Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
447,900 | 31,725,436,933 | IssuesEvent | 2023-09-10 22:13:09 | SINTEF/oteapi-optimade | https://api.github.com/repos/SINTEF/oteapi-optimade | closed | Pipeline figure not being shown in docs | bug documentation | Due to the added version part of the URL path (from mike), the reference to the pipeline figure under /img/ is not shown. | 1.0 | Pipeline figure not being shown in docs - Due to the added version part of the URL path (from mike), the reference to the pipeline figure under /img/ is not shown. | non_priority | pipeline figure not being shown in docs due to the added version part of the url path from mike the reference to the pipeline figure under img is not shown | 0 |
53,132 | 7,808,081,132 | IssuesEvent | 2018-06-11 18:58:46 | aforemny/elm-mdc | https://api.github.com/repos/aforemny/elm-mdc | closed | Handling onFocus on Textfield | documentation enhancement | It appears I cannot supply my own Options.onFocus for a Textfield is that right? Is that something that can be fixed?
I had a bit of a look at the source code and it doesn't appear that easy, at least not for me. Implementation.elm sets its own onFocus, and I suppose Elm doesn't handle multiple onFocus handlers. So it looks like in the update function you would need to check if the user has set an onFocus and chain that somehow. | 1.0 | Handling onFocus on Textfield - It appears I cannot supply my own Options.onFocus for a Textfield is that right? Is that something that can be fixed?
I had a bit of a look at the source code and it doesn't appear that easy, at least not for me. Implementation.elm sets its own onFocus, and I suppose Elm doesn't handle multiple onFocus handlers. So it looks like in the update function you would need to check if the user has set an onFocus and chain that somehow. | non_priority | handling onfocus on textfield it appears i cannot supply my own options onfocus for a textfield is that right is that something that can be fixed i had a bit of a look at the source code and it doesn t appear that easy at least not for me implementation elm sets its own onfocus and i suppose elm doesn t handle multiple onfocus handlers so it looks like in the update function you would need to check if the user has set an onfocus and chain that somehow | 0 |
316,898 | 23,653,896,327 | IssuesEvent | 2022-08-26 09:20:45 | dstansby/pfsspy | https://api.github.com/repos/dstansby/pfsspy | closed | Suggestions for documentation and UI | Documentation | - [x] You could mention the optional packages (`streamtracer`, `numba`) in the installation section. (For instance, for users with limited internet connection wanting to install the full package at once.) A link to `streamtracer` homepage would also be nice in the 'Improving performance ' section.
- [ ] You could add a few paragraphs at the beginning of the documentation to explain the general structure of the code and the terminology. From the example, I am guessing from the examples that `pfsspy.pfss` is the main function solving the PDE problem and that "tracers" are post-processing tools to reconstruct the values of the magnetic field from the abstract output of `pfss`. Maybe this could be explained more explicitly. By the way, wouldn't `solve` or `solve_pfss` be a more explicit name for `pfss`?
- [ ] Adding a string representation `__str__` to `Input` and `Output` might help new users to understand what they store.
These suggestions are not mandatory for a positive JOSS review. Do not feel any obligation to implement them. | 1.0 | Suggestions for documentation and UI - - [x] You could mention the optional packages (`streamtracer`, `numba`) in the installation section. (For instance, for users with limited internet connection wanting to install the full package at once.) A link to `streamtracer` homepage would also be nice in the 'Improving performance ' section.
- [ ] You could add a few paragraphs at the beginning of the documentation to explain the general structure of the code and the terminology. From the example, I am guessing from the examples that `pfsspy.pfss` is the main function solving the PDE problem and that "tracers" are post-processing tools to reconstruct the values of the magnetic field from the abstract output of `pfss`. Maybe this could be explained more explicitly. By the way, wouldn't `solve` or `solve_pfss` be a more explicit name for `pfss`?
- [ ] Adding a string representation `__str__` to `Input` and `Output` might help new users to understand what they store.
These suggestions are not mandatory for a positive JOSS review. Do not feel any obligation to implement them. | non_priority | suggestions for documentation and ui you could mention the optional packages streamtracer numba in the installation section for instance for users with limited internet connection wanting to install the full package at once a link to streamtracer homepage would also be nice in the improving performance section you could add a few paragraphs at the beginning of the documentation to explain the general structure of the code and the terminology from the example i am guessing from the examples that pfsspy pfss is the main function solving the pde problem and that tracers are post processing tools to reconstruct the values of the magnetic field from the abstract output of pfss maybe this could be explained more explicitly by the way wouldn t solve or solve pfss be a more explicit name for pfss adding a string representation str to input and output might help new users to understand what they store these suggestions are not mandatory for a positive joss review do not feel any obligation to implement them | 0 |
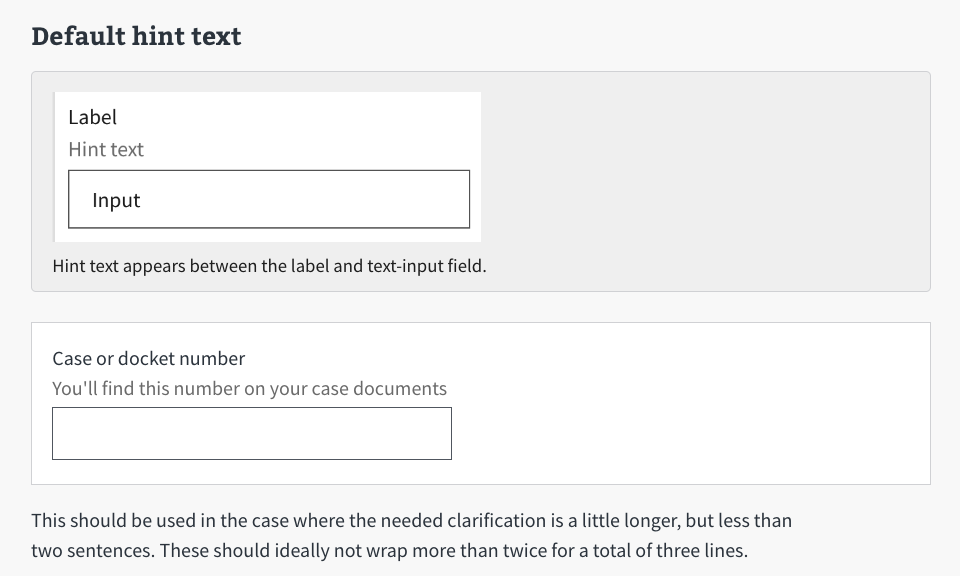
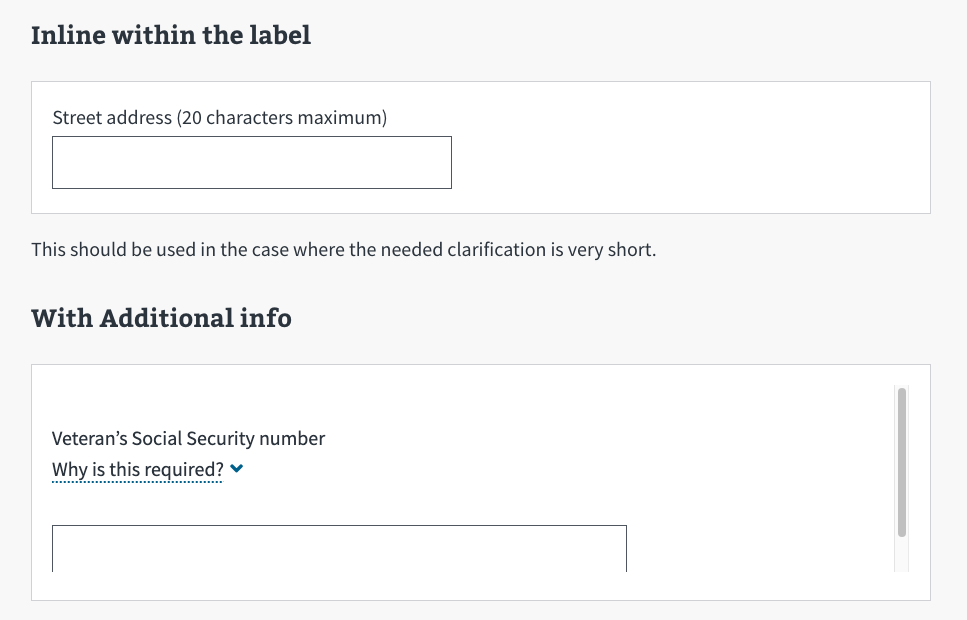
160,455 | 25,166,533,814 | IssuesEvent | 2022-11-10 21:25:19 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | opened | Update va-textinput web component | vsp-design-system-team va-text-input dst-engineering |
## Description
The Textinput web component needs to be updated to include two more text input with hint text examples.
## Details
Missing from Storybook are the hint text examples for text input (https://design.va.gov/components/form/#hint-text)
Text input with the “Default hint text”
Text input with “Inline within the label”
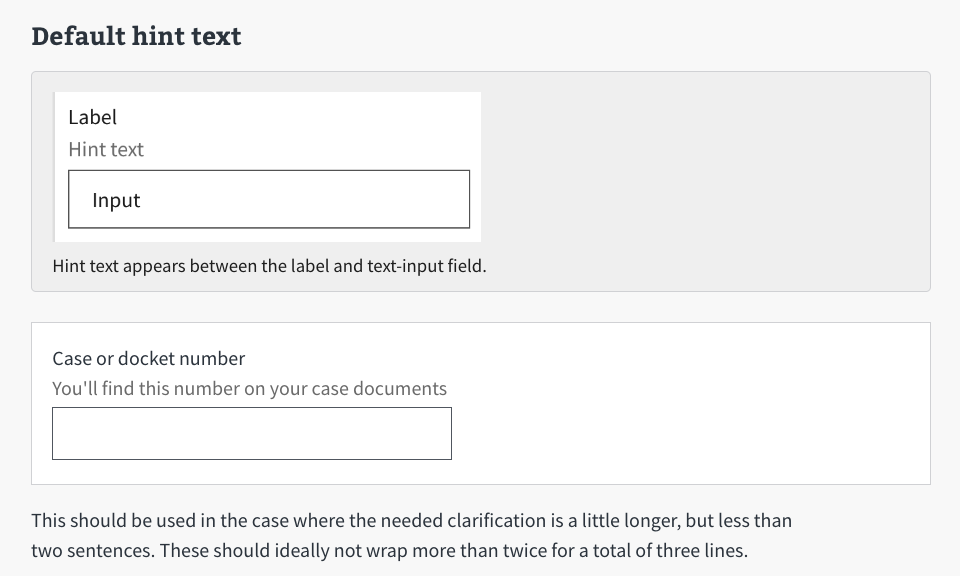
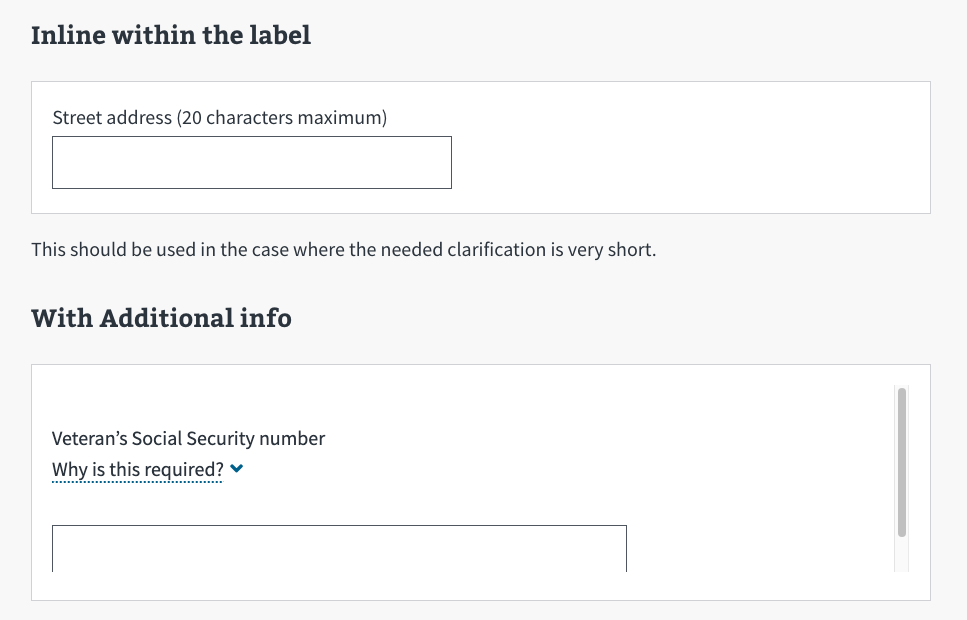
## Tasks
- [ ] update va-text input with Text input with the “Default hint text” and Text input with “Inline within the label” (see screenshots)
- [ ] update Storybook with the examples
- [ ] Review the updates with designer (confirm with Natalie that updates match Sketch library designs)
## Acceptance Criteria
- [ ] Component is updated in Storybook
- [ ] Component has had design review
| 1.0 | Update va-textinput web component -
## Description
The Textinput web component needs to be updated to include two more text input with hint text examples.
## Details
Missing from Storybook are the hint text examples for text input (https://design.va.gov/components/form/#hint-text)
Text input with the “Default hint text”
Text input with “Inline within the label”
## Tasks
- [ ] update va-text input with Text input with the “Default hint text” and Text input with “Inline within the label” (see screenshots)
- [ ] update Storybook with the examples
- [ ] Review the updates with designer (confirm with Natalie that updates match Sketch library designs)
## Acceptance Criteria
- [ ] Component is updated in Storybook
- [ ] Component has had design review
| non_priority | update va textinput web component description the textinput web component needs to be updated to include two more text input with hint text examples details missing from storybook are the hint text examples for text input text input with the “default hint text” text input with “inline within the label” tasks update va text input with text input with the “default hint text” and text input with “inline within the label” see screenshots update storybook with the examples review the updates with designer confirm with natalie that updates match sketch library designs acceptance criteria component is updated in storybook component has had design review | 0 |
10,444 | 7,189,141,694 | IssuesEvent | 2018-02-02 12:56:35 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Runtime Error with Qt GUI Application | stat:awaiting response type:bug/performance | ### System information
- **Have I written custom code (as opposed to using a stock example script provided in TensorFlow)**:
- **OS Platform and Distribution (e.g., Linux Ubuntu 16.04)**:
- **TensorFlow installed from source**:
- **TensorFlow version use master**:
- **Python version 2.7**:
- **Bazel version 0.9.0**:
- **GCC/Compiler version 5.4.0**:
- **Without CUDA/cuDNN**:
- **Without GPU**:
### Describe the problem
When I used QtCreator to build GUI Application, if include "tensorflow/core/lib/core/refcount.h", it will throw The program has unexpectedly finished.
.pro like
####
SOURCES += \
main.cpp \
mainwindow.cpp
HEADERS += \
mainwindow.h
FORMS += \
mainwindow.ui
#tensorflow
INCLUDEPATH += /home/face/Desktop/tensorflow/bazel-genfiles`
INCLUDEPATH += /home/face/Desktop/tensorflow`
INCLUDEPATH += /home/face/Desktop/tensorflow/tensorflow/contrib/makefile/gen/protobuf/include`
INCLUDEPATH += /home/face/Desktop/tensorflow/tensorflow/contrib/makefile/downloads/nsync/public`
INCLUDEPATH += /home/face/Desktop/eigen-eigen-5a0156e40feb`
LIBS += -L/home/face/Desktop/tensorflow/bazel-bin/tensorflow -ltensorflow_cc -ltensorflow_framework
main.cpp
####
#include "mainwindow.h"
#include <QApplication>
#include <tensorflow/core/platform/env.h>
#include <tensorflow/core/public/session.h>
int main(int argc, char *argv[])
{
QApplication a(argc, argv);
MainWindow w;
w.show();
return a.exec();
}
then if "tensorflow/core/lib/core/refcount.h" line 79
####
inline RefCounted::~RefCounted() {
DCHECK_EQ(ref_.load(), 0);
}
to
####
inline RefCounted::~RefCounted() {
//DCHECK_EQ(ref_.load(), 0);
}
it will work.
### Source code / logs
debug log like:
####
1 google::protobuf::internal::Mutex::Lock() 0x7fffde0c3516
2 google::protobuf::internal::OnShutdown(void ( *)()) 0x7fffde0c3833
3 call_init dl-init.c 72 0x7ffff7de76ba
4 call_init dl-init.c 30 0x7ffff7de77cb
5 _dl_init dl-init.c 120 0x7ffff7de77cb
6 dl_open_worker dl-open.c 575 0x7ffff7dec8e2
7 _dl_catch_error dl-error.c 187 0x7ffff7de7564
8 _dl_open dl-open.c 660 0x7ffff7debda9
9 dlopen_doit dlopen.c 66 0x7ffff18f0f09
10 _dl_catch_error dl-error.c 187 0x7ffff7de7564
11 _dlerror_run dlerror.c 163 0x7ffff18f1571
12 __dlopen dlopen.c 87 0x7ffff18f0fa1
13 ?? 0x7ffff33100e5
14 ?? 0x7ffff3309975
15 QFactoryLoader::instance(int) const 0x7ffff32ff07e
16 QPlatformThemeFactory::create(QString const&, QString const&) 0x7ffff0b30231
17 QGuiApplicationPrivate::createPlatformIntegration() 0x7ffff0b3aaf8
18 QGuiApplicationPrivate::createEventDispatcher() 0x7ffff0b3b4bd
19 QCoreApplicationPrivate::init() 0x7ffff331ab3b
20 QGuiApplicationPrivate::init() 0x7ffff0b3cf7b
21 QApplicationPrivate::init() 0x7ffff392d3b9
22 main main.cpp 103 0x402e3e
| True | Runtime Error with Qt GUI Application - ### System information
- **Have I written custom code (as opposed to using a stock example script provided in TensorFlow)**:
- **OS Platform and Distribution (e.g., Linux Ubuntu 16.04)**:
- **TensorFlow installed from source**:
- **TensorFlow version use master**:
- **Python version 2.7**:
- **Bazel version 0.9.0**:
- **GCC/Compiler version 5.4.0**:
- **Without CUDA/cuDNN**:
- **Without GPU**:
### Describe the problem
When I used QtCreator to build GUI Application, if include "tensorflow/core/lib/core/refcount.h", it will throw The program has unexpectedly finished.
.pro like
####
SOURCES += \
main.cpp \
mainwindow.cpp
HEADERS += \
mainwindow.h
FORMS += \
mainwindow.ui
#tensorflow
INCLUDEPATH += /home/face/Desktop/tensorflow/bazel-genfiles`
INCLUDEPATH += /home/face/Desktop/tensorflow`
INCLUDEPATH += /home/face/Desktop/tensorflow/tensorflow/contrib/makefile/gen/protobuf/include`
INCLUDEPATH += /home/face/Desktop/tensorflow/tensorflow/contrib/makefile/downloads/nsync/public`
INCLUDEPATH += /home/face/Desktop/eigen-eigen-5a0156e40feb`
LIBS += -L/home/face/Desktop/tensorflow/bazel-bin/tensorflow -ltensorflow_cc -ltensorflow_framework
main.cpp
####
#include "mainwindow.h"
#include <QApplication>
#include <tensorflow/core/platform/env.h>
#include <tensorflow/core/public/session.h>
int main(int argc, char *argv[])
{
QApplication a(argc, argv);
MainWindow w;
w.show();
return a.exec();
}
then if "tensorflow/core/lib/core/refcount.h" line 79
####
inline RefCounted::~RefCounted() {
DCHECK_EQ(ref_.load(), 0);
}
to
####
inline RefCounted::~RefCounted() {
//DCHECK_EQ(ref_.load(), 0);
}
it will work.
### Source code / logs
debug log like:
####
1 google::protobuf::internal::Mutex::Lock() 0x7fffde0c3516
2 google::protobuf::internal::OnShutdown(void ( *)()) 0x7fffde0c3833
3 call_init dl-init.c 72 0x7ffff7de76ba
4 call_init dl-init.c 30 0x7ffff7de77cb
5 _dl_init dl-init.c 120 0x7ffff7de77cb
6 dl_open_worker dl-open.c 575 0x7ffff7dec8e2
7 _dl_catch_error dl-error.c 187 0x7ffff7de7564
8 _dl_open dl-open.c 660 0x7ffff7debda9
9 dlopen_doit dlopen.c 66 0x7ffff18f0f09
10 _dl_catch_error dl-error.c 187 0x7ffff7de7564
11 _dlerror_run dlerror.c 163 0x7ffff18f1571
12 __dlopen dlopen.c 87 0x7ffff18f0fa1
13 ?? 0x7ffff33100e5
14 ?? 0x7ffff3309975
15 QFactoryLoader::instance(int) const 0x7ffff32ff07e
16 QPlatformThemeFactory::create(QString const&, QString const&) 0x7ffff0b30231
17 QGuiApplicationPrivate::createPlatformIntegration() 0x7ffff0b3aaf8
18 QGuiApplicationPrivate::createEventDispatcher() 0x7ffff0b3b4bd
19 QCoreApplicationPrivate::init() 0x7ffff331ab3b
20 QGuiApplicationPrivate::init() 0x7ffff0b3cf7b
21 QApplicationPrivate::init() 0x7ffff392d3b9
22 main main.cpp 103 0x402e3e
| non_priority | runtime error with qt gui application system information have i written custom code as opposed to using a stock example script provided in tensorflow os platform and distribution e g linux ubuntu tensorflow installed from source tensorflow version use master python version bazel version gcc compiler version without cuda cudnn without gpu describe the problem when i used qtcreator to build gui application if include tensorflow core lib core refcount h it will throw the program has unexpectedly finished pro like sources main cpp mainwindow cpp headers mainwindow h forms mainwindow ui tensorflow includepath home face desktop tensorflow bazel genfiles includepath home face desktop tensorflow includepath home face desktop tensorflow tensorflow contrib makefile gen protobuf include includepath home face desktop tensorflow tensorflow contrib makefile downloads nsync public includepath home face desktop eigen eigen libs l home face desktop tensorflow bazel bin tensorflow ltensorflow cc ltensorflow framework main cpp include mainwindow h include include include int main int argc char argv qapplication a argc argv mainwindow w w show return a exec then if tensorflow core lib core refcount h line inline refcounted refcounted dcheck eq ref load to inline refcounted refcounted dcheck eq ref load it will work source code logs debug log like google protobuf internal mutex lock google protobuf internal onshutdown void call init dl init c call init dl init c dl init dl init c dl open worker dl open c dl catch error dl error c dl open dl open c dlopen doit dlopen c dl catch error dl error c dlerror run dlerror c dlopen dlopen c qfactoryloader instance int const qplatformthemefactory create qstring const qstring const qguiapplicationprivate createplatformintegration qguiapplicationprivate createeventdispatcher qcoreapplicationprivate init qguiapplicationprivate init qapplicationprivate init main main cpp | 0 |
95,612 | 10,883,718,213 | IssuesEvent | 2019-11-18 06:03:44 | golang/go | https://api.github.com/repos/golang/go | closed | wiki: recommended Ubuntu port still does not have security fix release | Documentation NeedsInvestigation help wanted | Per https://github.com/golang/go/wiki/Ubuntu, the recommended Ubuntu 18.04 apt source is `longsleep/golang-backports`.
As of 5pm Pacific on October 22, that port does not have the Go 1.13.2 or Go 1.13.3 releases.
I'm not sure if this is the right place - if someone on the Go team maintains that package - but it seems bad that a recommended resource is not up to date several days after a security release.
It would be nice to maybe see instructions about what goes into the `.deb` file so we can reproduce it/upload on our own. | 1.0 | wiki: recommended Ubuntu port still does not have security fix release - Per https://github.com/golang/go/wiki/Ubuntu, the recommended Ubuntu 18.04 apt source is `longsleep/golang-backports`.
As of 5pm Pacific on October 22, that port does not have the Go 1.13.2 or Go 1.13.3 releases.
I'm not sure if this is the right place - if someone on the Go team maintains that package - but it seems bad that a recommended resource is not up to date several days after a security release.
It would be nice to maybe see instructions about what goes into the `.deb` file so we can reproduce it/upload on our own. | non_priority | wiki recommended ubuntu port still does not have security fix release per the recommended ubuntu apt source is longsleep golang backports as of pacific on october that port does not have the go or go releases i m not sure if this is the right place if someone on the go team maintains that package but it seems bad that a recommended resource is not up to date several days after a security release it would be nice to maybe see instructions about what goes into the deb file so we can reproduce it upload on our own | 0 |
78,540 | 15,026,524,994 | IssuesEvent | 2021-02-01 22:50:36 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] media field preview empty | No Code Attached Yet | ### Steps to reproduce the issue
in global configuration change site offline to yes
### Expected result
preview of image which as its not set yet is the blank default
### Actual result
it tries to load a non-existent file.
```
<div class="field-media-preview">
<div id="jform_offline_image_preview_empty">No image selected.</div>
<div id="jform_offline_image_preview_img">
<img src="" alt="Selected image." id="jform_offline_image_preview" class="media-preview" style="max-width:200px;max-height:200px;">
</div>
</div>
```

### Additional comments
I suspect this is a javascript issue a | 1.0 | [4.0] media field preview empty - ### Steps to reproduce the issue
in global configuration change site offline to yes
### Expected result
preview of image which as its not set yet is the blank default
### Actual result
it tries to load a non-existent file.
```
<div class="field-media-preview">
<div id="jform_offline_image_preview_empty">No image selected.</div>
<div id="jform_offline_image_preview_img">
<img src="" alt="Selected image." id="jform_offline_image_preview" class="media-preview" style="max-width:200px;max-height:200px;">
</div>
</div>
```

### Additional comments
I suspect this is a javascript issue a | non_priority | media field preview empty steps to reproduce the issue in global configuration change site offline to yes expected result preview of image which as its not set yet is the blank default actual result it tries to load a non existent file no image selected additional comments i suspect this is a javascript issue a | 0 |
13,869 | 16,627,145,432 | IssuesEvent | 2021-06-03 11:03:59 | arcus-azure/arcus.messaging | https://api.github.com/repos/arcus-azure/arcus.messaging | closed | Remove the 'old' Azure Service Bus message pump workings once the Arcus.BackgroundJobs package is updated | area:message-processing dependencies enhancement integration:service-bus | **Is your feature request related to a problem? Please describe.**
Since we rely in the Arcus.Messaging.ServiceBus.KeyRotation project on the Arcus.BackgroundJobs.* package (that uses again our messaging package), we have 'method not found's exceptions when we break the contract of the Azure Service Bus message pump.
**Describe the solution you'd like**
Once the Arcus.BackgroundJobs.* package is updated with our new messaging package, we can remove the 'old' workings of the message pump.
**Describe alternatives you've considered**
A clear and concise description of any alternative solutions or features you've considered.
**Additional context**
PR with backwards compatible Azure Service Bus message pump #175 | 1.0 | Remove the 'old' Azure Service Bus message pump workings once the Arcus.BackgroundJobs package is updated - **Is your feature request related to a problem? Please describe.**
Since we rely in the Arcus.Messaging.ServiceBus.KeyRotation project on the Arcus.BackgroundJobs.* package (that uses again our messaging package), we have 'method not found's exceptions when we break the contract of the Azure Service Bus message pump.
**Describe the solution you'd like**
Once the Arcus.BackgroundJobs.* package is updated with our new messaging package, we can remove the 'old' workings of the message pump.
**Describe alternatives you've considered**
A clear and concise description of any alternative solutions or features you've considered.
**Additional context**
PR with backwards compatible Azure Service Bus message pump #175 | non_priority | remove the old azure service bus message pump workings once the arcus backgroundjobs package is updated is your feature request related to a problem please describe since we rely in the arcus messaging servicebus keyrotation project on the arcus backgroundjobs package that uses again our messaging package we have method not found s exceptions when we break the contract of the azure service bus message pump describe the solution you d like once the arcus backgroundjobs package is updated with our new messaging package we can remove the old workings of the message pump describe alternatives you ve considered a clear and concise description of any alternative solutions or features you ve considered additional context pr with backwards compatible azure service bus message pump | 0 |
344,618 | 30,751,909,571 | IssuesEvent | 2023-07-28 20:08:26 | saltstack/salt | https://api.github.com/repos/saltstack/salt | opened | [Increase Test Coverage] Batch 43 | Tests | Increase the code coverage percent on the following files to at least 80%.
Please be aware that currently the percentage might be inaccurate if the module uses salt due to #64696
File | Percent
salt/utils/job.py 53
salt/utils/nacl.py 15
salt/utils/user.py 55
salt/utils/zeromq.py 73
salt/cloud/clouds/virtualbox.py 16
| 1.0 | [Increase Test Coverage] Batch 43 - Increase the code coverage percent on the following files to at least 80%.
Please be aware that currently the percentage might be inaccurate if the module uses salt due to #64696
File | Percent
salt/utils/job.py 53
salt/utils/nacl.py 15
salt/utils/user.py 55
salt/utils/zeromq.py 73
salt/cloud/clouds/virtualbox.py 16
| non_priority | batch increase the code coverage percent on the following files to at least please be aware that currently the percentage might be inaccurate if the module uses salt due to file percent salt utils job py salt utils nacl py salt utils user py salt utils zeromq py salt cloud clouds virtualbox py | 0 |
183,863 | 21,784,739,409 | IssuesEvent | 2022-05-14 01:09:19 | RG4421/azure-iot-platform-dotnet | https://api.github.com/repos/RG4421/azure-iot-platform-dotnet | closed | WS-2019-0333 (High) detected in handlebars-4.1.0.tgz - autoclosed | security vulnerability | ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz</a></p>
<p>Path to dependency file: azure-iot-platform-dotnet/src/webui/azure-iot-ux-fluent-controls/package.json</p>
<p>Path to vulnerable library: azure-iot-platform-dotnet/src/webui/azure-iot-ux-fluent-controls/node_modules/nyc/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- nyc-13.3.0.tgz (Root Library)
- istanbul-reports-2.1.1.tgz
- :x: **handlebars-4.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/azure-iot-platform-dotnet/commit/e1215c4c0b54ac624a08bdd584a503ed82b21d0d">e1215c4c0b54ac624a08bdd584a503ed82b21d0d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it's possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08>WS-2019-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1325">https://www.npmjs.com/advisories/1325</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.1.0","packageFilePaths":["/src/webui/azure-iot-ux-fluent-controls/package.json"],"isTransitiveDependency":true,"dependencyTree":"nyc:13.3.0;istanbul-reports:2.1.1;handlebars:4.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"handlebars - 4.5.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2019-0333","vulnerabilityDetails":"In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it\u0027s possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.","vulnerabilityUrl":"https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0333 (High) detected in handlebars-4.1.0.tgz - autoclosed - ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz</a></p>
<p>Path to dependency file: azure-iot-platform-dotnet/src/webui/azure-iot-ux-fluent-controls/package.json</p>
<p>Path to vulnerable library: azure-iot-platform-dotnet/src/webui/azure-iot-ux-fluent-controls/node_modules/nyc/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- nyc-13.3.0.tgz (Root Library)
- istanbul-reports-2.1.1.tgz
- :x: **handlebars-4.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/azure-iot-platform-dotnet/commit/e1215c4c0b54ac624a08bdd584a503ed82b21d0d">e1215c4c0b54ac624a08bdd584a503ed82b21d0d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it's possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08>WS-2019-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1325">https://www.npmjs.com/advisories/1325</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.1.0","packageFilePaths":["/src/webui/azure-iot-ux-fluent-controls/package.json"],"isTransitiveDependency":true,"dependencyTree":"nyc:13.3.0;istanbul-reports:2.1.1;handlebars:4.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"handlebars - 4.5.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2019-0333","vulnerabilityDetails":"In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it\u0027s possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.","vulnerabilityUrl":"https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in handlebars tgz autoclosed ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file azure iot platform dotnet src webui azure iot ux fluent controls package json path to vulnerable library azure iot platform dotnet src webui azure iot ux fluent controls node modules nyc node modules handlebars package json dependency hierarchy nyc tgz root library istanbul reports tgz x handlebars tgz vulnerable library found in head commit a href found in base branch master vulnerability details in handlebars versions prior to are vulnerable to prototype pollution using a malicious template it s possbile to add or modify properties to the object prototype this can also lead to dos and rce in certain conditions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree nyc istanbul reports handlebars isminimumfixversionavailable true minimumfixversion handlebars basebranches vulnerabilityidentifier ws vulnerabilitydetails in handlebars versions prior to are vulnerable to prototype pollution using a malicious template it possbile to add or modify properties to the object prototype this can also lead to dos and rce in certain conditions vulnerabilityurl | 0 |
242,466 | 20,250,782,403 | IssuesEvent | 2022-02-14 17:39:23 | mennaelkashef/eShop | https://api.github.com/repos/mennaelkashef/eShop | opened | No description entered by the user. | Hello! RULE-GOT-APPLIED DOES-NOT-CONTAIN-STRING Rule-works-on-convert-to-bug test instabug | # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2022-02-14 17:34:00 UTC
Email | kgomaa@instabug.com
Categories | Report a bug
Tags | test, Hello!, RULE-GOT-APPLIED, DOES-NOT-CONTAIN-STRING, Rule-works-on-convert-to-bug, instabug
App Version | 1.1 (1)
Session Duration | 24
Device | Google Android SDK built for arm64, OS Level 29
Display | 1080x2220 (xhdpi)
Location | Giza, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?utm_source=github&utm_medium=integrations) :point_left:
___
# :iphone: View Hierarchy
This bug was reported from **com.example.app.main.MainFragment**
Find its interactive view hierarchy with all its subviews here: :point_right: **[Check View Hierarchy](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-hierarchy-view=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
Used Memory | 68.8% - 1.34/1.95 GB
Used Storage | 49.6% - 2.88/5.81 GB
Connectivity | WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
key_name -1584268522: key value bla bla bla la
key_name 800329984: key value bla bla bla la
key_name -1214369878: key value bla bla bla la
key_name -368222842: key value bla bla bla la
key_name -1605190929: key value bla bla bla la
key_name -367957541: key value bla bla bla la
key_name -609870334: key value bla bla bla la
key_name -78245691: key value bla bla bla la
key_name 735154571: key value bla bla bla la
key_name -72503995: key value bla bla bla la
key_name -1737319729: key value bla bla bla la
key_name -1648420415: key value bla bla bla la
key_name -748298342: key value bla bla bla la
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.survey.SurveyFragment was paused.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.survey.SurveyFragment was stopped.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was created.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was started.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was resumed.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.survey.SurveyFragment was detached.
17:33:58 Tap in "Sdk version: 10..." of type "androidx.appcompat.widget.AppCompatTextView" in "com.example.app.main.MainActivity"
17:33:58 com.example.app.main.MainActivity was paused.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
17:34:00 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
17:34:01 D/IB-BaseReportingPresenter( 9198): receive a view hierarchy inspection action, action value: COMPLETED
17:34:01 D/IB-BaseReportingPresenter( 9198): receive a view hierarchy inspection action, action value: COMPLETED
17:34:01 I/com.example.ap( 9198): Waiting for a blocking GC Instrumentation
17:34:01 I/com.example.ap( 9198): Explicit concurrent copying GC freed 29335(1979KB) AllocSpace objects, 3(136KB) LOS objects, 47% free, 6778KB/12MB, paused 8us total 7.162ms
17:34:01 I/com.example.ap( 9198): WaitForGcToComplete blocked Instrumentation on Instrumentation for 7.283ms
17:34:01 D/LeakCanary( 9198): Rescheduling check for retained objects in 2000ms because found only 3 retained objects (< 5 while app visible)
17:34:01 D/EGL_emulation( 9198): eglMakeCurrent: 0x78eb9d4a00: ver 3 0 (tinfo 0x78eb9ce520)
17:34:02 D/IB-BaseReportingPresenter( 9198): checkUserEmailValid :non-empty-email
17:34:02 D/IB-ActionsOrchestrator( 9198): runAction
17:34:02 D/IB-AttachmentsUtility( 9198): encryptAttachments
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using HttpUrlConnection or Okhttp requests, [**check the details mentioned here**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations#section-network-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations). | 1.0 | No description entered by the user. - # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2022-02-14 17:34:00 UTC
Email | kgomaa@instabug.com
Categories | Report a bug
Tags | test, Hello!, RULE-GOT-APPLIED, DOES-NOT-CONTAIN-STRING, Rule-works-on-convert-to-bug, instabug
App Version | 1.1 (1)
Session Duration | 24
Device | Google Android SDK built for arm64, OS Level 29
Display | 1080x2220 (xhdpi)
Location | Giza, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?utm_source=github&utm_medium=integrations) :point_left:
___
# :iphone: View Hierarchy
This bug was reported from **com.example.app.main.MainFragment**
Find its interactive view hierarchy with all its subviews here: :point_right: **[Check View Hierarchy](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-hierarchy-view=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
Used Memory | 68.8% - 1.34/1.95 GB
Used Storage | 49.6% - 2.88/5.81 GB
Connectivity | WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
key_name -1584268522: key value bla bla bla la
key_name 800329984: key value bla bla bla la
key_name -1214369878: key value bla bla bla la
key_name -368222842: key value bla bla bla la
key_name -1605190929: key value bla bla bla la
key_name -367957541: key value bla bla bla la
key_name -609870334: key value bla bla bla la
key_name -78245691: key value bla bla bla la
key_name 735154571: key value bla bla bla la
key_name -72503995: key value bla bla bla la
key_name -1737319729: key value bla bla bla la
key_name -1648420415: key value bla bla bla la
key_name -748298342: key value bla bla bla la
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.survey.SurveyFragment was paused.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.survey.SurveyFragment was stopped.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was created.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was started.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was resumed.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.survey.SurveyFragment was detached.
17:33:58 Tap in "Sdk version: 10..." of type "androidx.appcompat.widget.AppCompatTextView" in "com.example.app.main.MainActivity"
17:33:58 com.example.app.main.MainActivity was paused.
17:33:58 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
17:34:00 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
17:34:01 D/IB-BaseReportingPresenter( 9198): receive a view hierarchy inspection action, action value: COMPLETED
17:34:01 D/IB-BaseReportingPresenter( 9198): receive a view hierarchy inspection action, action value: COMPLETED
17:34:01 I/com.example.ap( 9198): Waiting for a blocking GC Instrumentation
17:34:01 I/com.example.ap( 9198): Explicit concurrent copying GC freed 29335(1979KB) AllocSpace objects, 3(136KB) LOS objects, 47% free, 6778KB/12MB, paused 8us total 7.162ms
17:34:01 I/com.example.ap( 9198): WaitForGcToComplete blocked Instrumentation on Instrumentation for 7.283ms
17:34:01 D/LeakCanary( 9198): Rescheduling check for retained objects in 2000ms because found only 3 retained objects (< 5 while app visible)
17:34:01 D/EGL_emulation( 9198): eglMakeCurrent: 0x78eb9d4a00: ver 3 0 (tinfo 0x78eb9ce520)
17:34:02 D/IB-BaseReportingPresenter( 9198): checkUserEmailValid :non-empty-email
17:34:02 D/IB-ActionsOrchestrator( 9198): runAction
17:34:02 D/IB-AttachmentsUtility( 9198): encryptAttachments
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8442?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using HttpUrlConnection or Okhttp requests, [**check the details mentioned here**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations#section-network-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations). | non_priority | no description entered by the user clipboard bug details no description entered by the user key value reported at utc email kgomaa instabug com categories report a bug tags test hello rule got applied does not contain string rule works on convert to bug instabug app version session duration device google android sdk built for os level display xhdpi location giza egypt en point right point left iphone view hierarchy this bug was reported from com example app main mainfragment find its interactive view hierarchy with all its subviews here point right point left chart with downwards trend session profiler here is what the app was doing right before the bug was reported key value used memory gb used storage gb connectivity wifi battery unplugged orientation portrait find all the changes that happened in the parameters mentioned above during the last seconds before the bug was reported here point right point left bust in silhouette user info user attributes key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la key name key value bla bla bla la mag right logs user steps here are the last steps done by the user right before the bug was reported in activity com example app main mainactivity fragment com example app survey surveyfragment was paused in activity com example app main mainactivity fragment com example app survey surveyfragment was stopped in activity com example app main mainactivity fragment com example app main mainfragment was created in activity com example app main mainactivity fragment com example app main mainfragment was started in activity com example app main mainactivity fragment com example app main mainfragment was resumed in activity com example app main mainactivity fragment com example app survey surveyfragment was detached tap in sdk version of type androidx appcompat widget appcompattextview in com example app main mainactivity com example app main mainactivity was paused in activity com example app main mainactivity fragment com example app main mainfragment was paused tap in androidx constraintlayout widget constraintlayout in com example app main mainactivity find all the user steps done by the user throughout the session here point right point left console log here are the last console logs logged right before the bug was reported d ib basereportingpresenter receive a view hierarchy inspection action action value completed d ib basereportingpresenter receive a view hierarchy inspection action action value completed i com example ap waiting for a blocking gc instrumentation i com example ap explicit concurrent copying gc freed allocspace objects los objects free paused total i com example ap waitforgctocomplete blocked instrumentation on instrumentation for d leakcanary rescheduling check for retained objects in because found only retained objects while app visible d egl emulation eglmakecurrent ver tinfo d ib basereportingpresenter checkuseremailvalid non empty email d ib actionsorchestrator runaction d ib attachmentsutility encryptattachments find all the logged console logs throughout the session here point right point left warning looking for more details network log we are unable to capture your network requests automatically if you are using httpurlconnection or okhttp requests user events start capturing custom user events to send them along with each report instabug log start adding instabug logs to see them right inside each report you receive | 0 |
265,661 | 23,187,301,357 | IssuesEvent | 2022-08-01 09:29:30 | bitcoin/bitcoin | https://api.github.com/repos/bitcoin/bitcoin | closed | CI, tracing: run tracepoint interface tests in the CI | Feature Tests | The first tracepoint tests were merged in #24358. However, they are skipped in the CI. I've already done some experiments running them in the CI in https://github.com/bitcoin/bitcoin/issues/23296, however I haven't been successful with it yet. The main issue was the limited capabilities inside the CirrusCI docker container.
An option would be to ask CirrusCI for help, another would be to run this part in a VM, if it's not to much overhead. | 1.0 | CI, tracing: run tracepoint interface tests in the CI - The first tracepoint tests were merged in #24358. However, they are skipped in the CI. I've already done some experiments running them in the CI in https://github.com/bitcoin/bitcoin/issues/23296, however I haven't been successful with it yet. The main issue was the limited capabilities inside the CirrusCI docker container.
An option would be to ask CirrusCI for help, another would be to run this part in a VM, if it's not to much overhead. | non_priority | ci tracing run tracepoint interface tests in the ci the first tracepoint tests were merged in however they are skipped in the ci i ve already done some experiments running them in the ci in however i haven t been successful with it yet the main issue was the limited capabilities inside the cirrusci docker container an option would be to ask cirrusci for help another would be to run this part in a vm if it s not to much overhead | 0 |
118,538 | 17,594,176,860 | IssuesEvent | 2021-08-17 01:03:50 | jtimberlake/rl-bakery | https://api.github.com/repos/jtimberlake/rl-bakery | opened | CVE-2021-29517 (Medium) detected in tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2021-29517 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: rl-bakery/requirements.txt</p>
<p>Path to vulnerable library: rl-bakery/requirements.txt,rl-bakery</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. A malicious user could trigger a division by 0 in `Conv3D` implementation. The implementation(https://github.com/tensorflow/tensorflow/blob/42033603003965bffac51ae171b51801565e002d/tensorflow/core/kernels/conv_ops_3d.cc#L143-L145) does a modulo operation based on user controlled input. Thus, when `filter` has a 0 as the fifth element, this results in a division by 0. Additionally, if the shape of the two tensors is not valid, an Eigen assertion can be triggered, resulting in a program crash. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29517>CVE-2021-29517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-84mw-34w6-2q43">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-84mw-34w6-2q43</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0","packageFilePaths":["/requirements.txt","rl-bakery"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.5.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-29517","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. A malicious user could trigger a division by 0 in `Conv3D` implementation. The implementation(https://github.com/tensorflow/tensorflow/blob/42033603003965bffac51ae171b51801565e002d/tensorflow/core/kernels/conv_ops_3d.cc#L143-L145) does a modulo operation based on user controlled input. Thus, when `filter` has a 0 as the fifth element, this results in a division by 0. Additionally, if the shape of the two tensors is not valid, an Eigen assertion can be triggered, resulting in a program crash. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29517","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-29517 (Medium) detected in tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl - ## CVE-2021-29517 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: rl-bakery/requirements.txt</p>
<p>Path to vulnerable library: rl-bakery/requirements.txt,rl-bakery</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. A malicious user could trigger a division by 0 in `Conv3D` implementation. The implementation(https://github.com/tensorflow/tensorflow/blob/42033603003965bffac51ae171b51801565e002d/tensorflow/core/kernels/conv_ops_3d.cc#L143-L145) does a modulo operation based on user controlled input. Thus, when `filter` has a 0 as the fifth element, this results in a division by 0. Additionally, if the shape of the two tensors is not valid, an Eigen assertion can be triggered, resulting in a program crash. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29517>CVE-2021-29517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-84mw-34w6-2q43">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-84mw-34w6-2q43</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0","packageFilePaths":["/requirements.txt","rl-bakery"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.5.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-29517","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. A malicious user could trigger a division by 0 in `Conv3D` implementation. The implementation(https://github.com/tensorflow/tensorflow/blob/42033603003965bffac51ae171b51801565e002d/tensorflow/core/kernels/conv_ops_3d.cc#L143-L145) does a modulo operation based on user controlled input. Thus, when `filter` has a 0 as the fifth element, this results in a division by 0. Additionally, if the shape of the two tensors is not valid, an Eigen assertion can be triggered, resulting in a program crash. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29517","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file rl bakery requirements txt path to vulnerable library rl bakery requirements txt rl bakery dependency hierarchy x tensorflow whl vulnerable library found in base branch master vulnerability details tensorflow is an end to end open source platform for machine learning a malicious user could trigger a division by in implementation the implementation does a modulo operation based on user controlled input thus when filter has a as the fifth element this results in a division by additionally if the shape of the two tensors is not valid an eigen assertion can be triggered resulting in a program crash the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree tensorflow isminimumfixversionavailable true minimumfixversion tensorflow basebranches vulnerabilityidentifier cve vulnerabilitydetails tensorflow is an end to end open source platform for machine learning a malicious user could trigger a division by in implementation the implementation does a modulo operation based on user controlled input thus when filter has a as the fifth element this results in a division by additionally if the shape of the two tensors is not valid an eigen assertion can be triggered resulting in a program crash the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range vulnerabilityurl | 0 |
50,161 | 21,036,278,102 | IssuesEvent | 2022-03-31 08:09:46 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | [filebeat][windows-7] got some failed tests for test_symlink_rotated – filebeat.tests.system.test_harvester.Test | Filebeat flaky-test Stalled Team:Services windows-7 | ## Failed Test
* **Test Name:** ` test_symlink_rotated – filebeat.tests.system.test_harvester.Test`
* **Link:** https://github.com/elastic/beats/blob/f23f05a33fb570f7100a80d9ae31ab720ad96d1d/filebeat/tests/system/test_harvester.py#L566
* **Branch:** https://github.com/elastic/beats/pull/19803
* **Artifact Link:** https://beats-ci.elastic.co/blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/branches/PR-19803/runs/7/nodes/1911/log/?start=0
### Stacktrace
```
[2020-10-30T13:59:13.706Z] C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat>mage build unitTest
[2020-10-30T13:59:26.626Z] >> build: Building filebeat
[2020-10-30T14:00:34.798Z] >> go test: Unit Testing
[2020-10-30T14:01:43.449Z] SUMMARY:
[2020-10-30T14:01:43.449Z] Fail: 0
[2020-10-30T14:01:43.449Z] Skip: 5
[2020-10-30T14:01:43.449Z] Pass: 631
[2020-10-30T14:01:43.449Z] Packages: 26
[2020-10-30T14:01:43.449Z] Duration: 1m5.6816407s
[2020-10-30T14:01:43.449Z] Coverage Report: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-go-unit.html
[2020-10-30T14:01:43.449Z] JUnit Report: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-go-unit.xml
[2020-10-30T14:01:43.449Z] Output File: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-go-unit.out
[2020-10-30T14:01:43.449Z] >> go test: Unit Test Passed
[2020-10-30T14:01:53.676Z] >> python test: Unit Testing
[2020-10-30T14:02:09.135Z] ERROR: Could not install packages due to an EnvironmentError: [WinError 5] Access is denied: 'C:\\Users\\jenkins\\AppData\\Local\\Temp\\pip-uninstall-gc041_7j\\pip.exe'
[2020-10-30T14:02:09.135Z] Consider using the `--user` option or check the permissions.
[2020-10-30T14:02:09.135Z]
[2020-10-30T14:02:41.384Z] warn: failed to upgrade pip (ignoring): running "null\build\ve\windows\Scripts\pip install -U pip" failed with exit code 1============================= test session starts =============================
[2020-10-30T14:02:41.384Z] platform win32 -- Python 3.8.6, pytest-6.0.1, py-1.9.0, pluggy-0.13.1
[2020-10-30T14:02:41.384Z] rootdir: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats, configfile: pytest.ini
[2020-10-30T14:02:41.384Z] plugins: rerunfailures-9.0, timeout-1.3.4
[2020-10-30T14:02:41.384Z] timeout: 90.0s
[2020-10-30T14:02:41.384Z] timeout method: thread
[2020-10-30T14:02:41.384Z] timeout func_only: True
[2020-10-30T14:02:41.384Z] collected 321 items
[2020-10-30T14:02:41.384Z]
[2020-10-30T14:02:41.384Z] tests\system\test_autodiscover.py ss [ 0%]
[2020-10-30T14:02:43.639Z] tests\system\test_base.py ......ss [ 3%]
[2020-10-30T14:02:45.812Z] tests\system\test_cmd.py ... [ 4%]
[2020-10-30T14:02:47.059Z] tests\system\test_container.py .. [ 4%]
[2020-10-30T14:03:08.282Z] tests\system\test_crawler.py ......s.......... [ 9%]
[2020-10-30T14:03:08.854Z] tests\system\test_deprecated.py .. [ 10%]
[2020-10-30T14:03:11.154Z] tests\system\test_fields.py .... [ 11%]
[2020-10-30T14:03:13.081Z] tests\system\test_generate.py ... [ 12%]
[2020-10-30T14:03:38.076Z] tests\system\test_harvester.py ................F.... [ 19%]
[2020-10-30T14:03:39.109Z] tests\system\test_index_pattern.py .. [ 19%]
[2020-10-30T14:04:04.696Z] tests\system\test_input.py .........ss........... [ 26%]
[2020-10-30T14:04:10.888Z] tests\system\test_json.py .............. [ 31%]
[2020-10-30T14:04:11.820Z] tests\system\test_keystore.py .. [ 31%]
[2020-10-30T14:04:11.820Z] tests\system\test_load.py sss [ 32%]
[2020-10-30T14:04:12.078Z] tests\system\test_modules.py sssssssssssssssssssssssssssssssssssssssssss [ 46%]
[2020-10-30T14:04:12.336Z] ssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssss [ 68%]
[2020-10-30T14:04:12.336Z] sssssss [ 70%]
[2020-10-30T14:04:27.555Z] tests\system\test_multiline.py ......... [ 73%]
[2020-10-30T14:04:27.555Z] tests\system\test_pipeline.py s [ 73%]
[2020-10-30T14:04:33.636Z] tests\system\test_processors.py ............. [ 77%]
[2020-10-30T14:04:33.898Z] tests\system\test_publisher.py . [ 78%]
[2020-10-30T14:04:33.898Z] tests\system\test_redis.py s [ 78%]
[2020-10-30T14:05:00.935Z] tests\system\test_registrar.py sss........ssss......ss.. [ 86%]
[2020-10-30T14:05:00.935Z] tests\system\test_registrar_upgrade.py sssss [ 87%]
[2020-10-30T14:05:22.468Z] tests\system\test_reload_inputs.py ....... [ 90%]
[2020-10-30T14:05:31.083Z] tests\system\test_reload_modules.py ...s.. [ 91%]
[2020-10-30T14:05:31.083Z] tests\system\test_setup.py s [ 92%]
[2020-10-30T14:05:41.370Z] tests\system\test_shutdown.py ..s.. [ 93%]
[2020-10-30T14:05:42.529Z] tests\system\test_stdin.py ... [ 94%]
[2020-10-30T14:05:44.223Z] tests\system\test_syslog.py ...ss [ 96%]
[2020-10-30T14:05:46.005Z] tests\system\test_tcp.py ... [ 97%]
[2020-10-30T14:05:48.231Z] tests\system\test_tcp_tls.py ..... [ 98%]
[2020-10-30T14:05:48.488Z] tests\system\test_udp.py . [ 99%]
[2020-10-30T14:05:48.488Z] tests\system\test_unix.py sss [100%]
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] ================================== FAILURES ===================================
[2020-10-30T14:05:48.488Z] __________________________ Test.test_symlink_rotated __________________________
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] self = <test_harvester.Test testMethod=test_symlink_rotated>
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] def test_symlink_rotated(self):
[2020-10-30T14:05:48.488Z] """
[2020-10-30T14:05:48.488Z] Test what happens if symlink removed and points to a new file
[2020-10-30T14:05:48.488Z] """
[2020-10-30T14:05:48.488Z] self.render_config_template(
[2020-10-30T14:05:48.488Z] path=os.path.abspath(self.working_dir) + "/log/symlink.log",
[2020-10-30T14:05:48.488Z] symlinks="true",
[2020-10-30T14:05:48.488Z] close_removed="false",
[2020-10-30T14:05:48.488Z] clean_removed="false",
[2020-10-30T14:05:48.488Z] )
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] os.mkdir(self.working_dir + "/log/")
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.489Z] logfile1 = self.working_dir + "/log/test1.log"
[2020-10-30T14:05:48.489Z] logfile2 = self.working_dir + "/log/test2.log"
[2020-10-30T14:05:48.489Z] symlink = self.working_dir + "/log/symlink.log"
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] if os.name == "nt":
[2020-10-30T14:05:48.489Z] import win32file
[2020-10-30T14:05:48.489Z] win32file.CreateSymbolicLink(symlink, logfile1, 0)
[2020-10-30T14:05:48.489Z] else:
[2020-10-30T14:05:48.489Z] os.symlink(logfile1, symlink)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] with open(logfile1, 'a') as file:
[2020-10-30T14:05:48.489Z] file.write("Hello World1\n")
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] with open(logfile2, 'a') as file:
[2020-10-30T14:05:48.489Z] file.write("Hello World2\n")
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] filebeat = self.start_beat()
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] # Make sure some state is written
[2020-10-30T14:05:48.489Z] self.wait_until(
[2020-10-30T14:05:48.489Z] lambda: len(self.get_registry()) > 0,
[2020-10-30T14:05:48.489Z] max_timeout=10)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] # Make sure symlink is skipped
[2020-10-30T14:05:48.489Z] self.wait_until(
[2020-10-30T14:05:48.489Z] lambda: self.output_has(lines=1),
[2020-10-30T14:05:48.489Z] max_timeout=10)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] os.remove(symlink)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] if os.name == "nt":
[2020-10-30T14:05:48.489Z] import win32file
[2020-10-30T14:05:48.489Z] > win32file.CreateSymbolicLink(symlink, logfile2, 0)
[2020-10-30T14:05:48.489Z] E pywintypes.error: (5, 'CreateSymbolicLink', 'Access is denied.')
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] tests\system\test_harvester.py:611: error
[2020-10-30T14:05:48.489Z] - generated xml file: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-python-unit.xml -
[2020-10-30T14:05:48.489Z] ============================ slowest 20 durations =============================
[2020-10-30T14:05:48.489Z] 11.35s call filebeat/tests/system/test_harvester.py::Test::test_close_timeout
[2020-10-30T14:05:48.489Z] 6.03s call filebeat/tests/system/test_registrar.py::Test::test_restart_state
[2020-10-30T14:05:48.489Z] 4.81s call filebeat/tests/system/test_shutdown.py::Test::test_shutdown_wait_timeout
[2020-10-30T14:05:48.489Z] 4.43s call filebeat/tests/system/test_input.py::Test::test_harvester_limit
[2020-10-30T14:05:48.489Z] 4.42s call filebeat/tests/system/test_reload_inputs.py::Test::test_reload_add
[2020-10-30T14:05:48.489Z] 4.31s call filebeat/tests/system/test_crawler.py::Test::test_encodings
[2020-10-30T14:05:48.489Z] 4.20s call filebeat/tests/system/test_crawler.py::Test::test_multiple_appends
[2020-10-30T14:05:48.489Z] 3.72s call filebeat/tests/system/test_input.py::Test::test_rotating_close_inactive_low_write_rate
[2020-10-30T14:05:48.489Z] 3.65s call filebeat/tests/system/test_input.py::Test::test_close_inactive_file_rotation_and_removal2
[2020-10-30T14:05:48.489Z] 3.53s call filebeat/tests/system/test_multiline.py::Test::test_close_timeout_with_multiline
[2020-10-30T14:05:48.489Z] 3.45s call filebeat/tests/system/test_reload_inputs.py::Test::test_start_stop_replace
[2020-10-30T14:05:48.489Z] 3.44s call filebeat/tests/system/test_reload_inputs.py::Test::test_reload_same_input
[2020-10-30T14:05:48.489Z] 3.44s call filebeat/tests/system/test_reload_inputs.py::Test::test_reload_same_config
[2020-10-30T14:05:48.489Z] 3.34s call filebeat/tests/system/test_reload_modules.py::Test::test_start_stop
[2020-10-30T14:05:48.489Z] 3.33s call filebeat/tests/system/test_reload_inputs.py::Test::test_start_stop
[2020-10-30T14:05:48.489Z] 3.33s call filebeat/tests/system/test_registrar.py::Test::test_state_after_rotation_ignore_older
[2020-10-30T14:05:48.489Z] 3.32s call filebeat/tests/system/test_registrar.py::Test::test_state_after_rotation
[2020-10-30T14:05:48.489Z] 3.16s call filebeat/tests/system/test_shutdown.py::Test::test_shutdown
[2020-10-30T14:05:48.489Z] 2.54s call filebeat/tests/system/test_multiline.py::Test::test_timeout
[2020-10-30T14:05:48.489Z] 2.35s call filebeat/tests/system/test_registrar.py::Test::test_ignore_older_state_clean_inactive
[2020-10-30T14:05:48.489Z] =========================== short test summary info ===========================
[2020-10-30T14:05:48.489Z] FAILED tests\system\test_harvester.py::Test::test_symlink_rotated - pywintype...
[2020-10-30T14:05:48.489Z] =========== 1 failed, 164 passed, 156 skipped in 191.52s (0:03:11) ============
[2020-10-30T14:05:48.750Z] >> python test: Unit Testing Complete
[2020-10-30T14:05:48.750Z] Error: running "null\build\ve\windows\Scripts\pytest.exe --timeout=90 --durations=20 --junit-xml=build/TEST-python-unit.xml tests\system\test_autodiscover.py tests\system\test_base.py tests\system\test_cmd.py tests\system\test_container.py tests\system\test_crawler.py tests\system\test_deprecated.py tests\system\test_fields.py tests\system\test_generate.py tests\system\test_harvester.py tests\system\test_index_pattern.py tests\system\test_input.py tests\system\test_json.py tests\system\test_keystore.py tests\system\test_load.py tests\system\test_modules.py tests\system\test_multiline.py tests\system\test_pipeline.py tests\system\test_processors.py tests\system\test_publisher.py tests\system\test_redis.py tests\system\test_registrar.py tests\system\test_registrar_upgrade.py tests\system\test_reload_inputs.py tests\system\test_reload_modules.py tests\system\test_setup.py tests\system\test_shutdown.py tests\system\test_stdin.py tests\system\test_syslog.py tests\system\test_tcp.py tests\system\test_tcp_tls.py tests\system\test_udp.py tests\system\test_unix.py" failed with exit code 1
script returned exit code 1[2020-10-30T14:05:49.116Z]
``` | 1.0 | [filebeat][windows-7] got some failed tests for test_symlink_rotated – filebeat.tests.system.test_harvester.Test - ## Failed Test
* **Test Name:** ` test_symlink_rotated – filebeat.tests.system.test_harvester.Test`
* **Link:** https://github.com/elastic/beats/blob/f23f05a33fb570f7100a80d9ae31ab720ad96d1d/filebeat/tests/system/test_harvester.py#L566
* **Branch:** https://github.com/elastic/beats/pull/19803
* **Artifact Link:** https://beats-ci.elastic.co/blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/branches/PR-19803/runs/7/nodes/1911/log/?start=0
### Stacktrace
```
[2020-10-30T13:59:13.706Z] C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat>mage build unitTest
[2020-10-30T13:59:26.626Z] >> build: Building filebeat
[2020-10-30T14:00:34.798Z] >> go test: Unit Testing
[2020-10-30T14:01:43.449Z] SUMMARY:
[2020-10-30T14:01:43.449Z] Fail: 0
[2020-10-30T14:01:43.449Z] Skip: 5
[2020-10-30T14:01:43.449Z] Pass: 631
[2020-10-30T14:01:43.449Z] Packages: 26
[2020-10-30T14:01:43.449Z] Duration: 1m5.6816407s
[2020-10-30T14:01:43.449Z] Coverage Report: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-go-unit.html
[2020-10-30T14:01:43.449Z] JUnit Report: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-go-unit.xml
[2020-10-30T14:01:43.449Z] Output File: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-go-unit.out
[2020-10-30T14:01:43.449Z] >> go test: Unit Test Passed
[2020-10-30T14:01:53.676Z] >> python test: Unit Testing
[2020-10-30T14:02:09.135Z] ERROR: Could not install packages due to an EnvironmentError: [WinError 5] Access is denied: 'C:\\Users\\jenkins\\AppData\\Local\\Temp\\pip-uninstall-gc041_7j\\pip.exe'
[2020-10-30T14:02:09.135Z] Consider using the `--user` option or check the permissions.
[2020-10-30T14:02:09.135Z]
[2020-10-30T14:02:41.384Z] warn: failed to upgrade pip (ignoring): running "null\build\ve\windows\Scripts\pip install -U pip" failed with exit code 1============================= test session starts =============================
[2020-10-30T14:02:41.384Z] platform win32 -- Python 3.8.6, pytest-6.0.1, py-1.9.0, pluggy-0.13.1
[2020-10-30T14:02:41.384Z] rootdir: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats, configfile: pytest.ini
[2020-10-30T14:02:41.384Z] plugins: rerunfailures-9.0, timeout-1.3.4
[2020-10-30T14:02:41.384Z] timeout: 90.0s
[2020-10-30T14:02:41.384Z] timeout method: thread
[2020-10-30T14:02:41.384Z] timeout func_only: True
[2020-10-30T14:02:41.384Z] collected 321 items
[2020-10-30T14:02:41.384Z]
[2020-10-30T14:02:41.384Z] tests\system\test_autodiscover.py ss [ 0%]
[2020-10-30T14:02:43.639Z] tests\system\test_base.py ......ss [ 3%]
[2020-10-30T14:02:45.812Z] tests\system\test_cmd.py ... [ 4%]
[2020-10-30T14:02:47.059Z] tests\system\test_container.py .. [ 4%]
[2020-10-30T14:03:08.282Z] tests\system\test_crawler.py ......s.......... [ 9%]
[2020-10-30T14:03:08.854Z] tests\system\test_deprecated.py .. [ 10%]
[2020-10-30T14:03:11.154Z] tests\system\test_fields.py .... [ 11%]
[2020-10-30T14:03:13.081Z] tests\system\test_generate.py ... [ 12%]
[2020-10-30T14:03:38.076Z] tests\system\test_harvester.py ................F.... [ 19%]
[2020-10-30T14:03:39.109Z] tests\system\test_index_pattern.py .. [ 19%]
[2020-10-30T14:04:04.696Z] tests\system\test_input.py .........ss........... [ 26%]
[2020-10-30T14:04:10.888Z] tests\system\test_json.py .............. [ 31%]
[2020-10-30T14:04:11.820Z] tests\system\test_keystore.py .. [ 31%]
[2020-10-30T14:04:11.820Z] tests\system\test_load.py sss [ 32%]
[2020-10-30T14:04:12.078Z] tests\system\test_modules.py sssssssssssssssssssssssssssssssssssssssssss [ 46%]
[2020-10-30T14:04:12.336Z] ssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssss [ 68%]
[2020-10-30T14:04:12.336Z] sssssss [ 70%]
[2020-10-30T14:04:27.555Z] tests\system\test_multiline.py ......... [ 73%]
[2020-10-30T14:04:27.555Z] tests\system\test_pipeline.py s [ 73%]
[2020-10-30T14:04:33.636Z] tests\system\test_processors.py ............. [ 77%]
[2020-10-30T14:04:33.898Z] tests\system\test_publisher.py . [ 78%]
[2020-10-30T14:04:33.898Z] tests\system\test_redis.py s [ 78%]
[2020-10-30T14:05:00.935Z] tests\system\test_registrar.py sss........ssss......ss.. [ 86%]
[2020-10-30T14:05:00.935Z] tests\system\test_registrar_upgrade.py sssss [ 87%]
[2020-10-30T14:05:22.468Z] tests\system\test_reload_inputs.py ....... [ 90%]
[2020-10-30T14:05:31.083Z] tests\system\test_reload_modules.py ...s.. [ 91%]
[2020-10-30T14:05:31.083Z] tests\system\test_setup.py s [ 92%]
[2020-10-30T14:05:41.370Z] tests\system\test_shutdown.py ..s.. [ 93%]
[2020-10-30T14:05:42.529Z] tests\system\test_stdin.py ... [ 94%]
[2020-10-30T14:05:44.223Z] tests\system\test_syslog.py ...ss [ 96%]
[2020-10-30T14:05:46.005Z] tests\system\test_tcp.py ... [ 97%]
[2020-10-30T14:05:48.231Z] tests\system\test_tcp_tls.py ..... [ 98%]
[2020-10-30T14:05:48.488Z] tests\system\test_udp.py . [ 99%]
[2020-10-30T14:05:48.488Z] tests\system\test_unix.py sss [100%]
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] ================================== FAILURES ===================================
[2020-10-30T14:05:48.488Z] __________________________ Test.test_symlink_rotated __________________________
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] self = <test_harvester.Test testMethod=test_symlink_rotated>
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] def test_symlink_rotated(self):
[2020-10-30T14:05:48.488Z] """
[2020-10-30T14:05:48.488Z] Test what happens if symlink removed and points to a new file
[2020-10-30T14:05:48.488Z] """
[2020-10-30T14:05:48.488Z] self.render_config_template(
[2020-10-30T14:05:48.488Z] path=os.path.abspath(self.working_dir) + "/log/symlink.log",
[2020-10-30T14:05:48.488Z] symlinks="true",
[2020-10-30T14:05:48.488Z] close_removed="false",
[2020-10-30T14:05:48.488Z] clean_removed="false",
[2020-10-30T14:05:48.488Z] )
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.488Z] os.mkdir(self.working_dir + "/log/")
[2020-10-30T14:05:48.488Z]
[2020-10-30T14:05:48.489Z] logfile1 = self.working_dir + "/log/test1.log"
[2020-10-30T14:05:48.489Z] logfile2 = self.working_dir + "/log/test2.log"
[2020-10-30T14:05:48.489Z] symlink = self.working_dir + "/log/symlink.log"
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] if os.name == "nt":
[2020-10-30T14:05:48.489Z] import win32file
[2020-10-30T14:05:48.489Z] win32file.CreateSymbolicLink(symlink, logfile1, 0)
[2020-10-30T14:05:48.489Z] else:
[2020-10-30T14:05:48.489Z] os.symlink(logfile1, symlink)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] with open(logfile1, 'a') as file:
[2020-10-30T14:05:48.489Z] file.write("Hello World1\n")
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] with open(logfile2, 'a') as file:
[2020-10-30T14:05:48.489Z] file.write("Hello World2\n")
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] filebeat = self.start_beat()
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] # Make sure some state is written
[2020-10-30T14:05:48.489Z] self.wait_until(
[2020-10-30T14:05:48.489Z] lambda: len(self.get_registry()) > 0,
[2020-10-30T14:05:48.489Z] max_timeout=10)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] # Make sure symlink is skipped
[2020-10-30T14:05:48.489Z] self.wait_until(
[2020-10-30T14:05:48.489Z] lambda: self.output_has(lines=1),
[2020-10-30T14:05:48.489Z] max_timeout=10)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] os.remove(symlink)
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] if os.name == "nt":
[2020-10-30T14:05:48.489Z] import win32file
[2020-10-30T14:05:48.489Z] > win32file.CreateSymbolicLink(symlink, logfile2, 0)
[2020-10-30T14:05:48.489Z] E pywintypes.error: (5, 'CreateSymbolicLink', 'Access is denied.')
[2020-10-30T14:05:48.489Z]
[2020-10-30T14:05:48.489Z] tests\system\test_harvester.py:611: error
[2020-10-30T14:05:48.489Z] - generated xml file: C:\Users\jenkins\workspace\Beats_beats_PR-19803\src\github.com\elastic\beats\filebeat\build\TEST-python-unit.xml -
[2020-10-30T14:05:48.489Z] ============================ slowest 20 durations =============================
[2020-10-30T14:05:48.489Z] 11.35s call filebeat/tests/system/test_harvester.py::Test::test_close_timeout
[2020-10-30T14:05:48.489Z] 6.03s call filebeat/tests/system/test_registrar.py::Test::test_restart_state
[2020-10-30T14:05:48.489Z] 4.81s call filebeat/tests/system/test_shutdown.py::Test::test_shutdown_wait_timeout
[2020-10-30T14:05:48.489Z] 4.43s call filebeat/tests/system/test_input.py::Test::test_harvester_limit
[2020-10-30T14:05:48.489Z] 4.42s call filebeat/tests/system/test_reload_inputs.py::Test::test_reload_add
[2020-10-30T14:05:48.489Z] 4.31s call filebeat/tests/system/test_crawler.py::Test::test_encodings
[2020-10-30T14:05:48.489Z] 4.20s call filebeat/tests/system/test_crawler.py::Test::test_multiple_appends
[2020-10-30T14:05:48.489Z] 3.72s call filebeat/tests/system/test_input.py::Test::test_rotating_close_inactive_low_write_rate
[2020-10-30T14:05:48.489Z] 3.65s call filebeat/tests/system/test_input.py::Test::test_close_inactive_file_rotation_and_removal2
[2020-10-30T14:05:48.489Z] 3.53s call filebeat/tests/system/test_multiline.py::Test::test_close_timeout_with_multiline
[2020-10-30T14:05:48.489Z] 3.45s call filebeat/tests/system/test_reload_inputs.py::Test::test_start_stop_replace
[2020-10-30T14:05:48.489Z] 3.44s call filebeat/tests/system/test_reload_inputs.py::Test::test_reload_same_input
[2020-10-30T14:05:48.489Z] 3.44s call filebeat/tests/system/test_reload_inputs.py::Test::test_reload_same_config
[2020-10-30T14:05:48.489Z] 3.34s call filebeat/tests/system/test_reload_modules.py::Test::test_start_stop
[2020-10-30T14:05:48.489Z] 3.33s call filebeat/tests/system/test_reload_inputs.py::Test::test_start_stop
[2020-10-30T14:05:48.489Z] 3.33s call filebeat/tests/system/test_registrar.py::Test::test_state_after_rotation_ignore_older
[2020-10-30T14:05:48.489Z] 3.32s call filebeat/tests/system/test_registrar.py::Test::test_state_after_rotation
[2020-10-30T14:05:48.489Z] 3.16s call filebeat/tests/system/test_shutdown.py::Test::test_shutdown
[2020-10-30T14:05:48.489Z] 2.54s call filebeat/tests/system/test_multiline.py::Test::test_timeout
[2020-10-30T14:05:48.489Z] 2.35s call filebeat/tests/system/test_registrar.py::Test::test_ignore_older_state_clean_inactive
[2020-10-30T14:05:48.489Z] =========================== short test summary info ===========================
[2020-10-30T14:05:48.489Z] FAILED tests\system\test_harvester.py::Test::test_symlink_rotated - pywintype...
[2020-10-30T14:05:48.489Z] =========== 1 failed, 164 passed, 156 skipped in 191.52s (0:03:11) ============
[2020-10-30T14:05:48.750Z] >> python test: Unit Testing Complete
[2020-10-30T14:05:48.750Z] Error: running "null\build\ve\windows\Scripts\pytest.exe --timeout=90 --durations=20 --junit-xml=build/TEST-python-unit.xml tests\system\test_autodiscover.py tests\system\test_base.py tests\system\test_cmd.py tests\system\test_container.py tests\system\test_crawler.py tests\system\test_deprecated.py tests\system\test_fields.py tests\system\test_generate.py tests\system\test_harvester.py tests\system\test_index_pattern.py tests\system\test_input.py tests\system\test_json.py tests\system\test_keystore.py tests\system\test_load.py tests\system\test_modules.py tests\system\test_multiline.py tests\system\test_pipeline.py tests\system\test_processors.py tests\system\test_publisher.py tests\system\test_redis.py tests\system\test_registrar.py tests\system\test_registrar_upgrade.py tests\system\test_reload_inputs.py tests\system\test_reload_modules.py tests\system\test_setup.py tests\system\test_shutdown.py tests\system\test_stdin.py tests\system\test_syslog.py tests\system\test_tcp.py tests\system\test_tcp_tls.py tests\system\test_udp.py tests\system\test_unix.py" failed with exit code 1
script returned exit code 1[2020-10-30T14:05:49.116Z]
``` | non_priority | got some failed tests for test symlink rotated – filebeat tests system test harvester test failed test test name test symlink rotated – filebeat tests system test harvester test link branch artifact link stacktrace c users jenkins workspace beats beats pr src github com elastic beats filebeat mage build unittest build building filebeat go test unit testing summary fail skip pass packages duration coverage report c users jenkins workspace beats beats pr src github com elastic beats filebeat build test go unit html junit report c users jenkins workspace beats beats pr src github com elastic beats filebeat build test go unit xml output file c users jenkins workspace beats beats pr src github com elastic beats filebeat build test go unit out go test unit test passed python test unit testing error could not install packages due to an environmenterror access is denied c users jenkins appdata local temp pip uninstall pip exe consider using the user option or check the permissions warn failed to upgrade pip ignoring running null build ve windows scripts pip install u pip failed with exit code test session starts platform python pytest py pluggy rootdir c users jenkins workspace beats beats pr src github com elastic beats configfile pytest ini plugins rerunfailures timeout timeout timeout method thread timeout func only true collected items tests system test autodiscover py ss tests system test base py ss tests system test cmd py tests system test container py tests system test crawler py s tests system test deprecated py tests system test fields py tests system test generate py tests system test harvester py f tests system test index pattern py tests system test input py ss tests system test json py tests system test keystore py tests system test load py sss tests system test modules py sssssssssssssssssssssssssssssssssssssssssss ssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssss sssssss tests system test multiline py tests system test pipeline py s tests system test processors py tests system test publisher py tests system test redis py s tests system test registrar py sss ssss ss tests system test registrar upgrade py sssss tests system test reload inputs py tests system test reload modules py s tests system test setup py s tests system test shutdown py s tests system test stdin py tests system test syslog py ss tests system test tcp py tests system test tcp tls py tests system test udp py tests system test unix py sss failures test test symlink rotated self def test symlink rotated self test what happens if symlink removed and points to a new file self render config template path os path abspath self working dir log symlink log symlinks true close removed false clean removed false os mkdir self working dir log self working dir log log self working dir log log symlink self working dir log symlink log if os name nt import createsymboliclink symlink else os symlink symlink with open a as file file write hello n with open a as file file write hello n filebeat self start beat make sure some state is written self wait until lambda len self get registry max timeout make sure symlink is skipped self wait until lambda self output has lines max timeout os remove symlink if os name nt import createsymboliclink symlink e pywintypes error createsymboliclink access is denied tests system test harvester py error generated xml file c users jenkins workspace beats beats pr src github com elastic beats filebeat build test python unit xml slowest durations call filebeat tests system test harvester py test test close timeout call filebeat tests system test registrar py test test restart state call filebeat tests system test shutdown py test test shutdown wait timeout call filebeat tests system test input py test test harvester limit call filebeat tests system test reload inputs py test test reload add call filebeat tests system test crawler py test test encodings call filebeat tests system test crawler py test test multiple appends call filebeat tests system test input py test test rotating close inactive low write rate call filebeat tests system test input py test test close inactive file rotation and call filebeat tests system test multiline py test test close timeout with multiline call filebeat tests system test reload inputs py test test start stop replace call filebeat tests system test reload inputs py test test reload same input call filebeat tests system test reload inputs py test test reload same config call filebeat tests system test reload modules py test test start stop call filebeat tests system test reload inputs py test test start stop call filebeat tests system test registrar py test test state after rotation ignore older call filebeat tests system test registrar py test test state after rotation call filebeat tests system test shutdown py test test shutdown call filebeat tests system test multiline py test test timeout call filebeat tests system test registrar py test test ignore older state clean inactive short test summary info failed tests system test harvester py test test symlink rotated pywintype failed passed skipped in python test unit testing complete error running null build ve windows scripts pytest exe timeout durations junit xml build test python unit xml tests system test autodiscover py tests system test base py tests system test cmd py tests system test container py tests system test crawler py tests system test deprecated py tests system test fields py tests system test generate py tests system test harvester py tests system test index pattern py tests system test input py tests system test json py tests system test keystore py tests system test load py tests system test modules py tests system test multiline py tests system test pipeline py tests system test processors py tests system test publisher py tests system test redis py tests system test registrar py tests system test registrar upgrade py tests system test reload inputs py tests system test reload modules py tests system test setup py tests system test shutdown py tests system test stdin py tests system test syslog py tests system test tcp py tests system test tcp tls py tests system test udp py tests system test unix py failed with exit code script returned exit code | 0 |
208,718 | 15,930,705,295 | IssuesEvent | 2021-04-14 01:32:50 | bean-pod/switchboard | https://api.github.com/repos/bean-pod/switchboard | closed | Acceptance test for #50 As a user, I want to provide custom configuration to my sender devices | acceptance test | Steps:
- Start the frontend and backend
- Start the sample sender and sample receiver
- Select the webcam on the sample sender
- Click start on both sample apps
- Start a stream between the two devices, from channel 1 of the sender to channer 1 of the receiver
- A stream should appear at our default resolution of 1280x720 and the default FPS of 7.5
- Delete the stream
- Close the sample sender and receiver
- Open the device details page of the sender
- Click on "Upload" in the configuration section
- Upload a file with the following contents
```
{
"camera": {
"video_size": "800x600",
"framerate": "30"
}
}
```
- Open the sample sender and select the webcam streaming. Open the sample receiver.
- Click start on both devices
- Open the create stream page and create a stream between channel 1 of both devices
- A stream should appear at resolution of 800x600 and 30 fps | 1.0 | Acceptance test for #50 As a user, I want to provide custom configuration to my sender devices - Steps:
- Start the frontend and backend
- Start the sample sender and sample receiver
- Select the webcam on the sample sender
- Click start on both sample apps
- Start a stream between the two devices, from channel 1 of the sender to channer 1 of the receiver
- A stream should appear at our default resolution of 1280x720 and the default FPS of 7.5
- Delete the stream
- Close the sample sender and receiver
- Open the device details page of the sender
- Click on "Upload" in the configuration section
- Upload a file with the following contents
```
{
"camera": {
"video_size": "800x600",
"framerate": "30"
}
}
```
- Open the sample sender and select the webcam streaming. Open the sample receiver.
- Click start on both devices
- Open the create stream page and create a stream between channel 1 of both devices
- A stream should appear at resolution of 800x600 and 30 fps | non_priority | acceptance test for as a user i want to provide custom configuration to my sender devices steps start the frontend and backend start the sample sender and sample receiver select the webcam on the sample sender click start on both sample apps start a stream between the two devices from channel of the sender to channer of the receiver a stream should appear at our default resolution of and the default fps of delete the stream close the sample sender and receiver open the device details page of the sender click on upload in the configuration section upload a file with the following contents camera video size framerate open the sample sender and select the webcam streaming open the sample receiver click start on both devices open the create stream page and create a stream between channel of both devices a stream should appear at resolution of and fps | 0 |
273,887 | 20,819,403,678 | IssuesEvent | 2022-03-18 13:57:56 | Lesser-cuckoo/qintodo-native-cuckoo | https://api.github.com/repos/Lesser-cuckoo/qintodo-native-cuckoo | closed | READMEの作成 | documentation | ## なぜこの変更が必要なのか(必須)
- 開発環境の構築方法やデバッグ方法を共有するため
- ブランチの運用ルールなどを共有するため
## どうやって実装するのか(必須)
- Next.js版をベースに適宜変更
-
## 作業が競合しそうな issue
-
| 1.0 | READMEの作成 - ## なぜこの変更が必要なのか(必須)
- 開発環境の構築方法やデバッグ方法を共有するため
- ブランチの運用ルールなどを共有するため
## どうやって実装するのか(必須)
- Next.js版をベースに適宜変更
-
## 作業が競合しそうな issue
-
| non_priority | readmeの作成 なぜこの変更が必要なのか(必須) 開発環境の構築方法やデバッグ方法を共有するため ブランチの運用ルールなどを共有するため どうやって実装するのか(必須) next js版をベースに適宜変更 作業が競合しそうな issue | 0 |
12,968 | 8,053,521,205 | IssuesEvent | 2018-08-01 23:29:05 | xamarin/xamarin-android | https://api.github.com/repos/xamarin/xamarin-android | closed | Improve performance of JniTypeManager:TryRegisterNativeMembers | Area: App Runtime Area: Performance | `JniTypeManager:TryRegisterNativeMembers` uses a lot of reflection and is very slow.
Looks like we might save over 100ms just for the XA template. It take us 140ms to just look for registration methods, even when we don't find any.
140 0 4 Java.Interop.JniRuntime/JniTypeManager:TryRegisterNativeMembers (Java.Interop.JniType,System.Type,string)
122 0 543 System.Attribute:GetCustomAttribute (System.Reflection.MemberInfo,System.Type,bool) | True | Improve performance of JniTypeManager:TryRegisterNativeMembers - `JniTypeManager:TryRegisterNativeMembers` uses a lot of reflection and is very slow.
Looks like we might save over 100ms just for the XA template. It take us 140ms to just look for registration methods, even when we don't find any.
140 0 4 Java.Interop.JniRuntime/JniTypeManager:TryRegisterNativeMembers (Java.Interop.JniType,System.Type,string)
122 0 543 System.Attribute:GetCustomAttribute (System.Reflection.MemberInfo,System.Type,bool) | non_priority | improve performance of jnitypemanager tryregisternativemembers jnitypemanager tryregisternativemembers uses a lot of reflection and is very slow looks like we might save over just for the xa template it take us to just look for registration methods even when we don t find any java interop jniruntime jnitypemanager tryregisternativemembers java interop jnitype system type string system attribute getcustomattribute system reflection memberinfo system type bool | 0 |
288,834 | 24,940,116,316 | IssuesEvent | 2022-10-31 18:11:50 | elyra-ai/elyra | https://api.github.com/repos/elyra-ai/elyra | opened | Investigate CI tests execution order | component:test kind:investigative component:script-debugger | **Describe the issue**
Follow up issue to problems found in #2971 with respect to the execution order of integration test files.
In the PR above a new test file was created containing tests for the script debugger, although all tests would fail remotely, unless the new test file runs first.
Investigate which test file might be affecting the script debugger tests to fail remotely and why.
**Expected behavior**
CI tests should run independent of each other.
Make sure the test environment is always cleaned up and reset at the end of tests.
The integration test files should be able to run in alphabetical order as expected.
**Context information**
- Elyra version: v3.13.0-dev
- Installation source: src
- Operating system: macos | 1.0 | Investigate CI tests execution order - **Describe the issue**
Follow up issue to problems found in #2971 with respect to the execution order of integration test files.
In the PR above a new test file was created containing tests for the script debugger, although all tests would fail remotely, unless the new test file runs first.
Investigate which test file might be affecting the script debugger tests to fail remotely and why.
**Expected behavior**
CI tests should run independent of each other.
Make sure the test environment is always cleaned up and reset at the end of tests.
The integration test files should be able to run in alphabetical order as expected.
**Context information**
- Elyra version: v3.13.0-dev
- Installation source: src
- Operating system: macos | non_priority | investigate ci tests execution order describe the issue follow up issue to problems found in with respect to the execution order of integration test files in the pr above a new test file was created containing tests for the script debugger although all tests would fail remotely unless the new test file runs first investigate which test file might be affecting the script debugger tests to fail remotely and why expected behavior ci tests should run independent of each other make sure the test environment is always cleaned up and reset at the end of tests the integration test files should be able to run in alphabetical order as expected context information elyra version dev installation source src operating system macos | 0 |
27,588 | 21,947,719,645 | IssuesEvent | 2022-05-24 03:43:04 | mne-tools/mne-nirs | https://api.github.com/repos/mne-tools/mne-nirs | closed | Rework tests to be more unit like | infrastructure | Currently the tests are a mix of system tests and unit tests. I should use the example scripts as the system tests, and make sure the unit tests are small and fast. | 1.0 | Rework tests to be more unit like - Currently the tests are a mix of system tests and unit tests. I should use the example scripts as the system tests, and make sure the unit tests are small and fast. | non_priority | rework tests to be more unit like currently the tests are a mix of system tests and unit tests i should use the example scripts as the system tests and make sure the unit tests are small and fast | 0 |
310,741 | 26,739,358,277 | IssuesEvent | 2023-01-30 11:50:33 | galaxyproject/training-material | https://api.github.com/repos/galaxyproject/training-material | closed | Galaxy 101 - display in UCSC from history item | bug galaxy-interface galaxy-release-testing | This can no longer be done in the history in 23.0:
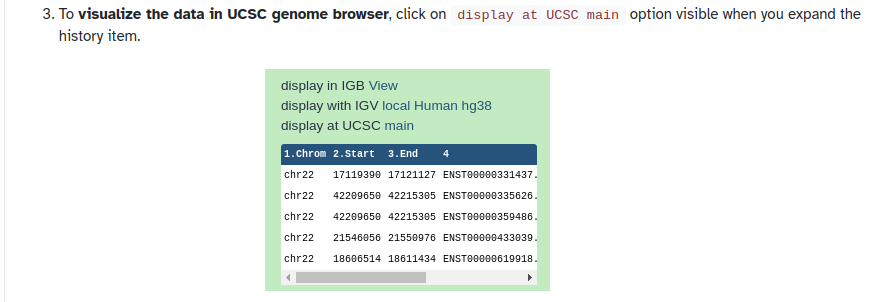
But it can be done by clicking the "visualize" icon for a dataset:
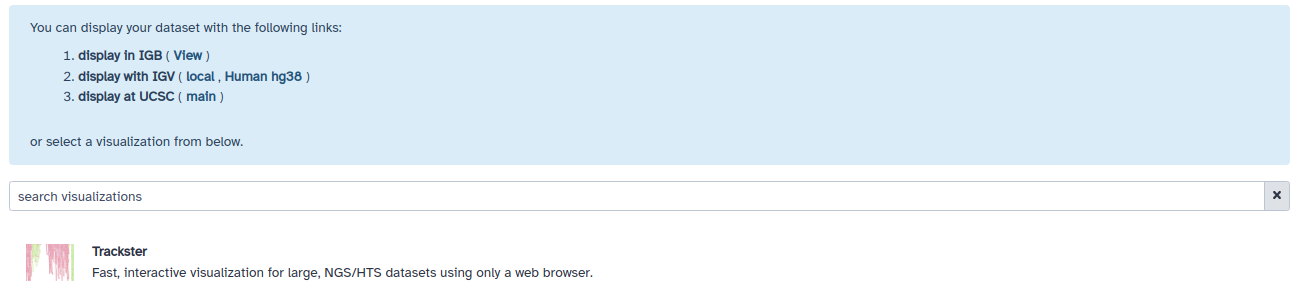
Not sure if this was intentionally left out (and the tutorial needs updating) or it's a bug in 23.0? | 1.0 | Galaxy 101 - display in UCSC from history item - This can no longer be done in the history in 23.0:
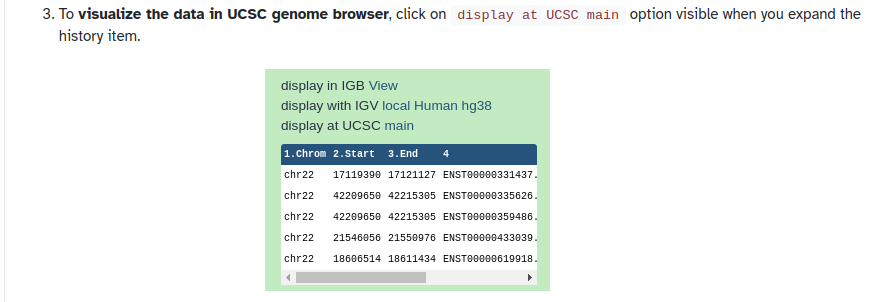
But it can be done by clicking the "visualize" icon for a dataset:
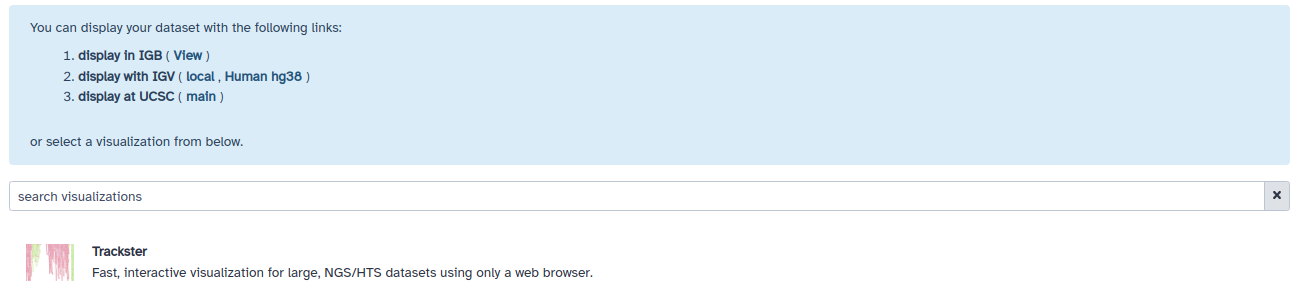
Not sure if this was intentionally left out (and the tutorial needs updating) or it's a bug in 23.0? | non_priority | galaxy display in ucsc from history item this can no longer be done in the history in but it can be done by clicking the visualize icon for a dataset not sure if this was intentionally left out and the tutorial needs updating or it s a bug in | 0 |
199,652 | 15,052,730,362 | IssuesEvent | 2021-02-03 15:30:10 | sillsdev/TheCombine | https://api.github.com/repos/sillsdev/TheCombine | opened | Console error during `npm run test-frontend -- VernDialog` | component: DataEntry test | Three instance of:
```
console.error
Material-UI: Unable to set focus to a ListItem whose component has not been rendered.
at node_modules/@material-ui/core/ListItem/ListItem.js:168:17
at commitHookEffectListMount (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:10345:26)
at commitLifeCycles (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:10401:9)
at commitLayoutEffects (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:13295:7)
at HTMLUnknownElement.callCallback (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:9972:14)
at HTMLUnknownElement.callTheUserObjectsOperation (node_modules/jsdom/lib/jsdom/living/generated/EventListener.js:26:30)
at innerInvokeEventListeners (node_modules/jsdom/lib/jsdom/living/events/EventTarget-impl.js:318:25)
at invokeEventListeners (node_modules/jsdom/lib/jsdom/living/events/EventTarget-impl.js:274:3)
``` | 1.0 | Console error during `npm run test-frontend -- VernDialog` - Three instance of:
```
console.error
Material-UI: Unable to set focus to a ListItem whose component has not been rendered.
at node_modules/@material-ui/core/ListItem/ListItem.js:168:17
at commitHookEffectListMount (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:10345:26)
at commitLifeCycles (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:10401:9)
at commitLayoutEffects (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:13295:7)
at HTMLUnknownElement.callCallback (node_modules/react-test-renderer/cjs/react-test-renderer.development.js:9972:14)
at HTMLUnknownElement.callTheUserObjectsOperation (node_modules/jsdom/lib/jsdom/living/generated/EventListener.js:26:30)
at innerInvokeEventListeners (node_modules/jsdom/lib/jsdom/living/events/EventTarget-impl.js:318:25)
at invokeEventListeners (node_modules/jsdom/lib/jsdom/living/events/EventTarget-impl.js:274:3)
``` | non_priority | console error during npm run test frontend verndialog three instance of console error material ui unable to set focus to a listitem whose component has not been rendered at node modules material ui core listitem listitem js at commithookeffectlistmount node modules react test renderer cjs react test renderer development js at commitlifecycles node modules react test renderer cjs react test renderer development js at commitlayouteffects node modules react test renderer cjs react test renderer development js at htmlunknownelement callcallback node modules react test renderer cjs react test renderer development js at htmlunknownelement calltheuserobjectsoperation node modules jsdom lib jsdom living generated eventlistener js at innerinvokeeventlisteners node modules jsdom lib jsdom living events eventtarget impl js at invokeeventlisteners node modules jsdom lib jsdom living events eventtarget impl js | 0 |
49,038 | 20,426,018,185 | IssuesEvent | 2022-02-24 04:02:08 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | opened | Use GitHib issue forms | Language Service internal | https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/configuring-issue-templates-for-your-repository#creating-issue-forms
Perhaps with separate fields for:
* Log output - Enable `"C_Cpp.loggingLevel": "Debug"` and provide the contents of the C/C++ output channel leading up to the issue.
* Log Diagnostics output - Run `C/C++: Log Diagnostics` with the source file open that is reproducing the issue.
* 'c_cpp_properties.json` contents
* Any explicitly set `C_cpp` settings
* Call Stacks - If the issue is a crash or hang, how to attach a debugger to cpptools or cpptools-srv to get call stacks.
| 1.0 | Use GitHib issue forms - https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/configuring-issue-templates-for-your-repository#creating-issue-forms
Perhaps with separate fields for:
* Log output - Enable `"C_Cpp.loggingLevel": "Debug"` and provide the contents of the C/C++ output channel leading up to the issue.
* Log Diagnostics output - Run `C/C++: Log Diagnostics` with the source file open that is reproducing the issue.
* 'c_cpp_properties.json` contents
* Any explicitly set `C_cpp` settings
* Call Stacks - If the issue is a crash or hang, how to attach a debugger to cpptools or cpptools-srv to get call stacks.
| non_priority | use githib issue forms perhaps with separate fields for log output enable c cpp logginglevel debug and provide the contents of the c c output channel leading up to the issue log diagnostics output run c c log diagnostics with the source file open that is reproducing the issue c cpp properties json contents any explicitly set c cpp settings call stacks if the issue is a crash or hang how to attach a debugger to cpptools or cpptools srv to get call stacks | 0 |
204,756 | 23,272,770,553 | IssuesEvent | 2022-08-05 02:15:43 | renfei/renfeid | https://api.github.com/repos/renfei/renfeid | closed | CVE-2022-29622 (High) detected in formidable-2.0.1.tgz - autoclosed | security vulnerability | ## CVE-2022-29622 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>formidable-2.0.1.tgz</b></p></summary>
<p>A node.js module for parsing form data, especially file uploads.</p>
<p>Library home page: <a href="https://registry.npmjs.org/formidable/-/formidable-2.0.1.tgz">https://registry.npmjs.org/formidable/-/formidable-2.0.1.tgz</a></p>
<p>Path to dependency file: /renfeid-ui/package.json</p>
<p>Path to vulnerable library: /renfeid-ui/node_modules/formidable/package.json</p>
<p>
Dependency Hierarchy:
- :x: **formidable-2.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/renfei/renfeid/commit/bbb49fd012660b8933a94bf6defc5f83dc3ec40a">bbb49fd012660b8933a94bf6defc5f83dc3ec40a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An arbitrary file upload vulnerability in formidable v3.1.4 allows attackers to execute arbitrary code via a crafted filename. NOTE: some third parties dispute this issue because the product has common use cases in which uploading arbitrary files is the desired behavior. Also, there are configuration options in all versions that can change the default behavior of how files are handled.
Mend Note: After conducting further research, Mend has determined that this is a controversial case - Mend security team suggest to refer to it as a risky feature and not as critical vulnerability
<p>Publish Date: 2022-05-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29622>CVE-2022-29622</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-05-16</p>
<p>Fix Resolution: formidable - 3.2.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-29622 (High) detected in formidable-2.0.1.tgz - autoclosed - ## CVE-2022-29622 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>formidable-2.0.1.tgz</b></p></summary>
<p>A node.js module for parsing form data, especially file uploads.</p>
<p>Library home page: <a href="https://registry.npmjs.org/formidable/-/formidable-2.0.1.tgz">https://registry.npmjs.org/formidable/-/formidable-2.0.1.tgz</a></p>
<p>Path to dependency file: /renfeid-ui/package.json</p>
<p>Path to vulnerable library: /renfeid-ui/node_modules/formidable/package.json</p>
<p>
Dependency Hierarchy:
- :x: **formidable-2.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/renfei/renfeid/commit/bbb49fd012660b8933a94bf6defc5f83dc3ec40a">bbb49fd012660b8933a94bf6defc5f83dc3ec40a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An arbitrary file upload vulnerability in formidable v3.1.4 allows attackers to execute arbitrary code via a crafted filename. NOTE: some third parties dispute this issue because the product has common use cases in which uploading arbitrary files is the desired behavior. Also, there are configuration options in all versions that can change the default behavior of how files are handled.
Mend Note: After conducting further research, Mend has determined that this is a controversial case - Mend security team suggest to refer to it as a risky feature and not as critical vulnerability
<p>Publish Date: 2022-05-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29622>CVE-2022-29622</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-05-16</p>
<p>Fix Resolution: formidable - 3.2.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in formidable tgz autoclosed cve high severity vulnerability vulnerable library formidable tgz a node js module for parsing form data especially file uploads library home page a href path to dependency file renfeid ui package json path to vulnerable library renfeid ui node modules formidable package json dependency hierarchy x formidable tgz vulnerable library found in head commit a href found in base branch master vulnerability details an arbitrary file upload vulnerability in formidable allows attackers to execute arbitrary code via a crafted filename note some third parties dispute this issue because the product has common use cases in which uploading arbitrary files is the desired behavior also there are configuration options in all versions that can change the default behavior of how files are handled mend note after conducting further research mend has determined that this is a controversial case mend security team suggest to refer to it as a risky feature and not as critical vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution formidable step up your open source security game with mend | 0 |
107,043 | 16,748,427,513 | IssuesEvent | 2021-06-11 18:49:05 | sharethrough/mikro-orm | https://api.github.com/repos/sharethrough/mikro-orm | closed | CVE-2020-28500 (Medium) detected in lodash-4.17.20.tgz, lodash-4.17.15.tgz - autoclosed | security vulnerability | ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.20.tgz</b>, <b>lodash-4.17.15.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.20.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz</a></p>
<p>Path to dependency file: mikro-orm/docs/package.json</p>
<p>Path to vulnerable library: mikro-orm/docs/node_modules/lodash</p>
<p>
Dependency Hierarchy:
- plugin-client-redirects-2.0.0-beta.0.tgz (Root Library)
- :x: **lodash-4.17.20.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: mikro-orm/docs/package.json</p>
<p>Path to vulnerable library: mikro-orm/docs/node_modules/lodash</p>
<p>
Dependency Hierarchy:
- core-2.0.0-beta.0.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- portfinder-1.0.28.tgz
- async-2.6.3.tgz
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/sharethrough/mikro-orm/commit/36ba319629e171ff276cb2202ec06ccd2db2c0ed">36ba319629e171ff276cb2202ec06ccd2db2c0ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash-4.17.21</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.20","packageFilePaths":["/docs/package.json"],"isTransitiveDependency":true,"dependencyTree":"@docusaurus/plugin-client-redirects:2.0.0-beta.0;lodash:4.17.20","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash-4.17.21"},{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.15","packageFilePaths":["/docs/package.json"],"isTransitiveDependency":true,"dependencyTree":"@docusaurus/core:2.0.0-beta.0;webpack-dev-server:3.11.2;portfinder:1.0.28;async:2.6.3;lodash:4.17.15","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash-4.17.21"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-28500 (Medium) detected in lodash-4.17.20.tgz, lodash-4.17.15.tgz - autoclosed - ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.20.tgz</b>, <b>lodash-4.17.15.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.20.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz</a></p>
<p>Path to dependency file: mikro-orm/docs/package.json</p>
<p>Path to vulnerable library: mikro-orm/docs/node_modules/lodash</p>
<p>
Dependency Hierarchy:
- plugin-client-redirects-2.0.0-beta.0.tgz (Root Library)
- :x: **lodash-4.17.20.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: mikro-orm/docs/package.json</p>
<p>Path to vulnerable library: mikro-orm/docs/node_modules/lodash</p>
<p>
Dependency Hierarchy:
- core-2.0.0-beta.0.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- portfinder-1.0.28.tgz
- async-2.6.3.tgz
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/sharethrough/mikro-orm/commit/36ba319629e171ff276cb2202ec06ccd2db2c0ed">36ba319629e171ff276cb2202ec06ccd2db2c0ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash-4.17.21</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.20","packageFilePaths":["/docs/package.json"],"isTransitiveDependency":true,"dependencyTree":"@docusaurus/plugin-client-redirects:2.0.0-beta.0;lodash:4.17.20","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash-4.17.21"},{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.15","packageFilePaths":["/docs/package.json"],"isTransitiveDependency":true,"dependencyTree":"@docusaurus/core:2.0.0-beta.0;webpack-dev-server:3.11.2;portfinder:1.0.28;async:2.6.3;lodash:4.17.15","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash-4.17.21"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in lodash tgz lodash tgz autoclosed cve medium severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file mikro orm docs package json path to vulnerable library mikro orm docs node modules lodash dependency hierarchy plugin client redirects beta tgz root library x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file mikro orm docs package json path to vulnerable library mikro orm docs node modules lodash dependency hierarchy core beta tgz root library webpack dev server tgz portfinder tgz async tgz x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree docusaurus plugin client redirects beta lodash isminimumfixversionavailable true minimumfixversion lodash packagetype javascript node js packagename lodash packageversion packagefilepaths istransitivedependency true dependencytree docusaurus core beta webpack dev server portfinder async lodash isminimumfixversionavailable true minimumfixversion lodash basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions vulnerabilityurl | 0 |
50,124 | 21,032,807,367 | IssuesEvent | 2022-03-31 03:31:21 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | WebApp:Web App Persistent Storage gets disabled after each deployment | Web Apps Service Attention customer-reported | > ### `az feedback` auto-generates most of the information requested below, as of CLI version 2.0.62
**Describe the bug**
WEBSITES_ENABLE_APP_SERVICE_STORAGE=true will be overwrite to false automatically with below cmdlet
az webapp config set --linux-fx-version
or
az webapp config container set
**To Reproduce**
Save application details into variables so we don't have to repeat them in every upcoming command
APP='--subscription [subid] --resource-group [rgname] --name [appname]'
Enable persistent storage in the application as explained in official docs https://docs.microsoft.com/en-us/azure/app-service/configure-custom-container?pivots=container-linux#use-persistent-shared-storage
az webapp config appsettings set $APP \\
--settings WEBSITES_ENABLE_APP_SERVICE_STORAGE=true \\
--query='[?name=='WEBSITES_ENABLE_APP_SERVICE_STORAGE'].{Name:name, Value:value}' \\
--output=table
Output:
Name Value
----------------------------------- -------
WEBSITES_ENABLE_APP_SERVICE_STORAGE true
run any of below cmdlet will reset WEBSITES_ENABLE_APP_SERVICE_STORAGE to false
az webapp config set $APP --linux-fx-version 'DOCKER|xxxxxxx'
or
az webapp config container set $APP \\
--docker-registry-server-url https://lupmixregistry.azurecr.io \\
--docker-registry-server-user $DOCKER_REGISTRY_USER \\
--docker-registry-server-password $DOCKER_REGISTRY_PASSWROD \\
--docker-custom-image-name '[acrname].azurecr.io/[path]' \\
**Expected behavior**
WEBSITES_ENABLE_APP_SERVICE_STORAGE should be intact once customer config it.
**Environment summary**
Linux Container app , https://docs.microsoft.com/en-us/azure/app-service/faq-app-service-linux#i-m-using-my-own-custom-container--i-want-the-platform-to-mount-an-smb-share-to-the---home---directory- say by default is false , that totally fine . but you can't automatic reset it to false again .
**Additional context**
https://github.com/Azure/azure-cli/blob/ed1fe586d24b5d78127c0b616cd7e32b765d0bfc/src/azure-cli/azure/cli/command_modules/appservice/custom.py
in update_site_configs() , CLI will reset the key to false when linux-fx-version startwith 'docker'
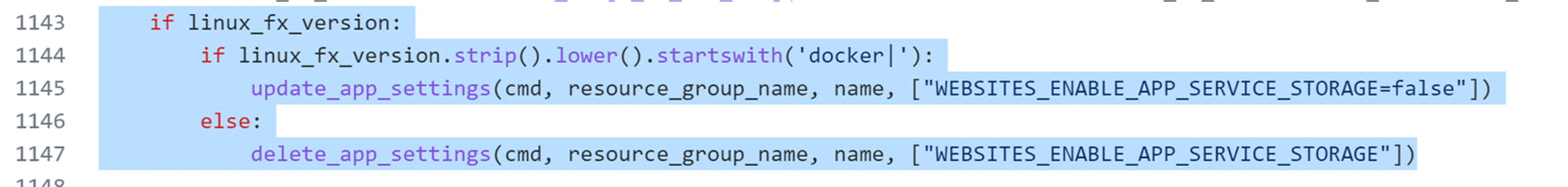
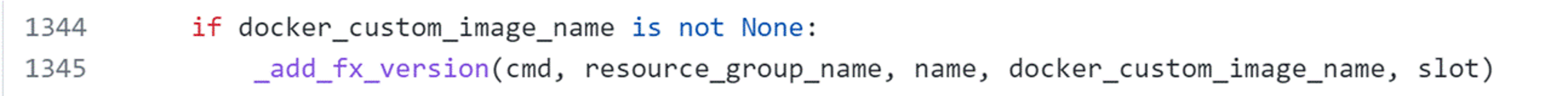
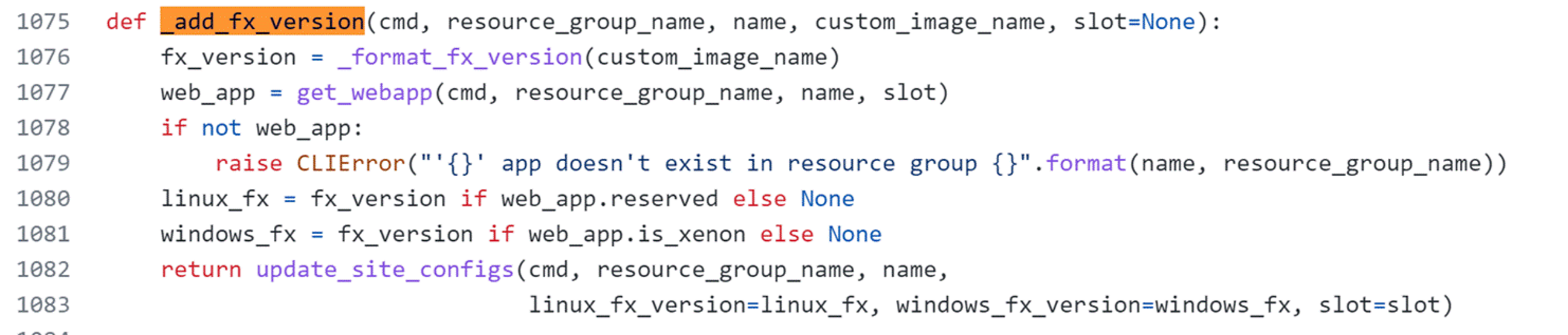
| 1.0 | WebApp:Web App Persistent Storage gets disabled after each deployment - > ### `az feedback` auto-generates most of the information requested below, as of CLI version 2.0.62
**Describe the bug**
WEBSITES_ENABLE_APP_SERVICE_STORAGE=true will be overwrite to false automatically with below cmdlet
az webapp config set --linux-fx-version
or
az webapp config container set
**To Reproduce**
Save application details into variables so we don't have to repeat them in every upcoming command
APP='--subscription [subid] --resource-group [rgname] --name [appname]'
Enable persistent storage in the application as explained in official docs https://docs.microsoft.com/en-us/azure/app-service/configure-custom-container?pivots=container-linux#use-persistent-shared-storage
az webapp config appsettings set $APP \\
--settings WEBSITES_ENABLE_APP_SERVICE_STORAGE=true \\
--query='[?name=='WEBSITES_ENABLE_APP_SERVICE_STORAGE'].{Name:name, Value:value}' \\
--output=table
Output:
Name Value
----------------------------------- -------
WEBSITES_ENABLE_APP_SERVICE_STORAGE true
run any of below cmdlet will reset WEBSITES_ENABLE_APP_SERVICE_STORAGE to false
az webapp config set $APP --linux-fx-version 'DOCKER|xxxxxxx'
or
az webapp config container set $APP \\
--docker-registry-server-url https://lupmixregistry.azurecr.io \\
--docker-registry-server-user $DOCKER_REGISTRY_USER \\
--docker-registry-server-password $DOCKER_REGISTRY_PASSWROD \\
--docker-custom-image-name '[acrname].azurecr.io/[path]' \\
**Expected behavior**
WEBSITES_ENABLE_APP_SERVICE_STORAGE should be intact once customer config it.
**Environment summary**
Linux Container app , https://docs.microsoft.com/en-us/azure/app-service/faq-app-service-linux#i-m-using-my-own-custom-container--i-want-the-platform-to-mount-an-smb-share-to-the---home---directory- say by default is false , that totally fine . but you can't automatic reset it to false again .
**Additional context**
https://github.com/Azure/azure-cli/blob/ed1fe586d24b5d78127c0b616cd7e32b765d0bfc/src/azure-cli/azure/cli/command_modules/appservice/custom.py
in update_site_configs() , CLI will reset the key to false when linux-fx-version startwith 'docker'
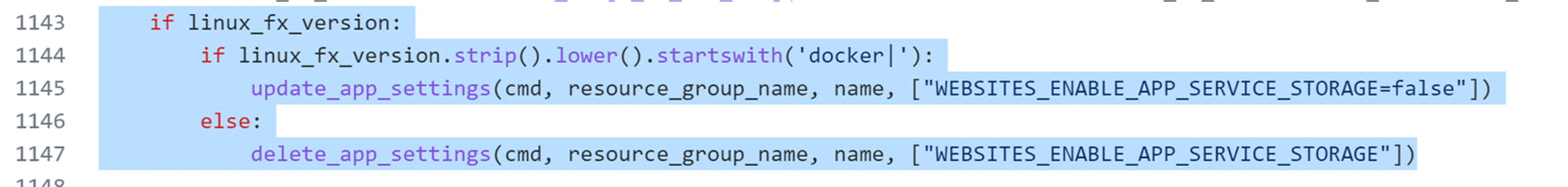
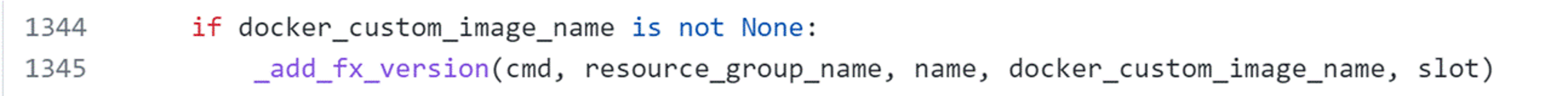
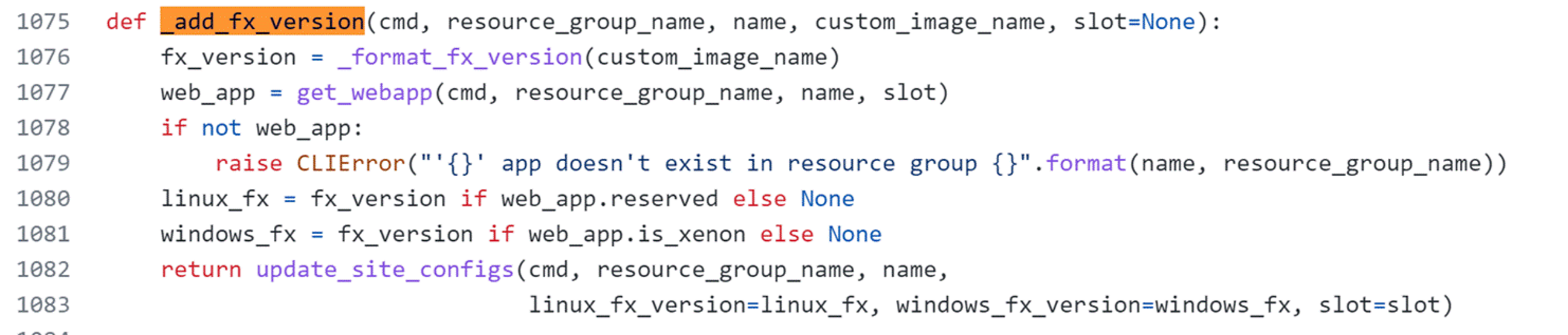
| non_priority | webapp web app persistent storage gets disabled after each deployment az feedback auto generates most of the information requested below as of cli version describe the bug websites enable app service storage true will be overwrite to false automatically with below cmdlet az webapp config set linux fx version or az webapp config container set to reproduce save application details into variables so we don t have to repeat them in every upcoming command app subscription resource group name enable persistent storage in the application as explained in official docs az webapp config appsettings set app settings websites enable app service storage true query name name value value output table output name value websites enable app service storage true run any of below cmdlet will reset websites enable app service storage to false az webapp config set app linux fx version docker xxxxxxx or az webapp config container set app docker registry server url docker registry server user docker registry user docker registry server password docker registry passwrod docker custom image name azurecr io expected behavior websites enable app service storage should be intact once customer config it environment summary linux container app say by default is false that totally fine but you can t automatic reset it to false again additional context in update site configs cli will reset the key to false when linux fx version startwith docker | 0 |
127,993 | 27,171,266,709 | IssuesEvent | 2023-02-17 19:40:47 | mozilla/foundation.mozilla.org | https://api.github.com/repos/mozilla/foundation.mozilla.org | opened | [PNI Refactor] Add documentation to pni-sort-dropdown.js | engineering buyer's guide 🛍 code cleanup needs grooming | Add documentation (in [JSDoc style](https://jsdoc.app/)) to `source/js/buyers-guide/search/pni-sort-dropdown.js`.
e.g.,
```js
/**
* Represents a book.
* @constructor
* @param {string} title - The title of the book.
* @param {string} author - The author of the book.
*/
function Book(title, author) {
}
```
| 1.0 | [PNI Refactor] Add documentation to pni-sort-dropdown.js - Add documentation (in [JSDoc style](https://jsdoc.app/)) to `source/js/buyers-guide/search/pni-sort-dropdown.js`.
e.g.,
```js
/**
* Represents a book.
* @constructor
* @param {string} title - The title of the book.
* @param {string} author - The author of the book.
*/
function Book(title, author) {
}
```
| non_priority | add documentation to pni sort dropdown js add documentation in to source js buyers guide search pni sort dropdown js e g js represents a book constructor param string title the title of the book param string author the author of the book function book title author | 0 |
192,489 | 22,215,961,103 | IssuesEvent | 2022-06-08 01:41:27 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | reopened | CVE-2014-5471 (Medium) detected in linux-yocto-4.12v3.1.10 | security vulnerability | ## CVE-2014-5471 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.1.10</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/isofs/isofs.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/isofs/rock.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Stack consumption vulnerability in the parse_rock_ridge_inode_internal function in fs/isofs/rock.c in the Linux kernel through 3.16.1 allows local users to cause a denial of service (uncontrolled recursion, and system crash or reboot) via a crafted iso9660 image with a CL entry referring to a directory entry that has a CL entry.
<p>Publish Date: 2014-09-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-5471>CVE-2014-5471</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5471">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5471</a></p>
<p>Release Date: 2014-09-01</p>
<p>Fix Resolution: v3.17-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2014-5471 (Medium) detected in linux-yocto-4.12v3.1.10 - ## CVE-2014-5471 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.1.10</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/isofs/isofs.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/isofs/rock.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Stack consumption vulnerability in the parse_rock_ridge_inode_internal function in fs/isofs/rock.c in the Linux kernel through 3.16.1 allows local users to cause a denial of service (uncontrolled recursion, and system crash or reboot) via a crafted iso9660 image with a CL entry referring to a directory entry that has a CL entry.
<p>Publish Date: 2014-09-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-5471>CVE-2014-5471</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5471">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5471</a></p>
<p>Release Date: 2014-09-01</p>
<p>Fix Resolution: v3.17-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux yocto cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files fs isofs isofs h fs isofs rock c vulnerability details stack consumption vulnerability in the parse rock ridge inode internal function in fs isofs rock c in the linux kernel through allows local users to cause a denial of service uncontrolled recursion and system crash or reboot via a crafted image with a cl entry referring to a directory entry that has a cl entry publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
76,910 | 21,624,946,563 | IssuesEvent | 2022-05-05 00:04:03 | aws/aws-cdk | https://api.github.com/repos/aws/aws-cdk | closed | imagebuilder: ExecuteBash action in Component cannot use redirection | bug p1 response-requested effort/small @aws-cdk/aws-imagebuilder | ### Describe the bug
In ImageBuilder, Component , Action, ExecuteBash : I want to output a bash command to a file but the `data` field which contain a yaml string do not allow ">" character.
### Expected Behavior
Somehow to be able to do piping and write result to file
### Current Behavior
I get the error :
```
Resource handler returned message: "The value supplied for parameter 'data' is not valid. Invalid step name 'Loading ssh keys' in phase 'build'. Allowed characters are combinations of numbers [0-9], english letters [a-z,A-Z] and special characters [-_]. (Service: Imagebuilder, Status Code: 400, Request ID: 23c0489b-3b59-49d5-b66c-95d55a2f15d7)" (RequestToken: 8e6f8f54-361f-c4bb-30e3-43ab5db2c7ad, HandlerErrorCode: GeneralServiceException)
```
### Reproduction Steps
To reproduce:
```python
class Failed(Stack):
def __init__(self, scope: Construct, construct_id: str, **kwargs) -> None:
super().__init__(scope, construct_id,description=f"",
**kwargs)
myComponent = imagebuilder.CfnComponent(self, "SetupComponent",
name="SetupComponent",
platform="Linux",
version="1.0.0",
data="""
schemaVersion: 1.0
phases:
-
name: build
steps:
-
name: "Loading ssh keys"
action: ExecuteBash
inputs:
commands:
- "aws secretsmanager get-secret-value --region ap-southeast-2 --secret-id REPLACE_SECRET_PUB --query SecretString --output text > amiKey.pub"
""",
description="Setup",
)
```
I tried to format it similar to the example as https://docs.aws.amazon.com/imagebuilder/latest/userguide/toe-action-modules.html#action-modules-executebash :
```python
class Failed(Stack):
def __init__(self, scope: Construct, construct_id: str, **kwargs) -> None:
super().__init__(scope, construct_id,description=f"",
**kwargs)
myComponent = imagebuilder.CfnComponent(self, "SetupComponent",
name="SetupComponent",
platform="Linux",
version="1.0.0",
data="""
schemaVersion: 1.0
phases:
-
name: build
steps:
-
name: "Loading ssh keys"
action: ExecuteBash
inputs:
commands:
- |
aws secretsmanager get-secret-value --region ap-southeast-2 --secret-id REPLACE_SECRET_PUB --query SecretString --output text > amiKey.pub
""",
description="Setup",
)
```
But still have the error
### Possible Solution
NA
### Additional Information/Context
NA
### CDK CLI Version
2.20.0 (build 738ef49)
### Framework Version
NA
### Node.js Version
v16.13.2
### OS
Ubuntu 18.04.5 LTS
### Language
Python
### Language Version
Python 3.6.9
### Other information
NA | 1.0 | imagebuilder: ExecuteBash action in Component cannot use redirection - ### Describe the bug
In ImageBuilder, Component , Action, ExecuteBash : I want to output a bash command to a file but the `data` field which contain a yaml string do not allow ">" character.
### Expected Behavior
Somehow to be able to do piping and write result to file
### Current Behavior
I get the error :
```
Resource handler returned message: "The value supplied for parameter 'data' is not valid. Invalid step name 'Loading ssh keys' in phase 'build'. Allowed characters are combinations of numbers [0-9], english letters [a-z,A-Z] and special characters [-_]. (Service: Imagebuilder, Status Code: 400, Request ID: 23c0489b-3b59-49d5-b66c-95d55a2f15d7)" (RequestToken: 8e6f8f54-361f-c4bb-30e3-43ab5db2c7ad, HandlerErrorCode: GeneralServiceException)
```
### Reproduction Steps
To reproduce:
```python
class Failed(Stack):
def __init__(self, scope: Construct, construct_id: str, **kwargs) -> None:
super().__init__(scope, construct_id,description=f"",
**kwargs)
myComponent = imagebuilder.CfnComponent(self, "SetupComponent",
name="SetupComponent",
platform="Linux",
version="1.0.0",
data="""
schemaVersion: 1.0
phases:
-
name: build
steps:
-
name: "Loading ssh keys"
action: ExecuteBash
inputs:
commands:
- "aws secretsmanager get-secret-value --region ap-southeast-2 --secret-id REPLACE_SECRET_PUB --query SecretString --output text > amiKey.pub"
""",
description="Setup",
)
```
I tried to format it similar to the example as https://docs.aws.amazon.com/imagebuilder/latest/userguide/toe-action-modules.html#action-modules-executebash :
```python
class Failed(Stack):
def __init__(self, scope: Construct, construct_id: str, **kwargs) -> None:
super().__init__(scope, construct_id,description=f"",
**kwargs)
myComponent = imagebuilder.CfnComponent(self, "SetupComponent",
name="SetupComponent",
platform="Linux",
version="1.0.0",
data="""
schemaVersion: 1.0
phases:
-
name: build
steps:
-
name: "Loading ssh keys"
action: ExecuteBash
inputs:
commands:
- |
aws secretsmanager get-secret-value --region ap-southeast-2 --secret-id REPLACE_SECRET_PUB --query SecretString --output text > amiKey.pub
""",
description="Setup",
)
```
But still have the error
### Possible Solution
NA
### Additional Information/Context
NA
### CDK CLI Version
2.20.0 (build 738ef49)
### Framework Version
NA
### Node.js Version
v16.13.2
### OS
Ubuntu 18.04.5 LTS
### Language
Python
### Language Version
Python 3.6.9
### Other information
NA | non_priority | imagebuilder executebash action in component cannot use redirection describe the bug in imagebuilder component action executebash i want to output a bash command to a file but the data field which contain a yaml string do not allow character expected behavior somehow to be able to do piping and write result to file current behavior i get the error resource handler returned message the value supplied for parameter data is not valid invalid step name loading ssh keys in phase build allowed characters are combinations of numbers english letters and special characters service imagebuilder status code request id requesttoken handlererrorcode generalserviceexception reproduction steps to reproduce python class failed stack def init self scope construct construct id str kwargs none super init scope construct id description f kwargs mycomponent imagebuilder cfncomponent self setupcomponent name setupcomponent platform linux version data schemaversion phases name build steps name loading ssh keys action executebash inputs commands aws secretsmanager get secret value region ap southeast secret id replace secret pub query secretstring output text amikey pub description setup i tried to format it similar to the example as python class failed stack def init self scope construct construct id str kwargs none super init scope construct id description f kwargs mycomponent imagebuilder cfncomponent self setupcomponent name setupcomponent platform linux version data schemaversion phases name build steps name loading ssh keys action executebash inputs commands aws secretsmanager get secret value region ap southeast secret id replace secret pub query secretstring output text amikey pub description setup but still have the error possible solution na additional information context na cdk cli version build framework version na node js version os ubuntu lts language python language version python other information na | 0 |
344,571 | 30,751,713,043 | IssuesEvent | 2023-07-28 19:56:46 | saltstack/salt | https://api.github.com/repos/saltstack/salt | opened | [Increase Test Coverage] Batch 130 | Tests | Increase the code coverage percent on the following files to at least 80%.
Please be aware that currently the percentage might be inaccurate if the module uses salt due to #64696
File | Percent
salt/returners/syslog_return.py 68
salt/runners/auth.py 31
salt/runners/config.py 33
salt/runners/error.py 25
salt/runners/event.py 57
| 1.0 | [Increase Test Coverage] Batch 130 - Increase the code coverage percent on the following files to at least 80%.
Please be aware that currently the percentage might be inaccurate if the module uses salt due to #64696
File | Percent
salt/returners/syslog_return.py 68
salt/runners/auth.py 31
salt/runners/config.py 33
salt/runners/error.py 25
salt/runners/event.py 57
| non_priority | batch increase the code coverage percent on the following files to at least please be aware that currently the percentage might be inaccurate if the module uses salt due to file percent salt returners syslog return py salt runners auth py salt runners config py salt runners error py salt runners event py | 0 |
15,677 | 10,335,069,903 | IssuesEvent | 2019-09-03 09:44:00 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Host is empty in the remote-exec provision part | question service/virtual-machine | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
Terraform v0.12.5
provider "azurerm" {
version = "1.31.0"
}
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* `azurerm_public_ip`
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
variable "admin_username" {
default = "thisisausernamemyfriend"
}
variable "admin_password" {
default = "**************"
}
# Configure the Microsoft Azure Provider.
provider "azurerm" {
version = "1.31.0"
}
# Create a resource group
resource "azurerm_resource_group" "iha-TF-Cloudacademy" {
name = "ihaTFResourceGroup" #TODO change!
location = "westeurope"
}
# Create virtual network
resource "azurerm_virtual_network" "vnet" {
name = "ihaTFVnet"
address_space = ["10.0.0.0/16"]
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
}
# Create subnet
resource "azurerm_subnet" "subnet" {
name = "myTFSubnet"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
virtual_network_name = "${azurerm_virtual_network.vnet.name}"
address_prefix = "10.0.1.0/24"
}
# Create public IP
resource "azurerm_public_ip" "publicip" {
name = "ihaTFPublicIP"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
allocation_method = "Dynamic"
}
# Create Network Security Group and rule
resource "azurerm_network_security_group" "iha-Cloudacdamey-nsg" {
name = "ihaTFNSG"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
security_rule {
name = "SSH"
priority = 1001
direction = "Inbound"
access = "Allow"
protocol = "Tcp"
source_port_range = "*"
destination_port_range = "22"
source_address_prefix = "*"
destination_address_prefix = "*"
}
}
# Create network interface
resource "azurerm_network_interface" "nic" {
name = "ihaNIC"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
network_security_group_id = "${azurerm_network_security_group.iha-Cloudacdamey-nsg.id}"
ip_configuration {
name = "ihaNICConfg"
subnet_id = "${azurerm_subnet.subnet.id}"
private_ip_address_allocation = "Dynamic"
public_ip_address_id = "${azurerm_public_ip.publicip.id}"
}
}
# Create a Linux virtual machine
resource "azurerm_virtual_machine" "vm" {
name = "ihaTFVM"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
network_interface_ids = ["${azurerm_network_interface.nic.id}"]
vm_size = "Standard_DS1_v2"
storage_os_disk {
name = "myOsDisk"
caching = "ReadWrite"
create_option = "FromImage"
managed_disk_type = "Premium_LRS"
}
storage_image_reference {
publisher = "Canonical"
offer = "UbuntuServer"
sku = "18.04-LTS"
version = "latest"
}
os_profile {
computer_name = "ihaTFVM"
admin_username = "${var.admin_username}"
admin_password = "${var.admin_password}"
}
os_profile_linux_config {
disable_password_authentication = false
}
# Here you can see how terraform is able to provision a instance
provisioner "remote-exec" {
# Install Python for Ansible
inline = ["while [ ! -f /var/lib/cloud/instance/boot-finished ]; do echo 'Waiting for cloud-init...'; sleep 1; done; sudo rm /var/lib/apt/lists/* ; sudo apt-get update ; sudo apt-get install -y python python-pip "]
connection {
user = "${var.admin_username}"
password = "${var.admin_password}"
host = "${azurerm_public_ip.publicip.ip_address}"
}
}
# Here we run provision from local disc to VM-instance with the help of Ansible
provisioner "local-exec" {
#we dont want host-key-check because we don't knew the assigned eip
command = "ANSIBLE_HOST_KEY_CHECKING=False Ansible-playbook -u ${var.admin_username} -i '${azurerm_public_ip.publicip.ip_address}' -T 300 ../provision/playbook.yml"
}
}
data "azurerm_public_ip" "test" {
name = "${azurerm_public_ip.publicip.name}"
resource_group_name = "${azurerm_virtual_machine.vm.resource_group_name}"
}
output "public_ip_address" {
value = "${data.azurerm_public_ip.test.ip_address}"
}
```
### Debug Output
```
azurerm_virtual_machine.vm (remote-exec): Connecting to remote host via SSH...
azurerm_virtual_machine.vm (remote-exec): Host: <<--- this is empty!
azurerm_virtual_machine.vm (remote-exec): User: thisisausernamemyfriend
azurerm_virtual_machine.vm (remote-exec): Password: true
azurerm_virtual_machine.vm (remote-exec): Private key: false
azurerm_virtual_machine.vm (remote-exec): Certificate: false
azurerm_virtual_machine.vm (remote-exec): SSH Agent: false
azurerm_virtual_machine.vm (remote-exec): Checking Host Key: false
-snip-
Error: timeout - last error: dial tcp :22: connectex: No connection could be made because the target machine actively refused it.
```
<!---
Please provide a link to a GitHub Gist containing the complete debug output. Please do NOT paste the debug output in the issue; just paste a link to the Gist.
To obtain the debug output, see the [Terraform documentation on debugging](https://www.terraform.io/docs/internals/debugging.html).
--->
----
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
---
### Expected Behavior
<!--- What should have happened? --->
host = "${azurerm_public_ip.publicip.ip_address}"
should have an ip-address for connecting to the generated vm.
### Actual Behavior
The host is empty - so no connection could established to the new vm.
The funny thing is - if i comment the provision part. i get an ip-address outputed to the cli.
<!--- What actually happened? --->
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform apply`
### Important Factoids
<!--- Are there anything atypical about your accounts that we should know? For example: Running in a Azure China/Germany/Government? --->
---
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Such as vendor documentation?
--->
* #0000
| 1.0 | Host is empty in the remote-exec provision part - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
Terraform v0.12.5
provider "azurerm" {
version = "1.31.0"
}
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* `azurerm_public_ip`
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
variable "admin_username" {
default = "thisisausernamemyfriend"
}
variable "admin_password" {
default = "**************"
}
# Configure the Microsoft Azure Provider.
provider "azurerm" {
version = "1.31.0"
}
# Create a resource group
resource "azurerm_resource_group" "iha-TF-Cloudacademy" {
name = "ihaTFResourceGroup" #TODO change!
location = "westeurope"
}
# Create virtual network
resource "azurerm_virtual_network" "vnet" {
name = "ihaTFVnet"
address_space = ["10.0.0.0/16"]
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
}
# Create subnet
resource "azurerm_subnet" "subnet" {
name = "myTFSubnet"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
virtual_network_name = "${azurerm_virtual_network.vnet.name}"
address_prefix = "10.0.1.0/24"
}
# Create public IP
resource "azurerm_public_ip" "publicip" {
name = "ihaTFPublicIP"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
allocation_method = "Dynamic"
}
# Create Network Security Group and rule
resource "azurerm_network_security_group" "iha-Cloudacdamey-nsg" {
name = "ihaTFNSG"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
security_rule {
name = "SSH"
priority = 1001
direction = "Inbound"
access = "Allow"
protocol = "Tcp"
source_port_range = "*"
destination_port_range = "22"
source_address_prefix = "*"
destination_address_prefix = "*"
}
}
# Create network interface
resource "azurerm_network_interface" "nic" {
name = "ihaNIC"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
network_security_group_id = "${azurerm_network_security_group.iha-Cloudacdamey-nsg.id}"
ip_configuration {
name = "ihaNICConfg"
subnet_id = "${azurerm_subnet.subnet.id}"
private_ip_address_allocation = "Dynamic"
public_ip_address_id = "${azurerm_public_ip.publicip.id}"
}
}
# Create a Linux virtual machine
resource "azurerm_virtual_machine" "vm" {
name = "ihaTFVM"
location = "westeurope"
resource_group_name = "${azurerm_resource_group.iha-TF-Cloudacademy.name}"
network_interface_ids = ["${azurerm_network_interface.nic.id}"]
vm_size = "Standard_DS1_v2"
storage_os_disk {
name = "myOsDisk"
caching = "ReadWrite"
create_option = "FromImage"
managed_disk_type = "Premium_LRS"
}
storage_image_reference {
publisher = "Canonical"
offer = "UbuntuServer"
sku = "18.04-LTS"
version = "latest"
}
os_profile {
computer_name = "ihaTFVM"
admin_username = "${var.admin_username}"
admin_password = "${var.admin_password}"
}
os_profile_linux_config {
disable_password_authentication = false
}
# Here you can see how terraform is able to provision a instance
provisioner "remote-exec" {
# Install Python for Ansible
inline = ["while [ ! -f /var/lib/cloud/instance/boot-finished ]; do echo 'Waiting for cloud-init...'; sleep 1; done; sudo rm /var/lib/apt/lists/* ; sudo apt-get update ; sudo apt-get install -y python python-pip "]
connection {
user = "${var.admin_username}"
password = "${var.admin_password}"
host = "${azurerm_public_ip.publicip.ip_address}"
}
}
# Here we run provision from local disc to VM-instance with the help of Ansible
provisioner "local-exec" {
#we dont want host-key-check because we don't knew the assigned eip
command = "ANSIBLE_HOST_KEY_CHECKING=False Ansible-playbook -u ${var.admin_username} -i '${azurerm_public_ip.publicip.ip_address}' -T 300 ../provision/playbook.yml"
}
}
data "azurerm_public_ip" "test" {
name = "${azurerm_public_ip.publicip.name}"
resource_group_name = "${azurerm_virtual_machine.vm.resource_group_name}"
}
output "public_ip_address" {
value = "${data.azurerm_public_ip.test.ip_address}"
}
```
### Debug Output
```
azurerm_virtual_machine.vm (remote-exec): Connecting to remote host via SSH...
azurerm_virtual_machine.vm (remote-exec): Host: <<--- this is empty!
azurerm_virtual_machine.vm (remote-exec): User: thisisausernamemyfriend
azurerm_virtual_machine.vm (remote-exec): Password: true
azurerm_virtual_machine.vm (remote-exec): Private key: false
azurerm_virtual_machine.vm (remote-exec): Certificate: false
azurerm_virtual_machine.vm (remote-exec): SSH Agent: false
azurerm_virtual_machine.vm (remote-exec): Checking Host Key: false
-snip-
Error: timeout - last error: dial tcp :22: connectex: No connection could be made because the target machine actively refused it.
```
<!---
Please provide a link to a GitHub Gist containing the complete debug output. Please do NOT paste the debug output in the issue; just paste a link to the Gist.
To obtain the debug output, see the [Terraform documentation on debugging](https://www.terraform.io/docs/internals/debugging.html).
--->
----
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
---
### Expected Behavior
<!--- What should have happened? --->
host = "${azurerm_public_ip.publicip.ip_address}"
should have an ip-address for connecting to the generated vm.
### Actual Behavior
The host is empty - so no connection could established to the new vm.
The funny thing is - if i comment the provision part. i get an ip-address outputed to the cli.
<!--- What actually happened? --->
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform apply`
### Important Factoids
<!--- Are there anything atypical about your accounts that we should know? For example: Running in a Azure China/Germany/Government? --->
---
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Such as vendor documentation?
--->
* #0000
| non_priority | host is empty in the remote exec provision part please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one of these scenarios we recommend opening an issue in the instead community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform and azurerm provider version terraform provider azurerm version affected resource s azurerm public ip terraform configuration files hcl variable admin username default thisisausernamemyfriend variable admin password default configure the microsoft azure provider provider azurerm version create a resource group resource azurerm resource group iha tf cloudacademy name ihatfresourcegroup todo change location westeurope create virtual network resource azurerm virtual network vnet name ihatfvnet address space location westeurope resource group name azurerm resource group iha tf cloudacademy name create subnet resource azurerm subnet subnet name mytfsubnet resource group name azurerm resource group iha tf cloudacademy name virtual network name azurerm virtual network vnet name address prefix create public ip resource azurerm public ip publicip name ihatfpublicip location westeurope resource group name azurerm resource group iha tf cloudacademy name allocation method dynamic create network security group and rule resource azurerm network security group iha cloudacdamey nsg name ihatfnsg location westeurope resource group name azurerm resource group iha tf cloudacademy name security rule name ssh priority direction inbound access allow protocol tcp source port range destination port range source address prefix destination address prefix create network interface resource azurerm network interface nic name ihanic location westeurope resource group name azurerm resource group iha tf cloudacademy name network security group id azurerm network security group iha cloudacdamey nsg id ip configuration name ihanicconfg subnet id azurerm subnet subnet id private ip address allocation dynamic public ip address id azurerm public ip publicip id create a linux virtual machine resource azurerm virtual machine vm name ihatfvm location westeurope resource group name azurerm resource group iha tf cloudacademy name network interface ids vm size standard storage os disk name myosdisk caching readwrite create option fromimage managed disk type premium lrs storage image reference publisher canonical offer ubuntuserver sku lts version latest os profile computer name ihatfvm admin username var admin username admin password var admin password os profile linux config disable password authentication false here you can see how terraform is able to provision a instance provisioner remote exec install python for ansible inline do echo waiting for cloud init sleep done sudo rm var lib apt lists sudo apt get update sudo apt get install y python python pip connection user var admin username password var admin password host azurerm public ip publicip ip address here we run provision from local disc to vm instance with the help of ansible provisioner local exec we dont want host key check because we don t knew the assigned eip command ansible host key checking false ansible playbook u var admin username i azurerm public ip publicip ip address t provision playbook yml data azurerm public ip test name azurerm public ip publicip name resource group name azurerm virtual machine vm resource group name output public ip address value data azurerm public ip test ip address debug output azurerm virtual machine vm remote exec connecting to remote host via ssh azurerm virtual machine vm remote exec host this is empty azurerm virtual machine vm remote exec user thisisausernamemyfriend azurerm virtual machine vm remote exec password true azurerm virtual machine vm remote exec private key false azurerm virtual machine vm remote exec certificate false azurerm virtual machine vm remote exec ssh agent false azurerm virtual machine vm remote exec checking host key false snip error timeout last error dial tcp connectex no connection could be made because the target machine actively refused it please provide a link to a github gist containing the complete debug output please do not paste the debug output in the issue just paste a link to the gist to obtain the debug output see the panic output expected behavior host azurerm public ip publicip ip address should have an ip address for connecting to the generated vm actual behavior the host is empty so no connection could established to the new vm the funny thing is if i comment the provision part i get an ip address outputed to the cli steps to reproduce terraform apply important factoids references information about referencing github issues are there any other github issues open or closed or pull requests that should be linked here such as vendor documentation | 0 |
74,254 | 9,777,329,765 | IssuesEvent | 2019-06-07 08:49:27 | vuetifyjs/vuetify | https://api.github.com/repos/vuetifyjs/vuetify | closed | [Bug Report] v-slot:body not overriding default body in datatable | C: VDatatable T: documentation | ### Versions and Environment
**Vuetify:** 2.0.0-beta.0
**Vue:** 2.6.10
**Browsers:** Chrome 73.0.3683.103
**OS:** Windows 10
### Steps to reproduce
create basic implantation of datatable using version 2.0beta.0
add props fixed-rows and hide-default-headers
add template v-slot:header={props:{header}} for custom header
add template v-slot:body={items} for custom body
### Expected Behavior
body should only have two column 'item.name' and "content" given custom body template
### Actual Behavior
body displays all data in object
### Reproduction Link
<a href="https://codepen.io/kylejoeckel/pen/VOGNEq" target="_blank">https://codepen.io/kylejoeckel/pen/VOGNEq</a>
### Other comments
this may be another documentation issue but i figured id submit it anyways..
<!-- generated by vuetify-issue-helper. DO NOT REMOVE --> | 1.0 | [Bug Report] v-slot:body not overriding default body in datatable - ### Versions and Environment
**Vuetify:** 2.0.0-beta.0
**Vue:** 2.6.10
**Browsers:** Chrome 73.0.3683.103
**OS:** Windows 10
### Steps to reproduce
create basic implantation of datatable using version 2.0beta.0
add props fixed-rows and hide-default-headers
add template v-slot:header={props:{header}} for custom header
add template v-slot:body={items} for custom body
### Expected Behavior
body should only have two column 'item.name' and "content" given custom body template
### Actual Behavior
body displays all data in object
### Reproduction Link
<a href="https://codepen.io/kylejoeckel/pen/VOGNEq" target="_blank">https://codepen.io/kylejoeckel/pen/VOGNEq</a>
### Other comments
this may be another documentation issue but i figured id submit it anyways..
<!-- generated by vuetify-issue-helper. DO NOT REMOVE --> | non_priority | v slot body not overriding default body in datatable versions and environment vuetify beta vue browsers chrome os windows steps to reproduce create basic implantation of datatable using version add props fixed rows and hide default headers add template v slot header props header for custom header add template v slot body items for custom body expected behavior body should only have two column item name and content given custom body template actual behavior body displays all data in object reproduction link other comments this may be another documentation issue but i figured id submit it anyways | 0 |
117,716 | 17,512,707,628 | IssuesEvent | 2021-08-11 01:07:59 | HelioGuilherme66/RIDE | https://api.github.com/repos/HelioGuilherme66/RIDE | closed | CVE-2020-5311 (High) detected in Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2020-5311 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/12/ad/61f8dfba88c4e56196bf6d056cdbba64dc9c5dfdfbc97d02e6472feed913/Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/12/ad/61f8dfba88c4e56196bf6d056cdbba64dc9c5dfdfbc97d02e6472feed913/Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/RIDE/requirements.txt</p>
<p>Path to vulnerable library: /RIDE/requirements.txt,/RIDE</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/HelioGuilherme66/RIDE/commit/20649d7dc0b190fc9513ff06e808b5f6718213ad">20649d7dc0b190fc9513ff06e808b5f6718213ad</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
libImaging/SgiRleDecode.c in Pillow before 6.2.2 has an SGI buffer overflow.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-5311>CVE-2020-5311</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5311">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5311</a></p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: 7.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-5311 (High) detected in Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2020-5311 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/12/ad/61f8dfba88c4e56196bf6d056cdbba64dc9c5dfdfbc97d02e6472feed913/Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/12/ad/61f8dfba88c4e56196bf6d056cdbba64dc9c5dfdfbc97d02e6472feed913/Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/RIDE/requirements.txt</p>
<p>Path to vulnerable library: /RIDE/requirements.txt,/RIDE</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-6.2.2-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/HelioGuilherme66/RIDE/commit/20649d7dc0b190fc9513ff06e808b5f6718213ad">20649d7dc0b190fc9513ff06e808b5f6718213ad</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
libImaging/SgiRleDecode.c in Pillow before 6.2.2 has an SGI buffer overflow.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-5311>CVE-2020-5311</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5311">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5311</a></p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: 7.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in pillow whl cve high severity vulnerability vulnerable library pillow whl python imaging library fork library home page a href path to dependency file tmp ws scm ride requirements txt path to vulnerable library ride requirements txt ride dependency hierarchy x pillow whl vulnerable library found in head commit a href vulnerability details libimaging sgirledecode c in pillow before has an sgi buffer overflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
294,079 | 25,344,092,760 | IssuesEvent | 2022-11-19 02:31:18 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | kernel: tests: Evaluate "platform_allow" usage in kernel tests. | Enhancement area: Tests | **Problem**
Platform_allow lists in kernel's testcase.yamls are incorrectly blocking testing scope.
**Describe the solution you'd like**
Every test scenario under tests/kernel which defines platform_allow has to be evaluated. Platform_allow lists should be replaced with other filtration means. To limit the CI execution scope one can use integration_platforms which will also enforce such test execution in the CI (skips are turned to errors in the CI for integration_platforms). Platform_allow lists should only be allowed for cases where there is no other means of filtration or tests are not portable (e.g. ones which require dedicated overlays for each platform).
**Describe alternatives you've considered**
I don't see other approach to fix the issue.
**Additional context**
IMO it is more a bug than an enhancement but due to the scope I put it under "enhancement". This problem is also not limited to kernel tests, but due to the scope I believe evaluation of platform_allow abuse can be limited to kernel tests in this task and we will continue solving the issue in following tasks.
Platform_allow is abused and used incorrectly. Looking at examples it seems it was often added just to limit the CI execution scope. Or because a developer only tested the solution on certain boards and didn't care about other platforms. Platform_allow is a hard filter preventing testing on anything outside of it. It also makes tests hard to maintain, since it needs constant updating with new boards being added (which is not happening in most cases...).
This evaluation is especially important in context of on-target testing and selecting "tier 1" boards. Kernel tests will be crucial for such boards. However, it seems there might be quite many artificial skips due to platform_allow misuse.
An example showing the problem: https://github.com/zephyrproject-rtos/zephyr/blob/main/tests/kernel/gen_isr_table/testcase.yaml#L11
The platforms in platform_allow seem totally arbitrarily selected and blocks testing on vast majority of platforms. | 1.0 | kernel: tests: Evaluate "platform_allow" usage in kernel tests. - **Problem**
Platform_allow lists in kernel's testcase.yamls are incorrectly blocking testing scope.
**Describe the solution you'd like**
Every test scenario under tests/kernel which defines platform_allow has to be evaluated. Platform_allow lists should be replaced with other filtration means. To limit the CI execution scope one can use integration_platforms which will also enforce such test execution in the CI (skips are turned to errors in the CI for integration_platforms). Platform_allow lists should only be allowed for cases where there is no other means of filtration or tests are not portable (e.g. ones which require dedicated overlays for each platform).
**Describe alternatives you've considered**
I don't see other approach to fix the issue.
**Additional context**
IMO it is more a bug than an enhancement but due to the scope I put it under "enhancement". This problem is also not limited to kernel tests, but due to the scope I believe evaluation of platform_allow abuse can be limited to kernel tests in this task and we will continue solving the issue in following tasks.
Platform_allow is abused and used incorrectly. Looking at examples it seems it was often added just to limit the CI execution scope. Or because a developer only tested the solution on certain boards and didn't care about other platforms. Platform_allow is a hard filter preventing testing on anything outside of it. It also makes tests hard to maintain, since it needs constant updating with new boards being added (which is not happening in most cases...).
This evaluation is especially important in context of on-target testing and selecting "tier 1" boards. Kernel tests will be crucial for such boards. However, it seems there might be quite many artificial skips due to platform_allow misuse.
An example showing the problem: https://github.com/zephyrproject-rtos/zephyr/blob/main/tests/kernel/gen_isr_table/testcase.yaml#L11
The platforms in platform_allow seem totally arbitrarily selected and blocks testing on vast majority of platforms. | non_priority | kernel tests evaluate platform allow usage in kernel tests problem platform allow lists in kernel s testcase yamls are incorrectly blocking testing scope describe the solution you d like every test scenario under tests kernel which defines platform allow has to be evaluated platform allow lists should be replaced with other filtration means to limit the ci execution scope one can use integration platforms which will also enforce such test execution in the ci skips are turned to errors in the ci for integration platforms platform allow lists should only be allowed for cases where there is no other means of filtration or tests are not portable e g ones which require dedicated overlays for each platform describe alternatives you ve considered i don t see other approach to fix the issue additional context imo it is more a bug than an enhancement but due to the scope i put it under enhancement this problem is also not limited to kernel tests but due to the scope i believe evaluation of platform allow abuse can be limited to kernel tests in this task and we will continue solving the issue in following tasks platform allow is abused and used incorrectly looking at examples it seems it was often added just to limit the ci execution scope or because a developer only tested the solution on certain boards and didn t care about other platforms platform allow is a hard filter preventing testing on anything outside of it it also makes tests hard to maintain since it needs constant updating with new boards being added which is not happening in most cases this evaluation is especially important in context of on target testing and selecting tier boards kernel tests will be crucial for such boards however it seems there might be quite many artificial skips due to platform allow misuse an example showing the problem the platforms in platform allow seem totally arbitrarily selected and blocks testing on vast majority of platforms | 0 |
66,097 | 19,982,224,682 | IssuesEvent | 2022-01-30 03:58:26 | idaholab/moose | https://api.github.com/repos/idaholab/moose | opened | CNSFV needs boundary checking | T: defect P: normal C: Modules/Navier Stokes | ## Bug Description
We accidentally set a BC to pressure instead of rho and were getting unexplainable negative temperatures forming
This could be avoided if CNSFV had the same BC checking as INSFV
## Steps to Reproduce
Do a problem with an outside outlet, forget a BC on the mass equation, or set it to an auxvariable
## Impact
Source of confusion
User friendliness | 1.0 | CNSFV needs boundary checking - ## Bug Description
We accidentally set a BC to pressure instead of rho and were getting unexplainable negative temperatures forming
This could be avoided if CNSFV had the same BC checking as INSFV
## Steps to Reproduce
Do a problem with an outside outlet, forget a BC on the mass equation, or set it to an auxvariable
## Impact
Source of confusion
User friendliness | non_priority | cnsfv needs boundary checking bug description we accidentally set a bc to pressure instead of rho and were getting unexplainable negative temperatures forming this could be avoided if cnsfv had the same bc checking as insfv steps to reproduce do a problem with an outside outlet forget a bc on the mass equation or set it to an auxvariable impact source of confusion user friendliness | 0 |
129,385 | 12,406,125,489 | IssuesEvent | 2020-05-21 18:33:02 | apache/trafficcontrol | https://api.github.com/repos/apache/trafficcontrol | closed | Update /servers/details to use data from the new tables | TO Client (Go) Traffic Ops documentation enhancement | ## I'm submitting a ...
- new feature / enhancement request
## Description
The `/servers/details` endpoint need to be updated to utilize data from the new tables added by whatever PR resolves #4611.
This depends on #4611
## Traffic Control components affected ...
- Documentation
- Traffic Ops
- Traffic Ops client (Go)
## Acceptance Criteria
* `/servers/details` in API 1.x:
* Uses the tables to provide the right legacy output for the `GET` method (should be unchanged)
* `/servers/details` in API 2.x:
* Provides the proper representations of cache servers as outlined in the blueprint for the `GET` method
* New behavior adheres to the API guidelines (where applicable)
* All behavior changes have been documented
* The Traffic Ops Go client has been updated (v2 only) to return the new structures
* Any associated unit and/or client/API integration tests have been updated to
test the new structure and all pass.
See the [Additional Server Interfaces blueprint](https://github.com/apache/trafficcontrol/blob/master/blueprints/multi-interface-servers.md#serversdetails) for details.
| 1.0 | Update /servers/details to use data from the new tables - ## I'm submitting a ...
- new feature / enhancement request
## Description
The `/servers/details` endpoint need to be updated to utilize data from the new tables added by whatever PR resolves #4611.
This depends on #4611
## Traffic Control components affected ...
- Documentation
- Traffic Ops
- Traffic Ops client (Go)
## Acceptance Criteria
* `/servers/details` in API 1.x:
* Uses the tables to provide the right legacy output for the `GET` method (should be unchanged)
* `/servers/details` in API 2.x:
* Provides the proper representations of cache servers as outlined in the blueprint for the `GET` method
* New behavior adheres to the API guidelines (where applicable)
* All behavior changes have been documented
* The Traffic Ops Go client has been updated (v2 only) to return the new structures
* Any associated unit and/or client/API integration tests have been updated to
test the new structure and all pass.
See the [Additional Server Interfaces blueprint](https://github.com/apache/trafficcontrol/blob/master/blueprints/multi-interface-servers.md#serversdetails) for details.
| non_priority | update servers details to use data from the new tables i m submitting a new feature enhancement request description the servers details endpoint need to be updated to utilize data from the new tables added by whatever pr resolves this depends on traffic control components affected documentation traffic ops traffic ops client go acceptance criteria servers details in api x uses the tables to provide the right legacy output for the get method should be unchanged servers details in api x provides the proper representations of cache servers as outlined in the blueprint for the get method new behavior adheres to the api guidelines where applicable all behavior changes have been documented the traffic ops go client has been updated only to return the new structures any associated unit and or client api integration tests have been updated to test the new structure and all pass see the for details | 0 |
10,635 | 3,411,599,493 | IssuesEvent | 2015-12-05 06:26:02 | KrisSiegel/msngr.js | https://api.github.com/repos/KrisSiegel/msngr.js | opened | Write up changelog for 4.0.0 | documentation | - [ ] Write up changelog for 4.0 outlining all of the additions, removals and breaking changes | 1.0 | Write up changelog for 4.0.0 - - [ ] Write up changelog for 4.0 outlining all of the additions, removals and breaking changes | non_priority | write up changelog for write up changelog for outlining all of the additions removals and breaking changes | 0 |
190,239 | 22,047,337,239 | IssuesEvent | 2022-05-30 04:18:48 | pazhanivel07/linux-4.19.72 | https://api.github.com/repos/pazhanivel07/linux-4.19.72 | closed | CVE-2020-25672 (High) detected in linux-yoctov5.4.51 - autoclosed | security vulnerability | ## CVE-2020-25672 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/linux-4.19.72/commit/ce28e4f7a922d93d9b737061ae46827305c8c30a">ce28e4f7a922d93d9b737061ae46827305c8c30a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak vulnerability was found in Linux kernel in llcp_sock_connect
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25672>CVE-2020-25672</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-25672">https://nvd.nist.gov/vuln/detail/CVE-2020-25672</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: linux-libc-headers - 5.13;linux-yocto - 4.8.26+gitAUTOINC+1c60e003c7_27efc3ba68,5.4.20+gitAUTOINC+c11911d4d1_f4d7dbafb1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-25672 (High) detected in linux-yoctov5.4.51 - autoclosed - ## CVE-2020-25672 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/linux-4.19.72/commit/ce28e4f7a922d93d9b737061ae46827305c8c30a">ce28e4f7a922d93d9b737061ae46827305c8c30a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/llcp_sock.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak vulnerability was found in Linux kernel in llcp_sock_connect
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25672>CVE-2020-25672</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-25672">https://nvd.nist.gov/vuln/detail/CVE-2020-25672</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: linux-libc-headers - 5.13;linux-yocto - 4.8.26+gitAUTOINC+1c60e003c7_27efc3ba68,5.4.20+gitAUTOINC+c11911d4d1_f4d7dbafb1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux autoclosed cve high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files net nfc llcp sock c net nfc llcp sock c vulnerability details a memory leak vulnerability was found in linux kernel in llcp sock connect publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux libc headers linux yocto gitautoinc gitautoinc step up your open source security game with whitesource | 0 |
144,311 | 11,612,220,549 | IssuesEvent | 2020-02-26 08:31:41 | swiss-art-research-net/rdmi | https://api.github.com/repos/swiss-art-research-net/rdmi | closed | WKT | Testing Needed fix | This does not produce WKT really. The structure should be expressed according to the format
> POINT(lat long)
example:
> POINT(7.029336 46.287932)
I do presume we do need one link just having 4 value:
constant "POINT("
xpath plSubstance_tgn_lat
xpath plSubstance_tgn_long
constant ")"
https://github.com/swiss-art-research-net/rdmi/blob/92add6fb2f43e29e4d9ed49dc2ebcb12b1502459/3M_Mapping/Reference_data_model_mapping/smartup/mappings-Place.x3ml#L167-L208 | 1.0 | WKT - This does not produce WKT really. The structure should be expressed according to the format
> POINT(lat long)
example:
> POINT(7.029336 46.287932)
I do presume we do need one link just having 4 value:
constant "POINT("
xpath plSubstance_tgn_lat
xpath plSubstance_tgn_long
constant ")"
https://github.com/swiss-art-research-net/rdmi/blob/92add6fb2f43e29e4d9ed49dc2ebcb12b1502459/3M_Mapping/Reference_data_model_mapping/smartup/mappings-Place.x3ml#L167-L208 | non_priority | wkt this does not produce wkt really the structure should be expressed according to the format point lat long example point i do presume we do need one link just having value constant point xpath plsubstance tgn lat xpath plsubstance tgn long constant | 0 |
149,660 | 13,285,960,679 | IssuesEvent | 2020-08-24 08:59:12 | HyperGAN/HyperGAN | https://api.github.com/repos/HyperGAN/HyperGAN | closed | --device cpu doesn't work | bug documentation | This flag in general doesn't work correctly since the move to pytorch.
CPU training should error out. We should consider making CPU sampling work however. | 1.0 | --device cpu doesn't work - This flag in general doesn't work correctly since the move to pytorch.
CPU training should error out. We should consider making CPU sampling work however. | non_priority | device cpu doesn t work this flag in general doesn t work correctly since the move to pytorch cpu training should error out we should consider making cpu sampling work however | 0 |
24,379 | 11,034,688,252 | IssuesEvent | 2019-12-07 07:44:51 | benchmarkdebricked/vue | https://api.github.com/repos/benchmarkdebricked/vue | opened | WS-2019-0310 (Medium) detected in https-proxy-agent-1.0.0.tgz | security vulnerability | ## WS-2019-0310 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https-proxy-agent-1.0.0.tgz</b></p></summary>
<p>An HTTP(s) proxy `http.Agent` implementation for HTTPS</p>
<p>Library home page: <a href="https://registry.npmjs.org/https-proxy-agent/-/https-proxy-agent-1.0.0.tgz">https://registry.npmjs.org/https-proxy-agent/-/https-proxy-agent-1.0.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/vue/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/vue/node_modules/proxy-agent/node_modules/https-proxy-agent/package.json</p>
<p>
Dependency Hierarchy:
- nightwatch-0.9.21.tgz (Root Library)
- proxy-agent-2.0.0.tgz
- :x: **https-proxy-agent-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/vue/commit/2db5c80c9d731fbf55bff8418d8fa8226d53a915">2db5c80c9d731fbf55bff8418d8fa8226d53a915</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a Machine-In-The-Middle vulnerability found in https-proxy-agent before 2.2.3. There is a failure of TLS enforcement on the socket. Attacker may intercept unencrypted communications.
<p>Publish Date: 2019-12-01
<p>URL: <a href=https://github.com/TooTallNate/node-https-proxy-agent/commit/36d8cf509f877fa44f4404fce57ebaf9410fe51b>WS-2019-0310</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1184">https://www.npmjs.com/advisories/1184</a></p>
<p>Release Date: 2019-12-01</p>
<p>Fix Resolution: https-proxy-agent - 2.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0310 (Medium) detected in https-proxy-agent-1.0.0.tgz - ## WS-2019-0310 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https-proxy-agent-1.0.0.tgz</b></p></summary>
<p>An HTTP(s) proxy `http.Agent` implementation for HTTPS</p>
<p>Library home page: <a href="https://registry.npmjs.org/https-proxy-agent/-/https-proxy-agent-1.0.0.tgz">https://registry.npmjs.org/https-proxy-agent/-/https-proxy-agent-1.0.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/vue/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/vue/node_modules/proxy-agent/node_modules/https-proxy-agent/package.json</p>
<p>
Dependency Hierarchy:
- nightwatch-0.9.21.tgz (Root Library)
- proxy-agent-2.0.0.tgz
- :x: **https-proxy-agent-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/vue/commit/2db5c80c9d731fbf55bff8418d8fa8226d53a915">2db5c80c9d731fbf55bff8418d8fa8226d53a915</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a Machine-In-The-Middle vulnerability found in https-proxy-agent before 2.2.3. There is a failure of TLS enforcement on the socket. Attacker may intercept unencrypted communications.
<p>Publish Date: 2019-12-01
<p>URL: <a href=https://github.com/TooTallNate/node-https-proxy-agent/commit/36d8cf509f877fa44f4404fce57ebaf9410fe51b>WS-2019-0310</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1184">https://www.npmjs.com/advisories/1184</a></p>
<p>Release Date: 2019-12-01</p>
<p>Fix Resolution: https-proxy-agent - 2.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in https proxy agent tgz ws medium severity vulnerability vulnerable library https proxy agent tgz an http s proxy http agent implementation for https library home page a href path to dependency file tmp ws scm vue package json path to vulnerable library tmp ws scm vue node modules proxy agent node modules https proxy agent package json dependency hierarchy nightwatch tgz root library proxy agent tgz x https proxy agent tgz vulnerable library found in head commit a href vulnerability details there is a machine in the middle vulnerability found in https proxy agent before there is a failure of tls enforcement on the socket attacker may intercept unencrypted communications publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution https proxy agent step up your open source security game with whitesource | 0 |
8,926 | 3,808,649,700 | IssuesEvent | 2016-03-25 16:02:43 | jig08/sQuick_new | https://api.github.com/repos/jig08/sQuick_new | opened | Renaming classes and variables | code refactoring | Renaming classes and variables so that their names are *intention revealing*
Courtesy: @theseion | 1.0 | Renaming classes and variables - Renaming classes and variables so that their names are *intention revealing*
Courtesy: @theseion | non_priority | renaming classes and variables renaming classes and variables so that their names are intention revealing courtesy theseion | 0 |
107,803 | 23,483,520,372 | IssuesEvent | 2022-08-17 12:42:48 | trezor/trezor-firmware | https://api.github.com/repos/trezor/trezor-firmware | opened | Model R: EIP712 signing flow | code tr | Currently, some of the features are missing - for example, the possibility to cancel viewing a field while scrolling, or the overall possibility to cancel it at the beginning (as uncovered by device tests).
It goes mostly together with the `should_show_more` functionality.
There is also a question of whether to support EIP712 full-data viewing or not - as on `model 1` we have only blind signing because of screen-size limitations, and `model R` has the same issue. | 1.0 | Model R: EIP712 signing flow - Currently, some of the features are missing - for example, the possibility to cancel viewing a field while scrolling, or the overall possibility to cancel it at the beginning (as uncovered by device tests).
It goes mostly together with the `should_show_more` functionality.
There is also a question of whether to support EIP712 full-data viewing or not - as on `model 1` we have only blind signing because of screen-size limitations, and `model R` has the same issue. | non_priority | model r signing flow currently some of the features are missing for example the possibility to cancel viewing a field while scrolling or the overall possibility to cancel it at the beginning as uncovered by device tests it goes mostly together with the should show more functionality there is also a question of whether to support full data viewing or not as on model we have only blind signing because of screen size limitations and model r has the same issue | 0 |
232,920 | 18,924,291,940 | IssuesEvent | 2021-11-17 07:42:57 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | reopened | Extension pty terminals should respect dimension overrides | integration-test-failure insiders-released | https://dev.azure.com/monacotools/Monaco/_build/results?buildId=142815&view=logs&j=4d2898ab-dfbe-557e-92e7-aaac158fdd2f&t=dccbe8b6-2cf2-56ce-ca99-720e7791a9c0&l=423
```
1) vscode API - terminal
Terminal
Extension pty terminals
should respect dimension overrides:
Error: Timeout of 60000ms exceeded. For async tests and hooks, ensure "done()" is called; if returning a Promise, ensure it resolves. (/__w/1/s/extensions/vscode-api-tests/out/singlefolder-tests/terminal.test.js)
at listOnTimeout (internal/timers.js:554:17)
at processTimers (internal/timers.js:497:7)
``` | 1.0 | Extension pty terminals should respect dimension overrides - https://dev.azure.com/monacotools/Monaco/_build/results?buildId=142815&view=logs&j=4d2898ab-dfbe-557e-92e7-aaac158fdd2f&t=dccbe8b6-2cf2-56ce-ca99-720e7791a9c0&l=423
```
1) vscode API - terminal
Terminal
Extension pty terminals
should respect dimension overrides:
Error: Timeout of 60000ms exceeded. For async tests and hooks, ensure "done()" is called; if returning a Promise, ensure it resolves. (/__w/1/s/extensions/vscode-api-tests/out/singlefolder-tests/terminal.test.js)
at listOnTimeout (internal/timers.js:554:17)
at processTimers (internal/timers.js:497:7)
``` | non_priority | extension pty terminals should respect dimension overrides vscode api terminal terminal extension pty terminals should respect dimension overrides error timeout of exceeded for async tests and hooks ensure done is called if returning a promise ensure it resolves w s extensions vscode api tests out singlefolder tests terminal test js at listontimeout internal timers js at processtimers internal timers js | 0 |
101,043 | 16,490,752,827 | IssuesEvent | 2021-05-25 03:12:42 | valdisiljuconoks/episerverless | https://api.github.com/repos/valdisiljuconoks/episerverless | opened | WS-2019-0332 (Medium) detected in handlebars-1.3.0.tgz | security vulnerability | ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-1.3.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-1.3.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-1.3.0.tgz</a></p>
<p>Path to dependency file: episerverless/src/Web/modules/_protected/Shell/Shell/10.10.6.0/ClientResources/lib/xstyle/package.json</p>
<p>Path to vulnerable library: episerverless/packages/EPiServer.CMS.UI.10.10.6/content/modules/_protected/Shell/Shell/10.10.6.0/ClientResources/lib/xstyle/node_modules/handlebars/package.json,episerverless/packages/EPiServer.CMS.UI.10.10.6/content/modules/_protected/Shell/Shell/10.10.6.0/ClientResources/lib/xstyle/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- intern-geezer-2.2.3.tgz (Root Library)
- istanbul-0.2.16.tgz
- :x: **handlebars-1.3.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.
<p>Publish Date: 2019-11-17
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7>WS-2019-0332</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0332 (Medium) detected in handlebars-1.3.0.tgz - ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-1.3.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-1.3.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-1.3.0.tgz</a></p>
<p>Path to dependency file: episerverless/src/Web/modules/_protected/Shell/Shell/10.10.6.0/ClientResources/lib/xstyle/package.json</p>
<p>Path to vulnerable library: episerverless/packages/EPiServer.CMS.UI.10.10.6/content/modules/_protected/Shell/Shell/10.10.6.0/ClientResources/lib/xstyle/node_modules/handlebars/package.json,episerverless/packages/EPiServer.CMS.UI.10.10.6/content/modules/_protected/Shell/Shell/10.10.6.0/ClientResources/lib/xstyle/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- intern-geezer-2.2.3.tgz (Root Library)
- istanbul-0.2.16.tgz
- :x: **handlebars-1.3.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.
<p>Publish Date: 2019-11-17
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7>WS-2019-0332</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in handlebars tgz ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file episerverless src web modules protected shell shell clientresources lib xstyle package json path to vulnerable library episerverless packages episerver cms ui content modules protected shell shell clientresources lib xstyle node modules handlebars package json episerverless packages episerver cms ui content modules protected shell shell clientresources lib xstyle node modules handlebars package json dependency hierarchy intern geezer tgz root library istanbul tgz x handlebars tgz vulnerable library vulnerability details arbitrary code execution vulnerability found in handlebars before lookup helper fails to validate templates attack may submit templates that execute arbitrary javascript in the system it is due to an incomplete fix for a ws publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
304,350 | 23,061,904,675 | IssuesEvent | 2022-07-25 10:41:15 | julia-actions/julia-runtest | https://api.github.com/repos/julia-actions/julia-runtest | opened | Document kwargs.jl | documentation | Currently it's not clear what this file does, which makes following and understand the script in `action.yml` a lot harder than it needs to be. A brief description would improve this already. | 1.0 | Document kwargs.jl - Currently it's not clear what this file does, which makes following and understand the script in `action.yml` a lot harder than it needs to be. A brief description would improve this already. | non_priority | document kwargs jl currently it s not clear what this file does which makes following and understand the script in action yml a lot harder than it needs to be a brief description would improve this already | 0 |
298,343 | 22,492,129,288 | IssuesEvent | 2022-06-23 03:05:48 | cogent3/cogent3 | https://api.github.com/repos/cogent3/cogent3 | opened | document using a dotplot to evaluate alignment quality | documentation enhancement help wanted | **Describe the solution you'd like**
The dotplot algorithm can show both matching segments between sequences AND the path an alignment algorithm has chosen.
Write a gallery document that shows this feature, explaining how it's useful.
The document should demonstrate using an aligner with bad parameter values. Apply it to the brca1.fasta file. Embellish the following with explanatory text of alignment parameters, what a dotplot shows, how to modify the dotplot display, etc...
```python
from cogent3 import load_aligned_seqs
from cogent3.app.align import progressive_align
seqs = load_aligned_seqs("/Users/gavin/repos/Cogent3/doc/data/brca1.fasta", moltype="dna").degap()
seqs = seqs.take_seqs(['LeafNose',
'FalseVamp',
'RoundEare',
'Sloth',
'Anteater',
'HairyArma'])
# bad idea! make gap extension unlikely
aligner = progressive_align("nucleotide", indel_length=1e-9, indel_rate=1e-2)
aln = aligner(seqs)
aln[2200:2500].dotplot("HairyArma", "RoundEare").show()
aln[2270:2500] # showing poorly aligned segment
# run with aligner defaults
aligner = progressive_align("nucleotide")
aln = aligner(seqs)
aln[2200:2500].dotplot("HairyArma", "RoundEare").show()
aln[2270:2500] # showing poorly aligned segment
``` | 1.0 | document using a dotplot to evaluate alignment quality - **Describe the solution you'd like**
The dotplot algorithm can show both matching segments between sequences AND the path an alignment algorithm has chosen.
Write a gallery document that shows this feature, explaining how it's useful.
The document should demonstrate using an aligner with bad parameter values. Apply it to the brca1.fasta file. Embellish the following with explanatory text of alignment parameters, what a dotplot shows, how to modify the dotplot display, etc...
```python
from cogent3 import load_aligned_seqs
from cogent3.app.align import progressive_align
seqs = load_aligned_seqs("/Users/gavin/repos/Cogent3/doc/data/brca1.fasta", moltype="dna").degap()
seqs = seqs.take_seqs(['LeafNose',
'FalseVamp',
'RoundEare',
'Sloth',
'Anteater',
'HairyArma'])
# bad idea! make gap extension unlikely
aligner = progressive_align("nucleotide", indel_length=1e-9, indel_rate=1e-2)
aln = aligner(seqs)
aln[2200:2500].dotplot("HairyArma", "RoundEare").show()
aln[2270:2500] # showing poorly aligned segment
# run with aligner defaults
aligner = progressive_align("nucleotide")
aln = aligner(seqs)
aln[2200:2500].dotplot("HairyArma", "RoundEare").show()
aln[2270:2500] # showing poorly aligned segment
``` | non_priority | document using a dotplot to evaluate alignment quality describe the solution you d like the dotplot algorithm can show both matching segments between sequences and the path an alignment algorithm has chosen write a gallery document that shows this feature explaining how it s useful the document should demonstrate using an aligner with bad parameter values apply it to the fasta file embellish the following with explanatory text of alignment parameters what a dotplot shows how to modify the dotplot display etc python from import load aligned seqs from app align import progressive align seqs load aligned seqs users gavin repos doc data fasta moltype dna degap seqs seqs take seqs leafnose falsevamp roundeare sloth anteater hairyarma bad idea make gap extension unlikely aligner progressive align nucleotide indel length indel rate aln aligner seqs aln dotplot hairyarma roundeare show aln showing poorly aligned segment run with aligner defaults aligner progressive align nucleotide aln aligner seqs aln dotplot hairyarma roundeare show aln showing poorly aligned segment | 0 |
58,850 | 14,352,073,235 | IssuesEvent | 2020-11-30 03:15:46 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 93: gnome-shell-3.34.5: 2 advisories [4.3] | 1.severity: security | [search](https://search.nix.gsc.io/?q=gnome-shell&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=gnome-shell+in%3Apath&type=Code)
* [ ] [CVE-2019-3820](https://nvd.nist.gov/vuln/detail/CVE-2019-3820) CVSSv3=4.3 (nixos-20.03)
* [ ] [CVE-2020-17489](https://nvd.nist.gov/vuln/detail/CVE-2020-17489) CVSSv3=4.3 (nixos-20.03)
Scanned versions: nixos-20.03: 0d0660fde3b.
Cc @hedning
Cc @lethalman
Cc @worldofpeace
| True | Vulnerability roundup 93: gnome-shell-3.34.5: 2 advisories [4.3] - [search](https://search.nix.gsc.io/?q=gnome-shell&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=gnome-shell+in%3Apath&type=Code)
* [ ] [CVE-2019-3820](https://nvd.nist.gov/vuln/detail/CVE-2019-3820) CVSSv3=4.3 (nixos-20.03)
* [ ] [CVE-2020-17489](https://nvd.nist.gov/vuln/detail/CVE-2020-17489) CVSSv3=4.3 (nixos-20.03)
Scanned versions: nixos-20.03: 0d0660fde3b.
Cc @hedning
Cc @lethalman
Cc @worldofpeace
| non_priority | vulnerability roundup gnome shell advisories nixos nixos scanned versions nixos cc hedning cc lethalman cc worldofpeace | 0 |
101,677 | 11,254,459,619 | IssuesEvent | 2020-01-11 23:55:59 | aws-samples/aws-serverless-airline-booking | https://api.github.com/repos/aws-samples/aws-serverless-airline-booking | closed | [Docs] Add README for back-end | documentation | After bonus episode, push README upstream to each back-end service, including integration tests instructions for those trying to run that locally.
**Tasks**
* **Catalog**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
* **Booking**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
* **Loyalty**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
* **Payment**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
| 1.0 | [Docs] Add README for back-end - After bonus episode, push README upstream to each back-end service, including integration tests instructions for those trying to run that locally.
**Tasks**
* **Catalog**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
* **Booking**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
* **Loyalty**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
* **Payment**
- [x] Add Implementation
- [x] Add high-level architecture
- [x] Add Integrations
- [x] Add Tech debt/decision making thoughts
| non_priority | add readme for back end after bonus episode push readme upstream to each back end service including integration tests instructions for those trying to run that locally tasks catalog add implementation add high level architecture add integrations add tech debt decision making thoughts booking add implementation add high level architecture add integrations add tech debt decision making thoughts loyalty add implementation add high level architecture add integrations add tech debt decision making thoughts payment add implementation add high level architecture add integrations add tech debt decision making thoughts | 0 |
264,662 | 28,211,102,696 | IssuesEvent | 2023-04-05 04:30:39 | osrf/ros2_test_cases | https://api.github.com/repos/osrf/ros2_test_cases | opened | Introducing ros2 security | tutorials security fastdds debian jammy amd64 generation-1 advanced docs iron | Check the documentation for the 'Introducing ros2 security' page
## Setup
- DDS vendor: FastDDS
- BuildType: Debian
- Os: Ubuntu Jammy
- Chip: Amd64
## Links
- [Introducing ros2 security page](https://docs.ros.org/en/rolling/Tutorials/Advanced/Security/Introducing-ros2-security.html)
## Checks
- [ ] **I was able to follow the documentation.**
- [ ] **The documentation seemed clear to me.**
- [ ] **The documentation didn't have any obvious errors.**
---
*You can find the code used to generate this test case [here](https://github.com/audrow/yatm)* | True | Introducing ros2 security - Check the documentation for the 'Introducing ros2 security' page
## Setup
- DDS vendor: FastDDS
- BuildType: Debian
- Os: Ubuntu Jammy
- Chip: Amd64
## Links
- [Introducing ros2 security page](https://docs.ros.org/en/rolling/Tutorials/Advanced/Security/Introducing-ros2-security.html)
## Checks
- [ ] **I was able to follow the documentation.**
- [ ] **The documentation seemed clear to me.**
- [ ] **The documentation didn't have any obvious errors.**
---
*You can find the code used to generate this test case [here](https://github.com/audrow/yatm)* | non_priority | introducing security check the documentation for the introducing security page setup dds vendor fastdds buildtype debian os ubuntu jammy chip links checks i was able to follow the documentation the documentation seemed clear to me the documentation didn t have any obvious errors you can find the code used to generate this test case | 0 |
442,976 | 30,868,790,053 | IssuesEvent | 2023-08-03 09:51:36 | HishamWattar/cooks-kingdom | https://api.github.com/repos/HishamWattar/cooks-kingdom | closed | Add admin endpoint api/admin/user/approve-chef/:id | documentation API tests | This endpoint will approve a chef request in case a user wanted to become a chef | 1.0 | Add admin endpoint api/admin/user/approve-chef/:id - This endpoint will approve a chef request in case a user wanted to become a chef | non_priority | add admin endpoint api admin user approve chef id this endpoint will approve a chef request in case a user wanted to become a chef | 0 |
104,326 | 16,613,613,523 | IssuesEvent | 2021-06-02 14:18:18 | Thanraj/linux-4.1.15 | https://api.github.com/repos/Thanraj/linux-4.1.15 | opened | CVE-2019-2024 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2019-2024 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/media/usb/em28xx/em28xx-dvb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/media/usb/em28xx/em28xx-dvb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In em28xx_unregister_dvb of em28xx-dvb.c, there is a possible use after free issue. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-111761954References: Upstream kernel
<p>Publish Date: 2019-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2024>CVE-2019-2024</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d">https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d</a></p>
<p>Release Date: 2019-03-05</p>
<p>Fix Resolution: v4.16-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-2024 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2019-2024 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Thanraj/linux-4.1.15/commits/5e3fb3e332499e1ad10a0969e55582af1027b085">5e3fb3e332499e1ad10a0969e55582af1027b085</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/media/usb/em28xx/em28xx-dvb.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linux-4.1.15/drivers/media/usb/em28xx/em28xx-dvb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In em28xx_unregister_dvb of em28xx-dvb.c, there is a possible use after free issue. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-111761954References: Upstream kernel
<p>Publish Date: 2019-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2024>CVE-2019-2024</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d">https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d</a></p>
<p>Release Date: 2019-03-05</p>
<p>Fix Resolution: v4.16-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files linux drivers media usb dvb c linux drivers media usb dvb c vulnerability details in unregister dvb of dvb c there is a possible use after free issue this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android kernelandroid id a upstream kernel publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
134,840 | 30,196,173,174 | IssuesEvent | 2023-07-04 21:25:25 | cashubtc/cashu | https://api.github.com/repos/cashubtc/cashu | opened | [Wallet] Find a way to properly give a wallet a name | wallet code health | Right now we initialize a wallet with a db path and a name. The treatment is very messy (we use os.path.join, we use ctx["WALLET_NAME"] and all sorts of things). Find a better way to do this. | 1.0 | [Wallet] Find a way to properly give a wallet a name - Right now we initialize a wallet with a db path and a name. The treatment is very messy (we use os.path.join, we use ctx["WALLET_NAME"] and all sorts of things). Find a better way to do this. | non_priority | find a way to properly give a wallet a name right now we initialize a wallet with a db path and a name the treatment is very messy we use os path join we use ctx and all sorts of things find a better way to do this | 0 |
137,596 | 20,171,089,286 | IssuesEvent | 2022-02-10 10:28:23 | owncloud/web | https://api.github.com/repos/owncloud/web | closed | Spaces polishing | feature:files Topic:UX-Design Interaction:Squad | those kind of buttons have a clickable size of 40x40 px in the design
nested icon size is 24x24
visual prominence should be taken back via less prominent bg color, but this can be part of design polishing imo


_Originally posted by @tbsbdr in https://github.com/owncloud/web/pull/6254#r794407285_
Link to all Figma Designs:
https://www.figma.com/file/EqAiB1wY7cYaMaitjyzup3/Current-oC-Web-UI-Kit-(WIP)?node-id=1450%3A135419
| 1.0 | Spaces polishing - those kind of buttons have a clickable size of 40x40 px in the design
nested icon size is 24x24
visual prominence should be taken back via less prominent bg color, but this can be part of design polishing imo


_Originally posted by @tbsbdr in https://github.com/owncloud/web/pull/6254#r794407285_
Link to all Figma Designs:
https://www.figma.com/file/EqAiB1wY7cYaMaitjyzup3/Current-oC-Web-UI-Kit-(WIP)?node-id=1450%3A135419
| non_priority | spaces polishing those kind of buttons have a clickable size of px in the design nested icon size is visual prominence should be taken back via less prominent bg color but this can be part of design polishing imo originally posted by tbsbdr in link to all figma designs | 0 |
48,650 | 6,100,757,436 | IssuesEvent | 2017-06-20 13:19:17 | geetsisbac/WCVVENIXYFVIRBXH3BYTI6TE | https://api.github.com/repos/geetsisbac/WCVVENIXYFVIRBXH3BYTI6TE | reopened | IQZ4wnxOD3RmRqTriUexFepK46VzgOOKKRW9j3cJKc8H+ST710dDfRVvshGwLhMxjbRsP4gTx8C0hByiObJppg9NDpWTUbM9/jmumaX+KB5zOeoNWTkcZ4pZ9B3Et8FO7W4mBP02r323zbPdwaWMicoA0/Z3vS54T2nF9TN5I+k= | design | Dr50xeuv2Acl0q9ROwapAY4wUMDoEiMANh4NQI9PyA91CzBv1UWtr6LoqnfbmVUUFCwU9+CAzOZJpS4SWfmGPW83jgmx9Nl2MQAsJ+yn6dGq0IS/XCkMikM+AAJdjReUYPw5ZYBahYnUPnl08H22Kl+B1wLUrVVkmcB2AtzKoYxuYhFiEOoQ6+musIX9yeQA77eEE+xNvT4cMOgouCltuTx2A2UWrpxhzLFC0xelUjoZjbch/0QT858af7QjoFYL77eEE+xNvT4cMOgouCltubMcCY6GdNKRfbVLOhj8fOf55/AnLBlB6An9UCPSnpUBdciFp108T++B9VwQlOWuf++3hBPsTb0+HDDoKLgpbbnPXvcLTT3RHfAaGUjVd7JCEipEYGMW9fbP8htQNd1pHZ2SEd63WedGcqKonXyT9gnvt4QT7E29Phww6Ci4KW25PnEGieLhlIBDxUTMCkuZqW5wzulLme6BKRSEwHnNjOzvt4QT7E29Phww6Ci4KW250Eyc6G54k/qMRwxyc0ozTjKMMGbY2nVVTLSXy+XmS63vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltua7DQwG853iO6wlFpjQ/X2ggSQgtnuY21BMTCzBQDy1Z77eEE+xNvT4cMOgouCltuZBInrbA4JnK3X1Czj5aHK99pi8rwuk0PZKZlhK1PIdGoey9Fkx2EWQupmZ0J6FAO62ZuXetzVxtx91MaDTDiTLITsMsFLnrvxID6EIxMkBkOPlyxvrRR2puoLiBVE3LTxJ/FZJwt6sHt7GsYZqm+uzvt4QT7E29Phww6Ci4KW25xrJ+xKqXMIDAAXP5WCohBSpLif/DI/0ohoauAMv5O6yxZkkIbfNY6KxAjT8C+/RQ77eEE+xNvT4cMOgouCltuQhRFTVowH6siX9Qq9A6leJpV8kvge7pqUsmLCPC8CZrjHnmUK0uNkSu1UZ/sUa7JO+3hBPsTb0+HDDoKLgpbblP8+wseEXEO4THOWsOU9xHhPxwvtoEJI9sYhXEm9VFe8C4ou8ZbUjBUIx1QL4Oi5qHzDGAfZh8YLinwG4NLo74CRFhhGSECQkoQYkK2L13aSGd4gjRTezSggyzYU82Rofvt4QT7E29Phww6Ci4KW25WyIPZ/PIw0EM7DV7Gfu0tLZZ1l0Lfxs3XIep3cY4AN+bYkW7qtaB0PvuL6v6dznFHWg7t/V64PpXzecMepVxcZmrDV/4NadPGYsasD1ayGZi4VtfgN8+lUpMkG1aNeh+77eEE+xNvT4cMOgouCltuYPKg5W9RwGrFaG0Mf+jWZJaviAJVfzTv0k28HJAlBVQ77eEE+xNvT4cMOgouCltuVzsTsKfyK5HqOAFBdw9BPyARP1tkbZK3Ki0B1OGgRbW77eEE+xNvT4cMOgouCltuVVQQA5GyGtfdOYyKzc0CYQ6Wvc4UVJVJVXk0ZDXgPz0anz7e5YZE8LxkdS8NFK0Pk58ykVlHQjefmgXAwAfkcTvt4QT7E29Phww6Ci4KW25unm478zrItxbfHbA3kyD3Oz36bZtoa1aGmV/5CRCCo8Vdie69yWV1ocLf2HxgrAiccjEnk6+mGKZItXFbyhBR47iPIjME347zW9extBftV7Zs9fX9XfWElNf3XdS980J77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbn01vYnq4sZ7sKoJd5JynLmFWA1GG2Ks8G9at0y8n5aPO+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25W94i0cXTnc5urOLIwechBBA0F4GcyZ4h51ycDMLCsTJM25S+9WnxwIrIxkwoY6eo3IJMsVpyLjAiQX5trNbxt04Rq1v5/aZRqCKe7ZR1BnXrN/FyTUa04DDGwOiZTuCfDjmNcEgRkiqUz3q5bFcS8CEJp+DxQwHdbRyVwvamPnzvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuS00i6o8imDzMsMriQ3HqdhGLmDyl4I3/Lpvs3E5JS6577eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbblFXEKYM/3EFnWVa3oAlYEKWuV1Vr6n78j8/VqtQgHjbkASPQPvQAVPh8RUwBr/7bTvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltufi1hv6hYZcLmz3k5hkFVPfC3PSBne/oOpF5J/W07yka77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbmT6Ob5AVxPxy0PFrYu4WaiWWEoMugOjOdTKG4+UD1sS/MUBaK++upIE/GN8jJrfkHvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuXt0C0e1EgZyaACPRcdaCl5AUl982wZpsJahohl8gYYH77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbmLZzYIRXKJG4Ik10H+xIRHg0Wtbvv+iEF36pqbOJHrCbYGUrjuuFxYk+Eid839EnPvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuUw1WYU0gfY+U7J0QSYXqaz6GvknJfGu/yJL+C/wmRCoXE12hNex6FfiyMrMArVvPe+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25aPOoISEra5Mnkd78SoqwuxNBef9NBP4YPBguXn3K9kLvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuQooWV+7Hx4r80fzF5bsW1FeqyDFe+xFAIry5g4MrdpyMsbnFt6fLhj/U47KCnnTje+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25+wT9o3ofnHRymfRRMkeviSpmT+b57v+t3TEJOtR2/5zvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuZ/yU7bzT+snMuvg6I+Pu8wpAi/006OA/NsX5mrIxe9IyyrCGUHEjQ6IVirQwtG51++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25xgoR+RK16dXqmZo4Z4TZEb3dA5bw7IsaTuMQehBRWpzvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuUZgHBNlnIouVPLVvu91/P2uw6FDGD/JGjmTBD5pTZwzXFs7c58sjuE958Ur35th3++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25dyAEv5hq/A6kPOk5Nrvx7smIjBIFptCG+UMXwOKtuq/vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuVveItHF053ObqziyMHnIQTaDRkTyGtlCkXmXexprTxfzzNdZeeIqqgYSF7vVAWd+++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25M0yr7sHvIh4xgoiBnf40MGT376U54aiaGKfm+iLWQDkhCafg8UMB3W0clcL2pj5877eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbnqAxz74YXLHBybr19/6ON+QTE8LU6xJq4YUYgho+h/s++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25RVxCmDP9xBZ1lWt6AJWBCsKUqUReqcVRjQxa8ZV1HLtAEj0D70AFT4fEVMAa/+2077eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbl8zCHD9RXw+FpZCyLf/iJ4Vnvi5xyvhvs7Cd8ix8ivqO+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25qMSz1dBT8ThI/rguivM2JD5s2GcPknPFq9ZXec11Iv+CfxGUc6izJR+VsnJkTQv377eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbmvorLNMx322KawcozPgKHbYkq8uYK9s/KWghqrzWF8/e+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25i2c2CEVyiRuCJNdB/sSER3IlIcZJd9BO6R63CnHBpwazVN75+tO8VF0mmk/bOYRV77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbn/4H10Ua6te0/rhxO8P4B4jZPz/03uSGIUgxjlQD/WNlxNdoTXsehX4sjKzAK1bz3vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltucC28WZlJlLJ6c33PDoXLntxM/z/D6gGG/Uuwxtf1bBv77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbkp6Lh/6aABXmR/cerPOZDKAZFKuFl6MpAKw4xTzioNnjLG5xbeny4Y/1OOygp5043vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuRlRFzb3nC2B+I8/Rv565+X7we28qQw/MEkwpTO32udV77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbkF/X+8+bZQf/q821d5iOgMoaBq8OzxFtkWYy+P4boeLx/cJvMaVVcyCnqzz9w3/RHvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltueIUrs4IpSphGvTiJ7wfrQ3XMA+phFj+H8Em3BSiaO2d77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbnQ1F9lPnOhXUBlYNfmnUPEoR0qFJHLehawhnZaoKjPHzyQN/ljsHGjYM74NFZQIkLvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuXsvYeGFbFvJUryKDXtkT2JRWo8668Qs0hfaE9f3qKmp77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbblb3iLRxdOdzm6s4sjB5yEEojIBBeRdCIT4kELHejwRa3DcriTfCm8z4na60Ly0rIvvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuXhmyC0b7xW80bUR5TxwyMd8bX59WAEv60F1eIY8N8zTmTkalv1ix+vni7XI8iSMU19TDfq889ufX1DbgQTPPoZvshWBqIIdhIDy1TJ/If+ccCHkKduKB6bsHluEpg7tu5JbbxM+Fyd3kVj623AkTAeNWT1AnYK9EUK+IbKXdVJmbZmM7GN21NDNJv/tvfgvyQ== | 1.0 | IQZ4wnxOD3RmRqTriUexFepK46VzgOOKKRW9j3cJKc8H+ST710dDfRVvshGwLhMxjbRsP4gTx8C0hByiObJppg9NDpWTUbM9/jmumaX+KB5zOeoNWTkcZ4pZ9B3Et8FO7W4mBP02r323zbPdwaWMicoA0/Z3vS54T2nF9TN5I+k= - Dr50xeuv2Acl0q9ROwapAY4wUMDoEiMANh4NQI9PyA91CzBv1UWtr6LoqnfbmVUUFCwU9+CAzOZJpS4SWfmGPW83jgmx9Nl2MQAsJ+yn6dGq0IS/XCkMikM+AAJdjReUYPw5ZYBahYnUPnl08H22Kl+B1wLUrVVkmcB2AtzKoYxuYhFiEOoQ6+musIX9yeQA77eEE+xNvT4cMOgouCltuTx2A2UWrpxhzLFC0xelUjoZjbch/0QT858af7QjoFYL77eEE+xNvT4cMOgouCltubMcCY6GdNKRfbVLOhj8fOf55/AnLBlB6An9UCPSnpUBdciFp108T++B9VwQlOWuf++3hBPsTb0+HDDoKLgpbbnPXvcLTT3RHfAaGUjVd7JCEipEYGMW9fbP8htQNd1pHZ2SEd63WedGcqKonXyT9gnvt4QT7E29Phww6Ci4KW25PnEGieLhlIBDxUTMCkuZqW5wzulLme6BKRSEwHnNjOzvt4QT7E29Phww6Ci4KW250Eyc6G54k/qMRwxyc0ozTjKMMGbY2nVVTLSXy+XmS63vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltua7DQwG853iO6wlFpjQ/X2ggSQgtnuY21BMTCzBQDy1Z77eEE+xNvT4cMOgouCltuZBInrbA4JnK3X1Czj5aHK99pi8rwuk0PZKZlhK1PIdGoey9Fkx2EWQupmZ0J6FAO62ZuXetzVxtx91MaDTDiTLITsMsFLnrvxID6EIxMkBkOPlyxvrRR2puoLiBVE3LTxJ/FZJwt6sHt7GsYZqm+uzvt4QT7E29Phww6Ci4KW25xrJ+xKqXMIDAAXP5WCohBSpLif/DI/0ohoauAMv5O6yxZkkIbfNY6KxAjT8C+/RQ77eEE+xNvT4cMOgouCltuQhRFTVowH6siX9Qq9A6leJpV8kvge7pqUsmLCPC8CZrjHnmUK0uNkSu1UZ/sUa7JO+3hBPsTb0+HDDoKLgpbblP8+wseEXEO4THOWsOU9xHhPxwvtoEJI9sYhXEm9VFe8C4ou8ZbUjBUIx1QL4Oi5qHzDGAfZh8YLinwG4NLo74CRFhhGSECQkoQYkK2L13aSGd4gjRTezSggyzYU82Rofvt4QT7E29Phww6Ci4KW25WyIPZ/PIw0EM7DV7Gfu0tLZZ1l0Lfxs3XIep3cY4AN+bYkW7qtaB0PvuL6v6dznFHWg7t/V64PpXzecMepVxcZmrDV/4NadPGYsasD1ayGZi4VtfgN8+lUpMkG1aNeh+77eEE+xNvT4cMOgouCltuYPKg5W9RwGrFaG0Mf+jWZJaviAJVfzTv0k28HJAlBVQ77eEE+xNvT4cMOgouCltuVzsTsKfyK5HqOAFBdw9BPyARP1tkbZK3Ki0B1OGgRbW77eEE+xNvT4cMOgouCltuVVQQA5GyGtfdOYyKzc0CYQ6Wvc4UVJVJVXk0ZDXgPz0anz7e5YZE8LxkdS8NFK0Pk58ykVlHQjefmgXAwAfkcTvt4QT7E29Phww6Ci4KW25unm478zrItxbfHbA3kyD3Oz36bZtoa1aGmV/5CRCCo8Vdie69yWV1ocLf2HxgrAiccjEnk6+mGKZItXFbyhBR47iPIjME347zW9extBftV7Zs9fX9XfWElNf3XdS980J77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbn01vYnq4sZ7sKoJd5JynLmFWA1GG2Ks8G9at0y8n5aPO+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25W94i0cXTnc5urOLIwechBBA0F4GcyZ4h51ycDMLCsTJM25S+9WnxwIrIxkwoY6eo3IJMsVpyLjAiQX5trNbxt04Rq1v5/aZRqCKe7ZR1BnXrN/FyTUa04DDGwOiZTuCfDjmNcEgRkiqUz3q5bFcS8CEJp+DxQwHdbRyVwvamPnzvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuS00i6o8imDzMsMriQ3HqdhGLmDyl4I3/Lpvs3E5JS6577eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbblFXEKYM/3EFnWVa3oAlYEKWuV1Vr6n78j8/VqtQgHjbkASPQPvQAVPh8RUwBr/7bTvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltufi1hv6hYZcLmz3k5hkFVPfC3PSBne/oOpF5J/W07yka77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbmT6Ob5AVxPxy0PFrYu4WaiWWEoMugOjOdTKG4+UD1sS/MUBaK++upIE/GN8jJrfkHvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuXt0C0e1EgZyaACPRcdaCl5AUl982wZpsJahohl8gYYH77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbmLZzYIRXKJG4Ik10H+xIRHg0Wtbvv+iEF36pqbOJHrCbYGUrjuuFxYk+Eid839EnPvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuUw1WYU0gfY+U7J0QSYXqaz6GvknJfGu/yJL+C/wmRCoXE12hNex6FfiyMrMArVvPe+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25aPOoISEra5Mnkd78SoqwuxNBef9NBP4YPBguXn3K9kLvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuQooWV+7Hx4r80fzF5bsW1FeqyDFe+xFAIry5g4MrdpyMsbnFt6fLhj/U47KCnnTje+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25+wT9o3ofnHRymfRRMkeviSpmT+b57v+t3TEJOtR2/5zvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuZ/yU7bzT+snMuvg6I+Pu8wpAi/006OA/NsX5mrIxe9IyyrCGUHEjQ6IVirQwtG51++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25xgoR+RK16dXqmZo4Z4TZEb3dA5bw7IsaTuMQehBRWpzvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuUZgHBNlnIouVPLVvu91/P2uw6FDGD/JGjmTBD5pTZwzXFs7c58sjuE958Ur35th3++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25dyAEv5hq/A6kPOk5Nrvx7smIjBIFptCG+UMXwOKtuq/vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuVveItHF053ObqziyMHnIQTaDRkTyGtlCkXmXexprTxfzzNdZeeIqqgYSF7vVAWd+++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25M0yr7sHvIh4xgoiBnf40MGT376U54aiaGKfm+iLWQDkhCafg8UMB3W0clcL2pj5877eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbnqAxz74YXLHBybr19/6ON+QTE8LU6xJq4YUYgho+h/s++3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25RVxCmDP9xBZ1lWt6AJWBCsKUqUReqcVRjQxa8ZV1HLtAEj0D70AFT4fEVMAa/+2077eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbl8zCHD9RXw+FpZCyLf/iJ4Vnvi5xyvhvs7Cd8ix8ivqO+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25qMSz1dBT8ThI/rguivM2JD5s2GcPknPFq9ZXec11Iv+CfxGUc6izJR+VsnJkTQv377eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbmvorLNMx322KawcozPgKHbYkq8uYK9s/KWghqrzWF8/e+3hBPsTb0+HDDoKLgpbbnvt4QT7E29Phww6Ci4KW25i2c2CEVyiRuCJNdB/sSER3IlIcZJd9BO6R63CnHBpwazVN75+tO8VF0mmk/bOYRV77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbn/4H10Ua6te0/rhxO8P4B4jZPz/03uSGIUgxjlQD/WNlxNdoTXsehX4sjKzAK1bz3vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltucC28WZlJlLJ6c33PDoXLntxM/z/D6gGG/Uuwxtf1bBv77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbkp6Lh/6aABXmR/cerPOZDKAZFKuFl6MpAKw4xTzioNnjLG5xbeny4Y/1OOygp5043vt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuRlRFzb3nC2B+I8/Rv565+X7we28qQw/MEkwpTO32udV77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbkF/X+8+bZQf/q821d5iOgMoaBq8OzxFtkWYy+P4boeLx/cJvMaVVcyCnqzz9w3/RHvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltueIUrs4IpSphGvTiJ7wfrQ3XMA+phFj+H8Em3BSiaO2d77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbbnQ1F9lPnOhXUBlYNfmnUPEoR0qFJHLehawhnZaoKjPHzyQN/ljsHGjYM74NFZQIkLvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuXsvYeGFbFvJUryKDXtkT2JRWo8668Qs0hfaE9f3qKmp77eEE+xNvT4cMOgouCltue+3hBPsTb0+HDDoKLgpbblb3iLRxdOdzm6s4sjB5yEEojIBBeRdCIT4kELHejwRa3DcriTfCm8z4na60Ly0rIvvt4QT7E29Phww6Ci4KW2577eEE+xNvT4cMOgouCltuXhmyC0b7xW80bUR5TxwyMd8bX59WAEv60F1eIY8N8zTmTkalv1ix+vni7XI8iSMU19TDfq889ufX1DbgQTPPoZvshWBqIIdhIDy1TJ/If+ccCHkKduKB6bsHluEpg7tu5JbbxM+Fyd3kVj623AkTAeNWT1AnYK9EUK+IbKXdVJmbZmM7GN21NDNJv/tvfgvyQ== | non_priority | jmumax k xckmikm di hddoklgpbblfxekym mubak upie yjl c umxwoktuq h s fpzcylf e hddoklgpbbn z hddoklgpbbkf x bzqf phfj if tvfgvyq | 0 |
278,022 | 21,057,978,959 | IssuesEvent | 2022-04-01 06:34:38 | junrong98/ped | https://api.github.com/repos/junrong98/ped | opened | No visuals were provided in User Guide | type.DocumentationBug severity.Low | There were no visuals provided in the User Guide to aid the reader.
For example:

Although it provides example of how to use the command, it would be better if images were provided to show the *before* and *after* each command execution.
<!--session: 1648794272385-f7c35d87-e511-4afb-bb63-97524a8089be-->
<!--Version: Web v3.4.2--> | 1.0 | No visuals were provided in User Guide - There were no visuals provided in the User Guide to aid the reader.
For example:

Although it provides example of how to use the command, it would be better if images were provided to show the *before* and *after* each command execution.
<!--session: 1648794272385-f7c35d87-e511-4afb-bb63-97524a8089be-->
<!--Version: Web v3.4.2--> | non_priority | no visuals were provided in user guide there were no visuals provided in the user guide to aid the reader for example although it provides example of how to use the command it would be better if images were provided to show the before and after each command execution | 0 |
176,402 | 21,411,028,038 | IssuesEvent | 2022-04-22 05:58:34 | pazhanivel07/frameworks_base_Aosp10_r33 | https://api.github.com/repos/pazhanivel07/frameworks_base_Aosp10_r33 | opened | CVE-2020-0391 (High) detected in baseandroid-10.0.0_r46 | security vulnerability | ## CVE-2020-0391 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_base_Aosp10_r33/commit/d0a412c03562493a433dc7e698ff88ab06a3468a">d0a412c03562493a433dc7e698ff88ab06a3468a</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/services/core/java/com/android/server/pm/PackageManagerService.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In applyPolicy of PackageManagerService.java, there is possible arbitrary command execution as System due to an unenforced protected-broadcast. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11Android ID: A-158570769
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0391>CVE-2020-0391</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2020-09-01">https://source.android.com/security/bulletin/2020-09-01</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-9.0.0_r60,android-10.0.0_r46</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-0391 (High) detected in baseandroid-10.0.0_r46 - ## CVE-2020-0391 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_base_Aosp10_r33/commit/d0a412c03562493a433dc7e698ff88ab06a3468a">d0a412c03562493a433dc7e698ff88ab06a3468a</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/services/core/java/com/android/server/pm/PackageManagerService.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In applyPolicy of PackageManagerService.java, there is possible arbitrary command execution as System due to an unenforced protected-broadcast. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11Android ID: A-158570769
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0391>CVE-2020-0391</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2020-09-01">https://source.android.com/security/bulletin/2020-09-01</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-9.0.0_r60,android-10.0.0_r46</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in baseandroid cve high severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch main vulnerable source files services core java com android server pm packagemanagerservice java vulnerability details in applypolicy of packagemanagerservice java there is possible arbitrary command execution as system due to an unenforced protected broadcast this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android android step up your open source security game with whitesource | 0 |
450,210 | 31,885,459,799 | IssuesEvent | 2023-09-16 22:20:56 | lumapu/ahoy | https://api.github.com/repos/lumapu/ahoy | closed | Feature Request: Exclude internal Flash Pins, Power Limit über Serial / Control | documentation enhancement stale | ### Platform
ESP8266
### Model name
NodeMCU LoLin v3
### nRF24L01+ Module
nRF24L01+ plus
### Antenna
external antenna
### Power Stabilization
~100uF Elko
### Connection diagram
## Connection diagram I used:
| nRF24L01+ Pin | ESP8266 GPIO |
| ------------- | -------------- |
| Pin 1 GND [*] | GND |
| Pin 2 +3.3V | +3.3V |
| Pin 3 CE | GPIO2 CE D4 |
| Pin 4 CSN | GPIO15 CS D8 |
| Pin 5 SCK | GPIO14 SCLK D5 |
| Pin 6 MOSI | GPIO13 MOSI D7 |
| Pin 7 MISO | GPIO12 MISO D6 |
| Pin 8 IRQ | GPIO0 IRQ D3 |
Display SSH1306 D1 = SCL, D2 = SDA
Note: [*] GND Pin 1 has a square mark on the nRF24L01+ module
### Connection picture
- [ ] I will attach/upload an Image of my wiring
### Version
0.5.66
### Github Hash
f8fe044
### Build & Flash Method
ESP Tools (flash)
### Desktop
Windows
### Setup
### Device Host Name
- Device Name: AHOY-DTU
### WiFi
- SSID: YOUR_WIFI_SSID *don't paste here*
- Password: YOUR_WIFI_PWD *don't paste here*
### Inverter
#### Inverter 0
- Address: 1141752123456
- Name: HM-400
- Active Power Limit: 65535
- Active Power Limit Control Type: no powerlimit
- Max Module Power (Wp): 385
- Module Name: Unten_O
#### Inverter 1
- Address: 1141752123456
- Name: HM-400
- Active Power Limit: 65535
- Active Power Limit Control Type: no powerlimit
- Max Module Power (Wp): 385
- Module Name: Unten_W
### General
- Interval [s]: 30
- Max retries per Payload: 5
### NTP Server
- NTP Server / IP: pool.ntp.org
- NTP Port: 123
### MQTT
- Broker / Server IP:
- Port: 1883
- Username (optional):
- Password (optional):
- Topic: inverter
### System Config
#### Pinout (Wemos)
- CS: D8 (GPIO15)
- CE: D4 (GPIO2)
- IRQ: D3 (GPIO0)
#### Radio (NRF24L01+)
- Amplifier Power Level: MIN
#### Serial Console
- print inverter data: [ ]
- Serial Debug: [ ]
- Interval [s]: 5
- Reboot device after successful save: [x]
- SAVE
### Debug Serial Log output
_No response_
### Error description
Nach Eingabe eines Powerlimits in % über >Serial / Control< bei beiden Invertern, hatte sich die Seite fast komplett verabschiedet!
Eine Auswahl der Inverter war nicht mehr möglich, da leer und auch der Schaltflächenframe. Auch eine Aktualisierung der Website blieb erfolglos.
... reboot! 😩
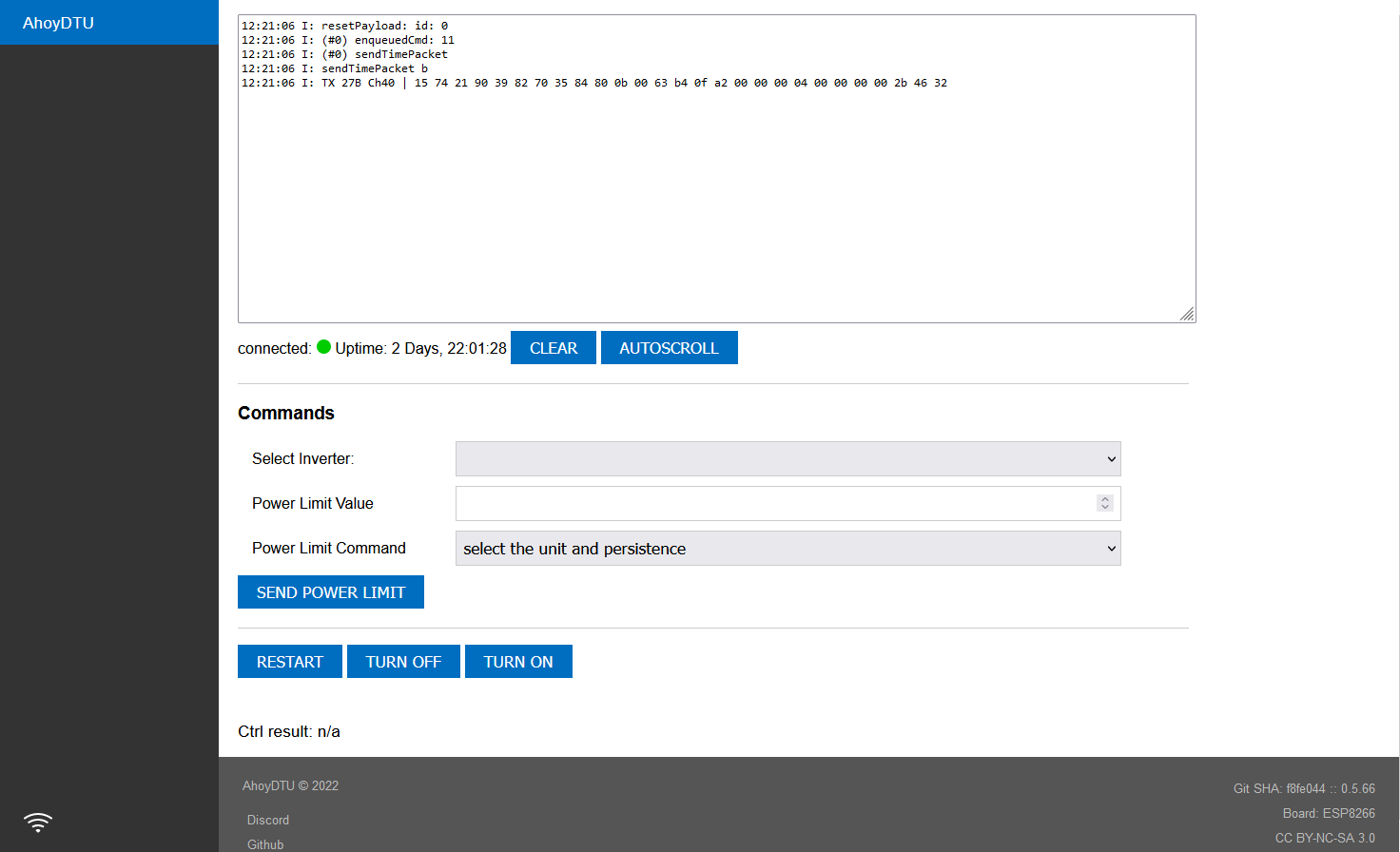
| 1.0 | Feature Request: Exclude internal Flash Pins, Power Limit über Serial / Control - ### Platform
ESP8266
### Model name
NodeMCU LoLin v3
### nRF24L01+ Module
nRF24L01+ plus
### Antenna
external antenna
### Power Stabilization
~100uF Elko
### Connection diagram
## Connection diagram I used:
| nRF24L01+ Pin | ESP8266 GPIO |
| ------------- | -------------- |
| Pin 1 GND [*] | GND |
| Pin 2 +3.3V | +3.3V |
| Pin 3 CE | GPIO2 CE D4 |
| Pin 4 CSN | GPIO15 CS D8 |
| Pin 5 SCK | GPIO14 SCLK D5 |
| Pin 6 MOSI | GPIO13 MOSI D7 |
| Pin 7 MISO | GPIO12 MISO D6 |
| Pin 8 IRQ | GPIO0 IRQ D3 |
Display SSH1306 D1 = SCL, D2 = SDA
Note: [*] GND Pin 1 has a square mark on the nRF24L01+ module
### Connection picture
- [ ] I will attach/upload an Image of my wiring
### Version
0.5.66
### Github Hash
f8fe044
### Build & Flash Method
ESP Tools (flash)
### Desktop
Windows
### Setup
### Device Host Name
- Device Name: AHOY-DTU
### WiFi
- SSID: YOUR_WIFI_SSID *don't paste here*
- Password: YOUR_WIFI_PWD *don't paste here*
### Inverter
#### Inverter 0
- Address: 1141752123456
- Name: HM-400
- Active Power Limit: 65535
- Active Power Limit Control Type: no powerlimit
- Max Module Power (Wp): 385
- Module Name: Unten_O
#### Inverter 1
- Address: 1141752123456
- Name: HM-400
- Active Power Limit: 65535
- Active Power Limit Control Type: no powerlimit
- Max Module Power (Wp): 385
- Module Name: Unten_W
### General
- Interval [s]: 30
- Max retries per Payload: 5
### NTP Server
- NTP Server / IP: pool.ntp.org
- NTP Port: 123
### MQTT
- Broker / Server IP:
- Port: 1883
- Username (optional):
- Password (optional):
- Topic: inverter
### System Config
#### Pinout (Wemos)
- CS: D8 (GPIO15)
- CE: D4 (GPIO2)
- IRQ: D3 (GPIO0)
#### Radio (NRF24L01+)
- Amplifier Power Level: MIN
#### Serial Console
- print inverter data: [ ]
- Serial Debug: [ ]
- Interval [s]: 5
- Reboot device after successful save: [x]
- SAVE
### Debug Serial Log output
_No response_
### Error description
Nach Eingabe eines Powerlimits in % über >Serial / Control< bei beiden Invertern, hatte sich die Seite fast komplett verabschiedet!
Eine Auswahl der Inverter war nicht mehr möglich, da leer und auch der Schaltflächenframe. Auch eine Aktualisierung der Website blieb erfolglos.
... reboot! 😩
| non_priority | feature request exclude internal flash pins power limit über serial control platform model name nodemcu lolin module plus antenna external antenna power stabilization elko connection diagram connection diagram i used pin gpio pin gnd gnd pin pin ce ce pin csn cs pin sck sclk pin mosi mosi pin miso miso pin irq irq display scl sda note gnd pin has a square mark on the module connection picture i will attach upload an image of my wiring version github hash build flash method esp tools flash desktop windows setup device host name device name ahoy dtu wifi ssid your wifi ssid don t paste here password your wifi pwd don t paste here inverter inverter address name hm active power limit active power limit control type no powerlimit max module power wp module name unten o inverter address name hm active power limit active power limit control type no powerlimit max module power wp module name unten w general interval max retries per payload ntp server ntp server ip pool ntp org ntp port mqtt broker server ip port username optional password optional topic inverter system config pinout wemos cs ce irq radio amplifier power level min serial console print inverter data serial debug interval reboot device after successful save save debug serial log output no response error description nach eingabe eines powerlimits in über serial control bei beiden invertern hatte sich die seite fast komplett verabschiedet eine auswahl der inverter war nicht mehr möglich da leer und auch der schaltflächenframe auch eine aktualisierung der website blieb erfolglos reboot 😩 | 0 |
115,426 | 11,873,986,198 | IssuesEvent | 2020-03-26 18:12:31 | cyberark/docs-cyberark-conjur-service-broker | https://api.github.com/repos/cyberark/docs-cyberark-conjur-service-broker | opened | Add instructions for getting Service Broker app logs | component/pcf kind/documentation | Add troubleshooting instructions such as:
> If you encounter errors during run time, or more detailed logs are required, you can also collect logs from the deployed application. To find these logs, navigate to the VMware Tanzu Apps Manager tile. Find the organization and space for the CyberArk Conjur Service Broker, which is typically `cyberark-conjur-org` and `cyberark-conjur-space`. From there, you can view detailed application logs.
Which is modeled on the troubleshooting instructions [here](https://docs.pivotal.io/partners/ecs-service-broker/troubleshooting.html).
| 1.0 | Add instructions for getting Service Broker app logs - Add troubleshooting instructions such as:
> If you encounter errors during run time, or more detailed logs are required, you can also collect logs from the deployed application. To find these logs, navigate to the VMware Tanzu Apps Manager tile. Find the organization and space for the CyberArk Conjur Service Broker, which is typically `cyberark-conjur-org` and `cyberark-conjur-space`. From there, you can view detailed application logs.
Which is modeled on the troubleshooting instructions [here](https://docs.pivotal.io/partners/ecs-service-broker/troubleshooting.html).
| non_priority | add instructions for getting service broker app logs add troubleshooting instructions such as if you encounter errors during run time or more detailed logs are required you can also collect logs from the deployed application to find these logs navigate to the vmware tanzu apps manager tile find the organization and space for the cyberark conjur service broker which is typically cyberark conjur org and cyberark conjur space from there you can view detailed application logs which is modeled on the troubleshooting instructions | 0 |
30,543 | 7,227,932,540 | IssuesEvent | 2018-02-11 02:40:00 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | closed | [RyuJIT] Update emitIns_R_AR to support SSE4.1 instructions without VEX-encoding | arch-x64 arch-x86 area-CodeGen | The SSE4.1 instruction `movntdqa` (used by HW intrinsic `LoadAlignedVector128NonTemporal`) can be correctly generated with VEX-encoding.
However, with legacy SSE encoding, RyuJIT compiles `movntdqa xmm0, xmmword ptr [rdi]` to
```
66 0F 38 2F
```
and the correct encoding should be
```
66 0f 38 2a 07
```
cc @CarolEidt @tannergooding | 1.0 | [RyuJIT] Update emitIns_R_AR to support SSE4.1 instructions without VEX-encoding - The SSE4.1 instruction `movntdqa` (used by HW intrinsic `LoadAlignedVector128NonTemporal`) can be correctly generated with VEX-encoding.
However, with legacy SSE encoding, RyuJIT compiles `movntdqa xmm0, xmmword ptr [rdi]` to
```
66 0F 38 2F
```
and the correct encoding should be
```
66 0f 38 2a 07
```
cc @CarolEidt @tannergooding | non_priority | update emitins r ar to support instructions without vex encoding the instruction movntdqa used by hw intrinsic can be correctly generated with vex encoding however with legacy sse encoding ryujit compiles movntdqa xmmword ptr to and the correct encoding should be cc caroleidt tannergooding | 0 |
12,306 | 7,845,703,998 | IssuesEvent | 2018-06-19 13:40:51 | commercialhaskell/stack | https://api.github.com/repos/commercialhaskell/stack | closed | Avoid rebuilding "sandbox" when profiling options turned off | type: performance | Hello, I have an issue. Steps to reproduce:
1. `cd myproject`
2. `stack build --library-profiling --executable-profiling` to build "sandbox" and `myproject` with profiling options
3. `stack build`
Expected behaviour:
Reconfigure `myproject` and rebuild it without profiling options like `cabal clean && cabal configure && cabal build` would.
Actual behaviour:
Stack rebuilds all "sandbox" without profiling options which takes a lot of time.
Use case: when testing `myproject` runtime error occures and developer want to see a stacktrace (which requires profiling options). He/she rebuilds project (with "sandbox") with profiling options, fixes issue and turns profiling options off (to speed up compilation).
| True | Avoid rebuilding "sandbox" when profiling options turned off - Hello, I have an issue. Steps to reproduce:
1. `cd myproject`
2. `stack build --library-profiling --executable-profiling` to build "sandbox" and `myproject` with profiling options
3. `stack build`
Expected behaviour:
Reconfigure `myproject` and rebuild it without profiling options like `cabal clean && cabal configure && cabal build` would.
Actual behaviour:
Stack rebuilds all "sandbox" without profiling options which takes a lot of time.
Use case: when testing `myproject` runtime error occures and developer want to see a stacktrace (which requires profiling options). He/she rebuilds project (with "sandbox") with profiling options, fixes issue and turns profiling options off (to speed up compilation).
| non_priority | avoid rebuilding sandbox when profiling options turned off hello i have an issue steps to reproduce cd myproject stack build library profiling executable profiling to build sandbox and myproject with profiling options stack build expected behaviour reconfigure myproject and rebuild it without profiling options like cabal clean cabal configure cabal build would actual behaviour stack rebuilds all sandbox without profiling options which takes a lot of time use case when testing myproject runtime error occures and developer want to see a stacktrace which requires profiling options he she rebuilds project with sandbox with profiling options fixes issue and turns profiling options off to speed up compilation | 0 |
23,969 | 11,993,808,979 | IssuesEvent | 2020-04-08 12:41:50 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Training is looping | Pri2 cognitive-services/svc cxp forms-recognizer/subsvc product-question triaged | When running this in a Jupyter Notebook I found that the training step was looping and not quitting after the first successful training. I replaced quit() with break and it worked fine after that.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 18818774-5076-cb76-ee9e-4ecb632b6caa
* Version Independent ID: 22d60153-50fc-024e-6249-edc796dcdf19
* Content: [Quickstart: Train a model and extract form data using the REST API with Python - Form Recognizer - Azure Cognitive Services](https://docs.microsoft.com/en-us/azure/cognitive-services/form-recognizer/quickstarts/python-train-extract#feedback)
* Content Source: [articles/cognitive-services/form-recognizer/quickstarts/python-train-extract.md](https://github.com/Microsoft/azure-docs/blob/master/articles/cognitive-services/form-recognizer/quickstarts/python-train-extract.md)
* Service: **cognitive-services**
* Sub-service: **forms-recognizer**
* GitHub Login: @PatrickFarley
* Microsoft Alias: **pafarley** | 1.0 | Training is looping - When running this in a Jupyter Notebook I found that the training step was looping and not quitting after the first successful training. I replaced quit() with break and it worked fine after that.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 18818774-5076-cb76-ee9e-4ecb632b6caa
* Version Independent ID: 22d60153-50fc-024e-6249-edc796dcdf19
* Content: [Quickstart: Train a model and extract form data using the REST API with Python - Form Recognizer - Azure Cognitive Services](https://docs.microsoft.com/en-us/azure/cognitive-services/form-recognizer/quickstarts/python-train-extract#feedback)
* Content Source: [articles/cognitive-services/form-recognizer/quickstarts/python-train-extract.md](https://github.com/Microsoft/azure-docs/blob/master/articles/cognitive-services/form-recognizer/quickstarts/python-train-extract.md)
* Service: **cognitive-services**
* Sub-service: **forms-recognizer**
* GitHub Login: @PatrickFarley
* Microsoft Alias: **pafarley** | non_priority | training is looping when running this in a jupyter notebook i found that the training step was looping and not quitting after the first successful training i replaced quit with break and it worked fine after that document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service cognitive services sub service forms recognizer github login patrickfarley microsoft alias pafarley | 0 |
44,094 | 23,490,301,015 | IssuesEvent | 2022-08-17 18:01:50 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | [wasm] `dotnet-runtime-perf`: `wasm-opt` failing with `unexpected expression typeemcc`, and killed with `SIGSEGV (-11)` | arch-wasm tenet-performance blocking-clean-ci-optional | This is on `dotnet-runtime-perf`, build `20220817.1` - `wasm.x64.micro.net7.0.Partition6`.
```
Linking with emcc with -O2. This may take a while ...
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-ld" -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm --allow-undefined --allow-undefined /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/pinvoke.o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/driver.o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/corebindings.o /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libicudata.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libicui18n.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libicuuc.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-debugger-stub-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-diagnostics_tracing-stub-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-hot_reload-stub-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-marshal-ilgen-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-ee-interp.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-icall-table.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-ilgen.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-profiler-aot.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-wasm-eh-js.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmonosgen-2.0.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libSystem.IO.Compression.Native.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libSystem.Native.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libSystem.Security.Cryptography.Native.Browser.a -L/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/emscripten/cache/sysroot/lib/wasm32-emscripten -lGL -lal -lhtml5 -lstubs -lnoexit -lc -ldlmalloc -lcompiler_rt -lc++ -lc++abi -lsockets -mllvm -combiner-global-alias-analysis=false -mllvm -enable-emscripten-cxx-exceptions -mllvm -enable-emscripten-sjlj -mllvm -disable-lsr --import-undefined --export-if-defined=malloc --export-if-defined=memalign --export-if-defined=memset --export-if-defined=htons --export-if-defined=ntohs --export-if-defined=free --export-if-defined=__start_em_asm --export-if-defined=__stop_em_asm --export=stackSave --export=stackRestore --export=stackAlloc --export=__wasm_call_ctors --export=__errno_location --export=malloc --export=free --export=__cxa_is_pointer_type --export=__cxa_can_catch --export=setThrew --export=ntohs --export=htons --export=__dl_seterr --export=htonl --export=emscripten_builtin_memalign --export-table -z stack-size=5242880 --initial-memory=536870912 --no-entry --max-memory=2147483648 --global-base=1024
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-emscripten-finalize" -g --dyncalls-i64 /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm --detect-features
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Node.linux-x64/7.0.0-rc.1.22411.1/tools/bin/node" /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/emscripten/src/compiler.js /home/helixbot/work/BA7809D8/t/tmpm883pqdf.json
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-opt" --strip-dwarf --post-emscripten -O2 --low-memory-unused --zero-filled-memory --strip-debug --strip-producers /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -g --mvp-features --enable-mutable-globals
unexpected expression typeemcc : error : '/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-opt --strip-dwarf --post-emscripten -O2 --low-memory-unused --zero-filled-memory --strip-debug --strip-producers /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -g --mvp-features --enable-mutable-globals' failed (received SIGSEGV (-11)) [/home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/bin/for-running/MicroBenchmarks/7bd6633c-d19a-41df-b328-fc32f56dcd0d/BenchmarkDotNet.Autogenerated.csproj]
/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.WebAssembly.Sdk/7.0.0-ci/Sdk/WasmApp.Native.targets(423,5): error MSB3073: The command "emcc "@/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/src/emcc-default.rsp" "@/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/src/emcc-link.rsp" "@/home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/emcc-link.rsp"" exited with code 1. [/home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/bin/for-running/MicroBenchmarks/7bd6633c-d19a-41df-b328-fc32f56dcd0d/BenchmarkDotNet.Autogenerated.csproj]
```
cc @radekdoulik | True | [wasm] `dotnet-runtime-perf`: `wasm-opt` failing with `unexpected expression typeemcc`, and killed with `SIGSEGV (-11)` - This is on `dotnet-runtime-perf`, build `20220817.1` - `wasm.x64.micro.net7.0.Partition6`.
```
Linking with emcc with -O2. This may take a while ...
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-ld" -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm --allow-undefined --allow-undefined /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/pinvoke.o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/driver.o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/corebindings.o /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libicudata.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libicui18n.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libicuuc.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-debugger-stub-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-diagnostics_tracing-stub-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-hot_reload-stub-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-component-marshal-ilgen-static.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-ee-interp.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-icall-table.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-ilgen.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-profiler-aot.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmono-wasm-eh-js.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libmonosgen-2.0.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libSystem.IO.Compression.Native.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libSystem.Native.a /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/libSystem.Security.Cryptography.Native.Browser.a -L/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/emscripten/cache/sysroot/lib/wasm32-emscripten -lGL -lal -lhtml5 -lstubs -lnoexit -lc -ldlmalloc -lcompiler_rt -lc++ -lc++abi -lsockets -mllvm -combiner-global-alias-analysis=false -mllvm -enable-emscripten-cxx-exceptions -mllvm -enable-emscripten-sjlj -mllvm -disable-lsr --import-undefined --export-if-defined=malloc --export-if-defined=memalign --export-if-defined=memset --export-if-defined=htons --export-if-defined=ntohs --export-if-defined=free --export-if-defined=__start_em_asm --export-if-defined=__stop_em_asm --export=stackSave --export=stackRestore --export=stackAlloc --export=__wasm_call_ctors --export=__errno_location --export=malloc --export=free --export=__cxa_is_pointer_type --export=__cxa_can_catch --export=setThrew --export=ntohs --export=htons --export=__dl_seterr --export=htonl --export=emscripten_builtin_memalign --export-table -z stack-size=5242880 --initial-memory=536870912 --no-entry --max-memory=2147483648 --global-base=1024
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-emscripten-finalize" -g --dyncalls-i64 /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm --detect-features
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Node.linux-x64/7.0.0-rc.1.22411.1/tools/bin/node" /home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/emscripten/src/compiler.js /home/helixbot/work/BA7809D8/t/tmpm883pqdf.json
"/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-opt" --strip-dwarf --post-emscripten -O2 --low-memory-unused --zero-filled-memory --strip-debug --strip-producers /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -g --mvp-features --enable-mutable-globals
unexpected expression typeemcc : error : '/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.Emscripten.3.1.12.Sdk.linux-x64/7.0.0-rc.1.22411.1/tools/bin/wasm-opt --strip-dwarf --post-emscripten -O2 --low-memory-unused --zero-filled-memory --strip-debug --strip-producers /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -o /home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/dotnet.wasm -g --mvp-features --enable-mutable-globals' failed (received SIGSEGV (-11)) [/home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/bin/for-running/MicroBenchmarks/7bd6633c-d19a-41df-b328-fc32f56dcd0d/BenchmarkDotNet.Autogenerated.csproj]
/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NET.Runtime.WebAssembly.Sdk/7.0.0-ci/Sdk/WasmApp.Native.targets(423,5): error MSB3073: The command "emcc "@/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/src/emcc-default.rsp" "@/home/helixbot/work/BA7809D8/p/dotnet/packs/Microsoft.NETCore.App.Runtime.Mono.browser-wasm/7.0.0-ci/runtimes/browser-wasm/native/src/emcc-link.rsp" "@/home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/obj/BenchmarkDotNet.Autogenerated/Release/net7.0/browser-wasm/wasm/for-publish/emcc-link.rsp"" exited with code 1. [/home/helixbot/work/BA7809D8/w/9C4E085D/e/performance/artifacts/bin/for-running/MicroBenchmarks/7bd6633c-d19a-41df-b328-fc32f56dcd0d/BenchmarkDotNet.Autogenerated.csproj]
```
cc @radekdoulik | non_priority | dotnet runtime perf wasm opt failing with unexpected expression typeemcc and killed with sigsegv this is on dotnet runtime perf build wasm micro linking with emcc with this may take a while home helixbot work p dotnet packs microsoft net runtime emscripten sdk linux rc tools bin wasm ld o home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm allow undefined allow undefined home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish pinvoke o home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish driver o home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish corebindings o home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libicudata a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libicuuc a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono component debugger stub static a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono component diagnostics tracing stub static a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono component hot reload stub static a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono component marshal ilgen static a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono ee interp a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono icall table a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono ilgen a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono profiler aot a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmono wasm eh js a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libmonosgen a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libsystem io compression native a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libsystem native a home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native libsystem security cryptography native browser a l home helixbot work p dotnet packs microsoft net runtime emscripten sdk linux rc tools emscripten cache sysroot lib emscripten lgl lal lstubs lnoexit lc ldlmalloc lcompiler rt lc lc abi lsockets mllvm combiner global alias analysis false mllvm enable emscripten cxx exceptions mllvm enable emscripten sjlj mllvm disable lsr import undefined export if defined malloc export if defined memalign export if defined memset export if defined htons export if defined ntohs export if defined free export if defined start em asm export if defined stop em asm export stacksave export stackrestore export stackalloc export wasm call ctors export errno location export malloc export free export cxa is pointer type export cxa can catch export setthrew export ntohs export htons export dl seterr export htonl export emscripten builtin memalign export table z stack size initial memory no entry max memory global base home helixbot work p dotnet packs microsoft net runtime emscripten sdk linux rc tools bin wasm emscripten finalize g dyncalls home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm o home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm detect features home helixbot work p dotnet packs microsoft net runtime emscripten node linux rc tools bin node home helixbot work p dotnet packs microsoft net runtime emscripten sdk linux rc tools emscripten src compiler js home helixbot work t json home helixbot work p dotnet packs microsoft net runtime emscripten sdk linux rc tools bin wasm opt strip dwarf post emscripten low memory unused zero filled memory strip debug strip producers home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm o home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm g mvp features enable mutable globals unexpected expression typeemcc error home helixbot work p dotnet packs microsoft net runtime emscripten sdk linux rc tools bin wasm opt strip dwarf post emscripten low memory unused zero filled memory strip debug strip producers home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm o home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish dotnet wasm g mvp features enable mutable globals failed received sigsegv home helixbot work p dotnet packs microsoft net runtime webassembly sdk ci sdk wasmapp native targets error the command emcc home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native src emcc default rsp home helixbot work p dotnet packs microsoft netcore app runtime mono browser wasm ci runtimes browser wasm native src emcc link rsp home helixbot work w e performance artifacts obj benchmarkdotnet autogenerated release browser wasm wasm for publish emcc link rsp exited with code cc radekdoulik | 0 |
189,409 | 22,047,033,580 | IssuesEvent | 2022-05-30 03:45:17 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | closed | CVE-2022-30594 (High) detected in linuxv4.19 - autoclosed | security vulnerability | ## CVE-2022-30594 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel before 5.17.2 mishandles seccomp permissions. The PTRACE_SEIZE code path allows attackers to bypass intended restrictions on setting the PT_SUSPEND_SECCOMP flag.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-30594>CVE-2022-30594</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-30594">https://www.linuxkernelcves.com/cves/CVE-2022-30594</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: v4.9.311,v4.14.276,v4.19.238,v5.4.189,v5.10.110,v5.15.33,v5.16.19,v5.17.2,v5.18-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-30594 (High) detected in linuxv4.19 - autoclosed - ## CVE-2022-30594 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel before 5.17.2 mishandles seccomp permissions. The PTRACE_SEIZE code path allows attackers to bypass intended restrictions on setting the PT_SUSPEND_SECCOMP flag.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-30594>CVE-2022-30594</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-30594">https://www.linuxkernelcves.com/cves/CVE-2022-30594</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: v4.9.311,v4.14.276,v4.19.238,v5.4.189,v5.10.110,v5.15.33,v5.16.19,v5.17.2,v5.18-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in autoclosed cve high severity vulnerability vulnerable library linux kernel source tree library home page a href found in base branch master vulnerable source files vulnerability details the linux kernel before mishandles seccomp permissions the ptrace seize code path allows attackers to bypass intended restrictions on setting the pt suspend seccomp flag publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
273,988 | 29,865,519,012 | IssuesEvent | 2023-06-20 03:14:00 | renfei/renfeid | https://api.github.com/repos/renfei/renfeid | closed | CVE-2023-28708 (Medium) detected in tomcat-embed-core-9.0.71.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2023-28708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.71.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>
Dependency Hierarchy:
<p>Found in HEAD commit: <a href="https://github.com/renfei/renfeid/commit/f224243aad6f68d7bf267204c3303e851b76164c">f224243aad6f68d7bf267204c3303e851b76164c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
When using the RemoteIpFilter with requests received from a reverse proxy via HTTP that include the X-Forwarded-Proto header set to https, session cookies created by Apache Tomcat 11.0.0-M1 to 11.0.0.-M2, 10.1.0-M1 to 10.1.5, 9.0.0-M1 to 9.0.71 and 8.5.0 to 8.5.85 did not include the secure attribute. This could result in the user agent transmitting the session cookie over an insecure channel.
<p>Publish Date: 2023-03-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28708>CVE-2023-28708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/hdksc59z3s7tm39x0pp33mtwdrt8qr67">https://lists.apache.org/thread/hdksc59z3s7tm39x0pp33mtwdrt8qr67</a></p>
<p>Release Date: 2023-03-22</p>
<p>Fix Resolution: 9.0.72</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-28708 (Medium) detected in tomcat-embed-core-9.0.71.jar - autoclosed - ## CVE-2023-28708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.71.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>
Dependency Hierarchy:
<p>Found in HEAD commit: <a href="https://github.com/renfei/renfeid/commit/f224243aad6f68d7bf267204c3303e851b76164c">f224243aad6f68d7bf267204c3303e851b76164c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
When using the RemoteIpFilter with requests received from a reverse proxy via HTTP that include the X-Forwarded-Proto header set to https, session cookies created by Apache Tomcat 11.0.0-M1 to 11.0.0.-M2, 10.1.0-M1 to 10.1.5, 9.0.0-M1 to 9.0.71 and 8.5.0 to 8.5.85 did not include the secure attribute. This could result in the user agent transmitting the session cookie over an insecure channel.
<p>Publish Date: 2023-03-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28708>CVE-2023-28708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/hdksc59z3s7tm39x0pp33mtwdrt8qr67">https://lists.apache.org/thread/hdksc59z3s7tm39x0pp33mtwdrt8qr67</a></p>
<p>Release Date: 2023-03-22</p>
<p>Fix Resolution: 9.0.72</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tomcat embed core jar autoclosed cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href dependency hierarchy found in head commit a href found in base branch master vulnerability details when using the remoteipfilter with requests received from a reverse proxy via http that include the x forwarded proto header set to https session cookies created by apache tomcat to to to and to did not include the secure attribute this could result in the user agent transmitting the session cookie over an insecure channel publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
31,883 | 15,115,959,391 | IssuesEvent | 2021-02-09 05:45:24 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Timing Discrepency betweeen Tflite Benchmarking Tool and Android Studio Inference Time | TF 1.15 comp:lite stat:awaiting tensorflower type:performance | <em>Please make sure that this is an issue related to performance of TensorFlow.
As per our
[GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md),
we only address code/doc bugs, performance issues, feature requests and
build/installation issues on GitHub. tag:performance_template</em>
**System information**
- Have I written custom code (as opposed to using a stock example script provided in TensorFlow):
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04):
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device:
- TensorFlow installed from (source or binary): Source
- TensorFlow version (use command below): 1.15
- Python version: 3.6
- Bazel version (if compiling from source):
- GCC/Compiler version (if compiling from source):
- CUDA/cuDNN version:
- GPU model and memory:
You can collect some of this information using our environment capture
[script](https://github.com/tensorflow/tensorflow/tree/master/tools/tf_env_collect.sh)
You can also obtain the TensorFlow version with:
1. TF 1.0: `python -c "import tensorflow as tf; print(tf.GIT_VERSION, tf.VERSION)"`
2. TF 2.0: `python -c "import tensorflow as tf; print(tf.version.GIT_VERSION, tf.version.VERSION)"`
**Describe the current behavior**
While Benchmarking the model using the benchmarking tool the timing reported did not match that as viewed while running inference on the model on an APK. In almost all instances, the timing reported was almost twice as that seen on the Benchmarking tool. The GPU delegate is used to run inference on this model.
To measure timing on the APK we employed both the methods.
i) Using the getLastNativeInferenceDurationNanoseconds() function provided by Tflite
ii) Using the SystemClock.uptimeMillis() function provided in the os.SystemClock library.
The code for the same is:
long str_time = SystemClock.uptimeMillis();
tflite_intep.run(inp,out);
System.out.println("Inference Time :"+(SystemClock.uptimeMillis()-str_time));
In this instance the output from both the getLastNativeInferenceDurationNanoseconds() as well as the Benchmarking tool is 35.421 ms while that shown in the logcat from the SystemClock function is 70.33 ms.
**Describe the expected behavior**
The timing shown in all 3 scenarios need to match or at least be within a reasonable amount from each other.
**Standalone code to reproduce the issue**
Provide a reproducible test case that is the bare minimum necessary to generate
the problem. If possible, please share a link to Colab/Jupyter/any notebook.
**Other info / logs** Include any logs or source code that would be helpful to
diagnose the problem. If including tracebacks, please include the full
traceback. Large logs and files should be attached.
Please do let me know if any furthur information is needed. | True | Timing Discrepency betweeen Tflite Benchmarking Tool and Android Studio Inference Time - <em>Please make sure that this is an issue related to performance of TensorFlow.
As per our
[GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md),
we only address code/doc bugs, performance issues, feature requests and
build/installation issues on GitHub. tag:performance_template</em>
**System information**
- Have I written custom code (as opposed to using a stock example script provided in TensorFlow):
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04):
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device:
- TensorFlow installed from (source or binary): Source
- TensorFlow version (use command below): 1.15
- Python version: 3.6
- Bazel version (if compiling from source):
- GCC/Compiler version (if compiling from source):
- CUDA/cuDNN version:
- GPU model and memory:
You can collect some of this information using our environment capture
[script](https://github.com/tensorflow/tensorflow/tree/master/tools/tf_env_collect.sh)
You can also obtain the TensorFlow version with:
1. TF 1.0: `python -c "import tensorflow as tf; print(tf.GIT_VERSION, tf.VERSION)"`
2. TF 2.0: `python -c "import tensorflow as tf; print(tf.version.GIT_VERSION, tf.version.VERSION)"`
**Describe the current behavior**
While Benchmarking the model using the benchmarking tool the timing reported did not match that as viewed while running inference on the model on an APK. In almost all instances, the timing reported was almost twice as that seen on the Benchmarking tool. The GPU delegate is used to run inference on this model.
To measure timing on the APK we employed both the methods.
i) Using the getLastNativeInferenceDurationNanoseconds() function provided by Tflite
ii) Using the SystemClock.uptimeMillis() function provided in the os.SystemClock library.
The code for the same is:
long str_time = SystemClock.uptimeMillis();
tflite_intep.run(inp,out);
System.out.println("Inference Time :"+(SystemClock.uptimeMillis()-str_time));
In this instance the output from both the getLastNativeInferenceDurationNanoseconds() as well as the Benchmarking tool is 35.421 ms while that shown in the logcat from the SystemClock function is 70.33 ms.
**Describe the expected behavior**
The timing shown in all 3 scenarios need to match or at least be within a reasonable amount from each other.
**Standalone code to reproduce the issue**
Provide a reproducible test case that is the bare minimum necessary to generate
the problem. If possible, please share a link to Colab/Jupyter/any notebook.
**Other info / logs** Include any logs or source code that would be helpful to
diagnose the problem. If including tracebacks, please include the full
traceback. Large logs and files should be attached.
Please do let me know if any furthur information is needed. | non_priority | timing discrepency betweeen tflite benchmarking tool and android studio inference time please make sure that this is an issue related to performance of tensorflow as per our we only address code doc bugs performance issues feature requests and build installation issues on github tag performance template system information have i written custom code as opposed to using a stock example script provided in tensorflow os platform and distribution e g linux ubuntu mobile device e g iphone pixel samsung galaxy if the issue happens on mobile device tensorflow installed from source or binary source tensorflow version use command below python version bazel version if compiling from source gcc compiler version if compiling from source cuda cudnn version gpu model and memory you can collect some of this information using our environment capture you can also obtain the tensorflow version with tf python c import tensorflow as tf print tf git version tf version tf python c import tensorflow as tf print tf version git version tf version version describe the current behavior while benchmarking the model using the benchmarking tool the timing reported did not match that as viewed while running inference on the model on an apk in almost all instances the timing reported was almost twice as that seen on the benchmarking tool the gpu delegate is used to run inference on this model to measure timing on the apk we employed both the methods i using the getlastnativeinferencedurationnanoseconds function provided by tflite ii using the systemclock uptimemillis function provided in the os systemclock library the code for the same is long str time systemclock uptimemillis tflite intep run inp out system out println inference time systemclock uptimemillis str time in this instance the output from both the getlastnativeinferencedurationnanoseconds as well as the benchmarking tool is ms while that shown in the logcat from the systemclock function is ms describe the expected behavior the timing shown in all scenarios need to match or at least be within a reasonable amount from each other standalone code to reproduce the issue provide a reproducible test case that is the bare minimum necessary to generate the problem if possible please share a link to colab jupyter any notebook other info logs include any logs or source code that would be helpful to diagnose the problem if including tracebacks please include the full traceback large logs and files should be attached please do let me know if any furthur information is needed | 0 |
183,183 | 21,714,482,767 | IssuesEvent | 2022-05-10 16:30:51 | svg-GHC-2/test_django.nv | https://api.github.com/repos/svg-GHC-2/test_django.nv | closed | CVE-2019-19844 (High) detected in Django-1.8.3-py2.py3-none-any.whl - autoclosed | security vulnerability | ## CVE-2019-19844 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.3-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/a3/e1/0f3c17b1caa559ba69513ff72e250377c268d5bd3e8ad2b22809c7e2e907/Django-1.8.3-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/a3/e1/0f3c17b1caa559ba69513ff72e250377c268d5bd3e8ad2b22809c7e2e907/Django-1.8.3-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Django-1.8.3-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/9c82557a12ed8d1bf704180a7d351aa1518ef16c">9c82557a12ed8d1bf704180a7d351aa1518ef16c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Django before 1.11.27, 2.x before 2.2.9, and 3.x before 3.0.1 allows account takeover. A suitably crafted email address (that is equal to an existing user's email address after case transformation of Unicode characters) would allow an attacker to be sent a password reset token for the matched user account. (One mitigation in the new releases is to send password reset tokens only to the registered user email address.)
<p>Publish Date: 2019-12-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19844>CVE-2019-19844</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19844">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19844</a></p>
<p>Release Date: 2020-01-08</p>
<p>Fix Resolution: 1.11.27;2.2.9;3.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"Django","packageVersion":"1.8.3","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"Django:1.8.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.11.27;2.2.9;3.0.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-19844","vulnerabilityDetails":"Django before 1.11.27, 2.x before 2.2.9, and 3.x before 3.0.1 allows account takeover. A suitably crafted email address (that is equal to an existing user\u0027s email address after case transformation of Unicode characters) would allow an attacker to be sent a password reset token for the matched user account. (One mitigation in the new releases is to send password reset tokens only to the registered user email address.)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19844","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-19844 (High) detected in Django-1.8.3-py2.py3-none-any.whl - autoclosed - ## CVE-2019-19844 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.3-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/a3/e1/0f3c17b1caa559ba69513ff72e250377c268d5bd3e8ad2b22809c7e2e907/Django-1.8.3-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/a3/e1/0f3c17b1caa559ba69513ff72e250377c268d5bd3e8ad2b22809c7e2e907/Django-1.8.3-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Django-1.8.3-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/9c82557a12ed8d1bf704180a7d351aa1518ef16c">9c82557a12ed8d1bf704180a7d351aa1518ef16c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Django before 1.11.27, 2.x before 2.2.9, and 3.x before 3.0.1 allows account takeover. A suitably crafted email address (that is equal to an existing user's email address after case transformation of Unicode characters) would allow an attacker to be sent a password reset token for the matched user account. (One mitigation in the new releases is to send password reset tokens only to the registered user email address.)
<p>Publish Date: 2019-12-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19844>CVE-2019-19844</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19844">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19844</a></p>
<p>Release Date: 2020-01-08</p>
<p>Fix Resolution: 1.11.27;2.2.9;3.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"Django","packageVersion":"1.8.3","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"Django:1.8.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.11.27;2.2.9;3.0.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-19844","vulnerabilityDetails":"Django before 1.11.27, 2.x before 2.2.9, and 3.x before 3.0.1 allows account takeover. A suitably crafted email address (that is equal to an existing user\u0027s email address after case transformation of Unicode characters) would allow an attacker to be sent a password reset token for the matched user account. (One mitigation in the new releases is to send password reset tokens only to the registered user email address.)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19844","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in django none any whl autoclosed cve high severity vulnerability vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x django none any whl vulnerable library found in head commit a href found in base branch main vulnerability details django before x before and x before allows account takeover a suitably crafted email address that is equal to an existing user s email address after case transformation of unicode characters would allow an attacker to be sent a password reset token for the matched user account one mitigation in the new releases is to send password reset tokens only to the registered user email address publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree django isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails django before x before and x before allows account takeover a suitably crafted email address that is equal to an existing user email address after case transformation of unicode characters would allow an attacker to be sent a password reset token for the matched user account one mitigation in the new releases is to send password reset tokens only to the registered user email address vulnerabilityurl | 0 |
30,841 | 11,855,502,084 | IssuesEvent | 2020-03-25 04:31:04 | emilwareus/NodeGoat | https://api.github.com/repos/emilwareus/NodeGoat | opened | CVE-2020-8116 (High) detected in dot-prop-4.2.0.tgz | security vulnerability | ## CVE-2020-8116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dot-prop-4.2.0.tgz</b></p></summary>
<p>Get, set, or delete a property from a nested object using a dot path</p>
<p>Library home page: <a href="https://registry.npmjs.org/dot-prop/-/dot-prop-4.2.0.tgz">https://registry.npmjs.org/dot-prop/-/dot-prop-4.2.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/NodeGoat/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/NodeGoat/node_modules/dot-prop/package.json</p>
<p>
Dependency Hierarchy:
- grunt-nodemon-0.4.2.tgz (Root Library)
- nodemon-1.18.9.tgz
- update-notifier-2.5.0.tgz
- configstore-3.1.2.tgz
- :x: **dot-prop-4.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/emilwareus/NodeGoat/commit/6e82e4fc2f213cdeef00afe959aabbe797616a0a">6e82e4fc2f213cdeef00afe959aabbe797616a0a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in dot-prop npm package version 5.1.0 and earlier allows an attacker to add arbitrary properties to JavaScript language constructs such as objects.
<p>Publish Date: 2020-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8116>CVE-2020-8116</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116</a></p>
<p>Release Date: 2020-02-04</p>
<p>Fix Resolution: dot-prop - 5.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-8116 (High) detected in dot-prop-4.2.0.tgz - ## CVE-2020-8116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dot-prop-4.2.0.tgz</b></p></summary>
<p>Get, set, or delete a property from a nested object using a dot path</p>
<p>Library home page: <a href="https://registry.npmjs.org/dot-prop/-/dot-prop-4.2.0.tgz">https://registry.npmjs.org/dot-prop/-/dot-prop-4.2.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/NodeGoat/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/NodeGoat/node_modules/dot-prop/package.json</p>
<p>
Dependency Hierarchy:
- grunt-nodemon-0.4.2.tgz (Root Library)
- nodemon-1.18.9.tgz
- update-notifier-2.5.0.tgz
- configstore-3.1.2.tgz
- :x: **dot-prop-4.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/emilwareus/NodeGoat/commit/6e82e4fc2f213cdeef00afe959aabbe797616a0a">6e82e4fc2f213cdeef00afe959aabbe797616a0a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in dot-prop npm package version 5.1.0 and earlier allows an attacker to add arbitrary properties to JavaScript language constructs such as objects.
<p>Publish Date: 2020-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8116>CVE-2020-8116</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8116</a></p>
<p>Release Date: 2020-02-04</p>
<p>Fix Resolution: dot-prop - 5.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in dot prop tgz cve high severity vulnerability vulnerable library dot prop tgz get set or delete a property from a nested object using a dot path library home page a href path to dependency file tmp ws scm nodegoat package json path to vulnerable library tmp ws scm nodegoat node modules dot prop package json dependency hierarchy grunt nodemon tgz root library nodemon tgz update notifier tgz configstore tgz x dot prop tgz vulnerable library found in head commit a href vulnerability details prototype pollution vulnerability in dot prop npm package version and earlier allows an attacker to add arbitrary properties to javascript language constructs such as objects publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution dot prop step up your open source security game with whitesource | 0 |
20,179 | 11,410,602,893 | IssuesEvent | 2020-02-01 00:05:33 | Azure/azure-rest-api-specs | https://api.github.com/repos/Azure/azure-rest-api-specs | closed | Cannot set BackendIPConfigurations on ApplicationGateway | Network Service Attention | (Area: network management)
I created an ApplicationGateway through the portal. I then wanted to add a BackendIPConfiguration to the BackendAddressPool. I wrote the following code (pardon the hideous variable names, this was trying to prove to myself that the problem existed):
```
var nm = new NetworkManagementClient(credentials);
nm.SubscriptionId = credentials.DefaultSubscriptionId;
var a = nm.ApplicationGateways.GetAsync("itowlsonacs7", "k8s-aaging-test-ingress-1").Result;
var bep = a.BackendAddressPools[0];
if (bep.BackendIPConfigurations == null)
{
bep.BackendIPConfigurations = new List<NetworkInterfaceIPConfigurationInner>();
bep.BackendAddresses = null;
}
bep.BackendIPConfigurations.Add(new NetworkInterfaceIPConfigurationInner("/subscriptions/21dd4ed1-9ce5-4633-b202-a27b157920dc/resourceGroups/itowlsonacs7/providers/Microsoft.Network/networkInterfaces/k8s-agent-DB1C7F54-nic-0/ipConfigurations/ipconfig1"));
var after = nm.ApplicationGateways.BeginCreateOrUpdateAsync("itowlsonacs7", "k8s-aaging-test-ingress-1", a).Result;
```
The CreateOrUpdate was apparently accepted (no exception occurred), but the BackendIPConfiguration was _not_ set on the gateway, nor did the gateway go into updating state.
It's possible there's a bug in the above code, but I've seen a similar issue when creating gateways from code, where all gateway properties _except_ BackendIPConfigurations were set correctly. So I suspect something is amiss in the library or in the networking Swagger spec.
I _can_ set BackendIPConfigurations via the portal, but looking at the network trace in dev tools, this seems to be performing an ARM batch update of both the gateway _and_ the NIC. The application gateway SDK docs don't mention this as being required. | 1.0 | Cannot set BackendIPConfigurations on ApplicationGateway - (Area: network management)
I created an ApplicationGateway through the portal. I then wanted to add a BackendIPConfiguration to the BackendAddressPool. I wrote the following code (pardon the hideous variable names, this was trying to prove to myself that the problem existed):
```
var nm = new NetworkManagementClient(credentials);
nm.SubscriptionId = credentials.DefaultSubscriptionId;
var a = nm.ApplicationGateways.GetAsync("itowlsonacs7", "k8s-aaging-test-ingress-1").Result;
var bep = a.BackendAddressPools[0];
if (bep.BackendIPConfigurations == null)
{
bep.BackendIPConfigurations = new List<NetworkInterfaceIPConfigurationInner>();
bep.BackendAddresses = null;
}
bep.BackendIPConfigurations.Add(new NetworkInterfaceIPConfigurationInner("/subscriptions/21dd4ed1-9ce5-4633-b202-a27b157920dc/resourceGroups/itowlsonacs7/providers/Microsoft.Network/networkInterfaces/k8s-agent-DB1C7F54-nic-0/ipConfigurations/ipconfig1"));
var after = nm.ApplicationGateways.BeginCreateOrUpdateAsync("itowlsonacs7", "k8s-aaging-test-ingress-1", a).Result;
```
The CreateOrUpdate was apparently accepted (no exception occurred), but the BackendIPConfiguration was _not_ set on the gateway, nor did the gateway go into updating state.
It's possible there's a bug in the above code, but I've seen a similar issue when creating gateways from code, where all gateway properties _except_ BackendIPConfigurations were set correctly. So I suspect something is amiss in the library or in the networking Swagger spec.
I _can_ set BackendIPConfigurations via the portal, but looking at the network trace in dev tools, this seems to be performing an ARM batch update of both the gateway _and_ the NIC. The application gateway SDK docs don't mention this as being required. | non_priority | cannot set backendipconfigurations on applicationgateway area network management i created an applicationgateway through the portal i then wanted to add a backendipconfiguration to the backendaddresspool i wrote the following code pardon the hideous variable names this was trying to prove to myself that the problem existed var nm new networkmanagementclient credentials nm subscriptionid credentials defaultsubscriptionid var a nm applicationgateways getasync aaging test ingress result var bep a backendaddresspools if bep backendipconfigurations null bep backendipconfigurations new list bep backendaddresses null bep backendipconfigurations add new networkinterfaceipconfigurationinner subscriptions resourcegroups providers microsoft network networkinterfaces agent nic ipconfigurations var after nm applicationgateways begincreateorupdateasync aaging test ingress a result the createorupdate was apparently accepted no exception occurred but the backendipconfiguration was not set on the gateway nor did the gateway go into updating state it s possible there s a bug in the above code but i ve seen a similar issue when creating gateways from code where all gateway properties except backendipconfigurations were set correctly so i suspect something is amiss in the library or in the networking swagger spec i can set backendipconfigurations via the portal but looking at the network trace in dev tools this seems to be performing an arm batch update of both the gateway and the nic the application gateway sdk docs don t mention this as being required | 0 |
108,946 | 11,616,137,202 | IssuesEvent | 2020-02-26 15:15:41 | MikeLimaSierra/Nuclear.Test | https://api.github.com/repos/MikeLimaSierra/Nuclear.Test | opened | document vs integration | documentation enhancement pkg: console | external tools
path to exe
arguments: -d $(BinDir) -p $(TargetName).dll -v 7
check use output window | 1.0 | document vs integration - external tools
path to exe
arguments: -d $(BinDir) -p $(TargetName).dll -v 7
check use output window | non_priority | document vs integration external tools path to exe arguments d bindir p targetname dll v check use output window | 0 |
29,542 | 8,367,390,913 | IssuesEvent | 2018-10-04 12:06:34 | gravitystorm/openstreetmap-carto | https://api.github.com/repos/gravitystorm/openstreetmap-carto | opened | Labels of amenity=school on buildings look generic | amenity-points bug buildings text | School names should look always the same (slanted text with darker school area color), however on buildings the name is rendered as if there was no school.
### Expected behavior
[Simple node](https://www.openstreetmap.org/node/1235505214)

### Actual behavior
[Building with school](https://www.openstreetmap.org/way/100280428)

| 1.0 | Labels of amenity=school on buildings look generic - School names should look always the same (slanted text with darker school area color), however on buildings the name is rendered as if there was no school.
### Expected behavior
[Simple node](https://www.openstreetmap.org/node/1235505214)

### Actual behavior
[Building with school](https://www.openstreetmap.org/way/100280428)

| non_priority | labels of amenity school on buildings look generic school names should look always the same slanted text with darker school area color however on buildings the name is rendered as if there was no school expected behavior actual behavior | 0 |
23,433 | 11,885,755,143 | IssuesEvent | 2020-03-27 20:18:07 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [Connectors UI] ServiceNow action type shouldn't be present in the Type filter list in Connectors tab | Feature:UIActions Team:Alerting Services bug | ServiceNow should be removed from the Type filter list on the connectors tab, because it is not on the “Select a connector” page
**Steps to reproduce:**
1. Navigate to Alerts and Actions -> Connectors
2. Create a few connectors to get some records in the table
3. Open Type filter dropdown
4. Observe that ServiceNow is present:

**Expected behavior:**
ServiceNow shouldn't be in the Type filter list
| 1.0 | [Connectors UI] ServiceNow action type shouldn't be present in the Type filter list in Connectors tab - ServiceNow should be removed from the Type filter list on the connectors tab, because it is not on the “Select a connector” page
**Steps to reproduce:**
1. Navigate to Alerts and Actions -> Connectors
2. Create a few connectors to get some records in the table
3. Open Type filter dropdown
4. Observe that ServiceNow is present:

**Expected behavior:**
ServiceNow shouldn't be in the Type filter list
| non_priority | servicenow action type shouldn t be present in the type filter list in connectors tab servicenow should be removed from the type filter list on the connectors tab because it is not on the “select a connector” page steps to reproduce navigate to alerts and actions connectors create a few connectors to get some records in the table open type filter dropdown observe that servicenow is present expected behavior servicenow shouldn t be in the type filter list | 0 |
70,810 | 13,535,645,149 | IssuesEvent | 2020-09-16 07:54:17 | hypergraph-xyz/desktop | https://api.github.com/repos/hypergraph-xyz/desktop | closed | Add route for own profile | bug code | Currently when you visit your own profile, the url is `/profiles/:key`, just like if you were visiting another profile. This is a problem for analytics, because you can't tell when people are looking at their _own_ profile. Add a route like `/profile` that makes this possible. | 1.0 | Add route for own profile - Currently when you visit your own profile, the url is `/profiles/:key`, just like if you were visiting another profile. This is a problem for analytics, because you can't tell when people are looking at their _own_ profile. Add a route like `/profile` that makes this possible. | non_priority | add route for own profile currently when you visit your own profile the url is profiles key just like if you were visiting another profile this is a problem for analytics because you can t tell when people are looking at their own profile add a route like profile that makes this possible | 0 |
84,859 | 7,936,083,271 | IssuesEvent | 2018-07-09 08:16:27 | edenlabllc/ehealth.web | https://api.github.com/repos/edenlabllc/ehealth.web | closed | Get Contract by ID | FE FE/nhs.admin epic/NHS_admin_portal epic/contracts status/test | As NHS Admin I want see details of each contract through admin portal
[spec](https://edenlab.atlassian.net/wiki/x/MoCeHw)
[apiary](https://uaehealthapi.docs.apiary.io/reference/contracts/contracts/get-contract-details) | 1.0 | Get Contract by ID - As NHS Admin I want see details of each contract through admin portal
[spec](https://edenlab.atlassian.net/wiki/x/MoCeHw)
[apiary](https://uaehealthapi.docs.apiary.io/reference/contracts/contracts/get-contract-details) | non_priority | get contract by id as nhs admin i want see details of each contract through admin portal | 0 |
38,112 | 5,166,731,423 | IssuesEvent | 2017-01-17 16:55:10 | palantir/atlasdb | https://api.github.com/repos/palantir/atlasdb | closed | Flaky test: LazyClosableIteratorTest | component: testing | Message:
```
java.lang.RuntimeException: Failure during run 66
```
Failed builds:
- https://circleci.com/gh/palantir/atlasdb/2612
- https://circleci.com/gh/palantir/atlasdb/2655
- https://circleci.com/gh/palantir/atlasdb/2693
- https://circleci.com/gh/palantir/atlasdb/2789
- https://circleci.com/gh/palantir/atlasdb/2790
| 1.0 | Flaky test: LazyClosableIteratorTest - Message:
```
java.lang.RuntimeException: Failure during run 66
```
Failed builds:
- https://circleci.com/gh/palantir/atlasdb/2612
- https://circleci.com/gh/palantir/atlasdb/2655
- https://circleci.com/gh/palantir/atlasdb/2693
- https://circleci.com/gh/palantir/atlasdb/2789
- https://circleci.com/gh/palantir/atlasdb/2790
| non_priority | flaky test lazyclosableiteratortest message java lang runtimeexception failure during run failed builds | 0 |
75,062 | 15,391,326,691 | IssuesEvent | 2021-03-03 14:26:47 | Madhusuthanan-B/FOO | https://api.github.com/repos/Madhusuthanan-B/FOO | opened | CVE-2021-27515 (High) detected in url-parse-1.4.7.tgz | security vulnerability | ## CVE-2021-27515 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: FOO/package.json</p>
<p>Path to vulnerable library: FOO/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.901.6.tgz (Root Library)
- webpack-dev-server-3.10.3.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Madhusuthanan-B/FOO/commit/b157124c24c1ddf938f36ca47f9212b09527a6a9">b157124c24c1ddf938f36ca47f9212b09527a6a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse before 1.5.0 mishandles certain uses of backslash such as http:\/ and interprets the URI as a relative path.
<p>Publish Date: 2021-02-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27515>CVE-2021-27515</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515</a></p>
<p>Release Date: 2021-02-22</p>
<p>Fix Resolution: 1.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-27515 (High) detected in url-parse-1.4.7.tgz - ## CVE-2021-27515 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: FOO/package.json</p>
<p>Path to vulnerable library: FOO/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.901.6.tgz (Root Library)
- webpack-dev-server-3.10.3.tgz
- sockjs-client-1.4.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Madhusuthanan-B/FOO/commit/b157124c24c1ddf938f36ca47f9212b09527a6a9">b157124c24c1ddf938f36ca47f9212b09527a6a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse before 1.5.0 mishandles certain uses of backslash such as http:\/ and interprets the URI as a relative path.
<p>Publish Date: 2021-02-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27515>CVE-2021-27515</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515</a></p>
<p>Release Date: 2021-02-22</p>
<p>Fix Resolution: 1.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in url parse tgz cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file foo package json path to vulnerable library foo node modules url parse package json dependency hierarchy build angular tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library found in head commit a href found in base branch master vulnerability details url parse before mishandles certain uses of backslash such as http and interprets the uri as a relative path publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
36,716 | 9,880,843,840 | IssuesEvent | 2019-06-24 13:31:46 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | "gradle eclipse" fails on 7.x due to :x-pack:plugin:vectors project | :Core/Infra/Build :Search/Ranking | This is only valid for 7.x and the `gradlew eclipse` command (or `gradlew cleanEclipse eclipse`) fail with the following output:
```
FAILURE: Build failed with an exception.
* Where:
Build file 'W:\Eclipse_workspace_7x\elasticsearch\x-pack\build.gradle' line: 9
* What went wrong:
A problem occurred evaluating project ':x-pack:plugin:vectors'.
> Project with path 'plugin:core-tests' could not be found in project ':x-pack'.
```
Removing [these lines](https://github.com/elastic/elasticsearch/blob/7.x/x-pack/plugin/vectors/build.gradle#L17-L19) makes the command succeed. | 1.0 | "gradle eclipse" fails on 7.x due to :x-pack:plugin:vectors project - This is only valid for 7.x and the `gradlew eclipse` command (or `gradlew cleanEclipse eclipse`) fail with the following output:
```
FAILURE: Build failed with an exception.
* Where:
Build file 'W:\Eclipse_workspace_7x\elasticsearch\x-pack\build.gradle' line: 9
* What went wrong:
A problem occurred evaluating project ':x-pack:plugin:vectors'.
> Project with path 'plugin:core-tests' could not be found in project ':x-pack'.
```
Removing [these lines](https://github.com/elastic/elasticsearch/blob/7.x/x-pack/plugin/vectors/build.gradle#L17-L19) makes the command succeed. | non_priority | gradle eclipse fails on x due to x pack plugin vectors project this is only valid for x and the gradlew eclipse command or gradlew cleaneclipse eclipse fail with the following output failure build failed with an exception where build file w eclipse workspace elasticsearch x pack build gradle line what went wrong a problem occurred evaluating project x pack plugin vectors project with path plugin core tests could not be found in project x pack removing makes the command succeed | 0 |
85,480 | 10,441,708,554 | IssuesEvent | 2019-09-18 11:28:36 | e-WindLidar/OpenLidarModuleDefinitions | https://api.github.com/repos/e-WindLidar/OpenLidarModuleDefinitions | closed | Create readme.md file | documentation | The repository needs a simple readme.md file. This should explain the OpenLidar concept and the repository. | 1.0 | Create readme.md file - The repository needs a simple readme.md file. This should explain the OpenLidar concept and the repository. | non_priority | create readme md file the repository needs a simple readme md file this should explain the openlidar concept and the repository | 0 |
405,350 | 27,514,482,956 | IssuesEvent | 2023-03-06 11:02:41 | tiiuae/vmd | https://api.github.com/repos/tiiuae/vmd | closed | Research WASM component model as binary target in the context of vmd | documentation | Bringing this up as a high level topic and putting together some notes below. My initial assessment is that we do not want to implement vmd-server and/or common types/protocols using WASM component system such as Spin at this stage.
TLDR; It's too immature both standard and implementation wise and it might conflict with our needs of highly privileged low level access on the host system.
However I'll leave some of my research and links below if anyone else could see something possibly interesting in this approach.
# Overview
Research the possibility of using the [WebAssembly component model](https://github.com/WebAssembly/component-model) as a binary target for vmd.
# Motivation
WASM component model might bring benefits in the context of vmd. From a research perspective it makes sense to get an idea of it's possible benefits and shortcomings.
At high level the component model offers the following:
> 1. Define a portable, load- and run-time-efficient binary format for separately-compiled components built from WebAssembly core modules that enable portable, cross-language composition.
> 2. Support the definition of portable, virtualizable, statically-analyzable, capability-safe, language-agnostic interfaces, especially those being defined by [WASI](https://github.com/WebAssembly/WASI/blob/main/README.md).
In the context of security:
> A component runtime implements built-in host functionality as wasm components to reduce the [Trusted Computing Base](https://en.wikipedia.org/wiki/Trusted_computing_base).
Furthermore the component model brings benefits in terms of using different languages and frameworks together as it defines a unified type-interface between the components.
> 1. A host defines imports in terms of explicit high-level value types (e.g.,
> numbers, strings, lists, records and variants) that can be automatically
> bound to the calling component's source-language values.
> 2. A host returns non-value, non-copied resources (like files, storage
> connections and requests/responses) to components via unforgeable handles
> (analogous to Unix file descriptors).
> 3. A host exposes non-blocking and/or streaming I/O to components through
> language-neutral interfaces that can be bound to different components'
> source languages' concurrency features (such as promises, futures,
> async/await and coroutines).
> 4. A host passes configuration (e.g., values from config files and secrets) to
> a component through imports of typed high-level values and handles.
Refer to the [high level overview](https://github.com/WebAssembly/component-model/tree/main/design/high-level) for more use cases and value propositions.
# Implementation
In the scope of this research we consider one of the more mature implementations of the component model which is [Spin](https://developer.fermyon.com/spin/index). As runtime we consider [wasmtime](https://docs.wasmtime.dev/) which adheres to the [WASI](https://wasi.dev/) standard.
At very high level implementing wasm component system for vmd could mean that the transport protocol requests and type interfaces are implemented as components.
# Possible shortcomings/open questions
- TLS support including newer standards and mutual TLS.
- Maturity of implementations and standards (Spin, wasmtime, WASI).
- Maybe there is functionality we need, but it doesn't yet exist in the implementation.
- Might conflict with needs of low level access on the host system.
| 1.0 | Research WASM component model as binary target in the context of vmd - Bringing this up as a high level topic and putting together some notes below. My initial assessment is that we do not want to implement vmd-server and/or common types/protocols using WASM component system such as Spin at this stage.
TLDR; It's too immature both standard and implementation wise and it might conflict with our needs of highly privileged low level access on the host system.
However I'll leave some of my research and links below if anyone else could see something possibly interesting in this approach.
# Overview
Research the possibility of using the [WebAssembly component model](https://github.com/WebAssembly/component-model) as a binary target for vmd.
# Motivation
WASM component model might bring benefits in the context of vmd. From a research perspective it makes sense to get an idea of it's possible benefits and shortcomings.
At high level the component model offers the following:
> 1. Define a portable, load- and run-time-efficient binary format for separately-compiled components built from WebAssembly core modules that enable portable, cross-language composition.
> 2. Support the definition of portable, virtualizable, statically-analyzable, capability-safe, language-agnostic interfaces, especially those being defined by [WASI](https://github.com/WebAssembly/WASI/blob/main/README.md).
In the context of security:
> A component runtime implements built-in host functionality as wasm components to reduce the [Trusted Computing Base](https://en.wikipedia.org/wiki/Trusted_computing_base).
Furthermore the component model brings benefits in terms of using different languages and frameworks together as it defines a unified type-interface between the components.
> 1. A host defines imports in terms of explicit high-level value types (e.g.,
> numbers, strings, lists, records and variants) that can be automatically
> bound to the calling component's source-language values.
> 2. A host returns non-value, non-copied resources (like files, storage
> connections and requests/responses) to components via unforgeable handles
> (analogous to Unix file descriptors).
> 3. A host exposes non-blocking and/or streaming I/O to components through
> language-neutral interfaces that can be bound to different components'
> source languages' concurrency features (such as promises, futures,
> async/await and coroutines).
> 4. A host passes configuration (e.g., values from config files and secrets) to
> a component through imports of typed high-level values and handles.
Refer to the [high level overview](https://github.com/WebAssembly/component-model/tree/main/design/high-level) for more use cases and value propositions.
# Implementation
In the scope of this research we consider one of the more mature implementations of the component model which is [Spin](https://developer.fermyon.com/spin/index). As runtime we consider [wasmtime](https://docs.wasmtime.dev/) which adheres to the [WASI](https://wasi.dev/) standard.
At very high level implementing wasm component system for vmd could mean that the transport protocol requests and type interfaces are implemented as components.
# Possible shortcomings/open questions
- TLS support including newer standards and mutual TLS.
- Maturity of implementations and standards (Spin, wasmtime, WASI).
- Maybe there is functionality we need, but it doesn't yet exist in the implementation.
- Might conflict with needs of low level access on the host system.
| non_priority | research wasm component model as binary target in the context of vmd bringing this up as a high level topic and putting together some notes below my initial assessment is that we do not want to implement vmd server and or common types protocols using wasm component system such as spin at this stage tldr it s too immature both standard and implementation wise and it might conflict with our needs of highly privileged low level access on the host system however i ll leave some of my research and links below if anyone else could see something possibly interesting in this approach overview research the possibility of using the as a binary target for vmd motivation wasm component model might bring benefits in the context of vmd from a research perspective it makes sense to get an idea of it s possible benefits and shortcomings at high level the component model offers the following define a portable load and run time efficient binary format for separately compiled components built from webassembly core modules that enable portable cross language composition support the definition of portable virtualizable statically analyzable capability safe language agnostic interfaces especially those being defined by in the context of security a component runtime implements built in host functionality as wasm components to reduce the furthermore the component model brings benefits in terms of using different languages and frameworks together as it defines a unified type interface between the components a host defines imports in terms of explicit high level value types e g numbers strings lists records and variants that can be automatically bound to the calling component s source language values a host returns non value non copied resources like files storage connections and requests responses to components via unforgeable handles analogous to unix file descriptors a host exposes non blocking and or streaming i o to components through language neutral interfaces that can be bound to different components source languages concurrency features such as promises futures async await and coroutines a host passes configuration e g values from config files and secrets to a component through imports of typed high level values and handles refer to the for more use cases and value propositions implementation in the scope of this research we consider one of the more mature implementations of the component model which is as runtime we consider which adheres to the standard at very high level implementing wasm component system for vmd could mean that the transport protocol requests and type interfaces are implemented as components possible shortcomings open questions tls support including newer standards and mutual tls maturity of implementations and standards spin wasmtime wasi maybe there is functionality we need but it doesn t yet exist in the implementation might conflict with needs of low level access on the host system | 0 |
336,709 | 30,217,518,463 | IssuesEvent | 2023-07-05 16:38:23 | apache/lucene | https://api.github.com/repos/apache/lucene | opened | Reproducible TestDrillSideways failure | type:test | ### Description
The following gradle command fails reproducibly on `branch_9x` with the following error:
```
> java.lang.AssertionError
> at __randomizedtesting.SeedInfo.seed([EA93FFB2BD206B3C:98DFDABD0C40DD4F]:0)
> at junit@4.13.1/org.junit.Assert.fail(Assert.java:87)
> at junit@4.13.1/org.junit.Assert.assertTrue(Assert.java:42)
> at junit@4.13.1/org.junit.Assert.assertFalse(Assert.java:65)
> at junit@4.13.1/org.junit.Assert.assertFalse(Assert.java:75)
> at org.apache.lucene.facet.TestDrillSideways.verifyEquals(TestDrillSideways.java:1776)
> at org.apache.lucene.facet.TestDrillSideways.testRandom(TestDrillSideways.java:1338)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
> at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
> at java.base/java.lang.reflect.Method.invoke(Method.java:568)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$8.evaluate(RandomizedRunner.java:946)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:982)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:48)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:45)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
> at junit@4.13.1/org.junit.rules.RunRules.evaluate(RunRules.java:20)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:390)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:843)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:490)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:38)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:47)
> at junit@4.13.1/org.junit.rules.RunRules.evaluate(RunRules.java:20)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:390)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:850)
> at java.base/java.lang.Thread.run(Thread.java:833)
2> NOTE: reproduce with: gradlew test --tests TestDrillSideways.testRandom -Dtests.seed=EA93FFB2BD206B3C -Dtests.locale=ar-OM -Dtests.timezone=Asia/Damascus -Dtests.asserts=true -Dtests.file.encoding=UTF-8
```
### Gradle command to reproduce
`./gradlew test --tests TestDrillSideways.testRandom -Dtests.seed=EA93FFB2BD206B3C -Dtests.locale=ar-OM -Dtests.timezone=Asia/Damascus -Dtests.asserts=true -Dtests.file.encoding=UTF-8` | 1.0 | Reproducible TestDrillSideways failure - ### Description
The following gradle command fails reproducibly on `branch_9x` with the following error:
```
> java.lang.AssertionError
> at __randomizedtesting.SeedInfo.seed([EA93FFB2BD206B3C:98DFDABD0C40DD4F]:0)
> at junit@4.13.1/org.junit.Assert.fail(Assert.java:87)
> at junit@4.13.1/org.junit.Assert.assertTrue(Assert.java:42)
> at junit@4.13.1/org.junit.Assert.assertFalse(Assert.java:65)
> at junit@4.13.1/org.junit.Assert.assertFalse(Assert.java:75)
> at org.apache.lucene.facet.TestDrillSideways.verifyEquals(TestDrillSideways.java:1776)
> at org.apache.lucene.facet.TestDrillSideways.testRandom(TestDrillSideways.java:1338)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
> at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
> at java.base/java.lang.reflect.Method.invoke(Method.java:568)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$8.evaluate(RandomizedRunner.java:946)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:982)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:48)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:45)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
> at junit@4.13.1/org.junit.rules.RunRules.evaluate(RunRules.java:20)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:390)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:843)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:490)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:38)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
> at org.apache.lucene.test_framework@9.8.0-SNAPSHOT/org.apache.lucene.tests.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:47)
> at junit@4.13.1/org.junit.rules.RunRules.evaluate(RunRules.java:20)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:390)
> at randomizedtesting.runner@2.8.1/com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:850)
> at java.base/java.lang.Thread.run(Thread.java:833)
2> NOTE: reproduce with: gradlew test --tests TestDrillSideways.testRandom -Dtests.seed=EA93FFB2BD206B3C -Dtests.locale=ar-OM -Dtests.timezone=Asia/Damascus -Dtests.asserts=true -Dtests.file.encoding=UTF-8
```
### Gradle command to reproduce
`./gradlew test --tests TestDrillSideways.testRandom -Dtests.seed=EA93FFB2BD206B3C -Dtests.locale=ar-OM -Dtests.timezone=Asia/Damascus -Dtests.asserts=true -Dtests.file.encoding=UTF-8` | non_priority | reproducible testdrillsideways failure description the following gradle command fails reproducibly on branch with the following error java lang assertionerror at randomizedtesting seedinfo seed at junit org junit assert fail assert java at junit org junit assert asserttrue assert java at junit org junit assert assertfalse assert java at junit org junit assert assertfalse assert java at org apache lucene facet testdrillsideways verifyequals testdrillsideways java at org apache lucene facet testdrillsideways testrandom testdrillsideways java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner invoke randomizedrunner java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at org apache lucene test framework snapshot org apache lucene tests util testrulesetupteardownchained evaluate testrulesetupteardownchained java at org apache lucene test framework snapshot org apache lucene tests util abstractbeforeafterrule evaluate abstractbeforeafterrule java at org apache lucene test framework snapshot org apache lucene tests util testrulethreadandtestname evaluate testrulethreadandtestname java at org apache lucene test framework snapshot org apache lucene tests util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at org apache lucene test framework snapshot org apache lucene tests util testrulemarkfailure evaluate testrulemarkfailure java at junit org junit rules runrules evaluate runrules java at randomizedtesting runner com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at randomizedtesting runner com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at randomizedtesting runner com carrotsearch randomizedtesting threadleakcontrol forktimeoutingtask threadleakcontrol java at randomizedtesting runner com carrotsearch randomizedtesting threadleakcontrol evaluate threadleakcontrol java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner runsingletest randomizedrunner java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at randomizedtesting runner com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at org apache lucene test framework snapshot org apache lucene tests util abstractbeforeafterrule evaluate abstractbeforeafterrule java at randomizedtesting runner com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene test framework snapshot org apache lucene tests util testrulestoreclassname evaluate testrulestoreclassname java at randomizedtesting runner com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at randomizedtesting runner com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at randomizedtesting runner com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at randomizedtesting runner com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene test framework snapshot org apache lucene tests util testruleassertionsrequired evaluate testruleassertionsrequired java at org apache lucene test framework snapshot org apache lucene tests util abstractbeforeafterrule evaluate abstractbeforeafterrule java at org apache lucene test framework snapshot org apache lucene tests util testrulemarkfailure evaluate testrulemarkfailure java at org apache lucene test framework snapshot org apache lucene tests util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at org apache lucene test framework snapshot org apache lucene tests util testruleignoretestsuites evaluate testruleignoretestsuites java at junit org junit rules runrules evaluate runrules java at randomizedtesting runner com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at randomizedtesting runner com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at randomizedtesting runner com carrotsearch randomizedtesting threadleakcontrol lambda forktimeoutingtask threadleakcontrol java at java base java lang thread run thread java note reproduce with gradlew test tests testdrillsideways testrandom dtests seed dtests locale ar om dtests timezone asia damascus dtests asserts true dtests file encoding utf gradle command to reproduce gradlew test tests testdrillsideways testrandom dtests seed dtests locale ar om dtests timezone asia damascus dtests asserts true dtests file encoding utf | 0 |
370,458 | 25,907,942,772 | IssuesEvent | 2022-12-15 11:45:21 | Programmiermethoden/Dungeon | https://api.github.com/repos/Programmiermethoden/Dungeon | opened | [DSL] Document DSL implementation | documentation | The interaction of different systems in the DSL implementation should be documented in a single place (Wiki?) for future reference. | 1.0 | [DSL] Document DSL implementation - The interaction of different systems in the DSL implementation should be documented in a single place (Wiki?) for future reference. | non_priority | document dsl implementation the interaction of different systems in the dsl implementation should be documented in a single place wiki for future reference | 0 |
242,040 | 20,190,767,719 | IssuesEvent | 2022-02-11 05:04:22 | apache/pulsar | https://api.github.com/repos/apache/pulsar | closed | Flaky-test: testConsumeTxnMessage | component/test flaky-tests | https://github.com/apache/pulsar/runs/5151178465?check_suite_focus=true
```
Error: testConsumeTxnMessage(org.apache.pulsar.testclient.PerformanceTransactionTest) Time elapsed: 1.248 s <<< FAILURE!
java.lang.AssertionError: expected [null] but found [org.apache.pulsar.client.impl.MessageImpl@59e073f3]
at org.testng.Assert.fail(Assert.java:99)
at org.testng.Assert.failNotSame(Assert.java:1033)
at org.testng.Assert.assertNull(Assert.java:965)
at org.testng.Assert.assertNull(Assert.java:953)
at org.apache.pulsar.testclient.PerformanceTransactionTest.testConsumeTxnMessage(PerformanceTransactionTest.java:235)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
at org.testng.internal.InvokeMethodRunnable.runOne(InvokeMethodRunnable.java:45)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:73)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:11)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:829)
``` | 2.0 | Flaky-test: testConsumeTxnMessage - https://github.com/apache/pulsar/runs/5151178465?check_suite_focus=true
```
Error: testConsumeTxnMessage(org.apache.pulsar.testclient.PerformanceTransactionTest) Time elapsed: 1.248 s <<< FAILURE!
java.lang.AssertionError: expected [null] but found [org.apache.pulsar.client.impl.MessageImpl@59e073f3]
at org.testng.Assert.fail(Assert.java:99)
at org.testng.Assert.failNotSame(Assert.java:1033)
at org.testng.Assert.assertNull(Assert.java:965)
at org.testng.Assert.assertNull(Assert.java:953)
at org.apache.pulsar.testclient.PerformanceTransactionTest.testConsumeTxnMessage(PerformanceTransactionTest.java:235)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
at org.testng.internal.InvokeMethodRunnable.runOne(InvokeMethodRunnable.java:45)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:73)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:11)
at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:829)
``` | non_priority | flaky test testconsumetxnmessage error testconsumetxnmessage org apache pulsar testclient performancetransactiontest time elapsed s failure java lang assertionerror expected but found at org testng assert fail assert java at org testng assert failnotsame assert java at org testng assert assertnull assert java at org testng assert assertnull assert java at org apache pulsar testclient performancetransactiontest testconsumetxnmessage performancetransactiontest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal invokemethodrunnable runone invokemethodrunnable java at org testng internal invokemethodrunnable call invokemethodrunnable java at org testng internal invokemethodrunnable call invokemethodrunnable java at java base java util concurrent futuretask run futuretask java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java | 0 |
331,702 | 29,047,933,293 | IssuesEvent | 2023-05-13 20:19:37 | IntellectualSites/FastAsyncWorldEdit | https://api.github.com/repos/IntellectualSites/FastAsyncWorldEdit | closed | Console Startup Error FAWE 1.19.4 | Custom Worlds | Requires Testing third-party | ### Server Implementation
Paper
### Server Version
1.19.4
### Describe the bug
Error on loading in console
### To Reproduce
Just starting the server
### Expected behaviour
No error?
### Screenshots / Videos
_No response_
### Error log (if applicable)
[10:49:13 INFO]: Preparing level "NewWorld" [10:49:14 ERROR]: Could not pass event WorldInitEvent to FastAsyncWorldEdit v2.6.2-SNAPSHOT-415;2987550 java.lang.IllegalArgumentException: Invalid key. Must be [a-z0-9/._-]: at com.google.common.base.Preconditions.checkArgument(Preconditions.java:220) ~[guava-31.1-jre.jar:?] at org.bukkit.NamespacedKey.<init>(NamespacedKey.java:86) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at org.bukkit.craftbukkit.v1_19_R3.util.CraftNamespacedKey.fromMinecraft(CraftNamespacedKey.java:24) ~[purpur-1.19.4.jar:git-Purpur-1952] at java.util.stream.ReferencePipeline$3$1.accept(ReferencePipeline.java:197) ~[?:?] at java.util.stream.ReferencePipeline$2$1.accept(ReferencePipeline.java:179) ~[?:?] at java.util.stream.ReferencePipeline$3$1.accept(ReferencePipeline.java:197) ~[?:?] at java.util.Iterator.forEachRemaining(Iterator.java:133) ~[?:?] at java.util.Spliterators$IteratorSpliterator.forEachRemaining(Spliterators.java:1845) ~[?:?] at java.util.stream.AbstractPipeline.copyInto(AbstractPipeline.java:509) ~[?:?] at java.util.stream.AbstractPipeline.wrapAndCopyInto(AbstractPipeline.java:499) ~[?:?] at java.util.stream.ReduceOps$ReduceOp.evaluateSequential(ReduceOps.java:921) ~[?:?] at java.util.stream.AbstractPipeline.evaluate(AbstractPipeline.java:234) ~[?:?] at java.util.stream.ReferencePipeline.collect(ReferencePipeline.java:682) ~[?:?] at com.sk89q.worldedit.bukkit.adapter.impl.fawe.v1_19_R3.PaperweightFaweAdapter.getRegisteredBiomes(PaperweightFaweAdapter.java:608) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.sk89q.worldedit.bukkit.WorldEditPlugin.setupBiomes(WorldEditPlugin.java:321) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.sk89q.worldedit.bukkit.WorldEditPlugin.setupWorldData(WorldEditPlugin.java:244) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.sk89q.worldedit.bukkit.WorldEditPlugin$WorldInitListener.onWorldInit(WorldEditPlugin.java:646) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.destroystokyo.paper.event.executor.MethodHandleEventExecutor.execute(MethodHandleEventExecutor.java:40) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at co.aikar.timings.TimedEventExecutor.execute(TimedEventExecutor.java:81) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:git-Purpur-1952] at org.bukkit.plugin.RegisteredListener.callEvent(RegisteredListener.java:70) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at io.papermc.paper.plugin.manager.PaperEventManager.callEvent(PaperEventManager.java:54) ~[purpur-1.19.4.jar:git-Purpur-1952] at io.papermc.paper.plugin.manager.PaperPluginManagerImpl.callEvent(PaperPluginManagerImpl.java:126) ~[purpur-1.19.4.jar:git-Purpur-1952] at org.bukkit.plugin.SimplePluginManager.callEvent(SimplePluginManager.java:617) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at net.minecraft.server.MinecraftServer.initWorld(MinecraftServer.java:660) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.loadWorld0(MinecraftServer.java:613) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.loadLevel(MinecraftServer.java:442) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.dedicated.DedicatedServer.initServer(DedicatedServer.java:344) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.runServer(MinecraftServer.java:1120) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.lambda$spin$0(MinecraftServer.java:325) ~[purpur-1.19.4.jar:git-Purpur-1952] at java.lang.Thread.run(Thread.java:833) ~[?:?]
### Fawe Debugpaste
https://athion.net/ISPaster/paste/view/41828f6b207b4b938d5c43d19087580c
### Fawe Version
2.6.2-SNAPSHOT-415;2987550
### Checklist
- [X] I have included a Fawe debugpaste.
- [X] I am using the newest build from https://ci.athion.net/job/FastAsyncWorldEdit/ and the issue still persists.
### Anything else?
_No response_ | 1.0 | Console Startup Error FAWE 1.19.4 | Custom Worlds - ### Server Implementation
Paper
### Server Version
1.19.4
### Describe the bug
Error on loading in console
### To Reproduce
Just starting the server
### Expected behaviour
No error?
### Screenshots / Videos
_No response_
### Error log (if applicable)
[10:49:13 INFO]: Preparing level "NewWorld" [10:49:14 ERROR]: Could not pass event WorldInitEvent to FastAsyncWorldEdit v2.6.2-SNAPSHOT-415;2987550 java.lang.IllegalArgumentException: Invalid key. Must be [a-z0-9/._-]: at com.google.common.base.Preconditions.checkArgument(Preconditions.java:220) ~[guava-31.1-jre.jar:?] at org.bukkit.NamespacedKey.<init>(NamespacedKey.java:86) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at org.bukkit.craftbukkit.v1_19_R3.util.CraftNamespacedKey.fromMinecraft(CraftNamespacedKey.java:24) ~[purpur-1.19.4.jar:git-Purpur-1952] at java.util.stream.ReferencePipeline$3$1.accept(ReferencePipeline.java:197) ~[?:?] at java.util.stream.ReferencePipeline$2$1.accept(ReferencePipeline.java:179) ~[?:?] at java.util.stream.ReferencePipeline$3$1.accept(ReferencePipeline.java:197) ~[?:?] at java.util.Iterator.forEachRemaining(Iterator.java:133) ~[?:?] at java.util.Spliterators$IteratorSpliterator.forEachRemaining(Spliterators.java:1845) ~[?:?] at java.util.stream.AbstractPipeline.copyInto(AbstractPipeline.java:509) ~[?:?] at java.util.stream.AbstractPipeline.wrapAndCopyInto(AbstractPipeline.java:499) ~[?:?] at java.util.stream.ReduceOps$ReduceOp.evaluateSequential(ReduceOps.java:921) ~[?:?] at java.util.stream.AbstractPipeline.evaluate(AbstractPipeline.java:234) ~[?:?] at java.util.stream.ReferencePipeline.collect(ReferencePipeline.java:682) ~[?:?] at com.sk89q.worldedit.bukkit.adapter.impl.fawe.v1_19_R3.PaperweightFaweAdapter.getRegisteredBiomes(PaperweightFaweAdapter.java:608) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.sk89q.worldedit.bukkit.WorldEditPlugin.setupBiomes(WorldEditPlugin.java:321) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.sk89q.worldedit.bukkit.WorldEditPlugin.setupWorldData(WorldEditPlugin.java:244) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.sk89q.worldedit.bukkit.WorldEditPlugin$WorldInitListener.onWorldInit(WorldEditPlugin.java:646) ~[FastAsyncWorldEdit-Bukkit-2.6.2-SNAPSHOT-415.jar:?] at com.destroystokyo.paper.event.executor.MethodHandleEventExecutor.execute(MethodHandleEventExecutor.java:40) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at co.aikar.timings.TimedEventExecutor.execute(TimedEventExecutor.java:81) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:git-Purpur-1952] at org.bukkit.plugin.RegisteredListener.callEvent(RegisteredListener.java:70) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at io.papermc.paper.plugin.manager.PaperEventManager.callEvent(PaperEventManager.java:54) ~[purpur-1.19.4.jar:git-Purpur-1952] at io.papermc.paper.plugin.manager.PaperPluginManagerImpl.callEvent(PaperPluginManagerImpl.java:126) ~[purpur-1.19.4.jar:git-Purpur-1952] at org.bukkit.plugin.SimplePluginManager.callEvent(SimplePluginManager.java:617) ~[purpur-api-1.19.4-R0.1-SNAPSHOT.jar:?] at net.minecraft.server.MinecraftServer.initWorld(MinecraftServer.java:660) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.loadWorld0(MinecraftServer.java:613) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.loadLevel(MinecraftServer.java:442) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.dedicated.DedicatedServer.initServer(DedicatedServer.java:344) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.runServer(MinecraftServer.java:1120) ~[purpur-1.19.4.jar:git-Purpur-1952] at net.minecraft.server.MinecraftServer.lambda$spin$0(MinecraftServer.java:325) ~[purpur-1.19.4.jar:git-Purpur-1952] at java.lang.Thread.run(Thread.java:833) ~[?:?]
### Fawe Debugpaste
https://athion.net/ISPaster/paste/view/41828f6b207b4b938d5c43d19087580c
### Fawe Version
2.6.2-SNAPSHOT-415;2987550
### Checklist
- [X] I have included a Fawe debugpaste.
- [X] I am using the newest build from https://ci.athion.net/job/FastAsyncWorldEdit/ and the issue still persists.
### Anything else?
_No response_ | non_priority | console startup error fawe custom worlds server implementation paper server version describe the bug error on loading in console to reproduce just starting the server expected behaviour no error screenshots videos no response error log if applicable preparing level newworld could not pass event worldinitevent to fastasyncworldedit snapshot java lang illegalargumentexception invalid key must be at com google common base preconditions checkargument preconditions java at org bukkit namespacedkey namespacedkey java at org bukkit craftbukkit util craftnamespacedkey fromminecraft craftnamespacedkey java at java util stream referencepipeline accept referencepipeline java at java util stream referencepipeline accept referencepipeline java at java util stream referencepipeline accept referencepipeline java at java util iterator foreachremaining iterator java at java util spliterators iteratorspliterator foreachremaining spliterators java at java util stream abstractpipeline copyinto abstractpipeline java at java util stream abstractpipeline wrapandcopyinto abstractpipeline java at java util stream reduceops reduceop evaluatesequential reduceops java at java util stream abstractpipeline evaluate abstractpipeline java at java util stream referencepipeline collect referencepipeline java at com worldedit bukkit adapter impl fawe paperweightfaweadapter getregisteredbiomes paperweightfaweadapter java at com worldedit bukkit worldeditplugin setupbiomes worldeditplugin java at com worldedit bukkit worldeditplugin setupworlddata worldeditplugin java at com worldedit bukkit worldeditplugin worldinitlistener onworldinit worldeditplugin java at com destroystokyo paper event executor methodhandleeventexecutor execute methodhandleeventexecutor java at co aikar timings timedeventexecutor execute timedeventexecutor java at org bukkit plugin registeredlistener callevent registeredlistener java at io papermc paper plugin manager papereventmanager callevent papereventmanager java at io papermc paper plugin manager paperpluginmanagerimpl callevent paperpluginmanagerimpl java at org bukkit plugin simplepluginmanager callevent simplepluginmanager java at net minecraft server minecraftserver initworld minecraftserver java at net minecraft server minecraftserver minecraftserver java at net minecraft server minecraftserver loadlevel minecraftserver java at net minecraft server dedicated dedicatedserver initserver dedicatedserver java at net minecraft server minecraftserver runserver minecraftserver java at net minecraft server minecraftserver lambda spin minecraftserver java at java lang thread run thread java fawe debugpaste fawe version snapshot checklist i have included a fawe debugpaste i am using the newest build from and the issue still persists anything else no response | 0 |
273,060 | 23,724,395,439 | IssuesEvent | 2022-08-30 18:09:24 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | Set sizeSlug in core/image (Template) don't work. | Needs Testing [Status] Stale [Block] Image | **Describe the bug**
I've developed a custom block with Template.
```
const PROJECT_TEMPLATE = [
[ 'core/image', { sizeSlug: 'full', align: 'wide' } ],
];
<InnerBlocks
template={ PROJECT_TEMPLATE }
/>
<figure class="wp-block-image alignwide size-large"><img src="http://127.0.0.1:8080/wp-content/uploads/slider-1-1024x431.jpg" alt="" class="wp-image-1647" srcset="http://127.0.0.1:8080/wp-content/uploads/slider-1-1024x431.jpg 1024w, http://127.0.0.1:8080/wp-content/uploads/slider-1-300x126.jpg 300w, http://127.0.0.1:8080/wp-content/uploads/slider-1-768x323.jpg 768w, http://127.0.0.1:8080/wp-content/uploads/slider-1-1536x647.jpg 1536w, http://127.0.0.1:8080/wp-content/uploads/slider-1.jpg 1900w" sizes="(max-width: 1024px) 100vw, 1024px"></figure>
```
If you add an image then the image is added to the block at large size (it's default when I see that right) and the settings panel's Image Size select field shows the image size as large. I think that is wrong. Setting the align works correctly.
**To reproduce**
Steps to reproduce the behavior:
1. Add an image block
2. Select an image
3. In the block settings view the Image Size select field
4. The selected option is large
**Expected behavior**
As the image was added at full size (see Template) don't show the select field value as large. The class should also be set accordingly <figure class="wp-block-image alignwide size-full">
**Editor version:**
- WordPress version: 5.4.1
- Does the website has Gutenberg plugin installed, or is it using the block editor that comes by default? default
**Desktop:**
- OS: mac
- Browser chrome
- Version 81 | 1.0 | Set sizeSlug in core/image (Template) don't work. - **Describe the bug**
I've developed a custom block with Template.
```
const PROJECT_TEMPLATE = [
[ 'core/image', { sizeSlug: 'full', align: 'wide' } ],
];
<InnerBlocks
template={ PROJECT_TEMPLATE }
/>
<figure class="wp-block-image alignwide size-large"><img src="http://127.0.0.1:8080/wp-content/uploads/slider-1-1024x431.jpg" alt="" class="wp-image-1647" srcset="http://127.0.0.1:8080/wp-content/uploads/slider-1-1024x431.jpg 1024w, http://127.0.0.1:8080/wp-content/uploads/slider-1-300x126.jpg 300w, http://127.0.0.1:8080/wp-content/uploads/slider-1-768x323.jpg 768w, http://127.0.0.1:8080/wp-content/uploads/slider-1-1536x647.jpg 1536w, http://127.0.0.1:8080/wp-content/uploads/slider-1.jpg 1900w" sizes="(max-width: 1024px) 100vw, 1024px"></figure>
```
If you add an image then the image is added to the block at large size (it's default when I see that right) and the settings panel's Image Size select field shows the image size as large. I think that is wrong. Setting the align works correctly.
**To reproduce**
Steps to reproduce the behavior:
1. Add an image block
2. Select an image
3. In the block settings view the Image Size select field
4. The selected option is large
**Expected behavior**
As the image was added at full size (see Template) don't show the select field value as large. The class should also be set accordingly <figure class="wp-block-image alignwide size-full">
**Editor version:**
- WordPress version: 5.4.1
- Does the website has Gutenberg plugin installed, or is it using the block editor that comes by default? default
**Desktop:**
- OS: mac
- Browser chrome
- Version 81 | non_priority | set sizeslug in core image template don t work describe the bug i ve developed a custom block with template const project template innerblocks template project template if you add an image then the image is added to the block at large size it s default when i see that right and the settings panel s image size select field shows the image size as large i think that is wrong setting the align works correctly to reproduce steps to reproduce the behavior add an image block select an image in the block settings view the image size select field the selected option is large expected behavior as the image was added at full size see template don t show the select field value as large the class should also be set accordingly editor version wordpress version does the website has gutenberg plugin installed or is it using the block editor that comes by default default desktop os mac browser chrome version | 0 |
2,956 | 4,099,707,970 | IssuesEvent | 2016-06-03 13:44:10 | DinisCruz/BSIMM-Graphs | https://api.github.com/repos/DinisCruz/BSIMM-Graphs | closed | Data_Files.set_File_Data - Path Traversal | risk - medium risk - to fix security T1 - Injection | Current implementation of Data_Files.set_File_Data ([here](https://github.com/DinisCruz/BSIMM-Graphs/blob/master/src/backend/Data-Files.coffee#L56-L65) and below) is vulnerable by design to an [Path Traversal](https://www.owasp.org/index.php/Path_Traversal) attack.
This will allow any caller to write into files outside the expected [data folder](https://github.com/DinisCruz/BSIMM-Graphs/blob/master/src/backend/Data-Files.coffee#L8)
```coffee
set_File_Data: (filename, file_Contents) ->
if not filename or not file_Contents
return null
if typeof file_Contents isnt 'string'
return null
file_Path = @.find filename
if file_Path is null or file_Path.file_Not_Exists()
file_Path = @.data_Path.path_Combine filename
file_Path.file_Write file_Contents
return file_Path
```
At the moment this method is not wired to a controller, but that is exactly what will happen next (since the point of this method is to allow the existing BSIMM mappings to be edited
Here is the test that proves the issue
```coffee
describe '_securtiy | A1 - Injection', ->
# https://github.com/DinisCruz/BSIMM-Graphs/issues/21
it 'Issue 19 - Data_Files.set_File_Data - Path Traversal', ->
using new Data_Files(), ->
folder_Name = 'outside-data-root'
file_Name = 'some-file.txt'
file_Content = 'some content'
target_Folder = @.data_Path.path_Combine('../' + folder_Name) # Create target folder
.folder_Create()
.assert_Folder_Exists() # Confirm it exists
target_Folder.path_Combine(file_Name) # Create target File
.file_Write(file_Content)
.assert_File_Exists() # Confirm it exists
payload = "../#{folder_Name}/#{file_Name}"
new_Content = 'new - content'
@.data_Path.path_Combine(payload)
.file_Contents().assert_Is file_Content # Confirm original content is there
@.set_File_Data payload, new_Content
@.data_Path.path_Combine(payload)
.file_Contents().assert_Is_Not file_Content # Confirm original content is NOT there
.assert_Is new_Content # Confirm that it has been changed
target_Folder.folder_Delete_Recursive().assert_Is_True() # Delete temp folder
``` | True | Data_Files.set_File_Data - Path Traversal - Current implementation of Data_Files.set_File_Data ([here](https://github.com/DinisCruz/BSIMM-Graphs/blob/master/src/backend/Data-Files.coffee#L56-L65) and below) is vulnerable by design to an [Path Traversal](https://www.owasp.org/index.php/Path_Traversal) attack.
This will allow any caller to write into files outside the expected [data folder](https://github.com/DinisCruz/BSIMM-Graphs/blob/master/src/backend/Data-Files.coffee#L8)
```coffee
set_File_Data: (filename, file_Contents) ->
if not filename or not file_Contents
return null
if typeof file_Contents isnt 'string'
return null
file_Path = @.find filename
if file_Path is null or file_Path.file_Not_Exists()
file_Path = @.data_Path.path_Combine filename
file_Path.file_Write file_Contents
return file_Path
```
At the moment this method is not wired to a controller, but that is exactly what will happen next (since the point of this method is to allow the existing BSIMM mappings to be edited
Here is the test that proves the issue
```coffee
describe '_securtiy | A1 - Injection', ->
# https://github.com/DinisCruz/BSIMM-Graphs/issues/21
it 'Issue 19 - Data_Files.set_File_Data - Path Traversal', ->
using new Data_Files(), ->
folder_Name = 'outside-data-root'
file_Name = 'some-file.txt'
file_Content = 'some content'
target_Folder = @.data_Path.path_Combine('../' + folder_Name) # Create target folder
.folder_Create()
.assert_Folder_Exists() # Confirm it exists
target_Folder.path_Combine(file_Name) # Create target File
.file_Write(file_Content)
.assert_File_Exists() # Confirm it exists
payload = "../#{folder_Name}/#{file_Name}"
new_Content = 'new - content'
@.data_Path.path_Combine(payload)
.file_Contents().assert_Is file_Content # Confirm original content is there
@.set_File_Data payload, new_Content
@.data_Path.path_Combine(payload)
.file_Contents().assert_Is_Not file_Content # Confirm original content is NOT there
.assert_Is new_Content # Confirm that it has been changed
target_Folder.folder_Delete_Recursive().assert_Is_True() # Delete temp folder
``` | non_priority | data files set file data path traversal current implementation of data files set file data and below is vulnerable by design to an attack this will allow any caller to write into files outside the expected coffee set file data filename file contents if not filename or not file contents return null if typeof file contents isnt string return null file path find filename if file path is null or file path file not exists file path data path path combine filename file path file write file contents return file path at the moment this method is not wired to a controller but that is exactly what will happen next since the point of this method is to allow the existing bsimm mappings to be edited here is the test that proves the issue coffee describe securtiy injection it issue data files set file data path traversal using new data files folder name outside data root file name some file txt file content some content target folder data path path combine folder name create target folder folder create assert folder exists confirm it exists target folder path combine file name create target file file write file content assert file exists confirm it exists payload folder name file name new content new content data path path combine payload file contents assert is file content confirm original content is there set file data payload new content data path path combine payload file contents assert is not file content confirm original content is not there assert is new content confirm that it has been changed target folder folder delete recursive assert is true delete temp folder | 0 |
317,195 | 27,219,542,880 | IssuesEvent | 2023-02-21 03:11:58 | Uuvana-Studios/longvinter-windows-client | https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client | opened | The issue of "Killed player" log not being recorded in the server log | Bug Not Tested | Hello admins, while I was opening an unofficial server, I found an issue and have a question. From a certain moment, it seems that the "Killed player" log is not being recorded in the server log anymore. Could you tell me why it disappeared? | 1.0 | The issue of "Killed player" log not being recorded in the server log - Hello admins, while I was opening an unofficial server, I found an issue and have a question. From a certain moment, it seems that the "Killed player" log is not being recorded in the server log anymore. Could you tell me why it disappeared? | non_priority | the issue of killed player log not being recorded in the server log hello admins while i was opening an unofficial server i found an issue and have a question from a certain moment it seems that the killed player log is not being recorded in the server log anymore could you tell me why it disappeared | 0 |
230,107 | 18,499,196,173 | IssuesEvent | 2021-10-19 12:06:03 | TEAMMATES/teammates | https://api.github.com/repos/TEAMMATES/teammates | opened | Add support for E2E tests with Edge browser | a-Testing c.Task | [Selenium 4](https://github.com/SeleniumHQ/selenium/releases/tag/selenium-4.0.0) was released few days ago and boasts many new features and improvements, among which is support for testing using Edge.
We should take advantage of this and at the same time make sure that E2E tests can pass in Windows. | 1.0 | Add support for E2E tests with Edge browser - [Selenium 4](https://github.com/SeleniumHQ/selenium/releases/tag/selenium-4.0.0) was released few days ago and boasts many new features and improvements, among which is support for testing using Edge.
We should take advantage of this and at the same time make sure that E2E tests can pass in Windows. | non_priority | add support for tests with edge browser was released few days ago and boasts many new features and improvements among which is support for testing using edge we should take advantage of this and at the same time make sure that tests can pass in windows | 0 |
248,777 | 26,830,686,741 | IssuesEvent | 2023-02-02 15:49:09 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [APM] Clicking "View span in Discover" outside of the default space does not work as expected | bug Team:APM Feature:Security/Spaces apm:platform [zube]: 8.0 | **Versions**
Kibana: (if relevant) 7.9
In APM, you can look at span details and from there click on `View Span in Discover`.
When inside the default space, this correctly takes you the Discover app where you can explore the `apm*` index pattern, filtered by the `span.id`.
This does not work correctly when outside of the default space. It seems as if the index pattern isn't available outside of the default space, so the Discover app does not show any relevant information.
| True | [APM] Clicking "View span in Discover" outside of the default space does not work as expected - **Versions**
Kibana: (if relevant) 7.9
In APM, you can look at span details and from there click on `View Span in Discover`.
When inside the default space, this correctly takes you the Discover app where you can explore the `apm*` index pattern, filtered by the `span.id`.
This does not work correctly when outside of the default space. It seems as if the index pattern isn't available outside of the default space, so the Discover app does not show any relevant information.
| non_priority | clicking view span in discover outside of the default space does not work as expected versions kibana if relevant in apm you can look at span details and from there click on view span in discover when inside the default space this correctly takes you the discover app where you can explore the apm index pattern filtered by the span id this does not work correctly when outside of the default space it seems as if the index pattern isn t available outside of the default space so the discover app does not show any relevant information | 0 |
2,074 | 3,268,452,552 | IssuesEvent | 2015-10-23 11:35:42 | vector-im/vector-web | https://api.github.com/repos/vector-im/vector-web | opened | Hide/show message timestamps & edit button with JS rather than CSS | maintenance p3 performance | We're bloating up the DOM quite a lot with precalculating invisible timestamps and edit menu images - we should surely just use React to add them into the DOM on mouseover. | True | Hide/show message timestamps & edit button with JS rather than CSS - We're bloating up the DOM quite a lot with precalculating invisible timestamps and edit menu images - we should surely just use React to add them into the DOM on mouseover. | non_priority | hide show message timestamps edit button with js rather than css we re bloating up the dom quite a lot with precalculating invisible timestamps and edit menu images we should surely just use react to add them into the dom on mouseover | 0 |
272,153 | 20,734,891,249 | IssuesEvent | 2022-03-14 12:54:18 | twoics/MapTarget | https://api.github.com/repos/twoics/MapTarget | closed | Map | documentation enhancement | **What is required**
- Need to rewrite the map creation module so that its map creation methods return an object of type `folium.Map`.
- Necessary to set different icons for different types of objects (for example: for coffee shops - the icon of coffee, etc.)
- Document and make the code readable | 1.0 | Map - **What is required**
- Need to rewrite the map creation module so that its map creation methods return an object of type `folium.Map`.
- Necessary to set different icons for different types of objects (for example: for coffee shops - the icon of coffee, etc.)
- Document and make the code readable | non_priority | map what is required need to rewrite the map creation module so that its map creation methods return an object of type folium map necessary to set different icons for different types of objects for example for coffee shops the icon of coffee etc document and make the code readable | 0 |
300,979 | 26,007,767,137 | IssuesEvent | 2022-12-20 21:14:17 | nodejs/node-addon-api | https://api.github.com/repos/nodejs/node-addon-api | closed | [Test] Coverage for class property descriptor | test good first issue never-stale | | class | methods |
|-------------------------|----------------------------------------------------------------------------------------------------------------------------------|
|ClassPropertyDescriptor | |
|Covered| ClassPropertyDescriptor(napi_property_descriptor desc)|
See addon_data.cc and addon_data.js
| 1.0 | [Test] Coverage for class property descriptor - | class | methods |
|-------------------------|----------------------------------------------------------------------------------------------------------------------------------|
|ClassPropertyDescriptor | |
|Covered| ClassPropertyDescriptor(napi_property_descriptor desc)|
See addon_data.cc and addon_data.js
| non_priority | coverage for class property descriptor class methods classpropertydescriptor covered classpropertydescriptor napi property descriptor desc see addon data cc and addon data js | 0 |
248,746 | 26,823,620,726 | IssuesEvent | 2023-02-02 11:15:06 | ministryofjustice/modernisation-platform | https://api.github.com/repos/ministryofjustice/modernisation-platform | closed | Spike: How can we prevent or monitor excessive usage in member AWS accounts | security risk register | ## User Story
Eg using up lots of IPs, large instances, lots of resources etc.
Org level alerting so that it can see everything in the OU
Could be a billing thing
<!--
As a… [who is the user?]
I need/want/expect to… [what does the user want to do?]
So that… [why does the user want to do this?]
-->
## User Type(s)
<!--
Does this impact specific user types?
Can it link to a persona?
-->
## Value
<!-- Describe the value and purpose of the changes -->
## Questions / Assumptions / Hypothesis
<!-- Additional information to explain approach taken
### Hypothesis
If we... [do a thing]
Then... [this will happ]
### Proposal
A proposal that is something testable, don't worry whether it works or not, it's a place for ideas.
-->
## Definition of done
<!-- Checklist for definition of done and acceptance criteria, for example: -->
- [ ] readme has been updated
- [ ] user docs have been updated
- [ ] another team member has reviewed
- [ ] tests are green
- [ ] UR test OR added to continual research plan
## Reference
[How to write good user stories](https://www.gov.uk/service-manual/agile-delivery/writing-user-stories)
| True | Spike: How can we prevent or monitor excessive usage in member AWS accounts - ## User Story
Eg using up lots of IPs, large instances, lots of resources etc.
Org level alerting so that it can see everything in the OU
Could be a billing thing
<!--
As a… [who is the user?]
I need/want/expect to… [what does the user want to do?]
So that… [why does the user want to do this?]
-->
## User Type(s)
<!--
Does this impact specific user types?
Can it link to a persona?
-->
## Value
<!-- Describe the value and purpose of the changes -->
## Questions / Assumptions / Hypothesis
<!-- Additional information to explain approach taken
### Hypothesis
If we... [do a thing]
Then... [this will happ]
### Proposal
A proposal that is something testable, don't worry whether it works or not, it's a place for ideas.
-->
## Definition of done
<!-- Checklist for definition of done and acceptance criteria, for example: -->
- [ ] readme has been updated
- [ ] user docs have been updated
- [ ] another team member has reviewed
- [ ] tests are green
- [ ] UR test OR added to continual research plan
## Reference
[How to write good user stories](https://www.gov.uk/service-manual/agile-delivery/writing-user-stories)
| non_priority | spike how can we prevent or monitor excessive usage in member aws accounts user story eg using up lots of ips large instances lots of resources etc org level alerting so that it can see everything in the ou could be a billing thing as a… i need want expect to… so that… user type s does this impact specific user types can it link to a persona value questions assumptions hypothesis additional information to explain approach taken hypothesis if we then proposal a proposal that is something testable don t worry whether it works or not it s a place for ideas definition of done readme has been updated user docs have been updated another team member has reviewed tests are green ur test or added to continual research plan reference | 0 |
10,544 | 4,074,266,747 | IssuesEvent | 2016-05-28 09:54:26 | SleepyTrousers/EnderIO | https://api.github.com/repos/SleepyTrousers/EnderIO | closed | [Request] Enhance texture pack posibilities by changing texture mappings | Code Complete Suggestion | Currently a number of the machines with custom models draw all their textures from the same few files making it very difficult to make any texture pack more varied then the current plain grey gradients.
For example the Combustion generator draws textures for it's top and sides from the standard machine sides texture and then tiles them, making it necessary for any machine textures to also tile.
| 1.0 | [Request] Enhance texture pack posibilities by changing texture mappings - Currently a number of the machines with custom models draw all their textures from the same few files making it very difficult to make any texture pack more varied then the current plain grey gradients.
For example the Combustion generator draws textures for it's top and sides from the standard machine sides texture and then tiles them, making it necessary for any machine textures to also tile.
| non_priority | enhance texture pack posibilities by changing texture mappings currently a number of the machines with custom models draw all their textures from the same few files making it very difficult to make any texture pack more varied then the current plain grey gradients for example the combustion generator draws textures for it s top and sides from the standard machine sides texture and then tiles them making it necessary for any machine textures to also tile | 0 |
52,353 | 27,523,563,637 | IssuesEvent | 2023-03-06 16:29:57 | ARK-Builders/arklib | https://api.github.com/repos/ARK-Builders/arklib | opened | Missing file causes index loading from file to fail and leads to complete rebuild | bug performance | 1. Build index of some folder using `ark-cli monitor`.
2. Verify `.ark/index` exists.
3. Remove a file from the folder. Verify the index has entry with its path.
4. Load index.
Last step fails, the index is completely rebuilt in this case.
Pay attention to `WARN` lines:
```
[kirill@lenovo TEST]$ RUST_LOG=info ark-cli monitor
Building index of folder /tmp/TEST
[2023-03-06T16:21:33Z INFO arklib] Index has not been registered before
[2023-03-06T16:21:33Z INFO arklib::index] Loading the index from file
[2023-03-06T16:21:33Z WARN arklib::index] No persisted index was found by path /tmp/TEST/.ark/index
[2023-03-06T16:21:33Z INFO arklib::index] Building the index from scratch
[2023-03-06T16:21:36Z INFO arklib::index] Index built
[2023-03-06T16:21:36Z INFO arklib::index] Storing the index to file
[2023-03-06T16:21:36Z INFO arklib] Index was registered
Build succeeded in 3.667931346s
Updating succeeded in 158.747289ms
^C
[kirill@lenovo TEST]$ RUST_LOG=info ark-cli monitor #just load index from the file and check for updates
Building index of folder /tmp/TEST
[2023-03-06T16:21:57Z INFO arklib] Index has not been registered before
[2023-03-06T16:21:57Z INFO arklib::index] Loading the index from file
[2023-03-06T16:21:58Z INFO arklib::index] Storing the index to file
[2023-03-06T16:21:58Z INFO arklib] Index was registered
Build succeeded in 297.370813ms
^C
[kirill@lenovo TEST]$ grep gagarin .ark/index
1678115269692 200433-880886451 gagarin.jpg
[kirill@lenovo TEST]$ mv gagarin.jpg /tmp/
[kirill@lenovo TEST]$ RUST_LOG=info ark-cli monitor #must load the index and remove disappeared resource
Building index of folder /tmp/TEST
[2023-03-06T16:22:43Z INFO arklib] Index has not been registered before
[2023-03-06T16:22:43Z INFO arklib::index] Loading the index from file
[2023-03-06T16:22:43Z WARN arklib::index] No such file or directory (os error 2)
[2023-03-06T16:22:43Z INFO arklib::index] Building the index from scratch
[2023-03-06T16:22:47Z INFO arklib::index] Index built
[2023-03-06T16:22:47Z INFO arklib::index] Storing the index to file
[2023-03-06T16:22:47Z INFO arklib] Index was registered
Build succeeded in 3.651734571s
```
Thanks @mdrlzy for discovering this bug. | True | Missing file causes index loading from file to fail and leads to complete rebuild - 1. Build index of some folder using `ark-cli monitor`.
2. Verify `.ark/index` exists.
3. Remove a file from the folder. Verify the index has entry with its path.
4. Load index.
Last step fails, the index is completely rebuilt in this case.
Pay attention to `WARN` lines:
```
[kirill@lenovo TEST]$ RUST_LOG=info ark-cli monitor
Building index of folder /tmp/TEST
[2023-03-06T16:21:33Z INFO arklib] Index has not been registered before
[2023-03-06T16:21:33Z INFO arklib::index] Loading the index from file
[2023-03-06T16:21:33Z WARN arklib::index] No persisted index was found by path /tmp/TEST/.ark/index
[2023-03-06T16:21:33Z INFO arklib::index] Building the index from scratch
[2023-03-06T16:21:36Z INFO arklib::index] Index built
[2023-03-06T16:21:36Z INFO arklib::index] Storing the index to file
[2023-03-06T16:21:36Z INFO arklib] Index was registered
Build succeeded in 3.667931346s
Updating succeeded in 158.747289ms
^C
[kirill@lenovo TEST]$ RUST_LOG=info ark-cli monitor #just load index from the file and check for updates
Building index of folder /tmp/TEST
[2023-03-06T16:21:57Z INFO arklib] Index has not been registered before
[2023-03-06T16:21:57Z INFO arklib::index] Loading the index from file
[2023-03-06T16:21:58Z INFO arklib::index] Storing the index to file
[2023-03-06T16:21:58Z INFO arklib] Index was registered
Build succeeded in 297.370813ms
^C
[kirill@lenovo TEST]$ grep gagarin .ark/index
1678115269692 200433-880886451 gagarin.jpg
[kirill@lenovo TEST]$ mv gagarin.jpg /tmp/
[kirill@lenovo TEST]$ RUST_LOG=info ark-cli monitor #must load the index and remove disappeared resource
Building index of folder /tmp/TEST
[2023-03-06T16:22:43Z INFO arklib] Index has not been registered before
[2023-03-06T16:22:43Z INFO arklib::index] Loading the index from file
[2023-03-06T16:22:43Z WARN arklib::index] No such file or directory (os error 2)
[2023-03-06T16:22:43Z INFO arklib::index] Building the index from scratch
[2023-03-06T16:22:47Z INFO arklib::index] Index built
[2023-03-06T16:22:47Z INFO arklib::index] Storing the index to file
[2023-03-06T16:22:47Z INFO arklib] Index was registered
Build succeeded in 3.651734571s
```
Thanks @mdrlzy for discovering this bug. | non_priority | missing file causes index loading from file to fail and leads to complete rebuild build index of some folder using ark cli monitor verify ark index exists remove a file from the folder verify the index has entry with its path load index last step fails the index is completely rebuilt in this case pay attention to warn lines rust log info ark cli monitor building index of folder tmp test index has not been registered before loading the index from file no persisted index was found by path tmp test ark index building the index from scratch index built storing the index to file index was registered build succeeded in updating succeeded in c rust log info ark cli monitor just load index from the file and check for updates building index of folder tmp test index has not been registered before loading the index from file storing the index to file index was registered build succeeded in c grep gagarin ark index gagarin jpg mv gagarin jpg tmp rust log info ark cli monitor must load the index and remove disappeared resource building index of folder tmp test index has not been registered before loading the index from file no such file or directory os error building the index from scratch index built storing the index to file index was registered build succeeded in thanks mdrlzy for discovering this bug | 0 |
138,142 | 11,184,949,208 | IssuesEvent | 2019-12-31 21:16:02 | dhenry-KCI/FredCo-Post-Go-Live- | https://api.github.com/repos/dhenry-KCI/FredCo-Post-Go-Live- | closed | 11 month extension letter | Ready for Retest | language needs to be updated we no longer use the attachments referenced in the highlighted. I thought these changes were made on this report?
A should read "Please log into your citizen portal account and complete the _extension request detail_ page for this permit to submit your request...."
B should read "Please log into your citizen portal account and to submit your request to void..."
| 1.0 | 11 month extension letter - language needs to be updated we no longer use the attachments referenced in the highlighted. I thought these changes were made on this report?
A should read "Please log into your citizen portal account and complete the _extension request detail_ page for this permit to submit your request...."
B should read "Please log into your citizen portal account and to submit your request to void..."
| non_priority | month extension letter language needs to be updated we no longer use the attachments referenced in the highlighted i thought these changes were made on this report a should read please log into your citizen portal account and complete the extension request detail page for this permit to submit your request b should read please log into your citizen portal account and to submit your request to void | 0 |
31,034 | 25,280,827,189 | IssuesEvent | 2022-11-16 15:40:06 | alan-turing-institute/the-turing-way | https://api.github.com/repos/alan-turing-institute/the-turing-way | closed | [BUG] Build error depending on venv directory | bug infrastructure | <!-- Use this template to raise issues about installing or running _The Turing Way_ locally on your computer. If you would like to raise an issue about fixing typos, or formatting issues in chapters, please use the Editor's Issue template. -->
### Description
<!-- Use this section to clearly and concisely describe the bug.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
Book build fails *when* ~~(and only when) using~~ a python virtual environment ~~which~~ is located in the `book/website` directory.
Update: The build seems to fail if there is a virtual environment in the `book/website` directory irrespective of if it is being used.
This is what the README suggests to do.
https://github.com/alan-turing-institute/the-turing-way/blob/2d9f6a57b65c58fb9caf1f03672e02c536225682/book/README.md?plain=1#L67-L72
The build works if I create the virtual environment in another directory, or install the requirements outside of a virtual environment.
#### Expected behaviour
<!-- Tell us what you thought would happen.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
Book builds
#### Actual behaviour
<!-- Tell us what actually happens.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
Error during `jupyter-book build .`. Logs below.
### How to reproduce
<!-- Use this section to describe the steps that a user would take to experience this bug.
For example:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error -->
1. `cd book/website`
2. `python -m venv ./venv`
3. `source ./venv/bin/activate`
4. `pip install -r requirements.txt`
5. `jupyter-book build .`
### Your personal set up
<!-- Tell us a little about the system you're using or tested this bug in. -->
OS:
<!-- Such as linux or OSX.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
- [x] Linux (Ubuntu, Fedora, Arch)
- [x] OSX
- Browser:
<!-- Such as Chrome or Firefox.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
- n/a
Dependencies:
<!-- Such as `jupyter-book` or `datascience`. You can generate a list of this using `pip freeze` or `conda list` depending on the package manager you are using. YOU MAY SKIP THIS SECTION-->
- Reproduced with Python 3.9, 3.10
### Failure Logs
<!-- Please include any relevant log snippets or files here. You may also include screenshots. -->
<details>
```none
Exception occurred:
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 953, in async_execute_cell
raise DeadKernelError("Kernel died")
nbclient.exceptions.DeadKernelError: Kernel died
The full traceback has been saved in /tmp/sphinx-err-5epqes8h.log, if you want to report the issue to the developers.
Please also report this if it was a user error, so that a better error message can be provided next time.
A bug report can be filed in the tracker at <https://github.com/sphinx-doc/sphinx/issues>. Thanks!
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 730, in _async_poll_for_reply
msg = await ensure_async(self.kc.shell_channel.get_msg(timeout=new_timeout))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 96, in ensure_async
result = await obj
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_client/channels.py", line 224, in get_msg
ready = await self.socket.poll(timeout)
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 949, in async_execute_cell
exec_reply = await self.task_poll_for_reply
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/sphinx.py", line 167, in build_sphinx
app.build(force_all, filenames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/application.py", line 330, in build
self.builder.build_update()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 286, in build_update
self.build(to_build,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 300, in build
updated_docnames = set(self.read())
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 407, in read
self._read_serial(docnames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 428, in _read_serial
self.read_doc(docname)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 468, in read_doc
doctree = read_doc(self.app, self.env, self.env.doc2path(docname))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 181, in read_doc
pub.publish()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/core.py", line 217, in publish
self.document = self.reader.read(self.source, self.parser,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 101, in read
self.parse()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/readers/__init__.py", line 78, in parse
self.parser.parse(self.input, document)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/parser.py", line 67, in parse
ntbk = generate_notebook_outputs(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/execution.py", line 137, in generate_notebook_outputs
result = single_nb_execution(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_cache/executors/utils.py", line 51, in single_nb_execution
executenb(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 1204, in execute
return NotebookClient(nb=nb, resources=resources, km=km, **kwargs).execute()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 84, in wrapped
return just_run(coro(*args, **kwargs))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 62, in just_run
return loop.run_until_complete(coro)
File "/usr/lib/python3.10/asyncio/base_events.py", line 646, in run_until_complete
return future.result()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 663, in async_execute
await self.async_execute_cell(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 953, in async_execute_cell
raise DeadKernelError("Kernel died")
nbclient.exceptions.DeadKernelError: Kernel died
The above exception was the direct cause of the following exception:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/bin/jupyter-book", line 8, in <module>
sys.exit(main())
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1130, in __call__
return self.main(*args, **kwargs)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1055, in main
rv = self.invoke(ctx)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1657, in invoke
return _process_result(sub_ctx.command.invoke(sub_ctx))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1404, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 760, in invoke
return __callback(*args, **kwargs)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/cli/main.py", line 323, in build
builder_specific_actions(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/cli/main.py", line 531, in builder_specific_actions
raise RuntimeError(_message_box(msg, color="red", doprint=False)) from result
RuntimeError:
===============================================================================
There was an error in building your book. Look above for the cause.
===============================================================================
```
</details>
And the log file
<details>
```bash
vagrant@ubuntu2204:~/the-turing-way/book/website$ cat /tmp/sphinx-err-5epqes8h.log
# Sphinx version: 4.5.0
# Python version: 3.10.4 (CPython)
# Docutils version: 0.17.1 release
# Jinja2 version: 3.1.2
# Last messages:
# reading sources... [ 55%] venv/lib/python3.10/site-packages/latexcodec-2.0.1.dist-info/AUTHORS
# reading sources... [ 55%] venv/lib/python3.10/site-packages/latexcodec-2.0.1.dist-info/LICENSE
# reading sources... [ 55%] venv/lib/python3.10/site-packages/matplotlib/backends/web_backend/nbagg_uat
# Executing: venv/lib/python3.10/site-packages/matplotlib/backends/web_backend/nbagg_uat in: /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/matplotlib/backends/web_backend
# reading sources... [ 55%] venv/lib/python3.10/site-packages/mdit_py_plugins/container/README
# reading sources... [ 55%] venv/lib/python3.10/site-packages/mdit_py_plugins/deflist/README
# reading sources... [ 56%] venv/lib/python3.10/site-packages/mdit_py_plugins/texmath/README
# reading sources... [ 56%] venv/lib/python3.10/site-packages/mistune-0.8.4.dist-info/DESCRIPTION
# reading sources... [ 56%] venv/lib/python3.10/site-packages/nbclient/tests/files/Autokill
# Executing: venv/lib/python3.10/site-packages/nbclient/tests/files/Autokill in: /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/tests/files
# Loaded extensions:
# sphinx.ext.mathjax (4.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/ext/mathjax.py
# sphinxcontrib.applehelp (1.0.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/applehelp/__init__.py
# sphinxcontrib.devhelp (1.0.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/devhelp/__init__.py
# sphinxcontrib.htmlhelp (2.0.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/htmlhelp/__init__.py
# sphinxcontrib.serializinghtml (1.1.5) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/serializinghtml/__init__.py
# sphinxcontrib.qthelp (1.0.3) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/qthelp/__init__.py
# alabaster (0.7.12) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/alabaster/__init__.py
# sphinx_togglebutton (0.3.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_togglebutton/__init__.py
# sphinx_copybutton (0.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_copybutton/__init__.py
# myst_nb (0.13.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/__init__.py
# jupyter_book (0.13.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/__init__.py
# sphinx_thebe (0.1.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_thebe/__init__.py
# sphinx_comments (0.0.3) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_comments/__init__.py
# sphinx_external_toc (0.2.4) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_external_toc/__init__.py
# sphinx.ext.intersphinx (4.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/ext/intersphinx.py
# sphinx_design (0.1.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_design/__init__.py
# sphinx_book_theme (unknown version) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_book_theme/__init__.py
# sphinxcontrib.bibtex (2.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/bibtex/__init__.py
# sphinx_jupyterbook_latex (unknown version) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_jupyterbook_latex/__init__.py
# pydata_sphinx_theme (unknown version) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/pydata_sphinx_theme/__init__.py
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 730, in _async_poll_for_reply
msg = await ensure_async(self.kc.shell_channel.get_msg(timeout=new_timeout))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 96, in ensure_async
result = await obj
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_client/channels.py", line 224, in get_msg
ready = await self.socket.poll(timeout)
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 949, in async_execute_cell
exec_reply = await self.task_poll_for_reply
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/sphinx.py", line 167, in build_sphinx
app.build(force_all, filenames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/application.py", line 330, in build
self.builder.build_update()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 286, in build_update
self.build(to_build,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 300, in build
updated_docnames = set(self.read())
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 407, in read
self._read_serial(docnames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 428, in _read_serial
self.read_doc(docname)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 468, in read_doc
doctree = read_doc(self.app, self.env, self.env.doc2path(docname))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 181, in read_doc
pub.publish()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/core.py", line 217, in publish
self.document = self.reader.read(self.source, self.parser,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 101, in read
self.parse()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/readers/__init__.py", line 78, in parse
self.parser.parse(self.input, document)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/parser.py", line 67, in parse
ntbk = generate_notebook_outputs(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/execution.py", line 137, in generate_notebook_outputs
result = single_nb_execution(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_cache/executors/utils.py", line 51, in single_nb_execution
executenb(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 1204, in execute
return NotebookClient(nb=nb, resources=resources, km=km, **kwargs).execute()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 84, in wrapped
return just_run(coro(*args, **kwargs))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 62, in just_run
return loop.run_until_complete(coro)
File "/usr/lib/python3.10/asyncio/base_events.py", line 646, in run_until_complete
return future.result()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 663, in async_execute
await self.async_execute_cell(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 953, in async_execute_cell
raise DeadKernelError("Kernel died")
nbclient.exceptions.DeadKernelError: Kernel died
```
</details> | 1.0 | [BUG] Build error depending on venv directory - <!-- Use this template to raise issues about installing or running _The Turing Way_ locally on your computer. If you would like to raise an issue about fixing typos, or formatting issues in chapters, please use the Editor's Issue template. -->
### Description
<!-- Use this section to clearly and concisely describe the bug.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
Book build fails *when* ~~(and only when) using~~ a python virtual environment ~~which~~ is located in the `book/website` directory.
Update: The build seems to fail if there is a virtual environment in the `book/website` directory irrespective of if it is being used.
This is what the README suggests to do.
https://github.com/alan-turing-institute/the-turing-way/blob/2d9f6a57b65c58fb9caf1f03672e02c536225682/book/README.md?plain=1#L67-L72
The build works if I create the virtual environment in another directory, or install the requirements outside of a virtual environment.
#### Expected behaviour
<!-- Tell us what you thought would happen.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
Book builds
#### Actual behaviour
<!-- Tell us what actually happens.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
Error during `jupyter-book build .`. Logs below.
### How to reproduce
<!-- Use this section to describe the steps that a user would take to experience this bug.
For example:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error -->
1. `cd book/website`
2. `python -m venv ./venv`
3. `source ./venv/bin/activate`
4. `pip install -r requirements.txt`
5. `jupyter-book build .`
### Your personal set up
<!-- Tell us a little about the system you're using or tested this bug in. -->
OS:
<!-- Such as linux or OSX.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
- [x] Linux (Ubuntu, Fedora, Arch)
- [x] OSX
- Browser:
<!-- Such as Chrome or Firefox.
We suggest using bullets (indicated by * or -) or checkboxes [ ] (filled checkbox [x]) here -->
- n/a
Dependencies:
<!-- Such as `jupyter-book` or `datascience`. You can generate a list of this using `pip freeze` or `conda list` depending on the package manager you are using. YOU MAY SKIP THIS SECTION-->
- Reproduced with Python 3.9, 3.10
### Failure Logs
<!-- Please include any relevant log snippets or files here. You may also include screenshots. -->
<details>
```none
Exception occurred:
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 953, in async_execute_cell
raise DeadKernelError("Kernel died")
nbclient.exceptions.DeadKernelError: Kernel died
The full traceback has been saved in /tmp/sphinx-err-5epqes8h.log, if you want to report the issue to the developers.
Please also report this if it was a user error, so that a better error message can be provided next time.
A bug report can be filed in the tracker at <https://github.com/sphinx-doc/sphinx/issues>. Thanks!
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 730, in _async_poll_for_reply
msg = await ensure_async(self.kc.shell_channel.get_msg(timeout=new_timeout))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 96, in ensure_async
result = await obj
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_client/channels.py", line 224, in get_msg
ready = await self.socket.poll(timeout)
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 949, in async_execute_cell
exec_reply = await self.task_poll_for_reply
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/sphinx.py", line 167, in build_sphinx
app.build(force_all, filenames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/application.py", line 330, in build
self.builder.build_update()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 286, in build_update
self.build(to_build,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 300, in build
updated_docnames = set(self.read())
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 407, in read
self._read_serial(docnames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 428, in _read_serial
self.read_doc(docname)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 468, in read_doc
doctree = read_doc(self.app, self.env, self.env.doc2path(docname))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 181, in read_doc
pub.publish()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/core.py", line 217, in publish
self.document = self.reader.read(self.source, self.parser,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 101, in read
self.parse()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/readers/__init__.py", line 78, in parse
self.parser.parse(self.input, document)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/parser.py", line 67, in parse
ntbk = generate_notebook_outputs(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/execution.py", line 137, in generate_notebook_outputs
result = single_nb_execution(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_cache/executors/utils.py", line 51, in single_nb_execution
executenb(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 1204, in execute
return NotebookClient(nb=nb, resources=resources, km=km, **kwargs).execute()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 84, in wrapped
return just_run(coro(*args, **kwargs))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 62, in just_run
return loop.run_until_complete(coro)
File "/usr/lib/python3.10/asyncio/base_events.py", line 646, in run_until_complete
return future.result()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 663, in async_execute
await self.async_execute_cell(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 953, in async_execute_cell
raise DeadKernelError("Kernel died")
nbclient.exceptions.DeadKernelError: Kernel died
The above exception was the direct cause of the following exception:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/bin/jupyter-book", line 8, in <module>
sys.exit(main())
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1130, in __call__
return self.main(*args, **kwargs)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1055, in main
rv = self.invoke(ctx)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1657, in invoke
return _process_result(sub_ctx.command.invoke(sub_ctx))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 1404, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/click/core.py", line 760, in invoke
return __callback(*args, **kwargs)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/cli/main.py", line 323, in build
builder_specific_actions(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/cli/main.py", line 531, in builder_specific_actions
raise RuntimeError(_message_box(msg, color="red", doprint=False)) from result
RuntimeError:
===============================================================================
There was an error in building your book. Look above for the cause.
===============================================================================
```
</details>
And the log file
<details>
```bash
vagrant@ubuntu2204:~/the-turing-way/book/website$ cat /tmp/sphinx-err-5epqes8h.log
# Sphinx version: 4.5.0
# Python version: 3.10.4 (CPython)
# Docutils version: 0.17.1 release
# Jinja2 version: 3.1.2
# Last messages:
# reading sources... [ 55%] venv/lib/python3.10/site-packages/latexcodec-2.0.1.dist-info/AUTHORS
# reading sources... [ 55%] venv/lib/python3.10/site-packages/latexcodec-2.0.1.dist-info/LICENSE
# reading sources... [ 55%] venv/lib/python3.10/site-packages/matplotlib/backends/web_backend/nbagg_uat
# Executing: venv/lib/python3.10/site-packages/matplotlib/backends/web_backend/nbagg_uat in: /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/matplotlib/backends/web_backend
# reading sources... [ 55%] venv/lib/python3.10/site-packages/mdit_py_plugins/container/README
# reading sources... [ 55%] venv/lib/python3.10/site-packages/mdit_py_plugins/deflist/README
# reading sources... [ 56%] venv/lib/python3.10/site-packages/mdit_py_plugins/texmath/README
# reading sources... [ 56%] venv/lib/python3.10/site-packages/mistune-0.8.4.dist-info/DESCRIPTION
# reading sources... [ 56%] venv/lib/python3.10/site-packages/nbclient/tests/files/Autokill
# Executing: venv/lib/python3.10/site-packages/nbclient/tests/files/Autokill in: /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/tests/files
# Loaded extensions:
# sphinx.ext.mathjax (4.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/ext/mathjax.py
# sphinxcontrib.applehelp (1.0.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/applehelp/__init__.py
# sphinxcontrib.devhelp (1.0.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/devhelp/__init__.py
# sphinxcontrib.htmlhelp (2.0.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/htmlhelp/__init__.py
# sphinxcontrib.serializinghtml (1.1.5) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/serializinghtml/__init__.py
# sphinxcontrib.qthelp (1.0.3) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/qthelp/__init__.py
# alabaster (0.7.12) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/alabaster/__init__.py
# sphinx_togglebutton (0.3.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_togglebutton/__init__.py
# sphinx_copybutton (0.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_copybutton/__init__.py
# myst_nb (0.13.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/__init__.py
# jupyter_book (0.13.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/__init__.py
# sphinx_thebe (0.1.2) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_thebe/__init__.py
# sphinx_comments (0.0.3) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_comments/__init__.py
# sphinx_external_toc (0.2.4) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_external_toc/__init__.py
# sphinx.ext.intersphinx (4.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/ext/intersphinx.py
# sphinx_design (0.1.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_design/__init__.py
# sphinx_book_theme (unknown version) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_book_theme/__init__.py
# sphinxcontrib.bibtex (2.5.0) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinxcontrib/bibtex/__init__.py
# sphinx_jupyterbook_latex (unknown version) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx_jupyterbook_latex/__init__.py
# pydata_sphinx_theme (unknown version) from /home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/pydata_sphinx_theme/__init__.py
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 730, in _async_poll_for_reply
msg = await ensure_async(self.kc.shell_channel.get_msg(timeout=new_timeout))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 96, in ensure_async
result = await obj
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_client/channels.py", line 224, in get_msg
ready = await self.socket.poll(timeout)
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 949, in async_execute_cell
exec_reply = await self.task_poll_for_reply
asyncio.exceptions.CancelledError
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_book/sphinx.py", line 167, in build_sphinx
app.build(force_all, filenames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/application.py", line 330, in build
self.builder.build_update()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 286, in build_update
self.build(to_build,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 300, in build
updated_docnames = set(self.read())
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 407, in read
self._read_serial(docnames)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 428, in _read_serial
self.read_doc(docname)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/builders/__init__.py", line 468, in read_doc
doctree = read_doc(self.app, self.env, self.env.doc2path(docname))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 181, in read_doc
pub.publish()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/core.py", line 217, in publish
self.document = self.reader.read(self.source, self.parser,
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/sphinx/io.py", line 101, in read
self.parse()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/docutils/readers/__init__.py", line 78, in parse
self.parser.parse(self.input, document)
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/parser.py", line 67, in parse
ntbk = generate_notebook_outputs(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/myst_nb/execution.py", line 137, in generate_notebook_outputs
result = single_nb_execution(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/jupyter_cache/executors/utils.py", line 51, in single_nb_execution
executenb(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 1204, in execute
return NotebookClient(nb=nb, resources=resources, km=km, **kwargs).execute()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 84, in wrapped
return just_run(coro(*args, **kwargs))
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/util.py", line 62, in just_run
return loop.run_until_complete(coro)
File "/usr/lib/python3.10/asyncio/base_events.py", line 646, in run_until_complete
return future.result()
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 663, in async_execute
await self.async_execute_cell(
File "/home/vagrant/the-turing-way/book/website/venv/lib/python3.10/site-packages/nbclient/client.py", line 953, in async_execute_cell
raise DeadKernelError("Kernel died")
nbclient.exceptions.DeadKernelError: Kernel died
```
</details> | non_priority | build error depending on venv directory description use this section to clearly and concisely describe the bug we suggest using bullets indicated by or or checkboxes filled checkbox here book build fails when and only when using a python virtual environment which is located in the book website directory update the build seems to fail if there is a virtual environment in the book website directory irrespective of if it is being used this is what the readme suggests to do the build works if i create the virtual environment in another directory or install the requirements outside of a virtual environment expected behaviour tell us what you thought would happen we suggest using bullets indicated by or or checkboxes filled checkbox here book builds actual behaviour tell us what actually happens we suggest using bullets indicated by or or checkboxes filled checkbox here error during jupyter book build logs below how to reproduce use this section to describe the steps that a user would take to experience this bug for example go to click on scroll down to see error cd book website python m venv venv source venv bin activate pip install r requirements txt jupyter book build your personal set up os such as linux or osx we suggest using bullets indicated by or or checkboxes filled checkbox here linux ubuntu fedora arch osx browser such as chrome or firefox we suggest using bullets indicated by or or checkboxes filled checkbox here n a dependencies reproduced with python failure logs none exception occurred file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute cell raise deadkernelerror kernel died nbclient exceptions deadkernelerror kernel died the full traceback has been saved in tmp sphinx err log if you want to report the issue to the developers please also report this if it was a user error so that a better error message can be provided next time a bug report can be filed in the tracker at thanks traceback most recent call last file home vagrant the turing way book website venv lib site packages nbclient client py line in async poll for reply msg await ensure async self kc shell channel get msg timeout new timeout file home vagrant the turing way book website venv lib site packages nbclient util py line in ensure async result await obj file home vagrant the turing way book website venv lib site packages jupyter client channels py line in get msg ready await self socket poll timeout asyncio exceptions cancellederror during handling of the above exception another exception occurred traceback most recent call last file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute cell exec reply await self task poll for reply asyncio exceptions cancellederror during handling of the above exception another exception occurred traceback most recent call last file home vagrant the turing way book website venv lib site packages jupyter book sphinx py line in build sphinx app build force all filenames file home vagrant the turing way book website venv lib site packages sphinx application py line in build self builder build update file home vagrant the turing way book website venv lib site packages sphinx builders init py line in build update self build to build file home vagrant the turing way book website venv lib site packages sphinx builders init py line in build updated docnames set self read file home vagrant the turing way book website venv lib site packages sphinx builders init py line in read self read serial docnames file home vagrant the turing way book website venv lib site packages sphinx builders init py line in read serial self read doc docname file home vagrant the turing way book website venv lib site packages sphinx builders init py line in read doc doctree read doc self app self env self env docname file home vagrant the turing way book website venv lib site packages sphinx io py line in read doc pub publish file home vagrant the turing way book website venv lib site packages docutils core py line in publish self document self reader read self source self parser file home vagrant the turing way book website venv lib site packages sphinx io py line in read self parse file home vagrant the turing way book website venv lib site packages docutils readers init py line in parse self parser parse self input document file home vagrant the turing way book website venv lib site packages myst nb parser py line in parse ntbk generate notebook outputs file home vagrant the turing way book website venv lib site packages myst nb execution py line in generate notebook outputs result single nb execution file home vagrant the turing way book website venv lib site packages jupyter cache executors utils py line in single nb execution executenb file home vagrant the turing way book website venv lib site packages nbclient client py line in execute return notebookclient nb nb resources resources km km kwargs execute file home vagrant the turing way book website venv lib site packages nbclient util py line in wrapped return just run coro args kwargs file home vagrant the turing way book website venv lib site packages nbclient util py line in just run return loop run until complete coro file usr lib asyncio base events py line in run until complete return future result file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute await self async execute cell file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute cell raise deadkernelerror kernel died nbclient exceptions deadkernelerror kernel died the above exception was the direct cause of the following exception traceback most recent call last file home vagrant the turing way book website venv bin jupyter book line in sys exit main file home vagrant the turing way book website venv lib site packages click core py line in call return self main args kwargs file home vagrant the turing way book website venv lib site packages click core py line in main rv self invoke ctx file home vagrant the turing way book website venv lib site packages click core py line in invoke return process result sub ctx command invoke sub ctx file home vagrant the turing way book website venv lib site packages click core py line in invoke return ctx invoke self callback ctx params file home vagrant the turing way book website venv lib site packages click core py line in invoke return callback args kwargs file home vagrant the turing way book website venv lib site packages jupyter book cli main py line in build builder specific actions file home vagrant the turing way book website venv lib site packages jupyter book cli main py line in builder specific actions raise runtimeerror message box msg color red doprint false from result runtimeerror there was an error in building your book look above for the cause and the log file bash vagrant the turing way book website cat tmp sphinx err log sphinx version python version cpython docutils version release version last messages reading sources venv lib site packages latexcodec dist info authors reading sources venv lib site packages latexcodec dist info license reading sources venv lib site packages matplotlib backends web backend nbagg uat executing venv lib site packages matplotlib backends web backend nbagg uat in home vagrant the turing way book website venv lib site packages matplotlib backends web backend reading sources venv lib site packages mdit py plugins container readme reading sources venv lib site packages mdit py plugins deflist readme reading sources venv lib site packages mdit py plugins texmath readme reading sources venv lib site packages mistune dist info description reading sources venv lib site packages nbclient tests files autokill executing venv lib site packages nbclient tests files autokill in home vagrant the turing way book website venv lib site packages nbclient tests files loaded extensions sphinx ext mathjax from home vagrant the turing way book website venv lib site packages sphinx ext mathjax py sphinxcontrib applehelp from home vagrant the turing way book website venv lib site packages sphinxcontrib applehelp init py sphinxcontrib devhelp from home vagrant the turing way book website venv lib site packages sphinxcontrib devhelp init py sphinxcontrib htmlhelp from home vagrant the turing way book website venv lib site packages sphinxcontrib htmlhelp init py sphinxcontrib serializinghtml from home vagrant the turing way book website venv lib site packages sphinxcontrib serializinghtml init py sphinxcontrib qthelp from home vagrant the turing way book website venv lib site packages sphinxcontrib qthelp init py alabaster from home vagrant the turing way book website venv lib site packages alabaster init py sphinx togglebutton from home vagrant the turing way book website venv lib site packages sphinx togglebutton init py sphinx copybutton from home vagrant the turing way book website venv lib site packages sphinx copybutton init py myst nb from home vagrant the turing way book website venv lib site packages myst nb init py jupyter book from home vagrant the turing way book website venv lib site packages jupyter book init py sphinx thebe from home vagrant the turing way book website venv lib site packages sphinx thebe init py sphinx comments from home vagrant the turing way book website venv lib site packages sphinx comments init py sphinx external toc from home vagrant the turing way book website venv lib site packages sphinx external toc init py sphinx ext intersphinx from home vagrant the turing way book website venv lib site packages sphinx ext intersphinx py sphinx design from home vagrant the turing way book website venv lib site packages sphinx design init py sphinx book theme unknown version from home vagrant the turing way book website venv lib site packages sphinx book theme init py sphinxcontrib bibtex from home vagrant the turing way book website venv lib site packages sphinxcontrib bibtex init py sphinx jupyterbook latex unknown version from home vagrant the turing way book website venv lib site packages sphinx jupyterbook latex init py pydata sphinx theme unknown version from home vagrant the turing way book website venv lib site packages pydata sphinx theme init py traceback most recent call last file home vagrant the turing way book website venv lib site packages nbclient client py line in async poll for reply msg await ensure async self kc shell channel get msg timeout new timeout file home vagrant the turing way book website venv lib site packages nbclient util py line in ensure async result await obj file home vagrant the turing way book website venv lib site packages jupyter client channels py line in get msg ready await self socket poll timeout asyncio exceptions cancellederror during handling of the above exception another exception occurred traceback most recent call last file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute cell exec reply await self task poll for reply asyncio exceptions cancellederror during handling of the above exception another exception occurred traceback most recent call last file home vagrant the turing way book website venv lib site packages jupyter book sphinx py line in build sphinx app build force all filenames file home vagrant the turing way book website venv lib site packages sphinx application py line in build self builder build update file home vagrant the turing way book website venv lib site packages sphinx builders init py line in build update self build to build file home vagrant the turing way book website venv lib site packages sphinx builders init py line in build updated docnames set self read file home vagrant the turing way book website venv lib site packages sphinx builders init py line in read self read serial docnames file home vagrant the turing way book website venv lib site packages sphinx builders init py line in read serial self read doc docname file home vagrant the turing way book website venv lib site packages sphinx builders init py line in read doc doctree read doc self app self env self env docname file home vagrant the turing way book website venv lib site packages sphinx io py line in read doc pub publish file home vagrant the turing way book website venv lib site packages docutils core py line in publish self document self reader read self source self parser file home vagrant the turing way book website venv lib site packages sphinx io py line in read self parse file home vagrant the turing way book website venv lib site packages docutils readers init py line in parse self parser parse self input document file home vagrant the turing way book website venv lib site packages myst nb parser py line in parse ntbk generate notebook outputs file home vagrant the turing way book website venv lib site packages myst nb execution py line in generate notebook outputs result single nb execution file home vagrant the turing way book website venv lib site packages jupyter cache executors utils py line in single nb execution executenb file home vagrant the turing way book website venv lib site packages nbclient client py line in execute return notebookclient nb nb resources resources km km kwargs execute file home vagrant the turing way book website venv lib site packages nbclient util py line in wrapped return just run coro args kwargs file home vagrant the turing way book website venv lib site packages nbclient util py line in just run return loop run until complete coro file usr lib asyncio base events py line in run until complete return future result file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute await self async execute cell file home vagrant the turing way book website venv lib site packages nbclient client py line in async execute cell raise deadkernelerror kernel died nbclient exceptions deadkernelerror kernel died | 0 |
43,024 | 23,079,457,216 | IssuesEvent | 2022-07-26 05:20:57 | mdn/content | https://api.github.com/repos/mdn/content | closed | "While it is not always possible to maintain 60fps, it is important to maintain a high and steady frame rate for all animations." | needs-triage Content:Performance | ### MDN URL
https://developer.mozilla.org/en-US/docs/Web/Performance/Animation_performance_and_frame_rate
### What specific section or headline is this issue about?
Animation performance and frame rate
### What information was incorrect, unhelpful, or incomplete?
"Users expect all interface interactions to be smooth and all user interfaces to be responsive."
Just because users may *expect* more and more websites to inflict "smooth" animation, motion sickness, migraines, and so on, doesn't mean every user *wants* them to.
"While it is not always possible to maintain 60fps, it is important to maintain a high and steady frame rate for all animations."
### What did you expect to see?
I was trying to see if user css could reduce frame rates on a per-domain basis, so I could read Google Docs without getting migraines.
### Do you have any supporting links, references, or citations?
_No response_
### Do you have anything more you want to share?
_No response_
### MDN metadata
<!-- Do not make changes below this line -->
<details>
<summary>Page report details</summary>
* Folder: `en-us/web/performance/animation_performance_and_frame_rate`
* MDN URL: https://developer.mozilla.org/en-US/docs/Web/Performance/Animation_performance_and_frame_rate
* GitHub URL: https://github.com/mdn/content/blob/main/files/en-us/web/performance/animation_performance_and_frame_rate/index.md
* Last commit: https://github.com/mdn/content/commit/c9dc772a9deb0a379518cc6a0aff23182daceeda
* Document last modified: 2022-07-23T04:09:16.000Z
</details> | True | "While it is not always possible to maintain 60fps, it is important to maintain a high and steady frame rate for all animations." - ### MDN URL
https://developer.mozilla.org/en-US/docs/Web/Performance/Animation_performance_and_frame_rate
### What specific section or headline is this issue about?
Animation performance and frame rate
### What information was incorrect, unhelpful, or incomplete?
"Users expect all interface interactions to be smooth and all user interfaces to be responsive."
Just because users may *expect* more and more websites to inflict "smooth" animation, motion sickness, migraines, and so on, doesn't mean every user *wants* them to.
"While it is not always possible to maintain 60fps, it is important to maintain a high and steady frame rate for all animations."
### What did you expect to see?
I was trying to see if user css could reduce frame rates on a per-domain basis, so I could read Google Docs without getting migraines.
### Do you have any supporting links, references, or citations?
_No response_
### Do you have anything more you want to share?
_No response_
### MDN metadata
<!-- Do not make changes below this line -->
<details>
<summary>Page report details</summary>
* Folder: `en-us/web/performance/animation_performance_and_frame_rate`
* MDN URL: https://developer.mozilla.org/en-US/docs/Web/Performance/Animation_performance_and_frame_rate
* GitHub URL: https://github.com/mdn/content/blob/main/files/en-us/web/performance/animation_performance_and_frame_rate/index.md
* Last commit: https://github.com/mdn/content/commit/c9dc772a9deb0a379518cc6a0aff23182daceeda
* Document last modified: 2022-07-23T04:09:16.000Z
</details> | non_priority | while it is not always possible to maintain it is important to maintain a high and steady frame rate for all animations mdn url what specific section or headline is this issue about animation performance and frame rate what information was incorrect unhelpful or incomplete users expect all interface interactions to be smooth and all user interfaces to be responsive just because users may expect more and more websites to inflict smooth animation motion sickness migraines and so on doesn t mean every user wants them to while it is not always possible to maintain it is important to maintain a high and steady frame rate for all animations what did you expect to see i was trying to see if user css could reduce frame rates on a per domain basis so i could read google docs without getting migraines do you have any supporting links references or citations no response do you have anything more you want to share no response mdn metadata page report details folder en us web performance animation performance and frame rate mdn url github url last commit document last modified | 0 |
121,554 | 10,173,291,557 | IssuesEvent | 2019-08-08 12:48:27 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | ICE: Unexpected non-scalars in register inputs of `asm!` | A-inline-assembly C-bug E-needstest I-ICE | Unexpected non-scalars in register inputs of `asm!` can ICE the compiler.
To reproduce:
``` rust
#![feature(asm)]
fn main() {
unsafe {
asm!("" :: "r"(""));
}
}
```
This mistake goes uncaught until it reaches [this line of code](https://github.com/rust-lang/rust/blob/master/src/librustc_trans/mir/operand.rs#L80) where it `bug!`s. I would expect it to have been caught earlier, during `asm!` argument validation.
I've found a similar case which dumps core, which will be the subject of a separate bug.
## Meta
`rustc --version --verbose`:
rustc 1.14.0-nightly (c59cb71d9 2016-10-26)
binary: rustc
commit-hash: c59cb71d976ceabf00c7da0224a795fab530601e
commit-date: 2016-10-26
host: x86_64-unknown-linux-gnu
release: 1.14.0-nightly
LLVM version: 3.9
Backtrace:
```
thread 'rustc' panicked at 'Box<Any>', ../src/librustc_errors/lib.rs:655
stack backtrace:
1: 0x7eff0357f908 - std::sys::backtrace::tracing::imp::write::h22f199c1dbb72ba2
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/sys/unix/backtrace/tracing/gcc_s.rs:42
2: 0x7eff0358efbf - std::panicking::default_hook::{{closure}}::h9a389c462b6a22dd
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:247
3: 0x7eff0358c2d5 - std::panicking::default_hook::h852b4223c1c00c59
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:257
4: 0x7eff0358c9e7 - std::panicking::rust_panic_with_hook::hcd9d05f53fa0dafc
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:451
5: 0x7efeffa1c5fa - std::panicking::begin_panic::h2f463d37998ebeba
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:413
6: 0x7efeffa2c22a - rustc_errors::Handler::bug::haca77c19c882b432
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_errors/lib.rs:655
7: 0x7eff00a752a1 - rustc::session::opt_span_bug_fmt::{{closure}}::hfeb850fbe828b399
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/session/mod.rs:727
8: 0x7eff009b038e - rustc::session::opt_span_bug_fmt::h46e45438a860a75e
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:978
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/session/mod.rs:723
9: 0x7eff009b01d2 - rustc::session::bug_fmt::hde22f071bf5a80ea
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/session/mod.rs:707
10: 0x7eff02138c58 - <collections::vec::Vec<T> as core::iter::traits::FromIterator<T>>::from_iter::hc5cbb62358ceb057
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/operand.rs:82
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/rvalue.rs:168
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/ops.rs:2648
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/option.rs:383
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/iter/mod.rs:960
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcollections/vec.rs:1632
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcollections/vec.rs:1540
11: 0x7eff021d8e65 - rustc_trans::mir::rvalue::<impl rustc_trans::mir::MirContext<'bcx, 'tcx>>::trans_rvalue::h2a14de75e2fd4285
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/iter/iterator.rs:1196
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/rvalue.rs:167
12: 0x7eff021c7a16 - rustc_trans::mir::block::<impl rustc_trans::mir::MirContext<'bcx, 'tcx>>::trans_block::he67d3259f79e4177
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/statement.rs:36
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/block.rs:103
13: 0x7eff021c5e26 - rustc_trans::mir::trans_mir::h2fb44ecb31cfdffa
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/mod.rs:319
14: 0x7eff02169d8d - rustc_trans::base::trans_closure::h941de14309416d66
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1041
15: 0x7eff021e50a9 - rustc_trans::trans_item::TransItem::define::h2e690ccd1ee22f95
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1061
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/trans_item.rs:85
16: 0x7eff0216d08b - rustc_trans::base::trans_crate::h9b06de31ed8799d1
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1641
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/dep_graph/graph.rs:77
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1639
17: 0x7eff039132a8 - rustc_driver::driver::phase_4_translate_to_llvm::hc3883ea2c4750179
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:1046
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/util/common.rs:38
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:1044
18: 0x7eff03948f77 - rustc_driver::driver::compile_input::{{closure}}::h9162a2fa292aeb3f
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:206
19: 0x7eff03940774 - rustc_driver::driver::phase_3_run_analysis_passes::{{closure}}::h1928c4704cfe9c61
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:1000
20: 0x7eff03911011 - rustc_driver::driver::phase_3_run_analysis_passes::he578df6b8805151c
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:949
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/thread/local.rs:245
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:946
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:933
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/thread/local.rs:245
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:930
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:719
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:869
21: 0x7eff038fa2d6 - rustc_driver::driver::compile_input::h5b63ccd49eeeb98b
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:172
22: 0x7eff03923109 - rustc_driver::run_compiler::h98c7274e7cb1d11d
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:224
23: 0x7eff03865018 - std::panicking::try::do_call::h99ed0da044e497c3
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:1148
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:137
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:1082
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panic.rs:255
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:356
24: 0x7eff03596eca - __rust_maybe_catch_panic
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libpanic_unwind/lib.rs:97
25: 0x7eff03883028 - <F as alloc::boxed::FnBox<A>>::call_box::hbdd5a14cd8e33b97
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:332
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panic.rs:311
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/thread/mod.rs:278
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/liballoc/boxed.rs:595
26: 0x7eff0358ac84 - std::sys::thread::Thread::new::thread_start::h50b05608a499d2b2
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/liballoc/boxed.rs:605
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/sys/common/thread.rs:21
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/sys/unix/thread.rs:84
27: 0x7efefb8b7453 - start_thread
28: 0x7eff0325a7de - __GI___clone
29: 0x0 - <unknown>
```
| 1.0 | ICE: Unexpected non-scalars in register inputs of `asm!` - Unexpected non-scalars in register inputs of `asm!` can ICE the compiler.
To reproduce:
``` rust
#![feature(asm)]
fn main() {
unsafe {
asm!("" :: "r"(""));
}
}
```
This mistake goes uncaught until it reaches [this line of code](https://github.com/rust-lang/rust/blob/master/src/librustc_trans/mir/operand.rs#L80) where it `bug!`s. I would expect it to have been caught earlier, during `asm!` argument validation.
I've found a similar case which dumps core, which will be the subject of a separate bug.
## Meta
`rustc --version --verbose`:
rustc 1.14.0-nightly (c59cb71d9 2016-10-26)
binary: rustc
commit-hash: c59cb71d976ceabf00c7da0224a795fab530601e
commit-date: 2016-10-26
host: x86_64-unknown-linux-gnu
release: 1.14.0-nightly
LLVM version: 3.9
Backtrace:
```
thread 'rustc' panicked at 'Box<Any>', ../src/librustc_errors/lib.rs:655
stack backtrace:
1: 0x7eff0357f908 - std::sys::backtrace::tracing::imp::write::h22f199c1dbb72ba2
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/sys/unix/backtrace/tracing/gcc_s.rs:42
2: 0x7eff0358efbf - std::panicking::default_hook::{{closure}}::h9a389c462b6a22dd
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:247
3: 0x7eff0358c2d5 - std::panicking::default_hook::h852b4223c1c00c59
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:257
4: 0x7eff0358c9e7 - std::panicking::rust_panic_with_hook::hcd9d05f53fa0dafc
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:451
5: 0x7efeffa1c5fa - std::panicking::begin_panic::h2f463d37998ebeba
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:413
6: 0x7efeffa2c22a - rustc_errors::Handler::bug::haca77c19c882b432
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_errors/lib.rs:655
7: 0x7eff00a752a1 - rustc::session::opt_span_bug_fmt::{{closure}}::hfeb850fbe828b399
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/session/mod.rs:727
8: 0x7eff009b038e - rustc::session::opt_span_bug_fmt::h46e45438a860a75e
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:978
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/session/mod.rs:723
9: 0x7eff009b01d2 - rustc::session::bug_fmt::hde22f071bf5a80ea
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/session/mod.rs:707
10: 0x7eff02138c58 - <collections::vec::Vec<T> as core::iter::traits::FromIterator<T>>::from_iter::hc5cbb62358ceb057
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/operand.rs:82
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/rvalue.rs:168
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/ops.rs:2648
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/option.rs:383
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/iter/mod.rs:960
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcollections/vec.rs:1632
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcollections/vec.rs:1540
11: 0x7eff021d8e65 - rustc_trans::mir::rvalue::<impl rustc_trans::mir::MirContext<'bcx, 'tcx>>::trans_rvalue::h2a14de75e2fd4285
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libcore/iter/iterator.rs:1196
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/rvalue.rs:167
12: 0x7eff021c7a16 - rustc_trans::mir::block::<impl rustc_trans::mir::MirContext<'bcx, 'tcx>>::trans_block::he67d3259f79e4177
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/statement.rs:36
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/block.rs:103
13: 0x7eff021c5e26 - rustc_trans::mir::trans_mir::h2fb44ecb31cfdffa
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/mir/mod.rs:319
14: 0x7eff02169d8d - rustc_trans::base::trans_closure::h941de14309416d66
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1041
15: 0x7eff021e50a9 - rustc_trans::trans_item::TransItem::define::h2e690ccd1ee22f95
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1061
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/trans_item.rs:85
16: 0x7eff0216d08b - rustc_trans::base::trans_crate::h9b06de31ed8799d1
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1641
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/dep_graph/graph.rs:77
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_trans/base.rs:1639
17: 0x7eff039132a8 - rustc_driver::driver::phase_4_translate_to_llvm::hc3883ea2c4750179
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:1046
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/util/common.rs:38
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:1044
18: 0x7eff03948f77 - rustc_driver::driver::compile_input::{{closure}}::h9162a2fa292aeb3f
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:206
19: 0x7eff03940774 - rustc_driver::driver::phase_3_run_analysis_passes::{{closure}}::h1928c4704cfe9c61
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:1000
20: 0x7eff03911011 - rustc_driver::driver::phase_3_run_analysis_passes::he578df6b8805151c
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:949
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/thread/local.rs:245
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:946
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:933
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/thread/local.rs:245
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:930
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc/ty/context.rs:719
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:869
21: 0x7eff038fa2d6 - rustc_driver::driver::compile_input::h5b63ccd49eeeb98b
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/driver.rs:172
22: 0x7eff03923109 - rustc_driver::run_compiler::h98c7274e7cb1d11d
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:224
23: 0x7eff03865018 - std::panicking::try::do_call::h99ed0da044e497c3
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:1148
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:137
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/librustc_driver/lib.rs:1082
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panic.rs:255
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:356
24: 0x7eff03596eca - __rust_maybe_catch_panic
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libpanic_unwind/lib.rs:97
25: 0x7eff03883028 - <F as alloc::boxed::FnBox<A>>::call_box::hbdd5a14cd8e33b97
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panicking.rs:332
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/panic.rs:311
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/thread/mod.rs:278
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/liballoc/boxed.rs:595
26: 0x7eff0358ac84 - std::sys::thread::Thread::new::thread_start::h50b05608a499d2b2
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/liballoc/boxed.rs:605
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/sys/common/thread.rs:21
at /buildslave/rust-buildbot/slave/nightly-dist-rustc-linux/build/obj/../src/libstd/sys/unix/thread.rs:84
27: 0x7efefb8b7453 - start_thread
28: 0x7eff0325a7de - __GI___clone
29: 0x0 - <unknown>
```
| non_priority | ice unexpected non scalars in register inputs of asm unexpected non scalars in register inputs of asm can ice the compiler to reproduce rust fn main unsafe asm r this mistake goes uncaught until it reaches where it bug s i would expect it to have been caught earlier during asm argument validation i ve found a similar case which dumps core which will be the subject of a separate bug meta rustc version verbose rustc nightly binary rustc commit hash commit date host unknown linux gnu release nightly llvm version backtrace thread rustc panicked at box src librustc errors lib rs stack backtrace std sys backtrace tracing imp write at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd sys unix backtrace tracing gcc s rs std panicking default hook closure at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panicking rs std panicking default hook at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panicking rs std panicking rust panic with hook at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panicking rs std panicking begin panic at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panicking rs rustc errors handler bug at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc errors lib rs rustc session opt span bug fmt closure at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc session mod rs rustc session opt span bug fmt at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc ty context rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc session mod rs rustc session bug fmt at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc session mod rs as core iter traits fromiterator from iter at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans mir operand rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans mir rvalue rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libcore ops rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libcore option rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libcore iter mod rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libcollections vec rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libcollections vec rs rustc trans mir rvalue trans rvalue at buildslave rust buildbot slave nightly dist rustc linux build obj src libcore iter iterator rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans mir rvalue rs rustc trans mir block trans block at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans mir statement rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans mir block rs rustc trans mir trans mir at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans mir mod rs rustc trans base trans closure at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans base rs rustc trans trans item transitem define at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans base rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans trans item rs rustc trans base trans crate at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans base rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc dep graph graph rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc trans base rs rustc driver driver phase translate to llvm at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver driver rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc util common rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver driver rs rustc driver driver compile input closure at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver driver rs rustc driver driver phase run analysis passes closure at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver driver rs rustc driver driver phase run analysis passes at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc ty context rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd thread local rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc ty context rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc ty context rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd thread local rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc ty context rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc ty context rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver driver rs rustc driver driver compile input at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver driver rs rustc driver run compiler at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver lib rs std panicking try do call at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver lib rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver lib rs at buildslave rust buildbot slave nightly dist rustc linux build obj src librustc driver lib rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panic rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panicking rs rust maybe catch panic at buildslave rust buildbot slave nightly dist rustc linux build obj src libpanic unwind lib rs call box at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panicking rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd panic rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd thread mod rs at buildslave rust buildbot slave nightly dist rustc linux build obj src liballoc boxed rs std sys thread thread new thread start at buildslave rust buildbot slave nightly dist rustc linux build obj src liballoc boxed rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd sys common thread rs at buildslave rust buildbot slave nightly dist rustc linux build obj src libstd sys unix thread rs start thread gi clone | 0 |
161,625 | 12,554,704,602 | IssuesEvent | 2020-06-07 03:08:46 | QubesOS/updates-status | https://api.github.com/repos/QubesOS/updates-status | closed | core-admin v4.1.11 (r4.1) | r4.1-dom0-cur-test | Update of core-admin to v4.1.11 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-core-admin/commit/6d19496ab5eae95431edb5e7d43d36451083229a
[Changes since previous version](https://github.com/QubesOS/qubes-core-admin/compare/v4.1.10...v4.1.11):
QubesOS/qubes-core-admin@6d19496a version 4.1.11
QubesOS/qubes-core-admin@e5edbc53 Merge remote-tracking branch 'origin/pr/332'
QubesOS/qubes-core-admin@3b963030 Merge remote-tracking branch 'origin/pr/331'
QubesOS/qubes-core-admin@46f09f89 Merge remote-tracking branch 'origin/pr/326'
QubesOS/qubes-core-admin@8420adf9 tests: improve audio tests
QubesOS/qubes-core-admin@a6efd6a3 Merge remote-tracking branch 'origin/pr/334'
QubesOS/qubes-core-admin@6605bf40 collections.Callable -> collections.abc.Callable
QubesOS/qubes-core-admin@f9538a57 tests/file: run_until_complete(); coro_maybe() for single arg
QubesOS/qubes-core-admin@9122a14f tests/file: use self.loop
QubesOS/qubes-core-admin@30661902 tests: fix qvm-copy-to-vm test
QubesOS/qubes-core-admin@1b7e2a5c tests: ensure proper cleanup of auxiliary process
QubesOS/qubes-core-admin@dd50e300 Fix multiple qmemman issues
QubesOS/qubes-core-admin@b11d6e05 ext/admin: workaround for extension's __init__() called multiple times
QubesOS/qubes-core-admin@0341cc52 tests: teardown fixes
QubesOS/qubes-core-admin@a90e7e36 travis: include core-qrexec in tests
QubesOS/qubes-core-admin@3f96c72e api/admin: (ext/admin) limit listing VMs based on qrexec policy
QubesOS/qubes-core-admin@8f0ec59f Merge remote-tracking branch 'origin/pr/330'
QubesOS/qubes-core-admin@577e4b24 gui: fixes from Marek's comments
QubesOS/qubes-core-admin@f130ec0b gui: improvements of feature keyboard layout checks
QubesOS/qubes-core-admin@5cb0e61a tests: adapt tests for keyboard-layout
QubesOS/qubes-core-admin@732e291a gui: drop legacy qubes-keyboard support
QubesOS/qubes-core-admin@29020d0c Merge branch 'feature-pre-set'
QubesOS/qubes-core-admin@d05592ba Add pre- events to vm features
QubesOS/qubes-core-admin@ddc13d6b Merge remote-tracking branch 'origin/pr/329'
QubesOS/qubes-core-admin@d8f80c96 tests: make PEP8 happier
QubesOS/qubes-core-admin@40156c3e tests: fix already registered event impl
QubesOS/qubes-core-admin@879ee9e7 api/internal: extract get_system_info() function
Referenced issues:
QubesOS/qubes-issues#4890
QubesOS/qubes-issues#5099
QubesOS/qubes-issues#5509
If you're release manager, you can issue GPG-inline signed command:
* `Upload core-admin 6d19496ab5eae95431edb5e7d43d36451083229a r4.1 current repo` (available 7 days from now)
* `Upload core-admin 6d19496ab5eae95431edb5e7d43d36451083229a r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload core-admin 6d19496ab5eae95431edb5e7d43d36451083229a r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| 1.0 | core-admin v4.1.11 (r4.1) - Update of core-admin to v4.1.11 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-core-admin/commit/6d19496ab5eae95431edb5e7d43d36451083229a
[Changes since previous version](https://github.com/QubesOS/qubes-core-admin/compare/v4.1.10...v4.1.11):
QubesOS/qubes-core-admin@6d19496a version 4.1.11
QubesOS/qubes-core-admin@e5edbc53 Merge remote-tracking branch 'origin/pr/332'
QubesOS/qubes-core-admin@3b963030 Merge remote-tracking branch 'origin/pr/331'
QubesOS/qubes-core-admin@46f09f89 Merge remote-tracking branch 'origin/pr/326'
QubesOS/qubes-core-admin@8420adf9 tests: improve audio tests
QubesOS/qubes-core-admin@a6efd6a3 Merge remote-tracking branch 'origin/pr/334'
QubesOS/qubes-core-admin@6605bf40 collections.Callable -> collections.abc.Callable
QubesOS/qubes-core-admin@f9538a57 tests/file: run_until_complete(); coro_maybe() for single arg
QubesOS/qubes-core-admin@9122a14f tests/file: use self.loop
QubesOS/qubes-core-admin@30661902 tests: fix qvm-copy-to-vm test
QubesOS/qubes-core-admin@1b7e2a5c tests: ensure proper cleanup of auxiliary process
QubesOS/qubes-core-admin@dd50e300 Fix multiple qmemman issues
QubesOS/qubes-core-admin@b11d6e05 ext/admin: workaround for extension's __init__() called multiple times
QubesOS/qubes-core-admin@0341cc52 tests: teardown fixes
QubesOS/qubes-core-admin@a90e7e36 travis: include core-qrexec in tests
QubesOS/qubes-core-admin@3f96c72e api/admin: (ext/admin) limit listing VMs based on qrexec policy
QubesOS/qubes-core-admin@8f0ec59f Merge remote-tracking branch 'origin/pr/330'
QubesOS/qubes-core-admin@577e4b24 gui: fixes from Marek's comments
QubesOS/qubes-core-admin@f130ec0b gui: improvements of feature keyboard layout checks
QubesOS/qubes-core-admin@5cb0e61a tests: adapt tests for keyboard-layout
QubesOS/qubes-core-admin@732e291a gui: drop legacy qubes-keyboard support
QubesOS/qubes-core-admin@29020d0c Merge branch 'feature-pre-set'
QubesOS/qubes-core-admin@d05592ba Add pre- events to vm features
QubesOS/qubes-core-admin@ddc13d6b Merge remote-tracking branch 'origin/pr/329'
QubesOS/qubes-core-admin@d8f80c96 tests: make PEP8 happier
QubesOS/qubes-core-admin@40156c3e tests: fix already registered event impl
QubesOS/qubes-core-admin@879ee9e7 api/internal: extract get_system_info() function
Referenced issues:
QubesOS/qubes-issues#4890
QubesOS/qubes-issues#5099
QubesOS/qubes-issues#5509
If you're release manager, you can issue GPG-inline signed command:
* `Upload core-admin 6d19496ab5eae95431edb5e7d43d36451083229a r4.1 current repo` (available 7 days from now)
* `Upload core-admin 6d19496ab5eae95431edb5e7d43d36451083229a r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload core-admin 6d19496ab5eae95431edb5e7d43d36451083229a r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| non_priority | core admin update of core admin to for qubes see comments below for details built from qubesos qubes core admin version qubesos qubes core admin merge remote tracking branch origin pr qubesos qubes core admin merge remote tracking branch origin pr qubesos qubes core admin merge remote tracking branch origin pr qubesos qubes core admin tests improve audio tests qubesos qubes core admin merge remote tracking branch origin pr qubesos qubes core admin collections callable collections abc callable qubesos qubes core admin tests file run until complete coro maybe for single arg qubesos qubes core admin tests file use self loop qubesos qubes core admin tests fix qvm copy to vm test qubesos qubes core admin tests ensure proper cleanup of auxiliary process qubesos qubes core admin fix multiple qmemman issues qubesos qubes core admin ext admin workaround for extension s init called multiple times qubesos qubes core admin tests teardown fixes qubesos qubes core admin travis include core qrexec in tests qubesos qubes core admin api admin ext admin limit listing vms based on qrexec policy qubesos qubes core admin merge remote tracking branch origin pr qubesos qubes core admin gui fixes from marek s comments qubesos qubes core admin gui improvements of feature keyboard layout checks qubesos qubes core admin tests adapt tests for keyboard layout qubesos qubes core admin gui drop legacy qubes keyboard support qubesos qubes core admin merge branch feature pre set qubesos qubes core admin add pre events to vm features qubesos qubes core admin merge remote tracking branch origin pr qubesos qubes core admin tests make happier qubesos qubes core admin tests fix already registered event impl qubesos qubes core admin api internal extract get system info function referenced issues qubesos qubes issues qubesos qubes issues qubesos qubes issues if you re release manager you can issue gpg inline signed command upload core admin current repo available days from now upload core admin current dists repo you can choose subset of distributions like vm vm available days from now upload core admin security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it | 0 |
347,854 | 24,902,010,321 | IssuesEvent | 2022-10-28 22:11:20 | PubInv/general-alarm-device | https://api.github.com/repos/PubInv/general-alarm-device | opened | Fully document screws for the case.... | documentation Hardware | The Enclosure is working well, but to complete my verification of it, I tried to use screws on the sides which pin the whole thing together. I tried M1 and M1.75 screws and they are definitely too small. (Note: we cannot reach a nut on these screws.) M3 machine screws won't start.
I have ordered M2 screws to try them, but do not have any on hand. We may have to make the holes large and have them receive M3 screws. But maybe the M2 screws will work fine when i have them. | 1.0 | Fully document screws for the case.... - The Enclosure is working well, but to complete my verification of it, I tried to use screws on the sides which pin the whole thing together. I tried M1 and M1.75 screws and they are definitely too small. (Note: we cannot reach a nut on these screws.) M3 machine screws won't start.
I have ordered M2 screws to try them, but do not have any on hand. We may have to make the holes large and have them receive M3 screws. But maybe the M2 screws will work fine when i have them. | non_priority | fully document screws for the case the enclosure is working well but to complete my verification of it i tried to use screws on the sides which pin the whole thing together i tried and screws and they are definitely too small note we cannot reach a nut on these screws machine screws won t start i have ordered screws to try them but do not have any on hand we may have to make the holes large and have them receive screws but maybe the screws will work fine when i have them | 0 |
153,411 | 24,122,559,431 | IssuesEvent | 2022-09-20 20:08:40 | phetsims/greenhouse-effect | https://api.github.com/repos/phetsims/greenhouse-effect | closed | Make Celsius the default unit | design:polish | Celsius is a more naturally understood unit than Kelvin, and in recent interviews, users made a point to switch the units to *C before exploring. In today's design meeting we decided to proceed with using Celsius as the default unit for all screens.
Kelvin was the default unit because it is necessary when using the equation related to blackbody radiation and radiative balance. However, there are other primary learning goals that aren't tied to Kelvin, so the interpretability of the temperature is also important.
We considered swapping the order of the radio buttons and ListBox items to C > K > F, but we like keeping C in proximity to both K and F, so we are sticking with K > C > F.
@jbphet please update the default units to Celsius. | 1.0 | Make Celsius the default unit - Celsius is a more naturally understood unit than Kelvin, and in recent interviews, users made a point to switch the units to *C before exploring. In today's design meeting we decided to proceed with using Celsius as the default unit for all screens.
Kelvin was the default unit because it is necessary when using the equation related to blackbody radiation and radiative balance. However, there are other primary learning goals that aren't tied to Kelvin, so the interpretability of the temperature is also important.
We considered swapping the order of the radio buttons and ListBox items to C > K > F, but we like keeping C in proximity to both K and F, so we are sticking with K > C > F.
@jbphet please update the default units to Celsius. | non_priority | make celsius the default unit celsius is a more naturally understood unit than kelvin and in recent interviews users made a point to switch the units to c before exploring in today s design meeting we decided to proceed with using celsius as the default unit for all screens kelvin was the default unit because it is necessary when using the equation related to blackbody radiation and radiative balance however there are other primary learning goals that aren t tied to kelvin so the interpretability of the temperature is also important we considered swapping the order of the radio buttons and listbox items to c k f but we like keeping c in proximity to both k and f so we are sticking with k c f jbphet please update the default units to celsius | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.