Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3
values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17
values | text_combine stringlengths 95 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
153,921 | 12,168,626,007 | IssuesEvent | 2020-04-27 12:59:37 | WoWManiaUK/Redemption | https://api.github.com/repos/WoWManiaUK/Redemption | closed | [NPC] Blood Prince Council - Crimson Hall doors | Fix - Ready to Test | **What is Happening:**
ones the raid in ICC kills 1st group of trash mobs on way Crimson Hall and the doors for room of Blood Prince Council open , players can enter room clear trash in it and engage Blood Prince Council to fight what will make doors to enter room close , how ever if the raid wipes on Blood Prince Co... | 1.0 | [NPC] Blood Prince Council - Crimson Hall doors - **What is Happening:**
ones the raid in ICC kills 1st group of trash mobs on way Crimson Hall and the doors for room of Blood Prince Council open , players can enter room clear trash in it and engage Blood Prince Council to fight what will make doors to enter room cl... | test | blood prince council crimson hall doors what is happening ones the raid in icc kills group of trash mobs on way crimson hall and the doors for room of blood prince council open players can enter room clear trash in it and engage blood prince council to fight what will make doors to enter room close ... | 1 |
79,460 | 7,716,456,444 | IssuesEvent | 2018-05-23 10:44:20 | Caphyon/clang-power-tools | https://api.github.com/repos/Caphyon/clang-power-tools | closed | Use Pester for PowerShell unit tests | in progress test | [Pester](https://github.com/pester/Pester) is de-facto standard unit test framework for writing PowerShell unit tests.
[msbuild_translation_tests.ps1](../blob/master/ClangPowerTools/ClangPowerTools/msbuild_translation_tests.ps1) should be rewritten with the help of this framework. | 1.0 | Use Pester for PowerShell unit tests - [Pester](https://github.com/pester/Pester) is de-facto standard unit test framework for writing PowerShell unit tests.
[msbuild_translation_tests.ps1](../blob/master/ClangPowerTools/ClangPowerTools/msbuild_translation_tests.ps1) should be rewritten with the help of this framewo... | test | use pester for powershell unit tests is de facto standard unit test framework for writing powershell unit tests blob master clangpowertools clangpowertools msbuild translation tests should be rewritten with the help of this framework | 1 |
58,354 | 14,271,303,946 | IssuesEvent | 2020-11-21 11:48:20 | LibreHealthIO/lh-ehr | https://api.github.com/repos/LibreHealthIO/lh-ehr | reopened | A lot of vulnerabilities in OpenEMR disclosed | Web Security | I found a report with [a decently sized list of vulnerabilities in OpenEMR](https://github.com/zeropwn/vulnerability-reports-and-pocs/blob/master/OpenEMR%20-%20Vulnerability%20Report.pdf) published on May 1<sup>st</sup> of this year.
Not sure if these exist in our code, but we should check.
| True | A lot of vulnerabilities in OpenEMR disclosed - I found a report with [a decently sized list of vulnerabilities in OpenEMR](https://github.com/zeropwn/vulnerability-reports-and-pocs/blob/master/OpenEMR%20-%20Vulnerability%20Report.pdf) published on May 1<sup>st</sup> of this year.
Not sure if these exist in our cod... | non_test | a lot of vulnerabilities in openemr disclosed i found a report with published on may st of this year not sure if these exist in our code but we should check | 0 |
46,919 | 13,056,002,298 | IssuesEvent | 2020-07-30 03:21:31 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | [phys-services] Delete I3TRandom (Trac #2137) | Incomplete Migration Migrated from Trac combo core defect | Migrated from https://code.icecube.wisc.edu/ticket/2137
```json
{
"status": "closed",
"changetime": "2019-02-13T14:14:43",
"description": "nobody uses it",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1550067283824229",
"component": "combo core",
"summary... | 1.0 | [phys-services] Delete I3TRandom (Trac #2137) - Migrated from https://code.icecube.wisc.edu/ticket/2137
```json
{
"status": "closed",
"changetime": "2019-02-13T14:14:43",
"description": "nobody uses it",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1550067283824229... | non_test | delete trac migrated from json status closed changetime description nobody uses it reporter kjmeagher cc resolution fixed ts component combo core summary delete priority normal ... | 0 |
176,324 | 13,636,121,746 | IssuesEvent | 2020-09-25 04:58:08 | jakeegan/Blink-Controlled-Speech-Synthesizer | https://api.github.com/repos/jakeegan/Blink-Controlled-Speech-Synthesizer | opened | Test word predictor | Test | Test word predictor on a testing dataset and report accuracy, recall, and precision. | 1.0 | Test word predictor - Test word predictor on a testing dataset and report accuracy, recall, and precision. | test | test word predictor test word predictor on a testing dataset and report accuracy recall and precision | 1 |
268,907 | 28,932,260,479 | IssuesEvent | 2023-05-09 01:06:49 | developerone12/WebGoat-WhiteSource-Bolt | https://api.github.com/repos/developerone12/WebGoat-WhiteSource-Bolt | opened | CVE-2022-25869 (Medium) detected in angular-1.2.16.js, angular-1.2.16.min.js | Mend: dependency security vulnerability | ## CVE-2022-25869 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>angular-1.2.16.js</b>, <b>angular-1.2.16.min.js</b></p></summary>
<p>
<details><summary><b>angular-1.2.16.js</b></... | True | CVE-2022-25869 (Medium) detected in angular-1.2.16.js, angular-1.2.16.min.js - ## CVE-2022-25869 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>angular-1.2.16.js</b>, <b>angular-1.... | non_test | cve medium detected in angular js angular min js cve medium severity vulnerability vulnerable libraries angular js angular min js angular js angularjs is an mvc framework for building web applications the core features include html enhanced with c... | 0 |
184,679 | 14,289,809,779 | IssuesEvent | 2020-11-23 19:51:47 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | blugelabs/bluge: search/searcher/search_match_all_test.go; 34 LoC | fresh small test |
Found a possible issue in [blugelabs/bluge](https://www.github.com/blugelabs/bluge) at [search/searcher/search_match_all_test.go](https://github.com/blugelabs/bluge/blob/c304a6733af6b14a0e57acb8085f7e88bae98560/search/searcher/search_match_all_test.go#L95-L128)
The below snippet of Go code triggered static analysis w... | 1.0 | blugelabs/bluge: search/searcher/search_match_all_test.go; 34 LoC -
Found a possible issue in [blugelabs/bluge](https://www.github.com/blugelabs/bluge) at [search/searcher/search_match_all_test.go](https://github.com/blugelabs/bluge/blob/c304a6733af6b14a0e57acb8085f7e88bae98560/search/searcher/search_match_all_test.go... | test | blugelabs bluge search searcher search match all test go loc found a possible issue in at the below snippet of go code triggered static analysis which searches for goroutines and or defer statements which capture loop variables click here to show the line s of go which triggered the analyze... | 1 |
413,322 | 12,065,004,892 | IssuesEvent | 2020-04-16 09:14:38 | ShortTechDE/ingenious | https://api.github.com/repos/ShortTechDE/ingenious | opened | Infinite infinite scrolling when link is not plain | bug priority | An example would be [shorttech.de/#](https://shorttech.de/#). Could be solved with Regex etc. | 1.0 | Infinite infinite scrolling when link is not plain - An example would be [shorttech.de/#](https://shorttech.de/#). Could be solved with Regex etc. | non_test | infinite infinite scrolling when link is not plain an example would be could be solved with regex etc | 0 |
487,296 | 14,021,814,805 | IssuesEvent | 2020-10-29 21:58:38 | Pemigrade/Acorn | https://api.github.com/repos/Pemigrade/Acorn | closed | Display mute reasons to players who are muted | Feature Request High Priority | **Brief Description**
<!-- A clear and concise description of what you want to happen. -->
Players should be given the permission node that allows them to see when they are muted, and why.
**Why do you want the feature?**
<!-- The reasons why you want to see the feature implemented. -->
A lot of the time when some... | 1.0 | Display mute reasons to players who are muted - **Brief Description**
<!-- A clear and concise description of what you want to happen. -->
Players should be given the permission node that allows them to see when they are muted, and why.
**Why do you want the feature?**
<!-- The reasons why you want to see the featu... | non_test | display mute reasons to players who are muted brief description players should be given the permission node that allows them to see when they are muted and why why do you want the feature a lot of the time when some players are muted they are confused and ask a staff member to explain for them wh... | 0 |
301,883 | 26,107,229,187 | IssuesEvent | 2022-12-27 14:43:24 | status-im/status-mobile | https://api.github.com/repos/status-im/status-mobile | opened | No aceessibility label on mention suggest list | e2e test blocker | # Bug Report
## Problem
No way to locate a particular element
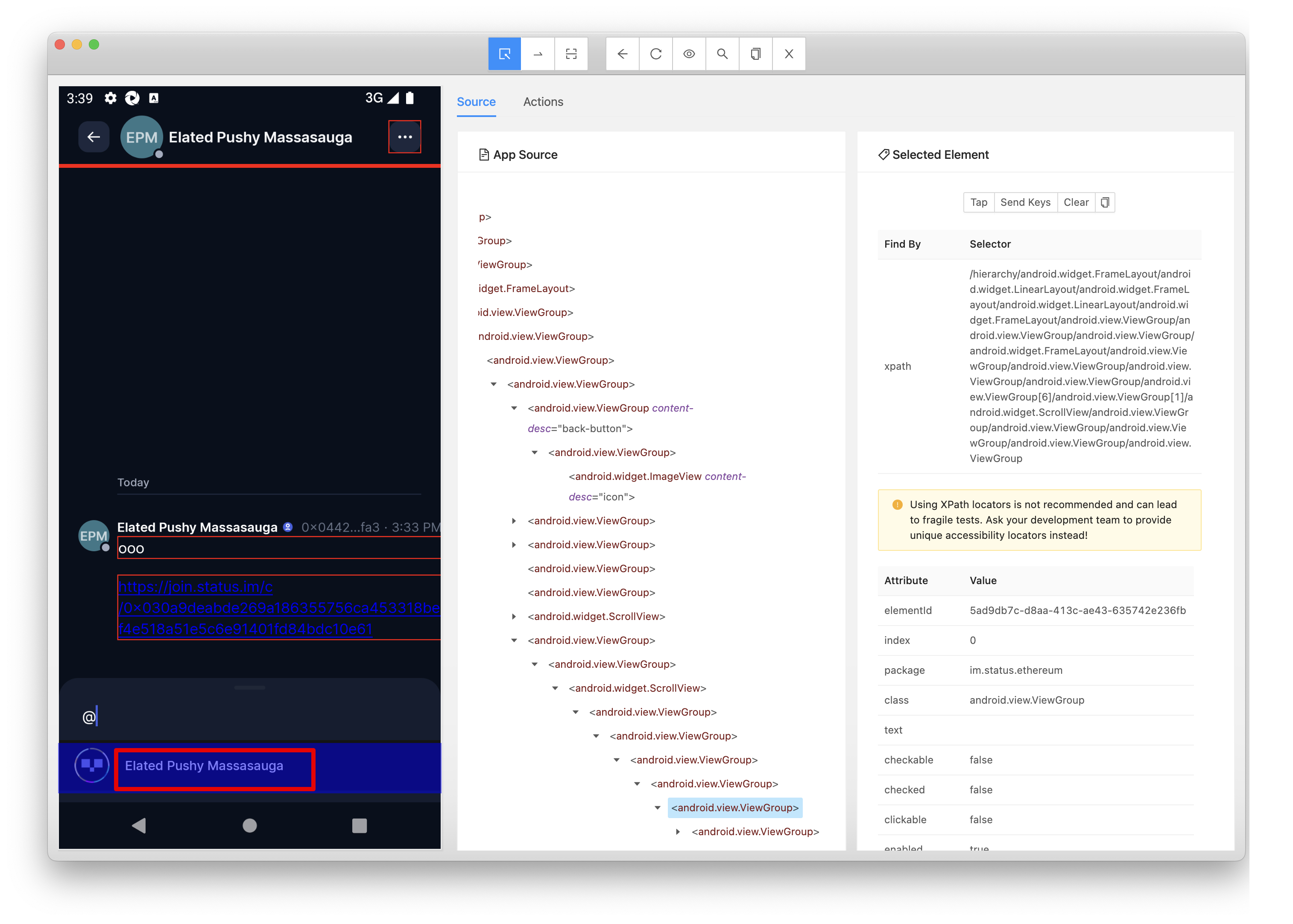
On UI 1.20 it was the part of //*[@content-desc='suggestions-list']
## Acceptance criteria
accessibility id for ... | 1.0 | No aceessibility label on mention suggest list - # Bug Report
## Problem
No way to locate a particular element
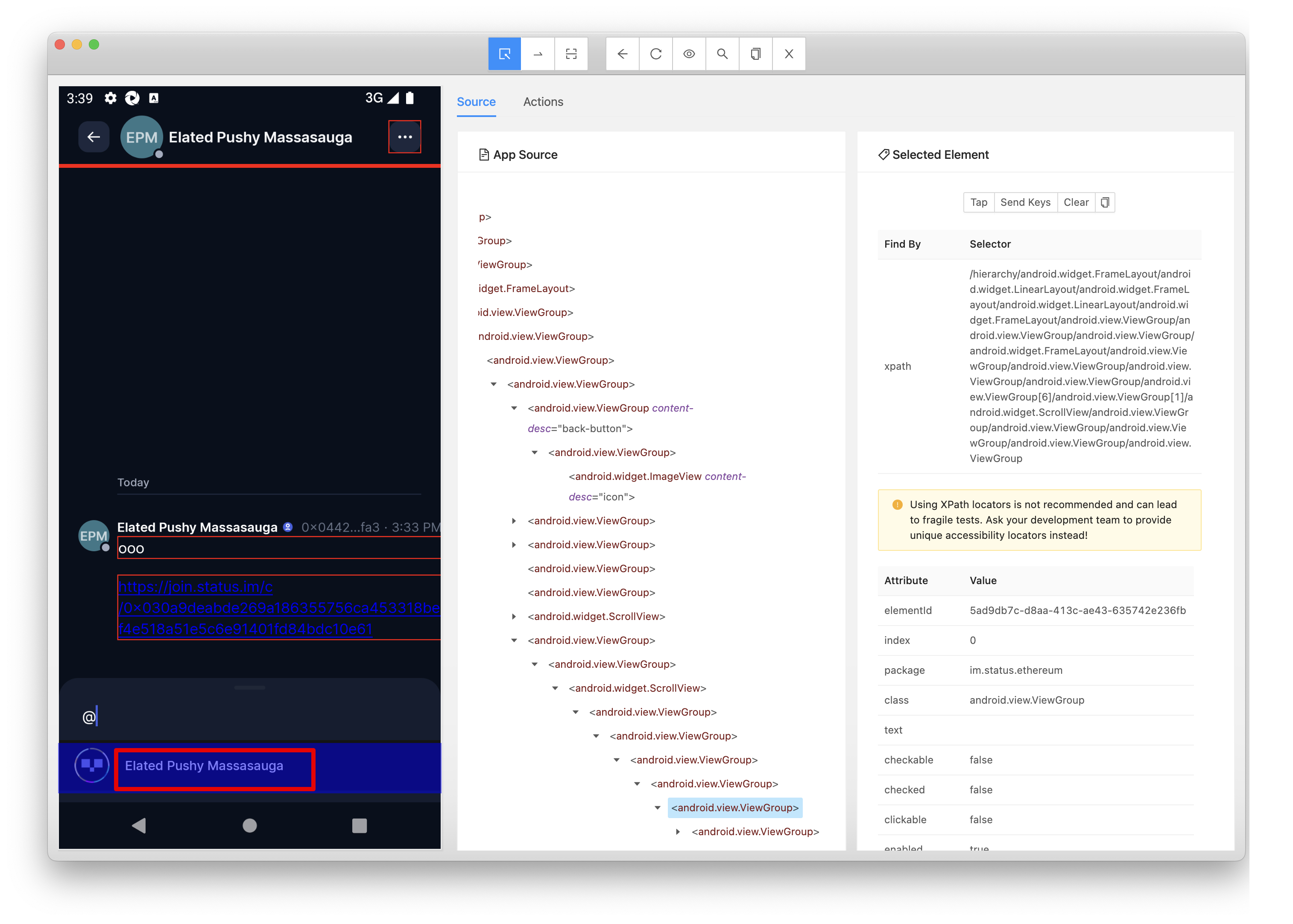
On UI 1.20 it was the part of //*[@content-desc='suggestions-list']... | test | no aceessibility label on mention suggest list bug report problem no way to locate a particular element on ui it was the part of acceptance criteria accessibility id for suggestion list in input field | 1 |
195,806 | 6,918,578,178 | IssuesEvent | 2017-11-29 12:44:40 | htpcBeginner/AtoMiC-ToolKit | https://api.github.com/repos/htpcBeginner/AtoMiC-ToolKit | closed | Feature Request - OpenVPN | Enhancement Priority: Low | Hi!
I'd like to respectfully request an OpenVPN feature that ties into whatever VPN provider we use - perhaps PIA initially for simplicity. It'd be even cooler if this somehow tied into whatever torrent client we use so that P2P traffic could be encrypted. Thanks!
**** UPDATE From Tom ****
- [X] Added [OpenVPN]... | 1.0 | Feature Request - OpenVPN - Hi!
I'd like to respectfully request an OpenVPN feature that ties into whatever VPN provider we use - perhaps PIA initially for simplicity. It'd be even cooler if this somehow tied into whatever torrent client we use so that P2P traffic could be encrypted. Thanks!
**** UPDATE From Tom... | non_test | feature request openvpn hi i d like to respectfully request an openvpn feature that ties into whatever vpn provider we use perhaps pia initially for simplicity it d be even cooler if this somehow tied into whatever torrent client we use so that traffic could be encrypted thanks update from tom ... | 0 |
537 | 2,511,426,086 | IssuesEvent | 2015-01-14 07:36:32 | OpenConext/OpenConext-dashboard | https://api.github.com/repos/OpenConext/OpenConext-dashboard | closed | Design tweaks | Design | User feedback reveals some design tweaks:
- Recently used filter is unclear -> Used in last 3 months / Never used is better
- Dropdown list of ISPs is unclear
- Line height can be less to accommodate more content on the apps overview page
- Label 'Added' is unclear. -> Application added to SURFconext (or better)
... | 1.0 | Design tweaks - User feedback reveals some design tweaks:
- Recently used filter is unclear -> Used in last 3 months / Never used is better
- Dropdown list of ISPs is unclear
- Line height can be less to accommodate more content on the apps overview page
- Label 'Added' is unclear. -> Application added to SURFcone... | non_test | design tweaks user feedback reveals some design tweaks recently used filter is unclear used in last months never used is better dropdown list of isps is unclear line height can be less to accommodate more content on the apps overview page label added is unclear application added to surfcone... | 0 |
216,628 | 16,777,665,807 | IssuesEvent | 2021-06-15 00:43:46 | quarkusio/quarkus | https://api.github.com/repos/quarkusio/quarkus | closed | quarkus:dev displays exception (warning) for @Disabled tests | area/continuous-testing kind/bug | ## Describe the bug
The current version `2.0.0.CR3` of `quarkus:dev` displays warnings with exception stacktraces for tests classes that are annotated with `@Disabled`.
## To reproduce
- Have the following test:
```java
@Disabled
public class CoffeeIT {
@Test
void testHello() {
// ...
... | 1.0 | quarkus:dev displays exception (warning) for @Disabled tests - ## Describe the bug
The current version `2.0.0.CR3` of `quarkus:dev` displays warnings with exception stacktraces for tests classes that are annotated with `@Disabled`.
## To reproduce
- Have the following test:
```java
@Disabled
public class Co... | test | quarkus dev displays exception warning for disabled tests describe the bug the current version of quarkus dev displays warnings with exception stacktraces for tests classes that are annotated with disabled to reproduce have the following test java disabled public class coff... | 1 |
250,876 | 21,367,444,042 | IssuesEvent | 2022-04-20 04:21:55 | Uuvana-Studios/longvinter-windows-client | https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client | closed | Electricity Bug | Bug Not Tested | **Describe the bug**
Despite fully upgrading house and having a total of 80 energy and allowing 3 turrets. The electricity amount always changes back down to 60 and deactivating a turret as a result.
**Screenshot**
`
- The struct fields links don't know the path to the struct's page, and are linking to `.html` | 1.0 | Subdoc Bugs exposed by libjxl - # https://old.lucaversari.it/jpeg_xl_data/docs/JxlColorProfile.html
- Here there's a data member `icc` whose type is `::(unnamed struct at /fast-data/libjxl/lib/include/jxl/cms_interface.h:47:3)`
- The struct fields links don't know the path to the struct's page, and are linking to `... | non_test | subdoc bugs exposed by libjxl here there s a data member icc whose type is unnamed struct at fast data libjxl lib include jxl cms interface h the struct fields links don t know the path to the struct s page and are linking to html | 0 |
7,792 | 3,606,214,736 | IssuesEvent | 2016-02-04 10:14:45 | hpi-swt2/wimi-portal | https://api.github.com/repos/hpi-swt2/wimi-portal | closed | Stundenzettel | bug Priorität 1 ready-for-code-review | **Aktuell**
1. Wenn ich als Nutzer den Link auf einen Stundenzettel habe, so kann ich diesen einreichen, obwohl es nicht mein eigener ist.
2. Es gibt zwei unterschiedliche Stundenzettel Seiten
3. Fremde Nutzer können meine Stundenzettel sehen
4. Als FG-Beauftragter gibt es eine Auflistung der Hiwis unter 'Research ... | 1.0 | Stundenzettel - **Aktuell**
1. Wenn ich als Nutzer den Link auf einen Stundenzettel habe, so kann ich diesen einreichen, obwohl es nicht mein eigener ist.
2. Es gibt zwei unterschiedliche Stundenzettel Seiten
3. Fremde Nutzer können meine Stundenzettel sehen
4. Als FG-Beauftragter gibt es eine Auflistung der Hiwis ... | non_test | stundenzettel aktuell wenn ich als nutzer den link auf einen stundenzettel habe so kann ich diesen einreichen obwohl es nicht mein eigener ist es gibt zwei unterschiedliche stundenzettel seiten fremde nutzer können meine stundenzettel sehen als fg beauftragter gibt es eine auflistung der hiwis ... | 0 |
78,423 | 7,641,200,173 | IssuesEvent | 2018-05-08 03:19:14 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Normalize Test Logging | Azure PS Team Engineering Test Tsar | ### Description
Normalize test logging across scenario and unit tests to:
- [ ] Use a consistent logging mechanism across xunit tests
- [ ] Write logs to a separate file per test
- [ ] Do not retain logs for tests that pass
- [ ] Ensure that logs contain full debug messages
### Cost: 8
| 1.0 | Normalize Test Logging - ### Description
Normalize test logging across scenario and unit tests to:
- [ ] Use a consistent logging mechanism across xunit tests
- [ ] Write logs to a separate file per test
- [ ] Do not retain logs for tests that pass
- [ ] Ensure that logs contain full debug messages
### Cost... | test | normalize test logging description normalize test logging across scenario and unit tests to use a consistent logging mechanism across xunit tests write logs to a separate file per test do not retain logs for tests that pass ensure that logs contain full debug messages cost | 1 |
43,007 | 17,388,412,767 | IssuesEvent | 2021-08-02 01:44:07 | Azure/azure-libraries-for-java | https://api.github.com/repos/Azure/azure-libraries-for-java | closed | Add VM extension fails as additional PATCH request sent and VM purchase plan cannot be updated | ARM Mgmt Service Attention | I followed the sample to add a VM extension but this fails with my set up. The reason is reported as failure to update purchase plan. On inspection is appears that a PATCH is sent to update the VM, before the add extension API call. As the PATCH on the VM fails the VM extension call never gets processed.
If howev... | 1.0 | Add VM extension fails as additional PATCH request sent and VM purchase plan cannot be updated - I followed the sample to add a VM extension but this fails with my set up. The reason is reported as failure to update purchase plan. On inspection is appears that a PATCH is sent to update the VM, before the add extensio... | non_test | add vm extension fails as additional patch request sent and vm purchase plan cannot be updated i followed the sample to add a vm extension but this fails with my set up the reason is reported as failure to update purchase plan on inspection is appears that a patch is sent to update the vm before the add extensio... | 0 |
50,150 | 6,062,207,110 | IssuesEvent | 2017-06-14 08:51:47 | mattbearman/lime | https://api.github.com/repos/mattbearman/lime | opened | test | question test | ## [View in BugMuncher Control Panel](https://app.bugmuncher.com/websites/a53d1139bceee3b3730c237aff8217d824ad1ccc/feedback/990b6796b1670dde25216fef582f1425c20f1d7b) ##
## Details ##
**Submitted:** June 14, 2017 08:51
**Category:** Question
**Sender Email:**
**Website:** BugMuncher
**URL:** https://www.bugmuncher... | 1.0 | test - ## [View in BugMuncher Control Panel](https://app.bugmuncher.com/websites/a53d1139bceee3b3730c237aff8217d824ad1ccc/feedback/990b6796b1670dde25216fef582f1425c20f1d7b) ##
## Details ##
**Submitted:** June 14, 2017 08:51
**Category:** Question
**Sender Email:**
**Website:** BugMuncher
**URL:** https://www.bug... | test | test details submitted june category question sender email website bugmuncher url operating system linux browser firefox browser size x user agent mozilla ubuntu linux rv gecko firefox description ... | 1 |
323,627 | 27,741,238,394 | IssuesEvent | 2023-03-15 14:25:10 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | modification of max char length in Client Server columnt - IPv6 address length cut and replaced with … - for better search possibility | Ready to Test | We suggest the possibility of changing the width of the Client or Server column width to accommodate the length of IPv6 addresses. So they don't get cut and are searchable by browser search function.

| 1.0 | modification of max char length in Client Server columnt - IPv6 address length cut and replaced with … - for better search possibility - We suggest the possibility of changing the width of the Client or Server column width to accommodate the length of IPv6 addresses. So they don't get cut and are searchable by browser ... | test | modification of max char length in client server columnt address length cut and replaced with … for better search possibility we suggest the possibility of changing the width of the client or server column width to accommodate the length of addresses so they don t get cut and are searchable by browser search... | 1 |
224,234 | 17,673,411,210 | IssuesEvent | 2021-08-23 09:16:53 | jac-uk/admin | https://api.github.com/repos/jac-uk/admin | closed | 'About the role' html editor exposes site to XSS | enhancement Pen Test | Pen test result:
"It is also possible to store javascript (stored xss) on the job listiing page by using the javascript URL handler. See the following page and click on the click me : https://apply-staging.judicialappointments.digital/vacancy/WmISjsHC7bokFK5qupsC/" | 1.0 | 'About the role' html editor exposes site to XSS - Pen test result:
"It is also possible to store javascript (stored xss) on the job listiing page by using the javascript URL handler. See the following page and click on the click me : https://apply-staging.judicialappointments.digital/vacancy/WmISjsHC7bokFK5qupsC/" | test | about the role html editor exposes site to xss pen test result it is also possible to store javascript stored xss on the job listiing page by using the javascript url handler see the following page and click on the click me | 1 |
205,458 | 15,615,433,489 | IssuesEvent | 2021-03-19 19:11:20 | ThatGuySam/doesitarm | https://api.github.com/repos/ThatGuySam/doesitarm | closed | QGIS, Needs M1 Testing | Needs M1 Testing Needs Reported Status New App Request |
**The official name of the app**
QGIS
**Is there a supported build available on a public/release channel?**
Yes
**Proposed App Status**
Unknown
**Proposed App Category**
Geospatial mapping
**Related Issue Tracker Link or discussion**
https://www.reddit.com/r/QGIS/comments/hgsfv1/qgis_for_apple_si... | 1.0 | QGIS, Needs M1 Testing -
**The official name of the app**
QGIS
**Is there a supported build available on a public/release channel?**
Yes
**Proposed App Status**
Unknown
**Proposed App Category**
Geospatial mapping
**Related Issue Tracker Link or discussion**
https://www.reddit.com/r/QGIS/comments... | test | qgis needs testing the official name of the app qgis is there a supported build available on a public release channel yes proposed app status unknown proposed app category geospatial mapping related issue tracker link or discussion an official app download link ... | 1 |
104,587 | 8,982,863,572 | IssuesEvent | 2019-01-31 04:12:53 | danleyb2/helpdesk | https://api.github.com/repos/danleyb2/helpdesk | opened | property creation and support email configuration | testing | testing / bug fixing of
- [ ] Creation of Properties
- [ ] Support Email Configuration and Editing | 1.0 | property creation and support email configuration - testing / bug fixing of
- [ ] Creation of Properties
- [ ] Support Email Configuration and Editing | test | property creation and support email configuration testing bug fixing of creation of properties support email configuration and editing | 1 |
49,556 | 13,454,367,221 | IssuesEvent | 2020-09-09 03:30:47 | ErezDasa/RB2 | https://api.github.com/repos/ErezDasa/RB2 | opened | CVE-2020-5405 (Medium) detected in spring-cloud-config-client-2.0.1.RELEASE.jar | security vulnerability | ## CVE-2020-5405 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-cloud-config-client-2.0.1.RELEASE.jar</b></p></summary>
<p>This project is a Spring configuration client.</p>
... | True | CVE-2020-5405 (Medium) detected in spring-cloud-config-client-2.0.1.RELEASE.jar - ## CVE-2020-5405 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-cloud-config-client-2.0.1.REL... | non_test | cve medium detected in spring cloud config client release jar cve medium severity vulnerability vulnerable library spring cloud config client release jar this project is a spring configuration client library home page a href path to dependency file tmp ws scm infra ... | 0 |
162,363 | 12,652,753,338 | IssuesEvent | 2020-06-17 04:38:17 | ansible/awx | https://api.github.com/repos/ansible/awx | closed | Unable to Sync Inventory Source - Ansible Tower | component:api priority:high state:needs_test type:bug | ##### ISSUE TYPE
- Bug Report
##### SUMMARY
An inventory configured with inventory source Ansible Tower is unable to sync
##### ENVIRONMENT
* AWX version: 11.2.0
* AWX install method: docker on linux
* Ansible version: 2.9.9
* Operating System: RHEL7
* Web Browser: Chrome
##### STEPS TO REPRODUCE
N... | 1.0 | Unable to Sync Inventory Source - Ansible Tower - ##### ISSUE TYPE
- Bug Report
##### SUMMARY
An inventory configured with inventory source Ansible Tower is unable to sync
##### ENVIRONMENT
* AWX version: 11.2.0
* AWX install method: docker on linux
* Ansible version: 2.9.9
* Operating System: RHEL7
* We... | test | unable to sync inventory source ansible tower issue type bug report summary an inventory configured with inventory source ansible tower is unable to sync environment awx version awx install method docker on linux ansible version operating system web bro... | 1 |
66,629 | 7,008,869,222 | IssuesEvent | 2017-12-19 17:01:50 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] TruncateTranslogIT#testCorruptTranslogTruncation fails | :Translog jenkins test | https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.x+multijob-darwin-compatibility/365/console.
```
TruncateTranslogIT.testCorruptTranslogTruncation <<< FAILURES!
> Throwable #1: java.lang.AssertionError: all shards should be failed due to a corrupted translog
> at __randomizedtesting.SeedInf... | 1.0 | [CI] TruncateTranslogIT#testCorruptTranslogTruncation fails - https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.x+multijob-darwin-compatibility/365/console.
```
TruncateTranslogIT.testCorruptTranslogTruncation <<< FAILURES!
> Throwable #1: java.lang.AssertionError: all shards should be failed due... | test | truncatetranslogit testcorrupttranslogtruncation fails truncatetranslogit testcorrupttranslogtruncation failures throwable java lang assertionerror all shards should be failed due to a corrupted translog at randomizedtesting seedinfo seed at org elasticsearch index tr... | 1 |
131,008 | 10,678,140,330 | IssuesEvent | 2019-10-21 16:41:24 | kubernetes/sig-release | https://api.github.com/repos/kubernetes/sig-release | closed | Implement release blocking job criteria | priority/important-longterm sig/release sig/testing | This is an umbrella issue for followup work to https://github.com/kubernetes/sig-release/pull/346
That PR describes aspirational release blocking job criteria. This issue is intended to track the followup work, including:
- ~assignment of owners to all jobs~
- ~descriptions added to all release-master-blocking jo... | 1.0 | Implement release blocking job criteria - This is an umbrella issue for followup work to https://github.com/kubernetes/sig-release/pull/346
That PR describes aspirational release blocking job criteria. This issue is intended to track the followup work, including:
- ~assignment of owners to all jobs~
- ~descriptio... | test | implement release blocking job criteria this is an umbrella issue for followup work to that pr describes aspirational release blocking job criteria this issue is intended to track the followup work including assignment of owners to all jobs descriptions added to all release master blocking jobs ... | 1 |
302,345 | 26,139,958,532 | IssuesEvent | 2022-12-29 16:57:39 | w3c/csswg-drafts | https://api.github.com/repos/w3c/csswg-drafts | closed | [css-pseudo] ::first-line and line-height | css-inline-3 css-pseudo-4 Closed Accepted by CSSWG Resolution Needs Testcase (WPT) | Specs: https://www.w3.org/TR/css-pseudo-4/#first-line-pseudo
The part of the specs related to the issue raised:
```
The ::first-line pseudo-element’s generated box behaves similar to that of an inline-level element, but with certain restrictions. The following CSS properties apply to a ::first-line pseudo-elemen... | 1.0 | [css-pseudo] ::first-line and line-height - Specs: https://www.w3.org/TR/css-pseudo-4/#first-line-pseudo
The part of the specs related to the issue raised:
```
The ::first-line pseudo-element’s generated box behaves similar to that of an inline-level element, but with certain restrictions. The following CSS prop... | test | first line and line height specs the part of the specs related to the issue raised the first line pseudo element’s generated box behaves similar to that of an inline level element but with certain restrictions the following css properties apply to a first line pseudo element all font pr... | 1 |
82,699 | 10,270,721,819 | IssuesEvent | 2019-08-23 12:25:37 | Automattic/wp-calypso | https://api.github.com/repos/Automattic/wp-calypso | opened | Importer: Handle longer author names better | Design Import Site Importer [Type] Enhancement | We should find a better way to display super long author names like the one below:
<img width="784" alt="Screenshot 2019-08-23 at 17 49 46" src="https://user-images.githubusercontent.com/18581859/63592380-199afa80-c5cf-11e9-8ab6-7e1ea31ce7dd.png">
<img width="747" alt="Screenshot 2019-08-23 at 17 53 00" src="https:... | 1.0 | Importer: Handle longer author names better - We should find a better way to display super long author names like the one below:
<img width="784" alt="Screenshot 2019-08-23 at 17 49 46" src="https://user-images.githubusercontent.com/18581859/63592380-199afa80-c5cf-11e9-8ab6-7e1ea31ce7dd.png">
<img width="747" alt="... | non_test | importer handle longer author names better we should find a better way to display super long author names like the one below img width alt screenshot at src img width alt screenshot at src noticed when reporting | 0 |
156,239 | 12,302,281,375 | IssuesEvent | 2020-05-11 16:42:57 | MathiasMen/FreeFit | https://api.github.com/repos/MathiasMen/FreeFit | closed | ExerciseEditor: Create test to verify deletion of Exercise works | Testing | Extend `ExerciseEditorValidator`. | 1.0 | ExerciseEditor: Create test to verify deletion of Exercise works - Extend `ExerciseEditorValidator`. | test | exerciseeditor create test to verify deletion of exercise works extend exerciseeditorvalidator | 1 |
144,536 | 11,623,382,907 | IssuesEvent | 2020-02-27 08:50:39 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: X-Pack Saved Object API Integration Tests -- security_and_spaces.x-pack/test/saved_object_api_integration/security_and_spaces/apis/find·ts - saved objects security and spaces enabled find user with no access within the space_1 space "after all" hook for "finding a hiddentype should return 403 with forbidd... | failed-test | A test failed on a tracked branch
```
Error: [GET http://elastic:changeme@localhost:6151/api/status] request failed (attempt=5/5) -- and ran out of retries
at KbnClientRequester.request (/dev/shm/workspace/kibana/packages/kbn-dev-utils/target/kbn_client/kbn_client_requester.js:99:23)
at process._tickCallback (... | 1.0 | Failing test: X-Pack Saved Object API Integration Tests -- security_and_spaces.x-pack/test/saved_object_api_integration/security_and_spaces/apis/find·ts - saved objects security and spaces enabled find user with no access within the space_1 space "after all" hook for "finding a hiddentype should return 403 with forbidd... | test | failing test x pack saved object api integration tests security and spaces x pack test saved object api integration security and spaces apis find·ts saved objects security and spaces enabled find user with no access within the space space after all hook for finding a hiddentype should return with forbidden... | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.