Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 5
112
| repo_url
stringlengths 34
141
| action
stringclasses 3
values | title
stringlengths 1
757
| labels
stringlengths 4
664
| body
stringlengths 3
261k
| index
stringclasses 10
values | text_combine
stringlengths 96
261k
| label
stringclasses 2
values | text
stringlengths 96
232k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
36,184
| 7,868,196,105
|
IssuesEvent
|
2018-06-23 18:22:39
|
libarchive/libarchive
|
https://api.github.com/repos/libarchive/libarchive
|
closed
|
test failures dependant with gcc -O0
|
OpSys-All Priority-Medium Type-Defect
|
Original [issue 108](https://code.google.com/p/libarchive/issues/detail?id=108) created by Google Code user `ferringb` on 2010-08-26T11:42:11.000Z:
```
<b>What steps will reproduce the problem?</b>
1. gcc 4.4.4; haven't yet tested with alternate versions.
2. compile with either explicitly forced CFLAGS to '' (not unset, forced to empty), or forced to -O0; end result is the same
3. make check. if it doesn't fail, while ! ./libarchive_test 118; do :; done; . It will bail sooner or later on test 118 (test_write_format_xar).
4. curse a fair amount while trying to run this down.
Attached is a set of 'valgrind --tool=memcheck --track-origins=yes -v libarchive_test 118' specifically varied between CFLAGS="-O0", and CFLAGS="-O1" (haven't tried -O3, but -O2 behaves fine same for -O1).
Spotted this at first in the libtransform work, finally nailed down the flags as the variable and that mainline/trunk has the same issue. The test failures are attached, but they're partially irrelevant- the failure directly maps back to the unitialization issue that appears in -O0 only.
Been trying to run this one down myself, but frankly I'm making zero headway in identifying how this varying- traced the implicated stack vars out and all are initialized as best I can tell. Possible it's just gcc sucking ass, but a second opinion on that from y'all is desired.
```
See attachment: [log-cflags-O0](http://libarchive.github.io/google-code/issue-108/comment-0/log-cflags-O0)
See attachment: [log-cflags-O1](http://libarchive.github.io/google-code/issue-108/comment-0/log-cflags-O1)
See attachment: [test_write_format_xar.log](http://libarchive.github.io/google-code/issue-108/comment-0/test_write_format_xar.log)
|
1.0
|
test failures dependant with gcc -O0 - Original [issue 108](https://code.google.com/p/libarchive/issues/detail?id=108) created by Google Code user `ferringb` on 2010-08-26T11:42:11.000Z:
```
<b>What steps will reproduce the problem?</b>
1. gcc 4.4.4; haven't yet tested with alternate versions.
2. compile with either explicitly forced CFLAGS to '' (not unset, forced to empty), or forced to -O0; end result is the same
3. make check. if it doesn't fail, while ! ./libarchive_test 118; do :; done; . It will bail sooner or later on test 118 (test_write_format_xar).
4. curse a fair amount while trying to run this down.
Attached is a set of 'valgrind --tool=memcheck --track-origins=yes -v libarchive_test 118' specifically varied between CFLAGS="-O0", and CFLAGS="-O1" (haven't tried -O3, but -O2 behaves fine same for -O1).
Spotted this at first in the libtransform work, finally nailed down the flags as the variable and that mainline/trunk has the same issue. The test failures are attached, but they're partially irrelevant- the failure directly maps back to the unitialization issue that appears in -O0 only.
Been trying to run this one down myself, but frankly I'm making zero headway in identifying how this varying- traced the implicated stack vars out and all are initialized as best I can tell. Possible it's just gcc sucking ass, but a second opinion on that from y'all is desired.
```
See attachment: [log-cflags-O0](http://libarchive.github.io/google-code/issue-108/comment-0/log-cflags-O0)
See attachment: [log-cflags-O1](http://libarchive.github.io/google-code/issue-108/comment-0/log-cflags-O1)
See attachment: [test_write_format_xar.log](http://libarchive.github.io/google-code/issue-108/comment-0/test_write_format_xar.log)
|
defect
|
test failures dependant with gcc original created by google code user ferringb on what steps will reproduce the problem gcc haven t yet tested with alternate versions compile with either explicitly forced cflags to not unset forced to empty or forced to end result is the same make check if it doesn t fail while libarchive test do done it will bail sooner or later on test test write format xar curse a fair amount while trying to run this down attached is a set of valgrind tool memcheck track origins yes v libarchive test specifically varied between cflags quot quot and cflags quot quot haven t tried but behaves fine same for spotted this at first in the libtransform work finally nailed down the flags as the variable and that mainline trunk has the same issue the test failures are attached but they re partially irrelevant the failure directly maps back to the unitialization issue that appears in only been trying to run this one down myself but frankly i m making zero headway in identifying how this varying traced the implicated stack vars out and all are initialized as best i can tell possible it s just gcc sucking ass but a second opinion on that from y all is desired see attachment see attachment see attachment
| 1
|
47,274
| 13,212,793,145
|
IssuesEvent
|
2020-08-16 09:14:43
|
TIBCOSoftware/spotfire-wrapper
|
https://api.github.com/repos/TIBCOSoftware/spotfire-wrapper
|
closed
|
CVE-2020-7598 (High) detected in minimist-0.0.10.tgz
|
security vulnerability
|
## CVE-2020-7598 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/spotfire-wrapper/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/spotfire-wrapper/node_modules/optimist/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.1.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","isTransitiveDependency":true,"dependencyTree":"karma:4.1.0;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.2"}],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-7598 (High) detected in minimist-0.0.10.tgz - ## CVE-2020-7598 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/spotfire-wrapper/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/spotfire-wrapper/node_modules/optimist/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.1.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","isTransitiveDependency":true,"dependencyTree":"karma:4.1.0;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.2"}],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve high detected in minimist tgz cve high severity vulnerability vulnerable library minimist tgz parse argument options library home page a href path to dependency file tmp ws scm spotfire wrapper package json path to vulnerable library tmp ws scm spotfire wrapper node modules optimist node modules minimist package json dependency hierarchy karma tgz root library optimist tgz x minimist tgz vulnerable library vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl
| 0
|
33,019
| 27,150,165,937
|
IssuesEvent
|
2023-02-17 00:07:35
|
cal-itp/eligibility-server
|
https://api.github.com/repos/cal-itp/eligibility-server
|
closed
|
resolve nightly downtime alerts
|
bug infrastructure
|
[Discussion thread.](https://cal-itp.slack.com/archives/C022HHSEE3F/p1669650929276489) In short, we have intentional nightly downtime, and this is leading to downtime alerts. We should either decide that we're ok with that downtime and adjust the monitoring to expect that (eliminating what is effectively a false positive), or make it so that downtime isn't necessary.
|
1.0
|
resolve nightly downtime alerts - [Discussion thread.](https://cal-itp.slack.com/archives/C022HHSEE3F/p1669650929276489) In short, we have intentional nightly downtime, and this is leading to downtime alerts. We should either decide that we're ok with that downtime and adjust the monitoring to expect that (eliminating what is effectively a false positive), or make it so that downtime isn't necessary.
|
non_defect
|
resolve nightly downtime alerts in short we have intentional nightly downtime and this is leading to downtime alerts we should either decide that we re ok with that downtime and adjust the monitoring to expect that eliminating what is effectively a false positive or make it so that downtime isn t necessary
| 0
|
12,516
| 14,813,997,057
|
IssuesEvent
|
2021-01-14 03:33:19
|
Lothrazar/Cyclic
|
https://api.github.com/repos/Lothrazar/Cyclic
|
closed
|
Robot Entity Crash
|
1.12 CausedByOthermod cannot replicate compatibility old version
|
Minecraft Version: 1.12.2
Forge Version: 14.23.5.2854
Mod Version: 1.20.3
Single Player or Server: Single Player
Describe problem (what you were doing; what happened; what should have happened):
While I'm loading the game Cyclic keeps giving crashing my game and saying that there is a kill.entity.robot error. I thought this was a problem with fast workbenches but I installed fast workbenches and it still crashes.
Log file link:
[crash-2020-10-21_09.58.38-client.txt](https://github.com/Lothrazar/Cyclic/files/5416417/crash-2020-10-21_09.58.38-client.txt)
Video/images/gifs (direct upload or link):
If your bug is related to anything causing LAG you need to measure the lag by taking a sample https://minecraft.curseforge.com/projects/sampler
Sorry if I didn't give enough info here is the modpack which causes cyclic to crash the game, take cyclic out and everything else works fine https://drive.google.com/drive/folders/1W5XrM5mH4oJCOpVI_G08FkdEm0I_G7QR?usp=sharing
|
True
|
Robot Entity Crash - Minecraft Version: 1.12.2
Forge Version: 14.23.5.2854
Mod Version: 1.20.3
Single Player or Server: Single Player
Describe problem (what you were doing; what happened; what should have happened):
While I'm loading the game Cyclic keeps giving crashing my game and saying that there is a kill.entity.robot error. I thought this was a problem with fast workbenches but I installed fast workbenches and it still crashes.
Log file link:
[crash-2020-10-21_09.58.38-client.txt](https://github.com/Lothrazar/Cyclic/files/5416417/crash-2020-10-21_09.58.38-client.txt)
Video/images/gifs (direct upload or link):
If your bug is related to anything causing LAG you need to measure the lag by taking a sample https://minecraft.curseforge.com/projects/sampler
Sorry if I didn't give enough info here is the modpack which causes cyclic to crash the game, take cyclic out and everything else works fine https://drive.google.com/drive/folders/1W5XrM5mH4oJCOpVI_G08FkdEm0I_G7QR?usp=sharing
|
non_defect
|
robot entity crash minecraft version forge version mod version single player or server single player describe problem what you were doing what happened what should have happened while i m loading the game cyclic keeps giving crashing my game and saying that there is a kill entity robot error i thought this was a problem with fast workbenches but i installed fast workbenches and it still crashes log file link video images gifs direct upload or link if your bug is related to anything causing lag you need to measure the lag by taking a sample sorry if i didn t give enough info here is the modpack which causes cyclic to crash the game take cyclic out and everything else works fine
| 0
|
20,123
| 2,622,188,637
|
IssuesEvent
|
2015-03-04 00:22:02
|
byzhang/cudpp
|
https://api.github.com/repos/byzhang/cudpp
|
closed
|
Switch from custom build steps to cuda.rules file
|
auto-migrated Priority-Medium Type-Enhancement
|
```
This will make building (and adding files) much easier on windows. Get the
latest cuda.rules file from the CUDA SDK.
```
Original issue reported on code.google.com by `harr...@gmail.com` on 16 Jun 2009 at 7:06
|
1.0
|
Switch from custom build steps to cuda.rules file - ```
This will make building (and adding files) much easier on windows. Get the
latest cuda.rules file from the CUDA SDK.
```
Original issue reported on code.google.com by `harr...@gmail.com` on 16 Jun 2009 at 7:06
|
non_defect
|
switch from custom build steps to cuda rules file this will make building and adding files much easier on windows get the latest cuda rules file from the cuda sdk original issue reported on code google com by harr gmail com on jun at
| 0
|
301,714
| 9,223,392,126
|
IssuesEvent
|
2019-03-12 03:15:08
|
smithjd/sql-pet
|
https://api.github.com/repos/smithjd/sql-pet
|
closed
|
directions on how to fix this docker issue
|
Priority: High bug
|
I ran the command twice, directions on how to fix this would be nice
system2("docker", docker_cmd, stdout = TRUE, stderr = TRUE)
running command ''docker' run -d --name cattle --publish 5432:5432 postgres:10 2>&1' had status 125[1] "docker: Error response from daemon: Conflict. The container name \"/cattle\" is already in use by container \"88322d93920807238616b35e77b9bbcc3020459b6d45559671f45a5bb5f689ab\". You have to remove (or rename) that container to be able to reuse that name."
[2] "See 'docker run --help'."
attr(,"status")
[1] 125
|
1.0
|
directions on how to fix this docker issue - I ran the command twice, directions on how to fix this would be nice
system2("docker", docker_cmd, stdout = TRUE, stderr = TRUE)
running command ''docker' run -d --name cattle --publish 5432:5432 postgres:10 2>&1' had status 125[1] "docker: Error response from daemon: Conflict. The container name \"/cattle\" is already in use by container \"88322d93920807238616b35e77b9bbcc3020459b6d45559671f45a5bb5f689ab\". You have to remove (or rename) that container to be able to reuse that name."
[2] "See 'docker run --help'."
attr(,"status")
[1] 125
|
non_defect
|
directions on how to fix this docker issue i ran the command twice directions on how to fix this would be nice docker docker cmd stdout true stderr true running command docker run d name cattle publish postgres had status docker error response from daemon conflict the container name cattle is already in use by container you have to remove or rename that container to be able to reuse that name see docker run help attr status
| 0
|
6,697
| 2,610,271,422
|
IssuesEvent
|
2015-02-26 19:26:51
|
chrsmith/scribefire-chrome
|
https://api.github.com/repos/chrsmith/scribefire-chrome
|
closed
|
Entry status
|
auto-migrated Priority-Medium Type-Defect
|
```
What's the problem?
Up until recently ScribeFire used to show in the Posts drop-down entry list
whether posts where [scheduled] or [draft] as well as nothing next to entries
actually posted.
That appears to have changed and there's now just a list of entries with
nothing indicating their actual state.
What browser are you using?
Firefox - 3.6.12
What version of ScribeFire are you running?
1.4.30
```
-----
Original issue reported on code.google.com by `win...@gmail.com` on 29 Nov 2010 at 6:30
|
1.0
|
Entry status - ```
What's the problem?
Up until recently ScribeFire used to show in the Posts drop-down entry list
whether posts where [scheduled] or [draft] as well as nothing next to entries
actually posted.
That appears to have changed and there's now just a list of entries with
nothing indicating their actual state.
What browser are you using?
Firefox - 3.6.12
What version of ScribeFire are you running?
1.4.30
```
-----
Original issue reported on code.google.com by `win...@gmail.com` on 29 Nov 2010 at 6:30
|
defect
|
entry status what s the problem up until recently scribefire used to show in the posts drop down entry list whether posts where or as well as nothing next to entries actually posted that appears to have changed and there s now just a list of entries with nothing indicating their actual state what browser are you using firefox what version of scribefire are you running original issue reported on code google com by win gmail com on nov at
| 1
|
75,767
| 26,039,131,747
|
IssuesEvent
|
2022-12-22 08:51:02
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
The website does not adapt to mobile form-factors.
|
T-Defect
|
### Steps to reproduce
Login.
### Outcome
#### What did you expect?
The website should adapt to the form-factor of my display.
#### What happened instead?
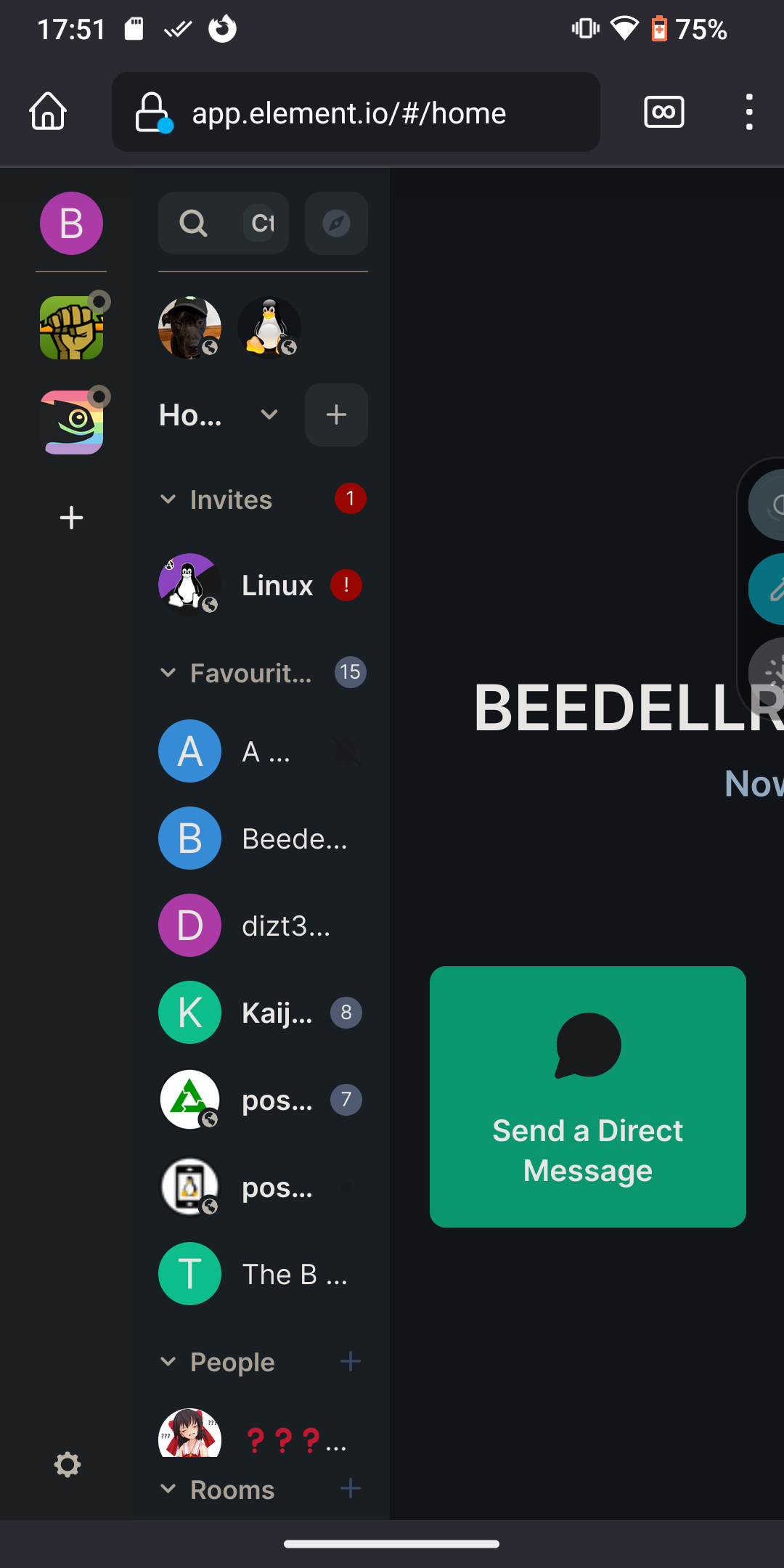
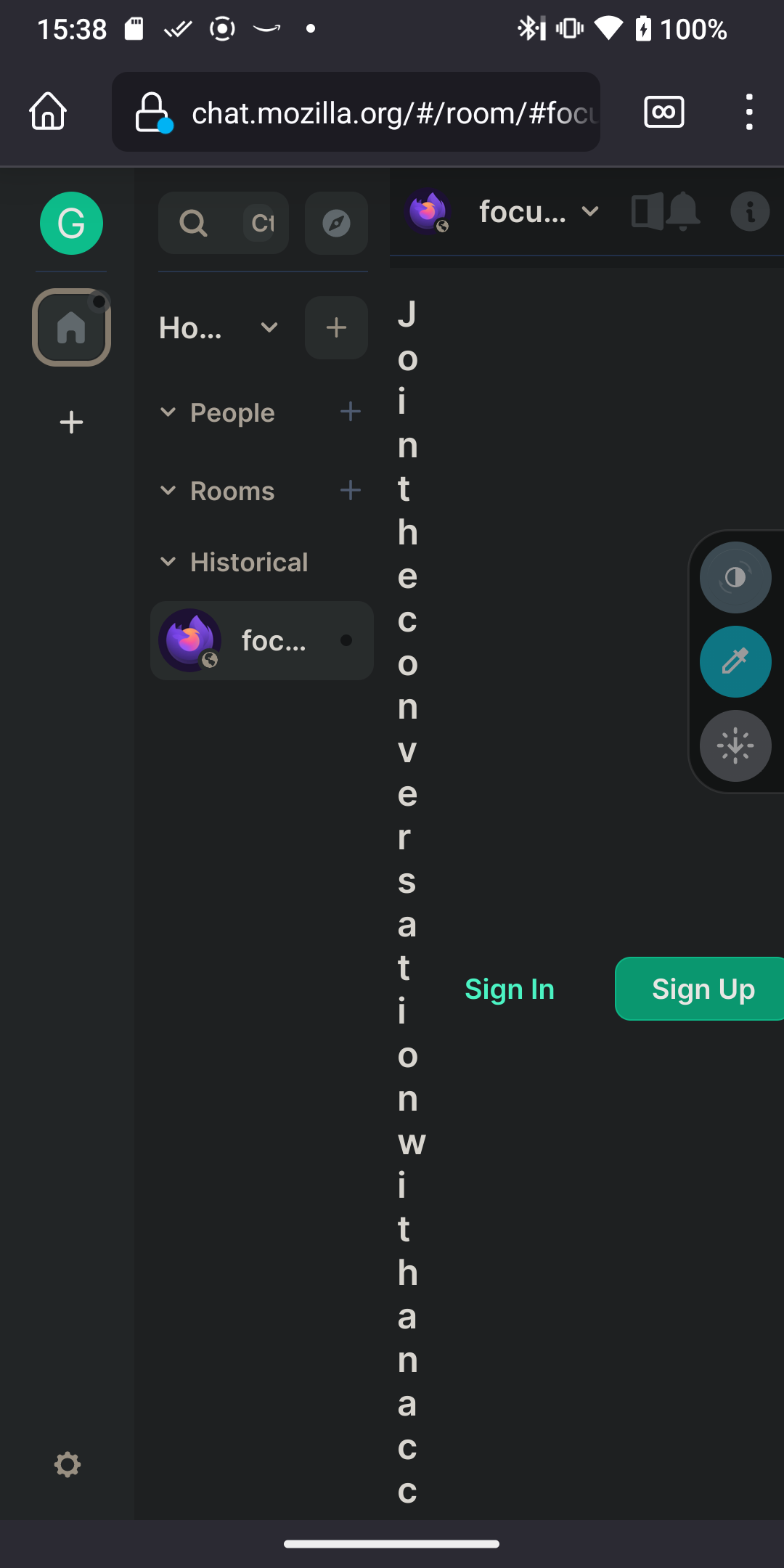
### Operating system
Android 13; CalyxOS 4.4.0; build TQ1A.221205.011.22404000
### Browser information
https://play.google.com/store/apps/details?id=org.mozilla.fenix 110.0a1 (Build #2015922795), d07de1e02+ AC: 110.0.20221221024602, 35a3cae7a7 GV: 110.0a1-20221220093956 AS: 96.1.3 2022-12-21T05:08:50.670314
### URL for webapp
_No response_
### Application version
_No response_
### Homeserver
matrix.org
### Will you send logs?
Yes
|
1.0
|
The website does not adapt to mobile form-factors. - ### Steps to reproduce
Login.
### Outcome
#### What did you expect?
The website should adapt to the form-factor of my display.
#### What happened instead?
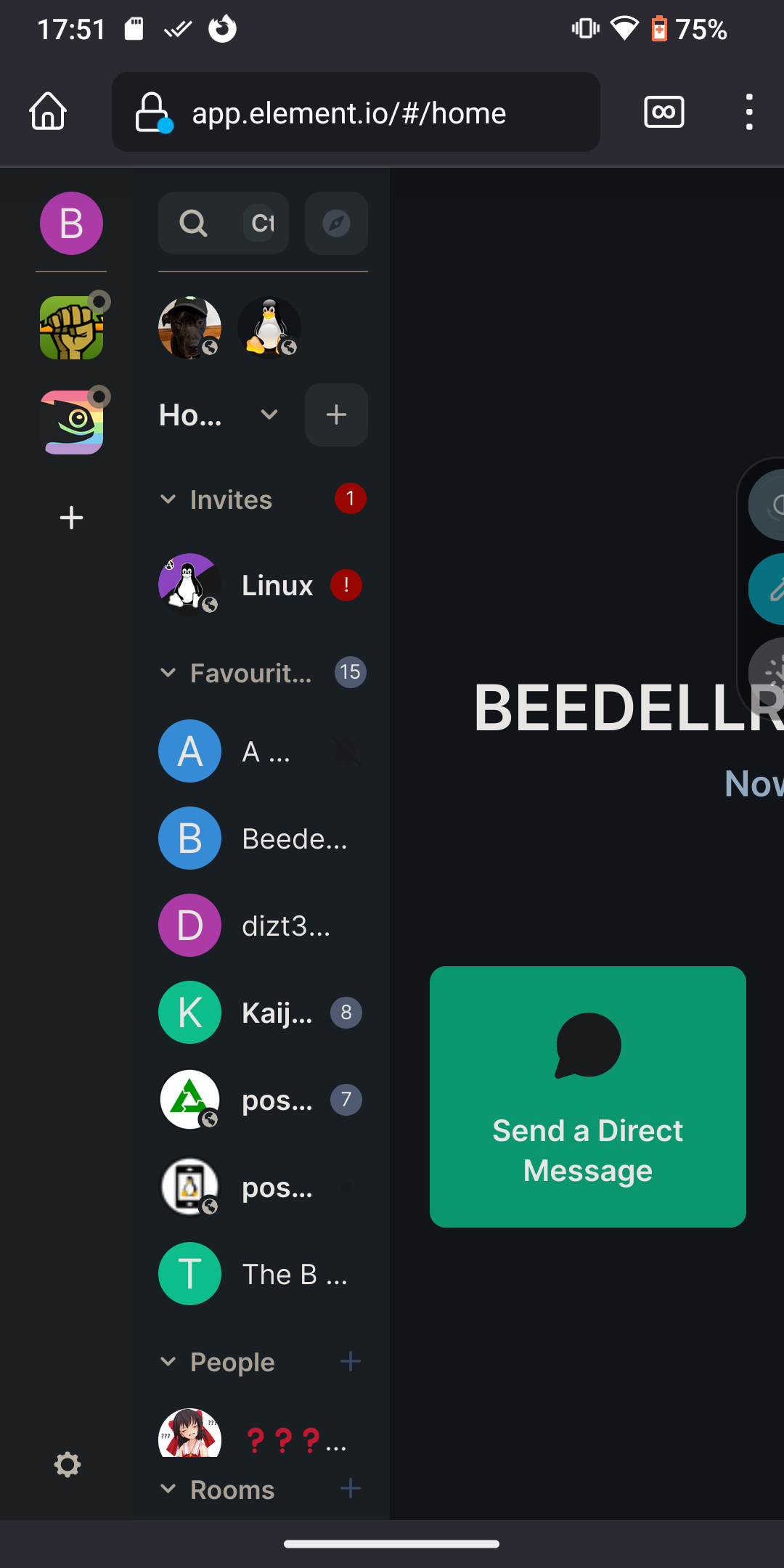
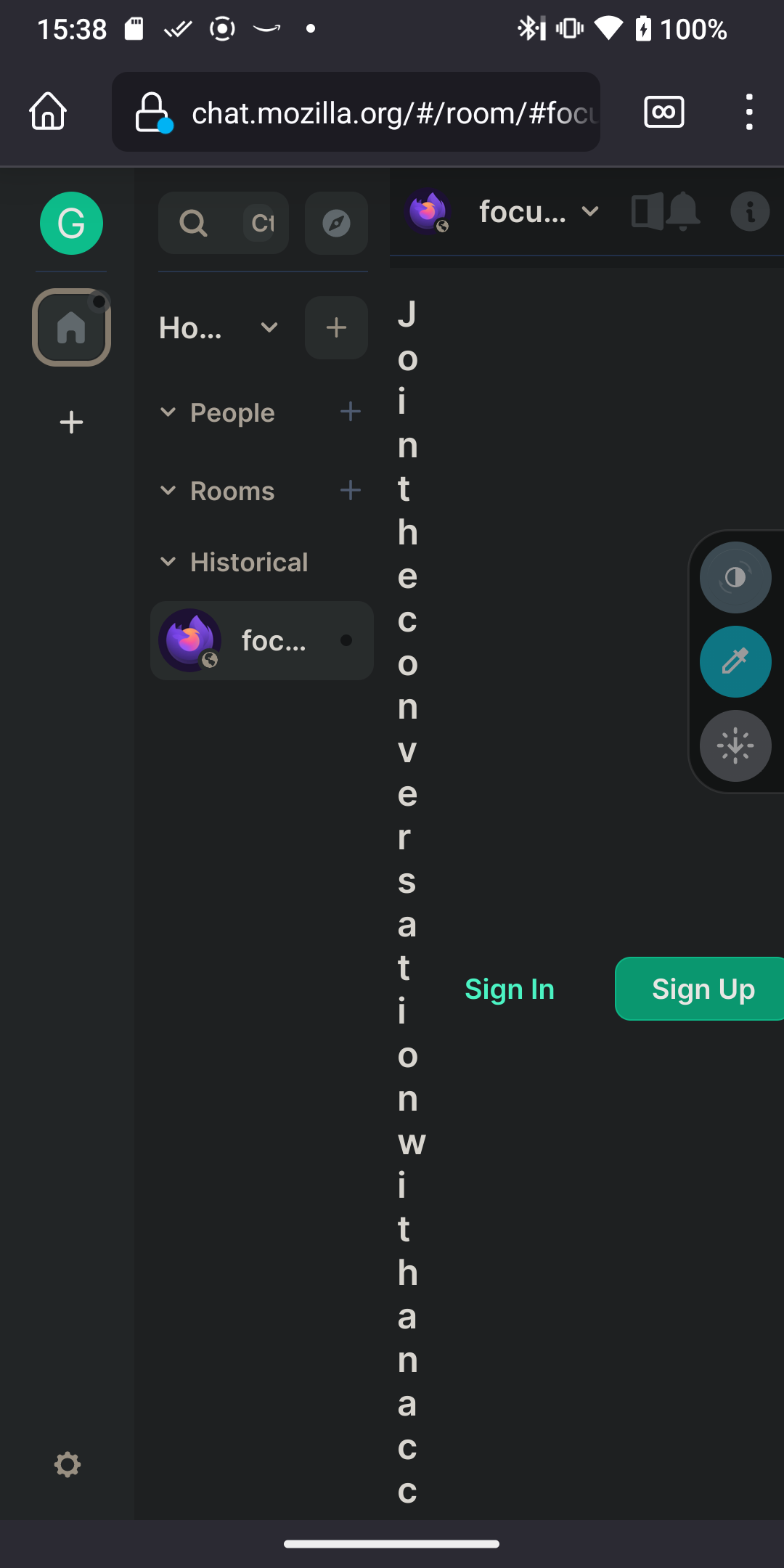
### Operating system
Android 13; CalyxOS 4.4.0; build TQ1A.221205.011.22404000
### Browser information
https://play.google.com/store/apps/details?id=org.mozilla.fenix 110.0a1 (Build #2015922795), d07de1e02+ AC: 110.0.20221221024602, 35a3cae7a7 GV: 110.0a1-20221220093956 AS: 96.1.3 2022-12-21T05:08:50.670314
### URL for webapp
_No response_
### Application version
_No response_
### Homeserver
matrix.org
### Will you send logs?
Yes
|
defect
|
the website does not adapt to mobile form factors steps to reproduce login outcome what did you expect the website should adapt to the form factor of my display what happened instead operating system android calyxos build browser information build ac gv as url for webapp no response application version no response homeserver matrix org will you send logs yes
| 1
|
22,039
| 30,555,679,922
|
IssuesEvent
|
2023-07-20 11:32:09
|
firebase/firebase-cpp-sdk
|
https://api.github.com/repos/firebase/firebase-cpp-sdk
|
reopened
|
[C++] Nightly Integration Testing Report for Firestore
|
type: process nightly-testing
|
<hidden value="integration-test-status-comment"></hidden>
### ✅ [build against repo] Integration test succeeded!
Requested by @sunmou99 on commit 38a46399f0972e11900bce80f9dfd1b4b1dd27ee
Last updated: Wed Jul 19 05:02 PDT 2023
**[View integration test log & download artifacts](https://github.com/firebase/firebase-cpp-sdk/actions/runs/5597731343)**
<hidden value="integration-test-status-comment"></hidden>
***
### ✅ [build against SDK] Integration test succeeded!
Requested by @firebase-workflow-trigger[bot] on commit 38a46399f0972e11900bce80f9dfd1b4b1dd27ee
Last updated: Wed Jul 19 07:54 PDT 2023
**[View integration test log & download artifacts](https://github.com/firebase/firebase-cpp-sdk/actions/runs/5599509572)**
<hidden value="integration-test-status-comment"></hidden>
***
### ✅ [build against tip] Integration test succeeded!
Requested by @sunmou99 on commit 38a46399f0972e11900bce80f9dfd1b4b1dd27ee
Last updated: Wed Jul 19 04:40 PDT 2023
**[View integration test log & download artifacts](https://github.com/firebase/firebase-cpp-sdk/actions/runs/5598272643)**
|
1.0
|
[C++] Nightly Integration Testing Report for Firestore -
<hidden value="integration-test-status-comment"></hidden>
### ✅ [build against repo] Integration test succeeded!
Requested by @sunmou99 on commit 38a46399f0972e11900bce80f9dfd1b4b1dd27ee
Last updated: Wed Jul 19 05:02 PDT 2023
**[View integration test log & download artifacts](https://github.com/firebase/firebase-cpp-sdk/actions/runs/5597731343)**
<hidden value="integration-test-status-comment"></hidden>
***
### ✅ [build against SDK] Integration test succeeded!
Requested by @firebase-workflow-trigger[bot] on commit 38a46399f0972e11900bce80f9dfd1b4b1dd27ee
Last updated: Wed Jul 19 07:54 PDT 2023
**[View integration test log & download artifacts](https://github.com/firebase/firebase-cpp-sdk/actions/runs/5599509572)**
<hidden value="integration-test-status-comment"></hidden>
***
### ✅ [build against tip] Integration test succeeded!
Requested by @sunmou99 on commit 38a46399f0972e11900bce80f9dfd1b4b1dd27ee
Last updated: Wed Jul 19 04:40 PDT 2023
**[View integration test log & download artifacts](https://github.com/firebase/firebase-cpp-sdk/actions/runs/5598272643)**
|
non_defect
|
nightly integration testing report for firestore ✅ nbsp integration test succeeded requested by on commit last updated wed jul pdt ✅ nbsp integration test succeeded requested by firebase workflow trigger on commit last updated wed jul pdt ✅ nbsp integration test succeeded requested by on commit last updated wed jul pdt
| 0
|
49,402
| 13,186,676,688
|
IssuesEvent
|
2020-08-13 00:57:34
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
g4-tankresponse - sparse docs (Trac #1309)
|
Incomplete Migration Migrated from Trac combo simulation defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1309">https://code.icecube.wisc.edu/ticket/1309</a>, reported by nega and owned by jgonzalez</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:10",
"description": "`index.rst` feels incomplete.\n\ninline doxygen is sparse",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1550067190995086",
"component": "combo simulation",
"summary": "g4-tankresponse - sparse docs",
"priority": "normal",
"keywords": "",
"time": "2015-08-28T23:38:09",
"milestone": "",
"owner": "jgonzalez",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
g4-tankresponse - sparse docs (Trac #1309) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1309">https://code.icecube.wisc.edu/ticket/1309</a>, reported by nega and owned by jgonzalez</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:10",
"description": "`index.rst` feels incomplete.\n\ninline doxygen is sparse",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1550067190995086",
"component": "combo simulation",
"summary": "g4-tankresponse - sparse docs",
"priority": "normal",
"keywords": "",
"time": "2015-08-28T23:38:09",
"milestone": "",
"owner": "jgonzalez",
"type": "defect"
}
```
</p>
</details>
|
defect
|
tankresponse sparse docs trac migrated from json status closed changetime description index rst feels incomplete n ninline doxygen is sparse reporter nega cc resolution fixed ts component combo simulation summary tankresponse sparse docs priority normal keywords time milestone owner jgonzalez type defect
| 1
|
61,154
| 17,023,619,817
|
IssuesEvent
|
2021-07-03 02:57:40
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
Problems with parallel ways and zoom levels
|
Component: mapnik Priority: major Resolution: wontfix Type: defect
|
**[Submitted to the original trac issue database at 8.31am, Wednesday, 28th July 2010]**
These cycleways display perfectly fine whilst zoomed in:
http://osm.org/go/eusTTF0Ow-
but when zoomed out they become less clear and interfere with the border of the adjacent road
http://osm.org/go/eusTR_bD--
Could the rendering be changed to squeeze the cycleway out a few pixels to one side at this point?
|
1.0
|
Problems with parallel ways and zoom levels - **[Submitted to the original trac issue database at 8.31am, Wednesday, 28th July 2010]**
These cycleways display perfectly fine whilst zoomed in:
http://osm.org/go/eusTTF0Ow-
but when zoomed out they become less clear and interfere with the border of the adjacent road
http://osm.org/go/eusTR_bD--
Could the rendering be changed to squeeze the cycleway out a few pixels to one side at this point?
|
defect
|
problems with parallel ways and zoom levels these cycleways display perfectly fine whilst zoomed in but when zoomed out they become less clear and interfere with the border of the adjacent road could the rendering be changed to squeeze the cycleway out a few pixels to one side at this point
| 1
|
49,931
| 13,187,296,125
|
IssuesEvent
|
2020-08-13 02:57:51
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
[filterscripts] MESE Filter Throws Key Error (Trac #2331)
|
Incomplete Migration Migrated from Trac defect jeb + pnf
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/2331">https://code.icecube.wisc.edu/ticket/2331</a>, reported by olivas and owned by blaufuss</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-06-28T22:27:43",
"description": "This is with the latest trunk of combo r174135.\n\nERROR (I3Module): MeseFilter_precut: Exception thrown (I3Module.cxx:123 in void I3Module::Do(void (I3Module::*)()))\nTraceback (most recent call last):\n File \"/home/olivas/icecube/combo/trunk/build/filterscripts/resources/scripts/SimulationFiltering.py\", line 387, in <module>\n main(opts)\n File \"/home/olivas/icecube/combo/trunk/build/filterscripts/resources/scripts/SimulationFiltering.py\", line 344, in main\n tray.Execute()\n File \"/home/olivas/icecube/combo/trunk/build/lib/I3Tray.py\", line 256, in Execute\n super(I3Tray, self).Execute()\n File \"/home/olivas/icecube/combo/trunk/build/lib/icecube/filterscripts/mesefilter.py\", line 127, in precut\n layer_veto_charge = frame['L4VetoLayer0'].value + frame['L4VetoLayer1'].value\nKeyError: 'L4VetoLayer0'\n",
"reporter": "olivas",
"cc": "",
"resolution": "fixed",
"_ts": "1561760863704892",
"component": "jeb + pnf",
"summary": "[filterscripts] MESE Filter Throws Key Error",
"priority": "blocker",
"keywords": "",
"time": "2019-06-22T02:23:41",
"milestone": "Autumnal Equinox 2019",
"owner": "blaufuss",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
[filterscripts] MESE Filter Throws Key Error (Trac #2331) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/2331">https://code.icecube.wisc.edu/ticket/2331</a>, reported by olivas and owned by blaufuss</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-06-28T22:27:43",
"description": "This is with the latest trunk of combo r174135.\n\nERROR (I3Module): MeseFilter_precut: Exception thrown (I3Module.cxx:123 in void I3Module::Do(void (I3Module::*)()))\nTraceback (most recent call last):\n File \"/home/olivas/icecube/combo/trunk/build/filterscripts/resources/scripts/SimulationFiltering.py\", line 387, in <module>\n main(opts)\n File \"/home/olivas/icecube/combo/trunk/build/filterscripts/resources/scripts/SimulationFiltering.py\", line 344, in main\n tray.Execute()\n File \"/home/olivas/icecube/combo/trunk/build/lib/I3Tray.py\", line 256, in Execute\n super(I3Tray, self).Execute()\n File \"/home/olivas/icecube/combo/trunk/build/lib/icecube/filterscripts/mesefilter.py\", line 127, in precut\n layer_veto_charge = frame['L4VetoLayer0'].value + frame['L4VetoLayer1'].value\nKeyError: 'L4VetoLayer0'\n",
"reporter": "olivas",
"cc": "",
"resolution": "fixed",
"_ts": "1561760863704892",
"component": "jeb + pnf",
"summary": "[filterscripts] MESE Filter Throws Key Error",
"priority": "blocker",
"keywords": "",
"time": "2019-06-22T02:23:41",
"milestone": "Autumnal Equinox 2019",
"owner": "blaufuss",
"type": "defect"
}
```
</p>
</details>
|
defect
|
mese filter throws key error trac migrated from json status closed changetime description this is with the latest trunk of combo n nerror mesefilter precut exception thrown cxx in void do void ntraceback most recent call last n file home olivas icecube combo trunk build filterscripts resources scripts simulationfiltering py line in n main opts n file home olivas icecube combo trunk build filterscripts resources scripts simulationfiltering py line in main n tray execute n file home olivas icecube combo trunk build lib py line in execute n super self execute n file home olivas icecube combo trunk build lib icecube filterscripts mesefilter py line in precut n layer veto charge frame value frame value nkeyerror n reporter olivas cc resolution fixed ts component jeb pnf summary mese filter throws key error priority blocker keywords time milestone autumnal equinox owner blaufuss type defect
| 1
|
1,237
| 5,268,229,308
|
IssuesEvent
|
2017-02-05 08:46:44
|
viktorradnai/flightgear-ask21
|
https://api.github.com/repos/viktorradnai/flightgear-ask21
|
opened
|
Rework Aircraft Rating?
|
enhancement maintainability question
|
In the -set file as well as on the wiki, we still have the following rating
**_FDM_**: 2: FDM tuned for cruise configuration.
**_Systems_**: 2: Working electrical system, fuel feed cockpit controls, stable autopilot
**_Cockpit_**: 2: 2D panel in 3D cockpit, or incomplete 3D panel
**_Model_**: 3: Accurate 3D model with animated control surfaces, gear detailing (retraction, rotation), prop
In my opinion this is not quite correct, e.g. **Cockpit** should IMO be improved to a 4 as we have
" 3D panel and accurately modelled 3D cockpit, plain texturing. Hotspots for majority of controls"
**Systems** should be corrected to 4 (note here that the ASK21 has very few systems to model). I have added a limit system which I will push after tooltips are solved. Later we can also add a bit more code to this so that e.g. the spoilers stuck/break if operated above 250km/h or that the wings brake under too heave load. Also, what I've thought of is to add fake spoilers to the wing connected to a rain property decreasing lift and increasing drag when flying in rain :D
**Model** could be increased to 4: Accurate 3D model with animated control surfaces, gear, prop, livery support (if applicable). or maybe even 5 as we already have shader effects etc. but I think for a 5 we should improve the exterior model a bit further.
About the **FDM** I'm not sure how realistic it is.
|
True
|
Rework Aircraft Rating? - In the -set file as well as on the wiki, we still have the following rating
**_FDM_**: 2: FDM tuned for cruise configuration.
**_Systems_**: 2: Working electrical system, fuel feed cockpit controls, stable autopilot
**_Cockpit_**: 2: 2D panel in 3D cockpit, or incomplete 3D panel
**_Model_**: 3: Accurate 3D model with animated control surfaces, gear detailing (retraction, rotation), prop
In my opinion this is not quite correct, e.g. **Cockpit** should IMO be improved to a 4 as we have
" 3D panel and accurately modelled 3D cockpit, plain texturing. Hotspots for majority of controls"
**Systems** should be corrected to 4 (note here that the ASK21 has very few systems to model). I have added a limit system which I will push after tooltips are solved. Later we can also add a bit more code to this so that e.g. the spoilers stuck/break if operated above 250km/h or that the wings brake under too heave load. Also, what I've thought of is to add fake spoilers to the wing connected to a rain property decreasing lift and increasing drag when flying in rain :D
**Model** could be increased to 4: Accurate 3D model with animated control surfaces, gear, prop, livery support (if applicable). or maybe even 5 as we already have shader effects etc. but I think for a 5 we should improve the exterior model a bit further.
About the **FDM** I'm not sure how realistic it is.
|
non_defect
|
rework aircraft rating in the set file as well as on the wiki we still have the following rating fdm fdm tuned for cruise configuration systems working electrical system fuel feed cockpit controls stable autopilot cockpit panel in cockpit or incomplete panel model accurate model with animated control surfaces gear detailing retraction rotation prop in my opinion this is not quite correct e g cockpit should imo be improved to a as we have panel and accurately modelled cockpit plain texturing hotspots for majority of controls systems should be corrected to note here that the has very few systems to model i have added a limit system which i will push after tooltips are solved later we can also add a bit more code to this so that e g the spoilers stuck break if operated above h or that the wings brake under too heave load also what i ve thought of is to add fake spoilers to the wing connected to a rain property decreasing lift and increasing drag when flying in rain d model could be increased to accurate model with animated control surfaces gear prop livery support if applicable or maybe even as we already have shader effects etc but i think for a we should improve the exterior model a bit further about the fdm i m not sure how realistic it is
| 0
|
38,355
| 12,536,727,691
|
IssuesEvent
|
2020-06-05 01:03:16
|
tamirverthim/lets-be-bad-guys
|
https://api.github.com/repos/tamirverthim/lets-be-bad-guys
|
opened
|
CVE-2020-13596 (Medium) detected in Django-1.9.6-py2.py3-none-any.whl
|
security vulnerability
|
## CVE-2020-13596 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.9.6-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/cb/97/081df31f2a3850988b92ad4464e95f9e4b257aa5a34e120bca89c260de96/Django-1.9.6-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/cb/97/081df31f2a3850988b92ad4464e95f9e4b257aa5a34e120bca89c260de96/Django-1.9.6-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/lets-be-bad-guys/requirements.txt</p>
<p>Path to vulnerable library: /lets-be-bad-guys/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Django-1.9.6-py2.py3-none-any.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in Django 2.2 before 2.2.13 and 3.0 before 3.0.7. Query parameters generated by the Django admin ForeignKeyRawIdWidget were not properly URL encoded, leading to a possibility of an XSS attack.
<p>Publish Date: 2020-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13596>CVE-2020-13596</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.djangoproject.com/weblog/2020/jun/03/security-releases/">https://www.djangoproject.com/weblog/2020/jun/03/security-releases/</a></p>
<p>Release Date: 2020-06-03</p>
<p>Fix Resolution: 3.0.7,2.2.13</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"Django","packageVersion":"1.9.6","isTransitiveDependency":false,"dependencyTree":"Django:1.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.0.7,2.2.13"}],"vulnerabilityIdentifier":"CVE-2020-13596","vulnerabilityDetails":"An issue was discovered in Django 2.2 before 2.2.13 and 3.0 before 3.0.7. Query parameters generated by the Django admin ForeignKeyRawIdWidget were not properly URL encoded, leading to a possibility of an XSS attack.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13596","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-13596 (Medium) detected in Django-1.9.6-py2.py3-none-any.whl - ## CVE-2020-13596 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.9.6-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/cb/97/081df31f2a3850988b92ad4464e95f9e4b257aa5a34e120bca89c260de96/Django-1.9.6-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/cb/97/081df31f2a3850988b92ad4464e95f9e4b257aa5a34e120bca89c260de96/Django-1.9.6-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/lets-be-bad-guys/requirements.txt</p>
<p>Path to vulnerable library: /lets-be-bad-guys/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Django-1.9.6-py2.py3-none-any.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in Django 2.2 before 2.2.13 and 3.0 before 3.0.7. Query parameters generated by the Django admin ForeignKeyRawIdWidget were not properly URL encoded, leading to a possibility of an XSS attack.
<p>Publish Date: 2020-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13596>CVE-2020-13596</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.djangoproject.com/weblog/2020/jun/03/security-releases/">https://www.djangoproject.com/weblog/2020/jun/03/security-releases/</a></p>
<p>Release Date: 2020-06-03</p>
<p>Fix Resolution: 3.0.7,2.2.13</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"Django","packageVersion":"1.9.6","isTransitiveDependency":false,"dependencyTree":"Django:1.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.0.7,2.2.13"}],"vulnerabilityIdentifier":"CVE-2020-13596","vulnerabilityDetails":"An issue was discovered in Django 2.2 before 2.2.13 and 3.0 before 3.0.7. Query parameters generated by the Django admin ForeignKeyRawIdWidget were not properly URL encoded, leading to a possibility of an XSS attack.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13596","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve medium detected in django none any whl cve medium severity vulnerability vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file tmp ws scm lets be bad guys requirements txt path to vulnerable library lets be bad guys requirements txt dependency hierarchy x django none any whl vulnerable library vulnerability details an issue was discovered in django before and before query parameters generated by the django admin foreignkeyrawidwidget were not properly url encoded leading to a possibility of an xss attack publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails an issue was discovered in django before and before query parameters generated by the django admin foreignkeyrawidwidget were not properly url encoded leading to a possibility of an xss attack vulnerabilityurl
| 0
|
59,518
| 17,023,150,025
|
IssuesEvent
|
2021-07-03 00:35:57
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
API 0.4 does not modify timestamps on new objects
|
Component: rails_port Priority: major Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 4.40pm, Thursday, 22nd March 2007]**
When a node,seg,way is updated, the timestamp is not updated. The timestamp in the current_ table should be the current timestamp
|
1.0
|
API 0.4 does not modify timestamps on new objects - **[Submitted to the original trac issue database at 4.40pm, Thursday, 22nd March 2007]**
When a node,seg,way is updated, the timestamp is not updated. The timestamp in the current_ table should be the current timestamp
|
defect
|
api does not modify timestamps on new objects when a node seg way is updated the timestamp is not updated the timestamp in the current table should be the current timestamp
| 1
|
67,562
| 20,994,789,931
|
IssuesEvent
|
2022-03-29 12:38:50
|
vector-im/element-ios
|
https://api.github.com/repos/vector-im/element-ios
|
opened
|
Local contacts are not recognised by their MXID
|
T-Defect A-Spaces S-Minor O-Uncommon Z-Spaces-Testing A-Invitations
|
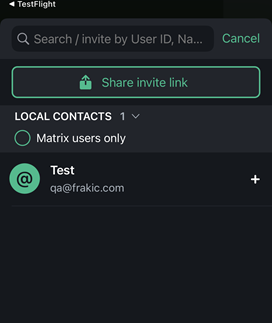
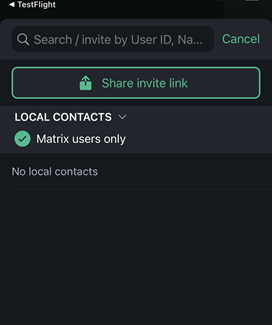
### Steps to reproduce
1. Where are you starting? What can you see?
-I have a contact saved in my phone with their MXID like so:
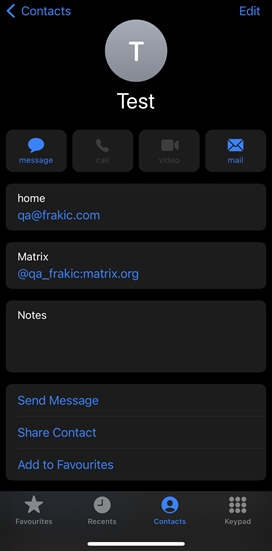
2. What do you click?
-I go to an existing space and tap Invite people:
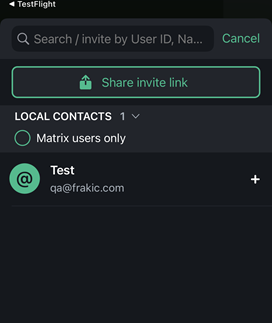
3. More steps…
-I turn on the "Matrix users only" filter
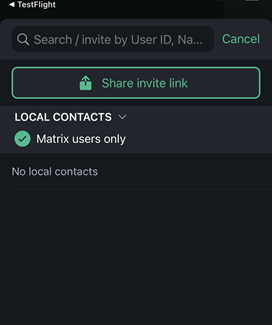
### Outcome
#### What did you expect?
I expected that contact to be recognised by their MXID.
#### What happened instead?
The contact is only recognised by their email address.
### Your phone model
iPhone 11 Pro
### Operating system version
iOS 15.4
### Application version
1.8.9 (20220328134736)
### Homeserver
matrix.org
### Will you send logs?
No
|
1.0
|
Local contacts are not recognised by their MXID - ### Steps to reproduce
1. Where are you starting? What can you see?
-I have a contact saved in my phone with their MXID like so:
2. What do you click?
-I go to an existing space and tap Invite people:
3. More steps…
-I turn on the "Matrix users only" filter
### Outcome
#### What did you expect?
I expected that contact to be recognised by their MXID.
#### What happened instead?
The contact is only recognised by their email address.
### Your phone model
iPhone 11 Pro
### Operating system version
iOS 15.4
### Application version
1.8.9 (20220328134736)
### Homeserver
matrix.org
### Will you send logs?
No
|
defect
|
local contacts are not recognised by their mxid steps to reproduce where are you starting what can you see i have a contact saved in my phone with their mxid like so what do you click i go to an existing space and tap invite people more steps… i turn on the matrix users only filter outcome what did you expect i expected that contact to be recognised by their mxid what happened instead the contact is only recognised by their email address your phone model iphone pro operating system version ios application version homeserver matrix org will you send logs no
| 1
|
15,121
| 8,773,942,449
|
IssuesEvent
|
2018-12-18 18:18:45
|
bitshares/bitshares-core
|
https://api.github.com/repos/bitshares/bitshares-core
|
opened
|
get_key_references performance issue?
|
6 Performance
|
**Bug Description**
If a key is in authorities of many accounts, `get_key_references` API will return all of them and will subscribe to all of them, this could lead to potential performance issues. This API is used by GUI to get related accounts when importing a key.
**Impacts**
Describe which portion(s) of BitShares Core may be impacted by this bug. Please tick at least one box.
- [x] API (the application programming interface)
- [ ] Build (the build process or something prior to compiled code)
- [ ] CLI (the command line wallet)
- [ ] Deployment (the deployment process after building such as Docker, Travis, etc.)
- [ ] DEX (the Decentralized EXchange, market engine, etc.)
- [ ] P2P (the peer-to-peer network for transaction/block propagation)
- [x] Performance (system or user efficiency, etc.)
- [ ] Protocol (the blockchain logic, consensus, validation, etc.)
- [ ] Security (the security of system or user data, etc.)
- [ ] UX (the User Experience)
- [ ] Other (please add below)
## CORE TEAM TASK LIST
- [ ] Evaluate / Prioritize Bug Report
- [ ] Refine User Stories / Requirements
- [ ] Define Test Cases
- [ ] Design / Develop Solution
- [ ] Perform QA/Testing
- [ ] Update Documentation
|
True
|
get_key_references performance issue? - **Bug Description**
If a key is in authorities of many accounts, `get_key_references` API will return all of them and will subscribe to all of them, this could lead to potential performance issues. This API is used by GUI to get related accounts when importing a key.
**Impacts**
Describe which portion(s) of BitShares Core may be impacted by this bug. Please tick at least one box.
- [x] API (the application programming interface)
- [ ] Build (the build process or something prior to compiled code)
- [ ] CLI (the command line wallet)
- [ ] Deployment (the deployment process after building such as Docker, Travis, etc.)
- [ ] DEX (the Decentralized EXchange, market engine, etc.)
- [ ] P2P (the peer-to-peer network for transaction/block propagation)
- [x] Performance (system or user efficiency, etc.)
- [ ] Protocol (the blockchain logic, consensus, validation, etc.)
- [ ] Security (the security of system or user data, etc.)
- [ ] UX (the User Experience)
- [ ] Other (please add below)
## CORE TEAM TASK LIST
- [ ] Evaluate / Prioritize Bug Report
- [ ] Refine User Stories / Requirements
- [ ] Define Test Cases
- [ ] Design / Develop Solution
- [ ] Perform QA/Testing
- [ ] Update Documentation
|
non_defect
|
get key references performance issue bug description if a key is in authorities of many accounts get key references api will return all of them and will subscribe to all of them this could lead to potential performance issues this api is used by gui to get related accounts when importing a key impacts describe which portion s of bitshares core may be impacted by this bug please tick at least one box api the application programming interface build the build process or something prior to compiled code cli the command line wallet deployment the deployment process after building such as docker travis etc dex the decentralized exchange market engine etc the peer to peer network for transaction block propagation performance system or user efficiency etc protocol the blockchain logic consensus validation etc security the security of system or user data etc ux the user experience other please add below core team task list evaluate prioritize bug report refine user stories requirements define test cases design develop solution perform qa testing update documentation
| 0
|
198
| 2,519,740,043
|
IssuesEvent
|
2015-01-18 09:01:05
|
mbunkus/mtx-trac-import-test
|
https://api.github.com/repos/mbunkus/mtx-trac-import-test
|
opened
|
mkvextract can't extract SSA subtitles written with older mkvmerge
|
C: mkvextract P: normal R: fixed T: defect
|
**Reported by tobias on 22 Aug 2003 13:29 UTC**
Hi,
I tried to extract the SSA subtitles from the sample video in the URL using:
$ mkvextract tracks mewmew-vorbis-ssa.mkv 1:mewmew.avi 2:mewmew.ogg
3:mewmew_info.ssa 4:mewmew_dut.ssa 5:mewmew_info2.ssa 6:mewmew_fin.ssa
7:mewmew_fre.ssa 8:mewmew_ger.ssa 9:mewmew_heb.ssa 10:mewmew_hun.ssa
11:mewmew_ita.ssa 12:mewmew_jpn.ssa 13:mewmew_nor.ssa 14:mewmew_pol.ssa
15:mewmew_por.ssa 16:mewmew_rus.ssa 17:mewmew_spa.ssa 18:mewmew_swe.ssa
The Video and Audio are extracted succesfully, however the subtitles can
not be extracted, because they have an unsupported CodecID (which, according
to the specs, is correct, the correct ID is "S_TEXT/SSA"):
Warning: Unsupported CodecID 'S_SSA' for ID 10. Skipping track.
However mkvinfo shows that this file was created using an older version of
mkvmerge:
$ mkvinfo mewmew-vorbis-ssa.mkv
[+ Muxing application: libebml v0.4.4 + libmatroska v0.4.4
| + Writing application: mkvmerge v0.5.0
[...](...]
|)
My System: Debian sid, mkvtoolnix Version 0.6.3-1 and corresponding libs.
My question as a user would be: How can I access these subtitles?
As a developer I would suggest to let mkvextract detect the faulty CodecID
and warn the user about it and extract it nevertheless.
Migrated-From: https://trac.bunkus.org/ticket/12
|
1.0
|
mkvextract can't extract SSA subtitles written with older mkvmerge - **Reported by tobias on 22 Aug 2003 13:29 UTC**
Hi,
I tried to extract the SSA subtitles from the sample video in the URL using:
$ mkvextract tracks mewmew-vorbis-ssa.mkv 1:mewmew.avi 2:mewmew.ogg
3:mewmew_info.ssa 4:mewmew_dut.ssa 5:mewmew_info2.ssa 6:mewmew_fin.ssa
7:mewmew_fre.ssa 8:mewmew_ger.ssa 9:mewmew_heb.ssa 10:mewmew_hun.ssa
11:mewmew_ita.ssa 12:mewmew_jpn.ssa 13:mewmew_nor.ssa 14:mewmew_pol.ssa
15:mewmew_por.ssa 16:mewmew_rus.ssa 17:mewmew_spa.ssa 18:mewmew_swe.ssa
The Video and Audio are extracted succesfully, however the subtitles can
not be extracted, because they have an unsupported CodecID (which, according
to the specs, is correct, the correct ID is "S_TEXT/SSA"):
Warning: Unsupported CodecID 'S_SSA' for ID 10. Skipping track.
However mkvinfo shows that this file was created using an older version of
mkvmerge:
$ mkvinfo mewmew-vorbis-ssa.mkv
[+ Muxing application: libebml v0.4.4 + libmatroska v0.4.4
| + Writing application: mkvmerge v0.5.0
[...](...]
|)
My System: Debian sid, mkvtoolnix Version 0.6.3-1 and corresponding libs.
My question as a user would be: How can I access these subtitles?
As a developer I would suggest to let mkvextract detect the faulty CodecID
and warn the user about it and extract it nevertheless.
Migrated-From: https://trac.bunkus.org/ticket/12
|
defect
|
mkvextract can t extract ssa subtitles written with older mkvmerge reported by tobias on aug utc hi i tried to extract the ssa subtitles from the sample video in the url using mkvextract tracks mewmew vorbis ssa mkv mewmew avi mewmew ogg mewmew info ssa mewmew dut ssa mewmew ssa mewmew fin ssa mewmew fre ssa mewmew ger ssa mewmew heb ssa mewmew hun ssa mewmew ita ssa mewmew jpn ssa mewmew nor ssa mewmew pol ssa mewmew por ssa mewmew rus ssa mewmew spa ssa mewmew swe ssa the video and audio are extracted succesfully however the subtitles can not be extracted because they have an unsupported codecid which according to the specs is correct the correct id is s text ssa warning unsupported codecid s ssa for id skipping track however mkvinfo shows that this file was created using an older version of mkvmerge mkvinfo mewmew vorbis ssa mkv muxing application libebml libmatroska writing application mkvmerge my system debian sid mkvtoolnix version and corresponding libs my question as a user would be how can i access these subtitles as a developer i would suggest to let mkvextract detect the faulty codecid and warn the user about it and extract it nevertheless migrated from
| 1
|
79,816
| 29,184,904,922
|
IssuesEvent
|
2023-05-19 14:41:33
|
dotCMS/core
|
https://api.github.com/repos/dotCMS/core
|
opened
|
Favorite Pages: Fix Stuck State in the New Pages Portlet When Changing Sites
|
Type : Defect Team : Lunik OKR : Core Features Priority : 3 Average
|
### Problem Statement
When a user changes the site within the new pages portlet, the page list gets stuck in a loading state.
### Steps to Reproduce
1. Navigate to the new pages portlet in the DotCMS backend.
2. Change the site from the dropdown menu.
3. Observe the page list getting stuck in loading state.
### Acceptance Criteria
- Change the site should refresh the page list.
- User should be able to have bookmarks cross-sites.
### External Links
N/A
### Assumptions & Initiation Needs
- The new pages portlet should be functioning correctly.
- The user should have access to change the site within the new pages portlet.
### Quality Assurance Notes & Workarounds
N/A
|
1.0
|
Favorite Pages: Fix Stuck State in the New Pages Portlet When Changing Sites - ### Problem Statement
When a user changes the site within the new pages portlet, the page list gets stuck in a loading state.
### Steps to Reproduce
1. Navigate to the new pages portlet in the DotCMS backend.
2. Change the site from the dropdown menu.
3. Observe the page list getting stuck in loading state.
### Acceptance Criteria
- Change the site should refresh the page list.
- User should be able to have bookmarks cross-sites.
### External Links
N/A
### Assumptions & Initiation Needs
- The new pages portlet should be functioning correctly.
- The user should have access to change the site within the new pages portlet.
### Quality Assurance Notes & Workarounds
N/A
|
defect
|
favorite pages fix stuck state in the new pages portlet when changing sites problem statement when a user changes the site within the new pages portlet the page list gets stuck in a loading state steps to reproduce navigate to the new pages portlet in the dotcms backend change the site from the dropdown menu observe the page list getting stuck in loading state acceptance criteria change the site should refresh the page list user should be able to have bookmarks cross sites external links n a assumptions initiation needs the new pages portlet should be functioning correctly the user should have access to change the site within the new pages portlet quality assurance notes workarounds n a
| 1
|
107,573
| 13,485,573,444
|
IssuesEvent
|
2020-09-11 08:14:14
|
pupilfirst/pupilfirst
|
https://api.github.com/repos/pupilfirst/pupilfirst
|
opened
|
Improve Targets Overview in Reports page
|
design enhancement
|
extracted out from #461
- [ ] Show split of "Completed", "Rejected", "Pending Review" and "Not Attempted"
|
1.0
|
Improve Targets Overview in Reports page - extracted out from #461
- [ ] Show split of "Completed", "Rejected", "Pending Review" and "Not Attempted"
|
non_defect
|
improve targets overview in reports page extracted out from show split of completed rejected pending review and not attempted
| 0
|
304,458
| 26,277,808,110
|
IssuesEvent
|
2023-01-07 01:13:42
|
airbytehq/airbyte
|
https://api.github.com/repos/airbytehq/airbyte
|
closed
|
SAT: DX improvements to make writing new connector easier
|
type/enhancement area/connectors Acceptance Tests team/extensibility autoteam team/connector-ops
|
## Tell us about the problem you're trying to solve
Currently when a developer writes a new connector enabling SAT and running them is very very last step. Instead, SAT can be used during all development processes from the very beginning till the end. SAT messages can follow the breakdown of the developing process and lead developers to missing or incomplete parts of the implementation.
## Describe the solution you’d like
Improve SAT message and SAT tests so they can be used right after the connector's code was generated by the template generator. This ticket is an epic for all improvement tickets.
## Additional context
For better DX SAT should be able to test connector without building docker.
TBD
Development process:
* implement spec
* implement check
* implement discovery
* implement full table read
* fill all streams with data
* implement incremental read
* implement
|
1.0
|
SAT: DX improvements to make writing new connector easier - ## Tell us about the problem you're trying to solve
Currently when a developer writes a new connector enabling SAT and running them is very very last step. Instead, SAT can be used during all development processes from the very beginning till the end. SAT messages can follow the breakdown of the developing process and lead developers to missing or incomplete parts of the implementation.
## Describe the solution you’d like
Improve SAT message and SAT tests so they can be used right after the connector's code was generated by the template generator. This ticket is an epic for all improvement tickets.
## Additional context
For better DX SAT should be able to test connector without building docker.
TBD
Development process:
* implement spec
* implement check
* implement discovery
* implement full table read
* fill all streams with data
* implement incremental read
* implement
|
non_defect
|
sat dx improvements to make writing new connector easier tell us about the problem you re trying to solve currently when a developer writes a new connector enabling sat and running them is very very last step instead sat can be used during all development processes from the very beginning till the end sat messages can follow the breakdown of the developing process and lead developers to missing or incomplete parts of the implementation describe the solution you’d like improve sat message and sat tests so they can be used right after the connector s code was generated by the template generator this ticket is an epic for all improvement tickets additional context for better dx sat should be able to test connector without building docker tbd development process implement spec implement check implement discovery implement full table read fill all streams with data implement incremental read implement
| 0
|
33,386
| 7,108,966,866
|
IssuesEvent
|
2018-01-17 03:07:07
|
Guake/guake
|
https://api.github.com/repos/Guake/guake
|
closed
|
Closing only remaining tab freezes Guake
|
Type: Defect
|
If I have multiple tabs open, I can close them individually with `Ctrl+Shit+W`. However, if only one tab exists and I press `Ctrl+Shift+W`, Guake will become unresponsive. This only started when I upgraded to Xubuntu 17.10 - when I was on Xubuntu 16.04 it worked as expected.
Version: Guake Terminal 0.8.8
Python: 2.7.14
|
1.0
|
Closing only remaining tab freezes Guake - If I have multiple tabs open, I can close them individually with `Ctrl+Shit+W`. However, if only one tab exists and I press `Ctrl+Shift+W`, Guake will become unresponsive. This only started when I upgraded to Xubuntu 17.10 - when I was on Xubuntu 16.04 it worked as expected.
Version: Guake Terminal 0.8.8
Python: 2.7.14
|
defect
|
closing only remaining tab freezes guake if i have multiple tabs open i can close them individually with ctrl shit w however if only one tab exists and i press ctrl shift w guake will become unresponsive this only started when i upgraded to xubuntu when i was on xubuntu it worked as expected version guake terminal python
| 1
|
48,156
| 13,067,484,606
|
IssuesEvent
|
2020-07-31 00:36:24
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
closed
|
[PROPOSAL] tables path is wrong (Trac #1875)
|
Migrated from Trac combo simulation defect
|
In I3PropagatorServicePROPOSAL.cxx, line 117, the correct path should be "/PROPOSAL/resources/tables"
Migrated from https://code.icecube.wisc.edu/ticket/1875
```json
{
"status": "closed",
"changetime": "2016-10-28T16:26:16",
"description": "In I3PropagatorServicePROPOSAL.cxx, line 117, the correct path should be \"/PROPOSAL/resources/tables\"\n",
"reporter": "aturcati",
"cc": "",
"resolution": "fixed",
"_ts": "1477671976188966",
"component": "combo simulation",
"summary": "[PROPOSAL] tables path is wrong",
"priority": "normal",
"keywords": "",
"time": "2016-10-01T15:11:00",
"milestone": "",
"owner": "jsoedingrekso",
"type": "defect"
}
```
|
1.0
|
[PROPOSAL] tables path is wrong (Trac #1875) - In I3PropagatorServicePROPOSAL.cxx, line 117, the correct path should be "/PROPOSAL/resources/tables"
Migrated from https://code.icecube.wisc.edu/ticket/1875
```json
{
"status": "closed",
"changetime": "2016-10-28T16:26:16",
"description": "In I3PropagatorServicePROPOSAL.cxx, line 117, the correct path should be \"/PROPOSAL/resources/tables\"\n",
"reporter": "aturcati",
"cc": "",
"resolution": "fixed",
"_ts": "1477671976188966",
"component": "combo simulation",
"summary": "[PROPOSAL] tables path is wrong",
"priority": "normal",
"keywords": "",
"time": "2016-10-01T15:11:00",
"milestone": "",
"owner": "jsoedingrekso",
"type": "defect"
}
```
|
defect
|
tables path is wrong trac in cxx line the correct path should be proposal resources tables migrated from json status closed changetime description in cxx line the correct path should be proposal resources tables n reporter aturcati cc resolution fixed ts component combo simulation summary tables path is wrong priority normal keywords time milestone owner jsoedingrekso type defect
| 1
|
813,378
| 30,455,531,203
|
IssuesEvent
|
2023-07-16 20:57:35
|
Vatsim-Scandinavia/handover
|
https://api.github.com/repos/Vatsim-Scandinavia/handover
|
opened
|
Theming
|
back-end enhancement front-end medium priority
|
Today it's hardcoded in the blade template. It should be more dynamic to allow other divisions to adjust to their needs.
- [ ] Theme colors
- [ ] Theme DPP details
- [ ] Might be we should upgrade Bootstrap once we're at on it as well.
|
1.0
|
Theming - Today it's hardcoded in the blade template. It should be more dynamic to allow other divisions to adjust to their needs.
- [ ] Theme colors
- [ ] Theme DPP details
- [ ] Might be we should upgrade Bootstrap once we're at on it as well.
|
non_defect
|
theming today it s hardcoded in the blade template it should be more dynamic to allow other divisions to adjust to their needs theme colors theme dpp details might be we should upgrade bootstrap once we re at on it as well
| 0
|
805,453
| 29,520,489,037
|
IssuesEvent
|
2023-06-05 00:57:53
|
acmutd/jury
|
https://api.github.com/repos/acmutd/jury
|
closed
|
Show list of all projects
|
new feature high priority A: Frontend A: Backend
|
### Is your feature request related to a problem? Please describe.
_No response_
### Describe the solution you'd like
Table view of projects; simply pull all projects from the database
### Additional context

|
1.0
|
Show list of all projects - ### Is your feature request related to a problem? Please describe.
_No response_
### Describe the solution you'd like
Table view of projects; simply pull all projects from the database
### Additional context

|
non_defect
|
show list of all projects is your feature request related to a problem please describe no response describe the solution you d like table view of projects simply pull all projects from the database additional context
| 0
|
4,080
| 6,290,584,295
|
IssuesEvent
|
2017-07-19 21:52:48
|
Microsoft/vscode-cpptools
|
https://api.github.com/repos/Microsoft/vscode-cpptools
|
closed
|
Relative Include Paths On Dependencies Not Being Detected With Intellisense
|
Language Service question
|
_From @weshoke on July 19, 2017 4:18_
<!-- Do you have a question? Please ask it on http://stackoverflow.com/questions/tagged/vscode. -->
<!-- Use Help > Report Issues to prefill these. -->
- VSCode Version: Version 1.14.1 (1.14.1)
- OS Version: 10.12.4 (16E195)
Steps to Reproduce:
1. Open a C++ project and set strict semantic checking for IntelliSense
2. Observer that include dependencies in other directories are unresolved due to the folder not being included explicitly. However, from the perspective of the C++ compiler when it's processing the dependency, the include path of the file itself is available and thus the second order dependency is valid
For example for folder structure
```
/path
inc_p.h
/subpath
/inc1.h
/subsubpath/inc2.h
```
If inc_p.h includes "subpath/inc1.h" and inc1.h includes "subsubpath/inc2.h", inc_p.h will have a red squiggly error since inc2.h is not detected by IntelliSense despite the code compiling just fine.
<!-- Launch with `code --disable-extensions` to check. -->
Reproduces without extensions: Yes
_Copied from original issue: Microsoft/vscode#30979_
|
1.0
|
Relative Include Paths On Dependencies Not Being Detected With Intellisense - _From @weshoke on July 19, 2017 4:18_
<!-- Do you have a question? Please ask it on http://stackoverflow.com/questions/tagged/vscode. -->
<!-- Use Help > Report Issues to prefill these. -->
- VSCode Version: Version 1.14.1 (1.14.1)
- OS Version: 10.12.4 (16E195)
Steps to Reproduce:
1. Open a C++ project and set strict semantic checking for IntelliSense
2. Observer that include dependencies in other directories are unresolved due to the folder not being included explicitly. However, from the perspective of the C++ compiler when it's processing the dependency, the include path of the file itself is available and thus the second order dependency is valid
For example for folder structure
```
/path
inc_p.h
/subpath
/inc1.h
/subsubpath/inc2.h
```
If inc_p.h includes "subpath/inc1.h" and inc1.h includes "subsubpath/inc2.h", inc_p.h will have a red squiggly error since inc2.h is not detected by IntelliSense despite the code compiling just fine.
<!-- Launch with `code --disable-extensions` to check. -->
Reproduces without extensions: Yes
_Copied from original issue: Microsoft/vscode#30979_
|
non_defect
|
relative include paths on dependencies not being detected with intellisense from weshoke on july report issues to prefill these vscode version version os version steps to reproduce open a c project and set strict semantic checking for intellisense observer that include dependencies in other directories are unresolved due to the folder not being included explicitly however from the perspective of the c compiler when it s processing the dependency the include path of the file itself is available and thus the second order dependency is valid for example for folder structure path inc p h subpath h subsubpath h if inc p h includes subpath h and h includes subsubpath h inc p h will have a red squiggly error since h is not detected by intellisense despite the code compiling just fine reproduces without extensions yes copied from original issue microsoft vscode
| 0
|
63,755
| 17,929,083,573
|
IssuesEvent
|
2021-09-10 06:36:33
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
Emoji selection/picker should favor emojis which are used more often
|
T-Defect
|
### Steps to reproduce
In a message input field when I start writing `:sweat`, the first-selected emoji is 😓. Before, it was 😅.
### What happened?
### What did you expect?
When I write `:sweat` I expected Element to present me with a fuzzy-search result over the names and descriptions of the emojis **sorted by most often used**.
### What happened?
The 😓 emoji is always presented first so I can't simply press enter to auto-fill it in.
Me and me and others I know have gotten quite used to using 😅 in chat. However, now the ordering has changed and it's become a hassle to quickly select that emoji. IIRC Even earlier, that emoji was reachable via `:embarrassed` but that stopped working.
I'd suggest ordering emoji by how often they've been used locally.
### Operating system
Debian Stable
### Application version
Element version: 1.8.2 Olm version: 3.2.3
### How did you install the app?
https://packages.riot.im/debian
### Homeserver
matrix.org
### Have you submitted a rageshake?
No
|
1.0
|
Emoji selection/picker should favor emojis which are used more often - ### Steps to reproduce
In a message input field when I start writing `:sweat`, the first-selected emoji is 😓. Before, it was 😅.
### What happened?
### What did you expect?
When I write `:sweat` I expected Element to present me with a fuzzy-search result over the names and descriptions of the emojis **sorted by most often used**.
### What happened?
The 😓 emoji is always presented first so I can't simply press enter to auto-fill it in.
Me and me and others I know have gotten quite used to using 😅 in chat. However, now the ordering has changed and it's become a hassle to quickly select that emoji. IIRC Even earlier, that emoji was reachable via `:embarrassed` but that stopped working.
I'd suggest ordering emoji by how often they've been used locally.
### Operating system
Debian Stable
### Application version
Element version: 1.8.2 Olm version: 3.2.3
### How did you install the app?
https://packages.riot.im/debian
### Homeserver
matrix.org
### Have you submitted a rageshake?
No
|
defect
|
emoji selection picker should favor emojis which are used more often steps to reproduce in a message input field when i start writing sweat the first selected emoji is 😓 before it was 😅 what happened what did you expect when i write sweat i expected element to present me with a fuzzy search result over the names and descriptions of the emojis sorted by most often used what happened the 😓 emoji is always presented first so i can t simply press enter to auto fill it in me and me and others i know have gotten quite used to using 😅 in chat however now the ordering has changed and it s become a hassle to quickly select that emoji iirc even earlier that emoji was reachable via embarrassed but that stopped working i d suggest ordering emoji by how often they ve been used locally operating system debian stable application version element version olm version how did you install the app homeserver matrix org have you submitted a rageshake no
| 1
|
116,480
| 24,923,772,189
|
IssuesEvent
|
2022-10-31 04:34:52
|
appsmithorg/appsmith
|
https://api.github.com/repos/appsmithorg/appsmith
|
closed
|
[Bug]: Promises don't work unless returned from a function body
|
Bug High Production FE Coders Pod JS Promises
|
### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Use `showAlert()` inside a `.then` or `.catch` and observe that the trigger does not take place unless another `showAlert()` is present outside the promises structure.
### Steps To Reproduce
[](https://www.loom.com/share/de5143ea6db9487ca4f0c607201f1c96)
### Environment
Deploy Preview
### Version
Cloud
|
1.0
|
[Bug]: Promises don't work unless returned from a function body - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Use `showAlert()` inside a `.then` or `.catch` and observe that the trigger does not take place unless another `showAlert()` is present outside the promises structure.
### Steps To Reproduce
[](https://www.loom.com/share/de5143ea6db9487ca4f0c607201f1c96)
### Environment
Deploy Preview
### Version
Cloud
|
non_defect
|
promises don t work unless returned from a function body is there an existing issue for this i have searched the existing issues current behavior use showalert inside a then or catch and observe that the trigger does not take place unless another showalert is present outside the promises structure steps to reproduce environment deploy preview version cloud
| 0
|
213,815
| 7,260,705,202
|
IssuesEvent
|
2018-02-18 13:18:08
|
GiantsLoveDeathMetal/foolscap
|
https://api.github.com/repos/GiantsLoveDeathMetal/foolscap
|
closed
|
Default Filter out Tags
|
HIGH PRIORITY Quality of Life enhancement neat
|
This can be used to create list sections.
e.g. `textbook` tag can always be filtered out unless specified.
Call a `directory` list to list all the sections. e.g:
- `general`
- `textbooks`
- `work`
|
1.0
|
Default Filter out Tags - This can be used to create list sections.
e.g. `textbook` tag can always be filtered out unless specified.
Call a `directory` list to list all the sections. e.g:
- `general`
- `textbooks`
- `work`
|
non_defect
|
default filter out tags this can be used to create list sections e g textbook tag can always be filtered out unless specified call a directory list to list all the sections e g general textbooks work
| 0
|
9,907
| 2,616,009,737
|
IssuesEvent
|
2015-03-02 00:53:21
|
jasonhall/bwapi
|
https://api.github.com/repos/jasonhall/bwapi
|
closed
|
Zerg Hatchery mutating into Lair reports isTraining() == true
|
auto-migrated Component-Logic Priority-Low Type-Defect
|
```
Happens with Hatchery mutating. May also happen on other morphings, such as
refineries, hives, sunkens/spores, greater spire, maybe even addons.
```
Original issue reported on code.google.com by `darkp...@gmail.com` on 15 Jan 2010 at 8:51
|
1.0
|
Zerg Hatchery mutating into Lair reports isTraining() == true - ```
Happens with Hatchery mutating. May also happen on other morphings, such as
refineries, hives, sunkens/spores, greater spire, maybe even addons.
```
Original issue reported on code.google.com by `darkp...@gmail.com` on 15 Jan 2010 at 8:51
|
defect
|
zerg hatchery mutating into lair reports istraining true happens with hatchery mutating may also happen on other morphings such as refineries hives sunkens spores greater spire maybe even addons original issue reported on code google com by darkp gmail com on jan at
| 1
|
43,490
| 7,047,992,917
|
IssuesEvent
|
2018-01-02 15:53:51
|
orientechnologies/orientdb
|
https://api.github.com/repos/orientechnologies/orientdb
|
closed
|
function takes no string-variable as query-string
|
documentation
|
### OrientDB Version: 2.2.23
## Expected behavior
Writing a function "mergeCDR" like this:
```
var db = orient.getDatabase();
var sqlString = "select rid FROM index:".concat(indexName).concat(" WHERE key = [?,?,?,?] ");
return db.query(sqlString, imsi, charging_id, ggsn, phone_ip);
```
Is saved with no problem, executed with 5 parameters and completes with no error. I would expect a well-known RID to be returned.
## Actual behavior
No errors, but also **no results**.
When I do **not** put the positional parameters to the query in a WHERE clause, then the function runs with no errors but (as expected) returns the 5 requested entries from the index:
```
var db = orient.getDatabase();
var sqlString = "select rid FROM index:".concat(indexName).concat(" LIMIT 5");
return db.query(sqlString);
```
When I rewrite the function like this:
```
var db = orient.getDatabase();
return db.query("select rid FROM index:myindexname WHERE key = [?,?,?,?] ", imsi, charging_id, ggsn, phone_ip);
```
then the well-known RID is properly returned.
|
1.0
|
function takes no string-variable as query-string - ### OrientDB Version: 2.2.23
## Expected behavior
Writing a function "mergeCDR" like this:
```
var db = orient.getDatabase();
var sqlString = "select rid FROM index:".concat(indexName).concat(" WHERE key = [?,?,?,?] ");
return db.query(sqlString, imsi, charging_id, ggsn, phone_ip);
```
Is saved with no problem, executed with 5 parameters and completes with no error. I would expect a well-known RID to be returned.
## Actual behavior
No errors, but also **no results**.
When I do **not** put the positional parameters to the query in a WHERE clause, then the function runs with no errors but (as expected) returns the 5 requested entries from the index:
```
var db = orient.getDatabase();
var sqlString = "select rid FROM index:".concat(indexName).concat(" LIMIT 5");
return db.query(sqlString);
```
When I rewrite the function like this:
```
var db = orient.getDatabase();
return db.query("select rid FROM index:myindexname WHERE key = [?,?,?,?] ", imsi, charging_id, ggsn, phone_ip);
```
then the well-known RID is properly returned.
|
non_defect
|
function takes no string variable as query string orientdb version expected behavior writing a function mergecdr like this var db orient getdatabase var sqlstring select rid from index concat indexname concat where key return db query sqlstring imsi charging id ggsn phone ip is saved with no problem executed with parameters and completes with no error i would expect a well known rid to be returned actual behavior no errors but also no results when i do not put the positional parameters to the query in a where clause then the function runs with no errors but as expected returns the requested entries from the index var db orient getdatabase var sqlstring select rid from index concat indexname concat limit return db query sqlstring when i rewrite the function like this var db orient getdatabase return db query select rid from index myindexname where key imsi charging id ggsn phone ip then the well known rid is properly returned
| 0
|
181,296
| 21,658,615,168
|
IssuesEvent
|
2022-05-06 16:34:50
|
tamirverthim/NodeGoat
|
https://api.github.com/repos/tamirverthim/NodeGoat
|
opened
|
CVE-2022-29167 (High) detected in hawk-3.1.3.tgz
|
security vulnerability
|
## CVE-2022-29167 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hawk-3.1.3.tgz</b></p></summary>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz">https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **hawk-3.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tamirverthim/NodeGoat/commit/3de6c5862c1fef83d38a1fec17b579f1a5e328fb">3de6c5862c1fef83d38a1fec17b579f1a5e328fb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker's input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.
<p>Publish Date: 2022-05-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167>CVE-2022-29167</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq">https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq</a></p>
<p>Release Date: 2022-05-05</p>
<p>Fix Resolution: hawk - 9.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hawk","packageVersion":"3.1.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-retire:0.3.12;request:2.67.0;hawk:3.1.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hawk - 9.0.1","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-29167","vulnerabilityDetails":"Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker\u0027s input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2022-29167 (High) detected in hawk-3.1.3.tgz - ## CVE-2022-29167 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hawk-3.1.3.tgz</b></p></summary>
<p>HTTP Hawk Authentication Scheme</p>
<p>Library home page: <a href="https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz">https://registry.npmjs.org/hawk/-/hawk-3.1.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hawk/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **hawk-3.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tamirverthim/NodeGoat/commit/3de6c5862c1fef83d38a1fec17b579f1a5e328fb">3de6c5862c1fef83d38a1fec17b579f1a5e328fb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker's input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.
<p>Publish Date: 2022-05-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167>CVE-2022-29167</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq">https://github.com/mozilla/hawk/security/advisories/GHSA-44pw-h2cw-w3vq</a></p>
<p>Release Date: 2022-05-05</p>
<p>Fix Resolution: hawk - 9.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hawk","packageVersion":"3.1.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-retire:0.3.12;request:2.67.0;hawk:3.1.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hawk - 9.0.1","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-29167","vulnerabilityDetails":"Hawk is an HTTP authentication scheme providing mechanisms for making authenticated HTTP requests with partial cryptographic verification of the request and response, covering the HTTP method, request URI, host, and optionally the request payload. Hawk used a regular expression to parse `Host` HTTP header (`Hawk.utils.parseHost()`), which was subject to regular expression DoS attack - meaning each added character in the attacker\u0027s input increases the computation time exponentially. `parseHost()` was patched in `9.0.1` to use built-in `URL` class to parse hostname instead. `Hawk.authenticate()` accepts `options` argument. If that contains `host` and `port`, those would be used instead of a call to `utils.parseHost()`.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29167","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve high detected in hawk tgz cve high severity vulnerability vulnerable library hawk tgz http hawk authentication scheme library home page a href path to dependency file package json path to vulnerable library node modules hawk package json dependency hierarchy grunt retire tgz root library request tgz x hawk tgz vulnerable library found in head commit a href found in base branch master vulnerability details hawk is an http authentication scheme providing mechanisms for making authenticated http requests with partial cryptographic verification of the request and response covering the http method request uri host and optionally the request payload hawk used a regular expression to parse host http header hawk utils parsehost which was subject to regular expression dos attack meaning each added character in the attacker s input increases the computation time exponentially parsehost was patched in to use built in url class to parse hostname instead hawk authenticate accepts options argument if that contains host and port those would be used instead of a call to utils parsehost publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hawk isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree grunt retire request hawk isminimumfixversionavailable true minimumfixversion hawk isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails hawk is an http authentication scheme providing mechanisms for making authenticated http requests with partial cryptographic verification of the request and response covering the http method request uri host and optionally the request payload hawk used a regular expression to parse host http header hawk utils parsehost which was subject to regular expression dos attack meaning each added character in the attacker input increases the computation time exponentially parsehost was patched in to use built in url class to parse hostname instead hawk authenticate accepts options argument if that contains host and port those would be used instead of a call to utils parsehost vulnerabilityurl
| 0
|
267,051
| 23,276,712,450
|
IssuesEvent
|
2022-08-05 07:58:12
|
wazuh/wazuh-qa
|
https://api.github.com/repos/wazuh/wazuh-qa
|
opened
|
QA testing - Updated Amazon Linux SCA texts, YML formatting and OS detection rule bug
|
team/qa feature/sca type/qa-testing status/not-tracked target/4.3.7
|
| Target version | Related issue | Related PR |
|--------------------|--------------------|-----------------|
| 4.3.7 | https://github.com/wazuh/wazuh/pull/14483 | https://github.com/wazuh/wazuh/issues/14258 |
<!-- Important: No section may be left blank. If not, delete it directly (in principle only Steps to reproduce could be left blank in case of not proceeding, although there are always exceptions). -->
## Description
Amazon Linux SCA policy was not working due to a wrong OS detection rule. This Issue solves that problem.
## Proposed checks
<!-- Indicate through a list of checkboxes the suggested checks to be carried out by the QA tester -->
- [ ] Verify Amazon Linux SCA policy is loaded when starting the agent in an Amazon Linux System
...
## Expected results
<!-- Indicate expected results such as behaviors, logs... -->
When using an Amazon Linux platform, our wazuh-agent will run the Amazon Linux SCA policy
## Configuration and considerations
<!--
Indicate considerations to take into account when performing the testing that may not be very intuitive.
If any configuration has to be applied, it should be indicated as far as possible.
-->
None.
|
1.0
|
QA testing - Updated Amazon Linux SCA texts, YML formatting and OS detection rule bug - | Target version | Related issue | Related PR |
|--------------------|--------------------|-----------------|
| 4.3.7 | https://github.com/wazuh/wazuh/pull/14483 | https://github.com/wazuh/wazuh/issues/14258 |
<!-- Important: No section may be left blank. If not, delete it directly (in principle only Steps to reproduce could be left blank in case of not proceeding, although there are always exceptions). -->
## Description
Amazon Linux SCA policy was not working due to a wrong OS detection rule. This Issue solves that problem.
## Proposed checks
<!-- Indicate through a list of checkboxes the suggested checks to be carried out by the QA tester -->
- [ ] Verify Amazon Linux SCA policy is loaded when starting the agent in an Amazon Linux System
...
## Expected results
<!-- Indicate expected results such as behaviors, logs... -->
When using an Amazon Linux platform, our wazuh-agent will run the Amazon Linux SCA policy
## Configuration and considerations
<!--
Indicate considerations to take into account when performing the testing that may not be very intuitive.
If any configuration has to be applied, it should be indicated as far as possible.
-->
None.
|
non_defect
|
qa testing updated amazon linux sca texts yml formatting and os detection rule bug target version related issue related pr description amazon linux sca policy was not working due to a wrong os detection rule this issue solves that problem proposed checks verify amazon linux sca policy is loaded when starting the agent in an amazon linux system expected results when using an amazon linux platform our wazuh agent will run the amazon linux sca policy configuration and considerations indicate considerations to take into account when performing the testing that may not be very intuitive if any configuration has to be applied it should be indicated as far as possible none
| 0
|
156,128
| 12,297,423,794
|
IssuesEvent
|
2020-05-11 08:49:07
|
prettier/prettier
|
https://api.github.com/repos/prettier/prettier
|
closed
|
Modern CSS color function syntax
|
lang:css/scss/less type:tests
|
**Prettier 2.0.5**
[Playground link](https://prettier.io/playground/#N4Igxg9gdgLgprEAuEAzCEAEwA6VOaQA2EATkpqQOYBGAFAAwA0mAjAEwAcL7ArLwEoA3HgLEyFajQCGjFh26Y+vFgwB0gkfkIQS5TAAsAzkTqsAnIq4BSFrwbXhonXorGisi1c63M93+qazuL6HvS8AGxq7ObWmAwWauYAzGxRvJyYAPR+Dk7aIRREYAZ0kdGxbOZqnBFKyVER7Nm5jloEWQBULmR0RgBKAOIAQvHxGgxsLf7CmJ1ZeAC+IEwgEAAOMACW0EbIoNKkpBAA7gAKhwh7KNJEJ9IAnnurNKTSYADWcDAAyuvvWygVGQMFIAFc4KsDDAALZEADqBi28CM-zAcB+V2RWwAbsiHshwEZniBAUY4KQYGc3lQYdJkKhbuTVgArIwAD2Gb0+3x+0hhcAAMoC4AymZCQGz2T9AVQiHAAIpgiDwMVEZkgf6kcmkQlgYkrTWkQEweFbAAmMAMyE4zCNEHJ8Le60J61IcB1ONFqwAjsr4NSNtcQNIjABaKBwODm6OG91+rbu6nSWn0pCM9US8kwrYg8FZ2XypUq0Xp8WrGDSGhmy3WpDsCtvLZEWUAYQgMLphI9vENYPJABUq9cMxqcRCAJJQGOwH5gY2bACC05+MAe8rV5MWiyAA)
```sh
--parser css
```
**Input:**
```css
foo {
color: rgb(0, 128, 255);
color: rgba(0, 128, 255, 0.5);
color: hsl(198, 28%, 50%);
color: hsla(198, 28%, 50%, 0.5);
color: lab(56.29% 019.93 16.58 / 50%);
color: lch(56.29% 19.86 236.62 / 50%);
/* color(sRGB 0 0.50 1 / 50%); */
}
```
**Output:**
```css
foo {
color: rgb(0, 128, 255);
color: rgba(0, 128, 255, 0.5);
color: hsl(198, 28%, 50%);
color: hsla(198, 28%, 50%, 0.5);
color: lab(56.29% 019.93 16.58 / 50%);
color: lch(56.29% 19.86 236.62 / 50%);
/* color(sRGB 0 0.50 1 / 50%); */
}
```
**Expected behavior:**
```css
foo {
color: rgb(0 128 255);
color: rgb(0 128 255 / 50%);
color: hsl(198deg 28% 50%);
color: hsl(198deg 28% 50% / 50%);
color: lab(56.29% 019.93 16.58 / 50%);
color: lch(56.29% 19.86 236.62deg / 50%);
/* color(sRGB 0 0.50 1 / 50%); */
}
```
Notes:
- in general, [use the modern comma-free syntax instead of the legacy comma-based syntax](https://twitter.com/mathias/status/1253242715304857601) ("legacy" is how the CSS Color spec refers to it)
- use `rgb()` with the new syntax instead of `rgba()` (which is a legacy function)
- use `hsl()` with the new syntax instead of `hsla()` (which is a legacy function)
- consider being opinionated w.r.t. how to represent alpha values. IMHO using percentage notation is most readable, as it clarifies the range: e.g. `70%` vs `0.7`
- consider being opinionated about using the `deg` suffix where applicable, e.g. in the first parameter for `hsl()` and the last non-alpha parameter for `lch()`. Again, because this clarifies that the range lies between `0-360`.
- the `color()` syntax is not yet supported by the parser, but that's a separate issue.
- optionally, consider being opinionated about preferring `#rrggbba`/`#rgba` hex notation over `rgb()` notation, or the other way around
|
1.0
|
Modern CSS color function syntax - **Prettier 2.0.5**
[Playground link](https://prettier.io/playground/#N4Igxg9gdgLgprEAuEAzCEAEwA6VOaQA2EATkpqQOYBGAFAAwA0mAjAEwAcL7ArLwEoA3HgLEyFajQCGjFh26Y+vFgwB0gkfkIQS5TAAsAzkTqsAnIq4BSFrwbXhonXorGisi1c63M93+qazuL6HvS8AGxq7ObWmAwWauYAzGxRvJyYAPR+Dk7aIRREYAZ0kdGxbOZqnBFKyVER7Nm5jloEWQBULmR0RgBKAOIAQvHxGgxsLf7CmJ1ZeAC+IEwgEAAOMACW0EbIoNKkpBAA7gAKhwh7KNJEJ9IAnnurNKTSYADWcDAAyuvvWygVGQMFIAFc4KsDDAALZEADqBi28CM-zAcB+V2RWwAbsiHshwEZniBAUY4KQYGc3lQYdJkKhbuTVgArIwAD2Gb0+3x+0hhcAAMoC4AymZCQGz2T9AVQiHAAIpgiDwMVEZkgf6kcmkQlgYkrTWkQEweFbAAmMAMyE4zCNEHJ8Le60J61IcB1ONFqwAjsr4NSNtcQNIjABaKBwODm6OG91+rbu6nSWn0pCM9US8kwrYg8FZ2XypUq0Xp8WrGDSGhmy3WpDsCtvLZEWUAYQgMLphI9vENYPJABUq9cMxqcRCAJJQGOwH5gY2bACC05+MAe8rV5MWiyAA)
```sh
--parser css
```
**Input:**
```css
foo {
color: rgb(0, 128, 255);
color: rgba(0, 128, 255, 0.5);
color: hsl(198, 28%, 50%);
color: hsla(198, 28%, 50%, 0.5);
color: lab(56.29% 019.93 16.58 / 50%);
color: lch(56.29% 19.86 236.62 / 50%);
/* color(sRGB 0 0.50 1 / 50%); */
}
```
**Output:**
```css
foo {
color: rgb(0, 128, 255);
color: rgba(0, 128, 255, 0.5);
color: hsl(198, 28%, 50%);
color: hsla(198, 28%, 50%, 0.5);
color: lab(56.29% 019.93 16.58 / 50%);
color: lch(56.29% 19.86 236.62 / 50%);
/* color(sRGB 0 0.50 1 / 50%); */
}
```
**Expected behavior:**
```css
foo {
color: rgb(0 128 255);
color: rgb(0 128 255 / 50%);
color: hsl(198deg 28% 50%);
color: hsl(198deg 28% 50% / 50%);
color: lab(56.29% 019.93 16.58 / 50%);
color: lch(56.29% 19.86 236.62deg / 50%);
/* color(sRGB 0 0.50 1 / 50%); */
}
```
Notes:
- in general, [use the modern comma-free syntax instead of the legacy comma-based syntax](https://twitter.com/mathias/status/1253242715304857601) ("legacy" is how the CSS Color spec refers to it)
- use `rgb()` with the new syntax instead of `rgba()` (which is a legacy function)
- use `hsl()` with the new syntax instead of `hsla()` (which is a legacy function)
- consider being opinionated w.r.t. how to represent alpha values. IMHO using percentage notation is most readable, as it clarifies the range: e.g. `70%` vs `0.7`
- consider being opinionated about using the `deg` suffix where applicable, e.g. in the first parameter for `hsl()` and the last non-alpha parameter for `lch()`. Again, because this clarifies that the range lies between `0-360`.
- the `color()` syntax is not yet supported by the parser, but that's a separate issue.
- optionally, consider being opinionated about preferring `#rrggbba`/`#rgba` hex notation over `rgb()` notation, or the other way around
|
non_defect
|
modern css color function syntax prettier sh parser css input css foo color rgb color rgba color hsl color hsla color lab color lch color srgb output css foo color rgb color rgba color hsl color hsla color lab color lch color srgb expected behavior css foo color rgb color rgb color hsl color hsl color lab color lch color srgb notes in general legacy is how the css color spec refers to it use rgb with the new syntax instead of rgba which is a legacy function use hsl with the new syntax instead of hsla which is a legacy function consider being opinionated w r t how to represent alpha values imho using percentage notation is most readable as it clarifies the range e g vs consider being opinionated about using the deg suffix where applicable e g in the first parameter for hsl and the last non alpha parameter for lch again because this clarifies that the range lies between the color syntax is not yet supported by the parser but that s a separate issue optionally consider being opinionated about preferring rrggbba rgba hex notation over rgb notation or the other way around
| 0
|
60,479
| 17,023,437,743
|
IssuesEvent
|
2021-07-03 02:01:56
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
Vietnamese (vi) locale breaks diary pages
|
Component: website Priority: major Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 2.36am, Wednesday, 8th July 2009]**
The Vietnamese locale introduced in r16313 breaks all diary-related pages, due to an outdated reference to `{{language}}` where there shouldve been a reference to `{{language_link}}`. A fixed version is attached.
|
1.0
|
Vietnamese (vi) locale breaks diary pages - **[Submitted to the original trac issue database at 2.36am, Wednesday, 8th July 2009]**
The Vietnamese locale introduced in r16313 breaks all diary-related pages, due to an outdated reference to `{{language}}` where there shouldve been a reference to `{{language_link}}`. A fixed version is attached.
|
defect
|
vietnamese vi locale breaks diary pages the vietnamese locale introduced in breaks all diary related pages due to an outdated reference to language where there shouldve been a reference to language link a fixed version is attached
| 1
|
39,234
| 15,895,107,420
|
IssuesEvent
|
2021-04-11 12:49:44
|
odk-x/tool-suite-X
|
https://api.github.com/repos/odk-x/tool-suite-X
|
closed
|
Fix Null Pointer OnItemSelected in MainActivity
|
Services bug
|
Here is the error:
Fatal Exception: java.lang.NullPointerException: Attempt to invoke virtual method 'void android.view.View.setFocusableInTouchMode(boolean)' on a null object reference
at org.opendatakit.services.MainActivity.onOptionsItemSelected(MainActivity.java:164)
at android.app.Activity.onMenuItemSelected(Activity.java:4137)
at androidx.fragment.app.FragmentActivity.onMenuItemSelected(FragmentActivity.java:340)
at androidx.appcompat.app.AppCompatActivity.onMenuItemSelected(AppCompatActivity.java:228)
at androidx.appcompat.view.WindowCallbackWrapper.onMenuItemSelected(WindowCallbackWrapper.java:109)
at androidx.appcompat.app.AppCompatDelegateImpl.onMenuItemSelected(AppCompatDelegateImpl.java:1176)
at androidx.appcompat.view.menu.MenuBuilder.dispatchMenuItemSelected(MenuBuilder.java:834)
at androidx.appcompat.view.menu.MenuItemImpl.invoke(MenuItemImpl.java:158)
at androidx.appcompat.view.menu.MenuBuilder.performItemAction(MenuBuilder.java:985)
at androidx.appcompat.view.menu.MenuPopup.onItemClick(MenuPopup.java:128)
at android.widget.AdapterView.performItemClick(AdapterView.java:330)
at android.widget.AbsListView.performItemClick(AbsListView.java:1190)
at android.widget.AbsListView$PerformClick.run(AbsListView.java:3198)
at android.widget.AbsListView.onTouchUp(AbsListView.java:4128)
at android.widget.AbsListView.onTouchEvent(AbsListView.java:3886)
at androidx.appcompat.widget.DropDownListView.onTouchEvent(DropDownListView.java:217)
at androidx.appcompat.widget.MenuPopupWindow$MenuDropDownListView.onTouchEvent(MenuPopupWindow.java:138)
at android.view.View.dispatchTouchEvent(View.java:13415)
at android.view.ViewGroup.dispatchTransformedTouchEvent(ViewGroup.java:3054)
at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:2741)
at android.view.ViewGroup.dispatchTransformedTouchEvent(ViewGroup.java:3060)
at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:2755)
at android.view.ViewGroup.dispatchTransformedTouchEvent(ViewGroup.java:3060)
at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:2755)
at android.widget.PopupWindow$PopupDecorView.dispatchTouchEvent(PopupWindow.java:2554)
at android.view.View.dispatchPointerEvent(View.java:13674)
at android.view.ViewRootImpl$ViewPostImeInputStage.processPointerEvent(ViewRootImpl.java:5482)
at android.view.ViewRootImpl$ViewPostImeInputStage.onProcess(ViewRootImpl.java:5285)
at android.view.ViewRootImpl$InputStage.deliver(ViewRootImpl.java:4788)
at android.view.ViewRootImpl$InputStage.onDeliverToNext(ViewRootImpl.java:4841)
at android.view.ViewRootImpl$InputStage.forward(ViewRootImpl.java:4807)
at android.view.ViewRootImpl$AsyncInputStage.forward(ViewRootImpl.java:4947)
at android.view.ViewRootImpl$InputStage.apply(ViewRootImpl.java:4815)
at android.view.ViewRootImpl$AsyncInputStage.apply(ViewRootImpl.java:5004)
at android.view.ViewRootImpl$InputStage.deliver(ViewRootImpl.java:4788)
at android.view.ViewRootImpl$InputStage.onDeliverToNext(ViewRootImpl.java:4841)
at android.view.ViewRootImpl$InputStage.forward(ViewRootImpl.java:4807)
at android.view.ViewRootImpl$InputStage.apply(ViewRootImpl.java:4815)
at android.view.ViewRootImpl$InputStage.deliver(ViewRootImpl.java:4788)
at android.view.ViewRootImpl.deliverInputEvent(ViewRootImpl.java:7505)
at android.view.ViewRootImpl.doProcessInputEvents(ViewRootImpl.java:7474)
at android.view.ViewRootImpl.enqueueInputEvent(ViewRootImpl.java:7435)
at android.view.ViewRootImpl$WindowInputEventReceiver.onInputEvent(ViewRootImpl.java:7630)
at android.view.InputEventReceiver.dispatchInputEvent(InputEventReceiver.java:188)
at android.os.MessageQueue.nativePollOnce(MessageQueue.java)
at android.os.MessageQueue.next(MessageQueue.java:336)
at android.os.Looper.loop(Looper.java:174)
at android.app.ActivityThread.main(ActivityThread.java:7356)
at java.lang.reflect.Method.invoke(Method.java)
at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:492)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:930)
|
1.0
|
Fix Null Pointer OnItemSelected in MainActivity - Here is the error:
Fatal Exception: java.lang.NullPointerException: Attempt to invoke virtual method 'void android.view.View.setFocusableInTouchMode(boolean)' on a null object reference
at org.opendatakit.services.MainActivity.onOptionsItemSelected(MainActivity.java:164)
at android.app.Activity.onMenuItemSelected(Activity.java:4137)
at androidx.fragment.app.FragmentActivity.onMenuItemSelected(FragmentActivity.java:340)
at androidx.appcompat.app.AppCompatActivity.onMenuItemSelected(AppCompatActivity.java:228)
at androidx.appcompat.view.WindowCallbackWrapper.onMenuItemSelected(WindowCallbackWrapper.java:109)
at androidx.appcompat.app.AppCompatDelegateImpl.onMenuItemSelected(AppCompatDelegateImpl.java:1176)
at androidx.appcompat.view.menu.MenuBuilder.dispatchMenuItemSelected(MenuBuilder.java:834)
at androidx.appcompat.view.menu.MenuItemImpl.invoke(MenuItemImpl.java:158)
at androidx.appcompat.view.menu.MenuBuilder.performItemAction(MenuBuilder.java:985)
at androidx.appcompat.view.menu.MenuPopup.onItemClick(MenuPopup.java:128)
at android.widget.AdapterView.performItemClick(AdapterView.java:330)
at android.widget.AbsListView.performItemClick(AbsListView.java:1190)
at android.widget.AbsListView$PerformClick.run(AbsListView.java:3198)
at android.widget.AbsListView.onTouchUp(AbsListView.java:4128)
at android.widget.AbsListView.onTouchEvent(AbsListView.java:3886)
at androidx.appcompat.widget.DropDownListView.onTouchEvent(DropDownListView.java:217)
at androidx.appcompat.widget.MenuPopupWindow$MenuDropDownListView.onTouchEvent(MenuPopupWindow.java:138)
at android.view.View.dispatchTouchEvent(View.java:13415)
at android.view.ViewGroup.dispatchTransformedTouchEvent(ViewGroup.java:3054)
at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:2741)
at android.view.ViewGroup.dispatchTransformedTouchEvent(ViewGroup.java:3060)
at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:2755)
at android.view.ViewGroup.dispatchTransformedTouchEvent(ViewGroup.java:3060)
at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:2755)
at android.widget.PopupWindow$PopupDecorView.dispatchTouchEvent(PopupWindow.java:2554)
at android.view.View.dispatchPointerEvent(View.java:13674)
at android.view.ViewRootImpl$ViewPostImeInputStage.processPointerEvent(ViewRootImpl.java:5482)
at android.view.ViewRootImpl$ViewPostImeInputStage.onProcess(ViewRootImpl.java:5285)
at android.view.ViewRootImpl$InputStage.deliver(ViewRootImpl.java:4788)
at android.view.ViewRootImpl$InputStage.onDeliverToNext(ViewRootImpl.java:4841)
at android.view.ViewRootImpl$InputStage.forward(ViewRootImpl.java:4807)
at android.view.ViewRootImpl$AsyncInputStage.forward(ViewRootImpl.java:4947)
at android.view.ViewRootImpl$InputStage.apply(ViewRootImpl.java:4815)
at android.view.ViewRootImpl$AsyncInputStage.apply(ViewRootImpl.java:5004)
at android.view.ViewRootImpl$InputStage.deliver(ViewRootImpl.java:4788)
at android.view.ViewRootImpl$InputStage.onDeliverToNext(ViewRootImpl.java:4841)
at android.view.ViewRootImpl$InputStage.forward(ViewRootImpl.java:4807)
at android.view.ViewRootImpl$InputStage.apply(ViewRootImpl.java:4815)
at android.view.ViewRootImpl$InputStage.deliver(ViewRootImpl.java:4788)
at android.view.ViewRootImpl.deliverInputEvent(ViewRootImpl.java:7505)
at android.view.ViewRootImpl.doProcessInputEvents(ViewRootImpl.java:7474)
at android.view.ViewRootImpl.enqueueInputEvent(ViewRootImpl.java:7435)
at android.view.ViewRootImpl$WindowInputEventReceiver.onInputEvent(ViewRootImpl.java:7630)
at android.view.InputEventReceiver.dispatchInputEvent(InputEventReceiver.java:188)
at android.os.MessageQueue.nativePollOnce(MessageQueue.java)
at android.os.MessageQueue.next(MessageQueue.java:336)
at android.os.Looper.loop(Looper.java:174)
at android.app.ActivityThread.main(ActivityThread.java:7356)
at java.lang.reflect.Method.invoke(Method.java)
at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:492)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:930)
|
non_defect
|
fix null pointer onitemselected in mainactivity here is the error fatal exception java lang nullpointerexception attempt to invoke virtual method void android view view setfocusableintouchmode boolean on a null object reference at org opendatakit services mainactivity onoptionsitemselected mainactivity java at android app activity onmenuitemselected activity java at androidx fragment app fragmentactivity onmenuitemselected fragmentactivity java at androidx appcompat app appcompatactivity onmenuitemselected appcompatactivity java at androidx appcompat view windowcallbackwrapper onmenuitemselected windowcallbackwrapper java at androidx appcompat app appcompatdelegateimpl onmenuitemselected appcompatdelegateimpl java at androidx appcompat view menu menubuilder dispatchmenuitemselected menubuilder java at androidx appcompat view menu menuitemimpl invoke menuitemimpl java at androidx appcompat view menu menubuilder performitemaction menubuilder java at androidx appcompat view menu menupopup onitemclick menupopup java at android widget adapterview performitemclick adapterview java at android widget abslistview performitemclick abslistview java at android widget abslistview performclick run abslistview java at android widget abslistview ontouchup abslistview java at android widget abslistview ontouchevent abslistview java at androidx appcompat widget dropdownlistview ontouchevent dropdownlistview java at androidx appcompat widget menupopupwindow menudropdownlistview ontouchevent menupopupwindow java at android view view dispatchtouchevent view java at android view viewgroup dispatchtransformedtouchevent viewgroup java at android view viewgroup dispatchtouchevent viewgroup java at android view viewgroup dispatchtransformedtouchevent viewgroup java at android view viewgroup dispatchtouchevent viewgroup java at android view viewgroup dispatchtransformedtouchevent viewgroup java at android view viewgroup dispatchtouchevent viewgroup java at android widget popupwindow popupdecorview dispatchtouchevent popupwindow java at android view view dispatchpointerevent view java at android view viewrootimpl viewpostimeinputstage processpointerevent viewrootimpl java at android view viewrootimpl viewpostimeinputstage onprocess viewrootimpl java at android view viewrootimpl inputstage deliver viewrootimpl java at android view viewrootimpl inputstage ondelivertonext viewrootimpl java at android view viewrootimpl inputstage forward viewrootimpl java at android view viewrootimpl asyncinputstage forward viewrootimpl java at android view viewrootimpl inputstage apply viewrootimpl java at android view viewrootimpl asyncinputstage apply viewrootimpl java at android view viewrootimpl inputstage deliver viewrootimpl java at android view viewrootimpl inputstage ondelivertonext viewrootimpl java at android view viewrootimpl inputstage forward viewrootimpl java at android view viewrootimpl inputstage apply viewrootimpl java at android view viewrootimpl inputstage deliver viewrootimpl java at android view viewrootimpl deliverinputevent viewrootimpl java at android view viewrootimpl doprocessinputevents viewrootimpl java at android view viewrootimpl enqueueinputevent viewrootimpl java at android view viewrootimpl windowinputeventreceiver oninputevent viewrootimpl java at android view inputeventreceiver dispatchinputevent inputeventreceiver java at android os messagequeue nativepollonce messagequeue java at android os messagequeue next messagequeue java at android os looper loop looper java at android app activitythread main activitythread java at java lang reflect method invoke method java at com android internal os runtimeinit methodandargscaller run runtimeinit java at com android internal os zygoteinit main zygoteinit java
| 0
|
71,764
| 23,791,131,994
|
IssuesEvent
|
2022-09-02 14:38:15
|
decentraland/unity-renderer
|
https://api.github.com/repos/decentraland/unity-renderer
|
opened
|
Opening the backpack multiple times makes the emotes swap position
|
major defect
|
**Description:**
The assigned emotes get swapped if the player enters the backpack's emote menu multiple times when some of the spots are unassigned. In the backpack the position of the assigned emotes is rearranged, however, on the emote wheel one emote often gets duplicated.
**Steps to reproduce:**
1. Load into the game as a guest or via a wallet.
2. Enter the Emote section in the Backpack ('I').
3. Set the emotes while leaving some spaces empty.
4. Exit the backpack.
5. Enter and exit the backpack multiple times by using the 'I' button.
6. Observe the issue.
**Results:**
Entering the backpack's emote section multiple times makes the assigned emotes swap.
**Expected results:**
The emotes are not afflicted with random swapping.
**Notes:**
- The issue occurs on both the guest and wallet accounts.
- The issue occurs only on the special emotes configuration: https://play.decentraland.zone/?NETWORK=mainnet&realm=hela&position=97%2C97&renderer-version=1.0.51910-20220901164430.commit-1e215aa&kernel-branch=feat%2Ffetch-emotes.
- Please see the attached video for reference: vid.
- Platforms: Web Client.
|
1.0
|
Opening the backpack multiple times makes the emotes swap position - **Description:**
The assigned emotes get swapped if the player enters the backpack's emote menu multiple times when some of the spots are unassigned. In the backpack the position of the assigned emotes is rearranged, however, on the emote wheel one emote often gets duplicated.
**Steps to reproduce:**
1. Load into the game as a guest or via a wallet.
2. Enter the Emote section in the Backpack ('I').
3. Set the emotes while leaving some spaces empty.
4. Exit the backpack.
5. Enter and exit the backpack multiple times by using the 'I' button.
6. Observe the issue.
**Results:**
Entering the backpack's emote section multiple times makes the assigned emotes swap.
**Expected results:**
The emotes are not afflicted with random swapping.
**Notes:**
- The issue occurs on both the guest and wallet accounts.
- The issue occurs only on the special emotes configuration: https://play.decentraland.zone/?NETWORK=mainnet&realm=hela&position=97%2C97&renderer-version=1.0.51910-20220901164430.commit-1e215aa&kernel-branch=feat%2Ffetch-emotes.
- Please see the attached video for reference: vid.
- Platforms: Web Client.
|
defect
|
opening the backpack multiple times makes the emotes swap position description the assigned emotes get swapped if the player enters the backpack s emote menu multiple times when some of the spots are unassigned in the backpack the position of the assigned emotes is rearranged however on the emote wheel one emote often gets duplicated steps to reproduce load into the game as a guest or via a wallet enter the emote section in the backpack i set the emotes while leaving some spaces empty exit the backpack enter and exit the backpack multiple times by using the i button observe the issue results entering the backpack s emote section multiple times makes the assigned emotes swap expected results the emotes are not afflicted with random swapping notes the issue occurs on both the guest and wallet accounts the issue occurs only on the special emotes configuration please see the attached video for reference vid platforms web client
| 1
|
499
| 3,487,672,205
|
IssuesEvent
|
2016-01-02 05:08:47
|
MovingBlocks/Terasology
|
https://api.github.com/repos/MovingBlocks/Terasology
|
closed
|
Allow EntityRef.toFullDescription() to run in modules
|
Architecture Contributor-friendly Security
|
This makes a nice JSON String describing the entity, but it uses some engine-y stuff that runs into the module sandboxing. Needs one of those fancy privileged blocks to stop the calls into privileged code from triggering security warnings (without making it OK to use that code in general)
Pretty easy! With a little bit of architecture/security flair. There are a few other privileged blocks to draw inspiration from.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/5960564-allow-entityref-tofulldescription-to-run-in-modules?utm_campaign=plugin&utm_content=tracker%2F5279&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F5279&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
1.0
|
Allow EntityRef.toFullDescription() to run in modules - This makes a nice JSON String describing the entity, but it uses some engine-y stuff that runs into the module sandboxing. Needs one of those fancy privileged blocks to stop the calls into privileged code from triggering security warnings (without making it OK to use that code in general)
Pretty easy! With a little bit of architecture/security flair. There are a few other privileged blocks to draw inspiration from.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/5960564-allow-entityref-tofulldescription-to-run-in-modules?utm_campaign=plugin&utm_content=tracker%2F5279&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F5279&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
non_defect
|
allow entityref tofulldescription to run in modules this makes a nice json string describing the entity but it uses some engine y stuff that runs into the module sandboxing needs one of those fancy privileged blocks to stop the calls into privileged code from triggering security warnings without making it ok to use that code in general pretty easy with a little bit of architecture security flair there are a few other privileged blocks to draw inspiration from want to back this issue we accept bounties via
| 0
|
333,447
| 24,375,150,304
|
IssuesEvent
|
2022-10-03 23:45:08
|
astrophpeter/blast
|
https://api.github.com/repos/astrophpeter/blast
|
closed
|
[Bug] Fix broken links in documentation
|
bug documentation Difficulty: intermediate
|
# **🐞 Bug Report**
## **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
*The links in https://blast.readthedocs.io/en/latest/developer_guide/dev_system_pages.html are broken. e.g., 0.0.0.0:8000/admin goes to https://blast.readthedocs.io/en/latest/developer_guide/0.0.0.0:8000/admin/ when it should go to http://0.0.0.0:8000/admin. For some reason readthedocs appends https://blast.readthedocs.io/en/latest/developer_guide/ to the link, we need to fix it. Several other links on this page do the same thing! We should fix them all.
|
1.0
|
[Bug] Fix broken links in documentation - # **🐞 Bug Report**
## **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
*The links in https://blast.readthedocs.io/en/latest/developer_guide/dev_system_pages.html are broken. e.g., 0.0.0.0:8000/admin goes to https://blast.readthedocs.io/en/latest/developer_guide/0.0.0.0:8000/admin/ when it should go to http://0.0.0.0:8000/admin. For some reason readthedocs appends https://blast.readthedocs.io/en/latest/developer_guide/ to the link, we need to fix it. Several other links on this page do the same thing! We should fix them all.
|
non_defect
|
fix broken links in documentation 🐞 bug report describe the bug the links in are broken e g admin goes to when it should go to for some reason readthedocs appends to the link we need to fix it several other links on this page do the same thing we should fix them all
| 0
|
125,948
| 17,861,742,627
|
IssuesEvent
|
2021-09-06 02:19:16
|
Galaxy-Software-Service/WebGoat
|
https://api.github.com/repos/Galaxy-Software-Service/WebGoat
|
reopened
|
CVE-2018-20821 (Medium) detected in multiple libraries
|
security vulnerability
|
## CVE-2018-20821 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-25.1.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: WebGoat/docs/package.json</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-4.0.2.tgz (Root Library)
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Galaxy-Software-Service/WebGoat/commit/12040d57fd51ffa0b6407f8b4e9cc04e47656d2d">12040d57fd51ffa0b6407f8b4e9cc04e47656d2d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The parsing component in LibSass through 3.5.5 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Parser::parse_css_variable_value in parser.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20821>CVE-2018-20821</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.14.1","isTransitiveDependency":true,"dependencyTree":"gulp-sass:4.0.2;node-sass:4.14.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"LibSass - 3.6.0"}],"vulnerabilityIdentifier":"CVE-2018-20821","vulnerabilityDetails":"The parsing component in LibSass through 3.5.5 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Parser::parse_css_variable_value in parser.cpp).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20821","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2018-20821 (Medium) detected in multiple libraries - ## CVE-2018-20821 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-25.1.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: WebGoat/docs/package.json</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-4.0.2.tgz (Root Library)
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Galaxy-Software-Service/WebGoat/commit/12040d57fd51ffa0b6407f8b4e9cc04e47656d2d">12040d57fd51ffa0b6407f8b4e9cc04e47656d2d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The parsing component in LibSass through 3.5.5 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Parser::parse_css_variable_value in parser.cpp).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20821>CVE-2018-20821</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20821</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.14.1","isTransitiveDependency":true,"dependencyTree":"gulp-sass:4.0.2;node-sass:4.14.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"LibSass - 3.6.0"}],"vulnerabilityIdentifier":"CVE-2018-20821","vulnerabilityDetails":"The parsing component in LibSass through 3.5.5 allows attackers to cause a denial-of-service (uncontrolled recursion in Sass::Parser::parse_css_variable_value in parser.cpp).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20821","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries opennmsopennms source node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file webgoat docs package json path to vulnerable library webgoat docs node modules node sass package json dependency hierarchy gulp sass tgz root library x node sass tgz vulnerable library found in head commit a href found in base branch master vulnerability details the parsing component in libsass through allows attackers to cause a denial of service uncontrolled recursion in sass parser parse css variable value in parser cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails the parsing component in libsass through allows attackers to cause a denial of service uncontrolled recursion in sass parser parse css variable value in parser cpp vulnerabilityurl
| 0
|
63,772
| 17,933,479,723
|
IssuesEvent
|
2021-09-10 12:34:05
|
jOOQ/jOOQ
|
https://api.github.com/repos/jOOQ/jOOQ
|
opened
|
Create Index with H2 Dialect generates invalid SQL due to double-quotes
|
T: Defect
|
### Expected behavior
An SQL like:
create index if not exists "aaa_transactions_start_desc" on table_name(transaction_start desc)
### Actual behavior
An SQL Like:
create index if not exists "aaa_transactions_start_desc" on "table_name"("transaction_start" desc)
It is rejected by H2 with:
Caused by: org.h2.jdbc.JdbcSQLSyntaxErrorException: Table "table_name" not found; SQL statement:
create index if not exists "aaa_transactions_start_desc" on "table_name"("transaction_start" desc) [42102-200]
at org.h2.message.DbException.getJdbcSQLException(DbException.java:453)
at org.h2.message.DbException.getJdbcSQLException(DbException.java:429)
at org.h2.message.DbException.get(DbException.java:205)
at org.h2.message.DbException.get(DbException.java:181)
at org.h2.command.ddl.CreateIndex.update(CreateIndex.java:70)
at org.h2.command.CommandContainer.update(CommandContainer.java:198)
at org.h2.command.Command.executeUpdate(Command.java:251)
at org.h2.jdbc.JdbcPreparedStatement.execute(JdbcPreparedStatement.java:240)
at org.jooq.tools.jdbc.DefaultPreparedStatement.execute(DefaultPreparedStatement.java:214)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:458)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:375)
... 39 common frames omitted
By fixing manually the issue around the table name, there is the same unexpected double-quotes around the field `transaction_start`.
### Steps to reproduce the problem
I consider code like:
try (CreateIndexIncludeStep createIndexNotConcurrently = dsl.createIndexIfNotExists(t + "_start_desc")
.on(DSL.table(DSL.name(t)), DSL.field(DSL.name("transaction_start")).desc())) {
String sql = createIndexNotConcurrently.getSQL();
}
### Versions
- jOOQ: 3.14.13
- Java: 1.11
- Database (include vendor): H2
|
1.0
|
Create Index with H2 Dialect generates invalid SQL due to double-quotes - ### Expected behavior
An SQL like:
create index if not exists "aaa_transactions_start_desc" on table_name(transaction_start desc)
### Actual behavior
An SQL Like:
create index if not exists "aaa_transactions_start_desc" on "table_name"("transaction_start" desc)
It is rejected by H2 with:
Caused by: org.h2.jdbc.JdbcSQLSyntaxErrorException: Table "table_name" not found; SQL statement:
create index if not exists "aaa_transactions_start_desc" on "table_name"("transaction_start" desc) [42102-200]
at org.h2.message.DbException.getJdbcSQLException(DbException.java:453)
at org.h2.message.DbException.getJdbcSQLException(DbException.java:429)
at org.h2.message.DbException.get(DbException.java:205)
at org.h2.message.DbException.get(DbException.java:181)
at org.h2.command.ddl.CreateIndex.update(CreateIndex.java:70)
at org.h2.command.CommandContainer.update(CommandContainer.java:198)
at org.h2.command.Command.executeUpdate(Command.java:251)
at org.h2.jdbc.JdbcPreparedStatement.execute(JdbcPreparedStatement.java:240)
at org.jooq.tools.jdbc.DefaultPreparedStatement.execute(DefaultPreparedStatement.java:214)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:458)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:375)
... 39 common frames omitted
By fixing manually the issue around the table name, there is the same unexpected double-quotes around the field `transaction_start`.
### Steps to reproduce the problem
I consider code like:
try (CreateIndexIncludeStep createIndexNotConcurrently = dsl.createIndexIfNotExists(t + "_start_desc")
.on(DSL.table(DSL.name(t)), DSL.field(DSL.name("transaction_start")).desc())) {
String sql = createIndexNotConcurrently.getSQL();
}
### Versions
- jOOQ: 3.14.13
- Java: 1.11
- Database (include vendor): H2
|
defect
|
create index with dialect generates invalid sql due to double quotes expected behavior an sql like create index if not exists aaa transactions start desc on table name transaction start desc actual behavior an sql like create index if not exists aaa transactions start desc on table name transaction start desc it is rejected by with caused by org jdbc jdbcsqlsyntaxerrorexception table table name not found sql statement create index if not exists aaa transactions start desc on table name transaction start desc at org message dbexception getjdbcsqlexception dbexception java at org message dbexception getjdbcsqlexception dbexception java at org message dbexception get dbexception java at org message dbexception get dbexception java at org command ddl createindex update createindex java at org command commandcontainer update commandcontainer java at org command command executeupdate command java at org jdbc jdbcpreparedstatement execute jdbcpreparedstatement java at org jooq tools jdbc defaultpreparedstatement execute defaultpreparedstatement java at org jooq impl abstractquery execute abstractquery java at org jooq impl abstractquery execute abstractquery java common frames omitted by fixing manually the issue around the table name there is the same unexpected double quotes around the field transaction start steps to reproduce the problem i consider code like try createindexincludestep createindexnotconcurrently dsl createindexifnotexists t start desc on dsl table dsl name t dsl field dsl name transaction start desc string sql createindexnotconcurrently getsql versions jooq java database include vendor
| 1
|
252,613
| 8,038,126,304
|
IssuesEvent
|
2018-07-30 14:36:01
|
allenlol/zSpigot-Issues
|
https://api.github.com/repos/allenlol/zSpigot-Issues
|
closed
|
Mobs are not spawning
|
bug low priority
|
Mobs are not spawning in regular world. Including Spawner Eggs, Natural Spawn, Spawner etc.
|
1.0
|
Mobs are not spawning - Mobs are not spawning in regular world. Including Spawner Eggs, Natural Spawn, Spawner etc.
|
non_defect
|
mobs are not spawning mobs are not spawning in regular world including spawner eggs natural spawn spawner etc
| 0
|
70,744
| 23,301,446,659
|
IssuesEvent
|
2022-08-07 11:40:10
|
primefaces/primeng
|
https://api.github.com/repos/primefaces/primeng
|
opened
|
Table: VirtualScroll + Lazy Load shows loadingbody too frequently
|
defect
|
### Describe the bug
This behavior seems a regression from the previous virtualscroll implementation. You can verify in the PrimeNg demo that when scrolling a table with lazy loading and virtual scrolling, the rows very frequently become their loadingbody templates, especially when reaching specific thresholds.
https://user-images.githubusercontent.com/42315498/183288701-23e0c31f-7f2e-408f-8a35-068607d6b4b9.mp4
### Environment
nil
### Reproducer
_No response_
### Angular version
14.1.1
### PrimeNG version
14.0.0
### Build / Runtime
Angular CLI App
### Language
TypeScript
### Node version (for AoT issues node --version)
14.19.3
### Browser(s)
_No response_
### Steps to reproduce the behavior
Please check the video. Scrolling on the simplest table implementation reproduces this issue.
### Expected behavior
I'd expect only the newly loaded rows to behave like that, and to load them before they appear in the view for a better user experience. With a normal implementation like this, the user would see the table very frequently reload its rows, which is unacceptable.
|
1.0
|
Table: VirtualScroll + Lazy Load shows loadingbody too frequently - ### Describe the bug
This behavior seems a regression from the previous virtualscroll implementation. You can verify in the PrimeNg demo that when scrolling a table with lazy loading and virtual scrolling, the rows very frequently become their loadingbody templates, especially when reaching specific thresholds.
https://user-images.githubusercontent.com/42315498/183288701-23e0c31f-7f2e-408f-8a35-068607d6b4b9.mp4
### Environment
nil
### Reproducer
_No response_
### Angular version
14.1.1
### PrimeNG version
14.0.0
### Build / Runtime
Angular CLI App
### Language
TypeScript
### Node version (for AoT issues node --version)
14.19.3
### Browser(s)
_No response_
### Steps to reproduce the behavior
Please check the video. Scrolling on the simplest table implementation reproduces this issue.
### Expected behavior
I'd expect only the newly loaded rows to behave like that, and to load them before they appear in the view for a better user experience. With a normal implementation like this, the user would see the table very frequently reload its rows, which is unacceptable.
|
defect
|
table virtualscroll lazy load shows loadingbody too frequently describe the bug this behavior seems a regression from the previous virtualscroll implementation you can verify in the primeng demo that when scrolling a table with lazy loading and virtual scrolling the rows very frequently become their loadingbody templates especially when reaching specific thresholds environment nil reproducer no response angular version primeng version build runtime angular cli app language typescript node version for aot issues node version browser s no response steps to reproduce the behavior please check the video scrolling on the simplest table implementation reproduces this issue expected behavior i d expect only the newly loaded rows to behave like that and to load them before they appear in the view for a better user experience with a normal implementation like this the user would see the table very frequently reload its rows which is unacceptable
| 1
|
83,013
| 10,318,194,250
|
IssuesEvent
|
2019-08-30 14:26:12
|
excellaco/tcp-angular
|
https://api.github.com/repos/excellaco/tcp-angular
|
closed
|
Code Coverage
|
documentation enhancement
|
- 85%
- Nothing red
- Meaningful tests in each spec file, or comments to where to find examples
- good comments on why to write tests in that manner
|
1.0
|
Code Coverage - - 85%
- Nothing red
- Meaningful tests in each spec file, or comments to where to find examples
- good comments on why to write tests in that manner
|
non_defect
|
code coverage nothing red meaningful tests in each spec file or comments to where to find examples good comments on why to write tests in that manner
| 0
|
57,105
| 15,688,660,044
|
IssuesEvent
|
2021-03-25 14:54:22
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
'the following users may not exist' dialog should only show if a profile lookup is an explicit fail
|
A-Create-Room P1 S-Minor T-Defect
|
general errors and timeouts should not trigger it. it's particularly embarassing if the invited user was proposed by the userdir in the first place.
|
1.0
|
'the following users may not exist' dialog should only show if a profile lookup is an explicit fail - general errors and timeouts should not trigger it. it's particularly embarassing if the invited user was proposed by the userdir in the first place.
|
defect
|
the following users may not exist dialog should only show if a profile lookup is an explicit fail general errors and timeouts should not trigger it it s particularly embarassing if the invited user was proposed by the userdir in the first place
| 1
|
220,977
| 16,991,887,706
|
IssuesEvent
|
2021-06-30 21:50:02
|
strimzi/strimzi-kafka-operator
|
https://api.github.com/repos/strimzi/strimzi-kafka-operator
|
opened
|
Deploying Standalone User Operator CA Secret Format
|
documentation
|
**Suggestion / Problem**
I was trying to deploy the Standalone User Operator against AWS MSK and using TLS as Auth. For this I created an AWS Private certificate authority, and then a Subordinate CA that could issue certificates.
I added them as secrets using
```
kubectl create --save-config --dry-run=client secret generic strimzi-subordinate-cert --from-file=keys/subordinate.crt -o yaml | kubectl apply -f -
kubectl create --save-config --dry-run=client secret generic strimzi-subordinate-key --from-file=keys/subordinate.key -o yaml | kubectl apply -f -
```
and tried my operator but it was failing with a NPE pointing at https://github.com/strimzi/strimzi-kafka-operator/blob/main/operator-common/src/main/java/io/strimzi/operator/cluster/model/Ca.java#L731.
I could not figure out what was going on, and started to look at base64 re-encoding the certificate, so I searched the docs to find that and founhttps://strimzi.io/docs/operators/in-development/using.html#proc-accessing-kafka-using-nodeports-str which casually mentions `kubectl get secret KAFKA-CLUSTER-NAME-cluster-ca-cert -o jsonpath='{.data.ca\.crt}' | base64 -d > ca.crt`. With that I relized the key the secret had to have, and then I found https://github.com/strimzi/strimzi-kafka-operator/blob/main/operator-common/src/main/java/io/strimzi/operator/cluster/model/Ca.java#L85-L86 which confirmed this.
I think it would be really helpful to add a simple hint to this in the linked [document](https://strimzi.io/docs/operators/in-development/deploying.html#deploying-the-user-operator-standalone-str).
**Documentation Link**
https://strimzi.io/docs/operators/in-development/deploying.html#deploying-the-user-operator-standalone-str
|
1.0
|
Deploying Standalone User Operator CA Secret Format - **Suggestion / Problem**
I was trying to deploy the Standalone User Operator against AWS MSK and using TLS as Auth. For this I created an AWS Private certificate authority, and then a Subordinate CA that could issue certificates.
I added them as secrets using
```
kubectl create --save-config --dry-run=client secret generic strimzi-subordinate-cert --from-file=keys/subordinate.crt -o yaml | kubectl apply -f -
kubectl create --save-config --dry-run=client secret generic strimzi-subordinate-key --from-file=keys/subordinate.key -o yaml | kubectl apply -f -
```
and tried my operator but it was failing with a NPE pointing at https://github.com/strimzi/strimzi-kafka-operator/blob/main/operator-common/src/main/java/io/strimzi/operator/cluster/model/Ca.java#L731.
I could not figure out what was going on, and started to look at base64 re-encoding the certificate, so I searched the docs to find that and founhttps://strimzi.io/docs/operators/in-development/using.html#proc-accessing-kafka-using-nodeports-str which casually mentions `kubectl get secret KAFKA-CLUSTER-NAME-cluster-ca-cert -o jsonpath='{.data.ca\.crt}' | base64 -d > ca.crt`. With that I relized the key the secret had to have, and then I found https://github.com/strimzi/strimzi-kafka-operator/blob/main/operator-common/src/main/java/io/strimzi/operator/cluster/model/Ca.java#L85-L86 which confirmed this.
I think it would be really helpful to add a simple hint to this in the linked [document](https://strimzi.io/docs/operators/in-development/deploying.html#deploying-the-user-operator-standalone-str).
**Documentation Link**
https://strimzi.io/docs/operators/in-development/deploying.html#deploying-the-user-operator-standalone-str
|
non_defect
|
deploying standalone user operator ca secret format suggestion problem i was trying to deploy the standalone user operator against aws msk and using tls as auth for this i created an aws private certificate authority and then a subordinate ca that could issue certificates i added them as secrets using kubectl create save config dry run client secret generic strimzi subordinate cert from file keys subordinate crt o yaml kubectl apply f kubectl create save config dry run client secret generic strimzi subordinate key from file keys subordinate key o yaml kubectl apply f and tried my operator but it was failing with a npe pointing at i could not figure out what was going on and started to look at re encoding the certificate so i searched the docs to find that and foun which casually mentions kubectl get secret kafka cluster name cluster ca cert o jsonpath data ca crt d ca crt with that i relized the key the secret had to have and then i found which confirmed this i think it would be really helpful to add a simple hint to this in the linked documentation link
| 0
|
10,815
| 8,182,261,508
|
IssuesEvent
|
2018-08-29 03:56:02
|
AOSC-Dev/aosc-os-abbs
|
https://api.github.com/repos/AOSC-Dev/aosc-os-abbs
|
closed
|
graphicsmagick, imagemagick: Disable PS, EPS, PDF, and XPS coders
|
security to-stable
|
Cross-References: openSUSE-SU-2018:2516-1
https://www.kb.cert.org/vuls/id/332928
Architectural progress
--------------------------------
- [x] AMD64 (`amd64`)
- [x] AArch64 (`arm64`)
- [x] ARMv7 (`armel`)
- [x] PowerPC 64-bit BE (`ppc64`)
- [x] PowerPC 32-bit BE (`powerpc`)
|
True
|
graphicsmagick, imagemagick: Disable PS, EPS, PDF, and XPS coders - Cross-References: openSUSE-SU-2018:2516-1
https://www.kb.cert.org/vuls/id/332928
Architectural progress
--------------------------------
- [x] AMD64 (`amd64`)
- [x] AArch64 (`arm64`)
- [x] ARMv7 (`armel`)
- [x] PowerPC 64-bit BE (`ppc64`)
- [x] PowerPC 32-bit BE (`powerpc`)
|
non_defect
|
graphicsmagick imagemagick disable ps eps pdf and xps coders cross references opensuse su architectural progress armel powerpc bit be powerpc bit be powerpc
| 0
|
2,058
| 2,603,975,662
|
IssuesEvent
|
2015-02-24 19:01:25
|
chrsmith/nishazi6
|
https://api.github.com/repos/chrsmith/nishazi6
|
opened
|
沈阳生殖器软疣
|
auto-migrated Priority-Medium Type-Defect
|
```
沈阳生殖器软疣〓沈陽軍區政治部醫院性病〓TEL:024-31023308��
�成立于1946年,68年專注于性傳播疾病的研究和治療。位于沈�
��市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷史�
��久、設備精良、技術權威、專家云集,是預防、保健、醫療
、科研康復為一體的綜合性醫院。是國家首批公立甲等部隊��
�院、全國首批醫療規范定點單位,是第四軍醫大學、東南大�
��等知名高等院校的教學醫院。曾被中國人民解放軍空軍后勤
部衛生部評為衛生工作先進單位,先后兩次榮立集體二等功��
�
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:17
|
1.0
|
沈阳生殖器软疣 - ```
沈阳生殖器软疣〓沈陽軍區政治部醫院性病〓TEL:024-31023308��
�成立于1946年,68年專注于性傳播疾病的研究和治療。位于沈�
��市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷史�
��久、設備精良、技術權威、專家云集,是預防、保健、醫療
、科研康復為一體的綜合性醫院。是國家首批公立甲等部隊��
�院、全國首批醫療規范定點單位,是第四軍醫大學、東南大�
��等知名高等院校的教學醫院。曾被中國人民解放軍空軍后勤
部衛生部評為衛生工作先進單位,先后兩次榮立集體二等功��
�
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:17
|
defect
|
沈阳生殖器软疣 沈阳生殖器软疣〓沈陽軍區政治部醫院性病〓tel: �� � , 。位于沈� �� 。是一所與新中國同建立共輝煌的歷史� ��久、設備精良、技術權威、專家云集,是預防、保健、醫療 、科研康復為一體的綜合性醫院。是國家首批公立甲等部隊�� �院、全國首批醫療規范定點單位,是第四軍醫大學、東南大� ��等知名高等院校的教學醫院。曾被中國人民解放軍空軍后勤 部衛生部評為衛生工作先進單位,先后兩次榮立集體二等功�� � original issue reported on code google com by gmail com on jun at
| 1
|
13,386
| 3,143,868,269
|
IssuesEvent
|
2015-09-14 09:55:20
|
nikomatsakis/lalrpop
|
https://api.github.com/repos/nikomatsakis/lalrpop
|
closed
|
add ability for grammars to have context values, type/lifetime parameters
|
design-work-needed
|
You should be able to thread context values and types through your grammar. I envision that you should be able to write something like:
```
grammar<'input, T:Eq>(value: &'input T) {
...
}
```
and then reference `'input` and `T` from the types of nonterminals and `value` from the action code. More specifically, I imagine your action code would be given an `&mut` borrow of `value`.
One of the main uses for this is so that when we synthesize a tokenizer, we can have a lifetime (`'input`) corresponding to the input string. I'm not entirely clear though on whether that connects to this? Perhaps the tokenizer should just operate on an iterator over `(usize, char)` pairs (like `str.char_indinces()`) and users can choose to supply the string as context input?
|
1.0
|
add ability for grammars to have context values, type/lifetime parameters - You should be able to thread context values and types through your grammar. I envision that you should be able to write something like:
```
grammar<'input, T:Eq>(value: &'input T) {
...
}
```
and then reference `'input` and `T` from the types of nonterminals and `value` from the action code. More specifically, I imagine your action code would be given an `&mut` borrow of `value`.
One of the main uses for this is so that when we synthesize a tokenizer, we can have a lifetime (`'input`) corresponding to the input string. I'm not entirely clear though on whether that connects to this? Perhaps the tokenizer should just operate on an iterator over `(usize, char)` pairs (like `str.char_indinces()`) and users can choose to supply the string as context input?
|
non_defect
|
add ability for grammars to have context values type lifetime parameters you should be able to thread context values and types through your grammar i envision that you should be able to write something like grammar value input t and then reference input and t from the types of nonterminals and value from the action code more specifically i imagine your action code would be given an mut borrow of value one of the main uses for this is so that when we synthesize a tokenizer we can have a lifetime input corresponding to the input string i m not entirely clear though on whether that connects to this perhaps the tokenizer should just operate on an iterator over usize char pairs like str char indinces and users can choose to supply the string as context input
| 0
|
195,207
| 14,707,802,865
|
IssuesEvent
|
2021-01-04 22:16:48
|
elastic/elasticsearch
|
https://api.github.com/repos/elastic/elasticsearch
|
closed
|
1.2.840.113549.1.1.4 Signature not available for BCJSSE in fips mode
|
:Security/FIPS >test-failure Team:Security
|
<!--
Please fill out the following information, and ensure you have attempted
to reproduce locally
-->
**Build scan**:
https://gradle-enterprise.elastic.co/s/sl7mn5m3gqtts/console-log?task=:client:sniffer:test
**Repro line**:
**Reproduces locally?**:
**Applicable branches**:
**Failure history**:
<!--
Link to build stats and possible indication of when this started failing and how often it fails
<https://build-stats.elastic.co/app/kibana>
-->
**Failure excerpt**:
```
: Test class org.elasticsearch.client.sniff.SniffOnFailureListenerTests |
-- | --
| 2> Dec 26, 2020 5:01:56 AM org.bouncycastle.jsse.provider.ProvKeyManagerFactorySpi getDefaultKeyStore |
| 2> INFO: Initializing empty key store |
| 2> Dec 26, 2020 5:01:56 AM org.bouncycastle.jsse.provider.ProvTrustManagerFactorySpi getDefaultTrustStore |
| 2> INFO: Initializing with trust store at path: /dev/shm/elastic+elasticsearch+master+matrix-java-periodic-fips/ES_RUNTIME_JAVA/java11/nodes/general-purpose/client/sniffer/build/fips-resources/cacerts.bcfks |
| 2> java.lang.ExceptionInInitializerError |
| at __randomizedtesting.SeedInfo.seed([E9613EC44B53D6F:A6FD937FBFBB3E3D]:0) |
| at java.base/javax.crypto.ProviderVerifier.verify(ProviderVerifier.java:128) |
| at java.base/javax.crypto.JceSecurity.verifyProvider(JceSecurity.java:191) |
| at java.base/javax.crypto.JceSecurity.getVerificationResult(JceSecurity.java:217) |
| at java.base/javax.crypto.JceSecurity.getInstance(JceSecurity.java:141) |
| at java.base/javax.crypto.Mac.getInstance(Mac.java:273) |
| at org.bouncycastle.jcajce.provider.ProvBCFKS$BCFIPSKeyStoreSpi.calculateMac(Unknown Source) |
| at org.bouncycastle.jcajce.provider.ProvBCFKS$BCFIPSKeyStoreSpi.verifyMac(Unknown Source) |
| at org.bouncycastle.jcajce.provider.ProvBCFKS$BCFIPSKeyStoreSpi.engineLoad(Unknown Source) |
| at java.base/java.security.KeyStore.load(KeyStore.java:1479) |
| at org.bouncycastle.jsse.provider.ProvTrustManagerFactorySpi.getDefaultTrustStore(ProvTrustManagerFactorySpi.java:98) |
| at org.bouncycastle.jsse.provider.ProvSSLContextSpi.getDefaultTrustManagers(ProvSSLContextSpi.java:302) |
| at org.bouncycastle.jsse.provider.DefaultSSLContextSpi$LazyManagers.<clinit>(DefaultSSLContextSpi.java:57) |
| at org.bouncycastle.jsse.provider.DefaultSSLContextSpi.<init>(DefaultSSLContextSpi.java:86) |
| at org.bouncycastle.jsse.provider.BouncyCastleJsseProvider$7.createInstance(BouncyCastleJsseProvider.java:217) |
| at org.bouncycastle.jsse.provider.BouncyCastleJsseProvider$BcJsseService.newInstance(BouncyCastleJsseProvider.java:373) |
| at java.base/sun.security.jca.GetInstance.getInstance(GetInstance.java:236) |
| at java.base/sun.security.jca.GetInstance.getInstance(GetInstance.java:164) |
| at java.base/javax.net.ssl.SSLContext.getInstance(SSLContext.java:168) |
| at java.base/javax.net.ssl.SSLContext.getDefault(SSLContext.java:99) |
| at org.elasticsearch.client.RestClientBuilder.createHttpClient(RestClientBuilder.java:222) |
| at java.base/java.security.AccessController.doPrivileged(Native Method) |
| at org.elasticsearch.client.RestClientBuilder.build(RestClientBuilder.java:201) |
| at org.elasticsearch.client.sniff.SniffOnFailureListenerTests.testSetSniffer(SniffOnFailureListenerTests.java:49) |
| |
| Caused by: |
| java.lang.SecurityException: Framework jar verification can not be initialized |
| at java.base/javax.crypto.JarVerifier.<clinit>(JarVerifier.java:198) |
| ... 23 more |
| |
| Caused by: |
| java.security.PrivilegedActionException: java.security.NoSuchAlgorithmException: 1.2.840.113549.1.1.4 Signature not available |
| at java.base/java.security.AccessController.doPrivileged(Native Method) |
| at java.base/javax.crypto.JarVerifier.<clinit>(JarVerifier.java:166) |
| ... 23 more |
| |
| Caused by: |
| java.security.NoSuchAlgorithmException: 1.2.840.113549.1.1.4 Signature not available |
| at java.base/java.security.Signature.getInstance(Signature.java:267) |
| at org.bouncycastle.jcajce.provider.X509CertificateObject.getSignatureFromProvider(Unknown Source) |
| at org.bouncycastle.jcajce.provider.X509CertificateObject.verify(Unknown Source) |
| at java.base/javax.crypto.JarVerifier.testSignatures(JarVerifier.java:735) |
| at java.base/javax.crypto.JarVerifier$1.run(JarVerifier.java:192) |
| at java.base/javax.crypto.JarVerifier$1.run(JarVerifier.java:167) |
| ... 25 more
```
It's not obvious what triggers this and it is only occured in certain tests and not always or when starting elasticsearch in fips mode. I presume it has to do with a combination of jdk provider and version. @BigPandaToo has been seeing this locally too IIRC
It looks like we are hitting https://bugs.openjdk.java.net/browse/JDK-8198743 and the appropriate workaround would be to add the SunRsaSign provider too in the list of providers we pack for CI in fips_java.security file, but we should look into why this is not always triggered and the verification of what jar causes this ( I.e. where is the md5withrsa signature used)
|
1.0
|
1.2.840.113549.1.1.4 Signature not available for BCJSSE in fips mode - <!--
Please fill out the following information, and ensure you have attempted
to reproduce locally
-->
**Build scan**:
https://gradle-enterprise.elastic.co/s/sl7mn5m3gqtts/console-log?task=:client:sniffer:test
**Repro line**:
**Reproduces locally?**:
**Applicable branches**:
**Failure history**:
<!--
Link to build stats and possible indication of when this started failing and how often it fails
<https://build-stats.elastic.co/app/kibana>
-->
**Failure excerpt**:
```
: Test class org.elasticsearch.client.sniff.SniffOnFailureListenerTests |
-- | --
| 2> Dec 26, 2020 5:01:56 AM org.bouncycastle.jsse.provider.ProvKeyManagerFactorySpi getDefaultKeyStore |
| 2> INFO: Initializing empty key store |
| 2> Dec 26, 2020 5:01:56 AM org.bouncycastle.jsse.provider.ProvTrustManagerFactorySpi getDefaultTrustStore |
| 2> INFO: Initializing with trust store at path: /dev/shm/elastic+elasticsearch+master+matrix-java-periodic-fips/ES_RUNTIME_JAVA/java11/nodes/general-purpose/client/sniffer/build/fips-resources/cacerts.bcfks |
| 2> java.lang.ExceptionInInitializerError |
| at __randomizedtesting.SeedInfo.seed([E9613EC44B53D6F:A6FD937FBFBB3E3D]:0) |
| at java.base/javax.crypto.ProviderVerifier.verify(ProviderVerifier.java:128) |
| at java.base/javax.crypto.JceSecurity.verifyProvider(JceSecurity.java:191) |
| at java.base/javax.crypto.JceSecurity.getVerificationResult(JceSecurity.java:217) |
| at java.base/javax.crypto.JceSecurity.getInstance(JceSecurity.java:141) |
| at java.base/javax.crypto.Mac.getInstance(Mac.java:273) |
| at org.bouncycastle.jcajce.provider.ProvBCFKS$BCFIPSKeyStoreSpi.calculateMac(Unknown Source) |
| at org.bouncycastle.jcajce.provider.ProvBCFKS$BCFIPSKeyStoreSpi.verifyMac(Unknown Source) |
| at org.bouncycastle.jcajce.provider.ProvBCFKS$BCFIPSKeyStoreSpi.engineLoad(Unknown Source) |
| at java.base/java.security.KeyStore.load(KeyStore.java:1479) |
| at org.bouncycastle.jsse.provider.ProvTrustManagerFactorySpi.getDefaultTrustStore(ProvTrustManagerFactorySpi.java:98) |
| at org.bouncycastle.jsse.provider.ProvSSLContextSpi.getDefaultTrustManagers(ProvSSLContextSpi.java:302) |
| at org.bouncycastle.jsse.provider.DefaultSSLContextSpi$LazyManagers.<clinit>(DefaultSSLContextSpi.java:57) |
| at org.bouncycastle.jsse.provider.DefaultSSLContextSpi.<init>(DefaultSSLContextSpi.java:86) |
| at org.bouncycastle.jsse.provider.BouncyCastleJsseProvider$7.createInstance(BouncyCastleJsseProvider.java:217) |
| at org.bouncycastle.jsse.provider.BouncyCastleJsseProvider$BcJsseService.newInstance(BouncyCastleJsseProvider.java:373) |
| at java.base/sun.security.jca.GetInstance.getInstance(GetInstance.java:236) |
| at java.base/sun.security.jca.GetInstance.getInstance(GetInstance.java:164) |
| at java.base/javax.net.ssl.SSLContext.getInstance(SSLContext.java:168) |
| at java.base/javax.net.ssl.SSLContext.getDefault(SSLContext.java:99) |
| at org.elasticsearch.client.RestClientBuilder.createHttpClient(RestClientBuilder.java:222) |
| at java.base/java.security.AccessController.doPrivileged(Native Method) |
| at org.elasticsearch.client.RestClientBuilder.build(RestClientBuilder.java:201) |
| at org.elasticsearch.client.sniff.SniffOnFailureListenerTests.testSetSniffer(SniffOnFailureListenerTests.java:49) |
| |
| Caused by: |
| java.lang.SecurityException: Framework jar verification can not be initialized |
| at java.base/javax.crypto.JarVerifier.<clinit>(JarVerifier.java:198) |
| ... 23 more |
| |
| Caused by: |
| java.security.PrivilegedActionException: java.security.NoSuchAlgorithmException: 1.2.840.113549.1.1.4 Signature not available |
| at java.base/java.security.AccessController.doPrivileged(Native Method) |
| at java.base/javax.crypto.JarVerifier.<clinit>(JarVerifier.java:166) |
| ... 23 more |
| |
| Caused by: |
| java.security.NoSuchAlgorithmException: 1.2.840.113549.1.1.4 Signature not available |
| at java.base/java.security.Signature.getInstance(Signature.java:267) |
| at org.bouncycastle.jcajce.provider.X509CertificateObject.getSignatureFromProvider(Unknown Source) |
| at org.bouncycastle.jcajce.provider.X509CertificateObject.verify(Unknown Source) |
| at java.base/javax.crypto.JarVerifier.testSignatures(JarVerifier.java:735) |
| at java.base/javax.crypto.JarVerifier$1.run(JarVerifier.java:192) |
| at java.base/javax.crypto.JarVerifier$1.run(JarVerifier.java:167) |
| ... 25 more
```
It's not obvious what triggers this and it is only occured in certain tests and not always or when starting elasticsearch in fips mode. I presume it has to do with a combination of jdk provider and version. @BigPandaToo has been seeing this locally too IIRC
It looks like we are hitting https://bugs.openjdk.java.net/browse/JDK-8198743 and the appropriate workaround would be to add the SunRsaSign provider too in the list of providers we pack for CI in fips_java.security file, but we should look into why this is not always triggered and the verification of what jar causes this ( I.e. where is the md5withrsa signature used)
|
non_defect
|
signature not available for bcjsse in fips mode please fill out the following information and ensure you have attempted to reproduce locally build scan repro line reproduces locally applicable branches failure history link to build stats and possible indication of when this started failing and how often it fails failure excerpt test class org elasticsearch client sniff sniffonfailurelistenertests dec am org bouncycastle jsse provider provkeymanagerfactoryspi getdefaultkeystore info initializing empty key store dec am org bouncycastle jsse provider provtrustmanagerfactoryspi getdefaulttruststore info initializing with trust store at path dev shm elastic elasticsearch master matrix java periodic fips es runtime java nodes general purpose client sniffer build fips resources cacerts bcfks java lang exceptionininitializererror at randomizedtesting seedinfo seed at java base javax crypto providerverifier verify providerverifier java at java base javax crypto jcesecurity verifyprovider jcesecurity java at java base javax crypto jcesecurity getverificationresult jcesecurity java at java base javax crypto jcesecurity getinstance jcesecurity java at java base javax crypto mac getinstance mac java at org bouncycastle jcajce provider provbcfks bcfipskeystorespi calculatemac unknown source at org bouncycastle jcajce provider provbcfks bcfipskeystorespi verifymac unknown source at org bouncycastle jcajce provider provbcfks bcfipskeystorespi engineload unknown source at java base java security keystore load keystore java at org bouncycastle jsse provider provtrustmanagerfactoryspi getdefaulttruststore provtrustmanagerfactoryspi java at org bouncycastle jsse provider provsslcontextspi getdefaulttrustmanagers provsslcontextspi java at org bouncycastle jsse provider defaultsslcontextspi lazymanagers defaultsslcontextspi java at org bouncycastle jsse provider defaultsslcontextspi defaultsslcontextspi java at org bouncycastle jsse provider bouncycastlejsseprovider createinstance bouncycastlejsseprovider java at org bouncycastle jsse provider bouncycastlejsseprovider bcjsseservice newinstance bouncycastlejsseprovider java at java base sun security jca getinstance getinstance getinstance java at java base sun security jca getinstance getinstance getinstance java at java base javax net ssl sslcontext getinstance sslcontext java at java base javax net ssl sslcontext getdefault sslcontext java at org elasticsearch client restclientbuilder createhttpclient restclientbuilder java at java base java security accesscontroller doprivileged native method at org elasticsearch client restclientbuilder build restclientbuilder java at org elasticsearch client sniff sniffonfailurelistenertests testsetsniffer sniffonfailurelistenertests java caused by java lang securityexception framework jar verification can not be initialized at java base javax crypto jarverifier jarverifier java more caused by java security privilegedactionexception java security nosuchalgorithmexception signature not available at java base java security accesscontroller doprivileged native method at java base javax crypto jarverifier jarverifier java more caused by java security nosuchalgorithmexception signature not available at java base java security signature getinstance signature java at org bouncycastle jcajce provider getsignaturefromprovider unknown source at org bouncycastle jcajce provider verify unknown source at java base javax crypto jarverifier testsignatures jarverifier java at java base javax crypto jarverifier run jarverifier java at java base javax crypto jarverifier run jarverifier java more it s not obvious what triggers this and it is only occured in certain tests and not always or when starting elasticsearch in fips mode i presume it has to do with a combination of jdk provider and version bigpandatoo has been seeing this locally too iirc it looks like we are hitting and the appropriate workaround would be to add the sunrsasign provider too in the list of providers we pack for ci in fips java security file but we should look into why this is not always triggered and the verification of what jar causes this i e where is the signature used
| 0
|
152,570
| 5,849,272,240
|
IssuesEvent
|
2017-05-10 23:16:50
|
VulcanDev/FinalProjectICS4U
|
https://api.github.com/repos/VulcanDev/FinalProjectICS4U
|
closed
|
Need framework for map generation.
|
addition high priority
|
Need a class to handle the generation of a 2D array map using a coordinate grid to place different stars.
Don't need to worry about the actual random generation of stars, etc. That can be managed later, just need the system in place to actually create the map right now.
|
1.0
|
Need framework for map generation. - Need a class to handle the generation of a 2D array map using a coordinate grid to place different stars.
Don't need to worry about the actual random generation of stars, etc. That can be managed later, just need the system in place to actually create the map right now.
|
non_defect
|
need framework for map generation need a class to handle the generation of a array map using a coordinate grid to place different stars don t need to worry about the actual random generation of stars etc that can be managed later just need the system in place to actually create the map right now
| 0
|
33,570
| 7,166,451,778
|
IssuesEvent
|
2018-01-29 17:15:40
|
mozilla-services/screenshots
|
https://api.github.com/repos/mozilla-services/screenshots
|
closed
|
registrationInfo is undefined Error
|
defect firefox
|
This happened on Januar 13th with the nightly from 13th or 12th or 11th. (sadly didn't write down the version number and forgot to report instantly)
EDIT: I just pressed the screenshot button and got the tutorial with this error on the bottomright.
Maybe it happened because of my mouse. (sometimes it doubleclicks, I still have to investigate that)
|
1.0
|
registrationInfo is undefined Error - 
This happened on Januar 13th with the nightly from 13th or 12th or 11th. (sadly didn't write down the version number and forgot to report instantly)
EDIT: I just pressed the screenshot button and got the tutorial with this error on the bottomright.
Maybe it happened because of my mouse. (sometimes it doubleclicks, I still have to investigate that)
|
defect
|
registrationinfo is undefined error this happened on januar with the nightly from or or sadly didn t write down the version number and forgot to report instantly edit i just pressed the screenshot button and got the tutorial with this error on the bottomright maybe it happened because of my mouse sometimes it doubleclicks i still have to investigate that
| 1
|
54,477
| 13,728,853,995
|
IssuesEvent
|
2020-10-04 13:33:37
|
combatopera/aridity
|
https://api.github.com/repos/combatopera/aridity
|
opened
|
refactoring opportunities post v36
|
defect
|
review changes between 35 and 36, there is some duplication and perhaps other low-hanging improvements
|
1.0
|
refactoring opportunities post v36 - review changes between 35 and 36, there is some duplication and perhaps other low-hanging improvements
|
defect
|
refactoring opportunities post review changes between and there is some duplication and perhaps other low hanging improvements
| 1
|
731,466
| 25,217,564,449
|
IssuesEvent
|
2022-11-14 10:16:45
|
authelia/authelia
|
https://api.github.com/repos/authelia/authelia
|
opened
|
LDAP + groups cause bad gateway
|
priority/4/normal type/bug/unconfirmed status/needs-triage
|
### Version
v4.37.1
### Deployment Method
Docker
### Reverse Proxy
Traefik
### Reverse Proxy Version
2.5.7
### Description
When I access a domain protected by a subject group subject rule, I get a bad gateway error. When I use a file backend instead of the LDAP server it works. When I remove the subject rule, it also works. Authelia reads the group from the LDAP server correctly.
### Reproduction
Here is my traefik middleware file:
```
http:
middlewares:
authelia:
forwardAuth:
address: http://authelia:9091/api/verify?rd=https%3A%2F%2Fauth.example.com%2F
trustForwardHeader: true
authResponseHeaders:
- "Remote-User"
- "Remote-Groups"
- "Remote-Email"
- "Remote-Name"
authelia-basic:
forwardAuth:
address: http://authelia:9091/api/verify?auth=basic
trustForwardHeader: true
authResponseHeaders:
- "Remote-User"
- "Remote-Groups"
- "Remote-Email"
- "Remote-Name"
securityHeaders:
headers:
customResponseHeaders:
X-Robots-Tag: "none,noarchive,nosnippet,notranslate,noimageindex"
server: ""
X-Forwarded-Proto: "https"
sslProxyHeaders:
X-Forwarded-Proto: https
referrerPolicy: "strict-origin-when-cross-origin"
hostsProxyHeaders:
- "X-Forwarded-Host"
customRequestHeaders:
X-Forwarded-Proto: "https"
contentTypeNosniff: true
browserXssFilter: true
forceSTSHeader: true
stsIncludeSubdomains: true
stsSeconds: 63072000
stsPreload: true
tls:
options:
default:
minVersion: VersionTLS12
cipherSuites:
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305
- TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305
```
### Expectations
_No response_
### Logs
```shell
time="2022-11-14T10:49:45+01:00" level=debug msg="Check authorization of subject username= groups= ip=157.97.134.67 and object https://flame.jokaendler.eu/ (method GET)."
time="2022-11-14T10:49:45+01:00" level=info msg="Access to https://flame.jokaendler.eu/ (method GET) is not authorized to user <anonymous>, responding with status code 302 with location redirect to https://auth.jokaendler.eu/?rd=https%3A%2F%2Fflame.jokaendler.eu%2F&rm=GET" method=GET path=/api/verify remote_ip=157.97.134.67
```
### Configuration
```yaml
authentication_backend:
password_reset:
disable: true
refresh_interval: 5m
file:
path: /config/users_database.yml #this is where your authorized users are stored
password:
algorithm: argon2id
iterations: 1
key_length: 32
salt_length: 16
memory: 1024
parallelism: 8
# ldap:
# implementation: custom
# url: ldap://openldap:389
# timeout: 5s
# start_tls: false
# tls:
# server_name: openldap.jokaendler.eu
# skip_verify: true
# minimum_version: TLS1.2
# base_dn: DC=example,DC=com
# additional_users_dn: OU=users
# users_filter: (&(|({username_attribute}={input})({mail_attribute}={input}))(objectClass=person))
# username_attribute: uid
# mail_attribute: Email
# display_name_attribute: displayName
# additional_groups_dn: OU=groups
# groups_filter: (&(member={dn})(objectClass=groupOfNames))
# group_name_attribute: cn
# user: cn=admin,DC=example,DC=com
# password: "…"
access_control:
default_policy: deny
rules:
- domain: "auth.example.com" #This should be your authentication URL
policy: bypass
- domain:
- "api.example.com"
policy: bypass
# admin rights:
- domain:
- "flame.example.com“
policy: two_factor
subject:
- ['group:admins']
session:
name: authelia_session
secret: "…"
expiration: 3600 # 1 hour
inactivity: 300 # 5 minutes
remember_me_duration: 24h
domain: example.com # Should match whatever your root protected domain is
redis:
host: redis
port: 6379
password: "…"
database_index: 0
maximum_active_connections: 10
minimum_idle_connections: 0
regulation:
max_retries: 3
find_time: 10m
ban_time: 4h
storage:
local:
path: /config/db.sqlite3 #this is your databse. You could use a mysql database if you wanted, but we're going to use this one.
encryption_key: "…"
```
### Documentation
_No response_
|
1.0
|
LDAP + groups cause bad gateway - ### Version
v4.37.1
### Deployment Method
Docker
### Reverse Proxy
Traefik
### Reverse Proxy Version
2.5.7
### Description
When I access a domain protected by a subject group subject rule, I get a bad gateway error. When I use a file backend instead of the LDAP server it works. When I remove the subject rule, it also works. Authelia reads the group from the LDAP server correctly.
### Reproduction
Here is my traefik middleware file:
```
http:
middlewares:
authelia:
forwardAuth:
address: http://authelia:9091/api/verify?rd=https%3A%2F%2Fauth.example.com%2F
trustForwardHeader: true
authResponseHeaders:
- "Remote-User"
- "Remote-Groups"
- "Remote-Email"
- "Remote-Name"
authelia-basic:
forwardAuth:
address: http://authelia:9091/api/verify?auth=basic
trustForwardHeader: true
authResponseHeaders:
- "Remote-User"
- "Remote-Groups"
- "Remote-Email"
- "Remote-Name"
securityHeaders:
headers:
customResponseHeaders:
X-Robots-Tag: "none,noarchive,nosnippet,notranslate,noimageindex"
server: ""
X-Forwarded-Proto: "https"
sslProxyHeaders:
X-Forwarded-Proto: https
referrerPolicy: "strict-origin-when-cross-origin"
hostsProxyHeaders:
- "X-Forwarded-Host"
customRequestHeaders:
X-Forwarded-Proto: "https"
contentTypeNosniff: true
browserXssFilter: true
forceSTSHeader: true
stsIncludeSubdomains: true
stsSeconds: 63072000
stsPreload: true
tls:
options:
default:
minVersion: VersionTLS12
cipherSuites:
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305
- TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305
```
### Expectations
_No response_
### Logs
```shell
time="2022-11-14T10:49:45+01:00" level=debug msg="Check authorization of subject username= groups= ip=157.97.134.67 and object https://flame.jokaendler.eu/ (method GET)."
time="2022-11-14T10:49:45+01:00" level=info msg="Access to https://flame.jokaendler.eu/ (method GET) is not authorized to user <anonymous>, responding with status code 302 with location redirect to https://auth.jokaendler.eu/?rd=https%3A%2F%2Fflame.jokaendler.eu%2F&rm=GET" method=GET path=/api/verify remote_ip=157.97.134.67
```
### Configuration
```yaml
authentication_backend:
password_reset:
disable: true
refresh_interval: 5m
file:
path: /config/users_database.yml #this is where your authorized users are stored
password:
algorithm: argon2id
iterations: 1
key_length: 32
salt_length: 16
memory: 1024
parallelism: 8
# ldap:
# implementation: custom
# url: ldap://openldap:389
# timeout: 5s
# start_tls: false
# tls:
# server_name: openldap.jokaendler.eu
# skip_verify: true
# minimum_version: TLS1.2
# base_dn: DC=example,DC=com
# additional_users_dn: OU=users
# users_filter: (&(|({username_attribute}={input})({mail_attribute}={input}))(objectClass=person))
# username_attribute: uid
# mail_attribute: Email
# display_name_attribute: displayName
# additional_groups_dn: OU=groups
# groups_filter: (&(member={dn})(objectClass=groupOfNames))
# group_name_attribute: cn
# user: cn=admin,DC=example,DC=com
# password: "…"
access_control:
default_policy: deny
rules:
- domain: "auth.example.com" #This should be your authentication URL
policy: bypass
- domain:
- "api.example.com"
policy: bypass
# admin rights:
- domain:
- "flame.example.com“
policy: two_factor
subject:
- ['group:admins']
session:
name: authelia_session
secret: "…"
expiration: 3600 # 1 hour
inactivity: 300 # 5 minutes
remember_me_duration: 24h
domain: example.com # Should match whatever your root protected domain is
redis:
host: redis
port: 6379
password: "…"
database_index: 0
maximum_active_connections: 10
minimum_idle_connections: 0
regulation:
max_retries: 3
find_time: 10m
ban_time: 4h
storage:
local:
path: /config/db.sqlite3 #this is your databse. You could use a mysql database if you wanted, but we're going to use this one.
encryption_key: "…"
```
### Documentation
_No response_
|
non_defect
|
ldap groups cause bad gateway version deployment method docker reverse proxy traefik reverse proxy version description when i access a domain protected by a subject group subject rule i get a bad gateway error when i use a file backend instead of the ldap server it works when i remove the subject rule it also works authelia reads the group from the ldap server correctly reproduction here is my traefik middleware file http middlewares authelia forwardauth address trustforwardheader true authresponseheaders remote user remote groups remote email remote name authelia basic forwardauth address trustforwardheader true authresponseheaders remote user remote groups remote email remote name securityheaders headers customresponseheaders x robots tag none noarchive nosnippet notranslate noimageindex server x forwarded proto https sslproxyheaders x forwarded proto https referrerpolicy strict origin when cross origin hostsproxyheaders x forwarded host customrequestheaders x forwarded proto https contenttypenosniff true browserxssfilter true forcestsheader true stsincludesubdomains true stsseconds stspreload true tls options default minversion ciphersuites tls ecdhe ecdsa with aes gcm tls ecdhe rsa with aes gcm tls ecdhe ecdsa with aes gcm tls ecdhe rsa with aes gcm tls ecdhe ecdsa with tls ecdhe rsa with expectations no response logs shell time level debug msg check authorization of subject username groups ip and object method get time level info msg access to method get is not authorized to user responding with status code with location redirect to method get path api verify remote ip configuration yaml authentication backend password reset disable true refresh interval file path config users database yml this is where your authorized users are stored password algorithm iterations key length salt length memory parallelism ldap implementation custom url ldap openldap timeout start tls false tls server name openldap jokaendler eu skip verify true minimum version base dn dc example dc com additional users dn ou users users filter username attribute input mail attribute input objectclass person username attribute uid mail attribute email display name attribute displayname additional groups dn ou groups groups filter member dn objectclass groupofnames group name attribute cn user cn admin dc example dc com password … access control default policy deny rules domain auth example com this should be your authentication url policy bypass domain api example com policy bypass admin rights domain flame example com“ policy two factor subject session name authelia session secret … expiration hour inactivity minutes remember me duration domain example com should match whatever your root protected domain is redis host redis port password … database index maximum active connections minimum idle connections regulation max retries find time ban time storage local path config db this is your databse you could use a mysql database if you wanted but we re going to use this one encryption key … documentation no response
| 0
|
57,345
| 15,731,098,981
|
IssuesEvent
|
2021-03-29 16:40:01
|
danmar/testissues
|
https://api.github.com/repos/danmar/testissues
|
opened
|
false positive::memory leak (Trac #354)
|
False positive Incomplete Migration Migrated from Trac defect hyd_danmar
|
Migrated from https://trac.cppcheck.net/ticket/354
```json
{
"status": "closed",
"changetime": "2009-06-05T10:42:12",
"description": "Hi friends,\n\ni checked the sources of the xvidcore-1.2.2. \ncppcheck printed a false postive on following source code:\n\n{{{\n/*****************************************************************************\n * xvid_malloc\n *\n * This function allocates 'size' bytes (usable by the user) on the heap and\n * takes care of the requested 'alignment'.\n * In order to align the allocated memory block, the xvid_malloc allocates\n * 'size' bytes + 'alignment' bytes. So try to keep alignment very small\n * when allocating small pieces of memory.\n *\n * NB : a block allocated by xvid_malloc _must_ be freed with xvid_free\n * (the libc free will return an error)\n *\n * Returned value : - NULL on error\n * - Pointer to the allocated aligned block\n *\n ****************************************************************************/\n\nvoid *\nxvid_malloc(size_t size,\n\t\t\tuint8_t alignment)\n{\n\tuint8_t *mem_ptr;\n\n\tif (!alignment) {\n\n\t\t/* We have not to satisfy any alignment */\n\t\tif ((mem_ptr = (uint8_t *) malloc(size + 1)) != NULL) {\n\n\t\t\t/* Store (mem_ptr - \"real allocated memory\") in *(mem_ptr-1) */\n\t\t\t*mem_ptr = (uint8_t)1;\n\n\t\t\t/* Return the mem_ptr pointer */\n\t\t\treturn ((void *)(mem_ptr+1));\n\t\t}\n\t} else {\n\t\tuint8_t *tmp;\n\n\t\t/* Allocate the required size memory + alignment so we\n\t\t * can realign the data if necessary */\n\t\tif ((tmp = (uint8_t *) malloc(size + alignment)) != NULL) {\n\n\t\t\t/* Align the tmp pointer */\n\t\t\tmem_ptr =\n\t\t\t\t(uint8_t *) ((ptr_t) (tmp + alignment - 1) &\n\t\t\t\t\t\t\t (~(ptr_t) (alignment - 1)));\n\n\t\t\t/* Special case where malloc have already satisfied the alignment\n\t\t\t * We must add alignment to mem_ptr because we must store\n\t\t\t * (mem_ptr - tmp) in *(mem_ptr-1)\n\t\t\t * If we do not add alignment to mem_ptr then *(mem_ptr-1) points\n\t\t\t * to a forbidden memory space */\n\t\t\tif (mem_ptr == tmp)\n\t\t\t\tmem_ptr += alignment;\n\n\t\t\t/* (mem_ptr - tmp) is stored in *(mem_ptr-1) so we are able to retrieve\n\t\t\t * the real malloc block allocated and free it in xvid_free */\n\t\t\t*(mem_ptr - 1) = (uint8_t) (mem_ptr - tmp);\n\n\t\t\t/* Return the aligned pointer */\n\t\t\treturn ((void *)mem_ptr);\n\t\t}\n\t}\n\n\treturn(NULL);\n}\n\n}}}\n\nThis is a function to allocate memory from xvidcore/src/utils/mem_align.c.\n\ncppcheck prints\n\n{{{\n[xvidcore/src/utils/mem_align.c:62]: (error) Memory leak: mem_ptr\n}}}\n\nBest regards\n\nMartin\n\n\n",
"reporter": "ettlmartin",
"cc": "mfranz",
"resolution": "fixed",
"_ts": "1244198532000000",
"component": "False positive",
"summary": "false positive::memory leak",
"priority": "",
"keywords": "",
"time": "2009-06-03T23:30:05",
"milestone": "1.33",
"owner": "hyd_danmar",
"type": "defect"
}
```
|
1.0
|
false positive::memory leak (Trac #354) - Migrated from https://trac.cppcheck.net/ticket/354
```json
{
"status": "closed",
"changetime": "2009-06-05T10:42:12",
"description": "Hi friends,\n\ni checked the sources of the xvidcore-1.2.2. \ncppcheck printed a false postive on following source code:\n\n{{{\n/*****************************************************************************\n * xvid_malloc\n *\n * This function allocates 'size' bytes (usable by the user) on the heap and\n * takes care of the requested 'alignment'.\n * In order to align the allocated memory block, the xvid_malloc allocates\n * 'size' bytes + 'alignment' bytes. So try to keep alignment very small\n * when allocating small pieces of memory.\n *\n * NB : a block allocated by xvid_malloc _must_ be freed with xvid_free\n * (the libc free will return an error)\n *\n * Returned value : - NULL on error\n * - Pointer to the allocated aligned block\n *\n ****************************************************************************/\n\nvoid *\nxvid_malloc(size_t size,\n\t\t\tuint8_t alignment)\n{\n\tuint8_t *mem_ptr;\n\n\tif (!alignment) {\n\n\t\t/* We have not to satisfy any alignment */\n\t\tif ((mem_ptr = (uint8_t *) malloc(size + 1)) != NULL) {\n\n\t\t\t/* Store (mem_ptr - \"real allocated memory\") in *(mem_ptr-1) */\n\t\t\t*mem_ptr = (uint8_t)1;\n\n\t\t\t/* Return the mem_ptr pointer */\n\t\t\treturn ((void *)(mem_ptr+1));\n\t\t}\n\t} else {\n\t\tuint8_t *tmp;\n\n\t\t/* Allocate the required size memory + alignment so we\n\t\t * can realign the data if necessary */\n\t\tif ((tmp = (uint8_t *) malloc(size + alignment)) != NULL) {\n\n\t\t\t/* Align the tmp pointer */\n\t\t\tmem_ptr =\n\t\t\t\t(uint8_t *) ((ptr_t) (tmp + alignment - 1) &\n\t\t\t\t\t\t\t (~(ptr_t) (alignment - 1)));\n\n\t\t\t/* Special case where malloc have already satisfied the alignment\n\t\t\t * We must add alignment to mem_ptr because we must store\n\t\t\t * (mem_ptr - tmp) in *(mem_ptr-1)\n\t\t\t * If we do not add alignment to mem_ptr then *(mem_ptr-1) points\n\t\t\t * to a forbidden memory space */\n\t\t\tif (mem_ptr == tmp)\n\t\t\t\tmem_ptr += alignment;\n\n\t\t\t/* (mem_ptr - tmp) is stored in *(mem_ptr-1) so we are able to retrieve\n\t\t\t * the real malloc block allocated and free it in xvid_free */\n\t\t\t*(mem_ptr - 1) = (uint8_t) (mem_ptr - tmp);\n\n\t\t\t/* Return the aligned pointer */\n\t\t\treturn ((void *)mem_ptr);\n\t\t}\n\t}\n\n\treturn(NULL);\n}\n\n}}}\n\nThis is a function to allocate memory from xvidcore/src/utils/mem_align.c.\n\ncppcheck prints\n\n{{{\n[xvidcore/src/utils/mem_align.c:62]: (error) Memory leak: mem_ptr\n}}}\n\nBest regards\n\nMartin\n\n\n",
"reporter": "ettlmartin",
"cc": "mfranz",
"resolution": "fixed",
"_ts": "1244198532000000",
"component": "False positive",
"summary": "false positive::memory leak",
"priority": "",
"keywords": "",
"time": "2009-06-03T23:30:05",
"milestone": "1.33",
"owner": "hyd_danmar",
"type": "defect"
}
```
|
defect
|
false positive memory leak trac migrated from json status closed changetime description hi friends n ni checked the sources of the xvidcore ncppcheck printed a false postive on following source code n n n n xvid malloc n n this function allocates size bytes usable by the user on the heap and n takes care of the requested alignment n in order to align the allocated memory block the xvid malloc allocates n size bytes alignment bytes so try to keep alignment very small n when allocating small pieces of memory n n nb a block allocated by xvid malloc must be freed with xvid free n the libc free will return an error n n returned value null on error n pointer to the allocated aligned block n n n nvoid nxvid malloc size t size n t t t alignment n n t mem ptr n n tif alignment n n t t we have not to satisfy any alignment n t tif mem ptr t malloc size null n n t t t store mem ptr real allocated memory in mem ptr n t t t mem ptr t n n t t t return the mem ptr pointer n t t treturn void mem ptr n t t n t else n t t tmp n n t t allocate the required size memory alignment so we n t t can realign the data if necessary n t tif tmp t malloc size alignment null n n t t t align the tmp pointer n t t tmem ptr n t t t t t ptr t tmp alignment n t t t t t t t ptr t alignment n n t t t special case where malloc have already satisfied the alignment n t t t we must add alignment to mem ptr because we must store n t t t mem ptr tmp in mem ptr n t t t if we do not add alignment to mem ptr then mem ptr points n t t t to a forbidden memory space n t t tif mem ptr tmp n t t t tmem ptr alignment n n t t t mem ptr tmp is stored in mem ptr so we are able to retrieve n t t t the real malloc block allocated and free it in xvid free n t t t mem ptr t mem ptr tmp n n t t t return the aligned pointer n t t treturn void mem ptr n t t n t n n treturn null n n n n nthis is a function to allocate memory from xvidcore src utils mem align c n ncppcheck prints n n n error memory leak mem ptr n n nbest regards n nmartin n n n reporter ettlmartin cc mfranz resolution fixed ts component false positive summary false positive memory leak priority keywords time milestone owner hyd danmar type defect
| 1
|
252,559
| 8,037,638,506
|
IssuesEvent
|
2018-07-30 13:17:12
|
TrailblazingTech/LSOA
|
https://api.github.com/repos/TrailblazingTech/LSOA
|
opened
|
Observation Screen: "Use Last Sample" does not show the previous sample (although it saves to the db correctly)
|
Effort: Medium Priority: High nit/bug
|
1.0
|
Observation Screen: "Use Last Sample" does not show the previous sample (although it saves to the db correctly) - https://www.dropbox.com/s/1utoc2fiol8y9zq/Screenshot%202018-07-30%2009.13.11.png?dl=0
When you click "Use Last Sample", the image or video from the previous sample does not load properly. I re-wrote a lot of the state machine logic behind the video/image/annotated image on this page. It probably just needs to be wired up correctly to hide/show the proper elements.
|
non_defect
|
observation screen use last sample does not show the previous sample although it saves to the db correctly when you click use last sample the image or video from the previous sample does not load properly i re wrote a lot of the state machine logic behind the video image annotated image on this page it probably just needs to be wired up correctly to hide show the proper elements
| 0
|
|
56,915
| 15,442,268,679
|
IssuesEvent
|
2021-03-08 07:26:46
|
SAP/fundamental-ngx
|
https://api.github.com/repos/SAP/fundamental-ngx
|
opened
|
segmentedButton: buttons with icon examples not availalble.
|
Defect Hunting core
|
#### Is this a bug, enhancement, or feature request?
bug
#### Briefly describe your proposal.
Segmented button with icon example not available. as per the fiori spec below highlighted examlples are not available.
<img width="330" alt="Screenshot 2021-03-08 at 12 53 24 PM" src="https://user-images.githubusercontent.com/53534379/110288068-758c6f00-800d-11eb-8fb0-c9f8fbb4d8ad.png">
#### Which versions of Angular and Fundamental Library for Angular are affected? (If this is a feature request, use current version.)
#### If this is a bug, please provide steps for reproducing it.
Step1: Open URL (https://fundamental-ngx.netlify.app/#/core/segmentedButton)
step 2: scroll to see the example and found that button with icon missing.
#### Please provide relevant source code if applicable.
#### Is there anything else we should know?
|
1.0
|
segmentedButton: buttons with icon examples not availalble. - #### Is this a bug, enhancement, or feature request?
bug
#### Briefly describe your proposal.
Segmented button with icon example not available. as per the fiori spec below highlighted examlples are not available.
<img width="330" alt="Screenshot 2021-03-08 at 12 53 24 PM" src="https://user-images.githubusercontent.com/53534379/110288068-758c6f00-800d-11eb-8fb0-c9f8fbb4d8ad.png">
#### Which versions of Angular and Fundamental Library for Angular are affected? (If this is a feature request, use current version.)
#### If this is a bug, please provide steps for reproducing it.
Step1: Open URL (https://fundamental-ngx.netlify.app/#/core/segmentedButton)
step 2: scroll to see the example and found that button with icon missing.
#### Please provide relevant source code if applicable.
#### Is there anything else we should know?
|
defect
|
segmentedbutton buttons with icon examples not availalble is this a bug enhancement or feature request bug briefly describe your proposal segmented button with icon example not available as per the fiori spec below highlighted examlples are not available img width alt screenshot at pm src which versions of angular and fundamental library for angular are affected if this is a feature request use current version if this is a bug please provide steps for reproducing it open url step scroll to see the example and found that button with icon missing please provide relevant source code if applicable is there anything else we should know
| 1
|
175,371
| 6,550,240,764
|
IssuesEvent
|
2017-09-05 10:12:36
|
OpenRefine/OpenRefine
|
https://api.github.com/repos/OpenRefine/OpenRefine
|
closed
|
Merge ColumnGroup model and Protograph
|
component-Logic enhancement imported overlay-model priority-Low
|
_Original author: iainsproat (June 17, 2010 11:08:53)_
The ColumnGroup model and the Schema alignment protograph are both tree structures describing the relationship between columns. These models could be merged.
Benefit:
When importing data with a tree structure, such as an Xml file or Json, the columngroup model is automatically created. When opening the schema alignment dialog, the column relationship is shown as flat - all the tree data is lost and has to be recreated by the user. If merged the tree would be retained.
Problems:
If the combined protograph is altered in the schema alignment dialog, then the exported data would not match the structure of the original as the columngroup is also changed. This may not be intended.
_Original issue: http://code.google.com/p/google-refine/issues/detail?id=76_
## <bountysource-plugin>
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/62869-merge-columngroup-model-and-protograph?utm_campaign=plugin&utm_content=tracker%2F32795&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F32795&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
1.0
|
Merge ColumnGroup model and Protograph - _Original author: iainsproat (June 17, 2010 11:08:53)_
The ColumnGroup model and the Schema alignment protograph are both tree structures describing the relationship between columns. These models could be merged.
Benefit:
When importing data with a tree structure, such as an Xml file or Json, the columngroup model is automatically created. When opening the schema alignment dialog, the column relationship is shown as flat - all the tree data is lost and has to be recreated by the user. If merged the tree would be retained.
Problems:
If the combined protograph is altered in the schema alignment dialog, then the exported data would not match the structure of the original as the columngroup is also changed. This may not be intended.
_Original issue: http://code.google.com/p/google-refine/issues/detail?id=76_
## <bountysource-plugin>
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/62869-merge-columngroup-model-and-protograph?utm_campaign=plugin&utm_content=tracker%2F32795&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F32795&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
non_defect
|
merge columngroup model and protograph original author iainsproat june the columngroup model and the schema alignment protograph are both tree structures describing the relationship between columns these models could be merged benefit when importing data with a tree structure such as an xml file or json the columngroup model is automatically created when opening the schema alignment dialog the column relationship is shown as flat all the tree data is lost and has to be recreated by the user if merged the tree would be retained problems if the combined protograph is altered in the schema alignment dialog then the exported data would not match the structure of the original as the columngroup is also changed this may not be intended original issue want to back this issue we accept bounties via
| 0
|
88,450
| 11,097,748,111
|
IssuesEvent
|
2019-12-16 13:58:36
|
WordPress/gutenberg
|
https://api.github.com/repos/WordPress/gutenberg
|
opened
|
Replace nav-menus.php with interface based on Navigation block
|
Needs Design [Block] Navigation [Feature] Widgets [Type] Enhancement
|
With Full Site Editing and the Navigation block, users will have a very intuitive interface for creating and editing menus. Not everyone will be able to access this, however, because some may not want to or may not be able to install a theme that supports Full Site Editing.
We should therefore investigate replacing the menu interface in `nav-menus.php` with a new interface built using the same components that the Navigation block uses.
This is closely related to the work in upgrading `widgets.php` to support blocks.
Consideration should also be given to replacing the menu interface in `customize.php`
---
`nav-menus.php` screen:
<img width="1440" alt="Screen Shot 2019-12-16 at 14 35 49" src="https://user-images.githubusercontent.com/612155/70912102-88371480-2013-11ea-91f4-952dd56705a0.png">
Navigation block:
<img width="1095" alt="Screen Shot 2019-12-16 at 14 47 06" src="https://user-images.githubusercontent.com/612155/70912107-89684180-2013-11ea-865b-4a685ef64e03.png">
cc. @mtias
|
1.0
|
Replace nav-menus.php with interface based on Navigation block - With Full Site Editing and the Navigation block, users will have a very intuitive interface for creating and editing menus. Not everyone will be able to access this, however, because some may not want to or may not be able to install a theme that supports Full Site Editing.
We should therefore investigate replacing the menu interface in `nav-menus.php` with a new interface built using the same components that the Navigation block uses.
This is closely related to the work in upgrading `widgets.php` to support blocks.
Consideration should also be given to replacing the menu interface in `customize.php`
---
`nav-menus.php` screen:
<img width="1440" alt="Screen Shot 2019-12-16 at 14 35 49" src="https://user-images.githubusercontent.com/612155/70912102-88371480-2013-11ea-91f4-952dd56705a0.png">
Navigation block:
<img width="1095" alt="Screen Shot 2019-12-16 at 14 47 06" src="https://user-images.githubusercontent.com/612155/70912107-89684180-2013-11ea-865b-4a685ef64e03.png">
cc. @mtias
|
non_defect
|
replace nav menus php with interface based on navigation block with full site editing and the navigation block users will have a very intuitive interface for creating and editing menus not everyone will be able to access this however because some may not want to or may not be able to install a theme that supports full site editing we should therefore investigate replacing the menu interface in nav menus php with a new interface built using the same components that the navigation block uses this is closely related to the work in upgrading widgets php to support blocks consideration should also be given to replacing the menu interface in customize php nav menus php screen img width alt screen shot at src navigation block img width alt screen shot at src cc mtias
| 0
|
718,515
| 24,720,558,397
|
IssuesEvent
|
2022-10-20 10:19:18
|
GQDeltex/ft_transcendence
|
https://api.github.com/repos/GQDeltex/ft_transcendence
|
closed
|
addon for make_test
|
priority
|
Can we please add that make test open this URL https://www.youtube.com/watch?v=Ur1XtSyjbxM&ab_channel=Don%27tlockthings
This is very important
|
1.0
|
addon for make_test - Can we please add that make test open this URL https://www.youtube.com/watch?v=Ur1XtSyjbxM&ab_channel=Don%27tlockthings
This is very important
|
non_defect
|
addon for make test can we please add that make test open this url this is very important
| 0
|
17,533
| 3,011,416,693
|
IssuesEvent
|
2015-07-28 17:46:39
|
USGS-EROS/espa
|
https://api.github.com/repos/USGS-EROS/espa
|
closed
|
Figure out why Hadoop is issuing "error importing function definition for `module`"
|
Priority-Low Type-Defect
|
```
Hadoop streaming issues
2014-07-14 13:06.59 17504 [science.py]:272 /bin/sh: module: line 1: syntax error: unexpected
end of file
/bin/sh: error importing function definition for `module'
when running streaming jobs where scripts depend on other scripts. This does not stop
code from executing but does result in warnings.
Find and fix.
```
Original issue reported on code.google.com by `davehill75` on 2014-07-14 18:18:10
|
1.0
|
Figure out why Hadoop is issuing "error importing function definition for `module`" - ```
Hadoop streaming issues
2014-07-14 13:06.59 17504 [science.py]:272 /bin/sh: module: line 1: syntax error: unexpected
end of file
/bin/sh: error importing function definition for `module'
when running streaming jobs where scripts depend on other scripts. This does not stop
code from executing but does result in warnings.
Find and fix.
```
Original issue reported on code.google.com by `davehill75` on 2014-07-14 18:18:10
|
defect
|
figure out why hadoop is issuing error importing function definition for module hadoop streaming issues bin sh module line syntax error unexpected end of file bin sh error importing function definition for module when running streaming jobs where scripts depend on other scripts this does not stop code from executing but does result in warnings find and fix original issue reported on code google com by on
| 1
|
13,326
| 2,753,744,365
|
IssuesEvent
|
2015-04-25 00:55:56
|
hubdotcom/marlon-tools
|
https://api.github.com/repos/hubdotcom/marlon-tools
|
closed
|
Move the proxy server to github
|
auto-migrated Priority-Medium Type-Defect
|
```
Really nice little script the proxy server is, would be cool if it was moved to
github so it could perhaps encourage further development.
```
Original issue reported on code.google.com by `bi...@itaccess.org` on 5 Nov 2013 at 10:09
|
1.0
|
Move the proxy server to github - ```
Really nice little script the proxy server is, would be cool if it was moved to
github so it could perhaps encourage further development.
```
Original issue reported on code.google.com by `bi...@itaccess.org` on 5 Nov 2013 at 10:09
|
defect
|
move the proxy server to github really nice little script the proxy server is would be cool if it was moved to github so it could perhaps encourage further development original issue reported on code google com by bi itaccess org on nov at
| 1
|
749,371
| 26,161,246,922
|
IssuesEvent
|
2022-12-31 15:16:37
|
gamefreedomgit/Maelstrom
|
https://api.github.com/repos/gamefreedomgit/Maelstrom
|
closed
|
[Death Knight][Ability][Death Gate] auto learn
|
Class: Death Knight Quest - Cataclysm (1-60) Priority: High Status: Confirmed
|
[//]: # (REMBEMBER! Add links to things related to the bug using for example:)
[//]: # (http://wowhead.com/)
[//]: # (cata-twinhead.twinstar.cz)
**Description:**
You auto learn Death Gate while leveling, instead of after completing The Light of Dawn
**How to reproduce:**
Just level up to 60
**How it should work:**
You learn it as a questreward from The Light of Dawn
**Database links:**
/?quest=12801
/?spell=50977
|
1.0
|
[Death Knight][Ability][Death Gate] auto learn - [//]: # (REMBEMBER! Add links to things related to the bug using for example:)
[//]: # (http://wowhead.com/)
[//]: # (cata-twinhead.twinstar.cz)
**Description:**
You auto learn Death Gate while leveling, instead of after completing The Light of Dawn
**How to reproduce:**
Just level up to 60
**How it should work:**
You learn it as a questreward from The Light of Dawn
**Database links:**
/?quest=12801
/?spell=50977
|
non_defect
|
auto learn rembember add links to things related to the bug using for example cata twinhead twinstar cz description you auto learn death gate while leveling instead of after completing the light of dawn how to reproduce just level up to how it should work you learn it as a questreward from the light of dawn database links quest spell
| 0
|
78,464
| 27,533,098,192
|
IssuesEvent
|
2023-03-07 00:10:07
|
scipy/scipy
|
https://api.github.com/repos/scipy/scipy
|
opened
|
BUG: <scipy.interpolate.SmoothSphereBivariateSpline gives constant output for non-constant input>
|
defect
|
### Describe your issue.
I use `scipy.interpolate.SmoothSphereBivariateSpline` to interpolate points on a sphere, but the interpolation fails in the sense that the resulting function does not interpolate the points at all, regardless of smoothing. I provide an example where I try to interpolate the points `(0,0,-1)`,`(0,90,-1)`,`(0,-90,-1)`,`(90,0,1)`,`(180,0,-1)`,`(270,0,1)` (represented as lon-lat-value, but I do the necessary conversions in the code example) with a smoothing of 10. This should give a central meridian at -1. , an identic antipode and two zones around 1. at 90° east and west of 0 respectively. This is not what the interpolator gives: it provides a uniform value of around -0.3. Is there something that I fundamentally not understand on how scipy.interpolate works? The first figure shows the distribution and values of the input points, the second figure the output of the interpolator on a regular grid, plotted on a world map using cartopy.

### Reproducing Code Example
```python
from scipy.interpolate import SmoothSphereBivariateSpline
import numpy as np
conf_lon=np.deg2rad(np.array([0,0,0,90,180,270]))
conf_lat=np.deg2rad(np.array([0,90,-90,00,00,00]))
values_for_this_rad=np.array([-1,-1,-1,1,-1,1])
# convert to colatitude
colats_decim = (np.pi/2)-conf_lat
lons_decim = conf_lon
interpolator = SmoothSphereBivariateSpline(theta=colats_decim, phi=lons_decim,
r=values_for_this_rad,
s=10)
# interpolator is basically a constant function
print(interpolator.get_knots(),interpolator.get_coeffs())
# plotting
import matplotlib.pyplot as plt
import cartopy.crs as ccrs
import matplotlib.colors as colors
# plot input of interpolator
fig = plt.figure(figsize=(14, 10))
ax = fig.add_subplot(1, 1, 1,projection=ccrs.Robinson(central_longitude=0))
ax.set_global()
im = ax.scatter(np.rad2deg(conf_lon), np.rad2deg(conf_lat), c=values_for_this_rad,transform=ccrs.PlateCarree(), norm=colors.CenteredNorm())
ax.coastlines()
fig.colorbar(im, ax=ax, location='bottom')
# plot output of interpolator on a regular grid
fig2 = plt.figure(figsize=(14, 10))
ax2 = fig2.add_subplot(1, 1, 1,projection=ccrs.Robinson(central_longitude=0))
ax2.set_global()
lon,lat=np.meshgrid(np.arange(360),np.arange(-90,90))
lon=lon.flatten()
lat=lat.flatten()
values=[]
for i in range(len(lon)):
values.append(interpolator((np.pi/2)-np.deg2rad(lat)[i],np.deg2rad(lon)[i]))
im = ax2.scatter(lon, lat, c=values,transform=ccrs.PlateCarree(), norm=colors.CenteredNorm())
ax2.coastlines()
fig2.colorbar(im, ax=ax2, location='bottom')
plt.show()
```
### Error message
```shell
No error message
code output:
(array([0. , 0. , 0. , 0. , 3.14159265,
3.14159265, 3.14159265, 3.14159265]), array([0. , 0. , 0. , 0. , 6.28318531,
6.28318531, 6.28318531, 6.28318531])) [-0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333
-0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333
-0.33333333 -0.33333333 -0.33333333 -0.33333333]
```
### SciPy/NumPy/Python version and system information
```shell
1.10.1 1.24.2 sys.version_info(major=3, minor=11, micro=0, releaselevel='final', serial=0)
lapack_armpl_info:
NOT AVAILABLE
lapack_mkl_info:
NOT AVAILABLE
openblas_lapack_info:
NOT AVAILABLE
openblas_clapack_info:
NOT AVAILABLE
flame_info:
NOT AVAILABLE
accelerate_info:
NOT AVAILABLE
atlas_3_10_threads_info:
NOT AVAILABLE
atlas_3_10_info:
NOT AVAILABLE
atlas_threads_info:
NOT AVAILABLE
atlas_info:
NOT AVAILABLE
lapack_info:
libraries = ['lapack', 'blas', 'lapack', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
language = f77
blas_armpl_info:
NOT AVAILABLE
blas_mkl_info:
NOT AVAILABLE
blis_info:
NOT AVAILABLE
openblas_info:
NOT AVAILABLE
atlas_3_10_blas_threads_info:
NOT AVAILABLE
atlas_3_10_blas_info:
NOT AVAILABLE
atlas_blas_threads_info:
NOT AVAILABLE
atlas_blas_info:
NOT AVAILABLE
blas_info:
libraries = ['cblas', 'blas', 'cblas', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
include_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/include']
language = c
define_macros = [('HAVE_CBLAS', None)]
blas_opt_info:
define_macros = [('NO_ATLAS_INFO', 1), ('HAVE_CBLAS', None)]
libraries = ['cblas', 'blas', 'cblas', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
include_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/include']
language = c
lapack_opt_info:
libraries = ['lapack', 'blas', 'lapack', 'blas', 'cblas', 'blas', 'cblas', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
language = c
define_macros = [('NO_ATLAS_INFO', 1), ('HAVE_CBLAS', None)]
include_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/include']
Supported SIMD extensions in this NumPy install:
baseline = SSE,SSE2,SSE3
found = SSSE3,SSE41,POPCNT,SSE42,AVX,F16C,FMA3,AVX2,AVX512F,AVX512CD,AVX512_SKX
not found = AVX512_KNL,AVX512_KNM,AVX512_CLX,AVX512_CNL,AVX512_ICL
```
|
1.0
|
BUG: <scipy.interpolate.SmoothSphereBivariateSpline gives constant output for non-constant input> - ### Describe your issue.
I use `scipy.interpolate.SmoothSphereBivariateSpline` to interpolate points on a sphere, but the interpolation fails in the sense that the resulting function does not interpolate the points at all, regardless of smoothing. I provide an example where I try to interpolate the points `(0,0,-1)`,`(0,90,-1)`,`(0,-90,-1)`,`(90,0,1)`,`(180,0,-1)`,`(270,0,1)` (represented as lon-lat-value, but I do the necessary conversions in the code example) with a smoothing of 10. This should give a central meridian at -1. , an identic antipode and two zones around 1. at 90° east and west of 0 respectively. This is not what the interpolator gives: it provides a uniform value of around -0.3. Is there something that I fundamentally not understand on how scipy.interpolate works? The first figure shows the distribution and values of the input points, the second figure the output of the interpolator on a regular grid, plotted on a world map using cartopy.

### Reproducing Code Example
```python
from scipy.interpolate import SmoothSphereBivariateSpline
import numpy as np
conf_lon=np.deg2rad(np.array([0,0,0,90,180,270]))
conf_lat=np.deg2rad(np.array([0,90,-90,00,00,00]))
values_for_this_rad=np.array([-1,-1,-1,1,-1,1])
# convert to colatitude
colats_decim = (np.pi/2)-conf_lat
lons_decim = conf_lon
interpolator = SmoothSphereBivariateSpline(theta=colats_decim, phi=lons_decim,
r=values_for_this_rad,
s=10)
# interpolator is basically a constant function
print(interpolator.get_knots(),interpolator.get_coeffs())
# plotting
import matplotlib.pyplot as plt
import cartopy.crs as ccrs
import matplotlib.colors as colors
# plot input of interpolator
fig = plt.figure(figsize=(14, 10))
ax = fig.add_subplot(1, 1, 1,projection=ccrs.Robinson(central_longitude=0))
ax.set_global()
im = ax.scatter(np.rad2deg(conf_lon), np.rad2deg(conf_lat), c=values_for_this_rad,transform=ccrs.PlateCarree(), norm=colors.CenteredNorm())
ax.coastlines()
fig.colorbar(im, ax=ax, location='bottom')
# plot output of interpolator on a regular grid
fig2 = plt.figure(figsize=(14, 10))
ax2 = fig2.add_subplot(1, 1, 1,projection=ccrs.Robinson(central_longitude=0))
ax2.set_global()
lon,lat=np.meshgrid(np.arange(360),np.arange(-90,90))
lon=lon.flatten()
lat=lat.flatten()
values=[]
for i in range(len(lon)):
values.append(interpolator((np.pi/2)-np.deg2rad(lat)[i],np.deg2rad(lon)[i]))
im = ax2.scatter(lon, lat, c=values,transform=ccrs.PlateCarree(), norm=colors.CenteredNorm())
ax2.coastlines()
fig2.colorbar(im, ax=ax2, location='bottom')
plt.show()
```
### Error message
```shell
No error message
code output:
(array([0. , 0. , 0. , 0. , 3.14159265,
3.14159265, 3.14159265, 3.14159265]), array([0. , 0. , 0. , 0. , 6.28318531,
6.28318531, 6.28318531, 6.28318531])) [-0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333
-0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333 -0.33333333
-0.33333333 -0.33333333 -0.33333333 -0.33333333]
```
### SciPy/NumPy/Python version and system information
```shell
1.10.1 1.24.2 sys.version_info(major=3, minor=11, micro=0, releaselevel='final', serial=0)
lapack_armpl_info:
NOT AVAILABLE
lapack_mkl_info:
NOT AVAILABLE
openblas_lapack_info:
NOT AVAILABLE
openblas_clapack_info:
NOT AVAILABLE
flame_info:
NOT AVAILABLE
accelerate_info:
NOT AVAILABLE
atlas_3_10_threads_info:
NOT AVAILABLE
atlas_3_10_info:
NOT AVAILABLE
atlas_threads_info:
NOT AVAILABLE
atlas_info:
NOT AVAILABLE
lapack_info:
libraries = ['lapack', 'blas', 'lapack', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
language = f77
blas_armpl_info:
NOT AVAILABLE
blas_mkl_info:
NOT AVAILABLE
blis_info:
NOT AVAILABLE
openblas_info:
NOT AVAILABLE
atlas_3_10_blas_threads_info:
NOT AVAILABLE
atlas_3_10_blas_info:
NOT AVAILABLE
atlas_blas_threads_info:
NOT AVAILABLE
atlas_blas_info:
NOT AVAILABLE
blas_info:
libraries = ['cblas', 'blas', 'cblas', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
include_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/include']
language = c
define_macros = [('HAVE_CBLAS', None)]
blas_opt_info:
define_macros = [('NO_ATLAS_INFO', 1), ('HAVE_CBLAS', None)]
libraries = ['cblas', 'blas', 'cblas', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
include_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/include']
language = c
lapack_opt_info:
libraries = ['lapack', 'blas', 'lapack', 'blas', 'cblas', 'blas', 'cblas', 'blas']
library_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/lib']
language = c
define_macros = [('NO_ATLAS_INFO', 1), ('HAVE_CBLAS', None)]
include_dirs = ['/home/gcl/BR/d.soergel/anaconda3/envs/mergemod/include']
Supported SIMD extensions in this NumPy install:
baseline = SSE,SSE2,SSE3
found = SSSE3,SSE41,POPCNT,SSE42,AVX,F16C,FMA3,AVX2,AVX512F,AVX512CD,AVX512_SKX
not found = AVX512_KNL,AVX512_KNM,AVX512_CLX,AVX512_CNL,AVX512_ICL
```
|
defect
|
bug describe your issue i use scipy interpolate smoothspherebivariatespline to interpolate points on a sphere but the interpolation fails in the sense that the resulting function does not interpolate the points at all regardless of smoothing i provide an example where i try to interpolate the points represented as lon lat value but i do the necessary conversions in the code example with a smoothing of this should give a central meridian at an identic antipode and two zones around at ° east and west of respectively this is not what the interpolator gives it provides a uniform value of around is there something that i fundamentally not understand on how scipy interpolate works the first figure shows the distribution and values of the input points the second figure the output of the interpolator on a regular grid plotted on a world map using cartopy reproducing code example python from scipy interpolate import smoothspherebivariatespline import numpy as np conf lon np np array conf lat np np array values for this rad np array convert to colatitude colats decim np pi conf lat lons decim conf lon interpolator smoothspherebivariatespline theta colats decim phi lons decim r values for this rad s interpolator is basically a constant function print interpolator get knots interpolator get coeffs plotting import matplotlib pyplot as plt import cartopy crs as ccrs import matplotlib colors as colors plot input of interpolator fig plt figure figsize ax fig add subplot projection ccrs robinson central longitude ax set global im ax scatter np conf lon np conf lat c values for this rad transform ccrs platecarree norm colors centerednorm ax coastlines fig colorbar im ax ax location bottom plot output of interpolator on a regular grid plt figure figsize add subplot projection ccrs robinson central longitude set global lon lat np meshgrid np arange np arange lon lon flatten lat lat flatten values for i in range len lon values append interpolator np pi np lat np lon im scatter lon lat c values transform ccrs platecarree norm colors centerednorm coastlines colorbar im ax location bottom plt show error message shell no error message code output array array scipy numpy python version and system information shell sys version info major minor micro releaselevel final serial lapack armpl info not available lapack mkl info not available openblas lapack info not available openblas clapack info not available flame info not available accelerate info not available atlas threads info not available atlas info not available atlas threads info not available atlas info not available lapack info libraries library dirs language blas armpl info not available blas mkl info not available blis info not available openblas info not available atlas blas threads info not available atlas blas info not available atlas blas threads info not available atlas blas info not available blas info libraries library dirs include dirs language c define macros blas opt info define macros libraries library dirs include dirs language c lapack opt info libraries library dirs language c define macros include dirs supported simd extensions in this numpy install baseline sse found popcnt avx skx not found knl knm clx cnl icl
| 1
|
261,514
| 19,714,977,981
|
IssuesEvent
|
2022-01-13 10:05:55
|
coopdigital/coop-frontend
|
https://api.github.com/repos/coopdigital/coop-frontend
|
closed
|
[Component] Hero Component for Storybook docs
|
documentation enhancement storybook
|
TODO:
- [ ] Move the Hero component from coop-ds-storybook to this repo, under the react-ui package
- [ ] Remove the pcss imports from jsx
- [ ] Remove the pcss file from component directory
- [ ] Have component styles installed at react-ui package root level as a package dependency
- [ ] Import component style .pcss at a global level in `.storybook/preview.js`
- [ ] Have stories attached to the component that cover all states of the component
- [ ] Remove enzyme and react test renderer from imports and replace with react testing library
- [ ] Add tests for the component using jest and testing-library/react
- [ ] Remove any static html examples from component directory
- [ ] Avoid any state management work for the time being, if it can be avoided.
|
1.0
|
[Component] Hero Component for Storybook docs - TODO:
- [ ] Move the Hero component from coop-ds-storybook to this repo, under the react-ui package
- [ ] Remove the pcss imports from jsx
- [ ] Remove the pcss file from component directory
- [ ] Have component styles installed at react-ui package root level as a package dependency
- [ ] Import component style .pcss at a global level in `.storybook/preview.js`
- [ ] Have stories attached to the component that cover all states of the component
- [ ] Remove enzyme and react test renderer from imports and replace with react testing library
- [ ] Add tests for the component using jest and testing-library/react
- [ ] Remove any static html examples from component directory
- [ ] Avoid any state management work for the time being, if it can be avoided.
|
non_defect
|
hero component for storybook docs todo move the hero component from coop ds storybook to this repo under the react ui package remove the pcss imports from jsx remove the pcss file from component directory have component styles installed at react ui package root level as a package dependency import component style pcss at a global level in storybook preview js have stories attached to the component that cover all states of the component remove enzyme and react test renderer from imports and replace with react testing library add tests for the component using jest and testing library react remove any static html examples from component directory avoid any state management work for the time being if it can be avoided
| 0
|
253,347
| 19,098,946,342
|
IssuesEvent
|
2021-11-29 19:58:17
|
AP6YC/ClusterValidityIndices.jl
|
https://api.github.com/repos/AP6YC/ClusterValidityIndices.jl
|
closed
|
Quickstart docs
|
documentation
|
From https://github.com/openjournals/joss-reviews/issues/3527#issuecomment-946230234
Both the README and docs should have installation instructions for the package. They should also both contain a usage quickstart.
|
1.0
|
Quickstart docs - From https://github.com/openjournals/joss-reviews/issues/3527#issuecomment-946230234
Both the README and docs should have installation instructions for the package. They should also both contain a usage quickstart.
|
non_defect
|
quickstart docs from both the readme and docs should have installation instructions for the package they should also both contain a usage quickstart
| 0
|
132,153
| 18,266,154,447
|
IssuesEvent
|
2021-10-04 08:41:50
|
artsking/linux-3.0.35_CVE-2020-15436_withPatch
|
https://api.github.com/repos/artsking/linux-3.0.35_CVE-2020-15436_withPatch
|
closed
|
CVE-2016-8666 (High) detected in linux-stable-rtv3.8.6 - autoclosed
|
security vulnerability
|
## CVE-2016-8666 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35_CVE-2020-15436_withPatch/commit/594a70cb9871ddd73cf61197bb1a2a1b1777a7ae">594a70cb9871ddd73cf61197bb1a2a1b1777a7ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/af_inet.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The IP stack in the Linux kernel before 4.6 allows remote attackers to cause a denial of service (stack consumption and panic) or possibly have unspecified other impact by triggering use of the GRO path for packets with tunnel stacking, as demonstrated by interleaved IPv4 headers and GRE headers, a related issue to CVE-2016-7039.
<p>Publish Date: 2016-10-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-8666>CVE-2016-8666</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-8666">https://nvd.nist.gov/vuln/detail/CVE-2016-8666</a></p>
<p>Release Date: 2016-10-16</p>
<p>Fix Resolution: 4.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2016-8666 (High) detected in linux-stable-rtv3.8.6 - autoclosed - ## CVE-2016-8666 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35_CVE-2020-15436_withPatch/commit/594a70cb9871ddd73cf61197bb1a2a1b1777a7ae">594a70cb9871ddd73cf61197bb1a2a1b1777a7ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/af_inet.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The IP stack in the Linux kernel before 4.6 allows remote attackers to cause a denial of service (stack consumption and panic) or possibly have unspecified other impact by triggering use of the GRO path for packets with tunnel stacking, as demonstrated by interleaved IPv4 headers and GRE headers, a related issue to CVE-2016-7039.
<p>Publish Date: 2016-10-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-8666>CVE-2016-8666</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-8666">https://nvd.nist.gov/vuln/detail/CVE-2016-8666</a></p>
<p>Release Date: 2016-10-16</p>
<p>Fix Resolution: 4.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in linux stable autoclosed cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files net af inet c vulnerability details the ip stack in the linux kernel before allows remote attackers to cause a denial of service stack consumption and panic or possibly have unspecified other impact by triggering use of the gro path for packets with tunnel stacking as demonstrated by interleaved headers and gre headers a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
37,777
| 8,517,475,548
|
IssuesEvent
|
2018-11-01 08:09:31
|
GoldenSoftwareLtd/gedemin
|
https://api.github.com/repos/GoldenSoftwareLtd/gedemin
|
closed
|
Валютное платежной поручение.
|
Bank Priority-Medium Type-Defect
|
Originally reported on Google Code with ID 3032
```
Столкнулись с тем что при экспорте выгружаются не все данные.Да и в документе ввода
отсутвует возможность их внести.
Поэтому приходится в клиент-банке после импорта донабирать информацию.
Хорошо бы в гедемине иметь форму ввода информации идентичную клиент- банковской.
В приложеном файле формат для импорта в клиент-банк
```
Reported by `PogoSG` on 2013-02-08 08:23:54
<hr>
- _Attachment: [Формат для импорта (валюта).doc](https://storage.googleapis.com/google-code-attachments/gedemin/issue-3032/comment-0/Формат для импорта %28валюта%29.doc)_
|
1.0
|
Валютное платежной поручение. - Originally reported on Google Code with ID 3032
```
Столкнулись с тем что при экспорте выгружаются не все данные.Да и в документе ввода
отсутвует возможность их внести.
Поэтому приходится в клиент-банке после импорта донабирать информацию.
Хорошо бы в гедемине иметь форму ввода информации идентичную клиент- банковской.
В приложеном файле формат для импорта в клиент-банк
```
Reported by `PogoSG` on 2013-02-08 08:23:54
<hr>
- _Attachment: [Формат для импорта (валюта).doc](https://storage.googleapis.com/google-code-attachments/gedemin/issue-3032/comment-0/Формат для импорта %28валюта%29.doc)_
|
defect
|
валютное платежной поручение originally reported on google code with id столкнулись с тем что при экспорте выгружаются не все данные да и в документе ввода отсутвует возможность их внести поэтому приходится в клиент банке после импорта донабирать информацию хорошо бы в гедемине иметь форму ввода информации идентичную клиент банковской в приложеном файле формат для импорта в клиент банк reported by pogosg on attachment для импорта doc
| 1
|
805,157
| 29,509,799,682
|
IssuesEvent
|
2023-06-03 19:36:29
|
VisualText/vscode-nlp
|
https://api.github.com/repos/VisualText/vscode-nlp
|
closed
|
Large numbers of files in TextView should not do all checks
|
enhancement priority high
|
Checking for log files really slows things down when there are lots of files.
|
1.0
|
Large numbers of files in TextView should not do all checks - Checking for log files really slows things down when there are lots of files.
|
non_defect
|
large numbers of files in textview should not do all checks checking for log files really slows things down when there are lots of files
| 0
|
81,332
| 30,803,949,691
|
IssuesEvent
|
2023-08-01 05:19:17
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
closed
|
[🐛 Bug]: CFT chrome Binary (version 115.x) is not getting downloaded with Selenium 4.11.0
|
I-defect needs-triaging
|
### What happened?
CFT chrome Binary (version 115.x) is not getting downloaded with Selenium 4.11.0.
I am able to download 113, 114, 116, 117 etc... but not able to download CFT chrome binary (115.x) version.
Please refer attached screenshot:
It's having the chrome browser versions: 114.0.5735.133 116.0.5845.49 117.0.5922.0
But not having 115.x version.
<img width="1343" alt="Screenshot 2023-08-01 at 10 28 50 AM" src="https://github.com/SeleniumHQ/selenium/assets/6771652/99df4a6b-3c55-4dfe-b1f0-42e67f424f39">
---Note: chromedriver.exe (115.x) is getting downloaded in .cache.
refer screenshot:
<img width="948" alt="Screenshot 2023-08-01 at 10 30 13 AM" src="https://github.com/SeleniumHQ/selenium/assets/6771652/50e03596-f1bb-427b-819e-16c7021f785b">
### How can we reproduce the issue?
```shell
Using this sample code:
import org.openqa.selenium.WebDriver;
import org.openqa.selenium.chrome.ChromeDriver;
import org.openqa.selenium.chrome.ChromeOptions;
import org.openqa.selenium.manager.SeleniumManager;
public class BrowserLaunch {
public static void main(String[] args) {
ChromeOptions co = new ChromeOptions();
co.setBrowserVersion("115"); //not downloading 115 CFT chrome browser version
co.setBrowserVersion("stable"); //with "stable" also, not downloading 115 CFT chrome browser version
String browserPath = SeleniumManager.getInstance().getDriverPath(co, false).getBrowserPath();
String driverPath = SeleniumManager.getInstance().getDriverPath(co, false).driverPath;
System.out.println(browserPath);
System.out.println(driverPath);
WebDriver driver = new ChromeDriver(co);//here, launching regular chrome, not CFT chrome
driver.get("https://www.google.com");
System.out.println(driver.getTitle());
}
}
--After running this code, its launching regular chrome browser not the CFT chrome browser.
Note: chromedriver.exe (115) is getting downloaded in the .cache directory.
```
### Relevant log output
```shell
When I try to print:
=========================
String browserPath = SeleniumManager.getInstance().getDriverPath(co, false).getBrowserPath();
String driverPath = SeleniumManager.getInstance().getDriverPath(co, false).driverPath;
System.out.println(browserPath);
System.out.println(driverPath);
=========================
This is console output:
/Applications/Google Chrome.app/Contents/MacOS/Google Chrome
/Users/naveenautomationlabs/.cache/selenium/chromedriver/mac-x64/115.0.5790.102/chromedriver
SLF4J: Failed to load class "org.slf4j.impl.StaticLoggerBinder".
SLF4J: Defaulting to no-operation (NOP) logger implementation
SLF4J: See http://www.slf4j.org/codes.html#StaticLoggerBinder for further details.
Google
```
### Operating System
MAC OS
### Selenium version
Java 4.11.0
### What are the browser(s) and version(s) where you see this issue?
Chrome CFT 115.x
### What are the browser driver(s) and version(s) where you see this issue?
chromedriver 115.x
### Are you using Selenium Grid?
_No response_
|
1.0
|
[🐛 Bug]: CFT chrome Binary (version 115.x) is not getting downloaded with Selenium 4.11.0 - ### What happened?
CFT chrome Binary (version 115.x) is not getting downloaded with Selenium 4.11.0.
I am able to download 113, 114, 116, 117 etc... but not able to download CFT chrome binary (115.x) version.
Please refer attached screenshot:
It's having the chrome browser versions: 114.0.5735.133 116.0.5845.49 117.0.5922.0
But not having 115.x version.
<img width="1343" alt="Screenshot 2023-08-01 at 10 28 50 AM" src="https://github.com/SeleniumHQ/selenium/assets/6771652/99df4a6b-3c55-4dfe-b1f0-42e67f424f39">
---Note: chromedriver.exe (115.x) is getting downloaded in .cache.
refer screenshot:
<img width="948" alt="Screenshot 2023-08-01 at 10 30 13 AM" src="https://github.com/SeleniumHQ/selenium/assets/6771652/50e03596-f1bb-427b-819e-16c7021f785b">
### How can we reproduce the issue?
```shell
Using this sample code:
import org.openqa.selenium.WebDriver;
import org.openqa.selenium.chrome.ChromeDriver;
import org.openqa.selenium.chrome.ChromeOptions;
import org.openqa.selenium.manager.SeleniumManager;
public class BrowserLaunch {
public static void main(String[] args) {
ChromeOptions co = new ChromeOptions();
co.setBrowserVersion("115"); //not downloading 115 CFT chrome browser version
co.setBrowserVersion("stable"); //with "stable" also, not downloading 115 CFT chrome browser version
String browserPath = SeleniumManager.getInstance().getDriverPath(co, false).getBrowserPath();
String driverPath = SeleniumManager.getInstance().getDriverPath(co, false).driverPath;
System.out.println(browserPath);
System.out.println(driverPath);
WebDriver driver = new ChromeDriver(co);//here, launching regular chrome, not CFT chrome
driver.get("https://www.google.com");
System.out.println(driver.getTitle());
}
}
--After running this code, its launching regular chrome browser not the CFT chrome browser.
Note: chromedriver.exe (115) is getting downloaded in the .cache directory.
```
### Relevant log output
```shell
When I try to print:
=========================
String browserPath = SeleniumManager.getInstance().getDriverPath(co, false).getBrowserPath();
String driverPath = SeleniumManager.getInstance().getDriverPath(co, false).driverPath;
System.out.println(browserPath);
System.out.println(driverPath);
=========================
This is console output:
/Applications/Google Chrome.app/Contents/MacOS/Google Chrome
/Users/naveenautomationlabs/.cache/selenium/chromedriver/mac-x64/115.0.5790.102/chromedriver
SLF4J: Failed to load class "org.slf4j.impl.StaticLoggerBinder".
SLF4J: Defaulting to no-operation (NOP) logger implementation
SLF4J: See http://www.slf4j.org/codes.html#StaticLoggerBinder for further details.
Google
```
### Operating System
MAC OS
### Selenium version
Java 4.11.0
### What are the browser(s) and version(s) where you see this issue?
Chrome CFT 115.x
### What are the browser driver(s) and version(s) where you see this issue?
chromedriver 115.x
### Are you using Selenium Grid?
_No response_
|
defect
|
cft chrome binary version x is not getting downloaded with selenium what happened cft chrome binary version x is not getting downloaded with selenium i am able to download etc but not able to download cft chrome binary x version please refer attached screenshot it s having the chrome browser versions but not having x version img width alt screenshot at am src note chromedriver exe x is getting downloaded in cache refer screenshot img width alt screenshot at am src how can we reproduce the issue shell using this sample code import org openqa selenium webdriver import org openqa selenium chrome chromedriver import org openqa selenium chrome chromeoptions import org openqa selenium manager seleniummanager public class browserlaunch public static void main string args chromeoptions co new chromeoptions co setbrowserversion not downloading cft chrome browser version co setbrowserversion stable with stable also not downloading cft chrome browser version string browserpath seleniummanager getinstance getdriverpath co false getbrowserpath string driverpath seleniummanager getinstance getdriverpath co false driverpath system out println browserpath system out println driverpath webdriver driver new chromedriver co here launching regular chrome not cft chrome driver get system out println driver gettitle after running this code its launching regular chrome browser not the cft chrome browser note chromedriver exe is getting downloaded in the cache directory relevant log output shell when i try to print string browserpath seleniummanager getinstance getdriverpath co false getbrowserpath string driverpath seleniummanager getinstance getdriverpath co false driverpath system out println browserpath system out println driverpath this is console output applications google chrome app contents macos google chrome users naveenautomationlabs cache selenium chromedriver mac chromedriver failed to load class org impl staticloggerbinder defaulting to no operation nop logger implementation see for further details google operating system mac os selenium version java what are the browser s and version s where you see this issue chrome cft x what are the browser driver s and version s where you see this issue chromedriver x are you using selenium grid no response
| 1
|
1,287
| 2,603,748,069
|
IssuesEvent
|
2015-02-24 17:43:12
|
chrsmith/bwapi
|
https://api.github.com/repos/chrsmith/bwapi
|
closed
|
getGroundHeight returns 0 for tiles with creep.
|
auto-migrated Priority-Medium Type-Defect
|
```
> What steps will reproduce the problem?
eg
editing the ExampleAI::OnFrame
// for(x, y) etc
int height = Broodwar->getGroundHeight(x*4+2, y*4+2)
Color c;
// Set colour based on the height
// 0->Red, 1->Orange, 2->Green
Broodwar->drawDotMap(x*32+16,y*32+16, c)
Play as zerg starting on high ground (eg astral balance)
> What is the expected output? What do you see instead?
Creep gets the colour corresponding to 0, no matter the height of the
underlying ground. Creating a creep colony shows the colours changing.
> What version of the product are you using? On what operating system?
2.4
> Please provide any additional information below.
```
-----
Original issue reported on code.google.com by `danielst...@gmail.com` on 11 Dec 2009 at 12:23
|
1.0
|
getGroundHeight returns 0 for tiles with creep. - ```
> What steps will reproduce the problem?
eg
editing the ExampleAI::OnFrame
// for(x, y) etc
int height = Broodwar->getGroundHeight(x*4+2, y*4+2)
Color c;
// Set colour based on the height
// 0->Red, 1->Orange, 2->Green
Broodwar->drawDotMap(x*32+16,y*32+16, c)
Play as zerg starting on high ground (eg astral balance)
> What is the expected output? What do you see instead?
Creep gets the colour corresponding to 0, no matter the height of the
underlying ground. Creating a creep colony shows the colours changing.
> What version of the product are you using? On what operating system?
2.4
> Please provide any additional information below.
```
-----
Original issue reported on code.google.com by `danielst...@gmail.com` on 11 Dec 2009 at 12:23
|
defect
|
getgroundheight returns for tiles with creep what steps will reproduce the problem eg editing the exampleai onframe for x y etc int height broodwar getgroundheight x y color c set colour based on the height red orange green broodwar drawdotmap x y c play as zerg starting on high ground eg astral balance what is the expected output what do you see instead creep gets the colour corresponding to no matter the height of the underlying ground creating a creep colony shows the colours changing what version of the product are you using on what operating system please provide any additional information below original issue reported on code google com by danielst gmail com on dec at
| 1
|
10,454
| 2,622,160,308
|
IssuesEvent
|
2015-03-04 00:09:48
|
byzhang/terrastore
|
https://api.github.com/repos/byzhang/terrastore
|
closed
|
Map/Reduce mappers shouldn't be called with modifiable values.
|
auto-migrated Milestone-0.8.1 Priority-Medium Project-Terrastore Type-Defect
|
```
Map/Reduce mappers are currently passed the stored value as a modifiable map.
This is an unnecessary waste of cpu and memory resources, given that values are
transformed into modifiable maps upfront, and mappers don't modify any value
anyways.
```
Original issue reported on code.google.com by `sergio.b...@gmail.com` on 15 Jan 2011 at 5:07
|
1.0
|
Map/Reduce mappers shouldn't be called with modifiable values. - ```
Map/Reduce mappers are currently passed the stored value as a modifiable map.
This is an unnecessary waste of cpu and memory resources, given that values are
transformed into modifiable maps upfront, and mappers don't modify any value
anyways.
```
Original issue reported on code.google.com by `sergio.b...@gmail.com` on 15 Jan 2011 at 5:07
|
defect
|
map reduce mappers shouldn t be called with modifiable values map reduce mappers are currently passed the stored value as a modifiable map this is an unnecessary waste of cpu and memory resources given that values are transformed into modifiable maps upfront and mappers don t modify any value anyways original issue reported on code google com by sergio b gmail com on jan at
| 1
|
34,151
| 7,370,281,635
|
IssuesEvent
|
2018-03-13 07:47:52
|
hazelcast/hazelcast
|
https://api.github.com/repos/hazelcast/hazelcast
|
closed
|
RetryableHazelcastException when shutting down an instance
|
Interface: ICache Source: Internal Team: Core Type: Defect
|
```
36:04,867 [10.216.1.11]:5701 [jet] [0.6-SNAPSHOT] Error while shutting down service[CacheService[hz:impl:cacheService]]: HazelcastInstance[[10.216.1.11]:5701] is not active!
com.hazelcast.spi.exception.RetryableHazelcastException: HazelcastInstance[[10.216.1.11]:5701] is not active!
at com.hazelcast.spi.impl.NodeEngineImpl.getService(NodeEngineImpl.java:358)
at com.hazelcast.cache.impl.AbstractCacheService.deleteCache(AbstractCacheService.java:333)
at com.hazelcast.cache.impl.AbstractCacheService.reset(AbstractCacheService.java:169)
at com.hazelcast.cache.impl.AbstractCacheService.shutdown(AbstractCacheService.java:192)
at com.hazelcast.spi.impl.servicemanager.impl.ServiceManagerImpl.shutdownService(ServiceManagerImpl.java:311)
at com.hazelcast.spi.impl.servicemanager.impl.ServiceManagerImpl.shutdown(ServiceManagerImpl.java:302)
at com.hazelcast.spi.impl.NodeEngineImpl.shutdown(NodeEngineImpl.java:464)
at com.hazelcast.instance.Node.shutdownServices(Node.java:490)
at com.hazelcast.instance.Node.shutdown(Node.java:454)
at com.hazelcast.instance.LifecycleServiceImpl.shutdown(LifecycleServiceImpl.java:98)
at com.hazelcast.instance.LifecycleServiceImpl.shutdown(LifecycleServiceImpl.java:81)
at com.hazelcast.instance.HazelcastInstanceFactory.shutdownAll(HazelcastInstanceFactory.java:289)
at com.hazelcast.instance.HazelcastInstanceFactory.shutdownAll(HazelcastInstanceFactory.java:259)
at com.hazelcast.core.Hazelcast.shutdownAll(Hazelcast.java:40)
at com.hazelcast.jet.Jet.shutdownAll(Jet.java:90)
at CacheJournalSource.main(CacheJournalSource.java:62)
```
To reproduce it just shutdown an instance which has a configured cache on it.
|
1.0
|
RetryableHazelcastException when shutting down an instance - ```
36:04,867 [10.216.1.11]:5701 [jet] [0.6-SNAPSHOT] Error while shutting down service[CacheService[hz:impl:cacheService]]: HazelcastInstance[[10.216.1.11]:5701] is not active!
com.hazelcast.spi.exception.RetryableHazelcastException: HazelcastInstance[[10.216.1.11]:5701] is not active!
at com.hazelcast.spi.impl.NodeEngineImpl.getService(NodeEngineImpl.java:358)
at com.hazelcast.cache.impl.AbstractCacheService.deleteCache(AbstractCacheService.java:333)
at com.hazelcast.cache.impl.AbstractCacheService.reset(AbstractCacheService.java:169)
at com.hazelcast.cache.impl.AbstractCacheService.shutdown(AbstractCacheService.java:192)
at com.hazelcast.spi.impl.servicemanager.impl.ServiceManagerImpl.shutdownService(ServiceManagerImpl.java:311)
at com.hazelcast.spi.impl.servicemanager.impl.ServiceManagerImpl.shutdown(ServiceManagerImpl.java:302)
at com.hazelcast.spi.impl.NodeEngineImpl.shutdown(NodeEngineImpl.java:464)
at com.hazelcast.instance.Node.shutdownServices(Node.java:490)
at com.hazelcast.instance.Node.shutdown(Node.java:454)
at com.hazelcast.instance.LifecycleServiceImpl.shutdown(LifecycleServiceImpl.java:98)
at com.hazelcast.instance.LifecycleServiceImpl.shutdown(LifecycleServiceImpl.java:81)
at com.hazelcast.instance.HazelcastInstanceFactory.shutdownAll(HazelcastInstanceFactory.java:289)
at com.hazelcast.instance.HazelcastInstanceFactory.shutdownAll(HazelcastInstanceFactory.java:259)
at com.hazelcast.core.Hazelcast.shutdownAll(Hazelcast.java:40)
at com.hazelcast.jet.Jet.shutdownAll(Jet.java:90)
at CacheJournalSource.main(CacheJournalSource.java:62)
```
To reproduce it just shutdown an instance which has a configured cache on it.
|
defect
|
retryablehazelcastexception when shutting down an instance error while shutting down service hazelcastinstance is not active com hazelcast spi exception retryablehazelcastexception hazelcastinstance is not active at com hazelcast spi impl nodeengineimpl getservice nodeengineimpl java at com hazelcast cache impl abstractcacheservice deletecache abstractcacheservice java at com hazelcast cache impl abstractcacheservice reset abstractcacheservice java at com hazelcast cache impl abstractcacheservice shutdown abstractcacheservice java at com hazelcast spi impl servicemanager impl servicemanagerimpl shutdownservice servicemanagerimpl java at com hazelcast spi impl servicemanager impl servicemanagerimpl shutdown servicemanagerimpl java at com hazelcast spi impl nodeengineimpl shutdown nodeengineimpl java at com hazelcast instance node shutdownservices node java at com hazelcast instance node shutdown node java at com hazelcast instance lifecycleserviceimpl shutdown lifecycleserviceimpl java at com hazelcast instance lifecycleserviceimpl shutdown lifecycleserviceimpl java at com hazelcast instance hazelcastinstancefactory shutdownall hazelcastinstancefactory java at com hazelcast instance hazelcastinstancefactory shutdownall hazelcastinstancefactory java at com hazelcast core hazelcast shutdownall hazelcast java at com hazelcast jet jet shutdownall jet java at cachejournalsource main cachejournalsource java to reproduce it just shutdown an instance which has a configured cache on it
| 1
|
133,523
| 18,298,929,811
|
IssuesEvent
|
2021-10-05 23:46:51
|
bsbtd/Teste
|
https://api.github.com/repos/bsbtd/Teste
|
opened
|
CVE-2021-35516 (High) detected in commons-compress-1.20.jar, commons-compress-1.8.1.jar
|
security vulnerability
|
## CVE-2021-35516 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>commons-compress-1.20.jar</b>, <b>commons-compress-1.8.1.jar</b></p></summary>
<p>
<details><summary><b>commons-compress-1.20.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE, DEFLATE64, LZ4,
Brotli, Zstandard and ar, cpio, jar, tar, zip, dump, 7z, arj.</p>
<p>Library home page: <a href="https://commons.apache.org/proper/commons-compress/">https://commons.apache.org/proper/commons-compress/</a></p>
<p>Path to dependency file: Teste/opentelemetry-java/exporters/jaeger/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.20/b8df472b31e1f17c232d2ad78ceb1c84e00c641b/commons-compress-1.20.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.20/b8df472b31e1f17c232d2ad78ceb1c84e00c641b/commons-compress-1.20.jar</p>
<p>
Dependency Hierarchy:
- testcontainers-1.13.0.jar (Root Library)
- :x: **commons-compress-1.20.jar** (Vulnerable Library)
</details>
<details><summary><b>commons-compress-1.8.1.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with compression and archive formats.
These include: bzip2, gzip, pack200, lzma, xz, Snappy, traditional Unix Compress and ar, cpio, jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: Teste/liferay-portal/modules/etl/talend/talend-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/commons/commons-compress/1.8.1/commons-compress-1.8.1.jar,/home/wss-scanner/.m2/repository/org/apache/commons/commons-compress/1.8.1/commons-compress-1.8.1.jar,/home/wss-scanner/.m2/repository/org/apache/commons/commons-compress/1.8.1/commons-compress-1.8.1.jar</p>
<p>
Dependency Hierarchy:
- components-api-0.25.3.jar (Root Library)
- daikon-0.27.0.jar
- avro-1.8.1.jar
- :x: **commons-compress-1.8.1.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/bsbtd/Teste/commit/64dde89c50c07496423c4d4a865f2e16b92399ad">64dde89c50c07496423c4d4a865f2e16b92399ad</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When reading a specially crafted 7Z archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' sevenz package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35516>CVE-2021-35516</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-35516 (High) detected in commons-compress-1.20.jar, commons-compress-1.8.1.jar - ## CVE-2021-35516 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>commons-compress-1.20.jar</b>, <b>commons-compress-1.8.1.jar</b></p></summary>
<p>
<details><summary><b>commons-compress-1.20.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with
compression and archive formats. These include: bzip2, gzip, pack200,
lzma, xz, Snappy, traditional Unix Compress, DEFLATE, DEFLATE64, LZ4,
Brotli, Zstandard and ar, cpio, jar, tar, zip, dump, 7z, arj.</p>
<p>Library home page: <a href="https://commons.apache.org/proper/commons-compress/">https://commons.apache.org/proper/commons-compress/</a></p>
<p>Path to dependency file: Teste/opentelemetry-java/exporters/jaeger/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.20/b8df472b31e1f17c232d2ad78ceb1c84e00c641b/commons-compress-1.20.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.commons/commons-compress/1.20/b8df472b31e1f17c232d2ad78ceb1c84e00c641b/commons-compress-1.20.jar</p>
<p>
Dependency Hierarchy:
- testcontainers-1.13.0.jar (Root Library)
- :x: **commons-compress-1.20.jar** (Vulnerable Library)
</details>
<details><summary><b>commons-compress-1.8.1.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with compression and archive formats.
These include: bzip2, gzip, pack200, lzma, xz, Snappy, traditional Unix Compress and ar, cpio, jar, tar, zip, dump, 7z, arj.</p>
<p>Path to dependency file: Teste/liferay-portal/modules/etl/talend/talend-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/commons/commons-compress/1.8.1/commons-compress-1.8.1.jar,/home/wss-scanner/.m2/repository/org/apache/commons/commons-compress/1.8.1/commons-compress-1.8.1.jar,/home/wss-scanner/.m2/repository/org/apache/commons/commons-compress/1.8.1/commons-compress-1.8.1.jar</p>
<p>
Dependency Hierarchy:
- components-api-0.25.3.jar (Root Library)
- daikon-0.27.0.jar
- avro-1.8.1.jar
- :x: **commons-compress-1.8.1.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/bsbtd/Teste/commit/64dde89c50c07496423c4d4a865f2e16b92399ad">64dde89c50c07496423c4d4a865f2e16b92399ad</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When reading a specially crafted 7Z archive, Compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs. This could be used to mount a denial of service attack against services that use Compress' sevenz package.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35516>CVE-2021-35516</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://commons.apache.org/proper/commons-compress/security-reports.html">https://commons.apache.org/proper/commons-compress/security-reports.html</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: org.apache.commons:commons-compress:1.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in commons compress jar commons compress jar cve high severity vulnerability vulnerable libraries commons compress jar commons compress jar commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress deflate brotli zstandard and ar cpio jar tar zip dump arj library home page a href path to dependency file teste opentelemetry java exporters jaeger build gradle path to vulnerable library home wss scanner gradle caches modules files org apache commons commons compress commons compress jar home wss scanner gradle caches modules files org apache commons commons compress commons compress jar dependency hierarchy testcontainers jar root library x commons compress jar vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress and ar cpio jar tar zip dump arj path to dependency file teste liferay portal modules etl talend talend common pom xml path to vulnerable library home wss scanner repository org apache commons commons compress commons compress jar home wss scanner repository org apache commons commons compress commons compress jar home wss scanner repository org apache commons commons compress commons compress jar dependency hierarchy components api jar root library daikon jar avro jar x commons compress jar vulnerable library found in head commit a href vulnerability details when reading a specially crafted archive compress can be made to allocate large amounts of memory that finally leads to an out of memory error even for very small inputs this could be used to mount a denial of service attack against services that use compress sevenz package publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache commons commons compress step up your open source security game with whitesource
| 0
|
194,024
| 15,395,150,872
|
IssuesEvent
|
2021-03-03 18:50:25
|
anchore/anchore-engine
|
https://api.github.com/repos/anchore/anchore-engine
|
opened
|
[docs] Add information about how the layer cache is managed and GC'd after image analysis
|
documentation
|
Per #914 , add documentation with more explanation of the cache growth and GC behavior.
|
1.0
|
[docs] Add information about how the layer cache is managed and GC'd after image analysis - Per #914 , add documentation with more explanation of the cache growth and GC behavior.
|
non_defect
|
add information about how the layer cache is managed and gc d after image analysis per add documentation with more explanation of the cache growth and gc behavior
| 0
|
16,672
| 2,928,179,134
|
IssuesEvent
|
2015-06-27 00:09:27
|
ariya/phantomjs
|
https://api.github.com/repos/ariya/phantomjs
|
closed
|
require(json)
|
old.Priority-Medium old.Status-New old.Type-Defect
|
_**[james.r....@gmail.com](http://code.google.com/u/118167286440686316509/) commented:**_
> nodejs parses json files, and i would like to request that phantomjs do the same, even though the commonjs spec does not require this
>
> http://nodejs.org/api/modules.html#modules_file_modules
>
> > `.json` files are parsed as JSON text files
**Disclaimer:**
This issue was migrated on 2013-03-15 from the project's former issue tracker on Google Code, [Issue #1057](http://code.google.com/p/phantomjs/issues/detail?id=1057).
:star2: **2** people had starred this issue at the time of migration.
|
1.0
|
require(json) - _**[james.r....@gmail.com](http://code.google.com/u/118167286440686316509/) commented:**_
> nodejs parses json files, and i would like to request that phantomjs do the same, even though the commonjs spec does not require this
>
> http://nodejs.org/api/modules.html#modules_file_modules
>
> > `.json` files are parsed as JSON text files
**Disclaimer:**
This issue was migrated on 2013-03-15 from the project's former issue tracker on Google Code, [Issue #1057](http://code.google.com/p/phantomjs/issues/detail?id=1057).
:star2: **2** people had starred this issue at the time of migration.
|
defect
|
require json commented nodejs parses json files and i would like to request that phantomjs do the same even though the commonjs spec does not require this gt json files are parsed as json text files disclaimer this issue was migrated on from the project s former issue tracker on google code nbsp people had starred this issue at the time of migration
| 1
|
29,782
| 5,890,581,625
|
IssuesEvent
|
2017-05-17 15:14:12
|
gwaldron/osgearth
|
https://api.github.com/repos/gwaldron/osgearth
|
closed
|
osgEarthDrivers xyz
|
defect
|
message:
> DynamicLibrary::failed loading "osgPlugins-3.5.6/mingw_osgdb_106&lyrs=s&x=3&y=0&z=2.dll
the url is http://mt.google.com/vt/v=ap.106&lyrs=y&x=${x}&y=${y}&z=${z}
profile provided, <profile>spherical-mercator</profile>
environment:
windows 10
msys64
OpenSceneGraph/master
osgQt/master
osgEarth/master
PS: openstreetmap with xyz driver works fine
|
1.0
|
osgEarthDrivers xyz - message:
> DynamicLibrary::failed loading "osgPlugins-3.5.6/mingw_osgdb_106&lyrs=s&x=3&y=0&z=2.dll
the url is http://mt.google.com/vt/v=ap.106&lyrs=y&x=${x}&y=${y}&z=${z}
profile provided, <profile>spherical-mercator</profile>
environment:
windows 10
msys64
OpenSceneGraph/master
osgQt/master
osgEarth/master
PS: openstreetmap with xyz driver works fine
|
defect
|
osgearthdrivers xyz message dynamiclibrary failed loading osgplugins mingw osgdb lyrs s x y z dll the url is profile provided spherical mercator environment windows openscenegraph master osgqt master osgearth master ps openstreetmap with xyz driver works fine
| 1
|
21,557
| 6,177,734,494
|
IssuesEvent
|
2017-07-02 04:26:53
|
oppia/oppia
|
https://api.github.com/repos/oppia/oppia
|
closed
|
Flaky e2e test in the misc suite
|
loc: full-stack owner: @seanlip (e2e tests) TODO: code type: bug (minor)
|
The misc e2e test suite keeps failing occasionally with the following error. This is a flaky error that often goes away on a test re-run.
This is quite irritating and necessitates multiple test restarts. It should be fixed.
(@Andimeo -- is this the error you noticed?)
```
Specs: /home/travis/build/oppia/oppia/core/tests/protractor/libraryPagesTour.js
[00:00:53] I/hosted - Using the selenium server at http://localhost:4444/wd/hub
Spec started
Started
Library pages tour
✓ visits the library index page (4 secs)
. ✗ visits the top rated page (15 secs)
- Failed: No element found using locator: by.repeater(item in localValue track by $index").row("ManagedPromise::5744 {[[PromiseStatus]]: "fulfilled"}")"
at WebDriverError (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/error.js:27:5)
at NoSuchElementError (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/error.js:242:5)
at /home/travis/build/oppia/node_modules/protractor/built/element.js:707:27
at ManagedPromise.invokeCallback_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:1379:14)
at TaskQueue.execute_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2913:14)
at TaskQueue.executeNext_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2896:21)
at asyncRun (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2775:27)
at /home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:639:7
at process._tickCallback (internal/process/next_tick.js:103:7)Error
at ElementArrayFinder.applyAction_ (/home/travis/build/oppia/node_modules/protractor/built/element.js:397:27)
at ElementArrayFinder._this.(anonymous function) [as clear] (/home/travis/build/oppia/node_modules/protractor/built/element.js:100:30)
at ElementFinder.(anonymous function) [as clear] (/home/travis/build/oppia/node_modules/protractor/built/element.js:728:22)
at Object.setValue (/home/travis/build/oppia/oppia/core/tests/protractor_utils/forms.js:183:41)
at /home/travis/build/oppia/oppia/core/tests/protractor_utils/users.js:85:35
at /home/travis/build/oppia/oppia/core/tests/protractor_utils/admin.js:40:9
at /home/travis/build/oppia/node_modules/protractor/built/element.js:697:32
at ManagedPromise.invokeCallback_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:1379:14)
at TaskQueue.execute_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2913:14)
at TaskQueue.executeNext_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2896:21)
From: Task: Run it("visits the top rated page") in control flow
at Object.<anonymous> (/home/travis/build/oppia/node_modules/jasminewd2/index.js:79:14)
From asynchronous test:
Error
at Suite.<anonymous> (/home/travis/build/oppia/oppia/core/tests/protractor/libraryPagesTour.js:41:3)
at Object.<anonymous> (/home/travis/build/oppia/oppia/core/tests/protractor/libraryPagesTour.js:26:1)
at Module._compile (module.js:570:32)
at Object.Module._extensions..js (module.js:579:10)
at Module.load (module.js:487:32)
at tryModuleLoad (module.js:446:12)
```
|
1.0
|
Flaky e2e test in the misc suite - The misc e2e test suite keeps failing occasionally with the following error. This is a flaky error that often goes away on a test re-run.
This is quite irritating and necessitates multiple test restarts. It should be fixed.
(@Andimeo -- is this the error you noticed?)
```
Specs: /home/travis/build/oppia/oppia/core/tests/protractor/libraryPagesTour.js
[00:00:53] I/hosted - Using the selenium server at http://localhost:4444/wd/hub
Spec started
Started
Library pages tour
✓ visits the library index page (4 secs)
. ✗ visits the top rated page (15 secs)
- Failed: No element found using locator: by.repeater(item in localValue track by $index").row("ManagedPromise::5744 {[[PromiseStatus]]: "fulfilled"}")"
at WebDriverError (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/error.js:27:5)
at NoSuchElementError (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/error.js:242:5)
at /home/travis/build/oppia/node_modules/protractor/built/element.js:707:27
at ManagedPromise.invokeCallback_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:1379:14)
at TaskQueue.execute_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2913:14)
at TaskQueue.executeNext_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2896:21)
at asyncRun (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2775:27)
at /home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:639:7
at process._tickCallback (internal/process/next_tick.js:103:7)Error
at ElementArrayFinder.applyAction_ (/home/travis/build/oppia/node_modules/protractor/built/element.js:397:27)
at ElementArrayFinder._this.(anonymous function) [as clear] (/home/travis/build/oppia/node_modules/protractor/built/element.js:100:30)
at ElementFinder.(anonymous function) [as clear] (/home/travis/build/oppia/node_modules/protractor/built/element.js:728:22)
at Object.setValue (/home/travis/build/oppia/oppia/core/tests/protractor_utils/forms.js:183:41)
at /home/travis/build/oppia/oppia/core/tests/protractor_utils/users.js:85:35
at /home/travis/build/oppia/oppia/core/tests/protractor_utils/admin.js:40:9
at /home/travis/build/oppia/node_modules/protractor/built/element.js:697:32
at ManagedPromise.invokeCallback_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:1379:14)
at TaskQueue.execute_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2913:14)
at TaskQueue.executeNext_ (/home/travis/build/oppia/node_modules/selenium-webdriver/lib/promise.js:2896:21)
From: Task: Run it("visits the top rated page") in control flow
at Object.<anonymous> (/home/travis/build/oppia/node_modules/jasminewd2/index.js:79:14)
From asynchronous test:
Error
at Suite.<anonymous> (/home/travis/build/oppia/oppia/core/tests/protractor/libraryPagesTour.js:41:3)
at Object.<anonymous> (/home/travis/build/oppia/oppia/core/tests/protractor/libraryPagesTour.js:26:1)
at Module._compile (module.js:570:32)
at Object.Module._extensions..js (module.js:579:10)
at Module.load (module.js:487:32)
at tryModuleLoad (module.js:446:12)
```
|
non_defect
|
flaky test in the misc suite the misc test suite keeps failing occasionally with the following error this is a flaky error that often goes away on a test re run this is quite irritating and necessitates multiple test restarts it should be fixed andimeo is this the error you noticed specs home travis build oppia oppia core tests protractor librarypagestour js i hosted using the selenium server at spec started started library pages tour ✓ visits the library index page secs ✗ visits the top rated page secs failed no element found using locator by repeater item in localvalue track by index row managedpromise fulfilled at webdrivererror home travis build oppia node modules selenium webdriver lib error js at nosuchelementerror home travis build oppia node modules selenium webdriver lib error js at home travis build oppia node modules protractor built element js at managedpromise invokecallback home travis build oppia node modules selenium webdriver lib promise js at taskqueue execute home travis build oppia node modules selenium webdriver lib promise js at taskqueue executenext home travis build oppia node modules selenium webdriver lib promise js at asyncrun home travis build oppia node modules selenium webdriver lib promise js at home travis build oppia node modules selenium webdriver lib promise js at process tickcallback internal process next tick js error at elementarrayfinder applyaction home travis build oppia node modules protractor built element js at elementarrayfinder this anonymous function home travis build oppia node modules protractor built element js at elementfinder anonymous function home travis build oppia node modules protractor built element js at object setvalue home travis build oppia oppia core tests protractor utils forms js at home travis build oppia oppia core tests protractor utils users js at home travis build oppia oppia core tests protractor utils admin js at home travis build oppia node modules protractor built element js at managedpromise invokecallback home travis build oppia node modules selenium webdriver lib promise js at taskqueue execute home travis build oppia node modules selenium webdriver lib promise js at taskqueue executenext home travis build oppia node modules selenium webdriver lib promise js from task run it visits the top rated page in control flow at object home travis build oppia node modules index js from asynchronous test error at suite home travis build oppia oppia core tests protractor librarypagestour js at object home travis build oppia oppia core tests protractor librarypagestour js at module compile module js at object module extensions js module js at module load module js at trymoduleload module js
| 0
|
36,521
| 17,773,274,388
|
IssuesEvent
|
2021-08-30 15:57:34
|
fkk-cz/noire_vehicles
|
https://api.github.com/repos/fkk-cz/noire_vehicles
|
closed
|
Mitsubishi Lancer EVO IX Top Speed
|
performance issue
|
The top speed is only 120, I feel like it should most def be faster than this
|
True
|
Mitsubishi Lancer EVO IX Top Speed - The top speed is only 120, I feel like it should most def be faster than this
|
non_defect
|
mitsubishi lancer evo ix top speed the top speed is only i feel like it should most def be faster than this
| 0
|
81,341
| 30,811,838,361
|
IssuesEvent
|
2023-08-01 10:56:20
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
Compound Type pass refinements
|
T-Defect S-Tolerable A-Session-Mgmt O-Frequent A-Threads Z-Compound
|
### Steps to reproduce
Refinements to the Compound Type pass discussed internally.
All of the following elements should be mapped to `font.body.sm.*` tokens.
- [x] Thread summary in main timeline
- [x] Thread summary in threads panel
- [x] Thread panel `Show:` dropdown label and menu
- [x] Sessions `Show:` dropdown label and menu
- [x] Session tile secondary line
- [x] Session details
### Outcome
All of them have been reported/documented on Figma already.
https://www.figma.com/file/GmiEFTUaqAulfYzou1Rwrz/Review%3A-Germain's-Typography-and-Color-pass?type=design&mode=design&t=wgfm1Gpx16bVB6an-0
|
1.0
|
Compound Type pass refinements - ### Steps to reproduce
Refinements to the Compound Type pass discussed internally.
All of the following elements should be mapped to `font.body.sm.*` tokens.
- [x] Thread summary in main timeline
- [x] Thread summary in threads panel
- [x] Thread panel `Show:` dropdown label and menu
- [x] Sessions `Show:` dropdown label and menu
- [x] Session tile secondary line
- [x] Session details
### Outcome
All of them have been reported/documented on Figma already.
https://www.figma.com/file/GmiEFTUaqAulfYzou1Rwrz/Review%3A-Germain's-Typography-and-Color-pass?type=design&mode=design&t=wgfm1Gpx16bVB6an-0
|
defect
|
compound type pass refinements steps to reproduce refinements to the compound type pass discussed internally all of the following elements should be mapped to font body sm tokens thread summary in main timeline thread summary in threads panel thread panel show dropdown label and menu sessions show dropdown label and menu session tile secondary line session details outcome all of them have been reported documented on figma already
| 1
|
89,534
| 10,603,398,591
|
IssuesEvent
|
2019-10-10 15:54:28
|
czbiohub/tabula-muris-senis
|
https://api.github.com/repos/czbiohub/tabula-muris-senis
|
closed
|
Facs sorted data - assayed genes
|
documentation
|
Hi,
we (Charlotte and I) are trying to convert the existing h5ad files to a merged `SingleCellExperiment` object to be used in R/Bioconductor via the https://github.com/csoneson/TabulaMurisData package.
I noticed upon loading the files via scanpy that not all subsets share the same set of genes.
```
>>> adata_facs_bat.X
<1561x22899 sparse matrix of type '<class 'numpy.float32'>'
with 2728411 stored elements in Compressed Sparse Row format>
>>> adata_facs_Bladder.X
<1740x16553 sparse matrix of type '<class 'numpy.float32'>'
with 8153961 stored elements in Compressed Sparse Row format>
>>> adata_facs_Brain_Myeloid.X
<8956x22899 sparse matrix of type '<class 'numpy.float32'>'
with 15979574 stored elements in Compressed Sparse Row format>
>>> adata_facs_Brain_NonMyeloid.X
<4614x22899 sparse matrix of type '<class 'numpy.float32'>'
with 12401088 stored elements in Compressed Sparse Row format>
>>> adata_facs_Diaphragm.X
<1608x22899 sparse matrix of type '<class 'numpy.float32'>'
with 2776493 stored elements in Compressed Sparse Row format>
>>> adata_facs_gat.X
<2531x22899 sparse matrix of type '<class 'numpy.float32'>'
with 7571811 stored elements in Compressed Sparse Row format>
>>> adata_facs_Heart.X
<3104x21190 sparse matrix of type '<class 'numpy.float32'>'
with 10448154 stored elements in Compressed Sparse Row format>
>>> adata_facs_Kidney.X
<1400x22899 sparse matrix of type '<class 'numpy.float32'>'
with 2173284 stored elements in Compressed Sparse Row format>
>>> adata_facs_Large_Intestine.X
<5942x22899 sparse matrix of type '<class 'numpy.float32'>'
with 22461504 stored elements in Compressed Sparse Row format>
>>> adata_facs_Limb_Muscle.X
<2334x22899 sparse matrix of type '<class 'numpy.float32'>'
with 4077488 stored elements in Compressed Sparse Row format>
>>> adata_facs_Liver.X
<1679x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5148416 stored elements in Compressed Sparse Row format>
>>> adata_facs_Lung.X
<3532x22899 sparse matrix of type '<class 'numpy.float32'>'
with 7385690 stored elements in Compressed Sparse Row format>
>>> adata_facs_Mammary_Gland.X
<3132x17232 sparse matrix of type '<class 'numpy.float32'>'
with 11823042 stored elements in Compressed Sparse Row format>
>>> adata_facs_Marrow.X
<9734x22899 sparse matrix of type '<class 'numpy.float32'>'
with 26197974 stored elements in Compressed Sparse Row format>
>>> adata_facs_mat.X
<1960x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5013970 stored elements in Compressed Sparse Row format>
>>> adata_facs_Pancreas.X
<2551x22899 sparse matrix of type '<class 'numpy.float32'>'
with 9105733 stored elements in Compressed Sparse Row format>
>>> adata_facs_scat.X
<2723x22899 sparse matrix of type '<class 'numpy.float32'>'
with 7491027 stored elements in Compressed Sparse Row format>
>>> adata_facs_Skin.X
<3468x22899 sparse matrix of type '<class 'numpy.float32'>'
with 10444947 stored elements in Compressed Sparse Row format>
>>> adata_facs_Spleen.X
<2812x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5185231 stored elements in Compressed Sparse Row format>
>>> adata_facs_Thymus.X
<2629x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5565327 stored elements in Compressed Sparse Row format>
>>> adata_facs_Tongue.X
<2776x22899 sparse matrix of type '<class 'numpy.float32'>'
with 11608627 stored elements in Compressed Sparse Row format>
>>> adata_facs_Trachea.X
<2353x22899 sparse matrix of type '<class 'numpy.float32'>'
with 6583927 stored elements in Compressed Sparse Row format>
```
I see the majority have 22899 genes in them, so I was wondering whether additional steps were applied to the files that have less - ideally, filtered out if not detected in any cell?
For the droplet data, this problem does not show up and all subsets 19860 genes.
Would it be possible to have the "original data" uploaded also for Bladder, MammaryGland, and Heart? (assuming the genes are all in the same order)
I'm tagging @csoneson to follow up on this one.
Thanks in advance!
Federico
|
1.0
|
Facs sorted data - assayed genes - Hi,
we (Charlotte and I) are trying to convert the existing h5ad files to a merged `SingleCellExperiment` object to be used in R/Bioconductor via the https://github.com/csoneson/TabulaMurisData package.
I noticed upon loading the files via scanpy that not all subsets share the same set of genes.
```
>>> adata_facs_bat.X
<1561x22899 sparse matrix of type '<class 'numpy.float32'>'
with 2728411 stored elements in Compressed Sparse Row format>
>>> adata_facs_Bladder.X
<1740x16553 sparse matrix of type '<class 'numpy.float32'>'
with 8153961 stored elements in Compressed Sparse Row format>
>>> adata_facs_Brain_Myeloid.X
<8956x22899 sparse matrix of type '<class 'numpy.float32'>'
with 15979574 stored elements in Compressed Sparse Row format>
>>> adata_facs_Brain_NonMyeloid.X
<4614x22899 sparse matrix of type '<class 'numpy.float32'>'
with 12401088 stored elements in Compressed Sparse Row format>
>>> adata_facs_Diaphragm.X
<1608x22899 sparse matrix of type '<class 'numpy.float32'>'
with 2776493 stored elements in Compressed Sparse Row format>
>>> adata_facs_gat.X
<2531x22899 sparse matrix of type '<class 'numpy.float32'>'
with 7571811 stored elements in Compressed Sparse Row format>
>>> adata_facs_Heart.X
<3104x21190 sparse matrix of type '<class 'numpy.float32'>'
with 10448154 stored elements in Compressed Sparse Row format>
>>> adata_facs_Kidney.X
<1400x22899 sparse matrix of type '<class 'numpy.float32'>'
with 2173284 stored elements in Compressed Sparse Row format>
>>> adata_facs_Large_Intestine.X
<5942x22899 sparse matrix of type '<class 'numpy.float32'>'
with 22461504 stored elements in Compressed Sparse Row format>
>>> adata_facs_Limb_Muscle.X
<2334x22899 sparse matrix of type '<class 'numpy.float32'>'
with 4077488 stored elements in Compressed Sparse Row format>
>>> adata_facs_Liver.X
<1679x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5148416 stored elements in Compressed Sparse Row format>
>>> adata_facs_Lung.X
<3532x22899 sparse matrix of type '<class 'numpy.float32'>'
with 7385690 stored elements in Compressed Sparse Row format>
>>> adata_facs_Mammary_Gland.X
<3132x17232 sparse matrix of type '<class 'numpy.float32'>'
with 11823042 stored elements in Compressed Sparse Row format>
>>> adata_facs_Marrow.X
<9734x22899 sparse matrix of type '<class 'numpy.float32'>'
with 26197974 stored elements in Compressed Sparse Row format>
>>> adata_facs_mat.X
<1960x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5013970 stored elements in Compressed Sparse Row format>
>>> adata_facs_Pancreas.X
<2551x22899 sparse matrix of type '<class 'numpy.float32'>'
with 9105733 stored elements in Compressed Sparse Row format>
>>> adata_facs_scat.X
<2723x22899 sparse matrix of type '<class 'numpy.float32'>'
with 7491027 stored elements in Compressed Sparse Row format>
>>> adata_facs_Skin.X
<3468x22899 sparse matrix of type '<class 'numpy.float32'>'
with 10444947 stored elements in Compressed Sparse Row format>
>>> adata_facs_Spleen.X
<2812x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5185231 stored elements in Compressed Sparse Row format>
>>> adata_facs_Thymus.X
<2629x22899 sparse matrix of type '<class 'numpy.float32'>'
with 5565327 stored elements in Compressed Sparse Row format>
>>> adata_facs_Tongue.X
<2776x22899 sparse matrix of type '<class 'numpy.float32'>'
with 11608627 stored elements in Compressed Sparse Row format>
>>> adata_facs_Trachea.X
<2353x22899 sparse matrix of type '<class 'numpy.float32'>'
with 6583927 stored elements in Compressed Sparse Row format>
```
I see the majority have 22899 genes in them, so I was wondering whether additional steps were applied to the files that have less - ideally, filtered out if not detected in any cell?
For the droplet data, this problem does not show up and all subsets 19860 genes.
Would it be possible to have the "original data" uploaded also for Bladder, MammaryGland, and Heart? (assuming the genes are all in the same order)
I'm tagging @csoneson to follow up on this one.
Thanks in advance!
Federico
|
non_defect
|
facs sorted data assayed genes hi we charlotte and i are trying to convert the existing files to a merged singlecellexperiment object to be used in r bioconductor via the package i noticed upon loading the files via scanpy that not all subsets share the same set of genes adata facs bat x with stored elements in compressed sparse row format adata facs bladder x with stored elements in compressed sparse row format adata facs brain myeloid x with stored elements in compressed sparse row format adata facs brain nonmyeloid x with stored elements in compressed sparse row format adata facs diaphragm x with stored elements in compressed sparse row format adata facs gat x with stored elements in compressed sparse row format adata facs heart x with stored elements in compressed sparse row format adata facs kidney x with stored elements in compressed sparse row format adata facs large intestine x with stored elements in compressed sparse row format adata facs limb muscle x with stored elements in compressed sparse row format adata facs liver x with stored elements in compressed sparse row format adata facs lung x with stored elements in compressed sparse row format adata facs mammary gland x with stored elements in compressed sparse row format adata facs marrow x with stored elements in compressed sparse row format adata facs mat x with stored elements in compressed sparse row format adata facs pancreas x with stored elements in compressed sparse row format adata facs scat x with stored elements in compressed sparse row format adata facs skin x with stored elements in compressed sparse row format adata facs spleen x with stored elements in compressed sparse row format adata facs thymus x with stored elements in compressed sparse row format adata facs tongue x with stored elements in compressed sparse row format adata facs trachea x with stored elements in compressed sparse row format i see the majority have genes in them so i was wondering whether additional steps were applied to the files that have less ideally filtered out if not detected in any cell for the droplet data this problem does not show up and all subsets genes would it be possible to have the original data uploaded also for bladder mammarygland and heart assuming the genes are all in the same order i m tagging csoneson to follow up on this one thanks in advance federico
| 0
|
152,610
| 19,690,700,272
|
IssuesEvent
|
2022-01-12 06:27:43
|
DavidSpek/pipelines
|
https://api.github.com/repos/DavidSpek/pipelines
|
opened
|
WS-2022-0008 (Medium) detected in node-forge-0.9.0.tgz, node-forge-0.9.1.tgz
|
security vulnerability
|
## WS-2022-0008 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-forge-0.9.0.tgz</b>, <b>node-forge-0.9.1.tgz</b></p></summary>
<p>
<details><summary><b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /frontend/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.1.tgz (Root Library)
- webpack-dev-server-3.10.3.tgz
- selfsigned-1.10.7.tgz
- :x: **node-forge-0.9.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>node-forge-0.9.1.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.1.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.1.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /frontend/node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- storage-4.1.3.tgz (Root Library)
- common-2.2.3.tgz
- google-auth-library-5.5.1.tgz
- gtoken-4.1.3.tgz
- google-p12-pem-2.0.3.tgz
- :x: **node-forge-0.9.1.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The forge.debug API had a potential prototype pollution issue if called with untrusted input. The API was only used for internal debug purposes in a safe way and never documented or advertised. It is suspected that uses of this API, if any exist, would likely not have used untrusted inputs in a vulnerable way.
<p>Publish Date: 2022-01-08
<p>URL: <a href=https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562>WS-2022-0008</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5rrq-pxf6-6jx5">https://github.com/advisories/GHSA-5rrq-pxf6-6jx5</a></p>
<p>Release Date: 2022-01-08</p>
<p>Fix Resolution: node-forge - 1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2022-0008 (Medium) detected in node-forge-0.9.0.tgz, node-forge-0.9.1.tgz - ## WS-2022-0008 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-forge-0.9.0.tgz</b>, <b>node-forge-0.9.1.tgz</b></p></summary>
<p>
<details><summary><b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /frontend/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.1.tgz (Root Library)
- webpack-dev-server-3.10.3.tgz
- selfsigned-1.10.7.tgz
- :x: **node-forge-0.9.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>node-forge-0.9.1.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.1.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.1.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /frontend/node_modules/google-p12-pem/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- storage-4.1.3.tgz (Root Library)
- common-2.2.3.tgz
- google-auth-library-5.5.1.tgz
- gtoken-4.1.3.tgz
- google-p12-pem-2.0.3.tgz
- :x: **node-forge-0.9.1.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The forge.debug API had a potential prototype pollution issue if called with untrusted input. The API was only used for internal debug purposes in a safe way and never documented or advertised. It is suspected that uses of this API, if any exist, would likely not have used untrusted inputs in a vulnerable way.
<p>Publish Date: 2022-01-08
<p>URL: <a href=https://github.com/digitalbazaar/forge/commit/51228083550dde97701ac8e06c629a5184117562>WS-2022-0008</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5rrq-pxf6-6jx5">https://github.com/advisories/GHSA-5rrq-pxf6-6jx5</a></p>
<p>Release Date: 2022-01-08</p>
<p>Fix Resolution: node-forge - 1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
ws medium detected in node forge tgz node forge tgz ws medium severity vulnerability vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file frontend package json path to vulnerable library frontend node modules node forge package json dependency hierarchy react scripts tgz root library webpack dev server tgz selfsigned tgz x node forge tgz vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file frontend package json path to vulnerable library frontend node modules google pem node modules node forge package json dependency hierarchy storage tgz root library common tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library found in base branch master vulnerability details the forge debug api had a potential prototype pollution issue if called with untrusted input the api was only used for internal debug purposes in a safe way and never documented or advertised it is suspected that uses of this api if any exist would likely not have used untrusted inputs in a vulnerable way publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge step up your open source security game with whitesource
| 0
|
205,744
| 16,007,857,853
|
IssuesEvent
|
2021-04-20 06:44:59
|
razorRun/react-native-vlc-media-player
|
https://api.github.com/repos/razorRun/react-native-vlc-media-player
|
opened
|
New feature requests and bug fixes
|
documentation help wanted
|
At the moment I am bit tide up with other work.I won’t be able to attend to issues or new requests for next couple of months. If you have any urgent request one option is to add a bounty in following site https://www.bountysource.com/ someone will attend to it. I will help when ever I can if someone has questions regarding development/maintenance of this plugin
|
1.0
|
New feature requests and bug fixes - At the moment I am bit tide up with other work.I won’t be able to attend to issues or new requests for next couple of months. If you have any urgent request one option is to add a bounty in following site https://www.bountysource.com/ someone will attend to it. I will help when ever I can if someone has questions regarding development/maintenance of this plugin
|
non_defect
|
new feature requests and bug fixes at the moment i am bit tide up with other work i won’t be able to attend to issues or new requests for next couple of months if you have any urgent request one option is to add a bounty in following site someone will attend to it i will help when ever i can if someone has questions regarding development maintenance of this plugin
| 0
|
729,496
| 25,130,163,134
|
IssuesEvent
|
2022-11-09 14:37:56
|
BIDMCDigitalPsychiatry/LAMP-platform
|
https://api.github.com/repos/BIDMCDigitalPsychiatry/LAMP-platform
|
closed
|
Changes to Jewels A and B
|
bug 7day frontend priority MEDIUM
|
In **Jewels B** the jewel shapes are really similar and hard to differentiate (look at the attached screenshots). We need to make sure that they are always differentiable.


For both **Jewels A** and **Jewels B**, can we make the following changes:
1. Increase the size of the jewels.
2. Change the background color every time someone moves up a level.
|
1.0
|
Changes to Jewels A and B - In **Jewels B** the jewel shapes are really similar and hard to differentiate (look at the attached screenshots). We need to make sure that they are always differentiable.


For both **Jewels A** and **Jewels B**, can we make the following changes:
1. Increase the size of the jewels.
2. Change the background color every time someone moves up a level.
|
non_defect
|
changes to jewels a and b in jewels b the jewel shapes are really similar and hard to differentiate look at the attached screenshots we need to make sure that they are always differentiable for both jewels a and jewels b can we make the following changes increase the size of the jewels change the background color every time someone moves up a level
| 0
|
58,378
| 3,088,981,604
|
IssuesEvent
|
2015-08-25 19:17:10
|
pavel-pimenov/flylinkdc-r5xx
|
https://api.github.com/repos/pavel-pimenov/flylinkdc-r5xx
|
opened
|
Не работает установка ограничений избранному пользователю если он оне в сети
|
bug imported Priority-Medium
|
_From [mike.kor...@gmail.com](https://code.google.com/u/101495626515388303633/) on October 13, 2014 20:19:44_
1. Добавляем пользователей в друзья
2. Когда кто-то из них уходит с хаба пытаемся установить ему ограничение на скачивание или еще как-то отредактировать запись о нем - ничего не получается.
**Attachment:** [Fly_x64_r17690_friends_bug.png Fly_x64_r17690_friends_bug2.png](http://code.google.com/p/flylinkdc/issues/detail?id=1501)
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=1501_
|
1.0
|
Не работает установка ограничений избранному пользователю если он оне в сети - _From [mike.kor...@gmail.com](https://code.google.com/u/101495626515388303633/) on October 13, 2014 20:19:44_
1. Добавляем пользователей в друзья
2. Когда кто-то из них уходит с хаба пытаемся установить ему ограничение на скачивание или еще как-то отредактировать запись о нем - ничего не получается.
**Attachment:** [Fly_x64_r17690_friends_bug.png Fly_x64_r17690_friends_bug2.png](http://code.google.com/p/flylinkdc/issues/detail?id=1501)
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=1501_
|
non_defect
|
не работает установка ограничений избранному пользователю если он оне в сети from on october добавляем пользователей в друзья когда кто то из них уходит с хаба пытаемся установить ему ограничение на скачивание или еще как то отредактировать запись о нем ничего не получается attachment original issue
| 0
|
6,908
| 6,658,950,188
|
IssuesEvent
|
2017-10-01 03:13:56
|
Daniel-Mietchen/ideas
|
https://api.github.com/repos/Daniel-Mietchen/ideas
|
opened
|
Look into mentions of visa issues in full-text research papers outside law
|
communities hackathon infrastructure research
|
e.g. as per "Three participants scheduled to participate in the witness seminar did not participate, one for personal reasons and two because of difficulties getting visas to the UK."
from
https://hyp.is/Nen9IqZAEee2qgf7bzx9MQ/wellcomeopenresearch.org/articles/2-63/v1
or "Visa restrictions and travel bans were enacted even by nations such as Canada that never saw an Ebola case."
from
https://www.ncbi.nlm.nih.gov/pmc/articles/PMC5616166/
|
1.0
|
Look into mentions of visa issues in full-text research papers outside law - e.g. as per "Three participants scheduled to participate in the witness seminar did not participate, one for personal reasons and two because of difficulties getting visas to the UK."
from
https://hyp.is/Nen9IqZAEee2qgf7bzx9MQ/wellcomeopenresearch.org/articles/2-63/v1
or "Visa restrictions and travel bans were enacted even by nations such as Canada that never saw an Ebola case."
from
https://www.ncbi.nlm.nih.gov/pmc/articles/PMC5616166/
|
non_defect
|
look into mentions of visa issues in full text research papers outside law e g as per three participants scheduled to participate in the witness seminar did not participate one for personal reasons and two because of difficulties getting visas to the uk from or visa restrictions and travel bans were enacted even by nations such as canada that never saw an ebola case from
| 0
|
311,365
| 23,383,993,781
|
IssuesEvent
|
2022-08-11 12:14:23
|
singularity-data/risingwave-docs
|
https://api.github.com/repos/singularity-data/risingwave-docs
|
opened
|
Update IN () as it now accepts a null value
|
documentation
|
### Related code PR
https://github.com/singularity-data/risingwave/pull/3974
### Which part(s) of the docs might be affected or should be updated? And how?
https://www.risingwave.dev/docs/latest/sql-function-comparison/#comparison-predicate
Update IN().
Skip Release Notes.
### Reference
_No response_
|
1.0
|
Update IN () as it now accepts a null value - ### Related code PR
https://github.com/singularity-data/risingwave/pull/3974
### Which part(s) of the docs might be affected or should be updated? And how?
https://www.risingwave.dev/docs/latest/sql-function-comparison/#comparison-predicate
Update IN().
Skip Release Notes.
### Reference
_No response_
|
non_defect
|
update in as it now accepts a null value related code pr which part s of the docs might be affected or should be updated and how update in skip release notes reference no response
| 0
|
11,455
| 2,651,605,266
|
IssuesEvent
|
2015-03-16 12:48:56
|
douglasdrumond/cloaked-computing-machine
|
https://api.github.com/repos/douglasdrumond/cloaked-computing-machine
|
opened
|
[CLOSED] When MMOpenFilesInTabs is set to 1, files are opened in the topmost window but not in new tabs
|
auto-migrated Priority-Medium Type-Defect
|
<a href="https://github.com/GoogleCodeExporter"><img src="https://avatars.githubusercontent.com/u/9614759?v=3" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [GoogleCodeExporter](https://github.com/GoogleCodeExporter)**
_Monday Mar 16, 2015 at 09:15 GMT_
_Originally opened as https://github.com/douglasdrumond/macvim/issues/28_
----
```
When MMOpenFilesInTabs is set to 1, files are opened in the topmost window
but not in new tabs. Instead, they are opened in a new buffer which takes
over the current tab.
```
Original issue reported on code.google.com by `m...@tolton.com` on 7 Nov 2007 at 6:34
|
1.0
|
[CLOSED] When MMOpenFilesInTabs is set to 1, files are opened in the topmost window but not in new tabs - <a href="https://github.com/GoogleCodeExporter"><img src="https://avatars.githubusercontent.com/u/9614759?v=3" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [GoogleCodeExporter](https://github.com/GoogleCodeExporter)**
_Monday Mar 16, 2015 at 09:15 GMT_
_Originally opened as https://github.com/douglasdrumond/macvim/issues/28_
----
```
When MMOpenFilesInTabs is set to 1, files are opened in the topmost window
but not in new tabs. Instead, they are opened in a new buffer which takes
over the current tab.
```
Original issue reported on code.google.com by `m...@tolton.com` on 7 Nov 2007 at 6:34
|
defect
|
when mmopenfilesintabs is set to files are opened in the topmost window but not in new tabs issue by monday mar at gmt originally opened as when mmopenfilesintabs is set to files are opened in the topmost window but not in new tabs instead they are opened in a new buffer which takes over the current tab original issue reported on code google com by m tolton com on nov at
| 1
|
175,696
| 27,961,288,808
|
IssuesEvent
|
2023-03-24 15:50:36
|
apache/camel-karavan
|
https://api.github.com/repos/apache/camel-karavan
|
closed
|
Browsing kamelets/components - Clicking "custom only" popup window with last kamelet
|
bug designer
|
<img width="2058" alt="Screenshot 2023-03-24 at 16 17 08" src="https://user-images.githubusercontent.com/477100/227566653-0df96595-8d23-4213-bd8d-84fa53626cb8.png">
clicking that "toggler" for custom only then show the last component/kamelet in a popup. To reproduce then you need to click on a kamelet/component first, then close the dialog, and then click that toggler
|
1.0
|
Browsing kamelets/components - Clicking "custom only" popup window with last kamelet - <img width="2058" alt="Screenshot 2023-03-24 at 16 17 08" src="https://user-images.githubusercontent.com/477100/227566653-0df96595-8d23-4213-bd8d-84fa53626cb8.png">
clicking that "toggler" for custom only then show the last component/kamelet in a popup. To reproduce then you need to click on a kamelet/component first, then close the dialog, and then click that toggler
|
non_defect
|
browsing kamelets components clicking custom only popup window with last kamelet img width alt screenshot at src clicking that toggler for custom only then show the last component kamelet in a popup to reproduce then you need to click on a kamelet component first then close the dialog and then click that toggler
| 0
|
185,461
| 21,789,497,648
|
IssuesEvent
|
2022-05-14 17:07:11
|
classicvalues/AA-ionic-login
|
https://api.github.com/repos/classicvalues/AA-ionic-login
|
closed
|
sails-disk-2.1.1.tgz: 3 vulnerabilities (highest severity is: 9.8) - autoclosed
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sails-disk-2.1.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-44906](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | minimist-0.0.8.tgz | Transitive | N/A | ❌ |
| [CVE-2021-43138](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | multiple | Transitive | N/A | ❌ |
| [CVE-2020-7598](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | minimist-0.0.8.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44906</summary>
### Vulnerable Library - <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- nedb-1.8.1.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-43138</summary>
### Vulnerable Libraries - <b>async-0.2.10.tgz</b>, <b>async-2.0.1.tgz</b></p>
<p>
### <b>async-0.2.10.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-0.2.10.tgz">https://registry.npmjs.org/async/-/async-0.2.10.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/@sailshq/nedb/node_modules/async/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- nedb-1.8.1.tgz
- :x: **async-0.2.10.tgz** (Vulnerable Library)
### <b>async-2.0.1.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-2.0.1.tgz">https://registry.npmjs.org/async/-/async-2.0.1.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/async/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- :x: **async-2.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Async before 2.6.4 and 3.x before 3.2.2, a malicious user can obtain privileges via the mapValues() method, aka lib/internal/iterator.js createObjectIterator prototype pollution.
<p>Publish Date: 2022-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138>CVE-2021-43138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43138">https://nvd.nist.gov/vuln/detail/CVE-2021-43138</a></p>
<p>Release Date: 2022-04-06</p>
<p>Fix Resolution: async - v3.2.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7598</summary>
### Vulnerable Library - <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- nedb-1.8.1.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;@sailshq/nedb:1.8.1;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 1.2.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"async","packageVersion":"0.2.10","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;@sailshq/nedb:1.8.1;async:0.2.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"async - v3.2.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"async","packageVersion":"2.0.1","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;async:2.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"async - v3.2.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-43138","vulnerabilityDetails":"In Async before 2.6.4 and 3.x before 3.2.2, a malicious user can obtain privileges via the mapValues() method, aka lib/internal/iterator.js createObjectIterator prototype pollution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;@sailshq/nedb:1.8.1;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> -->
|
True
|
sails-disk-2.1.1.tgz: 3 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sails-disk-2.1.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-44906](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | minimist-0.0.8.tgz | Transitive | N/A | ❌ |
| [CVE-2021-43138](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | multiple | Transitive | N/A | ❌ |
| [CVE-2020-7598](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | minimist-0.0.8.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44906</summary>
### Vulnerable Library - <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- nedb-1.8.1.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-43138</summary>
### Vulnerable Libraries - <b>async-0.2.10.tgz</b>, <b>async-2.0.1.tgz</b></p>
<p>
### <b>async-0.2.10.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-0.2.10.tgz">https://registry.npmjs.org/async/-/async-0.2.10.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/@sailshq/nedb/node_modules/async/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- nedb-1.8.1.tgz
- :x: **async-0.2.10.tgz** (Vulnerable Library)
### <b>async-2.0.1.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-2.0.1.tgz">https://registry.npmjs.org/async/-/async-2.0.1.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/async/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- :x: **async-2.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Async before 2.6.4 and 3.x before 3.2.2, a malicious user can obtain privileges via the mapValues() method, aka lib/internal/iterator.js createObjectIterator prototype pollution.
<p>Publish Date: 2022-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138>CVE-2021-43138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43138">https://nvd.nist.gov/vuln/detail/CVE-2021-43138</a></p>
<p>Release Date: 2022-04-06</p>
<p>Fix Resolution: async - v3.2.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7598</summary>
### Vulnerable Library - <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /Application/package.json</p>
<p>Path to vulnerable library: /Application/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- sails-disk-2.1.1.tgz (Root Library)
- nedb-1.8.1.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/classicvalues/AA-ionic-login/commit/3ac332c61bbe4c8a670d6fe4c93f8ff82860389b">3ac332c61bbe4c8a670d6fe4c93f8ff82860389b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;@sailshq/nedb:1.8.1;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 1.2.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"async","packageVersion":"0.2.10","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;@sailshq/nedb:1.8.1;async:0.2.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"async - v3.2.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"async","packageVersion":"2.0.1","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;async:2.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"async - v3.2.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-43138","vulnerabilityDetails":"In Async before 2.6.4 and 3.x before 3.2.2, a malicious user can obtain privileges via the mapValues() method, aka lib/internal/iterator.js createObjectIterator prototype pollution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/Application/package.json"],"isTransitiveDependency":true,"dependencyTree":"sails-disk:2.1.1;@sailshq/nedb:1.8.1;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> -->
|
non_defect
|
sails disk tgz vulnerabilities highest severity is autoclosed vulnerable library sails disk tgz path to dependency file application package json path to vulnerable library application node modules mkdirp node modules minimist package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high minimist tgz transitive n a high multiple transitive n a medium minimist tgz transitive n a details cve vulnerable library minimist tgz parse argument options library home page a href path to dependency file application package json path to vulnerable library application node modules mkdirp node modules minimist package json dependency hierarchy sails disk tgz root library nedb tgz mkdirp tgz x minimist tgz vulnerable library found in head commit a href found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist step up your open source security game with whitesource cve vulnerable libraries async tgz async tgz async tgz higher order functions and common patterns for asynchronous code library home page a href path to dependency file application package json path to vulnerable library application node modules sailshq nedb node modules async package json dependency hierarchy sails disk tgz root library nedb tgz x async tgz vulnerable library async tgz higher order functions and common patterns for asynchronous code library home page a href path to dependency file application package json path to vulnerable library application node modules async package json dependency hierarchy sails disk tgz root library x async tgz vulnerable library found in head commit a href found in base branch master vulnerability details in async before and x before a malicious user can obtain privileges via the mapvalues method aka lib internal iterator js createobjectiterator prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution async step up your open source security game with whitesource cve vulnerable library minimist tgz parse argument options library home page a href path to dependency file application package json path to vulnerable library application node modules mkdirp node modules minimist package json dependency hierarchy sails disk tgz root library nedb tgz mkdirp tgz x minimist tgz vulnerable library found in head commit a href found in base branch master vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist step up your open source security game with whitesource istransitivedependency true dependencytree sails disk sailshq nedb mkdirp minimist isminimumfixversionavailable true minimumfixversion minimist isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist is vulnerable to prototype pollution via file index js function setkey lines vulnerabilityurl istransitivedependency true dependencytree sails disk sailshq nedb async isminimumfixversionavailable true minimumfixversion async isbinary false packagetype javascript node js packagename async packageversion packagefilepaths istransitivedependency true dependencytree sails disk async isminimumfixversionavailable true minimumfixversion async isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in async before and x before a malicious user can obtain privileges via the mapvalues method aka lib internal iterator js createobjectiterator prototype pollution vulnerabilityurl istransitivedependency true dependencytree sails disk sailshq nedb mkdirp minimist isminimumfixversionavailable true minimumfixversion minimist isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl
| 0
|
57,947
| 7,108,434,062
|
IssuesEvent
|
2018-01-17 00:03:20
|
GSoft-Goldsmiths/iLost-main
|
https://api.github.com/repos/GSoft-Goldsmiths/iLost-main
|
closed
|
Reevaluate user needs
|
App UI Design
|
I called it UX, because it includes user interface but of course there is more to it, so User eXperience was chosen
|
1.0
|
Reevaluate user needs - I called it UX, because it includes user interface but of course there is more to it, so User eXperience was chosen
|
non_defect
|
reevaluate user needs i called it ux because it includes user interface but of course there is more to it so user experience was chosen
| 0
|
51,933
| 13,211,340,675
|
IssuesEvent
|
2020-08-15 22:25:53
|
icecube-trac/tix4
|
https://api.github.com/repos/icecube-trac/tix4
|
opened
|
paraboloid - coverage of private interfaces is weak (Trac #1305)
|
Incomplete Migration Migrated from Trac combo reconstruction defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1305">https://code.icecube.wisc.edu/projects/icecube/ticket/1305</a>, reported by negaand owned by kjmeagher</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-02-10T10:59:05",
"_ts": "1455101945934200",
"description": "a serialization and a \"known failure\" test will quickly bump coverage",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"time": "2015-08-28T23:07:43",
"component": "combo reconstruction",
"summary": "paraboloid - coverage of private interfaces is weak",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "kjmeagher",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
paraboloid - coverage of private interfaces is weak (Trac #1305) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1305">https://code.icecube.wisc.edu/projects/icecube/ticket/1305</a>, reported by negaand owned by kjmeagher</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-02-10T10:59:05",
"_ts": "1455101945934200",
"description": "a serialization and a \"known failure\" test will quickly bump coverage",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"time": "2015-08-28T23:07:43",
"component": "combo reconstruction",
"summary": "paraboloid - coverage of private interfaces is weak",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "kjmeagher",
"type": "defect"
}
```
</p>
</details>
|
defect
|
paraboloid coverage of private interfaces is weak trac migrated from json status closed changetime ts description a serialization and a known failure test will quickly bump coverage reporter nega cc resolution fixed time component combo reconstruction summary paraboloid coverage of private interfaces is weak priority normal keywords milestone owner kjmeagher type defect
| 1
|
54,256
| 13,505,908,722
|
IssuesEvent
|
2020-09-14 01:11:47
|
ba-st/Winter
|
https://api.github.com/repos/ba-st/Winter
|
closed
|
SpiderInvasion example problem
|
Type: Defect
|
The ship does not shoot. Bullet is created but not shown and do not collide.
|
1.0
|
SpiderInvasion example problem - The ship does not shoot. Bullet is created but not shown and do not collide.
|
defect
|
spiderinvasion example problem the ship does not shoot bullet is created but not shown and do not collide
| 1
|
13,042
| 5,289,623,907
|
IssuesEvent
|
2017-02-08 17:48:53
|
telegramdesktop/tdesktop
|
https://api.github.com/repos/telegramdesktop/tdesktop
|
closed
|
Makefiles implicitly depend on each other
|
auto closed build help wanted
|
In order to build the Telegram project, it is implicitly necessary to first build MetaEmoji and MetaStyle first. The programmer has to know that, otherwise the build of Telegram will result in cryptic error messages (see https://github.com/telegramdesktop/tdesktop/issues/117).
That’s what Makefiles are for.
The build run of Telegram should recursively depend on the others.
|
1.0
|
Makefiles implicitly depend on each other - In order to build the Telegram project, it is implicitly necessary to first build MetaEmoji and MetaStyle first. The programmer has to know that, otherwise the build of Telegram will result in cryptic error messages (see https://github.com/telegramdesktop/tdesktop/issues/117).
That’s what Makefiles are for.
The build run of Telegram should recursively depend on the others.
|
non_defect
|
makefiles implicitly depend on each other in order to build the telegram project it is implicitly necessary to first build metaemoji and metastyle first the programmer has to know that otherwise the build of telegram will result in cryptic error messages see that’s what makefiles are for the build run of telegram should recursively depend on the others
| 0
|
17,268
| 5,367,681,167
|
IssuesEvent
|
2017-02-22 05:34:57
|
oppia/oppia
|
https://api.github.com/repos/oppia/oppia
|
closed
|
Category images on library explorations need descriptive alt attributes
|
loc: frontend owner: @anthkris starter project TODO: code type: feature (minor)
|
The accessibility audit in issue #2862 identified that the category images on exploration "cards" in the library do not have an alt attribute.
<img width="840" alt="screen shot 2017-01-21 at 5 36 12 pm" src="https://cloud.githubusercontent.com/assets/10858542/22178582/242496f8-e000-11e6-9701-cbb366eaa4b4.png">
These category images display important content, allowing sighted users to easily see the category of an exploration. Therefore the alt attributes for these images should be descriptive, though they can be simple. Perhaps something along the lines of:
`alt="Physics exploration"` or even `alt="Physics"`
Because these images may be dynamically added, their alt tags may also need to be dynamically generated in Angular.
*Edit: Note that the "cards" are also used on the Profile page.
|
1.0
|
Category images on library explorations need descriptive alt attributes - The accessibility audit in issue #2862 identified that the category images on exploration "cards" in the library do not have an alt attribute.
<img width="840" alt="screen shot 2017-01-21 at 5 36 12 pm" src="https://cloud.githubusercontent.com/assets/10858542/22178582/242496f8-e000-11e6-9701-cbb366eaa4b4.png">
These category images display important content, allowing sighted users to easily see the category of an exploration. Therefore the alt attributes for these images should be descriptive, though they can be simple. Perhaps something along the lines of:
`alt="Physics exploration"` or even `alt="Physics"`
Because these images may be dynamically added, their alt tags may also need to be dynamically generated in Angular.
*Edit: Note that the "cards" are also used on the Profile page.
|
non_defect
|
category images on library explorations need descriptive alt attributes the accessibility audit in issue identified that the category images on exploration cards in the library do not have an alt attribute img width alt screen shot at pm src these category images display important content allowing sighted users to easily see the category of an exploration therefore the alt attributes for these images should be descriptive though they can be simple perhaps something along the lines of alt physics exploration or even alt physics because these images may be dynamically added their alt tags may also need to be dynamically generated in angular edit note that the cards are also used on the profile page
| 0
|
213,824
| 24,022,413,763
|
IssuesEvent
|
2022-09-15 08:45:35
|
sast-automation-dev/AltoroJ-25
|
https://api.github.com/repos/sast-automation-dev/AltoroJ-25
|
opened
|
swfobject-2.2.js: 1 vulnerabilities (highest severity is: 5.5)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>swfobject-2.2.js</b></p></summary>
<p>SWFObject is an easy-to-use and standards-friendly method to embed Flash content, which utilizes one small JavaScript file</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js">https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js</a></p>
<p>Path to dependency file: /WebContent/bank/stocks.jsp</p>
<p>Path to vulnerable library: /WebContent/bank/../util/swfobject.js,/WebContent/util/swfobject.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/AltoroJ-25/commit/61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8">61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2012-2400](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2400) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | swfobject-2.2.js | Direct | 3.3.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-2400</summary>
### Vulnerable Library - <b>swfobject-2.2.js</b></p>
<p>SWFObject is an easy-to-use and standards-friendly method to embed Flash content, which utilizes one small JavaScript file</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js">https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js</a></p>
<p>Path to dependency file: /WebContent/bank/stocks.jsp</p>
<p>Path to vulnerable library: /WebContent/bank/../util/swfobject.js,/WebContent/util/swfobject.js</p>
<p>
Dependency Hierarchy:
- :x: **swfobject-2.2.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/AltoroJ-25/commit/61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8">61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Unspecified vulnerability in wp-includes/js/swfobject.js in WordPress before 3.3.2 has unknown impact and attack vectors.
<p>Publish Date: 2012-04-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2400>CVE-2012-2400</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-2400">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-2400</a></p>
<p>Release Date: 2012-04-21</p>
<p>Fix Resolution: 3.3.2</p>
</p>
<p></p>
</details>
|
True
|
swfobject-2.2.js: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>swfobject-2.2.js</b></p></summary>
<p>SWFObject is an easy-to-use and standards-friendly method to embed Flash content, which utilizes one small JavaScript file</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js">https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js</a></p>
<p>Path to dependency file: /WebContent/bank/stocks.jsp</p>
<p>Path to vulnerable library: /WebContent/bank/../util/swfobject.js,/WebContent/util/swfobject.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/AltoroJ-25/commit/61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8">61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2012-2400](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2400) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | swfobject-2.2.js | Direct | 3.3.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-2400</summary>
### Vulnerable Library - <b>swfobject-2.2.js</b></p>
<p>SWFObject is an easy-to-use and standards-friendly method to embed Flash content, which utilizes one small JavaScript file</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js">https://cdnjs.cloudflare.com/ajax/libs/swfobject/2.2/swfobject.js</a></p>
<p>Path to dependency file: /WebContent/bank/stocks.jsp</p>
<p>Path to vulnerable library: /WebContent/bank/../util/swfobject.js,/WebContent/util/swfobject.js</p>
<p>
Dependency Hierarchy:
- :x: **swfobject-2.2.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/AltoroJ-25/commit/61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8">61e21c3da2cf5157cf3d5adcbb31ed71a3693eb8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Unspecified vulnerability in wp-includes/js/swfobject.js in WordPress before 3.3.2 has unknown impact and attack vectors.
<p>Publish Date: 2012-04-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2400>CVE-2012-2400</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-2400">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-2400</a></p>
<p>Release Date: 2012-04-21</p>
<p>Fix Resolution: 3.3.2</p>
</p>
<p></p>
</details>
|
non_defect
|
swfobject js vulnerabilities highest severity is vulnerable library swfobject js swfobject is an easy to use and standards friendly method to embed flash content which utilizes one small javascript file library home page a href path to dependency file webcontent bank stocks jsp path to vulnerable library webcontent bank util swfobject js webcontent util swfobject js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium swfobject js direct details cve vulnerable library swfobject js swfobject is an easy to use and standards friendly method to embed flash content which utilizes one small javascript file library home page a href path to dependency file webcontent bank stocks jsp path to vulnerable library webcontent bank util swfobject js webcontent util swfobject js dependency hierarchy x swfobject js vulnerable library found in head commit a href found in base branch master vulnerability details unspecified vulnerability in wp includes js swfobject js in wordpress before has unknown impact and attack vectors publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution
| 0
|
59,098
| 17,015,695,777
|
IssuesEvent
|
2021-07-02 11:42:31
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
opened
|
Town labels missing in Opencyclemap
|
Component: opencyclemap Priority: minor Type: defect
|
**[Submitted to the original trac issue database at 9.59am, Thursday, 15th September 2011]**
Paisley:
http://opencyclemap.org/?zoom=12&lat=55.85006&lon=-4.40583&layers=B0
Shows Gockston, Ferguslie Park, Arkleston (all smaller areas of Paisley). Expected to see Paisley; it appears at no zoom level.
The openstreetmap labelling of Paisley/Glasgow and the suburbs is more like what I'd expect:
http://www.openstreetmap.org/?lat=55.813&lon=-4.242&zoom=11&layers=M
Stirling:
http://opencyclemap.org/?zoom=12&lat=56.1287&lon=-3.92346&layers=B0
Shows Raploch, Riverside, Broomridge. Expected to see Stirling. Stirling disappears at zoom 10.
Also eg Dunfermline, Linlithgow, Gourock, Greenock, Port Glasgow, Largs - all disappear at zoom 12. This may be a different issue, since Paisley/Stirling seem to obscured at lower zooms by their suburbs, while these smaller towns mostly disappear with no other label nearby.
All of the above are tagged as Towns in OSM.
|
1.0
|
Town labels missing in Opencyclemap - **[Submitted to the original trac issue database at 9.59am, Thursday, 15th September 2011]**
Paisley:
http://opencyclemap.org/?zoom=12&lat=55.85006&lon=-4.40583&layers=B0
Shows Gockston, Ferguslie Park, Arkleston (all smaller areas of Paisley). Expected to see Paisley; it appears at no zoom level.
The openstreetmap labelling of Paisley/Glasgow and the suburbs is more like what I'd expect:
http://www.openstreetmap.org/?lat=55.813&lon=-4.242&zoom=11&layers=M
Stirling:
http://opencyclemap.org/?zoom=12&lat=56.1287&lon=-3.92346&layers=B0
Shows Raploch, Riverside, Broomridge. Expected to see Stirling. Stirling disappears at zoom 10.
Also eg Dunfermline, Linlithgow, Gourock, Greenock, Port Glasgow, Largs - all disappear at zoom 12. This may be a different issue, since Paisley/Stirling seem to obscured at lower zooms by their suburbs, while these smaller towns mostly disappear with no other label nearby.
All of the above are tagged as Towns in OSM.
|
defect
|
town labels missing in opencyclemap paisley shows gockston ferguslie park arkleston all smaller areas of paisley expected to see paisley it appears at no zoom level the openstreetmap labelling of paisley glasgow and the suburbs is more like what i d expect stirling shows raploch riverside broomridge expected to see stirling stirling disappears at zoom also eg dunfermline linlithgow gourock greenock port glasgow largs all disappear at zoom this may be a different issue since paisley stirling seem to obscured at lower zooms by their suburbs while these smaller towns mostly disappear with no other label nearby all of the above are tagged as towns in osm
| 1
|
134,872
| 18,512,751,225
|
IssuesEvent
|
2021-10-20 06:30:34
|
mgh3326/making_page
|
https://api.github.com/repos/mgh3326/making_page
|
closed
|
CVE-2021-3807 (High) detected in ansi-regex-4.1.0.tgz, ansi-regex-3.0.0.tgz - autoclosed
|
security vulnerability
|
## CVE-2021-3807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ansi-regex-4.1.0.tgz</b>, <b>ansi-regex-3.0.0.tgz</b></p></summary>
<p>
<details><summary><b>ansi-regex-4.1.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz</a></p>
<p>Path to dependency file: making_page/package.json</p>
<p>Path to vulnerable library: making_page/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- webpacker-4.2.0.tgz (Root Library)
- webpack-cli-3.3.10.tgz
- yargs-13.2.4.tgz
- cliui-5.0.0.tgz
- strip-ansi-5.2.0.tgz
- :x: **ansi-regex-4.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>ansi-regex-3.0.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz</a></p>
<p>Path to dependency file: making_page/package.json</p>
<p>Path to vulnerable library: making_page/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- webpacker-4.2.0.tgz (Root Library)
- node-sass-4.13.0.tgz
- npmlog-4.1.2.tgz
- gauge-2.7.4.tgz
- wide-align-1.1.3.tgz
- string-width-2.1.1.tgz
- strip-ansi-4.0.0.tgz
- :x: **ansi-regex-3.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/mgh3326/making_page/commit/3740fd55416fb0d9abd7c2b50d69bbe8e5649675">3740fd55416fb0d9abd7c2b50d69bbe8e5649675</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: ansi-regex - 5.0.1,6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-3807 (High) detected in ansi-regex-4.1.0.tgz, ansi-regex-3.0.0.tgz - autoclosed - ## CVE-2021-3807 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ansi-regex-4.1.0.tgz</b>, <b>ansi-regex-3.0.0.tgz</b></p></summary>
<p>
<details><summary><b>ansi-regex-4.1.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz</a></p>
<p>Path to dependency file: making_page/package.json</p>
<p>Path to vulnerable library: making_page/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- webpacker-4.2.0.tgz (Root Library)
- webpack-cli-3.3.10.tgz
- yargs-13.2.4.tgz
- cliui-5.0.0.tgz
- strip-ansi-5.2.0.tgz
- :x: **ansi-regex-4.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>ansi-regex-3.0.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz</a></p>
<p>Path to dependency file: making_page/package.json</p>
<p>Path to vulnerable library: making_page/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- webpacker-4.2.0.tgz (Root Library)
- node-sass-4.13.0.tgz
- npmlog-4.1.2.tgz
- gauge-2.7.4.tgz
- wide-align-1.1.3.tgz
- string-width-2.1.1.tgz
- strip-ansi-4.0.0.tgz
- :x: **ansi-regex-3.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/mgh3326/making_page/commit/3740fd55416fb0d9abd7c2b50d69bbe8e5649675">3740fd55416fb0d9abd7c2b50d69bbe8e5649675</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: ansi-regex - 5.0.1,6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in ansi regex tgz ansi regex tgz autoclosed cve high severity vulnerability vulnerable libraries ansi regex tgz ansi regex tgz ansi regex tgz regular expression for matching ansi escape codes library home page a href path to dependency file making page package json path to vulnerable library making page node modules ansi regex package json dependency hierarchy webpacker tgz root library webpack cli tgz yargs tgz cliui tgz strip ansi tgz x ansi regex tgz vulnerable library ansi regex tgz regular expression for matching ansi escape codes library home page a href path to dependency file making page package json path to vulnerable library making page node modules ansi regex package json dependency hierarchy webpacker tgz root library node sass tgz npmlog tgz gauge tgz wide align tgz string width tgz strip ansi tgz x ansi regex tgz vulnerable library found in head commit a href vulnerability details ansi regex is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ansi regex step up your open source security game with whitesource
| 0
|
9,911
| 2,616,010,021
|
IssuesEvent
|
2015-03-02 00:53:34
|
jasonhall/bwapi
|
https://api.github.com/repos/jasonhall/bwapi
|
closed
|
BWAPI identifies the positions of burrowed units
|
auto-migrated Component-Logic Priority-High Type-Defect
|
```
It seems like burrowed units (Zerg/Spidermines) are being identified by
bots in videos.
Burrowed units may have an "invisible/cloaked" property but they are in no
way noticable unless detected.
```
Original issue reported on code.google.com by `AHeinerm` on 28 Jan 2010 at 9:42
|
1.0
|
BWAPI identifies the positions of burrowed units - ```
It seems like burrowed units (Zerg/Spidermines) are being identified by
bots in videos.
Burrowed units may have an "invisible/cloaked" property but they are in no
way noticable unless detected.
```
Original issue reported on code.google.com by `AHeinerm` on 28 Jan 2010 at 9:42
|
defect
|
bwapi identifies the positions of burrowed units it seems like burrowed units zerg spidermines are being identified by bots in videos burrowed units may have an invisible cloaked property but they are in no way noticable unless detected original issue reported on code google com by aheinerm on jan at
| 1
|
108,282
| 13,612,156,251
|
IssuesEvent
|
2020-09-23 09:52:47
|
Automattic/wp-calypso
|
https://api.github.com/repos/Automattic/wp-calypso
|
closed
|
Gutenboarding: before domain is confirmed, check that it really is available
|
Design Needed Domains [Goal] Gutenboarding [Type] Task
|
via https://github.com/Automattic/wp-calypso/issues/40971#issuecomment-614828121
> The moment customer picks a domain - basically you have to assume that the suggestion endpoint is not always 100% accurate and might return unavailable domains. So, once a domain is selected, you should for it's availability via the is-available endpoint.
You can see it in action in the current domain search - at first I select a suggestion that turns out to unavailable and then one that's available and I'm allowed to proceed.
>
> https://cloudup.com/c0yynmBzeud
Some existing code:
https://github.com/Automattic/wp-calypso/blob/711190aee23edea9006c079d44b7b7cee5d9b977/client/lib/wpcom-undocumented/lib/undocumented.js#L482-L492
https://github.com/Automattic/wp-calypso/blob/f2c9d99b07e14ea938829e9b2e5b31b6fb388a90/client/lib/domains/registration/availability-messages.js
See details in pbAok1-Hb-p2#comment-1472
Related: https://github.com/Automattic/wp-calypso/issues/41219
## Design
Design for state when domain isn't available:
<img width="1240" alt="image" src="https://user-images.githubusercontent.com/87168/80486304-9d2d9800-8963-11ea-8950-4ec810a4d2bc.png">
@dubielzyk how should the "loading" state look like after selecting a domain from the list? I don't know how long it takes typically but we should make sure it doesn't look bad on slow connections or if API is slow to respond.
We can meanwhile implement this without the loading state.
|
1.0
|
Gutenboarding: before domain is confirmed, check that it really is available - via https://github.com/Automattic/wp-calypso/issues/40971#issuecomment-614828121
> The moment customer picks a domain - basically you have to assume that the suggestion endpoint is not always 100% accurate and might return unavailable domains. So, once a domain is selected, you should for it's availability via the is-available endpoint.
You can see it in action in the current domain search - at first I select a suggestion that turns out to unavailable and then one that's available and I'm allowed to proceed.
>
> https://cloudup.com/c0yynmBzeud
Some existing code:
https://github.com/Automattic/wp-calypso/blob/711190aee23edea9006c079d44b7b7cee5d9b977/client/lib/wpcom-undocumented/lib/undocumented.js#L482-L492
https://github.com/Automattic/wp-calypso/blob/f2c9d99b07e14ea938829e9b2e5b31b6fb388a90/client/lib/domains/registration/availability-messages.js
See details in pbAok1-Hb-p2#comment-1472
Related: https://github.com/Automattic/wp-calypso/issues/41219
## Design
Design for state when domain isn't available:
<img width="1240" alt="image" src="https://user-images.githubusercontent.com/87168/80486304-9d2d9800-8963-11ea-8950-4ec810a4d2bc.png">
@dubielzyk how should the "loading" state look like after selecting a domain from the list? I don't know how long it takes typically but we should make sure it doesn't look bad on slow connections or if API is slow to respond.
We can meanwhile implement this without the loading state.
|
non_defect
|
gutenboarding before domain is confirmed check that it really is available via the moment customer picks a domain basically you have to assume that the suggestion endpoint is not always accurate and might return unavailable domains so once a domain is selected you should for it s availability via the is available endpoint you can see it in action in the current domain search at first i select a suggestion that turns out to unavailable and then one that s available and i m allowed to proceed some existing code see details in hb comment related design design for state when domain isn t available img width alt image src dubielzyk how should the loading state look like after selecting a domain from the list i don t know how long it takes typically but we should make sure it doesn t look bad on slow connections or if api is slow to respond we can meanwhile implement this without the loading state
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.