Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
84,888 | 16,569,389,306 | IssuesEvent | 2021-05-30 04:30:32 | heclak/community-a4e-c | https://api.github.com/repos/heclak/community-a4e-c | closed | better alignment for controls indicator | Code/LUA | align controls indicator further down -- should be as close to bottom-right on a 16:9 monitor as possible:
VR target:
https://cdn.discordapp.com/attachments/765315037115187211/848387397963481128/20210530102757_1.jpg
https://cdn.discordapp.com/attachments/765315037115187211/848387875489710120/20210530102955_1.jpg | 1.0 | better alignment for controls indicator - align controls indicator further down -- should be as close to bottom-right on a 16:9 monitor as possible:
VR target:
https://cdn.discordapp.com/attachments/765315037115187211/848387397963481128/20210530102757_1.jpg
https://cdn.discordapp.com/attachments/765315037115187211/848387875489710120/20210530102955_1.jpg | non_priority | better alignment for controls indicator align controls indicator further down should be as close to bottom right on a monitor as possible vr target | 0 |
38,687 | 6,688,998,972 | IssuesEvent | 2017-10-08 20:53:55 | Moya/Moya | https://api.github.com/repos/Moya/Moya | opened | Changes in English docs not reflected in Chinese docs | documentation | **PLEASE DO NOT CLOSE THIS ISSUE**
This issue has been created to keep track of changes in the English documentation not translated into Chinese.
This issue will continuously be updated to reflect documents that are out of sync.
Documents apart from the README will be added once an initial Chinese counterpart has been written.
If you would like to update the Chinese documentation, please open a pull request and mention which part you've updated.
# To do list
## README
- [ ] #1355: Add link to migration guides in README
## Other
- [ ] The intro in this issue itself! | 1.0 | Changes in English docs not reflected in Chinese docs - **PLEASE DO NOT CLOSE THIS ISSUE**
This issue has been created to keep track of changes in the English documentation not translated into Chinese.
This issue will continuously be updated to reflect documents that are out of sync.
Documents apart from the README will be added once an initial Chinese counterpart has been written.
If you would like to update the Chinese documentation, please open a pull request and mention which part you've updated.
# To do list
## README
- [ ] #1355: Add link to migration guides in README
## Other
- [ ] The intro in this issue itself! | non_priority | changes in english docs not reflected in chinese docs please do not close this issue this issue has been created to keep track of changes in the english documentation not translated into chinese this issue will continuously be updated to reflect documents that are out of sync documents apart from the readme will be added once an initial chinese counterpart has been written if you would like to update the chinese documentation please open a pull request and mention which part you ve updated to do list readme add link to migration guides in readme other the intro in this issue itself | 0 |
432,531 | 30,287,041,910 | IssuesEvent | 2023-07-08 20:25:52 | Python-Dojo/Dojo-Helper-App | https://api.github.com/repos/Python-Dojo/Dojo-Helper-App | opened | Edit discord message | documentation | __See other messages about being careful with secrets__
- [ ] Edit the discord message in the channel to show how many issues are in each swim lane.
- [ ] Show if the code is currently passing (blocked by #4 ) and the current code coverage (blocked by #5 )
Avoid deleting the message and rewriting it as this will send a notification. | 1.0 | Edit discord message - __See other messages about being careful with secrets__
- [ ] Edit the discord message in the channel to show how many issues are in each swim lane.
- [ ] Show if the code is currently passing (blocked by #4 ) and the current code coverage (blocked by #5 )
Avoid deleting the message and rewriting it as this will send a notification. | non_priority | edit discord message see other messages about being careful with secrets edit the discord message in the channel to show how many issues are in each swim lane show if the code is currently passing blocked by and the current code coverage blocked by avoid deleting the message and rewriting it as this will send a notification | 0 |
74,334 | 15,342,410,247 | IssuesEvent | 2021-02-27 16:06:47 | turkdevops/karma | https://api.github.com/repos/turkdevops/karma | opened | CVE-2019-8331 (Medium) detected in bootstrap-3.3.2.min.js | security vulnerability | ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.2.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.2/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.2/js/bootstrap.min.js</a></p>
<p>Path to dependency file: karma/node_modules/knuth-shuffle-seeded/index.html</p>
<p>Path to vulnerable library: karma/node_modules/knuth-shuffle-seeded/index.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/karma/commit/7c03032a10da3be9eafae1355bcf84abf75d4fa6">7c03032a10da3be9eafae1355bcf84abf75d4fa6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-8331 (Medium) detected in bootstrap-3.3.2.min.js - ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.2.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.2/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.2/js/bootstrap.min.js</a></p>
<p>Path to dependency file: karma/node_modules/knuth-shuffle-seeded/index.html</p>
<p>Path to vulnerable library: karma/node_modules/knuth-shuffle-seeded/index.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/karma/commit/7c03032a10da3be9eafae1355bcf84abf75d4fa6">7c03032a10da3be9eafae1355bcf84abf75d4fa6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file karma node modules knuth shuffle seeded index html path to vulnerable library karma node modules knuth shuffle seeded index html dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap bootstrap sass step up your open source security game with whitesource | 0 |
304,441 | 26,276,530,242 | IssuesEvent | 2023-01-06 22:48:28 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | compose: TestComposeCompare failed | C-test-failure O-robot T-sql-sessions branch-release-22.2.0 | compose.TestComposeCompare [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800153?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800153?buildTab=artifacts#/) on release-22.2.0 @ [413dc596348780a8c81a450dc135135985ed70af](https://github.com/cockroachdb/cockroach/commits/413dc596348780a8c81a450dc135135985ed70af):
```
=== RUN TestComposeCompare
compose_test.go:65: -cockroach not set
--- FAIL: TestComposeCompare (0.00s)
```
<p>Parameters: <code>TAGS=bazel,gss</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #89361 compose: TestComposeCompare failed [C-test-failure O-robot T-sql-experience branch-release-22.2]
- #82867 compose: TestComposeCompare failed [C-test-failure O-robot T-sql-experience branch-master]
- #78068 compose: TestComposeCompare failed [C-test-failure O-robot T-sql-experience branch-release-22.1 sync-me-8]
- #73421 compose: TestComposeCompare failed [C-test-failure O-robot branch-release-21.2 sync-me-8]
</p>
</details>
/cc @cockroachdb/sql-experience
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestComposeCompare.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-22027 | 1.0 | compose: TestComposeCompare failed - compose.TestComposeCompare [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800153?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800153?buildTab=artifacts#/) on release-22.2.0 @ [413dc596348780a8c81a450dc135135985ed70af](https://github.com/cockroachdb/cockroach/commits/413dc596348780a8c81a450dc135135985ed70af):
```
=== RUN TestComposeCompare
compose_test.go:65: -cockroach not set
--- FAIL: TestComposeCompare (0.00s)
```
<p>Parameters: <code>TAGS=bazel,gss</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #89361 compose: TestComposeCompare failed [C-test-failure O-robot T-sql-experience branch-release-22.2]
- #82867 compose: TestComposeCompare failed [C-test-failure O-robot T-sql-experience branch-master]
- #78068 compose: TestComposeCompare failed [C-test-failure O-robot T-sql-experience branch-release-22.1 sync-me-8]
- #73421 compose: TestComposeCompare failed [C-test-failure O-robot branch-release-21.2 sync-me-8]
</p>
</details>
/cc @cockroachdb/sql-experience
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestComposeCompare.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-22027 | non_priority | compose testcomposecompare failed compose testcomposecompare with on release run testcomposecompare compose test go cockroach not set fail testcomposecompare parameters tags bazel gss help see also same failure on other branches compose testcomposecompare failed compose testcomposecompare failed compose testcomposecompare failed compose testcomposecompare failed cc cockroachdb sql experience jira issue crdb | 0 |
240,337 | 26,256,297,137 | IssuesEvent | 2023-01-06 01:13:59 | melvinhgf/one-click-hugo-cms | https://api.github.com/repos/melvinhgf/one-click-hugo-cms | opened | CVE-2020-7793 (High) detected in ua-parser-js-0.7.19.tgz | security vulnerability | ## CVE-2020-7793 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ua-parser-js-0.7.19.tgz</b></p></summary>
<p>Lightweight JavaScript-based user-agent string parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.19.tgz">https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.19.tgz</a></p>
<p>Path to dependency file: /one-click-hugo-cms/package.json</p>
<p>Path to vulnerable library: /node_modules/fbjs/node_modules/ua-parser-js/package.json</p>
<p>
Dependency Hierarchy:
- netlify-cms-2.9.1.tgz (Root Library)
- netlify-cms-app-2.9.1.tgz
- netlify-cms-widget-date-2.3.2.tgz
- react-datetime-2.16.3.tgz
- create-react-class-15.6.3.tgz
- fbjs-0.8.17.tgz
- :x: **ua-parser-js-0.7.19.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package ua-parser-js before 0.7.23 are vulnerable to Regular Expression Denial of Service (ReDoS) in multiple regexes (see linked commit for more info).
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7793>CVE-2020-7793</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (ua-parser-js): 0.7.23</p>
<p>Direct dependency fix Resolution (netlify-cms): 2.9.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7793 (High) detected in ua-parser-js-0.7.19.tgz - ## CVE-2020-7793 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ua-parser-js-0.7.19.tgz</b></p></summary>
<p>Lightweight JavaScript-based user-agent string parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.19.tgz">https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.19.tgz</a></p>
<p>Path to dependency file: /one-click-hugo-cms/package.json</p>
<p>Path to vulnerable library: /node_modules/fbjs/node_modules/ua-parser-js/package.json</p>
<p>
Dependency Hierarchy:
- netlify-cms-2.9.1.tgz (Root Library)
- netlify-cms-app-2.9.1.tgz
- netlify-cms-widget-date-2.3.2.tgz
- react-datetime-2.16.3.tgz
- create-react-class-15.6.3.tgz
- fbjs-0.8.17.tgz
- :x: **ua-parser-js-0.7.19.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package ua-parser-js before 0.7.23 are vulnerable to Regular Expression Denial of Service (ReDoS) in multiple regexes (see linked commit for more info).
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7793>CVE-2020-7793</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (ua-parser-js): 0.7.23</p>
<p>Direct dependency fix Resolution (netlify-cms): 2.9.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in ua parser js tgz cve high severity vulnerability vulnerable library ua parser js tgz lightweight javascript based user agent string parser library home page a href path to dependency file one click hugo cms package json path to vulnerable library node modules fbjs node modules ua parser js package json dependency hierarchy netlify cms tgz root library netlify cms app tgz netlify cms widget date tgz react datetime tgz create react class tgz fbjs tgz x ua parser js tgz vulnerable library vulnerability details the package ua parser js before are vulnerable to regular expression denial of service redos in multiple regexes see linked commit for more info publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution ua parser js direct dependency fix resolution netlify cms step up your open source security game with mend | 0 |
4,667 | 5,232,598,102 | IssuesEvent | 2017-01-30 09:59:47 | ethcore/parity | https://api.github.com/repos/ethcore/parity | closed | Dapps Identification | F1-security M6-rpcapi | Currently meta information about the dapp is derived from Referer header - i can be spoofed so it's not a perfect way.
Alternatives:
1. With always-proxy approach we can just use `Origin`, perhaps we should just display a big warning sign if the proxy is not configured (proxy solves localstorage clashes and dapps spoofing)
| True | Dapps Identification - Currently meta information about the dapp is derived from Referer header - i can be spoofed so it's not a perfect way.
Alternatives:
1. With always-proxy approach we can just use `Origin`, perhaps we should just display a big warning sign if the proxy is not configured (proxy solves localstorage clashes and dapps spoofing)
| non_priority | dapps identification currently meta information about the dapp is derived from referer header i can be spoofed so it s not a perfect way alternatives with always proxy approach we can just use origin perhaps we should just display a big warning sign if the proxy is not configured proxy solves localstorage clashes and dapps spoofing | 0 |
73,579 | 15,267,665,692 | IssuesEvent | 2021-02-22 10:22:46 | brave/brave-ios | https://api.github.com/repos/brave/brave-ios | closed | WebAuthn APIs should not be available in third party iframes | Epic: Security QA/Yes bug release-notes/include | <!-- Have you searched for similar issues on the repository?
Before submitting this issue, please visit our wiki for common ones: https://github.com/brave/browser-ios/wiki
For more, check out our community site: https://community.brave.com/ -->
### Description:
WebAuthn APIs are available in third party iframes
### Steps to Reproduce
1. Navigate to https://dustiest-limitation.000webhostapp.com/fido-frame.html
2. Verify that WebAuthn APIs are not available third party iframes.
**Actual result:** <!-- Add screenshots if needed -->
WebAuthn APIs are available
**Expected result:**
WebAuthn APIs should not be available
**Reproduces how often:** [Easily reproduced, Intermittent Issue]
Easily
**Brave Version:** <!-- Provide full details Eg: v1.4.2(17.09.08.16) -->
1.23.1 | True | WebAuthn APIs should not be available in third party iframes - <!-- Have you searched for similar issues on the repository?
Before submitting this issue, please visit our wiki for common ones: https://github.com/brave/browser-ios/wiki
For more, check out our community site: https://community.brave.com/ -->
### Description:
WebAuthn APIs are available in third party iframes
### Steps to Reproduce
1. Navigate to https://dustiest-limitation.000webhostapp.com/fido-frame.html
2. Verify that WebAuthn APIs are not available third party iframes.
**Actual result:** <!-- Add screenshots if needed -->
WebAuthn APIs are available
**Expected result:**
WebAuthn APIs should not be available
**Reproduces how often:** [Easily reproduced, Intermittent Issue]
Easily
**Brave Version:** <!-- Provide full details Eg: v1.4.2(17.09.08.16) -->
1.23.1 | non_priority | webauthn apis should not be available in third party iframes have you searched for similar issues on the repository before submitting this issue please visit our wiki for common ones for more check out our community site description webauthn apis are available in third party iframes steps to reproduce navigate to verify that webauthn apis are not available third party iframes actual result webauthn apis are available expected result webauthn apis should not be available reproduces how often easily brave version | 0 |
130,966 | 10,676,907,438 | IssuesEvent | 2019-10-21 14:34:39 | imixs/imixs-workflow | https://api.github.com/repos/imixs/imixs-workflow | closed | WorkflowRestService - validate resource UID | bug testing | In case of a POST request the optional UID must be validated against a existing $uniqueid. If the workitem does not has a uniqueid.
Error should only be thrown if:
(uid != null && !uid.isEmpty() && !workitem.getUniqueID().isEmpty() && !uid.equals(workitem.getUniqueID())) { | 1.0 | WorkflowRestService - validate resource UID - In case of a POST request the optional UID must be validated against a existing $uniqueid. If the workitem does not has a uniqueid.
Error should only be thrown if:
(uid != null && !uid.isEmpty() && !workitem.getUniqueID().isEmpty() && !uid.equals(workitem.getUniqueID())) { | non_priority | workflowrestservice validate resource uid in case of a post request the optional uid must be validated against a existing uniqueid if the workitem does not has a uniqueid error should only be thrown if uid null uid isempty workitem getuniqueid isempty uid equals workitem getuniqueid | 0 |
63,604 | 8,688,271,064 | IssuesEvent | 2018-12-03 15:44:40 | CICE-Consortium/CICE | https://api.github.com/repos/CICE-Consortium/CICE | reopened | create sample output pages for CICE v6 release | Documentation | Post simulation output for reference purposes, similar to our Icepack page, https://github.com/CICE-Consortium/Icepack/wiki/Icepack-Sample-output.
We might want multiple pages, from a selection of our tests. These could include
- [ ] box, 2001 configuration (see #151)
- [x] box, advection test
- [x] gx3 standard configuration
- [x] gx1 standard configuration, after 1 year
and others.
| 1.0 | create sample output pages for CICE v6 release - Post simulation output for reference purposes, similar to our Icepack page, https://github.com/CICE-Consortium/Icepack/wiki/Icepack-Sample-output.
We might want multiple pages, from a selection of our tests. These could include
- [ ] box, 2001 configuration (see #151)
- [x] box, advection test
- [x] gx3 standard configuration
- [x] gx1 standard configuration, after 1 year
and others.
| non_priority | create sample output pages for cice release post simulation output for reference purposes similar to our icepack page we might want multiple pages from a selection of our tests these could include box configuration see box advection test standard configuration standard configuration after year and others | 0 |
159,035 | 12,452,511,590 | IssuesEvent | 2020-05-27 12:25:41 | testground/testground | https://api.github.com/repos/testground/testground | closed | sidecar errors for a test run should be shown in test output | area/sidecar area/test-plan kind/enhancement | #### Version information:
b1773a47ede14f027c74b253a1a01caec0a6256d
x86_64 / debian
#### Description:
when debugging / setting up a new test, a logic error meant multiple containers were requesting the same configured IP address from the sidecar. The sidecar in it's docker logs reports an error "address already in use" in failing to perform this action, but the observed behavior when running the test is that the context for the `configureNetwork` command times out, and no error is provided besides that the command failed.
It would be great for the underlying sidecar error to be exposed in the diagnostic errors for the test to help with investigation / debugging
| 1.0 | sidecar errors for a test run should be shown in test output - #### Version information:
b1773a47ede14f027c74b253a1a01caec0a6256d
x86_64 / debian
#### Description:
when debugging / setting up a new test, a logic error meant multiple containers were requesting the same configured IP address from the sidecar. The sidecar in it's docker logs reports an error "address already in use" in failing to perform this action, but the observed behavior when running the test is that the context for the `configureNetwork` command times out, and no error is provided besides that the command failed.
It would be great for the underlying sidecar error to be exposed in the diagnostic errors for the test to help with investigation / debugging
| non_priority | sidecar errors for a test run should be shown in test output version information debian description when debugging setting up a new test a logic error meant multiple containers were requesting the same configured ip address from the sidecar the sidecar in it s docker logs reports an error address already in use in failing to perform this action but the observed behavior when running the test is that the context for the configurenetwork command times out and no error is provided besides that the command failed it would be great for the underlying sidecar error to be exposed in the diagnostic errors for the test to help with investigation debugging | 0 |
73,801 | 19,825,277,616 | IssuesEvent | 2022-01-20 05:19:57 | google/xls | https://api.github.com/repos/google/xls | closed | XLSCC - Create bazel rules to convert cc file to xls ir | build xlscc | While the DSLX front-end has rules to convert .x files to xls ir, the second xlscc frontend does not. This issue is to address that so that both frontends can be used within BUILD rules to generate xls ir and as part of the codegen flow, verilog. | 1.0 | XLSCC - Create bazel rules to convert cc file to xls ir - While the DSLX front-end has rules to convert .x files to xls ir, the second xlscc frontend does not. This issue is to address that so that both frontends can be used within BUILD rules to generate xls ir and as part of the codegen flow, verilog. | non_priority | xlscc create bazel rules to convert cc file to xls ir while the dslx front end has rules to convert x files to xls ir the second xlscc frontend does not this issue is to address that so that both frontends can be used within build rules to generate xls ir and as part of the codegen flow verilog | 0 |
4,048 | 3,671,553,811 | IssuesEvent | 2016-02-22 08:13:58 | MISP/MISP | https://api.github.com/repos/MISP/MISP | opened | style problem with filters on view event page with firefox | bug usability | When using Firefox (44.0.2) there is a style problem with the filters on the view event page.

With chrome it is displayed correctly
 | True | style problem with filters on view event page with firefox - When using Firefox (44.0.2) there is a style problem with the filters on the view event page.

With chrome it is displayed correctly
 | non_priority | style problem with filters on view event page with firefox when using firefox there is a style problem with the filters on the view event page with chrome it is displayed correctly | 0 |
22,472 | 6,246,277,151 | IssuesEvent | 2017-07-13 03:21:26 | xceedsoftware/wpftoolkit | https://api.github.com/repos/xceedsoftware/wpftoolkit | closed | Empty MaskedTextBox with a Value set. | CodePlex | <b>BoucherS[CodePlex]</b> <br />Based on discussion
http://wpftoolkit.codeplex.com/discussions/399301, the Masked TextBox with an initial Value starts empty.
| 1.0 | Empty MaskedTextBox with a Value set. - <b>BoucherS[CodePlex]</b> <br />Based on discussion
http://wpftoolkit.codeplex.com/discussions/399301, the Masked TextBox with an initial Value starts empty.
| non_priority | empty maskedtextbox with a value set bouchers based on discussion the masked textbox with an initial value starts empty | 0 |
48,817 | 5,971,028,609 | IssuesEvent | 2017-05-31 00:48:02 | Microsoft/PTVS | https://api.github.com/repos/Microsoft/PTVS | opened | Tests failing to load Microsoft.VisualStudio.Validation assembly | Tests | Example:
```
Test Name: ImportClassifications
Test Outcome: Failed
Result Message:
Test method PythonToolsMockTests.ClassifierTests.ImportClassifications threw exception:
System.IO.FileLoadException: Could not load file or assembly 'Microsoft.VisualStudio.Validation, Version=15.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a' or one of its dependencies. The located assembly's manifest definition does not match the assembly reference. (Exception from HRESULT: 0x80131040)
```
In 15.3, they've changed the version of that assembly from 15.0.0.0 to 15.3.0.0. devenv.exe.config has a bindingRedirect for it.
| 1.0 | Tests failing to load Microsoft.VisualStudio.Validation assembly - Example:
```
Test Name: ImportClassifications
Test Outcome: Failed
Result Message:
Test method PythonToolsMockTests.ClassifierTests.ImportClassifications threw exception:
System.IO.FileLoadException: Could not load file or assembly 'Microsoft.VisualStudio.Validation, Version=15.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a' or one of its dependencies. The located assembly's manifest definition does not match the assembly reference. (Exception from HRESULT: 0x80131040)
```
In 15.3, they've changed the version of that assembly from 15.0.0.0 to 15.3.0.0. devenv.exe.config has a bindingRedirect for it.
| non_priority | tests failing to load microsoft visualstudio validation assembly example test name importclassifications test outcome failed result message test method pythontoolsmocktests classifiertests importclassifications threw exception system io fileloadexception could not load file or assembly microsoft visualstudio validation version culture neutral publickeytoken or one of its dependencies the located assembly s manifest definition does not match the assembly reference exception from hresult in they ve changed the version of that assembly from to devenv exe config has a bindingredirect for it | 0 |
323,487 | 27,730,397,352 | IssuesEvent | 2023-03-15 07:31:47 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: name clusters after running test | C-enhancement T-testeng | **Is your feature request related to a problem? Please describe.**
The clusters get scraped by our internal Prom/Grafana instance, so it's helpful if the cluster name "means something".
**Describe the solution you'd like**
Switch from `$USER-1678829488-01-n10cpu8` to something like`$USER-nameoftestbutsanitizedandshortenedifnecessary-YYMMDD-nonce`
**Describe alternatives you've considered**
**Additional context**
[Slack (internal)](https://cockroachlabs.slack.com/archives/C023S0V4YEB/p1678844786969369?thread_ts=1678841298.001839&cid=C023S0V4YEB) | 1.0 | roachtest: name clusters after running test - **Is your feature request related to a problem? Please describe.**
The clusters get scraped by our internal Prom/Grafana instance, so it's helpful if the cluster name "means something".
**Describe the solution you'd like**
Switch from `$USER-1678829488-01-n10cpu8` to something like`$USER-nameoftestbutsanitizedandshortenedifnecessary-YYMMDD-nonce`
**Describe alternatives you've considered**
**Additional context**
[Slack (internal)](https://cockroachlabs.slack.com/archives/C023S0V4YEB/p1678844786969369?thread_ts=1678841298.001839&cid=C023S0V4YEB) | non_priority | roachtest name clusters after running test is your feature request related to a problem please describe the clusters get scraped by our internal prom grafana instance so it s helpful if the cluster name means something describe the solution you d like switch from user to something like user nameoftestbutsanitizedandshortenedifnecessary yymmdd nonce describe alternatives you ve considered additional context | 0 |
316,206 | 23,619,460,054 | IssuesEvent | 2022-08-24 19:01:30 | HITK-TECH-Community/Community-Website | https://api.github.com/repos/HITK-TECH-Community/Community-Website | closed | Adding issue forms for the repo | documentation | I want to add a few issue forms so that it will be convenient for new contributors to open issues. There are already issue templates for this project but they are deprecated now, issue forms instead work way better. I plan to create **Bug Report**, **Documentation**, and **Feature Request** forms.
**_The Bug Report issue form will have the following fields_**
- **Description of the bug**
- **How to Reproduce**
- **Expected behavior**
- **Urgency indicator**
- **Desktop Info (OS, Version, Browser, etc):**
**_The Documentation issue form will have the following fields_**
- **Description for documentation**
**_The Feature Request issue form will have the following fields_**
- **Is your feature request related to a problem? Please describe.**
- **Describe the solution you'd like**
- **Describe alternatives you've considered**
| 1.0 | Adding issue forms for the repo - I want to add a few issue forms so that it will be convenient for new contributors to open issues. There are already issue templates for this project but they are deprecated now, issue forms instead work way better. I plan to create **Bug Report**, **Documentation**, and **Feature Request** forms.
**_The Bug Report issue form will have the following fields_**
- **Description of the bug**
- **How to Reproduce**
- **Expected behavior**
- **Urgency indicator**
- **Desktop Info (OS, Version, Browser, etc):**
**_The Documentation issue form will have the following fields_**
- **Description for documentation**
**_The Feature Request issue form will have the following fields_**
- **Is your feature request related to a problem? Please describe.**
- **Describe the solution you'd like**
- **Describe alternatives you've considered**
| non_priority | adding issue forms for the repo i want to add a few issue forms so that it will be convenient for new contributors to open issues there are already issue templates for this project but they are deprecated now issue forms instead work way better i plan to create bug report documentation and feature request forms the bug report issue form will have the following fields description of the bug how to reproduce expected behavior urgency indicator desktop info os version browser etc the documentation issue form will have the following fields description for documentation the feature request issue form will have the following fields is your feature request related to a problem please describe describe the solution you d like describe alternatives you ve considered | 0 |
190,869 | 14,581,997,684 | IssuesEvent | 2020-12-18 11:37:39 | TIS2020-FMFI/krokovy-motor | https://api.github.com/repos/TIS2020-FMFI/krokovy-motor | closed | Odovzdanie finálnej verzie zadávateľovi. | deployment management testing | prebehlo stretnutie so zadávateľom
aplikovali sme zmeny ku vyhladavaniu minim
otestovali sme celkovú funkcionalitu
zadávateľ bol spokojný s výsledným projektom
odovzdali sme mu program vo formáte jar | 1.0 | Odovzdanie finálnej verzie zadávateľovi. - prebehlo stretnutie so zadávateľom
aplikovali sme zmeny ku vyhladavaniu minim
otestovali sme celkovú funkcionalitu
zadávateľ bol spokojný s výsledným projektom
odovzdali sme mu program vo formáte jar | non_priority | odovzdanie finálnej verzie zadávateľovi prebehlo stretnutie so zadávateľom aplikovali sme zmeny ku vyhladavaniu minim otestovali sme celkovú funkcionalitu zadávateľ bol spokojný s výsledným projektom odovzdali sme mu program vo formáte jar | 0 |
12,710 | 5,229,356,358 | IssuesEvent | 2017-01-29 02:25:24 | sebnitu/BaseWeb | https://api.github.com/repos/sebnitu/BaseWeb | closed | Update `Getting Started` page with new build scripts | Build Scripts Docs Update | Currently it still has the old information of Jake. This should be updated to reflect the new Gulp build scripts. | 1.0 | Update `Getting Started` page with new build scripts - Currently it still has the old information of Jake. This should be updated to reflect the new Gulp build scripts. | non_priority | update getting started page with new build scripts currently it still has the old information of jake this should be updated to reflect the new gulp build scripts | 0 |
365,721 | 25,549,323,501 | IssuesEvent | 2022-11-29 21:51:33 | SOunit/angularjs-memo | https://api.github.com/repos/SOunit/angularjs-memo | opened | fetch cart item count | documentation | # steps
- add ng-app
- add ng-controller
- add ng-init
- use $http
- set `$scope.cartItemsCount = response.data`
- show `cartItemsCount`
# point
- use ng-init to init data
- | 1.0 | fetch cart item count - # steps
- add ng-app
- add ng-controller
- add ng-init
- use $http
- set `$scope.cartItemsCount = response.data`
- show `cartItemsCount`
# point
- use ng-init to init data
- | non_priority | fetch cart item count steps add ng app add ng controller add ng init use http set scope cartitemscount response data show cartitemscount point use ng init to init data | 0 |
322,493 | 27,611,708,697 | IssuesEvent | 2023-03-09 16:24:26 | neondatabase/neon | https://api.github.com/repos/neondatabase/neon | opened | Spurious `cargo test` failures | a/test/flaky | We've had a few slack threads on these already:
- https://neondb.slack.com/archives/C04DGM6SMTM/p1673017754801879
- https://neondb.slack.com/archives/C033RQ5SPDH/p1676811125248989
They are essentially about these failures [build-neon job](https://github.com/neondatabase/neon/actions/runs/4376092920/jobs/7657714851):
```
failures:
v14::xlog_utils::tests::test_find_end_of_wal_crossing_segment_followed_by_small_one
v14::xlog_utils::tests::test_find_end_of_wal_last_crossing_segment
v14::xlog_utils::tests::test_find_end_of_wal_simple
v15::xlog_utils::tests::test_find_end_of_wal_crossing_segment_followed_by_small_one
v15::xlog_utils::tests::test_find_end_of_wal_last_crossing_segment
v15::xlog_utils::tests::test_find_end_of_wal_simple
test result: FAILED. 25 passed; 6 failed; 0 ignored; 0 measured; 0 filtered out; finished in 2.16s
error: test failed, to rerun pass `-p postgres_ffi --lib`
```
These seem quite rare. | 1.0 | Spurious `cargo test` failures - We've had a few slack threads on these already:
- https://neondb.slack.com/archives/C04DGM6SMTM/p1673017754801879
- https://neondb.slack.com/archives/C033RQ5SPDH/p1676811125248989
They are essentially about these failures [build-neon job](https://github.com/neondatabase/neon/actions/runs/4376092920/jobs/7657714851):
```
failures:
v14::xlog_utils::tests::test_find_end_of_wal_crossing_segment_followed_by_small_one
v14::xlog_utils::tests::test_find_end_of_wal_last_crossing_segment
v14::xlog_utils::tests::test_find_end_of_wal_simple
v15::xlog_utils::tests::test_find_end_of_wal_crossing_segment_followed_by_small_one
v15::xlog_utils::tests::test_find_end_of_wal_last_crossing_segment
v15::xlog_utils::tests::test_find_end_of_wal_simple
test result: FAILED. 25 passed; 6 failed; 0 ignored; 0 measured; 0 filtered out; finished in 2.16s
error: test failed, to rerun pass `-p postgres_ffi --lib`
```
These seem quite rare. | non_priority | spurious cargo test failures we ve had a few slack threads on these already they are essentially about these failures failures xlog utils tests test find end of wal crossing segment followed by small one xlog utils tests test find end of wal last crossing segment xlog utils tests test find end of wal simple xlog utils tests test find end of wal crossing segment followed by small one xlog utils tests test find end of wal last crossing segment xlog utils tests test find end of wal simple test result failed passed failed ignored measured filtered out finished in error test failed to rerun pass p postgres ffi lib these seem quite rare | 0 |
116,925 | 17,395,961,181 | IssuesEvent | 2021-08-02 13:30:36 | hygieia/hygieia | https://api.github.com/repos/hygieia/hygieia | closed | CVE-2021-32640 (Medium) detected in ws-7.4.4.tgz - autoclosed | security vulnerability | ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ws-7.4.4.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.4.4.tgz">https://registry.npmjs.org/ws/-/ws-7.4.4.tgz</a></p>
<p>Path to dependency file: hygieia/package.json</p>
<p>Path to vulnerable library: hygieia/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- socket.io-2.4.1.tgz (Root Library)
- engine.io-3.5.0.tgz
- :x: **ws-7.4.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/hygieia/commit/5ab87822afd91cf2c356b709e4d7762392cfc200">5ab87822afd91cf2c356b709e4d7762392cfc200</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: ws - 7.4.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-32640 (Medium) detected in ws-7.4.4.tgz - autoclosed - ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ws-7.4.4.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.4.4.tgz">https://registry.npmjs.org/ws/-/ws-7.4.4.tgz</a></p>
<p>Path to dependency file: hygieia/package.json</p>
<p>Path to vulnerable library: hygieia/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- socket.io-2.4.1.tgz (Root Library)
- engine.io-3.5.0.tgz
- :x: **ws-7.4.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/hygieia/commit/5ab87822afd91cf2c356b709e4d7762392cfc200">5ab87822afd91cf2c356b709e4d7762392cfc200</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: ws - 7.4.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in ws tgz autoclosed cve medium severity vulnerability vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file hygieia package json path to vulnerable library hygieia node modules ws package json dependency hierarchy socket io tgz root library engine io tgz x ws tgz vulnerable library found in head commit a href found in base branch master vulnerability details ws is an open source websocket client and server library for node js a specially crafted value of the sec websocket protocol header can be used to significantly slow down a ws server the vulnerability has been fixed in ws in vulnerable versions of ws the issue can be mitigated by reducing the maximum allowed length of the request headers using the and or the options publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ws step up your open source security game with whitesource | 0 |
126,629 | 12,294,902,408 | IssuesEvent | 2020-05-11 02:00:21 | MarkOoi1/macromonitor | https://api.github.com/repos/MarkOoi1/macromonitor | opened | Tactics | documentation | Document the workflow / design of the functionality
Document the dependencies and file structure of the build
Add new tasks to execute the work | 1.0 | Tactics - Document the workflow / design of the functionality
Document the dependencies and file structure of the build
Add new tasks to execute the work | non_priority | tactics document the workflow design of the functionality document the dependencies and file structure of the build add new tasks to execute the work | 0 |
313,605 | 26,939,386,526 | IssuesEvent | 2023-02-08 00:09:03 | saleor/saleor-dashboard | https://api.github.com/repos/saleor/saleor-dashboard | closed | Cypress test fail: should create page with DROPDOWN attribute | stale tests | **Known bug for versions:**
v37: true
**Additional Info:**
Spec: Tests for pages
**Created Ticket**
For: QA
Link: https://github.com/saleor/saleor-dashboard/issues/2782 | 1.0 | Cypress test fail: should create page with DROPDOWN attribute - **Known bug for versions:**
v37: true
**Additional Info:**
Spec: Tests for pages
**Created Ticket**
For: QA
Link: https://github.com/saleor/saleor-dashboard/issues/2782 | non_priority | cypress test fail should create page with dropdown attribute known bug for versions true additional info spec tests for pages created ticket for qa link | 0 |
193,128 | 22,216,067,946 | IssuesEvent | 2022-06-08 01:52:31 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2016-8650 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2016-8650 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/mpi/mpi-pow.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/mpi/mpi-pow.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/mpi/mpi-pow.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The mpi_powm function in lib/mpi/mpi-pow.c in the Linux kernel through 4.8.11 does not ensure that memory is allocated for limb data, which allows local users to cause a denial of service (stack memory corruption and panic) via an add_key system call for an RSA key with a zero exponent.
<p>Publish Date: 2016-11-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-8650>CVE-2016-8650</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-8650">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-8650</a></p>
<p>Release Date: 2016-11-28</p>
<p>Fix Resolution: v4.9-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-8650 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2016-8650 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/mpi/mpi-pow.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/mpi/mpi-pow.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/mpi/mpi-pow.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The mpi_powm function in lib/mpi/mpi-pow.c in the Linux kernel through 4.8.11 does not ensure that memory is allocated for limb data, which allows local users to cause a denial of service (stack memory corruption and panic) via an add_key system call for an RSA key with a zero exponent.
<p>Publish Date: 2016-11-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-8650>CVE-2016-8650</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-8650">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-8650</a></p>
<p>Release Date: 2016-11-28</p>
<p>Fix Resolution: v4.9-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files lib mpi mpi pow c lib mpi mpi pow c lib mpi mpi pow c vulnerability details the mpi powm function in lib mpi mpi pow c in the linux kernel through does not ensure that memory is allocated for limb data which allows local users to cause a denial of service stack memory corruption and panic via an add key system call for an rsa key with a zero exponent publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
28,166 | 5,203,212,647 | IssuesEvent | 2017-01-24 12:04:32 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Datatable drag & drop fail on Firefox | defect | Rows gets stuck floating over the datatable if the mouse pointer passes outside the browser window.
I've observed it only on Firefox.
Is there any option or configuration to prevent this behaviour?
| 1.0 | Datatable drag & drop fail on Firefox - Rows gets stuck floating over the datatable if the mouse pointer passes outside the browser window.
I've observed it only on Firefox.
Is there any option or configuration to prevent this behaviour?
| non_priority | datatable drag drop fail on firefox rows gets stuck floating over the datatable if the mouse pointer passes outside the browser window i ve observed it only on firefox is there any option or configuration to prevent this behaviour | 0 |
38,873 | 12,604,361,824 | IssuesEvent | 2020-06-11 14:51:36 | strikingraghu/spring-framework-petclinic | https://api.github.com/repos/strikingraghu/spring-framework-petclinic | opened | CVE-2018-14042 (Medium) detected in bootstrap-3.3.6.jar | security vulnerability | ## CVE-2018-14042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6.jar</b></p></summary>
<p>WebJar for Bootstrap</p>
<p>Library home page: <a href="http://webjars.org">http://webjars.org</a></p>
<p>Path to vulnerable library: /spring-framework-petclinic/target/petclinic/WEB-INF/lib/bootstrap-3.3.6.jar,epository/org/webjars/bootstrap/3.3.6/bootstrap-3.3.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/strikingraghu/spring-framework-petclinic/commit/08887eade2099e8e1be3fd68f3a665a75cdae3eb">08887eade2099e8e1be3fd68f3a665a75cdae3eb</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.webjars","packageName":"bootstrap","packageVersion":"3.3.6","isTransitiveDependency":false,"dependencyTree":"org.webjars:bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0"}],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-14042 (Medium) detected in bootstrap-3.3.6.jar - ## CVE-2018-14042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6.jar</b></p></summary>
<p>WebJar for Bootstrap</p>
<p>Library home page: <a href="http://webjars.org">http://webjars.org</a></p>
<p>Path to vulnerable library: /spring-framework-petclinic/target/petclinic/WEB-INF/lib/bootstrap-3.3.6.jar,epository/org/webjars/bootstrap/3.3.6/bootstrap-3.3.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/strikingraghu/spring-framework-petclinic/commit/08887eade2099e8e1be3fd68f3a665a75cdae3eb">08887eade2099e8e1be3fd68f3a665a75cdae3eb</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.webjars","packageName":"bootstrap","packageVersion":"3.3.6","isTransitiveDependency":false,"dependencyTree":"org.webjars:bootstrap:3.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0"}],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in bootstrap jar cve medium severity vulnerability vulnerable library bootstrap jar webjar for bootstrap library home page a href path to vulnerable library spring framework petclinic target petclinic web inf lib bootstrap jar epository org webjars bootstrap bootstrap jar dependency hierarchy x bootstrap jar vulnerable library found in head commit a href vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the data container property of tooltip vulnerabilityurl | 0 |
98,143 | 16,360,344,737 | IssuesEvent | 2021-05-14 08:29:44 | w3ctag/design-reviews | https://api.github.com/repos/w3ctag/design-reviews | reopened | Early TAG design review for captureTab | Needs explainer Needs security & privacy review Review type: early review Topic: media Venue: WebRTC | I'm requesting a TAG review of capture-current-tab.
Summary: in a number of scenarios (most prominently sharing Web slides in a Web teleconference), offering the possibility to video-capture the current tab (or a cropped view of the current tab) provides a smoother
and easier to understand UX than what's possible using the Screen Capture API. The WebRTC WG has rough consensus that this is a useful scenario to address and is exploring approaches to enable that scenario;
we are seeking input from the TAG on how to do that safely and consistently with the rest of the platform.
- Explainer: Two rough approaches have been discussed:
* getCurrentBrowseringContextMedia - explainer at
https://docs.google.com/document/d/1CIQH2ygvw7eTGO__Pcds_D46Gcn-iPAqESQqOsHHfkI/edit#heading=h.bj2aavkeqqud
related discussions at
https://github.com/w3c/mediacapture-screen-share/pull/148 and
https://github.com/w3c/mediacapture-screen-share/issues/156, with
concerns around cross-origin protections (see below)
* getTabMedia() secured by COEP sketched in
https://docs.google.com/presentation/d/1CeNeno5XuDhm1mpnVyE9eT14YKZgZUtgQsJfC8uqEpA/edit#slide=id.gaef31c926d_1_72 (slides 16-28)
- Security and Privacy self-review
The gist of our request for input is on the privacy and security trade-off given that in a number of cases, the content to be captured from a given tab will include cross-origin content (e.g. Web slides that integrate a video hosted on a streaming service), possibly nested several times.
In general, we recognize that an API that allows to capture a single tab reduces some privacy risk compared to the generic screen sharing API (with less risk to share unintended content), but creates a bigger security attack surface where a Web site could embed third-party content and social-engineer the user to get it captured to gain access to cross-origin information.
In particular, there is active discussion on whether embedded origins should opt-in or opt-out of that possibility:
https://github.com/w3c/mediacapture-screen-share/issues/156
The trade-off is discussed in slides
https://docs.google.com/presentation/d/1CeNeno5XuDhm1mpnVyE9eT14YKZgZUtgQsJfC8uqEpA/edit#slide=id.gaef31c926d_1_37
from 11 to 28
- GitHub repo (if you prefer feedback filed there):
https://github.com/w3c/mediacapture-screen-share/
- Primary contacts (and their relationship to the specification):
- Elad Alon (@eladalon1983, Google), Jan-Ivar Bruaroey (@jan-ivar, Mozilla) have been shepherding the discussions in this space
- Organization/project driving the design: WebRTC WG
Further details:
- [X] I have reviewed the TAG's [API Design
Principles](https://w3ctag.github.io/design-principles/)
- The group where the incubation/design work on this is being done (or is intended to be done in the future): WebRTC WG
- The group where standardization of this work is intended to be done ("unknown" if not known): WebRTC WG
- Existing major pieces of multi-stakeholder review or discussion of this design: (see above)
- Major unresolved issues with or opposition to this design: (as described above, the security model for cross-origin content)
- This work is being funded by: N/A
We'd prefer the TAG provide feedback as (please delete all but the desired option):
🐛 open issues in our GitHub repo for **each point of feedback** | True | Early TAG design review for captureTab - I'm requesting a TAG review of capture-current-tab.
Summary: in a number of scenarios (most prominently sharing Web slides in a Web teleconference), offering the possibility to video-capture the current tab (or a cropped view of the current tab) provides a smoother
and easier to understand UX than what's possible using the Screen Capture API. The WebRTC WG has rough consensus that this is a useful scenario to address and is exploring approaches to enable that scenario;
we are seeking input from the TAG on how to do that safely and consistently with the rest of the platform.
- Explainer: Two rough approaches have been discussed:
* getCurrentBrowseringContextMedia - explainer at
https://docs.google.com/document/d/1CIQH2ygvw7eTGO__Pcds_D46Gcn-iPAqESQqOsHHfkI/edit#heading=h.bj2aavkeqqud
related discussions at
https://github.com/w3c/mediacapture-screen-share/pull/148 and
https://github.com/w3c/mediacapture-screen-share/issues/156, with
concerns around cross-origin protections (see below)
* getTabMedia() secured by COEP sketched in
https://docs.google.com/presentation/d/1CeNeno5XuDhm1mpnVyE9eT14YKZgZUtgQsJfC8uqEpA/edit#slide=id.gaef31c926d_1_72 (slides 16-28)
- Security and Privacy self-review
The gist of our request for input is on the privacy and security trade-off given that in a number of cases, the content to be captured from a given tab will include cross-origin content (e.g. Web slides that integrate a video hosted on a streaming service), possibly nested several times.
In general, we recognize that an API that allows to capture a single tab reduces some privacy risk compared to the generic screen sharing API (with less risk to share unintended content), but creates a bigger security attack surface where a Web site could embed third-party content and social-engineer the user to get it captured to gain access to cross-origin information.
In particular, there is active discussion on whether embedded origins should opt-in or opt-out of that possibility:
https://github.com/w3c/mediacapture-screen-share/issues/156
The trade-off is discussed in slides
https://docs.google.com/presentation/d/1CeNeno5XuDhm1mpnVyE9eT14YKZgZUtgQsJfC8uqEpA/edit#slide=id.gaef31c926d_1_37
from 11 to 28
- GitHub repo (if you prefer feedback filed there):
https://github.com/w3c/mediacapture-screen-share/
- Primary contacts (and their relationship to the specification):
- Elad Alon (@eladalon1983, Google), Jan-Ivar Bruaroey (@jan-ivar, Mozilla) have been shepherding the discussions in this space
- Organization/project driving the design: WebRTC WG
Further details:
- [X] I have reviewed the TAG's [API Design
Principles](https://w3ctag.github.io/design-principles/)
- The group where the incubation/design work on this is being done (or is intended to be done in the future): WebRTC WG
- The group where standardization of this work is intended to be done ("unknown" if not known): WebRTC WG
- Existing major pieces of multi-stakeholder review or discussion of this design: (see above)
- Major unresolved issues with or opposition to this design: (as described above, the security model for cross-origin content)
- This work is being funded by: N/A
We'd prefer the TAG provide feedback as (please delete all but the desired option):
🐛 open issues in our GitHub repo for **each point of feedback** | non_priority | early tag design review for capturetab i m requesting a tag review of capture current tab summary in a number of scenarios most prominently sharing web slides in a web teleconference offering the possibility to video capture the current tab or a cropped view of the current tab provides a smoother and easier to understand ux than what s possible using the screen capture api the webrtc wg has rough consensus that this is a useful scenario to address and is exploring approaches to enable that scenario we are seeking input from the tag on how to do that safely and consistently with the rest of the platform explainer two rough approaches have been discussed getcurrentbrowseringcontextmedia explainer at related discussions at and with concerns around cross origin protections see below gettabmedia secured by coep sketched in slides security and privacy self review the gist of our request for input is on the privacy and security trade off given that in a number of cases the content to be captured from a given tab will include cross origin content e g web slides that integrate a video hosted on a streaming service possibly nested several times in general we recognize that an api that allows to capture a single tab reduces some privacy risk compared to the generic screen sharing api with less risk to share unintended content but creates a bigger security attack surface where a web site could embed third party content and social engineer the user to get it captured to gain access to cross origin information in particular there is active discussion on whether embedded origins should opt in or opt out of that possibility the trade off is discussed in slides from to github repo if you prefer feedback filed there primary contacts and their relationship to the specification elad alon google jan ivar bruaroey jan ivar mozilla have been shepherding the discussions in this space organization project driving the design webrtc wg further details i have reviewed the tag s api design principles the group where the incubation design work on this is being done or is intended to be done in the future webrtc wg the group where standardization of this work is intended to be done unknown if not known webrtc wg existing major pieces of multi stakeholder review or discussion of this design see above major unresolved issues with or opposition to this design as described above the security model for cross origin content this work is being funded by n a we d prefer the tag provide feedback as please delete all but the desired option 🐛 open issues in our github repo for each point of feedback | 0 |
271,277 | 29,418,908,084 | IssuesEvent | 2023-05-31 01:01:43 | Palem1988/EIPs | https://api.github.com/repos/Palem1988/EIPs | opened | CVE-2023-24824 (High) detected in commonmarker-0.17.9.gem | Mend: dependency security vulnerability | ## CVE-2023-24824 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commonmarker-0.17.9.gem</b></p></summary>
<p>A fast, safe, extensible parser for CommonMark. This wraps the official libcmark library.</p>
<p>Library home page: <a href="https://rubygems.org/gems/commonmarker-0.17.9.gem">https://rubygems.org/gems/commonmarker-0.17.9.gem</a></p>
<p>Path to dependency file: /EIPs/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/commonmarker-0.17.9.gem</p>
<p>
Dependency Hierarchy:
- github-pages-179.gem (Root Library)
- jekyll-commonmark-ghpages-0.1.5.gem
- :x: **commonmarker-0.17.9.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
cmark-gfm is GitHub's fork of cmark, a CommonMark parsing and rendering library and program in C. A polynomial time complexity issue in cmark-gfm may lead to unbounded resource exhaustion and subsequent denial of service. This CVE covers quadratic complexity issues when parsing text which leads with either large numbers of `>` or `-` characters. This issue has been addressed in version 0.29.0.gfm.10. Users are advised to upgrade. Users unable to upgrade should validate that their input comes from trusted sources.
<p>Publish Date: 2023-03-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24824>CVE-2023-24824</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-48wp-p9qv-4j64">https://github.com/advisories/GHSA-48wp-p9qv-4j64</a></p>
<p>Release Date: 2023-03-31</p>
<p>Fix Resolution: commonmarker - 0.23.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-24824 (High) detected in commonmarker-0.17.9.gem - ## CVE-2023-24824 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commonmarker-0.17.9.gem</b></p></summary>
<p>A fast, safe, extensible parser for CommonMark. This wraps the official libcmark library.</p>
<p>Library home page: <a href="https://rubygems.org/gems/commonmarker-0.17.9.gem">https://rubygems.org/gems/commonmarker-0.17.9.gem</a></p>
<p>Path to dependency file: /EIPs/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/commonmarker-0.17.9.gem</p>
<p>
Dependency Hierarchy:
- github-pages-179.gem (Root Library)
- jekyll-commonmark-ghpages-0.1.5.gem
- :x: **commonmarker-0.17.9.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
cmark-gfm is GitHub's fork of cmark, a CommonMark parsing and rendering library and program in C. A polynomial time complexity issue in cmark-gfm may lead to unbounded resource exhaustion and subsequent denial of service. This CVE covers quadratic complexity issues when parsing text which leads with either large numbers of `>` or `-` characters. This issue has been addressed in version 0.29.0.gfm.10. Users are advised to upgrade. Users unable to upgrade should validate that their input comes from trusted sources.
<p>Publish Date: 2023-03-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24824>CVE-2023-24824</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-48wp-p9qv-4j64">https://github.com/advisories/GHSA-48wp-p9qv-4j64</a></p>
<p>Release Date: 2023-03-31</p>
<p>Fix Resolution: commonmarker - 0.23.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in commonmarker gem cve high severity vulnerability vulnerable library commonmarker gem a fast safe extensible parser for commonmark this wraps the official libcmark library library home page a href path to dependency file eips gemfile lock path to vulnerable library var lib gems cache commonmarker gem dependency hierarchy github pages gem root library jekyll commonmark ghpages gem x commonmarker gem vulnerable library vulnerability details cmark gfm is github s fork of cmark a commonmark parsing and rendering library and program in c a polynomial time complexity issue in cmark gfm may lead to unbounded resource exhaustion and subsequent denial of service this cve covers quadratic complexity issues when parsing text which leads with either large numbers of or characters this issue has been addressed in version gfm users are advised to upgrade users unable to upgrade should validate that their input comes from trusted sources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commonmarker step up your open source security game with mend | 0 |
288,615 | 31,861,509,938 | IssuesEvent | 2023-09-15 11:16:25 | nidhi7598/linux-v4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564 | opened | CVE-2022-26490 (High) detected in linuxlinux-4.19.294 | Mend: dependency security vulnerability | ## CVE-2022-26490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
st21nfca_connectivity_event_received in drivers/nfc/st21nfca/se.c in the Linux kernel through 5.16.12 has EVT_TRANSACTION buffer overflows because of untrusted length parameters.
<p>Publish Date: 2022-03-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-26490>CVE-2022-26490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-26490">https://www.linuxkernelcves.com/cves/CVE-2022-26490</a></p>
<p>Release Date: 2022-03-06</p>
<p>Fix Resolution: v4.9.309,v4.14.274,v4.19.237,v5.4.188,v5.10.109,v5.15.32,v5.16.18</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-26490 (High) detected in linuxlinux-4.19.294 - ## CVE-2022-26490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
st21nfca_connectivity_event_received in drivers/nfc/st21nfca/se.c in the Linux kernel through 5.16.12 has EVT_TRANSACTION buffer overflows because of untrusted length parameters.
<p>Publish Date: 2022-03-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-26490>CVE-2022-26490</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-26490">https://www.linuxkernelcves.com/cves/CVE-2022-26490</a></p>
<p>Release Date: 2022-03-06</p>
<p>Fix Resolution: v4.9.309,v4.14.274,v4.19.237,v5.4.188,v5.10.109,v5.15.32,v5.16.18</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files vulnerability details connectivity event received in drivers nfc se c in the linux kernel through has evt transaction buffer overflows because of untrusted length parameters publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
316,964 | 23,657,970,371 | IssuesEvent | 2022-08-26 13:05:50 | ra3xdh/qucs_s | https://api.github.com/repos/ra3xdh/qucs_s | closed | "BJT" examples in schematic\ngspice folder | bug documentation | I tested and cleaned up the "BJT" examples in schematic\ngspice folder.
All simulated as shown in the online Help except "BJT-noise.sch".
The noise level are orders of magnitude higher than shown in the Help. Either I made a typo or something is wrong...
https://qucs-help.readthedocs.io/en/spice4qucs/ASim.html
[BJT_examples_ngspice.zip](https://github.com/ra3xdh/qucs_s/files/9365892/BJT_examples_ngspice.zip)
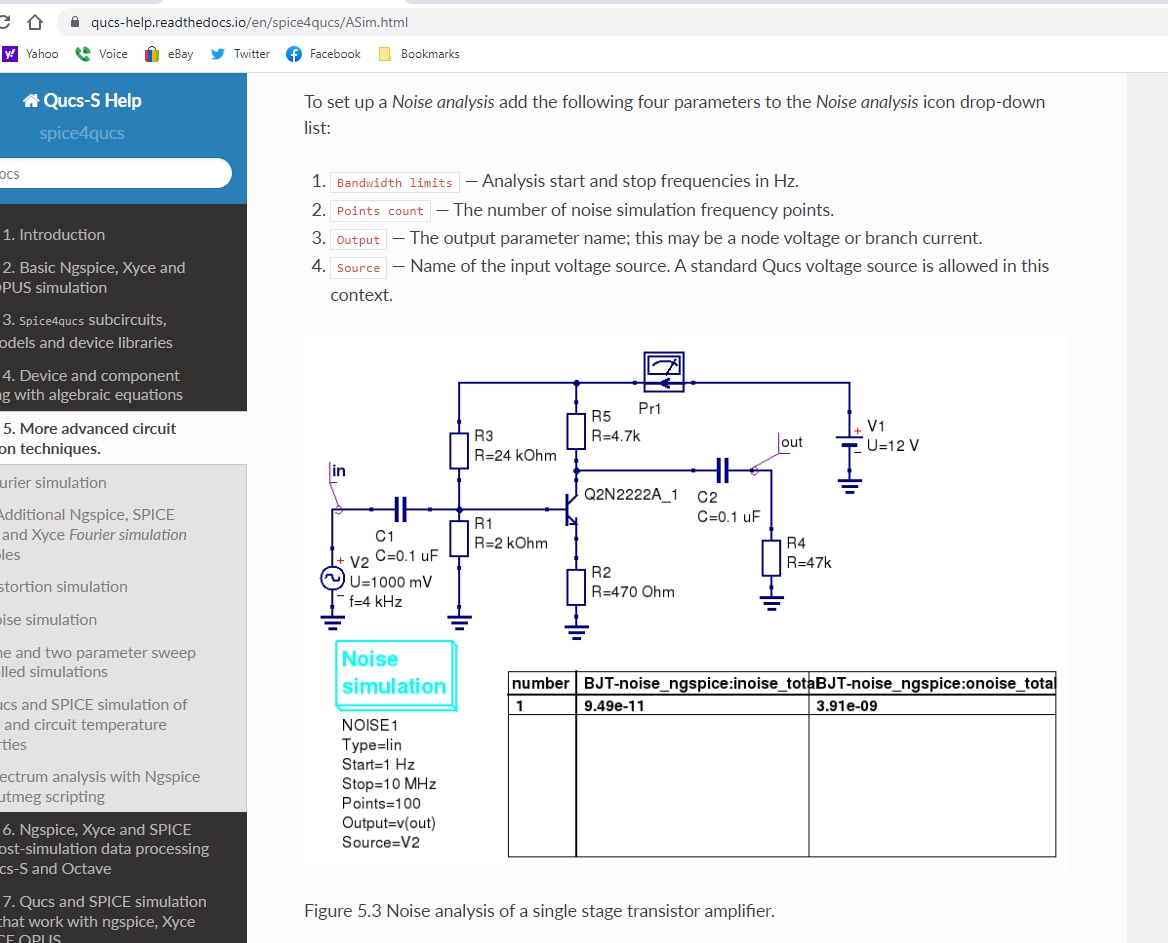
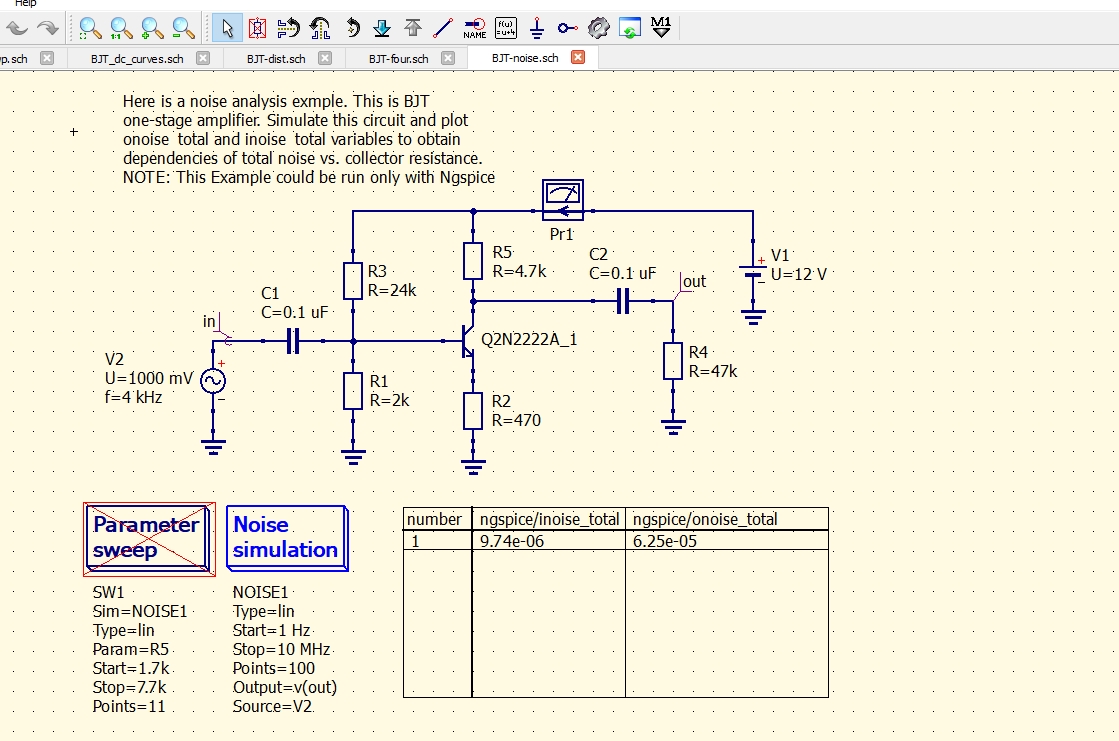
| 1.0 | "BJT" examples in schematic\ngspice folder - I tested and cleaned up the "BJT" examples in schematic\ngspice folder.
All simulated as shown in the online Help except "BJT-noise.sch".
The noise level are orders of magnitude higher than shown in the Help. Either I made a typo or something is wrong...
https://qucs-help.readthedocs.io/en/spice4qucs/ASim.html
[BJT_examples_ngspice.zip](https://github.com/ra3xdh/qucs_s/files/9365892/BJT_examples_ngspice.zip)
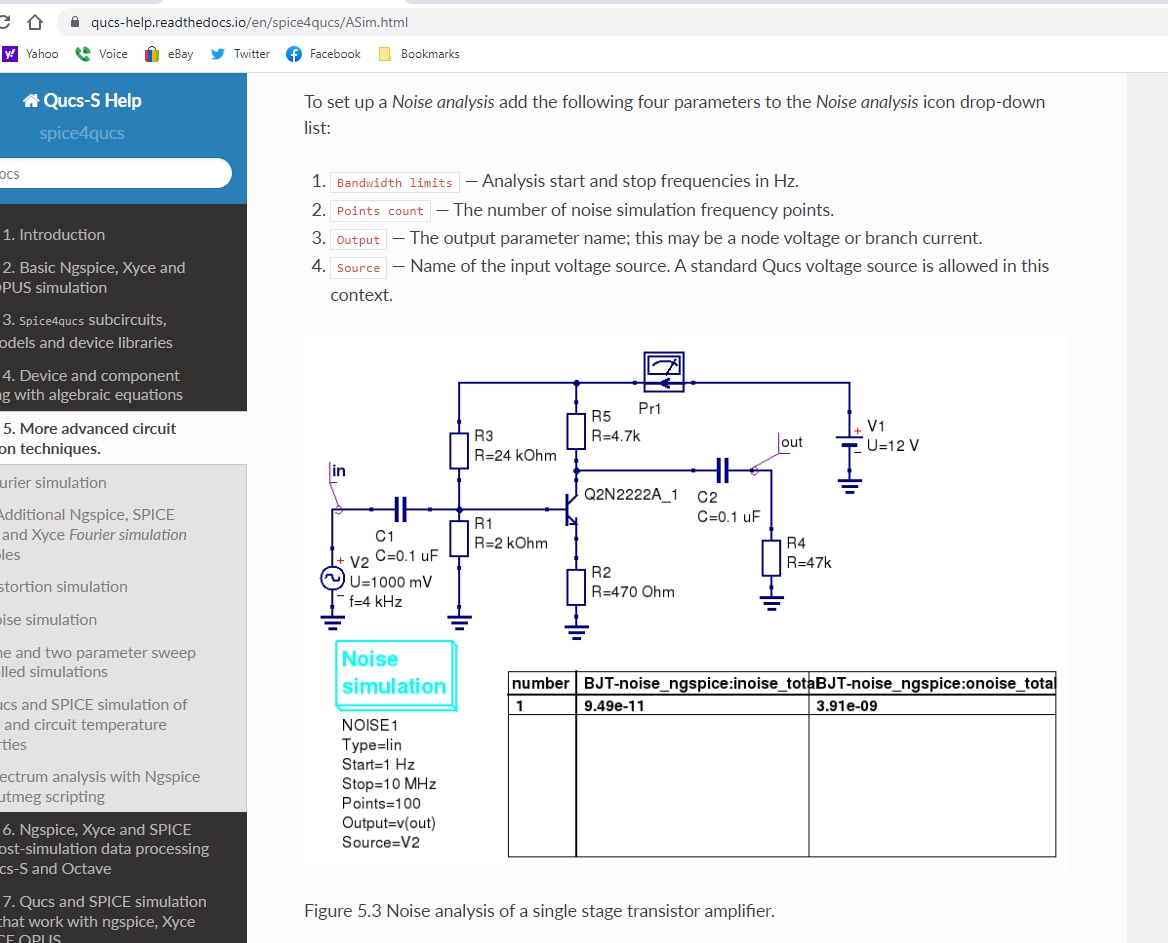
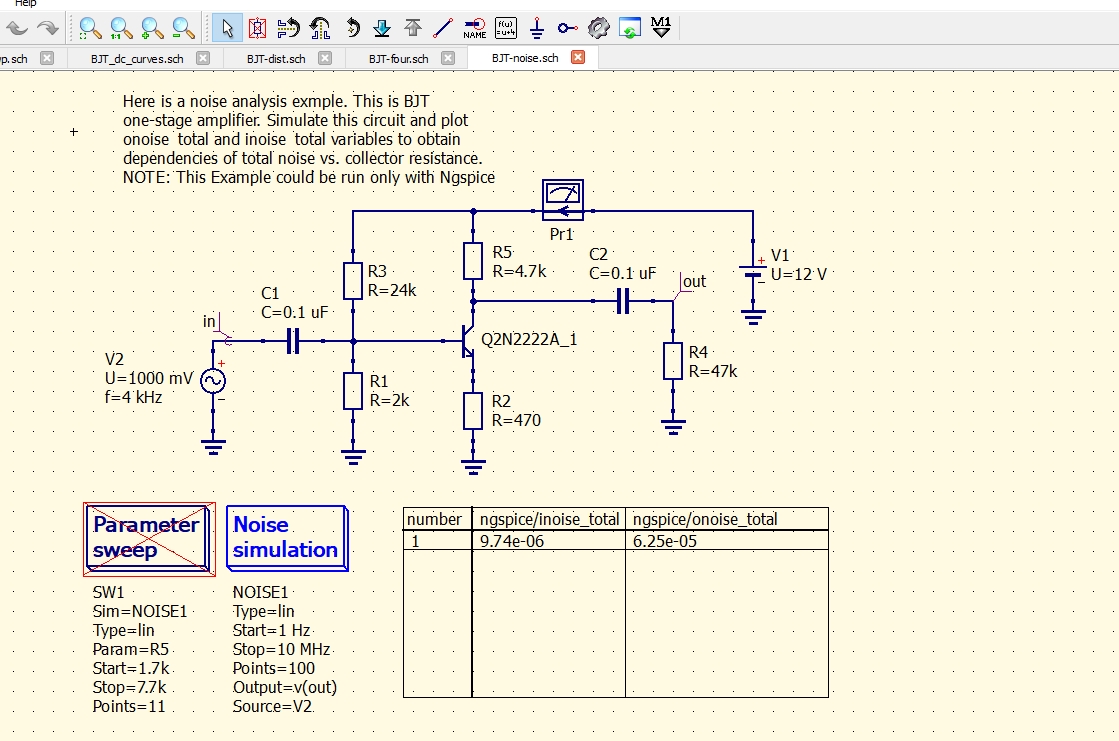
| non_priority | bjt examples in schematic ngspice folder i tested and cleaned up the bjt examples in schematic ngspice folder all simulated as shown in the online help except bjt noise sch the noise level are orders of magnitude higher than shown in the help either i made a typo or something is wrong | 0 |
323,373 | 23,945,103,271 | IssuesEvent | 2022-09-12 06:25:33 | Jack0Chan/pyuppaal | https://api.github.com/repos/Jack0Chan/pyuppaal | closed | pyuppaal接口升级 | documentation enhancement | - [X] pyuppaal.load(model_path: str) -> UModel
- [X] Verifyta的接口全部暴露给pyuppaal,比如
- [X] pyuppaal.set_verifyta_path()
- [X] pyuppaal.simple_verify()
- [X] pyuppaal.cmds()等
- [X] pyuppaal.get_communication_graph()
- [X] 升级后的文档结构 | 1.0 | pyuppaal接口升级 - - [X] pyuppaal.load(model_path: str) -> UModel
- [X] Verifyta的接口全部暴露给pyuppaal,比如
- [X] pyuppaal.set_verifyta_path()
- [X] pyuppaal.simple_verify()
- [X] pyuppaal.cmds()等
- [X] pyuppaal.get_communication_graph()
- [X] 升级后的文档结构 | non_priority | pyuppaal接口升级 pyuppaal load model path str umodel verifyta的接口全部暴露给pyuppaal,比如 pyuppaal set verifyta path pyuppaal simple verify pyuppaal cmds 等 pyuppaal get communication graph 升级后的文档结构 | 0 |
17,063 | 22,500,934,572 | IssuesEvent | 2022-06-23 11:46:31 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | closed | Update vulnerable versions of Go, Netty and Spring for 1.3.8 | kind/toil support area/security team/distributed team/process-automation release/1.3.9 | **Description**
According to Snyk, Zeebe 1.3.8 uses:
- io.netty:netty-common 4.1.72.Final -> CVE-2022-24823, CWE-200, CWE-378 :heavy_check_mark:
- org.springframework:spring-beans 5.3.18 -> CVE-2022-22970, CWE-400 :heavy_check_mark:
- org.springframework:spring-context 5.3.18 -> CVE-2022-22968, CWE-178 :heavy_check_mark:
- io.netty:netty-handler 4.1.72.Final -> CWE-295 :heavy_check_mark:
- go 1.15.15 -> CVE-2021-38297, CVE-2022-23806
We should update these versions.
The go update is a bit more involved so we should just backport the upgrade to go 1.17 once that's done: https://github.com/camunda/zeebe/issues/9270
Related support case: https://jira.camunda.com/browse/SUPPORT-13714 | 1.0 | Update vulnerable versions of Go, Netty and Spring for 1.3.8 - **Description**
According to Snyk, Zeebe 1.3.8 uses:
- io.netty:netty-common 4.1.72.Final -> CVE-2022-24823, CWE-200, CWE-378 :heavy_check_mark:
- org.springframework:spring-beans 5.3.18 -> CVE-2022-22970, CWE-400 :heavy_check_mark:
- org.springframework:spring-context 5.3.18 -> CVE-2022-22968, CWE-178 :heavy_check_mark:
- io.netty:netty-handler 4.1.72.Final -> CWE-295 :heavy_check_mark:
- go 1.15.15 -> CVE-2021-38297, CVE-2022-23806
We should update these versions.
The go update is a bit more involved so we should just backport the upgrade to go 1.17 once that's done: https://github.com/camunda/zeebe/issues/9270
Related support case: https://jira.camunda.com/browse/SUPPORT-13714 | non_priority | update vulnerable versions of go netty and spring for description according to snyk zeebe uses io netty netty common final cve cwe cwe heavy check mark org springframework spring beans cve cwe heavy check mark org springframework spring context cve cwe heavy check mark io netty netty handler final cwe heavy check mark go cve cve we should update these versions the go update is a bit more involved so we should just backport the upgrade to go once that s done related support case | 0 |
446,265 | 31,465,995,305 | IssuesEvent | 2023-08-30 02:03:14 | Studio-42/elFinder | https://api.github.com/repos/Studio-42/elFinder | closed | elFinder Anatomy Diagrams | documentation stale | This is just a suggestion to the awesome chief/developers/contributor....
Having visual diagrams (flaw charts) for the elFinder system and the different behaviors would help us better understand the built-in code and how to "programmaticaly" interact with elFinder. For example, having a diagram for the multi-file download user action would help us understand the main functions associated with this task, which will, in turn, help us identify reusable functions to be used in custom codes such as size(), filesize(), countSize(), $userFolderInfo['size'], $this->uploadTotalSize, etc.
I hope to see such resources in the wiki area.
Thank you! | 1.0 | elFinder Anatomy Diagrams - This is just a suggestion to the awesome chief/developers/contributor....
Having visual diagrams (flaw charts) for the elFinder system and the different behaviors would help us better understand the built-in code and how to "programmaticaly" interact with elFinder. For example, having a diagram for the multi-file download user action would help us understand the main functions associated with this task, which will, in turn, help us identify reusable functions to be used in custom codes such as size(), filesize(), countSize(), $userFolderInfo['size'], $this->uploadTotalSize, etc.
I hope to see such resources in the wiki area.
Thank you! | non_priority | elfinder anatomy diagrams this is just a suggestion to the awesome chief developers contributor having visual diagrams flaw charts for the elfinder system and the different behaviors would help us better understand the built in code and how to programmaticaly interact with elfinder for example having a diagram for the multi file download user action would help us understand the main functions associated with this task which will in turn help us identify reusable functions to be used in custom codes such as size filesize countsize userfolderinfo this uploadtotalsize etc i hope to see such resources in the wiki area thank you | 0 |
284,549 | 24,607,533,674 | IssuesEvent | 2022-10-14 17:44:07 | Moonshine-IDE/Moonshine-IDE | https://api.github.com/repos/Moonshine-IDE/Moonshine-IDE | closed | Update Moonshine-Domino-CRUD Template URL | enhancement test ready | I used a temporary URL when we were originally setting up the `Moonshine-Domino-CRUD` template for FormBuilder and DominoVisualEditor:
> https://moonshine-ide.com/downloads/Moonshine-Domino-CRUD/dev/template.zip
I would like to change this before the release (I confirmed this is working now):
> https://moonshine-ide.com/downloads/Moonshine-Domino-CRUD/prod/template.zip
It would be nice if we could automatically use the first URL for the Development build, but this should wait until after the 3.3.3 release.
I'll also need to update this production path with an official version of the zip. I have been doing some test updates for quick fixes. | 1.0 | Update Moonshine-Domino-CRUD Template URL - I used a temporary URL when we were originally setting up the `Moonshine-Domino-CRUD` template for FormBuilder and DominoVisualEditor:
> https://moonshine-ide.com/downloads/Moonshine-Domino-CRUD/dev/template.zip
I would like to change this before the release (I confirmed this is working now):
> https://moonshine-ide.com/downloads/Moonshine-Domino-CRUD/prod/template.zip
It would be nice if we could automatically use the first URL for the Development build, but this should wait until after the 3.3.3 release.
I'll also need to update this production path with an official version of the zip. I have been doing some test updates for quick fixes. | non_priority | update moonshine domino crud template url i used a temporary url when we were originally setting up the moonshine domino crud template for formbuilder and dominovisualeditor i would like to change this before the release i confirmed this is working now it would be nice if we could automatically use the first url for the development build but this should wait until after the release i ll also need to update this production path with an official version of the zip i have been doing some test updates for quick fixes | 0 |
282,687 | 30,889,404,255 | IssuesEvent | 2023-08-04 02:40:23 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | reopened | CVE-2022-1678 (High) detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2022-1678 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/tcp_output.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux Kernel from 4.18 to 4.19, an improper update of sock reference in TCP pacing can lead to memory/netns leak, which can be used by remote clients.
<p>Publish Date: 2022-05-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1678>CVE-2022-1678</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-1678">https://www.linuxkernelcves.com/cves/CVE-2022-1678</a></p>
<p>Release Date: 2022-05-25</p>
<p>Fix Resolution: v4.20-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-1678 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2022-1678 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/tcp_output.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux Kernel from 4.18 to 4.19, an improper update of sock reference in TCP pacing can lead to memory/netns leak, which can be used by remote clients.
<p>Publish Date: 2022-05-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1678>CVE-2022-1678</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-1678">https://www.linuxkernelcves.com/cves/CVE-2022-1678</a></p>
<p>Release Date: 2022-05-25</p>
<p>Fix Resolution: v4.20-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files net tcp output c vulnerability details an issue was discovered in the linux kernel from to an improper update of sock reference in tcp pacing can lead to memory netns leak which can be used by remote clients publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
20,812 | 6,110,222,559 | IssuesEvent | 2017-06-21 14:38:18 | fabric8io/fabric8-ux | https://api.github.com/repos/fabric8io/fabric8-ux | closed | Convert Sass to Less in Platform | code in progress | Convert the existing Sass style structure to Less in order to properly consume PatternFly, as well as restructure the style framework. | 1.0 | Convert Sass to Less in Platform - Convert the existing Sass style structure to Less in order to properly consume PatternFly, as well as restructure the style framework. | non_priority | convert sass to less in platform convert the existing sass style structure to less in order to properly consume patternfly as well as restructure the style framework | 0 |
150 | 2,663,329,629 | IssuesEvent | 2015-03-20 03:54:17 | ventuso/Fi-Test | https://api.github.com/repos/ventuso/Fi-Test | closed | Single Deal added on Merchant web page shows up twice on phone | bug service | Added a single deal on the merchant web page.
When I connect to my merchant through FI and click on DEALS.
The deal I added shows up twice.

| 1.0 | Single Deal added on Merchant web page shows up twice on phone - Added a single deal on the merchant web page.
When I connect to my merchant through FI and click on DEALS.
The deal I added shows up twice.

| non_priority | single deal added on merchant web page shows up twice on phone added a single deal on the merchant web page when i connect to my merchant through fi and click on deals the deal i added shows up twice | 0 |
134,903 | 10,935,228,642 | IssuesEvent | 2019-11-24 16:55:08 | strongbox/strongbox | https://api.github.com/repos/strongbox/strongbox | closed | Integration Tests fail in strongbox-web-core due to message mismatch with non english locale | bug hacktoberfest help wanted in progress testing | # Bug Description
Integration tests in strongbox-web-core fail when run on a system with non english locale.
# Steps To Reproduce
1. Clone repo
2. Set system locale to something other than english (tested on german)
3. Build repo with `mvn clean install -Dintegration.tests`
# Expected Behavior
Tests should not be affected by locale of the building system
# Environment
* Strongbox Version: 1.0-SNAPSHOT
* OS: Windows 10 x64 - German
* Maven version (please provide the full output of `mvn --version`):
`Apache Maven 3.6.1 (d66c9c0b3152b2e69ee9bac180bb8fcc8e6af555; 2019-04-04T21:00:29+02:00)
Maven home: C:\Program Files\JetBrains\IntelliJ IDEA 2019.2\plugins\maven\lib\maven3
Java version: 1.8.0_202, vendor: Oracle Corporation, runtime: C:\Program Files\Java\jre1.8.0_202
Default locale: de_AT, platform encoding: Cp1252
OS name: "windows 10", version: "10.0", arch: "amd64", family: "windows"`
# Proposed Solution
Implement fix similar to [Issue 1466/Pull 1467](https://github.com/strongbox/strongbox/pull/1467)
# Known Workarounds
Change system locale to english
# Useful Links <!-- Remove if unrelated -->
* [Similar Issue](https://github.com/strongbox/strongbox/issues/1466) | 1.0 | Integration Tests fail in strongbox-web-core due to message mismatch with non english locale - # Bug Description
Integration tests in strongbox-web-core fail when run on a system with non english locale.
# Steps To Reproduce
1. Clone repo
2. Set system locale to something other than english (tested on german)
3. Build repo with `mvn clean install -Dintegration.tests`
# Expected Behavior
Tests should not be affected by locale of the building system
# Environment
* Strongbox Version: 1.0-SNAPSHOT
* OS: Windows 10 x64 - German
* Maven version (please provide the full output of `mvn --version`):
`Apache Maven 3.6.1 (d66c9c0b3152b2e69ee9bac180bb8fcc8e6af555; 2019-04-04T21:00:29+02:00)
Maven home: C:\Program Files\JetBrains\IntelliJ IDEA 2019.2\plugins\maven\lib\maven3
Java version: 1.8.0_202, vendor: Oracle Corporation, runtime: C:\Program Files\Java\jre1.8.0_202
Default locale: de_AT, platform encoding: Cp1252
OS name: "windows 10", version: "10.0", arch: "amd64", family: "windows"`
# Proposed Solution
Implement fix similar to [Issue 1466/Pull 1467](https://github.com/strongbox/strongbox/pull/1467)
# Known Workarounds
Change system locale to english
# Useful Links <!-- Remove if unrelated -->
* [Similar Issue](https://github.com/strongbox/strongbox/issues/1466) | non_priority | integration tests fail in strongbox web core due to message mismatch with non english locale bug description integration tests in strongbox web core fail when run on a system with non english locale steps to reproduce clone repo set system locale to something other than english tested on german build repo with mvn clean install dintegration tests expected behavior tests should not be affected by locale of the building system environment strongbox version snapshot os windows german maven version please provide the full output of mvn version apache maven maven home c program files jetbrains intellij idea plugins maven lib java version vendor oracle corporation runtime c program files java default locale de at platform encoding os name windows version arch family windows proposed solution implement fix similar to known workarounds change system locale to english useful links | 0 |
139,744 | 12,879,042,440 | IssuesEvent | 2020-07-11 19:50:02 | sanzoko/twttr-cln | https://api.github.com/repos/sanzoko/twttr-cln | closed | Update readme | documentation | Update the readme with:
- [x] Project description
- [ ] Project spin up instructions | 1.0 | Update readme - Update the readme with:
- [x] Project description
- [ ] Project spin up instructions | non_priority | update readme update the readme with project description project spin up instructions | 0 |
339,574 | 30,456,667,054 | IssuesEvent | 2023-07-17 00:20:11 | ROCmSoftwarePlatform/MIOpen | https://api.github.com/repos/ROCmSoftwarePlatform/MIOpen | closed | Improve tensor operations tests | testing urgency_normal value_unknown | Current implementation of test_tensor_ops has very limited functionality:
- it doesn't allow to specify any tensor sizes
- it doesn't properly check tensors compatibility and may cause crashes for randomly generated cases
- it performs extra data initialization and copy even if verification is disabled
- it doesn't support strides configuration and doesn't perform strides correctness check
Some of the issues were addressed in #2208 but the others have to be fixed to perform proper validation and performance testing of #2221
The main goals are:
- remove hardcoded maximum tensor limitation
- add stride configuration
- fix tensor compatibility and stride configuration checks
- minimize data transfers and initializations for performance validation | 1.0 | Improve tensor operations tests - Current implementation of test_tensor_ops has very limited functionality:
- it doesn't allow to specify any tensor sizes
- it doesn't properly check tensors compatibility and may cause crashes for randomly generated cases
- it performs extra data initialization and copy even if verification is disabled
- it doesn't support strides configuration and doesn't perform strides correctness check
Some of the issues were addressed in #2208 but the others have to be fixed to perform proper validation and performance testing of #2221
The main goals are:
- remove hardcoded maximum tensor limitation
- add stride configuration
- fix tensor compatibility and stride configuration checks
- minimize data transfers and initializations for performance validation | non_priority | improve tensor operations tests current implementation of test tensor ops has very limited functionality it doesn t allow to specify any tensor sizes it doesn t properly check tensors compatibility and may cause crashes for randomly generated cases it performs extra data initialization and copy even if verification is disabled it doesn t support strides configuration and doesn t perform strides correctness check some of the issues were addressed in but the others have to be fixed to perform proper validation and performance testing of the main goals are remove hardcoded maximum tensor limitation add stride configuration fix tensor compatibility and stride configuration checks minimize data transfers and initializations for performance validation | 0 |
149,738 | 19,585,477,713 | IssuesEvent | 2022-01-05 06:01:57 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | On editing custom or default created space the available feature count is not visible for security. | bug Team:Security impact:low v7.17.0 | **Describe the bug:**
On editing custom or default created space the available feature count is not visible for security.
**Build Details:**
VERSION: 7.17.0-SNAPSHOT
BUILD: 46363
COMMIT: 25a4c8fdd78971cf1bed342086bee4fee6d145de
ARTIFACT: https://snapshots.elastic.co/7.17.0-4c03db4e/summary-7.17.0-SNAPSHOT.html
**Preconditions:**
Elastic 7.17.0-SNAPSHOT environment should be deployed.
**Steps to Reproduce:**
1. Navigate to Stack Management under Security app.
2. Go to Spaces under Kibana.
3. Then, edit the default or custom created space.
4. Observe that on editing custom or default created space the available feature count is not visible for security.
**Actual Result:**
On editing custom or default created space the available feature count is not visible for security.
**Expected Result:**
On editing custom or default created space the available feature count should be visible for security.
**What's Working:**
On editing Custom or default created space the available feature count is visible for security on 8.0.0-SNAPSHOT build.
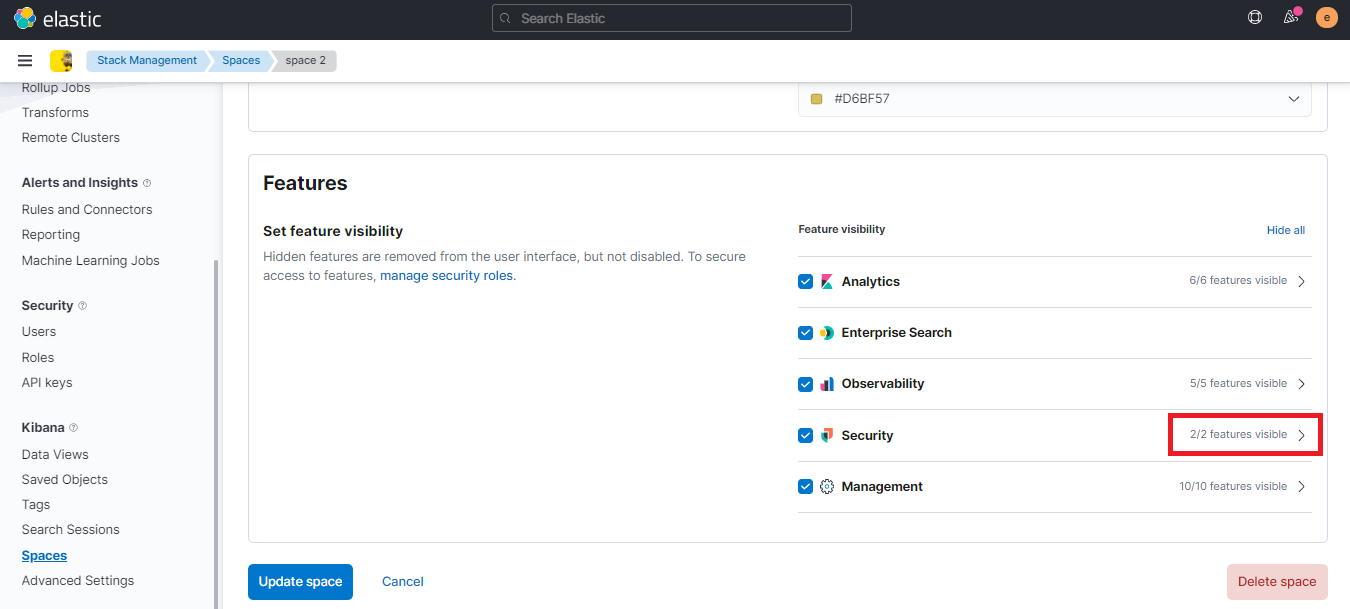
**Screenshot:**
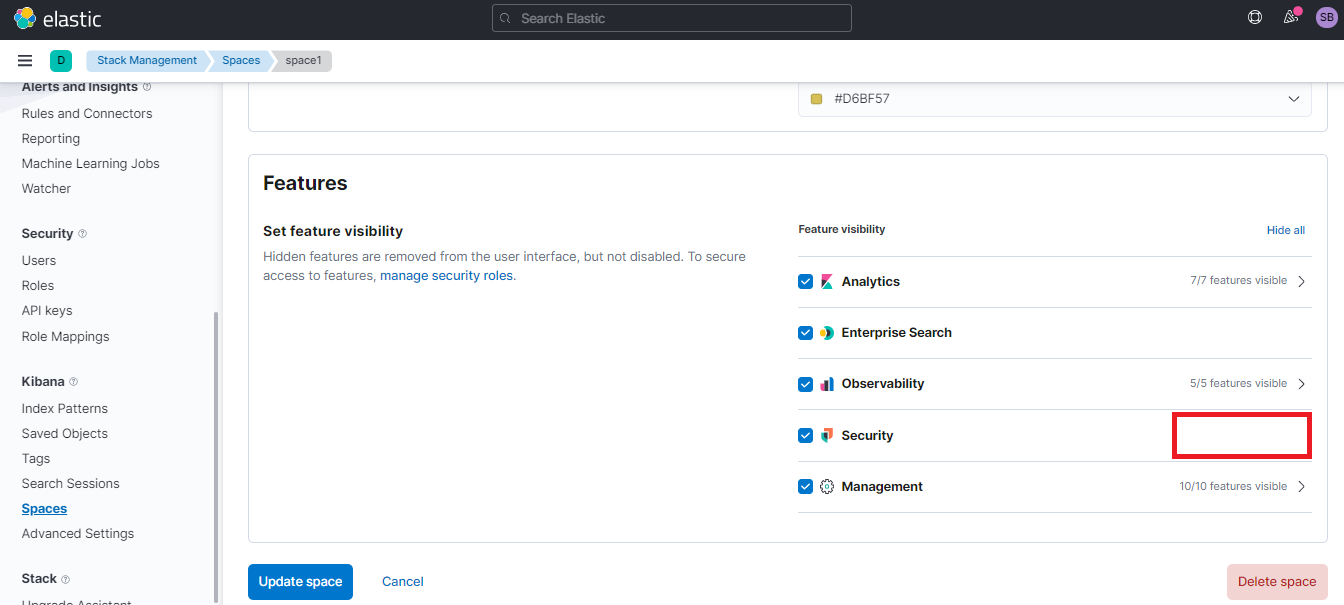
| True | On editing custom or default created space the available feature count is not visible for security. - **Describe the bug:**
On editing custom or default created space the available feature count is not visible for security.
**Build Details:**
VERSION: 7.17.0-SNAPSHOT
BUILD: 46363
COMMIT: 25a4c8fdd78971cf1bed342086bee4fee6d145de
ARTIFACT: https://snapshots.elastic.co/7.17.0-4c03db4e/summary-7.17.0-SNAPSHOT.html
**Preconditions:**
Elastic 7.17.0-SNAPSHOT environment should be deployed.
**Steps to Reproduce:**
1. Navigate to Stack Management under Security app.
2. Go to Spaces under Kibana.
3. Then, edit the default or custom created space.
4. Observe that on editing custom or default created space the available feature count is not visible for security.
**Actual Result:**
On editing custom or default created space the available feature count is not visible for security.
**Expected Result:**
On editing custom or default created space the available feature count should be visible for security.
**What's Working:**
On editing Custom or default created space the available feature count is visible for security on 8.0.0-SNAPSHOT build.
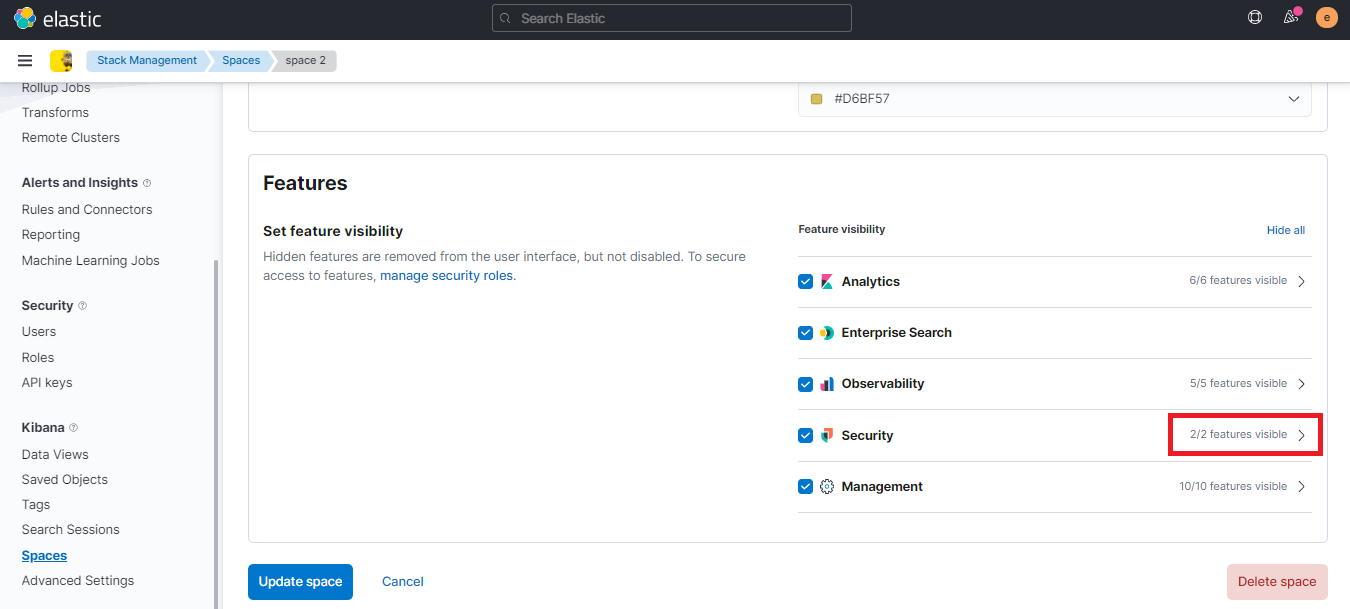
**Screenshot:**
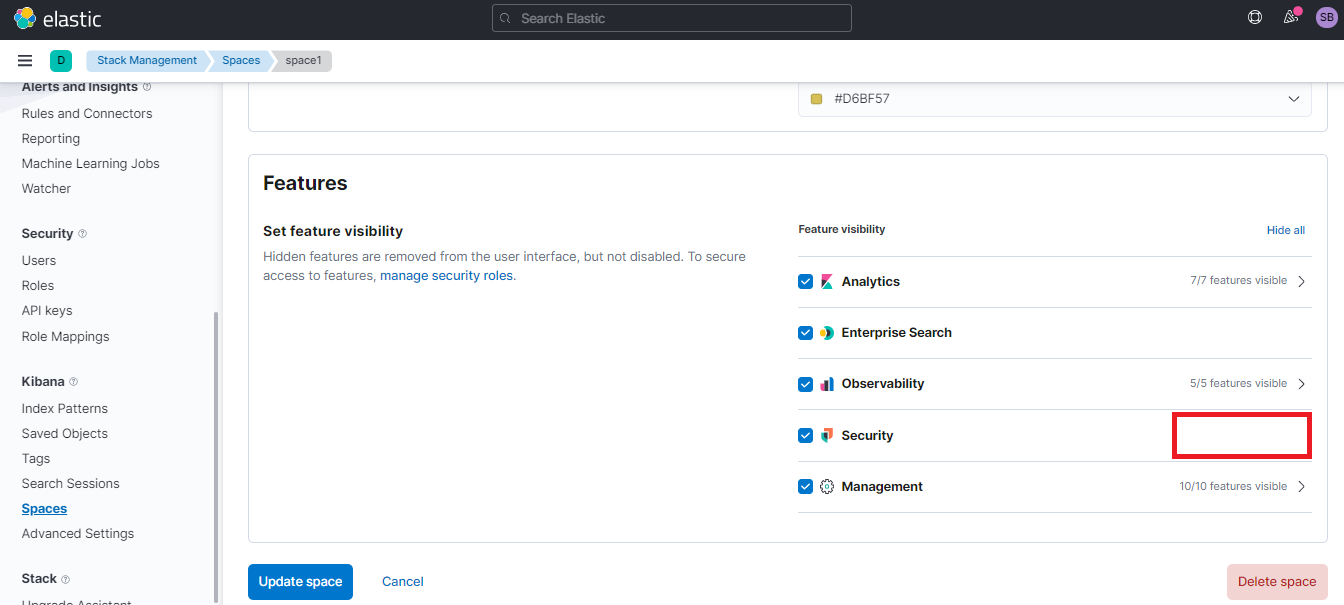
| non_priority | on editing custom or default created space the available feature count is not visible for security describe the bug on editing custom or default created space the available feature count is not visible for security build details version snapshot build commit artifact preconditions elastic snapshot environment should be deployed steps to reproduce navigate to stack management under security app go to spaces under kibana then edit the default or custom created space observe that on editing custom or default created space the available feature count is not visible for security actual result on editing custom or default created space the available feature count is not visible for security expected result on editing custom or default created space the available feature count should be visible for security what s working on editing custom or default created space the available feature count is visible for security on snapshot build screenshot | 0 |
123,815 | 12,219,031,838 | IssuesEvent | 2020-05-01 20:42:38 | SAP/fundamental-ngx | https://api.github.com/repos/SAP/fundamental-ngx | opened | New component docs need updating | bug documentation | #### Is this a bug, enhancement, or feature request?
Bug / docs
#### Briefly describe your proposal.
New component documentation is very dated and irrelevant | 1.0 | New component docs need updating - #### Is this a bug, enhancement, or feature request?
Bug / docs
#### Briefly describe your proposal.
New component documentation is very dated and irrelevant | non_priority | new component docs need updating is this a bug enhancement or feature request bug docs briefly describe your proposal new component documentation is very dated and irrelevant | 0 |
52,214 | 22,091,445,175 | IssuesEvent | 2022-06-01 06:24:20 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | ElastiCache creates/deletes node on every apply | bug service/elasticache service/logs | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* aws_elasticache_replication_group
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
resource "aws_cloudwatch_log_group" "elasticache_log_group" {
provider = aws.org
name = var.elasticache_cluster_id
tags = {
Environment = var.env
Application = "elasticache"
}
}
resource "aws_elasticache_replication_group" "env_elasticache_replication_group" {
provider = aws.org
replication_group_description = "env elasticache replication group"
apply_immediately = true
automatic_failover_enabled = var.multi_az_enabled == true ? true : false
replication_group_id = var.elasticache_cluster_id
multi_az_enabled = var.multi_az_enabled
maintenance_window = var.preferred_maintenance_window
engine_version = var.elasticache_engine_version
node_type = var.elasticache_node_type[var.env]
number_cache_clusters = var.elasticache_node_count[var.env]
parameter_group_name = var.elasticache_parameter_group
port = 6379
security_group_ids = [aws_security_group.env_main_sg.id, aws_security_group.env_internal_ingress_sg.id]
subnet_group_name = aws_elasticache_subnet_group.env_elasticache_subnets.name
log_delivery_configuration {
destination = aws_cloudwatch_log_group.elasticache_log_group.name
destination_type = "cloudwatch-logs"
log_format = "text"
log_type = "slow-log"
}
}
resource "aws_elasticache_subnet_group" "env_elasticache_subnets" {
provider = aws.org
name = "env-elasticache-subnets"
subnet_ids = module.env_vpc.private_subnets
}
resource "aws_elasticache_cluster" "env_elasticache" {
provider = aws.org
cluster_id = var.elasticache_cluster_id
replication_group_id = aws_elasticache_replication_group.env_elasticache_replication_group.id
}
```
### Debug Output
(https://gist.github.com/FarhanSajid1/270183fc55647d1f0e6bec4583d07c85)
### Expected Behavior
The nodes are resized and an additional instance is **not** created
### Actual Behavior
An additional instance is created after the nodes are resized
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. use the terraform template from above, first deploy by setting the instance size to `cache.t2.medium`
2. after that is completed, bump the instance size and re-run
| 2.0 | ElastiCache creates/deletes node on every apply - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* aws_elasticache_replication_group
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
resource "aws_cloudwatch_log_group" "elasticache_log_group" {
provider = aws.org
name = var.elasticache_cluster_id
tags = {
Environment = var.env
Application = "elasticache"
}
}
resource "aws_elasticache_replication_group" "env_elasticache_replication_group" {
provider = aws.org
replication_group_description = "env elasticache replication group"
apply_immediately = true
automatic_failover_enabled = var.multi_az_enabled == true ? true : false
replication_group_id = var.elasticache_cluster_id
multi_az_enabled = var.multi_az_enabled
maintenance_window = var.preferred_maintenance_window
engine_version = var.elasticache_engine_version
node_type = var.elasticache_node_type[var.env]
number_cache_clusters = var.elasticache_node_count[var.env]
parameter_group_name = var.elasticache_parameter_group
port = 6379
security_group_ids = [aws_security_group.env_main_sg.id, aws_security_group.env_internal_ingress_sg.id]
subnet_group_name = aws_elasticache_subnet_group.env_elasticache_subnets.name
log_delivery_configuration {
destination = aws_cloudwatch_log_group.elasticache_log_group.name
destination_type = "cloudwatch-logs"
log_format = "text"
log_type = "slow-log"
}
}
resource "aws_elasticache_subnet_group" "env_elasticache_subnets" {
provider = aws.org
name = "env-elasticache-subnets"
subnet_ids = module.env_vpc.private_subnets
}
resource "aws_elasticache_cluster" "env_elasticache" {
provider = aws.org
cluster_id = var.elasticache_cluster_id
replication_group_id = aws_elasticache_replication_group.env_elasticache_replication_group.id
}
```
### Debug Output
(https://gist.github.com/FarhanSajid1/270183fc55647d1f0e6bec4583d07c85)
### Expected Behavior
The nodes are resized and an additional instance is **not** created
### Actual Behavior
An additional instance is created after the nodes are resized
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. use the terraform template from above, first deploy by setting the instance size to `cache.t2.medium`
2. after that is completed, bump the instance size and re-run
| non_priority | elasticache creates deletes node on every apply community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform cli and terraform aws provider version affected resource s aws elasticache replication group terraform configuration files please include all terraform configurations required to reproduce the bug bug reports without a functional reproduction may be closed without investigation hcl resource aws cloudwatch log group elasticache log group provider aws org name var elasticache cluster id tags environment var env application elasticache resource aws elasticache replication group env elasticache replication group provider aws org replication group description env elasticache replication group apply immediately true automatic failover enabled var multi az enabled true true false replication group id var elasticache cluster id multi az enabled var multi az enabled maintenance window var preferred maintenance window engine version var elasticache engine version node type var elasticache node type number cache clusters var elasticache node count parameter group name var elasticache parameter group port security group ids subnet group name aws elasticache subnet group env elasticache subnets name log delivery configuration destination aws cloudwatch log group elasticache log group name destination type cloudwatch logs log format text log type slow log resource aws elasticache subnet group env elasticache subnets provider aws org name env elasticache subnets subnet ids module env vpc private subnets resource aws elasticache cluster env elasticache provider aws org cluster id var elasticache cluster id replication group id aws elasticache replication group env elasticache replication group id debug output expected behavior the nodes are resized and an additional instance is not created actual behavior an additional instance is created after the nodes are resized steps to reproduce use the terraform template from above first deploy by setting the instance size to cache medium after that is completed bump the instance size and re run | 0 |
273,687 | 29,831,061,640 | IssuesEvent | 2023-06-18 09:25:42 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | closed | CVE-2020-12655 (Medium) detected in linuxv5.2 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-12655 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/xfs/libxfs/xfs_alloc.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/xfs/libxfs/xfs_alloc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in xfs_agf_verify in fs/xfs/libxfs/xfs_alloc.c in the Linux kernel through 5.6.10. Attackers may trigger a sync of excessive duration via an XFS v5 image with crafted metadata, aka CID-d0c7feaf8767.
<p>Publish Date: 2020-05-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-12655>CVE-2020-12655</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12655">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12655</a></p>
<p>Release Date: 2020-05-05</p>
<p>Fix Resolution: v5.7-rc1</p>
</p>
</details>
<p></p>
| True | CVE-2020-12655 (Medium) detected in linuxv5.2 - autoclosed - ## CVE-2020-12655 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/xfs/libxfs/xfs_alloc.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/xfs/libxfs/xfs_alloc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in xfs_agf_verify in fs/xfs/libxfs/xfs_alloc.c in the Linux kernel through 5.6.10. Attackers may trigger a sync of excessive duration via an XFS v5 image with crafted metadata, aka CID-d0c7feaf8767.
<p>Publish Date: 2020-05-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-12655>CVE-2020-12655</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12655">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12655</a></p>
<p>Release Date: 2020-05-05</p>
<p>Fix Resolution: v5.7-rc1</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in base branch amp centos kernel vulnerable source files fs xfs libxfs xfs alloc c fs xfs libxfs xfs alloc c vulnerability details an issue was discovered in xfs agf verify in fs xfs libxfs xfs alloc c in the linux kernel through attackers may trigger a sync of excessive duration via an xfs image with crafted metadata aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
101,230 | 16,495,125,456 | IssuesEvent | 2021-05-25 09:31:24 | AlexRogalskiy/weather-sprites | https://api.github.com/repos/AlexRogalskiy/weather-sprites | opened | CVE-2020-11022 (Medium) detected in jquery-1.9.1.js, jquery-1.8.1.min.js | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.9.1.js</b>, <b>jquery-1.8.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.9.1.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js</a></p>
<p>Path to dependency file: weather-sprites/core/node_modules/tinygradient/bower_components/tinycolor/index.html</p>
<p>Path to vulnerable library: weather-sprites/core/node_modules/tinygradient/bower_components/tinycolor/demo/jquery-1.9.1.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.1.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: weather-sprites/core/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: weather-sprites/core/node_modules/redeyed/examples/browser/index.html,weather-sprites/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/weather-sprites/commit/2ce48a8cabe2336d182640776b31c7d0a3cbef9b">2ce48a8cabe2336d182640776b31c7d0a3cbef9b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11022 (Medium) detected in jquery-1.9.1.js, jquery-1.8.1.min.js - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.9.1.js</b>, <b>jquery-1.8.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.9.1.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js</a></p>
<p>Path to dependency file: weather-sprites/core/node_modules/tinygradient/bower_components/tinycolor/index.html</p>
<p>Path to vulnerable library: weather-sprites/core/node_modules/tinygradient/bower_components/tinycolor/demo/jquery-1.9.1.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.1.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: weather-sprites/core/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: weather-sprites/core/node_modules/redeyed/examples/browser/index.html,weather-sprites/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/weather-sprites/commit/2ce48a8cabe2336d182640776b31c7d0a3cbef9b">2ce48a8cabe2336d182640776b31c7d0a3cbef9b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery js jquery min js cve medium severity vulnerability vulnerable libraries jquery js jquery min js jquery js javascript library for dom operations library home page a href path to dependency file weather sprites core node modules tinygradient bower components tinycolor index html path to vulnerable library weather sprites core node modules tinygradient bower components tinycolor demo jquery js dependency hierarchy x jquery js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file weather sprites core node modules redeyed examples browser index html path to vulnerable library weather sprites core node modules redeyed examples browser index html weather sprites node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
65,592 | 14,740,881,397 | IssuesEvent | 2021-01-07 09:46:13 | hiptest/ember-easy-datatable | https://api.github.com/repos/hiptest/ember-easy-datatable | opened | CVE-2020-15366 (Medium) detected in ajv-4.11.8.tgz | security vulnerability | ## CVE-2020-15366 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ajv-4.11.8.tgz</b></p></summary>
<p>Another JSON Schema Validator</p>
<p>Library home page: <a href="https://registry.npmjs.org/ajv/-/ajv-4.11.8.tgz">https://registry.npmjs.org/ajv/-/ajv-4.11.8.tgz</a></p>
<p>Path to dependency file: ember-easy-datatable/package.json</p>
<p>Path to vulnerable library: ember-easy-datatable/node_modules/ajv/package.json</p>
<p>
Dependency Hierarchy:
- ember-cli-eslint-3.1.0.tgz (Root Library)
- broccoli-lint-eslint-3.3.2.tgz
- eslint-3.19.0.tgz
- table-3.8.3.tgz
- :x: **ajv-4.11.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hiptest/ember-easy-datatable/commit/174fc2ea19b9aaaa080440d9cb938d1e9a2d6120">174fc2ea19b9aaaa080440d9cb938d1e9a2d6120</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in ajv.validate() in Ajv (aka Another JSON Schema Validator) 6.12.2. A carefully crafted JSON schema could be provided that allows execution of other code by prototype pollution. (While untrusted schemas are recommended against, the worst case of an untrusted schema should be a denial of service, not execution of code.)
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15366>CVE-2020-15366</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/ajv-validator/ajv/releases/tag/v6.12.3">https://github.com/ajv-validator/ajv/releases/tag/v6.12.3</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: ajv - 6.12.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ajv","packageVersion":"4.11.8","isTransitiveDependency":true,"dependencyTree":"ember-cli-eslint:3.1.0;broccoli-lint-eslint:3.3.2;eslint:3.19.0;table:3.8.3;ajv:4.11.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ajv - 6.12.3"}],"vulnerabilityIdentifier":"CVE-2020-15366","vulnerabilityDetails":"An issue was discovered in ajv.validate() in Ajv (aka Another JSON Schema Validator) 6.12.2. A carefully crafted JSON schema could be provided that allows execution of other code by prototype pollution. (While untrusted schemas are recommended against, the worst case of an untrusted schema should be a denial of service, not execution of code.)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15366","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-15366 (Medium) detected in ajv-4.11.8.tgz - ## CVE-2020-15366 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ajv-4.11.8.tgz</b></p></summary>
<p>Another JSON Schema Validator</p>
<p>Library home page: <a href="https://registry.npmjs.org/ajv/-/ajv-4.11.8.tgz">https://registry.npmjs.org/ajv/-/ajv-4.11.8.tgz</a></p>
<p>Path to dependency file: ember-easy-datatable/package.json</p>
<p>Path to vulnerable library: ember-easy-datatable/node_modules/ajv/package.json</p>
<p>
Dependency Hierarchy:
- ember-cli-eslint-3.1.0.tgz (Root Library)
- broccoli-lint-eslint-3.3.2.tgz
- eslint-3.19.0.tgz
- table-3.8.3.tgz
- :x: **ajv-4.11.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hiptest/ember-easy-datatable/commit/174fc2ea19b9aaaa080440d9cb938d1e9a2d6120">174fc2ea19b9aaaa080440d9cb938d1e9a2d6120</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in ajv.validate() in Ajv (aka Another JSON Schema Validator) 6.12.2. A carefully crafted JSON schema could be provided that allows execution of other code by prototype pollution. (While untrusted schemas are recommended against, the worst case of an untrusted schema should be a denial of service, not execution of code.)
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15366>CVE-2020-15366</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/ajv-validator/ajv/releases/tag/v6.12.3">https://github.com/ajv-validator/ajv/releases/tag/v6.12.3</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: ajv - 6.12.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ajv","packageVersion":"4.11.8","isTransitiveDependency":true,"dependencyTree":"ember-cli-eslint:3.1.0;broccoli-lint-eslint:3.3.2;eslint:3.19.0;table:3.8.3;ajv:4.11.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ajv - 6.12.3"}],"vulnerabilityIdentifier":"CVE-2020-15366","vulnerabilityDetails":"An issue was discovered in ajv.validate() in Ajv (aka Another JSON Schema Validator) 6.12.2. A carefully crafted JSON schema could be provided that allows execution of other code by prototype pollution. (While untrusted schemas are recommended against, the worst case of an untrusted schema should be a denial of service, not execution of code.)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15366","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in ajv tgz cve medium severity vulnerability vulnerable library ajv tgz another json schema validator library home page a href path to dependency file ember easy datatable package json path to vulnerable library ember easy datatable node modules ajv package json dependency hierarchy ember cli eslint tgz root library broccoli lint eslint tgz eslint tgz table tgz x ajv tgz vulnerable library found in head commit a href found in base branch master vulnerability details an issue was discovered in ajv validate in ajv aka another json schema validator a carefully crafted json schema could be provided that allows execution of other code by prototype pollution while untrusted schemas are recommended against the worst case of an untrusted schema should be a denial of service not execution of code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ajv isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails an issue was discovered in ajv validate in ajv aka another json schema validator a carefully crafted json schema could be provided that allows execution of other code by prototype pollution while untrusted schemas are recommended against the worst case of an untrusted schema should be a denial of service not execution of code vulnerabilityurl | 0 |
15,725 | 19,898,018,202 | IssuesEvent | 2022-01-25 02:50:33 | djcurill/two-wheels | https://api.github.com/repos/djcurill/two-wheels | opened | Post Scrape Data Processing | utility data processing | Create functions for cleaning & formatting data after scraping from the internet. We will need the following:
1. Extract price and convert to CAD
2. Extract brand from title and format
3. Extract model from title and format
4. Extract front travel and convert to number
5. Extract rear travel and convert to number
6. Extract the year of bike from title and format | 1.0 | Post Scrape Data Processing - Create functions for cleaning & formatting data after scraping from the internet. We will need the following:
1. Extract price and convert to CAD
2. Extract brand from title and format
3. Extract model from title and format
4. Extract front travel and convert to number
5. Extract rear travel and convert to number
6. Extract the year of bike from title and format | non_priority | post scrape data processing create functions for cleaning formatting data after scraping from the internet we will need the following extract price and convert to cad extract brand from title and format extract model from title and format extract front travel and convert to number extract rear travel and convert to number extract the year of bike from title and format | 0 |
29,885 | 11,782,219,652 | IssuesEvent | 2020-03-17 01:07:21 | LevyForchh/stat-engine | https://api.github.com/repos/LevyForchh/stat-engine | opened | CVE-2020-7598 (High) detected in minimist-0.0.5.tgz | security vulnerability | ## CVE-2020-7598 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.5.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.5.tgz</a></p>
<p>
Dependency Hierarchy:
- mapbox-gl-0.45.0.tgz (Root Library)
- geojson-rewind-0.3.1.tgz
- sharkdown-0.1.0.tgz
- :x: **minimist-0.0.5.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.5","isTransitiveDependency":true,"dependencyTree":"mapbox-gl:0.45.0;geojson-rewind:0.3.1;sharkdown:0.1.0;minimist:0.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.2"}],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7598 (High) detected in minimist-0.0.5.tgz - ## CVE-2020-7598 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.5.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.5.tgz</a></p>
<p>
Dependency Hierarchy:
- mapbox-gl-0.45.0.tgz (Root Library)
- geojson-rewind-0.3.1.tgz
- sharkdown-0.1.0.tgz
- :x: **minimist-0.0.5.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.5","isTransitiveDependency":true,"dependencyTree":"mapbox-gl:0.45.0;geojson-rewind:0.3.1;sharkdown:0.1.0;minimist:0.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.2"}],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in minimist tgz cve high severity vulnerability vulnerable library minimist tgz parse argument options library home page a href dependency hierarchy mapbox gl tgz root library geojson rewind tgz sharkdown tgz x minimist tgz vulnerable library vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl | 0 |
20,987 | 14,270,540,503 | IssuesEvent | 2020-11-21 07:36:33 | patternfly/patternfly-react | https://api.github.com/repos/patternfly/patternfly-react | closed | Overlapping text in demo previews | bug :bug: infrastructure wontfix | **Describe the issue. What is the expected and unexpected behavior?**
Card View, Master Detail, and Sticky Header Table demos all have overlapping text in their demo previews:
### Card View
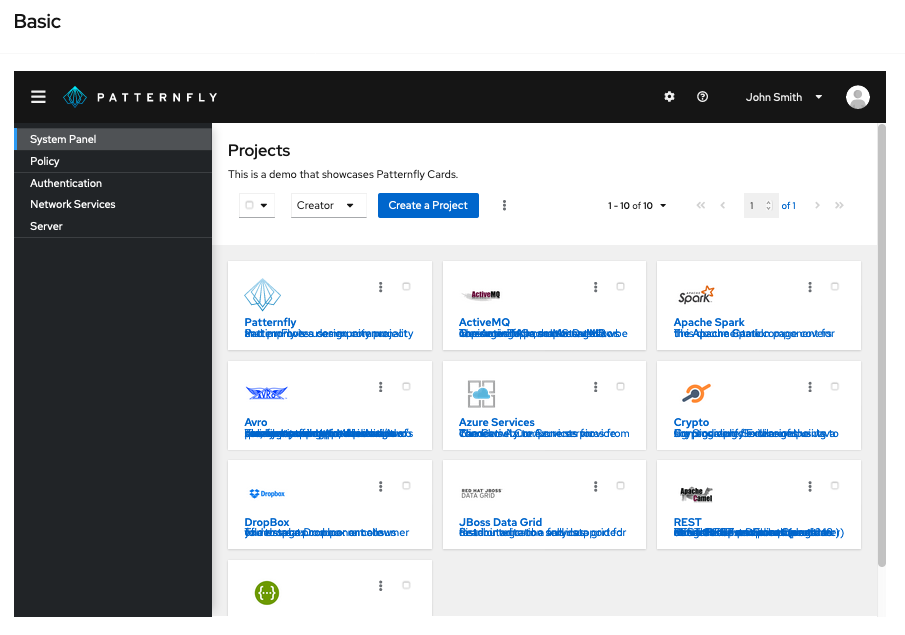
### Master Detail
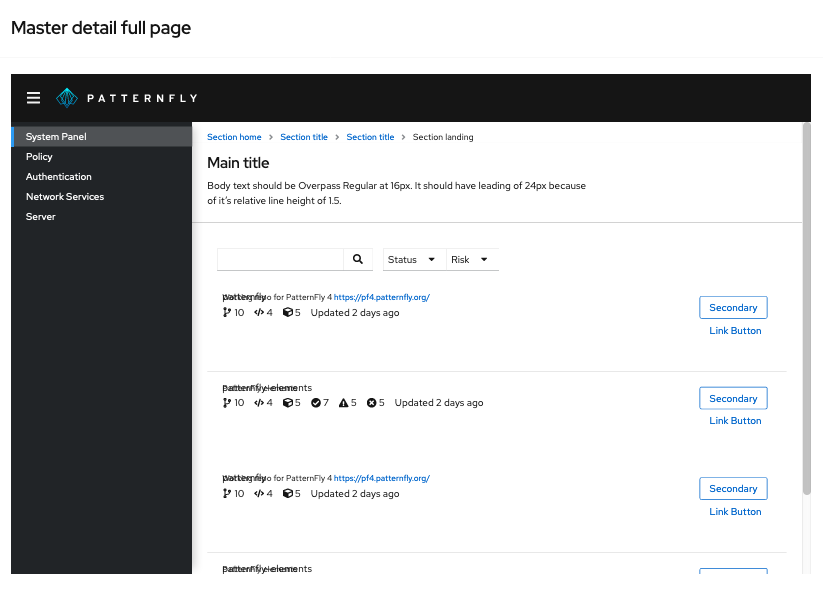
### Sticky Header Table
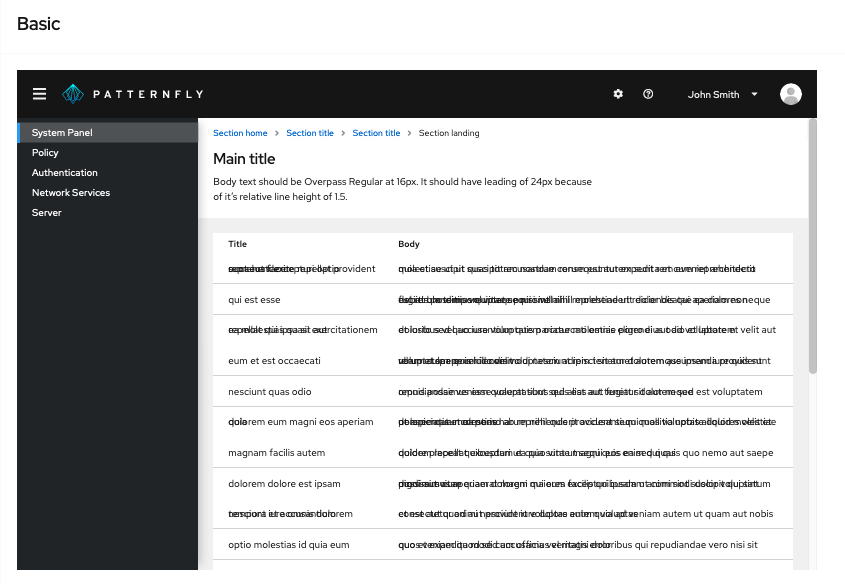
Opening an issue for these three demos per @seanforyou23 's comment here: https://github.com/patternfly/patternfly-react/pull/4417#pullrequestreview-437596180
**Is this a bug or enhancement? If this issue is a bug, is this issue blocking you or is there a work-around?**
bug 🐛
| 1.0 | Overlapping text in demo previews - **Describe the issue. What is the expected and unexpected behavior?**
Card View, Master Detail, and Sticky Header Table demos all have overlapping text in their demo previews:
### Card View
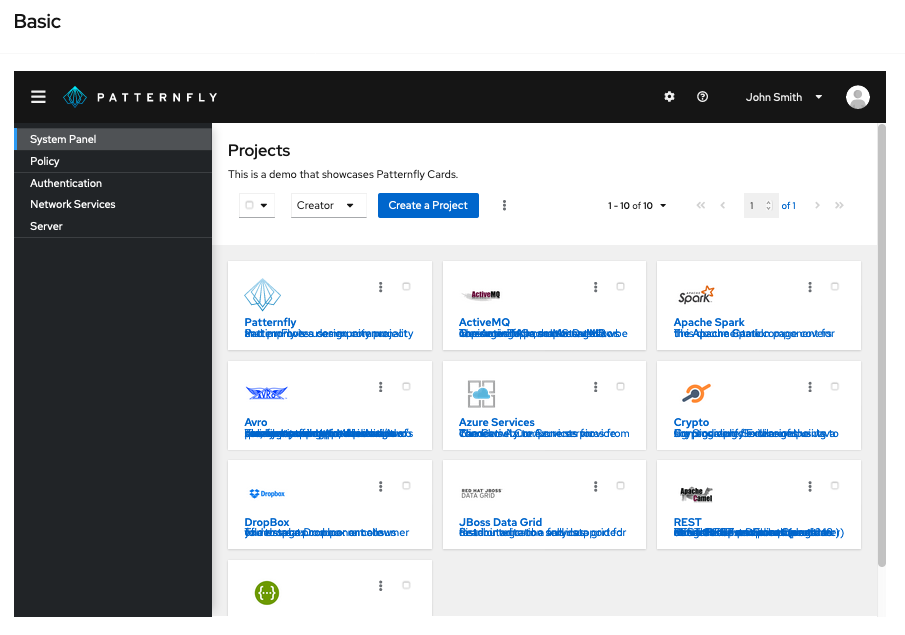
### Master Detail
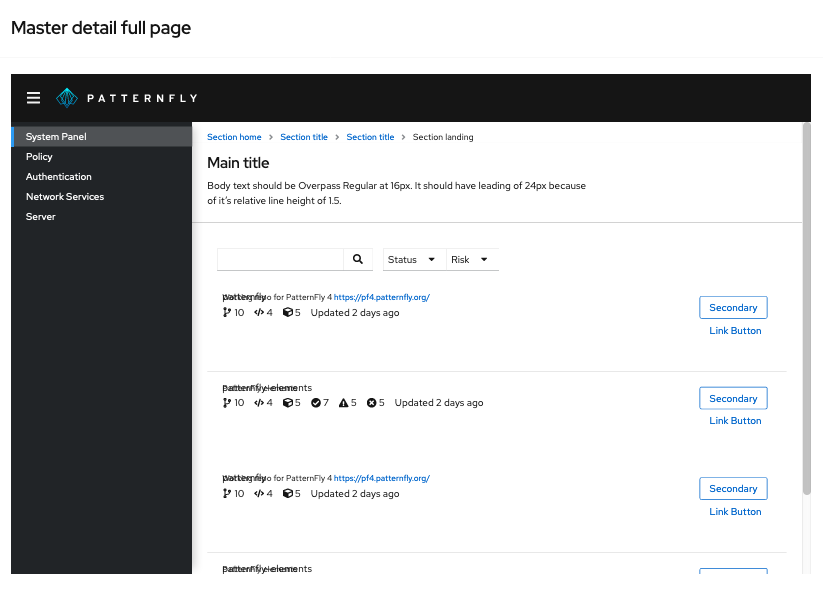
### Sticky Header Table
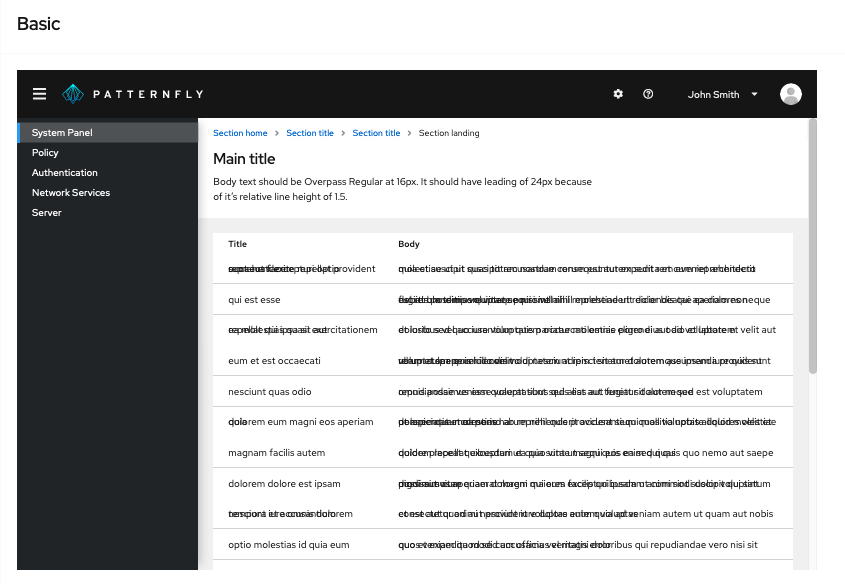
Opening an issue for these three demos per @seanforyou23 's comment here: https://github.com/patternfly/patternfly-react/pull/4417#pullrequestreview-437596180
**Is this a bug or enhancement? If this issue is a bug, is this issue blocking you or is there a work-around?**
bug 🐛
| non_priority | overlapping text in demo previews describe the issue what is the expected and unexpected behavior card view master detail and sticky header table demos all have overlapping text in their demo previews card view master detail sticky header table opening an issue for these three demos per s comment here is this a bug or enhancement if this issue is a bug is this issue blocking you or is there a work around bug 🐛 | 0 |
46,490 | 5,814,910,259 | IssuesEvent | 2017-05-05 06:34:09 | linkedpipes/etl | https://api.github.com/repos/linkedpipes/etl | closed | Excel to CSV: column end incremented | test | The "Column end" option in the Excel to CSV component is incremented by one. For example, when 2 is specified, 3 columns are produced. Pipeline to reproduce the issue is [here](https://github.com/linkedpipes/etl/files/954281/Local.Administrative.Units.LAU.2016-.test.column.end.jsonld.zip).
Tested using the develop version 9050cd725dc037e80aacf50275ac817a843cf82c. | 1.0 | Excel to CSV: column end incremented - The "Column end" option in the Excel to CSV component is incremented by one. For example, when 2 is specified, 3 columns are produced. Pipeline to reproduce the issue is [here](https://github.com/linkedpipes/etl/files/954281/Local.Administrative.Units.LAU.2016-.test.column.end.jsonld.zip).
Tested using the develop version 9050cd725dc037e80aacf50275ac817a843cf82c. | non_priority | excel to csv column end incremented the column end option in the excel to csv component is incremented by one for example when is specified columns are produced pipeline to reproduce the issue is tested using the develop version | 0 |
65,865 | 6,976,822,635 | IssuesEvent | 2017-12-12 12:33:05 | riddlesio/issues | https://api.github.com/repos/riddlesio/issues | closed | Possible disadvantage for opponent when my bot uses too much memory | bug enhancement status:testing | I can't verify whether my memory consumption actually caused this malfunction in my opponent's bot, but it happened around the same time my bot's memory consumption exceeded 200MB:
[game replay](https://starapple.riddles.io/competitions/light-riders/matches/95078e8b-4b3b-4813-a7bc-746547ba99ce)
From my bot's log, on turn 54 it had consumed 22242816 words on the heap (probably about 178MB) and on turn 55 it had consumed 25579520 words (probably about 204MB). On turn 59 my opponent seemed to suffer some sort of error.
It may have been coincidence - maybe my opponent also ran out of memory at about that time, but I thought I should raise it here just in case.
Since seeing this error I've made it clear the old parts of the data structure periodically when it grows too large (previously skipped this to save processing time, because in most games it doesn't manage to exceed 200MB). | 1.0 | Possible disadvantage for opponent when my bot uses too much memory - I can't verify whether my memory consumption actually caused this malfunction in my opponent's bot, but it happened around the same time my bot's memory consumption exceeded 200MB:
[game replay](https://starapple.riddles.io/competitions/light-riders/matches/95078e8b-4b3b-4813-a7bc-746547ba99ce)
From my bot's log, on turn 54 it had consumed 22242816 words on the heap (probably about 178MB) and on turn 55 it had consumed 25579520 words (probably about 204MB). On turn 59 my opponent seemed to suffer some sort of error.
It may have been coincidence - maybe my opponent also ran out of memory at about that time, but I thought I should raise it here just in case.
Since seeing this error I've made it clear the old parts of the data structure periodically when it grows too large (previously skipped this to save processing time, because in most games it doesn't manage to exceed 200MB). | non_priority | possible disadvantage for opponent when my bot uses too much memory i can t verify whether my memory consumption actually caused this malfunction in my opponent s bot but it happened around the same time my bot s memory consumption exceeded from my bot s log on turn it had consumed words on the heap probably about and on turn it had consumed words probably about on turn my opponent seemed to suffer some sort of error it may have been coincidence maybe my opponent also ran out of memory at about that time but i thought i should raise it here just in case since seeing this error i ve made it clear the old parts of the data structure periodically when it grows too large previously skipped this to save processing time because in most games it doesn t manage to exceed | 0 |
447,834 | 31,724,042,734 | IssuesEvent | 2023-09-10 18:39:40 | amityahav/vectory | https://api.github.com/repos/amityahav/vectory | opened | Add examples with real data,vectors | documentation enhancement good first issue | it would be nice to have a real example of vectorized documents inserted to the database and also semantic search them and get results with a decent recall | 1.0 | Add examples with real data,vectors - it would be nice to have a real example of vectorized documents inserted to the database and also semantic search them and get results with a decent recall | non_priority | add examples with real data vectors it would be nice to have a real example of vectorized documents inserted to the database and also semantic search them and get results with a decent recall | 0 |
69,824 | 8,461,529,994 | IssuesEvent | 2018-10-22 22:09:29 | aspnet/AspNetCore | https://api.github.com/repos/aspnet/AspNetCore | closed | Add fallback addresses | needs design repo:Routing | _From @rynowak on Wednesday, September 27, 2017 12:09:01 PM_
We want the dispatchers to be able to work with 'fallback' addresses
This is an address which works like a conventional route - it can generate a URL when no other address matches
_Copied from original issue: aspnet/Routing#458_ | 1.0 | Add fallback addresses - _From @rynowak on Wednesday, September 27, 2017 12:09:01 PM_
We want the dispatchers to be able to work with 'fallback' addresses
This is an address which works like a conventional route - it can generate a URL when no other address matches
_Copied from original issue: aspnet/Routing#458_ | non_priority | add fallback addresses from rynowak on wednesday september pm we want the dispatchers to be able to work with fallback addresses this is an address which works like a conventional route it can generate a url when no other address matches copied from original issue aspnet routing | 0 |
148,033 | 13,223,837,858 | IssuesEvent | 2020-08-17 17:58:52 | LakshyaKhatri/Crime-Count-Bot | https://api.github.com/repos/LakshyaKhatri/Crime-Count-Bot | closed | Roadmap for this Project | documentation enhancement | Here's a basic roadmap for this project:
SLC (Simple Lovable Complete)
---
- [ ] Create a hello world bot and test it locally
- [ ] Write some basic tests and set up a CI pipeline
- [ ] Create a docker image and deploy it on Azure
- [ ] Set up a CD pipeline
Growing The Project
---
- [ ] Update this section for more things | 1.0 | Roadmap for this Project - Here's a basic roadmap for this project:
SLC (Simple Lovable Complete)
---
- [ ] Create a hello world bot and test it locally
- [ ] Write some basic tests and set up a CI pipeline
- [ ] Create a docker image and deploy it on Azure
- [ ] Set up a CD pipeline
Growing The Project
---
- [ ] Update this section for more things | non_priority | roadmap for this project here s a basic roadmap for this project slc simple lovable complete create a hello world bot and test it locally write some basic tests and set up a ci pipeline create a docker image and deploy it on azure set up a cd pipeline growing the project update this section for more things | 0 |
154,231 | 13,542,092,166 | IssuesEvent | 2020-09-16 16:48:13 | Interacao-Humano-Computador/2020.1-UVaJudge | https://api.github.com/repos/Interacao-Humano-Computador/2020.1-UVaJudge | opened | Create meeting minutes | documentation | ## Description
We already had 2 meetings, we need to organize the minutes.
# Tasks
- [ ] Write meeting minutes
- [ ] Put them on the wiki or website, wherever it looks best
- [ ] The same goes for meetings with the professor
| 1.0 | Create meeting minutes - ## Description
We already had 2 meetings, we need to organize the minutes.
# Tasks
- [ ] Write meeting minutes
- [ ] Put them on the wiki or website, wherever it looks best
- [ ] The same goes for meetings with the professor
| non_priority | create meeting minutes description we already had meetings we need to organize the minutes tasks write meeting minutes put them on the wiki or website wherever it looks best the same goes for meetings with the professor | 0 |
32,204 | 7,511,126,856 | IssuesEvent | 2018-04-11 04:51:07 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | reopened | [4.0] com_banners. Drag and drop ordering fails. Undefined method createTagsHelper | No Code Attached Yet | ### Steps to reproduce the issue
- Joomla 4.
- Create 3 or more new banners inside same category.
- Order list by "Ordering" column.

- Reorder banners with drag and drop feature.

- Click "Banners" in left menu to reload current banners list.
==> New ordering is lost:

### Additional comm.
No warnings or errors in developer tools.
| 1.0 | [4.0] com_banners. Drag and drop ordering fails. Undefined method createTagsHelper - ### Steps to reproduce the issue
- Joomla 4.
- Create 3 or more new banners inside same category.
- Order list by "Ordering" column.

- Reorder banners with drag and drop feature.

- Click "Banners" in left menu to reload current banners list.
==> New ordering is lost:

### Additional comm.
No warnings or errors in developer tools.
| non_priority | com banners drag and drop ordering fails undefined method createtagshelper steps to reproduce the issue joomla create or more new banners inside same category order list by ordering column reorder banners with drag and drop feature click banners in left menu to reload current banners list new ordering is lost additional comm no warnings or errors in developer tools | 0 |
154,037 | 24,232,890,917 | IssuesEvent | 2022-09-26 19:58:06 | ethereum/solidity | https://api.github.com/repos/ethereum/solidity | closed | Support for immutable in function parameters | language design :rage4: | ## Abstract
Consider something like EIP-2535 (Diamonds) that allows for swapping out functions for upgrades. This introduces some trust required from the user to make sure functions stay the same as they were before (or at least don't turn malicious). Without immutable as a variable modifier that's hard because every storage or memory variable passed can be modified by it; regardless of if it's needed. I think reducing this possible attack surface could be good for upgradable contracts.
If I'm missing a keyword or solution that does this already, I'd be glad to hear about it.
## Motivation
```sol
function mySwappableCheckFunction(System storage system, uint256 userId) external returns(bool) {
//Do good stuff, we're only reading system here, not modifying
return ...;
}
```
Let's consider the example above, but assume that somehow the owner intentionally or unintentionally swapped out this function for a malicious one;
```sol
function mySwappableCheckFunction(System storage system, uint256 userId) external returns(bool) {
//Do evil stuff, We can do anything we want to system; all members are exposed
return ...;
}
```
This would mean that even though mySwappableCheckFunction only reads from system, it will still maintain the access to it. Meaning that intentionally or not someone can write to it. Marking this as immutable would solve the problem while also adding the nice syntax sugar of not allowing modification to something that you indicated shouldn't be modified.
Solution:
```sol
function mySwappableCheckFunction(System immutable storage system, uint256 userId) external returns(bool) {
//My evil function is now limited, it can only return bad results;
//We can't modify system here, so our exploit surface is limited
return ...;
}
```
## Specification
```sol
// SPDX-License-Identifier: MIT
pragma solidity >=0.8.9;
contract Test {
function test(uint256 immutable myTest) external returns(bool) {
myTest = 1;
return myTest == 0;
}
}
```
Should not compile, while not assigning to myTest should. I'm not sure about the EVM if it should block this access at bytecode level, but I think having support for this at Solidity level is already very nice (since the user can verify generated bytecode with the open source version to see if it has been altered).
## Backwards Compatibility
N/A. Older versions would just remain as they are | 1.0 | Support for immutable in function parameters - ## Abstract
Consider something like EIP-2535 (Diamonds) that allows for swapping out functions for upgrades. This introduces some trust required from the user to make sure functions stay the same as they were before (or at least don't turn malicious). Without immutable as a variable modifier that's hard because every storage or memory variable passed can be modified by it; regardless of if it's needed. I think reducing this possible attack surface could be good for upgradable contracts.
If I'm missing a keyword or solution that does this already, I'd be glad to hear about it.
## Motivation
```sol
function mySwappableCheckFunction(System storage system, uint256 userId) external returns(bool) {
//Do good stuff, we're only reading system here, not modifying
return ...;
}
```
Let's consider the example above, but assume that somehow the owner intentionally or unintentionally swapped out this function for a malicious one;
```sol
function mySwappableCheckFunction(System storage system, uint256 userId) external returns(bool) {
//Do evil stuff, We can do anything we want to system; all members are exposed
return ...;
}
```
This would mean that even though mySwappableCheckFunction only reads from system, it will still maintain the access to it. Meaning that intentionally or not someone can write to it. Marking this as immutable would solve the problem while also adding the nice syntax sugar of not allowing modification to something that you indicated shouldn't be modified.
Solution:
```sol
function mySwappableCheckFunction(System immutable storage system, uint256 userId) external returns(bool) {
//My evil function is now limited, it can only return bad results;
//We can't modify system here, so our exploit surface is limited
return ...;
}
```
## Specification
```sol
// SPDX-License-Identifier: MIT
pragma solidity >=0.8.9;
contract Test {
function test(uint256 immutable myTest) external returns(bool) {
myTest = 1;
return myTest == 0;
}
}
```
Should not compile, while not assigning to myTest should. I'm not sure about the EVM if it should block this access at bytecode level, but I think having support for this at Solidity level is already very nice (since the user can verify generated bytecode with the open source version to see if it has been altered).
## Backwards Compatibility
N/A. Older versions would just remain as they are | non_priority | support for immutable in function parameters abstract consider something like eip diamonds that allows for swapping out functions for upgrades this introduces some trust required from the user to make sure functions stay the same as they were before or at least don t turn malicious without immutable as a variable modifier that s hard because every storage or memory variable passed can be modified by it regardless of if it s needed i think reducing this possible attack surface could be good for upgradable contracts if i m missing a keyword or solution that does this already i d be glad to hear about it motivation sol function myswappablecheckfunction system storage system userid external returns bool do good stuff we re only reading system here not modifying return let s consider the example above but assume that somehow the owner intentionally or unintentionally swapped out this function for a malicious one sol function myswappablecheckfunction system storage system userid external returns bool do evil stuff we can do anything we want to system all members are exposed return this would mean that even though myswappablecheckfunction only reads from system it will still maintain the access to it meaning that intentionally or not someone can write to it marking this as immutable would solve the problem while also adding the nice syntax sugar of not allowing modification to something that you indicated shouldn t be modified solution sol function myswappablecheckfunction system immutable storage system userid external returns bool my evil function is now limited it can only return bad results we can t modify system here so our exploit surface is limited return specification sol spdx license identifier mit pragma solidity contract test function test immutable mytest external returns bool mytest return mytest should not compile while not assigning to mytest should i m not sure about the evm if it should block this access at bytecode level but i think having support for this at solidity level is already very nice since the user can verify generated bytecode with the open source version to see if it has been altered backwards compatibility n a older versions would just remain as they are | 0 |
152,959 | 19,702,050,445 | IssuesEvent | 2022-01-12 17:34:33 | harrinry/serverless-s3-local | https://api.github.com/repos/harrinry/serverless-s3-local | opened | CVE-2021-23337 (High) detected in lodash-4.17.15.tgz | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- eslint-5.16.0.tgz (Root Library)
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/serverless-s3-local/commit/507b173aed811d0cf6803c485e5541679b085b68">507b173aed811d0cf6803c485e5541679b085b68</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.15","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"eslint:5.16.0;lodash:4.17.15","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-23337 (High) detected in lodash-4.17.15.tgz - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- eslint-5.16.0.tgz (Root Library)
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/serverless-s3-local/commit/507b173aed811d0cf6803c485e5541679b085b68">507b173aed811d0cf6803c485e5541679b085b68</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.15","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"eslint:5.16.0;lodash:4.17.15","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in lodash tgz cve high severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file package json path to vulnerable library node modules lodash package json dependency hierarchy eslint tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree eslint lodash isminimumfixversionavailable true minimumfixversion lodash isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to command injection via the template function vulnerabilityurl | 0 |
48,789 | 10,279,259,723 | IssuesEvent | 2019-08-25 21:26:26 | atomist/sdm-pack-aspect | https://api.github.com/repos/atomist/sdm-pack-aspect | closed | Code Inspection: Tslint on build | code-inspection | ### no-floating-promises
- [`lib/analysis/offline/spider/analyzeCommand.ts:164`](https://github.com/atomist/sdm-pack-aspect/blob/6dd267011af706320719df0ef837931412c7e7aa/lib/analysis/offline/spider/analyzeCommand.ts#L164): _(error)_ Promises must be handled appropriately
[atomist:code-inspection:build=@atomist/atomist-sdm] | 1.0 | Code Inspection: Tslint on build - ### no-floating-promises
- [`lib/analysis/offline/spider/analyzeCommand.ts:164`](https://github.com/atomist/sdm-pack-aspect/blob/6dd267011af706320719df0ef837931412c7e7aa/lib/analysis/offline/spider/analyzeCommand.ts#L164): _(error)_ Promises must be handled appropriately
[atomist:code-inspection:build=@atomist/atomist-sdm] | non_priority | code inspection tslint on build no floating promises error promises must be handled appropriately | 0 |
9,563 | 3,293,370,568 | IssuesEvent | 2015-10-30 18:37:13 | coreos/rkt | https://api.github.com/repos/coreos/rkt | closed | docs: expand on actool usage | dependency/appc spec kind/documentation | An "I wish" reported from coreos.com/rkt/docs/latest/getting-started-guide.html
> I wish this page told me how to install actool, because I downloaded a zip folder and don't know what to do next
I'm not sure what the next steps here should be. | 1.0 | docs: expand on actool usage - An "I wish" reported from coreos.com/rkt/docs/latest/getting-started-guide.html
> I wish this page told me how to install actool, because I downloaded a zip folder and don't know what to do next
I'm not sure what the next steps here should be. | non_priority | docs expand on actool usage an i wish reported from coreos com rkt docs latest getting started guide html i wish this page told me how to install actool because i downloaded a zip folder and don t know what to do next i m not sure what the next steps here should be | 0 |
3,387 | 2,761,401,187 | IssuesEvent | 2015-04-28 17:02:14 | Atmosphere/nettosphere | https://api.github.com/repos/Atmosphere/nettosphere | closed | [websocket] Allow TextWebSocketFrame to be passed as binary | 2.3.1 Documentation Enhancement | Right now `TextWebSocketFrame.toString` is always called. We should allow passing the bytes directly to a `WebSocketProcessor` | 1.0 | [websocket] Allow TextWebSocketFrame to be passed as binary - Right now `TextWebSocketFrame.toString` is always called. We should allow passing the bytes directly to a `WebSocketProcessor` | non_priority | allow textwebsocketframe to be passed as binary right now textwebsocketframe tostring is always called we should allow passing the bytes directly to a websocketprocessor | 0 |
14,294 | 8,982,441,263 | IssuesEvent | 2019-01-31 02:06:11 | OctopusDeploy/Issues | https://api.github.com/repos/OctopusDeploy/Issues | closed | Package upload timestamp missing on previous versions dialog | area/modelling area/usability kind/bug | # Prerequisites
- [x] I have verified the problem exists in the latest version
- [x] I have searched [open](https://github.com/OctopusDeploy/Issues/issues) and [closed](https://github.com/OctopusDeploy/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already reported
- [x] I have written a descriptive issue title
- [x] I have linked the original source of this report
- [x] I have tagged the issue appropriately (area/*, kind/bug, tag/regression?)
# The bug
The package upload timestamp and release notes are no longer shown on previous versions dialog when creating a list, when using the built in feed.
## What I expected to happen
The package upload timestamp and release notes should be visible.
## Steps to reproduce
1. Create a project
2. Add a step that uses a package from the built in repository
3. Start to a release for that project
4. Under Packages, click 'select version',
-> publish date should be visible
### Screen capture
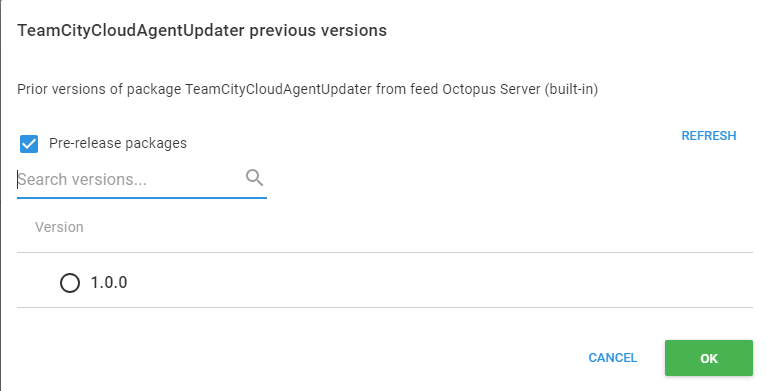
Should be:
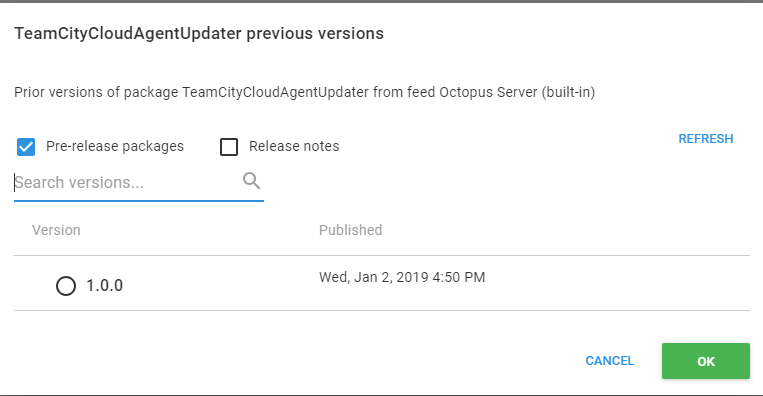
## Affected versions
**Octopus Server:** 2019.1.0 - 2019.1.1
## Workarounds
Nothing good.
## Links
source: [community slack](https://octopususergroup.slack.com/archives/C6UEBB7R9/p1548861962173400) | True | Package upload timestamp missing on previous versions dialog - # Prerequisites
- [x] I have verified the problem exists in the latest version
- [x] I have searched [open](https://github.com/OctopusDeploy/Issues/issues) and [closed](https://github.com/OctopusDeploy/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already reported
- [x] I have written a descriptive issue title
- [x] I have linked the original source of this report
- [x] I have tagged the issue appropriately (area/*, kind/bug, tag/regression?)
# The bug
The package upload timestamp and release notes are no longer shown on previous versions dialog when creating a list, when using the built in feed.
## What I expected to happen
The package upload timestamp and release notes should be visible.
## Steps to reproduce
1. Create a project
2. Add a step that uses a package from the built in repository
3. Start to a release for that project
4. Under Packages, click 'select version',
-> publish date should be visible
### Screen capture
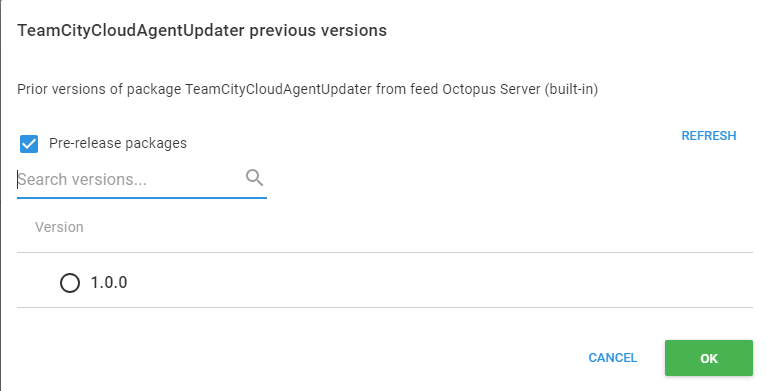
Should be:
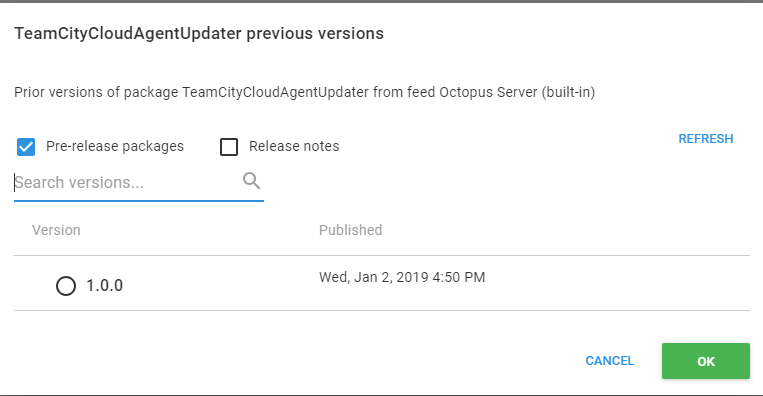
## Affected versions
**Octopus Server:** 2019.1.0 - 2019.1.1
## Workarounds
Nothing good.
## Links
source: [community slack](https://octopususergroup.slack.com/archives/C6UEBB7R9/p1548861962173400) | non_priority | package upload timestamp missing on previous versions dialog prerequisites i have verified the problem exists in the latest version i have searched and issues to make sure it isn t already reported i have written a descriptive issue title i have linked the original source of this report i have tagged the issue appropriately area kind bug tag regression the bug the package upload timestamp and release notes are no longer shown on previous versions dialog when creating a list when using the built in feed what i expected to happen the package upload timestamp and release notes should be visible steps to reproduce create a project add a step that uses a package from the built in repository start to a release for that project under packages click select version publish date should be visible screen capture should be affected versions octopus server workarounds nothing good links source | 0 |
198,615 | 14,988,839,587 | IssuesEvent | 2021-01-29 02:15:26 | zerolab-fe/awesome-nodejs | https://api.github.com/repos/zerolab-fe/awesome-nodejs | closed | chai | Testing | 在👆 Title 处填写包名,并补充下面信息:
```json
{
"repoUrl": "https://github.com/chaijs/chai",
"description": "Chai 是一个针对 Node.js 和浏览器的行为驱动测试和测试驱动测试的诊断库,可与任何 JavaScript 测试框架集成。"
}
```
| 1.0 | chai - 在👆 Title 处填写包名,并补充下面信息:
```json
{
"repoUrl": "https://github.com/chaijs/chai",
"description": "Chai 是一个针对 Node.js 和浏览器的行为驱动测试和测试驱动测试的诊断库,可与任何 JavaScript 测试框架集成。"
}
```
| non_priority | chai 在👆 title 处填写包名,并补充下面信息: json repourl description chai 是一个针对 node js 和浏览器的行为驱动测试和测试驱动测试的诊断库,可与任何 javascript 测试框架集成。 | 0 |
27,609 | 13,324,991,636 | IssuesEvent | 2020-08-27 09:17:04 | PowerShell/vscode-powershell | https://api.github.com/repos/PowerShell/vscode-powershell | closed | Make the progress of searching PS function implement faster | Area-Symbols & References Issue-Performance | First, Thanks to your contributions to this project.
_**The weakness about PowerShell plugin**_
I used this plugin for a long time. I find the progress of searching PS function implement is slow. So, I prefer to use "git grep" to find the implements of functions, it's faster enough than this plugin. The statue is that it's slow and cost lots of memory. When I click the definition of a function, the plugin begin to search, after a long time, it find the implement, but I check my PC station memory usage, the vscode used 30GB, My PC holds 32GB memory totally. I'm not sure that how do you implement this feature which can find a implement. My working repo's disk usage is about 28GB.
**_My idea about how to tackle with this weakness_**
Base on PowerShell SDK, and use syntax analysis tool to build a function implement index **_in advance_**, after this we can find the definition of a function more quickly. 😁 Here is my idea.
The content of example.ps1 file
```powershell
function A { # line 1
} # line 2
# line 3
function B { # line 4
} # line 5
```
And the index will be built like this
```txt
function A, example.ps1:1 # function A at line 1 of example.ps1
function B, example.ps1:4 # function B at line 4 of example.ps1
```
| True | Make the progress of searching PS function implement faster - First, Thanks to your contributions to this project.
_**The weakness about PowerShell plugin**_
I used this plugin for a long time. I find the progress of searching PS function implement is slow. So, I prefer to use "git grep" to find the implements of functions, it's faster enough than this plugin. The statue is that it's slow and cost lots of memory. When I click the definition of a function, the plugin begin to search, after a long time, it find the implement, but I check my PC station memory usage, the vscode used 30GB, My PC holds 32GB memory totally. I'm not sure that how do you implement this feature which can find a implement. My working repo's disk usage is about 28GB.
**_My idea about how to tackle with this weakness_**
Base on PowerShell SDK, and use syntax analysis tool to build a function implement index **_in advance_**, after this we can find the definition of a function more quickly. 😁 Here is my idea.
The content of example.ps1 file
```powershell
function A { # line 1
} # line 2
# line 3
function B { # line 4
} # line 5
```
And the index will be built like this
```txt
function A, example.ps1:1 # function A at line 1 of example.ps1
function B, example.ps1:4 # function B at line 4 of example.ps1
```
| non_priority | make the progress of searching ps function implement faster first thanks to your contributions to this project the weakness about powershell plugin i used this plugin for a long time i find the progress of searching ps function implement is slow so i prefer to use git grep to find the implements of functions it s faster enough than this plugin the statue is that it s slow and cost lots of memory when i click the definition of a function the plugin begin to search after a long time it find the implement but i check my pc station memory usage the vscode used my pc holds memory totally i m not sure that how do you implement this feature which can find a implement my working repo s disk usage is about my idea about how to tackle with this weakness base on powershell sdk and use syntax analysis tool to build a function implement index in advance after this we can find the definition of a function more quickly 😁 here is my idea the content of example file powershell function a line line line function b line line and the index will be built like this txt function a example function a at line of example function b example function b at line of example | 0 |
30,420 | 14,544,297,762 | IssuesEvent | 2020-12-15 17:59:18 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | opened | [Perf, Stress] Exceptions thrown in setup are not logged to console | Central-EngSys Performance Stress | Any exceptions thrown in the setup stages result in the cleanup stages being executed. Most of the time the previous failure results in a new exception being thrown in cleanup.
The output logs this error but it is not useful to understand the real issue.
The test framework should log the first exception thrown in any step that results in a bailout of execution. | True | [Perf, Stress] Exceptions thrown in setup are not logged to console - Any exceptions thrown in the setup stages result in the cleanup stages being executed. Most of the time the previous failure results in a new exception being thrown in cleanup.
The output logs this error but it is not useful to understand the real issue.
The test framework should log the first exception thrown in any step that results in a bailout of execution. | non_priority | exceptions thrown in setup are not logged to console any exceptions thrown in the setup stages result in the cleanup stages being executed most of the time the previous failure results in a new exception being thrown in cleanup the output logs this error but it is not useful to understand the real issue the test framework should log the first exception thrown in any step that results in a bailout of execution | 0 |
1,429 | 10,114,080,659 | IssuesEvent | 2019-07-30 18:18:42 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Clarification requested regarding Onboarding Limitation | assigned-to-author automation/svc doc-enhancement triaged | The documentation above states - "This leaves you with 3 resource groups to select for deployment.". Please clarify what exactly constitutes a deployment?
Is it correct to say, if we have hundreds of VMs in our subscription, all of them MUST be grouped within 3 resource groups in order to enable Change Tracking / Inventory management?
Thanks for your response.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: e55a5e66-a86b-1b40-e3fc-c3c3d8504a90
* Version Independent ID: 1ba2dda1-a573-281c-9ddd-6c74c18bcb16
* Content: [Learn how to onboard Update Management, Change Tracking, and Inventory solutions for multiple VMs in Azure Automation](https://docs.microsoft.com/en-us/azure/automation/automation-onboard-solutions-from-browse#feedback)
* Content Source: [articles/automation/automation-onboard-solutions-from-browse.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/automation-onboard-solutions-from-browse.md)
* Service: **automation**
* GitHub Login: @bobbytreed
* Microsoft Alias: **robreed** | 1.0 | Clarification requested regarding Onboarding Limitation - The documentation above states - "This leaves you with 3 resource groups to select for deployment.". Please clarify what exactly constitutes a deployment?
Is it correct to say, if we have hundreds of VMs in our subscription, all of them MUST be grouped within 3 resource groups in order to enable Change Tracking / Inventory management?
Thanks for your response.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: e55a5e66-a86b-1b40-e3fc-c3c3d8504a90
* Version Independent ID: 1ba2dda1-a573-281c-9ddd-6c74c18bcb16
* Content: [Learn how to onboard Update Management, Change Tracking, and Inventory solutions for multiple VMs in Azure Automation](https://docs.microsoft.com/en-us/azure/automation/automation-onboard-solutions-from-browse#feedback)
* Content Source: [articles/automation/automation-onboard-solutions-from-browse.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/automation-onboard-solutions-from-browse.md)
* Service: **automation**
* GitHub Login: @bobbytreed
* Microsoft Alias: **robreed** | non_priority | clarification requested regarding onboarding limitation the documentation above states this leaves you with resource groups to select for deployment please clarify what exactly constitutes a deployment is it correct to say if we have hundreds of vms in our subscription all of them must be grouped within resource groups in order to enable change tracking inventory management thanks for your response document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service automation github login bobbytreed microsoft alias robreed | 0 |
188,241 | 22,046,248,145 | IssuesEvent | 2022-05-30 02:16:41 | milagan/flask-web-template | https://api.github.com/repos/milagan/flask-web-template | opened | CVE-2019-16784 (High) detected in PyInstaller-3.5.tar.gz | security vulnerability | ## CVE-2019-16784 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyInstaller-3.5.tar.gz</b></p></summary>
<p>PyInstaller bundles a Python application and all its dependencies into a single package.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/e2/c9/0b44b2ea87ba36395483a672fddd07e6a9cb2b8d3c4a28d7ae76c7e7e1e5/PyInstaller-3.5.tar.gz">https://files.pythonhosted.org/packages/e2/c9/0b44b2ea87ba36395483a672fddd07e6a9cb2b8d3c4a28d7ae76c7e7e1e5/PyInstaller-3.5.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /ource-ArchiveExtractor_6351e790-0ee8-444c-855c-b983ee73ef25/20190922212702_88751/20190922212629_depth_0/PyInstaller-3.5.tar/PyInstaller-3.5</p>
<p>
Dependency Hierarchy:
- :x: **PyInstaller-3.5.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In PyInstaller before version 3.6, only on Windows, a local privilege escalation vulnerability is present in this particular case: If a software using PyInstaller in "onefile" mode is launched by a privileged user (at least more than the current one) which have his "TempPath" resolving to a world writable directory. This is the case for example if the software is launched as a service or as a scheduled task using a system account (TempPath will be C:\Windows\Temp). In order to be exploitable the software has to be (re)started after the attacker launch the exploit program, so for a service launched at startup, a service restart is needed (e.g. after a crash or an upgrade).
<p>Publish Date: 2020-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16784>CVE-2019-16784</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/pyinstaller/pyinstaller/security/advisories/GHSA-7fcj-pq9j-wh2r">https://github.com/pyinstaller/pyinstaller/security/advisories/GHSA-7fcj-pq9j-wh2r</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: v3.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-16784 (High) detected in PyInstaller-3.5.tar.gz - ## CVE-2019-16784 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyInstaller-3.5.tar.gz</b></p></summary>
<p>PyInstaller bundles a Python application and all its dependencies into a single package.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/e2/c9/0b44b2ea87ba36395483a672fddd07e6a9cb2b8d3c4a28d7ae76c7e7e1e5/PyInstaller-3.5.tar.gz">https://files.pythonhosted.org/packages/e2/c9/0b44b2ea87ba36395483a672fddd07e6a9cb2b8d3c4a28d7ae76c7e7e1e5/PyInstaller-3.5.tar.gz</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /ource-ArchiveExtractor_6351e790-0ee8-444c-855c-b983ee73ef25/20190922212702_88751/20190922212629_depth_0/PyInstaller-3.5.tar/PyInstaller-3.5</p>
<p>
Dependency Hierarchy:
- :x: **PyInstaller-3.5.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In PyInstaller before version 3.6, only on Windows, a local privilege escalation vulnerability is present in this particular case: If a software using PyInstaller in "onefile" mode is launched by a privileged user (at least more than the current one) which have his "TempPath" resolving to a world writable directory. This is the case for example if the software is launched as a service or as a scheduled task using a system account (TempPath will be C:\Windows\Temp). In order to be exploitable the software has to be (re)started after the attacker launch the exploit program, so for a service launched at startup, a service restart is needed (e.g. after a crash or an upgrade).
<p>Publish Date: 2020-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16784>CVE-2019-16784</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/pyinstaller/pyinstaller/security/advisories/GHSA-7fcj-pq9j-wh2r">https://github.com/pyinstaller/pyinstaller/security/advisories/GHSA-7fcj-pq9j-wh2r</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: v3.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in pyinstaller tar gz cve high severity vulnerability vulnerable library pyinstaller tar gz pyinstaller bundles a python application and all its dependencies into a single package library home page a href path to dependency file requirements txt path to vulnerable library ource archiveextractor depth pyinstaller tar pyinstaller dependency hierarchy x pyinstaller tar gz vulnerable library vulnerability details in pyinstaller before version only on windows a local privilege escalation vulnerability is present in this particular case if a software using pyinstaller in onefile mode is launched by a privileged user at least more than the current one which have his temppath resolving to a world writable directory this is the case for example if the software is launched as a service or as a scheduled task using a system account temppath will be c windows temp in order to be exploitable the software has to be re started after the attacker launch the exploit program so for a service launched at startup a service restart is needed e g after a crash or an upgrade publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
101,226 | 8,782,263,935 | IssuesEvent | 2018-12-19 23:19:51 | angusmoore/arphit | https://api.github.com/repos/angusmoore/arphit | opened | Single argument xlim broken by #213 | bug tests | Need to add tests for single argument xlim. There are none, so the changes in #213 weren't caught as breaking. | 1.0 | Single argument xlim broken by #213 - Need to add tests for single argument xlim. There are none, so the changes in #213 weren't caught as breaking. | non_priority | single argument xlim broken by need to add tests for single argument xlim there are none so the changes in weren t caught as breaking | 0 |
264,751 | 28,212,784,585 | IssuesEvent | 2023-04-05 06:31:21 | hshivhare67/platform_frameworks_av_AOSP10_r33_CVE-2023-20933 | https://api.github.com/repos/hshivhare67/platform_frameworks_av_AOSP10_r33_CVE-2023-20933 | closed | CVE-2021-0520 (High) detected in multiple libraries - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-0520 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>avandroid-10.0.0_r33</b>, <b>avandroid-10.0.0_r33</b>, <b>avandroid-10.0.0_r33</b>, <b>avandroid-10.0.0_r33</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In several functions of MemoryFileSystem.cpp and related files, there is a possible use after free due to a race condition. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-10Android ID: A-176237595
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-0520>CVE-2021-0520</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-06-01">https://source.android.com/security/bulletin/2021-06-01</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution: android-11.0.0_r38</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-0520 (High) detected in multiple libraries - autoclosed - ## CVE-2021-0520 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>avandroid-10.0.0_r33</b>, <b>avandroid-10.0.0_r33</b>, <b>avandroid-10.0.0_r33</b>, <b>avandroid-10.0.0_r33</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In several functions of MemoryFileSystem.cpp and related files, there is a possible use after free due to a race condition. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-10Android ID: A-176237595
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-0520>CVE-2021-0520</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-06-01">https://source.android.com/security/bulletin/2021-06-01</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution: android-11.0.0_r38</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries autoclosed cve high severity vulnerability vulnerable libraries avandroid avandroid avandroid avandroid vulnerability details in several functions of memoryfilesystem cpp and related files there is a possible use after free due to a race condition this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend | 0 |
63,355 | 17,606,158,832 | IssuesEvent | 2021-08-17 17:21:04 | TykTechnologies/tyk-operator | https://api.github.com/repos/TykTechnologies/tyk-operator | closed | 404 not found | defect | Hi,
I've been trying to getting tyk gateway to work but i haven't been successful.
At first, i tried using the API Definitions templates with the Ingress but it worked for some seconds and then puff, it stopped working without me changing anything. Only sending more requests. Not even restarting the pods corrected it.
I have tried with TLS and without TLS, only using API Definitions without the Ingress (templating). and still nothing.
Sometimes it works but then stops working (rarely works).
The errors are mostly 404 Not found errors but sometimes they don't even reach the gateway.
I have the log_level at debug but it isn't helpful.
Does anyone know what is going on with this?
Here goes my files and some screenshots of the API Definitions and such.
Thank you.




| 1.0 | 404 not found - Hi,
I've been trying to getting tyk gateway to work but i haven't been successful.
At first, i tried using the API Definitions templates with the Ingress but it worked for some seconds and then puff, it stopped working without me changing anything. Only sending more requests. Not even restarting the pods corrected it.
I have tried with TLS and without TLS, only using API Definitions without the Ingress (templating). and still nothing.
Sometimes it works but then stops working (rarely works).
The errors are mostly 404 Not found errors but sometimes they don't even reach the gateway.
I have the log_level at debug but it isn't helpful.
Does anyone know what is going on with this?
Here goes my files and some screenshots of the API Definitions and such.
Thank you.




| non_priority | not found hi i ve been trying to getting tyk gateway to work but i haven t been successful at first i tried using the api definitions templates with the ingress but it worked for some seconds and then puff it stopped working without me changing anything only sending more requests not even restarting the pods corrected it i have tried with tls and without tls only using api definitions without the ingress templating and still nothing sometimes it works but then stops working rarely works the errors are mostly not found errors but sometimes they don t even reach the gateway i have the log level at debug but it isn t helpful does anyone know what is going on with this here goes my files and some screenshots of the api definitions and such thank you | 0 |
42,240 | 12,883,943,787 | IssuesEvent | 2020-07-13 01:02:22 | Mohib-hub/sample-app-web | https://api.github.com/repos/Mohib-hub/sample-app-web | opened | CVE-2020-7693 (Medium) detected in sockjs-0.3.19.tgz | security vulnerability | ## CVE-2020-7693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sockjs-0.3.19.tgz</b></p></summary>
<p>SockJS-node is a server counterpart of SockJS-client a JavaScript library that provides a WebSocket-like object in the browser. SockJS gives you a coherent, cross-browser, Javascript API which creates a low latency, full duplex, cross-domain communication</p>
<p>Library home page: <a href="https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz">https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/sample-app-web/Local/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/sample-app-web/Local/node_modules/sockjs/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-3.10.3.tgz (Root Library)
- :x: **sockjs-0.3.19.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693>CVE-2020-7693</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sockjs/sockjs-node/pull/265">https://github.com/sockjs/sockjs-node/pull/265</a></p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution: sockjs - 0.3.20</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"sockjs","packageVersion":"0.3.19","isTransitiveDependency":true,"dependencyTree":"webpack-dev-server:3.10.3;sockjs:0.3.19","isMinimumFixVersionAvailable":true,"minimumFixVersion":"sockjs - 0.3.20"}],"vulnerabilityIdentifier":"CVE-2020-7693","vulnerabilityDetails":"Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7693 (Medium) detected in sockjs-0.3.19.tgz - ## CVE-2020-7693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sockjs-0.3.19.tgz</b></p></summary>
<p>SockJS-node is a server counterpart of SockJS-client a JavaScript library that provides a WebSocket-like object in the browser. SockJS gives you a coherent, cross-browser, Javascript API which creates a low latency, full duplex, cross-domain communication</p>
<p>Library home page: <a href="https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz">https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/sample-app-web/Local/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/sample-app-web/Local/node_modules/sockjs/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-3.10.3.tgz (Root Library)
- :x: **sockjs-0.3.19.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693>CVE-2020-7693</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sockjs/sockjs-node/pull/265">https://github.com/sockjs/sockjs-node/pull/265</a></p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution: sockjs - 0.3.20</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"sockjs","packageVersion":"0.3.19","isTransitiveDependency":true,"dependencyTree":"webpack-dev-server:3.10.3;sockjs:0.3.19","isMinimumFixVersionAvailable":true,"minimumFixVersion":"sockjs - 0.3.20"}],"vulnerabilityIdentifier":"CVE-2020-7693","vulnerabilityDetails":"Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in sockjs tgz cve medium severity vulnerability vulnerable library sockjs tgz sockjs node is a server counterpart of sockjs client a javascript library that provides a websocket like object in the browser sockjs gives you a coherent cross browser javascript api which creates a low latency full duplex cross domain communication library home page a href path to dependency file tmp ws scm sample app web local package json path to vulnerable library tmp ws scm sample app web local node modules sockjs package json dependency hierarchy webpack dev server tgz root library x sockjs tgz vulnerable library vulnerability details incorrect handling of upgrade header with the value websocket leads in crashing of containers hosting sockjs apps this affects the package sockjs before publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution sockjs isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails incorrect handling of upgrade header with the value websocket leads in crashing of containers hosting sockjs apps this affects the package sockjs before vulnerabilityurl | 0 |
194,662 | 15,437,384,344 | IssuesEvent | 2021-03-07 16:30:32 | joselitofilho/ginkgoTestExplorer | https://api.github.com/repos/joselitofilho/ginkgoTestExplorer | closed | Update the features of our extension on the README.md file. | documentation | ### Description
Create a new section on the [README.md](https://github.com/joselitofilho/ginkgoTestExplorer/blob/main/README.md) file to specify the features of our extension:
- Generate gifs or images.
- Write a summary about the feature. | 1.0 | Update the features of our extension on the README.md file. - ### Description
Create a new section on the [README.md](https://github.com/joselitofilho/ginkgoTestExplorer/blob/main/README.md) file to specify the features of our extension:
- Generate gifs or images.
- Write a summary about the feature. | non_priority | update the features of our extension on the readme md file description create a new section on the file to specify the features of our extension generate gifs or images write a summary about the feature | 0 |
301,481 | 26,052,213,492 | IssuesEvent | 2022-12-22 20:00:43 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | closed | [Schema Registry]Deploy test resources failing in nightly runs | Client Schema Registry test-reliability | Schema Registry nightly test runs are failing with:
> Error message:
> Retry : Exception calling "Invoke" with "0" argument(s): "The running command stopped because the preference variable "ErrorActionPreference" or common parameter is set to Stop: 4:44:39 AM - The deployment 't9332dac163b4402f' failed with error(s). Showing 2 out of 2 error(s).
> Status Message: Custom schema type is only supported with API version 2022-10 or later. TrackingId:f513cb55-640e-4096-8bfc-223aa4964f2a_M6SN1_M6SN1_G13, SystemTracker:t9332dac163b4402f-custom.servicebus.windows.net:$schemagroups/azsdk_js_test_group, Timestamp:2022-12-16T04:44:30 CorrelationId: 689606e6-63b2-487b-96e0-6ed033c39e0f (Code:UnsupportedMediaType)
> Status Message: Json schema type is only supported with API version 2022-10 or later. TrackingId:bfa82bf4-a3ac-400d-946f-ff4e4eca8ac1_M11SN1_M11SN1_G4, SystemTracker:t9332dac163b4402f-json.servicebus.windows.net:$schemagroups/azsdk_js_test_group, Timestamp:2022-12-16T04:44:30 CorrelationId: 689606e6-63b2-487b-96e0-6ed033c39e0f (Code:UnsupportedMediaType)
> CorrelationId: 689606e6-63b2-487b-96e0-6ed033c39e0f"
> At D:\a\_work\1\s\eng\common\TestResources\New-TestResources.ps1:736 char:23
> $deployment = Retry {
> ~~~~~~~
> CategoryInfo : NotSpecified: (:) [Write-Error], MethodInvocationException
> FullyQualifiedErrorId : ActionPreferenceStopException,Retry
> ##[error]PowerShell exited with code '1'.
For more details check here:
https://dev.azure.com/azure-sdk/internal/_build/results?buildId=2060427&view=results | 1.0 | [Schema Registry]Deploy test resources failing in nightly runs - Schema Registry nightly test runs are failing with:
> Error message:
> Retry : Exception calling "Invoke" with "0" argument(s): "The running command stopped because the preference variable "ErrorActionPreference" or common parameter is set to Stop: 4:44:39 AM - The deployment 't9332dac163b4402f' failed with error(s). Showing 2 out of 2 error(s).
> Status Message: Custom schema type is only supported with API version 2022-10 or later. TrackingId:f513cb55-640e-4096-8bfc-223aa4964f2a_M6SN1_M6SN1_G13, SystemTracker:t9332dac163b4402f-custom.servicebus.windows.net:$schemagroups/azsdk_js_test_group, Timestamp:2022-12-16T04:44:30 CorrelationId: 689606e6-63b2-487b-96e0-6ed033c39e0f (Code:UnsupportedMediaType)
> Status Message: Json schema type is only supported with API version 2022-10 or later. TrackingId:bfa82bf4-a3ac-400d-946f-ff4e4eca8ac1_M11SN1_M11SN1_G4, SystemTracker:t9332dac163b4402f-json.servicebus.windows.net:$schemagroups/azsdk_js_test_group, Timestamp:2022-12-16T04:44:30 CorrelationId: 689606e6-63b2-487b-96e0-6ed033c39e0f (Code:UnsupportedMediaType)
> CorrelationId: 689606e6-63b2-487b-96e0-6ed033c39e0f"
> At D:\a\_work\1\s\eng\common\TestResources\New-TestResources.ps1:736 char:23
> $deployment = Retry {
> ~~~~~~~
> CategoryInfo : NotSpecified: (:) [Write-Error], MethodInvocationException
> FullyQualifiedErrorId : ActionPreferenceStopException,Retry
> ##[error]PowerShell exited with code '1'.
For more details check here:
https://dev.azure.com/azure-sdk/internal/_build/results?buildId=2060427&view=results | non_priority | deploy test resources failing in nightly runs schema registry nightly test runs are failing with error message retry exception calling invoke with argument s the running command stopped because the preference variable erroractionpreference or common parameter is set to stop am the deployment failed with error s showing out of error s status message custom schema type is only supported with api version or later trackingid systemtracker custom servicebus windows net schemagroups azsdk js test group timestamp correlationid code unsupportedmediatype status message json schema type is only supported with api version or later trackingid systemtracker json servicebus windows net schemagroups azsdk js test group timestamp correlationid code unsupportedmediatype correlationid at d a work s eng common testresources new testresources char deployment retry categoryinfo notspecified methodinvocationexception fullyqualifiederrorid actionpreferencestopexception retry powershell exited with code for more details check here | 0 |
367,278 | 25,730,722,802 | IssuesEvent | 2022-12-07 20:05:20 | neondatabase/website | https://api.github.com/repos/neondatabase/website | closed | Move project data size content | a/documentation | Move the information about checking the project data size out of the Technical Preview Free Tier topic. This content should be moved to a section about managing projects. | 1.0 | Move project data size content - Move the information about checking the project data size out of the Technical Preview Free Tier topic. This content should be moved to a section about managing projects. | non_priority | move project data size content move the information about checking the project data size out of the technical preview free tier topic this content should be moved to a section about managing projects | 0 |
297,335 | 22,350,913,341 | IssuesEvent | 2022-06-15 11:59:39 | PlasmoHQ/plasmo | https://api.github.com/repos/PlasmoHQ/plasmo | opened | EXP | with-react-router | documentation good first issue | ### What is the example you wish to see?
This is a good first issue if you want to contribute to our framework!
[React Router](https://github.com/remix-run/react-router) is required for React apps that span multiple pages.
### Is there any context that might help us understand?
This would be a highly impactful addition to the examples.
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
- [X] I checked the [current issues](https://github.com/PlasmoHQ/plasmo/issues) for duplicate problems. | 1.0 | EXP | with-react-router - ### What is the example you wish to see?
This is a good first issue if you want to contribute to our framework!
[React Router](https://github.com/remix-run/react-router) is required for React apps that span multiple pages.
### Is there any context that might help us understand?
This would be a highly impactful addition to the examples.
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
- [X] I checked the [current issues](https://github.com/PlasmoHQ/plasmo/issues) for duplicate problems. | non_priority | exp with react router what is the example you wish to see this is a good first issue if you want to contribute to our framework is required for react apps that span multiple pages is there any context that might help us understand this would be a highly impactful addition to the examples code of conduct i agree to follow this project s code of conduct i checked the for duplicate problems | 0 |
427,953 | 29,872,555,700 | IssuesEvent | 2023-06-20 09:25:54 | microsoft/fluentui | https://api.github.com/repos/microsoft/fluentui | closed | [Docs]: Add an example of Dialog usage without DialogTrigger | Area: Documentation Component: Dialog Status: In PR Fluent UI react-components (v9) | ### Library
React Components / v9 (@fluentui/react-components)
### Describe the feature that you would like added
- `DialogTrigger` manages focus handling (restoration) when a `Dialog` gets closed
- `Dialog` can be used without triggers
- We need a documentation example for that case (#27914)
### Have you discussed this feature with our team
N/A
### Additional context
_No response_
### Validations
- [X] Check that there isn't already an issue that request the same feature to avoid creating a duplicate. | 1.0 | [Docs]: Add an example of Dialog usage without DialogTrigger - ### Library
React Components / v9 (@fluentui/react-components)
### Describe the feature that you would like added
- `DialogTrigger` manages focus handling (restoration) when a `Dialog` gets closed
- `Dialog` can be used without triggers
- We need a documentation example for that case (#27914)
### Have you discussed this feature with our team
N/A
### Additional context
_No response_
### Validations
- [X] Check that there isn't already an issue that request the same feature to avoid creating a duplicate. | non_priority | add an example of dialog usage without dialogtrigger library react components fluentui react components describe the feature that you would like added dialogtrigger manages focus handling restoration when a dialog gets closed dialog can be used without triggers we need a documentation example for that case have you discussed this feature with our team n a additional context no response validations check that there isn t already an issue that request the same feature to avoid creating a duplicate | 0 |
132,383 | 12,506,044,744 | IssuesEvent | 2020-06-02 11:53:09 | s-gbz/meme-scout-25 | https://api.github.com/repos/s-gbz/meme-scout-25 | opened | README verschönern & updaten | documentation task | - [ ] Kurze Einleitung/ Vorstellung für Nutzer erstellen
- [ ] Mockups/ Screenshots einpflegen
- [ ] Verwendete Technologien updaten | 1.0 | README verschönern & updaten - - [ ] Kurze Einleitung/ Vorstellung für Nutzer erstellen
- [ ] Mockups/ Screenshots einpflegen
- [ ] Verwendete Technologien updaten | non_priority | readme verschönern updaten kurze einleitung vorstellung für nutzer erstellen mockups screenshots einpflegen verwendete technologien updaten | 0 |
116,247 | 24,885,820,938 | IssuesEvent | 2022-10-28 07:40:36 | roanlinde/nodegoat | https://api.github.com/repos/roanlinde/nodegoat | opened | CVE: 2019-20920 found in handlebars - Version: 4.0.5 [JS] | Severity: High Veracode Dependency Scanning | Veracode Software Composition Analysis
===============================
Attribute | Details
| --- | --- |
Library | handlebars
Description | Handlebars provides the power necessary to let you build semantic templates effectively with no frustration
Language | JS
Vulnerability | Arbitrary Code Execution
Vulnerability description | handlebars is vulnerable to arbitrary code execution. The lookup helper does not properly validate templates, allowing the execution of JavaScript code in templates. This vulnerability exists due to an incomplete fix for https://www.sourceclear.com/vulnerability-database/security/arbitrary-code-execution/javascript/sid-21954/summary.
CVE | 2019-20920
CVSS score | 6.8
Vulnerability present in version/s | 4.0.0-4.5.2
Found library version/s | 4.0.5
Vulnerability fixed in version | 4.5.3
Library latest version | 4.7.7
Fix |
Links:
- https://sca.analysiscenter.veracode.com/vulnerability-database/libraries/2710?version=4.0.5
- https://sca.analysiscenter.veracode.com/vulnerability-database/vulnerabilities/21989
- Patch: https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7 | 1.0 | CVE: 2019-20920 found in handlebars - Version: 4.0.5 [JS] - Veracode Software Composition Analysis
===============================
Attribute | Details
| --- | --- |
Library | handlebars
Description | Handlebars provides the power necessary to let you build semantic templates effectively with no frustration
Language | JS
Vulnerability | Arbitrary Code Execution
Vulnerability description | handlebars is vulnerable to arbitrary code execution. The lookup helper does not properly validate templates, allowing the execution of JavaScript code in templates. This vulnerability exists due to an incomplete fix for https://www.sourceclear.com/vulnerability-database/security/arbitrary-code-execution/javascript/sid-21954/summary.
CVE | 2019-20920
CVSS score | 6.8
Vulnerability present in version/s | 4.0.0-4.5.2
Found library version/s | 4.0.5
Vulnerability fixed in version | 4.5.3
Library latest version | 4.7.7
Fix |
Links:
- https://sca.analysiscenter.veracode.com/vulnerability-database/libraries/2710?version=4.0.5
- https://sca.analysiscenter.veracode.com/vulnerability-database/vulnerabilities/21989
- Patch: https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7 | non_priority | cve found in handlebars version veracode software composition analysis attribute details library handlebars description handlebars provides the power necessary to let you build semantic templates effectively with no frustration language js vulnerability arbitrary code execution vulnerability description handlebars is vulnerable to arbitrary code execution the lookup helper does not properly validate templates allowing the execution of javascript code in templates this vulnerability exists due to an incomplete fix for cve cvss score vulnerability present in version s found library version s vulnerability fixed in version library latest version fix links patch | 0 |
49,143 | 20,618,471,557 | IssuesEvent | 2022-03-07 15:18:26 | gradido/gradido | https://api.github.com/repos/gradido/gradido | closed | 🐛 [Bug] updateUserInfos allows unsecure password | bug service: login server service: backend | ## 🐛 Bugreport
<!-- Describe your issue in detail. Include screenshots if needed. Give us as much information as possible. Use a clear and concise description of what the bug is.-->
`updateUserInfos` allows unsecure password. When using the password change feature in the user profile, the user can, due to missing client side validation, send unsecure passwords like `123` as password change request to the backend. The unsecure password is accepted. | 2.0 | 🐛 [Bug] updateUserInfos allows unsecure password - ## 🐛 Bugreport
<!-- Describe your issue in detail. Include screenshots if needed. Give us as much information as possible. Use a clear and concise description of what the bug is.-->
`updateUserInfos` allows unsecure password. When using the password change feature in the user profile, the user can, due to missing client side validation, send unsecure passwords like `123` as password change request to the backend. The unsecure password is accepted. | non_priority | 🐛 updateuserinfos allows unsecure password 🐛 bugreport updateuserinfos allows unsecure password when using the password change feature in the user profile the user can due to missing client side validation send unsecure passwords like as password change request to the backend the unsecure password is accepted | 0 |
1,279 | 3,547,912,784 | IssuesEvent | 2016-01-20 12:02:01 | ben-garside/XCP | https://api.github.com/repos/ben-garside/XCP | opened | add re-allocation on item page | requirement | Allow a user to click abutton to reallocate the stream of the item (good for resolving assignment errors). This will alow have to follow to init process; allocate, get data, validate data, collate content. | 1.0 | add re-allocation on item page - Allow a user to click abutton to reallocate the stream of the item (good for resolving assignment errors). This will alow have to follow to init process; allocate, get data, validate data, collate content. | non_priority | add re allocation on item page allow a user to click abutton to reallocate the stream of the item good for resolving assignment errors this will alow have to follow to init process allocate get data validate data collate content | 0 |
73,164 | 15,252,861,600 | IssuesEvent | 2021-02-20 04:59:05 | gate5/struts-2.3.20 | https://api.github.com/repos/gate5/struts-2.3.20 | closed | CVE-2019-8331 (Medium) detected in bootstrap-2.1.1.min.js - autoclosed | security vulnerability | ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-2.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/2.1.1/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/2.1.1/bootstrap.min.js</a></p>
<p>Path to vulnerable library: struts-2.3.20/apps/showcase/src/main/webapp/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-2.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gate5/struts-2.3.20/commit/1d3a9da2b49a075b9122e05e19a483fc66b5aaf4">1d3a9da2b49a075b9122e05e19a483fc66b5aaf4</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
| True | CVE-2019-8331 (Medium) detected in bootstrap-2.1.1.min.js - autoclosed - ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-2.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/2.1.1/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/2.1.1/bootstrap.min.js</a></p>
<p>Path to vulnerable library: struts-2.3.20/apps/showcase/src/main/webapp/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-2.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gate5/struts-2.3.20/commit/1d3a9da2b49a075b9122e05e19a483fc66b5aaf4">1d3a9da2b49a075b9122e05e19a483fc66b5aaf4</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in bootstrap min js autoclosed cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library struts apps showcase src main webapp js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap bootstrap sass | 0 |
89,013 | 25,566,216,568 | IssuesEvent | 2022-11-30 14:29:02 | gitpod-io/gitpod | https://api.github.com/repos/gitpod-io/gitpod | closed | Epic: Require a Gitpod project for prebuilds | feature: prebuilds meta: never-stale team: webapp aspect: cost efficiency type: epic | Now that projects are usable across git providers, Gitpod should limit prebuilds to repos with a project.
- [ ] Check for project before running prebuild
- [ ] Change documentation to explain that prebuilds require a project
- [ ] Post announcement about new prebuild requirement in changelog
| 1.0 | Epic: Require a Gitpod project for prebuilds - Now that projects are usable across git providers, Gitpod should limit prebuilds to repos with a project.
- [ ] Check for project before running prebuild
- [ ] Change documentation to explain that prebuilds require a project
- [ ] Post announcement about new prebuild requirement in changelog
| non_priority | epic require a gitpod project for prebuilds now that projects are usable across git providers gitpod should limit prebuilds to repos with a project check for project before running prebuild change documentation to explain that prebuilds require a project post announcement about new prebuild requirement in changelog | 0 |
233,126 | 17,851,950,655 | IssuesEvent | 2021-09-04 08:25:20 | OPGG-HACKTHON/gameflix | https://api.github.com/repos/OPGG-HACKTHON/gameflix | opened | 사용자 게임 조회 기능 구현 | bug documentation enhancement | - [ ] GET /users/{user-id}/games
- [ ] GET /users/{user-id}/games/{game-slug}
- [ ] swagger 문서 수정 | 1.0 | 사용자 게임 조회 기능 구현 - - [ ] GET /users/{user-id}/games
- [ ] GET /users/{user-id}/games/{game-slug}
- [ ] swagger 문서 수정 | non_priority | 사용자 게임 조회 기능 구현 get users user id games get users user id games game slug swagger 문서 수정 | 0 |
93,123 | 26,867,599,232 | IssuesEvent | 2023-02-04 03:32:52 | trickerer/Trinity-Bots | https://api.github.com/repos/trickerer/Trinity-Bots | closed | [AC] [Crash] [Core] AC update requires NPCBot Changes | bug update request build | **Description:**
https://github.com/azerothcore/azerothcore-wotlk/commit/bf30c66ba48cede909a98cb132959c979c032b3b
AC changed recently `(Unit* /*summoner*/) {}` to `(WorldObject* /*summoner*/) {}`
_I believe_ NPCBots may need to be updated accordingly.
AzerothCore:**
**Current behaviour:**
```
5>D:\azerothcore\src\server\game\AI\NpcBots\bpet_ai.h(36,14): error C3668: 'bot_pet_ai::IsSummonedBy': method with override specifier 'override' did not override any base class methods (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
5>D:\azerothcore\src\server\game\AI\NpcBots\bpet_ai.h(36,14): error C4263: 'void bot_pet_ai::IsSummonedBy(Unit *)': member function does not override any base class virtual member function (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
5>D:\azerothcore\src\server\game\AI\NpcBots\bpet_ai.h(174,1): error C4264: 'void CreatureAI::IsSummonedBy(WorldObject *)': no override available for virtual member function from base 'CreatureAI'; function is hidden (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
3>boss_high_interrogator_gerstahn.cpp
5>D:\azerothcore\src\server\game\AI\CreatureAI.h(129,18): message : see declaration of 'CreatureAI::IsSummonedBy' (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
5>D:\azerothcore\src\server\game\AI\CreatureAI.h(69,7): message : see declaration of 'CreatureAI' (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
```
**Expected behaviour:**
Should be able to compile
**Steps to reproduce the problem:**
1. AC, with NPCBots.patch and latest commit
**TC / AC rev. hash/commit:**
CHANGEME Copy the first line of the `worldserver` or `authserver` startup.
For example: TrinityCore rev. 0000000000 2000-01-09 11:31:41 +0100 (my branch) (Win64, Debug, Static) (worldserver)
**Operating system:** Windows 11
| 1.0 | [AC] [Crash] [Core] AC update requires NPCBot Changes - **Description:**
https://github.com/azerothcore/azerothcore-wotlk/commit/bf30c66ba48cede909a98cb132959c979c032b3b
AC changed recently `(Unit* /*summoner*/) {}` to `(WorldObject* /*summoner*/) {}`
_I believe_ NPCBots may need to be updated accordingly.
AzerothCore:**
**Current behaviour:**
```
5>D:\azerothcore\src\server\game\AI\NpcBots\bpet_ai.h(36,14): error C3668: 'bot_pet_ai::IsSummonedBy': method with override specifier 'override' did not override any base class methods (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
5>D:\azerothcore\src\server\game\AI\NpcBots\bpet_ai.h(36,14): error C4263: 'void bot_pet_ai::IsSummonedBy(Unit *)': member function does not override any base class virtual member function (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
5>D:\azerothcore\src\server\game\AI\NpcBots\bpet_ai.h(174,1): error C4264: 'void CreatureAI::IsSummonedBy(WorldObject *)': no override available for virtual member function from base 'CreatureAI'; function is hidden (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
3>boss_high_interrogator_gerstahn.cpp
5>D:\azerothcore\src\server\game\AI\CreatureAI.h(129,18): message : see declaration of 'CreatureAI::IsSummonedBy' (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
5>D:\azerothcore\src\server\game\AI\CreatureAI.h(69,7): message : see declaration of 'CreatureAI' (compiling source file D:\BUILD STUFF\repos\azerothcore\src\server\game\AI\NpcBots\bpet_hunter.cpp)
```
**Expected behaviour:**
Should be able to compile
**Steps to reproduce the problem:**
1. AC, with NPCBots.patch and latest commit
**TC / AC rev. hash/commit:**
CHANGEME Copy the first line of the `worldserver` or `authserver` startup.
For example: TrinityCore rev. 0000000000 2000-01-09 11:31:41 +0100 (my branch) (Win64, Debug, Static) (worldserver)
**Operating system:** Windows 11
| non_priority | ac update requires npcbot changes description ac changed recently unit summoner to worldobject summoner i believe npcbots may need to be updated accordingly azerothcore current behaviour d azerothcore src server game ai npcbots bpet ai h error bot pet ai issummonedby method with override specifier override did not override any base class methods compiling source file d build stuff repos azerothcore src server game ai npcbots bpet hunter cpp d azerothcore src server game ai npcbots bpet ai h error void bot pet ai issummonedby unit member function does not override any base class virtual member function compiling source file d build stuff repos azerothcore src server game ai npcbots bpet hunter cpp d azerothcore src server game ai npcbots bpet ai h error void creatureai issummonedby worldobject no override available for virtual member function from base creatureai function is hidden compiling source file d build stuff repos azerothcore src server game ai npcbots bpet hunter cpp boss high interrogator gerstahn cpp d azerothcore src server game ai creatureai h message see declaration of creatureai issummonedby compiling source file d build stuff repos azerothcore src server game ai npcbots bpet hunter cpp d azerothcore src server game ai creatureai h message see declaration of creatureai compiling source file d build stuff repos azerothcore src server game ai npcbots bpet hunter cpp expected behaviour should be able to compile steps to reproduce the problem ac with npcbots patch and latest commit tc ac rev hash commit changeme copy the first line of the worldserver or authserver startup for example trinitycore rev my branch debug static worldserver operating system windows | 0 |
8,134 | 7,245,256,895 | IssuesEvent | 2018-02-14 17:28:41 | AdguardTeam/AdguardFilters | https://api.github.com/repos/AdguardTeam/AdguardFilters | closed | Convert ABP #?# syntax | Infrastructure | According to https://adblockplus.org/development-builds/new-syntax-for-advanced-element-hiding-rules, ABP will use `#?#` instead of `##` to distinguish element hiding rules which make use of `-abp-has` and `-abp-properties` pseudo classes.
We need to convert `#?#` to `##`, `-abp-has(...)` to `[-ext-has='...']`, and discard if `-abp-properties` is used. | 1.0 | Convert ABP #?# syntax - According to https://adblockplus.org/development-builds/new-syntax-for-advanced-element-hiding-rules, ABP will use `#?#` instead of `##` to distinguish element hiding rules which make use of `-abp-has` and `-abp-properties` pseudo classes.
We need to convert `#?#` to `##`, `-abp-has(...)` to `[-ext-has='...']`, and discard if `-abp-properties` is used. | non_priority | convert abp syntax according to abp will use instead of to distinguish element hiding rules which make use of abp has and abp properties pseudo classes we need to convert to abp has to and discard if abp properties is used | 0 |
5,480 | 3,930,247,249 | IssuesEvent | 2016-04-25 07:01:59 | kolliSuman/issues | https://api.github.com/repos/kolliSuman/issues | closed | QA_MIPS Assembly Language Programming - 1_Prerequisites_p1 | Category: Usability Developed By: VLEAD Release Number: Production Severity: S2 Status: Open |
Defect Description :
In the "MIPS Assembly Language Programming - 1 " experiment, the minimum requirement to run the experiment is not displayed in the page instead a page or Scrolling should appear providing information on minimum requirement to run this experiment, information like Bandwidth,Device Resolution,Hardware Configuration and Software Required.
Actual Result :
In the "MIPS Assembly Language Programming - 1 " experiment, the minimum requirement to run the experiment is not displayed in the page.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0Bandwidth : 100Mbps
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/computer-organization-iiith/blob/master/test-cases/integration_test-cases/MIPS%20Assembly%20Language%20Programming%20-%201/MIPS%20Assembly%20Language%20Programming%20-%201_23_Prerequisites_p1.org | True | QA_MIPS Assembly Language Programming - 1_Prerequisites_p1 -
Defect Description :
In the "MIPS Assembly Language Programming - 1 " experiment, the minimum requirement to run the experiment is not displayed in the page instead a page or Scrolling should appear providing information on minimum requirement to run this experiment, information like Bandwidth,Device Resolution,Hardware Configuration and Software Required.
Actual Result :
In the "MIPS Assembly Language Programming - 1 " experiment, the minimum requirement to run the experiment is not displayed in the page.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0Bandwidth : 100Mbps
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/computer-organization-iiith/blob/master/test-cases/integration_test-cases/MIPS%20Assembly%20Language%20Programming%20-%201/MIPS%20Assembly%20Language%20Programming%20-%201_23_Prerequisites_p1.org | non_priority | qa mips assembly language programming prerequisites defect description in the mips assembly language programming experiment the minimum requirement to run the experiment is not displayed in the page instead a page or scrolling should appear providing information on minimum requirement to run this experiment information like bandwidth device resolution hardware configuration and software required actual result in the mips assembly language programming experiment the minimum requirement to run the experiment is not displayed in the page environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor test step link | 0 |
21,756 | 3,919,244,228 | IssuesEvent | 2016-04-21 15:08:59 | w3c/html | https://api.github.com/repos/w3c/html | opened | @title should allow LF to render consistently, especially given textarea[title] attribute values. | Needs tests | Moved from Bugzilla: https://www.w3.org/Bugs/Public/show_bug.cgi?id=19899
This might be worth considering, especially if implementations do allow LF in the title attribute. Marked for testing.
>The specification currently states that the attribute, if specified, must have a value that contains no "LF" (U+000A) or "CR" (U+000D) characters.
>
>I would like to request that this restricition is reconsidered for Textarea input fields which, by their nature, are designed to span multiple lines and a placeholder hint to show a user an example of the data to enter should also be able to span multiple lines.
>
>An example of this requirement is where a textarea is used to create a list of items e.g.
>
>```
>Please enter areas of work:
> Area A
> Area B
> Area C
>```
>The specification suggests the alternative use of Title but in most browsers this does not display in as helpful a manner and is, anyway, currently discouraged by the W3C, see:
>
>http://dev.w3.org/html5/spec/global-attributes.html#attr-title
>Relying on the title attribute is currently discouraged as many user agents do not expose the attribute in an accessible manner as required by this specification
>
>The use of this feature is becoming increasingly common, there is a clear demand for this feature to be supported (as can be seen by a quick Google search) and the decision to disallow line breaks imposes a decision that should really be left to individual website developers as to what best suits their own requirements. | 1.0 | @title should allow LF to render consistently, especially given textarea[title] attribute values. - Moved from Bugzilla: https://www.w3.org/Bugs/Public/show_bug.cgi?id=19899
This might be worth considering, especially if implementations do allow LF in the title attribute. Marked for testing.
>The specification currently states that the attribute, if specified, must have a value that contains no "LF" (U+000A) or "CR" (U+000D) characters.
>
>I would like to request that this restricition is reconsidered for Textarea input fields which, by their nature, are designed to span multiple lines and a placeholder hint to show a user an example of the data to enter should also be able to span multiple lines.
>
>An example of this requirement is where a textarea is used to create a list of items e.g.
>
>```
>Please enter areas of work:
> Area A
> Area B
> Area C
>```
>The specification suggests the alternative use of Title but in most browsers this does not display in as helpful a manner and is, anyway, currently discouraged by the W3C, see:
>
>http://dev.w3.org/html5/spec/global-attributes.html#attr-title
>Relying on the title attribute is currently discouraged as many user agents do not expose the attribute in an accessible manner as required by this specification
>
>The use of this feature is becoming increasingly common, there is a clear demand for this feature to be supported (as can be seen by a quick Google search) and the decision to disallow line breaks imposes a decision that should really be left to individual website developers as to what best suits their own requirements. | non_priority | title should allow lf to render consistently especially given textarea attribute values moved from bugzilla this might be worth considering especially if implementations do allow lf in the title attribute marked for testing the specification currently states that the attribute if specified must have a value that contains no lf u or cr u characters i would like to request that this restricition is reconsidered for textarea input fields which by their nature are designed to span multiple lines and a placeholder hint to show a user an example of the data to enter should also be able to span multiple lines an example of this requirement is where a textarea is used to create a list of items e g please enter areas of work area a area b area c the specification suggests the alternative use of title but in most browsers this does not display in as helpful a manner and is anyway currently discouraged by the see relying on the title attribute is currently discouraged as many user agents do not expose the attribute in an accessible manner as required by this specification the use of this feature is becoming increasingly common there is a clear demand for this feature to be supported as can be seen by a quick google search and the decision to disallow line breaks imposes a decision that should really be left to individual website developers as to what best suits their own requirements | 0 |
184,294 | 21,784,849,285 | IssuesEvent | 2022-05-14 01:32:41 | manishshanker/react-redux-d3-webpack-es6-seed | https://api.github.com/repos/manishshanker/react-redux-d3-webpack-es6-seed | closed | WS-2017-3737 (Medium) detected in shelljs-0.6.1.tgz - autoclosed | security vulnerability | ## WS-2017-3737 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shelljs-0.6.1.tgz</b></p></summary>
<p>Portable Unix shell commands for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/shelljs/-/shelljs-0.6.1.tgz">https://registry.npmjs.org/shelljs/-/shelljs-0.6.1.tgz</a></p>
<p>Path to dependency file: /react-redux-d3-webpack-es6-seed/package.json</p>
<p>Path to vulnerable library: /tmp/git/react-redux-d3-webpack-es6-seed/node_modules/shelljs/package.json</p>
<p>
Dependency Hierarchy:
- eslint-2.8.0.tgz (Root Library)
- :x: **shelljs-0.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/manishshanker/react-redux-d3-webpack-es6-seed/commits/3ccf14cd8defb56555cefdb2c27d2f7af0ac1059">3ccf14cd8defb56555cefdb2c27d2f7af0ac1059</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Shelljs 0.8.3 and before are vulnerable to Command Injection. Commands can be invoked from shell.exec(), those commands will include input from external sources, to be passed as arguments to system executables and allowing an attacker to inject arbitrary commands.
<p>Publish Date: 2019-06-16
<p>URL: <a href=https://github.com/shelljs/shelljs/commit/7a9f8e5b7547132ea3f7e4fa47356a94d1156bb3>WS-2017-3737</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2017-3737 (Medium) detected in shelljs-0.6.1.tgz - autoclosed - ## WS-2017-3737 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shelljs-0.6.1.tgz</b></p></summary>
<p>Portable Unix shell commands for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/shelljs/-/shelljs-0.6.1.tgz">https://registry.npmjs.org/shelljs/-/shelljs-0.6.1.tgz</a></p>
<p>Path to dependency file: /react-redux-d3-webpack-es6-seed/package.json</p>
<p>Path to vulnerable library: /tmp/git/react-redux-d3-webpack-es6-seed/node_modules/shelljs/package.json</p>
<p>
Dependency Hierarchy:
- eslint-2.8.0.tgz (Root Library)
- :x: **shelljs-0.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/manishshanker/react-redux-d3-webpack-es6-seed/commits/3ccf14cd8defb56555cefdb2c27d2f7af0ac1059">3ccf14cd8defb56555cefdb2c27d2f7af0ac1059</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Shelljs 0.8.3 and before are vulnerable to Command Injection. Commands can be invoked from shell.exec(), those commands will include input from external sources, to be passed as arguments to system executables and allowing an attacker to inject arbitrary commands.
<p>Publish Date: 2019-06-16
<p>URL: <a href=https://github.com/shelljs/shelljs/commit/7a9f8e5b7547132ea3f7e4fa47356a94d1156bb3>WS-2017-3737</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in shelljs tgz autoclosed ws medium severity vulnerability vulnerable library shelljs tgz portable unix shell commands for node js library home page a href path to dependency file react redux webpack seed package json path to vulnerable library tmp git react redux webpack seed node modules shelljs package json dependency hierarchy eslint tgz root library x shelljs tgz vulnerable library found in head commit a href vulnerability details shelljs and before are vulnerable to command injection commands can be invoked from shell exec those commands will include input from external sources to be passed as arguments to system executables and allowing an attacker to inject arbitrary commands publish date url a href cvss score details base score metrics not available step up your open source security game with whitesource | 0 |
89,657 | 25,868,248,029 | IssuesEvent | 2022-12-13 23:09:44 | openzim/javascript-libzim | https://api.github.com/repos/openzim/javascript-libzim | closed | Fails to read File `arrayBuffers` in Electron | bug build downstream | The good news is that the WASM loads correctly and initializes correctly inside the Electron framework.
The bad news is that the File System fails to read passed `arrayBuffer` of ZIM file. It produces an exception `stream.node.contents.slice is not a function`. It needs debugging.
It's not necessarily a tragedy, because I could build the Electron and NWJS versions using the NODEFS File System instead of the WORKERFS File System, but it would be ideal if I didn't have to use two different binaries, one for the PWA and one for Electron. Sigh. `¯\(°_o)/¯`
<img alt="image" src="https://user-images.githubusercontent.com/4304337/206733829-28e32d9e-db54-4827-b3e9-cd3b3af3815f.png"> | 1.0 | Fails to read File `arrayBuffers` in Electron - The good news is that the WASM loads correctly and initializes correctly inside the Electron framework.
The bad news is that the File System fails to read passed `arrayBuffer` of ZIM file. It produces an exception `stream.node.contents.slice is not a function`. It needs debugging.
It's not necessarily a tragedy, because I could build the Electron and NWJS versions using the NODEFS File System instead of the WORKERFS File System, but it would be ideal if I didn't have to use two different binaries, one for the PWA and one for Electron. Sigh. `¯\(°_o)/¯`
<img alt="image" src="https://user-images.githubusercontent.com/4304337/206733829-28e32d9e-db54-4827-b3e9-cd3b3af3815f.png"> | non_priority | fails to read file arraybuffers in electron the good news is that the wasm loads correctly and initializes correctly inside the electron framework the bad news is that the file system fails to read passed arraybuffer of zim file it produces an exception stream node contents slice is not a function it needs debugging it s not necessarily a tragedy because i could build the electron and nwjs versions using the nodefs file system instead of the workerfs file system but it would be ideal if i didn t have to use two different binaries one for the pwa and one for electron sigh ¯ ° o ¯ img alt image src | 0 |
352,982 | 25,093,589,781 | IssuesEvent | 2022-11-08 08:34:10 | cloudflare/cloudflare-docs | https://api.github.com/repos/cloudflare/cloudflare-docs | closed | Better explain what happens when a cache tag purge occures with Cache Reserve enabled | documentation content:edit | ### Which Cloudflare product does this pertain to?
Cache
### Existing documentation URL(s)
- https://developers.cloudflare.com/cache/about/cache-reserve/#purge
### Section that requires update
https://github.com/cloudflare/cloudflare-docs/blob/2637c7216a37e8006c5a31eb730217036fd10e24/content/cache/about/cache-reserve.md?plain=1#L107
### What needs to change?
I'm not sure I fully understand what the documentation is saying here.
is it saying that Cache Reserve will _immediaitly_ make a request to the origin server to revalidate the URLs, of which there could be thousands if not millions?
OR
is it saying that the resource will be marked as _stale_ rather than immediaitly being evicted?
### How should it change?
Clarify what happens (either immediialty or on subsequent requests)
### Additional information
_No response_ | 1.0 | Better explain what happens when a cache tag purge occures with Cache Reserve enabled - ### Which Cloudflare product does this pertain to?
Cache
### Existing documentation URL(s)
- https://developers.cloudflare.com/cache/about/cache-reserve/#purge
### Section that requires update
https://github.com/cloudflare/cloudflare-docs/blob/2637c7216a37e8006c5a31eb730217036fd10e24/content/cache/about/cache-reserve.md?plain=1#L107
### What needs to change?
I'm not sure I fully understand what the documentation is saying here.
is it saying that Cache Reserve will _immediaitly_ make a request to the origin server to revalidate the URLs, of which there could be thousands if not millions?
OR
is it saying that the resource will be marked as _stale_ rather than immediaitly being evicted?
### How should it change?
Clarify what happens (either immediialty or on subsequent requests)
### Additional information
_No response_ | non_priority | better explain what happens when a cache tag purge occures with cache reserve enabled which cloudflare product does this pertain to cache existing documentation url s section that requires update what needs to change i m not sure i fully understand what the documentation is saying here is it saying that cache reserve will immediaitly make a request to the origin server to revalidate the urls of which there could be thousands if not millions or is it saying that the resource will be marked as stale rather than immediaitly being evicted how should it change clarify what happens either immediialty or on subsequent requests additional information no response | 0 |
3,662 | 6,137,747,025 | IssuesEvent | 2017-06-26 13:08:00 | OpenSRP/opensrp-client | https://api.github.com/repos/OpenSRP/opensrp-client | closed | BZ4.6 Ability to submit aggregated data to calculate coverage rate | Confirm Requirements PATH BID Zambia | - [ ] Need a list of what coverage rates need to be calculated and where this information would be viewed. | 1.0 | BZ4.6 Ability to submit aggregated data to calculate coverage rate - - [ ] Need a list of what coverage rates need to be calculated and where this information would be viewed. | non_priority | ability to submit aggregated data to calculate coverage rate need a list of what coverage rates need to be calculated and where this information would be viewed | 0 |
254,566 | 19,252,125,991 | IssuesEvent | 2021-12-09 07:07:08 | kubesphere/kube-design | https://api.github.com/repos/kubesphere/kube-design | closed | The documentation of the Menu needs to be improved | documentation next | - [ ] How to bind events to menu item?
- [ ] Can menu item be disabled?
@tracer1023 | 1.0 | The documentation of the Menu needs to be improved - - [ ] How to bind events to menu item?
- [ ] Can menu item be disabled?
@tracer1023 | non_priority | the documentation of the menu needs to be improved how to bind events to menu item can menu item be disabled | 0 |
27,646 | 13,341,061,700 | IssuesEvent | 2020-08-28 15:20:49 | kframework/kore | https://api.github.com/repos/kframework/kore | opened | Use hashing to compare SideCondition | appetite: S bug investigate performance | We should investigate using `Hashed` to compare `SideCondition`s because that is heavily used. | True | Use hashing to compare SideCondition - We should investigate using `Hashed` to compare `SideCondition`s because that is heavily used. | non_priority | use hashing to compare sidecondition we should investigate using hashed to compare sidecondition s because that is heavily used | 0 |
27,409 | 5,003,475,784 | IssuesEvent | 2016-12-11 22:32:20 | ironjan/klausurtool-ror | https://api.github.com/repos/ironjan/klausurtool-ror | closed | Ausleihe Weight accepts floats | defect | ## How does this problem happen?
1. First I select a folder instance to lend
2. In the lending form I enter "3,7" (depends on locale)
## What does happen? What do you expect to happen instead?
3,7g is accepted. We don't have float weights... therefore these should be rejected as invalid.
| 1.0 | Ausleihe Weight accepts floats - ## How does this problem happen?
1. First I select a folder instance to lend
2. In the lending form I enter "3,7" (depends on locale)
## What does happen? What do you expect to happen instead?
3,7g is accepted. We don't have float weights... therefore these should be rejected as invalid.
| non_priority | ausleihe weight accepts floats how does this problem happen first i select a folder instance to lend in the lending form i enter depends on locale what does happen what do you expect to happen instead is accepted we don t have float weights therefore these should be rejected as invalid | 0 |
346,764 | 24,887,223,302 | IssuesEvent | 2022-10-28 08:49:35 | songivan00/ped | https://api.github.com/repos/songivan00/ped | opened | Inconsistent naming convention for exam | severity.Low type.DocumentationBug | 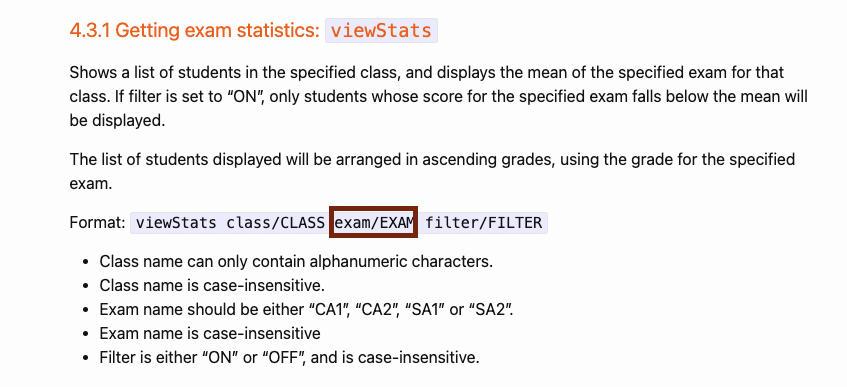
Small flaw but naming convention should be consistent throughout the UG, the exam name was called NAME at the start of the UG.
<!--session: 1666943941242-6358995f-a616-4a7c-a8f1-6a6e2d00776b-->
<!--Version: Web v3.4.4--> | 1.0 | Inconsistent naming convention for exam - 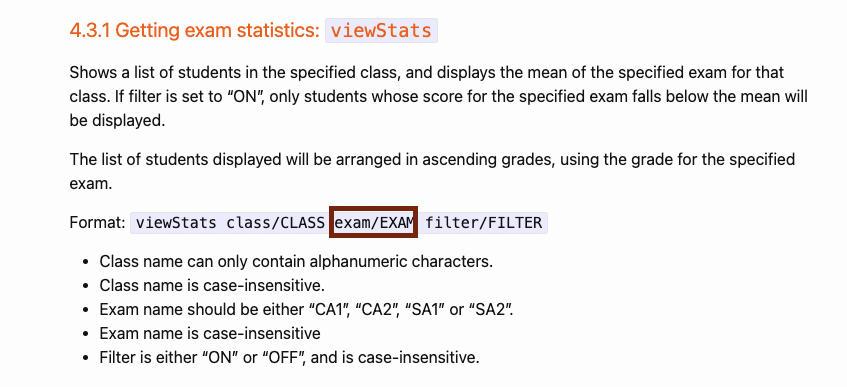
Small flaw but naming convention should be consistent throughout the UG, the exam name was called NAME at the start of the UG.
<!--session: 1666943941242-6358995f-a616-4a7c-a8f1-6a6e2d00776b-->
<!--Version: Web v3.4.4--> | non_priority | inconsistent naming convention for exam small flaw but naming convention should be consistent throughout the ug the exam name was called name at the start of the ug | 0 |
47,399 | 7,324,815,779 | IssuesEvent | 2018-03-03 01:07:42 | snowplow/snowplow | https://api.github.com/repos/snowplow/snowplow | closed | Update JS Tracker documentation to include new v2.9.0 version | documentation | @ihortom would you mind tackling this one? Mike's documentation is under this branch:
https://github.com/mhadam/snowplow.wiki-fork/tree/js-2.9.0 | 1.0 | Update JS Tracker documentation to include new v2.9.0 version - @ihortom would you mind tackling this one? Mike's documentation is under this branch:
https://github.com/mhadam/snowplow.wiki-fork/tree/js-2.9.0 | non_priority | update js tracker documentation to include new version ihortom would you mind tackling this one mike s documentation is under this branch | 0 |
27,339 | 28,130,777,272 | IssuesEvent | 2023-03-31 22:44:25 | pulumi/pulumi-databricks | https://api.github.com/repos/pulumi/pulumi-databricks | closed | Numerous Catalog Grants not supported | impact/usability kind/bug resolution/fixed | ### What happened?
Various catalog grants like "USE_SCHEMA" and "MODIFY" return "not allowed on catalog", despite their functionality existing in terraform and the databricks UI. https://registry.terraform.io/providers/databricks/databricks/latest/docs/resources/grants
https://docs.databricks.com/data-governance/unity-catalog/manage-privileges/privileges.html#inheritance
### Steps to reproduce
Set a grant to a catalog with privileges like "USE_SCHEMA", "MODIFY", etc.
### Expected Behavior
These should be valid privileges
### Actual Behavior
Error: says they aren't allowed on catalogs
`error: diffing urn:pulumi:dev::databricks-workspaces::databricks:index/grants:Grants::yellowCatalogGrant: USE_SCHEMA is not allowed on catalog`
### Output of `pulumi about`
```
CLI
Version 3.44.1
Go Version go1.19.2
Go Compiler gc
Plugins
NAME VERSION
aws 5.18.0
databricks 1.4.0
nodejs unknown
Host
OS darwin
Version 12.4
Arch arm64
```
### Additional context
_No response_
### Contributing
Vote on this issue by adding a 👍 reaction.
To contribute a fix for this issue, leave a comment (and link to your pull request, if you've opened one already).
| True | Numerous Catalog Grants not supported - ### What happened?
Various catalog grants like "USE_SCHEMA" and "MODIFY" return "not allowed on catalog", despite their functionality existing in terraform and the databricks UI. https://registry.terraform.io/providers/databricks/databricks/latest/docs/resources/grants
https://docs.databricks.com/data-governance/unity-catalog/manage-privileges/privileges.html#inheritance
### Steps to reproduce
Set a grant to a catalog with privileges like "USE_SCHEMA", "MODIFY", etc.
### Expected Behavior
These should be valid privileges
### Actual Behavior
Error: says they aren't allowed on catalogs
`error: diffing urn:pulumi:dev::databricks-workspaces::databricks:index/grants:Grants::yellowCatalogGrant: USE_SCHEMA is not allowed on catalog`
### Output of `pulumi about`
```
CLI
Version 3.44.1
Go Version go1.19.2
Go Compiler gc
Plugins
NAME VERSION
aws 5.18.0
databricks 1.4.0
nodejs unknown
Host
OS darwin
Version 12.4
Arch arm64
```
### Additional context
_No response_
### Contributing
Vote on this issue by adding a 👍 reaction.
To contribute a fix for this issue, leave a comment (and link to your pull request, if you've opened one already).
| non_priority | numerous catalog grants not supported what happened various catalog grants like use schema and modify return not allowed on catalog despite their functionality existing in terraform and the databricks ui steps to reproduce set a grant to a catalog with privileges like use schema modify etc expected behavior these should be valid privileges actual behavior error says they aren t allowed on catalogs error diffing urn pulumi dev databricks workspaces databricks index grants grants yellowcataloggrant use schema is not allowed on catalog output of pulumi about cli version go version go compiler gc plugins name version aws databricks nodejs unknown host os darwin version arch additional context no response contributing vote on this issue by adding a 👍 reaction to contribute a fix for this issue leave a comment and link to your pull request if you ve opened one already | 0 |
75,359 | 25,784,262,137 | IssuesEvent | 2022-12-09 18:45:48 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | Facility API Data fields are not locked | Defect VAMC ⭐️ Facilities Vet Center | ## Describe the defect
First reported in [slack here](https://dsva.slack.com/archives/C02730UEZPS/p1670519492899479)
For both VAMC Facilities and Vet Centers, the fields that are populated by the facility API are supposed to be locked down for all editors except true Admins.
## To Reproduce
Steps to reproduce the behavior:
1. Logn as Ryan.S___
2. Go to https://staging.cms.va.gov/node/1705/edit
3. Scroll down to 'Facility Data' field group.
4. See that all the fields in that group are editable.
### Cause
[This PR](https://github.com/department-of-veterans-affairs/va.gov-cms/pull/11809) updated the contrib module field_group to a newer version. The hypothesis is that the module bump changed the html structure of the field group in a way that made our custom javascript that locks down the fields, not be able to find the fields.
This update was released to prod at ~3:30PM ET on Wed December 7th. There error was noticed at Noon ET on December 8th
**Risk:** Data may have been inadvertently changed by an editor.
**Mitigation:** Re-running the migration with an update flag will cause any changed data to be set back to its proper value.
## AC / Expected behavior
- [ ] Logged in as an admin. All fields in the facility api field group are editable
- [ ] health_care_local_facility
- [ ] vet_center
- [ ] vet_center_mobile_vet_center
- [ ] vet_center_outstation
- [ ] Logged in as facility editor. All fields in the facility api field group are disabled so that they are greyed out and can not be edited.
- [ ] health_care_local_facility
- [ ] vet_center
- [ ] vet_center_mobile_vet_center
- [ ] vet_center_outstation
## Screenshots
If applicable, add screenshots to help explain your problem.
## Additional context
Add any other context about the problem here. Reach out to the Product Managers to determine if it should be escalated as critical (prevents users from accomplishing their work with no known workaround and needs to be addressed within 2 business days).
## Desktop (please complete the following information if relevant, or delete)
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
## Labels
(You can delete this section once it's complete)
- [x] Issue type (red) (defaults to "Defect")
- [ ] CMS subsystem (green)
- [ ] CMS practice area (blue)
- [x] CMS workstream (orange) (not needed for bug tickets)
- [ ] CMS-supported product (black)
### CMS Team
Please check the team(s) that will do this work.
- [ ] `Program`
- [ ] `Platform CMS Team`
- [ ] `Sitewide Crew`
- [ ] `⭐️ Sitewide CMS`
- [ ] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
| 1.0 | Facility API Data fields are not locked - ## Describe the defect
First reported in [slack here](https://dsva.slack.com/archives/C02730UEZPS/p1670519492899479)
For both VAMC Facilities and Vet Centers, the fields that are populated by the facility API are supposed to be locked down for all editors except true Admins.
## To Reproduce
Steps to reproduce the behavior:
1. Logn as Ryan.S___
2. Go to https://staging.cms.va.gov/node/1705/edit
3. Scroll down to 'Facility Data' field group.
4. See that all the fields in that group are editable.
### Cause
[This PR](https://github.com/department-of-veterans-affairs/va.gov-cms/pull/11809) updated the contrib module field_group to a newer version. The hypothesis is that the module bump changed the html structure of the field group in a way that made our custom javascript that locks down the fields, not be able to find the fields.
This update was released to prod at ~3:30PM ET on Wed December 7th. There error was noticed at Noon ET on December 8th
**Risk:** Data may have been inadvertently changed by an editor.
**Mitigation:** Re-running the migration with an update flag will cause any changed data to be set back to its proper value.
## AC / Expected behavior
- [ ] Logged in as an admin. All fields in the facility api field group are editable
- [ ] health_care_local_facility
- [ ] vet_center
- [ ] vet_center_mobile_vet_center
- [ ] vet_center_outstation
- [ ] Logged in as facility editor. All fields in the facility api field group are disabled so that they are greyed out and can not be edited.
- [ ] health_care_local_facility
- [ ] vet_center
- [ ] vet_center_mobile_vet_center
- [ ] vet_center_outstation
## Screenshots
If applicable, add screenshots to help explain your problem.
## Additional context
Add any other context about the problem here. Reach out to the Product Managers to determine if it should be escalated as critical (prevents users from accomplishing their work with no known workaround and needs to be addressed within 2 business days).
## Desktop (please complete the following information if relevant, or delete)
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
## Labels
(You can delete this section once it's complete)
- [x] Issue type (red) (defaults to "Defect")
- [ ] CMS subsystem (green)
- [ ] CMS practice area (blue)
- [x] CMS workstream (orange) (not needed for bug tickets)
- [ ] CMS-supported product (black)
### CMS Team
Please check the team(s) that will do this work.
- [ ] `Program`
- [ ] `Platform CMS Team`
- [ ] `Sitewide Crew`
- [ ] `⭐️ Sitewide CMS`
- [ ] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
| non_priority | facility api data fields are not locked describe the defect first reported in for both vamc facilities and vet centers the fields that are populated by the facility api are supposed to be locked down for all editors except true admins to reproduce steps to reproduce the behavior logn as ryan s go to scroll down to facility data field group see that all the fields in that group are editable cause updated the contrib module field group to a newer version the hypothesis is that the module bump changed the html structure of the field group in a way that made our custom javascript that locks down the fields not be able to find the fields this update was released to prod at et on wed december there error was noticed at noon et on december risk data may have been inadvertently changed by an editor mitigation re running the migration with an update flag will cause any changed data to be set back to its proper value ac expected behavior logged in as an admin all fields in the facility api field group are editable health care local facility vet center vet center mobile vet center vet center outstation logged in as facility editor all fields in the facility api field group are disabled so that they are greyed out and can not be edited health care local facility vet center vet center mobile vet center vet center outstation screenshots if applicable add screenshots to help explain your problem additional context add any other context about the problem here reach out to the product managers to determine if it should be escalated as critical prevents users from accomplishing their work with no known workaround and needs to be addressed within business days desktop please complete the following information if relevant or delete os browser version labels you can delete this section once it s complete issue type red defaults to defect cms subsystem green cms practice area blue cms workstream orange not needed for bug tickets cms supported product black cms team please check the team s that will do this work program platform cms team sitewide crew ⭐️ sitewide cms ⭐️ public websites ⭐️ facilities ⭐️ user support | 0 |
52,682 | 7,780,204,194 | IssuesEvent | 2018-06-05 19:16:11 | GoogleCloudPlatform/google-cloud-python | https://api.github.com/repos/GoogleCloudPlatform/google-cloud-python | closed | BigQuery: Show examples of how to use list_jobs() parameters | api: bigquery documentation type: feature request | Expand the `bigquery_list_jobs` snippet to include examples of more of the possible arguments (`all_users`, `min_creation_time`, `max_creation_time`).
(Follow up on https://github.com/GoogleCloudPlatform/google-cloud-python/pull/5429) | 1.0 | BigQuery: Show examples of how to use list_jobs() parameters - Expand the `bigquery_list_jobs` snippet to include examples of more of the possible arguments (`all_users`, `min_creation_time`, `max_creation_time`).
(Follow up on https://github.com/GoogleCloudPlatform/google-cloud-python/pull/5429) | non_priority | bigquery show examples of how to use list jobs parameters expand the bigquery list jobs snippet to include examples of more of the possible arguments all users min creation time max creation time follow up on | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.