Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 5
112
| repo_url
stringlengths 34
141
| action
stringclasses 3
values | title
stringlengths 1
757
| labels
stringlengths 4
664
| body
stringlengths 3
261k
| index
stringclasses 10
values | text_combine
stringlengths 96
261k
| label
stringclasses 2
values | text
stringlengths 96
232k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
155,752
| 24,512,050,182
|
IssuesEvent
|
2022-10-10 22:55:11
|
alanpjohn/next-notion-portfolio
|
https://api.github.com/repos/alanpjohn/next-notion-portfolio
|
opened
|
Restructure project page to include github contributions and featured projects
|
priority:low design
|
The projects page is a little bland right now.
It looks good on mobile devices but looks empty on wide screens.
- [ ] Improve user experience for wider screen devices
- [ ] Add GitHub contributions to break down projects into sections for better display
|
1.0
|
Restructure project page to include github contributions and featured projects - The projects page is a little bland right now.
It looks good on mobile devices but looks empty on wide screens.
- [ ] Improve user experience for wider screen devices
- [ ] Add GitHub contributions to break down projects into sections for better display
|
non_defect
|
restructure project page to include github contributions and featured projects the projects page is a little bland right now it looks good on mobile devices but looks empty on wide screens improve user experience for wider screen devices add github contributions to break down projects into sections for better display
| 0
|
449,680
| 31,856,792,275
|
IssuesEvent
|
2023-09-15 08:04:04
|
facebookresearch/detectron2
|
https://api.github.com/repos/facebookresearch/detectron2
|
opened
|
out of range
|
documentation
|
## 📚 Documentation Issue
This issue category is for problems about existing documentation, not for asking how-to questions.
* Provide a link to an existing documentation/comment/tutorial:
* How should the above documentation/comment/tutorial improve:
|
1.0
|
out of range - ## 📚 Documentation Issue
This issue category is for problems about existing documentation, not for asking how-to questions.
* Provide a link to an existing documentation/comment/tutorial:
* How should the above documentation/comment/tutorial improve:
|
non_defect
|
out of range 📚 documentation issue this issue category is for problems about existing documentation not for asking how to questions provide a link to an existing documentation comment tutorial how should the above documentation comment tutorial improve
| 0
|
110,403
| 13,906,784,436
|
IssuesEvent
|
2020-10-20 11:45:10
|
httpwg/httpbis-issues
|
https://api.github.com/repos/httpwg/httpbis-issues
|
closed
|
Bodies on GET (and other) requests (Trac #19)
|
Migrated from Trac design p1-messaging
|
Is a request body allowed on GET? Other requests?
Migrated from https://trac.ietf.org/ticket/19
```json
{
"status": "closed",
"changetime": "2012-11-29T03:56:27",
"_ts": "1354161387038002",
"description": "Is a request body allowed on GET? Other requests?",
"reporter": "mnot@pobox.com",
"cc": "",
"resolution": "fixed",
"time": "2007-12-20T03:12:56",
"component": "p1-messaging",
"summary": "Bodies on GET (and other) requests",
"priority": "normal",
"keywords": "",
"milestone": "02",
"owner": "",
"type": "design",
"severity": "Active WG Document"
}
```
|
1.0
|
Bodies on GET (and other) requests (Trac #19) - Is a request body allowed on GET? Other requests?
Migrated from https://trac.ietf.org/ticket/19
```json
{
"status": "closed",
"changetime": "2012-11-29T03:56:27",
"_ts": "1354161387038002",
"description": "Is a request body allowed on GET? Other requests?",
"reporter": "mnot@pobox.com",
"cc": "",
"resolution": "fixed",
"time": "2007-12-20T03:12:56",
"component": "p1-messaging",
"summary": "Bodies on GET (and other) requests",
"priority": "normal",
"keywords": "",
"milestone": "02",
"owner": "",
"type": "design",
"severity": "Active WG Document"
}
```
|
non_defect
|
bodies on get and other requests trac is a request body allowed on get other requests migrated from json status closed changetime ts description is a request body allowed on get other requests reporter mnot pobox com cc resolution fixed time component messaging summary bodies on get and other requests priority normal keywords milestone owner type design severity active wg document
| 0
|
48,622
| 13,392,331,493
|
IssuesEvent
|
2020-09-03 01:03:15
|
doc-ai/snipe-it
|
https://api.github.com/repos/doc-ai/snipe-it
|
opened
|
CVE-2020-7720 (High) detected in node-forge-0.7.1.tgz
|
security vulnerability
|
## CVE-2020-7720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.7.1.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.1.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/snipe-it/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/snipe-it/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-2.1.11.tgz (Root Library)
- webpack-dev-server-2.11.2.tgz
- selfsigned-1.10.2.tgz
- :x: **node-forge-0.7.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package node-forge are vulnerable to Prototype Pollution via the util.setPath function.
<p>Publish Date: 2020-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720>CVE-2020-7720</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-forge","packageVersion":"0.7.1","isTransitiveDependency":true,"dependencyTree":"laravel-mix:2.1.11;webpack-dev-server:2.11.2;selfsigned:1.10.2;node-forge:0.7.1","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2020-7720","vulnerabilityDetails":"All versions of package node-forge are vulnerable to Prototype Pollution via the util.setPath function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-7720 (High) detected in node-forge-0.7.1.tgz - ## CVE-2020-7720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.7.1.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.7.1.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.7.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/snipe-it/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/snipe-it/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-2.1.11.tgz (Root Library)
- webpack-dev-server-2.11.2.tgz
- selfsigned-1.10.2.tgz
- :x: **node-forge-0.7.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package node-forge are vulnerable to Prototype Pollution via the util.setPath function.
<p>Publish Date: 2020-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720>CVE-2020-7720</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-forge","packageVersion":"0.7.1","isTransitiveDependency":true,"dependencyTree":"laravel-mix:2.1.11;webpack-dev-server:2.11.2;selfsigned:1.10.2;node-forge:0.7.1","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2020-7720","vulnerabilityDetails":"All versions of package node-forge are vulnerable to Prototype Pollution via the util.setPath function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7720","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve high detected in node forge tgz cve high severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file tmp ws scm snipe it package json path to vulnerable library tmp ws scm snipe it node modules node forge package json dependency hierarchy laravel mix tgz root library webpack dev server tgz selfsigned tgz x node forge tgz vulnerable library vulnerability details all versions of package node forge are vulnerable to prototype pollution via the util setpath function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails all versions of package node forge are vulnerable to prototype pollution via the util setpath function vulnerabilityurl
| 0
|
46,171
| 13,055,862,312
|
IssuesEvent
|
2020-07-30 02:57:27
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
libX11/Xft/Xext not found by ROOT port configure script on some (newer) linux distros (Trac #682)
|
Incomplete Migration Migrated from Trac defect tools/ports
|
Migrated from https://code.icecube.wisc.edu/ticket/682
```json
{
"status": "closed",
"changetime": "2012-10-31T19:07:59",
"description": "On linux Mint 12 the ROOT install script is not able to find the libX11.so, libXft.so and libXext.so libraries, because only a limited list of directories is tested. On my system, libX11.so (and Xft, Xext) live under /usr/lib/i386-linux-gnu, which is not included in that list. I thought of just adding it to the list, which would solve my problem, but I suffered from the dangerous illusion that I could also solve it in an intelligent way, namely by querying the libdir using \"pkg-config\". I tested on 3 different linux systems that pkg-config was installed and gives the correct answer.\n\nAfter applying the following patch to the main configure script, ROOT got built on my system.\n\n{{{\n--- old/configure\t2011-11-24 17:11:19.000000000 +0100\n+++ new/configure\t2012-06-01 16:05:06.001012273 +0200\n@@ -2155,8 +2155,14 @@\n # Check for X11 and Xpm library (for X11 use always shared lib)\n #\n if test ! \"x$enable_x11\" = \"xno\" ; then\n+ if type pkg-config; then\n+\tpkgcnf_libx11dir=`pkg-config --variable=libdir x11`\n+\tpkgcnf_libxftdir=`pkg-config --variable=libdir xft`\n+\tpkgcnf_libxextdir=`pkg-config --variable=libdir xext`\n+ fi\n check_library \"libX11\" \"yes\" \"$x11libdir\" \\\n ${finkdir:+$finkdir/lib} \\\n+\t$pkgcnf_libx11dir \\\n /usr/lib /usr/X11R6/lib /usr/lib/X11 /usr/openwin/lib \\\n /usr/local/lib /usr/local/lib/X11 /usr/local/X11R6/lib \\\n /usr/X11/lib /usr/lib/X11R5\n@@ -2234,6 +2240,7 @@\n \n check_library \"libXft\" \"$enable_shared\" \"$xftlibdir\" \\\n ${finkdir:+$finkdir/lib} \\\n+\t$pkgcnf_libxftdir \\\n /usr/local/lib /usr/lib /usr/lib/X11 \\\n /usr/local/lib/X11 /usr/X11R6/lib /usr/local/X11R6/lib \\\n /usr/X11/lib\n@@ -2246,6 +2253,7 @@\n \n check_library \"libXext\" \"$enable_shared\" \"$xextlibdir\" \\\n ${finkdir:+$finkdir/lib} \\\n+\t$pkgcnf_libxextdir \\\n /usr/local/lib /usr/lib /usr/lib/X11 \\\n /usr/local/lib/X11 /usr/X11R6/lib /usr/local/X11R6/lib \\\n /usr/X11/lib\n}}}",
"reporter": "boersma",
"cc": "",
"resolution": "fixed",
"_ts": "1351710479000000",
"component": "tools/ports",
"summary": "libX11/Xft/Xext not found by ROOT port configure script on some (newer) linux distros",
"priority": "normal",
"keywords": "libX11 configure darwinports port ROOT",
"time": "2012-06-01T14:27:28",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
|
1.0
|
libX11/Xft/Xext not found by ROOT port configure script on some (newer) linux distros (Trac #682) - Migrated from https://code.icecube.wisc.edu/ticket/682
```json
{
"status": "closed",
"changetime": "2012-10-31T19:07:59",
"description": "On linux Mint 12 the ROOT install script is not able to find the libX11.so, libXft.so and libXext.so libraries, because only a limited list of directories is tested. On my system, libX11.so (and Xft, Xext) live under /usr/lib/i386-linux-gnu, which is not included in that list. I thought of just adding it to the list, which would solve my problem, but I suffered from the dangerous illusion that I could also solve it in an intelligent way, namely by querying the libdir using \"pkg-config\". I tested on 3 different linux systems that pkg-config was installed and gives the correct answer.\n\nAfter applying the following patch to the main configure script, ROOT got built on my system.\n\n{{{\n--- old/configure\t2011-11-24 17:11:19.000000000 +0100\n+++ new/configure\t2012-06-01 16:05:06.001012273 +0200\n@@ -2155,8 +2155,14 @@\n # Check for X11 and Xpm library (for X11 use always shared lib)\n #\n if test ! \"x$enable_x11\" = \"xno\" ; then\n+ if type pkg-config; then\n+\tpkgcnf_libx11dir=`pkg-config --variable=libdir x11`\n+\tpkgcnf_libxftdir=`pkg-config --variable=libdir xft`\n+\tpkgcnf_libxextdir=`pkg-config --variable=libdir xext`\n+ fi\n check_library \"libX11\" \"yes\" \"$x11libdir\" \\\n ${finkdir:+$finkdir/lib} \\\n+\t$pkgcnf_libx11dir \\\n /usr/lib /usr/X11R6/lib /usr/lib/X11 /usr/openwin/lib \\\n /usr/local/lib /usr/local/lib/X11 /usr/local/X11R6/lib \\\n /usr/X11/lib /usr/lib/X11R5\n@@ -2234,6 +2240,7 @@\n \n check_library \"libXft\" \"$enable_shared\" \"$xftlibdir\" \\\n ${finkdir:+$finkdir/lib} \\\n+\t$pkgcnf_libxftdir \\\n /usr/local/lib /usr/lib /usr/lib/X11 \\\n /usr/local/lib/X11 /usr/X11R6/lib /usr/local/X11R6/lib \\\n /usr/X11/lib\n@@ -2246,6 +2253,7 @@\n \n check_library \"libXext\" \"$enable_shared\" \"$xextlibdir\" \\\n ${finkdir:+$finkdir/lib} \\\n+\t$pkgcnf_libxextdir \\\n /usr/local/lib /usr/lib /usr/lib/X11 \\\n /usr/local/lib/X11 /usr/X11R6/lib /usr/local/X11R6/lib \\\n /usr/X11/lib\n}}}",
"reporter": "boersma",
"cc": "",
"resolution": "fixed",
"_ts": "1351710479000000",
"component": "tools/ports",
"summary": "libX11/Xft/Xext not found by ROOT port configure script on some (newer) linux distros",
"priority": "normal",
"keywords": "libX11 configure darwinports port ROOT",
"time": "2012-06-01T14:27:28",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
|
defect
|
xft xext not found by root port configure script on some newer linux distros trac migrated from json status closed changetime description on linux mint the root install script is not able to find the so libxft so and libxext so libraries because only a limited list of directories is tested on my system so and xft xext live under usr lib linux gnu which is not included in that list i thought of just adding it to the list which would solve my problem but i suffered from the dangerous illusion that i could also solve it in an intelligent way namely by querying the libdir using pkg config i tested on different linux systems that pkg config was installed and gives the correct answer n nafter applying the following patch to the main configure script root got built on my system n n n old configure n new configure n n check for and xpm library for use always shared lib n n if test x enable xno then n if type pkg config then n tpkgcnf pkg config variable libdir n tpkgcnf libxftdir pkg config variable libdir xft n tpkgcnf libxextdir pkg config variable libdir xext n fi n check library yes n finkdir finkdir lib n t pkgcnf n usr lib usr lib usr lib usr openwin lib n usr local lib usr local lib usr local lib n usr lib usr lib n n n check library libxft enable shared xftlibdir n finkdir finkdir lib n t pkgcnf libxftdir n usr local lib usr lib usr lib n usr local lib usr lib usr local lib n usr lib n n n check library libxext enable shared xextlibdir n finkdir finkdir lib n t pkgcnf libxextdir n usr local lib usr lib usr lib n usr local lib usr lib usr local lib n usr lib n reporter boersma cc resolution fixed ts component tools ports summary xft xext not found by root port configure script on some newer linux distros priority normal keywords configure darwinports port root time milestone owner nega type defect
| 1
|
215,496
| 24,173,572,301
|
IssuesEvent
|
2022-09-22 21:48:32
|
timf-app-demo/NodeGoat-remediate-renovate
|
https://api.github.com/repos/timf-app-demo/NodeGoat-remediate-renovate
|
opened
|
CVE-2021-44906 (High) detected in multiple libraries
|
security vulnerability
|
## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.5.tgz</b>, <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.10.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/prettyjson/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- prettyjson-1.2.1.tgz
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/timf-app-demo/NodeGoat-remediate-renovate/commit/d06382d3a4b66d3c1d5bc3f50ac841d47cd8378b">d06382d3a4b66d3c1d5bc3f50ac841d47cd8378b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
</details>
<p></p>
|
True
|
CVE-2021-44906 (High) detected in multiple libraries - ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.5.tgz</b>, <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.10.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/prettyjson/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- prettyjson-1.2.1.tgz
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/timf-app-demo/NodeGoat-remediate-renovate/commit/d06382d3a4b66d3c1d5bc3f50ac841d47cd8378b">d06382d3a4b66d3c1d5bc3f50ac841d47cd8378b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
</details>
<p></p>
|
non_defect
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules mkdirp node modules minimist package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz fsevents tgz node pre gyp tgz mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules prettyjson node modules minimist package json dependency hierarchy forever tgz root library prettyjson tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz fsevents tgz node pre gyp tgz rc tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules minimist package json dependency hierarchy forever tgz root library optimist tgz x minimist tgz vulnerable library found in head commit a href found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimist
| 0
|
175,350
| 13,547,475,192
|
IssuesEvent
|
2020-09-17 04:12:46
|
kubernetes/kubernetes
|
https://api.github.com/repos/kubernetes/kubernetes
|
closed
|
e2e test failure: error: failed to create clusterrolebinding: clusterrolebindings.rbac.authorization.k8s.io "e2e-test-cluster-admin-binding" already exists
|
kind/failing-test sig/autoscaling
|
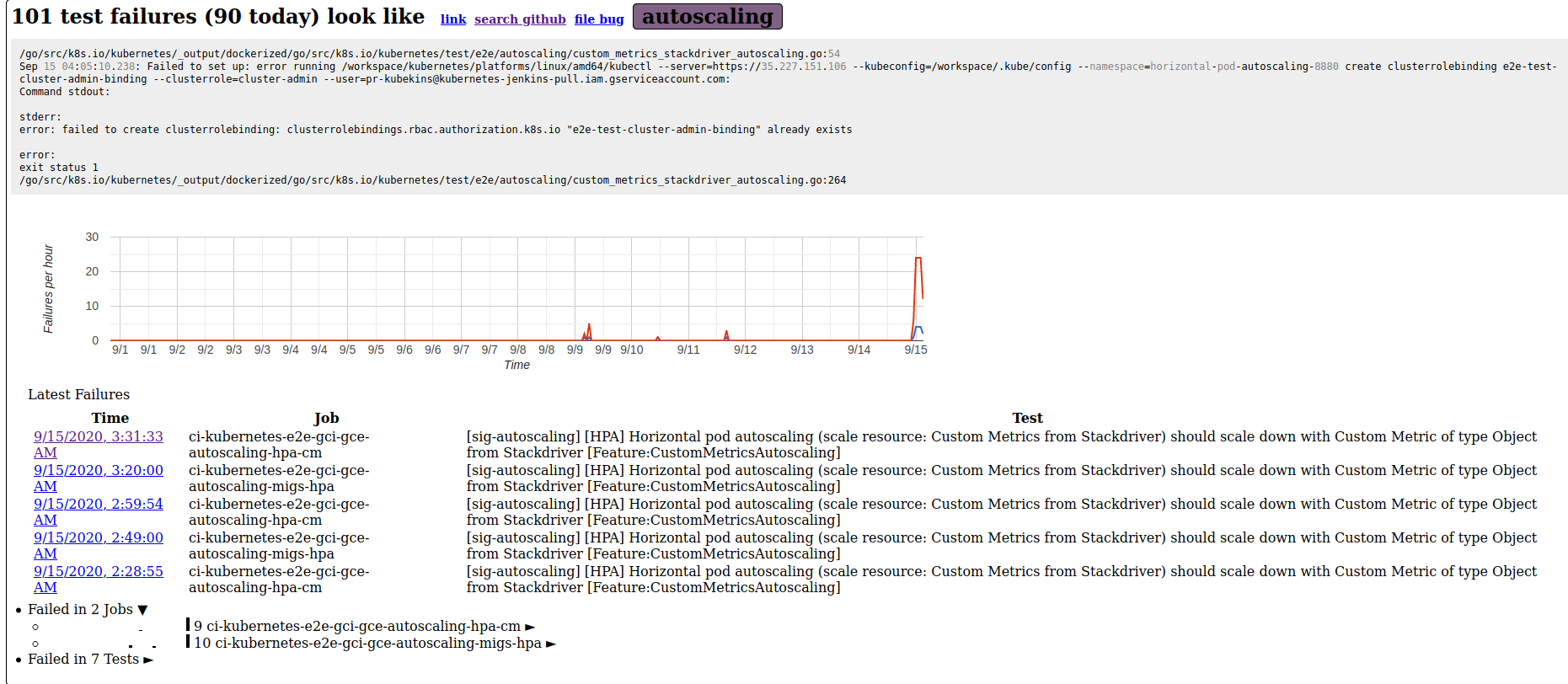
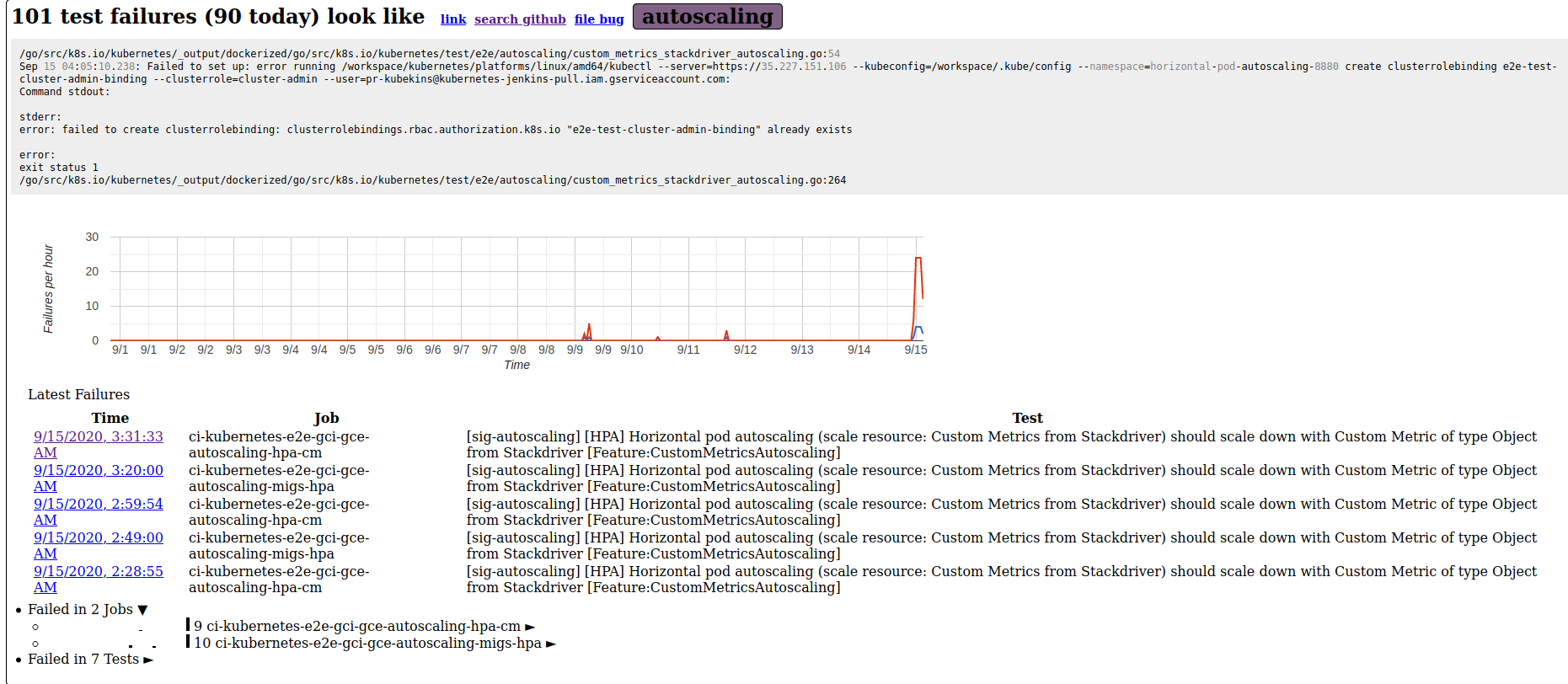
### Failure cluster [5b6df9d4650b8c2ce8e4](https://go.k8s.io/triage#5b6df9d4650b8c2ce8e4)
##### Error text:
```
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/autoscaling/custom_metrics_stackdriver_autoscaling.go:54
Sep 15 04:05:10.238: Failed to set up: error running /workspace/kubernetes/platforms/linux/amd64/kubectl --server=https://35.227.151.106 --kubeconfig=/workspace/.kube/config --namespace=horizontal-pod-autoscaling-8880 create clusterrolebinding e2e-test-cluster-admin-binding --clusterrole=cluster-admin --user=pr-kubekins@kubernetes-jenkins-pull.iam.gserviceaccount.com:
Command stdout:
stderr:
error: failed to create clusterrolebinding: clusterrolebindings.rbac.authorization.k8s.io "e2e-test-cluster-admin-binding" already exists
error:
exit status 1
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/autoscaling/custom_metrics_stackdriver_autoscaling.go:264
```
#### Recent failures:
[9/15/2020, 3:31:33 AM ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm/1305771124411338752)
[9/15/2020, 3:20:00 AM ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa/1305768225241305090)
[9/15/2020, 2:59:54 AM ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm/1305763192298803200)
[9/15/2020, 2:49:00 AM ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa/1305760424309821440)
[9/15/2020, 2:28:55 AM ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm/1305755390901751810)
/kind failing-test
<!-- If this is a flake, please add: /kind flake -->
/sig autoscaling
Looks like it just started happening today (@ 2020-09-15 03:54:19 +0000 UTC)
|
1.0
|
e2e test failure: error: failed to create clusterrolebinding: clusterrolebindings.rbac.authorization.k8s.io "e2e-test-cluster-admin-binding" already exists - ### Failure cluster [5b6df9d4650b8c2ce8e4](https://go.k8s.io/triage#5b6df9d4650b8c2ce8e4)
##### Error text:
```
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/autoscaling/custom_metrics_stackdriver_autoscaling.go:54
Sep 15 04:05:10.238: Failed to set up: error running /workspace/kubernetes/platforms/linux/amd64/kubectl --server=https://35.227.151.106 --kubeconfig=/workspace/.kube/config --namespace=horizontal-pod-autoscaling-8880 create clusterrolebinding e2e-test-cluster-admin-binding --clusterrole=cluster-admin --user=pr-kubekins@kubernetes-jenkins-pull.iam.gserviceaccount.com:
Command stdout:
stderr:
error: failed to create clusterrolebinding: clusterrolebindings.rbac.authorization.k8s.io "e2e-test-cluster-admin-binding" already exists
error:
exit status 1
/go/src/k8s.io/kubernetes/_output/dockerized/go/src/k8s.io/kubernetes/test/e2e/autoscaling/custom_metrics_stackdriver_autoscaling.go:264
```
#### Recent failures:
[9/15/2020, 3:31:33 AM ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm/1305771124411338752)
[9/15/2020, 3:20:00 AM ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa/1305768225241305090)
[9/15/2020, 2:59:54 AM ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm/1305763192298803200)
[9/15/2020, 2:49:00 AM ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-migs-hpa/1305760424309821440)
[9/15/2020, 2:28:55 AM ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm](https://prow.k8s.io/view/gcs/kubernetes-jenkins/logs/ci-kubernetes-e2e-gci-gce-autoscaling-hpa-cm/1305755390901751810)
/kind failing-test
<!-- If this is a flake, please add: /kind flake -->
/sig autoscaling
Looks like it just started happening today (@ 2020-09-15 03:54:19 +0000 UTC)
|
non_defect
|
test failure error failed to create clusterrolebinding clusterrolebindings rbac authorization io test cluster admin binding already exists failure cluster error text go src io kubernetes output dockerized go src io kubernetes test autoscaling custom metrics stackdriver autoscaling go sep failed to set up error running workspace kubernetes platforms linux kubectl server kubeconfig workspace kube config namespace horizontal pod autoscaling create clusterrolebinding test cluster admin binding clusterrole cluster admin user pr kubekins kubernetes jenkins pull iam gserviceaccount com command stdout stderr error failed to create clusterrolebinding clusterrolebindings rbac authorization io test cluster admin binding already exists error exit status go src io kubernetes output dockerized go src io kubernetes test autoscaling custom metrics stackdriver autoscaling go recent failures kind failing test sig autoscaling looks like it just started happening today utc
| 0
|
95,238
| 8,553,442,094
|
IssuesEvent
|
2018-11-08 00:54:09
|
zfsonlinux/zfs
|
https://api.github.com/repos/zfsonlinux/zfs
|
closed
|
Test case: zfs_mount_006_pos
|
Type: Test Suite
|
I being debugged the zfs-test scripts about zfs_mount,,I found that the scipts as zfs_mount_pos_005,zfs_mount_pos_006,zfs_mount_007_pos,zfs_mount_009_neg,zfs_mount_010_neg.ksh execute failure, through see the file-linux.run, found these scripts needs investigation, I try to debuged zfs_mount_pos_005,zfs_mount_pos_006,zfs_mount_010_neg.ksh, on my machine(linux 2.6.33)
through debug, I found that The cause of zfs_mount_pos_005 failure is same to the zfs_mount_010_neg.ksh
The two scipts verify "If the filesystem 's mountpoint is currently in use, will mount failed"
but in my machine, I execute the operation of these scipts, The results are as follows:
```
- [root@A22832414_00 /]# zpool list
- NAME SIZE ALLOC FREE EXPANDSZ FRAG CAP DEDUP HEALTH ALTROOT
- raid0 192M 384K 192M - 1% 0% 1.00x ONLINE -
- [root@A22832414_00 /]# zfs create raid0/fs1
- [root@A22832414_00 /]# zfs set mountpoint=/home/liuliu/ raid0/fs1
- [root@A22832414_00 /]# zfs umount -f raid0/fs1
- [root@A22832414_00 /]# cd /home/liuliu/ /* Building mountpoint is currently in use scenarios */
- [root@A22832414_00 liuliu]# zfs mount raid0/fs1 /* mount success is different to scipts verify */
- [root@A22832414_00 liuliu]#
```
From the above known, in linux, Even if the mountpoint is currently in use, can also be mounted, so
the scipts as zfs_mount_pos_005 and zfs_mount_010_neg excute failed.
the zfs_mount_pos_006 verify "If filesystem 's mountpoint be the identical of existing filesystem,it will mount failed"
but in my machine, I execute the operation of the scipt, The results are as follows:
```
[root@A22832414_00 liuliu]# zfs list
NAME USED AVAIL REFER MOUNTPOINT
raid0 110K 160M 19K /raid0
zpool11 907M 400M 24.0K /zpool11
zpool11/testvol28070 155M 555M 9.33K -
zpool11/testvol28071 188M 588M 8K -
zpool11/testvol28072 188M 588M 8K -
zpool11/testvol28073 188M 588M 9.33K -
zpool11/testvol28074 188M 588M 9.33K -
[root@A22832414_00 liuliu]# zfs create raid0/fs1
[root@A22832414_00 liuliu]# zfs set mountpoint=/home/liuliu/ raid0/fs1
[root@A22832414_00 liuliu]# zfs create raid0/fs2
[root@A22832414_00 liuliu]# zfs umount raid0/fs2
[root@A22832414_00 liuliu]# zfs set mountpoint=/home/liuliu/ raid0/fs2
[root@A22832414_00 liuliu]# zfs mount
raid0 /raid0
zpool11 /zpool11
raid0/fs1 /home/liuliu
[root@A22832414_00 liuliu]# zfs mount raid0/fs2
[root@A22832414_00 liuliu]# zfs mount
raid0 /raid0
zpool11 /zpool11
raid0/fs1 /home/liuliu
raid0/fs2 /home/liuliu
[root@A22832414_00 liuliu]#
```
From the above known, in linux, Even if the mountpoint be the identical of existing filesystem, can also be mounted, so the scipts as zfs_mount_pos_006 excute failed.
Analysis:
Overlay mount is default in Linux, zfs's code only limits the mountpoint is not empty,The following
```
/*
* Determine if the mountpoint is empty. If so, refuse to perform the
* mount. We don't perform this check if 'remount' is
* specified or if overlay option(-O) is given
*/
if ((flags & MS_OVERLAY) == 0 && !remount &&
!dir_is_empty(mountpoint)) {
zfs_error_aux(hdl, dgettext(TEXT_DOMAIN,
"directory is not empty"));
return (zfs_error_fmt(hdl, EZFS_MOUNTFAILED,
dgettext(TEXT_DOMAIN, "cannot mount '%s'"), mountpoint));
}
```
so ,if the mountpoint is empty, Even if the mountpoint be the identical of existing filesystem, can also be mounted, and after mount will overlay before mount, see all the scipts about zfs_mount, find that not verfiy "if mountpoint is not empty,will mount filesystem failed",so I add one scipt about it,code is the follow:
```
#!/IDE0/ztest/zfs-tests/bin/bash -p
#
# CDDL HEADER START
#
# The contents of this file are subject to the terms of the
# Common Development and Distribution License (the "License").
# You may not use this file except in compliance with the License.
#
# You can obtain a copy of the license at usr/src/OPENSOLARIS.LICENSE
# or http://www.opensolaris.org/os/licensing.
# See the License for the specific language governing permissions
# and limitations under the License.
#
# When distributing Covered Code, include this CDDL HEADER in each
# file and include the License file at usr/src/OPENSOLARIS.LICENSE.
# If applicable, add the following below this CDDL HEADER, with the
# fields enclosed by brackets "[]" replaced with your own identifying
# information: Portions Copyright [yyyy] [name of copyright owner]
#
# CDDL HEADER END
#
#
# Copyright 2007 Sun Microsystems, Inc. All rights reserved.
# Use is subject to license terms.
#
. $STF_SUITE/include/libtest.shlib
. $STF_SUITE/tests/functional/cli_root/zfs_mount/zfs_mount.kshlib
#
# DESCRIPTION:
# Invoke "zfs mount <filesystem>" with a filesystem
# but its mountpoint is not empty,
# it will fail with a return code of 1
# and issue an error message.
#
# STRATEGY:
#1. Make sure that the ZFS filesystem is unmounted.
#2. Apply 'zfs set mountpoint=path <filesystem>'.
#3. Create a file in the given mountpoint.
#3. Invoke 'zfs mount <filesystem>'.
#4. Verify that mount failed with return code of 1.
#
verify_runnable "both"
function cleanup
{
log_must $ZFS set mountpoint=$TESTDIR $TESTPOOL/$TESTFS
log_must force_unmount $TESTPOOL/$TESTFS
return 0
}
typeset -i ret=0
log_assert "Verify that '$ZFS $mountcmd' with a filesystem " \
"whose mountpoint is currently not empty will fail with return code 1."
log_onexit cleanup
unmounted $TESTPOOL/$TESTFS || \
log_must cleanup
[[ -d $TESTDIR ]] || \
log_must $MKDIR -p $TESTDIR
log_must $TOUCH $TESTDIR/$TESTFILE0
$ZFS $mountcmd $TESTPOOL/$TESTFS
ret=$?
(( ret == 1 )) || \
log_fail "'$ZFS $mountcmd $TESTPOOL/$TESTFS' " \
"unexpected return code of $ret."
log_note "Make sure the filesystem $TESTPOOL/$TESTFS is unmounted"
unmounted $TESTPOOL/$TESTFS || \
log_fail Filesystem $TESTPOOL/$TESTFS is mounted
log_pass "'$ZFS $mountcmd' with a filesystem " \
"whose mountpoint is currently not empty failed with return code 1."
```
Thank you!
|
1.0
|
Test case: zfs_mount_006_pos - I being debugged the zfs-test scripts about zfs_mount,,I found that the scipts as zfs_mount_pos_005,zfs_mount_pos_006,zfs_mount_007_pos,zfs_mount_009_neg,zfs_mount_010_neg.ksh execute failure, through see the file-linux.run, found these scripts needs investigation, I try to debuged zfs_mount_pos_005,zfs_mount_pos_006,zfs_mount_010_neg.ksh, on my machine(linux 2.6.33)
through debug, I found that The cause of zfs_mount_pos_005 failure is same to the zfs_mount_010_neg.ksh
The two scipts verify "If the filesystem 's mountpoint is currently in use, will mount failed"
but in my machine, I execute the operation of these scipts, The results are as follows:
```
- [root@A22832414_00 /]# zpool list
- NAME SIZE ALLOC FREE EXPANDSZ FRAG CAP DEDUP HEALTH ALTROOT
- raid0 192M 384K 192M - 1% 0% 1.00x ONLINE -
- [root@A22832414_00 /]# zfs create raid0/fs1
- [root@A22832414_00 /]# zfs set mountpoint=/home/liuliu/ raid0/fs1
- [root@A22832414_00 /]# zfs umount -f raid0/fs1
- [root@A22832414_00 /]# cd /home/liuliu/ /* Building mountpoint is currently in use scenarios */
- [root@A22832414_00 liuliu]# zfs mount raid0/fs1 /* mount success is different to scipts verify */
- [root@A22832414_00 liuliu]#
```
From the above known, in linux, Even if the mountpoint is currently in use, can also be mounted, so
the scipts as zfs_mount_pos_005 and zfs_mount_010_neg excute failed.
the zfs_mount_pos_006 verify "If filesystem 's mountpoint be the identical of existing filesystem,it will mount failed"
but in my machine, I execute the operation of the scipt, The results are as follows:
```
[root@A22832414_00 liuliu]# zfs list
NAME USED AVAIL REFER MOUNTPOINT
raid0 110K 160M 19K /raid0
zpool11 907M 400M 24.0K /zpool11
zpool11/testvol28070 155M 555M 9.33K -
zpool11/testvol28071 188M 588M 8K -
zpool11/testvol28072 188M 588M 8K -
zpool11/testvol28073 188M 588M 9.33K -
zpool11/testvol28074 188M 588M 9.33K -
[root@A22832414_00 liuliu]# zfs create raid0/fs1
[root@A22832414_00 liuliu]# zfs set mountpoint=/home/liuliu/ raid0/fs1
[root@A22832414_00 liuliu]# zfs create raid0/fs2
[root@A22832414_00 liuliu]# zfs umount raid0/fs2
[root@A22832414_00 liuliu]# zfs set mountpoint=/home/liuliu/ raid0/fs2
[root@A22832414_00 liuliu]# zfs mount
raid0 /raid0
zpool11 /zpool11
raid0/fs1 /home/liuliu
[root@A22832414_00 liuliu]# zfs mount raid0/fs2
[root@A22832414_00 liuliu]# zfs mount
raid0 /raid0
zpool11 /zpool11
raid0/fs1 /home/liuliu
raid0/fs2 /home/liuliu
[root@A22832414_00 liuliu]#
```
From the above known, in linux, Even if the mountpoint be the identical of existing filesystem, can also be mounted, so the scipts as zfs_mount_pos_006 excute failed.
Analysis:
Overlay mount is default in Linux, zfs's code only limits the mountpoint is not empty,The following
```
/*
* Determine if the mountpoint is empty. If so, refuse to perform the
* mount. We don't perform this check if 'remount' is
* specified or if overlay option(-O) is given
*/
if ((flags & MS_OVERLAY) == 0 && !remount &&
!dir_is_empty(mountpoint)) {
zfs_error_aux(hdl, dgettext(TEXT_DOMAIN,
"directory is not empty"));
return (zfs_error_fmt(hdl, EZFS_MOUNTFAILED,
dgettext(TEXT_DOMAIN, "cannot mount '%s'"), mountpoint));
}
```
so ,if the mountpoint is empty, Even if the mountpoint be the identical of existing filesystem, can also be mounted, and after mount will overlay before mount, see all the scipts about zfs_mount, find that not verfiy "if mountpoint is not empty,will mount filesystem failed",so I add one scipt about it,code is the follow:
```
#!/IDE0/ztest/zfs-tests/bin/bash -p
#
# CDDL HEADER START
#
# The contents of this file are subject to the terms of the
# Common Development and Distribution License (the "License").
# You may not use this file except in compliance with the License.
#
# You can obtain a copy of the license at usr/src/OPENSOLARIS.LICENSE
# or http://www.opensolaris.org/os/licensing.
# See the License for the specific language governing permissions
# and limitations under the License.
#
# When distributing Covered Code, include this CDDL HEADER in each
# file and include the License file at usr/src/OPENSOLARIS.LICENSE.
# If applicable, add the following below this CDDL HEADER, with the
# fields enclosed by brackets "[]" replaced with your own identifying
# information: Portions Copyright [yyyy] [name of copyright owner]
#
# CDDL HEADER END
#
#
# Copyright 2007 Sun Microsystems, Inc. All rights reserved.
# Use is subject to license terms.
#
. $STF_SUITE/include/libtest.shlib
. $STF_SUITE/tests/functional/cli_root/zfs_mount/zfs_mount.kshlib
#
# DESCRIPTION:
# Invoke "zfs mount <filesystem>" with a filesystem
# but its mountpoint is not empty,
# it will fail with a return code of 1
# and issue an error message.
#
# STRATEGY:
#1. Make sure that the ZFS filesystem is unmounted.
#2. Apply 'zfs set mountpoint=path <filesystem>'.
#3. Create a file in the given mountpoint.
#3. Invoke 'zfs mount <filesystem>'.
#4. Verify that mount failed with return code of 1.
#
verify_runnable "both"
function cleanup
{
log_must $ZFS set mountpoint=$TESTDIR $TESTPOOL/$TESTFS
log_must force_unmount $TESTPOOL/$TESTFS
return 0
}
typeset -i ret=0
log_assert "Verify that '$ZFS $mountcmd' with a filesystem " \
"whose mountpoint is currently not empty will fail with return code 1."
log_onexit cleanup
unmounted $TESTPOOL/$TESTFS || \
log_must cleanup
[[ -d $TESTDIR ]] || \
log_must $MKDIR -p $TESTDIR
log_must $TOUCH $TESTDIR/$TESTFILE0
$ZFS $mountcmd $TESTPOOL/$TESTFS
ret=$?
(( ret == 1 )) || \
log_fail "'$ZFS $mountcmd $TESTPOOL/$TESTFS' " \
"unexpected return code of $ret."
log_note "Make sure the filesystem $TESTPOOL/$TESTFS is unmounted"
unmounted $TESTPOOL/$TESTFS || \
log_fail Filesystem $TESTPOOL/$TESTFS is mounted
log_pass "'$ZFS $mountcmd' with a filesystem " \
"whose mountpoint is currently not empty failed with return code 1."
```
Thank you!
|
non_defect
|
test case zfs mount pos i being debugged the zfs test scripts about zfs mount i found that the scipts as zfs mount pos zfs mount pos zfs mount pos zfs mount neg zfs mount neg ksh execute failure through see the file linux run found these scripts needs investigation i try to debuged zfs mount pos zfs mount pos zfs mount neg ksh on my machine linux through debug i found that the cause of zfs mount pos failure is same to the zfs mount neg ksh the two scipts verify if the filesystem s mountpoint is currently in use will mount failed but in my machine i execute the operation of these scipts the results are as follows zpool list name size alloc free expandsz frag cap dedup health altroot online zfs create zfs set mountpoint home liuliu zfs umount f cd home liuliu building mountpoint is currently in use scenarios zfs mount mount success is different to scipts verify from the above known in linux even if the mountpoint is currently in use can also be mounted so the scipts as zfs mount pos and zfs mount neg excute failed the zfs mount pos verify if filesystem s mountpoint be the identical of existing filesystem it will mount failed but in my machine i execute the operation of the scipt the results are as follows zfs list name used avail refer mountpoint zfs create zfs set mountpoint home liuliu zfs create zfs umount zfs set mountpoint home liuliu zfs mount home liuliu zfs mount zfs mount home liuliu home liuliu from the above known in linux even if the mountpoint be the identical of existing filesystem can also be mounted so the scipts as zfs mount pos excute failed analysis overlay mount is default in linux zfs s code only limits the mountpoint is not empty the following determine if the mountpoint is empty if so refuse to perform the mount we don t perform this check if remount is specified or if overlay option o is given if flags ms overlay remount dir is empty mountpoint zfs error aux hdl dgettext text domain directory is not empty return zfs error fmt hdl ezfs mountfailed dgettext text domain cannot mount s mountpoint so if the mountpoint is empty even if the mountpoint be the identical of existing filesystem can also be mounted and after mount will overlay before mount see all the scipts about zfs mount find that not verfiy if mountpoint is not empty will mount filesystem failed so i add one scipt about it code is the follow ztest zfs tests bin bash p cddl header start the contents of this file are subject to the terms of the common development and distribution license the license you may not use this file except in compliance with the license you can obtain a copy of the license at usr src opensolaris license or see the license for the specific language governing permissions and limitations under the license when distributing covered code include this cddl header in each file and include the license file at usr src opensolaris license if applicable add the following below this cddl header with the fields enclosed by brackets replaced with your own identifying information portions copyright cddl header end copyright sun microsystems inc all rights reserved use is subject to license terms stf suite include libtest shlib stf suite tests functional cli root zfs mount zfs mount kshlib description invoke zfs mount with a filesystem but its mountpoint is not empty it will fail with a return code of and issue an error message strategy make sure that the zfs filesystem is unmounted apply zfs set mountpoint path create a file in the given mountpoint invoke zfs mount verify that mount failed with return code of verify runnable both function cleanup log must zfs set mountpoint testdir testpool testfs log must force unmount testpool testfs return typeset i ret log assert verify that zfs mountcmd with a filesystem whose mountpoint is currently not empty will fail with return code log onexit cleanup unmounted testpool testfs log must cleanup log must mkdir p testdir log must touch testdir zfs mountcmd testpool testfs ret ret log fail zfs mountcmd testpool testfs unexpected return code of ret log note make sure the filesystem testpool testfs is unmounted unmounted testpool testfs log fail filesystem testpool testfs is mounted log pass zfs mountcmd with a filesystem whose mountpoint is currently not empty failed with return code thank you
| 0
|
64,812
| 18,912,890,195
|
IssuesEvent
|
2021-11-16 15:42:56
|
NREL/EnergyPlus
|
https://api.github.com/repos/NREL/EnergyPlus
|
closed
|
Exhaust Absorption Chiller input processing issue when having more than one input objects
|
Defect
|
Issue overview
--------------
It was reported that EnergyPlus will give severe error message about the Exhaust turbine processing problems when there are more than one micro turbines defined in the file for absorption chillers / chillerheaters. The process error will be a fatal error that would terminate the simulation.
The root cause was found to be due to the incorrect override of the current reading object after a loop. Then at the beginning of the loop to read another chillerheater object. The problems is about the number of Absorption ChillerHeater objects (problematic if >1) rather than the number of micro turbines.
A code revision is needed to correct the issue.
### Details
Some additional details for this issue (if relevant):
- Platform (Operating system, version): All
- Version of EnergyPlus (if using an intermediate build, include SHA): v9.6
- Helpdesk ticket number: 16052
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [x] Defect file added (list location of defect file [here](https://github.com/NREL/EnergyPlusDevSupport/blob/master/DefectFiles/9000s/9158/9158_Exhaust_ChillerHeater_MicroTurbine_Multiple_Objects.idf))
- [x] Ticket added to Pivotal for defect (development team task)
- [x] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect)
|
1.0
|
Exhaust Absorption Chiller input processing issue when having more than one input objects - Issue overview
--------------
It was reported that EnergyPlus will give severe error message about the Exhaust turbine processing problems when there are more than one micro turbines defined in the file for absorption chillers / chillerheaters. The process error will be a fatal error that would terminate the simulation.
The root cause was found to be due to the incorrect override of the current reading object after a loop. Then at the beginning of the loop to read another chillerheater object. The problems is about the number of Absorption ChillerHeater objects (problematic if >1) rather than the number of micro turbines.
A code revision is needed to correct the issue.
### Details
Some additional details for this issue (if relevant):
- Platform (Operating system, version): All
- Version of EnergyPlus (if using an intermediate build, include SHA): v9.6
- Helpdesk ticket number: 16052
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [x] Defect file added (list location of defect file [here](https://github.com/NREL/EnergyPlusDevSupport/blob/master/DefectFiles/9000s/9158/9158_Exhaust_ChillerHeater_MicroTurbine_Multiple_Objects.idf))
- [x] Ticket added to Pivotal for defect (development team task)
- [x] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect)
|
defect
|
exhaust absorption chiller input processing issue when having more than one input objects issue overview it was reported that energyplus will give severe error message about the exhaust turbine processing problems when there are more than one micro turbines defined in the file for absorption chillers chillerheaters the process error will be a fatal error that would terminate the simulation the root cause was found to be due to the incorrect override of the current reading object after a loop then at the beginning of the loop to read another chillerheater object the problems is about the number of absorption chillerheater objects problematic if rather than the number of micro turbines a code revision is needed to correct the issue details some additional details for this issue if relevant platform operating system version all version of energyplus if using an intermediate build include sha helpdesk ticket number checklist add to this list or remove from it as applicable this is a simple templated set of guidelines defect file added list location of defect file ticket added to pivotal for defect development team task pull request created the pull request will have additional tasks related to reviewing changes that fix this defect
| 1
|
530,105
| 15,416,115,467
|
IssuesEvent
|
2021-03-05 04:16:51
|
worldanvil/worldanvil-bug-tracker
|
https://api.github.com/repos/worldanvil/worldanvil-bug-tracker
|
closed
|
Athena sidebar editor not saving excerpt changes
|
Feature: Articles & Templates Priority: Moderate Severity: Minor Status: Reproduced Type: Bug
|
**World Anvil Username:**
Lethann
**Describe the Issue**
In the Athena view I click on an article to get the preview on the right to show for that article. Adding tags and an icon work fine, but any changes in the excerpt box are not saved. Going into the Design tab and editing it there works fine.
**To Reproduce**
1. go to Articles & Categories (Athena)
2. click on any article
3. use preview on the right of screen to edit the excerpt box
4. click on another article/refresh page/open edited article
5. go back to original article and excerpt is still empty/unchanged.
|
1.0
|
Athena sidebar editor not saving excerpt changes -
**World Anvil Username:**
Lethann
**Describe the Issue**
In the Athena view I click on an article to get the preview on the right to show for that article. Adding tags and an icon work fine, but any changes in the excerpt box are not saved. Going into the Design tab and editing it there works fine.
**To Reproduce**
1. go to Articles & Categories (Athena)
2. click on any article
3. use preview on the right of screen to edit the excerpt box
4. click on another article/refresh page/open edited article
5. go back to original article and excerpt is still empty/unchanged.
|
non_defect
|
athena sidebar editor not saving excerpt changes world anvil username lethann describe the issue in the athena view i click on an article to get the preview on the right to show for that article adding tags and an icon work fine but any changes in the excerpt box are not saved going into the design tab and editing it there works fine to reproduce go to articles categories athena click on any article use preview on the right of screen to edit the excerpt box click on another article refresh page open edited article go back to original article and excerpt is still empty unchanged
| 0
|
183,598
| 21,772,136,625
|
IssuesEvent
|
2022-05-13 10:06:57
|
michaelmeaney/IdentityServer
|
https://api.github.com/repos/michaelmeaney/IdentityServer
|
opened
|
bootstrap-3.3.6.min.js: 6 vulnerabilities (highest severity is: 6.1)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-8331](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | bootstrap - 3.4.0, 4.0.0-beta.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0, 4.0.0-beta.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-8331","vulnerabilityDetails":"In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14040","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20677","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20676","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0, 4.0.0-beta.2","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> -->
|
True
|
bootstrap-3.3.6.min.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-8331](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.6.min.js | Direct | bootstrap - 3.4.0, 4.0.0-beta.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.3.6.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /clients/src/MvcHybridBackChannel/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/michaelmeaney/IdentityServer/commit/5d935ff804f203a3184f8e88d1ef723ac77c79e5">5d935ff804f203a3184f8e88d1ef723ac77c79e5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0, 4.0.0-beta.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-8331","vulnerabilityDetails":"In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14040","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20677","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20676","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0, 4.0.0-beta.2","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> -->
|
non_defect
|
bootstrap min js vulnerabilities highest severity is vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium bootstrap min js direct bootstrap bootstrap sass medium bootstrap min js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap min js direct bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter medium bootstrap min js direct bootstrap medium bootstrap min js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap min js direct bootstrap beta details cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap bootstrap sass step up your open source security game with whitesource cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap step up your open source security game with whitesource cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter step up your open source security game with whitesource cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap step up your open source security game with whitesource cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap step up your open source security game with whitesource cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library clients src mvchybridbackchannel wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap beta step up your open source security game with whitesource istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap bootstrap sass isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before and x before xss is possible in the tooltip or popover data template attribute vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion org webjars npm bootstrap org webjars bootstrap isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the collapse data parent attribute vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the affix configuration target property vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the tooltip data viewport attribute vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion org webjars npm bootstrap org webjars bootstrap isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the data container property of tooltip vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap beta isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve vulnerabilityurl
| 0
|
23,386
| 3,807,229,913
|
IssuesEvent
|
2016-03-25 06:28:28
|
drewandersonnz/trac2github
|
https://api.github.com/repos/drewandersonnz/trac2github
|
closed
|
Set Zend_Mail to UTF-8
|
P: trivial T: defect
|
**Reported by drew on 4 Oct 2012 21:10 UTC**
admin.onlysport.org/application/controllers/ProfileController.php:160: $mail = new Zend_Mail();
admin.onlysport.org/application/controllers/EmailController.php:167: $mail = new Zend_Mail();
admin.onlysport.org/crons/error_email.php:32:$mail = new Zend_Mail('utf-8');
onlysport.org/application/controllers/ProfileController.php:96: $mail = new Zend_Mail();
onlysport.org/application/controllers/ContactController.php:38: $mail = new Zend_Mail();
onlysport.org/application/controllers/AuthController.php:29: $mail = new Zend_Mail();
onlysport.org/application/controllers/AuthController.php:209: $mail = new Zend_Mail();
onlysport.org/application/controllers/AuthController.php:271: $mail = new Zend_Mail();
onlysport.org/application/controllers/ReportController.php:47: $mail = new Zend_Mail();
|
1.0
|
Set Zend_Mail to UTF-8 - **Reported by drew on 4 Oct 2012 21:10 UTC**
admin.onlysport.org/application/controllers/ProfileController.php:160: $mail = new Zend_Mail();
admin.onlysport.org/application/controllers/EmailController.php:167: $mail = new Zend_Mail();
admin.onlysport.org/crons/error_email.php:32:$mail = new Zend_Mail('utf-8');
onlysport.org/application/controllers/ProfileController.php:96: $mail = new Zend_Mail();
onlysport.org/application/controllers/ContactController.php:38: $mail = new Zend_Mail();
onlysport.org/application/controllers/AuthController.php:29: $mail = new Zend_Mail();
onlysport.org/application/controllers/AuthController.php:209: $mail = new Zend_Mail();
onlysport.org/application/controllers/AuthController.php:271: $mail = new Zend_Mail();
onlysport.org/application/controllers/ReportController.php:47: $mail = new Zend_Mail();
|
defect
|
set zend mail to utf reported by drew on oct utc admin onlysport org application controllers profilecontroller php mail new zend mail admin onlysport org application controllers emailcontroller php mail new zend mail admin onlysport org crons error email php mail new zend mail utf onlysport org application controllers profilecontroller php mail new zend mail onlysport org application controllers contactcontroller php mail new zend mail onlysport org application controllers authcontroller php mail new zend mail onlysport org application controllers authcontroller php mail new zend mail onlysport org application controllers authcontroller php mail new zend mail onlysport org application controllers reportcontroller php mail new zend mail
| 1
|
78,103
| 27,323,802,679
|
IssuesEvent
|
2023-02-24 22:52:40
|
OpenMS/OpenMS
|
https://api.github.com/repos/OpenMS/OpenMS
|
closed
|
TOPPView crashes when right-clicking layer of a view that was closed
|
defect TOPPView bug
|
If you close a view and then right click on the still available layer, it crashes hard.
|
1.0
|
TOPPView crashes when right-clicking layer of a view that was closed - If you close a view and then right click on the still available layer, it crashes hard.
|
defect
|
toppview crashes when right clicking layer of a view that was closed if you close a view and then right click on the still available layer it crashes hard
| 1
|
35,628
| 14,786,574,906
|
IssuesEvent
|
2021-01-12 05:51:21
|
microsoft/botframework-cli
|
https://api.github.com/repos/microsoft/botframework-cli
|
closed
|
No way to use in Azure Pipelines YAML
|
Bot Services customer-replied-to customer-reported
|
It's not easy to use the BF CLI in Azure Pipelines. It's hard to install globally (usually get errors), and it's hard to make use of if you only install it locally.
Please provide an example of installing and using the BF CLI in an Azure Pipelines YAML.
|
1.0
|
No way to use in Azure Pipelines YAML - It's not easy to use the BF CLI in Azure Pipelines. It's hard to install globally (usually get errors), and it's hard to make use of if you only install it locally.
Please provide an example of installing and using the BF CLI in an Azure Pipelines YAML.
|
non_defect
|
no way to use in azure pipelines yaml it s not easy to use the bf cli in azure pipelines it s hard to install globally usually get errors and it s hard to make use of if you only install it locally please provide an example of installing and using the bf cli in an azure pipelines yaml
| 0
|
32,087
| 6,711,959,906
|
IssuesEvent
|
2017-10-13 07:23:44
|
opencaching/opencaching-pl
|
https://api.github.com/repos/opencaching/opencaching-pl
|
closed
|
Invalid target redirect after logon on OCPL
|
Component_Core Priority_High Type_Defect
|
Steps to reproduce:
1. Logout from the service
2. Go to https://opencaching.pl/myneighborhood.php - redirects correctly to https://opencaching.pl/login.php?target=myneighborhood.php
3. Successful logon redirects to https://opencaching.plmyneighborhood.php without a slash ('/') in the middle, which is resolved to bad address
|
1.0
|
Invalid target redirect after logon on OCPL - Steps to reproduce:
1. Logout from the service
2. Go to https://opencaching.pl/myneighborhood.php - redirects correctly to https://opencaching.pl/login.php?target=myneighborhood.php
3. Successful logon redirects to https://opencaching.plmyneighborhood.php without a slash ('/') in the middle, which is resolved to bad address
|
defect
|
invalid target redirect after logon on ocpl steps to reproduce logout from the service go to redirects correctly to successful logon redirects to without a slash in the middle which is resolved to bad address
| 1
|
43,998
| 11,900,129,506
|
IssuesEvent
|
2020-03-30 10:07:14
|
ShaikASK/Testing
|
https://api.github.com/repos/ShaikASK/Testing
|
opened
|
Candidate : Common Details form 2 : Blank screen is displayed with "Previous", "Skip" and "Save & Continue" button upon clicking on skip button displayed in common details form 2 when there is no other webform
|
Defect P2
|
Steps To Replicate :
1.Launch the URL
2.Sign in as Candidate (candidate workflow used --> Accenture W2 : No Webform )
3.Sign the Offer Letter
4.Navigated to Common Details form 1 (Ensure that it should have only common details webform 1 & 2)
5.Fill common details form 1 and click on Save & Continue button
6.Navigated to common details form 2
7.Click on skip button
Experienced Behavior : Observed that blank screen is displayed with "Previous", "Skip" and "Save & Continue" button upon clicking on skip button displayed in common details form 2 when there is no other webform (Please Refer Screen Shot)
Expected Behavior : Ensure that it should not display black screen but it should display alert message that please fill all the required webform details
|
1.0
|
Candidate : Common Details form 2 : Blank screen is displayed with "Previous", "Skip" and "Save & Continue" button upon clicking on skip button displayed in common details form 2 when there is no other webform - Steps To Replicate :
1.Launch the URL
2.Sign in as Candidate (candidate workflow used --> Accenture W2 : No Webform )
3.Sign the Offer Letter
4.Navigated to Common Details form 1 (Ensure that it should have only common details webform 1 & 2)
5.Fill common details form 1 and click on Save & Continue button
6.Navigated to common details form 2
7.Click on skip button
Experienced Behavior : Observed that blank screen is displayed with "Previous", "Skip" and "Save & Continue" button upon clicking on skip button displayed in common details form 2 when there is no other webform (Please Refer Screen Shot)
Expected Behavior : Ensure that it should not display black screen but it should display alert message that please fill all the required webform details
|
defect
|
candidate common details form blank screen is displayed with previous skip and save continue button upon clicking on skip button displayed in common details form when there is no other webform steps to replicate launch the url sign in as candidate candidate workflow used accenture no webform sign the offer letter navigated to common details form ensure that it should have only common details webform fill common details form and click on save continue button navigated to common details form click on skip button experienced behavior observed that blank screen is displayed with previous skip and save continue button upon clicking on skip button displayed in common details form when there is no other webform please refer screen shot expected behavior ensure that it should not display black screen but it should display alert message that please fill all the required webform details
| 1
|
75,971
| 26,186,739,401
|
IssuesEvent
|
2023-01-03 02:07:49
|
vector-im/element-android
|
https://api.github.com/repos/vector-im/element-android
|
opened
|
After the image or video is viewed, it will automatically jump to the end of the timeline.
|
T-Defect
|
### Steps to reproduce
1. Enter a session;
2. Scroll up for a certain distance, and stop at the position where there is an image;
3. Click on the image, and press "Back" when finished viewing.
### Outcome
#### What did you expect?
The timeline remains at its current position.
#### What happened instead?
After the image is viewed, the timeline always scrolls to the end automatically. This is not friendly to users who want to browse through historical messages for a long time.
### Your phone model
HMD TA-1054; Mi 9T
### Operating system version
Android 8.1; MIUI 12.5 by xiaomi.eu (based on Android 11)
### Application version and app store
Element 1.5.18 (Google Play)
### Homeserver
Synapse 1.74.0
### Will you send logs?
No
### Are you willing to provide a PR?
No
|
1.0
|
After the image or video is viewed, it will automatically jump to the end of the timeline. - ### Steps to reproduce
1. Enter a session;
2. Scroll up for a certain distance, and stop at the position where there is an image;
3. Click on the image, and press "Back" when finished viewing.
### Outcome
#### What did you expect?
The timeline remains at its current position.
#### What happened instead?
After the image is viewed, the timeline always scrolls to the end automatically. This is not friendly to users who want to browse through historical messages for a long time.
### Your phone model
HMD TA-1054; Mi 9T
### Operating system version
Android 8.1; MIUI 12.5 by xiaomi.eu (based on Android 11)
### Application version and app store
Element 1.5.18 (Google Play)
### Homeserver
Synapse 1.74.0
### Will you send logs?
No
### Are you willing to provide a PR?
No
|
defect
|
after the image or video is viewed it will automatically jump to the end of the timeline steps to reproduce enter a session scroll up for a certain distance and stop at the position where there is an image click on the image and press back when finished viewing outcome what did you expect the timeline remains at its current position what happened instead after the image is viewed the timeline always scrolls to the end automatically this is not friendly to users who want to browse through historical messages for a long time your phone model hmd ta mi operating system version android miui by xiaomi eu based on android application version and app store element google play homeserver synapse will you send logs no are you willing to provide a pr no
| 1
|
6,688
| 3,437,722,200
|
IssuesEvent
|
2015-12-13 13:03:36
|
joomla/joomla-cms
|
https://api.github.com/repos/joomla/joomla-cms
|
opened
|
Regression - Missing Error message - Com_messages
|
No Code Attached Yet
|
#### Steps to reproduce the issue
Go to Messages
Create New
Select "No user" as recipient
Enter Title and Subject
Click Send
#### Expected result
Error message that I need to select a user (although I'm not sure why there is a No User option)
#### Actual result
Empty error div
In 3.4.5 you would get an error message
Save failed with the following error: Invalid recipient
|
1.0
|
Regression - Missing Error message - Com_messages - #### Steps to reproduce the issue
Go to Messages
Create New
Select "No user" as recipient
Enter Title and Subject
Click Send
#### Expected result
Error message that I need to select a user (although I'm not sure why there is a No User option)
#### Actual result
Empty error div
In 3.4.5 you would get an error message
Save failed with the following error: Invalid recipient
|
non_defect
|
regression missing error message com messages steps to reproduce the issue go to messages create new select no user as recipient enter title and subject click send expected result error message that i need to select a user although i m not sure why there is a no user option actual result empty error div in you would get an error message save failed with the following error invalid recipient
| 0
|
39,044
| 9,179,058,841
|
IssuesEvent
|
2019-03-05 01:33:03
|
amnh/PCG
|
https://api.github.com/repos/amnh/PCG
|
closed
|
The evaluation model doesn't perform work when it should
|
defect performance/optimization refactor verification/testing
|
The evaluation model report a `NoOp` value from the following script:
load("graph.bin")
report(data,"cost.data")
Thus script should preform I/O work attempting to deserialize the `"graph.bin"` file contents, and on a success, report the graph state that was deserialized.
I think one prudent solution might be to remove the `NoOp` value from the `EvalUnit` along with the `Monoid` and `MonadPlus` instances from the `Evaluation` monad. I believe we will only want to operate over non-empty structures (such as `NonEmpty Command`) with something like [`traverse1`](http://hackage.haskell.org/package/semigroupoids-5.3.2/docs/Data-Semigroup-Traversable.html), so the `NoOp` value is probably better left as unrepresented.
Once resolved, we should add integration tests to ensure that the evaluation model works on a variety of use cases for retrieving input and writing output, not just `READ`/`REPORT` commands.
|
1.0
|
The evaluation model doesn't perform work when it should - The evaluation model report a `NoOp` value from the following script:
load("graph.bin")
report(data,"cost.data")
Thus script should preform I/O work attempting to deserialize the `"graph.bin"` file contents, and on a success, report the graph state that was deserialized.
I think one prudent solution might be to remove the `NoOp` value from the `EvalUnit` along with the `Monoid` and `MonadPlus` instances from the `Evaluation` monad. I believe we will only want to operate over non-empty structures (such as `NonEmpty Command`) with something like [`traverse1`](http://hackage.haskell.org/package/semigroupoids-5.3.2/docs/Data-Semigroup-Traversable.html), so the `NoOp` value is probably better left as unrepresented.
Once resolved, we should add integration tests to ensure that the evaluation model works on a variety of use cases for retrieving input and writing output, not just `READ`/`REPORT` commands.
|
defect
|
the evaluation model doesn t perform work when it should the evaluation model report a noop value from the following script load graph bin report data cost data thus script should preform i o work attempting to deserialize the graph bin file contents and on a success report the graph state that was deserialized i think one prudent solution might be to remove the noop value from the evalunit along with the monoid and monadplus instances from the evaluation monad i believe we will only want to operate over non empty structures such as nonempty command with something like so the noop value is probably better left as unrepresented once resolved we should add integration tests to ensure that the evaluation model works on a variety of use cases for retrieving input and writing output not just read report commands
| 1
|
348,475
| 10,442,919,090
|
IssuesEvent
|
2019-09-18 13:58:12
|
brave/brave-browser
|
https://api.github.com/repos/brave/brave-browser
|
closed
|
Add callback to GetBalanceReport
|
QA/No dev-concern feature/rewards priority/P5
|
We need to add callback to `GetBalanceReport` inside `vendor/bat-native-ledger/include/bat/ledger/ledger.h`.
Right now we are passing result back via pointer. To be consistent let's return it via callback.
|
1.0
|
Add callback to GetBalanceReport - We need to add callback to `GetBalanceReport` inside `vendor/bat-native-ledger/include/bat/ledger/ledger.h`.
Right now we are passing result back via pointer. To be consistent let's return it via callback.
|
non_defect
|
add callback to getbalancereport we need to add callback to getbalancereport inside vendor bat native ledger include bat ledger ledger h right now we are passing result back via pointer to be consistent let s return it via callback
| 0
|
390,736
| 11,562,379,596
|
IssuesEvent
|
2020-02-20 02:16:53
|
CitiesSkylinesMods/TMPE
|
https://api.github.com/repos/CitiesSkylinesMods/TMPE
|
opened
|
Further enhancements to menu tooltips/keybinds
|
Accessibility DESPAWN TOOLS Localisation PRIORITY SIGNS Settings UI Usability VEHICLE RESTRICTIONS enhancement
|
While testing #656 I noticed some issues with tooltips and keybinds, I think maybe a separate PR could imrpove things a little if time permits...
I just added a keybind to Parking Restrictions for first time and got this:

Also, I think we should change where tool-select keybind is shown, if that's possible? For example, this is what Priority Signs tooltip currently looks like:

I would suggest cleaning it to something like:
>Priority Signs (Shift + P)
>
> When tool is active, you can:
> Shift+Click: ...
> Ctrl+Click: ...
> Ctrl+Shift+Click: ...
Also, is it possible to have keybind (ie, the shortcut key strings, _not_ their effect) in different colour such as yellow?
Following tools are still missing keybinds:
* Timed Traffic Lights and Manual Traffic Lights
* I hope we can one day merge all traffic lights in to one completely refactored tool
* _So ignore these for now_
* Disable Despawning
* Keybind would toggle state
* Vehicle Restrictions
* Clear Traffic
* _Doesn't need a keybind IMO_
|
1.0
|
Further enhancements to menu tooltips/keybinds - While testing #656 I noticed some issues with tooltips and keybinds, I think maybe a separate PR could imrpove things a little if time permits...
I just added a keybind to Parking Restrictions for first time and got this:

Also, I think we should change where tool-select keybind is shown, if that's possible? For example, this is what Priority Signs tooltip currently looks like:

I would suggest cleaning it to something like:
>Priority Signs (Shift + P)
>
> When tool is active, you can:
> Shift+Click: ...
> Ctrl+Click: ...
> Ctrl+Shift+Click: ...
Also, is it possible to have keybind (ie, the shortcut key strings, _not_ their effect) in different colour such as yellow?
Following tools are still missing keybinds:
* Timed Traffic Lights and Manual Traffic Lights
* I hope we can one day merge all traffic lights in to one completely refactored tool
* _So ignore these for now_
* Disable Despawning
* Keybind would toggle state
* Vehicle Restrictions
* Clear Traffic
* _Doesn't need a keybind IMO_
|
non_defect
|
further enhancements to menu tooltips keybinds while testing i noticed some issues with tooltips and keybinds i think maybe a separate pr could imrpove things a little if time permits i just added a keybind to parking restrictions for first time and got this also i think we should change where tool select keybind is shown if that s possible for example this is what priority signs tooltip currently looks like i would suggest cleaning it to something like priority signs shift p when tool is active you can shift click ctrl click ctrl shift click also is it possible to have keybind ie the shortcut key strings not their effect in different colour such as yellow following tools are still missing keybinds timed traffic lights and manual traffic lights i hope we can one day merge all traffic lights in to one completely refactored tool so ignore these for now disable despawning keybind would toggle state vehicle restrictions clear traffic doesn t need a keybind imo
| 0
|
70,032
| 22,793,861,940
|
IssuesEvent
|
2022-07-10 12:17:05
|
FreeRADIUS/freeradius-server
|
https://api.github.com/repos/FreeRADIUS/freeradius-server
|
closed
|
[defect]: missing ATTRIBUTE 178 in dictionary.erx#L233
|
defect
|
### What type of defect/bug is this?
incorrect 3rd party API usage
### How can the issue be reproduced?
request
`echo "Acct-Session-Id=5273,ERX-Update-Service:1='svc-allow-ipoe(1000000,1000000)'" | radclient -x 172.20.20.254:3799 coa testsecret`
response
```
Sent CoA-Request Id 110 from 0.0.0.0:23604 to 172.20.20.254:3799 length 66
Acct-Session-Id = "5273"
ERX-Update-Service:1 = "svc-allow-ipoe(1000000,1000000)"
Received CoA-NAK Id 110 from 172.20.20.254:3799 to 172.20.20.1:23604 length 55
Error-Cause = Invalid-Request
Attr-26.4874.178 = 0x31323220457865637574696f6e206661696c757265
(0) -: Expected CoA-ACK got CoA-NAK
```
response after fix attribute in https://github.com/FreeRADIUS/freeradius-server/blob/master/share/dictionary/radius/dictionary.erx#L233 by adding line
`ATTRIBUTE ERX-Action-Reason 178 string`
```
Sent CoA-Request Id 169 from 0.0.0.0:18201 to 172.20.20.254:3799 length 66
Acct-Session-Id = "5273"
ERX-Update-Service:1 = "svc-allow-ipoe(1000000,1000000)"
Received CoA-NAK Id 169 from 172.20.20.254:3799 to 172.20.20.1:18201 length 55
Error-Cause = Invalid-Request
ERX-Action-Reason = "122 Execution failure"
(0) -: Expected CoA-ACK got CoA-NAK
```
### Log output from the FreeRADIUS client
```shell
# echo "Acct-Session-Id=5273,ERX-Update-Service:1='svc-allow-ipoe(1000000,1000000)'" | radclient -x 172.20.20.254:3799 coa testsecret
Sent CoA-Request Id 110 from 0.0.0.0:23604 to 172.20.20.254:3799 length 66
Acct-Session-Id = "5273"
ERX-Update-Service:1 = "svc-allow-ipoe(1000000,1000000)"
Received CoA-NAK Id 110 from 172.20.20.254:3799 to 172.20.20.1:23604 length 55
Error-Cause = Invalid-Request
Attr-26.4874.178 = 0x31323220457865637574696f6e206661696c757265
(0) -: Expected CoA-ACK got CoA-NAK
```
### Relevant log output from client utilities
_No response_
### Backtrace from LLDB or GDB
_No response_
|
1.0
|
[defect]: missing ATTRIBUTE 178 in dictionary.erx#L233 - ### What type of defect/bug is this?
incorrect 3rd party API usage
### How can the issue be reproduced?
request
`echo "Acct-Session-Id=5273,ERX-Update-Service:1='svc-allow-ipoe(1000000,1000000)'" | radclient -x 172.20.20.254:3799 coa testsecret`
response
```
Sent CoA-Request Id 110 from 0.0.0.0:23604 to 172.20.20.254:3799 length 66
Acct-Session-Id = "5273"
ERX-Update-Service:1 = "svc-allow-ipoe(1000000,1000000)"
Received CoA-NAK Id 110 from 172.20.20.254:3799 to 172.20.20.1:23604 length 55
Error-Cause = Invalid-Request
Attr-26.4874.178 = 0x31323220457865637574696f6e206661696c757265
(0) -: Expected CoA-ACK got CoA-NAK
```
response after fix attribute in https://github.com/FreeRADIUS/freeradius-server/blob/master/share/dictionary/radius/dictionary.erx#L233 by adding line
`ATTRIBUTE ERX-Action-Reason 178 string`
```
Sent CoA-Request Id 169 from 0.0.0.0:18201 to 172.20.20.254:3799 length 66
Acct-Session-Id = "5273"
ERX-Update-Service:1 = "svc-allow-ipoe(1000000,1000000)"
Received CoA-NAK Id 169 from 172.20.20.254:3799 to 172.20.20.1:18201 length 55
Error-Cause = Invalid-Request
ERX-Action-Reason = "122 Execution failure"
(0) -: Expected CoA-ACK got CoA-NAK
```
### Log output from the FreeRADIUS client
```shell
# echo "Acct-Session-Id=5273,ERX-Update-Service:1='svc-allow-ipoe(1000000,1000000)'" | radclient -x 172.20.20.254:3799 coa testsecret
Sent CoA-Request Id 110 from 0.0.0.0:23604 to 172.20.20.254:3799 length 66
Acct-Session-Id = "5273"
ERX-Update-Service:1 = "svc-allow-ipoe(1000000,1000000)"
Received CoA-NAK Id 110 from 172.20.20.254:3799 to 172.20.20.1:23604 length 55
Error-Cause = Invalid-Request
Attr-26.4874.178 = 0x31323220457865637574696f6e206661696c757265
(0) -: Expected CoA-ACK got CoA-NAK
```
### Relevant log output from client utilities
_No response_
### Backtrace from LLDB or GDB
_No response_
|
defect
|
missing attribute in dictionary erx what type of defect bug is this incorrect party api usage how can the issue be reproduced request echo acct session id erx update service svc allow ipoe radclient x coa testsecret response sent coa request id from to length acct session id erx update service svc allow ipoe received coa nak id from to length error cause invalid request attr expected coa ack got coa nak response after fix attribute in by adding line attribute erx action reason string sent coa request id from to length acct session id erx update service svc allow ipoe received coa nak id from to length error cause invalid request erx action reason execution failure expected coa ack got coa nak log output from the freeradius client shell echo acct session id erx update service svc allow ipoe radclient x coa testsecret sent coa request id from to length acct session id erx update service svc allow ipoe received coa nak id from to length error cause invalid request attr expected coa ack got coa nak relevant log output from client utilities no response backtrace from lldb or gdb no response
| 1
|
50,984
| 13,188,015,945
|
IssuesEvent
|
2020-08-13 05:18:48
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
closed
|
CMake trips on partial ROOT install (Trac #1774)
|
Migrated from Trac cmake defect
|
When only parts of ROOT is installed cmake seems to set the ROOT_FOUND flag to false but the USE_ROOT to true which confuses cmake.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1774">https://code.icecube.wisc.edu/ticket/1774</a>, reported by sflis and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-09-18T05:46:12",
"description": "When only parts of ROOT is installed cmake seems to set the ROOT_FOUND flag to false but the USE_ROOT to true which confuses cmake. ",
"reporter": "sflis",
"cc": "",
"resolution": "worksforme",
"_ts": "1568785572410829",
"component": "cmake",
"summary": "CMake trips on partial ROOT install",
"priority": "normal",
"keywords": "",
"time": "2016-07-07T11:26:58",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
CMake trips on partial ROOT install (Trac #1774) - When only parts of ROOT is installed cmake seems to set the ROOT_FOUND flag to false but the USE_ROOT to true which confuses cmake.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1774">https://code.icecube.wisc.edu/ticket/1774</a>, reported by sflis and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-09-18T05:46:12",
"description": "When only parts of ROOT is installed cmake seems to set the ROOT_FOUND flag to false but the USE_ROOT to true which confuses cmake. ",
"reporter": "sflis",
"cc": "",
"resolution": "worksforme",
"_ts": "1568785572410829",
"component": "cmake",
"summary": "CMake trips on partial ROOT install",
"priority": "normal",
"keywords": "",
"time": "2016-07-07T11:26:58",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
defect
|
cmake trips on partial root install trac when only parts of root is installed cmake seems to set the root found flag to false but the use root to true which confuses cmake migrated from json status closed changetime description when only parts of root is installed cmake seems to set the root found flag to false but the use root to true which confuses cmake reporter sflis cc resolution worksforme ts component cmake summary cmake trips on partial root install priority normal keywords time milestone long term future owner nega type defect
| 1
|
36,752
| 8,114,738,476
|
IssuesEvent
|
2018-08-15 02:17:33
|
DotJoshJohnson/vscode-xml
|
https://api.github.com/repos/DotJoshJohnson/vscode-xml
|
closed
|
Allow custom xqueryExecutionArguments ordering
|
Defect Module: XQuery Execution SemVer: Patch Stale
|
**Description**
I'm not sure if this is more like feature request or bug report. It seems to me that `$(script)` is being replaced by output file when is set as last in the argument array.
```json
"xmlTools.xqueryExecutionArguments": [
"-i", "$(input)",
"-o", "$(input).output.xml",
"-c", "$(script)"
],
```
When I try to execute query with setup above, I will receive error message:
```
Stopped at ./, 1/15:
Unknown command: abraed.output.xml. Try 'help'.
```
Reason why I'm reporting this instead of just reordering argument array is the fact that BaseX seems to require fixed position of arguments: `-i file.xml -o file.output.xml -c query.xq`.
I have also tried this query in command line and everything worked fine, when I change position of the output file nothing is written into it.
**Extension Version**
2.3.1
**VS Code Version**
1.24.1
**Operating System**
Windows 10 (1803)
|
1.0
|
Allow custom xqueryExecutionArguments ordering - **Description**
I'm not sure if this is more like feature request or bug report. It seems to me that `$(script)` is being replaced by output file when is set as last in the argument array.
```json
"xmlTools.xqueryExecutionArguments": [
"-i", "$(input)",
"-o", "$(input).output.xml",
"-c", "$(script)"
],
```
When I try to execute query with setup above, I will receive error message:
```
Stopped at ./, 1/15:
Unknown command: abraed.output.xml. Try 'help'.
```
Reason why I'm reporting this instead of just reordering argument array is the fact that BaseX seems to require fixed position of arguments: `-i file.xml -o file.output.xml -c query.xq`.
I have also tried this query in command line and everything worked fine, when I change position of the output file nothing is written into it.
**Extension Version**
2.3.1
**VS Code Version**
1.24.1
**Operating System**
Windows 10 (1803)
|
defect
|
allow custom xqueryexecutionarguments ordering description i m not sure if this is more like feature request or bug report it seems to me that script is being replaced by output file when is set as last in the argument array json xmltools xqueryexecutionarguments i input o input output xml c script when i try to execute query with setup above i will receive error message stopped at unknown command abraed output xml try help reason why i m reporting this instead of just reordering argument array is the fact that basex seems to require fixed position of arguments i file xml o file output xml c query xq i have also tried this query in command line and everything worked fine when i change position of the output file nothing is written into it extension version vs code version operating system windows
| 1
|
230,428
| 18,669,241,846
|
IssuesEvent
|
2021-10-30 11:38:44
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
opened
|
Failing test: Jest Tests.x-pack/plugins/security/public/management/users/edit_user - EditUserPage changes password of current user when submitting form and closes dialog
|
failed-test
|
A test failed on a tracked branch
```
Error: thrown: "Exceeded timeout of 5000 ms for a test.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/x-pack/plugins/security/public/management/users/edit_user/edit_user_page.test.tsx:231:3
at _dispatchDescribe (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-circus/build/index.js:67:26)
at describe (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-circus/build/index.js:30:5)
at Object.<anonymous> (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/x-pack/plugins/security/public/management/users/edit_user/edit_user_page.test.tsx:31:1)
at Runtime._execModule (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runtime/build/index.js:1299:24)
at Runtime._loadModule (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runtime/build/index.js:898:12)
at Runtime.requireModule (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runtime/build/index.js:746:10)
at jestAdapter (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:106:13)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at runTestInternal (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runner/build/runTest.js:380:16)
at runTest (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runner/build/runTest.js:472:34)
at Object.worker (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runner/build/testWorker.js:133:12)
```
First failure: [CI Build - 7.16](https://buildkite.com/elastic/kibana-hourly/builds/2199#6d1d8214-47aa-4868-a294-c25f7afd73dd)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Tests.x-pack/plugins/security/public/management/users/edit_user","test.name":"EditUserPage changes password of current user when submitting form and closes dialog","test.failCount":1}} -->
|
1.0
|
Failing test: Jest Tests.x-pack/plugins/security/public/management/users/edit_user - EditUserPage changes password of current user when submitting form and closes dialog - A test failed on a tracked branch
```
Error: thrown: "Exceeded timeout of 5000 ms for a test.
Use jest.setTimeout(newTimeout) to increase the timeout value, if this is a long-running test."
at /opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/x-pack/plugins/security/public/management/users/edit_user/edit_user_page.test.tsx:231:3
at _dispatchDescribe (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-circus/build/index.js:67:26)
at describe (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-circus/build/index.js:30:5)
at Object.<anonymous> (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/x-pack/plugins/security/public/management/users/edit_user/edit_user_page.test.tsx:31:1)
at Runtime._execModule (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runtime/build/index.js:1299:24)
at Runtime._loadModule (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runtime/build/index.js:898:12)
at Runtime.requireModule (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runtime/build/index.js:746:10)
at jestAdapter (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-circus/build/legacy-code-todo-rewrite/jestAdapter.js:106:13)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at runTestInternal (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runner/build/runTest.js:380:16)
at runTest (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runner/build/runTest.js:472:34)
at Object.worker (/opt/local-ssd/buildkite/builds/kb-c2-16-0935c9d826d638d7/elastic/kibana-hourly/kibana/node_modules/jest-runner/build/testWorker.js:133:12)
```
First failure: [CI Build - 7.16](https://buildkite.com/elastic/kibana-hourly/builds/2199#6d1d8214-47aa-4868-a294-c25f7afd73dd)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Tests.x-pack/plugins/security/public/management/users/edit_user","test.name":"EditUserPage changes password of current user when submitting form and closes dialog","test.failCount":1}} -->
|
non_defect
|
failing test jest tests x pack plugins security public management users edit user edituserpage changes password of current user when submitting form and closes dialog a test failed on a tracked branch error thrown exceeded timeout of ms for a test use jest settimeout newtimeout to increase the timeout value if this is a long running test at opt local ssd buildkite builds kb elastic kibana hourly kibana x pack plugins security public management users edit user edit user page test tsx at dispatchdescribe opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest circus build index js at describe opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest circus build index js at object opt local ssd buildkite builds kb elastic kibana hourly kibana x pack plugins security public management users edit user edit user page test tsx at runtime execmodule opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest runtime build index js at runtime loadmodule opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest runtime build index js at runtime requiremodule opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest runtime build index js at jestadapter opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest circus build legacy code todo rewrite jestadapter js at processticksandrejections node internal process task queues at runtestinternal opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest runner build runtest js at runtest opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest runner build runtest js at object worker opt local ssd buildkite builds kb elastic kibana hourly kibana node modules jest runner build testworker js first failure
| 0
|
27,009
| 4,857,612,872
|
IssuesEvent
|
2016-11-12 18:06:37
|
FrancescoCioria/smooth-release
|
https://api.github.com/repos/FrancescoCioria/smooth-release
|
closed
|
only first "info" subtitle is logged!
|
defect in review
|
## description
only first "info" subtitle is logged!
## how to reproduce
- {optional: describe steps to reproduce defect}
## specs
to work with `elegant-status` we should move the empty line `\n` from the beginning to the end of an `info` log
## misc
{optional: other useful info}
|
1.0
|
only first "info" subtitle is logged! - ## description
only first "info" subtitle is logged!
## how to reproduce
- {optional: describe steps to reproduce defect}
## specs
to work with `elegant-status` we should move the empty line `\n` from the beginning to the end of an `info` log
## misc
{optional: other useful info}
|
defect
|
only first info subtitle is logged description only first info subtitle is logged how to reproduce optional describe steps to reproduce defect specs to work with elegant status we should move the empty line n from the beginning to the end of an info log misc optional other useful info
| 1
|
75,000
| 25,475,929,818
|
IssuesEvent
|
2022-11-25 14:27:01
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
Chat effects on receive in encrypted rooms have stopped working
|
T-Defect
|
### Steps to reproduce
Seems to be caused by the same thing as https://github.com/vector-im/element-web/issues/23784
1. Receive 🎉 message in encrypted room
### Outcome
#### What did you expect?
Confetti to be thrown
#### What happened instead?
Nothing
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No
|
1.0
|
Chat effects on receive in encrypted rooms have stopped working - ### Steps to reproduce
Seems to be caused by the same thing as https://github.com/vector-im/element-web/issues/23784
1. Receive 🎉 message in encrypted room
### Outcome
#### What did you expect?
Confetti to be thrown
#### What happened instead?
Nothing
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No
|
defect
|
chat effects on receive in encrypted rooms have stopped working steps to reproduce seems to be caused by the same thing as receive 🎉 message in encrypted room outcome what did you expect confetti to be thrown what happened instead nothing operating system no response browser information no response url for webapp no response application version no response homeserver no response will you send logs no
| 1
|
40,228
| 20,680,913,773
|
IssuesEvent
|
2022-03-10 13:50:21
|
TEAMMATES/teammates
|
https://api.github.com/repos/TEAMMATES/teammates
|
closed
|
Copying question from another session: optimize fetching of available questions
|
p.High a-Performance
|
Current: copying question requires fetching of all questions from all sessions available to a user.
<img width="1000" alt="Screenshot 2021-08-16 at 6 48 14 PM" src="https://user-images.githubusercontent.com/7261051/129552612-0a5d48e9-3a92-4817-923b-0eb697b2a7c5.png">
Problems:
- If the user has large number of sessions, this will introduce a burst of parallel API calls
- If the user knows exactly which question/s s/he want, this is a wasted effort and a major noise in the table
- Even if the user needs to scroll to find out the question/s s/he want, chances are s/he might have found it/them by the time the middle of table is visited; that means the bottom half of the table is wasted
Solutions:
- Fetch only questions from a few sessions at a time
- Add option to "Load more" (similarly, only from the next few sessions) if the user has not found the question/s s/he want
- Allow user to decide which session to populate the question list from
|
True
|
Copying question from another session: optimize fetching of available questions - Current: copying question requires fetching of all questions from all sessions available to a user.
<img width="1000" alt="Screenshot 2021-08-16 at 6 48 14 PM" src="https://user-images.githubusercontent.com/7261051/129552612-0a5d48e9-3a92-4817-923b-0eb697b2a7c5.png">
Problems:
- If the user has large number of sessions, this will introduce a burst of parallel API calls
- If the user knows exactly which question/s s/he want, this is a wasted effort and a major noise in the table
- Even if the user needs to scroll to find out the question/s s/he want, chances are s/he might have found it/them by the time the middle of table is visited; that means the bottom half of the table is wasted
Solutions:
- Fetch only questions from a few sessions at a time
- Add option to "Load more" (similarly, only from the next few sessions) if the user has not found the question/s s/he want
- Allow user to decide which session to populate the question list from
|
non_defect
|
copying question from another session optimize fetching of available questions current copying question requires fetching of all questions from all sessions available to a user img width alt screenshot at pm src problems if the user has large number of sessions this will introduce a burst of parallel api calls if the user knows exactly which question s s he want this is a wasted effort and a major noise in the table even if the user needs to scroll to find out the question s s he want chances are s he might have found it them by the time the middle of table is visited that means the bottom half of the table is wasted solutions fetch only questions from a few sessions at a time add option to load more similarly only from the next few sessions if the user has not found the question s s he want allow user to decide which session to populate the question list from
| 0
|
347,185
| 24,887,654,987
|
IssuesEvent
|
2022-10-28 09:09:56
|
LianGuoYang/ped
|
https://api.github.com/repos/LianGuoYang/ped
|
opened
|
Unmark command in UG
|
severity.Medium type.DocumentationBug
|
Problem: After I accidentally `mark` the wrong tasks, how do I `unmark` the task? Unable to find `unmark` command in UG.
<!--session: 1666944379215-89d987dc-dd49-4833-bdca-37dd58201917-->
<!--Version: Web v3.4.4-->
|
1.0
|
Unmark command in UG - Problem: After I accidentally `mark` the wrong tasks, how do I `unmark` the task? Unable to find `unmark` command in UG.
<!--session: 1666944379215-89d987dc-dd49-4833-bdca-37dd58201917-->
<!--Version: Web v3.4.4-->
|
non_defect
|
unmark command in ug problem after i accidentally mark the wrong tasks how do i unmark the task unable to find unmark command in ug
| 0
|
48,436
| 25,527,336,954
|
IssuesEvent
|
2022-11-29 04:17:26
|
iree-org/iree
|
https://api.github.com/repos/iree-org/iree
|
opened
|
Optimize "padding" operations created by im2col
|
performance ⚡
|
### What happened?
Im2Col creates padding operations that have 6 parallel dimensions and that have non permutation maps. This result in poor code generation in iree.
Ex:
```
%5 = tensor.empty() : tensor<2x1280x3x3x8x8xf16>
%6 = linalg.generic {indexing_maps = [affine_map<(d0, d1, d2, d3, d4, d5) -> (d0, d1, d4 + d2, d5 + d3)>, affine_map<(d0, d1, d2, d3, d4, d5) -> (d0, d1, d2, d3, d4, d5)>], iterator_types = ["parallel", "parallel", "parallel", "parallel", "parallel", "parallel"]} ins(%4 : tensor<2x1280x10x10xf16>) outs(%5 : tensor<2x1280x3x3x8x8xf16>) {
^bb0(%in: f16, %out: f16):
linalg.yield %in : f16
} -> tensor<2x1280x3x3x8x8xf16>
```
To get good performance we need to:
1. Improve distribution, here the higher dims are not distributed creating large serialized loops
2. Get vectorization or better coalescing for the load and stores
### Steps to reproduce your issue
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
### What component(s) does this issue relate to?
_No response_
### Version information
_No response_
### Additional context
_No response_
|
True
|
Optimize "padding" operations created by im2col - ### What happened?
Im2Col creates padding operations that have 6 parallel dimensions and that have non permutation maps. This result in poor code generation in iree.
Ex:
```
%5 = tensor.empty() : tensor<2x1280x3x3x8x8xf16>
%6 = linalg.generic {indexing_maps = [affine_map<(d0, d1, d2, d3, d4, d5) -> (d0, d1, d4 + d2, d5 + d3)>, affine_map<(d0, d1, d2, d3, d4, d5) -> (d0, d1, d2, d3, d4, d5)>], iterator_types = ["parallel", "parallel", "parallel", "parallel", "parallel", "parallel"]} ins(%4 : tensor<2x1280x10x10xf16>) outs(%5 : tensor<2x1280x3x3x8x8xf16>) {
^bb0(%in: f16, %out: f16):
linalg.yield %in : f16
} -> tensor<2x1280x3x3x8x8xf16>
```
To get good performance we need to:
1. Improve distribution, here the higher dims are not distributed creating large serialized loops
2. Get vectorization or better coalescing for the load and stores
### Steps to reproduce your issue
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
### What component(s) does this issue relate to?
_No response_
### Version information
_No response_
### Additional context
_No response_
|
non_defect
|
optimize padding operations created by what happened creates padding operations that have parallel dimensions and that have non permutation maps this result in poor code generation in iree ex tensor empty tensor linalg generic indexing maps iterator types ins tensor outs tensor in out linalg yield in tensor to get good performance we need to improve distribution here the higher dims are not distributed creating large serialized loops get vectorization or better coalescing for the load and stores steps to reproduce your issue go to click on scroll down to see error what component s does this issue relate to no response version information no response additional context no response
| 0
|
63,450
| 17,660,176,491
|
IssuesEvent
|
2021-08-21 10:29:53
|
Gogo1951/GogoLoot
|
https://api.github.com/repos/Gogo1951/GogoLoot
|
closed
|
Game Crashed when Attempting to Loot when Bags were Full
|
Type - Defect GogoLoot - Application
|
Had an issue where I was running SM boosts and went full out with mousewheel looting, just spamming it as fast as I could. I noticed my bags were getting full, then a saw a bag full message, then the game froze and I had to Alt F4 out. Seemed to happen as soon as tried to loot with full bags. Certainly was spamming the loot action too... but not sure what the cause was.
|
1.0
|
Game Crashed when Attempting to Loot when Bags were Full - Had an issue where I was running SM boosts and went full out with mousewheel looting, just spamming it as fast as I could. I noticed my bags were getting full, then a saw a bag full message, then the game froze and I had to Alt F4 out. Seemed to happen as soon as tried to loot with full bags. Certainly was spamming the loot action too... but not sure what the cause was.
|
defect
|
game crashed when attempting to loot when bags were full had an issue where i was running sm boosts and went full out with mousewheel looting just spamming it as fast as i could i noticed my bags were getting full then a saw a bag full message then the game froze and i had to alt out seemed to happen as soon as tried to loot with full bags certainly was spamming the loot action too but not sure what the cause was
| 1
|
7,181
| 2,610,356,140
|
IssuesEvent
|
2015-02-26 19:55:19
|
chrsmith/scribefire-chrome
|
https://api.github.com/repos/chrsmith/scribefire-chrome
|
closed
|
the right to left alignment is not working
|
auto-migrated Priority-Medium Type-Defect
|
```
What's the problem?
I am writing in Hebrew , but when I set the "right ti left" option on' it does
not realy align the text to the right
for instance if I try to color the text (to mark it ) the coloring starts only
from the second word
If I am writing a question mark at the end of the sentence it appears at the
beginning .
What browser are you using?
Chrome
What version of ScribeFire are you running?
1.9
```
-----
Original issue reported on code.google.com by `avni.g...@gmail.com` on 22 Oct 2011 at 2:52
|
1.0
|
the right to left alignment is not working - ```
What's the problem?
I am writing in Hebrew , but when I set the "right ti left" option on' it does
not realy align the text to the right
for instance if I try to color the text (to mark it ) the coloring starts only
from the second word
If I am writing a question mark at the end of the sentence it appears at the
beginning .
What browser are you using?
Chrome
What version of ScribeFire are you running?
1.9
```
-----
Original issue reported on code.google.com by `avni.g...@gmail.com` on 22 Oct 2011 at 2:52
|
defect
|
the right to left alignment is not working what s the problem i am writing in hebrew but when i set the right ti left option on it does not realy align the text to the right for instance if i try to color the text to mark it the coloring starts only from the second word if i am writing a question mark at the end of the sentence it appears at the beginning what browser are you using chrome what version of scribefire are you running original issue reported on code google com by avni g gmail com on oct at
| 1
|
72,479
| 24,134,659,548
|
IssuesEvent
|
2022-09-21 10:14:22
|
vector-im/element-android
|
https://api.github.com/repos/vector-im/element-android
|
closed
|
Leaving a room doesn't remove it from "All Chat" list with New App Layout Enabled
|
T-Defect S-Minor O-Occasional Z-AppLayout
|
### Steps to reproduce
1. Enable new app layout underneath the labs flag
2. Go into a chatroom **yueworuewo**
3. Leave the chatroom, click okay
4. You should be automatically directed back to the homepage
5. Notice the room ( **yueworuewo** ) is not removed from the "All Chats" list.
https://user-images.githubusercontent.com/16907963/190526220-59e24b41-2ca3-4ca7-8bc0-a272c8e13373.mov
### Outcome
#### What did you expect?
Leaving a room should take to back to the "All Chats" page with while showing the correct rooms I am apart of.
#### What happened instead?
The room I just left is still in the list of chats.
### Your phone model
Pixel 6
### Operating system version
Android 13
### Application version and app store
1.4.36
### Homeserver
_No response_
### Will you send logs?
Yes
### Are you willing to provide a PR?
No
|
1.0
|
Leaving a room doesn't remove it from "All Chat" list with New App Layout Enabled - ### Steps to reproduce
1. Enable new app layout underneath the labs flag
2. Go into a chatroom **yueworuewo**
3. Leave the chatroom, click okay
4. You should be automatically directed back to the homepage
5. Notice the room ( **yueworuewo** ) is not removed from the "All Chats" list.
https://user-images.githubusercontent.com/16907963/190526220-59e24b41-2ca3-4ca7-8bc0-a272c8e13373.mov
### Outcome
#### What did you expect?
Leaving a room should take to back to the "All Chats" page with while showing the correct rooms I am apart of.
#### What happened instead?
The room I just left is still in the list of chats.
### Your phone model
Pixel 6
### Operating system version
Android 13
### Application version and app store
1.4.36
### Homeserver
_No response_
### Will you send logs?
Yes
### Are you willing to provide a PR?
No
|
defect
|
leaving a room doesn t remove it from all chat list with new app layout enabled steps to reproduce enable new app layout underneath the labs flag go into a chatroom yueworuewo leave the chatroom click okay you should be automatically directed back to the homepage notice the room yueworuewo is not removed from the all chats list outcome what did you expect leaving a room should take to back to the all chats page with while showing the correct rooms i am apart of what happened instead the room i just left is still in the list of chats your phone model pixel operating system version android application version and app store homeserver no response will you send logs yes are you willing to provide a pr no
| 1
|
2,477
| 2,607,904,401
|
IssuesEvent
|
2015-02-26 00:15:01
|
chrsmithdemos/zen-coding
|
https://api.github.com/repos/chrsmithdemos/zen-coding
|
closed
|
TextMate Snippet "mirroring" functionality not working on nested elements. (Developer Preview)
|
auto-migrated Milestone-0.7 Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. Have the lastest Dev Preview
2. Modify your Zen-Coding snippets to the following:
'input':'<input type="text" class="text" value="${1}" name="${2:name}"
id="${2}" />'
3. Try expanding p>input, it doesn't work. However, if you do input only it
works perfectly
```
-----
Original issue reported on code.google.com by `kuroir` on 10 May 2010 at 6:17
|
1.0
|
TextMate Snippet "mirroring" functionality not working on nested elements. (Developer Preview) - ```
What steps will reproduce the problem?
1. Have the lastest Dev Preview
2. Modify your Zen-Coding snippets to the following:
'input':'<input type="text" class="text" value="${1}" name="${2:name}"
id="${2}" />'
3. Try expanding p>input, it doesn't work. However, if you do input only it
works perfectly
```
-----
Original issue reported on code.google.com by `kuroir` on 10 May 2010 at 6:17
|
defect
|
textmate snippet mirroring functionality not working on nested elements developer preview what steps will reproduce the problem have the lastest dev preview modify your zen coding snippets to the following input input type text class text value name name id try expanding p input it doesn t work however if you do input only it works perfectly original issue reported on code google com by kuroir on may at
| 1
|
5,901
| 2,610,217,666
|
IssuesEvent
|
2015-02-26 19:09:16
|
chrsmith/somefinders
|
https://api.github.com/repos/chrsmith/somefinders
|
opened
|
конвертер mswrd632 wpc
|
auto-migrated Priority-Medium Type-Defect
|
```
'''Вергилий Калинин'''
Привет всем не подскажите где можно найти
.конвертер mswrd632 wpc. как то выкладывали уже
'''Адий Фомичёв'''
Вот хороший сайт где можно скачать
http://bit.ly/1ar8lnJ
'''Володар Беспалов'''
Просит ввести номер мобилы!Не опасно ли это?
'''Авангард Мишин'''
Неа все ок у меня ничего не списало
'''Аврор Вишняков'''
Неа все ок у меня ничего не списало
Информация о файле: конвертер mswrd632 wpc
Загружен: В этом месяце
Скачан раз: 215
Рейтинг: 424
Средняя скорость скачивания: 269
Похожих файлов: 17
```
-----
Original issue reported on code.google.com by `kondense...@gmail.com` on 17 Dec 2013 at 12:00
|
1.0
|
конвертер mswrd632 wpc - ```
'''Вергилий Калинин'''
Привет всем не подскажите где можно найти
.конвертер mswrd632 wpc. как то выкладывали уже
'''Адий Фомичёв'''
Вот хороший сайт где можно скачать
http://bit.ly/1ar8lnJ
'''Володар Беспалов'''
Просит ввести номер мобилы!Не опасно ли это?
'''Авангард Мишин'''
Неа все ок у меня ничего не списало
'''Аврор Вишняков'''
Неа все ок у меня ничего не списало
Информация о файле: конвертер mswrd632 wpc
Загружен: В этом месяце
Скачан раз: 215
Рейтинг: 424
Средняя скорость скачивания: 269
Похожих файлов: 17
```
-----
Original issue reported on code.google.com by `kondense...@gmail.com` on 17 Dec 2013 at 12:00
|
defect
|
конвертер wpc вергилий калинин привет всем не подскажите где можно найти конвертер wpc как то выкладывали уже адий фомичёв вот хороший сайт где можно скачать володар беспалов просит ввести номер мобилы не опасно ли это авангард мишин неа все ок у меня ничего не списало аврор вишняков неа все ок у меня ничего не списало информация о файле конвертер wpc загружен в этом месяце скачан раз рейтинг средняя скорость скачивания похожих файлов original issue reported on code google com by kondense gmail com on dec at
| 1
|
447,067
| 31,593,842,916
|
IssuesEvent
|
2023-09-05 02:41:16
|
envoyproxy/gateway
|
https://api.github.com/repos/envoyproxy/gateway
|
closed
|
Add Metallb installation docs in Quickstart
|
documentation area/installation
|
*Description*:
The Quickstart docs today assume that the user is leveraging a K8s cluster that has a LB implementation that provides a `LoadBalancerIP` to the managed Envoy Proxy Service . in many cases especially on prem clusters on clusters created with `kind` this may not exist.
This can cause a user to think that the service is unhealthy, see here
https://github.com/envoyproxy/gateway/issues/1823#issuecomment-1691949817
So it would be good to enhance the docs outlining this and also providing steps to the user to install a LB implementation like `metallb` https://metallb.universe.tf
[optional *Relevant Links*:]
>Any extra documentation required to understand the issue.
|
1.0
|
Add Metallb installation docs in Quickstart - *Description*:
The Quickstart docs today assume that the user is leveraging a K8s cluster that has a LB implementation that provides a `LoadBalancerIP` to the managed Envoy Proxy Service . in many cases especially on prem clusters on clusters created with `kind` this may not exist.
This can cause a user to think that the service is unhealthy, see here
https://github.com/envoyproxy/gateway/issues/1823#issuecomment-1691949817
So it would be good to enhance the docs outlining this and also providing steps to the user to install a LB implementation like `metallb` https://metallb.universe.tf
[optional *Relevant Links*:]
>Any extra documentation required to understand the issue.
|
non_defect
|
add metallb installation docs in quickstart description the quickstart docs today assume that the user is leveraging a cluster that has a lb implementation that provides a loadbalancerip to the managed envoy proxy service in many cases especially on prem clusters on clusters created with kind this may not exist this can cause a user to think that the service is unhealthy see here so it would be good to enhance the docs outlining this and also providing steps to the user to install a lb implementation like metallb any extra documentation required to understand the issue
| 0
|
13,482
| 2,760,274,719
|
IssuesEvent
|
2015-04-28 11:05:54
|
bridgedotnet/Bridge
|
https://api.github.com/repos/bridgedotnet/Bridge
|
closed
|
[Core] Unable to cast null values
|
defect
|
```C#
using Bridge;
using Bridge.Html5;
using System;
namespace Demo
{
public class App
{
[Ready]
public static void Main()
{
var test = (string)null;
}
}
}
```
The code causes JavaScript exception **Cannot read property 'constructor' of null**
|
1.0
|
[Core] Unable to cast null values - ```C#
using Bridge;
using Bridge.Html5;
using System;
namespace Demo
{
public class App
{
[Ready]
public static void Main()
{
var test = (string)null;
}
}
}
```
The code causes JavaScript exception **Cannot read property 'constructor' of null**
|
defect
|
unable to cast null values c using bridge using bridge using system namespace demo public class app public static void main var test string null the code causes javascript exception cannot read property constructor of null
| 1
|
81,959
| 10,265,419,990
|
IssuesEvent
|
2019-08-22 18:48:03
|
department-of-veterans-affairs/va.gov-team
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-team
|
closed
|
Communicate va.gov-team repo consolidation strategy
|
content-ia-team documentation ia
|
## User Story
As a team member building with or on VSP, I need to navigate VSP documentation easily so I can build things in a self-service and agile manner.
## Goal
Team members are easily able to navigate through the VSP documentation.
## Acceptance Criteria
- [x] An artifact that communicates the recommended IA for VSP documentation
- [x] An artifact that communicates how we consolidate (i.e. not "migrating" but rather copying)
- [x] Review this artifact and recommendations with DSVA
- [x] Communicate approach across VSP
|
1.0
|
Communicate va.gov-team repo consolidation strategy - ## User Story
As a team member building with or on VSP, I need to navigate VSP documentation easily so I can build things in a self-service and agile manner.
## Goal
Team members are easily able to navigate through the VSP documentation.
## Acceptance Criteria
- [x] An artifact that communicates the recommended IA for VSP documentation
- [x] An artifact that communicates how we consolidate (i.e. not "migrating" but rather copying)
- [x] Review this artifact and recommendations with DSVA
- [x] Communicate approach across VSP
|
non_defect
|
communicate va gov team repo consolidation strategy user story as a team member building with or on vsp i need to navigate vsp documentation easily so i can build things in a self service and agile manner goal team members are easily able to navigate through the vsp documentation acceptance criteria an artifact that communicates the recommended ia for vsp documentation an artifact that communicates how we consolidate i e not migrating but rather copying review this artifact and recommendations with dsva communicate approach across vsp
| 0
|
49,319
| 13,186,610,695
|
IssuesEvent
|
2020-08-13 00:44:22
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
[finiteReco] Broken example script (Trac #1177)
|
Incomplete Migration Migrated from Trac combo reconstruction defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1177">https://code.icecube.wisc.edu/ticket/1177</a>, reported by olivas and owned by seuler</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "newExampleWithTraySegment.py - This depends on a driver file that isn't generally accessible.\n\nFails with the error :FATAL (I3PhotonicsService): Level 2 driver file /data/sim/scratch/test_pt/photonics-prod/tables/SPICEMie_i3coords/driverfiles/SPICEMie_i3coords_level2_muon_resampled.list does not exist\n\n\n",
"reporter": "olivas",
"cc": "",
"resolution": "fixed",
"_ts": "1550067117911749",
"component": "combo reconstruction",
"summary": "[finiteReco] Broken example script",
"priority": "blocker",
"keywords": "",
"time": "2015-08-19T02:24:30",
"milestone": "",
"owner": "seuler",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
[finiteReco] Broken example script (Trac #1177) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1177">https://code.icecube.wisc.edu/ticket/1177</a>, reported by olivas and owned by seuler</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "newExampleWithTraySegment.py - This depends on a driver file that isn't generally accessible.\n\nFails with the error :FATAL (I3PhotonicsService): Level 2 driver file /data/sim/scratch/test_pt/photonics-prod/tables/SPICEMie_i3coords/driverfiles/SPICEMie_i3coords_level2_muon_resampled.list does not exist\n\n\n",
"reporter": "olivas",
"cc": "",
"resolution": "fixed",
"_ts": "1550067117911749",
"component": "combo reconstruction",
"summary": "[finiteReco] Broken example script",
"priority": "blocker",
"keywords": "",
"time": "2015-08-19T02:24:30",
"milestone": "",
"owner": "seuler",
"type": "defect"
}
```
</p>
</details>
|
defect
|
broken example script trac migrated from json status closed changetime description newexamplewithtraysegment py this depends on a driver file that isn t generally accessible n nfails with the error fatal level driver file data sim scratch test pt photonics prod tables spicemie driverfiles spicemie muon resampled list does not exist n n n reporter olivas cc resolution fixed ts component combo reconstruction summary broken example script priority blocker keywords time milestone owner seuler type defect
| 1
|
24,044
| 3,901,571,341
|
IssuesEvent
|
2016-04-18 11:27:42
|
Tariq-Abuhashim/google-glog
|
https://api.github.com/repos/Tariq-Abuhashim/google-glog
|
closed
|
Possible Race condition at logging.cc:1012 google::RawLog__SetLastTime
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. run a multithreaded program that uses google-glog with valgrind
--tool=helgrind
What is the expected output? What do you see instead?
I expect zero error reports from valgrind and I get a lot of errors.
What version of the product are you using? On what operating system?
google-glog 0.3.1
valgrind 3.5.0
g++ 4.1.2 20080704 (Red Hat 4.1.2-48)
CentOS 5.2
Please provide any additional information below.
This is the output of valgrind:
==12505== at 0x403B4DE: google::RawLog__SetLastTime(tm const&, int)
(raw_logging.cc:78)
==12505== by 0x403411A: google::LogMessage::Init(char const*, int, int, void
(google::LogMessage::*)()) (logging.cc:1012)
==12505== by 0x4034B12: google::LogMessage::LogMessage(char const*, int)
(logging.cc:944)
google::RawLog__SetLastTime calls memcpy on a static variable and there is not
lock around it to protect it from concurrent accesses.
Modifying logging.cc at line 1012 like below may fix this problem:
{
MutexLock l(&log_mutex);
RawLog__SetLastTime(data_->tm_time_, usecs);
}
or if this is not really a race condition let me know so I can create a
valgrind suppression rule.
```
Original issue reported on code.google.com by `Horacio....@gmail.com` on 31 Aug 2010 at 3:29
|
1.0
|
Possible Race condition at logging.cc:1012 google::RawLog__SetLastTime - ```
What steps will reproduce the problem?
1. run a multithreaded program that uses google-glog with valgrind
--tool=helgrind
What is the expected output? What do you see instead?
I expect zero error reports from valgrind and I get a lot of errors.
What version of the product are you using? On what operating system?
google-glog 0.3.1
valgrind 3.5.0
g++ 4.1.2 20080704 (Red Hat 4.1.2-48)
CentOS 5.2
Please provide any additional information below.
This is the output of valgrind:
==12505== at 0x403B4DE: google::RawLog__SetLastTime(tm const&, int)
(raw_logging.cc:78)
==12505== by 0x403411A: google::LogMessage::Init(char const*, int, int, void
(google::LogMessage::*)()) (logging.cc:1012)
==12505== by 0x4034B12: google::LogMessage::LogMessage(char const*, int)
(logging.cc:944)
google::RawLog__SetLastTime calls memcpy on a static variable and there is not
lock around it to protect it from concurrent accesses.
Modifying logging.cc at line 1012 like below may fix this problem:
{
MutexLock l(&log_mutex);
RawLog__SetLastTime(data_->tm_time_, usecs);
}
or if this is not really a race condition let me know so I can create a
valgrind suppression rule.
```
Original issue reported on code.google.com by `Horacio....@gmail.com` on 31 Aug 2010 at 3:29
|
defect
|
possible race condition at logging cc google rawlog setlasttime what steps will reproduce the problem run a multithreaded program that uses google glog with valgrind tool helgrind what is the expected output what do you see instead i expect zero error reports from valgrind and i get a lot of errors what version of the product are you using on what operating system google glog valgrind g red hat centos please provide any additional information below this is the output of valgrind at google rawlog setlasttime tm const int raw logging cc by google logmessage init char const int int void google logmessage logging cc by google logmessage logmessage char const int logging cc google rawlog setlasttime calls memcpy on a static variable and there is not lock around it to protect it from concurrent accesses modifying logging cc at line like below may fix this problem mutexlock l log mutex rawlog setlasttime data tm time usecs or if this is not really a race condition let me know so i can create a valgrind suppression rule original issue reported on code google com by horacio gmail com on aug at
| 1
|
70,106
| 22,946,809,781
|
IssuesEvent
|
2022-07-19 01:23:20
|
babymiles77/issue_test
|
https://api.github.com/repos/babymiles77/issue_test
|
closed
|
[Defect] 오디언스 adid에 빈값이 들어와 푸시 전송이 안되는 이슈
|
defect lv3
|
## 발생 환경
- Device: [e.g. iPhone6]
- OS: [e.g. iOS8.1]
- Version [e.g. SDK v2.0]
- apk [tway37.ipa]
## 설명/연관이슈
오디언스 adid에 빈값이 들어와 푸시 전송이 안되는 이슈
## 재현과정(optional)
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
## 스크린샷

## 기대 결과
1. SKAN 호출
2. SKAN로 인하여, 오디언스의 adid에 빈값으로 들어온 것을 확인
3. 해당 오디언스로 푸시 전송
## 발생 결과
1. SKAN 호출
2. SKAN로 인하여, 오디언스의 adid에 빈값으로 들어온 것을 확인
3. 푸시 수신되지 않음
## Side Effect(optional)
1. Push message
2. Growth Scenario Push message
|
1.0
|
[Defect] 오디언스 adid에 빈값이 들어와 푸시 전송이 안되는 이슈 - ## 발생 환경
- Device: [e.g. iPhone6]
- OS: [e.g. iOS8.1]
- Version [e.g. SDK v2.0]
- apk [tway37.ipa]
## 설명/연관이슈
오디언스 adid에 빈값이 들어와 푸시 전송이 안되는 이슈
## 재현과정(optional)
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
## 스크린샷

## 기대 결과
1. SKAN 호출
2. SKAN로 인하여, 오디언스의 adid에 빈값으로 들어온 것을 확인
3. 해당 오디언스로 푸시 전송
## 발생 결과
1. SKAN 호출
2. SKAN로 인하여, 오디언스의 adid에 빈값으로 들어온 것을 확인
3. 푸시 수신되지 않음
## Side Effect(optional)
1. Push message
2. Growth Scenario Push message
|
defect
|
오디언스 adid에 빈값이 들어와 푸시 전송이 안되는 이슈 발생 환경 device os version apk 설명 연관이슈 오디언스 adid에 빈값이 들어와 푸시 전송이 안되는 이슈 재현과정 optional go to click on scroll down to see error 스크린샷 기대 결과 skan 호출 skan로 인하여 오디언스의 adid에 빈값으로 들어온 것을 확인 해당 오디언스로 푸시 전송 발생 결과 skan 호출 skan로 인하여 오디언스의 adid에 빈값으로 들어온 것을 확인 푸시 수신되지 않음 side effect optional push message growth scenario push message
| 1
|
28,392
| 5,247,685,844
|
IssuesEvent
|
2017-02-01 13:50:23
|
bridgedotnet/Bridge
|
https://api.github.com/repos/bridgedotnet/Bridge
|
closed
|
string.Format gives enum number(s) not names
|
defect
|
### Expected
A B C
A B
0 3 4
0 3
### Actual
0 3 4
0 3
0 3 4
0 3
### Steps To Reproduce
[Bridge Fiddle](http://live.bridge.net/#c9f9eb7fa3ab3d29a9be5c90fccbb24e)
``` csharp
public static class Program {
public enum SimpleEnum {
A,
B = 3,
C,
D = 10
}
public enum ByteEnum : byte {
A,
B = 3,
}
[Ready]
public static void Main (string[] args) {
Console.WriteLine(string.Format("{0} {1} {2}", SimpleEnum.A, SimpleEnum.B, SimpleEnum.C));
Console.WriteLine(string.Format("{0} {1}", ByteEnum.A, ByteEnum.B));
Console.WriteLine(string.Format("{0} {1} {2}", (int)SimpleEnum.A, (int)SimpleEnum.B, (int)SimpleEnum.C));
Console.WriteLine(string.Format("{0} {1}", (int)ByteEnum.A, (int)ByteEnum.B));
}
}
```
|
1.0
|
string.Format gives enum number(s) not names - ### Expected
A B C
A B
0 3 4
0 3
### Actual
0 3 4
0 3
0 3 4
0 3
### Steps To Reproduce
[Bridge Fiddle](http://live.bridge.net/#c9f9eb7fa3ab3d29a9be5c90fccbb24e)
``` csharp
public static class Program {
public enum SimpleEnum {
A,
B = 3,
C,
D = 10
}
public enum ByteEnum : byte {
A,
B = 3,
}
[Ready]
public static void Main (string[] args) {
Console.WriteLine(string.Format("{0} {1} {2}", SimpleEnum.A, SimpleEnum.B, SimpleEnum.C));
Console.WriteLine(string.Format("{0} {1}", ByteEnum.A, ByteEnum.B));
Console.WriteLine(string.Format("{0} {1} {2}", (int)SimpleEnum.A, (int)SimpleEnum.B, (int)SimpleEnum.C));
Console.WriteLine(string.Format("{0} {1}", (int)ByteEnum.A, (int)ByteEnum.B));
}
}
```
|
defect
|
string format gives enum number s not names expected a b c a b actual steps to reproduce csharp public static class program public enum simpleenum a b c d public enum byteenum byte a b public static void main string args console writeline string format simpleenum a simpleenum b simpleenum c console writeline string format byteenum a byteenum b console writeline string format int simpleenum a int simpleenum b int simpleenum c console writeline string format int byteenum a int byteenum b
| 1
|
242,600
| 26,277,751,562
|
IssuesEvent
|
2023-01-07 01:06:01
|
billmcchesney1/pacbot
|
https://api.github.com/repos/billmcchesney1/pacbot
|
closed
|
CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - autoclosed
|
security vulnerability
|
## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- cli-1.6.8.tgz (Root Library)
- less-2.7.3.tgz
- request-2.81.0.tgz
- http-signature-1.1.1.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/pacbot/commit/acf9a0620c1a37cee4f2896d71e1c3731c5c7b06">acf9a0620c1a37cee4f2896d71e1c3731c5c7b06</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution (json-schema): 0.4.0</p>
<p>Direct dependency fix Resolution (@angular/cli): 1.7.0</p>
</p>
</details>
<p></p>
|
True
|
CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - autoclosed - ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>
Dependency Hierarchy:
- cli-1.6.8.tgz (Root Library)
- less-2.7.3.tgz
- request-2.81.0.tgz
- http-signature-1.1.1.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/pacbot/commit/acf9a0620c1a37cee4f2896d71e1c3731c5c7b06">acf9a0620c1a37cee4f2896d71e1c3731c5c7b06</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution (json-schema): 0.4.0</p>
<p>Direct dependency fix Resolution (@angular/cli): 1.7.0</p>
</p>
</details>
<p></p>
|
non_defect
|
cve high detected in json schema tgz autoclosed cve high severity vulnerability vulnerable library json schema tgz json schema validation and specifications library home page a href dependency hierarchy cli tgz root library less tgz request tgz http signature tgz jsprim tgz x json schema tgz vulnerable library found in head commit a href found in base branch master vulnerability details json schema is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution json schema direct dependency fix resolution angular cli
| 0
|
50,642
| 13,547,515,756
|
IssuesEvent
|
2020-09-17 04:19:58
|
sourcegraph/sourcegraph
|
https://api.github.com/repos/sourcegraph/sourcegraph
|
closed
|
secrets: use base64 and make interface private
|
estimate/2d team/cloud team/security
|
This is a placeholder issue for tracking refactoring of secrets package.
|
True
|
secrets: use base64 and make interface private - This is a placeholder issue for tracking refactoring of secrets package.
|
non_defect
|
secrets use and make interface private this is a placeholder issue for tracking refactoring of secrets package
| 0
|
14,128
| 2,789,927,095
|
IssuesEvent
|
2015-05-08 22:28:25
|
google/google-visualization-api-issues
|
https://api.github.com/repos/google/google-visualization-api-issues
|
opened
|
bar chart & select event no longer working in IE8
|
Priority-Medium Type-Defect
|
Original [issue 534](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=534) created by orwant on 2011-02-24T05:28:27.000Z:
<b>What steps will reproduce the problem? Please provide a link to a</b>
<b>demonstration page if at all possible, or attach code.</b>
1.http://184.73.185.64/test.html
2.Seems that columns with values of 2 or less are not being recognized in IE as clickable
3. Used to work in IE8 still works in chrome, FF, and safari
Bar chart and select event
Are you using the test environment (version 1.1)? NO
<b>(If you are not sure, answer NO)</b>
<b>What operating system and browser are you using?</b>
IE8 and Windows 7.
IE8 and XP
Code is attached
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
|
1.0
|
bar chart & select event no longer working in IE8 - Original [issue 534](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=534) created by orwant on 2011-02-24T05:28:27.000Z:
<b>What steps will reproduce the problem? Please provide a link to a</b>
<b>demonstration page if at all possible, or attach code.</b>
1.http://184.73.185.64/test.html
2.Seems that columns with values of 2 or less are not being recognized in IE as clickable
3. Used to work in IE8 still works in chrome, FF, and safari
Bar chart and select event
Are you using the test environment (version 1.1)? NO
<b>(If you are not sure, answer NO)</b>
<b>What operating system and browser are you using?</b>
IE8 and Windows 7.
IE8 and XP
Code is attached
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
|
defect
|
bar chart select event no longer working in original created by orwant on what steps will reproduce the problem please provide a link to a demonstration page if at all possible or attach code seems that columns with values of or less are not being recognized in ie as clickable used to work in still works in chrome ff and safari bar chart and select event are you using the test environment version no if you are not sure answer no what operating system and browser are you using and windows and xp code is attached for developers viewing this issue please click the star icon to be notified of future changes and to let us know how many of you are interested in seeing it resolved
| 1
|
16,991
| 23,407,749,323
|
IssuesEvent
|
2022-08-12 14:24:03
|
woocommerce/woocommerce-blocks
|
https://api.github.com/repos/woocommerce/woocommerce-blocks
|
opened
|
Klarna Payments doesn't work with the Cart & Checkout Blocks
|
plugin incompatibility
|
## This is a ticket that just **highlights the incompatibly of Klarna Payments** with the Cart and Checkout Blocks and tracks user reports
As a merchant, the best course of action right now if you are using a plugin that isn't working with the Cart and Checkout Blocks is to notify the developer of the extension and ask if they can add support.
### It's up to extension developers to add support for the new checkout flow offered via the Cart and Checkout Blocks.
Currently it's up to extension developers to add support for the new checkout flow offered via the Cart and Checkout Blocks. We have some [documentation for Third-party developers](https://github.com/woocommerce/woocommerce-blocks/tree/trunk/docs#third-party-developers) and some [Developer Resources](https://github.com/woocommerce/woocommerce-blocks/tree/trunk/docs#developer-resources) available to help with their integration efforts.
You can keep on top of the [status of the Cart & Checkout Blocks in this documentation](https://docs.woocommerce.com/document/cart-checkout-blocks-support-status/).
|
True
|
Klarna Payments doesn't work with the Cart & Checkout Blocks - ## This is a ticket that just **highlights the incompatibly of Klarna Payments** with the Cart and Checkout Blocks and tracks user reports
As a merchant, the best course of action right now if you are using a plugin that isn't working with the Cart and Checkout Blocks is to notify the developer of the extension and ask if they can add support.
### It's up to extension developers to add support for the new checkout flow offered via the Cart and Checkout Blocks.
Currently it's up to extension developers to add support for the new checkout flow offered via the Cart and Checkout Blocks. We have some [documentation for Third-party developers](https://github.com/woocommerce/woocommerce-blocks/tree/trunk/docs#third-party-developers) and some [Developer Resources](https://github.com/woocommerce/woocommerce-blocks/tree/trunk/docs#developer-resources) available to help with their integration efforts.
You can keep on top of the [status of the Cart & Checkout Blocks in this documentation](https://docs.woocommerce.com/document/cart-checkout-blocks-support-status/).
|
non_defect
|
klarna payments doesn t work with the cart checkout blocks this is a ticket that just highlights the incompatibly of klarna payments with the cart and checkout blocks and tracks user reports as a merchant the best course of action right now if you are using a plugin that isn t working with the cart and checkout blocks is to notify the developer of the extension and ask if they can add support it s up to extension developers to add support for the new checkout flow offered via the cart and checkout blocks currently it s up to extension developers to add support for the new checkout flow offered via the cart and checkout blocks we have some and some available to help with their integration efforts you can keep on top of the
| 0
|
23,664
| 3,851,865,292
|
IssuesEvent
|
2016-04-06 05:27:46
|
GPF/imame4all
|
https://api.github.com/repos/GPF/imame4all
|
closed
|
iMame4all not recognizing iCade Jr iphone 4 ios 6.1
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1.Factory reset of my phone
2.Installation of Cydia
3.Installation of Imame4all
What is the expected output? What do you see instead?
I pair up the iphone to the icade. This is working for other games. When I
open imame4all and move the joystick I do not receive the detected iCade
message.
What version of the product are you using? On what operating system?
Iphone4
IOS6
imame4all v1.10.0
Please provide any additional information below.
I have tested this on an iphone 4s with 5.0.1 ios and it is working as expected.
I have performed two factory resets of the phone and only installed cydia and
imame4all with no other applications but still have this issue
```
Original issue reported on code.google.com by `jmic...@gmail.com` on 5 Feb 2013 at 11:36
|
1.0
|
iMame4all not recognizing iCade Jr iphone 4 ios 6.1 - ```
What steps will reproduce the problem?
1.Factory reset of my phone
2.Installation of Cydia
3.Installation of Imame4all
What is the expected output? What do you see instead?
I pair up the iphone to the icade. This is working for other games. When I
open imame4all and move the joystick I do not receive the detected iCade
message.
What version of the product are you using? On what operating system?
Iphone4
IOS6
imame4all v1.10.0
Please provide any additional information below.
I have tested this on an iphone 4s with 5.0.1 ios and it is working as expected.
I have performed two factory resets of the phone and only installed cydia and
imame4all with no other applications but still have this issue
```
Original issue reported on code.google.com by `jmic...@gmail.com` on 5 Feb 2013 at 11:36
|
defect
|
not recognizing icade jr iphone ios what steps will reproduce the problem factory reset of my phone installation of cydia installation of what is the expected output what do you see instead i pair up the iphone to the icade this is working for other games when i open and move the joystick i do not receive the detected icade message what version of the product are you using on what operating system please provide any additional information below i have tested this on an iphone with ios and it is working as expected i have performed two factory resets of the phone and only installed cydia and with no other applications but still have this issue original issue reported on code google com by jmic gmail com on feb at
| 1
|
12,297
| 2,689,695,836
|
IssuesEvent
|
2015-03-31 12:11:54
|
brunoduartec/duartec-projects
|
https://api.github.com/repos/brunoduartec/duartec-projects
|
closed
|
Problemas na tese
|
auto-migrated Priority-Medium Type-Defect
|
```
Resolver problemas na tese
```
Original issue reported on code.google.com by `bruno.duartec` on 29 Jan 2015 at 11:21
Attachments:
* [tese-issues.txt](https://storage.googleapis.com/google-code-attachments/duartec-projects/issue-1/comment-0/tese-issues.txt)
|
1.0
|
Problemas na tese - ```
Resolver problemas na tese
```
Original issue reported on code.google.com by `bruno.duartec` on 29 Jan 2015 at 11:21
Attachments:
* [tese-issues.txt](https://storage.googleapis.com/google-code-attachments/duartec-projects/issue-1/comment-0/tese-issues.txt)
|
defect
|
problemas na tese resolver problemas na tese original issue reported on code google com by bruno duartec on jan at attachments
| 1
|
186,083
| 6,733,383,093
|
IssuesEvent
|
2017-10-18 14:40:56
|
CS2103AUG2017-F11-B1/main
|
https://api.github.com/repos/CS2103AUG2017-F11-B1/main
|
opened
|
As a user I can have a temp delete 'folder' after I delete a contact and contact will be deleted after a week
|
priority.Low type.Enhancement
|
So that I can re-add the contact back if I change my mind.
|
1.0
|
As a user I can have a temp delete 'folder' after I delete a contact and contact will be deleted after a week - So that I can re-add the contact back if I change my mind.
|
non_defect
|
as a user i can have a temp delete folder after i delete a contact and contact will be deleted after a week so that i can re add the contact back if i change my mind
| 0
|
20,279
| 11,425,592,984
|
IssuesEvent
|
2020-02-03 20:08:59
|
microsoft/BotBuilder-Samples
|
https://api.github.com/repos/microsoft/BotBuilder-Samples
|
closed
|
MultiTurnPromptBot responds out of order when run via Microsoft Teams
|
Bot Services Support customer-replied-to customer-reported
|
## Sample information
1. Sample type: Sample
2. Sample language: dotnetcore
3. Sample name: MultiTurnPromptBot
## Describe the bug
Conversation is out of order when run via Teams
## To Reproduce
Steps to reproduce the behavior:
1. Publish to team.
2. Run in teams
3. Notice questions are re-asked and appear out of order.
## Expected behavior
Waterfall steps should be maintained
## Screenshots
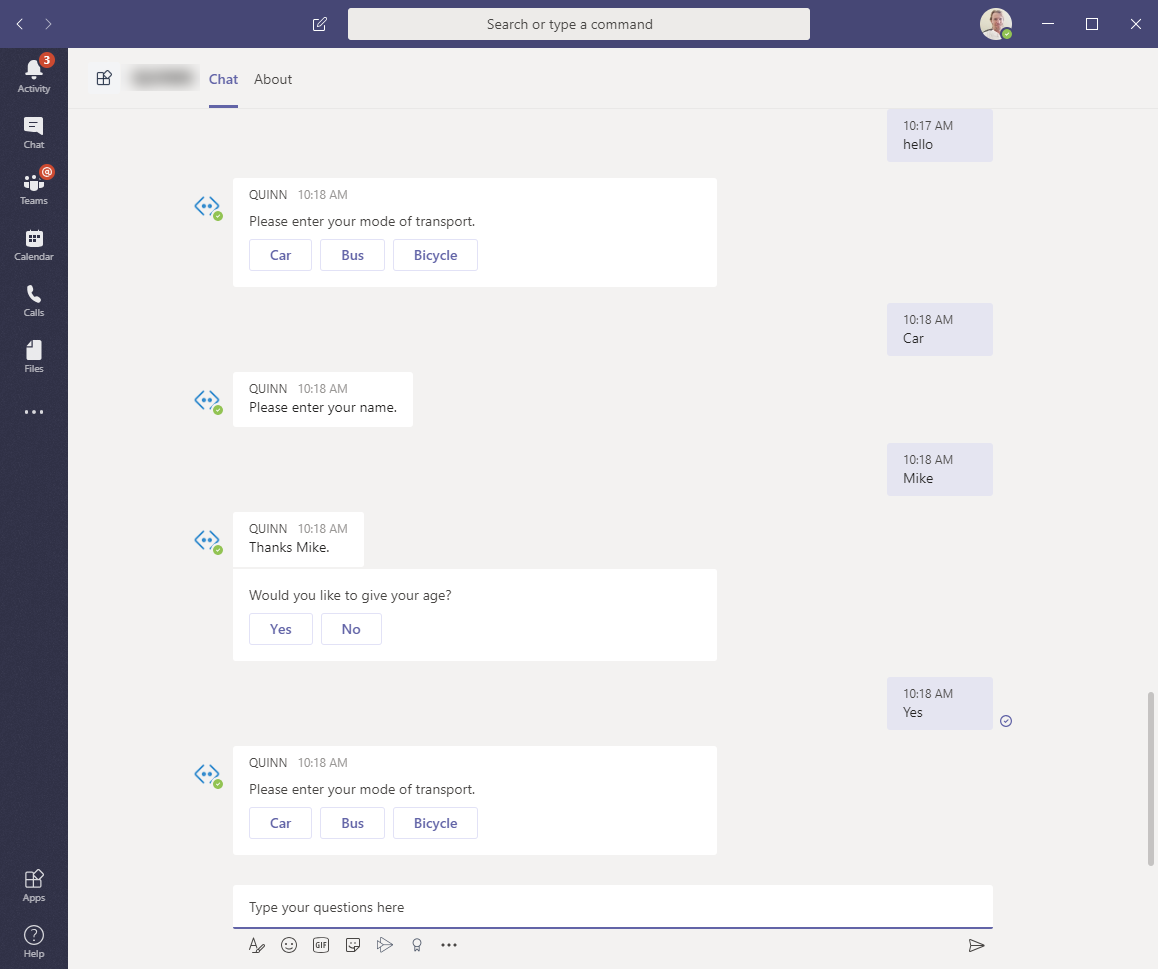
|
1.0
|
MultiTurnPromptBot responds out of order when run via Microsoft Teams - ## Sample information
1. Sample type: Sample
2. Sample language: dotnetcore
3. Sample name: MultiTurnPromptBot
## Describe the bug
Conversation is out of order when run via Teams
## To Reproduce
Steps to reproduce the behavior:
1. Publish to team.
2. Run in teams
3. Notice questions are re-asked and appear out of order.
## Expected behavior
Waterfall steps should be maintained
## Screenshots
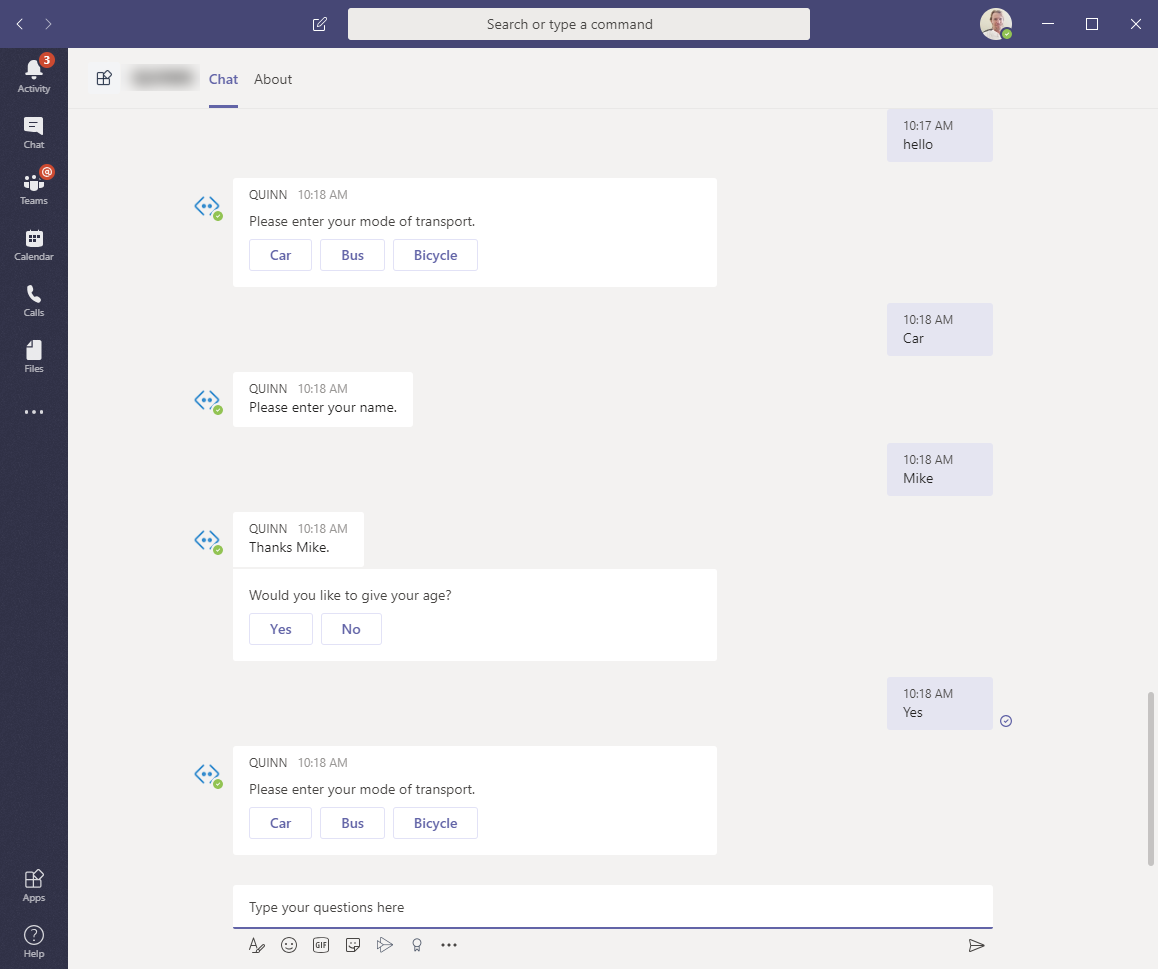
|
non_defect
|
multiturnpromptbot responds out of order when run via microsoft teams sample information sample type sample sample language dotnetcore sample name multiturnpromptbot describe the bug conversation is out of order when run via teams to reproduce steps to reproduce the behavior publish to team run in teams notice questions are re asked and appear out of order expected behavior waterfall steps should be maintained screenshots
| 0
|
80,061
| 29,951,462,944
|
IssuesEvent
|
2023-06-23 01:47:29
|
FreeRADIUS/freeradius-server
|
https://api.github.com/repos/FreeRADIUS/freeradius-server
|
opened
|
[defect]: autconf doesn't recurse
|
defect
|
### What type of defect/bug is this?
Crash or memory corruption (segv, abort, etc...)
### How can the issue be reproduced?
(v3.2.2)
```
$ autoconf --version
autoconf (GNU Autoconf) 2.69
$ find . -name configure | xargs rm
$ aclocal && autoconf
$ find . -name configure
./configure
````
https://www.gnu.org/software/autoconf/manual/autoconf-2.69/html_node/Subdirectories.html says
> please do not use:
AC_CONFIG_SUBDIRS([$my_subdirs])
and yet:
```
$ grep AC_CONFIG_SUBDIRS configure.ac
AC_CONFIG_SUBDIRS($mysubdirs)
```
### Log output from the FreeRADIUS daemon
```shell
n/a
```
### Relevant log output from client utilities
_No response_
### Backtrace from LLDB or GDB
_No response_
|
1.0
|
[defect]: autconf doesn't recurse - ### What type of defect/bug is this?
Crash or memory corruption (segv, abort, etc...)
### How can the issue be reproduced?
(v3.2.2)
```
$ autoconf --version
autoconf (GNU Autoconf) 2.69
$ find . -name configure | xargs rm
$ aclocal && autoconf
$ find . -name configure
./configure
````
https://www.gnu.org/software/autoconf/manual/autoconf-2.69/html_node/Subdirectories.html says
> please do not use:
AC_CONFIG_SUBDIRS([$my_subdirs])
and yet:
```
$ grep AC_CONFIG_SUBDIRS configure.ac
AC_CONFIG_SUBDIRS($mysubdirs)
```
### Log output from the FreeRADIUS daemon
```shell
n/a
```
### Relevant log output from client utilities
_No response_
### Backtrace from LLDB or GDB
_No response_
|
defect
|
autconf doesn t recurse what type of defect bug is this crash or memory corruption segv abort etc how can the issue be reproduced autoconf version autoconf gnu autoconf find name configure xargs rm aclocal autoconf find name configure configure says please do not use ac config subdirs and yet grep ac config subdirs configure ac ac config subdirs mysubdirs log output from the freeradius daemon shell n a relevant log output from client utilities no response backtrace from lldb or gdb no response
| 1
|
110,982
| 17,009,681,746
|
IssuesEvent
|
2021-07-02 01:06:12
|
tamirdahan/keycloak
|
https://api.github.com/repos/tamirdahan/keycloak
|
opened
|
CVE-2014-0114 (Medium) detected in commons-beanutils-1.9.2.jar
|
security vulnerability
|
## CVE-2014-0114 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-beanutils-1.9.2.jar</b></p></summary>
<p>Apache Commons BeanUtils provides an easy-to-use but flexible wrapper around reflection and introspection.</p>
<p>Path to dependency file: keycloak/testsuite/model/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.9.2/commons-beanutils-1.9.2.jar,/home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.9.2/commons-beanutils-1.9.2.jar</p>
<p>
Dependency Hierarchy:
- java-client-6.1.0.jar (Root Library)
- commons-validator-1.6.jar
- :x: **commons-beanutils-1.9.2.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"commons-beanutils","packageName":"commons-beanutils","packageVersion":"1.9.2","packageFilePaths":["/testsuite/model/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"io.appium:java-client:6.1.0;commons-validator:commons-validator:1.6;commons-beanutils:commons-beanutils:1.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2014-0114","vulnerabilityDetails":"Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to \"manipulate\" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2014-0114 (Medium) detected in commons-beanutils-1.9.2.jar - ## CVE-2014-0114 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-beanutils-1.9.2.jar</b></p></summary>
<p>Apache Commons BeanUtils provides an easy-to-use but flexible wrapper around reflection and introspection.</p>
<p>Path to dependency file: keycloak/testsuite/model/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.9.2/commons-beanutils-1.9.2.jar,/home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.9.2/commons-beanutils-1.9.2.jar</p>
<p>
Dependency Hierarchy:
- java-client-6.1.0.jar (Root Library)
- commons-validator-1.6.jar
- :x: **commons-beanutils-1.9.2.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"commons-beanutils","packageName":"commons-beanutils","packageVersion":"1.9.2","packageFilePaths":["/testsuite/model/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"io.appium:java-client:6.1.0;commons-validator:commons-validator:1.6;commons-beanutils:commons-beanutils:1.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2014-0114","vulnerabilityDetails":"Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to \"manipulate\" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve medium detected in commons beanutils jar cve medium severity vulnerability vulnerable library commons beanutils jar apache commons beanutils provides an easy to use but flexible wrapper around reflection and introspection path to dependency file keycloak testsuite model pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils commons beanutils jar home wss scanner repository commons beanutils commons beanutils commons beanutils jar dependency hierarchy java client jar root library commons validator jar x commons beanutils jar vulnerable library found in base branch master vulnerability details apache commons beanutils as distributed in lib commons beanutils jar in apache struts x through and in other products requiring commons beanutils through does not suppress the class property which allows remote attackers to manipulate the classloader and execute arbitrary code via the class parameter as demonstrated by the passing of this parameter to the getclass method of the actionform object in struts publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons beanutils commons beanutils org apache struts core isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree io appium java client commons validator commons validator commons beanutils commons beanutils isminimumfixversionavailable true minimumfixversion commons beanutils commons beanutils org apache struts core basebranches vulnerabilityidentifier cve vulnerabilitydetails apache commons beanutils as distributed in lib commons beanutils jar in apache struts x through and in other products requiring commons beanutils through does not suppress the class property which allows remote attackers to manipulate the classloader and execute arbitrary code via the class parameter as demonstrated by the passing of this parameter to the getclass method of the actionform object in struts vulnerabilityurl
| 0
|
45,524
| 12,833,347,102
|
IssuesEvent
|
2020-07-07 09:11:09
|
beefproject/beef
|
https://api.github.com/repos/beefproject/beef
|
closed
|
Hello, beef and facebook
|
Defect Module
|
Hello, can anyone tell me why I don't log in when I click on a pop-up?

|
1.0
|
Hello, beef and facebook - Hello, can anyone tell me why I don't log in when I click on a pop-up?

|
defect
|
hello beef and facebook hello can anyone tell me why i don t log in when i click on a pop up
| 1
|
43,474
| 11,727,080,630
|
IssuesEvent
|
2020-03-10 15:25:56
|
idaholab/moose
|
https://api.github.com/repos/idaholab/moose
|
opened
|
Time reset with sub app happens too late
|
T: defect
|
## Bug Description
Here is a description of the procedure that led to finding this bug:
A master application has a single sub-application; we want to run a transient that starts from a steady-state solution of this problem.
The steady-state solution of the problem is obtained first. The master application uses a `Steady` executioner, but the sub-app runs a pseudo-transient so has `Transient` executioner. So far, everything works fine.
The transient is restarted from a checkpoint file. When restarting, the time (meaning the `FEProblem` member `_time`) in the sub-app is reset too late. We experienced this when
evaluating a postprocessor on `INITIAL`. On `INITIAL` the value of `_time` is the last time of the pseudo-transient that the transient is restarted from. The postprocessor is `0` if `t < 0.5` and `1` otherwise. For the first timestep at `time = 0`, it evaluates to `1`. Here is an example output:
```
sub0: +----------------+----------------+----------------+----------------+
sub0: | time | sub_average | time_step_pp | trip_valve |
sub0: +----------------+----------------+----------------+----------------+
sub0: | 0.000000e+00 | 5.625000e-01 | 6.400000e-01 | 1.000000e+00 |
sub0: | 1.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 2.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 3.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 4.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 5.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 6.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 7.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 8.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 9.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 1.000000e+00 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: +----------------+----------------+----------------+----------------+
```
The first value in the rightmost column should be a 0.
## Steps to Reproduce
I will push a branch with an example.
## Impact
Specific models using `Controls` and restarting from pseudo-transients do not work.
|
1.0
|
Time reset with sub app happens too late - ## Bug Description
Here is a description of the procedure that led to finding this bug:
A master application has a single sub-application; we want to run a transient that starts from a steady-state solution of this problem.
The steady-state solution of the problem is obtained first. The master application uses a `Steady` executioner, but the sub-app runs a pseudo-transient so has `Transient` executioner. So far, everything works fine.
The transient is restarted from a checkpoint file. When restarting, the time (meaning the `FEProblem` member `_time`) in the sub-app is reset too late. We experienced this when
evaluating a postprocessor on `INITIAL`. On `INITIAL` the value of `_time` is the last time of the pseudo-transient that the transient is restarted from. The postprocessor is `0` if `t < 0.5` and `1` otherwise. For the first timestep at `time = 0`, it evaluates to `1`. Here is an example output:
```
sub0: +----------------+----------------+----------------+----------------+
sub0: | time | sub_average | time_step_pp | trip_valve |
sub0: +----------------+----------------+----------------+----------------+
sub0: | 0.000000e+00 | 5.625000e-01 | 6.400000e-01 | 1.000000e+00 |
sub0: | 1.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 2.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 3.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 4.000000e-01 | 5.625000e-01 | 1.000000e-01 | 0.000000e+00 |
sub0: | 5.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 6.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 7.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 8.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 9.000000e-01 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: | 1.000000e+00 | 5.625000e-01 | 1.000000e-01 | 1.000000e+00 |
sub0: +----------------+----------------+----------------+----------------+
```
The first value in the rightmost column should be a 0.
## Steps to Reproduce
I will push a branch with an example.
## Impact
Specific models using `Controls` and restarting from pseudo-transients do not work.
|
defect
|
time reset with sub app happens too late bug description here is a description of the procedure that led to finding this bug a master application has a single sub application we want to run a transient that starts from a steady state solution of this problem the steady state solution of the problem is obtained first the master application uses a steady executioner but the sub app runs a pseudo transient so has transient executioner so far everything works fine the transient is restarted from a checkpoint file when restarting the time meaning the feproblem member time in the sub app is reset too late we experienced this when evaluating a postprocessor on initial on initial the value of time is the last time of the pseudo transient that the transient is restarted from the postprocessor is if t and otherwise for the first timestep at time it evaluates to here is an example output time sub average time step pp trip valve the first value in the rightmost column should be a steps to reproduce i will push a branch with an example impact specific models using controls and restarting from pseudo transients do not work
| 1
|
13,113
| 2,732,902,774
|
IssuesEvent
|
2015-04-17 10:06:40
|
tiku01/oryx-editor
|
https://api.github.com/repos/tiku01/oryx-editor
|
closed
|
Grouping toolbar button active after moving a group of shapes
|
auto-migrated Component-Editor Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. create some shapes
2. select those shapes
3. group the shapes
4. move the group
What is the expected output?
the ungroup button is active.
What do you see instead?
the group button is active.
```
Original issue reported on code.google.com by `NicoPete...@gmail.com` on 6 Oct 2008 at 3:38
|
1.0
|
Grouping toolbar button active after moving a group of shapes - ```
What steps will reproduce the problem?
1. create some shapes
2. select those shapes
3. group the shapes
4. move the group
What is the expected output?
the ungroup button is active.
What do you see instead?
the group button is active.
```
Original issue reported on code.google.com by `NicoPete...@gmail.com` on 6 Oct 2008 at 3:38
|
defect
|
grouping toolbar button active after moving a group of shapes what steps will reproduce the problem create some shapes select those shapes group the shapes move the group what is the expected output the ungroup button is active what do you see instead the group button is active original issue reported on code google com by nicopete gmail com on oct at
| 1
|
11,075
| 2,632,356,886
|
IssuesEvent
|
2015-03-08 01:36:36
|
marmarek/test
|
https://api.github.com/repos/marmarek/test
|
closed
|
When starting a domain, manager should start qrexec_daemon, too
|
C: qubes-manager duplicate P: major T: defect
|
**Reported by rafal on 25 Mar 2011 13:12 UTC**
... just like it is done in current qvm-start.
|
1.0
|
When starting a domain, manager should start qrexec_daemon, too - **Reported by rafal on 25 Mar 2011 13:12 UTC**
... just like it is done in current qvm-start.
|
defect
|
when starting a domain manager should start qrexec daemon too reported by rafal on mar utc just like it is done in current qvm start
| 1
|
56,048
| 14,913,021,720
|
IssuesEvent
|
2021-01-22 13:34:02
|
gwaldron/osgearth
|
https://api.github.com/repos/gwaldron/osgearth
|
closed
|
MapNode doesn't survive change in osgViewer::Viewer
|
defect
|
This code fails on the second iteration of the loop with OpenGL errors and a missing globe.
```
#include <osgViewer/Viewer>
#include <osgGA/TrackballManipulator>
#include <osgDB/ReadFile>
int main(int argc, char** argv)
{
osg::ArgumentParser arguments(&argc,argv);
osg::ref_ptr<osg::Node> node = osgDB::readRefNodeFile("simple.earth");
for(int i=0; i<2; ++i)
{
osgViewer::Viewer viewer(arguments);
viewer.setSceneData(node.get());
viewer.setCameraManipulator(new osgGA::TrackballManipulator());
viewer.run();
}
return 0;
}
```
WORKAROUND: reload or recreate the node for each new Viewer instance.
|
1.0
|
MapNode doesn't survive change in osgViewer::Viewer - This code fails on the second iteration of the loop with OpenGL errors and a missing globe.
```
#include <osgViewer/Viewer>
#include <osgGA/TrackballManipulator>
#include <osgDB/ReadFile>
int main(int argc, char** argv)
{
osg::ArgumentParser arguments(&argc,argv);
osg::ref_ptr<osg::Node> node = osgDB::readRefNodeFile("simple.earth");
for(int i=0; i<2; ++i)
{
osgViewer::Viewer viewer(arguments);
viewer.setSceneData(node.get());
viewer.setCameraManipulator(new osgGA::TrackballManipulator());
viewer.run();
}
return 0;
}
```
WORKAROUND: reload or recreate the node for each new Viewer instance.
|
defect
|
mapnode doesn t survive change in osgviewer viewer this code fails on the second iteration of the loop with opengl errors and a missing globe include include include int main int argc char argv osg argumentparser arguments argc argv osg ref ptr node osgdb readrefnodefile simple earth for int i i i osgviewer viewer viewer arguments viewer setscenedata node get viewer setcameramanipulator new osgga trackballmanipulator viewer run return workaround reload or recreate the node for each new viewer instance
| 1
|
71,031
| 23,419,517,480
|
IssuesEvent
|
2022-08-13 13:23:47
|
openzfs/zfs
|
https://api.github.com/repos/openzfs/zfs
|
closed
|
Intermittent stat Input/output errors on 0.8.6
|
Type: Defect Status: Stale
|
### System information
Type | Version/Name
--- | ---
Distribution Name | CentOS
Distribution Version | 7-9.2009.1
Linux Kernel | 3.10.0-1160.21.1
Architecture | x86_64
ZFS Version | 0.8.6-1
SPL Version | 0.8.6-1
### Describe the problem you're observing
We upgraded a large pool from 0.6.5.8-1 to 0.8.6-1 recently and have had intermittent Input/output errors using stat for files that have been at rest for years. We can see this happening in the logs from a batch borg that runs nightly while it scans over the filesystem. When borg runs again or when we manually check these files, they succeed without stat errors.
The pool was upgraded 4/1 - you can see the errors appearing shortly after in the histogram: `2021-04-01.10:47:28 zpool upgrade Pool1`
This system has been running for years with the same pool, without error. We have a parallel system still running with 0.6.5.8-1 that continues without error.
<img width="1198" alt="Screen Shot 2021-04-16 at 10 12 03 AM" src="https://user-images.githubusercontent.com/16848553/115037214-3a971a00-9e9c-11eb-82fc-16b0a8bd8d73.png">
<img width="1198" alt="Screen Shot 2021-04-16 at 10 19 02 AM" src="https://user-images.githubusercontent.com/16848553/115038118-37e8f480-9e9d-11eb-9935-2425fb2ef4d6.png">
```
NAME SIZE ALLOC FREE CKPOINT EXPANDSZ FRAG CAP DEDUP HEALTH ALTROOT
Pool1 308T 292T 15.8T - - 36% 94% 1.00x ONLINE -
```
### Describe how to reproduce the problem
We are unable to reproduce this on demand. Attempting to observe one of the files that failed a stat after the fact works correctly.
### Include any warning/errors/backtraces from the system logs
Nothing is reported that we can find, beyond the userspace errno.
|
1.0
|
Intermittent stat Input/output errors on 0.8.6 - ### System information
Type | Version/Name
--- | ---
Distribution Name | CentOS
Distribution Version | 7-9.2009.1
Linux Kernel | 3.10.0-1160.21.1
Architecture | x86_64
ZFS Version | 0.8.6-1
SPL Version | 0.8.6-1
### Describe the problem you're observing
We upgraded a large pool from 0.6.5.8-1 to 0.8.6-1 recently and have had intermittent Input/output errors using stat for files that have been at rest for years. We can see this happening in the logs from a batch borg that runs nightly while it scans over the filesystem. When borg runs again or when we manually check these files, they succeed without stat errors.
The pool was upgraded 4/1 - you can see the errors appearing shortly after in the histogram: `2021-04-01.10:47:28 zpool upgrade Pool1`
This system has been running for years with the same pool, without error. We have a parallel system still running with 0.6.5.8-1 that continues without error.
<img width="1198" alt="Screen Shot 2021-04-16 at 10 12 03 AM" src="https://user-images.githubusercontent.com/16848553/115037214-3a971a00-9e9c-11eb-82fc-16b0a8bd8d73.png">
<img width="1198" alt="Screen Shot 2021-04-16 at 10 19 02 AM" src="https://user-images.githubusercontent.com/16848553/115038118-37e8f480-9e9d-11eb-9935-2425fb2ef4d6.png">
```
NAME SIZE ALLOC FREE CKPOINT EXPANDSZ FRAG CAP DEDUP HEALTH ALTROOT
Pool1 308T 292T 15.8T - - 36% 94% 1.00x ONLINE -
```
### Describe how to reproduce the problem
We are unable to reproduce this on demand. Attempting to observe one of the files that failed a stat after the fact works correctly.
### Include any warning/errors/backtraces from the system logs
Nothing is reported that we can find, beyond the userspace errno.
|
defect
|
intermittent stat input output errors on system information type version name distribution name centos distribution version linux kernel architecture zfs version spl version describe the problem you re observing we upgraded a large pool from to recently and have had intermittent input output errors using stat for files that have been at rest for years we can see this happening in the logs from a batch borg that runs nightly while it scans over the filesystem when borg runs again or when we manually check these files they succeed without stat errors the pool was upgraded you can see the errors appearing shortly after in the histogram zpool upgrade this system has been running for years with the same pool without error we have a parallel system still running with that continues without error img width alt screen shot at am src img width alt screen shot at am src name size alloc free ckpoint expandsz frag cap dedup health altroot online describe how to reproduce the problem we are unable to reproduce this on demand attempting to observe one of the files that failed a stat after the fact works correctly include any warning errors backtraces from the system logs nothing is reported that we can find beyond the userspace errno
| 1
|
47,025
| 13,056,020,595
|
IssuesEvent
|
2020-07-30 03:24:49
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
[MuonGun] Exclude stochastic losses outside active volume in Track::GetEnery() (Trac #2325)
|
Incomplete Migration Migrated from Trac combo simulation defect
|
Migrated from https://code.icecube.wisc.edu/ticket/2325
```json
{
"status": "closed",
"changetime": "2019-09-04T12:51:21",
"description": "MuonGun::Track assumes that all daughters attached to a muon in I3MCTree are stochastic losses in the active volume, and uses the the difference between the sum of daughter energies and I3MMCTrack::GetElost() as an estimate of the continuous loss rate. PROPOSAL now seems to attach muon decay products to I3MCTree even if they are outside the volume. In the attached example from jsoedingrekso, an up-going muon decays in low Earth orbit at 180 TeV. This makes the estimated continuous loss rate negative, and MuonGun::Track() claims that the muon _gains_ energy as it propagates.\n\nThis could be fixed by only including stochastic losses between Ti and Tf.",
"reporter": "jvansanten",
"cc": "jsoedingrekso",
"resolution": "duplicate",
"_ts": "1567601481373936",
"component": "combo simulation",
"summary": "[MuonGun] Exclude stochastic losses outside active volume in Track::GetEnery()",
"priority": "normal",
"keywords": "",
"time": "2019-06-12T07:56:13",
"milestone": "Autumnal Equinox 2019",
"owner": "jvansanten",
"type": "defect"
}
```
|
1.0
|
[MuonGun] Exclude stochastic losses outside active volume in Track::GetEnery() (Trac #2325) - Migrated from https://code.icecube.wisc.edu/ticket/2325
```json
{
"status": "closed",
"changetime": "2019-09-04T12:51:21",
"description": "MuonGun::Track assumes that all daughters attached to a muon in I3MCTree are stochastic losses in the active volume, and uses the the difference between the sum of daughter energies and I3MMCTrack::GetElost() as an estimate of the continuous loss rate. PROPOSAL now seems to attach muon decay products to I3MCTree even if they are outside the volume. In the attached example from jsoedingrekso, an up-going muon decays in low Earth orbit at 180 TeV. This makes the estimated continuous loss rate negative, and MuonGun::Track() claims that the muon _gains_ energy as it propagates.\n\nThis could be fixed by only including stochastic losses between Ti and Tf.",
"reporter": "jvansanten",
"cc": "jsoedingrekso",
"resolution": "duplicate",
"_ts": "1567601481373936",
"component": "combo simulation",
"summary": "[MuonGun] Exclude stochastic losses outside active volume in Track::GetEnery()",
"priority": "normal",
"keywords": "",
"time": "2019-06-12T07:56:13",
"milestone": "Autumnal Equinox 2019",
"owner": "jvansanten",
"type": "defect"
}
```
|
defect
|
exclude stochastic losses outside active volume in track getenery trac migrated from json status closed changetime description muongun track assumes that all daughters attached to a muon in are stochastic losses in the active volume and uses the the difference between the sum of daughter energies and getelost as an estimate of the continuous loss rate proposal now seems to attach muon decay products to even if they are outside the volume in the attached example from jsoedingrekso an up going muon decays in low earth orbit at tev this makes the estimated continuous loss rate negative and muongun track claims that the muon gains energy as it propagates n nthis could be fixed by only including stochastic losses between ti and tf reporter jvansanten cc jsoedingrekso resolution duplicate ts component combo simulation summary exclude stochastic losses outside active volume in track getenery priority normal keywords time milestone autumnal equinox owner jvansanten type defect
| 1
|
17,471
| 3,008,041,851
|
IssuesEvent
|
2015-07-27 19:09:14
|
TASVideos/BizHawk
|
https://api.github.com/repos/TASVideos/BizHawk
|
closed
|
Lua doesn't work in GDI+
|
auto-migrated Core-EmuHawk Priority-Critical Type-Defect
|
```
In GDI+ mode:
- Load a ROM.
- Open Lua Console.
- Load a script such as ButtonCount.lua.
- Unpause emulation.
Then BizHawk crashes with the following error:
http://i19.photobucket.com/albums/b185/jhchan8/gdiluaerror.png
Crashes occur in both 1.9.3 and 1.9.4.
OS is Windows 7 Home Premium (older computer that couldn't run BizHawk without
GDI+).
```
Original issue reported on code.google.com by `justinhc...@hotmail.com` on 7 Apr 2015 at 5:49
|
1.0
|
Lua doesn't work in GDI+ - ```
In GDI+ mode:
- Load a ROM.
- Open Lua Console.
- Load a script such as ButtonCount.lua.
- Unpause emulation.
Then BizHawk crashes with the following error:
http://i19.photobucket.com/albums/b185/jhchan8/gdiluaerror.png
Crashes occur in both 1.9.3 and 1.9.4.
OS is Windows 7 Home Premium (older computer that couldn't run BizHawk without
GDI+).
```
Original issue reported on code.google.com by `justinhc...@hotmail.com` on 7 Apr 2015 at 5:49
|
defect
|
lua doesn t work in gdi in gdi mode load a rom open lua console load a script such as buttoncount lua unpause emulation then bizhawk crashes with the following error crashes occur in both and os is windows home premium older computer that couldn t run bizhawk without gdi original issue reported on code google com by justinhc hotmail com on apr at
| 1
|
328,710
| 9,999,167,944
|
IssuesEvent
|
2019-07-12 09:57:15
|
latepaul/puttysessmgr
|
https://api.github.com/repos/latepaul/puttysessmgr
|
closed
|
Save to config file
|
High Priority enhancement
|
Save to a config file so changes in categories persist between instances of the script running.
|
1.0
|
Save to config file - Save to a config file so changes in categories persist between instances of the script running.
|
non_defect
|
save to config file save to a config file so changes in categories persist between instances of the script running
| 0
|
261,267
| 22,710,575,872
|
IssuesEvent
|
2022-07-05 18:53:37
|
danbudris/vulnerabilityProcessor
|
https://api.github.com/repos/danbudris/vulnerabilityProcessor
|
opened
|
LOW vulnerability in 0 packages affecting 1 resources
|
hey there test severity/LOW
|
Issue auto cut by Vulnerability Processor
Processor Version: `v0.0.0-dev`
Message Source: `EventBridge`
Finding Source: `inspectorV2`
LOW vulnerability CVE-2016-9085 detected in 1 resources
- arn:aws:ecr:us-east-1:555555555555:repository/myrepo/sha256:7308b29228bde15a52a49b2f4a4cf95d5e2610e5ca67cdae32430e4b18effd91
Associated Pull Requests:
-
|
1.0
|
LOW vulnerability in 0 packages affecting 1 resources - Issue auto cut by Vulnerability Processor
Processor Version: `v0.0.0-dev`
Message Source: `EventBridge`
Finding Source: `inspectorV2`
LOW vulnerability CVE-2016-9085 detected in 1 resources
- arn:aws:ecr:us-east-1:555555555555:repository/myrepo/sha256:7308b29228bde15a52a49b2f4a4cf95d5e2610e5ca67cdae32430e4b18effd91
Associated Pull Requests:
-
|
non_defect
|
low vulnerability in packages affecting resources issue auto cut by vulnerability processor processor version dev message source eventbridge finding source low vulnerability cve detected in resources arn aws ecr us east repository myrepo associated pull requests
| 0
|
75,552
| 25,913,021,295
|
IssuesEvent
|
2022-12-15 15:18:52
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
opened
|
[🐛 Bug]: Hanging issue with selenium-webdriver 4.5.0
|
I-defect needs-triaging
|
### What happened?
please see https://stackoverflow.com/questions/74722080/rails-capybara-using-session-visiting-a-page-and-having-ruby-debug-cause/74802398
### How can we reproduce the issue?
```shell
please see https://stackoverflow.com/questions/74722080/rails-capybara-using-session-visiting-a-page-and-having-ruby-debug-cause/74802398
```
### Relevant log output
```shell
not applicable.
```
### Operating System
macOS
### Selenium version
Ruby 3.1.3, selenium-webdriver 4.5.0
### What are the browser(s) and version(s) where you see this issue?
not applicable
### What are the browser driver(s) and version(s) where you see this issue?
not applicable
### Are you using Selenium Grid?
not applicable
|
1.0
|
[🐛 Bug]: Hanging issue with selenium-webdriver 4.5.0 - ### What happened?
please see https://stackoverflow.com/questions/74722080/rails-capybara-using-session-visiting-a-page-and-having-ruby-debug-cause/74802398
### How can we reproduce the issue?
```shell
please see https://stackoverflow.com/questions/74722080/rails-capybara-using-session-visiting-a-page-and-having-ruby-debug-cause/74802398
```
### Relevant log output
```shell
not applicable.
```
### Operating System
macOS
### Selenium version
Ruby 3.1.3, selenium-webdriver 4.5.0
### What are the browser(s) and version(s) where you see this issue?
not applicable
### What are the browser driver(s) and version(s) where you see this issue?
not applicable
### Are you using Selenium Grid?
not applicable
|
defect
|
hanging issue with selenium webdriver what happened please see how can we reproduce the issue shell please see relevant log output shell not applicable operating system macos selenium version ruby selenium webdriver what are the browser s and version s where you see this issue not applicable what are the browser driver s and version s where you see this issue not applicable are you using selenium grid not applicable
| 1
|
276,001
| 8,583,118,598
|
IssuesEvent
|
2018-11-13 18:50:15
|
StrangeLoopGames/EcoIssues
|
https://api.github.com/repos/StrangeLoopGames/EcoIssues
|
closed
|
Staging: too many tailings
|
High Priority
|
**Version:** 0.7.8.0 beta staging-52b819ac debug
Refers to - https://github.com/StrangeLoopGames/Eco/pull/3523
@craig-jong
No efficiency
**Expected behavior:**

10 bar, 25 tailings from 100 ores
**Actual behavior:**
10 bar, 30 tailings from 100 ores.
Max efficiency
**Expected behavior:**
10 bar, 5 tailings from 20 ores
**Actual behavior:**
10 bar, 10 tailings from 20 ores
|
1.0
|
Staging: too many tailings - **Version:** 0.7.8.0 beta staging-52b819ac debug
Refers to - https://github.com/StrangeLoopGames/Eco/pull/3523
@craig-jong
No efficiency
**Expected behavior:**

10 bar, 25 tailings from 100 ores
**Actual behavior:**
10 bar, 30 tailings from 100 ores.
Max efficiency
**Expected behavior:**
10 bar, 5 tailings from 20 ores
**Actual behavior:**
10 bar, 10 tailings from 20 ores
|
non_defect
|
staging too many tailings version beta staging debug refers to craig jong no efficiency expected behavior bar tailings from ores actual behavior bar tailings from ores max efficiency expected behavior bar tailings from ores actual behavior bar tailings from ores
| 0
|
55,800
| 14,692,426,975
|
IssuesEvent
|
2021-01-03 02:02:49
|
department-of-veterans-affairs/va.gov-cms
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms
|
opened
|
Spotlight panel link teasers: Can add 3, but only 1 gets saved.
|
Defect
|
**Describe the defect**
When adding 3 link teasers to the Spotlight panel, only 1 gets saved.
**To Reproduce**
Steps to reproduce the behavior:
1. Edit node 15068
2. Add two more link teasers in the Spotlight panel
3. Save.
4. See that only 1 is saved.
**Expected behavior**
I should be able to add 1, 2, 3, but not 4 or 0.
**Screenshots**

|
1.0
|
Spotlight panel link teasers: Can add 3, but only 1 gets saved. - **Describe the defect**
When adding 3 link teasers to the Spotlight panel, only 1 gets saved.
**To Reproduce**
Steps to reproduce the behavior:
1. Edit node 15068
2. Add two more link teasers in the Spotlight panel
3. Save.
4. See that only 1 is saved.
**Expected behavior**
I should be able to add 1, 2, 3, but not 4 or 0.
**Screenshots**

|
defect
|
spotlight panel link teasers can add but only gets saved describe the defect when adding link teasers to the spotlight panel only gets saved to reproduce steps to reproduce the behavior edit node add two more link teasers in the spotlight panel save see that only is saved expected behavior i should be able to add but not or screenshots
| 1
|
76,217
| 26,321,703,230
|
IssuesEvent
|
2023-01-10 00:38:46
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
Room visibility in a Space (and setting a Space logo) doesn't work
|
T-Defect X-Needs-Info
|
### Steps to reproduce
One user set up a space.
They then made me Admin of that space.
There are 2 users in the space, both with Admin level permissions.
(I am not able to set the logo for the space, it allows me to see the panel, upload the image and select "save" but when I close the modal it hasn't changed).
From Spaces home I can only see one room even though the other user can see 4 rooms - all of which are set as visibility at Space level (see the screenshot - this is not the space in question but is exactly the same setting for the rooms in question)
<img width="583" alt="Screenshot 2022-10-19 at 16 57 13" src="https://user-images.githubusercontent.com/89144281/197006077-c9efa0b0-da46-4c10-b262-ba77996045f0.png">
### Outcome
#### What did you expect?
To be able to see the rooms in the space that have this ☝️ setting even if i'm not a member of those rooms.
#### What happened instead?
They don't show up.
(I was able to set the logo on iOS but am not able to see the rooms on my iOS device either)
### Operating system
MacOS
### Application version
Element Nightly version: 2022102001 Olm version: 3.2.12
### How did you install the app?
element.io
### Homeserver
ems.one.host & matrix.org
### Will you send logs?
No
|
1.0
|
Room visibility in a Space (and setting a Space logo) doesn't work - ### Steps to reproduce
One user set up a space.
They then made me Admin of that space.
There are 2 users in the space, both with Admin level permissions.
(I am not able to set the logo for the space, it allows me to see the panel, upload the image and select "save" but when I close the modal it hasn't changed).
From Spaces home I can only see one room even though the other user can see 4 rooms - all of which are set as visibility at Space level (see the screenshot - this is not the space in question but is exactly the same setting for the rooms in question)
<img width="583" alt="Screenshot 2022-10-19 at 16 57 13" src="https://user-images.githubusercontent.com/89144281/197006077-c9efa0b0-da46-4c10-b262-ba77996045f0.png">
### Outcome
#### What did you expect?
To be able to see the rooms in the space that have this ☝️ setting even if i'm not a member of those rooms.
#### What happened instead?
They don't show up.
(I was able to set the logo on iOS but am not able to see the rooms on my iOS device either)
### Operating system
MacOS
### Application version
Element Nightly version: 2022102001 Olm version: 3.2.12
### How did you install the app?
element.io
### Homeserver
ems.one.host & matrix.org
### Will you send logs?
No
|
defect
|
room visibility in a space and setting a space logo doesn t work steps to reproduce one user set up a space they then made me admin of that space there are users in the space both with admin level permissions i am not able to set the logo for the space it allows me to see the panel upload the image and select save but when i close the modal it hasn t changed from spaces home i can only see one room even though the other user can see rooms all of which are set as visibility at space level see the screenshot this is not the space in question but is exactly the same setting for the rooms in question img width alt screenshot at src outcome what did you expect to be able to see the rooms in the space that have this ☝️ setting even if i m not a member of those rooms what happened instead they don t show up i was able to set the logo on ios but am not able to see the rooms on my ios device either operating system macos application version element nightly version olm version how did you install the app element io homeserver ems one host matrix org will you send logs no
| 1
|
245,703
| 7,889,714,661
|
IssuesEvent
|
2018-06-28 05:59:32
|
bleehu/Compound_X
|
https://api.github.com/repos/bleehu/Compound_X
|
closed
|
Gripe: Edit Skill Requirements and Class Passives to reflect Systematized Skills
|
Greenlit - Awaiting Review Gripe Priority - Med
|
For example:
Using grenades requires 10 skill in explosives, which is no feasible in early levels because skill points at lvl1 have decreased by 50.
Pilot passively gives 10 in piloting (a skill which no longer exists).
|
1.0
|
Gripe: Edit Skill Requirements and Class Passives to reflect Systematized Skills - For example:
Using grenades requires 10 skill in explosives, which is no feasible in early levels because skill points at lvl1 have decreased by 50.
Pilot passively gives 10 in piloting (a skill which no longer exists).
|
non_defect
|
gripe edit skill requirements and class passives to reflect systematized skills for example using grenades requires skill in explosives which is no feasible in early levels because skill points at have decreased by pilot passively gives in piloting a skill which no longer exists
| 0
|
40,894
| 10,215,963,898
|
IssuesEvent
|
2019-08-15 09:11:35
|
zotonic/zotonic
|
https://api.github.com/repos/zotonic/zotonic
|
closed
|
Fontawesome and material design paths to fonts are wrong.
|
defect presentation (css)
|
We bumped on a similar bug to #939 with font-awesome.
The css file contains relative paths to font files which do not work when the css files are concatenated.
The url below will 404 because the path to the font is relative.
```
https://gotokoala.com/lib-min/css/main~logon~/font-awesome-4/css/font-awesome.min~/material-design/fonts/fontawesome-webfont.woff?v=4.2.0
```
Should a similar update procedure like the one in bootstrap be put in place?
|
1.0
|
Fontawesome and material design paths to fonts are wrong. - We bumped on a similar bug to #939 with font-awesome.
The css file contains relative paths to font files which do not work when the css files are concatenated.
The url below will 404 because the path to the font is relative.
```
https://gotokoala.com/lib-min/css/main~logon~/font-awesome-4/css/font-awesome.min~/material-design/fonts/fontawesome-webfont.woff?v=4.2.0
```
Should a similar update procedure like the one in bootstrap be put in place?
|
defect
|
fontawesome and material design paths to fonts are wrong we bumped on a similar bug to with font awesome the css file contains relative paths to font files which do not work when the css files are concatenated the url below will because the path to the font is relative should a similar update procedure like the one in bootstrap be put in place
| 1
|
191,675
| 6,840,522,890
|
IssuesEvent
|
2017-11-11 01:03:20
|
uber/pyro
|
https://api.github.com/repos/uber/pyro
|
reopened
|
reproduce vae sample results
|
bug high priority
|
in the documentation there is a figure showing the ELBO for the test dataset.
after 50 epochs, the ELBO reaches below -80.
when running the vae sample, after 200 epochs the ELBO reaches -100.
is it a bug in the sample code ?
|
1.0
|
reproduce vae sample results - in the documentation there is a figure showing the ELBO for the test dataset.
after 50 epochs, the ELBO reaches below -80.
when running the vae sample, after 200 epochs the ELBO reaches -100.
is it a bug in the sample code ?
|
non_defect
|
reproduce vae sample results in the documentation there is a figure showing the elbo for the test dataset after epochs the elbo reaches below when running the vae sample after epochs the elbo reaches is it a bug in the sample code
| 0
|
39,617
| 9,565,479,848
|
IssuesEvent
|
2019-05-05 12:52:51
|
jmc2obj/j-mc-2-obj
|
https://api.github.com/repos/jmc2obj/j-mc-2-obj
|
closed
|
Textures Missing In Blender
|
Priority-Medium Type-Defect auto-migrated
|
```
What steps will reproduce the problem?
1.Importing the map
2.Exporting as .obj, .mtl, and textures
3.
What is the expected output? What do you see instead?
I expect to see the textures attatched to the model, and rather, the textures
are void, and nothing has a texture, but they have color.
What version of the product are you using? On what operating system?
0.2-dev281 or, I update, and get the same results. I am using Vista SP 2
Please describe your error as detailed as possible.
I select and import my MC world, and export it as obj. I also hit the export
MC textures, and it appears to do things. I open Blender 2.62a and import the
obj. position it, turn on enviroment lighting (all it does is light it up to
see) position the camera and render. No textures, plants disappear.
Please provide any additional information below.
I like how the program exports ONLY geometry I want it to.
Please provide the map if possible.
```
Original issue reported on code.google.com by `foch...@gmail.com` on 28 Jul 2013 at 6:36
Attachments:
- [level.dat](https://storage.googleapis.com/google-code-attachments/j-mc-2-obj/issue-75/comment-0/level.dat)
|
1.0
|
Textures Missing In Blender - ```
What steps will reproduce the problem?
1.Importing the map
2.Exporting as .obj, .mtl, and textures
3.
What is the expected output? What do you see instead?
I expect to see the textures attatched to the model, and rather, the textures
are void, and nothing has a texture, but they have color.
What version of the product are you using? On what operating system?
0.2-dev281 or, I update, and get the same results. I am using Vista SP 2
Please describe your error as detailed as possible.
I select and import my MC world, and export it as obj. I also hit the export
MC textures, and it appears to do things. I open Blender 2.62a and import the
obj. position it, turn on enviroment lighting (all it does is light it up to
see) position the camera and render. No textures, plants disappear.
Please provide any additional information below.
I like how the program exports ONLY geometry I want it to.
Please provide the map if possible.
```
Original issue reported on code.google.com by `foch...@gmail.com` on 28 Jul 2013 at 6:36
Attachments:
- [level.dat](https://storage.googleapis.com/google-code-attachments/j-mc-2-obj/issue-75/comment-0/level.dat)
|
defect
|
textures missing in blender what steps will reproduce the problem importing the map exporting as obj mtl and textures what is the expected output what do you see instead i expect to see the textures attatched to the model and rather the textures are void and nothing has a texture but they have color what version of the product are you using on what operating system or i update and get the same results i am using vista sp please describe your error as detailed as possible i select and import my mc world and export it as obj i also hit the export mc textures and it appears to do things i open blender and import the obj position it turn on enviroment lighting all it does is light it up to see position the camera and render no textures plants disappear please provide any additional information below i like how the program exports only geometry i want it to please provide the map if possible original issue reported on code google com by foch gmail com on jul at attachments
| 1
|
794,880
| 28,053,264,801
|
IssuesEvent
|
2023-03-29 07:40:46
|
AY2223S2-CS2103T-T09-4/tp
|
https://api.github.com/repos/AY2223S2-CS2103T-T09-4/tp
|
closed
|
Aggregating and Summarizing Data v1.3
|
type.Story priority.High
|
As a user, I can see my aggregated data of my clients, so that I can quickly view my progress in my career
|
1.0
|
Aggregating and Summarizing Data v1.3 - As a user, I can see my aggregated data of my clients, so that I can quickly view my progress in my career
|
non_defect
|
aggregating and summarizing data as a user i can see my aggregated data of my clients so that i can quickly view my progress in my career
| 0
|
4,769
| 3,080,596,706
|
IssuesEvent
|
2015-08-21 23:34:17
|
catapult-project/catapult
|
https://api.github.com/repos/catapult-project/catapult
|
closed
|
PiReportToHTMLTests spams stdout
|
Code Health
|
map_runner.py neesds to allow a nop-progress-reporter to be passed in.
|
1.0
|
PiReportToHTMLTests spams stdout - map_runner.py neesds to allow a nop-progress-reporter to be passed in.
|
non_defect
|
pireporttohtmltests spams stdout map runner py neesds to allow a nop progress reporter to be passed in
| 0
|
81,437
| 30,846,590,172
|
IssuesEvent
|
2023-08-02 14:05:54
|
mampfes/hacs_waste_collection_schedule
|
https://api.github.com/repos/mampfes/hacs_waste_collection_schedule
|
closed
|
hausmuell_info not working for all addresses
|
source defect
|
> Hey @5ila5 leider gibt es hier ein Problem mit der Stadt "Zella-Mehlis", da diese 3 Ortsteile hat.
> Unter der API https://schmalkalden-meiningen.hausmuell.info/search/search_orte.php kommt Zella-Mehlis mit der ort-id `10457` zurück.
> Der Ortsteil `Stadt` hat die id `10458`
>
> Sucht man nun nach Straßen, so wird im Python-Skript die ort-id und nicht die ortsteil-id genommen.
> unter https://schmalkalden-meiningen.hausmuell.info/search/search_strassen.php liefert die ort-id von Zella-Mehlis `10457` eine leere Liste zurück.
> Die Ort-Id von dem Ortsteil hingegen (`10458`) liefert die Straßennamen zurück.
> Dadurch kommt es zum Fehler `"strasse provided but not found in search results."`.
>
> Im Python-Skript gibt es auch nur ein Beispiel mit einem Orsteil, aber ohne Straßen
> https://github.com/mampfes/hacs_waste_collection_schedule/blob/master/custom_components/waste_collection_schedule/waste_collection_schedule/source/hausmuell_info.py#L48
> Lasse ich Straße und Hausnummer in meinem Fall weg, kommt es jedoch dennoch zum Fehler
>
> eine Anpassung müsste also hier erfolgen:
> https://github.com/mampfes/hacs_waste_collection_schedule/blob/master/custom_components/waste_collection_schedule/waste_collection_schedule/source/hausmuell_info.py#L242
>
> Alternativ wäre eine direkte Eingabe von den IDs sinnvoll :)
>
>
_Originally posted by @Maqsyo in https://github.com/mampfes/hacs_waste_collection_schedule/discussions/590#discussioncomment-6528073_
|
1.0
|
hausmuell_info not working for all addresses - > Hey @5ila5 leider gibt es hier ein Problem mit der Stadt "Zella-Mehlis", da diese 3 Ortsteile hat.
> Unter der API https://schmalkalden-meiningen.hausmuell.info/search/search_orte.php kommt Zella-Mehlis mit der ort-id `10457` zurück.
> Der Ortsteil `Stadt` hat die id `10458`
>
> Sucht man nun nach Straßen, so wird im Python-Skript die ort-id und nicht die ortsteil-id genommen.
> unter https://schmalkalden-meiningen.hausmuell.info/search/search_strassen.php liefert die ort-id von Zella-Mehlis `10457` eine leere Liste zurück.
> Die Ort-Id von dem Ortsteil hingegen (`10458`) liefert die Straßennamen zurück.
> Dadurch kommt es zum Fehler `"strasse provided but not found in search results."`.
>
> Im Python-Skript gibt es auch nur ein Beispiel mit einem Orsteil, aber ohne Straßen
> https://github.com/mampfes/hacs_waste_collection_schedule/blob/master/custom_components/waste_collection_schedule/waste_collection_schedule/source/hausmuell_info.py#L48
> Lasse ich Straße und Hausnummer in meinem Fall weg, kommt es jedoch dennoch zum Fehler
>
> eine Anpassung müsste also hier erfolgen:
> https://github.com/mampfes/hacs_waste_collection_schedule/blob/master/custom_components/waste_collection_schedule/waste_collection_schedule/source/hausmuell_info.py#L242
>
> Alternativ wäre eine direkte Eingabe von den IDs sinnvoll :)
>
>
_Originally posted by @Maqsyo in https://github.com/mampfes/hacs_waste_collection_schedule/discussions/590#discussioncomment-6528073_
|
defect
|
hausmuell info not working for all addresses hey leider gibt es hier ein problem mit der stadt zella mehlis da diese ortsteile hat unter der api kommt zella mehlis mit der ort id zurück der ortsteil stadt hat die id sucht man nun nach straßen so wird im python skript die ort id und nicht die ortsteil id genommen unter liefert die ort id von zella mehlis eine leere liste zurück die ort id von dem ortsteil hingegen liefert die straßennamen zurück dadurch kommt es zum fehler strasse provided but not found in search results im python skript gibt es auch nur ein beispiel mit einem orsteil aber ohne straßen lasse ich straße und hausnummer in meinem fall weg kommt es jedoch dennoch zum fehler eine anpassung müsste also hier erfolgen alternativ wäre eine direkte eingabe von den ids sinnvoll originally posted by maqsyo in
| 1
|
9,467
| 2,615,151,966
|
IssuesEvent
|
2015-03-01 06:29:26
|
chrsmith/reaver-wps
|
https://api.github.com/repos/chrsmith/reaver-wps
|
opened
|
it is not working at all at me
|
auto-migrated Priority-Triage Type-Defect
|
```
A few things to consider before submitting an issue:
0. We write documentation for a reason, if you have not read it and are
having problems with Reaver these pages are required reading before
submitting an issue:
http://code.google.com/p/reaver-wps/wiki/HintsAndTips
http://code.google.com/p/reaver-wps/wiki/README
http://code.google.com/p/reaver-wps/wiki/FAQ
http://code.google.com/p/reaver-wps/wiki/SupportedWirelessDrivers
1. Reaver will only work if your card is in monitor mode. If you do not
know what monitor mode is then you should learn more about 802.11 hacking
in linux before using Reaver.
2. Using Reaver against access points you do not own or have permission to
attack is illegal. If you cannot answer basic questions (i.e. model
number, distance away, etc) about the device you are attacking then do not
post your issue here. We will not help you break the law.
3. Please look through issues that have already been posted and make sure
your question has not already been asked here: http://code.google.com/p
/reaver-wps/issues/list
4. Often times we need packet captures of mon0 while Reaver is running to
troubleshoot the issue (tcpdump -i mon0 -s0 -w broken_reaver.pcap). Issue
reports with pcap files attached will receive more serious consideration.
Answer the following questions for every issue submitted:
0. What version of Reaver are you using? (Only defects against the latest
version will be considered.)
1. What operating system are you using (Linux is the only supported OS)?
bt5
2. Is your wireless card in monitor mode (yes/no)?
yes
3. What is the signal strength of the Access Point you are trying to crack?
how do I found this? with aireplay -9 mon0 command? if its this command the
signal is -66 with a tp link usb wireless model tl-wn822n
09:26:42 Ping (min/avg/max): 1.527ms/18.093ms/62.419ms Power: -66.57
4. What is the manufacturer and model # of the device you are trying to
crack?
vodafone in italy
5. What is the entire command line string you are supplying to reaver?
./reaver -i mon0 -b 00:24:89:XX:XX:XX -vv
6. Please describe what you think the issue is.
I have nu clue
7. Paste the output from Reaver below.
[+] Trying pin 12345670
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
```
Original issue reported on code.google.com by `gabethui...@yahoo.com` on 27 Jan 2012 at 1:44
|
1.0
|
it is not working at all at me - ```
A few things to consider before submitting an issue:
0. We write documentation for a reason, if you have not read it and are
having problems with Reaver these pages are required reading before
submitting an issue:
http://code.google.com/p/reaver-wps/wiki/HintsAndTips
http://code.google.com/p/reaver-wps/wiki/README
http://code.google.com/p/reaver-wps/wiki/FAQ
http://code.google.com/p/reaver-wps/wiki/SupportedWirelessDrivers
1. Reaver will only work if your card is in monitor mode. If you do not
know what monitor mode is then you should learn more about 802.11 hacking
in linux before using Reaver.
2. Using Reaver against access points you do not own or have permission to
attack is illegal. If you cannot answer basic questions (i.e. model
number, distance away, etc) about the device you are attacking then do not
post your issue here. We will not help you break the law.
3. Please look through issues that have already been posted and make sure
your question has not already been asked here: http://code.google.com/p
/reaver-wps/issues/list
4. Often times we need packet captures of mon0 while Reaver is running to
troubleshoot the issue (tcpdump -i mon0 -s0 -w broken_reaver.pcap). Issue
reports with pcap files attached will receive more serious consideration.
Answer the following questions for every issue submitted:
0. What version of Reaver are you using? (Only defects against the latest
version will be considered.)
1. What operating system are you using (Linux is the only supported OS)?
bt5
2. Is your wireless card in monitor mode (yes/no)?
yes
3. What is the signal strength of the Access Point you are trying to crack?
how do I found this? with aireplay -9 mon0 command? if its this command the
signal is -66 with a tp link usb wireless model tl-wn822n
09:26:42 Ping (min/avg/max): 1.527ms/18.093ms/62.419ms Power: -66.57
4. What is the manufacturer and model # of the device you are trying to
crack?
vodafone in italy
5. What is the entire command line string you are supplying to reaver?
./reaver -i mon0 -b 00:24:89:XX:XX:XX -vv
6. Please describe what you think the issue is.
I have nu clue
7. Paste the output from Reaver below.
[+] Trying pin 12345670
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
[!] WARNING: Receive timeout occurred
[+] Sending EAPOL START request
```
Original issue reported on code.google.com by `gabethui...@yahoo.com` on 27 Jan 2012 at 1:44
|
defect
|
it is not working at all at me a few things to consider before submitting an issue we write documentation for a reason if you have not read it and are having problems with reaver these pages are required reading before submitting an issue reaver will only work if your card is in monitor mode if you do not know what monitor mode is then you should learn more about hacking in linux before using reaver using reaver against access points you do not own or have permission to attack is illegal if you cannot answer basic questions i e model number distance away etc about the device you are attacking then do not post your issue here we will not help you break the law please look through issues that have already been posted and make sure your question has not already been asked here reaver wps issues list often times we need packet captures of while reaver is running to troubleshoot the issue tcpdump i w broken reaver pcap issue reports with pcap files attached will receive more serious consideration answer the following questions for every issue submitted what version of reaver are you using only defects against the latest version will be considered what operating system are you using linux is the only supported os is your wireless card in monitor mode yes no yes what is the signal strength of the access point you are trying to crack how do i found this with aireplay command if its this command the signal is with a tp link usb wireless model tl ping min avg max power what is the manufacturer and model of the device you are trying to crack vodafone in italy what is the entire command line string you are supplying to reaver reaver i b xx xx xx vv please describe what you think the issue is i have nu clue paste the output from reaver below trying pin sending eapol start request warning receive timeout occurred sending eapol start request warning receive timeout occurred sending eapol start request warning receive timeout occurred sending eapol start request warning receive timeout occurred sending eapol start request warning receive timeout occurred sending eapol start request original issue reported on code google com by gabethui yahoo com on jan at
| 1
|
630,169
| 20,099,467,952
|
IssuesEvent
|
2022-02-07 00:57:12
|
apcountryman/picolibrary-microchip-megaavr0
|
https://api.github.com/repos/apcountryman/picolibrary-microchip-megaavr0
|
closed
|
Add GPIO push-pull I/O pin toggle interactive test
|
priority-normal status-awaiting_review type-feature
|
Add GPIO push-pull I/O pin (`::picolibrary::Microchip::megaAVR0::GPIO::Push_Pull_IO_Pin`) toggle interactive test (`test-interactive-picolibrary-microchip-megaavr0-gpio-push_pull_io_pin-port-toggle` and `test-interactive-picolibrary-microchip-megaavr0-gpio-push_pull_io_pin-vport-toggle`).
- [x] Add the `test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/` directory to the build
- [x] Add `test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/CMakeLists.txt`
- [x] The test should be defined in `test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/main.cc`
- [x] The test should perform the following sequence of operations:
- [x] Configure the clock
- [x] Initialize the interactive testing log (`::picolibrary::Testing::Interactive::Microchip::megaAVR0::Log::initialize()`)
- [x] Construct an push-pull I/O pin (`::picolibrary::Microchip::megaAVR0::GPIO::Push_Pull_IO_Pin`)
- [x] Construct a 500 millisecond delayer (lambda wrapping a call to `avr-libcpp::delay_ms()`)
- [x] Run the picolibrary GPIO output pin toggle interactive test helper (`::picolibrary::Testing::Interactive::GPIO::toggle()`)
- [x] The test should accept the following build parameters:
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_PORT`: pin PORT
- This build parameter should be used to derive `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_VPORT`
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_MASK`: pin mask
- [x] Add ATmega4809 Arduino Nano Every test build configuration (`configuration/testing-interactive-atmega4809-arduino-nano-every/test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/CMakeLists.txt`
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_PORT`: `PORTE`
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_MASK`: `1 << 2`
|
1.0
|
Add GPIO push-pull I/O pin toggle interactive test - Add GPIO push-pull I/O pin (`::picolibrary::Microchip::megaAVR0::GPIO::Push_Pull_IO_Pin`) toggle interactive test (`test-interactive-picolibrary-microchip-megaavr0-gpio-push_pull_io_pin-port-toggle` and `test-interactive-picolibrary-microchip-megaavr0-gpio-push_pull_io_pin-vport-toggle`).
- [x] Add the `test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/` directory to the build
- [x] Add `test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/CMakeLists.txt`
- [x] The test should be defined in `test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/main.cc`
- [x] The test should perform the following sequence of operations:
- [x] Configure the clock
- [x] Initialize the interactive testing log (`::picolibrary::Testing::Interactive::Microchip::megaAVR0::Log::initialize()`)
- [x] Construct an push-pull I/O pin (`::picolibrary::Microchip::megaAVR0::GPIO::Push_Pull_IO_Pin`)
- [x] Construct a 500 millisecond delayer (lambda wrapping a call to `avr-libcpp::delay_ms()`)
- [x] Run the picolibrary GPIO output pin toggle interactive test helper (`::picolibrary::Testing::Interactive::GPIO::toggle()`)
- [x] The test should accept the following build parameters:
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_PORT`: pin PORT
- This build parameter should be used to derive `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_VPORT`
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_MASK`: pin mask
- [x] Add ATmega4809 Arduino Nano Every test build configuration (`configuration/testing-interactive-atmega4809-arduino-nano-every/test/interactive/picolibrary/microchip/megaavr0/gpio/push_pull_io_pin/toggle/CMakeLists.txt`
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_PORT`: `PORTE`
- [x] `PICOLIBRARY_MICROCHIP_MEGAAVR_GPIO_PUSH_PULL_IO_PIN_TOGGLE_INTERACTIVE_TEST_PIN_MASK`: `1 << 2`
|
non_defect
|
add gpio push pull i o pin toggle interactive test add gpio push pull i o pin picolibrary microchip gpio push pull io pin toggle interactive test test interactive picolibrary microchip gpio push pull io pin port toggle and test interactive picolibrary microchip gpio push pull io pin vport toggle add the test interactive picolibrary microchip gpio push pull io pin toggle directory to the build add test interactive picolibrary microchip gpio push pull io pin toggle cmakelists txt the test should be defined in test interactive picolibrary microchip gpio push pull io pin toggle main cc the test should perform the following sequence of operations configure the clock initialize the interactive testing log picolibrary testing interactive microchip log initialize construct an push pull i o pin picolibrary microchip gpio push pull io pin construct a millisecond delayer lambda wrapping a call to avr libcpp delay ms run the picolibrary gpio output pin toggle interactive test helper picolibrary testing interactive gpio toggle the test should accept the following build parameters picolibrary microchip megaavr gpio push pull io pin toggle interactive test pin port pin port this build parameter should be used to derive picolibrary microchip megaavr gpio push pull io pin toggle interactive test pin vport picolibrary microchip megaavr gpio push pull io pin toggle interactive test pin mask pin mask add arduino nano every test build configuration configuration testing interactive arduino nano every test interactive picolibrary microchip gpio push pull io pin toggle cmakelists txt picolibrary microchip megaavr gpio push pull io pin toggle interactive test pin port porte picolibrary microchip megaavr gpio push pull io pin toggle interactive test pin mask
| 0
|
60,241
| 17,023,378,140
|
IssuesEvent
|
2021-07-03 01:42:54
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
outdated URI in INSTALL file
|
Component: merkaartor Priority: minor Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 8.05pm, Tuesday, 24th March 2009]**
the INSTALL file in the svn points to a non-existing page in the wiki, http://wiki.openstreetmap.org/index.php/Merkaartor_doc_0.12.
one gets redirected to an existing page, "Merkaartor/Documentation", which does not provide the information the INSTALL file promises.
perhaps the INSTALL file should point to http://wiki.openstreetmap.org/wiki/Merkaartor/Compiling instead?
|
1.0
|
outdated URI in INSTALL file - **[Submitted to the original trac issue database at 8.05pm, Tuesday, 24th March 2009]**
the INSTALL file in the svn points to a non-existing page in the wiki, http://wiki.openstreetmap.org/index.php/Merkaartor_doc_0.12.
one gets redirected to an existing page, "Merkaartor/Documentation", which does not provide the information the INSTALL file promises.
perhaps the INSTALL file should point to http://wiki.openstreetmap.org/wiki/Merkaartor/Compiling instead?
|
defect
|
outdated uri in install file the install file in the svn points to a non existing page in the wiki one gets redirected to an existing page merkaartor documentation which does not provide the information the install file promises perhaps the install file should point to instead
| 1
|
38,266
| 2,845,468,307
|
IssuesEvent
|
2015-05-29 03:21:39
|
HellscreamWoW/Tracker
|
https://api.github.com/repos/HellscreamWoW/Tracker
|
closed
|
Azuremyst isle buggy mobs
|
Priority-High Type-Creature
|
In Azuremyst isle while exploring as level 4 night elf, I encountered mobs that cannot be seen, they attack me while walking on the road to Azure Watch from the docks. I encountered mostly Nightstalker mobs, they are like underground I think and made me think they are invisible, maybe there are other mobs in this zone that are underground or maybe they are invisible.
http://www.wowhead.com/zone=3524/azuremyst-isle
|
1.0
|
Azuremyst isle buggy mobs - In Azuremyst isle while exploring as level 4 night elf, I encountered mobs that cannot be seen, they attack me while walking on the road to Azure Watch from the docks. I encountered mostly Nightstalker mobs, they are like underground I think and made me think they are invisible, maybe there are other mobs in this zone that are underground or maybe they are invisible.
http://www.wowhead.com/zone=3524/azuremyst-isle
|
non_defect
|
azuremyst isle buggy mobs in azuremyst isle while exploring as level night elf i encountered mobs that cannot be seen they attack me while walking on the road to azure watch from the docks i encountered mostly nightstalker mobs they are like underground i think and made me think they are invisible maybe there are other mobs in this zone that are underground or maybe they are invisible
| 0
|
117,900
| 11,958,570,116
|
IssuesEvent
|
2020-04-04 18:34:31
|
ericdeansanchez/imgix-rs
|
https://api.github.com/repos/ericdeansanchez/imgix-rs
|
opened
|
Improve documentation of `lib` function
|
documentation good first issue help wanted
|
The following,
```text
/// Set the `lib` or library.
```
Would read better if it said,
```text
/// Set the library version.
```
https://github.com/ericdeansanchez/imgix-rs/blob/98f28ee2aa809e0cedb95128785f0e1282a8c324/src/imgix/lib.rs#L170
|
1.0
|
Improve documentation of `lib` function - The following,
```text
/// Set the `lib` or library.
```
Would read better if it said,
```text
/// Set the library version.
```
https://github.com/ericdeansanchez/imgix-rs/blob/98f28ee2aa809e0cedb95128785f0e1282a8c324/src/imgix/lib.rs#L170
|
non_defect
|
improve documentation of lib function the following text set the lib or library would read better if it said text set the library version
| 0
|
12,213
| 2,685,472,320
|
IssuesEvent
|
2015-03-30 01:21:37
|
IssueMigrationTest/Test5
|
https://api.github.com/repos/IssueMigrationTest/Test5
|
closed
|
sys.maxsize support
|
auto-migrated Priority-Medium Type-Defect
|
**Issue by jason.mi...@gmail.com**
_15 Jun 2011 at 2:55 GMT_
_Originally opened on Google Code_
----
```
sys lib has sys.maxint but no sys.maxsize
The future trend of python is to obsolete sys.maxint
```
|
1.0
|
sys.maxsize support - **Issue by jason.mi...@gmail.com**
_15 Jun 2011 at 2:55 GMT_
_Originally opened on Google Code_
----
```
sys lib has sys.maxint but no sys.maxsize
The future trend of python is to obsolete sys.maxint
```
|
defect
|
sys maxsize support issue by jason mi gmail com jun at gmt originally opened on google code sys lib has sys maxint but no sys maxsize the future trend of python is to obsolete sys maxint
| 1
|
30,566
| 6,175,417,740
|
IssuesEvent
|
2017-07-01 02:06:53
|
cakephp/cakephp
|
https://api.github.com/repos/cakephp/cakephp
|
closed
|
Different dirty behaviour between newEntity($data) and patchEntity($entity, $data)
|
Defect On hold ORM
|
This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.4.5
* Platform and Target: PHP 7.1.4, Apache 2.4.25, MySQL 5.7.16
### What you did
I save a model `NocForm` which has one `Document` association
```php
// In my controller
private function saveForm($id)
{
$this->loadModel('NocForms');
$data = $this->request->data;
if (empty($id)) {
$form = $this->NocForms->newEntity($data);
} else {
$form = $this->NocForms->getForm($id);
$form = $this->NocForms->patchEntity($form, $data);
}
if ($form->errors() || !$this->NocForms->save($form)) {
$this->addDangerMessage('There was a problem saving your form');
return;
}
}
```
Inside `$data` I have a bunch of `NocForm` fields, and also this `tmp_file` field which comes from a file input. Irrespective of whether I pass a file to my file input or not, `tmp_file` will be set. The contents will change accordingly when a file is included.
> *Note*: If relevant, the file input `name` is `document[tmp_file]`
```json
{
"document": {
"tmp_file": {
"tmp_name": "",
"error": 4,
"name": "",
"type": "",
"size": 0
}
}
}
```
Inside `DocumentsTable` I have the following events defined. `beforeMarshal` checks for the `tmp_file` property and if a file is actually contained in it, and if found it extracts the information relevant to me. If no file is found to be attached I simply unset the field.
```php
public function beforeMarshal(Event $event, ArrayObject $data, ArrayObject $options)
{
if (!empty($data['tmp_file'])) {
$file = $data['tmp_file'];
if (!empty($file['tmp_name'])) {
$data['extension'] = pathinfo($file['name'], PATHINFO_EXTENSION);
$data['content_type'] = mime_content_type($file['tmp_name']);
$data['file_size'] = filesize($file['tmp_name']);
$data['date_uploaded'] = new \Cake\I18n\Time();
$data['file_path'] = md5(uniqid()).'.'.$data['extension'];
} else {
unset($data['tmp_file']);
}
}
}
```
`beforeSave` will check if we are saving a new file, and uploads it to our bucket if so.
```php
public function beforeSave(Event $event, EntityInterface $entity, ArrayObject $options)
{
if (!empty($entity->tmp_file)) {
$file = $entity->tmp_file;
$bucket = new BucketWrapper();
$bucket->save($entity->file_path, $file['tmp_name']);
if (!$entity->dirty('name')) {
$entity->name = $file['name'];
}
}
}
```
### What happened
When creating a *new* `NocForm` without uploading a file, `save()` returns false with no errors. What seems to be the issue is that when creating a new `NocForm`, `document` is marked as dirty even though inside `DocumentsTable` the `beforeMarshal` event empties its `ArrayObject $data`.
When *updating an existing* `NocForm` which does not have a `Document`, it's `document` field is *not* marked as `dirty`.
In fact, if I refactor my code from this
```php
if (empty($id)) {
$form = $this->NocForms->newEntity($data);
} else {
$form = $this->NocForms->getForm($id);
$form = $this->NocForms->patchEntity($form, $data);
}
```
to this
```php
if (empty($id)) {
$form = $this->NocForms->newEntity();
} else {
$form = $this->NocForms->getForm($id);
}
$form = $this->NocForms->patchEntity($form, $data);
```
It works fine in all cases. Naturally I don't want to have a potential issue based around remembering to never use `newEntity($data)`
### What you expected to happen
I expect `newEntity($data)` and `patchEntity($entity, $data)` to work identically when dealing with a new entity.
|
1.0
|
Different dirty behaviour between newEntity($data) and patchEntity($entity, $data) - This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.4.5
* Platform and Target: PHP 7.1.4, Apache 2.4.25, MySQL 5.7.16
### What you did
I save a model `NocForm` which has one `Document` association
```php
// In my controller
private function saveForm($id)
{
$this->loadModel('NocForms');
$data = $this->request->data;
if (empty($id)) {
$form = $this->NocForms->newEntity($data);
} else {
$form = $this->NocForms->getForm($id);
$form = $this->NocForms->patchEntity($form, $data);
}
if ($form->errors() || !$this->NocForms->save($form)) {
$this->addDangerMessage('There was a problem saving your form');
return;
}
}
```
Inside `$data` I have a bunch of `NocForm` fields, and also this `tmp_file` field which comes from a file input. Irrespective of whether I pass a file to my file input or not, `tmp_file` will be set. The contents will change accordingly when a file is included.
> *Note*: If relevant, the file input `name` is `document[tmp_file]`
```json
{
"document": {
"tmp_file": {
"tmp_name": "",
"error": 4,
"name": "",
"type": "",
"size": 0
}
}
}
```
Inside `DocumentsTable` I have the following events defined. `beforeMarshal` checks for the `tmp_file` property and if a file is actually contained in it, and if found it extracts the information relevant to me. If no file is found to be attached I simply unset the field.
```php
public function beforeMarshal(Event $event, ArrayObject $data, ArrayObject $options)
{
if (!empty($data['tmp_file'])) {
$file = $data['tmp_file'];
if (!empty($file['tmp_name'])) {
$data['extension'] = pathinfo($file['name'], PATHINFO_EXTENSION);
$data['content_type'] = mime_content_type($file['tmp_name']);
$data['file_size'] = filesize($file['tmp_name']);
$data['date_uploaded'] = new \Cake\I18n\Time();
$data['file_path'] = md5(uniqid()).'.'.$data['extension'];
} else {
unset($data['tmp_file']);
}
}
}
```
`beforeSave` will check if we are saving a new file, and uploads it to our bucket if so.
```php
public function beforeSave(Event $event, EntityInterface $entity, ArrayObject $options)
{
if (!empty($entity->tmp_file)) {
$file = $entity->tmp_file;
$bucket = new BucketWrapper();
$bucket->save($entity->file_path, $file['tmp_name']);
if (!$entity->dirty('name')) {
$entity->name = $file['name'];
}
}
}
```
### What happened
When creating a *new* `NocForm` without uploading a file, `save()` returns false with no errors. What seems to be the issue is that when creating a new `NocForm`, `document` is marked as dirty even though inside `DocumentsTable` the `beforeMarshal` event empties its `ArrayObject $data`.
When *updating an existing* `NocForm` which does not have a `Document`, it's `document` field is *not* marked as `dirty`.
In fact, if I refactor my code from this
```php
if (empty($id)) {
$form = $this->NocForms->newEntity($data);
} else {
$form = $this->NocForms->getForm($id);
$form = $this->NocForms->patchEntity($form, $data);
}
```
to this
```php
if (empty($id)) {
$form = $this->NocForms->newEntity();
} else {
$form = $this->NocForms->getForm($id);
}
$form = $this->NocForms->patchEntity($form, $data);
```
It works fine in all cases. Naturally I don't want to have a potential issue based around remembering to never use `newEntity($data)`
### What you expected to happen
I expect `newEntity($data)` and `patchEntity($entity, $data)` to work identically when dealing with a new entity.
|
defect
|
different dirty behaviour between newentity data and patchentity entity data this is a multiple allowed bug enhancement feature discussion rfc cakephp version platform and target php apache mysql what you did i save a model nocform which has one document association php in my controller private function saveform id this loadmodel nocforms data this request data if empty id form this nocforms newentity data else form this nocforms getform id form this nocforms patchentity form data if form errors this nocforms save form this adddangermessage there was a problem saving your form return inside data i have a bunch of nocform fields and also this tmp file field which comes from a file input irrespective of whether i pass a file to my file input or not tmp file will be set the contents will change accordingly when a file is included note if relevant the file input name is document json document tmp file tmp name error name type size inside documentstable i have the following events defined beforemarshal checks for the tmp file property and if a file is actually contained in it and if found it extracts the information relevant to me if no file is found to be attached i simply unset the field php public function beforemarshal event event arrayobject data arrayobject options if empty data file data if empty file data pathinfo file pathinfo extension data mime content type file data filesize file data new cake time data uniqid data else unset data beforesave will check if we are saving a new file and uploads it to our bucket if so php public function beforesave event event entityinterface entity arrayobject options if empty entity tmp file file entity tmp file bucket new bucketwrapper bucket save entity file path file if entity dirty name entity name file what happened when creating a new nocform without uploading a file save returns false with no errors what seems to be the issue is that when creating a new nocform document is marked as dirty even though inside documentstable the beforemarshal event empties its arrayobject data when updating an existing nocform which does not have a document it s document field is not marked as dirty in fact if i refactor my code from this php if empty id form this nocforms newentity data else form this nocforms getform id form this nocforms patchentity form data to this php if empty id form this nocforms newentity else form this nocforms getform id form this nocforms patchentity form data it works fine in all cases naturally i don t want to have a potential issue based around remembering to never use newentity data what you expected to happen i expect newentity data and patchentity entity data to work identically when dealing with a new entity
| 1
|
17,936
| 3,013,795,399
|
IssuesEvent
|
2015-07-29 11:17:14
|
yawlfoundation/yawl
|
https://api.github.com/repos/yawlfoundation/yawl
|
closed
|
role id and role name are mixed up in saving spec and parsing distribution set
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. connect an external orgData source following tutorial
http://yaug.org/content/creating-custom-organisation-data-source
2. load users and roles, assign roles to users select different values for
rolename and roleid
3. create workflow, assign task to a role
What is the expected output? What do you see instead?
- task should be offered to owners of that role
- but resource service complains about empty distribution set for assigned role
- change entry in spec to role name value manually -> works
What version of the product are you using? On what operating system?
2.3.5 on tomcat (4study). win7 and debian
Please provide any additional information below.
please see thread in yawl forum with additional info
http://www.yawlfoundation.org/forum/viewtopic.php?f=6&t=934&sid=9ba8fdc11c65e01a
3bc73bb37f270689
```
Original issue reported on code.google.com by `anwim...@gmail.com` on 14 Feb 2014 at 9:49
|
1.0
|
role id and role name are mixed up in saving spec and parsing distribution set - ```
What steps will reproduce the problem?
1. connect an external orgData source following tutorial
http://yaug.org/content/creating-custom-organisation-data-source
2. load users and roles, assign roles to users select different values for
rolename and roleid
3. create workflow, assign task to a role
What is the expected output? What do you see instead?
- task should be offered to owners of that role
- but resource service complains about empty distribution set for assigned role
- change entry in spec to role name value manually -> works
What version of the product are you using? On what operating system?
2.3.5 on tomcat (4study). win7 and debian
Please provide any additional information below.
please see thread in yawl forum with additional info
http://www.yawlfoundation.org/forum/viewtopic.php?f=6&t=934&sid=9ba8fdc11c65e01a
3bc73bb37f270689
```
Original issue reported on code.google.com by `anwim...@gmail.com` on 14 Feb 2014 at 9:49
|
defect
|
role id and role name are mixed up in saving spec and parsing distribution set what steps will reproduce the problem connect an external orgdata source following tutorial load users and roles assign roles to users select different values for rolename and roleid create workflow assign task to a role what is the expected output what do you see instead task should be offered to owners of that role but resource service complains about empty distribution set for assigned role change entry in spec to role name value manually works what version of the product are you using on what operating system on tomcat and debian please provide any additional information below please see thread in yawl forum with additional info original issue reported on code google com by anwim gmail com on feb at
| 1
|
665,669
| 22,324,916,266
|
IssuesEvent
|
2022-06-14 09:45:27
|
edgedb/edgedb-cli
|
https://api.github.com/repos/edgedb/edgedb-cli
|
closed
|
`migration create --non-interactive` should use the fast path for the initial migration
|
enhancement high-priority developer experience
|
Currently, the initial migration (from empty schema) is not treated differently from subsequent migrations and uses the statement-by-statement `describe` approach, which could be fairly slow if the schema is large. Initial migrations are unabiguous and safe, and so a `START MIGRATION {...}; POPULATE MIGRATION; DESCRIBE CURRENT MIGRATION AS JSON` can be used to generate the migration script.
|
1.0
|
`migration create --non-interactive` should use the fast path for the initial migration - Currently, the initial migration (from empty schema) is not treated differently from subsequent migrations and uses the statement-by-statement `describe` approach, which could be fairly slow if the schema is large. Initial migrations are unabiguous and safe, and so a `START MIGRATION {...}; POPULATE MIGRATION; DESCRIBE CURRENT MIGRATION AS JSON` can be used to generate the migration script.
|
non_defect
|
migration create non interactive should use the fast path for the initial migration currently the initial migration from empty schema is not treated differently from subsequent migrations and uses the statement by statement describe approach which could be fairly slow if the schema is large initial migrations are unabiguous and safe and so a start migration populate migration describe current migration as json can be used to generate the migration script
| 0
|
787,520
| 27,720,295,574
|
IssuesEvent
|
2023-03-14 20:03:05
|
TEIC/TEI
|
https://api.github.com/repos/TEIC/TEI
|
closed
|
GitHub jobs failing due to permissions error
|
Priority: Release Blocker
|
In GitHub, the test job fail when running the Tests from the Stylesheets repo due to a permissions error:
https://github.com/TEIC/TEI/actions/runs/4224874009/jobs/7336394765#step:6:72
From what I can tell, this is a fairly widespread issue for containers running in GitHub runners due to a recent debian security upgrade (see threads here: https://github.com/actions/runner-images/issues/6775 and https://github.com/actions/checkout/issues/1169)
Following the advice from https://github.com/actions/checkout/issues/1169, I _think_ marking the directory as safe in Git after the [checkout step](https://github.com/TEIC/TEI/blob/b49da7f1651746181737b125a591621f7438cdc7/.github/workflows/test.yml#L22-L27) would work to solve the issue until `actions/checkout` implements a fix:
```yaml
- name: Checkout Stylesheets repo
uses: actions/checkout@v3
with:
repository: TEIC/Stylesheets
ref: dev
path: Stylesheets
- name: Fix permissions
run: git config --system --add safe.directory /github/workspace
```
|
1.0
|
GitHub jobs failing due to permissions error - In GitHub, the test job fail when running the Tests from the Stylesheets repo due to a permissions error:
https://github.com/TEIC/TEI/actions/runs/4224874009/jobs/7336394765#step:6:72
From what I can tell, this is a fairly widespread issue for containers running in GitHub runners due to a recent debian security upgrade (see threads here: https://github.com/actions/runner-images/issues/6775 and https://github.com/actions/checkout/issues/1169)
Following the advice from https://github.com/actions/checkout/issues/1169, I _think_ marking the directory as safe in Git after the [checkout step](https://github.com/TEIC/TEI/blob/b49da7f1651746181737b125a591621f7438cdc7/.github/workflows/test.yml#L22-L27) would work to solve the issue until `actions/checkout` implements a fix:
```yaml
- name: Checkout Stylesheets repo
uses: actions/checkout@v3
with:
repository: TEIC/Stylesheets
ref: dev
path: Stylesheets
- name: Fix permissions
run: git config --system --add safe.directory /github/workspace
```
|
non_defect
|
github jobs failing due to permissions error in github the test job fail when running the tests from the stylesheets repo due to a permissions error from what i can tell this is a fairly widespread issue for containers running in github runners due to a recent debian security upgrade see threads here and following the advice from i think marking the directory as safe in git after the would work to solve the issue until actions checkout implements a fix yaml name checkout stylesheets repo uses actions checkout with repository teic stylesheets ref dev path stylesheets name fix permissions run git config system add safe directory github workspace
| 0
|
23,079
| 3,756,243,715
|
IssuesEvent
|
2016-03-13 06:50:16
|
TASVideos/BizHawk
|
https://api.github.com/repos/TASVideos/BizHawk
|
closed
|
Bizhawk throws an exeption when movie folder contains alot of movies
|
auto-migrated Core-EmuHawk OpSys-Any Priority-High Type-Defect
|
```
What steps will reproduce the problem?
1. Have a selection of movies in the movies folder
2. 10 is enough, but the more you have the easier to trigger the bug
3.
What is the expected output? What do you see instead?
When loading a movie, the expected result is to see the relevant movie file for
me to play and/or continue.
This along standing bug that's annoyed me for ages, but it time to get it known
before a new bizhawk release is put out.
Sometimes, more often than not. If I as I build up a list of movie files,
bizhawk will through up an exception after it has tried to scan through all the
movie files.
Normally the exception window can be closed and just hit the rescan button and
the relevant movie will eventually show. Sometimes it can take 2 or 3 re
attempts but will get their in the end.
What version of the product are you using? On what operating system?
Any recent bizhawk version, Windows 8.1 64bit
Please provide any additional information below.
Its almost as if bizhawk is unzipping every movie file to search for the
correct hash but it takes too long and bizhawk gets fed up of waiting and
causes an exception.
```
Original issue reported on code.google.com by `MThompso...@gmail.com` on 16 Jun 2015 at 8:09
Attachments:
* [bizcrash.png](https://storage.googleapis.com/google-code-attachments/bizhawk/issue-435/comment-0/bizcrash.png)
* [bizcrash.txt](https://storage.googleapis.com/google-code-attachments/bizhawk/issue-435/comment-0/bizcrash.txt)
|
1.0
|
Bizhawk throws an exeption when movie folder contains alot of movies - ```
What steps will reproduce the problem?
1. Have a selection of movies in the movies folder
2. 10 is enough, but the more you have the easier to trigger the bug
3.
What is the expected output? What do you see instead?
When loading a movie, the expected result is to see the relevant movie file for
me to play and/or continue.
This along standing bug that's annoyed me for ages, but it time to get it known
before a new bizhawk release is put out.
Sometimes, more often than not. If I as I build up a list of movie files,
bizhawk will through up an exception after it has tried to scan through all the
movie files.
Normally the exception window can be closed and just hit the rescan button and
the relevant movie will eventually show. Sometimes it can take 2 or 3 re
attempts but will get their in the end.
What version of the product are you using? On what operating system?
Any recent bizhawk version, Windows 8.1 64bit
Please provide any additional information below.
Its almost as if bizhawk is unzipping every movie file to search for the
correct hash but it takes too long and bizhawk gets fed up of waiting and
causes an exception.
```
Original issue reported on code.google.com by `MThompso...@gmail.com` on 16 Jun 2015 at 8:09
Attachments:
* [bizcrash.png](https://storage.googleapis.com/google-code-attachments/bizhawk/issue-435/comment-0/bizcrash.png)
* [bizcrash.txt](https://storage.googleapis.com/google-code-attachments/bizhawk/issue-435/comment-0/bizcrash.txt)
|
defect
|
bizhawk throws an exeption when movie folder contains alot of movies what steps will reproduce the problem have a selection of movies in the movies folder is enough but the more you have the easier to trigger the bug what is the expected output what do you see instead when loading a movie the expected result is to see the relevant movie file for me to play and or continue this along standing bug that s annoyed me for ages but it time to get it known before a new bizhawk release is put out sometimes more often than not if i as i build up a list of movie files bizhawk will through up an exception after it has tried to scan through all the movie files normally the exception window can be closed and just hit the rescan button and the relevant movie will eventually show sometimes it can take or re attempts but will get their in the end what version of the product are you using on what operating system any recent bizhawk version windows please provide any additional information below its almost as if bizhawk is unzipping every movie file to search for the correct hash but it takes too long and bizhawk gets fed up of waiting and causes an exception original issue reported on code google com by mthompso gmail com on jun at attachments
| 1
|
89,467
| 25,806,164,708
|
IssuesEvent
|
2022-12-11 12:32:42
|
NFFT/nfft
|
https://api.github.com/repos/NFFT/nfft
|
closed
|
[configure] Change of shebang
|
question build routine
|
As already discussed in #122, the shebang of a shell script should be chosen as general as possible in order to avoid unintended behaviour of the build routine on machines where the actual installation path of Bash differs.
Since `./configure` is a result of the execution of `./bootstrap.sh` which actually requires Bash itself, we should think about adjusting the shebang of `./configure` to Bash as language since we already need it just to create this file.
Furthermore, the current shebang, `#! /bin/sh`, contains a rather obsolete space between the exclamation mark and the path which may cause problems. For instance, VSCodium is unable to consider this file syntactically correct and, hence, lists 919 errors, 81 warnings (plus 130 further errors and warnings which are suppressed) originating from this file. On the other hand, `./bootstrap.sh` does not render any warning.
Despite the possibility that this might be just a temporary bug of the IDE or one of its plugins which can be fixed in a future version, we should discuss if we really need this generality of `./configure`. For instance, it contains several setting lines just to ensure compatibility with Bash. Since it is a temporary file created during the execution of `./bootstrap.sh`, which only works with Bash, this generality (`sh` instead of `bash` as environment variable) is in my opinion not required.
What do you think about this topic?
|
1.0
|
[configure] Change of shebang - As already discussed in #122, the shebang of a shell script should be chosen as general as possible in order to avoid unintended behaviour of the build routine on machines where the actual installation path of Bash differs.
Since `./configure` is a result of the execution of `./bootstrap.sh` which actually requires Bash itself, we should think about adjusting the shebang of `./configure` to Bash as language since we already need it just to create this file.
Furthermore, the current shebang, `#! /bin/sh`, contains a rather obsolete space between the exclamation mark and the path which may cause problems. For instance, VSCodium is unable to consider this file syntactically correct and, hence, lists 919 errors, 81 warnings (plus 130 further errors and warnings which are suppressed) originating from this file. On the other hand, `./bootstrap.sh` does not render any warning.
Despite the possibility that this might be just a temporary bug of the IDE or one of its plugins which can be fixed in a future version, we should discuss if we really need this generality of `./configure`. For instance, it contains several setting lines just to ensure compatibility with Bash. Since it is a temporary file created during the execution of `./bootstrap.sh`, which only works with Bash, this generality (`sh` instead of `bash` as environment variable) is in my opinion not required.
What do you think about this topic?
|
non_defect
|
change of shebang as already discussed in the shebang of a shell script should be chosen as general as possible in order to avoid unintended behaviour of the build routine on machines where the actual installation path of bash differs since configure is a result of the execution of bootstrap sh which actually requires bash itself we should think about adjusting the shebang of configure to bash as language since we already need it just to create this file furthermore the current shebang bin sh contains a rather obsolete space between the exclamation mark and the path which may cause problems for instance vscodium is unable to consider this file syntactically correct and hence lists errors warnings plus further errors and warnings which are suppressed originating from this file on the other hand bootstrap sh does not render any warning despite the possibility that this might be just a temporary bug of the ide or one of its plugins which can be fixed in a future version we should discuss if we really need this generality of configure for instance it contains several setting lines just to ensure compatibility with bash since it is a temporary file created during the execution of bootstrap sh which only works with bash this generality sh instead of bash as environment variable is in my opinion not required what do you think about this topic
| 0
|
13,543
| 9,986,026,315
|
IssuesEvent
|
2019-07-10 18:02:52
|
terraform-providers/terraform-provider-azurerm
|
https://api.github.com/repos/terraform-providers/terraform-provider-azurerm
|
closed
|
Provision to pass taint value for the agents in AKS cluster
|
enhancement service/kubernetes-cluster
|
Currently, we do not have an option to pass the taint value to the agents created in AKS. Please refer for more details https://github.com/terraform-providers/terraform-provider-azurerm/issues/3753.
|
1.0
|
Provision to pass taint value for the agents in AKS cluster - Currently, we do not have an option to pass the taint value to the agents created in AKS. Please refer for more details https://github.com/terraform-providers/terraform-provider-azurerm/issues/3753.
|
non_defect
|
provision to pass taint value for the agents in aks cluster currently we do not have an option to pass the taint value to the agents created in aks please refer for more details
| 0
|
32,289
| 6,758,663,346
|
IssuesEvent
|
2017-10-24 14:49:21
|
primefaces/primeng
|
https://api.github.com/repos/primefaces/primeng
|
closed
|
programatic element (pre-)selection on datatable fails when using dataKey
|
defect pending-review
|
I'm submitting
```
[ x ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
Please fork the plunkr below and create a case demonstrating your bug report. Issues without a plunkr have much less possibility to be reviewed.
http://plnkr.co/edit/UZiAHEmvc3IldUTHTNyH?p=preview
**Current behavior**
Setting a selected item on a datatable that uses a dataKey does not work in single selction mode. The selection object and the selection keys are not correctly initialized, when selection is a single object instead of an array.
**Expected behavior**
Setting the selected item as object in single selection mode should use the datakey property to check equality.
**Minimal reproduction of the problem with instructions**
http://plnkr.co/edit/UZiAHEmvc3IldUTHTNyH?p=preview
** Issue and Fix
https://github.com/primefaces/primeng/blob/d75ad835f4434cccc02f1fbed644c4340188b7ac/src/app/components/datatable/datatable.ts#L851-L855
if(this._selection) {
if (Array.isArray(this._selection)) {
for(let data of this._selection) {
this.selectionKeys[String(this.objectUtils.resolveFieldData(data, this.dataKey))] = 1;
}
}
else {
this.selectionKeys[String(this.objectUtils.resolveFieldData(this._selection, this.dataKey))] = 1;
}
}
* **PrimeNG version:** 4.1.2
|
1.0
|
programatic element (pre-)selection on datatable fails when using dataKey - I'm submitting
```
[ x ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
Please fork the plunkr below and create a case demonstrating your bug report. Issues without a plunkr have much less possibility to be reviewed.
http://plnkr.co/edit/UZiAHEmvc3IldUTHTNyH?p=preview
**Current behavior**
Setting a selected item on a datatable that uses a dataKey does not work in single selction mode. The selection object and the selection keys are not correctly initialized, when selection is a single object instead of an array.
**Expected behavior**
Setting the selected item as object in single selection mode should use the datakey property to check equality.
**Minimal reproduction of the problem with instructions**
http://plnkr.co/edit/UZiAHEmvc3IldUTHTNyH?p=preview
** Issue and Fix
https://github.com/primefaces/primeng/blob/d75ad835f4434cccc02f1fbed644c4340188b7ac/src/app/components/datatable/datatable.ts#L851-L855
if(this._selection) {
if (Array.isArray(this._selection)) {
for(let data of this._selection) {
this.selectionKeys[String(this.objectUtils.resolveFieldData(data, this.dataKey))] = 1;
}
}
else {
this.selectionKeys[String(this.objectUtils.resolveFieldData(this._selection, this.dataKey))] = 1;
}
}
* **PrimeNG version:** 4.1.2
|
defect
|
programatic element pre selection on datatable fails when using datakey i m submitting bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see plunkr case bug reports please fork the plunkr below and create a case demonstrating your bug report issues without a plunkr have much less possibility to be reviewed current behavior setting a selected item on a datatable that uses a datakey does not work in single selction mode the selection object and the selection keys are not correctly initialized when selection is a single object instead of an array expected behavior setting the selected item as object in single selection mode should use the datakey property to check equality minimal reproduction of the problem with instructions issue and fix if this selection if array isarray this selection for let data of this selection this selectionkeys else this selectionkeys primeng version
| 1
|
140,041
| 31,819,871,293
|
IssuesEvent
|
2023-09-14 00:48:55
|
Jaovitosr/Chatbot
|
https://api.github.com/repos/Jaovitosr/Chatbot
|
opened
|
number of library items not fully displayed -> show as tooltip
|
good first issue type: enhancement groups FirstTimeCodeContribution
|
From jabref created by [ghost](https://github.com/ghost): JabRef/jabref#10208
### JabRef version
5.9 (latest release)
### Operating system
Windows
### Details on version and operating system
Windows 10 22H2
### Checked with the latest development build
- [X] I made a backup of my libraries before testing the latest development version.
- [X] I have tested the latest development version and the problem persists
### Steps to reproduce the behaviour
I have downloaded 2 databases in BibTeX format: one is an arcade game database (45974 items), the other a game console/computer database (134352)
Please look at screenshot. The number of items in the library is not fully displayed (see at the left). Only 4 digits are displayed, the rest in front of it is gone. Could it be fixed so I see the currect number of items? I know it are A LOT but it's possible to have such a big library :)


Attached are the 2 bib files
[games.zip](https://github.com/JabRef/jabref/files/12431909/games.zip)
### Appendix
...
<details>
<summary>Log File</summary>
```
Paste an excerpt of your log file here
```
</details>
|
1.0
|
number of library items not fully displayed -> show as tooltip - From jabref created by [ghost](https://github.com/ghost): JabRef/jabref#10208
### JabRef version
5.9 (latest release)
### Operating system
Windows
### Details on version and operating system
Windows 10 22H2
### Checked with the latest development build
- [X] I made a backup of my libraries before testing the latest development version.
- [X] I have tested the latest development version and the problem persists
### Steps to reproduce the behaviour
I have downloaded 2 databases in BibTeX format: one is an arcade game database (45974 items), the other a game console/computer database (134352)
Please look at screenshot. The number of items in the library is not fully displayed (see at the left). Only 4 digits are displayed, the rest in front of it is gone. Could it be fixed so I see the currect number of items? I know it are A LOT but it's possible to have such a big library :)


Attached are the 2 bib files
[games.zip](https://github.com/JabRef/jabref/files/12431909/games.zip)
### Appendix
...
<details>
<summary>Log File</summary>
```
Paste an excerpt of your log file here
```
</details>
|
non_defect
|
number of library items not fully displayed show as tooltip from jabref created by jabref jabref jabref version latest release operating system windows details on version and operating system windows checked with the latest development build i made a backup of my libraries before testing the latest development version i have tested the latest development version and the problem persists steps to reproduce the behaviour i have downloaded databases in bibtex format one is an arcade game database items the other a game console computer database please look at screenshot the number of items in the library is not fully displayed see at the left only digits are displayed the rest in front of it is gone could it be fixed so i see the currect number of items i know it are a lot but it s possible to have such a big library attached are the bib files appendix log file paste an excerpt of your log file here
| 0
|
64,078
| 18,164,318,267
|
IssuesEvent
|
2021-09-27 13:11:55
|
vector-im/element-ios
|
https://api.github.com/repos/vector-im/element-ios
|
closed
|
Spaces still visible after logging in with another account
|
T-Defect
|
### Steps to reproduce
1. Login with Alice
2. Logout
3. Login with Bob
### What happened?
### What did you expect?
Space list in the left panel to be refreshed with Bob's account
### What happened?
Space list in the left panel still with Alice's account
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
1.6.1
### Homeserver
_No response_
### Have you submitted a rageshake?
Yes
|
1.0
|
Spaces still visible after logging in with another account - ### Steps to reproduce
1. Login with Alice
2. Logout
3. Login with Bob
### What happened?
### What did you expect?
Space list in the left panel to be refreshed with Bob's account
### What happened?
Space list in the left panel still with Alice's account
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
1.6.1
### Homeserver
_No response_
### Have you submitted a rageshake?
Yes
|
defect
|
spaces still visible after logging in with another account steps to reproduce login with alice logout login with bob what happened what did you expect space list in the left panel to be refreshed with bob s account what happened space list in the left panel still with alice s account your phone model no response operating system version no response application version homeserver no response have you submitted a rageshake yes
| 1
|
427,430
| 29,812,463,371
|
IssuesEvent
|
2023-06-16 16:06:54
|
aws-amplify/amplify-ui
|
https://api.github.com/repos/aws-amplify/amplify-ui
|
closed
|
Bug(Docs): Value input for Ratings demo breaks if you hit backspace
|
bug Documentation
|
### Before creating a new issue, please confirm:
- [X] I have [searched for duplicate or closed issues](https://github.com/aws-amplify/amplify-ui/issues?q=is%3Aissue+) and [discussions](https://github.com/aws-amplify/amplify-ui/discussions).
- [X] I have tried disabling all browser extensions or using a different browser
- [X] I have tried deleting the node_modules folder and reinstalling my dependencies
- [X] I have read the guide for [submitting bug reports](https://github.com/aws-amplify/amplify-ui/blob/main/CONTRIBUTING.md#bug-reports).
### On which framework/platform are you having an issue?
Other
### Which UI component?
Other
### How is your app built?
n/a
### What browsers are you seeing the problem on?
_No response_
### Please describe your bug.
On the [Ratings doc page](https://ui.docs.amplify.aws/react/components/rating) in the demo, if you hit backspace/delete on the value input, the value turns to `NaN` which breaks the demo and you can no longer type in the input; you need to reload the page to reset it. Hitting backspace on the maxValue input causing the page to crash.
<img width="400" alt="Screenshot of Ratings doc page which shows the Demo section, the value input reads NaN and the component preview does not show up" src="https://github.com/aws-amplify/amplify-ui/assets/376920/57a4d281-6d50-4da6-bfe1-0689f692dfcf">
### What's the expected behaviour?
You should be able to clear out the value input and enter a new value.
### Help us reproduce the bug!
Tab or click into the value input and hit backspace or try to delete the number.
### Code Snippet
```typescript
// Put your code below this line.
```
### Additional information and screenshots
_No response_
|
1.0
|
Bug(Docs): Value input for Ratings demo breaks if you hit backspace - ### Before creating a new issue, please confirm:
- [X] I have [searched for duplicate or closed issues](https://github.com/aws-amplify/amplify-ui/issues?q=is%3Aissue+) and [discussions](https://github.com/aws-amplify/amplify-ui/discussions).
- [X] I have tried disabling all browser extensions or using a different browser
- [X] I have tried deleting the node_modules folder and reinstalling my dependencies
- [X] I have read the guide for [submitting bug reports](https://github.com/aws-amplify/amplify-ui/blob/main/CONTRIBUTING.md#bug-reports).
### On which framework/platform are you having an issue?
Other
### Which UI component?
Other
### How is your app built?
n/a
### What browsers are you seeing the problem on?
_No response_
### Please describe your bug.
On the [Ratings doc page](https://ui.docs.amplify.aws/react/components/rating) in the demo, if you hit backspace/delete on the value input, the value turns to `NaN` which breaks the demo and you can no longer type in the input; you need to reload the page to reset it. Hitting backspace on the maxValue input causing the page to crash.
<img width="400" alt="Screenshot of Ratings doc page which shows the Demo section, the value input reads NaN and the component preview does not show up" src="https://github.com/aws-amplify/amplify-ui/assets/376920/57a4d281-6d50-4da6-bfe1-0689f692dfcf">
### What's the expected behaviour?
You should be able to clear out the value input and enter a new value.
### Help us reproduce the bug!
Tab or click into the value input and hit backspace or try to delete the number.
### Code Snippet
```typescript
// Put your code below this line.
```
### Additional information and screenshots
_No response_
|
non_defect
|
bug docs value input for ratings demo breaks if you hit backspace before creating a new issue please confirm i have and i have tried disabling all browser extensions or using a different browser i have tried deleting the node modules folder and reinstalling my dependencies i have read the guide for on which framework platform are you having an issue other which ui component other how is your app built n a what browsers are you seeing the problem on no response please describe your bug on the in the demo if you hit backspace delete on the value input the value turns to nan which breaks the demo and you can no longer type in the input you need to reload the page to reset it hitting backspace on the maxvalue input causing the page to crash img width alt screenshot of ratings doc page which shows the demo section the value input reads nan and the component preview does not show up src what s the expected behaviour you should be able to clear out the value input and enter a new value help us reproduce the bug tab or click into the value input and hit backspace or try to delete the number code snippet typescript put your code below this line additional information and screenshots no response
| 0
|
208,645
| 7,156,936,988
|
IssuesEvent
|
2018-01-26 18:01:41
|
appirio-tech/connect-app
|
https://api.github.com/repos/appirio-tech/connect-app
|
closed
|
Top bar navigation icons not showing on narrow screen size
|
ACCEPTED Priority
|
### Expected behavior
Top bar icons should be visible at all times.
### Actual behavior
After the SVG refactor we lost the icons on narrow screens.
Expected:
Current:
|
1.0
|
Top bar navigation icons not showing on narrow screen size - ### Expected behavior
Top bar icons should be visible at all times.
### Actual behavior
After the SVG refactor we lost the icons on narrow screens.
Expected:
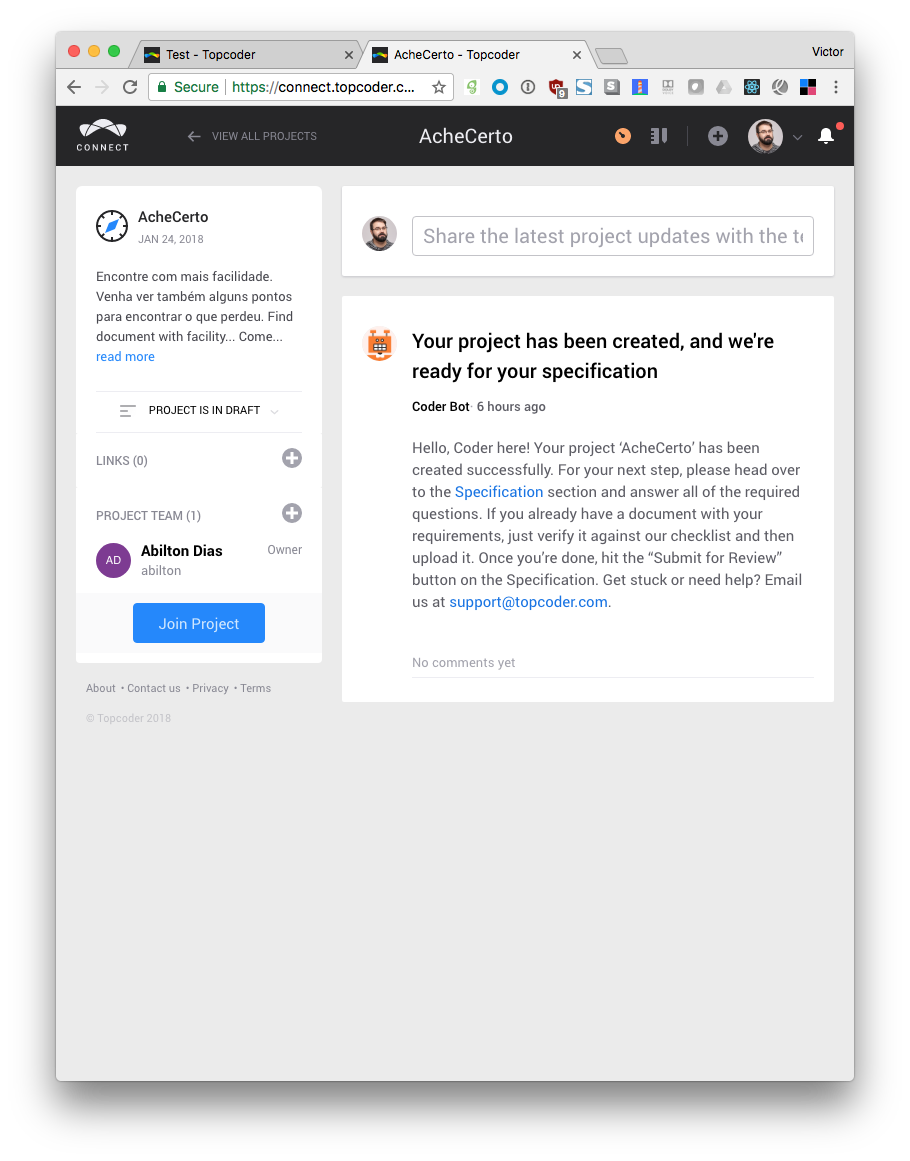
Current:
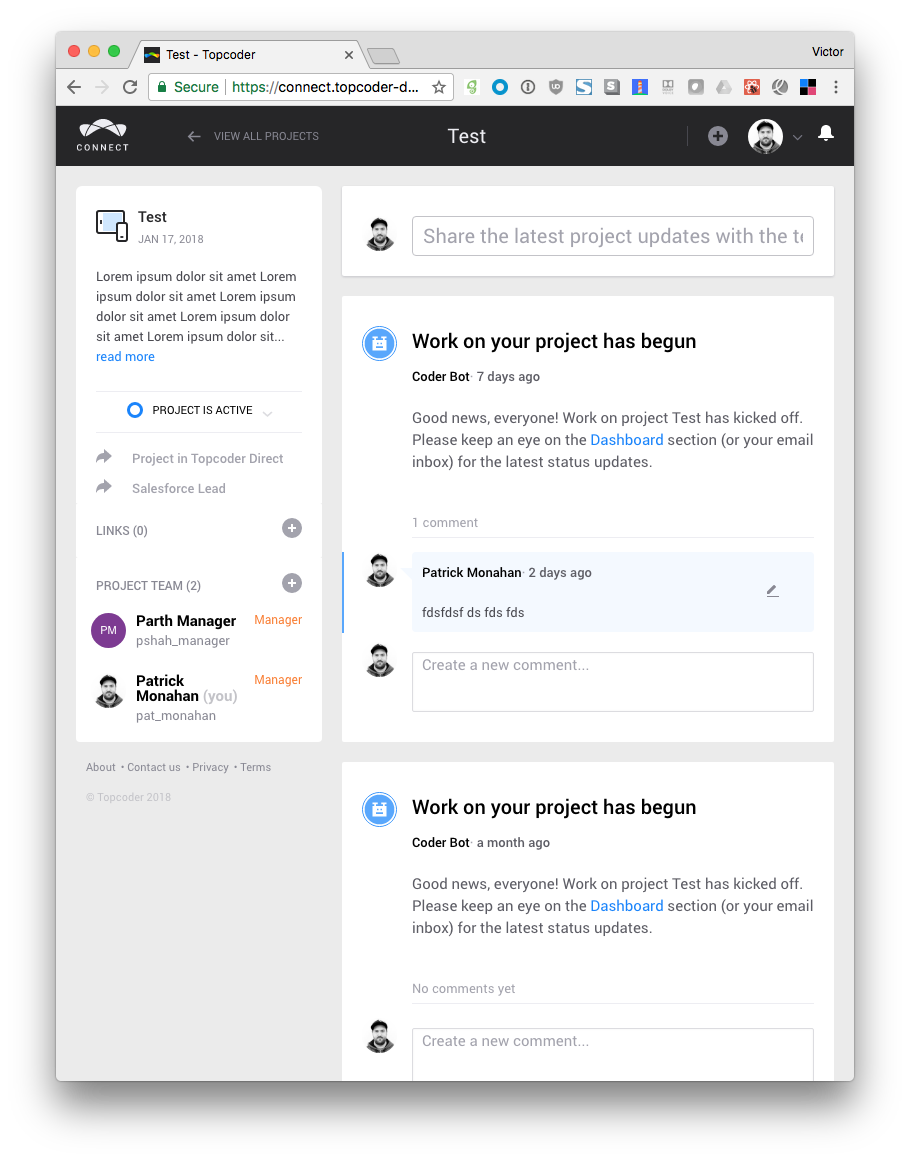
|
non_defect
|
top bar navigation icons not showing on narrow screen size expected behavior top bar icons should be visible at all times actual behavior after the svg refactor we lost the icons on narrow screens expected current
| 0
|
136,082
| 18,722,304,700
|
IssuesEvent
|
2021-11-03 13:09:40
|
KDWSS/dd-trace-java
|
https://api.github.com/repos/KDWSS/dd-trace-java
|
opened
|
CVE-2021-25329 (High) detected in multiple libraries
|
security vulnerability
|
## CVE-2021-25329 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tomcat-embed-core-7.0.37.jar</b>, <b>tomcat-embed-core-9.0.39.jar</b>, <b>tomcat-embed-core-8.5.34.jar</b>, <b>tomcat-embed-core-9.0.34.jar</b>, <b>tomcat-embed-core-7.0.0.jar</b>, <b>tomcat-embed-core-9.0.41.jar</b>, <b>tomcat-embed-core-8.5.35.jar</b></p></summary>
<p>
<details><summary><b>tomcat-embed-core-7.0.37.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/jsp-2.3/jsp-2.3.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.37/13754cedeae4b94451b4563111fad71dab9ae619/tomcat-embed-core-7.0.37.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.37/13754cedeae4b94451b4563111fad71dab9ae619/tomcat-embed-core-7.0.37.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-7.0.37.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-9.0.39.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.39/d82e926b31f06e96fccf552e41f1b8b1615d96dc/tomcat-embed-core-9.0.39.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.5.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.3.5.RELEASE.jar
- :x: **tomcat-embed-core-9.0.39.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-8.5.34.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-webmvc-3.1/spring-webmvc-3.1.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.34/a038040d68a90397f95dd1e11b979fe364a5000f/tomcat-embed-core-8.5.34.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.17.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.17.RELEASE.jar
- :x: **tomcat-embed-core-8.5.34.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-9.0.34.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-openliberty/application/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.34/tomcat-embed-core-9.0.34.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.7.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.2.7.RELEASE.jar
- :x: **tomcat-embed-core-9.0.34.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-7.0.0.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/java-concurrent/lambda-testing/lambda-testing.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.0/a5d50d1a993f78091f62d1b4afcd553fe7295ebb/tomcat-embed-core-7.0.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.0/a5d50d1a993f78091f62d1b4afcd553fe7295ebb/tomcat-embed-core-7.0.0.jar,/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.0/a5d50d1a993f78091f62d1b4afcd553fe7295ebb/tomcat-embed-core-7.0.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-7.0.0.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-9.0.41.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.41/a43e9711e85073187d04b137882b4b7957180ef0/tomcat-embed-core-9.0.41.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.4.1.jar (Root Library)
- spring-boot-starter-tomcat-2.4.1.jar
- tomcat-embed-websocket-9.0.41.jar
- :x: **tomcat-embed-core-9.0.41.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-8.5.35.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot/springboot.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.35/9c459829e1aa72669203dbbf6648dc3b6314644c/tomcat-embed-core-8.5.35.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.35/9c459829e1aa72669203dbbf6648dc3b6314644c/tomcat-embed-core-8.5.35.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.18.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.18.RELEASE.jar
- tomcat-embed-websocket-8.5.35.jar
- :x: **tomcat-embed-core-8.5.35.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329>CVE-2021-25329</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"7.0.37","packageFilePaths":["/dd-java-agent/instrumentation/jsp-2.3/jsp-2.3.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.tomcat.embed:tomcat-embed-core:7.0.37","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.39","packageFilePaths":["/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.3.5.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.3.5.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:9.0.39","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.34","packageFilePaths":["/dd-java-agent/instrumentation/spring-webmvc-3.1/spring-webmvc-3.1.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.17.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.17.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.34","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.34","packageFilePaths":["/dd-smoke-tests/springboot-openliberty/application/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.2.7.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.2.7.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:9.0.34","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"7.0.0","packageFilePaths":["/dd-java-agent/instrumentation/java-concurrent/lambda-testing/lambda-testing.gradle","/dd-java-agent/instrumentation/java-concurrent/java-concurrent.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.tomcat.embed:tomcat-embed-core:7.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.41","packageFilePaths":["/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.4.1;org.springframework.boot:spring-boot-starter-tomcat:2.4.1;org.apache.tomcat.embed:tomcat-embed-websocket:9.0.41;org.apache.tomcat.embed:tomcat-embed-core:9.0.41","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.35","packageFilePaths":["/dd-smoke-tests/springboot/springboot.gradle","/dd-smoke-tests/springboot-grpc/springboot-grpc.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.18.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.18.RELEASE;org.apache.tomcat.embed:tomcat-embed-websocket:8.5.35;org.apache.tomcat.embed:tomcat-embed-core:8.5.35","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-25329","vulnerabilityDetails":"The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329","cvss3Severity":"high","cvss3Score":"7.0","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2021-25329 (High) detected in multiple libraries - ## CVE-2021-25329 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tomcat-embed-core-7.0.37.jar</b>, <b>tomcat-embed-core-9.0.39.jar</b>, <b>tomcat-embed-core-8.5.34.jar</b>, <b>tomcat-embed-core-9.0.34.jar</b>, <b>tomcat-embed-core-7.0.0.jar</b>, <b>tomcat-embed-core-9.0.41.jar</b>, <b>tomcat-embed-core-8.5.35.jar</b></p></summary>
<p>
<details><summary><b>tomcat-embed-core-7.0.37.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/jsp-2.3/jsp-2.3.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.37/13754cedeae4b94451b4563111fad71dab9ae619/tomcat-embed-core-7.0.37.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.37/13754cedeae4b94451b4563111fad71dab9ae619/tomcat-embed-core-7.0.37.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-7.0.37.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-9.0.39.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.39/d82e926b31f06e96fccf552e41f1b8b1615d96dc/tomcat-embed-core-9.0.39.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.5.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.3.5.RELEASE.jar
- :x: **tomcat-embed-core-9.0.39.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-8.5.34.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-webmvc-3.1/spring-webmvc-3.1.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.34/a038040d68a90397f95dd1e11b979fe364a5000f/tomcat-embed-core-8.5.34.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.17.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.17.RELEASE.jar
- :x: **tomcat-embed-core-8.5.34.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-9.0.34.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-openliberty/application/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.34/tomcat-embed-core-9.0.34.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.7.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.2.7.RELEASE.jar
- :x: **tomcat-embed-core-9.0.34.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-7.0.0.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/java-concurrent/lambda-testing/lambda-testing.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.0/a5d50d1a993f78091f62d1b4afcd553fe7295ebb/tomcat-embed-core-7.0.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.0/a5d50d1a993f78091f62d1b4afcd553fe7295ebb/tomcat-embed-core-7.0.0.jar,/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/7.0.0/a5d50d1a993f78091f62d1b4afcd553fe7295ebb/tomcat-embed-core-7.0.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-7.0.0.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-9.0.41.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.41/a43e9711e85073187d04b137882b4b7957180ef0/tomcat-embed-core-9.0.41.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.4.1.jar (Root Library)
- spring-boot-starter-tomcat-2.4.1.jar
- tomcat-embed-websocket-9.0.41.jar
- :x: **tomcat-embed-core-9.0.41.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-8.5.35.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Path to dependency file: dd-trace-java/dd-smoke-tests/springboot/springboot.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.35/9c459829e1aa72669203dbbf6648dc3b6314644c/tomcat-embed-core-8.5.35.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.35/9c459829e1aa72669203dbbf6648dc3b6314644c/tomcat-embed-core-8.5.35.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.18.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.18.RELEASE.jar
- tomcat-embed-websocket-8.5.35.jar
- :x: **tomcat-embed-core-8.5.35.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329>CVE-2021-25329</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"7.0.37","packageFilePaths":["/dd-java-agent/instrumentation/jsp-2.3/jsp-2.3.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.tomcat.embed:tomcat-embed-core:7.0.37","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.39","packageFilePaths":["/dd-java-agent/instrumentation/spring-cloud-zuul-2/spring-cloud-zuul-2.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.3.5.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.3.5.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:9.0.39","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.34","packageFilePaths":["/dd-java-agent/instrumentation/spring-webmvc-3.1/spring-webmvc-3.1.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.17.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.17.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.34","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.34","packageFilePaths":["/dd-smoke-tests/springboot-openliberty/application/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.2.7.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.2.7.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:9.0.34","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"7.0.0","packageFilePaths":["/dd-java-agent/instrumentation/java-concurrent/lambda-testing/lambda-testing.gradle","/dd-java-agent/instrumentation/java-concurrent/java-concurrent.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.tomcat.embed:tomcat-embed-core:7.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.41","packageFilePaths":["/dd-smoke-tests/springboot-mongo/springboot-mongo.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.4.1;org.springframework.boot:spring-boot-starter-tomcat:2.4.1;org.apache.tomcat.embed:tomcat-embed-websocket:9.0.41;org.apache.tomcat.embed:tomcat-embed-core:9.0.41","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.35","packageFilePaths":["/dd-smoke-tests/springboot/springboot.gradle","/dd-smoke-tests/springboot-grpc/springboot-grpc.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.18.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.18.RELEASE;org.apache.tomcat.embed:tomcat-embed-websocket:8.5.35;org.apache.tomcat.embed:tomcat-embed-core:8.5.35","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-25329","vulnerabilityDetails":"The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329","cvss3Severity":"high","cvss3Score":"7.0","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries tomcat embed core jar tomcat embed core jar tomcat embed core jar tomcat embed core jar tomcat embed core jar tomcat embed core jar tomcat embed core jar tomcat embed core jar core tomcat implementation library home page a href path to dependency file dd trace java dd java agent instrumentation jsp jsp gradle path to vulnerable library caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file dd trace java dd java agent instrumentation spring cloud zuul spring cloud zuul gradle path to vulnerable library home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file dd trace java dd java agent instrumentation spring webmvc spring webmvc gradle path to vulnerable library home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file dd trace java dd smoke tests springboot openliberty application pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation path to dependency file dd trace java dd java agent instrumentation java concurrent lambda testing lambda testing gradle path to vulnerable library caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file dd trace java dd smoke tests springboot mongo springboot mongo gradle path to vulnerable library home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web jar root library spring boot starter tomcat jar tomcat embed websocket jar x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation path to dependency file dd trace java dd smoke tests springboot springboot gradle path to vulnerable library home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar tomcat embed websocket jar x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details the fix for cve was incomplete when using apache tomcat to to to or to with a configuration edge case that was highly unlikely to be used the tomcat instance was still vulnerable to cve note that both the previously published prerequisites for cve and the previously published mitigations for cve also apply to this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency false dependencytree org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web org springframework boot spring boot starter tomcat org apache tomcat embed tomcat embed websocket org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed websocket org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat basebranches vulnerabilityidentifier cve vulnerabilitydetails the fix for cve was incomplete when using apache tomcat to to to or to with a configuration edge case that was highly unlikely to be used the tomcat instance was still vulnerable to cve note that both the previously published prerequisites for cve and the previously published mitigations for cve also apply to this issue vulnerabilityurl
| 0
|
29,927
| 5,959,372,417
|
IssuesEvent
|
2017-05-29 10:50:06
|
PowerDNS/pdns
|
https://api.github.com/repos/PowerDNS/pdns
|
closed
|
Lua newDS:check() method does not match upper level domain if subdomain is added before upper level domain
|
defect rec
|
- Program: Recursor
- Issue type: Bug report
### Short description
<!-- Explain in a few sentences what the issue/request is -->
Lua newDS:check() method does not match upper level domain if subdomain is added before upper level domain.
### Environment
<!-- Tell us about the environment -->
- Operating system: Linux
- Software version: 4.0.4
- Software source: compiled myself and Archlinux repository as well, own compiled pdns-recursor binary running PLD Linux compiled with ./bootstrap ;./configure --prefix=/opt/… --with-lua; make; make install and PLD-Linux packet prepared by myself.
### Steps to reproduce
1. Create lua script:
```
domains = newDS()
domains:add("www.example.com")
domains:add("example.com")
function check_domain(domain)
pdnslog('Checking domain: ' .. domain)
domainname = newDN(domain)
if (domains:check(domainname)) then
pdnslog('Domain ' .. domain .. ' found', pdns.loglevels.Warning)
else
pdnslog('Domain ' .. domain .. ' NOT found', pdns.loglevels.Warning)
end
end
pdnslog('domains in suffix match group: ' .. domains:toString(), pdns.loglevels.Warning)
check_domain("example.com")
check_domain("www.example.com")
check_domain("generic.example.com")
```
<!-- Tell us step-by-step how the issue can be triggered. Please include your configuration files and any (Lua) scripts that are loaded. -->
2. Run pdns recursor: pdns_recursor --daemon=no --quiet=no
3. Reload lua script using: reload-lua-script $lua_script_path
### Expected behaviour
I'd expect domains:check(domainname) would return true for all of the three domains added to domains newDS.
### Actual behaviour
Only one domain, www.example.com return true when checked agains domains newDS:
```
May 29 12:32:01 domains in suffix match group: www.example.com., example.com.
May 29 12:32:01 Checking domain: example.com
May 29 12:32:01 Domain example.com NOT found
May 29 12:32:01 Checking domain: www.example.com
May 29 12:32:01 Domain www.example.com found
May 29 12:32:01 Checking domain: generic.example.com
May 29 12:32:01 Domain generic.example.com NOT found
May 29 12:32:01 0 (Re)loaded lua script from '/etc/pdns-recursor/lua/hazard-bug.lua'
```
### Other information
Version 4.0.5-rc1 compiled myself works as expected, but i could not find any issue describing above problem.
|
1.0
|
Lua newDS:check() method does not match upper level domain if subdomain is added before upper level domain - - Program: Recursor
- Issue type: Bug report
### Short description
<!-- Explain in a few sentences what the issue/request is -->
Lua newDS:check() method does not match upper level domain if subdomain is added before upper level domain.
### Environment
<!-- Tell us about the environment -->
- Operating system: Linux
- Software version: 4.0.4
- Software source: compiled myself and Archlinux repository as well, own compiled pdns-recursor binary running PLD Linux compiled with ./bootstrap ;./configure --prefix=/opt/… --with-lua; make; make install and PLD-Linux packet prepared by myself.
### Steps to reproduce
1. Create lua script:
```
domains = newDS()
domains:add("www.example.com")
domains:add("example.com")
function check_domain(domain)
pdnslog('Checking domain: ' .. domain)
domainname = newDN(domain)
if (domains:check(domainname)) then
pdnslog('Domain ' .. domain .. ' found', pdns.loglevels.Warning)
else
pdnslog('Domain ' .. domain .. ' NOT found', pdns.loglevels.Warning)
end
end
pdnslog('domains in suffix match group: ' .. domains:toString(), pdns.loglevels.Warning)
check_domain("example.com")
check_domain("www.example.com")
check_domain("generic.example.com")
```
<!-- Tell us step-by-step how the issue can be triggered. Please include your configuration files and any (Lua) scripts that are loaded. -->
2. Run pdns recursor: pdns_recursor --daemon=no --quiet=no
3. Reload lua script using: reload-lua-script $lua_script_path
### Expected behaviour
I'd expect domains:check(domainname) would return true for all of the three domains added to domains newDS.
### Actual behaviour
Only one domain, www.example.com return true when checked agains domains newDS:
```
May 29 12:32:01 domains in suffix match group: www.example.com., example.com.
May 29 12:32:01 Checking domain: example.com
May 29 12:32:01 Domain example.com NOT found
May 29 12:32:01 Checking domain: www.example.com
May 29 12:32:01 Domain www.example.com found
May 29 12:32:01 Checking domain: generic.example.com
May 29 12:32:01 Domain generic.example.com NOT found
May 29 12:32:01 0 (Re)loaded lua script from '/etc/pdns-recursor/lua/hazard-bug.lua'
```
### Other information
Version 4.0.5-rc1 compiled myself works as expected, but i could not find any issue describing above problem.
|
defect
|
lua newds check method does not match upper level domain if subdomain is added before upper level domain program recursor issue type bug report short description lua newds check method does not match upper level domain if subdomain is added before upper level domain environment operating system linux software version software source compiled myself and archlinux repository as well own compiled pdns recursor binary running pld linux compiled with bootstrap configure prefix opt … with lua make make install and pld linux packet prepared by myself steps to reproduce create lua script domains newds domains add domains add example com function check domain domain pdnslog checking domain domain domainname newdn domain if domains check domainname then pdnslog domain domain found pdns loglevels warning else pdnslog domain domain not found pdns loglevels warning end end pdnslog domains in suffix match group domains tostring pdns loglevels warning check domain example com check domain check domain generic example com run pdns recursor pdns recursor daemon no quiet no reload lua script using reload lua script lua script path expected behaviour i d expect domains check domainname would return true for all of the three domains added to domains newds actual behaviour only one domain return true when checked agains domains newds may domains in suffix match group example com may checking domain example com may domain example com not found may checking domain may domain found may checking domain generic example com may domain generic example com not found may re loaded lua script from etc pdns recursor lua hazard bug lua other information version compiled myself works as expected but i could not find any issue describing above problem
| 1
|
276,162
| 30,349,490,953
|
IssuesEvent
|
2023-07-11 17:48:30
|
KOSASIH/Farmatica
|
https://api.github.com/repos/KOSASIH/Farmatica
|
opened
|
h2-2.1.214.jar: 1 vulnerabilities (highest severity is: 7.8)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>h2-2.1.214.jar</b></p></summary>
<p>H2 Database Engine</p>
<p>Library home page: <a href="https://h2database.com">https://h2database.com</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/h2database/h2/2.1.214/h2-2.1.214.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/Farmatica/commit/bffdd75d8cf4f30a7f41839a581efdc74de85069">bffdd75d8cf4f30a7f41839a581efdc74de85069</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (h2 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-45868](https://www.mend.io/vulnerability-database/CVE-2022-45868) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.8 | h2-2.1.214.jar | Direct | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-45868</summary>
### Vulnerable Library - <b>h2-2.1.214.jar</b></p>
<p>H2 Database Engine</p>
<p>Library home page: <a href="https://h2database.com">https://h2database.com</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/h2database/h2/2.1.214/h2-2.1.214.jar</p>
<p>
Dependency Hierarchy:
- :x: **h2-2.1.214.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/Farmatica/commit/bffdd75d8cf4f30a7f41839a581efdc74de85069">bffdd75d8cf4f30a7f41839a581efdc74de85069</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The web-based admin console in H2 Database Engine through 2.1.214 can be started via the CLI with the argument -webAdminPassword, which allows the user to specify the password in cleartext for the web admin console. Consequently, a local user (or an attacker that has obtained local access through some means) would be able to discover the password by listing processes and their arguments. NOTE: the vendor states "This is not a vulnerability of H2 Console ... Passwords should never be passed on the command line and every qualified DBA or system administrator is expected to know that."
<p>Publish Date: 2022-11-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-45868>CVE-2022-45868</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
True
|
h2-2.1.214.jar: 1 vulnerabilities (highest severity is: 7.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>h2-2.1.214.jar</b></p></summary>
<p>H2 Database Engine</p>
<p>Library home page: <a href="https://h2database.com">https://h2database.com</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/h2database/h2/2.1.214/h2-2.1.214.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/Farmatica/commit/bffdd75d8cf4f30a7f41839a581efdc74de85069">bffdd75d8cf4f30a7f41839a581efdc74de85069</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (h2 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-45868](https://www.mend.io/vulnerability-database/CVE-2022-45868) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.8 | h2-2.1.214.jar | Direct | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-45868</summary>
### Vulnerable Library - <b>h2-2.1.214.jar</b></p>
<p>H2 Database Engine</p>
<p>Library home page: <a href="https://h2database.com">https://h2database.com</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/h2database/h2/2.1.214/h2-2.1.214.jar</p>
<p>
Dependency Hierarchy:
- :x: **h2-2.1.214.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/Farmatica/commit/bffdd75d8cf4f30a7f41839a581efdc74de85069">bffdd75d8cf4f30a7f41839a581efdc74de85069</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The web-based admin console in H2 Database Engine through 2.1.214 can be started via the CLI with the argument -webAdminPassword, which allows the user to specify the password in cleartext for the web admin console. Consequently, a local user (or an attacker that has obtained local access through some means) would be able to discover the password by listing processes and their arguments. NOTE: the vendor states "This is not a vulnerability of H2 Console ... Passwords should never be passed on the command line and every qualified DBA or system administrator is expected to know that."
<p>Publish Date: 2022-11-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-45868>CVE-2022-45868</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
non_defect
|
jar vulnerabilities highest severity is vulnerable library jar database engine library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in version remediation available high jar direct n a details cve vulnerable library jar database engine library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com jar dependency hierarchy x jar vulnerable library found in head commit a href found in base branch main vulnerability details the web based admin console in database engine through can be started via the cli with the argument webadminpassword which allows the user to specify the password in cleartext for the web admin console consequently a local user or an attacker that has obtained local access through some means would be able to discover the password by listing processes and their arguments note the vendor states this is not a vulnerability of console passwords should never be passed on the command line and every qualified dba or system administrator is expected to know that publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend
| 0
|
74,835
| 25,348,681,119
|
IssuesEvent
|
2022-11-19 14:02:53
|
pymc-devs/pymc
|
https://api.github.com/repos/pymc-devs/pymc
|
closed
|
Broken link in PyMC3 docs
|
defects docs
|
A Google search of "bayesian linear regression pymc" leads me to [this old page](https://docs.pymc.io/en/v3/pymc-examples/examples/generalized_linear_models/GLM-linear.html), which has the handy link at the top:
> Note
>
> You are not reading the most recent version of this documentation. [v4.1.3](https://docs.pymc.io/en/v4.1.3/pymc-examples/examples/generalized_linear_models/GLM-linear.html) is the latest version available.
Unfortunately this link looks broken. The correct link seems to be [https://www.pymc.io/projects/docs/en/stable/learn/core_notebooks/GLM_linear.html](https://www.pymc.io/projects/docs/en/stable/learn/core_notebooks/GLM_linear.html).
|
1.0
|
Broken link in PyMC3 docs - A Google search of "bayesian linear regression pymc" leads me to [this old page](https://docs.pymc.io/en/v3/pymc-examples/examples/generalized_linear_models/GLM-linear.html), which has the handy link at the top:
> Note
>
> You are not reading the most recent version of this documentation. [v4.1.3](https://docs.pymc.io/en/v4.1.3/pymc-examples/examples/generalized_linear_models/GLM-linear.html) is the latest version available.
Unfortunately this link looks broken. The correct link seems to be [https://www.pymc.io/projects/docs/en/stable/learn/core_notebooks/GLM_linear.html](https://www.pymc.io/projects/docs/en/stable/learn/core_notebooks/GLM_linear.html).
|
defect
|
broken link in docs a google search of bayesian linear regression pymc leads me to which has the handy link at the top note you are not reading the most recent version of this documentation is the latest version available unfortunately this link looks broken the correct link seems to be
| 1
|
468,529
| 13,484,597,210
|
IssuesEvent
|
2020-09-11 06:40:17
|
mjuenema/python-terrascript
|
https://api.github.com/repos/mjuenema/python-terrascript
|
closed
|
Remove support for Python 3.5
|
Priority: Low enhancement
|
As 3.5 approaches its end-of-life date (2020-09-13)[https://devguide.python.org/#status-of-python-branches], we should also drop support for it and stop building it.
This would allow for us to pick up 3.9 being released on (2020-10-04)[https://devguide.python.org/#status-of-python-branches] and in the long run make for less workarounds for legacy.
|
1.0
|
Remove support for Python 3.5 - As 3.5 approaches its end-of-life date (2020-09-13)[https://devguide.python.org/#status-of-python-branches], we should also drop support for it and stop building it.
This would allow for us to pick up 3.9 being released on (2020-10-04)[https://devguide.python.org/#status-of-python-branches] and in the long run make for less workarounds for legacy.
|
non_defect
|
remove support for python as approaches its end of life date we should also drop support for it and stop building it this would allow for us to pick up being released on and in the long run make for less workarounds for legacy
| 0
|
6,799
| 2,610,280,339
|
IssuesEvent
|
2015-02-26 19:29:37
|
chrsmith/scribefire-chrome
|
https://api.github.com/repos/chrsmith/scribefire-chrome
|
closed
|
Spell Checking
|
auto-migrated Type-Defect
|
```
What new feature do you want? Spell Checking!
```
-----
Original issue reported on code.google.com by `jefftsch...@gmail.com` on 3 Jul 2011 at 11:13
* Merged into: #299
|
1.0
|
Spell Checking - ```
What new feature do you want? Spell Checking!
```
-----
Original issue reported on code.google.com by `jefftsch...@gmail.com` on 3 Jul 2011 at 11:13
* Merged into: #299
|
defect
|
spell checking what new feature do you want spell checking original issue reported on code google com by jefftsch gmail com on jul at merged into
| 1
|
123,409
| 17,772,227,700
|
IssuesEvent
|
2021-08-30 14:52:31
|
kapseliboi/RDocumentation-app
|
https://api.github.com/repos/kapseliboi/RDocumentation-app
|
opened
|
CVE-2018-1000620 (High) detected in cryptiles-3.1.2.tgz, cryptiles-2.0.5.tgz
|
security vulnerability
|
## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>cryptiles-3.1.2.tgz</b>, <b>cryptiles-2.0.5.tgz</b></p></summary>
<p>
<details><summary><b>cryptiles-3.1.2.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz</a></p>
<p>Path to dependency file: RDocumentation-app/package.json</p>
<p>Path to vulnerable library: RDocumentation-app/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- request-2.83.0.tgz (Root Library)
- hawk-6.0.2.tgz
- :x: **cryptiles-3.1.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: RDocumentation-app/package.json</p>
<p>Path to vulnerable library: RDocumentation-app/node_modules/node-sass/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.7.2.tgz (Root Library)
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/RDocumentation-app/commit/ea1d4334329f74384d2d1b67f98e875da0b95310">ea1d4334329f74384d2d1b67f98e875da0b95310</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2018-1000620 (High) detected in cryptiles-3.1.2.tgz, cryptiles-2.0.5.tgz - ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>cryptiles-3.1.2.tgz</b>, <b>cryptiles-2.0.5.tgz</b></p></summary>
<p>
<details><summary><b>cryptiles-3.1.2.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz</a></p>
<p>Path to dependency file: RDocumentation-app/package.json</p>
<p>Path to vulnerable library: RDocumentation-app/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- request-2.83.0.tgz (Root Library)
- hawk-6.0.2.tgz
- :x: **cryptiles-3.1.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: RDocumentation-app/package.json</p>
<p>Path to vulnerable library: RDocumentation-app/node_modules/node-sass/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.7.2.tgz (Root Library)
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/RDocumentation-app/commit/ea1d4334329f74384d2d1b67f98e875da0b95310">ea1d4334329f74384d2d1b67f98e875da0b95310</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in cryptiles tgz cryptiles tgz cve high severity vulnerability vulnerable libraries cryptiles tgz cryptiles tgz cryptiles tgz general purpose crypto utilities library home page a href path to dependency file rdocumentation app package json path to vulnerable library rdocumentation app node modules cryptiles package json dependency hierarchy request tgz root library hawk tgz x cryptiles tgz vulnerable library cryptiles tgz general purpose crypto utilities library home page a href path to dependency file rdocumentation app package json path to vulnerable library rdocumentation app node modules node sass node modules cryptiles package json dependency hierarchy node sass tgz root library request tgz hawk tgz x cryptiles tgz vulnerable library found in head commit a href found in base branch master vulnerability details eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
76,992
| 26,709,233,779
|
IssuesEvent
|
2023-01-27 21:27:38
|
scipy/scipy
|
https://api.github.com/repos/scipy/scipy
|
reopened
|
BUG: Constraint minimization with the truncated normal distribution
|
defect
|
### Describe your issue.
I try to approximate a probability distribution within a known bound using truncated normal distribution and the `minimize` function from `scipy.optimize`. But I run into the "Inequality constraints incompatible" issue although I am sure that the inequality constraints are satisfied.
### Reproducing Code Example
```python
from scipy.stats import truncnorm
from scipy.optimize import minimize
# Sample data
a, b, loc, scale = -1, 1, 0.5, 0.1
r = truncnorm.rvs(a, b, loc=loc, scale=scale, size=1000)
# Boundary condition (by absolute range instead of by how many deviations away)
xa = 0
xb = 1
def cost(params, r):
return truncnorm.nnlf(params, r)
constraints = [
{'type': 'ineq', 'fun': lambda params: params[2] + params[0] * params[3] - xa},
{'type': 'ineq', 'fun': lambda params: xb - (params[2] + params[1] * params[3])},
]
init_params = (-0.5, 0.5, 0.3, 0.3) # (a, b, loc, scale)
res = minimize(cost, init_params, args=(r,), constraints=constraints)
print(res)
```
### Error message
```shell
RuntimeWarning: invalid value encountered in subtract
df = fun(x) - f0
message: Inequality constraints incompatible
success: False
status: 4
fun: inf
x: [-5.000e-01 5.000e-01 3.000e-01 3.000e-01]
nit: 1
jac: [ nan nan nan nan]
nfev: 5
njev: 1
```
### SciPy/NumPy/Python version information
1.10.0 1.24.1 sys.version_info(major=3, minor=9, micro=2, releaselevel='final', serial=0)
|
1.0
|
BUG: Constraint minimization with the truncated normal distribution - ### Describe your issue.
I try to approximate a probability distribution within a known bound using truncated normal distribution and the `minimize` function from `scipy.optimize`. But I run into the "Inequality constraints incompatible" issue although I am sure that the inequality constraints are satisfied.
### Reproducing Code Example
```python
from scipy.stats import truncnorm
from scipy.optimize import minimize
# Sample data
a, b, loc, scale = -1, 1, 0.5, 0.1
r = truncnorm.rvs(a, b, loc=loc, scale=scale, size=1000)
# Boundary condition (by absolute range instead of by how many deviations away)
xa = 0
xb = 1
def cost(params, r):
return truncnorm.nnlf(params, r)
constraints = [
{'type': 'ineq', 'fun': lambda params: params[2] + params[0] * params[3] - xa},
{'type': 'ineq', 'fun': lambda params: xb - (params[2] + params[1] * params[3])},
]
init_params = (-0.5, 0.5, 0.3, 0.3) # (a, b, loc, scale)
res = minimize(cost, init_params, args=(r,), constraints=constraints)
print(res)
```
### Error message
```shell
RuntimeWarning: invalid value encountered in subtract
df = fun(x) - f0
message: Inequality constraints incompatible
success: False
status: 4
fun: inf
x: [-5.000e-01 5.000e-01 3.000e-01 3.000e-01]
nit: 1
jac: [ nan nan nan nan]
nfev: 5
njev: 1
```
### SciPy/NumPy/Python version information
1.10.0 1.24.1 sys.version_info(major=3, minor=9, micro=2, releaselevel='final', serial=0)
|
defect
|
bug constraint minimization with the truncated normal distribution describe your issue i try to approximate a probability distribution within a known bound using truncated normal distribution and the minimize function from scipy optimize but i run into the inequality constraints incompatible issue although i am sure that the inequality constraints are satisfied reproducing code example python from scipy stats import truncnorm from scipy optimize import minimize sample data a b loc scale r truncnorm rvs a b loc loc scale scale size boundary condition by absolute range instead of by how many deviations away xa xb def cost params r return truncnorm nnlf params r constraints type ineq fun lambda params params params params xa type ineq fun lambda params xb params params params init params a b loc scale res minimize cost init params args r constraints constraints print res error message shell runtimewarning invalid value encountered in subtract df fun x message inequality constraints incompatible success false status fun inf x nit jac nfev njev scipy numpy python version information sys version info major minor micro releaselevel final serial
| 1
|
45,587
| 12,890,556,112
|
IssuesEvent
|
2020-07-13 16:11:24
|
autodesk-forks/MaterialX
|
https://api.github.com/repos/autodesk-forks/MaterialX
|
closed
|
Address static analysis issues found in Javascript code
|
Defect
|
There are a number of issues found through static analysis via Codacy.
The important issues should be addressed esp what appear to be security issues:
https://app.codacy.com/gh/autodesk-forks/MaterialX/issues?bid=18872641&filters=W3siaWQiOiJMYW5ndWFnZSIsInZhbHVlcyI6WyJKYXZhc2NyaXB0Il19LHsiaWQiOiJDYXRlZ29yeSIsInZhbHVlcyI6WyJTZWN1cml0eSJdfSx7ImlkIjoiTGV2ZWwiLCJ2YWx1ZXMiOltdfSx7ImlkIjoiUGF0dGVybiIsInZhbHVlcyI6W119LHsiaWQiOiJBdXRob3IiLCJ2YWx1ZXMiOltdfV0=
|
1.0
|
Address static analysis issues found in Javascript code - There are a number of issues found through static analysis via Codacy.
The important issues should be addressed esp what appear to be security issues:
https://app.codacy.com/gh/autodesk-forks/MaterialX/issues?bid=18872641&filters=W3siaWQiOiJMYW5ndWFnZSIsInZhbHVlcyI6WyJKYXZhc2NyaXB0Il19LHsiaWQiOiJDYXRlZ29yeSIsInZhbHVlcyI6WyJTZWN1cml0eSJdfSx7ImlkIjoiTGV2ZWwiLCJ2YWx1ZXMiOltdfSx7ImlkIjoiUGF0dGVybiIsInZhbHVlcyI6W119LHsiaWQiOiJBdXRob3IiLCJ2YWx1ZXMiOltdfV0=
|
defect
|
address static analysis issues found in javascript code there are a number of issues found through static analysis via codacy the important issues should be addressed esp what appear to be security issues
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.