Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3
values | title stringlengths 1 744 | labels stringlengths 4 574 | body stringlengths 9 211k | index stringclasses 10
values | text_combine stringlengths 96 211k | label stringclasses 2
values | text stringlengths 96 188k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
144,148 | 11,596,224,834 | IssuesEvent | 2020-02-24 18:31:50 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Not able to add group at project level | [zube]: To Test kind/bug-qa | **What kind of request is this (question/bug/enhancement/feature request):**
Bug
**Steps to reproduce (least amount of steps as possible):**
- Install Rancher 2.4 `master-head (02/21/2020)` commit id: 264d9235b
- Create a cluster
- Add a new user as Cluster Member for this cluster. (A user with a group)
- Log... | 1.0 | Not able to add group at project level - **What kind of request is this (question/bug/enhancement/feature request):**
Bug
**Steps to reproduce (least amount of steps as possible):**
- Install Rancher 2.4 `master-head (02/21/2020)` commit id: 264d9235b
- Create a cluster
- Add a new user as Cluster Member for t... | non_process | not able to add group at project level what kind of request is this question bug enhancement feature request bug steps to reproduce least amount of steps as possible install rancher master head commit id create a cluster add a new user as cluster member for this cluster ... | 0 |
12,936 | 15,301,995,031 | IssuesEvent | 2021-02-24 14:16:01 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | opened | Release 4.1 - March 2021 | P1 release team-XProduct type: process | # Status of Bazel 4.1
This release will use Bazel 4.0.0 as its baseline and we will apply selected cherry-picks and backports on top of it. Please request cherry-picks that you'd like to get into Bazel 4.1.0 here via a comment.
- Expected release date: March 2021
- [List of release blockers](https://github.com/b... | 1.0 | Release 4.1 - March 2021 - # Status of Bazel 4.1
This release will use Bazel 4.0.0 as its baseline and we will apply selected cherry-picks and backports on top of it. Please request cherry-picks that you'd like to get into Bazel 4.1.0 here via a comment.
- Expected release date: March 2021
- [List of release blo... | process | release march status of bazel this release will use bazel as its baseline and we will apply selected cherry picks and backports on top of it please request cherry picks that you d like to get into bazel here via a comment expected release date march to report a release... | 1 |
81,686 | 15,630,110,597 | IssuesEvent | 2021-03-22 01:23:24 | johnnymythology/material-blog-jp | https://api.github.com/repos/johnnymythology/material-blog-jp | closed | CVE-2018-19826 (Medium) detected in node-sass-v4.11.0 - autoclosed | security vulnerability | ## CVE-2018-19826 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=ht... | True | CVE-2018-19826 (Medium) detected in node-sass-v4.11.0 - autoclosed - ## CVE-2018-19826 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rain... | non_process | cve medium detected in node sass autoclosed cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matc... | 0 |
4,718 | 7,552,661,150 | IssuesEvent | 2018-04-19 01:38:48 | UnbFeelings/unb-feelings-docs | https://api.github.com/repos/UnbFeelings/unb-feelings-docs | opened | [Não Conformidade] Backlog | Desenvolvimento Processo | @UnbFeelings/devel
A auditoria do [Backlog](https://github.com/UnbFeelings/unb-feelings-docs/wiki/Processo#2011-requisitos-da-release), que é um produto gerado do sub processo **requisitos**, foi feita com base nos [critérios](https://github.com/UnbFeelings/unb-feelings-GQA/wiki/Crit%C3%A9rios-de-Avalia%C3%A7%C3%A... | 1.0 | [Não Conformidade] Backlog - @UnbFeelings/devel
A auditoria do [Backlog](https://github.com/UnbFeelings/unb-feelings-docs/wiki/Processo#2011-requisitos-da-release), que é um produto gerado do sub processo **requisitos**, foi feita com base nos [critérios](https://github.com/UnbFeelings/unb-feelings-GQA/wiki/Crit%... | process | backlog unbfeelings devel a auditoria do que é um produto gerado do sub processo requisitos foi feita com base nos pré estabelecidos para poder verificar se o processo foi utilizado o resultado da auditoria pode ser acessado através da seguinte página descrição foi identificado o... | 1 |
19,095 | 25,147,998,811 | IssuesEvent | 2022-11-10 07:41:05 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | Processing: Cannot choose attribute for "Class Identifier" in SAGA Supervised Classification for Grids | Processing Bug | ### What is the bug or the crash?
I am using SAGA-GIS tool _Supervised Classification for Grids_. One of the options of this tool is _Class Identifier_. It serves the purpose of indicating which of the fields of _Training Areas_, an optional input shape, contains the definitions of the classes. The SAGA-GIS version 7.... | 1.0 | Processing: Cannot choose attribute for "Class Identifier" in SAGA Supervised Classification for Grids - ### What is the bug or the crash?
I am using SAGA-GIS tool _Supervised Classification for Grids_. One of the options of this tool is _Class Identifier_. It serves the purpose of indicating which of the fields of _T... | process | processing cannot choose attribute for class identifier in saga supervised classification for grids what is the bug or the crash i am using saga gis tool supervised classification for grids one of the options of this tool is class identifier it serves the purpose of indicating which of the fields of t... | 1 |
67,171 | 16,827,450,784 | IssuesEvent | 2021-06-17 20:41:51 | coq/coq | https://api.github.com/repos/coq/coq | closed | Neither "make -j 12" nor "make -j 12 coqide" builds coqide | part: build | ```
$ dune exec -- dev/shim/coqide-prelude
File "ide/coqide/coqOps.ml", line 701, characters 31-44:
Error: This expression has type
(Doc.id * (unit, Doc.id) Util.union) Interface.value ->
unit Coq.task
but an expression was expected of type
Interface.add_rty Interface.value -> '... | 1.0 | Neither "make -j 12" nor "make -j 12 coqide" builds coqide - ```
$ dune exec -- dev/shim/coqide-prelude
File "ide/coqide/coqOps.ml", line 701, characters 31-44:
Error: This expression has type
(Doc.id * (unit, Doc.id) Util.union) Interface.value ->
unit Coq.task
but an expression was expe... | non_process | neither make j nor make j coqide builds coqide dune exec dev shim coqide prelude file ide coqide coqops ml line characters error this expression has type doc id unit doc id util union interface value unit coq task but an expression was expected o... | 0 |
7,898 | 11,084,025,656 | IssuesEvent | 2019-12-13 15:40:38 | NationalSecurityAgency/ghidra | https://api.github.com/repos/NationalSecurityAgency/ghidra | closed | Sleigh: Motorola 6805: typo in BSET instruction | Feature: Processor/6805 Type: Bug | **Describe the bug**
`BSET` instruction looks like erroneous copy of `BCLR` one.
https://github.com/NationalSecurityAgency/ghidra/blob/7e4dd35859e40233cd1b71248e0da411f0ac0812/Ghidra/Processors/6805/data/languages/6805.slaspec#L243
https://github.com/NationalSecurityAgency/ghidra/blob/7e4dd35859e40233cd1b71248e0... | 1.0 | Sleigh: Motorola 6805: typo in BSET instruction - **Describe the bug**
`BSET` instruction looks like erroneous copy of `BCLR` one.
https://github.com/NationalSecurityAgency/ghidra/blob/7e4dd35859e40233cd1b71248e0da411f0ac0812/Ghidra/Processors/6805/data/languages/6805.slaspec#L243
https://github.com/NationalSecu... | process | sleigh motorola typo in bset instruction describe the bug bset instruction looks like erroneous copy of bclr one please fix it with bset n direct is bit n direct local mask n direct direct mask | 1 |
1,749 | 4,442,357,847 | IssuesEvent | 2016-08-19 13:12:35 | neuropoly/spinalcordtoolbox | https://api.github.com/repos/neuropoly/spinalcordtoolbox | closed | enables creation of centerline from a series of points | enhancement priority: medium sct_process_segmentation | ~~~
xuanwu_20160624_yaou_MS013/t1 $ sct_process_segmentation -i t1_mask_viewer.nii.gz -p centerline
----------------------------------------------------------------------------------------------------
Spinal Cord Toolbox (version dev-3e107b779165b4feb9871fa193dec8c660108832)
Running /Users/julien/code/spinalcordtoo... | 1.0 | enables creation of centerline from a series of points - ~~~
xuanwu_20160624_yaou_MS013/t1 $ sct_process_segmentation -i t1_mask_viewer.nii.gz -p centerline
----------------------------------------------------------------------------------------------------
Spinal Cord Toolbox (version dev-3e107b779165b4feb9871fa193... | process | enables creation of centerline from a series of points xuanwu yaou sct process segmentation i mask viewer nii gz p centerline spinal cord toolbox version dev running users julien code spinalco... | 1 |
37,411 | 8,390,634,001 | IssuesEvent | 2018-10-09 13:10:11 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | opened | Tasks : Self Assigned "Tasks" are getting" displayed under HR admin "Dashboard" screen | Dashboard Defect HR Admin Module HR User Module P3 Tasks | Steps To Replicate :
1.Launch the URL
2.Sign in as HR user
3.Create a Task (Self Assigned) and save it
4.Sign in as HR admin user
5.Check the "Dashboard" screen
Experienced Behavior : Observed that Self Assigned "Tasks" are getting" displayed under HR admin "Dashboard" screen (Refer Screen Shot)
Expecte... | 1.0 | Tasks : Self Assigned "Tasks" are getting" displayed under HR admin "Dashboard" screen - Steps To Replicate :
1.Launch the URL
2.Sign in as HR user
3.Create a Task (Self Assigned) and save it
4.Sign in as HR admin user
5.Check the "Dashboard" screen
Experienced Behavior : Observed that Self Assigned "Tas... | non_process | tasks self assigned tasks are getting displayed under hr admin dashboard screen steps to replicate launch the url sign in as hr user create a task self assigned and save it sign in as hr admin user check the dashboard screen experienced behavior observed that self assigned tas... | 0 |
13,105 | 15,496,597,201 | IssuesEvent | 2021-03-11 02:58:51 | dluiscosta/weather_api | https://api.github.com/repos/dluiscosta/weather_api | opened | Automatically run tests on MR | development process enhancement | Automatically run tests on MR, displaying their results and preventing the merging to ```master``` if any tests fail.
This requires #10. | 1.0 | Automatically run tests on MR - Automatically run tests on MR, displaying their results and preventing the merging to ```master``` if any tests fail.
This requires #10. | process | automatically run tests on mr automatically run tests on mr displaying their results and preventing the merging to master if any tests fail this requires | 1 |
7,509 | 10,588,520,117 | IssuesEvent | 2019-10-09 02:21:52 | kubeflow/testing | https://api.github.com/repos/kubeflow/testing | closed | Create a Google group with viewer only access to the CI infrastructure | kind/process priority/p1 | We should create a suitable google group to grant folks viewer only access to ci infrastructure to support debugging tests.
/cc @jinchihe | 1.0 | Create a Google group with viewer only access to the CI infrastructure - We should create a suitable google group to grant folks viewer only access to ci infrastructure to support debugging tests.
/cc @jinchihe | process | create a google group with viewer only access to the ci infrastructure we should create a suitable google group to grant folks viewer only access to ci infrastructure to support debugging tests cc jinchihe | 1 |
350,846 | 10,509,605,338 | IssuesEvent | 2019-09-27 11:26:36 | getkirby/kirby | https://api.github.com/repos/getkirby/kirby | closed | [Panel] e.nextSibling.focus is not a function on multiselect field | priority: high 🔥 type: bug 🐛 | **Describe the bug**
Error occured when navigate right (no next siblings) selected options on multiselect field
**To Reproduce**
Steps to reproduce the behavior:
1. Go to panel
2. Add multiselect field with options to any page
3. Edit page and select some options
4. Navigate selected options with `right` a... | 1.0 | [Panel] e.nextSibling.focus is not a function on multiselect field - **Describe the bug**
Error occured when navigate right (no next siblings) selected options on multiselect field
**To Reproduce**
Steps to reproduce the behavior:
1. Go to panel
2. Add multiselect field with options to any page
3. Edit page... | non_process | e nextsibling focus is not a function on multiselect field describe the bug error occured when navigate right no next siblings selected options on multiselect field to reproduce steps to reproduce the behavior go to panel add multiselect field with options to any page edit page and s... | 0 |
22,245 | 30,799,251,119 | IssuesEvent | 2023-07-31 23:01:52 | h4sh5/npm-auto-scanner | https://api.github.com/repos/h4sh5/npm-auto-scanner | opened | developer_backup_test529 1.999.0 has 2 guarddog issues | npm-install-script npm-silent-process-execution | ```{"npm-install-script":[{"code":" \"preinstall\": \"node preinstall.js\",","location":"package/package.json:7","message":"The package.json has a script automatically running when the package is installed"}],"npm-silent-process-execution":[{"code":"const child = spawn('node', ['index.js'], {\n detached: true,\n s... | 1.0 | developer_backup_test529 1.999.0 has 2 guarddog issues - ```{"npm-install-script":[{"code":" \"preinstall\": \"node preinstall.js\",","location":"package/package.json:7","message":"The package.json has a script automatically running when the package is installed"}],"npm-silent-process-execution":[{"code":"const chil... | process | developer backup has guarddog issues npm install script npm silent process execution n detached true n stdio ignore n location package preinstall js message this package is silently executing another executable | 1 |
10,140 | 7,094,279,712 | IssuesEvent | 2018-01-13 01:13:44 | owncloud/core | https://api.github.com/repos/owncloud/core | closed | Optimize reading quota/free space on PROPFIND | bug performance status/STALE | @icewind1991 I did some debugging and I noticed that when you do a PROPFIND it will return the quota/free space for every subfolder too.
The problem is that getFileInfo() is likely to be called multiple times on the same node and so far we don't cache it. This means that this will cause additional DB queries, one for ... | True | Optimize reading quota/free space on PROPFIND - @icewind1991 I did some debugging and I noticed that when you do a PROPFIND it will return the quota/free space for every subfolder too.
The problem is that getFileInfo() is likely to be called multiple times on the same node and so far we don't cache it. This means that... | non_process | optimize reading quota free space on propfind i did some debugging and i noticed that when you do a propfind it will return the quota free space for every subfolder too the problem is that getfileinfo is likely to be called multiple times on the same node and so far we don t cache it this means that this will... | 0 |
10,454 | 13,234,960,609 | IssuesEvent | 2020-08-18 17:11:26 | googleapis/repo-automation-bots | https://api.github.com/repos/googleapis/repo-automation-bots | closed | Support @octokit/webhooks versions > 7.1.1 by changing import strategy | priority: p1 type: process | [@octokit/webhooks.js](https://www.npmjs.com/package/@octokit/webhooks) changed the way they export the `Webhooks` type i[n a recent commit](https://github.com/octokit/webhooks.js/commit/12a266a34ad4781975038a8a78908481460f5fce#diff-41df78d86ed4de80aae9b0b9560feb2b) and this [breaks the release-please tests](https://gi... | 1.0 | Support @octokit/webhooks versions > 7.1.1 by changing import strategy - [@octokit/webhooks.js](https://www.npmjs.com/package/@octokit/webhooks) changed the way they export the `Webhooks` type i[n a recent commit](https://github.com/octokit/webhooks.js/commit/12a266a34ad4781975038a8a78908481460f5fce#diff-41df78d86ed4de... | process | support octokit webhooks versions by changing import strategy changed the way they export the webhooks type i and this for versions above the fix should be fairly straightforward but it will require some testing to ensure nothing else is broken | 1 |
15,421 | 2,852,680,702 | IssuesEvent | 2015-06-01 14:49:32 | tokland/pysheng | https://api.github.com/repos/tokland/pysheng | closed | error from GUI | auto-migrated Priority-Medium Type-Defect | ```
What steps will reproduce the problem?
1. follow installation instructions
2. run pysheng-gui
What is the expected output? What do you see instead?
GUI does not open, following error is printed:
Traceback (most recent call last):
File "pysheng-gui", line 14, in <module>
sys.exit(main(sys.argv[1:]))
File ... | 1.0 | error from GUI - ```
What steps will reproduce the problem?
1. follow installation instructions
2. run pysheng-gui
What is the expected output? What do you see instead?
GUI does not open, following error is printed:
Traceback (most recent call last):
File "pysheng-gui", line 14, in <module>
sys.exit(main(sys.a... | non_process | error from gui what steps will reproduce the problem follow installation instructions run pysheng gui what is the expected output what do you see instead gui does not open following error is printed traceback most recent call last file pysheng gui line in sys exit main sys argv ... | 0 |
20,557 | 27,217,797,394 | IssuesEvent | 2023-02-21 00:35:50 | cse442-at-ub/project_s23-iweatherify | https://api.github.com/repos/cse442-at-ub/project_s23-iweatherify | opened | As a beginner participant, I want to read possible semester long projects so that I can see the thought process behind what idea got picked | Processing Task Sprint 1 | **Acceptance tests**
*Test 1*
1) Refer to https://docs.google.com/document/d/1fQDM2_rvD49LgCHpRX-fh-yX0UqBG1fgJzAu0D9KsRQ/edit?usp=sharing | 1.0 | As a beginner participant, I want to read possible semester long projects so that I can see the thought process behind what idea got picked - **Acceptance tests**
*Test 1*
1) Refer to https://docs.google.com/document/d/1fQDM2_rvD49LgCHpRX-fh-yX0UqBG1fgJzAu0D9KsRQ/edit?usp=sharing | process | as a beginner participant i want to read possible semester long projects so that i can see the thought process behind what idea got picked acceptance tests test refer to | 1 |
21,317 | 28,565,849,385 | IssuesEvent | 2023-04-21 02:00:09 | lizhihao6/get-daily-arxiv-noti | https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti | opened | New submissions for Fri, 21 Apr 23 | event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB | ## Keyword: events
### Introducing Construct Theory as a Standard Methodology for Inclusive AI Models
- **Authors:** Susanna Raj, Sudha Jamthe, Yashaswini Viswanath, Suresh Lokiah
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs... | 2.0 | New submissions for Fri, 21 Apr 23 - ## Keyword: events
### Introducing Construct Theory as a Standard Methodology for Inclusive AI Models
- **Authors:** Susanna Raj, Sudha Jamthe, Yashaswini Viswanath, Suresh Lokiah
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- ... | process | new submissions for fri apr keyword events introducing construct theory as a standard methodology for inclusive ai models authors susanna raj sudha jamthe yashaswini viswanath suresh lokiah subjects computer vision and pattern recognition cs cv artificial intelligence cs ai ... | 1 |
10,605 | 13,431,565,123 | IssuesEvent | 2020-09-07 07:12:12 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | Missing parent "GO:0140423 JSON effector-mediated suppression of pattern-triggered immunity' | high priority missing parentage multi-species process |
I'm back on PHI base today.
This term:
GO:0140423 effector-mediated suppression of pattern-triggered immunity
still doesn't seem to be a descendant of
GO:0140404 effector-mediated modulation of host innate immune response by symbiont
I'm sure we keep adding this?
| 1.0 | Missing parent "GO:0140423 JSON effector-mediated suppression of pattern-triggered immunity' -
I'm back on PHI base today.
This term:
GO:0140423 effector-mediated suppression of pattern-triggered immunity
still doesn't seem to be a descendant of
GO:0140404 effector-mediated modulation of host innate i... | process | missing parent go json effector mediated suppression of pattern triggered immunity i m back on phi base today this term go effector mediated suppression of pattern triggered immunity still doesn t seem to be a descendant of go effector mediated modulation of host innate immune response by ... | 1 |
18,974 | 24,962,395,936 | IssuesEvent | 2022-11-01 16:31:43 | OpenDataScotland/the_od_bods | https://api.github.com/repos/OpenDataScotland/the_od_bods | closed | Add name conversion for publisher "Na h-Eileanan an Iar" to "Comhairle nan Eilean Siar" | bug good first issue data processing | **Describe the bug**
For some reason, datasets by the Local Authority "Comhairle nan Eilean Siar" are being published under its constituency name "Na h-Eileanan an Iar" instead. The LA name on JKAN orgs is correct, so not going to change that, but we need to treat the incoming feed so it matches the org name.
Source... | 1.0 | Add name conversion for publisher "Na h-Eileanan an Iar" to "Comhairle nan Eilean Siar" - **Describe the bug**
For some reason, datasets by the Local Authority "Comhairle nan Eilean Siar" are being published under its constituency name "Na h-Eileanan an Iar" instead. The LA name on JKAN orgs is correct, so not going t... | process | add name conversion for publisher na h eileanan an iar to comhairle nan eilean siar describe the bug for some reason datasets by the local authority comhairle nan eilean siar are being published under its constituency name na h eileanan an iar instead the la name on jkan orgs is correct so not going t... | 1 |
677 | 3,147,522,960 | IssuesEvent | 2015-09-15 08:39:52 | e-government-ua/i | https://api.github.com/repos/e-government-ua/i | closed | На дашборде в разделе "Звіни" блоке "Експорт" добавить такой-же комбобокс с доступными БП, как и в блоке с "Статистика" и для каждого БП брать свой набор параметров, беря их из патернов /pattern/export | active bug hi priority In process of testing test | 1) сейчас набор параметров захардкоден жестко:
exportLink: function (exportParams) {
var data = {
'sID_BP': 'dnepr_spravka_o_doxodax',
'sID_State_BP': 'usertask1',
'sDateAt': exportParams.from,
'sDateTo': exportParams.to,
'saFields': '${nID_Task};${sDateCreate}... | 1.0 | На дашборде в разделе "Звіни" блоке "Експорт" добавить такой-же комбобокс с доступными БП, как и в блоке с "Статистика" и для каждого БП брать свой набор параметров, беря их из патернов /pattern/export - 1) сейчас набор параметров захардкоден жестко:
exportLink: function (exportParams) {
var data = {
... | process | на дашборде в разделе звіни блоке експорт добавить такой же комбобокс с доступными бп как и в блоке с статистика и для каждого бп брать свой набор параметров беря их из патернов pattern export сейчас набор параметров захардкоден жестко exportlink function exportparams var data ... | 1 |
9,231 | 12,260,985,416 | IssuesEvent | 2020-05-06 19:15:39 | cranec-project/Covid-19 | https://api.github.com/repos/cranec-project/Covid-19 | opened | moving prone patients | At overwhelm stage Critical ICU process Specific need Tech:Mechanics Ventilation | Patients with ARDS often benefit from being in a prone position for extended periods of time. the problem si moving them in and out of the prone position, especially if they are heavy, under the twin constraints of:
1. not disconnecting any tubes, etc.
2. using PPE | 1.0 | moving prone patients - Patients with ARDS often benefit from being in a prone position for extended periods of time. the problem si moving them in and out of the prone position, especially if they are heavy, under the twin constraints of:
1. not disconnecting any tubes, etc.
2. using PPE | process | moving prone patients patients with ards often benefit from being in a prone position for extended periods of time the problem si moving them in and out of the prone position especially if they are heavy under the twin constraints of not disconnecting any tubes etc using ppe | 1 |
818,270 | 30,681,463,874 | IssuesEvent | 2023-07-26 09:26:08 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | Windows: Mesh entities are not rendered in viewport | kind/bug needs-triage sig/content priority/critical | **Describe the bug**
Ground and shaderball entities in newly created levels are not rendered. Additionally, newly created entities with Mesh component added and asset assigned to it are also not rendering properly. All assets were processed in Asset Processor.
The issue does not occur on Linux.
**Steps to reproduc... | 1.0 | Windows: Mesh entities are not rendered in viewport - **Describe the bug**
Ground and shaderball entities in newly created levels are not rendered. Additionally, newly created entities with Mesh component added and asset assigned to it are also not rendering properly. All assets were processed in Asset Processor.
The... | non_process | windows mesh entities are not rendered in viewport describe the bug ground and shaderball entities in newly created levels are not rendered additionally newly created entities with mesh component added and asset assigned to it are also not rendering properly all assets were processed in asset processor the... | 0 |
17,760 | 23,677,533,437 | IssuesEvent | 2022-08-28 10:08:30 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | Show feature count of Processing outputs | Processing Feature Request | **Feature description.**
The insights from outputs generated with **_Processing_** tools, especially those related with overlays or aggregations, would be more immediate if the 'Show feature count' was toggled on automatically when these layers are added to the `Layers panel`.
This could also be a check box showin... | 1.0 | Show feature count of Processing outputs - **Feature description.**
The insights from outputs generated with **_Processing_** tools, especially those related with overlays or aggregations, would be more immediate if the 'Show feature count' was toggled on automatically when these layers are added to the `Layers panel`... | process | show feature count of processing outputs feature description the insights from outputs generated with processing tools especially those related with overlays or aggregations would be more immediate if the show feature count was toggled on automatically when these layers are added to the layers panel ... | 1 |
3,689 | 6,717,068,183 | IssuesEvent | 2017-10-14 16:43:52 | TraningManagementSystem/tms | https://api.github.com/repos/TraningManagementSystem/tms | closed | サービス(ビジネスロジック)実装の手前まで案内する | dev process | ### Description
サービス(ビジネスロジック)実装の手前まで案内する
----
### Details
必要なのは、主に自動生成とスクラッチのつなぎの部分のみだと考える。
----
### Relation Issue
なし
---- | 1.0 | サービス(ビジネスロジック)実装の手前まで案内する - ### Description
サービス(ビジネスロジック)実装の手前まで案内する
----
### Details
必要なのは、主に自動生成とスクラッチのつなぎの部分のみだと考える。
----
### Relation Issue
なし
---- | process | サービス(ビジネスロジック)実装の手前まで案内する description サービス(ビジネスロジック)実装の手前まで案内する details 必要なのは、主に自動生成とスクラッチのつなぎの部分のみだと考える。 relation issue なし | 1 |
821,213 | 30,811,038,652 | IssuesEvent | 2023-08-01 10:23:34 | telerik/kendo-react | https://api.github.com/repos/telerik/kendo-react | reopened | Switching between views in the Scheduler causes misalignment | bug pkg:scheduler Priority 1 SEV: High | When switching between the timeline view and other views, items are misaligned.
Steps to reproduce:
1. Choose vertical orientation
2. Select Timeline, observe the alignment of the items
3. Select any other view and then Timeline again
https://stackblitz.com/edit/react-6n6zxv-klygr2?file=app/main.tsx
![sched... | 1.0 | Switching between views in the Scheduler causes misalignment - When switching between the timeline view and other views, items are misaligned.
Steps to reproduce:
1. Choose vertical orientation
2. Select Timeline, observe the alignment of the items
3. Select any other view and then Timeline again
https://stack... | non_process | switching between views in the scheduler causes misalignment when switching between the timeline view and other views items are misaligned steps to reproduce choose vertical orientation select timeline observe the alignment of the items select any other view and then timeline again ... | 0 |
181 | 2,588,005,216 | IssuesEvent | 2015-02-17 22:01:21 | GsDevKit/gsDevKitHome | https://api.github.com/repos/GsDevKit/gsDevKitHome | closed | More definitive `script is finished` needed for installServer and friends | in process | Here's the current end of processing:
```
Bulk migrate of 0 candidate classes
No instance migrations performed.[12/12/2014 19:09:10.134 UTC]
gci login: currSession 1 rpc gem processId 2424 OOB keep-alive interval 0
---Starting backup to '/home/notroot/gsDevKitHome/gemstone/stones/Dario/backups//tode.dbf' (... | 1.0 | More definitive `script is finished` needed for installServer and friends - Here's the current end of processing:
```
Bulk migrate of 0 candidate classes
No instance migrations performed.[12/12/2014 19:09:10.134 UTC]
gci login: currSession 1 rpc gem processId 2424 OOB keep-alive interval 0
---Starting back... | process | more definitive script is finished needed for installserver and friends here s the current end of processing bulk migrate of candidate classes no instance migrations performed gci login currsession rpc gem processid oob keep alive interval starting backup to home notroot gsdevkitho... | 1 |
421,211 | 28,311,103,395 | IssuesEvent | 2023-04-10 15:28:00 | LuongXuanThang20110724/Web_TalkDesk | https://api.github.com/repos/LuongXuanThang20110724/Web_TalkDesk | closed | Code UI "ServiceLevel" | documentation | - [x] 1. Sử dụng và tinh chỉnh lại component Feature2
- [x] 2. Sử dụng và tinh chỉnh lại select "filter"
- [x] 3. Sử dụng và tinh chỉnh lại "Times"
- [x] 4. Sử dụng và tinh chỉnh lại "Stacked Bar Chart"
- [x] 5. Code "Pie Chart With Needle"
- [x] 6. Review hoàn chỉnh | 1.0 | Code UI "ServiceLevel" - - [x] 1. Sử dụng và tinh chỉnh lại component Feature2
- [x] 2. Sử dụng và tinh chỉnh lại select "filter"
- [x] 3. Sử dụng và tinh chỉnh lại "Times"
- [x] 4. Sử dụng và tinh chỉnh lại "Stacked Bar Chart"
- [x] 5. Code "Pie Chart With Needle"
- [x] 6. Review hoàn chỉnh | non_process | code ui servicelevel sử dụng và tinh chỉnh lại component sử dụng và tinh chỉnh lại select filter sử dụng và tinh chỉnh lại times sử dụng và tinh chỉnh lại stacked bar chart code pie chart with needle review hoàn chỉnh | 0 |
60,577 | 7,359,877,476 | IssuesEvent | 2018-03-10 12:31:08 | w3c/EasyChecks | https://api.github.com/repos/w3c/EasyChecks | closed | URI | wai-redesign-before | current URI is https://www.w3.org/WAI/eval/preliminary
(because once upon a time, this page was called "Preliminary Review of Web Sites for Accessibility")
In-progress prototype has http://w3c.github.io/wai-website/test-evaluate/easychecks/
Given that we expect to change the title when we revise resource, and it... | 1.0 | URI - current URI is https://www.w3.org/WAI/eval/preliminary
(because once upon a time, this page was called "Preliminary Review of Web Sites for Accessibility")
In-progress prototype has http://w3c.github.io/wai-website/test-evaluate/easychecks/
Given that we expect to change the title when we revise resource, ... | non_process | uri current uri is because once upon a time this page was called preliminary review of web sites for accessibility in progress prototype has given that we expect to change the title when we revise resource and it might not end up being easy checks i mildly propose that we do not use easychecks ... | 0 |
10,829 | 13,610,191,308 | IssuesEvent | 2020-09-23 06:56:36 | peopledoc/procrastinate | https://api.github.com/repos/peopledoc/procrastinate | closed | Use setuptools_scm in setup.py | Contains: Only Python Good for: newcomers Type: Process | Our setup.py makes exactly what setuptools_scm provides, so we could get rid of some code for a part that is completely process boilerplate.
I think it could be nice to switch to it.
https://pypi.org/project/setuptools-scm/ | 1.0 | Use setuptools_scm in setup.py - Our setup.py makes exactly what setuptools_scm provides, so we could get rid of some code for a part that is completely process boilerplate.
I think it could be nice to switch to it.
https://pypi.org/project/setuptools-scm/ | process | use setuptools scm in setup py our setup py makes exactly what setuptools scm provides so we could get rid of some code for a part that is completely process boilerplate i think it could be nice to switch to it | 1 |
112 | 2,546,288,699 | IssuesEvent | 2015-01-29 22:47:17 | tinkerpop/tinkerpop3 | https://api.github.com/repos/tinkerpop/tinkerpop3 | opened | There are no lambdas. [proposal] | enhancement process | What if there was only `Traversal`. This would greatly reduce the complexity of many steps. No such think as functions vs. traversals. What is `choose{it.name[0] == 'm'}` then? I'm glad you asked -- `choose(__.filter{it.name[0] == 'm'})`. People could write the lamda form (the first expression), but it is encoded as a ... | 1.0 | There are no lambdas. [proposal] - What if there was only `Traversal`. This would greatly reduce the complexity of many steps. No such think as functions vs. traversals. What is `choose{it.name[0] == 'm'}` then? I'm glad you asked -- `choose(__.filter{it.name[0] == 'm'})`. People could write the lamda form (the first e... | process | there are no lambdas what if there was only traversal this would greatly reduce the complexity of many steps no such think as functions vs traversals what is choose it name m then i m glad you asked choose filter it name m people could write the lamda form the first expression b... | 1 |
88,608 | 3,779,723,904 | IssuesEvent | 2016-03-18 09:47:23 | radar2go/radar-beta | https://api.github.com/repos/radar2go/radar-beta | closed | Oznaka notifikacije | enhancement priority | Fajn bi bilo da je v appu oznaceno ce imas kako notifikacijo. Neko oznako na fotki in potem v posamezni kategoriji. Ce ti je negdo poslal zahtev za prijateljstvo oznaka na people
Ce mas notifikacijo oznako na notifikacijo.
Enima ni najbolj jasna oznaka za dodajanje prijateljev. Meni pa je.
Moznost je da ko si z nek... | 1.0 | Oznaka notifikacije - Fajn bi bilo da je v appu oznaceno ce imas kako notifikacijo. Neko oznako na fotki in potem v posamezni kategoriji. Ce ti je negdo poslal zahtev za prijateljstvo oznaka na people
Ce mas notifikacijo oznako na notifikacijo.
Enima ni najbolj jasna oznaka za dodajanje prijateljev. Meni pa je.
Moz... | non_process | oznaka notifikacije fajn bi bilo da je v appu oznaceno ce imas kako notifikacijo neko oznako na fotki in potem v posamezni kategoriji ce ti je negdo poslal zahtev za prijateljstvo oznaka na people ce mas notifikacijo oznako na notifikacijo enima ni najbolj jasna oznaka za dodajanje prijateljev meni pa je moz... | 0 |
196,861 | 15,611,918,162 | IssuesEvent | 2021-03-19 14:49:45 | k-roffle/knitting-frontend | https://api.github.com/repos/k-roffle/knitting-frontend | closed | 이슈 템플릿 나오도록 수정 | Documentation Low Other bug | ## Bug 제안 사유
이슈 템플릿이 이슈 등록 시 나오지 않습니다
<!-- 왜 이 Bug를 제안하게 되었는지 간략하게 적어주세요. -->
## 재현 상황
이슈 추가 버튼을 누릅니다
<!-- Bug를 재현할 수 있는 순서를 적어주세요. -->
## 예상 동작
이슈 추가 버튼을 누르면 템플릿이 나와야 합니다
<!-- 예상 동작에 대한 명확하고 간결한 설명을 적어주세요. -->
## 스크린샷
<!-- 문제 해결에 도움이 되는 스크린샷이 있다면 추가해주세요. -->
## Desktop 스펙
- OS:
- Browser:
- V... | 1.0 | 이슈 템플릿 나오도록 수정 - ## Bug 제안 사유
이슈 템플릿이 이슈 등록 시 나오지 않습니다
<!-- 왜 이 Bug를 제안하게 되었는지 간략하게 적어주세요. -->
## 재현 상황
이슈 추가 버튼을 누릅니다
<!-- Bug를 재현할 수 있는 순서를 적어주세요. -->
## 예상 동작
이슈 추가 버튼을 누르면 템플릿이 나와야 합니다
<!-- 예상 동작에 대한 명확하고 간결한 설명을 적어주세요. -->
## 스크린샷
<!-- 문제 해결에 도움이 되는 스크린샷이 있다면 추가해주세요. -->
## Desktop 스펙
- OS:... | non_process | 이슈 템플릿 나오도록 수정 bug 제안 사유 이슈 템플릿이 이슈 등록 시 나오지 않습니다 재현 상황 이슈 추가 버튼을 누릅니다 예상 동작 이슈 추가 버튼을 누르면 템플릿이 나와야 합니다 스크린샷 desktop 스펙 os browser version mobile 스펙 device os browser version 부가 설명 | 0 |
1,186 | 3,687,740,468 | IssuesEvent | 2016-02-25 09:49:19 | dita-ot/dita-ot | https://api.github.com/repos/dita-ot/dita-ot | closed | Resolve coderef before conref | bug preprocess | Currently, the preprocessing order of operations resolves coderefs late — after conref resolution is complete. This can result in coderefs not being resolved. For example:
* Topic A contains an example with a coderef in it.
* Topic B conrefs the example from topic A.
At the time the file lists are generated, Top... | 1.0 | Resolve coderef before conref - Currently, the preprocessing order of operations resolves coderefs late — after conref resolution is complete. This can result in coderefs not being resolved. For example:
* Topic A contains an example with a coderef in it.
* Topic B conrefs the example from topic A.
At the time t... | process | resolve coderef before conref currently the preprocessing order of operations resolves coderefs late — after conref resolution is complete this can result in coderefs not being resolved for example topic a contains an example with a coderef in it topic b conrefs the example from topic a at the time t... | 1 |
18,199 | 24,254,773,124 | IssuesEvent | 2022-09-27 16:48:13 | AltTesterBot/test | https://api.github.com/repos/AltTesterBot/test | closed | setup a pipeline process | doing process gitlab | We need to figure out a way to:
* build automatically
* run the python unit tests
* run some of the Appium tests?
* dist to pypi (pip) when merged to master
---
<sub>You can find the original issue from GitLab [here](https://gitlab.com/altom/altunity/altunitytester/-/issues/5).</sub>
| 1.0 | setup a pipeline process - We need to figure out a way to:
* build automatically
* run the python unit tests
* run some of the Appium tests?
* dist to pypi (pip) when merged to master
---
<sub>You can find the original issue from GitLab [here](https://gitlab.com/altom/altunity/altunitytester/-/issues/5).</sub>
| process | setup a pipeline process we need to figure out a way to build automatically run the python unit tests run some of the appium tests dist to pypi pip when merged to master you can find the original issue from gitlab | 1 |
30,806 | 14,674,622,204 | IssuesEvent | 2020-12-30 15:43:45 | sergiorribeiro/webmetry | https://api.github.com/repos/sergiorribeiro/webmetry | opened | [Controller] Controller/api/v1/hedge_fund_accounting_report_records/ending_balance_share_class_records | controller needs squad prodops transaction-performance | The transaction **`Controller/api/v1/hedge_fund_accounting_report_records/ending_balance_share_class_records` (Controller)** violated a performance threshold.
## Violations:
- [2020-12-30] Maximum execution duration during the current week was exceeded. Duration: **`1.4 min`**. Limit: **`30 s`**. <!-- /// -->
... | True | [Controller] Controller/api/v1/hedge_fund_accounting_report_records/ending_balance_share_class_records - The transaction **`Controller/api/v1/hedge_fund_accounting_report_records/ending_balance_share_class_records` (Controller)** violated a performance threshold.
## Violations:
- [2020-12-30] Maximum execution duratio... | non_process | controller api hedge fund accounting report records ending balance share class records the transaction controller api hedge fund accounting report records ending balance share class records controller violated a performance threshold violations maximum execution duration during the current wee... | 0 |
190,986 | 22,192,267,718 | IssuesEvent | 2022-06-07 01:09:09 | opentok/opentok-react-native-samples | https://api.github.com/repos/opentok/opentok-react-native-samples | opened | opentok-react-native-0.20.1.tgz: 3 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opentok-react-native-0.20.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /BasicVideoChat/package.json</p>
<p>Path to vulnerable library: /Signaling/node_... | True | opentok-react-native-0.20.1.tgz: 3 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opentok-react-native-0.20.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: ... | non_process | opentok react native tgz vulnerabilities highest severity is vulnerable library opentok react native tgz path to dependency file basicvideochat package json path to vulnerable library signaling node modules follow redirects package json basicvideochat node modules follow re... | 0 |
438,915 | 30,668,851,842 | IssuesEvent | 2023-07-25 20:32:34 | jetstream-cloud/js2docs | https://api.github.com/repos/jetstream-cloud/js2docs | opened | [documentation] Add article for extending volume | documentation | ## Opportunity
This seems like a fairly common things users will want to do, and we get a good number of tickets asking how to do this. Here is an example of a ticket, including my reply:
https://access-ci.atlassian.net/browse/ATS-1987
## Resolution
We should add a page on the public docs for how to do this. | 1.0 | [documentation] Add article for extending volume - ## Opportunity
This seems like a fairly common things users will want to do, and we get a good number of tickets asking how to do this. Here is an example of a ticket, including my reply:
https://access-ci.atlassian.net/browse/ATS-1987
## Resolution
We should a... | non_process | add article for extending volume opportunity this seems like a fairly common things users will want to do and we get a good number of tickets asking how to do this here is an example of a ticket including my reply resolution we should add a page on the public docs for how to do this | 0 |
94,177 | 8,475,697,565 | IssuesEvent | 2018-10-24 19:41:00 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: hotspotsplits/nodes=4 failed | C-test-failure O-robot | SHA: https://github.com/cockroachdb/cockroach/commits/0dba537ae88e495ddf29b4c347b4c30ee99bd046
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace... | 1.0 | roachtest: hotspotsplits/nodes=4 failed - SHA: https://github.com/cockroachdb/cockroach/commits/0dba537ae88e495ddf29b4c347b4c30ee99bd046
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For exa... | non_process | roachtest hotspotsplits nodes failed sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which contr... | 0 |
21,710 | 30,210,241,146 | IssuesEvent | 2023-07-05 12:19:54 | GispoCoding/eis_toolkit | https://api.github.com/repos/GispoCoding/eis_toolkit | closed | Add Cell-Based Association | enhancement Preprocessing | **Cell-Based Association** (CBA) is used as a pre-processing method for geological data, such as geological maps and structural data. This method allows identifying specific associations of geological features across a given area (i.e. geological environments) using a regular square grid. Associations of geological fea... | 1.0 | Add Cell-Based Association - **Cell-Based Association** (CBA) is used as a pre-processing method for geological data, such as geological maps and structural data. This method allows identifying specific associations of geological features across a given area (i.e. geological environments) using a regular square grid. A... | process | add cell based association cell based association cba is used as a pre processing method for geological data such as geological maps and structural data this method allows identifying specific associations of geological features across a given area i e geological environments using a regular square grid a... | 1 |
99,677 | 8,708,076,053 | IssuesEvent | 2018-12-06 09:52:56 | club-soda/club-soda-guide | https://api.github.com/repos/club-soda/club-soda-guide | closed | Filter Beer, Wine, Cider and Spirits by ABV | Nisha - Consumer please-test priority-3 question | As a customer viewing all drinks,
I'd like to filter Beer, Wine, Cider and Spirits by ABV levels: 0.05, 0.5, 1-2.5 and 2.5 - 8%,
so I only see drinks I am comfortable drinking | 1.0 | Filter Beer, Wine, Cider and Spirits by ABV - As a customer viewing all drinks,
I'd like to filter Beer, Wine, Cider and Spirits by ABV levels: 0.05, 0.5, 1-2.5 and 2.5 - 8%,
so I only see drinks I am comfortable drinking | non_process | filter beer wine cider and spirits by abv as a customer viewing all drinks i d like to filter beer wine cider and spirits by abv levels and so i only see drinks i am comfortable drinking | 0 |
389,165 | 26,801,396,440 | IssuesEvent | 2023-02-01 15:20:00 | GillianPlatform/Gillian | https://api.github.com/repos/GillianPlatform/Gillian | closed | Deploy docs | documentation admin | We now have sphinx and odoc documentation ready, we just need to actually deploy it somewhere.
Related to #142 | 1.0 | Deploy docs - We now have sphinx and odoc documentation ready, we just need to actually deploy it somewhere.
Related to #142 | non_process | deploy docs we now have sphinx and odoc documentation ready we just need to actually deploy it somewhere related to | 0 |
17,683 | 23,520,366,515 | IssuesEvent | 2022-08-19 04:48:50 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Is it possible to add a method that kills the process tree? | area-System.Diagnostics.Process untriaged | .Net standard does not provide any method to kill a process tree. | 1.0 | Is it possible to add a method that kills the process tree? - .Net standard does not provide any method to kill a process tree. | process | is it possible to add a method that kills the process tree net standard does not provide any method to kill a process tree | 1 |
95,026 | 27,362,103,365 | IssuesEvent | 2023-02-27 16:30:10 | opensafely-core/databuilder | https://api.github.com/repos/opensafely-core/databuilder | closed | Add sequence operations to generative tests | databuilder-1 | See `tests.generative.variable_strategies.known_missing_operations` for the missing operations.
At the time of writing they are:
```
AggregateByPatient.CombineAsSet,
Function.In,
Function.StringContains,
```
(Note that there may be other non-sequence-related operations mentioned there which a... | 1.0 | Add sequence operations to generative tests - See `tests.generative.variable_strategies.known_missing_operations` for the missing operations.
At the time of writing they are:
```
AggregateByPatient.CombineAsSet,
Function.In,
Function.StringContains,
```
(Note that there may be other non-seque... | non_process | add sequence operations to generative tests see tests generative variable strategies known missing operations for the missing operations at the time of writing they are aggregatebypatient combineasset function in function stringcontains note that there may be other non seque... | 0 |
6,367 | 9,417,975,792 | IssuesEvent | 2019-04-10 18:03:22 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [Cards] Internal issue: b/129758049 | [Cards] type:Process | This was filed as an internal issue. If you are a Googler, please visit [b/129758049](http://b/129758049) for more details.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/129758049](http://b/129758049)
- Blocked by: https://github.com/material-components/mate... | 1.0 | [Cards] Internal issue: b/129758049 - This was filed as an internal issue. If you are a Googler, please visit [b/129758049](http://b/129758049) for more details.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/129758049](http://b/129758049)
- Blocked by: https... | process | internal issue b this was filed as an internal issue if you are a googler please visit for more details internal data associated internal bug blocked by blocked by blocked by blocked by blocked by blocked by blocked by | 1 |
13,181 | 15,609,758,979 | IssuesEvent | 2021-03-19 12:20:09 | hashicorp/packer | https://api.github.com/repos/hashicorp/packer | closed | Post-Processor: Delete docker image in local build machine after pushing to remote registry | enhancement post-processor/docker remote-plugin/docker | I do not want docker images piling up in my jenkins-slave. Is there any way to not commit images to local build machine and able to push docker image to remote registry?
I tried with "export" in builder and "docker-import" in post-processor but its still keeps a copy.
Thanks,
Karthik | 1.0 | Post-Processor: Delete docker image in local build machine after pushing to remote registry - I do not want docker images piling up in my jenkins-slave. Is there any way to not commit images to local build machine and able to push docker image to remote registry?
I tried with "export" in builder and "docker-import" ... | process | post processor delete docker image in local build machine after pushing to remote registry i do not want docker images piling up in my jenkins slave is there any way to not commit images to local build machine and able to push docker image to remote registry i tried with export in builder and docker import ... | 1 |
242,170 | 26,257,124,273 | IssuesEvent | 2023-01-06 02:25:48 | Hans-Zamorano-Matamala/mean_entrenamiento | https://api.github.com/repos/Hans-Zamorano-Matamala/mean_entrenamiento | opened | CVE-2022-21704 (Medium) detected in log4js-0.6.38.tgz | security vulnerability | ## CVE-2022-21704 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4js-0.6.38.tgz</b></p></summary>
<p>Port of Log4js to work with node.</p>
<p>Library home page: <a href="https://... | True | CVE-2022-21704 (Medium) detected in log4js-0.6.38.tgz - ## CVE-2022-21704 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4js-0.6.38.tgz</b></p></summary>
<p>Port of Log4js to wor... | non_process | cve medium detected in tgz cve medium severity vulnerability vulnerable library tgz port of to work with node library home page a href path to dependency file client package json path to vulnerable library client node modules package json dependency hi... | 0 |
24,045 | 23,264,099,428 | IssuesEvent | 2022-08-04 15:44:40 | Kitware/dive | https://api.github.com/repos/Kitware/dive | opened | Future Attribute Features | Type: Feature Request Affects: Usability | Additional Features to add to Attributes and the Attribute Details panel in the future.
Detection Attribute String Graphing:
- Graphing of attributes using a system to display the text/boolean values instead of the numerical values.
- This would require using sometime similar to the event viewer where the colo... | True | Future Attribute Features - Additional Features to add to Attributes and the Attribute Details panel in the future.
Detection Attribute String Graphing:
- Graphing of attributes using a system to display the text/boolean values instead of the numerical values.
- This would require using sometime similar to the... | non_process | future attribute features additional features to add to attributes and the attribute details panel in the future detection attribute string graphing graphing of attributes using a system to display the text boolean values instead of the numerical values this would require using sometime similar to the... | 0 |
9,920 | 12,960,217,173 | IssuesEvent | 2020-07-20 14:04:44 | prisma/prisma | https://api.github.com/repos/prisma/prisma | opened | Add a time limit to Buildkite jobs | kind/improvement process/candidate | Noticed that a job I started had a mistake on my end, and so it kept going for a couple of hours: https://buildkite.com/prisma/prisma2-test/builds/1864
We should probably have an upper limit on the job duration (like 30 mins or something) | 1.0 | Add a time limit to Buildkite jobs - Noticed that a job I started had a mistake on my end, and so it kept going for a couple of hours: https://buildkite.com/prisma/prisma2-test/builds/1864
We should probably have an upper limit on the job duration (like 30 mins or something) | process | add a time limit to buildkite jobs noticed that a job i started had a mistake on my end and so it kept going for a couple of hours we should probably have an upper limit on the job duration like mins or something | 1 |
9,733 | 11,783,283,507 | IssuesEvent | 2020-03-17 05:02:16 | hhxsv5/laravel-s | https://api.github.com/repos/hhxsv5/laravel-s | closed | laravelS和laravel-excel3.1冲突,导致报错无法导出数据 | compatibility | [2019-10-21 16:53:27] [TRACE] Swoole is running, press Ctrl+C to quit.
PHP Fatal error: Method Encore\Admin\Grid\Tools\Paginator::__toString() must not throw an exception, caught BadMethodCallException: Method Illuminate\Database\Eloquent\Collection::firstItem does not exist. in /www/wwwroot/XXX/storage/framework/vie... | True | laravelS和laravel-excel3.1冲突,导致报错无法导出数据 - [2019-10-21 16:53:27] [TRACE] Swoole is running, press Ctrl+C to quit.
PHP Fatal error: Method Encore\Admin\Grid\Tools\Paginator::__toString() must not throw an exception, caught BadMethodCallException: Method Illuminate\Database\Eloquent\Collection::firstItem does not exist. ... | non_process | laravels和laravel ,导致报错无法导出数据 swoole is running press ctrl c to quit php fatal error method encore admin grid tools paginator tostring must not throw an exception caught badmethodcallexception method illuminate database eloquent collection firstitem does not exist in www wwwroot xxx storage frame... | 0 |
5,482 | 8,356,217,461 | IssuesEvent | 2018-10-02 17:50:45 | HumanCellAtlas/dcp-community | https://api.github.com/repos/HumanCellAtlas/dcp-community | closed | Updates to RFC template from reviews | rfc-process | - [x] **User Stories** are *Required* rather than *Optional*
- [x] **Motivation** reference more generic PM plans instead of a _Thematic_ roadmap
- [x] **Prior Art** add _Community Standards_ as another example
- [x] **Acceptance Criteria** add new optional section suggested by @kbergin | 1.0 | Updates to RFC template from reviews - - [x] **User Stories** are *Required* rather than *Optional*
- [x] **Motivation** reference more generic PM plans instead of a _Thematic_ roadmap
- [x] **Prior Art** add _Community Standards_ as another example
- [x] **Acceptance Criteria** add new optional section sugge... | process | updates to rfc template from reviews user stories are required rather than optional motivation reference more generic pm plans instead of a thematic roadmap prior art add community standards as another example acceptance criteria add new optional section suggested by ... | 1 |
360,107 | 25,273,532,751 | IssuesEvent | 2022-11-16 10:57:57 | fedotkin/dotnet | https://api.github.com/repos/fedotkin/dotnet | closed | Root folder workarounds | documentation master | Root folder looks not good! There is no git ignore settings and readme-file looks ugly.
1. Rename Readme.txt file to [README.md](../trey-nash/README.md). Update content by short repository summary, .NET framework info, links and dotnet logo. Note: Readme-file is added on the first UI steps during a repo creation.
... | 1.0 | Root folder workarounds - Root folder looks not good! There is no git ignore settings and readme-file looks ugly.
1. Rename Readme.txt file to [README.md](../trey-nash/README.md). Update content by short repository summary, .NET framework info, links and dotnet logo. Note: Readme-file is added on the first UI steps ... | non_process | root folder workarounds root folder looks not good there is no git ignore settings and readme file looks ugly rename readme txt file to trey nash readme md update content by short repository summary net framework info links and dotnet logo note readme file is added on the first ui steps during a r... | 0 |
344,849 | 24,831,313,368 | IssuesEvent | 2022-10-26 03:56:18 | casey/just | https://api.github.com/repos/casey/just | closed | Make a video | documentation | I think a quick terminalcast is probably the best way to convey what just does.
- make a new folder
- cd into that folder
- start a new project
- initialize a rust project
- demonstrate every feature
- show error messages | 1.0 | Make a video - I think a quick terminalcast is probably the best way to convey what just does.
- make a new folder
- cd into that folder
- start a new project
- initialize a rust project
- demonstrate every feature
- show error messages | non_process | make a video i think a quick terminalcast is probably the best way to convey what just does make a new folder cd into that folder start a new project initialize a rust project demonstrate every feature show error messages | 0 |
14,361 | 17,382,011,840 | IssuesEvent | 2021-07-31 22:58:03 | AcademySoftwareFoundation/OpenCue | https://api.github.com/repos/AcademySoftwareFoundation/OpenCue | closed | Upgrade PySide to a more recent version. | process | **Describe the process**
Newer versions of Python 3 / pip on Windows no longer provide the version of PySide2 that we're using:
```
> pip3 install PySide2==5.11.2
ERROR: Could not find a version that satisfies the requirement PySide2==5.11.2 (from versions: 5.14.0, 5.14.1, 5.14.2, 5.14.2.1, 5.14.2.2, 5.14.2.3, 5.... | 1.0 | Upgrade PySide to a more recent version. - **Describe the process**
Newer versions of Python 3 / pip on Windows no longer provide the version of PySide2 that we're using:
```
> pip3 install PySide2==5.11.2
ERROR: Could not find a version that satisfies the requirement PySide2==5.11.2 (from versions: 5.14.0, 5.14.... | process | upgrade pyside to a more recent version describe the process newer versions of python pip on windows no longer provide the version of that we re using install error could not find a version that satisfies the requirement from versions ... | 1 |
119,785 | 12,042,806,482 | IssuesEvent | 2020-04-14 11:16:06 | poliastro/poliastro | https://api.github.com/repos/poliastro/poliastro | opened | Recommended conda instructions might leave user with older version | bug documentation | After following the official installation instructions for conda, @simium ended up with poliastro 0.9.1. This deserves a bit of investigation, but I suspect that having an old `base` environment and conda dependency solving played a role. We should either:
* Recommend installing exact versions: `conda install -c con... | 1.0 | Recommended conda instructions might leave user with older version - After following the official installation instructions for conda, @simium ended up with poliastro 0.9.1. This deserves a bit of investigation, but I suspect that having an old `base` environment and conda dependency solving played a role. We should ei... | non_process | recommended conda instructions might leave user with older version after following the official installation instructions for conda simium ended up with poliastro this deserves a bit of investigation but i suspect that having an old base environment and conda dependency solving played a role we should ei... | 0 |
15,287 | 19,286,484,705 | IssuesEvent | 2021-12-11 03:04:10 | q191201771/lal | https://api.github.com/repos/q191201771/lal | closed | 建议…可以做一个web后台监管系统 | #Feature *In process *Indefinite delay | 1.实时更新推拉流的客户端数量,ip,带宽流量等
2.分布式集群管理,一键添加或删除流服务器节点
3.实时监控播放正在推流内容,类似于监控室画面
4.根据时间段,播放量等可过滤直播回放视频列表
等等以及其他需要监管的数据信息。 | 1.0 | 建议…可以做一个web后台监管系统 - 1.实时更新推拉流的客户端数量,ip,带宽流量等
2.分布式集群管理,一键添加或删除流服务器节点
3.实时监控播放正在推流内容,类似于监控室画面
4.根据时间段,播放量等可过滤直播回放视频列表
等等以及其他需要监管的数据信息。 | process | 建议…可以做一个web后台监管系统 实时更新推拉流的客户端数量,ip,带宽流量等 分布式集群管理,一键添加或删除流服务器节点 实时监控播放正在推流内容,类似于监控室画面 根据时间段,播放量等可过滤直播回放视频列表 等等以及其他需要监管的数据信息。 | 1 |
271,410 | 23,602,892,163 | IssuesEvent | 2022-08-24 05:02:05 | istio/istio | https://api.github.com/repos/istio/istio | closed | Renaming base chart as istio base | kind/enhancement area/test and release area/environments area/user experience lifecycle/stale | (This is used to request new product features, please visit <https://discuss.istio.io> for questions on using Istio)
**Describe the feature request**
Rename Istio base chart name to istio-base
**Describe alternatives you've considered**
The chart name cannot have "base" name, since there a lot of base projects ... | 1.0 | Renaming base chart as istio base - (This is used to request new product features, please visit <https://discuss.istio.io> for questions on using Istio)
**Describe the feature request**
Rename Istio base chart name to istio-base
**Describe alternatives you've considered**
The chart name cannot have "base" name,... | non_process | renaming base chart as istio base this is used to request new product features please visit for questions on using istio describe the feature request rename istio base chart name to istio base describe alternatives you ve considered the chart name cannot have base name since there a lot of ba... | 0 |
666,304 | 22,349,638,188 | IssuesEvent | 2022-06-15 10:51:21 | codeklasse/codeklasse.de | https://api.github.com/repos/codeklasse/codeklasse.de | opened | Change regular text font | priority:high | Averta is too pricy for our use case.
We should find another simple font for text usage. | 1.0 | Change regular text font - Averta is too pricy for our use case.
We should find another simple font for text usage. | non_process | change regular text font averta is too pricy for our use case we should find another simple font for text usage | 0 |
789,482 | 27,791,678,161 | IssuesEvent | 2023-03-17 09:24:13 | VeriFIT/mata | https://api.github.com/repos/VeriFIT/mata | opened | Complementation over non-existent states | For:library Module:nfa Type:discussion Priority:low | In classical complement algorithm implemented in `Mata::Nfa::complement_classical`, we call `Mata::Nfa::Nfa::size()` which returns domain size of initial/final state sets. Those might contain “deleted” states (final/initial at some point but not now, yet still allocated with `false` value in `NumberPredicate`), so when... | 1.0 | Complementation over non-existent states - In classical complement algorithm implemented in `Mata::Nfa::complement_classical`, we call `Mata::Nfa::Nfa::size()` which returns domain size of initial/final state sets. Those might contain “deleted” states (final/initial at some point but not now, yet still allocated with `... | non_process | complementation over non existent states in classical complement algorithm implemented in mata nfa complement classical we call mata nfa nfa size which returns domain size of initial final state sets those might contain “deleted” states final initial at some point but not now yet still allocated with ... | 0 |
176,120 | 14,564,010,015 | IssuesEvent | 2020-12-17 03:58:26 | MakeContributions/markdown-dungeon | https://api.github.com/repos/MakeContributions/markdown-dungeon | closed | Shouldn't We Add Translations | beginner documentation good first issue help wanted | Recently, there has been many commits to the `english` folder and fresh rooms and dungeons have been added.
But, the new files have not been translated into portuguese (I think chinese is a seperate dungeon).
So, shouldn't we update the translations?
>Inviting some maintainers for their feedback: @ming-tsai, ... | 1.0 | Shouldn't We Add Translations - Recently, there has been many commits to the `english` folder and fresh rooms and dungeons have been added.
But, the new files have not been translated into portuguese (I think chinese is a seperate dungeon).
So, shouldn't we update the translations?
>Inviting some maintainers ... | non_process | shouldn t we add translations recently there has been many commits to the english folder and fresh rooms and dungeons have been added but the new files have not been translated into portuguese i think chinese is a seperate dungeon so shouldn t we update the translations inviting some maintainers ... | 0 |
12,544 | 14,975,634,863 | IssuesEvent | 2021-01-28 06:33:59 | darktable-org/darktable | https://api.github.com/repos/darktable-org/darktable | closed | Support for Dual Demosaicing (e.g. 3-pass+fast and AMaZE+VNG4) | feature: new scope: image processing | Last year RawTherapee added support for "[Dual Demosaicing](https://rawpedia.rawtherapee.com/Demosaicing#Dual_Demosaic)", which uses two different types of demosaicing on the same image, with each type being used on the parts of the image that it would work best with.
This feature has been very well received on RawT... | 1.0 | Support for Dual Demosaicing (e.g. 3-pass+fast and AMaZE+VNG4) - Last year RawTherapee added support for "[Dual Demosaicing](https://rawpedia.rawtherapee.com/Demosaicing#Dual_Demosaic)", which uses two different types of demosaicing on the same image, with each type being used on the parts of the image that it would wo... | process | support for dual demosaicing e g pass fast and amaze last year rawtherapee added support for which uses two different types of demosaicing on the same image with each type being used on the parts of the image that it would work best with this feature has been very well received on rawtherapee and it... | 1 |
6,388 | 9,462,590,267 | IssuesEvent | 2019-04-17 15:44:36 | openopps/openopps-platform | https://api.github.com/repos/openopps/openopps-platform | closed | Change security clearance values to match USAJOBS | Apply Process Requirements Ready State Dept. | Who: Internship applicants
What: Security clearance values
Why: To match USAJOBS
Modify the security clearance dropdown on the internship application to match the new values in USAJOBS.

| 1.0 | Change security clearance values to match USAJOBS - Who: Internship applicants
What: Security clearance values
Why: To match USAJOBS
Modify the security clearance dropdown on the internship application to match the new values in USAJOBS.
 | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.... | True | mysql-connector-java-5.1.25.jar: 9 vulnerabilities (highest severity is: 8.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>L... | non_process | mysql connector java jar vulnerabilities highest severity is vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library epository mysql mysql connector java mysql connect... | 0 |
2,558 | 5,313,781,930 | IssuesEvent | 2017-02-13 13:18:51 | openvstorage/volumedriver | https://api.github.com/repos/openvstorage/volumedriver | closed | Directories can be renamed | process_wontfix type_feature | While volumes cannot be renamed, directories can. This results in the model being out-of-sync with reality. We would either need an event that informs us about the directory rename, or block directory renames at all.
If we decide that renaming directories (or volumes for that matter) need to be possible and an event... | 1.0 | Directories can be renamed - While volumes cannot be renamed, directories can. This results in the model being out-of-sync with reality. We would either need an event that informs us about the directory rename, or block directory renames at all.
If we decide that renaming directories (or volumes for that matter) nee... | process | directories can be renamed while volumes cannot be renamed directories can this results in the model being out of sync with reality we would either need an event that informs us about the directory rename or block directory renames at all if we decide that renaming directories or volumes for that matter nee... | 1 |
16,003 | 28,435,927,718 | IssuesEvent | 2023-04-15 10:02:43 | makingdevices/TC-Logger-Device | https://api.github.com/repos/makingdevices/TC-Logger-Device | opened | [Requisite][1.2b] Thermocouple Reading | Baseline Requirement | The logger device needs to work with Thermocouples type K. In addition, the speed will be for at least 2Hz or 2 reading every second. The precision will be +-0.1C
Process Design:
- [ ] Find IC chip for thermocouple readings
- [ ] Implement the communication between main IC and ADC
Validation Design:
- [ ] T... | 1.0 | [Requisite][1.2b] Thermocouple Reading - The logger device needs to work with Thermocouples type K. In addition, the speed will be for at least 2Hz or 2 reading every second. The precision will be +-0.1C
Process Design:
- [ ] Find IC chip for thermocouple readings
- [ ] Implement the communication between main IC... | non_process | thermocouple reading the logger device needs to work with thermocouples type k in addition the speed will be for at least or reading every second the precision will be process design find ic chip for thermocouple readings implement the communication between main ic and adc validation... | 0 |
11,628 | 14,485,577,197 | IssuesEvent | 2020-12-10 17:45:53 | Feryi/5a | https://api.github.com/repos/Feryi/5a | opened | complete_size_estimating_template | process_dashboard | - completar el formato de estimcion de LOC con los valores obtenidos | 1.0 | complete_size_estimating_template - - completar el formato de estimcion de LOC con los valores obtenidos | process | complete size estimating template completar el formato de estimcion de loc con los valores obtenidos | 1 |
187,837 | 15,109,399,037 | IssuesEvent | 2021-02-08 17:47:57 | commercialhaskell/stackage | https://api.github.com/repos/commercialhaskell/stackage | closed | Docker images not automatically built? | type:documentation | The latest LTS versions seem to not have dockers [HERE](https://hub.docker.com/r/fpco/stack-build-small/).
Has something gone wrong in the automatic builds, or is there a certain release schedule for the newest LTS versions? | 1.0 | Docker images not automatically built? - The latest LTS versions seem to not have dockers [HERE](https://hub.docker.com/r/fpco/stack-build-small/).
Has something gone wrong in the automatic builds, or is there a certain release schedule for the newest LTS versions? | non_process | docker images not automatically built the latest lts versions seem to not have dockers has something gone wrong in the automatic builds or is there a certain release schedule for the newest lts versions | 0 |
36,840 | 8,153,877,234 | IssuesEvent | 2018-08-23 00:01:59 | primefaces/primereact | https://api.github.com/repos/primefaces/primereact | closed | Tooltip does not remove event listeners | defect | ```
[X ] bug report
[ ] feature request
[ ] support request => Please do not submit support request here, instead see https://forum.primefaces.org/viewforum.php?f=57
```
**Current behavior**
Tooltip does not remove event listeners in componentWillUnmount().
After it is displayed once, it remains there forever.... | 1.0 | Tooltip does not remove event listeners - ```
[X ] bug report
[ ] feature request
[ ] support request => Please do not submit support request here, instead see https://forum.primefaces.org/viewforum.php?f=57
```
**Current behavior**
Tooltip does not remove event listeners in componentWillUnmount().
After it is... | non_process | tooltip does not remove event listeners bug report feature request support request please do not submit support request here instead see current behavior tooltip does not remove event listeners in componentwillunmount after it is displayed once it remains there forever expec... | 0 |
2,160 | 5,006,506,047 | IssuesEvent | 2016-12-12 14:21:47 | openvstorage/framework | https://api.github.com/repos/openvstorage/framework | closed | No such file or directory: '/opt/OpenvStorage/config/framework.json' | process_wontfix | I follow this quick install guide : https://openvstorage.gitbooks.io/administration/content/Installation/quickinstall.html
and cluster install guide : https://openvstorage.gitbooks.io/administration/content/Installation/quickinstall.html
In the first config : ovs setup
ERROR: Failed to setup first node
ERROR: N... | 1.0 | No such file or directory: '/opt/OpenvStorage/config/framework.json' - I follow this quick install guide : https://openvstorage.gitbooks.io/administration/content/Installation/quickinstall.html
and cluster install guide : https://openvstorage.gitbooks.io/administration/content/Installation/quickinstall.html
In the fi... | process | no such file or directory opt openvstorage config framework json i follow this quick install guide and cluster install guide in the first config ovs setup error failed to setup first node error no authentication methods available rolling back setup of current node an unexpec... | 1 |
266,874 | 28,480,075,727 | IssuesEvent | 2023-04-18 01:23:01 | tomdgl397/juice-shop | https://api.github.com/repos/tomdgl397/juice-shop | opened | CVE-2023-28484 (Medium) detected in reactos0.4.13-dev | Mend: dependency security vulnerability | ## CVE-2023-28484 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>reactos0.4.13-dev</b></p></summary>
<p>
<p>A free Windows-compatible Operating System</p>
<p>Library home page: <a h... | True | CVE-2023-28484 (Medium) detected in reactos0.4.13-dev - ## CVE-2023-28484 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>reactos0.4.13-dev</b></p></summary>
<p>
<p>A free Windows-co... | non_process | cve medium detected in dev cve medium severity vulnerability vulnerable library dev a free windows compatible operating system library home page a href found in head commit a href vulnerable source files node modules vendor libxml xmls... | 0 |
253,456 | 27,300,617,836 | IssuesEvent | 2023-02-24 01:23:38 | panasalap/linux-4.19.72_1 | https://api.github.com/repos/panasalap/linux-4.19.72_1 | closed | CVE-2020-27152 (Medium) detected in linux-yoctov5.4.51 - autoclosed | security vulnerability | ## CVE-2020-27152 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://gi... | True | CVE-2020-27152 (Medium) detected in linux-yoctov5.4.51 - autoclosed - ## CVE-2020-27152 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yo... | non_process | cve medium detected in linux autoclosed cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files ... | 0 |
31,971 | 4,309,303,608 | IssuesEvent | 2016-07-21 15:36:02 | vincenthz/hs-foundation | https://api.github.com/repos/vincenthz/hs-foundation | opened | FilePath API | design enhancement | * [ ] extension manipulation
* [ ] path dropping / append filename
* [ ] parent
* [ ] windows support
* [ ] OS support (`readdir`)
| 1.0 | FilePath API - * [ ] extension manipulation
* [ ] path dropping / append filename
* [ ] parent
* [ ] windows support
* [ ] OS support (`readdir`)
| non_process | filepath api extension manipulation path dropping append filename parent windows support os support readdir | 0 |
764,986 | 26,827,297,475 | IssuesEvent | 2023-02-02 13:46:51 | GenomicMedLab/cool-seq-tool | https://api.github.com/repos/GenomicMedLab/cool-seq-tool | opened | `get_mane_data` raises `IndexError` | bug priority:medium | ```
File "cool_seq_tool/data_sources/mane_transcript.py", line 428, in <lambda>
copy_df["ac_no_version_as_int"] = copy_df["tx_ac"].apply(lambda x: int(x.split(".")[0].split("NM_00")[1])) # noqa: E501
IndexError: list index out of range
```
I'm not sure why I split on `NM_00`, it should just be `NM_` | 1.0 | `get_mane_data` raises `IndexError` - ```
File "cool_seq_tool/data_sources/mane_transcript.py", line 428, in <lambda>
copy_df["ac_no_version_as_int"] = copy_df["tx_ac"].apply(lambda x: int(x.split(".")[0].split("NM_00")[1])) # noqa: E501
IndexError: list index out of range
```
I'm not sure why I split on `N... | non_process | get mane data raises indexerror file cool seq tool data sources mane transcript py line in copy df copy df apply lambda x int x split split nm noqa indexerror list index out of range i m not sure why i split on nm it should just be nm | 0 |
171,202 | 6,481,225,039 | IssuesEvent | 2017-08-18 15:07:14 | knowmetools/km-api | https://api.github.com/repos/knowmetools/km-api | closed | Site is inaccessible | Priority: Critical Status: In Progress Type: Bug | ### Bug Report
#### Expected Behavior
We expect the site to be accessible after a deployment.
#### Actual Behavior
Any connections to the site time out. This is caused by a few different issues.
1. We have `SECURE_SSl_REDIRECT` set to `True`, but our load balancer is not listening on port 443. This is th... | 1.0 | Site is inaccessible - ### Bug Report
#### Expected Behavior
We expect the site to be accessible after a deployment.
#### Actual Behavior
Any connections to the site time out. This is caused by a few different issues.
1. We have `SECURE_SSl_REDIRECT` set to `True`, but our load balancer is not listening ... | non_process | site is inaccessible bug report expected behavior we expect the site to be accessible after a deployment actual behavior any connections to the site time out this is caused by a few different issues we have secure ssl redirect set to true but our load balancer is not listening ... | 0 |
564,656 | 16,738,151,160 | IssuesEvent | 2021-06-11 06:18:32 | mchen162/it115-explore-california | https://api.github.com/repos/mchen162/it115-explore-california | opened | Tour Information Link Error | bug priority 4 severity 4 | **Describe the bug**
When clicking the Tour Information Link the user is given a 404 File not found error.
**To Reproduce**
Steps to reproduce the behavior:
1. Hover over Resources item at the navigation bar located at the top.
2. Click on "Tour Information"
4. See error
**Expected behavior**
A working Tour... | 1.0 | Tour Information Link Error - **Describe the bug**
When clicking the Tour Information Link the user is given a 404 File not found error.
**To Reproduce**
Steps to reproduce the behavior:
1. Hover over Resources item at the navigation bar located at the top.
2. Click on "Tour Information"
4. See error
**Expec... | non_process | tour information link error describe the bug when clicking the tour information link the user is given a file not found error to reproduce steps to reproduce the behavior hover over resources item at the navigation bar located at the top click on tour information see error expecte... | 0 |
11,988 | 14,737,168,371 | IssuesEvent | 2021-01-07 01:03:53 | kdjstudios/SABillingGitlab | https://api.github.com/repos/kdjstudios/SABillingGitlab | closed | 001- NCSM - Unable to upload | anc-ops anc-process anp-important anp-urgent ant-support has attachment | In GitLab by @kdjstudios on Apr 23, 2018, 09:14
**Submitted by:** "Jesus Corchado" <jesus.corchado@answernet.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/2018-04-20-73483/conversation
**Server:** Internal
**Client/Site:** Multiple
**Account:** NA
**Issue:**
I’m trying to process the b... | 1.0 | 001- NCSM - Unable to upload - In GitLab by @kdjstudios on Apr 23, 2018, 09:14
**Submitted by:** "Jesus Corchado" <jesus.corchado@answernet.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/2018-04-20-73483/conversation
**Server:** Internal
**Client/Site:** Multiple
**Account:** NA
**Issue:*... | process | ncsm unable to upload in gitlab by kdjstudios on apr submitted by jesus corchado helpdesk server internal client site multiple account na issue i’m trying to process the billing for the ncsm cycles on the sites but i keep getting an error i am using the ... | 1 |
54,965 | 11,355,192,556 | IssuesEvent | 2020-01-24 19:26:42 | stan-dev/math | https://api.github.com/repos/stan-dev/math | closed | There are some error-checking functions we can lift out of loops | code cleanup | ## Description
This:
```
for (i=...)
check_foo(...x[i]...);
```
can sometimes be replaced by:
```
check_foo(x)
```
and should be.
## Example
```
- for (size_t i = 0; i < ns.size(); ++i) {
- check_bounded(function, "element of outcome array", ns[i], lb,
- theta.size());
... | 1.0 | There are some error-checking functions we can lift out of loops - ## Description
This:
```
for (i=...)
check_foo(...x[i]...);
```
can sometimes be replaced by:
```
check_foo(x)
```
and should be.
## Example
```
- for (size_t i = 0; i < ns.size(); ++i) {
- check_bounded(function, "elemen... | non_process | there are some error checking functions we can lift out of loops description this for i check foo x can sometimes be replaced by check foo x and should be example for size t i i ns size i check bounded function element ... | 0 |
21,074 | 28,017,797,697 | IssuesEvent | 2023-03-28 01:08:23 | HaoNguyenNhat/CNPMNC | https://api.github.com/repos/HaoNguyenNhat/CNPMNC | opened | Đánh giá và phản hồi chất lượng | DG HUY NN HÀO 5 point IN PROCESS | Là khách hàng chính thức tôi muốn đánh giá và phản hồi về chất lượng dịch vụ trên website để giúp cửa hàng cải thiện | 1.0 | Đánh giá và phản hồi chất lượng - Là khách hàng chính thức tôi muốn đánh giá và phản hồi về chất lượng dịch vụ trên website để giúp cửa hàng cải thiện | process | đánh giá và phản hồi chất lượng là khách hàng chính thức tôi muốn đánh giá và phản hồi về chất lượng dịch vụ trên website để giúp cửa hàng cải thiện | 1 |
20,544 | 27,194,085,199 | IssuesEvent | 2023-02-20 02:36:57 | cse442-at-ub/project_s23-team-infinity | https://api.github.com/repos/cse442-at-ub/project_s23-team-infinity | opened | Settle the basic environment for React.js | Processing Task | 1. Install Node.js and NPM (Node Package Manager)
2. Create a basic app name 'my-app' by running 'npx create-react-app my-app' command in the terminal
3. Open the directory by running 'cd my-app' command
4. start the app by running 'npm start' command, default hosted at localhost:3000 | 1.0 | Settle the basic environment for React.js - 1. Install Node.js and NPM (Node Package Manager)
2. Create a basic app name 'my-app' by running 'npx create-react-app my-app' command in the terminal
3. Open the directory by running 'cd my-app' command
4. start the app by running 'npm start' command, default hosted at local... | process | settle the basic environment for react js install node js and npm node package manager create a basic app name my app by running npx create react app my app command in the terminal open the directory by running cd my app command start the app by running npm start command default hosted at local... | 1 |
610,200 | 18,900,547,880 | IssuesEvent | 2021-11-16 00:04:43 | googleapis/google-cloud-go | https://api.github.com/repos/googleapis/google-cloud-go | reopened | storage: TestIntegration_MultiChunkWriteGRPC failed | type: bug api: storage priority: p1 flakybot: issue flakybot: flaky | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: e33350cfcabcddcda1a90069383d39c68deb977a
b... | 1.0 | storage: TestIntegration_MultiChunkWriteGRPC failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
-... | non_process | storage testintegration multichunkwritegrpc failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output integration test go rpc error code ... | 0 |
453,595 | 13,085,208,603 | IssuesEvent | 2020-08-02 00:48:09 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | drivers: i2c_nios2: device config_info content mutated | Stale area: NIOS2 bug priority: low | The device config_info structure is intended to be read-only, and so
the generic pointer stored in struct device is a pointer-to-const.
The i2c_nios2 driver removes this qualifier when casting the pointer to
the device-specific type. This removal is a violation of MISRA 11.8
as it evokes undefined behavior.
Whe... | 1.0 | drivers: i2c_nios2: device config_info content mutated - The device config_info structure is intended to be read-only, and so
the generic pointer stored in struct device is a pointer-to-const.
The i2c_nios2 driver removes this qualifier when casting the pointer to
the device-specific type. This removal is a violati... | non_process | drivers device config info content mutated the device config info structure is intended to be read only and so the generic pointer stored in struct device is a pointer to const the driver removes this qualifier when casting the pointer to the device specific type this removal is a violation of misra ... | 0 |
12,797 | 15,180,672,570 | IssuesEvent | 2021-02-15 00:49:16 | Geonovum/disgeo-arch | https://api.github.com/repos/Geonovum/disgeo-arch | closed | 5.2.3.1 Afgeleide opslag | Flexibiliteit In Behandeling In behandeling - voorstel processen e.d. Processen Functies Componenten | Dit hoort niet bij opslag. Bij opslag moet benoemd worden, dat in verband met performance en/of beter nog disaster recovery het is toegestaan om een synchrone kopie van de data te hebben. Daarnaast kan het mogelijk zijn om aggregaties van informatie te maken tbv business intelligence oid.
We moeten naar meer data bi... | 2.0 | 5.2.3.1 Afgeleide opslag - Dit hoort niet bij opslag. Bij opslag moet benoemd worden, dat in verband met performance en/of beter nog disaster recovery het is toegestaan om een synchrone kopie van de data te hebben. Daarnaast kan het mogelijk zijn om aggregaties van informatie te maken tbv business intelligence oid.
... | process | afgeleide opslag dit hoort niet bij opslag bij opslag moet benoemd worden dat in verband met performance en of beter nog disaster recovery het is toegestaan om een synchrone kopie van de data te hebben daarnaast kan het mogelijk zijn om aggregaties van informatie te maken tbv business intelligence oid ... | 1 |
203,328 | 15,362,626,120 | IssuesEvent | 2021-03-01 19:44:16 | seattle-uat/universal-application-tool | https://api.github.com/repos/seattle-uat/universal-application-tool | closed | Refactor BrowserTest to have a superclass with common methods | testing | **Describe the solution you'd like**
We should have multiple browser tests for different parts of the system. They are likely to share methods (for example, a method to go to a specific page) - these methods should be in a superclass the other tests extend
**Additional context**
See PR comment on https://github.co... | 1.0 | Refactor BrowserTest to have a superclass with common methods - **Describe the solution you'd like**
We should have multiple browser tests for different parts of the system. They are likely to share methods (for example, a method to go to a specific page) - these methods should be in a superclass the other tests exten... | non_process | refactor browsertest to have a superclass with common methods describe the solution you d like we should have multiple browser tests for different parts of the system they are likely to share methods for example a method to go to a specific page these methods should be in a superclass the other tests exten... | 0 |
640,030 | 20,771,506,955 | IssuesEvent | 2022-03-16 05:34:13 | VolmitSoftware/Iris | https://api.github.com/repos/VolmitSoftware/Iris | closed | Iris Crashing | High Priority | ### Problem
1. Install Iris on 1.17.1 purpur
2. Teleport to a value like 12k and 10k
3. Render a few chunks
4. Server will crash with the error attached
### Solution
None
### Minecraft Version
1.17.1
### Iris Version
1.9.5
### Log
https://mclo.gs/PiIzMBv | 1.0 | Iris Crashing - ### Problem
1. Install Iris on 1.17.1 purpur
2. Teleport to a value like 12k and 10k
3. Render a few chunks
4. Server will crash with the error attached
### Solution
None
### Minecraft Version
1.17.1
### Iris Version
1.9.5
### Log
https://mclo.gs/PiIzMBv | non_process | iris crashing problem install iris on purpur teleport to a value like and render a few chunks server will crash with the error attached solution none minecraft version iris version log | 0 |
48,952 | 3,001,067,496 | IssuesEvent | 2015-07-24 08:37:31 | lua-carbon/carbon | https://api.github.com/repos/lua-carbon/carbon | opened | Generate instance IDs | difficulty:easy feature priority:high | It'd be great to have a running track of all objects by some sort of ID. | 1.0 | Generate instance IDs - It'd be great to have a running track of all objects by some sort of ID. | non_process | generate instance ids it d be great to have a running track of all objects by some sort of id | 0 |
18,103 | 24,127,930,512 | IssuesEvent | 2022-09-21 03:32:38 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | fail to merge rasters on macOS | Feedback stale Processing Bug | ### What is the bug or the crash?
When I was trying to merge 3 rasters, the GDAL command output:
**Process gdal_merge.py failed to start. Either gdal_merge.py is missing, or you may have insufficient permissions to run the program.**
The whole log is:
Processing algorithm…
Algorithm 'Merge' starting…
Input para... | 1.0 | fail to merge rasters on macOS - ### What is the bug or the crash?
When I was trying to merge 3 rasters, the GDAL command output:
**Process gdal_merge.py failed to start. Either gdal_merge.py is missing, or you may have insufficient permissions to run the program.**
The whole log is:
Processing algorithm…
Algori... | process | fail to merge rasters on macos what is the bug or the crash when i was trying to merge rasters the gdal command output process gdal merge py failed to start either gdal merge py is missing or you may have insufficient permissions to run the program the whole log is processing algorithm… algori... | 1 |
14,208 | 10,132,152,382 | IssuesEvent | 2019-08-01 21:29:35 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | IoT Device Provisioning Resource | new-resource service/iothub | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not l... | 1.0 | IoT Device Provisioning Resource - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers priorit... | non_process | iot device provisioning resource community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the ... | 0 |
3,283 | 2,754,188,590 | IssuesEvent | 2015-04-25 12:26:07 | willsALMANJ/Zutilo | https://api.github.com/repos/willsALMANJ/Zutilo | closed | Fix german translation of docs | documentation translation | This is just a reminder to fix the german translation of the docs, I (or someone) needs to finish at:
https://github.com/willsALMANJ/Zutilo/blob/master/chrome/locale/de/zutilo/README.html
todo:
* convert back to markdown without word wraps using pandoc -> document this in #20
* remove word wraps manually if n... | 1.0 | Fix german translation of docs - This is just a reminder to fix the german translation of the docs, I (or someone) needs to finish at:
https://github.com/willsALMANJ/Zutilo/blob/master/chrome/locale/de/zutilo/README.html
todo:
* convert back to markdown without word wraps using pandoc -> document this in #20
... | non_process | fix german translation of docs this is just a reminder to fix the german translation of the docs i or someone needs to finish at todo convert back to markdown without word wraps using pandoc document this in remove word wraps manually if necessary fix the translation from about the midd... | 0 |
21,528 | 29,810,657,454 | IssuesEvent | 2023-06-16 14:49:37 | googleapis/google-cloud-java | https://api.github.com/repos/googleapis/google-cloud-java | closed | Enable versions in titles of release PRs | type: process priority: p3 | Currently the release PRs for this repo have the title `chore: release main` (e.g. https://github.com/googleapis/google-cloud-java/pull/9427). It would be great if we could have the version number as well as if it is a snapshot version in the title so it's easier to tell what version is getting released instead of havi... | 1.0 | Enable versions in titles of release PRs - Currently the release PRs for this repo have the title `chore: release main` (e.g. https://github.com/googleapis/google-cloud-java/pull/9427). It would be great if we could have the version number as well as if it is a snapshot version in the title so it's easier to tell what ... | process | enable versions in titles of release prs currently the release prs for this repo have the title chore release main e g it would be great if we could have the version number as well as if it is a snapshot version in the title so it s easier to tell what version is getting released instead of having to click int... | 1 |
11,438 | 14,259,876,253 | IssuesEvent | 2020-11-20 09:00:03 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | annotations to defense response to fungus, incompatible interaction | multi-species process quick fix | There are 16 annotations from
Proteomics of the response of Arabidopsis thaliana to infection with Alternaria brassicicola.
Abstract
We have studied the proteome of the model plant Arabidopsis thaliana infected with a necrotrophic fungal pathogen, Alternaria brassicicola. The Arabidopsis-A. brassicicola host-pat... | 1.0 | annotations to defense response to fungus, incompatible interaction - There are 16 annotations from
Proteomics of the response of Arabidopsis thaliana to infection with Alternaria brassicicola.
Abstract
We have studied the proteome of the model plant Arabidopsis thaliana infected with a necrotrophic fungal path... | process | annotations to defense response to fungus incompatible interaction there are annotations from proteomics of the response of arabidopsis thaliana to infection with alternaria brassicicola abstract we have studied the proteome of the model plant arabidopsis thaliana infected with a necrotrophic fungal patho... | 1 |
6,706 | 9,815,575,684 | IssuesEvent | 2019-06-13 12:58:01 | linnovate/root | https://api.github.com/repos/linnovate/root | closed | in tasks and projects, "no select" option when selecting an assignee changes the status to assigned | 2.0.7 Fixed Process bug Projects Tasks | create a new task/ project
click on select assignee
click on "no select"
the status is changed to assigned
| 1.0 | in tasks and projects, "no select" option when selecting an assignee changes the status to assigned - create a new task/ project
click on select assignee
click on "no select"
the status is changed to assigned
.
arrest of cell cycle progression | exact
cessation of cell cycle | exact
termination of cell cycle | exact
This term is only for use with cell which are ... | 1.0 | GO:0007050 cell cycle arrest - GO:0007050 cell cycle arrest
Definition
A regulatory process that halts progression through the cell cycle during one of the normal phases (G1, S, G2, M).
arrest of cell cycle progression | exact
cessation of cell cycle | exact
termination of cell cycle | exact
This term is o... | process | go cell cycle arrest go cell cycle arrest definition a regulatory process that halts progression through the cell cycle during one of the normal phases s m arrest of cell cycle progression exact cessation of cell cycle exact termination of cell cycle exact this term is only for use wi... | 1 |
710,575 | 24,423,413,525 | IssuesEvent | 2022-10-05 22:57:47 | mikezimm/drilldown7 | https://api.github.com/repos/mikezimm/drilldown7 | closed | Only get list definitions when the prop pane is loaded | enhancement High Priority complete | ## See SecureScript7 for code to load on propPaneStart
Maybe try loading _getListDefinitions at time of opening prop pane.
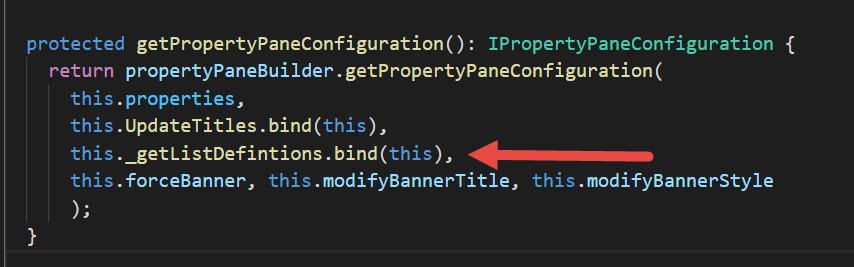
| 1.0 | Only get list definitions when the prop pane is loaded - ## See SecureScript7 for code to load on propPaneStart
Maybe try loading _getListDefinitions at time of opening prop pane.
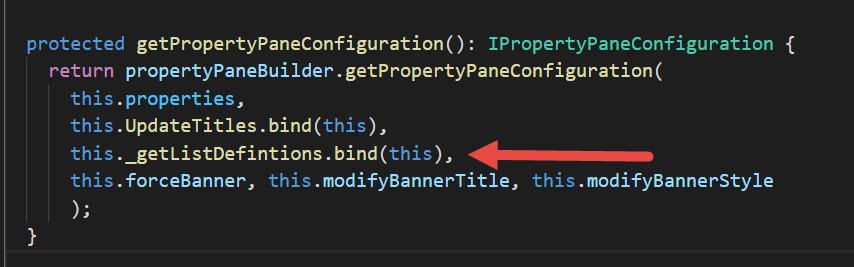
| non_process | only get list definitions when the prop pane is loaded see for code to load on proppanestart maybe try loading getlistdefinitions at time of opening prop pane | 0 |
21,984 | 30,482,266,287 | IssuesEvent | 2023-07-17 21:24:53 | bisq-network/proposals | https://api.github.com/repos/bisq-network/proposals | closed | Safely compensate traders requiring arbitration | was:approved a:proposal re:processes | ### Rationale
After #386, the arbitrator does not pay one security deposit for security reasons, as an evil burningman could take profit from creating self trades. This is bad for the traders, who need to wait a long time to be reimbursed, and get no compensation for the time spent and the inconveniences caused. The... | 1.0 | Safely compensate traders requiring arbitration - ### Rationale
After #386, the arbitrator does not pay one security deposit for security reasons, as an evil burningman could take profit from creating self trades. This is bad for the traders, who need to wait a long time to be reimbursed, and get no compensation for... | process | safely compensate traders requiring arbitration rationale after the arbitrator does not pay one security deposit for security reasons as an evil burningman could take profit from creating self trades this is bad for the traders who need to wait a long time to be reimbursed and get no compensation for t... | 1 |
540,884 | 15,818,961,580 | IssuesEvent | 2021-04-05 16:47:43 | dmwm/WMCore | https://api.github.com/repos/dmwm/WMCore | closed | Investigate PSet configuration upload to central CouchDB | CouchDB Medium Priority New Feature Python3 ToDo | **Impact of the new feature**
ReqMgr2 / CouchDB
**Is your feature request related to a problem? Please describe.**
Yes, it's related to the tightly coupling of WMCore, WMControl and CMSSW, and the complications affecting the support of multiple python versions and job configuration (Pset) upload to the WM system.
... | 1.0 | Investigate PSet configuration upload to central CouchDB - **Impact of the new feature**
ReqMgr2 / CouchDB
**Is your feature request related to a problem? Please describe.**
Yes, it's related to the tightly coupling of WMCore, WMControl and CMSSW, and the complications affecting the support of multiple python vers... | non_process | investigate pset configuration upload to central couchdb impact of the new feature couchdb is your feature request related to a problem please describe yes it s related to the tightly coupling of wmcore wmcontrol and cmssw and the complications affecting the support of multiple python versions a... | 0 |
771,231 | 27,075,857,307 | IssuesEvent | 2023-02-14 10:31:13 | sygmaprotocol/sygma-fee-oracle | https://api.github.com/repos/sygmaprotocol/sygma-fee-oracle | opened | Refactor conversion rate pairs property | Priority: P2 | <!--- Provide a general summary of the issue in the Title above -->
Currently, fee oracle requires us to define all possible conversion pairs manually. This, paired with the format of this configuration property, makes it really hard to maintain this in any real production environment.
It would be ideal for removing ... | 1.0 | Refactor conversion rate pairs property - <!--- Provide a general summary of the issue in the Title above -->
Currently, fee oracle requires us to define all possible conversion pairs manually. This, paired with the format of this configuration property, makes it really hard to maintain this in any real production envi... | non_process | refactor conversion rate pairs property currently fee oracle requires us to define all possible conversion pairs manually this paired with the format of this configuration property makes it really hard to maintain this in any real production environment it would be ideal for removing this as a configuration ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.