Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 5
112
| repo_url
stringlengths 34
141
| action
stringclasses 3
values | title
stringlengths 1
757
| labels
stringlengths 4
664
| body
stringlengths 3
261k
| index
stringclasses 10
values | text_combine
stringlengths 96
261k
| label
stringclasses 2
values | text
stringlengths 96
232k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
703,379
| 24,156,455,414
|
IssuesEvent
|
2022-09-22 08:07:11
|
googleapis/nodejs-ai-platform
|
https://api.github.com/repos/googleapis/nodejs-ai-platform
|
closed
|
AI platform create batch prediction job text entity extraction: should create a text entity extraction batch prediction job failed
|
type: bug priority: p1 flakybot: issue api: vertex-ai
|
This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: e1c5cd6b5d03afb03911ba9aa685457aa359a602
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/69dc3b23-298d-461c-9279-cd7551a90fc9), [Sponge](http://sponge2/69dc3b23-298d-461c-9279-cd7551a90fc9)
status: failed
<details><summary>Test output</summary><br><pre>Command failed: node ./create-batch-prediction-job-text-entity-extraction.js temp_create_batch_prediction_text_entity_extraction_testb2a69827-22a8-4e2f-a39e-ce54904090b5 6305215400179138560 gs://ucaip-samples-test-output/inputs/batch_predict_TEN/ten_inputs.jsonl gs://ucaip-samples-test-output/ ucaip-sample-tests us-central1
16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
Error: Command failed: node ./create-batch-prediction-job-text-entity-extraction.js temp_create_batch_prediction_text_entity_extraction_testb2a69827-22a8-4e2f-a39e-ce54904090b5 6305215400179138560 gs://ucaip-samples-test-output/inputs/batch_predict_TEN/ten_inputs.jsonl gs://ucaip-samples-test-output/ ucaip-sample-tests us-central1
16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
at checkExecSyncError (child_process.js:635:11)
at Object.execSync (child_process.js:671:15)
at execSync (test/create-batch-prediction-job-text-entity-extraction.test.js:23:28)
at Context.<anonymous> (test/create-batch-prediction-job-text-entity-extraction.test.js:44:20)
at processImmediate (internal/timers.js:461:21)</pre></details>
|
1.0
|
AI platform create batch prediction job text entity extraction: should create a text entity extraction batch prediction job failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: e1c5cd6b5d03afb03911ba9aa685457aa359a602
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/69dc3b23-298d-461c-9279-cd7551a90fc9), [Sponge](http://sponge2/69dc3b23-298d-461c-9279-cd7551a90fc9)
status: failed
<details><summary>Test output</summary><br><pre>Command failed: node ./create-batch-prediction-job-text-entity-extraction.js temp_create_batch_prediction_text_entity_extraction_testb2a69827-22a8-4e2f-a39e-ce54904090b5 6305215400179138560 gs://ucaip-samples-test-output/inputs/batch_predict_TEN/ten_inputs.jsonl gs://ucaip-samples-test-output/ ucaip-sample-tests us-central1
16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
Error: Command failed: node ./create-batch-prediction-job-text-entity-extraction.js temp_create_batch_prediction_text_entity_extraction_testb2a69827-22a8-4e2f-a39e-ce54904090b5 6305215400179138560 gs://ucaip-samples-test-output/inputs/batch_predict_TEN/ten_inputs.jsonl gs://ucaip-samples-test-output/ ucaip-sample-tests us-central1
16 UNAUTHENTICATED: Request had invalid authentication credentials. Expected OAuth 2 access token, login cookie or other valid authentication credential. See https://developers.google.com/identity/sign-in/web/devconsole-project.
at checkExecSyncError (child_process.js:635:11)
at Object.execSync (child_process.js:671:15)
at execSync (test/create-batch-prediction-job-text-entity-extraction.test.js:23:28)
at Context.<anonymous> (test/create-batch-prediction-job-text-entity-extraction.test.js:44:20)
at processImmediate (internal/timers.js:461:21)</pre></details>
|
non_defect
|
ai platform create batch prediction job text entity extraction should create a text entity extraction batch prediction job failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output command failed node create batch prediction job text entity extraction js temp create batch prediction text entity extraction gs ucaip samples test output inputs batch predict ten ten inputs jsonl gs ucaip samples test output ucaip sample tests us unauthenticated request had invalid authentication credentials expected oauth access token login cookie or other valid authentication credential see error command failed node create batch prediction job text entity extraction js temp create batch prediction text entity extraction gs ucaip samples test output inputs batch predict ten ten inputs jsonl gs ucaip samples test output ucaip sample tests us unauthenticated request had invalid authentication credentials expected oauth access token login cookie or other valid authentication credential see at checkexecsyncerror child process js at object execsync child process js at execsync test create batch prediction job text entity extraction test js at context test create batch prediction job text entity extraction test js at processimmediate internal timers js
| 0
|
4,912
| 3,898,280,173
|
IssuesEvent
|
2016-04-17 00:03:06
|
lionheart/openradar-mirror
|
https://api.github.com/repos/lionheart/openradar-mirror
|
opened
|
14887462: Launching an app can temporarily leave a white pixelated remnant in the upper left corner of the screen
|
classification:ui/usability reproducible:always status:open
|
#### Description
Summary:
Depending on your Springboard app layout, launching an app can temporarily leave a white pixelated remnant in the upper left corner of the screen.
Steps to Reproduce:
1. Organize applications on a Springboard page so an app with a long name (Google Maps works) is the second app on the second row.
2. Pull down to search for an app
3. Search for any app (other than the one you positioned) and launch
Expected Results:
Smooth animation into the home screen of the launched app
Actual Results:
Toward the end of the zoom animation, the right edge of the title of the app with the long name gets temporarily "stuck" in the upper left corner of the screen before the animation completes.
Version:
iOS 7 beta 6 (first appeared in beta 5)
Configuration:
App with long, one-line name in second position of second row in Springboard.
Attachments:
-
Product Version: iOS 7 beta 5, 6
Created: 2013-08-31T23:01:38.745797
Originated: 2013-08-31T00:00:00
Open Radar Link: http://www.openradar.me/14887462
|
True
|
14887462: Launching an app can temporarily leave a white pixelated remnant in the upper left corner of the screen - #### Description
Summary:
Depending on your Springboard app layout, launching an app can temporarily leave a white pixelated remnant in the upper left corner of the screen.
Steps to Reproduce:
1. Organize applications on a Springboard page so an app with a long name (Google Maps works) is the second app on the second row.
2. Pull down to search for an app
3. Search for any app (other than the one you positioned) and launch
Expected Results:
Smooth animation into the home screen of the launched app
Actual Results:
Toward the end of the zoom animation, the right edge of the title of the app with the long name gets temporarily "stuck" in the upper left corner of the screen before the animation completes.
Version:
iOS 7 beta 6 (first appeared in beta 5)
Configuration:
App with long, one-line name in second position of second row in Springboard.
Attachments:
-
Product Version: iOS 7 beta 5, 6
Created: 2013-08-31T23:01:38.745797
Originated: 2013-08-31T00:00:00
Open Radar Link: http://www.openradar.me/14887462
|
non_defect
|
launching an app can temporarily leave a white pixelated remnant in the upper left corner of the screen description summary depending on your springboard app layout launching an app can temporarily leave a white pixelated remnant in the upper left corner of the screen steps to reproduce organize applications on a springboard page so an app with a long name google maps works is the second app on the second row pull down to search for an app search for any app other than the one you positioned and launch expected results smooth animation into the home screen of the launched app actual results toward the end of the zoom animation the right edge of the title of the app with the long name gets temporarily stuck in the upper left corner of the screen before the animation completes version ios beta first appeared in beta configuration app with long one line name in second position of second row in springboard attachments product version ios beta created originated open radar link
| 0
|
26,341
| 11,297,130,675
|
IssuesEvent
|
2020-01-17 04:43:03
|
drakeg/drakeweb.org
|
https://api.github.com/repos/drakeg/drakeweb.org
|
opened
|
CVE-2017-16137 (Medium) detected in debug-0.7.4.tgz
|
security vulnerability
|
## CVE-2017-16137 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>debug-0.7.4.tgz</b></p></summary>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-0.7.4.tgz">https://registry.npmjs.org/debug/-/debug-0.7.4.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/drakeweb.org/wp-content/themes/decode/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/debug/package.json,/tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- tiny-lr-fork-0.0.5.tgz
- :x: **debug-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/drakeg/drakeweb.org/commit/3759e4bc84151f770a6f4cc54da1c6232f666a6e">3759e4bc84151f770a6f4cc54da1c6232f666a6e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16137">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16137</a></p>
<p>Release Date: 2019-06-05</p>
<p>Fix Resolution: 2.6.9,3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2017-16137 (Medium) detected in debug-0.7.4.tgz - ## CVE-2017-16137 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>debug-0.7.4.tgz</b></p></summary>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-0.7.4.tgz">https://registry.npmjs.org/debug/-/debug-0.7.4.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/drakeweb.org/wp-content/themes/decode/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/debug/package.json,/tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- tiny-lr-fork-0.0.5.tgz
- :x: **debug-0.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/drakeg/drakeweb.org/commit/3759e4bc84151f770a6f4cc54da1c6232f666a6e">3759e4bc84151f770a6f4cc54da1c6232f666a6e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16137">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16137</a></p>
<p>Release Date: 2019-06-05</p>
<p>Fix Resolution: 2.6.9,3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve medium detected in debug tgz cve medium severity vulnerability vulnerable library debug tgz small debugging utility library home page a href path to dependency file tmp ws scm drakeweb org wp content themes decode package json path to vulnerable library tmp ws scm drakeweb org wp content plugins press this node modules debug package json tmp ws scm drakeweb org wp content plugins press this node modules debug package json dependency hierarchy grunt contrib watch tgz root library tiny lr fork tgz x debug tgz vulnerable library found in head commit a href vulnerability details the debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter it takes around characters to block for seconds making this a low severity issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
1,850
| 2,603,972,459
|
IssuesEvent
|
2015-02-24 19:00:36
|
chrsmith/nishazi6
|
https://api.github.com/repos/chrsmith/nishazi6
|
opened
|
沈阳生殖器疣的早期症状
|
auto-migrated Priority-Medium Type-Defect
|
```
沈阳生殖器疣的早期症状〓沈陽軍區政治部醫院性病〓TEL:02
4-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治療�
��位于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝�
��的歷史悠久、設備精良、技術權威、專家云集,是預防、保
健、醫療、科研康復為一體的綜合性醫院。是國家首批公立��
�等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學�
��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍
空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集��
�二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:00
|
1.0
|
沈阳生殖器疣的早期症状 - ```
沈阳生殖器疣的早期症状〓沈陽軍區政治部醫院性病〓TEL:02
4-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治療�
��位于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝�
��的歷史悠久、設備精良、技術權威、專家云集,是預防、保
健、醫療、科研康復為一體的綜合性醫院。是國家首批公立��
�等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學�
��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍
空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集��
�二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:00
|
defect
|
沈阳生殖器疣的早期症状 沈阳生殖器疣的早期症状〓沈陽軍區政治部醫院性病〓tel: 〓 , � �� 。是一所與新中國同建立共輝� ��的歷史悠久、設備精良、技術權威、專家云集,是預防、保 健、醫療、科研康復為一體的綜合性醫院。是國家首批公立�� �等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學� ��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍 空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集�� �二等功。 original issue reported on code google com by gmail com on jun at
| 1
|
16,488
| 2,904,873,066
|
IssuesEvent
|
2015-06-18 20:27:26
|
vrapper/vrapper
|
https://api.github.com/repos/vrapper/vrapper
|
closed
|
net.sourceforge.vrapper.platform.VrapperPlatformException after 'o' on last line of file
|
Defect
|
I hit the stacktrace below when pressing 'o' (in command mode) on the last line of a java file, using vrapper 0.56. The last line is like this (space matters):
~~~~
}
~~~~
When I do 'o', the cursor moves as follows:
~~~~
}
| <- the cursor
~~~~
Then if I go back into command mode by pressing ESC, I get:
~~~~
net.sourceforge.vrapper.platform.VrapperPlatformException: Failed to set mark for M 25706
at net.sourceforge.vrapper.eclipse.platform.EclipseCursorAndSelection.setMark(EclipseCursorAndSelection.java:520)
at net.sourceforge.vrapper.vim.modes.InsertMode.saveTypedText(InsertMode.java:253)
at net.sourceforge.vrapper.vim.modes.InsertMode.leaveMode(InsertMode.java:194)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.changeMode(DefaultEditorAdaptor.java:373)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.changeModeSafely(DefaultEditorAdaptor.java:218)
at net.sourceforge.vrapper.vim.modes.InsertMode.handleKey(InsertMode.java:336)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.handleKey0(DefaultEditorAdaptor.java:667)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.handleKeyOffRecord(DefaultEditorAdaptor.java:404)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.handleKey(DefaultEditorAdaptor.java:399)
at net.sourceforge.vrapper.eclipse.interceptor.VimInputInterceptorFactory$VimInputInterceptor.verifyKey(VimInputInterceptorFactory.java:188)
at org.eclipse.jface.text.TextViewer$VerifyKeyListenersManager.verifyKey(TextViewer.java:492)
at org.eclipse.swt.custom.StyledTextListener.handleEvent(StyledTextListener.java:66)
at org.eclipse.swt.widgets.EventTable.sendEvent(EventTable.java:84)
at org.eclipse.swt.widgets.Display.sendEvent(Display.java:4454)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1388)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1412)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1397)
at org.eclipse.swt.widgets.Widget.notifyListeners(Widget.java:1182)
at org.eclipse.swt.custom.StyledText.handleKeyDown(StyledText.java:5981)
at org.eclipse.swt.custom.StyledText$7.handleEvent(StyledText.java:5663)
at org.eclipse.swt.widgets.EventTable.sendEvent(EventTable.java:84)
at org.eclipse.swt.widgets.Display.sendEvent(Display.java:4454)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1388)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1412)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1397)
at org.eclipse.swt.widgets.Widget.sendKeyEvent(Widget.java:1424)
at org.eclipse.swt.widgets.Widget.gtk_key_press_event(Widget.java:824)
at org.eclipse.swt.widgets.Control.gtk_key_press_event(Control.java:3293)
at org.eclipse.swt.widgets.Composite.gtk_key_press_event(Composite.java:769)
at org.eclipse.swt.widgets.Widget.windowProc(Widget.java:2098)
at org.eclipse.swt.widgets.Control.windowProc(Control.java:5534)
at org.eclipse.swt.widgets.Display.windowProc(Display.java:4668)
at org.eclipse.swt.internal.gtk.OS._gtk_main_do_event(Native Method)
at org.eclipse.swt.internal.gtk.OS.gtk_main_do_event(OS.java:9106)
at org.eclipse.swt.widgets.Display.eventProc(Display.java:1253)
at org.eclipse.swt.internal.gtk.OS._g_main_context_iteration(Native Method)
at org.eclipse.swt.internal.gtk.OS.g_main_context_iteration(OS.java:2477)
at org.eclipse.swt.widgets.Display.readAndDispatch(Display.java:3407)
at org.eclipse.e4.ui.internal.workbench.swt.PartRenderingEngine$9.run(PartRenderingEngine.java:1151)
at org.eclipse.core.databinding.observable.Realm.runWithDefault(Realm.java:332)
at org.eclipse.e4.ui.internal.workbench.swt.PartRenderingEngine.run(PartRenderingEngine.java:1032)
at org.eclipse.e4.ui.internal.workbench.E4Workbench.createAndRunUI(E4Workbench.java:148)
at org.eclipse.ui.internal.Workbench$5.run(Workbench.java:636)
at org.eclipse.core.databinding.observable.Realm.runWithDefault(Realm.java:332)
at org.eclipse.ui.internal.Workbench.createAndRunWorkbench(Workbench.java:579)
at org.eclipse.ui.PlatformUI.createAndRunWorkbench(PlatformUI.java:150)
at org.eclipse.ui.internal.ide.application.IDEApplication.start(IDEApplication.java:135)
at org.eclipse.equinox.internal.app.EclipseAppHandle.run(EclipseAppHandle.java:196)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.runApplication(EclipseAppLauncher.java:134)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.start(EclipseAppLauncher.java:104)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:380)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:235)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:483)
at org.eclipse.equinox.launcher.Main.invokeFramework(Main.java:648)
at org.eclipse.equinox.launcher.Main.basicRun(Main.java:603)
at org.eclipse.equinox.launcher.Main.run(Main.java:1465)
Caused by: org.eclipse.jface.text.BadLocationException
at org.eclipse.jface.text.AbstractDocument.addPosition(AbstractDocument.java:355)
at org.eclipse.core.internal.filebuffers.SynchronizableDocument.addPosition(SynchronizableDocument.java:236)
at org.eclipse.jface.text.AbstractDocument.addPosition(AbstractDocument.java:376)
at net.sourceforge.vrapper.eclipse.platform.EclipseCursorAndSelection.setMark(EclipseCursorAndSelection.java:518)
... 58 more
~~~~
I do not hit the bug if:
* the " }" is not on the last line, or
* if there's no space before "}".
|
1.0
|
net.sourceforge.vrapper.platform.VrapperPlatformException after 'o' on last line of file - I hit the stacktrace below when pressing 'o' (in command mode) on the last line of a java file, using vrapper 0.56. The last line is like this (space matters):
~~~~
}
~~~~
When I do 'o', the cursor moves as follows:
~~~~
}
| <- the cursor
~~~~
Then if I go back into command mode by pressing ESC, I get:
~~~~
net.sourceforge.vrapper.platform.VrapperPlatformException: Failed to set mark for M 25706
at net.sourceforge.vrapper.eclipse.platform.EclipseCursorAndSelection.setMark(EclipseCursorAndSelection.java:520)
at net.sourceforge.vrapper.vim.modes.InsertMode.saveTypedText(InsertMode.java:253)
at net.sourceforge.vrapper.vim.modes.InsertMode.leaveMode(InsertMode.java:194)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.changeMode(DefaultEditorAdaptor.java:373)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.changeModeSafely(DefaultEditorAdaptor.java:218)
at net.sourceforge.vrapper.vim.modes.InsertMode.handleKey(InsertMode.java:336)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.handleKey0(DefaultEditorAdaptor.java:667)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.handleKeyOffRecord(DefaultEditorAdaptor.java:404)
at net.sourceforge.vrapper.vim.DefaultEditorAdaptor.handleKey(DefaultEditorAdaptor.java:399)
at net.sourceforge.vrapper.eclipse.interceptor.VimInputInterceptorFactory$VimInputInterceptor.verifyKey(VimInputInterceptorFactory.java:188)
at org.eclipse.jface.text.TextViewer$VerifyKeyListenersManager.verifyKey(TextViewer.java:492)
at org.eclipse.swt.custom.StyledTextListener.handleEvent(StyledTextListener.java:66)
at org.eclipse.swt.widgets.EventTable.sendEvent(EventTable.java:84)
at org.eclipse.swt.widgets.Display.sendEvent(Display.java:4454)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1388)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1412)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1397)
at org.eclipse.swt.widgets.Widget.notifyListeners(Widget.java:1182)
at org.eclipse.swt.custom.StyledText.handleKeyDown(StyledText.java:5981)
at org.eclipse.swt.custom.StyledText$7.handleEvent(StyledText.java:5663)
at org.eclipse.swt.widgets.EventTable.sendEvent(EventTable.java:84)
at org.eclipse.swt.widgets.Display.sendEvent(Display.java:4454)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1388)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1412)
at org.eclipse.swt.widgets.Widget.sendEvent(Widget.java:1397)
at org.eclipse.swt.widgets.Widget.sendKeyEvent(Widget.java:1424)
at org.eclipse.swt.widgets.Widget.gtk_key_press_event(Widget.java:824)
at org.eclipse.swt.widgets.Control.gtk_key_press_event(Control.java:3293)
at org.eclipse.swt.widgets.Composite.gtk_key_press_event(Composite.java:769)
at org.eclipse.swt.widgets.Widget.windowProc(Widget.java:2098)
at org.eclipse.swt.widgets.Control.windowProc(Control.java:5534)
at org.eclipse.swt.widgets.Display.windowProc(Display.java:4668)
at org.eclipse.swt.internal.gtk.OS._gtk_main_do_event(Native Method)
at org.eclipse.swt.internal.gtk.OS.gtk_main_do_event(OS.java:9106)
at org.eclipse.swt.widgets.Display.eventProc(Display.java:1253)
at org.eclipse.swt.internal.gtk.OS._g_main_context_iteration(Native Method)
at org.eclipse.swt.internal.gtk.OS.g_main_context_iteration(OS.java:2477)
at org.eclipse.swt.widgets.Display.readAndDispatch(Display.java:3407)
at org.eclipse.e4.ui.internal.workbench.swt.PartRenderingEngine$9.run(PartRenderingEngine.java:1151)
at org.eclipse.core.databinding.observable.Realm.runWithDefault(Realm.java:332)
at org.eclipse.e4.ui.internal.workbench.swt.PartRenderingEngine.run(PartRenderingEngine.java:1032)
at org.eclipse.e4.ui.internal.workbench.E4Workbench.createAndRunUI(E4Workbench.java:148)
at org.eclipse.ui.internal.Workbench$5.run(Workbench.java:636)
at org.eclipse.core.databinding.observable.Realm.runWithDefault(Realm.java:332)
at org.eclipse.ui.internal.Workbench.createAndRunWorkbench(Workbench.java:579)
at org.eclipse.ui.PlatformUI.createAndRunWorkbench(PlatformUI.java:150)
at org.eclipse.ui.internal.ide.application.IDEApplication.start(IDEApplication.java:135)
at org.eclipse.equinox.internal.app.EclipseAppHandle.run(EclipseAppHandle.java:196)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.runApplication(EclipseAppLauncher.java:134)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.start(EclipseAppLauncher.java:104)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:380)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:235)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:483)
at org.eclipse.equinox.launcher.Main.invokeFramework(Main.java:648)
at org.eclipse.equinox.launcher.Main.basicRun(Main.java:603)
at org.eclipse.equinox.launcher.Main.run(Main.java:1465)
Caused by: org.eclipse.jface.text.BadLocationException
at org.eclipse.jface.text.AbstractDocument.addPosition(AbstractDocument.java:355)
at org.eclipse.core.internal.filebuffers.SynchronizableDocument.addPosition(SynchronizableDocument.java:236)
at org.eclipse.jface.text.AbstractDocument.addPosition(AbstractDocument.java:376)
at net.sourceforge.vrapper.eclipse.platform.EclipseCursorAndSelection.setMark(EclipseCursorAndSelection.java:518)
... 58 more
~~~~
I do not hit the bug if:
* the " }" is not on the last line, or
* if there's no space before "}".
|
defect
|
net sourceforge vrapper platform vrapperplatformexception after o on last line of file i hit the stacktrace below when pressing o in command mode on the last line of a java file using vrapper the last line is like this space matters when i do o the cursor moves as follows the cursor then if i go back into command mode by pressing esc i get net sourceforge vrapper platform vrapperplatformexception failed to set mark for m at net sourceforge vrapper eclipse platform eclipsecursorandselection setmark eclipsecursorandselection java at net sourceforge vrapper vim modes insertmode savetypedtext insertmode java at net sourceforge vrapper vim modes insertmode leavemode insertmode java at net sourceforge vrapper vim defaulteditoradaptor changemode defaulteditoradaptor java at net sourceforge vrapper vim defaulteditoradaptor changemodesafely defaulteditoradaptor java at net sourceforge vrapper vim modes insertmode handlekey insertmode java at net sourceforge vrapper vim defaulteditoradaptor defaulteditoradaptor java at net sourceforge vrapper vim defaulteditoradaptor handlekeyoffrecord defaulteditoradaptor java at net sourceforge vrapper vim defaulteditoradaptor handlekey defaulteditoradaptor java at net sourceforge vrapper eclipse interceptor viminputinterceptorfactory viminputinterceptor verifykey viminputinterceptorfactory java at org eclipse jface text textviewer verifykeylistenersmanager verifykey textviewer java at org eclipse swt custom styledtextlistener handleevent styledtextlistener java at org eclipse swt widgets eventtable sendevent eventtable java at org eclipse swt widgets display sendevent display java at org eclipse swt widgets widget sendevent widget java at org eclipse swt widgets widget sendevent widget java at org eclipse swt widgets widget sendevent widget java at org eclipse swt widgets widget notifylisteners widget java at org eclipse swt custom styledtext handlekeydown styledtext java at org eclipse swt custom styledtext handleevent styledtext java at org eclipse swt widgets eventtable sendevent eventtable java at org eclipse swt widgets display sendevent display java at org eclipse swt widgets widget sendevent widget java at org eclipse swt widgets widget sendevent widget java at org eclipse swt widgets widget sendevent widget java at org eclipse swt widgets widget sendkeyevent widget java at org eclipse swt widgets widget gtk key press event widget java at org eclipse swt widgets control gtk key press event control java at org eclipse swt widgets composite gtk key press event composite java at org eclipse swt widgets widget windowproc widget java at org eclipse swt widgets control windowproc control java at org eclipse swt widgets display windowproc display java at org eclipse swt internal gtk os gtk main do event native method at org eclipse swt internal gtk os gtk main do event os java at org eclipse swt widgets display eventproc display java at org eclipse swt internal gtk os g main context iteration native method at org eclipse swt internal gtk os g main context iteration os java at org eclipse swt widgets display readanddispatch display java at org eclipse ui internal workbench swt partrenderingengine run partrenderingengine java at org eclipse core databinding observable realm runwithdefault realm java at org eclipse ui internal workbench swt partrenderingengine run partrenderingengine java at org eclipse ui internal workbench createandrunui java at org eclipse ui internal workbench run workbench java at org eclipse core databinding observable realm runwithdefault realm java at org eclipse ui internal workbench createandrunworkbench workbench java at org eclipse ui platformui createandrunworkbench platformui java at org eclipse ui internal ide application ideapplication start ideapplication java at org eclipse equinox internal app eclipseapphandle run eclipseapphandle java at org eclipse core runtime internal adaptor eclipseapplauncher runapplication eclipseapplauncher java at org eclipse core runtime internal adaptor eclipseapplauncher start eclipseapplauncher java at org eclipse core runtime adaptor eclipsestarter run eclipsestarter java at org eclipse core runtime adaptor eclipsestarter run eclipsestarter java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org eclipse equinox launcher main invokeframework main java at org eclipse equinox launcher main basicrun main java at org eclipse equinox launcher main run main java caused by org eclipse jface text badlocationexception at org eclipse jface text abstractdocument addposition abstractdocument java at org eclipse core internal filebuffers synchronizabledocument addposition synchronizabledocument java at org eclipse jface text abstractdocument addposition abstractdocument java at net sourceforge vrapper eclipse platform eclipsecursorandselection setmark eclipsecursorandselection java more i do not hit the bug if the is not on the last line or if there s no space before
| 1
|
136,410
| 30,543,215,856
|
IssuesEvent
|
2023-07-20 00:06:58
|
grpc/grpc-java
|
https://api.github.com/repos/grpc/grpc-java
|
opened
|
AsyncServletOutputStreamWriterConcurrencyTest is too slow
|
code health
|
On my laptop, the single `linCheck` test takes over four minutes. I believe this is adding roughly that amount of time to the total build. This test class should either not be part of the normal test execution, or be configured in such a way to take considerably less time (max of 30s?).
|
1.0
|
AsyncServletOutputStreamWriterConcurrencyTest is too slow - On my laptop, the single `linCheck` test takes over four minutes. I believe this is adding roughly that amount of time to the total build. This test class should either not be part of the normal test execution, or be configured in such a way to take considerably less time (max of 30s?).
|
non_defect
|
asyncservletoutputstreamwriterconcurrencytest is too slow on my laptop the single lincheck test takes over four minutes i believe this is adding roughly that amount of time to the total build this test class should either not be part of the normal test execution or be configured in such a way to take considerably less time max of
| 0
|
46,773
| 13,055,973,976
|
IssuesEvent
|
2020-07-30 03:16:44
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
[I3OmDb] Not compiling for icerec/V05-00-02 (Trac #1853)
|
Incomplete Migration Migrated from Trac combo reconstruction defect
|
Migrated from https://code.icecube.wisc.edu/ticket/1853
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:24",
"description": "Does not compile for me when using clang however gcc works. Forward declaration wrongly executed.\n\n{{{\n[ 88%] Building CXX object STTools/CMakeFiles/STTools-pybindings.dir/private/pybindings/algorithms/seededRT/I3SeededRTConfigurationService.cxx.o\nIn file included from /home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/private/I3OmDb/I3OmDbFactory.cxx:2:\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:1280:8: error: 'Om_s' redeclared with 'private' access\nstruct Om_s \n ^\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:977:8: note: previously declared 'public' here\nstruct Om_s;\n ^\n1 error generated.\nmake[2]: *** [I3Db/CMakeFiles/I3Db.dir/private/I3OmDb/I3OmDbFactory.cxx.o] Error 1\nmake[2]: Target `I3Db/CMakeFiles/I3Db.dir/build' not remade because of errors.\nmake[1]: *** [I3Db/CMakeFiles/I3Db.dir/all] Error 2\n}}}\n",
"reporter": "maryon",
"cc": "",
"resolution": "fixed",
"_ts": "1550067204154158",
"component": "combo reconstruction",
"summary": "[I3OmDb] Not compiling for icerec/V05-00-02",
"priority": "blocker",
"keywords": "I3OmDb icerec",
"time": "2016-09-09T11:50:36",
"milestone": "",
"owner": "joertlin",
"type": "defect"
}
```
|
1.0
|
[I3OmDb] Not compiling for icerec/V05-00-02 (Trac #1853) - Migrated from https://code.icecube.wisc.edu/ticket/1853
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:24",
"description": "Does not compile for me when using clang however gcc works. Forward declaration wrongly executed.\n\n{{{\n[ 88%] Building CXX object STTools/CMakeFiles/STTools-pybindings.dir/private/pybindings/algorithms/seededRT/I3SeededRTConfigurationService.cxx.o\nIn file included from /home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/private/I3OmDb/I3OmDbFactory.cxx:2:\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:1280:8: error: 'Om_s' redeclared with 'private' access\nstruct Om_s \n ^\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:977:8: note: previously declared 'public' here\nstruct Om_s;\n ^\n1 error generated.\nmake[2]: *** [I3Db/CMakeFiles/I3Db.dir/private/I3OmDb/I3OmDbFactory.cxx.o] Error 1\nmake[2]: Target `I3Db/CMakeFiles/I3Db.dir/build' not remade because of errors.\nmake[1]: *** [I3Db/CMakeFiles/I3Db.dir/all] Error 2\n}}}\n",
"reporter": "maryon",
"cc": "",
"resolution": "fixed",
"_ts": "1550067204154158",
"component": "combo reconstruction",
"summary": "[I3OmDb] Not compiling for icerec/V05-00-02",
"priority": "blocker",
"keywords": "I3OmDb icerec",
"time": "2016-09-09T11:50:36",
"milestone": "",
"owner": "joertlin",
"type": "defect"
}
```
|
defect
|
not compiling for icerec trac migrated from json status closed changetime description does not compile for me when using clang however gcc works forward declaration wrongly executed n n n building cxx object sttools cmakefiles sttools pybindings dir private pybindings algorithms seededrt cxx o nin file included from home maryon software meta projects icerec src private cxx n home maryon software meta projects icerec src public h error om s redeclared with private access nstruct om s n n home maryon software meta projects icerec src public h note previously declared public here nstruct om s n error generated nmake error nmake target cmakefiles dir build not remade because of errors nmake error n n reporter maryon cc resolution fixed ts component combo reconstruction summary not compiling for icerec priority blocker keywords icerec time milestone owner joertlin type defect
| 1
|
101,843
| 4,142,052,406
|
IssuesEvent
|
2016-06-14 08:40:43
|
donjar/kontes-terbuka
|
https://api.github.com/repos/donjar/kontes-terbuka
|
closed
|
Rules page before contest
|
priority:high
|
Tampilkan peraturan satu kali saja sebelum masuk ke kontes. Contoh: codeforces
|
1.0
|
Rules page before contest - Tampilkan peraturan satu kali saja sebelum masuk ke kontes. Contoh: codeforces
|
non_defect
|
rules page before contest tampilkan peraturan satu kali saja sebelum masuk ke kontes contoh codeforces
| 0
|
37,609
| 8,469,545,975
|
IssuesEvent
|
2018-10-23 23:30:04
|
techo/voluntariado-eventual
|
https://api.github.com/repos/techo/voluntariado-eventual
|
opened
|
El país de los usuarios importados de pilote está mal
|
Defecto v1.0
|
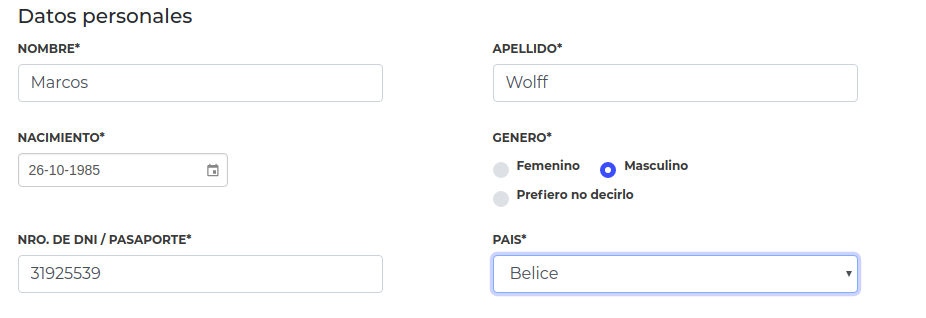
**Describí el error**
El país de los usuarios importados de pilote está mal
**Para reproducirlo**
Pasos para reproducir el comportamiento:
1. Con un usuario importado de Pilote ir a "Mi perfil"
2. Verificar que el país en la plataforma no es el mismo que se cargó en Pilote
**Comportamiento esperado**
Debería ser el mismo país
**Capturas de pantalla**
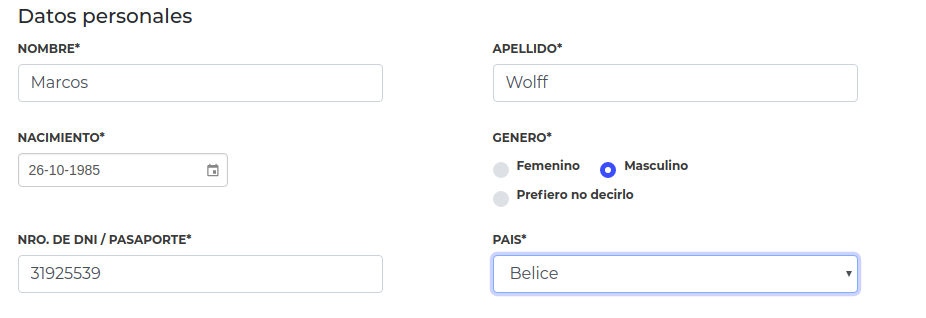
|
1.0
|
El país de los usuarios importados de pilote está mal - **Describí el error**
El país de los usuarios importados de pilote está mal
**Para reproducirlo**
Pasos para reproducir el comportamiento:
1. Con un usuario importado de Pilote ir a "Mi perfil"
2. Verificar que el país en la plataforma no es el mismo que se cargó en Pilote
**Comportamiento esperado**
Debería ser el mismo país
**Capturas de pantalla**
|
defect
|
el país de los usuarios importados de pilote está mal describí el error el país de los usuarios importados de pilote está mal para reproducirlo pasos para reproducir el comportamiento con un usuario importado de pilote ir a mi perfil verificar que el país en la plataforma no es el mismo que se cargó en pilote comportamiento esperado debería ser el mismo país capturas de pantalla
| 1
|
773,622
| 27,163,939,374
|
IssuesEvent
|
2023-02-17 14:04:42
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
www.thetimes.co.uk - design is broken
|
browser-firefox priority-normal os-mac engine-gecko
|
<!-- @browser: Firefox 110.0 -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/110.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/118335 -->
**URL**: https://www.thetimes.co.uk/
**Browser / Version**: Firefox 110.0
**Operating System**: Mac OS X 10.15
**Tested Another Browser**: Yes Chrome
**Problem type**: Design is broken
**Description**: Images not loaded
**Steps to Reproduce**:
Updated to 110.0 images won't load. Worked fine on 109
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2023/2/4980d49d-7c6f-4b33-9b95-e67718ad15a5.jpg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
www.thetimes.co.uk - design is broken - <!-- @browser: Firefox 110.0 -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:109.0) Gecko/20100101 Firefox/110.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/118335 -->
**URL**: https://www.thetimes.co.uk/
**Browser / Version**: Firefox 110.0
**Operating System**: Mac OS X 10.15
**Tested Another Browser**: Yes Chrome
**Problem type**: Design is broken
**Description**: Images not loaded
**Steps to Reproduce**:
Updated to 110.0 images won't load. Worked fine on 109
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2023/2/4980d49d-7c6f-4b33-9b95-e67718ad15a5.jpg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_defect
|
design is broken url browser version firefox operating system mac os x tested another browser yes chrome problem type design is broken description images not loaded steps to reproduce updated to images won t load worked fine on view the screenshot img alt screenshot src browser configuration none from with ❤️
| 0
|
80,476
| 30,302,219,007
|
IssuesEvent
|
2023-07-10 06:59:53
|
gperftools/gperftools
|
https://api.github.com/repos/gperftools/gperftools
|
closed
|
google-perftools 1.7 heap-checker_unittest hangs when glibc 2.14
|
Type-Defect Priority-Medium Status-CannotReproduce
|
Originally reported on Google Code with ID 342
```
Hello,
I have a problem with google-perftools unit tests.
The unit test (heap-checker) hangs during the HEAPCHECK=normal phase.
lt-heap-checker process just grows bigger and bigger, and nothnig else happens.
The problem occurs only with glibc 2.14. With other glibc versions everything is perfect.
Probably the problem is related to the __memalign_hook function.
```
Reported by `igor@chub.in` on 2011-06-06 07:08:57
|
1.0
|
google-perftools 1.7 heap-checker_unittest hangs when glibc 2.14 - Originally reported on Google Code with ID 342
```
Hello,
I have a problem with google-perftools unit tests.
The unit test (heap-checker) hangs during the HEAPCHECK=normal phase.
lt-heap-checker process just grows bigger and bigger, and nothnig else happens.
The problem occurs only with glibc 2.14. With other glibc versions everything is perfect.
Probably the problem is related to the __memalign_hook function.
```
Reported by `igor@chub.in` on 2011-06-06 07:08:57
|
defect
|
google perftools heap checker unittest hangs when glibc originally reported on google code with id hello i have a problem with google perftools unit tests the unit test heap checker hangs during the heapcheck normal phase lt heap checker process just grows bigger and bigger and nothnig else happens the problem occurs only with glibc with other glibc versions everything is perfect probably the problem is related to the memalign hook function reported by igor chub in on
| 1
|
40,543
| 10,037,629,179
|
IssuesEvent
|
2019-07-18 13:35:12
|
iconduit/iconduit
|
https://api.github.com/repos/iconduit/iconduit
|
closed
|
HTML tag attribute values are not being escaped
|
defect priority tags
|
Turns out [html-tag](https://github.com/jonschlinkert/html-tag) doesn't escape tag attribute values (jonschlinkert/html-tag#1) 🤯
I guess I need to write my own tag HTML generation.
|
1.0
|
HTML tag attribute values are not being escaped - Turns out [html-tag](https://github.com/jonschlinkert/html-tag) doesn't escape tag attribute values (jonschlinkert/html-tag#1) 🤯
I guess I need to write my own tag HTML generation.
|
defect
|
html tag attribute values are not being escaped turns out doesn t escape tag attribute values jonschlinkert html tag 🤯 i guess i need to write my own tag html generation
| 1
|
267,440
| 20,203,534,079
|
IssuesEvent
|
2022-02-11 17:35:53
|
CGI-FR/IoT-Hub-Portal
|
https://api.github.com/repos/CGI-FR/IoT-Hub-Portal
|
closed
|
Task: Activate swagger documentation
|
documentation .NET
|
Story: #217
**Description**
Activate Swagger documentation
|
1.0
|
Task: Activate swagger documentation - Story: #217
**Description**
Activate Swagger documentation
|
non_defect
|
task activate swagger documentation story description activate swagger documentation
| 0
|
255,790
| 27,504,310,231
|
IssuesEvent
|
2023-03-06 01:06:55
|
ghuangsnl/spring-boot
|
https://api.github.com/repos/ghuangsnl/spring-boot
|
opened
|
CVE-2022-4492 (High) detected in undertow-core-2.1.3.Final.jar
|
security vulnerability
|
## CVE-2022-4492 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>undertow-core-2.1.3.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Path to dependency file: /spring-boot-tests/spring-boot-smoke-tests/spring-boot-smoke-test-undertow-ssl/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/io.undertow/undertow-core/2.1.3.Final/ea86fcf86ad8d283c5b14a6820061a6bd203839e/undertow-core-2.1.3.Final.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.undertow/undertow-core/2.1.3.Final/ea86fcf86ad8d283c5b14a6820061a6bd203839e/undertow-core-2.1.3.Final.jar,/canner/.gradle/caches/modules-2/files-2.1/io.undertow/undertow-core/2.1.3.Final/ea86fcf86ad8d283c5b14a6820061a6bd203839e/undertow-core-2.1.3.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-2.1.3.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghuangsnl/spring-boot/commit/275c27d9dd5c88d8db426ebfb734d89d3f8e7412">275c27d9dd5c88d8db426ebfb734d89d3f8e7412</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The undertow client is not checking the server identity presented by the server certificate in https connections. This is a compulsory step (at least it should be performed by default) in https and in http/2. I would add it to any TLS client protocol.
<p>Publish Date: 2023-02-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-4492>CVE-2022-4492</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-4492 (High) detected in undertow-core-2.1.3.Final.jar - ## CVE-2022-4492 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>undertow-core-2.1.3.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Path to dependency file: /spring-boot-tests/spring-boot-smoke-tests/spring-boot-smoke-test-undertow-ssl/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/io.undertow/undertow-core/2.1.3.Final/ea86fcf86ad8d283c5b14a6820061a6bd203839e/undertow-core-2.1.3.Final.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.undertow/undertow-core/2.1.3.Final/ea86fcf86ad8d283c5b14a6820061a6bd203839e/undertow-core-2.1.3.Final.jar,/canner/.gradle/caches/modules-2/files-2.1/io.undertow/undertow-core/2.1.3.Final/ea86fcf86ad8d283c5b14a6820061a6bd203839e/undertow-core-2.1.3.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-2.1.3.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghuangsnl/spring-boot/commit/275c27d9dd5c88d8db426ebfb734d89d3f8e7412">275c27d9dd5c88d8db426ebfb734d89d3f8e7412</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The undertow client is not checking the server identity presented by the server certificate in https connections. This is a compulsory step (at least it should be performed by default) in https and in http/2. I would add it to any TLS client protocol.
<p>Publish Date: 2023-02-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-4492>CVE-2022-4492</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in undertow core final jar cve high severity vulnerability vulnerable library undertow core final jar undertow path to dependency file spring boot tests spring boot smoke tests spring boot smoke test undertow ssl build gradle path to vulnerable library canner gradle caches modules files io undertow undertow core final undertow core final jar home wss scanner gradle caches modules files io undertow undertow core final undertow core final jar canner gradle caches modules files io undertow undertow core final undertow core final jar dependency hierarchy x undertow core final jar vulnerable library found in head commit a href vulnerability details the undertow client is not checking the server identity presented by the server certificate in https connections this is a compulsory step at least it should be performed by default in https and in http i would add it to any tls client protocol publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend
| 0
|
652,118
| 21,522,662,910
|
IssuesEvent
|
2022-04-28 15:26:05
|
magento/pwa-studio
|
https://api.github.com/repos/magento/pwa-studio
|
reopened
|
[bug]: RootComponents can't have // commented code in their files
|
bug help wanted Priority: P2 Severity: S3 Progress: done
|
**Describe the bug**
Leaving code comments in RootComponents/Category/category.js prevents webpack from running after a restart
**To reproduce**
Steps to reproduce the behavior:
0. Start watcher with `yarn run watch:venia`
1. Go to packages/venia-ui/lib/RootComponents/Category/category.js
2. comment out
`
if (totalPagesFromData === null) {
return fullPageLoadingIndicator;
}
` with this `//` comment style
3. Note that it seems to compile normally without errors
4. Now restart the watcher
5. It should give you an error like below
<img width="1307" alt="Screenshot 2020-03-11 at 11 36 45" src="https://user-images.githubusercontent.com/19858728/76408037-9be0e580-638c-11ea-9287-b8a508cc35ef.png">
6. Now go ahead and remove the piece of code that we've just commented.
7. Restart watcher and note it now work properly
**Expected behavior**
Run's without a problem when you comment code
**Additional context**
It seem sto happen when the code has an `if()` statement in the code that's been commented.
Now for the weirdest part: when you use multiline comments like `/* */` the problem doesn't appear. So I think somewhere in the RootComponentsPlugin it somehow read's these comments
**Please complete the following device information:**
- Device [e.g. iPhone6, PC, Mac, Pixel3]:
- OS [e.g. iOS8.1, Windows 10]:
- Browser [e.g. Chrome, Safari]:
- Browser Version [e.g. 22]:
- Magento Version:
- PWA Studio Version:
- NPM version `npm -v`:
- Node Version `node -v`:
<!-- Complete the following sections to help us apply appropriate labels! -->
**Please let us know what packages this bug is in regards to:**
- [ ] `venia-concept`
- [ ] `venia-ui`
- [x] `pwa-buildpack`
- [ ] `peregrine`
- [ ] `pwa-devdocs`
- [ ] `upward-js`
- [ ] `upward-spec`
- [ ] `create-pwa`
|
1.0
|
[bug]: RootComponents can't have // commented code in their files - **Describe the bug**
Leaving code comments in RootComponents/Category/category.js prevents webpack from running after a restart
**To reproduce**
Steps to reproduce the behavior:
0. Start watcher with `yarn run watch:venia`
1. Go to packages/venia-ui/lib/RootComponents/Category/category.js
2. comment out
`
if (totalPagesFromData === null) {
return fullPageLoadingIndicator;
}
` with this `//` comment style
3. Note that it seems to compile normally without errors
4. Now restart the watcher
5. It should give you an error like below
<img width="1307" alt="Screenshot 2020-03-11 at 11 36 45" src="https://user-images.githubusercontent.com/19858728/76408037-9be0e580-638c-11ea-9287-b8a508cc35ef.png">
6. Now go ahead and remove the piece of code that we've just commented.
7. Restart watcher and note it now work properly
**Expected behavior**
Run's without a problem when you comment code
**Additional context**
It seem sto happen when the code has an `if()` statement in the code that's been commented.
Now for the weirdest part: when you use multiline comments like `/* */` the problem doesn't appear. So I think somewhere in the RootComponentsPlugin it somehow read's these comments
**Please complete the following device information:**
- Device [e.g. iPhone6, PC, Mac, Pixel3]:
- OS [e.g. iOS8.1, Windows 10]:
- Browser [e.g. Chrome, Safari]:
- Browser Version [e.g. 22]:
- Magento Version:
- PWA Studio Version:
- NPM version `npm -v`:
- Node Version `node -v`:
<!-- Complete the following sections to help us apply appropriate labels! -->
**Please let us know what packages this bug is in regards to:**
- [ ] `venia-concept`
- [ ] `venia-ui`
- [x] `pwa-buildpack`
- [ ] `peregrine`
- [ ] `pwa-devdocs`
- [ ] `upward-js`
- [ ] `upward-spec`
- [ ] `create-pwa`
|
non_defect
|
rootcomponents can t have commented code in their files describe the bug leaving code comments in rootcomponents category category js prevents webpack from running after a restart to reproduce steps to reproduce the behavior start watcher with yarn run watch venia go to packages venia ui lib rootcomponents category category js comment out if totalpagesfromdata null return fullpageloadingindicator with this comment style note that it seems to compile normally without errors now restart the watcher it should give you an error like below img width alt screenshot at src now go ahead and remove the piece of code that we ve just commented restart watcher and note it now work properly expected behavior run s without a problem when you comment code additional context it seem sto happen when the code has an if statement in the code that s been commented now for the weirdest part when you use multiline comments like the problem doesn t appear so i think somewhere in the rootcomponentsplugin it somehow read s these comments please complete the following device information device os browser browser version magento version pwa studio version npm version npm v node version node v please let us know what packages this bug is in regards to venia concept venia ui pwa buildpack peregrine pwa devdocs upward js upward spec create pwa
| 0
|
61,152
| 17,023,619,496
|
IssuesEvent
|
2021-07-03 02:57:33
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
[water] group of lakes (within a relation) mislabeled, all with the same name
|
Component: mapnik Priority: minor Resolution: worksforme Type: defect
|
**[Submitted to the original trac issue database at 7.26pm, Monday, 26th July 2010]**
When looking in OSM for lakes of 7 laux (group of lakes in French Alps), I see all the lakes labeled with the same name ("Lac de la Motte") :
http://www.openstreetmap.org/?lat=45.2415&lon=6.0863&zoom=14&layers=B000FTF
Whereas when looking at the OSM data in JOSM, each lake is correctly labeled with its different name.
|
1.0
|
[water] group of lakes (within a relation) mislabeled, all with the same name - **[Submitted to the original trac issue database at 7.26pm, Monday, 26th July 2010]**
When looking in OSM for lakes of 7 laux (group of lakes in French Alps), I see all the lakes labeled with the same name ("Lac de la Motte") :
http://www.openstreetmap.org/?lat=45.2415&lon=6.0863&zoom=14&layers=B000FTF
Whereas when looking at the OSM data in JOSM, each lake is correctly labeled with its different name.
|
defect
|
group of lakes within a relation mislabeled all with the same name when looking in osm for lakes of laux group of lakes in french alps i see all the lakes labeled with the same name lac de la motte whereas when looking at the osm data in josm each lake is correctly labeled with its different name
| 1
|
441,408
| 30,782,388,523
|
IssuesEvent
|
2023-07-31 10:56:00
|
authgear/docs
|
https://api.github.com/repos/authgear/docs
|
closed
|
Provide examples for including user attributes in JWT
|
documentation
|
A very common use case that can be achieved by the new event hook feature
```typescript
import { EventUserSessionJWTPreCreate, HookResponse } from "https://deno.land/x/authgear_deno_hook@v0.3.0/mod.ts";
export default async function(e: EventUserSessionJWTPreCreate): Promise<HookResponse> {
// Write your hook with the help of the type definition.
return {
mutations:{
jwt: {
payload:{
...e.payload.jwt.payload,
standard_attributes: e.payload.user.standard_attributes,
custom_attributes: e.payload.user.custom_attributes
}
}
},
is_allowed: true
};
}
```
|
1.0
|
Provide examples for including user attributes in JWT - A very common use case that can be achieved by the new event hook feature
```typescript
import { EventUserSessionJWTPreCreate, HookResponse } from "https://deno.land/x/authgear_deno_hook@v0.3.0/mod.ts";
export default async function(e: EventUserSessionJWTPreCreate): Promise<HookResponse> {
// Write your hook with the help of the type definition.
return {
mutations:{
jwt: {
payload:{
...e.payload.jwt.payload,
standard_attributes: e.payload.user.standard_attributes,
custom_attributes: e.payload.user.custom_attributes
}
}
},
is_allowed: true
};
}
```
|
non_defect
|
provide examples for including user attributes in jwt a very common use case that can be achieved by the new event hook feature typescript import eventusersessionjwtprecreate hookresponse from export default async function e eventusersessionjwtprecreate promise write your hook with the help of the type definition return mutations jwt payload e payload jwt payload standard attributes e payload user standard attributes custom attributes e payload user custom attributes is allowed true
| 0
|
20,547
| 3,374,014,215
|
IssuesEvent
|
2015-11-24 10:50:45
|
contao/core
|
https://api.github.com/repos/contao/core
|
closed
|
Discrepancy with $this->date between EventReader and EventList
|
defect
|
All the event templates use the variable `$this->date`. However, the Event modules do not fill this variable with the same values. While the EventList module fills this variable with just the date, e.g. `2015-09-14` the EventReader module on the other hand fills this variable with the date wrapped within an HTML `<time>` tag, e.g.
```html
<time datetime="2016-05-23T00:00:00+02:00">2016-05-23</time>
```
So, if you select the default [_event_list_](https://github.com/contao/core/blob/3.5.3/system/modules/calendar/templates/events/event_list.html5) template in the _EventReader_ (for whatever reason) it will produce invalid HTML:
```html
<h2><a href="" title="The Contao NRW-Day (<time datetime="2016-05-23T00:00:00+02:00">2016-05-23</time>)"></a></h2>
```
This is also reproducible in the Contao Online Demo.
The reason why the EventReader module produces a different value for `$this->date` is probably because the default [_event_full_](https://github.com/contao/core/blob/3.5.3/system/modules/calendar/templates/events/event_full.html5#L5) template has this line in it:
```php
<p class="info"><?= $this->date ?></p>
```
which in the end will produce
```html
<p class="info"><time datetime="2016-05-23T00:00:00+02:00">2016-05-23</time></p>
```
But in the teaser and list template, the variable is used within the title attribute of the link.
See also [3.5.3 Event Reader zeigt nur Teaserinhalt und seltsame Zeichen ](https://community.contao.org/de/showthread.php?59126-3-5-3-Event-Reader-zeigt-nur-Teaserinhalt-und-seltsame-Zeichen)
|
1.0
|
Discrepancy with $this->date between EventReader and EventList - All the event templates use the variable `$this->date`. However, the Event modules do not fill this variable with the same values. While the EventList module fills this variable with just the date, e.g. `2015-09-14` the EventReader module on the other hand fills this variable with the date wrapped within an HTML `<time>` tag, e.g.
```html
<time datetime="2016-05-23T00:00:00+02:00">2016-05-23</time>
```
So, if you select the default [_event_list_](https://github.com/contao/core/blob/3.5.3/system/modules/calendar/templates/events/event_list.html5) template in the _EventReader_ (for whatever reason) it will produce invalid HTML:
```html
<h2><a href="" title="The Contao NRW-Day (<time datetime="2016-05-23T00:00:00+02:00">2016-05-23</time>)"></a></h2>
```
This is also reproducible in the Contao Online Demo.
The reason why the EventReader module produces a different value for `$this->date` is probably because the default [_event_full_](https://github.com/contao/core/blob/3.5.3/system/modules/calendar/templates/events/event_full.html5#L5) template has this line in it:
```php
<p class="info"><?= $this->date ?></p>
```
which in the end will produce
```html
<p class="info"><time datetime="2016-05-23T00:00:00+02:00">2016-05-23</time></p>
```
But in the teaser and list template, the variable is used within the title attribute of the link.
See also [3.5.3 Event Reader zeigt nur Teaserinhalt und seltsame Zeichen ](https://community.contao.org/de/showthread.php?59126-3-5-3-Event-Reader-zeigt-nur-Teaserinhalt-und-seltsame-Zeichen)
|
defect
|
discrepancy with this date between eventreader and eventlist all the event templates use the variable this date however the event modules do not fill this variable with the same values while the eventlist module fills this variable with just the date e g the eventreader module on the other hand fills this variable with the date wrapped within an html tag e g html so if you select the default template in the eventreader for whatever reason it will produce invalid html html this is also reproducible in the contao online demo the reason why the eventreader module produces a different value for this date is probably because the default template has this line in it php date which in the end will produce html but in the teaser and list template the variable is used within the title attribute of the link see also
| 1
|
39,299
| 5,072,376,657
|
IssuesEvent
|
2016-12-26 22:28:05
|
kubernetes/kubernetes
|
https://api.github.com/repos/kubernetes/kubernetes
|
closed
|
Support for cookie based session affinity
|
kind/design priority/backlog team/cluster (deprecated - do not use)
|
Creating a new issue as https://github.com/GoogleCloudPlatform/kubernetes/issues/2867 is closed.
To add support for sticky sessions based on Cookies. If no one is working on this, I'd like to pick it up. Will need some help with the design for the same. If you have any thoughts please comment here.
An approach I have thought is to set a randomised string in a cookie for every new request (new = requests without the set cookie), create a map from this string to the service pod IP and the next time you see this cookie, you serve it with the mapped pod IP.
|
1.0
|
Support for cookie based session affinity - Creating a new issue as https://github.com/GoogleCloudPlatform/kubernetes/issues/2867 is closed.
To add support for sticky sessions based on Cookies. If no one is working on this, I'd like to pick it up. Will need some help with the design for the same. If you have any thoughts please comment here.
An approach I have thought is to set a randomised string in a cookie for every new request (new = requests without the set cookie), create a map from this string to the service pod IP and the next time you see this cookie, you serve it with the mapped pod IP.
|
non_defect
|
support for cookie based session affinity creating a new issue as is closed to add support for sticky sessions based on cookies if no one is working on this i d like to pick it up will need some help with the design for the same if you have any thoughts please comment here an approach i have thought is to set a randomised string in a cookie for every new request new requests without the set cookie create a map from this string to the service pod ip and the next time you see this cookie you serve it with the mapped pod ip
| 0
|
71,162
| 23,478,114,141
|
IssuesEvent
|
2022-08-17 08:10:49
|
jOOQ/jOOQ
|
https://api.github.com/repos/jOOQ/jOOQ
|
closed
|
PostgreSQL arrays don't deserialise correctly when using XML MULTISET emulation
|
T: Defect C: Functionality C: DB: PostgreSQL P: Medium E: All Editions
|
In PostgreSQL, when fetching an array such as `ARRAY['a', 'b']::TEXT[]`, the XML emulation may produce a query like this:
```sql
select (
select xmlelement(
name result,
xmlagg(xmlelement(
name record,
xmlelement(name "v0", "v0")
))
)
from (
select null as "v0"
union all
select cast('{"a","b"}' as varchar[]) as "a"
) as "t"
)
```
Which results in an XML document like this:
```xml
<?xml version="1.0" encoding="UTF-8"?>
<result>
<record>
<v0 />
</record>
<record>
<v0>
<element>a</element>
<element>b</element>
</v0>
</record>
</result>
```
This isn't being deserialised correctly by jOOQ. The following stack trace is produced:
```
org.jooq.exception.DataAccessException: SQL [select (select xmlelement(name result, xmlagg(xmlelement(name record, xmlelement(name "v0", "v0")))) from (select cast(? as varchar[]) as "v0" union all select cast(? as varchar[]) as "a") as "t") -- SQL rendered with a free trial version of jOOQ 3.18.0-SNAPSHOT]; Error while reading field: multiset(
select null "a"
union all
select array['a', 'b'] "a"
), at JDBC index: 1
at org.jooq_3.18.0-SNAPSHOT.POSTGRES.debug(Unknown Source)
at org.jooq.impl.Tools.translate(Tools.java:3300)
at org.jooq.impl.DefaultExecuteContext.sqlException(DefaultExecuteContext.java:678)
at org.jooq.impl.CursorImpl$CursorIterator.fetchNext(CursorImpl.java:1464)
at org.jooq.impl.CursorImpl$CursorIterator.hasNext(CursorImpl.java:1425)
at org.jooq.impl.CursorImpl.fetchNext(CursorImpl.java:238)
at org.jooq.impl.Tools.fetchOne(Tools.java:2592)
at org.jooq.impl.ResultQueryTrait.fetchOne(ResultQueryTrait.java:509)
at org.jooq.impl.Tools.attach(Tools.java:1518)
at org.jooq.impl.DefaultDSLContext.fetchOne(DefaultDSLContext.java:4662)
at org.jooq.impl.DefaultDSLContext.lambda$55(DefaultDSLContext.java:4682)
at org.jooq.impl.Tools.attach(Tools.java:1518)
at org.jooq.impl.DefaultDSLContext.fetchValue(DefaultDSLContext.java:4682)
at org.jooq.test.all.testcases.MultisetTests.lambda$211(MultisetTests.java:1491)
at org.jooq.test.jOOQAbstractTest.withDSLContext(jOOQAbstractTest.java:2062)
at org.jooq.test.jOOQAbstractTest.bindAndInlineWithDSLContexts(jOOQAbstractTest.java:2055)
at org.jooq.test.BaseTest.bindAndInlineWithDSLContexts(BaseTest.java:1728)
at org.jooq.test.all.testcases.MultisetTests.lambda$210(MultisetTests.java:1484)
at org.jooq.test.all.testcases.MultisetTests.lambda$453(MultisetTests.java:2984)
at org.jooq.test.all.testcases.MultisetTests.lambda$456(MultisetTests.java:3002)
at org.jooq.test.all.testcases.MultisetTests.testRecordLevelListenerResults(MultisetTests.java:3041)
at org.jooq.test.all.testcases.MultisetTests.testRecordLevelListenerResults(MultisetTests.java:3029)
at org.jooq.test.all.testcases.MultisetTests.testMultisetEmulations(MultisetTests.java:3002)
at org.jooq.test.all.testcases.MultisetTests.testMultisetEmulations(MultisetTests.java:2984)
at org.jooq.test.all.testcases.MultisetTests.assertMultisetDataType(MultisetTests.java:1483)
at org.jooq.test.all.testcases.MultisetTests.assertMultisetDataType(MultisetTests.java:1461)
at org.jooq.test.all.testcases.MultisetTests.assertMultisetDataType(MultisetTests.java:1457)
at org.jooq.test.all.testcases.MultisetTests.testMultisetProjectionDataTypeArray(MultisetTests.java:1714)
at org.jooq.test.jOOQAbstractTest.testMultisetProjectionDataTypeArray(jOOQAbstractTest.java:5333)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:61)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:61)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.eclipse.jdt.internal.junit4.runner.JUnit4TestReference.run(JUnit4TestReference.java:93)
at org.eclipse.jdt.internal.junit.runner.TestExecution.run(TestExecution.java:40)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.runTests(RemoteTestRunner.java:529)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.runTests(RemoteTestRunner.java:756)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.run(RemoteTestRunner.java:452)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.main(RemoteTestRunner.java:210)
Caused by: java.sql.SQLException: Error while reading field: multiset(
select null "a"
union all
select array['a', 'b'] "a"
), at JDBC index: 1
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.setValue(CursorImpl.java:1590)
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.apply(CursorImpl.java:1525)
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.apply(CursorImpl.java:1)
at org.jooq.impl.RecordDelegate.operate(RecordDelegate.java:144)
at org.jooq.impl.CursorImpl$CursorIterator.fetchNext(CursorImpl.java:1449)
... 57 more
Caused by: org.jooq.exception.DataAccessException: Could not read the XML string
at org.jooq.impl.XMLHandler.read(XMLHandler.java:173)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.readMultisetXML(DefaultBinding.java:4109)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.lambda$2(DefaultBinding.java:4084)
at org.jooq.impl.Tools.apply(Tools.java:2080)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.readMultiset(DefaultBinding.java:4082)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.readMultiset(DefaultBinding.java:4047)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.get0(DefaultBinding.java:4040)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.get0(DefaultBinding.java:1)
at org.jooq.impl.DefaultBinding$InternalBinding.get(DefaultBinding.java:1025)
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.setValue(CursorImpl.java:1580)
... 61 more
Caused by: java.lang.IndexOutOfBoundsException: Index 1 out of bounds for length 1
at java.base/jdk.internal.util.Preconditions.outOfBounds(Preconditions.java:64)
at java.base/jdk.internal.util.Preconditions.outOfBoundsCheckIndex(Preconditions.java:70)
at java.base/jdk.internal.util.Preconditions.checkIndex(Preconditions.java:266)
at java.base/java.util.Objects.checkIndex(Objects.java:359)
at java.base/java.util.ArrayList.get(ArrayList.java:427)
at org.jooq.impl.XMLHandler.startElement(XMLHandler.java:244)
at oracle.xml.parser.v2.NonValidatingParser.parseElement(NonValidatingParser.java:1701)
at oracle.xml.parser.v2.NonValidatingParser.parseRootElement(NonValidatingParser.java:461)
at oracle.xml.parser.v2.NonValidatingParser.parseDocument(NonValidatingParser.java:407)
at oracle.xml.parser.v2.XMLParser.parse(XMLParser.java:254)
at oracle.xml.jaxp.JXSAXParser.parse(JXSAXParser.java:298)
at oracle.xml.jaxp.JXSAXParser.parse(JXSAXParser.java:236)
at org.jooq.impl.XMLHandler.read(XMLHandler.java:169)
... 70 more
```
This seems to require a generic improvement to the XML deserialisation logic, independently of it being used by `MULTISET`. To be investigated.
|
1.0
|
PostgreSQL arrays don't deserialise correctly when using XML MULTISET emulation - In PostgreSQL, when fetching an array such as `ARRAY['a', 'b']::TEXT[]`, the XML emulation may produce a query like this:
```sql
select (
select xmlelement(
name result,
xmlagg(xmlelement(
name record,
xmlelement(name "v0", "v0")
))
)
from (
select null as "v0"
union all
select cast('{"a","b"}' as varchar[]) as "a"
) as "t"
)
```
Which results in an XML document like this:
```xml
<?xml version="1.0" encoding="UTF-8"?>
<result>
<record>
<v0 />
</record>
<record>
<v0>
<element>a</element>
<element>b</element>
</v0>
</record>
</result>
```
This isn't being deserialised correctly by jOOQ. The following stack trace is produced:
```
org.jooq.exception.DataAccessException: SQL [select (select xmlelement(name result, xmlagg(xmlelement(name record, xmlelement(name "v0", "v0")))) from (select cast(? as varchar[]) as "v0" union all select cast(? as varchar[]) as "a") as "t") -- SQL rendered with a free trial version of jOOQ 3.18.0-SNAPSHOT]; Error while reading field: multiset(
select null "a"
union all
select array['a', 'b'] "a"
), at JDBC index: 1
at org.jooq_3.18.0-SNAPSHOT.POSTGRES.debug(Unknown Source)
at org.jooq.impl.Tools.translate(Tools.java:3300)
at org.jooq.impl.DefaultExecuteContext.sqlException(DefaultExecuteContext.java:678)
at org.jooq.impl.CursorImpl$CursorIterator.fetchNext(CursorImpl.java:1464)
at org.jooq.impl.CursorImpl$CursorIterator.hasNext(CursorImpl.java:1425)
at org.jooq.impl.CursorImpl.fetchNext(CursorImpl.java:238)
at org.jooq.impl.Tools.fetchOne(Tools.java:2592)
at org.jooq.impl.ResultQueryTrait.fetchOne(ResultQueryTrait.java:509)
at org.jooq.impl.Tools.attach(Tools.java:1518)
at org.jooq.impl.DefaultDSLContext.fetchOne(DefaultDSLContext.java:4662)
at org.jooq.impl.DefaultDSLContext.lambda$55(DefaultDSLContext.java:4682)
at org.jooq.impl.Tools.attach(Tools.java:1518)
at org.jooq.impl.DefaultDSLContext.fetchValue(DefaultDSLContext.java:4682)
at org.jooq.test.all.testcases.MultisetTests.lambda$211(MultisetTests.java:1491)
at org.jooq.test.jOOQAbstractTest.withDSLContext(jOOQAbstractTest.java:2062)
at org.jooq.test.jOOQAbstractTest.bindAndInlineWithDSLContexts(jOOQAbstractTest.java:2055)
at org.jooq.test.BaseTest.bindAndInlineWithDSLContexts(BaseTest.java:1728)
at org.jooq.test.all.testcases.MultisetTests.lambda$210(MultisetTests.java:1484)
at org.jooq.test.all.testcases.MultisetTests.lambda$453(MultisetTests.java:2984)
at org.jooq.test.all.testcases.MultisetTests.lambda$456(MultisetTests.java:3002)
at org.jooq.test.all.testcases.MultisetTests.testRecordLevelListenerResults(MultisetTests.java:3041)
at org.jooq.test.all.testcases.MultisetTests.testRecordLevelListenerResults(MultisetTests.java:3029)
at org.jooq.test.all.testcases.MultisetTests.testMultisetEmulations(MultisetTests.java:3002)
at org.jooq.test.all.testcases.MultisetTests.testMultisetEmulations(MultisetTests.java:2984)
at org.jooq.test.all.testcases.MultisetTests.assertMultisetDataType(MultisetTests.java:1483)
at org.jooq.test.all.testcases.MultisetTests.assertMultisetDataType(MultisetTests.java:1461)
at org.jooq.test.all.testcases.MultisetTests.assertMultisetDataType(MultisetTests.java:1457)
at org.jooq.test.all.testcases.MultisetTests.testMultisetProjectionDataTypeArray(MultisetTests.java:1714)
at org.jooq.test.jOOQAbstractTest.testMultisetProjectionDataTypeArray(jOOQAbstractTest.java:5333)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:61)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:61)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.eclipse.jdt.internal.junit4.runner.JUnit4TestReference.run(JUnit4TestReference.java:93)
at org.eclipse.jdt.internal.junit.runner.TestExecution.run(TestExecution.java:40)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.runTests(RemoteTestRunner.java:529)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.runTests(RemoteTestRunner.java:756)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.run(RemoteTestRunner.java:452)
at org.eclipse.jdt.internal.junit.runner.RemoteTestRunner.main(RemoteTestRunner.java:210)
Caused by: java.sql.SQLException: Error while reading field: multiset(
select null "a"
union all
select array['a', 'b'] "a"
), at JDBC index: 1
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.setValue(CursorImpl.java:1590)
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.apply(CursorImpl.java:1525)
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.apply(CursorImpl.java:1)
at org.jooq.impl.RecordDelegate.operate(RecordDelegate.java:144)
at org.jooq.impl.CursorImpl$CursorIterator.fetchNext(CursorImpl.java:1449)
... 57 more
Caused by: org.jooq.exception.DataAccessException: Could not read the XML string
at org.jooq.impl.XMLHandler.read(XMLHandler.java:173)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.readMultisetXML(DefaultBinding.java:4109)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.lambda$2(DefaultBinding.java:4084)
at org.jooq.impl.Tools.apply(Tools.java:2080)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.readMultiset(DefaultBinding.java:4082)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.readMultiset(DefaultBinding.java:4047)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.get0(DefaultBinding.java:4040)
at org.jooq.impl.DefaultBinding$DefaultResultBinding.get0(DefaultBinding.java:1)
at org.jooq.impl.DefaultBinding$InternalBinding.get(DefaultBinding.java:1025)
at org.jooq.impl.CursorImpl$CursorIterator$CursorRecordInitialiser.setValue(CursorImpl.java:1580)
... 61 more
Caused by: java.lang.IndexOutOfBoundsException: Index 1 out of bounds for length 1
at java.base/jdk.internal.util.Preconditions.outOfBounds(Preconditions.java:64)
at java.base/jdk.internal.util.Preconditions.outOfBoundsCheckIndex(Preconditions.java:70)
at java.base/jdk.internal.util.Preconditions.checkIndex(Preconditions.java:266)
at java.base/java.util.Objects.checkIndex(Objects.java:359)
at java.base/java.util.ArrayList.get(ArrayList.java:427)
at org.jooq.impl.XMLHandler.startElement(XMLHandler.java:244)
at oracle.xml.parser.v2.NonValidatingParser.parseElement(NonValidatingParser.java:1701)
at oracle.xml.parser.v2.NonValidatingParser.parseRootElement(NonValidatingParser.java:461)
at oracle.xml.parser.v2.NonValidatingParser.parseDocument(NonValidatingParser.java:407)
at oracle.xml.parser.v2.XMLParser.parse(XMLParser.java:254)
at oracle.xml.jaxp.JXSAXParser.parse(JXSAXParser.java:298)
at oracle.xml.jaxp.JXSAXParser.parse(JXSAXParser.java:236)
at org.jooq.impl.XMLHandler.read(XMLHandler.java:169)
... 70 more
```
This seems to require a generic improvement to the XML deserialisation logic, independently of it being used by `MULTISET`. To be investigated.
|
defect
|
postgresql arrays don t deserialise correctly when using xml multiset emulation in postgresql when fetching an array such as array text the xml emulation may produce a query like this sql select select xmlelement name result xmlagg xmlelement name record xmlelement name from select null as union all select cast a b as varchar as a as t which results in an xml document like this xml a b this isn t being deserialised correctly by jooq the following stack trace is produced org jooq exception dataaccessexception sql as union all select cast as varchar as a as t sql rendered with a free trial version of jooq snapshot error while reading field multiset select null a union all select array a at jdbc index at org jooq snapshot postgres debug unknown source at org jooq impl tools translate tools java at org jooq impl defaultexecutecontext sqlexception defaultexecutecontext java at org jooq impl cursorimpl cursoriterator fetchnext cursorimpl java at org jooq impl cursorimpl cursoriterator hasnext cursorimpl java at org jooq impl cursorimpl fetchnext cursorimpl java at org jooq impl tools fetchone tools java at org jooq impl resultquerytrait fetchone resultquerytrait java at org jooq impl tools attach tools java at org jooq impl defaultdslcontext fetchone defaultdslcontext java at org jooq impl defaultdslcontext lambda defaultdslcontext java at org jooq impl tools attach tools java at org jooq impl defaultdslcontext fetchvalue defaultdslcontext java at org jooq test all testcases multisettests lambda multisettests java at org jooq test jooqabstracttest withdslcontext jooqabstracttest java at org jooq test jooqabstracttest bindandinlinewithdslcontexts jooqabstracttest java at org jooq test basetest bindandinlinewithdslcontexts basetest java at org jooq test all testcases multisettests lambda multisettests java at org jooq test all testcases multisettests lambda multisettests java at org jooq test all testcases multisettests lambda multisettests java at org jooq test all testcases multisettests testrecordlevellistenerresults multisettests java at org jooq test all testcases multisettests testrecordlevellistenerresults multisettests java at org jooq test all testcases multisettests testmultisetemulations multisettests java at org jooq test all testcases multisettests testmultisetemulations multisettests java at org jooq test all testcases multisettests assertmultisetdatatype multisettests java at org jooq test all testcases multisettests assertmultisetdatatype multisettests java at org jooq test all testcases multisettests assertmultisetdatatype multisettests java at org jooq test all testcases multisettests testmultisetprojectiondatatypearray multisettests java at org jooq test jooqabstracttest testmultisetprojectiondatatypearray jooqabstracttest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit internal runners statements runbefores evaluate runbefores java at org junit internal runners statements runafters evaluate runafters java at org junit rules testwatcher evaluate testwatcher java at org junit rules testwatcher evaluate testwatcher java at org junit runners parentrunner evaluate parentrunner java at org junit runners evaluate java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit internal runners statements runbefores evaluate runbefores java at org junit internal runners statements runafters evaluate runafters java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org eclipse jdt internal runner run java at org eclipse jdt internal junit runner testexecution run testexecution java at org eclipse jdt internal junit runner remotetestrunner runtests remotetestrunner java at org eclipse jdt internal junit runner remotetestrunner runtests remotetestrunner java at org eclipse jdt internal junit runner remotetestrunner run remotetestrunner java at org eclipse jdt internal junit runner remotetestrunner main remotetestrunner java caused by java sql sqlexception error while reading field multiset select null a union all select array a at jdbc index at org jooq impl cursorimpl cursoriterator cursorrecordinitialiser setvalue cursorimpl java at org jooq impl cursorimpl cursoriterator cursorrecordinitialiser apply cursorimpl java at org jooq impl cursorimpl cursoriterator cursorrecordinitialiser apply cursorimpl java at org jooq impl recorddelegate operate recorddelegate java at org jooq impl cursorimpl cursoriterator fetchnext cursorimpl java more caused by org jooq exception dataaccessexception could not read the xml string at org jooq impl xmlhandler read xmlhandler java at org jooq impl defaultbinding defaultresultbinding readmultisetxml defaultbinding java at org jooq impl defaultbinding defaultresultbinding lambda defaultbinding java at org jooq impl tools apply tools java at org jooq impl defaultbinding defaultresultbinding readmultiset defaultbinding java at org jooq impl defaultbinding defaultresultbinding readmultiset defaultbinding java at org jooq impl defaultbinding defaultresultbinding defaultbinding java at org jooq impl defaultbinding defaultresultbinding defaultbinding java at org jooq impl defaultbinding internalbinding get defaultbinding java at org jooq impl cursorimpl cursoriterator cursorrecordinitialiser setvalue cursorimpl java more caused by java lang indexoutofboundsexception index out of bounds for length at java base jdk internal util preconditions outofbounds preconditions java at java base jdk internal util preconditions outofboundscheckindex preconditions java at java base jdk internal util preconditions checkindex preconditions java at java base java util objects checkindex objects java at java base java util arraylist get arraylist java at org jooq impl xmlhandler startelement xmlhandler java at oracle xml parser nonvalidatingparser parseelement nonvalidatingparser java at oracle xml parser nonvalidatingparser parserootelement nonvalidatingparser java at oracle xml parser nonvalidatingparser parsedocument nonvalidatingparser java at oracle xml parser xmlparser parse xmlparser java at oracle xml jaxp jxsaxparser parse jxsaxparser java at oracle xml jaxp jxsaxparser parse jxsaxparser java at org jooq impl xmlhandler read xmlhandler java more this seems to require a generic improvement to the xml deserialisation logic independently of it being used by multiset to be investigated
| 1
|
171,371
| 13,230,219,985
|
IssuesEvent
|
2020-08-18 09:27:51
|
elastic/elasticsearch
|
https://api.github.com/repos/elastic/elasticsearch
|
closed
|
[CI] Failures in JdbcPreparedStatementIT.testConstantKeywordField
|
:Query Languages/SQL >test-failure Team:QL
|
**Build scan**:
https://gradle-enterprise.elastic.co/s/hnwhcemwfw6d4
**Repro line**:
```
./gradlew ':x-pack:plugin:sql:qa:jdbc:multi-node:v7.10.0#bwcTest' --tests "org.elasticsearch.xpack.sql.qa.jdbc.multi_node.JdbcPreparedStatementIT.testConstantKeywordField" \
-Dtests.seed=FAAE2116E1E1A3F2 \
-Dtests.security.manager=true \
-Dtests.locale=mt-MT \
-Dtests.timezone=America/Anguilla \
-Druntime.java=11 \
-Dtests.fips.enabled=true
```
**Reproduces locally?**:
No
**Applicable branches**:
master
**Failure history**:
Five failures since Aug 17th so far, on master, 7.x and 7.9
First failure probably this one: https://gradle-enterprise.elastic.co/s/wnria74d4wdkc
**Failure excerpt**:
```
java.lang.AssertionError: expected:<1001> but was:<1003>
at __randomizedtesting.SeedInfo.seed([FAAE2116E1E1A3F2:11DCA4D592802DBE]:0)
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at org.elasticsearch.xpack.sql.qa.jdbc.PreparedStatementTestCase.testConstantKeywordField(PreparedStatementTestCase.java:242)
```
|
1.0
|
[CI] Failures in JdbcPreparedStatementIT.testConstantKeywordField - **Build scan**:
https://gradle-enterprise.elastic.co/s/hnwhcemwfw6d4
**Repro line**:
```
./gradlew ':x-pack:plugin:sql:qa:jdbc:multi-node:v7.10.0#bwcTest' --tests "org.elasticsearch.xpack.sql.qa.jdbc.multi_node.JdbcPreparedStatementIT.testConstantKeywordField" \
-Dtests.seed=FAAE2116E1E1A3F2 \
-Dtests.security.manager=true \
-Dtests.locale=mt-MT \
-Dtests.timezone=America/Anguilla \
-Druntime.java=11 \
-Dtests.fips.enabled=true
```
**Reproduces locally?**:
No
**Applicable branches**:
master
**Failure history**:
Five failures since Aug 17th so far, on master, 7.x and 7.9
First failure probably this one: https://gradle-enterprise.elastic.co/s/wnria74d4wdkc
**Failure excerpt**:
```
java.lang.AssertionError: expected:<1001> but was:<1003>
at __randomizedtesting.SeedInfo.seed([FAAE2116E1E1A3F2:11DCA4D592802DBE]:0)
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at org.elasticsearch.xpack.sql.qa.jdbc.PreparedStatementTestCase.testConstantKeywordField(PreparedStatementTestCase.java:242)
```
|
non_defect
|
failures in jdbcpreparedstatementit testconstantkeywordfield build scan repro line gradlew x pack plugin sql qa jdbc multi node bwctest tests org elasticsearch xpack sql qa jdbc multi node jdbcpreparedstatementit testconstantkeywordfield dtests seed dtests security manager true dtests locale mt mt dtests timezone america anguilla druntime java dtests fips enabled true reproduces locally no applicable branches master failure history five failures since aug so far on master x and first failure probably this one failure excerpt java lang assertionerror expected but was at randomizedtesting seedinfo seed at org junit assert fail assert java at org junit assert failnotequals assert java at org junit assert assertequals assert java at org junit assert assertequals assert java at org elasticsearch xpack sql qa jdbc preparedstatementtestcase testconstantkeywordfield preparedstatementtestcase java
| 0
|
239,307
| 7,788,662,022
|
IssuesEvent
|
2018-06-07 06:05:27
|
gardener/gardener
|
https://api.github.com/repos/gardener/gardener
|
closed
|
Technical user cannot read cloudprofile
|
area/usability exp/beginner kind/bug platform/all priority/normal size/xs topology/garden
|
For CI/CD purposes we created a technical user (service account) like
```
kubectl create serviceaccount -n garden-<project> <tech-user>
kubectl set subject rolebinding garden-project-members --serviceaccount <tech-user> --namespace garden-<project>
```
Unfortunately, this service account cannot read cloudprofile in order to figure out the Kubernetes version to use for creating shoots. That is probably because cloudprofile is not namespaced, but on the cluster scope and there is no corresponding clusterrolebinding.
|
1.0
|
Technical user cannot read cloudprofile - For CI/CD purposes we created a technical user (service account) like
```
kubectl create serviceaccount -n garden-<project> <tech-user>
kubectl set subject rolebinding garden-project-members --serviceaccount <tech-user> --namespace garden-<project>
```
Unfortunately, this service account cannot read cloudprofile in order to figure out the Kubernetes version to use for creating shoots. That is probably because cloudprofile is not namespaced, but on the cluster scope and there is no corresponding clusterrolebinding.
|
non_defect
|
technical user cannot read cloudprofile for ci cd purposes we created a technical user service account like kubectl create serviceaccount n garden kubectl set subject rolebinding garden project members serviceaccount namespace garden unfortunately this service account cannot read cloudprofile in order to figure out the kubernetes version to use for creating shoots that is probably because cloudprofile is not namespaced but on the cluster scope and there is no corresponding clusterrolebinding
| 0
|
118,774
| 4,755,744,170
|
IssuesEvent
|
2016-10-24 11:53:09
|
architecture-building-systems/CEAforArcGIS
|
https://api.github.com/repos/architecture-building-systems/CEAforArcGIS
|
reopened
|
Radiation data missing from reference-case-zug
|
bug easy peasy Priority 1
|
Steps to reproduce:
1. Download reference-case-zug from repo
2. run data helper
3. run Demand script with weather=Zug
4. ???
5. Boom!!
```
Executing: DemandTool C:\reference-case-zug\baseline Zug
Start Time: Thu Sep 29 16:28:43 2016
Running script DemandTool...
Using python: C:\Python27\ArcGIS10.4\python.exe
Path to demand script: C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py
Adding path to PYTHONPATH: C:\Users\darthoma\Documents\GitHub\CEAforArcGIS
Running demand calculation for scenario C:\reference-case-zug\baseline
Running demand calculation with weather file C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\databases\CH\Weather\Zug.epw
reading input files
Traceback (most recent call last):
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py", line 187, in <module>
run_as_script(scenario_path=args.scenario, weather_path=args.weather)
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py", line 176, in run_as_script
demand_calculation(locator=locator, weather_path=weather_path, gv=gv)
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py", line 92, in demand_calculation
building_properties = BuildingProperties(locator, gv)
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\thermal_loads.py", line 849, in __init__
solar = pd.read_csv(locator.get_radiation()).set_index('Name')
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 474, in parser_f
return _read(filepath_or_buffer, kwds)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 250, in _read
parser = TextFileReader(filepath_or_buffer, **kwds)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 566, in __init__
self._make_engine(self.engine)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 705, in _make_engine
self._engine = CParserWrapper(self.f, **self.options)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 1072, in __init__
self._reader = _parser.TextReader(src, **kwds)
File "pandas\parser.pyx", line 350, in pandas.parser.TextReader.__cinit__ (pandas\parser.c:3160)
File "pandas\parser.pyx", line 594, in pandas.parser.TextReader._setup_parser_source (pandas\parser.c:5905)
IOError: File C:\reference-case-zug\baseline\outputs\data\solar-radiation\radiation.csv does not exist
Completed script DemandTool...
Succeeded at Thu Sep 29 16:28:49 2016 (Elapsed Time: 6.03 seconds)
```
|
1.0
|
Radiation data missing from reference-case-zug - Steps to reproduce:
1. Download reference-case-zug from repo
2. run data helper
3. run Demand script with weather=Zug
4. ???
5. Boom!!
```
Executing: DemandTool C:\reference-case-zug\baseline Zug
Start Time: Thu Sep 29 16:28:43 2016
Running script DemandTool...
Using python: C:\Python27\ArcGIS10.4\python.exe
Path to demand script: C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py
Adding path to PYTHONPATH: C:\Users\darthoma\Documents\GitHub\CEAforArcGIS
Running demand calculation for scenario C:\reference-case-zug\baseline
Running demand calculation with weather file C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\databases\CH\Weather\Zug.epw
reading input files
Traceback (most recent call last):
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py", line 187, in <module>
run_as_script(scenario_path=args.scenario, weather_path=args.weather)
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py", line 176, in run_as_script
demand_calculation(locator=locator, weather_path=weather_path, gv=gv)
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\demand_main.py", line 92, in demand_calculation
building_properties = BuildingProperties(locator, gv)
File "C:\Users\darthoma\Documents\GitHub\CEAforArcGIS\cea\demand\thermal_loads.py", line 849, in __init__
solar = pd.read_csv(locator.get_radiation()).set_index('Name')
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 474, in parser_f
return _read(filepath_or_buffer, kwds)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 250, in _read
parser = TextFileReader(filepath_or_buffer, **kwds)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 566, in __init__
self._make_engine(self.engine)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 705, in _make_engine
self._engine = CParserWrapper(self.f, **self.options)
File "C:\Python27\ArcGIS10.4\lib\site-packages\pandas\io\parsers.py", line 1072, in __init__
self._reader = _parser.TextReader(src, **kwds)
File "pandas\parser.pyx", line 350, in pandas.parser.TextReader.__cinit__ (pandas\parser.c:3160)
File "pandas\parser.pyx", line 594, in pandas.parser.TextReader._setup_parser_source (pandas\parser.c:5905)
IOError: File C:\reference-case-zug\baseline\outputs\data\solar-radiation\radiation.csv does not exist
Completed script DemandTool...
Succeeded at Thu Sep 29 16:28:49 2016 (Elapsed Time: 6.03 seconds)
```
|
non_defect
|
radiation data missing from reference case zug steps to reproduce download reference case zug from repo run data helper run demand script with weather zug boom executing demandtool c reference case zug baseline zug start time thu sep running script demandtool using python c python exe path to demand script c users darthoma documents github ceaforarcgis cea demand demand main py adding path to pythonpath c users darthoma documents github ceaforarcgis running demand calculation for scenario c reference case zug baseline running demand calculation with weather file c users darthoma documents github ceaforarcgis cea databases ch weather zug epw reading input files traceback most recent call last file c users darthoma documents github ceaforarcgis cea demand demand main py line in run as script scenario path args scenario weather path args weather file c users darthoma documents github ceaforarcgis cea demand demand main py line in run as script demand calculation locator locator weather path weather path gv gv file c users darthoma documents github ceaforarcgis cea demand demand main py line in demand calculation building properties buildingproperties locator gv file c users darthoma documents github ceaforarcgis cea demand thermal loads py line in init solar pd read csv locator get radiation set index name file c lib site packages pandas io parsers py line in parser f return read filepath or buffer kwds file c lib site packages pandas io parsers py line in read parser textfilereader filepath or buffer kwds file c lib site packages pandas io parsers py line in init self make engine self engine file c lib site packages pandas io parsers py line in make engine self engine cparserwrapper self f self options file c lib site packages pandas io parsers py line in init self reader parser textreader src kwds file pandas parser pyx line in pandas parser textreader cinit pandas parser c file pandas parser pyx line in pandas parser textreader setup parser source pandas parser c ioerror file c reference case zug baseline outputs data solar radiation radiation csv does not exist completed script demandtool succeeded at thu sep elapsed time seconds
| 0
|
61,295
| 17,023,659,741
|
IssuesEvent
|
2021-07-03 03:09:19
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
Tag list loses focus while being edited when pointer moves in map
|
Component: potlatch2 Priority: minor Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 8.30pm, Tuesday, 7th December 2010]**
This is annoying and leads to truncated tags. It is especially likely when you start a tag with the = shortcut and the mouse pointer is already in the map window. It then needs to move just a pixel to affect the tag edit.
|
1.0
|
Tag list loses focus while being edited when pointer moves in map - **[Submitted to the original trac issue database at 8.30pm, Tuesday, 7th December 2010]**
This is annoying and leads to truncated tags. It is especially likely when you start a tag with the = shortcut and the mouse pointer is already in the map window. It then needs to move just a pixel to affect the tag edit.
|
defect
|
tag list loses focus while being edited when pointer moves in map this is annoying and leads to truncated tags it is especially likely when you start a tag with the shortcut and the mouse pointer is already in the map window it then needs to move just a pixel to affect the tag edit
| 1
|
31,613
| 6,558,595,263
|
IssuesEvent
|
2017-09-06 22:09:01
|
CenturyLinkCloud/mdw
|
https://api.github.com/repos/CenturyLinkCloud/mdw
|
opened
|
RuntimeUI always displays the latest definition of a process
|
defect
|
Runtime info is correct according to the instance. However, the layout and other definition data is always taken from the latest.
|
1.0
|
RuntimeUI always displays the latest definition of a process - Runtime info is correct according to the instance. However, the layout and other definition data is always taken from the latest.
|
defect
|
runtimeui always displays the latest definition of a process runtime info is correct according to the instance however the layout and other definition data is always taken from the latest
| 1
|
278,149
| 30,702,214,548
|
IssuesEvent
|
2023-07-27 01:12:03
|
snykiotcubedev/arangodb-3.7.6
|
https://api.github.com/repos/snykiotcubedev/arangodb-3.7.6
|
reopened
|
CVE-2018-19838 (Medium) detected in node-sass-4.14.1.tgz
|
Mend: dependency security vulnerability
|
## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/arangodb-3.7.6/commit/fce8f85f1c2f070c8e6a8e76d17210a2117d3833">fce8f85f1c2f070c8e6a8e76d17210a2117d3833</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, functions inside ast.cpp for IMPLEMENT_AST_OPERATORS expansion allow attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, as demonstrated by recursive calls involving clone(), cloneChildren(), and copy().
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19838>CVE-2018-19838</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-12-04</p>
<p>Fix Resolution: 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2018-19838 (Medium) detected in node-sass-4.14.1.tgz - ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/arangodb-3.7.6/commit/fce8f85f1c2f070c8e6a8e76d17210a2117d3833">fce8f85f1c2f070c8e6a8e76d17210a2117d3833</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, functions inside ast.cpp for IMPLEMENT_AST_OPERATORS expansion allow attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, as demonstrated by recursive calls involving clone(), cloneChildren(), and copy().
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-19838>CVE-2018-19838</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-12-04</p>
<p>Fix Resolution: 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve medium detected in node sass tgz cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href dependency hierarchy x node sass tgz vulnerable library found in head commit a href found in base branch main vulnerability details in libsass prior to functions inside ast cpp for implement ast operators expansion allow attackers to cause a denial of service resulting from stack consumption via a crafted sass file as demonstrated by recursive calls involving clone clonechildren and copy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend
| 0
|
3,898
| 2,610,083,646
|
IssuesEvent
|
2015-02-26 18:25:32
|
chrsmith/dsdsdaadf
|
https://api.github.com/repos/chrsmith/dsdsdaadf
|
opened
|
深圳白头粉刺怎么祛除
|
auto-migrated Priority-Medium Type-Defect
|
```
深圳白头粉刺怎么祛除【深圳韩方科颜全国热线400-869-1818,24
小时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩��
�秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,�
��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹
”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内��
�业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上�
��痘痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 6:51
|
1.0
|
深圳白头粉刺怎么祛除 - ```
深圳白头粉刺怎么祛除【深圳韩方科颜全国热线400-869-1818,24
小时QQ4008691818】深圳韩方科颜专业祛痘连锁机构,机构以韩��
�秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,�
��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹
”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内��
�业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上�
��痘痘。
```
-----
Original issue reported on code.google.com by `szft...@163.com` on 14 May 2014 at 6:51
|
defect
|
深圳白头粉刺怎么祛除 深圳白头粉刺怎么祛除【 , 】深圳韩方科颜专业祛痘连锁机构,机构以韩�� �秘方——韩方科颜这一国妆准字号治疗型权威,祛痘佳品,� ��方科颜专业祛痘连锁机构,采用韩国秘方配合专业“不反弹 ”健康祛痘技术并结合先进“先进豪华彩光”仪,开创国内�� �业治疗粉刺、痤疮签约包治先河,成功消除了许多顾客脸上� ��痘痘。 original issue reported on code google com by szft com on may at
| 1
|
267,494
| 28,509,063,752
|
IssuesEvent
|
2023-04-19 01:32:08
|
dpteam/RK3188_TABLET
|
https://api.github.com/repos/dpteam/RK3188_TABLET
|
closed
|
CVE-2020-29370 (High) detected in linuxv3.0.70 - autoclosed
|
Mend: dependency security vulnerability
|
## CVE-2020-29370 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0.70</b></p></summary>
<p>
<p>Development tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git>https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in kmem_cache_alloc_bulk in mm/slub.c in the Linux kernel before 5.5.11. The slowpath lacks the required TID increment, aka CID-fd4d9c7d0c71.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29370>CVE-2020-29370</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.6-rc7,v5.5.11,v5.4.28</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-29370 (High) detected in linuxv3.0.70 - autoclosed - ## CVE-2020-29370 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0.70</b></p></summary>
<p>
<p>Development tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git>https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in kmem_cache_alloc_bulk in mm/slub.c in the Linux kernel before 5.5.11. The slowpath lacks the required TID increment, aka CID-fd4d9c7d0c71.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29370>CVE-2020-29370</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.6-rc7,v5.5.11,v5.4.28</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in autoclosed cve high severity vulnerability vulnerable library development tree library home page a href found in head commit a href found in base branch master vulnerable source files mm slub c vulnerability details an issue was discovered in kmem cache alloc bulk in mm slub c in the linux kernel before the slowpath lacks the required tid increment aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
773
| 2,514,285,997
|
IssuesEvent
|
2015-01-15 10:01:37
|
olga-jane/prizm
|
https://api.github.com/repos/olga-jane/prizm
|
closed
|
Save settings
|
MEDIUM priority POSTPONED System design
|
1) to save visual sizes (column width, window position etc)
2) to save something like "last entered date" for new pipe.
Some information about settings:
app.config is used for application settings, could not be modified by application in non-admin windows credentials
user.config is used for windows user settings, could be updated by application but applied to certain windows user
Please discuss before coding.
|
1.0
|
Save settings - 1) to save visual sizes (column width, window position etc)
2) to save something like "last entered date" for new pipe.
Some information about settings:
app.config is used for application settings, could not be modified by application in non-admin windows credentials
user.config is used for windows user settings, could be updated by application but applied to certain windows user
Please discuss before coding.
|
non_defect
|
save settings to save visual sizes column width window position etc to save something like last entered date for new pipe some information about settings app config is used for application settings could not be modified by application in non admin windows credentials user config is used for windows user settings could be updated by application but applied to certain windows user please discuss before coding
| 0
|
64,001
| 18,102,945,023
|
IssuesEvent
|
2021-09-22 15:57:06
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
Unable to Create account with Sign in with Google
|
T-Defect
|
### Steps to reproduce
1. Clicked Create account at staging.element.io
2. Click Sign in with Google
3. Sign in with a person gmail account with 2FA turned off
4. Get the following error on the next screen
### What happened?
### What did you expect?
A prompt to create a new Matrix account
### What happened?
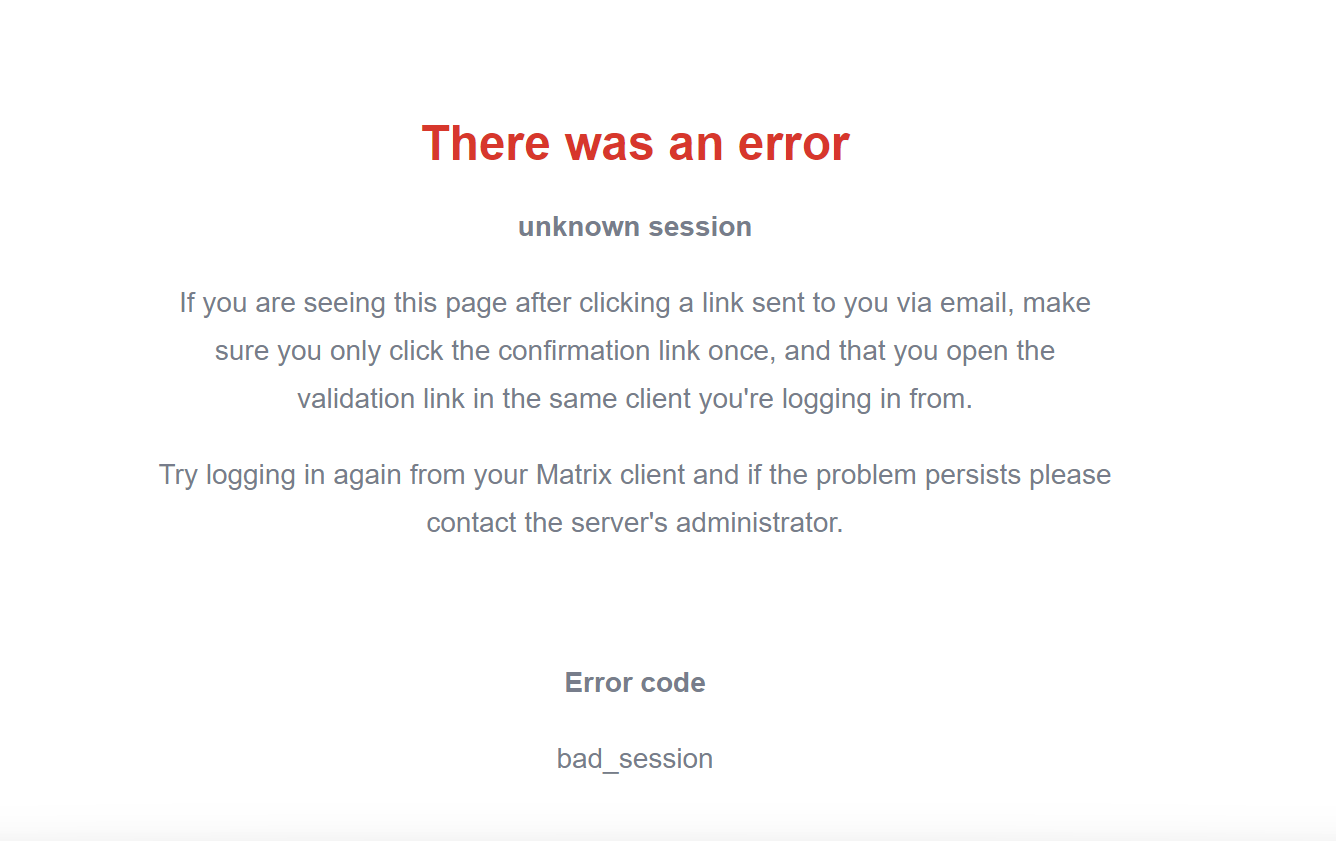
at URL https://matrix-client.matrix.org/_synapse/client/new_user_consent#
### Operating system
Windows
### Browser information
Chrome 94.0.4606.54
### URL for webapp
staging.element.io
### Homeserver
matrix.org
### Have you submitted a rageshake?
No
|
1.0
|
Unable to Create account with Sign in with Google - ### Steps to reproduce
1. Clicked Create account at staging.element.io
2. Click Sign in with Google
3. Sign in with a person gmail account with 2FA turned off
4. Get the following error on the next screen
### What happened?
### What did you expect?
A prompt to create a new Matrix account
### What happened?
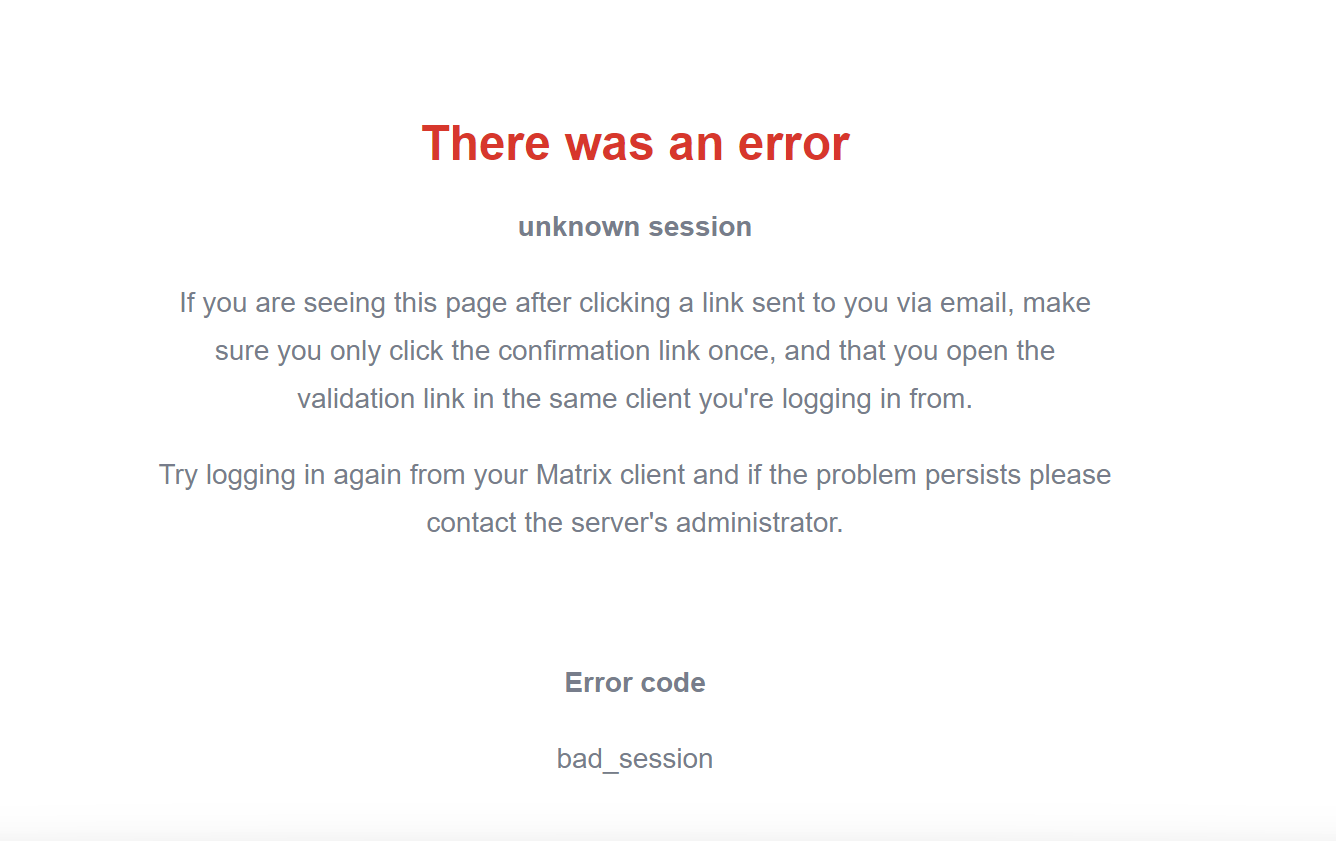
at URL https://matrix-client.matrix.org/_synapse/client/new_user_consent#
### Operating system
Windows
### Browser information
Chrome 94.0.4606.54
### URL for webapp
staging.element.io
### Homeserver
matrix.org
### Have you submitted a rageshake?
No
|
defect
|
unable to create account with sign in with google steps to reproduce clicked create account at staging element io click sign in with google sign in with a person gmail account with turned off get the following error on the next screen what happened what did you expect a prompt to create a new matrix account what happened at url operating system windows browser information chrome url for webapp staging element io homeserver matrix org have you submitted a rageshake no
| 1
|
291,981
| 21,945,332,105
|
IssuesEvent
|
2022-05-23 23:26:58
|
ExtraKeys/awards
|
https://api.github.com/repos/ExtraKeys/awards
|
opened
|
Universal Clacker Award Template
|
documentation
|
```swift
//
// UniversalClackerAwardTemplate.swift
// UIKeyCommand
//
// Designed in Missouri, bitch.
// Copyright © ExtraKeys. No rights reserved.
//
import SwiftUI
struct UCA: View {
var body: some View {
VStack {
Group {
Image(systemName: "command.circle")
.imageScale(.small)
.font(.largeTitle)
.padding(.top)
.offset(x: 0, y: 0)
.foregroundColor(Color(.quarternaryLabel))
.frame(height: 45)
.clipped()
Text("1 of FEW")
.font(.system(size: 12, weight: .thin, design: .default))
.padding(.all, 0)
.frame(minWidth: .infinity, minHeight: .infinity, alignment: .top)
.clipped()
.foregroundColor(Color(.tertiaryLabel))
.fixedSize(horizontal: true, vertical: true)
Text("UNIVERSAL")
.font(.system(size: 72, weight: .bold, design: .default))
.foregroundColor(Color(.displayP3, red: 48/255, green: 126/255, blue: 251/255))
.frame(maxWidth: .infinity, maxHeight: 77, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.multilineTextAlignment(.center)
.padding(.horizontal, 0)
.opacity(1)
.shadow(color: Color.purple.opacity(0.28), radius: 6, x: 0, y: 2)
.shadow(color: Color.purple, radius: 1, x: 0, y: 4)
Text("Ⓒ Ⓛ Ⓐ Ⓒ Ⓚ Ⓔ Ⓡ")
.font(.system(size: 41, weight: .light, design: .rounded))
.foregroundColor(Color.red.opacity(0.84))
.frame(maxWidth: .infinity, maxHeight: 50, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.padding(.horizontal)
.opacity(1)
.shadow(color: Color.pink.opacity(0.85), radius: 4, x: 1, y: 1)
Text("Award")
.underline()
.font(.system(size: 31, weight: .heavy, design: .serif))
.foregroundColor(Color.purple.opacity(0.77))
.frame(maxWidth: .infinity, maxHeight: 34, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.padding(.horizontal, 0)
.opacity(0.84)
Text("Unmatched foresight, consistency, competency, innovation, and support.")
.font(.system(size: 11, weight: .semibold, design: .default))
.foregroundColor(Color.blue.opacity(0.83))
.frame(width: 417, height: 20, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.fixedSize(horizontal: false, vertical: true)
.padding(.vertical, 0)
Image("myImage")
.renderingMode(.original)
.resizable()
.aspectRatio(contentMode: .fit)
.padding(.top, 10)
.frame(width: 286, height: 290)
.clipped()
.shadow(color: Color(.displayP3, red: 0/255, green: 0/255, blue: 107/255), radius: 9, x: 0, y: 4)
Text("CRUD")
.frame(maxWidth: .infinity, maxHeight: .infinity, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.font(.system(size: 75, weight: .bold, design: .monospaced))
.padding(.top, 0)
.lineSpacing(0)
.foregroundColor(Color(.displayP3, red: 0/255, green: 0/255, blue: 107/255))
.shadow(color: Color(.displayP3, red: 0/255, green: 0/255, blue: 107/255).opacity(0.64), radius: 3, x: 0, y: 2)
.fixedSize(horizontal: true, vertical: true)
Text("Misters Big Old Bitch")
.font(.system(size: 16, weight: .thin, design: .rounded))
.foregroundColor(Color.red)
.frame(width: 417, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.fixedSize(horizontal: false, vertical: true)
.padding(.top, 1)
VStack {
ZStack {
VStack(spacing: 0) {
EmptyView()
}
.frame(maxWidth: .infinity, maxHeight: .infinity)
.clipped()
.mask(Group {
EmptyView()
})
.shadow(color: Color(.sRGBLinear, red: 0/255, green: 0/255, blue: 0/255).opacity(0.5), radius: 8, x: 0, y: 4)
.foregroundColor(Color.primary)
}
}
.frame(maxWidth: .infinity)
.clipped()
.padding(0)
.background(Group {
Text("Blimpists, Inc.")
.italic()
.font(.system(size: 27, weight: .semibold, design: .serif))
.multilineTextAlignment(.leading)
.foregroundColor(Color(.systemGray3))
.multilineTextAlignment(.leading)
.padding(.bottom, 0)
.opacity(0.53)
Text("Hello, World!")
.frame(maxWidth: 380, maxHeight: 530, alignment: .center)
.clipped()
.multilineTextAlignment(.leading)
.font(.system(size: 14, weight: .medium, design: .default))
.multilineTextAlignment(.leading)
.foregroundColor(Color.blue)
.lineSpacing(4)
.opacity(0)
}, alignment: .center)
.padding()
.foregroundColor(Color.primary)
.background(Image(systemName: "keyboard")
.imageScale(.large)
.offset(x: 0, y: 90)
.fixedSize(horizontal: true, vertical: false)
.font(.system(size: 110, weight: .thin, design: .default))
.colorMultiply(Color(.tertiaryLabel).opacity(0.84))
.foregroundColor(Color.secondary.opacity(0.74)), alignment: .center)
.padding(.bottom, 60)
}
Group {
HStack {
VisualEffectView(style: .systemUltraThinMaterial)
.frame(width: 50, height: 50)
.clipped()
.overlay(Group {
EmptyView()
}, alignment: .center)
.mask(Circle()
.foregroundColor(Color.purple)
.mask(RoundedRectangle(cornerRadius: 16, style: .continuous)))
.overlay(Image(systemName: "option")
.font(.system(size: 23, weight: .light, design: .default)), alignment: .center)
Spacer()
VisualEffectView(style: .systemUltraThinMaterial)
.frame(width: 50, height: 50)
.clipped()
.overlay(Group {
EmptyView()
}, alignment: .center)
.mask(Circle())
.overlay(Image(systemName: "control")
.font(.system(size: 21, weight: .light, design: .default))
.offset(x: 0, y: -2), alignment: .center)
}
.padding(.horizontal, 47)
.padding(.bottom, 32)
}
}
.frame(maxWidth: .infinity, maxHeight: .infinity, alignment: .top)
.clipped()
.foregroundColor(Color.white)
.background(Group {
EmptyView()
}, alignment: .center)
}
}
struct UCA_Previews: PreviewProvider {
static var previews: some View {
UCA()
}
}
struct VisualEffectView: UIViewRepresentable {
let style: UIBlurEffect.Style
func makeUIView(context: Context) -> UIVisualEffectView {
return UIVisualEffectView(effect: UIBlurEffect(style: style))
}
func updateUIView(_ uiView: UIVisualEffectView, context: Context) {
uiView.effect = UIBlurEffect(style: style)
}
}
```
|
1.0
|
Universal Clacker Award Template - ```swift
//
// UniversalClackerAwardTemplate.swift
// UIKeyCommand
//
// Designed in Missouri, bitch.
// Copyright © ExtraKeys. No rights reserved.
//
import SwiftUI
struct UCA: View {
var body: some View {
VStack {
Group {
Image(systemName: "command.circle")
.imageScale(.small)
.font(.largeTitle)
.padding(.top)
.offset(x: 0, y: 0)
.foregroundColor(Color(.quarternaryLabel))
.frame(height: 45)
.clipped()
Text("1 of FEW")
.font(.system(size: 12, weight: .thin, design: .default))
.padding(.all, 0)
.frame(minWidth: .infinity, minHeight: .infinity, alignment: .top)
.clipped()
.foregroundColor(Color(.tertiaryLabel))
.fixedSize(horizontal: true, vertical: true)
Text("UNIVERSAL")
.font(.system(size: 72, weight: .bold, design: .default))
.foregroundColor(Color(.displayP3, red: 48/255, green: 126/255, blue: 251/255))
.frame(maxWidth: .infinity, maxHeight: 77, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.multilineTextAlignment(.center)
.padding(.horizontal, 0)
.opacity(1)
.shadow(color: Color.purple.opacity(0.28), radius: 6, x: 0, y: 2)
.shadow(color: Color.purple, radius: 1, x: 0, y: 4)
Text("Ⓒ Ⓛ Ⓐ Ⓒ Ⓚ Ⓔ Ⓡ")
.font(.system(size: 41, weight: .light, design: .rounded))
.foregroundColor(Color.red.opacity(0.84))
.frame(maxWidth: .infinity, maxHeight: 50, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.padding(.horizontal)
.opacity(1)
.shadow(color: Color.pink.opacity(0.85), radius: 4, x: 1, y: 1)
Text("Award")
.underline()
.font(.system(size: 31, weight: .heavy, design: .serif))
.foregroundColor(Color.purple.opacity(0.77))
.frame(maxWidth: .infinity, maxHeight: 34, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.padding(.horizontal, 0)
.opacity(0.84)
Text("Unmatched foresight, consistency, competency, innovation, and support.")
.font(.system(size: 11, weight: .semibold, design: .default))
.foregroundColor(Color.blue.opacity(0.83))
.frame(width: 417, height: 20, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.fixedSize(horizontal: false, vertical: true)
.padding(.vertical, 0)
Image("myImage")
.renderingMode(.original)
.resizable()
.aspectRatio(contentMode: .fit)
.padding(.top, 10)
.frame(width: 286, height: 290)
.clipped()
.shadow(color: Color(.displayP3, red: 0/255, green: 0/255, blue: 107/255), radius: 9, x: 0, y: 4)
Text("CRUD")
.frame(maxWidth: .infinity, maxHeight: .infinity, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.font(.system(size: 75, weight: .bold, design: .monospaced))
.padding(.top, 0)
.lineSpacing(0)
.foregroundColor(Color(.displayP3, red: 0/255, green: 0/255, blue: 107/255))
.shadow(color: Color(.displayP3, red: 0/255, green: 0/255, blue: 107/255).opacity(0.64), radius: 3, x: 0, y: 2)
.fixedSize(horizontal: true, vertical: true)
Text("Misters Big Old Bitch")
.font(.system(size: 16, weight: .thin, design: .rounded))
.foregroundColor(Color.red)
.frame(width: 417, alignment: .top)
.clipped()
.multilineTextAlignment(.center)
.fixedSize(horizontal: false, vertical: true)
.padding(.top, 1)
VStack {
ZStack {
VStack(spacing: 0) {
EmptyView()
}
.frame(maxWidth: .infinity, maxHeight: .infinity)
.clipped()
.mask(Group {
EmptyView()
})
.shadow(color: Color(.sRGBLinear, red: 0/255, green: 0/255, blue: 0/255).opacity(0.5), radius: 8, x: 0, y: 4)
.foregroundColor(Color.primary)
}
}
.frame(maxWidth: .infinity)
.clipped()
.padding(0)
.background(Group {
Text("Blimpists, Inc.")
.italic()
.font(.system(size: 27, weight: .semibold, design: .serif))
.multilineTextAlignment(.leading)
.foregroundColor(Color(.systemGray3))
.multilineTextAlignment(.leading)
.padding(.bottom, 0)
.opacity(0.53)
Text("Hello, World!")
.frame(maxWidth: 380, maxHeight: 530, alignment: .center)
.clipped()
.multilineTextAlignment(.leading)
.font(.system(size: 14, weight: .medium, design: .default))
.multilineTextAlignment(.leading)
.foregroundColor(Color.blue)
.lineSpacing(4)
.opacity(0)
}, alignment: .center)
.padding()
.foregroundColor(Color.primary)
.background(Image(systemName: "keyboard")
.imageScale(.large)
.offset(x: 0, y: 90)
.fixedSize(horizontal: true, vertical: false)
.font(.system(size: 110, weight: .thin, design: .default))
.colorMultiply(Color(.tertiaryLabel).opacity(0.84))
.foregroundColor(Color.secondary.opacity(0.74)), alignment: .center)
.padding(.bottom, 60)
}
Group {
HStack {
VisualEffectView(style: .systemUltraThinMaterial)
.frame(width: 50, height: 50)
.clipped()
.overlay(Group {
EmptyView()
}, alignment: .center)
.mask(Circle()
.foregroundColor(Color.purple)
.mask(RoundedRectangle(cornerRadius: 16, style: .continuous)))
.overlay(Image(systemName: "option")
.font(.system(size: 23, weight: .light, design: .default)), alignment: .center)
Spacer()
VisualEffectView(style: .systemUltraThinMaterial)
.frame(width: 50, height: 50)
.clipped()
.overlay(Group {
EmptyView()
}, alignment: .center)
.mask(Circle())
.overlay(Image(systemName: "control")
.font(.system(size: 21, weight: .light, design: .default))
.offset(x: 0, y: -2), alignment: .center)
}
.padding(.horizontal, 47)
.padding(.bottom, 32)
}
}
.frame(maxWidth: .infinity, maxHeight: .infinity, alignment: .top)
.clipped()
.foregroundColor(Color.white)
.background(Group {
EmptyView()
}, alignment: .center)
}
}
struct UCA_Previews: PreviewProvider {
static var previews: some View {
UCA()
}
}
struct VisualEffectView: UIViewRepresentable {
let style: UIBlurEffect.Style
func makeUIView(context: Context) -> UIVisualEffectView {
return UIVisualEffectView(effect: UIBlurEffect(style: style))
}
func updateUIView(_ uiView: UIVisualEffectView, context: Context) {
uiView.effect = UIBlurEffect(style: style)
}
}
```
|
non_defect
|
universal clacker award template swift universalclackerawardtemplate swift uikeycommand designed in missouri bitch copyright © extrakeys no rights reserved import swiftui struct uca view var body some view vstack group image systemname command circle imagescale small font largetitle padding top offset x y foregroundcolor color quarternarylabel frame height clipped text of few font system size weight thin design default padding all frame minwidth infinity minheight infinity alignment top clipped foregroundcolor color tertiarylabel fixedsize horizontal true vertical true text universal font system size weight bold design default foregroundcolor color red green blue frame maxwidth infinity maxheight alignment top clipped multilinetextalignment center multilinetextalignment center padding horizontal opacity shadow color color purple opacity radius x y shadow color color purple radius x y text ⓒ ⓛ ⓐ ⓒ ⓚ ⓔ ⓡ font system size weight light design rounded foregroundcolor color red opacity frame maxwidth infinity maxheight alignment top clipped multilinetextalignment center padding horizontal opacity shadow color color pink opacity radius x y text award underline font system size weight heavy design serif foregroundcolor color purple opacity frame maxwidth infinity maxheight alignment top clipped multilinetextalignment center padding horizontal opacity text unmatched foresight consistency competency innovation and support font system size weight semibold design default foregroundcolor color blue opacity frame width height alignment top clipped multilinetextalignment center fixedsize horizontal false vertical true padding vertical image myimage renderingmode original resizable aspectratio contentmode fit padding top frame width height clipped shadow color color red green blue radius x y text crud frame maxwidth infinity maxheight infinity alignment top clipped multilinetextalignment center font system size weight bold design monospaced padding top linespacing foregroundcolor color red green blue shadow color color red green blue opacity radius x y fixedsize horizontal true vertical true text misters big old bitch font system size weight thin design rounded foregroundcolor color red frame width alignment top clipped multilinetextalignment center fixedsize horizontal false vertical true padding top vstack zstack vstack spacing emptyview frame maxwidth infinity maxheight infinity clipped mask group emptyview shadow color color srgblinear red green blue opacity radius x y foregroundcolor color primary frame maxwidth infinity clipped padding background group text blimpists inc italic font system size weight semibold design serif multilinetextalignment leading foregroundcolor color multilinetextalignment leading padding bottom opacity text hello world frame maxwidth maxheight alignment center clipped multilinetextalignment leading font system size weight medium design default multilinetextalignment leading foregroundcolor color blue linespacing opacity alignment center padding foregroundcolor color primary background image systemname keyboard imagescale large offset x y fixedsize horizontal true vertical false font system size weight thin design default colormultiply color tertiarylabel opacity foregroundcolor color secondary opacity alignment center padding bottom group hstack visualeffectview style systemultrathinmaterial frame width height clipped overlay group emptyview alignment center mask circle foregroundcolor color purple mask roundedrectangle cornerradius style continuous overlay image systemname option font system size weight light design default alignment center spacer visualeffectview style systemultrathinmaterial frame width height clipped overlay group emptyview alignment center mask circle overlay image systemname control font system size weight light design default offset x y alignment center padding horizontal padding bottom frame maxwidth infinity maxheight infinity alignment top clipped foregroundcolor color white background group emptyview alignment center struct uca previews previewprovider static var previews some view uca struct visualeffectview uiviewrepresentable let style uiblureffect style func makeuiview context context uivisualeffectview return uivisualeffectview effect uiblureffect style style func updateuiview uiview uivisualeffectview context context uiview effect uiblureffect style style
| 0
|
10,030
| 2,618,932,198
|
IssuesEvent
|
2015-03-03 00:00:42
|
chrsmith/open-ig
|
https://api.github.com/repos/chrsmith/open-ig
|
closed
|
diplo felület
|
auto-migrated Priority-Medium Type-Defect
|
```
Game version: 0.95.124
5. szintre átlépve sem nyílt meg a diplomácia felület.
```
Original issue reported on code.google.com by `baga...@freemail.hu` on 31 Dec 2012 at 1:30
Attachments:
* [save-2012-12-31-14-30-05-150.xml.gz](https://storage.googleapis.com/google-code-attachments/open-ig/issue-708/comment-0/save-2012-12-31-14-30-05-150.xml.gz)
|
1.0
|
diplo felület - ```
Game version: 0.95.124
5. szintre átlépve sem nyílt meg a diplomácia felület.
```
Original issue reported on code.google.com by `baga...@freemail.hu` on 31 Dec 2012 at 1:30
Attachments:
* [save-2012-12-31-14-30-05-150.xml.gz](https://storage.googleapis.com/google-code-attachments/open-ig/issue-708/comment-0/save-2012-12-31-14-30-05-150.xml.gz)
|
defect
|
diplo felület game version szintre átlépve sem nyílt meg a diplomácia felület original issue reported on code google com by baga freemail hu on dec at attachments
| 1
|
7,615
| 2,610,407,708
|
IssuesEvent
|
2015-02-26 20:12:29
|
chrsmith/republic-at-war
|
https://api.github.com/repos/chrsmith/republic-at-war
|
opened
|
GC Auto-resolve Raiding / Mace Windu
|
auto-migrated Priority-Medium Type-Defect
|
```
Raids including Mace Windu have a near 100% win chance when using auto-resolve.
This was missed during the initial 1.0 testing period as B1s offset this. With
B1 auto-resolve balanced, this has become a serious issue.
A solution may be to limit each side to having 1 or 2 hero units with raiding
abilities (Mace Windu would not be one of them).
```
-----
Original issue reported on code.google.com by `KillerHurdz@netscape.net` on 1 May 2012 at 1:58
|
1.0
|
GC Auto-resolve Raiding / Mace Windu - ```
Raids including Mace Windu have a near 100% win chance when using auto-resolve.
This was missed during the initial 1.0 testing period as B1s offset this. With
B1 auto-resolve balanced, this has become a serious issue.
A solution may be to limit each side to having 1 or 2 hero units with raiding
abilities (Mace Windu would not be one of them).
```
-----
Original issue reported on code.google.com by `KillerHurdz@netscape.net` on 1 May 2012 at 1:58
|
defect
|
gc auto resolve raiding mace windu raids including mace windu have a near win chance when using auto resolve this was missed during the initial testing period as offset this with auto resolve balanced this has become a serious issue a solution may be to limit each side to having or hero units with raiding abilities mace windu would not be one of them original issue reported on code google com by killerhurdz netscape net on may at
| 1
|
72,881
| 24,343,526,342
|
IssuesEvent
|
2022-10-02 01:57:57
|
naev/naev
|
https://api.github.com/repos/naev/naev
|
closed
|
Bug with outfit names
|
Type-Defect Priority-High
|
LJ_Dude
—
昨日 06:14
Nightly windows, seems like the outfit names aren't displaying properly when hovering the cursor over.
|
1.0
|
Bug with outfit names - LJ_Dude
—
昨日 06:14
Nightly windows, seems like the outfit names aren't displaying properly when hovering the cursor over.
|
defect
|
bug with outfit names lj dude — 昨日 nightly windows seems like the outfit names aren t displaying properly when hovering the cursor over
| 1
|
14,292
| 17,189,978,400
|
IssuesEvent
|
2021-07-16 09:31:34
|
franzholz/tt_products
|
https://api.github.com/repos/franzholz/tt_products
|
closed
|
Wrong password when FE user is created by tt_products
|
compatibility
|
When tt_products creates a FE user on order finalize, the random generated password is not hashed correctly so when the user tries to log in with the password (s)he receive error.
https://docs.typo3.org/m/typo3/reference-coreapi/master/en-us/ApiOverview/PasswordHashing/Index.html#creating-a-hash
|
True
|
Wrong password when FE user is created by tt_products - When tt_products creates a FE user on order finalize, the random generated password is not hashed correctly so when the user tries to log in with the password (s)he receive error.
https://docs.typo3.org/m/typo3/reference-coreapi/master/en-us/ApiOverview/PasswordHashing/Index.html#creating-a-hash
|
non_defect
|
wrong password when fe user is created by tt products when tt products creates a fe user on order finalize the random generated password is not hashed correctly so when the user tries to log in with the password s he receive error
| 0
|
183,140
| 21,706,844,391
|
IssuesEvent
|
2022-05-10 10:22:31
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
closed
|
[Security Solutions] User risk - Add links to documentation and dashboards
|
Team: SecuritySolution NeededFor:Threat Hunting Team:Threat Hunting:Explore v8.3.0
|
**Describe the feature:**
When the documentation and dashboards are ready and we have access to their links we have to update user risk tabs to add the links.
* User page callOut
* User information modal
* User details / risk tab dashboard button
<img width="458" alt="Screenshot 2022-05-02 at 10 37 43" src="https://user-images.githubusercontent.com/1490444/166209656-0b26a069-2547-4a4e-9692-fe0be92b263b.png">
<img width="1776" alt="Screenshot 2022-05-02 at 10 29 14" src="https://user-images.githubusercontent.com/1490444/166209651-aea2e01c-a87e-45c1-a868-452f87339338.png">
<img width="1787" alt="Screenshot 2022-05-02 at 10 11 56" src="https://user-images.githubusercontent.com/1490444/166209640-24973f3e-ad4e-487d-9c02-628ec126d83c.png">
|
True
|
[Security Solutions] User risk - Add links to documentation and dashboards - **Describe the feature:**
When the documentation and dashboards are ready and we have access to their links we have to update user risk tabs to add the links.
* User page callOut
* User information modal
* User details / risk tab dashboard button
<img width="458" alt="Screenshot 2022-05-02 at 10 37 43" src="https://user-images.githubusercontent.com/1490444/166209656-0b26a069-2547-4a4e-9692-fe0be92b263b.png">
<img width="1776" alt="Screenshot 2022-05-02 at 10 29 14" src="https://user-images.githubusercontent.com/1490444/166209651-aea2e01c-a87e-45c1-a868-452f87339338.png">
<img width="1787" alt="Screenshot 2022-05-02 at 10 11 56" src="https://user-images.githubusercontent.com/1490444/166209640-24973f3e-ad4e-487d-9c02-628ec126d83c.png">
|
non_defect
|
user risk add links to documentation and dashboards describe the feature when the documentation and dashboards are ready and we have access to their links we have to update user risk tabs to add the links user page callout user information modal user details risk tab dashboard button img width alt screenshot at src img width alt screenshot at src img width alt screenshot at src
| 0
|
41,881
| 10,688,747,339
|
IssuesEvent
|
2019-10-22 18:53:29
|
STEllAR-GROUP/phylanx
|
https://api.github.com/repos/STEllAR-GROUP/phylanx
|
closed
|
RuntimeError: this client_base has no valid shared state: HPX(no_state)
|
platform: KERAS type: defect
|
The following code
```python
from phylanx import Phylanx, PhylanxSession, execution_tree
import numpy as np
PhylanxSession.init(1)
def variable(value, dtype=None, name=None):
if dtype is None:
dtype = "float64"
from phylanx.ast.physl import PhySL
if isinstance(value, PhySL.eval_wrapper):
return execution_tree.variable(value.code(), dtype)
if isinstance(value, execution_tree.variable):
return value
return execution_tree.variable(value, dtype=dtype, name=name)
def eval(x):
return x.eval()
@Phylanx
def sum_eager(x, axis, keepdims):
return np.sum(x, axis, keepdims)
def sum(x, axis=None, keepdims=False):
return sum_eager.lazy(x, axis, keepdims)
@Phylanx
def reshape_eager(x, shape):
return np.reshape(x, shape)
def reshape(x, shape):
return reshape_eager.lazy(x, shape)
@Phylanx
def squeeze_eager(x, axis):
return np.squeeze(x, axis)
def squeeze(x, axis):
return squeeze_eager.lazy(x, axis)
y_test = variable(np.array([0, 0, 2, 0]))
print("y_test:",eval(y_test))
y_test = reshape(y_test,(4,1))
y_test = squeeze(y_test, 1)
print("y_test:",eval(y_test))
sum_y_test = sum(y_test)
print("sum_y_test:", eval(sum_y_test))
```
produces:
```pytb
y_test: [0 0 2 0]
y_test: [0 0 2 0]
Traceback (most recent call last):
File "test12.py", line 48, in <module>
print("sum_y_test:", eval(sum_y_test))
File "test12.py", line 17, in eval
return x.eval()
File "C:\Repos\phylanx\cmake-build-debug\python\build\lib.win-amd64-3.6\phylanx\ast\physl.py", line 508, in eval
*self.args, **self.kwargs)
RuntimeError: this client_base has no valid shared state: HPX(no_state)
```
If we comment out `y_test = reshape(y_test,(4,1))` and `y_test = squeeze(y_test, 1)` it works properly:
```pytb
y_test: [0 0 2 0]
y_test: [0 0 2 0]
sum_y_test: 2
```
|
1.0
|
RuntimeError: this client_base has no valid shared state: HPX(no_state) - The following code
```python
from phylanx import Phylanx, PhylanxSession, execution_tree
import numpy as np
PhylanxSession.init(1)
def variable(value, dtype=None, name=None):
if dtype is None:
dtype = "float64"
from phylanx.ast.physl import PhySL
if isinstance(value, PhySL.eval_wrapper):
return execution_tree.variable(value.code(), dtype)
if isinstance(value, execution_tree.variable):
return value
return execution_tree.variable(value, dtype=dtype, name=name)
def eval(x):
return x.eval()
@Phylanx
def sum_eager(x, axis, keepdims):
return np.sum(x, axis, keepdims)
def sum(x, axis=None, keepdims=False):
return sum_eager.lazy(x, axis, keepdims)
@Phylanx
def reshape_eager(x, shape):
return np.reshape(x, shape)
def reshape(x, shape):
return reshape_eager.lazy(x, shape)
@Phylanx
def squeeze_eager(x, axis):
return np.squeeze(x, axis)
def squeeze(x, axis):
return squeeze_eager.lazy(x, axis)
y_test = variable(np.array([0, 0, 2, 0]))
print("y_test:",eval(y_test))
y_test = reshape(y_test,(4,1))
y_test = squeeze(y_test, 1)
print("y_test:",eval(y_test))
sum_y_test = sum(y_test)
print("sum_y_test:", eval(sum_y_test))
```
produces:
```pytb
y_test: [0 0 2 0]
y_test: [0 0 2 0]
Traceback (most recent call last):
File "test12.py", line 48, in <module>
print("sum_y_test:", eval(sum_y_test))
File "test12.py", line 17, in eval
return x.eval()
File "C:\Repos\phylanx\cmake-build-debug\python\build\lib.win-amd64-3.6\phylanx\ast\physl.py", line 508, in eval
*self.args, **self.kwargs)
RuntimeError: this client_base has no valid shared state: HPX(no_state)
```
If we comment out `y_test = reshape(y_test,(4,1))` and `y_test = squeeze(y_test, 1)` it works properly:
```pytb
y_test: [0 0 2 0]
y_test: [0 0 2 0]
sum_y_test: 2
```
|
defect
|
runtimeerror this client base has no valid shared state hpx no state the following code python from phylanx import phylanx phylanxsession execution tree import numpy as np phylanxsession init def variable value dtype none name none if dtype is none dtype from phylanx ast physl import physl if isinstance value physl eval wrapper return execution tree variable value code dtype if isinstance value execution tree variable return value return execution tree variable value dtype dtype name name def eval x return x eval phylanx def sum eager x axis keepdims return np sum x axis keepdims def sum x axis none keepdims false return sum eager lazy x axis keepdims phylanx def reshape eager x shape return np reshape x shape def reshape x shape return reshape eager lazy x shape phylanx def squeeze eager x axis return np squeeze x axis def squeeze x axis return squeeze eager lazy x axis y test variable np array print y test eval y test y test reshape y test y test squeeze y test print y test eval y test sum y test sum y test print sum y test eval sum y test produces pytb y test y test traceback most recent call last file py line in print sum y test eval sum y test file py line in eval return x eval file c repos phylanx cmake build debug python build lib win phylanx ast physl py line in eval self args self kwargs runtimeerror this client base has no valid shared state hpx no state if we comment out y test reshape y test and y test squeeze y test it works properly pytb y test y test sum y test
| 1
|
283,403
| 8,719,422,925
|
IssuesEvent
|
2018-12-08 00:45:21
|
aowen87/BAR
|
https://api.github.com/repos/aowen87/BAR
|
closed
|
Data level comparison wizard creates unparseable expression
|
bug crash likelihood medium priority reviewed severity high wrong results
|
Open Wave.visit
Open data level comparison wizard.
Choose 'Between different time slices on same mesh'
select pressure as donor field
Use Absolute time with index 0
Conn_cmfe
simply place it on target mesh for later use
After clicking finish, open the expressions window and look at the created expression:
conn_cmfe(<<[0]i:pressure>>, <quadmesh>)
The expression parser will complain about the double "<<"
This may be related to #1640, though I couldn't tell for certain from that ticket's description.
-----------------------REDMINE MIGRATION-----------------------
This ticket was migrated from Redmine. As such, not all
information was able to be captured in the transition. Below is
a complete record of the original redmine ticket.
Ticket number: 1828
Status: Resolved
Project: VisIt
Tracker: Bug
Priority: High
Subject: Data level comparison wizard creates unparseable expression
Assigned to: Kathleen Biagas
Category:
Target version: 2.7.3
Author: Kathleen Biagas
Start: 05/01/2014
Due date:
% Done: 0
Estimated time:
Created: 05/01/2014 12:19 pm
Updated: 05/16/2014 01:05 pm
Likelihood: 3 - Occasional
Severity: 4 - Crash / Wrong Results
Found in version: 2.7.1
Impact:
Expected Use:
OS: All
Support Group: Any
Description:
Open Wave.visit
Open data level comparison wizard.
Choose 'Between different time slices on same mesh'
select pressure as donor field
Use Absolute time with index 0
Conn_cmfe
simply place it on target mesh for later use
After clicking finish, open the expressions window and look at the created expression:
conn_cmfe(<<[0]i:pressure>>, <quadmesh>)
The expression parser will complain about the double "<<"
This may be related to #1640, though I couldn't tell for certain from that ticket's description.
Comments:
SVN revision 23328 (2.7RC)M /src/gui/QvisCMFEWizard.C
|
1.0
|
Data level comparison wizard creates unparseable expression - Open Wave.visit
Open data level comparison wizard.
Choose 'Between different time slices on same mesh'
select pressure as donor field
Use Absolute time with index 0
Conn_cmfe
simply place it on target mesh for later use
After clicking finish, open the expressions window and look at the created expression:
conn_cmfe(<<[0]i:pressure>>, <quadmesh>)
The expression parser will complain about the double "<<"
This may be related to #1640, though I couldn't tell for certain from that ticket's description.
-----------------------REDMINE MIGRATION-----------------------
This ticket was migrated from Redmine. As such, not all
information was able to be captured in the transition. Below is
a complete record of the original redmine ticket.
Ticket number: 1828
Status: Resolved
Project: VisIt
Tracker: Bug
Priority: High
Subject: Data level comparison wizard creates unparseable expression
Assigned to: Kathleen Biagas
Category:
Target version: 2.7.3
Author: Kathleen Biagas
Start: 05/01/2014
Due date:
% Done: 0
Estimated time:
Created: 05/01/2014 12:19 pm
Updated: 05/16/2014 01:05 pm
Likelihood: 3 - Occasional
Severity: 4 - Crash / Wrong Results
Found in version: 2.7.1
Impact:
Expected Use:
OS: All
Support Group: Any
Description:
Open Wave.visit
Open data level comparison wizard.
Choose 'Between different time slices on same mesh'
select pressure as donor field
Use Absolute time with index 0
Conn_cmfe
simply place it on target mesh for later use
After clicking finish, open the expressions window and look at the created expression:
conn_cmfe(<<[0]i:pressure>>, <quadmesh>)
The expression parser will complain about the double "<<"
This may be related to #1640, though I couldn't tell for certain from that ticket's description.
Comments:
SVN revision 23328 (2.7RC)M /src/gui/QvisCMFEWizard.C
|
non_defect
|
data level comparison wizard creates unparseable expression open wave visit open data level comparison wizard choose between different time slices on same mesh select pressure as donor field use absolute time with index conn cmfe simply place it on target mesh for later use after clicking finish open the expressions window and look at the created expression conn cmfe the expression parser will complain about the double this may be related to though i couldn t tell for certain from that ticket s description redmine migration this ticket was migrated from redmine as such not all information was able to be captured in the transition below is a complete record of the original redmine ticket ticket number status resolved project visit tracker bug priority high subject data level comparison wizard creates unparseable expression assigned to kathleen biagas category target version author kathleen biagas start due date done estimated time created pm updated pm likelihood occasional severity crash wrong results found in version impact expected use os all support group any description open wave visit open data level comparison wizard choose between different time slices on same mesh select pressure as donor field use absolute time with index conn cmfe simply place it on target mesh for later use after clicking finish open the expressions window and look at the created expression conn cmfe the expression parser will complain about the double this may be related to though i couldn t tell for certain from that ticket s description comments svn revision m src gui qviscmfewizard c
| 0
|
119,088
| 12,014,194,042
|
IssuesEvent
|
2020-04-10 10:45:37
|
benzoferrari123/pinerf
|
https://api.github.com/repos/benzoferrari123/pinerf
|
closed
|
Provide More Detail in README
|
documentation
|
The README does not detail much about the operation of the system and how it works. More detail may be added.
|
1.0
|
Provide More Detail in README - The README does not detail much about the operation of the system and how it works. More detail may be added.
|
non_defect
|
provide more detail in readme the readme does not detail much about the operation of the system and how it works more detail may be added
| 0
|
333,613
| 24,382,448,185
|
IssuesEvent
|
2022-10-04 08:58:45
|
geosolutions-it/MapStore2
|
https://api.github.com/repos/geosolutions-it/MapStore2
|
opened
|
User Guide - Aliases and tooltips for Table widget
|
Documentation User Guide C040-COMUNE_GE-2022-SUPPORT
|
## Description
<!-- A few sentences describing the documentation request -->
<!-- screenshot, video, or link to mockup/prototype are welcome -->
Add new Aliases and tooltips on Table widget in the [User Guide](https://mapstore.readthedocs.io/en/latest/user-guide/exploring-maps/)
*Documentation section involved*
- [x] User Guide
- [ ] Developer Guide
## Other useful information
https://github.com/geosolutions-it/MapStore2/issues/8559
|
1.0
|
User Guide - Aliases and tooltips for Table widget - ## Description
<!-- A few sentences describing the documentation request -->
<!-- screenshot, video, or link to mockup/prototype are welcome -->
Add new Aliases and tooltips on Table widget in the [User Guide](https://mapstore.readthedocs.io/en/latest/user-guide/exploring-maps/)
*Documentation section involved*
- [x] User Guide
- [ ] Developer Guide
## Other useful information
https://github.com/geosolutions-it/MapStore2/issues/8559
|
non_defect
|
user guide aliases and tooltips for table widget description add new aliases and tooltips on table widget in the documentation section involved user guide developer guide other useful information
| 0
|
71,478
| 23,644,776,764
|
IssuesEvent
|
2022-08-25 20:47:00
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
reopened
|
CPU churn on incremental sync after load
|
T-Defect A-Performance P1 S-Major A-Timeline O-Occasional
|
@dbkr says: 'I looked at the CPU churn on an incremental sync after load recently, and a lot of it was caused by the Constant Time Dispatcher now dispatching a separate Refresh event for every `roomstate.member` event, causing each `RoomTile` to refresh separately (if power levels change in a room, a `roomstate.member` event will be emitted for every member in the room).'
|
1.0
|
CPU churn on incremental sync after load - @dbkr says: 'I looked at the CPU churn on an incremental sync after load recently, and a lot of it was caused by the Constant Time Dispatcher now dispatching a separate Refresh event for every `roomstate.member` event, causing each `RoomTile` to refresh separately (if power levels change in a room, a `roomstate.member` event will be emitted for every member in the room).'
|
defect
|
cpu churn on incremental sync after load dbkr says i looked at the cpu churn on an incremental sync after load recently and a lot of it was caused by the constant time dispatcher now dispatching a separate refresh event for every roomstate member event causing each roomtile to refresh separately if power levels change in a room a roomstate member event will be emitted for every member in the room
| 1
|
36,136
| 7,867,147,112
|
IssuesEvent
|
2018-06-23 04:16:27
|
StrikeNP/trac_test
|
https://api.github.com/repos/StrikeNP/trac_test
|
closed
|
Rename Ncm_initial to Nc_in_cloud0 and Ncm_in_cloud to Nc_in_cloud (Trac #513)
|
Migrated from Trac clubb_src defect raut@uwm.edu
|
We've used the name Ncm_initial for years, but the "m" denotes layer average, whereas in fact Ncm_initial is an overall within-cloud value. This caused confusion for years (see ticket:490). Therefore, let's rename Ncm_initial everywhere to Nc_in_cloud0. The zero denotes that it is an initial value that's a scalar, not a profile vector. Ncm_initial will need to be renamed everywhere in the source code and all input/case_setups/...model.in files.
Second, CLUBB uses the variable name "Ncm_in_cloud", but this may seem contradictory, because "m" denotes layer average, but "in_cloud" denotes a within-cloud average. Therefore let's change it to Nc_in_cloud.
Both these changes should leave the output of the standard CLUBB simulations bit-for-bit identical with the old results. Let's check this before committing the new code.
Attachments:
[plot_explicit_ta_configs.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_explicit_ta_configs.maff)
[plot_new_pdf_config_1_plot_2.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_new_pdf_config_1_plot_2.maff)
[plot_combo_pdf_run_3.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_combo_pdf_run_3.maff)
[plot_input_fields_rtp3_thlp3_1.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_input_fields_rtp3_thlp3_1.maff)
[plot_new_pdf_20180522_test_1.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_new_pdf_20180522_test_1.maff)
[plot_attempts_8_10.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_attempts_8_10.maff)
[plot_attempt_8_only.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_attempt_8_only.maff)
[plot_beta_1p3.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_beta_1p3.maff)
[plot_beta_1p3_all.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_beta_1p3_all.maff)
Migrated from http://carson.math.uwm.edu/trac/clubb/ticket/513
```json
{
"status": "closed",
"changetime": "2013-08-28T17:15:43",
"description": "\nWe've used the name Ncm_initial for years, but the \"m\" denotes layer average, whereas in fact Ncm_initial is an overall within-cloud value. This caused confusion for years (see ticket:490). Therefore, let's rename Ncm_initial everywhere to Nc_in_cloud0. The zero denotes that it is an initial value that's a scalar, not a profile vector. Ncm_initial will need to be renamed everywhere in the source code and all input/case_setups/...model.in files.\n\nSecond, CLUBB uses the variable name \"Ncm_in_cloud\", but this may seem contradictory, because \"m\" denotes layer average, but \"in_cloud\" denotes a within-cloud average. Therefore let's change it to Nc_in_cloud.\n\nBoth these changes should leave the output of the standard CLUBB simulations bit-for-bit identical with the old results. Let's check this before committing the new code.",
"reporter": "vlarson@uwm.edu",
"cc": "vlarson@uwm.edu, bmg2@uwm.edu",
"resolution": "fixed",
"_ts": "1377710143501379",
"component": "clubb_src",
"summary": "Rename Ncm_initial to Nc_in_cloud0 and Ncm_in_cloud to Nc_in_cloud",
"priority": "minor",
"keywords": "",
"time": "2012-07-02T21:15:45",
"milestone": "3. Refactor CLUBB",
"owner": "raut@uwm.edu",
"type": "defect"
}
```
|
1.0
|
Rename Ncm_initial to Nc_in_cloud0 and Ncm_in_cloud to Nc_in_cloud (Trac #513) -
We've used the name Ncm_initial for years, but the "m" denotes layer average, whereas in fact Ncm_initial is an overall within-cloud value. This caused confusion for years (see ticket:490). Therefore, let's rename Ncm_initial everywhere to Nc_in_cloud0. The zero denotes that it is an initial value that's a scalar, not a profile vector. Ncm_initial will need to be renamed everywhere in the source code and all input/case_setups/...model.in files.
Second, CLUBB uses the variable name "Ncm_in_cloud", but this may seem contradictory, because "m" denotes layer average, but "in_cloud" denotes a within-cloud average. Therefore let's change it to Nc_in_cloud.
Both these changes should leave the output of the standard CLUBB simulations bit-for-bit identical with the old results. Let's check this before committing the new code.
Attachments:
[plot_explicit_ta_configs.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_explicit_ta_configs.maff)
[plot_new_pdf_config_1_plot_2.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_new_pdf_config_1_plot_2.maff)
[plot_combo_pdf_run_3.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_combo_pdf_run_3.maff)
[plot_input_fields_rtp3_thlp3_1.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_input_fields_rtp3_thlp3_1.maff)
[plot_new_pdf_20180522_test_1.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_new_pdf_20180522_test_1.maff)
[plot_attempts_8_10.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_attempts_8_10.maff)
[plot_attempt_8_only.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_attempt_8_only.maff)
[plot_beta_1p3.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_beta_1p3.maff)
[plot_beta_1p3_all.maff](https://github.com/larson-group/trac_attachment_archive/blob/master/trac_test/822/plot_beta_1p3_all.maff)
Migrated from http://carson.math.uwm.edu/trac/clubb/ticket/513
```json
{
"status": "closed",
"changetime": "2013-08-28T17:15:43",
"description": "\nWe've used the name Ncm_initial for years, but the \"m\" denotes layer average, whereas in fact Ncm_initial is an overall within-cloud value. This caused confusion for years (see ticket:490). Therefore, let's rename Ncm_initial everywhere to Nc_in_cloud0. The zero denotes that it is an initial value that's a scalar, not a profile vector. Ncm_initial will need to be renamed everywhere in the source code and all input/case_setups/...model.in files.\n\nSecond, CLUBB uses the variable name \"Ncm_in_cloud\", but this may seem contradictory, because \"m\" denotes layer average, but \"in_cloud\" denotes a within-cloud average. Therefore let's change it to Nc_in_cloud.\n\nBoth these changes should leave the output of the standard CLUBB simulations bit-for-bit identical with the old results. Let's check this before committing the new code.",
"reporter": "vlarson@uwm.edu",
"cc": "vlarson@uwm.edu, bmg2@uwm.edu",
"resolution": "fixed",
"_ts": "1377710143501379",
"component": "clubb_src",
"summary": "Rename Ncm_initial to Nc_in_cloud0 and Ncm_in_cloud to Nc_in_cloud",
"priority": "minor",
"keywords": "",
"time": "2012-07-02T21:15:45",
"milestone": "3. Refactor CLUBB",
"owner": "raut@uwm.edu",
"type": "defect"
}
```
|
defect
|
rename ncm initial to nc in and ncm in cloud to nc in cloud trac we ve used the name ncm initial for years but the m denotes layer average whereas in fact ncm initial is an overall within cloud value this caused confusion for years see ticket therefore let s rename ncm initial everywhere to nc in the zero denotes that it is an initial value that s a scalar not a profile vector ncm initial will need to be renamed everywhere in the source code and all input case setups model in files second clubb uses the variable name ncm in cloud but this may seem contradictory because m denotes layer average but in cloud denotes a within cloud average therefore let s change it to nc in cloud both these changes should leave the output of the standard clubb simulations bit for bit identical with the old results let s check this before committing the new code attachments migrated from json status closed changetime description nwe ve used the name ncm initial for years but the m denotes layer average whereas in fact ncm initial is an overall within cloud value this caused confusion for years see ticket therefore let s rename ncm initial everywhere to nc in the zero denotes that it is an initial value that s a scalar not a profile vector ncm initial will need to be renamed everywhere in the source code and all input case setups model in files n nsecond clubb uses the variable name ncm in cloud but this may seem contradictory because m denotes layer average but in cloud denotes a within cloud average therefore let s change it to nc in cloud n nboth these changes should leave the output of the standard clubb simulations bit for bit identical with the old results let s check this before committing the new code reporter vlarson uwm edu cc vlarson uwm edu uwm edu resolution fixed ts component clubb src summary rename ncm initial to nc in and ncm in cloud to nc in cloud priority minor keywords time milestone refactor clubb owner raut uwm edu type defect
| 1
|
664,588
| 22,282,174,453
|
IssuesEvent
|
2022-06-11 03:25:26
|
oppia/oppia-android
|
https://api.github.com/repos/oppia/oppia-android
|
closed
|
Require that all a classes that should have tests, have a corresponding test file (& in the right location) [Blocked: #59, #1724]
|
Type: Improvement Priority: Nice-to-have good second issue
|
**Is your feature request related to a problem? Please describe.**
Code can be introduced today without tests.
**Describe the solution you'd like**
In order to ensure the app has good testing coverage, we should require all new code have test files present. Later work can ensure that code coverage itself is properly met.
In particular, I think we should ensure there's an exact 'Test' file corresponding to each new file, but in the test directory. Unfortunately, we cannot do this until #59 (Bazel migration stage 2) is completed since that will reorganize the project into its final directory structure. There are also some files which probably do not require dedicated tests since they would be trivial/change detector tests that are covered by other integration tests:
- Components (which will eventually be automatically generated once #1720 is completed)
- Modules
- Data structure only classes (if these even exist--most pure data structures are represented via protos)
- Presenters (they should share a test with their fragment/activity/view counterpart)
|
1.0
|
Require that all a classes that should have tests, have a corresponding test file (& in the right location) [Blocked: #59, #1724] - **Is your feature request related to a problem? Please describe.**
Code can be introduced today without tests.
**Describe the solution you'd like**
In order to ensure the app has good testing coverage, we should require all new code have test files present. Later work can ensure that code coverage itself is properly met.
In particular, I think we should ensure there's an exact 'Test' file corresponding to each new file, but in the test directory. Unfortunately, we cannot do this until #59 (Bazel migration stage 2) is completed since that will reorganize the project into its final directory structure. There are also some files which probably do not require dedicated tests since they would be trivial/change detector tests that are covered by other integration tests:
- Components (which will eventually be automatically generated once #1720 is completed)
- Modules
- Data structure only classes (if these even exist--most pure data structures are represented via protos)
- Presenters (they should share a test with their fragment/activity/view counterpart)
|
non_defect
|
require that all a classes that should have tests have a corresponding test file in the right location is your feature request related to a problem please describe code can be introduced today without tests describe the solution you d like in order to ensure the app has good testing coverage we should require all new code have test files present later work can ensure that code coverage itself is properly met in particular i think we should ensure there s an exact test file corresponding to each new file but in the test directory unfortunately we cannot do this until bazel migration stage is completed since that will reorganize the project into its final directory structure there are also some files which probably do not require dedicated tests since they would be trivial change detector tests that are covered by other integration tests components which will eventually be automatically generated once is completed modules data structure only classes if these even exist most pure data structures are represented via protos presenters they should share a test with their fragment activity view counterpart
| 0
|
49,427
| 13,186,706,080
|
IssuesEvent
|
2020-08-13 01:03:10
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
[cmake] test dependencies (Trac #1367)
|
Incomplete Migration Migrated from Trac cmake defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1367">https://code.icecube.wisc.edu/ticket/1367</a>, reported by david.schultz and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-12T00:03:13",
"description": "Doing only `make icetray-test` is insufficient to build all the dependencies the test depends on. Building the entire metaproject solves this, so it's some internal dependency.",
"reporter": "david.schultz",
"cc": "nega",
"resolution": "fixed",
"_ts": "1547251393300533",
"component": "cmake",
"summary": "[cmake] test dependencies",
"priority": "normal",
"keywords": "",
"time": "2015-09-23T16:14:35",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
[cmake] test dependencies (Trac #1367) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1367">https://code.icecube.wisc.edu/ticket/1367</a>, reported by david.schultz and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-12T00:03:13",
"description": "Doing only `make icetray-test` is insufficient to build all the dependencies the test depends on. Building the entire metaproject solves this, so it's some internal dependency.",
"reporter": "david.schultz",
"cc": "nega",
"resolution": "fixed",
"_ts": "1547251393300533",
"component": "cmake",
"summary": "[cmake] test dependencies",
"priority": "normal",
"keywords": "",
"time": "2015-09-23T16:14:35",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
defect
|
test dependencies trac migrated from json status closed changetime description doing only make icetray test is insufficient to build all the dependencies the test depends on building the entire metaproject solves this so it s some internal dependency reporter david schultz cc nega resolution fixed ts component cmake summary test dependencies priority normal keywords time milestone owner nega type defect
| 1
|
46,726
| 13,055,965,579
|
IssuesEvent
|
2020-07-30 03:15:23
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
CMake trips on partial ROOT install (Trac #1774)
|
Incomplete Migration Migrated from Trac cmake defect
|
Migrated from https://code.icecube.wisc.edu/ticket/1774
```json
{
"status": "closed",
"changetime": "2019-09-18T05:46:12",
"description": "When only parts of ROOT is installed cmake seems to set the ROOT_FOUND flag to false but the USE_ROOT to true which confuses cmake. ",
"reporter": "sflis",
"cc": "",
"resolution": "worksforme",
"_ts": "1568785572410829",
"component": "cmake",
"summary": "CMake trips on partial ROOT install",
"priority": "normal",
"keywords": "",
"time": "2016-07-07T11:26:58",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
|
1.0
|
CMake trips on partial ROOT install (Trac #1774) - Migrated from https://code.icecube.wisc.edu/ticket/1774
```json
{
"status": "closed",
"changetime": "2019-09-18T05:46:12",
"description": "When only parts of ROOT is installed cmake seems to set the ROOT_FOUND flag to false but the USE_ROOT to true which confuses cmake. ",
"reporter": "sflis",
"cc": "",
"resolution": "worksforme",
"_ts": "1568785572410829",
"component": "cmake",
"summary": "CMake trips on partial ROOT install",
"priority": "normal",
"keywords": "",
"time": "2016-07-07T11:26:58",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
|
defect
|
cmake trips on partial root install trac migrated from json status closed changetime description when only parts of root is installed cmake seems to set the root found flag to false but the use root to true which confuses cmake reporter sflis cc resolution worksforme ts component cmake summary cmake trips on partial root install priority normal keywords time milestone long term future owner nega type defect
| 1
|
172,600
| 6,514,518,571
|
IssuesEvent
|
2017-08-26 01:35:13
|
minetest/minetest
|
https://api.github.com/repos/minetest/minetest
|
closed
|
Game doesn't always disregard image filename extensions in the context of a mod's code
|
@ Script API Bug Low priority Possible close
|
In a mod, when you specify an image to be used as a texture, according to the API you should be able to supply simply the base filename, or a filename with any image extension regardless of the actual file's contents. For example, consider the following code:
``` lua
minetest.register_node("tv:screen_7", {
description = "TV",
tile_images = {"tv_screen_7.png"},
is_ground_content = true,
groups = {snappy=1,bendy=2,cracky=1,melty=2,level=2},
drop = 'tv:screen_1',
light_source = 8,
})
```
Deprecated use of tile_images aside, the referenced file, "tv_screen_7.png" is actually stored on disk as a JPEG image, with the wrong file extension.
https://raw.github.com/Jordach/Minetest-Mods./master/tv/textures/tv_screen_7.png
According to the API, this should still work, but it doesn't. If the mod references the image with the wrong extension, or with no extension at all, the game does not load the image and warns the user of this.
If given the exact on-disk name of the image, and the image is properly named according to its content, the above code will load it just fine. That is, if I rename the image on disk to "tv_screen_7.jpg" and change the above code to match, it works fine.
While talking about this in IRC:
[08-23 12:36] [celeron55] i found the problem, and it is kind of odd
[08-23 12:36] [celeron55] the checking of different file extensions is done at the filesystem level, not at cache level (in which the stuff from the server ends up)
|
1.0
|
Game doesn't always disregard image filename extensions in the context of a mod's code - In a mod, when you specify an image to be used as a texture, according to the API you should be able to supply simply the base filename, or a filename with any image extension regardless of the actual file's contents. For example, consider the following code:
``` lua
minetest.register_node("tv:screen_7", {
description = "TV",
tile_images = {"tv_screen_7.png"},
is_ground_content = true,
groups = {snappy=1,bendy=2,cracky=1,melty=2,level=2},
drop = 'tv:screen_1',
light_source = 8,
})
```
Deprecated use of tile_images aside, the referenced file, "tv_screen_7.png" is actually stored on disk as a JPEG image, with the wrong file extension.
https://raw.github.com/Jordach/Minetest-Mods./master/tv/textures/tv_screen_7.png
According to the API, this should still work, but it doesn't. If the mod references the image with the wrong extension, or with no extension at all, the game does not load the image and warns the user of this.
If given the exact on-disk name of the image, and the image is properly named according to its content, the above code will load it just fine. That is, if I rename the image on disk to "tv_screen_7.jpg" and change the above code to match, it works fine.
While talking about this in IRC:
[08-23 12:36] [celeron55] i found the problem, and it is kind of odd
[08-23 12:36] [celeron55] the checking of different file extensions is done at the filesystem level, not at cache level (in which the stuff from the server ends up)
|
non_defect
|
game doesn t always disregard image filename extensions in the context of a mod s code in a mod when you specify an image to be used as a texture according to the api you should be able to supply simply the base filename or a filename with any image extension regardless of the actual file s contents for example consider the following code lua minetest register node tv screen description tv tile images tv screen png is ground content true groups snappy bendy cracky melty level drop tv screen light source deprecated use of tile images aside the referenced file tv screen png is actually stored on disk as a jpeg image with the wrong file extension according to the api this should still work but it doesn t if the mod references the image with the wrong extension or with no extension at all the game does not load the image and warns the user of this if given the exact on disk name of the image and the image is properly named according to its content the above code will load it just fine that is if i rename the image on disk to tv screen jpg and change the above code to match it works fine while talking about this in irc i found the problem and it is kind of odd the checking of different file extensions is done at the filesystem level not at cache level in which the stuff from the server ends up
| 0
|
301,473
| 26,051,369,919
|
IssuesEvent
|
2022-12-22 19:03:55
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
kvnemesis: add AddSSTable
|
C-enhancement A-testing T-kv
|
We should extend kvnemesis to issue AddSSTable requests.
Jira issue: CRDB-7281
|
1.0
|
kvnemesis: add AddSSTable - We should extend kvnemesis to issue AddSSTable requests.
Jira issue: CRDB-7281
|
non_defect
|
kvnemesis add addsstable we should extend kvnemesis to issue addsstable requests jira issue crdb
| 0
|
90,147
| 15,856,080,620
|
IssuesEvent
|
2021-04-08 01:28:25
|
rgordon95/react-redux-todo-list-demo
|
https://api.github.com/repos/rgordon95/react-redux-todo-list-demo
|
opened
|
CVE-2020-7660 (High) detected in serialize-javascript-1.6.1.tgz
|
security vulnerability
|
## CVE-2020-7660 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.6.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular expressions and functions.</p>
<p>Library home page: <a href="https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.6.1.tgz">https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.6.1.tgz</a></p>
<p>Path to dependency file: /react-redux-todo-list-demo/package.json</p>
<p>Path to vulnerable library: react-redux-todo-list-demo/node_modules/serialize-javascript/package.json</p>
<p>
Dependency Hierarchy:
- webpack-4.17.2.tgz (Root Library)
- uglifyjs-webpack-plugin-1.3.0.tgz
- :x: **serialize-javascript-1.6.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
serialize-javascript prior to 3.1.0 allows remote attackers to inject arbitrary code via the function "deleteFunctions" within "index.js".
<p>Publish Date: 2020-06-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7660>CVE-2020-7660</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7660">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7660</a></p>
<p>Release Date: 2020-06-01</p>
<p>Fix Resolution: serialize-javascript - 3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-7660 (High) detected in serialize-javascript-1.6.1.tgz - ## CVE-2020-7660 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.6.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular expressions and functions.</p>
<p>Library home page: <a href="https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.6.1.tgz">https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.6.1.tgz</a></p>
<p>Path to dependency file: /react-redux-todo-list-demo/package.json</p>
<p>Path to vulnerable library: react-redux-todo-list-demo/node_modules/serialize-javascript/package.json</p>
<p>
Dependency Hierarchy:
- webpack-4.17.2.tgz (Root Library)
- uglifyjs-webpack-plugin-1.3.0.tgz
- :x: **serialize-javascript-1.6.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
serialize-javascript prior to 3.1.0 allows remote attackers to inject arbitrary code via the function "deleteFunctions" within "index.js".
<p>Publish Date: 2020-06-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7660>CVE-2020-7660</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7660">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7660</a></p>
<p>Release Date: 2020-06-01</p>
<p>Fix Resolution: serialize-javascript - 3.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in serialize javascript tgz cve high severity vulnerability vulnerable library serialize javascript tgz serialize javascript to a superset of json that includes regular expressions and functions library home page a href path to dependency file react redux todo list demo package json path to vulnerable library react redux todo list demo node modules serialize javascript package json dependency hierarchy webpack tgz root library uglifyjs webpack plugin tgz x serialize javascript tgz vulnerable library vulnerability details serialize javascript prior to allows remote attackers to inject arbitrary code via the function deletefunctions within index js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution serialize javascript step up your open source security game with whitesource
| 0
|
67,835
| 21,182,932,918
|
IssuesEvent
|
2022-04-08 09:43:29
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
Unable to leave or join the room "#offtopic:grapheneos.org"
|
T-Defect X-Cannot-Reproduce S-Major A-Room-View O-Uncommon
|
### Steps to reproduce
1. I have been in the room #offtopic:grapheneos.org for a while now.
1. I discovered this issue by right clicking on the room and choosing the "Low Priority" option. I get the error message "Error leaving room Not a known room".
1. I then try to leave the room (with the intention of re-joining it). I get the error message "Error leaving room Not a known room".
1. I then try to join #offtopic:grapheneos.org to see if that works. I get the following error message, which brought me here to file this issue:
```
#offtopic:grapheneos.org is not accessible at this time.
Try again later, or ask a room admin to check if you have access.
M_UNKNOWN was returned while trying to access the room. If you think you're seeing this message in error, please [submit a bug report](https://github.com/vector-im/element-web/issues/new/choose).
```
### Outcome
#### What did you expect?
I expect that the room is accessible. I should be able to leave and join the room.
#### What happened instead?
It's not clear if the room exists or not. I'm unable to "leave" the room. I'm unable to "join" the room.
### Operating system
Arch Linux
### Application version
Element version: 1.10.8, Olm version: 3.2.8
### How did you install the app?
Arch package via pacman
### Homeserver
meowchat.xyz, Synapse {"server_version":"1.55.2","python_version":"3.9.2"}
### Will you send logs?
Yes
|
1.0
|
Unable to leave or join the room "#offtopic:grapheneos.org" - ### Steps to reproduce
1. I have been in the room #offtopic:grapheneos.org for a while now.
1. I discovered this issue by right clicking on the room and choosing the "Low Priority" option. I get the error message "Error leaving room Not a known room".
1. I then try to leave the room (with the intention of re-joining it). I get the error message "Error leaving room Not a known room".
1. I then try to join #offtopic:grapheneos.org to see if that works. I get the following error message, which brought me here to file this issue:
```
#offtopic:grapheneos.org is not accessible at this time.
Try again later, or ask a room admin to check if you have access.
M_UNKNOWN was returned while trying to access the room. If you think you're seeing this message in error, please [submit a bug report](https://github.com/vector-im/element-web/issues/new/choose).
```
### Outcome
#### What did you expect?
I expect that the room is accessible. I should be able to leave and join the room.
#### What happened instead?
It's not clear if the room exists or not. I'm unable to "leave" the room. I'm unable to "join" the room.
### Operating system
Arch Linux
### Application version
Element version: 1.10.8, Olm version: 3.2.8
### How did you install the app?
Arch package via pacman
### Homeserver
meowchat.xyz, Synapse {"server_version":"1.55.2","python_version":"3.9.2"}
### Will you send logs?
Yes
|
defect
|
unable to leave or join the room offtopic grapheneos org steps to reproduce i have been in the room offtopic grapheneos org for a while now i discovered this issue by right clicking on the room and choosing the low priority option i get the error message error leaving room not a known room i then try to leave the room with the intention of re joining it i get the error message error leaving room not a known room i then try to join offtopic grapheneos org to see if that works i get the following error message which brought me here to file this issue offtopic grapheneos org is not accessible at this time try again later or ask a room admin to check if you have access m unknown was returned while trying to access the room if you think you re seeing this message in error please outcome what did you expect i expect that the room is accessible i should be able to leave and join the room what happened instead it s not clear if the room exists or not i m unable to leave the room i m unable to join the room operating system arch linux application version element version olm version how did you install the app arch package via pacman homeserver meowchat xyz synapse server version python version will you send logs yes
| 1
|
426,697
| 29,580,266,593
|
IssuesEvent
|
2023-06-07 04:55:46
|
risingwavelabs/risingwave-docs
|
https://api.github.com/repos/risingwavelabs/risingwave-docs
|
closed
|
Document `SHOW INDEXES`
|
documentation
|
### Related code PR
https://github.com/risingwavelabs/risingwave/pull/9835
### Which part(s) of the docs might be affected or should be updated? And how?
Command
### Reference
_No response_
|
1.0
|
Document `SHOW INDEXES` - ### Related code PR
https://github.com/risingwavelabs/risingwave/pull/9835
### Which part(s) of the docs might be affected or should be updated? And how?
Command
### Reference
_No response_
|
non_defect
|
document show indexes related code pr which part s of the docs might be affected or should be updated and how command reference no response
| 0
|
84,566
| 10,410,527,286
|
IssuesEvent
|
2019-09-13 11:39:21
|
EventStore/EventStore
|
https://api.github.com/repos/EventStore/EventStore
|
closed
|
AWS EBS snapshot backup way to go?
|
area/documentation kind/question subsystem/Core Database
|
Currently we have a test setup on AWS. For EventStore persistence we use AWS EBS volumes. Would it be sufficient and reliable enough to just create EBS snapshots? Our first test round was looking good but differs from the backup procedure described here https://eventstore.org/docs/server/database-backup/index.html
And is really necessary to do this step in case of a restore?
> Create a copy of chaser.chk and call it truncate.chk.
|
1.0
|
AWS EBS snapshot backup way to go? - Currently we have a test setup on AWS. For EventStore persistence we use AWS EBS volumes. Would it be sufficient and reliable enough to just create EBS snapshots? Our first test round was looking good but differs from the backup procedure described here https://eventstore.org/docs/server/database-backup/index.html
And is really necessary to do this step in case of a restore?
> Create a copy of chaser.chk and call it truncate.chk.
|
non_defect
|
aws ebs snapshot backup way to go currently we have a test setup on aws for eventstore persistence we use aws ebs volumes would it be sufficient and reliable enough to just create ebs snapshots our first test round was looking good but differs from the backup procedure described here and is really necessary to do this step in case of a restore create a copy of chaser chk and call it truncate chk
| 0
|
68,446
| 21,664,564,413
|
IssuesEvent
|
2022-05-07 01:47:03
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
Animation when hovering quick reaction jumps 1px in Chrome
|
T-Defect A-Aggregations A-Reactions
|
When hovering a quick reaction in Chrome, it fades in as expected, but then jumps 1px at the end.
Firefox does not exhibit this jumping behaviour.
|
1.0
|
Animation when hovering quick reaction jumps 1px in Chrome - When hovering a quick reaction in Chrome, it fades in as expected, but then jumps 1px at the end.
Firefox does not exhibit this jumping behaviour.
|
defect
|
animation when hovering quick reaction jumps in chrome when hovering a quick reaction in chrome it fades in as expected but then jumps at the end firefox does not exhibit this jumping behaviour
| 1
|
178,104
| 21,509,287,454
|
IssuesEvent
|
2022-04-28 01:24:44
|
yaroschiffelers/vue-scheme
|
https://api.github.com/repos/yaroschiffelers/vue-scheme
|
closed
|
WS-2018-0236 (Medium) detected in mem-1.1.0.tgz - autoclosed
|
security vulnerability
|
## WS-2018-0236 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mem-1.1.0.tgz</b></p></summary>
<p>Memoize functions - An optimization used to speed up consecutive function calls by caching the result of calls with identical input</p>
<p>Library home page: <a href="https://registry.npmjs.org/mem/-/mem-1.1.0.tgz">https://registry.npmjs.org/mem/-/mem-1.1.0.tgz</a></p>
<p>Path to dependency file: /vue-scheme/package.json</p>
<p>Path to vulnerable library: /tmp/git/vue-scheme/node_modules/mem/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-unit-jest-3.9.0.tgz (Root Library)
- jest-23.6.0.tgz
- jest-cli-23.6.0.tgz
- yargs-11.1.0.tgz
- os-locale-2.1.0.tgz
- :x: **mem-1.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/yaroschiffelers/vue-scheme/commits/00fbbf1249d4b7cb16b6f1046bb6b647c82893a2">00fbbf1249d4b7cb16b6f1046bb6b647c82893a2</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In nodejs-mem before version 4.0.0 there is a memory leak due to old results not being removed from the cache despite reaching maxAge. Exploitation of this can lead to exhaustion of memory and subsequent denial of service.
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1623744>WS-2018-0236</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1623744">https://bugzilla.redhat.com/show_bug.cgi?id=1623744</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 4.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2018-0236 (Medium) detected in mem-1.1.0.tgz - autoclosed - ## WS-2018-0236 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mem-1.1.0.tgz</b></p></summary>
<p>Memoize functions - An optimization used to speed up consecutive function calls by caching the result of calls with identical input</p>
<p>Library home page: <a href="https://registry.npmjs.org/mem/-/mem-1.1.0.tgz">https://registry.npmjs.org/mem/-/mem-1.1.0.tgz</a></p>
<p>Path to dependency file: /vue-scheme/package.json</p>
<p>Path to vulnerable library: /tmp/git/vue-scheme/node_modules/mem/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-unit-jest-3.9.0.tgz (Root Library)
- jest-23.6.0.tgz
- jest-cli-23.6.0.tgz
- yargs-11.1.0.tgz
- os-locale-2.1.0.tgz
- :x: **mem-1.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/yaroschiffelers/vue-scheme/commits/00fbbf1249d4b7cb16b6f1046bb6b647c82893a2">00fbbf1249d4b7cb16b6f1046bb6b647c82893a2</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In nodejs-mem before version 4.0.0 there is a memory leak due to old results not being removed from the cache despite reaching maxAge. Exploitation of this can lead to exhaustion of memory and subsequent denial of service.
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1623744>WS-2018-0236</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1623744">https://bugzilla.redhat.com/show_bug.cgi?id=1623744</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 4.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
ws medium detected in mem tgz autoclosed ws medium severity vulnerability vulnerable library mem tgz memoize functions an optimization used to speed up consecutive function calls by caching the result of calls with identical input library home page a href path to dependency file vue scheme package json path to vulnerable library tmp git vue scheme node modules mem package json dependency hierarchy cli plugin unit jest tgz root library jest tgz jest cli tgz yargs tgz os locale tgz x mem tgz vulnerable library found in head commit a href vulnerability details in nodejs mem before version there is a memory leak due to old results not being removed from the cache despite reaching maxage exploitation of this can lead to exhaustion of memory and subsequent denial of service publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
73,971
| 24,890,751,074
|
IssuesEvent
|
2022-10-28 11:48:18
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
closed
|
Sometimes the thread list shows out of order
|
T-Defect X-Blocked S-Major O-Uncommon A-Threads
|
### Steps to reproduce
1. Be in the threads list of a room with a lot of threads
2. Scroll right up to the top and then down to the bottom again
3. Notice threads appear out of order
### Outcome
#### What did you expect?
Thread order should be consistent
#### What happened instead?
The last thread shown at the bottom of the list was from 6 days ago
### Operating system
OS X
### Application version
Element Nightly version: 2022041301 Olm version: 3.2.8
### How did you install the app?
Nightly
### Homeserver
matrix.org
### Will you send logs?
No
|
1.0
|
Sometimes the thread list shows out of order - ### Steps to reproduce
1. Be in the threads list of a room with a lot of threads
2. Scroll right up to the top and then down to the bottom again
3. Notice threads appear out of order
### Outcome
#### What did you expect?
Thread order should be consistent
#### What happened instead?
The last thread shown at the bottom of the list was from 6 days ago
### Operating system
OS X
### Application version
Element Nightly version: 2022041301 Olm version: 3.2.8
### How did you install the app?
Nightly
### Homeserver
matrix.org
### Will you send logs?
No
|
defect
|
sometimes the thread list shows out of order steps to reproduce be in the threads list of a room with a lot of threads scroll right up to the top and then down to the bottom again notice threads appear out of order outcome what did you expect thread order should be consistent what happened instead the last thread shown at the bottom of the list was from days ago operating system os x application version element nightly version olm version how did you install the app nightly homeserver matrix org will you send logs no
| 1
|
42,120
| 10,819,637,897
|
IssuesEvent
|
2019-11-08 14:47:52
|
raz0red/wii-mednafen
|
https://api.github.com/repos/raz0red/wii-mednafen
|
closed
|
Gamecube support?
|
Priority-Medium Type-Defect auto-migrated
|
```
Is there any chance of getting a version of this that runs on Gamecube? Or a
way that I could compile it for Gamecube myself?
```
Original issue reported on code.google.com by `dustin...@gmail.com` on 2 Mar 2012 at 4:14
|
1.0
|
Gamecube support? - ```
Is there any chance of getting a version of this that runs on Gamecube? Or a
way that I could compile it for Gamecube myself?
```
Original issue reported on code.google.com by `dustin...@gmail.com` on 2 Mar 2012 at 4:14
|
defect
|
gamecube support is there any chance of getting a version of this that runs on gamecube or a way that i could compile it for gamecube myself original issue reported on code google com by dustin gmail com on mar at
| 1
|
101,841
| 12,710,058,727
|
IssuesEvent
|
2020-06-23 13:20:57
|
easably/platform-player-extension
|
https://api.github.com/repos/easably/platform-player-extension
|
opened
|
Find 4 top video sources and pictures for them
|
design player
|
Yor are to find 4 top resources in youtube about learning languages.
Also find 16 top links in youtube about learning languages.
And find 16 pictures to fulfill links in the player youtube window.
|
1.0
|
Find 4 top video sources and pictures for them - Yor are to find 4 top resources in youtube about learning languages.
Also find 16 top links in youtube about learning languages.
And find 16 pictures to fulfill links in the player youtube window.
|
non_defect
|
find top video sources and pictures for them yor are to find top resources in youtube about learning languages also find top links in youtube about learning languages and find pictures to fulfill links in the player youtube window
| 0
|
267,838
| 28,509,250,372
|
IssuesEvent
|
2023-04-19 01:48:31
|
dpteam/RK3188_TABLET
|
https://api.github.com/repos/dpteam/RK3188_TABLET
|
closed
|
CVE-2016-1237 (Medium) detected in linux-yocto-4.12v3.1.10 - autoclosed
|
Mend: dependency security vulnerability
|
## CVE-2016-1237 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.1.10</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (5)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs2acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs2acl.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
nfsd in the Linux kernel through 4.6.3 allows local users to bypass intended file-permission restrictions by setting a POSIX ACL, related to nfs2acl.c, nfs3acl.c, and nfs4acl.c.
<p>Publish Date: 2016-06-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1237>CVE-2016-1237</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-1237">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-1237</a></p>
<p>Release Date: 2016-06-29</p>
<p>Fix Resolution: v4.7-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2016-1237 (Medium) detected in linux-yocto-4.12v3.1.10 - autoclosed - ## CVE-2016-1237 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.1.10</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (5)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs2acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4acl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs2acl.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
nfsd in the Linux kernel through 4.6.3 allows local users to bypass intended file-permission restrictions by setting a POSIX ACL, related to nfs2acl.c, nfs3acl.c, and nfs4acl.c.
<p>Publish Date: 2016-06-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1237>CVE-2016-1237</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-1237">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-1237</a></p>
<p>Release Date: 2016-06-29</p>
<p>Fix Resolution: v4.7-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve medium detected in linux yocto autoclosed cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files fs nfsd c fs nfsd c fs nfsd c fs nfsd c fs nfsd c vulnerability details nfsd in the linux kernel through allows local users to bypass intended file permission restrictions by setting a posix acl related to c c and c publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
1,895
| 2,603,973,113
|
IssuesEvent
|
2015-02-24 19:00:46
|
chrsmith/nishazi6
|
https://api.github.com/repos/chrsmith/nishazi6
|
opened
|
沈阳阴茎有水泡是怎么回事
|
auto-migrated Priority-Medium Type-Defect
|
```
沈阳阴茎有水泡是怎么回事〓沈陽軍區政治部醫院性病〓TEL��
�024-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治�
��。位于沈陽市沈河區二緯路32號。是一所與新中國同建立共�
��煌的歷史悠久、設備精良、技術權威、專家云集,是預防、
保健、醫療、科研康復為一體的綜合性醫院。是國家首批公��
�甲等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大�
��、東南大學等知名高等院校的教學醫院。曾被中國人民解放
軍空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立��
�體二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:04
|
1.0
|
沈阳阴茎有水泡是怎么回事 - ```
沈阳阴茎有水泡是怎么回事〓沈陽軍區政治部醫院性病〓TEL��
�024-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治�
��。位于沈陽市沈河區二緯路32號。是一所與新中國同建立共�
��煌的歷史悠久、設備精良、技術權威、專家云集,是預防、
保健、醫療、科研康復為一體的綜合性醫院。是國家首批公��
�甲等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大�
��、東南大學等知名高等院校的教學醫院。曾被中國人民解放
軍空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立��
�體二等功。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:04
|
defect
|
沈阳阴茎有水泡是怎么回事 沈阳阴茎有水泡是怎么回事〓沈陽軍區政治部醫院性病〓tel�� � 〓 , � ��。 。是一所與新中國同建立共� ��煌的歷史悠久、設備精良、技術權威、專家云集,是預防、 保健、醫療、科研康復為一體的綜合性醫院。是國家首批公�� �甲等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大� ��、東南大學等知名高等院校的教學醫院。曾被中國人民解放 軍空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立�� �體二等功。 original issue reported on code google com by gmail com on jun at
| 1
|
5,003
| 3,131,194,314
|
IssuesEvent
|
2015-09-09 13:42:34
|
owncloud/gallery
|
https://api.github.com/repos/owncloud/gallery
|
closed
|
Generate thumbnails on demand
|
coder wanted enhancement performance sponsor needed
|
Background thumbnail generation is coming in 8.2. We're tracking it here: https://github.com/owncloud/gallery/issues/18
In the meantime or in addition, we could offer a button to generate these thumbnails on demand in order to make the app usable from the first load.
I think this should sit in the user preferences and thus relies on the completion of this task:
- [ ] [Add a user settings button and section](https://github.com/owncloud/gallery/issues/4)
Since @libasys already did implement such a button in his fork, maybe he'd like to share his views on how it should work?
AFAIK, If we use EventSource, then the user has to stay on the settings page until the process is over.
If we create a cron job, then the user has to stay logged in and this will only be a temporary solution until 8.2 is delivered.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/8523400-generate-thumbnails-on-demand?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
1.0
|
Generate thumbnails on demand - Background thumbnail generation is coming in 8.2. We're tracking it here: https://github.com/owncloud/gallery/issues/18
In the meantime or in addition, we could offer a button to generate these thumbnails on demand in order to make the app usable from the first load.
I think this should sit in the user preferences and thus relies on the completion of this task:
- [ ] [Add a user settings button and section](https://github.com/owncloud/gallery/issues/4)
Since @libasys already did implement such a button in his fork, maybe he'd like to share his views on how it should work?
AFAIK, If we use EventSource, then the user has to stay on the settings page until the process is over.
If we create a cron job, then the user has to stay logged in and this will only be a temporary solution until 8.2 is delivered.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/8523400-generate-thumbnails-on-demand?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F9328526&utm_medium=issues&utm_source=github).
</bountysource-plugin>
|
non_defect
|
generate thumbnails on demand background thumbnail generation is coming in we re tracking it here in the meantime or in addition we could offer a button to generate these thumbnails on demand in order to make the app usable from the first load i think this should sit in the user preferences and thus relies on the completion of this task since libasys already did implement such a button in his fork maybe he d like to share his views on how it should work afaik if we use eventsource then the user has to stay on the settings page until the process is over if we create a cron job then the user has to stay logged in and this will only be a temporary solution until is delivered want to back this issue we accept bounties via
| 0
|
5,323
| 2,610,185,321
|
IssuesEvent
|
2015-02-26 18:58:52
|
chrsmith/quchuseban
|
https://api.github.com/repos/chrsmith/quchuseban
|
opened
|
关于去除色斑的有效方法
|
auto-migrated Priority-Medium Type-Defect
|
```
《摘要》
化妆是女性的必修课,但是化妆品内的重金属成分会使肌肤��
�到损害,清晰不彻底会沉淀在肌肤表层形成色斑。所以,选�
��化妆品是一定要挑选合格的适合自己肤质的产品,并且要把
彩妆彻底清洁干净。去除色斑的有效方法,
《客户案例》
我是电脑用的时间长太了,又经常熬夜才会长了很多斑��
�就是大家都知道的辐射斑,有了斑,就想快点把
斑去掉,可如何快速去斑呢?我用过很多据说能快速去斑的方�
��,和大家分享一下:<br>
果酸蜕皮:就是用含果酸的化妆品把脸上的皮褪掉,这��
�就没斑了,这个太危险了,后果是皮肤对光就越
敏感,变得干燥,太阳晒一晒马上就会起红疹,出现色素沉��
�反而比原来更加严重。<br>
激光祛斑:就是把光打到皮下,可以将色素团击碎,体��
�组织将其吸收或者排泄掉。这种方法虽然方便,
但不宜频繁使用,对皮肤伤害很大,而且很容易反弹。<br>
各类祛斑霜:不知道里面含了什么化学成分,让我肚子��
�了一星期。<br>
通过以上的各种快速去斑方法的尝试,我认为快速去斑��
�行不通的,后来我就瞄上了精华祛斑,也就是「黛芙薇尔精�
��液」,当时订购了两个周期,本来就是想试试,在用完第一
个周期的时候,我朋友说好
像有点变淡了,当时挺高兴的,就接着用,没想到最后还真��
�把那些辐射斑去掉了,到现在都没反弹,在这里我要对那些�
��快速去斑的姐妹说,还是相信精华祛斑吧,虽然速度是慢点
,可安全有保证。
阅读了去除色斑的有效方法,再看脸上容易长斑的原因:
《色斑形成原因》
内部因素
一、压力
当人受到压力时,就会分泌肾上腺素,为对付压力而做��
�备。如果长期受到压力,人体新陈代谢的平衡就会遭到破坏�
��皮肤所需的营养供应趋于缓慢,色素母细胞就会变得很活跃
。
二、荷尔蒙分泌失调
避孕药里所含的女性荷尔蒙雌激素,会刺激麦拉宁细胞��
�分泌而形成不均匀的斑点,因避孕药而形成的斑点,虽然在�
��药中断后会停止,但仍会在皮肤上停留很长一段时间。怀孕
中因女性荷尔蒙雌激素的增加,从怀孕4—5个月开始会容易出
现斑,这时候出现的斑点在产后大部分会消失。可是,新陈��
�谢不正常、肌肤裸露在强烈的紫外线下、精神上受到压力等�
��因,都会使斑加深。有时新长出的斑,产后也不会消失,所
以需要更加注意。
三、新陈代谢缓慢
肝的新陈代谢功能不正常或卵巢功能减退时也会出现斑��
�因为新陈代谢不顺畅、或内分泌失调,使身体处于敏感状态�
��,从而加剧色素问题。我们常说的便秘会形成斑,其实就是
内分泌失调导致过敏体质而形成的。另外,身体状态不正常��
�时候,紫外线的照射也会加速斑的形成。
四、错误的使用化妆品
使用了不适合自己皮肤的化妆品,会导致皮肤过敏。在��
�疗的过程中如过量照射到紫外线,皮肤会为了抵御外界的侵�
��,在有炎症的部位聚集麦拉宁色素,这样会出现色素沉着的
问题。
外部因素
一、紫外线
照射紫外线的时候,人体为了保护皮肤,会在基底层产��
�很多麦拉宁色素。所以为了保护皮肤,会在敏感部位聚集更�
��的色素。经常裸露在强烈的阳光底下不仅促进皮肤的老化,
还会引起黑斑、雀斑等色素沉着的皮肤疾患。
二、不良的清洁习惯
因强烈的清洁习惯使皮肤变得敏感,这样会刺激皮肤。��
�皮肤敏感时,人体为了保护皮肤,黑色素细胞会分泌很多麦�
��宁色素,当色素过剩时就出现了斑、瑕疵等皮肤色素沉着的
问题。
三、遗传基因
父母中有长斑的,则本人长斑的概率就很高,这种情况��
�一定程度上就可判定是遗传基因的作用。所以家里特别是长�
��有长斑的人,要注意避免引发长斑的重要因素之一——紫外
线照射,这是预防斑必须注意的。
《有疑问帮你解决》
1,黛芙薇尔精华液真的有效果吗?真的可以把脸上的黄褐��
�去掉吗?
答:黛芙薇尔精华液DNA精华能够有效的修复周围难以触��
�的色斑,其独有的纳豆成分为皮肤的美白与靓丽,提供了必�
��可少的营养物质,可以有效的去除黄褐斑,黄褐斑,黄褐斑
,蝴蝶斑,晒斑、妊娠斑等。它它完全突破了传统的美肤时��
�,宛如在皮肤中注入了一杯兼具活化、再生、滋养等功效的�
��尾酒,同时为脸部提供大量有机维生素精华,脸部的改变显
而易见。自产品上市以来,老顾客纷纷介绍新顾客,71%的新��
�客都是通过老顾客介绍而来,口碑由此而来!
2,服用黛芙薇尔美白,会伤身体吗?有副作用吗?
答:黛芙薇尔精华液应用了精纯复合配方和领先的分类��
�斑科技,并将“DNA美肤系统”疗法应用到了该产品中,能彻�
��祛除黄褐斑,蝴蝶斑,妊娠斑,晒斑,黄褐斑,老年斑,有
效淡化黄褐斑至接近肤色。黛芙薇尔通过法国、美国、台湾��
�地的专家通力协作,超过10年的研究以全新的DNA肌肤修复技��
�,挑战传统化学护肤理念,不懈追寻发现破译大自然的美丽�
��迹,令每一位爱美的女性都能享受到科技创新所带来的自然
之美。
专为亚洲女性肤质研制,精心呵护女性美丽,多年来,为数��
�百万计的女性解除了黄褐斑困扰。深得广大女性朋友的信赖!
3,去除黄褐斑之后,会反弹吗?
答:很多曾经长了黄褐斑的人士,自从选择了黛芙薇尔��
�白,就一劳永逸。这款祛斑产品是经过数十位权威祛斑专家�
��据斑的形成原因精心研制而成用事实说话,让消费者打分。
树立权威品牌!我们的很多新客户都是老客户介绍而来,请问�
��如果效果不好,会有客户转介绍吗?
4,你们的价格有点贵,能不能便宜一点?
答:如果您使用西药最少需要2000元,煎服的药最少需要3
000元,做手术最少是5000元,而这些毫无疑问,不会对彻底去�
��你的斑点有任何帮助!一分价钱,一份价值,我们现在做的��
�是一个口碑,一个品牌,价钱并不高。如果花这点钱把你的�
��褐斑彻底去除,你还会觉得贵吗?你还会再去花那么多冤枉��
�,不但斑没去掉,还把自己的皮肤弄的越来越糟吗
5,我适合用黛芙薇尔精华液吗?
答:黛芙薇尔适用人群:
1、生理紊乱引起的黄褐斑人群
2、生育引起的妊娠斑人群
3、年纪增长引起的老年斑人群
4、化妆品色素沉积、辐射斑人群
5、长期日照引起的日晒斑人群
6、肌肤暗淡急需美白的人群
《祛斑小方法》
去除色斑的有效方法,同时为您分享祛斑小方法
1.杏仁(去皮、捣烂)适量,用蛋清将杏仁未调匀,每晚睡前搽�
��,次晨用白酒洗去。
2.柿叶研细末,入熔化的凡士林搅拌为膏,外涂即可。
```
-----
Original issue reported on code.google.com by `additive...@gmail.com` on 1 Jul 2014 at 3:37
|
1.0
|
关于去除色斑的有效方法 - ```
《摘要》
化妆是女性的必修课,但是化妆品内的重金属成分会使肌肤��
�到损害,清晰不彻底会沉淀在肌肤表层形成色斑。所以,选�
��化妆品是一定要挑选合格的适合自己肤质的产品,并且要把
彩妆彻底清洁干净。去除色斑的有效方法,
《客户案例》
我是电脑用的时间长太了,又经常熬夜才会长了很多斑��
�就是大家都知道的辐射斑,有了斑,就想快点把
斑去掉,可如何快速去斑呢?我用过很多据说能快速去斑的方�
��,和大家分享一下:<br>
果酸蜕皮:就是用含果酸的化妆品把脸上的皮褪掉,这��
�就没斑了,这个太危险了,后果是皮肤对光就越
敏感,变得干燥,太阳晒一晒马上就会起红疹,出现色素沉��
�反而比原来更加严重。<br>
激光祛斑:就是把光打到皮下,可以将色素团击碎,体��
�组织将其吸收或者排泄掉。这种方法虽然方便,
但不宜频繁使用,对皮肤伤害很大,而且很容易反弹。<br>
各类祛斑霜:不知道里面含了什么化学成分,让我肚子��
�了一星期。<br>
通过以上的各种快速去斑方法的尝试,我认为快速去斑��
�行不通的,后来我就瞄上了精华祛斑,也就是「黛芙薇尔精�
��液」,当时订购了两个周期,本来就是想试试,在用完第一
个周期的时候,我朋友说好
像有点变淡了,当时挺高兴的,就接着用,没想到最后还真��
�把那些辐射斑去掉了,到现在都没反弹,在这里我要对那些�
��快速去斑的姐妹说,还是相信精华祛斑吧,虽然速度是慢点
,可安全有保证。
阅读了去除色斑的有效方法,再看脸上容易长斑的原因:
《色斑形成原因》
内部因素
一、压力
当人受到压力时,就会分泌肾上腺素,为对付压力而做��
�备。如果长期受到压力,人体新陈代谢的平衡就会遭到破坏�
��皮肤所需的营养供应趋于缓慢,色素母细胞就会变得很活跃
。
二、荷尔蒙分泌失调
避孕药里所含的女性荷尔蒙雌激素,会刺激麦拉宁细胞��
�分泌而形成不均匀的斑点,因避孕药而形成的斑点,虽然在�
��药中断后会停止,但仍会在皮肤上停留很长一段时间。怀孕
中因女性荷尔蒙雌激素的增加,从怀孕4—5个月开始会容易出
现斑,这时候出现的斑点在产后大部分会消失。可是,新陈��
�谢不正常、肌肤裸露在强烈的紫外线下、精神上受到压力等�
��因,都会使斑加深。有时新长出的斑,产后也不会消失,所
以需要更加注意。
三、新陈代谢缓慢
肝的新陈代谢功能不正常或卵巢功能减退时也会出现斑��
�因为新陈代谢不顺畅、或内分泌失调,使身体处于敏感状态�
��,从而加剧色素问题。我们常说的便秘会形成斑,其实就是
内分泌失调导致过敏体质而形成的。另外,身体状态不正常��
�时候,紫外线的照射也会加速斑的形成。
四、错误的使用化妆品
使用了不适合自己皮肤的化妆品,会导致皮肤过敏。在��
�疗的过程中如过量照射到紫外线,皮肤会为了抵御外界的侵�
��,在有炎症的部位聚集麦拉宁色素,这样会出现色素沉着的
问题。
外部因素
一、紫外线
照射紫外线的时候,人体为了保护皮肤,会在基底层产��
�很多麦拉宁色素。所以为了保护皮肤,会在敏感部位聚集更�
��的色素。经常裸露在强烈的阳光底下不仅促进皮肤的老化,
还会引起黑斑、雀斑等色素沉着的皮肤疾患。
二、不良的清洁习惯
因强烈的清洁习惯使皮肤变得敏感,这样会刺激皮肤。��
�皮肤敏感时,人体为了保护皮肤,黑色素细胞会分泌很多麦�
��宁色素,当色素过剩时就出现了斑、瑕疵等皮肤色素沉着的
问题。
三、遗传基因
父母中有长斑的,则本人长斑的概率就很高,这种情况��
�一定程度上就可判定是遗传基因的作用。所以家里特别是长�
��有长斑的人,要注意避免引发长斑的重要因素之一——紫外
线照射,这是预防斑必须注意的。
《有疑问帮你解决》
1,黛芙薇尔精华液真的有效果吗?真的可以把脸上的黄褐��
�去掉吗?
答:黛芙薇尔精华液DNA精华能够有效的修复周围难以触��
�的色斑,其独有的纳豆成分为皮肤的美白与靓丽,提供了必�
��可少的营养物质,可以有效的去除黄褐斑,黄褐斑,黄褐斑
,蝴蝶斑,晒斑、妊娠斑等。它它完全突破了传统的美肤时��
�,宛如在皮肤中注入了一杯兼具活化、再生、滋养等功效的�
��尾酒,同时为脸部提供大量有机维生素精华,脸部的改变显
而易见。自产品上市以来,老顾客纷纷介绍新顾客,71%的新��
�客都是通过老顾客介绍而来,口碑由此而来!
2,服用黛芙薇尔美白,会伤身体吗?有副作用吗?
答:黛芙薇尔精华液应用了精纯复合配方和领先的分类��
�斑科技,并将“DNA美肤系统”疗法应用到了该产品中,能彻�
��祛除黄褐斑,蝴蝶斑,妊娠斑,晒斑,黄褐斑,老年斑,有
效淡化黄褐斑至接近肤色。黛芙薇尔通过法国、美国、台湾��
�地的专家通力协作,超过10年的研究以全新的DNA肌肤修复技��
�,挑战传统化学护肤理念,不懈追寻发现破译大自然的美丽�
��迹,令每一位爱美的女性都能享受到科技创新所带来的自然
之美。
专为亚洲女性肤质研制,精心呵护女性美丽,多年来,为数��
�百万计的女性解除了黄褐斑困扰。深得广大女性朋友的信赖!
3,去除黄褐斑之后,会反弹吗?
答:很多曾经长了黄褐斑的人士,自从选择了黛芙薇尔��
�白,就一劳永逸。这款祛斑产品是经过数十位权威祛斑专家�
��据斑的形成原因精心研制而成用事实说话,让消费者打分。
树立权威品牌!我们的很多新客户都是老客户介绍而来,请问�
��如果效果不好,会有客户转介绍吗?
4,你们的价格有点贵,能不能便宜一点?
答:如果您使用西药最少需要2000元,煎服的药最少需要3
000元,做手术最少是5000元,而这些毫无疑问,不会对彻底去�
��你的斑点有任何帮助!一分价钱,一份价值,我们现在做的��
�是一个口碑,一个品牌,价钱并不高。如果花这点钱把你的�
��褐斑彻底去除,你还会觉得贵吗?你还会再去花那么多冤枉��
�,不但斑没去掉,还把自己的皮肤弄的越来越糟吗
5,我适合用黛芙薇尔精华液吗?
答:黛芙薇尔适用人群:
1、生理紊乱引起的黄褐斑人群
2、生育引起的妊娠斑人群
3、年纪增长引起的老年斑人群
4、化妆品色素沉积、辐射斑人群
5、长期日照引起的日晒斑人群
6、肌肤暗淡急需美白的人群
《祛斑小方法》
去除色斑的有效方法,同时为您分享祛斑小方法
1.杏仁(去皮、捣烂)适量,用蛋清将杏仁未调匀,每晚睡前搽�
��,次晨用白酒洗去。
2.柿叶研细末,入熔化的凡士林搅拌为膏,外涂即可。
```
-----
Original issue reported on code.google.com by `additive...@gmail.com` on 1 Jul 2014 at 3:37
|
defect
|
关于去除色斑的有效方法 《摘要》 化妆是女性的必修课,但是化妆品内的重金属成分会使肌肤�� �到损害,清晰不彻底会沉淀在肌肤表层形成色斑。所以,选� ��化妆品是一定要挑选合格的适合自己肤质的产品,并且要把 彩妆彻底清洁干净。去除色斑的有效方法, 《客户案例》 我是电脑用的时间长太了,又经常熬夜才会长了很多斑�� �就是大家都知道的辐射斑,有了斑,就想快点把 斑去掉,可如何快速去斑呢 我用过很多据说能快速去斑的方� ��,和大家分享一下: 果酸蜕皮:就是用含果酸的化妆品把脸上的皮褪掉,这�� �就没斑了,这个太危险了,后果是皮肤对光就越 敏感,变得干燥,太阳晒一晒马上就会起红疹,出现色素沉�� �反而比原来更加严重。 激光祛斑:就是把光打到皮下,可以将色素团击碎,体�� �组织将其吸收或者排泄掉。这种方法虽然方便, 但不宜频繁使用,对皮肤伤害很大,而且很容易反弹。 各类祛斑霜:不知道里面含了什么化学成分,让我肚子�� �了一星期。 通过以上的各种快速去斑方法的尝试,我认为快速去斑�� �行不通的,后来我就瞄上了精华祛斑,也就是「黛芙薇尔精� ��液」,当时订购了两个周期,本来就是想试试,在用完第一 个周期的时候,我朋友说好 像有点变淡了,当时挺高兴的,就接着用,没想到最后还真�� �把那些辐射斑去掉了,到现在都没反弹,在这里我要对那些� ��快速去斑的姐妹说,还是相信精华祛斑吧,虽然速度是慢点 ,可安全有保证。 阅读了去除色斑的有效方法,再看脸上容易长斑的原因: 《色斑形成原因》 内部因素 一、压力 当人受到压力时,就会分泌肾上腺素,为对付压力而做�� �备。如果长期受到压力,人体新陈代谢的平衡就会遭到破坏� ��皮肤所需的营养供应趋于缓慢,色素母细胞就会变得很活跃 。 二、荷尔蒙分泌失调 避孕药里所含的女性荷尔蒙雌激素,会刺激麦拉宁细胞�� �分泌而形成不均匀的斑点,因避孕药而形成的斑点,虽然在� ��药中断后会停止,但仍会在皮肤上停留很长一段时间。怀孕 中因女性荷尔蒙雌激素的增加, — 现斑,这时候出现的斑点在产后大部分会消失。可是,新陈�� �谢不正常、肌肤裸露在强烈的紫外线下、精神上受到压力等� ��因,都会使斑加深。有时新长出的斑,产后也不会消失,所 以需要更加注意。 三、新陈代谢缓慢 肝的新陈代谢功能不正常或卵巢功能减退时也会出现斑�� �因为新陈代谢不顺畅、或内分泌失调,使身体处于敏感状态� ��,从而加剧色素问题。我们常说的便秘会形成斑,其实就是 内分泌失调导致过敏体质而形成的。另外,身体状态不正常�� �时候,紫外线的照射也会加速斑的形成。 四、错误的使用化妆品 使用了不适合自己皮肤的化妆品,会导致皮肤过敏。在�� �疗的过程中如过量照射到紫外线,皮肤会为了抵御外界的侵� ��,在有炎症的部位聚集麦拉宁色素,这样会出现色素沉着的 问题。 外部因素 一、紫外线 照射紫外线的时候,人体为了保护皮肤,会在基底层产�� �很多麦拉宁色素。所以为了保护皮肤,会在敏感部位聚集更� ��的色素。经常裸露在强烈的阳光底下不仅促进皮肤的老化, 还会引起黑斑、雀斑等色素沉着的皮肤疾患。 二、不良的清洁习惯 因强烈的清洁习惯使皮肤变得敏感,这样会刺激皮肤。�� �皮肤敏感时,人体为了保护皮肤,黑色素细胞会分泌很多麦� ��宁色素,当色素过剩时就出现了斑、瑕疵等皮肤色素沉着的 问题。 三、遗传基因 父母中有长斑的,则本人长斑的概率就很高,这种情况�� �一定程度上就可判定是遗传基因的作用。所以家里特别是长� ��有长斑的人,要注意避免引发长斑的重要因素之一——紫外 线照射,这是预防斑必须注意的。 《有疑问帮你解决》 黛芙薇尔精华液真的有效果吗 真的可以把脸上的黄褐�� �去掉吗 答:黛芙薇尔精华液dna精华能够有效的修复周围难以触�� �的色斑,其独有的纳豆成分为皮肤的美白与靓丽,提供了必� ��可少的营养物质,可以有效的去除黄褐斑,黄褐斑,黄褐斑 ,蝴蝶斑,晒斑、妊娠斑等。它它完全突破了传统的美肤时�� �,宛如在皮肤中注入了一杯兼具活化、再生、滋养等功效的� ��尾酒,同时为脸部提供大量有机维生素精华,脸部的改变显 而易见。自产品上市以来,老顾客纷纷介绍新顾客, 的新�� �客都是通过老顾客介绍而来,口碑由此而来 ,服用黛芙薇尔美白,会伤身体吗 有副作用吗 答:黛芙薇尔精华液应用了精纯复合配方和领先的分类�� �斑科技,并将“dna美肤系统”疗法应用到了该产品中,能彻� ��祛除黄褐斑,蝴蝶斑,妊娠斑,晒斑,黄褐斑,老年斑,有 效淡化黄褐斑至接近肤色。黛芙薇尔通过法国、美国、台湾�� �地的专家通力协作, �� �,挑战传统化学护肤理念,不懈追寻发现破译大自然的美丽� ��迹,令每一位爱美的女性都能享受到科技创新所带来的自然 之美。 专为亚洲女性肤质研制,精心呵护女性美丽,多年来,为数�� �百万计的女性解除了黄褐斑困扰。深得广大女性朋友的信赖 ,去除黄褐斑之后,会反弹吗 答:很多曾经长了黄褐斑的人士,自从选择了黛芙薇尔�� �白,就一劳永逸。这款祛斑产品是经过数十位权威祛斑专家� ��据斑的形成原因精心研制而成用事实说话,让消费者打分。 树立权威品牌 我们的很多新客户都是老客户介绍而来,请问� ��如果效果不好,会有客户转介绍吗 ,你们的价格有点贵,能不能便宜一点 答: , , ,而这些毫无疑问,不会对彻底去� ��你的斑点有任何帮助 一分价钱,一份价值,我们现在做的�� �是一个口碑,一个品牌,价钱并不高。如果花这点钱把你的� ��褐斑彻底去除,你还会觉得贵吗 你还会再去花那么多冤枉�� �,不但斑没去掉,还把自己的皮肤弄的越来越糟吗 ,我适合用黛芙薇尔精华液吗 答:黛芙薇尔适用人群: 、生理紊乱引起的黄褐斑人群 、生育引起的妊娠斑人群 、年纪增长引起的老年斑人群 、化妆品色素沉积、辐射斑人群 、长期日照引起的日晒斑人群 、肌肤暗淡急需美白的人群 《祛斑小方法》 去除色斑的有效方法,同时为您分享祛斑小方法 杏仁 去皮、捣烂 适量,用蛋清将杏仁未调匀,每晚睡前搽� ��,次晨用白酒洗去。 柿叶研细末,入熔化的凡士林搅拌为膏,外涂即可。 original issue reported on code google com by additive gmail com on jul at
| 1
|
28,658
| 7,010,589,216
|
IssuesEvent
|
2017-12-20 00:06:59
|
mauricioarielramirez/ProyectoProgramacionMovil
|
https://api.github.com/repos/mauricioarielramirez/ProyectoProgramacionMovil
|
opened
|
Aplicar estilo de íconos de items de listview
|
code enhancement refactor UI
|
La idea es agregar un ícono a la izquierda de cada item de los listviews.
- [ ] Agregar ítem genérico para todos los casos del `simple_list_item`
- [ ] Realizar las modificaciones en cada caso particular que se necesite un ícono diferente más significativo.
|
1.0
|
Aplicar estilo de íconos de items de listview - La idea es agregar un ícono a la izquierda de cada item de los listviews.
- [ ] Agregar ítem genérico para todos los casos del `simple_list_item`
- [ ] Realizar las modificaciones en cada caso particular que se necesite un ícono diferente más significativo.
|
non_defect
|
aplicar estilo de íconos de items de listview la idea es agregar un ícono a la izquierda de cada item de los listviews agregar ítem genérico para todos los casos del simple list item realizar las modificaciones en cada caso particular que se necesite un ícono diferente más significativo
| 0
|
51,280
| 13,207,406,831
|
IssuesEvent
|
2020-08-14 22:59:10
|
icecube-trac/tix4
|
https://api.github.com/repos/icecube-trac/tix4
|
opened
|
BUILD_* doesn't toggle build of pybindings (Trac #130)
|
Incomplete Migration Migrated from Trac cmake defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/130">https://code.icecube.wisc.edu/projects/icecube/ticket/130</a>, reported by troyand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2014-11-23T03:37:56",
"_ts": "1416713876900096",
"description": "then you get a failure at cmake time",
"reporter": "troy",
"cc": "",
"resolution": "fixed",
"time": "2008-09-07T18:34:09",
"component": "cmake",
"summary": "BUILD_* doesn't toggle build of pybindings",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
BUILD_* doesn't toggle build of pybindings (Trac #130) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/130">https://code.icecube.wisc.edu/projects/icecube/ticket/130</a>, reported by troyand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2014-11-23T03:37:56",
"_ts": "1416713876900096",
"description": "then you get a failure at cmake time",
"reporter": "troy",
"cc": "",
"resolution": "fixed",
"time": "2008-09-07T18:34:09",
"component": "cmake",
"summary": "BUILD_* doesn't toggle build of pybindings",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
|
defect
|
build doesn t toggle build of pybindings trac migrated from json status closed changetime ts description then you get a failure at cmake time reporter troy cc resolution fixed time component cmake summary build doesn t toggle build of pybindings priority normal keywords milestone owner troy type defect
| 1
|
25,067
| 4,186,290,325
|
IssuesEvent
|
2016-06-23 14:06:17
|
jbs1/testingtrac
|
https://api.github.com/repos/jbs1/testingtrac
|
closed
|
arXMLiv XML Target Tracker Bug (Trac #1234)
|
defect Incomplete Migration Migrated from Trac project
|
Migrated from https://trac.kwarc.info/ticket/1234
```json
{
"status": "closed",
"changetime": "2007-09-23T05:03:06",
"description": "This is the tracker bug for the XML Target Language for the arXMLiv Translation. \n\nWe will use it to discuss the Target Language in general. \nAll build system bugs should be made dependent on this, so that we can generate\na dependency tree rooted in this bug to see our progress and plan the attack.",
"severity": "normal",
"reporter": "kohlhase",
"cc": "",
"resolution": "wontfix",
"include_gantt": "0",
"_ts": "1190523786000000",
"component": "project",
"summary": "arXMLiv XML Target Tracker Bug",
"priority": "high",
"keywords": "",
"dependencies": "",
"time": "2006-05-31T04:22:31",
"milestone": "first release",
"owner": "kohlhase",
"type": "defect",
"due_close": "",
"due_assign": ""
}
```
|
1.0
|
arXMLiv XML Target Tracker Bug (Trac #1234) - Migrated from https://trac.kwarc.info/ticket/1234
```json
{
"status": "closed",
"changetime": "2007-09-23T05:03:06",
"description": "This is the tracker bug for the XML Target Language for the arXMLiv Translation. \n\nWe will use it to discuss the Target Language in general. \nAll build system bugs should be made dependent on this, so that we can generate\na dependency tree rooted in this bug to see our progress and plan the attack.",
"severity": "normal",
"reporter": "kohlhase",
"cc": "",
"resolution": "wontfix",
"include_gantt": "0",
"_ts": "1190523786000000",
"component": "project",
"summary": "arXMLiv XML Target Tracker Bug",
"priority": "high",
"keywords": "",
"dependencies": "",
"time": "2006-05-31T04:22:31",
"milestone": "first release",
"owner": "kohlhase",
"type": "defect",
"due_close": "",
"due_assign": ""
}
```
|
defect
|
arxmliv xml target tracker bug trac migrated from json status closed changetime description this is the tracker bug for the xml target language for the arxmliv translation n nwe will use it to discuss the target language in general nall build system bugs should be made dependent on this so that we can generate na dependency tree rooted in this bug to see our progress and plan the attack severity normal reporter kohlhase cc resolution wontfix include gantt ts component project summary arxmliv xml target tracker bug priority high keywords dependencies time milestone first release owner kohlhase type defect due close due assign
| 1
|
355,886
| 25,176,052,543
|
IssuesEvent
|
2022-11-11 09:21:40
|
RichDom2185/pe
|
https://api.github.com/repos/RichDom2185/pe
|
opened
|
Inconsistent formatting of DG
|
type.DocumentationBug severity.VeryLow
|
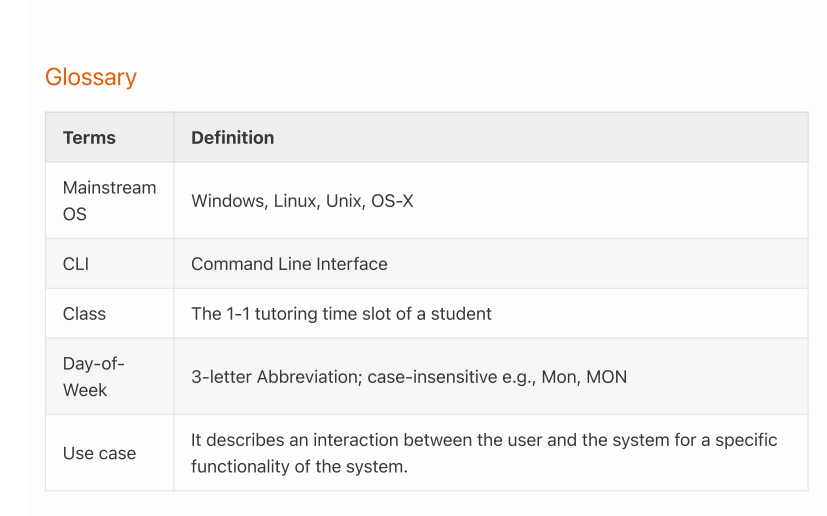
There is a full stop in the last definition that is not present in the others.
<!--session: 1668154065008-52adc948-2a6b-43f0-ae21-9d8349f474cf-->
<!--Version: Web v3.4.4-->
|
1.0
|
Inconsistent formatting of DG - 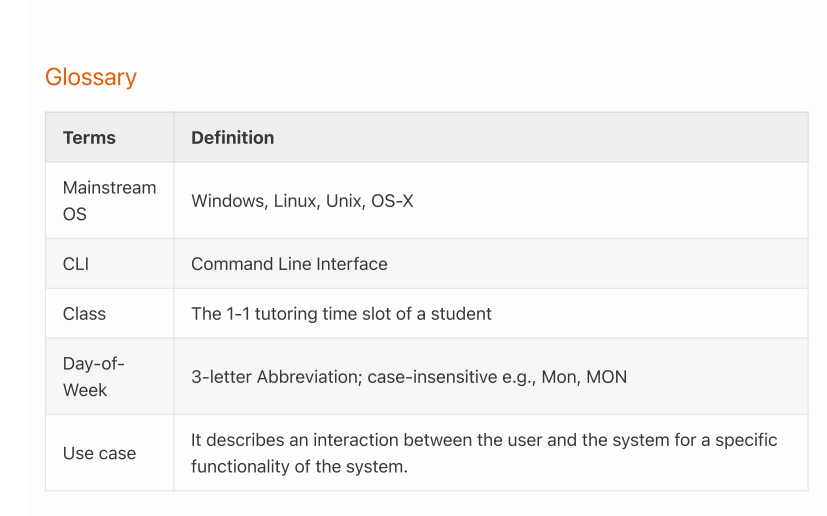
There is a full stop in the last definition that is not present in the others.
<!--session: 1668154065008-52adc948-2a6b-43f0-ae21-9d8349f474cf-->
<!--Version: Web v3.4.4-->
|
non_defect
|
inconsistent formatting of dg there is a full stop in the last definition that is not present in the others
| 0
|
77,527
| 27,041,904,345
|
IssuesEvent
|
2023-02-13 06:23:37
|
vector-im/element-android
|
https://api.github.com/repos/vector-im/element-android
|
opened
|
The app becomes unresponsive after the voice message finishes playing.
|
T-Defect
|
### Steps to reproduce
1. Let the other party send you a voice message, or send one by yourself;
2. Play it.
### Outcome
#### What did you expect?
n/a
#### What happened instead?
Once the voice message playback ends, the app freezes, crashes and restarts automatically.
### Your phone model
HMD TA-1054; Mi 9T
### Operating system version
Android 8.1; MIUI 12.5 by xiaomi.eu (based on Android 11)
### Application version and app store
Element 1.5.24 (Google Play)
### Homeserver
Synapse 1.76.0
### Will you send logs?
Yes
### Are you willing to provide a PR?
Yes
|
1.0
|
The app becomes unresponsive after the voice message finishes playing. - ### Steps to reproduce
1. Let the other party send you a voice message, or send one by yourself;
2. Play it.
### Outcome
#### What did you expect?
n/a
#### What happened instead?
Once the voice message playback ends, the app freezes, crashes and restarts automatically.
### Your phone model
HMD TA-1054; Mi 9T
### Operating system version
Android 8.1; MIUI 12.5 by xiaomi.eu (based on Android 11)
### Application version and app store
Element 1.5.24 (Google Play)
### Homeserver
Synapse 1.76.0
### Will you send logs?
Yes
### Are you willing to provide a PR?
Yes
|
defect
|
the app becomes unresponsive after the voice message finishes playing steps to reproduce let the other party send you a voice message or send one by yourself play it outcome what did you expect n a what happened instead once the voice message playback ends the app freezes crashes and restarts automatically your phone model hmd ta mi operating system version android miui by xiaomi eu based on android application version and app store element google play homeserver synapse will you send logs yes are you willing to provide a pr yes
| 1
|
7,255
| 2,610,360,427
|
IssuesEvent
|
2015-02-26 19:56:38
|
chrsmith/scribefire-chrome
|
https://api.github.com/repos/chrsmith/scribefire-chrome
|
closed
|
No Spell Check in chrome
|
auto-migrated Priority-Medium Type-Defect
|
```
What's the problem?
Google chrome spell check does not appear to be using
What browser are you using?
Google Chrome 17.0.963.56 (Official Build 121963) m
OS Windows
WebKit 535.11 (@107413)
JavaScript V8 3.7.12.22
Flash 11,1,102,62
User Agent Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like
Gecko) Chrome/17.0.963.56 Safari/535.11
What version of ScribeFire are you running? 4.1
```
-----
Original issue reported on code.google.com by `ZanePe...@gmail.com` on 17 Feb 2012 at 5:07
|
1.0
|
No Spell Check in chrome - ```
What's the problem?
Google chrome spell check does not appear to be using
What browser are you using?
Google Chrome 17.0.963.56 (Official Build 121963) m
OS Windows
WebKit 535.11 (@107413)
JavaScript V8 3.7.12.22
Flash 11,1,102,62
User Agent Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like
Gecko) Chrome/17.0.963.56 Safari/535.11
What version of ScribeFire are you running? 4.1
```
-----
Original issue reported on code.google.com by `ZanePe...@gmail.com` on 17 Feb 2012 at 5:07
|
defect
|
no spell check in chrome what s the problem google chrome spell check does not appear to be using what browser are you using google chrome official build m os windows webkit javascript flash user agent mozilla windows nt applewebkit khtml like gecko chrome safari what version of scribefire are you running original issue reported on code google com by zanepe gmail com on feb at
| 1
|
51,886
| 13,211,333,763
|
IssuesEvent
|
2020-08-15 22:23:00
|
icecube-trac/tix4
|
https://api.github.com/repos/icecube-trac/tix4
|
opened
|
[genie-icetray] needs tests (Trac #1215)
|
Incomplete Migration Migrated from Trac combo reconstruction defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1215">https://code.icecube.wisc.edu/projects/icecube/ticket/1215</a>, reported by david.schultzand owned by kclark</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:35",
"_ts": "1550067215093672",
"description": "I can't find any tests. Python tests should be in `resources/test/`.",
"reporter": "david.schultz",
"cc": "melanie.day",
"resolution": "fixed",
"time": "2015-08-19T19:44:22",
"component": "combo reconstruction",
"summary": "[genie-icetray] needs tests",
"priority": "critical",
"keywords": "",
"milestone": "",
"owner": "kclark",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
[genie-icetray] needs tests (Trac #1215) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1215">https://code.icecube.wisc.edu/projects/icecube/ticket/1215</a>, reported by david.schultzand owned by kclark</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:35",
"_ts": "1550067215093672",
"description": "I can't find any tests. Python tests should be in `resources/test/`.",
"reporter": "david.schultz",
"cc": "melanie.day",
"resolution": "fixed",
"time": "2015-08-19T19:44:22",
"component": "combo reconstruction",
"summary": "[genie-icetray] needs tests",
"priority": "critical",
"keywords": "",
"milestone": "",
"owner": "kclark",
"type": "defect"
}
```
</p>
</details>
|
defect
|
needs tests trac migrated from json status closed changetime ts description i can t find any tests python tests should be in resources test reporter david schultz cc melanie day resolution fixed time component combo reconstruction summary needs tests priority critical keywords milestone owner kclark type defect
| 1
|
247,910
| 7,925,099,105
|
IssuesEvent
|
2018-07-05 19:21:16
|
PMA-2020/ppp
|
https://api.github.com/repos/PMA-2020/ppp
|
opened
|
Template #1 ("old template") issue - inconsistent left/right column widths
|
graphical issue low priority
|
## Description
Some questions are not obeying the correct left and right column width %s. It appears to me that the "grouped" questions (distinguished visually as questions that have a double-line border) are correct, but non-grouped questions are not (single-line border).
---
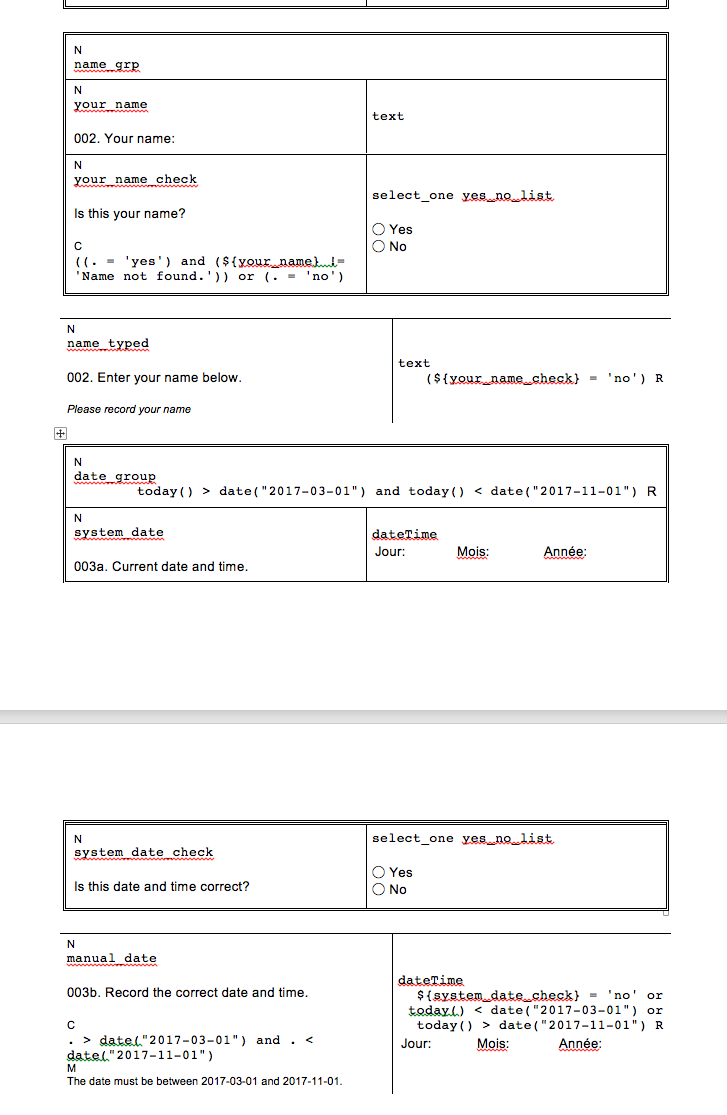
|
1.0
|
Template #1 ("old template") issue - inconsistent left/right column widths - ## Description
Some questions are not obeying the correct left and right column width %s. It appears to me that the "grouped" questions (distinguished visually as questions that have a double-line border) are correct, but non-grouped questions are not (single-line border).
---
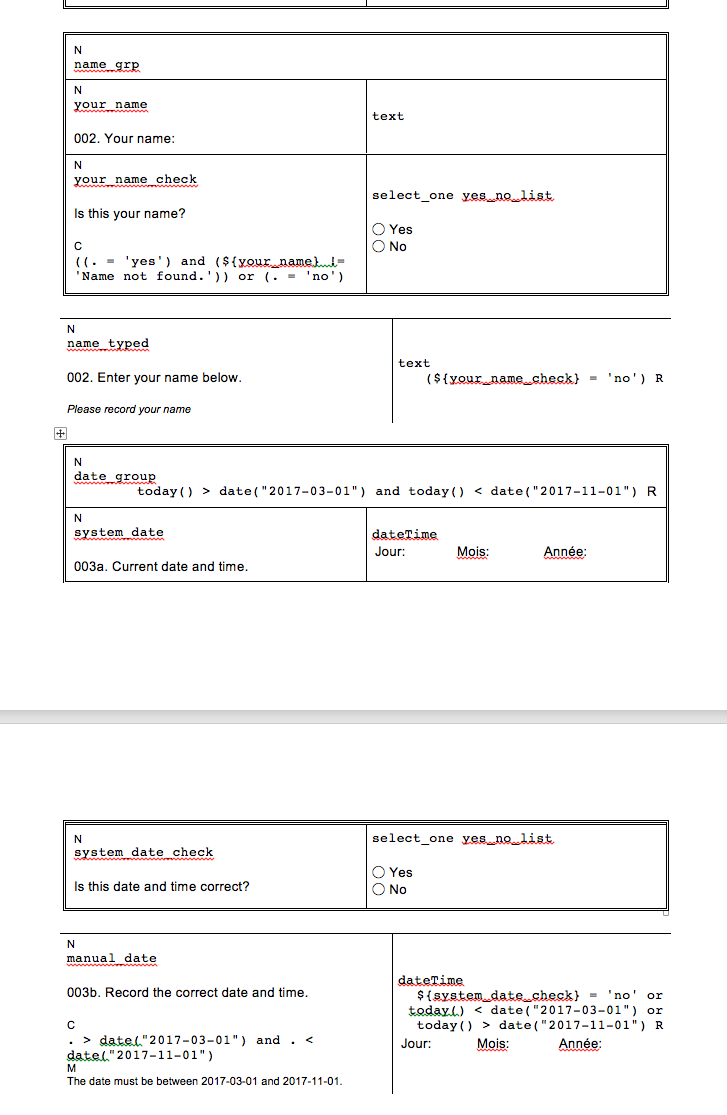
|
non_defect
|
template old template issue inconsistent left right column widths description some questions are not obeying the correct left and right column width s it appears to me that the grouped questions distinguished visually as questions that have a double line border are correct but non grouped questions are not single line border
| 0
|
2,860
| 2,607,963,419
|
IssuesEvent
|
2015-02-26 00:41:14
|
chrsmithdemos/leveldb
|
https://api.github.com/repos/chrsmithdemos/leveldb
|
closed
|
unknown size of return string of leveldb_property_value()
|
auto-migrated Priority-Medium Type-Defect
|
```
1. call leveldb_property_value() with "leveldb.stats"
2. strlen(leveldb_property_value("leveldb.stats"))
strlen doesn't find any '\0' terminator.
CopyString() is implemented as malloc(size) - memcpy().
Add size_t *size to leveldb_property_value() like leveldb_get() or return a
real null-terminated string.
```
-----
Original issue reported on code.google.com by `theo.bertozzi` on 20 Aug 2011 at 3:08
|
1.0
|
unknown size of return string of leveldb_property_value() - ```
1. call leveldb_property_value() with "leveldb.stats"
2. strlen(leveldb_property_value("leveldb.stats"))
strlen doesn't find any '\0' terminator.
CopyString() is implemented as malloc(size) - memcpy().
Add size_t *size to leveldb_property_value() like leveldb_get() or return a
real null-terminated string.
```
-----
Original issue reported on code.google.com by `theo.bertozzi` on 20 Aug 2011 at 3:08
|
defect
|
unknown size of return string of leveldb property value call leveldb property value with leveldb stats strlen leveldb property value leveldb stats strlen doesn t find any terminator copystring is implemented as malloc size memcpy add size t size to leveldb property value like leveldb get or return a real null terminated string original issue reported on code google com by theo bertozzi on aug at
| 1
|
74,001
| 24,899,467,497
|
IssuesEvent
|
2022-10-28 19:12:25
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
opened
|
[🐛 Bug]: Can't npm install selenium-webdriver/chrome
|
I-defect needs-triaging
|
### What happened?
I can not install the nodejs selenium webdriver.
### How can we reproduce the issue?
```shell
The docker step is optional, as it also happens on my Linux laptop.
docker run -it node:16 bash
npm install --save selenium-webdriver/chrome
```
### Relevant log output
```shell
npm ERR! code 128
npm ERR! An unknown git error occurred
npm ERR! command git --no-replace-objects ls-remote ssh://git@github.com/selenium-webdriver/chrome.git
npm ERR! Warning: Permanently added 'github.com,140.82.121.4' (ECDSA) to the list of known hosts.
npm ERR! git@github.com: Permission denied (publickey).
npm ERR! fatal: Could not read from remote repository.
npm ERR!
npm ERR! Please make sure you have the correct access rights
npm ERR! and the repository exists.
npm ERR! A complete log of this run can be found in:
npm ERR! /root/.npm/_logs/2022-10-28T19_10_27_576Z-debug-0.log
```
### Operating System
Ubuntu
### Selenium version
Not got this far yet
### What are the browser(s) and version(s) where you see this issue?
Not got this far yet
### What are the browser driver(s) and version(s) where you see this issue?
Not got this far yet
### Are you using Selenium Grid?
Not got this far yet
|
1.0
|
[🐛 Bug]: Can't npm install selenium-webdriver/chrome - ### What happened?
I can not install the nodejs selenium webdriver.
### How can we reproduce the issue?
```shell
The docker step is optional, as it also happens on my Linux laptop.
docker run -it node:16 bash
npm install --save selenium-webdriver/chrome
```
### Relevant log output
```shell
npm ERR! code 128
npm ERR! An unknown git error occurred
npm ERR! command git --no-replace-objects ls-remote ssh://git@github.com/selenium-webdriver/chrome.git
npm ERR! Warning: Permanently added 'github.com,140.82.121.4' (ECDSA) to the list of known hosts.
npm ERR! git@github.com: Permission denied (publickey).
npm ERR! fatal: Could not read from remote repository.
npm ERR!
npm ERR! Please make sure you have the correct access rights
npm ERR! and the repository exists.
npm ERR! A complete log of this run can be found in:
npm ERR! /root/.npm/_logs/2022-10-28T19_10_27_576Z-debug-0.log
```
### Operating System
Ubuntu
### Selenium version
Not got this far yet
### What are the browser(s) and version(s) where you see this issue?
Not got this far yet
### What are the browser driver(s) and version(s) where you see this issue?
Not got this far yet
### Are you using Selenium Grid?
Not got this far yet
|
defect
|
can t npm install selenium webdriver chrome what happened i can not install the nodejs selenium webdriver how can we reproduce the issue shell the docker step is optional as it also happens on my linux laptop docker run it node bash npm install save selenium webdriver chrome relevant log output shell npm err code npm err an unknown git error occurred npm err command git no replace objects ls remote ssh git github com selenium webdriver chrome git npm err warning permanently added github com ecdsa to the list of known hosts npm err git github com permission denied publickey npm err fatal could not read from remote repository npm err npm err please make sure you have the correct access rights npm err and the repository exists npm err a complete log of this run can be found in npm err root npm logs debug log operating system ubuntu selenium version not got this far yet what are the browser s and version s where you see this issue not got this far yet what are the browser driver s and version s where you see this issue not got this far yet are you using selenium grid not got this far yet
| 1
|
62,759
| 17,189,970,264
|
IssuesEvent
|
2021-07-16 09:30:56
|
snowplow/snowplow-android-tracker
|
https://api.github.com/repos/snowplow/snowplow-android-tracker
|
closed
|
Set application install timestamp on device timestamp field
|
priority:high status:completed type:defect
|
**Describe the bug**
Currently, the application install event store the first-run timestamp on the trueTimestamp field.
This can cause issues on data-modelling because the true_timestamp is directly assigned to the derived_timestamp.
If the device time is wrong it causes a wrong derived_timestamp in the data-modelling too.
**Expected behavior**
The first-run timestamp should be stored on the deviceTimestamp field of the event, like it used to be in the tracker v1.x.
Clone of: https://github.com/snowplow/snowplow-objc-tracker/issues/625
|
1.0
|
Set application install timestamp on device timestamp field - **Describe the bug**
Currently, the application install event store the first-run timestamp on the trueTimestamp field.
This can cause issues on data-modelling because the true_timestamp is directly assigned to the derived_timestamp.
If the device time is wrong it causes a wrong derived_timestamp in the data-modelling too.
**Expected behavior**
The first-run timestamp should be stored on the deviceTimestamp field of the event, like it used to be in the tracker v1.x.
Clone of: https://github.com/snowplow/snowplow-objc-tracker/issues/625
|
defect
|
set application install timestamp on device timestamp field describe the bug currently the application install event store the first run timestamp on the truetimestamp field this can cause issues on data modelling because the true timestamp is directly assigned to the derived timestamp if the device time is wrong it causes a wrong derived timestamp in the data modelling too expected behavior the first run timestamp should be stored on the devicetimestamp field of the event like it used to be in the tracker x clone of
| 1
|
63,599
| 17,785,706,049
|
IssuesEvent
|
2021-08-31 10:46:14
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
No encrypted search results despite message index being available
|
T-Defect
|
### Steps to reproduce
1. After rebuilding the encrypted search index (because I was suffering from https://github.com/vector-im/element-web/issues/14229)
2. I try to search in an encrypted room
3. And search never returns any results even for content that I see right there in the timeline


### What happened?
Search isn't working. Files panel shows no files despite hundreds being shared in that room.

### What did you expect?
Search working correctly
### Operating system
Arch Linux
### Application version
Element version: 1.7.34; olm version: 3.2.3
### How did you install the app?
pacman
### Homeserver
bubu1.eu
### Have you submitted a rageshake?
Yes
|
1.0
|
No encrypted search results despite message index being available - ### Steps to reproduce
1. After rebuilding the encrypted search index (because I was suffering from https://github.com/vector-im/element-web/issues/14229)
2. I try to search in an encrypted room
3. And search never returns any results even for content that I see right there in the timeline


### What happened?
Search isn't working. Files panel shows no files despite hundreds being shared in that room.

### What did you expect?
Search working correctly
### Operating system
Arch Linux
### Application version
Element version: 1.7.34; olm version: 3.2.3
### How did you install the app?
pacman
### Homeserver
bubu1.eu
### Have you submitted a rageshake?
Yes
|
defect
|
no encrypted search results despite message index being available steps to reproduce after rebuilding the encrypted search index because i was suffering from i try to search in an encrypted room and search never returns any results even for content that i see right there in the timeline what happened search isn t working files panel shows no files despite hundreds being shared in that room what did you expect search working correctly operating system arch linux application version element version olm version how did you install the app pacman homeserver eu have you submitted a rageshake yes
| 1
|
211
| 2,519,740,215
|
IssuesEvent
|
2015-01-18 09:01:23
|
mbunkus/mtx-trac-import-test
|
https://api.github.com/repos/mbunkus/mtx-trac-import-test
|
opened
|
Bad MKV Files Created With MMG 0.7.7
|
C: mmg (mkvmerge GUI) P: normal R: invalid T: defect
|
**Reported by shoalx2003 on 2 Dec 2003 16:53 UTC**
Here is the command line that MMG 0.7.7 creates after I input all desired
options:
"mkvmerge" -o "4.mkv" --default-track 1 --aspect-ratio "16/9" --fourcc
"DX50" -d 1 -A -S "F:\Rips1\2.mkv" --language 0:eng --track-name "0:English
Language" --default-track 0 --fourcc "DX50" -s 0 -D -A "F:\Rips1\NewFile
JAP.ssa" --language 22145:eng --track-name "22145:English Language" --fourcc
"DX50" -a 22145 -D -S "F:\Rips1\p-eng.ogg" --language 19944:jpn --track-name
"19944:Japanese Language" --default-track 19944 --fourcc "DX50" -a 19944 -D
-S "F:\Rips1\p-jap.ogg"
The file created just doesn't run -- neither Core Media Player 4 RC5 Build45
or Classic Media Player 6.4.6.7 will run it.
The MKV source was compressed with DivX 5.1.1 at a resolution of 640x360,
23.976fps using VirtualDubMod 1.5.4.1 All Inclusive. The audio tracks are q0
OGG VBR, compressed with oggenc.exe 1.0.1.
I tried using MMG 0.7.5 a while ago, and a similar problem occured. However,
the video at least played, but the sound was all screwed up. The files used
in this latest attempt all play just fine by themselves, but merged the
resulting MKV just craps out.
If any of this was covered in the documentation, I apologize. There is quite
a bit of reading to do to cover it all, and I just haven't had the time.
Oh, I'm using Windows XP Professional, with a FULLY sufficient PC for
playing any kind of video.
Migrated-From: https://trac.bunkus.org/ticket/20
|
1.0
|
Bad MKV Files Created With MMG 0.7.7 - **Reported by shoalx2003 on 2 Dec 2003 16:53 UTC**
Here is the command line that MMG 0.7.7 creates after I input all desired
options:
"mkvmerge" -o "4.mkv" --default-track 1 --aspect-ratio "16/9" --fourcc
"DX50" -d 1 -A -S "F:\Rips1\2.mkv" --language 0:eng --track-name "0:English
Language" --default-track 0 --fourcc "DX50" -s 0 -D -A "F:\Rips1\NewFile
JAP.ssa" --language 22145:eng --track-name "22145:English Language" --fourcc
"DX50" -a 22145 -D -S "F:\Rips1\p-eng.ogg" --language 19944:jpn --track-name
"19944:Japanese Language" --default-track 19944 --fourcc "DX50" -a 19944 -D
-S "F:\Rips1\p-jap.ogg"
The file created just doesn't run -- neither Core Media Player 4 RC5 Build45
or Classic Media Player 6.4.6.7 will run it.
The MKV source was compressed with DivX 5.1.1 at a resolution of 640x360,
23.976fps using VirtualDubMod 1.5.4.1 All Inclusive. The audio tracks are q0
OGG VBR, compressed with oggenc.exe 1.0.1.
I tried using MMG 0.7.5 a while ago, and a similar problem occured. However,
the video at least played, but the sound was all screwed up. The files used
in this latest attempt all play just fine by themselves, but merged the
resulting MKV just craps out.
If any of this was covered in the documentation, I apologize. There is quite
a bit of reading to do to cover it all, and I just haven't had the time.
Oh, I'm using Windows XP Professional, with a FULLY sufficient PC for
playing any kind of video.
Migrated-From: https://trac.bunkus.org/ticket/20
|
defect
|
bad mkv files created with mmg reported by on dec utc here is the command line that mmg creates after i input all desired options mkvmerge o mkv default track aspect ratio fourcc d a s f mkv language eng track name english language default track fourcc s d a f newfile jap ssa language eng track name english language fourcc a d s f p eng ogg language jpn track name japanese language default track fourcc a d s f p jap ogg the file created just doesn t run neither core media player or classic media player will run it the mkv source was compressed with divx at a resolution of using virtualdubmod all inclusive the audio tracks are ogg vbr compressed with oggenc exe i tried using mmg a while ago and a similar problem occured however the video at least played but the sound was all screwed up the files used in this latest attempt all play just fine by themselves but merged the resulting mkv just craps out if any of this was covered in the documentation i apologize there is quite a bit of reading to do to cover it all and i just haven t had the time oh i m using windows xp professional with a fully sufficient pc for playing any kind of video migrated from
| 1
|
76,721
| 3,491,399,697
|
IssuesEvent
|
2016-01-04 15:33:56
|
karma-runner/karma
|
https://api.github.com/repos/karma-runner/karma
|
closed
|
Karma chrashes with: Fatal error: Wrong length [0.13.16 regression]
|
priority: high type: bug-upstream
|
I've just updated from 0.13.15 where everything was fine to 0.13.16 and run tests. Karma has crashed with IE runner (with chrome and firefox there are no problems):
```
> karma start --single-run
25 12 2015 10:42:06.907:DEBUG [config]: autoWatch set to false, because of singleRun
25 12 2015 10:42:06.914:DEBUG [plugin]: Loading karma-* from E:\Dropbox\repo\browser-id3-writer\node_modules
25 12 2015 10:42:06.918:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-chai.
25 12 2015 10:42:06.920:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-chrome-launcher.
25 12 2015 10:42:06.931:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-coverage.
25 12 2015 10:42:07.270:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-firefox-launcher.
25 12 2015 10:42:07.274:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-ie-launcher.
25 12 2015 10:42:07.321:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-mocha.
25 12 2015 10:42:07.399:DEBUG [preprocessor.coverage]: Processing "E:/Dropbox/repo/browser-id3-writer/src/browser-id3-writer.js".
25 12 2015 10:42:07.508:INFO [karma]: Karma v0.13.16 server started at http://localhost:9876/
25 12 2015 10:42:07.517:INFO [launcher]: Starting browser IE
25 12 2015 10:42:07.518:DEBUG [temp-dir]: Creating temp dir at C:\Users\12C2~1\AppData\Local\Temp\karma-54524961
25 12 2015 10:42:07.523:DEBUG [launcher]: C:\Program Files\Internet Explorer\iexplore.exe http://localhost:9876/?id=54524961
25 12 2015 10:42:07.858:DEBUG [web-server]: serving: E:\Dropbox\repo\browser-id3-writer\node_modules\karma\static/client.html
25 12 2015 10:42:07.890:DEBUG [web-server]: serving: E:\Dropbox\repo\browser-id3-writer\node_modules\karma\static/karma.js
25 12 2015 10:42:08.021:DEBUG [karma]: A browser has connected on socket SBAFIfzlxXRz6LWaAAAA
25 12 2015 10:42:08.035:DEBUG [web-server]: upgrade /socket.io/?EIO=3&transport=websocket&sid=SBAFIfzlxXRz6LWaAAAA
25 12 2015 10:42:08.082:INFO [IE 11.0.0 (Windows 10 0.0.0)]: Connected on socket SBAFIfzlxXRz6LWaAAAA with id 54524961
25 12 2015 10:42:08.085:DEBUG [launcher]: IE (id 54524961) captured in 0.576 secs
25 12 2015 10:42:08.095:DEBUG [web-server]: serving: E:\Dropbox\repo\browser-id3-writer\node_modules\karma\static/context.html
IE 11.0.0 (Windows 10 0.0.0): Executed 1 of 1 SUCCESS (0.018 secs / 0 secs)
25 12 2015 10:42:08.230:DEBUG [karma]: Run complete, exiting.
25 12 2015 10:42:08.236:DEBUG [launcher]: Disconnecting all browsers
25 12 2015 10:42:08.239:ERROR [karma]: [RangeError: Wrong length!]
RangeError: Wrong length!
at RangeError (native)
at strictToLength (E:\Dropbox\repo\browser-id3-writer\node_modules\core-js\modules\_typed-array.js:94:36)
at E:\Dropbox\repo\browser-id3-writer\node_modules\core-js\modules\_typed-array.js:404:44
at new Uint8Array (E:\Dropbox\repo\browser-id3-writer\node_modules\core-js\modules\es6.typed.uint8-array.js:3:12)
at allocate (buffer.js:98:17)
at new Buffer (buffer.js:49:12)
at BufferPool.reset (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\BufferPool.js:57:26)
at Receiver.endPacket (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:247:68)
at Receiver.opcodes.1.finish (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:483:12)
at Receiver.expectHandler (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:451:33)
at Receiver.add (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:95:24)
at Socket.realHandler (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\WebSocket.js:800:20)
at emitOne (events.js:77:13)
at Socket.emit (events.js:169:7)
at readableAddChunk (_stream_readable.js:146:16)
at Socket.Readable.push (_stream_readable.js:110:10)
25 12 2015 10:42:08.253:DEBUG [launcher]: Disconnecting all browsers
25 12 2015 10:42:08.258:DEBUG [coverage]: Writing coverage to E:/Dropbox/repo/browser-id3-writer/coverage
25 12 2015 10:42:08.457:DEBUG [launcher]: Killed extra IE process 3724
25 12 2015 10:42:08.457:DEBUG [launcher]: Process IE exited with code 0
25 12 2015 10:42:08.458:DEBUG [temp-dir]: Cleaning temp dir C:\Users\12C2~1\AppData\Local\Temp\karma-54524961
25 12 2015 10:42:08.462:DEBUG [launcher]: Finished all browsers
npm ERR! Windows_NT 10.0.10586
npm ERR! argv "C:\\Program Files\\nodejs\\node.exe" "C:\\Program Files\\nodejs\\node_modules\\npm\\bin\\npm-cli.js" "run" "test"
npm ERR! node v5.3.0
npm ERR! npm v3.3.12
npm ERR! code ELIFECYCLE
npm ERR! browser-id3-writer@0.0.0-semantically-released test: `karma start --single-run`
npm ERR! Exit status 1
npm ERR!
npm ERR! Failed at the browser-id3-writer@0.0.0-semantically-released test script 'karma start --single-run'.
npm ERR! Make sure you have the latest version of node.js and npm installed.
npm ERR! If you do, this is most likely a problem with the browser-id3-writer package,
npm ERR! not with npm itself.
npm ERR! Tell the author that this fails on your system:
npm ERR! karma start --single-run
npm ERR! You can get their info via:
npm ERR! npm owner ls browser-id3-writer
npm ERR! There is likely additional logging output above.
npm ERR! Please include the following file with any support request:
npm ERR! E:\Dropbox\repo\browser-id3-writer\npm-debug.log
```
|
1.0
|
Karma chrashes with: Fatal error: Wrong length [0.13.16 regression] - I've just updated from 0.13.15 where everything was fine to 0.13.16 and run tests. Karma has crashed with IE runner (with chrome and firefox there are no problems):
```
> karma start --single-run
25 12 2015 10:42:06.907:DEBUG [config]: autoWatch set to false, because of singleRun
25 12 2015 10:42:06.914:DEBUG [plugin]: Loading karma-* from E:\Dropbox\repo\browser-id3-writer\node_modules
25 12 2015 10:42:06.918:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-chai.
25 12 2015 10:42:06.920:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-chrome-launcher.
25 12 2015 10:42:06.931:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-coverage.
25 12 2015 10:42:07.270:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-firefox-launcher.
25 12 2015 10:42:07.274:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-ie-launcher.
25 12 2015 10:42:07.321:DEBUG [plugin]: Loading plugin E:\Dropbox\repo\browser-id3-writer\node_modules/karma-mocha.
25 12 2015 10:42:07.399:DEBUG [preprocessor.coverage]: Processing "E:/Dropbox/repo/browser-id3-writer/src/browser-id3-writer.js".
25 12 2015 10:42:07.508:INFO [karma]: Karma v0.13.16 server started at http://localhost:9876/
25 12 2015 10:42:07.517:INFO [launcher]: Starting browser IE
25 12 2015 10:42:07.518:DEBUG [temp-dir]: Creating temp dir at C:\Users\12C2~1\AppData\Local\Temp\karma-54524961
25 12 2015 10:42:07.523:DEBUG [launcher]: C:\Program Files\Internet Explorer\iexplore.exe http://localhost:9876/?id=54524961
25 12 2015 10:42:07.858:DEBUG [web-server]: serving: E:\Dropbox\repo\browser-id3-writer\node_modules\karma\static/client.html
25 12 2015 10:42:07.890:DEBUG [web-server]: serving: E:\Dropbox\repo\browser-id3-writer\node_modules\karma\static/karma.js
25 12 2015 10:42:08.021:DEBUG [karma]: A browser has connected on socket SBAFIfzlxXRz6LWaAAAA
25 12 2015 10:42:08.035:DEBUG [web-server]: upgrade /socket.io/?EIO=3&transport=websocket&sid=SBAFIfzlxXRz6LWaAAAA
25 12 2015 10:42:08.082:INFO [IE 11.0.0 (Windows 10 0.0.0)]: Connected on socket SBAFIfzlxXRz6LWaAAAA with id 54524961
25 12 2015 10:42:08.085:DEBUG [launcher]: IE (id 54524961) captured in 0.576 secs
25 12 2015 10:42:08.095:DEBUG [web-server]: serving: E:\Dropbox\repo\browser-id3-writer\node_modules\karma\static/context.html
IE 11.0.0 (Windows 10 0.0.0): Executed 1 of 1 SUCCESS (0.018 secs / 0 secs)
25 12 2015 10:42:08.230:DEBUG [karma]: Run complete, exiting.
25 12 2015 10:42:08.236:DEBUG [launcher]: Disconnecting all browsers
25 12 2015 10:42:08.239:ERROR [karma]: [RangeError: Wrong length!]
RangeError: Wrong length!
at RangeError (native)
at strictToLength (E:\Dropbox\repo\browser-id3-writer\node_modules\core-js\modules\_typed-array.js:94:36)
at E:\Dropbox\repo\browser-id3-writer\node_modules\core-js\modules\_typed-array.js:404:44
at new Uint8Array (E:\Dropbox\repo\browser-id3-writer\node_modules\core-js\modules\es6.typed.uint8-array.js:3:12)
at allocate (buffer.js:98:17)
at new Buffer (buffer.js:49:12)
at BufferPool.reset (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\BufferPool.js:57:26)
at Receiver.endPacket (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:247:68)
at Receiver.opcodes.1.finish (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:483:12)
at Receiver.expectHandler (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:451:33)
at Receiver.add (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\Receiver.js:95:24)
at Socket.realHandler (E:\Dropbox\repo\browser-id3-writer\node_modules\ws\lib\WebSocket.js:800:20)
at emitOne (events.js:77:13)
at Socket.emit (events.js:169:7)
at readableAddChunk (_stream_readable.js:146:16)
at Socket.Readable.push (_stream_readable.js:110:10)
25 12 2015 10:42:08.253:DEBUG [launcher]: Disconnecting all browsers
25 12 2015 10:42:08.258:DEBUG [coverage]: Writing coverage to E:/Dropbox/repo/browser-id3-writer/coverage
25 12 2015 10:42:08.457:DEBUG [launcher]: Killed extra IE process 3724
25 12 2015 10:42:08.457:DEBUG [launcher]: Process IE exited with code 0
25 12 2015 10:42:08.458:DEBUG [temp-dir]: Cleaning temp dir C:\Users\12C2~1\AppData\Local\Temp\karma-54524961
25 12 2015 10:42:08.462:DEBUG [launcher]: Finished all browsers
npm ERR! Windows_NT 10.0.10586
npm ERR! argv "C:\\Program Files\\nodejs\\node.exe" "C:\\Program Files\\nodejs\\node_modules\\npm\\bin\\npm-cli.js" "run" "test"
npm ERR! node v5.3.0
npm ERR! npm v3.3.12
npm ERR! code ELIFECYCLE
npm ERR! browser-id3-writer@0.0.0-semantically-released test: `karma start --single-run`
npm ERR! Exit status 1
npm ERR!
npm ERR! Failed at the browser-id3-writer@0.0.0-semantically-released test script 'karma start --single-run'.
npm ERR! Make sure you have the latest version of node.js and npm installed.
npm ERR! If you do, this is most likely a problem with the browser-id3-writer package,
npm ERR! not with npm itself.
npm ERR! Tell the author that this fails on your system:
npm ERR! karma start --single-run
npm ERR! You can get their info via:
npm ERR! npm owner ls browser-id3-writer
npm ERR! There is likely additional logging output above.
npm ERR! Please include the following file with any support request:
npm ERR! E:\Dropbox\repo\browser-id3-writer\npm-debug.log
```
|
non_defect
|
karma chrashes with fatal error wrong length i ve just updated from where everything was fine to and run tests karma has crashed with ie runner with chrome and firefox there are no problems karma start single run debug autowatch set to false because of singlerun debug loading karma from e dropbox repo browser writer node modules debug loading plugin e dropbox repo browser writer node modules karma chai debug loading plugin e dropbox repo browser writer node modules karma chrome launcher debug loading plugin e dropbox repo browser writer node modules karma coverage debug loading plugin e dropbox repo browser writer node modules karma firefox launcher debug loading plugin e dropbox repo browser writer node modules karma ie launcher debug loading plugin e dropbox repo browser writer node modules karma mocha debug processing e dropbox repo browser writer src browser writer js info karma server started at info starting browser ie debug creating temp dir at c users appdata local temp karma debug c program files internet explorer iexplore exe debug serving e dropbox repo browser writer node modules karma static client html debug serving e dropbox repo browser writer node modules karma static karma js debug a browser has connected on socket debug upgrade socket io eio transport websocket sid info connected on socket with id debug ie id captured in secs debug serving e dropbox repo browser writer node modules karma static context html ie windows executed of success secs secs debug run complete exiting debug disconnecting all browsers error rangeerror wrong length at rangeerror native at stricttolength e dropbox repo browser writer node modules core js modules typed array js at e dropbox repo browser writer node modules core js modules typed array js at new e dropbox repo browser writer node modules core js modules typed array js at allocate buffer js at new buffer buffer js at bufferpool reset e dropbox repo browser writer node modules ws lib bufferpool js at receiver endpacket e dropbox repo browser writer node modules ws lib receiver js at receiver opcodes finish e dropbox repo browser writer node modules ws lib receiver js at receiver expecthandler e dropbox repo browser writer node modules ws lib receiver js at receiver add e dropbox repo browser writer node modules ws lib receiver js at socket realhandler e dropbox repo browser writer node modules ws lib websocket js at emitone events js at socket emit events js at readableaddchunk stream readable js at socket readable push stream readable js debug disconnecting all browsers debug writing coverage to e dropbox repo browser writer coverage debug killed extra ie process debug process ie exited with code debug cleaning temp dir c users appdata local temp karma debug finished all browsers npm err windows nt npm err argv c program files nodejs node exe c program files nodejs node modules npm bin npm cli js run test npm err node npm err npm npm err code elifecycle npm err browser writer semantically released test karma start single run npm err exit status npm err npm err failed at the browser writer semantically released test script karma start single run npm err make sure you have the latest version of node js and npm installed npm err if you do this is most likely a problem with the browser writer package npm err not with npm itself npm err tell the author that this fails on your system npm err karma start single run npm err you can get their info via npm err npm owner ls browser writer npm err there is likely additional logging output above npm err please include the following file with any support request npm err e dropbox repo browser writer npm debug log
| 0
|
413,199
| 12,061,293,269
|
IssuesEvent
|
2020-04-15 23:20:32
|
grpc/grpc
|
https://api.github.com/repos/grpc/grpc
|
closed
|
Valgrind reports memory leak in timer_thread()
|
disposition/stale kind/bug lang/core priority/P2
|
### What version of gRPC and what language are you using?
1.23.0, C++.
### What operating system (Linux, Windows,...) and version?
Ubuntu 18.04
### What runtime / compiler are you using (e.g. python version or version of gcc)
gcc 7.4.0
### What did you do?
When running the Arrow Flight tests on Valgrind, I get the following kind of traces:
```
==29953== 336 bytes in 1 blocks are possibly lost in loss record 96 of 111
==29953== at 0x4035C05: calloc (vg_replace_malloc.c:762)
==29953== by 0x40134A6: allocate_dtv (dl-tls.c:286)
==29953== by 0x40134A6: _dl_allocate_tls (dl-tls.c:530)
==29953== by 0x6F8E227: allocate_stack (allocatestack.c:627)
==29953== by 0x6F8E227: pthread_create@@GLIBC_2.2.5 (pthread_create.c:644)
==29953== by 0x4F18704: grpc_core::Thread::Thread(char const*, void (*)(void*), void*, bool*, grpc_core::Thread::Options const&) (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x4E33053: start_timer_thread_and_unlock() (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x4E335D4: timer_thread(void*) (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x4F18545: grpc_core::(anonymous namespace)::ThreadInternalsPosix::ThreadInternalsPosix(char const*, void (*)(void*), void*, bool*, grpc_core::Thread::Options const&)::{lambda(void*)#1}::_FUN(void*) (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x6F8D6DA: start_thread (pthread_create.c:463)
==29953== by 0x744E88E: clone (clone.S:95)
```
That stack trace looks a bit weird: from what I can see, `timer_thread` is supposed to be _started_ by `start_timer_thread_and_unlock`, but here it looks as though the former called the latter as well.
|
1.0
|
Valgrind reports memory leak in timer_thread() - ### What version of gRPC and what language are you using?
1.23.0, C++.
### What operating system (Linux, Windows,...) and version?
Ubuntu 18.04
### What runtime / compiler are you using (e.g. python version or version of gcc)
gcc 7.4.0
### What did you do?
When running the Arrow Flight tests on Valgrind, I get the following kind of traces:
```
==29953== 336 bytes in 1 blocks are possibly lost in loss record 96 of 111
==29953== at 0x4035C05: calloc (vg_replace_malloc.c:762)
==29953== by 0x40134A6: allocate_dtv (dl-tls.c:286)
==29953== by 0x40134A6: _dl_allocate_tls (dl-tls.c:530)
==29953== by 0x6F8E227: allocate_stack (allocatestack.c:627)
==29953== by 0x6F8E227: pthread_create@@GLIBC_2.2.5 (pthread_create.c:644)
==29953== by 0x4F18704: grpc_core::Thread::Thread(char const*, void (*)(void*), void*, bool*, grpc_core::Thread::Options const&) (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x4E33053: start_timer_thread_and_unlock() (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x4E335D4: timer_thread(void*) (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x4F18545: grpc_core::(anonymous namespace)::ThreadInternalsPosix::ThreadInternalsPosix(char const*, void (*)(void*), void*, bool*, grpc_core::Thread::Options const&)::{lambda(void*)#1}::_FUN(void*) (in /home/antoine/arrow/dev/cpp/build-test/debug/libarrow_flight.so.15.0.0)
==29953== by 0x6F8D6DA: start_thread (pthread_create.c:463)
==29953== by 0x744E88E: clone (clone.S:95)
```
That stack trace looks a bit weird: from what I can see, `timer_thread` is supposed to be _started_ by `start_timer_thread_and_unlock`, but here it looks as though the former called the latter as well.
|
non_defect
|
valgrind reports memory leak in timer thread what version of grpc and what language are you using c what operating system linux windows and version ubuntu what runtime compiler are you using e g python version or version of gcc gcc what did you do when running the arrow flight tests on valgrind i get the following kind of traces bytes in blocks are possibly lost in loss record of at calloc vg replace malloc c by allocate dtv dl tls c by dl allocate tls dl tls c by allocate stack allocatestack c by pthread create glibc pthread create c by grpc core thread thread char const void void void bool grpc core thread options const in home antoine arrow dev cpp build test debug libarrow flight so by start timer thread and unlock in home antoine arrow dev cpp build test debug libarrow flight so by timer thread void in home antoine arrow dev cpp build test debug libarrow flight so by grpc core anonymous namespace threadinternalsposix threadinternalsposix char const void void void bool grpc core thread options const lambda void fun void in home antoine arrow dev cpp build test debug libarrow flight so by start thread pthread create c by clone clone s that stack trace looks a bit weird from what i can see timer thread is supposed to be started by start timer thread and unlock but here it looks as though the former called the latter as well
| 0
|
50,788
| 13,187,745,226
|
IssuesEvent
|
2020-08-13 04:26:18
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
closed
|
env-shell inserts non-existant root path into LD_LIBRARY_PATH (Trac #1372)
|
Migrated from Trac cmake defect
|
When USE_ROOT is set to False env-shell.sh puts /USE_ROOT/IS/OFF/lib into the user's $LD_LIBRARY_PATH. This does no harm since no one is ever going to have that path, but introduces pointless clutter and wastes the dynamic linker's time. Maybe we could have it just skip adding the root library path when USE_ROOT is turned off.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1372">https://code.icecube.wisc.edu/ticket/1372</a>, reported by cweaver and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-12T00:03:39",
"description": "When USE_ROOT is set to False env-shell.sh puts /USE_ROOT/IS/OFF/lib into the user's $LD_LIBRARY_PATH. This does no harm since no one is ever going to have that path, but introduces pointless clutter and wastes the dynamic linker's time. Maybe we could have it just skip adding the root library path when USE_ROOT is turned off. ",
"reporter": "cweaver",
"cc": "david.schultz",
"resolution": "fixed",
"_ts": "1547251419341678",
"component": "cmake",
"summary": "env-shell inserts non-existant root path into LD_LIBRARY_PATH",
"priority": "minor",
"keywords": "",
"time": "2015-09-30T19:03:27",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
env-shell inserts non-existant root path into LD_LIBRARY_PATH (Trac #1372) - When USE_ROOT is set to False env-shell.sh puts /USE_ROOT/IS/OFF/lib into the user's $LD_LIBRARY_PATH. This does no harm since no one is ever going to have that path, but introduces pointless clutter and wastes the dynamic linker's time. Maybe we could have it just skip adding the root library path when USE_ROOT is turned off.
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1372">https://code.icecube.wisc.edu/ticket/1372</a>, reported by cweaver and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-12T00:03:39",
"description": "When USE_ROOT is set to False env-shell.sh puts /USE_ROOT/IS/OFF/lib into the user's $LD_LIBRARY_PATH. This does no harm since no one is ever going to have that path, but introduces pointless clutter and wastes the dynamic linker's time. Maybe we could have it just skip adding the root library path when USE_ROOT is turned off. ",
"reporter": "cweaver",
"cc": "david.schultz",
"resolution": "fixed",
"_ts": "1547251419341678",
"component": "cmake",
"summary": "env-shell inserts non-existant root path into LD_LIBRARY_PATH",
"priority": "minor",
"keywords": "",
"time": "2015-09-30T19:03:27",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
defect
|
env shell inserts non existant root path into ld library path trac when use root is set to false env shell sh puts use root is off lib into the user s ld library path this does no harm since no one is ever going to have that path but introduces pointless clutter and wastes the dynamic linker s time maybe we could have it just skip adding the root library path when use root is turned off migrated from json status closed changetime description when use root is set to false env shell sh puts use root is off lib into the user s ld library path this does no harm since no one is ever going to have that path but introduces pointless clutter and wastes the dynamic linker s time maybe we could have it just skip adding the root library path when use root is turned off reporter cweaver cc david schultz resolution fixed ts component cmake summary env shell inserts non existant root path into ld library path priority minor keywords time milestone owner nega type defect
| 1
|
19,873
| 3,268,016,476
|
IssuesEvent
|
2015-10-23 08:53:19
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
closed
|
FileUpload (advanced, multiple) throws JS error in IE10
|
5.2.15 5.3.1 defect
|
PrimeFaces 5.2
We use the Primefaces FileUploader in mode=advanced and multiple=true. If you select multiple files at once (click choose, select 2 or more files, accept) you will only get a single file in the preview of the upload queue. It doesn't matter how many files you select, you will always only get a single file. Pressing upload results in a JS error
```
SCRIPT5007: Die Eigenschaft "children" eines undefinierten oder Nullverweises kann nicht abgerufen werden.
fileupload.js.xhtml, Zeile 1 Zeichen 24948
```
The highlighted code in the JS debugger of IE10 is this:
```
g.row.children(".ui-fileupload-progress").find("> .ui-progressbar > .ui-progressbar-value").css({width:f+"%",display:"block"})
```
If you select the files one after another (choose, select file, accept, choose, select file, accept, ...) you will see all files in the upload queue and no error will be thrown when you press upload.
|
1.0
|
FileUpload (advanced, multiple) throws JS error in IE10 - PrimeFaces 5.2
We use the Primefaces FileUploader in mode=advanced and multiple=true. If you select multiple files at once (click choose, select 2 or more files, accept) you will only get a single file in the preview of the upload queue. It doesn't matter how many files you select, you will always only get a single file. Pressing upload results in a JS error
```
SCRIPT5007: Die Eigenschaft "children" eines undefinierten oder Nullverweises kann nicht abgerufen werden.
fileupload.js.xhtml, Zeile 1 Zeichen 24948
```
The highlighted code in the JS debugger of IE10 is this:
```
g.row.children(".ui-fileupload-progress").find("> .ui-progressbar > .ui-progressbar-value").css({width:f+"%",display:"block"})
```
If you select the files one after another (choose, select file, accept, choose, select file, accept, ...) you will see all files in the upload queue and no error will be thrown when you press upload.
|
defect
|
fileupload advanced multiple throws js error in primefaces we use the primefaces fileuploader in mode advanced and multiple true if you select multiple files at once click choose select or more files accept you will only get a single file in the preview of the upload queue it doesn t matter how many files you select you will always only get a single file pressing upload results in a js error die eigenschaft children eines undefinierten oder nullverweises kann nicht abgerufen werden fileupload js xhtml zeile zeichen the highlighted code in the js debugger of is this g row children ui fileupload progress find ui progressbar ui progressbar value css width f display block if you select the files one after another choose select file accept choose select file accept you will see all files in the upload queue and no error will be thrown when you press upload
| 1
|
28,159
| 5,201,804,608
|
IssuesEvent
|
2017-01-24 06:54:43
|
TNGSB/eWallet
|
https://api.github.com/repos/TNGSB/eWallet
|
closed
|
e-Wallet_Mobile App (Utilities - Astro Reversal) 20012017 #26
|
Defect - Medium (Sev-3) Live Environment
|
Mobile App does not display reversal status for utility payment.
Defect Description : User to perform a "reversal" scenario for utility payment however, mobile application does not indicate the transaction is successful/failed/reverse.
Attached screenshot for POT.


|
1.0
|
e-Wallet_Mobile App (Utilities - Astro Reversal) 20012017 #26 - Mobile App does not display reversal status for utility payment.
Defect Description : User to perform a "reversal" scenario for utility payment however, mobile application does not indicate the transaction is successful/failed/reverse.
Attached screenshot for POT.


|
defect
|
e wallet mobile app utilities astro reversal mobile app does not display reversal status for utility payment defect description user to perform a reversal scenario for utility payment however mobile application does not indicate the transaction is successful failed reverse attached screenshot for pot
| 1
|
129,417
| 17,780,288,610
|
IssuesEvent
|
2021-08-31 02:52:54
|
eoscostarica/proton-affiliate
|
https://api.github.com/repos/eoscostarica/proton-affiliate
|
closed
|
Admin input to add referrers
|
UI / UX Design
|
As an admin I want to add referrers directly so they don't need to apply.
|
1.0
|
Admin input to add referrers - As an admin I want to add referrers directly so they don't need to apply.
|
non_defect
|
admin input to add referrers as an admin i want to add referrers directly so they don t need to apply
| 0
|
17,445
| 12,037,091,955
|
IssuesEvent
|
2020-04-13 21:05:50
|
OBOFoundry/OBOFoundry.github.io
|
https://api.github.com/repos/OBOFoundry/OBOFoundry.github.io
|
closed
|
OBO-discuss link needed for ontology registration FAQ
|
attn: Technical WG usability feature website
|
The FAQ for ontology registration instructs the user to announce their ontology on the OBO-discuss list, but there is no link to the list. It would be helpful to have it.
http://obofoundry.org/faq/how-do-i-register-my-ontology.html
|
True
|
OBO-discuss link needed for ontology registration FAQ - The FAQ for ontology registration instructs the user to announce their ontology on the OBO-discuss list, but there is no link to the list. It would be helpful to have it.
http://obofoundry.org/faq/how-do-i-register-my-ontology.html
|
non_defect
|
obo discuss link needed for ontology registration faq the faq for ontology registration instructs the user to announce their ontology on the obo discuss list but there is no link to the list it would be helpful to have it
| 0
|
50,959
| 13,188,001,043
|
IssuesEvent
|
2020-08-13 05:16:03
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
closed
|
[Steamshovel] artists python files don't like being called on their own which confuses the documentation (Trac #1736)
|
Migrated from Trac combo core defect
|
It is not clear to me exactly how steamshovel loads these artist files but it causes problems with sphinx documentation. These can be tested by running the file directly for example calling `python ${I3_SRC}/CommonVariables/python/artists/direct_hits.py` instead of calling sphinx and it gets the same result.
* common_variables/artists/direct_hits.py
* common_variables/artists/hit_multiplicity.py
* common_variables/artists/hit_statistics.py
* common_variables/artists/track_characteristics.py
* millipede/artists.py
* steamshovel/artists/LEDPowerHouse.py
* steamshovel/artists/ParticleUncertainty.py
* steamshovel/sessions/IT73.py
* steamshovel/sessions/Minimum.py
Full error messages below
```text
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:15: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.direct_hits'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py", line 5, in <module>
class I3DirectHitsValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py", line 10, in I3DirectHitsValues
requiredTypes = [ direct_hits.I3DirectHitsValues ]
AttributeError: 'module' object has no attribute 'I3DirectHitsValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:23: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_multiplicity'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py", line 4, in <module>
class I3HitMultiplicityValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py", line 9, in I3HitMultiplicityValues
requiredTypes = [ hit_multiplicity.I3HitMultiplicityValues ]
AttributeError: 'module' object has no attribute 'I3HitMultiplicityValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:31: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_statistics'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py", line 5, in <module>
class I3HitStatisticsValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py", line 10, in I3HitStatisticsValues
requiredTypes = [ hit_statistics.I3HitStatisticsValues ]
AttributeError: 'module' object has no attribute 'I3HitStatisticsValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:39: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.track_characteristics'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py", line 5, in <module>
class I3TrackCharacteristicsValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py", line 10, in I3TrackCharacteristicsValues
requiredTypes = [ track_characteristics.I3TrackCharacteristicsValues ]
AttributeError: 'module' object has no attribute 'I3TrackCharacteristicsValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.ipdf.rst:23: WARNING: autodoc: failed to import module u'icecube.ipdf.test_bug'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/ipdf/test_bug.py", line 3, in <module>
scenario = window.gl.scenario
NameError: name 'window' is not defined
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.millipede.rst:15: WARNING: autodoc: failed to import module u'icecube.millipede.artists'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/millipede/artists.py", line 7, in <module>
from icecube.steamshovel.artists.MPLArtist import MPLArtist
ImportError: No module named MPLArtist
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:70: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.LEDPowerHouse'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/LEDPowerHouse.py", line 9, in <module>
import serial
ImportError: No module named serial
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:78: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.ParticleUncertainty'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/ParticleUncertainty.py", line 6, in <module>
from .AnimatedParticle import PosAtTime
ImportError: No module named AnimatedParticle
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:15: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.IT73'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py", line 124, in <module>
_dumpScenario()
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py", line 6, in _dumpScenario
scenario = window.gl.scenario
NameError: global name 'window' is not defined
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:23: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.Minimum'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py", line 47, in <module>
_dumpScenario()
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py", line 6, in _dumpScenario
scenario = window.gl.scenario
NameError: global name 'window' is not defined
```
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1736">https://code.icecube.wisc.edu/ticket/1736</a>, reported by kjmeagher and owned by hdembinski</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:12:38",
"description": "It is not clear to me exactly how steamshovel loads these artist files but it causes problems with sphinx documentation. These can be tested by running the file directly for example calling `python ${I3_SRC}/CommonVariables/python/artists/direct_hits.py` instead of calling sphinx and it gets the same result.\n\n* common_variables/artists/direct_hits.py\n* common_variables/artists/hit_multiplicity.py\n* common_variables/artists/hit_statistics.py\n* common_variables/artists/track_characteristics.py\n* millipede/artists.py\n* steamshovel/artists/LEDPowerHouse.py\n* steamshovel/artists/ParticleUncertainty.py\n* steamshovel/sessions/IT73.py\n* steamshovel/sessions/Minimum.py\n\nFull error messages below\n{{{\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:15: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.direct_hits'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py\", line 5, in <module>\n class I3DirectHitsValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py\", line 10, in I3DirectHitsValues\n requiredTypes = [ direct_hits.I3DirectHitsValues ]\nAttributeError: 'module' object has no attribute 'I3DirectHitsValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:23: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_multiplicity'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py\", line 4, in <module>\n class I3HitMultiplicityValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py\", line 9, in I3HitMultiplicityValues\n requiredTypes = [ hit_multiplicity.I3HitMultiplicityValues ]\nAttributeError: 'module' object has no attribute 'I3HitMultiplicityValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:31: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_statistics'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py\", line 5, in <module>\n class I3HitStatisticsValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py\", line 10, in I3HitStatisticsValues\n requiredTypes = [ hit_statistics.I3HitStatisticsValues ]\nAttributeError: 'module' object has no attribute 'I3HitStatisticsValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:39: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.track_characteristics'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py\", line 5, in <module>\n class I3TrackCharacteristicsValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py\", line 10, in I3TrackCharacteristicsValues\n requiredTypes = [ track_characteristics.I3TrackCharacteristicsValues ]\nAttributeError: 'module' object has no attribute 'I3TrackCharacteristicsValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.ipdf.rst:23: WARNING: autodoc: failed to import module u'icecube.ipdf.test_bug'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/ipdf/test_bug.py\", line 3, in <module>\n scenario = window.gl.scenario\nNameError: name 'window' is not defined\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.millipede.rst:15: WARNING: autodoc: failed to import module u'icecube.millipede.artists'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/millipede/artists.py\", line 7, in <module>\n from icecube.steamshovel.artists.MPLArtist import MPLArtist\nImportError: No module named MPLArtist\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:70: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.LEDPowerHouse'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/LEDPowerHouse.py\", line 9, in <module>\n import serial\nImportError: No module named serial\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:78: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.ParticleUncertainty'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/ParticleUncertainty.py\", line 6, in <module>\n from .AnimatedParticle import PosAtTime\nImportError: No module named AnimatedParticle\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:15: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.IT73'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py\", line 124, in <module>\n _dumpScenario()\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py\", line 6, in _dumpScenario\n scenario = window.gl.scenario\nNameError: global name 'window' is not defined\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:23: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.Minimum'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py\", line 47, in <module>\n _dumpScenario()\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py\", line 6, in _dumpScenario\n scenario = window.gl.scenario\nNameError: global name 'window' is not defined\n}}}",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1550067158057333",
"component": "combo core",
"summary": "[Steamshovel] artists python files don't like being called on their own which confuses the documentation",
"priority": "normal",
"keywords": "documentation",
"time": "2016-06-10T07:42:38",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
[Steamshovel] artists python files don't like being called on their own which confuses the documentation (Trac #1736) - It is not clear to me exactly how steamshovel loads these artist files but it causes problems with sphinx documentation. These can be tested by running the file directly for example calling `python ${I3_SRC}/CommonVariables/python/artists/direct_hits.py` instead of calling sphinx and it gets the same result.
* common_variables/artists/direct_hits.py
* common_variables/artists/hit_multiplicity.py
* common_variables/artists/hit_statistics.py
* common_variables/artists/track_characteristics.py
* millipede/artists.py
* steamshovel/artists/LEDPowerHouse.py
* steamshovel/artists/ParticleUncertainty.py
* steamshovel/sessions/IT73.py
* steamshovel/sessions/Minimum.py
Full error messages below
```text
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:15: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.direct_hits'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py", line 5, in <module>
class I3DirectHitsValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py", line 10, in I3DirectHitsValues
requiredTypes = [ direct_hits.I3DirectHitsValues ]
AttributeError: 'module' object has no attribute 'I3DirectHitsValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:23: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_multiplicity'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py", line 4, in <module>
class I3HitMultiplicityValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py", line 9, in I3HitMultiplicityValues
requiredTypes = [ hit_multiplicity.I3HitMultiplicityValues ]
AttributeError: 'module' object has no attribute 'I3HitMultiplicityValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:31: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_statistics'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py", line 5, in <module>
class I3HitStatisticsValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py", line 10, in I3HitStatisticsValues
requiredTypes = [ hit_statistics.I3HitStatisticsValues ]
AttributeError: 'module' object has no attribute 'I3HitStatisticsValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:39: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.track_characteristics'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py", line 5, in <module>
class I3TrackCharacteristicsValues(PyArtist):
File "/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py", line 10, in I3TrackCharacteristicsValues
requiredTypes = [ track_characteristics.I3TrackCharacteristicsValues ]
AttributeError: 'module' object has no attribute 'I3TrackCharacteristicsValues'
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.ipdf.rst:23: WARNING: autodoc: failed to import module u'icecube.ipdf.test_bug'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/ipdf/test_bug.py", line 3, in <module>
scenario = window.gl.scenario
NameError: name 'window' is not defined
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.millipede.rst:15: WARNING: autodoc: failed to import module u'icecube.millipede.artists'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/millipede/artists.py", line 7, in <module>
from icecube.steamshovel.artists.MPLArtist import MPLArtist
ImportError: No module named MPLArtist
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:70: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.LEDPowerHouse'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/LEDPowerHouse.py", line 9, in <module>
import serial
ImportError: No module named serial
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:78: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.ParticleUncertainty'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/ParticleUncertainty.py", line 6, in <module>
from .AnimatedParticle import PosAtTime
ImportError: No module named AnimatedParticle
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:15: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.IT73'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py", line 124, in <module>
_dumpScenario()
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py", line 6, in _dumpScenario
scenario = window.gl.scenario
NameError: global name 'window' is not defined
/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:23: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.Minimum'; the following exception was raised:
Traceback (most recent call last):
File "/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py", line 385, in import_object
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py", line 47, in <module>
_dumpScenario()
File "/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py", line 6, in _dumpScenario
scenario = window.gl.scenario
NameError: global name 'window' is not defined
```
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1736">https://code.icecube.wisc.edu/ticket/1736</a>, reported by kjmeagher and owned by hdembinski</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:12:38",
"description": "It is not clear to me exactly how steamshovel loads these artist files but it causes problems with sphinx documentation. These can be tested by running the file directly for example calling `python ${I3_SRC}/CommonVariables/python/artists/direct_hits.py` instead of calling sphinx and it gets the same result.\n\n* common_variables/artists/direct_hits.py\n* common_variables/artists/hit_multiplicity.py\n* common_variables/artists/hit_statistics.py\n* common_variables/artists/track_characteristics.py\n* millipede/artists.py\n* steamshovel/artists/LEDPowerHouse.py\n* steamshovel/artists/ParticleUncertainty.py\n* steamshovel/sessions/IT73.py\n* steamshovel/sessions/Minimum.py\n\nFull error messages below\n{{{\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:15: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.direct_hits'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py\", line 5, in <module>\n class I3DirectHitsValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/direct_hits.py\", line 10, in I3DirectHitsValues\n requiredTypes = [ direct_hits.I3DirectHitsValues ]\nAttributeError: 'module' object has no attribute 'I3DirectHitsValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:23: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_multiplicity'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py\", line 4, in <module>\n class I3HitMultiplicityValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_multiplicity.py\", line 9, in I3HitMultiplicityValues\n requiredTypes = [ hit_multiplicity.I3HitMultiplicityValues ]\nAttributeError: 'module' object has no attribute 'I3HitMultiplicityValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:31: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.hit_statistics'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py\", line 5, in <module>\n class I3HitStatisticsValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/hit_statistics.py\", line 10, in I3HitStatisticsValues\n requiredTypes = [ hit_statistics.I3HitStatisticsValues ]\nAttributeError: 'module' object has no attribute 'I3HitStatisticsValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.common_variables.artists.rst:39: WARNING: autodoc: failed to import module u'icecube.common_variables.artists.track_characteristics'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py\", line 5, in <module>\n class I3TrackCharacteristicsValues(PyArtist):\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/common_variables/artists/track_characteristics.py\", line 10, in I3TrackCharacteristicsValues\n requiredTypes = [ track_characteristics.I3TrackCharacteristicsValues ]\nAttributeError: 'module' object has no attribute 'I3TrackCharacteristicsValues'\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.ipdf.rst:23: WARNING: autodoc: failed to import module u'icecube.ipdf.test_bug'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/ipdf/test_bug.py\", line 3, in <module>\n scenario = window.gl.scenario\nNameError: name 'window' is not defined\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.millipede.rst:15: WARNING: autodoc: failed to import module u'icecube.millipede.artists'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/millipede/artists.py\", line 7, in <module>\n from icecube.steamshovel.artists.MPLArtist import MPLArtist\nImportError: No module named MPLArtist\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:70: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.LEDPowerHouse'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/LEDPowerHouse.py\", line 9, in <module>\n import serial\nImportError: No module named serial\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.artists.rst:78: WARNING: autodoc: failed to import module u'icecube.steamshovel.artists.ParticleUncertainty'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/artists/ParticleUncertainty.py\", line 6, in <module>\n from .AnimatedParticle import PosAtTime\nImportError: No module named AnimatedParticle\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:15: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.IT73'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py\", line 124, in <module>\n _dumpScenario()\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/IT73.py\", line 6, in _dumpScenario\n scenario = window.gl.scenario\nNameError: global name 'window' is not defined\n/Users/kmeagher/icecube/combo/release/sphinx_build/source/python/icecube.steamshovel.sessions.rst:23: WARNING: autodoc: failed to import module u'icecube.steamshovel.sessions.Minimum'; the following exception was raised:\nTraceback (most recent call last):\n File \"/private/var/folders/rc/g_4_lyp9039cj1586zzg88f40000gn/T/pip-build-A327aa/sphinx/sphinx/ext/autodoc.py\", line 385, in import_object\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py\", line 47, in <module>\n _dumpScenario()\n File \"/Users/kmeagher/icecube/combo/release/lib/icecube/steamshovel/sessions/Minimum.py\", line 6, in _dumpScenario\n scenario = window.gl.scenario\nNameError: global name 'window' is not defined\n}}}",
"reporter": "kjmeagher",
"cc": "",
"resolution": "fixed",
"_ts": "1550067158057333",
"component": "combo core",
"summary": "[Steamshovel] artists python files don't like being called on their own which confuses the documentation",
"priority": "normal",
"keywords": "documentation",
"time": "2016-06-10T07:42:38",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
</p>
</details>
|
defect
|
artists python files don t like being called on their own which confuses the documentation trac it is not clear to me exactly how steamshovel loads these artist files but it causes problems with sphinx documentation these can be tested by running the file directly for example calling python src commonvariables python artists direct hits py instead of calling sphinx and it gets the same result common variables artists direct hits py common variables artists hit multiplicity py common variables artists hit statistics py common variables artists track characteristics py millipede artists py steamshovel artists ledpowerhouse py steamshovel artists particleuncertainty py steamshovel sessions py steamshovel sessions minimum py full error messages below text users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists direct hits the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube common variables artists direct hits py line in class pyartist file users kmeagher icecube combo release lib icecube common variables artists direct hits py line in requiredtypes attributeerror module object has no attribute users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists hit multiplicity the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube common variables artists hit multiplicity py line in class pyartist file users kmeagher icecube combo release lib icecube common variables artists hit multiplicity py line in requiredtypes attributeerror module object has no attribute users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists hit statistics the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube common variables artists hit statistics py line in class pyartist file users kmeagher icecube combo release lib icecube common variables artists hit statistics py line in requiredtypes attributeerror module object has no attribute users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists track characteristics the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube common variables artists track characteristics py line in class pyartist file users kmeagher icecube combo release lib icecube common variables artists track characteristics py line in requiredtypes attributeerror module object has no attribute users kmeagher icecube combo release sphinx build source python icecube ipdf rst warning autodoc failed to import module u icecube ipdf test bug the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube ipdf test bug py line in scenario window gl scenario nameerror name window is not defined users kmeagher icecube combo release sphinx build source python icecube millipede rst warning autodoc failed to import module u icecube millipede artists the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube millipede artists py line in from icecube steamshovel artists mplartist import mplartist importerror no module named mplartist users kmeagher icecube combo release sphinx build source python icecube steamshovel artists rst warning autodoc failed to import module u icecube steamshovel artists ledpowerhouse the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube steamshovel artists ledpowerhouse py line in import serial importerror no module named serial users kmeagher icecube combo release sphinx build source python icecube steamshovel artists rst warning autodoc failed to import module u icecube steamshovel artists particleuncertainty the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube steamshovel artists particleuncertainty py line in from animatedparticle import posattime importerror no module named animatedparticle users kmeagher icecube combo release sphinx build source python icecube steamshovel sessions rst warning autodoc failed to import module u icecube steamshovel sessions the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube steamshovel sessions py line in dumpscenario file users kmeagher icecube combo release lib icecube steamshovel sessions py line in dumpscenario scenario window gl scenario nameerror global name window is not defined users kmeagher icecube combo release sphinx build source python icecube steamshovel sessions rst warning autodoc failed to import module u icecube steamshovel sessions minimum the following exception was raised traceback most recent call last file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object file users kmeagher icecube combo release lib icecube steamshovel sessions minimum py line in dumpscenario file users kmeagher icecube combo release lib icecube steamshovel sessions minimum py line in dumpscenario scenario window gl scenario nameerror global name window is not defined migrated from json status closed changetime description it is not clear to me exactly how steamshovel loads these artist files but it causes problems with sphinx documentation these can be tested by running the file directly for example calling python src commonvariables python artists direct hits py instead of calling sphinx and it gets the same result n n common variables artists direct hits py n common variables artists hit multiplicity py n common variables artists hit statistics py n common variables artists track characteristics py n millipede artists py n steamshovel artists ledpowerhouse py n steamshovel artists particleuncertainty py n steamshovel sessions py n steamshovel sessions minimum py n nfull error messages below n n users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists direct hits the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube common variables artists direct hits py line in n class pyartist n file users kmeagher icecube combo release lib icecube common variables artists direct hits py line in n requiredtypes nattributeerror module object has no attribute n users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists hit multiplicity the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube common variables artists hit multiplicity py line in n class pyartist n file users kmeagher icecube combo release lib icecube common variables artists hit multiplicity py line in n requiredtypes nattributeerror module object has no attribute n users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists hit statistics the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube common variables artists hit statistics py line in n class pyartist n file users kmeagher icecube combo release lib icecube common variables artists hit statistics py line in n requiredtypes nattributeerror module object has no attribute n users kmeagher icecube combo release sphinx build source python icecube common variables artists rst warning autodoc failed to import module u icecube common variables artists track characteristics the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube common variables artists track characteristics py line in n class pyartist n file users kmeagher icecube combo release lib icecube common variables artists track characteristics py line in n requiredtypes nattributeerror module object has no attribute n users kmeagher icecube combo release sphinx build source python icecube ipdf rst warning autodoc failed to import module u icecube ipdf test bug the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube ipdf test bug py line in n scenario window gl scenario nnameerror name window is not defined n users kmeagher icecube combo release sphinx build source python icecube millipede rst warning autodoc failed to import module u icecube millipede artists the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube millipede artists py line in n from icecube steamshovel artists mplartist import mplartist nimporterror no module named mplartist n users kmeagher icecube combo release sphinx build source python icecube steamshovel artists rst warning autodoc failed to import module u icecube steamshovel artists ledpowerhouse the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube steamshovel artists ledpowerhouse py line in n import serial nimporterror no module named serial n users kmeagher icecube combo release sphinx build source python icecube steamshovel artists rst warning autodoc failed to import module u icecube steamshovel artists particleuncertainty the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube steamshovel artists particleuncertainty py line in n from animatedparticle import posattime nimporterror no module named animatedparticle n users kmeagher icecube combo release sphinx build source python icecube steamshovel sessions rst warning autodoc failed to import module u icecube steamshovel sessions the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube steamshovel sessions py line in n dumpscenario n file users kmeagher icecube combo release lib icecube steamshovel sessions py line in dumpscenario n scenario window gl scenario nnameerror global name window is not defined n users kmeagher icecube combo release sphinx build source python icecube steamshovel sessions rst warning autodoc failed to import module u icecube steamshovel sessions minimum the following exception was raised ntraceback most recent call last n file private var folders rc g t pip build sphinx sphinx ext autodoc py line in import object n file users kmeagher icecube combo release lib icecube steamshovel sessions minimum py line in n dumpscenario n file users kmeagher icecube combo release lib icecube steamshovel sessions minimum py line in dumpscenario n scenario window gl scenario nnameerror global name window is not defined n reporter kjmeagher cc resolution fixed ts component combo core summary artists python files don t like being called on their own which confuses the documentation priority normal keywords documentation time milestone owner hdembinski type defect
| 1
|
232,955
| 25,718,920,131
|
IssuesEvent
|
2022-12-07 12:21:25
|
Nexmo/nexmo-sms-contest-app
|
https://api.github.com/repos/Nexmo/nexmo-sms-contest-app
|
opened
|
sass-rails-5.1.0.gem: 19 vulnerabilities (highest severity is: 9.8)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sass-rails-5.1.0.gem</b></p></summary>
<p></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (sass-rails version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-8165](https://www.mend.io/vulnerability-database/CVE-2020-8165) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | activesupport-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-31163](https://www.mend.io/vulnerability-database/CVE-2022-31163) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tzinfo-1.2.5.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22885](https://www.mend.io/vulnerability-database/CVE-2021-22885) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-8164](https://www.mend.io/vulnerability-database/CVE-2020-8164) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22902](https://www.mend.io/vulnerability-database/CVE-2021-22902) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22904](https://www.mend.io/vulnerability-database/CVE-2021-22904) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-8264](https://www.mend.io/vulnerability-database/CVE-2020-8264) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22942](https://www.mend.io/vulnerability-database/CVE-2021-22942) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-22577](https://www.mend.io/vulnerability-database/CVE-2022-22577) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-27777](https://www.mend.io/vulnerability-database/CVE-2022-27777) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionview-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-15169](https://www.mend.io/vulnerability-database/CVE-2020-15169) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionview-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-44528](https://www.mend.io/vulnerability-database/CVE-2021-44528) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22881](https://www.mend.io/vulnerability-database/CVE-2021-22881) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-32209](https://www.mend.io/vulnerability-database/CVE-2022-32209) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | rails-html-sanitizer-1.3.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-23634](https://www.mend.io/vulnerability-database/CVE-2022-23634) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-23633](https://www.mend.io/vulnerability-database/CVE-2022-23633) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-3704](https://www.mend.io/vulnerability-database/CVE-2022-3704) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.4 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-5267](https://www.mend.io/vulnerability-database/CVE-2020-5267) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | actionview-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-8166](https://www.mend.io/vulnerability-database/CVE-2020-8166) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.3 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8165</summary>
### Vulnerable Library - <b>activesupport-6.0.0.gem</b></p>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-6.0.0.gem">https://rubygems.org/gems/activesupport-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activesupport-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **activesupport-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization of untrusted data vulnernerability exists in rails < 5.2.4.3, rails < 6.0.3.1 that can allow an attacker to unmarshal user-provided objects in MemCacheStore and RedisCacheStore potentially resulting in an RCE.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8165>CVE-2020-8165</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-2p68-f74v-9wc6">https://github.com/advisories/GHSA-2p68-f74v-9wc6</a></p>
<p>Release Date: 2020-06-19</p>
<p>Fix Resolution: 5.2.4.3,6.0.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-31163</summary>
### Vulnerable Library - <b>tzinfo-1.2.5.gem</b></p>
<p>TZInfo provides daylight savings aware transformations between times in different time zones.</p>
<p>Library home page: <a href="https://rubygems.org/gems/tzinfo-1.2.5.gem">https://rubygems.org/gems/tzinfo-1.2.5.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/tzinfo-1.2.5.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- activesupport-6.0.0.gem
- :x: **tzinfo-1.2.5.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
TZInfo is a Ruby library that provides access to time zone data and allows times to be converted using time zone rules. Versions prior to 0.36.1, as well as those prior to 1.2.10 when used with the Ruby data source tzinfo-data, are vulnerable to relative path traversal. With the Ruby data source, time zones are defined in Ruby files. There is one file per time zone. Time zone files are loaded with `require` on demand. In the affected versions, `TZInfo::Timezone.get` fails to validate time zone identifiers correctly, allowing a new line character within the identifier. With Ruby version 1.9.3 and later, `TZInfo::Timezone.get` can be made to load unintended files with `require`, executing them within the Ruby process. Versions 0.3.61 and 1.2.10 include fixes to correctly validate time zone identifiers. Versions 2.0.0 and later are not vulnerable. Version 0.3.61 can still load arbitrary files from the Ruby load path if their name follows the rules for a valid time zone identifier and the file has a prefix of `tzinfo/definition` within a directory in the load path. Applications should ensure that untrusted files are not placed in a directory on the load path. As a workaround, the time zone identifier can be validated before passing to `TZInfo::Timezone.get` by ensuring it matches the regular expression `\A[A-Za-z0-9+\-_]+(?:\/[A-Za-z0-9+\-_]+)*\z`.
<p>Publish Date: 2022-07-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31163>CVE-2022-31163</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tzinfo/tzinfo/security/advisories/GHSA-5cm2-9h8c-rvfx">https://github.com/tzinfo/tzinfo/security/advisories/GHSA-5cm2-9h8c-rvfx</a></p>
<p>Release Date: 2022-07-22</p>
<p>Fix Resolution: tzinfo - 0.3.61,1.2.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22885</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A possible information disclosure / unintended method execution vulnerability in Action Pack >= 2.0.0 when using the `redirect_to` or `polymorphic_url`helper with untrusted user input.
<p>Publish Date: 2021-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22885>CVE-2021-22885</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-hjg4-8q5f-x6fm">https://github.com/advisories/GHSA-hjg4-8q5f-x6fm</a></p>
<p>Release Date: 2021-05-27</p>
<p>Fix Resolution: actionpack - 5.2.4.6,5.2.6,6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8164</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization of untrusted data vulnerability exists in rails < 5.2.4.3, rails < 6.0.3.1 which can allow an attacker to supply information can be inadvertently leaked fromStrong Parameters.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8164>CVE-2020-8164</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-8727-m6gj-mc37">https://github.com/advisories/GHSA-8727-m6gj-mc37</a></p>
<p>Release Date: 2020-06-19</p>
<p>Fix Resolution: 5.2.4.3,6.0.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22902</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The actionpack ruby gem (a framework for handling and responding to web requests in Rails) before 6.0.3.7, 6.1.3.2 suffers from a possible denial of service vulnerability in the Mime type parser of Action Dispatch. Carefully crafted Accept headers can cause the mime type parser in Action Dispatch to do catastrophic backtracking in the regular expression engine.
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22902>CVE-2021-22902</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: actionpack - 6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22904</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The actionpack ruby gem before 6.1.3.2, 6.0.3.7, 5.2.4.6, 5.2.6 suffers from a possible denial of service vulnerability in the Token Authentication logic in Action Controller due to a too permissive regular expression. Impacted code uses `authenticate_or_request_with_http_token` or `authenticate_with_http_token` for request authentication.
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22904>CVE-2021-22904</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: actionpack - 5.2.4.6,5.2.6,6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8264</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In actionpack gem >= 6.0.0, a possible XSS vulnerability exists when an application is running in development mode allowing an attacker to send or embed (in another page) a specially crafted URL which can allow the attacker to execute JavaScript in the context of the local application. This vulnerability is in the Actionable Exceptions middleware.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8264>CVE-2020-8264</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: v6.0.3.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22942</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A possible open redirect vulnerability in the Host Authorization middleware in Action Pack >= 6.0.0 that could allow attackers to redirect users to a malicious website.
<p>Publish Date: 2021-10-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22942>CVE-2021-22942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=2021-22942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=2021-22942</a></p>
<p>Release Date: 2021-10-18</p>
<p>Fix Resolution: actionpack - 6.0.4.1,6.1.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-22577</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An XSS Vulnerability in Action Pack >= 5.2.0 and < 5.2.0 that could allow an attacker to bypass CSP for non HTML like responses.
<p>Publish Date: 2022-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22577>CVE-2022-22577</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-mm33-5vfq-3mm3">https://github.com/advisories/GHSA-mm33-5vfq-3mm3</a></p>
<p>Release Date: 2022-05-26</p>
<p>Fix Resolution: actionpack - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-27777</summary>
### Vulnerable Library - <b>actionview-6.0.0.gem</b></p>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.0.gem">https://rubygems.org/gems/actionview-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionview-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **actionview-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A XSS Vulnerability in Action View tag helpers >= 5.2.0 and < 5.2.0 which would allow an attacker to inject content if able to control input into specific attributes.
<p>Publish Date: 2022-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-27777>CVE-2022-27777</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-ch3h-j2vf-95pv">https://github.com/advisories/GHSA-ch3h-j2vf-95pv</a></p>
<p>Release Date: 2022-05-26</p>
<p>Fix Resolution: actionview - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-15169</summary>
### Vulnerable Library - <b>actionview-6.0.0.gem</b></p>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.0.gem">https://rubygems.org/gems/actionview-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionview-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **actionview-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Action View before versions 5.2.4.4 and 6.0.3.3 there is a potential Cross-Site Scripting (XSS) vulnerability in Action View's translation helpers. Views that allow the user to control the default (not found) value of the `t` and `translate` helpers could be susceptible to XSS attacks. When an HTML-unsafe string is passed as the default for a missing translation key named html or ending in _html, the default string is incorrectly marked as HTML-safe and not escaped. This is patched in versions 6.0.3.3 and 5.2.4.4. A workaround without upgrading is proposed in the source advisory.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15169>CVE-2020-15169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://rubygems.org/gems/actionview/versions/6.0.3.3">https://rubygems.org/gems/actionview/versions/6.0.3.3</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 6.0.3.3, 5.2.4.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-44528</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A open redirect vulnerability exists in Action Pack >= 6.0.0 that could allow an attacker to craft a "X-Forwarded-Host" headers in combination with certain "allowed host" formats can cause the Host Authorization middleware in Action Pack to redirect users to a malicious website.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44528>CVE-2021-44528</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-qphc-hf5q-v8fc">https://github.com/advisories/GHSA-qphc-hf5q-v8fc</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution: actionpack - 6.0.4.2,6.1.4.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22881</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Host Authorization middleware in Action Pack before 6.1.2.1, 6.0.3.5 suffers from an open redirect vulnerability. Specially crafted `Host` headers in combination with certain "allowed host" formats can cause the Host Authorization middleware in Action Pack to redirect users to a malicious website. Impacted applications will have allowed hosts with a leading dot. When an allowed host contains a leading dot, a specially crafted `Host` header can be used to redirect to a malicious website.
<p>Publish Date: 2021-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22881>CVE-2021-22881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://discuss.rubyonrails.org/t/cve-2021-22881-possible-open-redirect-in-host-authorization-middleware/77130">https://discuss.rubyonrails.org/t/cve-2021-22881-possible-open-redirect-in-host-authorization-middleware/77130</a></p>
<p>Release Date: 2021-02-11</p>
<p>Fix Resolution: 6.0.3.5,6.1.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-32209</summary>
### Vulnerable Library - <b>rails-html-sanitizer-1.3.0.gem</b></p>
<p>HTML sanitization for Rails applications</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-html-sanitizer-1.3.0.gem">https://rubygems.org/gems/rails-html-sanitizer-1.3.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rails-html-sanitizer-1.3.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **rails-html-sanitizer-1.3.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
# Possible XSS Vulnerability in Rails::Html::SanitizerThere is a possible XSS vulnerability with certain configurations of Rails::Html::Sanitizer.This vulnerability has been assigned the CVE identifier CVE-2022-32209.Versions Affected: ALLNot affected: NONEFixed Versions: v1.4.3## ImpactA possible XSS vulnerability with certain configurations of Rails::Html::Sanitizer may allow an attacker to inject content if the application developer has overridden the sanitizer's allowed tags to allow both `select` and `style` elements.Code is only impacted if allowed tags are being overridden. This may be done via application configuration:```ruby# In config/application.rbconfig.action_view.sanitized_allowed_tags = ["select", "style"]```see https://guides.rubyonrails.org/configuring.html#configuring-action-viewOr it may be done with a `:tags` option to the Action View helper `sanitize`:```<%= sanitize @comment.body, tags: ["select", "style"] %>```see https://api.rubyonrails.org/classes/ActionView/Helpers/SanitizeHelper.html#method-i-sanitizeOr it may be done with Rails::Html::SafeListSanitizer directly:```ruby# class-level optionRails::Html::SafeListSanitizer.allowed_tags = ["select", "style"]```or```ruby# instance-level optionRails::Html::SafeListSanitizer.new.sanitize(@article.body, tags: ["select", "style"])```All users overriding the allowed tags by any of the above mechanisms to include both "select" and "style" should either upgrade or use one of the workarounds immediately.## ReleasesThe FIXED releases are available at the normal locations.## WorkaroundsRemove either `select` or `style` from the overridden allowed tags.## CreditsThis vulnerability was responsibly reported by [windshock](https://hackerone.com/windshock?type=user).
<p>Publish Date: 2022-06-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-32209>CVE-2022-32209</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://discuss.rubyonrails.org/t/cve-2022-32209-possible-xss-vulnerability-in-rails-sanitizer/80800">https://discuss.rubyonrails.org/t/cve-2022-32209-possible-xss-vulnerability-in-rails-sanitizer/80800</a></p>
<p>Release Date: 2022-06-24</p>
<p>Fix Resolution: rails-html-sanitizer - 1.4.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23634</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Puma is a Ruby/Rack web server built for parallelism. Prior to `puma` version `5.6.2`, `puma` may not always call `close` on the response body. Rails, prior to version `7.0.2.2`, depended on the response body being closed in order for its `CurrentAttributes` implementation to work correctly. The combination of these two behaviors (Puma not closing the body + Rails' Executor implementation) causes information leakage. This problem is fixed in Puma versions 5.6.2 and 4.3.11. This problem is fixed in Rails versions 7.02.2, 6.1.4.6, 6.0.4.6, and 5.2.6.2. Upgrading to a patched Rails _or_ Puma version fixes the vulnerability.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23634>CVE-2022-23634</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9">https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: puma - 4.3.11, 5.6.2; actionpack - 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23633</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Action Pack is a framework for handling and responding to web requests. Under certain circumstances response bodies will not be closed. In the event a response is *not* notified of a `close`, `ActionDispatch::Executor` will not know to reset thread local state for the next request. This can lead to data being leaked to subsequent requests.This has been fixed in Rails 7.0.2.1, 6.1.4.5, 6.0.4.5, and 5.2.6.1. Upgrading is highly recommended, but to work around this problem a middleware described in GHSA-wh98-p28r-vrc9 can be used.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23633>CVE-2022-23633</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9">https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2
</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-3704</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability classified as problematic has been found in Ruby on Rails. This affects an unknown part of the file actionpack/lib/action_dispatch/middleware/templates/routes/_table.html.erb. The manipulation leads to cross site scripting. It is possible to initiate the attack remotely. The name of the patch is be177e4566747b73ff63fd5f529fab564e475ed4. It is recommended to apply a patch to fix this issue. The associated identifier of this vulnerability is VDB-212319.
<p>Publish Date: 2022-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3704>CVE-2022-3704</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-5267</summary>
### Vulnerable Library - <b>actionview-6.0.0.gem</b></p>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.0.gem">https://rubygems.org/gems/actionview-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionview-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **actionview-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In ActionView before versions 6.0.2.2 and 5.2.4.2, there is a possible XSS vulnerability in ActionView's JavaScript literal escape helpers. Views that use the `j` or `escape_javascript` methods may be susceptible to XSS attacks. The issue is fixed in versions 6.0.2.2 and 5.2.4.2.
<p>Publish Date: 2020-03-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5267>CVE-2020-5267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5267">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5267</a></p>
<p>Release Date: 2020-10-05</p>
<p>Fix Resolution: actionview:6.0.2.2, 5.2.4.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8166</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A CSRF forgery vulnerability exists in rails < 5.2.5, rails < 6.0.4 that makes it possible for an attacker to, given a global CSRF token such as the one present in the authenticity_token meta tag, forge a per-form CSRF token.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8166>CVE-2020-8166</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jp5v-5gx4-jmj9">https://github.com/advisories/GHSA-jp5v-5gx4-jmj9</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: 5.2.4.3,6.0.3.1</p>
</p>
<p></p>
</details>
|
True
|
sass-rails-5.1.0.gem: 19 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sass-rails-5.1.0.gem</b></p></summary>
<p></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (sass-rails version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-8165](https://www.mend.io/vulnerability-database/CVE-2020-8165) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | activesupport-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-31163](https://www.mend.io/vulnerability-database/CVE-2022-31163) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tzinfo-1.2.5.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22885](https://www.mend.io/vulnerability-database/CVE-2021-22885) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-8164](https://www.mend.io/vulnerability-database/CVE-2020-8164) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22902](https://www.mend.io/vulnerability-database/CVE-2021-22902) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22904](https://www.mend.io/vulnerability-database/CVE-2021-22904) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-8264](https://www.mend.io/vulnerability-database/CVE-2020-8264) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22942](https://www.mend.io/vulnerability-database/CVE-2021-22942) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-22577](https://www.mend.io/vulnerability-database/CVE-2022-22577) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-27777](https://www.mend.io/vulnerability-database/CVE-2022-27777) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionview-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-15169](https://www.mend.io/vulnerability-database/CVE-2020-15169) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionview-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-44528](https://www.mend.io/vulnerability-database/CVE-2021-44528) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2021-22881](https://www.mend.io/vulnerability-database/CVE-2021-22881) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-32209](https://www.mend.io/vulnerability-database/CVE-2022-32209) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | rails-html-sanitizer-1.3.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-23634](https://www.mend.io/vulnerability-database/CVE-2022-23634) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-23633](https://www.mend.io/vulnerability-database/CVE-2022-23633) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2022-3704](https://www.mend.io/vulnerability-database/CVE-2022-3704) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.4 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-5267](https://www.mend.io/vulnerability-database/CVE-2020-5267) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | actionview-6.0.0.gem | Transitive | N/A* | ❌ |
| [CVE-2020-8166](https://www.mend.io/vulnerability-database/CVE-2020-8166) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.3 | actionpack-6.0.0.gem | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8165</summary>
### Vulnerable Library - <b>activesupport-6.0.0.gem</b></p>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-6.0.0.gem">https://rubygems.org/gems/activesupport-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activesupport-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **activesupport-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization of untrusted data vulnernerability exists in rails < 5.2.4.3, rails < 6.0.3.1 that can allow an attacker to unmarshal user-provided objects in MemCacheStore and RedisCacheStore potentially resulting in an RCE.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8165>CVE-2020-8165</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-2p68-f74v-9wc6">https://github.com/advisories/GHSA-2p68-f74v-9wc6</a></p>
<p>Release Date: 2020-06-19</p>
<p>Fix Resolution: 5.2.4.3,6.0.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-31163</summary>
### Vulnerable Library - <b>tzinfo-1.2.5.gem</b></p>
<p>TZInfo provides daylight savings aware transformations between times in different time zones.</p>
<p>Library home page: <a href="https://rubygems.org/gems/tzinfo-1.2.5.gem">https://rubygems.org/gems/tzinfo-1.2.5.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/tzinfo-1.2.5.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- activesupport-6.0.0.gem
- :x: **tzinfo-1.2.5.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
TZInfo is a Ruby library that provides access to time zone data and allows times to be converted using time zone rules. Versions prior to 0.36.1, as well as those prior to 1.2.10 when used with the Ruby data source tzinfo-data, are vulnerable to relative path traversal. With the Ruby data source, time zones are defined in Ruby files. There is one file per time zone. Time zone files are loaded with `require` on demand. In the affected versions, `TZInfo::Timezone.get` fails to validate time zone identifiers correctly, allowing a new line character within the identifier. With Ruby version 1.9.3 and later, `TZInfo::Timezone.get` can be made to load unintended files with `require`, executing them within the Ruby process. Versions 0.3.61 and 1.2.10 include fixes to correctly validate time zone identifiers. Versions 2.0.0 and later are not vulnerable. Version 0.3.61 can still load arbitrary files from the Ruby load path if their name follows the rules for a valid time zone identifier and the file has a prefix of `tzinfo/definition` within a directory in the load path. Applications should ensure that untrusted files are not placed in a directory on the load path. As a workaround, the time zone identifier can be validated before passing to `TZInfo::Timezone.get` by ensuring it matches the regular expression `\A[A-Za-z0-9+\-_]+(?:\/[A-Za-z0-9+\-_]+)*\z`.
<p>Publish Date: 2022-07-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31163>CVE-2022-31163</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tzinfo/tzinfo/security/advisories/GHSA-5cm2-9h8c-rvfx">https://github.com/tzinfo/tzinfo/security/advisories/GHSA-5cm2-9h8c-rvfx</a></p>
<p>Release Date: 2022-07-22</p>
<p>Fix Resolution: tzinfo - 0.3.61,1.2.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22885</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A possible information disclosure / unintended method execution vulnerability in Action Pack >= 2.0.0 when using the `redirect_to` or `polymorphic_url`helper with untrusted user input.
<p>Publish Date: 2021-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22885>CVE-2021-22885</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-hjg4-8q5f-x6fm">https://github.com/advisories/GHSA-hjg4-8q5f-x6fm</a></p>
<p>Release Date: 2021-05-27</p>
<p>Fix Resolution: actionpack - 5.2.4.6,5.2.6,6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8164</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A deserialization of untrusted data vulnerability exists in rails < 5.2.4.3, rails < 6.0.3.1 which can allow an attacker to supply information can be inadvertently leaked fromStrong Parameters.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8164>CVE-2020-8164</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-8727-m6gj-mc37">https://github.com/advisories/GHSA-8727-m6gj-mc37</a></p>
<p>Release Date: 2020-06-19</p>
<p>Fix Resolution: 5.2.4.3,6.0.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22902</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The actionpack ruby gem (a framework for handling and responding to web requests in Rails) before 6.0.3.7, 6.1.3.2 suffers from a possible denial of service vulnerability in the Mime type parser of Action Dispatch. Carefully crafted Accept headers can cause the mime type parser in Action Dispatch to do catastrophic backtracking in the regular expression engine.
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22902>CVE-2021-22902</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: actionpack - 6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22904</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The actionpack ruby gem before 6.1.3.2, 6.0.3.7, 5.2.4.6, 5.2.6 suffers from a possible denial of service vulnerability in the Token Authentication logic in Action Controller due to a too permissive regular expression. Impacted code uses `authenticate_or_request_with_http_token` or `authenticate_with_http_token` for request authentication.
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22904>CVE-2021-22904</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: actionpack - 5.2.4.6,5.2.6,6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8264</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In actionpack gem >= 6.0.0, a possible XSS vulnerability exists when an application is running in development mode allowing an attacker to send or embed (in another page) a specially crafted URL which can allow the attacker to execute JavaScript in the context of the local application. This vulnerability is in the Actionable Exceptions middleware.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8264>CVE-2020-8264</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: v6.0.3.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22942</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A possible open redirect vulnerability in the Host Authorization middleware in Action Pack >= 6.0.0 that could allow attackers to redirect users to a malicious website.
<p>Publish Date: 2021-10-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22942>CVE-2021-22942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=2021-22942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=2021-22942</a></p>
<p>Release Date: 2021-10-18</p>
<p>Fix Resolution: actionpack - 6.0.4.1,6.1.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-22577</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An XSS Vulnerability in Action Pack >= 5.2.0 and < 5.2.0 that could allow an attacker to bypass CSP for non HTML like responses.
<p>Publish Date: 2022-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-22577>CVE-2022-22577</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-mm33-5vfq-3mm3">https://github.com/advisories/GHSA-mm33-5vfq-3mm3</a></p>
<p>Release Date: 2022-05-26</p>
<p>Fix Resolution: actionpack - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-27777</summary>
### Vulnerable Library - <b>actionview-6.0.0.gem</b></p>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.0.gem">https://rubygems.org/gems/actionview-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionview-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **actionview-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A XSS Vulnerability in Action View tag helpers >= 5.2.0 and < 5.2.0 which would allow an attacker to inject content if able to control input into specific attributes.
<p>Publish Date: 2022-05-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-27777>CVE-2022-27777</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-ch3h-j2vf-95pv">https://github.com/advisories/GHSA-ch3h-j2vf-95pv</a></p>
<p>Release Date: 2022-05-26</p>
<p>Fix Resolution: actionview - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-15169</summary>
### Vulnerable Library - <b>actionview-6.0.0.gem</b></p>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.0.gem">https://rubygems.org/gems/actionview-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionview-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **actionview-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Action View before versions 5.2.4.4 and 6.0.3.3 there is a potential Cross-Site Scripting (XSS) vulnerability in Action View's translation helpers. Views that allow the user to control the default (not found) value of the `t` and `translate` helpers could be susceptible to XSS attacks. When an HTML-unsafe string is passed as the default for a missing translation key named html or ending in _html, the default string is incorrectly marked as HTML-safe and not escaped. This is patched in versions 6.0.3.3 and 5.2.4.4. A workaround without upgrading is proposed in the source advisory.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15169>CVE-2020-15169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://rubygems.org/gems/actionview/versions/6.0.3.3">https://rubygems.org/gems/actionview/versions/6.0.3.3</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 6.0.3.3, 5.2.4.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-44528</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A open redirect vulnerability exists in Action Pack >= 6.0.0 that could allow an attacker to craft a "X-Forwarded-Host" headers in combination with certain "allowed host" formats can cause the Host Authorization middleware in Action Pack to redirect users to a malicious website.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44528>CVE-2021-44528</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-qphc-hf5q-v8fc">https://github.com/advisories/GHSA-qphc-hf5q-v8fc</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution: actionpack - 6.0.4.2,6.1.4.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22881</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Host Authorization middleware in Action Pack before 6.1.2.1, 6.0.3.5 suffers from an open redirect vulnerability. Specially crafted `Host` headers in combination with certain "allowed host" formats can cause the Host Authorization middleware in Action Pack to redirect users to a malicious website. Impacted applications will have allowed hosts with a leading dot. When an allowed host contains a leading dot, a specially crafted `Host` header can be used to redirect to a malicious website.
<p>Publish Date: 2021-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22881>CVE-2021-22881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://discuss.rubyonrails.org/t/cve-2021-22881-possible-open-redirect-in-host-authorization-middleware/77130">https://discuss.rubyonrails.org/t/cve-2021-22881-possible-open-redirect-in-host-authorization-middleware/77130</a></p>
<p>Release Date: 2021-02-11</p>
<p>Fix Resolution: 6.0.3.5,6.1.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-32209</summary>
### Vulnerable Library - <b>rails-html-sanitizer-1.3.0.gem</b></p>
<p>HTML sanitization for Rails applications</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-html-sanitizer-1.3.0.gem">https://rubygems.org/gems/rails-html-sanitizer-1.3.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rails-html-sanitizer-1.3.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **rails-html-sanitizer-1.3.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
# Possible XSS Vulnerability in Rails::Html::SanitizerThere is a possible XSS vulnerability with certain configurations of Rails::Html::Sanitizer.This vulnerability has been assigned the CVE identifier CVE-2022-32209.Versions Affected: ALLNot affected: NONEFixed Versions: v1.4.3## ImpactA possible XSS vulnerability with certain configurations of Rails::Html::Sanitizer may allow an attacker to inject content if the application developer has overridden the sanitizer's allowed tags to allow both `select` and `style` elements.Code is only impacted if allowed tags are being overridden. This may be done via application configuration:```ruby# In config/application.rbconfig.action_view.sanitized_allowed_tags = ["select", "style"]```see https://guides.rubyonrails.org/configuring.html#configuring-action-viewOr it may be done with a `:tags` option to the Action View helper `sanitize`:```<%= sanitize @comment.body, tags: ["select", "style"] %>```see https://api.rubyonrails.org/classes/ActionView/Helpers/SanitizeHelper.html#method-i-sanitizeOr it may be done with Rails::Html::SafeListSanitizer directly:```ruby# class-level optionRails::Html::SafeListSanitizer.allowed_tags = ["select", "style"]```or```ruby# instance-level optionRails::Html::SafeListSanitizer.new.sanitize(@article.body, tags: ["select", "style"])```All users overriding the allowed tags by any of the above mechanisms to include both "select" and "style" should either upgrade or use one of the workarounds immediately.## ReleasesThe FIXED releases are available at the normal locations.## WorkaroundsRemove either `select` or `style` from the overridden allowed tags.## CreditsThis vulnerability was responsibly reported by [windshock](https://hackerone.com/windshock?type=user).
<p>Publish Date: 2022-06-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-32209>CVE-2022-32209</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://discuss.rubyonrails.org/t/cve-2022-32209-possible-xss-vulnerability-in-rails-sanitizer/80800">https://discuss.rubyonrails.org/t/cve-2022-32209-possible-xss-vulnerability-in-rails-sanitizer/80800</a></p>
<p>Release Date: 2022-06-24</p>
<p>Fix Resolution: rails-html-sanitizer - 1.4.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23634</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Puma is a Ruby/Rack web server built for parallelism. Prior to `puma` version `5.6.2`, `puma` may not always call `close` on the response body. Rails, prior to version `7.0.2.2`, depended on the response body being closed in order for its `CurrentAttributes` implementation to work correctly. The combination of these two behaviors (Puma not closing the body + Rails' Executor implementation) causes information leakage. This problem is fixed in Puma versions 5.6.2 and 4.3.11. This problem is fixed in Rails versions 7.02.2, 6.1.4.6, 6.0.4.6, and 5.2.6.2. Upgrading to a patched Rails _or_ Puma version fixes the vulnerability.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23634>CVE-2022-23634</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9">https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: puma - 4.3.11, 5.6.2; actionpack - 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23633</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Action Pack is a framework for handling and responding to web requests. Under certain circumstances response bodies will not be closed. In the event a response is *not* notified of a `close`, `ActionDispatch::Executor` will not know to reset thread local state for the next request. This can lead to data being leaked to subsequent requests.This has been fixed in Rails 7.0.2.1, 6.1.4.5, 6.0.4.5, and 5.2.6.1. Upgrading is highly recommended, but to work around this problem a middleware described in GHSA-wh98-p28r-vrc9 can be used.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23633>CVE-2022-23633</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9">https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2
</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-3704</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability classified as problematic has been found in Ruby on Rails. This affects an unknown part of the file actionpack/lib/action_dispatch/middleware/templates/routes/_table.html.erb. The manipulation leads to cross site scripting. It is possible to initiate the attack remotely. The name of the patch is be177e4566747b73ff63fd5f529fab564e475ed4. It is recommended to apply a patch to fix this issue. The associated identifier of this vulnerability is VDB-212319.
<p>Publish Date: 2022-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3704>CVE-2022-3704</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-5267</summary>
### Vulnerable Library - <b>actionview-6.0.0.gem</b></p>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-6.0.0.gem">https://rubygems.org/gems/actionview-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionview-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-6.0.0.gem
- :x: **actionview-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In ActionView before versions 6.0.2.2 and 5.2.4.2, there is a possible XSS vulnerability in ActionView's JavaScript literal escape helpers. Views that use the `j` or `escape_javascript` methods may be susceptible to XSS attacks. The issue is fixed in versions 6.0.2.2 and 5.2.4.2.
<p>Publish Date: 2020-03-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5267>CVE-2020-5267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5267">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5267</a></p>
<p>Release Date: 2020-10-05</p>
<p>Fix Resolution: actionview:6.0.2.2, 5.2.4.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8166</summary>
### Vulnerable Library - <b>actionpack-6.0.0.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-6.0.0.gem</p>
<p>
Dependency Hierarchy:
- sass-rails-5.1.0.gem (Root Library)
- sprockets-rails-3.2.1.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A CSRF forgery vulnerability exists in rails < 5.2.5, rails < 6.0.4 that makes it possible for an attacker to, given a global CSRF token such as the one present in the authenticity_token meta tag, forge a per-form CSRF token.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8166>CVE-2020-8166</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jp5v-5gx4-jmj9">https://github.com/advisories/GHSA-jp5v-5gx4-jmj9</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: 5.2.4.3,6.0.3.1</p>
</p>
<p></p>
</details>
|
non_defect
|
sass rails gem vulnerabilities highest severity is vulnerable library sass rails gem path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem vulnerabilities cve severity cvss dependency type fixed in sass rails version remediation available high activesupport gem transitive n a high tzinfo gem transitive n a high actionpack gem transitive n a high actionpack gem transitive n a high actionpack gem transitive n a high actionpack gem transitive n a medium actionpack gem transitive n a medium actionpack gem transitive n a medium actionpack gem transitive n a medium actionview gem transitive n a medium actionview gem transitive n a medium actionpack gem transitive n a medium actionpack gem transitive n a medium rails html sanitizer gem transitive n a medium actionpack gem transitive n a medium actionpack gem transitive n a medium actionpack gem transitive n a medium actionview gem transitive n a medium actionpack gem transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library activesupport gem a toolkit of support libraries and ruby core extensions extracted from the rails framework rich support for multibyte strings internationalization time zones and testing library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activesupport gem dependency hierarchy sass rails gem root library sprockets rails gem x activesupport gem vulnerable library found in base branch main vulnerability details a deserialization of untrusted data vulnernerability exists in rails rails that can allow an attacker to unmarshal user provided objects in memcachestore and rediscachestore potentially resulting in an rce publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library tzinfo gem tzinfo provides daylight savings aware transformations between times in different time zones library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache tzinfo gem dependency hierarchy sass rails gem root library sprockets rails gem activesupport gem x tzinfo gem vulnerable library found in base branch main vulnerability details tzinfo is a ruby library that provides access to time zone data and allows times to be converted using time zone rules versions prior to as well as those prior to when used with the ruby data source tzinfo data are vulnerable to relative path traversal with the ruby data source time zones are defined in ruby files there is one file per time zone time zone files are loaded with require on demand in the affected versions tzinfo timezone get fails to validate time zone identifiers correctly allowing a new line character within the identifier with ruby version and later tzinfo timezone get can be made to load unintended files with require executing them within the ruby process versions and include fixes to correctly validate time zone identifiers versions and later are not vulnerable version can still load arbitrary files from the ruby load path if their name follows the rules for a valid time zone identifier and the file has a prefix of tzinfo definition within a directory in the load path applications should ensure that untrusted files are not placed in a directory on the load path as a workaround the time zone identifier can be validated before passing to tzinfo timezone get by ensuring it matches the regular expression a z publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tzinfo cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details a possible information disclosure unintended method execution vulnerability in action pack when using the redirect to or polymorphic url helper with untrusted user input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details a deserialization of untrusted data vulnerability exists in rails rails which can allow an attacker to supply information can be inadvertently leaked fromstrong parameters publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details the actionpack ruby gem a framework for handling and responding to web requests in rails before suffers from a possible denial of service vulnerability in the mime type parser of action dispatch carefully crafted accept headers can cause the mime type parser in action dispatch to do catastrophic backtracking in the regular expression engine publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details the actionpack ruby gem before suffers from a possible denial of service vulnerability in the token authentication logic in action controller due to a too permissive regular expression impacted code uses authenticate or request with http token or authenticate with http token for request authentication publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details in actionpack gem a possible xss vulnerability exists when an application is running in development mode allowing an attacker to send or embed in another page a specially crafted url which can allow the attacker to execute javascript in the context of the local application this vulnerability is in the actionable exceptions middleware publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details a possible open redirect vulnerability in the host authorization middleware in action pack that could allow attackers to redirect users to a malicious website publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details an xss vulnerability in action pack and that could allow an attacker to bypass csp for non html like responses publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionpack cve vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionview gem dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem x actionview gem vulnerable library found in base branch main vulnerability details a xss vulnerability in action view tag helpers and which would allow an attacker to inject content if able to control input into specific attributes publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionview cve vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionview gem dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem x actionview gem vulnerable library found in base branch main vulnerability details in action view before versions and there is a potential cross site scripting xss vulnerability in action view s translation helpers views that allow the user to control the default not found value of the t and translate helpers could be susceptible to xss attacks when an html unsafe string is passed as the default for a missing translation key named html or ending in html the default string is incorrectly marked as html safe and not escaped this is patched in versions and a workaround without upgrading is proposed in the source advisory publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details a open redirect vulnerability exists in action pack that could allow an attacker to craft a x forwarded host headers in combination with certain allowed host formats can cause the host authorization middleware in action pack to redirect users to a malicious website publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details the host authorization middleware in action pack before suffers from an open redirect vulnerability specially crafted host headers in combination with certain allowed host formats can cause the host authorization middleware in action pack to redirect users to a malicious website impacted applications will have allowed hosts with a leading dot when an allowed host contains a leading dot a specially crafted host header can be used to redirect to a malicious website publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library rails html sanitizer gem html sanitization for rails applications library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache rails html sanitizer gem dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem x rails html sanitizer gem vulnerable library found in base branch main vulnerability details possible xss vulnerability in rails html sanitizerthere is a possible xss vulnerability with certain configurations of rails html sanitizer this vulnerability has been assigned the cve identifier cve versions affected allnot affected nonefixed versions impacta possible xss vulnerability with certain configurations of rails html sanitizer may allow an attacker to inject content if the application developer has overridden the sanitizer s allowed tags to allow both select and style elements code is only impacted if allowed tags are being overridden this may be done via application configuration ruby in config application rbconfig action view sanitized allowed tags see it may be done with a tags option to the action view helper sanitize see it may be done with rails html safelistsanitizer directly ruby class level optionrails html safelistsanitizer allowed tags or ruby instance level optionrails html safelistsanitizer new sanitize article body tags all users overriding the allowed tags by any of the above mechanisms to include both select and style should either upgrade or use one of the workarounds immediately releasesthe fixed releases are available at the normal locations workaroundsremove either select or style from the overridden allowed tags creditsthis vulnerability was responsibly reported by publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rails html sanitizer cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details puma is a ruby rack web server built for parallelism prior to puma version puma may not always call close on the response body rails prior to version depended on the response body being closed in order for its currentattributes implementation to work correctly the combination of these two behaviors puma not closing the body rails executor implementation causes information leakage this problem is fixed in puma versions and this problem is fixed in rails versions and upgrading to a patched rails or puma version fixes the vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution puma actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details action pack is a framework for handling and responding to web requests under certain circumstances response bodies will not be closed in the event a response is not notified of a close actiondispatch executor will not know to reset thread local state for the next request this can lead to data being leaked to subsequent requests this has been fixed in rails and upgrading is highly recommended but to work around this problem a middleware described in ghsa can be used publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details a vulnerability classified as problematic has been found in ruby on rails this affects an unknown part of the file actionpack lib action dispatch middleware templates routes table html erb the manipulation leads to cross site scripting it is possible to initiate the attack remotely the name of the patch is it is recommended to apply a patch to fix this issue the associated identifier of this vulnerability is vdb publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href cve vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionview gem dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem x actionview gem vulnerable library found in base branch main vulnerability details in actionview before versions and there is a possible xss vulnerability in actionview s javascript literal escape helpers views that use the j or escape javascript methods may be susceptible to xss attacks the issue is fixed in versions and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionview cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy sass rails gem root library sprockets rails gem x actionpack gem vulnerable library found in base branch main vulnerability details a csrf forgery vulnerability exists in rails rails that makes it possible for an attacker to given a global csrf token such as the one present in the authenticity token meta tag forge a per form csrf token publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution
| 0
|
32,779
| 6,926,943,557
|
IssuesEvent
|
2017-11-30 20:59:15
|
energicryptocurrency/energi
|
https://api.github.com/repos/energicryptocurrency/energi
|
closed
|
Dark Gravity Wave as difficulty algorithm
|
Defect Required for Main Net
|
The difficulty algorithm currently is separated into 3 phases, first the bitcoin difficulty algorithm is used, then the Kimoto Gravity Well (KGW) algorithm is used, followed by the Dark Gravity Wave (DGW) algorithm. These are activated at various chain heights as they were implemented in Dash.
For Energi, we should always use the DGW algorithm starting from block 0. Note that this change requires restarting the testnet.
|
1.0
|
Dark Gravity Wave as difficulty algorithm - The difficulty algorithm currently is separated into 3 phases, first the bitcoin difficulty algorithm is used, then the Kimoto Gravity Well (KGW) algorithm is used, followed by the Dark Gravity Wave (DGW) algorithm. These are activated at various chain heights as they were implemented in Dash.
For Energi, we should always use the DGW algorithm starting from block 0. Note that this change requires restarting the testnet.
|
defect
|
dark gravity wave as difficulty algorithm the difficulty algorithm currently is separated into phases first the bitcoin difficulty algorithm is used then the kimoto gravity well kgw algorithm is used followed by the dark gravity wave dgw algorithm these are activated at various chain heights as they were implemented in dash for energi we should always use the dgw algorithm starting from block note that this change requires restarting the testnet
| 1
|
70,643
| 23,271,549,976
|
IssuesEvent
|
2022-08-05 00:02:59
|
openzfs/zfs
|
https://api.github.com/repos/openzfs/zfs
|
closed
|
zpool add allows mismatching redundancy after vdev removal
|
Type: Defect
|
<!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Ubuntu
Distribution Version | 22.04 LTS
Kernel Version | 5.15.53 (vanilla)
Architecture | x86_64
OpenZFS Version | 2.1.5
<!--
Command to find OpenZFS version:
zfs versionea39f75f64ff72e30900a36e00632f180f5f6676
Commands to find kernel version:
uname -r # Linux
freebsd-version -r # FreeBSD
-->
### Describe the problem you're observing
It is possible to (involuntarily) bypass the "mismatching redundancy" security check of `zpool add` after a vdev has been removed from the zpool.
This is due to the fact that once `indirect` vdevs are present, the internal `get_replication()` check fails, even as the pool has still a correct redundancy. Any subsequent zpool modification command will be allowed even if it actually changes the redundancy as the `zpool` command will make the assumption that the redundancy is already broken, as per:
https://github.com/openzfs/zfs/blob/e8cf3a4f7662f2d1c13684ce52b73ab0d9a12266/cmd/zpool/zpool_vdev.c#L810-L821
### Describe how to reproduce the problem
```
for i in a b c d e f special; do truncate -s 1G /dev/shm/$i; done
zpool create test mirror /dev/shm/{a,b} mirror /dev/shm/{c,d}
zpool add test special /dev/shm/special # this fails as it should ("mismatched replication level: pool uses mirror and new vdev is file")
zpool add test mirror /dev/shm/{e,f}
zpool remove test mirror-1 # corresponding to /dev/shm/{c,d}
zpool add test special /dev/shm/special # it works, it shouldn't
```
After the `zpool remove`, a manual call to `get_redundancy()` shows failure, while it should report the pool has having a correct redundancy:
```
invalid vdev specification
use '-f' to override the following errors:
mismatched replication level: both mirror and indirect vdevs are present
mismatched replication level: both indirect and mirror vdevs are present
```
We end up with this configuration:
```
# zpool status test
pool: test
state: ONLINE
remove: Removal of vdev 1 copied 62.5K in 0h0m, completed on Fri Jul 29 11:19:36 2022
144 memory used for removed device mappings
config:
NAME STATE READ WRITE CKSUM
test ONLINE 0 0 0
mirror-0 ONLINE 0 0 0
/dev/shm/a ONLINE 0 0 0
/dev/shm/b ONLINE 0 0 0
mirror-2 ONLINE 0 0 0
/dev/shm/e ONLINE 0 0 0
/dev/shm/f ONLINE 0 0 0
special
/dev/shm/special ONLINE 0 0 0
```
...which is highly dangerous, and we didn't override any check by using `-f` at any point.
|
1.0
|
zpool add allows mismatching redundancy after vdev removal - <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Ubuntu
Distribution Version | 22.04 LTS
Kernel Version | 5.15.53 (vanilla)
Architecture | x86_64
OpenZFS Version | 2.1.5
<!--
Command to find OpenZFS version:
zfs versionea39f75f64ff72e30900a36e00632f180f5f6676
Commands to find kernel version:
uname -r # Linux
freebsd-version -r # FreeBSD
-->
### Describe the problem you're observing
It is possible to (involuntarily) bypass the "mismatching redundancy" security check of `zpool add` after a vdev has been removed from the zpool.
This is due to the fact that once `indirect` vdevs are present, the internal `get_replication()` check fails, even as the pool has still a correct redundancy. Any subsequent zpool modification command will be allowed even if it actually changes the redundancy as the `zpool` command will make the assumption that the redundancy is already broken, as per:
https://github.com/openzfs/zfs/blob/e8cf3a4f7662f2d1c13684ce52b73ab0d9a12266/cmd/zpool/zpool_vdev.c#L810-L821
### Describe how to reproduce the problem
```
for i in a b c d e f special; do truncate -s 1G /dev/shm/$i; done
zpool create test mirror /dev/shm/{a,b} mirror /dev/shm/{c,d}
zpool add test special /dev/shm/special # this fails as it should ("mismatched replication level: pool uses mirror and new vdev is file")
zpool add test mirror /dev/shm/{e,f}
zpool remove test mirror-1 # corresponding to /dev/shm/{c,d}
zpool add test special /dev/shm/special # it works, it shouldn't
```
After the `zpool remove`, a manual call to `get_redundancy()` shows failure, while it should report the pool has having a correct redundancy:
```
invalid vdev specification
use '-f' to override the following errors:
mismatched replication level: both mirror and indirect vdevs are present
mismatched replication level: both indirect and mirror vdevs are present
```
We end up with this configuration:
```
# zpool status test
pool: test
state: ONLINE
remove: Removal of vdev 1 copied 62.5K in 0h0m, completed on Fri Jul 29 11:19:36 2022
144 memory used for removed device mappings
config:
NAME STATE READ WRITE CKSUM
test ONLINE 0 0 0
mirror-0 ONLINE 0 0 0
/dev/shm/a ONLINE 0 0 0
/dev/shm/b ONLINE 0 0 0
mirror-2 ONLINE 0 0 0
/dev/shm/e ONLINE 0 0 0
/dev/shm/f ONLINE 0 0 0
special
/dev/shm/special ONLINE 0 0 0
```
...which is highly dangerous, and we didn't override any check by using `-f` at any point.
|
defect
|
zpool add allows mismatching redundancy after vdev removal thank you for reporting an issue important please check our issue tracker before opening a new issue additional valuable information can be found in the openzfs documentation and mailing list archives please fill in as much of the template as possible system information type version name distribution name ubuntu distribution version lts kernel version vanilla architecture openzfs version command to find openzfs version zfs commands to find kernel version uname r linux freebsd version r freebsd describe the problem you re observing it is possible to involuntarily bypass the mismatching redundancy security check of zpool add after a vdev has been removed from the zpool this is due to the fact that once indirect vdevs are present the internal get replication check fails even as the pool has still a correct redundancy any subsequent zpool modification command will be allowed even if it actually changes the redundancy as the zpool command will make the assumption that the redundancy is already broken as per describe how to reproduce the problem for i in a b c d e f special do truncate s dev shm i done zpool create test mirror dev shm a b mirror dev shm c d zpool add test special dev shm special this fails as it should mismatched replication level pool uses mirror and new vdev is file zpool add test mirror dev shm e f zpool remove test mirror corresponding to dev shm c d zpool add test special dev shm special it works it shouldn t after the zpool remove a manual call to get redundancy shows failure while it should report the pool has having a correct redundancy invalid vdev specification use f to override the following errors mismatched replication level both mirror and indirect vdevs are present mismatched replication level both indirect and mirror vdevs are present we end up with this configuration zpool status test pool test state online remove removal of vdev copied in completed on fri jul memory used for removed device mappings config name state read write cksum test online mirror online dev shm a online dev shm b online mirror online dev shm e online dev shm f online special dev shm special online which is highly dangerous and we didn t override any check by using f at any point
| 1
|
43,896
| 11,874,415,198
|
IssuesEvent
|
2020-03-26 18:57:40
|
Cockatrice/Cockatrice
|
https://api.github.com/repos/Cockatrice/Cockatrice
|
closed
|
OS X: Crashes on removing cards from the deck until no cards of the type being removed are left
|
Defect - Crash OS - macOS
|
<b>OS:</b>
OS X 10.11.3
<b>Cockatrice version:</b>
cbea432 (2016-03-08)
<br>
Sometimes I get crashes when I try to remove instances of a specific card in my deck. I can single out one case where it crashes certainly. Load the deck I supplied, and remove the `Captain's Claws` cards from the deck. It crashes immediately that way.
It seems to be somehow tied to Captain's Claws being the only Articaft type cards in the deck, but I'm not sure. I can get around it by first adding another artifact, then removing the Captain's Claws, and then the artifact I added... So it's a bit fishy.
I also have quite a lot of similar random crashes, such as when typing in the card search box, but I can't single out them as well.
[Thopterzzz.cod.zip](https://github.com/Cockatrice/Cockatrice/files/169155/Thopterzzz.cod.zip)
|
1.0
|
OS X: Crashes on removing cards from the deck until no cards of the type being removed are left - <b>OS:</b>
OS X 10.11.3
<b>Cockatrice version:</b>
cbea432 (2016-03-08)
<br>
Sometimes I get crashes when I try to remove instances of a specific card in my deck. I can single out one case where it crashes certainly. Load the deck I supplied, and remove the `Captain's Claws` cards from the deck. It crashes immediately that way.
It seems to be somehow tied to Captain's Claws being the only Articaft type cards in the deck, but I'm not sure. I can get around it by first adding another artifact, then removing the Captain's Claws, and then the artifact I added... So it's a bit fishy.
I also have quite a lot of similar random crashes, such as when typing in the card search box, but I can't single out them as well.
[Thopterzzz.cod.zip](https://github.com/Cockatrice/Cockatrice/files/169155/Thopterzzz.cod.zip)
|
defect
|
os x crashes on removing cards from the deck until no cards of the type being removed are left os os x cockatrice version sometimes i get crashes when i try to remove instances of a specific card in my deck i can single out one case where it crashes certainly load the deck i supplied and remove the captain s claws cards from the deck it crashes immediately that way it seems to be somehow tied to captain s claws being the only articaft type cards in the deck but i m not sure i can get around it by first adding another artifact then removing the captain s claws and then the artifact i added so it s a bit fishy i also have quite a lot of similar random crashes such as when typing in the card search box but i can t single out them as well
| 1
|
13,411
| 2,755,671,198
|
IssuesEvent
|
2015-04-26 21:08:18
|
sm0svx/svxlink
|
https://api.github.com/repos/sm0svx/svxlink
|
closed
|
Suddenly stops speaking to the EchoLink directory server
|
C: EchoLib C: Module EchoLink T: defect
|
The EchoLink module can suddenly stop speaking to the EchoLink directory server which make the node disappear from the EchoLink network. It never recovers so SvxLink have to be restarted.
This was first noticed after the EchoLink Proxy protocol was implemented. I also saw it the first time after I had switch hardware, to a Cubieboard (ARM).
|
1.0
|
Suddenly stops speaking to the EchoLink directory server - The EchoLink module can suddenly stop speaking to the EchoLink directory server which make the node disappear from the EchoLink network. It never recovers so SvxLink have to be restarted.
This was first noticed after the EchoLink Proxy protocol was implemented. I also saw it the first time after I had switch hardware, to a Cubieboard (ARM).
|
defect
|
suddenly stops speaking to the echolink directory server the echolink module can suddenly stop speaking to the echolink directory server which make the node disappear from the echolink network it never recovers so svxlink have to be restarted this was first noticed after the echolink proxy protocol was implemented i also saw it the first time after i had switch hardware to a cubieboard arm
| 1
|
76,885
| 26,655,075,802
|
IssuesEvent
|
2023-01-25 16:16:34
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
loud continuous "helicopter" noise during video call from element-desktop to element on android
|
T-Defect
|
### Steps to reproduce
The sound only occurs during video call, NOT during audio-only call. Video works fine with no issues.
The sound can only be heard on the Android device. It makes it almost impossible for userB to hear sound coming from userA.
userA: Garuda linux, Element ver 1.11.20 Olm ver 3.2.12
userB: Android 9, element ver 1.5.18 Olm ver 3.2.12
I could upload a recording of the sound if necessary, but please confirm this would be helpful before I go to the trouble.
I can try to provide logs if requested but of what and which logs?
### Outcome
#### What did you expect?
Relatively clear audio.
#### What happened instead?
userA cannot communicate with userB (except perhaps through sign language)
### Operating system
Arch linux & Android pie
### Application version
olm 3.2.12 , element 1.11.20 / 1.5.18
### How did you install the app?
AUR / f-droid
### Homeserver
matrix.org
### Will you send logs?
No
|
1.0
|
loud continuous "helicopter" noise during video call from element-desktop to element on android - ### Steps to reproduce
The sound only occurs during video call, NOT during audio-only call. Video works fine with no issues.
The sound can only be heard on the Android device. It makes it almost impossible for userB to hear sound coming from userA.
userA: Garuda linux, Element ver 1.11.20 Olm ver 3.2.12
userB: Android 9, element ver 1.5.18 Olm ver 3.2.12
I could upload a recording of the sound if necessary, but please confirm this would be helpful before I go to the trouble.
I can try to provide logs if requested but of what and which logs?
### Outcome
#### What did you expect?
Relatively clear audio.
#### What happened instead?
userA cannot communicate with userB (except perhaps through sign language)
### Operating system
Arch linux & Android pie
### Application version
olm 3.2.12 , element 1.11.20 / 1.5.18
### How did you install the app?
AUR / f-droid
### Homeserver
matrix.org
### Will you send logs?
No
|
defect
|
loud continuous helicopter noise during video call from element desktop to element on android steps to reproduce the sound only occurs during video call not during audio only call video works fine with no issues the sound can only be heard on the android device it makes it almost impossible for userb to hear sound coming from usera usera garuda linux element ver olm ver userb android element ver olm ver i could upload a recording of the sound if necessary but please confirm this would be helpful before i go to the trouble i can try to provide logs if requested but of what and which logs outcome what did you expect relatively clear audio what happened instead usera cannot communicate with userb except perhaps through sign language operating system arch linux android pie application version olm element how did you install the app aur f droid homeserver matrix org will you send logs no
| 1
|
15,276
| 2,850,523,292
|
IssuesEvent
|
2015-05-31 17:05:47
|
damonkohler/android-scripting
|
https://api.github.com/repos/damonkohler/android-scripting
|
closed
|
fullSetProperty not working on perl
|
auto-migrated Priority-Medium Type-Defect
|
```
What device(s) are you experiencing the problem on?
Motorola Droid3
What firmware version are you running on the device?
2.3.3
Im trying to use the new fullscreenUI in perl, fullShow for instance works and
displays the page, but fullSetProperty drops me java.lang.NullPointerException.
Has anyone had same problem? I am running sl4a_r5x and followed the examples.
Btw the same code does work in python.
```
Original issue reported on code.google.com by `aod...@gmail.com` on 21 Mar 2012 at 8:17
|
1.0
|
fullSetProperty not working on perl - ```
What device(s) are you experiencing the problem on?
Motorola Droid3
What firmware version are you running on the device?
2.3.3
Im trying to use the new fullscreenUI in perl, fullShow for instance works and
displays the page, but fullSetProperty drops me java.lang.NullPointerException.
Has anyone had same problem? I am running sl4a_r5x and followed the examples.
Btw the same code does work in python.
```
Original issue reported on code.google.com by `aod...@gmail.com` on 21 Mar 2012 at 8:17
|
defect
|
fullsetproperty not working on perl what device s are you experiencing the problem on motorola what firmware version are you running on the device im trying to use the new fullscreenui in perl fullshow for instance works and displays the page but fullsetproperty drops me java lang nullpointerexception has anyone had same problem i am running and followed the examples btw the same code does work in python original issue reported on code google com by aod gmail com on mar at
| 1
|
376,078
| 11,138,183,193
|
IssuesEvent
|
2019-12-20 21:33:40
|
Sage-Bionetworks/dccvalidator
|
https://api.github.com/repos/Sage-Bionetworks/dccvalidator
|
closed
|
Replace synapser with reticulate + python client
|
high priority
|
This is one solution to #155 and would also enable us to support the specific JSON schema validation package already being used elsewhere for validation (#72).
|
1.0
|
Replace synapser with reticulate + python client - This is one solution to #155 and would also enable us to support the specific JSON schema validation package already being used elsewhere for validation (#72).
|
non_defect
|
replace synapser with reticulate python client this is one solution to and would also enable us to support the specific json schema validation package already being used elsewhere for validation
| 0
|
25,769
| 4,441,206,725
|
IssuesEvent
|
2016-08-19 08:21:45
|
MICommunity/psicquic
|
https://api.github.com/repos/MICommunity/psicquic
|
closed
|
does not load
|
auto-migrated Priority-Medium Type-Defect
|
```
Please see (and resolve) the issue on the Mantis,
http://cbio.mskcc.org/cytoscape/bugs/view.php?id=2770.
```
Original issue reported on code.google.com by `rod...@gmail.com` on 15 Oct 2012 at 1:47
|
1.0
|
does not load - ```
Please see (and resolve) the issue on the Mantis,
http://cbio.mskcc.org/cytoscape/bugs/view.php?id=2770.
```
Original issue reported on code.google.com by `rod...@gmail.com` on 15 Oct 2012 at 1:47
|
defect
|
does not load please see and resolve the issue on the mantis original issue reported on code google com by rod gmail com on oct at
| 1
|
39,353
| 9,414,113,251
|
IssuesEvent
|
2019-04-10 09:24:20
|
STEllAR-GROUP/phylanx
|
https://api.github.com/repos/STEllAR-GROUP/phylanx
|
closed
|
`fold` primitive does not support NumPy arrays.
|
category: PhySL category: primitives submodule: backend type: defect
|
```py
from phylanx import Phylanx
import numpy as np
@Phylanx
def fldl(elements, initial):
return fold_left(lambda a, b : a + b, initial, elements)
print(fldl(np.array([1, 2, 3]), 0))
```
returns `[1, 2, 3]` instead of `6`- The same is true for `fold_right`.
|
1.0
|
`fold` primitive does not support NumPy arrays. - ```py
from phylanx import Phylanx
import numpy as np
@Phylanx
def fldl(elements, initial):
return fold_left(lambda a, b : a + b, initial, elements)
print(fldl(np.array([1, 2, 3]), 0))
```
returns `[1, 2, 3]` instead of `6`- The same is true for `fold_right`.
|
defect
|
fold primitive does not support numpy arrays py from phylanx import phylanx import numpy as np phylanx def fldl elements initial return fold left lambda a b a b initial elements print fldl np array returns instead of the same is true for fold right
| 1
|
176,470
| 14,583,444,824
|
IssuesEvent
|
2020-12-18 14:00:42
|
plunder-app/kube-vip
|
https://api.github.com/repos/plunder-app/kube-vip
|
closed
|
containerd kube-vip alias is not working
|
bug documentation
|
I tried to set
`alias kube-vip="ctr run --rm --net-host docker.io/plndr/kube-vip:0.2.3 vip`
and then
```
kube-vip manifest pod \
--interface $INTERFACE \
--vip $VIP \
--controlplane \
--services \
--arp \
--leaderElection
```
as described in
https://github.com/plunder-app/kube-vip/blob/master/docs/hybrid/static/index.md .
With containerd 1.4.3 I get the error
`ctr: OCI runtime create failed: container_linux.go:370: starting container process caused: exec: "manifest": executable file not found in $PATH: unknown`
because the "manifest" is seen as the [CMD] argument to ctr.
**Solution:**
I fixed this by setting
`alias kube-vip="ctr run --rm --net-host docker.io/plndr/kube-vip:0.2.3 vip /kube-vip"`
instead, this should probably be updated in the docs.
- OS/Distro: Ubuntu 20.04
- Kubernetes Version: v1.19
- Kube-vip Version: 0.2.3
- containerd 1.4.3
|
1.0
|
containerd kube-vip alias is not working - I tried to set
`alias kube-vip="ctr run --rm --net-host docker.io/plndr/kube-vip:0.2.3 vip`
and then
```
kube-vip manifest pod \
--interface $INTERFACE \
--vip $VIP \
--controlplane \
--services \
--arp \
--leaderElection
```
as described in
https://github.com/plunder-app/kube-vip/blob/master/docs/hybrid/static/index.md .
With containerd 1.4.3 I get the error
`ctr: OCI runtime create failed: container_linux.go:370: starting container process caused: exec: "manifest": executable file not found in $PATH: unknown`
because the "manifest" is seen as the [CMD] argument to ctr.
**Solution:**
I fixed this by setting
`alias kube-vip="ctr run --rm --net-host docker.io/plndr/kube-vip:0.2.3 vip /kube-vip"`
instead, this should probably be updated in the docs.
- OS/Distro: Ubuntu 20.04
- Kubernetes Version: v1.19
- Kube-vip Version: 0.2.3
- containerd 1.4.3
|
non_defect
|
containerd kube vip alias is not working i tried to set alias kube vip ctr run rm net host docker io plndr kube vip vip and then kube vip manifest pod interface interface vip vip controlplane services arp leaderelection as described in with containerd i get the error ctr oci runtime create failed container linux go starting container process caused exec manifest executable file not found in path unknown because the manifest is seen as the argument to ctr solution i fixed this by setting alias kube vip ctr run rm net host docker io plndr kube vip vip kube vip instead this should probably be updated in the docs os distro ubuntu kubernetes version kube vip version containerd
| 0
|
493,377
| 14,231,504,718
|
IssuesEvent
|
2020-11-18 09:39:39
|
gardener/gardener
|
https://api.github.com/repos/gardener/gardener
|
closed
|
Make DNS Entry TTL configurable
|
kind/enhancement priority/normal
|
**How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also state the commands multiple times, e.g.
/area control-plane
/area auto-scaling
...
"/area" identifiers: audit-logging|auto-scaling|backup|certification|control-plane-migration|control-plane|cost|delivery|dev-productivity|disaster-recovery|documentation|high-availability|logging|metering|monitoring|networking|open-source|operations|ops-productivity|os|performance|quality|robustness|scalability|security|storage|testing|usability|user-management
"/kind" identifiers: api-change|bug|cleanup|discussion|enhancement|epic|impediment|poc|post-mortem|question|regression|task|technical-debt|test
"/priority" identifiers: normal|critical|blocker
-->
/kind enhancement
/priority normal
**What would you like to be added**:
The ttl of the DNS entry deployed by the gardenlet is currently set to [120](https://github.com/gardener/gardener/blob/master/charts/seed-dns/entry/values.yaml#L3).
Some dns providers enforce a minimum ttl of more than 120 e.g. 300.
To support such dns providers, it should be possible to make the ttl configurable.
|
1.0
|
Make DNS Entry TTL configurable - **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also state the commands multiple times, e.g.
/area control-plane
/area auto-scaling
...
"/area" identifiers: audit-logging|auto-scaling|backup|certification|control-plane-migration|control-plane|cost|delivery|dev-productivity|disaster-recovery|documentation|high-availability|logging|metering|monitoring|networking|open-source|operations|ops-productivity|os|performance|quality|robustness|scalability|security|storage|testing|usability|user-management
"/kind" identifiers: api-change|bug|cleanup|discussion|enhancement|epic|impediment|poc|post-mortem|question|regression|task|technical-debt|test
"/priority" identifiers: normal|critical|blocker
-->
/kind enhancement
/priority normal
**What would you like to be added**:
The ttl of the DNS entry deployed by the gardenlet is currently set to [120](https://github.com/gardener/gardener/blob/master/charts/seed-dns/entry/values.yaml#L3).
Some dns providers enforce a minimum ttl of more than 120 e.g. 300.
To support such dns providers, it should be possible to make the ttl configurable.
|
non_defect
|
make dns entry ttl configurable how to categorize this issue please select area kind and priority for this issue this helps the community categorizing it replace below todos or exchange the existing identifiers with those that fit best in your opinion if multiple identifiers make sense you can also state the commands multiple times e g area control plane area auto scaling area identifiers audit logging auto scaling backup certification control plane migration control plane cost delivery dev productivity disaster recovery documentation high availability logging metering monitoring networking open source operations ops productivity os performance quality robustness scalability security storage testing usability user management kind identifiers api change bug cleanup discussion enhancement epic impediment poc post mortem question regression task technical debt test priority identifiers normal critical blocker kind enhancement priority normal what would you like to be added the ttl of the dns entry deployed by the gardenlet is currently set to some dns providers enforce a minimum ttl of more than e g to support such dns providers it should be possible to make the ttl configurable
| 0
|
189,695
| 14,518,226,075
|
IssuesEvent
|
2020-12-13 22:46:08
|
FEUP-ESOF-2020-21/open-cx-t2g1-2b-2b
|
https://api.github.com/repos/FEUP-ESOF-2020-21/open-cx-t2g1-2b-2b
|
closed
|
Development of gherkin unit tests
|
Unit Tests
|
- [x] Create automated gherkin unit tests
- [x] Create a workflow to run gherkin tests
|
1.0
|
Development of gherkin unit tests - - [x] Create automated gherkin unit tests
- [x] Create a workflow to run gherkin tests
|
non_defect
|
development of gherkin unit tests create automated gherkin unit tests create a workflow to run gherkin tests
| 0
|
69,853
| 15,039,229,035
|
IssuesEvent
|
2021-02-02 18:23:32
|
RG4421/bulk-smasher
|
https://api.github.com/repos/RG4421/bulk-smasher
|
opened
|
CVE-2020-15168 (Medium) detected in node-fetch-1.7.3.tgz
|
security vulnerability
|
## CVE-2020-15168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-fetch-1.7.3.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js and io.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz</a></p>
<p>Path to dependency file: bulk-smasher/package.json</p>
<p>Path to vulnerable library: bulk-smasher/node_modules/isomorphic-fetch/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- react-bootstrap-alert-1.0.7.tgz (Root Library)
- alt-0.18.6.tgz
- flux-2.1.1.tgz
- fbemitter-2.1.1.tgz
- fbjs-0.8.17.tgz
- isomorphic-fetch-2.2.1.tgz
- :x: **node-fetch-1.7.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/bulk-smasher/commit/e30cfd5c0db7e1ce0a35991701b2219636cfc2b3">e30cfd5c0db7e1ce0a35991701b2219636cfc2b3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don't double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.
<p>Publish Date: 2020-09-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168>CVE-2020-15168</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r">https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.6.1,3.0.0-beta.9</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"1.7.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-bootstrap-alert:1.0.7;alt:0.18.6;flux:2.1.1;fbemitter:2.1.1;fbjs:0.8.17;isomorphic-fetch:2.2.1;node-fetch:1.7.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.6.1,3.0.0-beta.9"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-15168","vulnerabilityDetails":"node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don\u0027t double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-15168 (Medium) detected in node-fetch-1.7.3.tgz - ## CVE-2020-15168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-fetch-1.7.3.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js and io.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-1.7.3.tgz</a></p>
<p>Path to dependency file: bulk-smasher/package.json</p>
<p>Path to vulnerable library: bulk-smasher/node_modules/isomorphic-fetch/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- react-bootstrap-alert-1.0.7.tgz (Root Library)
- alt-0.18.6.tgz
- flux-2.1.1.tgz
- fbemitter-2.1.1.tgz
- fbjs-0.8.17.tgz
- isomorphic-fetch-2.2.1.tgz
- :x: **node-fetch-1.7.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/bulk-smasher/commit/e30cfd5c0db7e1ce0a35991701b2219636cfc2b3">e30cfd5c0db7e1ce0a35991701b2219636cfc2b3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don't double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.
<p>Publish Date: 2020-09-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168>CVE-2020-15168</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r">https://github.com/node-fetch/node-fetch/security/advisories/GHSA-w7rc-rwvf-8q5r</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.6.1,3.0.0-beta.9</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"1.7.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-bootstrap-alert:1.0.7;alt:0.18.6;flux:2.1.1;fbemitter:2.1.1;fbjs:0.8.17;isomorphic-fetch:2.2.1;node-fetch:1.7.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.6.1,3.0.0-beta.9"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-15168","vulnerabilityDetails":"node-fetch before versions 2.6.1 and 3.0.0-beta.9 did not honor the size option after following a redirect, which means that when a content size was over the limit, a FetchError would never get thrown and the process would end without failure. For most people, this fix will have a little or no impact. However, if you are relying on node-fetch to gate files above a size, the impact could be significant, for example: If you don\u0027t double-check the size of the data after fetch() has completed, your JS thread could get tied up doing work on a large file (DoS) and/or cost you money in computing.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15168","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve medium detected in node fetch tgz cve medium severity vulnerability vulnerable library node fetch tgz a light weight module that brings window fetch to node js and io js library home page a href path to dependency file bulk smasher package json path to vulnerable library bulk smasher node modules isomorphic fetch node modules node fetch package json dependency hierarchy react bootstrap alert tgz root library alt tgz flux tgz fbemitter tgz fbjs tgz isomorphic fetch tgz x node fetch tgz vulnerable library found in head commit a href found in base branch master vulnerability details node fetch before versions and beta did not honor the size option after following a redirect which means that when a content size was over the limit a fetcherror would never get thrown and the process would end without failure for most people this fix will have a little or no impact however if you are relying on node fetch to gate files above a size the impact could be significant for example if you don t double check the size of the data after fetch has completed your js thread could get tied up doing work on a large file dos and or cost you money in computing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution beta isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree react bootstrap alert alt flux fbemitter fbjs isomorphic fetch node fetch isminimumfixversionavailable true minimumfixversion beta basebranches vulnerabilityidentifier cve vulnerabilitydetails node fetch before versions and beta did not honor the size option after following a redirect which means that when a content size was over the limit a fetcherror would never get thrown and the process would end without failure for most people this fix will have a little or no impact however if you are relying on node fetch to gate files above a size the impact could be significant for example if you don double check the size of the data after fetch has completed your js thread could get tied up doing work on a large file dos and or cost you money in computing vulnerabilityurl
| 0
|
20,021
| 3,290,956,803
|
IssuesEvent
|
2015-10-30 04:34:38
|
prettydiff/prettydiff
|
https://api.github.com/repos/prettydiff/prettydiff
|
closed
|
ES6 method declaration defects
|
Defect QA
|
https://github.com/Glavin001/atom-beautify/issues/611
Sample input:
var obj = {
foo(a, b) {
return a + b
},
bar(x, y) {
return x * y
},
*quux(x, y) {
yield x
yield y
}
}
Becomes:
var obj = {
foo(a, b) {
return a + b
},
bar(x, y) {
return x * y
}, * quux(x, y) {
yield x
yield y
}
}
The defect is due to the `*` before the property name. Research at https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Functions/Method_definitions
The only operator allowed in this convention is `*` and it must occur before the reference label. This said Pretty Diff will look for `*` operators following a comma, preceding a word, and residing directly in an object.
|
1.0
|
ES6 method declaration defects - https://github.com/Glavin001/atom-beautify/issues/611
Sample input:
var obj = {
foo(a, b) {
return a + b
},
bar(x, y) {
return x * y
},
*quux(x, y) {
yield x
yield y
}
}
Becomes:
var obj = {
foo(a, b) {
return a + b
},
bar(x, y) {
return x * y
}, * quux(x, y) {
yield x
yield y
}
}
The defect is due to the `*` before the property name. Research at https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Functions/Method_definitions
The only operator allowed in this convention is `*` and it must occur before the reference label. This said Pretty Diff will look for `*` operators following a comma, preceding a word, and residing directly in an object.
|
defect
|
method declaration defects sample input var obj foo a b return a b bar x y return x y quux x y yield x yield y becomes var obj foo a b return a b bar x y return x y quux x y yield x yield y the defect is due to the before the property name research at the only operator allowed in this convention is and it must occur before the reference label this said pretty diff will look for operators following a comma preceding a word and residing directly in an object
| 1
|
70,119
| 22,956,385,675
|
IssuesEvent
|
2022-07-19 11:58:46
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
Glitches/Artefacts when scrolling room list
|
T-Defect
|
### Steps to reproduce
1. Have some rooms in your room list
2. Scroll
### Outcome
#### What did you expect?
No visual glitches / artefacts
#### What happened instead?
Visual glitches / artefacts appear
### Operating system
Ubuntu 22.04 LTS
### Application version
Element version: 1.11.0 Olm version: 3.2.8
### How did you install the app?
https://packages.element.io/debian/
### Homeserver
_No response_
### Will you send logs?
Yes
|
1.0
|
Glitches/Artefacts when scrolling room list - ### Steps to reproduce
1. Have some rooms in your room list
2. Scroll
### Outcome
#### What did you expect?
No visual glitches / artefacts
#### What happened instead?
Visual glitches / artefacts appear
### Operating system
Ubuntu 22.04 LTS
### Application version
Element version: 1.11.0 Olm version: 3.2.8
### How did you install the app?
https://packages.element.io/debian/
### Homeserver
_No response_
### Will you send logs?
Yes
|
defect
|
glitches artefacts when scrolling room list steps to reproduce have some rooms in your room list scroll outcome what did you expect no visual glitches artefacts what happened instead visual glitches artefacts appear operating system ubuntu lts application version element version olm version how did you install the app homeserver no response will you send logs yes
| 1
|
33,204
| 7,051,737,906
|
IssuesEvent
|
2018-01-03 13:12:02
|
maloep/romcollectionbrowser
|
https://api.github.com/repos/maloep/romcollectionbrowser
|
closed
|
scraping and import crashes when certain characters in filename
|
auto-migrated Priority-Medium Type-Defect
|
```
when importing a directory with a file named "720°.zip", import stops with no
error. Filename derived from: https://en.wikipedia.org/wiki/720%C2%B0
Removing the "°" character and importing again appears to work fine.
```
Original issue reported on code.google.com by `johns...@gmail.com` on 18 Feb 2013 at 9:42
|
1.0
|
scraping and import crashes when certain characters in filename - ```
when importing a directory with a file named "720°.zip", import stops with no
error. Filename derived from: https://en.wikipedia.org/wiki/720%C2%B0
Removing the "°" character and importing again appears to work fine.
```
Original issue reported on code.google.com by `johns...@gmail.com` on 18 Feb 2013 at 9:42
|
defect
|
scraping and import crashes when certain characters in filename when importing a directory with a file named ° zip import stops with no error filename derived from removing the ° character and importing again appears to work fine original issue reported on code google com by johns gmail com on feb at
| 1
|
48,696
| 13,184,719,915
|
IssuesEvent
|
2020-08-12 19:58:15
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
View -> Take Snapshot bad location (Trac #69)
|
Incomplete Migration Migrated from Trac defect glshovel
|
<details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/69
, reported by troy and owned by troy_</summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T03:35:42",
"description": "Let's try File -> Export Image",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"_ts": "1194752142000000",
"component": "glshovel",
"summary": "View -> Take Snapshot bad location",
"priority": "normal",
"keywords": "",
"time": "2007-06-21T11:31:10",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
View -> Take Snapshot bad location (Trac #69) - <details>
<summary>_Migrated from https://code.icecube.wisc.edu/ticket/69
, reported by troy and owned by troy_</summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T03:35:42",
"description": "Let's try File -> Export Image",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"_ts": "1194752142000000",
"component": "glshovel",
"summary": "View -> Take Snapshot bad location",
"priority": "normal",
"keywords": "",
"time": "2007-06-21T11:31:10",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
|
defect
|
view take snapshot bad location trac migrated from reported by troy and owned by troy json status closed changetime description let s try file export image reporter troy cc resolution duplicate ts component glshovel summary view take snapshot bad location priority normal keywords time milestone owner troy type defect
| 1
|
78,494
| 27,554,086,438
|
IssuesEvent
|
2023-03-07 16:42:02
|
vector-im/element-x-ios
|
https://api.github.com/repos/vector-im/element-x-ios
|
opened
|
Don't block initial sync on to-device messages.
|
T-Defect
|
### Steps to reproduce
https://github.com/matrix-org/matrix-rust-sdk/pull/1616 forces to-device messages on constantly.
As a result, if you don't use the app for a few hours (e.g. overnight), then on a busy account hundreds of to-device messages could easily stack up as new megolm sessions get shared with you; new olm sessions get set up; etc.
Previously, we would download these in a second /sync req, ensuring the first one returns as rapidly as possible (meaning the user isn't stuck looking at a spinner; instead we show them which rooms are active, including previews for unencrypted rooms, and then encrypted content would get resolved shortly afterwards once the second /sync returned). However, in practice, the implementation of this proved fiddly, with the to-device extension getting stuck off, breaking e2ee until the next launch, hence implementing a workaround.
This bug exists to remind us to remove the workaround and fix it properly, so that launch continues to be instant, no matter how long the app has been offline - rather than staring at a spinner waiting for a to-device backlog before the roomlist is usable. The proposed fix is to split consuming to-device msgs into a separate /sync loop (which then means that e2ee state can all be managed one place without getting entangled or blocking the SS loop used for scrolling around the app and receiving room msgs).
### Outcome
#### What did you expect?
Instant launch, no matter how long it's been since you last launched the app.
#### What happened instead?
The longer you've been offline, the longer you'll be shown stale content on launch.
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No
|
1.0
|
Don't block initial sync on to-device messages. - ### Steps to reproduce
https://github.com/matrix-org/matrix-rust-sdk/pull/1616 forces to-device messages on constantly.
As a result, if you don't use the app for a few hours (e.g. overnight), then on a busy account hundreds of to-device messages could easily stack up as new megolm sessions get shared with you; new olm sessions get set up; etc.
Previously, we would download these in a second /sync req, ensuring the first one returns as rapidly as possible (meaning the user isn't stuck looking at a spinner; instead we show them which rooms are active, including previews for unencrypted rooms, and then encrypted content would get resolved shortly afterwards once the second /sync returned). However, in practice, the implementation of this proved fiddly, with the to-device extension getting stuck off, breaking e2ee until the next launch, hence implementing a workaround.
This bug exists to remind us to remove the workaround and fix it properly, so that launch continues to be instant, no matter how long the app has been offline - rather than staring at a spinner waiting for a to-device backlog before the roomlist is usable. The proposed fix is to split consuming to-device msgs into a separate /sync loop (which then means that e2ee state can all be managed one place without getting entangled or blocking the SS loop used for scrolling around the app and receiving room msgs).
### Outcome
#### What did you expect?
Instant launch, no matter how long it's been since you last launched the app.
#### What happened instead?
The longer you've been offline, the longer you'll be shown stale content on launch.
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No
|
defect
|
don t block initial sync on to device messages steps to reproduce forces to device messages on constantly as a result if you don t use the app for a few hours e g overnight then on a busy account hundreds of to device messages could easily stack up as new megolm sessions get shared with you new olm sessions get set up etc previously we would download these in a second sync req ensuring the first one returns as rapidly as possible meaning the user isn t stuck looking at a spinner instead we show them which rooms are active including previews for unencrypted rooms and then encrypted content would get resolved shortly afterwards once the second sync returned however in practice the implementation of this proved fiddly with the to device extension getting stuck off breaking until the next launch hence implementing a workaround this bug exists to remind us to remove the workaround and fix it properly so that launch continues to be instant no matter how long the app has been offline rather than staring at a spinner waiting for a to device backlog before the roomlist is usable the proposed fix is to split consuming to device msgs into a separate sync loop which then means that state can all be managed one place without getting entangled or blocking the ss loop used for scrolling around the app and receiving room msgs outcome what did you expect instant launch no matter how long it s been since you last launched the app what happened instead the longer you ve been offline the longer you ll be shown stale content on launch your phone model no response operating system version no response application version no response homeserver no response will you send logs no
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.