Unnamed: 0 int64 3 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 2 742 | labels stringlengths 4 431 | body stringlengths 5 239k | index stringclasses 10 values | text_combine stringlengths 96 240k | label stringclasses 2 values | text stringlengths 96 200k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
317,395 | 27,235,328,142 | IssuesEvent | 2023-02-21 15:56:18 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: sysbench/oltp_update_index/nodes=3/cpu=32/conc=256 failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.sysbench/oltp_update_index/nodes=3/cpu=32/conc=256 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8772032?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8772032?buildTab=artifacts#/sysbench/oltp_update_index/nodes=3/cpu=32/conc=256) on master @ [dd2749ae4ab61eed2f99238acb74e8d3c6b4cb1d](https://github.com/cockroachdb/cockroach/commits/dd2749ae4ab61eed2f99238acb74e8d3c6b4cb1d):
```
test artifacts and logs in: /artifacts/sysbench/oltp_update_index/nodes=3/cpu=32/conc=256/run_1
(cluster.go:1956).Run: output in run_155040.686266349_n4_sysbench-dbdriverpgs: sysbench \
--db-driver=pgsql \
--pgsql-host={pghost:1} \
--pgsql-port=26257 \
--pgsql-user=root \
--pgsql-password= \
--pgsql-db=sysbench \
--report-interval=1 \
--time=600 \
--threads=256 \
--tables=10 \
--table_size=10000000 \
--auto_inc=false \
oltp_update_index prepare returned: context canceled
(monitor.go:127).Wait: monitor failure: monitor command failure: unexpected node event: 3: dead (exit status 7)
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=32</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/test-eng
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sysbench/oltp_update_index/nodes=3/cpu=32/conc=256.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: sysbench/oltp_update_index/nodes=3/cpu=32/conc=256 failed - roachtest.sysbench/oltp_update_index/nodes=3/cpu=32/conc=256 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8772032?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8772032?buildTab=artifacts#/sysbench/oltp_update_index/nodes=3/cpu=32/conc=256) on master @ [dd2749ae4ab61eed2f99238acb74e8d3c6b4cb1d](https://github.com/cockroachdb/cockroach/commits/dd2749ae4ab61eed2f99238acb74e8d3c6b4cb1d):
```
test artifacts and logs in: /artifacts/sysbench/oltp_update_index/nodes=3/cpu=32/conc=256/run_1
(cluster.go:1956).Run: output in run_155040.686266349_n4_sysbench-dbdriverpgs: sysbench \
--db-driver=pgsql \
--pgsql-host={pghost:1} \
--pgsql-port=26257 \
--pgsql-user=root \
--pgsql-password= \
--pgsql-db=sysbench \
--report-interval=1 \
--time=600 \
--threads=256 \
--tables=10 \
--table_size=10000000 \
--auto_inc=false \
oltp_update_index prepare returned: context canceled
(monitor.go:127).Wait: monitor failure: monitor command failure: unexpected node event: 3: dead (exit status 7)
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=32</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/test-eng
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sysbench/oltp_update_index/nodes=3/cpu=32/conc=256.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_usab | roachtest sysbench oltp update index nodes cpu conc failed roachtest sysbench oltp update index nodes cpu conc with on master test artifacts and logs in artifacts sysbench oltp update index nodes cpu conc run cluster go run output in run sysbench dbdriverpgs sysbench db driver pgsql pgsql host pghost pgsql port pgsql user root pgsql password pgsql db sysbench report interval time threads tables table size auto inc false oltp update index prepare returned context canceled monitor go wait monitor failure monitor command failure unexpected node event dead exit status parameters roachtest cloud gce roachtest cpu roachtest encrypted false roachtest ssd help see see cc cockroachdb test eng | 0 |
49,322 | 12,322,344,638 | IssuesEvent | 2020-05-13 10:10:49 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | opened | Error after running the program | type:build/install | I ran this program to check if Tensorflow is installed or not in jupyter notebook. And Got the following error.
import tensorflow as tf
hello = tf.constant('Hello, TensorFlow!')
sess = tf.Session()
print(sess.run(hello))
ERROR:root:Internal Python error in the inspect module.
Below is the traceback from this internal error.
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 3325, in run_code
exec(code_obj, self.user_global_ns, self.user_ns)
File "<ipython-input-8-25b92e4d5dec>", line 2, in <module>
hello = tf.constant('Hello, TensorFlow!')
AttributeError: module 'tensorflow' has no attribute 'constant'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 2039, in showtraceback
stb = value._render_traceback_()
AttributeError: 'AttributeError' object has no attribute '_render_traceback_'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow_internal.py", line 2453, in <module>
from tensorflow.python.util import deprecation
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\util\deprecation.py", line 25, in <module>
from tensorflow.python.platform import tf_logging as logging
ImportError: cannot import name 'tf_logging' from 'tensorflow.python.platform' (C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\python\platform\__init__.py)
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\ultratb.py", line 1101, in get_records
return _fixed_getinnerframes(etb, number_of_lines_of_context, tb_offset)
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\ultratb.py", line 319, in wrapped
return f(*args, **kwargs)
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\ultratb.py", line 353, in _fixed_getinnerframes
records = fix_frame_records_filenames(inspect.getinnerframes(etb, context))
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 1502, in getinnerframes
frameinfo = (tb.tb_frame,) + getframeinfo(tb, context)
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 1460, in getframeinfo
filename = getsourcefile(frame) or getfile(frame)
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 696, in getsourcefile
if getattr(getmodule(object, filename), '__loader__', None) is not None:
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 733, in getmodule
if ismodule(module) and hasattr(module, '__file__'):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 50, in __getattr__
module = self._load()
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 44, in _load
module = _importlib.import_module(self.__name__)
File "C:\Users\Vishal\Anaconda3\New\lib\importlib\__init__.py", line 127, in import_module
return _bootstrap._gcd_import(name[level:], package, level)
File "<frozen importlib._bootstrap>", line 1006, in _gcd_import
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 953, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "<frozen importlib._bootstrap>", line 1006, in _gcd_import
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 967, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 677, in _load_unlocked
File "<frozen importlib._bootstrap_external>", line 728, in exec_module
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\__init__.py", line 42, in <module>
from . _api.v2 import audio
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\_api\v2\audio\__init__.py", line 10, in <module>
from tensorflow.python.ops.gen_audio_ops import decode_wav
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\ops\gen_audio_ops.py", line 9, in <module>
from tensorflow.python import pywrap_tensorflow as _pywrap_tensorflow
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 50, in __getattr__
module = self._load()
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 44, in _load
module = _importlib.import_module(self.__name__)
File "C:\Users\Vishal\Anaconda3\New\lib\importlib\__init__.py", line 127, in import_module
return _bootstrap._gcd_import(name[level:], package, level)
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\__init__.py", line 49, in <module>
from tensorflow.python import pywrap_tensorflow
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow.py", line 74, in <module>
raise ImportError(msg)
ImportError: Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 3325, in run_code
exec(code_obj, self.user_global_ns, self.user_ns)
File "<ipython-input-8-25b92e4d5dec>", line 2, in <module>
hello = tf.constant('Hello, TensorFlow!')
AttributeError: module 'tensorflow' has no attribute 'constant'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 2039, in showtraceback
stb = value._render_traceback_()
AttributeError: 'AttributeError' object has no attribute '_render_traceback_'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow_internal.py", line 2453, in <module>
from tensorflow.python.util import deprecation
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\util\deprecation.py", line 25, in <module>
from tensorflow.python.platform import tf_logging as logging
ImportError: cannot import name 'tf_logging' from 'tensorflow.python.platform' (C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\python\platform\__init__.py)
Failed to load the native TensorFlow runtime.
| 1.0 | Error after running the program - I ran this program to check if Tensorflow is installed or not in jupyter notebook. And Got the following error.
import tensorflow as tf
hello = tf.constant('Hello, TensorFlow!')
sess = tf.Session()
print(sess.run(hello))
ERROR:root:Internal Python error in the inspect module.
Below is the traceback from this internal error.
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 3325, in run_code
exec(code_obj, self.user_global_ns, self.user_ns)
File "<ipython-input-8-25b92e4d5dec>", line 2, in <module>
hello = tf.constant('Hello, TensorFlow!')
AttributeError: module 'tensorflow' has no attribute 'constant'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 2039, in showtraceback
stb = value._render_traceback_()
AttributeError: 'AttributeError' object has no attribute '_render_traceback_'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow_internal.py", line 2453, in <module>
from tensorflow.python.util import deprecation
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\util\deprecation.py", line 25, in <module>
from tensorflow.python.platform import tf_logging as logging
ImportError: cannot import name 'tf_logging' from 'tensorflow.python.platform' (C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\python\platform\__init__.py)
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\ultratb.py", line 1101, in get_records
return _fixed_getinnerframes(etb, number_of_lines_of_context, tb_offset)
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\ultratb.py", line 319, in wrapped
return f(*args, **kwargs)
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\ultratb.py", line 353, in _fixed_getinnerframes
records = fix_frame_records_filenames(inspect.getinnerframes(etb, context))
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 1502, in getinnerframes
frameinfo = (tb.tb_frame,) + getframeinfo(tb, context)
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 1460, in getframeinfo
filename = getsourcefile(frame) or getfile(frame)
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 696, in getsourcefile
if getattr(getmodule(object, filename), '__loader__', None) is not None:
File "C:\Users\Vishal\Anaconda3\New\lib\inspect.py", line 733, in getmodule
if ismodule(module) and hasattr(module, '__file__'):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 50, in __getattr__
module = self._load()
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 44, in _load
module = _importlib.import_module(self.__name__)
File "C:\Users\Vishal\Anaconda3\New\lib\importlib\__init__.py", line 127, in import_module
return _bootstrap._gcd_import(name[level:], package, level)
File "<frozen importlib._bootstrap>", line 1006, in _gcd_import
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 953, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "<frozen importlib._bootstrap>", line 1006, in _gcd_import
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 967, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 677, in _load_unlocked
File "<frozen importlib._bootstrap_external>", line 728, in exec_module
File "<frozen importlib._bootstrap>", line 219, in _call_with_frames_removed
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\__init__.py", line 42, in <module>
from . _api.v2 import audio
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\_api\v2\audio\__init__.py", line 10, in <module>
from tensorflow.python.ops.gen_audio_ops import decode_wav
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\ops\gen_audio_ops.py", line 9, in <module>
from tensorflow.python import pywrap_tensorflow as _pywrap_tensorflow
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 50, in __getattr__
module = self._load()
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\__init__.py", line 44, in _load
module = _importlib.import_module(self.__name__)
File "C:\Users\Vishal\Anaconda3\New\lib\importlib\__init__.py", line 127, in import_module
return _bootstrap._gcd_import(name[level:], package, level)
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\__init__.py", line 49, in <module>
from tensorflow.python import pywrap_tensorflow
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow.py", line 74, in <module>
raise ImportError(msg)
ImportError: Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 3325, in run_code
exec(code_obj, self.user_global_ns, self.user_ns)
File "<ipython-input-8-25b92e4d5dec>", line 2, in <module>
hello = tf.constant('Hello, TensorFlow!')
AttributeError: module 'tensorflow' has no attribute 'constant'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\IPython\core\interactiveshell.py", line 2039, in showtraceback
stb = value._render_traceback_()
AttributeError: 'AttributeError' object has no attribute '_render_traceback_'
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\pywrap_tensorflow_internal.py", line 2453, in <module>
from tensorflow.python.util import deprecation
File "C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow_core\python\util\deprecation.py", line 25, in <module>
from tensorflow.python.platform import tf_logging as logging
ImportError: cannot import name 'tf_logging' from 'tensorflow.python.platform' (C:\Users\Vishal\Anaconda3\New\lib\site-packages\tensorflow\python\platform\__init__.py)
Failed to load the native TensorFlow runtime.
| non_usab | error after running the program i ran this program to check if tensorflow is installed or not in jupyter notebook and got the following error import tensorflow as tf hello tf constant hello tensorflow sess tf session print sess run hello error root internal python error in the inspect module below is the traceback from this internal error traceback most recent call last file c users vishal new lib site packages ipython core interactiveshell py line in run code exec code obj self user global ns self user ns file line in hello tf constant hello tensorflow attributeerror module tensorflow has no attribute constant during handling of the above exception another exception occurred traceback most recent call last file c users vishal new lib site packages ipython core interactiveshell py line in showtraceback stb value render traceback attributeerror attributeerror object has no attribute render traceback during handling of the above exception another exception occurred traceback most recent call last file c users vishal new lib site packages tensorflow core python pywrap tensorflow py line in from tensorflow python pywrap tensorflow internal import file c users vishal new lib site packages tensorflow core python pywrap tensorflow internal py line in from tensorflow python util import deprecation file c users vishal new lib site packages tensorflow core python util deprecation py line in from tensorflow python platform import tf logging as logging importerror cannot import name tf logging from tensorflow python platform c users vishal new lib site packages tensorflow python platform init py during handling of the above exception another exception occurred traceback most recent call last file c users vishal new lib site packages ipython core ultratb py line in get records return fixed getinnerframes etb number of lines of context tb offset file c users vishal new lib site packages ipython core ultratb py line in wrapped return f args kwargs file c users vishal new lib site packages ipython core ultratb py line in fixed getinnerframes records fix frame records filenames inspect getinnerframes etb context file c users vishal new lib inspect py line in getinnerframes frameinfo tb tb frame getframeinfo tb context file c users vishal new lib inspect py line in getframeinfo filename getsourcefile frame or getfile frame file c users vishal new lib inspect py line in getsourcefile if getattr getmodule object filename loader none is not none file c users vishal new lib inspect py line in getmodule if ismodule module and hasattr module file file c users vishal new lib site packages tensorflow init py line in getattr module self load file c users vishal new lib site packages tensorflow init py line in load module importlib import module self name file c users vishal new lib importlib init py line in import module return bootstrap gcd import name package level file line in gcd import file line in find and load file line in find and load unlocked file line in call with frames removed file line in gcd import file line in find and load file line in find and load unlocked file line in load unlocked file line in exec module file line in call with frames removed file c users vishal new lib site packages tensorflow core init py line in from api import audio file c users vishal new lib site packages tensorflow core api audio init py line in from tensorflow python ops gen audio ops import decode wav file c users vishal new lib site packages tensorflow core python ops gen audio ops py line in from tensorflow python import pywrap tensorflow as pywrap tensorflow file c users vishal new lib site packages tensorflow init py line in getattr module self load file c users vishal new lib site packages tensorflow init py line in load module importlib import module self name file c users vishal new lib importlib init py line in import module return bootstrap gcd import name package level file c users vishal new lib site packages tensorflow core python init py line in from tensorflow python import pywrap tensorflow file c users vishal new lib site packages tensorflow core python pywrap tensorflow py line in raise importerror msg importerror traceback most recent call last file c users vishal new lib site packages ipython core interactiveshell py line in run code exec code obj self user global ns self user ns file line in hello tf constant hello tensorflow attributeerror module tensorflow has no attribute constant during handling of the above exception another exception occurred traceback most recent call last file c users vishal new lib site packages ipython core interactiveshell py line in showtraceback stb value render traceback attributeerror attributeerror object has no attribute render traceback during handling of the above exception another exception occurred traceback most recent call last file c users vishal new lib site packages tensorflow core python pywrap tensorflow py line in from tensorflow python pywrap tensorflow internal import file c users vishal new lib site packages tensorflow core python pywrap tensorflow internal py line in from tensorflow python util import deprecation file c users vishal new lib site packages tensorflow core python util deprecation py line in from tensorflow python platform import tf logging as logging importerror cannot import name tf logging from tensorflow python platform c users vishal new lib site packages tensorflow python platform init py failed to load the native tensorflow runtime | 0 |
362,795 | 25,390,386,278 | IssuesEvent | 2022-11-22 03:08:20 | dadosfera/Bugsfera | https://api.github.com/repos/dadosfera/Bugsfera | opened | Unable to process data from google sheets when the spreadsheet has been created using MS Excel and other tools | moderate Documentation | ## Mandatory information:
##### There are customers are directly impacted by this bug. Which?
-------------------------------------------
#### Bug Category
- [ ] Connection Manager
- [ ] Connection Test
- [ ] Creating Pipeline
- [x] Executing Pipeline
- [ ] Cataloging Data Asset
- [ ] Other
#### Connector
- Singer
#### Plugin
- Google Sheets
##### Describe the bug
While executing a pipeline with plugin `google-sheets`, the following error is raised:
```shell
HTTP-error-code: 400 {'code': 400, 'message': 'This operation is not supported for this document', 'status': 'FAILED_PRECONDITION'}: Unknown Error Traceback (most recent call last): File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 111, in raise_for_error response.raise_for_status() File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/requests/models.py", line 940, in raise_for_status raise HTTPError(http_error_msg, response=self) requests.exceptions.HTTPError: 400 Client Error: Bad Request for url: https://sheets.googleapis.com/v4/spreadsheets/191O9Y_SANs1fRpC_QKFCf2I8j-11LR39?includeGridData=false&includeGridData=false During handling of the above exception, another exception occurred: Traceback (most recent call last): File ".meltano/extractors/tap-google-sheets/venv/bin/tap-google-sheets", line 8, in <module> sys.exit(main()) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/singer/utils.py", line 229, in wrapped return fnc(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/__init__.py", line 51, in main do_discover(client, spreadsheet_id) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/__init__.py", line 26, in do_discover catalog = discover(client, spreadsheet_id) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/discover.py", line 6, in discover schemas, field_metadata = get_schemas(client, spreadsheet_id) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/schema.py", line 307, in get_schemas endpoint=stream_name) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 265, in get return self.request(method='GET', path=path, api=api, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/backoff/_sync.py", line 94, in retry ret = target(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/backoff/_sync.py", line 94, in retry ret = target(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/singer/utils.py", line 95, in wrapper return func(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 259, in request raise_for_error(response) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 128, in raise_for_error raise ex(message) tap_google_sheets.client.GoogleBadRequestError: HTTP-error-code: 400 {'code': 400, 'message': 'This operation is not supported for this document', 'status': 'FAILED_PRECONDITION'}: Unknown Error
```
#### To Reproduce
Steps to reproduce the behavior:
1. Create a spreadsheet using MS Excel or a similar tool
2. Upload this spreadsheet to Google Sheets
3. Create a pipeline using the spreadsheet that you upload as a source
4. Executes the pipeline
This is a limitation of the Google Sheets API. Therefore, we should try to document this issue for the users, so they can convert their spreadsheet into a google spreadsheet before creating a pipeline.
#### How to detect if a spreadsheet was created by MS Excel
When a spreadsheet is created in MS Excel, it has the extension `xlsx` as you can see in the image below:

#### How to convert a MS Excel Spreadsheet into a Google Spreadsheet:
1. Click on the menu `File`
2. Save as Google SpreadSheet
#### Dadosfera Customer:
-------------------------------------------
- dadosfera
What environment of software are you using?
- [x] PRD
- [ ] Other
| 1.0 | Unable to process data from google sheets when the spreadsheet has been created using MS Excel and other tools - ## Mandatory information:
##### There are customers are directly impacted by this bug. Which?
-------------------------------------------
#### Bug Category
- [ ] Connection Manager
- [ ] Connection Test
- [ ] Creating Pipeline
- [x] Executing Pipeline
- [ ] Cataloging Data Asset
- [ ] Other
#### Connector
- Singer
#### Plugin
- Google Sheets
##### Describe the bug
While executing a pipeline with plugin `google-sheets`, the following error is raised:
```shell
HTTP-error-code: 400 {'code': 400, 'message': 'This operation is not supported for this document', 'status': 'FAILED_PRECONDITION'}: Unknown Error Traceback (most recent call last): File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 111, in raise_for_error response.raise_for_status() File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/requests/models.py", line 940, in raise_for_status raise HTTPError(http_error_msg, response=self) requests.exceptions.HTTPError: 400 Client Error: Bad Request for url: https://sheets.googleapis.com/v4/spreadsheets/191O9Y_SANs1fRpC_QKFCf2I8j-11LR39?includeGridData=false&includeGridData=false During handling of the above exception, another exception occurred: Traceback (most recent call last): File ".meltano/extractors/tap-google-sheets/venv/bin/tap-google-sheets", line 8, in <module> sys.exit(main()) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/singer/utils.py", line 229, in wrapped return fnc(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/__init__.py", line 51, in main do_discover(client, spreadsheet_id) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/__init__.py", line 26, in do_discover catalog = discover(client, spreadsheet_id) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/discover.py", line 6, in discover schemas, field_metadata = get_schemas(client, spreadsheet_id) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/schema.py", line 307, in get_schemas endpoint=stream_name) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 265, in get return self.request(method='GET', path=path, api=api, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/backoff/_sync.py", line 94, in retry ret = target(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/backoff/_sync.py", line 94, in retry ret = target(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/singer/utils.py", line 95, in wrapper return func(*args, **kwargs) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 259, in request raise_for_error(response) File "/app/.meltano/extractors/tap-google-sheets/venv/lib/python3.7/site-packages/tap_google_sheets/client.py", line 128, in raise_for_error raise ex(message) tap_google_sheets.client.GoogleBadRequestError: HTTP-error-code: 400 {'code': 400, 'message': 'This operation is not supported for this document', 'status': 'FAILED_PRECONDITION'}: Unknown Error
```
#### To Reproduce
Steps to reproduce the behavior:
1. Create a spreadsheet using MS Excel or a similar tool
2. Upload this spreadsheet to Google Sheets
3. Create a pipeline using the spreadsheet that you upload as a source
4. Executes the pipeline
This is a limitation of the Google Sheets API. Therefore, we should try to document this issue for the users, so they can convert their spreadsheet into a google spreadsheet before creating a pipeline.
#### How to detect if a spreadsheet was created by MS Excel
When a spreadsheet is created in MS Excel, it has the extension `xlsx` as you can see in the image below:

#### How to convert a MS Excel Spreadsheet into a Google Spreadsheet:
1. Click on the menu `File`
2. Save as Google SpreadSheet
#### Dadosfera Customer:
-------------------------------------------
- dadosfera
What environment of software are you using?
- [x] PRD
- [ ] Other
| non_usab | unable to process data from google sheets when the spreadsheet has been created using ms excel and other tools mandatory information there are customers are directly impacted by this bug which bug category connection manager connection test creating pipeline executing pipeline cataloging data asset other connector singer plugin google sheets describe the bug while executing a pipeline with plugin google sheets the following error is raised shell http error code code message this operation is not supported for this document status failed precondition unknown error traceback most recent call last file app meltano extractors tap google sheets venv lib site packages tap google sheets client py line in raise for error response raise for status file app meltano extractors tap google sheets venv lib site packages requests models py line in raise for status raise httperror http error msg response self requests exceptions httperror client error bad request for url during handling of the above exception another exception occurred traceback most recent call last file meltano extractors tap google sheets venv bin tap google sheets line in sys exit main file app meltano extractors tap google sheets venv lib site packages singer utils py line in wrapped return fnc args kwargs file app meltano extractors tap google sheets venv lib site packages tap google sheets init py line in main do discover client spreadsheet id file app meltano extractors tap google sheets venv lib site packages tap google sheets init py line in do discover catalog discover client spreadsheet id file app meltano extractors tap google sheets venv lib site packages tap google sheets discover py line in discover schemas field metadata get schemas client spreadsheet id file app meltano extractors tap google sheets venv lib site packages tap google sheets schema py line in get schemas endpoint stream name file app meltano extractors tap google sheets venv lib site packages tap google sheets client py line in get return self request method get path path api api kwargs file app meltano extractors tap google sheets venv lib site packages backoff sync py line in retry ret target args kwargs file app meltano extractors tap google sheets venv lib site packages backoff sync py line in retry ret target args kwargs file app meltano extractors tap google sheets venv lib site packages singer utils py line in wrapper return func args kwargs file app meltano extractors tap google sheets venv lib site packages tap google sheets client py line in request raise for error response file app meltano extractors tap google sheets venv lib site packages tap google sheets client py line in raise for error raise ex message tap google sheets client googlebadrequesterror http error code code message this operation is not supported for this document status failed precondition unknown error to reproduce steps to reproduce the behavior create a spreadsheet using ms excel or a similar tool upload this spreadsheet to google sheets create a pipeline using the spreadsheet that you upload as a source executes the pipeline this is a limitation of the google sheets api therefore we should try to document this issue for the users so they can convert their spreadsheet into a google spreadsheet before creating a pipeline how to detect if a spreadsheet was created by ms excel when a spreadsheet is created in ms excel it has the extension xlsx as you can see in the image below how to convert a ms excel spreadsheet into a google spreadsheet click on the menu file save as google spreadsheet dadosfera customer dadosfera what environment of software are you using prd other | 0 |
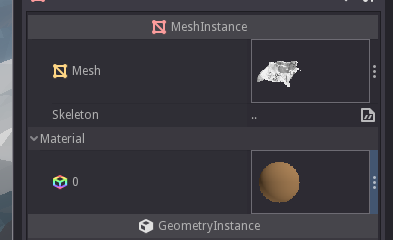
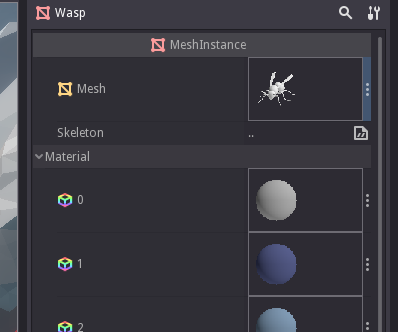
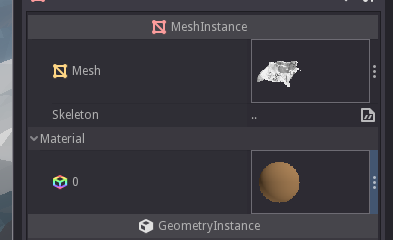
9,907 | 6,510,349,898 | IssuesEvent | 2017-08-25 02:41:32 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Sometimes resource thumbnails are shown in inspector, sometimes not | bug topic:editor usability | Godot 3.0 alpha1 official
Windows 10 64 bits
I noticed that I have no preview of the resources being in use here, I see there names now:

On the other hand, if I click on another MeshInstance in the same scene, I see thumbnails:
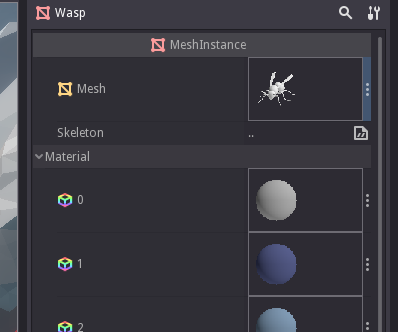
I used to see thumbnails in the first one a bit earlier in the same session, in which materials where black balls instead of brown. Not sure what caused them to disappear.
#9891 did occur earlier in the session, but I realize that now I can click on meshes without it happening, so maybe it's related?
Edit: I closed another unsaved scene, and now I can see thumbnails again in the first MeshInstance, and material thumbnails are back to brown color:
| True | Sometimes resource thumbnails are shown in inspector, sometimes not - Godot 3.0 alpha1 official
Windows 10 64 bits
I noticed that I have no preview of the resources being in use here, I see there names now:

On the other hand, if I click on another MeshInstance in the same scene, I see thumbnails:
I used to see thumbnails in the first one a bit earlier in the same session, in which materials where black balls instead of brown. Not sure what caused them to disappear.
#9891 did occur earlier in the session, but I realize that now I can click on meshes without it happening, so maybe it's related?
Edit: I closed another unsaved scene, and now I can see thumbnails again in the first MeshInstance, and material thumbnails are back to brown color:
| usab | sometimes resource thumbnails are shown in inspector sometimes not godot official windows bits i noticed that i have no preview of the resources being in use here i see there names now on the other hand if i click on another meshinstance in the same scene i see thumbnails i used to see thumbnails in the first one a bit earlier in the same session in which materials where black balls instead of brown not sure what caused them to disappear did occur earlier in the session but i realize that now i can click on meshes without it happening so maybe it s related edit i closed another unsaved scene and now i can see thumbnails again in the first meshinstance and material thumbnails are back to brown color | 1 |
291,920 | 21,944,202,288 | IssuesEvent | 2022-05-23 21:41:39 | interactions-py/library | https://api.github.com/repos/interactions-py/library | closed | [REQUEST] Implement clone channel method | documentation enhancement | ### Describe the feature.
It'd be very neat to have a way to automatically clone channels in a guild. I will create a PR that adds this feature as soon as this issue is public.
### Code of Conduct
- [X] I agree to follow the contribution requirements. | 1.0 | [REQUEST] Implement clone channel method - ### Describe the feature.
It'd be very neat to have a way to automatically clone channels in a guild. I will create a PR that adds this feature as soon as this issue is public.
### Code of Conduct
- [X] I agree to follow the contribution requirements. | non_usab | implement clone channel method describe the feature it d be very neat to have a way to automatically clone channels in a guild i will create a pr that adds this feature as soon as this issue is public code of conduct i agree to follow the contribution requirements | 0 |
78,151 | 7,622,029,228 | IssuesEvent | 2018-05-03 10:37:27 | tomato42/tlsfuzzer | https://api.github.com/repos/tomato42/tlsfuzzer | opened | TLS 1.3 and OpenPGP | help wanted new test script | - Verify that server will not try to use OpenPGP with TLS 1.3
- Verify that server will reject client Certificate if it includes OpenPGP certificate | 1.0 | TLS 1.3 and OpenPGP - - Verify that server will not try to use OpenPGP with TLS 1.3
- Verify that server will reject client Certificate if it includes OpenPGP certificate | non_usab | tls and openpgp verify that server will not try to use openpgp with tls verify that server will reject client certificate if it includes openpgp certificate | 0 |
516,426 | 14,982,008,643 | IssuesEvent | 2021-01-28 15:29:57 | kubernetes/release | https://api.github.com/repos/kubernetes/release | closed | Error importing kube-poroxy.tar for ARM64 with containerd | area/release-eng kind/bug needs-priority sig/release | <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!
If the matter is security related, please disclose it privately via https://kubernetes.io/security/
-->
#### What happened:
Since switching the kOps for ARM64 periodic tests to containerd container runtime, they are failing, not being able to create the cluster:
https://testgrid.k8s.io/kops-misc#kops-aws-arm64-conformance
[kOps logs](https://storage.googleapis.com/kubernetes-jenkins/logs/e2e-kops-aws-misc-arm64-conformance/1349280720744353792/artifacts/ip-172-20-36-171.eu-west-1.compute.internal/kops-configuration.log) from these tests show that there are issues importing the `kube-proxy.image` image:
```
I0113 09:16:05.009436 8756 load_image.go:159] running command ctr --namespace k8s.io images import
/var/cache/nodeup/sha256:1c7dc3f79c105657b765092b69b55d14ad530fe3db7d95cd664191f10bd60816_https___storage_googleapis_com_kubernetes-release_release_v1_20_1_bin_linux_arm64_kube-proxy_tar
W0113 09:16:06.571666 8756 executor.go:131] error running task "LoadImage.0" (9m58s remaining to succeed):
error loading docker image with 'ctr --namespace k8s.io images import
/var/cache/nodeup/sha256:1c7dc3f79c105657b765092b69b55d14ad530fe3db7d95cd664191f10bd60816_https___storage_googleapis_com_kubernetes-release_release_v1_20_1_bin_linux_arm64_kube-proxy_tar':
exit status 1: unpacking k8s.gcr.io/kube-proxy-arm64:v1.20.1 (sha256:6f6f747fa89f88a076fa6534946e392f0629a4c55f2f7413d855281d3af90e50)...
ctr: content digest sha256:e969937ccd0f155a9cc6e79c3d433679fb85853a3adbe6280dbba18a11202a2d: not found
```
containerd logs show similar thing:
```
time="2021-01-13T09:09:14.057352011Z" level=error msg="CreateContainer within sandbox
\"e87c5d542ae2bb38266df4c4a65351a7a6b63c08b961fdb828bc979aba3e5ba1\"
for &ContainerMetadata{Name:kube-proxy,Attempt:0,} failed"
error="rpc error: code = NotFound desc = failed to create containerd container:
error unpacking image: failed to resolve rootfs: content digest
sha256:9dee21b6b85b275630ede8fe219f62d68388c32a0fba11c05f2cff4fa38adfb6: not found"
```
Extracting the contents of the [kube-proxy.tar](https://storage.googleapis.com/kubernetes-release/release/v1.20.1/bin/linux/arm64/kube-proxy.tar) file can be noticed that the configuration JSON contains has the architecture set to "amd64":
```bash
$ cat 9dee21b6b85b275630ede8fe219f62d68388c32a0fba11c05f2cff4fa38adfb6.json | json_pp
{
"architecture" : "amd64",
...
```
#### How to reproduce it (as minimally and precisely as possible):
1. Start an instance with Ubuntu 20.04 and ARM64 CPU in AWS
2. Install containerd 1.4.3 from https://download.docker.com/linux/ubuntu/dists/focal/pool/stable/arm64/
3. Download https://storage.googleapis.com/kubernetes-release/release/v1.20.1/bin/linux/arm64/kube-proxy.tar
4. Try to import the image: `sudo ctr images import kube-proxy.tar`
#### Anything else we need to know?:
Issue was opened here because the problem seems to come from the `debian-iptables` image used as a base for `kube-proxy`.
Changing the architecture to "arm64" inside the config JSON makes the import succeed.
#### Environment:
- Cloud provider or hardware configuration: AWS with m6g.large instance type
- OS (e.g: `cat /etc/os-release`): Ubuntu 20.04 Focal ARM64
- Kernel (e.g. `uname -a`): n/a
- Others: | 1.0 | Error importing kube-poroxy.tar for ARM64 with containerd - <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!
If the matter is security related, please disclose it privately via https://kubernetes.io/security/
-->
#### What happened:
Since switching the kOps for ARM64 periodic tests to containerd container runtime, they are failing, not being able to create the cluster:
https://testgrid.k8s.io/kops-misc#kops-aws-arm64-conformance
[kOps logs](https://storage.googleapis.com/kubernetes-jenkins/logs/e2e-kops-aws-misc-arm64-conformance/1349280720744353792/artifacts/ip-172-20-36-171.eu-west-1.compute.internal/kops-configuration.log) from these tests show that there are issues importing the `kube-proxy.image` image:
```
I0113 09:16:05.009436 8756 load_image.go:159] running command ctr --namespace k8s.io images import
/var/cache/nodeup/sha256:1c7dc3f79c105657b765092b69b55d14ad530fe3db7d95cd664191f10bd60816_https___storage_googleapis_com_kubernetes-release_release_v1_20_1_bin_linux_arm64_kube-proxy_tar
W0113 09:16:06.571666 8756 executor.go:131] error running task "LoadImage.0" (9m58s remaining to succeed):
error loading docker image with 'ctr --namespace k8s.io images import
/var/cache/nodeup/sha256:1c7dc3f79c105657b765092b69b55d14ad530fe3db7d95cd664191f10bd60816_https___storage_googleapis_com_kubernetes-release_release_v1_20_1_bin_linux_arm64_kube-proxy_tar':
exit status 1: unpacking k8s.gcr.io/kube-proxy-arm64:v1.20.1 (sha256:6f6f747fa89f88a076fa6534946e392f0629a4c55f2f7413d855281d3af90e50)...
ctr: content digest sha256:e969937ccd0f155a9cc6e79c3d433679fb85853a3adbe6280dbba18a11202a2d: not found
```
containerd logs show similar thing:
```
time="2021-01-13T09:09:14.057352011Z" level=error msg="CreateContainer within sandbox
\"e87c5d542ae2bb38266df4c4a65351a7a6b63c08b961fdb828bc979aba3e5ba1\"
for &ContainerMetadata{Name:kube-proxy,Attempt:0,} failed"
error="rpc error: code = NotFound desc = failed to create containerd container:
error unpacking image: failed to resolve rootfs: content digest
sha256:9dee21b6b85b275630ede8fe219f62d68388c32a0fba11c05f2cff4fa38adfb6: not found"
```
Extracting the contents of the [kube-proxy.tar](https://storage.googleapis.com/kubernetes-release/release/v1.20.1/bin/linux/arm64/kube-proxy.tar) file can be noticed that the configuration JSON contains has the architecture set to "amd64":
```bash
$ cat 9dee21b6b85b275630ede8fe219f62d68388c32a0fba11c05f2cff4fa38adfb6.json | json_pp
{
"architecture" : "amd64",
...
```
#### How to reproduce it (as minimally and precisely as possible):
1. Start an instance with Ubuntu 20.04 and ARM64 CPU in AWS
2. Install containerd 1.4.3 from https://download.docker.com/linux/ubuntu/dists/focal/pool/stable/arm64/
3. Download https://storage.googleapis.com/kubernetes-release/release/v1.20.1/bin/linux/arm64/kube-proxy.tar
4. Try to import the image: `sudo ctr images import kube-proxy.tar`
#### Anything else we need to know?:
Issue was opened here because the problem seems to come from the `debian-iptables` image used as a base for `kube-proxy`.
Changing the architecture to "arm64" inside the config JSON makes the import succeed.
#### Environment:
- Cloud provider or hardware configuration: AWS with m6g.large instance type
- OS (e.g: `cat /etc/os-release`): Ubuntu 20.04 Focal ARM64
- Kernel (e.g. `uname -a`): n/a
- Others: | non_usab | error importing kube poroxy tar for with containerd please use this template while reporting a bug and provide as much info as possible not doing so may result in your bug not being addressed in a timely manner thanks if the matter is security related please disclose it privately via what happened since switching the kops for periodic tests to containerd container runtime they are failing not being able to create the cluster from these tests show that there are issues importing the kube proxy image image load image go running command ctr namespace io images import var cache nodeup https storage googleapis com kubernetes release release bin linux kube proxy tar executor go error running task loadimage remaining to succeed error loading docker image with ctr namespace io images import var cache nodeup https storage googleapis com kubernetes release release bin linux kube proxy tar exit status unpacking gcr io kube proxy ctr content digest not found containerd logs show similar thing time level error msg createcontainer within sandbox for containermetadata name kube proxy attempt failed error rpc error code notfound desc failed to create containerd container error unpacking image failed to resolve rootfs content digest not found extracting the contents of the file can be noticed that the configuration json contains has the architecture set to bash cat json json pp architecture how to reproduce it as minimally and precisely as possible start an instance with ubuntu and cpu in aws install containerd from download try to import the image sudo ctr images import kube proxy tar anything else we need to know issue was opened here because the problem seems to come from the debian iptables image used as a base for kube proxy changing the architecture to inside the config json makes the import succeed environment cloud provider or hardware configuration aws with large instance type os e g cat etc os release ubuntu focal kernel e g uname a n a others | 0 |
27,358 | 28,147,310,890 | IssuesEvent | 2023-04-02 16:30:17 | godotengine/godot-proposals | https://api.github.com/repos/godotengine/godot-proposals | closed | Make node-specific menus/buttons more obvious | topic:editor usability | ### Describe the project you are working on
Action RPG.
### Describe the problem or limitation you are having in your project
Some nodes, when clicked on in the SceneTree, make context-specific menus or buttons appear in the toolbar above the main editor viewport (to the right of the "Transform" and "View" menus in the 3D view).
Examples are MeshInstance3D (creates a Mesh menu) and Skeleton3D (creates a Skeleton3D menu and several buttons).
These menus/buttons are very unobtrusive, to the point that I generally don't notice they are there unless I'm specifically reminded to look there by a tutorial etc.
There are other Nodes that make node-specific controls appear in more obvious ways. Eg when Camera3D is clicked, the "toggle preview" button appears within the editor viewport, where it is much more likely to be noticed.
### Describe the feature / enhancement and how it helps to overcome the problem or limitation
Make the node-specific controls appear within the main editor viewport, similar to the Camera "toggle preview" button.
### Describe how your proposal will work, with code, pseudo-code, mock-ups, and/or diagrams

### If this enhancement will not be used often, can it be worked around with a few lines of script?
No, this is a basic editor UI enhancement.
### Is there a reason why this should be core and not an add-on in the asset library?
This is about editor usability. | True | Make node-specific menus/buttons more obvious - ### Describe the project you are working on
Action RPG.
### Describe the problem or limitation you are having in your project
Some nodes, when clicked on in the SceneTree, make context-specific menus or buttons appear in the toolbar above the main editor viewport (to the right of the "Transform" and "View" menus in the 3D view).
Examples are MeshInstance3D (creates a Mesh menu) and Skeleton3D (creates a Skeleton3D menu and several buttons).
These menus/buttons are very unobtrusive, to the point that I generally don't notice they are there unless I'm specifically reminded to look there by a tutorial etc.
There are other Nodes that make node-specific controls appear in more obvious ways. Eg when Camera3D is clicked, the "toggle preview" button appears within the editor viewport, where it is much more likely to be noticed.
### Describe the feature / enhancement and how it helps to overcome the problem or limitation
Make the node-specific controls appear within the main editor viewport, similar to the Camera "toggle preview" button.
### Describe how your proposal will work, with code, pseudo-code, mock-ups, and/or diagrams

### If this enhancement will not be used often, can it be worked around with a few lines of script?
No, this is a basic editor UI enhancement.
### Is there a reason why this should be core and not an add-on in the asset library?
This is about editor usability. | usab | make node specific menus buttons more obvious describe the project you are working on action rpg describe the problem or limitation you are having in your project some nodes when clicked on in the scenetree make context specific menus or buttons appear in the toolbar above the main editor viewport to the right of the transform and view menus in the view examples are creates a mesh menu and creates a menu and several buttons these menus buttons are very unobtrusive to the point that i generally don t notice they are there unless i m specifically reminded to look there by a tutorial etc there are other nodes that make node specific controls appear in more obvious ways eg when is clicked the toggle preview button appears within the editor viewport where it is much more likely to be noticed describe the feature enhancement and how it helps to overcome the problem or limitation make the node specific controls appear within the main editor viewport similar to the camera toggle preview button describe how your proposal will work with code pseudo code mock ups and or diagrams if this enhancement will not be used often can it be worked around with a few lines of script no this is a basic editor ui enhancement is there a reason why this should be core and not an add on in the asset library this is about editor usability | 1 |
257,681 | 22,201,104,501 | IssuesEvent | 2022-06-07 11:16:53 | mgba-emu/mgba | https://api.github.com/repos/mgba-emu/mgba | closed | mGBA 0.63 Windows 7 [Menu/Tools] inaccessible after ???, close and reopen | blocked:needs retest | Hi! First, love the emulator! It does everything good and works great!
I found a little glitch maybe, however... I am unable to reproduce it at will BUT it happened at least twice (0.63), can't remember happening on 0.61 (I updated maybe a weeks ago, start of September...).
What happens:
The Tools drop down menu (ONLY tools) is inaccessible/unopenable. However, shortcuts are still working (Alt-C for cheats) but the drop down menu is no where to be seen... I can also speculate (haven't tested it but once) but the menu seems to still be there (even though invisible). When I click below the Tools (that doesn't show a drop down) the log screen opens (at it should at that position).
Temp fix: Save state/close/reopen mGBA...
It's not a HUGE problem but can cause annoyance sometimes...
Continue the great work!
Vortaka
Windows 7, 64bit
I7 2600
16gb ram
P.S. If need of any more info, please email me! | 1.0 | mGBA 0.63 Windows 7 [Menu/Tools] inaccessible after ???, close and reopen - Hi! First, love the emulator! It does everything good and works great!
I found a little glitch maybe, however... I am unable to reproduce it at will BUT it happened at least twice (0.63), can't remember happening on 0.61 (I updated maybe a weeks ago, start of September...).
What happens:
The Tools drop down menu (ONLY tools) is inaccessible/unopenable. However, shortcuts are still working (Alt-C for cheats) but the drop down menu is no where to be seen... I can also speculate (haven't tested it but once) but the menu seems to still be there (even though invisible). When I click below the Tools (that doesn't show a drop down) the log screen opens (at it should at that position).
Temp fix: Save state/close/reopen mGBA...
It's not a HUGE problem but can cause annoyance sometimes...
Continue the great work!
Vortaka
Windows 7, 64bit
I7 2600
16gb ram
P.S. If need of any more info, please email me! | non_usab | mgba windows inaccessible after close and reopen hi first love the emulator it does everything good and works great i found a little glitch maybe however i am unable to reproduce it at will but it happened at least twice can t remember happening on i updated maybe a weeks ago start of september what happens the tools drop down menu only tools is inaccessible unopenable however shortcuts are still working alt c for cheats but the drop down menu is no where to be seen i can also speculate haven t tested it but once but the menu seems to still be there even though invisible when i click below the tools that doesn t show a drop down the log screen opens at it should at that position temp fix save state close reopen mgba it s not a huge problem but can cause annoyance sometimes continue the great work vortaka windows ram p s if need of any more info please email me | 0 |
12,666 | 8,032,696,137 | IssuesEvent | 2018-07-28 18:20:32 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Settings sometimes don't register when clicking enter | bug confirmed topic:editor usability | **Operating system or device, Godot version, GPU Model and driver (if graphics related):**
Ubuntu 17.04, [Build](https://bintray.com/calinou/godot/editor) fe08257
**Issue description:**
When setting something by clicking enter, it will sometimes go back to the previous value:
| True | Settings sometimes don't register when clicking enter - **Operating system or device, Godot version, GPU Model and driver (if graphics related):**
Ubuntu 17.04, [Build](https://bintray.com/calinou/godot/editor) fe08257
**Issue description:**
When setting something by clicking enter, it will sometimes go back to the previous value:
| usab | settings sometimes don t register when clicking enter operating system or device godot version gpu model and driver if graphics related ubuntu issue description when setting something by clicking enter it will sometimes go back to the previous value | 1 |
27,968 | 30,799,124,092 | IssuesEvent | 2023-07-31 22:52:13 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | Make client suggestion connection work with max_sessions_for_user | usability | **Describe the issue**
Clickhouse client can't load suggestions using single connection when max_sessions_for_user is set.
**How to reproduce**
- Create a user with `<max_sessions_for_user>2</max_sessions_for_user>` in profile
- Connect to the server with clickhouse-client in interactive mode (starts a session)
- Run another instance of interactive clickhouse-client. If will fail to load suggestions (due to the limitation on concurrent sessions) but then will continue working as usual.
**Expected behavior**
No error happen in this case.
**Error message and/or stacktrace**
```
ClickHouse client version 23.7.1.1.
Connecting to localhost:9000 as user maxsessions.
Connected to ClickHouse server version 23.7.1 revision 54464.
Cannot load data for command line suggestions: Code: 700. DB::Exception: Received from localhost:9000. DB::Exception: User 5eb5f051-64a4-19bc-ff75-494154bf67a9 has overflown session count 2. () (version 23.7.1.1)
dell9510 :) select 1
```
| True | Make client suggestion connection work with max_sessions_for_user - **Describe the issue**
Clickhouse client can't load suggestions using single connection when max_sessions_for_user is set.
**How to reproduce**
- Create a user with `<max_sessions_for_user>2</max_sessions_for_user>` in profile
- Connect to the server with clickhouse-client in interactive mode (starts a session)
- Run another instance of interactive clickhouse-client. If will fail to load suggestions (due to the limitation on concurrent sessions) but then will continue working as usual.
**Expected behavior**
No error happen in this case.
**Error message and/or stacktrace**
```
ClickHouse client version 23.7.1.1.
Connecting to localhost:9000 as user maxsessions.
Connected to ClickHouse server version 23.7.1 revision 54464.
Cannot load data for command line suggestions: Code: 700. DB::Exception: Received from localhost:9000. DB::Exception: User 5eb5f051-64a4-19bc-ff75-494154bf67a9 has overflown session count 2. () (version 23.7.1.1)
dell9510 :) select 1
```
| usab | make client suggestion connection work with max sessions for user describe the issue clickhouse client can t load suggestions using single connection when max sessions for user is set how to reproduce create a user with in profile connect to the server with clickhouse client in interactive mode starts a session run another instance of interactive clickhouse client if will fail to load suggestions due to the limitation on concurrent sessions but then will continue working as usual expected behavior no error happen in this case error message and or stacktrace clickhouse client version connecting to localhost as user maxsessions connected to clickhouse server version revision cannot load data for command line suggestions code db exception received from localhost db exception user has overflown session count version select | 1 |
539,710 | 15,793,579,471 | IssuesEvent | 2021-04-02 09:15:58 | yalla-coop/chiltern-music-therapy | https://api.github.com/repos/yalla-coop/chiltern-music-therapy | closed | Create Cards component | backlog client-reviewed components front-end priority-2 | __Related issue(s)__
Some of the cards requires components like #37 and #39 but aren't essential as content would just be fed into cards as children most likely
__Wireframe link__
https://www.figma.com/file/CcYmhfnXreAPxlfyEmGsAH/Chiltern-Music-Therapy?node-id=469%3A30652
---
### Acceptance Criteria:
_REMEMBER THAT WHOEVER WORKS ON THIS ISSUE MUST TICK OFF ALL THE POINTS IN THIS LIST UNLESS THERE IS CLEAR AGREEMENT IN THE COMMENTS TO SAY OTHERWISE. **DO NOT REVIEW A PR INVOLVING THIS ISSUE UNLESS THIS HAS BEEN DONE**_
**Note: If you see a solid green border around any of the cards ignore this. This is a bug on Figma not part of the design. Always inspect the component and look at the CSS to be sure of styling**
- [x] Basic card
- Simply includes information and possibly links
- [x] Link card
- Is basically a link that will take the user to another page
- You can see there are a few variations on these
- [x] Expandable card
- These cards when click should expand and then the content in the card should change
- Ensure prop is include to close card again (this would happen if in the parent component there are more than one card and another card gets clicked)
- [x] Info card
- [x] Make sure to use common margin component in styling #32
- [x] Add to storybook
| 1.0 | Create Cards component - __Related issue(s)__
Some of the cards requires components like #37 and #39 but aren't essential as content would just be fed into cards as children most likely
__Wireframe link__
https://www.figma.com/file/CcYmhfnXreAPxlfyEmGsAH/Chiltern-Music-Therapy?node-id=469%3A30652
---
### Acceptance Criteria:
_REMEMBER THAT WHOEVER WORKS ON THIS ISSUE MUST TICK OFF ALL THE POINTS IN THIS LIST UNLESS THERE IS CLEAR AGREEMENT IN THE COMMENTS TO SAY OTHERWISE. **DO NOT REVIEW A PR INVOLVING THIS ISSUE UNLESS THIS HAS BEEN DONE**_
**Note: If you see a solid green border around any of the cards ignore this. This is a bug on Figma not part of the design. Always inspect the component and look at the CSS to be sure of styling**
- [x] Basic card
- Simply includes information and possibly links
- [x] Link card
- Is basically a link that will take the user to another page
- You can see there are a few variations on these
- [x] Expandable card
- These cards when click should expand and then the content in the card should change
- Ensure prop is include to close card again (this would happen if in the parent component there are more than one card and another card gets clicked)
- [x] Info card
- [x] Make sure to use common margin component in styling #32
- [x] Add to storybook
| non_usab | create cards component related issue s some of the cards requires components like and but aren t essential as content would just be fed into cards as children most likely wireframe link acceptance criteria remember that whoever works on this issue must tick off all the points in this list unless there is clear agreement in the comments to say otherwise do not review a pr involving this issue unless this has been done note if you see a solid green border around any of the cards ignore this this is a bug on figma not part of the design always inspect the component and look at the css to be sure of styling basic card simply includes information and possibly links link card is basically a link that will take the user to another page you can see there are a few variations on these expandable card these cards when click should expand and then the content in the card should change ensure prop is include to close card again this would happen if in the parent component there are more than one card and another card gets clicked info card make sure to use common margin component in styling add to storybook | 0 |
22,064 | 18,444,486,528 | IssuesEvent | 2021-10-14 22:52:58 | bevyengine/bevy | https://api.github.com/repos/bevyengine/bevy | opened | Non-consuming method to check if events are empty | A-ECS C-Usability | ## What problem does this solve or what need does it fill?
Game logic commonly branches based on the presence or absence of events.
However, the only way to read events is to consume them.
You can of course drain and then reconstitute the events, but this is terrible.
## What solution would you like?
Add a `peek` method to events.
## What alternative(s) have you considered?
Use size hints to provide a dedicated `.is_empty` method on events instead.
| True | Non-consuming method to check if events are empty - ## What problem does this solve or what need does it fill?
Game logic commonly branches based on the presence or absence of events.
However, the only way to read events is to consume them.
You can of course drain and then reconstitute the events, but this is terrible.
## What solution would you like?
Add a `peek` method to events.
## What alternative(s) have you considered?
Use size hints to provide a dedicated `.is_empty` method on events instead.
| usab | non consuming method to check if events are empty what problem does this solve or what need does it fill game logic commonly branches based on the presence or absence of events however the only way to read events is to consume them you can of course drain and then reconstitute the events but this is terrible what solution would you like add a peek method to events what alternative s have you considered use size hints to provide a dedicated is empty method on events instead | 1 |
144,516 | 5,541,926,090 | IssuesEvent | 2017-03-22 14:01:04 | ReadyResponder/ReadyResponder | https://api.github.com/repos/ReadyResponder/ReadyResponder | closed | Timecards managed via text message | Claimed High Priority medium | Currently, timecards can be entered via the web UI. This creates the need for someone to do the clerical data entry. It would be much better if each individual volunteer could enter their own timecard through a text message.
People would text `arrive` to the ReadyResponder number when they arrive at the staging area. The capitalization should not matter. Upon receiving this message, the system should look up who sent the message, and see if there are any existing incomplete timecards for that person. These should be set to an `error` status. If no other timecards are found, create a new timecard for that person. The timecard should have the start time based on the time of the text. The status should be set to Incomplete. The system should respond to the user that a timecard has been started.
People would text `depart` when they are done and leaving the staging area. The system should look up the person who sent the message. It should then look for an open timecard, one that is `incomplete` and only has a start time. If more or less than one is found, they should all be set to an `error` status. The response should include an error message. Even if there is no correct timecard to complete, a new timecard with only this end_time should still be created, and immediately set to an error status. If only one is found, that timecard should be updated with the end time from the message, and a confirmation message returned.
ngrok is helpful in developing these features. | 1.0 | Timecards managed via text message - Currently, timecards can be entered via the web UI. This creates the need for someone to do the clerical data entry. It would be much better if each individual volunteer could enter their own timecard through a text message.
People would text `arrive` to the ReadyResponder number when they arrive at the staging area. The capitalization should not matter. Upon receiving this message, the system should look up who sent the message, and see if there are any existing incomplete timecards for that person. These should be set to an `error` status. If no other timecards are found, create a new timecard for that person. The timecard should have the start time based on the time of the text. The status should be set to Incomplete. The system should respond to the user that a timecard has been started.
People would text `depart` when they are done and leaving the staging area. The system should look up the person who sent the message. It should then look for an open timecard, one that is `incomplete` and only has a start time. If more or less than one is found, they should all be set to an `error` status. The response should include an error message. Even if there is no correct timecard to complete, a new timecard with only this end_time should still be created, and immediately set to an error status. If only one is found, that timecard should be updated with the end time from the message, and a confirmation message returned.
ngrok is helpful in developing these features. | non_usab | timecards managed via text message currently timecards can be entered via the web ui this creates the need for someone to do the clerical data entry it would be much better if each individual volunteer could enter their own timecard through a text message people would text arrive to the readyresponder number when they arrive at the staging area the capitalization should not matter upon receiving this message the system should look up who sent the message and see if there are any existing incomplete timecards for that person these should be set to an error status if no other timecards are found create a new timecard for that person the timecard should have the start time based on the time of the text the status should be set to incomplete the system should respond to the user that a timecard has been started people would text depart when they are done and leaving the staging area the system should look up the person who sent the message it should then look for an open timecard one that is incomplete and only has a start time if more or less than one is found they should all be set to an error status the response should include an error message even if there is no correct timecard to complete a new timecard with only this end time should still be created and immediately set to an error status if only one is found that timecard should be updated with the end time from the message and a confirmation message returned ngrok is helpful in developing these features | 0 |
13,269 | 8,407,114,138 | IssuesEvent | 2018-10-11 19:57:14 | LoopPerfect/buckaroo | https://api.github.com/repos/LoopPerfect/buckaroo | closed | Add should_remap_host_platform to .buckconfig when using quickstart | enhancement usability | Many packages assume that [`should_remap_host_platform`](https://buckbuild.com/files-and-dirs/buckconfig.html#cxx.should_remap_host_platform) is enabled. We should add this to the automatically generated `.buckconfig`. | True | Add should_remap_host_platform to .buckconfig when using quickstart - Many packages assume that [`should_remap_host_platform`](https://buckbuild.com/files-and-dirs/buckconfig.html#cxx.should_remap_host_platform) is enabled. We should add this to the automatically generated `.buckconfig`. | usab | add should remap host platform to buckconfig when using quickstart many packages assume that is enabled we should add this to the automatically generated buckconfig | 1 |
20,119 | 15,035,791,074 | IssuesEvent | 2021-02-02 14:32:43 | git4school/git4school-visu | https://api.github.com/repos/git4school/git4school-visu | closed | Hide "Graphs" menu when on home page | ready usability story | **Description**
We want to hide the _Graphs_ menu when the user is on the _home_ page for usability reasons. Indeed, it is currently possible to access the _overview_ graph in 2 different ways from the _home_ page.
**Hints**
It will therefore be necessary to make sure that the button to select an assignment does not reload it if there is nothing to load | True | Hide "Graphs" menu when on home page - **Description**
We want to hide the _Graphs_ menu when the user is on the _home_ page for usability reasons. Indeed, it is currently possible to access the _overview_ graph in 2 different ways from the _home_ page.
**Hints**
It will therefore be necessary to make sure that the button to select an assignment does not reload it if there is nothing to load | usab | hide graphs menu when on home page description we want to hide the graphs menu when the user is on the home page for usability reasons indeed it is currently possible to access the overview graph in different ways from the home page hints it will therefore be necessary to make sure that the button to select an assignment does not reload it if there is nothing to load | 1 |
34,737 | 4,952,729,723 | IssuesEvent | 2016-12-01 13:01:11 | astropy/astropy | https://api.github.com/repos/astropy/astropy | closed | Fix unit test fails on Windows / Appveyor | analytic_functions Bug io.ascii io.fits nddata testing Windows | When turning on continuous integration for Windows on AppVeyor in #2755 we told it to skip some unit tests that failed.
You can get a full list of these skipped tests in master using this full-text search:
https://github.com/astropy/astropy/search?utf8=%E2%9C%93&q=fails+on+AppVeyor
Here's a list:
- [x] `test_blackbody_scipy` and `test_blackbody_overflow` in `test_blackbody.py`
- [x] `test_setitem_invalid_shape` in `test_flag_collection.py`
- [ ] one test in `astropy.io.fits`
- [x] lots of tests in `astropy.io.ascii`
If someone with access to Windows could try to reproduce and fix these issues, that would be great!
| 1.0 | Fix unit test fails on Windows / Appveyor - When turning on continuous integration for Windows on AppVeyor in #2755 we told it to skip some unit tests that failed.
You can get a full list of these skipped tests in master using this full-text search:
https://github.com/astropy/astropy/search?utf8=%E2%9C%93&q=fails+on+AppVeyor
Here's a list:
- [x] `test_blackbody_scipy` and `test_blackbody_overflow` in `test_blackbody.py`
- [x] `test_setitem_invalid_shape` in `test_flag_collection.py`
- [ ] one test in `astropy.io.fits`
- [x] lots of tests in `astropy.io.ascii`
If someone with access to Windows could try to reproduce and fix these issues, that would be great!
| non_usab | fix unit test fails on windows appveyor when turning on continuous integration for windows on appveyor in we told it to skip some unit tests that failed you can get a full list of these skipped tests in master using this full text search here s a list test blackbody scipy and test blackbody overflow in test blackbody py test setitem invalid shape in test flag collection py one test in astropy io fits lots of tests in astropy io ascii if someone with access to windows could try to reproduce and fix these issues that would be great | 0 |
27,161 | 27,771,618,998 | IssuesEvent | 2023-03-16 14:47:30 | pulumi/pulumi-gcp | https://api.github.com/repos/pulumi/pulumi-gcp | closed | gcp.cloudfunctions.HttpCallbackFunction should support minInstances and maxInstances | impact/usability kind/enhancement help-wanted size/S good-first-issue | Both properties are not available in the `HttpCallbackFunctionArgs` type for the HttpCallbackFunction convenience constructor.
Once deployed, I can set the min and max instances through GCP console, so these properties are valid. | True | gcp.cloudfunctions.HttpCallbackFunction should support minInstances and maxInstances - Both properties are not available in the `HttpCallbackFunctionArgs` type for the HttpCallbackFunction convenience constructor.
Once deployed, I can set the min and max instances through GCP console, so these properties are valid. | usab | gcp cloudfunctions httpcallbackfunction should support mininstances and maxinstances both properties are not available in the httpcallbackfunctionargs type for the httpcallbackfunction convenience constructor once deployed i can set the min and max instances through gcp console so these properties are valid | 1 |
11,372 | 2,649,807,053 | IssuesEvent | 2015-03-15 09:35:16 | Grumbel/galapix | https://api.github.com/repos/Grumbel/galapix | closed | Google Code will close | auto-migrated Priority-Medium Type-Defect | ```
http://google-opensource.blogspot.com/2015/03/farewell-to-google-code.html
The option is migrating to any alternative and put the new url in the main page
(project home).
the big majority has opted for github, but us have until august to decide.
```
Original issue reported on code.google.com by `prflr88@gmail.com` on 14 Mar 2015 at 4:03 | 1.0 | Google Code will close - ```
http://google-opensource.blogspot.com/2015/03/farewell-to-google-code.html
The option is migrating to any alternative and put the new url in the main page
(project home).
the big majority has opted for github, but us have until august to decide.
```
Original issue reported on code.google.com by `prflr88@gmail.com` on 14 Mar 2015 at 4:03 | non_usab | google code will close the option is migrating to any alternative and put the new url in the main page project home the big majority has opted for github but us have until august to decide original issue reported on code google com by gmail com on mar at | 0 |
16,441 | 10,926,622,634 | IssuesEvent | 2019-11-22 15:04:56 | Zilliqa/scilla | https://api.github.com/repos/Zilliqa/scilla | opened | Mutable fields should be in scope in expressions | backwards-incompatible-change enhancement usability | Similar to how contract parameters are in scope in expression, so should mutable fields.
Note that
- We need to ensure that shadowing of fields and variables is implemented correctly. Also, we need to ensure that we issue appropriate warnings in case shadowing takes place.
- The cashflow analyser needs to implement the same scoping rules.
- This change probably isn't backward compatible, since a change to the scoping rules may cause unintended shadowing.
- This change eliminates the need for the `<-` syntax, which should be removed. The `:=` syntax should stay, though, since expressions may only read from mutable fields, not write to them. | True | Mutable fields should be in scope in expressions - Similar to how contract parameters are in scope in expression, so should mutable fields.
Note that
- We need to ensure that shadowing of fields and variables is implemented correctly. Also, we need to ensure that we issue appropriate warnings in case shadowing takes place.
- The cashflow analyser needs to implement the same scoping rules.
- This change probably isn't backward compatible, since a change to the scoping rules may cause unintended shadowing.
- This change eliminates the need for the `<-` syntax, which should be removed. The `:=` syntax should stay, though, since expressions may only read from mutable fields, not write to them. | usab | mutable fields should be in scope in expressions similar to how contract parameters are in scope in expression so should mutable fields note that we need to ensure that shadowing of fields and variables is implemented correctly also we need to ensure that we issue appropriate warnings in case shadowing takes place the cashflow analyser needs to implement the same scoping rules this change probably isn t backward compatible since a change to the scoping rules may cause unintended shadowing this change eliminates the need for the syntax which should be removed the syntax should stay though since expressions may only read from mutable fields not write to them | 1 |
11,252 | 9,022,916,806 | IssuesEvent | 2019-02-07 04:20:09 | sb/smallbasic-editor | https://api.github.com/repos/sb/smallbasic-editor | opened | Improve development cycle | type/infrastructure | As mentioned in the main `README` file, to have a fast edit/run cycle, you need:
* a separate CLI command needs to be run to listen to client editor changes.
* rebuild the generators whenever their models change.
We should look into how this cycle can be improved, so that Visual Studio can pick up these changes and recompile automatically. | 1.0 | Improve development cycle - As mentioned in the main `README` file, to have a fast edit/run cycle, you need:
* a separate CLI command needs to be run to listen to client editor changes.
* rebuild the generators whenever their models change.
We should look into how this cycle can be improved, so that Visual Studio can pick up these changes and recompile automatically. | non_usab | improve development cycle as mentioned in the main readme file to have a fast edit run cycle you need a separate cli command needs to be run to listen to client editor changes rebuild the generators whenever their models change we should look into how this cycle can be improved so that visual studio can pick up these changes and recompile automatically | 0 |
26,523 | 26,909,566,223 | IssuesEvent | 2023-02-06 22:10:49 | Ericsson/codechecker | https://api.github.com/repos/Ericsson/codechecker | closed | CodeChecker to support clang-tools like compilation database lookup (multi-root workspace) | analyzer :chart_with_upwards_trend: usability :+1: new feature :+1: | CodeChecker should support an analysis mode where for each source file,
it tries to find the closest compile_commands.json file up in the directory hierarchy starting from the source file.
clangd and clang-tidy works this way: https://clangd.llvm.org/installation.html
clangd will look in the parent directories of the files you edit looking for it, and also in subdirectories named build/. For example, if editing $SRC/gui/window.cpp, we search in $SRC/gui/, $SRC/gui/build/, $SRC/, $SRC/build/, …
This feature would allow the analaysis of multi-root projects also in the vscode plugin https://github.com/Ericsson/CodecheckerVSCodePlugin/issues/113 | True | CodeChecker to support clang-tools like compilation database lookup (multi-root workspace) - CodeChecker should support an analysis mode where for each source file,
it tries to find the closest compile_commands.json file up in the directory hierarchy starting from the source file.
clangd and clang-tidy works this way: https://clangd.llvm.org/installation.html
clangd will look in the parent directories of the files you edit looking for it, and also in subdirectories named build/. For example, if editing $SRC/gui/window.cpp, we search in $SRC/gui/, $SRC/gui/build/, $SRC/, $SRC/build/, …
This feature would allow the analaysis of multi-root projects also in the vscode plugin https://github.com/Ericsson/CodecheckerVSCodePlugin/issues/113 | usab | codechecker to support clang tools like compilation database lookup multi root workspace codechecker should support an analysis mode where for each source file it tries to find the closest compile commands json file up in the directory hierarchy starting from the source file clangd and clang tidy works this way clangd will look in the parent directories of the files you edit looking for it and also in subdirectories named build for example if editing src gui window cpp we search in src gui src gui build src src build … this feature would allow the analaysis of multi root projects also in the vscode plugin | 1 |
8,407 | 5,661,370,929 | IssuesEvent | 2017-04-10 17:12:13 | umts/probable-engine | https://api.github.com/repos/umts/probable-engine | closed | Inventory check for rentals/rental_schedule | enhancement usability | @owlee suggests adding an inventory check to the form on `rentals/rental_schedule`, specifically run when selecting dates (ajax?). Server side validations still apply.
| True | Inventory check for rentals/rental_schedule - @owlee suggests adding an inventory check to the form on `rentals/rental_schedule`, specifically run when selecting dates (ajax?). Server side validations still apply.
| usab | inventory check for rentals rental schedule owlee suggests adding an inventory check to the form on rentals rental schedule specifically run when selecting dates ajax server side validations still apply | 1 |
122,434 | 10,222,887,634 | IssuesEvent | 2019-08-16 08:08:53 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | The Cancle button is empty on upload blob dialog with AzCopy checked | :beetle: regression :gear: azcopy :gear: blobs 🧪 testing | **Storage Explorer Version:** 1.9.0
**Build:** 20190815.2
**Platform/OS:** Linux Ubuntu 19.04/Windows 10/macOS High Sierra
**Architecture:** ia32/x64
**Regression From:** Previous release(1.9.0)
**Steps to reproduce:**
1. Make sure AzCopy is checked.
2. Expand a storage account -> Blob Containers.
2. Create a new blob container -> Try to upload a blob to it.
3. Check the upload dialog.
**Expect Experience:**
The Cancel button shows well.
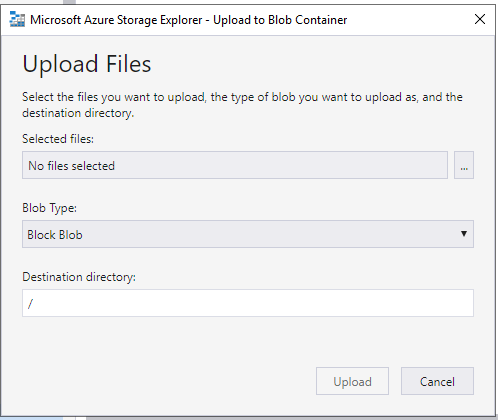
**Actual Experience:**
The Cancle button is empty for upload blob dialog
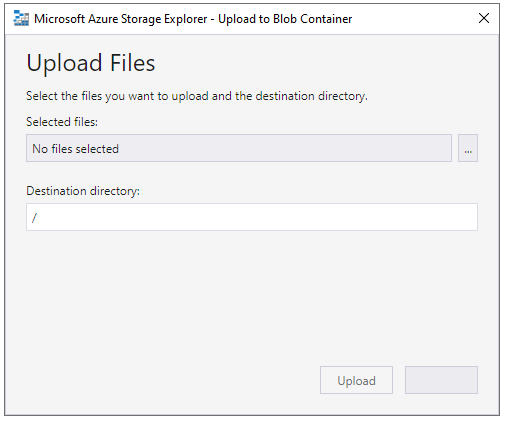
**More Info:**
1. This issue doesn't reproduce when AzCopy is unchecked.
2. This issue doesn't reproduce for one file share. | 1.0 | The Cancle button is empty on upload blob dialog with AzCopy checked - **Storage Explorer Version:** 1.9.0
**Build:** 20190815.2
**Platform/OS:** Linux Ubuntu 19.04/Windows 10/macOS High Sierra
**Architecture:** ia32/x64
**Regression From:** Previous release(1.9.0)
**Steps to reproduce:**
1. Make sure AzCopy is checked.
2. Expand a storage account -> Blob Containers.
2. Create a new blob container -> Try to upload a blob to it.
3. Check the upload dialog.
**Expect Experience:**
The Cancel button shows well.
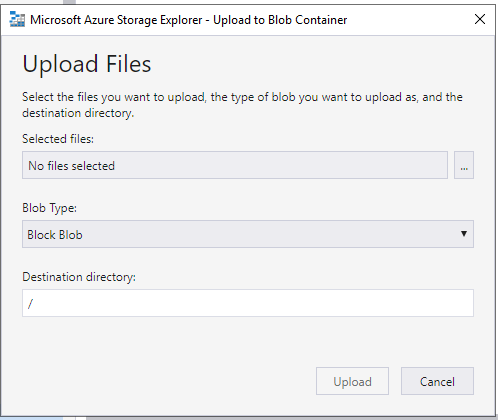
**Actual Experience:**
The Cancle button is empty for upload blob dialog
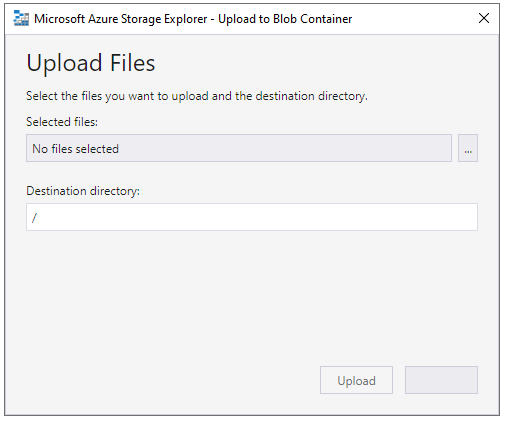
**More Info:**
1. This issue doesn't reproduce when AzCopy is unchecked.
2. This issue doesn't reproduce for one file share. | non_usab | the cancle button is empty on upload blob dialog with azcopy checked storage explorer version build platform os linux ubuntu windows macos high sierra architecture regression from previous release steps to reproduce make sure azcopy is checked expand a storage account blob containers create a new blob container try to upload a blob to it check the upload dialog expect experience the cancel button shows well actual experience the cancle button is empty for upload blob dialog more info this issue doesn t reproduce when azcopy is unchecked this issue doesn t reproduce for one file share | 0 |
334,524 | 29,871,810,699 | IssuesEvent | 2023-06-20 08:59:29 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | reopened | com.hazelcast.internal.metrics.impl.MetricsCompressorTest [HZ-2538] | Team: Core Type: Test-Failure Source: Internal to-jira | _master_ (commit 65933d5f0689250b39ad958322ee6fb77baaf936)
Failed on ibm-8: https://jenkins.hazelcast.com/view/Official%20Builds/job/Hazelcast-master-IbmJDK8-fips/56/testReport/com.hazelcast.internal.metrics.impl/MetricsCompressorTest/
Almost all tests in `com.hazelcast.internal.metrics.impl.MetricsCompressorTest` failed with the same expcetion.
<details><summary>Stacktrace (for testTwoMetrics_secondWithoutTags as example):</summary>
```
Wanted but not invoked:
defaultMetricDescriptorSupplier.get();
-> at com.hazelcast.internal.metrics.impl.DefaultMetricDescriptorSupplier.get(DefaultMetricDescriptorSupplier.java:32)
Actually, there were zero interactions with this mock.
at com.hazelcast.internal.metrics.impl.DefaultMetricDescriptorSupplier.get(DefaultMetricDescriptorSupplier.java:32)
at com.hazelcast.internal.metrics.impl.DefaultMetricDescriptorSupplier.get(DefaultMetricDescriptorSupplier.java:27)
at com.hazelcast.internal.metrics.impl.MetricsCompressorTest.testTwoMetrics_secondWithoutTags(MetricsCompressorTest.java:221)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:115)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:107)
at java.util.concurrent.FutureTask.run(FutureTask.java:277)
at java.lang.Thread.run(Thread.java:825)
```
</details>
Standard output can be found here - https://s3.console.aws.amazon.com/s3/buckets/j-artifacts/Hazelcast-master-IbmJDK8-fips/56/
| 1.0 | com.hazelcast.internal.metrics.impl.MetricsCompressorTest [HZ-2538] - _master_ (commit 65933d5f0689250b39ad958322ee6fb77baaf936)
Failed on ibm-8: https://jenkins.hazelcast.com/view/Official%20Builds/job/Hazelcast-master-IbmJDK8-fips/56/testReport/com.hazelcast.internal.metrics.impl/MetricsCompressorTest/
Almost all tests in `com.hazelcast.internal.metrics.impl.MetricsCompressorTest` failed with the same expcetion.
<details><summary>Stacktrace (for testTwoMetrics_secondWithoutTags as example):</summary>
```
Wanted but not invoked:
defaultMetricDescriptorSupplier.get();
-> at com.hazelcast.internal.metrics.impl.DefaultMetricDescriptorSupplier.get(DefaultMetricDescriptorSupplier.java:32)
Actually, there were zero interactions with this mock.
at com.hazelcast.internal.metrics.impl.DefaultMetricDescriptorSupplier.get(DefaultMetricDescriptorSupplier.java:32)
at com.hazelcast.internal.metrics.impl.DefaultMetricDescriptorSupplier.get(DefaultMetricDescriptorSupplier.java:27)
at com.hazelcast.internal.metrics.impl.MetricsCompressorTest.testTwoMetrics_secondWithoutTags(MetricsCompressorTest.java:221)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:115)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:107)
at java.util.concurrent.FutureTask.run(FutureTask.java:277)
at java.lang.Thread.run(Thread.java:825)
```
</details>
Standard output can be found here - https://s3.console.aws.amazon.com/s3/buckets/j-artifacts/Hazelcast-master-IbmJDK8-fips/56/
| non_usab | com hazelcast internal metrics impl metricscompressortest master commit failed on ibm almost all tests in com hazelcast internal metrics impl metricscompressortest failed with the same expcetion stacktrace for testtwometrics secondwithouttags as example wanted but not invoked defaultmetricdescriptorsupplier get at com hazelcast internal metrics impl defaultmetricdescriptorsupplier get defaultmetricdescriptorsupplier java actually there were zero interactions with this mock at com hazelcast internal metrics impl defaultmetricdescriptorsupplier get defaultmetricdescriptorsupplier java at com hazelcast internal metrics impl defaultmetricdescriptorsupplier get defaultmetricdescriptorsupplier java at com hazelcast internal metrics impl metricscompressortest testtwometrics secondwithouttags metricscompressortest java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at com hazelcast test failontimeoutstatement callablestatement call failontimeoutstatement java at com hazelcast test failontimeoutstatement callablestatement call failontimeoutstatement java at java util concurrent futuretask run futuretask java at java lang thread run thread java standard output can be found here | 0 |
22,019 | 7,110,037,066 | IssuesEvent | 2018-01-17 09:14:37 | opencv/opencv | https://api.github.com/repos/opencv/opencv | closed | building framework fails when older version of opencv is installed on macOS | category: build/install category: ios/osx | - OpenCV => 3.2
- Operating System / Platform => MacOS 10.12
- Compiler => XCode 8
##### Detailed description
The core/private.hpp header is mixed up with the installed version in /usr/local. this has the effect that certain defines like CV_INSTRUMENT_REGION() will crash the compilation throughout the code base. The main reason is that /usr/local/include is added to the import path for the platform/osx build. Not sure why, I worked around it by temporarily removing the opencv headers from my system.
##### Steps to reproduce
Install opencv 3.1 into /usr/local
checkout 3.2
run `cd platforms/osx;python build_framework.py --contrib=../../../opencv_contrib build`
| 1.0 | building framework fails when older version of opencv is installed on macOS - - OpenCV => 3.2
- Operating System / Platform => MacOS 10.12
- Compiler => XCode 8
##### Detailed description
The core/private.hpp header is mixed up with the installed version in /usr/local. this has the effect that certain defines like CV_INSTRUMENT_REGION() will crash the compilation throughout the code base. The main reason is that /usr/local/include is added to the import path for the platform/osx build. Not sure why, I worked around it by temporarily removing the opencv headers from my system.
##### Steps to reproduce
Install opencv 3.1 into /usr/local
checkout 3.2
run `cd platforms/osx;python build_framework.py --contrib=../../../opencv_contrib build`
| non_usab | building framework fails when older version of opencv is installed on macos opencv operating system platform macos compiler xcode detailed description the core private hpp header is mixed up with the installed version in usr local this has the effect that certain defines like cv instrument region will crash the compilation throughout the code base the main reason is that usr local include is added to the import path for the platform osx build not sure why i worked around it by temporarily removing the opencv headers from my system steps to reproduce install opencv into usr local checkout run cd platforms osx python build framework py contrib opencv contrib build | 0 |
1,991 | 3,455,448,347 | IssuesEvent | 2015-12-17 20:10:19 | RobDixonIII/Bloom | https://api.github.com/repos/RobDixonIII/Bloom | reopened | Add Buttons to Taxonomies Module | infrastructure | Add simple buttons to the taxonomies module to load the following modules into new tabs:
* Album
* Artist
* Library
* Person
* Playlist
* Song | 1.0 | Add Buttons to Taxonomies Module - Add simple buttons to the taxonomies module to load the following modules into new tabs:
* Album
* Artist
* Library
* Person
* Playlist
* Song | non_usab | add buttons to taxonomies module add simple buttons to the taxonomies module to load the following modules into new tabs album artist library person playlist song | 0 |
16,570 | 11,089,765,366 | IssuesEvent | 2019-12-14 20:54:45 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Tileset Zoom is not enough for pixel art | discussion enhancement topic:editor usability | **Godot version:**
3.2 beta 3
Perhaps its just my very poor eyesight. But the maximum zoom of the tileset editor is not sufficient for detailed pixel art games.
I realize its feature freeze but it would certainly help this impaired vision dev to increase the maximum zoom limit.
| True | Tileset Zoom is not enough for pixel art - **Godot version:**
3.2 beta 3
Perhaps its just my very poor eyesight. But the maximum zoom of the tileset editor is not sufficient for detailed pixel art games.
I realize its feature freeze but it would certainly help this impaired vision dev to increase the maximum zoom limit.
| usab | tileset zoom is not enough for pixel art godot version beta perhaps its just my very poor eyesight but the maximum zoom of the tileset editor is not sufficient for detailed pixel art games i realize its feature freeze but it would certainly help this impaired vision dev to increase the maximum zoom limit | 1 |
12,098 | 9,594,874,665 | IssuesEvent | 2019-05-09 14:52:20 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | [metricbeat] undocumented behavior of system/socket metricset when running in docker | :infrastructure Metricbeat [zube]: In Progress bug docs | For confirmed bugs, please report:
- Version: 7.0
- Operating System: linux
- Steps to Reproduce:
1. setup docker based on the configuration here: https://www.elastic.co/guide/en/beats/metricbeat/current/running-on-docker.html
```
docker run \
--user=root \
--name=metricbeat-test \
--mount type=bind,source=/proc,target=/hostfs/proc,readonly \
--mount type=bind,source=/sys/fs/cgroup,target=/hostfs/sys/fs/cgroup,readonly \
--mount type=bind,source=/,target=/hostfs,readonly \
--net=host \
--volume="$(pwd)/metricbeat.docker.yml:/usr/share/metricbeat/metricbeat.yml:ro" \
docker.elastic.co/beats/metricbeat:7.0.0 \
-e -system.hostfs=/hostfs
```
2. enable the system/socket metricset
3. Get some weird errors:
```
"system": {
"socket": {
"local": {
"port": 22,
"ip": "::"
}
}
},
"ecs": {
"version": "1.0.0"
},
"server": {
"ip": "::",
"port": 22
},
"error": {
"code": "process not found. inode=29023, tcp_state=LISTEN"
},
```
What's happening here is that the metricset is using netlink to actually grab socket data, and then using procfs to map the inodes back to processes. Even when running as `root` the container process doesn't have permissions to access the host symlinks in `/proc/$pid/fd`, hence the error. A temporary workaround is to use `--privileged`, which is a tad blunt. You can also omit the `--user=root`, although having metricbeat just monitor its own socket usage isn't that helpful, as an info message will tell you:
```
INFO socket/socket.go:81 socket process info will only be available for metricbeat because the process is running as a non-root user
```
It seems to be we should either alter the behavior of the metricset or document how to work around this. Having metricbeat monitor the host system from inside docker seems to be a supported use case, and I don't see anything on the above-linked page that would allow the socket metricset to just work. We may also want to document that without `--user=root` the metricset will just monitor itself, as `--user=root` is mentioned on the above-linked page, but never really explained. We may also want to do some kind of permissions check at runtime and print another info message similar to the one above. | 1.0 | [metricbeat] undocumented behavior of system/socket metricset when running in docker - For confirmed bugs, please report:
- Version: 7.0
- Operating System: linux
- Steps to Reproduce:
1. setup docker based on the configuration here: https://www.elastic.co/guide/en/beats/metricbeat/current/running-on-docker.html
```
docker run \
--user=root \
--name=metricbeat-test \
--mount type=bind,source=/proc,target=/hostfs/proc,readonly \
--mount type=bind,source=/sys/fs/cgroup,target=/hostfs/sys/fs/cgroup,readonly \
--mount type=bind,source=/,target=/hostfs,readonly \
--net=host \
--volume="$(pwd)/metricbeat.docker.yml:/usr/share/metricbeat/metricbeat.yml:ro" \
docker.elastic.co/beats/metricbeat:7.0.0 \
-e -system.hostfs=/hostfs
```
2. enable the system/socket metricset
3. Get some weird errors:
```
"system": {
"socket": {
"local": {
"port": 22,
"ip": "::"
}
}
},
"ecs": {
"version": "1.0.0"
},
"server": {
"ip": "::",
"port": 22
},
"error": {
"code": "process not found. inode=29023, tcp_state=LISTEN"
},
```
What's happening here is that the metricset is using netlink to actually grab socket data, and then using procfs to map the inodes back to processes. Even when running as `root` the container process doesn't have permissions to access the host symlinks in `/proc/$pid/fd`, hence the error. A temporary workaround is to use `--privileged`, which is a tad blunt. You can also omit the `--user=root`, although having metricbeat just monitor its own socket usage isn't that helpful, as an info message will tell you:
```
INFO socket/socket.go:81 socket process info will only be available for metricbeat because the process is running as a non-root user
```
It seems to be we should either alter the behavior of the metricset or document how to work around this. Having metricbeat monitor the host system from inside docker seems to be a supported use case, and I don't see anything on the above-linked page that would allow the socket metricset to just work. We may also want to document that without `--user=root` the metricset will just monitor itself, as `--user=root` is mentioned on the above-linked page, but never really explained. We may also want to do some kind of permissions check at runtime and print another info message similar to the one above. | non_usab | undocumented behavior of system socket metricset when running in docker for confirmed bugs please report version operating system linux steps to reproduce setup docker based on the configuration here docker run user root name metricbeat test mount type bind source proc target hostfs proc readonly mount type bind source sys fs cgroup target hostfs sys fs cgroup readonly mount type bind source target hostfs readonly net host volume pwd metricbeat docker yml usr share metricbeat metricbeat yml ro docker elastic co beats metricbeat e system hostfs hostfs enable the system socket metricset get some weird errors system socket local port ip ecs version server ip port error code process not found inode tcp state listen what s happening here is that the metricset is using netlink to actually grab socket data and then using procfs to map the inodes back to processes even when running as root the container process doesn t have permissions to access the host symlinks in proc pid fd hence the error a temporary workaround is to use privileged which is a tad blunt you can also omit the user root although having metricbeat just monitor its own socket usage isn t that helpful as an info message will tell you info socket socket go socket process info will only be available for metricbeat because the process is running as a non root user it seems to be we should either alter the behavior of the metricset or document how to work around this having metricbeat monitor the host system from inside docker seems to be a supported use case and i don t see anything on the above linked page that would allow the socket metricset to just work we may also want to document that without user root the metricset will just monitor itself as user root is mentioned on the above linked page but never really explained we may also want to do some kind of permissions check at runtime and print another info message similar to the one above | 0 |
10,222 | 8,441,563,983 | IssuesEvent | 2018-10-18 10:36:20 | geli-lms/geli | https://api.github.com/repos/geli-lms/geli | closed | Setup a BACKUP | enhancement infrastructure | # User Story
### As a:
Hoster
### I want:
to have a backup of ALL data
### so that:
we can restore the system if anything goes wrong.
## Storypoints:
## Acceptance criteria:
- [ ] a total serves crash is no problem
- [x] before a new version gets applied, a backup is done
- [ ] the backup is stored outside of the live server
- [x] an automatic backup is done every 24h
- [ ] a wiki/readme article about backuping is written
## Additional info:
To be discussed:
- what data we need to backup
- how do we backup them
- where do we store the backups
- how long do we store the backups? | 1.0 | Setup a BACKUP - # User Story
### As a:
Hoster
### I want:
to have a backup of ALL data
### so that:
we can restore the system if anything goes wrong.
## Storypoints:
## Acceptance criteria:
- [ ] a total serves crash is no problem
- [x] before a new version gets applied, a backup is done
- [ ] the backup is stored outside of the live server
- [x] an automatic backup is done every 24h
- [ ] a wiki/readme article about backuping is written
## Additional info:
To be discussed:
- what data we need to backup
- how do we backup them
- where do we store the backups
- how long do we store the backups? | non_usab | setup a backup user story as a hoster i want to have a backup of all data so that we can restore the system if anything goes wrong storypoints acceptance criteria a total serves crash is no problem before a new version gets applied a backup is done the backup is stored outside of the live server an automatic backup is done every a wiki readme article about backuping is written additional info to be discussed what data we need to backup how do we backup them where do we store the backups how long do we store the backups | 0 |
276,904 | 30,567,876,587 | IssuesEvent | 2023-07-20 19:18:30 | samq-democorp/easybuggy-lvp | https://api.github.com/repos/samq-democorp/easybuggy-lvp | opened | nekohtml-1.9.16.jar: 3 vulnerabilities (highest severity is: 7.5) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p></summary>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (nekohtml version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-28366](https://www.mend.io/vulnerability-database/CVE-2022-28366) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Direct | net.sourceforge.htmlunit:neko-htmlunit:2.27 | ✅ |
| [CVE-2022-29546](https://www.mend.io/vulnerability-database/CVE-2022-29546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Direct | net.sourceforge.htmlunit:neko-htmlunit:2.61.0 | ✅ |
| [CVE-2022-24839](https://www.mend.io/vulnerability-database/CVE-2022-24839) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Direct | net.sourceforge.nekohtml:nekohtml:1.9.22.noko2 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-28366</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Certain Neko-related HTML parsers allow a denial of service via crafted Processing Instruction (PI) input that causes excessive heap memory consumption. In particular, this issue exists in HtmlUnit-Neko through 2.26, and is fixed in 2.27. This issue also exists in CyberNeko HTML through 1.9.22 (also affecting OWASP AntiSamy before 1.6.6), but 1.9.22 is the last version of CyberNeko HTML. NOTE: this may be related to CVE-2022-24839.
<p>Publish Date: 2022-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-28366>CVE-2022-28366</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-g9hh-vvx3-v37v">https://github.com/advisories/GHSA-g9hh-vvx3-v37v</a></p>
<p>Release Date: 2022-04-21</p>
<p>Fix Resolution: net.sourceforge.htmlunit:neko-htmlunit:2.27</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-29546</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
HtmlUnit NekoHtml Parser before 2.61.0 suffers from a denial of service vulnerability. Crafted input associated with the parsing of Processing Instruction (PI) data leads to heap memory consumption. This is similar to CVE-2022-28366 but affects a much later version of the product.
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29546>CVE-2022-29546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: net.sourceforge.htmlunit:neko-htmlunit:2.61.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-24839</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
org.cyberneko.html is an html parser written in Java. The fork of `org.cyberneko.html` used by Nokogiri (Rubygem) raises a `java.lang.OutOfMemoryError` exception when parsing ill-formed HTML markup. Users are advised to upgrade to `>= 1.9.22.noko2`. Note: The upstream library `org.cyberneko.html` is no longer maintained. Nokogiri uses its own fork of this library located at https://github.com/sparklemotion/nekohtml and this CVE applies only to that fork. Other forks of nekohtml may have a similar vulnerability.
<p>Publish Date: 2022-04-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24839>CVE-2022-24839</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv">https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv</a></p>
<p>Release Date: 2022-04-11</p>
<p>Fix Resolution: net.sourceforge.nekohtml:nekohtml:1.9.22.noko2</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p> | True | nekohtml-1.9.16.jar: 3 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p></summary>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (nekohtml version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-28366](https://www.mend.io/vulnerability-database/CVE-2022-28366) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Direct | net.sourceforge.htmlunit:neko-htmlunit:2.27 | ✅ |
| [CVE-2022-29546](https://www.mend.io/vulnerability-database/CVE-2022-29546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Direct | net.sourceforge.htmlunit:neko-htmlunit:2.61.0 | ✅ |
| [CVE-2022-24839](https://www.mend.io/vulnerability-database/CVE-2022-24839) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Direct | net.sourceforge.nekohtml:nekohtml:1.9.22.noko2 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-28366</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Certain Neko-related HTML parsers allow a denial of service via crafted Processing Instruction (PI) input that causes excessive heap memory consumption. In particular, this issue exists in HtmlUnit-Neko through 2.26, and is fixed in 2.27. This issue also exists in CyberNeko HTML through 1.9.22 (also affecting OWASP AntiSamy before 1.6.6), but 1.9.22 is the last version of CyberNeko HTML. NOTE: this may be related to CVE-2022-24839.
<p>Publish Date: 2022-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-28366>CVE-2022-28366</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-g9hh-vvx3-v37v">https://github.com/advisories/GHSA-g9hh-vvx3-v37v</a></p>
<p>Release Date: 2022-04-21</p>
<p>Fix Resolution: net.sourceforge.htmlunit:neko-htmlunit:2.27</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-29546</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
HtmlUnit NekoHtml Parser before 2.61.0 suffers from a denial of service vulnerability. Crafted input associated with the parsing of Processing Instruction (PI) data leads to heap memory consumption. This is similar to CVE-2022-28366 but affects a much later version of the product.
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29546>CVE-2022-29546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: net.sourceforge.htmlunit:neko-htmlunit:2.61.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-24839</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/nekohtml-1.9.16.jar,/home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/easybuggy-lvp/commit/4afba820e35532010e5668591baf0bbbb1da4148">4afba820e35532010e5668591baf0bbbb1da4148</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
org.cyberneko.html is an html parser written in Java. The fork of `org.cyberneko.html` used by Nokogiri (Rubygem) raises a `java.lang.OutOfMemoryError` exception when parsing ill-formed HTML markup. Users are advised to upgrade to `>= 1.9.22.noko2`. Note: The upstream library `org.cyberneko.html` is no longer maintained. Nokogiri uses its own fork of this library located at https://github.com/sparklemotion/nekohtml and this CVE applies only to that fork. Other forks of nekohtml may have a similar vulnerability.
<p>Publish Date: 2022-04-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24839>CVE-2022-24839</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv">https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv</a></p>
<p>Release Date: 2022-04-11</p>
<p>Fix Resolution: net.sourceforge.nekohtml:nekohtml:1.9.22.noko2</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p> | non_usab | nekohtml jar vulnerabilities highest severity is vulnerable library nekohtml jar an html parser and tag balancer library home page a href path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib nekohtml jar home wss scanner repository net sourceforge nekohtml nekohtml nekohtml jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in nekohtml version remediation available high nekohtml jar direct net sourceforge htmlunit neko htmlunit high nekohtml jar direct net sourceforge htmlunit neko htmlunit high nekohtml jar direct net sourceforge nekohtml nekohtml details cve vulnerable library nekohtml jar an html parser and tag balancer library home page a href path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib nekohtml jar home wss scanner repository net sourceforge nekohtml nekohtml nekohtml jar dependency hierarchy x nekohtml jar vulnerable library found in head commit a href found in base branch master vulnerability details certain neko related html parsers allow a denial of service via crafted processing instruction pi input that causes excessive heap memory consumption in particular this issue exists in htmlunit neko through and is fixed in this issue also exists in cyberneko html through also affecting owasp antisamy before but is the last version of cyberneko html note this may be related to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution net sourceforge htmlunit neko htmlunit in order to enable automatic remediation please create cve vulnerable library nekohtml jar an html parser and tag balancer library home page a href path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib nekohtml jar home wss scanner repository net sourceforge nekohtml nekohtml nekohtml jar dependency hierarchy x nekohtml jar vulnerable library found in head commit a href found in base branch master vulnerability details htmlunit nekohtml parser before suffers from a denial of service vulnerability crafted input associated with the parsing of processing instruction pi data leads to heap memory consumption this is similar to cve but affects a much later version of the product publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution net sourceforge htmlunit neko htmlunit in order to enable automatic remediation please create cve vulnerable library nekohtml jar an html parser and tag balancer library home page a href path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib nekohtml jar home wss scanner repository net sourceforge nekohtml nekohtml nekohtml jar dependency hierarchy x nekohtml jar vulnerable library found in head commit a href found in base branch master vulnerability details org cyberneko html is an html parser written in java the fork of org cyberneko html used by nokogiri rubygem raises a java lang outofmemoryerror exception when parsing ill formed html markup users are advised to upgrade to note the upstream library org cyberneko html is no longer maintained nokogiri uses its own fork of this library located at and this cve applies only to that fork other forks of nekohtml may have a similar vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution net sourceforge nekohtml nekohtml in order to enable automatic remediation please create in order to enable automatic remediation for this issue please create | 0 |
22,854 | 20,368,594,408 | IssuesEvent | 2022-02-21 09:02:10 | prologdb/runtime | https://api.github.com/repos/prologdb/runtime | closed | Detailed Exceptions | usability embed | In every place where currently a `PrologRuntimeException` is being thrown, introduce an exception class (as a subclass of `PrologRuntimeException`) that clearly describes this failure mode, along with important information about the failure. | True | Detailed Exceptions - In every place where currently a `PrologRuntimeException` is being thrown, introduce an exception class (as a subclass of `PrologRuntimeException`) that clearly describes this failure mode, along with important information about the failure. | usab | detailed exceptions in every place where currently a prologruntimeexception is being thrown introduce an exception class as a subclass of prologruntimeexception that clearly describes this failure mode along with important information about the failure | 1 |
171,720 | 20,987,800,282 | IssuesEvent | 2022-03-29 06:14:12 | Satheesh575555/external_pdfium | https://api.github.com/repos/Satheesh575555/external_pdfium | opened | CVE-2018-6616 (Medium) detected in external_pdfiumtinker_edge_r-android9-1.0.2 | security vulnerability | ## CVE-2018-6616 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>external_pdfiumtinker_edge_r-android9-1.0.2</b></p></summary>
<p>
<p>Library home page: <a href=https://github.com/TinkerEdgeR-Android/external_pdfium.git>https://github.com/TinkerEdgeR-Android/external_pdfium.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/external_pdfium/commit/ac9e7ad2804cd2e179b787cb6e286be7591f4014">ac9e7ad2804cd2e179b787cb6e286be7591f4014</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/third_party/libopenjpeg20/t1.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In OpenJPEG 2.3.0, there is excessive iteration in the opj_t1_encode_cblks function of openjp2/t1.c. Remote attackers could leverage this vulnerability to cause a denial of service via a crafted bmp file.
<p>Publish Date: 2018-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-6616>CVE-2018-6616</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-6616">https://nvd.nist.gov/vuln/detail/CVE-2018-6616</a></p>
<p>Release Date: 2018-02-04</p>
<p>Fix Resolution: openjpeg2-tools - 2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-debuginfo - 2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-devel-docs - 2.3.1-1,2.3.1-1;openjpeg2 - 2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-devel - 2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-tools-debuginfo - 2.3.1-1,2.3.1-1;openjpeg2-debugsource - 2.3.1-1,2.3.1-1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-6616 (Medium) detected in external_pdfiumtinker_edge_r-android9-1.0.2 - ## CVE-2018-6616 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>external_pdfiumtinker_edge_r-android9-1.0.2</b></p></summary>
<p>
<p>Library home page: <a href=https://github.com/TinkerEdgeR-Android/external_pdfium.git>https://github.com/TinkerEdgeR-Android/external_pdfium.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/external_pdfium/commit/ac9e7ad2804cd2e179b787cb6e286be7591f4014">ac9e7ad2804cd2e179b787cb6e286be7591f4014</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/third_party/libopenjpeg20/t1.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In OpenJPEG 2.3.0, there is excessive iteration in the opj_t1_encode_cblks function of openjp2/t1.c. Remote attackers could leverage this vulnerability to cause a denial of service via a crafted bmp file.
<p>Publish Date: 2018-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-6616>CVE-2018-6616</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-6616">https://nvd.nist.gov/vuln/detail/CVE-2018-6616</a></p>
<p>Release Date: 2018-02-04</p>
<p>Fix Resolution: openjpeg2-tools - 2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-debuginfo - 2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-devel-docs - 2.3.1-1,2.3.1-1;openjpeg2 - 2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-devel - 2.3.1-1,2.3.1-1,2.3.1-1;openjpeg2-tools-debuginfo - 2.3.1-1,2.3.1-1;openjpeg2-debugsource - 2.3.1-1,2.3.1-1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve medium detected in external pdfiumtinker edge r cve medium severity vulnerability vulnerable library external pdfiumtinker edge r library home page a href found in head commit a href found in base branch master vulnerable source files third party c vulnerability details in openjpeg there is excessive iteration in the opj encode cblks function of c remote attackers could leverage this vulnerability to cause a denial of service via a crafted bmp file publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tools debuginfo devel docs devel tools debuginfo debugsource step up your open source security game with whitesource | 0 |
62,464 | 6,797,429,522 | IssuesEvent | 2017-11-01 22:52:03 | dondi/GRNsight | https://api.github.com/repos/dondi/GRNsight | closed | Add "syntactic" tests for graphml format | feature request priority 0 review requested testing | Need to add more tests for graphml format input files. @ebachoura and @eileenchoe can either split SIF and graphml or both work on both. Discuss with @dondi this week. | 1.0 | Add "syntactic" tests for graphml format - Need to add more tests for graphml format input files. @ebachoura and @eileenchoe can either split SIF and graphml or both work on both. Discuss with @dondi this week. | non_usab | add syntactic tests for graphml format need to add more tests for graphml format input files ebachoura and eileenchoe can either split sif and graphml or both work on both discuss with dondi this week | 0 |
27,315 | 28,089,806,620 | IssuesEvent | 2023-03-30 12:21:05 | humhub/humhub | https://api.github.com/repos/humhub/humhub | closed | Filtering for 'Country' in the Discovery module shows all countries | Kind:Enhancement Topic:Usability | When enabling `Use as Directory filter` on the Country attribute of user profiles the according dropw-down menu on the `People` pages shows all countries.
Enabling the option for `First name` creates a drop-down menu that only contains names People have entered into their profile.
As the list of all countries is very long, IMO a more intuitive way to present the `Country` filter would be using the pattern of the `First name` filter: showing only countries that have been entered into user profiles. | True | Filtering for 'Country' in the Discovery module shows all countries - When enabling `Use as Directory filter` on the Country attribute of user profiles the according dropw-down menu on the `People` pages shows all countries.
Enabling the option for `First name` creates a drop-down menu that only contains names People have entered into their profile.
As the list of all countries is very long, IMO a more intuitive way to present the `Country` filter would be using the pattern of the `First name` filter: showing only countries that have been entered into user profiles. | usab | filtering for country in the discovery module shows all countries when enabling use as directory filter on the country attribute of user profiles the according dropw down menu on the people pages shows all countries enabling the option for first name creates a drop down menu that only contains names people have entered into their profile as the list of all countries is very long imo a more intuitive way to present the country filter would be using the pattern of the first name filter showing only countries that have been entered into user profiles | 1 |
4,751 | 4,613,967,598 | IssuesEvent | 2016-09-25 09:39:33 | morganey-lang/Morganey | https://api.github.com/repos/morganey-lang/Morganey | opened | Compile Morganey with scala native | performance proposal research | https://github.com/scala-native/scala-native
I want to research the possibilities of using that thing to improve the performance of Morganey. | True | Compile Morganey with scala native - https://github.com/scala-native/scala-native
I want to research the possibilities of using that thing to improve the performance of Morganey. | non_usab | compile morganey with scala native i want to research the possibilities of using that thing to improve the performance of morganey | 0 |
21,787 | 17,761,886,462 | IssuesEvent | 2021-08-29 21:11:46 | godotengine/godot | https://api.github.com/repos/godotengine/godot | opened | Find Next shortcut not working when search bar is focused | bug topic:editor usability topic:input regression | ### Godot version
3a3c94b
### System information
W10
### Issue description
Title.
### Steps to reproduce
1. Open any script in Script Editor
2. Select some word that has multiple occurrences
3. Press Ctrl + F
4. Press F3
5. No effect, editor doesn't go to the next word
### Minimal reproduction project
_No response_ | True | Find Next shortcut not working when search bar is focused - ### Godot version
3a3c94b
### System information
W10
### Issue description
Title.
### Steps to reproduce
1. Open any script in Script Editor
2. Select some word that has multiple occurrences
3. Press Ctrl + F
4. Press F3
5. No effect, editor doesn't go to the next word
### Minimal reproduction project
_No response_ | usab | find next shortcut not working when search bar is focused godot version system information issue description title steps to reproduce open any script in script editor select some word that has multiple occurrences press ctrl f press no effect editor doesn t go to the next word minimal reproduction project no response | 1 |
778,673 | 27,324,585,334 | IssuesEvent | 2023-02-25 00:03:59 | Igalia/wolvic | https://api.github.com/repos/Igalia/wolvic | closed | Cant install the PICO XR build on Pico4. Its lloading till 90% than tells that "installation not possible". Did the latest Pico OS update, downloaded Wolvic apk through your website. Weird. | bug priority-high | Cant install the PICO XR build on Pico4. Its lloading till 90% than tells that "installation not possible". Did the latest Pico OS update, downloaded Wolvic apk through your website. Weird. | 1.0 | Cant install the PICO XR build on Pico4. Its lloading till 90% than tells that "installation not possible". Did the latest Pico OS update, downloaded Wolvic apk through your website. Weird. - Cant install the PICO XR build on Pico4. Its lloading till 90% than tells that "installation not possible". Did the latest Pico OS update, downloaded Wolvic apk through your website. Weird. | non_usab | cant install the pico xr build on its lloading till than tells that installation not possible did the latest pico os update downloaded wolvic apk through your website weird cant install the pico xr build on its lloading till than tells that installation not possible did the latest pico os update downloaded wolvic apk through your website weird | 0 |
24,548 | 23,898,415,267 | IssuesEvent | 2022-09-08 16:30:56 | tailscale/tailscale | https://api.github.com/repos/tailscale/tailscale | closed | tsconnect: resizing terminal window causes panic | L5 All users T6 Major usability needs-triage bug | ### What is the issue?
resizing terminal window causes a panic:
```
5:48:38.949 panic: runtime error: invalid memory address or nil pointer dereference [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.949 [signal 0xb code=0x0 addr=0x0 pc=0x0] [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 <empty string> [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 goroutine 6 [running]: [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 golang.org/x/crypto/ssh.(*Session).WindowChange(0x0, 0x18, 0x49) [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 golang.org/x/crypto@v0.0.0-20220427172511-eb4f295cb31f/ssh/session.go:251 +0xa [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 main.(*jsSSHSession).Resize(...) [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 tailscale.com/cmd/tsconnect/wasm/wasm_js.go:441 [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 main.(*jsIPN).ssh.func2({{}, 0x7ff80001000007a9, 0x1401348}, {0xfb0720, 0x2, 0x2}) [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 tailscale.com/cmd/tsconnect/wasm/wasm_js.go:335 +0x16 [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 syscall/js.handleEvent() [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 syscall/js/func.go:94 +0x26 [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
```
Browser: Firefox (also seen in Chrome) | True | tsconnect: resizing terminal window causes panic - ### What is the issue?
resizing terminal window causes a panic:
```
5:48:38.949 panic: runtime error: invalid memory address or nil pointer dereference [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.949 [signal 0xb code=0x0 addr=0x0 pc=0x0] [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 <empty string> [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 goroutine 6 [running]: [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 golang.org/x/crypto/ssh.(*Session).WindowChange(0x0, 0x18, 0x49) [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.950 golang.org/x/crypto@v0.0.0-20220427172511-eb4f295cb31f/ssh/session.go:251 +0xa [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 main.(*jsSSHSession).Resize(...) [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 tailscale.com/cmd/tsconnect/wasm/wasm_js.go:441 [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 main.(*jsIPN).ssh.func2({{}, 0x7ff80001000007a9, 0x1401348}, {0xfb0720, 0x2, 0x2}) [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 tailscale.com/cmd/tsconnect/wasm/wasm_js.go:335 +0x16 [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 syscall/js.handleEvent() [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
15:48:38.951 syscall/js/func.go:94 +0x26 [wasm_exec.js:22:13](http://localhost:31544/.cache/tailscale-go/misc/wasm/wasm_exec.js)
```
Browser: Firefox (also seen in Chrome) | usab | tsconnect resizing terminal window causes panic what is the issue resizing terminal window causes a panic panic runtime error invalid memory address or nil pointer dereference goroutine golang org x crypto ssh session windowchange golang org x crypto ssh session go main jssshsession resize tailscale com cmd tsconnect wasm wasm js go main jsipn ssh tailscale com cmd tsconnect wasm wasm js go syscall js handleevent syscall js func go browser firefox also seen in chrome | 1 |
16,330 | 9,370,019,669 | IssuesEvent | 2019-04-03 12:35:06 | arcus-azure/arcus.security | https://api.github.com/repos/arcus-azure/arcus.security | closed | Provide resiliency for service-side throttling for Azure Key Vault | azure-key-vault enhancement performance resiliency | Provide resiliency for service-side throttling by retrying `HTTP 429 TOO MANY REQUESTS`.
**Describe the solution you'd like**
These should be handled according by using Polly based on the recommended guidance documented [here](https://docs.microsoft.com/en-us/azure/key-vault/key-vault-ovw-throttling#recommended-client-side-throttling-method).
| True | Provide resiliency for service-side throttling for Azure Key Vault - Provide resiliency for service-side throttling by retrying `HTTP 429 TOO MANY REQUESTS`.
**Describe the solution you'd like**
These should be handled according by using Polly based on the recommended guidance documented [here](https://docs.microsoft.com/en-us/azure/key-vault/key-vault-ovw-throttling#recommended-client-side-throttling-method).
| non_usab | provide resiliency for service side throttling for azure key vault provide resiliency for service side throttling by retrying http too many requests describe the solution you d like these should be handled according by using polly based on the recommended guidance documented | 0 |
286,626 | 21,582,297,251 | IssuesEvent | 2022-05-02 20:08:13 | NOAA-FIMS/FIMS | https://api.github.com/repos/NOAA-FIMS/FIMS | closed | Questions: Do developers need to update documentation locally and check in updates? | kind: documentation kind: question | Hi @k-doering-NOAA ,
@Andrea-Havron-NOAA brought up a great question regarding call-doc-and-style-r.yml in the pull request #54. When working on a feature branch, do developers need to run devtools::check(), or devtools::document(), or roxygen2::roxygenise() locally and then check in updated documents (e.g., NAMESPACE)? I noticed that FIMS runs [call-doc-and-style-r.yml](https://github.com/NOAA-FIMS/FIMS/blob/main/.github/workflows/call-doc-and-style-r.yml) on main branch. I wonder if we need to run the workflow on feature branches as well and add NAMESPACE to .gitignore, so developers do not need to check in updated documentation to the repo. Thanks!
| 1.0 | Questions: Do developers need to update documentation locally and check in updates? - Hi @k-doering-NOAA ,
@Andrea-Havron-NOAA brought up a great question regarding call-doc-and-style-r.yml in the pull request #54. When working on a feature branch, do developers need to run devtools::check(), or devtools::document(), or roxygen2::roxygenise() locally and then check in updated documents (e.g., NAMESPACE)? I noticed that FIMS runs [call-doc-and-style-r.yml](https://github.com/NOAA-FIMS/FIMS/blob/main/.github/workflows/call-doc-and-style-r.yml) on main branch. I wonder if we need to run the workflow on feature branches as well and add NAMESPACE to .gitignore, so developers do not need to check in updated documentation to the repo. Thanks!
| non_usab | questions do developers need to update documentation locally and check in updates hi k doering noaa andrea havron noaa brought up a great question regarding call doc and style r yml in the pull request when working on a feature branch do developers need to run devtools check or devtools document or roxygenise locally and then check in updated documents e g namespace i noticed that fims runs on main branch i wonder if we need to run the workflow on feature branches as well and add namespace to gitignore so developers do not need to check in updated documentation to the repo thanks | 0 |
26,562 | 26,974,892,723 | IssuesEvent | 2023-02-09 08:50:16 | redpanda-data/documentation | https://api.github.com/repos/redpanda-data/documentation | opened | Provide more details on how to customize Helm charts | kubernetes usability improvement | ### Describe the Issue
Some users may not be familiar with Helm or how they can/should configure the charts.
We should provide more context in any relevant topics by taking some details from this Helm doc: https://helm.sh/docs/intro/using_helm/#customizing-the-chart-before-installing
### Updates to existing documentation
Any guides that deal with deploying Redpanda using Helm.
### New feature or content gap requests
<!--
If this is a new feature, provide material that will help the writer draft the new or updated content. If an issue only includes the name of a feature and release, it will be marked “More Info Needed” or “Blocked”. Ideally, the issue will provide:
- Links to internal wikis, PRDs, design docs, KIPs, training material, or slide decks.
- Links to engineering PRs that implement the update.
- Links to blog posts, if applicable.
- Identify specific Slack channels that the writer can join to get more details about the feature.
- Links to Slack conversations (RP and RP Community) about the issue.
- Names of SMEs who can answer questions and act as reviewers (at least one engineer and one PM).
- Any additional information that will be of use to the writer.
-->
### If new feature, in which release is it included or expected?
### If the requested update is from customer feedback or a Community slack conversation, provide a link:
### Additional notes
<!--
Documentation Issues must be distinct and not overlap. If filing an Issue for a feature that spans platform and cloud, you must file two separate Issues. Each Issue will drive the new content in GitHub for the respective platform or cloud doc.
Include:
- Relevant GitHub issues and pull requests
- Dependencies on other features or components
- Specific Redpanda contributors to notify
-->
| True | Provide more details on how to customize Helm charts - ### Describe the Issue
Some users may not be familiar with Helm or how they can/should configure the charts.
We should provide more context in any relevant topics by taking some details from this Helm doc: https://helm.sh/docs/intro/using_helm/#customizing-the-chart-before-installing
### Updates to existing documentation
Any guides that deal with deploying Redpanda using Helm.
### New feature or content gap requests
<!--
If this is a new feature, provide material that will help the writer draft the new or updated content. If an issue only includes the name of a feature and release, it will be marked “More Info Needed” or “Blocked”. Ideally, the issue will provide:
- Links to internal wikis, PRDs, design docs, KIPs, training material, or slide decks.
- Links to engineering PRs that implement the update.
- Links to blog posts, if applicable.
- Identify specific Slack channels that the writer can join to get more details about the feature.
- Links to Slack conversations (RP and RP Community) about the issue.
- Names of SMEs who can answer questions and act as reviewers (at least one engineer and one PM).
- Any additional information that will be of use to the writer.
-->
### If new feature, in which release is it included or expected?
### If the requested update is from customer feedback or a Community slack conversation, provide a link:
### Additional notes
<!--
Documentation Issues must be distinct and not overlap. If filing an Issue for a feature that spans platform and cloud, you must file two separate Issues. Each Issue will drive the new content in GitHub for the respective platform or cloud doc.
Include:
- Relevant GitHub issues and pull requests
- Dependencies on other features or components
- Specific Redpanda contributors to notify
-->
| usab | provide more details on how to customize helm charts describe the issue some users may not be familiar with helm or how they can should configure the charts we should provide more context in any relevant topics by taking some details from this helm doc updates to existing documentation any guides that deal with deploying redpanda using helm new feature or content gap requests if this is a new feature provide material that will help the writer draft the new or updated content if an issue only includes the name of a feature and release it will be marked “more info needed” or “blocked” ideally the issue will provide links to internal wikis prds design docs kips training material or slide decks links to engineering prs that implement the update links to blog posts if applicable identify specific slack channels that the writer can join to get more details about the feature links to slack conversations rp and rp community about the issue names of smes who can answer questions and act as reviewers at least one engineer and one pm any additional information that will be of use to the writer if new feature in which release is it included or expected if the requested update is from customer feedback or a community slack conversation provide a link additional notes documentation issues must be distinct and not overlap if filing an issue for a feature that spans platform and cloud you must file two separate issues each issue will drive the new content in github for the respective platform or cloud doc include relevant github issues and pull requests dependencies on other features or components specific redpanda contributors to notify | 1 |
106,802 | 11,498,642,914 | IssuesEvent | 2020-02-12 12:25:51 | FAIRplus/the-fair-cookbook | https://api.github.com/repos/FAIRplus/the-fair-cookbook | opened | Terminology and Ontology Services: | Findability Initial capability Interoperability documentation | # Recipe1: Anonymizing Patient Data
**identifier:**
**authors:**
Tony Burdett
Fuqi Xu
**maintainers:**
**version:**
**license**
## Ingredients:
Identifier Schema:
1. Metadata Model:
-
-
-
2. Vocabularies and Terminologies:
-
-
-
3. Data Format:
-
-
-
4. Tools and Software:
- OLS
-
-
## Objectives:
Deployment and Maintaining a vocabulary service
## Step by Step Process:
### Step1:
### Step2:
### Step3:
### Step4:
### Step5: ... | 1.0 | Terminology and Ontology Services: - # Recipe1: Anonymizing Patient Data
**identifier:**
**authors:**
Tony Burdett
Fuqi Xu
**maintainers:**
**version:**
**license**
## Ingredients:
Identifier Schema:
1. Metadata Model:
-
-
-
2. Vocabularies and Terminologies:
-
-
-
3. Data Format:
-
-
-
4. Tools and Software:
- OLS
-
-
## Objectives:
Deployment and Maintaining a vocabulary service
## Step by Step Process:
### Step1:
### Step2:
### Step3:
### Step4:
### Step5: ... | non_usab | terminology and ontology services anonymizing patient data identifier authors tony burdett fuqi xu maintainers version license ingredients identifier schema metadata model vocabularies and terminologies data format tools and software ols objectives deployment and maintaining a vocabulary service step by step process | 0 |
24,738 | 24,207,036,486 | IssuesEvent | 2022-09-25 11:33:40 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | reopened | After DB::Exception, clickhouse ask password again. | usability st-fixed comp-cli minor | I had run the query with tailing "FORMAT VERTICAL", But clickhouse server throw DB::Exception.
```
Exception on client:
Code: 73. DB::Exception: Unknown format VERTICAL
```
After this error, clickhouse client ask password agiain like this.
```
ch_7 :) select version();
SELECT version()
┌─version()─┐
│ 18.12.17 │
└───────────┘
select * from matt FORMAT VERTICAL;
Exception on client:
Code: 73. DB::Exception: Unknown format VERTICAL
Password for user matt_lee:
Connecting to database matt at localhost:9000 as user matt_lee.
Connected to ClickHouse server version 18.12.17 revision 54407.
ch_7 :)
```
But there's no password asking when syntax error of the other query. Is this really connection is closed ?
And one more thing is that why upper-case "VERTICAL" is not allowed ? | True | After DB::Exception, clickhouse ask password again. - I had run the query with tailing "FORMAT VERTICAL", But clickhouse server throw DB::Exception.
```
Exception on client:
Code: 73. DB::Exception: Unknown format VERTICAL
```
After this error, clickhouse client ask password agiain like this.
```
ch_7 :) select version();
SELECT version()
┌─version()─┐
│ 18.12.17 │
└───────────┘
select * from matt FORMAT VERTICAL;
Exception on client:
Code: 73. DB::Exception: Unknown format VERTICAL
Password for user matt_lee:
Connecting to database matt at localhost:9000 as user matt_lee.
Connected to ClickHouse server version 18.12.17 revision 54407.
ch_7 :)
```
But there's no password asking when syntax error of the other query. Is this really connection is closed ?
And one more thing is that why upper-case "VERTICAL" is not allowed ? | usab | after db exception clickhouse ask password again i had run the query with tailing format vertical but clickhouse server throw db exception exception on client code db exception unknown format vertical after this error clickhouse client ask password agiain like this ch select version select version ┌─version ─┐ │ │ └───────────┘ select from matt format vertical exception on client code db exception unknown format vertical password for user matt lee connecting to database matt at localhost as user matt lee connected to clickhouse server version revision ch but there s no password asking when syntax error of the other query is this really connection is closed and one more thing is that why upper case vertical is not allowed | 1 |
25,823 | 25,960,001,906 | IssuesEvent | 2022-12-18 19:28:10 | kubernetes/test-infra | https://api.github.com/repos/kubernetes/test-infra | closed | Prow presubmit job not able to create PV using PVC | kind/bug lifecycle/rotten sig/usability | <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!-->
**What happened**:
Seems like a presubmit prow job is not able to create a volume by using "volume claim template" described in the presubmit job yaml. I am trying to use the volume claim template to create a PV from volume snapshot "data source" in the yaml. The mount paths come up empty. The setup works fine when tested with a POD but not with prowjob yaml.
Eg:
volumes:
- name: try-vol
ephemeral:
volumeClaimTemplate:
spec:
accessModes:
- ReadWriteOnce
storageClassName: "xxx-xxx-x-x"
resources:
requests:
storage: 60Gi
dataSource:
name: snapshot
kind: VolumeSnapshot
apiGroup: snapshot.storage.k8s.io
**What you expected to happen**:
PV should have been created and the mount paths in the pod should have been populated.
**How to reproduce it (as minimally and precisely as possible)**:
**Please provide links to example occurrences, if any**:
N/A
**Anything else we need to know?**:
| True | Prow presubmit job not able to create PV using PVC - <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!-->
**What happened**:
Seems like a presubmit prow job is not able to create a volume by using "volume claim template" described in the presubmit job yaml. I am trying to use the volume claim template to create a PV from volume snapshot "data source" in the yaml. The mount paths come up empty. The setup works fine when tested with a POD but not with prowjob yaml.
Eg:
volumes:
- name: try-vol
ephemeral:
volumeClaimTemplate:
spec:
accessModes:
- ReadWriteOnce
storageClassName: "xxx-xxx-x-x"
resources:
requests:
storage: 60Gi
dataSource:
name: snapshot
kind: VolumeSnapshot
apiGroup: snapshot.storage.k8s.io
**What you expected to happen**:
PV should have been created and the mount paths in the pod should have been populated.
**How to reproduce it (as minimally and precisely as possible)**:
**Please provide links to example occurrences, if any**:
N/A
**Anything else we need to know?**:
| usab | prow presubmit job not able to create pv using pvc what happened seems like a presubmit prow job is not able to create a volume by using volume claim template described in the presubmit job yaml i am trying to use the volume claim template to create a pv from volume snapshot data source in the yaml the mount paths come up empty the setup works fine when tested with a pod but not with prowjob yaml eg volumes name try vol ephemeral volumeclaimtemplate spec accessmodes readwriteonce storageclassname xxx xxx x x resources requests storage datasource name snapshot kind volumesnapshot apigroup snapshot storage io what you expected to happen pv should have been created and the mount paths in the pod should have been populated how to reproduce it as minimally and precisely as possible please provide links to example occurrences if any n a anything else we need to know | 1 |
345,653 | 24,868,774,081 | IssuesEvent | 2022-10-27 13:51:54 | astanin/python-tabulate | https://api.github.com/repos/astanin/python-tabulate | closed | Update Mediawiki example in the README file | documentation | After pull request #210 Mediawiki format has changed.
The README file still shows the old output. | 1.0 | Update Mediawiki example in the README file - After pull request #210 Mediawiki format has changed.
The README file still shows the old output. | non_usab | update mediawiki example in the readme file after pull request mediawiki format has changed the readme file still shows the old output | 0 |
119,554 | 25,536,611,720 | IssuesEvent | 2022-11-29 12:28:47 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Iron helmet can be found in stores | Bug Code Design Unstable | ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [ ] My issue happened while using mods.
### What happened?

Simply, the makeshift armor isnt in stores anymore, the iron helmet still is. Happened on a residential Outpost, if that helps.
### Reproduction steps
1.Check stores for iron Helmets
### Bug prevalence
Happens every time I play
### Version
Faction test branch
### -
_No response_
### Which operating system did you encounter this bug on?
Windows
### Relevant error messages and crash reports
_No response_ | 1.0 | Iron helmet can be found in stores - ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [ ] My issue happened while using mods.
### What happened?

Simply, the makeshift armor isnt in stores anymore, the iron helmet still is. Happened on a residential Outpost, if that helps.
### Reproduction steps
1.Check stores for iron Helmets
### Bug prevalence
Happens every time I play
### Version
Faction test branch
### -
_No response_
### Which operating system did you encounter this bug on?
Windows
### Relevant error messages and crash reports
_No response_ | non_usab | iron helmet can be found in stores disclaimers i have searched the issue tracker to check if the issue has already been reported my issue happened while using mods what happened simply the makeshift armor isnt in stores anymore the iron helmet still is happened on a residential outpost if that helps reproduction steps check stores for iron helmets bug prevalence happens every time i play version faction test branch no response which operating system did you encounter this bug on windows relevant error messages and crash reports no response | 0 |
1,840 | 3,025,022,079 | IssuesEvent | 2015-08-03 03:55:34 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 21782270: Title of the Simulator window is mostly useless | classification:ui/usabiblity reproducible:always status:open | #### Description
See some screenshots at http://www.openradar.me/21782228
More than often, we don't know what kind of iPhone or Watch we are currently running. Sure, it's in the Window Title... But this one is mostly too small to read anything else than "Simulator" (which, really, shouldn't be part of the Window Title)
-
Product Version: Version 7.0 beta 3 (7A152u)
Created: 2015-07-11T19:00:33.350770
Originated: 2015-07-11T00:00:00
Open Radar Link: http://www.openradar.me/21782270 | True | 21782270: Title of the Simulator window is mostly useless - #### Description
See some screenshots at http://www.openradar.me/21782228
More than often, we don't know what kind of iPhone or Watch we are currently running. Sure, it's in the Window Title... But this one is mostly too small to read anything else than "Simulator" (which, really, shouldn't be part of the Window Title)
-
Product Version: Version 7.0 beta 3 (7A152u)
Created: 2015-07-11T19:00:33.350770
Originated: 2015-07-11T00:00:00
Open Radar Link: http://www.openradar.me/21782270 | usab | title of the simulator window is mostly useless description see some screenshots at more than often we don t know what kind of iphone or watch we are currently running sure it s in the window title but this one is mostly too small to read anything else than simulator which really shouldn t be part of the window title product version version beta created originated open radar link | 1 |
22,424 | 10,756,804,700 | IssuesEvent | 2019-10-31 12:01:17 | lnuon/EmpirEqual | https://api.github.com/repos/lnuon/EmpirEqual | opened | WS-2019-0103 (Medium) detected in handlebars-4.0.11.tgz, handlebars-4.0.5.tgz | security vulnerability | ## WS-2019-0103 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.11.tgz</b>, <b>handlebars-4.0.5.tgz</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.11.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/EmpirEqual/src/frontend/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/EmpirEqual/src/frontend/node_modules/react-scripts/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-1.1.4.tgz (Root Library)
- jest-20.0.4.tgz
- jest-cli-20.0.4.tgz
- istanbul-api-1.3.1.tgz
- istanbul-reports-1.3.0.tgz
- :x: **handlebars-4.0.11.tgz** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.5.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/EmpirEqual/src/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/EmpirEqual/src/frontend/node_modules/hbs/node_modules/handlebars/package.json,/tmp/ws-scm/EmpirEqual/src/frontend/node_modules/hbs/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- hbs-4.0.1.tgz (Root Library)
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/lnuon/EmpirEqual/commit/95570e41b1fabd86612a9a88d0ca4afa85bd659b">95570e41b1fabd86612a9a88d0ca4afa85bd659b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars.js before 4.1.0 has Remote Code Execution (RCE)
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://github.com/wycats/handlebars.js/issues/1267#issue-187151586>WS-2019-0103</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/wycats/handlebars.js/commit/edc6220d51139b32c28e51641fadad59a543ae57">https://github.com/wycats/handlebars.js/commit/edc6220d51139b32c28e51641fadad59a543ae57</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 4.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0103 (Medium) detected in handlebars-4.0.11.tgz, handlebars-4.0.5.tgz - ## WS-2019-0103 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.11.tgz</b>, <b>handlebars-4.0.5.tgz</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.11.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/EmpirEqual/src/frontend/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/EmpirEqual/src/frontend/node_modules/react-scripts/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-1.1.4.tgz (Root Library)
- jest-20.0.4.tgz
- jest-cli-20.0.4.tgz
- istanbul-api-1.3.1.tgz
- istanbul-reports-1.3.0.tgz
- :x: **handlebars-4.0.11.tgz** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.5.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/EmpirEqual/src/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/EmpirEqual/src/frontend/node_modules/hbs/node_modules/handlebars/package.json,/tmp/ws-scm/EmpirEqual/src/frontend/node_modules/hbs/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- hbs-4.0.1.tgz (Root Library)
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/lnuon/EmpirEqual/commit/95570e41b1fabd86612a9a88d0ca4afa85bd659b">95570e41b1fabd86612a9a88d0ca4afa85bd659b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars.js before 4.1.0 has Remote Code Execution (RCE)
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://github.com/wycats/handlebars.js/issues/1267#issue-187151586>WS-2019-0103</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/wycats/handlebars.js/commit/edc6220d51139b32c28e51641fadad59a543ae57">https://github.com/wycats/handlebars.js/commit/edc6220d51139b32c28e51641fadad59a543ae57</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 4.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | ws medium detected in handlebars tgz handlebars tgz ws medium severity vulnerability vulnerable libraries handlebars tgz handlebars tgz handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file tmp ws scm empirequal src frontend package json path to vulnerable library tmp ws scm empirequal src frontend node modules react scripts node modules handlebars package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz istanbul api tgz istanbul reports tgz x handlebars tgz vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file tmp ws scm empirequal src package json path to vulnerable library tmp ws scm empirequal src frontend node modules hbs node modules handlebars package json tmp ws scm empirequal src frontend node modules hbs node modules handlebars package json dependency hierarchy hbs tgz root library x handlebars tgz vulnerable library found in head commit a href vulnerability details handlebars js before has remote code execution rce publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
35,007 | 2,789,730,247 | IssuesEvent | 2015-05-08 21:07:46 | google/google-visualization-api-issues | https://api.github.com/repos/google/google-visualization-api-issues | opened | Automatic play option for Motion Chart | Priority-Low Type-Enhancement | Original [issue 42](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=42) created by google-admin on 2009-09-01T19:28:11.000Z:
<b>What would you like to see us add to this API?</b>
I would like to see the Motion Chart have an option to start playing as
soon as it is loaded (without having to press the play button).
<b>What component is this issue related to (PieChart, LineChart, DataTable,</b>
<b>Query, etc)?</b>
Motion Chart
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
| 1.0 | Automatic play option for Motion Chart - Original [issue 42](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=42) created by google-admin on 2009-09-01T19:28:11.000Z:
<b>What would you like to see us add to this API?</b>
I would like to see the Motion Chart have an option to start playing as
soon as it is loaded (without having to press the play button).
<b>What component is this issue related to (PieChart, LineChart, DataTable,</b>
<b>Query, etc)?</b>
Motion Chart
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
| non_usab | automatic play option for motion chart original created by google admin on what would you like to see us add to this api i would like to see the motion chart have an option to start playing as soon as it is loaded without having to press the play button what component is this issue related to piechart linechart datatable query etc motion chart for developers viewing this issue please click the star icon to be notified of future changes and to let us know how many of you are interested in seeing it resolved | 0 |
46,630 | 19,344,732,657 | IssuesEvent | 2021-12-15 09:38:09 | IBM-Cloud/terraform-provider-ibm | https://api.github.com/repos/IBM-Cloud/terraform-provider-ibm | closed | IBM Cloud Databases CLI Behavior Update | service/Cloud Databases | From James Thorne (IBM):
There's a behaviour change in the ibmcloud CLI that I wanted to give your team a heads up on in case it impacts you.
The `ibmcloud resource service-key-create` command has been broken for ICD services -- they've been working with the CLI team on a fix but it's coming with a behaviour change -- the [ROLE] parameter must now not be passed when working with ICD and other non-IAM-enabled services.
So
`ibmcloud resource service-key-create <key> Administrator --instance-name <name>`
is now just
`ibmcloud resource service-key-create <key> --instance-name <name>`
Does Terraform use the CLI and does that cause any issues on your end? The associated Resource Controller API is unchanged, as is the UI; the change just affects the ibmcloud CLI.
For more context the ticket is here: https://github.ibm.com/Bluemix/bluemix-cli/issues/3006 | 1.0 | IBM Cloud Databases CLI Behavior Update - From James Thorne (IBM):
There's a behaviour change in the ibmcloud CLI that I wanted to give your team a heads up on in case it impacts you.
The `ibmcloud resource service-key-create` command has been broken for ICD services -- they've been working with the CLI team on a fix but it's coming with a behaviour change -- the [ROLE] parameter must now not be passed when working with ICD and other non-IAM-enabled services.
So
`ibmcloud resource service-key-create <key> Administrator --instance-name <name>`
is now just
`ibmcloud resource service-key-create <key> --instance-name <name>`
Does Terraform use the CLI and does that cause any issues on your end? The associated Resource Controller API is unchanged, as is the UI; the change just affects the ibmcloud CLI.
For more context the ticket is here: https://github.ibm.com/Bluemix/bluemix-cli/issues/3006 | non_usab | ibm cloud databases cli behavior update from james thorne ibm there s a behaviour change in the ibmcloud cli that i wanted to give your team a heads up on in case it impacts you the ibmcloud resource service key create command has been broken for icd services they ve been working with the cli team on a fix but it s coming with a behaviour change the parameter must now not be passed when working with icd and other non iam enabled services so ibmcloud resource service key create administrator instance name is now just ibmcloud resource service key create instance name does terraform use the cli and does that cause any issues on your end the associated resource controller api is unchanged as is the ui the change just affects the ibmcloud cli for more context the ticket is here | 0 |
57,741 | 14,200,684,744 | IssuesEvent | 2020-11-16 06:05:41 | SCE-Development/Core-v4 | https://api.github.com/repos/SCE-Development/Core-v4 | closed | Add Authorization to Backend APIs | API Refactoring enhancement help wanted security | Right now we don't check for access level in our protected APIs. This is easy to add, see below
1. We need a new parameter for `checkIfTokenValid`, `accessLevel` [`api/main_endpoints/util/token-functions.js`](https://github.com/SCE-Development/Core-v4/blob/55ad626d991b3048a917b63abb68620a89911dad/api/main_endpoints/util/token-functions.js#L23)
The access level should default to `MEMBERSHIP_STATE.MEMBER` so we dont have to send it in all the time
```js
function checkIfTokenValid(request, accessLevel=MEMBERSHIP_STATE.MEMBER) {
// basically check if the user's access level >= accessLevel parameter
}
```
2. Refactor all the instances of `checkIfTokenValid` to send in the access level **don't use numbers!** use `MEMBERSHIP_STATE.ADMIN` as a parameter instead of something like `2` or `3`.
Example decoded response:
 | True | Add Authorization to Backend APIs - Right now we don't check for access level in our protected APIs. This is easy to add, see below
1. We need a new parameter for `checkIfTokenValid`, `accessLevel` [`api/main_endpoints/util/token-functions.js`](https://github.com/SCE-Development/Core-v4/blob/55ad626d991b3048a917b63abb68620a89911dad/api/main_endpoints/util/token-functions.js#L23)
The access level should default to `MEMBERSHIP_STATE.MEMBER` so we dont have to send it in all the time
```js
function checkIfTokenValid(request, accessLevel=MEMBERSHIP_STATE.MEMBER) {
// basically check if the user's access level >= accessLevel parameter
}
```
2. Refactor all the instances of `checkIfTokenValid` to send in the access level **don't use numbers!** use `MEMBERSHIP_STATE.ADMIN` as a parameter instead of something like `2` or `3`.
Example decoded response:
 | non_usab | add authorization to backend apis right now we don t check for access level in our protected apis this is easy to add see below we need a new parameter for checkiftokenvalid accesslevel the access level should default to membership state member so we dont have to send it in all the time js function checkiftokenvalid request accesslevel membership state member basically check if the user s access level accesslevel parameter refactor all the instances of checkiftokenvalid to send in the access level don t use numbers use membership state admin as a parameter instead of something like or example decoded response | 0 |
265,657 | 23,186,936,263 | IssuesEvent | 2022-08-01 09:12:19 | status-im/status-desktop | https://api.github.com/repos/status-im/status-desktop | closed | TestNet banner overlaps left panel | bug tested E:Bugfixes Settings S:2 | # Bug Report
## Description
<img width="1012" alt="image" src="https://user-images.githubusercontent.com/25482501/180727045-619eca13-9a3d-4b3f-8cef-83df9a184d84.png">
## Steps to reproduce
1. Start app
2. Enable TestNet in Settings/Wallet
| 1.0 | TestNet banner overlaps left panel - # Bug Report
## Description
<img width="1012" alt="image" src="https://user-images.githubusercontent.com/25482501/180727045-619eca13-9a3d-4b3f-8cef-83df9a184d84.png">
## Steps to reproduce
1. Start app
2. Enable TestNet in Settings/Wallet
| non_usab | testnet banner overlaps left panel bug report description img width alt image src steps to reproduce start app enable testnet in settings wallet | 0 |
11,709 | 7,372,593,308 | IssuesEvent | 2018-03-13 15:07:05 | surveyjs/editor | https://api.github.com/repos/surveyjs/editor | closed | Introduce Newby/Advanced/Expert mode. | usability issue | Collapse property grid by default.
Newby - just titles, visible if wizard
Advanced - all options, visible if expression, add to toolbox, convert question, ...
Expert - ability to accomplish any task (including JS code and CSS styles) in the editor | True | Introduce Newby/Advanced/Expert mode. - Collapse property grid by default.
Newby - just titles, visible if wizard
Advanced - all options, visible if expression, add to toolbox, convert question, ...
Expert - ability to accomplish any task (including JS code and CSS styles) in the editor | usab | introduce newby advanced expert mode collapse property grid by default newby just titles visible if wizard advanced all options visible if expression add to toolbox convert question expert ability to accomplish any task including js code and css styles in the editor | 1 |
121,471 | 12,126,687,183 | IssuesEvent | 2020-04-22 17:26:33 | Azure/azurehpc | https://api.github.com/repos/Azure/azurehpc | closed | question: deploy cycleserver into defined vnet | documentation | Hello,
I'm wondering how to skip the creating of the vnet and subnet while having pre-defined subnets available for the CycleServer deployment.
https://github.com/Azure/azurehpc/blob/master/examples/cycleserver/readme.md
Thanks for you guidance.
| 1.0 | question: deploy cycleserver into defined vnet - Hello,
I'm wondering how to skip the creating of the vnet and subnet while having pre-defined subnets available for the CycleServer deployment.
https://github.com/Azure/azurehpc/blob/master/examples/cycleserver/readme.md
Thanks for you guidance.
| non_usab | question deploy cycleserver into defined vnet hello i m wondering how to skip the creating of the vnet and subnet while having pre defined subnets available for the cycleserver deployment thanks for you guidance | 0 |
25,607 | 25,487,604,177 | IssuesEvent | 2022-11-26 16:16:18 | kitsudaiki/libKitsunemimiHanamiNetwork | https://api.github.com/repos/kitsudaiki/libKitsunemimiHanamiNetwork | opened | reconnection broken | Bug Usability | ## BUG-issue
### Description
Since the issue https://github.com/kitsudaiki/libKitsunemimiHanamiNetwork/issues/10, the reconnect doesn't work anymore. Only initial connection works. | True | reconnection broken - ## BUG-issue
### Description
Since the issue https://github.com/kitsudaiki/libKitsunemimiHanamiNetwork/issues/10, the reconnect doesn't work anymore. Only initial connection works. | usab | reconnection broken bug issue description since the issue the reconnect doesn t work anymore only initial connection works | 1 |
207,561 | 23,458,627,591 | IssuesEvent | 2022-08-16 11:10:41 | Gal-Doron/Baragon-test-6 | https://api.github.com/repos/Gal-Doron/Baragon-test-6 | opened | jackson-databind-2.9.9.jar: 50 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-14540](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2019-17531](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-16335](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-17267](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2020-8840](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.3 | ✅ |
| [CVE-2019-16942](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-16943](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-14893](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-14892](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2020-9546](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-9547](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-14379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-9548](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-20330](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2020-10968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10969](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11111](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11113](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11112](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10672](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10673](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11619](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-35728](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36189](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36188](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-11620](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10650](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10650) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-36181](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36180](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35490](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35490) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36183](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36182](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35491](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36187](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36186](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2021-20190](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2020-36179](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-24616](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14060](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14061](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14062](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-24750](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14195](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-25649](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2019-14439](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-36518](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.12.6.1 | ✅ |
| [CVE-2019-12814](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
| [CVE-2019-12384](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
## Details
> Partial details (19 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: 2.9.10.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-09-04</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20330</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10968</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968>CVE-2020-10968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10968">https://nvd.nist.gov/vuln/detail/CVE-2020-10968</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10969</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane.
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969>CVE-2020-10969</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11111</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.activemq.* (aka activemq-jms, activemq-core, activemq-pool, and activemq-pool-jms).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111>CVE-2020-11111</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11113</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.openjpa.ee.WASRegistryManagedRuntime (aka openjpa).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113>CVE-2020-11113</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11112</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | jackson-databind-2.9.9.jar: 50 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-14540](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2019-17531](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-16335](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-17267](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2020-8840](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.3 | ✅ |
| [CVE-2019-16942](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-16943](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-14893](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-14892](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2020-9546](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-9547](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-14379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-9548](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-20330](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2020-10968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10969](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11111](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11113](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11112](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10672](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10673](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11619](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-35728](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36189](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36188](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-11620](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10650](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10650) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-36181](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36180](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35490](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35490) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36183](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36182](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35491](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36187](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36186](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2021-20190](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2020-36179](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-24616](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14060](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14061](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14062](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-24750](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14195](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-25649](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2019-14439](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-36518](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.12.6.1 | ✅ |
| [CVE-2019-12814](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
| [CVE-2019-12384](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
## Details
> Partial details (19 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: 2.9.10.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-09-04</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20330</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10968</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968>CVE-2020-10968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10968">https://nvd.nist.gov/vuln/detail/CVE-2020-10968</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10969</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane.
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969>CVE-2020-10969</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11111</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.activemq.* (aka activemq-jms, activemq-core, activemq-pool, and activemq-pool-jms).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111>CVE-2020-11111</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11113</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.openjpa.ee.WASRegistryManagedRuntime (aka openjpa).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113>CVE-2020-11113</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11112</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonAgentService/pom.xml</p>
<p>Path to vulnerable library: /sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/sitory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_usab | jackson databind jar vulnerabilities highest severity is vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct medium jackson databind jar direct medium jackson databind jar direct details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the apache extra version x jar in the classpath and an attacker can provide a jndi service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to net sf ehcache hibernate ehcachejtatransactionmanagerlookup publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind through lacks certain xbean reflect jndi blocking as demonstrated by org apache xbean propertyeditor jndiconverter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the commons dbcp jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of org apache commons dbcp datasources sharedpooldatasource and org apache commons dbcp datasources peruserpooldatasource mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of com engine spy mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a flaw was discovered in fasterxml jackson databind in all versions before and where it would permit polymorphic deserialization of malicious objects using the xalan jndi gadget when used in conjunction with polymorphic type handling methods such as enabledefaulttyping or when jsontypeinfo is using id class or id minimal class or in any other way which objectmapper readvalue might instantiate objects from unsafe sources an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details a flaw was discovered in jackson databind in versions before and where it would permit polymorphic deserialization of a malicious object using commons configuration and jndi classes an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com ibatis sqlmap engine transaction jta jtatransactionconfig aka ibatis sqlmap publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details subtypevalidator java in fasterxml jackson databind before mishandles default typing when ehcache is used because of net sf ehcache transaction manager defaulttransactionmanagerlookup leading to remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to br com anteros dbcp anterosdbcpconfig aka anteros core publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before lacks certain net sf ehcache blocking publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org aoju bus proxy provider remoting rmiprovider aka bus proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to javax swing jeditorpane publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache activemq aka activemq jms activemq core activemq pool and activemq pool jms publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache openjpa ee wasregistrymanagedruntime aka openjpa publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonagentservice pom xml path to vulnerable library sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar sitory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
12,004 | 7,612,100,273 | IssuesEvent | 2018-05-01 16:18:06 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Edit Group for multiple nodes at the same time | feature proposal topic:editor usability |
It would be nice if it was possible to select multiple Nodes and set group for all of them togheter
Example of what happened: i created bounds for a map and i wanted to put them all in a group. Had to manually set groups for each Node.
Bonus: It would be nice if Groups were managed with a separate windows, where you can add groups, and then if you assingn a Node to a Group you'd have a drop down menu, to avoid misspelling related bugs.
| True | Edit Group for multiple nodes at the same time -
It would be nice if it was possible to select multiple Nodes and set group for all of them togheter
Example of what happened: i created bounds for a map and i wanted to put them all in a group. Had to manually set groups for each Node.
Bonus: It would be nice if Groups were managed with a separate windows, where you can add groups, and then if you assingn a Node to a Group you'd have a drop down menu, to avoid misspelling related bugs.
| usab | edit group for multiple nodes at the same time it would be nice if it was possible to select multiple nodes and set group for all of them togheter example of what happened i created bounds for a map and i wanted to put them all in a group had to manually set groups for each node bonus it would be nice if groups were managed with a separate windows where you can add groups and then if you assingn a node to a group you d have a drop down menu to avoid misspelling related bugs | 1 |
77,241 | 26,873,738,964 | IssuesEvent | 2023-02-04 19:46:38 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | closed | [🐛 Bug]: ProfilesIni fails on Ubuntu 22 using Firefox and Snap | I-defect needs-triaging | ### What happened?
org.openqa.selenium.firefox.ProfilesIni expects the Firefox profiles to be in ~/.mozilla/firefox when the platform is not Windows or Mac.
However, on Ubuntu 22 using Snap, the Firefox profiles are in ~/snap/firefox/common/.mozilla/firefox. That's the directory where profiles.ini is.
One possible solution is to change this:
`appData = new File(MessageFormat.format("{0}/.mozilla/firefox", System.getenv("HOME")));`
to this:
```
appData = new File(MessageFormat.format("{0}/.mozilla/firefox", System.getenv("HOME")));
if (!appData.exists()) {
appData = new File(MessageFormat.format("{0}/snap/firefox/common/.mozilla/firefox", System.getenv("HOME")));
}
```
A more complicated but cleaner solution would be to have a set of plugins that provide likely paths, the first one that has a profiles.ini wins.
### How can we reproduce the issue?
```shell
Install Ubuntu 22 and Firefox using Snap, then try to load a FF profile using ProfilesIni.
```
### Relevant log output
```shell
None, it just returns null on this platform.
```
### Operating System
Ubuntu 22
### Selenium version
4.7.2 (custom build incorporating #11545)
### What are the browser(s) and version(s) where you see this issue?
FF 109
### What are the browser driver(s) and version(s) where you see this issue?
n/a
### Are you using Selenium Grid?
n/a | 1.0 | [🐛 Bug]: ProfilesIni fails on Ubuntu 22 using Firefox and Snap - ### What happened?
org.openqa.selenium.firefox.ProfilesIni expects the Firefox profiles to be in ~/.mozilla/firefox when the platform is not Windows or Mac.
However, on Ubuntu 22 using Snap, the Firefox profiles are in ~/snap/firefox/common/.mozilla/firefox. That's the directory where profiles.ini is.
One possible solution is to change this:
`appData = new File(MessageFormat.format("{0}/.mozilla/firefox", System.getenv("HOME")));`
to this:
```
appData = new File(MessageFormat.format("{0}/.mozilla/firefox", System.getenv("HOME")));
if (!appData.exists()) {
appData = new File(MessageFormat.format("{0}/snap/firefox/common/.mozilla/firefox", System.getenv("HOME")));
}
```
A more complicated but cleaner solution would be to have a set of plugins that provide likely paths, the first one that has a profiles.ini wins.
### How can we reproduce the issue?
```shell
Install Ubuntu 22 and Firefox using Snap, then try to load a FF profile using ProfilesIni.
```
### Relevant log output
```shell
None, it just returns null on this platform.
```
### Operating System
Ubuntu 22
### Selenium version
4.7.2 (custom build incorporating #11545)
### What are the browser(s) and version(s) where you see this issue?
FF 109
### What are the browser driver(s) and version(s) where you see this issue?
n/a
### Are you using Selenium Grid?
n/a | non_usab | profilesini fails on ubuntu using firefox and snap what happened org openqa selenium firefox profilesini expects the firefox profiles to be in mozilla firefox when the platform is not windows or mac however on ubuntu using snap the firefox profiles are in snap firefox common mozilla firefox that s the directory where profiles ini is one possible solution is to change this appdata new file messageformat format mozilla firefox system getenv home to this appdata new file messageformat format mozilla firefox system getenv home if appdata exists appdata new file messageformat format snap firefox common mozilla firefox system getenv home a more complicated but cleaner solution would be to have a set of plugins that provide likely paths the first one that has a profiles ini wins how can we reproduce the issue shell install ubuntu and firefox using snap then try to load a ff profile using profilesini relevant log output shell none it just returns null on this platform operating system ubuntu selenium version custom build incorporating what are the browser s and version s where you see this issue ff what are the browser driver s and version s where you see this issue n a are you using selenium grid n a | 0 |
256,755 | 22,096,191,573 | IssuesEvent | 2022-06-01 10:19:43 | musescore/MuseScore | https://api.github.com/repos/musescore/MuseScore | closed | [MU4 Issue] Element duration line is not rendered for rasgueado and artificial harmonics | P2 Tested | **To Reproduce**
Steps to reproduce the behavior:
1. Open test file
[0____________rasg.gp.zip](https://github.com/musescore/MuseScore/files/8770324/0____________rasg.gp.zip)
2. Pay attention to the rasgueado marks
**Screenshots**
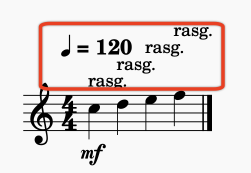
**Expected behavior**
Element duration line is rendered for rasgueado and artificial harmonics
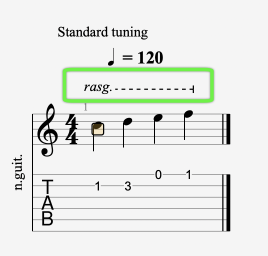
| 1.0 | [MU4 Issue] Element duration line is not rendered for rasgueado and artificial harmonics - **To Reproduce**
Steps to reproduce the behavior:
1. Open test file
[0____________rasg.gp.zip](https://github.com/musescore/MuseScore/files/8770324/0____________rasg.gp.zip)
2. Pay attention to the rasgueado marks
**Screenshots**
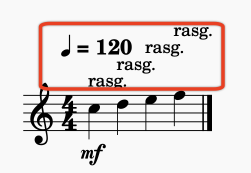
**Expected behavior**
Element duration line is rendered for rasgueado and artificial harmonics
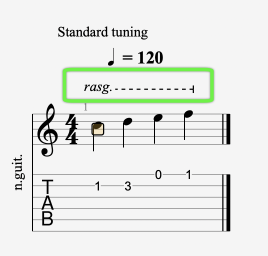
| non_usab | element duration line is not rendered for rasgueado and artificial harmonics to reproduce steps to reproduce the behavior open test file pay attention to the rasgueado marks screenshots expected behavior element duration line is rendered for rasgueado and artificial harmonics | 0 |
247,410 | 7,918,423,435 | IssuesEvent | 2018-07-04 13:16:24 | openaq/openaq-fetch | https://api.github.com/repos/openaq/openaq-fetch | closed | China - Sources (not useable yet) | help wanted high priority new data question | There are a ton of China air quality data sources. Here are some:
aepb.gov.cn
bjmemc.com.cn
cdemc.cn
cfhb.gov.cn
cepb.gov.cn
dl.gov.cn
dyhb.gov.cn
nbemc.gov.cn
sdein.gov.cn
fjepb.gov.cn
gsep.gansu.gov.cn
qhepb.gov.cn
gdep.gov.cn
gxepb.gov.cn
ghb.gov.cn
dloer.gov.cn
hebei.gov.cn
hljdep.gov.cn
hnep.gov.cn
hbepb.gov.cn
hbt.hunan.gov.cn
nmgepb.gov.cn
jshb.gov.cn
jxepb.gov.cn
shbj.klmy.gov.cn
lnemc.cn
lzhb.gov.cn
nnems.gov.cn
nxep.gov.cn
ordoshb.gov.cn
semc.gov.cn
sxhjjcz.com.cn
szhec.gov.cn
tjemc.org.cn
xzep.gov.cn
wlmqhb.gov.cn
whepb.gov.cn
xianemc.gov.cn
xnepb.gov.cn
xjepb.gov.cn
ynepb.gov.cn
zjepb.gov.cn
Sources from: aqicn.org/sources
There is also a site that provides an API to Chinese AQ data:
http://pm25.in/
However the issue is that from what I can tell, these data are not shared in their raw format only AQI (I have not clicked on each and everyone however).
Anyone know differently or find ones above that are shared our in raw format?
| 1.0 | China - Sources (not useable yet) - There are a ton of China air quality data sources. Here are some:
aepb.gov.cn
bjmemc.com.cn
cdemc.cn
cfhb.gov.cn
cepb.gov.cn
dl.gov.cn
dyhb.gov.cn
nbemc.gov.cn
sdein.gov.cn
fjepb.gov.cn
gsep.gansu.gov.cn
qhepb.gov.cn
gdep.gov.cn
gxepb.gov.cn
ghb.gov.cn
dloer.gov.cn
hebei.gov.cn
hljdep.gov.cn
hnep.gov.cn
hbepb.gov.cn
hbt.hunan.gov.cn
nmgepb.gov.cn
jshb.gov.cn
jxepb.gov.cn
shbj.klmy.gov.cn
lnemc.cn
lzhb.gov.cn
nnems.gov.cn
nxep.gov.cn
ordoshb.gov.cn
semc.gov.cn
sxhjjcz.com.cn
szhec.gov.cn
tjemc.org.cn
xzep.gov.cn
wlmqhb.gov.cn
whepb.gov.cn
xianemc.gov.cn
xnepb.gov.cn
xjepb.gov.cn
ynepb.gov.cn
zjepb.gov.cn
Sources from: aqicn.org/sources
There is also a site that provides an API to Chinese AQ data:
http://pm25.in/
However the issue is that from what I can tell, these data are not shared in their raw format only AQI (I have not clicked on each and everyone however).
Anyone know differently or find ones above that are shared our in raw format?
| non_usab | china sources not useable yet there are a ton of china air quality data sources here are some aepb gov cn bjmemc com cn cdemc cn cfhb gov cn cepb gov cn dl gov cn dyhb gov cn nbemc gov cn sdein gov cn fjepb gov cn gsep gansu gov cn qhepb gov cn gdep gov cn gxepb gov cn ghb gov cn dloer gov cn hebei gov cn hljdep gov cn hnep gov cn hbepb gov cn hbt hunan gov cn nmgepb gov cn jshb gov cn jxepb gov cn shbj klmy gov cn lnemc cn lzhb gov cn nnems gov cn nxep gov cn ordoshb gov cn semc gov cn sxhjjcz com cn szhec gov cn tjemc org cn xzep gov cn wlmqhb gov cn whepb gov cn xianemc gov cn xnepb gov cn xjepb gov cn ynepb gov cn zjepb gov cn sources from aqicn org sources there is also a site that provides an api to chinese aq data however the issue is that from what i can tell these data are not shared in their raw format only aqi i have not clicked on each and everyone however anyone know differently or find ones above that are shared our in raw format | 0 |
15,932 | 10,419,648,984 | IssuesEvent | 2019-09-15 18:06:31 | CC3301/csgo-strat-generator | https://api.github.com/repos/CC3301/csgo-strat-generator | closed | Sort buy command | usability | The buy command should represent the order in which the items should be bought. Due to the way that csgo handles these commands, the most important item should be on the first position in the buy command. | True | Sort buy command - The buy command should represent the order in which the items should be bought. Due to the way that csgo handles these commands, the most important item should be on the first position in the buy command. | usab | sort buy command the buy command should represent the order in which the items should be bought due to the way that csgo handles these commands the most important item should be on the first position in the buy command | 1 |
400,425 | 27,284,304,623 | IssuesEvent | 2023-02-23 12:24:30 | inbo/camtraptor | https://api.github.com/repos/inbo/camtraptor | opened | Search results on pkgdown website link to wrong page | bug documentation | 1. Go to https://inbo.github.io/camtraptor/index.html
2. Type "Read" in the search bar at the top
3. Click on the first suggested result in the dropdown: `Reference > Read a Camtrap DP — read_camtrap_dp`
4. Result link to: https://inbo.github.io/reference/read_camtrap_dp.html?q=Read#null
Rather than the expected: https://inbo.github.io/camtraptor/reference/read_camtrap_dp.html?q=Read#null
This also affects:
- [ ] https://trias-project.github.io/trias/
- [ ] https://inbo.github.io/movepub/
- [ ] https://inbo.github.io/etn/
`frictionless`, `bioRad`, `wateRinfo` and `rgbif` are not affected.
@PietrH can you debug this one? | 1.0 | Search results on pkgdown website link to wrong page - 1. Go to https://inbo.github.io/camtraptor/index.html
2. Type "Read" in the search bar at the top
3. Click on the first suggested result in the dropdown: `Reference > Read a Camtrap DP — read_camtrap_dp`
4. Result link to: https://inbo.github.io/reference/read_camtrap_dp.html?q=Read#null
Rather than the expected: https://inbo.github.io/camtraptor/reference/read_camtrap_dp.html?q=Read#null
This also affects:
- [ ] https://trias-project.github.io/trias/
- [ ] https://inbo.github.io/movepub/
- [ ] https://inbo.github.io/etn/
`frictionless`, `bioRad`, `wateRinfo` and `rgbif` are not affected.
@PietrH can you debug this one? | non_usab | search results on pkgdown website link to wrong page go to type read in the search bar at the top click on the first suggested result in the dropdown reference read a camtrap dp — read camtrap dp result link to rather than the expected this also affects frictionless biorad waterinfo and rgbif are not affected pietrh can you debug this one | 0 |
20,736 | 15,977,579,767 | IssuesEvent | 2021-04-17 05:49:07 | HauntedBees/Uprooted | https://api.github.com/repos/HauntedBees/Uprooted | closed | make enemies prioritize throwing ripe crops more | difficulty usability | especially(/exclusively?) mafioso
ed. note: can no longer reproduce; checked enemy attack plan and will always throw crops when ready, unless they want to shoot your crop. seems reasonable. | True | make enemies prioritize throwing ripe crops more - especially(/exclusively?) mafioso
ed. note: can no longer reproduce; checked enemy attack plan and will always throw crops when ready, unless they want to shoot your crop. seems reasonable. | usab | make enemies prioritize throwing ripe crops more especially exclusively mafioso ed note can no longer reproduce checked enemy attack plan and will always throw crops when ready unless they want to shoot your crop seems reasonable | 1 |
1,070 | 3,329,861,926 | IssuesEvent | 2015-11-11 06:07:40 | connolly/desc | https://api.github.com/repos/connolly/desc | opened | WL3-DC2-RQ0:T2 | DC2 DC2 RQ: Set requirements on DC2 simulated datasets Images to shear catalog I RQ wl | Determine the most useful applied shear and convergence. (Ray-tracing through the DC2 light cone, Gaussian shears from a cosmological power spectrum, or something even simpler?) | 1.0 | WL3-DC2-RQ0:T2 - Determine the most useful applied shear and convergence. (Ray-tracing through the DC2 light cone, Gaussian shears from a cosmological power spectrum, or something even simpler?) | non_usab | determine the most useful applied shear and convergence ray tracing through the light cone gaussian shears from a cosmological power spectrum or something even simpler | 0 |
24,143 | 23,391,823,632 | IssuesEvent | 2022-08-11 18:37:29 | linkedin/cruise-control | https://api.github.com/repos/linkedin/cruise-control | opened | NPE exception when calling topic_configuration endpoint | usability | ```
2022/08/10 01:57:51.461 ERROR [KafkaCruiseControlServlet] [qtp1636178473-23] [kafka-cruise-control] [] Error processing POST request '/topic_configuration' due to: 'com.linkedin.kafka.cruisecontrol.exception.KafkaCruiseControlException: java.lang.NullPointerException'.
java.util.concurrent.ExecutionException: com.linkedin.kafka.cruisecontrol.exception.KafkaCruiseControlException: java.lang.NullPointerException
at java.util.concurrent.CompletableFuture.reportGet(CompletableFuture.java:395) ~[?:?]
at java.util.concurrent.CompletableFuture.get(CompletableFuture.java:2022) ~[?:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.AbstractAsyncRequest.getResponse(AbstractAsyncRequest.java:57) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.AbstractRequest.handle(AbstractRequest.java:41) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.KafkaCruiseControlServlet.handlePost(KafkaCruiseControlServlet.java:229) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.KafkaCruiseControlServlet.doGetOrPost(KafkaCruiseControlServlet.java:127) [cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.KafkaCruiseControlServlet.doPost(KafkaCruiseControlServlet.java:106) [cruise-control-2.5.98.jar:?]
at javax.servlet.http.HttpServlet.service(HttpServlet.java:707) [javax.servlet-api-3.1.0.jar:3.1.0]
at javax.servlet.http.HttpServlet.service(HttpServlet.java:790) [javax.servlet-api-3.1.0.jar:3.1.0]
at org.xeril.util.servlet.ProxyServlet.service(ProxyServlet.java:61) [util-servlet-27.2.32.jar:?]
at javax.servlet.http.HttpServlet.service(HttpServlet.java:790) [javax.servlet-api-3.1.0.jar:3.1.0]
at org.eclipse.jetty.servlet.ServletHolder.handle(ServletHolder.java:857) [jetty-servlet-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.servlet.ServletHandler.doHandle(ServletHandler.java:535) [jetty-servlet-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.handle(ScopedHandler.java:146) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.security.SecurityHandler.handle(SecurityHandler.java:548) [jetty-security-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.HandlerWrapper.handle(HandlerWrapper.java:132) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextHandle(ScopedHandler.java:257) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.session.SessionHandler.doHandle(SessionHandler.java:1595) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextHandle(ScopedHandler.java:255) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ContextHandler.doHandle(ContextHandler.java:1340) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextScope(ScopedHandler.java:203) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.servlet.ServletHandler.doScope(ServletHandler.java:473) [jetty-servlet-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.session.SessionHandler.doScope(SessionHandler.java:1564) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextScope(ScopedHandler.java:201) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ContextHandler.doScope(ContextHandler.java:1242) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.handle(ScopedHandler.java:144) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at com.linkedin.emweb.ContextBasedHandlerImpl.handle(ContextBasedHandlerImpl.java:73) [emweb-impl-9.2.70.jar:?]
at com.linkedin.emweb.MapBasedHandlerImpl.handle(MapBasedHandlerImpl.java:480) [emweb-impl-9.2.70.jar:?]
at org.eclipse.jetty.server.handler.HandlerCollection.handle(HandlerCollection.java:126) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.HandlerWrapper.handle(HandlerWrapper.java:132) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.Server.handle(Server.java:503) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.HttpChannel.handle(HttpChannel.java:364) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.HttpConnection.onFillable(HttpConnection.java:260) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.io.AbstractConnection$ReadCallback.succeeded(AbstractConnection.java:305) [jetty-io-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.io.FillInterest.fillable(FillInterest.java:103) [jetty-io-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.io.ChannelEndPoint$2.run(ChannelEndPoint.java:118) [jetty-io-9.4.12.v20180830.jar:9.4.12.v20180830]
at com.linkedin.emweb.ThreadPoolWithTracking$QueuedRunnable.run(ThreadPoolWithTracking.java:424) [emweb-impl-9.2.70.jar:?]
at org.eclipse.jetty.util.thread.QueuedThreadPool.runJob(QueuedThreadPool.java:765) [jetty-util-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.util.thread.QueuedThreadPool$2.run(QueuedThreadPool.java:683) [jetty-util-9.4.12.v20180830.jar:9.4.12.v20180830]
at java.lang.Thread.run(Thread.java:829) [?:?]
Caused by: com.linkedin.kafka.cruisecontrol.exception.KafkaCruiseControlException: java.lang.NullPointerException
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.computeResult(GoalBasedOperationRunnable.java:167) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:149) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:69) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.OperationRunnable.run(OperationRunnable.java:45) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.run(GoalBasedOperationRunnable.java:36) ~[cruise-control-2.5.98.jar:?]
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515) ~[?:?]
at java.util.concurrent.FutureTask.run(FutureTask.java:264) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) ~[?:?]
... 1 more
Caused by: java.lang.NullPointerException
at com.linkedin.kafka.cruisecontrol.model.Host.removeReplica(Host.java:196) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.Rack.removeReplica(Rack.java:167) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.ClusterModel.removeReplica(ClusterModel.java:546) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.ClusterModel.deleteReplica(ClusterModel.java:905) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.ClusterModel.createOrDeleteReplicas(ClusterModel.java:1022) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.licruisecontrol.servlet.handler.async.runnable.LiUpdateTopicConfigurationRunnable.workWithClusterModel(LiUpdateTopicConfigurationRunnable.java:78) ~[likafka-cruise-control-impl_2.12-3.2.17.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.computeResult(GoalBasedOperationRunnable.java:161) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:149) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:69) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.OperationRunnable.run(OperationRunnable.java:45) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.run(GoalBasedOperationRunnable.java:36) ~[cruise-control-2.5.98.jar:?]
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515) ~[?:?]
at java.util.concurrent.FutureTask.run(FutureTask.java:264) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) ~[?:?]
``` | True | NPE exception when calling topic_configuration endpoint - ```
2022/08/10 01:57:51.461 ERROR [KafkaCruiseControlServlet] [qtp1636178473-23] [kafka-cruise-control] [] Error processing POST request '/topic_configuration' due to: 'com.linkedin.kafka.cruisecontrol.exception.KafkaCruiseControlException: java.lang.NullPointerException'.
java.util.concurrent.ExecutionException: com.linkedin.kafka.cruisecontrol.exception.KafkaCruiseControlException: java.lang.NullPointerException
at java.util.concurrent.CompletableFuture.reportGet(CompletableFuture.java:395) ~[?:?]
at java.util.concurrent.CompletableFuture.get(CompletableFuture.java:2022) ~[?:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.AbstractAsyncRequest.getResponse(AbstractAsyncRequest.java:57) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.AbstractRequest.handle(AbstractRequest.java:41) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.KafkaCruiseControlServlet.handlePost(KafkaCruiseControlServlet.java:229) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.KafkaCruiseControlServlet.doGetOrPost(KafkaCruiseControlServlet.java:127) [cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.KafkaCruiseControlServlet.doPost(KafkaCruiseControlServlet.java:106) [cruise-control-2.5.98.jar:?]
at javax.servlet.http.HttpServlet.service(HttpServlet.java:707) [javax.servlet-api-3.1.0.jar:3.1.0]
at javax.servlet.http.HttpServlet.service(HttpServlet.java:790) [javax.servlet-api-3.1.0.jar:3.1.0]
at org.xeril.util.servlet.ProxyServlet.service(ProxyServlet.java:61) [util-servlet-27.2.32.jar:?]
at javax.servlet.http.HttpServlet.service(HttpServlet.java:790) [javax.servlet-api-3.1.0.jar:3.1.0]
at org.eclipse.jetty.servlet.ServletHolder.handle(ServletHolder.java:857) [jetty-servlet-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.servlet.ServletHandler.doHandle(ServletHandler.java:535) [jetty-servlet-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.handle(ScopedHandler.java:146) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.security.SecurityHandler.handle(SecurityHandler.java:548) [jetty-security-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.HandlerWrapper.handle(HandlerWrapper.java:132) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextHandle(ScopedHandler.java:257) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.session.SessionHandler.doHandle(SessionHandler.java:1595) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextHandle(ScopedHandler.java:255) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ContextHandler.doHandle(ContextHandler.java:1340) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextScope(ScopedHandler.java:203) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.servlet.ServletHandler.doScope(ServletHandler.java:473) [jetty-servlet-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.session.SessionHandler.doScope(SessionHandler.java:1564) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.nextScope(ScopedHandler.java:201) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ContextHandler.doScope(ContextHandler.java:1242) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.ScopedHandler.handle(ScopedHandler.java:144) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at com.linkedin.emweb.ContextBasedHandlerImpl.handle(ContextBasedHandlerImpl.java:73) [emweb-impl-9.2.70.jar:?]
at com.linkedin.emweb.MapBasedHandlerImpl.handle(MapBasedHandlerImpl.java:480) [emweb-impl-9.2.70.jar:?]
at org.eclipse.jetty.server.handler.HandlerCollection.handle(HandlerCollection.java:126) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.handler.HandlerWrapper.handle(HandlerWrapper.java:132) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.Server.handle(Server.java:503) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.HttpChannel.handle(HttpChannel.java:364) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.server.HttpConnection.onFillable(HttpConnection.java:260) [jetty-server-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.io.AbstractConnection$ReadCallback.succeeded(AbstractConnection.java:305) [jetty-io-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.io.FillInterest.fillable(FillInterest.java:103) [jetty-io-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.io.ChannelEndPoint$2.run(ChannelEndPoint.java:118) [jetty-io-9.4.12.v20180830.jar:9.4.12.v20180830]
at com.linkedin.emweb.ThreadPoolWithTracking$QueuedRunnable.run(ThreadPoolWithTracking.java:424) [emweb-impl-9.2.70.jar:?]
at org.eclipse.jetty.util.thread.QueuedThreadPool.runJob(QueuedThreadPool.java:765) [jetty-util-9.4.12.v20180830.jar:9.4.12.v20180830]
at org.eclipse.jetty.util.thread.QueuedThreadPool$2.run(QueuedThreadPool.java:683) [jetty-util-9.4.12.v20180830.jar:9.4.12.v20180830]
at java.lang.Thread.run(Thread.java:829) [?:?]
Caused by: com.linkedin.kafka.cruisecontrol.exception.KafkaCruiseControlException: java.lang.NullPointerException
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.computeResult(GoalBasedOperationRunnable.java:167) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:149) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:69) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.OperationRunnable.run(OperationRunnable.java:45) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.run(GoalBasedOperationRunnable.java:36) ~[cruise-control-2.5.98.jar:?]
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515) ~[?:?]
at java.util.concurrent.FutureTask.run(FutureTask.java:264) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) ~[?:?]
... 1 more
Caused by: java.lang.NullPointerException
at com.linkedin.kafka.cruisecontrol.model.Host.removeReplica(Host.java:196) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.Rack.removeReplica(Rack.java:167) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.ClusterModel.removeReplica(ClusterModel.java:546) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.ClusterModel.deleteReplica(ClusterModel.java:905) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.model.ClusterModel.createOrDeleteReplicas(ClusterModel.java:1022) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.licruisecontrol.servlet.handler.async.runnable.LiUpdateTopicConfigurationRunnable.workWithClusterModel(LiUpdateTopicConfigurationRunnable.java:78) ~[likafka-cruise-control-impl_2.12-3.2.17.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.computeResult(GoalBasedOperationRunnable.java:161) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:149) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.UpdateTopicConfigurationRunnable.getResult(UpdateTopicConfigurationRunnable.java:69) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.OperationRunnable.run(OperationRunnable.java:45) ~[cruise-control-2.5.98.jar:?]
at com.linkedin.kafka.cruisecontrol.servlet.handler.async.runnable.GoalBasedOperationRunnable.run(GoalBasedOperationRunnable.java:36) ~[cruise-control-2.5.98.jar:?]
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515) ~[?:?]
at java.util.concurrent.FutureTask.run(FutureTask.java:264) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128) ~[?:?]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628) ~[?:?]
``` | usab | npe exception when calling topic configuration endpoint error error processing post request topic configuration due to com linkedin kafka cruisecontrol exception kafkacruisecontrolexception java lang nullpointerexception java util concurrent executionexception com linkedin kafka cruisecontrol exception kafkacruisecontrolexception java lang nullpointerexception at java util concurrent completablefuture reportget completablefuture java at java util concurrent completablefuture get completablefuture java at com linkedin kafka cruisecontrol servlet handler async abstractasyncrequest getresponse abstractasyncrequest java at com linkedin kafka cruisecontrol servlet handler abstractrequest handle abstractrequest java at com linkedin kafka cruisecontrol servlet kafkacruisecontrolservlet handlepost kafkacruisecontrolservlet java at com linkedin kafka cruisecontrol servlet kafkacruisecontrolservlet dogetorpost kafkacruisecontrolservlet java at com linkedin kafka cruisecontrol servlet kafkacruisecontrolservlet dopost kafkacruisecontrolservlet java at javax servlet http httpservlet service httpservlet java at javax servlet http httpservlet service httpservlet java at org xeril util servlet proxyservlet service proxyservlet java at javax servlet http httpservlet service httpservlet java at org eclipse jetty servlet servletholder handle servletholder java at org eclipse jetty servlet servlethandler dohandle servlethandler java at org eclipse jetty server handler scopedhandler handle scopedhandler java at org eclipse jetty security securityhandler handle securityhandler java at org eclipse jetty server handler handlerwrapper handle handlerwrapper java at org eclipse jetty server handler scopedhandler nexthandle scopedhandler java at org eclipse jetty server session sessionhandler dohandle sessionhandler java at org eclipse jetty server handler scopedhandler nexthandle scopedhandler java at org eclipse jetty server handler contexthandler dohandle contexthandler java at org eclipse jetty server handler scopedhandler nextscope scopedhandler java at org eclipse jetty servlet servlethandler doscope servlethandler java at org eclipse jetty server session sessionhandler doscope sessionhandler java at org eclipse jetty server handler scopedhandler nextscope scopedhandler java at org eclipse jetty server handler contexthandler doscope contexthandler java at org eclipse jetty server handler scopedhandler handle scopedhandler java at com linkedin emweb contextbasedhandlerimpl handle contextbasedhandlerimpl java at com linkedin emweb mapbasedhandlerimpl handle mapbasedhandlerimpl java at org eclipse jetty server handler handlercollection handle handlercollection java at org eclipse jetty server handler handlerwrapper handle handlerwrapper java at org eclipse jetty server server handle server java at org eclipse jetty server httpchannel handle httpchannel java at org eclipse jetty server httpconnection onfillable httpconnection java at org eclipse jetty io abstractconnection readcallback succeeded abstractconnection java at org eclipse jetty io fillinterest fillable fillinterest java at org eclipse jetty io channelendpoint run channelendpoint java at com linkedin emweb threadpoolwithtracking queuedrunnable run threadpoolwithtracking java at org eclipse jetty util thread queuedthreadpool runjob queuedthreadpool java at org eclipse jetty util thread queuedthreadpool run queuedthreadpool java at java lang thread run thread java caused by com linkedin kafka cruisecontrol exception kafkacruisecontrolexception java lang nullpointerexception at com linkedin kafka cruisecontrol servlet handler async runnable goalbasedoperationrunnable computeresult goalbasedoperationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable updatetopicconfigurationrunnable getresult updatetopicconfigurationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable updatetopicconfigurationrunnable getresult updatetopicconfigurationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable operationrunnable run operationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable goalbasedoperationrunnable run goalbasedoperationrunnable java at java util concurrent executors runnableadapter call executors java at java util concurrent futuretask run futuretask java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java more caused by java lang nullpointerexception at com linkedin kafka cruisecontrol model host removereplica host java at com linkedin kafka cruisecontrol model rack removereplica rack java at com linkedin kafka cruisecontrol model clustermodel removereplica clustermodel java at com linkedin kafka cruisecontrol model clustermodel deletereplica clustermodel java at com linkedin kafka cruisecontrol model clustermodel createordeletereplicas clustermodel java at com linkedin kafka licruisecontrol servlet handler async runnable liupdatetopicconfigurationrunnable workwithclustermodel liupdatetopicconfigurationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable goalbasedoperationrunnable computeresult goalbasedoperationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable updatetopicconfigurationrunnable getresult updatetopicconfigurationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable updatetopicconfigurationrunnable getresult updatetopicconfigurationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable operationrunnable run operationrunnable java at com linkedin kafka cruisecontrol servlet handler async runnable goalbasedoperationrunnable run goalbasedoperationrunnable java at java util concurrent executors runnableadapter call executors java at java util concurrent futuretask run futuretask java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java | 1 |
374,772 | 11,095,253,595 | IssuesEvent | 2019-12-16 08:41:24 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.pornhub.com - design is broken | browser-focus-geckoview engine-gecko ml-needsdiagnosis-false priority-critical | <!-- @browser: Firefox Mobile 71.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:71.0) Gecko/71.0 Firefox/71.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.pornhub.com/login?redirect=cTF12HAk8tJ2J22KE07_tGGQiqto0YEF9lJYAaDSjLMlAGijr-EbAOvmJcTgLA9A
**Browser / Version**: Firefox Mobile 71.0
**Operating System**: Android
**Tested Another Browser**: Unknown
**Problem type**: Design is broken
**Description**: redirect
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.pornhub.com - design is broken - <!-- @browser: Firefox Mobile 71.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:71.0) Gecko/71.0 Firefox/71.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.pornhub.com/login?redirect=cTF12HAk8tJ2J22KE07_tGGQiqto0YEF9lJYAaDSjLMlAGijr-EbAOvmJcTgLA9A
**Browser / Version**: Firefox Mobile 71.0
**Operating System**: Android
**Tested Another Browser**: Unknown
**Problem type**: Design is broken
**Description**: redirect
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_usab | design is broken url browser version firefox mobile operating system android tested another browser unknown problem type design is broken description redirect steps to reproduce browser configuration none from with ❤️ | 0 |
28,736 | 11,685,286,307 | IssuesEvent | 2020-03-05 08:48:13 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | Custom ETP: Choose which trackers and scripts to block | E8 Feature:FennecTransition Feature:Privacy&Security Feature:TrackingProtection eng:ready should | ## User Story
- As a user, I want to choose which type of trackers and scripts to block in my browser, so I can have full control over my privacy settings.
Note: currently users do not have the option of blocking all cookies if they choose to.
### Acceptance Criteria
- [x] I can go in my ETP settings and choose "custom" and decide on which trackers and scripts are blocked.
- [x] I can choose to block all cookies if I want.
- [ ] Telemetry Ticket to track how often users choose custom
Design Work
- [ ] Request for Comments from UX team
- [ ] N/A Usability testing if a new pattern or potentially confusing UI
- [x] Request for Comments from Fenix team and/or A/C, GV, Sync, etc as needed
- [x] Interaction details included
- [ ] N/A Accessibility - is this a review by someone, just keeping it in mind?
- [x] For existing UI changes, details are highlighted
- [x] Strings/content reviewed and approved
- [ ] Are they too long for the component in other locales
Deliverable
- [x] Assets uploaded to Google Drive
- [x] Links to deliverables (spec, assets) posted in comment 0
Deliverable Links
[UX Spec](https://share.goabstract.com/e02ea1ca-172f-4be9-abd5-03621246e434?mode=design&sha=7d9abedbe503d2fc1a494b4cf3b59e607c7b7a19)
| True | Custom ETP: Choose which trackers and scripts to block - ## User Story
- As a user, I want to choose which type of trackers and scripts to block in my browser, so I can have full control over my privacy settings.
Note: currently users do not have the option of blocking all cookies if they choose to.
### Acceptance Criteria
- [x] I can go in my ETP settings and choose "custom" and decide on which trackers and scripts are blocked.
- [x] I can choose to block all cookies if I want.
- [ ] Telemetry Ticket to track how often users choose custom
Design Work
- [ ] Request for Comments from UX team
- [ ] N/A Usability testing if a new pattern or potentially confusing UI
- [x] Request for Comments from Fenix team and/or A/C, GV, Sync, etc as needed
- [x] Interaction details included
- [ ] N/A Accessibility - is this a review by someone, just keeping it in mind?
- [x] For existing UI changes, details are highlighted
- [x] Strings/content reviewed and approved
- [ ] Are they too long for the component in other locales
Deliverable
- [x] Assets uploaded to Google Drive
- [x] Links to deliverables (spec, assets) posted in comment 0
Deliverable Links
[UX Spec](https://share.goabstract.com/e02ea1ca-172f-4be9-abd5-03621246e434?mode=design&sha=7d9abedbe503d2fc1a494b4cf3b59e607c7b7a19)
| non_usab | custom etp choose which trackers and scripts to block user story as a user i want to choose which type of trackers and scripts to block in my browser so i can have full control over my privacy settings note currently users do not have the option of blocking all cookies if they choose to acceptance criteria i can go in my etp settings and choose custom and decide on which trackers and scripts are blocked i can choose to block all cookies if i want telemetry ticket to track how often users choose custom design work request for comments from ux team n a usability testing if a new pattern or potentially confusing ui request for comments from fenix team and or a c gv sync etc as needed interaction details included n a accessibility is this a review by someone just keeping it in mind for existing ui changes details are highlighted strings content reviewed and approved are they too long for the component in other locales deliverable assets uploaded to google drive links to deliverables spec assets posted in comment deliverable links | 0 |
22,494 | 6,254,574,519 | IssuesEvent | 2017-07-14 02:49:12 | PowerPointLabs/PowerPointLabs | https://api.github.com/repos/PowerPointLabs/PowerPointLabs | opened | TextCollection should be organized into their respective labs | a-CodeQuality c.Task | Also needs to consider whether the text classes should be put into their respective labs folder, or a textcollection folder.
e.g. CropLab/CropLabText.cs or TextCollection/CropLabText.cs
A few options:
- Use a namespace
```
namespace PowerPointLabs.TextCollection
{
internal static class CropLabText { ... }
}
using PowerPointLabs.TextCollection;
string str = CropLabText.CropToShapeTooltip;
```
Pros: Separate TextCollection class for each lab, more readable when using the strings
Cons:
- Use partial class
```
internal static partial class TextCollection
{
public static string CropLabCropToShapeTooltip = "";
}
string str = TextCollection.CropLabCropToShapeTooltip;
```
Pros: A single class for all text
Cons: Needs to prefix the lab into the variable names, little difference from now other than file organization | 1.0 | TextCollection should be organized into their respective labs - Also needs to consider whether the text classes should be put into their respective labs folder, or a textcollection folder.
e.g. CropLab/CropLabText.cs or TextCollection/CropLabText.cs
A few options:
- Use a namespace
```
namespace PowerPointLabs.TextCollection
{
internal static class CropLabText { ... }
}
using PowerPointLabs.TextCollection;
string str = CropLabText.CropToShapeTooltip;
```
Pros: Separate TextCollection class for each lab, more readable when using the strings
Cons:
- Use partial class
```
internal static partial class TextCollection
{
public static string CropLabCropToShapeTooltip = "";
}
string str = TextCollection.CropLabCropToShapeTooltip;
```
Pros: A single class for all text
Cons: Needs to prefix the lab into the variable names, little difference from now other than file organization | non_usab | textcollection should be organized into their respective labs also needs to consider whether the text classes should be put into their respective labs folder or a textcollection folder e g croplab croplabtext cs or textcollection croplabtext cs a few options use a namespace namespace powerpointlabs textcollection internal static class croplabtext using powerpointlabs textcollection string str croplabtext croptoshapetooltip pros separate textcollection class for each lab more readable when using the strings cons use partial class internal static partial class textcollection public static string croplabcroptoshapetooltip string str textcollection croplabcroptoshapetooltip pros a single class for all text cons needs to prefix the lab into the variable names little difference from now other than file organization | 0 |
252,267 | 19,010,038,052 | IssuesEvent | 2021-11-23 08:11:45 | fremtind/jokul | https://api.github.com/repos/fremtind/jokul | closed | Komponentdok for Message box | 📚 documentation | **Må ha**
- [x] Eksempler på riktig og feil bruk
- [x] Live kodeeksempel
- [x] React-props oppsummert i bunnen
**Vil ha**
- [ ] Eksempler på bruk i teamene
- [x] Kontrollspørsmål for bruk
- [x] Lenker til relevante komponenter | 1.0 | Komponentdok for Message box - **Må ha**
- [x] Eksempler på riktig og feil bruk
- [x] Live kodeeksempel
- [x] React-props oppsummert i bunnen
**Vil ha**
- [ ] Eksempler på bruk i teamene
- [x] Kontrollspørsmål for bruk
- [x] Lenker til relevante komponenter | non_usab | komponentdok for message box må ha eksempler på riktig og feil bruk live kodeeksempel react props oppsummert i bunnen vil ha eksempler på bruk i teamene kontrollspørsmål for bruk lenker til relevante komponenter | 0 |
15,951 | 10,440,651,453 | IssuesEvent | 2019-09-18 09:09:12 | niftools/blender_nif_plugin | https://api.github.com/repos/niftools/blender_nif_plugin | closed | Export fails : No object selected | Improvement Usability | Traceback (most recent call last):
File "\io_scene_nif\operators\nif_export_op.py", line 164, in execute
return nif_export.NifExport(self, context).execute()
File "\io_scene_nif\nif_export.py", line 200, in execute
"Please select the object(s) to export,"
io_scene_nif.utility.nif_utils.NifError: Please select the object(s) to export, and run this script again.
location: <unknown location>:-1
| True | Export fails : No object selected - Traceback (most recent call last):
File "\io_scene_nif\operators\nif_export_op.py", line 164, in execute
return nif_export.NifExport(self, context).execute()
File "\io_scene_nif\nif_export.py", line 200, in execute
"Please select the object(s) to export,"
io_scene_nif.utility.nif_utils.NifError: Please select the object(s) to export, and run this script again.
location: <unknown location>:-1
| usab | export fails no object selected traceback most recent call last file io scene nif operators nif export op py line in execute return nif export nifexport self context execute file io scene nif nif export py line in execute please select the object s to export io scene nif utility nif utils niferror please select the object s to export and run this script again location | 1 |
193,384 | 22,216,144,508 | IssuesEvent | 2022-06-08 02:00:28 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2017-7273 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2017-7273 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-cypress.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The cp_report_fixup function in drivers/hid/hid-cypress.c in the Linux kernel 3.2 and 4.x before 4.9.4 allows physically proximate attackers to cause a denial of service (integer underflow) or possibly have unspecified other impact via a crafted HID report.
<p>Publish Date: 2017-03-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7273>CVE-2017-7273</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-7273">https://nvd.nist.gov/vuln/detail/CVE-2017-7273</a></p>
<p>Release Date: 2017-03-27</p>
<p>Fix Resolution: 4.9.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-7273 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2017-7273 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-cypress.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The cp_report_fixup function in drivers/hid/hid-cypress.c in the Linux kernel 3.2 and 4.x before 4.9.4 allows physically proximate attackers to cause a denial of service (integer underflow) or possibly have unspecified other impact via a crafted HID report.
<p>Publish Date: 2017-03-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7273>CVE-2017-7273</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-7273">https://nvd.nist.gov/vuln/detail/CVE-2017-7273</a></p>
<p>Release Date: 2017-03-27</p>
<p>Fix Resolution: 4.9.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files drivers hid hid cypress c vulnerability details the cp report fixup function in drivers hid hid cypress c in the linux kernel and x before allows physically proximate attackers to cause a denial of service integer underflow or possibly have unspecified other impact via a crafted hid report publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
10,882 | 6,970,715,208 | IssuesEvent | 2017-12-11 11:18:49 | theodi/csvlint | https://api.github.com/repos/theodi/csvlint | opened | Allow additional columns | f:enhancement-suggestion fn:Development fn:Usability | Allow for the extension of datasets with local information - additional columns outside of the provided schema - extendable.
- Validator should ignore any columns included in addition to those in the schema | True | Allow additional columns - Allow for the extension of datasets with local information - additional columns outside of the provided schema - extendable.
- Validator should ignore any columns included in addition to those in the schema | usab | allow additional columns allow for the extension of datasets with local information additional columns outside of the provided schema extendable validator should ignore any columns included in addition to those in the schema | 1 |
7,377 | 4,958,430,729 | IssuesEvent | 2016-12-02 09:45:27 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | How to disable the internal text editor? | bug topic:editor usability | Godot version:2.1.1
I set the external editor to sublime3,but when I edit a script,both the sublime3 and internal editor pop up.
How can I disable the internal editor? | True | How to disable the internal text editor? - Godot version:2.1.1
I set the external editor to sublime3,but when I edit a script,both the sublime3 and internal editor pop up.
How can I disable the internal editor? | usab | how to disable the internal text editor godot version i set the external editor to but when i edit a script both the and internal editor pop up how can i disable the internal editor | 1 |
67,825 | 21,180,716,152 | IssuesEvent | 2022-04-08 07:39:30 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | Hazelcast hangs in REPLICA_NOT_SYNC state [HZ-1013] | Type: Defect Team: Core Source: Community Module: Partitioning to-jira | <!--
Thanks for reporting your issue. Please share with us the following information, to help us resolve your issue quickly and efficiently.
-->
**Describe the bug**
Unfortunately, I don't have too much information I can share and also no reproduction case. We're experiencing problems with our Hazelcast nodes that seem to hang in `REPLICA_NOT_SYNC` state and even get unresponsive as it seems. Especially when starting the cluster we notice this. We're doing health checks each second that try to call `IPartitionService.isMemberStateSafe`. When we remove that from that from the health check our cluster seems to be fine after startup.
**Expected behavior**
Member state recovers to SAFE eventually and application does not hang.
**To Reproduce**
Unfortunately, no reproduction available. Calling `IPartitionService.isMemberStateSafe` concurrently might be a way.
**Additional context**
Hazelcast 4.1.5
JDK 11.0.12
Linux
Cluster size: 2
Application is not under load when this happens.
Might be related to https://github.com/hazelcast/hazelcast/issues/18778#issuecomment-86761475
**Excerpt of thread dump**
```
"ForkJoinPool.commonPool-worker-5" #114 daemon prio=5 os_prio=0 cpu=924.45ms elapsed=4695.40s tid=0x00007f3cb8203800 nid=0x1d0b waiting on condition [0x00007f3c9a0d7000]
java.lang.Thread.State: TIMED_WAITING (parking)
at jdk.internal.misc.Unsafe.park(java.base@11.0.12/Native Method)
- parking to wait for <0x00000007f170f5c8> (a java.util.concurrent.Semaphore$NonfairSync)
at java.util.concurrent.locks.LockSupport.parkNanos(java.base@11.0.12/LockSupport.java:234)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1079)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.tryAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1369)
at java.util.concurrent.Semaphore.tryAcquire(java.base@11.0.12/Semaphore.java:592)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.checkAndTriggerReplicaSync(PartitionReplicaStateChecker.java:238)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.getPartitionServiceState(PartitionReplicaStateChecker.java:107)
at com.hazelcast.internal.partition.impl.InternalPartitionServiceImpl.isMemberStateSafe(InternalPartitionServiceImpl.java:1107)
"ForkJoinPool.commonPool-worker-7" #120 daemon prio=5 os_prio=0 cpu=940.15ms elapsed=4695.04s tid=0x00007f3cf800b000 nid=0x1d11 waiting on condition [0x00007f3c9a5dc000]
java.lang.Thread.State: TIMED_WAITING (parking)
at jdk.internal.misc.Unsafe.park(java.base@11.0.12/Native Method)
- parking to wait for <0x00000007f21c61c0> (a java.util.concurrent.Semaphore$NonfairSync)
at java.util.concurrent.locks.LockSupport.parkNanos(java.base@11.0.12/LockSupport.java:234)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1079)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.tryAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1369)
at java.util.concurrent.Semaphore.tryAcquire(java.base@11.0.12/Semaphore.java:592)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.checkAndTriggerReplicaSync(PartitionReplicaStateChecker.java:238)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.getPartitionServiceState(PartitionReplicaStateChecker.java:107)
at com.hazelcast.internal.partition.impl.InternalPartitionServiceImpl.isMemberStateSafe(InternalPartitionServiceImpl.java:1107)
``` | 1.0 | Hazelcast hangs in REPLICA_NOT_SYNC state [HZ-1013] - <!--
Thanks for reporting your issue. Please share with us the following information, to help us resolve your issue quickly and efficiently.
-->
**Describe the bug**
Unfortunately, I don't have too much information I can share and also no reproduction case. We're experiencing problems with our Hazelcast nodes that seem to hang in `REPLICA_NOT_SYNC` state and even get unresponsive as it seems. Especially when starting the cluster we notice this. We're doing health checks each second that try to call `IPartitionService.isMemberStateSafe`. When we remove that from that from the health check our cluster seems to be fine after startup.
**Expected behavior**
Member state recovers to SAFE eventually and application does not hang.
**To Reproduce**
Unfortunately, no reproduction available. Calling `IPartitionService.isMemberStateSafe` concurrently might be a way.
**Additional context**
Hazelcast 4.1.5
JDK 11.0.12
Linux
Cluster size: 2
Application is not under load when this happens.
Might be related to https://github.com/hazelcast/hazelcast/issues/18778#issuecomment-86761475
**Excerpt of thread dump**
```
"ForkJoinPool.commonPool-worker-5" #114 daemon prio=5 os_prio=0 cpu=924.45ms elapsed=4695.40s tid=0x00007f3cb8203800 nid=0x1d0b waiting on condition [0x00007f3c9a0d7000]
java.lang.Thread.State: TIMED_WAITING (parking)
at jdk.internal.misc.Unsafe.park(java.base@11.0.12/Native Method)
- parking to wait for <0x00000007f170f5c8> (a java.util.concurrent.Semaphore$NonfairSync)
at java.util.concurrent.locks.LockSupport.parkNanos(java.base@11.0.12/LockSupport.java:234)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1079)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.tryAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1369)
at java.util.concurrent.Semaphore.tryAcquire(java.base@11.0.12/Semaphore.java:592)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.checkAndTriggerReplicaSync(PartitionReplicaStateChecker.java:238)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.getPartitionServiceState(PartitionReplicaStateChecker.java:107)
at com.hazelcast.internal.partition.impl.InternalPartitionServiceImpl.isMemberStateSafe(InternalPartitionServiceImpl.java:1107)
"ForkJoinPool.commonPool-worker-7" #120 daemon prio=5 os_prio=0 cpu=940.15ms elapsed=4695.04s tid=0x00007f3cf800b000 nid=0x1d11 waiting on condition [0x00007f3c9a5dc000]
java.lang.Thread.State: TIMED_WAITING (parking)
at jdk.internal.misc.Unsafe.park(java.base@11.0.12/Native Method)
- parking to wait for <0x00000007f21c61c0> (a java.util.concurrent.Semaphore$NonfairSync)
at java.util.concurrent.locks.LockSupport.parkNanos(java.base@11.0.12/LockSupport.java:234)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1079)
at java.util.concurrent.locks.AbstractQueuedSynchronizer.tryAcquireSharedNanos(java.base@11.0.12/AbstractQueuedSynchronizer.java:1369)
at java.util.concurrent.Semaphore.tryAcquire(java.base@11.0.12/Semaphore.java:592)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.checkAndTriggerReplicaSync(PartitionReplicaStateChecker.java:238)
at com.hazelcast.internal.partition.impl.PartitionReplicaStateChecker.getPartitionServiceState(PartitionReplicaStateChecker.java:107)
at com.hazelcast.internal.partition.impl.InternalPartitionServiceImpl.isMemberStateSafe(InternalPartitionServiceImpl.java:1107)
``` | non_usab | hazelcast hangs in replica not sync state thanks for reporting your issue please share with us the following information to help us resolve your issue quickly and efficiently describe the bug unfortunately i don t have too much information i can share and also no reproduction case we re experiencing problems with our hazelcast nodes that seem to hang in replica not sync state and even get unresponsive as it seems especially when starting the cluster we notice this we re doing health checks each second that try to call ipartitionservice ismemberstatesafe when we remove that from that from the health check our cluster seems to be fine after startup expected behavior member state recovers to safe eventually and application does not hang to reproduce unfortunately no reproduction available calling ipartitionservice ismemberstatesafe concurrently might be a way additional context hazelcast jdk linux cluster size application is not under load when this happens might be related to excerpt of thread dump forkjoinpool commonpool worker daemon prio os prio cpu elapsed tid nid waiting on condition java lang thread state timed waiting parking at jdk internal misc unsafe park java base native method parking to wait for a java util concurrent semaphore nonfairsync at java util concurrent locks locksupport parknanos java base locksupport java at java util concurrent locks abstractqueuedsynchronizer doacquiresharednanos java base abstractqueuedsynchronizer java at java util concurrent locks abstractqueuedsynchronizer tryacquiresharednanos java base abstractqueuedsynchronizer java at java util concurrent semaphore tryacquire java base semaphore java at com hazelcast internal partition impl partitionreplicastatechecker checkandtriggerreplicasync partitionreplicastatechecker java at com hazelcast internal partition impl partitionreplicastatechecker getpartitionservicestate partitionreplicastatechecker java at com hazelcast internal partition impl internalpartitionserviceimpl ismemberstatesafe internalpartitionserviceimpl java forkjoinpool commonpool worker daemon prio os prio cpu elapsed tid nid waiting on condition java lang thread state timed waiting parking at jdk internal misc unsafe park java base native method parking to wait for a java util concurrent semaphore nonfairsync at java util concurrent locks locksupport parknanos java base locksupport java at java util concurrent locks abstractqueuedsynchronizer doacquiresharednanos java base abstractqueuedsynchronizer java at java util concurrent locks abstractqueuedsynchronizer tryacquiresharednanos java base abstractqueuedsynchronizer java at java util concurrent semaphore tryacquire java base semaphore java at com hazelcast internal partition impl partitionreplicastatechecker checkandtriggerreplicasync partitionreplicastatechecker java at com hazelcast internal partition impl partitionreplicastatechecker getpartitionservicestate partitionreplicastatechecker java at com hazelcast internal partition impl internalpartitionserviceimpl ismemberstatesafe internalpartitionserviceimpl java | 0 |
19,972 | 14,855,890,483 | IssuesEvent | 2021-01-18 13:25:19 | raiden-network/raiden | https://api.github.com/repos/raiden-network/raiden | closed | Check minimal transfer expiration | Component / API Flag / Usability | In https://github.com/raiden-network/team/issues/894 we agreed to the minimal allowed value for transfer expiration that should be accepted by the client.
It needs to be checked that
- the client accepts transfers with the minimal and great expiration
- the client rejects transfers with lower expiration that the minimal value
The default expiration should stay the same
| True | Check minimal transfer expiration - In https://github.com/raiden-network/team/issues/894 we agreed to the minimal allowed value for transfer expiration that should be accepted by the client.
It needs to be checked that
- the client accepts transfers with the minimal and great expiration
- the client rejects transfers with lower expiration that the minimal value
The default expiration should stay the same
| usab | check minimal transfer expiration in we agreed to the minimal allowed value for transfer expiration that should be accepted by the client it needs to be checked that the client accepts transfers with the minimal and great expiration the client rejects transfers with lower expiration that the minimal value the default expiration should stay the same | 1 |
1,614 | 2,908,672,460 | IssuesEvent | 2015-06-20 00:35:07 | sandstorm-io/sandstorm | https://api.github.com/repos/sandstorm-io/sandstorm | closed | Admin page: confusing message after configuring an OAuth provider | bite-size self-hosting shell usability | After configuring an OAuth provider and clicking "save configuration", the config window closes and a message appears at the bottom of the setting page saying "Success! Your settings have been saved.". But, this only refers to the service config. The fact that I have checked the box to enable the login method (which is what caused the service config window to open) has _not_ been saved, requiring me to click "save" again.
I think that:
* Clicking "save configuration" on the service config should also immediately update the database to indicate that the service is enabled (without saving the rest of the stuff on the page).
* No "success" message should appear when the window closes; generally, the fact that the window closed is already enough feedback for the user that the settings were accepted. (You could still display an error if there is one.) | True | Admin page: confusing message after configuring an OAuth provider - After configuring an OAuth provider and clicking "save configuration", the config window closes and a message appears at the bottom of the setting page saying "Success! Your settings have been saved.". But, this only refers to the service config. The fact that I have checked the box to enable the login method (which is what caused the service config window to open) has _not_ been saved, requiring me to click "save" again.
I think that:
* Clicking "save configuration" on the service config should also immediately update the database to indicate that the service is enabled (without saving the rest of the stuff on the page).
* No "success" message should appear when the window closes; generally, the fact that the window closed is already enough feedback for the user that the settings were accepted. (You could still display an error if there is one.) | usab | admin page confusing message after configuring an oauth provider after configuring an oauth provider and clicking save configuration the config window closes and a message appears at the bottom of the setting page saying success your settings have been saved but this only refers to the service config the fact that i have checked the box to enable the login method which is what caused the service config window to open has not been saved requiring me to click save again i think that clicking save configuration on the service config should also immediately update the database to indicate that the service is enabled without saving the rest of the stuff on the page no success message should appear when the window closes generally the fact that the window closed is already enough feedback for the user that the settings were accepted you could still display an error if there is one | 1 |
4,914 | 3,898,334,503 | IssuesEvent | 2016-04-17 01:01:15 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 14847817: UIScrollView: Need updated frame when keyboard is being dismissed interactively | classification:ui/usability reproducible:always status:open | #### Description
Summary:
Setting UIScrollView's keyboardDismissMode property to interactive allows the user to manipulate the keyboard by dragging. However, there is no (easy) way to find out the updated frame of the keyboard.
The notifications UIKeyboardDidChangeFrameNotification and UIKeyboardWillChangeFrameNotification are only sent when the keyboard is displayed and dismissed. They are not sent as the frame of the keyboard is updated.
Either these notifications should fire every frame as the keyboard is being dragged, or UIScrollViewDelegate should have a new delegate method, something like -scrollView:didChangeKeyboardFrame:, where the second parameter is the frame of the keyboard converted to the scrollview's coordinate space.
Steps to Reproduce:
Expected Results:
Actual Results:
Regression:
Notes:
-
Product Version: 7 seed 5
Created: 2013-08-27T19:50:23.461411
Originated: 2013-08-27T13:49:00
Open Radar Link: http://www.openradar.me/14847817 | True | 14847817: UIScrollView: Need updated frame when keyboard is being dismissed interactively - #### Description
Summary:
Setting UIScrollView's keyboardDismissMode property to interactive allows the user to manipulate the keyboard by dragging. However, there is no (easy) way to find out the updated frame of the keyboard.
The notifications UIKeyboardDidChangeFrameNotification and UIKeyboardWillChangeFrameNotification are only sent when the keyboard is displayed and dismissed. They are not sent as the frame of the keyboard is updated.
Either these notifications should fire every frame as the keyboard is being dragged, or UIScrollViewDelegate should have a new delegate method, something like -scrollView:didChangeKeyboardFrame:, where the second parameter is the frame of the keyboard converted to the scrollview's coordinate space.
Steps to Reproduce:
Expected Results:
Actual Results:
Regression:
Notes:
-
Product Version: 7 seed 5
Created: 2013-08-27T19:50:23.461411
Originated: 2013-08-27T13:49:00
Open Radar Link: http://www.openradar.me/14847817 | usab | uiscrollview need updated frame when keyboard is being dismissed interactively description summary setting uiscrollview s keyboarddismissmode property to interactive allows the user to manipulate the keyboard by dragging however there is no easy way to find out the updated frame of the keyboard the notifications uikeyboarddidchangeframenotification and uikeyboardwillchangeframenotification are only sent when the keyboard is displayed and dismissed they are not sent as the frame of the keyboard is updated either these notifications should fire every frame as the keyboard is being dragged or uiscrollviewdelegate should have a new delegate method something like scrollview didchangekeyboardframe where the second parameter is the frame of the keyboard converted to the scrollview s coordinate space steps to reproduce expected results actual results regression notes product version seed created originated open radar link | 1 |
387,153 | 11,457,107,714 | IssuesEvent | 2020-02-06 22:47:50 | LinkedEarth/Pyleoclim_util | https://api.github.com/repos/LinkedEarth/Pyleoclim_util | closed | update interp function to allow for linear and spline | High Priority bug | Use this: https://docs.scipy.org/doc/scipy/reference/generated/scipy.interpolate.interp2d.html instead of the bumpy version | 1.0 | update interp function to allow for linear and spline - Use this: https://docs.scipy.org/doc/scipy/reference/generated/scipy.interpolate.interp2d.html instead of the bumpy version | non_usab | update interp function to allow for linear and spline use this instead of the bumpy version | 0 |
24,678 | 24,134,585,483 | IssuesEvent | 2022-09-21 10:10:50 | pypi/warehouse | https://api.github.com/repos/pypi/warehouse | opened | [FR] Multiline (and rich?) yank reason | UX/UI usability HTML feature request requires triaging needs discussion | **What's the problem this feature will solve?**
<!-- A clear and concise description of what the problem is. -->
Having a comprehensive explanation for yanking. I think it is important not to limit the maintainers with a very small input box. It would be useful to be able to show a descriptive message to the end-users too (related to FR #9837).
**Describe the solution you'd like**
<!-- A clear and concise description of what you want to happen. -->
I want `<textarea>` in the UI, not an `<input>`.
It could then also be displayed on the individual release pages and only the first line (maybe) would appear in badge tooltips (as suggested in #9837).
Not sure if allowing renderable Markdown would be safe but, I'd at least make the links clickable there too.
**Additional context**
<!-- Add any other context, links, etc. about the feature here. -->
N/A | True | [FR] Multiline (and rich?) yank reason - **What's the problem this feature will solve?**
<!-- A clear and concise description of what the problem is. -->
Having a comprehensive explanation for yanking. I think it is important not to limit the maintainers with a very small input box. It would be useful to be able to show a descriptive message to the end-users too (related to FR #9837).
**Describe the solution you'd like**
<!-- A clear and concise description of what you want to happen. -->
I want `<textarea>` in the UI, not an `<input>`.
It could then also be displayed on the individual release pages and only the first line (maybe) would appear in badge tooltips (as suggested in #9837).
Not sure if allowing renderable Markdown would be safe but, I'd at least make the links clickable there too.
**Additional context**
<!-- Add any other context, links, etc. about the feature here. -->
N/A | usab | multiline and rich yank reason what s the problem this feature will solve having a comprehensive explanation for yanking i think it is important not to limit the maintainers with a very small input box it would be useful to be able to show a descriptive message to the end users too related to fr describe the solution you d like i want in the ui not an it could then also be displayed on the individual release pages and only the first line maybe would appear in badge tooltips as suggested in not sure if allowing renderable markdown would be safe but i d at least make the links clickable there too additional context n a | 1 |
671,958 | 22,782,057,465 | IssuesEvent | 2022-07-08 21:08:02 | Templarian/MaterialDesign | https://api.github.com/repos/Templarian/MaterialDesign | closed | Currency icons for Ukrainian hryvnia | Icon Request High Priority | I have:
- [x] [Searched all issues](https://github.com/Templarian/MaterialDesign/issues) to make sure there isn't a request for this icon.
- [x] [Searched the current library](https://materialdesignicons.com/) to make sure the icon doesn't exist.
- [x] Only requested a single icon in this issue.
## Usage
* It will be used to show the currency sign for money value in hryvnia.
* It's sign is: ₴.
* The code is: UAH
* [Wikipedia](https://en.wikipedia.org/wiki/Ukrainian_hryvnia)
* [Hryvnia sign](https://en.wikipedia.org/wiki/Hryvnia_sign)
* [Unicode Character](http://www.fileformat.info/info/unicode/char/20b4/index.htm)
## Examples


| 1.0 | Currency icons for Ukrainian hryvnia - I have:
- [x] [Searched all issues](https://github.com/Templarian/MaterialDesign/issues) to make sure there isn't a request for this icon.
- [x] [Searched the current library](https://materialdesignicons.com/) to make sure the icon doesn't exist.
- [x] Only requested a single icon in this issue.
## Usage
* It will be used to show the currency sign for money value in hryvnia.
* It's sign is: ₴.
* The code is: UAH
* [Wikipedia](https://en.wikipedia.org/wiki/Ukrainian_hryvnia)
* [Hryvnia sign](https://en.wikipedia.org/wiki/Hryvnia_sign)
* [Unicode Character](http://www.fileformat.info/info/unicode/char/20b4/index.htm)
## Examples


| non_usab | currency icons for ukrainian hryvnia i have to make sure there isn t a request for this icon to make sure the icon doesn t exist only requested a single icon in this issue usage it will be used to show the currency sign for money value in hryvnia it s sign is ₴ the code is uah examples | 0 |
14,123 | 8,848,154,789 | IssuesEvent | 2019-01-08 05:37:42 | openstreetmap/iD | https://api.github.com/repos/openstreetmap/iD | closed | Swing to changes spot upon clicking Restore Changes | usability | If we click the Restore changes from previous session choice,
our field of view should perhaps swing to where those changes were. | True | Swing to changes spot upon clicking Restore Changes - If we click the Restore changes from previous session choice,
our field of view should perhaps swing to where those changes were. | usab | swing to changes spot upon clicking restore changes if we click the restore changes from previous session choice our field of view should perhaps swing to where those changes were | 1 |
9,955 | 6,529,246,106 | IssuesEvent | 2017-08-30 10:46:55 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Ability to translate and scale 3D nodes on two axes at once, locking the remaining axis | enhancement topic:editor usability | In Blender, it is possible to translate and scale 3D nodes on two axes at once (XY, YZ, or XZ) while locking the remaining axis (it is done by holding <kbd>Shift</kbd> while pressing an axis modifier key). This makes it easier and quicker to move or scale 3D geometry along a flat surface, for example.
Supporting this in Godot would make the 3D workflow more convenient. | True | Ability to translate and scale 3D nodes on two axes at once, locking the remaining axis - In Blender, it is possible to translate and scale 3D nodes on two axes at once (XY, YZ, or XZ) while locking the remaining axis (it is done by holding <kbd>Shift</kbd> while pressing an axis modifier key). This makes it easier and quicker to move or scale 3D geometry along a flat surface, for example.
Supporting this in Godot would make the 3D workflow more convenient. | usab | ability to translate and scale nodes on two axes at once locking the remaining axis in blender it is possible to translate and scale nodes on two axes at once xy yz or xz while locking the remaining axis it is done by holding shift while pressing an axis modifier key this makes it easier and quicker to move or scale geometry along a flat surface for example supporting this in godot would make the workflow more convenient | 1 |
269,616 | 23,452,672,316 | IssuesEvent | 2022-08-16 05:33:56 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: sqlsmith/setup=rand-tables/setting=no-mutations failed | C-test-failure O-robot O-roachtest branch-master | roachtest.sqlsmith/setup=rand-tables/setting=no-mutations [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6107800?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6107800?buildTab=artifacts#/sqlsmith/setup=rand-tables/setting=no-mutations) on master @ [f4042d47fa8062a612c38d4696eb6bee9cee7c21](https://github.com/cockroachdb/cockroach/commits/f4042d47fa8062a612c38d4696eb6bee9cee7c21):
```
test artifacts and logs in: /artifacts/sqlsmith/setup=rand-tables/setting=no-mutations/run_1
sqlsmith.go:265,sqlsmith.go:325,test_runner.go:896: error: pq: internal error: crdb_internal.set_compaction_concurrency(): compaction_concurrency must be > 0
stmt:
WITH
with_54090 (col_318446)
AS (
SELECT * FROM (VALUES ('1.190.141.9/6':::INET)) AS tab_131235 (col_318446)
EXCEPT SELECT * FROM (VALUES ('ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff':::INET)) AS tab_131236 (col_318447)
),
with_54091 (col_318448)
AS (
SELECT * FROM (VALUES (true), (true), (false), (false)) AS tab_131237 (col_318448)
UNION
SELECT
*
FROM
(
VALUES
(
crdb_internal.set_compaction_concurrency(7368933071913653453:::INT8::INT8, (-6393098846911290752):::INT8::INT8, (-909226569288498097):::INT8::INT8)::BOOL
),
(
st_dwithin('0107000060E6100000050000000103000060E61000000100000005000000985A039448C537C0241374C92DDE36C0D0B43B8888C3F7C10257FEC3FD0A6340411D589F574453C0314A413C7421FEC10C9B47D3F90A5E40E8AAC62795C52BC044B9490755B1F4C1B0741C60CF7B6340089865C266325040F0D374C42E67C941985A039448C537C0241374C92DDE36C0D0B43B8888C3F7C10101000060E61000008AAC5B226DD86040924486870C8150C0C0354EEB1B6EA9C10101000060E6100000C4B0EEB9860A41C02CE8C0B04C474D4042F5FB1447BB00420102000060E610000002000000B8447EF06F8F5D4018F05EA59DD42BC06ADFBA034D5DF041B2F7EC99E0CC6240F426FB136C0D51407C7EA0537F7AEC410104000060E610000005000000010100004030B5AF0AA5EE2B40A8FB05C5B6C92FC032EB383445AFF24101010000408E1CEA879BBB62C062896560372C4DC080C24CD9309B914101010000400A10A4DB10AA65405827C3C42733514040D78A31469CF7410101000040B4975B224FAD56401E46EAE8786B41405CEFC5C29EAFDEC10101000040E790549A342C65C06CCBAAD5F00E54C08133877A4C7EFAC1':::GEOGRAPHY::GEOGRAPHY, '01010000A0E610000000B9EC5CA9F63D40FAD3165317AB5040C4E1E0DBF54FFF41':::GEOGRAPHY::GEOGRAPHY, 'NaN':::FLOAT8::FLOAT8)::BOOL
)
)
AS tab_131238 (col_318449)
),
with_54092 (col_318450) AS (SELECT * FROM (VALUES (868781623:::OID), (3138052886:::OID)) AS tab_131239 (col_318450))
SELECT
'1.244.205.8/29':::INET AS col_318451
FROM
with_54090 AS cte_ref_15617
WHERE
true
ORDER BY
cte_ref_15617.col_318446, cte_ref_15617.col_318446
LIMIT
37:::INT8;
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sqlsmith/setup=rand-tables/setting=no-mutations.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: sqlsmith/setup=rand-tables/setting=no-mutations failed - roachtest.sqlsmith/setup=rand-tables/setting=no-mutations [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6107800?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6107800?buildTab=artifacts#/sqlsmith/setup=rand-tables/setting=no-mutations) on master @ [f4042d47fa8062a612c38d4696eb6bee9cee7c21](https://github.com/cockroachdb/cockroach/commits/f4042d47fa8062a612c38d4696eb6bee9cee7c21):
```
test artifacts and logs in: /artifacts/sqlsmith/setup=rand-tables/setting=no-mutations/run_1
sqlsmith.go:265,sqlsmith.go:325,test_runner.go:896: error: pq: internal error: crdb_internal.set_compaction_concurrency(): compaction_concurrency must be > 0
stmt:
WITH
with_54090 (col_318446)
AS (
SELECT * FROM (VALUES ('1.190.141.9/6':::INET)) AS tab_131235 (col_318446)
EXCEPT SELECT * FROM (VALUES ('ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff':::INET)) AS tab_131236 (col_318447)
),
with_54091 (col_318448)
AS (
SELECT * FROM (VALUES (true), (true), (false), (false)) AS tab_131237 (col_318448)
UNION
SELECT
*
FROM
(
VALUES
(
crdb_internal.set_compaction_concurrency(7368933071913653453:::INT8::INT8, (-6393098846911290752):::INT8::INT8, (-909226569288498097):::INT8::INT8)::BOOL
),
(
st_dwithin('0107000060E6100000050000000103000060E61000000100000005000000985A039448C537C0241374C92DDE36C0D0B43B8888C3F7C10257FEC3FD0A6340411D589F574453C0314A413C7421FEC10C9B47D3F90A5E40E8AAC62795C52BC044B9490755B1F4C1B0741C60CF7B6340089865C266325040F0D374C42E67C941985A039448C537C0241374C92DDE36C0D0B43B8888C3F7C10101000060E61000008AAC5B226DD86040924486870C8150C0C0354EEB1B6EA9C10101000060E6100000C4B0EEB9860A41C02CE8C0B04C474D4042F5FB1447BB00420102000060E610000002000000B8447EF06F8F5D4018F05EA59DD42BC06ADFBA034D5DF041B2F7EC99E0CC6240F426FB136C0D51407C7EA0537F7AEC410104000060E610000005000000010100004030B5AF0AA5EE2B40A8FB05C5B6C92FC032EB383445AFF24101010000408E1CEA879BBB62C062896560372C4DC080C24CD9309B914101010000400A10A4DB10AA65405827C3C42733514040D78A31469CF7410101000040B4975B224FAD56401E46EAE8786B41405CEFC5C29EAFDEC10101000040E790549A342C65C06CCBAAD5F00E54C08133877A4C7EFAC1':::GEOGRAPHY::GEOGRAPHY, '01010000A0E610000000B9EC5CA9F63D40FAD3165317AB5040C4E1E0DBF54FFF41':::GEOGRAPHY::GEOGRAPHY, 'NaN':::FLOAT8::FLOAT8)::BOOL
)
)
AS tab_131238 (col_318449)
),
with_54092 (col_318450) AS (SELECT * FROM (VALUES (868781623:::OID), (3138052886:::OID)) AS tab_131239 (col_318450))
SELECT
'1.244.205.8/29':::INET AS col_318451
FROM
with_54090 AS cte_ref_15617
WHERE
true
ORDER BY
cte_ref_15617.col_318446, cte_ref_15617.col_318446
LIMIT
37:::INT8;
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sqlsmith/setup=rand-tables/setting=no-mutations.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_usab | roachtest sqlsmith setup rand tables setting no mutations failed roachtest sqlsmith setup rand tables setting no mutations with on master test artifacts and logs in artifacts sqlsmith setup rand tables setting no mutations run sqlsmith go sqlsmith go test runner go error pq internal error crdb internal set compaction concurrency compaction concurrency must be stmt with with col as select from values inet as tab col except select from values ffff ffff ffff ffff ffff ffff ffff ffff inet as tab col with col as select from values true true false false as tab col union select from values crdb internal set compaction concurrency bool st dwithin geography geography geography geography nan bool as tab col with col as select from values oid oid as tab col select inet as col from with as cte ref where true order by cte ref col cte ref col limit parameters roachtest cloud gce roachtest cpu roachtest ssd help see see cc cockroachdb sql queries | 0 |
5,624 | 3,970,365,354 | IssuesEvent | 2016-05-04 06:49:05 | kolliSuman/issues | https://api.github.com/repos/kolliSuman/issues | closed | QA_Mohirs circle_Back to experiment_smk | Category: Usability Developed By: VLEAD Release Number: 1 Severity: S2 Status: Open | Defect Description :
In “Mohirs circle” experiment, back to the experiments link is not present instead back to the experiments link should be displayed on the experiment home page, where the user can easily get back and view the experiments
Actual Result :
In Mohirs circle” experiment, back to the experiments link is not present
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/strength-of-materials-nitk/blob/master/test-cases/integration_test-cases/Mohirs%20circle/Mohirs%20circle_14_Back%20to%20experiment_smk.org | True | QA_Mohirs circle_Back to experiment_smk - Defect Description :
In “Mohirs circle” experiment, back to the experiments link is not present instead back to the experiments link should be displayed on the experiment home page, where the user can easily get back and view the experiments
Actual Result :
In Mohirs circle” experiment, back to the experiments link is not present
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/strength-of-materials-nitk/blob/master/test-cases/integration_test-cases/Mohirs%20circle/Mohirs%20circle_14_Back%20to%20experiment_smk.org | usab | qa mohirs circle back to experiment smk defect description in “mohirs circle” experiment back to the experiments link is not present instead back to the experiments link should be displayed on the experiment home page where the user can easily get back and view the experiments actual result in mohirs circle” experiment back to the experiments link is not present environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor test step link | 1 |
167,654 | 13,038,710,773 | IssuesEvent | 2020-07-28 15:36:17 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: decommission/nodes=4/duration=1h0m0s failed | C-test-failure O-roachtest O-robot branch-provisional_202007271721_v20.1.4 release-blocker | [(roachtest).decommission/nodes=4/duration=1h0m0s failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2122385&tab=buildLog) on [provisional_202007271721_v20.1.4@9a822f51a64af9eebcf9ea5e5ecc0fdfcc1521fa](https://github.com/cockroachdb/cockroach/commits/9a822f51a64af9eebcf9ea5e5ecc0fdfcc1521fa):
```
The test failed on branch=provisional_202007271721_v20.1.4, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/decommission/nodes=4/duration=1h0m0s/run_1
decommission.go:262,decommission.go:47,test_runner.go:754: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start -a=--join 10.128.0.45:26257 --attrs=node1 teamcity-2122385-1595896218-01-n4cpu4:1 returned: exit status 1
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start -a=--join 10.128.0.45:26257 --attrs=node1 teamcity-2122385-1595896218-01-n4cpu4:1 returned
| stderr:
|
| stdout:
| teamcity-2122385-1595896218-01-n4cpu4: starting nodes
| teamcity-2122385-1595896218-01-n4cpu4: initializing clusterI200728 00:34:59.441576 21 cockroach.go:163 unable to initialize cluster: ~
| if ! test -e /mnt/data1/cockroach/cluster-bootstrapped ; then
| COCKROACH_CONNECT_TIMEOUT=0 ./cockroach init --url 'postgres://root@localhost:26257?sslmode=disable' && touch /mnt/data1/cockroach/cluster-bootstrapped
| fi
| warning: --url specifies user/password, but command "init" does not accept user/password details - details ignored
| *
| * ERROR: ERROR: rpc error: code = Unknown desc = already connected to cluster
| *
| E200728 00:34:59.408191 1 cli/error.go:373 ERROR: rpc error: code = Unknown desc = already connected to cluster
| ERROR: rpc error: code = Unknown desc = already connected to cluster
| Failed running "init": exit status 1
Wraps: (2) exit status 1
Error types: (1) *main.withCommandDetails (2) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/decommission/nodes=4/duration=1h0m0s](https://teamcity.cockroachdb.com/viewLog.html?buildId=2122385&tab=artifacts#/decommission/nodes=4/duration=1h0m0s)
Related:
- #51713 roachtest: decommission/nodes=4/duration=1h0m0s failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adecommission%2Fnodes%3D4%2Fduration%3D1h0m0s.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: decommission/nodes=4/duration=1h0m0s failed - [(roachtest).decommission/nodes=4/duration=1h0m0s failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2122385&tab=buildLog) on [provisional_202007271721_v20.1.4@9a822f51a64af9eebcf9ea5e5ecc0fdfcc1521fa](https://github.com/cockroachdb/cockroach/commits/9a822f51a64af9eebcf9ea5e5ecc0fdfcc1521fa):
```
The test failed on branch=provisional_202007271721_v20.1.4, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/decommission/nodes=4/duration=1h0m0s/run_1
decommission.go:262,decommission.go:47,test_runner.go:754: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start -a=--join 10.128.0.45:26257 --attrs=node1 teamcity-2122385-1595896218-01-n4cpu4:1 returned: exit status 1
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start -a=--join 10.128.0.45:26257 --attrs=node1 teamcity-2122385-1595896218-01-n4cpu4:1 returned
| stderr:
|
| stdout:
| teamcity-2122385-1595896218-01-n4cpu4: starting nodes
| teamcity-2122385-1595896218-01-n4cpu4: initializing clusterI200728 00:34:59.441576 21 cockroach.go:163 unable to initialize cluster: ~
| if ! test -e /mnt/data1/cockroach/cluster-bootstrapped ; then
| COCKROACH_CONNECT_TIMEOUT=0 ./cockroach init --url 'postgres://root@localhost:26257?sslmode=disable' && touch /mnt/data1/cockroach/cluster-bootstrapped
| fi
| warning: --url specifies user/password, but command "init" does not accept user/password details - details ignored
| *
| * ERROR: ERROR: rpc error: code = Unknown desc = already connected to cluster
| *
| E200728 00:34:59.408191 1 cli/error.go:373 ERROR: rpc error: code = Unknown desc = already connected to cluster
| ERROR: rpc error: code = Unknown desc = already connected to cluster
| Failed running "init": exit status 1
Wraps: (2) exit status 1
Error types: (1) *main.withCommandDetails (2) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/decommission/nodes=4/duration=1h0m0s](https://teamcity.cockroachdb.com/viewLog.html?buildId=2122385&tab=artifacts#/decommission/nodes=4/duration=1h0m0s)
Related:
- #51713 roachtest: decommission/nodes=4/duration=1h0m0s failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Adecommission%2Fnodes%3D4%2Fduration%3D1h0m0s.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_usab | roachtest decommission nodes duration failed on the test failed on branch provisional cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts decommission nodes duration run decommission go decommission go test runner go home agent work go src github com cockroachdb cockroach bin roachprod start a join attrs teamcity returned exit status home agent work go src github com cockroachdb cockroach bin roachprod start a join attrs teamcity returned stderr stdout teamcity starting nodes teamcity initializing cockroach go unable to initialize cluster if test e mnt cockroach cluster bootstrapped then cockroach connect timeout cockroach init url postgres root localhost sslmode disable touch mnt cockroach cluster bootstrapped fi warning url specifies user password but command init does not accept user password details details ignored error error rpc error code unknown desc already connected to cluster cli error go error rpc error code unknown desc already connected to cluster error rpc error code unknown desc already connected to cluster failed running init exit status wraps exit status error types main withcommanddetails exec exiterror more artifacts related roachtest decommission nodes duration failed powered by | 0 |
114,428 | 17,209,456,835 | IssuesEvent | 2021-07-19 00:12:31 | turkdevops/javascript-sdk | https://api.github.com/repos/turkdevops/javascript-sdk | opened | CVE-2021-29418 (Medium) detected in netmask-1.0.6.tgz | security vulnerability | ## CVE-2021-29418 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netmask-1.0.6.tgz</b></p></summary>
<p>Parse and lookup IP network blocks</p>
<p>Library home page: <a href="https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz">https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz</a></p>
<p>Path to dependency file: javascript-sdk/package.json</p>
<p>Path to vulnerable library: javascript-sdk/node_modules/netmask/package.json</p>
<p>
Dependency Hierarchy:
- nightwatch-0.9.21.tgz (Root Library)
- proxy-agent-2.0.0.tgz
- pac-proxy-agent-1.1.0.tgz
- pac-resolver-2.0.0.tgz
- :x: **netmask-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/javascript-sdk/commit/2ed96566365ee89d8a9b1250ccd7c049281ed09c">2ed96566365ee89d8a9b1250ccd7c049281ed09c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The netmask package before 2.0.1 for Node.js mishandles certain unexpected characters in an IP address string, such as an octal digit of 9. This (in some situations) allows attackers to bypass access control that is based on IP addresses. NOTE: this issue exists because of an incomplete fix for CVE-2021-28918.
<p>Publish Date: 2021-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29418>CVE-2021-29418</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://vuln.ryotak.me/advisories/6.txt">https://vuln.ryotak.me/advisories/6.txt</a></p>
<p>Release Date: 2021-03-30</p>
<p>Fix Resolution: 2.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-29418 (Medium) detected in netmask-1.0.6.tgz - ## CVE-2021-29418 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netmask-1.0.6.tgz</b></p></summary>
<p>Parse and lookup IP network blocks</p>
<p>Library home page: <a href="https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz">https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz</a></p>
<p>Path to dependency file: javascript-sdk/package.json</p>
<p>Path to vulnerable library: javascript-sdk/node_modules/netmask/package.json</p>
<p>
Dependency Hierarchy:
- nightwatch-0.9.21.tgz (Root Library)
- proxy-agent-2.0.0.tgz
- pac-proxy-agent-1.1.0.tgz
- pac-resolver-2.0.0.tgz
- :x: **netmask-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/javascript-sdk/commit/2ed96566365ee89d8a9b1250ccd7c049281ed09c">2ed96566365ee89d8a9b1250ccd7c049281ed09c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The netmask package before 2.0.1 for Node.js mishandles certain unexpected characters in an IP address string, such as an octal digit of 9. This (in some situations) allows attackers to bypass access control that is based on IP addresses. NOTE: this issue exists because of an incomplete fix for CVE-2021-28918.
<p>Publish Date: 2021-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29418>CVE-2021-29418</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://vuln.ryotak.me/advisories/6.txt">https://vuln.ryotak.me/advisories/6.txt</a></p>
<p>Release Date: 2021-03-30</p>
<p>Fix Resolution: 2.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve medium detected in netmask tgz cve medium severity vulnerability vulnerable library netmask tgz parse and lookup ip network blocks library home page a href path to dependency file javascript sdk package json path to vulnerable library javascript sdk node modules netmask package json dependency hierarchy nightwatch tgz root library proxy agent tgz pac proxy agent tgz pac resolver tgz x netmask tgz vulnerable library found in head commit a href found in base branch master vulnerability details the netmask package before for node js mishandles certain unexpected characters in an ip address string such as an octal digit of this in some situations allows attackers to bypass access control that is based on ip addresses note this issue exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
75,030 | 9,816,967,812 | IssuesEvent | 2019-06-13 15:41:11 | MontrealCorpusTools/PolyglotDB | https://api.github.com/repos/MontrealCorpusTools/PolyglotDB | opened | Subannotation documentation | documentation | There needs to be more explanation of subannotation enrichment (like the functionality developed for AutoVOT, as well as more generally). The name "subannotation" is still not great, but since annotation is used to refer to linguistic annotations like words/phones/etc, I'm not sure what a better name would be. Meta-annotation seems clunky. Regardless, some explanation of what subannotations are and how they differ from annotations is needed at some place.
User documentation:
- [ ] Add page for "Subannotation enrichment" to https://polyglotdb.readthedocs.io/en/latest/enrichment.html (might be a subset of Enrichment via CSV files)
- [ ] Add page for querying/exporting subannotations to https://polyglotdb.readthedocs.io/en/latest/queries.html
API documentation:
- [ ] Docstrings for subannotation import functions
(There isn't currently a place for the subannotation from CSV functions to be in the API documentation, this will be part of #137) | 1.0 | Subannotation documentation - There needs to be more explanation of subannotation enrichment (like the functionality developed for AutoVOT, as well as more generally). The name "subannotation" is still not great, but since annotation is used to refer to linguistic annotations like words/phones/etc, I'm not sure what a better name would be. Meta-annotation seems clunky. Regardless, some explanation of what subannotations are and how they differ from annotations is needed at some place.
User documentation:
- [ ] Add page for "Subannotation enrichment" to https://polyglotdb.readthedocs.io/en/latest/enrichment.html (might be a subset of Enrichment via CSV files)
- [ ] Add page for querying/exporting subannotations to https://polyglotdb.readthedocs.io/en/latest/queries.html
API documentation:
- [ ] Docstrings for subannotation import functions
(There isn't currently a place for the subannotation from CSV functions to be in the API documentation, this will be part of #137) | non_usab | subannotation documentation there needs to be more explanation of subannotation enrichment like the functionality developed for autovot as well as more generally the name subannotation is still not great but since annotation is used to refer to linguistic annotations like words phones etc i m not sure what a better name would be meta annotation seems clunky regardless some explanation of what subannotations are and how they differ from annotations is needed at some place user documentation add page for subannotation enrichment to might be a subset of enrichment via csv files add page for querying exporting subannotations to api documentation docstrings for subannotation import functions there isn t currently a place for the subannotation from csv functions to be in the api documentation this will be part of | 0 |
15,814 | 5,188,078,134 | IssuesEvent | 2017-01-20 18:49:01 | phetsims/unit-rates | https://api.github.com/repos/phetsims/unit-rates | closed | check for memory leaks | dev:code-review type:wontfix | Code review #52, checklist item:
> - [ ] Does a heap comparison using Chrome Developer Tools indicate a memory leak? (Describing this process is beyond the scope of this document.)
In implementation-notes.md, @schmitzware indicated:
> - When profiling memory usage, if asserts are enabled the sim will leak memory because of the
> SUN/buttons/RectangularPushButton's being used. Apparently SUN buttons dispose fails when assertions are enabled, so the disposes are turned off if asserts are turned on (see sun/#212)
> - FuzzMouse memory testing seems to stabilize around 30Mb, though I have a sneaking suspicion a few URNumberLineMarkers are still not getting disposed of properly.
So it sounds like heap companions have been done, but more investigation may be needed.
I'm not going to do this as part of code review, since I think that it makes sense only after the sim is feature complete (which it's not yet).
| 1.0 | check for memory leaks - Code review #52, checklist item:
> - [ ] Does a heap comparison using Chrome Developer Tools indicate a memory leak? (Describing this process is beyond the scope of this document.)
In implementation-notes.md, @schmitzware indicated:
> - When profiling memory usage, if asserts are enabled the sim will leak memory because of the
> SUN/buttons/RectangularPushButton's being used. Apparently SUN buttons dispose fails when assertions are enabled, so the disposes are turned off if asserts are turned on (see sun/#212)
> - FuzzMouse memory testing seems to stabilize around 30Mb, though I have a sneaking suspicion a few URNumberLineMarkers are still not getting disposed of properly.
So it sounds like heap companions have been done, but more investigation may be needed.
I'm not going to do this as part of code review, since I think that it makes sense only after the sim is feature complete (which it's not yet).
| non_usab | check for memory leaks code review checklist item does a heap comparison using chrome developer tools indicate a memory leak describing this process is beyond the scope of this document in implementation notes md schmitzware indicated when profiling memory usage if asserts are enabled the sim will leak memory because of the sun buttons rectangularpushbutton s being used apparently sun buttons dispose fails when assertions are enabled so the disposes are turned off if asserts are turned on see sun fuzzmouse memory testing seems to stabilize around though i have a sneaking suspicion a few urnumberlinemarkers are still not getting disposed of properly so it sounds like heap companions have been done but more investigation may be needed i m not going to do this as part of code review since i think that it makes sense only after the sim is feature complete which it s not yet | 0 |
128,403 | 5,064,775,880 | IssuesEvent | 2016-12-23 08:44:45 | praekeltfoundation/gem-bbb-indo | https://api.github.com/repos/praekeltfoundation/gem-bbb-indo | closed | Add Email to Registration | enhancement priority - highest qa | _Language: Indonesian
Device Make: Xiaomi
Device Model: Mi5
App Version: 0.0.9
Logged by: Pippa_
Add a new field to registration: Email and enable registration to be successful if either email or mobile number is completed (or both). Error text: _We need either your phone number or email address_
Two users during testing did not remember their phone number so we need to give them an option of inputting mobile number or email address or both. | 1.0 | Add Email to Registration - _Language: Indonesian
Device Make: Xiaomi
Device Model: Mi5
App Version: 0.0.9
Logged by: Pippa_
Add a new field to registration: Email and enable registration to be successful if either email or mobile number is completed (or both). Error text: _We need either your phone number or email address_
Two users during testing did not remember their phone number so we need to give them an option of inputting mobile number or email address or both. | non_usab | add email to registration language indonesian device make xiaomi device model app version logged by pippa add a new field to registration email and enable registration to be successful if either email or mobile number is completed or both error text we need either your phone number or email address two users during testing did not remember their phone number so we need to give them an option of inputting mobile number or email address or both | 0 |
6,261 | 4,203,527,873 | IssuesEvent | 2016-06-28 05:57:42 | Virtual-Labs/structural-dynamics-iiith | https://api.github.com/repos/Virtual-Labs/structural-dynamics-iiith | closed | QA_Impulse Response of SDOF_Prerequisites_p1 | Category: Usability Developed by: VLEAD Release Number: Production Resolved Severity: S2 | Defect Description :
In the "Impulse Response of SDOF" experiment, the minimum requirement to run the experiment is not displayed in the page instead a page or Scrolling should appear providing information on minimum requirement to run this experiment, information like Bandwidth,Device Resolution,Hardware Configuration and Software Required.
Actual Result :
In the "Impulse Response of SDOF" experiment, the minimum requirement to run the experiment is not displayed in the page.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/structural-dynamics-iiith/blob/master/test-cases/integration_test-cases/Impulse%20Response%20of%20SDOF/Impulse%20Response%20of%20SDOF_17_Prerequisites_p1.org
Attachment:

| True | QA_Impulse Response of SDOF_Prerequisites_p1 - Defect Description :
In the "Impulse Response of SDOF" experiment, the minimum requirement to run the experiment is not displayed in the page instead a page or Scrolling should appear providing information on minimum requirement to run this experiment, information like Bandwidth,Device Resolution,Hardware Configuration and Software Required.
Actual Result :
In the "Impulse Response of SDOF" experiment, the minimum requirement to run the experiment is not displayed in the page.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/structural-dynamics-iiith/blob/master/test-cases/integration_test-cases/Impulse%20Response%20of%20SDOF/Impulse%20Response%20of%20SDOF_17_Prerequisites_p1.org
Attachment:

| usab | qa impulse response of sdof prerequisites defect description in the impulse response of sdof experiment the minimum requirement to run the experiment is not displayed in the page instead a page or scrolling should appear providing information on minimum requirement to run this experiment information like bandwidth device resolution hardware configuration and software required actual result in the impulse response of sdof experiment the minimum requirement to run the experiment is not displayed in the page environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor test step link attachment | 1 |
445,317 | 12,828,935,799 | IssuesEvent | 2020-07-06 21:36:28 | alerj/docigp | https://api.github.com/repos/alerj/docigp | closed | Alterar a cor das badges dos transportes | priority 1 | - [x] Se o valor for transporte positivo, colocar `badge-success` nos transportes do mês atual e do mês seguinte. Se for negativo, `badge-danger`.

| 1.0 | Alterar a cor das badges dos transportes - - [x] Se o valor for transporte positivo, colocar `badge-success` nos transportes do mês atual e do mês seguinte. Se for negativo, `badge-danger`.

| non_usab | alterar a cor das badges dos transportes se o valor for transporte positivo colocar badge success nos transportes do mês atual e do mês seguinte se for negativo badge danger | 0 |
383 | 2,587,529,181 | IssuesEvent | 2015-02-17 19:03:06 | mavlink/qgroundcontrol | https://api.github.com/repos/mavlink/qgroundcontrol | opened | Rename "Connect" button on toolbar to "Open" | component-theming/usability difficulty-easy | The opposite would now be "Closed" instead of "Disconnect". These are both shorter words in English and also make more sense since the ManageLinks option is in the toolbar. | True | Rename "Connect" button on toolbar to "Open" - The opposite would now be "Closed" instead of "Disconnect". These are both shorter words in English and also make more sense since the ManageLinks option is in the toolbar. | usab | rename connect button on toolbar to open the opposite would now be closed instead of disconnect these are both shorter words in english and also make more sense since the managelinks option is in the toolbar | 1 |
101,727 | 16,525,372,026 | IssuesEvent | 2021-05-26 19:21:26 | OSWeekends/EventPoints | https://api.github.com/repos/OSWeekends/EventPoints | opened | CVE-2021-23368 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2021-23368 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.5.tgz</b>, <b>postcss-7.0.21.tgz</b>, <b>postcss-7.0.35.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.5.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.5.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.5.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- postcss-loader-3.0.0.tgz
- :x: **postcss-7.0.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.21.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- resolve-url-loader-3.1.3.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.35.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- postcss-normalize-8.0.1.tgz
- postcss-browser-comments-3.0.0.tgz
- :x: **postcss-7.0.35.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/OSWeekends/EventPoints/commit/abf2c9dcf38a40d49f6f8c5344a09f668e48fff4">abf2c9dcf38a40d49f6f8c5344a09f668e48fff4</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution: postcss -8.2.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23368 (Medium) detected in multiple libraries - ## CVE-2021-23368 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.5.tgz</b>, <b>postcss-7.0.21.tgz</b>, <b>postcss-7.0.35.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.5.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.5.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.5.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- postcss-loader-3.0.0.tgz
- :x: **postcss-7.0.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.21.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- resolve-url-loader-3.1.3.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.35.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- postcss-normalize-8.0.1.tgz
- postcss-browser-comments-3.0.0.tgz
- :x: **postcss-7.0.35.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/OSWeekends/EventPoints/commit/abf2c9dcf38a40d49f6f8c5344a09f668e48fff4">abf2c9dcf38a40d49f6f8c5344a09f668e48fff4</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution: postcss -8.2.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries postcss tgz postcss tgz postcss tgz postcss tgz tool for transforming styles with js plugins library home page a href dependency hierarchy react scripts tgz root library postcss loader tgz x postcss tgz vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href dependency hierarchy react scripts tgz root library resolve url loader tgz x postcss tgz vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href dependency hierarchy react scripts tgz root library postcss normalize tgz postcss browser comments tgz x postcss tgz vulnerable library found in head commit a href vulnerability details the package postcss from and before are vulnerable to regular expression denial of service redos during source map parsing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution postcss step up your open source security game with whitesource | 0 |
323,476 | 27,728,799,544 | IssuesEvent | 2023-03-15 05:57:46 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | closed | [Event Hubs] Subscribed to multiple partitions failed on China cloud. | Client Event Hubs test-sovereign-cloud | We are running live Tests against other clouds like US Gov and Azure China Cloud. The goal is to check whether new azure sdk package work with other clouds or not.
**Error Description:**
Live test `when subscribed to multiple partitions` failed in all environments on `China` cloud in [weekly pipeline](https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1609120&view=logs&j=90d65a40-c17a-520d-9c6f-63e72be21f54&t=46b4abb8-2fd4-54f0-4720-3b6e44bf3729).
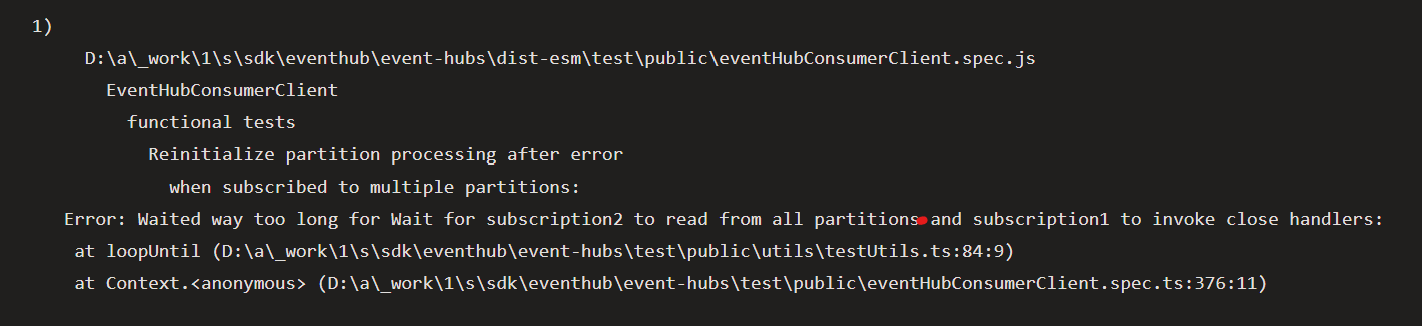
After investigation, error message: `Waited way too long for Wait for subscription2 to read from all partitions and subscription1 to invoke close handlers` is thrown from method `loopUntil`, but we cannot reproduce this problem locally.
**Expected behavior:**
Test `when subscribed to multiple partitions` can pass on `China` cloud like it on `Public` and `UsGov` clouds.
@benbp , @xirzec , @lilyjma , @jsquire , @deyaaeldeen for notification. | 1.0 | [Event Hubs] Subscribed to multiple partitions failed on China cloud. - We are running live Tests against other clouds like US Gov and Azure China Cloud. The goal is to check whether new azure sdk package work with other clouds or not.
**Error Description:**
Live test `when subscribed to multiple partitions` failed in all environments on `China` cloud in [weekly pipeline](https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1609120&view=logs&j=90d65a40-c17a-520d-9c6f-63e72be21f54&t=46b4abb8-2fd4-54f0-4720-3b6e44bf3729).
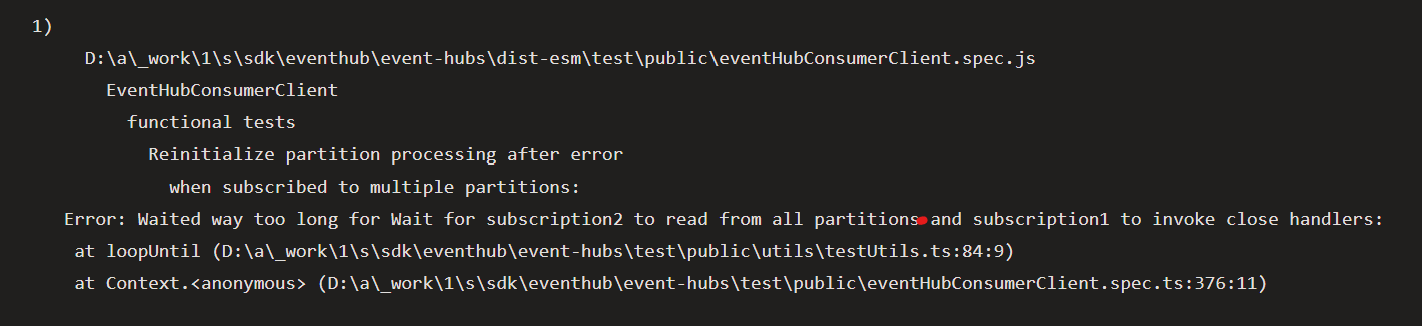
After investigation, error message: `Waited way too long for Wait for subscription2 to read from all partitions and subscription1 to invoke close handlers` is thrown from method `loopUntil`, but we cannot reproduce this problem locally.
**Expected behavior:**
Test `when subscribed to multiple partitions` can pass on `China` cloud like it on `Public` and `UsGov` clouds.
@benbp , @xirzec , @lilyjma , @jsquire , @deyaaeldeen for notification. | non_usab | subscribed to multiple partitions failed on china cloud we are running live tests against other clouds like us gov and azure china cloud the goal is to check whether new azure sdk package work with other clouds or not error description live test when subscribed to multiple partitions failed in all environments on china cloud in after investigation error message waited way too long for wait for to read from all partitions and to invoke close handlers is thrown from method loopuntil but we cannot reproduce this problem locally expected behavior test when subscribed to multiple partitions can pass on china cloud like it on public and usgov clouds benbp xirzec lilyjma jsquire deyaaeldeen for notification | 0 |
73,658 | 15,278,812,135 | IssuesEvent | 2021-02-23 02:24:01 | MohamedElashri/blog-theme | https://api.github.com/repos/MohamedElashri/blog-theme | closed | CVE-2017-1000048 (High) detected in qs-6.2.3.tgz - autoclosed | security vulnerability | ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.2.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.2.3.tgz">https://registry.npmjs.org/qs/-/qs-6.2.3.tgz</a></p>
<p>Path to dependency file: blog-theme/package.json</p>
<p>Path to vulnerable library: blog-theme/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.26.13.tgz (Root Library)
- :x: **qs-6.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/MohamedElashri/blog-theme/commit/c7939ca9cfb9a703f690395b2e84f88cab3b01f4">c7939ca9cfb9a703f690395b2e84f88cab3b01f4</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-1000048">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution: 6.0.4,6.1.2,6.2.3,6.3.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-1000048 (High) detected in qs-6.2.3.tgz - autoclosed - ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.2.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.2.3.tgz">https://registry.npmjs.org/qs/-/qs-6.2.3.tgz</a></p>
<p>Path to dependency file: blog-theme/package.json</p>
<p>Path to vulnerable library: blog-theme/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.26.13.tgz (Root Library)
- :x: **qs-6.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/MohamedElashri/blog-theme/commit/c7939ca9cfb9a703f690395b2e84f88cab3b01f4">c7939ca9cfb9a703f690395b2e84f88cab3b01f4</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-1000048">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution: 6.0.4,6.1.2,6.2.3,6.3.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_usab | cve high detected in qs tgz autoclosed cve high severity vulnerability vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file blog theme package json path to vulnerable library blog theme node modules qs package json dependency hierarchy browser sync tgz root library x qs tgz vulnerable library found in head commit a href found in base branch main vulnerability details the web framework using ljharb s qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
15,552 | 10,130,511,528 | IssuesEvent | 2019-08-01 17:08:19 | openstreetmap/iD | https://api.github.com/repos/openstreetmap/iD | closed | Don't default to generic preset favorites for new users | usability | When launching iD 3 for the first time, the generic Point, Line, and Area presets are the defaults favorites. The intention is to help longtime iD users with the transition by starting them off with the legacy workflow option. They can remove or customize these at any time.
<img width="250" alt="Screen Shot 2019-08-01 at 12 33 39 PM" src="https://user-images.githubusercontent.com/2046746/62311051-e4c8d700-b458-11e9-9cf6-185bf8dc7dea.png">
However, new users shouldn't have to worry about the old workflow. For brand new sessions we should present just the single Add Feature button. Users who want the generic favorites can add them manually.
<img width="188" alt="Screen Shot 2019-08-01 at 12 33 54 PM" src="https://user-images.githubusercontent.com/2046746/62311445-d9c27680-b459-11e9-8d79-7bc5c5c68a4e.png">
Re: #6684, #6665
| True | Don't default to generic preset favorites for new users - When launching iD 3 for the first time, the generic Point, Line, and Area presets are the defaults favorites. The intention is to help longtime iD users with the transition by starting them off with the legacy workflow option. They can remove or customize these at any time.
<img width="250" alt="Screen Shot 2019-08-01 at 12 33 39 PM" src="https://user-images.githubusercontent.com/2046746/62311051-e4c8d700-b458-11e9-9cf6-185bf8dc7dea.png">
However, new users shouldn't have to worry about the old workflow. For brand new sessions we should present just the single Add Feature button. Users who want the generic favorites can add them manually.
<img width="188" alt="Screen Shot 2019-08-01 at 12 33 54 PM" src="https://user-images.githubusercontent.com/2046746/62311445-d9c27680-b459-11e9-8d79-7bc5c5c68a4e.png">
Re: #6684, #6665
| usab | don t default to generic preset favorites for new users when launching id for the first time the generic point line and area presets are the defaults favorites the intention is to help longtime id users with the transition by starting them off with the legacy workflow option they can remove or customize these at any time img width alt screen shot at pm src however new users shouldn t have to worry about the old workflow for brand new sessions we should present just the single add feature button users who want the generic favorites can add them manually img width alt screen shot at pm src re | 1 |
394,178 | 11,633,022,990 | IssuesEvent | 2020-02-28 07:07:58 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.netflix.com - see bug description | browser-firefox engine-gecko priority-critical | <!-- @browser: Firefox 75.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/49174 -->
**URL**: https://www.netflix.com/br-en/
**Browser / Version**: Firefox 75.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: Netflix Site Error
**Steps to Reproduce**:
Netflix Site Error
We were unable to process your request.
Please go to the Netflix home page by clicking the button below.
Netflix Home
<details><summary>View the screenshot</summary><img alt='Screenshot' src='https://webcompat.com/uploads/2020/2/c5209710-0a5a-40c0-a28f-628dc3b4073d.jpeg'></details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20200227094956</li><li>channel: nightly</li><li>hasTouchScreen: false</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2020/2/51b0008b-58ee-43d1-b95d-86e3367d693b)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.netflix.com - see bug description - <!-- @browser: Firefox 75.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:75.0) Gecko/20100101 Firefox/75.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/49174 -->
**URL**: https://www.netflix.com/br-en/
**Browser / Version**: Firefox 75.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: Netflix Site Error
**Steps to Reproduce**:
Netflix Site Error
We were unable to process your request.
Please go to the Netflix home page by clicking the button below.
Netflix Home
<details><summary>View the screenshot</summary><img alt='Screenshot' src='https://webcompat.com/uploads/2020/2/c5209710-0a5a-40c0-a28f-628dc3b4073d.jpeg'></details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20200227094956</li><li>channel: nightly</li><li>hasTouchScreen: false</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2020/2/51b0008b-58ee-43d1-b95d-86e3367d693b)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_usab | see bug description url browser version firefox operating system windows tested another browser yes problem type something else description netflix site error steps to reproduce netflix site error we were unable to process your request please go to the netflix home page by clicking the button below netflix home view the screenshot img alt screenshot src browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel nightly hastouchscreen false mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️ | 0 |
16,593 | 11,101,281,974 | IssuesEvent | 2019-12-16 21:05:29 | spanezz/staticsite | https://api.github.com/repos/spanezz/staticsite | closed | Taxonomies and series | usability | (from a conversation with @DonKult)
> > In the example you have a dropdown menu which is nice, but I would like
> > to link to a page showing all entries of the series, which is the page
> > of the associated tag, but reaching that seems hard:
> > url_for(taxonomy('tags').categories[page.meta.series])
> > I was kinda hoping for `url_for(page.meta.series_tag)` especially if
> > – not that I have tried – you have multiple taxonomies with series's…
> If the series is autogenerated from a tag, indeed a way to generate a
> link to the tag page would be enough. If the series is not
> autogenerated from a tag, we currently wouldn't have a recap page for
> the series.
>
> For the first case, the series feature could easily add a metadata to
> the page pointing to the series tag.
>
> For the second case, I'm thinking of mandating that series have to be
> tags. One can always create a 'series' taxonomy, if one doesn't want to
> add some series to the normal set of tags. This would also automatically
> provide each series with an RSS feed, and maybe simplify some of the
> series code, by just using tags code to track which pages belong to a
> series.
TL;DR: merge series and taxonomies, mandating the fact that a series is an entry in a taxonomy.
The `series` header can be used to both add a tag and state that it is used as a series.
Document that if one doesn't want to mix series in one's own tag, one can create a new taxonomy for series. That would also give an index pages to all the series in a website.
| True | Taxonomies and series - (from a conversation with @DonKult)
> > In the example you have a dropdown menu which is nice, but I would like
> > to link to a page showing all entries of the series, which is the page
> > of the associated tag, but reaching that seems hard:
> > url_for(taxonomy('tags').categories[page.meta.series])
> > I was kinda hoping for `url_for(page.meta.series_tag)` especially if
> > – not that I have tried – you have multiple taxonomies with series's…
> If the series is autogenerated from a tag, indeed a way to generate a
> link to the tag page would be enough. If the series is not
> autogenerated from a tag, we currently wouldn't have a recap page for
> the series.
>
> For the first case, the series feature could easily add a metadata to
> the page pointing to the series tag.
>
> For the second case, I'm thinking of mandating that series have to be
> tags. One can always create a 'series' taxonomy, if one doesn't want to
> add some series to the normal set of tags. This would also automatically
> provide each series with an RSS feed, and maybe simplify some of the
> series code, by just using tags code to track which pages belong to a
> series.
TL;DR: merge series and taxonomies, mandating the fact that a series is an entry in a taxonomy.
The `series` header can be used to both add a tag and state that it is used as a series.
Document that if one doesn't want to mix series in one's own tag, one can create a new taxonomy for series. That would also give an index pages to all the series in a website.
| usab | taxonomies and series from a conversation with donkult in the example you have a dropdown menu which is nice but i would like to link to a page showing all entries of the series which is the page of the associated tag but reaching that seems hard url for taxonomy tags categories i was kinda hoping for url for page meta series tag especially if – not that i have tried – you have multiple taxonomies with series s… if the series is autogenerated from a tag indeed a way to generate a link to the tag page would be enough if the series is not autogenerated from a tag we currently wouldn t have a recap page for the series for the first case the series feature could easily add a metadata to the page pointing to the series tag for the second case i m thinking of mandating that series have to be tags one can always create a series taxonomy if one doesn t want to add some series to the normal set of tags this would also automatically provide each series with an rss feed and maybe simplify some of the series code by just using tags code to track which pages belong to a series tl dr merge series and taxonomies mandating the fact that a series is an entry in a taxonomy the series header can be used to both add a tag and state that it is used as a series document that if one doesn t want to mix series in one s own tag one can create a new taxonomy for series that would also give an index pages to all the series in a website | 1 |
9,335 | 6,225,550,202 | IssuesEvent | 2017-07-10 16:25:40 | loconomics/loconomics | https://api.github.com/repos/loconomics/loconomics | opened | Ensure that all interactive elements are keyboard accessible | C: Usability F: Accessbility | Think about keyboard access, especially when developing interactive elements, such as menus, mouseover information, collapsable accordions, or media players. Use tabindex="0" to add an element that does not normally receive focus, such as <div> or <span>, into the navigation order when it is being used for interaction. Use scripting to capture and respond to keyboard events.
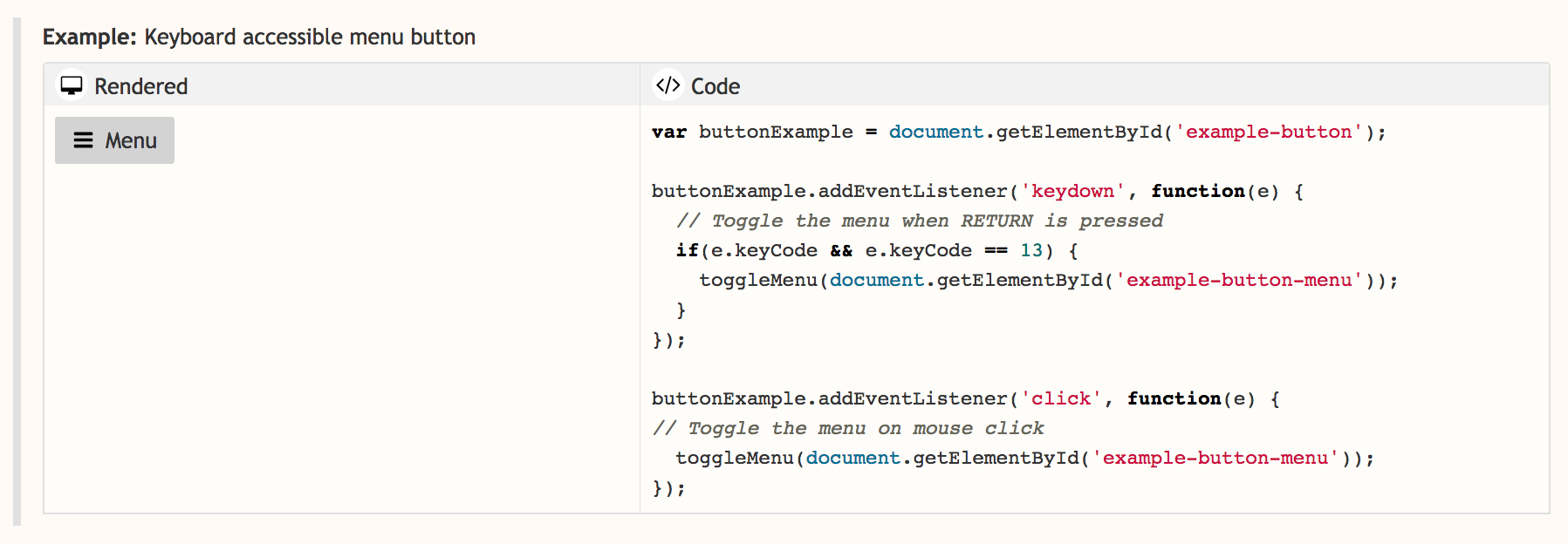
For more information
WCAG
[Keyboard 2.1.1](https://www.w3.org/WAI/WCAG20/quickref/#keyboard-operation-keyboard-operable) [(Understanding 2.1.1)](https://www.w3.org/TR/UNDERSTANDING-WCAG20/keyboard-operation-keyboard-operable.html)
User Story
[Describes how a user with RSI needs keyboard support](https://www.w3.org/WAI/intro/people-use-web/stories#reporter)
| True | Ensure that all interactive elements are keyboard accessible - Think about keyboard access, especially when developing interactive elements, such as menus, mouseover information, collapsable accordions, or media players. Use tabindex="0" to add an element that does not normally receive focus, such as <div> or <span>, into the navigation order when it is being used for interaction. Use scripting to capture and respond to keyboard events.
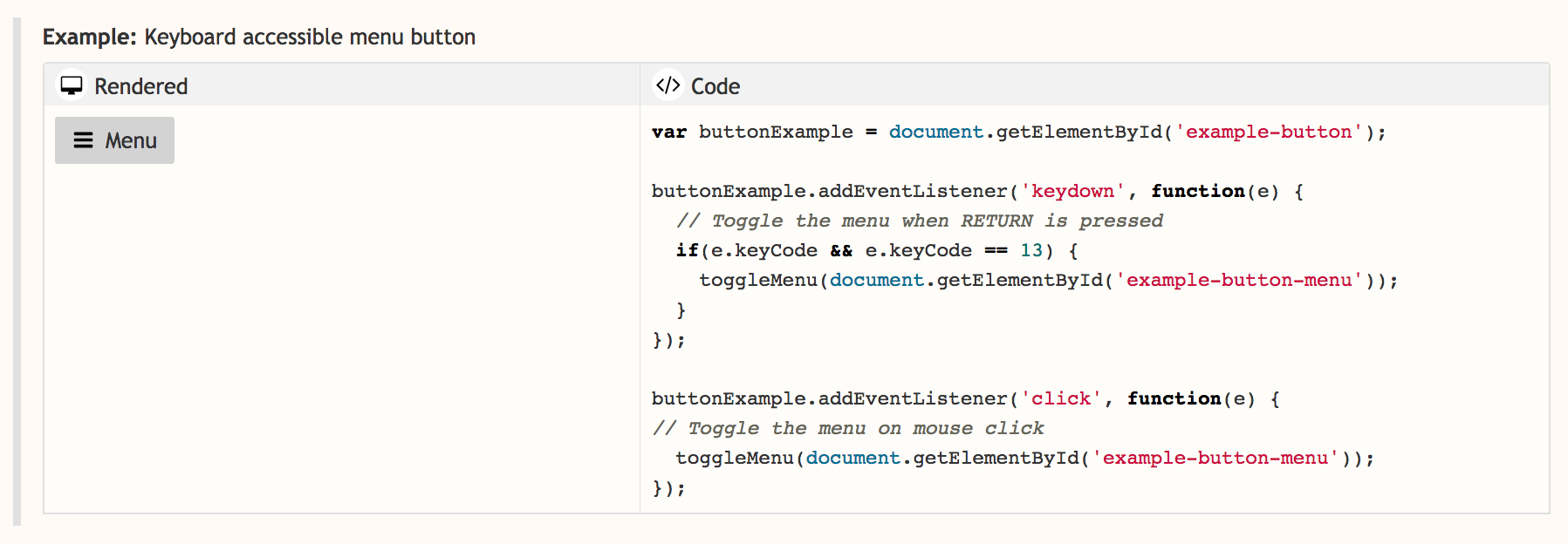
For more information
WCAG
[Keyboard 2.1.1](https://www.w3.org/WAI/WCAG20/quickref/#keyboard-operation-keyboard-operable) [(Understanding 2.1.1)](https://www.w3.org/TR/UNDERSTANDING-WCAG20/keyboard-operation-keyboard-operable.html)
User Story
[Describes how a user with RSI needs keyboard support](https://www.w3.org/WAI/intro/people-use-web/stories#reporter)
| usab | ensure that all interactive elements are keyboard accessible think about keyboard access especially when developing interactive elements such as menus mouseover information collapsable accordions or media players use tabindex to add an element that does not normally receive focus such as or into the navigation order when it is being used for interaction use scripting to capture and respond to keyboard events for more information wcag user story | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.