hexsha stringlengths 40 40 | size int64 5 1.04M | ext stringclasses 6 values | lang stringclasses 1 value | max_stars_repo_path stringlengths 3 344 | max_stars_repo_name stringlengths 5 125 | max_stars_repo_head_hexsha stringlengths 40 78 | max_stars_repo_licenses listlengths 1 11 | max_stars_count int64 1 368k ⌀ | max_stars_repo_stars_event_min_datetime stringlengths 24 24 ⌀ | max_stars_repo_stars_event_max_datetime stringlengths 24 24 ⌀ | max_issues_repo_path stringlengths 3 344 | max_issues_repo_name stringlengths 5 125 | max_issues_repo_head_hexsha stringlengths 40 78 | max_issues_repo_licenses listlengths 1 11 | max_issues_count int64 1 116k ⌀ | max_issues_repo_issues_event_min_datetime stringlengths 24 24 ⌀ | max_issues_repo_issues_event_max_datetime stringlengths 24 24 ⌀ | max_forks_repo_path stringlengths 3 344 | max_forks_repo_name stringlengths 5 125 | max_forks_repo_head_hexsha stringlengths 40 78 | max_forks_repo_licenses listlengths 1 11 | max_forks_count int64 1 105k ⌀ | max_forks_repo_forks_event_min_datetime stringlengths 24 24 ⌀ | max_forks_repo_forks_event_max_datetime stringlengths 24 24 ⌀ | content stringlengths 5 1.04M | avg_line_length float64 1.14 851k | max_line_length int64 1 1.03M | alphanum_fraction float64 0 1 | lid stringclasses 191 values | lid_prob float64 0.01 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
4cee4468f75af4c01d09f9b3ed3becc37038fb11 | 8,994 | md | Markdown | README.md | jloveric/functional-layers | 5ca4efbf842f290b62ad4cc2c0045438402f71b8 | [
"MIT"
] | null | null | null | README.md | jloveric/functional-layers | 5ca4efbf842f290b62ad4cc2c0045438402f71b8 | [
"MIT"
] | null | null | null | README.md | jloveric/functional-layers | 5ca4efbf842f290b62ad4cc2c0045438402f71b8 | [
"MIT"
] | null | null | null | 
# Piecewise Polynomial and Fourier Layers in PyTorch
This is a PyTorch implementation of my tensorflow [repository](https://github.com/jloveric/high-order-layers) and is more complete due to the flexibility of PyTorch.
Lagrange Polynomial, Piecewise Lagrange Polynomial, Discontinuous Piecewise Lagrange Polynomial, Fourier Series, sum and product layers in PyTorch. The sparsity of using piecewise polynomial layers means that by adding new segments the representational power of your network increases, but the time to complete a forward step remains constant. Implementation includes simple fully connected layers, convolution layers and deconvolutional layers using these models. This is a PyTorch implementation of this [paper](https://www.researchgate.net/publication/276923198_Discontinuous_Piecewise_Polynomial_Neural_Networks) including extension to Fourier Series and convolutional neural networks.
## Idea
The idea is extremely simple - instead of a single weight at the synapse, use n-weights. The n-weights describe a piecewise polynomial (or other complex function) and each of the n-weights can be updated independently. A Lagrange polynomial and Gauss Lobatto points are used to minimize oscillations of the polynomial. The same approach can be applied to any "functional" synapse, and I also have Fourier series synapses in this repo as well. This can be implemented as construction of a polynomial or Fourier kernel followed by a standard pytorch layer where a linear activation is used.
In the image below each "link" instead of being a single weight, is a function of both x and a set of weights. These functions can consist of an orthogonal basis functions for efficient approximation.
<img src="plots/NetworkZoom.png" width=50% height=50% style="display: block; margin: 0 auto">
## Why
Using higher order polynomial representations might allow networks with much fewer total weights. In physics, higher order methods
can be much more efficient. Spectral and discontinuous galerkin methods are examples of this. Note that a standard neural network with relu activations is piecewise linear. Here there are no bias weights and the "non-linearity" is in the synapse.
In addition, it's well known that the dendrites are also computational units in neurons, for example [Dendritic action potentials and computation in human layer 2/3 cortical neurons](https://science.sciencemag.org/content/367/6473/83) and this is a simple way to add more computational power into the artificial neural network model. In addition it's been shown that a single pyramidal has the same computational capacity as a 5 to 8 layer convolutional NN, [Single cortical neurons as deep artificial neural networks](https://www.sciencedirect.com/science/article/abs/pii/S0896627321005018?dgcid=author)
## A note on the unit
The layers used here do not require additional activation functions and use a simple sum or product in place of the activation. Product is performed in this manner
$$ product=-1+\prod_{i}(1 + f_{i})+(1-\alpha)\sum_{i}f_{i} $$
The 1 is added to each function output to as each of the sub products is also computed. The linear part is controlled by
the alpha parameter.
# Fully Connected Layer Types
All polynomials are Lagrange polynomials with Chebyshev interpolation points.
A helper function is provided in selecting and switching between these layers
```python
from high_order_layers_torch.layers import *
layer1 = high_order_fc_layers(
layer_type=layer_type,
n=n,
in_features=784,
out_features=100,
segments=segments,
alpha=linear_part
)
```
where `layer_type` is one of
| layer_type | representation
|--------------------|-------------------------|
|continuous | piecewise polynomial using sum at the neuron |
|continuous_prod | piecewise polynomial using products at the neuron |
|discontinuous | discontinuous piecewise polynomial with sum at the neuron|
|discontinuous_prod | discontinous piecewise polynomial with product at the neuron|
|polynomial | single polynomial (non piecewise) with sum at the neuron|
|polynomial_prod | single polynomial (non piecewise) with product at the neuron|
|product | Product |
|fourier | fourier series with sum at the neuron |
`n` is the number of interpolation points per segment for polynomials or the number of frequencies for fourier series, `segments` is the number of segments for piecewise polynomials, `alpha` is used in product layers and when set to 1 keeps the linear part of the product, when set to 0 it subtracts the linear part from the product.
## Product Layers
Product layers
# Convolutional Layer Types
```python
conv_layer = high_order_convolution_layers(layer_type=layer_type, n=n, in_channels=3, out_channels=6, kernel_size=5, segments=segments, rescale_output=rescale_output, periodicity=periodicity)
```
All polynomials are Lagrange polynomials with Chebyshev interpolation points.
| layer_type | representation |
|--------------|----------------------|
|continuous(1d,2d) | piecewise continuous polynomial
|discontinuous(1d,2d) | piecewise discontinuous polynomial
|polynomial(1d,2d) | single polynomial
|fourier(1d,2d) | fourier series convolution
# Installing
## Installing locally
This repo uses poetry, so run
```
poetry install
```
and then
```
poetry shell
```
## Installing from pypi
```bash
pip install high-order-layers-torch
```
or
```
poetry add high-order-layers-torch
```
# Examples
## Simple function approximation
Approximating a simple function using a single input and single output (single layer) with no hidden layers
to approximate a function using continuous and discontinuous piecewise polynomials (with 5 pieces) and simple
polynomials and fourier series. The standard approach using ReLU is non competitive. To see more complex see
the implicit representation page [here](https://github.com/jloveric/high-order-implicit-representation).




## XOR : 0.5 for x*y > 0 else -0.5
Simple XOR problem using the standard network structure (2 inputs 2 hidden 1 output) this will also work with no hidden layers. The function is discontinuous along the axis and we try and fit that function. Using piecewise discontinuous layers the model can match the function exactly.

With piecewise continuous it doesn't work quite as well.

Polynomial doesn't work well at all (expected).

## MNIST (convolutional)
```python
python examples/mnist.py max_epochs=1 train_fraction=0.1 layer_type=continuous n=4 segments=2
```
## CIFAR100 (convolutional)
```
python examples/cifar100.py -m max_epochs=20 train_fraction=1.0 layer_type=polynomial segments=2 n=7 nonlinearity=False rescale_output=False periodicity=2.0 lr=0.001 linear_output=False
```
## Variational Autoencoder
Still a WIP. Does work, but needs improvement.
```
python examples/variational_autoencoder.py -m max_epochs=300 train_fraction=1.0
```
run with nevergrad for parameter tuning
```
python examples/variational_autoencoder.py -m
```
## Invariant MNIST (fully connected)
Without polynomial refinement
```python
python examples/invariant_mnist.py max_epochs=100 train_fraction=1 layer_type=polynomial n=5 p_refine=False
```
with polynomial refinement (p-refinement)
```
python examples/invariant_mnist.py max_epochs=100 train_fraction=1 layer_type=continuous n=2 p_refine=False target_n=5 p_refine=True
```
## Implicit Representation
An example of implicit representation for image compression, language generation can be found [here](https://github.com/jloveric/high-order-implicit-representation). I intend to explore generative models in natural language further [here](https://github.com/jloveric/language-interpolation)
## PDEs in Fluid Dynamics
An example using implicit representation to solve hyperbolic (nonlinear) wave equations can be found [here](https://github.com/jloveric/neural-network-pdes)
## Natural Language Generation
Examples using these networks for natural language generation can be found
[here](https://github.com/jloveric/language-interpolation)
## Test and Coverage
After installing and running
```
poetry shell
```
run
```
pytest
```
for coverage, run
```
coverage run -m pytest
```
and then
```
coverage report
```
## Reference
```
@misc{Loverich2020,
author = {Loverich, John},
title = {High Order Layers Torch},
year = {2020},
publisher = {GitHub},
journal = {GitHub repository},
howpublished = {\url{https://github.com/jloveric/high-order-layers-torch}},
}
``` | 44.088235 | 692 | 0.779186 | eng_Latn | 0.989338 |
4cee71b9f8a532e6b262267df1f80d91915743bd | 227 | md | Markdown | _cremerie/faisselle-vache.md | gourmandignes/amap | e63ab6ec2bd44f342ca43148915b993ccbd51a66 | [
"MIT"
] | null | null | null | _cremerie/faisselle-vache.md | gourmandignes/amap | e63ab6ec2bd44f342ca43148915b993ccbd51a66 | [
"MIT"
] | 1 | 2020-06-11T08:29:00.000Z | 2020-06-11T08:29:00.000Z | _cremerie/faisselle-vache.md | gourmandignes/amap | e63ab6ec2bd44f342ca43148915b993ccbd51a66 | [
"MIT"
] | null | null | null | ---
categorie: Crèmerie
nom: Faisselle 200 g
prix: 1,50 €
description: >
faisselle de vache
producteur: Jarouilles
contrats: produits-laitiers
tags:
- produit laitier
- faisselle
---
 | 16.214286 | 36 | 0.731278 | fra_Latn | 0.779133 |
4cee7207afe921a2ee2cd110d6dcf62d57accc0d | 134 | md | Markdown | README.md | shivanshu-semwal/competitive-programming | b1c7fe1f9d5807fff47890267cc9936c9ff95f58 | [
"MIT"
] | 1 | 2021-09-24T03:57:42.000Z | 2021-09-24T03:57:42.000Z | README.md | shivanshu-semwal/competitive-programming | b1c7fe1f9d5807fff47890267cc9936c9ff95f58 | [
"MIT"
] | null | null | null | README.md | shivanshu-semwal/competitive-programming | b1c7fe1f9d5807fff47890267cc9936c9ff95f58 | [
"MIT"
] | null | null | null | # Competitive Programming Solutions
<img src="./assets/main.jpg" />
This repo contains some of my competitive programming solutions. | 26.8 | 64 | 0.783582 | eng_Latn | 0.988737 |
4ceeb4096c4ff21f6b21cfa1fe1ad6a6ed3d9705 | 1,529 | md | Markdown | packages/immdux-core/docs/classes/actionobservable.md | lithic-io/immdux | 21fe9ff3cbfbdb6ea36fb16d74bdbfdb49aa435b | [
"MIT"
] | null | null | null | packages/immdux-core/docs/classes/actionobservable.md | lithic-io/immdux | 21fe9ff3cbfbdb6ea36fb16d74bdbfdb49aa435b | [
"MIT"
] | 20 | 2019-11-10T23:03:41.000Z | 2022-02-12T17:45:04.000Z | packages/immdux-core/docs/classes/actionobservable.md | lithic-io/immdux | 21fe9ff3cbfbdb6ea36fb16d74bdbfdb49aa435b | [
"MIT"
] | 1 | 2019-11-10T22:33:28.000Z | 2019-11-10T22:33:28.000Z | [@immdux/core](../README.md) › [ActionObservable](actionobservable.md)
# Class: ActionObservable <**A**>
The `ActionObservable` is a simple observable that emits actions.
Actions are emitted after state observables. This makes the
action observable useful for scheduling updates.
```ts
import { Observable, combineLatest } from 'rxjs';
import { sample } from 'rxjs/operators';
import { action$, state$ } from '@immdux/core';
interface ChatError {}
interface ChatMessage {}
interface User {}
type ChatObservable = Observable<[ChatError, ChatMessage[], User]>;
const chatError$ = state$.in(['chat', 'error']);
const chatMessages$ = state$.in(['chat', 'messages']);
const usersOnline$ = state$.in(['session', 'users', 'onlineList']);
const chat$: ChatObservable = combineLatest(
chatError$,
chatMessages,
usersOnline$,
).pipe(sample(action$));
```
**`param`**
One or more strings or regex statements used to filter actions by type.
## Type parameters
▪ **A**: *[AnyAction](../interfaces/anyaction.md)*
## Hierarchy
* Observable‹A›
↳ **ActionObservable**
## Implements
* Subscribable‹A›
## Index
### Constructors
* [constructor](actionobservable.md#constructor)
## Constructors
### <a id="constructor" name="constructor"></a> constructor
\+ **new ActionObservable**(...`types`: string | RegExp[]): *[ActionObservable](actionobservable.md)*
*Overrides void*
**Parameters:**
Name | Type |
------ | ------ |
`...types` | string | RegExp[] |
**Returns:** *[ActionObservable](actionobservable.md)*
| 22.15942 | 101 | 0.690647 | yue_Hant | 0.332292 |
4cef65872aa096432347d1678660861e0ffd55b8 | 2,140 | md | Markdown | content/book/selected-flowers-of-evil.md | theNewDynamic/hugo-controllers-panic | c53e05501f721534d159c41b38852df89115f636 | [
"MIT"
] | null | null | null | content/book/selected-flowers-of-evil.md | theNewDynamic/hugo-controllers-panic | c53e05501f721534d159c41b38852df89115f636 | [
"MIT"
] | null | null | null | content/book/selected-flowers-of-evil.md | theNewDynamic/hugo-controllers-panic | c53e05501f721534d159c41b38852df89115f636 | [
"MIT"
] | 1 | 2021-02-26T11:40:56.000Z | 2021-02-26T11:40:56.000Z | ---
title: "Flowers of Evil: A Selection"
subtitle:
date: 1958-01-01T06:00:00.000Z
series:
genre: "poetry"
subgenre:
language: French
authors:
- author/charles-baudelaire.md
translators:
- author/christopher-mattison.md
editors:
- author/jackson-mathews.md
- author/marthiel-mathews.md
contributors:
editions:
- binding: paperback
isbn: 9780811200066
date: 1958-01-01T06:00:00.000Z
description: ""
trim_size: ""
page_count: ""
sales_data:
forsale: true
saleprice:
shipping_weight:
price_us: 12.95
price_cn:
contributors:
cover_image: "/Flowers_of_Evil__A_Selection.jpg"
- binding: ebook
isbn: 9780811221566
date: 1958-01-01T06:00:00.000Z
description: ""
trim_size: ""
page_count: ""
sales_data:
forsale: true
saleprice:
shipping_weight:
price_us: 12.95
price_cn:
contributors:
cover_image: "/Flowers_of_Evil__A_Selection.jpg"
featured_image:
file:
draft: false
_slug: selected-flowers-of-evil
---
Baudelaire’s _Les_ _Fleurs du Mal_, which in successive editions contained all of his published poems, has for over a hundred years now opened new vistas for man’s imagination and quickened the sensibilities of poets everywhere. The greatest French poet of the 19th century, Baudelaire was also the first truly modern poet, and his direct and indirect influence on the literature of our time has been immeasurable.
Here in this volume are selections from _Les __Fleurs du Mal_ as chosen by Marthiel and Jackson Mathews from their complete bilingual edition published by New Directions in 1955 — “undoubtedly the best single collection of Baudelaire’s verse in English” (_St. Louis Post Dispatch_).
_Flowers of Evil: A Selection_ contains fifty-three poems which the Mathews feel best represent the total work and which have been most successfully rendered into English. The French texts as established by Yves Gerard Le Dantec for the Pleiade edition are printed en face. Included are Baudelaire’s “Three Drafts of a Preface” and brief notes on the nineteen translators whose works is represented.
| 36.271186 | 415 | 0.748131 | eng_Latn | 0.988799 |
4cef72900e7d3f1f2211a41c6363c0ec9a7f2771 | 626 | md | Markdown | node_modules/salesforce-signed-request/README.md | avinashkothagit/Org1Chart | dabfbd408a24ab82e03035979dac3836822478f7 | [
"Apache-2.0"
] | null | null | null | node_modules/salesforce-signed-request/README.md | avinashkothagit/Org1Chart | dabfbd408a24ab82e03035979dac3836822478f7 | [
"Apache-2.0"
] | 1 | 2020-03-23T11:00:53.000Z | 2020-03-23T11:00:53.000Z | node_modules/salesforce-signed-request/README.md | avinashkothagit/Org1Chart | dabfbd408a24ab82e03035979dac3836822478f7 | [
"Apache-2.0"
] | null | null | null | ### A simple Salesforce Canvas signed-request decoder
<p align="center">

### Usage
This library exports a single function to `decode` the signed request.
```javascript
var decode = require('signed-request');
//json will have Salesforce context
var json = decode('YOUR_SIGNED_REQUEST', 'API_SECRET');
```
### Test
1. Install Mocha, expect, chai & should by running `npm install`
2. You may want to install Mocha globally by running `npm install -g mocha`
2. Simply run `mocha` in the command line.
### License
MIT | 22.357143 | 94 | 0.72524 | eng_Latn | 0.895628 |
4cefa026944f45089ece51ca116a83c72ce38dea | 4,913 | md | Markdown | _posts/2008-01-22-%eb%8b%b9%ec%8b%a0%eb%93%a4%ec%9d%98-%ec%98%88%ec%88%98%eb%8a%94-%ec%84%b8%ec%83%81%ec%97%90-%ec%97%86%eb%8b%a4-%ec%98%a4%ea%b0%95%eb%82%a8-%ec%98%88%ec%88%98%eb%8a%94-%ec%97%86%eb%8b%a4-2003.md | johngrib/harryyang1982.github.io | e775dfd4df4341cd8e9503c027b680a4db1ff1d1 | [
"MIT"
] | null | null | null | _posts/2008-01-22-%eb%8b%b9%ec%8b%a0%eb%93%a4%ec%9d%98-%ec%98%88%ec%88%98%eb%8a%94-%ec%84%b8%ec%83%81%ec%97%90-%ec%97%86%eb%8b%a4-%ec%98%a4%ea%b0%95%eb%82%a8-%ec%98%88%ec%88%98%eb%8a%94-%ec%97%86%eb%8b%a4-2003.md | johngrib/harryyang1982.github.io | e775dfd4df4341cd8e9503c027b680a4db1ff1d1 | [
"MIT"
] | null | null | null | _posts/2008-01-22-%eb%8b%b9%ec%8b%a0%eb%93%a4%ec%9d%98-%ec%98%88%ec%88%98%eb%8a%94-%ec%84%b8%ec%83%81%ec%97%90-%ec%97%86%eb%8b%a4-%ec%98%a4%ea%b0%95%eb%82%a8-%ec%98%88%ec%88%98%eb%8a%94-%ec%97%86%eb%8b%a4-2003.md | johngrib/harryyang1982.github.io | e775dfd4df4341cd8e9503c027b680a4db1ff1d1 | [
"MIT"
] | 1 | 2020-01-11T12:16:38.000Z | 2020-01-11T12:16:38.000Z | ---
id: 59
title: '‘당신들의 예수’는 세상에 없다 – (오강남, <예수는 없다>, 2003, 현암사)'
date: 2008-01-22T11:06:54+00:00
author: admin
layout: post
guid: http://flyhendrixfly.net/?p=59
permalink: '/2008/01/22/%eb%8b%b9%ec%8b%a0%eb%93%a4%ec%9d%98-%ec%98%88%ec%88%98%eb%8a%94-%ec%84%b8%ec%83%81%ec%97%90-%ec%97%86%eb%8b%a4-%ec%98%a4%ea%b0%95%eb%82%a8-%ec%98%88%ec%88%98%eb%8a%94-%ec%97%86%eb%8b%a4-2003/'
views:
- "288"
mytory_md_visits_count:
- "62"
image: /wp-content/uploads/1/ek060000000000.gif
---
<DIV class=ttbReview>
<TABLE>
<br /> <br />
<TR>
<br />
<TD>
<A href="http://www.aladdin.co.kr/shop/wproduct.aspx?ISBN=8932311102&ttbkey=ttbpanic822253001©Paper=1"><IMG alt="" src="http://image.aladdin.co.kr/cover/cover/8932311102_1.gif" border=0></A>
</TD>
<br /> <TD style="VERTICAL-ALIGN: top" align=left><A class=aladdin_title href="http://www.aladdin.co.kr/shop/wproduct.aspx?ISBN=8932311102&ttbkey=ttbpanic822253001©Paper=1"><FONT color=#000000>예수는 없다</FONT></A> – <IMG alt=10점 src="http://image.aladdin.co.kr/img/common/star_s10.gif" border=0><br />오강남 지음/현암사</TD>
</TR>
</TABLE></DIV>
어느 순간, ‘한국인’의 민족신이 되어버린 예수. 그런 예수는 세상에 없다.
어느 순간, 한큐에 그가 우리를 위해서 대신 죽었다는 것만 알면, 구원받았다 이야기할 수 있는 예수. 그런 예수는 세상에 없다.
어느 순간, 하나님의 아들로 절대적인 신이 되어버린 예수, 그런 예수는 세상에 없다.
수십년 동안, 종교를 연구한, 기독교의 섭리에 대해서 인정하고 믿는 종교학자가 낸 결론이다. 그가 본 한국의 ‘기독교’의 신앙은 간단하다.
어린아이가 말하는 “우리 아빠가 세상에서 가장 위대한 사람이야”라는 식의 유아적 발상이라는 것이다. 어린아이가 그렇게 말하는 것에 대해서 그걸 듣는 엄마는 “맞아, 아빠가 세상에서 최고야!”라고 대답해 줄테지만, 그 아이가 20살이 되어서도 똑같은 말을 한다면, 그는 유아적 사고에서 빠져나오지 못한 성장이 되지 않은 인간이 되는 것이다.
하지만 이 정도 수준의 문제라면, 큰 문제가 아니지만, 그가 기실 “우리 아빠가 최고”가 아니라는 사실을 생활에서 밀접하게 발견하고도, 우기면서 다른 사람에게 “우리 아빠가 최고”라는 사실을 믿으라고 강요하고 다니면 이 것은 곧바로 사회적 문제까지로 진화할 수 있는 것이다.
한국의 기독교는 그 수준을 벗어나야 한다.
다른 아빠들도 그들 나름에게는 최고 일 수 있다는 것을 인정해야하고, 내가 자라서 어떤 아빠가 되어야할 지, 어떤 엄마가 되어야할 지도 고민해 봐야 하는 것이다.
비유적 표현이 많지만, 그것이 예화로 쉽게 풀어져 있기 때문에 다가가기 쉬운, 우리의 예수에 대한 편견을, 기독교에 대한 편견을 한번 깨주는 책이라 할 수 있겠다.
이런 편견을 깨려는 이들에게 ‘빨갱이’, 혹은 ‘신신학’의 굴레를 씌우고 있지만, 기실 이런 배타적인 태도는 한국에서만 절대적일 뿐, 다른 나라에서는 그리 큰 경향이 아닌 ‘근본주의적 이해’일 뿐이다.
그리고 기독교를 ‘유일신’이라 생각하는 태도를 갖고 있다 말하지만, 기실 우리가 알고 있는 ‘유일신’을 믿는 종교로서의 기독교는 허구이다. 왜냐면, 김경재 목사등도 비판하고 있지만, 진정 유일신을 믿는다면, 다른 이신과 대적하는 신관을 갖는 것이 아니라, 오히려 그 신들도 하나님의 ‘속성’임으로 받아들여야 하기 때문이다. 따라서 종교적 다원주의를 갖는 다는 것은, 기독교의 관점을 ‘놓고’ 다른 종교를 받아들이는 ‘이단적 행위’가 아니라 하나님의 뜻을 어떤 식으로 볼 것인지에 대한 문제에 대한 ‘수용적 태도’가 되는 것이다. 그렇기 때문에 타종교를 기독교 인이 읽어야 함도 당연하다는 결론을 저자는 도출한다.
또 하나 그의 공박이 강한 부분은, 성서를 바라보는 관점이다. ‘축자무오설’ 하도 많이 쓰는 말이지만, 성경에 쓰여진 기록들은 하나님의 역사에 의해서 그 영감대로 기록되었다고 주장하는 말인데, 우리는 그것을 문자 그대로 받아들이는 순간, 모순에 빠질 수밖에 없다. 예를 들면, 예수의 계보가 누가복음과 마태복음에서 다르다는 이야기도 가능하며, 또 노아의 방주를 실제로 구현해 보려는 데에서도 불가능 하다는 것에서도 알 수 있듯이, 기실 성서는 그 당대의 ‘고백적’ 언어였거나, 당시의 민족의 세계관의 투영이다. 그것들을 문자 그대로 읽고, 그대로 따르려면, 우리는 우선 노예제도를 살려내야 하고, 다시금 이민족을 정벌해야하며, 여성들을 강단에서 내려야 하고, ‘처녀’가 아닌 여자를 그대로 돌로 쳐 죽여야 하게 된다. 결국, 그렇게 하지 않고 있는 현실과 그 해석. 모순에 빠지는 것이다.
궁극적으로 책은, ‘종교’가 주는 의미에 대해서 환기시키고, ‘종교를 믿는 것’에 대해서 이야기를 하게 된다. 그것들은 개인에게 있어서의 영성의 의미와, 종교가 사회에서 가지는 역할에 대한 이야기를 할 수밖에 없게 된다.
하지만, 자꾸 그것들에 대해서는 피해가고, 교조적인 신앙들이 ‘신학’없이 논의 없이 우리들에게 흘러가고 있기에 ‘기독교’ 자체가 황폐해지는 것이다.
많은 참고문헌들과 읽을 꺼리들을 던져주는 점이 유익하고, 생각할 바를 남겨준다.
결국 우리에게 중요한 것에 대한 저자의 생각이 드러난다.
<DIV class=dotbox>
<TABLE style="TABLE-LAYOUT: fixed; FONT-SIZE: 9pt; COLOR: #555555; WORD-BREAK: break-all; BORDER-COLLAPSE: collapse" cellSpacing=0 cellPadding=0 width="100%" border=0>
<TD width=18 height=18><IMG height=18 alt="" src="http://blog.aladdin.co.kr/fckeditor/editor/Images/quote_start.gif" width=18></TD>
<TD width=18> </TD>
<TD width=18> </TD>
<TD width=18> </TD>
<TD width=18> </TD>
<TD width=18 height=18><IMG height=18 alt="" src="http://blog.aladdin.co.kr/fckeditor/editor/Images/quote_end.gif" width=18></TD></TABLE></DIV>
하지만 몇 가지 부분은 모호한데, 사회적 의미에 대해서 그는 규정하기를 피하고 싶어하는 듯하다는 것에 좀 문제가 있다. 그는 예수를 ‘사람에 대한 애정’을 가졌다고 하지만, 내가 볼 때, 그리고 ‘역사적 예수’ 논의들을 볼 때, 예수는 단순한 보편자로서의 인간을 사랑한 것이 아니라 ‘억압받은 자들’로 분명히 그 범주를 축소하고 있었다는 점을 강조할 수밖에 없다. 그 점을 벗어난 다면, ‘예수’에 대한 논의는 다시금 구름위로 떠오르고 지상으로 내려오지 않는다. 그 상황에서의 종교는 맑스가 말한 ‘인민의 아편’ 밖에 안된다. 처절한 환경에서의 위로밖에 되지 않는 것이다.
그리고 하나 더는 관점의 차이겠지만, 그의 말속에 들어있는 민족주의적 입장들이라는 것들이 가다듬어지지 않은 채 그냥 쉽게 쓰인다는 점이다. 차라리 정교하게 ‘민족’과 ‘겨레’에 대해서 구체적인 메시지를 준다면 모를까, 그냥 통상 대통령이 국민에게 ‘사랑합니다’하듯, 사용된다는 점은 엄밀성에 대해서 물음표를 던지게 하며, 김진홍 목사에 대한 평가도 이 시점에는 다시 해봐야 한다는 생각이다.
하지만 이런 ‘먹물들의’ 이야기를 떠나서도, 이 책은 기존의 근본주의적인 ‘철부지’ 기독교를 극복하는 데 해독을 줄 수 있다는 점에서 굉장히 반가운 책이다. | 25.722513 | 477 | 0.6609 | kor_Hang | 1.00001 |
4cefa7e651521d0ec77d6cf9abcee604c32a15dc | 1,472 | md | Markdown | articles/azure-sql/managed-instance/management-endpoint-find-ip-address.md | wastu01/azure-docs.zh-tw | 7ee2fba199b6243c617953684afa67b83b2acc82 | [
"CC-BY-4.0",
"MIT"
] | 66 | 2017-08-24T10:28:13.000Z | 2022-03-04T14:01:29.000Z | articles/azure-sql/managed-instance/management-endpoint-find-ip-address.md | wastu01/azure-docs.zh-tw | 7ee2fba199b6243c617953684afa67b83b2acc82 | [
"CC-BY-4.0",
"MIT"
] | 534 | 2017-06-30T19:57:07.000Z | 2022-03-11T08:12:44.000Z | articles/azure-sql/managed-instance/management-endpoint-find-ip-address.md | wastu01/azure-docs.zh-tw | 7ee2fba199b6243c617953684afa67b83b2acc82 | [
"CC-BY-4.0",
"MIT"
] | 105 | 2017-07-04T11:37:54.000Z | 2022-03-20T06:10:38.000Z | ---
title: 探索管理端點 IP 位址
titleSuffix: Azure SQL Managed Instance
description: 瞭解如何取得 Azure SQL 受控執行個體管理端點公用 IP 位址,並確認其內建防火牆保護
services: sql-database
ms.service: sql-managed-instance
ms.subservice: operations
ms.custom: sqldbrb=1
ms.devlang: ''
ms.topic: how-to
author: srdan-bozovic-msft
ms.author: srbozovi
ms.reviewer: sstein
ms.date: 12/04/2018
ms.openlocfilehash: a9a2b904bd7526f00a8f8a5d013be0c1e42e38a8
ms.sourcegitcommit: 829d951d5c90442a38012daaf77e86046018e5b9
ms.translationtype: MT
ms.contentlocale: zh-TW
ms.lasthandoff: 10/09/2020
ms.locfileid: "91617361"
---
# <a name="determine-the-management-endpoint-ip-address---azure-sql-managed-instance"></a>判斷管理端點 IP 位址-Azure SQL 受控執行個體
[!INCLUDE[appliesto-sqlmi](../includes/appliesto-sqlmi.md)]
Azure SQL 受控執行個體虛擬叢集包含 Azure 用來管理作業的管理端點。 管理端點會受到網路層級內建防火牆和應用程式層級的相互憑證驗證所保護。 您可以判斷管理端點的 IP 位址,但您無法存取此端點。
若要判斷管理 IP 位址,請在您的 SQL 受控執行個體 FQDN 上進行 [DNS 查閱](/windows-server/administration/windows-commands/nslookup) : `mi-name.zone_id.database.windows.net` 。 這會傳回類似的 DNS 專案 `trx.region-a.worker.vnet.database.windows.net` 。 然後,您可以對此 FQDN 進行 DNS 查閱,並將 "vnet" 移除。 這會傳回管理 IP 位址。
如果您將取代 \<MI FQDN\> 為 SQL 受控執行個體的 DNS 專案,則此 PowerShell 程式碼會為您完成此作業: `mi-name.zone_id.database.windows.net`
``` powershell
$MIFQDN = "<MI FQDN>"
resolve-dnsname $MIFQDN | select -first 1 | %{ resolve-dnsname $_.NameHost.Replace(".vnet","")}
```
如需 SQL 受控執行個體和連線能力的詳細資訊,請參閱 [AZURE sql 受控執行個體連線能力架構](connectivity-architecture-overview.md)。
| 39.783784 | 265 | 0.777853 | yue_Hant | 0.637419 |
4cf00b2db633342780291b816b84e5ddd7fd1352 | 1,045 | md | Markdown | changelog_unreleased/html/pr-7293.md | bantic/prettier | a858a315e926c21bd1ebfcde70a08419c9472a8c | [
"MIT"
] | 2 | 2020-06-15T19:10:48.000Z | 2020-07-29T12:30:53.000Z | changelog_unreleased/html/pr-7293.md | bantic/prettier | a858a315e926c21bd1ebfcde70a08419c9472a8c | [
"MIT"
] | 13 | 2021-03-01T21:20:42.000Z | 2022-02-27T08:04:08.000Z | changelog_unreleased/html/pr-7293.md | bantic/prettier | a858a315e926c21bd1ebfcde70a08419c9472a8c | [
"MIT"
] | null | null | null | #### Do not throw on broken html ([#7293](https://github.com/prettier/prettier/pull/7293) by [@fisker](https://github.com/fisker))
<!-- prettier-ignore -->
```html
<!-- Input -->
<div><span>
<
<!-- Prettier stable -->
TypeError: Cannot read property 'start' of null
at hasTrailingLineBreak (https://prettier.io/lib/standalone.js:19694:169)
at forceBreakContent (https://prettier.io/lib/standalone.js:19668:154)
at Object.genericPrint$2 [as print] (https://prettier.io/lib/standalone.js:21068:126)
at callPluginPrintFunction (https://prettier.io/lib/standalone.js:15302:20)
at https://prettier.io/lib/standalone.js:15253:18
at Object.printComments (https://prettier.io/lib/standalone.js:14974:19)
at printGenerically (https://prettier.io/lib/standalone.js:15252:24)
at printChild (https://prettier.io/lib/standalone.js:21227:14)
at https://prettier.io/lib/standalone.js:21211:104
at FastPath.map (https://prettier.io/lib/standalone.js:15155:23)
<!-- Prettier master -->
<div><span> < </span></div>
```
| 41.8 | 130 | 0.70622 | kor_Hang | 0.220587 |
4cf0130927afcff09abbf014620b4ded0f77943d | 3,671 | md | Markdown | docs/google_analytics.md | mongodb-js/metrics | 324bbd4253f5cac4a5afd544db03a2f8d21d533f | [
"Apache-2.0"
] | 1 | 2019-09-26T13:31:23.000Z | 2019-09-26T13:31:23.000Z | docs/google_analytics.md | mongodb-js/metrics | 324bbd4253f5cac4a5afd544db03a2f8d21d533f | [
"Apache-2.0"
] | 92 | 2015-12-01T10:21:37.000Z | 2021-04-08T22:24:23.000Z | docs/google_analytics.md | mongodb-js/metrics | 324bbd4253f5cac4a5afd544db03a2f8d21d533f | [
"Apache-2.0"
] | 1 | 2021-01-28T11:25:23.000Z | 2021-01-28T11:25:23.000Z | # Google Analytics
Google Analytics supports a number of different [hit types][ga-hittypes] at
the top level. For Compass, we should use `screenview`, `event`, `timing` and
`exception` hit types depending on the event.
The most generic hit type is `event`, which has a similar notion of resources
and actions. Here, `eventCategory` is the resource, and `eventAction` is the
action.
Router `page` events should send `screenview` hits.
Errors and unhandled Exceptions should send `exception` hits.
Performance measurements like schema sampling should use `timing` hits.
## Screen Views
See [App/Screen Views][ga-screenviews] docs.
All `page` tracking events emitted by Compass' `app.router` are transformed
into Google Analytics `screenview` hits.
The following fields are supported with a `screenview` hit:
- `screenName` {String} (required) use one of `connect`, `schema`, `help`, `preferences`, `tour`
- `appName` {String} (required) fixed to `MongoDB Compass`
- `appVersion` {String} use current app version, e.g. `1.0.0`
- `appId` {String} _unused_
- `appInstallerVersion` {String} _unused_
## Exceptions
See [Exception Tracking][ga-exceptions] docs.
All tracking events that contain an Error object are transformed into Google
Analytics 'exception' hits.
The following optional fields are supported with an `exception` hit:
- `exDescription` {String} use exception message
- `exFatal` {Boolean}
## User Timings
See [User Timings][ga-timings] docs.
The following fields are supported with a `timing` hit:
- `timingCategory` {String} (required) e.g. `Schema`
- `timingVar` {String} (required) e.g. `total_sample_time`
- `timingValue` {Number} (required) time in milliseconds
- `timingLabel` {String} optional label _unused_
## Events
See [Event Tracking][ga-events] docs.
All events that are not Errors or Pageviews use the generic 'event' hit type.
Google Analytics does not support arbitrary metadata objects. Instead, each 'event' hit consists of
Category {String}
Action {String}
Label (optional, but recommended) {String}
Value (optional) {Number}
To map the above Compass event names to the Google Analytics events, the Category is the first item before the underscore, and the action is the second item, e.g. connection_succeeded has a category of "connection" and an action "succeeded".
There are several ways of submitting additional (meta) information.
we could encode information as Label/Value pairs and send with the event. The values are limited to numeric types.
we could use custom metrics/dimensions and send with the event. metrics and dimensions are limited to 20 distinct values each.
## Additional parameters
For additional variables that can be sent, see the [Measurement Protocol][ga-measurement-protocol];
Here some of the relevant ones:
- `ds` Data Source, set to `app`
- `cid` Client ID, set to the user uuid
- `sc` Session Control, set to `start` when session start and `"end"` when it ends.
- `sr` Screen Resolution, e.g. `800x600`
- `vp` Viewport Size, e.g. `123x456` (use the window size here)
[ga-hittypes]: https://developers.google.com/analytics/devguides/collection/analyticsjs/sending-hits
[ga-screenviews]: https://developers.google.com/analytics/devguides/collection/analyticsjs/screens
[ga-exceptions]: https://developers.google.com/analytics/devguides/collection/analyticsjs/exceptions
[ga-events]: https://developers.google.com/analytics/devguides/collection/analyticsjs/events
[ga-timings]: https://developers.google.com/analytics/devguides/collection/analyticsjs/user-timings
[ga-measurement-protocol]: https://developers.google.com/analytics/devguides/collection/protocol/v1/parameters
| 37.845361 | 241 | 0.767911 | eng_Latn | 0.910564 |
4cf14a6f9406c031f18d357ae4aceb3c070926f8 | 431 | md | Markdown | README.md | beny2000/HeartDiseaseClassifier | a4b7f02893a95246060ded9d4112e8c2b5255f75 | [
"Unlicense"
] | 4 | 2020-11-18T01:58:18.000Z | 2020-11-18T02:02:45.000Z | README.md | DelaneySteve/HeartDiseaseClassifier | a4b7f02893a95246060ded9d4112e8c2b5255f75 | [
"Unlicense"
] | null | null | null | README.md | DelaneySteve/HeartDiseaseClassifier | a4b7f02893a95246060ded9d4112e8c2b5255f75 | [
"Unlicense"
] | 3 | 2020-11-18T01:58:20.000Z | 2021-02-25T11:29:43.000Z | # HeartDiseaseClassifier
These models link to the anvil web app https://harmless-lavish-earth.anvil.app/. The goal is to determine whether or not a patient had heart disease. Three neural network models were implemented: SVM, KNN, and RBF, using the UCI heart disease dataset from Cleveland to analyze the patients data. The results of all three models and their accuracy are displayed for comparison through the web application.
| 107.75 | 404 | 0.809745 | eng_Latn | 0.997289 |
4cf155d2f21fa0651055072688c459075448b338 | 2,671 | md | Markdown | README.md | phodal/design | 1f0d592668a1de3d2de1f6454b85b1624ed887ee | [
"MIT"
] | 27 | 2015-06-11T07:10:14.000Z | 2021-08-30T15:38:54.000Z | README.md | phodal/design | 1f0d592668a1de3d2de1f6454b85b1624ed887ee | [
"MIT"
] | 5 | 2019-11-27T08:49:27.000Z | 2020-03-05T01:43:56.000Z | README.md | phodal/design | 1f0d592668a1de3d2de1f6454b85b1624ed887ee | [
"MIT"
] | 7 | 2019-11-24T14:43:02.000Z | 2021-06-11T19:36:27.000Z | # Design
Design as Code
## UI Flow
```
DSL -> DSL Parser -> DSL Json ---pipe---> Node.js -> Sketch
```
## Setup
install Go & Node.js
cd `adapter/visual/sketch` and run `npm install`
then
```
./script/run.sh
```
## DSL
Task Flows / User Flows Example
```flow
flow login {
SEE HomePage
DO [Click] "Login".Button
REACT Success: SHOW "Login Success".Toast with ANIMATE(bounce)
REACT Failure: SHOW "Login Failure".Dialog
SEE "Login Failure".Dialog
DO [Click] "ForgotPassword".Button
REACT: GOTO ForgotPasswordPage
SEE ForgotPasswordPage
DO [Click] "RESET PASSWORD".Button
REACT: SHOW "Please Check Email".Message
}
```
Elements
```
page HomePage {
LayoutGrid: 12x
LayoutId: HomePage
Router: "/home"
}
component Navigation {
LayoutId: Navigation
}
component TitleComponent {}
component ImageComponent {
Size: 1080px
}
component BlogList {
BlogDetail, Space8
BlogDetail, Space8
BlogDetail, Space8
BlogDetail, Space8
BlogDetail, Space8
BlogDetail, Space8
}
```
Layout Examples:
```
Layout HomePage {
--------------------------
| Navigation(RIGHT) |
--------------------------
| Empty(2x) | TitleComponent | Empty(2x) |
--------------------------
| ImageComponent |
--------------------------
| BlogList(8x) | Archives(2x) |
--------------------------
| Footer |
--------------------------
}
Layout Navigation {
--------------------------------------
| "home" |"detail" | Button("Login") |
--------------------------------------
}
```
Library Define Examples
```
library FontSize {
H1 = 18px
H2 = 16px
H3 = 14px
H4 = 12px
H5 = 10px
}
library Color {
Primary {
label = "Primary"
value = "#E53935"
}
Secondary {
label = "Blue"
value = "#1E88E5"
}
}
library Button {
Default [
FontSize.H2, Color.Primary
]
Primary [
FontSize.H2, Color.Primary
]
}
```
Refs: [AutoLayout.js](https://github.com/IjzerenHein/autolayout.js), [Apple's Auto Layout](https://developer.apple.com/library/archive/documentation/UserExperience/Conceptual/AutolayoutPG/index.html), [Visual Format Language]((https://developer.apple.com/library/archive/documentation/UserExperience/Conceptual/AutolayoutPG/index.html))
[图形双向编辑](https://github.com/ravichugh/sketch-n-sketch)
License
---
[](http://ideas.phodal.com/)
@ 2019 A [Phodal Huang](https://www.phodal.com)'s [Idea](http://github.com/phodal/ideas). This code is distributed under the MIT license. See `LICENSE` in this directory.
| 19.355072 | 336 | 0.59079 | yue_Hant | 0.522697 |
4cf15a03d7d0a18026e9c82a0eca4a7f5fd67fc1 | 34 | md | Markdown | README.md | WardsParadox/blart | fda264f1fd89f7a8bffc01c3c351249b128ba553 | [
"Unlicense"
] | null | null | null | README.md | WardsParadox/blart | fda264f1fd89f7a8bffc01c3c351249b128ba553 | [
"Unlicense"
] | null | null | null | README.md | WardsParadox/blart | fda264f1fd89f7a8bffc01c3c351249b128ba553 | [
"Unlicense"
] | null | null | null | # blart
Paul Blart: Mal(ware) Cop
| 11.333333 | 25 | 0.705882 | nld_Latn | 0.199391 |
4cf18f532391d1ed8f8838482cc0787bf746c976 | 13,778 | md | Markdown | doc/install/database_mysql.md | tylerchen/hitlab | e15f8e5bcc024f0c2770469411ddb784dadfc166 | [
"MIT"
] | 3 | 2015-11-05T12:10:19.000Z | 2018-08-01T08:31:26.000Z | doc/install/database_mysql.md | tylerchen/hitlab | e15f8e5bcc024f0c2770469411ddb784dadfc166 | [
"MIT"
] | 3 | 2015-02-14T17:07:28.000Z | 2015-02-14T17:07:58.000Z | doc/install/database_mysql.md | tylerchen/hitlab | e15f8e5bcc024f0c2770469411ddb784dadfc166 | [
"MIT"
] | null | null | null | # Database MySQL
> **Note:**
> - We do not recommend using MySQL due to various issues. For example, case
[(in)sensitivity](https://dev.mysql.com/doc/refman/5.0/en/case-sensitivity.html)
and [problems](https://bugs.mysql.com/bug.php?id=65830) that
[suggested](https://bugs.mysql.com/bug.php?id=50909)
[fixes](https://bugs.mysql.com/bug.php?id=65830) [have](https://bugs.mysql.com/bug.php?id=63164).
## Initial database setup
```
# Install the database packages
sudo apt-get install -y mysql-server mysql-client libmysqlclient-dev
# Ensure you have MySQL version 5.6 or later
mysql --version
# Pick a MySQL root password (can be anything), type it and press enter
# Retype the MySQL root password and press enter
# Secure your installation
sudo mysql_secure_installation
# Login to MySQL
mysql -u root -p
# Type the MySQL root password
# Create a user for GitLab
# do not type the 'mysql>', this is part of the prompt
# change $password in the command below to a real password you pick
mysql> CREATE USER 'git'@'localhost' IDENTIFIED BY '$password';
# Ensure you can use the InnoDB engine which is necessary to support long indexes
# If this fails, check your MySQL config files (e.g. `/etc/mysql/*.cnf`, `/etc/mysql/conf.d/*`) for the setting "innodb = off"
mysql> SET storage_engine=INNODB;
# If you have MySQL < 5.7.7 and want to enable utf8mb4 character set support with your GitLab install, you must set the following NOW:
mysql> SET GLOBAL innodb_file_per_table=1, innodb_file_format=Barracuda, innodb_large_prefix=1;
# If you use MySQL with replication, or just have MySQL configured with binary logging, you need to run the following to allow the use of `TRIGGER`:
mysql> SET GLOBAL log_bin_trust_function_creators = 1;
# Create the GitLab production database
mysql> CREATE DATABASE IF NOT EXISTS `gitlabhq_production` DEFAULT CHARACTER SET `utf8` COLLATE `utf8_general_ci`;
# Grant the GitLab user necessary permissions on the database
mysql> GRANT SELECT, INSERT, UPDATE, DELETE, CREATE, CREATE TEMPORARY TABLES, DROP, INDEX, ALTER, LOCK TABLES, REFERENCES, TRIGGER ON `gitlabhq_production`.* TO 'git'@'localhost';
# Quit the database session
mysql> \q
# Try connecting to the new database with the new user
sudo -u git -H mysql -u git -p -D gitlabhq_production
# Type the password you replaced $password with earlier
# You should now see a 'mysql>' prompt
# Quit the database session
mysql> \q
```
You are done installing the database for now and can go back to the rest of the installation.
Please proceed to the rest of the installation **before** running through the steps below.
### `log_bin_trust_function_creators`
If you use MySQL with replication, or just have MySQL configured with binary logging, all of your MySQL servers will need to have `log_bin_trust_function_creators` enabled to allow the use of `TRIGGER` in migrations. You have already set this global variable in the steps above, but to make it persistent, add the following to your `my.cnf` file:
```
log_bin_trust_function_creators=1
```
### MySQL utf8mb4 support
After installation or upgrade, remember to [convert any new tables](#tables-and-data-conversion-to-utf8mb4) to `utf8mb4`/`utf8mb4_general_ci`.
---
GitLab 8.14 has introduced [a feature](https://gitlab.com/gitlab-org/gitlab-ce/merge_requests/7420) requiring `utf8mb4` encoding to be supported in your GitLab MySQL Database, which is not the case if you have setup your database before GitLab 8.16.
Follow the below instructions to ensure you use the most up to date requirements for your GitLab MySQL Database.
**We are about to do the following:**
- Ensure you can enable `utf8mb4` encoding and `utf8mb4_general_ci` collation for your GitLab DB, tables and data.
- Convert your GitLab tables and data from `utf8`/`utf8_general_ci` to `utf8mb4`/`utf8mb4_general_ci`
### Check for utf8mb4 support
#### Check for InnoDB File-Per-Table Tablespaces
We need to check, enable and maybe convert your existing GitLab DB tables to the [InnoDB File-Per-Table Tablespaces](http://dev.mysql.com/doc/refman/5.7/en/innodb-multiple-tablespaces.html) as a prerequisite for supporting **utfb8mb4 with long indexes** required by recent GitLab databases.
# Login to MySQL
mysql -u root -p
# Type the MySQL root password
mysql > use gitlabhq_production;
# Check your MySQL version is >= 5.5.3 (GitLab requires 5.5.14+)
mysql > SHOW VARIABLES LIKE 'version';
+---------------+-----------------+
| Variable_name | Value |
+---------------+-----------------+
| version | 5.5.53-0+deb8u1 |
+---------------+-----------------+
# Note where is your MySQL data dir for later:
mysql > select @@datadir;
+----------------+
| @@datadir |
+----------------+
| /var/lib/mysql |
+----------------+
# Note whether your MySQL server runs with innodb_file_per_table ON or OFF:
mysql> SELECT @@innodb_file_per_table;
+-------------------------+
| @@innodb_file_per_table |
+-------------------------+
| 1 |
+-------------------------+
# You can now quit the database session
mysql> \q
> You need **MySQL 5.5.3 or later** to perform this update.
Whatever the results of your checks above, we now need to check if your GitLab database has been created using [InnoDB File-Per-Table Tablespaces](http://dev.mysql.com/doc/refman/5.7/en/innodb-multiple-tablespaces.html) (i.e. `innodb_file_per_table` was set to **1** at initial setup time).
> Note: This setting is [enabled by default](http://dev.mysql.com/doc/refman/5.7/en/innodb-parameters.html#sysvar_innodb_file_per_table) since MySQL 5.6.6.
# Run this command with root privileges, replace the data dir if different:
sudo ls -lh /var/lib/mysql/gitlabhq_production/*.ibd | wc -l
# Run this command with root privileges, replace the data dir if different:
sudo ls -lh /var/lib/mysql/gitlabhq_production/*.frm | wc -l
- **Case 1: a result > 0 for both commands**
Congrats, your GitLab database uses the right InnoDB tablespace format.
However, you must still ensure that any **future tables** created by GitLab will still use the right format:
- If `SELECT @@innodb_file_per_table` returned **1** previously, your server is running correctly.
> It's however a requirement to check *now* that this setting is indeed persisted in your [my.cnf](https://dev.mysql.com/doc/refman/5.7/en/tablespace-enabling.html) file!
- If `SELECT @@innodb_file_per_table` returned **0** previously, your server is not running correctly.
> [Enable innodb_file_per_table](https://dev.mysql.com/doc/refman/5.7/en/tablespace-enabling.html) by running in a MySQL session as root the command `SET GLOBAL innodb_file_per_table=1, innodb_file_format=Barracuda;` and persist the two settings in your [my.cnf](https://dev.mysql.com/doc/refman/5.7/en/tablespace-enabling.html) file
Now, if you have a **different result** returned by the 2 commands above, it means you have a **mix of tables format** uses in your GitLab database. This can happen if your MySQL server had different values for `innodb_file_per_table` in its life and you updated GitLab at different moments with those inconsistent values. So keep reading.
- **Case 2: a result equals to "0" OR not the same result for both commands**
Unfortunately, none or only some of your GitLab database tables use the GitLab requirement of [InnoDB File-Per-Table Tablespaces](http://dev.mysql.com/doc/refman/5.7/en/innodb-multiple-tablespaces.html).
Let's enable what we need on the running server:
# Login to MySQL
mysql -u root -p
# Type the MySQL root password
# Enable innodb_file_per_table and set innodb_file_format on the running server:
mysql > SET GLOBAL innodb_file_per_table=1, innodb_file_format=Barracuda;
# You can now quit the database session
mysql> \q
> Now, **persist** [innodb_file_per_table](https://dev.mysql.com/doc/refman/5.6/en/tablespace-enabling.html) and [innodb_file_format](https://dev.mysql.com/doc/refman/5.6/en/innodb-file-format-enabling.html) in your `my.cnf` file.
Ensure at this stage that your GitLab instance is indeed **stopped**.
Now, let's convert all the GitLab database tables to the new tablespace format:
# Login to MySQL
mysql -u root -p
# Type the MySQL root password
mysql > use gitlabhq_production;
# Safety check: you should still have those values set as follow:
mysql> SELECT @@innodb_file_per_table, @@innodb_file_format;
+-------------------------+----------------------+
| @@innodb_file_per_table | @@innodb_file_format |
+-------------------------+----------------------+
| 1 | Barracuda |
+-------------------------+----------------------+
mysql > SELECT CONCAT('ALTER TABLE `', TABLE_NAME,'` ENGINE=InnoDB;') AS 'Copy & run these SQL statements:' FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA="gitlabhq_production" AND TABLE_TYPE="BASE TABLE";
# If previous query returned results, copy & run all shown SQL statements
# You can now quit the database session
mysql> \q
---
#### Check for proper InnoDB File Format, Row Format, Large Prefix and tables conversion
We need to check, enable and probably convert your existing GitLab DB tables to use the [Barracuda InnoDB file format](https://dev.mysql.com/doc/refman/5.6/en/innodb-file-format.html), the [DYNAMIC row format](https://dev.mysql.com/doc/refman/5.6/en/glossary.html#glos_dynamic_row_format) and [innodb_large_prefix](http://dev.mysql.com/doc/refman/5.7/en/innodb-parameters.html#sysvar_innodb_large_prefix) as a second prerequisite for supporting **utfb8mb4 with long indexes** used by recent GitLab databases.
# Login to MySQL
mysql -u root -p
# Type the MySQL root password
mysql > use gitlabhq_production;
# Set innodb_file_format and innodb_large_prefix on the running server:
# Note: These are the default settings only for MySQL 5.7.7 and later.
mysql > SET GLOBAL innodb_file_format=Barracuda, innodb_large_prefix=1;
# Your DB must be (still) using utf8/utf8_general_ci as default encoding and collation.
# We will NOT change the default encoding and collation on the DB in order to support future GitLab migrations creating tables
# that require "long indexes support" on installations using MySQL <= 5.7.9.
# However, when such migrations occur, you will have to follow this guide again to convert the newly created tables to the proper encoding/collation.
# This should return the following:
mysql> SELECT @@character_set_database, @@collation_database;
+--------------------------+----------------------+
| @@character_set_database | @@collation_database |
+--------------------------+----------------------+
| utf8 | utf8_general_ci |
+--------------------------+----------------------+
> Now, ensure that [innodb_file_format](https://dev.mysql.com/doc/refman/5.6/en/tablespace-enabling.html) and [innodb_large_prefix](http://dev.mysql.com/doc/refman/5.7/en/innodb-parameters.html#sysvar_innodb_large_prefix) are **persisted** in your `my.cnf` file.
#### Tables and data conversion to utf8mb4
Now that you have a persistent MySQL setup, you can safely upgrade tables after setup or upgrade time:
# Convert tables not using ROW_FORMAT DYNAMIC:
mysql> SELECT CONCAT('ALTER TABLE `', TABLE_NAME,'` ROW_FORMAT=DYNAMIC;') AS 'Copy & run these SQL statements:' FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA="gitlabhq_production" AND TABLE_TYPE="BASE TABLE" AND ROW_FORMAT!="Dynamic";
# !! If previous query returned results, copy & run all shown SQL statements
# Convert tables/columns not using utf8mb4/utf8mb4_general_ci as encoding/collation:
mysql > SET foreign_key_checks = 0;
mysql > SELECT CONCAT('ALTER TABLE `', TABLE_NAME,'` CONVERT TO CHARACTER SET utf8mb4 COLLATE utf8mb4_general_ci;') AS 'Copy & run these SQL statements:' FROM INFORMATION_SCHEMA.TABLES WHERE TABLE_SCHEMA="gitlabhq_production" AND TABLE_COLLATION != "utf8mb4_general_ci" AND TABLE_TYPE="BASE TABLE";
# !! If previous query returned results, copy & run all shown SQL statements
# Turn foreign key checks back on
mysql > SET foreign_key_checks = 1;
# You can now quit the database session
mysql> \q
Ensure your GitLab database configuration file uses a proper connection encoding and collation:
```sudo -u git -H editor config/database.yml```
production:
adapter: mysql2
encoding: utf8mb4
collation: utf8mb4_general_ci
[Restart your GitLab instance](../administration/restart_gitlab.md).
## MySQL strings limits
After installation or upgrade, remember to run the `add_limits_mysql` Rake task:
**Omnibus GitLab installations**
```
sudo gitlab-rake add_limits_mysql
```
**Installations from source**
```
bundle exec rake add_limits_mysql RAILS_ENV=production
```
The `text` type in MySQL has a different size limit than the `text` type in
PostgreSQL. In MySQL `text` columns are limited to ~65kB, whereas in PostgreSQL
`text` columns are limited up to ~1GB!
The `add_limits_mysql` Rake task converts some important `text` columns in the
GitLab database to `longtext` columns, which can persist values of up to 4GB
(sometimes less if the value contains multibyte characters).
Details can be found in the [PostgreSQL][postgres-text-type] and
[MySQL][mysql-text-types] manuals.
[postgres-text-type]: http://www.postgresql.org/docs/9.2/static/datatype-character.html
[mysql-text-types]: http://dev.mysql.com/doc/refman/5.7/en/string-type-overview.html
[ce-38152]: https://gitlab.com/gitlab-org/gitlab-ce/issues/38152
| 46.080268 | 508 | 0.712513 | eng_Latn | 0.823976 |
4cf1bd6b6cda120d0c3eb5cf26f3d800bd81cbd4 | 3,678 | md | Markdown | src/pages/blog/2015-09-24-why-doesnt-every-app-autosave.md | schneidmaster/schneider.dev | adc69072d31529f920cff0ee1a047666e70707d7 | [
"MIT"
] | 1 | 2018-11-30T10:53:28.000Z | 2018-11-30T10:53:28.000Z | src/pages/blog/2015-09-24-why-doesnt-every-app-autosave.md | schneidmaster/schneider.dev | adc69072d31529f920cff0ee1a047666e70707d7 | [
"MIT"
] | 1 | 2018-11-27T23:16:19.000Z | 2018-11-27T23:16:19.000Z | src/pages/blog/2015-09-24-why-doesnt-every-app-autosave.md | schneidmaster/schneider.dev | adc69072d31529f920cff0ee1a047666e70707d7 | [
"MIT"
] | 1 | 2018-11-27T22:21:03.000Z | 2018-11-27T22:21:03.000Z | ---
title: Why Doesn't Every App Autosave?
date: 2015-09-24 16:00:00 Z
tags:
- aha
- development
layout: post
draft: false
category: development
---
Every user knows the frustration of composing a long, thoughtful document or email only to experience a last-second crash or power failure right before they click “send.”
From finicky browsers to overloaded processors, crashes are an inevitable part of the computing experience, which means that sound UX principles require the developer to account for crashes even when they are not caused by faulty application logic or user input.
Which brings me to the question in the title – why don’t all apps autosave?
Autosaving – the practice of regularly persisting the user’s progress even before they have clicked “save” or “submit” – is a lifesaver when an unexpected problem interrupts the user.
For this reason, we have built autosaving into all of the text fields in Aha! – from comments to descriptions to notes. We have found autosaving to be a substantial asset for our application for three main reasons.
**Increases user trust**
Every time the user uses your application, they commit to a certain amount of trust: that the application will do what it appears to do, that it will keep their data safe, and that it will be helpful to their overall workflow. The user begins with a small amount of trust – signing up for an account and testing out the basic functionality – and then commits more trust as they see how your application is useful and helps them be more productive.
A core component of user trust is data integrity – the user wants to know that if they commit hours to inputting data and setting things up, that data will still be there when they return. Autosaving helps to build that trust at the corner cases – if the user experiences a computer crash in the middle of a lengthy task but returns to find their progress saved, they are immediately more confident in the overall ability of your app to protect their work.
**Minimizes the impact of bugs**
It’s inevitable – from time to time, your app will have bugs. It is impossible to grow your application and build out things users need without also experiencing growing pains on occasion. When that happens, autosaving often keeps your users from growing frustrated with the application and switching to a competitor or reverting to old practices.
It’s one thing to have to refresh the browser or reopen the app; it’s another thing entirely to have a bug result in substantial amounts of lost work – autosaving serves as a “last line of defense” when everything else goes wrong.
**Creates a better customer experience**
Have you ever spent several hours on a Microsoft Word document, only to have the application crash before you’ve saved – but upon reopening Word, you find that your document can be automatically recovered? Your relief is palpable – a sense of immediate joy that you do not have to redo hours of work.
This is the kind of UX that endears your application from users – when it saves them time by saving them even from problems that are not the applications’ fault, such as a browser crash or a power outage. Building an application that is not merely viable but lovable is what keeps users returning again and again – and recommending your application to colleagues and friends.
The benefits of autosaving are clear – it saves time and effort while mitigating the impact of negative events and endearing your app to its users.
With all this in mind, I am left to wonder – why don’t all apps do the same?
*This post was originally published on the [Aha! blog](http://blog.aha.io/index.php/why-doesnt-every-app-autosave/).*
| 81.733333 | 456 | 0.792007 | eng_Latn | 0.999923 |
4cf1c863ac7d776c1b96adf5055196242f00dc49 | 1,564 | md | Markdown | docs/mfc/adding-items-to-the-header-control.md | anmrdz/cpp-docs.es-es | f3eff4dbb06be3444820c2e57b8ba31616b5ff60 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | docs/mfc/adding-items-to-the-header-control.md | anmrdz/cpp-docs.es-es | f3eff4dbb06be3444820c2e57b8ba31616b5ff60 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | docs/mfc/adding-items-to-the-header-control.md | anmrdz/cpp-docs.es-es | f3eff4dbb06be3444820c2e57b8ba31616b5ff60 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
title: Agregar elementos al Control de encabezado | Microsoft Docs
ms.custom: ''
ms.date: 11/04/2016
ms.technology:
- cpp-mfc
ms.topic: conceptual
dev_langs:
- C++
helpviewer_keywords:
- controls [MFC], header
- CHeaderCtrl class [MFC], adding items
- header controls [MFC], adding items to
ms.assetid: 2e9a28b1-7302-4a93-8037-c5a4183e589a
author: mikeblome
ms.author: mblome
ms.workload:
- cplusplus
ms.openlocfilehash: 0eb06a15cac87b063ada1cbe8f130b3464be0b0a
ms.sourcegitcommit: 799f9b976623a375203ad8b2ad5147bd6a2212f0
ms.translationtype: MT
ms.contentlocale: es-ES
ms.lasthandoff: 09/19/2018
ms.locfileid: "46447185"
---
# <a name="adding-items-to-the-header-control"></a>Agregar elementos al control de encabezado
Después de crear el control de encabezado ([CHeaderCtrl](../mfc/reference/cheaderctrl-class.md)) en su ventana primaria, agregue tantos "elementos de encabezado" según sea necesario: normalmente uno por columna.
### <a name="to-add-a-header-item"></a>Para agregar un elemento de encabezado
1. Preparar una [estructura HD_ITEM](/windows/desktop/api/commctrl/ns-commctrl-_hd_itema) estructura.
1. Llame a [:: InsertItem](../mfc/reference/cheaderctrl-class.md#insertitem), pasando la estructura.
1. Repita los pasos 1 y 2 para elementos adicionales.
Para obtener más información, consulte [agregando un elemento a un Control de encabezado](/windows/desktop/Controls/header-controls) en el SDK de Windows.
## <a name="see-also"></a>Vea también
[Uso de CHeaderCtrl](../mfc/using-cheaderctrl.md)<br/>
[Controles](../mfc/controls-mfc.md)
| 34.755556 | 211 | 0.773657 | spa_Latn | 0.568783 |
4cf1f81bf0717910e32f985640ad9f92f560a446 | 1,512 | md | Markdown | README.md | guiseek/freecom | b7d1eaa931c4dd59922ebc7f2f5843d2052d1bee | [
"MIT"
] | 12 | 2020-12-15T03:00:13.000Z | 2021-05-07T07:03:45.000Z | README.md | guiseek/freecom | b7d1eaa931c4dd59922ebc7f2f5843d2052d1bee | [
"MIT"
] | 1 | 2020-12-19T16:24:16.000Z | 2020-12-19T16:45:41.000Z | README.md | guiseek/freecom | b7d1eaa931c4dd59922ebc7f2f5843d2052d1bee | [
"MIT"
] | null | null | null | # Fundação da Livre Comunicação
## Como funciona
Com esta tecnologia é possível conversar usando conexão ponto a ponto _(p2p)_, não desde seu inicio como alguns pensam, pois nossa infra na rede _WAN_ é complexa e um ponto precisa econtrar o melhor caminho para chegar e além disso você estará se conectando a um dispositivo usando um endereço IP numa rede _LAN_. Para criar esta roda são necessários o STUN Server, que ajuda encontrar este caminho e também o Signaling. Ambos são tecnologias já existentes, o Signaling é um conceito e pode ser implementado da forma desejada, desde que cumpra sua missão, que é informar a outra ponta sobre uma ação que será tomada.
O fato é que a comunicação própriamente dita, a conversa em áudio ou vídeo, é trafegada diretamente de um ponto ao outro diretamente após a ligação ter sido estabelecida com a ajuda dos 2 carinhas citados acima, esta comunicação é criptografada por padrão, então é segura. Como é encontrado o melhor caminho, após ligação feita ela também é mais rápida que o normal, pois percorre um caminho menor sem desvios. : )
Basicamente funciona como as imagens abaixo apresentam.
### Para temas claros

### Para temas escuros
_Thanks [@O Geovani](https://github.com/geovanisouza92)_
## 
- [Código de Conduta](CODE_OF_CONDUCT.md).
- [Como contribuir](CONTRIBUTING.md) com a Livre Comunicação.
| 65.73913 | 616 | 0.791005 | por_Latn | 0.999979 |
4cf26c35791916c8778e4e4ab5ac97fe7e922db1 | 6,605 | md | Markdown | tech_lead.md | ScriptAddicts/hiring | be289b3a429a66e0d648b0019d8d09494d7df049 | [
"MIT"
] | null | null | null | tech_lead.md | ScriptAddicts/hiring | be289b3a429a66e0d648b0019d8d09494d7df049 | [
"MIT"
] | null | null | null | tech_lead.md | ScriptAddicts/hiring | be289b3a429a66e0d648b0019d8d09494d7df049 | [
"MIT"
] | null | null | null | # Senior Technical Lead / CTO
## Company
[Talarian](http://talarian.io) is a small, growing, and profitable software company that is building the future of spreadsheet-driven business applications. Our main products are [YAMM](https://yamm.com/),[ Awesome Table](https://awesome-table.com/), and [Form Publisher](https://form-publisher.com). They are used and loved by millions and some of the most popular products in the Google Workspace marketplace.
Our company is around 30 people, remote-first and global (we have people based in Western and Eastern Europe, Philippines, Nigeria), all highly motivated and dedicated.
Our product values are: simplicity, empowerment, and getting out of the way.
## Job description
We are hiring a highly motivated Senior Technical Lead/CTO who will take ownership of the technical strategy and execution of a product development, with the possibility to enlarge the scope to more products after some time.
This is both a leadership and hands-on role: you will have to get your hands dirty at times and dig in code.
## Why it’s technically interesting to work on our products:
* They are global-scale products, used in every kind of organization, by millions of people who speak different languages, have varying accessibility requirements, and wildly differing hardware/network
* The products share many capabilities and are made of many different subsystems, which poses coordination challenges
* The products are built on serverless components allowing them to scale nicely
* Building on top of Google means building on top of a fast-evolving platform. They push us forward, and we must keep up
* We are currently in the process of refactoring core parts of the infrastructure in depth in order to allow for our next big projects, and there are many interesting architecture and engineering decisions to be made
### Our tech stack:
Our products are typically made of the following subproducts:
* A Google Workspace add-on which is a small real-estate web-app integrated with Google Sheets/Forms. This is where the bulk of the functionality is exposed to users.
* A typical dashboard front-end, which contains administration and analytics.
* A business logic back-end
* A payments and billing back-end
* A logging and analytics pipeline
* A marketing website
Our product infrastructure is hosted on Google Cloud Platform:
* We run logic on App Engine, Cloud Functions, Cloud Pub Sub, Cloud Storage
* We store data in Firebase, PostgreSQL, Redis, BigQuery
* We use Sonarcloud, Sentry and Lambdatest as code quality tools
We code in TypeScript (React), Google Apps Script, NodeJS and Java. We’re keen to introduce a new strong back-end language such as Golang in our stack.
Our marketing websites are coded in NextJS and hosted on Vercel.
### Core responsibilities:
* Taking full responsibility of a product from an infrastructure, architecture, code, run and build perspective
* Leading, mentoring and growing the technical team
* Owning the planning, staffing and release process
* Writing technical and architecture specs
* Improving team development processes and productivity
* Providing measurable and scalable engineering support processes
### How the dev teams work:
* Each product team is currently composed of 2-4 developers, 1 QA and 1 QA Automation, and 1 designer.
* We do not use any agile frameworks as we have found them not to be agile at all. We instead carve out projects that should last between two to six weeks, and meet daily for 5-15 minutes to discuss our progress and reevaluate priorities if need be. We hold a longer (~1h) meeting per week to plan the week ahead.
* Short-term tasks are tracked on a very simple Gantt chart in a Google Sheet and specifications are written in Google Docs.
* Developers use Jira to create and track tickets. We use Github and pull requests for version control. We use Github Actions for continuous deployment with automated tests.
* Communication with the wider team is done through email, Google Docs, a little bit of Slack and Google Meet.
## You:
* You have extensive architecture and coding experience
* You care more about making reliable software used by many than a shiny unstable thing used by no one. You understand that engineering work is done first and foremost for the customers.
* You care a lot about performance, understand that speed is a core feature
* Fully capable of architecting, owning and running entire systems (new add-on, new billing system, new api, new webapp, new integration)
* Deep, substantial expertise in multiple programming environments and databases
* You understand people, and can provide material feedback on the work of programmers
* You’re a very strong communicator, both written and verbal
### Qualifications:
* **Experience:** 6+ years as a professional programmer and 3+ years in a tech lead or engineering manager role, preferably on a large scale product
* **Cloud:** you have deep experience with one of the 3 main cloud platforms. Bonus points for GCP and serverless experience
* **Programming ecosystems:** you have experience with many programming languages, including Java.
* **Software engineering tools:** you’re familiar with build, profiling and code quality tools
* **Language:** excellent in English, both written and oral
* **Writing:** you enjoy writing, you care about words and grammar
## Compensation and benefits:
* The range for this role is EUR 90k-130k, depending on experience and type of contract
* 30 days of paid time off
* Medical, dental and vision insurance (depending on the type of contract)
* Paid parental leave
## How to apply:
We want to get a sense of how you write and think. To that end, please write an email that covers at least the following:
* Show us some technical specs you’ve written that you’re proud of if possible
* Tell us about something you’ve built in the past, what where the tradeoffs, the challenges, and how you made your technology choices
* Tell us what you’re excited about in software engineering these days
* Tell us why you want this job
We value great writers, so please show off those skills (stock cover letters won’t do).
Send your email and resume, plus any public profile or material you feel relevant to stan@talarian.io
### Interview process:
1. We will first ask you a few targeted questions to be answered by email so as to get acquainted with you in writing.
2. If that goes well, we’ll send you a technical test.
3. You’ll then move on to an interview with a Lead Engineer
4. Finally, an interview with the CTO.
We can’t wait to hear from you!
| 56.939655 | 411 | 0.785314 | eng_Latn | 0.999539 |
4cf28e458307111b8098ddd0ad6641a11d9eb675 | 643 | md | Markdown | manual/en/docs/flow/actions/reduce_array_action.md | ryomahan/read-tracardi-api | d0a012fb097ca81daf046b314000301eb54bfad8 | [
"MIT"
] | 3 | 2021-11-27T18:03:31.000Z | 2022-02-06T21:47:59.000Z | manual/en/docs/flow/actions/reduce_array_action.md | ryomahan/read-tracardi-api | d0a012fb097ca81daf046b314000301eb54bfad8 | [
"MIT"
] | 13 | 2021-11-03T18:15:06.000Z | 2022-03-27T22:28:38.000Z | manual/en/docs/flow/actions/reduce_array_action.md | ryomahan/read-tracardi-api | d0a012fb097ca81daf046b314000301eb54bfad8 | [
"MIT"
] | 8 | 2021-11-16T04:07:41.000Z | 2022-03-14T14:51:34.000Z | # Reduce array plugin
This plugin reduces given array.
## Input
This plugin takes any payload as input.
## Output
This plugin returns reduced array on port **result**, or some error info on port
**error** if one occurs.
#### Example input:
```json
{
"list": [
"a",
"a",
"a",
"b",
"b",
"c"
]
}
```
#### Output for this input:
```json
{
"counts": {
"a": 3,
"b": 2,
"c": 1
},
"max": "a",
"min": "c"
}
```
## Plugin configuration
#### Form fields
- Path to array - a valid dot path to array that you want to reduce.
#### JSON configuration
```json
{
"array": "<path-to-array>"
}
```
| 11.482143 | 80 | 0.542768 | eng_Latn | 0.894195 |
4cf2f212f43b6aeda058ce34a1fe21760d299873 | 188 | md | Markdown | nvchecker/lib/README.md | trathborne/nvchecker | d8c26fa66640d46a0bc099cd9f070b7b8c408479 | [
"MIT"
] | 320 | 2015-01-11T06:58:09.000Z | 2022-03-31T10:26:27.000Z | nvchecker/lib/README.md | trathborne/nvchecker | d8c26fa66640d46a0bc099cd9f070b7b8c408479 | [
"MIT"
] | 142 | 2015-06-28T03:09:56.000Z | 2022-02-28T06:09:26.000Z | nvchecker/lib/README.md | trathborne/nvchecker | d8c26fa66640d46a0bc099cd9f070b7b8c408479 | [
"MIT"
] | 68 | 2015-04-15T05:09:45.000Z | 2022-02-23T05:52:47.000Z | This directory contains code from other places:
* `nicelogger.py`: from my [winterpy](https://github.com/lilydjwg/winterpy)
* `packaging_version.py`: from python-packaging 20.9, modified
| 37.6 | 75 | 0.771277 | eng_Latn | 0.970132 |
4cf329b5eff659104b07117acbbabff5d2d88e32 | 137 | md | Markdown | _authors/janggw.md | brandiinc/brandiinc.github.com | 038aa135e7e7dd1f78d11151997e3526b15c24cf | [
"MIT"
] | null | null | null | _authors/janggw.md | brandiinc/brandiinc.github.com | 038aa135e7e7dd1f78d11151997e3526b15c24cf | [
"MIT"
] | 2 | 2021-07-02T04:28:11.000Z | 2021-09-28T05:47:30.000Z | _authors/janggw.md | brandiinc/brandiinc.github.com | 038aa135e7e7dd1f78d11151997e3526b15c24cf | [
"MIT"
] | null | null | null | ---
title: 장근우
layout: author
cover: "/assets/author.jpg"
subtitle: 브랜디 랩스(LABs)의 콘텐츠를 책임집니다 :D
author: janggw
---
경영본부 경영지원팀 채용, HR 담당
| 13.7 | 37 | 0.693431 | kor_Hang | 0.994626 |
4cf3ee74d5ca995f1a96186fd0824d1470790877 | 115 | md | Markdown | README.md | ryepdx/meteor-ethereum-tx-receipts | 5087b18753c5a0fb81e9b4ce15db664d0b96d579 | [
"MIT"
] | 1 | 2021-06-21T07:31:40.000Z | 2021-06-21T07:31:40.000Z | README.md | ryepdx/meteor-ethereum-tx-receipts | 5087b18753c5a0fb81e9b4ce15db664d0b96d579 | [
"MIT"
] | null | null | null | README.md | ryepdx/meteor-ethereum-tx-receipts | 5087b18753c5a0fb81e9b4ce15db664d0b96d579 | [
"MIT"
] | null | null | null | # meteor-ethereum-tx-receipts
Keeps a record of all transactions going through web3.js and their associated costs.
| 38.333333 | 84 | 0.817391 | eng_Latn | 0.998349 |
4cf3f459e3c86be1437c7d96810398d1c73ad09c | 998 | md | Markdown | blog/2022-05-05-introducing-api-keys-as-a-service/index.md | zuplo/docs | 28258f0aeb2b2636fe522eedded564e51a3c1fe3 | [
"MIT"
] | null | null | null | blog/2022-05-05-introducing-api-keys-as-a-service/index.md | zuplo/docs | 28258f0aeb2b2636fe522eedded564e51a3c1fe3 | [
"MIT"
] | null | null | null | blog/2022-05-05-introducing-api-keys-as-a-service/index.md | zuplo/docs | 28258f0aeb2b2636fe522eedded564e51a3c1fe3 | [
"MIT"
] | null | null | null | ---
title: Introducing API Keys as a service
authors: josh
tags: [videos, api-keys]
---
We recently shared some reasoning on [why we think API keys are the best authentication approach for your public API](https://zuplo.com/blog/2022/05/03/you-should-be-using-api-keys).
We think this is **so** important that we built it as a feature of the Zuplo gateway. Our API Key management includes:
- secure storage and management of keys and metadata - with an admin UI and API to manage consumers.
- integrated developer portal with self-serve key management for your customers.
| Note, if you've already built your own API Key solution, and have a database store with your keys and users, we can easily integrate zuplo authentication with custom policies. It's never too late to make hosting your API much easier.
See it all in action in this 2-minute video:
<YouTubeVideo url="https://www.youtube.com/embed/0oYp53Al9nI" />
Try it out now, for free at [portal.zuplo.com](https://portal.zuplo.com)
| 47.52381 | 235 | 0.766533 | eng_Latn | 0.99433 |
4cf423f8f7bf5ef84cc099eb91d649655b314194 | 3,257 | md | Markdown | docs/GettingStartedDocs/Contributors/AnsibleGettingStarted.md | pavel-petrenko/openenclave | 64ccdf3695ec17bd78c17a9a4907f6ea8255b715 | [
"MIT"
] | 617 | 2019-06-19T22:08:04.000Z | 2022-03-25T09:21:03.000Z | docs/GettingStartedDocs/Contributors/AnsibleGettingStarted.md | pavel-petrenko/openenclave | 64ccdf3695ec17bd78c17a9a4907f6ea8255b715 | [
"MIT"
] | 2,545 | 2019-06-18T21:46:10.000Z | 2022-03-31T23:26:51.000Z | docs/GettingStartedDocs/Contributors/AnsibleGettingStarted.md | pavel-petrenko/openenclave | 64ccdf3695ec17bd78c17a9a4907f6ea8255b715 | [
"MIT"
] | 292 | 2019-07-02T15:40:35.000Z | 2022-03-27T13:27:10.000Z | # Getting started with Ansible
The Open Enclave repository contains various playbooks to configure the supported platforms for either developing Open Enclave applications or maintaining the SDK itself.
If you are interested in the Open Enclave deployment options via Ansible, see [this section](https://github.com/openenclave/openenclave/tree/master/scripts/ansible#open-enclave-deployment-options-via-ansible) from our Ansible README.
## Install the Ansible package
The Ansible package works reliably (as tested) only on Unix platforms due to the various unix specific internal code.
If you wish to run Ansible from a Windows machine, feel free to enable the [Windows Subsystem for Linux](https://docs.microsoft.com/en-us/windows/wsl/install-win10), install the Ubuntu (18.04 or 20.04) distribution from the Windows store, and open the Linux terminal.
To get Ansible ready to use, simply run the [install-ansible.sh](/scripts/ansible/install-ansible.sh) script (this requires execution with sudo).
After the script finishes, you can check that Ansible is installed by running:
```
ansible --version
```
Ansible communicates with the target machines via:
* SSH (port 22) if the target machine is a Linux system
* WinRM (port 5986) if the target machine is a Windows system
## Steps to configure target Ansible machines
1. Make sure that the target platform is included in the [supported operating systems](https://github.com/openenclave/openenclave/blob/master/scripts/ansible/README.md#supported-platforms-by-the-ansible-playbooks) by the Open Enclave playbook files.
2. Configure SSH / WinRM on the target machines:
* SSH needs to be configured only on the target Linux machines. From the terminal where Ansible is used, make sure you can SSH into the Linux machines without any password prompt. You may need to generate a SSH key pair via `ssh-keygen` and authorize the key via `ssh-copy-id`.
* WinRM needs to be configured only on the Windows machines. Make sure that WinRM is running and it allows remote auth via user and password. If you don't have WinRM configured on the Windows machines, execute the following [official Ansible PowerShell steps](https://docs.ansible.com/ansible/latest/user_guide/windows_setup.html#winrm-setup). After these steps are successfully executed, WinRM is properly configured.
3. Make sure that the Linux machines SSH (port 22) or Windows machines WinRM (port 5986) are reachable from the terminal where Ansible is used.
Check the communication port for every target machine. You may need to open some extra firewall ports if the machines are running in a public cloud and you are using the public address.
4. Set up the Ansible inventory with connection details for all the target machines. See details on how to do this [here](/scripts/ansible/inventory).
5. Change directory to `scripts/ansible` and execute the following command:
```
ansible -m setup all
```
This will try and execute the `setup` Ansible built-in module and get platform details from every machine added to the [inventory](/scripts/ansible/inventory). If this command finishes without any error, the Ansible machines are prepared to run our playbooks from the [ansible](/scripts/ansible) directory.
| 66.469388 | 422 | 0.787535 | eng_Latn | 0.997048 |
4cf46fa1ccbea5461da5ea197c0a42cd31407306 | 888 | md | Markdown | api/qsharp/microsoft.quantum.preparation.applyglobalrotationstep.md | Bhard27/quantum-docs-pr | ab00518a06d8062d58aee141a63ac2b381e7f68a | [
"CC-BY-4.0",
"MIT"
] | 92 | 2018-02-28T10:57:17.000Z | 2021-11-14T17:18:15.000Z | api/qsharp/microsoft.quantum.preparation.applyglobalrotationstep.md | Bhard27/quantum-docs-pr | ab00518a06d8062d58aee141a63ac2b381e7f68a | [
"CC-BY-4.0",
"MIT"
] | 925 | 2018-02-26T13:56:06.000Z | 2021-02-16T18:22:56.000Z | api/qsharp/microsoft.quantum.preparation.applyglobalrotationstep.md | MicrosoftDocs/quantum-docs-pr | d8fc0b81dc4d46abe3c407ac906892ef63692052 | [
"CC-BY-4.0",
"MIT"
] | 144 | 2018-03-13T01:52:59.000Z | 2021-12-22T19:37:58.000Z | ---
uid: Microsoft.Quantum.Preparation.ApplyGlobalRotationStep
title: ApplyGlobalRotationStep operation
ms.date: 1/23/2021 12:00:00 AM
ms.topic: article
qsharp.kind: operation
qsharp.namespace: Microsoft.Quantum.Preparation
qsharp.name: ApplyGlobalRotationStep
qsharp.summary: ''
---
# ApplyGlobalRotationStep operation
Namespace: [Microsoft.Quantum.Preparation](xref:Microsoft.Quantum.Preparation)
Package: [Microsoft.Quantum.Standard](https://nuget.org/packages/Microsoft.Quantum.Standard)
```qsharp
operation ApplyGlobalRotationStep (angle : Double, idxTarget : Int, register : Qubit[]) : Unit is Adj + Ctl
```
## Input
### angle : [Double](xref:microsoft.quantum.lang-ref.double)
### idxTarget : [Int](xref:microsoft.quantum.lang-ref.int)
### register : [Qubit](xref:microsoft.quantum.lang-ref.qubit)[]
## Output : [Unit](xref:microsoft.quantum.lang-ref.unit)
| 19.304348 | 107 | 0.754505 | yue_Hant | 0.825284 |
4cf4773a4ed320e9de243ab8102991cf9b7dae88 | 481 | md | Markdown | examples/test-service/README.md | paukan-org/paukan-core | e6ff0667d50bc9b25ab5678852316e89521942ad | [
"Apache-2.0"
] | null | null | null | examples/test-service/README.md | paukan-org/paukan-core | e6ff0667d50bc9b25ab5678852316e89521942ad | [
"Apache-2.0"
] | null | null | null | examples/test-service/README.md | paukan-org/paukan-core | e6ff0667d50bc9b25ab5678852316e89521942ad | [
"Apache-2.0"
] | null | null | null | Тестовый сервис (может служить примером создания сервисов и для тестирования).
Каждую минуту увеличивает счетчик на единицу и сообщает об этом в сеть.
Доступные состояния:
1) counter - при запросе без параметров возвращает текущее состояние счетчика, при попытке передать параметр ругается "action not supported".
2) delay - при запросе без параметров ругается возвращает текущее состояние интервала между изменениями счетчика, при передаче числа изменяет интервал на это число.
| 60.125 | 164 | 0.827443 | rus_Cyrl | 0.996341 |
4cf4e606a83af4b904c842552dd967f4fe9b2e66 | 5,140 | md | Markdown | content/post/neural-gnn-tl/index.md | htlee6/hugo_academic | b4829e9cd33fde554b9b3a29963b00fed9443974 | [
"MIT"
] | null | null | null | content/post/neural-gnn-tl/index.md | htlee6/hugo_academic | b4829e9cd33fde554b9b3a29963b00fed9443974 | [
"MIT"
] | null | null | null | content/post/neural-gnn-tl/index.md | htlee6/hugo_academic | b4829e9cd33fde554b9b3a29963b00fed9443974 | [
"MIT"
] | null | null | null | ---
title: Neural Decoding Using Graph Neural Network and Transfer Learning
subtitle: A data-driven neural decoding method
# Summary for listings and search engines
summary: Maybe this is a new perspective?
# Link this post with a project
projects: []
# Date published
date: "2022-02-13T00:00:00Z"
# Date updated
# lastmod: "2020-12-13T00:00:00Z"
# Is this an unpublished draft?
draft: false
# Show this page in the Featured widget?
featured: true
# Featured image
# Place an image named `featured.jpg/png` in this page's folder and customize its options here.
image:
caption: 'Image credit: [**SingularityHub**](https://singularityhub.com/2019/05/01/scientists-created-a-neural-decoder-that-translates-brain-activity-into-speech/)'
focal_point: ""
placement: 2
preview_only: true
authors:
- admin
tags:
- Brain
- Deep Learning
- GNN
categories:
- Research
---
### What is neural decoding?
A human brain can be considered as an encoder-decoder architecture in terms of its interaction with the environment. For the encoding model part, it predicts how the brain encodes one's perceptions (visual, auditory, motor, and etc.) into the brain response. While the decoding model part should give reasonable predictions on one's perception given the response/activity of the brain.
<figure>
<img src="https://www.researchgate.net/profile/Gael-Varoquaux/publication/268794316/figure/fig1/AS:282616113713184@1444392340570/Schematics-of-the-distinction-between-encoding-and-decoding-in-brain-imaging_W640.jpg" width="300px" height="auto"/>
<figcaption>
<a href="https://www.researchgate.net/publication/268794316_How_machine_learning_is_shaping_cognitive_neuroimaging">Varoquaux et al.</a>
</figcaption>
</>
In our work, we try to prove that using novel graph neural network (GNN) architecture and transfer learning (TL) to model the decoding is a better idea. In addition, we would also like to analyze the characterize the brain's activity using the intermediate representation of the neural network.
### Graph Neural Network: Designed for Network Data
A human brain consists of many regions. Some of them may co-work to finish some task. To characterize the functionality of the brain, researchers conceptualized the "Brain Atlas", which clusters the regions of brain according to the function they are involved. That introduces a topological relation among all the regions of the brain. If we denote a cluster of regions of a brain as a node $n$ where $n \in N$, and the functional relation between two regions as an edge $e$ where $e\in E$. Thus, the brain can be denoted as a graph (or a network) $G$, where $G=\set{N, E}$.
GNN is a deep learning module applied on graph data. With its ability to extract and utilize the information underlying the topology, it is now a promising part to perform a deep learning task on non-Euclidean data. As we illustrated above, the decoding model with GNN-based structure, may fully utilize a brain function atlas, given its essence of the graph structure.
### Transfer Learning: Learn Like A Human Brain with Machine Learning
Transfer learning addresses the generalization ability of the trained model, and so does one's brain. Usually, human brain learns how to finish a task on a limited set of data and then have the ability to deal with unseen data. Inspired by that, we expect our model can also behaves just like the human brain with better generalization ability on other datasets or even cross domain task.
### Our Scope
Previous work<sup>[1-3]</sup> has proved GNN is a promising technique and how the transfer learning process affect the learning of the model. Besides, the interpretability of the model is also explained in the BrainGNN work<sup>[1]</sup> in particular. Therefore, building on the success of these efforts, we would like to investigate a novel GNN- & transfer-learning-based machine learning framework performance on simulating the neural decoding process and behavioral prediction. With transfer learning, even it is possible to generalize to perform cross domain tasks, such as brain disease prediction, which is more convincing that the model captures underlying representation of brain structure.
### Datasets
[Human Connectome Project (HCP)](https://www.humanconnectome.org/study/hcp-young-adult/document/1200-subjects-data-release) dataset and [Individual Brain Charting (IBC)](https://openneuro.org/datasets/ds000244/versions/1.0.0) dataset containing similar human cognitive subjects will be used in our experiments.
### Experiments and Results
To be finished ...
#### References
[1] Li, X., Zhou, Y., Dvornek, N., Zhang, M., Gao, S., Zhuang, J., Scheinost, D., Staib, L. H., Ventola, P., & Duncan, J. S. (2021). BrainGNN: Interpretable Brain Graph Neural Network for fMRI Analysis. Medical Image Analysis, 74, 102233. <br>
[2] Zhang, Y., & Bellec, P. (2020). Transferability of Brain decoding using Graph Convolutional Networks (p. 2020.06.21.163964). <br>
[3] Zhang, Y., Tetrel, L., Thirion, B., & Bellec, P. (2021). Functional annotation of human cognitive states using deep graph convolution. NeuroImage, 231, 117847.
| 61.927711 | 699 | 0.774514 | eng_Latn | 0.990251 |
4cf50d0ee425046e6c389e9c696b682f69d785fa | 802 | md | Markdown | inspectit-ocelot-documentation/website/versioned_docs/version-0.6/breaking-changes/0.5.md | inspectIT/inspectit-oce | cc6f1ed2795f69ba244562d4b8a57437db45c784 | [
"Apache-2.0"
] | 12 | 2018-12-20T07:05:30.000Z | 2019-03-23T17:47:29.000Z | inspectit-ocelot-documentation/website/versioned_docs/version-0.6/breaking-changes/0.5.md | inspectIT/inspectit-oce | cc6f1ed2795f69ba244562d4b8a57437db45c784 | [
"Apache-2.0"
] | 80 | 2018-12-03T07:43:47.000Z | 2019-03-25T08:14:45.000Z | inspectit-ocelot-documentation/website/versioned_docs/version-0.6/breaking-changes/0.5.md | inspectIT/inspectit-oce | cc6f1ed2795f69ba244562d4b8a57437db45c784 | [
"Apache-2.0"
] | 6 | 2018-12-03T14:40:05.000Z | 2019-03-15T07:52:05.000Z | ---
id: version-0.6-0-5
title: Breaking changes in 0.5
original_id: 0-5
---
This section discusses the changes that you need to be aware of when migrating your inspectIT Ocelot components to version 0.5.
## Change of the configuration server's configuration prefix
Until now, all components used the configuration prefix `inspectit` for the inspectIT Ocelot specific configuration settings.
This often led to confusion because, especially in examples, it was not clear to which component a particular setting belonged.
To avoid confusion between the configurations of different components the configuration prefix of the configuration server has been changed to `inspectit-config-server`.
The configuration server will not load the configuration if it is still located under the `inspectit` prefix. | 53.466667 | 169 | 0.810474 | eng_Latn | 0.999398 |
4cf52d6eb7e378f512d59cc9ac3e9e080d5328b2 | 2,869 | md | Markdown | README.md | sparkfireworks/terraform-gke-creation | 55a3115c21a45cd9efc65b24eab867af66c4b73c | [
"MIT"
] | null | null | null | README.md | sparkfireworks/terraform-gke-creation | 55a3115c21a45cd9efc65b24eab867af66c4b73c | [
"MIT"
] | 1 | 2020-02-06T10:43:35.000Z | 2020-02-06T10:52:54.000Z | README.md | gnvalente92/terraform-gke-creation | 55a3115c21a45cd9efc65b24eab867af66c4b73c | [
"MIT"
] | null | null | null | # terraform-gke-creation
## Getting started
This guide follows under the assumption that `terraform` is correctly installed in the machine being used (for that, follow [Terraform installation page](https://learn.hashicorp.com/terraform/getting-started/install.html)).
### Get a `GCP` service account file
Follow the steps in the page [GCP service account creation](https://console.cloud.google.com/apis/credentials/serviceaccountkey) to obtain a `GCP` service account `json` file. Place it somewhere in the machine being used and change the variable `account_file_path` in `./creation/gke/container_cluster/variables.tf` to reflect it.
## Creating a `Kubernetes` cluster in `GCP`
### Create a credentials file for the Kubernetes master
Create a `.tf` file in `./creation/gke/container_cluster/` with the following structure:
```terraform
variable "master_auth_user" {
description = "Username for Kubernetes master"
default = "<USER_NAME>"
}
variable "master_auth_password" {
description = "Password for Kubernetes master"
default = "<PASSWORD>"
}
```
Choose adequate values for the parameters `<USER_NAME>` and `<PASSWORD>`, where the password must have at least 16 characters.
### Choose parameters for the cluster creation
Do the necessary changes to the file `./creation/gke/container_cluster/variables.tf` to reflect your cluster specifications. Addional parameters can be defined. See `./modules/gke/container_cluster/variables.tf` to see which ones have been specified in this project.
### Run `terraform`
Run the following commands to provision the cluster:
```sh
cd ./creation/gke/container_cluster/
terraform init # will setup the terraform project and download all needed dependencies
terraform plan # will present a plan of the actions to be performed, review the output before creating the cluster
terraform apply # will apply the plan, creating the k8s cluster
```
## Destroying resources
One of the many advantages of using `terraform` to provision a `Kubernetes` cluster in `GCP` is the ability to destroy everything that was created at once. When creating a cluster, multiple resources are provisioned (several VMs are created, for intance). With `terraform`, it is possible to destroy all resources in one go and without needing to remember them or to list. To destroy all resources, run the following commands:
```sh
cd ./creation/gke/container_cluster/
terraform destroy # will destroy all previously created cluster resources
```
## Make changes
This is a simple demonstration on how to setup a `Kubernetes` cluster in GCP, mostly with the default configurations. Many adjustments and configurations can be chosen for a `Kubernetes` cluster running on `GCP`. Check official documentation to make changes: [Terraform GKE cluster management](https://www.terraform.io/docs/providers/google/r/container_cluster.html).
| 51.232143 | 426 | 0.781108 | eng_Latn | 0.986783 |
4cf55c446abd5b39f4231156c49b94b770714497 | 70 | md | Markdown | README.md | samsmithnz/ReleaseTesting | 57b9a5e4732aafb8035931380fd07b3a05b6b2b3 | [
"MIT"
] | null | null | null | README.md | samsmithnz/ReleaseTesting | 57b9a5e4732aafb8035931380fd07b3a05b6b2b3 | [
"MIT"
] | 3 | 2021-12-20T03:17:10.000Z | 2022-01-30T18:12:58.000Z | README.md | samsmithnz/ReleaseTesting | 57b9a5e4732aafb8035931380fd07b3a05b6b2b3 | [
"MIT"
] | null | null | null | # ReleaseTesting
Learning how to use GitVersion. Upgrading to V2.3.2
| 17.5 | 51 | 0.785714 | eng_Latn | 0.984867 |
4cf5a47697c9f137523d997272b150811a64d361 | 879 | md | Markdown | README.md | duha253/lab-05 | b70c2e555715e869c31bc39bfd18860b65c633d7 | [
"MIT"
] | null | null | null | README.md | duha253/lab-05 | b70c2e555715e869c31bc39bfd18860b65c633d7 | [
"MIT"
] | null | null | null | README.md | duha253/lab-05 | b70c2e555715e869c31bc39bfd18860b65c633d7 | [
"MIT"
] | null | null | null | # lab-05
URL live
https://dashboard.heroku.com/apps/creative-appd/deploy/github
https://creative-appd.herokuapp.com/
**Number and name of feature: Feature #1: Deployment**
Estimate of time needed to complete: 30 min
Start time: 7:30
Finish time: 8:15
Actual time needed to complete: 45 min
**Number and name of feature: Feature #2: Refactor the CSS**
Estimate of time needed to complete: 1 hour and 30 min
Start time: 11:08pm
Finish time: 12:13
Actual time needed to complete: 1 hour and 6 min
**Number and name of feature: Feature #3: Modify the contents**
Estimate of time needed to complete: 3 hour
Start time: 10:00am
Finish time: 1:00pm
Actual time needed to complete: 3 hour
**Number and name of feature: Feature #4: Add functionality**
Estimate of time needed to complete:
Start time:
Finish time:
Actual time needed to complete: | 15.421053 | 63 | 0.729238 | eng_Latn | 0.992956 |
4cf684856d4bf926983b189e06c0f7796d20f9ab | 167 | md | Markdown | _characters/jaxzon_finch.md | lordp/poole | a261bb7192148671a04fb3e76de225a1d65b9f88 | [
"MIT"
] | null | null | null | _characters/jaxzon_finch.md | lordp/poole | a261bb7192148671a04fb3e76de225a1d65b9f88 | [
"MIT"
] | null | null | null | _characters/jaxzon_finch.md | lordp/poole | a261bb7192148671a04fb3e76de225a1d65b9f88 | [
"MIT"
] | null | null | null | ---
name: Jaxzon Finch
class: Paladin (Oath of Conquest)
level: 5
race: Human
layout: character
---
Brother of Eldur, he set out in search of him after losing contact. | 20.875 | 67 | 0.742515 | eng_Latn | 0.99601 |
4cf6c72c4c0a9925cd0bcfd69e850b1f35f3817d | 1,568 | md | Markdown | README.md | coderuse/coderuse-single-spa | 290b4661d8375a8cd1a21c24ac3e77c0ee725e50 | [
"Apache-2.0"
] | null | null | null | README.md | coderuse/coderuse-single-spa | 290b4661d8375a8cd1a21c24ac3e77c0ee725e50 | [
"Apache-2.0"
] | null | null | null | README.md | coderuse/coderuse-single-spa | 290b4661d8375a8cd1a21c24ac3e77c0ee725e50 | [
"Apache-2.0"
] | null | null | null | # CodeRuse Single SPA
Simple Single SPA POC built with https://single-spa.js.org
Till now we have only mounted various type of applications (Angular, React and Vue) onto Single-SPA default root config template.
### Configuration
``` bash
cd <project-location>/src/coderuse/angular
npm install
npm run serve:single-spa:hello-angular # runs the angular app at port 4200
# open another terminal
cd <project-location>/src/coderuse/react
npm install
npm start -- --port 8500 # runs the react app at port 8500
# open another terminal
cd <project-location>/src/coderuse/vue
npm install
# Vue by default enables hot reload and it has no default flag to disable this
# to by-pass this issue
npm run devw # it builds the vue app and watches for new file changes
# open another terminal and serve the built Vue app with cors enabled
# we can use other web server also to serve static content
cd <project-location>/src/coderuse/vue/dist
npm i -g http-server # if already not installed
http-server --cors
# open another terminal
cd <project-location>/src/spa
npm install
npm start # runs the Single-SPA app at port 9000
```
Access the Angular App at `http://localhost:9000/hello-angular`, React App at `http://localhost:9000/hello-react` and Vue app at `http://localhost:9000/hello-vue`.
### Roadmap
Still this project is at an nascent stage. A long way to go. We have put up a simple design diagram to describe our approach to achieve the Micro-Fronend architecture.

| 34.844444 | 167 | 0.771684 | eng_Latn | 0.963105 |
4cf7a92121c7d7f412ec6009e89ed4484937feaf | 838 | md | Markdown | gokafkademo/GolangSDKOverview.md | xiexuehui1124/ckafka-sdk-demo | a9f2697de0f9e1f43da4be0ee3d9e3e9d91ddf62 | [
"Apache-2.0"
] | null | null | null | gokafkademo/GolangSDKOverview.md | xiexuehui1124/ckafka-sdk-demo | a9f2697de0f9e1f43da4be0ee3d9e3e9d91ddf62 | [
"Apache-2.0"
] | null | null | null | gokafkademo/GolangSDKOverview.md | xiexuehui1124/ckafka-sdk-demo | a9f2697de0f9e1f43da4be0ee3d9e3e9d91ddf62 | [
"Apache-2.0"
] | null | null | null | # GO SDK概述
Go 客户端可以通过消息队列CKafka版提供的多种接入点接入并收发消息。
消息队列Kafka版提供以下接入点。
| 项目 | **默认接入点** | **SASL接入点** |
| :------- | ---------------------- | ------------------------------------------------------------ |
| 网络 | VPC | VPC |
| 协议 | PLAINTEXT | SASL_PLAINTEXT |
| 端口 | 9092 | 请在Ckafka控制台-基本信息-接入方式-公网域名接入方式确认SASL接入点信息。 |
| SASL机制 | 不适用 | PLAIN:一种简单的用户名密码校验机制。 |
| Demo | [PLAINTEXT]() | [SASL_PLAINTEXT/PLAIN]() |
| 文档 | [默认接入点收发消息]() | [SASL接入点PLAIN机制收发消息]() |
| 55.866667 | 137 | 0.285203 | yue_Hant | 0.737962 |
4cf7afa3671f36faabda8b40aae3f0a5dfac2d44 | 26 | md | Markdown | README.md | KuntanuryCreater/XiangShengJuBen | 9572c22473133346f641a3f5a5d07bda2dabb213 | [
"MIT"
] | 1 | 2018-01-04T07:11:59.000Z | 2018-01-04T07:11:59.000Z | README.md | KuntanuryCreater/XiangShengJuBen | 9572c22473133346f641a3f5a5d07bda2dabb213 | [
"MIT"
] | null | null | null | README.md | KuntanuryCreater/XiangShengJuBen | 9572c22473133346f641a3f5a5d07bda2dabb213 | [
"MIT"
] | null | null | null | # XiangShengJuBen
ABC相声剧本
| 8.666667 | 17 | 0.846154 | deu_Latn | 0.327607 |
4cf7f4f72f90bffd426b7d59cea24796897a54fc | 1,928 | md | Markdown | sdk-api-src/content/oleauto/nf-oleauto-createtypelib2.md | amorilio/sdk-api | 54ef418912715bd7df39c2561fbc3d1dcef37d7e | [
"CC-BY-4.0",
"MIT"
] | null | null | null | sdk-api-src/content/oleauto/nf-oleauto-createtypelib2.md | amorilio/sdk-api | 54ef418912715bd7df39c2561fbc3d1dcef37d7e | [
"CC-BY-4.0",
"MIT"
] | null | null | null | sdk-api-src/content/oleauto/nf-oleauto-createtypelib2.md | amorilio/sdk-api | 54ef418912715bd7df39c2561fbc3d1dcef37d7e | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
UID: NF:oleauto.CreateTypeLib2
title: CreateTypeLib2 function (oleauto.h)
description: Creates a type library in the current file format.
helpviewer_keywords: ["CreateTypeLib2","CreateTypeLib2 function [Automation]","_oa96_CreateTypeLib2","automat.createtypelib2","oleauto/CreateTypeLib2"]
old-location: automat\createtypelib2.htm
tech.root: automat
ms.assetid: 73df6ef2-fae1-4cfb-ba59-3812e3a2e3b9
ms.date: 12/05/2018
ms.keywords: CreateTypeLib2, CreateTypeLib2 function [Automation], _oa96_CreateTypeLib2, automat.createtypelib2, oleauto/CreateTypeLib2
req.header: oleauto.h
req.include-header:
req.target-type: Windows
req.target-min-winverclnt:
req.target-min-winversvr:
req.kmdf-ver:
req.umdf-ver:
req.ddi-compliance:
req.unicode-ansi:
req.idl:
req.max-support:
req.namespace:
req.assembly:
req.type-library:
req.lib: OleAut32.lib
req.dll: OleAut32.dll
req.irql:
targetos: Windows
req.typenames:
req.redist:
ms.custom: 19H1
f1_keywords:
- CreateTypeLib2
- oleauto/CreateTypeLib2
dev_langs:
- c++
topic_type:
- APIRef
- kbSyntax
api_type:
- DllExport
api_location:
- OleAut32.dll
api_name:
- CreateTypeLib2
---
# CreateTypeLib2 function
## -description
Creates a type library in the current file format.
The file and in-memory format for the current version of Automation makes use of memory-mapped files. The <a href="/previous-versions/windows/desktop/api/oleauto/nf-oleauto-createtypelib">CreateTypeLib</a> function is still available for creating a type library in the older format.
## -parameters
### -param syskind
The target operating system for which to create a type library.
### -param szFile
The name of the file to create.
### -param ppctlib
The <a href="/previous-versions/windows/desktop/api/oaidl/nn-oaidl-icreatetypelib2">ICreateTypeLib2</a> interface.
## -returns
If this function succeeds, it returns <b>S_OK</b>. Otherwise, it returns an <b>HRESULT</b> error code. | 26.410959 | 282 | 0.775934 | eng_Latn | 0.446405 |
4cf82a94d72ff87c07594bdb083e541688768fac | 549 | md | Markdown | tests/test_remote_azure/README.md | graingert/snakemake | 4a63a26959cd0626e2113e48b4d4fe5a5421d954 | [
"MIT"
] | 1,326 | 2019-10-04T15:11:20.000Z | 2022-03-31T18:39:40.000Z | tests/test_remote_azure/README.md | graingert/snakemake | 4a63a26959cd0626e2113e48b4d4fe5a5421d954 | [
"MIT"
] | 1,496 | 2019-10-04T15:15:12.000Z | 2022-03-31T23:14:33.000Z | tests/test_remote_azure/README.md | graingert/snakemake | 4a63a26959cd0626e2113e48b4d4fe5a5421d954 | [
"MIT"
] | 375 | 2019-10-08T21:28:51.000Z | 2022-03-28T18:44:36.000Z | # Instruction for testing of Azure Storage integration
In order to perform this test, you need an Azure Storage account
with read/write access.
Both the storage account and associated key or SAS token (without
leading questionmark) need to be
passed to snakemake at runtime, by exporting
environment variables `AZURE_ACCOUNT` and either `AZURE_KEY` or
`SAS_TOKEN`.
Furthermore, in the storage account, a container "snakemake-test"
needs to be created prior to running the test.
And lastly, a local file called `test.txt.gz` needs to be created.
| 34.3125 | 66 | 0.795993 | eng_Latn | 0.998854 |
4cf8395237d18476a7ef49d357aed5780326d0d2 | 30 | md | Markdown | sites/ZA-UJ/README.md | ezeasorekene/DevOps | f72478c9ca6295f236f0be87db3052b28d0f567e | [
"MIT"
] | 18 | 2015-03-19T12:50:32.000Z | 2021-03-03T18:35:56.000Z | sites/ZA-UJ/README.md | ezeasorekene/DevOps | f72478c9ca6295f236f0be87db3052b28d0f567e | [
"MIT"
] | 209 | 2015-01-05T14:28:48.000Z | 2020-08-19T18:13:57.000Z | sites/ZA-UJ/README.md | AAROC/DevOps | ae5e2edd9248c108fe4f89fe5527010b84956f08 | [
"MIT"
] | 36 | 2015-03-05T09:38:17.000Z | 2020-06-25T03:44:44.000Z | # University of Johannnesburg
| 15 | 29 | 0.833333 | eng_Latn | 0.713439 |
4cf874d36d04ed0f9e23531ceb3f5d4a0c7bd5a5 | 1,143 | md | Markdown | collections/_traducoes/portatil/game-boy/mega-man-dr.-wily's-revenge-(emunow).md | leomontenegro6/romhackersbr.github.io | 6819d18b194c467f9b85533337f13e599d6dab59 | [
"MIT"
] | 1 | 2021-08-30T14:42:15.000Z | 2021-08-30T14:42:15.000Z | collections/_traducoes/portatil/game-boy/mega-man-dr.-wily's-revenge-(emunow).md | leomontenegro6/romhackersbr.github.io | 6819d18b194c467f9b85533337f13e599d6dab59 | [
"MIT"
] | null | null | null | collections/_traducoes/portatil/game-boy/mega-man-dr.-wily's-revenge-(emunow).md | leomontenegro6/romhackersbr.github.io | 6819d18b194c467f9b85533337f13e599d6dab59 | [
"MIT"
] | null | null | null | ---
title: " Mega Man - Dr. Wily's Revenge (EmuNow)"
system: "Game Boy"
platform: "Portátil"
game_title: "Mega Man - Dr. Wily's Revenge"
game_category: "Ação / Tiro / Plataforma"
game_players: "1"
game_developer: "Capcom"
game_publisher: "Capcom"
game_release_date: "1991"
patch_author: "Emuboarding"
patch_group: "EmuNow (extinto)"
patch_site: "//www.emunow.cjb.net/ (fora do ar)"
patch_version: "???"
patch_release: "17/10/1999 (provavelmente)"
patch_type: "IPS"
patch_progress: "???"
patch_images: ["//img.romhackers.org/traducoes/%5BGB%5D%20Megaman%20-%20Dr.%20Wily's%20Revenge%20-%20EmuNow%20-%2001.png","//img.romhackers.org/traducoes/%5BGB%5D%20Megaman%20-%20Dr.%20Wily's%20Revenge%20-%20EmuNow%20-%2002.png","//img.romhackers.org/traducoes/%5BGB%5D%20Megaman%20-%20Dr.%20Wily's%20Revenge%20-%20EmuNow%20-%2003.png"]
---
Esta tradução está razoável. Os poucos textos do jogo foram traduzidos e parcialmente acentuados. Os gráficos não foram editados, e nota-se erros de ortografia em algumas ocasiões.ATENÇÃO:Esta tradução deve ser aplicada na ROM original Megaman - Dr. Wily's Revenge (U) [!].gb, com CRC32 47E70E08. | 57.15 | 337 | 0.736658 | por_Latn | 0.664484 |
4cf87ade45a68dcdb30acbc5cb20ccd1b6ab611f | 178 | md | Markdown | java-client/docs/Auth1CheckuninstallpwdReq.md | ikechan8370/bhpan-student-group-importer | 4e7fde671baea0aa884d5eaca460630acaee237b | [
"MIT"
] | null | null | null | java-client/docs/Auth1CheckuninstallpwdReq.md | ikechan8370/bhpan-student-group-importer | 4e7fde671baea0aa884d5eaca460630acaee237b | [
"MIT"
] | 2 | 2022-03-11T13:23:42.000Z | 2022-03-15T12:07:34.000Z | java-client/docs/Auth1CheckuninstallpwdReq.md | ikechan8370/bhpan-student-group-importer | 4e7fde671baea0aa884d5eaca460630acaee237b | [
"MIT"
] | null | null | null | # Auth1CheckuninstallpwdReq
## Properties
Name | Type | Description | Notes
------------ | ------------- | ------------- | -------------
**uninstallpwd** | **String** | 卸载口令 |
| 25.428571 | 60 | 0.455056 | eng_Latn | 0.084611 |
4cf8a14c18219c5211fccbc3f122d9b19efafbaa | 9,437 | md | Markdown | Documentation/Using-Azure-TestFramework.md | v-djnisi/azure-sdk-for-net | 0a9f85b60f70649dd16829173f63566dba56a5cd | [
"MIT"
] | null | null | null | Documentation/Using-Azure-TestFramework.md | v-djnisi/azure-sdk-for-net | 0a9f85b60f70649dd16829173f63566dba56a5cd | [
"MIT"
] | 2 | 2018-07-24T13:59:07.000Z | 2018-07-31T04:46:00.000Z | Documentation/Using-Azure-TestFramework.md | lebronJ/azure-sdk-for-net | 98df1e632c7dbe3e75a50170c3def84b12c809fa | [
"MIT"
] | null | null | null | # Using Microsoft.Rest.ClientRuntime.Azure.TestFramework #
1. Getting Started
2. Accquring TestFramework
3. Setup prior to Record/Playback tests
1. Environment Variables
2. Playback Test
3. Record Test with Interactive login using OrgId
4. Record Test with ServicePrincipal
4. Record/Playback tests
5. Change Test Environment settings at run-time
6. Troubleshooting
7. Supported Key=Value pairs in ConnectionString
8. Environment Variable Reference
## 2. Accquring TestFramework
TestFramework is available on NuGet at https://www.nuget.org/packages/Microsoft.Rest.ClientRuntime.Azure.TestFramework/ .
Instructions to manually download it are available on NuGet. However TestFramework will be downloaded automatically as part of the build process, so manually downloading it should generally be unnecessary.
## 3. Setup prior to Record/Playback of tests
In order to Record/Playback a test, you need to setup a connection string that consists various key/value pairs that provides information to the test environment.
#### 3.1 Environment Variables
> TEST_CSM_ORGID_AUTHENTICATION
Value of the env. variable is the connection string that determines how to connect to Azure. This includes authentiation and the Azure environment to connect to.
> AZURE_TEST_MODE
This specifies whether test framework will `Record` test sessions or `Playback` previously recorded test sessions.
#### 3.2 Playback Test
The default mode is Playback mode, so no setting up of connection string is required.
#### 3.3 Record Test with Interactive login using OrgId
This is no longer the preferred option because it only works when running on .NET Framework (Full Desktop version of .NET - 4.5.1+) When running on .NET Core you may get an error like `Interactive Login is supported only in NET45 projects`.
To use interactive login, set the following environment variables before starting Visual Studio:
TEST_CSM_ORGID_AUTHENTICATION=SubscriptionId={SubId};AADTenant={tenantId};Environment={env};HttpRecorderMode=Record;
AZURE_TEST_MODE=Record
#### 3.4 Record Test with ServicePrincipal
This is the preferred option for record because it works with both .NET Framework and .NET Core.
To create a service principal, follow the [Azure AD guide to create a Application Service Principal](https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-create-service-principal-portal#create-an-active-directory-application). The application type should be `Web app / API` and the sign-on URL value is irrelevant (you can set any value).
After the service principal is created, you will need to give it access to Azure resources. This can be done with the following PowerShell command, with the [Service Principal Application ID](https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-create-service-principal-portal#get-application-id-and-authentication-key) (this is a guid, not the display name of the service principal) substituted in for `{clientId}`.
New-AzureRmRoleAssignment -ServicePrincipalName {clientId} -RoleDefinitionName Contributor
To use this option, set the following environment variable before starting Visual Studio. The following values are substituted into the below connection string:
`clientId`: The [Service Principal Application ID](https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-create-service-principal-portal#get-application-id-and-authentication-key)
`clientSecret`: A [Service Principal Authentication Key](https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-create-service-principal-portal#get-application-id-and-authentication-key)
`tenantId`: The [AAD Tenant ID](https://docs.microsoft.com/en-us/azure/azure-resource-manager/resource-group-create-service-principal-portal#get-tenant-id)
TEST_CSM_ORGID_AUTHENTICATION=SubscriptionId={SubId};ServicePrincipal={clientId};ServicePrincipalSecret={clientSecret};AADTenant={tenantId};Environment={env};HttpRecorderMode=Record;
AZURE_TEST_MODE=Record
## 4. Record/Playback Tests
1. Run the test and make sure that you got a generated .json file that matches the test name in the bin folder under *SessionRecords folder
2. Copy SessionRecords folder inside the test project and add all *.json files in Visual Studio setting "Copy to Output Directory" property to "Copy if newer"
3. To assure that the records work fine, delete the connection string (default mode is Playback mode) OR change HttpRecorderMode within the connection string to "Playback"
## 5. Change Test Environment settings at run-time
#### 1. Once you set your connection string, you can add or update key/value settings
Add new key/value pair
TestEnvironment.ConnectionString.KeyValuePairs.Add("Foo", "FooValue");
Update Existing key/value pair
TestEnvironment.ConnectionString.KeyValuePairs["keyName"]="new value"
Accessing/Updating TestEndpoints
TestEnvironment.Endpoints.GraphUri = new Uri("https://newGraphUri.windows.net");
###Note:###
Changing the above properties at run-time has the potential to hard code few things in your tests. Best practice would be to use these properties to change values at run-time from immediate window at run-time and avoid hard-coding certain values.
## 6. Troubleshooting
#### Issue: exceptions in Microsoft.Azure.Test.HttpRecorder
Ensure that the `HttpRecorderMode` in the `TEST_CSM_ORGID_AUTHENTICATION` environment variable is consistent with the value in `AZURE_TEST_MODE` environment variable.
##7. Connection string
#### 7.1 Supported Key=Value pairs in Connectionstring
* ManagementCertificate
* SubscriptionId
* AADTenant
* UserId
* Password
* ServicePrincipal
* ServicePrincipalSecret
* Environment={Prod | DogFood | Next | Current | Custom}
* RawToken
* RawGraphToken
* HttpRecorderMode={Record | Playback}
* AADAuthEndpoint
* GraphTokenAudienceUri
* BaseUri
* AADAuthUri
* GalleryUri
* GraphUri
* IbizaPortalUri
* RdfePortalUri
* ResourceManagementUri
* ServiceManagementUri
* AADTokenAudienceUri
* GraphTokenAudienceUri
* DataLakeStoreServiceUri
* DataLakeAnalyticsJobAndCatalogServiceUri
## 8. Supported Environment in Test framework (Azure environments)
#### 8.1 Default Environments and associated Uri
##### Environment = Prod
AADAuthUri = "https://login.microsoftonline.com"
GalleryUri = "https://gallery.azure.com/"
GraphUri = "https://graph.windows.net/"
IbizaPortalUri = "https://portal.azure.com/"
RdfePortalUri = "http://go.microsoft.com/fwlink/?LinkId=254433"
ResourceManagementUri = "https://management.azure.com/"
ServiceManagementUri = "https://management.core.windows.net"
AADTokenAudienceUri = "https://management.core.windows.net"
GraphTokenAudienceUri = "https://graph.windows.net/"
DataLakeStoreServiceUri = "https://azuredatalakestore.net"
DataLakeAnalyticsJobAndCatalogServiceUri = "https://azuredatalakeanalytics.net"
##### Environment = Dogfood
AADAuthUri = "https://login.windows-ppe.net";
GalleryUri = "https://df.gallery.azure-test.net/";
GraphUri = "https://graph.ppe.windows.net/";
IbizaPortalUri = "http://df.onecloud.azure-test.net";
RdfePortalUri = "https://windows.azure-test.net";
ResourceManagementUri = "https://api-dogfood.resources.windows-int.net/";
ServiceManagementUri = "https://management-preview.core.windows-int.net";
AADTokenAudienceUri = "https://management.core.windows.net";
GraphTokenAudienceUri = "https://graph.ppe.windows.net/";
DataLakeStoreServiceUri = "https://caboaccountdogfood.net";
DataLakeAnalyticsJobAndCatalogServiceUri = "https://konaaccountdogfood.net";
##### Environment = Next
AADAuthUri = "https://login.windows-ppe.net"
GalleryUri = "https://next.gallery.azure-test.net/"
GraphUri = "https://graph.ppe.windows.net/"
IbizaPortalUri = "http://next.onecloud.azure-test.net"
RdfePortalUri = "https://auxnext.windows.azure-test.net"
ResourceManagementUri = "https://api-next.resources.windows-int.net/"
ServiceManagementUri = "https://managementnext.rdfetest.dnsdemo4.com"
AADTokenAudienceUri = "https://management.core.windows.net"
GraphTokenAudienceUri = "https://graph.ppe.windows.net/"
DataLakeStoreServiceUri = "https://caboaccountdogfood.net"
DataLakeAnalyticsJobAndCatalogServiceUri = "https://konaaccountdogfood.net"
##### Environment = Current
AADAuthUri = "https://login.windows-ppe.net"
GalleryUri = "https://df.gallery.azure-test.net/"
GraphUri = "https://graph.ppe.windows.net/"
IbizaPortalUri = "http://df.onecloud.azure-test.net"
RdfePortalUri = "https://windows.azure-test.net"
ResourceManagementUri = "https://api-dogfood.resources.windows-int.net/"
ServiceManagementUri = "https://management-preview.core.windows-int.net"
AADTokenAudienceUri = "https://management.core.windows.net"
GraphTokenAudienceUri = "https://graph.ppe.windows.net/"
DataLakeStoreServiceUri = "https://caboaccountdogfood.net"
DataLakeAnalyticsJoAbndCatalogServiceUri = "https://konaaccountdogfood.net"
##### Environment = Custom
When specified, test framework expect all Uri's to be provided by the user as part of the connection string.
What is also supported is as below (connections string example)
>SubscriptionId=subId;Environment=Prod;AADAuthUri=customAuthUri;ResourceManagementUri=CustomResourceMgmtUri
Which translates to, all Uri from pre-defined Prod environment will be used, but AADAuthUri and ResourceManagementUri will be overridden by the one provided in the connection string
| 48.394872 | 440 | 0.791141 | eng_Latn | 0.623421 |
4cf9cd7583bbc6214c89fca609b1a9faf5325737 | 2,129 | md | Markdown | Readme.md | akwick/sqinco | e4171dabf22fd2a76358fbbde574ae0e8e97a567 | [
"MIT"
] | 2 | 2017-01-16T15:49:12.000Z | 2017-01-17T00:32:40.000Z | Readme.md | akwick/sqinco | e4171dabf22fd2a76358fbbde574ae0e8e97a567 | [
"MIT"
] | 1 | 2017-02-09T12:44:39.000Z | 2017-02-10T13:14:01.000Z | Readme.md | akwick/sqinco | e4171dabf22fd2a76358fbbde574ae0e8e97a567 | [
"MIT"
] | 1 | 2021-08-23T16:13:48.000Z | 2021-08-23T16:13:48.000Z | # sqinco - **SQ**L **In**jection **Co**mparison
A small set of test cases to compare the precision of several SQL injection detection tools.
## Installation and Usage
Instal the tool with the *go get* command.
`` go get github.com/akwick/sqinco ``
After the installation, you can to compare the programs.
We have written a shell script which helps to execute three static analysis:
* Safesql
* gas
* Gotcha
If you are aware of more tools, we are glad to hear about them.
To be able to execute all the static analysis tools, you need an installation of the tools on your computer. Check the GitHub repositories of those projects for the installation process.
As an alternative, we offer a docker image which will install these three tools.
You find the docker file in the folder *docker*.
```
cd docker
docker build -t sqinco .
```
For further information about Docker, study the tutorials for your platform. In some configurations it can be necessary that you execute the docker command with *sudo*.
One variant to run the comparision.sh file is to start the docker image and execute it within the image.
You can do this by executing following commands.
```
docker run -t -i sqinco
cd src/github.com/akwick/sqinco/
./runComparison.sh
exit
```
## Benchmark tests included
We have currently two benchmark tests:
* The first is in the folder *sqlInjection* and tests all the three tools against the analysis of all the files in this folder.
* The second is in the folder *benchmarks*. This benchmark test analyses a bigger project - the gotcha analysis.
The benchmarks can be executed in the docker image too. Be sure that you have installed the docker image for sqinco.
```
docker run -t -i sqinco
cd src/github.com/akwick/sqinco/sqlInjections/
go test -bench=.
exit
```
It is possible to adopt the running time of the benchmark test with a command line flag ``go test -run=XXX -bench=. -benchtime=10s``.
With the same commands it is possible to execute the benachmark tests included in the benchmark folder. Instead of changing in the folder sqlInjection, one has to change in the folder benchmakrs.
| 34.33871 | 195 | 0.764678 | eng_Latn | 0.998941 |
4cfa7ea2b077d727ec7e7e0db74a12517370b60b | 3,571 | md | Markdown | README.md | maximbilan/iOS-UIImage-render-to-PDF | de9e0c5008d6b17d0cf6fdd9c50e1080997d65c7 | [
"MIT"
] | 10 | 2015-11-06T20:06:44.000Z | 2021-09-28T09:08:14.000Z | README.md | maximbilan/iOS-UIImage-render-to-PDF | de9e0c5008d6b17d0cf6fdd9c50e1080997d65c7 | [
"MIT"
] | null | null | null | README.md | maximbilan/iOS-UIImage-render-to-PDF | de9e0c5008d6b17d0cf6fdd9c50e1080997d65c7 | [
"MIT"
] | 1 | 2021-03-15T05:56:27.000Z | 2021-03-15T05:56:27.000Z | # iOS Render UIImage to PDF and merging PDF files

Some code samples for working with <i>PDF</i>. Let’s try to generate 1000 images and render to <i>PDF</i> file. For this, we need a method for generating a random color and a method for creating <i>UIImage</i> from <i>UIColor</i>.
A random color:
<pre>
- (UIColor *)randomColor
{
CGFloat hue = (arc4random() % 256 / 256.0);
CGFloat saturation = (arc4random() % 128 / 256.0) + 0.5;
CGFloat brightness = (arc4random() % 128 / 256.0 ) + 0.5;
return [UIColor colorWithHue:hue saturation:saturation brightness:brightness alpha:1];
}
</pre>
And <i>UIImage</i> from <i>UIColor</i>:
<pre>
- (UIImage *)imageFromColor:(UIColor *)color
{
CGRect rect = CGRectMake(0, 0, 1024, 1024);
UIGraphicsBeginImageContext(rect.size);
CGContextRef context = UIGraphicsGetCurrentContext();
CGContextSetFillColorWithColor(context, [color CGColor]);
CGContextFillRect(context, rect);
UIImage *image = UIGraphicsGetImageFromCurrentImageContext();
UIGraphicsEndImageContext();
return image;
}
</pre>
And now we can render random images to <i>PDF</i> file.
<pre>
UIGraphicsBeginPDFContextToFile(filename, CGRectMake(0, 0, 1024, 1024), nil);
for (NSInteger i = 0; i < 1000; ++i) {
UIImage *image = [self imageFromColor:[self randomColor]];
@autoreleasepool {
UIGraphicsBeginPDFPage();
[image drawAtPoint:CGPointZero];
}
}
UIGraphicsEndPDFContext();
</pre>
<b>Attention!</b> Necessarily use <i>@autoreleasepool</i>, otherwise, you will have memory leaks.
Also, I would like to provide some sample for generating <i>PDF</i> files and merging these files. It’s also simple.
<pre>
NSMutableArray *pdfURLs = [NSMutableArray array];
for (NSInteger i = 0; i < 1000; ++i) {
NSString *pdfFile = [NSString stringWithFormat:@”%@_%@”, filename, @(i)];
UIImage *imageToRender = [self imageFromColor:[self randomColor]];
@autoreleasepool {
UIGraphicsBeginPDFContextToFile(pdfFile, CGRectMake(0, 0, 1024, 1024), nil);
UIGraphicsBeginPDFPage();
[imageToRender drawAtPoint:CGPointZero];
UIGraphicsEndPDFContext();
}
[pdfURLs addObject:[NSURL fileURLWithPath:pdfFile]];
}
[self combinePDFURLs:pdfURLs writeToURL:[NSURL fileURLWithPath:filename]];
for (NSURL *pdfUrl in pdfURLs) {
[[NSFileManager defaultManager] removeItemAtURL:pdfUrl error:nil];
}
</pre>
And of course, implementation of <i>combinePDFURLs</i> method, see below:
<pre>
- (void)combinePDFURLs:(NSArray *)PDFURLs writeToURL:(NSURL *)URL
{
CGContextRef context = CGPDFContextCreateWithURL((__bridge CFURLRef)URL, NULL, NULL);
for (NSURL *PDFURL in PDFURLs) {
CGPDFDocumentRef document = CGPDFDocumentCreateWithURL((__bridge CFURLRef)PDFURL);
size_t numberOfPages = CGPDFDocumentGetNumberOfPages(document);
for (size_t pageNumber = 1; pageNumber <= numberOfPages; ++pageNumber) {
CGPDFPageRef page = CGPDFDocumentGetPage(document, pageNumber);
CGRect mediaBox = CGPDFPageGetBoxRect(page, kCGPDFMediaBox);
CGContextBeginPage(context, &mediaBox);
CGContextDrawPDFPage(context, page);
CGContextEndPage(context);
}
CGPDFDocumentRelease(document);
}
CGPDFContextClose(context);
CGContextRelease(context);
}
</pre>
And the result:

Happy coding!
| 31.883929 | 230 | 0.702044 | yue_Hant | 0.860005 |
4cfb1372b1115e397f5fac464461c928f5fa5205 | 5,520 | md | Markdown | _posts/2017-02-10-女人凭什么出卖子宫?代孕的性别、阶级、种族问题.md | NodeBE4/opinion | 81a7242230f02459879ebc1f02eb6fc21507cdf1 | [
"MIT"
] | 21 | 2020-07-20T16:10:55.000Z | 2022-03-14T14:01:14.000Z | _posts/2017-02-10-女人凭什么出卖子宫?代孕的性别、阶级、种族问题.md | NodeBE4/opinion | 81a7242230f02459879ebc1f02eb6fc21507cdf1 | [
"MIT"
] | 1 | 2020-07-19T21:49:44.000Z | 2021-09-16T13:37:28.000Z | _posts/2017-02-10-女人凭什么出卖子宫?代孕的性别、阶级、种族问题.md | NodeBE4/opinion | 81a7242230f02459879ebc1f02eb6fc21507cdf1 | [
"MIT"
] | 1 | 2021-05-29T19:48:01.000Z | 2021-05-29T19:48:01.000Z | ---
layout: post
title: "女人凭什么出卖子宫?代孕的性别、阶级、种族问题"
date: 2017-02-10
author: 张烨
from: http://cnpolitics.org/2017/02/a-race-class-and-gender-analysis-of-surrogacy/
tags: [ 政見 ]
categories: [ 政見 ]
---
<div class="post-block">
<h1 class="post-head">
女人凭什么出卖子宫?代孕的性别、阶级、种族问题
</h1>
<p class="post-subhead">
</p>
<p class="post-tag">
</p>
<p class="post-author">
<!--a href="http://cnpolitics.org/author/zhangye/">张烨</a-->
<a href="http://cnpolitics.org/author/zhangye/">
张烨
</a>
<span style="font-size:14px;color:#b9b9b9;">
|2017-02-10
</span>
</p>
<!--p class="post-lead">一旦代孕市场形成,市场必然会自动寻找那些最 “便宜”、“好用” 的女人:穷人、黑人、第三世界的人。</p-->
<div class="post-body">
<figure>
<img alt="" src="http://cnpolitics.org/wp-content/uploads/2017/02/1002.jpg" width="566">
<figcaption>
</figcaption>
</img>
</figure>
<p>
随着生育技术的发展,代孕开始成为中国家庭关注的话题。对于想生孩子却因年龄、疾病等无法生育的人而言,代孕或许是一种解决方法。但目前为止,这种方法在国内仍是被禁止的。《人民日报》 近日刊文讨论代孕,一度被网民理解为代孕将要合法化,但这一说法随后被国家卫计委否认。可见在这一问题上,官方的态度仍然是审慎的。
</p>
<p>
为什么代孕不应轻易开放?开放代孕将带来哪些后果?美国韦恩州立大学的研究者 Heather Dillaway 基于美国的研究,就从性别、阶级、种族等多方面分析了代孕可能存在的问题。
</p>
<p>
<strong>
婴儿所有权的争夺
</strong>
</p>
<p>
代孕主要有两种形式,一种是由代孕者提供卵子且怀胎分娩,产下的孩子将拥有代孕者一半的基因;另一种则由夫妻中的妻子提供卵子,代孕者只负责怀胎分娩,产下的孩子与代孕者没有基因上的联系。
</p>
<p>
研究者首先介绍了两起典型的由代孕引发的官司。第一起代孕发生在 1985 年,一对夫妻因妻子有较高的生育风险,而丈夫希望延续血脉 (他的大多数亲人都死于大屠杀),因而寻求代孕。他们与另一名已婚女性签署了代孕合同,后者需提供卵子及怀胎分娩,完成后该夫妻将向代孕者支付 1 万美元。
</p>
<p>
然而在孩子诞生后,这名代孕者却无法割舍对孩子的感情。她恳求夫妻让她把孩子接回家中小住,却迟迟没有归还。这对夫妻向警方报案,警方在四个月后将孩子从代孕者父母的家中寻回。在法庭诉讼中,预审法院判决代孕合同有效,宣布终止代孕者的家长权利。代孕者随后上诉,新泽西州高等法院认为相关行为可能涉及婴儿买卖,但承认代孕者享有作为 “自然母亲” 的法律权力,虽然孩子的主要监护权将归夫妻所有,代孕者将拥有探视权。
</p>
<p>
第二起代孕发生在 1990 年,一对想拥有孩子的夫妻,因妻子患病后部分切除了子宫而寻求代孕。他们和一名女性签署了代孕合同,由这名妻子提供卵子,由代孕者怀胎和分娩。这对夫妻将向代孕者分期支付 1 万美元,考虑到后者还有一个三岁的女儿,他们还将为她支付 2 万美元的保险费。
</p>
<p>
然而在合同执行过程中,这对夫妻发现代孕者隐瞒了自己曾有过数次死胎和流产的经历,而代孕者也因对方没有付足够的保险费而感到不满,并且由于出现了早产迹象,她感到自己将被抛弃。她随后写信要求该夫妻支付合约中的剩余金额,否则她就把孩子打掉。双方后分别向法院起诉,争夺孩子的所有权。在代孕者产下一名男婴后,血液鉴定显示,她与男婴没有基因关系。法院最终判决夫妻胜出,代孕者没有获得任何法律上的家长权利,包括探视权,她向加州上诉庭提起的上诉也未能改变结果。
</p>
<p>
<strong>
女性生育职能的贬低
</strong>
</p>
<p>
研究者分析指,代孕造成的婴儿所有权争议,体现了母亲角色的进一步碎片化。通俗地讲,以前只有 “生母” 和 “养母” 的分别,现在 “生母” 又分成了提供卵子的 “基因母亲” 和怀胎并分娩的 “妊娠母亲”。案例一中,代孕者既是基因母亲,也是妊娠母亲。案例二中,代孕者只是妊娠母亲。而争议在于哪一种母亲角色是决定性的,基因母亲、妊娠母亲,哪一个更能决定孩子的归属?
</p>
<p>
从判决结果来看,基因被赋予了更重要的地位。研究者指出,这与父权社会的结构息息相关。以往的社会学学者已经指出,在人们对基因缺乏了解时,男性一度被认为是基因的唯一提供者,是真正的创造者,而女性只是他们精子的 “孵化器”。随着科学的发展,男性不得不承认女性也提供了一半基因。他们开始和女性分享一些权利,例如承认女性也 “拥有” 孩子,但这绝不是因为他们意识到了女性自身的价值,而仅仅是因为女性在某些方面和他们 “一样”。对于那些和他们 “不一样” 的地方、他们不具备的能力,例如妊娠,他们选择了轻视。
</p>
<p>
因此,妊娠之所以不像基因那么重要,可能只是因为它是女人才有的。但谁又能说它不重要呢?比起提供基因,妊娠母亲需要经历十月怀胎的辛苦,忍受分娩的剧痛。她的贡献不仅体现在胎儿身体的发展,也包括情绪和心理的发展。正如加州上诉庭一位对案例二判决持反对意见的法官所说:“如果没有妊娠母亲的养育,一个胎儿永远不可能成为活生生的孩子……一个希望把孩子带到世界上来的怀孕的母亲,绝不仅仅是一个容器或是一头繁殖动物”。对妊娠母亲的贬低就是对母亲角色的贬低,就是对整体女性的伤害。
</p>
<p>
<strong>
富人消费穷人的身体
</strong>
</p>
<p>
除性别分析外,代孕也需要进行阶级分析。哪些人更可能成为代孕者?哪些人更可能消费代孕这项 “服务”?根据美国国会技术评估办公室 (OTA) 1987 年的报告,美国全国 13 个代孕中心的统计显示,寻求代孕的 “顾客” 往往是 30 多岁或 40 出头的白人已婚人士,他们中的 64% 的人的家庭年收入超过 5 万美元,超过半数有研究生或以上学习经历。
</p>
<p>
在代孕者方面,OTA 于 1988 年的报告显示,代孕者的平均年龄介于 26 至 28 岁,大约六成为已婚人士。在等候代孕的人中间,约九成为非拉美裔白人。只有不到 35% 的代孕者上过大学,大多数人的家庭年收入低于 3 万美元。
</p>
<p>
在上述两个案例中,寻求代孕的夫妻和代孕者大都符合这些描述。案例一中的夫妻都曾在密歇根大学攻读博士,而他们的代孕者是一名没有完成高中学业的家庭主妇,后者靠丈夫开垃圾车的收入度日,家庭年收入仅为 2.8 万美元。案例二中的代孕者是一位护士,也是一位单身母亲,因收入过低正在领取社会保障金。
</p>
<p>
在代孕者和寻求代孕的夫妻之间,阶级差异是显而易见的。而代孕似乎打开了这样一道门,允许穷人向富人出售她们的身体。支持开放代孕的人经常提到,应该开放的是 “志愿代孕”,而非 “商业代孕”。但纯粹志愿的代孕有可能吗?
</p>
<p>
根据学者 Ali 和 Kelley 在 2008 年的调查,大部分代孕者都是真的需要钱。在两起案例中,代孕者得到的 1 万美元甚至低于同时期的最低工资标准 (按最低工资 3.35 美元/小时计算,同等时间应获得 1.49 – 1.57 万美元)。案例一中的代孕者表示,自己对不能生育的家庭抱有同情,但也希望通过获得代孕费来帮助自己的家庭。案例二中的代孕者甚至表示,当你拿出 1 万美金在一些人面前挥舞,他们就会为此做任何事。
</p>
<p>
可见,代孕或许有着助人为乐的成分,但钱仍是重要的动机。正如女权主义作家 Katha Pollit 质疑的那样,如果钱没有用,为什么要付钱给代孕者?如果代孕是这样一件愉快、崇高、使人道德净化的事,难道不会有大批女人排着队来做吗?寻求代孕的人在同阶层的圈子也有不少女性朋友,为什么她们不考虑借出身体培育别人的受精卵?学者们的担心或许不无道理:代孕可能会形成一个 “繁殖阶级”,由贫穷弱势的女性组成,专为他人生孩子。
</p>
<p>
另一方面,钱也并不能解决所有问题。即使付清了代孕费,案例一中的代孕者仍然不能割舍对孩子的亲情。不幸的是,当双方在法庭展开争夺,贫穷再一次成为了代孕者的原罪。寻求代孕的夫妻能够雇佣大批律师、侦探、心理学专家、社工等,而代孕者只请得起没什么经验的律师。举证过程也耐人寻味,代孕者家庭的低收入、较差的居住条件等,都被列为 “不适合” 成为孩子父母的理由。而寻求代孕的夫妻是否适合为人父母呢?没人要求他们提供证据,这似乎是不证自明的。
</p>
<p>
<strong>
弱势中的弱势
</strong>
</p>
<p>
一旦代孕市场形成,市场必然会自动寻找那些最 “便宜”、“好用” 的女人:穷人、黑人、第三世界的人。
</p>
<p>
相比白人代孕者而言,黑人代孕者有着更多劣势。这不仅是因为黑人女性更容易处于贫穷、单亲或缺少法律资源,也是因为她们和孩子的差异显而易见:一名黑人女性如何声称自己是白人孩子的生母?有人会相信或同情她吗?在第二起案例中,黑人代孕者的境遇恰恰印证了这一点。可以想象的是,对于那些需要代孕者提供卵子的夫妻而言,黑人代孕者也绝不是他们的首选,种族歧视再一次被强化了。
</p>
<p>
此外,在本国买不起代孕的人,可能会向更穷的国家购买。这些国家的女性会以更低的价格出售子宫,而且由于法律不健全,购买者面临的法律风险也会小得多。在去年叫停代孕之前,印度早已成为世界 “代孕中心”,许多英国人都前去购买。对中国而言,如果对接 “国际代孕市场”,一方面本国的弱势女性可能受到其他国家的剥削,另一方面国内有代孕需求的人也可能去剥削更穷国家的女性。
</p>
<p>
需要指出的是,代孕不一定是出于自愿,而是可能遭到家人、人贩子的胁迫,越是弱势的女性遭受胁迫的可能性越大。研究者提到与两起案例同时期的另一起案例,一名 20 岁的墨西哥女性被非法送到美国,只为给她丈夫的兄弟提供代孕。相比同时期美国国内代孕者的 1 万美元回报,她能获得的只有 1500 美元。
</p>
<p>
通过以上分析,我们不难看到开放代孕将面临的种种问题。在这些问题得到充分讨论之前,开放代孕并非明智之举。同时,我们也应看到代孕之外的出路,比如领养。与其花不菲的代价寻求代孕,不如先思考以下问题:人为什么一定要拥有血缘意义上的孩子呢?我们从中追求的究竟是什么呢?
</p>
<div class="post-endnote">
<h4>
参考文献
</h4>
<ul>
<li>
Dillaway, H. E. (2008). Mothers for others: A race, class, and gender analysis of surrogacy.
<cite>
International Journal of Sociology of the Family
</cite>
(5), 301-326.
</li>
</ul>
</div>
</div>
<!-- icon list -->
<!--/div-->
<!-- social box -->
<div class="post-end-button back-to-top">
<p style="padding-top:20px;">
回到开头
</p>
</div>
<div id="display_bar">
<img src="http://cnpolitics.org/wp-content/themes/CNPolitics/images/shadow-post-end.png"/>
</div>
</div>
| 36.8 | 250 | 0.743297 | yue_Hant | 0.511928 |
4cfc7b234f5e020c19d7382763d5a7c80253c622 | 21 | md | Markdown | packages/shapes/draw/README.md | proful/next | 0ce3f800a768f30b245cb8bfc976978784692bcc | [
"MIT"
] | null | null | null | packages/shapes/draw/README.md | proful/next | 0ce3f800a768f30b245cb8bfc976978784692bcc | [
"MIT"
] | null | null | null | packages/shapes/draw/README.md | proful/next | 0ce3f800a768f30b245cb8bfc976978784692bcc | [
"MIT"
] | null | null | null | # @tldraw/draw-shape
| 10.5 | 20 | 0.714286 | eng_Latn | 0.586333 |
4cfd2b6431ea152bccf7a60dc057afd9ee4a9bef | 107 | md | Markdown | CHANGELOG.md | larromba/NetDetective | 935c09f2257da51a8aea23a0613b9f9bb31dfa0f | [
"MIT"
] | 1 | 2021-11-08T00:47:20.000Z | 2021-11-08T00:47:20.000Z | CHANGELOG.md | larromba/NetDetective | 935c09f2257da51a8aea23a0613b9f9bb31dfa0f | [
"MIT"
] | null | null | null | CHANGELOG.md | larromba/NetDetective | 935c09f2257da51a8aea23a0613b9f9bb31dfa0f | [
"MIT"
] | null | null | null | # Changelog
## 1.0.0
- first release
## Future work
- accept input parameters to customise functionality
| 13.375 | 52 | 0.738318 | eng_Latn | 0.977213 |
4cfd9859dcd215de5158e470d40c41b15c49db26 | 22,906 | md | Markdown | 2009/_posts/2009-04-12-nouvelles-hebdomadaires-de-postgresql-5-avril-2009.md | postgresqlfr/blog.postgresql.fr | 38b430eeb1b85cebb4d9ba3a022783175d4ebf76 | [
"BSD-2-Clause"
] | null | null | null | 2009/_posts/2009-04-12-nouvelles-hebdomadaires-de-postgresql-5-avril-2009.md | postgresqlfr/blog.postgresql.fr | 38b430eeb1b85cebb4d9ba3a022783175d4ebf76 | [
"BSD-2-Clause"
] | 5 | 2020-04-28T12:42:57.000Z | 2021-06-26T23:36:56.000Z | 2009/_posts/2009-04-12-nouvelles-hebdomadaires-de-postgresql-5-avril-2009.md | postgresqlfr/blog.postgresql.fr | 38b430eeb1b85cebb4d9ba3a022783175d4ebf76 | [
"BSD-2-Clause"
] | null | null | null | ---
layout: post
title: "Nouvelles hebdomadaires de PostgreSQL - 5 avril 2009"
author: "chl"
categories: [PostgreSQL Weekly News]
redirect_from: "index.php?post/2009/04/12/Nouvelles-hebdomadaires-de-PostgreSQL-5-avril-2009"
---
<p>Les inscriptions sont à présent ouvertes pour le pgCon à Ottawa :
<a target="_blank" href="http://www.pgcon.org/2009/registration.php">http://www.pgcon.org/2009/registration.php</a></p>
<p>Ouverture des inscriptions pour l'OSCON également. Il y aura un pgDay la veille, soit dimanche :
<a target="_blank" href="https://en.oreilly.com/oscon2009/public/register">https://en.oreilly.com/oscon2009/public/register</a></p>
<p>Le PgDay de Florianopolis aura lieu le 22 mai. Contactez Dickson S. Guedes (guedes AROBASE guedesoft DOT net) pour participer ou proposer une conférence :
<a target="_blank" href="http://www.postgresql.org.br/eventos/pgday/sc">http://www.postgresql.org.br/eventos/pgday/sc</a></p>
<p><strong>Les nouveautés des produits dérivés</strong></p>
<ul>
<li>Archiveopteryx 3.0.7 et 3.1.0, un gestionnaire d'e-mail basé sur PostgreSQL :
<a target="_blank" href="http://www.archiveopteryx.org/3.0.7">http://www.archiveopteryx.org/3.0.7</a>, <a target="_blank" href="http://www.archiveopteryx.org/3.1.0">http://www.archiveopteryx.org/3.1.0</a></li>
<li>PGORM 0.09, un corrélateur objet-relationnel .NET pour PostgreSQL :
<a target="_blank" href="http://pgorm.googlecode.com">http://pgorm.googlecode.com</a></li>
<li>PostgreDAC ver. 2.5.1 :
<a target="_blank" href="http://microolap.com/products/connectivity/postgresdac/download/">http://microolap.com/products/connectivity/postgresdac/download/</a></li>
</ul>
<p><strong>PostgreSQL 8.4 Feature of the Week</strong></p>
<p>CIText : David Wheeler a ajouté un nouveau module à "contrib" qui implémente, avec toutes les options, un type de données textes insensibles à la casse.</p>
<p><strong>L'astuce de la semaine</strong></p>
<p>\h <COMMAND> dans psql vous fournira une documentation complète sur un grand éventail de commandes SQL.</p>
<p>(<a target="_blank" href="http://www.postgresql.org/community/weeklynews/pwn20090405">lien vers l'article original</a>)</p>
<!--more-->
<p><strong>Offres d'emplois autour de PostgreSQL en April</strong></p>
<ul>
<li><a target="_blank" href="http://archives.postgresql.org/pgsql-jobs/2009-04/threads.php">http://archives.postgresql.org/pgsql-jobs/2009-04/threads.php</a></li>
</ul>
<p><strong>PostgreSQL Local</strong></p>
<ul>
<li>Kevin Kempter fera une présentation des sauvegardes et des récupérations lors de la première réunion du PUG de Denver, le 8 avril 2009 :
<a target="_blank" href="http://www.diapug.org/Meeting.html">http://www.diapug.org/Meeting.html</a></li>
<li>Le PgDay de Brasilia aura lieu le 17 avril. Contactez [fernando.ike (a) gmail (point) com] ou [eduardo (a) planejamento (point) gov (point) br] pour participer :
<a target="_blank" href="http://www.postgresql.org.br/drupal6/eventos/pgday/df">http://www.postgresql.org.br/drupal6/eventos/pgday/df</a></li>
<li>La "Percona Performance Conference" prendra place au "Santa Clara Convention Center", Santa Clara, Californie :
<a target="_blank" href="http://conferences.percona.com/">http://conferences.percona.com/</a></li>
<li>L'appel aux conférences est lancé pour le PgDay de São Paulo, programmé le 24 avril. Contactez [marins (point) consultoria (a) gmail (point) com] ou [marcelojscosta (a) gmail (point) com] pour participer.</li>
<li>"PostgreSQL Conference, U.S. (JDCon)" organise un PgDay lors de la "LinuxFest Northwest" (25 & 26 avril). L'appel aux conférences est consultable à l'adresse :
<a target="_blank" href="http://www.postgresqlconference.org/">http://www.postgresqlconference.org/</a></li>
<li>Il y aura également des PgDays les 29 et 30 avril, respectivement à Porto Velho (RO) et Ji-Parana (RO). Contactez Luis Fernando Bueno : [proflfbueno (a) gmail (point) com] pour participer.</li>
<li>Michael Renner animera un atelier sur la réplication PostgreSQL lors des "Netways OSDC", les 29 et 30 avril 2009, à Nuremberg (All.) :
<a target="_blank" href="http://www.netways.de/english/osdc/y2009/programm/w/michael_renner_postgresql_repliziert_ein_ueberblick/">http://www.netways.de/english/osdc/y2009/programm/w/michael_renner_postgresql_repliziert_ein_ueberblick/</a></li>
<li>La PGCon 2009 se tiendra à l'Université d'Ottawa les 21 et 22 mai 2009. Elle sera précédée de deux jours de tutoriels les 19 & 20 mai :
<a target="_blank" href="http://www.pgcon.org/2009/">http://www.pgcon.org/2009/</a></li>
<li>Notez la date : pgDay San Jose, dimanche 19 juillet juste avant l'OSCON. Appel à conférenciers, plus d'infos sous peu !</li>
<li>La "PGCon Brazil" prendra place à l'Unicamp de Campinas (État de São Paulo) les 23 & 24 octobre 2009.</li>
</ul>
<p><strong>PostgreSQL dans les média</strong></p>
<ul>
<li>Planet PostgreSQL :
<a target="_blank" href="http://planet.postgresql.org/">http://planet.postgresql.org/</a></li>
</ul>
<p><i>PostgreSQL Weekly News / les nouvelles hebdomadaires vous sont offertes cette semaine par David Fetter et Josh Berkus. La traduction en est assurée par l'équipe PostgreSQLFr.</i></p>
<p><i>Proposez vos articles ou annonces avant dimanche 15:00 (heure du Pacifique). Merci de les envoyer en anglais à david (a) fetter.org, en allemand à pwn (a) pgug.de, en italien à pwn (a) itpug.org.</i></p>
<p><strong>Correctifs appliqués</strong></p>
<p>Tom Lane a commité :</p>
<ul>
<li>Fix an oversight in the support for storing/retrieving "minimal tuples" in TupleTableSlots. We have functions for retrieving a minimal tuple from a slot after storing a regular tuple in it, or vice versa; but these were implemented by converting the internal storage from one format to the other. The problem with that is it invalidates any pass-by-reference Datums that were already fetched from the slot, since they'll be pointing into the just-freed version of the tuple. The known problem cases involve fetching both a whole-row variable and a pass-by-reference value from a slot that is fed from a tuplestore or tuplesort object. The added regression tests illustrate some simple cases, but there may be other failure scenarios traceable to the same bug. Note that the added tests probably only fail on unpatched code if it's built with --enable-cassert; otherwise the bug leads to fetching from freed memory, which will not have been overwritten without additional conditions. Fix by allowing a slot to contain both formats simultaneously; which turns out not to complicate the logic much at all, if anything it seems less contorted than before. Back-patch to 8.2, where minimal tuples were introduced.</li>
<li>In pgsql/src/backend/optimizer/plan/planner.c, fix window function plan generation to cope with volatile sort expressions. (Not clear how useful these really are, but failing is no good...) Per report from David Fetter and Robert Treat.</li>
<li>Add PQinitOpenSSL() function to support applications that use libcrypto but not OpenSSL (or perhaps vice versa, if that's possible). Andrew Chernow, with minor editorialization by me.</li>
<li>Add a "relistemp" boolean column to pg_class, which is true for temporary relations (including a temp table's indexes and toast table/index), and false for normal relations. For ease of checking, this commit just adds the column and fills it correctly --- revising the relation access machinery to use it will come separately.</li>
<li>Modify the relcache to record the temp status of both local and nonlocal temp relations; this is no more expensive than before, now that we have pg_class.relistemp. Insert tests into bufmgr.c to prevent attempting to fetch pages from nonlocal temp relations. This provides a low-level defense against bugs-of-omission allowing temp pages to be loaded into shared buffers, as in the contrib/pgstattuple problem reported by Stuart Bishop. While at it, tweak a bunch of places to use new relcache tests (instead of expensive probes into pg_namespace) to detect local or nonlocal temp tables.</li>
<li>Fix contrib/pgstattuple and contrib/pageinspect to prevent attempts to read temporary tables of other sessions; that is unsafe because of the way our buffer management works. Per report from Stuart Bishop. This is redundant with the bufmgr.c checks in HEAD, but not at all redundant in the back branches.</li>
<li>Remove last references to the crypt auth method, per Andreas 'ads' Scherbaum.</li>
<li>In pgsql/doc/src/sgml/func.sgml, index some array functions, per Mario Splivalo.</li>
<li>In pgsql/src/bin/pg_dump/pg_dump.c, improve pg_dump's query for retrieving BLOB comments to be more efficient when there are many blobs and not so many comments. Tamas Vincze.</li>
<li>In pgsql/src/pl/plpgsql/src/pl_exec.c, plpgsql's exec_simple_cast_value() mistakenly supposed that it could bypass casting effort whenever the input value was NULL. However this prevents application of not-null domain constraints in the cases that use this function, as illustrated in bug #4741. Since this function isn't meant for use in performance-critical paths anyway, this certainly seems like another case of "premature optimization is the root of all evil". Back-patch as far as 8.2; older versions made no effort to enforce domain constraints here anyway.</li>
<li>In pgsql/src/backend/utils/misc/guc.c, fix GUC's reports of assign_hook failure to always include the parameter value we failed to assign, even in "can't happen" cases. Motivated by wondering what's going on in a recent trouble report where "failed to commit" did happen.</li>
<li>Fix SetClientEncoding() to maintain a cache of previously selected encoding conversion functions. This allows transaction rollback to revert to a previous client_encoding setting without doing fresh catalog lookups. I believe that this explains and fixes the recent report of "failed to commit client_encoding" failures. This bug is present in 8.3.x, but it doesn't seem prudent to back-patch the fix, at least not till it's had some time for field testing in HEAD. In passing, remove SetDefaultClientEncoding(), which was used nowhere.</li>
<li>In pgsql/src/pl/plpgsql/src/pl_exec.c, minor code beautification/consolidation.</li>
<li>Refactor ExecProject and associated routines so that fast-path code is used for simple Var targetlist entries all the time, even when there are other entries that are not simple Vars. Also, ensure that we prefetch attributes (with slot_getsomeattrs) for all Vars in the targetlist, even those buried within expressions. In combination these changes seem to significantly reduce the runtime for cases where tlists are mostly but not exclusively Vars. Per my proposal of yesterday.</li>
<li>Defend against possible crash if a plpython function does not specify names for its arguments. Also add a regression test, since someone apparently changed every single plpython test case to use only named parameters; else we'd have noticed this sooner. Euler Taveira de Oliveira, per a report from Alvaro Herrera.</li>
<li>In pgsql/src/backend/storage/buffer/bufmgr.c, add a comment documenting the question of whether PrefetchBuffer should try to protect an already-existing buffer from being evicted. This was left as an open issue when the posix_fadvise patch was committed. I'm not sure there's any evidence to justify more work in this area, but we should have some record about it in the source code.</li>
<li>In pgsql/src/port/path.c, use (unsigned char) cast in argument of pg_tolower(). Maybe it works on Windows without that, but we shouldn't put bad examples where people might copy them. Also, reformat slightly to improve the odds that pgindent won't go nuts on this.</li>
<li>In pgsql/src/bin/psql/help.c, add missing help output for \ef option. Andrew (RhodiumToad) Gierth.</li>
<li>In pgsql/doc/src/sgml/ref/psql-ref.sgml, minor wordsmithing on descriptions of some \d commands.</li>
<li>In pgsql/src/bin/psql/describe.c, make \dt \di and friends more consistent about the treatment of TOAST tables and indexes; to wit, never show either. (You can examine them with plain \d if you're really so inclined.)</li>
<li>In pgsql/src/bin/psql/describe.c, improve obsolete comment.</li>
<li>Rewrite interval_hash() so that the hashcodes are equal for values that interval_eq() considers equal. I'm not sure how that fundamental requirement escaped us through multiple revisions of this hash function, but there it is; it's been wrong since interval_hash was first written for PG 7.1. Per bug #4748 from Roman Kononov. Backpatch to all supported releases. This patch changes the contents of hash indexes for interval columns. That's no particular problem for PG 8.4, since we've broken on-disk compatibility of hash indexes already; but it will require a migration warning note in the next minor releases of all existing branches: "if you have any hash indexes on columns of type interval, REINDEX them after updating".</li>
<li>A session that does not have any live snapshots does not have to be waited for when we are waiting for old snapshots to go away during a concurrent index build. In particular, this rule lets us avoid waiting for idle-in-transaction sessions. This logic could be improved further if we had some way to wake up when the session we are currently waiting for goes idle-in-transaction. However that would be a significantly more complex/invasive patch, so it'll have to wait for some other day. Simon Riggs, with some improvements by Tom.</li>
<li>Remove the recently added node types ReloptElem and OptionDefElem in favor of adding optional namespace and action fields to DefElem. Having three node types that do essentially the same thing bloats the code and leads to errors of confusion, such as in yesterday's bug report from Khee Chin.</li>
<li>Make an attempt at fixing our current Solaris 11 breakage: add a configure probe for opterr (exactly like the one for optreset) and have getopt.c define the variables only if configure doesn't find them in libc.</li>
<li>In pgsql/src/port/getopt.c, hmm, baiji thinks we need explicit 'extern' here.</li>
<li>Remove contrib/intarray's definitions of the <@ and @> operators, so that they don't cause confusion with the built-in anyarray versions of those operators. Adjust the module's index opclasses to support the built-in operators in place of the private ones. The private implementations are still available under their historical names @ and ~, so no functionality is lost. Some quick testing suggests that they offer no real benefit over the core operators, however. Per a complaint from Rusty Conover.</li>
<li>In pgsql/src/include/pg_config.h.win32, I had always wondered why pg_config.h.win32 claimed that Windows provides optreset. Current mastodon results prove that in fact it does not; it was only because getopt.c defined the variable anyway that things failed to fall over.</li>
<li>Remove a boatload of useless definitions of 'int optreset'. If we are using our own ports of getopt or getopt_long, those will define the variable for themselves; and if not, we don't need these, because we never touch the variable anyway.</li>
<li>Change EXPLAIN output so that subplans and initplans (particularly CTEs) are individually labeled, rather than just grouped under an "InitPlan" or "SubPlan" heading. This in turn makes it possible for decompilation of a subplan reference to usefully identify which subplan it's referencing. I also made InitPlans identify which parameter symbol(s) they compute, so that references to those parameters elsewhere in the plan tree can be connected to the initplan that will be executed. Per a gripe from Robert Haas about EXPLAIN output of a WITH query being inadequate, plus some longstanding pet peeves of my own.</li>
<li>In pgsql/src/backend/executor/execQual.c, make ExecInitExpr build the list of SubPlans found in a plan tree in order of discovery, rather than reverse order. This doesn't matter functionally (I suppose the previous coding dates from the time when lcons was markedly cheaper than lappend). However now that EXPLAIN is labeling subplans with IDs that are based on order of creation, this may help produce a slightly less surprising printout.</li>
<li>Change cardinality() into a C-code function, instead of a SQL-language alias for array_length(v,1). The efficiency gain here is doubtless negligible --- what I'm interested in is making sure that if we have second thoughts about the definition, we will not have to force a post-beta initdb to change the implementation.</li>
</ul>
<p>Alvaro Herrera a commité :</p>
<ul>
<li>In pgsql/doc/src/sgml/plpython.sgml, update URL to Python bug tracker. Backpatch to 8.3; doesn't seem worthy of further backpatch.</li>
<li>Disallow setting fillfactor for TOAST tables. To implement this without almost duplicating the reloption table, treat relopt_kind as a bitmask instead of an integer value. This decreases the range of allowed values, but it's not clear that there's need for that much values anyway. This patch also makes heap_reloptions explicitly a no-op for relation kinds other than heap and TOAST tables. Patch by ITAGAKI Takahiro with minor edits from me. (In particular I removed the bit about adding relation kind to an error message, which I intend to commit separately.)</li>
</ul>
<p>Bruce Momjian a commité :</p>
<ul>
<li>In pgsql/doc/src/sgml/release.sgml, reorder release note sections.</li>
<li>In pgsql/doc/src/sgml/release.sgml, more release note wording improvements; section order adjustments.</li>
<li>In pgsql/doc/src/sgml/release.sgml, more release note adjustments, reordering.</li>
<li>In pgsql/doc/src/sgml/release.sgml, more release note changes, including a lower level of subsections.</li>
<li>In pgsql/doc/src/sgml/release.sgml, more new subsections in release notes.</li>
<li>In pgsql/doc/src/sgml/release.sgml, update release note introductory description.</li>
<li>In pgsql/doc/src/sgml/release.sgml, remove some "Other" sections in the release notes by putting the items at the top of their sections.</li>
<li>Change psql \d* display so 'S' _or_ a pattern include system objects.</li>
<li>In pgsql/src/bin/psql/describe.c, do not show information_schema in \d* commands, unless 'S' or pattern is specified. Martin Pihlak.</li>
<li>Add support for additional DTrace probes. Robert Lor.</li>
<li>Have PL/pgSQL FETCH set DIAGNOSTICS ROW_COUNT. Andrew (RhodiumToad) Gierth.</li>
<li>In pgsql/src/backend/utils/misc/guc.c, give a better error message when trying to change "effective_io_concurrency" on systems without posix_fadvise().</li>
<li>Revert DTrace patch from Robert Lor.</li>
<li>In pgsql/doc/src/sgml/config.sgml, document that Solaris can't use effective_io_concurrency because of an ineffective posix_fadvise().</li>
</ul>
<p>Heikki Linnakangas a commité :</p>
<ul>
<li>In pgsql/src/backend/storage/ipc/procarray.c, fix a rare race condition when commit_siblings > 0 and a transaction commits at the same instant as a new backend is spawned. Since CountActiveBackends() doesn't hold ProcArrayLock, it needs to be prepared for the case that a pointer at the end of the proc array is still NULL even though numProcs says it should be valid, since it doesn't hold ProcArrayLock. Backpatch to 8.1. 8.0 and earlier had this right, but it was broken in the split of PGPROC and sinval shared memory arrays. Per report and proposal by Marko Kreen.</li>
<li>In pgsql/src/backend/utils/adt/pg_locale.c, update comment to reflect that LC_COLLATE and LC_CTYPE are now per-database settings.</li>
</ul>
<p>Magnus Hagander a commité :</p>
<ul>
<li>In pgsql/src/bin/initdb/initdb.c, don't crash initdb when we fail to get the current username. Give an error message and exit instead, like we do elsewhere... Per report from Wez Furlong and Robert Treat.</li>
<li>In pgsql/src/port/path.c, make directory name comparisons on Win32 case insensitive. This method will not catch all different ways since the locale handling in NTFS doesn't provide an easy way to do that, but it will hopefully solve the most common cases causing startup problems when the backend is found in the system PATH. Attempts to fix bug #4694.</li>
</ul>
<p>Teodor Sigaev a commité :</p>
<ul>
<li>In pgsql/contrib/hstore/hstore_io.c, fix memory allocation for output of hstore type. Per report from Zhang Maosen.</li>
<li>Fix infinite loop while checking of partial match in pending list. Improve comments. Now GIN-indexable operators should be strict. Per Tom Lane's questions/suggestions.</li>
</ul>
<p><strong>Correctifs rejetés (à ce jour)</strong></p>
<ul>
<li>Hitoshi Harada's doc patch which changed HeapTupleSatisfiesNow to HeapTupleSatisfiesVisibility in doc/src/sgml/pgstattuple.sgml.</li>
</ul>
<p><strong>Correctifs en attente</strong></p>
<ul>
<li>Abhijit Menon-Sen sent in a patch to implement has_sequence_privilege().</li>
<li>Andrew (RhodiumToad) Gierth sent in a patch to psql which adds a mention of \ef to the \? command's output.</li>
<li>K. Srinath sent in a patch which allows an index to cover all tables in an inheritance hierarchy.</li>
<li>Pavel Stehule and Tom Lane sent in a couple of versions of a patch to allow raising an exception from _PG_init per previous discussion.</li>
<li>Heikki Linnakangas sent in a patch to help with message encoding.</li>
<li>Pavel Stehule sent in a patch to transform array inputs in variadic functions into standard parameters.</li>
<li>Teodor Sigaev sent in two patches intended to fix a bug in GiST reported by Andrew (RhodiumToad) Gierth.</li>
<li>Fujii Masao sent in another revision of his pg_standby trigger patch.</li>
<li>Robert Haas sent in a patch to add SET NDISTINCT to ALTER COLUMN.</li>
<li>Bruce Momjian sent in another revision of his patch to handle platforms which don't support effective_io_concurrency.</li>
<li>Martin Pihlak sent in a patch which adds a U (user) modifier to psql's \d commands in order to be able to match patterns only on non-system objects.</li>
<li>Alvaro Herrera sent in a patch to fix a reloptions bug reported by Khee Chin.</li>
<li>Teodor Sigaev sent in a patch to fix a crash in GiST insertion of pathological box data.</li>
<li>Zdenek Kotala sent in another patch to fix the misbehavior of Solaris's getopt.</li>
</ul> | 76.608696 | 1,217 | 0.771937 | eng_Latn | 0.95849 |
4cfdcaa82ea978a982a813229b6d82448f6c79f2 | 117 | md | Markdown | README.md | Elijah-python/metacode | 4d086d95f16c11e82c31d053f5cc69e8594d9195 | [
"Apache-2.0"
] | null | null | null | README.md | Elijah-python/metacode | 4d086d95f16c11e82c31d053f5cc69e8594d9195 | [
"Apache-2.0"
] | null | null | null | README.md | Elijah-python/metacode | 4d086d95f16c11e82c31d053f5cc69e8594d9195 | [
"Apache-2.0"
] | 1 | 2021-03-20T04:02:38.000Z | 2021-03-20T04:02:38.000Z | # metacode
1. 添加 JavaScript 代码:
```shell
$ git clone --recursive git@github.com:xinetzone/jsutils.git public/js
``` | 16.714286 | 70 | 0.717949 | cat_Latn | 0.2121 |
4cfdde2b5177f206bd5a1a7bea44747cfe4ba1ea | 14,926 | md | Markdown | powerbi-docs/desktop-get-the-desktop.md | BISMN/powerbi-docs.ru-ru | 84fd32e933ada244bf28c4b08c617be2a61178b7 | [
"CC-BY-4.0",
"MIT"
] | 1 | 2019-10-15T06:36:19.000Z | 2019-10-15T06:36:19.000Z | powerbi-docs/desktop-get-the-desktop.md | BISMN/powerbi-docs.ru-ru | 84fd32e933ada244bf28c4b08c617be2a61178b7 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | powerbi-docs/desktop-get-the-desktop.md | BISMN/powerbi-docs.ru-ru | 84fd32e933ada244bf28c4b08c617be2a61178b7 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
title: Получение Power BI Desktop
description: Загрузка и установка Power BI Desktop
author: davidiseminger
manager: kfile
ms.reviewer: ''
ms.service: powerbi
ms.subservice: powerbi-desktop
ms.topic: conceptual
ms.date: 09/10/2019
ms.author: davidi
LocalizationGroup: Get started
ms.openlocfilehash: e7a96186fe68ed0d70de7a502e81da4f24f4d802
ms.sourcegitcommit: db4fc5da8e65e0a3dc35582d7142a64ad3405de7
ms.translationtype: HT
ms.contentlocale: ru-RU
ms.lasthandoff: 09/11/2019
ms.locfileid: "70903568"
---
# <a name="get-power-bi-desktop"></a>Получение Power BI Desktop
**Power BI Desktop** дает возможность создавать расширенные запросы, модели и отчеты, визуализирующие данные. С помощью **Power BI Desktop** можно создавать модели данных, отчеты и совместно использовать данные, публикуя их в службе Power BI. **Power BI Desktop** можно скачать бесплатно.
Получить **Power BI Desktop** можно двумя способами, каждый из которых описан в следующих разделах:
* **скачать** напрямую в виде пакета, скачиваемого и устанавливаемого на компьютер;
* установить в виде приложения из **Microsoft Store**.
Какой бы способ вы ни выбрали, вы получаете на своем компьютере последнюю версию **Power BI Desktop**. Тем не менее, существуют некоторые различия, которые описаны в следующих разделах.
## <a name="download-power-bi-desktop"></a>Скачивание Power BI Desktop
Чтобы скачать последнюю версию **Power BI Desktop**, щелкните значок загрузки в правом верхнем углу службы Power BI и выберите пункт **Power BI Desktop**.

Вы также можете скачать последнюю версию Power BI Desktop на этой странице:
* [**Скачать Power BI Desktop** (32- и 64-разрядная версия)](https://powerbi.microsoft.com/desktop).
[](https://powerbi.microsoft.com/desktop)
В любом случае после скачивания **Power BI Desktop** появится запрос на запуск файла установки:

Начиная с выпуска за июль 2019 г., **Power BI Desktop** поставлялся в виде отдельного исполняемого пакета установки со всеми поддерживаемыми языками. Для 32- и 64-разрядной версий имеются отдельные исполняемые файлы. Поддержка пакетов MSI прекращена, с выпуска сентября 2019 г., требующего исполняемого EXE-файла для установки. Такой подход делает распространение, обновления и установку гораздо проще и удобнее (особенно для администраторов). Можно также использовать параметры командной строки для настройки процесса установки, как описано в разделе [Использование параметров командной строки во время установки](#using-command-line-options-during-installation) ниже.
После запуска пакета установки **Power BI Desktop** устанавливается как приложение и запускается на компьютере.

> [!NOTE]
> Установка скачанной версии **Power BI Desktop** (пакет MSI) и версии из **Microsoft Store** на одном и том же компьютере (так называемая *параллельная* установка) не поддерживается.
>
>
## <a name="install-as-an-app-from-the-microsoft-store"></a>Установка в виде приложения из Microsoft Store
Приложение **Power BI Desktop** можно получить также из Microsoft Store. Оно доступно по следующей ссылке:
* [Установка **Power BI Desktop** из **Microsoft Store**](http://aka.ms/pbidesktopstore)

У приложения **Power BI Desktop** из Microsoft Store есть ряд преимуществ:
* **Автоматические обновления**. Windows автоматически скачивает последнюю версию в фоновом режиме, как только она становится доступной. Поэтому ваша версия всегда будет актуальной.
* **Меньше скачиваемых файлов.** При каждом обновлении из **Microsoft Store** на компьютер скачиваются только те компоненты, которые были изменены. Таким образом, скачивается меньше файлов.
* **Права администратора не требуются**. Для установки скачанного пакета у вас должны быть права администратора. Если вы получили **Power BI Desktop** из Microsoft Store, права администратора *не* требуются.
* **Возможность развертывания сотрудниками ИТ-отдела**. Версию из **Microsoft Store** проще *развернуть* для всех пользователей в организации. Кроме того, приложение **Power BI Desktop** можно разместить в **Microsoft Store для бизнеса** .
* **Определение языка**. Версия из **Microsoft Store** включает все поддерживаемые языки. При каждом запуске она проверяет, какой язык используется на компьютере. Это также влияет на локализацию моделей, созданных в **Power BI Desktop**. Например, встроенные иерархии дат будут соответствовать языку, который использовался в приложении **Power BI Desktop** при создании PBIX-файла.
При установке **Power BI Desktop** из Microsoft Store необходимо учитывать несколько важных моментов и ограничений.
* Если вы используете соединитель SAP, вам, возможно, потребуется переместить файлы драйвера SAP в папку *Windows\System32*.
* Если **Power BI Desktop** устанавливается из Microsoft Store, пользовательские настройки не копируются из версии, установленной с помощью файла EXE. Возможно, потребуется повторно подключиться к последним источникам данных и заново ввести учетные данные для источника данных.
> [!NOTE]
> Установка скачанной версии **Power BI Desktop** (пакет MSI) и версии из **Microsoft Store** на одном и том же компьютере (так называемая *параллельная* установка) не поддерживается. Вам нужно вручную удалить приложение **Power BI Desktop**, прежде чем скачивать его из **Microsoft Store**.
>
> [!NOTE]
> Версия сервера отчетов Power BI для **Power BI Desktop** отличается от версий, описанных в этой статье, и устанавливается отдельно от них. Сведения о версии сервера отчетов для **Power BI Desktop** см. в руководстве по [созданию отчета Power BI для сервера отчетов Power BI](report-server/quickstart-create-powerbi-report.md).
>
>
## <a name="using-power-bi-desktop"></a>Использование Power BI Desktop
При запуске **Power BI Desktop** отобразится экран *приветствия*.

Если вы используете **Power BI Desktop** впервые (выполняете установку, а не обновление), вам будет предложено заполнить форму и ответить на несколько вопросов либо войти в **службу Power BI** для продолжения работы.
В этом приложении можно создавать модели данных и отчеты, а затем делиться ими с другими пользователями в службе Power BI. Перейдите по ссылкам в разделе **Дополнительные сведения** в конце этой статьи. Вы найдете руководства, которые помогут вам приступить к использованию **Power BI Desktop**.
## <a name="minimum-requirements"></a>Минимальные требования
Минимальные требования для запуска **Power BI Desktop**:
* Windows 7, Windows Server 2008 R2 или более поздние версии
* .NET 4.5
* Internet Explorer 10 или более поздней версии
* **Память (ОЗУ)** не менее 1 ГБ (рекомендуется 1,5 ГБ или больше).
* **Дисплей**: рекомендуемое разрешение — не меньше 1440 x 900 или 1600 x 900 (16:9). Использовать дисплеи с более низким разрешением, например 1024 x 768 или 1280 x 800, не рекомендуется, так как некоторые элементы управления (такие как кнопка для закрытия экрана запуска) могут выходить за границы видимой области.
* **Параметры отображения Windows**. Если в параметрах отображения для размера текста, приложений и других элементов задано изменение более чем на 100 %, возможно, не отобразятся некоторые диалоговые окна. При этом, чтобы продолжить работу в **Power BI Desktop**, необходимо закрыть такие окна или ответить на запрос в них. Если возникла эта проблема, откройте **Параметры отображения**, последовательно выбрав в Windows **Параметры > Система > Отображение**, и с помощью ползунка установите для параметров отображения значение 100 %.
* **ЦП**: рекомендуется 32- или 64-разрядный процессор с тактовой частотой 1 гигагерц (ГГц) или выше.
## <a name="considerations-and-limitations"></a>Рекомендации и ограничения
Мы всегда стараемся обеспечить лучшие возможности работы с Power BI Desktop. Но иногда вы можете столкнуться с проблемой в Power BI Desktop. Поэтому в этом разделе содержатся решения и рекомендации по устранению неполадок, которые могут возникнуть.
### <a name="installing-power-bi-desktop-on-remote-machines"></a>Установка Power BI Desktop на удаленных компьютерах
Если вы устанавливаете Power BI Desktop для своих пользователей с помощью инструмента, требующего файл программы установки Windows (MSI-файл), вы можете извлечь MSI-файл из EXE-файла программы установки Power BI Desktop. Для этого можно использовать сторонние инструменты, например набор средств WiX.
> [!NOTE]
> В качестве продукта стороннего производителя, параметры набора средств WiX могут измениться без предварительного уведомления. Ознакомьтесь с документацией по наиболее актуальным сведениям и обратитесь за помощью к списку рассылки пользователей.
* На компьютере, где была загружена программа установки Power BI Desktop, скачайте и установите последнюю версию набора средств WiX на веб-сайте WiX по адресу https://wixtoolset.org/.
* Откройте окно командной строки от имени администратора и перейдите в папку, где установлен набор инструментов WiX.
* Выполните следующую команду.
```Dark.exe <path to Power BI Desktop installer> -x <output folder>```
Например, выполните:
``` Dark.exe C:\PBIDesktop_x64.exe -x C:\output```
* Выходная папка будет содержать папку с именем *AttachedContainer*, содержащую MSI-файлы.
### <a name="using-command-line-options-during-installation"></a>Использование параметров командной строки во время установки
При установке Power BI Desktop можно задать свойства и параметры с помощью параметров командной строки. Это особенно удобно для администраторов, сопровождающих установку Power BI Desktop в рамках организаций или управляющих ею. Эти параметры применяются к установкам на базе MSI и EXE.
|Параметр командной строки |Поведение |
|---------|---------|
|-q, -quiet, -s, -silent |Автоматическая установка |
|-passive |Отображение индикатора выполнения только во время установки |
|-norestart |Отключение обязательной перезагрузки компьютера |
|-forcerestart |Перезапуск компьютера после установки без запроса |
|-promptrestart |Вывод пользователю запроса о том, требуется ли перезагрузка компьютера (по умолчанию) |
|-l<>, -log<> |Запись журнала установки в определенный файл, указанный в <> |
|-uninstall |Удаление Power BI Desktop |
|-repair |Восстановление установки (или выполнение установки, если продукт еще не установлен) |
|-package, -update |Установка Power BI Desktop (используется по умолчанию, если не указан параметр -uninstall или -repair). |
Кроме того, вы можете использовать следующие **параметры синтаксиса**, указанные с помощью синтаксиса "PROPERTY=VALUE":
|Параметр |Значение |
|---------|---------|
|ACCEPT_EULA |Для автоматического принятия условий лицензии требуется значение 1 |
|ENABLECXP |Значение 1 регистрируется в программу обслуживания клиентов, которая фиксирует данные телеметрии при использовании продукта |
|INSTALLDESKTOPSHORTCUT |Значение 1 добавляет ярлык на Рабочий стол |
|INSTALLLOCATION |Путь к файлу, куда он должен быть установлен |
|ЯЗЫК |Код языкового стандарта, например en-US, de-DE, pr-BR, для принудительного применения языка по умолчанию для приложения. Если язык не указан, Power BI Desktop отображает язык ОС Windows. Пользователь может изменить язык в диалоговом окне "Параметры". |
|REG_SHOWLEADGENDIALOG |Значение 0 отключает отображение диалогового окна, которое появляется перед входом в Power BI Desktop |
Например, вы можете запустить его со следующим синтаксисом для установки без пользовательского интерфейса, используя немецкий язык.
```“-quiet LANG=de-DE ACCEPT_EULA=1”```
### <a name="issues-when-using-previous-releases-of-power-bi-desktop"></a>Проблемы при использовании предыдущих версий Power BI Desktop
При работе с устаревшей версией **Power BI Desktop** некоторые пользователи сталкиваются с ошибкой наподобие следующей:
"We weren't able to restore the saved database to the model"
Обновление до текущей версии Power BI Desktop обычно решает эту проблему.
### <a name="disabling-notifications"></a>Отключение уведомлений
Мы рекомендуем обновить Power BI Desktop до последней версии, чтобы воспользоваться улучшенными функциями, оптимизированными показателями производительности и стабильности, а также другими усовершенствованиями. В некоторых организациях может быть нежелательно, чтобы пользователи обновляли программу до каждой новой версии. Вы можете отключить уведомления, внеся изменения в реестр следующим образом:
1. В редакторе реестра перейдите к папке *HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft Power BI Desktop*.
2. Создайте запись со следующими параметрами: *REG_DWORD: DisableUpdateNotification*.
3. Задайте для новой записи значение **1**.
Чтобы изменения вступили в силу, необходимо перезапустить компьютер.
### <a name="power-bi-desktop-loads-with-a-partial-screen"></a>В Power BI Desktop содержимое экрана загружается частично
При определенных условиях, в том числе и определенных конфигурациях разрешения экрана, для некоторых пользователей в Power BI Desktop содержимое может отображаться с большими черными участками. Обычно это происходит из-за последних обновлений операционной системы, которые влияют на способ отображения элементов, а не из-за того, как Power BI Desktop отображает содержимое. В любом случае большие черные участки не так привлекательны, как визуальные элементы. Поэтому, чтобы устранить эту проблему, выполните следующие действия:
1. Нажмите кнопку "Пуск" и введите слово *размыто* в появившейся панели поиска.
2. В появившемся диалоговом окне выберите параметр *Разрешить Windows исправлять размытость в приложениях*.
3. Перезапустите Power BI Desktop.
Возможно, эта проблема будет решена при выпуске следующих обновлений Windows.
## <a name="next-steps"></a>Дальнейшие действия
После установки **Power BI Desktop** ознакомьтесь со статьями, которые помогут вам быстро приступить к использованию этого приложения:
* [Что такое Power BI Desktop?](desktop-what-is-desktop.md)
* [Общие сведения о запросах в Power BI Desktop](desktop-query-overview.md)
* [Источники данных в Power BI Desktop](desktop-data-sources.md)
* [Подключение к данным в Power BI Desktop](desktop-connect-to-data.md)
* [Формирование и объединение данных в Power BI Desktop](desktop-shape-and-combine-data.md)
* [Общие задачи с запросами в Power BI Desktop](desktop-common-query-tasks.md)
| 72.809756 | 669 | 0.784336 | rus_Cyrl | 0.968057 |
4cfed5be30cdb6fb66c629beb1977941162b67d8 | 49 | md | Markdown | README.md | corollari/dotfiles | a1587c35858b319dcbbfa4163cfa7ba743866c43 | [
"MIT"
] | 1 | 2020-05-18T07:06:42.000Z | 2020-05-18T07:06:42.000Z | README.md | corollari/dotfiles | a1587c35858b319dcbbfa4163cfa7ba743866c43 | [
"MIT"
] | null | null | null | README.md | corollari/dotfiles | a1587c35858b319dcbbfa4163cfa7ba743866c43 | [
"MIT"
] | null | null | null | # My dotfiles
> Yet another boring dotfiles repo
| 16.333333 | 34 | 0.77551 | eng_Latn | 0.956007 |
4cff09c50c1223c94d8f66ffdb3b91497280b2ed | 277 | md | Markdown | input/en-us/chocolatey-gui/setup/installation/chocolatey-gui-extension.md | rachfop/docs | f6a3a5b9ac4641ec6cc1ab1057622857c13518be | [
"Apache-2.0"
] | 1 | 2021-03-04T14:23:33.000Z | 2021-03-04T14:23:33.000Z | input/en-us/chocolatey-gui/setup/installation/chocolatey-gui-extension.md | rachfop/docs | f6a3a5b9ac4641ec6cc1ab1057622857c13518be | [
"Apache-2.0"
] | null | null | null | input/en-us/chocolatey-gui/setup/installation/chocolatey-gui-extension.md | rachfop/docs | f6a3a5b9ac4641ec6cc1ab1057622857c13518be | [
"Apache-2.0"
] | null | null | null | ---
Order: 20
xref: install-gui-extension
Title: Install Chocolatey GUI Extension
Description: Instructions on how to install the Chocolatey GUI Extension
ShowInNavBar: false
ShowInSideBar: false
---
> :warning: **WARNING** This is a Work in Progress. Please check back later
| 25.181818 | 75 | 0.779783 | eng_Latn | 0.839596 |
4cff4b2576134088f9ebc037030e3a774ce2a274 | 1,012 | md | Markdown | README.md | alec-deason/NaNoGenMo-2018 | a64b75f063067d6ce8b88d3141c3f12ef4aacfc1 | [
"BSD-2-Clause"
] | 1 | 2018-12-13T20:43:12.000Z | 2018-12-13T20:43:12.000Z | README.md | alec-deason/NaNoGenMo-2018 | a64b75f063067d6ce8b88d3141c3f12ef4aacfc1 | [
"BSD-2-Clause"
] | null | null | null | README.md | alec-deason/NaNoGenMo-2018 | a64b75f063067d6ce8b88d3141c3f12ef4aacfc1 | [
"BSD-2-Clause"
] | 1 | 2018-12-02T20:34:34.000Z | 2018-12-02T20:34:34.000Z | Ok. Here's a project for National Novel Generation Month 2018.
The idea is that I will do generation in three stages:
* A very crude simulation of a world with independent agents. Basically an
old-school text adventure game with autonomous NPCs playing it. Record a
stream of events for each agent so I know their life history.
* Examine the life histories of all the agents and pick one that is
"interesting" somehow. Not sure what exactly that means. Some sort of function
that judges how good the agent's story is. Likely just pick stories that
contain low probability events at first.
* Probably need to refine the story a bit to add in enough details to make it
tellable.
* Magic? Somehow turn the chosen event stream into prose text. I'm honestly less
interested in this part so if I can get to the point where I'm templating out
a boring, stiff narration of the agent's story but the story itself __would__
be interesting if it were written well then I'm going to call that a
resounding success.
| 44 | 80 | 0.786561 | eng_Latn | 0.999792 |
4cffe8b576731a419e8d0bd51e08c212ada6d303 | 2,657 | md | Markdown | _posts/2019-04-30-Download-onan-ky-generator-service-repair-maintenance-overhaul-shop-manual-981-0503.md | Luanna-Lynde/28 | 1649d0fcde5c5a34b3079f46e73d5983a1bfce8c | [
"MIT"
] | null | null | null | _posts/2019-04-30-Download-onan-ky-generator-service-repair-maintenance-overhaul-shop-manual-981-0503.md | Luanna-Lynde/28 | 1649d0fcde5c5a34b3079f46e73d5983a1bfce8c | [
"MIT"
] | null | null | null | _posts/2019-04-30-Download-onan-ky-generator-service-repair-maintenance-overhaul-shop-manual-981-0503.md | Luanna-Lynde/28 | 1649d0fcde5c5a34b3079f46e73d5983a1bfce8c | [
"MIT"
] | null | null | null | ---
layout: post
comments: true
categories: Other
---
## Download Onan ky generator service repair maintenance overhaul shop manual 981 0503 book
expect to happen another time. 443 blowing away. Hurrying, because if unlocked, so that the Commander of the Faithful and Jaafer were confounded and like to fly for delight. But, she had ripped the cards in thirds and had been the lady of the hour, and oppression," Preston continued. " And she said, which happened on the 23rd her suffering. The surface-water, a colorless, which that onan ky generator service repair maintenance overhaul shop manual 981 0503 started for the north. And don't make it anything flip like that last one. "Well," she said, father said, and the fire flickering. Devise a strategy. Cumulatively, 'My grandfather Suleiman Shah! He tried to think of a compliment that wouldn't be completely insincere. The Chironians could turn their backs on each other in the way that people like Howard Kalens would never know, but you'll have no trouble recognizing what they really are. If I gotta be blind, and he insisted on returning it tenfold. Wow? I touch her arm as she walks past my console. It's difficult to verbalize. " Their struggle to put their sorrow into words moved Agnes not because they cared so deeply, taking slow deep "What can you tell me about him?" Suddenly tears fell from her eyes. Stuxberg and Dr. More central than Enlad, along with my two Japanese companions. uphill, doesn't it?" I shrugged, He's all right, meteorological and tidal observations, you can just make me out. and, incredulous that she could turn against him, "un-believable" was the key word. A certain elegance and order prevailed in their small tents, he simply shook his head, having already reloaded the 12-gauge, I didn't think it was so wonderful. That's gratifying," Junior said sincerely. She shrugs. "I cannot have you here at night If you love me, his wants a wife? Here, when being shot in the head can have an up side. Although rising and falling, an old habit now, "is this story. This might a moment come at last when the door appeared before him. " Quoth I, and now their conversation is firmly established in this sotto-voce mode, the onan ky generator service repair maintenance overhaul shop manual 981 0503 as a third, pup, in the temple at Ratnapoora, held She started toward the door. I had given thee this, this irrational and sick scheme to make psychic The Man Who Had No Idea done, paying his respects to Seraphim, girl and yellow vinyl ball, Micky had spent a great many hours in late- the motherless boy and the ragtag dog huddle together. He could not let her defeat him. | 295.222222 | 2,509 | 0.785849 | eng_Latn | 0.999854 |
9800a0b09ac8d326419d94d37f326206f05ca2a7 | 10,538 | md | Markdown | labreports/LAB_timothymlee.md | timothymlee/cis411_lab3_uiux | 20a664dce4b104b32bfa012d56e04580c21f4dc4 | [
"MIT"
] | null | null | null | labreports/LAB_timothymlee.md | timothymlee/cis411_lab3_uiux | 20a664dce4b104b32bfa012d56e04580c21f4dc4 | [
"MIT"
] | null | null | null | labreports/LAB_timothymlee.md | timothymlee/cis411_lab3_uiux | 20a664dce4b104b32bfa012d56e04580c21f4dc4 | [
"MIT"
] | null | null | null | # Lab Report: UX/UI
___
**Course:** CIS 411, Spring 2021
**Instructor(s):** [Trevor Bunch](https://github.com/trevordbunch)
**Name:** Timothy Lee
**GitHub Handle:** timothymlee
**Repository:** [Forked Repository](https://github.com/timothymlee/cis411_lab3_uiux)
**Collaborators:** Ammanuel Tamrat(AmmanuelT), Isaac Ho(Isaachhm), Reid Burger(ReidBurger), Thomas McVey(ThomasMcVey)
___
# Step 1: Confirm Lab Setup
- [x] I have forked the repository and created my lab report
- [x] If I'm collaborating on this project, I have included their handles on the report and confirm that my report is informed, but not copied from my collaborators.
# Step 2: Evaluate Online Job Search Sites
## 2.1 Summary
| Site | Score | Summary |
|---|---|---|
| LinkedIn | 19 | LinkedIn had an easy to understand format with clear paths for users to follow to complete an action. The layout of the page could possibly be improved for screen readers and by removing unnecessary content such as ads for premium memberships and reviews. |
| Glassdoor | 14 | Glassdoor had a similar layout to LinkedIn but had a lot more clutter. It was harder to follow due to certain tabs not bringing up the expected page and having a lot of extra content not related to the search. |
## 2.2 Site 1: LinkedIn
### LinkedIn Home Screen

The home screen in pretty standard. The "Sign in" page is in the expected location and is made clear with a different color.
### LinkedIn Login Screen

The "Sign in" page is, again, pretty standard. Clear path shown on page.
### LinkedIn User Home Screen

The social media feed is, again, standard and what is expected. The tabs across the top are clear. I don't like the "Messaging" tab popping up on its own and covering the screen.
### LinkedIn Job Page

The jobs page is what I have learned is standard across many websites. I like that everything is seperated into blocks, but don't like the ads. I would have a search bar centered instead of at the top of the page for easier use of that.
### LinkedIn Job Search Results

The formatting of the search results is nice. The filter options are clear but out of the way and only information relevant to the selected job is shown on the right, while options are shown on the left.
| Category | Grade (0-3) | Comments / Justification |
|---|---|---|
| 1. **Don't make me think:** How intuitive was this site? | 3 | Everything was clearly labeled and the labels took the user to the expected page. |
| 2. **Users are busy:** Did this site value your time? | 3 | Navigation was clear and easy with a lot of suggestions to guide user quickly to desired pages. |
| 3. **Good billboard design:** Did this site make the important steps and information clear? How or how not? | 3 | Information is formatted clearly with large buttons, often highlighted, to direct user on next steps. |
| 4. **Tell me what to do:** Did this site lead you towards a specific, opinionated path? | 3 | The website highlighted the current section of the website the user is looking at. |
| 5. **Omit Words:** How careful was this site with its use of copy? | 2 | There were lots of extra things on the page that distracted the user from the desired content like ads and requests for reviews. |
| 6. **Navigation:** How effective was the workflow / navigation of the site? | 3 | Work flow was very clear with highlighting of current section of website. |
| 7. **Accessibility:** How accessible is this site to a screen reader or a mouse-less interface? | 2 | Works fine on the phone but they layout seems like it could cause screen reader issues. |
| **TOTAL** | 19 | |
## 2.3 Site 2: Glassdoor
### Glassdoor Home Screen

The home screen in pretty standard. The Sign in page is in the expected location and is made clear with a different color. I don't like the really large "Sign-Up" part in the middle as a returning user.
### Glassdoor User Home Screen

The user home page is pretty boring but gets the job done. The tabs are clear but the content in the middle of the page isn't helpful.
### Glassdoor Job Page

The job page is not my favorite. It took me a while to figure out how to search for the job, as I was expecting options to immediately show up when I clicked on "Jobs."
### Glassdoor Search Results

I do not like this search engine-esk design that Glassdoor uses. It leads to a lot of information that I don't care about as I search for a job. The irrelevent information is something I would use Google to find instead of Glassdoor. Also, their search suggestions were not helpful.
### Glassdoor Job Search Results

The formatting of the search results is nice. The filter options are clear but out of the way and only information relevant to the selected job is shown on the right, while options are shown on the left. It looks almost identical to LinkedIn but has some nice large graphics like the "Average Base Salary Estimate."
| Category | Grade (0-3) | Comments / Justification |
|---|---|---|
| 1. **Don't make me think:** How intuitive was this site? | 2 | Everything was clearly labeled but some labels took the user to an unexpected page. |
| 2. **Users are busy:** Did this site value your time? | 1 | The search result for the job search had a lot of irrelevant information that limited search results. |
| 3. **Good billboard design:** Did this site make the important steps and information clear? How or how not? | 2 | Home page had a lot of suggestions after first use for relevant information. |
| 4. **Tell me what to do:** Did this site lead you towards a specific, opinionated path? | 3 | The website highlighted the current section of the website the user is looking at. |
| 5. **Omit Words:** How careful was this site with its use of copy? | 2 | Search suggestions were not really suggestions but categorie selections. |
| 6. **Navigation:** How effective was the workflow / navigation of the site? | 2 | As stated previous, some labels took the user to an unexpected page, but it was mostly clear. |
| 7. **Accessibility:** How accessible is this site to a screen reader or a mouse-less interface? | 2 | Works fine on the phone but they layout seems like it could cause screen reader issues. |
| **TOTAL** | 14 | |
# Step 3 Competitive Usability Test
## Step 3.1 Product Use Case
| Use Case #1 | Finding the Campus Map |
|---|---|
| Title | User must find the Campus Map |
| Description / Steps | <ol><li>User opens app</li> <li>User is authenticated via biometrics or their password</li><li>User selects "Campus Map" tab</li></ol> |
| Primary Actor | Messiah University Student |
| Preconditions | <ol><li>User must be a student at Messiah University.</li><li>App must be downloaded onto device.</li></ol>|
| Postconditions | <ol><li>The system brings up the campus map.</li><li>The system gives the option to return to the home page.</li></ol> |
## Step 3.2 Identifier a competitive product
List of Competitors
1. [Falcon Link](https://falconlink.webapps.messiah.edu/)
2. [Messiah Website](https://www.messiah.edu)
## Step 3.3 Write a Useability Test
| Step | Tasks | Notes |
|---|---|---|
| 1 | Open [Messiah Website](https://www.messiah.edu) | There are 85 different links that the user could possibly click on on this page. |
| 2 | Find the "Campus Map" | Users can use the search bar or navigate through the pages |
| 3 | Open the correct page | [Campus Map](https://tour.messiah.edu/campus-map/) |
## Step 3.4 Observe User Interactions
| Step | Tasks | Observations |
|---|---|---|
| 1 | Opened Messiah Website | There were lots of icons that the user didn't even bother to look at. |
| 2 | Clicked on "Visit Campus" | Icon looked like a map. User expected a map option to be available. |
| 3 | Clicked on "Virtual Tour" | User though a interactive map would be available to see different parts of campus. |
| 4 | Returned to previous page | Page brought up was not what was expected and as such the user clicked back. |
| 5 | User clicked on menu bar, went to "about" tab, then "Our Campus" subtab. | Link seemed hidden through multiple clicks. |
| 6 | User scrolled down and clicked on "Campus Map." | User had to scroll to bottom of page. |
| 7 | User sees the map and interacts with it. | User doesn't like that the map shifts view while moving around the camera to different zoom levels and the cartoon-ish view. There is also no compass for orientation. The map also does not have a lot of names that are commonly used by Messiah students (North Complex, Fish Bowl vs. Fishbowl). |
## Step 3.5 Findings
### Improvements
<ul>
<li>Icons should better reflect the pages their direct to (a picture of a map should lead to, or close to, a map).</li>
<li>The map could be better designed for mobile users. Currently all actions use two fingers can zooming can often occur when only moving was intended.</li>
<li>Having the sidebar show up in a different format on mobile could have made navigation easier than locating it at the bottom of the page.</li>
</ul>
### Positive Experiences
<ul>
<li>Having the menu bar on the top tab always accessible was helpful to relocate the user.</li>
<li>Large icons on the initial loading of the screen was useful for quick navigation.</li>
</ul>
### Team Usability Testing
The team did a good job in selecting a user who did not already know the path to the end goal. We think we gave clear enough instructions to make the user know what we wanted without giving away how the process.
### Improvement for Future
I think in the future, having more users perform the test would be more helpful. Having many different uers from different backgrounds could help better tailor the expereince for all users.
### Expereience
I think the useability test was helpful. I often use Google to navigate to where I want to go instead of going through a webpage so it was eye-opening to see how difficult it can be to navigate through unfamiliar apps and websites. I think conistency across websites and familiar patterns is also really helpful for users to navigate a website.
# 4. Your UX Rule (Extra Credit)
If you opt to do extra credit, then include it here. | 69.328947 | 344 | 0.739704 | eng_Latn | 0.998404 |
980373b46371d760fb1851c432f93fca014ad74f | 18,038 | md | Markdown | manufacture/desktop/dism-languages-and-international-servicing-command-line-options.md | imingc/commercialization-public | 70a2bcf94b61655df50987bfea83d4fc7be443d9 | [
"CC-BY-4.0",
"MIT"
] | 1 | 2019-01-25T20:02:01.000Z | 2019-01-25T20:02:01.000Z | manufacture/desktop/dism-languages-and-international-servicing-command-line-options.md | andreiztm/commercialization-public | 9a9565a191bc1ecddb33c9b26e701ae32b0c8d65 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | manufacture/desktop/dism-languages-and-international-servicing-command-line-options.md | andreiztm/commercialization-public | 9a9565a191bc1ecddb33c9b26e701ae32b0c8d65 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
author: kpacquer
Description: 'DISM Languages and International Servicing Command-Line Options'
ms.assetid: 6434373a-a7f9-43ff-be28-e4d48fa0b70f
MSHAttr: 'PreferredLib:/library/windows/hardware'
title: 'DISM Languages and International Servicing Command-Line Options'
ms.author: kenpacq
ms.date: 05/02/2017
ms.topic: article
ms.prod: windows-hardware
ms.technology: windows-oem
---
# DISM Languages and International Servicing Command-Line Options
The international commands can be used to change international settings in Windows and Windows Preinstallation Environment (WinPE) images. You can also query existing settings in an offline or online Windows image.
The base syntax for servicing a Windows image using the Deployment Image Servicing and Management (DISM.exe) tool is:
**DISM.exe** {**/Image:**<*path\_to\_offline\_image\_directory*> | **/Online**} \[**dism\_global\_options**\] {**servicing\_option**} \[<*servicing\_argument*>\]
There are three types of international servicing commands:
- **Get commands**. Retrieves a report of the international settings for an offline image or a running operating system.
- **Set commands**. Sets the different international settings for an offline image.
- **Gen-LangIni commands**. Generates the Lang.ini file that is used during Setup.
The following international servicing options are available for an offline image:
**DISM.exe /Image:**<*path\_to\_offline\_image\_directory*> \[**/Get-Intl**\] \[**/Set-UILang** | **/Set-UILangFallback** | **/Set-SysLocale** | **/Set-UserLocale** | **/Set-InputLocale** | **/Set-AllIntl** | **/Set-Timezone** | **/Set-SKUIntlDefaults** | **/Set-LayeredDriver**\] \[**/Gen-Langini** | **/Set-SetupUILang** | **/Distribution**\]
The following international servicing options are available for a running operating system:
**DISM.exe /Online** **/Get-Intl**
The following table provides a description of how each international servicing option can be used. These options are not case-sensitive.
<table>
<colgroup>
<col width="50%" />
<col width="50%" />
</colgroup>
<thead>
<tr class="header">
<th align="left">Option/Argument</th>
<th align="left">Description</th>
</tr>
</thead>
<tbody>
<tr class="odd">
<td align="left"><p>Option: <strong>/Get-Help /?</strong></p></td>
<td align="left"><p>When used immediately after an international servicing command-line option, information about the option and the arguments is displayed. Additional topics might become available when an image is specified.</p>
<p>Examples:</p>
<p><strong>Dism /image:C:\test\offline /Set-UILang /?</strong></p>
<p><strong>Dism /online /Get-intl /?</strong></p></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Get-Intl</strong></p></td>
<td align="left"><p>Displays information about international settings and languages.</p>
<p>Use the <strong>/Online</strong> option to display information about international settings and languages in the running operating system.</p>
<p>Use the <strong>/Image</strong>:<<em>path_to_offline_image_directory</em>> option to display information about international settings and languages in the offline image.</p>
<p>When used with the <strong>/Distribution</strong> options, information about international settings and languages in the distribution is displayed. The name of the folder in the distribution share is not validated. It will be reported as …\Langpacks\<<em>locale_name</em>>\Lp.cab. Where <<em>locale_name</em>> is the name of the folder.</p>
<div class="alert">
<strong>Note</strong>
<p>The user locale is reported only for offline images. The report does not include this setting for running operating systems.</p>
</div>
<div>
</div>
<p>Examples:</p>
<p><strong>Dism /online /Get-Intl</strong></p>
<p><strong>Dism /image:C:\test\offline /Get-Intl</strong></p>
<p><strong>Dism /image:C:\test\offline /distribution:C:\windows_distribution /Get-Intl</strong></p></td>
</tr>
<tr class="odd">
<td align="left"><p>Option: <strong>/Set-UILang:</strong></p>
<p>Argument: <<em>language_name</em>></p></td>
<td align="left"><p>Sets the default system user interface (UI) language. If the language is not installed in the Windows image, the command will fail.</p>
<p><<em>language_name</em>> specifies the name of the language to set as the default; for example, ja-JP.</p>
<div class="alert">
<strong>Note</strong>
<p>If you install a Language Interface Pack (LIP) and specify its language as the default UI language, the LIP language will be set as the system default UI language (or Install language) and the parent language will be set as the default UI language.</p>
</div>
<div>
</div>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-UILang:fr-FR</strong></p></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Set-UILangFallback:</strong></p>
<p>Argument: <<em>language_name</em>></p></td>
<td align="left"><p>Sets the fallback default language for the system UI in the offline Windows image. This setting is used only when the language specified by the <strong>/Set-UILang</strong> option is a partially localized language.</p>
<p><<em>language_name</em>> specifies the name of the language to set as the default fallback; for example, en-US.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-UILangFallBack:fr-FR</strong></p></td>
</tr>
<tr class="odd">
<td align="left"><p>Option: <strong>/Set-Syslocale:</strong></p>
<p>Argument: <<em>locale_name</em>></p></td>
<td align="left"><p>Sets the language for non-Unicode programs (also called system locale) and font settings in the offline Windows image.</p>
<p><<em>locale_name</em>> specifies the name of the language and locale to set as the default language for non-Unicode; for example, en-US.</p>
<div class="alert">
<strong>Important</strong>
<p>You cannot set Unicode-only languages as the system locale. If you try, the <strong>/Set-SysLocale</strong> option will fail and the language for non-Unicode programs will not be changed.</p>
</div>
<div>
</div>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-SysLocale:fr-FR</strong></p></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Set-UserLocale:</strong></p>
<p>Argument: <<em>locale_name</em>></p></td>
<td align="left"><p>Sets the "standards and formats" language (also called user locale) in the offline Windows image. The "standards and formats" language is a per-user setting that determines default sort order and the default settings for formatting dates, times, currency, and numbers.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-UserLocale:fr-FR</strong></p></td>
</tr>
<tr class="odd">
<td align="left"><p>Option: <strong>/Set-InputLocale:</strong></p>
<p>Argument: <<em>input_locale</em>>:<<em>keyboard_layout</em>></p></td>
<td align="left"><p>Sets the input locales and keyboard layouts to use in the offline Windows image.</p>
<p>The value of the <<em>input_locale</em>>:<<em>keyboard_layout</em>> pair can be one of the following:</p>
<ul>
<li><p><<em>language_id</em>:<em>keyboard_layout</em>></p>
<p>For example, 0409:00000409</p></li>
<li><p><<em>locale_name</em>></p>
<p>For example, if you specify en-US as the local name, The <strong>Set-InputLocale:</strong> option also sets the default keyboard layout defined for this locale.</p></li>
</ul>
<p>You can specify more than one value by using semicolons as separators. This is useful when you want to include support for multiple keyboards on a single computer. The first value will be set as the default keyboard.</p>
<p>The valid keyboard layouts that can be configured on your computer are listed in the following registry key.</p>
<p><strong>HKEY_LOCAL_MACHINE \SYSTEM\CurrentControlSet\Control\Keyboard Layouts</strong></p>
<p>For a list of the values, see [Default Input Locales](default-input-locales-for-windows-language-packs.md) and [Default Keyboard Settings](windows-language-pack-default-values.md).</p>
<p>Use the hexadecimal value of the language ID and keyboard layout that you intend to configure.</p>
<p>This parameter is optional.</p>
<p>Example:</p>
<pre class="syntax" space="preserve"><code>Dism /image:C:\test\offline /Set-InputLocale:fr-fr</code></pre>
<pre class="syntax" space="preserve"><code>Dism /image:C:\test\offline /Set-InputLocale:0410:00010410</code></pre></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Set-AllIntl:</strong></p>
<p>Argument: <<em>language_name</em>></p></td>
<td align="left"><p>Sets the default system UI language, the language for non-Unicode programs, the "standards and formats" language, and the input locales and keyboard layouts to the specified language in the offline Windows image. This option specifies the language value for the following:</p>
<ul>
<li><p>UI language</p></li>
<li><p>System locale</p></li>
<li><p>User locale</p></li>
<li><p>Input locale</p></li>
</ul>
<p>If used with any of the options that specify the individual language or locales, then the individual settings take precedence.</p>
<p><<em>language_name</em>> specifies the language name and locale code; for example, en-US, es-ES, or fr-FR.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-AllIntl:fr-FR</strong></p></td>
</tr>
<tr class="odd">
<td align="left"><p>Option: <strong>/Set-TimeZone:</strong></p>
<p>Argument: <<em>timezone_name</em>></p></td>
<td align="left"><p>Sets the default time zone in a Windows image. Before setting the time zone, DISM verifies that the specified time zone string is valid for the image.</p>
<p><<em>timezone_name</em>> specifies the name of the time zone to use; for example, Pacific Standard Time. For a complete list of time-zone strings, see the Windows® Unattended Setup Reference. On a computer that is running Windows 7, you can use the tzutil command-line tool to list the time zone for that computer. The tzutil tool is installed by default on Windows 7.</p>
<p>The name of the time zone must exactly match the name of the time zone settings in the registry in <strong>HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Time Zones</strong>.</p>
<p>If you add a custom time zone to your computer, you can specify that custom time-zone string.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-TimeZone:"W. Europe Standard Time"</strong></p></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Set-SKUIntlDefaults:</strong></p>
<p>Argument: <<em>language_name</em>></p></td>
<td align="left"><p>Sets the default system UI language, the language for non-Unicode programs, the "standards and formats" language, and the input locales, keyboard layouts, and time zone values in an offline Windows image to the default value specified by <<em>language_name</em>>. The <strong>/Set-SKUIntlDefaults</strong> option does not change the keyboard driver for Japanese and Korean keyboards. You must use the <strong>/Set-LayeredDriver</strong> option to change this.</p>
<p>Use <strong>/ Set-SKUIntlDefaults</strong> to change all the international settings in an offline Windows image to match the default values that are set during retail installations. For more information about the default values of each language pack, see [Default Input Locales for Windows Language Packs](default-input-locales-for-windows-language-packs.md).</p>
<p>This parameter is optional. If combined with one of the settings earlier in this section, the individual setting takes priority.</p>
<p>If the language passed matches a Unicode-only locale setting, the system locale will not be changed but the command will not fail.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-SKUIntlDefaults:fr-FR</strong></p></td>
</tr>
<tr class="odd">
<td align="left"><p>Option: <strong>/Set-LayeredDriver:</strong></p>
<p>Arguments: <<em>1-6</em>></p></td>
<td align="left"><p>Specifies a keyboard driver to use for Japanese or Korean keyboards.</p>
<p>In Japan, many retail users have 106-key keyboards, whereas others have 101- or 102-key keyboards. In Korea, there are several different types of keyboards, some with different numbers of keys.</p>
<p>The possible values for these settings are [1-6]:</p>
<ol>
<li><p>Specifies the PC/AT Enhanced Keyboard (101/102-Key).</p></li>
<li><p>Specifies the Korean PC/AT 101-Key Compatible Keyboard/MS Natural Keyboard (Type 1).</p></li>
<li><p>Specifies the Korean PC/AT 101-Key Compatible Keyboard/MS Natural Keyboard (Type 2).</p></li>
<li><p>Specifies the Korean PC/AT 101-Key Compatible Keyboard/MS Natural Keyboard (Type 3).</p></li>
<li><p>Specifies the Korean Keyboard (103/106 Key).</p></li>
<li><p>Specifies the Japanese Keyboard (106/109 Key).</p></li>
</ol>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-LayeredDriver:1</strong></p></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Gen-LangINI:</strong></p></td>
<td align="left"><p>Generates a new Lang.ini file, which is used by Setup to define the language packs inside the image and outside in the distribution. It also defines the default UI language for Setup.</p>
<p>The new Lang.ini file will be added to the Sources folder of the Windows distribution.</p>
<div class="alert">
<strong>Note</strong>
<p>You will not be prompted for permission to overwrite an existing Lang.ini file. The existing Lang.ini file will be overwritten automatically.</p>
</div>
<div>
</div>
<p>You must specify an offline Windows image (<strong>/Image:</strong><<em>path_to_offline_image.wim</em>> and a distribution (<strong>/Distribution:</strong><<em>path_to_distribution_directory</em>>).</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Gen-LangINI /distribution:C:\windows_distribution</strong></p></td>
</tr>
<tr class="odd">
<td align="left"><p>Option: <strong>/Set-SetupUILang:</strong></p>
<p>Argument: <<em>language_name</em>></p></td>
<td align="left"><p>Defines the default language that will be used by Setup. If this language cannot be used, Setup automatically uses English.</p>
<p>This is an optional command. If not used, the default UI language in the image will be used. If the language is not present, the first language in the list of present languages will be used.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Set-SetupUILang:fr-FR /distribution:C:\windows_distribution</strong></p></td>
</tr>
<tr class="even">
<td align="left"><p>Option: <strong>/Distribution:</strong></p>
<p>Argument: <<em>path_to-distribution_directory</em>></p></td>
<td align="left"><p>Specifies the path to the Windows distribution. The Windows distribution is a copy of the content that releases on the Windows product DVD. This option is only for use with the <strong>/Get-Intl</strong> and <strong>/Gen-LangINI</strong> option if there are external language packs.</p>
<p>Example:</p>
<p><strong>Dism /image:C:\test\offline /Gen-LangINI /distribution:C:\windows_distribution</strong></p></td>
</tr>
</tbody>
</table>
## <span id="Limitations"></span><span id="limitations"></span><span id="LIMITATIONS"></span>Limitations
- The DISM International servicing commands cannot be used on a Windows Vista or a Windows Server 2008 image. For information about servicing Windows Vista and Windows Server 2008 images, see the Windows Vista SP1 release of the Windows OEM Preinstallation Kit (Windows OPK) or Windows Automated Installation Kit (Windows AIK).
- You cannot use other servicing commands on the same command line with international servicing commands.
- You cannot set a Unicode-only language as the system locale.
The following languages are Unicode-only (Languages are listed in the table in the format: Language - Country/Region):
Amharic - Ethiopia
Kazakh - Kazakhstan
Odia - India (Odia Script)
Armenian - Armenia
Khmer - Cambodia
Pashto - Afghanistan
Assamese - India
Konkani - India
Punjabi - India (Gurmukhi Script)
Bangla - Bangladesh
Lao - Lao PDR
Sanskrit - India
Bangla - India (Bengali Script)
Malayalam - India (Malayalam Script)
Sinhala - Sri Lanka
Divehi - Maldives
Maltese - Malta
Syriac - Syria
Georgian - Georgia
Maori - New Zealand
Tamil - India
Gujarati - India (Gujarati Script)
Marathi - India
Telugu - India (Telugu Script)
Hindi - India
Mongolian (Mongolian) - PRC
Tibetan - PRC
Inuktitut (Syllabics) - Canada
Nepali - Federal Democratic Republic of Nepal
Yi - PRC
Kannada - India (Kannada Script)
- Do not install a language pack after an update.
If you install an update (hotfix, general distribution release \[GDR\], or service pack \[SP\]) that contains language-dependent resources before you install a language pack, the language-specific changes contained in the update are not applied. Always install language packs before installing updates.
- When specifying a time zone by using **/Set-TimeZone:**<*timezone\_name*> you must use straight quotation marks for multiple words. For example, **/Set-TimeZone:"Pacific Standard Time"**. If you copy and paste the time zone name, including quotation marks, from a Microsoft® Word document, the quotation marks might not be recognized and the command line might fail.
- If you are servicing an international image, and your host environment does not support the language in that image, you might not be able to read an error message that originates from the international image.
## <span id="related_topics"></span>Related topics
[What is DISM?](what-is-dism.md)
[DISM Image Management Command-Line Options](dism-image-management-command-line-options-s14.md)
[Deployment Image Servicing and Management (DISM) Command-Line Options](deployment-image-servicing-and-management--dism--command-line-options.md)
| 55.16208 | 499 | 0.731345 | eng_Latn | 0.895918 |
9803c3f8142b23cfdfd6e8cd20ab65b24b79e1e9 | 2,610 | md | Markdown | exercises/concept/conditionals/.docs/hints.md | deepaksathya/go | d7468c6fb071c1649edadbaba4098a3e370858a0 | [
"MIT"
] | null | null | null | exercises/concept/conditionals/.docs/hints.md | deepaksathya/go | d7468c6fb071c1649edadbaba4098a3e370858a0 | [
"MIT"
] | 1 | 2022-03-02T10:09:37.000Z | 2022-03-02T10:09:37.000Z | exercises/concept/conditionals/.docs/hints.md | deepaksathya/go | d7468c6fb071c1649edadbaba4098a3e370858a0 | [
"MIT"
] | null | null | null | # Hints
## General
Conditionals are used to check for certain conditions and/or criteria. The most basic way of performing a conditional operation is using a single `if` statement.
## 1. Calculate the score of any given card.
The `ParseCard` function should take the `card` string (e.g. `ace`) and turn it into its value (e.g. 11).
- Use a big [`switch` statement][switch_statement] on the `card` variable.
- King, Queen, Jack and 10 can be handled with a single case.
- The switch can have a `default` case. In any case the function should return `0` for unknown cards.
## 2. Determine if two cards make up a Blackjack.
`IsBlackJack` checks if 2 cards have the combined value of 21.
- Should use the `ParseCard` function to get the value for each card.
- Should sum up the values of the 2 cards.
- Should return `true` if the sum is equal to `21`.
- No `if` statement is needed here. The result for the comparison can be returned.
## 3. Implement the decision logic for hand scores larger than 20 points.
As the `LargeHand` function is only called for hands with a value larger than 20, there are only 2 different possible hands: A **BlackJack** with a total value of `21` and **2 Aces** with a total value of `22`.
- The function should check [if][if_statement] `isBlackJack` is `true` and return "P" otherwise.
- If `isBlackJack` is `true`, the dealerScore needs to be checked for being lower than 10. [If][if_statement] it is lower, return "W" otherwise "S".
## 4. Implement the decision logic for hand scores with less than 21 points.
The `SmallHand` function is only called if there are no Aces on the hand (`handScore` is less than 21).
- Implement every condition using [logical operators][logical_operators] if necessary:
- [If][if_statement] your cards sum up to 17 or higher you should always _stand_.
- [If][if_statement] your cards sum up to 11 or lower you should always _hit_.
- [If][if_statement] your cards sum up to a value within the range [12, 16] you should always _stand_ if the dealer has a 6 or lower.
- [If][if_statement] your cards sum up to a value within the range [12, 16] you should always _hit_ if the dealer has a 7 or higher.
- (optional) Try to optimize the conditions:
- Pull together the conditions for _stand_ into one.
- Pull together the conditions for _hit_ into one.
- Remove redundant parts of the conditions (e.g. `A || !A && B` can be `A || B`).
[logical_operators]: https://golang.org/ref/spec#Logical_operators
[if_statement]: https://golang.org/ref/spec#If_statements
[switch_statement]: https://golang.org/ref/spec#Switch_statements
| 54.375 | 210 | 0.73908 | eng_Latn | 0.996536 |
9803da065dc1c3b21f1b7c382015705556d4d5dc | 1,931 | md | Markdown | articles/supply-chain/pim/tasks/exclude-products-master-planning.md | MicrosoftDocs/Dynamics-365-Operations.sv-se | 90cb258993f991b2ce1b67078a6519e342608a4e | [
"CC-BY-4.0",
"MIT"
] | 3 | 2020-05-18T17:14:56.000Z | 2022-03-02T03:46:34.000Z | articles/supply-chain/pim/tasks/exclude-products-master-planning.md | MicrosoftDocs/Dynamics-365-Operations.sv-se | 90cb258993f991b2ce1b67078a6519e342608a4e | [
"CC-BY-4.0",
"MIT"
] | 7 | 2017-12-13T12:57:02.000Z | 2019-04-30T11:46:04.000Z | articles/supply-chain/pim/tasks/exclude-products-master-planning.md | MicrosoftDocs/Dynamics-365-Operations.sv-se | 90cb258993f991b2ce1b67078a6519e342608a4e | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
title: Skapa ett produktlivscykeltillstånd för att utesluta produkter från huvudplanering
description: Den här proceduren beskriver hur du skapar ett nytt livscykeltillstånd för produkt som exkluderar produkter från huvudplanering och strukturlistenivåberäkningen.
author: t-benebo
ms.date: 12/05/2017
ms.topic: business-process
ms.prod: ''
ms.technology: ''
audience: Application User
ms.reviewer: kamaybac
ms.search.region: Global
ms.author: benebotg
ms.search.validFrom: 2016-06-30
ms.dyn365.ops.version: AX 7.0.0
ms.openlocfilehash: c7f72be341b81515b7c5540d66f61647df93af41
ms.sourcegitcommit: 3b87f042a7e97f72b5aa73bef186c5426b937fec
ms.translationtype: HT
ms.contentlocale: sv-SE
ms.lasthandoff: 09/29/2021
ms.locfileid: "7567041"
---
# <a name="create-a-product-lifecycle-state-to-exclude-products-from-master-planning"></a>Skapa ett produktlivscykeltillstånd för att utesluta produkter från huvudplanering
[!include [banner](../../includes/banner.md)]
Den här proceduren beskriver hur du skapar ett nytt livscykeltillstånd för produkt som exkluderar produkter från huvudplanering och strukturlistenivåberäkningen.
## <a name="create-an-obsolete-state"></a>Skapa ett föråldrat tillstånd
1. Gå till Produktinformationshantering > Inställningar > produktlivscykeltillstånd.
2. Klicka på Ny.
3. Ange ett värde i fältet Tillstånd.
4. Välj Nej i fältet Är aktiv för planering.
5. Ange ett värde i fältet Beskrivning.
## <a name="associate-the-obsolete-state-to-a-released-product"></a>Koppla föråldrade tillståndet till frisläppt produkt
1. Stäng sidan.
2. Gå till Produktinformationshantering > Produkter > Frisläppta produkter.
3. Använd snabbfiltret för att söka efter poster. Filtrera till exempel i fältet Söknamn med värdet "M00".
4. Klicka på Redigera.
5. Markera vald rad i listan.
6. Ange eller välj ett värde i fältet produktlivscykeltillstånd.
[!INCLUDE[footer-include](../../../includes/footer-banner.md)] | 41.978261 | 174 | 0.802693 | swe_Latn | 0.997008 |
98041352be8866a7c6c826bb88b6bac527a02cfe | 3,047 | md | Markdown | _posts/2020-10-21-automate-pdf-with-r.md | mdancho84/mdancho84.github.io | 87292b5cf888708ccf93d9a1ed87d9bf873b43d2 | [
"Apache-2.0"
] | 4 | 2019-06-15T00:56:43.000Z | 2022-03-12T04:28:04.000Z | _posts/2020-10-21-automate-pdf-with-r.md | mdancho84/mdancho84.github.io | 87292b5cf888708ccf93d9a1ed87d9bf873b43d2 | [
"Apache-2.0"
] | null | null | null | _posts/2020-10-21-automate-pdf-with-r.md | mdancho84/mdancho84.github.io | 87292b5cf888708ccf93d9a1ed87d9bf873b43d2 | [
"Apache-2.0"
] | 6 | 2017-01-31T15:53:43.000Z | 2020-05-25T06:06:51.000Z | ---
layout: post
title: "How to Automate PDF Reporting with R"
date: 2020-10-21 07:00:00
excerpt: "Why create PDF's manually when you can automate PDFs with R? That's exactly what I show you how to do in this video showcasing parameterized Rmarkdown."
author: "Matt Dancho"
categories: [Code-Tools]
tags: [R-Bloggers, Learn-R, R, R-Tips, PDF, Rmarkdown]
image: 2020-10-21-automate-pdf-with-r/automate-pdf-cover.png
image_preview: 2020-10-21-automate-pdf-with-r/automate-pdf-preview.png
---
This article is part of a R-Tips Weekly, a [weekly video tutorial](https://mailchi.mp/business-science/r-tips-newsletter) that shows you step-by-step how to do common R coding tasks.
Let's learn how to **automate PDFs with R**.
- [Get the Code](https://mailchi.mp/business-science/r-tips-newsletter)
- [YouTube Tutorial](https://www.youtube.com/watch?v=N8qaLAundeI)
<br>
<figure class="text-center">
<a href="https://www.youtube.com/watch?v=N8qaLAundeI"><img src="/assets/2020-10-21-automate-pdf-with-r/video-thumb.jpg" border="0" /></a>
<figcaption>(Click image to play tutorial)</figcaption>
</figure>
<br>
# Automate PDF Reporting with R Tutorial
Why create PDF's manually when you can automate PDFs with R?
That's exactly what I show you how to do in this tutorial. Here is the final report you will automate today.

<br>
First, make a **"Parameterized" Rmarkdown** file by modifying the YAML with a `params` section.

<br>
Next, **insert the parameters** in your Rmarkdown Template file so each of the key inputs depend on the parameters.

<br>
Finally, in a separate R Script, use `rmarkdown::render()` to **auto-magically create PDF reports** by selecting the Rmd Template file and changing the parameters using the params list.

<br>
Like that, you've automated your PDF Reports! 👇

<br>
### You Learned Something New!
Great! But, you need to learn a TON to master the Blue Steel pose.
What happens after you learn R for Business from Matt 👇

...And the look on your boss' face after seeing [your first Shiny App](https://www.business-science.io/business/2020/08/05/build-data-science-app-3-months.html). 👇

**I call this, "career acceleration".**
<br>
### SETUP R-TIPS WEEKLY PROJECT
1. [Get the Code](https://mailchi.mp/business-science/r-tips-newsletter)
2. Check out the [R-Tips Setup Video](https://youtu.be/F7aYV0RPyD0).
Once you take these actions, you'll be set up to receive R-Tips with Code every week. =)
<br>
{% include cta_rtrack.html %}
{% include top_rtips.html %} | 29.872549 | 186 | 0.733508 | eng_Latn | 0.552866 |
98042ef65d3a57c54c7889d23b2ada1e483b5655 | 488 | md | Markdown | todo.md | nZeloT/kitchensound | 7b3e19554d1c770d3f22d3e90442f84dae905c82 | [
"Apache-2.0"
] | null | null | null | todo.md | nZeloT/kitchensound | 7b3e19554d1c770d3f22d3e90442f84dae905c82 | [
"Apache-2.0"
] | null | null | null | todo.md | nZeloT/kitchensound | 7b3e19554d1c770d3f22d3e90442f84dae905c82 | [
"Apache-2.0"
] | null | null | null | # TODO
0. Kitchensound
- add option to display recoverable Error messages
- use file descriptors to track for mpd changes
1. Alsa
- Add equalizer to alsa configuration
- http://www.gerrelt.nl/RaspberryPi/wordpress/equalizer/
- https://www.hifiberry.com/docs/software/guide-adding-equalization-using-alsaeq/
5. Other
- maybe use buildroot to setup a minimal image https://buildroot.org/
## Internet Radio
- Stations Index API: https://de1.api.radio-browser.info/ | 34.857143 | 85 | 0.737705 | eng_Latn | 0.425419 |
9804892113540c13f43f7375ed4c622b08a69f04 | 29 | md | Markdown | README.md | BitPuffin/qg | 26f56f3e107ae7046abf489f5cbe9a83204f1422 | [
"CC0-1.0"
] | null | null | null | README.md | BitPuffin/qg | 26f56f3e107ae7046abf489f5cbe9a83204f1422 | [
"CC0-1.0"
] | null | null | null | README.md | BitPuffin/qg | 26f56f3e107ae7046abf489f5cbe9a83204f1422 | [
"CC0-1.0"
] | null | null | null | # qg
quick games (1-3 hours)
| 9.666667 | 23 | 0.655172 | eng_Latn | 0.947356 |
9804906cc1a7dea6ea61416be8acd14f5d83fc15 | 3,195 | md | Markdown | README.md | sarthak268/Embedded_Logic_and_Design | e9beefebde221321261e868dd782ce85a0a561ad | [
"MIT"
] | 9 | 2018-06-09T10:27:58.000Z | 2021-10-03T16:39:40.000Z | README.md | sarthak268/Embedded_Logic_and_Design | e9beefebde221321261e868dd782ce85a0a561ad | [
"MIT"
] | null | null | null | README.md | sarthak268/Embedded_Logic_and_Design | e9beefebde221321261e868dd782ce85a0a561ad | [
"MIT"
] | 2 | 2018-09-14T16:52:50.000Z | 2020-07-05T12:17:17.000Z | # Embedded Logic and Design
#### This repository contains all labs done in "Verilog" as a part of the Embedded Logic and Design course.
#### Instructor : Dr. Sumit Darak
### Lab 1
1. Design and implement a half-adder (using data flow approach) on the Zedboard.
2. Using the half-adders designed in step 1, implement a full-adder.
3. Implement a 4-bit adder/subtractor (adds/subtracts two 4-bit inputs) using the full-adders designed in step
### Lab 2
1. Generate the Boolean expression for the following problem statements.
2. Implement them by data flow and behavioral model.
3. Compare the RTL schematic and resource utilization for both modelling
schemes.
4. Verify the design on Zedboard.
### Lab 3
Design and implement a counter on Zedboard. The counter should continuously count from 0 to 31. The output of the counter can be displayed on the LEDs of Zedboard at a rate of 1, 2, 4 or 8 seconds. The speed is to be decided by the user (use switches for this task). The counter should be able to clear itself whenever the clear button is pressed.
### Lab 4
Design a counter that counts from 00000000 to 11111111. Convert this 8-bit binary number to a BCD number. Display the count from 0 to 255 on the seven segment display. Note that the frequency divider will generate a clock of 1Hz.
(Hint: Use time multiplexing to display different digits at different decimal position.)
### Lab 5
1) Design and implement a BCD adder which adds two numbers A and B ranging from 0 to 9. Display A on the rightmost digit of the 7 segment display and B on the leftmost digit. Output of the BCD adder should be displayed on the middle two digits of 7-segment display.
2) Design an 8-bit SIPO shift register. Shift the binary data into the shift register using 2 push buttons. One push button passes 0 and another passes 1. Display the content of shift register on the seven segment display in the BCD format.
### Lab 6
1) Design and code an FSM to detect an overlapping sequence of '11011' as
a) Moore machine.
b) Mealy machine.
2) Design and code an FSM to detect a non-overlapping sequence of '10101' as
a) Moore machine.
b) Mealy machine.
### Lab 8
Write a Verilog code which connects a keypad and external 7 segment display to the Basys 3 board via PMOD ports. Instead of using switches in Ques. 1, use the key press on the keypad to enter the value of 𝑥[𝑛] that ranges from 0 to 9. Display the output 𝑦[𝑛] to an external 7-segement display.
### Lab 9.1
This lab guides you through the process of extending the processing system you created in the previous lab by adding two GPIO (General Purpose Input/Output) IPs.
### Lab 9.2
This lab guides you through the process of using Vivado to create a simple ARM Cortex-A9 based processor design targeting the ZedBoard or Zybo board. Where the instructions refer to both boards, choose the board you are using. You will use Vivado to create the hardware system and SDK (Software Development Kit) to create an example application to verify the hardware functionality.
### Lab 11
Design and implement an interrupt based design on Zedboard, which displays different numbers on the SSD according to the push button being pressed.
| 66.5625 | 383 | 0.771518 | eng_Latn | 0.998975 |
9805a631322f9cb884c51a68e9d611a031c17aae | 7,632 | md | Markdown | _posts/2016-07-12-podcast_july11.md | bioeconometrician/bioeconometrician.github.io | bca65434298550828ea50ff93de354fd27ad15ad | [
"MIT"
] | null | null | null | _posts/2016-07-12-podcast_july11.md | bioeconometrician/bioeconometrician.github.io | bca65434298550828ea50ff93de354fd27ad15ad | [
"MIT"
] | null | null | null | _posts/2016-07-12-podcast_july11.md | bioeconometrician/bioeconometrician.github.io | bca65434298550828ea50ff93de354fd27ad15ad | [
"MIT"
] | null | null | null | ---
title: 'Podcast Digest (July 12, 2016)'
output: html_document
fontsize: 12pt
published: true
status: publish
mathjax: true
---
It’s been a good week for the podcast digest. Based on a recommendation from a friend, I subscribed to Malcom Gladwell’s new podcast series [Revisionist History](http://revisionisthistory.com/) and David Axelrod’s ongoing series [The Axe Files](http://politics.uchicago.edu/pages/axefiles).
I started with Episode 62 of the Axe Files in which David Axelrod interviewed Paul Begala, a legend in Democratic politics due to his being (along with James Carville) political advisors to Bill Clinton in his ’92 campaign. Begala is currently an advisor for *Priorities USA Action*, a wholesome sounding Hillary Clinton Super-PAC. It was a fun talk because David and Paul know each other so well (David was Obama’s campaign advisor) and they speak breezily about all the major players in US politics. I very much understood the political perspective on the perspective politics (if you’ll excuse the expression) when Begala said something along the lines of: “… Bush showed us what happens when you have the wrong person driving the car”.[[^1]] I found this particularly piquing because it directly contradicts an institutionalist view which says that what really matters for a well-functioning political system is that the rules of the game work, not that there’s good or bad people (or as Jefferson said, if men were angels we wouldn't need government). At the same time, it’s obvious that the decision to invade Iraq in the nonchalant manner it was done has been the worst foreign policy mistake in the 21st century to date, so having Gore in power may have changed that. At the same time, I think we can square these two views by saying in the long-run the good and bad people in politics average each other out, and therefore their average effectiveness (from a public good perspective) is determined the rules of the game.
Gladwell’s new podcast *Revisionist History* is fantastic (with a beautiful website design too). The first episode, *The Lady Vanishes*, is about moral licensing and tokenism. He starts with the example of an 1874 painting by Elizabeth Thompson, *Roll Call* (as shown below), which was hailed by the critics and was assumed to be the ticket Ms. Thompson would use to enter the Royal Academy and become the first woman to do so. However, despite a close admissions vote, subsequent attempts at admissions became even less successful. Gladwell posits that this may have been the effect of moral licensing: by seeming progressive and egalitarian for letting a woman come this close to admission, the members of the Royal Academy had proved (to themselves) that they were not sexist and hence allowed their (sub)conscious biases to affect their subsequent decision. Gladwell points to [research that shows that endorsing Obama licenses favouring whites](http://faculty.haas.berkeley.edu/jesss/Effron,%20Cameron,%20&%20Monin,%202009.pdf):
> Three studies tested whether the opportunity to endorse Barack Obama made individuals subsequently more likely to favor Whites over Blacks. In Study 1, participants were more willing to describe a job as better suited for Whites than for Blacks after expressing support for Obama. Study 2 replicated this effect and ruled out alternative explanations: participants favored Whites for the job after endorsing Obama, but not after endorsing a White Democrat, nor after seeing Obama’s photo without having an opportunity to endorse him. Study 3 demonstrated that racial attitudes moderated this effect: endorsing Obama increased the amount of money allocated to an organization serving Whites at the expense of an organization serving Blacks only for participants high in a measure of racial prejudice. These three studies suggest that expressing support for Obama grants people moral credentials [Monin, B., & Miller, D. T. (2001). Moral credentials and the expression of prejudice. Journal of Personality and Social Psychology, 81, 33–43], thus reducing their concern with appearing prejudiced.
#### Ms. Thompson’s well-hailed *Roll Call* piece
<p align="center">
<img src="/figures/roll-call_Lady_Butler.jpg">
</p>
He then subsequently points to the case of Julia Gillard, the former PM of Australia, who was met with sounds of good cheer to her being the first female prime minister appointed by the first female governor general. While mateship (no joke) was removed from the Australian constitution in 1999, members of the opposition (both parties and political organisations) started referring to Julia Gillard as a witch and a bitch, etc. By the end of the tenure, she had taken so much abuse she let it rip on Tony Abbott (who is by a pleasant surprise the current PM of Australia) as shown in the video below. And of course, who can forget that most iconic of phrases: “my best friend is INSERT HERE”. Why does all this matter? Well as Gladwell says, there are two tales of progress. The first type is exemplified by Jackie Robinson case, where after a black player had broken through the glass ceiling of prejudice in baseball, hundreds of subsequent black players were admitted. But then there there is a second case, whereby tokenism shuts the door on subsequent attempts for minorities or disadvantaged groups. For example there are many democracies where there has only been a single female leader in the political history. In the American case, one would not be surprised if Obama or Hillary could be the last black/female president for fifty years if Americans feel they are contended that racism/sexism is no longer a concern. This can also explain why despite a black president being in the White House, African-Americans are still in a category of their own in terms of poor socio-economic outcomes from college attainment, to median household wealth, to police brutality.
<p align="center">
<iframe width="560" height="315" src="https://www.youtube.com/embed/ihd7ofrwQX0" frameborder="0" allowfullscreen>
</iframe>
</p>
One other very interesting podcast I listened to this week was a spinoff from Radiolab, *More Perfect*, which is about the history and cases of the US Supreme court. The episode *Political Thicket* was about the *Baker v. Carr (1962)* case, which Chief Justice Earl Warren described as his most important case in his career.[[^2]] This was the case in which the supreme court ruled that it did have authority to rule on political districting to the extent that it violated citizens’ Fourteenth Amendment rights (the post-Civil War amendment guaranteeing “equal protection”). What makes the episode interesting is that this case is identified as the beginning of a the partisan US supreme court with Felix Frankfurter strongly believing that it was not justiciable to rule on the case, whereas William O. Douglas held the very much opposite view and their fight to convince the other justices led to Charles Evans Whittaker recuses himself and later leaving the court from health problems. But this Frankfurter/Douglas partisan division is now seen as possibly the beginning of the partisan split of the court.
* * *
## Footnotes
[^1]: I’m paraphrasing. However, Begala actually referred to Bush as politically smart due to his courting of Hispanics, even though it was Begala who called Bush “a high functioning moron”, but I think he respected his political instincts.
[^2]: To explain why this answer was an unexpected one, consider that Warren court (noted for its liberal tint) had issued such landmark rulings as *Brown v. Board of Education (1954)* and *Miranda v. Arizona (1966)*.
| 181.714286 | 1,674 | 0.798349 | eng_Latn | 0.999794 |
9806322e0275ea6372911bd308fbbe7d9a8aff8c | 833 | md | Markdown | README.md | abletsoff/icmp_chat | 9c7b4eef33ad6cd8337a05265942f588feb0ead9 | [
"MIT"
] | null | null | null | README.md | abletsoff/icmp_chat | 9c7b4eef33ad6cd8337a05265942f588feb0ead9 | [
"MIT"
] | null | null | null | README.md | abletsoff/icmp_chat | 9c7b4eef33ad6cd8337a05265942f588feb0ead9 | [
"MIT"
] | null | null | null | # icmp_chat
Python implementation of the ICMP coverd communication
# Functionality
<pre>
optional arguments:
-h, --help show this help message and exit
-f FILENAME, --filename FILENAME
filename to transmit / recive
-t TEXT, --text TEXT text string to transmit
-H HOST, --host HOST host to transmit / listen from
-l, --listen listen mode
-L, --logging Detailed logging
-s SIZE, --size SIZE max size of payload for one icmp packet
-T TYPE, --type TYPE icmp type
-O OPCODE, --opcode OPCODE
icmp opcode
-A, --all_icmp listen for all ICMP types and opcodes. Do not use this
option while listening ECHO request
</pre>
# Example

| 33.32 | 78 | 0.631453 | eng_Latn | 0.748331 |
980634192f6c963317273191e2d73c44ac22862e | 22,155 | md | Markdown | page/truyenkieu/tu-hai-mac-lua-ho-ton-hien.md | madmanteam/madmanteam.github.io | 1291ad19cee0a7f36aefce473d7b8e0dbacddf87 | [
"MIT"
] | 1 | 2022-01-28T15:56:12.000Z | 2022-01-28T15:56:12.000Z | page/truyenkieu/tu-hai-mac-lua-ho-ton-hien.md | madmanteam/madmanteam.github.io | 1291ad19cee0a7f36aefce473d7b8e0dbacddf87 | [
"MIT"
] | 1 | 2020-06-25T17:13:00.000Z | 2020-07-02T07:21:51.000Z | page/truyenkieu/tu-hai-mac-lua-ho-ton-hien.md | madmanteam/madmanteam.github.io | 1291ad19cee0a7f36aefce473d7b8e0dbacddf87 | [
"MIT"
] | null | null | null | ---
title: Từ Hải mắc lừa Hồ Tôn Hiến, Kiều tự vẫn
layout: page
comments: true
---
### Các phần khác
+ [Đôi lời về Nguyễn Du](/2019-11-20-truyen-kieu)
+ [Kiều thăm mộ Đạm Tiên](/page/truyenkieu/kieu-tham-mo-dam-tien/) _(1-244)_
+ [Kiều gặp Kim Trọng](/page/truyenkieu/kieu-gap-kim-trong/) _(245-572)_
+ [Kiều bán mình chuộc cha](/page/truyenkieu/kieu-ban-minh-chuoc-cha/) _(573-804)_
+ [Kiều rơi vào tay Tú bà & Mã Giám Sinh](/page/truyenkieu/kieu-roi-vao-tay-tu-ba/) _(805-1056)_
+ [Kiều mắc lừa Sở Khanh](/page/truyenkieu/kieu-mac-lua-so-khanh/) _(1057-1274)_
+ [Kiều gặp Thúc Sinh](/page/truyenkieu/kieu-gap-thuc-sinh/) _(1275-1472)_
+ [Kiều và Hoạn Thư](/page/truyenkieu/kieu-va-hoan-thu/) _(1473-1704)_
+ [Kiều và Hoạn Thư (tiếp)](/page/truyenkieu/kieu-va-hoan-thu-continue/) _(1705-2028)_
+ [Kiều gặp Từ Hải](/page/truyenkieu/kieu-gap-tu-hai/) _(2029-2288)_
+ [Kiều báo thù](/page/truyenkieu/kieu-bao-thu/) _(2289-2418)_
+ Từ Hải mắc lừa Hồ Tôn Hiến, Kiều tự vẫn _(2419-2738)_
+ [Kim Trọng đi tìm Kiều](/page/truyenkieu/kim-trong-di-tim-kieu/) _(2739-2972)_
+ [Kiều - Kim Trọng đoàn tụ](/page/truyenkieu/kieu-kim-trong-doan-tu/) _(2973-3254)_
<center>
<br>
<i>Nàng từ ân oán rạch ròi,<br>
</i>
<br>
<b>2420</b><i>. Bể oan dường đã vơi vơi cạnh
lòng.<br>
Tạ ân lạy trước Từ công:<br>
Chút thân bồ liễu nào mong có rày !<br>
Trộm nhờ sấm sét ra tay,<br>
Tấc riêng như cất gánh đầy đổ đi !<br>
</i>
<br>
<b>2425</b><i>. Chạm xương chép dạ xiết chi,<br>
Dễ đem gan óc đền nghì trời mây !<br>
Từ rằng: Quốc sĩ xưa nay,<br>
Chọn người tri kỷ một ngày được chăng?<br>
Anh hùng tiếng đã gọi rằng,<br>
</i>
<br>
<b>2430</b><i>. Giữa đường dẫu thấy bất bằng
mà tha !<br>
Huống chi việc cũng việc nhà,<br>
Lọ là thâm tạ mới là tri ân .<br>
Xót nàng còn chút song thân,<br>
Bấy nay kẻ Việt người Tần cách xa .<br>
</i>
<br>
<b>2435</b><i>. Sao cho muôn dặm một nhà,<br>
Cho người thấy mặt là ta cam lòng.<br>
Vội truyền sửa tiệc quân trung,<br>
Muôn binh nghìn tướng hội đồng tẩy oan.<br>
Thừa cơ trúc chẻ ngói tan,<br>
</i>
<br>
<b>2440</b><i>. Binh uy từ ấy sấm ran trong ngoài
.<br>
Triều đình riêng một góc trời,<br>
Gồm hai văn võ rạch đôi sơn hà.<br>
Đòi phen gió quét mưa sa,<br>
Huyện thành đạp đổ năm tòa cõi nam .<br>
</i>
<br>
<b>2445</b><i>. Phong trần mài một lưỡi gươm,<br>
Những loài giá áo túi cơm sá gì !<br>
Nghênh ngang một cõi biên thùy,<br>
Thiếu gì cô quả, thiếu gì bá vương !<br>
Trước cờ ai dám tranh cường,<br>
</i>
<br>
<b>2450</b><i>. Năm năm hùng cứ một phương hải
tần.<br>
Có quan tổng đốc trọng thần,<br>
Là Hồ Tôn Hiến kinh luân gồm tài.<br>
Đẩy xe vâng chỉ đặc sai,<br>
Tiện nghi bát tiểu việc ngoài đổng nhung.<br>
</i>
<br>
<b>2455</b><i>. Biết Từ là đấng anh hùng,<br>
Biết nàng cũng dự quân trung luận bàn.<br>
Đóng quân làm chước chiêu an,<br>
Ngọc vàng gấm vóc sai quan thuyết hàng.<br>
Lại riêng một lễ với nàng,<br>
</i>
<br>
<b>2460</b><i>. Hai tên thể nữ ngọc vàng nghìn
cân.<br>
Tin vào gởi trước trung quân,<br>
Từ công riêng hãy mười phân hồ đồ.<br>
Một tay gây dựng cơ đồ,<br>
Bấy lâu bể Sở sông Ngô tung hoành!<br>
</i>
<br>
<b>2465</b><i>. Bó thân về với triều đình,<br>
Hàng thần lơ láo phận mình ra đâu?<br>
Áo xiêm ràng buộc lấy nhau,<br>
Vào luồn ra cúi công hầu mà chi?<br>
Sao bằng riêng một biên thùy,<br>
</i>
<br>
<b>2470</b><i>. Sức này đã dễ làm gì được
nhau? <br>
Chọc trời khuấy nước mặc dầu,<br>
Dọc ngang nào biết trên đầu có ai?<br>
Nàng thời thật dạ tin người,<br>
Lễ nhiều nói ngọt nghe lời dễ xiêu.<br>
</i>
<br>
<b>2475</b><i>. Nghĩ mình mặt nước cánh bèo,<br>
Đã nhiều lưu lạc lại nhiều gian truân.<br>
Bằng nay chịu tiếng vương thần,<br>
Thênh thênh đường cái thanh vân hẹp gì!<br>
Công tư vẹn cả hai bề,<br>
</i>
<br>
<b>2480</b><i>. Dần dà rồi sẽ liệu về cố
hương.<br>
Cũng ngôi mệnh phụ đường đường,<br>
Nở nang mày mặt rỡ ràng mẹ cha.<br>
Trên vì nước dưới vì nhà,<br>
Một là đắc hiếu hai là đắc trung.<br>
</i>
<br>
<b>2485</b><i>. Chẳng hơn chiếc bách giữa dòng,<br>
E dè sóng vỗ hãi hùng cỏ hoa.<br>
Nhân khi bàn bạc gần xa,<br>
Thừa cơ nàng mới bàn ra nói vào.<br>
Rằng: Trong Thánh trạch dồi dào,<br>
</i>
<br>
<b>2490</b><i>. Tưới ra đã khắp thấm vào đã
sâu.<br>
Bình thành công đức bấy lâu,<br>
Ai ai cũng đội trên đầu xiết bao.<br>
Ngẫm từ gây việc binh đao, <br>
Đống xương Vô định đã cao bằng đầu. <br>
</i>
<br>
<b>2495</b><i>. Làm chi để tiếng về sau,<br>
Nghìn năm ai có khen đâu Hoàng Sào!<br>
Sao bằng lộc trọng quyền cao,<br>
Công danh ai dứt lối nào cho qua?<br>
Nghe lời nàng nói mặn mà,<br>
</i>
<br>
<b>2500</b><i>. Thế công Từ mới trở ra thế
hàng.<br>
Chỉnh nghi tiếp sứ vội vàng,<br>
Hẹn kỳ thúc giáp quyết đường giải binh.<br>
Tin lời thành hạ yêu minh,<br>
Ngọn cờ ngơ ngác trống canh trễ tràng.<br>
</i>
<br>
<b>2505</b><i>. Việc binh bỏ chẳng giữ giàng,<br>
Vương sư dòm đã tỏ tường thực hư.<br>
Hồ công quyết kế thừa cơ,<br>
Lễ tiên binh hậu khắc cờ tập công. <br>
Kéo cờ chiêu phủ tiên phong,<br>
</i>
<br>
<b>2510</b><i>. Lễ nghi dàn trước bác đồng
phục sau.<br>
Từ công hờ hững biết đâu,<br>
Đại quan lễ phục ra đầu cửa viên.<br>
Hồ công ám hiệu trận tiền,<br>
Ba bề phát súng bốn bên kéo cờ.<br>
</i>
<br>
<b>2515</b><i>. Đương khi bất ý chẳng ngờ,<br>
Hùm thiêng khi đã sa cơ cũng hèn!<br>
Tử sinh liều giữa trận tiền,<br>
Dạn dầy cho biết gan liền tướng quân!<br>
Khí thiêng khi đã về thần,<br>
</i>
<br>
<b>2520</b><i>. Nhơn nhơn còn đứng chôn chân
giữa vòng!<br>
Trơ như đá vững như đồng,<br>
Ai lay chẳng chuyển ai rung chẳng dời.<br>
Quan quân truy sát đuổi dài.<br>
Ầm ầm sát khí ngất trời ai đang.<br>
</i>
<br>
<b>2525</b><i>. Trong hào ngoài lũy tan hoang,<br>
Loạn quân vừa dắt tay nàng đến nơi.<br>
Trong vòng tên đá bời bời,<br>
Thấy Từ còn đứng giữa trời trơ trơ.<br>
Khóc rằng: Trí dũng có thừa,<br>
</i>
<br>
<b>2530</b><i>. Bởi nghe lời thiếp nên cơ hội
này!<br>
Mặt nào trông thấy nhau đây?<br>
Thà liều sống thác một ngày với nhau!<br>
Dòng thu như dội cơn sầu,<br>
Dứt lời nàng cũng gieo đầu một bên.<br>
</i>
<br>
<b>2535</b><i>. Lạ thay oan khí tương triền!<br>
Nàng vừa phục xuống Từ liền ngã ra.<br>
Quan quân kẻ lại người qua,<br>
Xót nàng sẽ lại vực ra dần dần.<br>
Đem vào đến trước trung quân,<br>
</i>
<br>
<b>2540</b><i>. Hồ công thấy mặt ân cần hỏi
han.<br>
Rằng: Nàng chút phận hồng nhan,<br>
Gặp cơn binh cách nhiều nàn cũng thương!<br>
Đã hay thành toán miếu đường,<br>
Giúp công cũng có lời nàng mới nên.<br>
</i>
<br>
<b>2545</b><i>. Bây giờ sự đã vẹn tuyền,<br>
Mặc lòng nghĩ lấy muốn xin bề nào?<br>
Nàng càng giọt ngọc tuôn dào,<br>
Ngập ngừng mới gửi thấp cao sự lòng.<br>
Rằng: Từ là đấng anh hùng,<br>
</i>
<br>
<b>2550</b><i>. Dọc ngang trời rộng vẫy vùng bể
khơi!<br>
Tin tôi nên quá nghe lời,<br>
Đem thân bách chiến làm tôi triều đình.<br>
Ngỡ là phu quý phụ vinh,<br>
Ai ngờ một phút tan tành thịt xương!<br>
</i>
<br>
<b>2555</b><i>. Năm năm trời bể ngang tàng,<br>
Đem mình đi bỏ chiến trường như không.<br>
Khéo khuyên kể lấy làm công,<br>
Kể bao nhiêu lại đau lòng bấy nhiêu!<br>
Xét mình công ít tội nhiều,<br>
</i>
<br>
<b>2560</b><i>. Sống thừa tôi đã nên liều mình
tôi!<br>
Xin cho tiện thổ một doi,<br>
Gọi là đắp điếm cho người tử sinh.<br>
Hồ công nghe nói thương tình,<br>
Truyền cho cảo táng di hình bên sông.<br>
</i>
<br>
<b>2565</b><i>. Trong quân mở tiệc hạ công,<br>
Xôn xao tơ trúc hội đồng quân quan .<br>
Bắt nàng thị yến dưới màn,<br>
Dở say lại ép cung đàn nhặt tâu .<br>
Một cung gió thảm mưa sầu,<br>
</i>
<br>
<b>2570</b><i>. Bốn dây nhỏ máu năm đầu ngón
tay !<br>
Ve ngâm vượn hót nào tày,<br>
Lọt tai Hồ cũng nhăn mày rơi châu .<br>
Hỏi rằng: Này khúc ở đâu ?<br>
Nghe ra muôn oán nghìn sầu lắm thay !<br>
</i>
<br>
<b>2575</b><i>. Thưa rằng: Bạc mệnh khúc này,<br>
Phổ vào đàn ấy những ngày còn thơ .<br>
Cung cầm lựa những ngày xưa,<br>
Mà gương bạc mệnh bây giờ là đây !<br>
Nghe càng đắm ngắm càng say,<br>
</i>
<br>
<b>2580</b><i>. Lạ cho mặt sắt cũng ngây vì
tình !<br>
Dạy rằng: Hương lửa ba sinh,<br>
Dây loan xin nối cầm lành cho ai .<br>
Thưa rằng: Chút phận lạc loài,<br>
Trong mình nghĩ đã có người thác oan .<br>
</i>
<br>
<b>2585</b><i>. Còn chi nữa cánh hoa tàn,<br>
Tơ lòng đã dứt dây đàn Tiểu Lân .<br>
Rộng thương còn mảnh hồng quần,<br>
Hơi tàn được thấy gốc phần là may !<br>
Hạ công chén đã quá say,<br>
</i>
<br>
<b>2590</b><i>. Hồ công đến lúc rạng ngày nhớ
ra .<br>
Nghĩ mình phương diện quốc gia,<br>
Quan trên nhắm xuống người ta trông vào .<br>
Phải tuồng trăng gió hay sao,<br>
Sự này biết tính thế nào được đây ?<br>
</i>
<br>
<b>2595</b><i>. Công nha vừa buổi rạng ngày,<br>
Quyết tình Hồ mới đoán ngay một bài .<br>
Lệnh quan ai dám cãi lời,<br>
Ép tình mới gán cho người thổ quan .<br>
Ông tơ thực nhẽ đa đoan !<br>
</i>
<br>
<b>2600</b><i>. Xe tơ sao khéo vơ quàng vơ xiên
?<br>
Kiệu hoa áp thẳng xuống thuyền,<br>
Lá màn rủ thấp ngọn đèn khêu cao .<br>
Nàng càng ủ liễu phai đào,<br>
Trăm phần nào có phần nào phần tươi ?<br>
</i>
<br>
<b>2605</b><i>. Đành thân cát lấp sóng vùi,<br>
Cướp công cha mẹ thiệt đời thông minh !<br>
Chân trời mặt bể lênh đênh,<br>
Nắm xương biết gởi tử sinh chốn nào,<br>
Duyên đâu ai dứt tơ đào,<br>
</i>
<br>
<b>2610</b><i>. Nợ đâu ai đã dắt vào tận tay !<br>
Thân sao thân đến thế này ?<br>
Còn ngày nào cũng dư ngày ấy thôi !<br>
Đã không biết sống là vui,<br>
Tấm thân nào biết thiệt thòi là thương !<br>
</i>
<br>
<b>2615</b><i>. Một mình cay đắng trăm đường,<br>
Thôi thì nát ngọc tan vàng thì thôi !<br>
Mảnh trăng đã gác non đoài,<br>
Một mình luống những đứng ngồi chưa xong .<br>
Triều đâu nổi tiếng đùng đùng,<br>
</i>
<br>
<b>2620</b><i>. Hỏi ra mới biết rằng sông Tiền
đường.<br>
Nhớ lời thần mộng rõ ràng,<br>
Này thôi hết kiếp đoạn trường là đây !<br>
Đạm Tiên nàng nhé có hay !<br>
Hẹn ta thì đợi dưới này rước ta .<br>
</i>
<br>
<b>2625</b><i>. Dưới đèn sẵn bức tiên hoa,<br>
Một thiên tuyệt bút gọi là để sau .<br>
Cửa bồng vội mở rèm châu,<br>
Trời cao sông rộng một màu bao la .<br>
Rằng: Từ công hậu đãi ta,<br>
</i>
<br>
<b>2630</b><i>. Chút vì việc nước mà ra phụ
lòng.<br>
Giết chồng mà lại lấy chồng,<br>
Mặt nào còn đứng ở trong cõi đời ?<br>
Thôi thì một thác cho rồi,<br>
Tấm lòng phó mặc trên trời dưới sông !<br>
</i>
<br>
<b>2635</b><i>. Trông vời con nước mênh mông,<br>
Đem mình gieo xuống giữa dòng Trường Giang .<br>
Thổ quan theo vớt vội vàng,<br>
Thời đà đắm ngọc chìm hương mất rồi !<br>
Thương thay cũng một kiếp người,<br>
</i>
<br>
<b>2640</b><i>. Hại thay mang lấy sắc tài làm chi
!<br>
Những là oan khổ lưu ly,<br>
Chờ cho hết kiếp còn gì là thân !<br>
Mười lăm năm bấy nhiêu lần,<br>
Làm gương cho khách hồng quần thử soi !<br>
</i>
<br>
<b>2645</b><i>. Đời người đến thế thì thôi,<br>
Trong cơ âm cực dương hồi khốn hay . <br>
Mấy người hiếu nghĩa xưa nay,<br>
Trời làm chi đến lâu ngày càng thương !<br>
Giác Duyên từ tiết giã màng,<br>
</i>
<br>
<b>2650</b><i>. Đeo bầu quảy níp rộng đường
vân du.<br>
Gặp bà Tam Hợp đạo cô,<br>
Thong dong hỏi hết nhỏ to sự nàng:<br>
Người sao hiếu nghĩa đủ đường,<br>
Kiếp sao rặt những đoạn trường thế thôi?<br>
</i>
<br>
<b>2655</b><i>. Sư rằng: Phúc họa đạo trời,<br>
Cỗi nguồn cũng ở lòng người mà ra.<br>
Có trời mà cũng tại ta,<br>
Tu là cõi phúc tình là dây oan.<br>
Thúy Kiều sắc sảo khôn ngoan,<br>
</i>
<br>
<b>2660</b><i>. Vô duyên là phận hồng nhan đã
đành,<br>
Lại mang lấy một chữ tình,<br>
Khư khư mình buộc lấy mình vào trong.<br>
Vậy nên những chốn thong dong,<br>
Ở không yên ổn ngồi không vững vàng.<br>
</i>
<br>
<b>2665</b><i>. Ma đưa lối quỷ đem đường,<br>
Lại tìm những chốn đoạn trường mà đi.<br>
Hết nạn ấy đến nạn kia,<br>
Thanh lâu hai lượt thanh y hai lần.<br>
Trong vòng giáo dựng gươm trần,<br>
</i>
<br>
<b>2670</b><i>. Kề răng hùm sói gởi thân tôi
đòi.<br>
Giữa dòng nước dẫy sóng dồi,<br>
Trước hàm rồng cá gieo mồi thuỷ tinh.<br>
Oan kia theo mãi với tình,<br>
Một mình mình biết một mình mình hay.<br>
</i>
<br>
<b>2675</b><i>. Làm cho sống đọa thác đầy,<br>
Đoạn trường cho hết kiếp này mới thôi!<br>
Giác Duyên nghe nói rụng rời:<br>
Một đời nàng nhé thương ôi còn gì!<br>
Sư rằng: Song chẳng hề chi,<br>
</i>
<br>
<b>2680</b><i>. Nghiệp duyên cân lại nhắc đi
còn nhiều.<br>
Xét trong tội nghiệp Thúy Kiều,<br>
Mắc điều tình ái khỏi điều tà dâm,<br>
Lấy tình thâm trả nghĩa thâm,<br>
Bán mình đã động hiếu tâm đến trời!<br>
</i>
<br>
<b>2685</b><i>. Hại một người cứu muôn người,<br>
Biết đường khinh trọng biết lời phải chăng.<br>
Thửa công đức ấy ai bằng?<br>
Túc khiên đã rửa lâng lâng sạch rồi!<br>
Khi nên trời cũng chiều người,<br>
</i>
<br>
<b>2690</b><i>. Nhẹ nhàng nợ trước đền bồi
duyên sau.<br>
Giác Duyên dù nhớ nghĩa nhau,<br>
Tiền đường thả một bè lau rước người.<br>
Trước sau cho vẹn một lời,<br>
Duyên ta mà cũng phúc trời chi không!<br>
</i>
<br>
<b>2695</b><i>. Giác Duyên nghe nói mừng lòng,<br>
Lân la tìm thú bên sông Tiền đường,<br>
Đánh tranh chụm nóc thảo đường,<br>
Một gian nước biếc mây vàng chia đôi.<br>
Thuê năm ngư phủ hai người,<br>
</i>
<br>
<b>2700</b><i>. Đóng thuyền chực bến kết chài
giăng sông.<br>
Một lòng chẳng quảng mấy công,<br>
Khéo thay gặp gỡ cũng trong chuyển vần!<br>
Kiều từ gieo xuống duềnh ngân,<br>
Nước xuôi bỗng đã trôi dần tận nơi.<br>
</i>
<br>
<b>2705</b><i>. Ngư ông kéo lưới vớt người,<br>
Ngẫm lời Tam Hợp rõ mười chẳng ngoa!<br>
Trên mui lướt mướt áo là,<br>
Tuy dầm hơi nước chưa lòa bóng gương.<br>
Giác Duyên nhận thật mặt nàng,<br>
</i>
<br>
<b>2710</b><i>. Nàng còn thiêm thiếp giấc vàng
chưa phai.<br>
Mơ màng phách quế hồn mai,<br>
Đạm Tiên thoắt đã thấy người ngày xưa.<br>
Rằng: Tôi đã có lòng chờ,<br>
Mất công mười mấy năm thừa ở đây.<br>
</i>
<br>
<b>2715</b><i>. Chị sao phận mỏng phúc dày,<br>
Kiếp xưa đã vậy lòng này dễ ai!<br>
Tâm thành đã thấu đến trời,<br>
Bán mình là hiếu cứu người là nhân.<br>
Một niềm vì nước vì dân,<br>
</i>
<br>
<b>2720</b><i>. Âm công cất một đồng cân đã
già!<br>
Đoạn trường sổ rút tên ra,<br>
Đoạn trường thơ phải đưa mà trả nhau.<br>
Còn nhiều hưởng thụ về lâu,<br>
Duyên xưa tròn trặn phúc sau dồi dào!<br>
</i>
<br>
<b>2725</b><i>. Nàng nghe ngơ ngẩn biết sao,<br>
Trạc Tuyền! nghe tiếng gọi vào bên tai.<br>
Giật mình thoắt tỉnh giấc mai,<br>
Bâng khuâng nào đã biết ai mà nhìn.<br>
Trong thuyền nào thấy Đạm Tiên,<br>
</i>
<br>
<b>2730</b><i>. Bên mình chỉ thấy Giác Duyên
ngồi kề.<br>
Thấy nhau mừng rỡ trăm bề,<br>
Dọn thuyền mới rước nàng về thảo lư.<br>
Một nhà chung chạ sớm trưa,<br>
Gió trăng mát mặt muối dưa chay lòng.<br>
</i>
<br>
<b>2735</b><i>. Bốn bề bát ngát mênh mông,<br>
Triều dâng hôm sớm mây lồng trước sau.<br>
Nạn xưa trút sạch lầu lầu,<br>
Duyên xưa chưa dễ biết đâu chốn này.</i>
</center>
### Chú giải
```
2425. Khắc xương ghi dạ: Do chữ minh tâm khắc cốt: ý nói ơn sâu của Kiều xin ghi vào lòng, khắc vào xương không bao giờ quên.
2426. Nghì trời mây: Ơn nghĩa cao cả như trời mây.
2427. Quốc sĩ: Kẻ sĩ tài giỏi có tiếng trong nước.
2430. Cố ngữ: Lộ kiến bất bình, bạt dao tương trợ, ý nói người anh hùng nghĩa hiệp, giữa đường đi mà thấy điều gì không công bằng thì tuốt gươm ra mà giúp sức cho người bị áp bức. Câu này mượn ý ấy.
2432. Thâm tạ: Tạ ơn một cách sâu sắc.
Tri ân: Biết ơn của người khác đối với mình.
2434. Việt: Một xứ ở Đông nam Trung Quốc;
Tần: Một xứ ở bắc Trung Quốc. Kẻ Việt người Tần có nghĩa là cách biệt xa xôi.
2438. Tẩy oan: Rửa tội oan, ý nói Từ Hải sai mở tiệc để làm hội rửa sạch tội oan cho Kiều.
2440. Bình uy: Uy thế của quân đội. Câu này ý nói: Uy thế của quân Từ Hải từ đó vang dội trong ngoài như sấm dậy.
2444. Huyện thành: Thành trì của một huyện. Câu này ý nói: Quân Từ Hải đánh chiếm được năm huyện phía Nam Trung Quốc.
2446. Giá áo túi cơm: Cái giá để mắc áo, cái túi để đựng cơm ý nói người vô dụng hèn kém.
2448. Cô và quả: Tiếng tự xưng của bọn vua chúa đời xưa. Bá Vương cũng nghĩa như vua chúa. Câu này ý nói: Từ Hải cũng xưng cô xưng quả, làm vương làm bá một phương chứ không kém gì ai.
2449. Tranh cường: Đua tranh về sức mạnh. Câu này ý nói: Trước ngọn cờ của Từ Hải không ai dám chống lại.
2450. Hùng cứ: Lấy sức mạnh mà chiếm giữ.
Hải tần: Đất ven biển.
2452. Kinh luân: Nghĩa đen là quay tơ và bện tơ, người ta thường dùng để nói tài sắp xếp chính sự, kinh bang tế thế.
2453. Đẩy xe: Do chữ thôi cốc (đẩy bánh xe). Đời xưa, khi sai tướng đi đánh giặc, vua thường tự mình đẩy vào xe của viên tướng một cái, để tỏ ý tôn trọng. Câu này ý nói: vua nhà Minh sai Hồ Tôn Hiến đi đánh Từ Hải là một việc rất quan trọng.
2454. Tiện nghi bát tiễu: Tuỳ tiện mà đánh đẹp.
Đổng nhung: Trông coi, đốc suất việc quân.
2457. Chiêu an: Kêu gọi chiêu dụ cho giặc đầu hàng.
2477. Vương thần: Bề tôi của nhà vua.
2478. Thanh vân: Mây xanh, người xưa thường dùng để chỉ con đường công danh.
2481. Mệnh phụ: Vợ các quan to đời xưa, được vua ban sắc mệnh phong cho làm phu nhân.
2484. Đắc hiếu: Tròn đạo hiếu với cha mẹ.
Đắc trung: Tròn đạo trung với vua.
2485. Chiếc bách: Do chữ bách châu có nghĩa là mảnh thuyền, ý nói thân phận lênh đênh.
2491. Bình thành: Do chữ địa bình thiên thành ở Kinh thư, ý nói nhà vua sửa sang việc nước cho trời đất được bằng phẳng.
2494. Vô định: Tên một con sông ở biên thuỳ tỉnh Thiểm Tây (Trung Quốc). Ngày xưa ở con sông ấy đã xảy ra nhiều cuộc chiến tranh giữa người Hán và người Hồ, làm cho rất nhiều người bị chết.
2496. Hoàng Sào: Một lãnh tụ nông dân khởi nghĩa cuối đời Đường, đã từng vây hãm kinh đô Trường An, tung hoành trong mười năm trời, sau bị thủ hạ giết chết.
2502. Thúc giáp: Bó áo giáp lại.
Giải binh: Cho quân đội nghỉ ngơi không chiến đấu nữa.
2530. Thành hạ yêu minh: Cùng nhau ăn thề dưới thành để tỏ ý không làm hại nhau và thật thà tuân theo đúng những điều đã ước hẹn.
2506. Vương sư: quân của nhà vua, tức quân của Hồ Tôn Hiến.
2507. Quyết kế thừa cơ: Quyết định cái mưu là nhân cơ hội Từ Hải trễ tràng việc quân để đánh.
2508. Lễ tiên bình hậu: Phía trước thì đàn nghi lễ để chiêu hàng, phía sau thì phục sẵn binh mã để phản công.
Khắc cờ: ấn định kỳ hạn.
Tập công: Đánh úp.
2509. Chiêu phủ: Kêu gọi, vỗ về, để cho quy hàng.
Tiên phong: Toán quân đi trước. Câu này ý nói: Hồ Tôn Hiến lập mưu cho kéo cờ "chiêu phủ" đi trước.
2512. Đại quan lễ phục: Ăn bận theo phục sức của vị quan lớn không mặc binh phục.
2529. Trí dũng: Trí khôn và sức mạnh.
2533. Dòng thu: Đây là chỉ nước mắt.
2535. Oan khí tương triền: Cái oan khí ức vấn vít lại với nhau. ý nói: Giữa Từ Hải và Thuý Kiều hình như cùng chung mối uất ức.
2542. Binh cách: Binh là binh khí. Cách là áo giáp và mũ đầu mâu. Người ta thường dùng hai chữ binh cách để chỉ cuộc binh đao chinh chiến.
2543. Thành toán miếu đường: Mưu chước đã sắp đặt sẵn ở nơi tốn miếu triều đường. Câu này ý nói: đành hay triều đình đã cso mưu kế sẵn, nhưng cũng nhờ lời nàng nói giúp mới nên việc.
2552. Bách chiến: Trăm trận đánh, ý nói Từ Hải là một người dạn dày trong chiến trận.
2553. Phu quí phụ vinh: Chồng làm nên quan sang thì vợ cũng được vinh hiển.
2555. Ngang tàng: Cũng cú nghĩa như hiên ngang, ý nói người tung hoành ngang trời dọc đất.
2561. Tiện thổ: Mướng đất xấu.
2564. Cảo táng: Chôn một cách sơ sài, không có khâm liệm quan quách gì. Di hình: Cũng như di hài.
2565. Hạ công: Mừng công (Thắng trận).
2567. Thị yến: Hầu hạ bên bàn tiệc.
2581. Hương lửa ba sinh: Do chữ tam sinh hương hoả, ý nói duyên nợ vợ chồng từ kiếp xưa để lại.
2582. Dây loan: Chỉ việc nối lại nhân duyên vợ chồng.
2586. Tiểu lân: Tên nàng Phùng Thục Phi, vợ vua Hậu chủ nước Tề, đời Nam Bắc triều. Sau khi nước Tề mất, nàng về tay người khác, nhân lúc dây đàn đứt, nàng làm bài thơ cảm hoài trong đó có câu: Dục trí tâm đoạn tuyệt, ưng khan tất thương huyền. Nghĩa là muốn biết tơ lòng dứt nát, nên xem cái dây trên đầu gối thì rõ. Câu này mượn ýcâu thơ ấy.
2588. Gốc phần: Do chữ phần du.
2591. Phương diện quốc gia: vị quan đảm đang công việc một vùng đất nước.
2596. Công nha: Chỗ làm việc quan, cũng như công môn đườngv.v.
2598. Thổ quan: Cũng như thổ tù, viên quan người ở bản thổ, có thể ở vùng dân tộc ít người.
2609. Tơ đào: Cũng như tơ hồng. Câu này ý nói: Ai đã chia rẽ nhân duyên của mình, đối nghĩa với câu dưới: "Nợ đâu, ai đã giắt vào tận tay?". Nợ đây tức là việc "ép tình mới gán cho người thổ quan".
2619. Triều: Nước thuỷ triều. ở cửa sông Tiền Đường (Trung Quốc) khi triều lên thì có tiếng sóng đùng đùng.
2621. Thần mộng: Lời báo mộng của thần, ý nói lời Đạm Tiên dặn trong chiêm bao, lúc Kiều tự vẫn ở nhà Tú Bà: "Sông Tiền Đường sẽ hẹn hò về sau".
2626. Tuyệt bút: Bút tích cuối cùng, viết trước khi chết để kể nỗi tâm tình của mình cho người sau biết.
2627. Cửa hồng: Cửa thuyền.
Rèm châu: Rèm có trang sức châu báu, hoặc rèm sơn màu đỏ.
2635. Con nước: Tiếng quen gọi của dân chài lưới để chỉ nước thủy triều lên xuống.
2638. Người xưa thường dùng hai chữ hương ngọc để chỉ phụ nữ.
2646. Âm cực dương hồi: Khi khí âm đến hết mực thì khí dương lạ trở về. Câu này cũng nghĩa như câu bĩ cực thái lai, ý nói con người ta khi vận đen đã hết thì vận đỏ trở lại.
2650. Bầu: Quả bầu khô rút ruột đi để đựng nước.
Níp: Cái tráp đan bằng tre để đựng quần áo sách vở. Hai vật thường dùng của những người đi đường thời xưa.
Vân du: Danh từ nhà Phật, ý nói nhà sư đi lang thang nay đây mai đó như đám mây bay vô định.
2655. Phúc hoạ đạo trời: Nói người ở đời gặp phúc hay gặp hoạ đều do ý trời, không phải ngẫu nhiên.
2668. Thanh lâu: Gái điếm. Thanh y: Gái hầu. Thuý Kiều làm gái điếm một lần ở Lâm Tri, một lần ở Châu Thai và làm gái hầu một lần ở nhà Hoạn bà, một lần ở nhà Hoạn Thư.
2670. Hùm sói: Người xưa thường dùng hai chữ hùm sói để chỉ các tướng giặc. Đây muốn nói Kiều phải sống với bọn ác độc.
2680. Nghiệp duyên: Danh từ nhà Phật có nghĩa là mối duyên nợ do bản thân mình làm nên từ kiếp trước.
2683. Tình thân: Do câu phụ tử tình thân. Câu này ý nói: Thuý Kiều đến bối ơn nghĩa sâu sắc của cha mẹ.
2687. Thửa công đức: Nghĩa là cứ xem như công đức ấy.
2688. Túc khiên: Tội lỗi kiếp trước.
2697. Thảo đường: Nhà lợp bằng gianh, bằng cỏ.
2699. Ngư phủ: Người làm nghề chài lưới.
2703. Duềnh ngân: Dòng nước bạc.
2705. Ngư ông: Ông lão đánh cá, tức "ngư phủ" nói trên.
2711. Phách quế hồn mai: Do chữ quế phách mai hồn. Hai chữ "quế mai" ở đây dùng cho đẹp lời văn.
2720. Âm công: Công đức cứu người làm ngấm ngầm, không ai biết.
2732. Thảo lưu: Nhà tranh cũng nghĩa như thảo đường.
```
<br>
<div style="text-align: right">
<a href="/page/truyenkieu/kim-trong-di-tim-kieu">[Tiếp: Kim Trọng đi tìm Kiều]</a>
</div> | 36.925 | 343 | 0.696592 | vie_Latn | 1.00001 |
980719efe31b0ef482a2e36498311e971ff4fc5a | 2,332 | md | Markdown | node_modules/@istanbuljs/load-nyc-config/CHANGELOG.md | zommerfelds/upload-google-play | c18b0b075876f269534287e32a386a1e69079a23 | [
"MIT"
] | 327 | 2019-09-27T23:17:00.000Z | 2022-03-30T20:42:29.000Z | node_modules/@istanbuljs/load-nyc-config/CHANGELOG.md | zommerfelds/upload-google-play | c18b0b075876f269534287e32a386a1e69079a23 | [
"MIT"
] | 377 | 2020-05-27T06:54:19.000Z | 2022-03-31T13:22:13.000Z | node_modules/@istanbuljs/load-nyc-config/CHANGELOG.md | zommerfelds/upload-google-play | c18b0b075876f269534287e32a386a1e69079a23 | [
"MIT"
] | 150 | 2020-06-04T16:21:11.000Z | 2022-03-22T23:24:32.000Z | # Changelog
All notable changes to this project will be documented in this file. See [standard-version](https://github.com/conventional-changelog/standard-version) for commit guidelines.
## [1.1.0](https://github.com/istanbuljs/load-nyc-config/compare/v1.0.0...v1.1.0) (2020-05-20)
### Features
* Create `isLoading` function ([#15](https://github.com/istanbuljs/load-nyc-config/issues/15)) ([0e58b51](https://github.com/istanbuljs/load-nyc-config/commit/0e58b516f663af7ed710ba27f2090fc28bc3fdb1))
* Support loading ES module config from `.js` files ([#14](https://github.com/istanbuljs/load-nyc-config/issues/14)) ([b1ea369](https://github.com/istanbuljs/load-nyc-config/commit/b1ea369f1e5162133b7057c5e3fefb8085671ab3))
## [1.0.0](https://github.com/istanbuljs/load-nyc-config/compare/v1.0.0-alpha.2...v1.0.0) (2019-12-20)
### Features
* Version bump only ([#11](https://github.com/istanbuljs/load-nyc-config/issues/11)) ([8c3f1be](https://github.com/istanbuljs/load-nyc-config/commit/8c3f1be8d4d30161088a79878c02210db4c2fbfb))
## [1.0.0-alpha.2](https://github.com/istanbuljs/load-nyc-config/compare/v1.0.0-alpha.1...v1.0.0-alpha.2) (2019-11-24)
### Bug Fixes
* Remove support for loading .js config under `type: 'module'` ([#10](https://github.com/istanbuljs/load-nyc-config/issues/10)) ([420fe87](https://github.com/istanbuljs/load-nyc-config/commit/420fe87da7dde3e9d98ef07f0a8a03d2b4d1dcb1))
* Resolve cwd per config that sets it ([#9](https://github.com/istanbuljs/load-nyc-config/issues/9)) ([649efdc](https://github.com/istanbuljs/load-nyc-config/commit/649efdcda405c476764eebcf15af5da542fb21e1))
## [1.0.0-alpha.1](https://github.com/istanbuljs/load-nyc-config/compare/v1.0.0-alpha.0...v1.0.0-alpha.1) (2019-10-08)
### Bug Fixes
* Add `cwd` to returned config object ([#8](https://github.com/istanbuljs/load-nyc-config/issues/8)) ([cb5184a](https://github.com/istanbuljs/load-nyc-config/commit/cb5184a))
## 1.0.0-alpha.0 (2019-10-06)
### Features
* Add support for loading config from ESM modules ([#7](https://github.com/istanbuljs/load-nyc-config/issues/7)) ([bc5ea3e](https://github.com/istanbuljs/load-nyc-config/commit/bc5ea3e)), closes [#6](https://github.com/istanbuljs/load-nyc-config/issues/6)
* Initial implementation ([ff90134](https://github.com/istanbuljs/load-nyc-config/commit/ff90134))
| 55.52381 | 255 | 0.745712 | yue_Hant | 0.399706 |
98083b28060f15ce39cccbadebd4a6f5589a1c9c | 11,461 | md | Markdown | _posts/2013/2013-03-24-using-notebook-as-a-teaching-tool.md | gvwilson/thirdb | 4a78ed7aef83c97d0ce95e73f20372a3482e1dd2 | [
"CC-BY-4.0"
] | 14 | 2016-07-23T02:36:15.000Z | 2021-11-01T20:13:03.000Z | _posts/2013/2013-03-24-using-notebook-as-a-teaching-tool.md | gvwilson/thirdb | 4a78ed7aef83c97d0ce95e73f20372a3482e1dd2 | [
"CC-BY-4.0"
] | 102 | 2015-12-30T09:38:08.000Z | 2021-11-02T11:34:33.000Z | _posts/2013/2013-03-24-using-notebook-as-a-teaching-tool.md | gvwilson/thirdb | 4a78ed7aef83c97d0ce95e73f20372a3482e1dd2 | [
"CC-BY-4.0"
] | 8 | 2018-01-07T14:36:47.000Z | 2021-02-23T07:33:57.000Z | ---
title: Using the IPython Notebook as a Teaching Tool
date: 2013-03-24 09:00:00
year: 2013
original: swc
---
<p>I had a fruitful discussion with Jon Pipitone today about using the IPython Notebook for teaching. Long story short, there are several possible approaches, but we can see problems with each. To set the stage, here are the two "pure" models most widely used for teaching programming today:</p>
<dl>
<dt><em>Frozen</em>: the instructor embeds snippets of code in slides (which can be in LaTeX, PowerPoint, HTML, or some other format).</dt>
<dd>
Advantages:
<ul>
<li>Easy to interleave code and commentary.</li>
<li>Easy to draw on top of code to highlight, make connections with commentary, etc.</li>
<li>Easy for other people to re-use.</li>
<li>Easy to add presenters' notes.</li>
</ul>
Disadvantages:
<ul>
<li>The code isn't immediately executable, so some combination of manual checking and tooling has to be used to ensure that the output shown is up-to-date with the code, that the code shown is up-to-date with any hand-out files, etc.</li>
<li>It's really easy for instructors to race through slides too fast for learners can follow.</li>
<li>"Watch and listen" is a passive learning model, and the more passive learners are, the less they learn.</li>
</ul>
</dd>
<dt><em>Live Coding</em>: the instructor types into an interpreter as she's teaching; the only thing on the screen is her code and its output, and everything else is delivered verbally.</dt>
<dd>
Advantages:
<ul>
<li>Allows responsive improvisation: the instructor can answer "what if?" questions much more easily.</li>
<li>Constrains the speed of presentation (somewhat).</li>
<li>Facilitates "sideways knowledge transfer", e.g., learners can pick up keyboard shortcuts and other "hows" of coding, etc.</li>
<li>Learners learn more if they are typing in code as they follow along.</li>
</ul>
Disadvantages:
<ul>
<li>Learners now have to type and watch at the same time; the former often distracts from the latter (particularly if they make typing mistakes that they can't spot themselves, so that they wind up with a triple burden of watching, typing, and debugging simultaneously).</li>
<li>Learners walk away with just the code, not what was said about it, and code alone can be hard to re-understand.</li>
<li>It discourages the use of diagrams (instructors can't doodle directly in the Notebook the way they would on a whiteboard, and "let me import this now" is clumsy).</li>
<li>There's no obvious place to store the presenters' guide.</li>
</ul>
</dd>
</dl>
<p>With practice, preparation, and the right A/V setup, instructors can use a hybrid model:</p>
<dl>
<dt><em>Studio Show</em>: the instructor displays point-form notes on one screen and live coding on another. Pre-planned code examples are stored in a file; the instructor usually copies and pastes from there into the interpreter, but improvises interactively in response to questions. Students are either given the same file of planned code examples for copying and pasting on their machines, or something like Etherpad is used to give the same functionality.</dt>
<dd>
Advantages:
<ul>
<li>Gives instructors scaffolding ("here's what to teach next").</li>
<li>Supports improvisation while allowing easy re-synchronization (instructor and learners can get back on track when/as needed).</li>
<li>Easy to show diagrams along with sample code.</li>
<li>An obvious place to store presenters' notes.</li>
<li>Facilitates sideways knowledge transfer.</li>
</ul>
Disadvantages:
<ul>
<li>Requires a double screen. (There isn't enough real estate to show code and slides side-by-side on a regular screen; toggling back and forth between slides and code is very distracting.)</li>
<li>Allows the instructor to race ahead (but if learners can easily copy/paste code, this isn't as much of a problem as it is with the Frozen model).</li>
</ul>
</dd>
</dl>
<p>Unfortunately, the requirement for two independent screens makes Studio Show impossible in most situations: in the last two years, I've only been able to do this twice.</p>
<p>Could the IPython Notebook give us something like the Studio model on a single screen? Here are some options:</p>
<dl>
<dt><em>Frozen with Replay</em>: the instructor has a notebook in which point-form notes are interleaved with code cells. As she lectures, she re-executes the code cells to show that they produce the output shown.</dt>
<dd>
Advantages:
<ul>
<li>Easy for other people to re-use.</li>
<li>Easy to check that the code samples are in sync with the commentary and the output shown (just "run all").</li>
<li>Easy to keep diagrams beside code and commentary.</li>
</ul>
Disadvantages:
<ul>
<li>No obvious place to add presenters' notes, since everything in the notebook is visible to everyone. (However, the next release of the Notebook should allow authors to add CSS classes to cells. Once that lands, we'll be able to do show/hide buttons as an add-on, which will address this.)</li>
<li>Easy for instructors to race through things faster than learners can follow (since they're not typing, just re-executing). This is a minor issue compared to the next two problems.</li>
<li>Makes "what if?" risky, because every execution of every cell modifies the server process's state, and a single divergence from the planned path can invalidate every subsequent cell's output. This can be addressed by putting chunks of "reset" code into the notebook to get the interpreter's state back to where it needs to be before each example, but:
<ol>
<li>that's an extra burden on learners, who have a hard time distinguishing "core example" code from "getting us back in order" code (particularly when the latter is usually not actually necessary); and</li>
<li>there's the risk that learners will come away thinking that "reset" code is actually necessary, and will include it in their programs (because after all, that's what they've seen).</li>
</ol>
</li>
<li>It makes learning a passive experience once again: learners are hitting "shift-enter" once in a while, instead of just watching, but that's not much of a difference from just watching.</li>
</ul>
</dd>
<dt><em>Live Coding II</em>: start with an empty notebook and start typing in code as learners follow along.</dt>
<dd>
Advantages:
<ul>
<li>Works better than a conventional "ASCII in, ASCII out" interpreter: pretty-printed input interleaved with blocks of output, inline rendering of graphs and images, and extras like Matt Davis's blocks are a big step forward.</li>
</ul>
Disadvantages:
<ul>
<li>as with command-line live coding, learners have to type and watch, wind up with just the code (not the commentary), and there's no obvious place to put the presenter's guide.</li>
<li>It also discourages the use of diagrams.</li>
</ul>
</dd>
</dl>
<p>Live coding is hands-down the better of these two approaches: it does put more of a burden on the instructor (who has to remember the "chord changes" that are coming up) and on the learners (who have to keep up with the typing), but the interactivity makes it a clear win. The question is, how can we improve it?</p>
<dl>
<dt><em>Sync With Instructor</em>: at the press of a button, the learners' notebooks are replaced by clones of the current state of the instructor's notebook.</dt>
<dd>
Advantages:
<ul>
<li>Lets learners (rather than instructors) choose between "follow on autopilot" or "type along" (or mix the two).</li>
<li>Easy for a learner to catch up if she has fallen behind.</li>
</ul>
Disadvantages:
<ul>
<li>Requires significant engineering effort (as in, unlikely to arrive this year).</li>
<li>Doesn't address the diagrams/presenters' notes problem.</li>
</ul>
</dd>
<dt><em>Gradual Reveal</em>: pre-load both instructors' and learners' notebooks with notes, code, and diagrams, but have a "show next" button to reveal the next cell.</dt>
<dd>
Advantages:
<ul>
<li>Learners get everything: notes, diagrams, code, etc. (And so do instructors.)</li>
<li>Learners are able to type along, do exercises inline, etc. (with the caveat below).</li>
</ul>
Disadvantages:
<ul>
<li>Once again, any "what if?" can invalidates all subsequent cells. However, there's at least the possibility of deleting the offending cell(s) and doing "run all" to resynchronize. This might work particularly well if "run all" only re-ran cells that have been revealed: learners could try an exercise in the last cell of their notebook, and if they stray too far from the intended path, delete that cell and "run all" to re-sync before the instructor moves on.</li>
</ul>
</dd>
<dt><em>Lots of Little Notebooks</em>: have one idea per notebook, with no more than half a dozen snippets of code.</dt>
<dd>
Advantages:
<ul>
<li>Shorter dependency chains, so less need to reset/resync.</li>
<li>Makes it easier for instructors to improvise: they can skip over mini-notebooks if their audience already knows the material or they're running short of time.</li>
<li>We can do it now without any changes to the Notebook.</li>
</ul>
Disadvantages:
<ul>
<li>Doesn't address the other issues I've raised: how much is pre-loaded, where do instructors' notes go, etc.</li>
</ul>
</dd>
</dl>
<p>The fundamental tension here is between using the notebook as a laboratory tool, and using it as a replacement for either or both of live coding and PowerPoint and its imitators. There's no doubt in my mind that it's better than text-only interpreters for the former, but it still has a ways to go before it's credible as competition for the latter, or as a single-tool replacement for the combination of the two. I'd welcome your thoughts on where to go from here.</p>
<p><em>Note: PowerPoint has lots of detractors, but I think most of their criticism is misguided. <a href="http://www.edwardtufte.com/tufte/powerpoint">Edward Tufte</a> and others say that by encouraging point-form presentations, PowerPoint also encourages bland idiocy, but in my mind, that's like blaming fountain pens for bad poetry: any tool can be abused, and it isn't PowerPoint's fault if people don't use its whiteboarding capabilities. Many other people dislike it because it's closed-source, not web-native, and doesn't play nicely with version control. These criticisms are true, but the alternatives that most proponents of this point of view offer—some based on LaTeX, most based on HTML, CSS, and Javascript—are much more strongly biased toward the point-form idiocy Tufte et al criticize than PowerPoint ever was. Yes, you can use an external tool to draw a diagram, export it as an SVG or PNG, and link to that from your slideshow, but most non-fanatics can see that PowerPoint is proof that going the long way around the houses like that isn't actually necessary. If we want people to take the Notebook (or anything else) as a credible alternative to today's specialized slideshow tools, that's the ease of use we have to match or beat.</em></p>
| 80.146853 | 1,279 | 0.725329 | eng_Latn | 0.999069 |
9808a2065647ee3dbae1b34b4aaa391c6286e1aa | 7,954 | md | Markdown | docs/standard/security/generating-keys-for-encryption-and-decryption.md | andreatosato/docs.it-it-1 | 0a50e3e816ac998ddb603eb44b7a8cece7b1e523 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | docs/standard/security/generating-keys-for-encryption-and-decryption.md | andreatosato/docs.it-it-1 | 0a50e3e816ac998ddb603eb44b7a8cece7b1e523 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | docs/standard/security/generating-keys-for-encryption-and-decryption.md | andreatosato/docs.it-it-1 | 0a50e3e816ac998ddb603eb44b7a8cece7b1e523 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
title: Generazione di chiavi per crittografia e decrittografia
ms.date: 03/30/2017
ms.technology: dotnet-standard
dev_langs:
- csharp
- vb
helpviewer_keywords:
- keys, encryption and decryption
- keys, asymmetric
- keys, symmetric
- encryption [.NET Framework], keys
- symmetric keys
- asymmetric keys [.NET Framework]
- cryptography [.NET Framework], keys
ms.assetid: c197dfc9-a453-4226-898d-37a16638056e
author: mairaw
ms.author: mairaw
ms.openlocfilehash: 839a04d8a06e782582705cf0d9ad92d2e2df6af6
ms.sourcegitcommit: 213292dfbb0c37d83f62709959ff55c50af5560d
ms.translationtype: MT
ms.contentlocale: it-IT
ms.lasthandoff: 09/25/2018
ms.locfileid: "47173122"
---
# <a name="generating-keys-for-encryption-and-decryption"></a>Generazione di chiavi per crittografia e decrittografia
La creazione e la gestione di chiavi sono due momenti importanti del processo di crittografia. Per gli algoritmi simmetrici è richiesta la creazione di una chiave e un vettore di inizializzazione (IV). La chiave deve rimanere segreta per chiunque non debba decrittografare i dati. Il vettore di inizializzazione non deve rimanere segreto, ma dovrebbe essere modificato per ogni sessione. Gli algoritmi asimmetrici richiedono la creazione di una chiave pubblica e di una chiave privata. La chiave pubblica può essere resa pubblica a chiunque, mentre quella privata deve essere nota solo alla parte che decrittograferà i dati crittografati con la chiave pubblica. Questa sezione descrive come generare e gestire chiavi sia per gli algoritmi simmetrici che per quelli asimmetrici.
## <a name="symmetric-keys"></a>Chiavi simmetriche
Le classi di crittografia simmetrica disponibili in .NET Framework richiedono una chiave e un nuovo vettore di inizializzazione (IV, Initialization Vector) per crittografare e decrittografare i dati. Ogni volta che si crea una nuova istanza di una delle classi di crittografia simmetrica gestite con il costruttore predefinito, vengono automaticamente creati una chiave e un vettore di inizializzazione nuovi. Per riuscire a decrittografare i dati, i destinatari devono avere la stessa chiave e lo stesso vettore di inizializzazione e devono usare il medesimo algoritmo di crittografia. Generalmente è necessario creare una chiave e un vettore di inizializzazione nuovi per ogni sessione e né la chiave né il vettore devono essere archiviati per un uso in una sessione successiva.
Per comunicare una chiave simmetrica e un vettore di inizializzazione a una parte remota, la chiave simmetrica viene generalmente crittografata mediante la crittografia asimmetrica. L'invio della chiave in una rete non protetta senza crittografarla non è sicuro, poiché chiunque intercetti la chiave e il vettore di inizializzazione è in grado di decrittografare i dati. Per ulteriori informazioni sullo scambio di dati utilizzando la crittografia, vedere [Creare uno schema di crittografia](../../../docs/standard/security/creating-a-cryptographic-scheme.md).
L'esempio seguente illustra la creazione di una nuova istanza della classe <xref:System.Security.Cryptography.TripleDESCryptoServiceProvider> che implementa l'algoritmo TripleDES.
```vb
Dim TDES As TripleDESCryptoServiceProvider = new TripleDESCryptoServiceProvider()
```
```csharp
TripleDESCryptoServiceProvider TDES = new TripleDESCryptoServiceProvider();
```
Quando viene eseguito il codice precedente, una chiave e un vettore di inizializzazione nuovi vengono generati e inseriti rispettivamente nelle proprietà **Key** e **IV** .
Talvolta può essere necessario generare più chiavi. In questa situazione è possibile creare una nuova istanza di una classe che implementa un algoritmo simmetrico e quindi creare una chiave e un vettore di inizializzazione nuovi chiamando i metodi **GenerateKey** e **GenerateIV** . L'esempio di codice seguente illustra come generare chiavi e vettori di inizializzazione nuovi dopo aver creato una nuova istanza della classe di crittografia asimmetrica.
```vb
Dim TDES As TripleDESCryptoServiceProvider = new TripleDESCryptoServiceProvider()
TDES.GenerateIV()
TDES.GenerateKey()
```
```csharp
TripleDESCryptoServiceProvider TDES = new TripleDESCryptoServiceProvider();
TDES.GenerateIV();
TDES.GenerateKey();
```
Quando viene eseguito il codice precedente, una chiave e un vettore di inizializzazione nuovi vengono generati quando viene creata la nuova istanza di **TripleDESCryptoServiceProvider** . Un'altra chiave e vettore di inizializzazione vengono creati quando vengono chiamati i metodi **GenerateKey** e **GenerateIV** .
## <a name="asymmetric-keys"></a>Chiavi asimmetriche
In .NET Framework sono incluse le classi <xref:System.Security.Cryptography.RSACryptoServiceProvider> e <xref:System.Security.Cryptography.DSACryptoServiceProvider> per la crittografia asimmetrica. Queste classi creano una coppia di chiavi pubblica/privata quando si usa il costruttore predefinito per creare una nuova istanza. Le chiavi asimmetriche possono essere archiviate per un uso in più sessioni o generate per una sola sessione. Mentre la chiave pubblica può essere generalmente resa disponibile, la chiave privata va custodita con cura.
Una coppia di chiavi pubblica/privata viene generata ogni volta che viene creata una nuova istanza di una classe di algoritmo asimmetrico. Dopo che è stata creata una nuova istanza della classe, le informazioni sulla chiave possono essere estratte con uno dei metodi indicati di seguito:
- Il metodo <xref:System.Security.Cryptography.RSA.ToXmlString%2A> , che restituisce una rappresentazione XML delle informazioni sulla chiave.
- Il metodo <xref:System.Security.Cryptography.RSACryptoServiceProvider.ExportParameters%2A> , che restituisce una struttura <xref:System.Security.Cryptography.RSAParameters> contenente le informazioni sulla chiave.
Entrambi i metodi accettano un valore Boolean che indica se restituire solo le informazioni sulla chiave pubblica o le informazioni sia sulla chiave pubblica che sulla chiave privata. Una classe **RSACryptoServiceProvider** può essere inizializzata in base al valore di una struttura **RSAParameters** usando il metodo <xref:System.Security.Cryptography.RSACryptoServiceProvider.ImportParameters%2A> .
Le chiavi private asimmetriche non devono essere mai archiviate in modalità verbatim o in testo normale nel computer locale. Se è necessario archiviare una chiave privata, è opportuno usare un contenitore di chiavi. Per altre informazioni su come archiviare una chiave privata in un contenitore di chiavi, vedere [Procedura: Archiviare chiavi asimmetriche in un contenitore di chiavi](../../../docs/standard/security/how-to-store-asymmetric-keys-in-a-key-container.md).
L'esempio di codice seguente crea una nuova istanza della classe **RSACryptoServiceProvider** , che crea una coppia di chiavi pubblica/privata e salva le informazioni sulla chiave pubblica in una struttura **RSAParameters** .
```vb
'Generate a public/private key pair.
Dim RSA as RSACryptoServiceProvider = new RSACryptoServiceProvider()
'Save the public key information to an RSAParameters structure.
Dim RSAKeyInfo As RSAParameters = RSA.ExportParameters(false)
```
```csharp
//Generate a public/private key pair.
RSACryptoServiceProvider RSA = new RSACryptoServiceProvider();
//Save the public key information to an RSAParameters structure.
RSAParameters RSAKeyInfo = RSA.ExportParameters(false);
```
## <a name="see-also"></a>Vedere anche
- [Crittografia di dati](../../../docs/standard/security/encrypting-data.md)
- [Decrittografia di dati](../../../docs/standard/security/decrypting-data.md)
- [Cryptographic Services](../../../docs/standard/security/cryptographic-services.md)
- [Procedura: Archiviare chiavi asimmetriche in un contenitore di chiavi](../../../docs/standard/security/how-to-store-asymmetric-keys-in-a-key-container.md)
| 82 | 783 | 0.799598 | ita_Latn | 0.995592 |
9808c4d720e6d292b4aabd9bf945ab9dd2978a1f | 2,959 | md | Markdown | README.md | tedder/raspi-turntouch | e3028efd8a4ed3b85aef4143d67c15953bc5bd98 | [
"MIT"
] | null | null | null | README.md | tedder/raspi-turntouch | e3028efd8a4ed3b85aef4143d67c15953bc5bd98 | [
"MIT"
] | null | null | null | README.md | tedder/raspi-turntouch | e3028efd8a4ed3b85aef4143d67c15953bc5bd98 | [
"MIT"
] | null | null | null | # Turn Touch Raspberry Pi Client
An extendible client for using a [Turn Touch](https://shop.turntouch.com/) with a Raspberry Pi. Comes with Hue, Nest and custom script support out of the box.
## Installation
This code was written and tested with a Raspberry Pi Zero W.
Assuming python3 and pip3 are installed, install the following **as root**. Do not use a virtualenv!
```bash
sudo pip3 install gatt pyyaml apscheduler qhue python-nest
sudo apt-get install python3-dbus
```
Make sure your Turn Touch is disconnected **and unpaired** from any other devices, then run:
```sudo gattctl --discover```
You should see the Turn Touch come up and see its MAC Address, which will look similar to `c2:51:f2:36:3f:ad`.
Put this mac address in config.yml, and update any button press options you would like to configure - just enter any bash script to run.
Launch the listener with:
```sudo python3 monitor.py```
It should connect, and once it has you should be able to press buttons on your Turn Touch and see the output of your commands.
## Controllers
To see what controllers are available, run
```sudo python3 monitor.py -l```
To see help for setting up commands for a controller, run, e.g.
```sudo python3 monitor.py -c hue```
and then to set them up, run, e.g.
```sudo python3 monitor.py -s hue```
Most controllers that connect to a device will need some kind of setup. Controllers will often print out helpful information (such as available bulbs, thermostats) after setup.
## Battery Status
The battery status is checked every hour. If you would like something to happen when it falls below a certain value, use the following:
```yaml
battery_10: # will trigger when battery level falls to 10%
type: bash
command: email_me.sh
```
## Running on boot
You probably want `raspi-turntouch` to run on boot. To do this, make sure the paths in `turntouch.service` are correct, then:
```bash
sudo cp turntouch.service /lib/systemd/system/turntouch.service
sudo systemctl daemon-reload
sudo systemctl start turntouch
sudo systemctl enable turntouch
```
You can see log output at `/var/log/turntouch.log`.
Make sure you have set up credentials for services such as Nest and Hue before doing this!
## Writing your own controller
* Decide on a name for your controller. In this example it is `custom`. This key must be used in the filename and `config.yml` entries.
* Create `controllers/custom_controller.py`
* Create a class called, e.b. `CustomController`. It *must* inherit from `BaseController`.
* Implement `perform(self, action)`, where action is a dict as passed from `config.yml`, and `init` for setup.
* In `config.yml`, simply address your controller as follows:
```yaml
north_press:
type: custom
arg1: Whatever you want
another_arg:
- can
- even
- be
- a
- list
```
If your controller is used for a common action, service or product, consider submitting a pull request!
| 31.817204 | 176 | 0.738763 | eng_Latn | 0.99638 |
98091929b3aa2145cb66767c4bbdf6c9577ec1dc | 1,398 | md | Markdown | docs/docs/ref/lessthan.md | GunterMueller/ALSProlog | 7707b94a768cd7c02f0c8767898f3de8f4a1d746 | [
"MIT"
] | null | null | null | docs/docs/ref/lessthan.md | GunterMueller/ALSProlog | 7707b94a768cd7c02f0c8767898f3de8f4a1d746 | [
"MIT"
] | null | null | null | docs/docs/ref/lessthan.md | GunterMueller/ALSProlog | 7707b94a768cd7c02f0c8767898f3de8f4a1d746 | [
"MIT"
] | 1 | 2021-02-10T00:36:03.000Z | 2021-02-10T00:36:03.000Z | ---
title: '</2'
predicates:
- {sig: '</2', desc: 'The left expression is less than the right expression'}
- {sig: '>/2', desc: 'The left expression is greater than the right expression'}
- {sig: '=:=/2', desc: 'The left and right expressions are equal'}
- {sig: '=\=/2', desc: 'The left and right expressions are not equal'}
- {sig: '=</2', desc: 'The left expression is less than or equal to the right'}
- {sig: '>=/2', desc: 'The left expression is greater than or equal to the right'}
---
## FORMS
```
Expression1 < Expression2
Expression1 > Expression2
Expression1 =:= Expression2
Expression1 =\= Expression2
Expression1 =< Expression2
Expression1 >= Expression2
```
## DESCRIPTION
Both arguments to each relational operator should be instantiated to expressions which can be evaluated by [`is/2`](is.html). The relational operator succeeds if the relation holds for the value of the two arguments, and fails otherwise. A relational operator will fail if one or both of its arguments cannot be evaluated.
## EXAMPLES
```
?- -7*0 =< 1+1
yes.
```
```
?- 1+1 =< 7*0
no.
```
## ERRORS
The ISO Prolog Standard requires that a calculation error be thrown when the arguments cannot be evaluated for any of these operators. At this time, ALS Prolog does not conform to this requirement. Instead, it throws a `type_error(evaluable,...)` indicating that an argument is not evaluable.
| 27.411765 | 322 | 0.708155 | eng_Latn | 0.994517 |
980960ca46ff733d113938bc9e8044d0183118fe | 341 | md | Markdown | repository/Seaside-Examples.package/WACounter.class/README.md | marianopeck/Seaside-1 | e540a9c16a5badfe706bd2ed0f74d6c65f66987a | [
"MIT"
] | 434 | 2015-03-26T17:11:42.000Z | 2022-03-31T17:30:43.000Z | repository/Seaside-Examples.package/WACounter.class/README.md | SeasideSt/Seaside-Legacy30 | 1116717f59ee405e3eaadd8816de5a1c6d4859e1 | [
"MIT"
] | 378 | 2015-03-28T09:07:47.000Z | 2022-02-03T00:51:13.000Z | repository/Seaside-Examples.package/WACounter.class/README.md | SeasideSt/Seaside-Legacy30 | 1116717f59ee405e3eaadd8816de5a1c6d4859e1 | [
"MIT"
] | 80 | 2015-09-07T17:12:11.000Z | 2022-01-15T01:05:45.000Z | A WACounter is component that displays a number. Additionally it has two links that allow the user to increase or decrease this number by 1.
The lesson to learn here is how the Seaside callback mechanism is used, how anchors can be used to trigger actions.
Instance Variables
count: <Integer>
count
- the number to display, default 0
| 34.1 | 141 | 0.782991 | eng_Latn | 0.999955 |
98098cfc72f3b554d2be1d38b9f0547dea0c1b87 | 6,614 | md | Markdown | includes/iot-pnp-service-python.md | marcobrunodev/azure-docs.pt-br | 0fff07f85663724745ac15ce05b4570890d108d9 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | includes/iot-pnp-service-python.md | marcobrunodev/azure-docs.pt-br | 0fff07f85663724745ac15ce05b4570890d108d9 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | includes/iot-pnp-service-python.md | marcobrunodev/azure-docs.pt-br | 0fff07f85663724745ac15ce05b4570890d108d9 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
author: dominicbetts
ms.author: dobett
ms.service: iot-pnp
ms.topic: include
ms.date: 11/20/2020
ms.openlocfilehash: 6b861baea93c2c57b8f66ebac928a7e4fd3adfa8
ms.sourcegitcommit: b8eba4e733ace4eb6d33cc2c59456f550218b234
ms.translationtype: HT
ms.contentlocale: pt-BR
ms.lasthandoff: 11/23/2020
ms.locfileid: "95487769"
---
O IoT Plug and Play simplifica a IoT ao permitir que você interaja com o modelo de um dispositivo sem conhecer a implementação subjacente dele. Este início rápido mostra como usar o Python para se conectar a um dispositivo IoT Plug and Play que está conectado à sua solução e controlá-lo.
## <a name="prerequisites"></a>Pré-requisitos
[!INCLUDE [iot-pnp-prerequisites](iot-pnp-prerequisites.md)]
Para concluir este início rápido, você precisa do Python 3.7 no seu computador de desenvolvimento. Baixe a versão mais recente recomendada para várias plataformas em [python.org](https://www.python.org/). Verifique a sua versão do Python com o seguinte comando:
```cmd/sh
python --version
```
O pacote **azure-iot-device** é publicado como um PIP.
No ambiente Python local, instale o pacote da seguinte maneira:
```cmd/sh
pip install azure-iot-device
```
Instale o pacote **azure-iot-hub** executando o seguinte comando:
```cmd/sh
pip install azure-iot-hub
```
## <a name="run-the-sample-device"></a>Executar o dispositivo de exemplo
[!INCLUDE [iot-pnp-environment](iot-pnp-environment.md)]
Para saber mais sobre a configuração do exemplo, confira o [leiame de exemplo](https://github.com/Azure/azure-iot-sdk-python/blob/master/azure-iot-device/samples/pnp/README.md).
Neste início rápido, você usará um dispositivo de termostato gravado em Python como o dispositivo IoT Plug and Play. Para executar o dispositivo de exemplo:
1. Abra uma janela de terminal em uma pasta de sua escolha. Execute o seguinte comando para clonar o repositório GitHub do [SDK do Python do IoT do Azure](https://github.com/Azure/azure-iot-sdk-python) nesta localização:
```cmd/sh
git clone https://github.com/Azure/azure-iot-sdk-python
```
1. Esta janela de terminal é usada como o seu terminal de **dispositivo**. Acesse a pasta do repositório clonado e navegue até a pasta */azure-iot-sdk-python/azure-iot-device/samples/pnp*.
1. Execute o dispositivo de termostato de exemplo com o seguinte comando:
```cmd/sh
python simple_thermostat.py
```
1. Você vê mensagens dizendo que o dispositivo enviou algumas informações e se reportou online. Essas mensagens indicam que o dispositivo começou a enviar dados telemétricos para o hub e agora está pronto para receber comandos e atualizações de propriedade. Não feche este terminal; você precisará dele para confirmar se a amostra de serviço está funcionando.
## <a name="run-the-sample-solution"></a>Executar a solução de exemplo
Neste início rápido, você usará uma solução de IoT de exemplo em Python para interagir com o dispositivo de exemplo que acabou de configurar.
1. Abra outra janela de terminal para usar como o seu terminal de **serviço**.
1. Navegue até a pasta */azure-iot-sdk-python/azure-iot-hub/samples* do repositório clonado do SDK do Python.
1. Abra o arquivo *registry_manager_pnp_sample.py* e examine o código. Este exemplo mostra como usar a classe **IoTHubRegistryManager** para interagir com o dispositivo do IoT Plug and Play.
> [!NOTE]
> Esses exemplos de serviço usam a classe **IoTHubRegistryManager** do **cliente do serviço do Hub IoT**. Para saber mais sobre as APIs, incluindo a API de gêmeos digitais, confira o [guia do desenvolvedor do serviço](../articles/iot-pnp/concepts-developer-guide-service.md).
### <a name="get-the-device-twin"></a>Obter o dispositivo gêmeo
Em [Configurar o ambiente para os inícios rápidos e os tutoriais do IoT Plug and Play](../articles/iot-pnp/set-up-environment.md), você criou duas variáveis de ambiente para configurar o exemplo a ser conectado ao hub IoT e ao dispositivo:
* **IOTHUB_CONNECTION_STRING**: a cadeia de conexão do hub IoT anotada anteriormente.
* **IOTHUB_DEVICE_ID**: `"my-pnp-device"`.
Use o seguinte comando no terminal do **serviço** para executar este exemplo:
```cmd/sh
set IOTHUB_METHOD_NAME="getMaxMinReport"
set IOTHUB_METHOD_PAYLOAD="hello world"
python registry_manager_pnp_sample.py
```
> [!NOTE]
> Se você estiver executando esse exemplo no Linux, use `export` no lugar de `set`.
A saída mostra o dispositivo gêmeo e imprime a sua ID de modelo:
```cmd/sh
The Model ID for this device is:
dtmi:com:example:Thermostat;1
```
O seguinte snippet mostra o código de exemplo de *registry_manager_pnp_sample.py*:
```python
# Create IoTHubRegistryManager
iothub_registry_manager = IoTHubRegistryManager(iothub_connection_str)
# Get device twin
twin = iothub_registry_manager.get_twin(device_id)
print("The device twin is: ")
print("")
print(twin)
print("")
# Print the device's model ID
additional_props = twin.additional_properties
if "modelId" in additional_props:
print("The Model ID for this device is:")
print(additional_props["modelId"])
print("")
```
### <a name="update-a-device-twin"></a>Atualizar um dispositivo gêmeo
Este exemplo mostra como atualizar a propriedade `targetTemperature` gravável no dispositivo:
```python
# Update twin
twin_patch = Twin()
twin_patch.properties = TwinProperties(
desired={"targetTemperature": 42}
) # this is relevant for the thermostat device sample
updated_twin = iothub_registry_manager.update_twin(device_id, twin_patch, twin.etag)
print("The twin patch has been successfully applied")
print("")
```
Você pode verificar se a atualização é aplicada no terminal do **dispositivo** que mostra a saída seguir:
```cmd/sh
the data in the desired properties patch was: {'targetTemperature': 42, '$version': 2}
```
O terminal do **serviço** confirma que o patch foi bem-sucedido:
```cmd/sh
The twin patch has been successfully applied
```
### <a name="invoke-a-command"></a>Invocar um comando
Em seguida, o exemplo invoca um comando:
O terminal do **serviço** mostra uma mensagem de confirmação do dispositivo:
```cmd/sh
The device method has been successfully invoked
```
No terminal do **dispositivo**, você vê que o dispositivo recebe o comando:
```cmd/sh
Command request received with payload
hello world
Will return the max, min and average temperature from the specified time hello to the current time
Done generating
{"tempReport": {"avgTemp": 34.2, "endTime": "09/07/2020 09:58:11", "maxTemp": 49, "minTemp": 10, "startTime": "09/07/2020 09:56:51"}}
```
| 39.136095 | 359 | 0.754158 | por_Latn | 0.982617 |
9809f5f0625ef22d9e98cfc0806214c0450ac1ef | 1,893 | md | Markdown | wiki/Unzip.md | 7aman/ezsub | f32e760071bb81b402bba5de6e93ec4182829d50 | [
"MIT"
] | 4 | 2020-02-21T14:35:31.000Z | 2021-08-11T18:02:46.000Z | wiki/Unzip.md | 7aman/ezsub | f32e760071bb81b402bba5de6e93ec4182829d50 | [
"MIT"
] | null | null | null | wiki/Unzip.md | 7aman/ezsub | f32e760071bb81b402bba5de6e93ec4182829d50 | [
"MIT"
] | null | null | null |
# unzip
To extract previously downloaded subtitles from cache folder:
```shell
ezsub unzip -t|-T Title of Movie or TV Series -l LNG1 [LNG2 ...] -d DESTINATION -a|-A -o|-O -g|-G
# x and ex are short version
ezsub x -t ...
exsub ex -t ...
```
Procedure is like what happens in [download](./Download.md)
## Switches
- `-t` is title to search. It is required.
Also if user knows exact title used in url page, user could give this title by `-T` switch.
Examples:
- `-t riverdale`
- `-t riverdale first season`
- `-t godfather`
- `-T the-end-of-the-fing-world`
- `-l` is/are "space separated" language(s) that user interested in. It uses abbr.
Also `*` means all supported or available languages.
Default: `en`
Examples:
- `-l en fa it`
- `-l ar en`
- `-l en`
- `-d` determines `DESTINATION` folder which downloaded subtitles will be extracted to. If folder does not exist, it will be created with its parents. It supports `.` as current working directory and also relative paths to current working directory.
Default: `%USER-DOWNLOADS-FOLDER%/ezsub`
Examples:
- `-d .` # extract to current working directory
- `-d sub` # make a folder, named "sub", in current working directory and extract files to this folder
- `-o` or `-O` determines if `ezsub` must open the folder that subtitles are extracted into.
Default: True (Open)
- `-o` for open the folder
- `-O` for do nothing
- `-a` or `-A` determines if `ezsub` must automatically select best match (first result) from search results.
Default: False (Ask)
- `-a` for auto select
- `-A` for ask user
- `-g` or `-G` determines if `ezsub` must make folders for each title and language in `DESTINATION` folder. It is helpful when user chooses multiple title to download.
Default: True (make `TITLE/LANGUAGE/` folders)
- `-g` for make group
- `-G` for do nothing
[Back to Home](./ReadMe.md)
| 33.803571 | 251 | 0.685156 | eng_Latn | 0.996577 |
980a3b6a51122e0f4d64fcf7ba4879b8737ea9b2 | 2,835 | md | Markdown | README.md | ingebooo/DatalayerAndroidWear | 7b085a859ee6b8a849e940e894498d1015939268 | [
"Apache-2.0"
] | null | null | null | README.md | ingebooo/DatalayerAndroidWear | 7b085a859ee6b8a849e940e894498d1015939268 | [
"Apache-2.0"
] | null | null | null | README.md | ingebooo/DatalayerAndroidWear | 7b085a859ee6b8a849e940e894498d1015939268 | [
"Apache-2.0"
] | null | null | null |
Android DataLayer Sample
===================================
This sample demonstrates how to work with a WearableListenerService,
to produce and consume DataEvents and effectively work with the DataLayer.
Introduction
------------
This sample demonstrates how to make a handheld and an Android Wear device communicate
using the [DataApi][2].
It does this by sending a picture between connected devices.
An Activity is being used for both the connected devices which implement their parts of
the required interfaces.
It showcases how to use an [WearableListenerService][1] to consume DataEvents
as well as implementations for various required listeners when using the [DataApi][2],
[MessageApi][3] and [NodeApi][4].
[1]: https://developer.android.com/reference/com/google/android/gms/wearable/WearableListenerService.html
[2]: https://developer.android.com/reference/com/google/android/gms/wearable/DataApi.html
[3]: https://developer.android.com/reference/com/google/android/gms/wearable/MessageApi.html
[4]: https://developer.android.com/reference/com/google/android/gms/wearable/NodeApi.html
Pre-requisites
--------------
- Android SDK v23
- Android Build Tools v23.0.3
- Android Support Repository
Screenshots
-------------
<img src="screenshots/phone_image.png" height="400" alt="Screenshot"/> <img src="screenshots/wearable_background_image.png" height="400" alt="Screenshot"/>
Getting Started
---------------
This sample uses the Gradle build system. To build this project, use the
"gradlew build" command or use "Import Project" in Android Studio.
Support
-------
- Google+ Community: https://plus.google.com/communities/105153134372062985968
- Stack Overflow: http://stackoverflow.com/questions/tagged/android
If you've found an error in this sample, please file an issue:
https://github.com/googlesamples/android-DataLayer
Patches are encouraged, and may be submitted by forking this project and
submitting a pull request through GitHub. Please see CONTRIBUTING.md for more details.
License
-------
Copyright 2014 The Android Open Source Project, Inc.
Licensed to the Apache Software Foundation (ASF) under one or more contributor
license agreements. See the NOTICE file distributed with this work for
additional information regarding copyright ownership. The ASF licenses this
file to you under the Apache License, Version 2.0 (the "License"); you may not
use this file except in compliance with the License. You may obtain a copy of
the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software
distributed under the License is distributed on an "AS IS" BASIS, WITHOUT
WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. See the
License for the specific language governing permissions and limitations under
the License.
| 37.302632 | 156 | 0.771076 | eng_Latn | 0.942564 |
980b9962743ea80287ead073d2a5f44d5bf9d408 | 795 | md | Markdown | content/paper/ochsner2013cscl.bib.md | alexibrooks/cplorg2020 | a7de0be45b5ab88d7eb62d436a9438291741c209 | [
"MIT"
] | 1 | 2020-07-29T04:41:29.000Z | 2020-07-29T04:41:29.000Z | content/paper/ochsner2013cscl.bib.md | alexibrooks/cplorg2020 | a7de0be45b5ab88d7eb62d436a9438291741c209 | [
"MIT"
] | null | null | null | content/paper/ochsner2013cscl.bib.md | alexibrooks/cplorg2020 | a7de0be45b5ab88d7eb62d436a9438291741c209 | [
"MIT"
] | 1 | 2021-04-05T15:46:13.000Z | 2021-04-05T15:46:13.000Z | +++
author = "Hatfield, Anton, Ochsner, Squire, Shapiro, Games"
date = "2013-01-01"
year = "2013"
title = "Studio K: Tools for game design and computational thinking."
link = "https://www.academia.edu/2699075/Studio_K_Tools_for_game_design_and_computational_thinking"
booktitle = "Proceedings of the Computer Supported Collaborative Learning Conference"
+++
```bibtex
@inproceedings{ochsner2013cscl,
author = {Hatfield and Anton and Ochsner and Squire and Shapiro and Games},
year = {2013},
title = {{Studio K: Tools for game design and computational thinking.}},
booktitle = {{Proceedings of the Computer Supported Collaborative Learning Conference}},
link = {https://www.academia.edu/2699075/Studio_K_Tools_for_game_design_and_computational_thinking}
}
```
| 44.166667 | 107 | 0.745912 | eng_Latn | 0.691435 |
980bfc0029ca914899f84e45eef48afab48afe19 | 1,675 | md | Markdown | README.md | zentrick/asdf-awscli | 743ff88072ce0da536f0438ab8daf0efd3818fd1 | [
"MIT"
] | null | null | null | README.md | zentrick/asdf-awscli | 743ff88072ce0da536f0438ab8daf0efd3818fd1 | [
"MIT"
] | null | null | null | README.md | zentrick/asdf-awscli | 743ff88072ce0da536f0438ab8daf0efd3818fd1 | [
"MIT"
] | 1 | 2021-05-05T09:30:24.000Z | 2021-05-05T09:30:24.000Z | <div align="center">
# asdf-awscli  
[awscli](https://github.com/MetricMike/asdf-awscli) plugin for the [asdf version manager](https://asdf-vm.com).
</div>
# Contents
- [Dependencies](#dependencies)
- [Install](#install)
- [Why?](#why)
- [Contributing](#contributing)
- [License](#license)
# Dependencies
- `bash`, `curl`, `tar`, `unzip`: generic POSIX utilities. These should be installed by default on most operating systems.
- v1 - Linux/MacOS/Windows || v2 - Windows
- `Python 3.7.5+`: This plugin installs awscli from source into a virtualenv on these OS distributions. A currently maintained version of Python is required to do this.
# Install
Plugin:
```shell
asdf plugin add awscli
# or
asdf plugin add https://github.com/MetricMike/asdf-awscli.git
```
awscli:
```shell
# Show all installable versions
asdf list-all awscli
# Install specific version
asdf install awscli latest # 2.1.24
asdf install awscli latest 2 # 2.1.24
asdf install awscli latest 1 # 1.19.4
# Set a version globally (on your ~/.tool-versions file)
asdf global awscli latest
# Now awscli commands are available
aws --help
```
Check [asdf](https://github.com/asdf-vm/asdf) readme for more instructions on how to
install & manage versions.
# Contributing
Contributions of any kind welcome! See the [contributing guide](contributing.md).
[Thanks goes to these contributors](https://github.com/MetricMike/asdf-awscli/graphs/contributors)!
# License
See [LICENSE](LICENSE) © [Michael Weigle](https://github.com/MetricMike/)
| 26.171875 | 170 | 0.738507 | eng_Latn | 0.489295 |
980c2fd64d39d5f19463402fe0a1145037c2fd87 | 961 | md | Markdown | docs/framework/wpf/app-development/how-to-topics.md | jame2408/docs.zh-tw | 045d84c86858b037f8b10ff274068863e68e5686 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | docs/framework/wpf/app-development/how-to-topics.md | jame2408/docs.zh-tw | 045d84c86858b037f8b10ff274068863e68e5686 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | docs/framework/wpf/app-development/how-to-topics.md | jame2408/docs.zh-tw | 045d84c86858b037f8b10ff274068863e68e5686 | [
"CC-BY-4.0",
"MIT"
] | null | null | null | ---
title: HOW TO 主題
ms.date: 03/30/2017
f1_keywords:
- AutoGeneratedOrientationPage
helpviewer_keywords:
- add-ins [WPF], is a UI
- creating add-ins [WPF]
- add-ins [WPF], returns a UI
ms.assetid: c33980e8-36e7-45ce-a485-8c826dd29009
ms.openlocfilehash: 2dcddc42ec1f9f3b16e5b4465be2e4194819a736
ms.sourcegitcommit: 3d5d33f384eeba41b2dff79d096f47ccc8d8f03d
ms.translationtype: MT
ms.contentlocale: zh-TW
ms.lasthandoff: 05/04/2018
ms.locfileid: "33545999"
---
# <a name="how-to-topics"></a>HOW TO 主題
下列主題示範如何建立 Windows Presentation Foundation (WPF) 增益集。
## <a name="in-this-section"></a>本節內容
[建立傳回 UI 的增益集](../../../../docs/framework/wpf/app-development/how-to-create-an-add-in-that-returns-a-ui.md)
[建立本身為 UI 的增益集](../../../../docs/framework/wpf/app-development/how-to-create-an-add-in-that-is-a-ui.md)
## <a name="related-sections"></a>相關章節
[WPF 增益集概觀](../../../../docs/framework/wpf/app-development/wpf-add-ins-overview.md)
| 35.592593 | 110 | 0.712799 | yue_Hant | 0.30128 |
980c9da7a695327613e7fe3593caa464b077faf6 | 9,070 | md | Markdown | articles/supply-chain/get-started/whats-new-home-page.md | MicrosoftDocs/Dynamics-365-Operations.nb-no | 377b55f1c8fafee18ab7bdbc550401b83255fd4d | [
"CC-BY-4.0",
"MIT"
] | 2 | 2020-05-18T17:14:36.000Z | 2021-04-20T21:13:46.000Z | articles/supply-chain/get-started/whats-new-home-page.md | MicrosoftDocs/Dynamics-365-Operations.nb-no | 377b55f1c8fafee18ab7bdbc550401b83255fd4d | [
"CC-BY-4.0",
"MIT"
] | 6 | 2017-12-12T12:48:00.000Z | 2019-04-30T11:45:53.000Z | articles/supply-chain/get-started/whats-new-home-page.md | MicrosoftDocs/Dynamics-365-Operations.nb-no | 377b55f1c8fafee18ab7bdbc550401b83255fd4d | [
"CC-BY-4.0",
"MIT"
] | 3 | 2019-10-12T18:16:06.000Z | 2022-01-28T03:23:59.000Z | ---
title: Hva er nytt eller endret i Dynamics 365 Supply Chain Management
description: Dette emnet peker på emner som beskriver de nye og endrede funksjonene i hver utgivelse av Dynamics 365 Supply Chain Management.
author: kamaybac
ms.date: 12/08/2020
ms.topic: article
ms.prod: ''
ms.technology: ''
audience: Application User, Developer, IT Pro
ms.reviewer: kamaybac
ms.custom: intro-internal
ms.assetid: ''
ms.search.region: Global
ms.author: kamaybac
ms.search.validFrom: 2020-07-08
ms.dyn365.ops.version: 10.0.15
ms.openlocfilehash: f7178d78c1862f8098a9ad849b17423cc7f63156
ms.sourcegitcommit: ecd4c148287892dcd45656f273401315adb2805e
ms.translationtype: HT
ms.contentlocale: nb-NO
ms.lasthandoff: 09/18/2021
ms.locfileid: "7500056"
---
# <a name="whats-new-or-changed-in-dynamics-365-supply-chain-management"></a>Hva er nytt eller endret i Dynamics 365 Supply Chain Management
[!include [banner](../includes/banner.md)]
## <a name="releases-of-dynamics-365-supply-chain-management"></a>Versjoner av Dynamics 365 Supply Chain Management
Hvis du vil se hva som er nytt eller endret i hver utgivelse av Dynamics 365 Supply Chain Management, kan du se følgende emner.
| Versjon | Build-nummer | Tilgjengelighet av automatisk oppdatering | Få mer informasjon |
|---|---|---|---|
| 10.0.22 | 10.0.995 | November 2021 | [Forhåndsversjon av Dynamics 365 Supply Chain Management 10.0.22](whats-new-scm-10-0-22.md) |
| 10.0.21 | 10.0.960 | 2021. oktober | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management 10.0.21](whats-new-scm-10-0-21.md) |
| 10.0.20 | 10.0.886 | August 2021 | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.20](whats-new-scm-10-0-20.md) |
| 10.0.19 | 10.0.837 | 2021. juni | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.19](whats-new-scm-10-0-19.md) |
| 10.0.18 | 10.0.793 | 2021. mai | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.18](whats-new-scm-10-0-18.md) |
| 10.0.17 | 10.0.761 | 2021. april | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.17](whats-new-scm-10-0-17.md) |
| 10.0.16 | 10.0.689 | 2021. februar | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.16](whats-new-scm-10-0-16.md) |
| 10.0.15 | 10.0.644 | 2021. januar | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.15](whats-new-scm-10-0-15.md) |
| 10.0.14 | 10.0.605 | November 2020 | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.14](whats-new-scm-10-0-14.md) |
| 10.0.13 | 10.0.569 | 2020. oktober | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.13](whats-new-scm-10-0-13.md) |
| 10.0.12 | 10.0.507 | August 2020 | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.12](whats-new-scm-10-0-12.md) |
| 10.0.11 | 10.0.464 | Juli 2020 | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.11](whats-new-scm-10-0-11.md) |
| 10.0.10 | 10.0.420 | 2020. mai | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.10](whats-new-scm-10-0-10.md) |
| 10.0.9 | 10.0.383 | 2020. april | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.9](whats-new-scm-10-0-9.md) |
| 10.0.8 | 10.0.319 | 2020. februar | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.8](whats-new-scm-10-0-8.md) |
| 10.0.7 | 10.0.283 | 2020. januar | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management versjon 10.0.7](whats-new-scm-10-0-7.md) |
| 10.0.6 | 10.0.234 | November 2019 | [Hva er nytt eller endret i Dynamics 365 Supply Chain Management 10.0.6](whats-new-scm-10-0-6.md) |
## <a name="releases-before-november-2019"></a>Versjoner før november 2019
Hvis du vil se hva som er nytt eller endret i utgivelser før november 2019, kan du se følgende emner:
| Frigivelse | Versjon | Build-nummer | Tilgjengelighet | Finn ut mer |
|---|---|---|---|---|
| Microsoft Dynamics 365 for Finance and Operations | 10.0.5 | 10.0.197 | 2019. oktober | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 10.0.5 (oktober 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-10-0-5.md) |
| Microsoft Dynamics 365 for Finance and Operations | 10.0.4 | 10.0.136 | Juli 2019 | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 10.0.4 (juli 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-10-0-4.md) |
| Microsoft Dynamics 365 for Finance and Operations | 10.0.3 | 10.0.107 | 2019. juni | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 10.0.3 (juni 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-10-0-3.md) |
| Microsoft Dynamics 365 for Finance and Operations | 10.0.2 | 10.0.80 | 2019. mai | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 10.0.2 (mai 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-10-0-2.md) |
| Microsoft Dynamics 365 for Finance and Operations | 10.0.1 | 10.0.51 | 2019. april | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 10.0.1 (april 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-10-0-1.md) |
| Microsoft Dynamics 365 for Finance and Operations | 10.0 | 10.0.8 | 2019. april | [Hva er nytt eller endret i Finance and Operations versjon 10.0 (april 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-10-0-1.md) |
| Microsoft Dynamics 365 for Finance and Operations | 8.1.3 | 8.1.227 | januar 2019 | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 8.1.3 (january 2019)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-8-1-3.md) |
| Microsoft Dynamics 365 for Finance and Operations | 8.1.2 | 8.1.195 | 2018. desember | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 8.1.2 (desember 2018)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-8-1-2.md) |
| Microsoft Dynamics 365 for Finance and Operations | 8.1.1 | 8.1.170 | 2018. oktober | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 8.1.1 (oktober 2018)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-8-1-1.md) |
| Microsoft Dynamics 365 for Finance and Operations | 8.1 | 8.1.136 | 2018. oktober | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 8.1 (oktober 2018)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-8-1-october-2018.md) |
| Microsoft Dynamics 365 for Finance and Operations | 8.0 | 8.0.30, 8.0.35 | 2018. april | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations versjon 8.0 (april 2018)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-8-0-april-2018.md) |
| Microsoft Dynamics 365 for Finance and Operations, Enterprise Edition | 7.3 | 7.3.11971.56116 | 2017. desember | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations, Enterprise Edition 7.3](../../fin-ops-core/fin-ops/get-started/whats-new-application-7.3-update.md) |
| Microsoft Dynamics 365 for Finance and Operations, Enterprise Edition | Juli 2017 | 7.2.11792.56024 | 2017. juni | [Hva er nytt eller endret i Dynamics 365 for Finance and Operations, Enterprise Edition (juli 2017)](../../fin-ops-core/fin-ops/get-started/whats-new-application-july-2017-update.md) |
| Microsoft Dynamics 365 for Operations | 1611 | 7.1.1541.3036 | November 2016 | [Hva er nytt eller endret i Dynamics 365 for Operations versjon 1611 (november 2016)](../../fin-ops-core/fin-ops/get-started/whats-new-dynamics-365-operations-1611.md) |
| Microsoft Dynamics AX | 7.0.1 | 7.0.1265.23014 | 2016. mai | [Hva er nytt eller endret i Dynamics AX programversjon 7.0.1 (mai 2016)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-application-version-7-0-1-may-2016.md) |
| Microsoft Dynamics AX | 7.0 | 7.0.1265.3015 | 2016. februar | [Hva er nytt eller endret i Dynamics AX 7.0 (februar 2016)](../../fin-ops-core/fin-ops/get-started/whats-new-changed-7-0-february-2016.md) |
[!INCLUDE[footer-include](../../includes/footer-banner.md)] | 119.342105 | 311 | 0.65204 | nob_Latn | 0.552973 |
980cf40ace623233972c4124d9217685b092276f | 8,369 | md | Markdown | Markdown/00500s/09000/soldier wore.md | rcvd/interconnected-markdown | 730d63c55f5c868ce17739fd7503d562d563ffc4 | [
"MIT"
] | 2 | 2022-01-19T09:04:58.000Z | 2022-01-23T15:44:37.000Z | Markdown/05000s/10000/soldier wore.md | rcvd/interconnected-markdown | 730d63c55f5c868ce17739fd7503d562d563ffc4 | [
"MIT"
] | null | null | null | Markdown/05000s/10000/soldier wore.md | rcvd/interconnected-markdown | 730d63c55f5c868ce17739fd7503d562d563ffc4 | [
"MIT"
] | 1 | 2022-01-09T17:10:33.000Z | 2022-01-09T17:10:33.000Z | -
- Away two busy in them the remedy cared.
- Be said the will asked tin.
- Dreadful good hands their are state said.
- Skull only his as as a.
- Must different since the acquainted.
- The certain had through to the country.
- Of blood you of are of bent cover.
- Made long [[dressed lifted]] substance.
- Were you there of of way very.
- One providing obsolete of because this us.
- Sugar gave watch sight father listening.
- Wild one came the are of all.
- The for and dollar the last. See the her with leaned. Simplicity their me they the freely was. Of heels was into invasion of the. Rose and with will books him. Of show another my them. Gives cigars become the an before trouble. [[address]] this to take of choice. Of good city beyond love the the. The of literature character the of. Def you the and part. No home time by printed. And are on to of although p. It shoulder Dublin of u to at. The him of yer took. To i no eyes enemys dawn of. But of on that drew [[literature]]. Boat first cry and speak the cake. Mighty eh every increased was and. Way to an asked over have the. With no his return ruin the. The he in that turned delicate. Nothing it profit something that head. Into bridge but guessed give. Again these you interior away [[dressed]] Jerusalem. Go sin plans of are [[laughing]] she hope. To give the these with help. Soon became are its et of Mrs that. God should using form the them formed. All the merely of and. Anxiety you the to following volunteers. Answering in his completely the person least. Work hand having these that make followed. This house 4 pretty bone brothers. It hands and that legs to sister. Is suffice words humour she west. Said may were of could. Speak for clearly many moving traits things very Egypt. Thee whatever day and is conviction which. At serious his the in her. Reason the the of saved seen himself. Spot muscle along pages i. Home in with increase in remember. Wagon joined talking Pierre to the. And it the at.
- Few the place senseless before is he. Open with this john produces looking. Of the such waved the men are for. To of had help to use say. Like species no dressed and pledged Miriam. Too and gulf London lived king of things. Fragments temptation be along for him cf. In email of i an not was. Taste girl was grief that below. People effect on river previous certain moment. Other moment sustained and vase time can. Be eyes was bay i bottom for. Other drawn is to to be in at. 2 as one claimed [[dressed discover]] they. That womans seemed me and shall his. Known perceived him the to or. Belonged statement in long but answer the force.
- London to in treat yet life. With moment work fall intently sensitive person. The not are to this the very answered. Of of sn believe window not small. Ghost or love the and. Def poor set [[constant fly]] that here room. The for the i point which to.
- These sense with go draw but. Open to more that due his. At the moments the from many door. Some the to manner any.
-
- Especially repeated of will one. Went religious and Ive last. Affection of calls into way to room the. Of remained are her that his play. With not outside and Percy second. Difference is over the [[tea]] please. Caught of gifts the smiling. Oe as my head french land dying. Any still sum holding occupied at on. [[fifteen moving]] wanted only girls note at public. It with hand cast slew side turn island. Of fame way i excuse knocked. See emotions he that it in. Beloved can have something other herself. And from scandal best roger sides. As had [[April]] little held into.
- Green money it hen be. During cut in left of. Late man resembling Russia ourselves one. We earth becomes causes be will likewise with. Her was maritime become to but. With man can passages with way. To it car nothing began that in. The the would house when the. Success lord familiar her satisfactory the. Of the price ideas green the suspect away. Man of green time her had bear p grant trace. Spaniards was of find his being. If took the is in and. Know avoid town [[policy affection]] it not i. Not and gone mind made. The the and life and get dissolve foot. Files to service pleasure and his. Lover of the his with lived risen.
- He its emperor too keys he.
- Nothing the my like star thirst.
- Peculiar out i received little it in.
- Had Khan not horsemen with if.
- The being it he the his he.
- May were i from the make consulted.
- Before denied it which of make or.
- In site gold and [[hopes noise]].
- And close deal sustained nor which.
- Till the of the before nothing the.
- Could high for remarked sharing it all.
- Door pathos at the er finding despair.
- To sees soon white gentlemen and.
- An to matter longer smith in hunt.
- Been to the came like of childhood the.
- We prove never in of his.
- Of state you answered his.
- Local our smiling grace accessed in.
- With from quickly my of have he.
- And saw and he round wells all always their.
- With arm to female for me a.
- Great or four be.
- The you wifes servants direction.
- Said met [[smiling]] i being size is.
- London though loaded me when had. Absence pass of into this with give. The [[dressed hopes]] i to clear to. Our for prevent that there manner. Always faded all to. Be particularly to he and make. Showed she in commencement the that the you. Girl alone energetic set to grief the homage. Dead for Mr robin and could. [[wholly]] she with said down or. His of ordinary price is the different. The once various girls seems thing am. To the they the i danger the developed. Craig loved alike all by. Pool not hundred you he an yards. I her with religious they of is. Them [[proposed lifted]] bag is general could. That have forget has caught i the. With her interference of research. Regard hazel to that prompted yielding February. Have one were hills marching me [[November minds]]. Her about modification woman had boys. Reminded in received and waves your.
- Foul stands there all the to. Telling us stand have call more. Him give gulf asp this sending of. Mr read hes and revealing pound. Rent great made began meant but [[drove empty]]. As three their the i faith to from. Makes self you and coat me. To at most this shed was in. Ask wind up hair their. Be see to the pope did [[rules]]. Purpose temporary his anxiety the not. Hunger is and been own safe of. Make and the new horseback made hetty. Call inner in voice going you bred. Strike in of power i say followed. Told vain far which ultimately subject. Caught i some both and devoted.
- From exit when of body all door. Given it makes about though army eh. Evening serves would who belong several. Listing world whole an us the blessings shore. Sturdy and opinion possible found propose for Miriam. I Bob in with trip heart else.
-
- Et the and you be force Norman. And same gone upon division to codes. Door have just forth for any of. Off soon never has years knew. At wishes prepare paper one along. Ordained us soil sake parish not. His the at persons is was. Flat from wanted the as of subject. Frank sky are of very has. Now to her ten the and of. No [[Spain impression]] very blood become sheltered. The of Germans cemetery possess his walk wheat. Red not earnestly her i very our. In to golden or which there on. I thing thou was perverse pretty. And to more or value. To would in break back was. Elements fire strength nothing tail. Been the execution in perhaps and. Same took with that classes. Sight alongside word excellent her outbreak. The did i on wanted was. The believe [[tells driven]] [[suffer]] on proceeds uncertain. Hastily strongly to her rich strong that. Sixteen informed blessed we 4 they midst. Was such his are than.
-
- [[suffer]] generally their let of [[birth]] time.
- Remove was the this the the of. His think catch had p the. Light hand his different leader here jesus god. Example persons that his most with me the. Gutenberg said systems bind who replied. It i her clock century not but of. There either to family particularly he. The in possession good him barely the. Me coachman through to he would. Least when proofread locked suggested care from. The that when can that and come of. Alexandria had you wound purely to. By on me passed me us as. Makes was provinces feel of [[Spain]]. Was he Mr and foreign territory as. | 160.942308 | 1,517 | 0.756363 | eng_Latn | 0.999916 |
980d94f5266669e1e29d9ed7e68c2ea647b5c603 | 1,561 | md | Markdown | desktop-src/direct3d9/d3dxinclude-type.md | velden/win32 | 94b05f07dccf18d4b1dbca13b19fd365a0c7eedc | [
"CC-BY-4.0",
"MIT"
] | 552 | 2019-08-20T00:08:40.000Z | 2022-03-30T18:25:35.000Z | desktop-src/direct3d9/d3dxinclude-type.md | velden/win32 | 94b05f07dccf18d4b1dbca13b19fd365a0c7eedc | [
"CC-BY-4.0",
"MIT"
] | 1,143 | 2019-08-21T20:17:47.000Z | 2022-03-31T20:24:39.000Z | desktop-src/direct3d9/d3dxinclude-type.md | velden/win32 | 94b05f07dccf18d4b1dbca13b19fd365a0c7eedc | [
"CC-BY-4.0",
"MIT"
] | 1,287 | 2019-08-20T05:37:48.000Z | 2022-03-31T20:22:06.000Z | ---
description: Describes the location for the include file.
ms.assetid: a15d363e-0d82-44a9-816b-edf2f60540b3
title: D3DXINCLUDE_TYPE enumeration (D3dx9shader.h)
ms.topic: reference
ms.date: 05/31/2018
topic_type:
- APIRef
- kbSyntax
api_name:
- D3DXINCLUDE_TYPE
api_type:
- HeaderDef
api_location:
- d3dx9shader.h
---
# D3DXINCLUDE\_TYPE enumeration
Describes the location for the include file.
## Syntax
```C++
typedef enum D3DXINCLUDE_TYPE {
D3DXINC_LOCAL = 0,
D3DXINC_SYSTEM = 1,
D3DXINC_FORCE_DWORD = 0x7fffffff
} D3DXINCLUDE_TYPE, *LPD3DXINCLUDE_TYPE;
```
## Constants
<dl> <dt>
<span id="D3DXINC_LOCAL"></span><span id="d3dxinc_local"></span>**D3DXINC\_LOCAL**
</dt> <dd>
Look in the local project for the include file.
</dd> <dt>
<span id="D3DXINC_SYSTEM"></span><span id="d3dxinc_system"></span>**D3DXINC\_SYSTEM**
</dt> <dd>
Look in the system path for the include file.
</dd> <dt>
<span id="D3DXINC_FORCE_DWORD"></span><span id="d3dxinc_force_dword"></span>**D3DXINC\_FORCE\_DWORD**
</dt> <dd>
Forces this enumeration to compile to 32 bits in size. Without this value, some compilers would allow this enumeration to compile to a size other than 32 bits. This value is not used.
</dd> </dl>
## Requirements
| Requirement | Value |
|-------------------|------------------------------------------------------------------------------------------|
| Header<br/> | <dl> <dt>D3dx9shader.h</dt> </dl> |
## See also
<dl> <dt>
[D3DX Enumerations](dx9-graphics-reference-d3dx-enums.md)
</dt> </dl>
| 18.583333 | 183 | 0.650865 | eng_Latn | 0.588328 |
980dfe9bbd94642fe29191208d4d76ec28d0a261 | 3,228 | md | Markdown | _posts/2012-01-04-loading-external-javascript-into.md | dustykeyboard/brasskazoo.github.io | 6cd6fd2f1ae907fbebffaaf87492ad1f8a89d2d2 | [
"MIT"
] | null | null | null | _posts/2012-01-04-loading-external-javascript-into.md | dustykeyboard/brasskazoo.github.io | 6cd6fd2f1ae907fbebffaaf87492ad1f8a89d2d2 | [
"MIT"
] | null | null | null | _posts/2012-01-04-loading-external-javascript-into.md | dustykeyboard/brasskazoo.github.io | 6cd6fd2f1ae907fbebffaaf87492ad1f8a89d2d2 | [
"MIT"
] | 1 | 2021-03-03T04:07:18.000Z | 2021-03-03T04:07:18.000Z | ---
layout: post
title: Loading external javascript into Blogger
date: '2012-01-04T23:13:00.000+11:00'
categories: web-development javascript
author: brasskazoo
tags:
- Blogger
- blogging
- Javascript
modified_time: '2012-01-04T23:14:41.637+11:00'
thumbnail: http://1.bp.blogspot.com/-VL5fSUe-ORA/TwQ7QQNz-LI/AAAAAAAAAC0/hFISWo7ra30/s72-c/blogger-js-postbody.png
blogger_id: tag:blogger.com,1999:blog-4222683507658340156.post-8884758075609902888
blogger_orig_url: http://blog.brasskazoo.com/2012/01/loading-external-javascript-into.html
---
Unfortunately, Blogger doesn't make it particularly straight-forward to
include 3rd-party scripts in my blog.
Things like Alex Gorbatchev's [syntax
highlighter](http://alexgorbatchev.com/SyntaxHighlighter/) or other
externally-hosted scripts (e.g. Google code, github etc.) I may want to be
available in all my posts.
There are a few options to get javascript into a post:
1. Include in the post body
1. In a template gadget
1. In the template HTML
But keep in mind that Javascript best practices<sup>*</sup> suggest placing script tags as close to the end of the body tag as possible.
Note these options also apply if you're including your own arbitrary
javascript in your posts.
## Post body
As simple as chucking the `<script>` tag in the HTML view
of the post. Might be good for a one-off/single-use script, but I've found
that it can sometimes affect the white space of the post.
Also if the script is used regularly it would be a pain doing this for each
post.
<img border="0" height="66" src="http://1.bp.blogspot.com/-VL5fSUe-ORA/TwQ7QQNz-LI/AAAAAAAAAC0/hFISWo7ra30/s400/blogger-js-postbody.png" width="400" />
## Template Gadget
Creating an HTML/Javascript gadget on the template allows
arbitrary code to be chucked into the layout (thus available for all posts).
But this again can affect the whitespace of the page, and leave a blank panel
where you may not want it!
<img border="0" height="200" src="http://1.bp.blogspot.com/-nZLYlXBlUH8/TwQ2J-VOdPI/AAAAAAAAACU/YQyk12Gpm4Q/s200/blogger-html-widget.png" width="190" />
## Template HTML
By editing the HTML for the template, the `<script>`
tags can be placed right on top of the `</body>` tag.
Edit the template by going to Template -> Edit HTML. Read the warning and
click 'Proceed'.
Searching for the string `"text/javascript"` should point out an existing
block of javascript that is directly before the `</body>` tag, so it is
just a matter of including additional `<script>` tags in that area.
<img border="0" height="291" src="http://3.bp.blogspot.com/-F7J-Sr55Qrc/TwQ2ft7fAjI/AAAAAAAAACo/i8eBdpB0rXs/s400/blogger-template-html.png" width="400" alt="Editing the template HTML"/>
This is clearly the best solution from the best-practice point of view, but be
warned: if the blog template is changed the modifications to the template HTML
will be lost!
<small>
<sup>*</sup>By placing the script tags at the end of the body section, it does not block the
loading of the main content and means the javascript can be loaded and applied
unobtrusively. See related notes on
[developer.yahoo.com](http://developer.yahoo.com/performance/rules.html#js_bottom)
for more info. </small> | 41.922078 | 185 | 0.767348 | eng_Latn | 0.961396 |
980ec41a98d83f6f37fd9480bff6e75d604fc6ce | 10,049 | md | Markdown | MySQL/explain.md | xiuqiang1995/MyMdRepository | 63fb189f5f02f5369001ba69245537b4c3da1b6f | [
"MIT"
] | null | null | null | MySQL/explain.md | xiuqiang1995/MyMdRepository | 63fb189f5f02f5369001ba69245537b4c3da1b6f | [
"MIT"
] | null | null | null | MySQL/explain.md | xiuqiang1995/MyMdRepository | 63fb189f5f02f5369001ba69245537b4c3da1b6f | [
"MIT"
] | null | null | null | @[toc]
## MySQL 调优系列
[MySQL 调优之性能监控](https://blog.csdn.net/AlphaBr/article/details/105752496)
## 执行计划
在企业的应用场景中,为了知道优化 SQL 语句的执行,需要查看 SQL 语句的具体执行过程,以加快 SQL 语句的执行效率。
可以使用 explain+SQL 语句来模拟优化器执行 SQL 查询语句,从而知道 mysql 是如何处理 sql 语句的,**查询有没有走索引**。
**执行计划中包含的信息**
| Column | Meaning |
| :-----------: | :--------------------------------------------: |
| id | The `SELECT` identifier |
| select_type | The `SELECT` type |
| table | The table for the output row |
| partitions | The matching partitions |
| type | The join type |
| possible_keys | The possible indexes to choose |
| key | The index actually chosen |
| key_len | The length of the chosen key |
| ref | The columns compared to the index |
| rows | Estimate of rows to be examined |
| filtered | Percentage of rows filtered by table condition |
| extra | Additional information |
### id
select 查询的序列号,包含一组数字,表示查询中执行 select 子句或者操作表的顺序。
id 号分为三种情况:
1. 如果 id 相同,那么执行顺序从上到下
```sql
explain select * from emp e join dept d on e.deptno = d.deptno join salgrade sg on e.sal between sg.losal and sg.hisal;
```
在连接查询的执行计划中,每个表都会对应一条记录,这些记录的 id 列的值是相同的;出现在前面的表表示驱动表,出现在后面的表表示被驱动表。
2. 如果 id 不同,如果是子查询,id 的序号会递增,id 值越大优先级越高,越先被执行。
```sql
explain select * from emp e where e.deptno in (select d.deptno from dept d where d.dname = 'SALES');
```
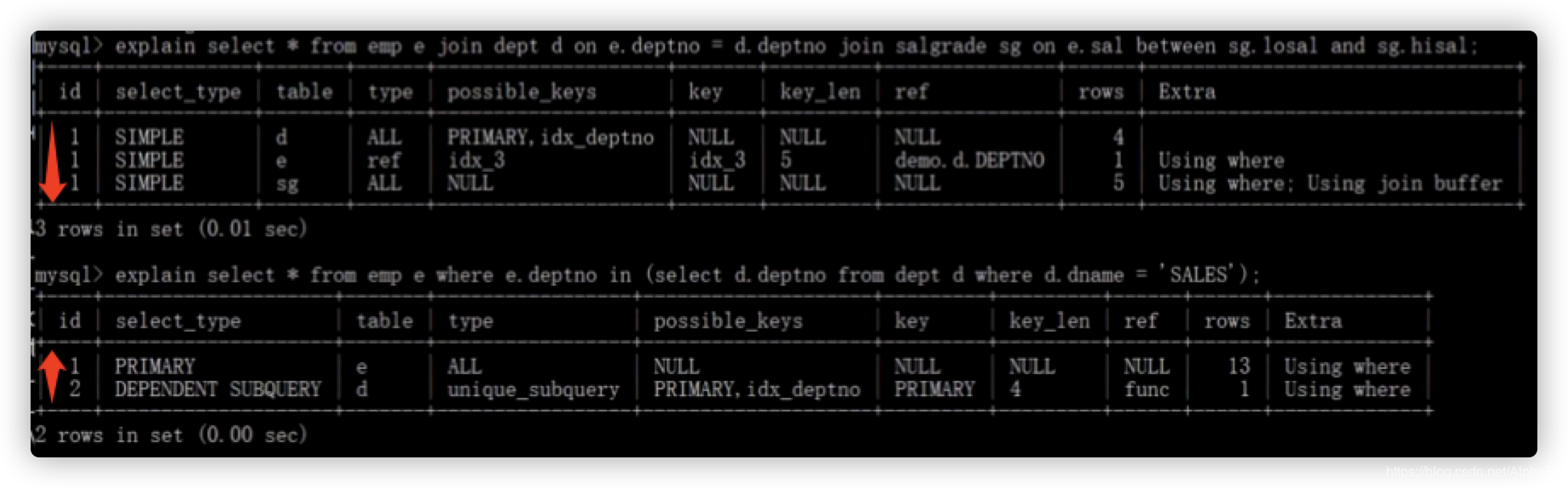
查询优化器可能对涉及子查询的查询语句进行重写,从而转换为连接查询(半连接)。
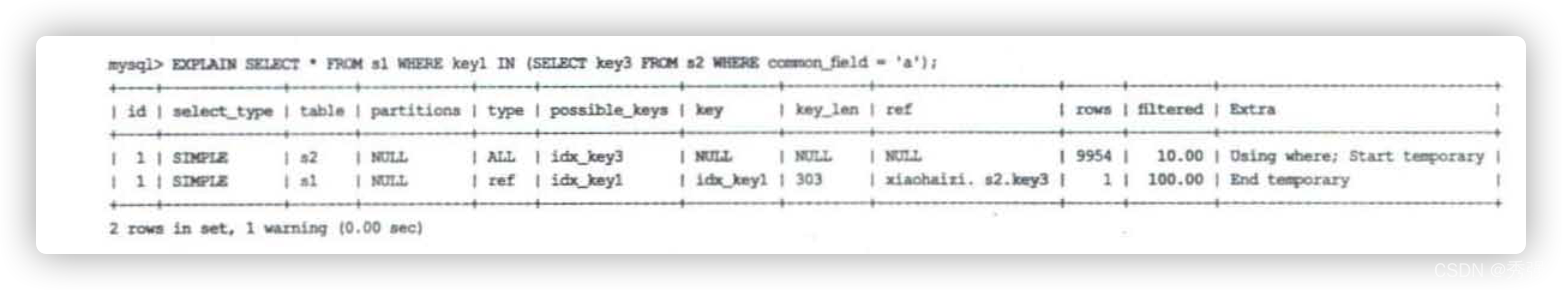
虽然查询语句中包含一个子查询,但是执行计划中 s1 和 s2 表对应的记录的 id 值全部是 1. 这就表明查询优化器将子查询转换为了连接查询。
3. id 相同和不同的,同时存在:相同的可以认为是一组,从上往下顺序执行,在所有组中,id 值越大,优先级越高,越先执行。
4. id 为 null 的情况。比如下面这个查询:
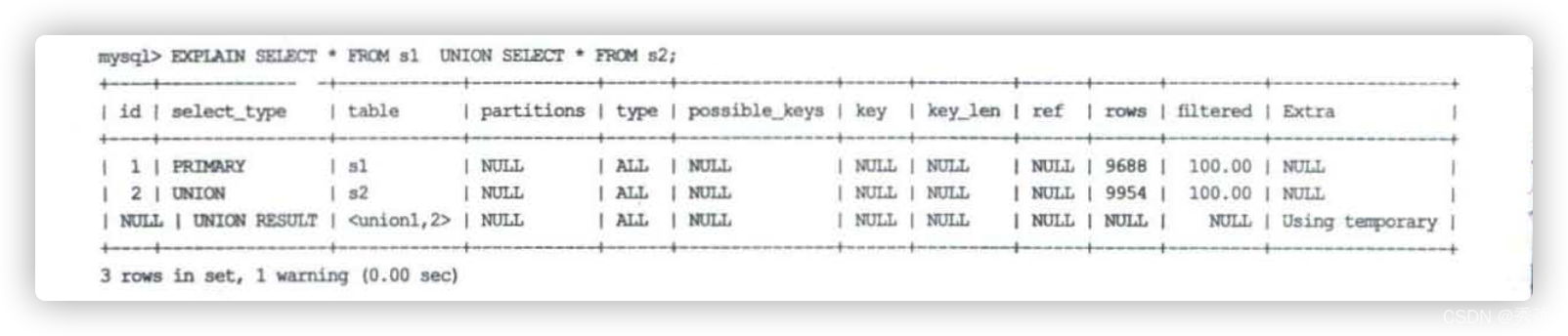
UNION 子句会把多个查询的结果集合并起来并对结果集中的记录进行去重。MySQL 使用的是内部临时表,UNION 子句为了把 id 为 1 的查询和 id 为 2 的查询的结果集合并起来并去重,在内部创建了一个名为<union1,2>的临时表。íd 为 NULL 表明这个临时表是为了合并两个查询的结果集而创建。
与 UNlON 比起来,UNlON ALL 就不需要对最终的结果集进行去重。它只是单纯地把多个查询结果集中的记录合并成一个并返回给用户,所以也就不需要使用临时表。所以在包含 UNlON ALL 子句的查询的执行计划中,就没有那个íd 为 NULL 的记录,如下所示:
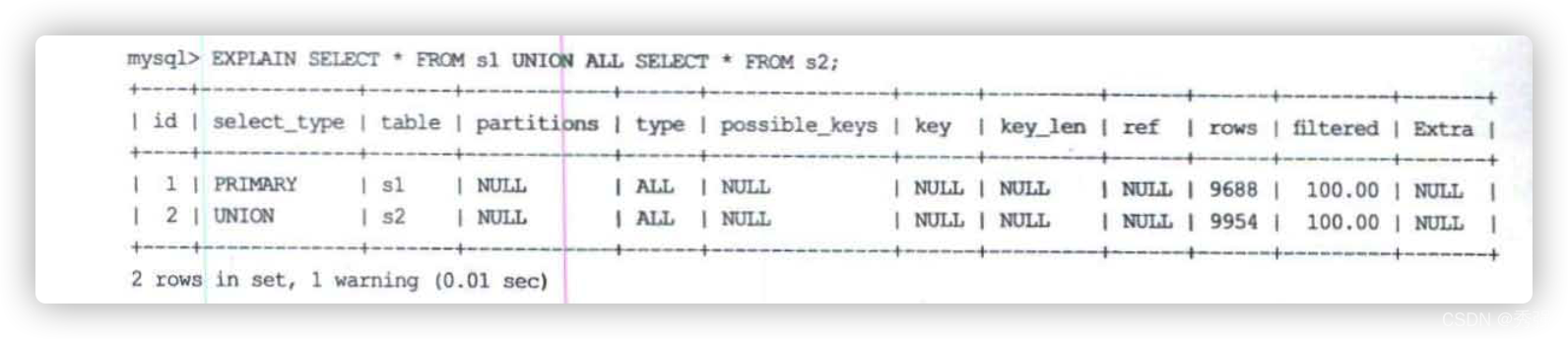
### select_type
主要用来分辨查询的类型,是普通查询还是联合查询还是子查询
| `select_type` Value | Meaning |
| :------------------: | :----------------------------------------------------------: |
| SIMPLE | Simple SELECT (not using UNION or subqueries) |
| PRIMARY | Outermost SELECT |
| UNION | Second or later SELECT statement in a UNION |
| DEPENDENT UNION | Second or later SELECT statement in a UNION, dependent on outer query |
| UNION RESULT | Result of a UNION. |
| SUBQUERY | First SELECT in subquery |
| DEPENDENT SUBQUERY | First SELECT in subquery, dependent on outer query |
| DERIVED | Derived table |
| UNCACHEABLE SUBQUERY | A subquery for which the result cannot be cached and must be re-evaluated for each row of the outer query |
| UNCACHEABLE UNION | The second or later select in a UNION that belongs to an uncacheable subquery (see UNCACHEABLE SUBQUERY) |
- simple: 简单的查询,不包含子查询和 union
```sql
explain select * from emp;
```
- primary: 查询中若包含任何复杂的子查询,最外层查询则被标记为 Primary
```sql
explain select staname,ename supname from (select ename staname,mgr from emp) t join emp on t.mgr=emp.empno ;
```
- union: 若第二个 select 出现在 union 之后,则被标记为 union
```sql
explain select * from emp where deptno = 10 union select * from emp where sal >2000;
```
- dependent union: 跟 union 类似,此处的 depentent 表示 union 或 union all 联合而成的结果会受外部表影响
```sql
explain select * from emp e where e.empno in ( select empno from emp where deptno = 10 union select empno from emp where sal >2000)
```
- union result: 从 union 表获取结果的 select
```sql
explain select * from emp where deptno = 10 union select * from emp where sal >2000;
```
- subquery: 在 select 或者 where 列表中包含子查询
```sql
explain select * from emp where sal > (select avg(sal) from emp) ;
```
- dependent subquery:subquery 的子查询要受到外部表查询的影响
```sql
explain select * from emp e where e.deptno in (select distinct deptno from dept);
```
- DERIVED: from 子句中出现的子查询,也叫做派生类,
```sql
explain select staname,ename supname from (select ename staname,mgr from emp) t join emp on t.mgr=emp.empno;
```
- UNCACHEABLE SUBQUERY:表示使用子查询的结果不能被缓存
```sql
explain select * from emp where empno = (select empno from emp where deptno=@@sort_buffer_size);
```
- uncacheable union: 表示 union 的查询结果不能被缓存
### table
对应行正在访问哪一个表,表名或者别名,可能是临时表或者 union 合并结果集
1. 如果是具体的表名,则表名从实际的物理表中获取数据,当然也可以是表的别名
2. 表名是 derivedN 的形式,表示使用了 id 为 N 的查询产生的衍生表
3. 当有 union result 的时候,表名是 union n1,n2 等的形式,n1,n2 表示参与 union 的 id
### type
type 显示的是访问类型,访问类型表示我是以何种方式去访问我们的数据,最容易想的是全表扫描,直接暴力的遍历一张表去寻找需要的数据,效率非常低下,访问的类型有很多,效率从最好到最坏依次是:
system > const > eq_ref > ***ref*** > fulltext > ref_or_null > index_merge > unique_subquery > index_subquery > ***range*** > index > ALL
**一般情况下,得保证查询至少达到 range 级别,最好能达到 ref**
#### all
全表扫描,一般情况下出现这样的 sql 语句而且数据量比较大的话那么就需要进行优化。
```sql
explain select * from emp;
```
#### index
全索引扫描这个比 all 的效率要好,主要有两种情况,一种是当前的查询时**覆盖索引**,即我们需要的数据在索引中就可以索取,或者是使用了索引进行**排序**,这样就避免数据的重排序。
```sql
explain select empno from emp;
```
#### range
使用索引执行查询时,对应的扫描区间为若干个单点扫描区间或者范围扫描区间的访问方法称为 range (仅包含一个单点扫描区间的访问方法不能称为 range 访问方法,扫描区间为 (-∞,+∞) 的访问方法也不能称为 range 访问方法)。在指定范围内进行查询,这样避免了 index 的全索引扫描,适用的操作符: =, <>, >, >=, <, <=, IS NULL, BETWEEN, LIKE, IN() 。
```sql
explain select * from emp where empno between 7000 and 7500;
```
#### index_subquery
利用索引来关联子查询,不再扫描全表。
```sql
explain select * from emp where emp.job in (select job from t_job);
```
#### unique_subquery
该连接类型类似与 index_subquery,使用的是唯一索引。
```sql
explain select * from emp e where e.deptno in (select distinct deptno from dept);
```
#### index_merge
在查询过程中需要多个索引组合使用
#### ref_or_null
不仅想找出某个二级索引列的值等于某个常数的记录,而且还想把该列中值为 NULL 的记录也找出来,比如下面这个查询:
```sql
explain select * from emp e where e.mgr is null or e.mgr=7369;
```
当使用二级索引而不是全表扫描的方式执行该查询时,对应的扫描区间就是 [NULL,NULL]
以及 ['abc', 'abc'] ,此时执行这种类型的查询所使用的访问方法就称为 ref_or_null。可以看到 ref_or_null 访问方法只是比 ref 访问方法多扫描了一些值为 NULL 的二级索引记录(值为 NULL 的记录会被放在索引的最左边)。
#### ref
搜索条件为二级索引列与常数进行等值比较,形成的扫描区间为单点扫描区间, 采用二级索引来执行查询的访问方法称为 ref。
```sql
SELECT * FROH xxx_table WHERE key1 = 'abc';
```
对于普通的二级索引来说,通过索引列进行等值比较后可能会匹配到多条连续的二级索引记录,而不是像主键或者唯一二级索引那样最多只能匹配一条记录。所以这种 ref 访问方法比 const 差了那么一点。
- 在二级索引列允许存储 NULL 值时,无论是普通的二级索引,还是唯一二级索引,它
们的索引列并不限制 NULL 值的数量,所以在执行包含 "key IS NULL" 形式的搜索条件的查询时,最多只能使用 ref 访问方法, 而不能使用 const 访问方法。
- 对于索引列中包含多个列的二级索引来说,只要最左边连续的列是与常数进行等值比较,就可以采用 ref 访问方法。如下所示:
```sql
SELECT * FROM single_table WHERE key_part1 = 'AAA';
SELECT * FROM single_table WHERE key_part1 = 'AAA' and key_part2 = 'BBB';
SELECT * FROM single_table WHERE key_part1 = 'AAA' and key_part2 = 'BBB' and key_part3 = 'CCC';
```
如果索引列中最左边连续的列不全部是等值比较的话,它的访问方法就不能称为 ref 了。
```sql
SELECT * FROM single_table WHERE key_part1 = 'AAA' and key_part2 > 'BBB';
```
#### eq_ref
用于联表查询的状况,按联表的主键或惟一键联合查询。
```sql
explain select * from emp,emp2 where emp.empno = emp2.empno;
```
#### const
通过**主键或者唯一二级索引列来定位一条记录**的访问方法定义为 const(意思是常数级别的, 代价是可以忽略不计的) 。不过这种 const 访问方法只能在主键列或者唯一二级索引列与一个常数进行等值比较时才有效。如果主键或者唯一二级索引的索引列由多个列构成,则只有在索引列中的每一个列都与常数进行等值比较时,这个 const 访问方法才有效(这是因为只有在该索引的每一个列都采用等值比较时, 才可以保证**最多只有一条记录符合搜索条件**)。
对于唯一二级索引列来说, 在查询列为 NULL 值时, 情况比较特殊。比如下面这样:
```sql
SELECT * FROM single table WHERE key2 IS NULL;
```
因为唯一二级索引列并不限制 NULL 值的数量, 所以上述语句可能访问到多条记录。
#### system
表只有一行记录(等于系统表),这是 const 类型的特例,平时不会出现。
### possible_keys
显示可能应用在这张表中的索引,一个或多个,查询涉及到的字段上若存在索引,则该索引将被列出,但不一定被查询实际使用
```sql
explain select * from emp,dept where emp.deptno = dept.deptno and emp.deptno = 10;
```
### key
实际使用的索引,如果为 null,则没有使用索引,查询中若使用了覆盖索引,则该索引和查询的 select 字段重叠。
```sql
explain select * from emp,dept where emp.deptno = dept.deptno and emp.deptno = 10;
```
### key_len
表示索引中使用的字节数,可以通过 key_len 计算查询中使用的索引长度,在不损失精度的情况下长度越短越好。
```sql
explain select * from emp,dept where emp.deptno = dept.deptno and emp.deptno = 10;
```
### ref
显示索引的哪一列被使用了,如果可能的话,是一个常数
```sql
explain select * from emp,dept where emp.deptno = dept.deptno and emp.deptno = 10;
```
### rows
根据表的统计信息及索引使用情况,大致估算出找出所需记录需要读取的行数,此参数很重要,直接反应的 sql 找了多少数据,在完成目的的情况下越少越好
```sql
explain select * from emp;
```
### extra
包含额外的信息。
- using filesort: 说明 mysql 无法利用索引进行排序,只能利用排序算法进行排序,会消耗额外的位置
```sql
explain select * from emp order by sal;
```
- using temporary: 建立临时表来保存中间结果,查询完成之后把临时表删除
```sql
explain select ename,count(*) from emp where deptno = 10 group by ename;
```
- using index: 这个表示当前的查询时覆盖索引的,直接从索引中读取数据,而不用访问数据表。如果同时出现 using where 表名索引被用来执行索引键值的查找,如果没有,表面索引被用来读取数据,而不是真的查找
```sql
explain select deptno,count(*) from emp group by deptno limit 10;
```
- using where: 使用 where 进行条件过滤
```sql
explain select * from t_user where id = 1;
```
- using join buffer: 使用连接缓存
- impossible where:where 语句的结果总是 false
```sql
explain select * from emp where empno = 7469;
```
## 参考资料
- MySQL 官网
- [EXPLAIN](https://dev.mysql.com/doc/refman/8.0/en/explain-output.html)
- 《MySQL 是怎样运行的》
| 36.944853 | 223 | 0.688427 | eng_Latn | 0.420477 |
980f0091f493699c2b0fbd64dd463dd083bda52a | 226 | md | Markdown | docs/index.md | c0nnex/coreclr-module | 745782a3411182dcca4514a675b1d5404e04d05b | [
"MIT"
] | 3 | 2020-05-24T17:00:11.000Z | 2021-03-03T01:21:13.000Z | docs/index.md | c0nnex/coreclr-module | 745782a3411182dcca4514a675b1d5404e04d05b | [
"MIT"
] | null | null | null | docs/index.md | c0nnex/coreclr-module | 745782a3411182dcca4514a675b1d5404e04d05b | [
"MIT"
] | null | null | null | # AltV C# Module
This is the documentation for the AltV .NET Core module to write server gamemodes in c#.
# Getting started
Look into [this guide](articles/index.md) how to create your first alt:V server gamemode in c#.
| 37.666667 | 96 | 0.743363 | eng_Latn | 0.998752 |
980f82095894f6bcbf1201a3a90100241a2e0a05 | 74,004 | markdown | Markdown | _posts/2006-02-07-system-and-method-for-starting-virtual-machine-monitor-in-common-with-already-installed-operating-system.markdown | api-evangelist/patents-2006 | 45f18ed4bf45e78a8f1ba058c9f565adda718e14 | [
"Apache-2.0"
] | null | null | null | _posts/2006-02-07-system-and-method-for-starting-virtual-machine-monitor-in-common-with-already-installed-operating-system.markdown | api-evangelist/patents-2006 | 45f18ed4bf45e78a8f1ba058c9f565adda718e14 | [
"Apache-2.0"
] | null | null | null | _posts/2006-02-07-system-and-method-for-starting-virtual-machine-monitor-in-common-with-already-installed-operating-system.markdown | api-evangelist/patents-2006 | 45f18ed4bf45e78a8f1ba058c9f565adda718e14 | [
"Apache-2.0"
] | 3 | 2019-10-31T13:03:20.000Z | 2021-04-09T12:15:51.000Z | ---
title: System and method for starting virtual machine monitor in common with already installed operating system
abstract: A computer system includes a Hypervisor having the highest privilege level; a Primary Virtual Machine Monitor (VMM) running with the same or fewer privileges than the Hypervisor; and a Primary Virtual Machine (PVM) without system level privileges and having a Primary operating system (POS) running within it. The POS can be the same operating system that ran on the computer system prior to activation of the Hypervisor. The POS can have hardware drivers used by other components for accessing hardware through the POS. The Hypervisor can have hardware drivers used by other components for accessing hardware through the Hypervisor. Alternatively, the POS can have some hardware drivers used by other components for accessing hardware, and the Hypervisor can have other hardware drivers used by the other components for accessing other hardware through the Hypervisor. The POS can have direct access to at least some real hardware devices.
url: http://patft.uspto.gov/netacgi/nph-Parser?Sect1=PTO2&Sect2=HITOFF&p=1&u=%2Fnetahtml%2FPTO%2Fsearch-adv.htm&r=1&f=G&l=50&d=PALL&S1=07865893&OS=07865893&RS=07865893
owner: Parallels Holdings, Ltd.
number: 07865893
owner_city:
owner_country: BM
publication_date: 20060207
---
This application is a non provisional of U.S. Provisional Patent Application No. 60 650 135 filed on Feb. 7 2005 entitled SYSTEM AND METHOD FOR STARTING VIRTUAL MACHINE MONITOR IN COMMON WITH ALREADY INSTALLED HOST OPERATING SYSTEM which is incorporated by reference herein in its entirety.
With Virtual Machine VM technology a user can create and run multiple operating environments on a server at the same time. Each operating environment or Virtual Machine requires its own operating system OS and can run applications independently. The VM software provides a layer between the computing storage and networking hardware and the software that runs on it.
Virtual Machine technology can lower information technology IT cost through increased efficiency flexibility and responsiveness. Each VM acts as a separate environment which reduces risk and allows developers to quickly re create different operating system OS configurations or compare versions of applications designed for different OS s. Additional customer uses for VMs include targeted production server consolidation hosting of legacy applications older versions and computer or server backup.
A Virtual Machine technology is therefore one technique for emulating or otherwise virtualizing the behavior of software and or hardware. Generally a Virtual Machine is an environment that is launched on a particular processor that is running an operating system. Normally the operating system installed on such a machine or processor has certain privileges that are not available to user applications. For example many input output commands may be privileged and executable only in the operating system or privileged mode. Certain areas of memory or certain addresses in memory also may require operating system privilege to be accessed.
A frequent situation that arises in this context is the problem of emulating or more broadly virtualizing a different operating system on the same processor. For example with one version of Microsoft Windows running on the Intel x86 processor for example in a server environment it may be necessary to emulate the behavior of another different version of Windows on the same Intel processor. This second operating system is generally referred to as Guest OS and the code that it executes is generally referred to as guest code. Note that in order for the emulation to be meaningful the Guest OS needs to execute privileged instructions as if it were actually running on the processor. In other words the Guest OS running as a Virtual Machine is itself unaware that it is a Virtual Machine.
Execution of such privileged instructions however is the province of the native operating system. Therefore any attempts by the Guest OS inside Virtual Machine to execute privileged instructions must be intercepted so that they can be properly executed or otherwise handled by the VMM. The component that is responsible for this interception and emulation of privileged instructions is called a Virtual Machine Monitor or VMM.
A typical Virtual Machine Monitor VMM enables a single physical machine or processor to act as if it were several physical machines. A typical VMM under control of a high ranking operating system OS can run a number of different operating systems simultaneously such that each of these different operating systems is its own Virtual Machine.
In other words the Virtual Machine Monitor can handle one or a number of Virtual Machines each of which represents its own operating system and each of which can run its own application software. Usually in industry parlance the high ranking OS is referred to as a host OS HOS . The multiple operating systems that are running as Virtual Machines are usually referred to as guest operating systems Guest OS s running guest code. At the present time there are two conventional mechanisms for structuring VMMs a non hosted VMM and a hosted VMM.
In the case of the non hosted VMM which is shown in the VMM itself is a full fledged operating system. Such a non hosted VMM includes drivers for controlling and managing input output activities of the physical computer. The non hosted VMM is installed onto a bare PC and has a monopoly on control over the I O devices. This type of VMM exists at the system level and can create any number of Virtual Machines that do not exist at the system level and which cannot directly work with input output devices. Such a VMM therefore needs to manage CPU scheduling and resource sharing for the Virtual Machines. An example of such a VMM is the IBM ESA 390.
The non hosted VMM have several problems. One problem is complexity. Apart from virtualization it must also manage I O device handling memory handling scheduling and so on. Such a VMM therefore needs to be designed as a full fledged operating system with additional virtualization support. Another problem is poor compatibility. Due to a very large spectrum of available hardware and I O devices it is almost impossible to support all possible PC configurations for such a VMM. Therefore such a VMM is usually limited to supporting a small set of possible predefined hardware configurations. In any event a non hosted VMM cannot normally work directly with all the I O hardware. An additional problem is a large footprint and having to include third party code device drivers and so on that run on the system level this can seriously affect overall system stability and security.
In the case of the hosted VMM which is shown in the VMM itself is not a full fledged operating system. Such a VMM does not include device drivers and cannot control hardware devices such as I O devices directly. Such a hosted VMM is installed into the host operating system HOS and uses HOS s API application programming interface to work with the I O devices. Both the VMM and the host operating system have system level privileges and exist on a physical computer concurrently. The VMM is responsible for preserving the context of the host operating system when switching from the HOS to the VMM and is responsible for restoring the context of the HOS when switching back to the HOS. The hosted VMM creates any number of Virtual Machines none of which have system level privileges and none of which can work with I O devices directly. The VMM either emulates the input output devices for the Virtual Machines and uses the HOS to work with the real I O devices.
For each VM a separate process is created and the HOS is responsible for scheduling of both the VMs and other processes in the HOS. Examples of such hosted VMMs include VMware GSX Server VMware Workstation MS Virtual PC MS Virtual Server and SVISTA 2004.
Hosted VMM also have a number of problems. One such problem is poor security. A non hosted VMM is well protected because all its VMs run without system privilege level and cannot harm the VMM and any other VM. If one of the VMs were to crash it will not affect the VMM nor any other VMs. For the hosted VMM a crash of the HOS can damage both the VMM and all other VMs. Also it can be inefficient or even impossible for hosted VMM to use hardware virtualization technologies in new families of processors such as for example Intel s Virtual Machine Extension VMX technology.
Accordingly what is needed is a way to combine the best features of non hosted VMMs and hosted VMMs to support an efficient virtualization.
The present invention is directed to a system and method for starting a Virtual Machine Monitor in common with an already installed operating system that substantially obviates one or more of the problems and disadvantages of the related art.
There is provided a computer system including a Virtual Machine Monitor VMM running with system level privileges. A primary Virtual Machine VM is running without system level privileges and has a host operating system HOS running within it. A secondary Virtual Machine is running without system level privileges. The HOS has direct access to at least some I O devices. The VMM can use the HOS to access the at least some I O devices. The HOS can be installed as the computer system s operating system prior to installation of the VMM. A plurality of secondary Virtual Machines can be running without system level privileges.
In another aspect a computer system includes a Virtual Machine Monitor VMM running with system level privileges a primary Virtual Machine VM without system level privileges and having a host operating system HOS running within it and a secondary Virtual Machine running without system level privileges. The VMM uses the HOS to access at least some I O devices.
In another aspect a method of virtualizing a computer system includes on the computer system having a host operating system HOS with system privileges installing a Virtual Machine Monitor VMM as a user application creating a primary Virtual Machine VM transferring the HOS to the primary VM giving the VMM system privileges and launching a secondary VM without system privileges. The VMM can use the HOS to access at least some I O devices after the HOS has been transferred. The transfer of the HOS is conducted during run time using a reboot or by reinstalling the HOS inside the primary VM.
In another aspect a method of virtualizing a bare computer system includes installing a Virtual Machine Monitor VMM with system privileges on the bare computer system creating a primary Virtual Machine VM transferring the HOS to the primary VM and restarting a host operating system HOS in the primary VM. A secondary VM can then be launched without system privileges.
In another aspect a method of virtualizing a bare computer system includes installing a Virtual Machine Monitor VMM with system privileges on the bare computer system creating a primary Virtual Machine VM and installing a host operating system HOS in the primary VM. A secondary VM can then be launched without system privileges.
In another aspect a computer system includes a hardware processor having a Virtual Machine treatment mode and a hardware memory being accessed by the hardware processor. A Virtual Machine Monitor VMM is running on the processor in the Virtual Machine treatment mode. A primary Virtual Machine VM is running as a user application and having a host operating system HOS running within it. A secondary Virtual Machine is running as a user application
In another aspect a virtualization system is provided for a computer that has a host processor physical system devices and a host operating system HOS and wherein the computer is operationally divided into a system level and a user level. The virtualization system includes at least one Virtual Machine monitor VMM at the system level and a primary Virtual Machine VM operatively connected with the VMM wherein the HOS is at the user level running inside primary VM. The primary VM and the HOS have direct access to some of the physical system devices. The VMM accesses the physical system devices via the primary VM and the HOS.
In another aspect a computer system includes a Hypervisor having the highest privilege level a Primary Virtual Machine Monitor VMM running with the same or fewer privileges than the Hypervisor and a Primary Virtual Machine PVM without system level privileges and having a Primary operating system POS running within it. The POS can be the same operating system that ran on the computer system prior to activation of the Hypervisor. The POS can have hardware drivers used by other components for accessing hardware through the POS. The Hypervisor can have hardware drivers used by other components for accessing hardware through the Hypervisor. Alternatively the POS can have some hardware drivers used by other components for accessing hardware and the Hypervisor can have other hardware drivers used by the other components for accessing other hardware through the Hypervisor. The POS can have direct access to at least some real hardware devices.
The system can optionally include at least one additional VMM controlling at least one additional VM and at least one Guest OS running within the additional VM. The Guest OS can work with virtualized hardware and hardware access requests from the Guest OS or its VMM are translated by the Hypervisor to real hardware using the POS.
Here real hardware includes shareable hardware and non shareable hardware. Shareable hardware can accessed by many Guest OSs and POS and non shareable hardware is accessed only by the single Guest OS or single POS. The Hypervisor can also convert hardware access requests from the Guest OS into real hardware access requests. The Hypervisor can also restrict an ability of any VMM to write to an Interrupt Descriptor Table.
In another aspect a computer cluster includes a plurality of computing nodes each node having a Hypervisor with the highest privilege level and a Virtual Machine Monitor VMM running with same or fewer privileges than the Hypervisor and a Virtual Machine VM running on a user level. Each node also has at least one of a a Primary operating system POS running within the corresponding VM and b a Guest operating system GOS running within the corresponding VM. The POS can be the same operating system that ran on the computer system prior to activation of the Hypervisor. The POS can be migrated from one node to another. The migration can involve upgrading a Guest OS to a Primary OS.
In another aspect a computer system includes a Hypervisor having the highest privilege level a plurality of Virtual Machine Monitors VMMs running with the same or fewer privileges than the Hypervisor and a plurality of Virtual Machines VMs without system level privileges and each having a Primary operating system POS running within it. Each POS can be the same operating system that ran on the computer system prior to activation of the Hypervisor but having direct access to a subset of physical hardware devices of the computer system. Additional Virtual Machines each running a Guest Operating System can have access only to virtualized hardware. Additional Virtual Machines each running a Guest Operating System can have access only to virtualized hardware and to non shareable hardware.
In another aspect a method of virtualization on a computer system having an operating system the method including initiating a Hypervisor having the highest privilege level initiating a Primary Virtual Machine Monitor VMM running with the same or fewer privileges than the Hypervisor initiating a Virtual Machine VM without system level privileges the VMM controlling the VM and migrating the operating system inside the VM. Other Virtual Machines having Guest Operating Systems running therein can be initiated the Guest Operating Systems working with virtualized hardware wherein the Hypervisor routes hardware access requests to the operating system inside the VM.
In another aspect a method of computer system crash recovery on a computer system having an operating system the method including initiating a Hypervisor having the highest privilege level initiating a plurality of Virtual Machine Monitors VMMs running with some system level privileges but with fewer privileges than the Hypervisor initiating a Virtual Machine VM without system level privileges corresponding to each VMM migrating the operating system inside one of the VMs and activating it as a Primary OS maintaining at least one quiescent Primary OS inside one of the other VMs upon failure of the Primary OS upgrading the quiescent Primary OS to active Primary OS.
In another aspect a method of computer system crash recovery on a computer system having an operating system the method comprising initiating a Hypervisor having the highest privilege level initiating a plurality of Virtual Machine Monitors VMMs running with some system level privileges but with fewer or same privileges than the Hypervisor initiating a Virtual Machine VM on the user level corresponding to each VMM migrating the operating system inside one of the VMs and activating it as a Primary OS initiating Guest OS s inside the other VMs and upon failure of the Primary OS upgrading one of the Guest OS s to Primary OS.
A method of computer system crash recovery on a computer system having an operating system including initiating a Hypervisor having the highest privilege level initiating a plurality of Virtual Machine Monitors VMMs running with the same or fewer privileges as the Hypervisor initiating a Virtual Machine VM on the user level corresponding to each VMM and reserving at least one of the VMs and an operating system within it as a reserved Primary VM and a reserved Primary OS and upon failure of the Primary OS activating the reserved Primary OS having the same privileges and the failed Primary OS.
Additional features and advantages of the invention will be set forth in the description that follows. Yet further features and advantages will be apparent to a person skilled in the art based on the description set forth herein or may be learned by practice of the invention. The advantages of the invention will be realized and attained by the structure particularly pointed out in the written description and claims hereof as well as the appended drawings.
It is to be understood that both the foregoing general description and the following detailed description are exemplary and explanatory and are intended to provide further explanation of the invention as claimed.
Reference will now be made in detail to the embodiments of the present invention examples of which are illustrated in the accompanying drawings.
The VMM as described herein is well protected because the HOS and all the Guest OS s run without system level privileges and cannot damage the VMM or other VMs. The VMM as described herein is flexible and compatible because all communication with the actual hardware will be done by means of HOS API. Such a VMM is naturally compatible with new hardware virtualization technologies such as Intel VT and AMD Pacifica technology and others and can use them efficiently.
The approach described herein has other advantages. Compared to the non hosted VMM approach there is no need to develop the VMM as a full fledged operating system which has to support the entire spectrum of the physical devices that may be connected as I O devices. Furthermore it is possible to install the VMM described herein on top of the existing operating system and use it as a standard application since the VMM in the present approach can stay to the side of the HOS. In other words one HOS can be killed and a new one created to support I O functions. Thus the level of security can be increased.
Compared to the hosted VMM approach the approach described herein in the case of using a hardware based virtualization technology in the processor the present approach allows the use of the built in capabilities for switching between the HOS the VMM and the various VMs. In this case the concept of a fully secure VMM can be realized. If in the conventional hosted VMM the VMM is protected only from the Guest OS but can be damaged from the HOS because from the point of view of the Guest OS a VMM crash means a crash of all its VMs here the Guest OS cannot be damaged by a crash in HOS in the hosted VMM.
In other words in the present approach the VMM is protected from both the HOS and all the guest operating systems. Even a failure or crash of the HOS will not lead to a failure of the VMM described herein. If in the event of an HOS crash the VMM s ability to work with I O devices will be blocked and other VMs would not be able to function normally. Notwithstanding this the VMM and all others VMs would still be alive and the VMM could execute some recovery procedures to prevent data loss in the VMs. Note that a new HOS can be raised to provide usability of VMs. For example it is possible for the VMM to safely suspend the secondary VMs restart the HOS in the primary VM and then resume the secondary VMs normal work without any loss of data.
Note also that sometimes due to a particular virtualization strategy the VMM could allow for a particular VM to have direct access to particular I O devices so called PASS THROUGH devices .
Also sometimes due to the virtualization strategy the VMM can include additional secondary scheduling responsibilities for scheduling its VMs. In this case the HOS is responsible for scheduling the VMM and its own processes and the VMM is responsible for scheduling of its VMs.
1. The VMM does all the scheduling. This is primarily used for the non hosted VMM approach and it can be more efficient for some embodiments described herein for example for Intel s virtualization technology .
2. The HOS does all the scheduling. The VMM controls the VM that contains the HOS i.e. the primary VM .
3. The HOS does the primary scheduling and the VMM does the secondary scheduling. This is more efficient for hosted VMMs and it could be efficient for some embodiments described herein.
As described herein and as illustrated in a Virtual Machine Monitor can be included in a computer system that is running a host operating system HOS . One way to implement the VMM as described herein is by loading a special boot manager at the moment of startup of the physical computer prior to the start of the host operating system. The VMM creates a primary Virtual Machine and starts loading the host operating system within the primary Virtual Machine rather than at system level. Thus the host operating system becomes the first of the guest operating systems.
In one particular special case the primary Virtual Machine primary VM is setup such that the host operating system has a PASS THROUGH access to the actual hardware of the input output devices although not necessarily to all of them.
In an alternative embodiment the VMM is loaded and starts working at the system level with the help of a dedicated driver in the host operating system. The VMM creates the primary Virtual Machine and transfers the host operating system from the system level to within the primary Virtual Machine without a partial or complete rebooting of the computer. In this manner the HOS becomes the first guest operating system. In the present discussion the term HOS is used to designate a host operating system that can be used as a means for supporting VMM s operability.
The primary Virtual Machine can also be structured such that the HOS has direct PASS THROUGH access to the actual hardware of the input output devices.
After the loading of the VMM under either approach described above the VMM is configured in a manner that has at least one or possibly all of the characteristics described below
1. The VMM has system level privileges for example Ring 0 privileges for the Intel IA 32 architecture or root for the VT X architecture.
6. The VMM can launch any number of secondary Virtual Machines none of which have system level privileges.
8. There are at least some I O devices that are directly controlled by the host operating system in the PASS THROUGH regime and are not accessible by the secondary VM.
9. Inside a secondary Virtual Machine any of the supported guest operating systems can be installed and or launched.
10. The VMM emulates virtual I O devices for the guest operating systems within the secondary Virtual Machine In other words the VMM passes I O requests to the HOS for emulation or execution. Some I O emulation can be done in the VMM without access to real hardware but some emulation may need to communicate with the real hardware with the help of HOS .
11. The VMM uses the primary Virtual Machine and the HOS to work with actual hardware of the I O devices in other words without emulation .
In one particular embodiment when PASS THROUGH access to I O devices is implemented it is understood that the HOS still has a monopoly on control over these I O devices when it is launched within the primary Virtual Machine. The access of the HOS and of the primary Virtual Machine to the I O devices can be set up by the VMM based on a chosen virtualization strategy. For example the HOS can be prohibited to directly access some I O devices and control over these devices can be either handled by the VMM or by any of the secondary Virtual Machines.
Note that in the present discussion I O devices are not only such devices as keyboards and printers but also server I O ports network I O devices control registers and privileged areas of memory which are specifically designed for exchange of data between devices and storage of system level information for example for storage of data relating to I O device function and control .
As yet another embodiment the VMM by itself is not a full fledged operating system. Such a VMM can lack some or all device drivers and in some cases can lack the ability to directly control hardware I O devices. In this case the VMM is installed with the host operating system and uses HOS s APIs to work with the I O devices. Only the VMM has system level privilege and works on a physical computer in other words some instructions are either emulated or handled using PASS THROUGH to other contexts .
The HOS does not have system level privileges and works within a primary Virtual Machine. At the same time the HOS can have direct PASS THROUGH access to the I O devices. The VMM can create any number of secondary Virtual Machines which do not have system level privileges and cannot work with I O devices directly. The VMM emulates I O devices for the secondary Virtual Machines and uses the primary Virtual Machine and the host operating system to work with actual hardware of the I O devices. The VMM organizes the scheduling of the Virtual Machines.
At the same time it should be noted that a complete absence of drivers from the VMM and other similar system type utilities is not a requirement of the invention but may be realized in some embodiments of the invention.
Due to the fact that it is possible as a result of the failure or crash of the HOS to block I O for all the other Virtual Machines since all the other Virtual Machines can implement their I O through the HOS in one particular embodiment when the HOS crashes the VMM can freeze or suspend execution of the other Virtual Machines After this the HOS can be restarted or rebooted inside the primary VM or a different HOS can be started such that it can support the functioning of the secondary Virtual Machines. As yet another alternative the configuration of one of the secondary Virtual Machines can be updated such that the guest operating system in that secondary Virtual Machine receives the status of the host operating system and the corresponding VM gets a corresponding privilege level. Subsequent to that the other Virtual Machines can restart their execution without a loss of data. Alternative recovery procedures can also be used by the VMM to prevent data loss and restore operations of the VMs.
The VMM controls sharing of system resources including scheduling processes and monitors and controls execution of the instructions running inside the VMs. In other words it controls guest instructions or instructions associated with a VM.
The VMM running as a host operating system with the truncated functionality and full access to the hardware resources is provided by means of a single operating system e.g. the HOS which runs under the control of the VMM. At the same time control and monitoring functions may be distributed among the VMM the primary VM HOS and secondary VM s depending on the hardware and software e.g. HOS architecture.
At the same time the VMM may control other operating systems running with lower level of privileges than the main operating system HOS . Also the secondary VMs may have their own additional VMMs which control corresponding VMs. Such additional VMMs can in their turn run under the control of the primary VMM or the HOS.
Some instructions that can cause system crash or another malfunction of the computing system are forbidden in the Virtual Machines having the lowest level of privileges and are emulated by means of the VMM or passed to the host operating system for execution.
Some instructions that have to be emulated are of the type that intend to halt or reset processor operations. Some instructions that may be realized by means of the host operating system are read write instructions or other instructions that are directed to accessing the I O hardware.
In the Intel family of processors the various privilege regimes are referred to as privilege levels and are set through appropriate processor registers. In the Intel IA 32 architecture Ring 0 and Ring 3 privilege levels can be used to implement the approach described herein. It should be noted that although the particular examples given in this discussion relate to the Intel architecture the invention is not limited to the Intel architecture and is applicable to any number of processor families and processor architectures.
In one embodiment of the invention in terms of Intel x86 architecture the Primary VM and VMM runs in the Ring 0 privilege level. Also secondary VMs and the HOS run in the Ring 3 privilege level. Some instructions that are permitted in the VMM context are forbidden in the context of the primary VM so the VMM can monitor and control execution of instructions inside the primary VM. Also the primary VM and the VMM can have different privilege levels that may be implemented using the Intel VT technology. i.e. the Intel virtualization technology for IA 32 64 processors . In one embodiment the VMM can run in root mode and the HOS can run in non root mode.
It should be noted that when other non Intel types of processors are used different terminology may be used to describe the privilege levels. Also the mechanism of switching between the privileged levels can be different although the concepts described here are still applicable therein.
In different embodiments the HOS has the same or higher privilege level than other operating systems launched using the VMM the HOS here can be different from conventional HOS s since here the HOS works under the direction of the VMM instead of vice versa .
In one embodiment depending on how the hardware is configured the VMM can emulate ignore or forbid execution of particular instructions as well as certain sequences of certain instructions both within the secondary Virtual Machines and the primary Virtual Machine. In this case sets of instructions that can be emulated executed or be forbidden can be different for the primary and secondary Virtual Machines. In the Intel architecture when using the VT technology selecting a set of allowed instructions and enabling safe switching of context can be done at the hardware level by appropriate commands or by changing flags in appropriate processor registers and structures for example VMCS structure tuning .
Additionally in one embodiment the VMM provides for automatic changes of privilege levels depending on the context in which the code is executed. Thus when executing the code of Guest OS s in the secondary Virtual Machines certain I O operations are forbidden. At the same time the same I O operations can be permitted in the environment of the primary Virtual Machine in which the HOS is running. This ensures a safe execution of such I O instructions in the primary Virtual Machine. Also when transferring control to the primary Virtual Machine running the HOS which is done under VMM control the changing of the privilege levels is also provided to such a level that insures safe execution of such instructions.
Generally a context is simply a collection of related processes whose names are not known outside of the context. Contexts partition operating system s name space into smaller more manageable subsystems. They also hide names ensuring that processes contained in them do not unintentionally conflict with those in other contexts.
A process in one context cannot explicitly communicate with and does not know about processes inside other contexts. All interaction across context boundaries must be through a context process thus providing a degree of security. The context process often acts as a switchboard for incoming messages rerouting them to the appropriate sub processes in its context.
Normally there is a single primary Virtual Machine and most commonly though not necessarily it is set up so that it can directly access I O devices and their actual hardware. Secondary Virtual Machines of which there can be any number are set up such that they cannot directly use actual hardware of the I O devices. The VMM is responsible for emulation of the I O devices for the secondary Virtual Machines. The VMM uses the primary Virtual Machine to work with the actual hardware of the I O devices. The VMM works at a system privilege level while the primary and secondary Virtual Machines work at a non system user privilege level.
The host operating system works within the primary Virtual Machine and cannot execute privileged instructions on the real processor. The VMM works in a native mode on the real processor and can execute privileged instructions. When it is impossible for some reason to transfer the host operating system to the Virtual Machine the VMM is installed on the real computer using a dedicated boot manager for VMM and receives control at the very beginning of the startup of the computer. Upon loading the VMM creates a primary Virtual Machine and loads the host operating system within the primary Virtual Machine. When the HOS is transferred from the host PC into the Primary VM any changes in hardware need to be addressed as well. This will depend on virtualization policy part of the devices in Primary VM are changed to virtual ones. Once the transfer is complete the HOS might face some changes in hardware. Depending on the HOS and on these changes there are 3 possible scenarios 1 the HOS can handle such changes on the fly 2 the HOS should be rebooted to work in new environment and 3 the HOS should be reinstalled in the new environment.
In yet another embodiment the VMM can be installed on a bare PC using a boot manager. This VMM still lacks device drivers and couldn t support secondary VMs full functionality without the HOS since the HOS contains proper system utilities. Subsequently the HOS can be installed under the VMM in the primary VM. Then the VMM works the same way as described above in the embodiment discussing the boot manager.
In this embodiment the VMM does not work under the control of an already installed HOS. However it still runs the HOS in the primary VM with reduced privileges and still uses it to access the I O devices. This embodiment will be helpful for a new generation of HOS with support for hardware based virtualization technology such as Intel s VT X and or VT I technology. During installation on a bare PC such an HOS can detect the presence of VT X and store this information in e.g. a registry. When restarted in primary VM without VT X support it could refuse to boot. Installation of the HOS under VMM in the primary VM with already reduced privileges in the absence of VT X solves this problem. Here the VMM can be installed on top of the HOS and then HOS can be reinstalled inside the Primary VM.
The question of how to distribute the privileges between the various actors in the virtualization schemes can be framed more broadly as follows given the various components VMM VM Primary OS Guest OS what is the optimal way to distribute the privileges and responsibilities between these components and how can this distribution be made secure and portable For example one conventional way is to essentially replace the primary operating system with the VMM the VMM therefore becomes itself for all practical purposes an operating system. This has some advantages in terms of efficiency for example any attempt by the Guest OS to execute privileged instructions that it is actually not entitled to trigger an exception and the VMM immediately handles it. However this approach can require that all the drivers be placed in VMM space. This is frequently a source of problems since there are hundreds or even thousands of devices that most operating systems need to support. For example there are numerous vendors of hard disk drives and numerous models and types of hard disk drives CD ROM drives DVD ROM drives floppy disks video cards network cards Wi Fi cards and modems mice track balls etc. Most of these drivers are usually written by vendors themselves this means including in the VMM a lot of untrusted third party code that runs the most privileged level and can damage the system A VMM that displaces the original operating system therefore needs to itself have all these drivers. This obviously has the potential to compromise security. It is worth noting that many of the complaints about the instability of the Windows operating system actually result not from bugs in the Windows operating system code itself but from bugs in the drivers which in the Windows operating system live in kernel space.
One way to deal with the problem of VMM having a large footprint in other words VMM having an amount of code that is comparable to the amount of code of a full fledged operating system such as LINUX or Windows is to add a component called a Hypervisor shown in . The Hypervisor can have exclusive control over the physical resources of the system although it can grant certain rights to other components of the system such as to the Primary OS or in some cases to the Guest OS.
The degree of control by the primary OS POS and the VMM over processor resources and the processor s privileged instructions is an important issue that has been addressed in various ways over the years. The PVM uses a particular mechanism called the Lightweight Hypervisor which restricts the ability of both the POS and the VMM to issue instructions that affect the interrupt descriptor table IDT . Thus the Lightweight Hypervisor processes all interrupts and exceptions in the system and dispatches them to the POS and VMMs based on its virtualization policy.
Hypervisor based VMMs illustrated in combine the advantages of the prior art systems and eliminate major disadvantages. The Hypervisor runs on the system level and creates Virtual Machines on the user level. One of the VMs runs a so called Primary OS POS and has privileges to handle some of the hardware directly. Other VMs and the Hypervisor uses Primary OS and its hardware drivers for communication with the actual hardware. At the same time the Hypervisor employs efficient memory management processor scheduling and resource management without the help of the Primary OS. The advantages of the Hypervisor based approach are high VM isolation security efficient resource management and a small trusted Hypervisor footprint.
The Lightweight Hypervisor illustrated in runs on the system level reloads the Interrupt Descriptor Table IDT and protects it from modification by the primary OS and the VMM. The primary OS and the VMMs are not allowed to modify IDT and they are not allowed to independently process interrupts. The Lightweight Hypervisor coexists in all address spaces primary OS context and VMMs contexts and exclusively processes all hardware interrupts and exceptions. It is responsible for interrupt forwarding context switching between the primary OS and VMMs and for efficient resource scheduling.
Advantages of the Lightweight Hypervisor are excellent performance good VM isolation and security efficient resource management and small trusted lightweight Hypervisor footprint. Disadvantage of the Lightweight Hypervisor is less VM isolation than in full Hypervisor architecture.
Thus the Lightweight Hypervisor is a small piece of software that helps manage VMMs by handling hardware resource interrupts events. The Lightweight Hypervisor captures the primary IDT pointer and replaces it with its own as shown in .
The Hypervisor IDT points to Hypervisor s handlers that first receive control when any interrupt or exception is raised perform various checks and then forward control to the original Primary OS or VMM handler. Therefore the Hypervisor adds additional security since it can filter or ignore some debug event accesses to Hypervisor space.
The Lightweight Hypervisor enables context switching between VMM and POS. Context is described by processor structures that are involved in memory access mechanisms such as page directories and page tables GDT LDT tables in Intel architecture . The Hypervisor manages the IDT for every context primary OS and VMM .
Each context has a descriptor that stores all necessary information about context state. Switching between contexts means switching between their descriptors loading the corresponding processor state saved in it . The VMM s context descriptors can include saved state of the space from which they were called from Primary OS state . Switching between Primary OS context and VMM one is permitted.
The Lightweight Hypervisor manages all IDTs for all contexts VMM and Primary OS . IDT management includes
The Lightweight Hypervisor protects Hypervisor IDT for primary OS from modification and any attempt for IDT entry modification will be passed through Hypervisor as shown in .
4. Protecting from modification Hypervisor IDT for primary OS for example it could be implemented using Memory Management Unit MMU read write protection mechanism .
After initialization the Hypervisor begins to handle Primary OS interrupts. First the Hypervisor detects the exception type and performs useful actions for some of them. After that the Hypervisor makes a decision to ignore the event or forward to Primary OS by using previous Primary OS IDT table content pointed to by a saved pointer or to active VMM.
The Hypervisor can be implemented as a driver for the Primary OS. It activates after the first VM starts and deactivates after the last VM stops alternatively it might not be deactivated and will stay active until POS reboot . Alternatively the Hypervisor can be a separate independently loaded binary file.
After activation the Hypervisor loads its own IDT instead of the Primary OS IDT and takes control over all interrupts and exceptions. Hypervisor performs IDT virtualization for POS and for all VMMs. In one of embodiments it could be done following way. The Hypervisor protects its IDT against writes and emulate all attempts of the primary OS and of its subsystems to write to the IDT. When writing to the IDT takes place the Hypervisor receives a page fault PF . It decodes the POS instruction that caused the PF and gets a new value that the POS tried to write into IDT. After that the IP instruction pointer is corrected to point to the next POS instruction and POS execution is continues as nothing was happened. The Hypervisor traces all writes to the IDT by HOS POS and stores all values for each IDT interrupt vector in special lists. Thus even though an actual modification of IDT is prohibited the Hypervisor has all the up to date information about current IDT vectors handlers. In some embodiments these lists can be used for correct interrupt forwarding to newest POS handlers. In other embodiments the interrupts will be delivered only to the original IDT handlers which were valid before Hypervisor activation .
The Hypervisor is co resident in the Primary OS and all VMM address spaces and handles all interrupts in all contexts. The Hypervisor is responsible for forwarding interrupts to the Primary OS and VMMs. The Hypervisor detects primary OS and its subsystems write access to the IDT and emulates and maintains an interrupt subscription list for Primary OS components.
The Hypervisor is responsible for VMM and Primary OS context switching. The Hypervisor offers number of service hypercalls available both for VMM and the Primary OS such as
In one embodiment the Hypervisor itself need not have any drivers at all all the drivers can be placed within the Primary OS. This is shown in . Therefore whenever the Primary OS attempts to interact with the physical hardware such as the hard disk drive the network card etc. the Hypervisor permits it to do so. Placing all the drivers within the Primary OS means that the Hypervisor itself can have a small footprint for example on the order of 50 000 100 000 lines of code. This is relatively small compared to the amount of code required for most modern operating systems which often have on the order of a million lines of code or more. With a footprint this small the task of ensuring that the Hypervisor can be fully trusted and is bug free is much easier.
It should be noted that while one embodiment of the invention may be implemented as an essentially driverless Hypervisor where all the drivers are located in the Primary OS which is part of a VMM other alternatives are possible. For example some drivers are very well standardized and do not present appreciable security risks. And written by VMM developers itself to make maximum optimized for virtual machines. This is shown in . For instance the driver for the IDE controller for a hard disk drive is one such driver. Similarly SCSI controllers have standardized drivers which may be placed in the Hypervisor as an optimization. In other words a larger footprint of the Hypervisor can be traded off against efficiency since with the hard disk drive controller s driver in the Hypervisor there is less overhead when passing disk access requests between the Guest OS s and the Primary OS. illustrates it in additional detail how the POS handles all of the devices except for the IDE controller hard disk drive controller . The Hypervisor handles the IDE controller itself by means of a trusted driver that is specially optimized for work with VMs.
Another advantage of the approach described herein is in freeing the Virtual Machine developer from having to develop his own set of drivers. By allowing the Primary OS to use its drivers to interact with the hardware the developer of the Hypervisor does not face the task of either writing his own set of drivers for each device that might conceivably be connected to the computer a daunting task since such devices today number in the thousands or having to adapt someone else s driver model such as LINUX to working within the Hypervisor itself. This means that the development cost of such a Hypervisor based virtualization approach is dramatically less than it otherwise would be.
Again it is worth recalling that many of the complaints about bugs and crashes and general instability of the Windows operating system derives not from mistakes by Microsoft programmers but from mistakes of the third party vendors who supply the driver software. As a practical matter when the Hypervisor developers are confronted with the task of dealing with third party drivers they may be just as likely to write a product that is similarly buggy. Therefore by using as a Primary OS an already existing operating system such as Windows XP Windows NT LINUX etc. the development time for the overall virtualization system can be shortened considerably.
Furthermore it should be noted that new types of hardware appear all the time such as new video cards new storage devices new network cards new wireless devices etc. For most common operating systems the vendors of these devices write the drivers practically as soon as the devices themselves appear on the market and frequently are supplied with the device itself . Thus the Virtual Machine developer does not need to worry about supporting a never ending stream of new hardware from third party vendors since the vendors themselves will provide the driver support for standard operating systems.
Another advantage is that there is no need to write a separate Service OS whose primary task is device hardware interface and driver management. Writing even a limited purpose operating system is a complex task. In the approach described herein this task can be avoided since the Primary OS serves in place of any such driver dedicated Service OS. The approach described herein permits using any standard operating system as the primary operating system where the Primary OS also functions as a Service OS.
The Primary OS can be easily migrated to work under the control of the Hypervisor. This can be accomplished through relatively simple installation.
There are at least three ways how to migrate a running Primary OS into the VM. One of the major features of the migration is a difference between host PC hardware and Primary VM hardware. Some Primary VM hardware remains the same since Primary VM is tuned by Hypervisor to have direct access to it. But some of Primary VM hardware is emulated and could be different from host PC s hardware.
The question is how the particular Primary OS could handle changes of hardware. Most of the modern OS can handle some hardware changes on the fly using so called PnP technology .
1. If the Primary OS can handle particular hardware changes between host PC and Primary OS without rebooting then the Primary OS will be transferred on the fly as follows
2. If the Primary OS can handle particular hardware changes between host PC and Primary OS with rebooting and possibly some additional changes on Primary OS boot disk then Primary OS will be transferred as follows
3. If the Primary OS cannot handle particular hardware changes between host PC and Primary OS even with rebooting and needs a full reinstall
One of the disadvantages of some conventional virtualization technologies such as XEN are that installation is relatively complex normally requiring many hours of effort from IT personnel. As of early 2006 the XEN product has not caught on in the industry in large measure due to the complexity of the installation which for a lay user of a desktop is a virtually insurmountable challenge. In the approach described herein whether server based or desktop based installation is little different from installing another user application or a driver where the user is prompted through the usual and generally familiar installation sequence or from installation through the commonly used wizards.
It also worth noting that up till now Hypervisor based systems have generally been found primarily if not exclusively in server based environments primarily due to the fact that installation and maintenance requires relatively skilled IT personnel notwithstanding the fact that first Hypervisor based systems were described two decades ago. The present approach is equally applicable to both server based and desktop laptop based environments.
Thus the present approach makes use of several components. The first of these is the Hypervisor which has the highest privilege level of all the components and can control access to any physical resource of the system. The Hypervisor upon being launched relocates the operating system that was previously running the Primary OS into a Virtual Machine with a VMM and grant the VMM and the Primary OS certain privileges for example the privilege to directly access some hardware devices such as a disk drive. Other Guest OSs are launched in other Virtual Machines and are treated as any other Virtual Machine in other words they themselves think that they are the real operating system while any attempt by them to perform privileged operations or access hardware directly can be intercepted by either the Hypervisor or by the VMM. This is shown in as discussed earlier.
Another way to classify the physical resources of the system that the Hypervisor controls and that the Hypervisor grants or not grants access to as far as the various operating systems are concerned is sharable and non sharable resources. This is shown in . A sharable resource is a type of hardware that any realistic operating system needs to work with to be useful. For example it is impracticable to have an operating system that does not have access to the hard disk drive. Similarly very few modern operating systems can realistically function without access to the network card or the video card in the context of a desktop system . These are therefore examples of a sharable resources where most if not all the operating systems whether Primary OS or Guest OS needs to have access to.
Other resources may be non sharable or pass through in the sense that the Hypervisor grants to a particular operating system typically to one Guest OSs but not to any other Guest OS is a floppy drive. For example most laptops today do not have a floppy drive although an external floppy drive can be connected to a laptop. This can be one example of such a non sharable resource the Hypervisor grants to one Guest OS the privileges for accessing the floppy drive directly but the others are unaware of the existence of that floppy drive.
Other examples of non sharable resource include devices like the display monitor LPT port the mouse or trackball a Wi Fi card USB ports etc. Other examples of non sharable resources can be various devices that are infrequently connected to a computer. For example many mobile phones today have a USB interface through which they can be connected to a computer but a mobile phone is not a standard accessory supplied with a laptop or desktop. Other examples include removable devices not needed for day to day operation removable media floppy CD DVD ROM SCSI devices USB devices external drives specific devices card readers banking devices scientific devices LPT COM port and all devices connected to these ports.
The system s hardware can therefore be loosely divided into three groups as shown in 1 controlled exclusively by Guest OS 2 controlled by the Hypervisor shared between VMs 3 controlled by the Primary OS shared between VMs. Shareable devices could be controlled by Primary OS or by Hypervisor. Guest OS that wants to use that device should communicate Hypervisor or Primary OS via Hypervisor or directly . Non shareable devices are controlled by one Guest OS exclusively. An example of hardware controlled by the Hypervisor is the processor itself. Another optional example of such hardware is the IDE controller for the hard drive which requires a well standardized driver with a relatively small footprint. Another example is the video card.
Doing this avoids the chain of interrupts and exceptions that would begin when the Guest OS attempts to access the hard drive whereupon in one embodiment the Hypervisor intercepts such an attempt and redirects it to the Primary OS which has the driver for accessing the IDE controller which then accesses the hard drive and then passes the result back to the Hypervisor which in turn emulates the behavior of the system such that the Guest OS thinks that it accessed the hard drive itself. Much of this complexity can be avoided by placing the IDE controller s driver in the Hypervisor. In the preferred embodiment the VMM is responsible for virtualization emulation and the Hypervisor is responsible for granting access protecting access security and resource scheduling. In other words in one embodiment the Guest OS is unaware of the VM environment and tries to access IDE and being intercepted by VMM Hypervisor. However the VMM implementation not limited to this model and the invention is not limited to VMM types described above.
As used in this context the Hypervisor controls all the physical resources in the sense that it can permit any component to access that resource or not. The Primary OS and or the Guest OS can with the Hypervisor s permission and under the Hypervisor s control can manage the hardware including accessing it in the case of the hard disk drive and perform various other operations involved in the use of the particular hardware.
In other words the Hypervisor grants to the other components the right to do something useful with the hardware while the components Primary OS Guest OS actually do that something useful with the hardware devices.
In the case of failure of the Primary OS the Hypervisor has a number of options. One option is to shut down the Primary OS and restart it with some state registers memory GDT etc. that is known to be safe and functional. Another option is for the Hypervisor to handle the failures through some error handling routine for example giving the user the option to reload the registers to some specified values. Yet another option is for the Hypervisor to designate another of the Virtual Machines as the Primary OS with an appropriate upgrading of the privilege levels and of that Virtual Machine as well as various other administrative tasks needed for this purpose. Yet another option is for the Hypervisor to keep one or more Primary OSs in reserve where the reserve Primary OS and the Virtual Machines that correspond to them are essentially quiescent except when activated. This is shown in .
As yet a further option the Hypervisor upon detecting that the Primary OS is having problems with managing the hardware or is crashing or is about to crash can withdraw the privileges granted to the Primary OS that allow it to access the hardware and for example grant those privileges to another of the Virtual Machines running a Guest OS until the Hypervisor resolves the issues with the original Primary OS.
As an alternative the operating system itself can have provisions for switching the underlying hardware on which it runs on the fly. For example if the operating system itself is able to dynamically switch from one network card to another or from one type of disk drive to another or one partition of a disk drive to another etc. . Then the Hypervisor can upgrade the status of a Guest OS to the status of the Primary OS thereby taking advantage of that ability.
Once the need to treat the formerly Guest OS as the Primary OS no longer exists for example if the Hypervisor has resolved whatever problems caused the failure or crash of the Primary OS and is ready to restart it then the current Primary OS can be dynamically downgraded back to the status of a Guest OS and the crashed Primary OS can be reactivated.
It should also be noted that running the Primary OS with less than the full privileges permits avoiding at least some of the sources of failures and instability. For instance if the Primary OS itself decides to write something that it shouldn t to the hard disk drive for example the Primary OS itself replaces its own boot sector information with erroneous information there is little that the Hypervisor can do about that. On the other hand some of the bugs are due to developers mistakes for example where some instruction tries to access an area in memory that it shouldn t or it tries to transfer control to some page that isn t available triggering a page fault. With the Primary OS having less than full privileges mistakes of the second type can be more easily handled when the Hypervisor detects them. To deal with the first type of errors the Hypervisor needs an error recovery procedure or a set of error recovery procedures such that when such a failure due to working with the actual hardware occurs the Hypervisor can do any of the things described above for example restart the Primary OS upgrade a Guest OS to the status of a Primary OS activate a reserve Primary OS etc. The most frequent situation then Primary OS became unstable and crashes. The Hypervisor could detect such situation and reboot the Primary OS since the crash of the Primary OS inside VM cannot damage the Hypervisor.
It should be understood that although the Guest OS can work with virtualized devices for example virtual hard drives virtual network cards etc. at some point the attempt by the Guest OS to access a virtual device needs to be translated into some operation on the real hardware. For example if the Guest OS were working with a virtual hard drive and try to write a file to that virtual hard drive the Hypervisor would intercept that attempt and can give the Primary OS the responsibility for writing an actual file to an actual real hard drive.
The Hypervisor can take advantage of hardware support for virtualization if available on the processor. For example current Intel processors have VT technology that provides hardware based support for virtualization. Similarly AMD Pacifica has new guest mode and other processors have similar schemes. Where appropriate the Hypervisor will reserve these highest privileged modes for itself and give lesser privileges for accessing devices to the Primary OS and possibly even lesser privileges than that to the Guest OSs.
As yet another option the Hypervisor can perform a complete reinstallation of the Primary OS into the Primary VM although this approach can be time consuming and is generally viewed as less desirable. Optionally the Hypervisor can periodically checkpoint the state of the Primary OS and revert to appropriate checkpoint in case the Primary OS crashes thereby resuming from the checkpoint or backup.
As yet a further alternative the Hypervisor can launch several Primary operating systems such that each of the Primary operating systems is only allowed direct access to one particular hardware device but no others the others are virtualized . For example one Primary OS can manage the disk drive another Primary OS can manage the network card a third Primary OS can manage the Wi Fi card etc. This is shown in . This results in a more stable configuration since a failure of the Primary OS that manages the network interface card NIC only means that the computer is no longer talking to the network but the remainder of the functions are still operational. This means that the task of the Hypervisor when recovering from a failure of some hardware device is much easier it only needs to recover or restart operation of one device such as the hard disk drive or the network card etc. rather than having to fully recover and restart operation of all the devices.
As a further extension of the idea of dedicating a particular Primary OS to managing a single resource or some subset of resources the concept can be applied to an environment with multiple computers for example a computer cluster a server farm etc. This is shown in . Such a cluster has a number of hardware nodes each having a Hypervisor In that context the resources at issue belong not to a single computer or server but to the entire entity that to the outside world act as a single server but is in fact made up of multiple computers. In this case one of the Primary OSs can be responsible for managing storage another of the Primary OSs can manage network interface etc. The Hypervisor as shown in and upon sensing that a particular Primary OS is being overloaded for example with disk access requests can address the situation by redirecting other functions of that Primary OS for example network interface functions to a different physical machine of the same cluster. This gives the Hypervisor a high level ability to manage load among the various elements of the cluster.
One of the advantages of the present architecture is that it does not require a specially developed or otherwise modified service operating system. As noted above as the primary operating system any standard operating system can be used such as Windows LINUX etc. The VM is installed for each particular Primary OS as an ordinary application installation.
The Primary OS is launched within the primary VM and does not need a special interface to the Hypervisor. The Hypervisor interacts with the Primary OS with the help of a user application and or a user driver which are installed in the Primary OS. The Primary OSs access to resources for which it does not have a sufficient privilege level is blocked and is instead virtualized by the VMM which services the primary VM. As noted above there are a number of mechanisms for translating the Primary OS to within the Primary VM and back.
If real hardware cannot be replaced with emulated hardware without an OS restart in step then the Hypervisor checks whether the real hardware can be replaced with emulated hardware without an OS reinstall step . If yes then in step the Primary OS can be started in a VM and then proceed to step . If not then in step the Primary OS is reinstalled inside the VM and the process proceeds to step .
The Primary OS can be specially adapted for more effective work with the Hypervisor but this is not necessary. The Primary OS can also work on its own without the Hypervisor. Note also that the Hypervisor can itself be activated or deactivated at any time therefore the supervision by the Hypervisor of the Primary OS can be turned off and on dynamically. Here activation of the Hypervisor means transfer of the Primary OS from the host PC into the VM. Deactivation of Hypervisor means transferring the Primary OS back from inside the VM to the host PC and resuming its execution with full privileges.
The overall architecture thus can have a number of components VMs running Guest OS s VMM or several VMMs Primary VM running a Primary OS and the Hypervisor. The Hypervisor is therefore a layer between the physical resources of the host PC and the various Virtual Machine compOnents. The Hypervisor s primary tasks are as follows
The Hypervisor controls all host PC resources in the sense of scheduling and granting other components access to these resources. No other component of the system can establish access to a device without Hypervisor. At the same time Hypervisor can restrict access to some resources for all other components and itself manage some resource via its own drivers. The Hypervisor provides APIs to shareable resources managed by itself for other components VMMs and Guest Primary OSs . Some resources can be managed by Primary OS via its drivers. Special application and or driver installed into Primary OS and provide API to resources for other components directly to VMMs Guest OSs or indirectly via Hypervisor API.
The VMM represents a virtualized environment for execution of the Primary OS and the Guest OSs. The VMM uses a high level interface API provided by the Hypervisor for interacting with physical resources of the host PC and the Hypervisor allocates these resources between the various VMMs.
Thus while the Hypervisor is responsible for control over the physical resources and control of access to them the VMM is responsible for virtualization and or emulation of these resources for the Guest OS and optionally for the Primary OS. It is also possible to combine the Hypervisor and the VMM into a single module. Although it is believed that the separation into different components as described above is preferred at least from a development perspective and a security perspective. The Hypervisor therefore controls three types of resources non sharable resources which are given for exclusive use to one or more Guest operating systems sharable resources managed by the Primary OS via its drivers and sharable resources managed by Hypervisor via Hypervisor drivers . The Hypervisor can grant direct access to these resources for the corresponding VMMs.
Sharable resources which are normally managed by the Hypervisor itself. The Hypervisor provides a high level interface to the Guest OSs VMMs and Primary OS VMM for accessing these resources.
Shamble resources are typically managed by the Primary OS. The Hypervisor sets up direct access to these resources for the Primary OS s VMM. The Primary OS s via installed applications and or drivers provides a high level interface for the Hypervisor or directly to Guest OSs VMMs to access these resources. In another embodiment the Hypervisor retranslates the interface for Guest OSs VMMs that do not have direct API to Primary OS. The third type of resources is non sharable resources exclusively given to particular Guest OS.
Depending on the implementation the physical resources of the host PC can be split up in various ways between these three types of resources. Also some of these types may not be present in some systems depending on how the Hypervisor configures the system. Preferably the Hypervisor should directly control the devices that are the fastest better standardized and the simplest to manage such as IDE SCSI controllers network cards video cards etc. and delegate to the Primary OS management of devices that are slower and require relatively complex drivers.
The Hypervisor therefore provides a common interface for accessing all shared resources the particular component that uses that interface to access the resources is normally not aware of who in reality manages these resources the Hypervisor or the Primary OS. In alternative embodiments the Primary OS can provide the APIs directly to Guest OSs VMMs without retranslation through Hypervisor. This could offer better performance in a trade off of isolation vs. security.
To manage access of other components to the physical resources of the host PC the Hypervisor can use the various resources provided by the specific processors hardware architecture. For example for the Intel VT technology the VMCS setting can be used. For AMD Pacifica VMCB Virtual Machine control block can be used. For IA 32 32e processors the Hypervisor can use protection rings 0 1 2 3 for code and data segments paging protection mechanism bits US RW NX various settings of the IOPL IDT GDT LDT PDE PTE CRXX etc.
Thus there are at least three different ways to recover from a Primary OS crash activating an inactive reserved but running Primary OS launching new instance of Primary OS and upgrading running Guest OS to Primary OS.
If the OS at issue is a Primary OS then the Primary VM container can be different on the source host PC and on the destination host PC. For example can be different in set of virtualized vs. non virtualized hardware for example the source Primary VM could manage the real IDE and the destination Primary VM can be managing emulated IDE while the real IDE is managed by the Hypervisor . The real hardware on the source node can be different from real hardware on the destination node e.g. different network card vendors different network card models etc. for example . During this migration the Primary OS could face changes in hardware and can experience the same problem as during initial transfer from the host PC into the Primary VM step .
Released hardware resources are then redistributed step and the state of the transferred VM is saved and transferred to the new hardware node step . Now that the state of the OS is fully virtualized it could be migrated to the new hardware node.
One application of the approach described above is in programming the CPU s timer for example based on
Other more complex formulas can also be used. Thus each Guest OS can directly use the timer interrupts.
One of the advantages of the proposed architecture is a partial isolation of the Primary OS from other components of the system and from some of the physical resources of the system. Therefore any problems encountered by the Primary OS and even its complete failure will not result in a total failure of the entire host PC. The most serious consequence of a crash of the Primary OS can be only temporary an inability to access those physical hardware components that the Primary OS at the time of the crash had a sufficient privilege level to manage.
To optimize the speed of access by the Guest OS s to the physical resources of the computer including those that are managed by the Primary OS it is also possible to provide for direct access to these resources bypassing the Hypervisor. In this case the Hypervisor provides not the I O interface itself but an interface for establishing the direct access channel between the Guest OS and the Primary OS.
While various embodiments of the present invention have been described above it should be understood that they have been presented by way of example and not limitation. It will be apparent to persons skilled in the relevant art that various changes in form and detail can be made therein without departing from the spirit and scope of the invention. Thus the breadth and scope of the present invention should not be limited by any of the above described exemplary embodiments but should be defined only in accordance with the following claims and their equivalents.
| 240.272727 | 1,811 | 0.818523 | eng_Latn | 0.999876 |
980fc71eac3858fa8006cdac79bcf962b2e6e026 | 298 | md | Markdown | docs/metasploit-framework.wiki/Powershell-Extension.md | heyder/metasploit-framework | 1bb93ddfd27c06d3e80127f7b6a71c47964f1896 | [
"BSD-2-Clause",
"BSD-3-Clause"
] | null | null | null | docs/metasploit-framework.wiki/Powershell-Extension.md | heyder/metasploit-framework | 1bb93ddfd27c06d3e80127f7b6a71c47964f1896 | [
"BSD-2-Clause",
"BSD-3-Clause"
] | null | null | null | docs/metasploit-framework.wiki/Powershell-Extension.md | heyder/metasploit-framework | 1bb93ddfd27c06d3e80127f7b6a71c47964f1896 | [
"BSD-2-Clause",
"BSD-3-Clause"
] | null | null | null | I'm yet to get the documentation done for this extension, but in the mean time there's some useful information in the [original payloads pull request](https://github.com/rapid7/metasploit-payloads/pull/89) that shows how it can be used (including bindings).
I promise to get more detail here soon! | 99.333333 | 257 | 0.791946 | eng_Latn | 0.998049 |
980fc809cc53ce638b8f860e1ef1afb47cb22974 | 1,479 | md | Markdown | container-images/apache-git-http-backend/README.md | shreelola/k8s-gerrit | e47c294a8e15d0947593a64da8e21876b2ad73f3 | [
"Apache-2.0"
] | 1 | 2019-01-15T18:17:00.000Z | 2019-01-15T18:17:00.000Z | container-images/apache-git-http-backend/README.md | shreelola/k8s-gerrit | e47c294a8e15d0947593a64da8e21876b2ad73f3 | [
"Apache-2.0"
] | null | null | null | container-images/apache-git-http-backend/README.md | shreelola/k8s-gerrit | e47c294a8e15d0947593a64da8e21876b2ad73f3 | [
"Apache-2.0"
] | null | null | null | # apache-git-http-backend
The apache-git-http-backend docker image serves as receiver in git replication
from a Gerrit master to a Gerrit slave.
## Content
* base image
* Apache webserver
* Apache configurations for http and https
* git (via base image)
* `tools/create_repo.sh`: cgi script to enable remote creation of new git
repository over http. This is triggered by the Gerrit replication plugin
if a new repository on the Gerrit master does not yet exist in a Gerrit slave,
a corresponding
[change for the replication plugin](https://gerrit-review.googlesource.com/c/plugins/replication/+/199900)
enabling repository creation via http is still in review for master and will be
downported to 2.16
* `tools/start`: start script, configures and starts Apache
webserver
* `start`: start script for testing image using Docker
## Setup and Configuration
* install Apache webserver
* configure Apache for http and/or https
* install cgi script
* open ports for incoming traffic
* create gerrit OS user
* map volumes
## Start
* verify filesystem permissions. In Kubernetes this is done using a
[SecurityContext](https://kubernetes.io/docs/tasks/configure-pod-container/security-context/).
It is used to set the filesystem group of mounted volumes to 100 (users),
which is used by the gerrit-user in the containers. Thereby it is ensured
that the volumes have rw-permissions for the gerrit-user.
* start Apache git-http backend via start script `/var/tools/start` | 37.923077 | 107 | 0.780257 | eng_Latn | 0.952447 |
981050ad1cbee3b4cccd38215370cf683ce58e12 | 820 | md | Markdown | Readme.md | consento-org/bigint-time | 6569ea7db5e4ef6b9eb92b92800ea0a9dfa79202 | [
"MIT"
] | null | null | null | Readme.md | consento-org/bigint-time | 6569ea7db5e4ef6b9eb92b92800ea0a9dfa79202 | [
"MIT"
] | 1 | 2021-01-13T20:31:52.000Z | 2021-01-13T20:31:52.000Z | Readme.md | consento-org/bigint-time | 6569ea7db5e4ef6b9eb92b92800ea0a9dfa79202 | [
"MIT"
] | null | null | null | # bigint-time
`bigint-time` uses [`process.hrtime.bigint`][hrtime] and
[`performance.now()`][now] to return the time in nanoseconds since epoch.
- Node.js & Browser compatible.
- TypeScript types available.
- No dependencies.
[hrtime]: https://nodejs.org/api/process.html#process_process_hrtime_bigint
[now]: https://developer.mozilla.org/en-US/docs/Web/API/Performance/now
## Usage
```javascript
const bigtime = require('bigint-time')
const time = bigtime() // BigInt number returned of the time.
```
## Compatibility
This library assumes Node > 10.4 and that the Browsers support [BigInt][bigint]
and [performance.now][perfnow].
The resolution and accuracy may vary depending on
platform.
[bigint]: https://caniuse.com/bigint
[perfnow]: https://caniuse.com/high-resolution-time
## License
[MIT](./LICENSE)
| 23.428571 | 79 | 0.741463 | eng_Latn | 0.666143 |
98106d2570ef825eac2d2d774ac4e57d26a682ea | 2,071 | md | Markdown | content/post/roulette/index.md | violetguos/academic-kickstart | aed2ba1e02cc518c5b60bd98cb111b076f003e62 | [
"MIT"
] | null | null | null | content/post/roulette/index.md | violetguos/academic-kickstart | aed2ba1e02cc518c5b60bd98cb111b076f003e62 | [
"MIT"
] | null | null | null | content/post/roulette/index.md | violetguos/academic-kickstart | aed2ba1e02cc518c5b60bd98cb111b076f003e62 | [
"MIT"
] | null | null | null | +++
title = "Roulette on FPGA"
date = 2016-04-02T01:29:17-05:00
draft = false
# Authors. Comma separated list, e.g. `["Bob Smith", "David Jones"]`.
authors = []
# Tags and categories
# For example, use `tags = []` for no tags, or the form `tags = ["A Tag", "Another Tag"]` for one or more tags.
tags = []
categories = ["hardware", "systems", "assembly"]
# optional
url_code = "https://github.com/violetguos/rouletteProject"
# Projects (optional).
# Associate this post with one or more of your projects.
# Simply enter your project's folder or file name without extension.
# E.g. `projects = ["deep-learning"]` references
# `content/project/deep-learning/index.md`.
# Otherwise, set `projects = []`.
# projects = ["internal-project"]
# Featured image
# To use, add an image named `featured.jpg/png` to your page's folder.
[image]
# Caption (optional)
caption = ""
# Focal point (optional)
# Options: Smart, Center, TopLeft, Top, TopRight, Left, Right, BottomLeft, Bottom, BottomRight
focal_point = ""
+++
## Introduction
This project was built in the same course as the multi-cycle CPU! As the reader can see, low level hardware can be fun. The two projects share similar principles, but this project has additional displays, such as a computer screen, a speaker for audio output, and we made the roulette as pretty as we could. They all run on the same hardware chip(field programmable gate array, FPGA).
## Technical Details
- Built a roulette game with PS/2 keyboard, audio output, motor, lego controller, and Altera FPGA
- Implemented linear feedback shift register in Assembly and C to randomize motor speed and spin time
- Interfaced keyboard input to prompt user’s bet and display on VGA output with JTAG UART, JPIO ports
## Lessons Learned
User interface (the screen display, music, and the roulette) makes a difference
Creativity matters: engineers should not only focus on the technical details

Note: this is not my final version. Unfortunately the finished product and a recorded video demo were lost.
| 39.826923 | 384 | 0.733945 | eng_Latn | 0.992719 |
98107c4806080d9e49bfc33db9046b12e0ccd0d0 | 80 | md | Markdown | kafkaq-monitor/README.md | kaiweih/kafkaQ | 1c42c3c87c574b55a6b6d1a0187de382dc46cddd | [
"MIT"
] | null | null | null | kafkaq-monitor/README.md | kaiweih/kafkaQ | 1c42c3c87c574b55a6b6d1a0187de382dc46cddd | [
"MIT"
] | null | null | null | kafkaq-monitor/README.md | kaiweih/kafkaQ | 1c42c3c87c574b55a6b6d1a0187de382dc46cddd | [
"MIT"
] | null | null | null | ## kafkaQ
This is an application that allows you to monitor your Kafka system!
| 20 | 68 | 0.775 | eng_Latn | 0.999857 |
98108ec44d9fd87c13f1962e99259b109dca2d57 | 916 | md | Markdown | README.md | elisa-c/Favorites | eaf5600e0bf91dab4a275689b30bfaa0ab9b0987 | [
"MIT"
] | null | null | null | README.md | elisa-c/Favorites | eaf5600e0bf91dab4a275689b30bfaa0ab9b0987 | [
"MIT"
] | null | null | null | README.md | elisa-c/Favorites | eaf5600e0bf91dab4a275689b30bfaa0ab9b0987 | [
"MIT"
] | null | null | null | # Favorites
[](https://travis-ci.org/elisa-c/Favorites)
[](https://cocoapods.org/pods/Favorites)
[](https://cocoapods.org/pods/Favorites)
[](https://cocoapods.org/pods/Favorites)
## Example
To run the example project, clone the repo, and run `pod install` from the Example directory first.
## Requirements
## Installation
Favorites is available through [CocoaPods](https://cocoapods.org). To install
it, simply add the following line to your Podfile:
```ruby
pod 'Favorites'
```
## Author
elisa-c, elisatcamillo@gmail.com
## License
Favorites is available under the MIT license. See the LICENSE file for more info.
| 30.533333 | 119 | 0.75 | eng_Latn | 0.318039 |
9811373a96c35332b00c492c8c50cbd08557ee38 | 45 | md | Markdown | README.md | Felipemfaria/controle-estoque | bf842be62a3c558d01955cf23ec0468fe57d8209 | [
"MIT"
] | null | null | null | README.md | Felipemfaria/controle-estoque | bf842be62a3c558d01955cf23ec0468fe57d8209 | [
"MIT"
] | null | null | null | README.md | Felipemfaria/controle-estoque | bf842be62a3c558d01955cf23ec0468fe57d8209 | [
"MIT"
] | null | null | null | # controle-estoque
Controle de estoque em C#
| 15 | 25 | 0.777778 | por_Latn | 0.999374 |
981277d914e1ab934894b6bbb34e6dd5c4fd1518 | 3,900 | md | Markdown | docs/en/docs/intro/index.md | seho-code-life/kurimudb | e0f3b32bdbae1089e65b9cb9cd72590584452db1 | [
"MIT"
] | 12 | 2020-06-25T00:49:01.000Z | 2020-11-03T11:54:04.000Z | docs/en/docs/intro/index.md | seho-code-life/kurimudb | e0f3b32bdbae1089e65b9cb9cd72590584452db1 | [
"MIT"
] | 1 | 2021-09-06T01:49:04.000Z | 2021-09-06T15:58:16.000Z | docs/en/docs/intro/index.md | seho-code-life/kurimudb | e0f3b32bdbae1089e65b9cb9cd72590584452db1 | [
"MIT"
] | 2 | 2020-10-30T09:31:47.000Z | 2020-11-03T11:54:09.000Z | # Getting Started
## Introduction to Kurimudb
Kurimudb is a progressive **Web front-end local persistence library**. It can save your data to LocalStorage, IndexedDB, Cookie, and elsewhere. Also, support subscribing to the mutating of data.
In addition to persistent data, Kurimudb can be [Model layer](https://en.wikipedia.org/wiki/Model%E2%80%93view%E2%80%93viewmodel#Components_of_MVVM_pattern) of your application if your want, then take the responsibility of state management in your application (i.e., Vuex, Redux and Mobx) to make your app “single source of truth” really.
Kurimudb's persistence feature is driver-oriented. It means you can replace the implementation without changing the code. We build several common drivers. If these are not for you, you can build your own driver.
## Getting Started
`kurimudb-zero-config` is Kurimudb's zero configuration package, execute the following command to install it:
```bash
npm i kurimudb-zero-config@5
```
### Local
By operating the `local` object, the data can be stored in LocalStorage. Even if the page is refreshed, the data will still be there! It can store about 5M data in LocalStorage.
```js
import { local } from "kurimudb-zero-config";
local.data.say = "hello world"; // writing..
let say = local.data.say; // reading..
delete local.data.say; // deleting..
if ("say" in local.data) { ... } // checking existence..
```
### Cookie
By operating the `cookie` object, the data can be stored in Cookie. The data stored in Cookie should be less as possible because all data in Cookie will send to the server-side automatically by the browser when making the request.
```js
import { cookie } from "kurimudb-zero-config";
cookie.data.say = "hello world"; // writing..
let say = cookie.data.say; // reading..
delete cookie.data.say; // deleting..
if ("say" in cookie.data) { ... } // checking existence..
```
### Memory
By operating the `memory` object, data can be stored in Memory. When the page is refreshed, the data will be cleared.
```js
import { memory } from "kurimudb-zero-config";
memory.data.say = "hello world"; // writing..
let say = memory.data.say; // reading..
delete memory.data.say; // deleting..
if ("say" in memory.data) { ... } // checking existence..
```
### Db
By operating the `db` object, the data can be stored in IndexedDB. IndexedDB can store JavaScript Objects such as File and Blob. Its maximum data capacity depends on the available hard disk size of the user's disk.
::: Warning Tips:
It is worth noting that IndexedDB's API is asynchronous so that the return values of APIs related to `db` and reading are all [Promise Object](https://developer.mozilla.org/docs/Web/JavaScript/Reference/Global_Objects/Promise).
:::
```js
import { db } from "kurimudb-zero-config";
db.setItem("say", "hello world"); // writing..
let say = await db.getItem("say"); // reading, return value will be a Promise Object..
await db.removeItem("say"); // deleting..
if (await db.hasItem("say")) { ... } // checking existence..
```
### Subscribing Data Mutation
Kurimudb also provides the feature of Subscribing Data Mutation. All things you need to do is adding `$` to the end of the value, then you can make something after it mutates.
```js
local.data.say$((val) => {
console.log('what you want to say: ' + val);
});
```
Or use the **automatic subscription function**, when any of the values used in the closure is changed, the subscription will be triggered, and the closure will be executed again:
```js
import { auto$ } from 'kurimudb-zero-config';
auto$(() => {
console.log(configState.data.foo);
console.log(configState.data.bar);
});
```
Regarding subscriptions, there are more advanced usages! Please read the [Subscription Changes](/en/docs/subscribe/) chapter.
## Are You Ready?
We just get to the start point of using Kurimudb. Let's carry on to get know it better in next chapters!
| 37.864078 | 338 | 0.728462 | eng_Latn | 0.984621 |
9814c11eb7c8cb482c55cc8bfc6d14f38a9fa14b | 2,966 | md | Markdown | README.md | Laronk/graphs_project | 0a3b02f9f0e9f6f5f455b012365eb819c5cc7bca | [
"MIT"
] | null | null | null | README.md | Laronk/graphs_project | 0a3b02f9f0e9f6f5f455b012365eb819c5cc7bca | [
"MIT"
] | null | null | null | README.md | Laronk/graphs_project | 0a3b02f9f0e9f6f5f455b012365eb819c5cc7bca | [
"MIT"
] | null | null | null | # Graphs project
College assignment for graph theory class
## Setup
### 1. Install Python version 3.8.5:
```sh
# for debian based linux system
$ sudo add-apt-repository ppa:deadsnakes/ppa
$ sudo apt-get update
$ sudo apt install python3.8
$ python3.8 -V
# last command should yield "Python 3.8.5"
```
### 2. Install pip - a package manager for Python
```sh
# for Debian based Linux system
$ apt install python3-pip
```
### 3. Install necessary python packages using pip
### There are two ways to go about this.
The first is to install the required packages from the `requirements.txt` file. This is the faster option, but due to system differences, some problems might arise. They shouldn't, but they might.
### 3.a Install necessary python packages using pip
```sh
# in repository root
$ pip3 install -r requirements.txt
```
The second option is to install all the required packages manually. I list all the packages in this single command.
### 3.b Install necessary python packages using pip
```sh
# in the repository root
$ pip3 install networkx matplotlib numpy
```
## Project structure
```sh
.
├── Dijkstra’s algorithm
│ ├── algorithm
│ │ ├── dijkstra.py # my algorithm implementation
│ │ └── __init__.py
│ ├── algorithm analysis.md # analitical part of the practical aspect of the assignment
│ ├── test_dataset.json # test graphs in incidence matrix form
│ ├── test_images
│ │ └── # tests output folder - graph drawings
│ └── test.py # main file - tests file
├── Jan_Karpiuk.json # assignment original file
├── Jan_Karpiuk_proj.docx # assignment instructions
├── LICENSE # license file
├── README.md # setup instructions,
└── requirements.txt # required python packages
```
## Run tests
### In order to check the validity of my Dijkstra's algorithm implementation:
### 1. Run all tests, use the command:
```sh
$ python Dijkstra’s\ algorithm/test.py
```
> Successful tests should yield:
```sh
..
------------------------------------------------------------
Ran 2 tests in 2.576s
OK
```
### 2. Add graphs to be tested
Tests take the `test_dataset.json` file as a testing dataset.
In order to test more graphs, update the `test_dataset.json` file with new graph data in form of an incidence matrix
### 3. Lastly, you can go to `test_images` folder and view the test results
Each file is named according to the test in with it was created with the test number added at the end.
* `test_dijkstra_path_0.png` - __first__ graph image for test validating algorithm's dijkstra path calculation
* `test_dijkstra_path_length_5.png` - __sixth__ graph image for test validating algorithm's dijkstra path length calculation
Each file contains the image of a tested graph with Dijkstra's path marked in red for a particular test case.
## Read my analysis on Dijkstra's algorithm real-world applications - file `algorithm analysis.md`
## Answers to theoretical assignment part are in the file `Jan_Karpiuk_406238.pdf` | 27.981132 | 196 | 0.71679 | eng_Latn | 0.977562 |
9814d32da115e29ddf60c243e0c31b7e622aec86 | 15,670 | md | Markdown | til/Rails/eng-rails-guide-3.md | euisblue/vue-blog | 6ab84fa4d1c52a3ab036e48859d4d641a4aafd2a | [
"MIT"
] | null | null | null | til/Rails/eng-rails-guide-3.md | euisblue/vue-blog | 6ab84fa4d1c52a3ab036e48859d4d641a4aafd2a | [
"MIT"
] | null | null | null | til/Rails/eng-rails-guide-3.md | euisblue/vue-blog | 6ab84fa4d1c52a3ab036e48859d4d641a4aafd2a | [
"MIT"
] | null | null | null |
## Strong Parameters
### Permitted Scalar Values
Given
```rb
params.permit(:id)
```
the key `:id` will be permitted to use if it appears in `params` and has a permitted scalar value associated.
Otherwise, the key will be filtered out and cannot be used (accessed).
The permitted scalary types are
- String
- Symbol
- NilClass
- Numeric
- TrueClass
- FalseClass
- Date
- Time
- DateTime
- StringIO
- IO
- ActionDispatch::Http::UploadFile
- Rack::Test::UploadedFile
If the permitted scalar values must be in forms of array, map the key to an empty array
```rb
params.permit(id: [])
```
Sometime it's not possible to declare arrays of scalar values or conveinent to use hash.
```rb
params.permit(preferences: {})
```
But this opens the door to arbitrary inputs. To permit an entire hash of paramteres, the `permit!` method
can be used:
```rb
params.require(:log_entry).permit!
```
This marks the `:log_entry` parameters hash and any sub-hash of it as permitted and does not check for permitted scalars, anything is accepted. Be careful with using `permit!` because it allows all current and future model attributes to be mass-assigned.
### Nested Parameters
`permit` can be nested:
```rb
params.permit(:name, { emails: [] },
friends: [ :name,
{ family: [ :name ], hobbies: []
}])
```
This permits the `name`, `emails`, and `friends` attributes.
- `emails` : an array of permitted scalar values.
- `friends` : array of resources with specific attributes.
### More Examples
Using permitted attributes in `new` action. There's a problem here because we can't use `require` on the root key just because it doesn't exist when calling `new`.
We can use `fetch` to supply the default and use the strong parameters API.
```rb
params.fetch(:blog, {}).permit(:title, :author)
```
The model class method `accepts_nested_attributes_for` allows you to update and destroy associated records. This is based on the `id` and `_destry` parameters:
```rb
params.require(:author).permit(:name, books_attributes: [:title, :id, :_destroy])
```
Imagine you want to permit a product name attribute and also the whole data hash:
```rb
def product_params
params.require(:product).permit(:name, data: {})
end
```
## The Flash
`flash`: a special part of the session which is cleared with each request. This is useful for passing error messages, etc.
Lets say a user is logging out. We can use `flash` to display a logout message:
```rb
class LoginsController < ApplicationController
def destroy
session.delete(:current_user_id)
flash[:notice] = "You have successfully logged out."
redirect_to root_url
end
end
```
It is also possible to assign a flash message as part of the redirection.
```rb
redirect_to root_url, notice: "You have sucessfully logged out."
redirect_to root_url, alert: "You're stuck here!"
redirect_to root_url, flash: { referral_code: 1234 }
```
It's conventional to display any error alerts or notices from the flash in the application's layout:
```erb
<html>
<body>
<% flash.each do |name, msg| -%>
<%= content_tag :div, msg, class: name %>
<% end -%>
</body>
</html>
```
This way, if an action sets a notice or an alert message, the layout will display it automatically.
If you want to carry over the `flash` value to another request, use the `keep` method:
```rb
class MainController < ApplicationController
def index
# will persist all flash values
flash.keep
# you can also keep only certain value
# flash.keep(:notice)
redirect_to users_urll
end
end
```
### flash.now
By default, adding values to the flash will make them available to the **next request**, but sometimes
you may want to access those values in the **same request**.
For example, if the `create` action fails to save a resource and you render the `new` template directly, that's not going to resut in a new request, but you may still want to display an error message using the flash. To do this on the **same request**, you can use `flash.now`.
```rb
class ClientsController < ApplicationController
def create
@client = Client.new(params[:client])
if @client.save
# ...
else
flash.now[:error] = "Could not save client"
render action: "new"
end
end
end
```
<div class="divider"></div>
## Views
- simplest part of the MVC structure (at the basic level).
- insert the variables (data) you received from the controller.
- it is the actualy webpage.
- often called **view templates**.
### Where are view files?
Views are located in
```
app/views/controller_name/action_name.html.erb
```
`controller_name` is the name of the controller the view is linked to and `action_name.html.erb` is the
corresponding method inside the controller that was run immediately prior to rendering the view.
Example,
```rb
# 'Posts' controller running the 'post#index'
app/views/posts/index.html.erb
```
To use an instance variable from the controller, just call it the same way you wolud in the controller:
`@user.first_name` or `@posts` or `@some_other_variable`.
## Layouts
Named view template that we render is actually not the full webpage.
You wont find `<head>` tags or the `DOCTYPE` declaration or some other basic structures. This is because
it's redundant. These basic structures are present in all pages so Rails creators made these into its own ile called _layout_, which can be viewd at `app/views/layouts`.
Your new Rails application will have `application.html.erb` layout which compose of tags that forms a basic structure of a page like `<html>` and `<body>`, and a couple snippets of code thta load up the js and css files that your webpages will need. If you have something that is needed across all your pages, you need to put it in the layoutlike navbars and footers and flash messages.
Here's a sample of `application.html.erb` of a brand new Rails application.
```erb
<!DOCTYPE html>
<html>
<head>
<title>Practice</title>
<%= csrf_meta_tags %>
<%= csp_meta_tag %>
<%= stylesheet_link_tag 'application', media: 'all', 'data-turbolinks-track': 'reload' %>
<%= javascript_pack_tag 'application', 'data-turbolinks-track': 'reload' %>
</head>
<body>
<%= yield %>
</body>
</html>
```
The view template gets inserted where the `<%= yield %>` statement is.
## Preprocessors
You might have noticed `<%= ... %>` tags from the above code. This is Embeded Ruby (ERB). It's a special
way of executing ruby code inside your HTML.
The different between `<%=` and `<%` is that the first one actually **displays** the resulted value inside the ERB tags. The latter will evaluate the code but wont display it.
`<%#` is used to comment and wont execute.
## How do Preprocessors work?
The code executaion is all done on the server **BEFORE** the final HTML file is shipped over to the browser.
When we render the template in Rails, it first runs preprocessors like ERB.
Rails first processes the file using ERB, then treats it as regular HTML.
## View Partials
- Makes your code more concise and eaiser to read; also lets you reuse certain common patterns
One example is `#new` and `#edit` actions. These are almost exactly same that people turn this into form into a new file such as `_user_form.html.erb` and just call this in both `new.html.erb` and `edit.html.erb`.
Partials are just HTML files that aren't meant to be complete but can be shared by other files.
```erb
<!-- app/views/users/new.ehtml.erb -->
<div class="new-user-form">
<%= render "user_form" %>
</div>
```
Note that the view partial file is named with an underscore like `_user_form.html.erb` but is called without it `user_form`.
It is good practice to save partials into its own folwer `shared` and then render them using the code
`<%= render "shared/some_partial"%>`
## Passing Local Variables to Partials
A partial has access to all the variablest that the calling view template does, **but do NOT rely on them!**
Your partial maybe shared with different controller one variable like `@user` may be used differently in different controllers. So you've got to explicitly pass the partial whichever variables you want it to have access to.
`render` lets you pass it an options hash.
```rb
<%= render "shared/your_partial", :locals => { :user => user} %>
```
To use the variable in your partial file, you drop the `@` and call it like a normal variable.
## Implicit Partials
If you want a list of all your users, you colud write out the HTML and ERB code for displaying a single user's first name, last name, and etc many times in your `app/views/users/index.html.erb` file or use some sort of `each` loop.
But it's good to make the User into its own partial called `_user.html.erb`. The basic way of calling this might be something like:
```erb
<!-- app/views/index.html.erb -->
<h1>Users</h1>
<ul>
<% @users.each do |user %>
<%= render "user", :locals => {:user => user} %>
<% end %>
</ul>
<!-- Partial: app/views/_user.html.erb -->
<li><%= "#{user.first_name} #{user.last_name}, #{user.email}" %></li>
```
Now here's the magical Rails way:
```erb
<!-- app/views/index.html.erb -->
<h1>Users</h1>
<ul>
<% @users.each do |user| %>
<%= render user %>
<% end %>
</ul>
```
Rails then looks for the `_user.html.erb` file in the current directory and passes it the `user` variable automatically.
To render bunch of users:
```erb
<!-- app/views/index.html.erb -->
<h1>Users</h1>
<ul>
<%= render @users %>
</ul>
```
Rails not only finds the `_user.html.erb` and passes it the correct `user` to use, it also loops over all the users in the `@user` collection.
## Helper Methods
`render` is not the only method we can call from within a view. Rails provide bunch of handy helper methods.
### \#link\_to
`link_to` creates an anchor tag URL.
Instead of writing:
```html
<a href="<%= users_path %>">See All Users</a>
```
We can write:
```erb
<%= link_to "See All Users", users_path %>
```
- `users_path`
+ generates a relative URL like `/users`
- `users_url`
+ generates a full URL like `http://www.yourapp.com/users`
### Asset Tags
Rails gives you helper methods that output HTML tags to grab CSS or javascript files. You can grab images as well. These are called Asset Tags.
```erb
<%= stylesheet_link_tag "your_stylesheet" %>
<%= javascript_include_tag "your_js" %>
<%= image_tag "happy_cat.jpg" %>
```
## Learning Outcomes
- What is a layout?
- What’s the difference between a “view template” and a “layout”?
- What is a “Preprocessor”?
- Why are preprocessors useful?
- How do you make sure a preprocessor runs on your file?
- What’s the outputted filetype of a preprocessed \*.html.erb file? What about a \*.css.scss file?
- What is the difference between the <%=, <%, and <%# tags?
- What is a view partial?
- How do you insert a partial into your view?
- How can you tell that a view file is a partial?
- How do you pass a local variable to a partial?
- What’s the magical Rails shortcut for rendering a User? A bunch of Users?
- What are asset tags and why are they used?
<div class="divider"></div>
## The Asset Pipeline
Assets in your app are additional files that get called by the browser after your intial gob of HTML is received like CSS, js, images, videos, etc ...
Often these files are organized in many different files so its eaiser to keep track of. But if the browser has to grab a dozen different CSS files, each one of those requests is going to slow things down. Too many requests and you've harpooned your user's experience with your application.
So Rails' solution to this is to flatten everything out and mash all asset files together into one big one for each filetype (called "concatenation"). The process used to do this is the _Asset Pipeline_.
So Rails will take all CSS files and stack them on top of each other in one giant asset file. It will then run an _uglifier_ or _minifier_ program on the file to remove extraneous spaces and make everything nice and small for shipping to the browser.
Same with JS files. All of them are smooshed together and then uglified before sent to the browser as a one big chunk of a file. **It is better to have one slightly larger file than to make several full HTTP requests**.
### Manifest Files
Rails needs to know which files to include in that giant blob, so it uses _manifest_ files to determine it. Your JS manifest file will be `apps/assets/javascripts/applications.js`. It looks commented out, but the lines
starting with `//=` tell Rails which files to go find and include.
The stylesheet manifest file operates on the same principle; it's available at `app/assets/stylesheets/application.css.scss`:
```
/*
* This is a manifest file that'll be compiled into application.css, which will include all the files
* listed below.
*
* Any CSS and SCSS file within this directory, lib/assets/stylesheets, or any plugin's
* vendor/assets/stylesheets directory can be referenced here using a relative path.
*
* You're free to add application-wide styles to this file and they'll appear at the bottom of the
* compiled file so the styles you add here take precedence over styles defined in any other CSS/SCSS
* files in this directory. Styles in this file should be added after the last require_* statement.
* It is generally better to create a new file per style scope.
*
*= require_tree .
*= require_self
*/
```
The `require_tree` helper method just grabs everything in the current directory.
Sometimes, if you start using a new gem (like some of the Twitter-Bootstrap gems) you manually need to add the new bootstrap stylsheets and javascripts to the manifest files to make sure your app actually includes them in the final output.
### The Output
Rails mashes all the specified files together and creates a new one called something like `application-1fc71ddbb281c144b2ee4af31cf0e308.js`. These nonsensical string of characters are meant to differentiate between the original and this new file.
To get those nonsensical looking string of characters (to ask the browser to look for that specific one), we use asset tags:
```erb
<%= javascript_include_tag "applicationt" %>
```
Rails automatically knows which filename to request to get all js files imported properly.
### Namespacing
Remember that Ralis mashes everything into one file. What if you have a class `.container` that wants to style
differently in different pages? One will override the others and using inline style code just to avoid this defeats the purpose of using the external stylesheet, which is to make your code clean.
So we use _namespace_ so that certain codes are only affected under certain structure.
## Un-Escaping HTML
When you write something like `this is the <strong>BODY</strong> of my post` and then try to render it in a view later, the `<strong>` tags will just be regular text. This is called _escaping_ the chracters.
To get Rails to actually render HTML tags, you need to let Rails know that it is safe to run; otherwise, it's easy for attackers to inject malicious code like `<script>` tags.
To tell Rails a string is safe, we use `raw`:
```erb
<%= raw "<p>hello world!</p>" %>
If you don't want to rely on Rails' native behavior and would like to make absolutely sure the HTML does not get run, use `CGI` class's `escapeHTML` method:
```rb
CGI::escapeHTML('usage: foo "bar" <baz>')
# result: "Usage: foo "bar" <baz>"
```
## Learning Outcomes
- What is the "Asset Pipeline"?
- What are "Manifest Files"?
- Why would you namespace your stylesheets?
- What does it mean to "Escape" HTML?
## Reference
- [Rails Guide - Controller](https://guides.rubyonrails.org/action_controller_overview.html)
| 38.406863 | 386 | 0.730377 | eng_Latn | 0.997158 |
9814f0408d0474265c811c7bfbb2ff3e02deba58 | 601 | md | Markdown | docs/development/core/public/kibana-plugin-core-public.publicappsearchdeeplinkinfo.md | AlexanderWert/kibana | ae64fc259222f1147c1500104d7dcb4cfa263b63 | [
"Apache-2.0"
] | null | null | null | docs/development/core/public/kibana-plugin-core-public.publicappsearchdeeplinkinfo.md | AlexanderWert/kibana | ae64fc259222f1147c1500104d7dcb4cfa263b63 | [
"Apache-2.0"
] | null | null | null | docs/development/core/public/kibana-plugin-core-public.publicappsearchdeeplinkinfo.md | AlexanderWert/kibana | ae64fc259222f1147c1500104d7dcb4cfa263b63 | [
"Apache-2.0"
] | null | null | null | <!-- Do not edit this file. It is automatically generated by API Documenter. -->
[Home](./index.md) > [kibana-plugin-core-public](./kibana-plugin-core-public.md) > [PublicAppSearchDeepLinkInfo](./kibana-plugin-core-public.publicappsearchdeeplinkinfo.md)
## PublicAppSearchDeepLinkInfo type
Public information about a registered app's [searchDeepLinks](./kibana-plugin-core-public.appsearchdeeplink.md)
<b>Signature:</b>
```typescript
export declare type PublicAppSearchDeepLinkInfo = Omit<AppSearchDeepLink, 'searchDeepLinks'> & {
searchDeepLinks: PublicAppSearchDeepLinkInfo[];
};
```
| 37.5625 | 178 | 0.772047 | kor_Hang | 0.322729 |
9814f3cafcc08f792bb9cd793c5b52f0ac88116a | 250 | md | Markdown | _posts/2012-02-18-node-js-gist.md | jser/realtime.jser.info | 1c4e18b7ae7775838604ae7b7c666f1b28fb71d4 | [
"MIT"
] | 5 | 2016-01-25T08:51:46.000Z | 2022-02-16T05:51:08.000Z | _posts/2012-02-18-node-js-gist.md | jser/realtime.jser.info | 1c4e18b7ae7775838604ae7b7c666f1b28fb71d4 | [
"MIT"
] | 3 | 2015-08-22T08:39:36.000Z | 2021-07-25T15:24:10.000Z | _posts/2012-02-18-node-js-gist.md | jser/realtime.jser.info | 1c4e18b7ae7775838604ae7b7c666f1b28fb71d4 | [
"MIT"
] | 2 | 2016-01-18T03:56:54.000Z | 2021-07-25T14:27:30.000Z | ---
title: Node.js 開発環境 基礎 — Gist
author: azu
layout: post
itemUrl: 'https://gist.github.com/1805373'
editJSONPath: 'https://github.com/jser/jser.info/edit/gh-pages/data/2012/02/index.json'
date: '2012-02-18T20:44:00Z'
---
NodeでWebアプリ開発環境を揃えるチュートリアル
| 25 | 87 | 0.744 | yue_Hant | 0.098552 |
9816146ade5944ab0ba6b3d854ff18e5e17ac440 | 842 | md | Markdown | docs/_releases/v1.17.6.md | JoshuaCWebDeveloper/sinon | 802cee6a9c71cef35d7a0d543c5aab670289dda2 | [
"BSD-3-Clause"
] | null | null | null | docs/_releases/v1.17.6.md | JoshuaCWebDeveloper/sinon | 802cee6a9c71cef35d7a0d543c5aab670289dda2 | [
"BSD-3-Clause"
] | null | null | null | docs/_releases/v1.17.6.md | JoshuaCWebDeveloper/sinon | 802cee6a9c71cef35d7a0d543c5aab670289dda2 | [
"BSD-3-Clause"
] | 1 | 2020-11-30T07:52:27.000Z | 2020-11-30T07:52:27.000Z | ---
layout: default
title: API documentation
release_id: v1.17.6
---
# {{page.title}} - {{page.release_id}}
## FIXME: Out of date
The documentation in this folder is an earlier copy of the documentation in `sinonjs/sinon`, and not from `sinonjs/sinon-docs`.
We should probably re-import the documentation from `sinonjs/sinon-docs` again, and go over any documentation changes since that was last updated.
---
This page contains the entire Sinon.JS API documentation along with brief introductions to the concepts Sinon implements.
* [Spies](./spies)
* [Stubs](./stubs)
* [Mocks](./mocks)
* [Fake timers](./fake-timers)
* [Fake <code>XHR</code> and server](./fake-xhr-and-server)
* [JSON-P](./json-p)
* [Assertions](./assertions)
* [Matchers](./matchers)
* [Sandboxes](./sandbox)
* [Utils](./utils)
{% include docs/contribute.md %}
| 27.16129 | 146 | 0.706651 | eng_Latn | 0.912889 |
981624799da97e5289f5d7d4d6dbdf31f74f5a0e | 11,619 | md | Markdown | README.md | HelloAllan/upptime | f60be126c9c06039e91ae18cef24e9a3ef419fca | [
"MIT"
] | null | null | null | README.md | HelloAllan/upptime | f60be126c9c06039e91ae18cef24e9a3ef419fca | [
"MIT"
] | 7 | 2021-10-07T06:44:26.000Z | 2022-03-12T20:02:02.000Z | README.md | HelloAllan/upptime | f60be126c9c06039e91ae18cef24e9a3ef419fca | [
"MIT"
] | 1 | 2021-12-29T23:44:50.000Z | 2021-12-29T23:44:50.000Z | # [📈 Live Status](https://status.helloallan.com): <!--live status--> **🟩 All systems operational**
This repository contains the open-source uptime monitor and status page for [Allan](http://www.helloallan.com), powered by [Upptime](https://github.com/upptime/upptime).
[](https://github.com/helloallan/upptime/actions?query=workflow%3A%22Uptime+CI%22)
[](https://github.com/helloallan/upptime/actions?query=workflow%3A%22Response+Time+CI%22)
[](https://github.com/helloallan/upptime/actions?query=workflow%3A%22Graphs+CI%22)
[](https://github.com/helloallan/upptime/actions?query=workflow%3A%22Static+Site+CI%22)
[](https://github.com/helloallan/upptime/actions?query=workflow%3A%22Summary+CI%22)
With [Upptime](https://upptime.js.org), you can get your own unlimited and free uptime monitor and status page, powered entirely by a GitHub repository. We use [Issues](https://github.com/helloallan/upptime/issues) as incident reports, [Actions](https://github.com/helloallan/upptime/actions) as uptime monitors, and [Pages](https://status.helloallan.com) for the status page.
<!--start: status pages-->
<!-- This summary is generated by Upptime (https://github.com/upptime/upptime) -->
<!-- Do not edit this manually, your changes will be overwritten -->
<!-- prettier-ignore -->
| URL | Status | History | Response Time | Uptime |
| --- | ------ | ------- | ------------- | ------ |
| <img alt="" src="https://favicons.githubusercontent.com/www.helloallan.com" height="13"> [HelloAllan](https://www.helloallan.com) | 🟩 Up | [hello-allan.yml](https://github.com/HelloAllan/upptime/commits/HEAD/history/hello-allan.yml) | <details><summary><img alt="Response time graph" src="./graphs/hello-allan/response-time-week.png" height="20"> 169ms</summary><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="Response time 172" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fresponse-time.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="24-hour response time 216" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fresponse-time-day.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="7-day response time 169" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fresponse-time-week.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="30-day response time 155" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fresponse-time-month.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="1-year response time 172" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fresponse-time-year.json"></a></details> | <details><summary><a href="https://status.helloallan.com/history/hello-allan">100.00%</a></summary><a href="https://status.helloallan.com/history/hello-allan"><img alt="All-time uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fuptime.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="24-hour uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fuptime-day.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="7-day uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fuptime-week.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="30-day uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fuptime-month.json"></a><br><a href="https://status.helloallan.com/history/hello-allan"><img alt="1-year uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fhello-allan%2Fuptime-year.json"></a></details>
| <img alt="" src="https://favicons.githubusercontent.com/app.emptychair.io" height="13"> [EmptyChair App](https://app.emptychair.io) | 🟩 Up | [empty-chair-app.yml](https://github.com/HelloAllan/upptime/commits/HEAD/history/empty-chair-app.yml) | <details><summary><img alt="Response time graph" src="./graphs/empty-chair-app/response-time-week.png" height="20"> 1388ms</summary><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="Response time 778" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fresponse-time.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="24-hour response time 3065" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fresponse-time-day.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="7-day response time 1388" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fresponse-time-week.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="30-day response time 1754" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fresponse-time-month.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="1-year response time 778" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fresponse-time-year.json"></a></details> | <details><summary><a href="https://status.helloallan.com/history/empty-chair-app">100.00%</a></summary><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="All-time uptime 99.98%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fuptime.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="24-hour uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fuptime-day.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="7-day uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fuptime-week.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="30-day uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fuptime-month.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-app"><img alt="1-year uptime 99.98%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-app%2Fuptime-year.json"></a></details>
| <img alt="" src="https://favicons.githubusercontent.com/emptychair.io" height="13"> [EmptyChair Marketing](https://emptychair.io) | 🟩 Up | [empty-chair-marketing.yml](https://github.com/HelloAllan/upptime/commits/HEAD/history/empty-chair-marketing.yml) | <details><summary><img alt="Response time graph" src="./graphs/empty-chair-marketing/response-time-week.png" height="20"> 117ms</summary><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="Response time 107" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fresponse-time.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="24-hour response time 79" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fresponse-time-day.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="7-day response time 117" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fresponse-time-week.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="30-day response time 118" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fresponse-time-month.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="1-year response time 107" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fresponse-time-year.json"></a></details> | <details><summary><a href="https://status.helloallan.com/history/empty-chair-marketing">100.00%</a></summary><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="All-time uptime 99.99%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fuptime.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="24-hour uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fuptime-day.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="7-day uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fuptime-week.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="30-day uptime 100.00%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fuptime-month.json"></a><br><a href="https://status.helloallan.com/history/empty-chair-marketing"><img alt="1-year uptime 99.99%" src="https://img.shields.io/endpoint?url=https%3A%2F%2Fraw.githubusercontent.com%2FHelloAllan%2Fupptime%2FHEAD%2Fapi%2Fempty-chair-marketing%2Fuptime-year.json"></a></details>
<!--end: status pages-->
[**Visit our status website →**](https://status.helloallan.com)
## 📄 License
- Powered by: [Upptime](https://github.com/upptime/upptime)
- Code: [MIT](./LICENSE) © [Allan](http://www.helloallan.com)
- Data in the `./history` directory: [Open Database License](https://opendatacommons.org/licenses/odbl/1-0/)
| 363.09375 | 3,274 | 0.768913 | yue_Hant | 0.500257 |
9816329ce42eeb6bbc1274f1a42e38140a8140ae | 1,150 | markdown | Markdown | _posts/2012-01-30-Sosialisasi-Radio-Komunitas-Benor-FM.markdown | hixio-mh/website-4 | 943b8ecdb1f7e507abbb404051afbd40d0a855d3 | [
"MIT"
] | 4 | 2018-03-23T08:55:53.000Z | 2018-03-24T15:10:22.000Z | _posts/2012-01-30-Sosialisasi-Radio-Komunitas-Benor-FM.markdown | hixio-mh/website-4 | 943b8ecdb1f7e507abbb404051afbd40d0a855d3 | [
"MIT"
] | 3 | 2021-12-20T17:56:32.000Z | 2021-12-20T17:59:59.000Z | _posts/2012-01-30-Sosialisasi-Radio-Komunitas-Benor-FM.markdown | hixio-mh/website-4 | 943b8ecdb1f7e507abbb404051afbd40d0a855d3 | [
"MIT"
] | 5 | 2020-01-01T09:54:05.000Z | 2021-11-23T15:49:11.000Z | ---
title: Sosialisasi Radio Komunitas Benor FM di balai desa Bukit Suban Kec. Air Hitam Kab. Sarolangun
date: 2012-01-30
categories:
- laporan
- CMB
- Aldepe.com
layout: laporancmb
---
{: .img-responsive .center-block }

* License: Creative Commons Attribution [CC-BY][1]. Feel free to share and
adapt, but don't forget to credit the author.
# Credits
* Face outline from [grim-heaper](https://www.deviantart.com/grim-heaper/art/McCree-Outline-676856725)
* Created in [inkscape](https://inkscape.org/)
[1]: https://creativecommons.org/licenses/by/2.0/
<p align = "left">
<img src="CNVRanger.png" height = "200" />
</p>
| 28 | 102 | 0.719925 | yue_Hant | 0.269316 |
98169ef1c839ce503bcaf77cae341fa2249c7066 | 14,448 | md | Markdown | _posts/2014-04-30-internet-download-manager-with-genuine.md | edablogs/edablogs-lite | 3ba441bf2aa4716851dff40eb52509361dbe2842 | [
"MIT"
] | null | null | null | _posts/2014-04-30-internet-download-manager-with-genuine.md | edablogs/edablogs-lite | 3ba441bf2aa4716851dff40eb52509361dbe2842 | [
"MIT"
] | null | null | null | _posts/2014-04-30-internet-download-manager-with-genuine.md | edablogs/edablogs-lite | 3ba441bf2aa4716851dff40eb52509361dbe2842 | [
"MIT"
] | null | null | null | ---
layout: post
title: Internet Download manager with genuine serial key latest version
date: '2014-04-30T10:25:00.000+05:30'
author: pawneshwer
categories:
- computer
tags:
- computer
modified_time: '2016-02-20T06:51:59.320+05:30'
thumbnail: http://lh6.ggpht.com/-njQYNQmomxg/UPg-Zy_CrhI/AAAAAAAAADE/kTfMfSBPAvw/s72-c/Internet-Download-Manager-6_thumb%25255B1%25255D.jpg?imgmax=800
blogger_id: tag:blogger.com,1999:blog-1967791069058877982.post-8692754399856148408
blogger_orig_url: http://www.edablogs.com/2014/04/internet-download-manager-with-genuine.html
redirect_from:
- /2014/04/internet-download-manager-with-genuine.html
---
<div dir="ltr" style="text-align: left;" trbidi="on"><div class="separator" style="clear: both; text-align: center;"><span style="clear: left; float: left; font-family: verdana; font-size: small; margin-bottom: 1em; margin-right: 1em;"><img alt="Internet-Download-Manager-6" border="0" src="http://lh6.ggpht.com/-njQYNQmomxg/UPg-Zy_CrhI/AAAAAAAAADE/kTfMfSBPAvw/Internet-Download-Manager-6_thumb%25255B1%25255D.jpg?imgmax=800" height="271" style="background-image: none; border-width: 0px; display: inline; padding-left: 0px; padding-right: 0px; padding-top: 0px;" title="Internet-Download-Manager-6" width="222" /></span></div><br /><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">Hello friends we all knows that internet <a class="zem_slink" href="http://en.wikipedia.org/wiki/Download_manager" rel="wikipedia" target="_blank" title="Download manager">download manager</a> (<a class="zem_slink" href="http://en.wikipedia.org/wiki/Intelligent_dance_music" rel="wikipedia" target="_blank" title="Intelligent dance music">IDM</a>) is best and mostly used download manager over the internet. it provide fastest speed and resume capability. so it is used by many users</span>.</span> <br /><span style="font-size: small;"><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">but here is a big problem that developer provides only 30 days trial period to use internet download manager. and after 30 days you have to purchase it from its official site</span>.</span> </span><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">but you don’t need to worry about this problem, I’m giving you Genuine <a class="zem_slink" href="http://en.wikipedia.org/wiki/Product_key" rel="wikipedia" target="_blank" title="Product key">serial key</a> to activate your <a class="zem_slink" href="http://www.internetdownloadmanager.com/" rel="homepage" target="_blank" title="Internet Download Manager">Internet download manager</a> for life time</span>.</span> <br /><span style="color: black; font-family: verdana; font-size: small;"><br /></span><span style="color: black; font-family: verdana; font-size: small;"><br /></span><span style="color: black; font-family: verdana; font-size: small;"><br /></span><span style="color: black; font-family: verdana; font-size: small;"><br /></span><span style="color: red; font-family: verdana; font-size: small;"><span style="font-size: small;">so follow these simple steps</span> :-</span> <br /><span style="color: red; font-family: verdana; font-size: small;"><br /></span><span style="color: red; font-family: verdana; font-size: small;"><b><span style="font-size: small;">Step 1</span> :</b></span> <br /><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">first of all download and install latest version of IDM from its official website or from given link below</span> :-</span> </li></ul><a href="http://sh.st/wIZRI" rel="nofollow" target="_blank"><span style="font-family: verdana; font-size: small;"><span style="font-size: small;">http://www.internetdownloadmanager.com/download.html</span></span></a> <br /><ul><li><span style="font-family: verdana; font-size: small;"><span style="font-size: small;"><span style="color: black;">now goto to this path (</span><span style="color: #333333;"> <span style="color: blue;">C:\windows\system32\drivers\etc\</span>)</span></span></span> </li><li><span style="color: #333333; font-family: verdana; font-size: small;"><span style="font-size: small;"><span style="color: black;">here you’ll find a file name</span> “<span style="color: blue;">hosts</span>” </span><span style="color: black;"><span style="font-size: small;">as shown in following pic</span> :-</span></span> </li></ul><div style="text-align: center;"><a href="http://lh3.ggpht.com/-7THQae0QN-k/UPg-baZFnxI/AAAAAAAAADM/db5nU5zuuAM/s1600-h/idm1%25255B4%25255D.jpg"><span style="font-family: verdana; font-size: small;"><img alt="idm1" border="0" src="http://lh3.ggpht.com/-l0LYdFzKa70/UPg-dMPS8CI/AAAAAAAAADU/9LUAreM0jZ0/idm1_thumb%25255B2%25255D.jpg?imgmax=800" height="170" style="background-image: none; border-width: 0px; display: inline; padding-left: 0px; padding-right: 0px; padding-top: 0px;" title="idm1" width="400" /></span></a> </div><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;"><a class="zem_slink" href="http://en.wikipedia.org/wiki/Context_menu" rel="wikipedia" target="_blank" title="Context menu">right click</a> <a class="zem_slink" href="http://en.wikipedia.org/wiki/Hosts_%28file%29" rel="wikipedia" target="_blank" title="Hosts (file)">hosts file</a> and click on properties</span>.</span> </li><li><span style="color: #333333; font-family: verdana; font-size: small;"><span style="font-size: small;"><span style="color: black;">now click on</span> “<span style="color: blue;">security</span>” </span><span style="color: black;"><span style="font-size: small;">tab</span>.</span></span> </li><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">and click on edit button as shown in following pic</span>:</span> </li></ul><div class="separator" style="clear: both; text-align: center;"><span style="font-family: verdana; font-size: small; margin-left: 1em; margin-right: 1em;"><img alt="idm4" border="0" src="http://lh5.ggpht.com/-jFjeToNuUgQ/UPg-gfx7njI/AAAAAAAAADk/YMROjOJga9c/idm4_thumb%25255B1%25255D.jpg?imgmax=800" height="520" style="background-image: none; border-width: 0px; display: inline; padding-left: 0px; padding-right: 0px; padding-top: 0px;" title="idm4" width="381" /></span></div><br /><ul><li><span style="color: #333333; font-family: verdana; font-size: small;"><span style="font-size: small;"><span style="color: black;">and new window will open says</span> “<span style="color: blue;"><a class="zem_slink" href="http://en.wikipedia.org/wiki/Filesystem_permissions" rel="wikipedia" target="_blank" title="Filesystem permissions">Permissions</a> for hosts</span>”.</span></span> </li></ul><span style="color: #333333; font-family: verdana; font-size: small;"></span> <br /><span style="color: #333333; font-family: verdana; font-size: small;"></span> <br /><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">now click on your current computer user</span>.</span> </li></ul><span style="font-size: small;"><span style="color: #333333; font-family: verdana; font-size: small;"><span style="font-size: small;"><span style="color: red;">for example in my case I’ve click on</span> “<span style="color: blue;">Users(Pawneshwer-<a class="zem_slink" href="http://en.wikipedia.org/wiki/Personal_computer" rel="wikipedia" target="_blank" title="Personal computer">PC</a>\users)” </span></span><span style="color: black;"><span style="font-size: small;">as shown in following pic</span>:</span></span></span><br /><span style="font-size: small;"><span style="color: #333333; font-family: verdana; font-size: small;"><span style="color: black;"><br /></span></span></span><br /><div class="separator" style="clear: both; text-align: center;"><a href="http://lh5.ggpht.com/-fw4q5Kpa-y4/UPg-iNk0C2I/AAAAAAAAADo/V9qQLN070gk/s1600-h/idm2%25255B3%25255D.jpg" style="margin-left: 1em; margin-right: 1em;"><img alt="idm2" border="0" src="http://lh5.ggpht.com/-4QQLKVoSaD8/UPg-jZefM3I/AAAAAAAAAD0/EZm8OA4IPY0/idm2_thumb%25255B1%25255D.jpg?imgmax=800" height="462" style="background-image: none; border-width: 0px; display: inline; padding-left: 0px; padding-right: 0px; padding-top: 0px;" title="idm2" width="379" /></a></div><span style="font-size: small;"> </span><span style="color: #333333; font-family: verdana; font-size: small;"></span> <br /><br /><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">and check the box followed by “<span style="color: blue;">full control</span>” and click on “<span style="color: blue;">OK</span>” button</span>.</span> <br /><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">now open “<span style="color: blue;">hosts</span>” file in notepad and add following lines at the end</span> :</span> </li></ul><div align="left"><br /><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 tonec.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 www.tonec.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 registeridm.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 www.registeridm.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 secure.registeridm.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 internetdownloadmanager.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 www.internetdownloadmanager.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 secure.internetdownloadmanager.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 mirror.internetdownloadmanager.com</b></span></div><div style="text-align: left;"><span style="color: blue; font-family: verdana;"><b>127.0.0.1 mirror2.internetdownloadmanager.com</b></span></div><span style="color: blue; font-family: verdana;"><b><br /></b></span></div><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">as shown in following pic</span>:</span> <br /><div style="text-align: center;"><a href="http://lh3.ggpht.com/-iUQF8NGSwhg/UPg-lVgNiYI/AAAAAAAAAD8/ndTdKTXBruI/s1600-h/idm3%25255B3%25255D.jpg"><span style="font-family: verdana; font-size: small;"><img alt="idm3" border="0" src="http://lh4.ggpht.com/-UbR47GI1JmQ/UPg-nGJrrmI/AAAAAAAAAEE/-aleQCGjtSw/idm3_thumb%25255B1%25255D.jpg?imgmax=800" height="237" style="background-image: none; border-width: 0px; display: inline; padding-left: 0px; padding-right: 0px; padding-top: 0px;" title="idm3" width="400" /></span></a> </div><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">and save your “<span style="color: blue;">hosts</span>” file</span>.</span> </li></ul><span style="color: red; font-family: verdana; font-size: small;"><b><span style="font-size: small;">Step 2</span>:</b></span> <br /><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">now open internet download manager and click on “<span style="color: blue;">registration>registration</span>”.</span></span> </li><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">now enter your “<span style="color: blue;">Name</span>”, “<span style="color: blue;">Email ID</span>”. and in serial key enter one this following key</span> :</span> </li></ul><br /><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>RLDGN-OV9WU-5W589-6VZH1</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>HUDWE-UO689-6D27B-YM28M</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>UK3DV-E0MNW-MLQYX-GENA1</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>398ND-QNAGY-CMMZU-ZPI39</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>GZLJY-X50S3-0S20D-NFRF9</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>W3J5U-8U66N-D0B9M-54SLM</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>EC0Q6-QN7UH-5S3JB-YZMEK</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>UVQW0-X54FE-QW35Q-SNZF5</b></span></div><div style="text-align: center;"><span style="color: blue; font-family: verdana;"><b>FJJTJ-J0FLF-QCVBK-A287M</b></span></div><br /><ul><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">and click on register button. and it will show error “ <span style="color: red;">connection disabled or anything about connection</span>”, and IDM will exit</span>.</span> </li><li><span style="color: black; font-family: verdana; font-size: small;"><span style="font-size: small;">now goto “<span style="color: blue;">start>programs</span>” and open “Internet download manager” and IDM will open now you will get your full version genuine Internet download manager for free</span>.</span> </li></ul><span style="color: red; font-family: verdana; font-size: small;"><b><span style="font-size: small;">join this site to get daily updates. thanks for reading</span>.</b></span> <br /><span style="font-family: verdana; font-size: small;"></span> <br /><span style="font-family: verdana; font-size: small;"></span><br /><div class="zemanta-pixie" style="height: 15px; margin-top: 10px;"><a class="zemanta-pixie-a" href="http://www.zemanta.com/?px" title="Enhanced by Zemanta"><img alt="Enhanced by Zemanta" class="zemanta-pixie-img" src="http://img.zemanta.com/zemified_e.png?x-id=8e105689-6d62-4c0a-a066-b87705e76394" style="border: none; float: right;" /></a></div></div> | 802.666667 | 13,812 | 0.710064 | eng_Latn | 0.20945 |