Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 1 853 | labels stringlengths 4 898 | body stringlengths 2 262k | index stringclasses 13 values | text_combine stringlengths 96 262k | label stringclasses 2 values | text stringlengths 96 250k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
55,101 | 11,386,578,945 | IssuesEvent | 2020-01-29 13:33:37 | googleapis/google-cloud-python | https://api.github.com/repos/googleapis/google-cloud-python | closed | Synthesis failed for billingbudgets | autosynth failure codegen type: process | Hello! Autosynth couldn't regenerate billingbudgets. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth-billingbudgets'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', 'synth.py', '--']
synthtool > Executing /tmpfs/src/git/autosynth/working_repo/billingbudgets/synth.py.
synthtool > Ensuring dependencies.
synthtool > Pulling artman image.
latest: Pulling from googleapis/artman
Digest: sha256:10a6d0342b8d62544810ac5ad86c3b21049ec0696608ac60175da8e513234344
Status: Image is up to date for googleapis/artman:latest
synthtool > Cloning googleapis.
synthtool > Running generator for google/cloud/billing/budgets/artman_billingbudgets_v1beta1.yaml.
synthtool > Generated code into /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1.
synthtool > Copy: /home/kbuilder/.cache/synthtool/googleapis/google/cloud/billing/budgets/v1beta1/budget_service.proto to /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1/google/cloud/billingbudgets_v1beta1/proto/budget_service.proto
synthtool > Copy: /home/kbuilder/.cache/synthtool/googleapis/google/cloud/billing/budgets/v1beta1/budget_model.proto to /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1/google/cloud/billingbudgets_v1beta1/proto/budget_model.proto
synthtool > Placed proto files into /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1/google/cloud/billingbudgets_v1beta1/proto.
synthtool > Replaced 'from google\\.cloud\\.billing\\.budgets_v1beta1' in google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2_grpc.py.
synthtool > Replaced 'from google\\.cloud\\.billing\\.budgets_v1beta1' in google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2.py.
synthtool > Replaced 'google-cloud-billingbudgets' in docs/conf.py.
synthtool > Replaced 'google-cloud-billingbudgets' in google/cloud/billing_budgets_v1beta1/gapic/budget_service_client.py.
.coveragerc
.flake8
MANIFEST.in
docs/_static/custom.css
docs/_templates/layout.html
noxfile.py.j2
setup.cfg
Running session blacken
Creating virtual environment (virtualenv) using python3.6 in .nox/blacken
pip install black==19.3b0
black docs google tests noxfile.py setup.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/__init__.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/__init__.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/__init__.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/enums.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/budget_service_client_config.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/transports/budget_service_grpc_transport.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_model_pb2_grpc.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/docs/conf.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2_grpc.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/types.py
error: cannot format /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2.py: Cannot parse: 273:11: '__doc__': """Request for CreateBudget
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/budget_service_client.py
error: cannot format /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_model_pb2.py: Cannot parse: 373:11: '__doc__': """A budget is a plan that describes what you expect to spend
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/noxfile.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/tests/unit/gapic/v1beta1/test_budget_service_client_v1beta1.py
All done! 💥 💔 💥
14 files reformatted, 4 files left unchanged, 2 files failed to reformat.
Command black docs google tests noxfile.py setup.py failed with exit code 123
Session blacken failed.
synthtool > Failed executing nox -s blacken:
None
synthtool > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 99, in <module>
main()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 764, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 717, in main
rv = self.invoke(ctx)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 956, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 555, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 91, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 205, in _call_with_frames_removed
File "/tmpfs/src/git/autosynth/working_repo/billingbudgets/synth.py", line 71, in <module>
s.shell.run(["nox", "-s", "blacken"], hide_output=False)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 39, in run
raise exc
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 33, in run
encoding="utf-8",
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/subprocess.py", line 418, in run
output=stdout, stderr=stderr)
subprocess.CalledProcessError: Command '['nox', '-s', 'blacken']' returned non-zero exit status 1.
Synthesis failed
```
Google internal developers can see the full log [here](https://sponge/7466e354-d120-4bf0-a156-1b9913bcb1fc).
| 1.0 | Synthesis failed for billingbudgets - Hello! Autosynth couldn't regenerate billingbudgets. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth-billingbudgets'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', 'synth.py', '--']
synthtool > Executing /tmpfs/src/git/autosynth/working_repo/billingbudgets/synth.py.
synthtool > Ensuring dependencies.
synthtool > Pulling artman image.
latest: Pulling from googleapis/artman
Digest: sha256:10a6d0342b8d62544810ac5ad86c3b21049ec0696608ac60175da8e513234344
Status: Image is up to date for googleapis/artman:latest
synthtool > Cloning googleapis.
synthtool > Running generator for google/cloud/billing/budgets/artman_billingbudgets_v1beta1.yaml.
synthtool > Generated code into /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1.
synthtool > Copy: /home/kbuilder/.cache/synthtool/googleapis/google/cloud/billing/budgets/v1beta1/budget_service.proto to /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1/google/cloud/billingbudgets_v1beta1/proto/budget_service.proto
synthtool > Copy: /home/kbuilder/.cache/synthtool/googleapis/google/cloud/billing/budgets/v1beta1/budget_model.proto to /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1/google/cloud/billingbudgets_v1beta1/proto/budget_model.proto
synthtool > Placed proto files into /home/kbuilder/.cache/synthtool/googleapis/artman-genfiles/python/billingbudgets-v1beta1/google/cloud/billingbudgets_v1beta1/proto.
synthtool > Replaced 'from google\\.cloud\\.billing\\.budgets_v1beta1' in google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2_grpc.py.
synthtool > Replaced 'from google\\.cloud\\.billing\\.budgets_v1beta1' in google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2.py.
synthtool > Replaced 'google-cloud-billingbudgets' in docs/conf.py.
synthtool > Replaced 'google-cloud-billingbudgets' in google/cloud/billing_budgets_v1beta1/gapic/budget_service_client.py.
.coveragerc
.flake8
MANIFEST.in
docs/_static/custom.css
docs/_templates/layout.html
noxfile.py.j2
setup.cfg
Running session blacken
Creating virtual environment (virtualenv) using python3.6 in .nox/blacken
pip install black==19.3b0
black docs google tests noxfile.py setup.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/__init__.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/__init__.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/__init__.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/enums.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/budget_service_client_config.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/transports/budget_service_grpc_transport.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_model_pb2_grpc.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/docs/conf.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2_grpc.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/types.py
error: cannot format /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_service_pb2.py: Cannot parse: 273:11: '__doc__': """Request for CreateBudget
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/gapic/budget_service_client.py
error: cannot format /tmpfs/src/git/autosynth/working_repo/billingbudgets/google/cloud/billing_budgets_v1beta1/proto/budget_model_pb2.py: Cannot parse: 373:11: '__doc__': """A budget is a plan that describes what you expect to spend
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/noxfile.py
reformatted /tmpfs/src/git/autosynth/working_repo/billingbudgets/tests/unit/gapic/v1beta1/test_budget_service_client_v1beta1.py
All done! 💥 💔 💥
14 files reformatted, 4 files left unchanged, 2 files failed to reformat.
Command black docs google tests noxfile.py setup.py failed with exit code 123
Session blacken failed.
synthtool > Failed executing nox -s blacken:
None
synthtool > Wrote metadata to synth.metadata.
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 99, in <module>
main()
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 764, in __call__
return self.main(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 717, in main
rv = self.invoke(ctx)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 956, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/click/core.py", line 555, in invoke
return callback(*args, **kwargs)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/__main__.py", line 91, in main
spec.loader.exec_module(synth_module) # type: ignore
File "<frozen importlib._bootstrap_external>", line 678, in exec_module
File "<frozen importlib._bootstrap>", line 205, in _call_with_frames_removed
File "/tmpfs/src/git/autosynth/working_repo/billingbudgets/synth.py", line 71, in <module>
s.shell.run(["nox", "-s", "blacken"], hide_output=False)
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 39, in run
raise exc
File "/tmpfs/src/git/autosynth/env/lib/python3.6/site-packages/synthtool/shell.py", line 33, in run
encoding="utf-8",
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/subprocess.py", line 418, in run
output=stdout, stderr=stderr)
subprocess.CalledProcessError: Command '['nox', '-s', 'blacken']' returned non-zero exit status 1.
Synthesis failed
```
Google internal developers can see the full log [here](https://sponge/7466e354-d120-4bf0-a156-1b9913bcb1fc).
| non_build | synthesis failed for billingbudgets hello autosynth couldn t regenerate billingbudgets broken heart here s the output from running synth py cloning into working repo switched to branch autosynth billingbudgets running synthtool synthtool executing tmpfs src git autosynth working repo billingbudgets synth py synthtool ensuring dependencies synthtool pulling artman image latest pulling from googleapis artman digest status image is up to date for googleapis artman latest synthtool cloning googleapis synthtool running generator for google cloud billing budgets artman billingbudgets yaml synthtool generated code into home kbuilder cache synthtool googleapis artman genfiles python billingbudgets synthtool copy home kbuilder cache synthtool googleapis google cloud billing budgets budget service proto to home kbuilder cache synthtool googleapis artman genfiles python billingbudgets google cloud billingbudgets proto budget service proto synthtool copy home kbuilder cache synthtool googleapis google cloud billing budgets budget model proto to home kbuilder cache synthtool googleapis artman genfiles python billingbudgets google cloud billingbudgets proto budget model proto synthtool placed proto files into home kbuilder cache synthtool googleapis artman genfiles python billingbudgets google cloud billingbudgets proto synthtool replaced from google cloud billing budgets in google cloud billing budgets proto budget service grpc py synthtool replaced from google cloud billing budgets in google cloud billing budgets proto budget service py synthtool replaced google cloud billingbudgets in docs conf py synthtool replaced google cloud billingbudgets in google cloud billing budgets gapic budget service client py coveragerc manifest in docs static custom css docs templates layout html noxfile py setup cfg running session blacken creating virtual environment virtualenv using in nox blacken pip install black black docs google tests noxfile py setup py reformatted tmpfs src git autosynth working repo billingbudgets google init py reformatted tmpfs src git autosynth working repo billingbudgets google cloud init py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets init py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets gapic enums py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets gapic budget service client config py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets gapic transports budget service grpc transport py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets proto budget model grpc py reformatted tmpfs src git autosynth working repo billingbudgets docs conf py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets proto budget service grpc py reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets types py error cannot format tmpfs src git autosynth working repo billingbudgets google cloud billing budgets proto budget service py cannot parse doc request for createbudget reformatted tmpfs src git autosynth working repo billingbudgets google cloud billing budgets gapic budget service client py error cannot format tmpfs src git autosynth working repo billingbudgets google cloud billing budgets proto budget model py cannot parse doc a budget is a plan that describes what you expect to spend reformatted tmpfs src git autosynth working repo billingbudgets noxfile py reformatted tmpfs src git autosynth working repo billingbudgets tests unit gapic test budget service client py all done 💥 💔 💥 files reformatted files left unchanged files failed to reformat command black docs google tests noxfile py setup py failed with exit code session blacken failed synthtool failed executing nox s blacken none synthtool wrote metadata to synth metadata traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src git autosynth env lib site packages synthtool main py line in main file tmpfs src git autosynth env lib site packages click core py line in call return self main args kwargs file tmpfs src git autosynth env lib site packages click core py line in main rv self invoke ctx file tmpfs src git autosynth env lib site packages click core py line in invoke return ctx invoke self callback ctx params file tmpfs src git autosynth env lib site packages click core py line in invoke return callback args kwargs file tmpfs src git autosynth env lib site packages synthtool main py line in main spec loader exec module synth module type ignore file line in exec module file line in call with frames removed file tmpfs src git autosynth working repo billingbudgets synth py line in s shell run hide output false file tmpfs src git autosynth env lib site packages synthtool shell py line in run raise exc file tmpfs src git autosynth env lib site packages synthtool shell py line in run encoding utf file home kbuilder pyenv versions lib subprocess py line in run output stdout stderr stderr subprocess calledprocesserror command returned non zero exit status synthesis failed google internal developers can see the full log | 0 |
21,674 | 7,057,437,074 | IssuesEvent | 2018-01-04 16:27:04 | Guake/guake | https://api.github.com/repos/Guake/guake | closed | Guake 3 Roadmap | Epic: GTK 3 port Priority:High Type: Build System; Packaging; Docs; Tanslations Type: Feature Request | Here is a task list and Roadmap for the Guake 3 release
# Version
- jump directly from guake version 0.8.x to 3.0.0.
- keep semver versioning
# Goals
- rewrite the core guake engine to more modular and more extensible
- plugin architecture
- port to gtk3, dconf, latest version of VTE
- dark theming (UI like sublime)
# Roadmap
## Guake 3.0 - "Proper Basis"
- [x] ~~**Rewrite the Build System for pip**: #873. even though Guake will still have hard dependency with system-level libraries such as libkeybinder, we need to switch to a clean pip compatible installation procedure. Drop all the makefile, autopen. I would like to put some build scripts to help bootstrapping their dev environment.~~
- [x] **move gettext Translation after all rewriten**: to keep the old translation we will reconstruct all Guake first THEN move back the `po` directory and update the translations, hoping gettext will be able to match translations
- [x] ~~**stricter code styling**: `validate` and `fiximports` will enforce more Pylint and pep8 checks. Stricter code style is not bad. use `_` to separate private/publicly available members in each class~~
- [ ] **no more global.py**
- [x] **Proper unit test integration**: #874
**Components**
- [x] **GuakeTerminal**: ported to gtk3 and new version of vte. add methods: search, save. Of course unit test
- [x] **GuakeTerminalPage**: replaces guakeTerminalBox. Allow to split the terminal horizontally and vertically. Provide accessor for visual position (`getTerminalByPos(0, 1)` to get terminal on first line, second column, `iterAllTerminals`` as an iterator all all terminals, `getCurrentTerminal`, `focusTerminalByPos(1, 0)` to focus second raw first column, `focusTerminalByShift(1,0)` to focus the terminal on the next row, `splitHorizontally`, `splitVertically`, `unplitHorizontally(deleteRight=True)`, `unsplitVertically(deleteBellow=True)`, and so on)
- [x] **GuakeTerminalTab**: merge all the `*_tab` functions from `Guake` class and the `GuakeNotebook` class. `Guake` class is too huge, lets apply the One Responsibility Principle. API Should be as simple as `addTab`, `splitCurTabVertically`, `unsplitCurTabVertically`. No more internal api hack
- [x] **GuakeWindow**: handle the placement of the Guake Window. Only that. Do exposes the tabs/page/terminal directly (using clean accessors), not by using proxy. #879
- [ ] **GuakeBinder**: proposal to bind events from keyboard/setting change to actions
- [x] **dconfhandler**: port gconfhandler to dconf
- [x] **dbus**: should be easy to port to gtk3
- [ ] **paletes.py**: port to a set of yams file => follow up #1053
- [ ] **Startup Script**: systemd scripts?
- [x] **Screen position computation**: rewrite the whole code, it is buggy, finding where to place the window is too complex, error prone, when fixing a bug another one appears. I do not see how to unit test it, since it depends on how gtk will position the window. Integration tests? => follow up #1054
- [ ] **Command line interface**: port CLI to guake3 branch
**Preferences** => follow up #1055
- [ ] **Rewrite preference window**. Too bloaty, difficult to modify and adapt. Find a more elegant disposition
- [ ] **Setting preference exposure**: too many files to modify when adding a setting, let's find a way to tell which setting gooes to which panel
**Plugin System** => #1052
- [ ] **Register/Unregister mechanism**: find a way for user to easily find and install new plugin. Probably like Sublime Text's Package Control. It a JSON file stores on github, user refresh periodicaly and are updated of new available packages on merge. Probably on https://github.come/Guake/plugins/plugins.xml
- [ ] **Python Event system** : Plugin will be able to react in python to some event:
- [ ] **2 Person review** : for plugin to be available to user, at least 2 person need code review
- [ ] **onion deployment**: plugins to be deployed using canary-like deployment. Users are packed into n different layers ("stable/unstable/cutting-edge" for instance) so they test plugins in advance
## Guake 3.1
| 1.0 | Guake 3 Roadmap - Here is a task list and Roadmap for the Guake 3 release
# Version
- jump directly from guake version 0.8.x to 3.0.0.
- keep semver versioning
# Goals
- rewrite the core guake engine to more modular and more extensible
- plugin architecture
- port to gtk3, dconf, latest version of VTE
- dark theming (UI like sublime)
# Roadmap
## Guake 3.0 - "Proper Basis"
- [x] ~~**Rewrite the Build System for pip**: #873. even though Guake will still have hard dependency with system-level libraries such as libkeybinder, we need to switch to a clean pip compatible installation procedure. Drop all the makefile, autopen. I would like to put some build scripts to help bootstrapping their dev environment.~~
- [x] **move gettext Translation after all rewriten**: to keep the old translation we will reconstruct all Guake first THEN move back the `po` directory and update the translations, hoping gettext will be able to match translations
- [x] ~~**stricter code styling**: `validate` and `fiximports` will enforce more Pylint and pep8 checks. Stricter code style is not bad. use `_` to separate private/publicly available members in each class~~
- [ ] **no more global.py**
- [x] **Proper unit test integration**: #874
**Components**
- [x] **GuakeTerminal**: ported to gtk3 and new version of vte. add methods: search, save. Of course unit test
- [x] **GuakeTerminalPage**: replaces guakeTerminalBox. Allow to split the terminal horizontally and vertically. Provide accessor for visual position (`getTerminalByPos(0, 1)` to get terminal on first line, second column, `iterAllTerminals`` as an iterator all all terminals, `getCurrentTerminal`, `focusTerminalByPos(1, 0)` to focus second raw first column, `focusTerminalByShift(1,0)` to focus the terminal on the next row, `splitHorizontally`, `splitVertically`, `unplitHorizontally(deleteRight=True)`, `unsplitVertically(deleteBellow=True)`, and so on)
- [x] **GuakeTerminalTab**: merge all the `*_tab` functions from `Guake` class and the `GuakeNotebook` class. `Guake` class is too huge, lets apply the One Responsibility Principle. API Should be as simple as `addTab`, `splitCurTabVertically`, `unsplitCurTabVertically`. No more internal api hack
- [x] **GuakeWindow**: handle the placement of the Guake Window. Only that. Do exposes the tabs/page/terminal directly (using clean accessors), not by using proxy. #879
- [ ] **GuakeBinder**: proposal to bind events from keyboard/setting change to actions
- [x] **dconfhandler**: port gconfhandler to dconf
- [x] **dbus**: should be easy to port to gtk3
- [ ] **paletes.py**: port to a set of yams file => follow up #1053
- [ ] **Startup Script**: systemd scripts?
- [x] **Screen position computation**: rewrite the whole code, it is buggy, finding where to place the window is too complex, error prone, when fixing a bug another one appears. I do not see how to unit test it, since it depends on how gtk will position the window. Integration tests? => follow up #1054
- [ ] **Command line interface**: port CLI to guake3 branch
**Preferences** => follow up #1055
- [ ] **Rewrite preference window**. Too bloaty, difficult to modify and adapt. Find a more elegant disposition
- [ ] **Setting preference exposure**: too many files to modify when adding a setting, let's find a way to tell which setting gooes to which panel
**Plugin System** => #1052
- [ ] **Register/Unregister mechanism**: find a way for user to easily find and install new plugin. Probably like Sublime Text's Package Control. It a JSON file stores on github, user refresh periodicaly and are updated of new available packages on merge. Probably on https://github.come/Guake/plugins/plugins.xml
- [ ] **Python Event system** : Plugin will be able to react in python to some event:
- [ ] **2 Person review** : for plugin to be available to user, at least 2 person need code review
- [ ] **onion deployment**: plugins to be deployed using canary-like deployment. Users are packed into n different layers ("stable/unstable/cutting-edge" for instance) so they test plugins in advance
## Guake 3.1
| build | guake roadmap here is a task list and roadmap for the guake release version jump directly from guake version x to keep semver versioning goals rewrite the core guake engine to more modular and more extensible plugin architecture port to dconf latest version of vte dark theming ui like sublime roadmap guake proper basis rewrite the build system for pip even though guake will still have hard dependency with system level libraries such as libkeybinder we need to switch to a clean pip compatible installation procedure drop all the makefile autopen i would like to put some build scripts to help bootstrapping their dev environment move gettext translation after all rewriten to keep the old translation we will reconstruct all guake first then move back the po directory and update the translations hoping gettext will be able to match translations stricter code styling validate and fiximports will enforce more pylint and checks stricter code style is not bad use to separate private publicly available members in each class no more global py proper unit test integration components guaketerminal ported to and new version of vte add methods search save of course unit test guaketerminalpage replaces guaketerminalbox allow to split the terminal horizontally and vertically provide accessor for visual position getterminalbypos to get terminal on first line second column iterallterminals as an iterator all all terminals getcurrentterminal focusterminalbypos to focus second raw first column focusterminalbyshift to focus the terminal on the next row splithorizontally splitvertically unplithorizontally deleteright true unsplitvertically deletebellow true and so on guaketerminaltab merge all the tab functions from guake class and the guakenotebook class guake class is too huge lets apply the one responsibility principle api should be as simple as addtab splitcurtabvertically unsplitcurtabvertically no more internal api hack guakewindow handle the placement of the guake window only that do exposes the tabs page terminal directly using clean accessors not by using proxy guakebinder proposal to bind events from keyboard setting change to actions dconfhandler port gconfhandler to dconf dbus should be easy to port to paletes py port to a set of yams file follow up startup script systemd scripts screen position computation rewrite the whole code it is buggy finding where to place the window is too complex error prone when fixing a bug another one appears i do not see how to unit test it since it depends on how gtk will position the window integration tests follow up command line interface port cli to branch preferences follow up rewrite preference window too bloaty difficult to modify and adapt find a more elegant disposition setting preference exposure too many files to modify when adding a setting let s find a way to tell which setting gooes to which panel plugin system register unregister mechanism find a way for user to easily find and install new plugin probably like sublime text s package control it a json file stores on github user refresh periodicaly and are updated of new available packages on merge probably on python event system plugin will be able to react in python to some event person review for plugin to be available to user at least person need code review onion deployment plugins to be deployed using canary like deployment users are packed into n different layers stable unstable cutting edge for instance so they test plugins in advance guake | 1 |
80,752 | 23,296,515,738 | IssuesEvent | 2022-08-06 17:03:21 | CosmosOS/Cosmos | https://api.github.com/repos/CosmosOS/Cosmos | closed | The system cannot find the file specified. | Area: Visual Studio Integration Area: Build | Have you checked Github Issues for similar errors? yes
**Exception**
Post the exception returned by Visual Studio - The system cannot find the file specified
** VS Output Logs **
There is no log other than the exception
**To Reproduce**
Describe any changes done to a clean kernel for this error to occur. - Tried to Build as an ISO
**Screenshots**
If applicable, add screenshots to help explain your problem.


**Context**
Before posting please confirm that the following are in order
[yes] Both Cosmos VS Extensions are installed
[yes] In the NuGet Package Manager "Include prerelease" is selected
[yes] The Cosmos NuGet package store is selected (NOT nuget.org) in 'Manage NuGet Packages'
[yes] The Cosmos NuGet packages are installed
Add any other context about the problem which might be helpful.
i do have the same issue as #2215 , i followed the available instructions there and i still facing the same issue.
Cosmos is installed on my other drive which is the E: drive. A successful installation without any issues
Apparently for some reason its trying to execute it as if its located on the C drive while its located on the E drive its properly installed its not like moved out from its original installation location im trying to find a way to edit it so it wont try to execute it as if its located on the C drive The same wanted executable is located on the E drive. | 1.0 | The system cannot find the file specified. - Have you checked Github Issues for similar errors? yes
**Exception**
Post the exception returned by Visual Studio - The system cannot find the file specified
** VS Output Logs **
There is no log other than the exception
**To Reproduce**
Describe any changes done to a clean kernel for this error to occur. - Tried to Build as an ISO
**Screenshots**
If applicable, add screenshots to help explain your problem.


**Context**
Before posting please confirm that the following are in order
[yes] Both Cosmos VS Extensions are installed
[yes] In the NuGet Package Manager "Include prerelease" is selected
[yes] The Cosmos NuGet package store is selected (NOT nuget.org) in 'Manage NuGet Packages'
[yes] The Cosmos NuGet packages are installed
Add any other context about the problem which might be helpful.
i do have the same issue as #2215 , i followed the available instructions there and i still facing the same issue.
Cosmos is installed on my other drive which is the E: drive. A successful installation without any issues
Apparently for some reason its trying to execute it as if its located on the C drive while its located on the E drive its properly installed its not like moved out from its original installation location im trying to find a way to edit it so it wont try to execute it as if its located on the C drive The same wanted executable is located on the E drive. | build | the system cannot find the file specified have you checked github issues for similar errors yes exception post the exception returned by visual studio the system cannot find the file specified vs output logs there is no log other than the exception to reproduce describe any changes done to a clean kernel for this error to occur tried to build as an iso screenshots if applicable add screenshots to help explain your problem context before posting please confirm that the following are in order both cosmos vs extensions are installed in the nuget package manager include prerelease is selected the cosmos nuget package store is selected not nuget org in manage nuget packages the cosmos nuget packages are installed add any other context about the problem which might be helpful i do have the same issue as i followed the available instructions there and i still facing the same issue cosmos is installed on my other drive which is the e drive a successful installation without any issues apparently for some reason its trying to execute it as if its located on the c drive while its located on the e drive its properly installed its not like moved out from its original installation location im trying to find a way to edit it so it wont try to execute it as if its located on the c drive the same wanted executable is located on the e drive | 1 |
79,701 | 15,586,199,916 | IssuesEvent | 2021-03-18 01:24:06 | sergioms/jackson_deserialization_poc | https://api.github.com/repos/sergioms/jackson_deserialization_poc | opened | CVE-2020-11111 (High) detected in jackson-databind-2.9.6.jar | security vulnerability | ## CVE-2020-11111 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: jackson_deserialization_poc/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.4.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.4.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.activemq.* (aka activemq-jms, activemq-core, activemq-pool, and activemq-pool-jms).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111>CVE-2020-11111</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11111 (High) detected in jackson-databind-2.9.6.jar - ## CVE-2020-11111 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: jackson_deserialization_poc/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.4.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.4.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.activemq.* (aka activemq-jms, activemq-core, activemq-pool, and activemq-pool-jms).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111>CVE-2020-11111</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_build | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file jackson deserialization poc pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache activemq aka activemq jms activemq core activemq pool and activemq pool jms publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
713,155 | 24,518,555,182 | IssuesEvent | 2022-10-11 07:44:43 | HiAvatar/backend | https://api.github.com/repos/HiAvatar/backend | closed | 영상 생성 요청에 대한 응답으로 videoUrl 추가 | Type: Enhancement Priority: High | ### Description
FE 요구사항으로 인해 영상 생성 요청에 대한 응답으로 videoUrl 추가
<br>
### Todo List
- [x] ProjectService, Dto 수정
<br>
### e.t.c (Optional)
(참조 및 링크 첨부하기)
| 1.0 | 영상 생성 요청에 대한 응답으로 videoUrl 추가 - ### Description
FE 요구사항으로 인해 영상 생성 요청에 대한 응답으로 videoUrl 추가
<br>
### Todo List
- [x] ProjectService, Dto 수정
<br>
### e.t.c (Optional)
(참조 및 링크 첨부하기)
| non_build | 영상 생성 요청에 대한 응답으로 videourl 추가 description fe 요구사항으로 인해 영상 생성 요청에 대한 응답으로 videourl 추가 todo list projectservice dto 수정 e t c optional 참조 및 링크 첨부하기 | 0 |
118,461 | 25,313,513,334 | IssuesEvent | 2022-11-17 19:29:00 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | Aggregation UI integration test has a flake | webapp team/code-insights | In the past few weeks we started to have `Error: Node is either not clickable or not an HTMLElement` error in [this](https://sourcegraph.com/-/editor?remote_url=git%40github.com%3Asourcegraph%2Fsourcegraph.git&branch=main&file=client%2Fweb%2Fsrc%2Fintegration%2Fsearch-aggregation.test.ts&start_row=297&start_col=9&end_row=297&end_col=9&editor=JetBrains&version=v2.0.1) integration test ([example of failed build on the main](https://buildkite.com/sourcegraph/sourcegraph/builds/183787#01847efd-8d92-4f37-9897-81664ff6c927))
We need to fix the test or mute it until we find a root problem there. | 1.0 | Aggregation UI integration test has a flake - In the past few weeks we started to have `Error: Node is either not clickable or not an HTMLElement` error in [this](https://sourcegraph.com/-/editor?remote_url=git%40github.com%3Asourcegraph%2Fsourcegraph.git&branch=main&file=client%2Fweb%2Fsrc%2Fintegration%2Fsearch-aggregation.test.ts&start_row=297&start_col=9&end_row=297&end_col=9&editor=JetBrains&version=v2.0.1) integration test ([example of failed build on the main](https://buildkite.com/sourcegraph/sourcegraph/builds/183787#01847efd-8d92-4f37-9897-81664ff6c927))
We need to fix the test or mute it until we find a root problem there. | non_build | aggregation ui integration test has a flake in the past few weeks we started to have error node is either not clickable or not an htmlelement error in integration test we need to fix the test or mute it until we find a root problem there | 0 |
179,744 | 30,292,974,816 | IssuesEvent | 2023-07-09 14:04:40 | mkdocs/mkdocs | https://api.github.com/repos/mkdocs/mkdocs | closed | Add ability to warn about pages existing in the docs directory but not included in the "nav" configuration | Enhancement Needs design decision | ## Use case
A team uses a CI system and would like to ensure documentation quality never regresses.
To this end, the CI job has a step that runs `mkdocs build --strict` which reports a failure if building the documentation results in any warnings or errors.
However, it can still happen that someone will write new documentation but forget to include it in the `nav` configuration. And MkDocs will detect this and report it. Here is an example output:
```
INFO - The following pages exist in the docs directory, but are not included in the "nav" configuration:
- README.md
- foo.md
```
## Feature request
Would it be possible to configure this INFO message to be a WARNING?
As a bonus, would it be possible to configure which files in the docs directory should be ignored by MkDocs completely? | 1.0 | Add ability to warn about pages existing in the docs directory but not included in the "nav" configuration - ## Use case
A team uses a CI system and would like to ensure documentation quality never regresses.
To this end, the CI job has a step that runs `mkdocs build --strict` which reports a failure if building the documentation results in any warnings or errors.
However, it can still happen that someone will write new documentation but forget to include it in the `nav` configuration. And MkDocs will detect this and report it. Here is an example output:
```
INFO - The following pages exist in the docs directory, but are not included in the "nav" configuration:
- README.md
- foo.md
```
## Feature request
Would it be possible to configure this INFO message to be a WARNING?
As a bonus, would it be possible to configure which files in the docs directory should be ignored by MkDocs completely? | non_build | add ability to warn about pages existing in the docs directory but not included in the nav configuration use case a team uses a ci system and would like to ensure documentation quality never regresses to this end the ci job has a step that runs mkdocs build strict which reports a failure if building the documentation results in any warnings or errors however it can still happen that someone will write new documentation but forget to include it in the nav configuration and mkdocs will detect this and report it here is an example output info the following pages exist in the docs directory but are not included in the nav configuration readme md foo md feature request would it be possible to configure this info message to be a warning as a bonus would it be possible to configure which files in the docs directory should be ignored by mkdocs completely | 0 |
417,301 | 28,110,323,094 | IssuesEvent | 2023-03-31 06:33:48 | russelltankaimin/ped | https://api.github.com/repos/russelltankaimin/ped | opened | [UG] Feature link is broken | type.DocumentationBug severity.Medium | ## Description:
Under Quick Start, Step 6, the word "Features" has embedded link, but when clicked, it does not seem to redirect anywhere.
## Steps to reproduce:
Scroll to Quick Start on your UG, then under step 6, click "Features.
## Expected
Redirected to Features Page
## Actual
No redirection to Features Page
## Picture

Notice the link is "#paperclip-features" but page has still not loaded.
## Reason for severity assessment:
Before I tested your app, I only know about the help and exit command from your UG. I suspect your customer base might end up clueless too on how to continue using the application.
## Potential fix
Not familiar with this but maybe you might have forgotten to include some hrefs? For my team, the #some-name will direct to some header called Some-Name. Perhaps it could have been supposed to be #features? All the best!👍
<!--session: 1680242640335-601a1fe5-8289-4b11-9417-f6e95371a316-->
<!--Version: Web v3.4.7--> | 1.0 | [UG] Feature link is broken - ## Description:
Under Quick Start, Step 6, the word "Features" has embedded link, but when clicked, it does not seem to redirect anywhere.
## Steps to reproduce:
Scroll to Quick Start on your UG, then under step 6, click "Features.
## Expected
Redirected to Features Page
## Actual
No redirection to Features Page
## Picture

Notice the link is "#paperclip-features" but page has still not loaded.
## Reason for severity assessment:
Before I tested your app, I only know about the help and exit command from your UG. I suspect your customer base might end up clueless too on how to continue using the application.
## Potential fix
Not familiar with this but maybe you might have forgotten to include some hrefs? For my team, the #some-name will direct to some header called Some-Name. Perhaps it could have been supposed to be #features? All the best!👍
<!--session: 1680242640335-601a1fe5-8289-4b11-9417-f6e95371a316-->
<!--Version: Web v3.4.7--> | non_build | feature link is broken description under quick start step the word features has embedded link but when clicked it does not seem to redirect anywhere steps to reproduce scroll to quick start on your ug then under step click features expected redirected to features page actual no redirection to features page picture notice the link is paperclip features but page has still not loaded reason for severity assessment before i tested your app i only know about the help and exit command from your ug i suspect your customer base might end up clueless too on how to continue using the application potential fix not familiar with this but maybe you might have forgotten to include some hrefs for my team the some name will direct to some header called some name perhaps it could have been supposed to be features all the best 👍 | 0 |
39,801 | 5,247,103,298 | IssuesEvent | 2017-02-01 11:50:54 | QualiSystems/Azure-Shell | https://api.github.com/repos/QualiSystems/Azure-Shell | closed | Fix app naming | bug in test P3 Version 8.0 | - Replace white spaces with dashes (-) instead of removing the whitespace
- The 15 chars limit is applicable only for windows machines. No need to apply for Linux
- From the API is is possible to give the vm resource a different name form the computer name. So for Windows machines we will only truncate the computer name to 15 chars and keep the original app name for the vm resource.
- The max length of the vm resource is 64 chars | 1.0 | Fix app naming - - Replace white spaces with dashes (-) instead of removing the whitespace
- The 15 chars limit is applicable only for windows machines. No need to apply for Linux
- From the API is is possible to give the vm resource a different name form the computer name. So for Windows machines we will only truncate the computer name to 15 chars and keep the original app name for the vm resource.
- The max length of the vm resource is 64 chars | non_build | fix app naming replace white spaces with dashes instead of removing the whitespace the chars limit is applicable only for windows machines no need to apply for linux from the api is is possible to give the vm resource a different name form the computer name so for windows machines we will only truncate the computer name to chars and keep the original app name for the vm resource the max length of the vm resource is chars | 0 |
78,085 | 14,946,415,716 | IssuesEvent | 2021-01-26 06:44:30 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Update startup_namer codelab for upcoming Flutter relase | d: codelabs passed first triage team | From [failing CI run](https://github.com/flutter/codelabs/pull/49/checks?check_run_id=1724535915#step:7:101):
```
Your application code is in startup_namer/step1_base/lib/main.dart.
+ flutter analyze
Analyzing step1_base...
error • Target of URI doesn't exist: 'package:integration_test/integration_test.dart' • integration_test/app_test.dart:10:8 • uri_does_not_exist
error • Target of URI doesn't exist: 'package:step1_base/main.dart' • integration_test/app_test.dart:12:8 • uri_does_not_exist
error • The function 'run' isn't defined • integration_test/app_test.dart:14:16 • undefined_function
error • Target of URI doesn't exist: 'package:integration_test/integration_test_driver.dart' • integration_test/driver.dart:6:8 • uri_does_not_exist
error • The function 'integrationDriver' isn't defined • integration_test/driver.dart:8:24 • undefined_function
``` | 1.0 | Update startup_namer codelab for upcoming Flutter relase - From [failing CI run](https://github.com/flutter/codelabs/pull/49/checks?check_run_id=1724535915#step:7:101):
```
Your application code is in startup_namer/step1_base/lib/main.dart.
+ flutter analyze
Analyzing step1_base...
error • Target of URI doesn't exist: 'package:integration_test/integration_test.dart' • integration_test/app_test.dart:10:8 • uri_does_not_exist
error • Target of URI doesn't exist: 'package:step1_base/main.dart' • integration_test/app_test.dart:12:8 • uri_does_not_exist
error • The function 'run' isn't defined • integration_test/app_test.dart:14:16 • undefined_function
error • Target of URI doesn't exist: 'package:integration_test/integration_test_driver.dart' • integration_test/driver.dart:6:8 • uri_does_not_exist
error • The function 'integrationDriver' isn't defined • integration_test/driver.dart:8:24 • undefined_function
``` | non_build | update startup namer codelab for upcoming flutter relase from your application code is in startup namer base lib main dart flutter analyze analyzing base error • target of uri doesn t exist package integration test integration test dart • integration test app test dart • uri does not exist error • target of uri doesn t exist package base main dart • integration test app test dart • uri does not exist error • the function run isn t defined • integration test app test dart • undefined function error • target of uri doesn t exist package integration test integration test driver dart • integration test driver dart • uri does not exist error • the function integrationdriver isn t defined • integration test driver dart • undefined function | 0 |
13,381 | 5,350,501,329 | IssuesEvent | 2017-02-19 02:37:07 | neomutt/neomutt | https://api.github.com/repos/neomutt/neomutt | opened | Functional and unit tests for CI | status:in-progress topic:automatization topic:build-process topic:lua-scripting topic:stability type:enhancement | following #222 and all the others discussion about testing. It took me some time, but I finally found out a decent way to implement functional and unit testing for (neo)mutt.
## functional tests
Those are tests being done using the mutt runtime, calling commands using mutt's eventloop. To achieve that, the Lua API is a good way to go #298.
So I've done exactly that: https://gist.github.com/35be5c581aaabf6f1c453cbc2a6e6147
A few tests that are ran by calling:
```
build/mutt -F tests/functional/test_runner.muttrc --batch
```
Those tests will be included in the Lua PR #298.
## unit tests
those ones are a bit trickier. The idea is to to access each header of mutt and test the API exposed through the compiled objects. I've achieved this by using [Luajit]+[FFI], and compiling mutt as a big shared library. To complete the testing toolchain (and load all the headers and symbols), I've stolen a bunch of lua files from neovim/neovim 😀 like [helpers.lua].
And then I wrote a test case for the lists (babysteps!): https://gist.github.com/b12b948616341d8dffd825ae9a5efcea
[FFI]:https://en.wikipedia.org/wiki/Foreign_function_interface
[Luajit]:http://luajit.org
[helpers.lua]:https://github.com/neovim/neovim/blob/master/test/unit/helpers.lua | 1.0 | Functional and unit tests for CI - following #222 and all the others discussion about testing. It took me some time, but I finally found out a decent way to implement functional and unit testing for (neo)mutt.
## functional tests
Those are tests being done using the mutt runtime, calling commands using mutt's eventloop. To achieve that, the Lua API is a good way to go #298.
So I've done exactly that: https://gist.github.com/35be5c581aaabf6f1c453cbc2a6e6147
A few tests that are ran by calling:
```
build/mutt -F tests/functional/test_runner.muttrc --batch
```
Those tests will be included in the Lua PR #298.
## unit tests
those ones are a bit trickier. The idea is to to access each header of mutt and test the API exposed through the compiled objects. I've achieved this by using [Luajit]+[FFI], and compiling mutt as a big shared library. To complete the testing toolchain (and load all the headers and symbols), I've stolen a bunch of lua files from neovim/neovim 😀 like [helpers.lua].
And then I wrote a test case for the lists (babysteps!): https://gist.github.com/b12b948616341d8dffd825ae9a5efcea
[FFI]:https://en.wikipedia.org/wiki/Foreign_function_interface
[Luajit]:http://luajit.org
[helpers.lua]:https://github.com/neovim/neovim/blob/master/test/unit/helpers.lua | build | functional and unit tests for ci following and all the others discussion about testing it took me some time but i finally found out a decent way to implement functional and unit testing for neo mutt functional tests those are tests being done using the mutt runtime calling commands using mutt s eventloop to achieve that the lua api is a good way to go so i ve done exactly that a few tests that are ran by calling build mutt f tests functional test runner muttrc batch those tests will be included in the lua pr unit tests those ones are a bit trickier the idea is to to access each header of mutt and test the api exposed through the compiled objects i ve achieved this by using and compiling mutt as a big shared library to complete the testing toolchain and load all the headers and symbols i ve stolen a bunch of lua files from neovim neovim 😀 like and then i wrote a test case for the lists babysteps | 1 |
65,350 | 16,240,724,037 | IssuesEvent | 2021-05-07 09:12:45 | woocommerce/storefront | https://api.github.com/repos/woocommerce/storefront | closed | Use @wordpress/browserslist-config in .browserslistrc | type: build | ## Is your feature request related to a problem? Please describe.
Feature request
## Describe the solution you'd like
At the moment, https://github.com/woocommerce/storefront/blob/trunk/.browserslistrc holds the definition of supported browsers hard coded. A better way would be to use [@wordpress/browserslist-config](https://www.npmjs.com/package/@wordpress/browserslist-config) to avoid having to update the supported browsers manually.
## Describe alternatives you've considered
No alternatives considered
## Additional context
This approach can be seen for other popular repos as well:
- [https://github.com/WordPress/gutenberg/](https://github.com/WordPress/gutenberg/blob/master/.browserslistrc)
- [https://github.com/WordPress/twentytwentyone/](https://github.com/WordPress/twentytwentyone/blob/06373b9f05a30f5714dfbbb6099d63d16581eb3b/package.json#L49-L51)
- [https://github.com/WordPress/twentytwenty/](https://github.com/WordPress/twentytwenty/blob/6d0a5240af108d02f58ec797fd49b32458a4c698/package.json#L29-L31)
- [https://github.com/WordPress/twentynineteen/](https://github.com/WordPress/twentynineteen/blob/b604f127c2cae10bd48bbbec0fbbbff2cd31f957/package.json#L32-L34) | 1.0 | Use @wordpress/browserslist-config in .browserslistrc - ## Is your feature request related to a problem? Please describe.
Feature request
## Describe the solution you'd like
At the moment, https://github.com/woocommerce/storefront/blob/trunk/.browserslistrc holds the definition of supported browsers hard coded. A better way would be to use [@wordpress/browserslist-config](https://www.npmjs.com/package/@wordpress/browserslist-config) to avoid having to update the supported browsers manually.
## Describe alternatives you've considered
No alternatives considered
## Additional context
This approach can be seen for other popular repos as well:
- [https://github.com/WordPress/gutenberg/](https://github.com/WordPress/gutenberg/blob/master/.browserslistrc)
- [https://github.com/WordPress/twentytwentyone/](https://github.com/WordPress/twentytwentyone/blob/06373b9f05a30f5714dfbbb6099d63d16581eb3b/package.json#L49-L51)
- [https://github.com/WordPress/twentytwenty/](https://github.com/WordPress/twentytwenty/blob/6d0a5240af108d02f58ec797fd49b32458a4c698/package.json#L29-L31)
- [https://github.com/WordPress/twentynineteen/](https://github.com/WordPress/twentynineteen/blob/b604f127c2cae10bd48bbbec0fbbbff2cd31f957/package.json#L32-L34) | build | use wordpress browserslist config in browserslistrc is your feature request related to a problem please describe feature request describe the solution you d like at the moment holds the definition of supported browsers hard coded a better way would be to use to avoid having to update the supported browsers manually describe alternatives you ve considered no alternatives considered additional context this approach can be seen for other popular repos as well | 1 |
96,568 | 8,617,577,191 | IssuesEvent | 2018-11-20 06:18:28 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | projecttesting20 : ApiV1RunsIdTestSuiteSummarySearchGetQueryParamPagesizeNegativeNumber | projecttesting20 | Project : projecttesting20
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=YWUxZTQxNjAtNjdiZS00ODlkLWI3NWItN2JjMDJjYmFkMjEx; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 20 Nov 2018 06:15:30 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/runs/NxvfwLrR/test-suite-summary/search?pageSize=-1
Request :
Response :
{
"timestamp" : "2018-11-20T06:15:31.099+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/runs/NxvfwLrR/test-suite-summary/search"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot --- | 1.0 | projecttesting20 : ApiV1RunsIdTestSuiteSummarySearchGetQueryParamPagesizeNegativeNumber - Project : projecttesting20
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=YWUxZTQxNjAtNjdiZS00ODlkLWI3NWItN2JjMDJjYmFkMjEx; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 20 Nov 2018 06:15:30 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/runs/NxvfwLrR/test-suite-summary/search?pageSize=-1
Request :
Response :
{
"timestamp" : "2018-11-20T06:15:31.099+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/runs/NxvfwLrR/test-suite-summary/search"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot --- | non_build | project job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api runs nxvfwlrr test suite summary search logs assertion resolved to result assertion resolved to result fx bot | 0 |
6,281 | 3,785,755,670 | IssuesEvent | 2016-03-20 18:25:11 | rbenv/rbenv | https://api.github.com/repos/rbenv/rbenv | closed | Failed to install Ruby 1.9.3 on OpenBSD 5.9 | ruby-build |
Compiling Ruby 1.9.3-p551 on OpenBSD 5.9 with the latest rbenv unfortunately fails as you can see below.
```
$ rbenv install 1.9.3-p551
Downloading yaml-0.1.6.tar.gz...
-> https://dqw8nmjcqpjn7.cloudfront.net/7da6971b4bd08a986dd2a61353bc422362bd0edcc67d7ebaac68c95f74182749
Installing yaml-0.1.6...
Installed yaml-0.1.6 to /home/onadmin/.rbenv/versions/1.9.3-p551
Downloading ruby-1.9.3-p551.tar.bz2...
-> https://cache.ruby-lang.org/pub/ruby/1.9/ruby-1.9.3-p551.tar.bz2
Installing ruby-1.9.3-p551...
BUILD FAILED (OpenBSD 5.9 using ruby-build 20160228-5-g522f3ba)
Inspect or clean up the working tree at /tmp/ruby-build.20160318124152.5233
Results logged to /tmp/ruby-build.20160318124152.5233.log
Last 10 log lines:
linking shared-object -test-/string/string.so
compiling wait_for_single_fd.c
installing default wait_for_single_fd libraries
linking shared-object -test-/wait_for_single_fd/wait_for_single_fd.so
compiling bigdecimal.c
cp: cannot overwrite directory ../../.ext/common/bigdecimal with non-directory ../.././ext/bigdecimal/lib/bigdecimal/newton.rb
*** Error 1 in target '../../.ext/common/bigdecimal/newton.rb'
*** Error 1 in ext/bigdecimal (Makefile:178 '../../.ext/common/bigdecimal/newton.rb': @ cp ../.././ext/bigdecimal/lib/bigdecimal/newton.rb ....)
*** Error 2 in . (exts.mk:64 'ext/bigdecimal/all')
*** Error 2 in /tmp/ruby-build.20160318124152.5233/ruby-1.9.3-p551 (Makefile:572 'build-ext')
```
Any ideas what could be going wrong?
Ruby build file is attached here:
[ruby-build.20160318124152.5233.log.txt](https://github.com/rbenv/rbenv/files/179573/ruby-build.20160318124152.5233.log.txt) | 1.0 | Failed to install Ruby 1.9.3 on OpenBSD 5.9 -
Compiling Ruby 1.9.3-p551 on OpenBSD 5.9 with the latest rbenv unfortunately fails as you can see below.
```
$ rbenv install 1.9.3-p551
Downloading yaml-0.1.6.tar.gz...
-> https://dqw8nmjcqpjn7.cloudfront.net/7da6971b4bd08a986dd2a61353bc422362bd0edcc67d7ebaac68c95f74182749
Installing yaml-0.1.6...
Installed yaml-0.1.6 to /home/onadmin/.rbenv/versions/1.9.3-p551
Downloading ruby-1.9.3-p551.tar.bz2...
-> https://cache.ruby-lang.org/pub/ruby/1.9/ruby-1.9.3-p551.tar.bz2
Installing ruby-1.9.3-p551...
BUILD FAILED (OpenBSD 5.9 using ruby-build 20160228-5-g522f3ba)
Inspect or clean up the working tree at /tmp/ruby-build.20160318124152.5233
Results logged to /tmp/ruby-build.20160318124152.5233.log
Last 10 log lines:
linking shared-object -test-/string/string.so
compiling wait_for_single_fd.c
installing default wait_for_single_fd libraries
linking shared-object -test-/wait_for_single_fd/wait_for_single_fd.so
compiling bigdecimal.c
cp: cannot overwrite directory ../../.ext/common/bigdecimal with non-directory ../.././ext/bigdecimal/lib/bigdecimal/newton.rb
*** Error 1 in target '../../.ext/common/bigdecimal/newton.rb'
*** Error 1 in ext/bigdecimal (Makefile:178 '../../.ext/common/bigdecimal/newton.rb': @ cp ../.././ext/bigdecimal/lib/bigdecimal/newton.rb ....)
*** Error 2 in . (exts.mk:64 'ext/bigdecimal/all')
*** Error 2 in /tmp/ruby-build.20160318124152.5233/ruby-1.9.3-p551 (Makefile:572 'build-ext')
```
Any ideas what could be going wrong?
Ruby build file is attached here:
[ruby-build.20160318124152.5233.log.txt](https://github.com/rbenv/rbenv/files/179573/ruby-build.20160318124152.5233.log.txt) | build | failed to install ruby on openbsd compiling ruby on openbsd with the latest rbenv unfortunately fails as you can see below rbenv install downloading yaml tar gz installing yaml installed yaml to home onadmin rbenv versions downloading ruby tar installing ruby build failed openbsd using ruby build inspect or clean up the working tree at tmp ruby build results logged to tmp ruby build log last log lines linking shared object test string string so compiling wait for single fd c installing default wait for single fd libraries linking shared object test wait for single fd wait for single fd so compiling bigdecimal c cp cannot overwrite directory ext common bigdecimal with non directory ext bigdecimal lib bigdecimal newton rb error in target ext common bigdecimal newton rb error in ext bigdecimal makefile ext common bigdecimal newton rb cp ext bigdecimal lib bigdecimal newton rb error in exts mk ext bigdecimal all error in tmp ruby build ruby makefile build ext any ideas what could be going wrong ruby build file is attached here | 1 |
4,148 | 3,297,543,342 | IssuesEvent | 2015-11-02 09:34:25 | systemd/systemd | https://api.github.com/repos/systemd/systemd | closed | Parallel make (-j12) failure | build-system needs-reporter-feedback | On my Arch Linux box with GNU Make 3.82, building via the official instructions:
```
./autogen.sh
./configure CFLAGS='-g -O0 -ftrapv' --enable-compat-libs --enable-kdbus --sysconfdir=/etc --localstatedir=/var --libdir=/usr/lib
make -j12
[...]
CC src/journal/libsystemd_journal_internal_la-journal-authenticate.lo
CC src/journal/libsystemd_journal_internal_la-fsprg.lo
CCLD libudev-internal.la
CC libsystemd_journal_la-libsystemd-journal.lo
libtool: link: `src/libudev/libudev.lo' is not a valid libtool object
make[2]: *** [libudev-internal.la] Error 1
make[2]: *** Waiting for unfinished jobs....
CC libsystemd_login_la-libsystemd-login.lo
make[1]: *** [all-recursive] Error 1
make: *** [all] Error 2
```
But building with `make -j1` works:
```
make -j1
[...]
CC src/libudev/libudev.lo
[...]
CCLD libudev-internal.la
[...]
```
It seems there is a missing dependency from `libudev-internal.la` to `src/libudev/libudev.lo` that (in my case) causes former target to be executed before the latter target is ready.
Has anybody else seen this? Is building with -jN (for N > 1) supported by systemd? | 1.0 | Parallel make (-j12) failure - On my Arch Linux box with GNU Make 3.82, building via the official instructions:
```
./autogen.sh
./configure CFLAGS='-g -O0 -ftrapv' --enable-compat-libs --enable-kdbus --sysconfdir=/etc --localstatedir=/var --libdir=/usr/lib
make -j12
[...]
CC src/journal/libsystemd_journal_internal_la-journal-authenticate.lo
CC src/journal/libsystemd_journal_internal_la-fsprg.lo
CCLD libudev-internal.la
CC libsystemd_journal_la-libsystemd-journal.lo
libtool: link: `src/libudev/libudev.lo' is not a valid libtool object
make[2]: *** [libudev-internal.la] Error 1
make[2]: *** Waiting for unfinished jobs....
CC libsystemd_login_la-libsystemd-login.lo
make[1]: *** [all-recursive] Error 1
make: *** [all] Error 2
```
But building with `make -j1` works:
```
make -j1
[...]
CC src/libudev/libudev.lo
[...]
CCLD libudev-internal.la
[...]
```
It seems there is a missing dependency from `libudev-internal.la` to `src/libudev/libudev.lo` that (in my case) causes former target to be executed before the latter target is ready.
Has anybody else seen this? Is building with -jN (for N > 1) supported by systemd? | build | parallel make failure on my arch linux box with gnu make building via the official instructions autogen sh configure cflags g ftrapv enable compat libs enable kdbus sysconfdir etc localstatedir var libdir usr lib make cc src journal libsystemd journal internal la journal authenticate lo cc src journal libsystemd journal internal la fsprg lo ccld libudev internal la cc libsystemd journal la libsystemd journal lo libtool link src libudev libudev lo is not a valid libtool object make error make waiting for unfinished jobs cc libsystemd login la libsystemd login lo make error make error but building with make works make cc src libudev libudev lo ccld libudev internal la it seems there is a missing dependency from libudev internal la to src libudev libudev lo that in my case causes former target to be executed before the latter target is ready has anybody else seen this is building with jn for n supported by systemd | 1 |
606,625 | 18,766,538,523 | IssuesEvent | 2021-11-06 02:32:02 | AY2122S1-CS2113T-W11-3/tp | https://api.github.com/repos/AY2122S1-CS2113T-W11-3/tp | closed | [PE-D] Listing of Lessons Not in Chronological Order | priority.High | ### Feature - `list lesson`
## Problem
The list feature for lessons are not in chronological order of the lessons but rather the chronological order of the input time.
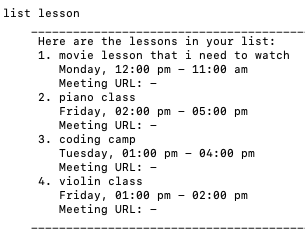
## Suggestion
List the lessons in chronological order the lesson time instead. (eg. in the screenshot above, the order should be `movie lesson`, `coding camp`, `violin class`, `piano class`.)
<!--session: 1635496993936-f323e22b-806c-4255-9050-2f429441bbc2-->
<!--Version: Web v3.4.1-->
-------------
Labels: `severity.Medium` `type.FeatureFlaw`
original: WU-LUOYU-SERENA/ped#4 | 1.0 | [PE-D] Listing of Lessons Not in Chronological Order - ### Feature - `list lesson`
## Problem
The list feature for lessons are not in chronological order of the lessons but rather the chronological order of the input time.
## Suggestion
List the lessons in chronological order the lesson time instead. (eg. in the screenshot above, the order should be `movie lesson`, `coding camp`, `violin class`, `piano class`.)
<!--session: 1635496993936-f323e22b-806c-4255-9050-2f429441bbc2-->
<!--Version: Web v3.4.1-->
-------------
Labels: `severity.Medium` `type.FeatureFlaw`
original: WU-LUOYU-SERENA/ped#4 | non_build | listing of lessons not in chronological order feature list lesson problem the list feature for lessons are not in chronological order of the lessons but rather the chronological order of the input time suggestion list the lessons in chronological order the lesson time instead eg in the screenshot above the order should be movie lesson coding camp violin class piano class labels severity medium type featureflaw original wu luoyu serena ped | 0 |
38,099 | 10,141,578,615 | IssuesEvent | 2019-08-03 15:30:33 | moby/moby | https://api.github.com/repos/moby/moby | closed | "make binary" command fails at last step | area/builder platform/arm | <!--
If you are reporting a new issue, make sure that we do not have any duplicates
already open. You can ensure this by searching the issue list for this
repository. If there is a duplicate, please close your issue and add a comment
to the existing issue instead.
If you suspect your issue is a bug, please edit your issue description to
include the BUG REPORT INFORMATION shown below. If you fail to provide this
information within 7 days, we cannot debug your issue and will close it. We
will, however, reopen it if you later provide the information.
For more information about reporting issues, see
https://github.com/moby/moby/blob/master/CONTRIBUTING.md#reporting-other-issues
---------------------------------------------------
GENERAL SUPPORT INFORMATION
---------------------------------------------------
The GitHub issue tracker is for bug reports and feature requests.
General support for **docker** can be found at the following locations:
- Docker Support Forums - https://forums.docker.com
- Slack - community.docker.com #general channel
- Post a question on StackOverflow, using the Docker tag
General support for **moby** can be found at the following locations:
- Moby Project Forums - https://forums.mobyproject.org
- Slack - community.docker.com #moby-project channel
- Post a question on StackOverflow, using the Moby tag
---------------------------------------------------
BUG REPORT INFORMATION
---------------------------------------------------
Use the commands below to provide key information from your environment:
You do NOT have to include this information if this is a FEATURE REQUEST
-->
**Description**
I have a Raspberry Pi with docker installed. I've cloned the moby/moby github repository on the Pi and issued the command `make binary` to create the binaries. The `make binary` command does not execute successfully and fails with an error message as shared below.
**Steps to reproduce the issue:**
1. Install docker on Raspberry Pi
2. Clone moby/moby github repository
3. Navigate your current directory to moby and run `make binary`. I got the below error in response to this command so I had to specify DOCKER_BUILDKIT=0 along with the make call.
Error on running `make binary`:
```
Makefile:152: The docker client CLI has moved to github.com/docker/cli. For a dev-test cycle involving the CLI, run:
DOCKER_CLI_PATH=/host/path/to/cli/binary make shell
then change the cli and compile into a binary at the same location.
DOCKER_BUILDKIT="1" docker build --build-arg=GO_VERSION --build-arg=CROSS=false -t "docker-dev:master" -f "Dockerfile" .
2019/08/01 19:44:23 http2: server: error reading preface from client /var/run/docker.sock: read unix @->/var/run/docker.sock: read: connection reset by peer
error during connect: Post http://%2Fvar%2Frun%2Fdocker.sock/v1.40/build?buildargs=%7B%22CROSS%22%3A%22false%22%2C%22GO_VERSION%22%3Anull%7D&buildid=579a155b0dcd7671b0aef7f557ff2bdcb94f4cc1b6ca3ba4459d7f32b30eec0a&cachefrom=%5B%5D&cgroupparent=&cpuperiod=0&cpuquota=0&cpusetcpus=&cpusetmems=&cpushares=0&dockerfile=Dockerfile&labels=%7B%7D&memory=0&memswap=0&networkmode=default&remote=client-session&rm=1&session=2ho0e8czxdfou2s8wwgbntt9l&shmsize=0&t=docker-dev%3Amaster&target=&ulimits=null&version=2: EOF
make: *** [Makefile:153: build] Error 1
```
Modified command : `make DOCKER_BUILDKIT=0 binary`
**Describe the results you received:**
Pasting here the last few lines of the output of the command make DOCKER_BUILDKIT=0 binary
```
Step 110/110 : COPY . /go/src/github.com/docker/docker
---> 5fe8d78fc1af
Successfully built 5fe8d78fc1af
Successfully tagged docker-dev:master
docker run --rm -i --privileged -e DOCKER_CROSSPLATFORMS -e BUILD_APT_MIRROR -e BUILDFLAGS -e KEEPBUNDLE -e DOCKER_BUILD_ARGS -e DOCKER_BUILD_GOGC -e DOCKER_BUILD_OPTS -e DOCKER_BUILD_PKGS -e DOCKER_BUILDKIT -e DOCKER_BASH_COMPLETION_PATH -e DOCKER_CLI_PATH -e DOCKER_DEBUG -e DOCKER_EXPERIMENTAL -e DOCKER_GITCOMMIT -e DOCKER_GRAPHDRIVER -e DOCKER_LDFLAGS -e DOCKER_PORT -e DOCKER_REMAP_ROOT -e DOCKER_STORAGE_OPTS -e DOCKER_TEST_HOST -e DOCKER_USERLANDPROXY -e DOCKERD_ARGS -e TEST_INTEGRATION_DIR -e TESTDEBUG -e TESTDIRS -e TESTFLAGS -e TIMEOUT -e VALIDATE_REPO -e VALIDATE_BRANCH -e VALIDATE_ORIGIN_BRANCH -e HTTP_PROXY -e HTTPS_PROXY -e NO_PROXY -e http_proxy -e https_proxy -e no_proxy -e VERSION -e PLATFORM -e DEFAULT_PRODUCT_LICENSE -e PRODUCT -v "/home/pi/go/src/moby/bundles:/go/src/github.com/docker/docker/bundles" -v "/home/pi/go/src/moby/.git:/go/src/github.com/docker/docker/.git" -v docker-dev-cache:/root/.cache -t "docker-dev:master" hack/make.sh binary
Removing bundles/
---> Making bundle: binary (in bundles/binary)
Building: bundles/binary-daemon/dockerd-dev
GOOS="" GOARCH="" GOARM=""
# github.com/docker/docker/cmd/dockerd
/usr/local/go/pkg/tool/linux_arm/link: running gcc failed: fork/exec /usr/bin/gcc: cannot allocate memory
make: *** [Makefile:132: binary] Error 2
```
**Describe the results you expected:**
```
Removing bundles/
---> Making bundle: binary (in bundles/binary)
Building: bundles/binary-daemon/dockerd-dev
GOOS="" GOARCH="" GOARM=""
Created binary: bundles/binary-daemon/dockerd-dev
Copying nested executables into bundles/binary-daemon
```
**Additional information you deem important (e.g. issue happens only occasionally):**
**Output of `docker version`:**
```
Client: Docker Engine - Community
Version: 19.03.1
API version: 1.40
Go version: go1.12.5
Git commit: 74b1e89
Built: Thu Jul 25 21:33:17 2019
OS/Arch: linux/arm
Experimental: false
Server: Docker Engine - Community
Engine:
Version: 19.03.1
API version: 1.40 (minimum version 1.12)
Go version: go1.12.5
Git commit: 74b1e89
Built: Thu Jul 25 21:27:09 2019
OS/Arch: linux/arm
Experimental: false
containerd:
Version: 1.2.6
GitCommit: 894b81a4b802e4eb2a91d1ce216b8817763c29fb
runc:
Version: 1.0.0-rc8
GitCommit: 425e105d5a03fabd737a126ad93d62a9eeede87f
docker-init:
Version: 0.18.0
GitCommit: fec3683
```
**Output of `docker info`:**
```
Client:
Debug Mode: false
Server:
Containers: 2
Running: 0
Paused: 0
Stopped: 2
Images: 88
Server Version: 19.03.1
Storage Driver: overlay2
Backing Filesystem: extfs
Supports d_type: true
Native Overlay Diff: true
Logging Driver: json-file
Cgroup Driver: cgroupfs
Plugins:
Volume: local
Network: bridge host ipvlan macvlan null overlay
Log: awslogs fluentd gcplogs gelf journald json-file local logentries splunk syslog
Swarm: inactive
Runtimes: runc
Default Runtime: runc
Init Binary: docker-init
containerd version: 894b81a4b802e4eb2a91d1ce216b8817763c29fb
runc version: 425e105d5a03fabd737a126ad93d62a9eeede87f
init version: fec3683
Security Options:
seccomp
Profile: default
Kernel Version: 4.19.57-v7+
Operating System: Raspbian GNU/Linux 10 (buster)
OSType: linux
Architecture: armv7l
CPUs: 4
Total Memory: 926.1MiB
Name: raspberrypi
ID: IJVJ:EY33:W32Y:JZFL:SJKN:CL65:GOFC:LNPB:4RUQ:W47C:46JT:TCLW
Docker Root Dir: /var/lib/docker
Debug Mode: false
Registry: https://index.docker.io/v1/
Labels:
Experimental: false
Insecure Registries:
127.0.0.0/8
Live Restore Enabled: false
WARNING: No swap limit support
WARNING: No cpu cfs quota support
WARNING: No cpu cfs period support
```
**Additional environment details (AWS, VirtualBox, physical, etc.):**
Hardware: Raspberry Pi 3B+
| 1.0 | "make binary" command fails at last step - <!--
If you are reporting a new issue, make sure that we do not have any duplicates
already open. You can ensure this by searching the issue list for this
repository. If there is a duplicate, please close your issue and add a comment
to the existing issue instead.
If you suspect your issue is a bug, please edit your issue description to
include the BUG REPORT INFORMATION shown below. If you fail to provide this
information within 7 days, we cannot debug your issue and will close it. We
will, however, reopen it if you later provide the information.
For more information about reporting issues, see
https://github.com/moby/moby/blob/master/CONTRIBUTING.md#reporting-other-issues
---------------------------------------------------
GENERAL SUPPORT INFORMATION
---------------------------------------------------
The GitHub issue tracker is for bug reports and feature requests.
General support for **docker** can be found at the following locations:
- Docker Support Forums - https://forums.docker.com
- Slack - community.docker.com #general channel
- Post a question on StackOverflow, using the Docker tag
General support for **moby** can be found at the following locations:
- Moby Project Forums - https://forums.mobyproject.org
- Slack - community.docker.com #moby-project channel
- Post a question on StackOverflow, using the Moby tag
---------------------------------------------------
BUG REPORT INFORMATION
---------------------------------------------------
Use the commands below to provide key information from your environment:
You do NOT have to include this information if this is a FEATURE REQUEST
-->
**Description**
I have a Raspberry Pi with docker installed. I've cloned the moby/moby github repository on the Pi and issued the command `make binary` to create the binaries. The `make binary` command does not execute successfully and fails with an error message as shared below.
**Steps to reproduce the issue:**
1. Install docker on Raspberry Pi
2. Clone moby/moby github repository
3. Navigate your current directory to moby and run `make binary`. I got the below error in response to this command so I had to specify DOCKER_BUILDKIT=0 along with the make call.
Error on running `make binary`:
```
Makefile:152: The docker client CLI has moved to github.com/docker/cli. For a dev-test cycle involving the CLI, run:
DOCKER_CLI_PATH=/host/path/to/cli/binary make shell
then change the cli and compile into a binary at the same location.
DOCKER_BUILDKIT="1" docker build --build-arg=GO_VERSION --build-arg=CROSS=false -t "docker-dev:master" -f "Dockerfile" .
2019/08/01 19:44:23 http2: server: error reading preface from client /var/run/docker.sock: read unix @->/var/run/docker.sock: read: connection reset by peer
error during connect: Post http://%2Fvar%2Frun%2Fdocker.sock/v1.40/build?buildargs=%7B%22CROSS%22%3A%22false%22%2C%22GO_VERSION%22%3Anull%7D&buildid=579a155b0dcd7671b0aef7f557ff2bdcb94f4cc1b6ca3ba4459d7f32b30eec0a&cachefrom=%5B%5D&cgroupparent=&cpuperiod=0&cpuquota=0&cpusetcpus=&cpusetmems=&cpushares=0&dockerfile=Dockerfile&labels=%7B%7D&memory=0&memswap=0&networkmode=default&remote=client-session&rm=1&session=2ho0e8czxdfou2s8wwgbntt9l&shmsize=0&t=docker-dev%3Amaster&target=&ulimits=null&version=2: EOF
make: *** [Makefile:153: build] Error 1
```
Modified command : `make DOCKER_BUILDKIT=0 binary`
**Describe the results you received:**
Pasting here the last few lines of the output of the command make DOCKER_BUILDKIT=0 binary
```
Step 110/110 : COPY . /go/src/github.com/docker/docker
---> 5fe8d78fc1af
Successfully built 5fe8d78fc1af
Successfully tagged docker-dev:master
docker run --rm -i --privileged -e DOCKER_CROSSPLATFORMS -e BUILD_APT_MIRROR -e BUILDFLAGS -e KEEPBUNDLE -e DOCKER_BUILD_ARGS -e DOCKER_BUILD_GOGC -e DOCKER_BUILD_OPTS -e DOCKER_BUILD_PKGS -e DOCKER_BUILDKIT -e DOCKER_BASH_COMPLETION_PATH -e DOCKER_CLI_PATH -e DOCKER_DEBUG -e DOCKER_EXPERIMENTAL -e DOCKER_GITCOMMIT -e DOCKER_GRAPHDRIVER -e DOCKER_LDFLAGS -e DOCKER_PORT -e DOCKER_REMAP_ROOT -e DOCKER_STORAGE_OPTS -e DOCKER_TEST_HOST -e DOCKER_USERLANDPROXY -e DOCKERD_ARGS -e TEST_INTEGRATION_DIR -e TESTDEBUG -e TESTDIRS -e TESTFLAGS -e TIMEOUT -e VALIDATE_REPO -e VALIDATE_BRANCH -e VALIDATE_ORIGIN_BRANCH -e HTTP_PROXY -e HTTPS_PROXY -e NO_PROXY -e http_proxy -e https_proxy -e no_proxy -e VERSION -e PLATFORM -e DEFAULT_PRODUCT_LICENSE -e PRODUCT -v "/home/pi/go/src/moby/bundles:/go/src/github.com/docker/docker/bundles" -v "/home/pi/go/src/moby/.git:/go/src/github.com/docker/docker/.git" -v docker-dev-cache:/root/.cache -t "docker-dev:master" hack/make.sh binary
Removing bundles/
---> Making bundle: binary (in bundles/binary)
Building: bundles/binary-daemon/dockerd-dev
GOOS="" GOARCH="" GOARM=""
# github.com/docker/docker/cmd/dockerd
/usr/local/go/pkg/tool/linux_arm/link: running gcc failed: fork/exec /usr/bin/gcc: cannot allocate memory
make: *** [Makefile:132: binary] Error 2
```
**Describe the results you expected:**
```
Removing bundles/
---> Making bundle: binary (in bundles/binary)
Building: bundles/binary-daemon/dockerd-dev
GOOS="" GOARCH="" GOARM=""
Created binary: bundles/binary-daemon/dockerd-dev
Copying nested executables into bundles/binary-daemon
```
**Additional information you deem important (e.g. issue happens only occasionally):**
**Output of `docker version`:**
```
Client: Docker Engine - Community
Version: 19.03.1
API version: 1.40
Go version: go1.12.5
Git commit: 74b1e89
Built: Thu Jul 25 21:33:17 2019
OS/Arch: linux/arm
Experimental: false
Server: Docker Engine - Community
Engine:
Version: 19.03.1
API version: 1.40 (minimum version 1.12)
Go version: go1.12.5
Git commit: 74b1e89
Built: Thu Jul 25 21:27:09 2019
OS/Arch: linux/arm
Experimental: false
containerd:
Version: 1.2.6
GitCommit: 894b81a4b802e4eb2a91d1ce216b8817763c29fb
runc:
Version: 1.0.0-rc8
GitCommit: 425e105d5a03fabd737a126ad93d62a9eeede87f
docker-init:
Version: 0.18.0
GitCommit: fec3683
```
**Output of `docker info`:**
```
Client:
Debug Mode: false
Server:
Containers: 2
Running: 0
Paused: 0
Stopped: 2
Images: 88
Server Version: 19.03.1
Storage Driver: overlay2
Backing Filesystem: extfs
Supports d_type: true
Native Overlay Diff: true
Logging Driver: json-file
Cgroup Driver: cgroupfs
Plugins:
Volume: local
Network: bridge host ipvlan macvlan null overlay
Log: awslogs fluentd gcplogs gelf journald json-file local logentries splunk syslog
Swarm: inactive
Runtimes: runc
Default Runtime: runc
Init Binary: docker-init
containerd version: 894b81a4b802e4eb2a91d1ce216b8817763c29fb
runc version: 425e105d5a03fabd737a126ad93d62a9eeede87f
init version: fec3683
Security Options:
seccomp
Profile: default
Kernel Version: 4.19.57-v7+
Operating System: Raspbian GNU/Linux 10 (buster)
OSType: linux
Architecture: armv7l
CPUs: 4
Total Memory: 926.1MiB
Name: raspberrypi
ID: IJVJ:EY33:W32Y:JZFL:SJKN:CL65:GOFC:LNPB:4RUQ:W47C:46JT:TCLW
Docker Root Dir: /var/lib/docker
Debug Mode: false
Registry: https://index.docker.io/v1/
Labels:
Experimental: false
Insecure Registries:
127.0.0.0/8
Live Restore Enabled: false
WARNING: No swap limit support
WARNING: No cpu cfs quota support
WARNING: No cpu cfs period support
```
**Additional environment details (AWS, VirtualBox, physical, etc.):**
Hardware: Raspberry Pi 3B+
| build | make binary command fails at last step if you are reporting a new issue make sure that we do not have any duplicates already open you can ensure this by searching the issue list for this repository if there is a duplicate please close your issue and add a comment to the existing issue instead if you suspect your issue is a bug please edit your issue description to include the bug report information shown below if you fail to provide this information within days we cannot debug your issue and will close it we will however reopen it if you later provide the information for more information about reporting issues see general support information the github issue tracker is for bug reports and feature requests general support for docker can be found at the following locations docker support forums slack community docker com general channel post a question on stackoverflow using the docker tag general support for moby can be found at the following locations moby project forums slack community docker com moby project channel post a question on stackoverflow using the moby tag bug report information use the commands below to provide key information from your environment you do not have to include this information if this is a feature request description i have a raspberry pi with docker installed i ve cloned the moby moby github repository on the pi and issued the command make binary to create the binaries the make binary command does not execute successfully and fails with an error message as shared below steps to reproduce the issue install docker on raspberry pi clone moby moby github repository navigate your current directory to moby and run make binary i got the below error in response to this command so i had to specify docker buildkit along with the make call error on running make binary makefile the docker client cli has moved to github com docker cli for a dev test cycle involving the cli run docker cli path host path to cli binary make shell then change the cli and compile into a binary at the same location docker buildkit docker build build arg go version build arg cross false t docker dev master f dockerfile server error reading preface from client var run docker sock read unix var run docker sock read connection reset by peer error during connect post eof make error modified command make docker buildkit binary describe the results you received pasting here the last few lines of the output of the command make docker buildkit binary step copy go src github com docker docker successfully built successfully tagged docker dev master docker run rm i privileged e docker crossplatforms e build apt mirror e buildflags e keepbundle e docker build args e docker build gogc e docker build opts e docker build pkgs e docker buildkit e docker bash completion path e docker cli path e docker debug e docker experimental e docker gitcommit e docker graphdriver e docker ldflags e docker port e docker remap root e docker storage opts e docker test host e docker userlandproxy e dockerd args e test integration dir e testdebug e testdirs e testflags e timeout e validate repo e validate branch e validate origin branch e http proxy e https proxy e no proxy e http proxy e https proxy e no proxy e version e platform e default product license e product v home pi go src moby bundles go src github com docker docker bundles v home pi go src moby git go src github com docker docker git v docker dev cache root cache t docker dev master hack make sh binary removing bundles making bundle binary in bundles binary building bundles binary daemon dockerd dev goos goarch goarm github com docker docker cmd dockerd usr local go pkg tool linux arm link running gcc failed fork exec usr bin gcc cannot allocate memory make error describe the results you expected removing bundles making bundle binary in bundles binary building bundles binary daemon dockerd dev goos goarch goarm created binary bundles binary daemon dockerd dev copying nested executables into bundles binary daemon additional information you deem important e g issue happens only occasionally output of docker version client docker engine community version api version go version git commit built thu jul os arch linux arm experimental false server docker engine community engine version api version minimum version go version git commit built thu jul os arch linux arm experimental false containerd version gitcommit runc version gitcommit docker init version gitcommit output of docker info client debug mode false server containers running paused stopped images server version storage driver backing filesystem extfs supports d type true native overlay diff true logging driver json file cgroup driver cgroupfs plugins volume local network bridge host ipvlan macvlan null overlay log awslogs fluentd gcplogs gelf journald json file local logentries splunk syslog swarm inactive runtimes runc default runtime runc init binary docker init containerd version runc version init version security options seccomp profile default kernel version operating system raspbian gnu linux buster ostype linux architecture cpus total memory name raspberrypi id ijvj jzfl sjkn gofc lnpb tclw docker root dir var lib docker debug mode false registry labels experimental false insecure registries live restore enabled false warning no swap limit support warning no cpu cfs quota support warning no cpu cfs period support additional environment details aws virtualbox physical etc hardware raspberry pi | 1 |
264,389 | 20,017,925,891 | IssuesEvent | 2022-02-01 13:55:36 | demisto/content-docs | https://api.github.com/repos/demisto/content-docs | opened | Issue with "Microsoft Policy And Compliance (Audit Log)" in @site/docs/reference/integrations/microsoft-policy-and-compliance-audit-log.md | documentation |
## Describe the problem
* Page: [Microsoft Policy And Compliance (Audit Log)](https://xsoar.pan.dev/docs/reference/integrations/microsoft-policy-and-compliance-audit-log)
* Source: https://github.com/demisto/content/blob/master//Packs/Office365AndAzureAuditLog/Integrations/MicrosoftPolicyAndComplianceAuditLog/README.md
Customer reports no information on why/how to set MS permissions for this integration.
## Suggested fix
Add more details or a link MS site on what permissions are required
| 1.0 | Issue with "Microsoft Policy And Compliance (Audit Log)" in @site/docs/reference/integrations/microsoft-policy-and-compliance-audit-log.md -
## Describe the problem
* Page: [Microsoft Policy And Compliance (Audit Log)](https://xsoar.pan.dev/docs/reference/integrations/microsoft-policy-and-compliance-audit-log)
* Source: https://github.com/demisto/content/blob/master//Packs/Office365AndAzureAuditLog/Integrations/MicrosoftPolicyAndComplianceAuditLog/README.md
Customer reports no information on why/how to set MS permissions for this integration.
## Suggested fix
Add more details or a link MS site on what permissions are required
| non_build | issue with microsoft policy and compliance audit log in site docs reference integrations microsoft policy and compliance audit log md describe the problem page source customer reports no information on why how to set ms permissions for this integration suggested fix add more details or a link ms site on what permissions are required | 0 |
44,752 | 11,499,243,645 | IssuesEvent | 2020-02-12 13:36:46 | pymor/pymor | https://api.github.com/repos/pymor/pymor | opened | Auto generate scripts from tutorials | buildsystem docs | and them into an easily discoverable directory (`docs/scripts`?).
Supersedes #573. | 1.0 | Auto generate scripts from tutorials - and them into an easily discoverable directory (`docs/scripts`?).
Supersedes #573. | build | auto generate scripts from tutorials and them into an easily discoverable directory docs scripts supersedes | 1 |
58,447 | 14,397,825,006 | IssuesEvent | 2020-12-03 08:45:56 | ballerina-platform/ballerina-standard-library | https://api.github.com/repos/ballerina-platform/ballerina-standard-library | closed | Update Readme.md when updating module dependencies | area/build | We now have a workflow to update the standard library dependencies. It will generate the [`stdlib_modules.json`](https://github.com/ballerina-platform/ballerina-standard-library/blob/main/release/resources/stdlib_modules.json) file with the correct levels and the dependencies. But this workflow still not updating the Readme.md, which contains the standard library dashboard.
When there is a change in levels, the status dashboard should also be updated. | 1.0 | Update Readme.md when updating module dependencies - We now have a workflow to update the standard library dependencies. It will generate the [`stdlib_modules.json`](https://github.com/ballerina-platform/ballerina-standard-library/blob/main/release/resources/stdlib_modules.json) file with the correct levels and the dependencies. But this workflow still not updating the Readme.md, which contains the standard library dashboard.
When there is a change in levels, the status dashboard should also be updated. | build | update readme md when updating module dependencies we now have a workflow to update the standard library dependencies it will generate the file with the correct levels and the dependencies but this workflow still not updating the readme md which contains the standard library dashboard when there is a change in levels the status dashboard should also be updated | 1 |
92,928 | 3,875,307,857 | IssuesEvent | 2016-04-12 00:15:27 | BYU-ARCLITE/Ayamel-Examples | https://api.github.com/repos/BYU-ARCLITE/Ayamel-Examples | closed | "Clone with Translation" Concatenating Words | Bug CaptionAider Priority 1 | For the purpose of creating a new track with translations, when a caption has two lines, the last word of the first line and the first word of the second line are concatenated. The results in an incorrect translation as shown below:

| 1.0 | "Clone with Translation" Concatenating Words - For the purpose of creating a new track with translations, when a caption has two lines, the last word of the first line and the first word of the second line are concatenated. The results in an incorrect translation as shown below:

| non_build | clone with translation concatenating words for the purpose of creating a new track with translations when a caption has two lines the last word of the first line and the first word of the second line are concatenated the results in an incorrect translation as shown below | 0 |
43,187 | 11,171,839,330 | IssuesEvent | 2019-12-28 23:33:06 | skypjack/entt | https://api.github.com/repos/skypjack/entt | opened | Remove in-repo Conan support | build system | Conan is switching to a different model (see [this issue](https://github.com/conan-io/conan-center-index/issues/550) for further details) and therefore the in-repo stuff is no longer required. | 1.0 | Remove in-repo Conan support - Conan is switching to a different model (see [this issue](https://github.com/conan-io/conan-center-index/issues/550) for further details) and therefore the in-repo stuff is no longer required. | build | remove in repo conan support conan is switching to a different model see for further details and therefore the in repo stuff is no longer required | 1 |
54,929 | 13,486,457,593 | IssuesEvent | 2020-09-11 09:29:14 | akka/akka | https://api.github.com/repos/akka/akka | closed | Make sbt clean out parts of local maven repo | 1 - triaged t:build | imported from https://www.assembla.com/spaces/akka/tickets/3939
We should clean out SNAPSHOT versions of akka artifacts from the local .m2 repo (at least during PR validation) to find broken version dependencies. See #13936
| 1.0 | Make sbt clean out parts of local maven repo - imported from https://www.assembla.com/spaces/akka/tickets/3939
We should clean out SNAPSHOT versions of akka artifacts from the local .m2 repo (at least during PR validation) to find broken version dependencies. See #13936
| build | make sbt clean out parts of local maven repo imported from we should clean out snapshot versions of akka artifacts from the local repo at least during pr validation to find broken version dependencies see | 1 |
68,288 | 17,209,655,287 | IssuesEvent | 2021-07-19 00:56:08 | t3kt/raytk | https://api.github.com/repos/t3kt/raytk | closed | Move op status from tags to parameters on opDefinition | build process infrastructure | Tags don't seem to handle clone-based updating properly. | 1.0 | Move op status from tags to parameters on opDefinition - Tags don't seem to handle clone-based updating properly. | build | move op status from tags to parameters on opdefinition tags don t seem to handle clone based updating properly | 1 |
32,327 | 12,103,028,721 | IssuesEvent | 2020-04-20 17:41:21 | Baneeishaque/educature-education | https://api.github.com/repos/Baneeishaque/educature-education | opened | CVE-2015-9251 (Medium) detected in jquery-2.2.4.min.js, jquery-1.11.0.min.js | security vulnerability | ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.2.4.min.js</b>, <b>jquery-1.11.0.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.2.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/educature-education/courses.html</p>
<p>Path to vulnerable library: /educature-education/js/vendor/jquery-2.2.4.min.js,/educature-education/js/vendor/jquery-2.2.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.0/jquery.min.js</a></p>
<p>Path to vulnerable library: /educature-education/Educature Education - Doc/js/jquery-1.11.0.min.js,/educature-education/Educature Education - Doc/js/jquery-1.11.0.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.0.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/educature-education/commit/fb910a573322109f6149cb994a649ec421e47511">fb910a573322109f6149cb994a649ec421e47511</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-9251 (Medium) detected in jquery-2.2.4.min.js, jquery-1.11.0.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.2.4.min.js</b>, <b>jquery-1.11.0.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.2.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/educature-education/courses.html</p>
<p>Path to vulnerable library: /educature-education/js/vendor/jquery-2.2.4.min.js,/educature-education/js/vendor/jquery-2.2.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.0/jquery.min.js</a></p>
<p>Path to vulnerable library: /educature-education/Educature Education - Doc/js/jquery-1.11.0.min.js,/educature-education/Educature Education - Doc/js/jquery-1.11.0.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.0.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/educature-education/commit/fb910a573322109f6149cb994a649ec421e47511">fb910a573322109f6149cb994a649ec421e47511</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_build | cve medium detected in jquery min js jquery min js cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm educature education courses html path to vulnerable library educature education js vendor jquery min js educature education js vendor jquery min js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library educature education educature education doc js jquery min js educature education educature education doc js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
517,576 | 15,016,439,387 | IssuesEvent | 2021-02-01 09:35:35 | rtCamp/web-stories-wp | https://api.github.com/repos/rtCamp/web-stories-wp | closed | Fix e2e tests | priority:high stage:wip | <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Bug Description
Most recent updates on the `feature/embed-stories` branch, the new PRs are failing the e2e tests checks.
It is highly likely that this was introduced in PR #190.
Tests are failing with a fatal error for exceeding the allowed memory usage as seen [here](https://github.com/rtCamp/web-stories-wp/runs/1776468263?check_suite_focus=true).
I did try increasing the memory limit and re-run the tests, in this case, there were navigation timeout [errors.](https://github.com/rtCamp/web-stories-wp/pull/257/checks?check_run_id=1783610167)
## Expected Behaviour
Tests should pass without any failures.
## Steps to Reproduce
- Create a new branch from `feature/embed-stories`
- Make changes if any.
- Raise PR against the base branch or run the tests locally.
---
_Do not alter or remove anything below. The following sections will be managed by moderators only._
## Acceptance Criteria
<!-- One or more bullet points for acceptance criteria. -->
## Implementation Brief
<!-- One or more bullet points for how to technically implement the feature. -->
| 1.0 | Fix e2e tests - <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Bug Description
Most recent updates on the `feature/embed-stories` branch, the new PRs are failing the e2e tests checks.
It is highly likely that this was introduced in PR #190.
Tests are failing with a fatal error for exceeding the allowed memory usage as seen [here](https://github.com/rtCamp/web-stories-wp/runs/1776468263?check_suite_focus=true).
I did try increasing the memory limit and re-run the tests, in this case, there were navigation timeout [errors.](https://github.com/rtCamp/web-stories-wp/pull/257/checks?check_run_id=1783610167)
## Expected Behaviour
Tests should pass without any failures.
## Steps to Reproduce
- Create a new branch from `feature/embed-stories`
- Make changes if any.
- Raise PR against the base branch or run the tests locally.
---
_Do not alter or remove anything below. The following sections will be managed by moderators only._
## Acceptance Criteria
<!-- One or more bullet points for acceptance criteria. -->
## Implementation Brief
<!-- One or more bullet points for how to technically implement the feature. -->
| non_build | fix tests bug description most recent updates on the feature embed stories branch the new prs are failing the tests checks it is highly likely that this was introduced in pr tests are failing with a fatal error for exceeding the allowed memory usage as seen i did try increasing the memory limit and re run the tests in this case there were navigation timeout expected behaviour tests should pass without any failures steps to reproduce create a new branch from feature embed stories make changes if any raise pr against the base branch or run the tests locally do not alter or remove anything below the following sections will be managed by moderators only acceptance criteria implementation brief | 0 |
53,027 | 6,671,499,500 | IssuesEvent | 2017-10-04 07:36:55 | idris-lang/Idris-dev | https://api.github.com/repos/idris-lang/Idris-dev | closed | Idris calls C compiler with arguments in wrong order | A-Confirmed C-Low Hanging Fruit G-C Backend S-Normal U-Language Design | After parsing `%flag` directives the Idris backend calls the C compiler with the flags in the opposite order, which breaks some order-dependent flags. For instance, the following directive:
```
%flag C "-L/usr/local/IUP/lib -Wl,-Bstatic -Wl,-liup -Wl,-Bdynamic"
```
will result in the following arguments to the C compiler:
```
"-Wl,-Bdynamic","-Wl,-liup","-Wl,-Bstatic","-L/usr/local/IUP/lib"
```
which obviously has the opposite effect.
| 1.0 | Idris calls C compiler with arguments in wrong order - After parsing `%flag` directives the Idris backend calls the C compiler with the flags in the opposite order, which breaks some order-dependent flags. For instance, the following directive:
```
%flag C "-L/usr/local/IUP/lib -Wl,-Bstatic -Wl,-liup -Wl,-Bdynamic"
```
will result in the following arguments to the C compiler:
```
"-Wl,-Bdynamic","-Wl,-liup","-Wl,-Bstatic","-L/usr/local/IUP/lib"
```
which obviously has the opposite effect.
| non_build | idris calls c compiler with arguments in wrong order after parsing flag directives the idris backend calls the c compiler with the flags in the opposite order which breaks some order dependent flags for instance the following directive flag c l usr local iup lib wl bstatic wl liup wl bdynamic will result in the following arguments to the c compiler wl bdynamic wl liup wl bstatic l usr local iup lib which obviously has the opposite effect | 0 |
41,022 | 10,604,061,374 | IssuesEvent | 2019-10-10 17:20:28 | grpc/grpc | https://api.github.com/repos/grpc/grpc | closed | C# build failing for unclear reason | infra/BUILDPONY kind/bug lang/C# | ERROR: type should be string, got "https://source.cloud.google.com/results/invocations/afc994a2-46fb-4a02-87e9-377c0c657f3d/targets\r\n\r\nEnd of relevant log output:\r\n\r\n```\r\n\r\nBuild succeeded.\r\n 0 Warning(s)\r\n 0 Error(s)\r\nTime Elapsed 00:00:15.38\r\n2019-05-15 17:03:47,245 FAILED: tools/run_tests/helper_scripts/build_csharp.sh [ret=134, pid=7043, time=16.1sec]\r\n2019-05-15 17:03:47,245 FAILED: Some tests failed\r\n adding: reports/ (stored 0%)\r\n+ DOCKER_EXIT_CODE=1\r\n++ mktemp\r\n+ TEMP_REPORTS_ZIP=/tmpfs/tmp/tmp.4SzwJ3J9Mx\r\n+ docker cp run_tests_ce16a783-f198-49a1-be8c-4291e7191955:/var/local/git/grpc/reports.zip /tmpfs/tmp/tmp.4SzwJ3J9Mx\r\n+ unzip -o /tmpfs/tmp/tmp.4SzwJ3J9Mx -d /tmpfs/src/github/grpc\r\nArchive: /tmpfs/tmp/tmp.4SzwJ3J9Mx\r\n creating: /tmpfs/src/github/grpc/reports/\r\n+ rm -f /tmpfs/tmp/tmp.4SzwJ3J9Mx\r\n+ docker rm -f run_tests_ce16a783-f198-49a1-be8c-4291e7191955\r\nrun_tests_ce16a783-f198-49a1-be8c-4291e7191955\r\n+ exit 1\r\nTraceback (most recent call last):\r\n File \"tools/run_tests/run_tests.py\", line 1540, in <module>\r\n env=env)\r\n File \"/usr/lib/python2.7/subprocess.py\", line 540, in check_call\r\n raise CalledProcessError(retcode, cmd)\r\nsubprocess.CalledProcessError: Command 'tools/run_tests/dockerize/build_docker_and_run_tests.sh' returned non-zero exit status 1\r\n2019-05-15 10:03:50,457 FAILED: run_tests_csharp_linux_opt_native [ret=1, pid=8980, time=147.7sec]\r\n```" | 1.0 | C# build failing for unclear reason - https://source.cloud.google.com/results/invocations/afc994a2-46fb-4a02-87e9-377c0c657f3d/targets
End of relevant log output:
```
Build succeeded.
0 Warning(s)
0 Error(s)
Time Elapsed 00:00:15.38
2019-05-15 17:03:47,245 FAILED: tools/run_tests/helper_scripts/build_csharp.sh [ret=134, pid=7043, time=16.1sec]
2019-05-15 17:03:47,245 FAILED: Some tests failed
adding: reports/ (stored 0%)
+ DOCKER_EXIT_CODE=1
++ mktemp
+ TEMP_REPORTS_ZIP=/tmpfs/tmp/tmp.4SzwJ3J9Mx
+ docker cp run_tests_ce16a783-f198-49a1-be8c-4291e7191955:/var/local/git/grpc/reports.zip /tmpfs/tmp/tmp.4SzwJ3J9Mx
+ unzip -o /tmpfs/tmp/tmp.4SzwJ3J9Mx -d /tmpfs/src/github/grpc
Archive: /tmpfs/tmp/tmp.4SzwJ3J9Mx
creating: /tmpfs/src/github/grpc/reports/
+ rm -f /tmpfs/tmp/tmp.4SzwJ3J9Mx
+ docker rm -f run_tests_ce16a783-f198-49a1-be8c-4291e7191955
run_tests_ce16a783-f198-49a1-be8c-4291e7191955
+ exit 1
Traceback (most recent call last):
File "tools/run_tests/run_tests.py", line 1540, in <module>
env=env)
File "/usr/lib/python2.7/subprocess.py", line 540, in check_call
raise CalledProcessError(retcode, cmd)
subprocess.CalledProcessError: Command 'tools/run_tests/dockerize/build_docker_and_run_tests.sh' returned non-zero exit status 1
2019-05-15 10:03:50,457 FAILED: run_tests_csharp_linux_opt_native [ret=1, pid=8980, time=147.7sec]
``` | build | c build failing for unclear reason end of relevant log output build succeeded warning s error s time elapsed failed tools run tests helper scripts build csharp sh failed some tests failed adding reports stored docker exit code mktemp temp reports zip tmpfs tmp tmp docker cp run tests var local git grpc reports zip tmpfs tmp tmp unzip o tmpfs tmp tmp d tmpfs src github grpc archive tmpfs tmp tmp creating tmpfs src github grpc reports rm f tmpfs tmp tmp docker rm f run tests run tests exit traceback most recent call last file tools run tests run tests py line in env env file usr lib subprocess py line in check call raise calledprocesserror retcode cmd subprocess calledprocesserror command tools run tests dockerize build docker and run tests sh returned non zero exit status failed run tests csharp linux opt native | 1 |
223,421 | 7,453,707,832 | IssuesEvent | 2018-03-29 12:56:04 | cilium/cilium | https://api.github.com/repos/cilium/cilium | opened | Disable CNP v2 CRD for new installations | priority/release-blocker | We can't install CNP v2 CRD for new clusters since the user might have already switched to v3, so we will only watch for CNP v2 in case the user is already running v2 on an existing cluster.
Unfortunately, if we don't install it for new clusters the e2e tests will fail because they use v2 policies so I've temporarily installing CNP v2 CRD until either:
1) We replace all k8s e2e tests with v3.
2) Or manually install the v2 cilium CRD on new testing clusters before running e2e. | 1.0 | Disable CNP v2 CRD for new installations - We can't install CNP v2 CRD for new clusters since the user might have already switched to v3, so we will only watch for CNP v2 in case the user is already running v2 on an existing cluster.
Unfortunately, if we don't install it for new clusters the e2e tests will fail because they use v2 policies so I've temporarily installing CNP v2 CRD until either:
1) We replace all k8s e2e tests with v3.
2) Or manually install the v2 cilium CRD on new testing clusters before running e2e. | non_build | disable cnp crd for new installations we can t install cnp crd for new clusters since the user might have already switched to so we will only watch for cnp in case the user is already running on an existing cluster unfortunately if we don t install it for new clusters the tests will fail because they use policies so i ve temporarily installing cnp crd until either we replace all tests with or manually install the cilium crd on new testing clusters before running | 0 |
302,510 | 9,260,941,832 | IssuesEvent | 2019-03-18 07:46:06 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | d2az0u4t6eqmie.cloudfront.net - see bug description | browser-firefox-mobile priority-important | <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: -->
**URL**: http://d2az0u4t6eqmie.cloudfront.net/creative/c/10/?cid=54
**Browser / Version**: Firefox Mobile 65.0
**Operating System**: Android
**Tested Another Browser**: No
**Problem type**: Something else
**Description**: spam
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | d2az0u4t6eqmie.cloudfront.net - see bug description - <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: -->
**URL**: http://d2az0u4t6eqmie.cloudfront.net/creative/c/10/?cid=54
**Browser / Version**: Firefox Mobile 65.0
**Operating System**: Android
**Tested Another Browser**: No
**Problem type**: Something else
**Description**: spam
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_build | cloudfront net see bug description url browser version firefox mobile operating system android tested another browser no problem type something else description spam steps to reproduce browser configuration none from with ❤️ | 0 |
802,631 | 29,042,458,887 | IssuesEvent | 2023-05-13 05:34:35 | IAmTamal/Milan | https://api.github.com/repos/IAmTamal/Milan | closed | [FEATURE] Adding the close icon when navbar is down in mobile view. | 🟨 priority: medium ⭐ goal: addition 🛠 status : under development 🤖 status : Asking updates | ### Description
How about changing the nav button to close button when a user opens the navbar in the mobile view.
### Screenshots
<img width="531" alt="Screenshot 2023-02-09 at 11 35 10 PM" src="https://user-images.githubusercontent.com/92542124/217899957-d4f0c59a-40f6-4b50-b314-75ac4b70115c.png">
### 🥦 Browser
Google Chrome
### 👀 Have you checked for similar open issues?
- [X] I checked and didn't find similar issue
### 🏢 Have you read the Contributing Guidelines?
- [X] I have read the [Contributing Guidelines](https://github.com/IAmTamal/Milan/blob/main/CONTRIBUTING.md)
### Are you willing to work on this issue ?
Yes I am willing to submit a PR! | 1.0 | [FEATURE] Adding the close icon when navbar is down in mobile view. - ### Description
How about changing the nav button to close button when a user opens the navbar in the mobile view.
### Screenshots
<img width="531" alt="Screenshot 2023-02-09 at 11 35 10 PM" src="https://user-images.githubusercontent.com/92542124/217899957-d4f0c59a-40f6-4b50-b314-75ac4b70115c.png">
### 🥦 Browser
Google Chrome
### 👀 Have you checked for similar open issues?
- [X] I checked and didn't find similar issue
### 🏢 Have you read the Contributing Guidelines?
- [X] I have read the [Contributing Guidelines](https://github.com/IAmTamal/Milan/blob/main/CONTRIBUTING.md)
### Are you willing to work on this issue ?
Yes I am willing to submit a PR! | non_build | adding the close icon when navbar is down in mobile view description how about changing the nav button to close button when a user opens the navbar in the mobile view screenshots img width alt screenshot at pm src 🥦 browser google chrome 👀 have you checked for similar open issues i checked and didn t find similar issue 🏢 have you read the contributing guidelines i have read the are you willing to work on this issue yes i am willing to submit a pr | 0 |
126,247 | 17,872,936,909 | IssuesEvent | 2021-09-06 19:13:13 | Virinas-code/Indecrypt-2 | https://api.github.com/repos/Virinas-code/Indecrypt-2 | closed | CVE-2012-6708 (Medium) detected in jquery-1.3.2.min.js, jquery-1.8.1.min.js - autoclosed | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.3.2.min.js</b>, <b>jquery-1.8.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.3.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.3.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.3.2/jquery.min.js</a></p>
<p>Path to dependency file: Indecrypt-2/static/jquery-ui-1.12.1.custom/node_modules/underscore.string/test/test.html</p>
<p>Path to vulnerable library: /static/jquery-ui-1.12.1.custom/node_modules/underscore.string/test/test_underscore/vendor/jquery.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.3.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: Indecrypt-2/static/jquery-ui-1.12.1.custom/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /static/jquery-ui-1.12.1.custom/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Virinas-code/Indecrypt-2/commit/be5e35bc27ca92f0532d889bc304ace229cc56cc">be5e35bc27ca92f0532d889bc304ace229cc56cc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2012-6708 (Medium) detected in jquery-1.3.2.min.js, jquery-1.8.1.min.js - autoclosed - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.3.2.min.js</b>, <b>jquery-1.8.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.3.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.3.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.3.2/jquery.min.js</a></p>
<p>Path to dependency file: Indecrypt-2/static/jquery-ui-1.12.1.custom/node_modules/underscore.string/test/test.html</p>
<p>Path to vulnerable library: /static/jquery-ui-1.12.1.custom/node_modules/underscore.string/test/test_underscore/vendor/jquery.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.3.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: Indecrypt-2/static/jquery-ui-1.12.1.custom/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /static/jquery-ui-1.12.1.custom/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Virinas-code/Indecrypt-2/commit/be5e35bc27ca92f0532d889bc304ace229cc56cc">be5e35bc27ca92f0532d889bc304ace229cc56cc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_build | cve medium detected in jquery min js jquery min js autoclosed cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to dependency file indecrypt static jquery ui custom node modules underscore string test test html path to vulnerable library static jquery ui custom node modules underscore string test test underscore vendor jquery js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file indecrypt static jquery ui custom node modules bower lib node modules redeyed examples browser index html path to vulnerable library static jquery ui custom node modules bower lib node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks the jquery strinput function does not differentiate selectors from html in a reliable fashion in vulnerable versions jquery determined whether the input was html by looking for the character anywhere in the string giving attackers more flexibility when attempting to construct a malicious payload in fixed versions jquery only deems the input to be html if it explicitly starts with the character limiting exploitability only to attackers who can control the beginning of a string which is far less common publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
7,464 | 3,984,205,070 | IssuesEvent | 2016-05-07 01:40:59 | freebroccolo/practical-foundations-for-higher-algebra | https://api.github.com/repos/freebroccolo/practical-foundations-for-higher-algebra | closed | Improve rendering performance | build latex | When everything is rendered in final mode it's a lot slower than I'd like and there's not even that much content yet. Even draft mode is a bit slow. I suspect a big part of the overhead is just due to the initial font loading since there's a ton of stuff going on just with that one part of the configuration. Maybe there's a nice way to profile the process.
Ideas:
- [ ] profile and figure out the slowest parts
- [ ] render all diagrams as `standalone` documents
- [ ] render all code snippets as `standalone` documents
- [ ] parallelize `standalone` rendering? (not sure if this is feasible; maybe with `pdfpages`)
- [ ] try precompiling the preamble (this probably won't work for `fontspec` parts)
- [x] try switching to `luajitlatex` | 1.0 | Improve rendering performance - When everything is rendered in final mode it's a lot slower than I'd like and there's not even that much content yet. Even draft mode is a bit slow. I suspect a big part of the overhead is just due to the initial font loading since there's a ton of stuff going on just with that one part of the configuration. Maybe there's a nice way to profile the process.
Ideas:
- [ ] profile and figure out the slowest parts
- [ ] render all diagrams as `standalone` documents
- [ ] render all code snippets as `standalone` documents
- [ ] parallelize `standalone` rendering? (not sure if this is feasible; maybe with `pdfpages`)
- [ ] try precompiling the preamble (this probably won't work for `fontspec` parts)
- [x] try switching to `luajitlatex` | build | improve rendering performance when everything is rendered in final mode it s a lot slower than i d like and there s not even that much content yet even draft mode is a bit slow i suspect a big part of the overhead is just due to the initial font loading since there s a ton of stuff going on just with that one part of the configuration maybe there s a nice way to profile the process ideas profile and figure out the slowest parts render all diagrams as standalone documents render all code snippets as standalone documents parallelize standalone rendering not sure if this is feasible maybe with pdfpages try precompiling the preamble this probably won t work for fontspec parts try switching to luajitlatex | 1 |
94,192 | 27,141,595,723 | IssuesEvent | 2023-02-16 16:43:14 | Scirra/Construct-3-bugs | https://api.github.com/repos/Scirra/Construct-3-bugs | closed | Whitelist plugins (Routine maintenance) | Build Service | Hello sir
Please add this
com.adjust.sdk@4.32.0
Reason Fixed import statement errors in case CocoaPods is forcing usage of frameworks
Thank you | 1.0 | Whitelist plugins (Routine maintenance) - Hello sir
Please add this
com.adjust.sdk@4.32.0
Reason Fixed import statement errors in case CocoaPods is forcing usage of frameworks
Thank you | build | whitelist plugins routine maintenance hello sir please add this com adjust sdk reason fixed import statement errors in case cocoapods is forcing usage of frameworks thank you | 1 |
114,439 | 11,847,560,944 | IssuesEvent | 2020-03-24 12:16:10 | quarkusio/quarkus | https://api.github.com/repos/quarkusio/quarkus | closed | Document how to enable DEBUG logging for @QuarkusTest | area/documentation area/testing kind/enhancement | I've tried to set system properties in `applications.properties` and for the `maven-surefire-plugin` with no success. | 1.0 | Document how to enable DEBUG logging for @QuarkusTest - I've tried to set system properties in `applications.properties` and for the `maven-surefire-plugin` with no success. | non_build | document how to enable debug logging for quarkustest i ve tried to set system properties in applications properties and for the maven surefire plugin with no success | 0 |
100,566 | 30,724,814,044 | IssuesEvent | 2023-07-27 18:44:28 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | Build failure: man-pages (options-docbook tag mismatch) | 0.kind: build failure | ### Steps To Reproduce
Steps to reproduce the behavior:
1. update nixpkgs from `0e1fc501c6072287c4dd49b1178d77b0c7918a0a` to `93d16f0f94354d4e5045c65c622afd2933a34fdf`
2. rebuild nixos
### Build log
```
error: builder for '/nix/store/hy9q33dj1lqzgdk0am06dm8rai5fipl1-options-docbook.xml.drv' failed with exit code 6;
last 10 log lines:
> options.xml:169: parser error : Opening and ending tag mismatch: varlistentry line 104 and variablelist
> </variablelist>
> ^
> options.xml:170: parser error : Opening and ending tag mismatch: variablelist line 5 and appendix
> </appendix>
> ^
> options.xml:170: parser error : Premature end of data in tag appendix line 2
> </appendix>
> ^
> unable to parse options.xml
For full logs, run 'nix log /nix/store/hy9q33dj1lqzgdk0am06dm8rai5fipl1-options-docbook.xml.drv'.
error: 1 dependencies of derivation '/nix/store/28kwc2mn5j6xmgy9v1f2yjblbyvcacgb-hm-module-docs-for-nmd.drv' failed to build
error: 1 dependencies of derivation '/nix/store/7yk4ffbahz63cyiyq2ddcrnq6hn23dng-nmd-documents.drv' failed to build
error: 1 dependencies of derivation '/nix/store/hf5yqlyiv96xz189v78w4d5i0pd6p53d-manual-combined.drv' failed to build
error: 1 dependencies of derivation '/nix/store/0xwv1ajh7fpxpyfgicfavnlas2ql180s-man-pages.drv' failed to build
error: 1 dependencies of derivation '/nix/store/d8lgq9pnar2g4vl11p0hgiaw8mjbpaa6-home-manager-path.drv' failed to build
error: 1 dependencies of derivation '/nix/store/93i7vn3hn2gsh7kicfskln1d0cg3zw6n-home-manager-generation.drv' failed to build
```
### Additional context
The failing package `options-docbook` seems to be a dependency of other packages among which `man-pages`.
### Notify maintainers
(i don't really see any for the packages involved)
### Metadata
Please run `nix-shell -p nix-info --run "nix-info -m"` and paste the result.
```console
[user@system:~]$ nix-shell -p nix-info --run "nix-info -m"
- system: `"x86_64-linux"`
- host os: `Linux 6.1.33, NixOS, 23.05 (Stoat), 23.05.20230614.ddf4688`
- multi-user?: `yes`
- sandbox: `yes`
- version: `nix-env (Nix) 2.13.3`
- channels(kiara): `"home-manager"`
- nixpkgs: `/nix/var/nix/profiles/per-user/root/channels/nixos`
```
| 1.0 | Build failure: man-pages (options-docbook tag mismatch) - ### Steps To Reproduce
Steps to reproduce the behavior:
1. update nixpkgs from `0e1fc501c6072287c4dd49b1178d77b0c7918a0a` to `93d16f0f94354d4e5045c65c622afd2933a34fdf`
2. rebuild nixos
### Build log
```
error: builder for '/nix/store/hy9q33dj1lqzgdk0am06dm8rai5fipl1-options-docbook.xml.drv' failed with exit code 6;
last 10 log lines:
> options.xml:169: parser error : Opening and ending tag mismatch: varlistentry line 104 and variablelist
> </variablelist>
> ^
> options.xml:170: parser error : Opening and ending tag mismatch: variablelist line 5 and appendix
> </appendix>
> ^
> options.xml:170: parser error : Premature end of data in tag appendix line 2
> </appendix>
> ^
> unable to parse options.xml
For full logs, run 'nix log /nix/store/hy9q33dj1lqzgdk0am06dm8rai5fipl1-options-docbook.xml.drv'.
error: 1 dependencies of derivation '/nix/store/28kwc2mn5j6xmgy9v1f2yjblbyvcacgb-hm-module-docs-for-nmd.drv' failed to build
error: 1 dependencies of derivation '/nix/store/7yk4ffbahz63cyiyq2ddcrnq6hn23dng-nmd-documents.drv' failed to build
error: 1 dependencies of derivation '/nix/store/hf5yqlyiv96xz189v78w4d5i0pd6p53d-manual-combined.drv' failed to build
error: 1 dependencies of derivation '/nix/store/0xwv1ajh7fpxpyfgicfavnlas2ql180s-man-pages.drv' failed to build
error: 1 dependencies of derivation '/nix/store/d8lgq9pnar2g4vl11p0hgiaw8mjbpaa6-home-manager-path.drv' failed to build
error: 1 dependencies of derivation '/nix/store/93i7vn3hn2gsh7kicfskln1d0cg3zw6n-home-manager-generation.drv' failed to build
```
### Additional context
The failing package `options-docbook` seems to be a dependency of other packages among which `man-pages`.
### Notify maintainers
(i don't really see any for the packages involved)
### Metadata
Please run `nix-shell -p nix-info --run "nix-info -m"` and paste the result.
```console
[user@system:~]$ nix-shell -p nix-info --run "nix-info -m"
- system: `"x86_64-linux"`
- host os: `Linux 6.1.33, NixOS, 23.05 (Stoat), 23.05.20230614.ddf4688`
- multi-user?: `yes`
- sandbox: `yes`
- version: `nix-env (Nix) 2.13.3`
- channels(kiara): `"home-manager"`
- nixpkgs: `/nix/var/nix/profiles/per-user/root/channels/nixos`
```
| build | build failure man pages options docbook tag mismatch steps to reproduce steps to reproduce the behavior update nixpkgs from to rebuild nixos build log error builder for nix store options docbook xml drv failed with exit code last log lines options xml parser error opening and ending tag mismatch varlistentry line and variablelist options xml parser error opening and ending tag mismatch variablelist line and appendix options xml parser error premature end of data in tag appendix line unable to parse options xml for full logs run nix log nix store options docbook xml drv error dependencies of derivation nix store hm module docs for nmd drv failed to build error dependencies of derivation nix store nmd documents drv failed to build error dependencies of derivation nix store manual combined drv failed to build error dependencies of derivation nix store man pages drv failed to build error dependencies of derivation nix store home manager path drv failed to build error dependencies of derivation nix store home manager generation drv failed to build additional context the failing package options docbook seems to be a dependency of other packages among which man pages notify maintainers i don t really see any for the packages involved metadata please run nix shell p nix info run nix info m and paste the result console nix shell p nix info run nix info m system linux host os linux nixos stoat multi user yes sandbox yes version nix env nix channels kiara home manager nixpkgs nix var nix profiles per user root channels nixos | 1 |
90,059 | 25,959,018,270 | IssuesEvent | 2022-12-18 16:33:00 | CosmosOS/Cosmos | https://api.github.com/repos/CosmosOS/Cosmos | closed | System.IO.FileLoaderException: Could not load file or assembly Cosmos.Debug.Kernel | Pending User Response Area: Visual Studio Integration Area: Build | 
Please help. | 1.0 | System.IO.FileLoaderException: Could not load file or assembly Cosmos.Debug.Kernel - 
Please help. | build | system io fileloaderexception could not load file or assembly cosmos debug kernel please help | 1 |
77,617 | 21,913,048,748 | IssuesEvent | 2022-05-21 11:14:13 | python/cpython | https://api.github.com/repos/python/cpython | closed | BUILD: AIX-64-bit segmentation fault using xlc-v11 | build 3.9 type-crash | BPO | [42309](https://bugs.python.org/issue42309)
--- | :---
Nosy | @aixtools, @kadler
<sup>*Note: these values reflect the state of the issue at the time it was migrated and might not reflect the current state.*</sup>
<details><summary>Show more details</summary><p>
GitHub fields:
```python
assignee = None
closed_at = None
created_at = <Date 2020-11-10.11:44:55.949>
labels = ['build', '3.9', 'type-crash']
title = 'BUILD: AIX-64-bit segmentation fault using xlc-v11'
updated_at = <Date 2021-01-06.16:41:47.483>
user = 'https://github.com/aixtools'
```
bugs.python.org fields:
```python
activity = <Date 2021-01-06.16:41:47.483>
actor = 'Michael.Felt'
assignee = 'none'
closed = False
closed_date = None
closer = None
components = ['Build']
creation = <Date 2020-11-10.11:44:55.949>
creator = 'Michael.Felt'
dependencies = []
files = []
hgrepos = []
issue_num = 42309
keywords = []
message_count = 6.0
messages = ['380654', '380693', '380951', '381094', '381104', '384511']
nosy_count = 2.0
nosy_names = ['Michael.Felt', 'kadler']
pr_nums = []
priority = 'normal'
resolution = None
stage = None
status = 'open'
superseder = None
type = 'crash'
url = 'https://bugs.python.org/issue42309'
versions = ['Python 3.9']
```
</p></details>
| 1.0 | BUILD: AIX-64-bit segmentation fault using xlc-v11 - BPO | [42309](https://bugs.python.org/issue42309)
--- | :---
Nosy | @aixtools, @kadler
<sup>*Note: these values reflect the state of the issue at the time it was migrated and might not reflect the current state.*</sup>
<details><summary>Show more details</summary><p>
GitHub fields:
```python
assignee = None
closed_at = None
created_at = <Date 2020-11-10.11:44:55.949>
labels = ['build', '3.9', 'type-crash']
title = 'BUILD: AIX-64-bit segmentation fault using xlc-v11'
updated_at = <Date 2021-01-06.16:41:47.483>
user = 'https://github.com/aixtools'
```
bugs.python.org fields:
```python
activity = <Date 2021-01-06.16:41:47.483>
actor = 'Michael.Felt'
assignee = 'none'
closed = False
closed_date = None
closer = None
components = ['Build']
creation = <Date 2020-11-10.11:44:55.949>
creator = 'Michael.Felt'
dependencies = []
files = []
hgrepos = []
issue_num = 42309
keywords = []
message_count = 6.0
messages = ['380654', '380693', '380951', '381094', '381104', '384511']
nosy_count = 2.0
nosy_names = ['Michael.Felt', 'kadler']
pr_nums = []
priority = 'normal'
resolution = None
stage = None
status = 'open'
superseder = None
type = 'crash'
url = 'https://bugs.python.org/issue42309'
versions = ['Python 3.9']
```
</p></details>
| build | build aix bit segmentation fault using xlc bpo nosy aixtools kadler note these values reflect the state of the issue at the time it was migrated and might not reflect the current state show more details github fields python assignee none closed at none created at labels title build aix bit segmentation fault using xlc updated at user bugs python org fields python activity actor michael felt assignee none closed false closed date none closer none components creation creator michael felt dependencies files hgrepos issue num keywords message count messages nosy count nosy names pr nums priority normal resolution none stage none status open superseder none type crash url versions | 1 |
680,474 | 23,271,922,391 | IssuesEvent | 2022-08-05 00:44:01 | zulip/zulip | https://api.github.com/repos/zulip/zulip | closed | api: Represent muted topics with stream IDs, not names (and maybe new `user_topic` model) | area: api priority: high release goal | I think the docs ([`/register`](https://zulip.com/api/register-queue#response), [`GET /events`](https://zulip.com/api/get-events#muted_topics)) are accurate about what servers currently do for `muted_topics`:
> Array of tuples, where each tuple describes a muted topic. The first element of tuple is the stream name in which the topic has to be muted, the second element is the topic name to be muted and the third element is an integer UNIX timestamp representing when the topic was muted.
We should use stream IDs instead of stream names.
While we're at it, we could switch over to a new model that would allow representing:
- "normal behavior for [a] (user, stream) pair"
- MUTED: "A normal muted topic. No notifications and unreads hidden."
- UNMUTED: "This topic will behave like an unmuted topic in an unmuted stream even if it belongs to a muted stream."
- FOLLOWED: "This topic will behave like `UNMUTED`, plus will also always trigger notifications."
Discussion continuing at https://chat.zulip.org/#narrow/stream/378-api-design/topic/stream.20IDs.20in.20.60muted_topics.60/near/1320601 | 1.0 | api: Represent muted topics with stream IDs, not names (and maybe new `user_topic` model) - I think the docs ([`/register`](https://zulip.com/api/register-queue#response), [`GET /events`](https://zulip.com/api/get-events#muted_topics)) are accurate about what servers currently do for `muted_topics`:
> Array of tuples, where each tuple describes a muted topic. The first element of tuple is the stream name in which the topic has to be muted, the second element is the topic name to be muted and the third element is an integer UNIX timestamp representing when the topic was muted.
We should use stream IDs instead of stream names.
While we're at it, we could switch over to a new model that would allow representing:
- "normal behavior for [a] (user, stream) pair"
- MUTED: "A normal muted topic. No notifications and unreads hidden."
- UNMUTED: "This topic will behave like an unmuted topic in an unmuted stream even if it belongs to a muted stream."
- FOLLOWED: "This topic will behave like `UNMUTED`, plus will also always trigger notifications."
Discussion continuing at https://chat.zulip.org/#narrow/stream/378-api-design/topic/stream.20IDs.20in.20.60muted_topics.60/near/1320601 | non_build | api represent muted topics with stream ids not names and maybe new user topic model i think the docs are accurate about what servers currently do for muted topics array of tuples where each tuple describes a muted topic the first element of tuple is the stream name in which the topic has to be muted the second element is the topic name to be muted and the third element is an integer unix timestamp representing when the topic was muted we should use stream ids instead of stream names while we re at it we could switch over to a new model that would allow representing normal behavior for user stream pair muted a normal muted topic no notifications and unreads hidden unmuted this topic will behave like an unmuted topic in an unmuted stream even if it belongs to a muted stream followed this topic will behave like unmuted plus will also always trigger notifications discussion continuing at | 0 |
46,890 | 11,905,254,113 | IssuesEvent | 2020-03-30 18:14:42 | csf-dev/CSF.EqualityRules | https://api.github.com/repos/csf-dev/CSF.EqualityRules | closed | For wider compatibility, this library should be multi-targeted | build/packaging enhancement | I would like to target my standard collection of frameworks:
* `netstandard1.0` (if possible)
* `netstandard2.0`
* `net45` | 1.0 | For wider compatibility, this library should be multi-targeted - I would like to target my standard collection of frameworks:
* `netstandard1.0` (if possible)
* `netstandard2.0`
* `net45` | build | for wider compatibility this library should be multi targeted i would like to target my standard collection of frameworks if possible | 1 |
105,535 | 9,086,362,317 | IssuesEvent | 2019-02-18 10:44:51 | nicklashersen/numpy | https://api.github.com/repos/nicklashersen/numpy | opened | Unittest add_data_files raises TypeError | testing | Assert that this branch https://codecov.io/gh/numpy/numpy/src/master/numpy/distutils/misc_util.py#L1291 is run correctly and raises an ValueError given some input.
| 1.0 | Unittest add_data_files raises TypeError - Assert that this branch https://codecov.io/gh/numpy/numpy/src/master/numpy/distutils/misc_util.py#L1291 is run correctly and raises an ValueError given some input.
| non_build | unittest add data files raises typeerror assert that this branch is run correctly and raises an valueerror given some input | 0 |
24,621 | 24,041,269,309 | IssuesEvent | 2022-09-16 02:12:39 | pulumi/service-requests | https://api.github.com/repos/pulumi/service-requests | opened | automatically assign stack permissions to a team by tag | kind/enhancement impact/usability | we recently had a request to be able to automatically assign a stack permissions based on tag | True | automatically assign stack permissions to a team by tag - we recently had a request to be able to automatically assign a stack permissions based on tag | non_build | automatically assign stack permissions to a team by tag we recently had a request to be able to automatically assign a stack permissions based on tag | 0 |
96,746 | 16,164,586,363 | IssuesEvent | 2021-05-01 08:16:58 | AlexRogalskiy/github-action-coverage-reporter | https://api.github.com/repos/AlexRogalskiy/github-action-coverage-reporter | opened | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: github-action-coverage-reporter/package.json</p>
<p>Path to vulnerable library: github-action-coverage-reporter/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsonlint-1.6.3.tgz (Root Library)
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-coverage-reporter/commit/5f5dca7fa71d37e389c57fc007f7006c480f2859">5f5dca7fa71d37e389c57fc007f7006c480f2859</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: github-action-coverage-reporter/package.json</p>
<p>Path to vulnerable library: github-action-coverage-reporter/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsonlint-1.6.3.tgz (Root Library)
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-coverage-reporter/commit/5f5dca7fa71d37e389c57fc007f7006c480f2859">5f5dca7fa71d37e389c57fc007f7006c480f2859</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_build | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file github action coverage reporter package json path to vulnerable library github action coverage reporter node modules underscore package json dependency hierarchy jsonlint tgz root library nomnom tgz x underscore tgz vulnerable library found in head commit a href vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore step up your open source security game with whitesource | 0 |
52,550 | 12,992,737,504 | IssuesEvent | 2020-07-23 07:31:57 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Tensorflow importing issue | TF 2.2 stalled stat:awaiting response subtype:windows type:build/install | <em>Please make sure that this is a build/installation issue. As per our [GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md), we only address code/doc bugs, performance issues, feature requests and build/installation issues on GitHub. tag:build_template</em>
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): windows 10
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device: none
- TensorFlow installed from (source or binary): tensorflow.org
- TensorFlow version: 2.2.0
- Python version: 3.8.3
- Installed using virtualenv? pip? conda?: pip
- Bazel version (if compiling from source):
- GCC/Compiler version (if compiling from source):
- CUDA/cuDNN version:
- GPU model and memory:
I can not import tensorflow, it shows an import issue that i tried to fix, but it is still not working. Any help is appreciated. Thanks a lot
Traceback (most recent call last):
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 28, in <module>
_pywrap_tensorflow_internal = swig_import_helper()
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 24, in swig_import_helper
_mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 242, in load_module
return load_dynamic(name, filename, file)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 342, in load_dynamic
return _load(spec)
ImportError: DLL load failed while importing _pywrap_tensorflow_internal: The specified module could not be found.
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "<pyshell#0>", line 1, in <module>
import tensorflow
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\__init__.py", line 41, in <module>
from tensorflow.python.tools import module_util as _module_util
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\__init__.py", line 50, in <module>
from tensorflow.python import pywrap_tensorflow
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 69, in <module>
raise ImportError(msg)
ImportError: Traceback (most recent call last):
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 28, in <module>
_pywrap_tensorflow_internal = swig_import_helper()
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 24, in swig_import_helper
_mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 242, in load_module
return load_dynamic(name, filename, file)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 342, in load_dynamic
return _load(spec)
ImportError: DLL load failed while importing _pywrap_tensorflow_internal: The specified module could not be found.
Failed to load the native TensorFlow runtime.
See https://www.tensorflow.org/install/errors
for some common reasons and solutions. Include the entire stack trace
above this error message when asking for help.
>>>
| 1.0 | Tensorflow importing issue - <em>Please make sure that this is a build/installation issue. As per our [GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md), we only address code/doc bugs, performance issues, feature requests and build/installation issues on GitHub. tag:build_template</em>
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): windows 10
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device: none
- TensorFlow installed from (source or binary): tensorflow.org
- TensorFlow version: 2.2.0
- Python version: 3.8.3
- Installed using virtualenv? pip? conda?: pip
- Bazel version (if compiling from source):
- GCC/Compiler version (if compiling from source):
- CUDA/cuDNN version:
- GPU model and memory:
I can not import tensorflow, it shows an import issue that i tried to fix, but it is still not working. Any help is appreciated. Thanks a lot
Traceback (most recent call last):
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 28, in <module>
_pywrap_tensorflow_internal = swig_import_helper()
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 24, in swig_import_helper
_mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 242, in load_module
return load_dynamic(name, filename, file)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 342, in load_dynamic
return _load(spec)
ImportError: DLL load failed while importing _pywrap_tensorflow_internal: The specified module could not be found.
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "<pyshell#0>", line 1, in <module>
import tensorflow
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\__init__.py", line 41, in <module>
from tensorflow.python.tools import module_util as _module_util
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\__init__.py", line 50, in <module>
from tensorflow.python import pywrap_tensorflow
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 69, in <module>
raise ImportError(msg)
ImportError: Traceback (most recent call last):
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 28, in <module>
_pywrap_tensorflow_internal = swig_import_helper()
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 24, in swig_import_helper
_mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 242, in load_module
return load_dynamic(name, filename, file)
File "C:\Users\david\AppData\Local\Programs\Python\Python38\lib\imp.py", line 342, in load_dynamic
return _load(spec)
ImportError: DLL load failed while importing _pywrap_tensorflow_internal: The specified module could not be found.
Failed to load the native TensorFlow runtime.
See https://www.tensorflow.org/install/errors
for some common reasons and solutions. Include the entire stack trace
above this error message when asking for help.
>>>
| build | tensorflow importing issue please make sure that this is a build installation issue as per our we only address code doc bugs performance issues feature requests and build installation issues on github tag build template system information os platform and distribution e g linux ubuntu windows mobile device e g iphone pixel samsung galaxy if the issue happens on mobile device none tensorflow installed from source or binary tensorflow org tensorflow version python version installed using virtualenv pip conda pip bazel version if compiling from source gcc compiler version if compiling from source cuda cudnn version gpu model and memory i can not import tensorflow it shows an import issue that i tried to fix but it is still not working any help is appreciated thanks a lot traceback most recent call last file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow py line in from tensorflow python pywrap tensorflow internal import file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow internal py line in pywrap tensorflow internal swig import helper file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow internal py line in swig import helper mod imp load module pywrap tensorflow internal fp pathname description file c users david appdata local programs python lib imp py line in load module return load dynamic name filename file file c users david appdata local programs python lib imp py line in load dynamic return load spec importerror dll load failed while importing pywrap tensorflow internal the specified module could not be found during handling of the above exception another exception occurred traceback most recent call last file line in import tensorflow file c users david appdata local programs python lib site packages tensorflow init py line in from tensorflow python tools import module util as module util file c users david appdata local programs python lib site packages tensorflow python init py line in from tensorflow python import pywrap tensorflow file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow py line in raise importerror msg importerror traceback most recent call last file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow py line in from tensorflow python pywrap tensorflow internal import file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow internal py line in pywrap tensorflow internal swig import helper file c users david appdata local programs python lib site packages tensorflow python pywrap tensorflow internal py line in swig import helper mod imp load module pywrap tensorflow internal fp pathname description file c users david appdata local programs python lib imp py line in load module return load dynamic name filename file file c users david appdata local programs python lib imp py line in load dynamic return load spec importerror dll load failed while importing pywrap tensorflow internal the specified module could not be found failed to load the native tensorflow runtime see for some common reasons and solutions include the entire stack trace above this error message when asking for help | 1 |
91,438 | 26,393,558,099 | IssuesEvent | 2023-01-12 17:26:01 | opensafely/documentation | https://api.github.com/repos/opensafely/documentation | closed | Add structure to URLs of databuilder docs | data builder databuilder-1 | The URL structure of the OpenSAFELY documentation is currently flat. It would be neater (and would make the docs source code easier to navigate) if the URLs were nested. For instance:
| old | new |
|-|-|
| https://docs.opensafely.org/data-builder-toc/ | https://docs.opensafely.org/data-builder/ |
| https://docs.opensafely.org/ehrql-intro/ | https://docs.opensafely.org/data-builder/ehrql/ |
| https://docs.opensafely.org/ehrql-tutorial/ | https://docs.opensafely.org/data-builder/ehrql/tutorial/ |
We can start with the databuilder (or is it data-builder?) docs since these are unused and we don't have to worry about redirects. | 2.0 | Add structure to URLs of databuilder docs - The URL structure of the OpenSAFELY documentation is currently flat. It would be neater (and would make the docs source code easier to navigate) if the URLs were nested. For instance:
| old | new |
|-|-|
| https://docs.opensafely.org/data-builder-toc/ | https://docs.opensafely.org/data-builder/ |
| https://docs.opensafely.org/ehrql-intro/ | https://docs.opensafely.org/data-builder/ehrql/ |
| https://docs.opensafely.org/ehrql-tutorial/ | https://docs.opensafely.org/data-builder/ehrql/tutorial/ |
We can start with the databuilder (or is it data-builder?) docs since these are unused and we don't have to worry about redirects. | build | add structure to urls of databuilder docs the url structure of the opensafely documentation is currently flat it would be neater and would make the docs source code easier to navigate if the urls were nested for instance old new we can start with the databuilder or is it data builder docs since these are unused and we don t have to worry about redirects | 1 |
31,676 | 6,583,685,708 | IssuesEvent | 2017-09-13 07:12:14 | yaoius/newsy | https://api.github.com/repos/yaoius/newsy | opened | Check boxes in issue templates shows bar on card | defect | ### Issue Description
Using check boxes for Issue templates gives a -/4 marker on cards that is undesirable. Change just to manual string input.
Priority
- [x] Trivial
- [ ] Minor
- [ ] Major
- [ ] Critical
| 1.0 | Check boxes in issue templates shows bar on card - ### Issue Description
Using check boxes for Issue templates gives a -/4 marker on cards that is undesirable. Change just to manual string input.
Priority
- [x] Trivial
- [ ] Minor
- [ ] Major
- [ ] Critical
| non_build | check boxes in issue templates shows bar on card issue description using check boxes for issue templates gives a marker on cards that is undesirable change just to manual string input priority trivial minor major critical | 0 |
72,190 | 19,072,737,818 | IssuesEvent | 2021-11-27 07:15:16 | hexops/mach | https://api.github.com/repos/hexops/mach | closed | update system_sdk to reflect new Zig macOS version targeting | build-system | Since https://github.com/ziglang/zig/pull/10215 Zig will ship versioned libc headers and allow specifying the following target triples for macOS:
> * supported triples:
>
> * x86_64-macos.10 (Catalina)
> * x86_64-macos.11 (Big Sur)
> * x86_64-macos.12 (Monterey)
> * aarch64-macos.11 (Big Sur)
> * aarch64-macos.12 (Monterey)
We should reflect this change by:
1. [ ] Revert the temporary hack to allow compilation with macOS 12 frameworks https://github.com/hexops/mach/commit/7d47233d7a5a97241ad16a148c153831ce5d555d
2. [ ] Default to the same macOS version as Zig (well, in reality Zig defaults to 10 but we only have an 11 SDK, so we'll default to that even when Zig targets 10 which is fine and we know works. In the future, we'll continue to target the same SDK as Zig)
3. [ ] When the target triple is `-macos.12`, have `system_sdk.zig` detect that and use the new https://github.com/hexops/sdk-macos-12.0
| 1.0 | update system_sdk to reflect new Zig macOS version targeting - Since https://github.com/ziglang/zig/pull/10215 Zig will ship versioned libc headers and allow specifying the following target triples for macOS:
> * supported triples:
>
> * x86_64-macos.10 (Catalina)
> * x86_64-macos.11 (Big Sur)
> * x86_64-macos.12 (Monterey)
> * aarch64-macos.11 (Big Sur)
> * aarch64-macos.12 (Monterey)
We should reflect this change by:
1. [ ] Revert the temporary hack to allow compilation with macOS 12 frameworks https://github.com/hexops/mach/commit/7d47233d7a5a97241ad16a148c153831ce5d555d
2. [ ] Default to the same macOS version as Zig (well, in reality Zig defaults to 10 but we only have an 11 SDK, so we'll default to that even when Zig targets 10 which is fine and we know works. In the future, we'll continue to target the same SDK as Zig)
3. [ ] When the target triple is `-macos.12`, have `system_sdk.zig` detect that and use the new https://github.com/hexops/sdk-macos-12.0
| build | update system sdk to reflect new zig macos version targeting since zig will ship versioned libc headers and allow specifying the following target triples for macos supported triples macos catalina macos big sur macos monterey macos big sur macos monterey we should reflect this change by revert the temporary hack to allow compilation with macos frameworks default to the same macos version as zig well in reality zig defaults to but we only have an sdk so we ll default to that even when zig targets which is fine and we know works in the future we ll continue to target the same sdk as zig when the target triple is macos have system sdk zig detect that and use the new | 1 |
20,194 | 6,827,411,907 | IssuesEvent | 2017-11-08 16:57:06 | zooniverse/Panoptes-Front-End | https://api.github.com/repos/zooniverse/Panoptes-Front-End | closed | Request: ability to "backup" a project | feature request project builder | It would be nice to be able to "save" a project in some form (to recover from accidental deletions of project parts by owners or collaborators -- see #1253 for example). Even if it were just a text dump of the JSON for the project, content pages, and associated workflows, it could save folks a lot of time and sadness. Could be an export (e.g. of JSON text) or just be a "backup" saved in Panoptes space (sorta like GitHub saves snapshots of repos as "releases").
| 1.0 | Request: ability to "backup" a project - It would be nice to be able to "save" a project in some form (to recover from accidental deletions of project parts by owners or collaborators -- see #1253 for example). Even if it were just a text dump of the JSON for the project, content pages, and associated workflows, it could save folks a lot of time and sadness. Could be an export (e.g. of JSON text) or just be a "backup" saved in Panoptes space (sorta like GitHub saves snapshots of repos as "releases").
| build | request ability to backup a project it would be nice to be able to save a project in some form to recover from accidental deletions of project parts by owners or collaborators see for example even if it were just a text dump of the json for the project content pages and associated workflows it could save folks a lot of time and sadness could be an export e g of json text or just be a backup saved in panoptes space sorta like github saves snapshots of repos as releases | 1 |
284,824 | 30,921,619,104 | IssuesEvent | 2023-08-06 01:06:54 | samq-democorp/GMQ-Java-Prioritize | https://api.github.com/repos/samq-democorp/GMQ-Java-Prioritize | closed | webgoat-container-v8.1.0.jar: 33 vulnerabilities (highest severity is: 9.8) reachable - autoclosed | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>webgoat-container-v8.1.0.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (webgoat-container-v8.1.0.jar version) | Remediation Available | Reachability |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- | --- |
| [CVE-2022-22965](https://www.mend.io/vulnerability-database/CVE-2022-22965) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-beans-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20873](https://www.mend.io/vulnerability-database/CVE-2023-20873) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22978](https://www.mend.io/vulnerability-database/CVE-2022-22978) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-1471](https://www.mend.io/vulnerability-database/CVE-2022-1471) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | snakeyaml-1.25.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-22112](https://www.mend.io/vulnerability-database/CVE-2021-22112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [WS-2019-0490](https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jcommander-1.35.jar | Transitive | N/A* | ❌ |
| [CVE-2019-14888](https://www.mend.io/vulnerability-database/CVE-2019-14888) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌ |
| [CVE-2022-4492](https://www.mend.io/vulnerability-database/CVE-2022-4492) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5398](https://www.mend.io/vulnerability-database/CVE-2020-5398) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-web-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-46877](https://www.mend.io/vulnerability-database/CVE-2021-46877) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-0084](https://www.mend.io/vulnerability-database/CVE-2022-0084) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | xnio-api-3.3.8.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-1319](https://www.mend.io/vulnerability-database/CVE-2022-1319) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20883](https://www.mend.io/vulnerability-database/CVE-2023-20883) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-boot-autoconfigure-2.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-1259](https://www.mend.io/vulnerability-database/CVE-2022-1259) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-1108](https://www.mend.io/vulnerability-database/CVE-2023-1108) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌ |
| [CVE-2021-42550](https://www.mend.io/vulnerability-database/CVE-2021-42550) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.6 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22950](https://www.mend.io/vulnerability-database/CVE-2022-22950) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20861](https://www.mend.io/vulnerability-database/CVE-2023-20861) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20863](https://www.mend.io/vulnerability-database/CVE-2023-20863) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5408](https://www.mend.io/vulnerability-database/CVE-2020-5408) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-security-core-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5421](https://www.mend.io/vulnerability-database/CVE-2020-5421) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-web-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [WS-2017-3767](https://github.com/spring-projects/spring-security/commit/eed71243cb86833e7edf230e5e43ad89b01142f9) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.3 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-3629](https://www.mend.io/vulnerability-database/CVE-2021-3629) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌ |
| [WS-2021-0616](https://github.com/FasterXML/jackson-databind/commit/3ccde7d938fea547e598fdefe9a82cff37fed5cb) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [WS-2020-0293](https://github.com/spring-projects/spring-security/commit/40e027c56d11b9b4c5071360bfc718165c937784) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22968](https://www.mend.io/vulnerability-database/CVE-2022-22968) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | spring-context-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22970](https://www.mend.io/vulnerability-database/CVE-2022-22970) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5397](https://www.mend.io/vulnerability-database/CVE-2020-5397) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-22060](https://www.mend.io/vulnerability-database/CVE-2021-22060) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 4.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-22096](https://www.mend.io/vulnerability-database/CVE-2021-22096) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 4.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (18 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-22965</summary>
### Vulnerable Library - <b>spring-beans-5.2.2.RELEASE.jar</b></p>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.2.RELEASE/spring-beans-5.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-2.2.2.RELEASE.jar
- spring-boot-2.2.2.RELEASE.jar
- spring-context-5.2.2.RELEASE.jar
- spring-aop-5.2.2.RELEASE.jar
- :x: **spring-beans-5.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.beans.CachedIntrospectionResults (Application)
-> org.springframework.data.util.DirectFieldAccessFallbackBeanWrapper (Extension)
-> org.springframework.context.annotation.CommonAnnotationBeanPostProcessor (Extension)
-> org.springframework.boot.autoconfigure.SharedMetadataReaderFactoryContextInitializer (Extension)
...
-> org.springframework.boot.autoconfigure.AutoConfigurationImportSelector (Extension)
-> org.springframework.boot.autoconfigure.SpringBootApplication (Extension)
-> ❌ org.owasp.webwolf.WebWolf (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A Spring MVC or Spring WebFlux application running on JDK 9+ may be vulnerable to remote code execution (RCE) via data binding. The specific exploit requires the application to run on Tomcat as a WAR deployment. If the application is deployed as a Spring Boot executable jar, i.e. the default, it is not vulnerable to the exploit. However, the nature of the vulnerability is more general, and there may be other ways to exploit it.
Mend Note: Converted from WS-2022-0107, on 2022-11-07.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22965>CVE-2022-22965</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.20.RELEASE,5.3.18</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2023-20873</summary>
### Vulnerable Library - <b>spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar</b></p>
<p>Spring Boot Actuator AutoConfigure</p>
<p>Library home page: <a href="https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-actuator-autoconfigure">https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-actuator-autoconfigure</a></p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-actuator-autoconfigure/2.2.2.RELEASE/spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-actuator-2.2.2.RELEASE.jar
- :x: **spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.boot.actuate.autoconfigure.cloudfoundry.reactive.ReactiveCloudFoundryActuatorAutoConfiguration$WebFilterChainPostProcessor (Application)
-> org.springframework.beans.factory.support.DefaultListableBeanFactory (Extension)
-> org.springframework.web.servlet.config.annotation.WebMvcConfigurationSupport (Extension)
-> org.thymeleaf.spring5.expression.Mvc (Extension)
...
-> org.thymeleaf.spring5.dialect.SpringStandardDialect (Extension)
-> org.thymeleaf.spring5.SpringTemplateEngine (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.5, 2.7.0 - 2.7.10, and older unsupported versions, an application that is deployed to Cloud Foundry could be susceptible to a security bypass. Users of affected versions should apply the following mitigation: 3.0.x users should upgrade to 3.0.6+. 2.7.x users should upgrade to 2.7.11+. Users of older, unsupported versions should upgrade to 3.0.6+ or 2.7.11+.
<p>Publish Date: 2023-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20873>CVE-2023-20873</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20873">https://spring.io/security/cve-2023-20873</a></p>
<p>Release Date: 2023-04-20</p>
<p>Fix Resolution: org.springframework.boot:spring-boot-actuator-autoconfigure:2.7.11,3.0.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-22978</summary>
### Vulnerable Library - <b>spring-security-web-5.2.1.RELEASE.jar</b></p>
<p>spring-security-web</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-web/5.2.1.RELEASE/spring-security-web-5.2.1.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-security-2.2.2.RELEASE.jar
- :x: **spring-security-web-5.2.1.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.security.web.util.matcher.RegexRequestMatcher (Application)
-> org.springframework.security.config.annotation.web.builders.HttpSecurity (Extension)
-> ❌ org.owasp.webwolf.WebSecurityConfig (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In spring security versions prior to 5.4.11+, 5.5.7+ , 5.6.4+ and older unsupported versions, RegexRequestMatcher can easily be misconfigured to be bypassed on some servlet containers. Applications using RegexRequestMatcher with `.` in the regular expression are possibly vulnerable to an authorization bypass.
<p>Publish Date: 2022-05-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22978>CVE-2022-22978</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2022-22978/">https://spring.io/security/cve-2022-22978/</a></p>
<p>Release Date: 2022-05-19</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:5.5.7,5.6.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-1471</summary>
### Vulnerable Library - <b>snakeyaml-1.25.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.25/snakeyaml-1.25.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-2.2.2.RELEASE.jar
- :x: **snakeyaml-1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.yaml.snakeyaml.LoaderOptions (Application)
-> org.yaml.snakeyaml.Yaml (Extension)
-> org.springframework.beans.factory.config.YamlMapFactoryBean (Extension)
-> org.springframework.beans.factory.support.DefaultListableBeanFactory (Extension)
-> org.thymeleaf.spring5.view.ThymeleafViewResolver (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization. We recommend upgrading to version 2.0 and beyond.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374">https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374</a></p>
<p>Release Date: 2022-12-01</p>
<p>Fix Resolution: org.yaml:snakeyaml:2.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2021-22112</summary>
### Vulnerable Library - <b>spring-security-web-5.2.1.RELEASE.jar</b></p>
<p>spring-security-web</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-web/5.2.1.RELEASE/spring-security-web-5.2.1.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-security-2.2.2.RELEASE.jar
- :x: **spring-security-web-5.2.1.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.security.web.context.HttpSessionSecurityContextRepository$SaveToSessionResponseWrapper (Application)
-> ❌ org.owasp.webgoat.idor.IDORViewOtherProfile (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security 5.4.x prior to 5.4.4, 5.3.x prior to 5.3.8.RELEASE, 5.2.x prior to 5.2.9.RELEASE, and older unsupported versions can fail to save the SecurityContext if it is changed more than once in a single request.A malicious user cannot cause the bug to happen (it must be programmed in). However, if the application's intent is to only allow the user to run with elevated privileges in a small portion of the application, the bug can be leveraged to extend those privileges to the rest of the application.
<p>Publish Date: 2021-02-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22112>CVE-2021-22112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22112">https://tanzu.vmware.com/security/cve-2021-22112</a></p>
<p>Release Date: 2021-02-23</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:5.2.9,5.3.8,5.4.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> WS-2019-0490</summary>
### Vulnerable Library - <b>jcommander-1.35.jar</b></p>
<p>A Java framework to parse command line options with annotations.</p>
<p>Library home page: <a href="http://beust.com/">http://beust.com/</a></p>
<p>Path to dependency file: /webgoat-container/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/beust/jcommander/1.35/jcommander-1.35.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- asciidoctorj-1.5.8.1.jar
- :x: **jcommander-1.35.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
<p>Publish Date: 2019-02-19
<p>URL: <a href=https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53>WS-2019-0490</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-19</p>
<p>Fix Resolution: com.beust:jcommander:1.75</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2019-14888</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in the Undertow HTTP server in versions before 2.0.28.SP1 when listening on HTTPS. An attacker can target the HTTPS port to carry out a Denial Of Service (DOS) to make the service unavailable on SSL.
<p>Publish Date: 2020-01-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14888>CVE-2019-14888</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security-tracker.debian.org/tracker/CVE-2019-14888">https://security-tracker.debian.org/tracker/CVE-2019-14888</a></p>
<p>Release Date: 2020-01-23</p>
<p>Fix Resolution: 2.0.29.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-4492</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
io.undertow.security.impl.ClientCertAuthenticationMechanism (Application)
-> io.undertow.servlet.core.DeploymentManagerImpl (Extension)
-> io.undertow.servlet.core.ServletContainerImpl (Extension)
-> org.springframework.web.context.ContextLoader (Extension)
...
-> org.springframework.web.servlet.mvc.ParameterizableViewController (Extension)
-> org.springframework.web.servlet.config.annotation.ViewControllerRegistry (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
The undertow client is not checking the server identity presented by the server certificate in https connections. This is a compulsory step (at least it should be performed by default) in https and in http/2. I would add it to any TLS client protocol.
<p>Publish Date: 2023-02-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-4492>CVE-2022-4492</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pfcc-3g6r-8rg8">https://github.com/advisories/GHSA-pfcc-3g6r-8rg8</a></p>
<p>Release Date: 2023-02-23</p>
<p>Fix Resolution: io.undertow:undertow-core:2.2.24.Final,2.3.5.Final, io.undertow:undertow-examples:2.2.24.Final,2.3.5.Final, io.undertow:undertow-benchmarks:2.2.24.Final,2.3.5.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2020-5398</summary>
### Vulnerable Library - <b>spring-web-5.2.2.RELEASE.jar</b></p>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /webgoat-container/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.2.2.RELEASE/spring-web-5.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **spring-web-5.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.http.ContentDisposition (Application)
-> org.springframework.web.multipart.support.StandardMultipartHttpServletRequest (Extension)
-> ❌ org.owasp.webgoat.password_reset.ResetLinkAssignmentForgotPassword (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Framework, versions 5.2.x prior to 5.2.3, versions 5.1.x prior to 5.1.13, and versions 5.0.x prior to 5.0.16, an application is vulnerable to a reflected file download (RFD) attack when it sets a "Content-Disposition" header in the response where the filename attribute is derived from user supplied input.
<p>Publish Date: 2020-01-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5398>CVE-2020-5398</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pivotal.io/security/cve-2020-5398">https://pivotal.io/security/cve-2020-5398</a></p>
<p>Release Date: 2020-01-17</p>
<p>Fix Resolution: org.springframework:spring-web:5.0.16.RELEASE,org.springframework:spring-web:5.1.13.RELEASE,org.springframework:spring-web:5.2.3.RELEASE</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2021-46877</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
com.fasterxml.jackson.databind.node.NodeSerialization (Application)
-> com.fasterxml.jackson.databind.node.BaseJsonNode (Extension)
-> com.fasterxml.jackson.databind.node.ArrayNode (Extension)
-> com.fasterxml.jackson.databind.json.JsonMapper (Extension)
-> ❌ org.owasp.webwolf.requests.Requests (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6,2.13.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42004</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42004>CVE-2022-42004</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.13.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-42003</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
com.fasterxml.jackson.databind.deser.std.StdDeserializer (Application)
-> com.fasterxml.jackson.databind.deser.std.StdDelegatingDeserializer (Extension)
-> com.fasterxml.jackson.databind.deser.DeserializerCache (Extension)
-> com.fasterxml.jackson.databind.deser.DefaultDeserializationContext$Impl (Extension)
-> com.fasterxml.jackson.databind.ObjectMapper (Extension)
-> ❌ org.owasp.webwolf.requests.Requests (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-0084</summary>
### Vulnerable Library - <b>xnio-api-3.3.8.Final.jar</b></p>
<p>The API JAR of the XNIO project</p>
<p>Library home page: <a href="http://www.jboss.org/xnio">http://www.jboss.org/xnio</a></p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jboss/xnio/xnio-api/3.3.8.Final/xnio-api-3.3.8.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- undertow-core-2.0.28.Final.jar
- :x: **xnio-api-3.3.8.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.xnio.StreamConnection (Application)
-> org.xnio.ssl.JsseXnioSsl (Extension)
-> io.undertow.server.handlers.proxy.mod_cluster.MCMPHandler (Extension)
-> org.springframework.http.converter.xml.MappingJackson2XmlHttpMessageConverter (Extension)
...
-> org.springframework.web.filter.FormContentFilter (Extension)
-> org.springframework.web.filter.FormContentFilter$FormContentRequestWrapper (Extension)
-> ❌ org.owasp.webgoat.missing_ac.MissingFunctionACUsers (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in XNIO, specifically in the notifyReadClosed method. The issue revealed this method was logging a message to another expected end. This flaw allows an attacker to send flawed requests to a server, possibly causing log contention-related performance concerns or an unwanted disk fill-up.
<p>Publish Date: 2022-08-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0084>CVE-2022-0084</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-08-26</p>
<p>Fix Resolution: org.jboss.xnio:xnio-api:3.8.8.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-1319</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
io.undertow.server.protocol.ajp.AjpReadListener (Application)
-> io.undertow.protocols.ssl.UndertowAcceptingSslChannel (Extension)
-> org.xnio._private.Messages (Extension)
-> org.springframework.web.servlet.FrameworkServlet (Extension)
...
-> org.springframework.web.servlet.handler.HandlerMappingIntrospector (Extension)
-> org.springframework.web.servlet.handler.HandlerMappingIntrospector$RequestAttributeChangeIgnoringWrapper (Extension)
-> ❌ org.owasp.webgoat.crypto.HashingAssignment (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Undertow. For an AJP 400 response, EAP 7 is improperly sending two response packets, and those packets have the reuse flag set even though JBoss EAP closes the connection. A failure occurs when the connection is reused after a 400 by CPING since it reads in the second SEND_HEADERS response packet instead of a CPONG.
<p>Publish Date: 2022-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1319>CVE-2022-1319</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-1319">https://www.cve.org/CVERecord?id=CVE-2022-1319</a></p>
<p>Release Date: 2022-08-31</p>
<p>Fix Resolution: io.undertow:undertow-core:2.2.18.Final,2.3.0.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2023-20883</summary>
### Vulnerable Library - <b>spring-boot-autoconfigure-2.2.2.RELEASE.jar</b></p>
<p>Spring Boot AutoConfigure</p>
<p>Library home page: <a href="https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-autoconfigure">https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-autoconfigure</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-autoconfigure/2.2.2.RELEASE/spring-boot-autoconfigure-2.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-2.2.2.RELEASE.jar
- :x: **spring-boot-autoconfigure-2.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.boot.autoconfigure.web.servlet.WebMvcAutoConfiguration$EnableWebMvcConfiguration (Application)
-> org.springframework.test.web.servlet.setup.StubWebApplicationContext$StubBeanFactory (Extension)
-> org.thymeleaf.spring5.view.ThymeleafViewResolver (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.6, 2.7.0 - 2.7.11, 2.6.0 - 2.6.14, 2.5.0 - 2.5.14 and older unsupported versions, there is potential for a denial-of-service (DoS) attack if Spring MVC is used together with a reverse proxy cache.
<p>Publish Date: 2023-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20883>CVE-2023-20883</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20883">https://spring.io/security/cve-2023-20883</a></p>
<p>Release Date: 2023-05-26</p>
<p>Fix Resolution: org.springframework.boot:spring-boot-autoconfigure:2.5.12,2.6.12,2.7.12,3.0.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2020-36518</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
com.fasterxml.jackson.databind.deser.std.UntypedObjectDeserializer$Vanilla (Application)
-> com.fasterxml.jackson.databind.json.JsonMapper (Extension)
-> ❌ org.owasp.webwolf.requests.Requests (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind before 2.13.0 allows a Java StackOverflow exception and denial of service via a large depth of nested objects.
Mend Note: After conducting further research, Mend has determined that all versions of com.fasterxml.jackson.core:jackson-databind up to version 2.13.2 are vulnerable to CVE-2020-36518.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-36518>CVE-2020-36518</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6.1,2.13.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-1259</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
io.undertow.server.protocol.framed.AbstractFramedStreamSinkChannel (Application)
-> io.undertow.server.protocol.framed.AbstractFramedChannel (Extension)
-> io.undertow.server.protocol.framed.AbstractFramedChannel$FrameReadListener (Extension)
-> org.springframework.web.filter.GenericFilterBean (Extension)
...
-> org.springframework.web.filter.FormContentFilter (Extension)
-> org.springframework.web.filter.FormContentFilter$FormContentRequestWrapper (Extension)
-> ❌ org.owasp.webgoat.crypto.HashingAssignment (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Undertow. A potential security issue in flow control handling by the browser over HTTP/2 may cause overhead or a denial of service in the server. This flaw exists because of an incomplete fix for CVE-2021-3629.
<p>Publish Date: 2022-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1259>CVE-2022-1259</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=2072339">https://bugzilla.redhat.com/show_bug.cgi?id=2072339</a></p>
<p>Release Date: 2022-08-31</p>
<p>Fix Resolution: io.undertow:undertow-core:2.3.6.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-1108</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Undertow: Infinite loop in SslConduit during close.
A flaw was found in undertow. This issue makes achieving a denial of service possible due to an unexpected handshake status updated in SslConduit, where the loop never terminates.
<p>Publish Date: 2023-03-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1108>CVE-2023-1108</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-1108">https://nvd.nist.gov/vuln/detail/CVE-2023-1108</a></p>
<p>Release Date: 2023-03-01</p>
<p>Fix Resolution: org.teiid:vdb-base-builder - 1.6.0;io.syndesis.server:server-runtime - 1.3.5,1.13.1;io.syndesis.meta:meta - 1.13.1,1.3.5,1.13.1</p>
</p>
<p></p>
</details> | True | webgoat-container-v8.1.0.jar: 33 vulnerabilities (highest severity is: 9.8) reachable - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>webgoat-container-v8.1.0.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (webgoat-container-v8.1.0.jar version) | Remediation Available | Reachability |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- | --- |
| [CVE-2022-22965](https://www.mend.io/vulnerability-database/CVE-2022-22965) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-beans-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20873](https://www.mend.io/vulnerability-database/CVE-2023-20873) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22978](https://www.mend.io/vulnerability-database/CVE-2022-22978) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-1471](https://www.mend.io/vulnerability-database/CVE-2022-1471) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | snakeyaml-1.25.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-22112](https://www.mend.io/vulnerability-database/CVE-2021-22112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [WS-2019-0490](https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | jcommander-1.35.jar | Transitive | N/A* | ❌ |
| [CVE-2019-14888](https://www.mend.io/vulnerability-database/CVE-2019-14888) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌ |
| [CVE-2022-4492](https://www.mend.io/vulnerability-database/CVE-2022-4492) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5398](https://www.mend.io/vulnerability-database/CVE-2020-5398) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-web-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-46877](https://www.mend.io/vulnerability-database/CVE-2021-46877) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-0084](https://www.mend.io/vulnerability-database/CVE-2022-0084) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | xnio-api-3.3.8.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-1319](https://www.mend.io/vulnerability-database/CVE-2022-1319) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20883](https://www.mend.io/vulnerability-database/CVE-2023-20883) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | spring-boot-autoconfigure-2.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-1259](https://www.mend.io/vulnerability-database/CVE-2022-1259) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-1108](https://www.mend.io/vulnerability-database/CVE-2023-1108) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌ |
| [CVE-2021-42550](https://www.mend.io/vulnerability-database/CVE-2021-42550) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.6 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22950](https://www.mend.io/vulnerability-database/CVE-2022-22950) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20861](https://www.mend.io/vulnerability-database/CVE-2023-20861) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2023-20863](https://www.mend.io/vulnerability-database/CVE-2023-20863) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-expression-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5408](https://www.mend.io/vulnerability-database/CVE-2020-5408) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-security-core-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5421](https://www.mend.io/vulnerability-database/CVE-2020-5421) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | spring-web-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [WS-2017-3767](https://github.com/spring-projects/spring-security/commit/eed71243cb86833e7edf230e5e43ad89b01142f9) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.3 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-3629](https://www.mend.io/vulnerability-database/CVE-2021-3629) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | undertow-core-2.0.28.Final.jar | Transitive | N/A* | ❌ |
| [WS-2021-0616](https://github.com/FasterXML/jackson-databind/commit/3ccde7d938fea547e598fdefe9a82cff37fed5cb) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | jackson-databind-2.10.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [WS-2020-0293](https://github.com/spring-projects/spring-security/commit/40e027c56d11b9b4c5071360bfc718165c937784) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | spring-security-web-5.2.1.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22968](https://www.mend.io/vulnerability-database/CVE-2022-22968) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | spring-context-5.2.2.RELEASE.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2022-22970](https://www.mend.io/vulnerability-database/CVE-2022-22970) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-5397](https://www.mend.io/vulnerability-database/CVE-2020-5397) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-22060](https://www.mend.io/vulnerability-database/CVE-2021-22060) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 4.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-22096](https://www.mend.io/vulnerability-database/CVE-2021-22096) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 4.3 | detected in multiple dependencies | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (18 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-22965</summary>
### Vulnerable Library - <b>spring-beans-5.2.2.RELEASE.jar</b></p>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.2.RELEASE/spring-beans-5.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-2.2.2.RELEASE.jar
- spring-boot-2.2.2.RELEASE.jar
- spring-context-5.2.2.RELEASE.jar
- spring-aop-5.2.2.RELEASE.jar
- :x: **spring-beans-5.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.beans.CachedIntrospectionResults (Application)
-> org.springframework.data.util.DirectFieldAccessFallbackBeanWrapper (Extension)
-> org.springframework.context.annotation.CommonAnnotationBeanPostProcessor (Extension)
-> org.springframework.boot.autoconfigure.SharedMetadataReaderFactoryContextInitializer (Extension)
...
-> org.springframework.boot.autoconfigure.AutoConfigurationImportSelector (Extension)
-> org.springframework.boot.autoconfigure.SpringBootApplication (Extension)
-> ❌ org.owasp.webwolf.WebWolf (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A Spring MVC or Spring WebFlux application running on JDK 9+ may be vulnerable to remote code execution (RCE) via data binding. The specific exploit requires the application to run on Tomcat as a WAR deployment. If the application is deployed as a Spring Boot executable jar, i.e. the default, it is not vulnerable to the exploit. However, the nature of the vulnerability is more general, and there may be other ways to exploit it.
Mend Note: Converted from WS-2022-0107, on 2022-11-07.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22965>CVE-2022-22965</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.20.RELEASE,5.3.18</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2023-20873</summary>
### Vulnerable Library - <b>spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar</b></p>
<p>Spring Boot Actuator AutoConfigure</p>
<p>Library home page: <a href="https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-actuator-autoconfigure">https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-actuator-autoconfigure</a></p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-actuator-autoconfigure/2.2.2.RELEASE/spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-actuator-2.2.2.RELEASE.jar
- :x: **spring-boot-actuator-autoconfigure-2.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.boot.actuate.autoconfigure.cloudfoundry.reactive.ReactiveCloudFoundryActuatorAutoConfiguration$WebFilterChainPostProcessor (Application)
-> org.springframework.beans.factory.support.DefaultListableBeanFactory (Extension)
-> org.springframework.web.servlet.config.annotation.WebMvcConfigurationSupport (Extension)
-> org.thymeleaf.spring5.expression.Mvc (Extension)
...
-> org.thymeleaf.spring5.dialect.SpringStandardDialect (Extension)
-> org.thymeleaf.spring5.SpringTemplateEngine (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.5, 2.7.0 - 2.7.10, and older unsupported versions, an application that is deployed to Cloud Foundry could be susceptible to a security bypass. Users of affected versions should apply the following mitigation: 3.0.x users should upgrade to 3.0.6+. 2.7.x users should upgrade to 2.7.11+. Users of older, unsupported versions should upgrade to 3.0.6+ or 2.7.11+.
<p>Publish Date: 2023-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20873>CVE-2023-20873</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20873">https://spring.io/security/cve-2023-20873</a></p>
<p>Release Date: 2023-04-20</p>
<p>Fix Resolution: org.springframework.boot:spring-boot-actuator-autoconfigure:2.7.11,3.0.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-22978</summary>
### Vulnerable Library - <b>spring-security-web-5.2.1.RELEASE.jar</b></p>
<p>spring-security-web</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-web/5.2.1.RELEASE/spring-security-web-5.2.1.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-security-2.2.2.RELEASE.jar
- :x: **spring-security-web-5.2.1.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.security.web.util.matcher.RegexRequestMatcher (Application)
-> org.springframework.security.config.annotation.web.builders.HttpSecurity (Extension)
-> ❌ org.owasp.webwolf.WebSecurityConfig (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In spring security versions prior to 5.4.11+, 5.5.7+ , 5.6.4+ and older unsupported versions, RegexRequestMatcher can easily be misconfigured to be bypassed on some servlet containers. Applications using RegexRequestMatcher with `.` in the regular expression are possibly vulnerable to an authorization bypass.
<p>Publish Date: 2022-05-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22978>CVE-2022-22978</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2022-22978/">https://spring.io/security/cve-2022-22978/</a></p>
<p>Release Date: 2022-05-19</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:5.5.7,5.6.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-1471</summary>
### Vulnerable Library - <b>snakeyaml-1.25.jar</b></p>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.25/snakeyaml-1.25.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-2.2.2.RELEASE.jar
- :x: **snakeyaml-1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.yaml.snakeyaml.LoaderOptions (Application)
-> org.yaml.snakeyaml.Yaml (Extension)
-> org.springframework.beans.factory.config.YamlMapFactoryBean (Extension)
-> org.springframework.beans.factory.support.DefaultListableBeanFactory (Extension)
-> org.thymeleaf.spring5.view.ThymeleafViewResolver (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
SnakeYaml's Constructor() class does not restrict types which can be instantiated during deserialization. Deserializing yaml content provided by an attacker can lead to remote code execution. We recommend using SnakeYaml's SafeConsturctor when parsing untrusted content to restrict deserialization. We recommend upgrading to version 2.0 and beyond.
<p>Publish Date: 2022-12-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1471>CVE-2022-1471</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374">https://bitbucket.org/snakeyaml/snakeyaml/issues/561/cve-2022-1471-vulnerability-in#comment-64634374</a></p>
<p>Release Date: 2022-12-01</p>
<p>Fix Resolution: org.yaml:snakeyaml:2.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2021-22112</summary>
### Vulnerable Library - <b>spring-security-web-5.2.1.RELEASE.jar</b></p>
<p>spring-security-web</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-web/5.2.1.RELEASE/spring-security-web-5.2.1.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-security-2.2.2.RELEASE.jar
- :x: **spring-security-web-5.2.1.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.security.web.context.HttpSessionSecurityContextRepository$SaveToSessionResponseWrapper (Application)
-> ❌ org.owasp.webgoat.idor.IDORViewOtherProfile (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security 5.4.x prior to 5.4.4, 5.3.x prior to 5.3.8.RELEASE, 5.2.x prior to 5.2.9.RELEASE, and older unsupported versions can fail to save the SecurityContext if it is changed more than once in a single request.A malicious user cannot cause the bug to happen (it must be programmed in). However, if the application's intent is to only allow the user to run with elevated privileges in a small portion of the application, the bug can be leveraged to extend those privileges to the rest of the application.
<p>Publish Date: 2021-02-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22112>CVE-2021-22112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22112">https://tanzu.vmware.com/security/cve-2021-22112</a></p>
<p>Release Date: 2021-02-23</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:5.2.9,5.3.8,5.4.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> WS-2019-0490</summary>
### Vulnerable Library - <b>jcommander-1.35.jar</b></p>
<p>A Java framework to parse command line options with annotations.</p>
<p>Library home page: <a href="http://beust.com/">http://beust.com/</a></p>
<p>Path to dependency file: /webgoat-container/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/beust/jcommander/1.35/jcommander-1.35.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- asciidoctorj-1.5.8.1.jar
- :x: **jcommander-1.35.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
<p>Publish Date: 2019-02-19
<p>URL: <a href=https://github.com/cbeust/jcommander/commit/3ae95595febbed9c13f367b6bda5c0be1c572c53>WS-2019-0490</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-19</p>
<p>Fix Resolution: com.beust:jcommander:1.75</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2019-14888</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in the Undertow HTTP server in versions before 2.0.28.SP1 when listening on HTTPS. An attacker can target the HTTPS port to carry out a Denial Of Service (DOS) to make the service unavailable on SSL.
<p>Publish Date: 2020-01-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14888>CVE-2019-14888</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security-tracker.debian.org/tracker/CVE-2019-14888">https://security-tracker.debian.org/tracker/CVE-2019-14888</a></p>
<p>Release Date: 2020-01-23</p>
<p>Fix Resolution: 2.0.29.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-4492</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
io.undertow.security.impl.ClientCertAuthenticationMechanism (Application)
-> io.undertow.servlet.core.DeploymentManagerImpl (Extension)
-> io.undertow.servlet.core.ServletContainerImpl (Extension)
-> org.springframework.web.context.ContextLoader (Extension)
...
-> org.springframework.web.servlet.mvc.ParameterizableViewController (Extension)
-> org.springframework.web.servlet.config.annotation.ViewControllerRegistry (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
The undertow client is not checking the server identity presented by the server certificate in https connections. This is a compulsory step (at least it should be performed by default) in https and in http/2. I would add it to any TLS client protocol.
<p>Publish Date: 2023-02-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-4492>CVE-2022-4492</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pfcc-3g6r-8rg8">https://github.com/advisories/GHSA-pfcc-3g6r-8rg8</a></p>
<p>Release Date: 2023-02-23</p>
<p>Fix Resolution: io.undertow:undertow-core:2.2.24.Final,2.3.5.Final, io.undertow:undertow-examples:2.2.24.Final,2.3.5.Final, io.undertow:undertow-benchmarks:2.2.24.Final,2.3.5.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2020-5398</summary>
### Vulnerable Library - <b>spring-web-5.2.2.RELEASE.jar</b></p>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /webgoat-container/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.2.2.RELEASE/spring-web-5.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **spring-web-5.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.http.ContentDisposition (Application)
-> org.springframework.web.multipart.support.StandardMultipartHttpServletRequest (Extension)
-> ❌ org.owasp.webgoat.password_reset.ResetLinkAssignmentForgotPassword (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Framework, versions 5.2.x prior to 5.2.3, versions 5.1.x prior to 5.1.13, and versions 5.0.x prior to 5.0.16, an application is vulnerable to a reflected file download (RFD) attack when it sets a "Content-Disposition" header in the response where the filename attribute is derived from user supplied input.
<p>Publish Date: 2020-01-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5398>CVE-2020-5398</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pivotal.io/security/cve-2020-5398">https://pivotal.io/security/cve-2020-5398</a></p>
<p>Release Date: 2020-01-17</p>
<p>Fix Resolution: org.springframework:spring-web:5.0.16.RELEASE,org.springframework:spring-web:5.1.13.RELEASE,org.springframework:spring-web:5.2.3.RELEASE</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2021-46877</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
com.fasterxml.jackson.databind.node.NodeSerialization (Application)
-> com.fasterxml.jackson.databind.node.BaseJsonNode (Extension)
-> com.fasterxml.jackson.databind.node.ArrayNode (Extension)
-> com.fasterxml.jackson.databind.json.JsonMapper (Extension)
-> ❌ org.owasp.webwolf.requests.Requests (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6,2.13.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42004</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42004>CVE-2022-42004</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.13.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-42003</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
com.fasterxml.jackson.databind.deser.std.StdDeserializer (Application)
-> com.fasterxml.jackson.databind.deser.std.StdDelegatingDeserializer (Extension)
-> com.fasterxml.jackson.databind.deser.DeserializerCache (Extension)
-> com.fasterxml.jackson.databind.deser.DefaultDeserializationContext$Impl (Extension)
-> com.fasterxml.jackson.databind.ObjectMapper (Extension)
-> ❌ org.owasp.webwolf.requests.Requests (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-0084</summary>
### Vulnerable Library - <b>xnio-api-3.3.8.Final.jar</b></p>
<p>The API JAR of the XNIO project</p>
<p>Library home page: <a href="http://www.jboss.org/xnio">http://www.jboss.org/xnio</a></p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jboss/xnio/xnio-api/3.3.8.Final/xnio-api-3.3.8.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- undertow-core-2.0.28.Final.jar
- :x: **xnio-api-3.3.8.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.xnio.StreamConnection (Application)
-> org.xnio.ssl.JsseXnioSsl (Extension)
-> io.undertow.server.handlers.proxy.mod_cluster.MCMPHandler (Extension)
-> org.springframework.http.converter.xml.MappingJackson2XmlHttpMessageConverter (Extension)
...
-> org.springframework.web.filter.FormContentFilter (Extension)
-> org.springframework.web.filter.FormContentFilter$FormContentRequestWrapper (Extension)
-> ❌ org.owasp.webgoat.missing_ac.MissingFunctionACUsers (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in XNIO, specifically in the notifyReadClosed method. The issue revealed this method was logging a message to another expected end. This flaw allows an attacker to send flawed requests to a server, possibly causing log contention-related performance concerns or an unwanted disk fill-up.
<p>Publish Date: 2022-08-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0084>CVE-2022-0084</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-08-26</p>
<p>Fix Resolution: org.jboss.xnio:xnio-api:3.8.8.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-1319</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
io.undertow.server.protocol.ajp.AjpReadListener (Application)
-> io.undertow.protocols.ssl.UndertowAcceptingSslChannel (Extension)
-> org.xnio._private.Messages (Extension)
-> org.springframework.web.servlet.FrameworkServlet (Extension)
...
-> org.springframework.web.servlet.handler.HandlerMappingIntrospector (Extension)
-> org.springframework.web.servlet.handler.HandlerMappingIntrospector$RequestAttributeChangeIgnoringWrapper (Extension)
-> ❌ org.owasp.webgoat.crypto.HashingAssignment (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Undertow. For an AJP 400 response, EAP 7 is improperly sending two response packets, and those packets have the reuse flag set even though JBoss EAP closes the connection. A failure occurs when the connection is reused after a 400 by CPING since it reads in the second SEND_HEADERS response packet instead of a CPONG.
<p>Publish Date: 2022-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1319>CVE-2022-1319</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-1319">https://www.cve.org/CVERecord?id=CVE-2022-1319</a></p>
<p>Release Date: 2022-08-31</p>
<p>Fix Resolution: io.undertow:undertow-core:2.2.18.Final,2.3.0.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2023-20883</summary>
### Vulnerable Library - <b>spring-boot-autoconfigure-2.2.2.RELEASE.jar</b></p>
<p>Spring Boot AutoConfigure</p>
<p>Library home page: <a href="https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-autoconfigure">https://projects.spring.io/spring-boot/#/spring-boot-parent/spring-boot-autoconfigure</a></p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot-autoconfigure/2.2.2.RELEASE/spring-boot-autoconfigure-2.2.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-2.2.2.RELEASE.jar
- :x: **spring-boot-autoconfigure-2.2.2.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.springframework.boot.autoconfigure.web.servlet.WebMvcAutoConfiguration$EnableWebMvcConfiguration (Application)
-> org.springframework.test.web.servlet.setup.StubWebApplicationContext$StubBeanFactory (Extension)
-> org.thymeleaf.spring5.view.ThymeleafViewResolver (Extension)
-> ❌ org.owasp.webgoat.MvcConfiguration (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In Spring Boot versions 3.0.0 - 3.0.6, 2.7.0 - 2.7.11, 2.6.0 - 2.6.14, 2.5.0 - 2.5.14 and older unsupported versions, there is potential for a denial-of-service (DoS) attack if Spring MVC is used together with a reverse proxy cache.
<p>Publish Date: 2023-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-20883>CVE-2023-20883</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/security/cve-2023-20883">https://spring.io/security/cve-2023-20883</a></p>
<p>Release Date: 2023-05-26</p>
<p>Fix Resolution: org.springframework.boot:spring-boot-autoconfigure:2.5.12,2.6.12,2.7.12,3.0.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2020-36518</summary>
### Vulnerable Library - <b>jackson-databind-2.10.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /webgoat-lessons/challenge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.1/jackson-databind-2.10.1.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-web-2.2.2.RELEASE.jar
- spring-boot-starter-json-2.2.2.RELEASE.jar
- :x: **jackson-databind-2.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
com.fasterxml.jackson.databind.deser.std.UntypedObjectDeserializer$Vanilla (Application)
-> com.fasterxml.jackson.databind.json.JsonMapper (Extension)
-> ❌ org.owasp.webwolf.requests.Requests (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind before 2.13.0 allows a Java StackOverflow exception and denial of service via a large depth of nested objects.
Mend Note: After conducting further research, Mend has determined that all versions of com.fasterxml.jackson.core:jackson-databind up to version 2.13.2 are vulnerable to CVE-2020-36518.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-36518>CVE-2020-36518</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6.1,2.13.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-1259</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
io.undertow.server.protocol.framed.AbstractFramedStreamSinkChannel (Application)
-> io.undertow.server.protocol.framed.AbstractFramedChannel (Extension)
-> io.undertow.server.protocol.framed.AbstractFramedChannel$FrameReadListener (Extension)
-> org.springframework.web.filter.GenericFilterBean (Extension)
...
-> org.springframework.web.filter.FormContentFilter (Extension)
-> org.springframework.web.filter.FormContentFilter$FormContentRequestWrapper (Extension)
-> ❌ org.owasp.webgoat.crypto.HashingAssignment (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was found in Undertow. A potential security issue in flow control handling by the browser over HTTP/2 may cause overhead or a denial of service in the server. This flaw exists because of an incomplete fix for CVE-2021-3629.
<p>Publish Date: 2022-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1259>CVE-2022-1259</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=2072339">https://bugzilla.redhat.com/show_bug.cgi?id=2072339</a></p>
<p>Release Date: 2022-08-31</p>
<p>Fix Resolution: io.undertow:undertow-core:2.3.6.Final</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-1108</summary>
### Vulnerable Library - <b>undertow-core-2.0.28.Final.jar</b></p>
<p>Undertow</p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/2.0.28.Final/undertow-core-2.0.28.Final.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-v8.1.0.jar (Root Library)
- spring-boot-starter-undertow-2.2.2.RELEASE.jar
- :x: **undertow-core-2.0.28.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-democorp/GMQ-Java-Prioritize/commit/411df46286164f4b431ef08daee03c73e487967a">411df46286164f4b431ef08daee03c73e487967a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Undertow: Infinite loop in SslConduit during close.
A flaw was found in undertow. This issue makes achieving a denial of service possible due to an unexpected handshake status updated in SslConduit, where the loop never terminates.
<p>Publish Date: 2023-03-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1108>CVE-2023-1108</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2023-1108">https://nvd.nist.gov/vuln/detail/CVE-2023-1108</a></p>
<p>Release Date: 2023-03-01</p>
<p>Fix Resolution: org.teiid:vdb-base-builder - 1.6.0;io.syndesis.server:server-runtime - 1.3.5,1.13.1;io.syndesis.meta:meta - 1.13.1,1.3.5,1.13.1</p>
</p>
<p></p>
</details> | non_build | webgoat container jar vulnerabilities highest severity is reachable autoclosed vulnerable library webgoat container jar path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in webgoat container jar version remediation available reachability critical spring beans release jar transitive n a the vulnerability is likely to be reachable critical spring boot actuator autoconfigure release jar transitive n a the vulnerability is likely to be reachable critical spring security web release jar transitive n a the vulnerability is likely to be reachable critical snakeyaml jar transitive n a the vulnerability is likely to be reachable high spring security web release jar transitive n a the vulnerability is likely to be reachable high jcommander jar transitive n a high undertow core final jar transitive n a high undertow core final jar transitive n a the vulnerability is likely to be reachable high spring web release jar transitive n a the vulnerability is likely to be reachable high jackson databind jar transitive n a the vulnerability is likely to be reachable high jackson databind jar transitive n a high jackson databind jar transitive n a the vulnerability is likely to be reachable high xnio api final jar transitive n a the vulnerability is likely to be reachable high undertow core final jar transitive n a the vulnerability is likely to be reachable high spring boot autoconfigure release jar transitive n a the vulnerability is likely to be reachable high jackson databind jar transitive n a the vulnerability is likely to be reachable high undertow core final jar transitive n a the vulnerability is likely to be reachable high undertow core final jar transitive n a medium detected in multiple dependencies transitive n a the vulnerability is likely to be reachable medium spring expression release jar transitive n a the vulnerability is likely to be reachable medium spring expression release jar transitive n a the vulnerability is likely to be reachable medium spring expression release jar transitive n a the vulnerability is likely to be reachable medium spring security core release jar transitive n a the vulnerability is likely to be reachable medium spring web release jar transitive n a the vulnerability is likely to be reachable medium spring security web release jar transitive n a the vulnerability is likely to be reachable medium undertow core final jar transitive n a medium jackson databind jar transitive n a the vulnerability is likely to be reachable medium spring security web release jar transitive n a the vulnerability is likely to be reachable medium spring context release jar transitive n a the vulnerability is likely to be reachable medium detected in multiple dependencies transitive n a the vulnerability is likely to be reachable medium detected in multiple dependencies transitive n a the vulnerability is likely to be reachable medium detected in multiple dependencies transitive n a the vulnerability is likely to be reachable medium detected in multiple dependencies transitive n a the vulnerability is likely to be reachable for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library spring beans release jar spring beans library home page a href path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository org springframework spring beans release spring beans release jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter release jar spring boot release jar spring context release jar spring aop release jar x spring beans release jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org springframework beans cachedintrospectionresults application org springframework data util directfieldaccessfallbackbeanwrapper extension org springframework context annotation commonannotationbeanpostprocessor extension org springframework boot autoconfigure sharedmetadatareaderfactorycontextinitializer extension org springframework boot autoconfigure autoconfigurationimportselector extension org springframework boot autoconfigure springbootapplication extension ❌ org owasp webwolf webwolf vulnerable component vulnerability details a spring mvc or spring webflux application running on jdk may be vulnerable to remote code execution rce via data binding the specific exploit requires the application to run on tomcat as a war deployment if the application is deployed as a spring boot executable jar i e the default it is not vulnerable to the exploit however the nature of the vulnerability is more general and there may be other ways to exploit it mend note converted from ws on publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans release cve vulnerable library spring boot actuator autoconfigure release jar spring boot actuator autoconfigure library home page a href path to dependency file webgoat server pom xml path to vulnerable library home wss scanner repository org springframework boot spring boot actuator autoconfigure release spring boot actuator autoconfigure release jar dependency hierarchy webgoat container jar root library spring boot starter actuator release jar x spring boot actuator autoconfigure release jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org springframework boot actuate autoconfigure cloudfoundry reactive reactivecloudfoundryactuatorautoconfiguration webfilterchainpostprocessor application org springframework beans factory support defaultlistablebeanfactory extension org springframework web servlet config annotation webmvcconfigurationsupport extension org thymeleaf expression mvc extension org thymeleaf dialect springstandarddialect extension org thymeleaf springtemplateengine extension ❌ org owasp webgoat mvcconfiguration vulnerable component vulnerability details in spring boot versions and older unsupported versions an application that is deployed to cloud foundry could be susceptible to a security bypass users of affected versions should apply the following mitigation x users should upgrade to x users should upgrade to users of older unsupported versions should upgrade to or publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework boot spring boot actuator autoconfigure cve vulnerable library spring security web release jar spring security web library home page a href path to dependency file webgoat server pom xml path to vulnerable library home wss scanner repository org springframework security spring security web release spring security web release jar dependency hierarchy webgoat container jar root library spring boot starter security release jar x spring security web release jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org springframework security web util matcher regexrequestmatcher application org springframework security config annotation web builders httpsecurity extension ❌ org owasp webwolf websecurityconfig vulnerable component vulnerability details in spring security versions prior to and older unsupported versions regexrequestmatcher can easily be misconfigured to be bypassed on some servlet containers applications using regexrequestmatcher with in the regular expression are possibly vulnerable to an authorization bypass publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security web cve vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter release jar x snakeyaml jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org yaml snakeyaml loaderoptions application org yaml snakeyaml yaml extension org springframework beans factory config yamlmapfactorybean extension org springframework beans factory support defaultlistablebeanfactory extension org thymeleaf view thymeleafviewresolver extension ❌ org owasp webgoat mvcconfiguration vulnerable component vulnerability details snakeyaml s constructor class does not restrict types which can be instantiated during deserialization deserializing yaml content provided by an attacker can lead to remote code execution we recommend using snakeyaml s safeconsturctor when parsing untrusted content to restrict deserialization we recommend upgrading to version and beyond publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml cve vulnerable library spring security web release jar spring security web library home page a href path to dependency file webgoat server pom xml path to vulnerable library home wss scanner repository org springframework security spring security web release spring security web release jar dependency hierarchy webgoat container jar root library spring boot starter security release jar x spring security web release jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org springframework security web context httpsessionsecuritycontextrepository savetosessionresponsewrapper application ❌ org owasp webgoat idor idorviewotherprofile vulnerable component vulnerability details spring security x prior to x prior to release x prior to release and older unsupported versions can fail to save the securitycontext if it is changed more than once in a single request a malicious user cannot cause the bug to happen it must be programmed in however if the application s intent is to only allow the user to run with elevated privileges in a small portion of the application the bug can be leveraged to extend those privileges to the rest of the application publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security web ws vulnerable library jcommander jar a java framework to parse command line options with annotations library home page a href path to dependency file webgoat container pom xml path to vulnerable library home wss scanner repository com beust jcommander jcommander jar dependency hierarchy webgoat container jar root library asciidoctorj jar x jcommander jar vulnerable library found in head commit a href found in base branch main vulnerability details inclusion of functionality from untrusted control sphere vulnerability found in jcommander before jcommander resolving dependencies over http instead of https publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com beust jcommander cve vulnerable library undertow core final jar undertow path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar dependency hierarchy webgoat container jar root library spring boot starter undertow release jar x undertow core final jar vulnerable library found in head commit a href found in base branch main vulnerability details a vulnerability was found in the undertow http server in versions before when listening on https an attacker can target the https port to carry out a denial of service dos to make the service unavailable on ssl publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution final cve vulnerable library undertow core final jar undertow path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar dependency hierarchy webgoat container jar root library spring boot starter undertow release jar x undertow core final jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used io undertow security impl clientcertauthenticationmechanism application io undertow servlet core deploymentmanagerimpl extension io undertow servlet core servletcontainerimpl extension org springframework web context contextloader extension org springframework web servlet mvc parameterizableviewcontroller extension org springframework web servlet config annotation viewcontrollerregistry extension ❌ org owasp webgoat mvcconfiguration vulnerable component vulnerability details the undertow client is not checking the server identity presented by the server certificate in https connections this is a compulsory step at least it should be performed by default in https and in http i would add it to any tls client protocol publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io undertow undertow core final final io undertow undertow examples final final io undertow undertow benchmarks final final cve vulnerable library spring web release jar spring web library home page a href path to dependency file webgoat container pom xml path to vulnerable library home wss scanner repository org springframework spring web release spring web release jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter json release jar x spring web release jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org springframework http contentdisposition application org springframework web multipart support standardmultiparthttpservletrequest extension ❌ org owasp webgoat password reset resetlinkassignmentforgotpassword vulnerable component vulnerability details in spring framework versions x prior to versions x prior to and versions x prior to an application is vulnerable to a reflected file download rfd attack when it sets a content disposition header in the response where the filename attribute is derived from user supplied input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web release org springframework spring web release org springframework spring web release cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file webgoat lessons challenge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter json release jar x jackson databind jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used com fasterxml jackson databind node nodeserialization application com fasterxml jackson databind node basejsonnode extension com fasterxml jackson databind node arraynode extension com fasterxml jackson databind json jsonmapper extension ❌ org owasp webwolf requests requests vulnerable component vulnerability details jackson databind x through x before and x before allows attackers to cause a denial of service gb transient heap usage per read in uncommon situations involving jsonnode jdk serialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file webgoat lessons challenge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter json release jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in beandeserializer deserializefromarray to prevent use of deeply nested arrays an application is vulnerable only with certain customized choices for deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file webgoat lessons challenge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter json release jar x jackson databind jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used com fasterxml jackson databind deser std stddeserializer application com fasterxml jackson databind deser std stddelegatingdeserializer extension com fasterxml jackson databind deser deserializercache extension com fasterxml jackson databind deser defaultdeserializationcontext impl extension com fasterxml jackson databind objectmapper extension ❌ org owasp webwolf requests requests vulnerable component vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting when the unwrap single value arrays feature is enabled additional fix version in and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library xnio api final jar the api jar of the xnio project library home page a href path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository org jboss xnio xnio api final xnio api final jar dependency hierarchy webgoat container jar root library spring boot starter undertow release jar undertow core final jar x xnio api final jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org xnio streamconnection application org xnio ssl jssexniossl extension io undertow server handlers proxy mod cluster mcmphandler extension org springframework http converter xml extension org springframework web filter formcontentfilter extension org springframework web filter formcontentfilter formcontentrequestwrapper extension ❌ org owasp webgoat missing ac missingfunctionacusers vulnerable component vulnerability details a flaw was found in xnio specifically in the notifyreadclosed method the issue revealed this method was logging a message to another expected end this flaw allows an attacker to send flawed requests to a server possibly causing log contention related performance concerns or an unwanted disk fill up publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution org jboss xnio xnio api final cve vulnerable library undertow core final jar undertow path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar dependency hierarchy webgoat container jar root library spring boot starter undertow release jar x undertow core final jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used io undertow server protocol ajp ajpreadlistener application io undertow protocols ssl undertowacceptingsslchannel extension org xnio private messages extension org springframework web servlet frameworkservlet extension org springframework web servlet handler handlermappingintrospector extension org springframework web servlet handler handlermappingintrospector requestattributechangeignoringwrapper extension ❌ org owasp webgoat crypto hashingassignment vulnerable component vulnerability details a flaw was found in undertow for an ajp response eap is improperly sending two response packets and those packets have the reuse flag set even though jboss eap closes the connection a failure occurs when the connection is reused after a by cping since it reads in the second send headers response packet instead of a cpong publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io undertow undertow core final final cve vulnerable library spring boot autoconfigure release jar spring boot autoconfigure library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository org springframework boot spring boot autoconfigure release spring boot autoconfigure release jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter release jar x spring boot autoconfigure release jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used org springframework boot autoconfigure web servlet webmvcautoconfiguration enablewebmvcconfiguration application org springframework test web servlet setup stubwebapplicationcontext stubbeanfactory extension org thymeleaf view thymeleafviewresolver extension ❌ org owasp webgoat mvcconfiguration vulnerable component vulnerability details in spring boot versions and older unsupported versions there is potential for a denial of service dos attack if spring mvc is used together with a reverse proxy cache publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework boot spring boot autoconfigure cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file webgoat lessons challenge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy webgoat container jar root library spring boot starter web release jar spring boot starter json release jar x jackson databind jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used com fasterxml jackson databind deser std untypedobjectdeserializer vanilla application com fasterxml jackson databind json jsonmapper extension ❌ org owasp webwolf requests requests vulnerable component vulnerability details jackson databind before allows a java stackoverflow exception and denial of service via a large depth of nested objects mend note after conducting further research mend has determined that all versions of com fasterxml jackson core jackson databind up to version are vulnerable to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library undertow core final jar undertow path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar dependency hierarchy webgoat container jar root library spring boot starter undertow release jar x undertow core final jar vulnerable library found in head commit a href found in base branch main reachability analysis this vulnerability is potentially used io undertow server protocol framed abstractframedstreamsinkchannel application io undertow server protocol framed abstractframedchannel extension io undertow server protocol framed abstractframedchannel framereadlistener extension org springframework web filter genericfilterbean extension org springframework web filter formcontentfilter extension org springframework web filter formcontentfilter formcontentrequestwrapper extension ❌ org owasp webgoat crypto hashingassignment vulnerable component vulnerability details a flaw was found in undertow a potential security issue in flow control handling by the browser over http may cause overhead or a denial of service in the server this flaw exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io undertow undertow core final cve vulnerable library undertow core final jar undertow path to dependency file webwolf pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar dependency hierarchy webgoat container jar root library spring boot starter undertow release jar x undertow core final jar vulnerable library found in head commit a href found in base branch main vulnerability details undertow infinite loop in sslconduit during close a flaw was found in undertow this issue makes achieving a denial of service possible due to an unexpected handshake status updated in sslconduit where the loop never terminates publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org teiid vdb base builder io syndesis server server runtime io syndesis meta meta | 0 |
90,107 | 25,975,935,971 | IssuesEvent | 2022-12-19 14:54:03 | Crocoblock/suggestions | https://api.github.com/repos/Crocoblock/suggestions | closed | Jet Woo builder - My Account | JetWooBuilder | it is possible with this wonderful plugin to customize the endpoints for each part of the account, except the "forgotten password" part, which poses a problem since there is no possibility to modify the style of the element, it would be necessary to create a widget and an endpoint | 1.0 | Jet Woo builder - My Account - it is possible with this wonderful plugin to customize the endpoints for each part of the account, except the "forgotten password" part, which poses a problem since there is no possibility to modify the style of the element, it would be necessary to create a widget and an endpoint | build | jet woo builder my account it is possible with this wonderful plugin to customize the endpoints for each part of the account except the forgotten password part which poses a problem since there is no possibility to modify the style of the element it would be necessary to create a widget and an endpoint | 1 |
498,150 | 14,401,860,326 | IssuesEvent | 2020-12-03 14:14:52 | luslab/clipseq | https://api.github.com/repos/luslab/clipseq | closed | Add an auto-download genome/annotation feature | low priority | Add option so if a species is supplied (and a `--download` flag maybe?) the fasta and gtf files are automatically downloaded from Gencode or Ensembl | 1.0 | Add an auto-download genome/annotation feature - Add option so if a species is supplied (and a `--download` flag maybe?) the fasta and gtf files are automatically downloaded from Gencode or Ensembl | non_build | add an auto download genome annotation feature add option so if a species is supplied and a download flag maybe the fasta and gtf files are automatically downloaded from gencode or ensembl | 0 |
84,288 | 24,270,100,565 | IssuesEvent | 2022-09-28 09:35:18 | Decathlon/vitamin-design | https://api.github.com/repos/Decathlon/vitamin-design | opened | [component] Text input | documentation 📝 enhancement 🚀 web 🔵 android 🟢 ios 🟡 build 🏗 | ### Duplicates ❌
- [X] I have searched the existing issues
### Which Figma library is concerned?
Not related to one Figma library
### Summary 💡
A text input is a field that allows users to enter text into.
### Dependencies 📦
_No response_
### Examples 🌈
_No response_
### Motivation 🔦
_No response_
### New 🆕
- [ ] Validated in a grooming session
### Backlog 📋
- [ ] Has a good summary
- [ ] Has example link(s)
### Design in progress 🏗
- [ ] Analysis _(functional & technical)_
- [ ] Design refinement
- [ ] Dev qualification _(properties, breakpoints, tokens etc.)_
- [ ] Documentation refinement _(inside the Figma branch)_
### Design review 👀
- [ ] Figma branch merged
- [ ] Documentation review _(and move the documentation into Vitamin Documentation Figma file)
### Ready to dev 👍
- [ ] Issues are created in all repositories affected _(vitamin-<web,android,ios,compose>)_
### Dev in progress 💻
- [ ] All issues are resolved _(to replace with issues links)_ | 1.0 | [component] Text input - ### Duplicates ❌
- [X] I have searched the existing issues
### Which Figma library is concerned?
Not related to one Figma library
### Summary 💡
A text input is a field that allows users to enter text into.
### Dependencies 📦
_No response_
### Examples 🌈
_No response_
### Motivation 🔦
_No response_
### New 🆕
- [ ] Validated in a grooming session
### Backlog 📋
- [ ] Has a good summary
- [ ] Has example link(s)
### Design in progress 🏗
- [ ] Analysis _(functional & technical)_
- [ ] Design refinement
- [ ] Dev qualification _(properties, breakpoints, tokens etc.)_
- [ ] Documentation refinement _(inside the Figma branch)_
### Design review 👀
- [ ] Figma branch merged
- [ ] Documentation review _(and move the documentation into Vitamin Documentation Figma file)
### Ready to dev 👍
- [ ] Issues are created in all repositories affected _(vitamin-<web,android,ios,compose>)_
### Dev in progress 💻
- [ ] All issues are resolved _(to replace with issues links)_ | build | text input duplicates ❌ i have searched the existing issues which figma library is concerned not related to one figma library summary 💡 a text input is a field that allows users to enter text into dependencies 📦 no response examples 🌈 no response motivation 🔦 no response new 🆕 validated in a grooming session backlog 📋 has a good summary has example link s design in progress 🏗 analysis functional technical design refinement dev qualification properties breakpoints tokens etc documentation refinement inside the figma branch design review 👀 figma branch merged documentation review and move the documentation into vitamin documentation figma file ready to dev 👍 issues are created in all repositories affected vitamin dev in progress 💻 all issues are resolved to replace with issues links | 1 |
33,169 | 9,039,564,119 | IssuesEvent | 2019-02-10 08:09:35 | mapstruct/mapstruct | https://api.github.com/repos/mapstruct/mapstruct | closed | Avoid circular dependency between "model" and "conversion" packages | build | Hey @filiphr, @agudian, @sjaakd, @chris922, by creating an architecture model for MapStruct using [Deptective](https://github.com/moditect/deptective/) I stumbled upon a circular dependendency between "model", "model.source.builtin" and "conversion". This can easily be resolved by removing the import of `SimpleConversion` in the `BuiltInMethod` class, which is solely used for the purposes of JavaDoc. Great job to keep the code base circle-free otherwise!
If you're interested, I've pushed the set-up for Deptective to my MapStruct repo [here](https://github.com/gunnarmorling/mapstruct/tree/deptective). Note this is based on a pending Deptective PR (https://github.com/moditect/deptective/pull/36). To see by yourself how that wrong dependency is reported, just run `mvn clean compile -pl processor`. This will fail the build due to the bad dependency and also create the dot file attached as PNG to that other PR.
Once Deptective is a bit more stable and we've done a first release and you like the idea, I can send a PR for adding it to MapStruct. | 1.0 | Avoid circular dependency between "model" and "conversion" packages - Hey @filiphr, @agudian, @sjaakd, @chris922, by creating an architecture model for MapStruct using [Deptective](https://github.com/moditect/deptective/) I stumbled upon a circular dependendency between "model", "model.source.builtin" and "conversion". This can easily be resolved by removing the import of `SimpleConversion` in the `BuiltInMethod` class, which is solely used for the purposes of JavaDoc. Great job to keep the code base circle-free otherwise!
If you're interested, I've pushed the set-up for Deptective to my MapStruct repo [here](https://github.com/gunnarmorling/mapstruct/tree/deptective). Note this is based on a pending Deptective PR (https://github.com/moditect/deptective/pull/36). To see by yourself how that wrong dependency is reported, just run `mvn clean compile -pl processor`. This will fail the build due to the bad dependency and also create the dot file attached as PNG to that other PR.
Once Deptective is a bit more stable and we've done a first release and you like the idea, I can send a PR for adding it to MapStruct. | build | avoid circular dependency between model and conversion packages hey filiphr agudian sjaakd by creating an architecture model for mapstruct using i stumbled upon a circular dependendency between model model source builtin and conversion this can easily be resolved by removing the import of simpleconversion in the builtinmethod class which is solely used for the purposes of javadoc great job to keep the code base circle free otherwise if you re interested i ve pushed the set up for deptective to my mapstruct repo note this is based on a pending deptective pr to see by yourself how that wrong dependency is reported just run mvn clean compile pl processor this will fail the build due to the bad dependency and also create the dot file attached as png to that other pr once deptective is a bit more stable and we ve done a first release and you like the idea i can send a pr for adding it to mapstruct | 1 |
31,999 | 7,472,377,873 | IssuesEvent | 2018-04-03 12:29:24 | incad/registrdigitalizace | https://api.github.com/repos/incad/registrdigitalizace | closed | Přehled nevyužívaných agend | Aplikace - Relief Zmigrováno z GoogleCode | ```
Přehled je rozdělen do dvou oddílů.
1. Agendy, které jsou momentálně dostupné pro uživatele z křižovatky.
Zpracovatel
ISO
2. Agendy, které již nejsou dostupné pro uživatele z křižovatky, ale
stále jsou součástí aplikace.
Autor
Exemplář
Vydavatel
Přívazek
Titul
DL Seznam jazyků
Adresa
Fyzický popis
Soubor XML
Grafika
Hudebniny
Mapy
Monografie
Rukopisy
Periodika
Speciální Dokumenty
Staré tisky
Digitální objekt (Zakázka)
+ Související vnorené agendy a zdroje použitých dynamických listů
Issue založeno na základě zápisu ze schůzky.
```
Original issue reported on code.google.com by `martin.n...@incad.cz` on 6 Jun 2013 at 9:19
| 1.0 | Přehled nevyužívaných agend - ```
Přehled je rozdělen do dvou oddílů.
1. Agendy, které jsou momentálně dostupné pro uživatele z křižovatky.
Zpracovatel
ISO
2. Agendy, které již nejsou dostupné pro uživatele z křižovatky, ale
stále jsou součástí aplikace.
Autor
Exemplář
Vydavatel
Přívazek
Titul
DL Seznam jazyků
Adresa
Fyzický popis
Soubor XML
Grafika
Hudebniny
Mapy
Monografie
Rukopisy
Periodika
Speciální Dokumenty
Staré tisky
Digitální objekt (Zakázka)
+ Související vnorené agendy a zdroje použitých dynamických listů
Issue založeno na základě zápisu ze schůzky.
```
Original issue reported on code.google.com by `martin.n...@incad.cz` on 6 Jun 2013 at 9:19
| non_build | přehled nevyužívaných agend přehled je rozdělen do dvou oddílů agendy které jsou momentálně dostupné pro uživatele z křižovatky zpracovatel iso agendy které již nejsou dostupné pro uživatele z křižovatky ale stále jsou součástí aplikace autor exemplář vydavatel přívazek titul dl seznam jazyků adresa fyzický popis soubor xml grafika hudebniny mapy monografie rukopisy periodika speciální dokumenty staré tisky digitální objekt zakázka související vnorené agendy a zdroje použitých dynamických listů issue založeno na základě zápisu ze schůzky original issue reported on code google com by martin n incad cz on jun at | 0 |
179,961 | 14,729,429,225 | IssuesEvent | 2021-01-06 11:27:23 | seqre/battleships | https://api.github.com/repos/seqre/battleships | closed | Translate README | documentation | - [ ] project info
- [ ] build info
- [ ] usage info
- [ ] protocol specification
| 1.0 | Translate README - - [ ] project info
- [ ] build info
- [ ] usage info
- [ ] protocol specification
| non_build | translate readme project info build info usage info protocol specification | 0 |
60,767 | 14,913,257,753 | IssuesEvent | 2021-01-22 13:54:07 | waruqi/tboox.github.io | https://api.github.com/repos/waruqi/tboox.github.io | opened | A luarocks build plugin for lua module with c/c++ based on xmake | /2021/01/22/luarocks-build-xmake-v1.0/ Gitalk | https://tboox.org/2021/01/22/luarocks-build-xmake-v1.0/
luarocks is a package management tool of lua, which provides the installation and integration of various lua modules.When users install lua modules, it will ... | 1.0 | A luarocks build plugin for lua module with c/c++ based on xmake - https://tboox.org/2021/01/22/luarocks-build-xmake-v1.0/
luarocks is a package management tool of lua, which provides the installation and integration of various lua modules.When users install lua modules, it will ... | build | a luarocks build plugin for lua module with c c based on xmake luarocks is a package management tool of lua which provides the installation and integration of various lua modules when users install lua modules it will | 1 |
75,618 | 20,910,301,607 | IssuesEvent | 2022-03-24 08:40:55 | PyAV-Org/PyAV | https://api.github.com/repos/PyAV-Org/PyAV | opened | 9.0.2 requires FFMpeg headers to clean source | build | Since the release of v9.0.2, doing a `python setup.py clean` resolves FFMpeg headers and fails if unable to locate them.
This project should never cleanup that other project, so seemingly has no need for those headers during its own cleanup. | 1.0 | 9.0.2 requires FFMpeg headers to clean source - Since the release of v9.0.2, doing a `python setup.py clean` resolves FFMpeg headers and fails if unable to locate them.
This project should never cleanup that other project, so seemingly has no need for those headers during its own cleanup. | build | requires ffmpeg headers to clean source since the release of doing a python setup py clean resolves ffmpeg headers and fails if unable to locate them this project should never cleanup that other project so seemingly has no need for those headers during its own cleanup | 1 |
33,925 | 9,215,528,845 | IssuesEvent | 2019-03-11 03:39:12 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Can't import tensorflow | stat:awaiting response subtype:windows type:build/install | <em>Please make sure that this is a build/installation issue. As per our [GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md), we only address code/doc bugs, performance issues, feature requests and build/installation issues on GitHub. tag:build_template</em>
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Windows 10 Enterprise
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device:
- TensorFlow installed from (source or binary): Not sure (pip install tensorflow-gpu in conda prompt)
- TensorFlow version: Latest stable release with GPU support
- Python version: 3.6.8
- Installed using virtualenv? pip? conda?: conda with a self-created virtual environment
- Bazel version (if compiling from source):
- GCC/Compiler version (if compiling from source):
- CUDA/cuDNN version: 10.0
- GPU model and memory: 1070-Ti
**Describe the problem**
Successfully installed tensorflow and keras through pip install in conda prompt. But then failed to import tensorflow.
**Provide the exact sequence of commands / steps that you executed before running into the problem**
import tensorflow as tf
**Any other info / logs**
---------------------------------------------------------------------------
ImportError Traceback (most recent call last)
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow.py in <module>
57
---> 58 from tensorflow.python.pywrap_tensorflow_internal import *
59 from tensorflow.python.pywrap_tensorflow_internal import __version__
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py in <module>
27 return _mod
---> 28 _pywrap_tensorflow_internal = swig_import_helper()
29 del swig_import_helper
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py in swig_import_helper()
23 try:
---> 24 _mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
25 finally:
~\.conda\envs\tensorflow\lib\imp.py in load_module(name, file, filename, details)
242 else:
--> 243 return load_dynamic(name, filename, file)
244 elif type_ == PKG_DIRECTORY:
~\.conda\envs\tensorflow\lib\imp.py in load_dynamic(name, path, file)
342 name=name, loader=loader, origin=path)
--> 343 return _load(spec)
344
ImportError: DLL load failed: 找不到指定的模組。
During handling of the above exception, another exception occurred:
ImportError Traceback (most recent call last)
<ipython-input-1-64156d691fe5> in <module>
----> 1 import tensorflow as tf
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\__init__.py in <module>
22
23 # pylint: disable=g-bad-import-order
---> 24 from tensorflow.python import pywrap_tensorflow # pylint: disable=unused-import
25
26 from tensorflow._api.v1 import app
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\__init__.py in <module>
47 import numpy as np
48
---> 49 from tensorflow.python import pywrap_tensorflow
50
51 # Protocol buffers
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow.py in <module>
72 for some common reasons and solutions. Include the entire stack trace
73 above this error message when asking for help.""" % traceback.format_exc()
---> 74 raise ImportError(msg)
75
76 # pylint: enable=wildcard-import,g-import-not-at-top,unused-import,line-too-long
ImportError: Traceback (most recent call last):
File "C:\Users\user\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\user\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 28, in <module>
_pywrap_tensorflow_internal = swig_import_helper()
File "C:\Users\user\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 24, in swig_import_helper
_mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
File "C:\Users\user\.conda\envs\tensorflow\lib\imp.py", line 243, in load_module
return load_dynamic(name, filename, file)
File "C:\Users\user\.conda\envs\tensorflow\lib\imp.py", line 343, in load_dynamic
return _load(spec)
ImportError: DLL load failed: 找不到指定的模組。
| 1.0 | Can't import tensorflow - <em>Please make sure that this is a build/installation issue. As per our [GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md), we only address code/doc bugs, performance issues, feature requests and build/installation issues on GitHub. tag:build_template</em>
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Windows 10 Enterprise
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device:
- TensorFlow installed from (source or binary): Not sure (pip install tensorflow-gpu in conda prompt)
- TensorFlow version: Latest stable release with GPU support
- Python version: 3.6.8
- Installed using virtualenv? pip? conda?: conda with a self-created virtual environment
- Bazel version (if compiling from source):
- GCC/Compiler version (if compiling from source):
- CUDA/cuDNN version: 10.0
- GPU model and memory: 1070-Ti
**Describe the problem**
Successfully installed tensorflow and keras through pip install in conda prompt. But then failed to import tensorflow.
**Provide the exact sequence of commands / steps that you executed before running into the problem**
import tensorflow as tf
**Any other info / logs**
---------------------------------------------------------------------------
ImportError Traceback (most recent call last)
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow.py in <module>
57
---> 58 from tensorflow.python.pywrap_tensorflow_internal import *
59 from tensorflow.python.pywrap_tensorflow_internal import __version__
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py in <module>
27 return _mod
---> 28 _pywrap_tensorflow_internal = swig_import_helper()
29 del swig_import_helper
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py in swig_import_helper()
23 try:
---> 24 _mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
25 finally:
~\.conda\envs\tensorflow\lib\imp.py in load_module(name, file, filename, details)
242 else:
--> 243 return load_dynamic(name, filename, file)
244 elif type_ == PKG_DIRECTORY:
~\.conda\envs\tensorflow\lib\imp.py in load_dynamic(name, path, file)
342 name=name, loader=loader, origin=path)
--> 343 return _load(spec)
344
ImportError: DLL load failed: 找不到指定的模組。
During handling of the above exception, another exception occurred:
ImportError Traceback (most recent call last)
<ipython-input-1-64156d691fe5> in <module>
----> 1 import tensorflow as tf
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\__init__.py in <module>
22
23 # pylint: disable=g-bad-import-order
---> 24 from tensorflow.python import pywrap_tensorflow # pylint: disable=unused-import
25
26 from tensorflow._api.v1 import app
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\__init__.py in <module>
47 import numpy as np
48
---> 49 from tensorflow.python import pywrap_tensorflow
50
51 # Protocol buffers
~\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow.py in <module>
72 for some common reasons and solutions. Include the entire stack trace
73 above this error message when asking for help.""" % traceback.format_exc()
---> 74 raise ImportError(msg)
75
76 # pylint: enable=wildcard-import,g-import-not-at-top,unused-import,line-too-long
ImportError: Traceback (most recent call last):
File "C:\Users\user\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow.py", line 58, in <module>
from tensorflow.python.pywrap_tensorflow_internal import *
File "C:\Users\user\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 28, in <module>
_pywrap_tensorflow_internal = swig_import_helper()
File "C:\Users\user\.conda\envs\tensorflow\lib\site-packages\tensorflow\python\pywrap_tensorflow_internal.py", line 24, in swig_import_helper
_mod = imp.load_module('_pywrap_tensorflow_internal', fp, pathname, description)
File "C:\Users\user\.conda\envs\tensorflow\lib\imp.py", line 243, in load_module
return load_dynamic(name, filename, file)
File "C:\Users\user\.conda\envs\tensorflow\lib\imp.py", line 343, in load_dynamic
return _load(spec)
ImportError: DLL load failed: 找不到指定的模組。
| build | can t import tensorflow please make sure that this is a build installation issue as per our we only address code doc bugs performance issues feature requests and build installation issues on github tag build template system information os platform and distribution e g linux ubuntu windows enterprise mobile device e g iphone pixel samsung galaxy if the issue happens on mobile device tensorflow installed from source or binary not sure pip install tensorflow gpu in conda prompt tensorflow version latest stable release with gpu support python version installed using virtualenv pip conda conda with a self created virtual environment bazel version if compiling from source gcc compiler version if compiling from source cuda cudnn version gpu model and memory ti describe the problem successfully installed tensorflow and keras through pip install in conda prompt but then failed to import tensorflow provide the exact sequence of commands steps that you executed before running into the problem import tensorflow as tf any other info logs importerror traceback most recent call last conda envs tensorflow lib site packages tensorflow python pywrap tensorflow py in from tensorflow python pywrap tensorflow internal import from tensorflow python pywrap tensorflow internal import version conda envs tensorflow lib site packages tensorflow python pywrap tensorflow internal py in return mod pywrap tensorflow internal swig import helper del swig import helper conda envs tensorflow lib site packages tensorflow python pywrap tensorflow internal py in swig import helper try mod imp load module pywrap tensorflow internal fp pathname description finally conda envs tensorflow lib imp py in load module name file filename details else return load dynamic name filename file elif type pkg directory conda envs tensorflow lib imp py in load dynamic name path file name name loader loader origin path return load spec importerror dll load failed 找不到指定的模組。 during handling of the above exception another exception occurred importerror traceback most recent call last in import tensorflow as tf conda envs tensorflow lib site packages tensorflow init py in pylint disable g bad import order from tensorflow python import pywrap tensorflow pylint disable unused import from tensorflow api import app conda envs tensorflow lib site packages tensorflow python init py in import numpy as np from tensorflow python import pywrap tensorflow protocol buffers conda envs tensorflow lib site packages tensorflow python pywrap tensorflow py in for some common reasons and solutions include the entire stack trace above this error message when asking for help traceback format exc raise importerror msg pylint enable wildcard import g import not at top unused import line too long importerror traceback most recent call last file c users user conda envs tensorflow lib site packages tensorflow python pywrap tensorflow py line in from tensorflow python pywrap tensorflow internal import file c users user conda envs tensorflow lib site packages tensorflow python pywrap tensorflow internal py line in pywrap tensorflow internal swig import helper file c users user conda envs tensorflow lib site packages tensorflow python pywrap tensorflow internal py line in swig import helper mod imp load module pywrap tensorflow internal fp pathname description file c users user conda envs tensorflow lib imp py line in load module return load dynamic name filename file file c users user conda envs tensorflow lib imp py line in load dynamic return load spec importerror dll load failed 找不到指定的模組。 | 1 |
33,800 | 9,205,511,819 | IssuesEvent | 2019-03-08 10:47:15 | qissue-bot/QGIS | https://api.github.com/repos/qissue-bot/QGIS | closed | Update GRASS 6.3 in QGIS building | Category: Build/Install Component: Affected QGIS version Component: Crashes QGIS or corrupts data Component: Easy fix? Component: Operating System Component: Pull Request or Patch supplied Component: Regression? Component: Resolution Priority: Low Project: QGIS Application Status: Closed Tracker: Bug report | ---
Author Name: **leo-lami -** (leo-lami -)
Original Redmine Issue: 841, https://issues.qgis.org/issues/841
Original Assignee: nobody -
---
QGIS 0.9.1 need of the last GRASS version:
http://grass.itc.it/grass63/source/grass-6.3.0RC2.tar.gz
for the new QGIS-GRASS modules.
Can you upfate it in Windows?
Thank you very much
Leonardo
| 1.0 | Update GRASS 6.3 in QGIS building - ---
Author Name: **leo-lami -** (leo-lami -)
Original Redmine Issue: 841, https://issues.qgis.org/issues/841
Original Assignee: nobody -
---
QGIS 0.9.1 need of the last GRASS version:
http://grass.itc.it/grass63/source/grass-6.3.0RC2.tar.gz
for the new QGIS-GRASS modules.
Can you upfate it in Windows?
Thank you very much
Leonardo
| build | update grass in qgis building author name leo lami leo lami original redmine issue original assignee nobody qgis need of the last grass version for the new qgis grass modules can you upfate it in windows thank you very much leonardo | 1 |
595,575 | 18,069,221,923 | IssuesEvent | 2021-09-20 23:28:42 | dtcenter/METexpress | https://api.github.com/repos/dtcenter/METexpress | closed | Metadata scripts need to delete models no longer in the database | priority: high type: enhancement requestor: NOAA/GSL | I've brought this up before, but the current METexpress metadata scripts can only add models to the metadata tables; they don't delete models that have been removed or renamed. We need to fix this for a) accuracy, and b) we don't want the size of our metadata to be over 16 MB or we start having mongodb troubles again. I would like Randy's help with this, as he designed the table reconciliation code initially.
### Time Estimate ###
1 day.
| 1.0 | Metadata scripts need to delete models no longer in the database - I've brought this up before, but the current METexpress metadata scripts can only add models to the metadata tables; they don't delete models that have been removed or renamed. We need to fix this for a) accuracy, and b) we don't want the size of our metadata to be over 16 MB or we start having mongodb troubles again. I would like Randy's help with this, as he designed the table reconciliation code initially.
### Time Estimate ###
1 day.
| non_build | metadata scripts need to delete models no longer in the database i ve brought this up before but the current metexpress metadata scripts can only add models to the metadata tables they don t delete models that have been removed or renamed we need to fix this for a accuracy and b we don t want the size of our metadata to be over mb or we start having mongodb troubles again i would like randy s help with this as he designed the table reconciliation code initially time estimate day | 0 |
299,882 | 9,205,939,229 | IssuesEvent | 2019-03-08 12:10:21 | qissue-bot/QGIS | https://api.github.com/repos/qissue-bot/QGIS | closed | PostGIS layers don't display data - geometry or attributes - since r9095 | Category: Data Provider Component: Affected QGIS version Component: Crashes QGIS or corrupts data Component: Easy fix? Component: Operating System Component: Pull Request or Patch supplied Component: Regression? Component: Resolution Priority: Low Project: QGIS Application Status: Closed Tracker: Bug report | ---
Author Name: **Steven Mizuno** (Steven Mizuno)
Original Redmine Issue: 1237, https://issues.qgis.org/issues/1237
Original Assignee: Jürgen Fischer
---
No data are retrieved due as the PG server log shows errors like:
```
```
There seems to be missing BEGIN statements in the feature/attribute retrieval area and deduceEndian() function, at the least.
There are DECLARE CURSOR ... statements and statements that use the cursor, but there are no transactions in effect.
| 1.0 | PostGIS layers don't display data - geometry or attributes - since r9095 - ---
Author Name: **Steven Mizuno** (Steven Mizuno)
Original Redmine Issue: 1237, https://issues.qgis.org/issues/1237
Original Assignee: Jürgen Fischer
---
No data are retrieved due as the PG server log shows errors like:
```
```
There seems to be missing BEGIN statements in the feature/attribute retrieval area and deduceEndian() function, at the least.
There are DECLARE CURSOR ... statements and statements that use the cursor, but there are no transactions in effect.
| non_build | postgis layers don t display data geometry or attributes since author name steven mizuno steven mizuno original redmine issue original assignee jürgen fischer no data are retrieved due as the pg server log shows errors like there seems to be missing begin statements in the feature attribute retrieval area and deduceendian function at the least there are declare cursor statements and statements that use the cursor but there are no transactions in effect | 0 |
27,629 | 8,013,497,059 | IssuesEvent | 2018-07-25 00:37:27 | habitat-sh/habitat | https://api.github.com/repos/habitat-sh/habitat | closed | Populate `results/last_build.env` after failed builds | A-plan-build E-easy I-linux I-windows L-shell S-needs-discussion V-devx | Building tooling around Habitat has led me to want `results/last_build.env` to be updated even in the case of a failed build.
To pass notifications, and hook into the build process, I'd love to be about to source the `results/last_build.env` file for both success and failure. Maybe adding a `$pkg_build_result` variable or similar if necessary.
Simple use case is my push notifications for studio, which on failure, can't easily provide details about the build that failed.
I run `build_notify` instead of `build` when I want to receive a push notification on completion:
```
# .studiorc
# Using pushover for notifications
push_notification() {
API_TOKEN="_____"
USER_TOKEN="_____"
if [ "$#" -eq 1 ]; then
INPUT=$1
elif [ "$#" -eq 0 ]; then
INPUT=$(cat)
else
echo "Invalid number of arguments."
exit 1
fi
curl -s \
--form-string "user=${USER_TOKEN}" \
--form-string "token=${API_TOKEN}" \
--form-string "message=${INPUT}" \
https://api.pushover.net/1/messages.json
}
build_notify() {
build
if [ $? -eq 0 ]; then
source results/last_build.env
push_notification "[${pkg_origin}/${pkg_name}/${pkg_version}] Build Completed Successfully"
else
push_notification "Build Failed"
fi
}
``` | 1.0 | Populate `results/last_build.env` after failed builds - Building tooling around Habitat has led me to want `results/last_build.env` to be updated even in the case of a failed build.
To pass notifications, and hook into the build process, I'd love to be about to source the `results/last_build.env` file for both success and failure. Maybe adding a `$pkg_build_result` variable or similar if necessary.
Simple use case is my push notifications for studio, which on failure, can't easily provide details about the build that failed.
I run `build_notify` instead of `build` when I want to receive a push notification on completion:
```
# .studiorc
# Using pushover for notifications
push_notification() {
API_TOKEN="_____"
USER_TOKEN="_____"
if [ "$#" -eq 1 ]; then
INPUT=$1
elif [ "$#" -eq 0 ]; then
INPUT=$(cat)
else
echo "Invalid number of arguments."
exit 1
fi
curl -s \
--form-string "user=${USER_TOKEN}" \
--form-string "token=${API_TOKEN}" \
--form-string "message=${INPUT}" \
https://api.pushover.net/1/messages.json
}
build_notify() {
build
if [ $? -eq 0 ]; then
source results/last_build.env
push_notification "[${pkg_origin}/${pkg_name}/${pkg_version}] Build Completed Successfully"
else
push_notification "Build Failed"
fi
}
``` | build | populate results last build env after failed builds building tooling around habitat has led me to want results last build env to be updated even in the case of a failed build to pass notifications and hook into the build process i d love to be about to source the results last build env file for both success and failure maybe adding a pkg build result variable or similar if necessary simple use case is my push notifications for studio which on failure can t easily provide details about the build that failed i run build notify instead of build when i want to receive a push notification on completion studiorc using pushover for notifications push notification api token user token if then input elif then input cat else echo invalid number of arguments exit fi curl s form string user user token form string token api token form string message input build notify build if then source results last build env push notification build completed successfully else push notification build failed fi | 1 |
408,901 | 11,954,034,880 | IssuesEvent | 2020-04-03 22:20:29 | GeyserMC/Geyser | https://api.github.com/repos/GeyserMC/Geyser | closed | Combat is inconsistent on bedrock | Confirmed Bug Priority: Medium | **Describe the bug**
Combat does not feel right at all on bedrock, even after waiting 3 seconds between hits it took around 4 hits with a diamond sword to kill a chicken.
**To Reproduce**
Steps to reproduce the behavior:
1. Join a geyser server
2. Find or spawn a chicken
3. Get a diamond sword
4. Try to kill the chicken, waiting 3 seconds between hits to ensure the combat cool down is satisfied
5. Observe the chicken dies in around 4 hits
**Expected behavior**
Combat should behave the same as it does on java, (Chickens should die in 1 or 2 hits with a diamond sword)
**Screenshots**
N/A
**Server version**
Latest Paper Build
**Geyser version**
Latest Geyser build
**Bedrock version**
1.14.30
**Additional context**
I've had reports that reverting to old combat mechanics on java solves this issue
| 1.0 | Combat is inconsistent on bedrock - **Describe the bug**
Combat does not feel right at all on bedrock, even after waiting 3 seconds between hits it took around 4 hits with a diamond sword to kill a chicken.
**To Reproduce**
Steps to reproduce the behavior:
1. Join a geyser server
2. Find or spawn a chicken
3. Get a diamond sword
4. Try to kill the chicken, waiting 3 seconds between hits to ensure the combat cool down is satisfied
5. Observe the chicken dies in around 4 hits
**Expected behavior**
Combat should behave the same as it does on java, (Chickens should die in 1 or 2 hits with a diamond sword)
**Screenshots**
N/A
**Server version**
Latest Paper Build
**Geyser version**
Latest Geyser build
**Bedrock version**
1.14.30
**Additional context**
I've had reports that reverting to old combat mechanics on java solves this issue
| non_build | combat is inconsistent on bedrock describe the bug combat does not feel right at all on bedrock even after waiting seconds between hits it took around hits with a diamond sword to kill a chicken to reproduce steps to reproduce the behavior join a geyser server find or spawn a chicken get a diamond sword try to kill the chicken waiting seconds between hits to ensure the combat cool down is satisfied observe the chicken dies in around hits expected behavior combat should behave the same as it does on java chickens should die in or hits with a diamond sword screenshots n a server version latest paper build geyser version latest geyser build bedrock version additional context i ve had reports that reverting to old combat mechanics on java solves this issue | 0 |
21,949 | 7,103,280,088 | IssuesEvent | 2018-01-16 03:50:02 | raxod502/straight.el | https://api.github.com/repos/raxod502/straight.el | closed | Failing to build info manual for web-server | bug build-system texinfo | I got the following when I run `M-x straight-rebuild-package web-server`:
```
Warning (straight): Command failed: makeinfo web-server.texi doclicense.texi gpl.texi (default-directory: "/Users/xcy/.emacs.d/straight/build/web-server/"):
web-server.texi:208: @verbatiminclude: could not find ../examples/000-hello-world.el
web-server.texi:217: @verbatiminclude: could not find ../examples/001-hello-world-utf8.el
web-server.texi:221: @verbatiminclude: could not find ../examples/002-hello-world-html.el
web-server.texi:239: @verbatiminclude: could not find ../examples/003-file-server.el
web-server.texi:254: @verbatiminclude: could not find ../examples/004-url-param-echo.el
web-server.texi:262: @verbatiminclude: could not find ../examples/005-post-echo.el
web-server.texi:288: @verbatiminclude: could not find ../examples/006-basic-authentication.el
web-server.texi:297: @verbatiminclude: could not find ../examples/007-org-mode-file-server.el
web-server.texi:306: @verbatiminclude: could not find ../examples/008-file-upload.el
web-server.texi:343: @verbatiminclude: could not find ../examples/009-web-socket.el
web-server.texi:354: @verbatiminclude: could not find ../examples/016-content-encoding-gzip.el
web-server.texi:365: @verbatiminclude: could not find ../examples/017-transfer-encoding-chunked.el
```
It does not fail when I try to build the info manual from the Git repository
```
~ $ cd ~/.emacs.d/straight/repos/emacs-web-server
~/.emacs.d/straight/repos/emacs-web-server $ cd doc
~/.emacs.d/straight/repos/emacs-web-server/doc $ makeinfo web-server.texi
~/.emacs.d/straight/repos/emacs-web-server/doc $
```
It seems we need to preserve the whole Git repository (all files & their directory structure) for building this package. | 1.0 | Failing to build info manual for web-server - I got the following when I run `M-x straight-rebuild-package web-server`:
```
Warning (straight): Command failed: makeinfo web-server.texi doclicense.texi gpl.texi (default-directory: "/Users/xcy/.emacs.d/straight/build/web-server/"):
web-server.texi:208: @verbatiminclude: could not find ../examples/000-hello-world.el
web-server.texi:217: @verbatiminclude: could not find ../examples/001-hello-world-utf8.el
web-server.texi:221: @verbatiminclude: could not find ../examples/002-hello-world-html.el
web-server.texi:239: @verbatiminclude: could not find ../examples/003-file-server.el
web-server.texi:254: @verbatiminclude: could not find ../examples/004-url-param-echo.el
web-server.texi:262: @verbatiminclude: could not find ../examples/005-post-echo.el
web-server.texi:288: @verbatiminclude: could not find ../examples/006-basic-authentication.el
web-server.texi:297: @verbatiminclude: could not find ../examples/007-org-mode-file-server.el
web-server.texi:306: @verbatiminclude: could not find ../examples/008-file-upload.el
web-server.texi:343: @verbatiminclude: could not find ../examples/009-web-socket.el
web-server.texi:354: @verbatiminclude: could not find ../examples/016-content-encoding-gzip.el
web-server.texi:365: @verbatiminclude: could not find ../examples/017-transfer-encoding-chunked.el
```
It does not fail when I try to build the info manual from the Git repository
```
~ $ cd ~/.emacs.d/straight/repos/emacs-web-server
~/.emacs.d/straight/repos/emacs-web-server $ cd doc
~/.emacs.d/straight/repos/emacs-web-server/doc $ makeinfo web-server.texi
~/.emacs.d/straight/repos/emacs-web-server/doc $
```
It seems we need to preserve the whole Git repository (all files & their directory structure) for building this package. | build | failing to build info manual for web server i got the following when i run m x straight rebuild package web server warning straight command failed makeinfo web server texi doclicense texi gpl texi default directory users xcy emacs d straight build web server web server texi verbatiminclude could not find examples hello world el web server texi verbatiminclude could not find examples hello world el web server texi verbatiminclude could not find examples hello world html el web server texi verbatiminclude could not find examples file server el web server texi verbatiminclude could not find examples url param echo el web server texi verbatiminclude could not find examples post echo el web server texi verbatiminclude could not find examples basic authentication el web server texi verbatiminclude could not find examples org mode file server el web server texi verbatiminclude could not find examples file upload el web server texi verbatiminclude could not find examples web socket el web server texi verbatiminclude could not find examples content encoding gzip el web server texi verbatiminclude could not find examples transfer encoding chunked el it does not fail when i try to build the info manual from the git repository cd emacs d straight repos emacs web server emacs d straight repos emacs web server cd doc emacs d straight repos emacs web server doc makeinfo web server texi emacs d straight repos emacs web server doc it seems we need to preserve the whole git repository all files their directory structure for building this package | 1 |
62,735 | 15,353,447,367 | IssuesEvent | 2021-03-01 08:35:17 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [SB] Tooltip text is not displayed | Bug P2 Process: Fixed Process: Tested QA Process: Tested dev Study builder | The tooltip text is not displayed for the following
1. Comprehension test questions table > When user mouse hovered on 'Edit' and 'Delete' icon
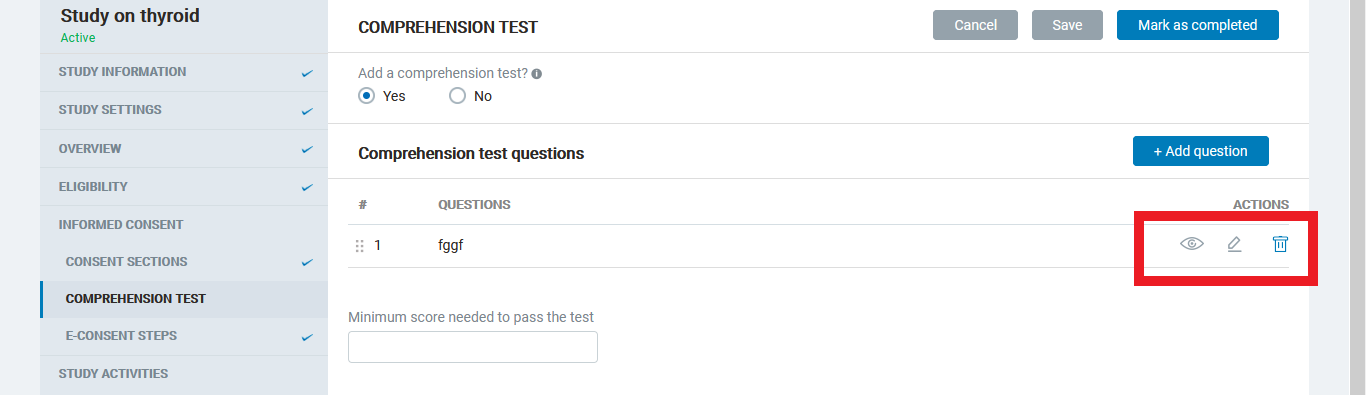
2. Add/Edit questionnaire > When user mouse hovered on 'View', 'Edit' and 'Delete' icon
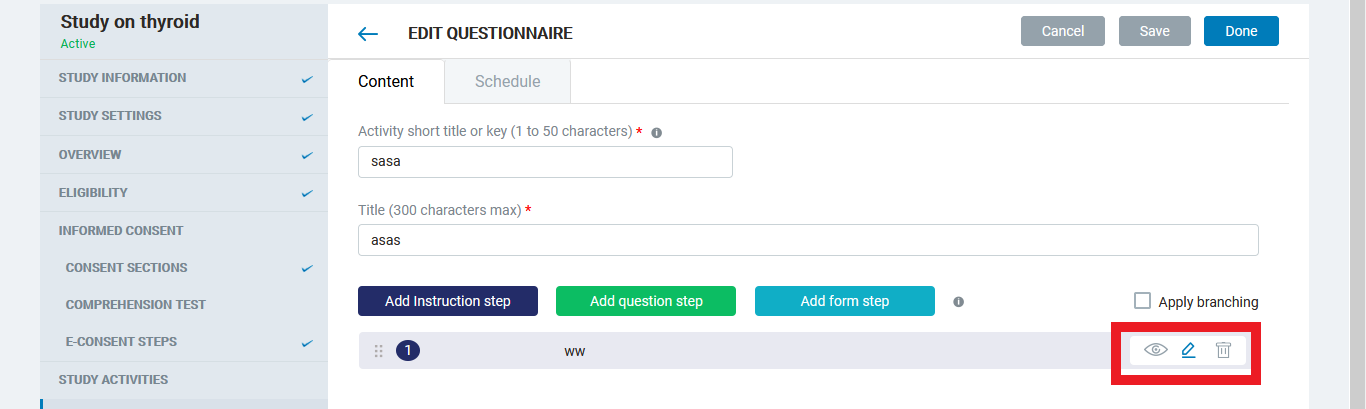
3. Add/Edit Form step > When user mouse hovered on 'View', 'Edit' and 'Delete' icon
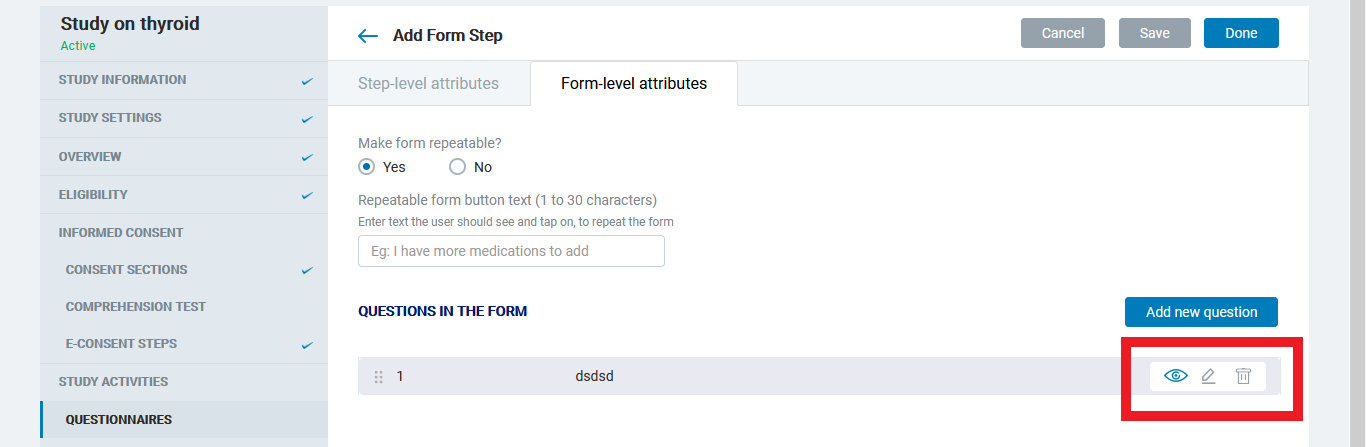
4. Consent section > Add more than one consent >Delete any one of the consent and user mouse hovered on 'View', 'Edit' and 'Delete' icon
5. Eligibility test / Validation token + Eligibility test > Add more than one questions > Delete any one of the question and user mouse hovered on 'View', 'Edit' and 'Delete' icon
6. Resources > Add more than one resource > Delete any one of the resources and user mouse hovered on 'View', 'Edit' and 'Delete' icon
| 1.0 | [SB] Tooltip text is not displayed - The tooltip text is not displayed for the following
1. Comprehension test questions table > When user mouse hovered on 'Edit' and 'Delete' icon
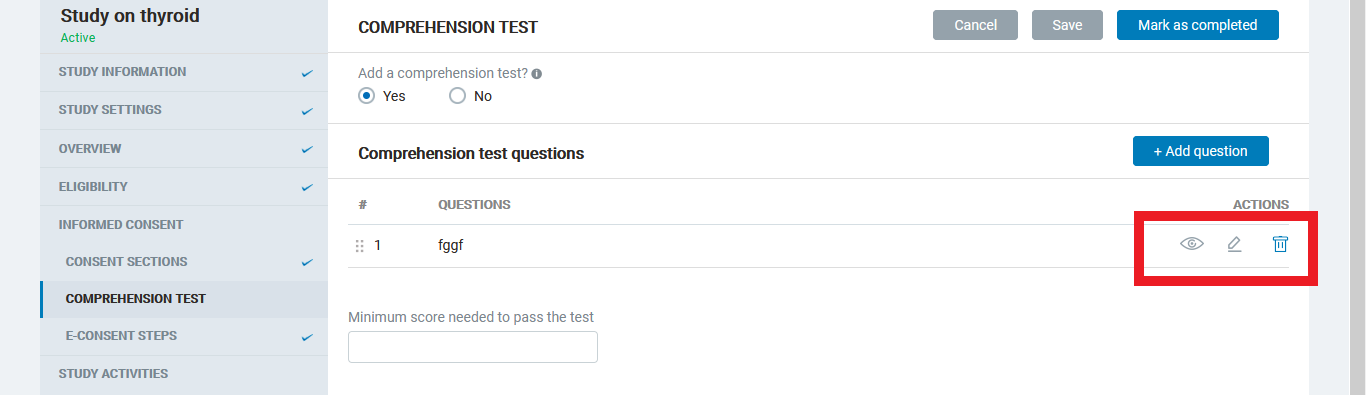
2. Add/Edit questionnaire > When user mouse hovered on 'View', 'Edit' and 'Delete' icon
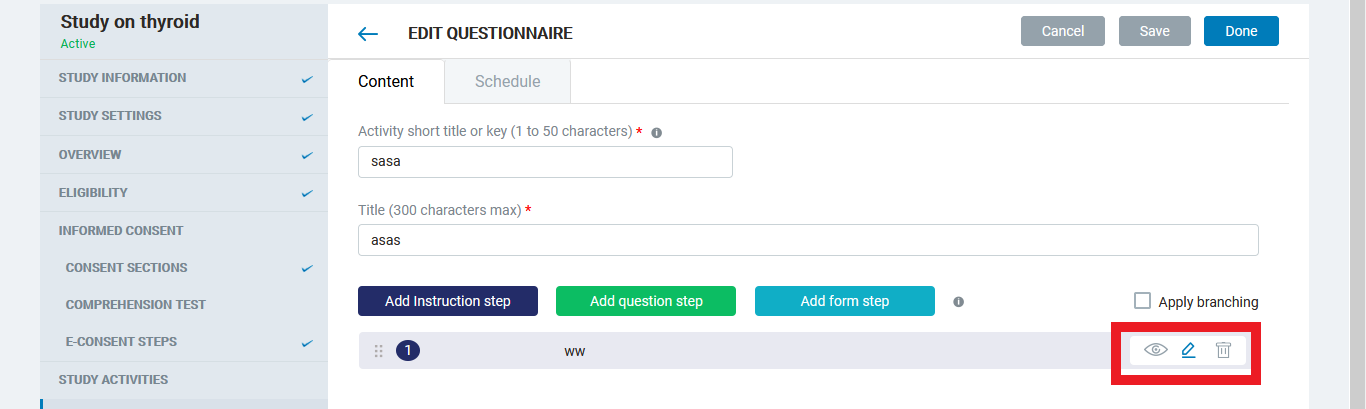
3. Add/Edit Form step > When user mouse hovered on 'View', 'Edit' and 'Delete' icon
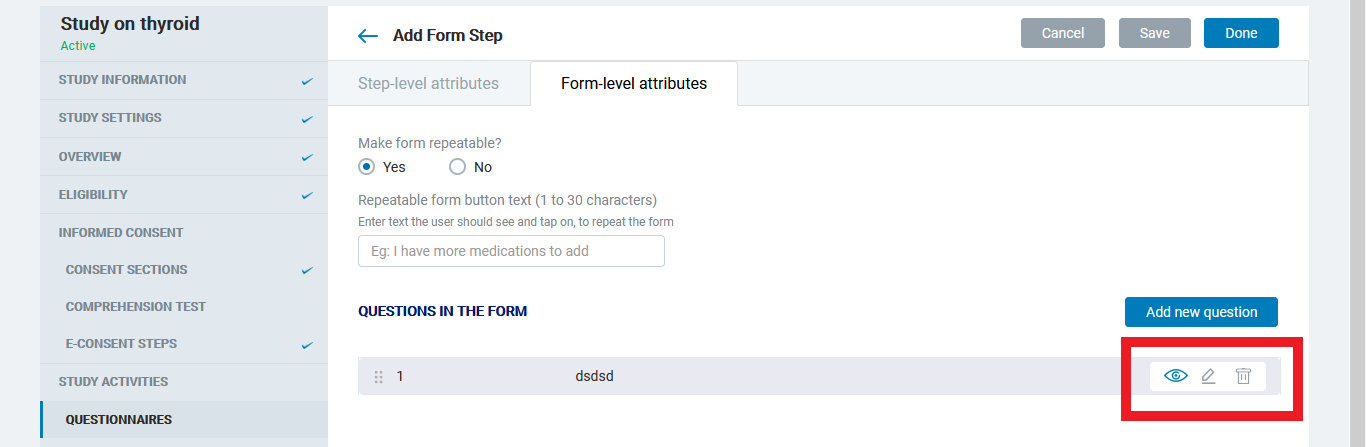
4. Consent section > Add more than one consent >Delete any one of the consent and user mouse hovered on 'View', 'Edit' and 'Delete' icon
5. Eligibility test / Validation token + Eligibility test > Add more than one questions > Delete any one of the question and user mouse hovered on 'View', 'Edit' and 'Delete' icon
6. Resources > Add more than one resource > Delete any one of the resources and user mouse hovered on 'View', 'Edit' and 'Delete' icon
| build | tooltip text is not displayed the tooltip text is not displayed for the following comprehension test questions table when user mouse hovered on edit and delete icon add edit questionnaire when user mouse hovered on view edit and delete icon add edit form step when user mouse hovered on view edit and delete icon consent section add more than one consent delete any one of the consent and user mouse hovered on view edit and delete icon eligibility test validation token eligibility test add more than one questions delete any one of the question and user mouse hovered on view edit and delete icon resources add more than one resource delete any one of the resources and user mouse hovered on view edit and delete icon | 1 |
32,486 | 8,869,322,649 | IssuesEvent | 2019-01-11 04:37:35 | xamarin/xamarin-android | https://api.github.com/repos/xamarin/xamarin-android | opened | ActivityNotFoundException when attempting to use a new Activity and other issues with outdated AndroidManifest.xml in projects configured to use Enhanced Fast Deployment | Area: App+Library Build Area: Commercial bug | ### Steps to Reproduce
1. Create a new Android application project.
2. Add the following lines to the *.csproj* file to enable Enhanced Fast Deployment:
```xml
<PropertyGroup>
<AndroidFastDeploymentType>Assemblies:Dexes</AndroidFastDeploymentType>
</PropertyGroup>
```
3. Add an additional `Activity` subclass to the project, similar to:
```csharp
public class SecondActivity : Activity {
protected override void OnCreate (Bundle savedInstanceState)
{
base.OnCreate (savedInstanceState);
SetContentView (Resource.Layout.activity_main);
}
}
```
4. Choose **Debug > Start Debugging** to build, deploy, and start debugging the app.
5. Choose **Debug > Stop Debugging**.
6. Add an `[Activity]` attribute to `SecondActivity` to make the build process generate an entry for it in *AndroidManifest.xml*.
7. Add a line to start the new activity from the `MainActivity.OnCreate()` override via an `Intent`:
```csharp
StartActivity (typeof (SecondActivity));
```
8. Choose **Debug > Start Debugging**.
### Actual Behavior
```
UNHANDLED EXCEPTION:
Android.Content.ActivityNotFoundException: Unable to find explicit activity class {AndroidApp1.AndroidApp1/md559d7fc296fc238aa7bec92ba27f2cb33.SecondActivity}; have you declared this activity in your AndroidManifest.xml?
```
The new activity cannot be started because the *AndroidManifest.xml* file has not been updated on-device. Indeed the timestamps on the *.apk* files in the *bin\\* directory show the time of the initial build from step 4 rather than the new build from step 8.
It looks like the issue might be that the `_BuildApkFastDev` target doesn't have `$(IntermediateOutputPath)android\AndroidManifest.xml` as an input, so the target is skipped:
```txt
2>Target "_BuildApkFastDev" in file "C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Xamarin\Android\Xamarin.Android.Common.Debugging.targets" from project "c:\Temp\AndroidApp1\AndroidApp1\AndroidApp1.csproj" (target "_CopyPackage" depends on it):
2>Skipping target "_BuildApkFastDev" because all output files are up-to-date with respect to the input files.
2>Input files: C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\Java.Interop.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v8.1\Mono.Android.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Core.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Xml.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\mscorlib.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Net.Http.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Runtime.Serialization.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.ServiceModel.Internals.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\Mono.Security.dll;c:\Temp\AndroidApp1\AndroidApp1\obj\AndroidApp1.csproj.nuget.g.props;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Current\Bin\Microsoft.Xaml.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\CommonExtensions\Microsoft\NuGet\NuGet.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Current\Microsoft.Common.targets\ImportAfter\Microsoft.NET.Build.Extensions.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\Microsoft.NET.Build.Extensions\Microsoft.NET.Build.Extensions.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\Microsoft.NET.Build.Extensions\Microsoft.NET.Build.Extensions.ConflictResolution.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\Microsoft.NET.Build.Extensions\Microsoft.NET.DefaultPackageConflictOverrides.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\NuGet\16.0\Microsoft.NuGet.targets;c:\Temp\AndroidApp1\AndroidApp1\obj\AndroidApp1.csproj.nuget.g.targets;obj\Debug\81\build.props;obj\Debug\81\adb.props
2>Output files: obj\Debug\81\android\bin\AndroidApp1.AndroidApp1.apk
2>Done building target "_BuildApkFastDev" in project "AndroidApp1.csproj".
```
[DiagnosticMSBuildOutput.zip](https://github.com/xamarin/xamarin-android/files/2748072/DiagnosticMSBuildOutput.zip)
### Expected Behavior
If I disable Enhanced Fast Deployment and go back to classic Fast Deployment, the `_BuildApkFastDev` target *does* build in this scenario, and the new activity starts successfully.
### Version Information
Microsoft Visual Studio Enterprise 2019 Int Preview
Version 16.0.0 Preview 2.0 [28509.60.d16.0]
VisualStudio.16.IntPreview/16.0.0-pre.2.0+28509.60.d16.0
Microsoft .NET Framework
Version 4.7.03056
Xamarin.Android SDK 9.1.103.6 (HEAD/1127dc3a) | 1.0 | ActivityNotFoundException when attempting to use a new Activity and other issues with outdated AndroidManifest.xml in projects configured to use Enhanced Fast Deployment - ### Steps to Reproduce
1. Create a new Android application project.
2. Add the following lines to the *.csproj* file to enable Enhanced Fast Deployment:
```xml
<PropertyGroup>
<AndroidFastDeploymentType>Assemblies:Dexes</AndroidFastDeploymentType>
</PropertyGroup>
```
3. Add an additional `Activity` subclass to the project, similar to:
```csharp
public class SecondActivity : Activity {
protected override void OnCreate (Bundle savedInstanceState)
{
base.OnCreate (savedInstanceState);
SetContentView (Resource.Layout.activity_main);
}
}
```
4. Choose **Debug > Start Debugging** to build, deploy, and start debugging the app.
5. Choose **Debug > Stop Debugging**.
6. Add an `[Activity]` attribute to `SecondActivity` to make the build process generate an entry for it in *AndroidManifest.xml*.
7. Add a line to start the new activity from the `MainActivity.OnCreate()` override via an `Intent`:
```csharp
StartActivity (typeof (SecondActivity));
```
8. Choose **Debug > Start Debugging**.
### Actual Behavior
```
UNHANDLED EXCEPTION:
Android.Content.ActivityNotFoundException: Unable to find explicit activity class {AndroidApp1.AndroidApp1/md559d7fc296fc238aa7bec92ba27f2cb33.SecondActivity}; have you declared this activity in your AndroidManifest.xml?
```
The new activity cannot be started because the *AndroidManifest.xml* file has not been updated on-device. Indeed the timestamps on the *.apk* files in the *bin\\* directory show the time of the initial build from step 4 rather than the new build from step 8.
It looks like the issue might be that the `_BuildApkFastDev` target doesn't have `$(IntermediateOutputPath)android\AndroidManifest.xml` as an input, so the target is skipped:
```txt
2>Target "_BuildApkFastDev" in file "C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Xamarin\Android\Xamarin.Android.Common.Debugging.targets" from project "c:\Temp\AndroidApp1\AndroidApp1\AndroidApp1.csproj" (target "_CopyPackage" depends on it):
2>Skipping target "_BuildApkFastDev" because all output files are up-to-date with respect to the input files.
2>Input files: C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\Java.Interop.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v8.1\Mono.Android.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Core.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Xml.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\mscorlib.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Net.Http.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.Runtime.Serialization.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\System.ServiceModel.Internals.dll;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\ReferenceAssemblies\Microsoft\Framework\MonoAndroid\v1.0\Mono.Security.dll;c:\Temp\AndroidApp1\AndroidApp1\obj\AndroidApp1.csproj.nuget.g.props;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Current\Bin\Microsoft.Xaml.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\Common7\IDE\CommonExtensions\Microsoft\NuGet\NuGet.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Current\Microsoft.Common.targets\ImportAfter\Microsoft.NET.Build.Extensions.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\Microsoft.NET.Build.Extensions\Microsoft.NET.Build.Extensions.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\Microsoft.NET.Build.Extensions\Microsoft.NET.Build.Extensions.ConflictResolution.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\Microsoft.NET.Build.Extensions\Microsoft.NET.DefaultPackageConflictOverrides.targets;C:\Program Files (x86)\Microsoft Visual Studio\2019\Preview\MSBuild\Microsoft\NuGet\16.0\Microsoft.NuGet.targets;c:\Temp\AndroidApp1\AndroidApp1\obj\AndroidApp1.csproj.nuget.g.targets;obj\Debug\81\build.props;obj\Debug\81\adb.props
2>Output files: obj\Debug\81\android\bin\AndroidApp1.AndroidApp1.apk
2>Done building target "_BuildApkFastDev" in project "AndroidApp1.csproj".
```
[DiagnosticMSBuildOutput.zip](https://github.com/xamarin/xamarin-android/files/2748072/DiagnosticMSBuildOutput.zip)
### Expected Behavior
If I disable Enhanced Fast Deployment and go back to classic Fast Deployment, the `_BuildApkFastDev` target *does* build in this scenario, and the new activity starts successfully.
### Version Information
Microsoft Visual Studio Enterprise 2019 Int Preview
Version 16.0.0 Preview 2.0 [28509.60.d16.0]
VisualStudio.16.IntPreview/16.0.0-pre.2.0+28509.60.d16.0
Microsoft .NET Framework
Version 4.7.03056
Xamarin.Android SDK 9.1.103.6 (HEAD/1127dc3a) | build | activitynotfoundexception when attempting to use a new activity and other issues with outdated androidmanifest xml in projects configured to use enhanced fast deployment steps to reproduce create a new android application project add the following lines to the csproj file to enable enhanced fast deployment xml assemblies dexes add an additional activity subclass to the project similar to csharp public class secondactivity activity protected override void oncreate bundle savedinstancestate base oncreate savedinstancestate setcontentview resource layout activity main choose debug start debugging to build deploy and start debugging the app choose debug stop debugging add an attribute to secondactivity to make the build process generate an entry for it in androidmanifest xml add a line to start the new activity from the mainactivity oncreate override via an intent csharp startactivity typeof secondactivity choose debug start debugging actual behavior unhandled exception android content activitynotfoundexception unable to find explicit activity class secondactivity have you declared this activity in your androidmanifest xml the new activity cannot be started because the androidmanifest xml file has not been updated on device indeed the timestamps on the apk files in the bin directory show the time of the initial build from step rather than the new build from step it looks like the issue might be that the buildapkfastdev target doesn t have intermediateoutputpath android androidmanifest xml as an input so the target is skipped txt target buildapkfastdev in file c program files microsoft visual studio preview msbuild xamarin android xamarin android common debugging targets from project c temp csproj target copypackage depends on it skipping target buildapkfastdev because all output files are up to date with respect to the input files input files c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid java interop dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid mono android dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid system core dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid system dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid system xml dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid mscorlib dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid system net http dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid system runtime serialization dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid system servicemodel internals dll c program files microsoft visual studio preview ide referenceassemblies microsoft framework monoandroid mono security dll c temp obj csproj nuget g props c program files microsoft visual studio preview msbuild current bin microsoft xaml targets c program files microsoft visual studio preview ide commonextensions microsoft nuget nuget targets c program files microsoft visual studio preview msbuild current microsoft common targets importafter microsoft net build extensions targets c program files microsoft visual studio preview msbuild microsoft microsoft net build extensions microsoft net build extensions targets c program files microsoft visual studio preview msbuild microsoft microsoft net build extensions microsoft net build extensions conflictresolution targets c program files microsoft visual studio preview msbuild microsoft microsoft net build extensions microsoft net defaultpackageconflictoverrides targets c program files microsoft visual studio preview msbuild microsoft nuget microsoft nuget targets c temp obj csproj nuget g targets obj debug build props obj debug adb props output files obj debug android bin apk done building target buildapkfastdev in project csproj expected behavior if i disable enhanced fast deployment and go back to classic fast deployment the buildapkfastdev target does build in this scenario and the new activity starts successfully version information microsoft visual studio enterprise int preview version preview visualstudio intpreview pre microsoft net framework version xamarin android sdk head | 1 |
54,500 | 13,359,057,030 | IssuesEvent | 2020-08-31 12:46:35 | microsoft/onnxruntime | https://api.github.com/repos/microsoft/onnxruntime | closed | Python 3.6 not found by FindPythonInterp | component:build stale | **Describe the bug**
When compiling the latest release, I got python >= 3.5 not found error in FindPythonInterp.
System has python 2.7 and 3.6 installed.
A workaround is to add `-DPython_ADDITIONAL_VERSION=3.6`.
**Urgency**
Can be manually worked around but should be fixed ASAP.
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Ubuntu 18.04
- ONNX Runtime installed from (source or binary): source
- ONNX Runtime version: latest release(1.2.0)
- Python version: 3.6
- GCC/Compiler version (if compiling from source): gcc8
- CUDA/cuDNN version: 10.2 | 1.0 | Python 3.6 not found by FindPythonInterp - **Describe the bug**
When compiling the latest release, I got python >= 3.5 not found error in FindPythonInterp.
System has python 2.7 and 3.6 installed.
A workaround is to add `-DPython_ADDITIONAL_VERSION=3.6`.
**Urgency**
Can be manually worked around but should be fixed ASAP.
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Ubuntu 18.04
- ONNX Runtime installed from (source or binary): source
- ONNX Runtime version: latest release(1.2.0)
- Python version: 3.6
- GCC/Compiler version (if compiling from source): gcc8
- CUDA/cuDNN version: 10.2 | build | python not found by findpythoninterp describe the bug when compiling the latest release i got python not found error in findpythoninterp system has python and installed a workaround is to add dpython additional version urgency can be manually worked around but should be fixed asap system information os platform and distribution e g linux ubuntu ubuntu onnx runtime installed from source or binary source onnx runtime version latest release python version gcc compiler version if compiling from source cuda cudnn version | 1 |
39,572 | 10,354,043,291 | IssuesEvent | 2019-09-05 12:59:10 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Provide a way for individual projects to specify which distributions they can run/test against | :Core/Infra/Build >enhancement | Related to #30874.
The distribution running in the integration tests, or started with the `run` task can be switched with the `tests.distribution` and `run.distribution` properties.
The problem is that no all projects are able to run with any distribution e.x. plugins being tested might depend on other plugins. On the other hand we want to make sure that the inputs are honored, so we can't silently match the distribution for some projects (i.e. use `zip` even trough `zip-oss` is required ), we want to ave tasks skipped in these cases.
To achieve this we need a better way to express distribution requirements for cluster formation so that projects can define distribution types that they need and the plugins can do all the setup without the individual projects having to deal with setting up the tasks to do so. | 1.0 | Provide a way for individual projects to specify which distributions they can run/test against - Related to #30874.
The distribution running in the integration tests, or started with the `run` task can be switched with the `tests.distribution` and `run.distribution` properties.
The problem is that no all projects are able to run with any distribution e.x. plugins being tested might depend on other plugins. On the other hand we want to make sure that the inputs are honored, so we can't silently match the distribution for some projects (i.e. use `zip` even trough `zip-oss` is required ), we want to ave tasks skipped in these cases.
To achieve this we need a better way to express distribution requirements for cluster formation so that projects can define distribution types that they need and the plugins can do all the setup without the individual projects having to deal with setting up the tasks to do so. | build | provide a way for individual projects to specify which distributions they can run test against related to the distribution running in the integration tests or started with the run task can be switched with the tests distribution and run distribution properties the problem is that no all projects are able to run with any distribution e x plugins being tested might depend on other plugins on the other hand we want to make sure that the inputs are honored so we can t silently match the distribution for some projects i e use zip even trough zip oss is required we want to ave tasks skipped in these cases to achieve this we need a better way to express distribution requirements for cluster formation so that projects can define distribution types that they need and the plugins can do all the setup without the individual projects having to deal with setting up the tasks to do so | 1 |
30,859 | 8,614,647,438 | IssuesEvent | 2018-11-19 18:06:06 | QuantEcon/lecture-source-jl | https://api.github.com/repos/QuantEcon/lecture-source-jl | opened | Fix QELAP in the build | build-infrastructure high-priority | We have an issue with building `QELAP` on the Linux because we need to manually install some dependency tarballs like `Ipopt`. Need to coordinate with Matt and get that working. | 1.0 | Fix QELAP in the build - We have an issue with building `QELAP` on the Linux because we need to manually install some dependency tarballs like `Ipopt`. Need to coordinate with Matt and get that working. | build | fix qelap in the build we have an issue with building qelap on the linux because we need to manually install some dependency tarballs like ipopt need to coordinate with matt and get that working | 1 |
86,409 | 10,741,241,721 | IssuesEvent | 2019-10-29 19:49:44 | Automattic/wp-calypso | https://api.github.com/repos/Automattic/wp-calypso | closed | Domains: Entering multiple keywords is an odd way to domain search | Design Domains FixTheFlows [Impact] High | <img width="1280" alt="Screen Shot 2019-04-23 at 10 24 31 AM" src="https://user-images.githubusercontent.com/2124984/56588766-00972400-65b2-11e9-8612-62af25b71ef5.png">
The domain search suggests using multiple keywords to describe your business, but then the keywords are strung together to suggest a domain. So if you put in "animal care dogs cats" you could get suggestions like "animalcaredogscats.care" which is a terrible suggestion for a business' domain name. :)
I don't have a solid "What I expected" for this one, it's something that needs further thought and probably guidance on the copy. Changing the language around domain search to avoid using the word "keywords" seems like a good start, since that has SEO-ish connotations. | 1.0 | Domains: Entering multiple keywords is an odd way to domain search - <img width="1280" alt="Screen Shot 2019-04-23 at 10 24 31 AM" src="https://user-images.githubusercontent.com/2124984/56588766-00972400-65b2-11e9-8612-62af25b71ef5.png">
The domain search suggests using multiple keywords to describe your business, but then the keywords are strung together to suggest a domain. So if you put in "animal care dogs cats" you could get suggestions like "animalcaredogscats.care" which is a terrible suggestion for a business' domain name. :)
I don't have a solid "What I expected" for this one, it's something that needs further thought and probably guidance on the copy. Changing the language around domain search to avoid using the word "keywords" seems like a good start, since that has SEO-ish connotations. | non_build | domains entering multiple keywords is an odd way to domain search img width alt screen shot at am src the domain search suggests using multiple keywords to describe your business but then the keywords are strung together to suggest a domain so if you put in animal care dogs cats you could get suggestions like animalcaredogscats care which is a terrible suggestion for a business domain name i don t have a solid what i expected for this one it s something that needs further thought and probably guidance on the copy changing the language around domain search to avoid using the word keywords seems like a good start since that has seo ish connotations | 0 |
233,630 | 17,873,423,330 | IssuesEvent | 2021-09-06 20:24:35 | duffn/terraform-provider-alertlogic | https://api.github.com/repos/duffn/terraform-provider-alertlogic | opened | Update docs to use markdown | documentation | It would be nice to have the docs generate some nice looking markdown, ala the AWS provider docs: https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/availability_zones. Backticks for code, some bolding where necessary, etc. | 1.0 | Update docs to use markdown - It would be nice to have the docs generate some nice looking markdown, ala the AWS provider docs: https://registry.terraform.io/providers/hashicorp/aws/latest/docs/data-sources/availability_zones. Backticks for code, some bolding where necessary, etc. | non_build | update docs to use markdown it would be nice to have the docs generate some nice looking markdown ala the aws provider docs backticks for code some bolding where necessary etc | 0 |
99,574 | 30,498,611,465 | IssuesEvent | 2023-07-18 12:36:52 | SigNoz/signoz | https://api.github.com/repos/SigNoz/signoz | closed | [EPIC]FE(Trace)Query Builder | enhancement frontend epic query-builder traces | This is the list of items that needed to be completed to get the first version of trace explorer working based on the PRD. The issues are ordered to reflect the development process of the traces explorer. Each issue will be independently worked on, and after merging, the explorer's state will have the working functionality until that point.
- [x] https://github.com/SigNoz/signoz/issues/2317
- [x] https://github.com/SigNoz/signoz/issues/2314
- [x] https://github.com/SigNoz/signoz/issues/2286
- [x] https://github.com/SigNoz/signoz/issues/2306
- [x] https://github.com/SigNoz/signoz/issues/2307
- [x] https://github.com/SigNoz/signoz/issues/2312
- [x] https://github.com/SigNoz/signoz/issues/2308
- [x] https://github.com/SigNoz/signoz/issues/2309
- [x] https://github.com/SigNoz/signoz/issues/2310
- [x] https://github.com/SigNoz/signoz/issues/2313
- [x] #2332
- [x] #2335
- [x] #2336
- [x] #2333
- [x] #2334
- [x] #2337
- [x] #2338
- [x] #2339 | 1.0 | [EPIC]FE(Trace)Query Builder - This is the list of items that needed to be completed to get the first version of trace explorer working based on the PRD. The issues are ordered to reflect the development process of the traces explorer. Each issue will be independently worked on, and after merging, the explorer's state will have the working functionality until that point.
- [x] https://github.com/SigNoz/signoz/issues/2317
- [x] https://github.com/SigNoz/signoz/issues/2314
- [x] https://github.com/SigNoz/signoz/issues/2286
- [x] https://github.com/SigNoz/signoz/issues/2306
- [x] https://github.com/SigNoz/signoz/issues/2307
- [x] https://github.com/SigNoz/signoz/issues/2312
- [x] https://github.com/SigNoz/signoz/issues/2308
- [x] https://github.com/SigNoz/signoz/issues/2309
- [x] https://github.com/SigNoz/signoz/issues/2310
- [x] https://github.com/SigNoz/signoz/issues/2313
- [x] #2332
- [x] #2335
- [x] #2336
- [x] #2333
- [x] #2334
- [x] #2337
- [x] #2338
- [x] #2339 | build | fe trace query builder this is the list of items that needed to be completed to get the first version of trace explorer working based on the prd the issues are ordered to reflect the development process of the traces explorer each issue will be independently worked on and after merging the explorer s state will have the working functionality until that point | 1 |
374,108 | 26,099,684,493 | IssuesEvent | 2022-12-27 04:35:58 | bounswe/bounswe2022group1 | https://api.github.com/repos/bounswe/bounswe2022group1 | closed | Frontend: CI&CD | Type: Documentation Status: Completed Frontend | **Issue Description:**
I spent some time with jenkins on this project but decided it was less of a requirement for us. That's why I needed a different CI&CD solution. Here I preferred to use "crontab". This way, this project will be updated every night, no matter what changes happen.
<img width="636" alt="Screen Shot 2022-12-27 at 07 33 32" src="https://user-images.githubusercontent.com/74508086/209611508-d438ebe4-7f87-463a-b4bd-23368908f2f4.png">
https://www.jenkins.io/
https://ceaksan.com/tr/crontab-nedir-nasil-kullanilir | 1.0 | Frontend: CI&CD - **Issue Description:**
I spent some time with jenkins on this project but decided it was less of a requirement for us. That's why I needed a different CI&CD solution. Here I preferred to use "crontab". This way, this project will be updated every night, no matter what changes happen.
<img width="636" alt="Screen Shot 2022-12-27 at 07 33 32" src="https://user-images.githubusercontent.com/74508086/209611508-d438ebe4-7f87-463a-b4bd-23368908f2f4.png">
https://www.jenkins.io/
https://ceaksan.com/tr/crontab-nedir-nasil-kullanilir | non_build | frontend ci cd issue description i spent some time with jenkins on this project but decided it was less of a requirement for us that s why i needed a different ci cd solution here i preferred to use crontab this way this project will be updated every night no matter what changes happen img width alt screen shot at src | 0 |
75,076 | 20,620,176,076 | IssuesEvent | 2022-03-07 16:40:57 | bitcoin/bitcoin | https://api.github.com/repos/bitcoin/bitcoin | closed | Build broken when enabling fuzzing on Apple M1 hw using homebrew llvm. | macOS Build system | Enabling fuzzing on macos (Monterey) with Apple M1 hw (arm64) breaks the build:
- I did the steps required to use llvm with homebrew (brew install llvm). Then passed CC & CXX env vars pointing their new respective binaries. Most fuzz tests compiled till I got to crc32c.
./configure --enable-fuzz --with-sanitizers=fuzzer,address,undefined CC=/opt/homebrew/opt/llvm/bin/clang CXX=/opt/homebrew/opt/llvm/bin/clang++ --disable-asm
CXXLD test/fuzz/fuzz
Undefined symbols for architecture arm64:
"crc32c::ExtendArm64(unsigned int, unsigned char const*, unsigned long)", referenced from:
crc32c::Extend(unsigned int, unsigned char const*, unsigned long) in libcrc32c.a(libcrc32c_a-crc32c.o)
ld: symbol(s) not found for architecture arm64
clang-13: error: linker command failed with exit code 1 (use -v to see invocation)
make[2]: *** [test/fuzz/fuzz] Error 1
make[1]: *** [all-recursive] Error 1
make: *** [all-recursive] Error 1
| 1.0 | Build broken when enabling fuzzing on Apple M1 hw using homebrew llvm. - Enabling fuzzing on macos (Monterey) with Apple M1 hw (arm64) breaks the build:
- I did the steps required to use llvm with homebrew (brew install llvm). Then passed CC & CXX env vars pointing their new respective binaries. Most fuzz tests compiled till I got to crc32c.
./configure --enable-fuzz --with-sanitizers=fuzzer,address,undefined CC=/opt/homebrew/opt/llvm/bin/clang CXX=/opt/homebrew/opt/llvm/bin/clang++ --disable-asm
CXXLD test/fuzz/fuzz
Undefined symbols for architecture arm64:
"crc32c::ExtendArm64(unsigned int, unsigned char const*, unsigned long)", referenced from:
crc32c::Extend(unsigned int, unsigned char const*, unsigned long) in libcrc32c.a(libcrc32c_a-crc32c.o)
ld: symbol(s) not found for architecture arm64
clang-13: error: linker command failed with exit code 1 (use -v to see invocation)
make[2]: *** [test/fuzz/fuzz] Error 1
make[1]: *** [all-recursive] Error 1
make: *** [all-recursive] Error 1
| build | build broken when enabling fuzzing on apple hw using homebrew llvm enabling fuzzing on macos monterey with apple hw breaks the build i did the steps required to use llvm with homebrew brew install llvm then passed cc cxx env vars pointing their new respective binaries most fuzz tests compiled till i got to configure enable fuzz with sanitizers fuzzer address undefined cc opt homebrew opt llvm bin clang cxx opt homebrew opt llvm bin clang disable asm cxxld test fuzz fuzz undefined symbols for architecture unsigned int unsigned char const unsigned long referenced from extend unsigned int unsigned char const unsigned long in a a o ld symbol s not found for architecture clang error linker command failed with exit code use v to see invocation make error make error make error | 1 |
36,958 | 2,813,918,744 | IssuesEvent | 2015-05-18 17:08:02 | synergy/synergy | https://api.github.com/repos/synergy/synergy | closed | Runaway logging causes GUI to freeze | bug priority-urgent | 1. **Open GUI**
2. Experience bug #4650 (or other runaway log bug)
3. Wait for server cursor to freeze
4. Service and GUI gobble up memory

```
INFO: accepted secure socket
ERROR: secure socket error: SSL
_ERROR_SSL
ERROR: error:140780E5:SSL routines:ssl23_read:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
ERROR: error:140790E5:SSL routines:ssl23_write:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
ERROR: error:140790E5:SSL routines:ssl23_write:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
ERROR: error:140790E5:SSL routines:ssl23_write:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
``` | 1.0 | Runaway logging causes GUI to freeze - 1. **Open GUI**
2. Experience bug #4650 (or other runaway log bug)
3. Wait for server cursor to freeze
4. Service and GUI gobble up memory

```
INFO: accepted secure socket
ERROR: secure socket error: SSL
_ERROR_SSL
ERROR: error:140780E5:SSL routines:ssl23_read:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
ERROR: error:140790E5:SSL routines:ssl23_write:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
ERROR: error:140790E5:SSL routines:ssl23_write:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
ERROR: error:140790E5:SSL routines:ssl23_write:ssl handshake failure
ERROR: secure socket error: SSL_ERROR_SSL
``` | non_build | runaway logging causes gui to freeze open gui experience bug or other runaway log bug wait for server cursor to freeze service and gui gobble up memory info accepted secure socket error secure socket error ssl error ssl error error ssl routines read ssl handshake failure error secure socket error ssl error ssl error error ssl routines write ssl handshake failure error secure socket error ssl error ssl error error ssl routines write ssl handshake failure error secure socket error ssl error ssl error error ssl routines write ssl handshake failure error secure socket error ssl error ssl | 0 |
15,705 | 11,671,402,284 | IssuesEvent | 2020-03-04 03:04:21 | radareorg/radare2 | https://api.github.com/repos/radareorg/radare2 | opened | Setup a GitHub Action for release multiple repositories | infrastructure | Currently all releases are done manually. But it's possible to run the release action on multiple repositories, so all related projects will be released simultaneously:
- radare2 itself
- radare2-lang
- radare2-bindings
- r2pipe repositories?
- radare2-extras
- something else? | 1.0 | Setup a GitHub Action for release multiple repositories - Currently all releases are done manually. But it's possible to run the release action on multiple repositories, so all related projects will be released simultaneously:
- radare2 itself
- radare2-lang
- radare2-bindings
- r2pipe repositories?
- radare2-extras
- something else? | non_build | setup a github action for release multiple repositories currently all releases are done manually but it s possible to run the release action on multiple repositories so all related projects will be released simultaneously itself lang bindings repositories extras something else | 0 |
12,077 | 9,575,541,149 | IssuesEvent | 2019-05-07 06:45:17 | fluencelabs/fluence | https://api.github.com/repos/fluencelabs/fluence | closed | Debugging simulator for backend development | rust ~infrastructure ~rust_sdk | Some kind of 'dev tool' that would allow to test backend without deploying it to the Fluence network. It should make development cycle (write-run-test-debug) shorter. | 1.0 | Debugging simulator for backend development - Some kind of 'dev tool' that would allow to test backend without deploying it to the Fluence network. It should make development cycle (write-run-test-debug) shorter. | non_build | debugging simulator for backend development some kind of dev tool that would allow to test backend without deploying it to the fluence network it should make development cycle write run test debug shorter | 0 |
43,674 | 11,276,996,178 | IssuesEvent | 2020-01-15 01:09:33 | streamnative/bookkeeper | https://api.github.com/repos/streamnative/bookkeeper | opened | ISSUE-1514: Clean up javadoc mojos execution | area/build help wanted triage/week-8 type/improvement | Original Issue: apache/bookkeeper#1514
---
**BUG REPORT**
1. Please describe the issue you observed:
- What did you do?
run "mvn clean install -DskipTests" on current master
- What did you expect to see?
build okay without warnings
- What did you see instead?
[ERROR] Failed to execute goal org.apache.maven.plugins:maven-javadoc-plugin:3.0.0:javadoc (default-cli) on project bookkeeper-tools-framework: An error has occurred in Javadoc report generation:
[ERROR] Exit code: 1 - javadoc: error - No public or protected classes found to document.
| 1.0 | ISSUE-1514: Clean up javadoc mojos execution - Original Issue: apache/bookkeeper#1514
---
**BUG REPORT**
1. Please describe the issue you observed:
- What did you do?
run "mvn clean install -DskipTests" on current master
- What did you expect to see?
build okay without warnings
- What did you see instead?
[ERROR] Failed to execute goal org.apache.maven.plugins:maven-javadoc-plugin:3.0.0:javadoc (default-cli) on project bookkeeper-tools-framework: An error has occurred in Javadoc report generation:
[ERROR] Exit code: 1 - javadoc: error - No public or protected classes found to document.
| build | issue clean up javadoc mojos execution original issue apache bookkeeper bug report please describe the issue you observed what did you do run mvn clean install dskiptests on current master what did you expect to see build okay without warnings what did you see instead failed to execute goal org apache maven plugins maven javadoc plugin javadoc default cli on project bookkeeper tools framework an error has occurred in javadoc report generation exit code javadoc error no public or protected classes found to document | 1 |
98,655 | 30,030,104,782 | IssuesEvent | 2023-06-27 09:02:21 | scikit-learn/scikit-learn | https://api.github.com/repos/scikit-learn/scikit-learn | closed | MAINT: Sphinx gallery bug after Sphinx min dependency increased to 6.0.0 | Documentation Build / CI | Sphinx gallery error when resolving links:
```
TypeError: list indices must be integers or slices, not str
```
See CI: https://app.circleci.com/pipelines/github/scikit-learn/scikit-learn/48046/workflows/c2bbef06-cb62-416d-98c5-29b211a01b93/jobs/240437 from #26677
This bug was introduced after sphinx 4.3.0 (thus introduced after #26627) and fixed in sphinx gallery 0.10.1, see: https://github.com/sphinx-gallery/sphinx-gallery/issues/879
Can we increase the min dep of sphinx gallery to 0.10.1 ?
| 1.0 | MAINT: Sphinx gallery bug after Sphinx min dependency increased to 6.0.0 - Sphinx gallery error when resolving links:
```
TypeError: list indices must be integers or slices, not str
```
See CI: https://app.circleci.com/pipelines/github/scikit-learn/scikit-learn/48046/workflows/c2bbef06-cb62-416d-98c5-29b211a01b93/jobs/240437 from #26677
This bug was introduced after sphinx 4.3.0 (thus introduced after #26627) and fixed in sphinx gallery 0.10.1, see: https://github.com/sphinx-gallery/sphinx-gallery/issues/879
Can we increase the min dep of sphinx gallery to 0.10.1 ?
| build | maint sphinx gallery bug after sphinx min dependency increased to sphinx gallery error when resolving links typeerror list indices must be integers or slices not str see ci from this bug was introduced after sphinx thus introduced after and fixed in sphinx gallery see can we increase the min dep of sphinx gallery to | 1 |
76,414 | 21,394,722,582 | IssuesEvent | 2022-04-21 10:27:35 | yatinappsmith/TestCaseRepo | https://api.github.com/repos/yatinappsmith/TestCaseRepo | opened | [TestCase] verify the functionality of document viewer by adding xls link | Automated App Viewers Pod UI Building Pod Document Viewer Widget | ### Steps
**Step1.** drag and drop file picker widget
**Expected** ensure that file picker widget placed on canvas
**Step2.** go to properties of document viewer
**Expected** ensure that document viewer properties panel opened
**Step3.** Click on document link textbox
**Expected** ensure that it is editable
**Step4.** Enter xls link inside document link text box
**Expected** ensure that textbox is error free
**Step5.** steps
**Expected** ensure that it is showing a preview of that xls file
### Expected behaviour
| 1.0 | [TestCase] verify the functionality of document viewer by adding xls link - ### Steps
**Step1.** drag and drop file picker widget
**Expected** ensure that file picker widget placed on canvas
**Step2.** go to properties of document viewer
**Expected** ensure that document viewer properties panel opened
**Step3.** Click on document link textbox
**Expected** ensure that it is editable
**Step4.** Enter xls link inside document link text box
**Expected** ensure that textbox is error free
**Step5.** steps
**Expected** ensure that it is showing a preview of that xls file
### Expected behaviour
| build | verify the functionality of document viewer by adding xls link steps drag and drop file picker widget expected ensure that file picker widget placed on canvas go to properties of document viewer expected ensure that document viewer properties panel opened click on document link textbox expected ensure that it is editable enter xls link inside document link text box expected ensure that textbox is error free steps expected ensure that it is showing a preview of that xls file expected behaviour | 1 |
116,869 | 11,944,080,543 | IssuesEvent | 2020-04-03 01:18:00 | StanfordMSL/msl_quad | https://api.github.com/repos/StanfordMSL/msl_quad | closed | Software Documentation - External Dependencies | Comp: Documentation Help Wanted! Priority: 3 - Normal Type: Task | We need to add a "External Dependencies" section under the "Hardware" section of our documentation. Specifically related to the onboard computers. See this link for full layout https://stanford-msl.slack.com/archives/CBLRMNEQ7/p1566425187004900
This will have subsections for each of the following:
- [ ] Raspberry PI
- [ ] Upboard
- [ ] ODroid
- [ ] TX2 | 1.0 | Software Documentation - External Dependencies - We need to add a "External Dependencies" section under the "Hardware" section of our documentation. Specifically related to the onboard computers. See this link for full layout https://stanford-msl.slack.com/archives/CBLRMNEQ7/p1566425187004900
This will have subsections for each of the following:
- [ ] Raspberry PI
- [ ] Upboard
- [ ] ODroid
- [ ] TX2 | non_build | software documentation external dependencies we need to add a external dependencies section under the hardware section of our documentation specifically related to the onboard computers see this link for full layout this will have subsections for each of the following raspberry pi upboard odroid | 0 |
17,724 | 23,625,621,372 | IssuesEvent | 2022-08-25 03:22:29 | MPMG-DCC-UFMG/C01 | https://api.github.com/repos/MPMG-DCC-UFMG/C01 | closed | Problema na visualização de passos de coleta dinâmica | [1] Bug [2] Alta Prioridade [E] Externa [0] Desenvolvimento [3] Processamento Dinâmico | ## Comportamento Esperado
Visualizar os parâmetros inseridos nos passos de coleta dinâmica assim como especificado no arquivo de configuração da coleta.
## Comportamento Atual
Alguns passos não exibem os parâmetros inseridos previamente, como se não estivessem especificados no arquivo de configuração. No entanto, a coleta ainda é executada como o esperado, mesmo que os parâmetros não apareçam na aba de edição.
## Passos para reproduzir o erro
1. Importar o arquivo de configuração abaixo
2. Acessar a aba "Processamento dinâmico"
3. Verirficar que alguns passos não exibem os parâmetros
## Especificações da Coleta
`{
"source_name": "[Realiza\u00e7\u00e3o-F01] Coleta de Servidores P\u00fablicos - Servidores Ativos de Itapeva",
"base_url": "https://e-gov.betha.com.br/transparencia/01037-108/recursos.faces?mun=5QecS5u6hOnx7T0IfpzfTXDJDYqFSDUS",
"obey_robots": false,
"data_path": "home/isabel/itapeva/servidores_empregados_ativos",
"request_type": "GET",
"form_request_type": "POST",
"antiblock_download_delay": 2,
"antiblock_autothrottle_enabled": false,
"antiblock_autothrottle_start_delay": 2,
"antiblock_autothrottle_max_delay": 10,
"antiblock_ip_rotation_enabled": false,
"antiblock_ip_rotation_type": "tor",
"antiblock_max_reqs_per_ip": 10,
"antiblock_max_reuse_rounds": 10,
"antiblock_proxy_list": "",
"antiblock_user_agent_rotation_enabled": false,
"antiblock_reqs_per_user_agent": 100,
"antiblock_user_agents_list": "",
"antiblock_insert_cookies_enabled": false,
"antiblock_cookies_list": "",
"captcha": "none",
"has_webdriver": false,
"webdriver_path": "",
"img_xpath": "",
"sound_xpath": "",
"dynamic_processing": true,
"skip_iter_errors": false,
"explore_links": false,
"link_extractor_max_depth": null,
"link_extractor_allow_url": "",
"link_extractor_allow_domains": "",
"link_extractor_tags": "",
"link_extractor_attrs": "",
"link_extractor_check_type": false,
"link_extractor_process_value": "",
"download_files": false,
"download_files_allow_url": "",
"download_files_allow_extensions": "",
"download_files_allow_domains": "",
"download_files_tags": "",
"download_files_attrs": "",
"download_files_process_value": "",
"download_files_check_large_content": true,
"download_imgs": false,
"steps": "{\"step\":\"root\",\"depth\":0,\"children\":[{\"step\":\"espere\",\"depth\":1,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"screenshot\",\"depth\":1,\"arguments\":{}},{\"step\":\"clique\",\"depth\":1,\"arguments\":{\"elemento\":\"\\\"//a[text()='Servidores/empregados ativos']\\\"\"}},{\"step\":\"espere\",\"depth\":1,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"screenshot\",\"depth\":1,\"arguments\":{}},{\"step\":\"para_cada\",\"depth\":1,\"iterator\":\"ano\",\"children\":[{\"step\":\"selecione\",\"depth\":2,\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[1]/label/span/select\\\"\",\"opcao\":\"ano\"}},{\"step\":\"espere\",\"depth\":2,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"se\",\"depth\":2,\"children\":[{\"step\":\"para_cada\",\"depth\":3,\"iterator\":\"mes\",\"children\":[{\"step\":\"selecione\",\"depth\":4,\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[2]/label/span/select\\\"\",\"opcao\":\"mes\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"imprime\",\"depth\":4,\"arguments\":{\"texto\":\"f\\\"Coletando dados de {mes} de {ano}\\\"\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='mainForm:consultar']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"6\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='btExpandirTodos']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"salva_pagina\",\"depth\":4,\"arguments\":{}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='btn_export_0']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='mainForm:exportType:3']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@title='Exportar consulta para o tipo de arquivo selecionado']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"20\"}},{\"step\":\"screenshot\",\"depth\":4,\"arguments\":{}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[4]/div/div/div/div/div/div/span[3]/span/a\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"para_cada\",\"depth\":4,\"iterator\":\"dado_servidor\",\"children\":[{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"dado_servidor\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"screenshot\",\"depth\":5,\"arguments\":{}},{\"step\":\"executar_em_iframe\",\"depth\":5,\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[4]/div/div/div/div/iframe\\\"\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[1]/div/span[1]/div[2]/span[2]/input\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[4]/div/div/div/div/div/table/tbody/tr[4]/td/input\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[4]/div/div/div/div/div/div/span[1]/span/input\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[4]/div/div/div/div/div/div/span[3]/span/a\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"screenshot\",\"depth\":5,\"arguments\":{}},{\"step\":\"sair_de_iframe\",\"depth\":5,\"arguments\":{}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[4]/div/div/a\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"2\"}}],\"iterable\":{\"call\":{\"step\":\"localiza_elementos\",\"arguments\":{\"xpath\":\"\\\"//tbody[*]//img\\\"\"}}}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='mainForm:novaConsulta']\\\"\"}},{\"step\":\"screenshot\",\"depth\":4,\"arguments\":{}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"4\"}}],\"iterable\":{\"call\":{\"step\":\"opcoes\",\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[2]/label/span/select\\\"\"}}}}],\"condition\":{\"call\":{\"step\":\"objeto\",\"arguments\":{\"objeto\":\"int(ano) >= 2021\"}}}}],\"iterable\":{\"call\":{\"step\":\"opcoes\",\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[1]/label/span/select\\\"\"}}}}]}",
"encoding_detection_method": 1,
"expected_runtime_category": "fast",
"templated_url_parameter_handlers": [],
"static_form_parameter_handlers": [],
"templated_url_response_handlers": [],
"static_form_response_handlers": [],
"crawler_id": 310,
"instance_id": "165512008958773"
}`
## Screenshots
Exemplo de passos que não apresentam os elementos especificados:

| 1.0 | Problema na visualização de passos de coleta dinâmica - ## Comportamento Esperado
Visualizar os parâmetros inseridos nos passos de coleta dinâmica assim como especificado no arquivo de configuração da coleta.
## Comportamento Atual
Alguns passos não exibem os parâmetros inseridos previamente, como se não estivessem especificados no arquivo de configuração. No entanto, a coleta ainda é executada como o esperado, mesmo que os parâmetros não apareçam na aba de edição.
## Passos para reproduzir o erro
1. Importar o arquivo de configuração abaixo
2. Acessar a aba "Processamento dinâmico"
3. Verirficar que alguns passos não exibem os parâmetros
## Especificações da Coleta
`{
"source_name": "[Realiza\u00e7\u00e3o-F01] Coleta de Servidores P\u00fablicos - Servidores Ativos de Itapeva",
"base_url": "https://e-gov.betha.com.br/transparencia/01037-108/recursos.faces?mun=5QecS5u6hOnx7T0IfpzfTXDJDYqFSDUS",
"obey_robots": false,
"data_path": "home/isabel/itapeva/servidores_empregados_ativos",
"request_type": "GET",
"form_request_type": "POST",
"antiblock_download_delay": 2,
"antiblock_autothrottle_enabled": false,
"antiblock_autothrottle_start_delay": 2,
"antiblock_autothrottle_max_delay": 10,
"antiblock_ip_rotation_enabled": false,
"antiblock_ip_rotation_type": "tor",
"antiblock_max_reqs_per_ip": 10,
"antiblock_max_reuse_rounds": 10,
"antiblock_proxy_list": "",
"antiblock_user_agent_rotation_enabled": false,
"antiblock_reqs_per_user_agent": 100,
"antiblock_user_agents_list": "",
"antiblock_insert_cookies_enabled": false,
"antiblock_cookies_list": "",
"captcha": "none",
"has_webdriver": false,
"webdriver_path": "",
"img_xpath": "",
"sound_xpath": "",
"dynamic_processing": true,
"skip_iter_errors": false,
"explore_links": false,
"link_extractor_max_depth": null,
"link_extractor_allow_url": "",
"link_extractor_allow_domains": "",
"link_extractor_tags": "",
"link_extractor_attrs": "",
"link_extractor_check_type": false,
"link_extractor_process_value": "",
"download_files": false,
"download_files_allow_url": "",
"download_files_allow_extensions": "",
"download_files_allow_domains": "",
"download_files_tags": "",
"download_files_attrs": "",
"download_files_process_value": "",
"download_files_check_large_content": true,
"download_imgs": false,
"steps": "{\"step\":\"root\",\"depth\":0,\"children\":[{\"step\":\"espere\",\"depth\":1,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"screenshot\",\"depth\":1,\"arguments\":{}},{\"step\":\"clique\",\"depth\":1,\"arguments\":{\"elemento\":\"\\\"//a[text()='Servidores/empregados ativos']\\\"\"}},{\"step\":\"espere\",\"depth\":1,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"screenshot\",\"depth\":1,\"arguments\":{}},{\"step\":\"para_cada\",\"depth\":1,\"iterator\":\"ano\",\"children\":[{\"step\":\"selecione\",\"depth\":2,\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[1]/label/span/select\\\"\",\"opcao\":\"ano\"}},{\"step\":\"espere\",\"depth\":2,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"se\",\"depth\":2,\"children\":[{\"step\":\"para_cada\",\"depth\":3,\"iterator\":\"mes\",\"children\":[{\"step\":\"selecione\",\"depth\":4,\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[2]/label/span/select\\\"\",\"opcao\":\"mes\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"imprime\",\"depth\":4,\"arguments\":{\"texto\":\"f\\\"Coletando dados de {mes} de {ano}\\\"\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='mainForm:consultar']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"6\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='btExpandirTodos']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"salva_pagina\",\"depth\":4,\"arguments\":{}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='btn_export_0']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='mainForm:exportType:3']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@title='Exportar consulta para o tipo de arquivo selecionado']\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"20\"}},{\"step\":\"screenshot\",\"depth\":4,\"arguments\":{}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[4]/div/div/div/div/div/div/span[3]/span/a\\\"\"}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"para_cada\",\"depth\":4,\"iterator\":\"dado_servidor\",\"children\":[{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"dado_servidor\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"screenshot\",\"depth\":5,\"arguments\":{}},{\"step\":\"executar_em_iframe\",\"depth\":5,\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[4]/div/div/div/div/iframe\\\"\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[1]/div/span[1]/div[2]/span[2]/input\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[4]/div/div/div/div/div/table/tbody/tr[4]/td/input\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"1\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[4]/div/div/div/div/div/div/span[1]/span/input\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"4\"}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[3]/div/div/div/form/div[4]/div/div/div/div/div/div/span[3]/span/a\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"2\"}},{\"step\":\"screenshot\",\"depth\":5,\"arguments\":{}},{\"step\":\"sair_de_iframe\",\"depth\":5,\"arguments\":{}},{\"step\":\"clique\",\"depth\":5,\"arguments\":{\"elemento\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[4]/div/div/a\\\"\"}},{\"step\":\"espere\",\"depth\":5,\"arguments\":{\"segundos\":\"2\"}}],\"iterable\":{\"call\":{\"step\":\"localiza_elementos\",\"arguments\":{\"xpath\":\"\\\"//tbody[*]//img\\\"\"}}}},{\"step\":\"clique\",\"depth\":4,\"arguments\":{\"elemento\":\"\\\"//input[@id='mainForm:novaConsulta']\\\"\"}},{\"step\":\"screenshot\",\"depth\":4,\"arguments\":{}},{\"step\":\"espere\",\"depth\":4,\"arguments\":{\"segundos\":\"4\"}}],\"iterable\":{\"call\":{\"step\":\"opcoes\",\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[2]/label/span/select\\\"\"}}}}],\"condition\":{\"call\":{\"step\":\"objeto\",\"arguments\":{\"objeto\":\"int(ano) >= 2021\"}}}}],\"iterable\":{\"call\":{\"step\":\"opcoes\",\"arguments\":{\"xpath\":\"\\\"/html/body/div[1]/div[1]/div/div/div/form/div[1]/div[1]/span/div/span/div[1]/div[1]/label/span/select\\\"\"}}}}]}",
"encoding_detection_method": 1,
"expected_runtime_category": "fast",
"templated_url_parameter_handlers": [],
"static_form_parameter_handlers": [],
"templated_url_response_handlers": [],
"static_form_response_handlers": [],
"crawler_id": 310,
"instance_id": "165512008958773"
}`
## Screenshots
Exemplo de passos que não apresentam os elementos especificados:

| non_build | problema na visualização de passos de coleta dinâmica comportamento esperado visualizar os parâmetros inseridos nos passos de coleta dinâmica assim como especificado no arquivo de configuração da coleta comportamento atual alguns passos não exibem os parâmetros inseridos previamente como se não estivessem especificados no arquivo de configuração no entanto a coleta ainda é executada como o esperado mesmo que os parâmetros não apareçam na aba de edição passos para reproduzir o erro importar o arquivo de configuração abaixo acessar a aba processamento dinâmico verirficar que alguns passos não exibem os parâmetros especificações da coleta source name coleta de servidores p servidores ativos de itapeva base url obey robots false data path home isabel itapeva servidores empregados ativos request type get form request type post antiblock download delay antiblock autothrottle enabled false antiblock autothrottle start delay antiblock autothrottle max delay antiblock ip rotation enabled false antiblock ip rotation type tor antiblock max reqs per ip antiblock max reuse rounds antiblock proxy list antiblock user agent rotation enabled false antiblock reqs per user agent antiblock user agents list antiblock insert cookies enabled false antiblock cookies list captcha none has webdriver false webdriver path img xpath sound xpath dynamic processing true skip iter errors false explore links false link extractor max depth null link extractor allow url link extractor allow domains link extractor tags link extractor attrs link extractor check type false link extractor process value download files false download files allow url download files allow extensions download files allow domains download files tags download files attrs download files process value download files check large content true download imgs false steps step root depth children step espere depth arguments segundos step screenshot depth arguments step para cada depth iterator ano children div div div div form div div span div span div div label span select opcao ano step espere depth arguments segundos step se depth children div div div div form div div span div span div div label span select opcao mes step espere depth arguments segundos step imprime depth arguments texto f coletando dados de mes de ano step clique depth arguments elemento input step espere depth arguments segundos step clique depth arguments elemento input step espere depth arguments segundos step salva pagina depth arguments step clique depth arguments elemento input step espere depth arguments segundos step clique depth arguments elemento input step espere depth arguments segundos step clique depth arguments elemento input step espere depth arguments segundos step screenshot depth arguments step clique depth arguments elemento html body div div div div div form div div div div div div div span span a step espere depth arguments segundos step para cada depth iterator dado servidor children div div div div form div div div div div iframe step clique depth arguments elemento html body div div div div div form div div span div span input step espere depth arguments segundos step clique depth arguments elemento html body div div div div div form div div div div div div table tbody tr td input step espere depth arguments segundos step clique depth arguments elemento html body div div div div div form div div div div div div div span span input step espere depth arguments segundos step clique depth arguments elemento html body div div div div div form div div div div div div div span span a step espere depth arguments segundos step screenshot depth arguments step sair de iframe depth arguments step clique depth arguments elemento html body div div div div div form div div div a step espere depth arguments segundos iterable call step localiza elementos arguments xpath tbody img step clique depth arguments elemento input step screenshot depth arguments step espere depth arguments segundos iterable call step opcoes arguments xpath html body div div div div div form div div span div span div div label span select condition call step objeto arguments objeto int ano iterable call step opcoes arguments xpath html body div div div div div form div div span div span div div label span select encoding detection method expected runtime category fast templated url parameter handlers static form parameter handlers templated url response handlers static form response handlers crawler id instance id screenshots exemplo de passos que não apresentam os elementos especificados | 0 |
23,119 | 21,048,236,133 | IssuesEvent | 2022-03-31 18:08:48 | CH-Earth/summa | https://api.github.com/repos/CH-Earth/summa | opened | Add a warning if SUMMA performs a relative humidity correction? | enhancement usability | #### Feature Requests
https://github.com/CH-Earth/summa/blob/fa9adf808229a45085defdc2bb8ef05836b9b3aa/build/source/engine/derivforce.f90#L276-L282
Might be helpful to users if this correction also prints a warning, so that it becomes easier to track what happens to the provided forcing data | True | Add a warning if SUMMA performs a relative humidity correction? - #### Feature Requests
https://github.com/CH-Earth/summa/blob/fa9adf808229a45085defdc2bb8ef05836b9b3aa/build/source/engine/derivforce.f90#L276-L282
Might be helpful to users if this correction also prints a warning, so that it becomes easier to track what happens to the provided forcing data | non_build | add a warning if summa performs a relative humidity correction feature requests might be helpful to users if this correction also prints a warning so that it becomes easier to track what happens to the provided forcing data | 0 |
75,603 | 20,907,652,616 | IssuesEvent | 2022-03-24 05:16:16 | google/mediapipe | https://api.github.com/repos/google/mediapipe | opened | Javascript failed to load @mediapipe/hands | type:build/install | I'm doing node js project with hand detection ,
It cause error on browser when I started by node app.js
hands_solution_simd_wasm_bin.js:9 Uncaught (in promise) RuntimeError: Aborted(native code called abort())
at abort (hands_solution_simd_wasm_bin.js:9)
at _abort (hands_solution_simd_wasm_bin.js:9)
at hands_solution_simd_wasm_bin.wasm:0x51ad24
at hands_solution_simd_wasm_bin.wasm:0x51abc9
at hands_solution_simd_wasm_bin.wasm:0x51ad99
at hands_solution_simd_wasm_bin.wasm:0x1f191
at hands_solution_simd_wasm_bin.wasm:0x198f7
at SolutionWasm$send [as send] (eval at new_ (hands_solution_simd_wasm_bin.js:9), <anonymous>:9:1)
at pa.h (hands.js:73)
at G (hands.js:14)
I think when Loading here, it cause above error.
what may be the problem ?
```
const hands = new Hands({locateFile: (file) => {
console.log("!!"+file);
return `https://cdn.jsdelivr.net/npm/@mediapipe/hands/${file}`;
}});
```
Full source code is
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="utf-8">
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/holistic@0.1/holistic.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/camera_utils/camera_utils.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/control_utils/control_utils.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/drawing_utils/drawing_utils.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/hands/hands.js" crossorigin="anonymous"></script>
</head>
<style>
body {
bottom: 0;
font-family: 'Titillium Web', sans-serif;
color: white;
left: 0;
margin: 0;
position: absolute;
right: 0;
top: 0;
transform-origin: 0px 0px;
overflow: hidden;
}
.container {
position: absolute;
background-color: #596e73;
width: 100%;
max-height: 100%;
}
.input_video {
display: none;
position: absolute;
top: 0;
left: 0;
right: 0;
bottom: 0;
&.selfie {
transform: scale(-1, 1);
}
}
.output_canvas {
max-width: 100%;
display: block;
position: relative;
left: 0;
top: 0;
}
</style>
<script type="module">
const videoElement = document.getElementsByClassName('input_video')[0];
const canvasElement = document.getElementsByClassName('output_canvas')[0];
const canvasCtx = canvasElement.getContext('2d');
function onResults(results) {
console.log("result come");
canvasCtx.save();
canvasCtx.clearRect(0, 0, canvasElement.width, canvasElement.height);
canvasCtx.drawImage(
results.image, 0, 0, canvasElement.width, canvasElement.height);
if (results.multiHandLandmarks) {
for (const landmarks of results.multiHandLandmarks) {
drawConnectors(canvasCtx, landmarks, HAND_CONNECTIONS,
{color: '#00FF00', lineWidth: 5});
drawLandmarks(canvasCtx, landmarks, {color: '#FF0000', lineWidth: 2});
}
}
canvasCtx.restore();
}
const hands = new Hands({locateFile: (file) => {
console.log("!!"+file);
return `https://cdn.jsdelivr.net/npm/@mediapipe/hands/${file}`;
}});
hands.setOptions({
maxNumHands: 2,
minDetectionConfidence: 0.5,
minTrackingConfidence: 0.5
});
hands.onResults(onResults);
const camera = new Camera(videoElement, {
onFrame: async () => {
await hands.send({image: videoElement});
},
width: 1280,
height: 720
});
camera.start();
</script>
<body>
<div class="container">
<video class="input_video"></video>
<canvas class="output_canvas" width="1280px" height="720px"></canvas>
</div>
</body>
</html>
```
| 1.0 | Javascript failed to load @mediapipe/hands - I'm doing node js project with hand detection ,
It cause error on browser when I started by node app.js
hands_solution_simd_wasm_bin.js:9 Uncaught (in promise) RuntimeError: Aborted(native code called abort())
at abort (hands_solution_simd_wasm_bin.js:9)
at _abort (hands_solution_simd_wasm_bin.js:9)
at hands_solution_simd_wasm_bin.wasm:0x51ad24
at hands_solution_simd_wasm_bin.wasm:0x51abc9
at hands_solution_simd_wasm_bin.wasm:0x51ad99
at hands_solution_simd_wasm_bin.wasm:0x1f191
at hands_solution_simd_wasm_bin.wasm:0x198f7
at SolutionWasm$send [as send] (eval at new_ (hands_solution_simd_wasm_bin.js:9), <anonymous>:9:1)
at pa.h (hands.js:73)
at G (hands.js:14)
I think when Loading here, it cause above error.
what may be the problem ?
```
const hands = new Hands({locateFile: (file) => {
console.log("!!"+file);
return `https://cdn.jsdelivr.net/npm/@mediapipe/hands/${file}`;
}});
```
Full source code is
```
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="utf-8">
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/holistic@0.1/holistic.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/camera_utils/camera_utils.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/control_utils/control_utils.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/drawing_utils/drawing_utils.js" crossorigin="anonymous"></script>
<script src="https://cdn.jsdelivr.net/npm/@mediapipe/hands/hands.js" crossorigin="anonymous"></script>
</head>
<style>
body {
bottom: 0;
font-family: 'Titillium Web', sans-serif;
color: white;
left: 0;
margin: 0;
position: absolute;
right: 0;
top: 0;
transform-origin: 0px 0px;
overflow: hidden;
}
.container {
position: absolute;
background-color: #596e73;
width: 100%;
max-height: 100%;
}
.input_video {
display: none;
position: absolute;
top: 0;
left: 0;
right: 0;
bottom: 0;
&.selfie {
transform: scale(-1, 1);
}
}
.output_canvas {
max-width: 100%;
display: block;
position: relative;
left: 0;
top: 0;
}
</style>
<script type="module">
const videoElement = document.getElementsByClassName('input_video')[0];
const canvasElement = document.getElementsByClassName('output_canvas')[0];
const canvasCtx = canvasElement.getContext('2d');
function onResults(results) {
console.log("result come");
canvasCtx.save();
canvasCtx.clearRect(0, 0, canvasElement.width, canvasElement.height);
canvasCtx.drawImage(
results.image, 0, 0, canvasElement.width, canvasElement.height);
if (results.multiHandLandmarks) {
for (const landmarks of results.multiHandLandmarks) {
drawConnectors(canvasCtx, landmarks, HAND_CONNECTIONS,
{color: '#00FF00', lineWidth: 5});
drawLandmarks(canvasCtx, landmarks, {color: '#FF0000', lineWidth: 2});
}
}
canvasCtx.restore();
}
const hands = new Hands({locateFile: (file) => {
console.log("!!"+file);
return `https://cdn.jsdelivr.net/npm/@mediapipe/hands/${file}`;
}});
hands.setOptions({
maxNumHands: 2,
minDetectionConfidence: 0.5,
minTrackingConfidence: 0.5
});
hands.onResults(onResults);
const camera = new Camera(videoElement, {
onFrame: async () => {
await hands.send({image: videoElement});
},
width: 1280,
height: 720
});
camera.start();
</script>
<body>
<div class="container">
<video class="input_video"></video>
<canvas class="output_canvas" width="1280px" height="720px"></canvas>
</div>
</body>
</html>
```
| build | javascript failed to load mediapipe hands i m doing node js project with hand detection it cause error on browser when i started by node app js hands solution simd wasm bin js uncaught in promise runtimeerror aborted native code called abort at abort hands solution simd wasm bin js at abort hands solution simd wasm bin js at hands solution simd wasm bin wasm at hands solution simd wasm bin wasm at hands solution simd wasm bin wasm at hands solution simd wasm bin wasm at hands solution simd wasm bin wasm at solutionwasm send eval at new hands solution simd wasm bin js at pa h hands js at g hands js i think when loading here it cause above error what may be the problem const hands new hands locatefile file console log file return full source code is body bottom font family titillium web sans serif color white left margin position absolute right top transform origin overflow hidden container position absolute background color width max height input video display none position absolute top left right bottom selfie transform scale output canvas max width display block position relative left top const videoelement document getelementsbyclassname input video const canvaselement document getelementsbyclassname output canvas const canvasctx canvaselement getcontext function onresults results console log result come canvasctx save canvasctx clearrect canvaselement width canvaselement height canvasctx drawimage results image canvaselement width canvaselement height if results multihandlandmarks for const landmarks of results multihandlandmarks drawconnectors canvasctx landmarks hand connections color linewidth drawlandmarks canvasctx landmarks color linewidth canvasctx restore const hands new hands locatefile file console log file return hands setoptions maxnumhands mindetectionconfidence mintrackingconfidence hands onresults onresults const camera new camera videoelement onframe async await hands send image videoelement width height camera start | 1 |
8,358 | 4,231,603,817 | IssuesEvent | 2016-07-04 16:49:53 | jeff1evesque/machine-learning | https://api.github.com/repos/jeff1evesque/machine-learning | opened | Link docker containers to allow unit testing | build enhancement | This issue is a continuation of #2153. However, this issue will be more of a focus on accessing the [environmental variables](https://docs.docker.com/v1.8/userguide/dockerlinks/#environment-variables) defined from the alias naming convention. Specifically, we will conditionally define necessary attributes within db_settings.py, as well as app.py, based on the linked docker container environmental variables. | 1.0 | Link docker containers to allow unit testing - This issue is a continuation of #2153. However, this issue will be more of a focus on accessing the [environmental variables](https://docs.docker.com/v1.8/userguide/dockerlinks/#environment-variables) defined from the alias naming convention. Specifically, we will conditionally define necessary attributes within db_settings.py, as well as app.py, based on the linked docker container environmental variables. | build | link docker containers to allow unit testing this issue is a continuation of however this issue will be more of a focus on accessing the defined from the alias naming convention specifically we will conditionally define necessary attributes within db settings py as well as app py based on the linked docker container environmental variables | 1 |
412,652 | 12,053,928,272 | IssuesEvent | 2020-04-15 10:12:32 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | Make alert ids and flow status ids constant | low-priority bug | Alert ids and flow status ids were constant, then in https://github.com/ntop/ntopng/issues/3221 a request was made to make them dynamic with the aim of simplifying their management. However, making them dynamic requires ntopng to keep additional mappings (alert id -> alert key, flow status id -> status key) that can go out of sync when redis is cleared. This, although improbable, yields issues such as:
- https://github.com/ntop/ntopng/issues/3728
- https://github.com/ntop/ntopng/issues/3727
For this reason, we believe having static, never-changing ids is the right choice (same as done in NetFlow for example).
So ntopng will have certain alert and certain flow ids reserved for built-in plugins. Then, it will leave other ranges for user plugin:
- alert ids <= 32k will be for ntopng, greater than 32k
- flow ids < 59 will be for ntopng, between 59 and 63 for user plugins
Flow ids are currently kept in a 64-bit bitmap. If in the future, even if this bitmap will be extended, ids 59-63 will still be guaranteed to be left for user plugins.
For builtin alerts, alert ids will be specified in the alerts definition lua files as:
```
return {
alert_id = 11,
....
}
```
For user script plugins, alert ids will be in the form
```
return {
alert_id = user_defined_alert_id_01,
....
}
```
Status page http://127.0.0.1:3000/lua/defs_overview.lua will offer an overview of currently used and free ids.
Mutatis mutandis, the same applies for flow ids.
-----
Doing this change breaks the current alert database and the flow statuses in nIndex but is essential and must be done as soon as possible. To avoid losing old data, a migration script should be executed upon ntopng startup.
The migration script:
- Will update the alert database to rewrite the alert ids. It will overwrite the previously computed dynamic ids with the new static ids.
- Will delete/recreate the flow status id column for those using nIndex. Need comments from @lucaderi on the feasibility of this.
Migration script will be executed both on the stable and on the dev releases. | 1.0 | Make alert ids and flow status ids constant - Alert ids and flow status ids were constant, then in https://github.com/ntop/ntopng/issues/3221 a request was made to make them dynamic with the aim of simplifying their management. However, making them dynamic requires ntopng to keep additional mappings (alert id -> alert key, flow status id -> status key) that can go out of sync when redis is cleared. This, although improbable, yields issues such as:
- https://github.com/ntop/ntopng/issues/3728
- https://github.com/ntop/ntopng/issues/3727
For this reason, we believe having static, never-changing ids is the right choice (same as done in NetFlow for example).
So ntopng will have certain alert and certain flow ids reserved for built-in plugins. Then, it will leave other ranges for user plugin:
- alert ids <= 32k will be for ntopng, greater than 32k
- flow ids < 59 will be for ntopng, between 59 and 63 for user plugins
Flow ids are currently kept in a 64-bit bitmap. If in the future, even if this bitmap will be extended, ids 59-63 will still be guaranteed to be left for user plugins.
For builtin alerts, alert ids will be specified in the alerts definition lua files as:
```
return {
alert_id = 11,
....
}
```
For user script plugins, alert ids will be in the form
```
return {
alert_id = user_defined_alert_id_01,
....
}
```
Status page http://127.0.0.1:3000/lua/defs_overview.lua will offer an overview of currently used and free ids.
Mutatis mutandis, the same applies for flow ids.
-----
Doing this change breaks the current alert database and the flow statuses in nIndex but is essential and must be done as soon as possible. To avoid losing old data, a migration script should be executed upon ntopng startup.
The migration script:
- Will update the alert database to rewrite the alert ids. It will overwrite the previously computed dynamic ids with the new static ids.
- Will delete/recreate the flow status id column for those using nIndex. Need comments from @lucaderi on the feasibility of this.
Migration script will be executed both on the stable and on the dev releases. | non_build | make alert ids and flow status ids constant alert ids and flow status ids were constant then in a request was made to make them dynamic with the aim of simplifying their management however making them dynamic requires ntopng to keep additional mappings alert id alert key flow status id status key that can go out of sync when redis is cleared this although improbable yields issues such as for this reason we believe having static never changing ids is the right choice same as done in netflow for example so ntopng will have certain alert and certain flow ids reserved for built in plugins then it will leave other ranges for user plugin alert ids will be for ntopng greater than flow ids will be for ntopng between and for user plugins flow ids are currently kept in a bit bitmap if in the future even if this bitmap will be extended ids will still be guaranteed to be left for user plugins for builtin alerts alert ids will be specified in the alerts definition lua files as return alert id for user script plugins alert ids will be in the form return alert id user defined alert id status page will offer an overview of currently used and free ids mutatis mutandis the same applies for flow ids doing this change breaks the current alert database and the flow statuses in nindex but is essential and must be done as soon as possible to avoid losing old data a migration script should be executed upon ntopng startup the migration script will update the alert database to rewrite the alert ids it will overwrite the previously computed dynamic ids with the new static ids will delete recreate the flow status id column for those using nindex need comments from lucaderi on the feasibility of this migration script will be executed both on the stable and on the dev releases | 0 |
88,640 | 10,576,356,813 | IssuesEvent | 2019-10-07 17:41:31 | xtermjs/xterm.js | https://api.github.com/repos/xtermjs/xterm.js | closed | Figure out how we call out contributions to satellite repos | type/documentation | We could call out all PRs merged across the org for example: https://github.com/issues?q=is%3Apr+org%3Axtermjs+merged%3A%3E2018-07-13+is%3Aclosed
This may be a little weird though as addons will get released separately and should have their own releases. | 1.0 | Figure out how we call out contributions to satellite repos - We could call out all PRs merged across the org for example: https://github.com/issues?q=is%3Apr+org%3Axtermjs+merged%3A%3E2018-07-13+is%3Aclosed
This may be a little weird though as addons will get released separately and should have their own releases. | non_build | figure out how we call out contributions to satellite repos we could call out all prs merged across the org for example this may be a little weird though as addons will get released separately and should have their own releases | 0 |
71,300 | 18,676,707,599 | IssuesEvent | 2021-10-31 17:29:30 | quicklisp/quicklisp-projects | https://api.github.com/repos/quicklisp/quicklisp-projects | closed | Please add compiler-macro-notes | canbuild | Please fetch from the releases: https://github.com/digikar99/compiler-macro-notes/releases
compiler-macro-notes provides two conditions `note` and `optimization-failure-note` and a couple of utilities for using these in macros and compiler-macros. | 1.0 | Please add compiler-macro-notes - Please fetch from the releases: https://github.com/digikar99/compiler-macro-notes/releases
compiler-macro-notes provides two conditions `note` and `optimization-failure-note` and a couple of utilities for using these in macros and compiler-macros. | build | please add compiler macro notes please fetch from the releases compiler macro notes provides two conditions note and optimization failure note and a couple of utilities for using these in macros and compiler macros | 1 |
72,526 | 19,303,260,506 | IssuesEvent | 2021-12-13 08:50:21 | alexrp/system-terminal | https://api.github.com/repos/alexrp/system-terminal | opened | Long term: Switch to a native library for driver implementations | type: feature state: approved area: build area: drivers | This would have a number of benefits:
* Some unfixable race conditions relating to signals (e.g. `SIGCONT`) will be resolved.
* No more duplicated code between Linux and macOS.
* Significantly reduced metadata size from removing P/Invoke declarations.
* Faster builds as CsWin32 will no longer be needed.
* Easier porting to new platforms.
The native library would probably be written in Zig. For this to as painless as possible, we would need alexrp/zig-msbuild-sdk#8 (and by extension dotnet/sdk#19929) to be implemented first. | 1.0 | Long term: Switch to a native library for driver implementations - This would have a number of benefits:
* Some unfixable race conditions relating to signals (e.g. `SIGCONT`) will be resolved.
* No more duplicated code between Linux and macOS.
* Significantly reduced metadata size from removing P/Invoke declarations.
* Faster builds as CsWin32 will no longer be needed.
* Easier porting to new platforms.
The native library would probably be written in Zig. For this to as painless as possible, we would need alexrp/zig-msbuild-sdk#8 (and by extension dotnet/sdk#19929) to be implemented first. | build | long term switch to a native library for driver implementations this would have a number of benefits some unfixable race conditions relating to signals e g sigcont will be resolved no more duplicated code between linux and macos significantly reduced metadata size from removing p invoke declarations faster builds as will no longer be needed easier porting to new platforms the native library would probably be written in zig for this to as painless as possible we would need alexrp zig msbuild sdk and by extension dotnet sdk to be implemented first | 1 |
177,626 | 14,635,064,875 | IssuesEvent | 2020-12-24 07:15:40 | cpp-lln-lab/CPP_BIDS | https://api.github.com/repos/cpp-lln-lab/CPP_BIDS | closed | set up a release protocol / checklist (see BIDS specs for ideas) | documentation | for example I forgot to update the version.txt in the last release | 1.0 | set up a release protocol / checklist (see BIDS specs for ideas) - for example I forgot to update the version.txt in the last release | non_build | set up a release protocol checklist see bids specs for ideas for example i forgot to update the version txt in the last release | 0 |
589,007 | 17,687,791,313 | IssuesEvent | 2021-08-24 05:42:58 | thoth-station/integration-tests | https://api.github.com/repos/thoth-station/integration-tests | closed | test metadata service | kind/feature priority/important-soon lifecycle/rotten | As a User of Thoth Service,
I want to retrieve the metadata of the latest TensorFlow version published on PyPI
so that I can verify which indices contain TF,
and so that I can see thoth's information on TF
/kind feature | 1.0 | test metadata service - As a User of Thoth Service,
I want to retrieve the metadata of the latest TensorFlow version published on PyPI
so that I can verify which indices contain TF,
and so that I can see thoth's information on TF
/kind feature | non_build | test metadata service as a user of thoth service i want to retrieve the metadata of the latest tensorflow version published on pypi so that i can verify which indices contain tf and so that i can see thoth s information on tf kind feature | 0 |
3,579 | 3,203,311,600 | IssuesEvent | 2015-10-02 18:21:44 | johnhbenetech/listTest | https://api.github.com/repos/johnhbenetech/listTest | opened | product.Disappearing_Languages | feature.Data_Collection feature.Distribution feature.Localization process.Community_Building process.Content_Standards_Development process.Crowdsourcing process.Pedagogical_Standards_Development technology.Content technology.Web user.Displaced user.Seniors user.Unconnected user.Underserved vertical.Education vertical.Global_Literacy | 1 Impact
1 Need
2 Mission fit
2 Legalilty
0 Money: current
1 Money: future
0 Cost
0 Talent
2 Technical Risk
0 Champion
0 Community: users
0 Community: partners
1 Portfolio fit
0 Exit strategies
0 Data/proof | 1.0 | product.Disappearing_Languages - 1 Impact
1 Need
2 Mission fit
2 Legalilty
0 Money: current
1 Money: future
0 Cost
0 Talent
2 Technical Risk
0 Champion
0 Community: users
0 Community: partners
1 Portfolio fit
0 Exit strategies
0 Data/proof | build | product disappearing languages impact need mission fit legalilty money current money future cost talent technical risk champion community users community partners portfolio fit exit strategies data proof | 1 |
98,887 | 30,213,161,042 | IssuesEvent | 2023-07-05 14:00:59 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | Build 106 for 8.8 with status FAILURE | automation ci-reported Team:Elastic-Agent-Data-Plane build-failures |
## :broken_heart: Build Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//pipeline) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//tests) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//changes) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//artifacts) [](http://beats_null.docs-preview.app.elstc.co/diff) [](https://ci-stats.elastic.co/app/apm/services/beats-ci/transactions/view?rangeFrom=2023-06-15T08:27:45.753Z&rangeTo=2023-06-15T08:47:45.753Z&transactionName=BUILD+Beats%2Fbeats%2F8.8&transactionType=job&latencyAggregationType=avg&traceId=c2b684152aaa60a4d5cf7a5e49804b46&transactionId=27ed18bc8c718311)
<!-- BUILD SUMMARY-->
<details><summary>Expand to view the summary</summary>
<p>
#### Build stats
* Start Time: 2023-06-15T08:37:45.753+0000
* Duration: 64 min 4 sec
#### Test stats :test_tube:
| Test | Results |
| ------------ | :-----------------------------: |
| Failed | 0 |
| Passed | 25306 |
| Skipped | 1794 |
| Total | 27100 |
</p>
</details>
<!-- TEST RESULTS IF ANY-->
<!-- STEPS ERRORS IF ANY -->
### Steps errors [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//pipeline)
<details><summary>Expand to view the steps failures</summary>
<p>
> Show only the first 10 steps failures
##### `x-pack/auditbeat-build - mage update build test`
<ul>
<li>Took 1 min 36 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/16250/log/?start=0">here</a></li>
<li>Description: <code>mage update build test</code></l1>
</ul>
##### `x-pack/auditbeat-windows-2016-windows-2016 - Install Python`
<ul>
<li>Took 1 min 7 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/10058/log/?start=0">here</a></li>
<li>Description: <code>.ci/scripts/install-tools.bat</code></l1>
</ul>
##### `x-pack/libbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 4 min 17 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/12277/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 4 min 33 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/12410/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 3 min 2 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/15709/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 3 min 3 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/17476/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-pythonIntegTest - mage pythonIntegTest`
<ul>
<li>Took 1 min 14 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/12118/log/?start=0">here</a></li>
<li>Description: <code>mage pythonIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-pythonIntegTest - mage pythonIntegTest`
<ul>
<li>Took 0 min 29 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/13119/log/?start=0">here</a></li>
<li>Description: <code>mage pythonIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-pythonIntegTest - mage pythonIntegTest`
<ul>
<li>Took 0 min 19 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/13398/log/?start=0">here</a></li>
<li>Description: <code>mage pythonIntegTest</code></l1>
</ul>
##### `Error signal`
<ul>
<li>Took 0 min 0 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/21021/log/?start=0">here</a></li>
<li>Description: <code>Error "hudson.AbortException: script returned exit code 1"</code></l1>
</ul>
</p>
</details>
| 1.0 | Build 106 for 8.8 with status FAILURE -
## :broken_heart: Build Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//pipeline) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//tests) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//changes) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//artifacts) [](http://beats_null.docs-preview.app.elstc.co/diff) [](https://ci-stats.elastic.co/app/apm/services/beats-ci/transactions/view?rangeFrom=2023-06-15T08:27:45.753Z&rangeTo=2023-06-15T08:47:45.753Z&transactionName=BUILD+Beats%2Fbeats%2F8.8&transactionType=job&latencyAggregationType=avg&traceId=c2b684152aaa60a4d5cf7a5e49804b46&transactionId=27ed18bc8c718311)
<!-- BUILD SUMMARY-->
<details><summary>Expand to view the summary</summary>
<p>
#### Build stats
* Start Time: 2023-06-15T08:37:45.753+0000
* Duration: 64 min 4 sec
#### Test stats :test_tube:
| Test | Results |
| ------------ | :-----------------------------: |
| Failed | 0 |
| Passed | 25306 |
| Skipped | 1794 |
| Total | 27100 |
</p>
</details>
<!-- TEST RESULTS IF ANY-->
<!-- STEPS ERRORS IF ANY -->
### Steps errors [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.8/detail/8.8/106//pipeline)
<details><summary>Expand to view the steps failures</summary>
<p>
> Show only the first 10 steps failures
##### `x-pack/auditbeat-build - mage update build test`
<ul>
<li>Took 1 min 36 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/16250/log/?start=0">here</a></li>
<li>Description: <code>mage update build test</code></l1>
</ul>
##### `x-pack/auditbeat-windows-2016-windows-2016 - Install Python`
<ul>
<li>Took 1 min 7 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/10058/log/?start=0">here</a></li>
<li>Description: <code>.ci/scripts/install-tools.bat</code></l1>
</ul>
##### `x-pack/libbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 4 min 17 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/12277/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 4 min 33 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/12410/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 3 min 2 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/15709/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 3 min 3 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/17476/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-pythonIntegTest - mage pythonIntegTest`
<ul>
<li>Took 1 min 14 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/12118/log/?start=0">here</a></li>
<li>Description: <code>mage pythonIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-pythonIntegTest - mage pythonIntegTest`
<ul>
<li>Took 0 min 29 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/13119/log/?start=0">here</a></li>
<li>Description: <code>mage pythonIntegTest</code></l1>
</ul>
##### `x-pack/metricbeat-pythonIntegTest - mage pythonIntegTest`
<ul>
<li>Took 0 min 19 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/13398/log/?start=0">here</a></li>
<li>Description: <code>mage pythonIntegTest</code></l1>
</ul>
##### `Error signal`
<ul>
<li>Took 0 min 0 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.8/runs/106/steps/21021/log/?start=0">here</a></li>
<li>Description: <code>Error "hudson.AbortException: script returned exit code 1"</code></l1>
</ul>
</p>
</details>
| build | build for with status failure broken heart build failed the below badges are clickable and redirect to their specific view in the ci or docs expand to view the summary build stats start time duration min sec test stats test tube test results failed passed skipped total steps errors expand to view the steps failures show only the first steps failures x pack auditbeat build mage update build test took min sec view more details a href description mage update build test x pack auditbeat windows windows install python took min sec view more details a href description ci scripts install tools bat x pack libbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest x pack metricbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest x pack metricbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest x pack metricbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest x pack metricbeat pythonintegtest mage pythonintegtest took min sec view more details a href description mage pythonintegtest x pack metricbeat pythonintegtest mage pythonintegtest took min sec view more details a href description mage pythonintegtest x pack metricbeat pythonintegtest mage pythonintegtest took min sec view more details a href description mage pythonintegtest error signal took min sec view more details a href description error hudson abortexception script returned exit code | 1 |
56,171 | 13,768,868,291 | IssuesEvent | 2020-10-07 17:43:59 | GoogleCloudPlatform/python-docs-samples | https://api.github.com/repos/GoogleCloudPlatform/python-docs-samples | closed | jobs.v3.api_client.email_alert_search_sample_test: test_email_alert_search_sample failed | :rotating_light: api: jobs buildcop: flaky buildcop: issue priority: p1 priority: p2 samples type: bug | Note: #2857 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: c45fb88095a9d5f4ea16283553e39c8759645eee
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/a33947ff-cc11-4456-b8f4-686bacfb5131), [Sponge](http://sponge2/a33947ff-cc11-4456-b8f4-686bacfb5131)
status: failed
<details><summary>Test output</summary><br><pre>Traceback (most recent call last):
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_sync.py", line 105, in retry
seconds = _next_wait(wait, jitter, elapsed, max_time_)
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_common.py", line 27, in _next_wait
value = next(wait)
StopIteration
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/workspace/jobs/v3/api_client/email_alert_search_sample_test.py", line 43, in test_email_alert_search_sample
eventually_consistent_test()
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_sync.py", line 108, in retry
raise e
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_sync.py", line 94, in retry
ret = target(*args, **kwargs)
File "/workspace/jobs/v3/api_client/email_alert_search_sample_test.py", line 41, in eventually_consistent_test
assert re.search(expected, out)
AssertionError: assert None
+ where None = <function search at 0x7fd9ae177488>('.*matchingJobs.*', "{'metadata': {'requestId': '06ba3dbc-4c30-49a4-9628-9ba2d29a9af9:APAb7ITygdHzBJ4uZPuu9g0WO0uREgSWcg=='}}\n")
+ where <function search at 0x7fd9ae177488> = re.search</pre></details> | 2.0 | jobs.v3.api_client.email_alert_search_sample_test: test_email_alert_search_sample failed - Note: #2857 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: c45fb88095a9d5f4ea16283553e39c8759645eee
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/a33947ff-cc11-4456-b8f4-686bacfb5131), [Sponge](http://sponge2/a33947ff-cc11-4456-b8f4-686bacfb5131)
status: failed
<details><summary>Test output</summary><br><pre>Traceback (most recent call last):
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_sync.py", line 105, in retry
seconds = _next_wait(wait, jitter, elapsed, max_time_)
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_common.py", line 27, in _next_wait
value = next(wait)
StopIteration
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/workspace/jobs/v3/api_client/email_alert_search_sample_test.py", line 43, in test_email_alert_search_sample
eventually_consistent_test()
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_sync.py", line 108, in retry
raise e
File "/workspace/jobs/v3/api_client/.nox/py-3-6/lib/python3.6/site-packages/backoff/_sync.py", line 94, in retry
ret = target(*args, **kwargs)
File "/workspace/jobs/v3/api_client/email_alert_search_sample_test.py", line 41, in eventually_consistent_test
assert re.search(expected, out)
AssertionError: assert None
+ where None = <function search at 0x7fd9ae177488>('.*matchingJobs.*', "{'metadata': {'requestId': '06ba3dbc-4c30-49a4-9628-9ba2d29a9af9:APAb7ITygdHzBJ4uZPuu9g0WO0uREgSWcg=='}}\n")
+ where <function search at 0x7fd9ae177488> = re.search</pre></details> | build | jobs api client email alert search sample test test email alert search sample failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output traceback most recent call last file workspace jobs api client nox py lib site packages backoff sync py line in retry seconds next wait wait jitter elapsed max time file workspace jobs api client nox py lib site packages backoff common py line in next wait value next wait stopiteration during handling of the above exception another exception occurred traceback most recent call last file workspace jobs api client email alert search sample test py line in test email alert search sample eventually consistent test file workspace jobs api client nox py lib site packages backoff sync py line in retry raise e file workspace jobs api client nox py lib site packages backoff sync py line in retry ret target args kwargs file workspace jobs api client email alert search sample test py line in eventually consistent test assert re search expected out assertionerror assert none where none matchingjobs metadata requestid n where re search | 1 |
389,070 | 26,796,993,297 | IssuesEvent | 2023-02-01 12:37:39 | Withding/withding | https://api.github.com/repos/Withding/withding | opened | 프로젝트 생성 단계에서 상품 추가 문서 수정부탁드립니다. | documentation | 문서가 기존에 협약했던거랑 다른거같아서요.
상품 리스트 가져올떄 상품의 속성들은 올바른데 여기서만 다르네요
https://github.com/Withding/withding/blob/develop/Backend/API/%ED%94%84%EB%A1%9C%EC%A0%9D%ED%8A%B8/%ED%94%84%EB%A1%9C%EC%A0%9D%ED%8A%B8%203%EB%8B%A8%EA%B3%84%20%EC%A0%80%EC%9E%A5.md
| 1.0 | 프로젝트 생성 단계에서 상품 추가 문서 수정부탁드립니다. - 문서가 기존에 협약했던거랑 다른거같아서요.
상품 리스트 가져올떄 상품의 속성들은 올바른데 여기서만 다르네요
https://github.com/Withding/withding/blob/develop/Backend/API/%ED%94%84%EB%A1%9C%EC%A0%9D%ED%8A%B8/%ED%94%84%EB%A1%9C%EC%A0%9D%ED%8A%B8%203%EB%8B%A8%EA%B3%84%20%EC%A0%80%EC%9E%A5.md
| non_build | 프로젝트 생성 단계에서 상품 추가 문서 수정부탁드립니다 문서가 기존에 협약했던거랑 다른거같아서요 상품 리스트 가져올떄 상품의 속성들은 올바른데 여기서만 다르네요 | 0 |
112,979 | 4,540,945,492 | IssuesEvent | 2016-09-09 16:08:09 | citp/OpenWPM | https://api.github.com/repos/citp/OpenWPM | opened | Investigate changes necessary to move to Python 3 | help wanted low-priority needs-investigation | Python 2.7 is being [slowly removed](https://wiki.ubuntu.com/XenialXerus/ReleaseNotes#Updated_Packages) from the default installs of Ubuntu, we should investigate what changes are necessary to port to Python 3. I'm guessing some of our dependencies will be 2.7+ only. | 1.0 | Investigate changes necessary to move to Python 3 - Python 2.7 is being [slowly removed](https://wiki.ubuntu.com/XenialXerus/ReleaseNotes#Updated_Packages) from the default installs of Ubuntu, we should investigate what changes are necessary to port to Python 3. I'm guessing some of our dependencies will be 2.7+ only. | non_build | investigate changes necessary to move to python python is being from the default installs of ubuntu we should investigate what changes are necessary to port to python i m guessing some of our dependencies will be only | 0 |
76,552 | 21,484,824,890 | IssuesEvent | 2022-04-26 21:46:28 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | nixos.tests.installer.lvm.x86_64-linux fails on hydra | 1.severity: channel blocker 0.kind: build failure | https://hydra.nixos.org/build/174875086
Currently blocking nixpkgs-unstable-small
To reproduce: check out nixpkgs cef053 and `nix-build '<nixpkgs/nixos/tests/installer.nix>' -A lvm` (haven't tested myself yet)
```
machine: must succeed: nixos-install < /dev/null >&2
machine # copying channel...
machine # [ 928.783595] systemd[1]: Starting Cleanup of Temporary Directories...
machine # [ 930.254457] systemd[1]: systemd-tmpfiles-clean.service: Deactivated successfully.
machine # [ 930.255433] systemd[1]: Finished Cleanup of Temporary Directories.
machine # building the configuration in /mnt/etc/nixos/configuration.nix...
machine # error: undefined variable 'boot'
machine #
machine # at /nix/var/nix/profiles/per-user/root/channels/nixos/nixos/modules/tasks/filesystems/xfs.nix:18:57:
machine #
machine # 17|
machine # 18| boot.initrd.extraUtilsCommands = mkIf (inInitrd && !boot.initrd.systemd.enable)
machine # | ^
machine # 19| ''
machine # (use '--show-trace' to show detailed location information)
machine: output:
Test "Perform the installation" failed with error: "command `nixos-install < /dev/null >&2` failed (exit code 1)"
``` | 1.0 | nixos.tests.installer.lvm.x86_64-linux fails on hydra - https://hydra.nixos.org/build/174875086
Currently blocking nixpkgs-unstable-small
To reproduce: check out nixpkgs cef053 and `nix-build '<nixpkgs/nixos/tests/installer.nix>' -A lvm` (haven't tested myself yet)
```
machine: must succeed: nixos-install < /dev/null >&2
machine # copying channel...
machine # [ 928.783595] systemd[1]: Starting Cleanup of Temporary Directories...
machine # [ 930.254457] systemd[1]: systemd-tmpfiles-clean.service: Deactivated successfully.
machine # [ 930.255433] systemd[1]: Finished Cleanup of Temporary Directories.
machine # building the configuration in /mnt/etc/nixos/configuration.nix...
machine # error: undefined variable 'boot'
machine #
machine # at /nix/var/nix/profiles/per-user/root/channels/nixos/nixos/modules/tasks/filesystems/xfs.nix:18:57:
machine #
machine # 17|
machine # 18| boot.initrd.extraUtilsCommands = mkIf (inInitrd && !boot.initrd.systemd.enable)
machine # | ^
machine # 19| ''
machine # (use '--show-trace' to show detailed location information)
machine: output:
Test "Perform the installation" failed with error: "command `nixos-install < /dev/null >&2` failed (exit code 1)"
``` | build | nixos tests installer lvm linux fails on hydra currently blocking nixpkgs unstable small to reproduce check out nixpkgs and nix build a lvm haven t tested myself yet machine must succeed nixos install machine copying channel machine systemd starting cleanup of temporary directories machine systemd systemd tmpfiles clean service deactivated successfully machine systemd finished cleanup of temporary directories machine building the configuration in mnt etc nixos configuration nix machine error undefined variable boot machine machine at nix var nix profiles per user root channels nixos nixos modules tasks filesystems xfs nix machine machine machine boot initrd extrautilscommands mkif ininitrd boot initrd systemd enable machine machine machine use show trace to show detailed location information machine output test perform the installation failed with error command nixos install failed exit code | 1 |
11,634 | 2,660,010,028 | IssuesEvent | 2015-03-19 01:32:36 | perfsonar/project | https://api.github.com/repos/perfsonar/project | closed | mesh config "http get" doesn't retry with all resolved addresses | Milestone-Release3.5 Priority-Medium Type-Defect | Original [issue 1013](https://code.google.com/p/perfsonar-ps/issues/detail?id=1013) created by arlake228 on 2014-11-04T13:31:00.000Z:
If a DNS name resolves to v4 and v6 addresses but v6 is either disabled on the client or unavailable on the server, the mesh config https_get routine, using IO::Socket::INET6 under the hood, will try the v6 address and fail, even though the v4 address is accessible. There is a MultiHomed flag that you can add to the IO::Socket::* modules, but when we did that, it went into an unhelpful infinite loop with the module version available in RedHat 6. There are a few options to fix this:
1) Find a better Perl module, that's available in RedHat 6 or EPEL6, and rewrite the https_get routine using it
2) Have the https_get routine do the address resolving, and iterate through the addresses itself
3) Package a newer version of the IO::Socket::INET6 module
I'm partial to # 1 if there's something we can use, but barring that, # 2 seems the way to go. I'd imagine # 3 would just lead to all sorts of pain. | 1.0 | mesh config "http get" doesn't retry with all resolved addresses - Original [issue 1013](https://code.google.com/p/perfsonar-ps/issues/detail?id=1013) created by arlake228 on 2014-11-04T13:31:00.000Z:
If a DNS name resolves to v4 and v6 addresses but v6 is either disabled on the client or unavailable on the server, the mesh config https_get routine, using IO::Socket::INET6 under the hood, will try the v6 address and fail, even though the v4 address is accessible. There is a MultiHomed flag that you can add to the IO::Socket::* modules, but when we did that, it went into an unhelpful infinite loop with the module version available in RedHat 6. There are a few options to fix this:
1) Find a better Perl module, that's available in RedHat 6 or EPEL6, and rewrite the https_get routine using it
2) Have the https_get routine do the address resolving, and iterate through the addresses itself
3) Package a newer version of the IO::Socket::INET6 module
I'm partial to # 1 if there's something we can use, but barring that, # 2 seems the way to go. I'd imagine # 3 would just lead to all sorts of pain. | non_build | mesh config http get doesn t retry with all resolved addresses original created by on if a dns name resolves to and addresses but is either disabled on the client or unavailable on the server the mesh config https get routine using io socket under the hood will try the address and fail even though the address is accessible there is a multihomed flag that you can add to the io socket modules but when we did that it went into an unhelpful infinite loop with the module version available in redhat there are a few options to fix this find a better perl module that s available in redhat or and rewrite the https get routine using it have the https get routine do the address resolving and iterate through the addresses itself package a newer version of the io socket module i m partial to nbsp if there s something we can use but barring that nbsp seems the way to go i d imagine nbsp would just lead to all sorts of pain | 0 |
105,355 | 23,039,000,818 | IssuesEvent | 2022-07-22 23:18:08 | iree-org/iree | https://api.github.com/repos/iree-org/iree | closed | Fuse reduction followed by broadcast into the consumer elementwise op | codegen performance ⚡ | ### Request description
A common pattern of a reduction is that the result is used again with the source with a broadcast.
For most cases when the reduction is fused into the consumer, the very next user of the reduced result would see two edges are coming from the same source. This may be useful to fuse the element-wise op into the previous dispatch region when a dispatch region formation is being done.
<img width="687" alt="image" src="https://user-images.githubusercontent.com/4314836/173956075-aa297b74-718a-4b07-8722-938da4e4c9c0.png">
### What component(s) does this issue relate to?
Compiler
### Additional context
_No response_ | 1.0 | Fuse reduction followed by broadcast into the consumer elementwise op - ### Request description
A common pattern of a reduction is that the result is used again with the source with a broadcast.
For most cases when the reduction is fused into the consumer, the very next user of the reduced result would see two edges are coming from the same source. This may be useful to fuse the element-wise op into the previous dispatch region when a dispatch region formation is being done.
<img width="687" alt="image" src="https://user-images.githubusercontent.com/4314836/173956075-aa297b74-718a-4b07-8722-938da4e4c9c0.png">
### What component(s) does this issue relate to?
Compiler
### Additional context
_No response_ | non_build | fuse reduction followed by broadcast into the consumer elementwise op request description a common pattern of a reduction is that the result is used again with the source with a broadcast for most cases when the reduction is fused into the consumer the very next user of the reduced result would see two edges are coming from the same source this may be useful to fuse the element wise op into the previous dispatch region when a dispatch region formation is being done img width alt image src what component s does this issue relate to compiler additional context no response | 0 |
234,166 | 17,935,816,275 | IssuesEvent | 2021-09-10 15:10:56 | SAP/fundamental-styles | https://api.github.com/repos/SAP/fundamental-styles | opened | Create style guide for the repo | documentation | Create a style guide that includes naming conventions, best practices, standards, etc. that are used in the library and that will help with onboarding new developers or external contributors. This will also help the PR review process by automating some of these checks.
Some examples of good style guides:
- https://github.com/airbnb/javascript/tree/master/react
- https://angular.io/guide/styleguide
- https://vuejs.org/v2/style-guide/ | 1.0 | Create style guide for the repo - Create a style guide that includes naming conventions, best practices, standards, etc. that are used in the library and that will help with onboarding new developers or external contributors. This will also help the PR review process by automating some of these checks.
Some examples of good style guides:
- https://github.com/airbnb/javascript/tree/master/react
- https://angular.io/guide/styleguide
- https://vuejs.org/v2/style-guide/ | non_build | create style guide for the repo create a style guide that includes naming conventions best practices standards etc that are used in the library and that will help with onboarding new developers or external contributors this will also help the pr review process by automating some of these checks some examples of good style guides | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.