Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
16,619 | 9,853,146,656 | IssuesEvent | 2019-06-19 14:14:49 | SAP/cloud-commerce-spartacus-storefront | https://api.github.com/repos/SAP/cloud-commerce-spartacus-storefront | opened | Document XSRF token security precautions | security type/doc | It's supported by default in Angular (if HttpClient is used, and we use it exclusively) but requires proper support on the backend and additional deployment measurements.
More info about Angular support: https://angular.io/guide/security#xsrf | True | Document XSRF token security precautions - It's supported by default in Angular (if HttpClient is used, and we use it exclusively) but requires proper support on the backend and additional deployment measurements.
More info about Angular support: https://angular.io/guide/security#xsrf | non_priority | document xsrf token security precautions it s supported by default in angular if httpclient is used and we use it exclusively but requires proper support on the backend and additional deployment measurements more info about angular support | 0 |
346,544 | 30,926,613,690 | IssuesEvent | 2023-08-06 15:02:07 | dialex/start-testing | https://api.github.com/repos/dialex/start-testing | closed | Test types | create 3.test types | - ✅ unit/integration/e2e https://martinfowler.com/articles/practical-test-pyramid.html
- ✅ risks instead of test types https://danashby.co.uk/2019/05/01/risk-based-testing-part-one-talking-about-risks-over-types-of-testing/
- ✅ designing tests https://dojo.ministryoftesting.com/lessons/designing-tests-what-s-the-difference-between-a-good-test-and-a-bad-test
- ❌ https://medium.com/@revelutions/how-cem-kaner-tests-software-17e3d6fc6157
- 💀 http://watirtight.com/2016/12/19/stop-saying-that.html
- ✅ what to test https://joshilewis.wordpress.com/2017/02/15/test-trade-offs/
- 💀 http://www.testingexcellence.com/choose-tests-automate/
- ❌ https://medium.com/@TuckerConnelly/on-continuous-delivery-7591d773296b#.qb0ykjulo
- ❌ https://www.ultimateqa.com/how-to-design-test-cases-for-testing-part-1-equivalence-partitioning/
- ❌ https://www.ultimateqa.com/proper-black-box-testing-case-design/
- 💀 https://watirmelon.blog/2017/12/20/ama-automated-unit-vs-component-tests/
- ❌ where to place them https://techbeacon.com/6-reasons-co-locate-your-app-automation-code
- ❌ less code https://testmuse.wordpress.com/2018/01/10/write-fewer-automated-checks-tests/
- ❌ http://watirtight.com/2016/12/19/stop-saying-that.html
- ❌ https://circleci.com/blog/component-vs-unit-testing/\
- ✅ fuzz testing https://responsibleautomation.wordpress.com/2023/05/31/kill-more-bugs-add-randomization-to-your-web-testing/
Types
- ✅ http://www.satisfice.com/tools/htsm.pdf
- 💀 https://www.ibm.com/developerworks/library/j-test/
- ❌ Contract https://docs.pact.io/faq/convinceme.html
- ✅ https://kentcdodds.com/blog/static-vs-unit-vs-integration-vs-e2e-tests
- ❌ Contract https://alexromanov.github.io/2021/07/12/should-you-use-contract-testing
- ❌ E2E / Unit https://medium.com/@TuckerConnelly/good-practices-for-testing-react-apps-3a64154fa3b1#.vpr2elq2k
- ❌ E2E http://marmelab.com/blog/2016/04/19/e2e-testing-with-node-and-es6.html
- 💀 E2E https://get-testy.com/top-5-pitfalls-writing-integration-tests/
- ✅ acceptance http://www.developsense.com/blog/2010/08/acceptance-tests-lets-change-the-title-too/
- ❌ acceptance criteria https://club.ministryoftesting.com/t/how-testers-can-help-with-acceptance-criteria/12227/4
- ⏩ BDD https://theitriskmanager.wordpress.com/2018/03/11/bdd-done-easy-the-cotswold-way/
- ✅ integration https://youtu.be/VGNxv9ilFbQ
- ✅ integraion is a scam https://www.youtube.com/watch?v=VDfX44fZoMc
- 💀 Black Box http://newsblur.com/site/2086404/maverick-tester
- 💀 Black box https://thelifeofoneman.com/definition-of-the-day-blackbox-testing
- 💀 http://cheezyworld.com/2010/11/09/ui-tests-not-brittle/
- 💀 http://cheezyworld.com/2010/11/21/ui-tests-default-dat/ | 1.0 | Test types - - ✅ unit/integration/e2e https://martinfowler.com/articles/practical-test-pyramid.html
- ✅ risks instead of test types https://danashby.co.uk/2019/05/01/risk-based-testing-part-one-talking-about-risks-over-types-of-testing/
- ✅ designing tests https://dojo.ministryoftesting.com/lessons/designing-tests-what-s-the-difference-between-a-good-test-and-a-bad-test
- ❌ https://medium.com/@revelutions/how-cem-kaner-tests-software-17e3d6fc6157
- 💀 http://watirtight.com/2016/12/19/stop-saying-that.html
- ✅ what to test https://joshilewis.wordpress.com/2017/02/15/test-trade-offs/
- 💀 http://www.testingexcellence.com/choose-tests-automate/
- ❌ https://medium.com/@TuckerConnelly/on-continuous-delivery-7591d773296b#.qb0ykjulo
- ❌ https://www.ultimateqa.com/how-to-design-test-cases-for-testing-part-1-equivalence-partitioning/
- ❌ https://www.ultimateqa.com/proper-black-box-testing-case-design/
- 💀 https://watirmelon.blog/2017/12/20/ama-automated-unit-vs-component-tests/
- ❌ where to place them https://techbeacon.com/6-reasons-co-locate-your-app-automation-code
- ❌ less code https://testmuse.wordpress.com/2018/01/10/write-fewer-automated-checks-tests/
- ❌ http://watirtight.com/2016/12/19/stop-saying-that.html
- ❌ https://circleci.com/blog/component-vs-unit-testing/\
- ✅ fuzz testing https://responsibleautomation.wordpress.com/2023/05/31/kill-more-bugs-add-randomization-to-your-web-testing/
Types
- ✅ http://www.satisfice.com/tools/htsm.pdf
- 💀 https://www.ibm.com/developerworks/library/j-test/
- ❌ Contract https://docs.pact.io/faq/convinceme.html
- ✅ https://kentcdodds.com/blog/static-vs-unit-vs-integration-vs-e2e-tests
- ❌ Contract https://alexromanov.github.io/2021/07/12/should-you-use-contract-testing
- ❌ E2E / Unit https://medium.com/@TuckerConnelly/good-practices-for-testing-react-apps-3a64154fa3b1#.vpr2elq2k
- ❌ E2E http://marmelab.com/blog/2016/04/19/e2e-testing-with-node-and-es6.html
- 💀 E2E https://get-testy.com/top-5-pitfalls-writing-integration-tests/
- ✅ acceptance http://www.developsense.com/blog/2010/08/acceptance-tests-lets-change-the-title-too/
- ❌ acceptance criteria https://club.ministryoftesting.com/t/how-testers-can-help-with-acceptance-criteria/12227/4
- ⏩ BDD https://theitriskmanager.wordpress.com/2018/03/11/bdd-done-easy-the-cotswold-way/
- ✅ integration https://youtu.be/VGNxv9ilFbQ
- ✅ integraion is a scam https://www.youtube.com/watch?v=VDfX44fZoMc
- 💀 Black Box http://newsblur.com/site/2086404/maverick-tester
- 💀 Black box https://thelifeofoneman.com/definition-of-the-day-blackbox-testing
- 💀 http://cheezyworld.com/2010/11/09/ui-tests-not-brittle/
- 💀 http://cheezyworld.com/2010/11/21/ui-tests-default-dat/ | non_priority | test types ✅ unit integration ✅ risks instead of test types ✅ designing tests ❌ 💀 ✅ what to test 💀 ❌ ❌ ❌ 💀 ❌ where to place them ❌ less code ❌ ❌ ✅ fuzz testing types ✅ 💀 ❌ contract ✅ ❌ contract ❌ unit ❌ 💀 ✅ acceptance ❌ acceptance criteria ⏩ bdd ✅ integration ✅ integraion is a scam 💀 black box 💀 black box 💀 💀 | 0 |
114,248 | 24,572,074,888 | IssuesEvent | 2022-10-13 09:24:52 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | opened | Tidy and refactor Navigation block codebase | [Type] Code Quality [Block] Navigation | Many aspects of the Navigation block codebase have grown over time. Let's see if we can simplify:
- Remove _excess_ duplication - let's avoid taking this too far.
- Reduce code "noise" in the primary `edit` definition - this may be by extracting hooks.
| 1.0 | Tidy and refactor Navigation block codebase - Many aspects of the Navigation block codebase have grown over time. Let's see if we can simplify:
- Remove _excess_ duplication - let's avoid taking this too far.
- Reduce code "noise" in the primary `edit` definition - this may be by extracting hooks.
| non_priority | tidy and refactor navigation block codebase many aspects of the navigation block codebase have grown over time let s see if we can simplify remove excess duplication let s avoid taking this too far reduce code noise in the primary edit definition this may be by extracting hooks | 0 |
165,841 | 20,622,730,097 | IssuesEvent | 2022-03-07 19:05:06 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 111: flatpak-builder-1.2.0: 1 advisory [6.5] | 1.severity: security | [search](https://search.nix.gsc.io/?q=flatpak-builder&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=flatpak-builder+in%3Apath&type=Code)
* [ ] [CVE-2022-21682](https://nvd.nist.gov/vuln/detail/CVE-2022-21682) CVSSv3=6.5 (nixos-unstable)
## CVE details
### CVE-2022-21682
Flatpak is a Linux application sandboxing and distribution framework. A path traversal vulnerability affects versions of Flatpak prior to 1.12.3 and 1.10.6. flatpak-builder applies `finish-args` last in the build. At this point the build directory will have the full access that is specified in the manifest, so running `flatpak build` against it will gain those permissions. Normally this will not be done, so this is not problem. However, if `--mirror-screenshots-url` is specified, then flatpak-builder will launch `flatpak build --nofilesystem=host appstream-utils mirror-screenshots` after finalization, which can lead to issues even with the `--nofilesystem=host` protection. In normal use, the only issue is that these empty directories can be created wherever the user has write permissions. However, a malicious application could replace the `appstream-util` binary and potentially do something more hostile. This has been resolved in Flatpak 1.12.3 and 1.10.6 by changing the behaviour of `--nofilesystem=home` and `--nofilesystem=host`.
-----
Scanned versions: nixos-unstable: 5aaed40d22f.
Cc @jtojnar
| True | Vulnerability roundup 111: flatpak-builder-1.2.0: 1 advisory [6.5] - [search](https://search.nix.gsc.io/?q=flatpak-builder&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=flatpak-builder+in%3Apath&type=Code)
* [ ] [CVE-2022-21682](https://nvd.nist.gov/vuln/detail/CVE-2022-21682) CVSSv3=6.5 (nixos-unstable)
## CVE details
### CVE-2022-21682
Flatpak is a Linux application sandboxing and distribution framework. A path traversal vulnerability affects versions of Flatpak prior to 1.12.3 and 1.10.6. flatpak-builder applies `finish-args` last in the build. At this point the build directory will have the full access that is specified in the manifest, so running `flatpak build` against it will gain those permissions. Normally this will not be done, so this is not problem. However, if `--mirror-screenshots-url` is specified, then flatpak-builder will launch `flatpak build --nofilesystem=host appstream-utils mirror-screenshots` after finalization, which can lead to issues even with the `--nofilesystem=host` protection. In normal use, the only issue is that these empty directories can be created wherever the user has write permissions. However, a malicious application could replace the `appstream-util` binary and potentially do something more hostile. This has been resolved in Flatpak 1.12.3 and 1.10.6 by changing the behaviour of `--nofilesystem=home` and `--nofilesystem=host`.
-----
Scanned versions: nixos-unstable: 5aaed40d22f.
Cc @jtojnar
| non_priority | vulnerability roundup flatpak builder advisory nixos unstable cve details cve flatpak is a linux application sandboxing and distribution framework a path traversal vulnerability affects versions of flatpak prior to and flatpak builder applies finish args last in the build at this point the build directory will have the full access that is specified in the manifest so running flatpak build against it will gain those permissions normally this will not be done so this is not problem however if mirror screenshots url is specified then flatpak builder will launch flatpak build nofilesystem host appstream utils mirror screenshots after finalization which can lead to issues even with the nofilesystem host protection in normal use the only issue is that these empty directories can be created wherever the user has write permissions however a malicious application could replace the appstream util binary and potentially do something more hostile this has been resolved in flatpak and by changing the behaviour of nofilesystem home and nofilesystem host scanned versions nixos unstable cc jtojnar | 0 |
357,074 | 25,176,319,948 | IssuesEvent | 2022-11-11 09:34:44 | Lan-Jingbo/pe | https://api.github.com/repos/Lan-Jingbo/pe | opened | A better "adj" is better | type.DocumentationBug severity.VeryLow | 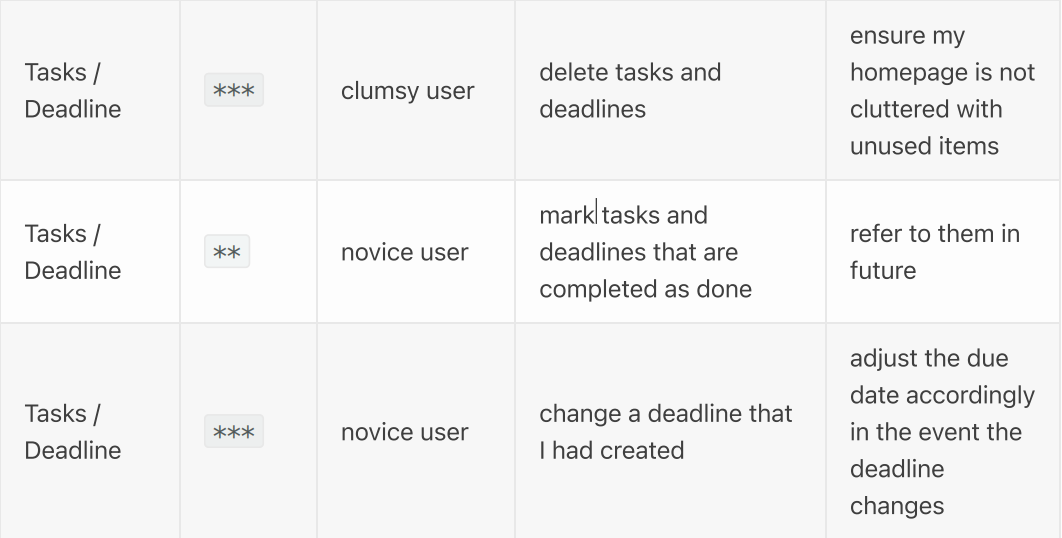
advice: think about new adj instead of "clumsy" and "novice"
<!--session: 1668157905148-bc616dd6-fb96-4a4b-a3f2-f8fcab420a18-->
<!--Version: Web v3.4.4--> | 1.0 | A better "adj" is better - 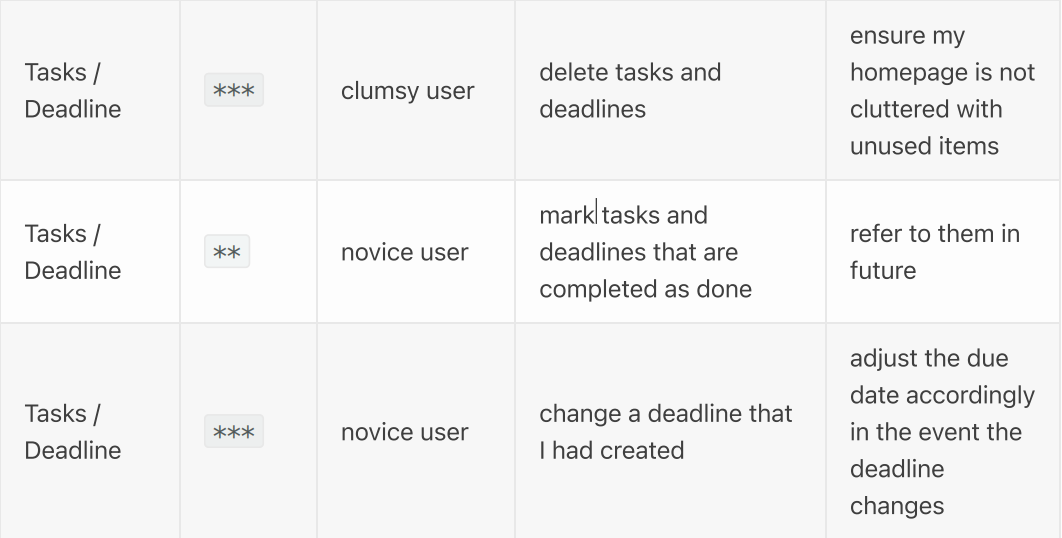
advice: think about new adj instead of "clumsy" and "novice"
<!--session: 1668157905148-bc616dd6-fb96-4a4b-a3f2-f8fcab420a18-->
<!--Version: Web v3.4.4--> | non_priority | a better adj is better advice think about new adj instead of clumsy and novice | 0 |
307,341 | 23,195,458,852 | IssuesEvent | 2022-08-01 15:58:32 | Open-EO/openeo-api | https://api.github.com/repos/Open-EO/openeo-api | closed | Job estimates for UDFs etc | documentation | Some job estimates may not be possible, e.g. for a UDF. For UDFs a back-end may not be able to give an estimate as the code is not really known/understood by the back-end automatically. Thus, we should clarify in the API how a back-end should reject estimates in such cases (e.g. a specific error code via HTTP 400) | 1.0 | Job estimates for UDFs etc - Some job estimates may not be possible, e.g. for a UDF. For UDFs a back-end may not be able to give an estimate as the code is not really known/understood by the back-end automatically. Thus, we should clarify in the API how a back-end should reject estimates in such cases (e.g. a specific error code via HTTP 400) | non_priority | job estimates for udfs etc some job estimates may not be possible e g for a udf for udfs a back end may not be able to give an estimate as the code is not really known understood by the back end automatically thus we should clarify in the api how a back end should reject estimates in such cases e g a specific error code via http | 0 |
7,711 | 7,000,057,081 | IssuesEvent | 2017-12-18 01:41:00 | ushahidi/platform | https://api.github.com/repos/ushahidi/platform | closed | USH-004 -- Abuse of Function | Bug Theme: Security and privacy | ### Expected behaviour
- Set the created and post_date server side, do not rely on the client.
### Actual behaviour
- It is possible to manipulate the variables "created" and"post_date" which leads to false post-chronology.
### Steps to reproduce the behaviour/error
| True | USH-004 -- Abuse of Function - ### Expected behaviour
- Set the created and post_date server side, do not rely on the client.
### Actual behaviour
- It is possible to manipulate the variables "created" and"post_date" which leads to false post-chronology.
### Steps to reproduce the behaviour/error
| non_priority | ush abuse of function expected behaviour set the created and post date server side do not rely on the client actual behaviour it is possible to manipulate the variables created and post date which leads to false post chronology steps to reproduce the behaviour error | 0 |
244,504 | 26,414,153,588 | IssuesEvent | 2023-01-13 14:40:15 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Improve documentation for Login Selector icons | good first issue Team:Security Feature:Security/Authentication docs | The icons that we render within the login selector supports everything that [EuiIcon](https://elastic.github.io/eui/#/display/icons) supports as a `type`:
* http/https URLs
* predefined ids listed here https://elastic.github.io/eui/#/display/icons
* `data:` URLs (incl. base64)
ex:
```yaml
xpack.security.authc.providers:
basic.basic1:
order: 0
icon: "logoElasticsearch"
hint: "Typically for administrators"
saml.saml1:
order: 1
realm: saml1
description: "Log in with SSO"
# Content of kibana-7.17.1-darwin-x86_64/src/plugins/home/public/assets/logos/system.svg
icon: 'data:image/svg+xml;utf8,<svg xmlns="http://www.w3.org/2000/svg" viewBox="0 0 1000 1000"><path d="M433.41 29.92c-9.81 5.14-15.18 10.04-19.15 17.74-1.87 3.74-9.57 43.43-17.28 88.49-23.58 140.32-43.19 243.98-72.61 384.3l-2.57 12.38-10.27-10.97c-19.61-20.31-45.76-25.92-67.71-14.48-14.71 7.47-24.05 20.31-34.55 46.93-7.7 20.32-9.11 22.18-15.64 23.58-3.97.7-39.22 1.4-78.45 1.4-67.94 0-71.91.23-81.72 4.9C7.54 596.8 1.94 631.82 22.49 651.9c13.08 12.84 17.04 13.31 88.72 13.54 106 0 125.38-3.04 145.69-24.05l7.94-8.17 6.3 13.54c12.14 25.45 28.72 38.76 51.6 41.56 24.52 2.8 42.49-10.97 56.03-43.19 13.31-31.98 39.93-147.56 63.28-272.93 5.6-29.88 10.51-54.4 11.21-54.4.7 0 26.85 140.09 58.14 311.22 31.28 170.91 58.37 314.73 60.24 319.17 4.2 10.51 9.11 15.87 19.85 21.25 18.45 9.57 43.19 3.04 54.4-14.01 5.14-7.71 7.24-16.34 13.07-57.67 12.36-85.22 33.84-204.06 36.87-204.06.7 0 4.67 5.37 8.4 11.91 14.48 24.75 37.82 38.06 66.54 38.29 29.18 0 40.63-9.34 72.15-58.84l16.11-25.21 57.2-1.17c56.5-1.17 57.44-1.17 63.27-6.77 7.94-7.47 11.44-19.15 10.27-34.09-1.4-15.88-8.17-28.72-20.08-37.12l-9.57-6.77-57.43-1.17c-69.58-1.4-77.51-.23-94.33 14.94-6.3 5.84-17.74 19.84-24.98 31.29-7.47 11.44-13.78 20.78-14.01 20.31-.24-.23-2.57-12.61-5.37-27.32-8.64-48.8-19.38-69.81-40.86-80.55-22.41-11.21-48.33-6.31-64.21 11.91-14.47 16.34-30.12 56.03-43.66 110.67-3.5 14.47-6.77 25.68-7.24 24.52-.23-1.4-26.38-142.66-57.9-314.03-63.04-342.74-58.6-323.83-78.21-333.87-10.96-5.61-28.71-6.08-38.51-.71z"/></svg>'
```
We should improve our documentation to make the supported icon formats more explicit, so that administrators can more easily customize their login experience. | True | Improve documentation for Login Selector icons - The icons that we render within the login selector supports everything that [EuiIcon](https://elastic.github.io/eui/#/display/icons) supports as a `type`:
* http/https URLs
* predefined ids listed here https://elastic.github.io/eui/#/display/icons
* `data:` URLs (incl. base64)
ex:
```yaml
xpack.security.authc.providers:
basic.basic1:
order: 0
icon: "logoElasticsearch"
hint: "Typically for administrators"
saml.saml1:
order: 1
realm: saml1
description: "Log in with SSO"
# Content of kibana-7.17.1-darwin-x86_64/src/plugins/home/public/assets/logos/system.svg
icon: 'data:image/svg+xml;utf8,<svg xmlns="http://www.w3.org/2000/svg" viewBox="0 0 1000 1000"><path d="M433.41 29.92c-9.81 5.14-15.18 10.04-19.15 17.74-1.87 3.74-9.57 43.43-17.28 88.49-23.58 140.32-43.19 243.98-72.61 384.3l-2.57 12.38-10.27-10.97c-19.61-20.31-45.76-25.92-67.71-14.48-14.71 7.47-24.05 20.31-34.55 46.93-7.7 20.32-9.11 22.18-15.64 23.58-3.97.7-39.22 1.4-78.45 1.4-67.94 0-71.91.23-81.72 4.9C7.54 596.8 1.94 631.82 22.49 651.9c13.08 12.84 17.04 13.31 88.72 13.54 106 0 125.38-3.04 145.69-24.05l7.94-8.17 6.3 13.54c12.14 25.45 28.72 38.76 51.6 41.56 24.52 2.8 42.49-10.97 56.03-43.19 13.31-31.98 39.93-147.56 63.28-272.93 5.6-29.88 10.51-54.4 11.21-54.4.7 0 26.85 140.09 58.14 311.22 31.28 170.91 58.37 314.73 60.24 319.17 4.2 10.51 9.11 15.87 19.85 21.25 18.45 9.57 43.19 3.04 54.4-14.01 5.14-7.71 7.24-16.34 13.07-57.67 12.36-85.22 33.84-204.06 36.87-204.06.7 0 4.67 5.37 8.4 11.91 14.48 24.75 37.82 38.06 66.54 38.29 29.18 0 40.63-9.34 72.15-58.84l16.11-25.21 57.2-1.17c56.5-1.17 57.44-1.17 63.27-6.77 7.94-7.47 11.44-19.15 10.27-34.09-1.4-15.88-8.17-28.72-20.08-37.12l-9.57-6.77-57.43-1.17c-69.58-1.4-77.51-.23-94.33 14.94-6.3 5.84-17.74 19.84-24.98 31.29-7.47 11.44-13.78 20.78-14.01 20.31-.24-.23-2.57-12.61-5.37-27.32-8.64-48.8-19.38-69.81-40.86-80.55-22.41-11.21-48.33-6.31-64.21 11.91-14.47 16.34-30.12 56.03-43.66 110.67-3.5 14.47-6.77 25.68-7.24 24.52-.23-1.4-26.38-142.66-57.9-314.03-63.04-342.74-58.6-323.83-78.21-333.87-10.96-5.61-28.71-6.08-38.51-.71z"/></svg>'
```
We should improve our documentation to make the supported icon formats more explicit, so that administrators can more easily customize their login experience. | non_priority | improve documentation for login selector icons the icons that we render within the login selector supports everything that supports as a type http https urls predefined ids listed here data urls incl ex yaml xpack security authc providers basic order icon logoelasticsearch hint typically for administrators saml order realm description log in with sso content of kibana darwin src plugins home public assets logos system svg icon data image svg xml we should improve our documentation to make the supported icon formats more explicit so that administrators can more easily customize their login experience | 0 |
260,663 | 19,681,165,694 | IssuesEvent | 2022-01-11 16:53:50 | MIT-LCP/mimic-code | https://api.github.com/repos/MIT-LCP/mimic-code | opened | Document deidentification of `anchor_age` | documentation mimic-iv | `anchor_age` is set to 91 for all patients over 89. The only difference between our approach between MIMIC-III and MIMIC-IV is that we use 91 rather than 300.
However this isn't explicitly documented online, I think? Didn't see it here https://mimic.mit.edu/docs/iv/modules/core/patients/
It probably should be! | 1.0 | Document deidentification of `anchor_age` - `anchor_age` is set to 91 for all patients over 89. The only difference between our approach between MIMIC-III and MIMIC-IV is that we use 91 rather than 300.
However this isn't explicitly documented online, I think? Didn't see it here https://mimic.mit.edu/docs/iv/modules/core/patients/
It probably should be! | non_priority | document deidentification of anchor age anchor age is set to for all patients over the only difference between our approach between mimic iii and mimic iv is that we use rather than however this isn t explicitly documented online i think didn t see it here it probably should be | 0 |
13,059 | 3,683,441,059 | IssuesEvent | 2016-02-24 14:06:36 | vivienlacourba/Unicorn | https://api.github.com/repos/vivienlacourba/Unicorn | closed | Write the tasklist parser | documentation task | **Reported by jean gui on 1 Jan 1970 00:20 UTC**
Write the code to unmarshall the tasklist in a form that will be usable | 1.0 | Write the tasklist parser - **Reported by jean gui on 1 Jan 1970 00:20 UTC**
Write the code to unmarshall the tasklist in a form that will be usable | non_priority | write the tasklist parser reported by jean gui on jan utc write the code to unmarshall the tasklist in a form that will be usable | 0 |
185,517 | 21,791,545,510 | IssuesEvent | 2022-05-15 01:07:50 | emilwareus/spring-boot | https://api.github.com/repos/emilwareus/spring-boot | opened | CVE-2022-22971 (Medium) detected in spring-messaging-5.2.0.M2.jar | security vulnerability | ## CVE-2022-22971 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-messaging-5.2.0.M2.jar</b></p></summary>
<p>Spring Messaging</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /spring-boot/spring-boot-project/spring-boot-actuator-autoconfigure/pom.xml</p>
<p>Path to vulnerable library: /2/repository/org/springframework/spring-messaging/5.2.0.M2/spring-messaging-5.2.0.M2.jar,/root/.m2/repository/org/springframework/spring-messaging/5.2.0.M2/spring-messaging-5.2.0.M2.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-messaging-5.2.0.M2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/emilwareus/spring-boot/commit/47fe1da3f868a49b21bc0b8762c2e956d09f8a18">47fe1da3f868a49b21bc0b8762c2e956d09f8a18</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, application with a STOMP over WebSocket endpoint is vulnerable to a denial of service attack by an authenticated user.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22971>CVE-2022-22971</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22971">https://tanzu.vmware.com/security/cve-2022-22971</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: org.springframework:spring-messaging:5.2.22,5.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-22971 (Medium) detected in spring-messaging-5.2.0.M2.jar - ## CVE-2022-22971 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-messaging-5.2.0.M2.jar</b></p></summary>
<p>Spring Messaging</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /spring-boot/spring-boot-project/spring-boot-actuator-autoconfigure/pom.xml</p>
<p>Path to vulnerable library: /2/repository/org/springframework/spring-messaging/5.2.0.M2/spring-messaging-5.2.0.M2.jar,/root/.m2/repository/org/springframework/spring-messaging/5.2.0.M2/spring-messaging-5.2.0.M2.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-messaging-5.2.0.M2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/emilwareus/spring-boot/commit/47fe1da3f868a49b21bc0b8762c2e956d09f8a18">47fe1da3f868a49b21bc0b8762c2e956d09f8a18</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, application with a STOMP over WebSocket endpoint is vulnerable to a denial of service attack by an authenticated user.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22971>CVE-2022-22971</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22971">https://tanzu.vmware.com/security/cve-2022-22971</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: org.springframework:spring-messaging:5.2.22,5.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in spring messaging jar cve medium severity vulnerability vulnerable library spring messaging jar spring messaging library home page a href path to dependency file spring boot spring boot project spring boot actuator autoconfigure pom xml path to vulnerable library repository org springframework spring messaging spring messaging jar root repository org springframework spring messaging spring messaging jar dependency hierarchy x spring messaging jar vulnerable library found in head commit a href found in base branch master vulnerability details in spring framework versions prior to and old unsupported versions application with a stomp over websocket endpoint is vulnerable to a denial of service attack by an authenticated user publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring messaging step up your open source security game with whitesource | 0 |
24,356 | 6,537,292,071 | IssuesEvent | 2017-08-31 21:44:29 | phw198/OutlookGoogleCalendarSync | https://api.github.com/repos/phw198/OutlookGoogleCalendarSync | closed | Multiple deletions | codeplex discussion dormant help wanted | <div><strong>This discussion was imported from <a href="http://outlookgooglecalendarsync.codeplex.com/discussions/662377" target="_blank">CodePlex</a></strong></div><hr/>
<div>
<p><strong><a href="http://www.codeplex.com/site/users/view/pablohf68" target="_blank">pablohf68</a></strong> wrote at 2017-04-04 02:14:</p><div class="markDownOutput ">Hello, for some synchronization problem, all my appointments were deleted, in Gmail, Outlook and in my smart phone (Samsung S7).
<br>
<br>
There is a way to recover them? <br>
<br>
I'm desperate, I had everything there. <br>
<br>
Thanks. <br>
<br>
Pablo.<br>
</div></div>
| 1.0 | Multiple deletions - <div><strong>This discussion was imported from <a href="http://outlookgooglecalendarsync.codeplex.com/discussions/662377" target="_blank">CodePlex</a></strong></div><hr/>
<div>
<p><strong><a href="http://www.codeplex.com/site/users/view/pablohf68" target="_blank">pablohf68</a></strong> wrote at 2017-04-04 02:14:</p><div class="markDownOutput ">Hello, for some synchronization problem, all my appointments were deleted, in Gmail, Outlook and in my smart phone (Samsung S7).
<br>
<br>
There is a way to recover them? <br>
<br>
I'm desperate, I had everything there. <br>
<br>
Thanks. <br>
<br>
Pablo.<br>
</div></div>
| non_priority | multiple deletions this discussion was imported from codeplex wrote at hello for some synchronization problem all my appointments were deleted in gmail outlook and in my smart phone samsung there is a way to recover them i m desperate i had everything there thanks pablo | 0 |
71,959 | 13,768,048,657 | IssuesEvent | 2020-10-07 16:32:01 | pulumi/pulumi | https://api.github.com/repos/pulumi/pulumi | closed | Support deprecation messages for enum values. | area/codegen | Related to: #4003
Add support for deprecation messages for specific enum values. Example below.
https://github.com/pulumi/pulumi-aws/blob/master/sdk/nodejs/lambda/runtimes.ts#L56-L69 | 1.0 | Support deprecation messages for enum values. - Related to: #4003
Add support for deprecation messages for specific enum values. Example below.
https://github.com/pulumi/pulumi-aws/blob/master/sdk/nodejs/lambda/runtimes.ts#L56-L69 | non_priority | support deprecation messages for enum values related to add support for deprecation messages for specific enum values example below | 0 |
28,255 | 4,385,240,368 | IssuesEvent | 2016-08-08 08:12:17 | Algatux/influxdb-bundle | https://api.github.com/repos/Algatux/influxdb-bundle | closed | Suggestion: Coveralls | enhancement testing | I suggest you to setup Coveralls: https://coveralls.io/
With this tools, you will get PR status for coverage.
Example:

| 1.0 | Suggestion: Coveralls - I suggest you to setup Coveralls: https://coveralls.io/
With this tools, you will get PR status for coverage.
Example:

| non_priority | suggestion coveralls i suggest you to setup coveralls with this tools you will get pr status for coverage example | 0 |
98,882 | 8,685,912,076 | IssuesEvent | 2018-12-03 09:21:16 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | reopened | FX Testing 3 : ApiV1DashboardCountTestsGetQueryParamPagesizeEmptyValue | FX Testing 3 | Project : FX Testing 3
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=NTMyNmEzN2QtNTNkYS00NzM1LWFlYzItODhkMDFhYWQ5ZTg1; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Mon, 03 Dec 2018 04:37:56 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/dashboard/count-tests?pageSize=
Request :
Response :
{
"timestamp" : "2018-12-03T04:37:57.436+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/dashboard/count-tests"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 500] resolved-to [404 != 500] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]Assertion [@StatusCode != 200] resolved-to [404 != 200] result [Passed]
--- FX Bot --- | 1.0 | FX Testing 3 : ApiV1DashboardCountTestsGetQueryParamPagesizeEmptyValue - Project : FX Testing 3
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=NTMyNmEzN2QtNTNkYS00NzM1LWFlYzItODhkMDFhYWQ5ZTg1; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Mon, 03 Dec 2018 04:37:56 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/dashboard/count-tests?pageSize=
Request :
Response :
{
"timestamp" : "2018-12-03T04:37:57.436+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/dashboard/count-tests"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 500] resolved-to [404 != 500] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]Assertion [@StatusCode != 200] resolved-to [404 != 200] result [Passed]
--- FX Bot --- | non_priority | fx testing project fx testing job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api dashboard count tests logs assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result fx bot | 0 |
7,306 | 3,962,184,883 | IssuesEvent | 2016-05-02 15:52:06 | RobotLocomotion/drake | https://api.github.com/repos/RobotLocomotion/drake | opened | Superbuild externals should use shallow clone | team: kitware type: build | I think the superbuild externals should use a shallow git clone. We don't typically want or need the full commit history of an external, and a build-from-scratch would go faster if all the git cloning were faster.
This forum post seems relevant, but I didn't immediately see any follow-up:
https://cmake.org/pipermail/cmake/2015-May/060571.html
| 1.0 | Superbuild externals should use shallow clone - I think the superbuild externals should use a shallow git clone. We don't typically want or need the full commit history of an external, and a build-from-scratch would go faster if all the git cloning were faster.
This forum post seems relevant, but I didn't immediately see any follow-up:
https://cmake.org/pipermail/cmake/2015-May/060571.html
| non_priority | superbuild externals should use shallow clone i think the superbuild externals should use a shallow git clone we don t typically want or need the full commit history of an external and a build from scratch would go faster if all the git cloning were faster this forum post seems relevant but i didn t immediately see any follow up | 0 |
285,844 | 31,155,668,859 | IssuesEvent | 2023-08-16 12:59:28 | nidhi7598/linux-4.1.15_CVE-2018-5873 | https://api.github.com/repos/nidhi7598/linux-4.1.15_CVE-2018-5873 | opened | CVE-2018-9415 (High) detected in linuxlinux-4.1.52 | Mend: dependency security vulnerability | ## CVE-2018-9415 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In driver_override_store and driver_override_show of bus.c, there is a possible double free due to improper locking. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation. Product: Android Versions: Android kernel Android ID: A-69129004 References: Upstream kernel.
<p>Publish Date: 2018-11-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-9415>CVE-2018-9415</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-11-06</p>
<p>Fix Resolution: v4.17-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-9415 (High) detected in linuxlinux-4.1.52 - ## CVE-2018-9415 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In driver_override_store and driver_override_show of bus.c, there is a possible double free due to improper locking. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation. Product: Android Versions: Android kernel Android ID: A-69129004 References: Upstream kernel.
<p>Publish Date: 2018-11-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-9415>CVE-2018-9415</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-11-06</p>
<p>Fix Resolution: v4.17-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files vulnerability details in driver override store and driver override show of bus c there is a possible double free due to improper locking this could lead to local escalation of privilege with system execution privileges needed user interaction is not needed for exploitation product android versions android kernel android id a references upstream kernel publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
233,695 | 19,029,265,800 | IssuesEvent | 2021-11-24 08:56:25 | nextcloud/deck | https://api.github.com/repos/nextcloud/deck | closed | Integration tests | tests 1. to develop | Our integration tests are still broken, they need to be adjusted to work with the latest guzzlehttp version of the server.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/75858083-integration-tests?utm_campaign=plugin&utm_content=tracker%2F52758431&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F52758431&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | Integration tests - Our integration tests are still broken, they need to be adjusted to work with the latest guzzlehttp version of the server.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/75858083-integration-tests?utm_campaign=plugin&utm_content=tracker%2F52758431&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F52758431&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_priority | integration tests our integration tests are still broken they need to be adjusted to work with the latest guzzlehttp version of the server want to back this issue we accept bounties via | 0 |
69,352 | 13,237,543,230 | IssuesEvent | 2020-08-18 21:54:58 | DataBiosphere/azul | https://api.github.com/repos/DataBiosphere/azul | closed | Terra handover fails with invalid characters in bundle version | bug code demoed orange | Here's the error as reported in Terra.
```
{
"statusCode": 400,
"source": "rawls",
"timestamp": 1595530086136,
"causes": [],
"stackTrace": [],
"message": "Invalid input: a0ca0624-ddf5-4b80-8ba6-a481002731be.2019-05-14T10:50:20.494000Z. Input may only contain alphanumeric characters, underscores, dashes, and periods."
}
```
For this export I only had the "Single-cell RNA-seq analysis of human pancreas from healthy individuals and type 2 diabetes patients" project selected. | 1.0 | Terra handover fails with invalid characters in bundle version - Here's the error as reported in Terra.
```
{
"statusCode": 400,
"source": "rawls",
"timestamp": 1595530086136,
"causes": [],
"stackTrace": [],
"message": "Invalid input: a0ca0624-ddf5-4b80-8ba6-a481002731be.2019-05-14T10:50:20.494000Z. Input may only contain alphanumeric characters, underscores, dashes, and periods."
}
```
For this export I only had the "Single-cell RNA-seq analysis of human pancreas from healthy individuals and type 2 diabetes patients" project selected. | non_priority | terra handover fails with invalid characters in bundle version here s the error as reported in terra statuscode source rawls timestamp causes stacktrace message invalid input input may only contain alphanumeric characters underscores dashes and periods for this export i only had the single cell rna seq analysis of human pancreas from healthy individuals and type diabetes patients project selected | 0 |
184,536 | 21,784,909,133 | IssuesEvent | 2022-05-14 01:46:09 | n-devs/example-scripts-react | https://api.github.com/repos/n-devs/example-scripts-react | closed | WS-2019-0493 (High) detected in handlebars-4.1.2.tgz - autoclosed | security vulnerability | ## WS-2019-0493 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /example-scripts-react/package.json</p>
<p>Path to vulnerable library: example-scripts-react/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-24.7.1.tgz (Root Library)
- jest-cli-24.8.0.tgz
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.6.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-14
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0493</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-11-14</p>
<p>Fix Resolution: handlebars - 3.0.8,4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0493 (High) detected in handlebars-4.1.2.tgz - autoclosed - ## WS-2019-0493 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /example-scripts-react/package.json</p>
<p>Path to vulnerable library: example-scripts-react/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-24.7.1.tgz (Root Library)
- jest-cli-24.8.0.tgz
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.6.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-14
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0493</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-11-14</p>
<p>Fix Resolution: handlebars - 3.0.8,4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in handlebars tgz autoclosed ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file example scripts react package json path to vulnerable library example scripts react node modules handlebars package json dependency hierarchy jest tgz root library jest cli tgz core tgz reporters tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details handlebars before and x before is vulnerable to arbitrary code execution the package s lookup helper fails to properly validate templates allowing attackers to submit templates that execute arbitrary javascript in the system publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
1,627 | 2,563,524,806 | IssuesEvent | 2015-02-06 13:47:23 | radare/radare2 | https://api.github.com/repos/radare/radare2 | closed | Cropped strings | blocker bug regression test-attached | It seems that aafea2ec4e1d4f22fd330ce6fd409b7e02a716ad is breaking the `./t/cmd_pd` tests by cropping the strings:
```
$ ./t/cmd_pd
[OK] 1 cmd_pd: ASCII Recognition
[XX] 2 cmd_pd: String capstone
Command: /usr/local/bin/radare2 -e scr.color=0 -N -q -i /tmp/r2-regressions//cmd_pd-rad.XBLmrn ../bins/elf/main > /tmp/r2-regressions//cmd_pd-out.oRqqMn 2> /tmp/r2-regressions//cmd_pd-err.VcqCeH
File: ../bins/elf/main
Script:
e asm.arch = x86
e scr.columns = 90
aa
pd 1 @ 0x0040050a
Diff: --- /tmp/r2-regressions//cmd_pd-exp.NYEY3V 2015-02-05 13:12:18.747575253 +0100
+++ /tmp/r2-regressions//cmd_pd-out.oRqqMn 2015-02-05 13:12:18.783575251 +0100
@@ -1 +1 @@
-| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello World" @ 0x4005c4
+| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello Wor" @ 0x4005c4
[XX] 3 cmd_pd: String udis86
Command: /usr/local/bin/radare2 -e scr.color=0 -N -q -i /tmp/r2-regressions//cmd_pd-rad.aH2GrP ../bins/elf/main > /tmp/r2-regressions//cmd_pd-out.PuWnAe 2> /tmp/r2-regressions//cmd_pd-err.D4Es56
File: ../bins/elf/main
Script: e asm.arch = x86.udis
e scr.columns = 90
aa
pd 1 @ 0x0040050a
Diff: --- /tmp/r2-regressions//cmd_pd-exp.70f6Cd 2015-02-05 13:12:18.795575251 +0100
+++ /tmp/r2-regressions//cmd_pd-out.PuWnAe 2015-02-05 13:12:18.835575249 +0100
@@ -1 +1 @@
-| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello World" @ 0x4005c4
+| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello Wor" @ 0x4005c4
zsh: exit 1 ./t/cmd_pd
``` | 1.0 | Cropped strings - It seems that aafea2ec4e1d4f22fd330ce6fd409b7e02a716ad is breaking the `./t/cmd_pd` tests by cropping the strings:
```
$ ./t/cmd_pd
[OK] 1 cmd_pd: ASCII Recognition
[XX] 2 cmd_pd: String capstone
Command: /usr/local/bin/radare2 -e scr.color=0 -N -q -i /tmp/r2-regressions//cmd_pd-rad.XBLmrn ../bins/elf/main > /tmp/r2-regressions//cmd_pd-out.oRqqMn 2> /tmp/r2-regressions//cmd_pd-err.VcqCeH
File: ../bins/elf/main
Script:
e asm.arch = x86
e scr.columns = 90
aa
pd 1 @ 0x0040050a
Diff: --- /tmp/r2-regressions//cmd_pd-exp.NYEY3V 2015-02-05 13:12:18.747575253 +0100
+++ /tmp/r2-regressions//cmd_pd-out.oRqqMn 2015-02-05 13:12:18.783575251 +0100
@@ -1 +1 @@
-| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello World" @ 0x4005c4
+| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello Wor" @ 0x4005c4
[XX] 3 cmd_pd: String udis86
Command: /usr/local/bin/radare2 -e scr.color=0 -N -q -i /tmp/r2-regressions//cmd_pd-rad.aH2GrP ../bins/elf/main > /tmp/r2-regressions//cmd_pd-out.PuWnAe 2> /tmp/r2-regressions//cmd_pd-err.D4Es56
File: ../bins/elf/main
Script: e asm.arch = x86.udis
e scr.columns = 90
aa
pd 1 @ 0x0040050a
Diff: --- /tmp/r2-regressions//cmd_pd-exp.70f6Cd 2015-02-05 13:12:18.795575251 +0100
+++ /tmp/r2-regressions//cmd_pd-out.PuWnAe 2015-02-05 13:12:18.835575249 +0100
@@ -1 +1 @@
-| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello World" @ 0x4005c4
+| 0x0040050a bfc4054000 mov edi, str.Hello_World ; "Hello Wor" @ 0x4005c4
zsh: exit 1 ./t/cmd_pd
``` | non_priority | cropped strings it seems that is breaking the t cmd pd tests by cropping the strings t cmd pd cmd pd ascii recognition cmd pd string capstone command usr local bin e scr color n q i tmp regressions cmd pd rad xblmrn bins elf main tmp regressions cmd pd out orqqmn tmp regressions cmd pd err vcqceh file bins elf main script e asm arch e scr columns aa pd diff tmp regressions cmd pd exp tmp regressions cmd pd out orqqmn mov edi str hello world hello world mov edi str hello world hello wor cmd pd string command usr local bin e scr color n q i tmp regressions cmd pd rad bins elf main tmp regressions cmd pd out puwnae tmp regressions cmd pd err file bins elf main script e asm arch udis e scr columns aa pd diff tmp regressions cmd pd exp tmp regressions cmd pd out puwnae mov edi str hello world hello world mov edi str hello world hello wor zsh exit t cmd pd | 0 |
126,765 | 12,298,985,663 | IssuesEvent | 2020-05-11 11:32:34 | baltic-guys/read-path | https://api.github.com/repos/baltic-guys/read-path | closed | Разработка пользовательского сценария | critical documentation | Создать модуль doc в который прописать пользовательский сценарий | 1.0 | Разработка пользовательского сценария - Создать модуль doc в который прописать пользовательский сценарий | non_priority | разработка пользовательского сценария создать модуль doc в который прописать пользовательский сценарий | 0 |
32,084 | 7,482,164,417 | IssuesEvent | 2018-04-04 23:42:28 | chrisblakley/Nebula | https://api.github.com/repos/chrisblakley/Nebula | closed | Add icon in user list for those who logged in today | Backend (Server) WP Admin / Shortcode / Widget | Users who have logged in today should have an icon in the "Last Seen" column. Users who have not don't need to have any icon at all. | 1.0 | Add icon in user list for those who logged in today - Users who have logged in today should have an icon in the "Last Seen" column. Users who have not don't need to have any icon at all. | non_priority | add icon in user list for those who logged in today users who have logged in today should have an icon in the last seen column users who have not don t need to have any icon at all | 0 |
428,313 | 29,951,952,132 | IssuesEvent | 2023-06-23 02:29:43 | ruby-passkeys/devise-passkeys | https://api.github.com/repos/ruby-passkeys/devise-passkeys | opened | Add documentation about how to override the `passkeys_authenticatable` for `Devise.add_module` | documentation good first issue | Previously in #13; I thought the module was not being defined inside the gem, but it's actually defined in: https://github.com/ruby-passkeys/devise-passkeys/blob/main/lib/devise/passkeys.rb#L26
Instead, the template repo overrides the module definition with its implementation-specific definitions, which is what we actually want to happen here; since each app will have to create its own set of controllers.
We should update the README to include documentation about how the step is needed (and why!); and use the code from the template repo as example code | 1.0 | Add documentation about how to override the `passkeys_authenticatable` for `Devise.add_module` - Previously in #13; I thought the module was not being defined inside the gem, but it's actually defined in: https://github.com/ruby-passkeys/devise-passkeys/blob/main/lib/devise/passkeys.rb#L26
Instead, the template repo overrides the module definition with its implementation-specific definitions, which is what we actually want to happen here; since each app will have to create its own set of controllers.
We should update the README to include documentation about how the step is needed (and why!); and use the code from the template repo as example code | non_priority | add documentation about how to override the passkeys authenticatable for devise add module previously in i thought the module was not being defined inside the gem but it s actually defined in instead the template repo overrides the module definition with its implementation specific definitions which is what we actually want to happen here since each app will have to create its own set of controllers we should update the readme to include documentation about how the step is needed and why and use the code from the template repo as example code | 0 |
77,173 | 9,982,372,467 | IssuesEvent | 2019-07-10 09:42:09 | uliska/luatemplates | https://api.github.com/repos/uliska/luatemplates | opened | self-documentation for *all* clients | documentation enhancement | self-documentation should also be possible for *all* clients at once.
This has to be highly configurable/templatable. | 1.0 | self-documentation for *all* clients - self-documentation should also be possible for *all* clients at once.
This has to be highly configurable/templatable. | non_priority | self documentation for all clients self documentation should also be possible for all clients at once this has to be highly configurable templatable | 0 |
51,705 | 27,204,467,385 | IssuesEvent | 2023-02-20 12:04:54 | CommunityToolkit/dotnet | https://api.github.com/repos/CommunityToolkit/dotnet | opened | Add ArrayPoolBufferWriter<T>.DangerousGetArray() API | feature request :mailbox_with_mail: high-performance 🚂 | ### Overview
Related to #614. The `ArrayPoolBufferWriter<T>` lacks the `DangerousGetArray()` API which `MemoryOwner<T>` and `SpanOwner<T>` have. We should add it there too to make it easier and clearer how to get the underlying array from a writer.
### API breakdown
```csharp
namespace CommunityToolkit.HighPerformance.Buffers;
public sealed class ArrayPoolBufferWriter<T> : IBuffer<T>, IMemoryOwner<T>
{
[MethodImpl(MethodImplOptions.AggressiveInlining)]
public ArraySegment<T> DangerousGetArray();
}
```
### Usage example
```csharp
ArraySegment<byte> segment = bufferWriter.DangerousGetArray();
stream.Write(segment.Array!, segment.Offset, segment.Count);
```
### Breaking change?
No
### Alternatives
Use `MemoryMarshal.TryGetArray`. That's less clear and less discoverable, so not ideal.
### Additional context
_No response_
### Help us help you
Yes, I'd like to be assigned to work on this item | True | Add ArrayPoolBufferWriter<T>.DangerousGetArray() API - ### Overview
Related to #614. The `ArrayPoolBufferWriter<T>` lacks the `DangerousGetArray()` API which `MemoryOwner<T>` and `SpanOwner<T>` have. We should add it there too to make it easier and clearer how to get the underlying array from a writer.
### API breakdown
```csharp
namespace CommunityToolkit.HighPerformance.Buffers;
public sealed class ArrayPoolBufferWriter<T> : IBuffer<T>, IMemoryOwner<T>
{
[MethodImpl(MethodImplOptions.AggressiveInlining)]
public ArraySegment<T> DangerousGetArray();
}
```
### Usage example
```csharp
ArraySegment<byte> segment = bufferWriter.DangerousGetArray();
stream.Write(segment.Array!, segment.Offset, segment.Count);
```
### Breaking change?
No
### Alternatives
Use `MemoryMarshal.TryGetArray`. That's less clear and less discoverable, so not ideal.
### Additional context
_No response_
### Help us help you
Yes, I'd like to be assigned to work on this item | non_priority | add arraypoolbufferwriter dangerousgetarray api overview related to the arraypoolbufferwriter lacks the dangerousgetarray api which memoryowner and spanowner have we should add it there too to make it easier and clearer how to get the underlying array from a writer api breakdown csharp namespace communitytoolkit highperformance buffers public sealed class arraypoolbufferwriter ibuffer imemoryowner public arraysegment dangerousgetarray usage example csharp arraysegment segment bufferwriter dangerousgetarray stream write segment array segment offset segment count breaking change no alternatives use memorymarshal trygetarray that s less clear and less discoverable so not ideal additional context no response help us help you yes i d like to be assigned to work on this item | 0 |
76,964 | 21,638,319,981 | IssuesEvent | 2022-05-05 16:06:37 | facebook/rocksdb | https://api.github.com/repos/facebook/rocksdb | closed | Generate rocksdb.pc (pkg-config) file in CMake | enhancement up-for-grabs Build | Target `gen-pc` in Makefile generates `rocksdb.pc`.
https://github.com/facebook/rocksdb/blob/21218316dabca5ffd02e5d10793fb1894e3870ae/Makefile#L2097-L2108
Please, add this target in CMakeLists.txt and also add `install` step for this file. | 1.0 | Generate rocksdb.pc (pkg-config) file in CMake - Target `gen-pc` in Makefile generates `rocksdb.pc`.
https://github.com/facebook/rocksdb/blob/21218316dabca5ffd02e5d10793fb1894e3870ae/Makefile#L2097-L2108
Please, add this target in CMakeLists.txt and also add `install` step for this file. | non_priority | generate rocksdb pc pkg config file in cmake target gen pc in makefile generates rocksdb pc please add this target in cmakelists txt and also add install step for this file | 0 |
190,277 | 15,225,511,512 | IssuesEvent | 2021-02-18 07:26:44 | zwave-js/node-zwave-js | https://api.github.com/repos/zwave-js/node-zwave-js | closed | Missing docs | Documentation 📚 | - [ ] ConfigManager methods
- [ ] Command Classes available commands (should be auto generated someway)
cc @AlCalzone | 1.0 | Missing docs - - [ ] ConfigManager methods
- [ ] Command Classes available commands (should be auto generated someway)
cc @AlCalzone | non_priority | missing docs configmanager methods command classes available commands should be auto generated someway cc alcalzone | 0 |
210,001 | 16,329,659,197 | IssuesEvent | 2021-05-12 07:37:16 | pester/Pester | https://api.github.com/repos/pester/Pester | closed | invoke-pester ConfigurationProperty documentation issue | Documentation | <!-- Thank you for using Pester and taking the time to report this issue!
Known issue: Documentation of Pester 5 is mostly out of date for all commands. See [Breaking changes](https://github.com/pester/Pester#breaking-changes)
Command Reference documentation on the website are generated from comment-based help in the functions and should be reported here.
All other documentation issues on https://pester.dev should be reported in the [docs-repo](https://github.com/pester/docs). -->
## Location
https://pester.dev/docs/commands/Invoke-Pester#pesterconfigurationdefaulttestresult
- Pester version: 5
- Function: invoke-pester ConfigurationProperty
## General summary of the issue
(Deprecated v4) Replace with ConfigurationProperty TestResult.**OutputFile** The path where ...
Should be:
(Deprecated v4) Replace with ConfigurationProperty TestResult.**OutputPath** The path where ...
| 1.0 | invoke-pester ConfigurationProperty documentation issue - <!-- Thank you for using Pester and taking the time to report this issue!
Known issue: Documentation of Pester 5 is mostly out of date for all commands. See [Breaking changes](https://github.com/pester/Pester#breaking-changes)
Command Reference documentation on the website are generated from comment-based help in the functions and should be reported here.
All other documentation issues on https://pester.dev should be reported in the [docs-repo](https://github.com/pester/docs). -->
## Location
https://pester.dev/docs/commands/Invoke-Pester#pesterconfigurationdefaulttestresult
- Pester version: 5
- Function: invoke-pester ConfigurationProperty
## General summary of the issue
(Deprecated v4) Replace with ConfigurationProperty TestResult.**OutputFile** The path where ...
Should be:
(Deprecated v4) Replace with ConfigurationProperty TestResult.**OutputPath** The path where ...
| non_priority | invoke pester configurationproperty documentation issue thank you for using pester and taking the time to report this issue known issue documentation of pester is mostly out of date for all commands see command reference documentation on the website are generated from comment based help in the functions and should be reported here all other documentation issues on should be reported in the location pester version function invoke pester configurationproperty general summary of the issue deprecated replace with configurationproperty testresult outputfile the path where should be deprecated replace with configurationproperty testresult outputpath the path where | 0 |
162,730 | 12,687,951,280 | IssuesEvent | 2020-06-20 19:17:44 | Oldes/Rebol-issues | https://api.github.com/repos/Oldes/Rebol-issues | closed | DECIMAL! picking acting as SELECT, though it PICKed in Rebol2 | Oldes.resolved Test.written Type.note | _Submitted by:_ _**Hostilefork**_
In #2311 about SET-PATH!, it's mentioned that there is a [comment in the source for path dispatch of arrays](https://github.com/rebol/rebol/blob/25033f897b2bd466068d7663563cd3ff64740b94/src/core/t-block.c#L536). It mentions another issue regarding picking of DECIMAL!:
/* Issues!!!
a/1.3
a/not-found: 10 error or append?
a/not-followed: 10 error or append?
*/
[@Oldes observed](https://chat.stackoverflow.com/transcript/message/42915238#42915238) that decimal picking is odd:
>> b: [1 2] b/1.0
== 2
In Rebol2 it gives 1, and in Red it's currently an error which may just be an oversight (*Syntax Error: invalid integer! at "b/1.0"*)
The reason it has its behavior in R3-Alpha is because only INTEGER! has the ability to do indexing, everything else is being looked at for equivalence. So the `b/1.0` is like `SELECT b 1.0`.
Rebol2 appears to just round the number down and use it as an index:
>> data: [a b]
== [a b]
>> data/0.5
== none
>> data/1.0
== a
>> data/1.8
== a
>> data/1.9999999
== a
>> data/2
== b
Since it is numeric, the SELECT behavior is almost certainly never what people intend. For the moment, Ren-C changes it to the Rebol2 behavior by adding IS_DECIMAL() branches, and letting Int32() convert it (VECTOR! was already doing this for some reason):
https://github.com/metaeducation/ren-c/pull/818
But a valid question is whether it should be an error, since selecting at index 1.99999 and getting the first thing is a bit random.
> "Should array indices start at 0 or 1? My compromise of 0.5 was rejected without, I thought, proper consideration." [Stan Kelly-Bootle](https://en.wikipedia.org/wiki/Stan_Kelly-Bootle)
---
<sup>**Imported from**: https://github.com/rebol/rebol-issues/issues/2312</sup>
Comments:
---
---
> **Hostilefork** added the **Type.note** on Jun 14, 2018
---
> **Oldes** added a commit to **[Oldes/Rebol3](https://github.com/Oldes/Rebol3/)** that referenced this issue on Jun 14, 2018:
> [FIX: DECIMAL! picking acting as SELECT, though it PICKed in Rebol2](https://github.com/Oldes/Rebol3/commit/6202a850c610bd2596cbb22d1fda21ab9dddbb23)
--- | 1.0 | DECIMAL! picking acting as SELECT, though it PICKed in Rebol2 - _Submitted by:_ _**Hostilefork**_
In #2311 about SET-PATH!, it's mentioned that there is a [comment in the source for path dispatch of arrays](https://github.com/rebol/rebol/blob/25033f897b2bd466068d7663563cd3ff64740b94/src/core/t-block.c#L536). It mentions another issue regarding picking of DECIMAL!:
/* Issues!!!
a/1.3
a/not-found: 10 error or append?
a/not-followed: 10 error or append?
*/
[@Oldes observed](https://chat.stackoverflow.com/transcript/message/42915238#42915238) that decimal picking is odd:
>> b: [1 2] b/1.0
== 2
In Rebol2 it gives 1, and in Red it's currently an error which may just be an oversight (*Syntax Error: invalid integer! at "b/1.0"*)
The reason it has its behavior in R3-Alpha is because only INTEGER! has the ability to do indexing, everything else is being looked at for equivalence. So the `b/1.0` is like `SELECT b 1.0`.
Rebol2 appears to just round the number down and use it as an index:
>> data: [a b]
== [a b]
>> data/0.5
== none
>> data/1.0
== a
>> data/1.8
== a
>> data/1.9999999
== a
>> data/2
== b
Since it is numeric, the SELECT behavior is almost certainly never what people intend. For the moment, Ren-C changes it to the Rebol2 behavior by adding IS_DECIMAL() branches, and letting Int32() convert it (VECTOR! was already doing this for some reason):
https://github.com/metaeducation/ren-c/pull/818
But a valid question is whether it should be an error, since selecting at index 1.99999 and getting the first thing is a bit random.
> "Should array indices start at 0 or 1? My compromise of 0.5 was rejected without, I thought, proper consideration." [Stan Kelly-Bootle](https://en.wikipedia.org/wiki/Stan_Kelly-Bootle)
---
<sup>**Imported from**: https://github.com/rebol/rebol-issues/issues/2312</sup>
Comments:
---
---
> **Hostilefork** added the **Type.note** on Jun 14, 2018
---
> **Oldes** added a commit to **[Oldes/Rebol3](https://github.com/Oldes/Rebol3/)** that referenced this issue on Jun 14, 2018:
> [FIX: DECIMAL! picking acting as SELECT, though it PICKed in Rebol2](https://github.com/Oldes/Rebol3/commit/6202a850c610bd2596cbb22d1fda21ab9dddbb23)
--- | non_priority | decimal picking acting as select though it picked in submitted by hostilefork in about set path it s mentioned that there is a it mentions another issue regarding picking of decimal issues a a not found error or append a not followed error or append that decimal picking is odd b b in it gives and in red it s currently an error which may just be an oversight syntax error invalid integer at b the reason it has its behavior in alpha is because only integer has the ability to do indexing everything else is being looked at for equivalence so the b is like select b appears to just round the number down and use it as an index data data none data a data a data a data b since it is numeric the select behavior is almost certainly never what people intend for the moment ren c changes it to the behavior by adding is decimal branches and letting convert it vector was already doing this for some reason but a valid question is whether it should be an error since selecting at index and getting the first thing is a bit random should array indices start at or my compromise of was rejected without i thought proper consideration imported from comments hostilefork added the type note on jun oldes added a commit to that referenced this issue on jun | 0 |
40,431 | 6,823,593,987 | IssuesEvent | 2017-11-08 00:50:11 | oracle/terraform-kubernetes-installer | https://api.github.com/repos/oracle/terraform-kubernetes-installer | closed | Provide instructions about how to upgrade k8s to newer version | documentation | Since there is no kubeadm, so can't use kubeadm to upgrade k8s.
It will be best if can provide a instruction for upgrade k8s with this installer. Thanks! | 1.0 | Provide instructions about how to upgrade k8s to newer version - Since there is no kubeadm, so can't use kubeadm to upgrade k8s.
It will be best if can provide a instruction for upgrade k8s with this installer. Thanks! | non_priority | provide instructions about how to upgrade to newer version since there is no kubeadm so can t use kubeadm to upgrade it will be best if can provide a instruction for upgrade with this installer thanks | 0 |
245,753 | 26,550,961,752 | IssuesEvent | 2023-01-20 07:39:40 | Trinadh465/linux-4.1.15 | https://api.github.com/repos/Trinadh465/linux-4.1.15 | opened | CVE-2016-7097 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2016-7097 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b>, <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The filesystem implementation in the Linux kernel through 4.8.2 preserves the setgid bit during a setxattr call, which allows local users to gain group privileges by leveraging the existence of a setgid program with restrictions on execute permissions.
<p>Publish Date: 2016-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-7097>CVE-2016-7097</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-7097">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-7097</a></p>
<p>Release Date: 2016-10-16</p>
<p>Fix Resolution: v4.9-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-7097 (Medium) detected in multiple libraries - ## CVE-2016-7097 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b>, <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The filesystem implementation in the Linux kernel through 4.8.2 preserves the setgid bit during a setxattr call, which allows local users to gain group privileges by leveraging the existence of a setgid program with restrictions on execute permissions.
<p>Publish Date: 2016-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-7097>CVE-2016-7097</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-7097">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-7097</a></p>
<p>Release Date: 2016-10-16</p>
<p>Fix Resolution: v4.9-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries linux stable linuxlinux linux stable linux stable linuxlinux linuxlinux linuxlinux linuxlinux linuxlinux linuxlinux linuxlinux linux stable linux stable linuxlinux vulnerability details the filesystem implementation in the linux kernel through preserves the setgid bit during a setxattr call which allows local users to gain group privileges by leveraging the existence of a setgid program with restrictions on execute permissions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
64,102 | 8,710,926,590 | IssuesEvent | 2018-12-06 17:42:04 | adobe/spectrum-css | https://api.github.com/repos/adobe/spectrum-css | closed | Poor Scrolling Performance on CSS Demo/Documentation Page in Chrome/Safari | documentation performance | ### Expected Behavior
Scrolling through demos/documentation should be buttery smooth.
### Actual Behavior
Scrolling is very jerky, making for a poor experience.
### Reproduce Scenario (including but not limited to)
Visit [the documentation](http://opensource.adobe.com/spectrum-css/) and scroll in certain browsers.
#### Steps to Reproduce
1. Open the documentation using Chrome or Safari.
1. Navigate to the [demo/documentation](http://opensource.adobe.com/spectrum-css/) page.
1. Scroll the page at high speed.
**\*** Firefox 63 does not exhibit this issue, though its Performance developer tools may provide further insights when investigating.
#### Browser name/version/os
* Chrome Version 70.0.3538.77 (Official Build) (64-bit)
* Safari Version 12.0.1 (14606.2.104.1.1)
Both tested on macOS 10.14.1.
#### Spectrum-CSS version
2.5.1
#### Sample Code that illustrates the problem
N/A
#### Screenshots (if applicable)
N/A | 1.0 | Poor Scrolling Performance on CSS Demo/Documentation Page in Chrome/Safari - ### Expected Behavior
Scrolling through demos/documentation should be buttery smooth.
### Actual Behavior
Scrolling is very jerky, making for a poor experience.
### Reproduce Scenario (including but not limited to)
Visit [the documentation](http://opensource.adobe.com/spectrum-css/) and scroll in certain browsers.
#### Steps to Reproduce
1. Open the documentation using Chrome or Safari.
1. Navigate to the [demo/documentation](http://opensource.adobe.com/spectrum-css/) page.
1. Scroll the page at high speed.
**\*** Firefox 63 does not exhibit this issue, though its Performance developer tools may provide further insights when investigating.
#### Browser name/version/os
* Chrome Version 70.0.3538.77 (Official Build) (64-bit)
* Safari Version 12.0.1 (14606.2.104.1.1)
Both tested on macOS 10.14.1.
#### Spectrum-CSS version
2.5.1
#### Sample Code that illustrates the problem
N/A
#### Screenshots (if applicable)
N/A | non_priority | poor scrolling performance on css demo documentation page in chrome safari expected behavior scrolling through demos documentation should be buttery smooth actual behavior scrolling is very jerky making for a poor experience reproduce scenario including but not limited to visit and scroll in certain browsers steps to reproduce open the documentation using chrome or safari navigate to the page scroll the page at high speed firefox does not exhibit this issue though its performance developer tools may provide further insights when investigating browser name version os chrome version official build bit safari version both tested on macos spectrum css version sample code that illustrates the problem n a screenshots if applicable n a | 0 |
54,785 | 13,925,979,095 | IssuesEvent | 2020-10-21 17:37:12 | polatengin/B05277 | https://api.github.com/repos/polatengin/B05277 | opened | CVE-2018-1000620 (High) detected in cryptiles-2.0.5.tgz | security vulnerability | ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: B05277/Chapter03/2-CompilingLessFilesToCSSFilesWithGrunt/package.json</p>
<p>Path to vulnerable library: B05277/Chapter03/2-CompilingLessFilesToCSSFilesWithGrunt/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-less-1.4.1.tgz (Root Library)
- less-2.7.3.tgz
- request-2.81.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/polatengin/B05277/commit/17c9aaaa23bce244f17eb788d2e53f21061314da">17c9aaaa23bce244f17eb788d2e53f21061314da</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-1000620 (High) detected in cryptiles-2.0.5.tgz - ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: B05277/Chapter03/2-CompilingLessFilesToCSSFilesWithGrunt/package.json</p>
<p>Path to vulnerable library: B05277/Chapter03/2-CompilingLessFilesToCSSFilesWithGrunt/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-less-1.4.1.tgz (Root Library)
- less-2.7.3.tgz
- request-2.81.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/polatengin/B05277/commit/17c9aaaa23bce244f17eb788d2e53f21061314da">17c9aaaa23bce244f17eb788d2e53f21061314da</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in cryptiles tgz cve high severity vulnerability vulnerable library cryptiles tgz general purpose crypto utilities library home page a href path to dependency file compilinglessfilestocssfileswithgrunt package json path to vulnerable library compilinglessfilestocssfileswithgrunt node modules cryptiles package json dependency hierarchy grunt contrib less tgz root library less tgz request tgz hawk tgz x cryptiles tgz vulnerable library found in head commit a href found in base branch master vulnerability details eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
128,605 | 18,063,393,204 | IssuesEvent | 2021-09-20 16:12:24 | turkdevops/playwright | https://api.github.com/repos/turkdevops/playwright | opened | CVE-2021-3807 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2021-3807 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ansi-regex-4.1.0.tgz</b>, <b>ansi-regex-2.1.1.tgz</b>, <b>ansi-regex-5.0.0.tgz</b></p></summary>
<p>
<details><summary><b>ansi-regex-4.1.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz</a></p>
<p>Path to dependency file: playwright/package.json</p>
<p>Path to vulnerable library: playwright/node_modules/yargs/node_modules/ansi-regex/package.json,playwright/node_modules/wrap-ansi/node_modules/ansi-regex/package.json,playwright/node_modules/cliui/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- webpack-cli-3.3.12.tgz (Root Library)
- yargs-13.3.2.tgz
- string-width-3.1.0.tgz
- strip-ansi-5.2.0.tgz
- :x: **ansi-regex-4.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>ansi-regex-2.1.1.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-2.1.1.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-2.1.1.tgz</a></p>
<p>Path to dependency file: playwright/package.json</p>
<p>Path to vulnerable library: playwright/node_modules/renderkid/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- html-webpack-plugin-4.5.2.tgz (Root Library)
- pretty-error-2.1.2.tgz
- renderkid-2.0.5.tgz
- strip-ansi-3.0.1.tgz
- :x: **ansi-regex-2.1.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ansi-regex-5.0.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz</a></p>
<p>Path to dependency file: playwright/package.json</p>
<p>Path to vulnerable library: playwright/node_modules/ansi-regex/package.json,playwright/packages/create-playwright/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- eslint-7.31.0.tgz (Root Library)
- strip-ansi-6.0.0.tgz
- :x: **ansi-regex-5.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/playwright/commit/2d130c23295d3d1b5f667670cd944de159affe05">2d130c23295d3d1b5f667670cd944de159affe05</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: ansi-regex - 5.0.1,6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3807 (Medium) detected in multiple libraries - ## CVE-2021-3807 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ansi-regex-4.1.0.tgz</b>, <b>ansi-regex-2.1.1.tgz</b>, <b>ansi-regex-5.0.0.tgz</b></p></summary>
<p>
<details><summary><b>ansi-regex-4.1.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-4.1.0.tgz</a></p>
<p>Path to dependency file: playwright/package.json</p>
<p>Path to vulnerable library: playwright/node_modules/yargs/node_modules/ansi-regex/package.json,playwright/node_modules/wrap-ansi/node_modules/ansi-regex/package.json,playwright/node_modules/cliui/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- webpack-cli-3.3.12.tgz (Root Library)
- yargs-13.3.2.tgz
- string-width-3.1.0.tgz
- strip-ansi-5.2.0.tgz
- :x: **ansi-regex-4.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>ansi-regex-2.1.1.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-2.1.1.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-2.1.1.tgz</a></p>
<p>Path to dependency file: playwright/package.json</p>
<p>Path to vulnerable library: playwright/node_modules/renderkid/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- html-webpack-plugin-4.5.2.tgz (Root Library)
- pretty-error-2.1.2.tgz
- renderkid-2.0.5.tgz
- strip-ansi-3.0.1.tgz
- :x: **ansi-regex-2.1.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ansi-regex-5.0.0.tgz</b></p></summary>
<p>Regular expression for matching ANSI escape codes</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz">https://registry.npmjs.org/ansi-regex/-/ansi-regex-5.0.0.tgz</a></p>
<p>Path to dependency file: playwright/package.json</p>
<p>Path to vulnerable library: playwright/node_modules/ansi-regex/package.json,playwright/packages/create-playwright/node_modules/ansi-regex/package.json</p>
<p>
Dependency Hierarchy:
- eslint-7.31.0.tgz (Root Library)
- strip-ansi-6.0.0.tgz
- :x: **ansi-regex-5.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/playwright/commit/2d130c23295d3d1b5f667670cd944de159affe05">2d130c23295d3d1b5f667670cd944de159affe05</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ansi-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3807>CVE-2021-3807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/">https://huntr.dev/bounties/5b3cf33b-ede0-4398-9974-800876dfd994/</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: ansi-regex - 5.0.1,6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries ansi regex tgz ansi regex tgz ansi regex tgz ansi regex tgz regular expression for matching ansi escape codes library home page a href path to dependency file playwright package json path to vulnerable library playwright node modules yargs node modules ansi regex package json playwright node modules wrap ansi node modules ansi regex package json playwright node modules cliui node modules ansi regex package json dependency hierarchy webpack cli tgz root library yargs tgz string width tgz strip ansi tgz x ansi regex tgz vulnerable library ansi regex tgz regular expression for matching ansi escape codes library home page a href path to dependency file playwright package json path to vulnerable library playwright node modules renderkid node modules ansi regex package json dependency hierarchy html webpack plugin tgz root library pretty error tgz renderkid tgz strip ansi tgz x ansi regex tgz vulnerable library ansi regex tgz regular expression for matching ansi escape codes library home page a href path to dependency file playwright package json path to vulnerable library playwright node modules ansi regex package json playwright packages create playwright node modules ansi regex package json dependency hierarchy eslint tgz root library strip ansi tgz x ansi regex tgz vulnerable library found in head commit a href found in base branch master vulnerability details ansi regex is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ansi regex step up your open source security game with whitesource | 0 |
282,710 | 21,315,896,523 | IssuesEvent | 2022-04-16 09:08:45 | warrencxw/pe | https://api.github.com/repos/warrencxw/pe | opened | Missing unmark feature in table of contents | severity.Low type.DocumentationBug |
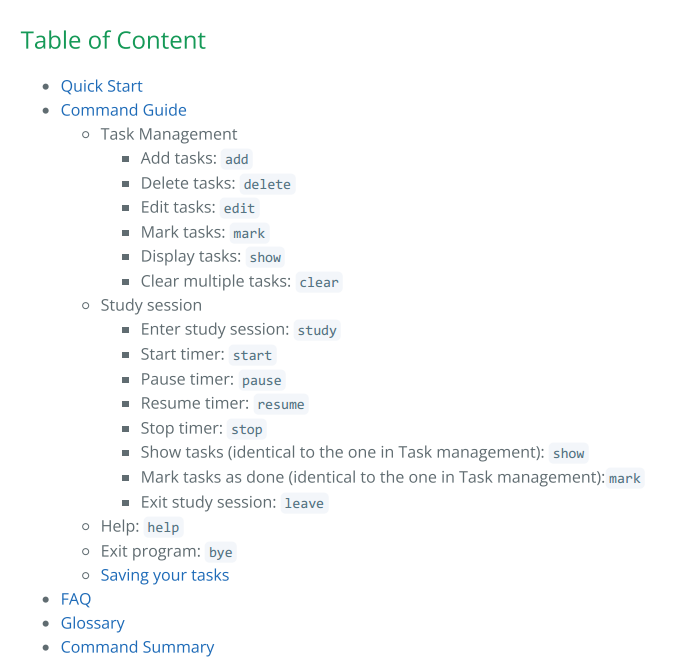
In the UG's table of contents, there is no mentioning of the `unmark` functionality. This can be exceptionally misleading when a user is attempting to look for a way to unmark task using the user guide and cannot find it.
<!--session: 1650096028979-949b02c2-1fd6-4db9-9b86-833d0cb39bcb-->
<!--Version: Web v3.4.2--> | 1.0 | Missing unmark feature in table of contents -
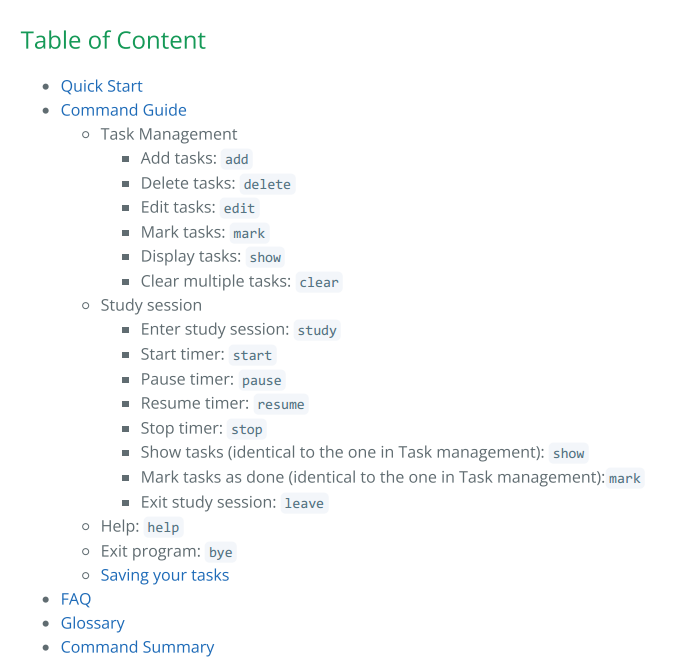
In the UG's table of contents, there is no mentioning of the `unmark` functionality. This can be exceptionally misleading when a user is attempting to look for a way to unmark task using the user guide and cannot find it.
<!--session: 1650096028979-949b02c2-1fd6-4db9-9b86-833d0cb39bcb-->
<!--Version: Web v3.4.2--> | non_priority | missing unmark feature in table of contents in the ug s table of contents there is no mentioning of the unmark functionality this can be exceptionally misleading when a user is attempting to look for a way to unmark task using the user guide and cannot find it | 0 |
107,190 | 16,751,651,621 | IssuesEvent | 2021-06-12 01:38:38 | gms-ws-demo/nibrs | https://api.github.com/repos/gms-ws-demo/nibrs | opened | CVE-2017-18640 (High) detected in multiple libraries | security vulnerability | ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>snakeyaml-1.19.jar</b>, <b>snakeyaml-1.17.jar</b>, <b>snakeyaml-1.23.jar</b></p></summary>
<p>
<details><summary><b>snakeyaml-1.19.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-validation/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
</details>
<details><summary><b>snakeyaml-1.17.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/snakeyaml-1.17.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.17/snakeyaml-1.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **snakeyaml-1.17.jar** (Vulnerable Library)
</details>
<details><summary><b>snakeyaml-1.23.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-2.1.5.RELEASE.jar
- :x: **snakeyaml-1.23.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Alias feature in SnakeYAML 1.18 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.26</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.yaml","packageName":"snakeyaml","packageVersion":"1.19","packageFilePaths":["/tools/nibrs-validation/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-validate-common/pom.xml","/web/nibrs-web/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-staging-data/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.yaml:snakeyaml:1.19","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.yaml:snakeyaml:1.26"},{"packageType":"Java","groupId":"org.yaml","packageName":"snakeyaml","packageVersion":"1.17","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.yaml:snakeyaml:1.17","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.yaml:snakeyaml:1.26"},{"packageType":"Java","groupId":"org.yaml","packageName":"snakeyaml","packageVersion":"1.23","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter:2.1.5.RELEASE;org.yaml:snakeyaml:1.23","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.yaml:snakeyaml:1.26"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-18640","vulnerabilityDetails":"The Alias feature in SnakeYAML 1.18 allows entity expansion during a load operation, a related issue to CVE-2003-1564.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-18640 (High) detected in multiple libraries - ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>snakeyaml-1.19.jar</b>, <b>snakeyaml-1.17.jar</b>, <b>snakeyaml-1.23.jar</b></p></summary>
<p>
<details><summary><b>snakeyaml-1.19.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-validation/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.19/snakeyaml-1.19.jar</p>
<p>
Dependency Hierarchy:
- :x: **snakeyaml-1.19.jar** (Vulnerable Library)
</details>
<details><summary><b>snakeyaml-1.17.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/snakeyaml-1.17.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.17/snakeyaml-1.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **snakeyaml-1.17.jar** (Vulnerable Library)
</details>
<details><summary><b>snakeyaml-1.23.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.23/snakeyaml-1.23.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-2.1.5.RELEASE.jar
- :x: **snakeyaml-1.23.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Alias feature in SnakeYAML 1.18 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.26</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.yaml","packageName":"snakeyaml","packageVersion":"1.19","packageFilePaths":["/tools/nibrs-validation/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-validate-common/pom.xml","/web/nibrs-web/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-staging-data/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.yaml:snakeyaml:1.19","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.yaml:snakeyaml:1.26"},{"packageType":"Java","groupId":"org.yaml","packageName":"snakeyaml","packageVersion":"1.17","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.yaml:snakeyaml:1.17","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.yaml:snakeyaml:1.26"},{"packageType":"Java","groupId":"org.yaml","packageName":"snakeyaml","packageVersion":"1.23","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter:2.1.5.RELEASE;org.yaml:snakeyaml:1.23","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.yaml:snakeyaml:1.26"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-18640","vulnerabilityDetails":"The Alias feature in SnakeYAML 1.18 allows entity expansion during a load operation, a related issue to CVE-2003-1564.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries snakeyaml jar snakeyaml jar snakeyaml jar snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file nibrs tools nibrs validation pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar nibrs web nibrs web target nibrs web web inf lib snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy x snakeyaml jar vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file nibrs tools nibrs fbi service pom xml path to vulnerable library nibrs tools nibrs fbi service target nibrs fbi service web inf lib snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy x snakeyaml jar vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file nibrs tools nibrs summary report common pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy spring boot starter web release jar root library spring boot starter release jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details the alias feature in snakeyaml allows entity expansion during a load operation a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org yaml snakeyaml isminimumfixversionavailable true minimumfixversion org yaml snakeyaml packagetype java groupid org yaml packagename snakeyaml packageversion packagefilepaths istransitivedependency false dependencytree org yaml snakeyaml isminimumfixversionavailable true minimumfixversion org yaml snakeyaml packagetype java groupid org yaml packagename snakeyaml packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter release org yaml snakeyaml isminimumfixversionavailable true minimumfixversion org yaml snakeyaml basebranches vulnerabilityidentifier cve vulnerabilitydetails the alias feature in snakeyaml allows entity expansion during a load operation a related issue to cve vulnerabilityurl | 0 |
15,102 | 10,254,341,258 | IssuesEvent | 2019-08-21 13:22:27 | aws/aws-cdk | https://api.github.com/repos/aws/aws-cdk | closed | imageName undefined when applying fromEcrRepository cdk 1.0.0 | bug needs-repro service/ecr | **Note: for support questions, please first reference our [documentation](https://docs.aws.amazon.com/cdk/api/latest), then use [Stackoverflow](https://stackoverflow.com/questions/ask?tags=aws-cdk)**. This repository's issues are intended for feature requests and bug reports.
* **I'm submitting a ...**
- [x ] :beetle: bug report
- [ ] :rocket: feature request
- [ ] :books: construct library gap
- [ ] :phone: security issue or vulnerability => Please see [policy](https://github.com/awslabs/aws-cdk/security/policy)
- [ ] :question: support request => Please see note at the top of this template.
* **What is the current behavior?**
*If the current behavior is a :beetle:bug:beetle:: Please provide the steps to reproduce*
I have the following Stack for a batch job. A deployed docker image exists in ECR
```js
export class BatchJobStack extends cdk.Stack {
constructor(scope: cdk.Construct, id: string, props?: cdk.StackProps) {
super(scope, id, props);
const repo = Repository.fromRepositoryArn(this, 'JobImage', 'arn:aws:ecr:XXXXXXX:XXXXXX:repository/XXXXXX-batch-job')
const image = EcrImage.fromEcrRepository(repo)
console.log("++++++++++" + image.imageName)
const jobRole = new iam.CfnRole(this, "job-role",{
path: '/service/',
roleName: "update-job-role",
assumeRolePolicyDocument : new iam.PolicyDocument({
statements: [
new iam.PolicyStatement(
{
principals: [
new iam.ServicePrincipal("ecs-tasks.amazonaws.com"),
new iam.ArnPrincipal("arn:aws:iam::XXXXXXXXXX:root")
],
actions: [ "sts:AssumeRole"]
})
]
}),
policies: [
{
policyDocument: new iam.PolicyDocument({
statements:[
new iam.PolicyStatement({
actions: ["kms:Decrypt"],
resources :[
`arn:aws:kms:${this.region}:${this.account}:alias/*`,
`arn:aws:kms:${this.region}:${this.account}:key/*`
]
}
),
new iam.PolicyStatement({
actions: ["secretsmanager:GetSecretValue"],
resources: ["arn:aws:secretsmanager:XXXXXXX:XXXXXXX:secret:XXXXXX"]
}
)
]
}
),
policyName: "job-policy"
}
]
})
const jobDef = new batch.CfnJobDefinition(this, "job-def", {
jobDefinitionName: "job",
type: "container",
retryStrategy: {
attempts: 2
},
containerProperties:
{
memory: 512,
vcpus: 1,
image: image.imageName,
command: ["python3", "do_sth.py"]
}
})
}
}
```
Execution of `cdk synth` the following error message comes up:
```sh
++++++++++undefined
/node_modules/@aws-cdk/core/lib/runtime.ts:141
throw new CfnSynthesisError(message);
^
Error: Resolution error: Supplied properties not correct for "CfnJobDefinitionProps"
containerProperties: supplied properties not correct for "ContainerPropertiesProperty"
image: required but missing.
Object creation stack:
at new Intrinsic (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/intrinsic.ts:28:26)
at new PostResolveToken (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/util.ts:83:5)
at CfnJobDefinition._toCloudFormation (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/cfn-resource.ts:222:29)
at /Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/stack.ts:556:56
at Array.map (<anonymous>)
at BatchJobAppCdk10Stack._toCloudFormation (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/stack.ts:556:32)
at BatchJobAppCdk10Stack.synthesize (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/stack.ts:518:51)
at Function.synth (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/construct.ts:59:28)
at App.synth (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/app.ts:128:36)
at process.<anonymous> (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/app.ts:111:45)
at Object.onceWrapper (events.js:291:20)
at process.emit (events.js:203:13)
at process.EventEmitter.emit (domain.js:471:20)
at process.emit (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/source-map-support/source-map-support.js:465:21)
at process.topLevelDomainCallback (domain.js:126:23)
at ValidationResult.assertSuccess (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/runtime.ts:141:13)
at cfnJobDefinitionPropsToCloudFormation (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/aws-batch/lib/batch.generated.ts:454:48)
at CfnJobDefinition.renderProperties (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/aws-batch/lib/batch.generated.ts:553:16)
at PostResolveToken.ret.Resources [as processor] (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/cfn-resource.ts:233:40)
at PostResolveToken.postProcess (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/util.ts:92:17)
at Object.postProcess (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:50:78)
at DefaultTokenResolver.resolveToken (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/resolvable.ts:133:32)
at resolve (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:131:29)
at Object.resolve (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:47:32)
at resolve (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:152:39)
Subprocess exited with error 1
```
As the console.log shows, the image name seems not to be set.
* **Please tell us about your environment:**
- CDK CLI Version: 1.0.0
- Module Version:1.0.0
- OS: [OSX High Sierra ]
- Language: [TypeScript ]
* **Other information** (e.g. detailed explanation, stacktraces, related issues, suggestions how to fix, links for us to have context, eg. associated pull-request, stackoverflow, gitter, etc)
- stack runs smoothly in cdk 0.33. (with undoing breaking changes)
| 1.0 | imageName undefined when applying fromEcrRepository cdk 1.0.0 - **Note: for support questions, please first reference our [documentation](https://docs.aws.amazon.com/cdk/api/latest), then use [Stackoverflow](https://stackoverflow.com/questions/ask?tags=aws-cdk)**. This repository's issues are intended for feature requests and bug reports.
* **I'm submitting a ...**
- [x ] :beetle: bug report
- [ ] :rocket: feature request
- [ ] :books: construct library gap
- [ ] :phone: security issue or vulnerability => Please see [policy](https://github.com/awslabs/aws-cdk/security/policy)
- [ ] :question: support request => Please see note at the top of this template.
* **What is the current behavior?**
*If the current behavior is a :beetle:bug:beetle:: Please provide the steps to reproduce*
I have the following Stack for a batch job. A deployed docker image exists in ECR
```js
export class BatchJobStack extends cdk.Stack {
constructor(scope: cdk.Construct, id: string, props?: cdk.StackProps) {
super(scope, id, props);
const repo = Repository.fromRepositoryArn(this, 'JobImage', 'arn:aws:ecr:XXXXXXX:XXXXXX:repository/XXXXXX-batch-job')
const image = EcrImage.fromEcrRepository(repo)
console.log("++++++++++" + image.imageName)
const jobRole = new iam.CfnRole(this, "job-role",{
path: '/service/',
roleName: "update-job-role",
assumeRolePolicyDocument : new iam.PolicyDocument({
statements: [
new iam.PolicyStatement(
{
principals: [
new iam.ServicePrincipal("ecs-tasks.amazonaws.com"),
new iam.ArnPrincipal("arn:aws:iam::XXXXXXXXXX:root")
],
actions: [ "sts:AssumeRole"]
})
]
}),
policies: [
{
policyDocument: new iam.PolicyDocument({
statements:[
new iam.PolicyStatement({
actions: ["kms:Decrypt"],
resources :[
`arn:aws:kms:${this.region}:${this.account}:alias/*`,
`arn:aws:kms:${this.region}:${this.account}:key/*`
]
}
),
new iam.PolicyStatement({
actions: ["secretsmanager:GetSecretValue"],
resources: ["arn:aws:secretsmanager:XXXXXXX:XXXXXXX:secret:XXXXXX"]
}
)
]
}
),
policyName: "job-policy"
}
]
})
const jobDef = new batch.CfnJobDefinition(this, "job-def", {
jobDefinitionName: "job",
type: "container",
retryStrategy: {
attempts: 2
},
containerProperties:
{
memory: 512,
vcpus: 1,
image: image.imageName,
command: ["python3", "do_sth.py"]
}
})
}
}
```
Execution of `cdk synth` the following error message comes up:
```sh
++++++++++undefined
/node_modules/@aws-cdk/core/lib/runtime.ts:141
throw new CfnSynthesisError(message);
^
Error: Resolution error: Supplied properties not correct for "CfnJobDefinitionProps"
containerProperties: supplied properties not correct for "ContainerPropertiesProperty"
image: required but missing.
Object creation stack:
at new Intrinsic (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/intrinsic.ts:28:26)
at new PostResolveToken (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/util.ts:83:5)
at CfnJobDefinition._toCloudFormation (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/cfn-resource.ts:222:29)
at /Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/stack.ts:556:56
at Array.map (<anonymous>)
at BatchJobAppCdk10Stack._toCloudFormation (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/stack.ts:556:32)
at BatchJobAppCdk10Stack.synthesize (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/stack.ts:518:51)
at Function.synth (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/construct.ts:59:28)
at App.synth (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/app.ts:128:36)
at process.<anonymous> (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/app.ts:111:45)
at Object.onceWrapper (events.js:291:20)
at process.emit (events.js:203:13)
at process.EventEmitter.emit (domain.js:471:20)
at process.emit (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/source-map-support/source-map-support.js:465:21)
at process.topLevelDomainCallback (domain.js:126:23)
at ValidationResult.assertSuccess (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/runtime.ts:141:13)
at cfnJobDefinitionPropsToCloudFormation (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/aws-batch/lib/batch.generated.ts:454:48)
at CfnJobDefinition.renderProperties (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/aws-batch/lib/batch.generated.ts:553:16)
at PostResolveToken.ret.Resources [as processor] (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/cfn-resource.ts:233:40)
at PostResolveToken.postProcess (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/util.ts:92:17)
at Object.postProcess (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:50:78)
at DefaultTokenResolver.resolveToken (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/resolvable.ts:133:32)
at resolve (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:131:29)
at Object.resolve (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:47:32)
at resolve (/Users/nikolaus.werner/PycharmProjects/ep-dna-ekg-reporting/batch-job-app-cdk-1.0/node_modules/@aws-cdk/core/lib/private/resolve.ts:152:39)
Subprocess exited with error 1
```
As the console.log shows, the image name seems not to be set.
* **Please tell us about your environment:**
- CDK CLI Version: 1.0.0
- Module Version:1.0.0
- OS: [OSX High Sierra ]
- Language: [TypeScript ]
* **Other information** (e.g. detailed explanation, stacktraces, related issues, suggestions how to fix, links for us to have context, eg. associated pull-request, stackoverflow, gitter, etc)
- stack runs smoothly in cdk 0.33. (with undoing breaking changes)
| non_priority | imagename undefined when applying fromecrrepository cdk note for support questions please first reference our then use this repository s issues are intended for feature requests and bug reports i m submitting a beetle bug report rocket feature request books construct library gap phone security issue or vulnerability please see question support request please see note at the top of this template what is the current behavior if the current behavior is a beetle bug beetle please provide the steps to reproduce i have the following stack for a batch job a deployed docker image exists in ecr js export class batchjobstack extends cdk stack constructor scope cdk construct id string props cdk stackprops super scope id props const repo repository fromrepositoryarn this jobimage arn aws ecr xxxxxxx xxxxxx repository xxxxxx batch job const image ecrimage fromecrrepository repo console log image imagename const jobrole new iam cfnrole this job role path service rolename update job role assumerolepolicydocument new iam policydocument statements new iam policystatement principals new iam serviceprincipal ecs tasks amazonaws com new iam arnprincipal arn aws iam xxxxxxxxxx root actions policies policydocument new iam policydocument statements new iam policystatement actions resources arn aws kms this region this account alias arn aws kms this region this account key new iam policystatement actions resources policyname job policy const jobdef new batch cfnjobdefinition this job def jobdefinitionname job type container retrystrategy attempts containerproperties memory vcpus image image imagename command execution of cdk synth the following error message comes up sh undefined node modules aws cdk core lib runtime ts throw new cfnsynthesiserror message error resolution error supplied properties not correct for cfnjobdefinitionprops containerproperties supplied properties not correct for containerpropertiesproperty image required but missing object creation stack at new intrinsic users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib private intrinsic ts at new postresolvetoken users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib util ts at cfnjobdefinition tocloudformation users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib cfn resource ts at users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib stack ts at array map at tocloudformation users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib stack ts at synthesize users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib stack ts at function synth users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib construct ts at app synth users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib app ts at process users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib app ts at object oncewrapper events js at process emit events js at process eventemitter emit domain js at process emit users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules source map support source map support js at process topleveldomaincallback domain js at validationresult assertsuccess users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib runtime ts at cfnjobdefinitionpropstocloudformation users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk aws batch lib batch generated ts at cfnjobdefinition renderproperties users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk aws batch lib batch generated ts at postresolvetoken ret resources users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib cfn resource ts at postresolvetoken postprocess users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib util ts at object postprocess users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib private resolve ts at defaulttokenresolver resolvetoken users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib resolvable ts at resolve users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib private resolve ts at object resolve users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib private resolve ts at resolve users nikolaus werner pycharmprojects ep dna ekg reporting batch job app cdk node modules aws cdk core lib private resolve ts subprocess exited with error as the console log shows the image name seems not to be set please tell us about your environment cdk cli version module version os language other information e g detailed explanation stacktraces related issues suggestions how to fix links for us to have context eg associated pull request stackoverflow gitter etc stack runs smoothly in cdk with undoing breaking changes | 0 |
9,048 | 7,540,542,594 | IssuesEvent | 2018-04-17 06:53:35 | molgenis/molgenis | https://api.github.com/repos/molgenis/molgenis | closed | Logout in R API does not log out | 5.2 bug mod:security | ### How to Reproduce
Based on analysis demo script:
http://www.molgenis.org/attachment/wiki/research/molgenis_research_demoanalysis_Smith_Kruglyak_2008.R
New session, not logged in, gives error instead of data (OK)
```
> yeastdata <- molgenis.get("base_yeast_geno_pheno_map")
> yeastdata
[1] X.html..head..title.Apache.Tomcat.7.0.78...Error.report..title..style.....H1..font.family.Tahoma
[2] Arial
[3] sans.serif.color.white.background.color..525D76.font.size.22px...H2..font.family.Tahoma
[4] Arial.1
[5] sans.serif.color.white.background.color..525D76.font.size.16px...H3..font.family.Tahoma
[6] Arial.2
[7] sans.serif.color.white.background.color..525D76.font.size.14px...BODY..font.family.Tahoma
[8] Arial.3
[9] sans.serif.color.black.background.color.white...B..font.family.Tahoma
[10] Arial.4
[11] sans.serif.color.white.background.color..525D76...P..font.family.Tahoma
[12] Arial.5
[13] sans.serif.background.white.color.black.font.size.12px..A..color...black..A.name..color...black..HR..color....525D76.......style....head..body..h1.HTTP.Status.401.....h1..HR.size.1.noshade.noshade..p..b.type..b..Status.report..p..p..b.message..b...u...u...p..p..b.description..b...u.This.request.requires.HTTP.authentication...u...p..HR.size.1.noshade.noshade..h3.Apache.Tomcat.7.0.78..h3...body...html.
<0 rows> (or 0-length row.names)
```
After logging in, data is downloadable (OK)
```
> molgenis.login("admin", "mrdemo")
Login success
> yeastdata[1:5,1:5]
marker_or_phenotype chr cm GSM238074 GSM238076
1 YAL069W_1 1 0.0483 1 1
2 L013C_11 1 0.3280 1 1
3 YAL067C_21 1 0.7544 1 1
4 YAL066W_31 1 1.0236 1 1
5 YAL065C_41 1 1.1626 1 1
>
```
After logging out, data is still downloadable (not OK)
```
> molgenis.logout()
Logout success
> yeastdata <- molgenis.get("base_yeast_geno_pheno_map")
> yeastdata[1:5,1:5]
marker_or_phenotype chr cm GSM238074 GSM238076
1 YAL069W_1 1 0.0483 1 1
2 L013C_11 1 0.3280 1 1
3 YAL067C_21 1 0.7544 1 1
4 YAL066W_31 1 1.0236 1 1
5 YAL065C_41 1 1.1626 1 1
>
```
### Expected behavior
Expected to see the "not authorized" error instead of the data.
| True | Logout in R API does not log out - ### How to Reproduce
Based on analysis demo script:
http://www.molgenis.org/attachment/wiki/research/molgenis_research_demoanalysis_Smith_Kruglyak_2008.R
New session, not logged in, gives error instead of data (OK)
```
> yeastdata <- molgenis.get("base_yeast_geno_pheno_map")
> yeastdata
[1] X.html..head..title.Apache.Tomcat.7.0.78...Error.report..title..style.....H1..font.family.Tahoma
[2] Arial
[3] sans.serif.color.white.background.color..525D76.font.size.22px...H2..font.family.Tahoma
[4] Arial.1
[5] sans.serif.color.white.background.color..525D76.font.size.16px...H3..font.family.Tahoma
[6] Arial.2
[7] sans.serif.color.white.background.color..525D76.font.size.14px...BODY..font.family.Tahoma
[8] Arial.3
[9] sans.serif.color.black.background.color.white...B..font.family.Tahoma
[10] Arial.4
[11] sans.serif.color.white.background.color..525D76...P..font.family.Tahoma
[12] Arial.5
[13] sans.serif.background.white.color.black.font.size.12px..A..color...black..A.name..color...black..HR..color....525D76.......style....head..body..h1.HTTP.Status.401.....h1..HR.size.1.noshade.noshade..p..b.type..b..Status.report..p..p..b.message..b...u...u...p..p..b.description..b...u.This.request.requires.HTTP.authentication...u...p..HR.size.1.noshade.noshade..h3.Apache.Tomcat.7.0.78..h3...body...html.
<0 rows> (or 0-length row.names)
```
After logging in, data is downloadable (OK)
```
> molgenis.login("admin", "mrdemo")
Login success
> yeastdata[1:5,1:5]
marker_or_phenotype chr cm GSM238074 GSM238076
1 YAL069W_1 1 0.0483 1 1
2 L013C_11 1 0.3280 1 1
3 YAL067C_21 1 0.7544 1 1
4 YAL066W_31 1 1.0236 1 1
5 YAL065C_41 1 1.1626 1 1
>
```
After logging out, data is still downloadable (not OK)
```
> molgenis.logout()
Logout success
> yeastdata <- molgenis.get("base_yeast_geno_pheno_map")
> yeastdata[1:5,1:5]
marker_or_phenotype chr cm GSM238074 GSM238076
1 YAL069W_1 1 0.0483 1 1
2 L013C_11 1 0.3280 1 1
3 YAL067C_21 1 0.7544 1 1
4 YAL066W_31 1 1.0236 1 1
5 YAL065C_41 1 1.1626 1 1
>
```
### Expected behavior
Expected to see the "not authorized" error instead of the data.
| non_priority | logout in r api does not log out how to reproduce based on analysis demo script new session not logged in gives error instead of data ok yeastdata molgenis get base yeast geno pheno map yeastdata x html head title apache tomcat error report title style font family tahoma arial sans serif color white background color font size font family tahoma arial sans serif color white background color font size font family tahoma arial sans serif color white background color font size body font family tahoma arial sans serif color black background color white b font family tahoma arial sans serif color white background color p font family tahoma arial sans serif background white color black font size a color black a name color black hr color style head body http status hr size noshade noshade p b type b status report p p b message b u u p p b description b u this request requires http authentication u p hr size noshade noshade apache tomcat body html or length row names after logging in data is downloadable ok molgenis login admin mrdemo login success yeastdata marker or phenotype chr cm after logging out data is still downloadable not ok molgenis logout logout success yeastdata molgenis get base yeast geno pheno map yeastdata marker or phenotype chr cm expected behavior expected to see the not authorized error instead of the data | 0 |
4,763 | 5,282,221,849 | IssuesEvent | 2017-02-07 18:18:44 | NuGet/NuGetGallery | https://api.github.com/repos/NuGet/NuGetGallery | closed | When changing a password user shouldn't re-enter the same password | Area: Gallery UI Area: Security | Please work on defining the minimal set of rules require here?
Example:
Should we preserve the last few passwords and prevent them?
Should we prevent similar passwords as well?
CC @blowdart
| True | When changing a password user shouldn't re-enter the same password - Please work on defining the minimal set of rules require here?
Example:
Should we preserve the last few passwords and prevent them?
Should we prevent similar passwords as well?
CC @blowdart
| non_priority | when changing a password user shouldn t re enter the same password please work on defining the minimal set of rules require here example should we preserve the last few passwords and prevent them should we prevent similar passwords as well cc blowdart | 0 |
5,707 | 13,025,338,909 | IssuesEvent | 2020-07-27 13:23:52 | motleystate/moonstone | https://api.github.com/repos/motleystate/moonstone | opened | Normalization optimization module | architecture module: normalization | The idea is to provide a way of optimizing a given normalization for a dataset. | 1.0 | Normalization optimization module - The idea is to provide a way of optimizing a given normalization for a dataset. | non_priority | normalization optimization module the idea is to provide a way of optimizing a given normalization for a dataset | 0 |
137,600 | 18,755,102,938 | IssuesEvent | 2021-11-05 09:43:29 | Dima2022/node-kms | https://api.github.com/repos/Dima2022/node-kms | opened | CVE-2021-33623 (High) detected in trim-newlines-1.0.0.tgz | security vulnerability | ## CVE-2021-33623 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: node-kms/package.json</p>
<p>Path to vulnerable library: node-kms/node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- gulp-doctoc-0.1.4.tgz (Root Library)
- gulp-util-2.2.20.tgz
- dateformat-1.0.12.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/node-kms/commit/0174d52c9bbe1d27d5a8e0359134e9ffdbe6db6f">0174d52c9bbe1d27d5a8e0359134e9ffdbe6db6f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"trim-newlines","packageVersion":"1.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-doctoc:0.1.4;gulp-util:2.2.20;dateformat:1.0.12;meow:3.7.0;trim-newlines:1.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"trim-newlines - 3.0.1, 4.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33623","vulnerabilityDetails":"The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-33623 (High) detected in trim-newlines-1.0.0.tgz - ## CVE-2021-33623 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: node-kms/package.json</p>
<p>Path to vulnerable library: node-kms/node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- gulp-doctoc-0.1.4.tgz (Root Library)
- gulp-util-2.2.20.tgz
- dateformat-1.0.12.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/node-kms/commit/0174d52c9bbe1d27d5a8e0359134e9ffdbe6db6f">0174d52c9bbe1d27d5a8e0359134e9ffdbe6db6f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"trim-newlines","packageVersion":"1.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-doctoc:0.1.4;gulp-util:2.2.20;dateformat:1.0.12;meow:3.7.0;trim-newlines:1.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"trim-newlines - 3.0.1, 4.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33623","vulnerabilityDetails":"The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in trim newlines tgz cve high severity vulnerability vulnerable library trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file node kms package json path to vulnerable library node kms node modules trim newlines package json dependency hierarchy gulp doctoc tgz root library gulp util tgz dateformat tgz meow tgz x trim newlines tgz vulnerable library found in head commit a href found in base branch master vulnerability details the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution trim newlines isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree gulp doctoc gulp util dateformat meow trim newlines isminimumfixversionavailable true minimumfixversion trim newlines basebranches vulnerabilityidentifier cve vulnerabilitydetails the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method vulnerabilityurl | 0 |
22,489 | 3,961,053,953 | IssuesEvent | 2016-05-02 10:45:20 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | sFlow Interface Gauge Showing sFlow Throughput Data | testing needed | At some point it looks like the interface gauge for our sFlow collection stopped displaying the throughput as provided by the sFlow data and began what seems to be the physical interface's data rates. I think it started after an update but I don't know which one | 1.0 | sFlow Interface Gauge Showing sFlow Throughput Data - At some point it looks like the interface gauge for our sFlow collection stopped displaying the throughput as provided by the sFlow data and began what seems to be the physical interface's data rates. I think it started after an update but I don't know which one | non_priority | sflow interface gauge showing sflow throughput data at some point it looks like the interface gauge for our sflow collection stopped displaying the throughput as provided by the sflow data and began what seems to be the physical interface s data rates i think it started after an update but i don t know which one | 0 |
204,902 | 15,954,405,649 | IssuesEvent | 2021-04-15 13:33:23 | srijan-sivakumar/redant | https://api.github.com/repos/srijan-sivakumar/redant | closed | Standardizing the Code | documentation enhancement | * Ops:
1. docstring doesn't match the actual return:
Ex: peer_ops
```js
def peer_status(self, node: str):
"""
Checks the status of the peers
Args:
node (str): Node on which command has to be executed.
Returns:
tuple: Tuple containing three elements (ret, out, err).
The first element 'ret' is of type 'int' and
is the return value
of command execution.
The second element 'out' is of type 'str'
and is the stdout value
of the command execution.
The third element 'err' is of type 'str'
and is the stderr value
of the command execution.
"""
cmd = 'gluster --xml peer status'
self.logger.info(f"Running {cmd} on node {node}")
ret = self.execute_command(node, cmd)
if ret['error_code'] != 0:
self.logger.error(ret['msg']['opErrstr'])
raise Exception(ret['msg']['opErrstr'])
self.logger.info(f"Successfully ran {cmd} on {node}")
return ret
```
Here we are returning just ret which is a dictionary but the docstring is stating it as tuple.
2. In tests we are not using the ret value:
Test: peer_probe_detach
```js
def run_test(self):
"""
In this testcase:
1) glusterd service is started
2) peer probe of a server
3) list the storage pool
4) peer detach
5) glusterd is stopped
"""
try:
server1 = self.server_list[0]
server2 = self.server_list[1]
self.redant.start_glusterd(server1)
self.redant.peer_probe(server2, server1)
self.redant.pool_list(server1)
self.redant.peer_detach(server1, server2)
self.redant.stop_glusterd(server1)
except Exception as e:
self.TEST_RES = False
print(f"Test is failed:{e}")
```
If we are not using the ret value then returning that might not be needed.
* Class names
In some classes SnakeCase is used while in some CamelCase. This is the initial stage so keeping the name formats standard will be better.
* Certain ops are not returning ret or anything.
```js
def volume_mount(self, server: str, volname: str,
path: str, node: str=None):
"""
Mounts the gluster volume to the client's filesystem.
Args:
node (str): The client node in the cluster where volume
mount is to be run
server (str): Hostname or IP address
volname (str): Name of volume to be mounted
path (str): The path of the mount directory(mount point)
"""
cmd = f"mount -t glusterfs {server}:/{volname} {path}"
self.logger.info(f"Running {cmd} on node {node}")
ret = self.execute_command(node=node, cmd=cmd)
if int(ret["error_code"]) != 0:
self.logger.error(ret["error_msg"])
raise Exception(ret["error_msg"])
self.logger.info(f"Successfully ran {cmd} on {node}")
def volume_unmount(self, path: str, node: str=None):
"""
Unmounts the gluster volume .
Args:
node (str): The client node in the cluster where volume
unmount is to be run
server (str): Hostname or IP address
volname (str): Name of volume to be mounted
path (str): The path of the mount directory(mount point)
"""
cmd = f"umount {path}"
self.logger.info(f"Running {cmd} on node {node}")
ret = self.execute_command(node=node, cmd=cmd)
if int(ret["error_code"]) != 0:
self.logger.error(ret["error_msg"])
raise Exception(ret["error_msg"])
self.logger.info(f"Successfully ran {cmd} on {node}")
```
| 1.0 | Standardizing the Code - * Ops:
1. docstring doesn't match the actual return:
Ex: peer_ops
```js
def peer_status(self, node: str):
"""
Checks the status of the peers
Args:
node (str): Node on which command has to be executed.
Returns:
tuple: Tuple containing three elements (ret, out, err).
The first element 'ret' is of type 'int' and
is the return value
of command execution.
The second element 'out' is of type 'str'
and is the stdout value
of the command execution.
The third element 'err' is of type 'str'
and is the stderr value
of the command execution.
"""
cmd = 'gluster --xml peer status'
self.logger.info(f"Running {cmd} on node {node}")
ret = self.execute_command(node, cmd)
if ret['error_code'] != 0:
self.logger.error(ret['msg']['opErrstr'])
raise Exception(ret['msg']['opErrstr'])
self.logger.info(f"Successfully ran {cmd} on {node}")
return ret
```
Here we are returning just ret which is a dictionary but the docstring is stating it as tuple.
2. In tests we are not using the ret value:
Test: peer_probe_detach
```js
def run_test(self):
"""
In this testcase:
1) glusterd service is started
2) peer probe of a server
3) list the storage pool
4) peer detach
5) glusterd is stopped
"""
try:
server1 = self.server_list[0]
server2 = self.server_list[1]
self.redant.start_glusterd(server1)
self.redant.peer_probe(server2, server1)
self.redant.pool_list(server1)
self.redant.peer_detach(server1, server2)
self.redant.stop_glusterd(server1)
except Exception as e:
self.TEST_RES = False
print(f"Test is failed:{e}")
```
If we are not using the ret value then returning that might not be needed.
* Class names
In some classes SnakeCase is used while in some CamelCase. This is the initial stage so keeping the name formats standard will be better.
* Certain ops are not returning ret or anything.
```js
def volume_mount(self, server: str, volname: str,
path: str, node: str=None):
"""
Mounts the gluster volume to the client's filesystem.
Args:
node (str): The client node in the cluster where volume
mount is to be run
server (str): Hostname or IP address
volname (str): Name of volume to be mounted
path (str): The path of the mount directory(mount point)
"""
cmd = f"mount -t glusterfs {server}:/{volname} {path}"
self.logger.info(f"Running {cmd} on node {node}")
ret = self.execute_command(node=node, cmd=cmd)
if int(ret["error_code"]) != 0:
self.logger.error(ret["error_msg"])
raise Exception(ret["error_msg"])
self.logger.info(f"Successfully ran {cmd} on {node}")
def volume_unmount(self, path: str, node: str=None):
"""
Unmounts the gluster volume .
Args:
node (str): The client node in the cluster where volume
unmount is to be run
server (str): Hostname or IP address
volname (str): Name of volume to be mounted
path (str): The path of the mount directory(mount point)
"""
cmd = f"umount {path}"
self.logger.info(f"Running {cmd} on node {node}")
ret = self.execute_command(node=node, cmd=cmd)
if int(ret["error_code"]) != 0:
self.logger.error(ret["error_msg"])
raise Exception(ret["error_msg"])
self.logger.info(f"Successfully ran {cmd} on {node}")
```
| non_priority | standardizing the code ops docstring doesn t match the actual return ex peer ops js def peer status self node str checks the status of the peers args node str node on which command has to be executed returns tuple tuple containing three elements ret out err the first element ret is of type int and is the return value of command execution the second element out is of type str and is the stdout value of the command execution the third element err is of type str and is the stderr value of the command execution cmd gluster xml peer status self logger info f running cmd on node node ret self execute command node cmd if ret self logger error ret raise exception ret self logger info f successfully ran cmd on node return ret here we are returning just ret which is a dictionary but the docstring is stating it as tuple in tests we are not using the ret value test peer probe detach js def run test self in this testcase glusterd service is started peer probe of a server list the storage pool peer detach glusterd is stopped try self server list self server list self redant start glusterd self redant peer probe self redant pool list self redant peer detach self redant stop glusterd except exception as e self test res false print f test is failed e if we are not using the ret value then returning that might not be needed class names in some classes snakecase is used while in some camelcase this is the initial stage so keeping the name formats standard will be better certain ops are not returning ret or anything js def volume mount self server str volname str path str node str none mounts the gluster volume to the client s filesystem args node str the client node in the cluster where volume mount is to be run server str hostname or ip address volname str name of volume to be mounted path str the path of the mount directory mount point cmd f mount t glusterfs server volname path self logger info f running cmd on node node ret self execute command node node cmd cmd if int ret self logger error ret raise exception ret self logger info f successfully ran cmd on node def volume unmount self path str node str none unmounts the gluster volume args node str the client node in the cluster where volume unmount is to be run server str hostname or ip address volname str name of volume to be mounted path str the path of the mount directory mount point cmd f umount path self logger info f running cmd on node node ret self execute command node node cmd cmd if int ret self logger error ret raise exception ret self logger info f successfully ran cmd on node | 0 |
13,364 | 5,346,521,496 | IssuesEvent | 2017-02-17 19:54:16 | elegantthemes/Divi-Beta | https://api.github.com/repos/elegantthemes/Divi-Beta | closed | BlueHost :: Builder Sync :: Blurb Module :: center / left orientation issue | BUILDER SYNC DESIGN SIGNOFF QUALITY ASSURED READY FOR REVIEW | ### Problem:
Text default orientation of the blurb module is different in VB (centered) and BB (left) which can cause a problem with syncing :
https://www.dropbox.com/s/0b647o4t3ufy0hi/95.gif?dl=0
## Attached PR
- https://github.com/elegantthemes/submodule-builder/pull/1732 | 1.0 | BlueHost :: Builder Sync :: Blurb Module :: center / left orientation issue - ### Problem:
Text default orientation of the blurb module is different in VB (centered) and BB (left) which can cause a problem with syncing :
https://www.dropbox.com/s/0b647o4t3ufy0hi/95.gif?dl=0
## Attached PR
- https://github.com/elegantthemes/submodule-builder/pull/1732 | non_priority | bluehost builder sync blurb module center left orientation issue problem text default orientation of the blurb module is different in vb centered and bb left which can cause a problem with syncing attached pr | 0 |
3,298 | 4,314,412,557 | IssuesEvent | 2016-07-22 14:24:55 | nodejs/node | https://api.github.com/repos/nodejs/node | closed | Please update minimatch | npm security | Hi,
there has been a recent security issue in minimatch.js
https://nodesecurity.io/advisories/118
Could you update the minimatch under deps/npm ?
thanks
| True | Please update minimatch - Hi,
there has been a recent security issue in minimatch.js
https://nodesecurity.io/advisories/118
Could you update the minimatch under deps/npm ?
thanks
| non_priority | please update minimatch hi there has been a recent security issue in minimatch js could you update the minimatch under deps npm thanks | 0 |
51,830 | 10,729,727,564 | IssuesEvent | 2019-10-28 16:05:08 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Firefox XPack UI Functional Tests.x-pack/test/functional/apps/code/file_tree·ts - Code File Tree "before all" hook | Team:Code failed-test | A test failed on a tracked branch
```
Error: retry.try timeout: Error: expected false to equal true
at Assertion.assert (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/packages/kbn-expect/expect.js:100:11)
at Assertion.be.Assertion.equal (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/packages/kbn-expect/expect.js:221:8)
at Assertion.(anonymous function) [as be] (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/packages/kbn-expect/expect.js:69:22)
at be (test/functional/apps/code/file_tree.ts:46:59)
at process._tickCallback (internal/process/next_tick.js:68:7)
at lastError (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/test/common/services/retry/retry_for_success.ts:28:9)
at onFailure (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/test/common/services/retry/retry_for_success.ts:68:13)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+master/JOB=x-pack-firefoxSmoke,node=linux-immutable/106/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Firefox XPack UI Functional Tests.x-pack/test/functional/apps/code/file_tree·ts","test.name":"Code File Tree \"before all\" hook","test.failCount":1}} --> | 1.0 | Failing test: Firefox XPack UI Functional Tests.x-pack/test/functional/apps/code/file_tree·ts - Code File Tree "before all" hook - A test failed on a tracked branch
```
Error: retry.try timeout: Error: expected false to equal true
at Assertion.assert (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/packages/kbn-expect/expect.js:100:11)
at Assertion.be.Assertion.equal (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/packages/kbn-expect/expect.js:221:8)
at Assertion.(anonymous function) [as be] (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/packages/kbn-expect/expect.js:69:22)
at be (test/functional/apps/code/file_tree.ts:46:59)
at process._tickCallback (internal/process/next_tick.js:68:7)
at lastError (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/test/common/services/retry/retry_for_success.ts:28:9)
at onFailure (/var/lib/jenkins/workspace/elastic+kibana+master/JOB/x-pack-firefoxSmoke/node/linux-immutable/kibana/test/common/services/retry/retry_for_success.ts:68:13)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+master/JOB=x-pack-firefoxSmoke,node=linux-immutable/106/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Firefox XPack UI Functional Tests.x-pack/test/functional/apps/code/file_tree·ts","test.name":"Code File Tree \"before all\" hook","test.failCount":1}} --> | non_priority | failing test firefox xpack ui functional tests x pack test functional apps code file tree·ts code file tree before all hook a test failed on a tracked branch error retry try timeout error expected false to equal true at assertion assert var lib jenkins workspace elastic kibana master job x pack firefoxsmoke node linux immutable kibana packages kbn expect expect js at assertion be assertion equal var lib jenkins workspace elastic kibana master job x pack firefoxsmoke node linux immutable kibana packages kbn expect expect js at assertion anonymous function var lib jenkins workspace elastic kibana master job x pack firefoxsmoke node linux immutable kibana packages kbn expect expect js at be test functional apps code file tree ts at process tickcallback internal process next tick js at lasterror var lib jenkins workspace elastic kibana master job x pack firefoxsmoke node linux immutable kibana test common services retry retry for success ts at onfailure var lib jenkins workspace elastic kibana master job x pack firefoxsmoke node linux immutable kibana test common services retry retry for success ts first failure | 0 |
84,822 | 15,728,297,591 | IssuesEvent | 2021-03-29 13:40:14 | ssobue/kotlin-boot | https://api.github.com/repos/ssobue/kotlin-boot | closed | CVE-2020-36188 (High) detected in jackson-databind-2.8.10.jar | security vulnerability | ## CVE-2020-36188 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /kotlin-boot/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.10/jackson-databind-2.8.10.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.10.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.JNDIConnectionSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36188>CVE-2020-36188</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2996">https://github.com/FasterXML/jackson-databind/issues/2996</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-36188 (High) detected in jackson-databind-2.8.10.jar - ## CVE-2020-36188 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /kotlin-boot/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.10/jackson-databind-2.8.10.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.10.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.JNDIConnectionSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36188>CVE-2020-36188</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2996">https://github.com/FasterXML/jackson-databind/issues/2996</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file kotlin boot pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com newrelic agent deps ch qos logback core db jndiconnectionsource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
235,359 | 19,340,484,655 | IssuesEvent | 2021-12-15 03:28:56 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | ICE: compiler/rustc_infer/src/infer/lexical_region_resolve/mod.rs:498:17: cannot relate region: LUB(ReErased, ReEmpty(U0)) | I-ICE E-needs-test P-low regression-from-stable-to-nightly T-compiler C-bug glacier | <!--
Thank you for finding an Internal Compiler Error! 🧊 If possible, try to provide
a minimal verifiable example. You can read "Rust Bug Minimization Patterns" for
how to create smaller examples.
http://blog.pnkfx.org/blog/2019/11/18/rust-bug-minimization-patterns/
-->
### Code
```Rust
trait StreamOnce {
type Position;
}
impl StreamOnce for &str {
type Position = usize;
}
fn follow(_: &str) -> <&str as StreamOnce>::Position {
String::new
}
```
### Meta
<!--
If you're using the stable version of the compiler, you should also check if the
bug also exists in the beta or nightly versions.
-->
`rustc --version --verbose`:
```
rustc 1.56.0-nightly (9c25eb7aa 2021-07-25)
binary: rustc
commit-hash: 9c25eb7aa3a71fb951564b0ddf131be59c2c951d
commit-date: 2021-07-25
host: x86_64-unknown-linux-gnu
release: 1.56.0-nightly
LLVM version: 12.0.1
```
### Error output
```
error[E0601]: `main` function not found in crate `mutant`
--> mutant.rs:1:1
|
1 | / trait StreamOnce {
2 | | type Position;
3 | | }
4 | | impl StreamOnce for &str {
... |
8 | | String::new
9 | | }
| |_^ consider adding a `main` function to `mutant.rs`
error[E0308]: mismatched types
--> mutant.rs:8:5
|
7 | fn follow(_: &str) -> <&str as StreamOnce>::Position {
| ------------------------------ expected `usize` because of return type
8 | String::new
| ^^^^^^^^^^^ expected `usize`, found fn item
|
= note: expected type `usize`
found fn item `fn() -> String {String::new}`
error: internal compiler error: compiler/rustc_infer/src/infer/lexical_region_resolve/mod.rs:498:17: cannot relate region: LUB(ReErased, ReEmpty(U0))
thread 'rustc' panicked at 'Box<dyn Any>', compiler/rustc_errors/src/lib.rs:1034:9
note: run with `RUST_BACKTRACE=1` environment variable to display a backtrace
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/issues/new?labels=C-bug%2C+I-ICE%2C+T-compiler&template=ice.md
note: rustc 1.56.0-nightly (9c25eb7aa 2021-07-25) running on x86_64-unknown-linux-gnu
query stack during panic:
#0 [typeck] type-checking `follow`
#1 [typeck_item_bodies] type-checking all item bodies
end of query stack
error: aborting due to 3 previous errors
Some errors have detailed explanations: E0308, E0601.
For more information about an error, try `rustc --explain E0308`.
```
<!--
Include a backtrace in the code block by setting `RUST_BACKTRACE=1` in your
environment. E.g. `RUST_BACKTRACE=1 cargo build`.
-->
<details><summary><strong>Backtrace</strong></summary>
<p>
```
error[E0601]: `main` function not found in crate `mutant`
--> mutant.rs:1:1
|
1 | / trait StreamOnce {
2 | | type Position;
3 | | }
4 | | impl StreamOnce for &str {
... |
8 | | String::new
9 | | }
| |_^ consider adding a `main` function to `mutant.rs`
error[E0308]: mismatched types
--> mutant.rs:8:5
|
7 | fn follow(_: &str) -> <&str as StreamOnce>::Position {
| ------------------------------ expected `usize` because of return type
8 | String::new
| ^^^^^^^^^^^ expected `usize`, found fn item
|
= note: expected type `usize`
found fn item `fn() -> String {String::new}`
error: internal compiler error: compiler/rustc_infer/src/infer/lexical_region_resolve/mod.rs:498:17: cannot relate region: LUB(ReErased, ReEmpty(U0))
thread 'rustc' panicked at 'Box<dyn Any>', compiler/rustc_errors/src/lib.rs:1034:9
stack backtrace:
0: std::panicking::begin_panic
1: std::panic::panic_any
2: rustc_errors::HandlerInner::bug
3: rustc_errors::Handler::bug
4: rustc_middle::ty::context::tls::with_opt
5: rustc_middle::util::bug::opt_span_bug_fmt
6: rustc_middle::util::bug::bug_fmt
7: rustc_infer::infer::lexical_region_resolve::LexicalResolver::lub_concrete_regions
8: rustc_infer::infer::lexical_region_resolve::LexicalResolver::expand_node
9: rustc_infer::infer::lexical_region_resolve::LexicalResolver::infer_variable_values
10: rustc_infer::infer::lexical_region_resolve::resolve
11: rustc_infer::infer::InferCtxt::resolve_regions_and_report_errors
12: rustc_typeck::check::regionck::<impl rustc_typeck::check::fn_ctxt::FnCtxt>::regionck_fn
13: rustc_infer::infer::InferCtxtBuilder::enter
14: rustc_typeck::check::typeck
15: rustc_query_system::query::plumbing::get_query_impl
16: <rustc_query_impl::Queries as rustc_middle::ty::query::QueryEngine>::typeck
17: rustc_middle::ty::<impl rustc_middle::ty::context::TyCtxt>::par_body_owners
18: rustc_typeck::check::typeck_item_bodies
19: rustc_query_system::query::plumbing::get_query_impl
20: <rustc_query_impl::Queries as rustc_middle::ty::query::QueryEngine>::typeck_item_bodies
21: rustc_session::utils::<impl rustc_session::session::Session>::time
22: rustc_typeck::check_crate
23: rustc_interface::passes::analysis
24: rustc_query_system::query::plumbing::get_query_impl
25: <rustc_query_impl::Queries as rustc_middle::ty::query::QueryEngine>::analysis
26: rustc_interface::queries::<impl rustc_interface::interface::Compiler>::enter
27: rustc_span::with_source_map
28: rustc_interface::interface::create_compiler_and_run
29: scoped_tls::ScopedKey<T>::set
note: Some details are omitted, run with `RUST_BACKTRACE=full` for a verbose backtrace.
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/issues/new?labels=C-bug%2C+I-ICE%2C+T-compiler&template=ice.md
note: rustc 1.56.0-nightly (9c25eb7aa 2021-07-25) running on x86_64-unknown-linux-gnu
query stack during panic:
#0 [typeck] type-checking `follow`
#1 [typeck_item_bodies] type-checking all item bodies
#2 [analysis] running analysis passes on this crate
end of query stack
error: aborting due to 3 previous errors
Some errors have detailed explanations: E0308, E0601.
For more information about an error, try `rustc --explain E0308`.
```
</p>
</details> | 1.0 | ICE: compiler/rustc_infer/src/infer/lexical_region_resolve/mod.rs:498:17: cannot relate region: LUB(ReErased, ReEmpty(U0)) - <!--
Thank you for finding an Internal Compiler Error! 🧊 If possible, try to provide
a minimal verifiable example. You can read "Rust Bug Minimization Patterns" for
how to create smaller examples.
http://blog.pnkfx.org/blog/2019/11/18/rust-bug-minimization-patterns/
-->
### Code
```Rust
trait StreamOnce {
type Position;
}
impl StreamOnce for &str {
type Position = usize;
}
fn follow(_: &str) -> <&str as StreamOnce>::Position {
String::new
}
```
### Meta
<!--
If you're using the stable version of the compiler, you should also check if the
bug also exists in the beta or nightly versions.
-->
`rustc --version --verbose`:
```
rustc 1.56.0-nightly (9c25eb7aa 2021-07-25)
binary: rustc
commit-hash: 9c25eb7aa3a71fb951564b0ddf131be59c2c951d
commit-date: 2021-07-25
host: x86_64-unknown-linux-gnu
release: 1.56.0-nightly
LLVM version: 12.0.1
```
### Error output
```
error[E0601]: `main` function not found in crate `mutant`
--> mutant.rs:1:1
|
1 | / trait StreamOnce {
2 | | type Position;
3 | | }
4 | | impl StreamOnce for &str {
... |
8 | | String::new
9 | | }
| |_^ consider adding a `main` function to `mutant.rs`
error[E0308]: mismatched types
--> mutant.rs:8:5
|
7 | fn follow(_: &str) -> <&str as StreamOnce>::Position {
| ------------------------------ expected `usize` because of return type
8 | String::new
| ^^^^^^^^^^^ expected `usize`, found fn item
|
= note: expected type `usize`
found fn item `fn() -> String {String::new}`
error: internal compiler error: compiler/rustc_infer/src/infer/lexical_region_resolve/mod.rs:498:17: cannot relate region: LUB(ReErased, ReEmpty(U0))
thread 'rustc' panicked at 'Box<dyn Any>', compiler/rustc_errors/src/lib.rs:1034:9
note: run with `RUST_BACKTRACE=1` environment variable to display a backtrace
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/issues/new?labels=C-bug%2C+I-ICE%2C+T-compiler&template=ice.md
note: rustc 1.56.0-nightly (9c25eb7aa 2021-07-25) running on x86_64-unknown-linux-gnu
query stack during panic:
#0 [typeck] type-checking `follow`
#1 [typeck_item_bodies] type-checking all item bodies
end of query stack
error: aborting due to 3 previous errors
Some errors have detailed explanations: E0308, E0601.
For more information about an error, try `rustc --explain E0308`.
```
<!--
Include a backtrace in the code block by setting `RUST_BACKTRACE=1` in your
environment. E.g. `RUST_BACKTRACE=1 cargo build`.
-->
<details><summary><strong>Backtrace</strong></summary>
<p>
```
error[E0601]: `main` function not found in crate `mutant`
--> mutant.rs:1:1
|
1 | / trait StreamOnce {
2 | | type Position;
3 | | }
4 | | impl StreamOnce for &str {
... |
8 | | String::new
9 | | }
| |_^ consider adding a `main` function to `mutant.rs`
error[E0308]: mismatched types
--> mutant.rs:8:5
|
7 | fn follow(_: &str) -> <&str as StreamOnce>::Position {
| ------------------------------ expected `usize` because of return type
8 | String::new
| ^^^^^^^^^^^ expected `usize`, found fn item
|
= note: expected type `usize`
found fn item `fn() -> String {String::new}`
error: internal compiler error: compiler/rustc_infer/src/infer/lexical_region_resolve/mod.rs:498:17: cannot relate region: LUB(ReErased, ReEmpty(U0))
thread 'rustc' panicked at 'Box<dyn Any>', compiler/rustc_errors/src/lib.rs:1034:9
stack backtrace:
0: std::panicking::begin_panic
1: std::panic::panic_any
2: rustc_errors::HandlerInner::bug
3: rustc_errors::Handler::bug
4: rustc_middle::ty::context::tls::with_opt
5: rustc_middle::util::bug::opt_span_bug_fmt
6: rustc_middle::util::bug::bug_fmt
7: rustc_infer::infer::lexical_region_resolve::LexicalResolver::lub_concrete_regions
8: rustc_infer::infer::lexical_region_resolve::LexicalResolver::expand_node
9: rustc_infer::infer::lexical_region_resolve::LexicalResolver::infer_variable_values
10: rustc_infer::infer::lexical_region_resolve::resolve
11: rustc_infer::infer::InferCtxt::resolve_regions_and_report_errors
12: rustc_typeck::check::regionck::<impl rustc_typeck::check::fn_ctxt::FnCtxt>::regionck_fn
13: rustc_infer::infer::InferCtxtBuilder::enter
14: rustc_typeck::check::typeck
15: rustc_query_system::query::plumbing::get_query_impl
16: <rustc_query_impl::Queries as rustc_middle::ty::query::QueryEngine>::typeck
17: rustc_middle::ty::<impl rustc_middle::ty::context::TyCtxt>::par_body_owners
18: rustc_typeck::check::typeck_item_bodies
19: rustc_query_system::query::plumbing::get_query_impl
20: <rustc_query_impl::Queries as rustc_middle::ty::query::QueryEngine>::typeck_item_bodies
21: rustc_session::utils::<impl rustc_session::session::Session>::time
22: rustc_typeck::check_crate
23: rustc_interface::passes::analysis
24: rustc_query_system::query::plumbing::get_query_impl
25: <rustc_query_impl::Queries as rustc_middle::ty::query::QueryEngine>::analysis
26: rustc_interface::queries::<impl rustc_interface::interface::Compiler>::enter
27: rustc_span::with_source_map
28: rustc_interface::interface::create_compiler_and_run
29: scoped_tls::ScopedKey<T>::set
note: Some details are omitted, run with `RUST_BACKTRACE=full` for a verbose backtrace.
note: the compiler unexpectedly panicked. this is a bug.
note: we would appreciate a bug report: https://github.com/rust-lang/rust/issues/new?labels=C-bug%2C+I-ICE%2C+T-compiler&template=ice.md
note: rustc 1.56.0-nightly (9c25eb7aa 2021-07-25) running on x86_64-unknown-linux-gnu
query stack during panic:
#0 [typeck] type-checking `follow`
#1 [typeck_item_bodies] type-checking all item bodies
#2 [analysis] running analysis passes on this crate
end of query stack
error: aborting due to 3 previous errors
Some errors have detailed explanations: E0308, E0601.
For more information about an error, try `rustc --explain E0308`.
```
</p>
</details> | non_priority | ice compiler rustc infer src infer lexical region resolve mod rs cannot relate region lub reerased reempty thank you for finding an internal compiler error 🧊 if possible try to provide a minimal verifiable example you can read rust bug minimization patterns for how to create smaller examples code rust trait streamonce type position impl streamonce for str type position usize fn follow str position string new meta if you re using the stable version of the compiler you should also check if the bug also exists in the beta or nightly versions rustc version verbose rustc nightly binary rustc commit hash commit date host unknown linux gnu release nightly llvm version error output error main function not found in crate mutant mutant rs trait streamonce type position impl streamonce for str string new consider adding a main function to mutant rs error mismatched types mutant rs fn follow str position expected usize because of return type string new expected usize found fn item note expected type usize found fn item fn string string new error internal compiler error compiler rustc infer src infer lexical region resolve mod rs cannot relate region lub reerased reempty thread rustc panicked at box compiler rustc errors src lib rs note run with rust backtrace environment variable to display a backtrace note the compiler unexpectedly panicked this is a bug note we would appreciate a bug report note rustc nightly running on unknown linux gnu query stack during panic type checking follow type checking all item bodies end of query stack error aborting due to previous errors some errors have detailed explanations for more information about an error try rustc explain include a backtrace in the code block by setting rust backtrace in your environment e g rust backtrace cargo build backtrace error main function not found in crate mutant mutant rs trait streamonce type position impl streamonce for str string new consider adding a main function to mutant rs error mismatched types mutant rs fn follow str position expected usize because of return type string new expected usize found fn item note expected type usize found fn item fn string string new error internal compiler error compiler rustc infer src infer lexical region resolve mod rs cannot relate region lub reerased reempty thread rustc panicked at box compiler rustc errors src lib rs stack backtrace std panicking begin panic std panic panic any rustc errors handlerinner bug rustc errors handler bug rustc middle ty context tls with opt rustc middle util bug opt span bug fmt rustc middle util bug bug fmt rustc infer infer lexical region resolve lexicalresolver lub concrete regions rustc infer infer lexical region resolve lexicalresolver expand node rustc infer infer lexical region resolve lexicalresolver infer variable values rustc infer infer lexical region resolve resolve rustc infer infer inferctxt resolve regions and report errors rustc typeck check regionck regionck fn rustc infer infer inferctxtbuilder enter rustc typeck check typeck rustc query system query plumbing get query impl typeck rustc middle ty par body owners rustc typeck check typeck item bodies rustc query system query plumbing get query impl typeck item bodies rustc session utils time rustc typeck check crate rustc interface passes analysis rustc query system query plumbing get query impl analysis rustc interface queries enter rustc span with source map rustc interface interface create compiler and run scoped tls scopedkey set note some details are omitted run with rust backtrace full for a verbose backtrace note the compiler unexpectedly panicked this is a bug note we would appreciate a bug report note rustc nightly running on unknown linux gnu query stack during panic type checking follow type checking all item bodies running analysis passes on this crate end of query stack error aborting due to previous errors some errors have detailed explanations for more information about an error try rustc explain | 0 |
6,770 | 15,208,603,161 | IssuesEvent | 2021-02-17 03:05:14 | Azure/azure-sdk | https://api.github.com/repos/Azure/azure-sdk | opened | Board Review: Document Translation (Python) | architecture board-review | Thank you for submitting this review request. Thorough review of your client library ensures that your APIs are consistent with the guidelines and the consumers of your client library have a consistently good experience when using Azure.
**The Architecture Board reviews [Track 2 libraries](https://azure.github.io/azure-sdk/general_introduction.html) only.** If your library does not meet this requirement, please reach out to [Architecture Board](adparch@microsoft.com) before creating the issue.
Please reference our [review process guidelines](https://azure.github.io/azure-sdk/policies_reviewprocess.html) to understand what is being asked for in the issue template.
To ensure consistency, all Tier-1 languages (C#, TypeScript, Java, Python) will generally be reviewed together. In expansive libraries, we will pair dynamic languages (Python, TypeScript) together, and strongly typed languages (C#, Java) together in separate meetings.
For Tier-2 languages (C, C++, Go, Android, iOS), the review will be on an as-needed basis.
**Before submitting, ensure you adjust the title of the issue appropriately.**
**Note that the required material must be included before a meeting can be scheduled.**
## Contacts and Timeline
* Responsible service team: ADP/translation team
* Main contacts: @mayurid
* Expected code complete date: TBD
* Expected release date: TBD
## About the Service
* Link to documentation introducing/describing the service: https://microsoft.sharepoint.com/:w:/r/teams/translator/internal/Shared%20Documents/Document%20Translator/User%20Documentation%20-%20Snyder.docx?d=we0ab3acd79134035be30ef45ded71027&csf=1&web=1&e=jDyN8D
* Link to the service REST APIs: https://github.com/Azure/azure-rest-api-specs/blob/master/specification/cognitiveservices/data-plane/TranslatorText/preview/v1.0-preview.1/TranslatorBatch.json
* Link to GitHub issue for previous review sessions, if applicable: https://github.com/Azure/azure-sdk/issues/1968
## About the client library
* Name of the client library: azure-ai-documenttranslation
* Languages for this review: Python
## Artifacts required (per language)
Please read through “API Review” section [here](https://azure.github.io/azure-sdk/policies_reviewprocess.html) to understand how these artifacts are generated. **It is critical that these artifacts are present and are in the right format. If not, the language architects cannot review them with the SDK Team’s API review tool.**
### .NET
* APIView Link:
* Link to Champion Scenarios/Quickstart samples:
### Java
* APIView Link:
* Link to Champion Scenarios/Quickstart samples:
### Python
* APIView Link: https://apiview.dev/Assemblies/Review/019355482c6245a5a404eef64740da1e
* Link to Champion Scenarios/Quickstart samples: will add shortly
### TypeScript
* APIView Link:
* Link to Champion Scenarios/Quickstart samples:
For all other languages, send a request to the Architecture Board to discuss the best format on individual basis.
## Thank you!
| 1.0 | Board Review: Document Translation (Python) - Thank you for submitting this review request. Thorough review of your client library ensures that your APIs are consistent with the guidelines and the consumers of your client library have a consistently good experience when using Azure.
**The Architecture Board reviews [Track 2 libraries](https://azure.github.io/azure-sdk/general_introduction.html) only.** If your library does not meet this requirement, please reach out to [Architecture Board](adparch@microsoft.com) before creating the issue.
Please reference our [review process guidelines](https://azure.github.io/azure-sdk/policies_reviewprocess.html) to understand what is being asked for in the issue template.
To ensure consistency, all Tier-1 languages (C#, TypeScript, Java, Python) will generally be reviewed together. In expansive libraries, we will pair dynamic languages (Python, TypeScript) together, and strongly typed languages (C#, Java) together in separate meetings.
For Tier-2 languages (C, C++, Go, Android, iOS), the review will be on an as-needed basis.
**Before submitting, ensure you adjust the title of the issue appropriately.**
**Note that the required material must be included before a meeting can be scheduled.**
## Contacts and Timeline
* Responsible service team: ADP/translation team
* Main contacts: @mayurid
* Expected code complete date: TBD
* Expected release date: TBD
## About the Service
* Link to documentation introducing/describing the service: https://microsoft.sharepoint.com/:w:/r/teams/translator/internal/Shared%20Documents/Document%20Translator/User%20Documentation%20-%20Snyder.docx?d=we0ab3acd79134035be30ef45ded71027&csf=1&web=1&e=jDyN8D
* Link to the service REST APIs: https://github.com/Azure/azure-rest-api-specs/blob/master/specification/cognitiveservices/data-plane/TranslatorText/preview/v1.0-preview.1/TranslatorBatch.json
* Link to GitHub issue for previous review sessions, if applicable: https://github.com/Azure/azure-sdk/issues/1968
## About the client library
* Name of the client library: azure-ai-documenttranslation
* Languages for this review: Python
## Artifacts required (per language)
Please read through “API Review” section [here](https://azure.github.io/azure-sdk/policies_reviewprocess.html) to understand how these artifacts are generated. **It is critical that these artifacts are present and are in the right format. If not, the language architects cannot review them with the SDK Team’s API review tool.**
### .NET
* APIView Link:
* Link to Champion Scenarios/Quickstart samples:
### Java
* APIView Link:
* Link to Champion Scenarios/Quickstart samples:
### Python
* APIView Link: https://apiview.dev/Assemblies/Review/019355482c6245a5a404eef64740da1e
* Link to Champion Scenarios/Quickstart samples: will add shortly
### TypeScript
* APIView Link:
* Link to Champion Scenarios/Quickstart samples:
For all other languages, send a request to the Architecture Board to discuss the best format on individual basis.
## Thank you!
| non_priority | board review document translation python thank you for submitting this review request thorough review of your client library ensures that your apis are consistent with the guidelines and the consumers of your client library have a consistently good experience when using azure the architecture board reviews only if your library does not meet this requirement please reach out to adparch microsoft com before creating the issue please reference our to understand what is being asked for in the issue template to ensure consistency all tier languages c typescript java python will generally be reviewed together in expansive libraries we will pair dynamic languages python typescript together and strongly typed languages c java together in separate meetings for tier languages c c go android ios the review will be on an as needed basis before submitting ensure you adjust the title of the issue appropriately note that the required material must be included before a meeting can be scheduled contacts and timeline responsible service team adp translation team main contacts mayurid expected code complete date tbd expected release date tbd about the service link to documentation introducing describing the service link to the service rest apis link to github issue for previous review sessions if applicable about the client library name of the client library azure ai documenttranslation languages for this review python artifacts required per language please read through “api review” section to understand how these artifacts are generated it is critical that these artifacts are present and are in the right format if not the language architects cannot review them with the sdk team’s api review tool net apiview link link to champion scenarios quickstart samples java apiview link link to champion scenarios quickstart samples python apiview link link to champion scenarios quickstart samples will add shortly typescript apiview link link to champion scenarios quickstart samples for all other languages send a request to the architecture board to discuss the best format on individual basis thank you | 0 |
214,891 | 16,616,942,495 | IssuesEvent | 2021-06-02 17:58:08 | Realm667/WolfenDoom | https://api.github.com/repos/Realm667/WolfenDoom | closed | C2M5_A: Open polygon seam on the scrolling terrain. | mapping playtesting rendering API (vulkan/opengl/soft) | While making your way to the front of the train, the west portion of the scrolling background terrain has an open, triangle-shaped seam.
| 1.0 | C2M5_A: Open polygon seam on the scrolling terrain. - While making your way to the front of the train, the west portion of the scrolling background terrain has an open, triangle-shaped seam.
| non_priority | a open polygon seam on the scrolling terrain while making your way to the front of the train the west portion of the scrolling background terrain has an open triangle shaped seam | 0 |
171,734 | 14,344,133,252 | IssuesEvent | 2020-11-28 13:02:27 | DanielGurevich1/8.1-comming-soon | https://api.github.com/repos/DanielGurevich1/8.1-comming-soon | opened | general form validator | documentation js js validation | single logic for any form in the page
validation rules can be detected based on data-* attribute values
on submit, if success: show success message in a "toast" component
on submit, if error: show error message in a "toast" component
js docs | 1.0 | general form validator - single logic for any form in the page
validation rules can be detected based on data-* attribute values
on submit, if success: show success message in a "toast" component
on submit, if error: show error message in a "toast" component
js docs | non_priority | general form validator single logic for any form in the page validation rules can be detected based on data attribute values on submit if success show success message in a toast component on submit if error show error message in a toast component js docs | 0 |
97,399 | 11,012,649,627 | IssuesEvent | 2019-12-04 18:44:13 | nanocurrency/nano-node | https://api.github.com/repos/nanocurrency/nano-node | closed | Wallet RPC action "receive" sets the wrong representative/ignores the wallet representative | bug documentation | This issue has been present since V14 or so, it is the same as #1019 - but was missing an important detail which is why it was closed as un-reproducible
**Description of bug:**
When you use the rpc `receive` action on a node/development wallet then the representative is set to the account itself, rather than the wallet representative.
Example, if you have an account in the node wallet:
`nano_1hmefcfq35td5f6rkh15hbpr4bkkhyyhmfhm7511jaka811bfp17xhkboyxo`
And you do an RPC `receive` for any block, the representative for that account will become `nano_1hmefcfq35td5f6rkh15hbpr4bkkhyyhmfhm7511jaka811bfp17xhkboyxo`
This issue **does not** occur when transactions are auto-received, only when they are received using the RPC receive action.
**Steps to reproduce the issue:**
1. Create a wallet via `wallet_create` with auto receive disabled
2. Create an account on the wallet via `account_create`
3. Use rpc `receive` to pocket the funds from the account
4. The representative for that account is now set to itself
**Describe the results you received:**
Accounts in the node/developer wallet always set the representative field to themselves when using rpc `receive`
**Describe the results you expected:**
Accounts use the wallet representative
**Additional information you deem important (e.g. issue happens only occasionally):**
Issue happens consistently and is repeatable.
**Environment**:
- Ubuntu 18.04
- Nodes V14, V15, V16, V17, V18, V19, V20 | 1.0 | Wallet RPC action "receive" sets the wrong representative/ignores the wallet representative - This issue has been present since V14 or so, it is the same as #1019 - but was missing an important detail which is why it was closed as un-reproducible
**Description of bug:**
When you use the rpc `receive` action on a node/development wallet then the representative is set to the account itself, rather than the wallet representative.
Example, if you have an account in the node wallet:
`nano_1hmefcfq35td5f6rkh15hbpr4bkkhyyhmfhm7511jaka811bfp17xhkboyxo`
And you do an RPC `receive` for any block, the representative for that account will become `nano_1hmefcfq35td5f6rkh15hbpr4bkkhyyhmfhm7511jaka811bfp17xhkboyxo`
This issue **does not** occur when transactions are auto-received, only when they are received using the RPC receive action.
**Steps to reproduce the issue:**
1. Create a wallet via `wallet_create` with auto receive disabled
2. Create an account on the wallet via `account_create`
3. Use rpc `receive` to pocket the funds from the account
4. The representative for that account is now set to itself
**Describe the results you received:**
Accounts in the node/developer wallet always set the representative field to themselves when using rpc `receive`
**Describe the results you expected:**
Accounts use the wallet representative
**Additional information you deem important (e.g. issue happens only occasionally):**
Issue happens consistently and is repeatable.
**Environment**:
- Ubuntu 18.04
- Nodes V14, V15, V16, V17, V18, V19, V20 | non_priority | wallet rpc action receive sets the wrong representative ignores the wallet representative this issue has been present since or so it is the same as but was missing an important detail which is why it was closed as un reproducible description of bug when you use the rpc receive action on a node development wallet then the representative is set to the account itself rather than the wallet representative example if you have an account in the node wallet nano and you do an rpc receive for any block the representative for that account will become nano this issue does not occur when transactions are auto received only when they are received using the rpc receive action steps to reproduce the issue create a wallet via wallet create with auto receive disabled create an account on the wallet via account create use rpc receive to pocket the funds from the account the representative for that account is now set to itself describe the results you received accounts in the node developer wallet always set the representative field to themselves when using rpc receive describe the results you expected accounts use the wallet representative additional information you deem important e g issue happens only occasionally issue happens consistently and is repeatable environment ubuntu nodes | 0 |
145,114 | 11,649,129,389 | IssuesEvent | 2020-03-02 00:33:54 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | opened | j9_extended.functional_x86-64_mac_xl testOSMXBeanRemote_0_FAILED Caused by: java.lang.IllegalArgumentException | test failure | Failure link
------------
From an internal build `Test_openjdk11_j9_extended.functional_x86-64_mac_xl_Nightly/6/`:
```
00:30:59 openjdk version "11.0.7-internal" 2020-04-14
00:30:59 OpenJDK Runtime Environment (build 11.0.7-internal+0-adhoc.jenkins.BuildJDK11x86-64macxlNightly)
00:30:59 Eclipse OpenJ9 VM (build ibm_sdk-ff26ace9d6, JRE 11 Mac OS X amd64-64-Bit 20200229_6 (JIT enabled, AOT enabled)
00:30:59 OpenJ9 - ff26ace9d6
00:30:59 OMR - c93afcc6b
00:30:59 JCL - e0e94184e0b based on jdk-11.0.7+5)
```
Optional info
-------------
Failure output (captured from console output)
---------------------------------------------
```
FAILED: runTestOSMXBean
java.lang.AssertionError: Unknown exception occurred: null
at org.testng.Assert.fail(Assert.java:85)
at org.openj9.test.management.TestOperatingSystemMXBean.test_processorInfo(TestOperatingSystemMXBean.java:637)
at org.openj9.test.management.TestOperatingSystemMXBean.runTestOSMXBean(TestOperatingSystemMXBean.java:174)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:124)
at org.testng.internal.Invoker.invokeMethod(Invoker.java:580)
at org.testng.internal.Invoker.invokeTestMethod(Invoker.java:716)
at org.testng.internal.Invoker.invokeTestMethods(Invoker.java:988)
at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:125)
at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:109)
at org.testng.TestRunner.privateRun(TestRunner.java:648)
at org.testng.TestRunner.run(TestRunner.java:505)
at org.testng.SuiteRunner.runTest(SuiteRunner.java:455)
at org.testng.SuiteRunner.runSequentially(SuiteRunner.java:450)
at org.testng.SuiteRunner.privateRun(SuiteRunner.java:415)
at org.testng.SuiteRunner.run(SuiteRunner.java:364)
at org.testng.SuiteRunnerWorker.runSuite(SuiteRunnerWorker.java:52)
at org.testng.SuiteRunnerWorker.run(SuiteRunnerWorker.java:84)
at org.testng.TestNG.runSuitesSequentially(TestNG.java:1208)
at org.testng.TestNG.runSuitesLocally(TestNG.java:1137)
at org.testng.TestNG.runSuites(TestNG.java:1049)
at org.testng.TestNG.run(TestNG.java:1017)
at org.testng.TestNG.privateMain(TestNG.java:1354)
at org.testng.TestNG.main(TestNG.java:1323)
Caused by: java.lang.reflect.UndeclaredThrowableException
at com.sun.proxy.$Proxy4.retrieveTotalProcessorUsage(Unknown Source)
at org.openj9.test.management.TestOperatingSystemMXBean.test_processorInfo(TestOperatingSystemMXBean.java:575)
... 25 more
Caused by: java.io.InvalidObjectException: Failed to invoke from(CompositeData)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory.invalidObjectException(DefaultMXBeanMappingFactory.java:1437)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$CompositeBuilderViaFrom.fromCompositeData(DefaultMXBeanMappingFactory.java:1024)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$CompositeMapping.fromNonNullOpenValue(DefaultMXBeanMappingFactory.java:922)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$NonNullMXBeanMapping.fromOpenValue(DefaultMXBeanMappingFactory.java:134)
at java.management/com.sun.jmx.mbeanserver.ConvertingMethod.fromOpenReturnValue(ConvertingMethod.java:131)
at java.management/com.sun.jmx.mbeanserver.MXBeanProxy.invoke(MXBeanProxy.java:168)
at java.management/javax.management.MBeanServerInvocationHandler.invoke(MBeanServerInvocationHandler.java:258)
... 27 more
Caused by: java.lang.reflect.InvocationTargetException
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at sun.reflect.misc.Trampoline.invoke(MethodUtil.java:71)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at java.base/sun.reflect.misc.MethodUtil.invoke(MethodUtil.java:260)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$CompositeBuilderViaFrom.fromCompositeData(DefaultMXBeanMappingFactory.java:1021)
... 32 more
Caused by: java.lang.IllegalArgumentException
at jdk.management/com.ibm.lang.management.ProcessorUsage.<init>(ProcessorUsage.java:92)
at jdk.management/com.ibm.lang.management.ProcessorUsage.from(ProcessorUsage.java:275)
... 43 more
===============================================
testOSMXBean
Tests run: 1, Failures: 1, Skips: 0
===============================================
===============================================
JLM_Tests_Suite
Total tests run: 1, Failures: 1, Skips: 0
===============================================
testOSMXBeanRemote_0_FAILED
testOSMXBeanRemote_1_FAILED failed similarly as well.
```
To rebuild the failed tests in <Jenkins URL>=https://ci.adoptopenjdk.net/job/Grinder, use the following links:
02:24:14 https://ci.adoptopenjdk.net/job/Grinder/parambuild/?JDK_VERSION=11&JDK_IMPL=openj9&BUILD_LIST=functional&PLATFORM=x86-64_mac_xl&TARGET=testOSMXBeanRemote_0
02:24:14 https://ci.adoptopenjdk.net/job/Grinder/parambuild/?JDK_VERSION=11&JDK_IMPL=openj9&BUILD_LIST=functional&PLATFORM=x86-64_mac_xl&TARGET=testOSMXBeanRemote_1 | 1.0 | j9_extended.functional_x86-64_mac_xl testOSMXBeanRemote_0_FAILED Caused by: java.lang.IllegalArgumentException - Failure link
------------
From an internal build `Test_openjdk11_j9_extended.functional_x86-64_mac_xl_Nightly/6/`:
```
00:30:59 openjdk version "11.0.7-internal" 2020-04-14
00:30:59 OpenJDK Runtime Environment (build 11.0.7-internal+0-adhoc.jenkins.BuildJDK11x86-64macxlNightly)
00:30:59 Eclipse OpenJ9 VM (build ibm_sdk-ff26ace9d6, JRE 11 Mac OS X amd64-64-Bit 20200229_6 (JIT enabled, AOT enabled)
00:30:59 OpenJ9 - ff26ace9d6
00:30:59 OMR - c93afcc6b
00:30:59 JCL - e0e94184e0b based on jdk-11.0.7+5)
```
Optional info
-------------
Failure output (captured from console output)
---------------------------------------------
```
FAILED: runTestOSMXBean
java.lang.AssertionError: Unknown exception occurred: null
at org.testng.Assert.fail(Assert.java:85)
at org.openj9.test.management.TestOperatingSystemMXBean.test_processorInfo(TestOperatingSystemMXBean.java:637)
at org.openj9.test.management.TestOperatingSystemMXBean.runTestOSMXBean(TestOperatingSystemMXBean.java:174)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:124)
at org.testng.internal.Invoker.invokeMethod(Invoker.java:580)
at org.testng.internal.Invoker.invokeTestMethod(Invoker.java:716)
at org.testng.internal.Invoker.invokeTestMethods(Invoker.java:988)
at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:125)
at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:109)
at org.testng.TestRunner.privateRun(TestRunner.java:648)
at org.testng.TestRunner.run(TestRunner.java:505)
at org.testng.SuiteRunner.runTest(SuiteRunner.java:455)
at org.testng.SuiteRunner.runSequentially(SuiteRunner.java:450)
at org.testng.SuiteRunner.privateRun(SuiteRunner.java:415)
at org.testng.SuiteRunner.run(SuiteRunner.java:364)
at org.testng.SuiteRunnerWorker.runSuite(SuiteRunnerWorker.java:52)
at org.testng.SuiteRunnerWorker.run(SuiteRunnerWorker.java:84)
at org.testng.TestNG.runSuitesSequentially(TestNG.java:1208)
at org.testng.TestNG.runSuitesLocally(TestNG.java:1137)
at org.testng.TestNG.runSuites(TestNG.java:1049)
at org.testng.TestNG.run(TestNG.java:1017)
at org.testng.TestNG.privateMain(TestNG.java:1354)
at org.testng.TestNG.main(TestNG.java:1323)
Caused by: java.lang.reflect.UndeclaredThrowableException
at com.sun.proxy.$Proxy4.retrieveTotalProcessorUsage(Unknown Source)
at org.openj9.test.management.TestOperatingSystemMXBean.test_processorInfo(TestOperatingSystemMXBean.java:575)
... 25 more
Caused by: java.io.InvalidObjectException: Failed to invoke from(CompositeData)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory.invalidObjectException(DefaultMXBeanMappingFactory.java:1437)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$CompositeBuilderViaFrom.fromCompositeData(DefaultMXBeanMappingFactory.java:1024)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$CompositeMapping.fromNonNullOpenValue(DefaultMXBeanMappingFactory.java:922)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$NonNullMXBeanMapping.fromOpenValue(DefaultMXBeanMappingFactory.java:134)
at java.management/com.sun.jmx.mbeanserver.ConvertingMethod.fromOpenReturnValue(ConvertingMethod.java:131)
at java.management/com.sun.jmx.mbeanserver.MXBeanProxy.invoke(MXBeanProxy.java:168)
at java.management/javax.management.MBeanServerInvocationHandler.invoke(MBeanServerInvocationHandler.java:258)
... 27 more
Caused by: java.lang.reflect.InvocationTargetException
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at sun.reflect.misc.Trampoline.invoke(MethodUtil.java:71)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at java.base/sun.reflect.misc.MethodUtil.invoke(MethodUtil.java:260)
at java.management/com.sun.jmx.mbeanserver.DefaultMXBeanMappingFactory$CompositeBuilderViaFrom.fromCompositeData(DefaultMXBeanMappingFactory.java:1021)
... 32 more
Caused by: java.lang.IllegalArgumentException
at jdk.management/com.ibm.lang.management.ProcessorUsage.<init>(ProcessorUsage.java:92)
at jdk.management/com.ibm.lang.management.ProcessorUsage.from(ProcessorUsage.java:275)
... 43 more
===============================================
testOSMXBean
Tests run: 1, Failures: 1, Skips: 0
===============================================
===============================================
JLM_Tests_Suite
Total tests run: 1, Failures: 1, Skips: 0
===============================================
testOSMXBeanRemote_0_FAILED
testOSMXBeanRemote_1_FAILED failed similarly as well.
```
To rebuild the failed tests in <Jenkins URL>=https://ci.adoptopenjdk.net/job/Grinder, use the following links:
02:24:14 https://ci.adoptopenjdk.net/job/Grinder/parambuild/?JDK_VERSION=11&JDK_IMPL=openj9&BUILD_LIST=functional&PLATFORM=x86-64_mac_xl&TARGET=testOSMXBeanRemote_0
02:24:14 https://ci.adoptopenjdk.net/job/Grinder/parambuild/?JDK_VERSION=11&JDK_IMPL=openj9&BUILD_LIST=functional&PLATFORM=x86-64_mac_xl&TARGET=testOSMXBeanRemote_1 | non_priority | extended functional mac xl testosmxbeanremote failed caused by java lang illegalargumentexception failure link from an internal build test extended functional mac xl nightly openjdk version internal openjdk runtime environment build internal adhoc jenkins eclipse vm build ibm sdk jre mac os x bit jit enabled aot enabled omr jcl based on jdk optional info failure output captured from console output failed runtestosmxbean java lang assertionerror unknown exception occurred null at org testng assert fail assert java at org test management testoperatingsystemmxbean test processorinfo testoperatingsystemmxbean java at org test management testoperatingsystemmxbean runtestosmxbean testoperatingsystemmxbean java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal invoker invokemethod invoker java at org testng internal invoker invoketestmethod invoker java at org testng internal invoker invoketestmethods invoker java at org testng internal testmethodworker invoketestmethods testmethodworker java at org testng internal testmethodworker run testmethodworker java at org testng testrunner privaterun testrunner java at org testng testrunner run testrunner java at org testng suiterunner runtest suiterunner java at org testng suiterunner runsequentially suiterunner java at org testng suiterunner privaterun suiterunner java at org testng suiterunner run suiterunner java at org testng suiterunnerworker runsuite suiterunnerworker java at org testng suiterunnerworker run suiterunnerworker java at org testng testng runsuitessequentially testng java at org testng testng runsuiteslocally testng java at org testng testng runsuites testng java at org testng testng run testng java at org testng testng privatemain testng java at org testng testng main testng java caused by java lang reflect undeclaredthrowableexception at com sun proxy retrievetotalprocessorusage unknown source at org test management testoperatingsystemmxbean test processorinfo testoperatingsystemmxbean java more caused by java io invalidobjectexception failed to invoke from compositedata at java management com sun jmx mbeanserver defaultmxbeanmappingfactory invalidobjectexception defaultmxbeanmappingfactory java at java management com sun jmx mbeanserver defaultmxbeanmappingfactory compositebuilderviafrom fromcompositedata defaultmxbeanmappingfactory java at java management com sun jmx mbeanserver defaultmxbeanmappingfactory compositemapping fromnonnullopenvalue defaultmxbeanmappingfactory java at java management com sun jmx mbeanserver defaultmxbeanmappingfactory nonnullmxbeanmapping fromopenvalue defaultmxbeanmappingfactory java at java management com sun jmx mbeanserver convertingmethod fromopenreturnvalue convertingmethod java at java management com sun jmx mbeanserver mxbeanproxy invoke mxbeanproxy java at java management javax management mbeanserverinvocationhandler invoke mbeanserverinvocationhandler java more caused by java lang reflect invocationtargetexception at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at sun reflect misc trampoline invoke methodutil java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at java base sun reflect misc methodutil invoke methodutil java at java management com sun jmx mbeanserver defaultmxbeanmappingfactory compositebuilderviafrom fromcompositedata defaultmxbeanmappingfactory java more caused by java lang illegalargumentexception at jdk management com ibm lang management processorusage processorusage java at jdk management com ibm lang management processorusage from processorusage java more testosmxbean tests run failures skips jlm tests suite total tests run failures skips testosmxbeanremote failed testosmxbeanremote failed failed similarly as well to rebuild the failed tests in use the following links | 0 |
88,732 | 17,652,108,483 | IssuesEvent | 2021-08-20 14:29:39 | cloud-native-toolkit/planning | https://api.github.com/repos/cloud-native-toolkit/planning | opened | Update links in starter kits readme files | documentation code pattern | The links in the readme files in the starter kits need to be updated
- Reference to Developer guide should point to https://cloudnativetoolkit.dev/ see [this issue](https://github.com/IBM/template-node-typescript/issues/34)
- Links to Cloud Native Toolkit should be https://cloudnativetoolkit.dev/images/catalyst.png | 1.0 | Update links in starter kits readme files - The links in the readme files in the starter kits need to be updated
- Reference to Developer guide should point to https://cloudnativetoolkit.dev/ see [this issue](https://github.com/IBM/template-node-typescript/issues/34)
- Links to Cloud Native Toolkit should be https://cloudnativetoolkit.dev/images/catalyst.png | non_priority | update links in starter kits readme files the links in the readme files in the starter kits need to be updated reference to developer guide should point to see links to cloud native toolkit should be | 0 |
171,743 | 13,246,584,509 | IssuesEvent | 2020-08-19 15:54:48 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | ccl/backupccl: TestBackupRestoreSubsetCreatedStats failed | C-test-failure O-robot branch-release-20.1 | [(ccl/backupccl).TestBackupRestoreSubsetCreatedStats failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2180692&tab=buildLog) on [release-20.1@ba8de96cc0c40e27818194e8e548b47063ea4ae6](https://github.com/cockroachdb/cockroach/commits/ba8de96cc0c40e27818194e8e548b47063ea4ae6):
```
I200814 05:16:05.265700 234500 sql/temporary_schema.go:575 [n1] temporary object cleaner next scheduled to run at 2020-08-14 05:46:05.217928109 +0000 UTC
I200814 05:16:05.265761 234616 sql/event_log.go:132 [n1,intExec=optInToDiagnosticsStatReporting] Event: "set_cluster_setting", target: 0, info: {SettingName:diagnostics.reporting.enabled Value:true User:root}
I200814 05:16:05.275246 233922 sql/event_log.go:132 [n1,intExec=set-setting] Event: "set_cluster_setting", target: 0, info: {SettingName:version Value:20.1 User:root}
I200814 05:16:05.288302 234993 sql/event_log.go:132 [n1,intExec=initializeClusterSecret] Event: "set_cluster_setting", target: 0, info: {SettingName:cluster.secret Value:a1b753b5-3af5-49a7-8d79-a3c324181747 User:root}
I200814 05:16:05.295257 234910 sql/event_log.go:132 [n1,intExec=create-default-db] Event: "create_database", target: 50, info: {DatabaseName:defaultdb Statement:CREATE DATABASE IF NOT EXISTS defaultdb User:root}
I200814 05:16:05.299452 234684 sql/event_log.go:132 [n1,intExec=create-default-db] Event: "create_database", target: 51, info: {DatabaseName:postgres Statement:CREATE DATABASE IF NOT EXISTS postgres User:root}
I200814 05:16:05.326846 234338 server/server.go:1798 [n1] done ensuring all necessary migrations have run
I200814 05:16:05.326890 234338 server/server.go:2040 [n1] serving sql connections
I200814 05:16:05.329305 235085 sqlmigrations/migrations.go:668 [n1] starting wait for upgrade finalization before schema change job migration
I200814 05:16:05.329554 235085 sqlmigrations/migrations.go:700 [n1] starting schema change job migration
I200814 05:16:05.332413 234338 testutils/testcluster/testcluster.go:760 WaitForFullReplication took: 637ns
I200814 05:16:05.334033 235083 server/server_update.go:55 [n1] no need to upgrade, cluster already at the newest version
I200814 05:16:05.339018 235086 sql/event_log.go:132 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:127.0.0.1:45103 Attrs: Locality:region=test,dc=dc1 ServerVersion:20.1 BuildTag:v20.1.4-50-gba8de96 StartedAt:1597382165203894472 LocalityAddress:[] ClusterName: SQLAddress:127.0.0.1:42823} ClusterID:43326666-240e-434d-9221-7de365cc45ba StartedAt:1597382165203894472 LastUp:1597382165203894472}
I200814 05:16:05.345137 235085 sqlmigrations/migrations.go:1124 [schema-change-job-migration] evaluating tables for creating jobs
I200814 05:16:05.345293 235085 sqlmigrations/migrations.go:719 [n1] schema change job migration completed
I200814 05:16:05.377042 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_database", target: 52, info: {DatabaseName:data Statement:CREATE DATABASE data User:root}
I200814 05:16:05.389114 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_table", target: 53, info: {TableName:data.public.bank Statement:CREATE TABLE IF NOT EXISTS bank (id INT8 PRIMARY KEY, balance INT8, payload STRING, FAMILY (id, balance, payload)) User:root}
I200814 05:16:05.390741 235012 kv/kvserver/replica_command.go:397 [n1,split,s1,r32/1:/{Table/36-Max}] initiating a split of this range at key /Table/53 [r33] (zone config)
I200814 05:16:05.402178 234338 workload/workloadsql/dataload.go:140 imported bank (0s, 1 rows)
I200814 05:16:05.404637 234338 testutils/testcluster/testcluster.go:760 WaitForFullReplication took: 814ns
I200814 05:16:05.408481 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "set_cluster_setting", target: 0, info: {SettingName:sql.stats.automatic_collection.enabled Value:false User:root}
I200814 05:16:05.413341 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_table", target: 54, info: {TableName:data.public.foo Statement:CREATE TABLE data.public.foo (a INT8) User:root}
I200814 05:16:05.415190 235593 kv/kvserver/replica_command.go:397 [n1,split,s1,r33/1:/{Table/53-Max}] initiating a split of this range at key /Table/54 [r34] (zone config)
I200814 05:16:05.431941 235637 jobs/registry.go:806 [n1] job 581015192940249089: stepping through state running with error <nil>
I200814 05:16:05.471687 235637 jobs/registry.go:806 [n1] job 581015192940249089: stepping through state succeeded with error <nil>
I200814 05:16:05.479543 235637 jobs/registry.go:961 [n1] job 581015192940249089: status succeeded after adoption finished
I200814 05:16:05.493664 235688 jobs/registry.go:806 [n1] job 581015193126895617: stepping through state running with error <nil>
I200814 05:16:05.522313 235688 jobs/registry.go:806 [n1] job 581015193126895617: stepping through state succeeded with error <nil>
I200814 05:16:05.527848 235688 jobs/registry.go:961 [n1] job 581015193126895617: status succeeded after adoption finished
I200814 05:16:05.580177 235720 jobs/registry.go:806 [n1] job 581015193377177601: stepping through state running with error <nil>
I200814 05:16:05.597380 235536 ccl/storageccl/export.go:102 [n1,s1,r33/1:/Table/5{3-4}] export [/Table/53/1,/Table/53/2)
I200814 05:16:05.597398 235535 ccl/storageccl/export.go:102 [n1,s1,r34/1:/{Table/54-Max}] export [/Table/54/1,/Table/54/2)
I200814 05:16:05.651922 235720 jobs/registry.go:806 [n1] job 581015193377177601: stepping through state succeeded with error <nil>
I200814 05:16:05.672342 235720 jobs/registry.go:961 [n1] job 581015193377177601: status succeeded after adoption finished
I200814 05:16:05.678836 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_database", target: 55, info: {DatabaseName:"data 2" Statement:CREATE DATABASE "data 2" User:root}
I200814 05:16:05.694782 235880 jobs/registry.go:806 [n1] job 581015193801228289: stepping through state running with error <nil>
I200814 05:16:05.700728 235862 kv/kvserver/replica_command.go:397 [n1,s1,r34/1:/{Table/54-Max}] initiating a split of this range at key /Table/56 [r35] (manual)
I200814 05:16:05.728144 235880 jobs/registry.go:806 [n1] job 581015193801228289: stepping through state succeeded with error <nil>
I200814 05:16:05.742431 235880 jobs/registry.go:961 [n1] job 581015193801228289: status succeeded after adoption finished
I200814 05:16:05.744279 234338 util/stop/stopper.go:539 quiescing
I200814 05:16:05.744448 235949 util/stop/stopper.go:539 quiescing
W200814 05:16:05.744867 235913 kv/kvserver/intentresolver/intent_resolver.go:745 failed to gc transaction record: could not GC completed transaction anchored at /Table/3/1/56/2/1: node unavailable; try another peer
--- FAIL: TestBackupRestoreSubsetCreatedStats (0.68s)
backup_test.go:3822: query 'SELECT name, "columnIDs", "rowCount", "distinctCount", "nullCount" FROM system.table_statistics': expected:
bank_stats, {1}, 1, 1, 0
bank_stats, {2}, 1, 1, 0
bank_stats, {3}, 1, 1, 0
got:
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestBackupRestoreSubsetCreatedStats PKG=./pkg/ccl/backupccl TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestBackupRestoreSubsetCreatedStats.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 1.0 | ccl/backupccl: TestBackupRestoreSubsetCreatedStats failed - [(ccl/backupccl).TestBackupRestoreSubsetCreatedStats failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2180692&tab=buildLog) on [release-20.1@ba8de96cc0c40e27818194e8e548b47063ea4ae6](https://github.com/cockroachdb/cockroach/commits/ba8de96cc0c40e27818194e8e548b47063ea4ae6):
```
I200814 05:16:05.265700 234500 sql/temporary_schema.go:575 [n1] temporary object cleaner next scheduled to run at 2020-08-14 05:46:05.217928109 +0000 UTC
I200814 05:16:05.265761 234616 sql/event_log.go:132 [n1,intExec=optInToDiagnosticsStatReporting] Event: "set_cluster_setting", target: 0, info: {SettingName:diagnostics.reporting.enabled Value:true User:root}
I200814 05:16:05.275246 233922 sql/event_log.go:132 [n1,intExec=set-setting] Event: "set_cluster_setting", target: 0, info: {SettingName:version Value:20.1 User:root}
I200814 05:16:05.288302 234993 sql/event_log.go:132 [n1,intExec=initializeClusterSecret] Event: "set_cluster_setting", target: 0, info: {SettingName:cluster.secret Value:a1b753b5-3af5-49a7-8d79-a3c324181747 User:root}
I200814 05:16:05.295257 234910 sql/event_log.go:132 [n1,intExec=create-default-db] Event: "create_database", target: 50, info: {DatabaseName:defaultdb Statement:CREATE DATABASE IF NOT EXISTS defaultdb User:root}
I200814 05:16:05.299452 234684 sql/event_log.go:132 [n1,intExec=create-default-db] Event: "create_database", target: 51, info: {DatabaseName:postgres Statement:CREATE DATABASE IF NOT EXISTS postgres User:root}
I200814 05:16:05.326846 234338 server/server.go:1798 [n1] done ensuring all necessary migrations have run
I200814 05:16:05.326890 234338 server/server.go:2040 [n1] serving sql connections
I200814 05:16:05.329305 235085 sqlmigrations/migrations.go:668 [n1] starting wait for upgrade finalization before schema change job migration
I200814 05:16:05.329554 235085 sqlmigrations/migrations.go:700 [n1] starting schema change job migration
I200814 05:16:05.332413 234338 testutils/testcluster/testcluster.go:760 WaitForFullReplication took: 637ns
I200814 05:16:05.334033 235083 server/server_update.go:55 [n1] no need to upgrade, cluster already at the newest version
I200814 05:16:05.339018 235086 sql/event_log.go:132 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:127.0.0.1:45103 Attrs: Locality:region=test,dc=dc1 ServerVersion:20.1 BuildTag:v20.1.4-50-gba8de96 StartedAt:1597382165203894472 LocalityAddress:[] ClusterName: SQLAddress:127.0.0.1:42823} ClusterID:43326666-240e-434d-9221-7de365cc45ba StartedAt:1597382165203894472 LastUp:1597382165203894472}
I200814 05:16:05.345137 235085 sqlmigrations/migrations.go:1124 [schema-change-job-migration] evaluating tables for creating jobs
I200814 05:16:05.345293 235085 sqlmigrations/migrations.go:719 [n1] schema change job migration completed
I200814 05:16:05.377042 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_database", target: 52, info: {DatabaseName:data Statement:CREATE DATABASE data User:root}
I200814 05:16:05.389114 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_table", target: 53, info: {TableName:data.public.bank Statement:CREATE TABLE IF NOT EXISTS bank (id INT8 PRIMARY KEY, balance INT8, payload STRING, FAMILY (id, balance, payload)) User:root}
I200814 05:16:05.390741 235012 kv/kvserver/replica_command.go:397 [n1,split,s1,r32/1:/{Table/36-Max}] initiating a split of this range at key /Table/53 [r33] (zone config)
I200814 05:16:05.402178 234338 workload/workloadsql/dataload.go:140 imported bank (0s, 1 rows)
I200814 05:16:05.404637 234338 testutils/testcluster/testcluster.go:760 WaitForFullReplication took: 814ns
I200814 05:16:05.408481 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "set_cluster_setting", target: 0, info: {SettingName:sql.stats.automatic_collection.enabled Value:false User:root}
I200814 05:16:05.413341 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_table", target: 54, info: {TableName:data.public.foo Statement:CREATE TABLE data.public.foo (a INT8) User:root}
I200814 05:16:05.415190 235593 kv/kvserver/replica_command.go:397 [n1,split,s1,r33/1:/{Table/53-Max}] initiating a split of this range at key /Table/54 [r34] (zone config)
I200814 05:16:05.431941 235637 jobs/registry.go:806 [n1] job 581015192940249089: stepping through state running with error <nil>
I200814 05:16:05.471687 235637 jobs/registry.go:806 [n1] job 581015192940249089: stepping through state succeeded with error <nil>
I200814 05:16:05.479543 235637 jobs/registry.go:961 [n1] job 581015192940249089: status succeeded after adoption finished
I200814 05:16:05.493664 235688 jobs/registry.go:806 [n1] job 581015193126895617: stepping through state running with error <nil>
I200814 05:16:05.522313 235688 jobs/registry.go:806 [n1] job 581015193126895617: stepping through state succeeded with error <nil>
I200814 05:16:05.527848 235688 jobs/registry.go:961 [n1] job 581015193126895617: status succeeded after adoption finished
I200814 05:16:05.580177 235720 jobs/registry.go:806 [n1] job 581015193377177601: stepping through state running with error <nil>
I200814 05:16:05.597380 235536 ccl/storageccl/export.go:102 [n1,s1,r33/1:/Table/5{3-4}] export [/Table/53/1,/Table/53/2)
I200814 05:16:05.597398 235535 ccl/storageccl/export.go:102 [n1,s1,r34/1:/{Table/54-Max}] export [/Table/54/1,/Table/54/2)
I200814 05:16:05.651922 235720 jobs/registry.go:806 [n1] job 581015193377177601: stepping through state succeeded with error <nil>
I200814 05:16:05.672342 235720 jobs/registry.go:961 [n1] job 581015193377177601: status succeeded after adoption finished
I200814 05:16:05.678836 235254 sql/event_log.go:132 [n1,client=127.0.0.1:50960,hostssl,user=root] Event: "create_database", target: 55, info: {DatabaseName:"data 2" Statement:CREATE DATABASE "data 2" User:root}
I200814 05:16:05.694782 235880 jobs/registry.go:806 [n1] job 581015193801228289: stepping through state running with error <nil>
I200814 05:16:05.700728 235862 kv/kvserver/replica_command.go:397 [n1,s1,r34/1:/{Table/54-Max}] initiating a split of this range at key /Table/56 [r35] (manual)
I200814 05:16:05.728144 235880 jobs/registry.go:806 [n1] job 581015193801228289: stepping through state succeeded with error <nil>
I200814 05:16:05.742431 235880 jobs/registry.go:961 [n1] job 581015193801228289: status succeeded after adoption finished
I200814 05:16:05.744279 234338 util/stop/stopper.go:539 quiescing
I200814 05:16:05.744448 235949 util/stop/stopper.go:539 quiescing
W200814 05:16:05.744867 235913 kv/kvserver/intentresolver/intent_resolver.go:745 failed to gc transaction record: could not GC completed transaction anchored at /Table/3/1/56/2/1: node unavailable; try another peer
--- FAIL: TestBackupRestoreSubsetCreatedStats (0.68s)
backup_test.go:3822: query 'SELECT name, "columnIDs", "rowCount", "distinctCount", "nullCount" FROM system.table_statistics': expected:
bank_stats, {1}, 1, 1, 0
bank_stats, {2}, 1, 1, 0
bank_stats, {3}, 1, 1, 0
got:
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestBackupRestoreSubsetCreatedStats PKG=./pkg/ccl/backupccl TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestBackupRestoreSubsetCreatedStats.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | ccl backupccl testbackuprestoresubsetcreatedstats failed on sql temporary schema go temporary object cleaner next scheduled to run at utc sql event log go event set cluster setting target info settingname diagnostics reporting enabled value true user root sql event log go event set cluster setting target info settingname version value user root sql event log go event set cluster setting target info settingname cluster secret value user root sql event log go event create database target info databasename defaultdb statement create database if not exists defaultdb user root sql event log go event create database target info databasename postgres statement create database if not exists postgres user root server server go done ensuring all necessary migrations have run server server go serving sql connections sqlmigrations migrations go starting wait for upgrade finalization before schema change job migration sqlmigrations migrations go starting schema change job migration testutils testcluster testcluster go waitforfullreplication took server server update go no need to upgrade cluster already at the newest version sql event log go event node join target info descriptor nodeid address attrs locality region test dc serverversion buildtag startedat localityaddress clustername sqladdress clusterid startedat lastup sqlmigrations migrations go evaluating tables for creating jobs sqlmigrations migrations go schema change job migration completed sql event log go event create database target info databasename data statement create database data user root sql event log go event create table target info tablename data public bank statement create table if not exists bank id primary key balance payload string family id balance payload user root kv kvserver replica command go initiating a split of this range at key table zone config workload workloadsql dataload go imported bank rows testutils testcluster testcluster go waitforfullreplication took sql event log go event set cluster setting target info settingname sql stats automatic collection enabled value false user root sql event log go event create table target info tablename data public foo statement create table data public foo a user root kv kvserver replica command go initiating a split of this range at key table zone config jobs registry go job stepping through state running with error jobs registry go job stepping through state succeeded with error jobs registry go job status succeeded after adoption finished jobs registry go job stepping through state running with error jobs registry go job stepping through state succeeded with error jobs registry go job status succeeded after adoption finished jobs registry go job stepping through state running with error ccl storageccl export go export table table ccl storageccl export go export table table jobs registry go job stepping through state succeeded with error jobs registry go job status succeeded after adoption finished sql event log go event create database target info databasename data statement create database data user root jobs registry go job stepping through state running with error kv kvserver replica command go initiating a split of this range at key table manual jobs registry go job stepping through state succeeded with error jobs registry go job status succeeded after adoption finished util stop stopper go quiescing util stop stopper go quiescing kv kvserver intentresolver intent resolver go failed to gc transaction record could not gc completed transaction anchored at table node unavailable try another peer fail testbackuprestoresubsetcreatedstats backup test go query select name columnids rowcount distinctcount nullcount from system table statistics expected bank stats bank stats bank stats got more parameters goflags json make stressrace tests testbackuprestoresubsetcreatedstats pkg pkg ccl backupccl testtimeout stressflags timeout powered by | 0 |
277,619 | 21,052,107,493 | IssuesEvent | 2022-03-31 21:31:54 | skalenetwork/IMA | https://api.github.com/repos/skalenetwork/IMA | opened | Missing docs for CHAIN_CONNECTOR_ROLE in S2S transfer | documentation bug | roll setup is missing: CHAIN_CONNECTOR_ROLE on the token manager linker for the message proxy on the new schain | 1.0 | Missing docs for CHAIN_CONNECTOR_ROLE in S2S transfer - roll setup is missing: CHAIN_CONNECTOR_ROLE on the token manager linker for the message proxy on the new schain | non_priority | missing docs for chain connector role in transfer roll setup is missing chain connector role on the token manager linker for the message proxy on the new schain | 0 |
68,134 | 7,088,260,134 | IssuesEvent | 2018-01-11 20:50:46 | Vizzuality/half-earth | https://api.github.com/repos/Vizzuality/half-earth | closed | New styles for barcharts | difficulty:easy ready-to-test-staging | Several spider-charts have been replaced by bar-charts, the bar=chart designs are slightly different from what we already had, this should be adjusted. | 1.0 | New styles for barcharts - Several spider-charts have been replaced by bar-charts, the bar=chart designs are slightly different from what we already had, this should be adjusted. | non_priority | new styles for barcharts several spider charts have been replaced by bar charts the bar chart designs are slightly different from what we already had this should be adjusted | 0 |
23,940 | 16,717,956,426 | IssuesEvent | 2021-06-10 01:12:41 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Build failed: Validate-DotNet/main #runtime-93068-.NET6 | area-Infrastructure untriaged | Build [#runtime-93068-.NET6](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=1173341) failed
## :x: : internal / Validate-DotNet failed
### Summary
**Finished** - Sun, 06 Jun 2021 03:20:03 GMT
**Duration** - 254 minutes
**Requested for** - DotNet Bot
**Reason** - manual
### Details
#### Validation Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/149) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Missing symbols for 5 modules in the package D:\workspace\_work\1\a\signed\shipping\assets\symbols\Microsoft.NETCore.App.Runtime.Mono.ios-arm.6.0.0-preview.6.21305.3.symbols.nupkg
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Missing symbols for 2 modules in the package D:\workspace\_work\1\a\signed\shipping\assets\symbols\Microsoft.NETCore.App.Runtime.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Missing symbols for 2 modules in the package D:\workspace\_work\1\a\signed\shipping\assets\symbols\Microsoft.NETCore.App.Runtime.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Symbols missing for 3/312 packages
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - PowerShell exited with code '1'.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/291) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/227) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/256) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - ValidateSymbols: Entry found in generated contract does not match ValidateSymbols.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - Steps were not validated for contract.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - Contract was not validated.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - PowerShell exited with code '1'.
#### Required Validation Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/161) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/260) - Number of checksums and assets don't match. Checksums: 182. Assets: 794. Assets with no corresponding checksum are:
assets/symbols/System.IO.Pipelines.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.DirectoryServices.Protocols.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Formats.Asn1.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Formats.Cbor.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.FileSystem.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.Packaging.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.Pipes.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Data.OleDb.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Net.Http.Json.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Cryptography.ProtectedData.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Data.Odbc.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.TypedParts.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.CodeDom.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Collections.Immutable.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.ComponentModel.Composition.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.ComponentModel.Composition.Registration.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.AttributedModel.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.Convention.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.Hosting.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.Runtime.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Permissions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Cryptography.Xml.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Diagnostics.DiagnosticSource.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Runtime.CompilerServices.Unsafe.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Memory.Data.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Resources.Extensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Net.Http.WinHttpHandler.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Numerics.Tensors.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Reflection.Context.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Reflection.Metadata.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Reflection.MetadataLoadContext.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Cryptography.Pkcs.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Management.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Configuration.ConfigurationManager.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
runtime.linux-arm.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-arm.Microsoft.NETCore.ILAsm
Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-x64
runtime.linux-arm64.Microsoft.NETCore.TestHost
runtime.linux-arm64.runtime.native.System.IO.Ports
runtime.linux-musl-arm.Microsoft.NETCore.DotNetAppHost
runtime.linux-musl-arm.Microsoft.NETCore.DotNetHost
Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.osx-x64
Microsoft.Win32.Registry
Microsoft.NETCore.TestHost
Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-x64
Microsoft.NETCore.App.Runtime.Mono.LLVM.osx-x64
Microsoft.NETCore.App.Runtime.Mono.tvossimulator-x64
Microsoft.NETCore.App.Runtime.Mono.tvossimulator-arm64
Microsoft.NETCore.App.Runtime.Mono.osx-arm64
Microsoft.NETCore.App.Runtime.Mono.osx-x64
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-musl-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-musl-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Principal.Windows.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.Win32.Registry.AccessControl
Microsoft.Win32.SystemEvents
assets/symbols/runtime.linux-arm.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
runtime.linux-arm.Microsoft.NETCore.DotNetAppHost
Microsoft.Windows.Compatibility
Microsoft.XmlSerializer.Generator
runtime.linux-arm.Microsoft.NETCore.DotNetHost
runtime.linux-arm.Microsoft.NETCore.DotNetHostResolver
runtime.linux-arm.Microsoft.NETCore.ILDAsm
Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-arm64
runtime.linux-arm.Microsoft.NETCore.TestHost
runtime.linux-arm64.Microsoft.NETCore.DotNetAppHost
runtime.linux-arm.runtime.native.System.IO.Ports
runtime.linux-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-arm64.Microsoft.NETCore.DotNetHost
runtime.linux-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-arm64.Microsoft.NETCore.ILAsm
runtime.linux-arm64.Microsoft.NETCore.ILDAsm
runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostResolver
Microsoft.NETCore.Platforms
Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-arm64
Microsoft.NETCore.App.Runtime.Mono.maccatalyst-arm64
Microsoft.NETCore.App.Runtime.osx-x64
Microsoft.NETCore.App.Runtime.Mono.win-x64
runtime.linux-musl-arm.Microsoft.NETCore.ILAsm
Microsoft.NETCore.App.Runtime.win-x64
Microsoft.NETCore.DotNetHostPolicy
Microsoft.NETCore.ILAsm
Microsoft.NETCore.ILDAsm
Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-arm.Microsoft.NETCore.ILDAsm
runtime.osx-x64.Microsoft.NETCore.DotNetAppHost
runtime.linux-musl-arm.Microsoft.NETCore.TestHost
runtime.osx-x64.Microsoft.NETCore.DotNetHost
runtime.osx-x64.Microsoft.NETCore.DotNetHostPolicy
runtime.win-arm.Microsoft.NETCore.DotNetAppHost
runtime.osx-x64.Microsoft.NETCore.ILDAsm
runtime.osx-x64.Microsoft.NETCore.DotNetHostResolver
runtime.osx-x64.Microsoft.NETCore.ILAsm
runtime.osx-x64.Microsoft.NETCore.TestHost
runtime.win-arm64.Microsoft.NETCore.DotNetAppHost
runtime.osx-x64.runtime.native.System.IO.Ports
runtime.win-arm.Microsoft.NETCore.DotNetHost
runtime.win-arm.Microsoft.NETCore.DotNetHostPolicy
runtime.win-arm.Microsoft.NETCore.DotNetHostResolver
runtime.win-arm.Microsoft.NETCore.ILAsm
runtime.osx-arm64.Microsoft.NETCore.TestHost
runtime.win-x64.Microsoft.NETCore.DotNetAppHost
runtime.win-arm.Microsoft.NETCore.ILDAsm
runtime.win-arm64.Microsoft.NETCore.DotNetHost
runtime.win-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.win-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.win-arm64.Microsoft.NETCore.ILAsm
runtime.win-arm64.Microsoft.NETCore.ILDAsm
runtime.win-arm64.Microsoft.NETCore.TestHost
runtime.win-x64.Microsoft.NETCore.DotNetHost
runtime.win-x64.Microsoft.NETCore.DotNetHostPolicy
Microsoft.NETCore.App.Runtime.Mono.linux-x64
runtime.win-x64.Microsoft.NETCore.DotNetHostResolver
runtime.win-x64.Microsoft.NETCore.ILAsm
runtime.win-x64.Microsoft.NETCore.ILDAsm
runtime.osx-arm64.Microsoft.NETCore.ILDAsm
runtime.win-arm.Microsoft.NETCore.TestHost
runtime.osx-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHost
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetAppHost
Microsoft.ILVerification
Microsoft.NET.Workload.Mono.ToolChain.Manifest-6.0.100
Microsoft.NETCore.App.Crossgen2.linux-arm
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-x64
Microsoft.NETCore.App.Runtime.Mono.android-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.browser-wasm
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Composite.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
runtime.win-x86.Microsoft.NETCore.DotNetHost
assets/symbols/Microsoft.NETCore.App.Runtime.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.BrowserDebugHost.Transport.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Private.CoreFx.OOB.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Win32.Registry.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Win32.Registry.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Win32.SystemEvents.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Windows.Compatibility.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.XmlSerializer.Generator.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
System.Reflection.MetadataLoadContext
System.Resources.Extensions
System.Runtime.Caching
System.Security.AccessControl
System.Runtime.CompilerServices.Unsafe
System.Security.Cryptography.Pkcs
System.Security.Permissions
System.Security.Cryptography.ProtectedData
System.Security.Cryptography.Xml
assets/symbols/System.ServiceModel.Syndication.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
Runtime/6.0.0-preview.6.21305.3/productVersion.txt
Runtime/6.0.0-preview.6.21305.3/runtime-productVersion.txt
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm
Microsoft.NETCore.App.Host.linux-musl-x64
Microsoft.NETCore.App.Host.linux-x64
Microsoft.NETCore.App.Host.osx-arm64
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm
assets/symbols/Microsoft.NETCore.App.Host.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.Android.Sample.Mono.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.iOS.Sample.Mono.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.MonoAOTCompiler.Task.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.RuntimeConfigParser.Task.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.wasm.Sample.Mono.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.WebAssembly.Sdk.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Sdk.IL.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Workload.Mono.ToolChain.Manifest-6.0.100.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-musl-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.tvossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
System.Security.Principal.Windows
System.IO.Pipes.AccessControl
System.IO.Pipelines
runtime.win-x86.Microsoft.NETCore.DotNetHostResolver
runtime.win-x86.Microsoft.NETCore.ILAsm
runtime.win-x86.Microsoft.NETCore.TestHost
runtime.win-x86.Microsoft.NETCore.ILDAsm
System.CodeDom
System.ComponentModel.Composition
System.Composition
System.Composition.AttributedModel
System.Data.Odbc
System.Composition.TypedParts
System.Data.OleDb
System.Diagnostics.PerformanceCounter
assets/symbols/System.Text.Encoding.CodePages.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Speech.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.ServiceProcess.ServiceController.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Text.Json.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Text.Encodings.Web.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Threading.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Threading.Tasks.Dataflow.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Threading.Channels.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Windows.Extensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.win-x86
Microsoft.NETCore.App.Runtime.Mono.win-x86
Microsoft.NETCore.DotNetAppHost
Microsoft.NETCore.DotNetHost
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-arm64.Microsoft.NETCore.ILAsm
runtime.linux-musl-x64.Microsoft.NETCore.DotNetAppHost
runtime.linux-musl-arm64.Microsoft.NETCore.ILDAsm
runtime.linux-musl-arm64.Microsoft.NETCore.TestHost
runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-x64.Microsoft.NETCore.DotNetHost
runtime.linux-x64.Microsoft.NETCore.DotNetAppHost
runtime.osx-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.osx-arm64.Microsoft.NETCore.DotNetHost
Microsoft.NETCore.App.Runtime.Mono.linux-arm64
runtime.linux-musl-x64.Microsoft.NETCore.TestHost
Microsoft.Extensions.Logging.Abstractions
Microsoft.Extensions.Logging
Microsoft.Extensions.Logging.Console
Microsoft.Extensions.Logging.Debug
Microsoft.Extensions.Logging.Configuration
Microsoft.Extensions.Logging.EventLog
Microsoft.Extensions.Logging.EventSource
Microsoft.Extensions.Options
Microsoft.Extensions.Logging.TraceSource
Microsoft.Extensions.Options.ConfigurationExtensions
Microsoft.NETCore.App.Composite
Microsoft.Extensions.Http
Microsoft.IO.Redist
Microsoft.NET.Runtime.iOS.Sample.Mono
Microsoft.NET.Runtime.Android.Sample.Mono
Microsoft.NET.Runtime.WebAssembly.Sdk
Microsoft.NET.Runtime.RuntimeConfigParser.Task
Microsoft.NET.Runtime.MonoAOTCompiler.Task
Microsoft.NET.Runtime.wasm.Sample.Mono
Microsoft.NET.Sdk.IL
Microsoft.NETCore.App.Crossgen2.linux-arm64
Microsoft.Extensions.Caching.Memory
Microsoft.NETCore.App.Crossgen2.linux-musl-x64
Microsoft.Extensions.Configuration.CommandLine
Microsoft.Extensions.Configuration.EnvironmentVariables
Microsoft.Extensions.Hosting.Systemd
Microsoft.Extensions.Configuration.FileExtensions
Microsoft.Extensions.Configuration.Json
Microsoft.Extensions.DependencyInjection
Microsoft.Extensions.DependencyInjection.Abstractions
Microsoft.NETCore.App.Crossgen2.osx-arm64
Microsoft.Extensions.FileProviders.Physical
Microsoft.Extensions.FileProviders.Composite
Microsoft.Extensions.FileSystemGlobbing
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x86
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-x64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm64
Microsoft.NETCore.App.Runtime.linux-arm
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-arm64
Microsoft.NETCore.App.Runtime.linux-arm64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.browser-wasm
Microsoft.NETCore.App.Runtime.Mono.ios-arm64
Microsoft.NETCore.App.Runtime.Mono.iossimulator-x86
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm64
Microsoft.NETCore.App.Crossgen2.win-x64
Microsoft.NETCore.App.Crossgen2.win-arm
Microsoft.NETCore.App.Crossgen2.win-x86
Microsoft.NETCore.App.Host.linux-arm
Microsoft.NETCore.App.Host.linux-musl-arm
Microsoft.NETCore.App.Host.linux-arm64
Microsoft.NETCore.App.Host.linux-musl-arm64
Microsoft.NETCore.App.Host.osx-x64
Microsoft.NETCore.App.Host.win-x64
Microsoft.NETCore.App.Host.win-arm
Microsoft.NETCore.App.Host.win-x86
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm64
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x86
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.browser-wasm
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvos-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.tvos-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.maccatalyst-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.maccatalyst-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
System.ServiceProcess.ServiceController
System.ServiceModel.Syndication
System.Text.Encoding.CodePages
System.Speech
System.Text.Json
System.Text.Encodings.Web
System.Threading.AccessControl
System.Threading.Tasks.Dataflow
System.Threading.Channels
System.Windows.Extensions
System.IO.Ports
System.Management
System.Collections.Immutable
System.ComponentModel.Composition.Registration
System.Composition.Convention
System.Composition.Hosting
System.Composition.Runtime
assets/symbols/Microsoft.IO.Redist.6.0.0-preview.6.21305.3.symbols.nupkg
System.Diagnostics.EventLog
System.Diagnostics.DiagnosticSource
System.DirectoryServices
System.DirectoryServices.AccountManagement
System.DirectoryServices.Protocols
System.Formats.Asn1
System.Formats.Cbor
System.IO.Packaging
assets/symbols/Microsoft.Extensions.DependencyInjection.Specification.Tests.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Xml.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.DependencyInjection.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.DependencyModel.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Diagnostics.EventLog.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.DirectoryServices.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Diagnostics.PerformanceCounter.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Drawing.Common.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.DirectoryServices.AccountManagement.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.Mono.tvos-arm64
Microsoft.NETCore.App.Runtime.osx-arm64
Microsoft.NETCore.App.Runtime.win-arm64
Microsoft.NETCore.App.Runtime.win-arm
Microsoft.Extensions.Options.DataAnnotations
Microsoft.Extensions.Primitives
Microsoft.Extensions.DependencyInjection.Specification.Tests
Microsoft.Extensions.FileProviders.Abstractions
Microsoft.Extensions.DependencyModel
Microsoft.NETCore.App.Runtime.linux-musl-x64
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x86
runtime.win-x86.Microsoft.NETCore.DotNetAppHost
Microsoft.NETCore.App.Host.win-arm64
runtime.win-x64.Microsoft.NETCore.TestHost
runtime.win-x86.Microsoft.NETCore.DotNetHostPolicy
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-musl-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.ios-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
System.Net.Http.Json
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
System.Memory.Data
System.Net.Http.WinHttpHandler
assets/symbols/Microsoft.NET.HostModel.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Net.HostModel.PGO.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.ILVerification.6.0.0-preview.6.21305.3.symbols.nupkg
System.Numerics.Tensors
System.Reflection.Context
System.Reflection.Metadata
assets/symbols/Microsoft.Extensions.Configuration.Json.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.Systemd.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.EventLog.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.EventSource.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.TraceSource.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Options.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Primitives.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.WindowsServices.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Ini.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.UserSecrets.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.EnvironmentVariables.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Runtime.Caching.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.Mono.maccatalyst-x64
runtime.linux-musl-x64.Microsoft.NETCore.ILAsm
runtime.linux-musl-x64.Microsoft.NETCore.ILDAsm
runtime.osx-arm64.Microsoft.NETCore.ILAsm
runtime.linux-x64.Microsoft.NETCore.DotNetHost
runtime.linux-x64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-x64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-x64.Microsoft.NETCore.ILAsm
runtime.linux-x64.Microsoft.NETCore.ILDAsm
Microsoft.NETCore.App.Runtime.Mono.linux-musl-x64
runtime.linux-x64.Microsoft.NETCore.TestHost
runtime.osx-arm64.Microsoft.NETCore.DotNetAppHost
runtime.linux-x64.runtime.native.System.IO.Ports
Microsoft.NETCore.App.Runtime.Mono.linux-arm
runtime.native.System.IO.Ports
Microsoft.NETCore.App.Crossgen2.linux-musl-arm64
Microsoft.NETCore.App.Crossgen2.linux-musl-arm
Microsoft.Extensions.Hosting.Abstractions
Microsoft.Extensions.Hosting.WindowsServices
dotnet-ilverify
Microsoft.Diagnostics.Tracing.EventSource.Redist
Microsoft.Bcl.AsyncInterfaces
Microsoft.Extensions.Caching.Abstractions
Microsoft.Extensions.Configuration
Microsoft.Extensions.Configuration.Abstractions
Microsoft.Extensions.Configuration.Binder
Microsoft.Extensions.Configuration.UserSecrets
Microsoft.Extensions.Configuration.Xml
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x64
Microsoft.Extensions.Hosting
Microsoft.Extensions.Configuration.Ini
assets/symbols/runtime.linux-arm.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvos-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-arm64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x86
Microsoft.NETCore.App.Runtime.linux-musl-arm64
Microsoft.NETCore.App.Runtime.linux-x64
Microsoft.NETCore.App.Runtime.Mono.android-arm
Microsoft.NETCore.App.Runtime.Mono.android-x64
Microsoft.NETCore.App.Runtime.Mono.android-x86
Microsoft.NETCore.App.Runtime.Mono.ios-arm
Microsoft.NETCore.App.Runtime.Mono.browser-wasm
Microsoft.NETCore.App.Runtime.Mono.iossimulator-arm64
Microsoft.NETCore.App.Runtime.Mono.iossimulator-x64
Microsoft.NETCore.App.Crossgen2.linux-x64
Microsoft.NETCore.App.Runtime.linux-musl-arm
Microsoft.NETCore.App.Crossgen2.osx-x64
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-musl-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-musl-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.iossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.iossimulator-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
System.Drawing.Common
System.IO.FileSystem.AccessControl
System.Configuration.ConfigurationManager
assets/symbols/Microsoft.Extensions.DependencyInjection.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileProviders.Composite.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileProviders.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileProviders.Physical.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileSystemGlobbing.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.HostFactoryResolver.Sources.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.CommandLine.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Binder.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Diagnostics.Tracing.EventSource.Redist.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Caching.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Bcl.AsyncInterfaces.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.AspNetCore.Internal.Transport.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/dotnet-pgo.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Crossgen2.win-arm64
Microsoft.NETCore.App.Ref
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x64
assets/symbols/Microsoft.NETCore.App.PGO.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Ref.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.tvossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.ios-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.iossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Http.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Configuration.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Console.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Debug.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Options.ConfigurationExtensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Options.DataAnnotations.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.FileExtensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Caching.Memory.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/ILCompiler.Reflection.ReadyToRun.Experimental.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/dotnet-ilverify.6.0.0-preview.6.21305.3.symbols.nupkg
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/263) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/178) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/244) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/278) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
#### Signing Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/56) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/131) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
#### Source Code Validation
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/62) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/74) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/105) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/120) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
#### Prep Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/36) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
### Changes
| 1.0 | Build failed: Validate-DotNet/main #runtime-93068-.NET6 - Build [#runtime-93068-.NET6](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=1173341) failed
## :x: : internal / Validate-DotNet failed
### Summary
**Finished** - Sun, 06 Jun 2021 03:20:03 GMT
**Duration** - 254 minutes
**Requested for** - DotNet Bot
**Reason** - manual
### Details
#### Validation Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/149) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Missing symbols for 5 modules in the package D:\workspace\_work\1\a\signed\shipping\assets\symbols\Microsoft.NETCore.App.Runtime.Mono.ios-arm.6.0.0-preview.6.21305.3.symbols.nupkg
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Missing symbols for 2 modules in the package D:\workspace\_work\1\a\signed\shipping\assets\symbols\Microsoft.NETCore.App.Runtime.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Missing symbols for 2 modules in the package D:\workspace\_work\1\a\signed\shipping\assets\symbols\Microsoft.NETCore.App.Runtime.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - (NETCORE_ENGINEERING_TELEMETRY=CheckSymbols) Symbols missing for 3/312 packages
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/282) - PowerShell exited with code '1'.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/291) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/227) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/256) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - ValidateSymbols: Entry found in generated contract does not match ValidateSymbols.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - Steps were not validated for contract.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - Contract was not validated.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/305) - PowerShell exited with code '1'.
#### Required Validation Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/161) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/260) - Number of checksums and assets don't match. Checksums: 182. Assets: 794. Assets with no corresponding checksum are:
assets/symbols/System.IO.Pipelines.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.DirectoryServices.Protocols.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Formats.Asn1.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Formats.Cbor.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.FileSystem.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.Packaging.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.Pipes.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Data.OleDb.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Net.Http.Json.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Cryptography.ProtectedData.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Data.Odbc.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.TypedParts.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.CodeDom.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Collections.Immutable.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.ComponentModel.Composition.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.ComponentModel.Composition.Registration.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.AttributedModel.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.Convention.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.Hosting.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Composition.Runtime.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Permissions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Cryptography.Xml.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Diagnostics.DiagnosticSource.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Runtime.CompilerServices.Unsafe.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Memory.Data.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Resources.Extensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Net.Http.WinHttpHandler.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Numerics.Tensors.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Reflection.Context.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Reflection.Metadata.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Reflection.MetadataLoadContext.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Cryptography.Pkcs.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Management.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Configuration.ConfigurationManager.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
runtime.linux-arm.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-arm.Microsoft.NETCore.ILAsm
Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-x64
runtime.linux-arm64.Microsoft.NETCore.TestHost
runtime.linux-arm64.runtime.native.System.IO.Ports
runtime.linux-musl-arm.Microsoft.NETCore.DotNetAppHost
runtime.linux-musl-arm.Microsoft.NETCore.DotNetHost
Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.osx-x64
Microsoft.Win32.Registry
Microsoft.NETCore.TestHost
Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-x64
Microsoft.NETCore.App.Runtime.Mono.LLVM.osx-x64
Microsoft.NETCore.App.Runtime.Mono.tvossimulator-x64
Microsoft.NETCore.App.Runtime.Mono.tvossimulator-arm64
Microsoft.NETCore.App.Runtime.Mono.osx-arm64
Microsoft.NETCore.App.Runtime.Mono.osx-x64
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-musl-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-musl-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Security.Principal.Windows.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.Win32.Registry.AccessControl
Microsoft.Win32.SystemEvents
assets/symbols/runtime.linux-arm.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
runtime.linux-arm.Microsoft.NETCore.DotNetAppHost
Microsoft.Windows.Compatibility
Microsoft.XmlSerializer.Generator
runtime.linux-arm.Microsoft.NETCore.DotNetHost
runtime.linux-arm.Microsoft.NETCore.DotNetHostResolver
runtime.linux-arm.Microsoft.NETCore.ILDAsm
Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-arm64
runtime.linux-arm.Microsoft.NETCore.TestHost
runtime.linux-arm64.Microsoft.NETCore.DotNetAppHost
runtime.linux-arm.runtime.native.System.IO.Ports
runtime.linux-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-arm64.Microsoft.NETCore.DotNetHost
runtime.linux-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-arm64.Microsoft.NETCore.ILAsm
runtime.linux-arm64.Microsoft.NETCore.ILDAsm
runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostResolver
Microsoft.NETCore.Platforms
Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-arm64
Microsoft.NETCore.App.Runtime.Mono.maccatalyst-arm64
Microsoft.NETCore.App.Runtime.osx-x64
Microsoft.NETCore.App.Runtime.Mono.win-x64
runtime.linux-musl-arm.Microsoft.NETCore.ILAsm
Microsoft.NETCore.App.Runtime.win-x64
Microsoft.NETCore.DotNetHostPolicy
Microsoft.NETCore.ILAsm
Microsoft.NETCore.ILDAsm
Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-arm.Microsoft.NETCore.ILDAsm
runtime.osx-x64.Microsoft.NETCore.DotNetAppHost
runtime.linux-musl-arm.Microsoft.NETCore.TestHost
runtime.osx-x64.Microsoft.NETCore.DotNetHost
runtime.osx-x64.Microsoft.NETCore.DotNetHostPolicy
runtime.win-arm.Microsoft.NETCore.DotNetAppHost
runtime.osx-x64.Microsoft.NETCore.ILDAsm
runtime.osx-x64.Microsoft.NETCore.DotNetHostResolver
runtime.osx-x64.Microsoft.NETCore.ILAsm
runtime.osx-x64.Microsoft.NETCore.TestHost
runtime.win-arm64.Microsoft.NETCore.DotNetAppHost
runtime.osx-x64.runtime.native.System.IO.Ports
runtime.win-arm.Microsoft.NETCore.DotNetHost
runtime.win-arm.Microsoft.NETCore.DotNetHostPolicy
runtime.win-arm.Microsoft.NETCore.DotNetHostResolver
runtime.win-arm.Microsoft.NETCore.ILAsm
runtime.osx-arm64.Microsoft.NETCore.TestHost
runtime.win-x64.Microsoft.NETCore.DotNetAppHost
runtime.win-arm.Microsoft.NETCore.ILDAsm
runtime.win-arm64.Microsoft.NETCore.DotNetHost
runtime.win-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.win-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.win-arm64.Microsoft.NETCore.ILAsm
runtime.win-arm64.Microsoft.NETCore.ILDAsm
runtime.win-arm64.Microsoft.NETCore.TestHost
runtime.win-x64.Microsoft.NETCore.DotNetHost
runtime.win-x64.Microsoft.NETCore.DotNetHostPolicy
Microsoft.NETCore.App.Runtime.Mono.linux-x64
runtime.win-x64.Microsoft.NETCore.DotNetHostResolver
runtime.win-x64.Microsoft.NETCore.ILAsm
runtime.win-x64.Microsoft.NETCore.ILDAsm
runtime.osx-arm64.Microsoft.NETCore.ILDAsm
runtime.win-arm.Microsoft.NETCore.TestHost
runtime.osx-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHost
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetAppHost
Microsoft.ILVerification
Microsoft.NET.Workload.Mono.ToolChain.Manifest-6.0.100
Microsoft.NETCore.App.Crossgen2.linux-arm
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-x64
Microsoft.NETCore.App.Runtime.Mono.android-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.browser-wasm
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Composite.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
runtime.win-x86.Microsoft.NETCore.DotNetHost
assets/symbols/Microsoft.NETCore.App.Runtime.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.BrowserDebugHost.Transport.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Private.CoreFx.OOB.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Win32.Registry.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Win32.Registry.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Win32.SystemEvents.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Windows.Compatibility.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.XmlSerializer.Generator.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
System.Reflection.MetadataLoadContext
System.Resources.Extensions
System.Runtime.Caching
System.Security.AccessControl
System.Runtime.CompilerServices.Unsafe
System.Security.Cryptography.Pkcs
System.Security.Permissions
System.Security.Cryptography.ProtectedData
System.Security.Cryptography.Xml
assets/symbols/System.ServiceModel.Syndication.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.CrossOsDiag.Private.CoreCLR.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
Runtime/6.0.0-preview.6.21305.3/productVersion.txt
Runtime/6.0.0-preview.6.21305.3/runtime-productVersion.txt
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm
Microsoft.NETCore.App.Host.linux-musl-x64
Microsoft.NETCore.App.Host.linux-x64
Microsoft.NETCore.App.Host.osx-arm64
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm
assets/symbols/Microsoft.NETCore.App.Host.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.Android.Sample.Mono.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.iOS.Sample.Mono.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.MonoAOTCompiler.Task.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.RuntimeConfigParser.Task.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.wasm.Sample.Mono.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Runtime.WebAssembly.Sdk.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Sdk.IL.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NET.Workload.Mono.ToolChain.Manifest-6.0.100.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-musl-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Host.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.tvossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
System.Security.Principal.Windows
System.IO.Pipes.AccessControl
System.IO.Pipelines
runtime.win-x86.Microsoft.NETCore.DotNetHostResolver
runtime.win-x86.Microsoft.NETCore.ILAsm
runtime.win-x86.Microsoft.NETCore.TestHost
runtime.win-x86.Microsoft.NETCore.ILDAsm
System.CodeDom
System.ComponentModel.Composition
System.Composition
System.Composition.AttributedModel
System.Data.Odbc
System.Composition.TypedParts
System.Data.OleDb
System.Diagnostics.PerformanceCounter
assets/symbols/System.Text.Encoding.CodePages.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Speech.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.ServiceProcess.ServiceController.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Text.Json.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Text.Encodings.Web.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Threading.AccessControl.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Threading.Tasks.Dataflow.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Threading.Channels.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Windows.Extensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.win-x86
Microsoft.NETCore.App.Runtime.Mono.win-x86
Microsoft.NETCore.DotNetAppHost
Microsoft.NETCore.DotNetHost
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-arm64.Microsoft.NETCore.ILAsm
runtime.linux-musl-x64.Microsoft.NETCore.DotNetAppHost
runtime.linux-musl-arm64.Microsoft.NETCore.ILDAsm
runtime.linux-musl-arm64.Microsoft.NETCore.TestHost
runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-musl-x64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-musl-x64.Microsoft.NETCore.DotNetHost
runtime.linux-x64.Microsoft.NETCore.DotNetAppHost
runtime.osx-arm64.Microsoft.NETCore.DotNetHostPolicy
runtime.osx-arm64.Microsoft.NETCore.DotNetHost
Microsoft.NETCore.App.Runtime.Mono.linux-arm64
runtime.linux-musl-x64.Microsoft.NETCore.TestHost
Microsoft.Extensions.Logging.Abstractions
Microsoft.Extensions.Logging
Microsoft.Extensions.Logging.Console
Microsoft.Extensions.Logging.Debug
Microsoft.Extensions.Logging.Configuration
Microsoft.Extensions.Logging.EventLog
Microsoft.Extensions.Logging.EventSource
Microsoft.Extensions.Options
Microsoft.Extensions.Logging.TraceSource
Microsoft.Extensions.Options.ConfigurationExtensions
Microsoft.NETCore.App.Composite
Microsoft.Extensions.Http
Microsoft.IO.Redist
Microsoft.NET.Runtime.iOS.Sample.Mono
Microsoft.NET.Runtime.Android.Sample.Mono
Microsoft.NET.Runtime.WebAssembly.Sdk
Microsoft.NET.Runtime.RuntimeConfigParser.Task
Microsoft.NET.Runtime.MonoAOTCompiler.Task
Microsoft.NET.Runtime.wasm.Sample.Mono
Microsoft.NET.Sdk.IL
Microsoft.NETCore.App.Crossgen2.linux-arm64
Microsoft.Extensions.Caching.Memory
Microsoft.NETCore.App.Crossgen2.linux-musl-x64
Microsoft.Extensions.Configuration.CommandLine
Microsoft.Extensions.Configuration.EnvironmentVariables
Microsoft.Extensions.Hosting.Systemd
Microsoft.Extensions.Configuration.FileExtensions
Microsoft.Extensions.Configuration.Json
Microsoft.Extensions.DependencyInjection
Microsoft.Extensions.DependencyInjection.Abstractions
Microsoft.NETCore.App.Crossgen2.osx-arm64
Microsoft.Extensions.FileProviders.Physical
Microsoft.Extensions.FileProviders.Composite
Microsoft.Extensions.FileSystemGlobbing
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x86
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-x64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm64
Microsoft.NETCore.App.Runtime.linux-arm
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-arm64
Microsoft.NETCore.App.Runtime.linux-arm64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.browser-wasm
Microsoft.NETCore.App.Runtime.Mono.ios-arm64
Microsoft.NETCore.App.Runtime.Mono.iossimulator-x86
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm64
Microsoft.NETCore.App.Crossgen2.win-x64
Microsoft.NETCore.App.Crossgen2.win-arm
Microsoft.NETCore.App.Crossgen2.win-x86
Microsoft.NETCore.App.Host.linux-arm
Microsoft.NETCore.App.Host.linux-musl-arm
Microsoft.NETCore.App.Host.linux-arm64
Microsoft.NETCore.App.Host.linux-musl-arm64
Microsoft.NETCore.App.Host.osx-x64
Microsoft.NETCore.App.Host.win-x64
Microsoft.NETCore.App.Host.win-arm
Microsoft.NETCore.App.Host.win-x86
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm64
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x86
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.browser-wasm
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.ios-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvos-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.tvos-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.maccatalyst-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.maccatalyst-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
System.ServiceProcess.ServiceController
System.ServiceModel.Syndication
System.Text.Encoding.CodePages
System.Speech
System.Text.Json
System.Text.Encodings.Web
System.Threading.AccessControl
System.Threading.Tasks.Dataflow
System.Threading.Channels
System.Windows.Extensions
System.IO.Ports
System.Management
System.Collections.Immutable
System.ComponentModel.Composition.Registration
System.Composition.Convention
System.Composition.Hosting
System.Composition.Runtime
assets/symbols/Microsoft.IO.Redist.6.0.0-preview.6.21305.3.symbols.nupkg
System.Diagnostics.EventLog
System.Diagnostics.DiagnosticSource
System.DirectoryServices
System.DirectoryServices.AccountManagement
System.DirectoryServices.Protocols
System.Formats.Asn1
System.Formats.Cbor
System.IO.Packaging
assets/symbols/Microsoft.Extensions.DependencyInjection.Specification.Tests.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Xml.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.DependencyInjection.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.DependencyModel.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-arm.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Diagnostics.EventLog.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.DirectoryServices.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Diagnostics.PerformanceCounter.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Drawing.Common.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.DirectoryServices.AccountManagement.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x86.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetHostPolicy.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.Mono.tvos-arm64
Microsoft.NETCore.App.Runtime.osx-arm64
Microsoft.NETCore.App.Runtime.win-arm64
Microsoft.NETCore.App.Runtime.win-arm
Microsoft.Extensions.Options.DataAnnotations
Microsoft.Extensions.Primitives
Microsoft.Extensions.DependencyInjection.Specification.Tests
Microsoft.Extensions.FileProviders.Abstractions
Microsoft.Extensions.DependencyModel
Microsoft.NETCore.App.Runtime.linux-musl-x64
Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x86
runtime.win-x86.Microsoft.NETCore.DotNetAppHost
Microsoft.NETCore.App.Host.win-arm64
runtime.win-x64.Microsoft.NETCore.TestHost
runtime.win-x86.Microsoft.NETCore.DotNetHostPolicy
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-musl-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.ios-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-musl-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
System.Net.Http.Json
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
System.Memory.Data
System.Net.Http.WinHttpHandler
assets/symbols/Microsoft.NET.HostModel.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Net.HostModel.PGO.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.ILVerification.6.0.0-preview.6.21305.3.symbols.nupkg
System.Numerics.Tensors
System.Reflection.Context
System.Reflection.Metadata
assets/symbols/Microsoft.Extensions.Configuration.Json.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.Systemd.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.EventLog.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.EventSource.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.TraceSource.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Options.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Primitives.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.WindowsServices.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Ini.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.UserSecrets.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.EnvironmentVariables.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.ILDAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.osx-x64.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.ILAsm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.DotNetHostResolver.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-musl-arm64.Microsoft.NETCore.TestHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/System.Runtime.Caching.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.win-x64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm64.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.Mono.maccatalyst-x64
runtime.linux-musl-x64.Microsoft.NETCore.ILAsm
runtime.linux-musl-x64.Microsoft.NETCore.ILDAsm
runtime.osx-arm64.Microsoft.NETCore.ILAsm
runtime.linux-x64.Microsoft.NETCore.DotNetHost
runtime.linux-x64.Microsoft.NETCore.DotNetHostPolicy
runtime.linux-x64.Microsoft.NETCore.DotNetHostResolver
runtime.linux-x64.Microsoft.NETCore.ILAsm
runtime.linux-x64.Microsoft.NETCore.ILDAsm
Microsoft.NETCore.App.Runtime.Mono.linux-musl-x64
runtime.linux-x64.Microsoft.NETCore.TestHost
runtime.osx-arm64.Microsoft.NETCore.DotNetAppHost
runtime.linux-x64.runtime.native.System.IO.Ports
Microsoft.NETCore.App.Runtime.Mono.linux-arm
runtime.native.System.IO.Ports
Microsoft.NETCore.App.Crossgen2.linux-musl-arm64
Microsoft.NETCore.App.Crossgen2.linux-musl-arm
Microsoft.Extensions.Hosting.Abstractions
Microsoft.Extensions.Hosting.WindowsServices
dotnet-ilverify
Microsoft.Diagnostics.Tracing.EventSource.Redist
Microsoft.Bcl.AsyncInterfaces
Microsoft.Extensions.Caching.Abstractions
Microsoft.Extensions.Configuration
Microsoft.Extensions.Configuration.Abstractions
Microsoft.Extensions.Configuration.Binder
Microsoft.Extensions.Configuration.UserSecrets
Microsoft.Extensions.Configuration.Xml
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.iossimulator-x64
Microsoft.Extensions.Hosting
Microsoft.Extensions.Configuration.Ini
assets/symbols/runtime.linux-arm.runtime.native.System.IO.Ports.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.maccatalyst-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvos-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.tvossimulator-arm64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-arm
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x64
Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.android-x86
Microsoft.NETCore.App.Runtime.linux-musl-arm64
Microsoft.NETCore.App.Runtime.linux-x64
Microsoft.NETCore.App.Runtime.Mono.android-arm
Microsoft.NETCore.App.Runtime.Mono.android-x64
Microsoft.NETCore.App.Runtime.Mono.android-x86
Microsoft.NETCore.App.Runtime.Mono.ios-arm
Microsoft.NETCore.App.Runtime.Mono.browser-wasm
Microsoft.NETCore.App.Runtime.Mono.iossimulator-arm64
Microsoft.NETCore.App.Runtime.Mono.iossimulator-x64
Microsoft.NETCore.App.Crossgen2.linux-x64
Microsoft.NETCore.App.Runtime.linux-musl-arm
Microsoft.NETCore.App.Crossgen2.osx-x64
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.android-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.linux-x64.Cross.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-musl-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.AOT.win-x64.Cross.browser-wasm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-musl-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.iossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.iossimulator-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
System.Drawing.Common
System.IO.FileSystem.AccessControl
System.Configuration.ConfigurationManager
assets/symbols/Microsoft.Extensions.DependencyInjection.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileProviders.Composite.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileProviders.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileProviders.Physical.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.FileSystemGlobbing.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.HostFactoryResolver.Sources.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.CommandLine.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Binder.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Diagnostics.Tracing.EventSource.Redist.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Caching.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Bcl.AsyncInterfaces.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.AspNetCore.Internal.Transport.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/dotnet-pgo.6.0.0-preview.6.21305.3.symbols.nupkg
Microsoft.NETCore.App.Crossgen2.win-arm64
Microsoft.NETCore.App.Ref
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-arm64
Microsoft.NETCore.App.Runtime.AOT.osx-x64.Cross.android-x64
assets/symbols/Microsoft.NETCore.App.PGO.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Ref.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.osx-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Crossgen2.win-x86.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.osx-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.win-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/runtime.linux-arm.Microsoft.NETCore.DotNetAppHost.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.tvossimulator-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.android-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.ios-arm.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.iossimulator-x64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.NETCore.App.Runtime.Mono.LLVM.AOT.linux-arm64.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Hosting.Abstractions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Http.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Configuration.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Console.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Logging.Debug.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Options.ConfigurationExtensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Options.DataAnnotations.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.FileExtensions.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Caching.Memory.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/Microsoft.Extensions.Configuration.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/ILCompiler.Reflection.ReadyToRun.Experimental.6.0.0-preview.6.21305.3.symbols.nupkg
assets/symbols/dotnet-ilverify.6.0.0-preview.6.21305.3.symbols.nupkg
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/263) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/178) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/244) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/278) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
#### Signing Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/56) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/131) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
#### Source Code Validation
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/62) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/74) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/105) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/120) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
#### Prep Ring
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1173341/logs/36) - Component Governance detected 1 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
### Changes
| non_priority | build failed validate dotnet main runtime build failed x internal validate dotnet failed summary finished sun jun gmt duration minutes requested for dotnet bot reason manual details validation ring warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency x netcore engineering telemetry checksymbols missing symbols for modules in the package d workspace work a signed shipping assets symbols microsoft netcore app runtime mono ios arm preview symbols nupkg x netcore engineering telemetry checksymbols missing symbols for modules in the package d workspace work a signed shipping assets symbols microsoft netcore app runtime win preview symbols nupkg x netcore engineering telemetry checksymbols missing symbols for modules in the package d workspace work a signed shipping assets symbols microsoft netcore app runtime win arm preview symbols nupkg x netcore engineering telemetry checksymbols symbols missing for packages x powershell exited with code warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency x validatesymbols entry found in generated contract does not match validatesymbols x steps were not validated for contract x contract was not validated x powershell exited with code required validation ring warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning number of checksums and assets don t match checksums assets assets with no corresponding checksum are assets symbols system io pipelines preview symbols nupkg assets symbols runtime linux microsoft netcore ilasm preview symbols nupkg assets symbols system directoryservices protocols preview symbols nupkg assets symbols system formats preview symbols nupkg assets symbols system formats cbor preview symbols nupkg assets symbols system io filesystem accesscontrol preview symbols nupkg assets symbols system io packaging preview symbols nupkg assets symbols system io pipes accesscontrol preview symbols nupkg assets symbols system data oledb preview symbols nupkg assets symbols system net http json preview symbols nupkg assets symbols system security cryptography protecteddata preview symbols nupkg assets symbols system data odbc preview symbols nupkg assets symbols system composition typedparts preview symbols nupkg assets symbols runtime win microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime win microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime win microsoft netcore ilasm preview symbols nupkg assets symbols runtime win microsoft netcore ildasm preview symbols nupkg assets symbols runtime win microsoft netcore testhost preview symbols nupkg assets symbols runtime win microsoft netcore ildasm preview symbols nupkg assets symbols runtime win microsoft netcore ilasm preview symbols nupkg assets symbols runtime win microsoft netcore testhost preview symbols nupkg assets symbols system codedom preview symbols nupkg assets symbols system collections immutable preview symbols nupkg assets symbols system componentmodel composition preview symbols nupkg assets symbols system composition preview symbols nupkg assets symbols system componentmodel composition registration preview symbols nupkg assets symbols system composition attributedmodel preview symbols nupkg assets symbols system composition convention preview symbols nupkg assets symbols system composition hosting preview symbols nupkg assets symbols runtime win microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols system composition runtime preview symbols nupkg assets symbols system security permissions preview symbols nupkg assets symbols system security cryptography xml preview symbols nupkg assets symbols runtime linux microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime win arm microsoft netcore ildasm preview symbols nupkg assets symbols runtime linux musl microsoft crossosdiag private coreclr preview symbols nupkg assets symbols runtime linux musl microsoft netcore ildasm preview symbols nupkg assets symbols runtime win microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime linux musl microsoft netcore ilasm preview symbols nupkg assets symbols runtime linux musl microsoft netcore ildasm preview symbols nupkg assets symbols runtime win arm microsoft netcore testhost preview symbols nupkg assets symbols runtime win microsoft netcore dotnethost preview symbols nupkg assets symbols system diagnostics diagnosticsource preview symbols nupkg assets symbols system io ports preview symbols nupkg assets symbols system runtime compilerservices unsafe preview symbols nupkg assets symbols system memory data preview symbols nupkg assets symbols system resources extensions preview symbols nupkg assets symbols system net http winhttphandler preview symbols nupkg assets symbols system numerics tensors preview symbols nupkg assets symbols system reflection context preview symbols nupkg assets symbols system reflection metadata preview symbols nupkg assets symbols system reflection metadataloadcontext preview symbols nupkg assets symbols system security cryptography pkcs preview symbols nupkg assets symbols system security accesscontrol preview symbols nupkg assets symbols system management preview symbols nupkg assets symbols runtime win microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime win microsoft netcore ilasm preview symbols nupkg assets symbols runtime win microsoft netcore ildasm preview symbols nupkg assets symbols runtime win microsoft netcore testhost preview symbols nupkg assets symbols system configuration configurationmanager preview symbols nupkg assets symbols runtime win microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime win microsoft netcore dotnethost preview symbols nupkg runtime linux arm microsoft netcore dotnethostpolicy runtime linux arm microsoft netcore ilasm microsoft netcore app runtime mono llvm aot linux runtime linux microsoft netcore testhost runtime linux runtime native system io ports runtime linux musl arm microsoft netcore dotnetapphost runtime linux musl arm microsoft netcore dotnethost microsoft netcore app runtime mono llvm aot osx microsoft registry microsoft netcore testhost microsoft netcore app runtime mono llvm linux microsoft netcore app runtime mono llvm osx microsoft netcore app runtime mono tvossimulator microsoft netcore app runtime mono tvossimulator microsoft netcore app runtime mono osx microsoft netcore app runtime mono osx assets symbols microsoft netcore app runtime aot osx cross android preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross ios arm preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross iossimulator preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross tvossimulator preview symbols nupkg assets symbols microsoft netcore app runtime aot win cross android preview symbols nupkg assets symbols microsoft netcore app host win preview symbols nupkg assets symbols microsoft netcore app linux musl arm preview symbols nupkg assets symbols microsoft netcore app win preview symbols nupkg assets symbols microsoft netcore app host linux arm preview symbols nupkg assets symbols microsoft netcore app host linux preview symbols nupkg assets symbols microsoft netcore app host linux musl arm preview symbols nupkg assets symbols microsoft netcore app runtime osx preview symbols nupkg assets symbols microsoft netcore app runtime win arm preview symbols nupkg assets symbols microsoft netcore dotnetapphost preview symbols nupkg assets symbols microsoft netcore dotnethost preview symbols nupkg assets symbols microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols microsoft netcore dotnethostresolver preview symbols nupkg assets symbols microsoft netcore ilasm preview symbols nupkg assets symbols runtime linux arm microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime linux arm microsoft netcore ilasm preview symbols nupkg assets symbols runtime linux arm microsoft netcore ildasm preview symbols nupkg assets symbols microsoft netcore app runtime mono win preview symbols nupkg assets symbols microsoft netcore app runtime mono win preview symbols nupkg assets symbols microsoft netcore app runtime linux musl preview symbols nupkg assets symbols system security principal windows preview symbols nupkg assets symbols runtime linux microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime linux microsoft crossosdiag private coreclr preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore ilasm preview symbols nupkg assets symbols runtime linux microsoft crossosdiag private coreclr preview symbols nupkg microsoft registry accesscontrol microsoft systemevents assets symbols runtime linux arm microsoft netcore testhost preview symbols nupkg runtime linux arm microsoft netcore dotnetapphost microsoft windows compatibility microsoft xmlserializer generator runtime linux arm microsoft netcore dotnethost runtime linux arm microsoft netcore dotnethostresolver runtime linux arm microsoft netcore ildasm microsoft netcore app runtime mono llvm aot linux runtime linux arm microsoft netcore testhost runtime linux microsoft netcore dotnetapphost runtime linux arm runtime native system io ports runtime linux microsoft netcore dotnethostpolicy runtime linux microsoft netcore dotnethost runtime linux microsoft netcore dotnethostresolver runtime linux microsoft netcore ilasm runtime linux microsoft netcore ildasm runtime linux musl arm microsoft netcore dotnethostpolicy runtime linux musl arm microsoft netcore dotnethostresolver microsoft netcore platforms microsoft netcore app runtime mono llvm linux microsoft netcore app runtime mono maccatalyst microsoft netcore app runtime osx microsoft netcore app runtime mono win runtime linux musl arm microsoft netcore ilasm microsoft netcore app runtime win microsoft netcore dotnethostpolicy microsoft netcore ilasm microsoft netcore ildasm microsoft netcore dotnethostresolver runtime linux musl arm microsoft netcore ildasm runtime osx microsoft netcore dotnetapphost runtime linux musl arm microsoft netcore testhost runtime osx microsoft netcore dotnethost runtime osx microsoft netcore dotnethostpolicy runtime win arm microsoft netcore dotnetapphost runtime osx microsoft netcore ildasm runtime osx microsoft netcore dotnethostresolver runtime osx microsoft netcore ilasm runtime osx microsoft netcore testhost runtime win microsoft netcore dotnetapphost runtime osx runtime native system io ports runtime win arm microsoft netcore dotnethost runtime win arm microsoft netcore dotnethostpolicy runtime win arm microsoft netcore dotnethostresolver runtime win arm microsoft netcore ilasm runtime osx microsoft netcore testhost runtime win microsoft netcore dotnetapphost runtime win arm microsoft netcore ildasm runtime win microsoft netcore dotnethost runtime win microsoft netcore dotnethostpolicy runtime win microsoft netcore dotnethostresolver runtime win microsoft netcore ilasm runtime win microsoft netcore ildasm runtime win microsoft netcore testhost runtime win microsoft netcore dotnethost runtime win microsoft netcore dotnethostpolicy microsoft netcore app runtime mono linux runtime win microsoft netcore dotnethostresolver runtime win microsoft netcore ilasm runtime win microsoft netcore ildasm runtime osx microsoft netcore ildasm runtime win arm microsoft netcore testhost runtime osx microsoft netcore dotnethostresolver runtime linux musl microsoft netcore dotnethost runtime linux musl microsoft netcore dotnetapphost microsoft ilverification microsoft net workload mono toolchain manifest microsoft netcore app linux arm microsoft netcore app runtime aot osx cross tvossimulator microsoft netcore app runtime mono android microsoft netcore app runtime aot osx cross browser wasm assets symbols microsoft netcore app runtime aot osx cross maccatalyst preview symbols nupkg assets symbols microsoft netcore app composite preview symbols nupkg assets symbols microsoft netcore app linux musl preview symbols nupkg assets symbols microsoft netcore app linux preview symbols nupkg assets symbols microsoft netcore app host osx preview symbols nupkg runtime win microsoft netcore dotnethost assets symbols microsoft netcore app runtime win preview symbols nupkg assets symbols microsoft netcore browserdebughost transport preview symbols nupkg assets symbols microsoft netcore ildasm preview symbols nupkg assets symbols microsoft netcore testhost preview symbols nupkg assets symbols microsoft private corefx oob preview symbols nupkg assets symbols microsoft registry preview symbols nupkg assets symbols microsoft registry accesscontrol preview symbols nupkg assets symbols microsoft systemevents preview symbols nupkg assets symbols microsoft windows compatibility preview symbols nupkg assets symbols microsoft xmlserializer generator preview symbols nupkg assets symbols runtime linux arm microsoft crossosdiag private coreclr preview symbols nupkg assets symbols runtime linux arm microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux arm microsoft netcore dotnethostpolicy preview symbols nupkg system reflection metadataloadcontext system resources extensions system runtime caching system security accesscontrol system runtime compilerservices unsafe system security cryptography pkcs system security permissions system security cryptography protecteddata system security cryptography xml assets symbols system servicemodel syndication preview symbols nupkg assets symbols runtime osx microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime linux microsoft netcore testhost preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime linux microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime linux musl microsoft netcore testhost preview symbols nupkg assets symbols runtime linux microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime linux musl arm microsoft crossosdiag private coreclr preview symbols nupkg assets symbols runtime linux microsoft netcore ildasm preview symbols nupkg assets symbols runtime linux microsoft netcore testhost preview symbols nupkg assets symbols runtime linux runtime native system io ports preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux musl microsoft crossosdiag private coreclr preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore ildasm preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore testhost preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnetapphost preview symbols nupkg runtime preview productversion txt runtime preview runtime productversion txt microsoft netcore app runtime aot osx cross ios arm microsoft netcore app host linux musl microsoft netcore app host linux microsoft netcore app host osx microsoft netcore app runtime aot linux cross android arm assets symbols microsoft netcore app host win preview symbols nupkg assets symbols microsoft netcore app runtime aot linux cross android preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross android preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross browser wasm preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross iossimulator preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross maccatalyst preview symbols nupkg assets symbols microsoft netcore app runtime aot win cross android arm preview symbols nupkg assets symbols microsoft netcore app runtime aot win cross android preview symbols nupkg assets symbols microsoft netcore app host win preview symbols nupkg assets symbols microsoft netcore app host win arm preview symbols nupkg assets symbols microsoft netcore app host osx preview symbols nupkg assets symbols microsoft net runtime android sample mono preview symbols nupkg assets symbols microsoft net runtime ios sample mono preview symbols nupkg assets symbols microsoft net runtime monoaotcompiler task preview symbols nupkg assets symbols microsoft net runtime runtimeconfigparser task preview symbols nupkg assets symbols microsoft net runtime wasm sample mono preview symbols nupkg assets symbols microsoft net runtime webassembly sdk preview symbols nupkg assets symbols microsoft net sdk il preview symbols nupkg assets symbols microsoft net workload mono toolchain manifest preview symbols nupkg assets symbols microsoft netcore app host linux musl preview symbols nupkg assets symbols microsoft netcore app host linux musl preview symbols nupkg assets symbols microsoft netcore app host linux preview symbols nupkg assets symbols microsoft netcore app runtime win preview symbols nupkg assets symbols microsoft netcore app runtime mono tvossimulator preview symbols nupkg assets symbols microsoft netcore app runtime mono android preview symbols nupkg assets symbols microsoft netcore app runtime mono linux arm preview symbols nupkg system security principal windows system io pipes accesscontrol system io pipelines runtime win microsoft netcore dotnethostresolver runtime win microsoft netcore ilasm runtime win microsoft netcore testhost runtime win microsoft netcore ildasm system codedom system componentmodel composition system composition system composition attributedmodel system data odbc system composition typedparts system data oledb system diagnostics performancecounter assets symbols system text encoding codepages preview symbols nupkg assets symbols system speech preview symbols nupkg assets symbols system serviceprocess servicecontroller preview symbols nupkg assets symbols system text json preview symbols nupkg assets symbols system text encodings web preview symbols nupkg assets symbols system threading accesscontrol preview symbols nupkg assets symbols system threading tasks dataflow preview symbols nupkg assets symbols system threading channels preview symbols nupkg assets symbols system windows extensions preview symbols nupkg assets symbols runtime linux microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime linux microsoft netcore ilasm preview symbols nupkg assets symbols runtime linux microsoft netcore ildasm preview symbols nupkg assets symbols runtime linux runtime native system io ports preview symbols nupkg assets symbols runtime native system io ports preview symbols nupkg assets symbols runtime osx microsoft netcore dotnethost preview symbols nupkg assets symbols runtime osx microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime osx microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime osx microsoft netcore ilasm preview symbols nupkg microsoft netcore app runtime win microsoft netcore app runtime mono win microsoft netcore dotnetapphost microsoft netcore dotnethost runtime linux musl microsoft netcore dotnethostpolicy runtime linux musl microsoft netcore dotnethostresolver runtime linux musl microsoft netcore ilasm runtime linux musl microsoft netcore dotnetapphost runtime linux musl microsoft netcore ildasm runtime linux musl microsoft netcore testhost runtime linux musl microsoft netcore dotnethostpolicy runtime linux musl microsoft netcore dotnethostresolver runtime linux musl microsoft netcore dotnethost runtime linux microsoft netcore dotnetapphost runtime osx microsoft netcore dotnethostpolicy runtime osx microsoft netcore dotnethost microsoft netcore app runtime mono linux runtime linux musl microsoft netcore testhost microsoft extensions logging abstractions microsoft extensions logging microsoft extensions logging console microsoft extensions logging debug microsoft extensions logging configuration microsoft extensions logging eventlog microsoft extensions logging eventsource microsoft extensions options microsoft extensions logging tracesource microsoft extensions options configurationextensions microsoft netcore app composite microsoft extensions http microsoft io redist microsoft net runtime ios sample mono microsoft net runtime android sample mono microsoft net runtime webassembly sdk microsoft net runtime runtimeconfigparser task microsoft net runtime monoaotcompiler task microsoft net runtime wasm sample mono microsoft net sdk il microsoft netcore app linux microsoft extensions caching memory microsoft netcore app linux musl microsoft extensions configuration commandline microsoft extensions configuration environmentvariables microsoft extensions hosting systemd microsoft extensions configuration fileextensions microsoft extensions configuration json microsoft extensions dependencyinjection microsoft extensions dependencyinjection abstractions microsoft netcore app osx microsoft extensions fileproviders physical microsoft extensions fileproviders composite microsoft extensions filesystemglobbing microsoft netcore app runtime aot osx cross iossimulator microsoft netcore app runtime aot osx cross maccatalyst microsoft netcore app runtime aot win cross android microsoft netcore app runtime linux arm microsoft netcore app runtime aot osx cross iossimulator microsoft netcore app runtime linux microsoft netcore app runtime aot win cross browser wasm microsoft netcore app runtime mono ios microsoft netcore app runtime mono iossimulator microsoft netcore app runtime aot osx cross ios microsoft netcore app win microsoft netcore app win arm microsoft netcore app win microsoft netcore app host linux arm microsoft netcore app host linux musl arm microsoft netcore app host linux microsoft netcore app host linux musl microsoft netcore app host osx microsoft netcore app host win microsoft netcore app host win arm microsoft netcore app host win microsoft netcore app runtime aot linux cross android microsoft netcore app runtime aot linux cross android microsoft netcore app runtime aot linux cross browser wasm assets symbols microsoft netcore app runtime aot linux cross android preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross android arm preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross ios preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross iossimulator preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross tvos preview symbols nupkg assets symbols microsoft netcore app runtime aot win cross android preview symbols nupkg assets symbols microsoft netcore app linux arm preview symbols nupkg assets symbols microsoft netcore app runtime mono linux preview symbols nupkg assets symbols microsoft netcore app runtime mono tvos preview symbols nupkg assets symbols microsoft netcore app runtime mono maccatalyst preview symbols nupkg assets symbols microsoft netcore app runtime mono maccatalyst preview symbols nupkg assets symbols microsoft netcore app runtime mono osx preview symbols nupkg system serviceprocess servicecontroller system servicemodel syndication system text encoding codepages system speech system text json system text encodings web system threading accesscontrol system threading tasks dataflow system threading channels system windows extensions system io ports system management system collections immutable system componentmodel composition registration system composition convention system composition hosting system composition runtime assets symbols microsoft io redist preview symbols nupkg system diagnostics eventlog system diagnostics diagnosticsource system directoryservices system directoryservices accountmanagement system directoryservices protocols system formats system formats cbor system io packaging assets symbols microsoft extensions dependencyinjection specification tests preview symbols nupkg assets symbols microsoft extensions configuration xml preview symbols nupkg assets symbols microsoft extensions dependencyinjection abstractions preview symbols nupkg assets symbols microsoft extensions dependencymodel preview symbols nupkg assets symbols runtime osx microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime osx microsoft netcore ildasm preview symbols nupkg assets symbols runtime osx microsoft netcore testhost preview symbols nupkg assets symbols runtime osx microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime osx microsoft netcore dotnethost preview symbols nupkg assets symbols runtime osx microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime osx microsoft netcore ilasm preview symbols nupkg assets symbols runtime win arm microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime win arm microsoft netcore dotnethost preview symbols nupkg assets symbols runtime win arm microsoft netcore dotnethostpolicy preview symbols nupkg assets symbols runtime win arm microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime win arm microsoft netcore ilasm preview symbols nupkg assets symbols system diagnostics eventlog preview symbols nupkg assets symbols system directoryservices preview symbols nupkg assets symbols system diagnostics performancecounter preview symbols nupkg assets symbols system drawing common preview symbols nupkg assets symbols system directoryservices accountmanagement preview symbols nupkg assets symbols runtime win microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime win microsoft netcore dotnethostpolicy preview symbols nupkg microsoft netcore app runtime mono tvos microsoft netcore app runtime osx microsoft netcore app runtime win microsoft netcore app runtime win arm microsoft extensions options dataannotations microsoft extensions primitives microsoft extensions dependencyinjection specification tests microsoft extensions fileproviders abstractions microsoft extensions dependencymodel microsoft netcore app runtime linux musl microsoft netcore app runtime aot linux cross android microsoft netcore app runtime aot osx cross android arm microsoft netcore app runtime aot osx cross android runtime win microsoft netcore dotnetapphost microsoft netcore app host win runtime win microsoft netcore testhost runtime win microsoft netcore dotnethostpolicy assets symbols microsoft netcore app runtime aot linux cross android preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross android preview symbols nupkg assets symbols microsoft netcore app runtime aot osx cross tvossimulator preview symbols nupkg assets symbols microsoft netcore app osx preview symbols nupkg assets symbols microsoft netcore app win preview symbols nupkg assets symbols microsoft netcore app runtime linux musl arm preview symbols nupkg assets symbols microsoft netcore app runtime linux preview symbols nupkg assets symbols microsoft netcore app runtime mono android arm preview symbols nupkg assets symbols microsoft netcore app runtime mono android preview symbols nupkg assets symbols microsoft netcore app runtime mono browser wasm preview symbols nupkg assets symbols microsoft netcore app runtime mono ios preview symbols nupkg assets symbols microsoft netcore app runtime mono linux musl preview symbols nupkg assets symbols microsoft netcore app runtime mono llvm aot osx preview symbols nupkg assets symbols microsoft netcore app runtime mono llvm linux preview symbols nupkg assets symbols microsoft netcore app runtime mono llvm osx preview symbols nupkg assets symbols microsoft netcore app runtime mono osx preview symbols nupkg system net http json assets symbols microsoft netcore app runtime mono linux preview symbols nupkg system memory data system net http winhttphandler assets symbols microsoft net hostmodel preview symbols nupkg assets symbols microsoft net hostmodel pgo preview symbols nupkg assets symbols microsoft ilverification preview symbols nupkg system numerics tensors system reflection context system reflection metadata assets symbols microsoft extensions configuration json preview symbols nupkg assets symbols microsoft extensions hosting systemd preview symbols nupkg assets symbols microsoft extensions logging abstractions preview symbols nupkg assets symbols microsoft extensions logging eventlog preview symbols nupkg assets symbols microsoft extensions logging eventsource preview symbols nupkg assets symbols microsoft extensions logging tracesource preview symbols nupkg assets symbols microsoft extensions options preview symbols nupkg assets symbols microsoft extensions primitives preview symbols nupkg assets symbols microsoft extensions hosting windowsservices preview symbols nupkg assets symbols microsoft extensions configuration ini preview symbols nupkg assets symbols microsoft extensions configuration usersecrets preview symbols nupkg assets symbols microsoft extensions configuration environmentvariables preview symbols nupkg assets symbols runtime osx microsoft netcore ildasm preview symbols nupkg assets symbols runtime osx microsoft netcore testhost preview symbols nupkg assets symbols runtime osx runtime native system io ports preview symbols nupkg assets symbols runtime linux microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux musl arm microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux musl microsoft netcore ilasm preview symbols nupkg assets symbols runtime linux musl microsoft netcore dotnethostresolver preview symbols nupkg assets symbols runtime linux musl microsoft netcore testhost preview symbols nupkg assets symbols system runtime caching preview symbols nupkg assets symbols runtime win microsoft netcore dotnetapphost preview symbols nupkg assets symbols runtime win microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux microsoft netcore dotnethost preview symbols nupkg assets symbols runtime linux microsoft netcore dotnetapphost preview symbols nupkg microsoft netcore app runtime mono maccatalyst runtime linux musl microsoft netcore ilasm runtime linux musl microsoft netcore ildasm runtime osx microsoft netcore ilasm runtime linux microsoft netcore dotnethost runtime linux microsoft netcore dotnethostpolicy runtime linux microsoft netcore dotnethostresolver runtime linux microsoft netcore ilasm runtime linux microsoft netcore ildasm microsoft netcore app runtime mono linux musl runtime linux microsoft netcore testhost runtime osx microsoft netcore dotnetapphost runtime linux runtime native system io ports microsoft netcore app runtime mono linux arm runtime native system io ports microsoft netcore app linux musl microsoft netcore app linux musl arm microsoft extensions hosting abstractions microsoft extensions hosting windowsservices dotnet ilverify microsoft diagnostics tracing eventsource redist microsoft bcl asyncinterfaces microsoft extensions caching abstractions microsoft extensions configuration microsoft extensions configuration abstractions microsoft extensions configuration binder microsoft extensions configuration usersecrets microsoft extensions configuration xml microsoft netcore app runtime aot osx cross iossimulator microsoft extensions hosting microsoft extensions configuration ini assets symbols runtime linux arm runtime native system io ports preview symbols nupkg microsoft netcore app runtime aot osx cross maccatalyst microsoft netcore app runtime aot osx cross tvos microsoft netcore app runtime aot osx cross tvossimulator microsoft netcore app runtime aot win cross android arm microsoft netcore app runtime aot win cross android microsoft netcore app runtime aot win cross android microsoft netcore app runtime linux musl microsoft netcore app runtime linux microsoft netcore app runtime mono android arm microsoft netcore app runtime mono android microsoft netcore app runtime mono android microsoft netcore app runtime mono ios arm microsoft netcore app runtime mono browser wasm microsoft netcore app runtime mono iossimulator microsoft netcore app runtime mono iossimulator microsoft netcore app linux microsoft netcore app runtime linux musl arm microsoft netcore app osx assets symbols microsoft netcore app runtime aot linux cross android arm preview symbols nupkg assets symbols microsoft netcore app runtime aot linux cross browser wasm preview symbols nupkg assets symbols microsoft netcore app linux musl preview symbols nupkg assets symbols microsoft netcore app runtime aot win cross browser wasm preview symbols nupkg assets symbols microsoft netcore app win arm preview symbols nupkg assets symbols microsoft netcore app runtime linux arm preview symbols nupkg assets symbols microsoft netcore app runtime linux musl preview symbols nupkg assets symbols microsoft netcore app runtime linux preview symbols nupkg assets symbols microsoft netcore app runtime mono iossimulator preview symbols nupkg assets symbols microsoft netcore app runtime mono iossimulator preview symbols nupkg assets symbols microsoft netcore app runtime mono llvm aot linux preview symbols nupkg assets symbols microsoft netcore app runtime mono llvm linux preview symbols nupkg system drawing common system io filesystem accesscontrol system configuration configurationmanager assets symbols microsoft extensions dependencyinjection preview symbols nupkg assets symbols microsoft extensions fileproviders composite preview symbols nupkg assets symbols microsoft extensions fileproviders abstractions preview symbols nupkg assets symbols microsoft extensions fileproviders physical preview symbols nupkg assets symbols microsoft extensions filesystemglobbing preview symbols nupkg assets symbols microsoft extensions hostfactoryresolver sources preview symbols nupkg assets symbols microsoft extensions hosting preview symbols nupkg assets symbols microsoft extensions configuration commandline preview symbols nupkg assets symbols microsoft extensions configuration binder preview symbols nupkg assets symbols microsoft extensions configuration abstractions preview symbols nupkg assets symbols microsoft diagnostics tracing eventsource redist preview symbols nupkg assets symbols microsoft extensions caching abstractions preview symbols nupkg assets symbols microsoft bcl asyncinterfaces preview symbols nupkg assets symbols microsoft aspnetcore internal transport preview symbols nupkg assets symbols dotnet pgo preview symbols nupkg microsoft netcore app win microsoft netcore app ref microsoft netcore app runtime aot osx cross android microsoft netcore app runtime aot osx cross android assets symbols microsoft netcore app pgo preview symbols nupkg assets symbols microsoft netcore app ref preview symbols nupkg assets symbols microsoft netcore app linux preview symbols nupkg assets symbols microsoft netcore app osx preview symbols nupkg assets symbols microsoft netcore app win preview symbols nupkg assets symbols microsoft netcore app runtime osx preview symbols nupkg assets symbols microsoft netcore app runtime win preview symbols nupkg assets symbols runtime linux arm microsoft netcore dotnetapphost preview symbols nupkg assets symbols microsoft netcore app runtime mono tvossimulator preview symbols nupkg assets symbols microsoft netcore app runtime mono android preview symbols nupkg assets symbols microsoft netcore app runtime mono ios arm preview symbols nupkg assets symbols microsoft netcore app runtime mono iossimulator preview symbols nupkg assets symbols microsoft netcore app runtime mono llvm aot linux preview symbols nupkg assets symbols microsoft extensions hosting abstractions preview symbols nupkg assets symbols microsoft extensions http preview symbols nupkg assets symbols microsoft extensions logging preview symbols nupkg assets symbols microsoft extensions logging configuration preview symbols nupkg assets symbols microsoft extensions logging console preview symbols nupkg assets symbols microsoft extensions logging debug preview symbols nupkg assets symbols microsoft extensions options configurationextensions preview symbols nupkg assets symbols microsoft extensions options dataannotations preview symbols nupkg assets symbols microsoft extensions configuration fileextensions preview symbols nupkg assets symbols microsoft extensions caching memory preview symbols nupkg assets symbols microsoft extensions configuration preview symbols nupkg assets symbols ilcompiler reflection readytorun experimental preview symbols nupkg assets symbols dotnet ilverify preview symbols nupkg warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency signing ring warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency source code validation warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency prep ring warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency changes | 0 |
25,003 | 12,198,218,850 | IssuesEvent | 2020-04-29 22:21:51 | edgexfoundry/app-service-configurable | https://api.github.com/repos/edgexfoundry/app-service-configurable | opened | Update export profiles for Security features | 3-high app-services geneva | Update the `http-export` and `mqtt-export` profiles to add the new `[SecretStoreExclusive]` section
Update the `http-export` and `sample` profiles to add the `SecretHeaderName` and `SecretPath` to the parameters for the `HTTPPost` functions .
Update the `mqtt-export` profile to add MQTTSecretSend function
Update documentation of the profiles | 1.0 | Update export profiles for Security features - Update the `http-export` and `mqtt-export` profiles to add the new `[SecretStoreExclusive]` section
Update the `http-export` and `sample` profiles to add the `SecretHeaderName` and `SecretPath` to the parameters for the `HTTPPost` functions .
Update the `mqtt-export` profile to add MQTTSecretSend function
Update documentation of the profiles | non_priority | update export profiles for security features update the http export and mqtt export profiles to add the new section update the http export and sample profiles to add the secretheadername and secretpath to the parameters for the httppost functions update the mqtt export profile to add mqttsecretsend function update documentation of the profiles | 0 |
136,185 | 11,042,980,698 | IssuesEvent | 2019-12-09 10:15:15 | aeternity/aeternity | https://api.github.com/repos/aeternity/aeternity | opened | Add throughput test for aec_chain_state:insert_block (micro block) | area/tests | Similar to #3046, but for micro blocks. | 1.0 | Add throughput test for aec_chain_state:insert_block (micro block) - Similar to #3046, but for micro blocks. | non_priority | add throughput test for aec chain state insert block micro block similar to but for micro blocks | 0 |
32,937 | 7,623,891,228 | IssuesEvent | 2018-05-03 16:14:58 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Malformed subcategory links in category list and blog articles | No Code Attached Yet | ### Steps to reproduce the issue
1. Create a category
2. Create a sub-category to that category
3. Create a Category Listing view and configure so sub-category link is created on the page
### Expected result
A link something like www.example.com/category-menu/2-subcategory
### Actual result
www.example.com/category-menu/2-subcategory?layout=
### System information (as much as possible)
This started happening in Joomla 3.8.7 and has been confirmed not to occur in 3.8.6
### Additional comments
This problem doesn't occur on category blog views. But the back-link to the subcategory in an article does end up with the empty layout variable.
| 1.0 | Malformed subcategory links in category list and blog articles - ### Steps to reproduce the issue
1. Create a category
2. Create a sub-category to that category
3. Create a Category Listing view and configure so sub-category link is created on the page
### Expected result
A link something like www.example.com/category-menu/2-subcategory
### Actual result
www.example.com/category-menu/2-subcategory?layout=
### System information (as much as possible)
This started happening in Joomla 3.8.7 and has been confirmed not to occur in 3.8.6
### Additional comments
This problem doesn't occur on category blog views. But the back-link to the subcategory in an article does end up with the empty layout variable.
| non_priority | malformed subcategory links in category list and blog articles steps to reproduce the issue create a category create a sub category to that category create a category listing view and configure so sub category link is created on the page expected result a link something like actual result system information as much as possible this started happening in joomla and has been confirmed not to occur in additional comments this problem doesn t occur on category blog views but the back link to the subcategory in an article does end up with the empty layout variable | 0 |
58,473 | 6,599,573,333 | IssuesEvent | 2017-09-16 21:36:13 | GMDevinity/BattleRoyaleIssues | https://api.github.com/repos/GMDevinity/BattleRoyaleIssues | closed | Unable to turn off flashlight when dead | Bug Needs Testing | Flashlight also sometimes doesn't work when alive either | 1.0 | Unable to turn off flashlight when dead - Flashlight also sometimes doesn't work when alive either | non_priority | unable to turn off flashlight when dead flashlight also sometimes doesn t work when alive either | 0 |
263,870 | 28,070,720,915 | IssuesEvent | 2023-03-29 18:51:15 | turkdevops/cirrus-ci-web | https://api.github.com/repos/turkdevops/cirrus-ci-web | closed | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- react-dev-utils-10.2.1.tgz
- globby-8.0.2.tgz
- fast-glob-2.2.7.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/cirrus-ci-web/commit/31e3781d9cd380020c335ba4f4897abf983dbc02">31e3781d9cd380020c335ba4f4897abf983dbc02</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz - autoclosed - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- react-dev-utils-10.2.1.tgz
- globby-8.0.2.tgz
- fast-glob-2.2.7.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/cirrus-ci-web/commit/31e3781d9cd380020c335ba4f4897abf983dbc02">31e3781d9cd380020c335ba4f4897abf983dbc02</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz autoclosed cve high severity vulnerability vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file package json path to vulnerable library node modules glob parent dependency hierarchy react scripts tgz root library react dev utils tgz globby tgz fast glob tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution react scripts step up your open source security game with mend | 0 |
270,650 | 29,047,047,461 | IssuesEvent | 2023-05-13 17:50:31 | tabacmend/JAVA-Demo-Smartfix | https://api.github.com/repos/tabacmend/JAVA-Demo-Smartfix | opened | log4j-core-2.14.0.jar: 4 vulnerabilities (highest severity is: 10.0) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (log4j-core version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-44228](https://www.mend.io/vulnerability-database/CVE-2021-44228) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 10.0 | log4j-core-2.14.0.jar | Direct | 2.15.0 | ✅ |
| [CVE-2021-45046](https://www.mend.io/vulnerability-database/CVE-2021-45046) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.0 | log4j-core-2.14.0.jar | Direct | 2.16.0 | ✅ |
| [CVE-2021-44832](https://www.mend.io/vulnerability-database/CVE-2021-44832) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.6 | log4j-core-2.14.0.jar | Direct | 2.17.1 | ✅ |
| [CVE-2021-45105](https://www.mend.io/vulnerability-database/CVE-2021-45105) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | log4j-core-2.14.0.jar | Direct | 2.17.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-44228</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44228>CVE-2021-44228</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: 2.15.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-45046</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45046>CVE-2021-45046</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-14</p>
<p>Fix Resolution: 2.16.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-44832</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 versions 2.0-beta7 through 2.17.0 (excluding security fix releases 2.3.2 and 2.12.4) are vulnerable to a remote code execution (RCE) attack when a configuration uses a JDBC Appender with a JNDI LDAP data source URI when an attacker has control of the target LDAP server. This issue is fixed by limiting JNDI data source names to the java protocol in Log4j2 versions 2.17.1, 2.12.4, and 2.3.2.
<p>Publish Date: 2021-12-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44832>CVE-2021-44832</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-28</p>
<p>Fix Resolution: 2.17.1</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-45105</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 versions 2.0-alpha1 through 2.16.0 (excluding 2.12.3 and 2.3.1) did not protect from uncontrolled recursion from self-referential lookups. This allows an attacker with control over Thread Context Map data to cause a denial of service when a crafted string is interpreted. This issue was fixed in Log4j 2.17.0, 2.12.3, and 2.3.1.
<p>Publish Date: 2021-12-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45105>CVE-2021-45105</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-18</p>
<p>Fix Resolution: 2.17.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p> | True | log4j-core-2.14.0.jar: 4 vulnerabilities (highest severity is: 10.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (log4j-core version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-44228](https://www.mend.io/vulnerability-database/CVE-2021-44228) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 10.0 | log4j-core-2.14.0.jar | Direct | 2.15.0 | ✅ |
| [CVE-2021-45046](https://www.mend.io/vulnerability-database/CVE-2021-45046) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.0 | log4j-core-2.14.0.jar | Direct | 2.16.0 | ✅ |
| [CVE-2021-44832](https://www.mend.io/vulnerability-database/CVE-2021-44832) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.6 | log4j-core-2.14.0.jar | Direct | 2.17.1 | ✅ |
| [CVE-2021-45105](https://www.mend.io/vulnerability-database/CVE-2021-45105) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.9 | log4j-core-2.14.0.jar | Direct | 2.17.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-44228</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 2.0-beta9 through 2.15.0 (excluding security releases 2.12.2, 2.12.3, and 2.3.1) JNDI features used in configuration, log messages, and parameters do not protect against attacker controlled LDAP and other JNDI related endpoints. An attacker who can control log messages or log message parameters can execute arbitrary code loaded from LDAP servers when message lookup substitution is enabled. From log4j 2.15.0, this behavior has been disabled by default. From version 2.16.0 (along with 2.12.2, 2.12.3, and 2.3.1), this functionality has been completely removed. Note that this vulnerability is specific to log4j-core and does not affect log4net, log4cxx, or other Apache Logging Services projects.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44228>CVE-2021-44228</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: 2.15.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-45046</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45046>CVE-2021-45046</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-14</p>
<p>Fix Resolution: 2.16.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-44832</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 versions 2.0-beta7 through 2.17.0 (excluding security fix releases 2.3.2 and 2.12.4) are vulnerable to a remote code execution (RCE) attack when a configuration uses a JDBC Appender with a JNDI LDAP data source URI when an attacker has control of the target LDAP server. This issue is fixed by limiting JNDI data source names to the java protocol in Log4j2 versions 2.17.1, 2.12.4, and 2.3.2.
<p>Publish Date: 2021-12-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-44832>CVE-2021-44832</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-28</p>
<p>Fix Resolution: 2.17.1</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-45105</summary>
### Vulnerable Library - <b>log4j-core-2.14.0.jar</b></p>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.14.0/log4j-core-2.14.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.14.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tabacmend/JAVA-Demo-Smartfix/commit/0388eaf0e0125e0578964d70af064b277bc75eb3">0388eaf0e0125e0578964d70af064b277bc75eb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Log4j2 versions 2.0-alpha1 through 2.16.0 (excluding 2.12.3 and 2.3.1) did not protect from uncontrolled recursion from self-referential lookups. This allows an attacker with control over Thread Context Map data to cause a denial of service when a crafted string is interpreted. This issue was fixed in Log4j 2.17.0, 2.12.3, and 2.3.1.
<p>Publish Date: 2021-12-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45105>CVE-2021-45105</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-18</p>
<p>Fix Resolution: 2.17.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p> | non_priority | core jar vulnerabilities highest severity is vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache logging core core jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in core version remediation available critical core jar direct critical core jar direct medium core jar direct medium core jar direct details cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details apache through excluding security releases and jndi features used in configuration log messages and parameters do not protect against attacker controlled ldap and other jndi related endpoints an attacker who can control log messages or log message parameters can execute arbitrary code loaded from ldap servers when message lookup substitution is enabled from this behavior has been disabled by default from version along with and this functionality has been completely removed note that this vulnerability is specific to core and does not affect or other apache logging services projects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution in order to enable automatic remediation please create cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details it was found that the fix to address cve in apache was incomplete in certain non default configurations this could allows attackers with control over thread context map mdc input data when the logging configuration uses a non default pattern layout with either a context lookup for example ctx loginid or a thread context map pattern x mdc or mdc to craft malicious input data using a jndi lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments java and java fix this issue by removing support for message lookup patterns and disabling jndi functionality by default publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution in order to enable automatic remediation please create cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details apache versions through excluding security fix releases and are vulnerable to a remote code execution rce attack when a configuration uses a jdbc appender with a jndi ldap data source uri when an attacker has control of the target ldap server this issue is fixed by limiting jndi data source names to the java protocol in versions and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution in order to enable automatic remediation please create cve vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details apache versions through excluding and did not protect from uncontrolled recursion from self referential lookups this allows an attacker with control over thread context map data to cause a denial of service when a crafted string is interpreted this issue was fixed in and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution in order to enable automatic remediation please create in order to enable automatic remediation for this issue please create | 0 |
273,468 | 20,793,583,368 | IssuesEvent | 2022-03-17 06:35:08 | postmanlabs/postman-app-support | https://api.github.com/repos/postmanlabs/postman-app-support | closed | There was an error importing this collection. Please try again. | bug product/documentation product/runtime | ### Is there an existing issue for this?
- [X] I have searched the tracker for existing similar issues
### Describe the Issue
There are similar issues and always worked by having the latest release. But I'm on the latest release.
`You are up to date! Postman v9.14.13 is the latest version.`
### Steps To Reproduce
Click on Run in Postman here -> https://documenter.getpostman.com/view/7726481/S1TWzcX6?version=latest
### Screenshots or Videos
### Environment Information
```markdown
- Operating System: Windows 10 Pro
- Platform Type: Native App / Postman Web
- Postman Version: Postman v9.14.13
```
### Additional Context?
_No response_ | 1.0 | There was an error importing this collection. Please try again. - ### Is there an existing issue for this?
- [X] I have searched the tracker for existing similar issues
### Describe the Issue
There are similar issues and always worked by having the latest release. But I'm on the latest release.
`You are up to date! Postman v9.14.13 is the latest version.`
### Steps To Reproduce
Click on Run in Postman here -> https://documenter.getpostman.com/view/7726481/S1TWzcX6?version=latest
### Screenshots or Videos
### Environment Information
```markdown
- Operating System: Windows 10 Pro
- Platform Type: Native App / Postman Web
- Postman Version: Postman v9.14.13
```
### Additional Context?
_No response_ | non_priority | there was an error importing this collection please try again is there an existing issue for this i have searched the tracker for existing similar issues describe the issue there are similar issues and always worked by having the latest release but i m on the latest release you are up to date postman is the latest version steps to reproduce click on run in postman here screenshots or videos environment information markdown operating system windows pro platform type native app postman web postman version postman additional context no response | 0 |
22,191 | 4,778,454,804 | IssuesEvent | 2016-10-27 19:21:01 | stealjs/steal | https://api.github.com/repos/stealjs/steal | closed | Add docs about circular dependencies | documentation | Please add docs about how Steal handles circular dependencies ([if it does?](https://github.com/stealjs/steal-tools/issues/382)).
I’m requesting this because last week I gave [a talk](http://www.chasenlehara.com/blog/introduction-to-javascript-modules) and briefly covered Steal. I was asked how Steal handles circular dependencies but I [couldn’t find](https://www.google.com/search?client=safari&rls=en&q=site:steal.js+module&ie=UTF-8&oe=UTF-8#q=site:stealjs.com+circular) any docs about it. | 1.0 | Add docs about circular dependencies - Please add docs about how Steal handles circular dependencies ([if it does?](https://github.com/stealjs/steal-tools/issues/382)).
I’m requesting this because last week I gave [a talk](http://www.chasenlehara.com/blog/introduction-to-javascript-modules) and briefly covered Steal. I was asked how Steal handles circular dependencies but I [couldn’t find](https://www.google.com/search?client=safari&rls=en&q=site:steal.js+module&ie=UTF-8&oe=UTF-8#q=site:stealjs.com+circular) any docs about it. | non_priority | add docs about circular dependencies please add docs about how steal handles circular dependencies i’m requesting this because last week i gave and briefly covered steal i was asked how steal handles circular dependencies but i any docs about it | 0 |
31,542 | 7,389,303,932 | IssuesEvent | 2018-03-16 08:06:42 | uncovery/uncovery_me | https://api.github.com/repos/uncovery/uncovery_me | closed | Create abstraction layer for tellraw | code upgrade | We need to create functions that allow an easier use of tellraw so that the code is readable and does not need to include JSON everywhere. | 1.0 | Create abstraction layer for tellraw - We need to create functions that allow an easier use of tellraw so that the code is readable and does not need to include JSON everywhere. | non_priority | create abstraction layer for tellraw we need to create functions that allow an easier use of tellraw so that the code is readable and does not need to include json everywhere | 0 |
165,807 | 26,227,490,611 | IssuesEvent | 2023-01-04 20:10:23 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | opened | PACT Act wizard | Research Design VA.gov frontend Drupal engineering Epic Needs refining ⭐️ Public Websites Product management | ## Product Outline
To be created: https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/product-management/product-outline-template.md
## High Level User Story/ies
As a Veteran, I need to understand if I qualify for additional benefits, due to the PACT Act.
## Hypothesis or Bet
**If** we create a wizard to help Veterans understand their benefit status, **then** we will see an uptick in benefit applications for qualifying Veterans.
### Key metrics
TBD
## Definition of done
### What must be true in order for you to consider this epic complete?
* A benefits "wizard" has been designed built, tested, & launched, and metrics for the wizard's use and funnels to benefit applications are being tracked.
* Collab Cycle has reviewed & signed off
## Design principles
Veteran-centered
- [X] `Single source of truth`: Increase reliability and consistency of content on VA.gov by providing a single source of truth.
- [ ] `Accessible, plain language`: Provide guardrails and guidelines to ensure content quality.
- [ ] `Purposely structured content`: Ensure Content API can deliver content whose meaning matches its structure.
- [ ] `Content lifecycle governance`: Produce tools, processes and policies to maintain content quality throughout its lifecycle.
### CMS Team
Please check the team(s) that will do this work.
- [ ] `Program`
- [ ] `Platform CMS Team`
- [ ] `Sitewide Crew`
- [ ] `⭐️ Sitewide CMS`
- [x] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
| 1.0 | PACT Act wizard - ## Product Outline
To be created: https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/product-management/product-outline-template.md
## High Level User Story/ies
As a Veteran, I need to understand if I qualify for additional benefits, due to the PACT Act.
## Hypothesis or Bet
**If** we create a wizard to help Veterans understand their benefit status, **then** we will see an uptick in benefit applications for qualifying Veterans.
### Key metrics
TBD
## Definition of done
### What must be true in order for you to consider this epic complete?
* A benefits "wizard" has been designed built, tested, & launched, and metrics for the wizard's use and funnels to benefit applications are being tracked.
* Collab Cycle has reviewed & signed off
## Design principles
Veteran-centered
- [X] `Single source of truth`: Increase reliability and consistency of content on VA.gov by providing a single source of truth.
- [ ] `Accessible, plain language`: Provide guardrails and guidelines to ensure content quality.
- [ ] `Purposely structured content`: Ensure Content API can deliver content whose meaning matches its structure.
- [ ] `Content lifecycle governance`: Produce tools, processes and policies to maintain content quality throughout its lifecycle.
### CMS Team
Please check the team(s) that will do this work.
- [ ] `Program`
- [ ] `Platform CMS Team`
- [ ] `Sitewide Crew`
- [ ] `⭐️ Sitewide CMS`
- [x] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
| non_priority | pact act wizard product outline to be created high level user story ies as a veteran i need to understand if i qualify for additional benefits due to the pact act hypothesis or bet if we create a wizard to help veterans understand their benefit status then we will see an uptick in benefit applications for qualifying veterans key metrics tbd definition of done what must be true in order for you to consider this epic complete a benefits wizard has been designed built tested launched and metrics for the wizard s use and funnels to benefit applications are being tracked collab cycle has reviewed signed off design principles veteran centered single source of truth increase reliability and consistency of content on va gov by providing a single source of truth accessible plain language provide guardrails and guidelines to ensure content quality purposely structured content ensure content api can deliver content whose meaning matches its structure content lifecycle governance produce tools processes and policies to maintain content quality throughout its lifecycle cms team please check the team s that will do this work program platform cms team sitewide crew ⭐️ sitewide cms ⭐️ public websites ⭐️ facilities ⭐️ user support | 0 |
116,613 | 14,984,518,616 | IssuesEvent | 2021-01-28 18:43:17 | crimethinc/website | https://api.github.com/repos/crimethinc/website | closed | [TCE] Replace icon font with SVG icons | :art: design :beginner: good first issue :paintbrush: frontend 💡 To Change Everything | # [crimethinc.com/tce](https://crimethinc.com/tce)
<img width="490" alt="screen shot 2019-03-05 at 9 08 56 pm" src="https://user-images.githubusercontent.com/4361/53857391-f631b400-3f8a-11e9-8eee-29a16e1d7ca4.png">
Icon font is used in the header nav. Maybe elsewhere too?
https://github.com/crimethinc/website/blob/1078fb874181cf77eeead05c4c84435ff48ab677/app/views/layouts/to_change_everything.html.erb#L69
https://github.com/crimethinc/website/blob/1078fb874181cf77eeead05c4c84435ff48ab677/app/views/layouts/to_change_everything.html.erb#L79
https://github.com/crimethinc/website/blob/1078fb874181cf77eeead05c4c84435ff48ab677/app/views/layouts/to_change_everything.html.erb#L89
***
**UPDATE:** all of the icons are now here, as SVGs.
https://github.com/crimethinc/website/tree/master/app/assets/images/to-change-everything/icons | 1.0 | [TCE] Replace icon font with SVG icons - # [crimethinc.com/tce](https://crimethinc.com/tce)
<img width="490" alt="screen shot 2019-03-05 at 9 08 56 pm" src="https://user-images.githubusercontent.com/4361/53857391-f631b400-3f8a-11e9-8eee-29a16e1d7ca4.png">
Icon font is used in the header nav. Maybe elsewhere too?
https://github.com/crimethinc/website/blob/1078fb874181cf77eeead05c4c84435ff48ab677/app/views/layouts/to_change_everything.html.erb#L69
https://github.com/crimethinc/website/blob/1078fb874181cf77eeead05c4c84435ff48ab677/app/views/layouts/to_change_everything.html.erb#L79
https://github.com/crimethinc/website/blob/1078fb874181cf77eeead05c4c84435ff48ab677/app/views/layouts/to_change_everything.html.erb#L89
***
**UPDATE:** all of the icons are now here, as SVGs.
https://github.com/crimethinc/website/tree/master/app/assets/images/to-change-everything/icons | non_priority | replace icon font with svg icons img width alt screen shot at pm src icon font is used in the header nav maybe elsewhere too update all of the icons are now here as svgs | 0 |
46,102 | 13,150,337,804 | IssuesEvent | 2020-08-09 10:57:32 | shaundmorris/ddf | https://api.github.com/repos/shaundmorris/ddf | closed | CVE-2018-19797 Medium Severity Vulnerability detected by WhiteSource | security vulnerability wontfix | ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.9.4</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/shaundmorris/ddf/commit/ea35fc52f05b85ef437e9a9e39a887ad51692ff0">ea35fc52f05b85ef437e9a9e39a887ad51692ff0</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (121)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/bind.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/base.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cencode.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.cpp
- /ddf/ui/node_modules/node-sass/src/callback_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass2scss.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/paths.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/json.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/string.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debugger.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/factory.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/operation.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/value.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.hpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /ddf/ui/node_modules/node-sass/src/binding.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/functions.h
- /ddf/ui/node_modules/node-sass/src/custom_function_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/values.cpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/b64/encode.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/number.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/c99func.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/backtrace.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/values.h
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/null.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/context.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debug.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19797>CVE-2018-19797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19797 Medium Severity Vulnerability detected by WhiteSource - ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.9.4</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/shaundmorris/ddf/commit/ea35fc52f05b85ef437e9a9e39a887ad51692ff0">ea35fc52f05b85ef437e9a9e39a887ad51692ff0</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (121)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/bind.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/base.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cencode.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.cpp
- /ddf/ui/node_modules/node-sass/src/callback_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass2scss.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/paths.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/json.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/string.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debugger.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/factory.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/operation.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/value.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.hpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /ddf/ui/node_modules/node-sass/src/binding.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/functions.h
- /ddf/ui/node_modules/node-sass/src/custom_function_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/values.cpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/b64/encode.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/number.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/c99func.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/backtrace.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/values.h
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/null.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/context.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debug.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19797>CVE-2018-19797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium severity vulnerability detected by whitesource cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries ddf ui node modules node sass src libsass src error handling cpp ddf ui node modules node sass src libsass src output cpp ddf ui node modules node sass src libsass src output hpp ddf ui node modules node sass src libsass src check nesting cpp ddf ui node modules node sass src libsass src sass values hpp ddf ui node modules node sass src libsass src check nesting hpp ddf ui node modules node sass src libsass src bind cpp ddf ui node modules node sass src libsass test test node cpp ddf ui node modules node sass src libsass src constants cpp ddf ui node modules node sass src libsass src eval hpp ddf ui node modules node sass src libsass src plugins cpp ddf ui node modules node sass src libsass include sass base h ddf ui node modules node sass src libsass src prelexer hpp ddf ui node modules node sass src libsass src subset map hpp ddf ui node modules node sass src libsass src extend cpp ddf ui node modules node sass src custom importer bridge cpp ddf ui node modules node sass src libsass contrib plugin cpp ddf ui node modules node sass src libsass src lexer hpp ddf ui node modules node sass src libsass src sass util cpp ddf ui node modules node sass src libsass test test superselector cpp ddf ui node modules node sass src libsass src cencode c ddf ui node modules node sass src libsass src ast fwd decl hpp ddf ui node modules node sass src libsass src string hpp ddf ui node modules node sass src libsass src file cpp ddf ui node modules node sass src callback bridge h ddf ui node modules node sass src libsass src subset map cpp ddf ui node modules node sass src libsass include h ddf ui node modules node sass src libsass src sass functions hpp ddf ui node modules node sass src libsass src emitter cpp ddf ui node modules node sass src libsass src environment cpp ddf ui node modules node sass src libsass src ast def macros hpp ddf ui node modules node sass src libsass src paths hpp ddf ui node modules node sass src libsass src expand cpp ddf ui node modules node sass src libsass src listize cpp ddf ui node modules node sass src libsass test test unification cpp ddf ui node modules node sass src libsass src source map cpp ddf ui node modules node sass src libsass src inspect cpp ddf ui node modules node sass src libsass src source map hpp ddf ui node modules node sass src sass types list h ddf ui node modules node sass src libsass src sass functions cpp ddf ui node modules node sass src libsass src json cpp ddf ui node modules node sass src libsass src sass util hpp ddf ui node modules node sass src libsass src position cpp ddf ui node modules node sass src libsass src listize hpp ddf ui node modules node sass src libsass src error handling hpp ddf ui node modules node sass src sass types string cpp ddf ui node modules node sass src libsass src eval cpp ddf ui node modules node sass src libsass src environment hpp ddf ui node modules node sass src sass types boolean h ddf ui node modules node sass src libsass src emitter hpp ddf ui node modules node sass src libsass src extend hpp ddf ui node modules node sass src libsass src lexer cpp ddf ui node modules node sass src libsass src functions cpp ddf ui node modules node sass src libsass src debugger hpp ddf ui node modules node sass src sass types factory cpp ddf ui node modules node sass src libsass src prelexer cpp ddf ui node modules node sass src sass types color cpp ddf ui node modules node sass src libsass src operation hpp ddf ui node modules node sass src libsass src ast cpp ddf ui node modules node sass src libsass src sass hpp ddf ui node modules node sass src libsass src constants hpp ddf ui node modules node sass src sass types boolean cpp ddf ui node modules node sass src libsass src context hpp ddf ui node modules node sass src sass types value h ddf ui node modules node sass src libsass src units cpp ddf ui node modules node sass src libsass src cssize hpp ddf ui node modules node sass src libsass src parser cpp ddf ui node modules node sass src libsass src functions hpp ddf ui node modules node sass src libsass src position hpp ddf ui node modules node sass src sass context wrapper cpp ddf ui node modules node sass src libsass src sass context hpp ddf ui node modules node sass src libsass src node cpp ddf ui node modules node sass src libsass src ast fwd decl cpp ddf ui node modules node sass src libsass src cssize cpp ddf ui node modules node sass src libsass src remove placeholders cpp ddf ui node modules node sass src binding cpp ddf ui node modules node sass src sass types list cpp ddf ui node modules node sass src libsass include sass functions h ddf ui node modules node sass src custom function bridge cpp ddf ui node modules node sass src custom importer bridge h ddf ui node modules node sass src libsass src color maps cpp ddf ui node modules node sass src libsass src string cpp ddf ui node modules node sass src sass types sass value wrapper h ddf ui node modules node sass src libsass src ast hpp ddf ui node modules node sass src libsass src values cpp ddf ui node modules node sass src sass context wrapper h ddf ui node modules node sass src libsass src encode h ddf ui node modules node sass src libsass src sass cpp ddf ui node modules node sass src libsass src cpp ddf ui node modules node sass src sass types number cpp ddf ui node modules node sass src libsass src c ddf ui node modules node sass src libsass src node hpp ddf ui node modules node sass src libsass src remove placeholders hpp ddf ui node modules node sass src libsass src util cpp ddf ui node modules node sass src libsass src memory sharedptr hpp ddf ui node modules node sass src libsass src backtrace hpp ddf ui node modules node sass src libsass include sass values h ddf ui node modules node sass src libsass test test subset map cpp ddf ui node modules node sass src libsass src cpp ddf ui node modules node sass src libsass src sass context cpp ddf ui node modules node sass src libsass src memory sharedptr cpp ddf ui node modules node sass src sass types null cpp ddf ui node modules node sass src libsass src expand hpp ddf ui node modules node sass src libsass src to value hpp ddf ui node modules node sass src libsass src context cpp ddf ui node modules node sass src libsass include sass context h ddf ui node modules node sass src libsass src to c cpp ddf ui node modules node sass src libsass src sass values cpp ddf ui node modules node sass src libsass src color maps hpp ddf ui node modules node sass src libsass src inspect hpp ddf ui node modules node sass src libsass script test leaks pl ddf ui node modules node sass src libsass src to c hpp ddf ui node modules node sass src libsass src util hpp ddf ui node modules node sass src sass types map cpp ddf ui node modules node sass src libsass src file hpp ddf ui node modules node sass src libsass src units hpp ddf ui node modules node sass src libsass src plugins hpp ddf ui node modules node sass src sass types color h ddf ui node modules node sass src libsass src to value cpp ddf ui node modules node sass src libsass src debug hpp ddf ui node modules node sass src libsass src parser hpp vulnerability details in libsass a null pointer dereference in the function sass selector list populate extends in sharedptr hpp used by ast cpp and ast selectors cpp may cause a denial of service application crash via a crafted sass input file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
52,644 | 22,334,126,118 | IssuesEvent | 2022-06-14 16:53:28 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Dashboard design enhancements for consistency | Service: Dev Need: 2-Should Have Type: Enhancement Product: Moped | [From this PR](https://github.com/cityofaustin/atd-moped/pull/663)
Welcome header should mirror the Project Title.
- [x] Change the size of font for "Good morning, Test!" to mirror the size of the "ALL PROJECTS" font size
- [x] change the Date to mirror the font size of the Project Title.
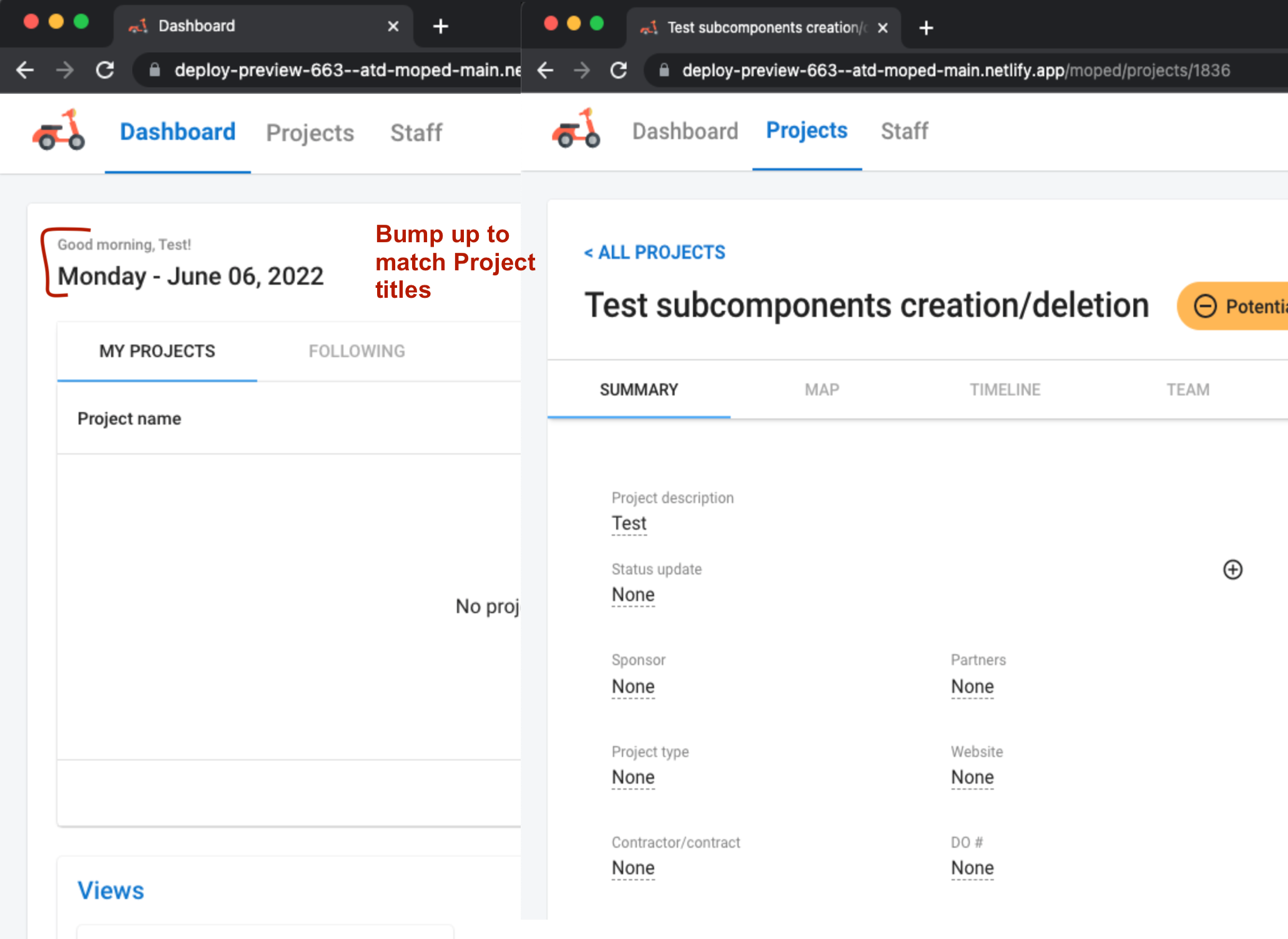 | 1.0 | Dashboard design enhancements for consistency - [From this PR](https://github.com/cityofaustin/atd-moped/pull/663)
Welcome header should mirror the Project Title.
- [x] Change the size of font for "Good morning, Test!" to mirror the size of the "ALL PROJECTS" font size
- [x] change the Date to mirror the font size of the Project Title.
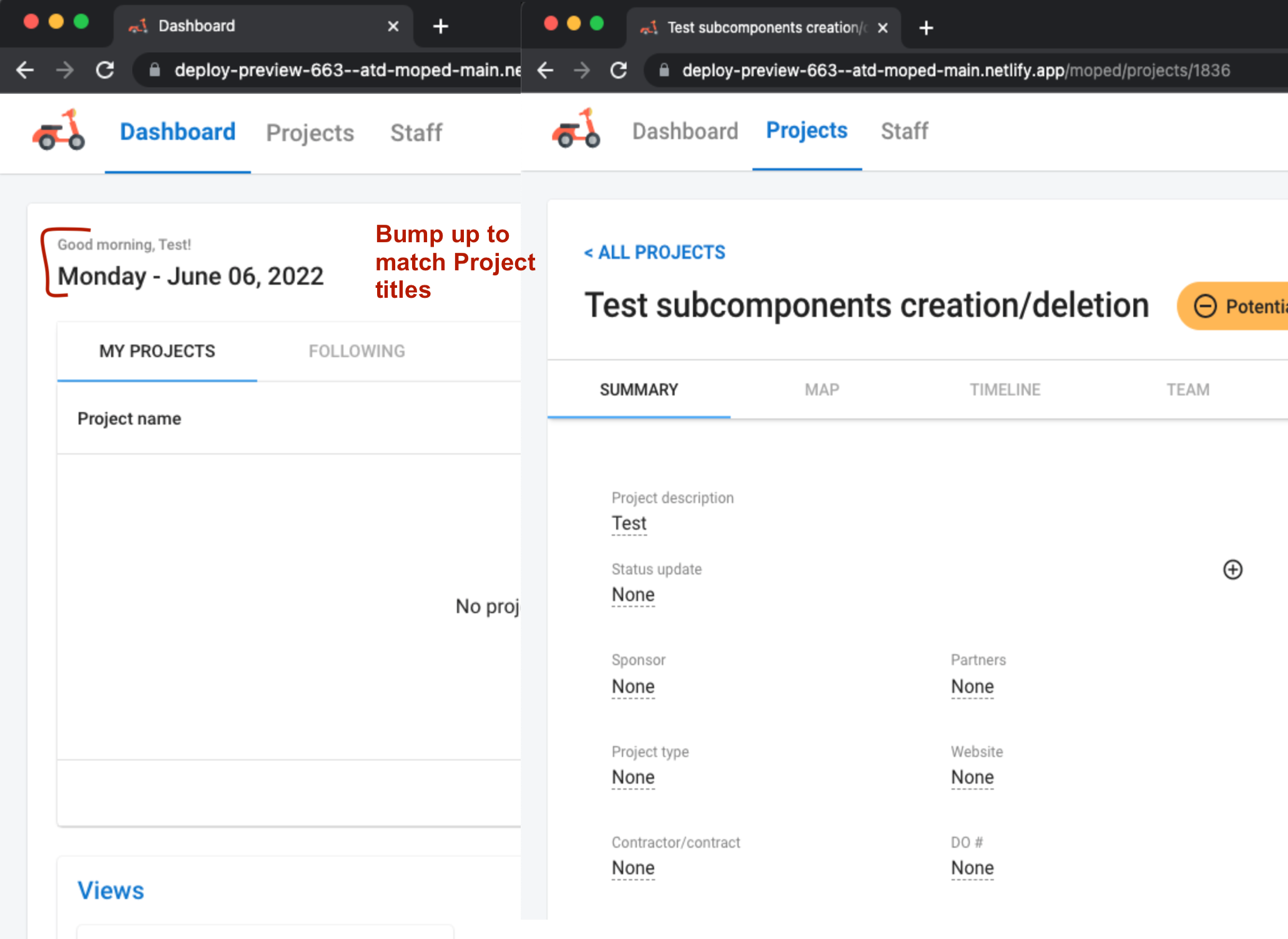 | non_priority | dashboard design enhancements for consistency welcome header should mirror the project title change the size of font for good morning test to mirror the size of the all projects font size change the date to mirror the font size of the project title | 0 |
64,067 | 14,657,155,804 | IssuesEvent | 2020-12-28 14:59:49 | turkdevops/grafana | https://api.github.com/repos/turkdevops/grafana | opened | WS-2020-0097 (High) detected in papaparse-4.6.3.js, papaparse-4.6.3.tgz | security vulnerability | ## WS-2020-0097 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>papaparse-4.6.3.js</b>, <b>papaparse-4.6.3.tgz</b></p></summary>
<p>
<details><summary><b>papaparse-4.6.3.js</b></p></summary>
<p>Fast and powerful CSV parser for the browser that supports web workers and streaming large files. Converts CSV to JSON and JSON to CSV.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/PapaParse/4.6.3/papaparse.js">https://cdnjs.cloudflare.com/ajax/libs/PapaParse/4.6.3/papaparse.js</a></p>
<p>Path to dependency file: grafana/packages/grafana-toolkit/node_modules/papaparse/player/player.html</p>
<p>Path to vulnerable library: grafana/packages/grafana-toolkit/node_modules/papaparse/player/../papaparse.js</p>
<p>
Dependency Hierarchy:
- :x: **papaparse-4.6.3.js** (Vulnerable Library)
</details>
<details><summary><b>papaparse-4.6.3.tgz</b></p></summary>
<p>Fast and powerful CSV parser for the browser that supports web workers and streaming large files. Converts CSV to JSON and JSON to CSV.</p>
<p>Library home page: <a href="https://registry.npmjs.org/papaparse/-/papaparse-4.6.3.tgz">https://registry.npmjs.org/papaparse/-/papaparse-4.6.3.tgz</a></p>
<p>Path to dependency file: grafana/node_modules/papaparse/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/papaparse/package.json</p>
<p>
Dependency Hierarchy:
- ui-7.0.0.tgz (Root Library)
- :x: **papaparse-4.6.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/494d3ade5b02fb069ecdd7a9a278fd2016f5f577">494d3ade5b02fb069ecdd7a9a278fd2016f5f577</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
papaparse before 5.2.0 are vulnerable to Regular Expression Denial of Service (ReDos). The parse function contains a malformed regular expression that takes exponentially longer to process non-numerical inputs. This allows attackers to stall systems and lead to Denial of Service.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://github.com/mholt/PapaParse/pull/779>WS-2020-0097</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1515">https://www.npmjs.com/advisories/1515</a></p>
<p>Release Date: 2020-05-26</p>
<p>Fix Resolution: papaparse - 5.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0097 (High) detected in papaparse-4.6.3.js, papaparse-4.6.3.tgz - ## WS-2020-0097 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>papaparse-4.6.3.js</b>, <b>papaparse-4.6.3.tgz</b></p></summary>
<p>
<details><summary><b>papaparse-4.6.3.js</b></p></summary>
<p>Fast and powerful CSV parser for the browser that supports web workers and streaming large files. Converts CSV to JSON and JSON to CSV.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/PapaParse/4.6.3/papaparse.js">https://cdnjs.cloudflare.com/ajax/libs/PapaParse/4.6.3/papaparse.js</a></p>
<p>Path to dependency file: grafana/packages/grafana-toolkit/node_modules/papaparse/player/player.html</p>
<p>Path to vulnerable library: grafana/packages/grafana-toolkit/node_modules/papaparse/player/../papaparse.js</p>
<p>
Dependency Hierarchy:
- :x: **papaparse-4.6.3.js** (Vulnerable Library)
</details>
<details><summary><b>papaparse-4.6.3.tgz</b></p></summary>
<p>Fast and powerful CSV parser for the browser that supports web workers and streaming large files. Converts CSV to JSON and JSON to CSV.</p>
<p>Library home page: <a href="https://registry.npmjs.org/papaparse/-/papaparse-4.6.3.tgz">https://registry.npmjs.org/papaparse/-/papaparse-4.6.3.tgz</a></p>
<p>Path to dependency file: grafana/node_modules/papaparse/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/papaparse/package.json</p>
<p>
Dependency Hierarchy:
- ui-7.0.0.tgz (Root Library)
- :x: **papaparse-4.6.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/494d3ade5b02fb069ecdd7a9a278fd2016f5f577">494d3ade5b02fb069ecdd7a9a278fd2016f5f577</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
papaparse before 5.2.0 are vulnerable to Regular Expression Denial of Service (ReDos). The parse function contains a malformed regular expression that takes exponentially longer to process non-numerical inputs. This allows attackers to stall systems and lead to Denial of Service.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://github.com/mholt/PapaParse/pull/779>WS-2020-0097</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1515">https://www.npmjs.com/advisories/1515</a></p>
<p>Release Date: 2020-05-26</p>
<p>Fix Resolution: papaparse - 5.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in papaparse js papaparse tgz ws high severity vulnerability vulnerable libraries papaparse js papaparse tgz papaparse js fast and powerful csv parser for the browser that supports web workers and streaming large files converts csv to json and json to csv library home page a href path to dependency file grafana packages grafana toolkit node modules papaparse player player html path to vulnerable library grafana packages grafana toolkit node modules papaparse player papaparse js dependency hierarchy x papaparse js vulnerable library papaparse tgz fast and powerful csv parser for the browser that supports web workers and streaming large files converts csv to json and json to csv library home page a href path to dependency file grafana node modules papaparse package json path to vulnerable library grafana node modules papaparse package json dependency hierarchy ui tgz root library x papaparse tgz vulnerable library found in head commit a href found in base branch master vulnerability details papaparse before are vulnerable to regular expression denial of service redos the parse function contains a malformed regular expression that takes exponentially longer to process non numerical inputs this allows attackers to stall systems and lead to denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution papaparse step up your open source security game with whitesource | 0 |
18,701 | 11,033,685,695 | IssuesEvent | 2019-12-07 00:00:47 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Get-AzNetworkServiceTag does not give the latest changes | Network - SDN Service Attention customer-reported | <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
- https://github.com/Azure/azure-powershell/blob/master/documentation/troubleshoot-module-load.md
-->
## Description
Get-AzNetworkServiceTag does not give the latest changes that are published on the weekly updated JSON that can be found at Microsoft Download Center here: https://www.microsoft.com/en-us/download/details.aspx?id=56519
Currently the Get-AzNetworkServiceTag returns changeNumber 63, while the Microsoft Download Center JSON gives changeNumber 84
## Steps to reproduce
```powershell
Get-AzNetworkServiceTag -Location westeurope
```
## Environment data
<!-- Please run $PSVersionTable and paste the output in the below code block -->
```
$PSVersionTable
Name Value
---- -----
PSVersion 5.1.14393.3053
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.14393.3053
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
```
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
```powershell
PS C:\Windows\system32> Get-Module -ListAvailable Az*
Directory: C:\Program Files\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 1.6.2 Az.Accounts {Disable-AzDataCollection, Disable-AzContextAutosave, Enable-AzDataCollection, Enable-AzContextAutosave...}
Script 1.0.1 Az.Advisor {Get-AzAdvisorRecommendation, Enable-AzAdvisorRecommendation, Disable-AzAdvisorRecommendation, Get-AzAdvisorConfiguration...}
Script 1.0.2 Az.Aks {Get-AzAks, New-AzAks, Remove-AzAks, Import-AzAksCredential...}
Script 1.1.1 Az.AnalysisServices {Resume-AzAnalysisServicesServer, Suspend-AzAnalysisServicesServer, Get-AzAnalysisServicesServer, Remove-AzAnalysisServicesServer...}
Script 1.3.0 Az.ApiManagement {Add-AzApiManagementApiToProduct, Add-AzApiManagementProductToGroup, Add-AzApiManagementRegion, Add-AzApiManagementUserToGroup...}
Script 1.0.2 Az.ApplicationInsights {Get-AzApplicationInsights, New-AzApplicationInsights, Remove-AzApplicationInsights, Set-AzApplicationInsightsPricingPlan...}
Script 1.3.2 Az.Automation {Get-AzAutomationHybridWorkerGroup, Remove-AzAutomationHybridWorkerGroup, Get-AzAutomationJobOutputRecord, Import-AzAutomationDscNodeConfiguration...}
Script 1.1.1 Az.Batch {Remove-AzBatchAccount, Get-AzBatchAccount, Get-AzBatchAccountKey, New-AzBatchAccount...}
Script 1.0.1 Az.Billing {Get-AzBillingInvoice, Get-AzBillingPeriod, Get-AzEnrollmentAccount, Get-AzConsumptionBudget...}
Script 1.3.1 Az.Cdn {Get-AzCdnProfile, Get-AzCdnProfileSsoUrl, New-AzCdnProfile, Remove-AzCdnProfile...}
Script 1.2.1 Az.CognitiveServices {Get-AzCognitiveServicesAccount, Get-AzCognitiveServicesAccountKey, Get-AzCognitiveServicesAccountSku, Get-AzCognitiveServicesAccountType...}
Script 2.5.0 Az.Compute {Remove-AzAvailabilitySet, Get-AzAvailabilitySet, New-AzAvailabilitySet, Update-AzAvailabilitySet...}
Script 1.0.1 Az.ContainerInstance {New-AzContainerGroup, Get-AzContainerGroup, Remove-AzContainerGroup, Get-AzContainerInstanceLog}
Script 1.1.0 Az.ContainerRegistry {New-AzContainerRegistry, Get-AzContainerRegistry, Update-AzContainerRegistry, Remove-AzContainerRegistry...}
Script 1.2.0 Az.DataFactory {Set-AzDataFactoryV2, Update-AzDataFactoryV2, Get-AzDataFactoryV2, Remove-AzDataFactoryV2...}
Script 1.0.1 Az.DataLakeAnalytics {Get-AzDataLakeAnalyticsDataSource, New-AzDataLakeAnalyticsCatalogCredential, Remove-AzDataLakeAnalyticsCatalogCredential, Set-AzDataLakeAnalyticsCatalogCredential...}
Script 1.2.2 Az.DataLakeStore {Get-AzDataLakeStoreTrustedIdProvider, Remove-AzDataLakeStoreTrustedIdProvider, Remove-AzDataLakeStoreFirewallRule, Set-AzDataLakeStoreTrustedIdProvider...}
Script 1.0.1 Az.DeploymentManager {Get-AzDeploymentManagerArtifactSource, New-AzDeploymentManagerArtifactSource, Set-AzDeploymentManagerArtifactSource, Remove-AzDeploymentManagerArtifactSource...}
Script 1.0.0 Az.DevTestLabs {Get-AzDtlAllowedVMSizesPolicy, Get-AzDtlAutoShutdownPolicy, Get-AzDtlAutoStartPolicy, Get-AzDtlVMsPerLabPolicy...}
Script 1.1.1 Az.Dns {Get-AzDnsRecordSet, New-AzDnsRecordConfig, Remove-AzDnsRecordSet, Set-AzDnsRecordSet...}
Script 1.2.2 Az.EventGrid {New-AzEventGridTopic, Get-AzEventGridTopic, Set-AzEventGridTopic, New-AzEventGridTopicKey...}
Script 1.4.0 Az.EventHub {New-AzEventHubNamespace, Get-AzEventHubNamespace, Set-AzEventHubNamespace, Remove-AzEventHubNamespace...}
Script 1.1.1 Az.FrontDoor {New-AzFrontDoor, Get-AzFrontDoor, Set-AzFrontDoor, Remove-AzFrontDoor...}
Script 2.0.1 Az.HDInsight {Get-AzHDInsightJob, New-AzHDInsightSqoopJobDefinition, Wait-AzHDInsightJob, New-AzHDInsightStreamingMapReduceJobDefinition...}
Script 1.2.1 Az.IotHub {Add-AzIotHubKey, Get-AzIotHubEventHubConsumerGroup, Get-AzIotHubConnectionString, Get-AzIotHubJob...}
Script 1.3.1 Az.KeyVault {Add-AzKeyVaultCertificate, Update-AzKeyVaultCertificate, Stop-AzKeyVaultCertificateOperation, Get-AzKeyVaultCertificateOperation...}
Script 1.3.1 Az.LogicApp {Get-AzIntegrationAccountAgreement, Get-AzIntegrationAccountAssembly, Get-AzIntegrationAccountBatchConfiguration, Get-AzIntegrationAccountCallbackUrl...}
Script 1.1.1 Az.MachineLearning {Move-AzMlCommitmentAssociation, Get-AzMlCommitmentAssociation, Get-AzMlCommitmentPlanUsageHistory, Remove-AzMlCommitmentPlan...}
Script 1.0.1 Az.ManagedServices {Get-AzManagedServicesAssignment, New-AzManagedServicesAssignment, Remove-AzManagedServicesAssignment, Get-AzManagedServicesDefinition...}
Script 1.0.1 Az.MarketplaceOrdering {Get-AzMarketplaceTerms, Set-AzMarketplaceTerms}
Script 1.1.0 Az.Media {Sync-AzMediaServiceStorageKey, Set-AzMediaServiceKey, Get-AzMediaServiceKey, Get-AzMediaServiceNameAvailability...}
Script 1.2.2 Az.Monitor {Get-AzMetricDefinition, Get-AzMetric, Remove-AzLogProfile, Get-AzLogProfile...}
Script 1.13.0 Az.Network {Add-AzApplicationGatewayAuthenticationCertificate, Get-AzApplicationGatewayAuthenticationCertificate, New-AzApplicationGatewayAuthenticationCertificate, Remove-AzApplicationGatewayAuthenticationCertificate...}
Script 1.1.0 Az.NotificationHubs {Get-AzNotificationHub, Get-AzNotificationHubAuthorizationRule, Get-AzNotificationHubListKey, Get-AzNotificationHubPNSCredential...}
Script 1.3.3 Az.OperationalInsights {New-AzOperationalInsightsAzureActivityLogDataSource, New-AzOperationalInsightsCustomLogDataSource, Disable-AzOperationalInsightsLinuxCustomLogCollection, Disable-AzOperationalInsightsIISLogCollection...}
Script 1.1.3 Az.PolicyInsights {Get-AzPolicyEvent, Get-AzPolicyState, Get-AzPolicyStateSummary, Get-AzPolicyRemediation...}
Script 1.1.0 Az.PowerBIEmbedded {Remove-AzPowerBIWorkspaceCollection, Get-AzPowerBIWorkspaceCollection, Get-AzPowerBIWorkspaceCollectionAccessKey, Get-AzPowerBIWorkspace...}
Script 1.4.4 Az.RecoveryServices {Get-AzRecoveryServicesBackupProperty, Get-AzRecoveryServicesVault, Get-AzRecoveryServicesVaultSettingsFile, New-AzRecoveryServicesVault...}
Script 1.1.0 Az.RedisCache {Remove-AzRedisCachePatchSchedule, New-AzRedisCacheScheduleEntry, Get-AzRedisCachePatchSchedule, New-AzRedisCachePatchSchedule...}
Script 1.0.2 Az.Relay {New-AzRelayNamespace, Get-AzRelayNamespace, Set-AzRelayNamespace, Remove-AzRelayNamespace...}
Script 1.6.2 Az.Resources {Get-AzProviderOperation, Remove-AzRoleAssignment, Get-AzRoleAssignment, New-AzRoleAssignment...}
Script 1.4.0 Az.ServiceBus {New-AzServiceBusNamespace, Get-AzServiceBusNamespace, Set-AzServiceBusNamespace, Remove-AzServiceBusNamespace...}
Script 1.1.2 Az.ServiceFabric {Add-AzServiceFabricApplicationCertificate, Add-AzServiceFabricClientCertificate, Add-AzServiceFabricClusterCertificate, Add-AzServiceFabricNode...}
Script 1.0.3 Az.SignalR {New-AzSignalR, Get-AzSignalR, Get-AzSignalRKey, New-AzSignalRKey...}
Script 1.14.1 Az.Sql {Get-AzSqlDatabaseTransparentDataEncryption, Get-AzSqlDatabaseTransparentDataEncryptionActivity, Set-AzSqlDatabaseTransparentDataEncryption, Get-AzSqlDatabaseUpgradeHint...}
Script 1.6.0 Az.Storage {Get-AzStorageAccount, Get-AzStorageAccountKey, New-AzStorageAccount, New-AzStorageAccountKey...}
Script 1.2.0 Az.StorageSync {Invoke-AzStorageSyncCompatibilityCheck, New-AzStorageSyncService, Get-AzStorageSyncService, Remove-AzStorageSyncService...}
Script 1.0.0 Az.StreamAnalytics {Get-AzStreamAnalyticsFunction, Get-AzStreamAnalyticsDefaultFunctionDefinition, New-AzStreamAnalyticsFunction, Remove-AzStreamAnalyticsFunction...}
Script 1.0.2 Az.TrafficManager {Add-AzTrafficManagerCustomHeaderToEndpoint, Remove-AzTrafficManagerCustomHeaderFromEndpoint, Add-AzTrafficManagerCustomHeaderToProfile, Remove-AzTrafficManagerCustomHeaderFromProfile...}
Script 1.4.1 Az.Websites {Get-AzAppServicePlan, Set-AzAppServicePlan, New-AzAppServicePlan, Remove-AzAppServicePlan...}
```
## Debug output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
```
## Error output
<!-- Please run Resolve-AzError and paste the output in the below code block -->
```
```
| 1.0 | Get-AzNetworkServiceTag does not give the latest changes - <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
- https://github.com/Azure/azure-powershell/blob/master/documentation/troubleshoot-module-load.md
-->
## Description
Get-AzNetworkServiceTag does not give the latest changes that are published on the weekly updated JSON that can be found at Microsoft Download Center here: https://www.microsoft.com/en-us/download/details.aspx?id=56519
Currently the Get-AzNetworkServiceTag returns changeNumber 63, while the Microsoft Download Center JSON gives changeNumber 84
## Steps to reproduce
```powershell
Get-AzNetworkServiceTag -Location westeurope
```
## Environment data
<!-- Please run $PSVersionTable and paste the output in the below code block -->
```
$PSVersionTable
Name Value
---- -----
PSVersion 5.1.14393.3053
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.14393.3053
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
```
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
```powershell
PS C:\Windows\system32> Get-Module -ListAvailable Az*
Directory: C:\Program Files\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 1.6.2 Az.Accounts {Disable-AzDataCollection, Disable-AzContextAutosave, Enable-AzDataCollection, Enable-AzContextAutosave...}
Script 1.0.1 Az.Advisor {Get-AzAdvisorRecommendation, Enable-AzAdvisorRecommendation, Disable-AzAdvisorRecommendation, Get-AzAdvisorConfiguration...}
Script 1.0.2 Az.Aks {Get-AzAks, New-AzAks, Remove-AzAks, Import-AzAksCredential...}
Script 1.1.1 Az.AnalysisServices {Resume-AzAnalysisServicesServer, Suspend-AzAnalysisServicesServer, Get-AzAnalysisServicesServer, Remove-AzAnalysisServicesServer...}
Script 1.3.0 Az.ApiManagement {Add-AzApiManagementApiToProduct, Add-AzApiManagementProductToGroup, Add-AzApiManagementRegion, Add-AzApiManagementUserToGroup...}
Script 1.0.2 Az.ApplicationInsights {Get-AzApplicationInsights, New-AzApplicationInsights, Remove-AzApplicationInsights, Set-AzApplicationInsightsPricingPlan...}
Script 1.3.2 Az.Automation {Get-AzAutomationHybridWorkerGroup, Remove-AzAutomationHybridWorkerGroup, Get-AzAutomationJobOutputRecord, Import-AzAutomationDscNodeConfiguration...}
Script 1.1.1 Az.Batch {Remove-AzBatchAccount, Get-AzBatchAccount, Get-AzBatchAccountKey, New-AzBatchAccount...}
Script 1.0.1 Az.Billing {Get-AzBillingInvoice, Get-AzBillingPeriod, Get-AzEnrollmentAccount, Get-AzConsumptionBudget...}
Script 1.3.1 Az.Cdn {Get-AzCdnProfile, Get-AzCdnProfileSsoUrl, New-AzCdnProfile, Remove-AzCdnProfile...}
Script 1.2.1 Az.CognitiveServices {Get-AzCognitiveServicesAccount, Get-AzCognitiveServicesAccountKey, Get-AzCognitiveServicesAccountSku, Get-AzCognitiveServicesAccountType...}
Script 2.5.0 Az.Compute {Remove-AzAvailabilitySet, Get-AzAvailabilitySet, New-AzAvailabilitySet, Update-AzAvailabilitySet...}
Script 1.0.1 Az.ContainerInstance {New-AzContainerGroup, Get-AzContainerGroup, Remove-AzContainerGroup, Get-AzContainerInstanceLog}
Script 1.1.0 Az.ContainerRegistry {New-AzContainerRegistry, Get-AzContainerRegistry, Update-AzContainerRegistry, Remove-AzContainerRegistry...}
Script 1.2.0 Az.DataFactory {Set-AzDataFactoryV2, Update-AzDataFactoryV2, Get-AzDataFactoryV2, Remove-AzDataFactoryV2...}
Script 1.0.1 Az.DataLakeAnalytics {Get-AzDataLakeAnalyticsDataSource, New-AzDataLakeAnalyticsCatalogCredential, Remove-AzDataLakeAnalyticsCatalogCredential, Set-AzDataLakeAnalyticsCatalogCredential...}
Script 1.2.2 Az.DataLakeStore {Get-AzDataLakeStoreTrustedIdProvider, Remove-AzDataLakeStoreTrustedIdProvider, Remove-AzDataLakeStoreFirewallRule, Set-AzDataLakeStoreTrustedIdProvider...}
Script 1.0.1 Az.DeploymentManager {Get-AzDeploymentManagerArtifactSource, New-AzDeploymentManagerArtifactSource, Set-AzDeploymentManagerArtifactSource, Remove-AzDeploymentManagerArtifactSource...}
Script 1.0.0 Az.DevTestLabs {Get-AzDtlAllowedVMSizesPolicy, Get-AzDtlAutoShutdownPolicy, Get-AzDtlAutoStartPolicy, Get-AzDtlVMsPerLabPolicy...}
Script 1.1.1 Az.Dns {Get-AzDnsRecordSet, New-AzDnsRecordConfig, Remove-AzDnsRecordSet, Set-AzDnsRecordSet...}
Script 1.2.2 Az.EventGrid {New-AzEventGridTopic, Get-AzEventGridTopic, Set-AzEventGridTopic, New-AzEventGridTopicKey...}
Script 1.4.0 Az.EventHub {New-AzEventHubNamespace, Get-AzEventHubNamespace, Set-AzEventHubNamespace, Remove-AzEventHubNamespace...}
Script 1.1.1 Az.FrontDoor {New-AzFrontDoor, Get-AzFrontDoor, Set-AzFrontDoor, Remove-AzFrontDoor...}
Script 2.0.1 Az.HDInsight {Get-AzHDInsightJob, New-AzHDInsightSqoopJobDefinition, Wait-AzHDInsightJob, New-AzHDInsightStreamingMapReduceJobDefinition...}
Script 1.2.1 Az.IotHub {Add-AzIotHubKey, Get-AzIotHubEventHubConsumerGroup, Get-AzIotHubConnectionString, Get-AzIotHubJob...}
Script 1.3.1 Az.KeyVault {Add-AzKeyVaultCertificate, Update-AzKeyVaultCertificate, Stop-AzKeyVaultCertificateOperation, Get-AzKeyVaultCertificateOperation...}
Script 1.3.1 Az.LogicApp {Get-AzIntegrationAccountAgreement, Get-AzIntegrationAccountAssembly, Get-AzIntegrationAccountBatchConfiguration, Get-AzIntegrationAccountCallbackUrl...}
Script 1.1.1 Az.MachineLearning {Move-AzMlCommitmentAssociation, Get-AzMlCommitmentAssociation, Get-AzMlCommitmentPlanUsageHistory, Remove-AzMlCommitmentPlan...}
Script 1.0.1 Az.ManagedServices {Get-AzManagedServicesAssignment, New-AzManagedServicesAssignment, Remove-AzManagedServicesAssignment, Get-AzManagedServicesDefinition...}
Script 1.0.1 Az.MarketplaceOrdering {Get-AzMarketplaceTerms, Set-AzMarketplaceTerms}
Script 1.1.0 Az.Media {Sync-AzMediaServiceStorageKey, Set-AzMediaServiceKey, Get-AzMediaServiceKey, Get-AzMediaServiceNameAvailability...}
Script 1.2.2 Az.Monitor {Get-AzMetricDefinition, Get-AzMetric, Remove-AzLogProfile, Get-AzLogProfile...}
Script 1.13.0 Az.Network {Add-AzApplicationGatewayAuthenticationCertificate, Get-AzApplicationGatewayAuthenticationCertificate, New-AzApplicationGatewayAuthenticationCertificate, Remove-AzApplicationGatewayAuthenticationCertificate...}
Script 1.1.0 Az.NotificationHubs {Get-AzNotificationHub, Get-AzNotificationHubAuthorizationRule, Get-AzNotificationHubListKey, Get-AzNotificationHubPNSCredential...}
Script 1.3.3 Az.OperationalInsights {New-AzOperationalInsightsAzureActivityLogDataSource, New-AzOperationalInsightsCustomLogDataSource, Disable-AzOperationalInsightsLinuxCustomLogCollection, Disable-AzOperationalInsightsIISLogCollection...}
Script 1.1.3 Az.PolicyInsights {Get-AzPolicyEvent, Get-AzPolicyState, Get-AzPolicyStateSummary, Get-AzPolicyRemediation...}
Script 1.1.0 Az.PowerBIEmbedded {Remove-AzPowerBIWorkspaceCollection, Get-AzPowerBIWorkspaceCollection, Get-AzPowerBIWorkspaceCollectionAccessKey, Get-AzPowerBIWorkspace...}
Script 1.4.4 Az.RecoveryServices {Get-AzRecoveryServicesBackupProperty, Get-AzRecoveryServicesVault, Get-AzRecoveryServicesVaultSettingsFile, New-AzRecoveryServicesVault...}
Script 1.1.0 Az.RedisCache {Remove-AzRedisCachePatchSchedule, New-AzRedisCacheScheduleEntry, Get-AzRedisCachePatchSchedule, New-AzRedisCachePatchSchedule...}
Script 1.0.2 Az.Relay {New-AzRelayNamespace, Get-AzRelayNamespace, Set-AzRelayNamespace, Remove-AzRelayNamespace...}
Script 1.6.2 Az.Resources {Get-AzProviderOperation, Remove-AzRoleAssignment, Get-AzRoleAssignment, New-AzRoleAssignment...}
Script 1.4.0 Az.ServiceBus {New-AzServiceBusNamespace, Get-AzServiceBusNamespace, Set-AzServiceBusNamespace, Remove-AzServiceBusNamespace...}
Script 1.1.2 Az.ServiceFabric {Add-AzServiceFabricApplicationCertificate, Add-AzServiceFabricClientCertificate, Add-AzServiceFabricClusterCertificate, Add-AzServiceFabricNode...}
Script 1.0.3 Az.SignalR {New-AzSignalR, Get-AzSignalR, Get-AzSignalRKey, New-AzSignalRKey...}
Script 1.14.1 Az.Sql {Get-AzSqlDatabaseTransparentDataEncryption, Get-AzSqlDatabaseTransparentDataEncryptionActivity, Set-AzSqlDatabaseTransparentDataEncryption, Get-AzSqlDatabaseUpgradeHint...}
Script 1.6.0 Az.Storage {Get-AzStorageAccount, Get-AzStorageAccountKey, New-AzStorageAccount, New-AzStorageAccountKey...}
Script 1.2.0 Az.StorageSync {Invoke-AzStorageSyncCompatibilityCheck, New-AzStorageSyncService, Get-AzStorageSyncService, Remove-AzStorageSyncService...}
Script 1.0.0 Az.StreamAnalytics {Get-AzStreamAnalyticsFunction, Get-AzStreamAnalyticsDefaultFunctionDefinition, New-AzStreamAnalyticsFunction, Remove-AzStreamAnalyticsFunction...}
Script 1.0.2 Az.TrafficManager {Add-AzTrafficManagerCustomHeaderToEndpoint, Remove-AzTrafficManagerCustomHeaderFromEndpoint, Add-AzTrafficManagerCustomHeaderToProfile, Remove-AzTrafficManagerCustomHeaderFromProfile...}
Script 1.4.1 Az.Websites {Get-AzAppServicePlan, Set-AzAppServicePlan, New-AzAppServicePlan, Remove-AzAppServicePlan...}
```
## Debug output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
```
## Error output
<!-- Please run Resolve-AzError and paste the output in the below code block -->
```
```
| non_priority | get aznetworkservicetag does not give the latest changes make sure you are able to reproduce this issue on the latest released version of az please search the existing issues to see if there has been a similar issue filed for issue related to importing a module please refer to our troubleshooting guide description get aznetworkservicetag does not give the latest changes that are published on the weekly updated json that can be found at microsoft download center here currently the get aznetworkservicetag returns changenumber while the microsoft download center json gives changenumber steps to reproduce powershell get aznetworkservicetag location westeurope environment data psversiontable name value psversion psedition desktop pscompatibleversions buildversion clrversion wsmanstackversion psremotingprotocolversion serializationversion module versions powershell ps c windows get module listavailable az directory c program files windowspowershell modules moduletype version name exportedcommands script az accounts disable azdatacollection disable azcontextautosave enable azdatacollection enable azcontextautosave script az advisor get azadvisorrecommendation enable azadvisorrecommendation disable azadvisorrecommendation get azadvisorconfiguration script az aks get azaks new azaks remove azaks import azakscredential script az analysisservices resume azanalysisservicesserver suspend azanalysisservicesserver get azanalysisservicesserver remove azanalysisservicesserver script az apimanagement add azapimanagementapitoproduct add azapimanagementproducttogroup add azapimanagementregion add azapimanagementusertogroup script az applicationinsights get azapplicationinsights new azapplicationinsights remove azapplicationinsights set azapplicationinsightspricingplan script az automation get azautomationhybridworkergroup remove azautomationhybridworkergroup get azautomationjoboutputrecord import azautomationdscnodeconfiguration script az batch remove azbatchaccount get azbatchaccount get azbatchaccountkey new azbatchaccount script az billing get azbillinginvoice get azbillingperiod get azenrollmentaccount get azconsumptionbudget script az cdn get azcdnprofile get azcdnprofilessourl new azcdnprofile remove azcdnprofile script az cognitiveservices get azcognitiveservicesaccount get azcognitiveservicesaccountkey get azcognitiveservicesaccountsku get azcognitiveservicesaccounttype script az compute remove azavailabilityset get azavailabilityset new azavailabilityset update azavailabilityset script az containerinstance new azcontainergroup get azcontainergroup remove azcontainergroup get azcontainerinstancelog script az containerregistry new azcontainerregistry get azcontainerregistry update azcontainerregistry remove azcontainerregistry script az datafactory set update get remove script az datalakeanalytics get azdatalakeanalyticsdatasource new azdatalakeanalyticscatalogcredential remove azdatalakeanalyticscatalogcredential set azdatalakeanalyticscatalogcredential script az datalakestore get azdatalakestoretrustedidprovider remove azdatalakestoretrustedidprovider remove azdatalakestorefirewallrule set azdatalakestoretrustedidprovider script az deploymentmanager get azdeploymentmanagerartifactsource new azdeploymentmanagerartifactsource set azdeploymentmanagerartifactsource remove azdeploymentmanagerartifactsource script az devtestlabs get azdtlallowedvmsizespolicy get azdtlautoshutdownpolicy get azdtlautostartpolicy get azdtlvmsperlabpolicy script az dns get azdnsrecordset new azdnsrecordconfig remove azdnsrecordset set azdnsrecordset script az eventgrid new azeventgridtopic get azeventgridtopic set azeventgridtopic new azeventgridtopickey script az eventhub new azeventhubnamespace get azeventhubnamespace set azeventhubnamespace remove azeventhubnamespace script az frontdoor new azfrontdoor get azfrontdoor set azfrontdoor remove azfrontdoor script az hdinsight get azhdinsightjob new azhdinsightsqoopjobdefinition wait azhdinsightjob new azhdinsightstreamingmapreducejobdefinition script az iothub add aziothubkey get aziothubeventhubconsumergroup get aziothubconnectionstring get aziothubjob script az keyvault add azkeyvaultcertificate update azkeyvaultcertificate stop azkeyvaultcertificateoperation get azkeyvaultcertificateoperation script az logicapp get azintegrationaccountagreement get azintegrationaccountassembly get azintegrationaccountbatchconfiguration get azintegrationaccountcallbackurl script az machinelearning move azmlcommitmentassociation get azmlcommitmentassociation get azmlcommitmentplanusagehistory remove azmlcommitmentplan script az managedservices get azmanagedservicesassignment new azmanagedservicesassignment remove azmanagedservicesassignment get azmanagedservicesdefinition script az marketplaceordering get azmarketplaceterms set azmarketplaceterms script az media sync azmediaservicestoragekey set azmediaservicekey get azmediaservicekey get azmediaservicenameavailability script az monitor get azmetricdefinition get azmetric remove azlogprofile get azlogprofile script az network add azapplicationgatewayauthenticationcertificate get azapplicationgatewayauthenticationcertificate new azapplicationgatewayauthenticationcertificate remove azapplicationgatewayauthenticationcertificate script az notificationhubs get aznotificationhub get aznotificationhubauthorizationrule get aznotificationhublistkey get aznotificationhubpnscredential script az operationalinsights new azoperationalinsightsazureactivitylogdatasource new azoperationalinsightscustomlogdatasource disable azoperationalinsightslinuxcustomlogcollection disable azoperationalinsightsiislogcollection script az policyinsights get azpolicyevent get azpolicystate get azpolicystatesummary get azpolicyremediation script az powerbiembedded remove azpowerbiworkspacecollection get azpowerbiworkspacecollection get azpowerbiworkspacecollectionaccesskey get azpowerbiworkspace script az recoveryservices get azrecoveryservicesbackupproperty get azrecoveryservicesvault get azrecoveryservicesvaultsettingsfile new azrecoveryservicesvault script az rediscache remove azrediscachepatchschedule new azrediscachescheduleentry get azrediscachepatchschedule new azrediscachepatchschedule script az relay new azrelaynamespace get azrelaynamespace set azrelaynamespace remove azrelaynamespace script az resources get azprovideroperation remove azroleassignment get azroleassignment new azroleassignment script az servicebus new azservicebusnamespace get azservicebusnamespace set azservicebusnamespace remove azservicebusnamespace script az servicefabric add azservicefabricapplicationcertificate add azservicefabricclientcertificate add azservicefabricclustercertificate add azservicefabricnode script az signalr new azsignalr get azsignalr get azsignalrkey new azsignalrkey script az sql get azsqldatabasetransparentdataencryption get azsqldatabasetransparentdataencryptionactivity set azsqldatabasetransparentdataencryption get azsqldatabaseupgradehint script az storage get azstorageaccount get azstorageaccountkey new azstorageaccount new azstorageaccountkey script az storagesync invoke azstoragesynccompatibilitycheck new azstoragesyncservice get azstoragesyncservice remove azstoragesyncservice script az streamanalytics get azstreamanalyticsfunction get azstreamanalyticsdefaultfunctiondefinition new azstreamanalyticsfunction remove azstreamanalyticsfunction script az trafficmanager add aztrafficmanagercustomheadertoendpoint remove aztrafficmanagercustomheaderfromendpoint add aztrafficmanagercustomheadertoprofile remove aztrafficmanagercustomheaderfromprofile script az websites get azappserviceplan set azappserviceplan new azappserviceplan remove azappserviceplan debug output error output | 0 |
316,636 | 23,641,879,714 | IssuesEvent | 2022-08-25 17:52:50 | thegetty/quire-docs | https://api.github.com/repos/thegetty/quire-docs | opened | V1 Docs: Add Regex Section | documentation 11ty | ### Before proceeding, check to make sure there isn’t an existing issue for your suggestion or a similar one.
- [X] I have searched the existing issues and determined this is new suggestion.
### Idea being proposed
Add a section, or incorporate into an existing section, that shares useful regex patterns.
### What contribution category does your proposal fall under?
Propose/write new section
### Supporting Information
_No response_ | 1.0 | V1 Docs: Add Regex Section - ### Before proceeding, check to make sure there isn’t an existing issue for your suggestion or a similar one.
- [X] I have searched the existing issues and determined this is new suggestion.
### Idea being proposed
Add a section, or incorporate into an existing section, that shares useful regex patterns.
### What contribution category does your proposal fall under?
Propose/write new section
### Supporting Information
_No response_ | non_priority | docs add regex section before proceeding check to make sure there isn’t an existing issue for your suggestion or a similar one i have searched the existing issues and determined this is new suggestion idea being proposed add a section or incorporate into an existing section that shares useful regex patterns what contribution category does your proposal fall under propose write new section supporting information no response | 0 |
63,736 | 12,371,367,450 | IssuesEvent | 2020-05-18 18:26:11 | dotnet/interactive | https://api.github.com/repos/dotnet/interactive | opened | change file extension for VS Code notebooks | Area-VS Code Extension | The current extension, `.dotnet-interactive`, is a placeholder. We should come up with something more concise. | 1.0 | change file extension for VS Code notebooks - The current extension, `.dotnet-interactive`, is a placeholder. We should come up with something more concise. | non_priority | change file extension for vs code notebooks the current extension dotnet interactive is a placeholder we should come up with something more concise | 0 |
154,430 | 12,214,223,679 | IssuesEvent | 2020-05-01 09:20:01 | torusresearch/torus-website | https://api.github.com/repos/torusresearch/torus-website | closed | [Brave - Export Key] Unable to export key, stuck at encrypting | bug test | Unable to export discord acc key, stuck at encrypting
<img width="1440" alt="Screenshot 2020-05-01 at 4 52 01 PM" src="https://user-images.githubusercontent.com/53069682/80794325-3ced5f00-8bcc-11ea-82b6-469e9be956cc.png">
| 1.0 | [Brave - Export Key] Unable to export key, stuck at encrypting - Unable to export discord acc key, stuck at encrypting
<img width="1440" alt="Screenshot 2020-05-01 at 4 52 01 PM" src="https://user-images.githubusercontent.com/53069682/80794325-3ced5f00-8bcc-11ea-82b6-469e9be956cc.png">
| non_priority | unable to export key stuck at encrypting unable to export discord acc key stuck at encrypting img width alt screenshot at pm src | 0 |
56,307 | 23,747,557,093 | IssuesEvent | 2022-08-31 17:21:01 | oasis-open/odata-rapid | https://api.github.com/repos/oasis-open/odata-rapid | closed | GraphQL client tutorial fails in step "Preview your service with GraphQL" | bug GraphQL Interoperability Jetsons sample service | Following the instructions in [GraphQL client tutorial](https://rapid.rocks/docs/tutorial/graphqlclient) fails in step [Preview your service with GraphQL](https://rapid.rocks/docs/tutorial/graphqlclient#preview-your-service-with-graphql):
~~~sh
yarn mesh dev
~~~
or equivalently
~~~sh
npx mesh dev
~~~
fail with error message
~~~
💡 🕸️ Mesh - Server Generating the unified schema...
💥 🕸️ Mesh - Jetsons Failed to generate the schema TypeError: Cannot read properties of undefined (reading '0')
at ODataHandler.getMeshSource (C:\temp\rapid-graphql-client-tutorial\node_modules\@graphql-mesh\odata\index.js:121:42)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at async C:\temp\rapid-graphql-client-tutorial\node_modules\@graphql-mesh\runtime\index.js:281:28
💥 🕸️ Mesh An error occured while writing the schema file: Error: Schemas couldn't be generated successfully. C...
💥 🕸️ Mesh An error occurred while building the artifacts: Error: Schemas couldn't be generated successfully. C...
💥 🕸️ Mesh - Server Error: Schemas couldn't be generated successfully. Check for the logs by running Mesh with DEBUG=1 e...
~~~
Replacing the baseUrl with https://services.odata.org/V4/(S(oygeljzs0rz0wq0k2vd4j3zk))/TripPinServiceRW/, so this seems to be a communication problem between GraphQL Mesh and the Jetsons service. | 1.0 | GraphQL client tutorial fails in step "Preview your service with GraphQL" - Following the instructions in [GraphQL client tutorial](https://rapid.rocks/docs/tutorial/graphqlclient) fails in step [Preview your service with GraphQL](https://rapid.rocks/docs/tutorial/graphqlclient#preview-your-service-with-graphql):
~~~sh
yarn mesh dev
~~~
or equivalently
~~~sh
npx mesh dev
~~~
fail with error message
~~~
💡 🕸️ Mesh - Server Generating the unified schema...
💥 🕸️ Mesh - Jetsons Failed to generate the schema TypeError: Cannot read properties of undefined (reading '0')
at ODataHandler.getMeshSource (C:\temp\rapid-graphql-client-tutorial\node_modules\@graphql-mesh\odata\index.js:121:42)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at async C:\temp\rapid-graphql-client-tutorial\node_modules\@graphql-mesh\runtime\index.js:281:28
💥 🕸️ Mesh An error occured while writing the schema file: Error: Schemas couldn't be generated successfully. C...
💥 🕸️ Mesh An error occurred while building the artifacts: Error: Schemas couldn't be generated successfully. C...
💥 🕸️ Mesh - Server Error: Schemas couldn't be generated successfully. Check for the logs by running Mesh with DEBUG=1 e...
~~~
Replacing the baseUrl with https://services.odata.org/V4/(S(oygeljzs0rz0wq0k2vd4j3zk))/TripPinServiceRW/, so this seems to be a communication problem between GraphQL Mesh and the Jetsons service. | non_priority | graphql client tutorial fails in step preview your service with graphql following the instructions in fails in step sh yarn mesh dev or equivalently sh npx mesh dev fail with error message 💡 🕸️ mesh server generating the unified schema 💥 🕸️ mesh jetsons failed to generate the schema typeerror cannot read properties of undefined reading at odatahandler getmeshsource c temp rapid graphql client tutorial node modules graphql mesh odata index js at processticksandrejections node internal process task queues at async c temp rapid graphql client tutorial node modules graphql mesh runtime index js 💥 🕸️ mesh an error occured while writing the schema file error schemas couldn t be generated successfully c 💥 🕸️ mesh an error occurred while building the artifacts error schemas couldn t be generated successfully c 💥 🕸️ mesh server error schemas couldn t be generated successfully check for the logs by running mesh with debug e replacing the baseurl with so this seems to be a communication problem between graphql mesh and the jetsons service | 0 |
11,586 | 3,507,845,416 | IssuesEvent | 2016-01-08 15:19:14 | agershun/alasql | https://api.github.com/repos/agershun/alasql | reopened | || operator | Documentation Question Solved: please test | ```||``` in SQLite is string concatination.
```sql
SELECT 'wolf' || 'hound';
wolfhound
```
Currently. in AlaSQL ```||``` is like JavaScript ```||```. Should we keep current behaviour or change it to SQLite way? | 1.0 | || operator - ```||``` in SQLite is string concatination.
```sql
SELECT 'wolf' || 'hound';
wolfhound
```
Currently. in AlaSQL ```||``` is like JavaScript ```||```. Should we keep current behaviour or change it to SQLite way? | non_priority | operator in sqlite is string concatination sql select wolf hound wolfhound currently in alasql is like javascript should we keep current behaviour or change it to sqlite way | 0 |
278,109 | 21,058,071,918 | IssuesEvent | 2022-04-01 06:41:56 | yusufaine/ped | https://api.github.com/repos/yusufaine/ped | opened | [UG] Addjob invalid sample command in command summary | type.DocumentationBug severity.High | Currently the add job command in the summary is as follows:
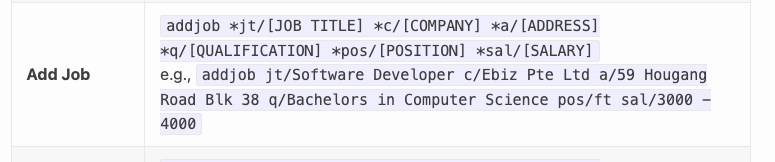
```
addjob jt/Software Developer c/Ebiz Pte Ltd a/59 Hougang Road Blk 38 q/Bachelors in Computer Science pos/ft sal/3000 - 4000
```
This command throws an error as seen in issue #9
<!--session: 1648793076586-50e6562d-99d8-453a-a06d-b22a3601f521-->
<!--Version: Web v3.4.2--> | 1.0 | [UG] Addjob invalid sample command in command summary - Currently the add job command in the summary is as follows:
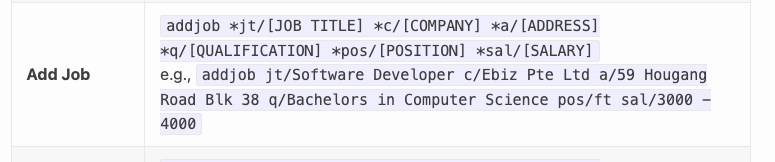
```
addjob jt/Software Developer c/Ebiz Pte Ltd a/59 Hougang Road Blk 38 q/Bachelors in Computer Science pos/ft sal/3000 - 4000
```
This command throws an error as seen in issue #9
<!--session: 1648793076586-50e6562d-99d8-453a-a06d-b22a3601f521-->
<!--Version: Web v3.4.2--> | non_priority | addjob invalid sample command in command summary currently the add job command in the summary is as follows addjob jt software developer c ebiz pte ltd a hougang road blk q bachelors in computer science pos ft sal this command throws an error as seen in issue | 0 |
124,199 | 26,419,460,428 | IssuesEvent | 2023-01-13 18:55:11 | pnp/pnpjs | https://api.github.com/repos/pnp/pnpjs | closed | renderListDataAsStream doesn't work in v3 as it used to in v2 | type: question status: answered area: code | ### Category
- [ ] Enhancement
- [x] Bug
- [ ] Question
- [ ] Documentation gap/issue
### Version
Please specify what version of the library you are using: [^3.7.0]
Please specify what version(s) of SharePoint you are targeting: [Online]
### Expected / Desired Behavior / Question
renderListDataAsStream returns data in v3 following https://pnp.github.io/pnpjs/sp/lists/#render-list-data-as-stream as it used to in v2
### Observed Behavior
The code below used to work on v2 (^2.11.0)
```
import { Web } from "@pnp/sp/webs";
const list = Web([url of site different than current site]).lists.getById([listId]);
const listViewXml = await (await list.views.getById(viewId).select("*").get()).ListViewXml;
const resultsViewItems = await list.renderListDataAsStream({
DatesInUtc: true,
OverrideViewXml: listViewXml
});
resultsViewItems.Row.forEach(item => {
console.log(item);
});
```
The code above adapted to v3 doesn't work at renderListDataAsStream throwing a "Cannot read properties of undefined (reading 'web')" error.
```
import { Web } from "@pnp/sp/webs";
const list = Web([url of site different than current site]).lists.getById(listId);
const view = list.views.getById(viewId);
const listViewXml = await (await view()).ListViewXml;
const resultsViewItems = await list.renderListDataAsStream({
DatesInUtc: true,
OverrideViewXml: listViewXml
});
resultsViewItems.Row.forEach(item => {
console.log(item);
});
```
I also tried initializing the list using spfi instead but same result
```
const sp: SPFI = spfi([url of site different than current site]).using(SPFx(this.props.context as any));
const list = sp.web.lists.getById(config.ListId);
```
### Steps to Reproduce
```
import { Web } from "@pnp/sp/webs";
const list = Web([url of site different than current site]).lists.getById(listId);
const view = list.views.getById(viewId);
const listViewXml = await (await view()).ListViewXml;
const resultsViewItems = await list.renderListDataAsStream({
DatesInUtc: true,
OverrideViewXml: listViewXml
});
resultsViewItems.Row.forEach(item => {
console.log(item);
});
``` | 1.0 | renderListDataAsStream doesn't work in v3 as it used to in v2 - ### Category
- [ ] Enhancement
- [x] Bug
- [ ] Question
- [ ] Documentation gap/issue
### Version
Please specify what version of the library you are using: [^3.7.0]
Please specify what version(s) of SharePoint you are targeting: [Online]
### Expected / Desired Behavior / Question
renderListDataAsStream returns data in v3 following https://pnp.github.io/pnpjs/sp/lists/#render-list-data-as-stream as it used to in v2
### Observed Behavior
The code below used to work on v2 (^2.11.0)
```
import { Web } from "@pnp/sp/webs";
const list = Web([url of site different than current site]).lists.getById([listId]);
const listViewXml = await (await list.views.getById(viewId).select("*").get()).ListViewXml;
const resultsViewItems = await list.renderListDataAsStream({
DatesInUtc: true,
OverrideViewXml: listViewXml
});
resultsViewItems.Row.forEach(item => {
console.log(item);
});
```
The code above adapted to v3 doesn't work at renderListDataAsStream throwing a "Cannot read properties of undefined (reading 'web')" error.
```
import { Web } from "@pnp/sp/webs";
const list = Web([url of site different than current site]).lists.getById(listId);
const view = list.views.getById(viewId);
const listViewXml = await (await view()).ListViewXml;
const resultsViewItems = await list.renderListDataAsStream({
DatesInUtc: true,
OverrideViewXml: listViewXml
});
resultsViewItems.Row.forEach(item => {
console.log(item);
});
```
I also tried initializing the list using spfi instead but same result
```
const sp: SPFI = spfi([url of site different than current site]).using(SPFx(this.props.context as any));
const list = sp.web.lists.getById(config.ListId);
```
### Steps to Reproduce
```
import { Web } from "@pnp/sp/webs";
const list = Web([url of site different than current site]).lists.getById(listId);
const view = list.views.getById(viewId);
const listViewXml = await (await view()).ListViewXml;
const resultsViewItems = await list.renderListDataAsStream({
DatesInUtc: true,
OverrideViewXml: listViewXml
});
resultsViewItems.Row.forEach(item => {
console.log(item);
});
``` | non_priority | renderlistdataasstream doesn t work in as it used to in category enhancement bug question documentation gap issue version please specify what version of the library you are using please specify what version s of sharepoint you are targeting expected desired behavior question renderlistdataasstream returns data in following as it used to in observed behavior the code below used to work on import web from pnp sp webs const list web lists getbyid const listviewxml await await list views getbyid viewid select get listviewxml const resultsviewitems await list renderlistdataasstream datesinutc true overrideviewxml listviewxml resultsviewitems row foreach item console log item the code above adapted to doesn t work at renderlistdataasstream throwing a cannot read properties of undefined reading web error import web from pnp sp webs const list web lists getbyid listid const view list views getbyid viewid const listviewxml await await view listviewxml const resultsviewitems await list renderlistdataasstream datesinutc true overrideviewxml listviewxml resultsviewitems row foreach item console log item i also tried initializing the list using spfi instead but same result const sp spfi spfi using spfx this props context as any const list sp web lists getbyid config listid steps to reproduce import web from pnp sp webs const list web lists getbyid listid const view list views getbyid viewid const listviewxml await await view listviewxml const resultsviewitems await list renderlistdataasstream datesinutc true overrideviewxml listviewxml resultsviewitems row foreach item console log item | 0 |
15,932 | 20,982,550,253 | IssuesEvent | 2022-03-28 21:35:34 | dotnet/docs | https://api.github.com/repos/dotnet/docs | closed | [Breaking change]: EncryptionPolicy.NoEncryption and EncryptionPolicy.AllowNoEncryption are obsolete | doc-idea :watch: Not Triaged breaking-change Pri1 source incompatible :checkered_flag: Release: .NET 7 | ### Description
https://github.com/dotnet/runtime/pull/66292 Marks `EncryptionPolicy.NoEncryption` and `EncryptionPolicy.AllowNoEncryption` as obsolete.
Original issue: https://github.com/dotnet/runtime/issues/65545
### Version
.NET 7 Preview 3
### Previous behavior
Using `EncryptionPolicy.NoEncryption` or `EncryptionPolicy.AllowNoEncryption` does not produce compiler warnings.
### New behavior
Using `EncryptionPolicy.NoEncryption` or `EncryptionPolicy.AllowNoEncryption` produces `SYSLIB0040` warning.
### Type of breaking change
- [ ] **Binary incompatible**: Existing binaries may encounter a breaking change in behavior, such as failure to load/execute or different run-time behavior.
- [X] **Source incompatible**: Source code may encounter a breaking change in behavior when targeting the new runtime/component/SDK, such as compile errors or different run-time behavior.
### Reason for change
While old SSL/TLS versions permitted NULL encryption it and while it may be useful for debugging, nobody should really be using it in production. NULL encryption is also no longer available as of Tls 1.3.
### Recommended action
Always use `EncryptionPolicy.RequireEncryption` (default value)
### Feature area
Networking
### Affected APIs
Any use of `EncryptionPolicy` enum. | True | [Breaking change]: EncryptionPolicy.NoEncryption and EncryptionPolicy.AllowNoEncryption are obsolete - ### Description
https://github.com/dotnet/runtime/pull/66292 Marks `EncryptionPolicy.NoEncryption` and `EncryptionPolicy.AllowNoEncryption` as obsolete.
Original issue: https://github.com/dotnet/runtime/issues/65545
### Version
.NET 7 Preview 3
### Previous behavior
Using `EncryptionPolicy.NoEncryption` or `EncryptionPolicy.AllowNoEncryption` does not produce compiler warnings.
### New behavior
Using `EncryptionPolicy.NoEncryption` or `EncryptionPolicy.AllowNoEncryption` produces `SYSLIB0040` warning.
### Type of breaking change
- [ ] **Binary incompatible**: Existing binaries may encounter a breaking change in behavior, such as failure to load/execute or different run-time behavior.
- [X] **Source incompatible**: Source code may encounter a breaking change in behavior when targeting the new runtime/component/SDK, such as compile errors or different run-time behavior.
### Reason for change
While old SSL/TLS versions permitted NULL encryption it and while it may be useful for debugging, nobody should really be using it in production. NULL encryption is also no longer available as of Tls 1.3.
### Recommended action
Always use `EncryptionPolicy.RequireEncryption` (default value)
### Feature area
Networking
### Affected APIs
Any use of `EncryptionPolicy` enum. | non_priority | encryptionpolicy noencryption and encryptionpolicy allownoencryption are obsolete description marks encryptionpolicy noencryption and encryptionpolicy allownoencryption as obsolete original issue version net preview previous behavior using encryptionpolicy noencryption or encryptionpolicy allownoencryption does not produce compiler warnings new behavior using encryptionpolicy noencryption or encryptionpolicy allownoencryption produces warning type of breaking change binary incompatible existing binaries may encounter a breaking change in behavior such as failure to load execute or different run time behavior source incompatible source code may encounter a breaking change in behavior when targeting the new runtime component sdk such as compile errors or different run time behavior reason for change while old ssl tls versions permitted null encryption it and while it may be useful for debugging nobody should really be using it in production null encryption is also no longer available as of tls recommended action always use encryptionpolicy requireencryption default value feature area networking affected apis any use of encryptionpolicy enum | 0 |
264,181 | 23,100,373,479 | IssuesEvent | 2022-07-27 01:40:53 | woowacourse-teams/2022-dallog | https://api.github.com/repos/woowacourse-teams/2022-dallog | closed | 테스트 격리를 실패시키는 TestFixture 제거한다. | backend refactor test | ## 🤷 구현할 기능
테스트 격리실패의 원인이 되는 테스트 fixture를 수정한다
## 🔨 상세 작업 내용
- [x] 객체로 생성된 TestFixture를 제거한다.
- [x] 객체로 생성한 TestFixture를 사용하는 테스트 코드를 변경한다.
- [x] 중복되는 테스트 코드를 제거한다.
## ⏰ 예상 소요 기간
2시간 | 1.0 | 테스트 격리를 실패시키는 TestFixture 제거한다. - ## 🤷 구현할 기능
테스트 격리실패의 원인이 되는 테스트 fixture를 수정한다
## 🔨 상세 작업 내용
- [x] 객체로 생성된 TestFixture를 제거한다.
- [x] 객체로 생성한 TestFixture를 사용하는 테스트 코드를 변경한다.
- [x] 중복되는 테스트 코드를 제거한다.
## ⏰ 예상 소요 기간
2시간 | non_priority | 테스트 격리를 실패시키는 testfixture 제거한다 🤷 구현할 기능 테스트 격리실패의 원인이 되는 테스트 fixture를 수정한다 🔨 상세 작업 내용 객체로 생성된 testfixture를 제거한다 객체로 생성한 testfixture를 사용하는 테스트 코드를 변경한다 중복되는 테스트 코드를 제거한다 ⏰ 예상 소요 기간 | 0 |
135,586 | 19,598,645,785 | IssuesEvent | 2022-01-05 21:18:45 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | [PM, Design] My VA - Payment Information and On-site Notification: Update all documentation to include error states | design product my-va-dashboard vsa-authenticated-exp needs-grooming planned-work onsite-notifications | ## Background
Technical discovery has been completed and shared for both the Payment information section and the On-site notification. The team has agreed on the error states. The design, FE documentation, test cases (and any other docs) need to be updated with this information.
## Tasks
On-site Notification
- [ ] Update any design documents to include error states for On-site notification
- [ ] Update any FE documentation to include error states for On-site notification
- [ ] Update test cases to include error states for On-site notification
Payment Information section
- [ ] Update any design documents to include error states for payment information section
- [ ] Update any FE documentation to include error states for payment information section
- [ ] Update test cases to include error states for payment information section
## Acceptance Criteria
- All documentation has been updated to include error states on both Payment Information and On-site Notification
| 1.0 | [PM, Design] My VA - Payment Information and On-site Notification: Update all documentation to include error states - ## Background
Technical discovery has been completed and shared for both the Payment information section and the On-site notification. The team has agreed on the error states. The design, FE documentation, test cases (and any other docs) need to be updated with this information.
## Tasks
On-site Notification
- [ ] Update any design documents to include error states for On-site notification
- [ ] Update any FE documentation to include error states for On-site notification
- [ ] Update test cases to include error states for On-site notification
Payment Information section
- [ ] Update any design documents to include error states for payment information section
- [ ] Update any FE documentation to include error states for payment information section
- [ ] Update test cases to include error states for payment information section
## Acceptance Criteria
- All documentation has been updated to include error states on both Payment Information and On-site Notification
| non_priority | my va payment information and on site notification update all documentation to include error states background technical discovery has been completed and shared for both the payment information section and the on site notification the team has agreed on the error states the design fe documentation test cases and any other docs need to be updated with this information tasks on site notification update any design documents to include error states for on site notification update any fe documentation to include error states for on site notification update test cases to include error states for on site notification payment information section update any design documents to include error states for payment information section update any fe documentation to include error states for payment information section update test cases to include error states for payment information section acceptance criteria all documentation has been updated to include error states on both payment information and on site notification | 0 |
64,318 | 6,899,570,019 | IssuesEvent | 2017-11-24 14:21:28 | dzhw/metadatamanagement | https://api.github.com/repos/dzhw/metadatamanagement | closed | Rework number of decimal places of values | category:variablemanagement points:8 prio:1 scope:research data centre status:testing type:bug | - Not enough decimal places are shown for weight variables:
https://metadatamanagement-test.cfapps.io/#!/en/variables/var-gra2005-ds1-wgt_t1d$?search-result-index=1
- For example school grades only need zero or one decimal place:
https://metadatamanagement-test.cfapps.io/#!/en/variables/var-gra2005-ds1-astu03c$?search-result-index=1
- Integer variables which were wrongly stored as float in stata datasets have zero decimal places:
https://metadatamanagement-test.cfapps.io/#!/en/variables/var-gra2005-ds4-end_y$?search-result-index=2
| 1.0 | Rework number of decimal places of values - - Not enough decimal places are shown for weight variables:
https://metadatamanagement-test.cfapps.io/#!/en/variables/var-gra2005-ds1-wgt_t1d$?search-result-index=1
- For example school grades only need zero or one decimal place:
https://metadatamanagement-test.cfapps.io/#!/en/variables/var-gra2005-ds1-astu03c$?search-result-index=1
- Integer variables which were wrongly stored as float in stata datasets have zero decimal places:
https://metadatamanagement-test.cfapps.io/#!/en/variables/var-gra2005-ds4-end_y$?search-result-index=2
| non_priority | rework number of decimal places of values not enough decimal places are shown for weight variables for example school grades only need zero or one decimal place integer variables which were wrongly stored as float in stata datasets have zero decimal places | 0 |
207,505 | 16,086,465,572 | IssuesEvent | 2021-04-26 11:53:26 | pompomsw/embedded-diagrams | https://api.github.com/repos/pompomsw/embedded-diagrams | closed | Set up commmitlint | documentation | ## Commitlint helps us make commit messages following the rule of Conventional Commits.
### ToDo
1. Create commitlint.config.js.
2. Add husky settings to package.json.
3. Set up GitHub Actions for commitlint | 1.0 | Set up commmitlint - ## Commitlint helps us make commit messages following the rule of Conventional Commits.
### ToDo
1. Create commitlint.config.js.
2. Add husky settings to package.json.
3. Set up GitHub Actions for commitlint | non_priority | set up commmitlint commitlint helps us make commit messages following the rule of conventional commits todo create commitlint config js add husky settings to package json set up github actions for commitlint | 0 |
11,124 | 4,891,331,589 | IssuesEvent | 2016-11-18 16:24:07 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | Rustdoc tests fail due to htmlparser python dependency | A-rustbuild | ```
Traceback (most recent call last):
File "/home/nagisa/Documents/rust/rust/src/etc/htmldocck.py", line 113, in <module>
from HTMLParser import HTMLParser
ImportError: No module named 'HTMLParser'
```
| 1.0 | Rustdoc tests fail due to htmlparser python dependency - ```
Traceback (most recent call last):
File "/home/nagisa/Documents/rust/rust/src/etc/htmldocck.py", line 113, in <module>
from HTMLParser import HTMLParser
ImportError: No module named 'HTMLParser'
```
| non_priority | rustdoc tests fail due to htmlparser python dependency traceback most recent call last file home nagisa documents rust rust src etc htmldocck py line in from htmlparser import htmlparser importerror no module named htmlparser | 0 |
126,823 | 17,970,735,365 | IssuesEvent | 2021-09-14 01:24:47 | ghuangsnl/spring-boot | https://api.github.com/repos/ghuangsnl/spring-boot | opened | CVE-2021-37137 (Medium) detected in netty-codec-4.1.50.Final.jar | security vulnerability | ## CVE-2021-37137 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-4.1.50.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Path to dependency file: spring-boot/spring-boot-tests/spring-boot-smoke-tests/spring-boot-smoke-test-jta-bitronix/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.netty/netty-codec/4.1.50.Final/cbcb646c9380c6cdc3f56603ae6418a11418ce0f/netty-codec-4.1.50.Final.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.netty/netty-codec/4.1.50.Final/cbcb646c9380c6cdc3f56603ae6418a11418ce0f/netty-codec-4.1.50.Final.jar</p>
<p>
Dependency Hierarchy:
- netty-bom-4.1.50.Final (Root Library)
- :x: **netty-codec-4.1.50.Final.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Snappy frame decoder function doesn't restrict the chunk length which may lead to excessive memory usage. Beside this it also may buffer reserved skippable chunks until the whole chunk was received which may lead to excessive memory usage as well.
This vulnerability can be triggered by supplying malicious input that decompresses to a very big size (via a network stream or a file) or by sending a huge skippable chunk
<p>Publish Date: 2021-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37137>CVE-2021-37137</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9vjp-v76f-g363">https://github.com/advisories/GHSA-9vjp-v76f-g363</a></p>
<p>Release Date: 2021-07-21</p>
<p>Fix Resolution: io.netty:netty-codec:4.1.68.Final</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-37137 (Medium) detected in netty-codec-4.1.50.Final.jar - ## CVE-2021-37137 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-4.1.50.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Path to dependency file: spring-boot/spring-boot-tests/spring-boot-smoke-tests/spring-boot-smoke-test-jta-bitronix/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.netty/netty-codec/4.1.50.Final/cbcb646c9380c6cdc3f56603ae6418a11418ce0f/netty-codec-4.1.50.Final.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.netty/netty-codec/4.1.50.Final/cbcb646c9380c6cdc3f56603ae6418a11418ce0f/netty-codec-4.1.50.Final.jar</p>
<p>
Dependency Hierarchy:
- netty-bom-4.1.50.Final (Root Library)
- :x: **netty-codec-4.1.50.Final.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Snappy frame decoder function doesn't restrict the chunk length which may lead to excessive memory usage. Beside this it also may buffer reserved skippable chunks until the whole chunk was received which may lead to excessive memory usage as well.
This vulnerability can be triggered by supplying malicious input that decompresses to a very big size (via a network stream or a file) or by sending a huge skippable chunk
<p>Publish Date: 2021-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37137>CVE-2021-37137</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9vjp-v76f-g363">https://github.com/advisories/GHSA-9vjp-v76f-g363</a></p>
<p>Release Date: 2021-07-21</p>
<p>Fix Resolution: io.netty:netty-codec:4.1.68.Final</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in netty codec final jar cve medium severity vulnerability vulnerable library netty codec final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients path to dependency file spring boot spring boot tests spring boot smoke tests spring boot smoke test jta bitronix build gradle path to vulnerable library home wss scanner gradle caches modules files io netty netty codec final netty codec final jar home wss scanner gradle caches modules files io netty netty codec final netty codec final jar dependency hierarchy netty bom final root library x netty codec final jar vulnerable library vulnerability details the snappy frame decoder function doesn t restrict the chunk length which may lead to excessive memory usage beside this it also may buffer reserved skippable chunks until the whole chunk was received which may lead to excessive memory usage as well this vulnerability can be triggered by supplying malicious input that decompresses to a very big size via a network stream or a file or by sending a huge skippable chunk publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io netty netty codec final step up your open source security game with whitesource | 0 |
194,393 | 14,677,162,182 | IssuesEvent | 2020-12-30 22:21:37 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | apigee-labs/transicator: changeserver/changes_api_test.go; 27 LoC | fresh small test |
Found a possible issue in [apigee-labs/transicator](https://www.github.com/apigee-labs/transicator) at [changeserver/changes_api_test.go](https://github.com/apigee-labs/transicator/blob/2d5dc596a5f2f5e13967e0f1943f248d88eac1e7/changeserver/changes_api_test.go#L374-L400)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable p used in defer or goroutine at line 379
[Click here to see the code in its original context.](https://github.com/apigee-labs/transicator/blob/2d5dc596a5f2f5e13967e0f1943f248d88eac1e7/changeserver/changes_api_test.go#L374-L400)
<details>
<summary>Click here to show the 27 line(s) of Go which triggered the analyzer.</summary>
```go
for _, p := range []string{"scope", "selector"} {
resultChan := make(chan *common.ChangeList, 1)
go func() {
lc := getChanges(fmt.Sprintf(
"%s/changes?since=%s&%s=foo", baseURL, lastChangeSequence, p))
resultChan <- lc
lc = getChanges(fmt.Sprintf(
"%s/changes?since=%s&%s=foo&block=30", baseURL, lastChangeSequence, p))
resultChan <- lc
}()
cl := <-resultChan
Expect(cl.Changes).Should(BeEmpty())
// Make sure that we don't get anything for a short time before we insert
Consistently(resultChan, time.Second).ShouldNot(Receive())
lastTestSequence++
_, err := insertStmt.Exec(lastTestSequence, "foo")
Expect(err).Should(Succeed())
cl = <-resultChan
Expect(len(cl.Changes)).Should(Equal(1))
Expect(compareSequence(cl, 0, lastTestSequence)).Should(BeTrue())
lastChangeSequence = cl.Changes[0].GetSequence()
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 2d5dc596a5f2f5e13967e0f1943f248d88eac1e7
| 1.0 | apigee-labs/transicator: changeserver/changes_api_test.go; 27 LoC -
Found a possible issue in [apigee-labs/transicator](https://www.github.com/apigee-labs/transicator) at [changeserver/changes_api_test.go](https://github.com/apigee-labs/transicator/blob/2d5dc596a5f2f5e13967e0f1943f248d88eac1e7/changeserver/changes_api_test.go#L374-L400)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable p used in defer or goroutine at line 379
[Click here to see the code in its original context.](https://github.com/apigee-labs/transicator/blob/2d5dc596a5f2f5e13967e0f1943f248d88eac1e7/changeserver/changes_api_test.go#L374-L400)
<details>
<summary>Click here to show the 27 line(s) of Go which triggered the analyzer.</summary>
```go
for _, p := range []string{"scope", "selector"} {
resultChan := make(chan *common.ChangeList, 1)
go func() {
lc := getChanges(fmt.Sprintf(
"%s/changes?since=%s&%s=foo", baseURL, lastChangeSequence, p))
resultChan <- lc
lc = getChanges(fmt.Sprintf(
"%s/changes?since=%s&%s=foo&block=30", baseURL, lastChangeSequence, p))
resultChan <- lc
}()
cl := <-resultChan
Expect(cl.Changes).Should(BeEmpty())
// Make sure that we don't get anything for a short time before we insert
Consistently(resultChan, time.Second).ShouldNot(Receive())
lastTestSequence++
_, err := insertStmt.Exec(lastTestSequence, "foo")
Expect(err).Should(Succeed())
cl = <-resultChan
Expect(len(cl.Changes)).Should(Equal(1))
Expect(compareSequence(cl, 0, lastTestSequence)).Should(BeTrue())
lastChangeSequence = cl.Changes[0].GetSequence()
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 2d5dc596a5f2f5e13967e0f1943f248d88eac1e7
| non_priority | apigee labs transicator changeserver changes api test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable p used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for p range string scope selector resultchan make chan common changelist go func lc getchanges fmt sprintf s changes since s s foo baseurl lastchangesequence p resultchan lc lc getchanges fmt sprintf s changes since s s foo block baseurl lastchangesequence p resultchan lc cl resultchan expect cl changes should beempty make sure that we don t get anything for a short time before we insert consistently resultchan time second shouldnot receive lasttestsequence err insertstmt exec lasttestsequence foo expect err should succeed cl resultchan expect len cl changes should equal expect comparesequence cl lasttestsequence should betrue lastchangesequence cl changes getsequence leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
66,377 | 8,000,655,590 | IssuesEvent | 2018-07-22 18:30:33 | cloudscribe/cloudscribe.SimpleContent | https://api.github.com/repos/cloudscribe/cloudscribe.SimpleContent | closed | Content Versions, including history and draft | enhancement has-design has-sponsorship | In SimpleContent we already have the ability to make a whole page a draft. But we don’t have the ability to make an edited version of that page a draft while the existing version remains live. And we don’t have the ability to review previous versions, and restore them.
And I think these requirements can be combined into one (in contrast with mojoPortal's approach where these were two separate things that could become confusing for editors). So "Content Versioning" would deliver management of past versions and a future draft version.
This would apply to content pages. Blog posts would only need the "history" part of this as draft content can already be handled adequately.
My initial ideas on this would be:
## History:
I think another tab: Content | Settings | History
History tab lists of previous versions with date/time and editor, with ability to “Restore to editor” or “Compare to current” (plus delete and delete all).
I’d suggest the “Compare” might perhaps open the page in a full browser window rather than a modal, with difference highlighting. (The modal approach means layout is rarely faithful and so comparison is not easy – anyone doing this kind of work can manage browser tabs and windows). This might be achieved by opening a page with URL param identifying the version to open, with this only working for users in an editing role. But the modal approach would be ok too.
## Draft content:
Regarding drafting once a page is already published, I’ve thought through a few ways and one nice simple implementation might be…
## On creating a new page…
Hide the “Is Published” check box and “Publication Date” in this context and instead have these controls:
[Save Draft] [Publish Now] [Publish Later:] […date/time picker…] [Delete]
[Developer Tools]
“Save Draft” sets “Is Published” to False on the Page.
“Publish Now” sets “Is Published” to True on the Page and sets “Publication Date” to now.
“Publish Later” sets “Is Published” to True on the Page and sets “Publication Date” to specified date/time. If none specified, do as “Save Draft”.
## On editing an existing page…
always edit the draft if one exists. Depending on how this is all stored, this could always be the most recent in the history. Don’t give the ability to edit a previous (published) version (it made things too confusing in mojo - editors can achieve that by restoring the published version into the editor).
Show the “Is Published” check box and “Publication Date” in this context, but call them “Page Is Published” and “Page Publication Date”.
Provide same set of buttons/controls:
[Save Draft] [Publish Now] [Publish Later:] […date/time picker…] [Delete]
(this allows a changeover in content to be scheduled).
There could well be some loopholes here!
I feel Content Versioning would be enabled globally. I cannot imagine why it would not be useful across the board, and it doesn't make the publishing workflow any harder. So perhaps just always there in SimpleContent - no need even to switch it on. The only reason not to would be the extra storage needed for the superseded versions, but that shouldn't be an issue these days, and there could be an Administrative capability to clean out history (All, or older than a specified period (e.g. 1 month, 6 months, 1 year).
Also useful in the Administration area would be a view of all Content History (descending date order by default, filterable by Editor or page), permitting View (but not restore).
Note this does not provide any differentiation in roles for editing and publishing – we think that’s rarely needed and makes things more complex, but a potential future enhancement. | 1.0 | Content Versions, including history and draft - In SimpleContent we already have the ability to make a whole page a draft. But we don’t have the ability to make an edited version of that page a draft while the existing version remains live. And we don’t have the ability to review previous versions, and restore them.
And I think these requirements can be combined into one (in contrast with mojoPortal's approach where these were two separate things that could become confusing for editors). So "Content Versioning" would deliver management of past versions and a future draft version.
This would apply to content pages. Blog posts would only need the "history" part of this as draft content can already be handled adequately.
My initial ideas on this would be:
## History:
I think another tab: Content | Settings | History
History tab lists of previous versions with date/time and editor, with ability to “Restore to editor” or “Compare to current” (plus delete and delete all).
I’d suggest the “Compare” might perhaps open the page in a full browser window rather than a modal, with difference highlighting. (The modal approach means layout is rarely faithful and so comparison is not easy – anyone doing this kind of work can manage browser tabs and windows). This might be achieved by opening a page with URL param identifying the version to open, with this only working for users in an editing role. But the modal approach would be ok too.
## Draft content:
Regarding drafting once a page is already published, I’ve thought through a few ways and one nice simple implementation might be…
## On creating a new page…
Hide the “Is Published” check box and “Publication Date” in this context and instead have these controls:
[Save Draft] [Publish Now] [Publish Later:] […date/time picker…] [Delete]
[Developer Tools]
“Save Draft” sets “Is Published” to False on the Page.
“Publish Now” sets “Is Published” to True on the Page and sets “Publication Date” to now.
“Publish Later” sets “Is Published” to True on the Page and sets “Publication Date” to specified date/time. If none specified, do as “Save Draft”.
## On editing an existing page…
always edit the draft if one exists. Depending on how this is all stored, this could always be the most recent in the history. Don’t give the ability to edit a previous (published) version (it made things too confusing in mojo - editors can achieve that by restoring the published version into the editor).
Show the “Is Published” check box and “Publication Date” in this context, but call them “Page Is Published” and “Page Publication Date”.
Provide same set of buttons/controls:
[Save Draft] [Publish Now] [Publish Later:] […date/time picker…] [Delete]
(this allows a changeover in content to be scheduled).
There could well be some loopholes here!
I feel Content Versioning would be enabled globally. I cannot imagine why it would not be useful across the board, and it doesn't make the publishing workflow any harder. So perhaps just always there in SimpleContent - no need even to switch it on. The only reason not to would be the extra storage needed for the superseded versions, but that shouldn't be an issue these days, and there could be an Administrative capability to clean out history (All, or older than a specified period (e.g. 1 month, 6 months, 1 year).
Also useful in the Administration area would be a view of all Content History (descending date order by default, filterable by Editor or page), permitting View (but not restore).
Note this does not provide any differentiation in roles for editing and publishing – we think that’s rarely needed and makes things more complex, but a potential future enhancement. | non_priority | content versions including history and draft in simplecontent we already have the ability to make a whole page a draft but we don’t have the ability to make an edited version of that page a draft while the existing version remains live and we don’t have the ability to review previous versions and restore them and i think these requirements can be combined into one in contrast with mojoportal s approach where these were two separate things that could become confusing for editors so content versioning would deliver management of past versions and a future draft version this would apply to content pages blog posts would only need the history part of this as draft content can already be handled adequately my initial ideas on this would be history i think another tab content settings history history tab lists of previous versions with date time and editor with ability to “restore to editor” or “compare to current” plus delete and delete all i’d suggest the “compare” might perhaps open the page in a full browser window rather than a modal with difference highlighting the modal approach means layout is rarely faithful and so comparison is not easy – anyone doing this kind of work can manage browser tabs and windows this might be achieved by opening a page with url param identifying the version to open with this only working for users in an editing role but the modal approach would be ok too draft content regarding drafting once a page is already published i’ve thought through a few ways and one nice simple implementation might be… on creating a new page… hide the “is published” check box and “publication date” in this context and instead have these controls “save draft” sets “is published” to false on the page “publish now” sets “is published” to true on the page and sets “publication date” to now “publish later” sets “is published” to true on the page and sets “publication date” to specified date time if none specified do as “save draft” on editing an existing page… always edit the draft if one exists depending on how this is all stored this could always be the most recent in the history don’t give the ability to edit a previous published version it made things too confusing in mojo editors can achieve that by restoring the published version into the editor show the “is published” check box and “publication date” in this context but call them “page is published” and “page publication date” provide same set of buttons controls this allows a changeover in content to be scheduled there could well be some loopholes here i feel content versioning would be enabled globally i cannot imagine why it would not be useful across the board and it doesn t make the publishing workflow any harder so perhaps just always there in simplecontent no need even to switch it on the only reason not to would be the extra storage needed for the superseded versions but that shouldn t be an issue these days and there could be an administrative capability to clean out history all or older than a specified period e g month months year also useful in the administration area would be a view of all content history descending date order by default filterable by editor or page permitting view but not restore note this does not provide any differentiation in roles for editing and publishing – we think that’s rarely needed and makes things more complex but a potential future enhancement | 0 |
11,584 | 17,496,799,843 | IssuesEvent | 2021-08-10 02:15:04 | goharbor/harbor | https://api.github.com/repos/goharbor/harbor | closed | Harbor 1.8.0: Robot account with pull and push permissions can't get tags from API | kind/requirement | **Expected behavior and actual behavior:**
I have a robot account with full pull and push permissions. It is already automatically pushing and pulling images as we speak. However I would like to trigger another robot account based on newer tags being pushed to my repository by fetching the tags using the API.
*Expected*
Get a list of all the available tags of a specific repository with the right permissions set
*Actual*
Above expected result does not seem possible and instead the API always returns a 403 Forbidden.
**Steps to reproduce the problem:**
1) Create project.
2) Add robot account with full push and pull permissions.
3) Use robot account to successfully push an image to this repository, resulting in both a check on the correct permissions as well as having at least one image with a tag registered in this repository.
4) Use the API with the same robot account both in a manual curl command as well as via the swagger API using the /repositories/{repo_name}/tags endpoint with a GET, obviously using the correct repo name as defined in the project.
5) Get a 403, regardless.
**Versions:**
- harbor version: 1.8.0
**Additional context:**
*Edit*:
More on this issue: a normal user account with the "guest" role to the project, is allowed to see all tags of the repositories. Seems counteruitive.
I would expect a robot account to be able to list all tags once this account even has only pull action. Since pulling every image would pretty much result in the same result.
This is a pretty useful robot endpoint to poll and automate on new pushed images to the Harbor registry. | 1.0 | Harbor 1.8.0: Robot account with pull and push permissions can't get tags from API - **Expected behavior and actual behavior:**
I have a robot account with full pull and push permissions. It is already automatically pushing and pulling images as we speak. However I would like to trigger another robot account based on newer tags being pushed to my repository by fetching the tags using the API.
*Expected*
Get a list of all the available tags of a specific repository with the right permissions set
*Actual*
Above expected result does not seem possible and instead the API always returns a 403 Forbidden.
**Steps to reproduce the problem:**
1) Create project.
2) Add robot account with full push and pull permissions.
3) Use robot account to successfully push an image to this repository, resulting in both a check on the correct permissions as well as having at least one image with a tag registered in this repository.
4) Use the API with the same robot account both in a manual curl command as well as via the swagger API using the /repositories/{repo_name}/tags endpoint with a GET, obviously using the correct repo name as defined in the project.
5) Get a 403, regardless.
**Versions:**
- harbor version: 1.8.0
**Additional context:**
*Edit*:
More on this issue: a normal user account with the "guest" role to the project, is allowed to see all tags of the repositories. Seems counteruitive.
I would expect a robot account to be able to list all tags once this account even has only pull action. Since pulling every image would pretty much result in the same result.
This is a pretty useful robot endpoint to poll and automate on new pushed images to the Harbor registry. | non_priority | harbor robot account with pull and push permissions can t get tags from api expected behavior and actual behavior i have a robot account with full pull and push permissions it is already automatically pushing and pulling images as we speak however i would like to trigger another robot account based on newer tags being pushed to my repository by fetching the tags using the api expected get a list of all the available tags of a specific repository with the right permissions set actual above expected result does not seem possible and instead the api always returns a forbidden steps to reproduce the problem create project add robot account with full push and pull permissions use robot account to successfully push an image to this repository resulting in both a check on the correct permissions as well as having at least one image with a tag registered in this repository use the api with the same robot account both in a manual curl command as well as via the swagger api using the repositories repo name tags endpoint with a get obviously using the correct repo name as defined in the project get a regardless versions harbor version additional context edit more on this issue a normal user account with the guest role to the project is allowed to see all tags of the repositories seems counteruitive i would expect a robot account to be able to list all tags once this account even has only pull action since pulling every image would pretty much result in the same result this is a pretty useful robot endpoint to poll and automate on new pushed images to the harbor registry | 0 |
409,179 | 27,724,866,036 | IssuesEvent | 2023-03-15 00:50:44 | DevelopingSpace/starchart | https://api.github.com/repos/DevelopingSpace/starchart | closed | Document and pick a LETS_ENCRYPT_DIRECTORY_URL for staging/prod | category: documentation category: certificates category: deployment | We expect the `LETS_ENCRYPT_DIRECTORY_URL` environment variable to be set. In our `.env.example` we specify the various options:
```ini
# Let's encrypt directory URL (the server we request the cert from)
# Staging: 'https://acme-staging-v02.api.letsencrypt.org/directory'
# Production 'https://acme-v02.api.letsencrypt.org/directory'
# Local development / testing docker container 'https://127.0.0.1:14000/dir'
```
In staging and production, we need to set the URL to use. Are we going to use the [Let's Encrypt Staging Environment](https://letsencrypt.org/docs/staging-environment/) or the [Production Environment](https://community.letsencrypt.org/t/acme-v2-production-environment-wildcards/55578)?
We need to update `DEPLOY.md` to indicate what we expect in staging and production.
This is needed for #43. | 1.0 | Document and pick a LETS_ENCRYPT_DIRECTORY_URL for staging/prod - We expect the `LETS_ENCRYPT_DIRECTORY_URL` environment variable to be set. In our `.env.example` we specify the various options:
```ini
# Let's encrypt directory URL (the server we request the cert from)
# Staging: 'https://acme-staging-v02.api.letsencrypt.org/directory'
# Production 'https://acme-v02.api.letsencrypt.org/directory'
# Local development / testing docker container 'https://127.0.0.1:14000/dir'
```
In staging and production, we need to set the URL to use. Are we going to use the [Let's Encrypt Staging Environment](https://letsencrypt.org/docs/staging-environment/) or the [Production Environment](https://community.letsencrypt.org/t/acme-v2-production-environment-wildcards/55578)?
We need to update `DEPLOY.md` to indicate what we expect in staging and production.
This is needed for #43. | non_priority | document and pick a lets encrypt directory url for staging prod we expect the lets encrypt directory url environment variable to be set in our env example we specify the various options ini let s encrypt directory url the server we request the cert from staging production local development testing docker container in staging and production we need to set the url to use are we going to use the or the we need to update deploy md to indicate what we expect in staging and production this is needed for | 0 |
6,114 | 7,478,114,361 | IssuesEvent | 2018-04-04 10:29:22 | Mte90/Share-Backported | https://api.github.com/repos/Mte90/Share-Backported | closed | Mastodon is missing the url | bug help wanted service | Actually the mastdon implementation has only one parameter insterad the other service 2 for message and url.
We need a way in teh doc to detect when the url is of mastodon and append the url. | 1.0 | Mastodon is missing the url - Actually the mastdon implementation has only one parameter insterad the other service 2 for message and url.
We need a way in teh doc to detect when the url is of mastodon and append the url. | non_priority | mastodon is missing the url actually the mastdon implementation has only one parameter insterad the other service for message and url we need a way in teh doc to detect when the url is of mastodon and append the url | 0 |
187,229 | 14,427,276,223 | IssuesEvent | 2020-12-06 03:00:40 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | mongodb/ftdc: vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go; 3 LoC | fresh test tiny vendored |
Found a possible issue in [mongodb/ftdc](https://www.github.com/mongodb/ftdc) at [vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go](https://github.com/mongodb/ftdc/blob/d5dbbae38209b053448f889ce16f57f1bee3d296/vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go#L94-L96)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to testCase at line 95 may start a goroutine
[Click here to see the code in its original context.](https://github.com/mongodb/ftdc/blob/d5dbbae38209b053448f889ce16f57f1bee3d296/vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go#L94-L96)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, testCase := range container.Tests {
runTest(t, filename, &testCase)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: d5dbbae38209b053448f889ce16f57f1bee3d296
| 1.0 | mongodb/ftdc: vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go; 3 LoC -
Found a possible issue in [mongodb/ftdc](https://www.github.com/mongodb/ftdc) at [vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go](https://github.com/mongodb/ftdc/blob/d5dbbae38209b053448f889ce16f57f1bee3d296/vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go#L94-L96)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to testCase at line 95 may start a goroutine
[Click here to see the code in its original context.](https://github.com/mongodb/ftdc/blob/d5dbbae38209b053448f889ce16f57f1bee3d296/vendor/go.mongodb.org/mongo-driver/x/network/connstring/connstring_spec_test.go#L94-L96)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, testCase := range container.Tests {
runTest(t, filename, &testCase)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: d5dbbae38209b053448f889ce16f57f1bee3d296
| non_priority | mongodb ftdc vendor go mongodb org mongo driver x network connstring connstring spec test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to testcase at line may start a goroutine click here to show the line s of go which triggered the analyzer go for testcase range container tests runtest t filename testcase leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
226,304 | 24,946,930,903 | IssuesEvent | 2022-11-01 01:38:05 | tctc008/WebGoat-develop | https://api.github.com/repos/tctc008/WebGoat-develop | closed | CVE-2022-40152 (High) detected in xstream-1.4.5.jar - autoclosed | security vulnerability | ## CVE-2022-40152 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/itory/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tctc008/WebGoat-develop/commit/538305d0b6f6b18a23725514424ebaebbf96f082">538305d0b6f6b18a23725514424ebaebbf96f082</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Xstream to seralize XML data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40152>CVE-2022-40152</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-40152 (High) detected in xstream-1.4.5.jar - autoclosed - ## CVE-2022-40152 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to dependency file: /webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/home/wss-scanner/.m2/repository/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar,/itory/com/thoughtworks/xstream/xstream/1.4.5/xstream-1.4.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tctc008/WebGoat-develop/commit/538305d0b6f6b18a23725514424ebaebbf96f082">538305d0b6f6b18a23725514424ebaebbf96f082</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Xstream to seralize XML data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40152>CVE-2022-40152</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in xstream jar autoclosed cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xstream xstream jar home wss scanner repository com thoughtworks xstream xstream xstream jar itory com thoughtworks xstream xstream xstream jar dependency hierarchy x xstream jar vulnerable library found in head commit a href found in base branch main vulnerability details those using xstream to seralize xml data may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
133,626 | 10,853,656,178 | IssuesEvent | 2019-11-13 15:05:56 | QubesOS/updates-status | https://api.github.com/repos/QubesOS/updates-status | closed | meta-packages v4.1.3 (r4.1) | r4.1-bullseye-cur-test r4.1-buster-cur-test r4.1-centos7-cur-test r4.1-dom0-cur-test r4.1-fc29-cur-test r4.1-fc30-cur-test r4.1-fc31-cur-test r4.1-stretch-cur-test | Update of meta-packages to v4.1.3 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-meta-packages/commit/0755bce434e62694b487f93ee4e067be28718d46
[Changes since previous version](https://github.com/QubesOS/qubes-meta-packages/compare/v4.1.2...v4.1.3):
QubesOS/qubes-meta-packages@0755bce version 4.1.3
QubesOS/qubes-meta-packages@0f58110 Merge remote-tracking branch 'origin/pr/10'
QubesOS/qubes-meta-packages@e38e230 Add dist suffix to keys
Referenced issues:
If you're release manager, you can issue GPG-inline signed command:
* `Upload meta-packages 0755bce434e62694b487f93ee4e067be28718d46 r4.1 current repo` (available 7 days from now)
* `Upload meta-packages 0755bce434e62694b487f93ee4e067be28718d46 r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload meta-packages 0755bce434e62694b487f93ee4e067be28718d46 r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| 8.0 | meta-packages v4.1.3 (r4.1) - Update of meta-packages to v4.1.3 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-meta-packages/commit/0755bce434e62694b487f93ee4e067be28718d46
[Changes since previous version](https://github.com/QubesOS/qubes-meta-packages/compare/v4.1.2...v4.1.3):
QubesOS/qubes-meta-packages@0755bce version 4.1.3
QubesOS/qubes-meta-packages@0f58110 Merge remote-tracking branch 'origin/pr/10'
QubesOS/qubes-meta-packages@e38e230 Add dist suffix to keys
Referenced issues:
If you're release manager, you can issue GPG-inline signed command:
* `Upload meta-packages 0755bce434e62694b487f93ee4e067be28718d46 r4.1 current repo` (available 7 days from now)
* `Upload meta-packages 0755bce434e62694b487f93ee4e067be28718d46 r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload meta-packages 0755bce434e62694b487f93ee4e067be28718d46 r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| non_priority | meta packages update of meta packages to for qubes see comments below for details built from qubesos qubes meta packages version qubesos qubes meta packages merge remote tracking branch origin pr qubesos qubes meta packages add dist suffix to keys referenced issues if you re release manager you can issue gpg inline signed command upload meta packages current repo available days from now upload meta packages current dists repo you can choose subset of distributions like vm vm available days from now upload meta packages security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it | 0 |
126,611 | 17,947,251,552 | IssuesEvent | 2021-09-12 02:53:06 | corbantjoyce/website | https://api.github.com/repos/corbantjoyce/website | closed | WS-2019-0424 (Medium) detected in elliptic-6.5.2.tgz - autoclosed | security vulnerability | ## WS-2019-0424 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: website/package.json</p>
<p>Path to vulnerable library: website/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.1.tgz (Root Library)
- webpack-4.42.0.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.1.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/corbantjoyce/website/commit/2d41f06ec8faa6317e843654af85f7dacef9b46e">2d41f06ec8faa6317e843654af85f7dacef9b46e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
all versions of elliptic are vulnerable to Timing Attack through side-channels.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0424 (Medium) detected in elliptic-6.5.2.tgz - autoclosed - ## WS-2019-0424 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: website/package.json</p>
<p>Path to vulnerable library: website/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.1.tgz (Root Library)
- webpack-4.42.0.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.1.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/corbantjoyce/website/commit/2d41f06ec8faa6317e843654af85f7dacef9b46e">2d41f06ec8faa6317e843654af85f7dacef9b46e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
all versions of elliptic are vulnerable to Timing Attack through side-channels.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in elliptic tgz autoclosed ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file website package json path to vulnerable library website node modules elliptic package json dependency hierarchy react scripts tgz root library webpack tgz node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in head commit a href found in base branch master vulnerability details all versions of elliptic are vulnerable to timing attack through side channels publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact none for more information on scores click a href step up your open source security game with whitesource | 0 |
136,388 | 11,048,228,266 | IssuesEvent | 2019-12-09 20:42:02 | Princeton-CDH/mep-django | https://api.github.com/repos/Princeton-CDH/mep-django | closed | Fix indexing handler for saving addresses | awaiting testing bug | On 12/5 Ian found a bug - he can't save addresses; gets an error page | 1.0 | Fix indexing handler for saving addresses - On 12/5 Ian found a bug - he can't save addresses; gets an error page | non_priority | fix indexing handler for saving addresses on ian found a bug he can t save addresses gets an error page | 0 |
119,714 | 12,037,539,254 | IssuesEvent | 2020-04-13 22:04:57 | perpetualintelligence/pidotapp-bugs | https://api.github.com/repos/perpetualintelligence/pidotapp-bugs | closed | Microsoft Translate and Azure File Storage can be selected | bug documentation internal | Enterprise integration with Microsoft Translate and Azure File Storage is not yet supported. Yet user can still select those and get an error message at the end. Why not just disable those till we support integration. | 1.0 | Microsoft Translate and Azure File Storage can be selected - Enterprise integration with Microsoft Translate and Azure File Storage is not yet supported. Yet user can still select those and get an error message at the end. Why not just disable those till we support integration. | non_priority | microsoft translate and azure file storage can be selected enterprise integration with microsoft translate and azure file storage is not yet supported yet user can still select those and get an error message at the end why not just disable those till we support integration | 0 |
261,384 | 22,742,171,263 | IssuesEvent | 2022-07-07 05:32:55 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: sqlsmith/setup=rand-tables/setting=no-mutations failed | C-test-failure O-robot O-roachtest branch-master | roachtest.sqlsmith/setup=rand-tables/setting=no-mutations [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5672143?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5672143?buildTab=artifacts#/sqlsmith/setup=rand-tables/setting=no-mutations) on master @ [03d5260a467b8640de41ee08054c1ce05f91966c](https://github.com/cockroachdb/cockroach/commits/03d5260a467b8640de41ee08054c1ce05f91966c):
```
test artifacts and logs in: /artifacts/sqlsmith/setup=rand-tables/setting=no-mutations/run_1
sqlsmith.go:265,sqlsmith.go:325,test_runner.go:896: error: pq: internal error: lookup for ComparisonExpr ((column1)[void] IS DISTINCT FROM (NULL)[unknown])[bool]'s CmpOp failed
stmt:
WITH
with_29346 (col_134830) AS (SELECT * FROM (VALUES ('':::VOID), ('':::VOID)) AS tab_71507 (col_134830)),
with_29347 (col_134831)
AS (SELECT * FROM (VALUES ('ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff':::INET)) AS tab_71508 (col_134831))
SELECT
NULL AS col_134832, COALESCE(cte_ref_8414.col_134830, cte_ref_8413.col_134830) AS col_134833, NULL AS col_134834
FROM
with_29346 AS cte_ref_8413,
with_29346 AS cte_ref_8414,
with_29347 AS cte_ref_8415,
defaultdb.public.table1@table1_pkey AS tab_71509;
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sqlsmith/setup=rand-tables/setting=no-mutations.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: sqlsmith/setup=rand-tables/setting=no-mutations failed - roachtest.sqlsmith/setup=rand-tables/setting=no-mutations [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5672143?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/5672143?buildTab=artifacts#/sqlsmith/setup=rand-tables/setting=no-mutations) on master @ [03d5260a467b8640de41ee08054c1ce05f91966c](https://github.com/cockroachdb/cockroach/commits/03d5260a467b8640de41ee08054c1ce05f91966c):
```
test artifacts and logs in: /artifacts/sqlsmith/setup=rand-tables/setting=no-mutations/run_1
sqlsmith.go:265,sqlsmith.go:325,test_runner.go:896: error: pq: internal error: lookup for ComparisonExpr ((column1)[void] IS DISTINCT FROM (NULL)[unknown])[bool]'s CmpOp failed
stmt:
WITH
with_29346 (col_134830) AS (SELECT * FROM (VALUES ('':::VOID), ('':::VOID)) AS tab_71507 (col_134830)),
with_29347 (col_134831)
AS (SELECT * FROM (VALUES ('ffff:ffff:ffff:ffff:ffff:ffff:ffff:ffff':::INET)) AS tab_71508 (col_134831))
SELECT
NULL AS col_134832, COALESCE(cte_ref_8414.col_134830, cte_ref_8413.col_134830) AS col_134833, NULL AS col_134834
FROM
with_29346 AS cte_ref_8413,
with_29346 AS cte_ref_8414,
with_29347 AS cte_ref_8415,
defaultdb.public.table1@table1_pkey AS tab_71509;
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sqlsmith/setup=rand-tables/setting=no-mutations.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest sqlsmith setup rand tables setting no mutations failed roachtest sqlsmith setup rand tables setting no mutations with on master test artifacts and logs in artifacts sqlsmith setup rand tables setting no mutations run sqlsmith go sqlsmith go test runner go error pq internal error lookup for comparisonexpr is distinct from null s cmpop failed stmt with with col as select from values void void as tab col with col as select from values ffff ffff ffff ffff ffff ffff ffff ffff inet as tab col select null as col coalesce cte ref col cte ref col as col null as col from with as cte ref with as cte ref with as cte ref defaultdb public pkey as tab parameters roachtest cloud gce roachtest cpu roachtest ssd help see see cc cockroachdb sql queries | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.