id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,904,501 | Using the System for Award Management SAM Exclusions List to Vet Subcontractors | Discover how leveraging the SAM Exclusions List can enhance your subcontractor vetting process for better compliance and risk management. | 0 | 2024-06-28T16:46:53 | https://www.govcon.me/blog/using_the_system_for_award_management_sam_exclusions_list_to_vet_subcontractors | contracting, compliance, technology | # Using the System for Award Management (SAM) Exclusions List to Vet Subcontractors
In today's rapidly evolving business landscape, ensuring compliance and minimizing risks are paramount, especially when it comes to vetting subcontractors. One powerful tool in the arsenal of diligent project managers and complian... | quantumcybersolution |
1,904,500 | How to Use Virtual Reality for Client Walkthroughs and Approvals | Unlock the power of Virtual Reality to revolutionize client walkthroughs and approvals by making presentations more interactive, immersive, and convincing. | 0 | 2024-06-28T16:46:26 | https://www.govcon.me/blog/how_to_use_virtual_reality_for_client_walkthroughs_and_approvals | virtualreality, clientinteraction, technology | # How to Use Virtual Reality for Client Walkthroughs and Approvals
In an age where technological advancements continuously reshape our world, one innovation stands tall: Virtual Reality (VR). Once a fantastical concept found in the realms of science fiction, VR now offers practical applications that can revolutionize ... | quantumcybersolution |
1,904,499 | Unassigned shards in Elasticsearch 7 and 8 | There are multiple reasons why shards might get unassigned, ranging from misconfigured allocation... | 0 | 2024-06-28T16:46:03 | https://dev.to/bidhanahdib/unassigned-shards-in-elasticsearch-7-and-8-2jlh | elasticsearch, devops, beginners, automation | There are multiple reasons why shards might get unassigned, ranging from misconfigured allocation settings to lack of disk space.
To reassign all unassigned shards in Elasticsearch, you can use the following steps:
https://bidhankhatri.com.np/system/unassigned-shards-in-elasticsearch/
| bidhanahdib |
1,904,498 | 2285. Maximum Total Importance of Roads | 2285. Maximum Total Importance of Roads Medium You are given an integer n denoting the number of... | 27,523 | 2024-06-28T16:42:31 | https://dev.to/mdarifulhaque/2285-maximum-total-importance-of-roads-5281 | php, leetcode, algorithms, programming | 2285\. Maximum Total Importance of Roads
Medium
You are given an integer `n` denoting the number of cities in a country. The cities are numbered from `0` to `n - 1`.
You are also given a 2D integer array roads where <code>roads[i] = [a<sub>i</sub>, b<sub>i</sub>]</code> denotes that there exists a **bidirectional** ... | mdarifulhaque |
1,904,463 | Security Analysis of BitPower | Introduction With the rapid development of blockchain technology, decentralized finance (DeFi)... | 0 | 2024-06-28T16:09:11 | https://dev.to/woy_ca2a85cabb11e9fa2bd0d/security-analysis-of-bitpower-27 | btc | Introduction
With the rapid development of blockchain technology, decentralized finance (DeFi) platforms have rapidly emerged around the world. As an outstanding representative of these platforms, BitPower has won wide attention and trust with its excellent security and transparency. This article will explore BitPower'... | woy_ca2a85cabb11e9fa2bd0d |
1,902,502 | Exploring the most powerful Open LLMs launched till now in June 2024 | In the recent months, there has been a huge excitement and interest around Generative AI, there are... | 0 | 2024-06-28T16:42:15 | https://dev.to/portkey/exploring-the-most-powerful-llms-launched-till-now-in-june-2024-59c1 | llm, ai, programming, news | In the recent months, there has been a huge excitement and interest around Generative AI, there are tons of announcements/new innovations! It has been great for overall ecosystem, however, quite difficult for individual dev to catch up!
Okay! While diving into this field of Generative AI, one of the commonly used term... | aravind |
1,904,497 | Using Reverse Auctions for Government Procurement | Explore the innovative approach of reverse auctions in government procurement, and how it drives efficiency and cost savings. | 0 | 2024-06-28T16:41:46 | https://www.govcon.me/blog/using_reverse_auctions_for_government_procurement | government, procurement, reverseauctions, technology | # Using Reverse Auctions for Government Procurement
When it comes to government procurement, efficiency, transparency, and cost savings are paramount. Traditional procurement methods often fall short of these goals, leading to delays, increased costs, and a lack of competition. Enter *reverse auctions*, a revolutionar... | quantumcybersolution |
1,899,343 | RETHV - Building Reth for the RISC-V platform | We describe how we managed to run Reth, the Rust Ethereum execution client maintained by Paradigm and... | 0 | 2024-06-28T16:41:18 | https://dev.to/quartztechnology/rethv-building-reth-for-the-risc-v-platform-17ji | reth, ethereum, riscv | We describe how we managed to run [Reth](https://github.com/paradigmxyz/reth), the Rust Ethereum execution client maintained by Paradigm and the open-source community, on a RISC-V environnement.
As we faced issues and learned many things, we wanted not only to share the finished PoC but also the journey itself. If you... | quartztechnology |
1,904,496 | BUILD YOUR DREAMS WITH INDIAN STOCK MARKET | what is stock market You can invest our money in various of company and as per your... | 0 | 2024-06-28T16:40:27 | https://dev.to/vamsi_777/build-your-dreams-with-indian-stock-market-4817 | nifty, sensex |
## what is stock market
You can invest our money in various of company and as per your intrest you can buy and sell shares in market with a proper research and analysis. Other wise they may loose money
## how to buy stocks
To buy and sell stocks we need a demat account and we need to take that demat account under... | vamsi_777 |
1,904,237 | Accelerated Integration: How We Met Our Deadline Ahead of Schedule. | Introduction: This story or blog is about an Journey of an Integration project. I am sure that today... | 0 | 2024-06-28T16:37:54 | https://dev.to/vaibhav9017/accelerated-integration-how-we-met-our-deadline-ahead-of-schedule-57fl | acceleratedintegration, teamwork, rapiddevelopment, deadlinedriven | **Introduction**: This story or blog is about an Journey of an Integration project. I am sure that today everyone is aware about Integration. What it is? right? But still, let me highlight the thing what is an Integration. In simple words or for better understanding, Integration is nothing but an communication or passi... | vaibhav9017 |
1,904,492 | How to Use Predictive Maintenance for Construction Equipment | Explore the transformative potential of predictive maintenance in construction, ensuring equipment efficiency and minimizing downtime. | 0 | 2024-06-28T16:36:19 | https://www.govcon.me/blog/how_to_use_predictive_maintenance_for_construction_equipment | predictivemaintenance, constructiontechnology, innovation | # How to Use Predictive Maintenance for Construction Equipment
Welcome to the future of construction technology! Predictive maintenance is revolutionizing the industry by maximizing equipment uptime and minimizing costly failures. Buckle up as we dive into how you can leverage this cutting-edge technology to keep your... | quantumcybersolution |
1,904,490 | God Explained With Math | How God is the origin we are all expressions of One! | 0 | 2024-06-28T16:34:06 | https://www.rics-notebook.com/blog/Personal/GodUniverse | esoteric, consciousness, meditation, alchemy | ## 🌌 God as the Origin: Expressions and the Universe
### The Origin of All
In esoteric philosophy, God is often seen as the origin and the starting point of everything. This perspective sees God as the fundamental source from which all existence emanates. The universe, in this view, is a manifestation of God's ... | eric_dequ |
1,904,489 | Using GSA eBuy for Targeted Government Contract Opportunities | Explore how to leverage the GSA eBuy platform to secure targeted government contracts and enhance your business growth. | 0 | 2024-06-28T16:31:31 | https://www.govcon.me/blog/using_gsa_ebuy_for_targeted_government_contract_opportunities | gsa, governmentcontracts, ebuy | # Using GSA eBuy for Targeted Government Contract Opportunities
Government contracts can be a goldmine for businesses, large and small. You might think that snaring one is akin to catching a unicorn, but with the right tools and strategies, it’s entirely achievable. One such tool is the **GSA eBuy** platform—an online... | quantumcybersolution |
1,904,487 | My Pen on CodePen | Check out this Pen I made! | 0 | 2024-06-28T16:30:30 | https://dev.to/gabrielcontasistema_75a18/my-pen-on-codepen-pfe | codepen | Check out this Pen I made!
{% codepen https://codepen.io/Gabrielcontasistema/pen/jOoomOJ %} | gabrielcontasistema_75a18 |
1,904,486 | My Pen on CodePen | Check out this Pen I made! | 0 | 2024-06-28T16:30:29 | https://dev.to/gabrielcontasistema_75a18/my-pen-on-codepen-jhg | codepen | Check out this Pen I made!
{% codepen https://codepen.io/Gabrielcontasistema/pen/jOoomOJ %} | gabrielcontasistema_75a18 |
1,904,484 | Transcend Receive Energy The Esoteric Path | Understanding consciousness, energy, and the practices that can lead to an elevated state of being. | 0 | 2024-06-28T16:28:58 | https://www.rics-notebook.com/blog/Personal/Consciousness | esoteric, consciousness, meditation, alchemy | # 🌌 Transcend & Receive Energy: The Esoteric Path
The path to elevated consciousness and higher energies is paved with ancient wisdom, scientific insights, and meditative practices. From Carl Jungs theories to Nikola Tesla's insights, there is a confluence of understanding that offers an in-depth look at the... | eric_dequ |
1,630,497 | React Hydration explained | If you are a frontend developer and have some experience with React, you may have heard the term... | 0 | 2024-06-28T16:27:37 | https://dev.to/saeedmosavat/react-hydration-explained-egh | react, javascript, webdev, frontend | If you are a frontend developer and have some experience with React, you may have heard the term "Hydration". In this article we will explore what it is, why we need it and how it works.
This is what the official react [documentation](https://react.dev/reference/react-dom/hydrate#:~:text=In%20React%2C%20%E2%80%9Chydra... | saeedmosavat |
1,904,483 | Using Government Contracting to Enter New Markets and Diversify Your Business | Discover how leveraging government contracts can open new avenues for market entry and diversification, ensuring long-term growth and stability for your business. | 0 | 2024-06-28T16:26:24 | https://www.govcon.me/blog/using_government_contracting_to_enter_new_markets_and_diversify_your_business | governmentcontracting, businessgrowth, marketdiversification | # Using Government Contracting to Enter New Markets and Diversify Your Business
Innovation and growth are cornerstones of a successful business strategy. For many companies, particularly small to mid-sized enterprises, breaking into new markets can feel like a daunting task. However, one often overlooked avenue for ma... | quantumcybersolution |
1,904,482 | How to Use Laser Scanning Technology for Precise Construction Measurements | Unlock the potential of laser scanning technology in construction for accurate and efficient measurements, saving time, reducing errors, and enhancing project outcomes. | 0 | 2024-06-28T16:26:11 | https://www.govcon.me/blog/how_to_use_laser_scanning_technology_for_precise_construction_measurements | construction, laserscanning, technology | # How to Use Laser Scanning Technology for Precise Construction Measurements
Construction has come a long way from the days of chalk lines and manually measured tape distances. Welcome to the future: a place where **laser scanning technology** revolutionizes how we plan, execute, and monitor construction projects. In ... | quantumcybersolution |
1,903,137 | 40 days of Kubernetes: Docker Fundamentals | To understand Kubernetes, we should understand the concept of containers. In the traditional way of... | 0 | 2024-06-28T16:14:18 | https://dev.to/ak_15/40-days-of-kubernetes-docker-fundamentals-193c | docker, fundamentals, kubernetes, cka | To understand Kubernetes, we should understand the concept of containers.
In the traditional way of development, the application deployment in local environments such as development and testing worked fine but would fail when promoted to production. The **"it works on my machine"** problem was never-ending.
When analy... | ak_15 |
1,904,480 | Elevate Your Web App Transforming Nextjs Project into a PWA | Delve into the journey of augmenting your Next.js project with PWA features, leveraging the pages directory for an organized and efficient structure. | 0 | 2024-06-28T16:23:51 | https://www.rics-notebook.com/blog/Next/PWA | nextjs, pwa, webdev, tutorial | ## 🚀 Elevate Your Web App: Transforming Next.js Project into a PWA
## Introduction
In a realm where user experience significantly drives engagement and retention, Progressive Web Apps (PWAs) have emerged as a cornerstone for modern web development practices. By intertwining the benefits of web and mobile apps, PWAs ... | eric_dequ |
1,904,479 | How Next router handles routing differently from React Router Dom | React and Next.js are similar in some ways, and different in others. One of those differences is in... | 0 | 2024-06-28T16:22:32 | https://dev.to/armstrong2035/how-next-router-handles-routing-differently-from-react-router-dom-o40 | **React** and **Next.js** are similar in some ways, and different in others. One of those differences is in how both frameworks handle routing. As someone who has used React for most of my career, I was surprised to find how different Next.js routing is from React Routing. Understanding these differences is crucial for... | armstrong2035 | |
1,904,478 | How to Overcome Creative Block as a Web Designer | You know those times when you want to design something but just don’t know how to start? It’s... | 0 | 2024-06-28T16:22:27 | https://dev.to/divine-ikechukwu/how-to-overcome-creative-block-as-a-web-designer-50mh | webdesign, design, webdev, productivity |
You know those times when you want to design something but just don’t know how to start? It’s always frustrating, isn’t it? You know you can do it, but your creative juices just aren’t flowing. This often happens a... | divine-ikechukwu |
1,904,477 | Using Capabilities Statements to Market Your Business to Government Agencies | Unlock the secrets of creating an impactful capabilities statement to effectively market your business to government agencies. | 0 | 2024-06-28T16:21:16 | https://www.govcon.me/blog/using_capabilities_statements_to_market_your_business_to_government_agencies | governmentcontracts, businessdevelopment, marketing | # Using Capabilities Statements to Market Your Business to Government Agencies
If you've ever aspired to land contracts with government agencies, you know it's a whole different ball game compared to traditional B2B marketing. One of the most powerful tools in your arsenal is the **Capabilities Statement**. ... | quantumcybersolution |
1,904,475 | TCP vs UDP Understanding the Differences | In this blog post, we will compare the key differences between TCP and UDP, two essential protocols used to send data over a network. We will discuss their features, use cases, and help you decide which protocol is best for your specific needs. 🚀 | 0 | 2024-06-28T16:18:44 | https://www.rics-notebook.com/blog/Networking_priciples/TCPvsUDP | tcp, udp, networking, devops | ## What is TCP? 🔗
TCP stands for Transmission Control Protocol. It is a connection-oriented
protocol that provides a reliable way to send data over a network. TCP
guarantees that all data will be delivered in the correct order and that no data
will be lost. TCP is often used for applications that require a reliable
c... | eric_dequ |
1,904,474 | FastAPI Beyond CRUD Part 15 - More Database And Schema Relationships | In this video, we enhance our SQLModel models by establishing additional database relationships... | 0 | 2024-06-28T16:17:21 | https://dev.to/jod35/fastapi-beyond-crud-part-15-more-database-and-schema-relationships-3g89 | fastapi, python, backenddevelopment, api | In this video, we enhance our SQLModel models by establishing additional database relationships within our application. We demonstrate how to efficiently retrieve data leveraging these relationships, with a specific focus on user reviews.
{%youtube HFsvl515eKM%} | jod35 |
1,904,470 | Using BetaSAMgov to Find and Pursue Government Contract Opportunities | Dive into the world of government contracts with Beta.SAM.gov! Learn how to navigate this invaluable resource and secure lucrative opportunities for your business. | 0 | 2024-06-28T16:16:09 | https://www.govcon.me/blog/using_betasamgov_to_find_and_pursue_government_contract_opportunities | governmentcontracts, betasamgov, businessopportunities | # Using Beta.SAM.gov to Find and Pursue Government Contract Opportunities
In today's rapidly evolving business landscape, government contracts can be a treasure trove of opportunities. Whether you're a small startup or a large enterprise, winning these contracts can pave the way for substantial growth and st... | quantumcybersolution |
1,904,469 | How to Use Geofencing for Enhanced Construction Site Security | Discover how geofencing technology can revolutionize security measures on construction sites by offering real-time alerts, precise monitoring, and robust protection. | 0 | 2024-06-28T16:16:04 | https://www.govcon.me/blog/how_to_use_geofencing_for_enhanced_construction_site_security | geofencing, construction, security, technology | # How to Use Geofencing for Enhanced Construction Site Security
In the ever-evolving landscape of construction, the integration of advanced technology is not merely beneficial but essential. Among the myriad of innovative solutions, geofencing stands out as a game-changer in ensuring robust security on construction si... | quantumcybersolution |
1,904,425 | My Journey as a Backend Developer: Tackling AI-Powered Sentiment Analysis for Course Reviews | INTRODUCTION My name is Adekolu Samuel Oluwaseun, an undergraduate student of Veritas... | 0 | 2024-06-28T16:14:51 | https://dev.to/samixx_yasuke/my-journey-as-a-backend-developer-tackling-ai-powered-sentiment-analysis-for-course-reviews-4doi | webdev, javascript, programming, node | ## INTRODUCTION
My name is Adekolu Samuel Oluwaseun, an undergraduate student of Veritas University Abuja studying Computer Science and Information Technology. I want to open up my journey as I talk about one of the most difficult backend projects I've worked on which I used as my final year project. But before that I... | samixx_yasuke |
547,571 | Answer: flutter remove back button on appbar | answer re: flutter remove back button... | 0 | 2020-12-20T07:03:59 | https://dev.to/satyaroutray1/answer-flutter-remove-back-button-on-appbar-57oa | {% stackoverflow 46713257 %} | satyaroutray1 | |
1,904,468 | Understanding RAID Levels | A comprehensive guide to understanding the different RAID levels and how they can improve performance, capacity, and fault tolerance of hard disk drives. | 0 | 2024-06-28T16:13:36 | https://www.rics-notebook.com/blog/Networking_priciples/Raid | raid, storage, technology, devops | # Understanding RAID Levels
RAID redundant array of independent disks is a technology that combines
multiple hard disk drives HDDs into a single logical unit. RAID provides
several benefits over using a single HDD, including improved performance,
increased capacity, and improved fault tolerance.
In this guide, we wil... | eric_dequ |
1,904,467 | 🌟 Explore the extraordinary of BitPower Loop! 🌟 | 1️⃣ Smart contract guarantee: All transactions are automatically executed by smart contracts to... | 0 | 2024-06-28T16:12:13 | https://dev.to/weq_24a494dd3a467ace6aca5/explore-the-extraordinary-of-bitpower-loop-a3o | btc | 1️⃣ Smart contract guarantee: All transactions are automatically executed by smart contracts to ensure security and transparency.
2️⃣ Decentralized lending: No third-party intermediary is required, reducing costs and increasing autonomy. Users can borrow and lend directly through smart contracts.
3️⃣ Funding pool mec... | weq_24a494dd3a467ace6aca5 |
1,904,466 | Unleashing the Power of Federal Business Opportunities FBO to Find Government Contract Leads | Dive deep into the world of Federal Business Opportunities (FBO) and discover how you can leverage this powerful platform to secure lucrative government contracts for your business. | 0 | 2024-06-28T16:11:01 | https://www.govcon.me/blog/unleashing_the_power_of_federal_business_opportunities_fbo_to_find_government_contract_leads | governmentcontracts, fbo, businessopportunities | ## Unleashing the Power of Federal Business Opportunities (FBO) to Find Government Contract Leads
If you're a business owner with aspirations of landing lucrative government contracts, you're in for a treat! Welcome to the incredible world of Federal Business Opportunities (FBO), a staple tool for companies ... | quantumcybersolution |
1,904,465 | Meesho 9th Anniversary Lucky Draw 2024: Celebrating Success with Rewards | Meesho, a pioneering force in India’s social commerce landscape since its inception in 2024, is... | 0 | 2024-06-28T16:10:43 | https://dev.to/meesho121/meesho-9th-anniversary-lucky-draw-2024-celebrating-success-with-rewards-bo9 |

Meesho, a pioneering force in India’s social commerce landscape since its inception in 2024, is marking 8th anniversary with an exhilarating lucky draw event in 2024. This celebration not only commemorates a signif... | meesho121 | |
1,904,464 | Styled Components vs TailwindCss (UIs Showdown) | As a front-end developer, when it comes to styling user interfaces, two popular options always come... | 0 | 2024-06-28T16:09:58 | https://dev.to/oladee/styled-components-vs-tailwindcss-uis-showdown-2jho | react, css | As a front-end developer, when it comes to styling user interfaces, two popular options always come to mind: Styled Components and Tailwind CSS. Both offer distinct approaches, and the "better" choice depends on your project's specific needs, although I have my preferred option of the two, but lets take on a journey to... | oladee |
1,904,462 | Quantum Networks | Discover how quantum networks are set to revolutionize modern communication, offering unparalleled security and efficiency. Learn about the basics of quantum communication and explore the potential applications and advantages of this cutting-edge technology. | 0 | 2024-06-28T16:08:29 | https://www.rics-notebook.com/blog/Networking_priciples/QuantumNetworks | internet, cybersecurity, quantum, devops | # Quantum Networks: The Future of Secure and Efficient Communication 🌐🔐
In today's digital age, our lives revolve around the internet and the vast network of computers that keep us connected. But as our reliance on these networks grows, so too do the risks of hacking, surveillance, and data breaches. Enter quan... | eric_dequ |
1,904,460 | Security Analysis of BitPower | Introduction With the rapid development of blockchain technology, decentralized finance (DeFi)... | 0 | 2024-06-28T16:08:07 | https://dev.to/woy_621fc0f3ac62fff68606e/security-analysis-of-bitpower-3lhl | btc | Introduction
With the rapid development of blockchain technology, decentralized finance (DeFi) platforms have rapidly emerged around the world. As an outstanding representative of these platforms, BitPower has won wide attention and trust with its excellent security and transparency. This article will explore BitPower'... | woy_621fc0f3ac62fff68606e |
1,904,039 | Understanding Two-Factor Authentication (2FA): How It Safeguards Your Accounts | In an era where online security threats loom large, safeguarding your digital accounts is paramount.... | 0 | 2024-06-28T16:07:13 | https://dev.to/verifyvault/understanding-two-factor-authentication-2fa-how-it-safeguards-your-accounts-5f9k | cybersecurity, opensource, github, security | In an era where online security threats loom large, safeguarding your digital accounts is paramount. Two-factor authentication (2FA) adds an essential layer of protection by requiring users to verify their identity in two distinct ways. Today, we unravel the concept of 2FA and showcase how VerifyVault seamlessly integr... | verifyvault |
1,904,459 | Security Analysis of BitPower | Introduction With the rapid development of blockchain technology, decentralized finance (DeFi)... | 0 | 2024-06-28T16:06:12 | https://dev.to/wot_ee4275f6aa8eafb35b941/security-analysis-of-bitpower-3lp4 | btc | Introduction
With the rapid development of blockchain technology, decentralized finance (DeFi) platforms have rapidly emerged around the world. As an outstanding representative of these platforms, BitPower has won wide attention and trust with its excellent security and transparency. This article will explore BitPower'... | wot_ee4275f6aa8eafb35b941 |
1,904,458 | BitPower: A revolutionary force that reshapes finance | BitPower: A revolutionary force that reshapes finance In an infinite digital world, BitPower shines... | 0 | 2024-06-28T16:06:02 | https://dev.to/pings_iman_934c7bc4590ba4/bitpower-a-revolutionary-force-that-reshapes-finance-2nke |
BitPower: A revolutionary force that reshapes finance
In an infinite digital world, BitPower shines like a star. It is not just a platform, but also a revolutionary force that re-empowers the public with financial p... | pings_iman_934c7bc4590ba4 | |
1,904,457 | How to Use Building Automation Systems for Energy Efficiency | Explore how building automation systems can revolutionize energy management and lead to substantial savings in commercial and residential properties. | 0 | 2024-06-28T16:05:57 | https://www.govcon.me/blog/how_to_use_building_automation_systems_for_energy_efficiency | buildingautomation, energyefficiency, smarttechnology | # How to Use Building Automation Systems for Energy Efficiency
In today's rapidly evolving technological landscape, building automation systems (BAS) stand out as game-changers for energy efficiency. These sophisticated systems, which integrate and automate various building technologies, offer the promise of redu... | quantumcybersolution |
1,904,456 | Understanding the Impacts of Federal Acquisition Streamlining Act FASA | Learn how FASA has simplified the federal procurement process and what it means for contractors, including key provisions and practical tips for compliance. | 0 | 2024-06-28T16:05:54 | https://www.govcon.me/blog/understanding_the_impacts_of_federal_acquisition_streamlining_act_fasa | governmentcontracting, fasa, federalprocurement, compliance | ## Understanding the Impacts of Federal Acquisition Streamlining Act (FASA)
The **Federal Acquisition Streamlining Act (FASA)** of 1994 brought significant reforms to the federal procurement process, making it simpler and inviting for contractors. This article delves into the core elements of FASA, its impacts on fede... | quantumcybersolution |
1,903,859 | Satan, Anime, or North Korea? 5 Unusual Linux Distributions | Here are some Linux distributions that you’ve probably never heard of ➡ Ubuntu Satanic... | 0 | 2024-06-28T16:04:45 | https://dev.to/ispmanager/satan-anime-or-north-korea-5-unusual-linux-distributions-2jkb | linux, anime, alternativedistributions, design | Here are some Linux distributions that you’ve probably never heard of ➡
## Ubuntu Satanic Edition
A distribution for true Satanists. The boot screen displays the devil, and it comes with a collection of heavy metal music.
**," a radiant ensemble that embodies sophistication and allure. Crafted from luxurious georgette fabric, this jumpsuit exudes elegance with every step you take.
| ruksanak5749 |
542,053 | 利用 Excel 陣列計算不重複項目 | 因為需要計算不重複項目, 發現大家的解決方案都是在 Excel 中使用陣列公式, 所以稍微瞭解了一下陣列的用法, 果然是神兵力器, 值得學一下。 Excel... | 0 | 2020-12-14T10:47:30 | https://dev.to/codemee/excel-4d33 | excel | 因為需要計算不重複項目, 發現大家的解決方案都是在 Excel 中使用陣列公式, 所以稍微瞭解了一下陣列的用法, 果然是神兵力器, 值得學一下。
## Excel 的陣列
如果你有以下的資料, 想要算出小計:

一般的作法可能是在 B4 建立公式 `=B2*B3`, 然後再複製公式到 C4 與 D4;有了這些資料後, 我們就可以計算總價, 也就是所有小計的總和。
我們可以改用陣列公式取代上述運算, 在大多數情況下能夠節省很多操作時間。
### 使用陣列計算出選取範圍內的個別結果
以下列步驟完成同樣的結果:
1. 選取小計範圍 B4:D4:
... | codemee |
1,904,452 | Bat Houses Unsung Heroes of Pest Control and Ecological Balance | Discover the incredible benefits of promoting bat houses and learn how these nocturnal heroes help maintain ecological balance, control pest populations, and support a healthier environment for all. | 0 | 2024-06-28T16:03:22 | https://www.rics-notebook.com/blog/Nature/BatHouse | bathouses, pestcontrol, ecologicalbalance, insectcontrol | # Bat Houses: Unsung Heroes of Pest Control and Ecological Balance 🦇🏡
Bats are often misunderstood and underappreciated creatures, but they play a crucial role in maintaining the delicate balance of our ecosystems. By promoting the use of bat houses, we can create safe habitats for these nocturnal heroes and reap th... | eric_dequ |
1,904,435 | Getting started with Passwordless Authentication | Passwordless authentication is an alternative to traditional password-based authentication that is... | 0 | 2024-06-28T16:02:44 | https://dev.to/userfront/getting-started-with-passwordless-authentication-2ao4 | webdev, authentication, passwordless, learning | Passwordless authentication is an alternative to traditional password-based authentication that is gaining traction among organizations aiming to bolster their security infrastructure while enhancing user experience. This article explores the concept of passwordless authentication, its benefits for organizations, vario... | userfront_devs |
1,904,448 | Titanic Dataset Analysis | Introduction The Titanic dataset, a well-known dataset in the data science and machine... | 0 | 2024-06-28T16:01:18 | https://dev.to/net_work_6c1ca76f29fa0c46/titanic-dataset-analysis-3abl | datascience, analytics, python, learning | ## Introduction
The Titanic dataset, a well-known dataset in the data science and machine learning communities, consists of information about the passengers aboard the RMS Titanic.
RMS Titanic was a British ocean liner that sank on 15 April 1912 after striking an iceberg on her maiden voyage from Southampton, England... | net_work_6c1ca76f29fa0c46 |
1,904,447 | Blockchain in Banking: Revolutionizing the Financial Sector | Introduction Blockchain technology, originally devised for Bitcoin, has evolved into... | 27,673 | 2024-06-28T16:01:17 | https://dev.to/rapidinnovation/blockchain-in-banking-revolutionizing-the-financial-sector-56ao | ## Introduction
Blockchain technology, originally devised for Bitcoin, has evolved into a
decentralized digital ledger that records transactions securely and
transparently. This technology is transforming the banking sector by enhancing
data security, transparency, and efficiency.
## What is Blockchain?
Blockchain i... | rapidinnovation | |
1,904,438 | My personal detox command | The original detox It is perfect but in termux i do not have it in my repositories,... | 0 | 2024-06-28T15:52:02 | https://dev.to/voyeg3r/my-personal-detox-command-2b2m | detox, termux, tools, rename | ## The original detox
It is perfect but in termux i do not have it in my repositories, so:
```sh
#!/bin/bash
#
# Script: dtx
# Description: Rename files by removing special characters and normalizing names.
#
# Usage: dtx [-d] [-h] files...
# Options:
# -d Dry run. Show the final result without renaming.
# -h ... | voyeg3r |
1,904,446 | Understanding the Federal Acquisition Regulation FAR Key Sections for Contractors | Navigate the intricate world of government contracts with a deep dive into the Federal Acquisition Regulation (FAR), focusing on the most crucial sections for contractors. | 0 | 2024-06-28T16:00:47 | https://www.govcon.me/blog/understanding_the_federal_acquisition_regulation_far_key_sections_for_contractors | federalacquisitionregulation, contractors, governmentcontracts | # Understanding the Federal Acquisition Regulation (FAR): Key Sections for Contractors
When it comes to government contracts, the Federal Acquisition Regulation (FAR) is the cornerstone guideline that bidders and contractors must understand. Yet, navigating FAR can often feel like deciphering a dense legal manuscript.... | quantumcybersolution |
1,904,445 | BitPower: A cutting-edge platform that revolutionizes decentralized lending | Introduction With the rapid development of blockchain technology, decentralized finance (DeFi) has... | 0 | 2024-06-28T16:00:45 | https://dev.to/aimm_l_6b8a62242513520c18/bitpower-a-cutting-edge-platform-that-revolutionizes-decentralized-lending-37ml | Introduction
With the rapid development of blockchain technology, decentralized finance (DeFi) has become an important trend in financial technology. As a leading platform in this field, BitPower provides global users with safe, efficient and convenient decentralized lending services through its innovative lending prot... | aimm_l_6b8a62242513520c18 | |
1,904,444 | Matlab | MATLAB short for Matrix Laboratory is a programming language developed by MathWorks. It is used for technical computing and is widely used in engineering, science, and mathematics. | 0 | 2024-06-28T15:58:15 | https://www.rics-notebook.com/blog/Matlab/Matlab | matlab, programming, software, development | ## **Introduction**
MATLAB short for Matrix Laboratory is a programming language developed by
MathWorks. It is used for technical computing and is widely used in engineering,
science, and mathematics. MATLAB is a powerful tool that can be used for a
variety of tasks, including:
- Data analysis
- Data visualization
- ... | eric_dequ |
1,904,355 | Turning Adobe Illustrator Into A People Generator (aka, A Dress Up Doll Maker) | The Problem I recently had a very tight ask: to populate an image with hundreds of unique characters... | 0 | 2024-06-28T15:56:10 | https://dev.to/kocreative/turning-adobe-illustrator-into-a-people-generator-aka-a-dress-up-doll-maker-29j1 | beginners, tutorial, codenewbie, illustrator | **The Problem**
I recently had a very tight ask: to populate an image with hundreds of unique characters in under 2 weeks. This is naturally quite a tall order, so I broke out the javascript.
I have never used javascript on anything other than After Effects, but I was aware that you could write and run scripts on othe... | kocreative |
1,904,443 | How to Use Augmented Reality for Construction Site Inspections | Discover how augmented reality (AR) is revolutionizing construction site inspections, enhancing accuracy, efficiency, and safety. | 0 | 2024-06-28T15:55:49 | https://www.govcon.me/blog/how_to_use_augmented_reality_for_construction_site_inspections | augmentedreality, constructiontechnology, innovation | # How to Use Augmented Reality for Construction Site Inspections
Welcome to the frontier where cutting-edge technology meets the rugged practicality of construction! Augmented Reality (AR) is no longer confined to gaming and entertainment—it’s revolutionizing the way construction site inspections are performed. Strap ... | quantumcybersolution |
1,904,442 | Understanding the Defense Federal Acquisition Regulation Supplement DFARS | Learn the key aspects of DFARS that contractors must comply with when working on defense-related contracts, including cybersecurity requirements and ethical considerations. | 0 | 2024-06-28T15:55:40 | https://www.govcon.me/blog/understanding_the_defense_federal_acquisition_regulation_supplement_dfars | governmentcontracting, dfars, cybersecurity, compliance | # Understanding the Defense Federal Acquisition Regulation Supplement (DFARS)
For contractors interested in working with the Department of Defense (DoD), a critical document to understand is the Defense Federal Acquisition Regulation Supplement (DFARS). This supplement to the Federal Acquisition Regulation (FAR) provi... | quantumcybersolution |
1,904,441 | Game title in html css only | Check out this Pen I made! | 0 | 2024-06-28T15:53:32 | https://dev.to/tidycoder/game-title-in-html-css-only-o7o | codepen, webdev, css, html | Check out this Pen I made!
{% codepen https://codepen.io/TidyCoder/pen/GRaampx %} | tidycoder |
1,904,440 | Understanding Sine Cosine and the Unit Circle Mapping Problems in a New Light | Sine and cosine functions are fundamental concepts in trigonometry that help us model periodic phenomena. By understanding these functions and their relationship to the unit circle, we can map problems in a new way and gain valuable insights into the world around us. | 0 | 2024-06-28T15:53:07 | https://www.rics-notebook.com/blog/Math/UnitCircle | trigonometry, mathematics, education, unitcircle | # 🔍 Introduction: Exploring the World of Sine and Cosine 🔍
Trigonometry is a fascinating branch of mathematics that deals with the relationships between the sides and angles of triangles. At the heart of trigonometry lie the sine and cosine functions, which are essential tools for modeling periodic phenomena and sol... | eric_dequ |
1,904,439 | HNG 11 will draw me closer to my dreams | Hello! My name is Tolulope Ajewole, and as a junior designer with ambitious aspirations for the next... | 0 | 2024-06-28T15:53:02 | https://dev.to/atjuiux/hng-11-will-draw-me-closer-to-my-dreams-294f | webdev, internship, infographics |
Hello! My name is Tolulope Ajewole, and as a junior designer with ambitious aspirations for the next two years, I've mapped out clear objectives to enhance my skills, accumulate valuable experience, and network within the design community. Additionally, I have some personal milestones I'm eager to achieve. To make m... | atjuiux |
1,902,487 | The Benefits of Using a UIF Calculator | The Unemployment Insurance Fund (UIF) provides financial support to workers who have lost their jobs... | 0 | 2024-06-27T11:40:58 | https://dev.to/dipcario23/the-benefits-of-using-a-uif-calculator-3mdh | The Unemployment Insurance Fund (UIF) provides financial support to workers who have lost their jobs or are unable to work due to illness, maternity, or adoption leave. Understanding how much you can claim from the UIF can be complex, and this is where a [UIF calculator](https://uifcalculator.co.za/) becomes invaluable... | dipcario23 | |
1,904,403 | Real-Time Capabilities in API Integration | As suggested by their name, real-time APIs allow applications to send and receive data in real time,... | 0 | 2024-06-28T15:51:53 | https://dev.to/apidna/real-time-capabilities-in-api-integration-45lj | api, webdev, realtime, learning | As suggested by their name, real-time APIs allow applications to send and receive data in real time, ensuring up-to-date information and immediate responses.
They are essential for applications demanding rapid response times, such as online gaming, financial trading, and IoT devices, aiming to minimise latency and ens... | itsrorymurphy |
1,904,437 | Understanding Indirect Cost Rates in Government Contracts | Dive into the complexities of indirect cost rates in government contracts and learn how they can impact your project’s budget and performance. | 0 | 2024-06-28T15:50:32 | https://www.govcon.me/blog/understanding_indirect_cost_rates_in_government_contracts | governmentcontracts, indirectcosts, finance | # Understanding Indirect Cost Rates in Government Contracts
Navigating the labyrinthine landscape of government contracts can be challenging, especially when it comes to understanding indirect cost rates. These rates can make or break your project's budget and performance, so it's crucial to grasp their nuan... | quantumcybersolution |
1,904,434 | Beyond Algorithms: A Futurist View of The Future of Machine Learning | Researchers and practitioners in machine learning (ML) are always exploring new frontiers of... | 0 | 2024-06-28T15:48:51 | https://dev.to/bytevillage/beyond-algorithms-a-futurist-view-of-the-future-of-machine-learning-4f5e | machinelearning, ai, ethics, python | **Researchers and practitioners in machine learning (ML) are always exploring new frontiers of artificial intelligence, which are quickly evolving. Algorithms have always led the charge in improvements of ML, but perhaps- just as our earlier medical advancements are slowly becoming available to everyone - we will also ... | bytevillage |
1,904,433 | Linear Algebra | Linear algebra is a branch of mathematics that deals with linear equations, matrices, and vector spaces. | 0 | 2024-06-28T15:48:00 | https://www.rics-notebook.com/blog/Math/LinearAlgebra | linearalgebra, math, calculus | ## **Introduction**
Linear algebra is a branch of mathematics that deals with linear equations,
matrices, and vector spaces. It is a fundamental tool in many fields, including
engineering, physics, computer science, and economics.
## **Important lessons learned**
There are many important lessons that students can le... | eric_dequ |
1,891,900 | Revenue Potential: Earn Money with Flutter and Google AdMob | Flutter, Google’s open-source UI toolkit, is widely used for creating natively compiled applications... | 0 | 2024-06-28T15:47:34 | https://dev.to/madisukma/revenue-potential-earn-money-with-flutter-and-google-admob-1ilk | admob, revenue, flutter | Flutter, Google’s open-source UI toolkit, is widely used for creating natively compiled applications across mobile, web, and desktop platforms from a single codebase. By incorporating Google AdMob, you can effectively monetize these apps. This guide will walk you through the process.
Google AdMob is a robust mobile a... | madisukma |
1,904,432 | How to Use Advanced Robotics for Precision Construction Tasks | Dive into the transformative world of advanced robotics in construction, exploring how innovative technologies are revolutionizing precision tasks for efficiency and accuracy. | 0 | 2024-06-28T15:45:42 | https://www.govcon.me/blog/how_to_use_advanced_robotics_for_precision_construction_tasks | robotics, construction, innovation, technology | # How to Use Advanced Robotics for Precision Construction Tasks
Welcome to the future of construction! Imagine a world where skyscrapers are built with laser-sharp precision, bridges are assembled with unerring accuracy, and homes are constructed in a fraction of the time—all thanks to advanced robotics. This isn'... | quantumcybersolution |
1,904,431 | Understanding Cost Accounting Standards CAS for Government Contracts | Dive into the world of Cost Accounting Standards (CAS) and discover how they shape government contracts, ensuring fairness, transparency, and fiscal responsibility. | 0 | 2024-06-28T15:45:13 | https://www.govcon.me/blog/understanding_cost_accounting_standards_cas_for_government_contracts | costaccounting, cas, governmentcontracts | # Understanding Cost Accounting Standards (CAS) for Government Contracts
Welcome to a deep dive into one of the most pivotal elements in government contracting: **Cost Accounting Standards (CAS)**. If you're aiming to secure a government contract, these standards are your guiding light towards fairness, transpare... | quantumcybersolution |
1,904,413 | A confusing task! | Have you ever felt a requirement was either impossible or atmost unrealistic? Like utterly confusing... | 0 | 2024-06-28T15:44:46 | https://dev.to/kramstyles/a-confusing-task-43d | backend, django, djangorest, webdev | Have you ever felt a requirement was either impossible or atmost unrealistic? Like utterly confusing and you can't wrap your head as to why such a task was given?
I'm helping a friend out on a task; he has this particularly intersting criteria he wants sorted out. Apparently he an expense tracker app he uses to store ... | kramstyles |
1,904,430 | BitPower: A cutting-edge platform that revolutionizes decentralized lending | Introduction With the rapid development of blockchain technology, decentralized finance (DeFi) has... | 0 | 2024-06-28T15:44:30 | https://dev.to/aimm_w_1761d19cef7fa886fd/bitpower-a-cutting-edge-platform-that-revolutionizes-decentralized-lending-35dd | Introduction
With the rapid development of blockchain technology, decentralized finance (DeFi) has become an important trend in financial technology. As a leading platform in this field, BitPower provides global users with safe, efficient and convenient decentralized lending services through its innovative lending prot... | aimm_w_1761d19cef7fa886fd | |
1,904,429 | Engineering Statistics An Essential Tool for Engineers | Engineering statistics is the application of statistical methods to engineering problems. It is a powerful tool that can be used to solve a wide variety of problems in engineering, including quality control, design of experiments, reliability engineering, risk analysis, and data mining. | 0 | 2024-06-28T15:42:53 | https://www.rics-notebook.com/blog/Math/EngineeringStats | engineering, statistics, methods | = **Introduction**
Engineering statistics is the application of statistical methods to engineering
problems. It is a broad field that includes topics such as probability,
sampling, estimation, hypothesis testing, and statistical inference. Engineering
statistics is used to solve a wide variety of problems in engineeri... | eric_dequ |
1,904,428 | Understanding Contract Financing Options for Government Projects | Dive into the myriad of contract financing options available for government projects and learn how to navigate this crucial aspect of doing business with the public sector. | 0 | 2024-06-28T15:40:06 | https://www.govcon.me/blog/understanding_contract_financing_options_for_government_projects | governmentcontracts, financing, smallbusiness | # Understanding Contract Financing Options for Government Projects
Securing a government contract is an arduous yet gratifying journey, especially for small businesses. Once the ink is dry and celebratory cheers have settled, the real challenge begins: financing the contract. While the government comes with its perks—... | quantumcybersolution |
1,904,424 | Exploring Number Theory and Digit Sums | Dive into the fascinating world of number theory and discover the potential of digit sum in finding new ways to Explore large numbers. Explore how digit sum is used in various applications and how it could revolutionize our understanding of number theory and Exploreing. | 0 | 2024-06-28T15:37:45 | https://www.rics-notebook.com/blog/Math/DigitSum | mathematics | ## Exploring Number Theory and Digit Sum: Unveiling New Possibilities in Exploreing Large Numbers 🔢🔍
Number theory, the study of integers and their properties, has captivated mathematicians for centuries. One particularly intriguing concept within number theory is digit sum, which is the sum of the digits of a given... | eric_dequ |
1,904,423 | My Journey into Mobile Development | My HNG Internship Journey in Mobile Development Mobile development lets me create... | 0 | 2024-06-28T15:37:11 | https://dev.to/monyasau/my-journey-into-mobile-development-3g52 | reactnative, react, mobile | ### My HNG Internship Journey in Mobile Development
Mobile development lets me create impactful applications. Joining the HNG Internship, I'm excited to improve my skills.
#### Mobile Development Platforms
**iOS Development:**
- **Pros:** High-quality user experience, revenue potential, secure ecosystem.
- **Cons:**... | monyasau |
1,904,058 | Test-Driven Development in Python using Unittest and Nose | Test-driven development implies that we first write unit tests for our modules before writing the... | 0 | 2024-06-28T15:36:47 | https://dev.to/h4ck3rd33p/test-driven-development-in-python-using-unittest-and-nosetest-24ck | testing, python | Test-driven development implies that we first write unit tests for our modules before writing the module itself. This way we know what we expect from our function and then write the function so that it passes the test cases. There are a total of 3 steps involved in TDD (Test-Driven Development).
1. Red - You write tes... | h4ck3rd33p |
1,904,422 | How to Use Advanced Analytics for Construction Resource Optimization | Discover how advanced analytics can revolutionize resource optimization in the construction industry, driving efficiency and cost savings like never before. | 0 | 2024-06-28T15:35:35 | https://www.govcon.me/blog/how_to_use_advanced_analytics_for_construction_resource_optimization | construction, analytics, optimization | # How to Use Advanced Analytics for Construction Resource Optimization
## Introduction
The construction industry is at the precipice of a technological revolution. With the advent of advanced analytics, companies can now harness data to optimize resources, reduce costs, and enhance efficiency on a scale previously de... | quantumcybersolution |
1,904,420 | Understanding and Utilizing the Defense Contract Audit Agency DCAA Compliance | Learn the importance of DCAA compliance for government contractors, including how to prepare for audits and ensure your accounting systems meet government standards. | 0 | 2024-06-28T15:34:59 | https://www.govcon.me/blog/understanding_and_utilizing_the_defense_contract_audit_agency_dcaa_compliance | governmentcontracting, dcaa, compliance, audit | Understanding and Utilizing the Defense Contract Audit Agency (DCAA) Compliance
===============================================================================
Government contracting opens a world of opportunities, but it also comes with its unique set of challenges, particularly in the realm of compliance. One of the... | quantumcybersolution |
1,904,419 | Maximum depth of a binary tree | A post by Shoeb Ahmed | 0 | 2024-06-28T15:34:49 | https://dev.to/shoeb_ahmed/maximum-depth-of-a-binary-tree-ahe |
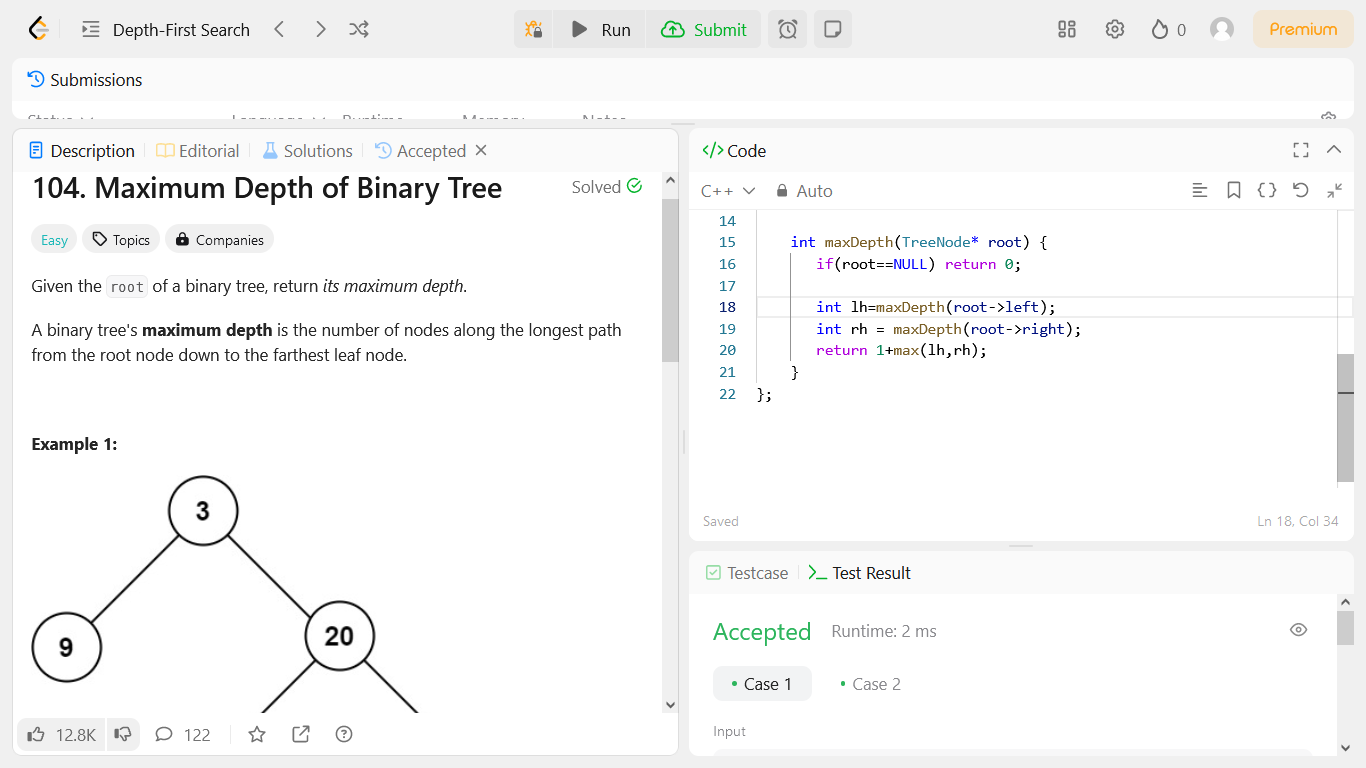 | shoeb_ahmed | |
1,904,417 | Calculus 3 The Advanced Study of Multivariable Calculus | Calculus 3 is a continuation of Calculus 1 and Calculus 2. It covers advanced topics in multivariable calculus, including vector calculus, line integrals, surface integrals, and volumes of revolution. | 0 | 2024-06-28T15:32:38 | https://www.rics-notebook.com/blog/Math/Calc3 | calculus, mathematics, education | - **Introduction**
Calculus 3 is a continuation of Calculus 1 and Calculus 2. It covers more
advanced topics in multivariable calculus, including vector calculus, line
integrals, surface integrals, and volumes of revolution. It is a challenging
course, but it is also an essential one for students who plan to study
eng... | eric_dequ |
1,904,426 | Running a Javascript VM in Golang: Data Transforms via User Scripts | Javascript VM in Golang Introduction Integrating user-defined scripts into backend... | 0 | 2024-06-28T15:39:57 | https://didil.medium.com/running-a-javascript-vm-in-golang-data-transforms-via-user-scripts-5560b0ced0d5 | javascript, backend, go | ---
title: Running a Javascript VM in Golang: Data Transforms via User Scripts
published: true
date: 2024-06-28 15:32:13 UTC
tags: javascript,backend,go,golang
canonical_url: https://didil.medium.com/running-a-javascript-vm-in-golang-data-transforms-via-user-scripts-5560b0ced0d5
---

## Introduction
Many programming conferences are held every ... | anogneva |
1,904,415 | Transitioning from Subcontractor to Prime Contractor Strategies for Growth | Unlock your potential by transforming from a subcontractor to a prime contractor. Explore strategic steps to ensure a seamless and successful transition. | 0 | 2024-06-28T15:29:52 | https://www.govcon.me/blog/transitioning_from_subcontractor_to_prime_contractor_strategies_for_growth | businessgrowth, contracting, strategy | # Transitioning from Subcontractor to Prime Contractor: Strategies for Growth
Breaking away from the subcontractor mold and stepping up as a prime contractor can be a game-changer for your business. It's akin to manifesting your business's latent potential and scaling new heights in terms of reputation, reve... | quantumcybersolution |
1,904,414 | New Caledonia WhatsApp Group Links | Latest 3800+ Caledonia WhatsApp Group Links, Join here latest and active WhatsApp Group Links New... | 0 | 2024-06-28T15:29:42 | https://dev.to/whatsapp_grouplinks_bf47/new-caledonia-whatsapp-group-links-2lae | webdev, website, seo, blog | Latest 3800+ Caledonia WhatsApp Group **[Links](https://bfatima.com/whatsapp-group-link/)**, Join here latest and active WhatsApp Group Links New Caledonia. you just scroll down and find here your favorite group links. join any **[group links](https://bfatima.com)** below.
New Caledonia is a French overseas territory ... | whatsapp_grouplinks_bf47 |
1,904,338 | APNs (Apple Push Notification service) using Laravel | In this post, I will discuss the only Laravel end functionality, assuming you have 'certificate.p12',... | 0 | 2024-06-28T15:28:40 | https://dev.to/asadut_zaman/apns-apple-push-notification-service-using-laravel-3odc | In this post, I will discuss the only Laravel end functionality, assuming you have 'certificate.p12', 'password', and 'app_bundel_id' from Apple
**Step 1**
If you have 'Certificates.p12' you need to convert this to 'Certificates.pem' file. I have stored my 'Certificates.p12' file in the 'storage' directory.
In .env ... | asadut_zaman | |
1,904,412 | Calculus 2 Advanced Concepts and Applications | Calculus 2 covers advanced topics in differentiation and integration, including Taylor series, sequences and series, and multivariable calculus. | 0 | 2024-06-28T15:27:31 | https://www.rics-notebook.com/blog/Math/Calc2 | calculus2, mathematics, engineering | ## Introduction
Calculus 2 is a continuation of Calculus 1, covering more advanced topics in
differentiation and integration, including Taylor series, sequences and series,
and multivariable calculus. It is a challenging course, but it is also an
essential one for students who plan to study engineering, science, or
ma... | eric_dequ |
1,904,411 | Solving User Authorization Issues for Deposits in a Fintech Project | The fintech world is constantly changing and securing financial transactions is of utmost importance.... | 0 | 2024-06-28T15:27:24 | https://dev.to/ubong_patrick/solving-user-authorization-issues-for-deposits-in-a-fintech-project-566l | The fintech world is constantly changing and securing financial transactions is of utmost importance. Recently, I faced a particularly challenging problem in a fintech project I was working on. The task was to ensure that only authorized users could make deposits into their accounts. Despite using JSON Web Tokens (JWT)... | ubong_patrick | |
1,904,405 | How to Query Spark Tables from Serverless SQL Pools in Azure Synapse | Introduction Say goodbye to constantly running Spark clusters! With the shared metadata... | 0 | 2024-06-28T15:27:06 | https://dev.to/ayush9892/how-to-query-spark-tables-from-serverless-sql-pools-in-azure-synapse-8e8 | azure, serverless, sql | ## Introduction
Say goodbye to constantly running Spark clusters! With the shared metadata functionality, you can shut down your Spark pools while still be able to query your Spark external tables using Serverless SQL Pool. In this blog we dive into, how Serverless SQL Pool streamlines your data workflow by automatical... | ayush9892 |
1,904,410 | 🌟 Explore the extraordinary of BitPower Loop! 🌟 | 1️⃣ Smart contract guarantee: All transactions are automatically executed by smart contracts to... | 0 | 2024-06-28T15:26:47 | https://dev.to/kjask_jklshd_cecbd37d6d57/explore-the-extraordinary-of-bitpower-loop-94g |
1️⃣ Smart contract guarantee: All transactions are automatically executed by smart contracts to ensure security and transparency.
2️⃣ Decentralized lending: No third-party intermediary is required, reducing costs a... | kjask_jklshd_cecbd37d6d57 | |
1,904,409 | How to Train Your Workforce for the Construction Technologies of Tomorrow | Discover how to equip your construction workforce with the skills they need to thrive in a technology-driven future! | 0 | 2024-06-28T15:25:28 | https://www.govcon.me/blog/how_to_train_your_workforce_for_the_construction_technologies_of_tomorrow | construction, technology, workforcedevelopment | # How to Train Your Workforce for the Construction Technologies of Tomorrow
As technology continues to revolutionize industries across the globe, the construction sector is no exception. The advent of Building Information Modeling (BIM), drones, augmented reality (AR), and artificial intelligence (AI) are reshaping th... | quantumcybersolution |
1,904,408 | First Contributions: learn how to contribute to open source projects | I followed the hands-on tutorial in the Readme of first contributions and made my first pull request... | 0 | 2024-06-28T15:24:59 | https://dev.to/ugreeen/first-contributions-learn-how-to-contribute-to-open-source-projects-32a8 | opensource, beginners, tutorial | I followed the hands-on tutorial in the Readme of first contributions and made my first pull request to the same repo.
{% embed https://github.com/firstcontributions/first-contributions %} | ugreeen |
1,904,394 | The Ultimate Guide to XML Code Formatter: Streamlining Your Data Management | https://ovdss.com/apps/xml-code-formatter Introduction to XML Extensible Markup Language (XML) is a... | 0 | 2024-06-28T15:18:01 | https://dev.to/johnalbort12/the-ultimate-guide-to-xml-code-formatter-streamlining-your-data-management-39ea | ERROR: type should be string, got "\n\n\n\n\n\n\nhttps://ovdss.com/apps/xml-code-formatter\n\n\nIntroduction to XML\nExtensible Markup Language (XML) is a widely-used format for encoding documents in a way that is both human-readable and machine-readable. XML is commonly used in web services, configuration files, and data storage, making it an essential tool for developers and data analysts.\n\nThe Importance of XML Formatting\nProperly formatted XML is crucial for ensuring that your data is easy to read, maintain, and debug. An XML code formatter is a tool that automatically organizes your XML code, making it cleaner and more structured. In this post, we'll explore the key features of an XML code formatter and how it can enhance your workflow.\n\n\nKey Features of an XML Code Formatter\n\n1. Instant Formatting\nOne of the standout features of a good XML code formatter is instant formatting. With just a click, your XML code is transformed from a jumbled mess into a neatly organized document. This feature saves time and reduces the effort needed to manually format code, allowing you to focus on more important tasks.\n\n2. User-Friendly Interface\nA user-friendly interface is essential for any tool to be effective. The best XML code formatters have intuitive designs that make it easy for users of all skill levels to navigate. Whether you're a seasoned developer or a beginner, a simple and clear interface ensures that you can quickly format your XML without any hassle.\n3. Optimized for Performance\nPerformance is key when dealing with large XML files. An XML code formatter optimized for performance can handle extensive documents without slowing down your workflow. Efficient algorithms and streamlined processes ensure that your files are formatted quickly and accurately, regardless of their size.\n4. Free and Accessible\nAccessibility is important, especially for individual developers and small teams. A free and accessible XML code formatter ensures that you can take advantage of its features without worrying about costs. Many high-quality XML code formatters are available online at no charge, making them an excellent resource for anyone working with XML.\n5. Customizable Settings\nEvery project has unique requirements, and a one-size-fits-all approach doesn't always work. XML code formatters with customizable settings allow you to tailor the formatting to meet your specific needs. Whether it's adjusting indentation, managing whitespace, or configuring tag attributes, customizable settings provide the flexibility you need for optimal results.\n\n\nHow to Use an XML Code Formatter\nUsing an XML code formatter is straightforward. Here are some steps to get you started:\nChoose Your Tool: Select an XML code formatter that fits your needs. Popular options include online tools like Code Beautify and Pretty Print, as well as IDE plugins for Visual Studio Code and IntelliJ IDEA.\nPaste Your XML Code: Copy your unformatted XML code and paste it into the formatter tool.\nAdjust Settings: If your formatter offers customizable settings, adjust them according to your preferences.\nFormat the Code: Click the format button and watch as your XML code is instantly transformed.\nReview and Use: Review the formatted code to ensure it meets your requirements, then copy and use it in your project.\n\nConclusion\nAn XML code formatter is an indispensable tool for anyone working with XML. With features like instant formatting, a user-friendly interface, performance optimization, free accessibility, and customizable settings, it greatly enhances your ability to manage and maintain XML documents. Incorporate an XML code formatter into your workflow to experience the benefits of clean, readable, and well-organized code.\n\n" | johnalbort12 | |
1,904,407 | Top 10 Strategies for Winning Federal Government Contracts | Unlock the secrets to securing federal government contracts with these top 10 strategies designed to make your proposals stand out and win. | 0 | 2024-06-28T15:24:44 | https://www.govcon.me/blog/top_10_strategies_for_winning_federal_government_contracts | governmentcontracts, businessstrategy, techinnovation | # Top 10 Strategies for Winning Federal Government Contracts
Securing federal government contracts can be a game-changer for businesses, offering a reliable revenue stream and significant growth opportunities. However, navigating the complex landscape of government procurement can be daunting. Fear not! We've dis... | quantumcybersolution |
1,904,406 | BitPower: A revolutionary force that reshapes finance | In an infinite digital world, BitPower shines like a star. It is not just a platform, but also a... | 0 | 2024-06-28T15:24:26 | https://dev.to/pingc_iman_034e9f20936ef4/bitpower-a-revolutionary-force-that-reshapes-finance-np0 |

In an infinite digital world, BitPower shines like a star. It is not just a platform, but also a revolutionary force that re-empowers the public with financial power. BitPower's advantages are like a sharp sword th... | pingc_iman_034e9f20936ef4 | |
1,904,404 | Calculus 1 The Foundations of Mathematics | Calculus 1 is a challenging but essential course that covers limits, derivatives, and integrals, and is a critical foundation for students who plan to study engineering, science, or mathematics. | 0 | 2024-06-28T15:22:23 | https://www.rics-notebook.com/blog/Math/Calc1 | calculus, mathematics, education | - **Introduction**
Calculus 1 is a foundational course in mathematics that covers limits,
derivatives, and integrals. It is a challenging course, but it is also an
essential one for students who plan to study engineering, science, or
mathematics.
- **Important lessons learned**
There are many important lessons that ... | eric_dequ |
1,904,395 | The Role of Independent Contractors in Government Projects Advantages Challenges and Best Practices | Understand the advantages and challenges of using independent contractors in government projects, including compliance considerations and tips for managing contractor relationships. | 0 | 2024-06-28T15:19:37 | https://www.govcon.me/blog/the_role_of_independent_contractors_in_government_projects_advantages_challenges_and_best_practices | governmentcontracting, independentcontractors, compliance, contractormanagement | # The Role of Independent Contractors in Government Projects: Advantages, Challenges, and Best Practices
Government contracting presents numerous opportunities and a dynamic environment for independent contractors. As public sector projects grow increasingly complex, government agencies often turn to independent contr... | quantumcybersolution |
1,904,385 | Mermaid Markdown | Using ChatGPT and Mermaid to Create System Architecture Diagrams | 0 | 2024-06-28T15:12:09 | https://www.rics-notebook.com/blog/Markdown/mermaid | markdown, documentation, mermaid | # Tutorial: Using ChatGPT and Mermaid to Create System Architecture Diagrams
## Introduction 📚
System architecture diagrams are a powerful tool for visualizing the components of a system and how they interact with each other. They can be used to communicate complex ideas to stakeholders, developers, and other techni... | eric_dequ |
1,904,392 | Benfords Law Unraveling the Secrets of Digits in the Digital Age | Discover the power of Benfords Law, a fascinating statistical principle that unveils hidden patterns in digits. | 0 | 2024-06-28T15:17:16 | https://www.rics-notebook.com/blog/Math/BenfordsLaw | datascience, fraud, ai | ## Benford's Law: Unraveling the Secrets of Digits in the Digital Age 🔍🌐
In the vast realm of mathematics, there exists a surprising and counterintuitive principle known as Benford's Law. This statistical phenomenon has far-reaching applications, from exposing financial fraud to ensuring the integrity of A... | eric_dequ |
1,904,391 | Data Warehousing and Analytics with Amazon Redshift | Data Warehousing and Analytics with Amazon Redshift In today's data-driven world,... | 0 | 2024-06-28T15:16:23 | https://dev.to/virajlakshitha/data-warehousing-and-analytics-with-amazon-redshift-31n5 | 
# Data Warehousing and Analytics with Amazon Redshift
In today's data-driven world, businesses need to extract meaningful insights from vast amounts of data. This is where data warehousing comes into play, providing a centralized r... | virajlakshitha | |
1,904,390 | How to Optimize Construction Project Schedules with Technology | Dive into the innovative tech tools transforming construction project scheduling, ensuring efficiency, reduced costs, and timely project completion. | 0 | 2024-06-28T15:15:20 | https://www.govcon.me/blog/how_to_optimize_construction_project_schedules_with_technology | construction, technology, projectmanagement | # How to Optimize Construction Project Schedules with Technology
In the bustling world of construction, managing schedules has always been a daunting task. However, with the rapid advancement in technology, the industry is witnessing a transformational shift, paving the way for optimized project management and executi... | quantumcybersolution |
1,904,368 | Why DeFi Protocols Should Migrate from Push Oracles to Pull Oracles: A Case for the Pyth Network | Introduction In the dynamic world of decentralized finance (DeFi), oracles play a crucial... | 0 | 2024-06-28T15:14:43 | https://dev.to/skandesh_304185c05025ba6c/why-defi-protocols-should-migrate-from-push-oracles-to-pull-oracles-a-case-for-the-pyth-network-522l | oracle, defi, blockchain, web3 | ##Introduction
In the dynamic world of decentralized finance (DeFi), oracles play a crucial role in bridging the gap between blockchain systems and real-world data. With the rapid evolution of DeFi, the need for accurate, timely, and reliable data has never been more critical. Traditionally, push oracles have been the... | skandesh_304185c05025ba6c |
1,904,384 | Is pixel-perfect front-end development still a thing? | Pixel-perfect front-end often sparks heated debates among developers. How come? While some view it as... | 0 | 2024-06-28T15:11:47 | https://dev.to/momciloo/is-pixel-perfect-front-end-development-still-a-thing-1ban | Pixel-perfect front-end often sparks heated debates among developers. How come? While some view it as a relic of the past, others view it as a crucial quality standard. Clearly, pixel-perfect has become a more popular goal with the advent of new tools and libraries.
However, the question remains: Does pixel-perfect st... | momciloo |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.