Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 5
112
| repo_url
stringlengths 34
141
| action
stringclasses 3
values | title
stringlengths 1
757
| labels
stringlengths 4
664
| body
stringlengths 3
261k
| index
stringclasses 10
values | text_combine
stringlengths 96
261k
| label
stringclasses 2
values | text
stringlengths 96
232k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
34,513
| 7,452,640,479
|
IssuesEvent
|
2018-03-29 09:05:48
|
jOOQ/jOOQ
|
https://api.github.com/repos/jOOQ/jOOQ
|
closed
|
Error when binding null values to UUID types in PostgreSQL
|
C: DB: PostgreSQL C: Functionality P: Medium T: Defect
|
There is an error when binding a null value to a UUID type in PostgreSQL:
```
Caused by: org.postgresql.util.PSQLException: ERROR: column "id" is of type uuid but expression is of type character varying
Hint: You will need to rewrite or cast the expression.
Position: 225
at org.postgresql.core.v3.QueryExecutorImpl.receiveErrorResponse(QueryExecutorImpl.java:2422)
at org.postgresql.core.v3.QueryExecutorImpl.processResults(QueryExecutorImpl.java:2167)
at org.postgresql.core.v3.QueryExecutorImpl.execute(QueryExecutorImpl.java:306)
at org.postgresql.jdbc.PgStatement.executeInternal(PgStatement.java:441)
at org.postgresql.jdbc.PgStatement.execute(PgStatement.java:365)
at org.postgresql.jdbc.PgPreparedStatement.executeWithFlags(PgPreparedStatement.java:155)
at org.postgresql.jdbc.PgPreparedStatement.execute(PgPreparedStatement.java:144)
...
at org.jooq.tools.jdbc.DefaultPreparedStatement.execute(DefaultPreparedStatement.java:209)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:429)
at org.jooq.impl.AbstractDMLQuery.execute(AbstractDMLQuery.java:452)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:347)
... 51 more
```
----
See also: https://stackoverflow.com/q/49490526/521799
|
1.0
|
Error when binding null values to UUID types in PostgreSQL - There is an error when binding a null value to a UUID type in PostgreSQL:
```
Caused by: org.postgresql.util.PSQLException: ERROR: column "id" is of type uuid but expression is of type character varying
Hint: You will need to rewrite or cast the expression.
Position: 225
at org.postgresql.core.v3.QueryExecutorImpl.receiveErrorResponse(QueryExecutorImpl.java:2422)
at org.postgresql.core.v3.QueryExecutorImpl.processResults(QueryExecutorImpl.java:2167)
at org.postgresql.core.v3.QueryExecutorImpl.execute(QueryExecutorImpl.java:306)
at org.postgresql.jdbc.PgStatement.executeInternal(PgStatement.java:441)
at org.postgresql.jdbc.PgStatement.execute(PgStatement.java:365)
at org.postgresql.jdbc.PgPreparedStatement.executeWithFlags(PgPreparedStatement.java:155)
at org.postgresql.jdbc.PgPreparedStatement.execute(PgPreparedStatement.java:144)
...
at org.jooq.tools.jdbc.DefaultPreparedStatement.execute(DefaultPreparedStatement.java:209)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:429)
at org.jooq.impl.AbstractDMLQuery.execute(AbstractDMLQuery.java:452)
at org.jooq.impl.AbstractQuery.execute(AbstractQuery.java:347)
... 51 more
```
----
See also: https://stackoverflow.com/q/49490526/521799
|
defect
|
error when binding null values to uuid types in postgresql there is an error when binding a null value to a uuid type in postgresql caused by org postgresql util psqlexception error column id is of type uuid but expression is of type character varying hint you will need to rewrite or cast the expression position at org postgresql core queryexecutorimpl receiveerrorresponse queryexecutorimpl java at org postgresql core queryexecutorimpl processresults queryexecutorimpl java at org postgresql core queryexecutorimpl execute queryexecutorimpl java at org postgresql jdbc pgstatement executeinternal pgstatement java at org postgresql jdbc pgstatement execute pgstatement java at org postgresql jdbc pgpreparedstatement executewithflags pgpreparedstatement java at org postgresql jdbc pgpreparedstatement execute pgpreparedstatement java at org jooq tools jdbc defaultpreparedstatement execute defaultpreparedstatement java at org jooq impl abstractquery execute abstractquery java at org jooq impl abstractdmlquery execute abstractdmlquery java at org jooq impl abstractquery execute abstractquery java more see also
| 1
|
81,707
| 31,393,971,824
|
IssuesEvent
|
2023-08-26 17:45:20
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
closed
|
[🐛 Bug]:
|
I-defect I-question needs-triaging
|
### What happened?
Please help me resolve this issue:

### How can we reproduce the issue?
```shell
package introduction;
public class Selenium {
public static void main(String[] args) {
System.setProperty("webdriver.chome.driver","C://Drivers/chromedriver.exe");
WebDriver driver = new ChromeDriver();
}
}
```
### Relevant log output
```shell
Exception in thread "main" java.lang.Error: Unresolved compilation problems:
WebDriver cannot be resolved to a type
ChromeDriver cannot be resolved to a type
at introduction/introduction.Selenium.main(Selenium.java:7)
```
### Operating System
Windows 10
### Selenium version
Java 4.11.0
### What are the browser(s) and version(s) where you see this issue?
Chrome 116
### What are the browser driver(s) and version(s) where you see this issue?
ChromeDriver 116.0.5845.96
### Are you using Selenium Grid?
No
|
1.0
|
[🐛 Bug]: - ### What happened?
Please help me resolve this issue:

### How can we reproduce the issue?
```shell
package introduction;
public class Selenium {
public static void main(String[] args) {
System.setProperty("webdriver.chome.driver","C://Drivers/chromedriver.exe");
WebDriver driver = new ChromeDriver();
}
}
```
### Relevant log output
```shell
Exception in thread "main" java.lang.Error: Unresolved compilation problems:
WebDriver cannot be resolved to a type
ChromeDriver cannot be resolved to a type
at introduction/introduction.Selenium.main(Selenium.java:7)
```
### Operating System
Windows 10
### Selenium version
Java 4.11.0
### What are the browser(s) and version(s) where you see this issue?
Chrome 116
### What are the browser driver(s) and version(s) where you see this issue?
ChromeDriver 116.0.5845.96
### Are you using Selenium Grid?
No
|
defect
|
what happened please help me resolve this issue how can we reproduce the issue shell package introduction public class selenium public static void main string args system setproperty webdriver chome driver c drivers chromedriver exe webdriver driver new chromedriver relevant log output shell exception in thread main java lang error unresolved compilation problems webdriver cannot be resolved to a type chromedriver cannot be resolved to a type at introduction introduction selenium main selenium java operating system windows selenium version java what are the browser s and version s where you see this issue chrome what are the browser driver s and version s where you see this issue chromedriver are you using selenium grid no
| 1
|
42,092
| 10,807,512,448
|
IssuesEvent
|
2019-11-07 08:35:37
|
vesoft-inc/nebula
|
https://api.github.com/repos/vesoft-inc/nebula
|
closed
|
could not get the inserted nodes if just create the schema
|
defect-p2
|
**Describe the bug(__must be provided__)**
**a. drop space and recreate, and create tag for node.**
```
I1024 18:21:30.446066 20151 ExecutionPlan.cpp:15] Parsing query: drop space aGraph;
I1024 18:21:30.446188 19927 ThriftClientManager.inl:21] Getting a client to 10.200.182.109:45500
I1024 18:21:30.446229 19927 MetaClient.cpp:311] Send request to meta [10.200.182.109:45500]
I1024 18:21:30.453719 19927 AsyncSocket.cpp:1931] this=0x7f49a49bb390, AsyncSocket::handleRead() got 45 bytes
I1024 18:21:35.161900 19926 SessionManager.cpp:89] Try to reclaim expired sessions out of 106 ones
I1024 18:21:38.826997 19927 AsyncSocket.cpp:1931] this=0x7f49a49bc510, AsyncSocket::handleRead() got 96 bytes
I1024 18:21:38.827157 20151 ExecutionPlan.cpp:15] Parsing query: create space aGraph(partition_num=1024, replica_factor=1);
I1024 18:21:38.827286 19927 ThriftClientManager.inl:21] Getting a client to 10.200.182.109:45500
I1024 18:21:38.827327 19927 MetaClient.cpp:311] Send request to meta [10.200.182.109:45500]
I1024 18:21:38.835907 19927 AsyncSocket.cpp:1931] this=0x7f49a49bb390, AsyncSocket::handleRead() got 50 bytes
I1024 18:21:45.154918 19927 AsyncSocket.cpp:1931] this=0x7f49a49bc510, AsyncSocket::handleRead() got 192 bytes
I1024 18:21:45.155086 20151 ExecutionPlan.cpp:15] Parsing query: create TAG user(vid string,userName string,xxxx);
```
**b. insert vertex/node to tag user;**
```
I1024 18:23:37.309913 20151 ExecutionPlan.cpp:15] Parsing query: INSERT VERTEX user(vid,userName,regTime,xxxxx) VALUES uuid('102
6069'):('1026001','xxx@126.com',xxxx)
I1024 18:23:37.317335 19927 AsyncSocket.cpp:1931] this=0x7f49a49bda10, AsyncSocket::handleRead() got 250 bytes
I1024 18:23:37.317378 20151 ExecutionPlan.cpp:15] Parsing query: INSERT VERTEX user(vid,userName,xxxx) VALUES
....
```
xxxx and xxx stands for something sensitive.
**c. fetch the inserted node, but get nothing**
```
I1024 18:30:31.771060 20151 ExecutionPlan.cpp:15] Parsing query: FETCH PROP ON user uuid('1026001') YIELD user.vid, user.userName
I1024 18:30:31.771090 20151 FetchVerticesExecutor.cpp:93] Executing FetchVertices: FETCH PROP ON user uuid(1026001) YIELD user.vid,user.userName
I1024 18:30:31.771111 20151 ServerBasedSchemaManager.cpp:26] Get Tag Schema Space 112, TagID 113, Version -1
I1024 18:30:31.771142 20151 StorageClient.h:188] No leader exists. Choose one random.
I1024 18:30:31.771178 19927 ThriftClientManager.inl:21] Getting a client to 10.200.182.109:44500
I1024 18:30:31.771200 19927 StorageClient.inl:180] Send request to storage [10.200.182.109:44500]
```
nothing returned
```
(user@10.200.182.111) [riskGraph]> FETCH PROP ON user uuid('1026001') YIELD user.vid, user.userName;
Execution succeeded (Time spent: 2017/2526 us)
```
**Your Environments(__must be provided__)**
* OS: `uname -a`
* Compliler: `g++ --version` or `clang++ --version`
* CPU: `lscpu`
```
Linux abc 3.10.0-693.5.2.el7.x86_64 #1 SMP Fri Oct 20 20:32:50 UTC 2017 x86_64 x86_64 x86_64 GNU/Linux
g++ (GCC) 4.8.5 20150623 (Red Hat 4.8.5-16)
Copyright (C) 2015 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
```
**How To Reproduce(__must be provided__)**
Steps to reproduce the behavior:
1. using nebula graph java client
2. do as described above. a,b,c
**Expected behavior**
the node which has inserted should return from fetch command.
**Additional context**
the problem seem that we insert nodes too soon after the schema (space and tag) has been created.
as there is a parameter load_data_interval_secs, default value 120s, it means graphd and storaged will reload schema from metad every 120s.
but i think it is a bad design, metadata/schema should sync to graphd and storaged after change, or reload meatadata when graphd or storaged receive requests that has unknow or new schema version.
|
1.0
|
could not get the inserted nodes if just create the schema - **Describe the bug(__must be provided__)**
**a. drop space and recreate, and create tag for node.**
```
I1024 18:21:30.446066 20151 ExecutionPlan.cpp:15] Parsing query: drop space aGraph;
I1024 18:21:30.446188 19927 ThriftClientManager.inl:21] Getting a client to 10.200.182.109:45500
I1024 18:21:30.446229 19927 MetaClient.cpp:311] Send request to meta [10.200.182.109:45500]
I1024 18:21:30.453719 19927 AsyncSocket.cpp:1931] this=0x7f49a49bb390, AsyncSocket::handleRead() got 45 bytes
I1024 18:21:35.161900 19926 SessionManager.cpp:89] Try to reclaim expired sessions out of 106 ones
I1024 18:21:38.826997 19927 AsyncSocket.cpp:1931] this=0x7f49a49bc510, AsyncSocket::handleRead() got 96 bytes
I1024 18:21:38.827157 20151 ExecutionPlan.cpp:15] Parsing query: create space aGraph(partition_num=1024, replica_factor=1);
I1024 18:21:38.827286 19927 ThriftClientManager.inl:21] Getting a client to 10.200.182.109:45500
I1024 18:21:38.827327 19927 MetaClient.cpp:311] Send request to meta [10.200.182.109:45500]
I1024 18:21:38.835907 19927 AsyncSocket.cpp:1931] this=0x7f49a49bb390, AsyncSocket::handleRead() got 50 bytes
I1024 18:21:45.154918 19927 AsyncSocket.cpp:1931] this=0x7f49a49bc510, AsyncSocket::handleRead() got 192 bytes
I1024 18:21:45.155086 20151 ExecutionPlan.cpp:15] Parsing query: create TAG user(vid string,userName string,xxxx);
```
**b. insert vertex/node to tag user;**
```
I1024 18:23:37.309913 20151 ExecutionPlan.cpp:15] Parsing query: INSERT VERTEX user(vid,userName,regTime,xxxxx) VALUES uuid('102
6069'):('1026001','xxx@126.com',xxxx)
I1024 18:23:37.317335 19927 AsyncSocket.cpp:1931] this=0x7f49a49bda10, AsyncSocket::handleRead() got 250 bytes
I1024 18:23:37.317378 20151 ExecutionPlan.cpp:15] Parsing query: INSERT VERTEX user(vid,userName,xxxx) VALUES
....
```
xxxx and xxx stands for something sensitive.
**c. fetch the inserted node, but get nothing**
```
I1024 18:30:31.771060 20151 ExecutionPlan.cpp:15] Parsing query: FETCH PROP ON user uuid('1026001') YIELD user.vid, user.userName
I1024 18:30:31.771090 20151 FetchVerticesExecutor.cpp:93] Executing FetchVertices: FETCH PROP ON user uuid(1026001) YIELD user.vid,user.userName
I1024 18:30:31.771111 20151 ServerBasedSchemaManager.cpp:26] Get Tag Schema Space 112, TagID 113, Version -1
I1024 18:30:31.771142 20151 StorageClient.h:188] No leader exists. Choose one random.
I1024 18:30:31.771178 19927 ThriftClientManager.inl:21] Getting a client to 10.200.182.109:44500
I1024 18:30:31.771200 19927 StorageClient.inl:180] Send request to storage [10.200.182.109:44500]
```
nothing returned
```
(user@10.200.182.111) [riskGraph]> FETCH PROP ON user uuid('1026001') YIELD user.vid, user.userName;
Execution succeeded (Time spent: 2017/2526 us)
```
**Your Environments(__must be provided__)**
* OS: `uname -a`
* Compliler: `g++ --version` or `clang++ --version`
* CPU: `lscpu`
```
Linux abc 3.10.0-693.5.2.el7.x86_64 #1 SMP Fri Oct 20 20:32:50 UTC 2017 x86_64 x86_64 x86_64 GNU/Linux
g++ (GCC) 4.8.5 20150623 (Red Hat 4.8.5-16)
Copyright (C) 2015 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
```
**How To Reproduce(__must be provided__)**
Steps to reproduce the behavior:
1. using nebula graph java client
2. do as described above. a,b,c
**Expected behavior**
the node which has inserted should return from fetch command.
**Additional context**
the problem seem that we insert nodes too soon after the schema (space and tag) has been created.
as there is a parameter load_data_interval_secs, default value 120s, it means graphd and storaged will reload schema from metad every 120s.
but i think it is a bad design, metadata/schema should sync to graphd and storaged after change, or reload meatadata when graphd or storaged receive requests that has unknow or new schema version.
|
defect
|
could not get the inserted nodes if just create the schema describe the bug must be provided a drop space and recreate and create tag for node executionplan cpp parsing query drop space agraph thriftclientmanager inl getting a client to metaclient cpp send request to meta asyncsocket cpp this asyncsocket handleread got bytes sessionmanager cpp try to reclaim expired sessions out of ones asyncsocket cpp this asyncsocket handleread got bytes executionplan cpp parsing query create space agraph partition num replica factor thriftclientmanager inl getting a client to metaclient cpp send request to meta asyncsocket cpp this asyncsocket handleread got bytes asyncsocket cpp this asyncsocket handleread got bytes executionplan cpp parsing query create tag user vid string username string xxxx b insert vertex node to tag user executionplan cpp parsing query insert vertex user vid username regtime xxxxx values uuid xxx com xxxx asyncsocket cpp this asyncsocket handleread got bytes executionplan cpp parsing query insert vertex user vid username xxxx values xxxx and xxx stands for something sensitive c fetch the inserted node, but get nothing executionplan cpp parsing query fetch prop on user uuid yield user vid user username fetchverticesexecutor cpp executing fetchvertices fetch prop on user uuid yield user vid user username serverbasedschemamanager cpp get tag schema space tagid version storageclient h no leader exists choose one random thriftclientmanager inl getting a client to storageclient inl send request to storage nothing returned user fetch prop on user uuid yield user vid user username execution succeeded time spent us your environments must be provided os uname a compliler g version or clang version cpu lscpu linux abc smp fri oct utc gnu linux g gcc red hat copyright c free software foundation inc this is free software see the source for copying conditions there is no warranty not even for merchantability or fitness for a particular purpose how to reproduce must be provided steps to reproduce the behavior using nebula graph java client do as described above a b c expected behavior the node which has inserted should return from fetch command additional context the problem seem that we insert nodes too soon after the schema space and tag has been created as there is a parameter load data interval secs default value it means graphd and storaged will reload schema from metad every but i think it is a bad design metadata schema should sync to graphd and storaged after change or reload meatadata when graphd or storaged receive requests that has unknow or new schema version
| 1
|
773,424
| 27,157,238,273
|
IssuesEvent
|
2023-02-17 08:57:38
|
bryntum/support
|
https://api.github.com/repos/bryntum/support
|
closed
|
Error appeared on drop event into empty scheduler
|
bug resolved high-priority forum large-account OEM
|
2 users complained about this.
3rd case here: https://forum.bryntum.com/posting.php?mode=reply&t=23744#preview
Error appears right after app init.
To reproduce open drag-between-schedulers demo, set `events: []` for second scheduler. Drag and drop event from 1st scheduler to empty one. See an error in console
<img width="555" alt="Screenshot 2023-02-02 at 09 03 37" src="https://user-images.githubusercontent.com/7203098/216213363-921d9ba8-e170-4dd3-b98b-29dbad91eee8.png">
[Forum post](https://forum.bryntum.com/viewtopic.php?f=44&t=23738&p=117579#p117579)
Hi Team,
As you might already be aware we use the two scheduler view and React as the front-end development library.
We have upgraded Bryntum from 5.0.1 to 5.2.2 and ever since we get TypeError: Cannot read properties of null (reading 'hasLinks') when moving the first event from the top grid to the bottom grid.
Here are the steps.
Drag and drop an event from the top grid to the bottom grid (No events in the bottom grid)

The whole scheduler goes to frozen mode. the event is not visible anymore where you dropped. Unless you do a full refresh the screen will remain the same.

Check the console and found the error as follows

I debugged the code in both 5.0.1 & 5.2.2 using the scheduler.umd.js
As you can see our scheduler worked fine when the version was 5.0.1. Please provide your assistance.



|
1.0
|
Error appeared on drop event into empty scheduler - 2 users complained about this.
3rd case here: https://forum.bryntum.com/posting.php?mode=reply&t=23744#preview
Error appears right after app init.
To reproduce open drag-between-schedulers demo, set `events: []` for second scheduler. Drag and drop event from 1st scheduler to empty one. See an error in console
<img width="555" alt="Screenshot 2023-02-02 at 09 03 37" src="https://user-images.githubusercontent.com/7203098/216213363-921d9ba8-e170-4dd3-b98b-29dbad91eee8.png">
[Forum post](https://forum.bryntum.com/viewtopic.php?f=44&t=23738&p=117579#p117579)
Hi Team,
As you might already be aware we use the two scheduler view and React as the front-end development library.
We have upgraded Bryntum from 5.0.1 to 5.2.2 and ever since we get TypeError: Cannot read properties of null (reading 'hasLinks') when moving the first event from the top grid to the bottom grid.
Here are the steps.
Drag and drop an event from the top grid to the bottom grid (No events in the bottom grid)

The whole scheduler goes to frozen mode. the event is not visible anymore where you dropped. Unless you do a full refresh the screen will remain the same.

Check the console and found the error as follows

I debugged the code in both 5.0.1 & 5.2.2 using the scheduler.umd.js
As you can see our scheduler worked fine when the version was 5.0.1. Please provide your assistance.



|
non_defect
|
error appeared on drop event into empty scheduler users complained about this case here error appears right after app init to reproduce open drag between schedulers demo set events for second scheduler drag and drop event from scheduler to empty one see an error in console img width alt screenshot at src hi team as you might already be aware we use the two scheduler view and react as the front end development library we have upgraded bryntum from to and ever since we get typeerror cannot read properties of null reading haslinks when moving the first event from the top grid to the bottom grid here are the steps drag and drop an event from the top grid to the bottom grid no events in the bottom grid the whole scheduler goes to frozen mode the event is not visible anymore where you dropped unless you do a full refresh the screen will remain the same check the console and found the error as follows i debugged the code in both using the scheduler umd js as you can see our scheduler worked fine when the version was please provide your assistance
| 0
|
68,083
| 9,122,162,039
|
IssuesEvent
|
2019-02-23 04:56:57
|
mlpack/mlpack
|
https://api.github.com/repos/mlpack/mlpack
|
opened
|
Ensmallen documentation yet to be removed
|
c: documentation s: unanswered t: bug report
|
<!--
Welcome! Unfortunately not all documentation is perfect, and if you're opening
a documentation issue we are interested in fixing it. Please fill out the
template below so that we can solve the problem more quickly; or, alternately,
open a PR with a fix, if you like.
-->
In mlpack/doc/tutorials, there exists tutorials for CNE and Optimizers, both of which have now been shifted to the ensmallen repository. Shouldn't they be removed?
<!-- Link to incorrect website or location of source file with bad
documentation. -->
<!-- Tell us what is wrong with the documentation so we can fix it. -->
|
1.0
|
Ensmallen documentation yet to be removed - <!--
Welcome! Unfortunately not all documentation is perfect, and if you're opening
a documentation issue we are interested in fixing it. Please fill out the
template below so that we can solve the problem more quickly; or, alternately,
open a PR with a fix, if you like.
-->
In mlpack/doc/tutorials, there exists tutorials for CNE and Optimizers, both of which have now been shifted to the ensmallen repository. Shouldn't they be removed?
<!-- Link to incorrect website or location of source file with bad
documentation. -->
<!-- Tell us what is wrong with the documentation so we can fix it. -->
|
non_defect
|
ensmallen documentation yet to be removed welcome unfortunately not all documentation is perfect and if you re opening a documentation issue we are interested in fixing it please fill out the template below so that we can solve the problem more quickly or alternately open a pr with a fix if you like in mlpack doc tutorials there exists tutorials for cne and optimizers both of which have now been shifted to the ensmallen repository shouldn t they be removed link to incorrect website or location of source file with bad documentation
| 0
|
346,844
| 10,420,622,085
|
IssuesEvent
|
2019-09-16 01:44:32
|
itsmeow/betteranimalsplus
|
https://api.github.com/repos/itsmeow/betteranimalsplus
|
closed
|
Picking up Feral Wolves with Carry On makes them invisible
|
bug mc:1.14 mod compat priority:low side:client
|
**Describe the bug** (Required)
Picking up certain tameable mobs (Feral Wolf and Lammergier) with [https://www.curseforge.com/minecraft/mc-mods/carry-on](Carry On) and placing them back down makes them invisible. They are still there, fully functional, just not visible. They are still invisible after reloading the world.
**To Reproduce** (Required unless not known)
Steps to reproduce the behavior:
0. Have Carry On and BA+ installed
1. Spawn tameable, such as Feral Wolf
2. Shift-rclick on feral wolf
3. Rclick on ground
**Expected behavior**
Mob gets placed down, fully visible.
**Screenshots**


(oddly, wolf still has its eyes and outline)
**Versions:**
- Forge Version: 28.1.1
- MC Version: 1.14.4
- Mod Version: BA+ 7.1.2 CarryOn 1.12.3
**Additional context**
May be a CarryOn problem, but given there isn't a crash I can't tell.
|
1.0
|
Picking up Feral Wolves with Carry On makes them invisible - **Describe the bug** (Required)
Picking up certain tameable mobs (Feral Wolf and Lammergier) with [https://www.curseforge.com/minecraft/mc-mods/carry-on](Carry On) and placing them back down makes them invisible. They are still there, fully functional, just not visible. They are still invisible after reloading the world.
**To Reproduce** (Required unless not known)
Steps to reproduce the behavior:
0. Have Carry On and BA+ installed
1. Spawn tameable, such as Feral Wolf
2. Shift-rclick on feral wolf
3. Rclick on ground
**Expected behavior**
Mob gets placed down, fully visible.
**Screenshots**


(oddly, wolf still has its eyes and outline)
**Versions:**
- Forge Version: 28.1.1
- MC Version: 1.14.4
- Mod Version: BA+ 7.1.2 CarryOn 1.12.3
**Additional context**
May be a CarryOn problem, but given there isn't a crash I can't tell.
|
non_defect
|
picking up feral wolves with carry on makes them invisible describe the bug required picking up certain tameable mobs feral wolf and lammergier with carry on and placing them back down makes them invisible they are still there fully functional just not visible they are still invisible after reloading the world to reproduce required unless not known steps to reproduce the behavior have carry on and ba installed spawn tameable such as feral wolf shift rclick on feral wolf rclick on ground expected behavior mob gets placed down fully visible screenshots oddly wolf still has its eyes and outline versions forge version mc version mod version ba carryon additional context may be a carryon problem but given there isn t a crash i can t tell
| 0
|
103,990
| 16,613,306,202
|
IssuesEvent
|
2021-06-02 14:00:49
|
Thanraj/linux-4.1.15
|
https://api.github.com/repos/Thanraj/linux-4.1.15
|
opened
|
CVE-2018-12896 (Medium) detected in linux-stable-rtv4.1.33
|
security vulnerability
|
## CVE-2018-12896 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/time/posix-timers.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/time/posix-timers.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel through 4.17.3. An Integer Overflow in kernel/time/posix-timers.c in the POSIX timer code is caused by the way the overrun accounting works. Depending on interval and expiry time values, the overrun can be larger than INT_MAX, but the accounting is int based. This basically makes the accounting values, which are visible to user space via timer_getoverrun(2) and siginfo::si_overrun, random. For example, a local user can cause a denial of service (signed integer overflow) via crafted mmap, futex, timer_create, and timer_settime system calls.
<p>Publish Date: 2018-07-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12896>CVE-2018-12896</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-12896">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-12896</a></p>
<p>Release Date: 2018-07-02</p>
<p>Fix Resolution: v4.19-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2018-12896 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2018-12896 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/time/posix-timers.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/kernel/time/posix-timers.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel through 4.17.3. An Integer Overflow in kernel/time/posix-timers.c in the POSIX timer code is caused by the way the overrun accounting works. Depending on interval and expiry time values, the overrun can be larger than INT_MAX, but the accounting is int based. This basically makes the accounting values, which are visible to user space via timer_getoverrun(2) and siginfo::si_overrun, random. For example, a local user can cause a denial of service (signed integer overflow) via crafted mmap, futex, timer_create, and timer_settime system calls.
<p>Publish Date: 2018-07-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12896>CVE-2018-12896</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-12896">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-12896</a></p>
<p>Release Date: 2018-07-02</p>
<p>Fix Resolution: v4.19-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files linux kernel time posix timers c linux kernel time posix timers c vulnerability details an issue was discovered in the linux kernel through an integer overflow in kernel time posix timers c in the posix timer code is caused by the way the overrun accounting works depending on interval and expiry time values the overrun can be larger than int max but the accounting is int based this basically makes the accounting values which are visible to user space via timer getoverrun and siginfo si overrun random for example a local user can cause a denial of service signed integer overflow via crafted mmap futex timer create and timer settime system calls publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
88,268
| 10,567,900,566
|
IssuesEvent
|
2019-10-06 08:50:03
|
sdispater/poetry
|
https://api.github.com/repos/sdispater/poetry
|
opened
|
Document how `add` a dependency with an exact version
|
Documentation
|
Hi, Poetry newbie here. Trying to get my dependencies specified in `requirements.txt` format into Poetry took me longer than expected. Here's what I've found.
- [x] I have searched the [issues](https://github.com/sdispater/poetry/issues) of this repo and believe that this is not a duplicate.
The short documentation section on [Exact [version] requirements](https://poetry.eustace.io/docs/versions/#exact-requirements), as opposed to others, includes no examples of the specific version format string and, this feels especially important for this case, a full Poetry command to add a specific version of a dependency.
I wanted to install a specific version of the `attrs` package (as an example), so I tried this:
- `poetry add attrs 19.1.0` results in
```
Using version ^19.2 for attrs
[PackageNotFound]
Package [19.1.0] not found.
```
Nothing added to `pyproject.toml`.
It seems that Poetry expects the version number to be a package name, which fits the usage string of the `add` command (`add [options here …] <name> (<name>)...`). That is fine.
- `poetry add attrs==19.1.0`
This is the format I expect to work as I'm used to it from `requirements.txt` and probably `setup.py` and other common, but older, approaches to specify requirements.
The line `attrs = "=19.1.0"` gets added to `pyproject.toml`. This doesn't look wrong per se, but my understanding is that the equality sign is at least redundant/superfluous here and, thus, should not have been added automatically.
And I'm not sure if it will actually work later on. Maybe Poetry assumes the second `=` is the start of the version number? That sounds like trouble.
Maybe Poetry should normalize `==` to `=` as a special case?
- `poetry add attrs=19.1.0`
This, to me, uses an unexpected format, coming from `requirements.txt` (where `==` seems to be/is common, though I'm not sure if a single `=` would work, too).
However, the line `attrs = "19.1.0"` gets added to `pyproject.toml` and it looks correct to me.
- `poetry add 'attrs 19.1.0'`
Okay, let's try to group package name and version number into arguments using quotes.
Again, the line `attrs = "19.1.0"` gets added to `pyproject.toml`.
This is fine, and not having to type `=` is nice (though the quotes then become necessary with this format), but should be documented.
- `poetry add 'attrs == 19.1.0'`
This, with spaces around the `==`, is what's in my `requirements.txt` files, because it it more readable than without spaces, and works perfectly fine there (even though it's not the output generated by, for example, `pip freeze`, unfortunately).
Result:
```
[ValueError]
too many values to unpack (expected 2)
```
Unexpected.
As I've learned from `attrs==19.1.0` (with out without quotes around the term, btw), this doesn't seem to be what Poetry expects.
However, I think it should be better at dealing with this, preferably even suggesting (or doing?) the right thing.
**tl;dr**
The documentation should make clear how to add a dependency with a specific version using `poetry add`.
And maybe a dependency version value like `=1.2.3` ending up in `pyproject.toml` (both manually and via Poetry commands) should be caught and and error be raised.
Thanks for reading.
|
1.0
|
Document how `add` a dependency with an exact version - Hi, Poetry newbie here. Trying to get my dependencies specified in `requirements.txt` format into Poetry took me longer than expected. Here's what I've found.
- [x] I have searched the [issues](https://github.com/sdispater/poetry/issues) of this repo and believe that this is not a duplicate.
The short documentation section on [Exact [version] requirements](https://poetry.eustace.io/docs/versions/#exact-requirements), as opposed to others, includes no examples of the specific version format string and, this feels especially important for this case, a full Poetry command to add a specific version of a dependency.
I wanted to install a specific version of the `attrs` package (as an example), so I tried this:
- `poetry add attrs 19.1.0` results in
```
Using version ^19.2 for attrs
[PackageNotFound]
Package [19.1.0] not found.
```
Nothing added to `pyproject.toml`.
It seems that Poetry expects the version number to be a package name, which fits the usage string of the `add` command (`add [options here …] <name> (<name>)...`). That is fine.
- `poetry add attrs==19.1.0`
This is the format I expect to work as I'm used to it from `requirements.txt` and probably `setup.py` and other common, but older, approaches to specify requirements.
The line `attrs = "=19.1.0"` gets added to `pyproject.toml`. This doesn't look wrong per se, but my understanding is that the equality sign is at least redundant/superfluous here and, thus, should not have been added automatically.
And I'm not sure if it will actually work later on. Maybe Poetry assumes the second `=` is the start of the version number? That sounds like trouble.
Maybe Poetry should normalize `==` to `=` as a special case?
- `poetry add attrs=19.1.0`
This, to me, uses an unexpected format, coming from `requirements.txt` (where `==` seems to be/is common, though I'm not sure if a single `=` would work, too).
However, the line `attrs = "19.1.0"` gets added to `pyproject.toml` and it looks correct to me.
- `poetry add 'attrs 19.1.0'`
Okay, let's try to group package name and version number into arguments using quotes.
Again, the line `attrs = "19.1.0"` gets added to `pyproject.toml`.
This is fine, and not having to type `=` is nice (though the quotes then become necessary with this format), but should be documented.
- `poetry add 'attrs == 19.1.0'`
This, with spaces around the `==`, is what's in my `requirements.txt` files, because it it more readable than without spaces, and works perfectly fine there (even though it's not the output generated by, for example, `pip freeze`, unfortunately).
Result:
```
[ValueError]
too many values to unpack (expected 2)
```
Unexpected.
As I've learned from `attrs==19.1.0` (with out without quotes around the term, btw), this doesn't seem to be what Poetry expects.
However, I think it should be better at dealing with this, preferably even suggesting (or doing?) the right thing.
**tl;dr**
The documentation should make clear how to add a dependency with a specific version using `poetry add`.
And maybe a dependency version value like `=1.2.3` ending up in `pyproject.toml` (both manually and via Poetry commands) should be caught and and error be raised.
Thanks for reading.
|
non_defect
|
document how add a dependency with an exact version hi poetry newbie here trying to get my dependencies specified in requirements txt format into poetry took me longer than expected here s what i ve found i have searched the of this repo and believe that this is not a duplicate the short documentation section on requirements as opposed to others includes no examples of the specific version format string and this feels especially important for this case a full poetry command to add a specific version of a dependency i wanted to install a specific version of the attrs package as an example so i tried this poetry add attrs results in using version for attrs package not found nothing added to pyproject toml it seems that poetry expects the version number to be a package name which fits the usage string of the add command add that is fine poetry add attrs this is the format i expect to work as i m used to it from requirements txt and probably setup py and other common but older approaches to specify requirements the line attrs gets added to pyproject toml this doesn t look wrong per se but my understanding is that the equality sign is at least redundant superfluous here and thus should not have been added automatically and i m not sure if it will actually work later on maybe poetry assumes the second is the start of the version number that sounds like trouble maybe poetry should normalize to as a special case poetry add attrs this to me uses an unexpected format coming from requirements txt where seems to be is common though i m not sure if a single would work too however the line attrs gets added to pyproject toml and it looks correct to me poetry add attrs okay let s try to group package name and version number into arguments using quotes again the line attrs gets added to pyproject toml this is fine and not having to type is nice though the quotes then become necessary with this format but should be documented poetry add attrs this with spaces around the is what s in my requirements txt files because it it more readable than without spaces and works perfectly fine there even though it s not the output generated by for example pip freeze unfortunately result too many values to unpack expected unexpected as i ve learned from attrs with out without quotes around the term btw this doesn t seem to be what poetry expects however i think it should be better at dealing with this preferably even suggesting or doing the right thing tl dr the documentation should make clear how to add a dependency with a specific version using poetry add and maybe a dependency version value like ending up in pyproject toml both manually and via poetry commands should be caught and and error be raised thanks for reading
| 0
|
68,402
| 21,661,843,063
|
IssuesEvent
|
2022-05-06 20:11:23
|
martinrotter/rssguard
|
https://api.github.com/repos/martinrotter/rssguard
|
closed
|
[BUG]: Images in nowebenging in 4.2.2 appear pixelated
|
Type-Defect
|
### Brief description of the issue
All images appear pixelated and changing the height in settings does not appear to fix this - if opened via right click the images appear okay, but there's no back button to go back to the article 
### How to reproduce the bug?
1. enable images in settings
2. fetch an article with images from a feed
### What was the expected result?
images to appear not pixelated
### What actually happened?
images appear pixelated as shown in screenshot
### Debug log
I don't know how to see log for an app image, using the AppImage on Linux Mint 20.3. If you can let me know how, I'll add the log.
### Operating system and version
* OS: Linux Mint 20.3
* RSS Guard version: 4.2.2 nowebengine
|
1.0
|
[BUG]: Images in nowebenging in 4.2.2 appear pixelated - ### Brief description of the issue
All images appear pixelated and changing the height in settings does not appear to fix this - if opened via right click the images appear okay, but there's no back button to go back to the article 
### How to reproduce the bug?
1. enable images in settings
2. fetch an article with images from a feed
### What was the expected result?
images to appear not pixelated
### What actually happened?
images appear pixelated as shown in screenshot
### Debug log
I don't know how to see log for an app image, using the AppImage on Linux Mint 20.3. If you can let me know how, I'll add the log.
### Operating system and version
* OS: Linux Mint 20.3
* RSS Guard version: 4.2.2 nowebengine
|
defect
|
images in nowebenging in appear pixelated brief description of the issue all images appear pixelated and changing the height in settings does not appear to fix this if opened via right click the images appear okay but there s no back button to go back to the article how to reproduce the bug enable images in settings fetch an article with images from a feed what was the expected result images to appear not pixelated what actually happened images appear pixelated as shown in screenshot debug log i don t know how to see log for an app image using the appimage on linux mint if you can let me know how i ll add the log operating system and version os linux mint rss guard version nowebengine
| 1
|
23,065
| 3,756,128,561
|
IssuesEvent
|
2016-03-13 04:20:35
|
StarsOCV/eve-tf2hud
|
https://api.github.com/repos/StarsOCV/eve-tf2hud
|
closed
|
No previous best popup
|
auto-migrated OpSys-All Priority-Medium Type-Defect
|
```
After I score higher the my previous best, the popup window telling me I did
does not appear.
I used to get this window in normal TF2
What steps will reproduce it?
1. Start tf2
2. Score a better score than previous
3. No window.
What version do you use?
3.40
What's your screen resolution?
1280 X 1024
Please provide any additional information below. #don't forget about
screenshots
```
Original issue reported on code.google.com by `naotg...@gmail.com` on 16 Feb 2014 at 6:35
|
1.0
|
No previous best popup - ```
After I score higher the my previous best, the popup window telling me I did
does not appear.
I used to get this window in normal TF2
What steps will reproduce it?
1. Start tf2
2. Score a better score than previous
3. No window.
What version do you use?
3.40
What's your screen resolution?
1280 X 1024
Please provide any additional information below. #don't forget about
screenshots
```
Original issue reported on code.google.com by `naotg...@gmail.com` on 16 Feb 2014 at 6:35
|
defect
|
no previous best popup after i score higher the my previous best the popup window telling me i did does not appear i used to get this window in normal what steps will reproduce it start score a better score than previous no window what version do you use what s your screen resolution x please provide any additional information below don t forget about screenshots original issue reported on code google com by naotg gmail com on feb at
| 1
|
201,473
| 22,972,126,848
|
IssuesEvent
|
2022-07-20 04:52:30
|
KOSASIH/zixstudio
|
https://api.github.com/repos/KOSASIH/zixstudio
|
closed
|
base-2.18.0.tgz: 9 vulnerabilities (highest severity is: 9.8) - autoclosed
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>base-2.18.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/prismjs/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-0691](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0691) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0686](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0686) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0155](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | follow-redirects-1.14.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2021-3801](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3801) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | prismjs-1.24.1.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-23647](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23647) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | prismjs-1.24.1.tgz | Transitive | 2.21.8-reference-updates.26 | ❌ |
| [CVE-2022-0536](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | follow-redirects-1.14.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2021-23566](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23566) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | nanoid-3.1.25.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0639](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0639) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0512](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-0691</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.9.
<p>Publish Date: 2022-02-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0691>CVE-2022-0691</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691</a></p>
<p>Release Date: 2022-02-21</p>
<p>Fix Resolution (url-parse): 1.5.9</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-0686</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.8.
<p>Publish Date: 2022-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0686>CVE-2022-0686</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686</a></p>
<p>Release Date: 2022-02-20</p>
<p>Fix Resolution (url-parse): 1.5.8</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0155</summary>
### Vulnerable Library - <b>follow-redirects-1.14.3.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/follow-redirects/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **follow-redirects-1.14.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
follow-redirects is vulnerable to Exposure of Private Personal Information to an Unauthorized Actor
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155>CVE-2022-0155</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/">https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution (follow-redirects): 1.14.7</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-3801</summary>
### Vulnerable Library - <b>prismjs-1.24.1.tgz</b></p>
<p>Lightweight, robust, elegant syntax highlighting. A spin-off project from Dabblet.</p>
<p>Library home page: <a href="https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz">https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/prismjs/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- refractor-3.4.0.tgz
- :x: **prismjs-1.24.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
prism is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3801>CVE-2021-3801</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3801">https://nvd.nist.gov/vuln/detail/CVE-2021-3801</a></p>
<p>Release Date: 2021-09-15</p>
<p>Fix Resolution (prismjs): 1.25.0</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23647</summary>
### Vulnerable Library - <b>prismjs-1.24.1.tgz</b></p>
<p>Lightweight, robust, elegant syntax highlighting. A spin-off project from Dabblet.</p>
<p>Library home page: <a href="https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz">https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/prismjs/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- refractor-3.4.0.tgz
- :x: **prismjs-1.24.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prism is a syntax highlighting library. Starting with version 1.14.0 and prior to version 1.27.0, Prism's command line plugin can be used by attackers to achieve a cross-site scripting attack. The command line plugin did not properly escape its output, leading to the input text being inserted into the DOM as HTML code. Server-side usage of Prism is not impacted. Websites that do not use the Command Line plugin are also not impacted. This bug has been fixed in v1.27.0. As a workaround, do not use the command line plugin on untrusted inputs, or sanitize all code blocks (remove all HTML code text) from all code blocks that use the command line plugin.
<p>Publish Date: 2022-02-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23647>CVE-2022-23647</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/PrismJS/prism/security/advisories/GHSA-3949-f494-cm99">https://github.com/PrismJS/prism/security/advisories/GHSA-3949-f494-cm99</a></p>
<p>Release Date: 2022-02-18</p>
<p>Fix Resolution (prismjs): 1.27.0</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.21.8-reference-updates.26</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0536</summary>
### Vulnerable Library - <b>follow-redirects-1.14.3.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/follow-redirects/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **follow-redirects-1.14.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM follow-redirects prior to 1.14.8.
<p>Publish Date: 2022-02-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536>CVE-2022-0536</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536</a></p>
<p>Release Date: 2022-02-09</p>
<p>Fix Resolution (follow-redirects): 1.14.8</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-23566</summary>
### Vulnerable Library - <b>nanoid-3.1.25.tgz</b></p>
<p>A tiny (108 bytes), secure URL-friendly unique string ID generator</p>
<p>Library home page: <a href="https://registry.npmjs.org/nanoid/-/nanoid-3.1.25.tgz">https://registry.npmjs.org/nanoid/-/nanoid-3.1.25.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/nanoid/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- :x: **nanoid-3.1.25.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package nanoid from 3.0.0 and before 3.1.31 are vulnerable to Information Exposure via the valueOf() function which allows to reproduce the last id generated.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23566>CVE-2021-23566</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution (nanoid): 3.1.31</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0639</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.7.
<p>Publish Date: 2022-02-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0639>CVE-2022-0639</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0639">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0639</a></p>
<p>Release Date: 2022-02-17</p>
<p>Fix Resolution (url-parse): 1.5.7</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0512</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.6.
<p>Publish Date: 2022-02-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512>CVE-2022-0512</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512</a></p>
<p>Release Date: 2022-02-14</p>
<p>Fix Resolution (url-parse): 1.5.6</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
True
|
base-2.18.0.tgz: 9 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>base-2.18.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/prismjs/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-0691](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0691) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0686](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0686) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0155](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | follow-redirects-1.14.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2021-3801](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3801) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | prismjs-1.24.1.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-23647](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23647) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | prismjs-1.24.1.tgz | Transitive | 2.21.8-reference-updates.26 | ❌ |
| [CVE-2022-0536](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | follow-redirects-1.14.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2021-23566](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23566) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | nanoid-3.1.25.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0639](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0639) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
| [CVE-2022-0512](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | url-parse-1.5.3.tgz | Transitive | 2.18.1-canary.9 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-0691</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.9.
<p>Publish Date: 2022-02-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0691>CVE-2022-0691</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0691</a></p>
<p>Release Date: 2022-02-21</p>
<p>Fix Resolution (url-parse): 1.5.9</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-0686</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.8.
<p>Publish Date: 2022-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0686>CVE-2022-0686</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0686</a></p>
<p>Release Date: 2022-02-20</p>
<p>Fix Resolution (url-parse): 1.5.8</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0155</summary>
### Vulnerable Library - <b>follow-redirects-1.14.3.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/follow-redirects/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **follow-redirects-1.14.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
follow-redirects is vulnerable to Exposure of Private Personal Information to an Unauthorized Actor
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155>CVE-2022-0155</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/">https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution (follow-redirects): 1.14.7</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-3801</summary>
### Vulnerable Library - <b>prismjs-1.24.1.tgz</b></p>
<p>Lightweight, robust, elegant syntax highlighting. A spin-off project from Dabblet.</p>
<p>Library home page: <a href="https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz">https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/prismjs/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- refractor-3.4.0.tgz
- :x: **prismjs-1.24.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
prism is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3801>CVE-2021-3801</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3801">https://nvd.nist.gov/vuln/detail/CVE-2021-3801</a></p>
<p>Release Date: 2021-09-15</p>
<p>Fix Resolution (prismjs): 1.25.0</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23647</summary>
### Vulnerable Library - <b>prismjs-1.24.1.tgz</b></p>
<p>Lightweight, robust, elegant syntax highlighting. A spin-off project from Dabblet.</p>
<p>Library home page: <a href="https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz">https://registry.npmjs.org/prismjs/-/prismjs-1.24.1.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/prismjs/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- refractor-3.4.0.tgz
- :x: **prismjs-1.24.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prism is a syntax highlighting library. Starting with version 1.14.0 and prior to version 1.27.0, Prism's command line plugin can be used by attackers to achieve a cross-site scripting attack. The command line plugin did not properly escape its output, leading to the input text being inserted into the DOM as HTML code. Server-side usage of Prism is not impacted. Websites that do not use the Command Line plugin are also not impacted. This bug has been fixed in v1.27.0. As a workaround, do not use the command line plugin on untrusted inputs, or sanitize all code blocks (remove all HTML code text) from all code blocks that use the command line plugin.
<p>Publish Date: 2022-02-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23647>CVE-2022-23647</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/PrismJS/prism/security/advisories/GHSA-3949-f494-cm99">https://github.com/PrismJS/prism/security/advisories/GHSA-3949-f494-cm99</a></p>
<p>Release Date: 2022-02-18</p>
<p>Fix Resolution (prismjs): 1.27.0</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.21.8-reference-updates.26</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0536</summary>
### Vulnerable Library - <b>follow-redirects-1.14.3.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.14.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/follow-redirects/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **follow-redirects-1.14.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM follow-redirects prior to 1.14.8.
<p>Publish Date: 2022-02-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536>CVE-2022-0536</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536</a></p>
<p>Release Date: 2022-02-09</p>
<p>Fix Resolution (follow-redirects): 1.14.8</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-23566</summary>
### Vulnerable Library - <b>nanoid-3.1.25.tgz</b></p>
<p>A tiny (108 bytes), secure URL-friendly unique string ID generator</p>
<p>Library home page: <a href="https://registry.npmjs.org/nanoid/-/nanoid-3.1.25.tgz">https://registry.npmjs.org/nanoid/-/nanoid-3.1.25.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/nanoid/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- :x: **nanoid-3.1.25.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package nanoid from 3.0.0 and before 3.1.31 are vulnerable to Information Exposure via the valueOf() function which allows to reproduce the last id generated.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23566>CVE-2021-23566</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution (nanoid): 3.1.31</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0639</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.7.
<p>Publish Date: 2022-02-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0639>CVE-2022-0639</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0639">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0639</a></p>
<p>Release Date: 2022-02-17</p>
<p>Fix Resolution (url-parse): 1.5.7</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0512</summary>
### Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- base-2.18.0.tgz (Root Library)
- client-2.18.0.tgz
- get-it-5.0.5.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KOSASIH/zixstudio/commit/25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1">25b7fcdf00ed5fc3dbc4b87f88bf0d88e80715d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.6.
<p>Publish Date: 2022-02-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512>CVE-2022-0512</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512</a></p>
<p>Release Date: 2022-02-14</p>
<p>Fix Resolution (url-parse): 1.5.6</p>
<p>Direct dependency fix Resolution (@sanity/base): 2.18.1-canary.9</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
non_defect
|
base tgz vulnerabilities highest severity is autoclosed vulnerable library base tgz path to dependency file studio package json path to vulnerable library studio node modules prismjs package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high url parse tgz transitive canary high url parse tgz transitive canary medium follow redirects tgz transitive canary medium prismjs tgz transitive canary medium prismjs tgz transitive reference updates medium follow redirects tgz transitive canary medium nanoid tgz transitive canary medium url parse tgz transitive canary medium url parse tgz transitive canary details cve vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file studio package json path to vulnerable library studio node modules url parse package json dependency hierarchy base tgz root library client tgz get it tgz x url parse tgz vulnerable library found in head commit a href found in base branch main vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file studio package json path to vulnerable library studio node modules url parse package json dependency hierarchy base tgz root library client tgz get it tgz x url parse tgz vulnerable library found in head commit a href found in base branch main vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library follow redirects tgz http and https modules that follow redirects library home page a href path to dependency file studio package json path to vulnerable library studio node modules follow redirects package json dependency hierarchy base tgz root library client tgz get it tgz x follow redirects tgz vulnerable library found in head commit a href found in base branch main vulnerability details follow redirects is vulnerable to exposure of private personal information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution follow redirects direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library prismjs tgz lightweight robust elegant syntax highlighting a spin off project from dabblet library home page a href path to dependency file studio package json path to vulnerable library studio node modules prismjs package json dependency hierarchy base tgz root library refractor tgz x prismjs tgz vulnerable library found in head commit a href found in base branch main vulnerability details prism is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution prismjs direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library prismjs tgz lightweight robust elegant syntax highlighting a spin off project from dabblet library home page a href path to dependency file studio package json path to vulnerable library studio node modules prismjs package json dependency hierarchy base tgz root library refractor tgz x prismjs tgz vulnerable library found in head commit a href found in base branch main vulnerability details prism is a syntax highlighting library starting with version and prior to version prism s command line plugin can be used by attackers to achieve a cross site scripting attack the command line plugin did not properly escape its output leading to the input text being inserted into the dom as html code server side usage of prism is not impacted websites that do not use the command line plugin are also not impacted this bug has been fixed in as a workaround do not use the command line plugin on untrusted inputs or sanitize all code blocks remove all html code text from all code blocks that use the command line plugin publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution prismjs direct dependency fix resolution sanity base reference updates step up your open source security game with mend cve vulnerable library follow redirects tgz http and https modules that follow redirects library home page a href path to dependency file studio package json path to vulnerable library studio node modules follow redirects package json dependency hierarchy base tgz root library client tgz get it tgz x follow redirects tgz vulnerable library found in head commit a href found in base branch main vulnerability details exposure of sensitive information to an unauthorized actor in npm follow redirects prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution follow redirects direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library nanoid tgz a tiny bytes secure url friendly unique string id generator library home page a href path to dependency file studio package json path to vulnerable library studio node modules nanoid package json dependency hierarchy base tgz root library x nanoid tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package nanoid from and before are vulnerable to information exposure via the valueof function which allows to reproduce the last id generated publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution nanoid direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file studio package json path to vulnerable library studio node modules url parse package json dependency hierarchy base tgz root library client tgz get it tgz x url parse tgz vulnerable library found in head commit a href found in base branch main vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution sanity base canary step up your open source security game with mend cve vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file studio package json path to vulnerable library studio node modules url parse package json dependency hierarchy base tgz root library client tgz get it tgz x url parse tgz vulnerable library found in head commit a href found in base branch main vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution sanity base canary step up your open source security game with mend
| 0
|
251,604
| 27,191,019,913
|
IssuesEvent
|
2023-02-19 19:59:48
|
WFS-Mend/vtrade-serverless
|
https://api.github.com/repos/WFS-Mend/vtrade-serverless
|
opened
|
serverless-2.22.0.tgz: 27 vulnerabilities (highest severity is: 9.8)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serverless-2.22.0.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (serverless version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-25912](https://www.mend.io/vulnerability-database/CVE-2022-25912) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | simple-git-2.31.0.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2022-48285](https://www.mend.io/vulnerability-database/CVE-2022-48285) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | jszip-3.5.0.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-24433](https://www.mend.io/vulnerability-database/CVE-2022-24433) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | simple-git-2.31.0.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2022-24066](https://www.mend.io/vulnerability-database/CVE-2022-24066) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | simple-git-2.31.0.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2021-31597](https://www.mend.io/vulnerability-database/CVE-2021-31597) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.4 | xmlhttprequest-ssl-1.5.5.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-42581](https://www.mend.io/vulnerability-database/CVE-2021-42581) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.1 | detected in multiple dependencies | Transitive | 3.0.0 | ❌ |
| [CVE-2020-28502](https://www.mend.io/vulnerability-database/CVE-2020-28502) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | xmlhttprequest-ssl-1.5.5.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-43138](https://www.mend.io/vulnerability-database/CVE-2021-43138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | detected in multiple dependencies | Transitive | 3.0.0 | ❌ |
| [CVE-2022-0355](https://www.mend.io/vulnerability-database/CVE-2022-0355) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | simple-get-2.8.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-25878](https://www.mend.io/vulnerability-database/CVE-2022-25878) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobufjs-6.10.2.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2020-28469](https://www.mend.io/vulnerability-database/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-5.1.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-33502](https://www.mend.io/vulnerability-database/CVE-2021-33502) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | normalize-url-4.5.0.tgz | Transitive | 2.23.0 | ❌ |
| [WS-2021-0152](https://github.com/Qix-/color-string/commit/0789e21284c33d89ebc4ab4ca6f759b9375ac9d3) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | color-string-1.5.4.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-38900](https://www.mend.io/vulnerability-database/CVE-2022-38900) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | decode-uri-component-0.2.0.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-3749](https://www.mend.io/vulnerability-database/CVE-2021-3749) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | axios-0.21.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-25881](https://www.mend.io/vulnerability-database/CVE-2022-25881) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-3807](https://www.mend.io/vulnerability-database/CVE-2021-3807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 2.23.0 | ❌ |
| [CVE-2022-25901](https://www.mend.io/vulnerability-database/CVE-2022-25901) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | cookiejar-2.1.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-31129](https://www.mend.io/vulnerability-database/CVE-2022-31129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-2.29.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-24785](https://www.mend.io/vulnerability-database/CVE-2022-24785) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-2.29.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-0155](https://www.mend.io/vulnerability-database/CVE-2022-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | follow-redirects-1.13.2.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-0235](https://www.mend.io/vulnerability-database/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.1.tgz | Transitive | 2.71.0 | ❌ |
| [CVE-2022-0536](https://www.mend.io/vulnerability-database/CVE-2022-0536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | follow-redirects-1.13.2.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-32640](https://www.mend.io/vulnerability-database/CVE-2021-32640) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | 2.23.0 | ❌ |
| [CVE-2021-23413](https://www.mend.io/vulnerability-database/CVE-2021-23413) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jszip-3.5.0.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-29060](https://www.mend.io/vulnerability-database/CVE-2021-29060) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | color-string-1.5.4.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-33987](https://www.mend.io/vulnerability-database/CVE-2022-33987) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | 3.19.0 | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (25 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-25912</summary>
### Vulnerable Library - <b>simple-git-2.31.0.tgz</b></p>
<p>Simple GIT interface for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz">https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **simple-git-2.31.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package simple-git before 3.15.0 are vulnerable to Remote Code Execution (RCE) when enabling the ext transport protocol, which makes it exploitable via clone() method. This vulnerability exists due to an incomplete fix of [CVE-2022-24066](https://security.snyk.io/vuln/SNYK-JS-SIMPLEGIT-2434306).
<p>Publish Date: 2022-12-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25912>CVE-2022-25912</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-25912">https://www.cve.org/CVERecord?id=CVE-2022-25912</a></p>
<p>Release Date: 2022-12-06</p>
<p>Fix Resolution (simple-git): 3.15.0</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-48285</summary>
### Vulnerable Library - <b>jszip-3.5.0.tgz</b></p>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **jszip-3.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
loadAsync in JSZip before 3.8.0 allows Directory Traversal via a crafted ZIP archive.
<p>Publish Date: 2023-01-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-48285>CVE-2022-48285</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-29</p>
<p>Fix Resolution (jszip): 3.8.0</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-24433</summary>
### Vulnerable Library - <b>simple-git-2.31.0.tgz</b></p>
<p>Simple GIT interface for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz">https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **simple-git-2.31.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package simple-git before 3.3.0 are vulnerable to Command Injection via argument injection. When calling the .fetch(remote, branch, handlerFn) function, both the remote and branch parameters are passed to the git fetch subcommand. By injecting some git options it was possible to get arbitrary command execution.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24433>CVE-2022-24433</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-3f95-r44v-8mrg">https://github.com/advisories/GHSA-3f95-r44v-8mrg</a></p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution (simple-git): 3.3.0</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-24066</summary>
### Vulnerable Library - <b>simple-git-2.31.0.tgz</b></p>
<p>Simple GIT interface for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz">https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **simple-git-2.31.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package simple-git before 3.5.0 are vulnerable to Command Injection due to an incomplete fix of [CVE-2022-24433](https://security.snyk.io/vuln/SNYK-JS-SIMPLEGIT-2421199) which only patches against the git fetch attack vector. A similar use of the --upload-pack feature of git is also supported for git clone, which the prior fix didn't cover.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24066>CVE-2022-24066</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-28xr-mwxg-3qc8">https://github.com/advisories/GHSA-28xr-mwxg-3qc8</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution (simple-git): 3.5.0</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2021-31597</summary>
### Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz">https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- socket.io-client-2.4.0.tgz
- engine.io-client-3.5.0.tgz
- :x: **xmlhttprequest-ssl-1.5.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The xmlhttprequest-ssl package before 1.6.1 for Node.js disables SSL certificate validation by default, because rejectUnauthorized (when the property exists but is undefined) is considered to be false within the https.request function of Node.js. In other words, no certificate is ever rejected.
<p>Publish Date: 2021-04-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-31597>CVE-2021-31597</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-31597">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-31597</a></p>
<p>Release Date: 2021-04-23</p>
<p>Fix Resolution (xmlhttprequest-ssl): 1.6.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2021-42581</summary>
### Vulnerable Libraries - <b>ramda-0.25.0.tgz</b>, <b>ramda-0.26.1.tgz</b></p>
<p>
### <b>ramda-0.25.0.tgz</b></p>
<p>A practical functional library for JavaScript programmers.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ramda/-/ramda-0.25.0.tgz">https://registry.npmjs.org/ramda/-/ramda-0.25.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-sdk-2.3.2.tgz
- :x: **ramda-0.25.0.tgz** (Vulnerable Library)
### <b>ramda-0.26.1.tgz</b></p>
<p>A practical functional library for JavaScript programmers.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ramda/-/ramda-0.26.1.tgz">https://registry.npmjs.org/ramda/-/ramda-0.26.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- cli-1.5.2.tgz
- template-1.1.4.tgz
- :x: **ramda-0.26.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
** DISPUTED ** Prototype poisoning in function mapObjIndexed in Ramda 0.27.0 and earlier allows attackers to compromise integrity or availability of application via supplying a crafted object (that contains an own property "__proto__") as an argument to the function. NOTE: the vendor disputes this because the observed behavior only means that a user can create objects that the user didn't know would contain custom prototypes.
<p>Publish Date: 2022-05-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-42581>CVE-2021-42581</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42581">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42581</a></p>
<p>Release Date: 2022-05-10</p>
<p>Fix Resolution (ramda): 0.27.1</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p><p>Fix Resolution (ramda): 0.27.1</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28502</summary>
### Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz">https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- socket.io-client-2.4.0.tgz
- engine.io-client-3.5.0.tgz
- :x: **xmlhttprequest-ssl-1.5.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package xmlhttprequest before 1.7.0; all versions of package xmlhttprequest-ssl. Provided requests are sent synchronously (async=False on xhr.open), malicious user input flowing into xhr.send could result in arbitrary code being injected and run.
<p>Publish Date: 2021-03-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28502>CVE-2020-28502</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4j5-c7cj-74xg">https://github.com/advisories/GHSA-h4j5-c7cj-74xg</a></p>
<p>Release Date: 2021-03-05</p>
<p>Fix Resolution (xmlhttprequest-ssl): 1.6.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-43138</summary>
### Vulnerable Libraries - <b>async-2.6.3.tgz</b>, <b>async-3.2.0.tgz</b></p>
<p>
### <b>async-2.6.3.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-2.6.3.tgz">https://registry.npmjs.org/async/-/async-2.6.3.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- kafka-node-5.0.0.tgz
- :x: **async-2.6.3.tgz** (Vulnerable Library)
### <b>async-3.2.0.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-3.2.0.tgz">https://registry.npmjs.org/async/-/async-3.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- archiver-5.2.0.tgz
- :x: **async-3.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Async before 2.6.4 and 3.x before 3.2.2, a malicious user can obtain privileges via the mapValues() method, aka lib/internal/iterator.js createObjectIterator prototype pollution.
<p>Publish Date: 2022-04-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43138>CVE-2021-43138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43138">https://nvd.nist.gov/vuln/detail/CVE-2021-43138</a></p>
<p>Release Date: 2022-04-06</p>
<p>Fix Resolution (async): 2.6.4</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p><p>Fix Resolution (async): 3.2.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-0355</summary>
### Vulnerable Library - <b>simple-get-2.8.1.tgz</b></p>
<p>Simplest way to make http get requests. Supports HTTPS, redirects, gzip/deflate, streams in < 100 lines.</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-get/-/simple-get-2.8.1.tgz">https://registry.npmjs.org/simple-get/-/simple-get-2.8.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- kafka-node-5.0.0.tgz
- snappy-6.3.5.tgz
- prebuild-install-5.3.0.tgz
- :x: **simple-get-2.8.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM simple-get prior to 4.0.1.
<p>Publish Date: 2022-01-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0355>CVE-2022-0355</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355</a></p>
<p>Release Date: 2022-01-26</p>
<p>Fix Resolution (simple-get): 2.8.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25878</summary>
### Vulnerable Library - <b>protobufjs-6.10.2.tgz</b></p>
<p>Protocol Buffers for JavaScript (& TypeScript).</p>
<p>Library home page: <a href="https://registry.npmjs.org/protobufjs/-/protobufjs-6.10.2.tgz">https://registry.npmjs.org/protobufjs/-/protobufjs-6.10.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- :x: **protobufjs-6.10.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package protobufjs before 6.11.3 are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype. This vulnerability can occur in multiple ways: 1. by providing untrusted user input to util.setProperty or to ReflectionObject.setParsedOption functions 2. by parsing/loading .proto files
<p>Publish Date: 2022-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25878>CVE-2022-25878</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878</a></p>
<p>Release Date: 2022-05-27</p>
<p>Fix Resolution (protobufjs): 6.10.3</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-5.1.1.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- chokidar-3.5.1.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33502</summary>
### Vulnerable Library - <b>normalize-url-4.5.0.tgz</b></p>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-4.5.0.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-4.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- got-11.8.1.tgz
- cacheable-request-7.0.1.tgz
- :x: **normalize-url-4.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution (normalize-url): 4.5.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2021-0152</summary>
### Vulnerable Library - <b>color-string-1.5.4.tgz</b></p>
<p>Parser and generator for CSS color strings</p>
<p>Library home page: <a href="https://registry.npmjs.org/color-string/-/color-string-1.5.4.tgz">https://registry.npmjs.org/color-string/-/color-string-1.5.4.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- winston-3.2.1.tgz
- diagnostics-1.1.1.tgz
- colorspace-1.1.2.tgz
- color-3.0.0.tgz
- :x: **color-string-1.5.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular Expression Denial of Service (ReDoS) was found in color-string before 1.5.5.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://github.com/Qix-/color-string/commit/0789e21284c33d89ebc4ab4ca6f759b9375ac9d3>WS-2021-0152</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution (color-string): 1.5.5</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-38900</summary>
### Vulnerable Library - <b>decode-uri-component-0.2.0.tgz</b></p>
<p>A better decodeURIComponent</p>
<p>Library home page: <a href="https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz">https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- download-8.0.0.tgz
- got-8.3.2.tgz
- cacheable-request-2.1.4.tgz
- normalize-url-2.0.1.tgz
- query-string-5.1.1.tgz
- :x: **decode-uri-component-0.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
decode-uri-component 0.2.0 is vulnerable to Improper Input Validation resulting in DoS.
<p>Publish Date: 2022-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38900>CVE-2022-38900</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-w573-4hg7-7wgq">https://github.com/advisories/GHSA-w573-4hg7-7wgq</a></p>
<p>Release Date: 2022-11-28</p>
<p>Fix Resolution (decode-uri-component): 0.2.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3749</summary>
### Vulnerable Library - <b>axios-0.21.1.tgz</b></p>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.1.tgz">https://registry.npmjs.org/axios/-/axios-0.21.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- :x: **axios-0.21.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
axios is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3749>CVE-2021-3749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/1e8f07fc-c384-4ff9-8498-0690de2e8c31/">https://huntr.dev/bounties/1e8f07fc-c384-4ff9-8498-0690de2e8c31/</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (axios): 0.21.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25881</summary>
### Vulnerable Libraries - <b>http-cache-semantics-4.1.0.tgz</b>, <b>http-cache-semantics-3.8.1.tgz</b></p>
<p>
### <b>http-cache-semantics-4.1.0.tgz</b></p>
<p>Parses Cache-Control and other headers. Helps building correct HTTP caches and proxies</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz">https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- got-11.8.1.tgz
- cacheable-request-7.0.1.tgz
- :x: **http-cache-semantics-4.1.0.tgz** (Vulnerable Library)
### <b>http-cache-semantics-3.8.1.tgz</b></p>
<p>Parses Cache-Control and other headers. Helps building correct HTTP caches and proxies</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-3.8.1.tgz">https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-3.8.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- download-8.0.0.tgz
- got-8.3.2.tgz
- cacheable-request-2.1.4.tgz
- :x: **http-cache-semantics-3.8.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects versions of the package http-cache-semantics before 4.1.1. The issue can be exploited via malicious request header values sent to a server, when that server reads the cache policy from the request using this library.
<p>Publish Date: 2023-01-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25881>CVE-2022-25881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-25881">https://www.cve.org/CVERecord?id=CVE-2022-25881</a></p>
<p>Release Date: 2023-01-31</p>
<p>Fix Resolution: http-cache-semantics - 4.1.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3807</summary>
### Vulnerable Libraries - <b>ansi-regex-3.0.0.tgz</b>, <b>ansi-regex-5.0.0.tgz</b></p>
<p>
### <b>ansi-regex-3.0.0.tgz</b></p>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- tabtab-3.0.2.tgz
- inquirer-6.5.2.tgz
- string-width-2.1.1.tgz
- strip-ansi-4.0.0.tgz
- :x: **ansi-regex-3.0.0.tgz** (Vulnerable Library)
### <b>ansi-regex-5.0.0.tgz</b></p>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- boxen-5.0.0.tgz
- wrap-ansi-7.0.0.tgz
- strip-ansi-6.0.0.tgz
- :x: **ansi-regex-5.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution (ansi-regex): 3.0.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p><p>Fix Resolution (ansi-regex): 5.0.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25901</summary>
### Vulnerable Library - <b>cookiejar-2.1.2.tgz</b></p>
<p>simple persistent cookiejar system</p>
<p>Library home page: <a href="https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.2.tgz">https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- json-refs-3.0.15.tgz
- path-loader-1.0.10.tgz
- superagent-3.8.3.tgz
- :x: **cookiejar-2.1.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the package cookiejar before 2.1.4 are vulnerable to Regular Expression Denial of Service (ReDoS) via the Cookie.parse function, which uses an insecure regular expression.
<p>Publish Date: 2023-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25901>CVE-2022-25901</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-18</p>
<p>Fix Resolution: cookiejar - 2.1.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-31129</summary>
### Vulnerable Library - <b>moment-2.29.1.tgz</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://registry.npmjs.org/moment/-/moment-2.29.1.tgz">https://registry.npmjs.org/moment/-/moment-2.29.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- :x: **moment-2.29.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
moment is a JavaScript date library for parsing, validating, manipulating, and formatting dates. Affected versions of moment were found to use an inefficient parsing algorithm. Specifically using string-to-date parsing in moment (more specifically rfc2822 parsing, which is tried by default) has quadratic (N^2) complexity on specific inputs. Users may notice a noticeable slowdown is observed with inputs above 10k characters. Users who pass user-provided strings without sanity length checks to moment constructor are vulnerable to (Re)DoS attacks. The problem is patched in 2.29.4, the patch can be applied to all affected versions with minimal tweaking. Users are advised to upgrade. Users unable to upgrade should consider limiting date lengths accepted from user input.
<p>Publish Date: 2022-07-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31129>CVE-2022-31129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g">https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g</a></p>
<p>Release Date: 2022-07-06</p>
<p>Fix Resolution: moment - 2.29.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24785</summary>
### Vulnerable Library - <b>moment-2.29.1.tgz</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://registry.npmjs.org/moment/-/moment-2.29.1.tgz">https://registry.npmjs.org/moment/-/moment-2.29.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- :x: **moment-2.29.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Moment.js is a JavaScript date library for parsing, validating, manipulating, and formatting dates. A path traversal vulnerability impacts npm (server) users of Moment.js between versions 1.0.1 and 2.29.1, especially if a user-provided locale string is directly used to switch moment locale. This problem is patched in 2.29.2, and the patch can be applied to all affected versions. As a workaround, sanitize the user-provided locale name before passing it to Moment.js.
<p>Publish Date: 2022-04-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24785>CVE-2022-24785</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4">https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4</a></p>
<p>Release Date: 2022-04-04</p>
<p>Fix Resolution (moment): 2.29.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0155</summary>
### Vulnerable Library - <b>follow-redirects-1.13.2.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- axios-0.21.1.tgz
- :x: **follow-redirects-1.13.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
follow-redirects is vulnerable to Exposure of Private Personal Information to an Unauthorized Actor
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0155>CVE-2022-0155</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/">https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution (follow-redirects): 1.14.7</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.1.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- :x: **node-fetch-2.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution (node-fetch): 2.6.7</p>
<p>Direct dependency fix Resolution (serverless): 2.71.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0536</summary>
### Vulnerable Library - <b>follow-redirects-1.13.2.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- axios-0.21.1.tgz
- :x: **follow-redirects-1.13.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM follow-redirects prior to 1.14.8.
<p>Publish Date: 2022-02-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0536>CVE-2022-0536</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536</a></p>
<p>Release Date: 2022-02-09</p>
<p>Fix Resolution (follow-redirects): 1.14.8</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-32640</summary>
### Vulnerable Libraries - <b>ws-7.4.3.tgz</b>, <b>ws-6.2.1.tgz</b></p>
<p>
### <b>ws-7.4.3.tgz</b></p>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.4.3.tgz">https://registry.npmjs.org/ws/-/ws-7.4.3.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- :x: **ws-7.4.3.tgz** (Vulnerable Library)
### <b>ws-6.2.1.tgz</b></p>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-6.2.1.tgz">https://registry.npmjs.org/ws/-/ws-6.2.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-sdk-2.3.2.tgz
- :x: **ws-6.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution (ws): 7.4.6</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p><p>Fix Resolution (ws): 6.2.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-23413</summary>
### Vulnerable Library - <b>jszip-3.5.0.tgz</b></p>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **jszip-3.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package jszip before 3.7.0. Crafting a new zip file with filenames set to Object prototype values (e.g __proto__, toString, etc) results in a returned object with a modified prototype instance.
<p>Publish Date: 2021-07-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23413>CVE-2021-23413</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413</a></p>
<p>Release Date: 2021-07-25</p>
<p>Fix Resolution (jszip): 3.7.0</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details>
|
True
|
serverless-2.22.0.tgz: 27 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serverless-2.22.0.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (serverless version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-25912](https://www.mend.io/vulnerability-database/CVE-2022-25912) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | simple-git-2.31.0.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2022-48285](https://www.mend.io/vulnerability-database/CVE-2022-48285) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | jszip-3.5.0.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-24433](https://www.mend.io/vulnerability-database/CVE-2022-24433) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | simple-git-2.31.0.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2022-24066](https://www.mend.io/vulnerability-database/CVE-2022-24066) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | simple-git-2.31.0.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2021-31597](https://www.mend.io/vulnerability-database/CVE-2021-31597) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.4 | xmlhttprequest-ssl-1.5.5.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-42581](https://www.mend.io/vulnerability-database/CVE-2021-42581) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.1 | detected in multiple dependencies | Transitive | 3.0.0 | ❌ |
| [CVE-2020-28502](https://www.mend.io/vulnerability-database/CVE-2020-28502) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | xmlhttprequest-ssl-1.5.5.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-43138](https://www.mend.io/vulnerability-database/CVE-2021-43138) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | detected in multiple dependencies | Transitive | 3.0.0 | ❌ |
| [CVE-2022-0355](https://www.mend.io/vulnerability-database/CVE-2022-0355) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | simple-get-2.8.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-25878](https://www.mend.io/vulnerability-database/CVE-2022-25878) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobufjs-6.10.2.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2020-28469](https://www.mend.io/vulnerability-database/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-5.1.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-33502](https://www.mend.io/vulnerability-database/CVE-2021-33502) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | normalize-url-4.5.0.tgz | Transitive | 2.23.0 | ❌ |
| [WS-2021-0152](https://github.com/Qix-/color-string/commit/0789e21284c33d89ebc4ab4ca6f759b9375ac9d3) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | color-string-1.5.4.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-38900](https://www.mend.io/vulnerability-database/CVE-2022-38900) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | decode-uri-component-0.2.0.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-3749](https://www.mend.io/vulnerability-database/CVE-2021-3749) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | axios-0.21.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-25881](https://www.mend.io/vulnerability-database/CVE-2022-25881) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-3807](https://www.mend.io/vulnerability-database/CVE-2021-3807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | 2.23.0 | ❌ |
| [CVE-2022-25901](https://www.mend.io/vulnerability-database/CVE-2022-25901) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | cookiejar-2.1.2.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-31129](https://www.mend.io/vulnerability-database/CVE-2022-31129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-2.29.1.tgz | Transitive | N/A* | ❌ |
| [CVE-2022-24785](https://www.mend.io/vulnerability-database/CVE-2022-24785) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-2.29.1.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-0155](https://www.mend.io/vulnerability-database/CVE-2022-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | follow-redirects-1.13.2.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-0235](https://www.mend.io/vulnerability-database/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.1.tgz | Transitive | 2.71.0 | ❌ |
| [CVE-2022-0536](https://www.mend.io/vulnerability-database/CVE-2022-0536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | follow-redirects-1.13.2.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-32640](https://www.mend.io/vulnerability-database/CVE-2021-32640) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | 2.23.0 | ❌ |
| [CVE-2021-23413](https://www.mend.io/vulnerability-database/CVE-2021-23413) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jszip-3.5.0.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2021-29060](https://www.mend.io/vulnerability-database/CVE-2021-29060) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | color-string-1.5.4.tgz | Transitive | 2.23.0 | ❌ |
| [CVE-2022-33987](https://www.mend.io/vulnerability-database/CVE-2022-33987) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | detected in multiple dependencies | Transitive | 3.19.0 | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (25 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-25912</summary>
### Vulnerable Library - <b>simple-git-2.31.0.tgz</b></p>
<p>Simple GIT interface for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz">https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **simple-git-2.31.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package simple-git before 3.15.0 are vulnerable to Remote Code Execution (RCE) when enabling the ext transport protocol, which makes it exploitable via clone() method. This vulnerability exists due to an incomplete fix of [CVE-2022-24066](https://security.snyk.io/vuln/SNYK-JS-SIMPLEGIT-2434306).
<p>Publish Date: 2022-12-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25912>CVE-2022-25912</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-25912">https://www.cve.org/CVERecord?id=CVE-2022-25912</a></p>
<p>Release Date: 2022-12-06</p>
<p>Fix Resolution (simple-git): 3.15.0</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-48285</summary>
### Vulnerable Library - <b>jszip-3.5.0.tgz</b></p>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **jszip-3.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
loadAsync in JSZip before 3.8.0 allows Directory Traversal via a crafted ZIP archive.
<p>Publish Date: 2023-01-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-48285>CVE-2022-48285</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-29</p>
<p>Fix Resolution (jszip): 3.8.0</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-24433</summary>
### Vulnerable Library - <b>simple-git-2.31.0.tgz</b></p>
<p>Simple GIT interface for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz">https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **simple-git-2.31.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package simple-git before 3.3.0 are vulnerable to Command Injection via argument injection. When calling the .fetch(remote, branch, handlerFn) function, both the remote and branch parameters are passed to the git fetch subcommand. By injecting some git options it was possible to get arbitrary command execution.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24433>CVE-2022-24433</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-3f95-r44v-8mrg">https://github.com/advisories/GHSA-3f95-r44v-8mrg</a></p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution (simple-git): 3.3.0</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2022-24066</summary>
### Vulnerable Library - <b>simple-git-2.31.0.tgz</b></p>
<p>Simple GIT interface for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz">https://registry.npmjs.org/simple-git/-/simple-git-2.31.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **simple-git-2.31.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package simple-git before 3.5.0 are vulnerable to Command Injection due to an incomplete fix of [CVE-2022-24433](https://security.snyk.io/vuln/SNYK-JS-SIMPLEGIT-2421199) which only patches against the git fetch attack vector. A similar use of the --upload-pack feature of git is also supported for git clone, which the prior fix didn't cover.
<p>Publish Date: 2022-04-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24066>CVE-2022-24066</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-28xr-mwxg-3qc8">https://github.com/advisories/GHSA-28xr-mwxg-3qc8</a></p>
<p>Release Date: 2022-04-01</p>
<p>Fix Resolution (simple-git): 3.5.0</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2021-31597</summary>
### Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz">https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- socket.io-client-2.4.0.tgz
- engine.io-client-3.5.0.tgz
- :x: **xmlhttprequest-ssl-1.5.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The xmlhttprequest-ssl package before 1.6.1 for Node.js disables SSL certificate validation by default, because rejectUnauthorized (when the property exists but is undefined) is considered to be false within the https.request function of Node.js. In other words, no certificate is ever rejected.
<p>Publish Date: 2021-04-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-31597>CVE-2021-31597</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-31597">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-31597</a></p>
<p>Release Date: 2021-04-23</p>
<p>Fix Resolution (xmlhttprequest-ssl): 1.6.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2021-42581</summary>
### Vulnerable Libraries - <b>ramda-0.25.0.tgz</b>, <b>ramda-0.26.1.tgz</b></p>
<p>
### <b>ramda-0.25.0.tgz</b></p>
<p>A practical functional library for JavaScript programmers.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ramda/-/ramda-0.25.0.tgz">https://registry.npmjs.org/ramda/-/ramda-0.25.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-sdk-2.3.2.tgz
- :x: **ramda-0.25.0.tgz** (Vulnerable Library)
### <b>ramda-0.26.1.tgz</b></p>
<p>A practical functional library for JavaScript programmers.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ramda/-/ramda-0.26.1.tgz">https://registry.npmjs.org/ramda/-/ramda-0.26.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- cli-1.5.2.tgz
- template-1.1.4.tgz
- :x: **ramda-0.26.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
** DISPUTED ** Prototype poisoning in function mapObjIndexed in Ramda 0.27.0 and earlier allows attackers to compromise integrity or availability of application via supplying a crafted object (that contains an own property "__proto__") as an argument to the function. NOTE: the vendor disputes this because the observed behavior only means that a user can create objects that the user didn't know would contain custom prototypes.
<p>Publish Date: 2022-05-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-42581>CVE-2021-42581</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42581">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42581</a></p>
<p>Release Date: 2022-05-10</p>
<p>Fix Resolution (ramda): 0.27.1</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p><p>Fix Resolution (ramda): 0.27.1</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28502</summary>
### Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz">https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- socket.io-client-2.4.0.tgz
- engine.io-client-3.5.0.tgz
- :x: **xmlhttprequest-ssl-1.5.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package xmlhttprequest before 1.7.0; all versions of package xmlhttprequest-ssl. Provided requests are sent synchronously (async=False on xhr.open), malicious user input flowing into xhr.send could result in arbitrary code being injected and run.
<p>Publish Date: 2021-03-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28502>CVE-2020-28502</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4j5-c7cj-74xg">https://github.com/advisories/GHSA-h4j5-c7cj-74xg</a></p>
<p>Release Date: 2021-03-05</p>
<p>Fix Resolution (xmlhttprequest-ssl): 1.6.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-43138</summary>
### Vulnerable Libraries - <b>async-2.6.3.tgz</b>, <b>async-3.2.0.tgz</b></p>
<p>
### <b>async-2.6.3.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-2.6.3.tgz">https://registry.npmjs.org/async/-/async-2.6.3.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- kafka-node-5.0.0.tgz
- :x: **async-2.6.3.tgz** (Vulnerable Library)
### <b>async-3.2.0.tgz</b></p>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-3.2.0.tgz">https://registry.npmjs.org/async/-/async-3.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- archiver-5.2.0.tgz
- :x: **async-3.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Async before 2.6.4 and 3.x before 3.2.2, a malicious user can obtain privileges via the mapValues() method, aka lib/internal/iterator.js createObjectIterator prototype pollution.
<p>Publish Date: 2022-04-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43138>CVE-2021-43138</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43138">https://nvd.nist.gov/vuln/detail/CVE-2021-43138</a></p>
<p>Release Date: 2022-04-06</p>
<p>Fix Resolution (async): 2.6.4</p>
<p>Direct dependency fix Resolution (serverless): 3.0.0</p><p>Fix Resolution (async): 3.2.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-0355</summary>
### Vulnerable Library - <b>simple-get-2.8.1.tgz</b></p>
<p>Simplest way to make http get requests. Supports HTTPS, redirects, gzip/deflate, streams in < 100 lines.</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-get/-/simple-get-2.8.1.tgz">https://registry.npmjs.org/simple-get/-/simple-get-2.8.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- kafka-node-5.0.0.tgz
- snappy-6.3.5.tgz
- prebuild-install-5.3.0.tgz
- :x: **simple-get-2.8.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM simple-get prior to 4.0.1.
<p>Publish Date: 2022-01-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0355>CVE-2022-0355</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355</a></p>
<p>Release Date: 2022-01-26</p>
<p>Fix Resolution (simple-get): 2.8.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25878</summary>
### Vulnerable Library - <b>protobufjs-6.10.2.tgz</b></p>
<p>Protocol Buffers for JavaScript (& TypeScript).</p>
<p>Library home page: <a href="https://registry.npmjs.org/protobufjs/-/protobufjs-6.10.2.tgz">https://registry.npmjs.org/protobufjs/-/protobufjs-6.10.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- :x: **protobufjs-6.10.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package protobufjs before 6.11.3 are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype. This vulnerability can occur in multiple ways: 1. by providing untrusted user input to util.setProperty or to ReflectionObject.setParsedOption functions 2. by parsing/loading .proto files
<p>Publish Date: 2022-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25878>CVE-2022-25878</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25878</a></p>
<p>Release Date: 2022-05-27</p>
<p>Fix Resolution (protobufjs): 6.10.3</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-5.1.1.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- chokidar-3.5.1.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33502</summary>
### Vulnerable Library - <b>normalize-url-4.5.0.tgz</b></p>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-4.5.0.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-4.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- got-11.8.1.tgz
- cacheable-request-7.0.1.tgz
- :x: **normalize-url-4.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution (normalize-url): 4.5.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2021-0152</summary>
### Vulnerable Library - <b>color-string-1.5.4.tgz</b></p>
<p>Parser and generator for CSS color strings</p>
<p>Library home page: <a href="https://registry.npmjs.org/color-string/-/color-string-1.5.4.tgz">https://registry.npmjs.org/color-string/-/color-string-1.5.4.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- platform-client-china-2.1.4.tgz
- utils-china-1.0.14.tgz
- winston-3.2.1.tgz
- diagnostics-1.1.1.tgz
- colorspace-1.1.2.tgz
- color-3.0.0.tgz
- :x: **color-string-1.5.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular Expression Denial of Service (ReDoS) was found in color-string before 1.5.5.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://github.com/Qix-/color-string/commit/0789e21284c33d89ebc4ab4ca6f759b9375ac9d3>WS-2021-0152</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution (color-string): 1.5.5</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-38900</summary>
### Vulnerable Library - <b>decode-uri-component-0.2.0.tgz</b></p>
<p>A better decodeURIComponent</p>
<p>Library home page: <a href="https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz">https://registry.npmjs.org/decode-uri-component/-/decode-uri-component-0.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- download-8.0.0.tgz
- got-8.3.2.tgz
- cacheable-request-2.1.4.tgz
- normalize-url-2.0.1.tgz
- query-string-5.1.1.tgz
- :x: **decode-uri-component-0.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
decode-uri-component 0.2.0 is vulnerable to Improper Input Validation resulting in DoS.
<p>Publish Date: 2022-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-38900>CVE-2022-38900</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-w573-4hg7-7wgq">https://github.com/advisories/GHSA-w573-4hg7-7wgq</a></p>
<p>Release Date: 2022-11-28</p>
<p>Fix Resolution (decode-uri-component): 0.2.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3749</summary>
### Vulnerable Library - <b>axios-0.21.1.tgz</b></p>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.1.tgz">https://registry.npmjs.org/axios/-/axios-0.21.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- :x: **axios-0.21.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
axios is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3749>CVE-2021-3749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/1e8f07fc-c384-4ff9-8498-0690de2e8c31/">https://huntr.dev/bounties/1e8f07fc-c384-4ff9-8498-0690de2e8c31/</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (axios): 0.21.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25881</summary>
### Vulnerable Libraries - <b>http-cache-semantics-4.1.0.tgz</b>, <b>http-cache-semantics-3.8.1.tgz</b></p>
<p>
### <b>http-cache-semantics-4.1.0.tgz</b></p>
<p>Parses Cache-Control and other headers. Helps building correct HTTP caches and proxies</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz">https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- got-11.8.1.tgz
- cacheable-request-7.0.1.tgz
- :x: **http-cache-semantics-4.1.0.tgz** (Vulnerable Library)
### <b>http-cache-semantics-3.8.1.tgz</b></p>
<p>Parses Cache-Control and other headers. Helps building correct HTTP caches and proxies</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-3.8.1.tgz">https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-3.8.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- download-8.0.0.tgz
- got-8.3.2.tgz
- cacheable-request-2.1.4.tgz
- :x: **http-cache-semantics-3.8.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects versions of the package http-cache-semantics before 4.1.1. The issue can be exploited via malicious request header values sent to a server, when that server reads the cache policy from the request using this library.
<p>Publish Date: 2023-01-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25881>CVE-2022-25881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-25881">https://www.cve.org/CVERecord?id=CVE-2022-25881</a></p>
<p>Release Date: 2023-01-31</p>
<p>Fix Resolution: http-cache-semantics - 4.1.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3807</summary>
### Vulnerable Libraries - <b>ansi-regex-3.0.0.tgz</b>, <b>ansi-regex-5.0.0.tgz</b></p>
<p>
### <b>ansi-regex-3.0.0.tgz</b></p>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-3.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- tabtab-3.0.2.tgz
- inquirer-6.5.2.tgz
- string-width-2.1.1.tgz
- strip-ansi-4.0.0.tgz
- :x: **ansi-regex-3.0.0.tgz** (Vulnerable Library)
### <b>ansi-regex-5.0.0.tgz</b></p>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- boxen-5.0.0.tgz
- wrap-ansi-7.0.0.tgz
- strip-ansi-6.0.0.tgz
- :x: **ansi-regex-5.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution (ansi-regex): 3.0.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p><p>Fix Resolution (ansi-regex): 5.0.1</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25901</summary>
### Vulnerable Library - <b>cookiejar-2.1.2.tgz</b></p>
<p>simple persistent cookiejar system</p>
<p>Library home page: <a href="https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.2.tgz">https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- json-refs-3.0.15.tgz
- path-loader-1.0.10.tgz
- superagent-3.8.3.tgz
- :x: **cookiejar-2.1.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the package cookiejar before 2.1.4 are vulnerable to Regular Expression Denial of Service (ReDoS) via the Cookie.parse function, which uses an insecure regular expression.
<p>Publish Date: 2023-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25901>CVE-2022-25901</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-18</p>
<p>Fix Resolution: cookiejar - 2.1.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-31129</summary>
### Vulnerable Library - <b>moment-2.29.1.tgz</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://registry.npmjs.org/moment/-/moment-2.29.1.tgz">https://registry.npmjs.org/moment/-/moment-2.29.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- :x: **moment-2.29.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
moment is a JavaScript date library for parsing, validating, manipulating, and formatting dates. Affected versions of moment were found to use an inefficient parsing algorithm. Specifically using string-to-date parsing in moment (more specifically rfc2822 parsing, which is tried by default) has quadratic (N^2) complexity on specific inputs. Users may notice a noticeable slowdown is observed with inputs above 10k characters. Users who pass user-provided strings without sanity length checks to moment constructor are vulnerable to (Re)DoS attacks. The problem is patched in 2.29.4, the patch can be applied to all affected versions with minimal tweaking. Users are advised to upgrade. Users unable to upgrade should consider limiting date lengths accepted from user input.
<p>Publish Date: 2022-07-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31129>CVE-2022-31129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g">https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g</a></p>
<p>Release Date: 2022-07-06</p>
<p>Fix Resolution: moment - 2.29.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24785</summary>
### Vulnerable Library - <b>moment-2.29.1.tgz</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://registry.npmjs.org/moment/-/moment-2.29.1.tgz">https://registry.npmjs.org/moment/-/moment-2.29.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- components-3.6.1.tgz
- :x: **moment-2.29.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Moment.js is a JavaScript date library for parsing, validating, manipulating, and formatting dates. A path traversal vulnerability impacts npm (server) users of Moment.js between versions 1.0.1 and 2.29.1, especially if a user-provided locale string is directly used to switch moment locale. This problem is patched in 2.29.2, and the patch can be applied to all affected versions. As a workaround, sanitize the user-provided locale name before passing it to Moment.js.
<p>Publish Date: 2022-04-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24785>CVE-2022-24785</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4">https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4</a></p>
<p>Release Date: 2022-04-04</p>
<p>Fix Resolution (moment): 2.29.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0155</summary>
### Vulnerable Library - <b>follow-redirects-1.13.2.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- axios-0.21.1.tgz
- :x: **follow-redirects-1.13.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
follow-redirects is vulnerable to Exposure of Private Personal Information to an Unauthorized Actor
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0155>CVE-2022-0155</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/">https://huntr.dev/bounties/fc524e4b-ebb6-427d-ab67-a64181020406/</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution (follow-redirects): 1.14.7</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.1.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- :x: **node-fetch-2.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution (node-fetch): 2.6.7</p>
<p>Direct dependency fix Resolution (serverless): 2.71.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0536</summary>
### Vulnerable Library - <b>follow-redirects-1.13.2.tgz</b></p>
<p>HTTP and HTTPS modules that follow redirects.</p>
<p>Library home page: <a href="https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz">https://registry.npmjs.org/follow-redirects/-/follow-redirects-1.13.2.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- axios-0.21.1.tgz
- :x: **follow-redirects-1.13.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM follow-redirects prior to 1.14.8.
<p>Publish Date: 2022-02-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0536>CVE-2022-0536</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0536</a></p>
<p>Release Date: 2022-02-09</p>
<p>Fix Resolution (follow-redirects): 1.14.8</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-32640</summary>
### Vulnerable Libraries - <b>ws-7.4.3.tgz</b>, <b>ws-6.2.1.tgz</b></p>
<p>
### <b>ws-7.4.3.tgz</b></p>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.4.3.tgz">https://registry.npmjs.org/ws/-/ws-7.4.3.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-client-3.11.0.tgz
- :x: **ws-7.4.3.tgz** (Vulnerable Library)
### <b>ws-6.2.1.tgz</b></p>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-6.2.1.tgz">https://registry.npmjs.org/ws/-/ws-6.2.1.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- platform-sdk-2.3.2.tgz
- :x: **ws-6.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution (ws): 7.4.6</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p><p>Fix Resolution (ws): 6.2.2</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-23413</summary>
### Vulnerable Library - <b>jszip-3.5.0.tgz</b></p>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- serverless-2.22.0.tgz (Root Library)
- enterprise-plugin-4.4.2.tgz
- :x: **jszip-3.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/WFS-Mend/vtrade-serverless/commit/c52b98a9d17fb727f467104ad99db0dca5b6e0f9">c52b98a9d17fb727f467104ad99db0dca5b6e0f9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package jszip before 3.7.0. Crafting a new zip file with filenames set to Object prototype values (e.g __proto__, toString, etc) results in a returned object with a modified prototype instance.
<p>Publish Date: 2021-07-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23413>CVE-2021-23413</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413</a></p>
<p>Release Date: 2021-07-25</p>
<p>Fix Resolution (jszip): 3.7.0</p>
<p>Direct dependency fix Resolution (serverless): 2.23.0</p>
</p>
<p></p>
</details>
|
non_defect
|
serverless tgz vulnerabilities highest severity is vulnerable library serverless tgz found in head commit a href vulnerabilities cve severity cvss dependency type fixed in serverless version remediation available critical simple git tgz transitive critical jszip tgz transitive critical simple git tgz transitive critical simple git tgz transitive critical xmlhttprequest ssl tgz transitive critical detected in multiple dependencies transitive high xmlhttprequest ssl tgz transitive high detected in multiple dependencies transitive high simple get tgz transitive high protobufjs tgz transitive high glob parent tgz transitive high normalize url tgz transitive high color string tgz transitive high decode uri component tgz transitive high axios tgz transitive high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive high cookiejar tgz transitive n a high moment tgz transitive n a high moment tgz transitive medium follow redirects tgz transitive medium node fetch tgz transitive medium follow redirects tgz transitive medium detected in multiple dependencies transitive medium jszip tgz transitive medium color string tgz transitive medium detected in multiple dependencies transitive for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library simple git tgz simple git interface for node js library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz x simple git tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package simple git before are vulnerable to remote code execution rce when enabling the ext transport protocol which makes it exploitable via clone method this vulnerability exists due to an incomplete fix of publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution simple git direct dependency fix resolution serverless cve vulnerable library jszip tgz create read and edit zip files with javascript library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz x jszip tgz vulnerable library found in head commit a href found in base branch master vulnerability details loadasync in jszip before allows directory traversal via a crafted zip archive publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution jszip direct dependency fix resolution serverless cve vulnerable library simple git tgz simple git interface for node js library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz x simple git tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package simple git before are vulnerable to command injection via argument injection when calling the fetch remote branch handlerfn function both the remote and branch parameters are passed to the git fetch subcommand by injecting some git options it was possible to get arbitrary command execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution simple git direct dependency fix resolution serverless cve vulnerable library simple git tgz simple git interface for node js library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz x simple git tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package simple git before are vulnerable to command injection due to an incomplete fix of which only patches against the git fetch attack vector a similar use of the upload pack feature of git is also supported for git clone which the prior fix didn t cover publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution simple git direct dependency fix resolution serverless cve vulnerable library xmlhttprequest ssl tgz xmlhttprequest for node library home page a href dependency hierarchy serverless tgz root library components tgz platform client china tgz utils china tgz socket io client tgz engine io client tgz x xmlhttprequest ssl tgz vulnerable library found in head commit a href found in base branch master vulnerability details the xmlhttprequest ssl package before for node js disables ssl certificate validation by default because rejectunauthorized when the property exists but is undefined is considered to be false within the https request function of node js in other words no certificate is ever rejected publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xmlhttprequest ssl direct dependency fix resolution serverless cve vulnerable libraries ramda tgz ramda tgz ramda tgz a practical functional library for javascript programmers library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz platform sdk tgz x ramda tgz vulnerable library ramda tgz a practical functional library for javascript programmers library home page a href dependency hierarchy serverless tgz root library cli tgz template tgz x ramda tgz vulnerable library found in head commit a href found in base branch master vulnerability details disputed prototype poisoning in function mapobjindexed in ramda and earlier allows attackers to compromise integrity or availability of application via supplying a crafted object that contains an own property proto as an argument to the function note the vendor disputes this because the observed behavior only means that a user can create objects that the user didn t know would contain custom prototypes publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ramda direct dependency fix resolution serverless fix resolution ramda direct dependency fix resolution serverless cve vulnerable library xmlhttprequest ssl tgz xmlhttprequest for node library home page a href dependency hierarchy serverless tgz root library components tgz platform client china tgz utils china tgz socket io client tgz engine io client tgz x xmlhttprequest ssl tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package xmlhttprequest before all versions of package xmlhttprequest ssl provided requests are sent synchronously async false on xhr open malicious user input flowing into xhr send could result in arbitrary code being injected and run publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xmlhttprequest ssl direct dependency fix resolution serverless cve vulnerable libraries async tgz async tgz async tgz higher order functions and common patterns for asynchronous code library home page a href dependency hierarchy serverless tgz root library components tgz platform client china tgz utils china tgz kafka node tgz x async tgz vulnerable library async tgz higher order functions and common patterns for asynchronous code library home page a href dependency hierarchy serverless tgz root library archiver tgz x async tgz vulnerable library found in head commit a href found in base branch master vulnerability details in async before and x before a malicious user can obtain privileges via the mapvalues method aka lib internal iterator js createobjectiterator prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution async direct dependency fix resolution serverless fix resolution async direct dependency fix resolution serverless cve vulnerable library simple get tgz simplest way to make http get requests supports https redirects gzip deflate streams in library home page a href dependency hierarchy serverless tgz root library components tgz platform client china tgz utils china tgz kafka node tgz snappy tgz prebuild install tgz x simple get tgz vulnerable library found in head commit a href found in base branch master vulnerability details exposure of sensitive information to an unauthorized actor in npm simple get prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution simple get direct dependency fix resolution serverless cve vulnerable library protobufjs tgz protocol buffers for javascript typescript library home page a href dependency hierarchy serverless tgz root library components tgz platform client china tgz utils china tgz x protobufjs tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package protobufjs before are vulnerable to prototype pollution which can allow an attacker to add modify properties of the object prototype this vulnerability can occur in multiple ways by providing untrusted user input to util setproperty or to reflectionobject setparsedoption functions by parsing loading proto files publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution protobufjs direct dependency fix resolution serverless cve vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution serverless cve vulnerable library normalize url tgz normalize a url library home page a href dependency hierarchy serverless tgz root library got tgz cacheable request tgz x normalize url tgz vulnerable library found in head commit a href found in base branch master vulnerability details the normalize url package before x before and x before for node js has a redos regular expression denial of service issue because it has exponential performance for data urls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution normalize url direct dependency fix resolution serverless ws vulnerable library color string tgz parser and generator for css color strings library home page a href dependency hierarchy serverless tgz root library components tgz platform client china tgz utils china tgz winston tgz diagnostics tgz colorspace tgz color tgz x color string tgz vulnerable library found in head commit a href found in base branch master vulnerability details regular expression denial of service redos was found in color string before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution color string direct dependency fix resolution serverless cve vulnerable library decode uri component tgz a better decodeuricomponent library home page a href dependency hierarchy serverless tgz root library download tgz got tgz cacheable request tgz normalize url tgz query string tgz x decode uri component tgz vulnerable library found in head commit a href found in base branch master vulnerability details decode uri component is vulnerable to improper input validation resulting in dos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution decode uri component direct dependency fix resolution serverless cve vulnerable library axios tgz promise based http client for the browser and node js library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz platform client tgz x axios tgz vulnerable library found in head commit a href found in base branch master vulnerability details axios is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution axios direct dependency fix resolution serverless cve vulnerable libraries http cache semantics tgz http cache semantics tgz http cache semantics tgz parses cache control and other headers helps building correct http caches and proxies library home page a href dependency hierarchy serverless tgz root library got tgz cacheable request tgz x http cache semantics tgz vulnerable library http cache semantics tgz parses cache control and other headers helps building correct http caches and proxies library home page a href dependency hierarchy serverless tgz root library download tgz got tgz cacheable request tgz x http cache semantics tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects versions of the package http cache semantics before the issue can be exploited via malicious request header values sent to a server when that server reads the cache policy from the request using this library publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution http cache semantics cve vulnerable libraries ansi regex tgz ansi regex tgz ansi regex tgz regular expression for matching ansi escape codes library home page a href dependency hierarchy serverless tgz root library tabtab tgz inquirer tgz string width tgz strip ansi tgz x ansi regex tgz vulnerable library ansi regex tgz regular expression for matching ansi escape codes library home page a href dependency hierarchy serverless tgz root library boxen tgz wrap ansi tgz strip ansi tgz x ansi regex tgz vulnerable library found in head commit a href found in base branch master vulnerability details ansi regex is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ansi regex direct dependency fix resolution serverless fix resolution ansi regex direct dependency fix resolution serverless cve vulnerable library cookiejar tgz simple persistent cookiejar system library home page a href dependency hierarchy serverless tgz root library json refs tgz path loader tgz superagent tgz x cookiejar tgz vulnerable library found in head commit a href found in base branch master vulnerability details versions of the package cookiejar before are vulnerable to regular expression denial of service redos via the cookie parse function which uses an insecure regular expression publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution cookiejar cve vulnerable library moment tgz parse validate manipulate and display dates library home page a href dependency hierarchy serverless tgz root library components tgz x moment tgz vulnerable library found in head commit a href found in base branch master vulnerability details moment is a javascript date library for parsing validating manipulating and formatting dates affected versions of moment were found to use an inefficient parsing algorithm specifically using string to date parsing in moment more specifically parsing which is tried by default has quadratic n complexity on specific inputs users may notice a noticeable slowdown is observed with inputs above characters users who pass user provided strings without sanity length checks to moment constructor are vulnerable to re dos attacks the problem is patched in the patch can be applied to all affected versions with minimal tweaking users are advised to upgrade users unable to upgrade should consider limiting date lengths accepted from user input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution moment cve vulnerable library moment tgz parse validate manipulate and display dates library home page a href dependency hierarchy serverless tgz root library components tgz x moment tgz vulnerable library found in head commit a href found in base branch master vulnerability details moment js is a javascript date library for parsing validating manipulating and formatting dates a path traversal vulnerability impacts npm server users of moment js between versions and especially if a user provided locale string is directly used to switch moment locale this problem is patched in and the patch can be applied to all affected versions as a workaround sanitize the user provided locale name before passing it to moment js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution moment direct dependency fix resolution serverless cve vulnerable library follow redirects tgz http and https modules that follow redirects library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz platform client tgz axios tgz x follow redirects tgz vulnerable library found in head commit a href found in base branch master vulnerability details follow redirects is vulnerable to exposure of private personal information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution follow redirects direct dependency fix resolution serverless cve vulnerable library node fetch tgz a light weight module that brings window fetch to node js library home page a href dependency hierarchy serverless tgz root library x node fetch tgz vulnerable library found in head commit a href found in base branch master vulnerability details node fetch is vulnerable to exposure of sensitive information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node fetch direct dependency fix resolution serverless cve vulnerable library follow redirects tgz http and https modules that follow redirects library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz platform client tgz axios tgz x follow redirects tgz vulnerable library found in head commit a href found in base branch master vulnerability details exposure of sensitive information to an unauthorized actor in npm follow redirects prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution follow redirects direct dependency fix resolution serverless cve vulnerable libraries ws tgz ws tgz ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz platform client tgz x ws tgz vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz platform sdk tgz x ws tgz vulnerable library found in head commit a href found in base branch master vulnerability details ws is an open source websocket client and server library for node js a specially crafted value of the sec websocket protocol header can be used to significantly slow down a ws server the vulnerability has been fixed in ws in vulnerable versions of ws the issue can be mitigated by reducing the maximum allowed length of the request headers using the and or the options publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ws direct dependency fix resolution serverless fix resolution ws direct dependency fix resolution serverless cve vulnerable library jszip tgz create read and edit zip files with javascript library home page a href dependency hierarchy serverless tgz root library enterprise plugin tgz x jszip tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package jszip before crafting a new zip file with filenames set to object prototype values e g proto tostring etc results in a returned object with a modified prototype instance publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jszip direct dependency fix resolution serverless
| 0
|
27,229
| 13,204,821,969
|
IssuesEvent
|
2020-08-14 16:39:31
|
hajimehoshi/ebiten
|
https://api.github.com/repos/hajimehoshi/ebiten
|
closed
|
graphicsdriver/opengl: Use an explicit way to detect GL context lost
|
os:android performance
|
https://developer.android.com/reference/android/opengl/GLSurfaceView.Renderer.html#egl-context-lost
> There are situations where the EGL rendering context will be lost. This typically happens when device wakes up after going to sleep. When the EGL context is lost, all OpenGL resources (such as textures) that are associated with that context will be automatically deleted. In order to keep rendering correctly, a renderer must recreate any lost resources that it still needs. The onSurfaceCreated(javax.microedition.khronos.opengles.GL10, javax.microedition.khronos.egl.EGLConfig) method is a convenient place to do this.
|
True
|
graphicsdriver/opengl: Use an explicit way to detect GL context lost - https://developer.android.com/reference/android/opengl/GLSurfaceView.Renderer.html#egl-context-lost
> There are situations where the EGL rendering context will be lost. This typically happens when device wakes up after going to sleep. When the EGL context is lost, all OpenGL resources (such as textures) that are associated with that context will be automatically deleted. In order to keep rendering correctly, a renderer must recreate any lost resources that it still needs. The onSurfaceCreated(javax.microedition.khronos.opengles.GL10, javax.microedition.khronos.egl.EGLConfig) method is a convenient place to do this.
|
non_defect
|
graphicsdriver opengl use an explicit way to detect gl context lost there are situations where the egl rendering context will be lost this typically happens when device wakes up after going to sleep when the egl context is lost all opengl resources such as textures that are associated with that context will be automatically deleted in order to keep rendering correctly a renderer must recreate any lost resources that it still needs the onsurfacecreated javax microedition khronos opengles javax microedition khronos egl eglconfig method is a convenient place to do this
| 0
|
15,530
| 5,140,730,055
|
IssuesEvent
|
2017-01-12 06:54:43
|
phetsims/john-travoltage
|
https://api.github.com/repos/phetsims/john-travoltage
|
opened
|
AppendageNode options.controls
|
dev:code-review
|
I see:
```js
if ( options.controls ) {
this.setAttribute( 'aria-controls', options.controls.join( ',' ));
}
```
but this option isn't noted in the default options, and doesn't have documentation. Can it have a default value with documentation mentioning what it does?
Code review for https://github.com/phetsims/john-travoltage/issues/128
|
1.0
|
AppendageNode options.controls - I see:
```js
if ( options.controls ) {
this.setAttribute( 'aria-controls', options.controls.join( ',' ));
}
```
but this option isn't noted in the default options, and doesn't have documentation. Can it have a default value with documentation mentioning what it does?
Code review for https://github.com/phetsims/john-travoltage/issues/128
|
non_defect
|
appendagenode options controls i see js if options controls this setattribute aria controls options controls join but this option isn t noted in the default options and doesn t have documentation can it have a default value with documentation mentioning what it does code review for
| 0
|
333,791
| 24,391,465,064
|
IssuesEvent
|
2022-10-04 15:32:00
|
G915-2-Data-Modeling-381/Project-1-eStreamingMovies
|
https://api.github.com/repos/G915-2-Data-Modeling-381/Project-1-eStreamingMovies
|
closed
|
10/4/2022 10:45AM - Model Draft Discussion Round 2
|
documentation Meeting
|
**GOAL: Review the CS381 Project Planning Document and the Project 1 Specification.**
**Attendance:**
- [x] Amber Garcia
- [x] Adrian Noa
- [x] Jasminder Garcha
- [x] Wade Li
- [ ] Oliver Vidal
**To-Dos:**
- [x] Schedule time for meeting with everyone's confirmation
- [ ] Read over the positives, negatives, and suggested features for the DM
- [x] Start drafting the CDM
- [ ] Creating Definitions for relationships and the business objects
**Notes:**
- View Notes for https://github.com/G915-2-Data-Modeling-381/Project-1-eStreamingMovies/issues/8 to push to this meeting
|
1.0
|
10/4/2022 10:45AM - Model Draft Discussion Round 2 - **GOAL: Review the CS381 Project Planning Document and the Project 1 Specification.**
**Attendance:**
- [x] Amber Garcia
- [x] Adrian Noa
- [x] Jasminder Garcha
- [x] Wade Li
- [ ] Oliver Vidal
**To-Dos:**
- [x] Schedule time for meeting with everyone's confirmation
- [ ] Read over the positives, negatives, and suggested features for the DM
- [x] Start drafting the CDM
- [ ] Creating Definitions for relationships and the business objects
**Notes:**
- View Notes for https://github.com/G915-2-Data-Modeling-381/Project-1-eStreamingMovies/issues/8 to push to this meeting
|
non_defect
|
model draft discussion round goal review the project planning document and the project specification attendance amber garcia adrian noa jasminder garcha wade li oliver vidal to dos schedule time for meeting with everyone s confirmation read over the positives negatives and suggested features for the dm start drafting the cdm creating definitions for relationships and the business objects notes view notes for to push to this meeting
| 0
|
2,090
| 2,603,976,182
|
IssuesEvent
|
2015-02-24 19:01:33
|
chrsmith/nishazi6
|
https://api.github.com/repos/chrsmith/nishazi6
|
opened
|
沈阳包皮上长水疱
|
auto-migrated Priority-Medium Type-Defect
|
```
沈阳包皮上长水疱〓沈陽軍區政治部醫院性病〓TEL:024-3102330
8〓成立于1946年,68年專注于性傳播疾病的研究和治療。位于�
��陽市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷�
��悠久、設備精良、技術權威、專家云集,是預防、保健、醫
療、科研康復為一體的綜合性醫院。是國家首批公立甲等部��
�醫院、全國首批醫療規范定點單位,是第四軍醫大學、東南�
��學等知名高等院校的教學醫院。曾被中國人民解放軍空軍后
勤部衛生部評為衛生工作先進單位,先后兩次榮立集體二等��
�。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:20
|
1.0
|
沈阳包皮上长水疱 - ```
沈阳包皮上长水疱〓沈陽軍區政治部醫院性病〓TEL:024-3102330
8〓成立于1946年,68年專注于性傳播疾病的研究和治療。位于�
��陽市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷�
��悠久、設備精良、技術權威、專家云集,是預防、保健、醫
療、科研康復為一體的綜合性醫院。是國家首批公立甲等部��
�醫院、全國首批醫療規范定點單位,是第四軍醫大學、東南�
��學等知名高等院校的教學醫院。曾被中國人民解放軍空軍后
勤部衛生部評為衛生工作先進單位,先后兩次榮立集體二等��
�。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:20
|
defect
|
沈阳包皮上长水疱 沈阳包皮上长水疱〓沈陽軍區政治部醫院性病〓tel: 〓 , 。位于� �� 。是一所與新中國同建立共輝煌的歷� ��悠久、設備精良、技術權威、專家云集,是預防、保健、醫 療、科研康復為一體的綜合性醫院。是國家首批公立甲等部�� �醫院、全國首批醫療規范定點單位,是第四軍醫大學、東南� ��學等知名高等院校的教學醫院。曾被中國人民解放軍空軍后 勤部衛生部評為衛生工作先進單位,先后兩次榮立集體二等�� �。 original issue reported on code google com by gmail com on jun at
| 1
|
55,150
| 13,966,021,571
|
IssuesEvent
|
2020-10-26 01:00:45
|
kenferrara/conjure-java
|
https://api.github.com/repos/kenferrara/conjure-java
|
opened
|
CVE-2020-27216 (High) detected in jetty-webapp-9.4.26.v20200117.jar
|
security vulnerability
|
## CVE-2020-27216 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-webapp-9.4.26.v20200117.jar</b></p></summary>
<p>Jetty web application support</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: conjure-java/conjure-java-server-verifier/build.gradle</p>
<p>Path to vulnerable library: /tmp/ws-ua_20200729191313_IAUXGS/downloadResource_JHGLGQ/20200729191727/jetty-webapp-9.4.26.v20200117.jar,20200729191313_IAUXGS/downloadResource_JHGLGQ/20200729191727/jetty-webapp-9.4.26.v20200117.jar</p>
<p>
Dependency Hierarchy:
- :x: **jetty-webapp-9.4.26.v20200117.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Eclipse Jetty versions 1.0 thru 9.4.32.v20200930, 10.0.0.alpha1 thru 10.0.0.beta2, and 11.0.0.alpha1 thru 11.0.0.beta2O, on Unix like systems, the system's temporary directory is shared between all users on that system. A collocated user can observe the process of creating a temporary sub directory in the shared temporary directory and race to complete the creation of the temporary subdirectory. If the attacker wins the race then they will have read and write permission to the subdirectory used to unpack web applications, including their WEB-INF/lib jar files and JSP files. If any code is ever executed out of this temporary directory, this can lead to a local privilege escalation vulnerability.
<p>Publish Date: 2020-10-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-27216>CVE-2020-27216</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.eclipse.org/bugs/show_bug.cgi?id=567921">https://bugs.eclipse.org/bugs/show_bug.cgi?id=567921</a></p>
<p>Release Date: 2020-10-20</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-runner:9.4.33,10.0.0.beta3,11.0.0.beta3;org.eclipse.jetty:jetty-webapp:9.4.33,10.0.0.beta3,11.0.0.beta3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-webapp","packageVersion":"9.4.26.v20200117","isTransitiveDependency":false,"dependencyTree":"org.eclipse.jetty:jetty-webapp:9.4.26.v20200117","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-runner:9.4.33,10.0.0.beta3,11.0.0.beta3;org.eclipse.jetty:jetty-webapp:9.4.33,10.0.0.beta3,11.0.0.beta3"}],"vulnerabilityIdentifier":"CVE-2020-27216","vulnerabilityDetails":"In Eclipse Jetty versions 1.0 thru 9.4.32.v20200930, 10.0.0.alpha1 thru 10.0.0.beta2, and 11.0.0.alpha1 thru 11.0.0.beta2O, on Unix like systems, the system\u0027s temporary directory is shared between all users on that system. A collocated user can observe the process of creating a temporary sub directory in the shared temporary directory and race to complete the creation of the temporary subdirectory. If the attacker wins the race then they will have read and write permission to the subdirectory used to unpack web applications, including their WEB-INF/lib jar files and JSP files. If any code is ever executed out of this temporary directory, this can lead to a local privilege escalation vulnerability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-27216","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-27216 (High) detected in jetty-webapp-9.4.26.v20200117.jar - ## CVE-2020-27216 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-webapp-9.4.26.v20200117.jar</b></p></summary>
<p>Jetty web application support</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: conjure-java/conjure-java-server-verifier/build.gradle</p>
<p>Path to vulnerable library: /tmp/ws-ua_20200729191313_IAUXGS/downloadResource_JHGLGQ/20200729191727/jetty-webapp-9.4.26.v20200117.jar,20200729191313_IAUXGS/downloadResource_JHGLGQ/20200729191727/jetty-webapp-9.4.26.v20200117.jar</p>
<p>
Dependency Hierarchy:
- :x: **jetty-webapp-9.4.26.v20200117.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Eclipse Jetty versions 1.0 thru 9.4.32.v20200930, 10.0.0.alpha1 thru 10.0.0.beta2, and 11.0.0.alpha1 thru 11.0.0.beta2O, on Unix like systems, the system's temporary directory is shared between all users on that system. A collocated user can observe the process of creating a temporary sub directory in the shared temporary directory and race to complete the creation of the temporary subdirectory. If the attacker wins the race then they will have read and write permission to the subdirectory used to unpack web applications, including their WEB-INF/lib jar files and JSP files. If any code is ever executed out of this temporary directory, this can lead to a local privilege escalation vulnerability.
<p>Publish Date: 2020-10-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-27216>CVE-2020-27216</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.eclipse.org/bugs/show_bug.cgi?id=567921">https://bugs.eclipse.org/bugs/show_bug.cgi?id=567921</a></p>
<p>Release Date: 2020-10-20</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-runner:9.4.33,10.0.0.beta3,11.0.0.beta3;org.eclipse.jetty:jetty-webapp:9.4.33,10.0.0.beta3,11.0.0.beta3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-webapp","packageVersion":"9.4.26.v20200117","isTransitiveDependency":false,"dependencyTree":"org.eclipse.jetty:jetty-webapp:9.4.26.v20200117","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-runner:9.4.33,10.0.0.beta3,11.0.0.beta3;org.eclipse.jetty:jetty-webapp:9.4.33,10.0.0.beta3,11.0.0.beta3"}],"vulnerabilityIdentifier":"CVE-2020-27216","vulnerabilityDetails":"In Eclipse Jetty versions 1.0 thru 9.4.32.v20200930, 10.0.0.alpha1 thru 10.0.0.beta2, and 11.0.0.alpha1 thru 11.0.0.beta2O, on Unix like systems, the system\u0027s temporary directory is shared between all users on that system. A collocated user can observe the process of creating a temporary sub directory in the shared temporary directory and race to complete the creation of the temporary subdirectory. If the attacker wins the race then they will have read and write permission to the subdirectory used to unpack web applications, including their WEB-INF/lib jar files and JSP files. If any code is ever executed out of this temporary directory, this can lead to a local privilege escalation vulnerability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-27216","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
cve high detected in jetty webapp jar cve high severity vulnerability vulnerable library jetty webapp jar jetty web application support library home page a href path to dependency file conjure java conjure java server verifier build gradle path to vulnerable library tmp ws ua iauxgs downloadresource jhglgq jetty webapp jar iauxgs downloadresource jhglgq jetty webapp jar dependency hierarchy x jetty webapp jar vulnerable library vulnerability details in eclipse jetty versions thru thru and thru on unix like systems the system s temporary directory is shared between all users on that system a collocated user can observe the process of creating a temporary sub directory in the shared temporary directory and race to complete the creation of the temporary subdirectory if the attacker wins the race then they will have read and write permission to the subdirectory used to unpack web applications including their web inf lib jar files and jsp files if any code is ever executed out of this temporary directory this can lead to a local privilege escalation vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org eclipse jetty jetty runner org eclipse jetty jetty webapp isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails in eclipse jetty versions thru thru and thru on unix like systems the system temporary directory is shared between all users on that system a collocated user can observe the process of creating a temporary sub directory in the shared temporary directory and race to complete the creation of the temporary subdirectory if the attacker wins the race then they will have read and write permission to the subdirectory used to unpack web applications including their web inf lib jar files and jsp files if any code is ever executed out of this temporary directory this can lead to a local privilege escalation vulnerability vulnerabilityurl
| 0
|
780,723
| 27,405,632,615
|
IssuesEvent
|
2023-03-01 06:26:48
|
WavesHQ/quantum
|
https://api.github.com/repos/WavesHQ/quantum
|
closed
|
Error code 3: when user send more than specified amount
|
area/ui-ux bug/major needs/triage priority/important-soon kind/bug
|
<!--
Please use this template while reporting a bug and provide as much info as possible.
If the matter is security related, please disclose it privately via security@defichain.com
-->
```
Ver: 0.14.0
Network: TestNet
Flow: DFC → ETH
Description: Error code 3: when user send more than specified amount
```
**Actual:**
– at **step 3 Validate**, if user encounters `Error code 3: BalanceNotMatched`
– The balance in the wallet's address does not equal to the amount filled in the form
– user has no other option but to select x and restart the tx
#### What you expected to happen:
TBC
**To reproduce:**
Select Source Network: Ethereum
Input `0.02` dETH > select `Review transaction`
at **step 1 Initiate**, paste `Ethereum address` in text field > Continue
at **step 2 Transact**, use MLW to send `0.3` dETH > when tx is sent > go back to **Quantum**, select `Verify transfer`
at **step 3 Validate**, `error:` Error code 3: BalanceNotMatched > `note:` user get back 0.1 dETH as specified amount is 0.02 dETH
#### Anything else we need to know?:
<img width="2108" alt="230224 Quantum - over sends amount" src="https://user-images.githubusercontent.com/65014479/221188855-a7d9ffee-84cd-42c9-858d-fcb64c5c7f0c.png">
|
1.0
|
Error code 3: when user send more than specified amount - <!--
Please use this template while reporting a bug and provide as much info as possible.
If the matter is security related, please disclose it privately via security@defichain.com
-->
```
Ver: 0.14.0
Network: TestNet
Flow: DFC → ETH
Description: Error code 3: when user send more than specified amount
```
**Actual:**
– at **step 3 Validate**, if user encounters `Error code 3: BalanceNotMatched`
– The balance in the wallet's address does not equal to the amount filled in the form
– user has no other option but to select x and restart the tx
#### What you expected to happen:
TBC
**To reproduce:**
Select Source Network: Ethereum
Input `0.02` dETH > select `Review transaction`
at **step 1 Initiate**, paste `Ethereum address` in text field > Continue
at **step 2 Transact**, use MLW to send `0.3` dETH > when tx is sent > go back to **Quantum**, select `Verify transfer`
at **step 3 Validate**, `error:` Error code 3: BalanceNotMatched > `note:` user get back 0.1 dETH as specified amount is 0.02 dETH
#### Anything else we need to know?:
<img width="2108" alt="230224 Quantum - over sends amount" src="https://user-images.githubusercontent.com/65014479/221188855-a7d9ffee-84cd-42c9-858d-fcb64c5c7f0c.png">
|
non_defect
|
error code when user send more than specified amount please use this template while reporting a bug and provide as much info as possible if the matter is security related please disclose it privately via security defichain com ver network testnet flow dfc → eth description error code when user send more than specified amount actual – at step validate if user encounters error code balancenotmatched – the balance in the wallet s address does not equal to the amount filled in the form – user has no other option but to select x and restart the tx what you expected to happen tbc to reproduce select source network ethereum input deth select review transaction at step initiate paste ethereum address in text field continue at step transact use mlw to send deth when tx is sent go back to quantum select verify transfer at step validate error error code balancenotmatched note user get back deth as specified amount is deth anything else we need to know img width alt quantum over sends amount src
| 0
|
58,951
| 16,963,865,365
|
IssuesEvent
|
2021-06-29 08:31:20
|
jOOQ/jOOQ
|
https://api.github.com/repos/jOOQ/jOOQ
|
closed
|
INSERT .. RETURNING emulation doesn't work on SQL Server when returning expressions or aliases
|
C: Functionality E: Enterprise Edition E: Professional Edition P: High R: Fixed T: Defect
|
The newly implemented `INSERT .. RETURNING` emulation in SQL Server that uses `OUTPUT` (#4498) currently cannot handle expressions yet.
This will be non-trivial to emulate, as `OUTPUT` column expressions need to refer to the DML table using `INSERTED` or `DELETED` pseudo tables, a qualification that has to be pushed down into the actual expression, possibly with table mapping?
----
Related:
- #8897
- #8899
|
1.0
|
INSERT .. RETURNING emulation doesn't work on SQL Server when returning expressions or aliases - The newly implemented `INSERT .. RETURNING` emulation in SQL Server that uses `OUTPUT` (#4498) currently cannot handle expressions yet.
This will be non-trivial to emulate, as `OUTPUT` column expressions need to refer to the DML table using `INSERTED` or `DELETED` pseudo tables, a qualification that has to be pushed down into the actual expression, possibly with table mapping?
----
Related:
- #8897
- #8899
|
defect
|
insert returning emulation doesn t work on sql server when returning expressions or aliases the newly implemented insert returning emulation in sql server that uses output currently cannot handle expressions yet this will be non trivial to emulate as output column expressions need to refer to the dml table using inserted or deleted pseudo tables a qualification that has to be pushed down into the actual expression possibly with table mapping related
| 1
|
2,150
| 2,603,977,143
|
IssuesEvent
|
2015-02-24 19:01:47
|
chrsmith/nishazi6
|
https://api.github.com/repos/chrsmith/nishazi6
|
opened
|
沈阳人乳头状病毒
|
auto-migrated Priority-Medium Type-Defect
|
```
沈阳人乳头状病毒〓沈陽軍區政治部醫院性病〓TEL:024-3102330
8〓成立于1946年,68年專注于性傳播疾病的研究和治療。位于�
��陽市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷�
��悠久、設備精良、技術權威、專家云集,是預防、保健、醫
療、科研康復為一體的綜合性醫院。是國家首批公立甲等部��
�醫院、全國首批醫療規范定點單位,是第四軍醫大學、東南�
��學等知名高等院校的教學醫院。曾被中國人民解放軍空軍后
勤部衛生部評為衛生工作先進單位,先后兩次榮立集體二等��
�。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:25
|
1.0
|
沈阳人乳头状病毒 - ```
沈阳人乳头状病毒〓沈陽軍區政治部醫院性病〓TEL:024-3102330
8〓成立于1946年,68年專注于性傳播疾病的研究和治療。位于�
��陽市沈河區二緯路32號。是一所與新中國同建立共輝煌的歷�
��悠久、設備精良、技術權威、專家云集,是預防、保健、醫
療、科研康復為一體的綜合性醫院。是國家首批公立甲等部��
�醫院、全國首批醫療規范定點單位,是第四軍醫大學、東南�
��學等知名高等院校的教學醫院。曾被中國人民解放軍空軍后
勤部衛生部評為衛生工作先進單位,先后兩次榮立集體二等��
�。
```
-----
Original issue reported on code.google.com by `q964105...@gmail.com` on 4 Jun 2014 at 8:25
|
defect
|
沈阳人乳头状病毒 沈阳人乳头状病毒〓沈陽軍區政治部醫院性病〓tel: 〓 , 。位于� �� 。是一所與新中國同建立共輝煌的歷� ��悠久、設備精良、技術權威、專家云集,是預防、保健、醫 療、科研康復為一體的綜合性醫院。是國家首批公立甲等部�� �醫院、全國首批醫療規范定點單位,是第四軍醫大學、東南� ��學等知名高等院校的教學醫院。曾被中國人民解放軍空軍后 勤部衛生部評為衛生工作先進單位,先后兩次榮立集體二等�� �。 original issue reported on code google com by gmail com on jun at
| 1
|
16,507
| 2,908,963,110
|
IssuesEvent
|
2015-06-20 07:47:28
|
anfichtn/arduinoha
|
https://api.github.com/repos/anfichtn/arduinoha
|
closed
|
Oregon scientific protocol
|
auto-migrated Priority-Medium Type-Defect
|
```
Dont know how to add this type of info other than here. So sorry if its
not correct. Thought this might help you.
If you would like it i have Kaku protocol also.
```
Original issue reported on code.google.com by `krul...@yahoo.com` on 6 Jan 2009 at 8:39
Attachments:
* [wmr928-weijenberg.pdf](https://storage.googleapis.com/google-code-attachments/arduinoha/issue-2/comment-0/wmr928-weijenberg.pdf)
|
1.0
|
Oregon scientific protocol - ```
Dont know how to add this type of info other than here. So sorry if its
not correct. Thought this might help you.
If you would like it i have Kaku protocol also.
```
Original issue reported on code.google.com by `krul...@yahoo.com` on 6 Jan 2009 at 8:39
Attachments:
* [wmr928-weijenberg.pdf](https://storage.googleapis.com/google-code-attachments/arduinoha/issue-2/comment-0/wmr928-weijenberg.pdf)
|
defect
|
oregon scientific protocol dont know how to add this type of info other than here so sorry if its not correct thought this might help you if you would like it i have kaku protocol also original issue reported on code google com by krul yahoo com on jan at attachments
| 1
|
47,636
| 2,982,658,546
|
IssuesEvent
|
2015-07-17 12:58:27
|
HPI-SWA-Teaching/SWT15-Project-13
|
https://api.github.com/repos/HPI-SWA-Teaching/SWT15-Project-13
|
closed
|
Shell-Script
|
priority: critical type: improvement
|
Das ist der vollständige Befehl zum Starten der REPL (unter Mac)
`/Applications/SWT2015.app/Contents/MacOS/Squeak -headless /Applications/SWT2015.app/Contents/Resources/SWT2015.image -repl` (eine Zeile)
und
`telnet 127.0.0.1 8080`.
Kennt sich jemand aus und schreibt dafür ein Script, sodass sie sich in einem Befehl starten lässt?
|
1.0
|
Shell-Script - Das ist der vollständige Befehl zum Starten der REPL (unter Mac)
`/Applications/SWT2015.app/Contents/MacOS/Squeak -headless /Applications/SWT2015.app/Contents/Resources/SWT2015.image -repl` (eine Zeile)
und
`telnet 127.0.0.1 8080`.
Kennt sich jemand aus und schreibt dafür ein Script, sodass sie sich in einem Befehl starten lässt?
|
non_defect
|
shell script das ist der vollständige befehl zum starten der repl unter mac applications app contents macos squeak headless applications app contents resources image repl eine zeile und telnet kennt sich jemand aus und schreibt dafür ein script sodass sie sich in einem befehl starten lässt
| 0
|
184,690
| 21,784,940,187
|
IssuesEvent
|
2022-05-14 01:53:09
|
Meathead98/vuetify
|
https://api.github.com/repos/Meathead98/vuetify
|
closed
|
WS-2020-0218 (High) detected in merge-1.2.1.tgz - autoclosed
|
security vulnerability
|
## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.1.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar to the jQuery.extend but more flexible. Works in Node.js and the browser.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge/-/merge-1.2.1.tgz">https://registry.npmjs.org/merge/-/merge-1.2.1.tgz</a></p>
<p>Path to dependency file: /vuetify/package.json</p>
<p>Path to vulnerable library: vuetify/node_modules/merge/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-21.2.1.tgz (Root Library)
- jest-haste-map-21.2.0.tgz
- sane-2.5.2.tgz
- exec-sh-0.2.2.tgz
- :x: **merge-1.2.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2020-0218 (High) detected in merge-1.2.1.tgz - autoclosed - ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.1.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar to the jQuery.extend but more flexible. Works in Node.js and the browser.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge/-/merge-1.2.1.tgz">https://registry.npmjs.org/merge/-/merge-1.2.1.tgz</a></p>
<p>Path to dependency file: /vuetify/package.json</p>
<p>Path to vulnerable library: vuetify/node_modules/merge/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-21.2.1.tgz (Root Library)
- jest-haste-map-21.2.0.tgz
- sane-2.5.2.tgz
- exec-sh-0.2.2.tgz
- :x: **merge-1.2.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
ws high detected in merge tgz autoclosed ws high severity vulnerability vulnerable library merge tgz merge multiple objects into one optionally creating a new cloned object similar to the jquery extend but more flexible works in node js and the browser library home page a href path to dependency file vuetify package json path to vulnerable library vuetify node modules merge package json dependency hierarchy jest cli tgz root library jest haste map tgz sane tgz exec sh tgz x merge tgz vulnerable library vulnerability details a prototype pollution vulnerability was found in merge before via the merge recursive function it can be tricked into adding or modifying properties of the object prototype these properties will be present on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution merge step up your open source security game with whitesource
| 0
|
165,796
| 20,620,536,807
|
IssuesEvent
|
2022-03-07 16:59:52
|
Baneeishaque/Gym_Class_Accounter
|
https://api.github.com/repos/Baneeishaque/Gym_Class_Accounter
|
opened
|
CVE-2017-9096 (High) detected in itextpdf-5.5.5.jar
|
security vulnerability
|
## CVE-2017-9096 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>itextpdf-5.5.5.jar</b></p></summary>
<p>iText, a free Java-PDF library</p>
<p>Library home page: <a href="http://itextpdf.com">http://itextpdf.com</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /s/modules-2/files-2.1/com.itextpdf/itextpdf/5.5.5/5781a6df5c14e4ad07f2bab7b228e8f3187c672d/itextpdf-5.5.5.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.itextpdf/itextpdf/5.5.5/5781a6df5c14e4ad07f2bab7b228e8f3187c672d/itextpdf-5.5.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **itextpdf-5.5.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/Gym_Class_Accounter/commit/d0b484ab35339c58b68f75b5f03b3958d80ce307">d0b484ab35339c58b68f75b5f03b3958d80ce307</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The XML parsers in iText before 5.5.12 and 7.x before 7.0.3 do not disable external entities, which might allow remote attackers to conduct XML external entity (XXE) attacks via a crafted PDF.
<p>Publish Date: 2017-11-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-9096>CVE-2017-9096</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096</a></p>
<p>Release Date: 2017-11-08</p>
<p>Fix Resolution: com.itextpdf:itextpdf:5.5.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2017-9096 (High) detected in itextpdf-5.5.5.jar - ## CVE-2017-9096 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>itextpdf-5.5.5.jar</b></p></summary>
<p>iText, a free Java-PDF library</p>
<p>Library home page: <a href="http://itextpdf.com">http://itextpdf.com</a></p>
<p>Path to dependency file: /app/build.gradle</p>
<p>Path to vulnerable library: /s/modules-2/files-2.1/com.itextpdf/itextpdf/5.5.5/5781a6df5c14e4ad07f2bab7b228e8f3187c672d/itextpdf-5.5.5.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.itextpdf/itextpdf/5.5.5/5781a6df5c14e4ad07f2bab7b228e8f3187c672d/itextpdf-5.5.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **itextpdf-5.5.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/Gym_Class_Accounter/commit/d0b484ab35339c58b68f75b5f03b3958d80ce307">d0b484ab35339c58b68f75b5f03b3958d80ce307</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The XML parsers in iText before 5.5.12 and 7.x before 7.0.3 do not disable external entities, which might allow remote attackers to conduct XML external entity (XXE) attacks via a crafted PDF.
<p>Publish Date: 2017-11-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-9096>CVE-2017-9096</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096</a></p>
<p>Release Date: 2017-11-08</p>
<p>Fix Resolution: com.itextpdf:itextpdf:5.5.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in itextpdf jar cve high severity vulnerability vulnerable library itextpdf jar itext a free java pdf library library home page a href path to dependency file app build gradle path to vulnerable library s modules files com itextpdf itextpdf itextpdf jar home wss scanner gradle caches modules files com itextpdf itextpdf itextpdf jar dependency hierarchy x itextpdf jar vulnerable library found in head commit a href vulnerability details the xml parsers in itext before and x before do not disable external entities which might allow remote attackers to conduct xml external entity xxe attacks via a crafted pdf publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com itextpdf itextpdf step up your open source security game with whitesource
| 0
|
102,374
| 11,296,613,036
|
IssuesEvent
|
2020-01-17 02:31:54
|
apache/pulsar
|
https://api.github.com/repos/apache/pulsar
|
closed
|
Update Functions state documentation for Python
|
component/documentation triage/week-33 type/task
|
Pulsar Functions documentation at http://pulsar.apache.org/docs/en/functions-state/ needs to be updated to note that Python functions support state, and to provide examples of how to use state with Python.
|
1.0
|
Update Functions state documentation for Python - Pulsar Functions documentation at http://pulsar.apache.org/docs/en/functions-state/ needs to be updated to note that Python functions support state, and to provide examples of how to use state with Python.
|
non_defect
|
update functions state documentation for python pulsar functions documentation at needs to be updated to note that python functions support state and to provide examples of how to use state with python
| 0
|
80,376
| 30,262,511,771
|
IssuesEvent
|
2023-07-07 09:16:45
|
cf-convention/discuss
|
https://api.github.com/repos/cf-convention/discuss
|
closed
|
error in canonical `units` of `atmosphere_convective`* quantities
|
defect standard name accepted
|
The three quantities `atmosphere_convective_available_potential_energy_wrt_surface`, `atmosphere_convective_inhibition` and `atmosphere_convective_inhibition_wrt_surface` have canonical units written as `J kg -1`, with a space between `kg` and `-1`. The string given is a legal unit, which is dimensionally equivalent to `J kg`, but I think the space is a typo and the unit should be `J kg-1`. Thanks.
|
1.0
|
error in canonical `units` of `atmosphere_convective`* quantities - The three quantities `atmosphere_convective_available_potential_energy_wrt_surface`, `atmosphere_convective_inhibition` and `atmosphere_convective_inhibition_wrt_surface` have canonical units written as `J kg -1`, with a space between `kg` and `-1`. The string given is a legal unit, which is dimensionally equivalent to `J kg`, but I think the space is a typo and the unit should be `J kg-1`. Thanks.
|
defect
|
error in canonical units of atmosphere convective quantities the three quantities atmosphere convective available potential energy wrt surface atmosphere convective inhibition and atmosphere convective inhibition wrt surface have canonical units written as j kg with a space between kg and the string given is a legal unit which is dimensionally equivalent to j kg but i think the space is a typo and the unit should be j kg thanks
| 1
|
4,384
| 6,562,481,242
|
IssuesEvent
|
2017-09-07 16:44:51
|
Phasedio/webapp
|
https://api.github.com/repos/Phasedio/webapp
|
closed
|
Teams within teams
|
enhancement Service wide feature
|
Something we have been hearing a lot from clients is to have ways of having groups of teams within a company. These teams would also have permissions so only specific users or groups of users could access them.
A way to think about this would be slack channels. You can make a new channel and only select some users to be a part of it or not.
The issues with this is the current structure of how teams are set out. @daveriedstra / @clouie87 I'm not sure if you guys have any ideas of how we could work this out but here's my thought on the issue. We put a new child node in to a company that holds user ids and then the id of the team that they are a part of. Then on Auth we figure out what company they are apart of as well look up the team they are in as well. For the teams them selfs in the db within the company we create a child node that holds team id nodes, with the name of the team and members apart of it.
So it looks a little like this:
```
{
company: {
members : {
USERID: TEAMID,
USERID: TEAMID,
...
},
teams : {
TEAMID : {
name : String,
members: {
USERID : True,
USERID : True
}
},
TEAMID : {
name : String,
members: {
USERID : True,
USERID : True
}
}
}
}
}
```


|
1.0
|
Teams within teams - Something we have been hearing a lot from clients is to have ways of having groups of teams within a company. These teams would also have permissions so only specific users or groups of users could access them.
A way to think about this would be slack channels. You can make a new channel and only select some users to be a part of it or not.
The issues with this is the current structure of how teams are set out. @daveriedstra / @clouie87 I'm not sure if you guys have any ideas of how we could work this out but here's my thought on the issue. We put a new child node in to a company that holds user ids and then the id of the team that they are a part of. Then on Auth we figure out what company they are apart of as well look up the team they are in as well. For the teams them selfs in the db within the company we create a child node that holds team id nodes, with the name of the team and members apart of it.
So it looks a little like this:
```
{
company: {
members : {
USERID: TEAMID,
USERID: TEAMID,
...
},
teams : {
TEAMID : {
name : String,
members: {
USERID : True,
USERID : True
}
},
TEAMID : {
name : String,
members: {
USERID : True,
USERID : True
}
}
}
}
}
```


|
non_defect
|
teams within teams something we have been hearing a lot from clients is to have ways of having groups of teams within a company these teams would also have permissions so only specific users or groups of users could access them a way to think about this would be slack channels you can make a new channel and only select some users to be a part of it or not the issues with this is the current structure of how teams are set out daveriedstra i m not sure if you guys have any ideas of how we could work this out but here s my thought on the issue we put a new child node in to a company that holds user ids and then the id of the team that they are a part of then on auth we figure out what company they are apart of as well look up the team they are in as well for the teams them selfs in the db within the company we create a child node that holds team id nodes with the name of the team and members apart of it so it looks a little like this company members userid teamid userid teamid teams teamid name string members userid true userid true teamid name string members userid true userid true
| 0
|
436,995
| 12,557,832,945
|
IssuesEvent
|
2020-06-07 14:10:03
|
Eastrall/Rhisis
|
https://api.github.com/repos/Eastrall/Rhisis
|
closed
|
Changing armour does not always update
|
bug priority: critical srv: world sys: inventory v0.4.x
|
# :beetle: Bug Report
**Rhisis version:** v0.4.x
## Expected Behavior
Armour is equipped and unequipped.
## Current Behavior
Player is either naked, or the switched armour doesn't update for the client.
## Steps to Reproduce
1. Equip armour dropped from mobs.
2. Relog and it will then update.
**Coincidentally, sometimes you can't reconnect to the game after this bug happens.**
|
1.0
|
Changing armour does not always update - # :beetle: Bug Report
**Rhisis version:** v0.4.x
## Expected Behavior
Armour is equipped and unequipped.
## Current Behavior
Player is either naked, or the switched armour doesn't update for the client.
## Steps to Reproduce
1. Equip armour dropped from mobs.
2. Relog and it will then update.
**Coincidentally, sometimes you can't reconnect to the game after this bug happens.**
|
non_defect
|
changing armour does not always update beetle bug report rhisis version x expected behavior armour is equipped and unequipped current behavior player is either naked or the switched armour doesn t update for the client steps to reproduce equip armour dropped from mobs relog and it will then update coincidentally sometimes you can t reconnect to the game after this bug happens
| 0
|
41,391
| 10,438,371,237
|
IssuesEvent
|
2019-09-18 01:53:18
|
line/armeria
|
https://api.github.com/repos/line/armeria
|
closed
|
gRPC-web client doesn't apply framing
|
defect
|
From slack, it seems that the gRPC web serialization format may not be working correctly on client side. Any of our formats should work both in server and client.
https://line-armeria.slack.com/archives/C1NGPBUH2/p1566800641169400?thread_ts=1566800641.169400&cid=C1NGPBUH2
|
1.0
|
gRPC-web client doesn't apply framing - From slack, it seems that the gRPC web serialization format may not be working correctly on client side. Any of our formats should work both in server and client.
https://line-armeria.slack.com/archives/C1NGPBUH2/p1566800641169400?thread_ts=1566800641.169400&cid=C1NGPBUH2
|
defect
|
grpc web client doesn t apply framing from slack it seems that the grpc web serialization format may not be working correctly on client side any of our formats should work both in server and client
| 1
|
30,248
| 6,060,422,992
|
IssuesEvent
|
2017-06-14 01:42:00
|
extnet/Ext.NET
|
https://api.github.com/repos/extnet/Ext.NET
|
opened
|
Drag and drop overlaps dragging DOM elements with selection
|
4.x defect sencha
|
Sencha forum thread: [Drag & Drop : Dragging selects text and image when mouse moves in chrome browser](https://www.sencha.com/forum/showthread.php?335100)
Drag and drop behaves strange, not inhibiting selection drag (as selecting text on the page) while the dom elements (or components) are dragged around.
Some affected EE examples:
- [Drag And Drop - Advanced - Drag with State](http://examples4.ext.net/#/DragDrop/Advanced/Drag_with_State/)
- [Drag And Drop - Advanced - Example 1](http://examples4.ext.net/#/DragDrop/Advanced/Example1/)
- [Drag And Drop - Advanced - Example 2](http://examples4.ext.net/#/DragDrop/Advanced/Example2/)
- [Drag And Drop - Advanced - Example 3](http://examples4.ext.net/#/DragDrop/Advanced/Example3/)
- [Toolbar - Plugins - ToolbarDroppable](http://examples4.ext.net/#/Toolbar/Plugins/ToolbarDroppable/)
|
1.0
|
Drag and drop overlaps dragging DOM elements with selection - Sencha forum thread: [Drag & Drop : Dragging selects text and image when mouse moves in chrome browser](https://www.sencha.com/forum/showthread.php?335100)
Drag and drop behaves strange, not inhibiting selection drag (as selecting text on the page) while the dom elements (or components) are dragged around.
Some affected EE examples:
- [Drag And Drop - Advanced - Drag with State](http://examples4.ext.net/#/DragDrop/Advanced/Drag_with_State/)
- [Drag And Drop - Advanced - Example 1](http://examples4.ext.net/#/DragDrop/Advanced/Example1/)
- [Drag And Drop - Advanced - Example 2](http://examples4.ext.net/#/DragDrop/Advanced/Example2/)
- [Drag And Drop - Advanced - Example 3](http://examples4.ext.net/#/DragDrop/Advanced/Example3/)
- [Toolbar - Plugins - ToolbarDroppable](http://examples4.ext.net/#/Toolbar/Plugins/ToolbarDroppable/)
|
defect
|
drag and drop overlaps dragging dom elements with selection sencha forum thread drag and drop behaves strange not inhibiting selection drag as selecting text on the page while the dom elements or components are dragged around some affected ee examples
| 1
|
27,301
| 4,958,076,542
|
IssuesEvent
|
2016-12-02 08:21:12
|
TNGSB/eWallet
|
https://api.github.com/repos/TNGSB/eWallet
|
closed
|
eWallet_MobileApp-Transfer(Live Env) #122
|
Defect - High (Sev-2) Live Environment
|
Defect Description :System allowed more than 65 characters input for Android and IOS
Test Description : To verify error message when the values input for "Search ID" textbox - alphanumeric more than 36 characters
Refer the attachment for POT.
[Defect_Mobile.App.122.xlsx](https://github.com/TNGSB/eWallet/files/602661/Defect_Mobile.App.122.xlsx)
|
1.0
|
eWallet_MobileApp-Transfer(Live Env) #122 - Defect Description :System allowed more than 65 characters input for Android and IOS
Test Description : To verify error message when the values input for "Search ID" textbox - alphanumeric more than 36 characters
Refer the attachment for POT.
[Defect_Mobile.App.122.xlsx](https://github.com/TNGSB/eWallet/files/602661/Defect_Mobile.App.122.xlsx)
|
defect
|
ewallet mobileapp transfer live env defect description system allowed more than characters input for android and ios test description to verify error message when the values input for search id textbox alphanumeric more than characters refer the attachment for pot
| 1
|
45,862
| 13,055,810,990
|
IssuesEvent
|
2020-07-30 02:48:29
|
icecube-trac/tix2
|
https://api.github.com/repos/icecube-trac/tix2
|
opened
|
new singleton implementation does not compile on RHEL4 (gcc 3.4.6)_ (Trac #151)
|
IceTray Incomplete Migration Migrated from Trac defect
|
Migrated from https://code.icecube.wisc.edu/ticket/151
```json
{
"status": "closed",
"changetime": "2009-01-08T14:51:17",
"description": "Compilation of the trunk of offline software ends with an error (error\ndump: see \"additional information\"). According to the error message an\nattempt is being made by the Singleton implementation to use the\nI3Factory() constructor. This happens both for I3ModuleFactory and for\nI3ServiceFactory.\n\nThe error does not occur under RHEL5 (gcc 4.1.2)",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1231426277000000",
"component": "IceTray",
"summary": "new singleton implementation does not compile on RHEL4 (gcc 3.4.6)_",
"priority": "normal",
"keywords": "",
"time": "2008-11-19T02:08:07",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
|
1.0
|
new singleton implementation does not compile on RHEL4 (gcc 3.4.6)_ (Trac #151) - Migrated from https://code.icecube.wisc.edu/ticket/151
```json
{
"status": "closed",
"changetime": "2009-01-08T14:51:17",
"description": "Compilation of the trunk of offline software ends with an error (error\ndump: see \"additional information\"). According to the error message an\nattempt is being made by the Singleton implementation to use the\nI3Factory() constructor. This happens both for I3ModuleFactory and for\nI3ServiceFactory.\n\nThe error does not occur under RHEL5 (gcc 4.1.2)",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1231426277000000",
"component": "IceTray",
"summary": "new singleton implementation does not compile on RHEL4 (gcc 3.4.6)_",
"priority": "normal",
"keywords": "",
"time": "2008-11-19T02:08:07",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
|
defect
|
new singleton implementation does not compile on gcc trac migrated from json status closed changetime description compilation of the trunk of offline software ends with an error error ndump see additional information according to the error message an nattempt is being made by the singleton implementation to use the constructor this happens both for and for n nthe error does not occur under gcc reporter blaufuss cc resolution fixed ts component icetray summary new singleton implementation does not compile on gcc priority normal keywords time milestone owner troy type defect
| 1
|
202,307
| 15,825,607,090
|
IssuesEvent
|
2021-04-06 06:06:52
|
IgniteUI/igniteui-angular
|
https://api.github.com/repos/IgniteUI/igniteui-angular
|
closed
|
Missing brackets around autoGenerate property of IgxGrid in IgxGridComponent API doc
|
bug documentation status: in-development version: 11.1.x
|
## Description
Missing brackets around autoGenerate property of IgxGrid in the first example in IgxGridComponent API documentation [here](https://www.infragistics.com/products/ignite-ui-angular/docs/typescript/latest/classes/igxgridcomponent.html)
|
1.0
|
Missing brackets around autoGenerate property of IgxGrid in IgxGridComponent API doc - ## Description
Missing brackets around autoGenerate property of IgxGrid in the first example in IgxGridComponent API documentation [here](https://www.infragistics.com/products/ignite-ui-angular/docs/typescript/latest/classes/igxgridcomponent.html)
|
non_defect
|
missing brackets around autogenerate property of igxgrid in igxgridcomponent api doc description missing brackets around autogenerate property of igxgrid in the first example in igxgridcomponent api documentation
| 0
|
78,880
| 3,518,701,577
|
IssuesEvent
|
2016-01-12 14:09:49
|
McStasMcXtrace/McWeb
|
https://api.github.com/repos/McStasMcXtrace/McWeb
|
closed
|
Mediawiki: import data from elearn1
|
Jakob/Peter Priority 800
|
Peter will attempt this during week 2. I may need the help of Pia for some parts
|
1.0
|
Mediawiki: import data from elearn1 - Peter will attempt this during week 2. I may need the help of Pia for some parts
|
non_defect
|
mediawiki import data from peter will attempt this during week i may need the help of pia for some parts
| 0
|
235,844
| 25,962,070,423
|
IssuesEvent
|
2022-12-19 01:03:15
|
michaeldotson/movie-app
|
https://api.github.com/repos/michaeldotson/movie-app
|
opened
|
CVE-2022-23517 (High) detected in rails-html-sanitizer-1.0.4.gem
|
security vulnerability
|
## CVE-2022-23517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rails-html-sanitizer-1.0.4.gem</b></p></summary>
<p>HTML sanitization for Rails applications</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-html-sanitizer-1.0.4.gem">https://rubygems.org/gems/rails-html-sanitizer-1.0.4.gem</a></p>
<p>Path to dependency file: /movie-app/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/rails-html-sanitizer-1.0.4.gem</p>
<p>
Dependency Hierarchy:
- web-console-3.7.0.gem (Root Library)
- actionview-5.2.2.gem
- :x: **rails-html-sanitizer-1.0.4.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
rails-html-sanitizer is responsible for sanitizing HTML fragments in Rails applications. Certain configurations of rails-html-sanitizer < 1.4.4 use an inefficient regular expression that is susceptible to excessive backtracking when attempting to sanitize certain SVG attributes. This may lead to a denial of service through CPU resource consumption. This issue has been patched in version 1.4.4.
<p>Publish Date: 2022-12-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23517>CVE-2022-23517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/rails-html-sanitizer/security/advisories/GHSA-5x79-w82f-gw8w">https://github.com/rails/rails-html-sanitizer/security/advisories/GHSA-5x79-w82f-gw8w</a></p>
<p>Release Date: 2022-12-14</p>
<p>Fix Resolution: rails-html-sanitizer - 1.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-23517 (High) detected in rails-html-sanitizer-1.0.4.gem - ## CVE-2022-23517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rails-html-sanitizer-1.0.4.gem</b></p></summary>
<p>HTML sanitization for Rails applications</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-html-sanitizer-1.0.4.gem">https://rubygems.org/gems/rails-html-sanitizer-1.0.4.gem</a></p>
<p>Path to dependency file: /movie-app/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/rails-html-sanitizer-1.0.4.gem</p>
<p>
Dependency Hierarchy:
- web-console-3.7.0.gem (Root Library)
- actionview-5.2.2.gem
- :x: **rails-html-sanitizer-1.0.4.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
rails-html-sanitizer is responsible for sanitizing HTML fragments in Rails applications. Certain configurations of rails-html-sanitizer < 1.4.4 use an inefficient regular expression that is susceptible to excessive backtracking when attempting to sanitize certain SVG attributes. This may lead to a denial of service through CPU resource consumption. This issue has been patched in version 1.4.4.
<p>Publish Date: 2022-12-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23517>CVE-2022-23517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/rails-html-sanitizer/security/advisories/GHSA-5x79-w82f-gw8w">https://github.com/rails/rails-html-sanitizer/security/advisories/GHSA-5x79-w82f-gw8w</a></p>
<p>Release Date: 2022-12-14</p>
<p>Fix Resolution: rails-html-sanitizer - 1.4.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in rails html sanitizer gem cve high severity vulnerability vulnerable library rails html sanitizer gem html sanitization for rails applications library home page a href path to dependency file movie app gemfile lock path to vulnerable library var lib gems cache rails html sanitizer gem dependency hierarchy web console gem root library actionview gem x rails html sanitizer gem vulnerable library vulnerability details rails html sanitizer is responsible for sanitizing html fragments in rails applications certain configurations of rails html sanitizer use an inefficient regular expression that is susceptible to excessive backtracking when attempting to sanitize certain svg attributes this may lead to a denial of service through cpu resource consumption this issue has been patched in version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rails html sanitizer step up your open source security game with mend
| 0
|
14,249
| 2,796,048,123
|
IssuesEvent
|
2015-05-12 03:16:22
|
CocoaPods/CocoaPods
|
https://api.github.com/repos/CocoaPods/CocoaPods
|
closed
|
Build Failed with 'Failure Reason: File name too long' when 'Copy Pods Resources' in 0.36.x.
|
d1:easy s1:awaiting input t2:defect
|
Hi, in my team project, we have a new member in. He `pod update` the project and build it, then got the error, so I try to do again got the same error of below:
> ...
sent 12960 bytes received 578 bytes 27076.00 bytes/sec
total size is 10522 speedup is 0.78
> /* com.apple.actool.errors */
: error: Failed to read file attributes for "/Users/PeterWang/mart-ios/Mart/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Curly/CurlySample/CurlySample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Moya/Demo/Demo/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/examples/FadeExample/FadeExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/extensions/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RHMVVMHelpers/RHMVVMHelpers/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RSBarcodes/RSBarcodesSample/RSBarcodesSample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SimpleAlert/SimpleAlertExample/SimpleAlertExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TinderLike/TinderLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TwitterLike/TwitterLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SwiftyJSON/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/XCGLogger/XCGLogger/Demo"
> Failure Reason: File name too long
> /* com.apple.actool.notices */
: warning: Failed to read file attributes for "/Users/PeterWang/mart-ios/Mart/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Curly/CurlySample/CurlySample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Moya/Demo/Demo/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/examples/FadeExample/FadeExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/extensions/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RHMVVMHelpers/RHMVVMHelpers/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RSBarcodes/RSBarcodesSample/RSBarcodesSample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SimpleAlert/SimpleAlertExample/SimpleAlertExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TinderLike/TinderLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TwitterLike/TwitterLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SwiftyJSON/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/XCGLogger/XCGLogger/Demo"
Failure Reason: File name too long
/* com.apple.actool.compilation-results */
/Users/PeterWang/Library/Developer/Xcode/DerivedData/Mart-adxfewucewqguhhjalskbnyynmdb/Build/Products/Debug-iphoneos/Mart.app/Assets.car
I go back to the old version, found out there no problem in 0.35.x. And I compare the 'Pods-resources.sh' found a little different at the last part of the shell.
In 0.35.x:
```
find "${PWD}" -name "*.xcassets" -print0 | xargs -0 actool --output-format human-readable-text --notices --warnings --platform "${PLATFORM_NAME}" --minimum-deployment-target "${IPHONEOS_DEPLOYMENT_TARGET}" ${TARGET_DEVICE_ARGS} --compress-pngs --compile "${BUILT_PRODUCTS_DIR}/${UNLOCALIZED_RESOURCES_FOLDER_PATH}"
```
In 0.36.x:
```
while read line; do XCASSET_FILES="$XCASSET_FILES '$line'"; done <<<$(find "$PWD" -name "*.xcassets" | egrep -v "^$PODS_ROOT")
echo $XCASSET_FILES | xargs actool --output-format human-readable-text --notices --warnings --platform "${PLATFORM_NAME}" --minimum-deployment-target "${IPHONEOS_DEPLOYMENT_TARGET}" ${TARGET_DEVICE_ARGS} --compress-pngs --compile "${BUILT_PRODUCTS_DIR}/${UNLOCALIZED_RESOURCES_FOLDER_PATH}"
```
I think it would read all the xcasset files in one command line and cause the issue.
Our project is swift/objective-c mixed project, and target iOS 7 and up.
Thanks ~
|
1.0
|
Build Failed with 'Failure Reason: File name too long' when 'Copy Pods Resources' in 0.36.x. - Hi, in my team project, we have a new member in. He `pod update` the project and build it, then got the error, so I try to do again got the same error of below:
> ...
sent 12960 bytes received 578 bytes 27076.00 bytes/sec
total size is 10522 speedup is 0.78
> /* com.apple.actool.errors */
: error: Failed to read file attributes for "/Users/PeterWang/mart-ios/Mart/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Curly/CurlySample/CurlySample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Moya/Demo/Demo/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/examples/FadeExample/FadeExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/extensions/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RHMVVMHelpers/RHMVVMHelpers/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RSBarcodes/RSBarcodesSample/RSBarcodesSample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SimpleAlert/SimpleAlertExample/SimpleAlertExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TinderLike/TinderLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TwitterLike/TwitterLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SwiftyJSON/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/XCGLogger/XCGLogger/Demo"
> Failure Reason: File name too long
> /* com.apple.actool.notices */
: warning: Failed to read file attributes for "/Users/PeterWang/mart-ios/Mart/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Curly/CurlySample/CurlySample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Moya/Demo/Demo/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/examples/FadeExample/FadeExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/Promissum/extensions/Alamofire/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RHMVVMHelpers/RHMVVMHelpers/Images.xcassets /Users/PeterWang/mart-ios/Vendor/RSBarcodes/RSBarcodesSample/RSBarcodesSample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SimpleAlert/SimpleAlertExample/SimpleAlertExample/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TinderLike/TinderLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SLPagingViewSwift/Demos/TwitterLike/TwitterLike/Images.xcassets /Users/PeterWang/mart-ios/Vendor/SwiftyJSON/Example/Images.xcassets /Users/PeterWang/mart-ios/Vendor/XCGLogger/XCGLogger/Demo"
Failure Reason: File name too long
/* com.apple.actool.compilation-results */
/Users/PeterWang/Library/Developer/Xcode/DerivedData/Mart-adxfewucewqguhhjalskbnyynmdb/Build/Products/Debug-iphoneos/Mart.app/Assets.car
I go back to the old version, found out there no problem in 0.35.x. And I compare the 'Pods-resources.sh' found a little different at the last part of the shell.
In 0.35.x:
```
find "${PWD}" -name "*.xcassets" -print0 | xargs -0 actool --output-format human-readable-text --notices --warnings --platform "${PLATFORM_NAME}" --minimum-deployment-target "${IPHONEOS_DEPLOYMENT_TARGET}" ${TARGET_DEVICE_ARGS} --compress-pngs --compile "${BUILT_PRODUCTS_DIR}/${UNLOCALIZED_RESOURCES_FOLDER_PATH}"
```
In 0.36.x:
```
while read line; do XCASSET_FILES="$XCASSET_FILES '$line'"; done <<<$(find "$PWD" -name "*.xcassets" | egrep -v "^$PODS_ROOT")
echo $XCASSET_FILES | xargs actool --output-format human-readable-text --notices --warnings --platform "${PLATFORM_NAME}" --minimum-deployment-target "${IPHONEOS_DEPLOYMENT_TARGET}" ${TARGET_DEVICE_ARGS} --compress-pngs --compile "${BUILT_PRODUCTS_DIR}/${UNLOCALIZED_RESOURCES_FOLDER_PATH}"
```
I think it would read all the xcasset files in one command line and cause the issue.
Our project is swift/objective-c mixed project, and target iOS 7 and up.
Thanks ~
|
defect
|
build failed with failure reason file name too long when copy pods resources in x hi in my team project we have a new member in he pod update the project and build it then got the error so i try to do again got the same error of below sent bytes received bytes bytes sec total size is speedup is com apple actool errors error failed to read file attributes for users peterwang mart ios mart images xcassets users peterwang mart ios vendor alamofire example images xcassets users peterwang mart ios vendor curly curlysample curlysample images xcassets users peterwang mart ios vendor moya demo demo images xcassets users peterwang mart ios vendor promissum examples fadeexample fadeexample images xcassets users peterwang mart ios vendor promissum extensions alamofire example images xcassets users peterwang mart ios vendor rhmvvmhelpers rhmvvmhelpers images xcassets users peterwang mart ios vendor rsbarcodes rsbarcodessample rsbarcodessample images xcassets users peterwang mart ios vendor simplealert simplealertexample simplealertexample images xcassets users peterwang mart ios vendor slpagingviewswift demos tinderlike tinderlike images xcassets users peterwang mart ios vendor slpagingviewswift demos twitterlike twitterlike images xcassets users peterwang mart ios vendor swiftyjson example images xcassets users peterwang mart ios vendor xcglogger xcglogger demo failure reason file name too long com apple actool notices warning failed to read file attributes for users peterwang mart ios mart images xcassets users peterwang mart ios vendor alamofire example images xcassets users peterwang mart ios vendor curly curlysample curlysample images xcassets users peterwang mart ios vendor moya demo demo images xcassets users peterwang mart ios vendor promissum examples fadeexample fadeexample images xcassets users peterwang mart ios vendor promissum extensions alamofire example images xcassets users peterwang mart ios vendor rhmvvmhelpers rhmvvmhelpers images xcassets users peterwang mart ios vendor rsbarcodes rsbarcodessample rsbarcodessample images xcassets users peterwang mart ios vendor simplealert simplealertexample simplealertexample images xcassets users peterwang mart ios vendor slpagingviewswift demos tinderlike tinderlike images xcassets users peterwang mart ios vendor slpagingviewswift demos twitterlike twitterlike images xcassets users peterwang mart ios vendor swiftyjson example images xcassets users peterwang mart ios vendor xcglogger xcglogger demo failure reason file name too long com apple actool compilation results users peterwang library developer xcode deriveddata mart adxfewucewqguhhjalskbnyynmdb build products debug iphoneos mart app assets car i go back to the old version found out there no problem in x and i compare the pods resources sh found a little different at the last part of the shell in x find pwd name xcassets xargs actool output format human readable text notices warnings platform platform name minimum deployment target iphoneos deployment target target device args compress pngs compile built products dir unlocalized resources folder path in x while read line do xcasset files xcasset files line done find pwd name xcassets egrep v pods root echo xcasset files xargs actool output format human readable text notices warnings platform platform name minimum deployment target iphoneos deployment target target device args compress pngs compile built products dir unlocalized resources folder path i think it would read all the xcasset files in one command line and cause the issue our project is swift objective c mixed project and target ios and up thanks
| 1
|
28,370
| 5,244,172,844
|
IssuesEvent
|
2017-01-31 22:41:54
|
bridgedotnet/Bridge
|
https://api.github.com/repos/bridgedotnet/Bridge
|
closed
|
List (s) give incorrect type FullName (s)
|
defect
|
[Bridge Fiddle](http://live.bridge.net/#f9543491757163d6696af0dca4795834)
[Dot Net Fiddle](https://dotnetfiddle.net/PYKzPK)
### Expected
System.Collections.Generic.List`1[[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]]
### Actual
Bridge.List$1$Bridge.Int32
### Steps To Reproduce
``` csharp
public class App
{
[Ready]
public static void Main()
{
List<int> value = new List<int>();
Console.WriteLine(value.GetType().FullName);
}
}
```
|
1.0
|
List (s) give incorrect type FullName (s) - [Bridge Fiddle](http://live.bridge.net/#f9543491757163d6696af0dca4795834)
[Dot Net Fiddle](https://dotnetfiddle.net/PYKzPK)
### Expected
System.Collections.Generic.List`1[[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]]
### Actual
Bridge.List$1$Bridge.Int32
### Steps To Reproduce
``` csharp
public class App
{
[Ready]
public static void Main()
{
List<int> value = new List<int>();
Console.WriteLine(value.GetType().FullName);
}
}
```
|
defect
|
list s give incorrect type fullname s expected system collections generic list actual bridge list bridge steps to reproduce csharp public class app public static void main list value new list console writeline value gettype fullname
| 1
|
69,240
| 22,291,343,949
|
IssuesEvent
|
2022-06-12 12:11:40
|
openzfs/zfs
|
https://api.github.com/repos/openzfs/zfs
|
closed
|
Multiple "zio error=61 type=1" errors not faulting a vdev
|
Type: Defect Status: Stale Status: Triage Needed
|
<!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | CentOS
Distribution Version | 7.8.2003
Linux Kernel | 3.10.0-1127.19.1.el7.x86_64
Architecture | x86_64
ZFS Version | 0.8.4-1
SPL Version | 0.8.4-1
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
We have a number of 10-drive raidz2 zpools on a system. The drives are in a JBOD connected to the system, with multipath providing pathing to each drive. We have seen drives begin to log multiple errors into syslog/dmesg, accumulating a large number of errors. We have yet to find the key, but at some point the zpool appears to go non-responsive (deeper information at this point is difficult due to pacemaker stoniths as this is a production filesystem).
An example of the errors are:
```
Feb 16 10:57:31 node0 kernel: [888148.088324] sd 2:3:77:0: [sdkh] tag#19 BRCM Debug mfi stat 0x2d, data len requested/completed 0x1000/0x0
Feb 16 10:57:31 node0 kernel: [888148.088341] sd 2:3:77:0: [sdkh] tag#19 FAILED Result: hostbyte=DID_OK driverbyte=DRIVER_SENSE cmd_age=9s
Feb 16 10:57:31 node0 kernel: [888148.088347] sd 2:3:77:0: [sdkh] tag#19 Sense Key : Medium Error [current]
Feb 16 10:57:31 node0 kernel: [888148.088349] sd 2:3:77:0: [sdkh] tag#19 Add. Sense: Unrecovered read error
Feb 16 10:57:31 node0 kernel: [888148.088352] sd 2:3:77:0: [sdkh] tag#19 CDB: Read(16) 88 00 00 00 00 00 a1 d6 69 a8 00 00 00 08 00 00
Feb 16 10:57:31 node0 kernel: [888148.088354] blk_update_request: critical medium error, dev sdkh, sector 2715183528
Feb 16 10:57:31 node0 kernel: [888148.088362] blk_update_request: critical medium error, dev dm-49, sector 2715183528
Feb 16 10:57:31 node0 kernel: [888148.088367] zio pool=node0-storage006 vdev=/dev/mapper/node0-storage006-6p1 error=61 type=1 offset=1390172917760 size=4096 flags=180880
```
It appears that ZFS never automatically faults the bad vdev, and instead keeps all vdevs online even though I/O to the underlying device is having issues.
I'm unsure if there's something else going on here keeping ZFS from faulting that drive, or if this is some kind of underlying bug.
### Describe how to reproduce the problem
### Include any warning/errors/backtraces from the system logs
<!--
*IMPORTANT* - Please mark logs and text output from terminal commands
or else Github will not display them correctly.
An example is provided below.
Example:
```
this is an example how log text should be marked (wrap it with ```)
```
-->
Log excerpt is above, this was taken from dmesg. We have also seen the following (though not seemingly as often as above):
```
Feb 16 01:05:26 node0 kernel: [852621.670537] sd 2:3:77:0: [sdkh] tag#6 FAILED Result: hostbyte=DID_OK driverbyte=DRIVER_SENSE cmd_age=2s
Feb 16 01:05:26 node0 kernel: [852621.670558] sd 2:3:77:0: [sdkh] tag#6 Sense Key : Hardware Error [current] [descriptor]
Feb 16 01:05:26 node0 kernel: [852621.670570] sd 2:3:77:0: [sdkh] tag#6 Add. Sense: Power-on or self-test failure(0)
Feb 16 01:05:26 node0 kernel: [852621.670580] sd 2:3:77:0: [sdkh] tag#6 CDB: Synchronize Cache(10) 35 00 00 00 00 00 00 00 00 00
Feb 16 01:05:26 node0 kernel: [852621.670664] blk_update_request: critical target error, dev dm-49, sector 0
Feb 16 01:05:26 node0 kernel: [852621.670673] zio pool=node0-storage006 vdev=/dev/mapper/node0-storage006-6p1 error=121 type=5 offset=0 size=0 flags=100480
```
We are working with the hardware vendor on the drive issues specifically, but it seems like ZFS should be able to handle this situation a bit better.
|
1.0
|
Multiple "zio error=61 type=1" errors not faulting a vdev - <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | CentOS
Distribution Version | 7.8.2003
Linux Kernel | 3.10.0-1127.19.1.el7.x86_64
Architecture | x86_64
ZFS Version | 0.8.4-1
SPL Version | 0.8.4-1
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
We have a number of 10-drive raidz2 zpools on a system. The drives are in a JBOD connected to the system, with multipath providing pathing to each drive. We have seen drives begin to log multiple errors into syslog/dmesg, accumulating a large number of errors. We have yet to find the key, but at some point the zpool appears to go non-responsive (deeper information at this point is difficult due to pacemaker stoniths as this is a production filesystem).
An example of the errors are:
```
Feb 16 10:57:31 node0 kernel: [888148.088324] sd 2:3:77:0: [sdkh] tag#19 BRCM Debug mfi stat 0x2d, data len requested/completed 0x1000/0x0
Feb 16 10:57:31 node0 kernel: [888148.088341] sd 2:3:77:0: [sdkh] tag#19 FAILED Result: hostbyte=DID_OK driverbyte=DRIVER_SENSE cmd_age=9s
Feb 16 10:57:31 node0 kernel: [888148.088347] sd 2:3:77:0: [sdkh] tag#19 Sense Key : Medium Error [current]
Feb 16 10:57:31 node0 kernel: [888148.088349] sd 2:3:77:0: [sdkh] tag#19 Add. Sense: Unrecovered read error
Feb 16 10:57:31 node0 kernel: [888148.088352] sd 2:3:77:0: [sdkh] tag#19 CDB: Read(16) 88 00 00 00 00 00 a1 d6 69 a8 00 00 00 08 00 00
Feb 16 10:57:31 node0 kernel: [888148.088354] blk_update_request: critical medium error, dev sdkh, sector 2715183528
Feb 16 10:57:31 node0 kernel: [888148.088362] blk_update_request: critical medium error, dev dm-49, sector 2715183528
Feb 16 10:57:31 node0 kernel: [888148.088367] zio pool=node0-storage006 vdev=/dev/mapper/node0-storage006-6p1 error=61 type=1 offset=1390172917760 size=4096 flags=180880
```
It appears that ZFS never automatically faults the bad vdev, and instead keeps all vdevs online even though I/O to the underlying device is having issues.
I'm unsure if there's something else going on here keeping ZFS from faulting that drive, or if this is some kind of underlying bug.
### Describe how to reproduce the problem
### Include any warning/errors/backtraces from the system logs
<!--
*IMPORTANT* - Please mark logs and text output from terminal commands
or else Github will not display them correctly.
An example is provided below.
Example:
```
this is an example how log text should be marked (wrap it with ```)
```
-->
Log excerpt is above, this was taken from dmesg. We have also seen the following (though not seemingly as often as above):
```
Feb 16 01:05:26 node0 kernel: [852621.670537] sd 2:3:77:0: [sdkh] tag#6 FAILED Result: hostbyte=DID_OK driverbyte=DRIVER_SENSE cmd_age=2s
Feb 16 01:05:26 node0 kernel: [852621.670558] sd 2:3:77:0: [sdkh] tag#6 Sense Key : Hardware Error [current] [descriptor]
Feb 16 01:05:26 node0 kernel: [852621.670570] sd 2:3:77:0: [sdkh] tag#6 Add. Sense: Power-on or self-test failure(0)
Feb 16 01:05:26 node0 kernel: [852621.670580] sd 2:3:77:0: [sdkh] tag#6 CDB: Synchronize Cache(10) 35 00 00 00 00 00 00 00 00 00
Feb 16 01:05:26 node0 kernel: [852621.670664] blk_update_request: critical target error, dev dm-49, sector 0
Feb 16 01:05:26 node0 kernel: [852621.670673] zio pool=node0-storage006 vdev=/dev/mapper/node0-storage006-6p1 error=121 type=5 offset=0 size=0 flags=100480
```
We are working with the hardware vendor on the drive issues specifically, but it seems like ZFS should be able to handle this situation a bit better.
|
defect
|
multiple zio error type errors not faulting a vdev thank you for reporting an issue important please check our issue tracker before opening a new issue additional valuable information can be found in the openzfs documentation and mailing list archives please fill in as much of the template as possible system information type version name distribution name centos distribution version linux kernel architecture zfs version spl version commands to find zfs spl versions modinfo zfs grep iw version modinfo spl grep iw version describe the problem you re observing we have a number of drive zpools on a system the drives are in a jbod connected to the system with multipath providing pathing to each drive we have seen drives begin to log multiple errors into syslog dmesg accumulating a large number of errors we have yet to find the key but at some point the zpool appears to go non responsive deeper information at this point is difficult due to pacemaker stoniths as this is a production filesystem an example of the errors are feb kernel sd tag brcm debug mfi stat data len requested completed feb kernel sd tag failed result hostbyte did ok driverbyte driver sense cmd age feb kernel sd tag sense key medium error feb kernel sd tag add sense unrecovered read error feb kernel sd tag cdb read feb kernel blk update request critical medium error dev sdkh sector feb kernel blk update request critical medium error dev dm sector feb kernel zio pool vdev dev mapper error type offset size flags it appears that zfs never automatically faults the bad vdev and instead keeps all vdevs online even though i o to the underlying device is having issues i m unsure if there s something else going on here keeping zfs from faulting that drive or if this is some kind of underlying bug describe how to reproduce the problem include any warning errors backtraces from the system logs important please mark logs and text output from terminal commands or else github will not display them correctly an example is provided below example this is an example how log text should be marked wrap it with log excerpt is above this was taken from dmesg we have also seen the following though not seemingly as often as above feb kernel sd tag failed result hostbyte did ok driverbyte driver sense cmd age feb kernel sd tag sense key hardware error feb kernel sd tag add sense power on or self test failure feb kernel sd tag cdb synchronize cache feb kernel blk update request critical target error dev dm sector feb kernel zio pool vdev dev mapper error type offset size flags we are working with the hardware vendor on the drive issues specifically but it seems like zfs should be able to handle this situation a bit better
| 1
|
5,201
| 5,544,371,301
|
IssuesEvent
|
2017-03-22 18:58:42
|
hydroshare/hydroshare
|
https://api.github.com/repos/hydroshare/hydroshare
|
closed
|
Renew HydroShare SSL certificate - expires on 5/12/2017
|
SECURITY
|
@dtarb - Our existing HydroShare SSL cert will expire on May 12, 2017.

|
True
|
Renew HydroShare SSL certificate - expires on 5/12/2017 - @dtarb - Our existing HydroShare SSL cert will expire on May 12, 2017.

|
non_defect
|
renew hydroshare ssl certificate expires on dtarb our existing hydroshare ssl cert will expire on may
| 0
|
20,191
| 3,314,629,937
|
IssuesEvent
|
2015-11-06 06:55:02
|
yinheli/lightweight-java-profiler
|
https://api.github.com/repos/yinheli/lightweight-java-profiler
|
closed
|
INVALID_METHODID
|
auto-migrated Priority-Medium Type-Defect
|
```
Using Ubuntu 14.04 64-bit. Built from @12 with patch from #3 applied. In both
JDK 7u55 and 6u45, when I run an application (Jenkins) with the agent loaded,
`traces.txt` is created but has no content. When I interrupt the process with
Ctrl-C, the following is printed:
{{{
One of your monitoring interfaces is having trouble resolving its stack traces.
GetMethodName on a jmethodID involved in a stacktrace resulted in an
INVALID_METHODID error which usually indicates its declaring class has been
unloaded.
}}}
```
Original issue reported on code.google.com by `jgl...@cloudbees.com` on 28 May 2014 at 5:16
|
1.0
|
INVALID_METHODID - ```
Using Ubuntu 14.04 64-bit. Built from @12 with patch from #3 applied. In both
JDK 7u55 and 6u45, when I run an application (Jenkins) with the agent loaded,
`traces.txt` is created but has no content. When I interrupt the process with
Ctrl-C, the following is printed:
{{{
One of your monitoring interfaces is having trouble resolving its stack traces.
GetMethodName on a jmethodID involved in a stacktrace resulted in an
INVALID_METHODID error which usually indicates its declaring class has been
unloaded.
}}}
```
Original issue reported on code.google.com by `jgl...@cloudbees.com` on 28 May 2014 at 5:16
|
defect
|
invalid methodid using ubuntu bit built from with patch from applied in both jdk and when i run an application jenkins with the agent loaded traces txt is created but has no content when i interrupt the process with ctrl c the following is printed one of your monitoring interfaces is having trouble resolving its stack traces getmethodname on a jmethodid involved in a stacktrace resulted in an invalid methodid error which usually indicates its declaring class has been unloaded original issue reported on code google com by jgl cloudbees com on may at
| 1
|
49,290
| 13,186,589,087
|
IssuesEvent
|
2020-08-13 00:39:45
|
icecube-trac/tix3
|
https://api.github.com/repos/icecube-trac/tix3
|
opened
|
cmake - I3_USE_ROOT macro set w/o root installed (Trac #1131)
|
Incomplete Migration Migrated from Trac cmake defect
|
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1131">https://code.icecube.wisc.edu/ticket/1131</a>, reported by nega and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-11T23:59:15",
"description": "if USE_ROOT is given to cmake, the C macro I3_USE_ROOT is set even if root isn't found.\n\nsee #1121",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1547251155701656",
"component": "cmake",
"summary": "cmake - I3_USE_ROOT macro set w/o root installed",
"priority": "blocker",
"keywords": "",
"time": "2015-08-17T18:43:53",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
cmake - I3_USE_ROOT macro set w/o root installed (Trac #1131) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1131">https://code.icecube.wisc.edu/ticket/1131</a>, reported by nega and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-01-11T23:59:15",
"description": "if USE_ROOT is given to cmake, the C macro I3_USE_ROOT is set even if root isn't found.\n\nsee #1121",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1547251155701656",
"component": "cmake",
"summary": "cmake - I3_USE_ROOT macro set w/o root installed",
"priority": "blocker",
"keywords": "",
"time": "2015-08-17T18:43:53",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
|
defect
|
cmake use root macro set w o root installed trac migrated from json status closed changetime description if use root is given to cmake the c macro use root is set even if root isn t found n nsee reporter nega cc resolution fixed ts component cmake summary cmake use root macro set w o root installed priority blocker keywords time milestone owner nega type defect
| 1
|
156,817
| 19,906,909,769
|
IssuesEvent
|
2022-01-25 13:43:28
|
Azure/AKS
|
https://api.github.com/repos/Azure/AKS
|
opened
|
CVE-2022-0185: heap overflow bug in legacy_parse_param()
|
security
|
William Liu and Jamie Hill-Daniel discovered that the file system context functionality in the Linux kernel contained an integer underflow vulnerability, leading to an out-of-bounds write. A local attacker could use this to cause a denial of service (system crash) or execute arbitrary code.
# Mitigation
Disable unprivileged user namespaces:
sysctl -w kernel.unprivileged_userns_clone=0
# AKS Information:
AKS is working on applied to the patched kernel. Will update this issue once the patch is available.
AKS
-- | --
|
True
|
CVE-2022-0185: heap overflow bug in legacy_parse_param() - William Liu and Jamie Hill-Daniel discovered that the file system context functionality in the Linux kernel contained an integer underflow vulnerability, leading to an out-of-bounds write. A local attacker could use this to cause a denial of service (system crash) or execute arbitrary code.
# Mitigation
Disable unprivileged user namespaces:
sysctl -w kernel.unprivileged_userns_clone=0
# AKS Information:
AKS is working on applied to the patched kernel. Will update this issue once the patch is available.
AKS
-- | --
|
non_defect
|
cve heap overflow bug in legacy parse param william liu and jamie hill daniel discovered that the file system context functionality in the linux kernel contained an integer underflow vulnerability leading to an out of bounds write a local attacker could use this to cause a denial of service system crash or execute arbitrary code mitigation disable unprivileged user namespaces sysctl w kernel unprivileged userns clone aks information aks is working on applied to the patched kernel will update this issue once the patch is available aks
| 0
|
92,368
| 26,666,767,342
|
IssuesEvent
|
2023-01-26 05:20:07
|
runatlantis/atlantis
|
https://api.github.com/repos/runatlantis/atlantis
|
opened
|
Add permissions to all github actions
|
build github-actions
|
<!--- Please keep this note for the community --->
### Community Note
- Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request. Searching for pre-existing feature requests helps us consolidate datapoints for identical requirements into a single place, thank you!
- Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request.
- If you are interested in working on this issue or have submitted a pull request, please leave a comment.
<!--- Thank you for keeping this note for the community --->
---
- [ ] I'd be willing to implement this feature ([contributing guide](https://github.com/runatlantis/atlantis/blob/main/CONTRIBUTING.md))
**Describe the user story**
<!--
A clear and concise description of what workflow is meant to be improved.
Example: "As a developer, I often want to do <something>, but I often face <problem>".
-->
Keep things secure by adding necessary permissions.
This can be used to generate the permissions.
https://app.stepsecurity.io/secureworkflow/runatlantis/atlantis
**Describe the solution you'd like**
<!--
A clear and concise description of what you want to happen. Consider that atlantis is used
by many people, and your particular use case might not make sense to implement in the core.
-->
**Describe the drawbacks of your solution**
<!--
This section is important not only to identify future issues, but also for us to see whether
you thought through your request. When filling it, ask yourself what are the problems we could
have maintaining what you propose. How often will it break?
-->
**Describe alternatives you've considered**
<!--
A clear and concise description of any alternative solutions or features you've considered,
and why you think they wouldn't be good enough.
-->
|
1.0
|
Add permissions to all github actions - <!--- Please keep this note for the community --->
### Community Note
- Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request. Searching for pre-existing feature requests helps us consolidate datapoints for identical requirements into a single place, thank you!
- Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request.
- If you are interested in working on this issue or have submitted a pull request, please leave a comment.
<!--- Thank you for keeping this note for the community --->
---
- [ ] I'd be willing to implement this feature ([contributing guide](https://github.com/runatlantis/atlantis/blob/main/CONTRIBUTING.md))
**Describe the user story**
<!--
A clear and concise description of what workflow is meant to be improved.
Example: "As a developer, I often want to do <something>, but I often face <problem>".
-->
Keep things secure by adding necessary permissions.
This can be used to generate the permissions.
https://app.stepsecurity.io/secureworkflow/runatlantis/atlantis
**Describe the solution you'd like**
<!--
A clear and concise description of what you want to happen. Consider that atlantis is used
by many people, and your particular use case might not make sense to implement in the core.
-->
**Describe the drawbacks of your solution**
<!--
This section is important not only to identify future issues, but also for us to see whether
you thought through your request. When filling it, ask yourself what are the problems we could
have maintaining what you propose. How often will it break?
-->
**Describe alternatives you've considered**
<!--
A clear and concise description of any alternative solutions or features you've considered,
and why you think they wouldn't be good enough.
-->
|
non_defect
|
add permissions to all github actions community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request searching for pre existing feature requests helps us consolidate datapoints for identical requirements into a single place thank you please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment i d be willing to implement this feature describe the user story a clear and concise description of what workflow is meant to be improved example as a developer i often want to do but i often face keep things secure by adding necessary permissions this can be used to generate the permissions describe the solution you d like a clear and concise description of what you want to happen consider that atlantis is used by many people and your particular use case might not make sense to implement in the core describe the drawbacks of your solution this section is important not only to identify future issues but also for us to see whether you thought through your request when filling it ask yourself what are the problems we could have maintaining what you propose how often will it break describe alternatives you ve considered a clear and concise description of any alternative solutions or features you ve considered and why you think they wouldn t be good enough
| 0
|
30,762
| 6,277,074,187
|
IssuesEvent
|
2017-07-18 11:13:24
|
contao/core-bundle
|
https://api.github.com/repos/contao/core-bundle
|
closed
|
Content element table - I can't shrink increased table sizes
|
defect
|
For table content elements exists an increase button. But no option to shrink the table size back.
<img width="525" alt="bildschirmfoto 2017-07-18 um 11 47 31" src="https://user-images.githubusercontent.com/26099903/28311153-045f5a8e-6baf-11e7-85d8-69f5b755551f.png">
|
1.0
|
Content element table - I can't shrink increased table sizes - For table content elements exists an increase button. But no option to shrink the table size back.
<img width="525" alt="bildschirmfoto 2017-07-18 um 11 47 31" src="https://user-images.githubusercontent.com/26099903/28311153-045f5a8e-6baf-11e7-85d8-69f5b755551f.png">
|
defect
|
content element table i can t shrink increased table sizes for table content elements exists an increase button but no option to shrink the table size back img width alt bildschirmfoto um src
| 1
|
34,261
| 7,431,749,030
|
IssuesEvent
|
2018-03-25 17:43:53
|
Yahkal/replicaisland
|
https://api.github.com/repos/Yahkal/replicaisland
|
closed
|
Rare random crashes on HTC Hero
|
Priority-Medium Type-Defect auto-migrated
|
```
Cannot be easily reproduced.
I went through the entire game without any big problem, but 3-4 times per
game I encountered strange blank+black screen. To get over it was necessary
to escape game with home button and kill the game with task killer tool.
I run RI on my HTC Hero, Android 1.5. Game once upgraded.
Probably won't be helpful by itself, perhaps any other user has similar
issue.
```
Original issue reported on code.google.com by `ales.najmann` on 18 Apr 2010 at 10:30
|
1.0
|
Rare random crashes on HTC Hero - ```
Cannot be easily reproduced.
I went through the entire game without any big problem, but 3-4 times per
game I encountered strange blank+black screen. To get over it was necessary
to escape game with home button and kill the game with task killer tool.
I run RI on my HTC Hero, Android 1.5. Game once upgraded.
Probably won't be helpful by itself, perhaps any other user has similar
issue.
```
Original issue reported on code.google.com by `ales.najmann` on 18 Apr 2010 at 10:30
|
defect
|
rare random crashes on htc hero cannot be easily reproduced i went through the entire game without any big problem but times per game i encountered strange blank black screen to get over it was necessary to escape game with home button and kill the game with task killer tool i run ri on my htc hero android game once upgraded probably won t be helpful by itself perhaps any other user has similar issue original issue reported on code google com by ales najmann on apr at
| 1
|
74,462
| 25,135,324,046
|
IssuesEvent
|
2022-11-09 18:06:28
|
SeleniumHQ/selenium
|
https://api.github.com/repos/SeleniumHQ/selenium
|
opened
|
[🐛 Bug]: selenium can't get dom elements in facebook
|
I-defect needs-triaging
|
### What happened?
**the problem the selenium can't see html elements that generated by javascript or dom in facebook page**
selenium see the javascript or dom code only and can't see rendered html code by javascript or dom
I hope you understand what I mean, thank you
### How can we reproduce the issue?
```shell
python code:
WebDriverWait(driver, 20).until(EC.frame_to_be_available_and_switch_to_it((By.CSS_SELECTOR,"iframe[title='reCAPTCHA']")))
WebDriverWait(driver, 20).until(EC.element_to_be_clickable((By.CSS_SELECTOR, "div.recaptcha-checkbox-border"))).click()
selenium after load the page view this code link below:
before dom and selenium view this code only and can't get elements after dom:
https://raw.githubusercontent.com/AhmedSheri123/license/main/source.html
```
### Relevant log output
```shell
c:\Users\****\Documents\****\****\project\venv\lib\site-packages\pydub\utils.py:170: RuntimeWarning:
DevTools listening on ws://127.0.0.1:11202/devtools/browser/0120b89b-8a42-45bc-a991-ead5c3c0de22
[8136:600:1109/194410.150:ERROR:device_event_log_impl.cc(215)] [19:44:10.150] USB: usb_device_handle_win.cc:1048 Failed to read descriptor
from node connection: A device attached to the system is not functioning. (0x1F)
[8136:600:1109/194410.154:ERROR:device_event_log_impl.cc(215)] [19:44:10.155] USB: usb_device_handle_win.cc:1048 Failed to read descriptor
from node connection: A device attached to the system is not functioning. (0x1F)
الاشتراك في فيسبوك | فيسبوك
['CDwindow-C8C8C349895E61EFDE57EDB5188B8D1E']
Traceback (most recent call last):
File "c:\Users\SHERI\Documents\mostql\MosaShaheen\facebook\main.py", line 120, in <module>
WebDriverWait(driver, 20).until(EC.frame_to_be_available_and_switch_to_it((By.CSS_SELECTOR,"iframe[title='reCAPTCHA']")))
File "c:\Users\SHERI\Documents\mostql\MosaShaheen\facebook\venv\lib\site-packages\selenium\webdriver\support\wait.py", line 90, in until
raise TimeoutException(message, screen, stacktrace)
selenium.common.exceptions.TimeoutException: Message:
Stacktrace:
Backtrace:
Ordinal0 [0x00D0ACD3+2075859]
Ordinal0 [0x00C9EE61+1633889]
Ordinal0 [0x00B9B7BD+571325]
Ordinal0 [0x00BCAC2F+764975]
Ordinal0 [0x00BCAE1B+765467]
Ordinal0 [0x00BFD0F2+970994]
Ordinal0 [0x00BE7364+881508]
Ordinal0 [0x00BFB56A+963946]
Ordinal0 [0x00BE7136+880950]
Ordinal0 [0x00BBFEFD+720637]
Ordinal0 [0x00BC0F3F+724799]
GetHandleVerifier [0x00FBEED2+2769538]
GetHandleVerifier [0x00FB0D95+2711877]
GetHandleVerifier [0x00D9A03A+521194]
GetHandleVerifier [0x00D98DA0+516432]
Ordinal0 [0x00CA682C+1665068]
Ordinal0 [0x00CAB128+1683752]
Ordinal0 [0x00CAB215+1683989]
Ordinal0 [0x00CB6484+1729668]
BaseThreadInitThunk [0x76A0FA29+25]
RtlGetAppContainerNamedObjectPath [0x776E7BBE+286]
RtlGetAppContainerNamedObjectPath [0x776E7B8E+238]
```
### Operating System
windows10
### Selenium version
4.5.0
### What are the browser(s) and version(s) where you see this issue?
chrome v- 107.0.5304.88
### What are the browser driver(s) and version(s) where you see this issue?
from webdriver_manager.chrome import ChromeDriverManager
### Are you using Selenium Grid?
_No response_
|
1.0
|
[🐛 Bug]: selenium can't get dom elements in facebook - ### What happened?
**the problem the selenium can't see html elements that generated by javascript or dom in facebook page**
selenium see the javascript or dom code only and can't see rendered html code by javascript or dom
I hope you understand what I mean, thank you
### How can we reproduce the issue?
```shell
python code:
WebDriverWait(driver, 20).until(EC.frame_to_be_available_and_switch_to_it((By.CSS_SELECTOR,"iframe[title='reCAPTCHA']")))
WebDriverWait(driver, 20).until(EC.element_to_be_clickable((By.CSS_SELECTOR, "div.recaptcha-checkbox-border"))).click()
selenium after load the page view this code link below:
before dom and selenium view this code only and can't get elements after dom:
https://raw.githubusercontent.com/AhmedSheri123/license/main/source.html
```
### Relevant log output
```shell
c:\Users\****\Documents\****\****\project\venv\lib\site-packages\pydub\utils.py:170: RuntimeWarning:
DevTools listening on ws://127.0.0.1:11202/devtools/browser/0120b89b-8a42-45bc-a991-ead5c3c0de22
[8136:600:1109/194410.150:ERROR:device_event_log_impl.cc(215)] [19:44:10.150] USB: usb_device_handle_win.cc:1048 Failed to read descriptor
from node connection: A device attached to the system is not functioning. (0x1F)
[8136:600:1109/194410.154:ERROR:device_event_log_impl.cc(215)] [19:44:10.155] USB: usb_device_handle_win.cc:1048 Failed to read descriptor
from node connection: A device attached to the system is not functioning. (0x1F)
الاشتراك في فيسبوك | فيسبوك
['CDwindow-C8C8C349895E61EFDE57EDB5188B8D1E']
Traceback (most recent call last):
File "c:\Users\SHERI\Documents\mostql\MosaShaheen\facebook\main.py", line 120, in <module>
WebDriverWait(driver, 20).until(EC.frame_to_be_available_and_switch_to_it((By.CSS_SELECTOR,"iframe[title='reCAPTCHA']")))
File "c:\Users\SHERI\Documents\mostql\MosaShaheen\facebook\venv\lib\site-packages\selenium\webdriver\support\wait.py", line 90, in until
raise TimeoutException(message, screen, stacktrace)
selenium.common.exceptions.TimeoutException: Message:
Stacktrace:
Backtrace:
Ordinal0 [0x00D0ACD3+2075859]
Ordinal0 [0x00C9EE61+1633889]
Ordinal0 [0x00B9B7BD+571325]
Ordinal0 [0x00BCAC2F+764975]
Ordinal0 [0x00BCAE1B+765467]
Ordinal0 [0x00BFD0F2+970994]
Ordinal0 [0x00BE7364+881508]
Ordinal0 [0x00BFB56A+963946]
Ordinal0 [0x00BE7136+880950]
Ordinal0 [0x00BBFEFD+720637]
Ordinal0 [0x00BC0F3F+724799]
GetHandleVerifier [0x00FBEED2+2769538]
GetHandleVerifier [0x00FB0D95+2711877]
GetHandleVerifier [0x00D9A03A+521194]
GetHandleVerifier [0x00D98DA0+516432]
Ordinal0 [0x00CA682C+1665068]
Ordinal0 [0x00CAB128+1683752]
Ordinal0 [0x00CAB215+1683989]
Ordinal0 [0x00CB6484+1729668]
BaseThreadInitThunk [0x76A0FA29+25]
RtlGetAppContainerNamedObjectPath [0x776E7BBE+286]
RtlGetAppContainerNamedObjectPath [0x776E7B8E+238]
```
### Operating System
windows10
### Selenium version
4.5.0
### What are the browser(s) and version(s) where you see this issue?
chrome v- 107.0.5304.88
### What are the browser driver(s) and version(s) where you see this issue?
from webdriver_manager.chrome import ChromeDriverManager
### Are you using Selenium Grid?
_No response_
|
defect
|
selenium can t get dom elements in facebook what happened the problem the selenium can t see html elements that generated by javascript or dom in facebook page selenium see the javascript or dom code only and can t see rendered html code by javascript or dom i hope you understand what i mean thank you how can we reproduce the issue shell python code webdriverwait driver until ec frame to be available and switch to it by css selector iframe webdriverwait driver until ec element to be clickable by css selector div recaptcha checkbox border click selenium after load the page view this code link below before dom and selenium view this code only and can t get elements after dom relevant log output shell c users documents project venv lib site packages pydub utils py runtimewarning devtools listening on ws devtools browser usb usb device handle win cc failed to read descriptor from node connection a device attached to the system is not functioning usb usb device handle win cc failed to read descriptor from node connection a device attached to the system is not functioning الاشتراك في فيسبوك فيسبوك traceback most recent call last file c users sheri documents mostql mosashaheen facebook main py line in webdriverwait driver until ec frame to be available and switch to it by css selector iframe file c users sheri documents mostql mosashaheen facebook venv lib site packages selenium webdriver support wait py line in until raise timeoutexception message screen stacktrace selenium common exceptions timeoutexception message stacktrace backtrace gethandleverifier gethandleverifier gethandleverifier gethandleverifier basethreadinitthunk rtlgetappcontainernamedobjectpath rtlgetappcontainernamedobjectpath operating system selenium version what are the browser s and version s where you see this issue chrome v what are the browser driver s and version s where you see this issue from webdriver manager chrome import chromedrivermanager are you using selenium grid no response
| 1
|
74,583
| 20,244,473,392
|
IssuesEvent
|
2022-02-14 12:26:36
|
spring-projects/spring-security
|
https://api.github.com/repos/spring-projects/spring-security
|
closed
|
Spring Security main build is broken on samples task
|
in: build type: bug
|
Example: https://github.com/spring-projects/spring-security/runs/5181928075?check_suite_focus=true
Our Spring Security CI build is broken on the main branch for the task "Check samples project".
The error is:
```
Execution failed for task ':includeRepo:servlet:java-configuration:data:compileJava'.
> Could not resolve all files for configuration ':includeRepo:servlet:java-configuration:data:compileClasspath'.
> Could not find org.springframework.security:spring-security-core:6.0.0-SNAPSHOT.
Searched in the following locations:
- https://repo.maven.apache.org/maven2/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/maven-metadata.xml
- https://repo.maven.apache.org/maven2/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/spring-security-core-6.0.0-SNAPSHOT.pom
- https://repo.spring.io/milestone/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/maven-metadata.xml
- https://repo.spring.io/milestone/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/spring-security-core-6.0.0-SNAPSHOT.pom
- https://repo.spring.io/snapshot/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/maven-metadata.xml
- https://repo.spring.io/snapshot/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/spring-security-core-6.0.0-SNAPSHOT.pom
Required by:
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-bom:6.0.0-SNAPSHOT:20220210.1[233](https://github.com/spring-projects/spring-security/runs/5181928075?check_suite_focus=true#step:5:233)00-223
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-config:6.0.0-SNAPSHOT:20220210.123302-221
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-data:6.0.0-SNAPSHOT:20220210.123304-222
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-web:6.0.0-SNAPSHOT:20220210.123312-222
```
|
1.0
|
Spring Security main build is broken on samples task - Example: https://github.com/spring-projects/spring-security/runs/5181928075?check_suite_focus=true
Our Spring Security CI build is broken on the main branch for the task "Check samples project".
The error is:
```
Execution failed for task ':includeRepo:servlet:java-configuration:data:compileJava'.
> Could not resolve all files for configuration ':includeRepo:servlet:java-configuration:data:compileClasspath'.
> Could not find org.springframework.security:spring-security-core:6.0.0-SNAPSHOT.
Searched in the following locations:
- https://repo.maven.apache.org/maven2/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/maven-metadata.xml
- https://repo.maven.apache.org/maven2/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/spring-security-core-6.0.0-SNAPSHOT.pom
- https://repo.spring.io/milestone/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/maven-metadata.xml
- https://repo.spring.io/milestone/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/spring-security-core-6.0.0-SNAPSHOT.pom
- https://repo.spring.io/snapshot/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/maven-metadata.xml
- https://repo.spring.io/snapshot/org/springframework/security/spring-security-core/6.0.0-SNAPSHOT/spring-security-core-6.0.0-SNAPSHOT.pom
Required by:
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-bom:6.0.0-SNAPSHOT:20220210.1[233](https://github.com/spring-projects/spring-security/runs/5181928075?check_suite_focus=true#step:5:233)00-223
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-config:6.0.0-SNAPSHOT:20220210.123302-221
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-data:6.0.0-SNAPSHOT:20220210.123304-222
project :includeRepo:servlet:java-configuration:data > org.springframework.security:spring-security-web:6.0.0-SNAPSHOT:20220210.123312-222
```
|
non_defect
|
spring security main build is broken on samples task example our spring security ci build is broken on the main branch for the task check samples project the error is execution failed for task includerepo servlet java configuration data compilejava could not resolve all files for configuration includerepo servlet java configuration data compileclasspath could not find org springframework security spring security core snapshot searched in the following locations required by project includerepo servlet java configuration data org springframework security spring security bom snapshot project includerepo servlet java configuration data org springframework security spring security config snapshot project includerepo servlet java configuration data org springframework security spring security data snapshot project includerepo servlet java configuration data org springframework security spring security web snapshot
| 0
|
23,197
| 3,776,036,986
|
IssuesEvent
|
2016-03-17 15:28:21
|
obophenotype/upheno
|
https://api.github.com/repos/obophenotype/upheno
|
closed
|
zp.owl issue
|
Priority-Medium Status-Accepted Type-Defect
|
Originally reported on Google Code with ID 48
```
1. Some BFO IDs need to be changed to RO IDs
2. 'abnormal' is repeated, in both text and equiv axioms. E.g
has_part some
(abnormal
and (BFO_0000052 some 'central nervous system')
and ('has component' some abnormal))
Should be
has_part some
(*quality*
and (*RO*_0000052 some 'central nervous system')
and ('has component' some abnormal))
```
Reported by `cmungall` on 2014-07-31 19:11:55
|
1.0
|
zp.owl issue - Originally reported on Google Code with ID 48
```
1. Some BFO IDs need to be changed to RO IDs
2. 'abnormal' is repeated, in both text and equiv axioms. E.g
has_part some
(abnormal
and (BFO_0000052 some 'central nervous system')
and ('has component' some abnormal))
Should be
has_part some
(*quality*
and (*RO*_0000052 some 'central nervous system')
and ('has component' some abnormal))
```
Reported by `cmungall` on 2014-07-31 19:11:55
|
defect
|
zp owl issue originally reported on google code with id some bfo ids need to be changed to ro ids abnormal is repeated in both text and equiv axioms e g has part some abnormal and bfo some central nervous system and has component some abnormal should be has part some quality and ro some central nervous system and has component some abnormal reported by cmungall on
| 1
|
9,134
| 27,603,832,100
|
IssuesEvent
|
2023-03-09 11:42:02
|
red-hat-storage/ocs-ci
|
https://api.github.com/repos/red-hat-storage/ocs-ci
|
opened
|
Add OBC support for 4.10 UI testing
|
MCG ui_automation
|
The `views.py::locators.4.10` dict doesn't have an `obc` entry so `
test_obc_creation_and_deletion` fails with a KeyError while trying to initialize ObcUI:
```
class ObcUI(PageNavigator):
"""
A class representation for abstraction of OBC-related OpenShift UI actions
"""
def __init__(self, driver):
super().__init__(driver)
ocs_version = f"{version.get_ocs_version_from_csv(only_major_minor=True)}"
self.obc_loc = locators[ocs_version]["obc"]
...
...
Message: KeyError: 'obc'
```
Runs:
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-Actions]-02/24/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9240/409505/409641/409643/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-three_dots]-02/24/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9240/409505/409641/409642/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-three_dots]-02/25/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9273/411686/411822/411824/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-three_dots]-02/25/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9273/411686/411822/411823/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
|
1.0
|
Add OBC support for 4.10 UI testing - The `views.py::locators.4.10` dict doesn't have an `obc` entry so `
test_obc_creation_and_deletion` fails with a KeyError while trying to initialize ObcUI:
```
class ObcUI(PageNavigator):
"""
A class representation for abstraction of OBC-related OpenShift UI actions
"""
def __init__(self, driver):
super().__init__(driver)
ocs_version = f"{version.get_ocs_version_from_csv(only_major_minor=True)}"
self.obc_loc = locators[ocs_version]["obc"]
...
...
Message: KeyError: 'obc'
```
Runs:
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-Actions]-02/24/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9240/409505/409641/409643/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-three_dots]-02/24/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9240/409505/409641/409642/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-three_dots]-02/25/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9273/411686/411822/411824/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
[test_obc_creation_and_deletion[openshift-storage.noobaa.io-noobaa-default-bucket-class-three_dots]-02/25/2023](https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#ocs/launches/432/9273/411686/411822/411823/log?item0Params=filter.eq.hasStats%3Dtrue%26filter.eq.hasChildren%3Dfalse%26filter.in.issueType%3Dti001%252Cti_1h7tquhpjupuu%252Cti_u7ukrfvrt1yu%252Cti_qxkzvw4t6ipf%252Cti_1h7u8s8jf8tvb)
|
non_defect
|
add obc support for ui testing the views py locators dict doesn t have an obc entry so test obc creation and deletion fails with a keyerror while trying to initialize obcui class obcui pagenavigator a class representation for abstraction of obc related openshift ui actions def init self driver super init driver ocs version f version get ocs version from csv only major minor true self obc loc locators message keyerror obc runs
| 0
|
2,357
| 2,607,897,566
|
IssuesEvent
|
2015-02-26 00:12:05
|
chrsmithdemos/zen-coding
|
https://api.github.com/repos/chrsmithdemos/zen-coding
|
closed
|
P is becoming padding instead of paragraph in Coda
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1. Make new document in Coda
2. Try div+p
3. the div is made but the p becomes padding
What is the expected output? What do you see instead?
<div></div>
<p></p>
<div></div>
padding:;
What version of the product are you using? On what operating system?
Latest Coda, OS X
Please provide any additional information below.
```
-----
Original issue reported on code.google.com by `dt.e...@gmail.com` on 22 Nov 2009 at 8:24
|
1.0
|
P is becoming padding instead of paragraph in Coda - ```
What steps will reproduce the problem?
1. Make new document in Coda
2. Try div+p
3. the div is made but the p becomes padding
What is the expected output? What do you see instead?
<div></div>
<p></p>
<div></div>
padding:;
What version of the product are you using? On what operating system?
Latest Coda, OS X
Please provide any additional information below.
```
-----
Original issue reported on code.google.com by `dt.e...@gmail.com` on 22 Nov 2009 at 8:24
|
defect
|
p is becoming padding instead of paragraph in coda what steps will reproduce the problem make new document in coda try div p the div is made but the p becomes padding what is the expected output what do you see instead padding what version of the product are you using on what operating system latest coda os x please provide any additional information below original issue reported on code google com by dt e gmail com on nov at
| 1
|
19,813
| 3,263,974,641
|
IssuesEvent
|
2015-10-22 09:05:37
|
hazelcast/hazelcast
|
https://api.github.com/repos/hazelcast/hazelcast
|
closed
|
[TEST-FAILURE] MigrationAwareServiceTest.testPartitionDataSize_whenBackupNodesTerminated_withSingleBackup
|
Team: Core Type: Defect
|
**Note:** This failure occurred on the Hazelcast-3.x-IbmJDK1.6 build job!
https://hazelcast-l337.ci.cloudbees.com/view/Official%20Builds/job/Hazelcast-3.x-IbmJDK1.6/663/
```
Error Message
expected:<542> but was:<517>
Stacktrace
java.lang.AssertionError: expected:<542> but was:<517>
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at com.hazelcast.spi.MigrationAwareServiceTest$3.run(MigrationAwareServiceTest.java:221)
at com.hazelcast.test.HazelcastTestSupport.assertTrueEventually(HazelcastTestSupport.java:751)
at com.hazelcast.test.HazelcastTestSupport.assertTrueEventually(HazelcastTestSupport.java:765)
at com.hazelcast.spi.MigrationAwareServiceTest.assertSize(MigrationAwareServiceTest.java:210)
at com.hazelcast.spi.MigrationAwareServiceTest.testPartitionDataSize_whenBackupNodesTerminated(MigrationAwareServiceTest.java:146)
at com.hazelcast.spi.MigrationAwareServiceTest.testPartitionDataSize_whenBackupNodesTerminated_withSingleBackup(MigrationAwareServiceTest.java:124)
```
|
1.0
|
[TEST-FAILURE] MigrationAwareServiceTest.testPartitionDataSize_whenBackupNodesTerminated_withSingleBackup - **Note:** This failure occurred on the Hazelcast-3.x-IbmJDK1.6 build job!
https://hazelcast-l337.ci.cloudbees.com/view/Official%20Builds/job/Hazelcast-3.x-IbmJDK1.6/663/
```
Error Message
expected:<542> but was:<517>
Stacktrace
java.lang.AssertionError: expected:<542> but was:<517>
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at com.hazelcast.spi.MigrationAwareServiceTest$3.run(MigrationAwareServiceTest.java:221)
at com.hazelcast.test.HazelcastTestSupport.assertTrueEventually(HazelcastTestSupport.java:751)
at com.hazelcast.test.HazelcastTestSupport.assertTrueEventually(HazelcastTestSupport.java:765)
at com.hazelcast.spi.MigrationAwareServiceTest.assertSize(MigrationAwareServiceTest.java:210)
at com.hazelcast.spi.MigrationAwareServiceTest.testPartitionDataSize_whenBackupNodesTerminated(MigrationAwareServiceTest.java:146)
at com.hazelcast.spi.MigrationAwareServiceTest.testPartitionDataSize_whenBackupNodesTerminated_withSingleBackup(MigrationAwareServiceTest.java:124)
```
|
defect
|
migrationawareservicetest testpartitiondatasize whenbackupnodesterminated withsinglebackup note this failure occurred on the hazelcast x build job error message expected but was stacktrace java lang assertionerror expected but was at org junit assert fail assert java at org junit assert failnotequals assert java at org junit assert assertequals assert java at org junit assert assertequals assert java at com hazelcast spi migrationawareservicetest run migrationawareservicetest java at com hazelcast test hazelcasttestsupport asserttrueeventually hazelcasttestsupport java at com hazelcast test hazelcasttestsupport asserttrueeventually hazelcasttestsupport java at com hazelcast spi migrationawareservicetest assertsize migrationawareservicetest java at com hazelcast spi migrationawareservicetest testpartitiondatasize whenbackupnodesterminated migrationawareservicetest java at com hazelcast spi migrationawareservicetest testpartitiondatasize whenbackupnodesterminated withsinglebackup migrationawareservicetest java
| 1
|
213,865
| 7,261,076,942
|
IssuesEvent
|
2018-02-18 17:10:47
|
sankichi92/LiveLog
|
https://api.github.com/repos/sankichi92/LiveLog
|
closed
|
Stats ページ周りをリファクタリングする
|
low priority
|
- モデル `Stats` を作成する
- `StatsController` を作成する
- `resources :stats, only: :show` を `routes.rb` に追加する
|
1.0
|
Stats ページ周りをリファクタリングする - - モデル `Stats` を作成する
- `StatsController` を作成する
- `resources :stats, only: :show` を `routes.rb` に追加する
|
non_defect
|
stats ページ周りをリファクタリングする モデル stats を作成する statscontroller を作成する resources stats only show を routes rb に追加する
| 0
|
368,154
| 25,779,199,685
|
IssuesEvent
|
2022-12-09 14:33:09
|
FabienArcellier/fixtup
|
https://api.github.com/repos/FabienArcellier/fixtup
|
opened
|
use docker logo into principle.excalidraw
|
documentation
|
we are going to change the block diagram to organize it on 2 lines.
![Uploading image.png…]()
The first line will display directory & docker. The second line will display dataset associated with directory and postgres, redis, ftp associated with docker. sqlite disappears.
|
1.0
|
use docker logo into principle.excalidraw - we are going to change the block diagram to organize it on 2 lines.
![Uploading image.png…]()
The first line will display directory & docker. The second line will display dataset associated with directory and postgres, redis, ftp associated with docker. sqlite disappears.
|
non_defect
|
use docker logo into principle excalidraw we are going to change the block diagram to organize it on lines the first line will display directory docker the second line will display dataset associated with directory and postgres redis ftp associated with docker sqlite disappears
| 0
|
132,318
| 18,680,657,509
|
IssuesEvent
|
2021-11-01 04:54:07
|
appsmithorg/appsmith
|
https://api.github.com/repos/appsmithorg/appsmith
|
closed
|
[Bug]: API & Query fields don't expand correctly
|
Bug Design System High Platform Pod New Developers Pod
|
### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
When writing code in the API URL, headers, params & form data, the fields don't expand to show the entire code block
When writing code in the mongo query, the fields expand but are transparent so the fields underneath are visible
### Steps To Reproduce
<img width="518" alt="Screenshot 2021-10-27 at 5 58 23 PM" src="https://user-images.githubusercontent.com/3897254/139065484-1d4f80f6-1fd6-45b1-9c41-85ca4aa1124e.png">
<img width="841" alt="Screenshot 2021-10-27 at 5 58 40 PM" src="https://user-images.githubusercontent.com/3897254/139065502-6cfb4ac9-93c2-4478-acd6-906180a0d8ea.png">
### Environment
Production
### Version
Cloud
|
1.0
|
[Bug]: API & Query fields don't expand correctly - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
When writing code in the API URL, headers, params & form data, the fields don't expand to show the entire code block
When writing code in the mongo query, the fields expand but are transparent so the fields underneath are visible
### Steps To Reproduce
<img width="518" alt="Screenshot 2021-10-27 at 5 58 23 PM" src="https://user-images.githubusercontent.com/3897254/139065484-1d4f80f6-1fd6-45b1-9c41-85ca4aa1124e.png">
<img width="841" alt="Screenshot 2021-10-27 at 5 58 40 PM" src="https://user-images.githubusercontent.com/3897254/139065502-6cfb4ac9-93c2-4478-acd6-906180a0d8ea.png">
### Environment
Production
### Version
Cloud
|
non_defect
|
api query fields don t expand correctly is there an existing issue for this i have searched the existing issues current behavior when writing code in the api url headers params form data the fields don t expand to show the entire code block when writing code in the mongo query the fields expand but are transparent so the fields underneath are visible steps to reproduce img width alt screenshot at pm src img width alt screenshot at pm src environment production version cloud
| 0
|
11,646
| 14,499,867,522
|
IssuesEvent
|
2020-12-11 17:15:47
|
elastic/beats
|
https://api.github.com/repos/elastic/beats
|
closed
|
Add documentation examples for adding fields to a module
|
:Processors Stalled libbeat needs_docs needs_team
|
Normally you'd configure `fields` and `fields_under_root` as
```
- type: log
paths:
- /your_data_path
fields:
field1: aaa
field2: bbb
field3: ccc
fields_under_root: true
```
However there's no example in the documentation on how to do this when using modules. For example:
```
- module: apache2
access:
enabled: true
var.paths:
input:
fields_under_root: true
fields.field1: aaa
fields.field2: bbb
fields.field3: ccc
error:
enabled: true
var.paths:
input:
fields_under_root: true
fields.field1: aaa
fields.field2: bbb
fields.field3: ccc
```
|
1.0
|
Add documentation examples for adding fields to a module - Normally you'd configure `fields` and `fields_under_root` as
```
- type: log
paths:
- /your_data_path
fields:
field1: aaa
field2: bbb
field3: ccc
fields_under_root: true
```
However there's no example in the documentation on how to do this when using modules. For example:
```
- module: apache2
access:
enabled: true
var.paths:
input:
fields_under_root: true
fields.field1: aaa
fields.field2: bbb
fields.field3: ccc
error:
enabled: true
var.paths:
input:
fields_under_root: true
fields.field1: aaa
fields.field2: bbb
fields.field3: ccc
```
|
non_defect
|
add documentation examples for adding fields to a module normally you d configure fields and fields under root as type log paths your data path fields aaa bbb ccc fields under root true however there s no example in the documentation on how to do this when using modules for example module access enabled true var paths input fields under root true fields aaa fields bbb fields ccc error enabled true var paths input fields under root true fields aaa fields bbb fields ccc
| 0
|
42,325
| 10,963,290,810
|
IssuesEvent
|
2019-11-27 19:18:59
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
closed
|
DataTable & ContextMenu: ContextMenu does not open for empty DataTables
|
defect
|
## 1) Environment
- PrimeFaces version: 7.0
- Does it work on the newest released PrimeFaces version? Version? No
- Does it work on the newest sources in GitHub? No
- Affected browsers: Firefox
## 2) Expected behavior
When right-clicking an empty row in a datatable the context menu is displayed.
## 3) Actual behavior
When right-clicking an empty row in a databale the default browser context menu is displayed (e.g. the PF context menu is not displayed).
The browser console indicates "TypeError: g is undefined."
## 4) Steps to reproduce
1) Create a DataTable and a context menu that is associated with the table. Ensure that the table is empty and that there is a emptyMessage attribute set on the data table.
2) Right click on the empty row.
I looked into it in detail and found that in my components.js file there is a variable "g" that is not instantiated in the scope of its use. There is however a variable "f" which looks like it should be used instead of "g". I believe "f" and "g" are used because the file was minified & obfuscated.
In the latest version of primefaces, this code is located in datatable.js ( primefaces/src/main/resources/META-INF/resources/primefaces/datatable/datatable.js ) and that "f" variable corresponds to "row" on line 882 and "g" corresponds to "$this" on line 903. The error is happening on line 903: `else if(row.hasClass('ui-datatable-empty-message') && !$this.cfg.disableContextMenuIfEmpty) {` because the "$this" variable is defined outside of the scope where it is used here (line 909).
I think replacing "$this" with "row" on line 903 will fix the issue.
## 5) Sample XHTML
```xml
<p:dataTable id="testTable" emptyMessage-"No Data">
<f:facet name="header">Table</f:facet>
<p:column headerText="Column 1"></p:column>
</p:dataTable>
<p:contextMenu for="testTable">
<p:menuitem value="Add" onclick="alert('added');" />
</p:contextMenu>
```
## 6) Sample bean
N/A - not relevant
|
1.0
|
DataTable & ContextMenu: ContextMenu does not open for empty DataTables - ## 1) Environment
- PrimeFaces version: 7.0
- Does it work on the newest released PrimeFaces version? Version? No
- Does it work on the newest sources in GitHub? No
- Affected browsers: Firefox
## 2) Expected behavior
When right-clicking an empty row in a datatable the context menu is displayed.
## 3) Actual behavior
When right-clicking an empty row in a databale the default browser context menu is displayed (e.g. the PF context menu is not displayed).
The browser console indicates "TypeError: g is undefined."
## 4) Steps to reproduce
1) Create a DataTable and a context menu that is associated with the table. Ensure that the table is empty and that there is a emptyMessage attribute set on the data table.
2) Right click on the empty row.
I looked into it in detail and found that in my components.js file there is a variable "g" that is not instantiated in the scope of its use. There is however a variable "f" which looks like it should be used instead of "g". I believe "f" and "g" are used because the file was minified & obfuscated.
In the latest version of primefaces, this code is located in datatable.js ( primefaces/src/main/resources/META-INF/resources/primefaces/datatable/datatable.js ) and that "f" variable corresponds to "row" on line 882 and "g" corresponds to "$this" on line 903. The error is happening on line 903: `else if(row.hasClass('ui-datatable-empty-message') && !$this.cfg.disableContextMenuIfEmpty) {` because the "$this" variable is defined outside of the scope where it is used here (line 909).
I think replacing "$this" with "row" on line 903 will fix the issue.
## 5) Sample XHTML
```xml
<p:dataTable id="testTable" emptyMessage-"No Data">
<f:facet name="header">Table</f:facet>
<p:column headerText="Column 1"></p:column>
</p:dataTable>
<p:contextMenu for="testTable">
<p:menuitem value="Add" onclick="alert('added');" />
</p:contextMenu>
```
## 6) Sample bean
N/A - not relevant
|
defect
|
datatable contextmenu contextmenu does not open for empty datatables environment primefaces version does it work on the newest released primefaces version version no does it work on the newest sources in github no affected browsers firefox expected behavior when right clicking an empty row in a datatable the context menu is displayed actual behavior when right clicking an empty row in a databale the default browser context menu is displayed e g the pf context menu is not displayed the browser console indicates typeerror g is undefined steps to reproduce create a datatable and a context menu that is associated with the table ensure that the table is empty and that there is a emptymessage attribute set on the data table right click on the empty row i looked into it in detail and found that in my components js file there is a variable g that is not instantiated in the scope of its use there is however a variable f which looks like it should be used instead of g i believe f and g are used because the file was minified obfuscated in the latest version of primefaces this code is located in datatable js primefaces src main resources meta inf resources primefaces datatable datatable js and that f variable corresponds to row on line and g corresponds to this on line the error is happening on line else if row hasclass ui datatable empty message this cfg disablecontextmenuifempty because the this variable is defined outside of the scope where it is used here line i think replacing this with row on line will fix the issue sample xhtml xml table sample bean n a not relevant
| 1
|
72,556
| 24,180,879,517
|
IssuesEvent
|
2022-09-23 08:46:58
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
opened
|
Carousel: Has no paginator link limit
|
:lady_beetle: defect :bangbang: needs-triage
|
### Describe the bug
Since PrimeFaces 11.0.0 the carousel component is missing the of the attribute "pageLinks" which was used to limit the displayed page links in the paginator area. So now there is a page link for every item in the carousel. For example, if you have 20 items in it, it will show 20 page links and so on. We need at least an option to disable the display of the page links to prevent an overflow of those.
### Reproducer
```
<div class="card">
<p:carousel circular="true">
<f:facet name="header">
<h5>Tabs</h5>
</f:facet>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab> <p:tab>
<p class="m-0 p-3">A</p>
</p:tab> <p:tab>
<p class="m-0 p-3">A</p>
</p:tab> <p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
</p:carousel>
</div>
```
### Expected behavior
_No response_
### PrimeFaces edition
_No response_
### PrimeFaces version
11.0.0
### Theme
Diamond
### JSF implementation
MyFaces
### JSF version
2.3
### Java version
Java 8
### Browser(s)
_No response_
|
1.0
|
Carousel: Has no paginator link limit - ### Describe the bug
Since PrimeFaces 11.0.0 the carousel component is missing the of the attribute "pageLinks" which was used to limit the displayed page links in the paginator area. So now there is a page link for every item in the carousel. For example, if you have 20 items in it, it will show 20 page links and so on. We need at least an option to disable the display of the page links to prevent an overflow of those.
### Reproducer
```
<div class="card">
<p:carousel circular="true">
<f:facet name="header">
<h5>Tabs</h5>
</f:facet>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
<p:tab>
<p class="m-0 p-3">A</p>
</p:tab> <p:tab>
<p class="m-0 p-3">A</p>
</p:tab> <p:tab>
<p class="m-0 p-3">A</p>
</p:tab> <p:tab>
<p class="m-0 p-3">A</p>
</p:tab>
</p:carousel>
</div>
```
### Expected behavior
_No response_
### PrimeFaces edition
_No response_
### PrimeFaces version
11.0.0
### Theme
Diamond
### JSF implementation
MyFaces
### JSF version
2.3
### Java version
Java 8
### Browser(s)
_No response_
|
defect
|
carousel has no paginator link limit describe the bug since primefaces the carousel component is missing the of the attribute pagelinks which was used to limit the displayed page links in the paginator area so now there is a page link for every item in the carousel for example if you have items in it it will show page links and so on we need at least an option to disable the display of the page links to prevent an overflow of those reproducer tabs a a a a a a a a expected behavior no response primefaces edition no response primefaces version theme diamond jsf implementation myfaces jsf version java version java browser s no response
| 1
|
517,842
| 15,020,426,254
|
IssuesEvent
|
2021-02-01 14:42:12
|
SentyFunBall/valour-vapp
|
https://api.github.com/repos/SentyFunBall/valour-vapp
|
opened
|
🐛 Bug - wrapper doesnt authenticate
|
bug high priority urgent
|
Describe the bug
title
To Reproduce
go to wrapper.py
there is no good authentication
Expected behavior
good authentication
Screenshots
If applicable, add screenshots to help explain your problem.
System Information:
-not needed-
Additional context
none
|
1.0
|
🐛 Bug - wrapper doesnt authenticate - Describe the bug
title
To Reproduce
go to wrapper.py
there is no good authentication
Expected behavior
good authentication
Screenshots
If applicable, add screenshots to help explain your problem.
System Information:
-not needed-
Additional context
none
|
non_defect
|
🐛 bug wrapper doesnt authenticate describe the bug title to reproduce go to wrapper py there is no good authentication expected behavior good authentication screenshots if applicable add screenshots to help explain your problem system information not needed additional context none
| 0
|
80,731
| 30,508,194,343
|
IssuesEvent
|
2023-07-18 18:34:30
|
vector-im/element-desktop
|
https://api.github.com/repos/vector-im/element-desktop
|
closed
|
Element is offline after the first log on
|
T-Defect Z-Linux X-Community-Supported-Platform Z-Suse
|
### Steps to reproduce
1. Log on the client for the first time
2. Verify the client
3. Restart the client
### Outcome
#### What did you expect?
I expect that when I start Element that I get log on as normal
#### What happened instead?
Everything works fine when I log on Element Desktop the first time, but after I restart the client is stuck being offline telling that "Connectivity to the server has been lost."
I know the server is working well since it works on other clients, and the browser version of element
### Operating system
OpenSUSE Tumbleweed
### Application version
Element-Desktop 1.11.15
### How did you install the app?
OpenSUSE repository
### Homeserver
element.ithvr.no
### Will you send logs?
Yes
|
1.0
|
Element is offline after the first log on - ### Steps to reproduce
1. Log on the client for the first time
2. Verify the client
3. Restart the client
### Outcome
#### What did you expect?
I expect that when I start Element that I get log on as normal
#### What happened instead?
Everything works fine when I log on Element Desktop the first time, but after I restart the client is stuck being offline telling that "Connectivity to the server has been lost."
I know the server is working well since it works on other clients, and the browser version of element
### Operating system
OpenSUSE Tumbleweed
### Application version
Element-Desktop 1.11.15
### How did you install the app?
OpenSUSE repository
### Homeserver
element.ithvr.no
### Will you send logs?
Yes
|
defect
|
element is offline after the first log on steps to reproduce log on the client for the first time verify the client restart the client outcome what did you expect i expect that when i start element that i get log on as normal what happened instead everything works fine when i log on element desktop the first time but after i restart the client is stuck being offline telling that connectivity to the server has been lost i know the server is working well since it works on other clients and the browser version of element operating system opensuse tumbleweed application version element desktop how did you install the app opensuse repository homeserver element ithvr no will you send logs yes
| 1
|
93,823
| 27,051,963,439
|
IssuesEvent
|
2023-02-13 13:52:17
|
gwaldron/osgearth
|
https://api.github.com/repos/gwaldron/osgearth
|
closed
|
Zip driver build issue
|
build-issue
|
Currently, there are several issues with osgearth's zip driver
1) libzip package searched as follows:
```
if(OSGEARTH_BUILD_ZIP_PLUGIN)
find_package(LIBZIP)
endif()
```
But script itself in CMakeModules called FindLibZip.cmake, and i think find_package is case sensitive.
2) There is probably typo in CMakeLists.txt for zip driver, `OSGEARTH_BUILD_ZIP_PLUGIN` option called here `BUILD_OSGEARTH_ZIP_PLUGIN`
3) If 1 and 2 is fixed, looks like produced library name will be the same as OpenSceneGraph's zip plugin (which is probably also optional, but anyway). Is it intended? Even if they didn't have the same name, which plugin will be used for zipped files?
|
1.0
|
Zip driver build issue - Currently, there are several issues with osgearth's zip driver
1) libzip package searched as follows:
```
if(OSGEARTH_BUILD_ZIP_PLUGIN)
find_package(LIBZIP)
endif()
```
But script itself in CMakeModules called FindLibZip.cmake, and i think find_package is case sensitive.
2) There is probably typo in CMakeLists.txt for zip driver, `OSGEARTH_BUILD_ZIP_PLUGIN` option called here `BUILD_OSGEARTH_ZIP_PLUGIN`
3) If 1 and 2 is fixed, looks like produced library name will be the same as OpenSceneGraph's zip plugin (which is probably also optional, but anyway). Is it intended? Even if they didn't have the same name, which plugin will be used for zipped files?
|
non_defect
|
zip driver build issue currently there are several issues with osgearth s zip driver libzip package searched as follows if osgearth build zip plugin find package libzip endif but script itself in cmakemodules called findlibzip cmake and i think find package is case sensitive there is probably typo in cmakelists txt for zip driver osgearth build zip plugin option called here build osgearth zip plugin if and is fixed looks like produced library name will be the same as openscenegraph s zip plugin which is probably also optional but anyway is it intended even if they didn t have the same name which plugin will be used for zipped files
| 0
|
165,304
| 12,836,768,209
|
IssuesEvent
|
2020-07-07 14:49:13
|
mui-org/material-ui
|
https://api.github.com/repos/mui-org/material-ui
|
reopened
|
[TablePagination] Snapshot test issue
|
component: Table test
|
Recent changes to compnent `TablePagination` break test.
```
<Typography color="inherit" variant="body2" className={classes.caption} id={labelId}>
{labelRowsPerPage}
</Typography>
```
[link](https://github.com/mui-org/material-ui/blob/3eb02f5498857bd01bb7924eed9b946f33e39052/packages/material-ui/src/TablePagination/TablePagination.js#L114)
The generated id is always new and snapshot doesn't/cann't match.
```
<p
class="MuiTypography-root MuiTablePagination-caption MuiTypography-body2 MuiTypography-colorInherit"
- id="mui-7460"
+ id="mui-62542"
>
```
- [+] The issue is present in the latest release.
- [+] I have searched the [issues](https://github.com/mui-org/material-ui/issues) of this repository and believe that this is not a duplicate.
## Environment 🌎
`@material-ui/core: 4.10.1`
`jest: 24.9.0`
|
1.0
|
[TablePagination] Snapshot test issue - Recent changes to compnent `TablePagination` break test.
```
<Typography color="inherit" variant="body2" className={classes.caption} id={labelId}>
{labelRowsPerPage}
</Typography>
```
[link](https://github.com/mui-org/material-ui/blob/3eb02f5498857bd01bb7924eed9b946f33e39052/packages/material-ui/src/TablePagination/TablePagination.js#L114)
The generated id is always new and snapshot doesn't/cann't match.
```
<p
class="MuiTypography-root MuiTablePagination-caption MuiTypography-body2 MuiTypography-colorInherit"
- id="mui-7460"
+ id="mui-62542"
>
```
- [+] The issue is present in the latest release.
- [+] I have searched the [issues](https://github.com/mui-org/material-ui/issues) of this repository and believe that this is not a duplicate.
## Environment 🌎
`@material-ui/core: 4.10.1`
`jest: 24.9.0`
|
non_defect
|
snapshot test issue recent changes to compnent tablepagination break test labelrowsperpage the generated id is always new and snapshot doesn t cann t match p class muitypography root muitablepagination caption muitypography muitypography colorinherit id mui id mui the issue is present in the latest release i have searched the of this repository and believe that this is not a duplicate environment 🌎 material ui core jest
| 0
|
720
| 2,587,684,868
|
IssuesEvent
|
2015-02-17 20:01:08
|
hazelcast/hazelcast
|
https://api.github.com/repos/hazelcast/hazelcast
|
closed
|
TransactionalMap.size() returns inconsistent results during a transaction
|
Team: Core Type: Defect
|
Hazelcast version: 3.4
Node type: in-cluster
Configuration: a basic unit-test setup
The problem is probably best described by the following JUnit example:
@Test
public void transactionalMapCanHaveNegativeSize() throws Exception {
final TransactionContext transactionContext =
hazelcastInstance.newTransactionContext(new TransactionOptions().setTransactionType(TransactionOptions.TransactionType.LOCAL));
transactionContext.beginTransaction();
final TransactionalMap<String, String> map = transactionContext.getMap("test-map");
map.put("k", "v");
map.remove("k");
assertEquals(0, map.size()); // failure: expected 0 got -1
}
I think the problem is in `TransactionalMap#remove(Object)`, where it overwrites the "insert" operation in its internal transaction map with a "remove" - so you end up with a remove for an object that never existed. Then when it comes to decide size, it counts the removal with negative size.
I think the right thing to do here is to remove the insertion `TxValueWrapper` from `txMap`.
I'm happy to write up a PR if the above is agreed - the reason I haven't already is that I'm surprised this hasn't been stumbled on before, so I'm wondering if there's some reason it would be intentional.
The work-around we're using is to get the size of the keyset (which returns the expected result).
|
1.0
|
TransactionalMap.size() returns inconsistent results during a transaction - Hazelcast version: 3.4
Node type: in-cluster
Configuration: a basic unit-test setup
The problem is probably best described by the following JUnit example:
@Test
public void transactionalMapCanHaveNegativeSize() throws Exception {
final TransactionContext transactionContext =
hazelcastInstance.newTransactionContext(new TransactionOptions().setTransactionType(TransactionOptions.TransactionType.LOCAL));
transactionContext.beginTransaction();
final TransactionalMap<String, String> map = transactionContext.getMap("test-map");
map.put("k", "v");
map.remove("k");
assertEquals(0, map.size()); // failure: expected 0 got -1
}
I think the problem is in `TransactionalMap#remove(Object)`, where it overwrites the "insert" operation in its internal transaction map with a "remove" - so you end up with a remove for an object that never existed. Then when it comes to decide size, it counts the removal with negative size.
I think the right thing to do here is to remove the insertion `TxValueWrapper` from `txMap`.
I'm happy to write up a PR if the above is agreed - the reason I haven't already is that I'm surprised this hasn't been stumbled on before, so I'm wondering if there's some reason it would be intentional.
The work-around we're using is to get the size of the keyset (which returns the expected result).
|
defect
|
transactionalmap size returns inconsistent results during a transaction hazelcast version node type in cluster configuration a basic unit test setup the problem is probably best described by the following junit example test public void transactionalmapcanhavenegativesize throws exception final transactioncontext transactioncontext hazelcastinstance newtransactioncontext new transactionoptions settransactiontype transactionoptions transactiontype local transactioncontext begintransaction final transactionalmap map transactioncontext getmap test map map put k v map remove k assertequals map size failure expected got i think the problem is in transactionalmap remove object where it overwrites the insert operation in its internal transaction map with a remove so you end up with a remove for an object that never existed then when it comes to decide size it counts the removal with negative size i think the right thing to do here is to remove the insertion txvaluewrapper from txmap i m happy to write up a pr if the above is agreed the reason i haven t already is that i m surprised this hasn t been stumbled on before so i m wondering if there s some reason it would be intentional the work around we re using is to get the size of the keyset which returns the expected result
| 1
|
61,903
| 14,643,128,346
|
IssuesEvent
|
2020-12-25 14:44:42
|
fu1771695yongxie/node
|
https://api.github.com/repos/fu1771695yongxie/node
|
opened
|
CVE-2019-10747 (High) detected in set-value-2.0.0.tgz, set-value-0.4.3.tgz
|
security vulnerability
|
## CVE-2019-10747 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>set-value-2.0.0.tgz</b>, <b>set-value-0.4.3.tgz</b></p></summary>
<p>
<details><summary><b>set-value-2.0.0.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz">https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz</a></p>
<p>Path to dependency file: node/deps/node-inspect/package.json</p>
<p>Path to vulnerable library: node/deps/node-inspect/node_modules/nyc/node_modules/set-value/package.json,node/deps/v8/tools/clusterfuzz/js_fuzzer/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- tap-10.7.3.tgz (Root Library)
- nyc-11.9.0.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- :x: **set-value-2.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>set-value-0.4.3.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz">https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz</a></p>
<p>Path to dependency file: node/deps/node-inspect/package.json</p>
<p>Path to vulnerable library: node/deps/node-inspect/node_modules/nyc/node_modules/union-value/node_modules/set-value/package.json,node/deps/v8/tools/clusterfuzz/js_fuzzer/node_modules/union-value/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- tap-10.7.3.tgz (Root Library)
- nyc-11.9.0.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- union-value-1.0.0.tgz
- :x: **set-value-0.4.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/node/commit/3059e1d5415bc8b2e7573d215723e6a29a000bc0">3059e1d5415bc8b2e7573d215723e6a29a000bc0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
set-value is vulnerable to Prototype Pollution in versions lower than 3.0.1. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using any of the constructor, prototype and _proto_ payloads.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10747>CVE-2019-10747</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f">https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f</a></p>
<p>Release Date: 2019-07-24</p>
<p>Fix Resolution: 2.0.1,3.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-10747 (High) detected in set-value-2.0.0.tgz, set-value-0.4.3.tgz - ## CVE-2019-10747 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>set-value-2.0.0.tgz</b>, <b>set-value-0.4.3.tgz</b></p></summary>
<p>
<details><summary><b>set-value-2.0.0.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz">https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz</a></p>
<p>Path to dependency file: node/deps/node-inspect/package.json</p>
<p>Path to vulnerable library: node/deps/node-inspect/node_modules/nyc/node_modules/set-value/package.json,node/deps/v8/tools/clusterfuzz/js_fuzzer/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- tap-10.7.3.tgz (Root Library)
- nyc-11.9.0.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- :x: **set-value-2.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>set-value-0.4.3.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz">https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz</a></p>
<p>Path to dependency file: node/deps/node-inspect/package.json</p>
<p>Path to vulnerable library: node/deps/node-inspect/node_modules/nyc/node_modules/union-value/node_modules/set-value/package.json,node/deps/v8/tools/clusterfuzz/js_fuzzer/node_modules/union-value/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- tap-10.7.3.tgz (Root Library)
- nyc-11.9.0.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- union-value-1.0.0.tgz
- :x: **set-value-0.4.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/node/commit/3059e1d5415bc8b2e7573d215723e6a29a000bc0">3059e1d5415bc8b2e7573d215723e6a29a000bc0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
set-value is vulnerable to Prototype Pollution in versions lower than 3.0.1. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using any of the constructor, prototype and _proto_ payloads.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10747>CVE-2019-10747</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f">https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f</a></p>
<p>Release Date: 2019-07-24</p>
<p>Fix Resolution: 2.0.1,3.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_defect
|
cve high detected in set value tgz set value tgz cve high severity vulnerability vulnerable libraries set value tgz set value tgz set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file node deps node inspect package json path to vulnerable library node deps node inspect node modules nyc node modules set value package json node deps tools clusterfuzz js fuzzer node modules set value package json dependency hierarchy tap tgz root library nyc tgz micromatch tgz snapdragon tgz base tgz cache base tgz x set value tgz vulnerable library set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file node deps node inspect package json path to vulnerable library node deps node inspect node modules nyc node modules union value node modules set value package json node deps tools clusterfuzz js fuzzer node modules union value node modules set value package json dependency hierarchy tap tgz root library nyc tgz micromatch tgz snapdragon tgz base tgz cache base tgz union value tgz x set value tgz vulnerable library found in head commit a href vulnerability details set value is vulnerable to prototype pollution in versions lower than the function mixin deep could be tricked into adding or modifying properties of object prototype using any of the constructor prototype and proto payloads publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
123,906
| 10,291,670,634
|
IssuesEvent
|
2019-08-27 13:00:07
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
teamcity: failed test: _duplicate_collated_string_key_direct=false
|
C-test-failure O-robot
|
The following tests appear to have failed on master (testrace): _duplicate_collated_string_key_direct=false
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+_duplicate_collated_string_key_direct=false).
[#1451542](https://teamcity.cockroachdb.com/viewLog.html?buildId=1451542):
```
_duplicate_collated_string_key_direct=false
--- FAIL: testrace/TestImportData/CSV:_duplicate_collated_string_key_direct=false (0.000s)
Test ended in panic.
------- Stdout: -------
I190823 14:38:02.665697 268 sql/event_log.go:130 [n1,client=127.0.0.1:42112,user=root] Event: "create_database", target: 57, info: {DatabaseName:d2 Statement:CREATE DATABASE d2 User:root}
W190823 14:38:02.722597 30 sql/schema_changer.go:949 [n1,scExec] waiting to update leases: error with attached stack trace:
github.com/cockroachdb/cockroach/pkg/sql.LeaseStore.WaitForOneVersion
/go/src/github.com/cockroachdb/cockroach/pkg/sql/lease.go:314
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChanger).waitToUpdateLeases
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:1201
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChanger).exec.func1
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:948
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChanger).exec
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:964
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChangeManager).Start.func1.1
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:1961
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChangeManager).Start.func1
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:2226
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:196
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1337
- error with embedded safe details: ID %d is not a table
-- arg 1: <sqlbase.ID>
- ID 54 is not a table
I190823 14:38:02.890630 1811 storage/replica_command.go:284 [n1,s1,r25/1:/{Table/56/1-Max}] initiating a split of this range at key /Table/58/1 [r27] (manual)
I190823 14:38:02.905536 1810 ccl/importccl/read_import_proc.go:83 [n1,import-distsql-ingest] could not fetch file size; falling back to per-file progress: bad ContentLength: -1
I190823 14:38:03.005641 1867 storage/replica_command.go:284 [n1,split,s1,r25/1:/Table/5{6/1-8/1}] initiating a split of this range at key /Table/58 [r28] (zone config)
I190823 14:38:03.065022 268 sql/event_log.go:130 [n1,client=127.0.0.1:42112,user=root] Event: "drop_database", target: 57, info: {DatabaseName:d2 Statement:DROP DATABASE d2 User:root DroppedSchemaObjects:[]}
```
Please assign, take a look and update the issue accordingly.
|
1.0
|
teamcity: failed test: _duplicate_collated_string_key_direct=false - The following tests appear to have failed on master (testrace): _duplicate_collated_string_key_direct=false
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+_duplicate_collated_string_key_direct=false).
[#1451542](https://teamcity.cockroachdb.com/viewLog.html?buildId=1451542):
```
_duplicate_collated_string_key_direct=false
--- FAIL: testrace/TestImportData/CSV:_duplicate_collated_string_key_direct=false (0.000s)
Test ended in panic.
------- Stdout: -------
I190823 14:38:02.665697 268 sql/event_log.go:130 [n1,client=127.0.0.1:42112,user=root] Event: "create_database", target: 57, info: {DatabaseName:d2 Statement:CREATE DATABASE d2 User:root}
W190823 14:38:02.722597 30 sql/schema_changer.go:949 [n1,scExec] waiting to update leases: error with attached stack trace:
github.com/cockroachdb/cockroach/pkg/sql.LeaseStore.WaitForOneVersion
/go/src/github.com/cockroachdb/cockroach/pkg/sql/lease.go:314
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChanger).waitToUpdateLeases
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:1201
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChanger).exec.func1
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:948
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChanger).exec
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:964
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChangeManager).Start.func1.1
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:1961
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChangeManager).Start.func1
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:2226
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:196
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1337
- error with embedded safe details: ID %d is not a table
-- arg 1: <sqlbase.ID>
- ID 54 is not a table
I190823 14:38:02.890630 1811 storage/replica_command.go:284 [n1,s1,r25/1:/{Table/56/1-Max}] initiating a split of this range at key /Table/58/1 [r27] (manual)
I190823 14:38:02.905536 1810 ccl/importccl/read_import_proc.go:83 [n1,import-distsql-ingest] could not fetch file size; falling back to per-file progress: bad ContentLength: -1
I190823 14:38:03.005641 1867 storage/replica_command.go:284 [n1,split,s1,r25/1:/Table/5{6/1-8/1}] initiating a split of this range at key /Table/58 [r28] (zone config)
I190823 14:38:03.065022 268 sql/event_log.go:130 [n1,client=127.0.0.1:42112,user=root] Event: "drop_database", target: 57, info: {DatabaseName:d2 Statement:DROP DATABASE d2 User:root DroppedSchemaObjects:[]}
```
Please assign, take a look and update the issue accordingly.
|
non_defect
|
teamcity failed test duplicate collated string key direct false the following tests appear to have failed on master testrace duplicate collated string key direct false you may want to check duplicate collated string key direct false fail testrace testimportdata csv duplicate collated string key direct false test ended in panic stdout sql event log go event create database target info databasename statement create database user root sql schema changer go waiting to update leases error with attached stack trace github com cockroachdb cockroach pkg sql leasestore waitforoneversion go src github com cockroachdb cockroach pkg sql lease go github com cockroachdb cockroach pkg sql schemachanger waittoupdateleases go src github com cockroachdb cockroach pkg sql schema changer go github com cockroachdb cockroach pkg sql schemachanger exec go src github com cockroachdb cockroach pkg sql schema changer go github com cockroachdb cockroach pkg sql schemachanger exec go src github com cockroachdb cockroach pkg sql schema changer go github com cockroachdb cockroach pkg sql schemachangemanager start go src github com cockroachdb cockroach pkg sql schema changer go github com cockroachdb cockroach pkg sql schemachangemanager start go src github com cockroachdb cockroach pkg sql schema changer go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go runtime goexit usr local go src runtime asm s error with embedded safe details id d is not a table arg id is not a table storage replica command go initiating a split of this range at key table manual ccl importccl read import proc go could not fetch file size falling back to per file progress bad contentlength storage replica command go initiating a split of this range at key table zone config sql event log go event drop database target info databasename statement drop database user root droppedschemaobjects please assign take a look and update the issue accordingly
| 0
|
218,343
| 24,353,897,456
|
IssuesEvent
|
2022-10-03 04:51:51
|
dotnet/aspnetcore
|
https://api.github.com/repos/dotnet/aspnetcore
|
closed
|
SecurityTokenInvalidAudienceException: IDX10206: Unable to validate audience. The 'audiences' parameter is empty. Microsoft.IdentityModel.Tokens.Validators.ValidateAudience(IEnumerable<string> audiences, SecurityToken securityToken, TokenValidationParameters validationParameters)
|
Needs: Author Feedback area-security
|
### Is there an existing issue for this?
- [X] I have searched the existing issues
### Describe the bug
I have a problem for use cookie authentication without ASP.NET Core Identity.
### Expected Behavior
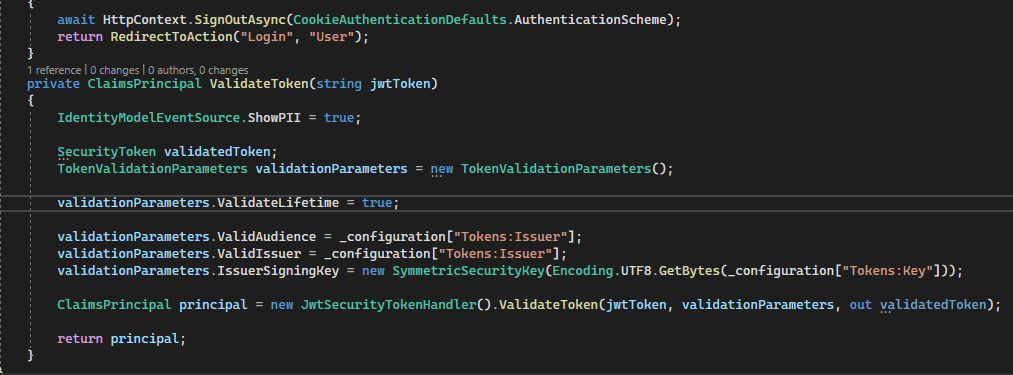

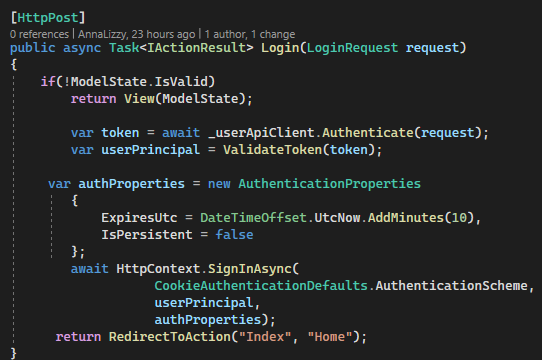
### Steps To Reproduce
_No response_
### Exceptions (if any)
_No response_
### .NET Version
.net core 3.1
### Anything else?
_No response_
|
True
|
SecurityTokenInvalidAudienceException: IDX10206: Unable to validate audience. The 'audiences' parameter is empty. Microsoft.IdentityModel.Tokens.Validators.ValidateAudience(IEnumerable<string> audiences, SecurityToken securityToken, TokenValidationParameters validationParameters) - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Describe the bug
I have a problem for use cookie authentication without ASP.NET Core Identity.
### Expected Behavior
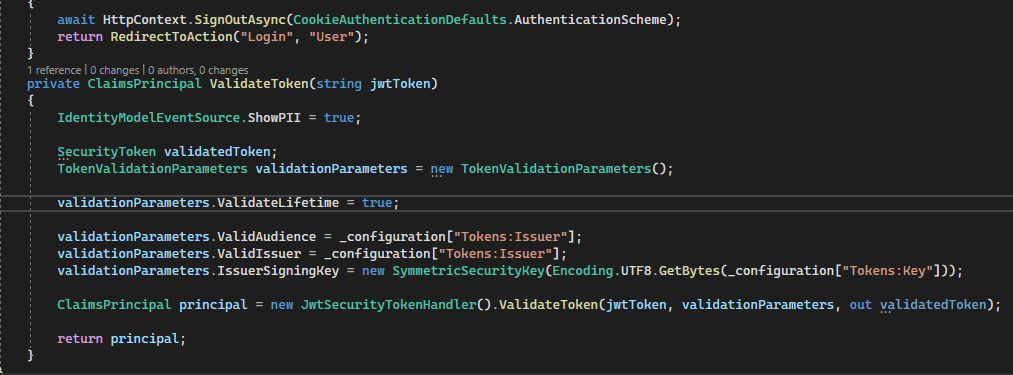

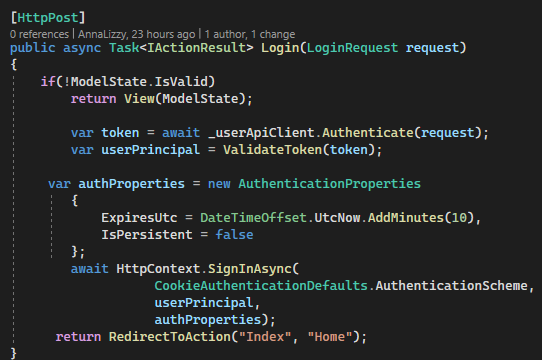
### Steps To Reproduce
_No response_
### Exceptions (if any)
_No response_
### .NET Version
.net core 3.1
### Anything else?
_No response_
|
non_defect
|
securitytokeninvalidaudienceexception unable to validate audience the audiences parameter is empty microsoft identitymodel tokens validators validateaudience ienumerable audiences securitytoken securitytoken tokenvalidationparameters validationparameters is there an existing issue for this i have searched the existing issues describe the bug i have a problem for use cookie authentication without asp net core identity expected behavior steps to reproduce no response exceptions if any no response net version net core anything else no response
| 0
|
9,207
| 3,028,577,571
|
IssuesEvent
|
2015-08-04 06:49:27
|
servo/string-cache
|
https://api.github.com/repos/servo/string-cache
|
closed
|
Add string-cache to Travis and Rust-CI
|
doc testing
|
And upload docs.
We're now tracking nightlies because of html5ever.
|
1.0
|
Add string-cache to Travis and Rust-CI - And upload docs.
We're now tracking nightlies because of html5ever.
|
non_defect
|
add string cache to travis and rust ci and upload docs we re now tracking nightlies because of
| 0
|
79,511
| 28,322,006,884
|
IssuesEvent
|
2023-04-11 02:30:49
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
No fallback solution for Elements if Matrix.org is unavailable.
|
T-Defect
|
### Steps to reproduce
1. Ban matrix.org.
2. Open element desktop
3. Ooops
### Outcome
#### What did you expect?
I was trying to share my Matrix server with friends in China, Matrix.org is blocked by gfw, and they cannot use element to connect to my server because if matrix.org is unavailable the application won't start in the first place and has no fallback solution.
Same thing happened to Android client too, I have no apple device but I believe this might be the same on iOS.
#### What happened instead?
It should at least provide a easy to use fallback solution for non tech user to select server they gonna use.
### Operating system
_No response_
### Application version
_No response_
### How did you install the app?
_No response_
### Homeserver
_No response_
### Will you send logs?
No
|
1.0
|
No fallback solution for Elements if Matrix.org is unavailable. - ### Steps to reproduce
1. Ban matrix.org.
2. Open element desktop
3. Ooops
### Outcome
#### What did you expect?
I was trying to share my Matrix server with friends in China, Matrix.org is blocked by gfw, and they cannot use element to connect to my server because if matrix.org is unavailable the application won't start in the first place and has no fallback solution.
Same thing happened to Android client too, I have no apple device but I believe this might be the same on iOS.
#### What happened instead?
It should at least provide a easy to use fallback solution for non tech user to select server they gonna use.
### Operating system
_No response_
### Application version
_No response_
### How did you install the app?
_No response_
### Homeserver
_No response_
### Will you send logs?
No
|
defect
|
no fallback solution for elements if matrix org is unavailable steps to reproduce ban matrix org open element desktop ooops outcome what did you expect i was trying to share my matrix server with friends in china matrix org is blocked by gfw and they cannot use element to connect to my server because if matrix org is unavailable the application won t start in the first place and has no fallback solution same thing happened to android client too i have no apple device but i believe this might be the same on ios what happened instead it should at least provide a easy to use fallback solution for non tech user to select server they gonna use operating system no response application version no response how did you install the app no response homeserver no response will you send logs no
| 1
|
18,337
| 3,047,320,779
|
IssuesEvent
|
2015-08-11 03:25:21
|
piccolo2d/piccolo2d.java
|
https://api.github.com/repos/piccolo2d/piccolo2d.java
|
closed
|
PSelectionEventHandler grip points do not scale with zoom
|
Component-Extras Milestone-1.3 Priority-Medium Status-Verified Toolkit-Piccolo2D.Java Type-Defect
|
Originally reported on Google Code with ID 72
```
The PSelectionEventHandler circuler grip points to resize a selected item
dont scale so a zoomed in item is obscured by the grip points easily.
```
Reported by `norderkid` on 2008-11-25 00:27:19
|
1.0
|
PSelectionEventHandler grip points do not scale with zoom - Originally reported on Google Code with ID 72
```
The PSelectionEventHandler circuler grip points to resize a selected item
dont scale so a zoomed in item is obscured by the grip points easily.
```
Reported by `norderkid` on 2008-11-25 00:27:19
|
defect
|
pselectioneventhandler grip points do not scale with zoom originally reported on google code with id the pselectioneventhandler circuler grip points to resize a selected item dont scale so a zoomed in item is obscured by the grip points easily reported by norderkid on
| 1
|
54,205
| 13,461,158,337
|
IssuesEvent
|
2020-09-09 14:29:09
|
AeroScripts/QuestieDev
|
https://api.github.com/repos/AeroScripts/QuestieDev
|
closed
|
Quest issue with "Cuergo's Gold"
|
Questie - Quest Issue Type - Defect
|
<!-- READ THIS FIRST
Hello, thanks for taking the time to report a bug!
Before you proceed, please verify that you're running the latest version of Questie. The easiest way to do this is via the Twitch client, but you can also download the latest version here: https://www.curseforge.com/wow/addons/questie
Questie is one of the most popular Classic WoW addons, with over 22M downloads. However, like almost all WoW addons, it's built and maintained by a team of volunteers. The current Questie team is:
* @AeroScripts / Aero#1357 (Discord)
* @BreakBB / TheCrux#1702 (Discord)
* @drejjmit / Drejjmit#8241 (Discord)
* @Dyaxler / Dyaxler#0086 (Discord)
* @gogo1951 / Gogo#0298 (Discord)
If you'd like to help, please consider making a donation. You can do so here: https://www.paypal.com/cgi-bin/webscr?cmd=_donations&business=aero1861%40gmail%2ecom&lc=CA&item_name=Questie%20Devs¤cy_code=USD&bn=PP%2dDonationsBF%3abtn_donate_LG%2egif%3aNonHosted
You can also help as a tester, developer or translator, please join the Questie Discord here https://discord.gg/fYcQfv7
-->
## Description
<!-- Explain in detail what problem you encountered. Is a quest not showing or showing again or an objective not showing or a spawn missing? -->
The objective is missing for Cuergo's Gold. Maybe because you trigger the mob spawn who drops the item? Let's just put it on the object that triggers the mob spawn.
## Wowhead link
<!-- If this issue is about a quest/npc/item/... then please include a link to it from Wowhead: https://classic.wowhead.com -->
* Cuergo's Gold - Quest - World of Warcraft || https://classic.wowhead.com/quest=2882/cuergos-gold
## Screenshots
<!-- If you can, add a screenshot to help explaining the problem (e.g. of your map where a quest is not shown but the NPC has an ! above him). Simply drag and drop the image in this input field, no need to upload it to any other image platform. -->
Github needs to get with the times. =P

## Questie version
<!--
Which version of Questie are you using? You can find it by:
- 1. Hovering over the Questie Minimap Icon
- 2. looking at your Questie.toc file (open it with any text editor).
It looks something like this: "v5.9.0" or "## Version: 5.9.0".
-->
|
1.0
|
Quest issue with "Cuergo's Gold" - <!-- READ THIS FIRST
Hello, thanks for taking the time to report a bug!
Before you proceed, please verify that you're running the latest version of Questie. The easiest way to do this is via the Twitch client, but you can also download the latest version here: https://www.curseforge.com/wow/addons/questie
Questie is one of the most popular Classic WoW addons, with over 22M downloads. However, like almost all WoW addons, it's built and maintained by a team of volunteers. The current Questie team is:
* @AeroScripts / Aero#1357 (Discord)
* @BreakBB / TheCrux#1702 (Discord)
* @drejjmit / Drejjmit#8241 (Discord)
* @Dyaxler / Dyaxler#0086 (Discord)
* @gogo1951 / Gogo#0298 (Discord)
If you'd like to help, please consider making a donation. You can do so here: https://www.paypal.com/cgi-bin/webscr?cmd=_donations&business=aero1861%40gmail%2ecom&lc=CA&item_name=Questie%20Devs¤cy_code=USD&bn=PP%2dDonationsBF%3abtn_donate_LG%2egif%3aNonHosted
You can also help as a tester, developer or translator, please join the Questie Discord here https://discord.gg/fYcQfv7
-->
## Description
<!-- Explain in detail what problem you encountered. Is a quest not showing or showing again or an objective not showing or a spawn missing? -->
The objective is missing for Cuergo's Gold. Maybe because you trigger the mob spawn who drops the item? Let's just put it on the object that triggers the mob spawn.
## Wowhead link
<!-- If this issue is about a quest/npc/item/... then please include a link to it from Wowhead: https://classic.wowhead.com -->
* Cuergo's Gold - Quest - World of Warcraft || https://classic.wowhead.com/quest=2882/cuergos-gold
## Screenshots
<!-- If you can, add a screenshot to help explaining the problem (e.g. of your map where a quest is not shown but the NPC has an ! above him). Simply drag and drop the image in this input field, no need to upload it to any other image platform. -->
Github needs to get with the times. =P

## Questie version
<!--
Which version of Questie are you using? You can find it by:
- 1. Hovering over the Questie Minimap Icon
- 2. looking at your Questie.toc file (open it with any text editor).
It looks something like this: "v5.9.0" or "## Version: 5.9.0".
-->
|
defect
|
quest issue with cuergo s gold read this first hello thanks for taking the time to report a bug before you proceed please verify that you re running the latest version of questie the easiest way to do this is via the twitch client but you can also download the latest version here questie is one of the most popular classic wow addons with over downloads however like almost all wow addons it s built and maintained by a team of volunteers the current questie team is aeroscripts aero discord breakbb thecrux discord drejjmit drejjmit discord dyaxler dyaxler discord gogo discord if you d like to help please consider making a donation you can do so here you can also help as a tester developer or translator please join the questie discord here description the objective is missing for cuergo s gold maybe because you trigger the mob spawn who drops the item let s just put it on the object that triggers the mob spawn wowhead link cuergo s gold quest world of warcraft screenshots github needs to get with the times p questie version which version of questie are you using you can find it by hovering over the questie minimap icon looking at your questie toc file open it with any text editor it looks something like this or version
| 1
|
604,667
| 18,716,265,943
|
IssuesEvent
|
2021-11-03 05:29:00
|
wso2/product-microgateway
|
https://api.github.com/repos/wso2/product-microgateway
|
opened
|
correct base64 url encoding for backend jwt
|
Type/Bug Priority/Normal
|
### Description:
The backend jwt created by enforcer includes "=" in its base64 url encoding. As per https://datatracker.ietf.org/doc/html/rfc7515#section-2 trailing '=' characters must be omitted.
```
Base64url Encoding
Base64 encoding using the URL- and filename-safe character set
defined in Section 5 of RFC 4648 [RFC4648], with all trailing '='
characters omitted (as permitted by Section 3.2) and without the
inclusion of any line breaks, whitespace, or other additional
characters. Note that the base64url encoding of the empty octet
sequence is the empty string.
```
A warning related to this also appears when trying to decode the backend jwt via a web jwt decoder.
### Steps to reproduce:
1. Add the following to config.toml
```
[enforcer]
[enforcer.jwtGenerator]
enabled = true
```
2. Start choreo connect with apim
3. Create, deploy and publish an API
4. Invoke the API from devportal
5. Get the jwt token received at the backend and check the encoding
We can use the following to fix this
```
Base64.getEncoder().withoutPadding().encodeToString(someByteArray);
```
### Affected Product Version:
<!-- Members can use Affected/*** labels -->
### Environment details (with versions):
- OS:
- Client:
- Env (Docker/K8s):
---
### Optional Fields
#### Related Issues:
<!-- Any related issues from this/other repositories-->
#### Suggested Labels:
<!--Only to be used by non-members-->
#### Suggested Assignees:
<!--Only to be used by non-members-->
|
1.0
|
correct base64 url encoding for backend jwt - ### Description:
The backend jwt created by enforcer includes "=" in its base64 url encoding. As per https://datatracker.ietf.org/doc/html/rfc7515#section-2 trailing '=' characters must be omitted.
```
Base64url Encoding
Base64 encoding using the URL- and filename-safe character set
defined in Section 5 of RFC 4648 [RFC4648], with all trailing '='
characters omitted (as permitted by Section 3.2) and without the
inclusion of any line breaks, whitespace, or other additional
characters. Note that the base64url encoding of the empty octet
sequence is the empty string.
```
A warning related to this also appears when trying to decode the backend jwt via a web jwt decoder.
### Steps to reproduce:
1. Add the following to config.toml
```
[enforcer]
[enforcer.jwtGenerator]
enabled = true
```
2. Start choreo connect with apim
3. Create, deploy and publish an API
4. Invoke the API from devportal
5. Get the jwt token received at the backend and check the encoding
We can use the following to fix this
```
Base64.getEncoder().withoutPadding().encodeToString(someByteArray);
```
### Affected Product Version:
<!-- Members can use Affected/*** labels -->
### Environment details (with versions):
- OS:
- Client:
- Env (Docker/K8s):
---
### Optional Fields
#### Related Issues:
<!-- Any related issues from this/other repositories-->
#### Suggested Labels:
<!--Only to be used by non-members-->
#### Suggested Assignees:
<!--Only to be used by non-members-->
|
non_defect
|
correct url encoding for backend jwt description the backend jwt created by enforcer includes in its url encoding as per trailing characters must be omitted encoding encoding using the url and filename safe character set defined in section of rfc with all trailing characters omitted as permitted by section and without the inclusion of any line breaks whitespace or other additional characters note that the encoding of the empty octet sequence is the empty string a warning related to this also appears when trying to decode the backend jwt via a web jwt decoder steps to reproduce add the following to config toml enabled true start choreo connect with apim create deploy and publish an api invoke the api from devportal get the jwt token received at the backend and check the encoding we can use the following to fix this getencoder withoutpadding encodetostring somebytearray affected product version environment details with versions os client env docker optional fields related issues suggested labels suggested assignees
| 0
|
703,071
| 24,145,923,780
|
IssuesEvent
|
2022-09-21 18:44:12
|
neevaco/neeva-android
|
https://api.github.com/repos/neevaco/neeva-android
|
opened
|
As you close last tab in Today, tab in Yesterday moves to today
|
bug Priority: Untriaged
|
**Describe the bug**
Unexpectedly moving tab from Yesterday to Today
Steps to reproduce the behavior:
1. Have tabs in Today and also in Yesterday
2. Close tabs in Today one by one
3. Observe that the tab at Yesterday moves to Today
🔒 [Link to conversation](https://neeva-makers.slack.com/archives/C031KKSCULA/p1663785626327539).
|
1.0
|
As you close last tab in Today, tab in Yesterday moves to today - **Describe the bug**
Unexpectedly moving tab from Yesterday to Today
Steps to reproduce the behavior:
1. Have tabs in Today and also in Yesterday
2. Close tabs in Today one by one
3. Observe that the tab at Yesterday moves to Today
🔒 [Link to conversation](https://neeva-makers.slack.com/archives/C031KKSCULA/p1663785626327539).
|
non_defect
|
as you close last tab in today tab in yesterday moves to today describe the bug unexpectedly moving tab from yesterday to today steps to reproduce the behavior have tabs in today and also in yesterday close tabs in today one by one observe that the tab at yesterday moves to today 🔒
| 0
|
675,733
| 23,103,058,307
|
IssuesEvent
|
2022-07-27 06:04:39
|
openmsupply/mobile
|
https://api.github.com/repos/openmsupply/mobile
|
closed
|
Kiribati: Delete patient medical record
|
Priority: high Feature Project: Kiribati COVID-19 Vax
|
## Is your feature request related to a problem? Please describe.
Add soft deletion of the patients to the "Patient Details" page.
--------
### More context:
**User Stories:**
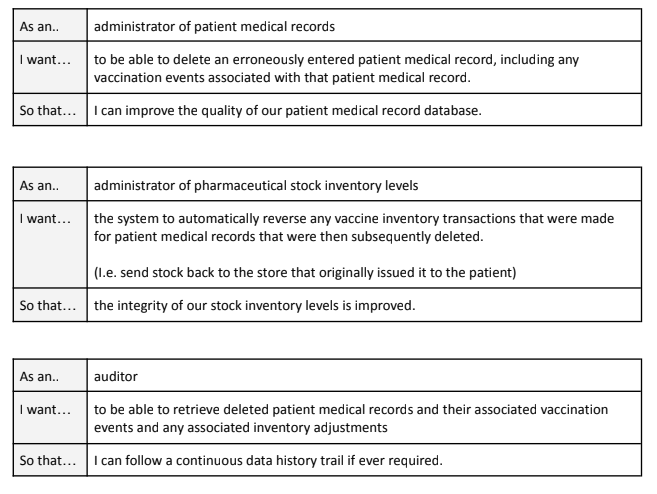
### Proposed solution
- The system will be updated to allow deletion of patient medical records via mSupply Desktop.
- Vaccination events associated with the deleted patient medical record will also be deleted.
- The system will be updated to make automatic stock inventory adjustments when deleting a vaccination event (e.g. the issuing store will be refunded the vaccine stock that was erroneously recorded as being administered to the patient).
- Deleted patient medical records and vaccination events will be kept in the back-end for auditing purposes.
Some other proposed solution details:
- **If there are vaccines dispensed to the patient on a different tablet - it will not be deleted!**
- If there are any dispensary transactions made with this patient on the current tablet, the patient will not be deleted.
- All the vaccination events associated with this patient will be deleted, and stock will be returned.
## Implementation
Not sure yet
## Additional context
Trello card: [(1.7.g + 1.7.h + 1.7.i) Delete patient medical record](https://trello.com/c/DpudXeHa/76-17g-17h-17i-delete-patient-medical-record)
- I'm not sure if there's a way of checking if this patient had transactions on another tablet. As we soft delete it shouldn't cause any problems even if there are any transactions on the other tablet. However, Adam reassured me that they do not use dispensing module at all.
|
1.0
|
Kiribati: Delete patient medical record - ## Is your feature request related to a problem? Please describe.
Add soft deletion of the patients to the "Patient Details" page.
--------
### More context:
**User Stories:**
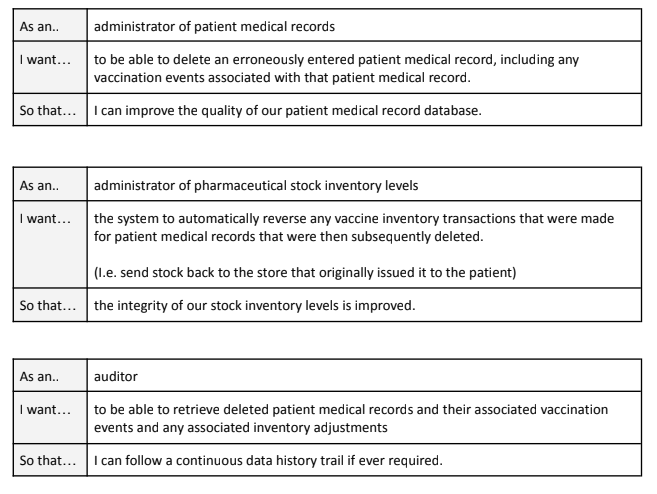
### Proposed solution
- The system will be updated to allow deletion of patient medical records via mSupply Desktop.
- Vaccination events associated with the deleted patient medical record will also be deleted.
- The system will be updated to make automatic stock inventory adjustments when deleting a vaccination event (e.g. the issuing store will be refunded the vaccine stock that was erroneously recorded as being administered to the patient).
- Deleted patient medical records and vaccination events will be kept in the back-end for auditing purposes.
Some other proposed solution details:
- **If there are vaccines dispensed to the patient on a different tablet - it will not be deleted!**
- If there are any dispensary transactions made with this patient on the current tablet, the patient will not be deleted.
- All the vaccination events associated with this patient will be deleted, and stock will be returned.
## Implementation
Not sure yet
## Additional context
Trello card: [(1.7.g + 1.7.h + 1.7.i) Delete patient medical record](https://trello.com/c/DpudXeHa/76-17g-17h-17i-delete-patient-medical-record)
- I'm not sure if there's a way of checking if this patient had transactions on another tablet. As we soft delete it shouldn't cause any problems even if there are any transactions on the other tablet. However, Adam reassured me that they do not use dispensing module at all.
|
non_defect
|
kiribati delete patient medical record is your feature request related to a problem please describe add soft deletion of the patients to the patient details page more context user stories proposed solution the system will be updated to allow deletion of patient medical records via msupply desktop vaccination events associated with the deleted patient medical record will also be deleted the system will be updated to make automatic stock inventory adjustments when deleting a vaccination event e g the issuing store will be refunded the vaccine stock that was erroneously recorded as being administered to the patient deleted patient medical records and vaccination events will be kept in the back end for auditing purposes some other proposed solution details if there are vaccines dispensed to the patient on a different tablet it will not be deleted if there are any dispensary transactions made with this patient on the current tablet the patient will not be deleted all the vaccination events associated with this patient will be deleted and stock will be returned implementation not sure yet additional context trello card i m not sure if there s a way of checking if this patient had transactions on another tablet as we soft delete it shouldn t cause any problems even if there are any transactions on the other tablet however adam reassured me that they do not use dispensing module at all
| 0
|
59,312
| 17,023,079,238
|
IssuesEvent
|
2021-07-03 00:17:29
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
slippy/tiles map zooming limits
|
Component: website Priority: major Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 2.44pm, Friday, 11th November 2005]**
zooming out when you're fully zoomed out should do nothing (currently it
doesn't change anything, but you then need two clicks to zoom back in)
likewise, zooming in when you're fully zoomed in should do nothing
|
1.0
|
slippy/tiles map zooming limits - **[Submitted to the original trac issue database at 2.44pm, Friday, 11th November 2005]**
zooming out when you're fully zoomed out should do nothing (currently it
doesn't change anything, but you then need two clicks to zoom back in)
likewise, zooming in when you're fully zoomed in should do nothing
|
defect
|
slippy tiles map zooming limits zooming out when you re fully zoomed out should do nothing currently it doesn t change anything but you then need two clicks to zoom back in likewise zooming in when you re fully zoomed in should do nothing
| 1
|
73,989
| 24,896,404,633
|
IssuesEvent
|
2022-10-28 16:12:39
|
vector-im/element-web
|
https://api.github.com/repos/vector-im/element-web
|
opened
|
Only WISIWIG-editing possible, when trying to correct an input - mode problems with the WISIWIG-mode
|
T-Defect
|
### Steps to reproduce
1. Where are you starting? What can you see? I start, with the editor set to ''show plain text''. Then I enter **b** *i* visual test; after Carriage Return the formatted line is visible. Then I try to correct it - but I do not get my input presented, instead the WISIWIG-editor mode comes up
2. What do you click?
3. More steps…
### Outcome
#### What did you expect?
I would prefer to get the data I have entered, when I try to correct my input
#### What happened instead?
The mode of the WISIWIG-editor changed back to ''show formatting''
This mode-changes happens too, if I look into another room and go back to my editing - then the mode ''show plain text'' is resetted and my partial input is gone.
### Operating system
macOS 13.0 (22A380)
### Browser information
Safari 16.1 (18614.2.9.1.12)
### URL for webapp
https://develop.element.io
### Application version
Version von Element: 1b9860187036-react-d92fdc1f5bfc-js-068fbb766099 Version von Olm: 3.2.12
### Homeserver
synod.im
### Will you send logs?
No
|
1.0
|
Only WISIWIG-editing possible, when trying to correct an input - mode problems with the WISIWIG-mode - ### Steps to reproduce
1. Where are you starting? What can you see? I start, with the editor set to ''show plain text''. Then I enter **b** *i* visual test; after Carriage Return the formatted line is visible. Then I try to correct it - but I do not get my input presented, instead the WISIWIG-editor mode comes up
2. What do you click?
3. More steps…
### Outcome
#### What did you expect?
I would prefer to get the data I have entered, when I try to correct my input
#### What happened instead?
The mode of the WISIWIG-editor changed back to ''show formatting''
This mode-changes happens too, if I look into another room and go back to my editing - then the mode ''show plain text'' is resetted and my partial input is gone.
### Operating system
macOS 13.0 (22A380)
### Browser information
Safari 16.1 (18614.2.9.1.12)
### URL for webapp
https://develop.element.io
### Application version
Version von Element: 1b9860187036-react-d92fdc1f5bfc-js-068fbb766099 Version von Olm: 3.2.12
### Homeserver
synod.im
### Will you send logs?
No
|
defect
|
only wisiwig editing possible when trying to correct an input mode problems with the wisiwig mode steps to reproduce where are you starting what can you see i start with the editor set to show plain text then i enter b i visual test after carriage return the formatted line is visible then i try to correct it but i do not get my input presented instead the wisiwig editor mode comes up what do you click more steps… outcome what did you expect i would prefer to get the data i have entered when i try to correct my input what happened instead the mode of the wisiwig editor changed back to show formatting this mode changes happens too if i look into another room and go back to my editing then the mode show plain text is resetted and my partial input is gone operating system macos browser information safari url for webapp application version version von element react js version von olm homeserver synod im will you send logs no
| 1
|
9,451
| 2,615,150,776
|
IssuesEvent
|
2015-03-01 06:28:10
|
chrsmith/reaver-wps
|
https://api.github.com/repos/chrsmith/reaver-wps
|
opened
|
WASH reporting WPS enable AP, but WPS is not configured
|
auto-migrated Priority-Triage Type-Defect
|
```
running r106 on BT5 R1 x64
looking at beacon frame it showed an entry for WPS
after clicking on it and viewing details, its status stated "Configured"
--> cracked without a problem
wash reported another AP as vulnerable
looking at beacon frame it showed an entry for WPS
however after clicking on it and viewing details, its status stated "Not
configured"
--> reached 99.99% and kept cycling the last PIN forever
is Wash WPS detection based only on the presence of WPS field in the beacon
frame?
```
Original issue reported on code.google.com by `jcdento...@gmail.com` on 22 Jan 2012 at 11:59
|
1.0
|
WASH reporting WPS enable AP, but WPS is not configured - ```
running r106 on BT5 R1 x64
looking at beacon frame it showed an entry for WPS
after clicking on it and viewing details, its status stated "Configured"
--> cracked without a problem
wash reported another AP as vulnerable
looking at beacon frame it showed an entry for WPS
however after clicking on it and viewing details, its status stated "Not
configured"
--> reached 99.99% and kept cycling the last PIN forever
is Wash WPS detection based only on the presence of WPS field in the beacon
frame?
```
Original issue reported on code.google.com by `jcdento...@gmail.com` on 22 Jan 2012 at 11:59
|
defect
|
wash reporting wps enable ap but wps is not configured running on looking at beacon frame it showed an entry for wps after clicking on it and viewing details its status stated configured cracked without a problem wash reported another ap as vulnerable looking at beacon frame it showed an entry for wps however after clicking on it and viewing details its status stated not configured reached and kept cycling the last pin forever is wash wps detection based only on the presence of wps field in the beacon frame original issue reported on code google com by jcdento gmail com on jan at
| 1
|
8,322
| 2,611,486,806
|
IssuesEvent
|
2015-02-27 05:27:49
|
chrsmith/switchlist
|
https://api.github.com/repos/chrsmith/switchlist
|
opened
|
built-in switchlist styles appear twice in binary
|
auto-migrated Priority-Medium Type-Defect
|
```
There are two copies of the switchlist styles in the binary - in the Resources
directory, and in the builtin-templates directory below that. There should be
only one.
```
Original issue reported on code.google.com by `rwbowdi...@gmail.com` on 11 Aug 2014 at 3:37
|
1.0
|
built-in switchlist styles appear twice in binary - ```
There are two copies of the switchlist styles in the binary - in the Resources
directory, and in the builtin-templates directory below that. There should be
only one.
```
Original issue reported on code.google.com by `rwbowdi...@gmail.com` on 11 Aug 2014 at 3:37
|
defect
|
built in switchlist styles appear twice in binary there are two copies of the switchlist styles in the binary in the resources directory and in the builtin templates directory below that there should be only one original issue reported on code google com by rwbowdi gmail com on aug at
| 1
|
68,883
| 21,939,883,861
|
IssuesEvent
|
2022-05-23 16:56:46
|
department-of-veterans-affairs/va.gov-cms
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms
|
closed
|
Some CMS admin forms frozen for many seconds upon load
|
Defect Critical defect Platform CMS Team ⭐️ Sitewide CMS
|
## Describe the defect
Some forms are frozen upon load, for about 30s. They cannot be interacted with, and the browser itself also becomes unresponsive.
On other forms, interacting with an element caused a slow response. This was seen on elements that do filtering.
https://dsva.slack.com/archives/CT4GZBM8F/p1652889323316019
https://dsva.slack.com/archives/C02HX4AQZ33/p1652801568091339
## To Reproduce
Example URLs (currently fixed):
* https://prod.cms.va.gov/node/add/vha_facility_nonclinical_service?field_service_name_and_descripti=1025&field_administration=375
* https://prod.cms.va.gov/admin/modules (filtering)
* https://prod.cms.va.gov/admin/modules/uninstall (filtering)
## Expected behavior
Forms should be responsive.
## Outcome
Through reviewing recent commits to the CMS, we were able to identify the PR https://github.com/department-of-veterans-affairs/va.gov-cms/pull/8994 as containing the code causing the defect. [We reverted out this code](https://github.com/department-of-veterans-affairs/va.gov-cms/pull/9102), which allowed system operation to return to normal.
Subsequently, @tjheffner did investigation to the root cause and [submitted a PR to fix the problematic code](https://github.com/department-of-veterans-affairs/va.gov-cms/pull/9103).
## Labels
(You can delete this section once it's complete)
- [x] Issue type (red) (defaults to "Defect")
- [ ] CMS subsystem (green)
- [ ] CMS practice area (blue)
- [x] CMS workstream (orange) (not needed for bug tickets)
- [ ] CMS-supported product (black)
### CMS Team
Please check the team(s) that will do this work.
- [X] `Platform CMS Team`
- [ ] `Sitewide program`
- [X] `⭐️ Sitewide CMS`
- [ ] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
|
2.0
|
Some CMS admin forms frozen for many seconds upon load - ## Describe the defect
Some forms are frozen upon load, for about 30s. They cannot be interacted with, and the browser itself also becomes unresponsive.
On other forms, interacting with an element caused a slow response. This was seen on elements that do filtering.
https://dsva.slack.com/archives/CT4GZBM8F/p1652889323316019
https://dsva.slack.com/archives/C02HX4AQZ33/p1652801568091339
## To Reproduce
Example URLs (currently fixed):
* https://prod.cms.va.gov/node/add/vha_facility_nonclinical_service?field_service_name_and_descripti=1025&field_administration=375
* https://prod.cms.va.gov/admin/modules (filtering)
* https://prod.cms.va.gov/admin/modules/uninstall (filtering)
## Expected behavior
Forms should be responsive.
## Outcome
Through reviewing recent commits to the CMS, we were able to identify the PR https://github.com/department-of-veterans-affairs/va.gov-cms/pull/8994 as containing the code causing the defect. [We reverted out this code](https://github.com/department-of-veterans-affairs/va.gov-cms/pull/9102), which allowed system operation to return to normal.
Subsequently, @tjheffner did investigation to the root cause and [submitted a PR to fix the problematic code](https://github.com/department-of-veterans-affairs/va.gov-cms/pull/9103).
## Labels
(You can delete this section once it's complete)
- [x] Issue type (red) (defaults to "Defect")
- [ ] CMS subsystem (green)
- [ ] CMS practice area (blue)
- [x] CMS workstream (orange) (not needed for bug tickets)
- [ ] CMS-supported product (black)
### CMS Team
Please check the team(s) that will do this work.
- [X] `Platform CMS Team`
- [ ] `Sitewide program`
- [X] `⭐️ Sitewide CMS`
- [ ] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
|
defect
|
some cms admin forms frozen for many seconds upon load describe the defect some forms are frozen upon load for about they cannot be interacted with and the browser itself also becomes unresponsive on other forms interacting with an element caused a slow response this was seen on elements that do filtering to reproduce example urls currently fixed filtering filtering expected behavior forms should be responsive outcome through reviewing recent commits to the cms we were able to identify the pr as containing the code causing the defect which allowed system operation to return to normal subsequently tjheffner did investigation to the root cause and labels you can delete this section once it s complete issue type red defaults to defect cms subsystem green cms practice area blue cms workstream orange not needed for bug tickets cms supported product black cms team please check the team s that will do this work platform cms team sitewide program ⭐️ sitewide cms ⭐️ public websites ⭐️ facilities ⭐️ user support
| 1
|
3,428
| 2,610,062,573
|
IssuesEvent
|
2015-02-26 18:18:23
|
chrsmith/jsjsj122
|
https://api.github.com/repos/chrsmith/jsjsj122
|
opened
|
黄岩治疗不育去哪里最好
|
auto-migrated Priority-Medium Type-Defect
|
```
黄岩治疗不育去哪里最好【台州五洲生殖医院】24小时健康咨
询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台州
市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、108�
��118、198及椒江一金清公交车直达枫南小区,乘坐107、105、109
、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费。尖端医疗设备,与世界同步。权威专家,成就专业典
范。人性化服务,一切以患者为中心。
看男科就选台州五洲生殖医院,专业男科为男人。
```
-----
Original issue reported on code.google.com by `poweragr...@gmail.com` on 30 May 2014 at 7:39
|
1.0
|
黄岩治疗不育去哪里最好 - ```
黄岩治疗不育去哪里最好【台州五洲生殖医院】24小时健康咨
询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台州
市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、108�
��118、198及椒江一金清公交车直达枫南小区,乘坐107、105、109
、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费。尖端医疗设备,与世界同步。权威专家,成就专业典
范。人性化服务,一切以患者为中心。
看男科就选台州五洲生殖医院,专业男科为男人。
```
-----
Original issue reported on code.google.com by `poweragr...@gmail.com` on 30 May 2014 at 7:39
|
defect
|
黄岩治疗不育去哪里最好 黄岩治疗不育去哪里最好【台州五洲生殖医院】 询热线 微信号tzwzszyy 医院地址 台州 (枫南大转盘旁)乘车线路 、 � �� 、 , 、 、 、 、 、 ,步行即可到院。 诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,�� �精,无精。包皮包茎,精索静脉曲张,淋病等。 台州五洲生殖医院是台州最大的男科医院,权威专家在线免�� �咨询,拥有专业完善的男科检查治疗设备,严格按照国家标� ��收费。尖端医疗设备,与世界同步。权威专家,成就专业典 范。人性化服务,一切以患者为中心。 看男科就选台州五洲生殖医院,专业男科为男人。 original issue reported on code google com by poweragr gmail com on may at
| 1
|
52,655
| 13,224,883,238
|
IssuesEvent
|
2020-08-17 20:02:30
|
icecube-trac/tix4
|
https://api.github.com/repos/icecube-trac/tix4
|
closed
|
make test -C TWRDistillery and python TWRDistillery/resources/scripts/TWRrecoTest.py (Trac #110)
|
Migrated from Trac cmake defect
|
I see a different output running in icerec (trunk, RC 1-6-0)
'make test -C TWRDistillery' --> Failed
(Troy recommended 'ctest -VV -R TWRDistillery::TWRrecoTest' --> Failed with
/Users/schlenst/prog/ice/icerec/trunk/src/TWRDistillery/private/twr-distillery/I3TWRReTrigger.cxx:127: FATAL: No DMADD file)
and
'python TWRDistillery/resources/scripts/TWRrecoTest.py' --> OK
Whats wrong? Thanks, Stefan
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/110">https://code.icecube.wisc.edu/projects/icecube/ticket/110</a>, reported by icecubeand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-09-06T17:23:26",
"_ts": "1189099406000000",
"description": "I see a different output running in icerec (trunk, RC 1-6-0)\n'make test -C TWRDistillery' --> Failed\n(Troy recommended 'ctest -VV -R TWRDistillery::TWRrecoTest' --> Failed with \n/Users/schlenst/prog/ice/icerec/trunk/src/TWRDistillery/private/twr-distillery/I3TWRReTrigger.cxx:127: FATAL: No DMADD file) \nand \n'python TWRDistillery/resources/scripts/TWRrecoTest.py' --> OK\n\nWhats wrong? Thanks, Stefan",
"reporter": "icecube",
"cc": "",
"resolution": "invalid",
"time": "2007-09-06T15:05:10",
"component": "cmake",
"summary": "make test -C TWRDistillery and python TWRDistillery/resources/scripts/TWRrecoTest.py",
"priority": "normal",
"keywords": "running tests",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
|
1.0
|
make test -C TWRDistillery and python TWRDistillery/resources/scripts/TWRrecoTest.py (Trac #110) - I see a different output running in icerec (trunk, RC 1-6-0)
'make test -C TWRDistillery' --> Failed
(Troy recommended 'ctest -VV -R TWRDistillery::TWRrecoTest' --> Failed with
/Users/schlenst/prog/ice/icerec/trunk/src/TWRDistillery/private/twr-distillery/I3TWRReTrigger.cxx:127: FATAL: No DMADD file)
and
'python TWRDistillery/resources/scripts/TWRrecoTest.py' --> OK
Whats wrong? Thanks, Stefan
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/110">https://code.icecube.wisc.edu/projects/icecube/ticket/110</a>, reported by icecubeand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-09-06T17:23:26",
"_ts": "1189099406000000",
"description": "I see a different output running in icerec (trunk, RC 1-6-0)\n'make test -C TWRDistillery' --> Failed\n(Troy recommended 'ctest -VV -R TWRDistillery::TWRrecoTest' --> Failed with \n/Users/schlenst/prog/ice/icerec/trunk/src/TWRDistillery/private/twr-distillery/I3TWRReTrigger.cxx:127: FATAL: No DMADD file) \nand \n'python TWRDistillery/resources/scripts/TWRrecoTest.py' --> OK\n\nWhats wrong? Thanks, Stefan",
"reporter": "icecube",
"cc": "",
"resolution": "invalid",
"time": "2007-09-06T15:05:10",
"component": "cmake",
"summary": "make test -C TWRDistillery and python TWRDistillery/resources/scripts/TWRrecoTest.py",
"priority": "normal",
"keywords": "running tests",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
|
defect
|
make test c twrdistillery and python twrdistillery resources scripts twrrecotest py trac i see a different output running in icerec trunk rc make test c twrdistillery failed troy recommended ctest vv r twrdistillery twrrecotest failed with users schlenst prog ice icerec trunk src twrdistillery private twr distillery cxx fatal no dmadd file and python twrdistillery resources scripts twrrecotest py ok whats wrong thanks stefan migrated from json status closed changetime ts description i see a different output running in icerec trunk rc n make test c twrdistillery failed n troy recommended ctest vv r twrdistillery twrrecotest failed with n users schlenst prog ice icerec trunk src twrdistillery private twr distillery cxx fatal no dmadd file nand n python twrdistillery resources scripts twrrecotest py ok n nwhats wrong thanks stefan reporter icecube cc resolution invalid time component cmake summary make test c twrdistillery and python twrdistillery resources scripts twrrecotest py priority normal keywords running tests milestone owner troy type defect
| 1
|
3,639
| 2,610,066,185
|
IssuesEvent
|
2015-02-26 18:19:28
|
chrsmith/jsjsj122
|
https://api.github.com/repos/chrsmith/jsjsj122
|
opened
|
临海看前列腺炎哪家最好
|
auto-migrated Priority-Medium Type-Defect
|
```
临海看前列腺炎哪家最好【台州五洲生殖医院】24小时健康咨
询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台州
市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、108�
��118、198及椒江一金清公交车直达枫南小区,乘坐107、105、109
、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费。尖端医疗设备,与世界同步。权威专家,成就专业典
范。人性化服务,一切以患者为中心。
看男科就选台州五洲生殖医院,专业男科为男人。
```
-----
Original issue reported on code.google.com by `poweragr...@gmail.com` on 30 May 2014 at 8:30
|
1.0
|
临海看前列腺炎哪家最好 - ```
临海看前列腺炎哪家最好【台州五洲生殖医院】24小时健康咨
询热线:0576-88066933-(扣扣800080609)-(微信号tzwzszyy)医院地址:台州
市椒江区枫南路229号(枫南大转盘旁)乘车线路:乘坐104、108�
��118、198及椒江一金清公交车直达枫南小区,乘坐107、105、109
、112、901、 902公交车到星星广场下车,步行即可到院。
诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,��
�精,无精。包皮包茎,精索静脉曲张,淋病等。
台州五洲生殖医院是台州最大的男科医院,权威专家在线免��
�咨询,拥有专业完善的男科检查治疗设备,严格按照国家标�
��收费。尖端医疗设备,与世界同步。权威专家,成就专业典
范。人性化服务,一切以患者为中心。
看男科就选台州五洲生殖医院,专业男科为男人。
```
-----
Original issue reported on code.google.com by `poweragr...@gmail.com` on 30 May 2014 at 8:30
|
defect
|
临海看前列腺炎哪家最好 临海看前列腺炎哪家最好【台州五洲生殖医院】 询热线 微信号tzwzszyy 医院地址 台州 (枫南大转盘旁)乘车线路 、 � �� 、 , 、 、 、 、 、 ,步行即可到院。 诊疗项目:阳痿,早泄,前列腺炎,前列腺增生,龟头炎,�� �精,无精。包皮包茎,精索静脉曲张,淋病等。 台州五洲生殖医院是台州最大的男科医院,权威专家在线免�� �咨询,拥有专业完善的男科检查治疗设备,严格按照国家标� ��收费。尖端医疗设备,与世界同步。权威专家,成就专业典 范。人性化服务,一切以患者为中心。 看男科就选台州五洲生殖医院,专业男科为男人。 original issue reported on code google com by poweragr gmail com on may at
| 1
|
167,612
| 26,522,925,327
|
IssuesEvent
|
2023-01-19 05:32:37
|
brave/brave-browser
|
https://api.github.com/repos/brave/brave-browser
|
closed
|
Add Swap Rewards slide in Rewards onboarding slideshow
|
feature/rewards design/needs-mock-up priority/P5 QA/Yes OS/Desktop feature/swap-rewards
|
## Description
Add a slide in the Rewards onboarding slideshow that promotes Swap Rewards. It would probably have to come at the end, since if the user clicks on it, it'll probably open up a new tab into brave://wallet (?). UI/UX TBD.
**Note:** Recall that there are 2 onboarding slideshow flows: one where the user actually enables Brave Rewards, and one where the user is only taking a tour but not necessarily enabling Brave Rewards.
|
1.0
|
Add Swap Rewards slide in Rewards onboarding slideshow - ## Description
Add a slide in the Rewards onboarding slideshow that promotes Swap Rewards. It would probably have to come at the end, since if the user clicks on it, it'll probably open up a new tab into brave://wallet (?). UI/UX TBD.
**Note:** Recall that there are 2 onboarding slideshow flows: one where the user actually enables Brave Rewards, and one where the user is only taking a tour but not necessarily enabling Brave Rewards.
|
non_defect
|
add swap rewards slide in rewards onboarding slideshow description add a slide in the rewards onboarding slideshow that promotes swap rewards it would probably have to come at the end since if the user clicks on it it ll probably open up a new tab into brave wallet ui ux tbd note recall that there are onboarding slideshow flows one where the user actually enables brave rewards and one where the user is only taking a tour but not necessarily enabling brave rewards
| 0
|
108,455
| 4,345,515,030
|
IssuesEvent
|
2016-07-29 12:59:22
|
wp-crm/wp-crm
|
https://api.github.com/repos/wp-crm/wp-crm
|
closed
|
Messages do not have option to be deleted and checkbox and trash button don't work
|
core bug high priority
|
http://screencast.com/t/B5ktGnqvK
http://screencast.com/t/1HGt5lXQ
relates to the add-on -https://github.com/wp-crm/wp-crm-group-messages
|
1.0
|
Messages do not have option to be deleted and checkbox and trash button don't work - http://screencast.com/t/B5ktGnqvK
http://screencast.com/t/1HGt5lXQ
relates to the add-on -https://github.com/wp-crm/wp-crm-group-messages
|
non_defect
|
messages do not have option to be deleted and checkbox and trash button don t work relates to the add on
| 0
|
31,190
| 6,443,911,949
|
IssuesEvent
|
2017-08-12 02:29:56
|
opendatakit/opendatakit
|
https://api.github.com/repos/opendatakit/opendatakit
|
closed
|
In filters "Where" clause is diabled
|
Aggregate Priority-Medium Type-Defect
|
Originally reported on Google Code with ID 1149
```
What steps will reproduce the problem?
1. Click on Add Filter
What is the expected output? What do you see instead?
I can mention the where clause for filtering data.
Instead of it where clause is disabled.
What version of the product are you using? On what operating system?
ODK Aggregate 1.4.7 on Windows Server 2008
Please provide any additional information below.
```
Reported by `piyushsh18` on 2015-06-08 05:18:01
<hr>
- _Attachment: Untitled.png<br>_
|
1.0
|
In filters "Where" clause is diabled - Originally reported on Google Code with ID 1149
```
What steps will reproduce the problem?
1. Click on Add Filter
What is the expected output? What do you see instead?
I can mention the where clause for filtering data.
Instead of it where clause is disabled.
What version of the product are you using? On what operating system?
ODK Aggregate 1.4.7 on Windows Server 2008
Please provide any additional information below.
```
Reported by `piyushsh18` on 2015-06-08 05:18:01
<hr>
- _Attachment: Untitled.png<br>_
|
defect
|
in filters where clause is diabled originally reported on google code with id what steps will reproduce the problem click on add filter what is the expected output what do you see instead i can mention the where clause for filtering data instead of it where clause is disabled what version of the product are you using on what operating system odk aggregate on windows server please provide any additional information below reported by on attachment untitled png
| 1
|
150,701
| 11,981,830,285
|
IssuesEvent
|
2020-04-07 11:53:17
|
act-rules/act-rules.github.io
|
https://api.github.com/repos/act-rules/act-rules.github.io
|
reopened
|
Test for (no) angle bracket around element names
|
test
|
The convention in ACT-R is to not put angle brackets around element names (`title`, not `<title>`) but it is not always respected. We should add a test for this.
|
1.0
|
Test for (no) angle bracket around element names - The convention in ACT-R is to not put angle brackets around element names (`title`, not `<title>`) but it is not always respected. We should add a test for this.
|
non_defect
|
test for no angle bracket around element names the convention in act r is to not put angle brackets around element names title not but it is not always respected we should add a test for this
| 0
|
55,917
| 14,792,866,818
|
IssuesEvent
|
2021-01-12 15:14:46
|
PowerDNS/pdns
|
https://api.github.com/repos/PowerDNS/pdns
|
opened
|
dnsdist: Ponder what to do about header-only queries
|
defect dnsdist
|
- Program: dnsdist
- Issue type: Bug report
### Short description
As reported by Arnaud Gavara on the mailing-list [1], dnsdist currently drops queries that have a `qdcount` of zero. That used to be fine (it was used by rfc7873 but it seems that nobody cared about it) but now that it is described as a conformance test in rfc8906 we might need to think about how to handle that.
The issue is that a lot of our rules, and likely a lot of custom Lua code, expect that a query has a qname, and qtype and a qclass, and I'm not sure how to deal with that in a compatible way. I don't want to break setups on an upgrade, even a major one, if I don't have to.
A good start might be to reply with `FORMERR` or `NOTIMP` instead of dropping the packet, as long until we can figure out a way to actually pass that query to the backend.
[1]: https://mailman.powerdns.com/pipermail/dnsdist/2020-September/000902.html
|
1.0
|
dnsdist: Ponder what to do about header-only queries -
- Program: dnsdist
- Issue type: Bug report
### Short description
As reported by Arnaud Gavara on the mailing-list [1], dnsdist currently drops queries that have a `qdcount` of zero. That used to be fine (it was used by rfc7873 but it seems that nobody cared about it) but now that it is described as a conformance test in rfc8906 we might need to think about how to handle that.
The issue is that a lot of our rules, and likely a lot of custom Lua code, expect that a query has a qname, and qtype and a qclass, and I'm not sure how to deal with that in a compatible way. I don't want to break setups on an upgrade, even a major one, if I don't have to.
A good start might be to reply with `FORMERR` or `NOTIMP` instead of dropping the packet, as long until we can figure out a way to actually pass that query to the backend.
[1]: https://mailman.powerdns.com/pipermail/dnsdist/2020-September/000902.html
|
defect
|
dnsdist ponder what to do about header only queries program dnsdist issue type bug report short description as reported by arnaud gavara on the mailing list dnsdist currently drops queries that have a qdcount of zero that used to be fine it was used by but it seems that nobody cared about it but now that it is described as a conformance test in we might need to think about how to handle that the issue is that a lot of our rules and likely a lot of custom lua code expect that a query has a qname and qtype and a qclass and i m not sure how to deal with that in a compatible way i don t want to break setups on an upgrade even a major one if i don t have to a good start might be to reply with formerr or notimp instead of dropping the packet as long until we can figure out a way to actually pass that query to the backend
| 1
|
62,875
| 17,204,565,484
|
IssuesEvent
|
2021-07-18 00:58:51
|
avereon/carta
|
https://api.github.com/repos/avereon/carta
|
closed
|
DesignTool blocks some action shortcuts
|
bug / defect
|
The DesignTool is blocking some action shortcuts like the wallpaper shortcuts.
|
1.0
|
DesignTool blocks some action shortcuts - The DesignTool is blocking some action shortcuts like the wallpaper shortcuts.
|
defect
|
designtool blocks some action shortcuts the designtool is blocking some action shortcuts like the wallpaper shortcuts
| 1
|
369,302
| 10,895,233,718
|
IssuesEvent
|
2019-11-19 10:15:28
|
loco-3d/crocoddyl
|
https://api.github.com/repos/loco-3d/crocoddyl
|
closed
|
Standarized unit-test for NumDiff, #133 - [merged]
|
gitlab merge request priority
|
In GitLab by @cmastalli on Mar 1, 2019, 16:54
_Merges topic/unittest -> devel_
This PR make a standarization for NumDiff unit-test. I run a stress test with this (>100 times).
|
1.0
|
Standarized unit-test for NumDiff, #133 - [merged] - In GitLab by @cmastalli on Mar 1, 2019, 16:54
_Merges topic/unittest -> devel_
This PR make a standarization for NumDiff unit-test. I run a stress test with this (>100 times).
|
non_defect
|
standarized unit test for numdiff in gitlab by cmastalli on mar merges topic unittest devel this pr make a standarization for numdiff unit test i run a stress test with this times
| 0
|
8,002
| 7,105,032,624
|
IssuesEvent
|
2018-01-16 12:10:00
|
linuxkit/linuxkit
|
https://api.github.com/repos/linuxkit/linuxkit
|
closed
|
Add functionlity CPU micrcode updates
|
kind/enhancement kind/security
|
For baremetal deployments we should have a package which updates the CPU microcode either from the debian or the alpine base packages. It likely only requires dumping the microcode binary in the right place in the rootfs and the kernel will take care of the rest.
|
True
|
Add functionlity CPU micrcode updates - For baremetal deployments we should have a package which updates the CPU microcode either from the debian or the alpine base packages. It likely only requires dumping the microcode binary in the right place in the rootfs and the kernel will take care of the rest.
|
non_defect
|
add functionlity cpu micrcode updates for baremetal deployments we should have a package which updates the cpu microcode either from the debian or the alpine base packages it likely only requires dumping the microcode binary in the right place in the rootfs and the kernel will take care of the rest
| 0
|
21,917
| 3,587,215,031
|
IssuesEvent
|
2016-01-30 05:06:04
|
mash99/crypto-js
|
https://api.github.com/repos/mash99/crypto-js
|
closed
|
Automatic key expiration
|
auto-migrated Priority-Medium Type-Defect
|
```
I am having a scenario where i want to secure the JSON data which i am sending
and storing at the client side, and i also want that, that data should be
protected, The way to protect this data i suppose is encryption of the data but
because the decryption logic and key is also at the client side (to decrypt the
encrypted JSON data).
So to protect it i was wondering if we can set something like expiration time
of key,
The way i was thinking this is to work that if someone is encrypting the data
with the key then encrypted data must have some intelligence that after a
period of time this data cannot be decrypted with the key with which it was
encrypted(or may be cannot be decrypted at all).
is it possible? i suppose yes , and i don't it is there in the library now.
so i am asking to all members to please provide this facility in this library,
or if it is not possible(which i suppose is not) or is not gonna solve a
problem please justify.
Thanks.
```
Original issue reported on code.google.com by `5i.aksha...@gmail.com` on 30 Jun 2014 at 1:17
|
1.0
|
Automatic key expiration - ```
I am having a scenario where i want to secure the JSON data which i am sending
and storing at the client side, and i also want that, that data should be
protected, The way to protect this data i suppose is encryption of the data but
because the decryption logic and key is also at the client side (to decrypt the
encrypted JSON data).
So to protect it i was wondering if we can set something like expiration time
of key,
The way i was thinking this is to work that if someone is encrypting the data
with the key then encrypted data must have some intelligence that after a
period of time this data cannot be decrypted with the key with which it was
encrypted(or may be cannot be decrypted at all).
is it possible? i suppose yes , and i don't it is there in the library now.
so i am asking to all members to please provide this facility in this library,
or if it is not possible(which i suppose is not) or is not gonna solve a
problem please justify.
Thanks.
```
Original issue reported on code.google.com by `5i.aksha...@gmail.com` on 30 Jun 2014 at 1:17
|
defect
|
automatic key expiration i am having a scenario where i want to secure the json data which i am sending and storing at the client side and i also want that that data should be protected the way to protect this data i suppose is encryption of the data but because the decryption logic and key is also at the client side to decrypt the encrypted json data so to protect it i was wondering if we can set something like expiration time of key the way i was thinking this is to work that if someone is encrypting the data with the key then encrypted data must have some intelligence that after a period of time this data cannot be decrypted with the key with which it was encrypted or may be cannot be decrypted at all is it possible i suppose yes and i don t it is there in the library now so i am asking to all members to please provide this facility in this library or if it is not possible which i suppose is not or is not gonna solve a problem please justify thanks original issue reported on code google com by aksha gmail com on jun at
| 1
|
71,246
| 23,506,548,703
|
IssuesEvent
|
2022-08-18 13:06:50
|
vector-im/element-call
|
https://api.github.com/repos/vector-im/element-call
|
closed
|
Investigation: Multiple group calls can be created in glare-like scenario
|
T-Defect
|
### Steps to reproduce
We seem to be able to end up with multiple group calls in the same room. In this case we saw, the room got created with a group call in February, and then on July 20th Matthew iphone joined and 4 hours later, created a second group call, before going silent.
So:
1. There may be some bug in our create-call-if-none-already logic
2. We should probably handle mutliple group calls in a room in *some* way, eg. always join the most recently added.
3. We probably want to guard against this in general. In EC we could add the call to initial_state when creating the room, but this wouldn't help other applications - I've brought this up on the MSC: https://github.com/matrix-org/matrix-spec-proposals/pull/3401/files#r711950320
### Outcome
#### What did you expect?
#### What happened instead?
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Will you send logs?
No
|
1.0
|
Investigation: Multiple group calls can be created in glare-like scenario - ### Steps to reproduce
We seem to be able to end up with multiple group calls in the same room. In this case we saw, the room got created with a group call in February, and then on July 20th Matthew iphone joined and 4 hours later, created a second group call, before going silent.
So:
1. There may be some bug in our create-call-if-none-already logic
2. We should probably handle mutliple group calls in a room in *some* way, eg. always join the most recently added.
3. We probably want to guard against this in general. In EC we could add the call to initial_state when creating the room, but this wouldn't help other applications - I've brought this up on the MSC: https://github.com/matrix-org/matrix-spec-proposals/pull/3401/files#r711950320
### Outcome
#### What did you expect?
#### What happened instead?
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Will you send logs?
No
|
defect
|
investigation multiple group calls can be created in glare like scenario steps to reproduce we seem to be able to end up with multiple group calls in the same room in this case we saw the room got created with a group call in february and then on july matthew iphone joined and hours later created a second group call before going silent so there may be some bug in our create call if none already logic we should probably handle mutliple group calls in a room in some way eg always join the most recently added we probably want to guard against this in general in ec we could add the call to initial state when creating the room but this wouldn t help other applications i ve brought this up on the msc outcome what did you expect what happened instead operating system no response browser information no response url for webapp no response will you send logs no
| 1
|
70,511
| 23,214,582,350
|
IssuesEvent
|
2022-08-02 13:08:46
|
primefaces/primereact
|
https://api.github.com/repos/primefaces/primereact
|
closed
|
Calendar: Min/Max fixes ported from PrimeFaces
|
defect
|
### Describe the bug
See: https://github.com/primefaces/primefaces/issues/9052
Also when using min and max of first day of year and last day of year it was not calculating correctly.
```js
let minDate = new Date("01/01/2022");
let maxDate = new Date("12/31/2022");
```
### Reproducer
_No response_
### PrimeReact version
8.3.0
### React version
18.x
### Language
ALL
### Build / Runtime
Next.js
### Browser(s)
_No response_
### Steps to reproduce the behavior
_No response_
### Expected behavior
_No response_
|
1.0
|
Calendar: Min/Max fixes ported from PrimeFaces - ### Describe the bug
See: https://github.com/primefaces/primefaces/issues/9052
Also when using min and max of first day of year and last day of year it was not calculating correctly.
```js
let minDate = new Date("01/01/2022");
let maxDate = new Date("12/31/2022");
```
### Reproducer
_No response_
### PrimeReact version
8.3.0
### React version
18.x
### Language
ALL
### Build / Runtime
Next.js
### Browser(s)
_No response_
### Steps to reproduce the behavior
_No response_
### Expected behavior
_No response_
|
defect
|
calendar min max fixes ported from primefaces describe the bug see also when using min and max of first day of year and last day of year it was not calculating correctly js let mindate new date let maxdate new date reproducer no response primereact version react version x language all build runtime next js browser s no response steps to reproduce the behavior no response expected behavior no response
| 1
|
2,405
| 8,528,812,834
|
IssuesEvent
|
2018-11-03 03:51:33
|
TabbycatDebate/tabbycat
|
https://api.github.com/repos/TabbycatDebate/tabbycat
|
opened
|
CSV api for adjudicators
|
awaiting maintainer feature wudc2019
|
To support #910 there should be a list of basic adj information in terms of name, institution etc. This would allow the feedback list to refer to primary keys.
|
True
|
CSV api for adjudicators - To support #910 there should be a list of basic adj information in terms of name, institution etc. This would allow the feedback list to refer to primary keys.
|
non_defect
|
csv api for adjudicators to support there should be a list of basic adj information in terms of name institution etc this would allow the feedback list to refer to primary keys
| 0
|
59,342
| 17,023,092,788
|
IssuesEvent
|
2021-07-03 00:20:58
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
Index out of bounds exception in java console
|
Component: applet Priority: major Resolution: fixed Type: defect
|
**[Submitted to the original trac issue database at 9.41pm, Wednesday, 28th December 2005]**
Not reproduceable yet.
Exception in thread "Thread-305" java.lang.ArrayIndexOutOfBoundsException: 0 >= 0
at java.util.Vector.elementAt(Unknown Source)
at org.openstreetmap.client.Tile.getEle(Tile.java:361)
at org.openstreetmap.client.ImFetch.run(Tile.java:437)
This is the log entries:
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.929931640625,61.7419302246182,16.94091796875,61.74453081889597&width=256&height=128
adding image 1541,14389
mousePressed in ModeManager with currentMode=org.openstreetmap.processing.OSMApplet$LineMode@aa2ef2 and overButton=false
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.7289239586037,16.951904296875,61.73152565113397&width=256&height=128
adding image 1542,14384
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.7289239586037,16.951904296875,61.73152565113397&width=256&height=128
adding image 1542,14384
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.73152565113397,16.951904296875,61.73412712398737&width=256&height=128
adding image 1542,14385
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.73152565113397,16.951904296875,61.73412712398737&width=256&height=128
adding image 1542,14385
Exception in thread "Thread-305" java.lang.ArrayIndexOutOfBoundsException: 0 >= 0
at java.util.Vector.elementAt(Unknown Source)
at org.openstreetmap.client.Tile.getEle(Tile.java:361)
at org.openstreetmap.client.ImFetch.run(Tile.java:437)
getting nodes and lines
trying url: http://www.openstreetmap.org/api/0.2/map?bbox=16.910602569580078,61.73166151838643,16.940643310546875,61.74182223008769
2005-dec-28 22:36:56 org.apache.commons.httpclient.auth.AuthChallengeProcessor selectAuthScheme
INFO: basic authentication scheme selected
GPX parser started...
Start of Document
End of Document
|
1.0
|
Index out of bounds exception in java console - **[Submitted to the original trac issue database at 9.41pm, Wednesday, 28th December 2005]**
Not reproduceable yet.
Exception in thread "Thread-305" java.lang.ArrayIndexOutOfBoundsException: 0 >= 0
at java.util.Vector.elementAt(Unknown Source)
at org.openstreetmap.client.Tile.getEle(Tile.java:361)
at org.openstreetmap.client.ImFetch.run(Tile.java:437)
This is the log entries:
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.929931640625,61.7419302246182,16.94091796875,61.74453081889597&width=256&height=128
adding image 1541,14389
mousePressed in ModeManager with currentMode=org.openstreetmap.processing.OSMApplet$LineMode@aa2ef2 and overButton=false
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.7289239586037,16.951904296875,61.73152565113397&width=256&height=128
adding image 1542,14384
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.7289239586037,16.951904296875,61.73152565113397&width=256&height=128
adding image 1542,14384
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.73152565113397,16.951904296875,61.73412712398737&width=256&height=128
adding image 1542,14385
Trying to download image http://www.openstreetmap.org/tile/0.1/wms?map=/usr/lib/cgi-bin/steve/wms.map&service=WMS&WMTVER=1.0.0&REQUEST=map&STYLES=&TRANSPARENT=TRUE&LAYERS=landsat,gpx&bbox=16.94091796875,61.73152565113397,16.951904296875,61.73412712398737&width=256&height=128
adding image 1542,14385
Exception in thread "Thread-305" java.lang.ArrayIndexOutOfBoundsException: 0 >= 0
at java.util.Vector.elementAt(Unknown Source)
at org.openstreetmap.client.Tile.getEle(Tile.java:361)
at org.openstreetmap.client.ImFetch.run(Tile.java:437)
getting nodes and lines
trying url: http://www.openstreetmap.org/api/0.2/map?bbox=16.910602569580078,61.73166151838643,16.940643310546875,61.74182223008769
2005-dec-28 22:36:56 org.apache.commons.httpclient.auth.AuthChallengeProcessor selectAuthScheme
INFO: basic authentication scheme selected
GPX parser started...
Start of Document
End of Document
|
defect
|
index out of bounds exception in java console not reproduceable yet exception in thread thread java lang arrayindexoutofboundsexception at java util vector elementat unknown source at org openstreetmap client tile getele tile java at org openstreetmap client imfetch run tile java this is the log entries trying to download image adding image mousepressed in modemanager with currentmode org openstreetmap processing osmapplet linemode and overbutton false trying to download image adding image trying to download image adding image trying to download image adding image trying to download image adding image exception in thread thread java lang arrayindexoutofboundsexception at java util vector elementat unknown source at org openstreetmap client tile getele tile java at org openstreetmap client imfetch run tile java getting nodes and lines trying url dec org apache commons httpclient auth authchallengeprocessor selectauthscheme info basic authentication scheme selected gpx parser started start of document end of document
| 1
|
264,614
| 8,317,578,233
|
IssuesEvent
|
2018-09-25 12:33:19
|
Neomer/EveryPrice
|
https://api.github.com/repos/Neomer/EveryPrice
|
opened
|
Отключать GPS при отсутствии в нем протребности
|
bug priority: High
|
Отключать работы с GPS при свернутом приложении и при неактивных активити, использующих GPS
|
1.0
|
Отключать GPS при отсутствии в нем протребности - Отключать работы с GPS при свернутом приложении и при неактивных активити, использующих GPS
|
non_defect
|
отключать gps при отсутствии в нем протребности отключать работы с gps при свернутом приложении и при неактивных активити использующих gps
| 0
|
107,907
| 13,529,172,505
|
IssuesEvent
|
2020-09-15 17:52:05
|
flutter/flutter
|
https://api.github.com/repos/flutter/flutter
|
closed
|
[Navigation Rail] Extended animation jumps on initially frame
|
f: material design framework passed first triage
|
As soon as the animation is non-zero, a const SizedBox is inserted which causing an unsmooth animation.

|
1.0
|
[Navigation Rail] Extended animation jumps on initially frame - As soon as the animation is non-zero, a const SizedBox is inserted which causing an unsmooth animation.

|
non_defect
|
extended animation jumps on initially frame as soon as the animation is non zero a const sizedbox is inserted which causing an unsmooth animation
| 0
|
365,297
| 25,528,155,728
|
IssuesEvent
|
2022-11-29 05:26:18
|
WSU-CPTS415-ParquetParkour/Amazon-CoPurchasing
|
https://api.github.com/repos/WSU-CPTS415-ParquetParkour/Amazon-CoPurchasing
|
opened
|
[TASK] Final report - Results and Findings
|
documentation
|
_Background_:
We need a segment which describes our findings from analyzing this dataset.
_Problem_:
What did our analyses reveal from this dataset?
_Success Criteria_:
1. From the prompt on Canvas: "How do you evaluate your solution to whatever empirical, algorithmic or theoretical question you have addressed and what do these evaluation methods tell you about your solution. It is not so important how well your method performs but rather how interesting and clever your experiments and analysis are. We are interested in seeing a clear and conclusive set of experiments which successfully evaluate the problem you set out to solve. Make sure to interpret the results and talk about what can we conclude and learn from your evaluations. Even if you have a theoretical project you should have something here to demonstrate the validity or value of your project (for example, proofs or runtime analysis)."
2. References are cited and included in a subsection at the end.
|
1.0
|
[TASK] Final report - Results and Findings - _Background_:
We need a segment which describes our findings from analyzing this dataset.
_Problem_:
What did our analyses reveal from this dataset?
_Success Criteria_:
1. From the prompt on Canvas: "How do you evaluate your solution to whatever empirical, algorithmic or theoretical question you have addressed and what do these evaluation methods tell you about your solution. It is not so important how well your method performs but rather how interesting and clever your experiments and analysis are. We are interested in seeing a clear and conclusive set of experiments which successfully evaluate the problem you set out to solve. Make sure to interpret the results and talk about what can we conclude and learn from your evaluations. Even if you have a theoretical project you should have something here to demonstrate the validity or value of your project (for example, proofs or runtime analysis)."
2. References are cited and included in a subsection at the end.
|
non_defect
|
final report results and findings background we need a segment which describes our findings from analyzing this dataset problem what did our analyses reveal from this dataset success criteria from the prompt on canvas how do you evaluate your solution to whatever empirical algorithmic or theoretical question you have addressed and what do these evaluation methods tell you about your solution it is not so important how well your method performs but rather how interesting and clever your experiments and analysis are we are interested in seeing a clear and conclusive set of experiments which successfully evaluate the problem you set out to solve make sure to interpret the results and talk about what can we conclude and learn from your evaluations even if you have a theoretical project you should have something here to demonstrate the validity or value of your project for example proofs or runtime analysis references are cited and included in a subsection at the end
| 0
|
110,094
| 13,904,071,873
|
IssuesEvent
|
2020-10-20 08:07:30
|
httpwg/httpbis-issues
|
https://api.github.com/repos/httpwg/httpbis-issues
|
opened
|
User-Agent guidelines (Trac #232)
|
Incomplete Migration Migrated from Trac design mnot@pobox.com p2-semantics
|
Migrated from https://trac.ietf.org/ticket/232
```json
{
"status": "closed",
"changetime": "2011-02-08T23:43:54",
"_ts": "1297208634000000",
"description": "UA strings have become quite long, which makes requests bigger than necessary, can reveal too much information about the user (including allowing them to be \"fingerprinted\"), and potentially can encourage inappropriate sniffing.\n\nGuidance should be provided regarding what's appropriate / inappropriate in a UA string, and the privacy aspect should be added to Security Considerations.\n\nSee also:\n https://bugzilla.mozilla.org/show_bug.cgi?id=572650\n http://blogs.msdn.com/b/ie/archive/2010/03/23/introducing-ie9-s-user-agent-string.aspx\n https://panopticlick.eff.org/",
"reporter": "mnot@pobox.com",
"cc": "",
"resolution": "fixed",
"time": "2010-07-24T12:04:37",
"component": "p2-semantics",
"summary": "User-Agent guidelines",
"priority": "normal",
"keywords": "",
"milestone": "12",
"owner": "mnot@pobox.com",
"type": "design",
"severity": "Active WG Document"
}
```
|
1.0
|
User-Agent guidelines (Trac #232) - Migrated from https://trac.ietf.org/ticket/232
```json
{
"status": "closed",
"changetime": "2011-02-08T23:43:54",
"_ts": "1297208634000000",
"description": "UA strings have become quite long, which makes requests bigger than necessary, can reveal too much information about the user (including allowing them to be \"fingerprinted\"), and potentially can encourage inappropriate sniffing.\n\nGuidance should be provided regarding what's appropriate / inappropriate in a UA string, and the privacy aspect should be added to Security Considerations.\n\nSee also:\n https://bugzilla.mozilla.org/show_bug.cgi?id=572650\n http://blogs.msdn.com/b/ie/archive/2010/03/23/introducing-ie9-s-user-agent-string.aspx\n https://panopticlick.eff.org/",
"reporter": "mnot@pobox.com",
"cc": "",
"resolution": "fixed",
"time": "2010-07-24T12:04:37",
"component": "p2-semantics",
"summary": "User-Agent guidelines",
"priority": "normal",
"keywords": "",
"milestone": "12",
"owner": "mnot@pobox.com",
"type": "design",
"severity": "Active WG Document"
}
```
|
non_defect
|
user agent guidelines trac migrated from json status closed changetime ts description ua strings have become quite long which makes requests bigger than necessary can reveal too much information about the user including allowing them to be fingerprinted and potentially can encourage inappropriate sniffing n nguidance should be provided regarding what s appropriate inappropriate in a ua string and the privacy aspect should be added to security considerations n nsee also n reporter mnot pobox com cc resolution fixed time component semantics summary user agent guidelines priority normal keywords milestone owner mnot pobox com type design severity active wg document
| 0
|
28,312
| 2,700,903,114
|
IssuesEvent
|
2015-04-04 18:00:22
|
tgstation/-tg-station
|
https://api.github.com/repos/tgstation/-tg-station
|
closed
|
Energy katana desc is not capitalized.
|
Consistency Issue Easy Fix Grammar and Formating Priority: High
|
"a katana infused with a strong energy"
The a should be capitalized, and there should probably be a period at the end there too.
@RemieRichards
|
1.0
|
Energy katana desc is not capitalized. - "a katana infused with a strong energy"
The a should be capitalized, and there should probably be a period at the end there too.
@RemieRichards
|
non_defect
|
energy katana desc is not capitalized a katana infused with a strong energy the a should be capitalized and there should probably be a period at the end there too remierichards
| 0
|
85,103
| 15,731,206,731
|
IssuesEvent
|
2021-03-29 16:47:44
|
wrbejar/bag-of-holding
|
https://api.github.com/repos/wrbejar/bag-of-holding
|
opened
|
WS-2019-0425 (Medium) detected in mocha-2.5.3.tgz
|
security vulnerability
|
## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.5.3.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz">https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz</a></p>
<p>Path to dependency file: bag-of-holding/package.json</p>
<p>Path to vulnerable library: bag-of-holding/node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-1.3.3.tgz (Root Library)
- node-sass-2.1.1.tgz
- :x: **mocha-2.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/wrbejar/bag-of-holding/commit/6087cf643d57f8f112ae650913c59bfc0a1033d6">6087cf643d57f8f112ae650913c59bfc0a1033d6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2020-05-07</p>
<p>Fix Resolution: https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"2.5.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-sass:1.3.3;node-sass:2.1.1;mocha:2.5.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559"}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2019-0425","vulnerabilityDetails":"Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.","vulnerabilityUrl":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
WS-2019-0425 (Medium) detected in mocha-2.5.3.tgz - ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.5.3.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz">https://registry.npmjs.org/mocha/-/mocha-2.5.3.tgz</a></p>
<p>Path to dependency file: bag-of-holding/package.json</p>
<p>Path to vulnerable library: bag-of-holding/node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-1.3.3.tgz (Root Library)
- node-sass-2.1.1.tgz
- :x: **mocha-2.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/wrbejar/bag-of-holding/commit/6087cf643d57f8f112ae650913c59bfc0a1033d6">6087cf643d57f8f112ae650913c59bfc0a1033d6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2020-05-07</p>
<p>Fix Resolution: https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"2.5.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-sass:1.3.3;node-sass:2.1.1;mocha:2.5.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559"}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2019-0425","vulnerabilityDetails":"Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.","vulnerabilityUrl":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_defect
|
ws medium detected in mocha tgz ws medium severity vulnerability vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file bag of holding package json path to vulnerable library bag of holding node modules mocha package json dependency hierarchy gulp sass tgz root library node sass tgz x mocha tgz vulnerable library found in head commit a href found in base branch master vulnerability details mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree gulp sass node sass mocha isminimumfixversionavailable true minimumfixversion vulnerabilityidentifier ws vulnerabilitydetails mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time vulnerabilityurl
| 0
|
76,875
| 7,548,045,658
|
IssuesEvent
|
2018-04-18 09:52:57
|
Kademi/kademi-dev
|
https://api.github.com/repos/Kademi/kademi-dev
|
closed
|
Stop/Go funnel goal
|
Ready to Test - Dev
|
Create a goal which allows manual control of progression.
All leads should initially stop. The administrator can click a button which will cause all leads stopped on that goal to proceed
|
1.0
|
Stop/Go funnel goal - Create a goal which allows manual control of progression.
All leads should initially stop. The administrator can click a button which will cause all leads stopped on that goal to proceed
|
non_defect
|
stop go funnel goal create a goal which allows manual control of progression all leads should initially stop the administrator can click a button which will cause all leads stopped on that goal to proceed
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.