Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
321,201 | 27,513,048,071 | IssuesEvent | 2023-03-06 10:08:11 | lawrimon/PDA_SWE | https://api.github.com/repos/lawrimon/PDA_SWE | closed | Test and refine Pytest workflow | task test | **Description:** The purpose of this task is to ensure that the Pytest workflow is functioning correctly. This involves testing the workflow on a sample failing and passing Python test, reviewing the output for any unexpected behaviour and refining the workflow as necessary. Any necessary refinements to the workflow should be made at this stage. | 1.0 | Test and refine Pytest workflow - **Description:** The purpose of this task is to ensure that the Pytest workflow is functioning correctly. This involves testing the workflow on a sample failing and passing Python test, reviewing the output for any unexpected behaviour and refining the workflow as necessary. Any necessary refinements to the workflow should be made at this stage. | non_priority | test and refine pytest workflow description the purpose of this task is to ensure that the pytest workflow is functioning correctly this involves testing the workflow on a sample failing and passing python test reviewing the output for any unexpected behaviour and refining the workflow as necessary any necessary refinements to the workflow should be made at this stage | 0 |
68,183 | 13,090,953,128 | IssuesEvent | 2020-08-03 05:13:25 | microsoft/appcenter-cli | https://api.github.com/repos/microsoft/appcenter-cli | closed | How to move sourcemap file after hermes to sourcemapOutputDir | CodePush question | 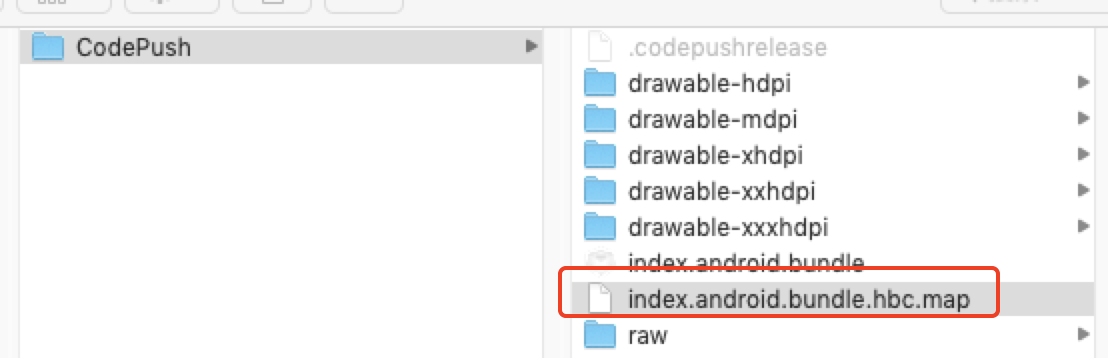
code-push will upload the sourcemap after hermes together. | 1.0 | How to move sourcemap file after hermes to sourcemapOutputDir - 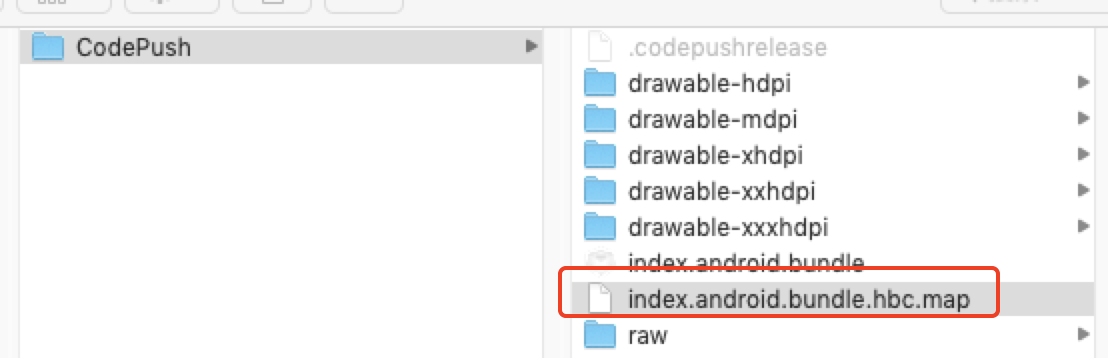
code-push will upload the sourcemap after hermes together. | non_priority | how to move sourcemap file after hermes to sourcemapoutputdir code push will upload the sourcemap after hermes together | 0 |
429,771 | 30,089,624,079 | IssuesEvent | 2023-06-29 11:18:06 | rerun-io/rerun | https://api.github.com/repos/rerun-io/rerun | closed | Release tool needs to deploy updated docs | 📖 documentation ⛴ release | `manual_build_release.yml` should produce the docs with the correct version.
`manual_release.yml` should tag latest. | 1.0 | Release tool needs to deploy updated docs - `manual_build_release.yml` should produce the docs with the correct version.
`manual_release.yml` should tag latest. | non_priority | release tool needs to deploy updated docs manual build release yml should produce the docs with the correct version manual release yml should tag latest | 0 |
62,659 | 12,229,715,351 | IssuesEvent | 2020-05-04 01:34:46 | PapirusDevelopmentTeam/papirus-icon-theme | https://api.github.com/repos/PapirusDevelopmentTeam/papirus-icon-theme | closed | [Icon request] gens-gs | hardcoded invalid | <!--
Before creating a new issue ensure that:
- The icon request is not a duplicate
- The app is not installed by snap (the snap packages have hardcoded paths to icons)
- The app is not a Windows application running under Wine/Crossover
- The title contains application or icon name (Ex: [Icon request] Boostnote)
NOTE:
You'll find most of necessary entries for the icon request in a app's desktop-file, usually placed in /usr/share/applications/ folder (Ex. /usr/share/applications/firefox.desktop).
-->
- **App Name:** Gens/GS
- **Icon Name:** /usr/share/gens/gensgs_48x48.png
- **Description:** Sega Genesis, Sega CD, and Sega 32X emulator
- **Webpage (optional):** https://segaretro.org/Gens/GS#Git_Repository
- **Original Icon:**

<!-- upload (or just drag and drop) the original app icon below -->
| 1.0 | [Icon request] gens-gs - <!--
Before creating a new issue ensure that:
- The icon request is not a duplicate
- The app is not installed by snap (the snap packages have hardcoded paths to icons)
- The app is not a Windows application running under Wine/Crossover
- The title contains application or icon name (Ex: [Icon request] Boostnote)
NOTE:
You'll find most of necessary entries for the icon request in a app's desktop-file, usually placed in /usr/share/applications/ folder (Ex. /usr/share/applications/firefox.desktop).
-->
- **App Name:** Gens/GS
- **Icon Name:** /usr/share/gens/gensgs_48x48.png
- **Description:** Sega Genesis, Sega CD, and Sega 32X emulator
- **Webpage (optional):** https://segaretro.org/Gens/GS#Git_Repository
- **Original Icon:**

<!-- upload (or just drag and drop) the original app icon below -->
| non_priority | gens gs before creating a new issue ensure that the icon request is not a duplicate the app is not installed by snap the snap packages have hardcoded paths to icons the app is not a windows application running under wine crossover the title contains application or icon name ex boostnote note you ll find most of necessary entries for the icon request in a app s desktop file usually placed in usr share applications folder ex usr share applications firefox desktop app name gens gs icon name usr share gens gensgs png description sega genesis sega cd and sega emulator webpage optional original icon | 0 |
186,229 | 14,394,659,721 | IssuesEvent | 2020-12-03 01:49:21 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | vbehar/openshift-flowdock-notifier: Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go; 15 LoC | fresh small test |
Found a possible issue in [vbehar/openshift-flowdock-notifier](https://www.github.com/vbehar/openshift-flowdock-notifier) at [Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go](https://github.com/vbehar/openshift-flowdock-notifier/blob/c9ba865c8a049a7a2fe934a9485aee21376b83f7/Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go#L78-L92)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/vbehar/openshift-flowdock-notifier/blob/c9ba865c8a049a7a2fe934a9485aee21376b83f7/Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go#L78-L92)
<details>
<summary>Click here to show the 15 line(s) of Go which triggered the analyzer.</summary>
```go
for _, expected := range expectedPods {
found := false
for _, actual := range actualPods {
if actual.UID == expected.UID {
if !reflect.DeepEqual(&expected, &actual) {
t.Errorf("pod was recorded incorrectly. expect: %#v, got: %#v", expected, actual)
}
found = true
break
}
}
if !found {
t.Errorf("pod %q was not found in %#v", expected.UID, actualPods)
}
}
```
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call at line 82 may store a reference to expected
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c9ba865c8a049a7a2fe934a9485aee21376b83f7
| 1.0 | vbehar/openshift-flowdock-notifier: Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go; 15 LoC -
Found a possible issue in [vbehar/openshift-flowdock-notifier](https://www.github.com/vbehar/openshift-flowdock-notifier) at [Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go](https://github.com/vbehar/openshift-flowdock-notifier/blob/c9ba865c8a049a7a2fe934a9485aee21376b83f7/Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go#L78-L92)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/vbehar/openshift-flowdock-notifier/blob/c9ba865c8a049a7a2fe934a9485aee21376b83f7/Godeps/_workspace/src/k8s.io/kubernetes/pkg/kubelet/pod/manager_test.go#L78-L92)
<details>
<summary>Click here to show the 15 line(s) of Go which triggered the analyzer.</summary>
```go
for _, expected := range expectedPods {
found := false
for _, actual := range actualPods {
if actual.UID == expected.UID {
if !reflect.DeepEqual(&expected, &actual) {
t.Errorf("pod was recorded incorrectly. expect: %#v, got: %#v", expected, actual)
}
found = true
break
}
}
if !found {
t.Errorf("pod %q was not found in %#v", expected.UID, actualPods)
}
}
```
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call at line 82 may store a reference to expected
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c9ba865c8a049a7a2fe934a9485aee21376b83f7
| non_priority | vbehar openshift flowdock notifier godeps workspace src io kubernetes pkg kubelet pod manager test go loc found a possible issue in at the below snippet of go code triggered static analysis which searches for goroutines and or defer statements which capture loop variables click here to show the line s of go which triggered the analyzer go for expected range expectedpods found false for actual range actualpods if actual uid expected uid if reflect deepequal expected actual t errorf pod was recorded incorrectly expect v got v expected actual found true break if found t errorf pod q was not found in v expected uid actualpods below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call at line may store a reference to expected leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
63,524 | 14,656,735,318 | IssuesEvent | 2020-12-28 14:04:56 | fu1771695yongxie/taro | https://api.github.com/repos/fu1771695yongxie/taro | opened | WS-2017-0421 (High) detected in ws-2.3.1.tgz | security vulnerability | ## WS-2017-0421 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ws-2.3.1.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-2.3.1.tgz">https://registry.npmjs.org/ws/-/ws-2.3.1.tgz</a></p>
<p>Path to dependency file: taro/packages/taro-components-rn/TCRNExample/package.json</p>
<p>Path to vulnerable library: taro/packages/taro-components-rn/TCRNExample/node_modules/react-devtools-core/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- react-native-0.55.4.tgz (Root Library)
- react-devtools-core-3.1.0.tgz
- :x: **ws-2.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/taro/commit/d6b9282bf207231f27f7ba5779aaa86a96d1e110">d6b9282bf207231f27f7ba5779aaa86a96d1e110</a></p>
<p>Found in base branch: <b>next</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected version of ws (0.2.6 through 3.3.0 excluding 0.3.4-2, 0.3.5-2, 0.3.5-3, 0.3.5-4, 1.1.5, 2.0.0-beta.0, 2.0.0-beta.1 and 2.0.0-beta.2) are vulnerable to A specially crafted value of the Sec-WebSocket-Extensions header that used Object.prototype property names as extension or parameter names could be used to make a ws server crash.
<p>Publish Date: 2017-11-08
<p>URL: <a href=https://github.com/websockets/ws/commit/c4fe46608acd61fbf7397eadc47378903f95b78a>WS-2017-0421</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/commit/c4fe46608acd61fbf7397eadc47378903f95b78a">https://github.com/websockets/ws/commit/c4fe46608acd61fbf7397eadc47378903f95b78a</a></p>
<p>Release Date: 2017-11-08</p>
<p>Fix Resolution: 3.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2017-0421 (High) detected in ws-2.3.1.tgz - ## WS-2017-0421 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ws-2.3.1.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-2.3.1.tgz">https://registry.npmjs.org/ws/-/ws-2.3.1.tgz</a></p>
<p>Path to dependency file: taro/packages/taro-components-rn/TCRNExample/package.json</p>
<p>Path to vulnerable library: taro/packages/taro-components-rn/TCRNExample/node_modules/react-devtools-core/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- react-native-0.55.4.tgz (Root Library)
- react-devtools-core-3.1.0.tgz
- :x: **ws-2.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/taro/commit/d6b9282bf207231f27f7ba5779aaa86a96d1e110">d6b9282bf207231f27f7ba5779aaa86a96d1e110</a></p>
<p>Found in base branch: <b>next</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected version of ws (0.2.6 through 3.3.0 excluding 0.3.4-2, 0.3.5-2, 0.3.5-3, 0.3.5-4, 1.1.5, 2.0.0-beta.0, 2.0.0-beta.1 and 2.0.0-beta.2) are vulnerable to A specially crafted value of the Sec-WebSocket-Extensions header that used Object.prototype property names as extension or parameter names could be used to make a ws server crash.
<p>Publish Date: 2017-11-08
<p>URL: <a href=https://github.com/websockets/ws/commit/c4fe46608acd61fbf7397eadc47378903f95b78a>WS-2017-0421</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/commit/c4fe46608acd61fbf7397eadc47378903f95b78a">https://github.com/websockets/ws/commit/c4fe46608acd61fbf7397eadc47378903f95b78a</a></p>
<p>Release Date: 2017-11-08</p>
<p>Fix Resolution: 3.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in ws tgz ws high severity vulnerability vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file taro packages taro components rn tcrnexample package json path to vulnerable library taro packages taro components rn tcrnexample node modules react devtools core node modules ws package json dependency hierarchy react native tgz root library react devtools core tgz x ws tgz vulnerable library found in head commit a href found in base branch next vulnerability details affected version of ws through excluding beta beta and beta are vulnerable to a specially crafted value of the sec websocket extensions header that used object prototype property names as extension or parameter names could be used to make a ws server crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
143,730 | 22,150,568,334 | IssuesEvent | 2022-06-03 16:18:04 | blopker/totem | https://api.github.com/repos/blopker/totem | closed | Hide self view | needs design | Design what the hidden self-view shoudl look like, and how people use it to see themselves when they want.
@sebasnieb | 1.0 | Hide self view - Design what the hidden self-view shoudl look like, and how people use it to see themselves when they want.
@sebasnieb | non_priority | hide self view design what the hidden self view shoudl look like and how people use it to see themselves when they want sebasnieb | 0 |
25,732 | 12,295,923,578 | IssuesEvent | 2020-05-11 05:39:02 | dotnet/fsharp | https://api.github.com/repos/dotnet/fsharp | opened | Completion commits opened namespace on the same line when cursor is at first line in file | Area-IDE Language Service bug | Latest VS
Trigger extended completion:

Commit it:
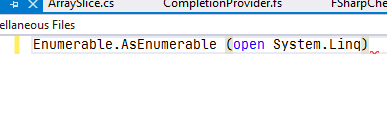
This is only if it's the first line in the file. | 1.0 | Completion commits opened namespace on the same line when cursor is at first line in file - Latest VS
Trigger extended completion:

Commit it:
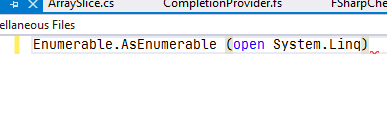
This is only if it's the first line in the file. | non_priority | completion commits opened namespace on the same line when cursor is at first line in file latest vs trigger extended completion commit it this is only if it s the first line in the file | 0 |
286,776 | 31,762,971,970 | IssuesEvent | 2023-09-12 06:56:36 | dagger/dagger | https://api.github.com/repos/dagger/dagger | closed | Support configuring additional options for secrets | kind/dx kind/security area/engine | Buildkit's full `SecretInfo` struct is as follows:
```go
type SecretInfo struct {
ID string
Target string
Mode int
UID int
GID int
Optional bool
IsEnv bool
}
```
We already support `ID`, `Target`, and `IsEnv` but maybe folks will have a use for `Mode`, `UID`, `GUID`, and/or `Optional`. | True | Support configuring additional options for secrets - Buildkit's full `SecretInfo` struct is as follows:
```go
type SecretInfo struct {
ID string
Target string
Mode int
UID int
GID int
Optional bool
IsEnv bool
}
```
We already support `ID`, `Target`, and `IsEnv` but maybe folks will have a use for `Mode`, `UID`, `GUID`, and/or `Optional`. | non_priority | support configuring additional options for secrets buildkit s full secretinfo struct is as follows go type secretinfo struct id string target string mode int uid int gid int optional bool isenv bool we already support id target and isenv but maybe folks will have a use for mode uid guid and or optional | 0 |
26,911 | 13,152,552,734 | IssuesEvent | 2020-08-09 22:59:13 | microsoft/STL | https://api.github.com/repos/microsoft/STL | closed | <execution>: cache thread::hardware_concurrency | performance | Currently <execution> does not cache `hardware_concurrency` value, like it used to in certain configurations.
`GetNativeSystemInfo` may be a system call, so it may defeat the speedup obtained by parallel algorithms.
Consider caching it again.
Note that since number of CPUs _may_ change at runtime, it may be a good idea to refresh the value after some `GetTickCount64` interval. | True | <execution>: cache thread::hardware_concurrency - Currently <execution> does not cache `hardware_concurrency` value, like it used to in certain configurations.
`GetNativeSystemInfo` may be a system call, so it may defeat the speedup obtained by parallel algorithms.
Consider caching it again.
Note that since number of CPUs _may_ change at runtime, it may be a good idea to refresh the value after some `GetTickCount64` interval. | non_priority | cache thread hardware concurrency currently does not cache hardware concurrency value like it used to in certain configurations getnativesysteminfo may be a system call so it may defeat the speedup obtained by parallel algorithms consider caching it again note that since number of cpus may change at runtime it may be a good idea to refresh the value after some interval | 0 |
302,644 | 26,157,723,207 | IssuesEvent | 2022-12-31 03:01:28 | apache/helix | https://api.github.com/repos/apache/helix | opened | [Failed CI Test] testCreateJob(org.apache.helix.rest.server.TestJobAccessor) | FailedTestTracking | This issue is created for tracking unstable test: testCreateJob(org.apache.helix.rest.server.TestJobAccessor) | 1.0 | [Failed CI Test] testCreateJob(org.apache.helix.rest.server.TestJobAccessor) - This issue is created for tracking unstable test: testCreateJob(org.apache.helix.rest.server.TestJobAccessor) | non_priority | testcreatejob org apache helix rest server testjobaccessor this issue is created for tracking unstable test testcreatejob org apache helix rest server testjobaccessor | 0 |
15,661 | 3,479,649,708 | IssuesEvent | 2015-12-28 21:58:22 | coala-analyzer/coala | https://api.github.com/repos/coala-analyzer/coala | closed | test issue | bounty test | will be closed in a minute
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/29446968-test-issue?utm_campaign=plugin&utm_content=tracker%2F2228228&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F2228228&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | test issue - will be closed in a minute
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/29446968-test-issue?utm_campaign=plugin&utm_content=tracker%2F2228228&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F2228228&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_priority | test issue will be closed in a minute want to back this issue we accept bounties via | 0 |
58,818 | 11,905,340,966 | IssuesEvent | 2020-03-30 18:23:48 | home-assistant/brands | https://api.github.com/repos/home-assistant/brands | opened | Tahoma is missing brand images | domain-missing has-codeowner |
## The problem
The Tahoma integration does not have brand images in
this repository.
We recently started this Brands repository, to create a centralized storage of all brand-related images. These images are used on our website and the Home Assistant frontend.
The following images are missing and would ideally be added:
- `src/tahoma/icon.png`
- `src/tahoma/logo.png`
- `src/tahoma/icon@2x.png`
- `src/tahoma/logo@2x.png`
For image specifications and requirements, please see [README.md](https://github.com/home-assistant/brands/blob/master/README.md).
## Updating the documentation repository
Our documentation repository already has a logo for this integration, however, it does not meet the image requirements of this new Brands repository.
If adding images to this repository, please open up a PR to the documentation repository as well, removing the `logo: tahoma.png` line from this file:
<https://github.com/home-assistant/home-assistant.io/blob/current/source/_integrations/tahoma.markdown>
**Note**: The documentation PR needs to be opened against the `current` branch.
**Note2**: Please leave the actual logo file in the documentation repository. It will be cleaned up differently.
## Additional information
For more information about this repository, read the [README.md](https://github.com/home-assistant/brands/blob/master/README.md) file of this repository. It contains information on how this repository works, and image specification and requirements.
## Codeowner mention
Hi there, @philklei! Mind taking a look at this issue as it is with an integration (tahoma) you are listed as a [codeowner](https://github.com/home-assistant/core/blob/dev/homeassistant/components/tahoma/manifest.json) for? Thanks!
Resolving this issue is not limited to codeowners! If you want to help us out, feel free to resolve this issue! Thanks already!
| 1.0 | Tahoma is missing brand images -
## The problem
The Tahoma integration does not have brand images in
this repository.
We recently started this Brands repository, to create a centralized storage of all brand-related images. These images are used on our website and the Home Assistant frontend.
The following images are missing and would ideally be added:
- `src/tahoma/icon.png`
- `src/tahoma/logo.png`
- `src/tahoma/icon@2x.png`
- `src/tahoma/logo@2x.png`
For image specifications and requirements, please see [README.md](https://github.com/home-assistant/brands/blob/master/README.md).
## Updating the documentation repository
Our documentation repository already has a logo for this integration, however, it does not meet the image requirements of this new Brands repository.
If adding images to this repository, please open up a PR to the documentation repository as well, removing the `logo: tahoma.png` line from this file:
<https://github.com/home-assistant/home-assistant.io/blob/current/source/_integrations/tahoma.markdown>
**Note**: The documentation PR needs to be opened against the `current` branch.
**Note2**: Please leave the actual logo file in the documentation repository. It will be cleaned up differently.
## Additional information
For more information about this repository, read the [README.md](https://github.com/home-assistant/brands/blob/master/README.md) file of this repository. It contains information on how this repository works, and image specification and requirements.
## Codeowner mention
Hi there, @philklei! Mind taking a look at this issue as it is with an integration (tahoma) you are listed as a [codeowner](https://github.com/home-assistant/core/blob/dev/homeassistant/components/tahoma/manifest.json) for? Thanks!
Resolving this issue is not limited to codeowners! If you want to help us out, feel free to resolve this issue! Thanks already!
| non_priority | tahoma is missing brand images the problem the tahoma integration does not have brand images in this repository we recently started this brands repository to create a centralized storage of all brand related images these images are used on our website and the home assistant frontend the following images are missing and would ideally be added src tahoma icon png src tahoma logo png src tahoma icon png src tahoma logo png for image specifications and requirements please see updating the documentation repository our documentation repository already has a logo for this integration however it does not meet the image requirements of this new brands repository if adding images to this repository please open up a pr to the documentation repository as well removing the logo tahoma png line from this file note the documentation pr needs to be opened against the current branch please leave the actual logo file in the documentation repository it will be cleaned up differently additional information for more information about this repository read the file of this repository it contains information on how this repository works and image specification and requirements codeowner mention hi there philklei mind taking a look at this issue as it is with an integration tahoma you are listed as a for thanks resolving this issue is not limited to codeowners if you want to help us out feel free to resolve this issue thanks already | 0 |
133,610 | 12,545,997,981 | IssuesEvent | 2020-06-05 19:55:31 | Azure-Samples/AzureSubscriptionBuilder | https://api.github.com/repos/Azure-Samples/AzureSubscriptionBuilder | closed | Fix broken pptx and PDF links | bug documentation | Links to the presentation content is broken. Files need to be moved to durable storage separate from the project itself. | 1.0 | Fix broken pptx and PDF links - Links to the presentation content is broken. Files need to be moved to durable storage separate from the project itself. | non_priority | fix broken pptx and pdf links links to the presentation content is broken files need to be moved to durable storage separate from the project itself | 0 |
274,199 | 29,929,668,349 | IssuesEvent | 2023-06-22 08:35:47 | amaybaum-local/vprofile-project8 | https://api.github.com/repos/amaybaum-local/vprofile-project8 | closed | CVE-2018-11040 (Medium, non-reachable) detected in spring-web-4.3.7.RELEASE.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2018-11040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.3.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /Users/alexmaybaum/.m2/repository/org/springframework/spring-web/4.3.7.RELEASE/spring-web-4.3.7.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-1.7.1.RELEASE.jar (Root Library)
- :x: **spring-web-4.3.7.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-local/vprofile-project8/commit/5eec2b68c36038bc971648668da557114972e048">5eec2b68c36038bc971648668da557114972e048</a></p>
<p>Found in base branch: <b>vp-rem</b></p>
</p>
</details>
<p></p>
<details><summary> <img src='https://whitesource-resources.whitesourcesoftware.com/viaGreen.png' width=19 height=20> Reachability Analysis</summary>
<p>
<p>The vulnerable code is not reachable.</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0.x prior to 5.0.7 and 4.3.x prior to 4.3.18 and older unsupported versions, allows web applications to enable cross-domain requests via JSONP (JSON with Padding) through AbstractJsonpResponseBodyAdvice for REST controllers and MappingJackson2JsonView for browser requests. Both are not enabled by default in Spring Framework nor Spring Boot, however, when MappingJackson2JsonView is configured in an application, JSONP support is automatically ready to use through the "jsonp" and "callback" JSONP parameters, enabling cross-domain requests.
<p>Publish Date: 2018-06-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11040>CVE-2018-11040</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040</a></p>
<p>Release Date: 2018-06-25</p>
<p>Fix Resolution: org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE</p>
</p>
</details>
<p></p>
| True | CVE-2018-11040 (Medium, non-reachable) detected in spring-web-4.3.7.RELEASE.jar - autoclosed - ## CVE-2018-11040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.3.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /Users/alexmaybaum/.m2/repository/org/springframework/spring-web/4.3.7.RELEASE/spring-web-4.3.7.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-1.7.1.RELEASE.jar (Root Library)
- :x: **spring-web-4.3.7.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-local/vprofile-project8/commit/5eec2b68c36038bc971648668da557114972e048">5eec2b68c36038bc971648668da557114972e048</a></p>
<p>Found in base branch: <b>vp-rem</b></p>
</p>
</details>
<p></p>
<details><summary> <img src='https://whitesource-resources.whitesourcesoftware.com/viaGreen.png' width=19 height=20> Reachability Analysis</summary>
<p>
<p>The vulnerable code is not reachable.</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0.x prior to 5.0.7 and 4.3.x prior to 4.3.18 and older unsupported versions, allows web applications to enable cross-domain requests via JSONP (JSON with Padding) through AbstractJsonpResponseBodyAdvice for REST controllers and MappingJackson2JsonView for browser requests. Both are not enabled by default in Spring Framework nor Spring Boot, however, when MappingJackson2JsonView is configured in an application, JSONP support is automatically ready to use through the "jsonp" and "callback" JSONP parameters, enabling cross-domain requests.
<p>Publish Date: 2018-06-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11040>CVE-2018-11040</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040</a></p>
<p>Release Date: 2018-06-25</p>
<p>Fix Resolution: org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE</p>
</p>
</details>
<p></p>
| non_priority | cve medium non reachable detected in spring web release jar autoclosed cve medium severity vulnerability vulnerable library spring web release jar spring web library home page a href path to dependency file pom xml path to vulnerable library users alexmaybaum repository org springframework spring web release spring web release jar dependency hierarchy spring rabbit release jar root library x spring web release jar vulnerable library found in head commit a href found in base branch vp rem reachability analysis the vulnerable code is not reachable vulnerability details spring framework versions x prior to and x prior to and older unsupported versions allows web applications to enable cross domain requests via jsonp json with padding through abstractjsonpresponsebodyadvice for rest controllers and for browser requests both are not enabled by default in spring framework nor spring boot however when is configured in an application jsonp support is automatically ready to use through the jsonp and callback jsonp parameters enabling cross domain requests publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release | 0 |
278,005 | 21,057,954,567 | IssuesEvent | 2022-04-01 06:32:43 | ian-from-dover/ped | https://api.github.com/repos/ian-from-dover/ped | opened | Command Summary does not have examples | severity.VeryLow type.DocumentationBug | ## Expected
The UG table header says that there will be examples in the table
## Actual

There are no example commands in the table
<!--session: 1648793079029-094b23bf-c065-4806-bff4-e64ce7b438fa-->
<!--Version: Web v3.4.2--> | 1.0 | Command Summary does not have examples - ## Expected
The UG table header says that there will be examples in the table
## Actual

There are no example commands in the table
<!--session: 1648793079029-094b23bf-c065-4806-bff4-e64ce7b438fa-->
<!--Version: Web v3.4.2--> | non_priority | command summary does not have examples expected the ug table header says that there will be examples in the table actual there are no example commands in the table | 0 |
267,122 | 20,190,108,831 | IssuesEvent | 2022-02-11 04:04:34 | bbhuston/gameops | https://api.github.com/repos/bbhuston/gameops | opened | Rename GCP folders and projects to conform with GCP security foundations nomenclature | documentation enhancement | Updating the GameOps GCP folders and projects to conform with the [GCP security foundations naming conventions](https://services.google.com/fh/files/misc/google-cloud-security-foundations-guide.pdf) will allow users to refer to officially supported Google documentation for additional information on security practices/architecture. | 1.0 | Rename GCP folders and projects to conform with GCP security foundations nomenclature - Updating the GameOps GCP folders and projects to conform with the [GCP security foundations naming conventions](https://services.google.com/fh/files/misc/google-cloud-security-foundations-guide.pdf) will allow users to refer to officially supported Google documentation for additional information on security practices/architecture. | non_priority | rename gcp folders and projects to conform with gcp security foundations nomenclature updating the gameops gcp folders and projects to conform with the will allow users to refer to officially supported google documentation for additional information on security practices architecture | 0 |
163,536 | 13,921,534,546 | IssuesEvent | 2020-10-21 12:05:08 | yewstack/yew | https://api.github.com/repos/yewstack/yew | closed | Implicitly convert value to Some(value) for Option<T> props | documentation | <!-- Please only include one feature request per issue, thank you! -->
**Describe the feature you'd like**
Implicitly converting `value` to `Some(value)` for a prop with type of `Option<T>`. Consider the following props
```rust
struct Props {
#[prop_or_default]
pub foo: Option<String>
}
```
If no prop value is passed for `foo` then that field will be initialized as `None` but when a value is to be passed, it must be passed as `foo=Some(value)`. It should be able to be passed as `foo=value` where `value` has a type of `String` (`&str`) and an implicit conversion should occur which converts to `Some(value)`. This is similar to conversion between `String` and `&str`.
**Is your feature request related to a problem? Please describe.**
Converting to `Some` when passing value to `Option<T>` props can get repetitive and can be abstracted away similar to conversion between `String` and `&str`.
**Describe alternatives you've considered**
Doing `Some(value)` every single time.
**Additional context**
None, that I can think of.
**Questionnaire**
<!-- Developing Yew is a community effort! -->
<!-- If you feel up to the challenge, please check one of the boxes below: -->
- [ ] I'm interested in implementing this myself but don't know where to start
- [ ] I would like to add this feature
- [x] I don't have time to add this right now, but maybe later
...and also my knowledge of proc macros is too limited to efficiently work on this | 1.0 | Implicitly convert value to Some(value) for Option<T> props - <!-- Please only include one feature request per issue, thank you! -->
**Describe the feature you'd like**
Implicitly converting `value` to `Some(value)` for a prop with type of `Option<T>`. Consider the following props
```rust
struct Props {
#[prop_or_default]
pub foo: Option<String>
}
```
If no prop value is passed for `foo` then that field will be initialized as `None` but when a value is to be passed, it must be passed as `foo=Some(value)`. It should be able to be passed as `foo=value` where `value` has a type of `String` (`&str`) and an implicit conversion should occur which converts to `Some(value)`. This is similar to conversion between `String` and `&str`.
**Is your feature request related to a problem? Please describe.**
Converting to `Some` when passing value to `Option<T>` props can get repetitive and can be abstracted away similar to conversion between `String` and `&str`.
**Describe alternatives you've considered**
Doing `Some(value)` every single time.
**Additional context**
None, that I can think of.
**Questionnaire**
<!-- Developing Yew is a community effort! -->
<!-- If you feel up to the challenge, please check one of the boxes below: -->
- [ ] I'm interested in implementing this myself but don't know where to start
- [ ] I would like to add this feature
- [x] I don't have time to add this right now, but maybe later
...and also my knowledge of proc macros is too limited to efficiently work on this | non_priority | implicitly convert value to some value for option props describe the feature you d like implicitly converting value to some value for a prop with type of option consider the following props rust struct props pub foo option if no prop value is passed for foo then that field will be initialized as none but when a value is to be passed it must be passed as foo some value it should be able to be passed as foo value where value has a type of string str and an implicit conversion should occur which converts to some value this is similar to conversion between string and str is your feature request related to a problem please describe converting to some when passing value to option props can get repetitive and can be abstracted away similar to conversion between string and str describe alternatives you ve considered doing some value every single time additional context none that i can think of questionnaire i m interested in implementing this myself but don t know where to start i would like to add this feature i don t have time to add this right now but maybe later and also my knowledge of proc macros is too limited to efficiently work on this | 0 |
16,562 | 6,224,793,524 | IssuesEvent | 2017-07-10 14:56:13 | mumble-voip/mumble | https://api.github.com/repos/mumble-voip/mumble | closed | plugins: Warning in sto/sto.cpp when compiling with MinGW | build | ```
sto\sto.cpp:55: warning: dereferencing type-punned pointer will break strict-aliasing rules [-Wstrict-aliasing]
if (* reinterpret_cast<DWORD *>(& posblock[52]) == 1) {
``` | 1.0 | plugins: Warning in sto/sto.cpp when compiling with MinGW - ```
sto\sto.cpp:55: warning: dereferencing type-punned pointer will break strict-aliasing rules [-Wstrict-aliasing]
if (* reinterpret_cast<DWORD *>(& posblock[52]) == 1) {
``` | non_priority | plugins warning in sto sto cpp when compiling with mingw sto sto cpp warning dereferencing type punned pointer will break strict aliasing rules if reinterpret cast posblock | 0 |
215,710 | 24,196,486,615 | IssuesEvent | 2022-09-24 01:05:23 | DavidSpek/kale | https://api.github.com/repos/DavidSpek/kale | opened | CVE-2022-35938 (High) detected in tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl, tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2022-35938 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl</b>, <b>tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl</b></p></summary>
<p>
<details><summary><b>tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/7b/c5/a97ed48fcc878e36bb05a3ea700c077360853c0994473a8f6b0ab4c2ddd2/tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/7b/c5/a97ed48fcc878e36bb05a3ea700c077360853c0994473a8f6b0ab4c2ddd2/tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /examples/dog-breed-classification/requirements/requirements.txt</p>
<p>Path to vulnerable library: /examples/dog-breed-classification/requirements/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</details>
<details><summary><b>tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/ef/73/205b5e7f8fe086ffe4165d984acb2c49fa3086f330f03099378753982d2e/tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/ef/73/205b5e7f8fe086ffe4165d984acb2c49fa3086f330f03099378753982d2e/tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /examples/taxi-cab-classification/requirements.txt</p>
<p>Path to vulnerable library: /examples/taxi-cab-classification/requirements.txt</p>
<p>
Dependency Hierarchy:
- tfx_bsl-0.21.4-cp27-cp27mu-manylinux2010_x86_64.whl (Root Library)
- :x: **tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. The `GatherNd` function takes arguments that determine the sizes of inputs and outputs. If the inputs given are greater than or equal to the sizes of the outputs, an out-of-bounds memory read or a crash is triggered. This issue has been patched in GitHub commit 4142e47e9e31db481781b955ed3ff807a781b494. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-35938>CVE-2022-35938</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-3m3g-pf5v-5hpj">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-3m3g-pf5v-5hpj</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-35938 (High) detected in tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl, tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl - ## CVE-2022-35938 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl</b>, <b>tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl</b></p></summary>
<p>
<details><summary><b>tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/7b/c5/a97ed48fcc878e36bb05a3ea700c077360853c0994473a8f6b0ab4c2ddd2/tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/7b/c5/a97ed48fcc878e36bb05a3ea700c077360853c0994473a8f6b0ab4c2ddd2/tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /examples/dog-breed-classification/requirements/requirements.txt</p>
<p>Path to vulnerable library: /examples/dog-breed-classification/requirements/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.0.0-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</details>
<details><summary><b>tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/ef/73/205b5e7f8fe086ffe4165d984acb2c49fa3086f330f03099378753982d2e/tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/ef/73/205b5e7f8fe086ffe4165d984acb2c49fa3086f330f03099378753982d2e/tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /examples/taxi-cab-classification/requirements.txt</p>
<p>Path to vulnerable library: /examples/taxi-cab-classification/requirements.txt</p>
<p>
Dependency Hierarchy:
- tfx_bsl-0.21.4-cp27-cp27mu-manylinux2010_x86_64.whl (Root Library)
- :x: **tensorflow-2.1.0-cp27-cp27mu-manylinux2010_x86_64.whl** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. The `GatherNd` function takes arguments that determine the sizes of inputs and outputs. If the inputs given are greater than or equal to the sizes of the outputs, an out-of-bounds memory read or a crash is triggered. This issue has been patched in GitHub commit 4142e47e9e31db481781b955ed3ff807a781b494. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-35938>CVE-2022-35938</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-3m3g-pf5v-5hpj">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-3m3g-pf5v-5hpj</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tensorflow whl tensorflow whl cve high severity vulnerability vulnerable libraries tensorflow whl tensorflow whl tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file examples dog breed classification requirements requirements txt path to vulnerable library examples dog breed classification requirements requirements txt dependency hierarchy x tensorflow whl vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file examples taxi cab classification requirements txt path to vulnerable library examples taxi cab classification requirements txt dependency hierarchy tfx bsl whl root library x tensorflow whl vulnerable library found in base branch master vulnerability details tensorflow is an open source platform for machine learning the gathernd function takes arguments that determine the sizes of inputs and outputs if the inputs given are greater than or equal to the sizes of the outputs an out of bounds memory read or a crash is triggered this issue has been patched in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
335,438 | 30,030,694,677 | IssuesEvent | 2023-06-27 09:23:30 | cotezos/umami-api-endpoints | https://api.github.com/repos/cotezos/umami-api-endpoints | closed | 🛑 QA Umami API mainnet - testing - do not use is down | status qa-umami-api-mainnet-testing-do-not-use | In [`f6d0d10`](https://github.com/cotezos/umami-api-endpoints/commit/f6d0d10a4172de1482fd258ee61ff09c37927173
), QA Umami API mainnet - testing - do not use (https://mainnet-qa.umamiwallet.com/monitor/blocks) was **down**:
- HTTP code: 503
- Response time: 653 ms
| 1.0 | 🛑 QA Umami API mainnet - testing - do not use is down - In [`f6d0d10`](https://github.com/cotezos/umami-api-endpoints/commit/f6d0d10a4172de1482fd258ee61ff09c37927173
), QA Umami API mainnet - testing - do not use (https://mainnet-qa.umamiwallet.com/monitor/blocks) was **down**:
- HTTP code: 503
- Response time: 653 ms
| non_priority | 🛑 qa umami api mainnet testing do not use is down in qa umami api mainnet testing do not use was down http code response time ms | 0 |
128,685 | 10,547,762,777 | IssuesEvent | 2019-10-03 02:38:39 | neetjn/core-routing | https://api.github.com/repos/neetjn/core-routing | closed | add test for legacy support | WIP test todo :spiral_notepad: | https://github.com/neetjn/core-routing/blob/e1fec08bd618414a0bff6a9046697dc2ec2c0b38/__test__/router.test.js#L5-L10
---
###### This issue was generated by [todo](https://todo.jasonet.co) based on a `TODO` comment in e1fec08bd618414a0bff6a9046697dc2ec2c0b38. It's been assigned to @neetjn because they committed the code. | 1.0 | add test for legacy support - https://github.com/neetjn/core-routing/blob/e1fec08bd618414a0bff6a9046697dc2ec2c0b38/__test__/router.test.js#L5-L10
---
###### This issue was generated by [todo](https://todo.jasonet.co) based on a `TODO` comment in e1fec08bd618414a0bff6a9046697dc2ec2c0b38. It's been assigned to @neetjn because they committed the code. | non_priority | add test for legacy support this issue was generated by based on a todo comment in it s been assigned to neetjn because they committed the code | 0 |
220,105 | 16,888,030,106 | IssuesEvent | 2021-06-23 04:57:36 | lspcontainers/lspcontainers.nvim | https://api.github.com/repos/lspcontainers/lspcontainers.nvim | closed | Support for podman | documentation good first issue | Podman has a docker compatible CLI, so just being able to substitute docker with podman with a config or something would already solve this. A workaround is `alias docker="podman"`, so I would also understand if this is rejected. | 1.0 | Support for podman - Podman has a docker compatible CLI, so just being able to substitute docker with podman with a config or something would already solve this. A workaround is `alias docker="podman"`, so I would also understand if this is rejected. | non_priority | support for podman podman has a docker compatible cli so just being able to substitute docker with podman with a config or something would already solve this a workaround is alias docker podman so i would also understand if this is rejected | 0 |
31,461 | 6,532,642,580 | IssuesEvent | 2017-08-31 00:28:53 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Scrolling to top problem on TreeTable with scrollable = true | 6.0.23 6.1.5 defect | Reported By PRO User
> On my page, after have edited a specifict row, I need to refresh the tree in order to update the color of the row (tree structure do not change).
If TreeTable isn't scrollable the position on my page not change, but if TreeTable is scrollabe and I specified "scrollHeight", the TreeTable scroll on the top.
Is there a way to avoid scrolling to the top (just update color of the cells). | 1.0 | Scrolling to top problem on TreeTable with scrollable = true - Reported By PRO User
> On my page, after have edited a specifict row, I need to refresh the tree in order to update the color of the row (tree structure do not change).
If TreeTable isn't scrollable the position on my page not change, but if TreeTable is scrollabe and I specified "scrollHeight", the TreeTable scroll on the top.
Is there a way to avoid scrolling to the top (just update color of the cells). | non_priority | scrolling to top problem on treetable with scrollable true reported by pro user on my page after have edited a specifict row i need to refresh the tree in order to update the color of the row tree structure do not change if treetable isn t scrollable the position on my page not change but if treetable is scrollabe and i specified scrollheight the treetable scroll on the top is there a way to avoid scrolling to the top just update color of the cells | 0 |
40,245 | 9,934,927,237 | IssuesEvent | 2019-07-02 15:25:41 | zfsonlinux/zfs | https://api.github.com/repos/zfsonlinux/zfs | closed | Snapshot automount (.zfs) still fails under chroot (OpenSSH ChrootDirectory) | Type: Defect | <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please search our issue tracker *before* making a new issue.
If you cannot find a similar issue, then create a new issue.
https://github.com/zfsonlinux/zfs/issues
*IMPORTANT* - This issue tracker is for *bugs* and *issues* only.
Please search the wiki and the mailing list archives before asking
questions on the mailing list.
https://github.com/zfsonlinux/zfs/wiki/Mailing-Lists
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Debian
Distribution Version | 9.9 (Stretch)
Linux Kernel | 4.9.0-9-amd64
Architecture | amd64
ZFS Version | 0.8.0-1
SPL Version | 0.8.0-1
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
When attempting to browse auto-mounting ZFS dataset snapshots (.zfs/snapshot directory) over a chrooted SFTP (OpenSSH’s `ChrootDirectory` directive), snapshot access fails with the following error:
`WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512`
Browsing snapshots in this manner works as intended if `ChrootDirectory` is not set (not a workable solution, due to needing to restrict SFTP client access to the filesystem), and also works correctly on FreeBSD (11.2-RELEASE, 12.0-RELEASE), presumably because of differing methods of auto-mounting snapshot access.
This appears to be extremely similar to #3778, and @behlendorf indicated various fixes landing in 0.6.x and 0.7.x, although perhaps it wasn’t fully resolved for all kinds of chroot? The error is clear, in that the `mount` operation is being called on the SFTP client’s view of the filesystem (where `/tank/backups/test01` appears as `/`), even though it should be resolved outside of the chroot.
I first ran into this issue on Ubuntu 18.04, running distro-provided zfs/spl 0.7.5, although attempted this reproduction on Debian with the latest 0.8.0 release to see whether the #3778 discussion/fixes were landed after Ubuntu’s version.
### Describe how to reproduce the problem
1. Create a new dataset for hosting restricted client content, e.g. `tank/backups/test01`, mounted at `/tank/backups/test01`.
2. Create some dummy files, and create a symlink at the top of the dataset, pointing to the hidden snapshots directory: `ln -s .zfs/snapshot snapshots`. **(The symlink is only so that SFTP clients don’t have to explicitly view hidden files, it’s not a prerequisite for reproducing the issue!)**
3. Create a few snapshots of the dataset: `zfs snapshot tank/backups/test01@one`, `zfs snapshot tank/backups/test01@two`.
4. Create a test user (e.g. test01) and configure OpenSSH to restrict access for that particular user, including ChrootDirectory, and restart `sshd`. E.g.:
```
Match User test01
ChrootDirectory /tank/backups/test01
ForceCommand internal-sftp -l INFO -u 022
PasswordAuthentication yes
```
5. Connect via SFTP as specified test user. Verify that dummy files and directories are successfully browsable.
6. Change into the `snapshots` symlink (.zfs/snapshot), and verify that snapshots list is accurate. **(The symlink is only so that SFTP clients don’t have to explicitly view hidden files, it’s not a prerequisite for reproducing the issue!)**
7. Attempt to enter one or more snapshot directories. No content will appear, and kernel log on host system will include one or more errors similar to above: `WARNING: Unable to automount /.zfs/snapshot/one/tank/backups/test01@one: 512`.
### Include any warning/errors/backtraces from the system logs
<!--
*IMPORTANT* - Please mark logs and text output from terminal commands
or else Github will not display them correctly.
An example is provided below.
Example:
```
this is an example how log text should be marked (wrap it with ```)
```
-->
```
[ 5061.371785] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5061.457781] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5061.464070] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5063.660823] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5063.747940] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5063.757878] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
``` | 1.0 | Snapshot automount (.zfs) still fails under chroot (OpenSSH ChrootDirectory) - <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please search our issue tracker *before* making a new issue.
If you cannot find a similar issue, then create a new issue.
https://github.com/zfsonlinux/zfs/issues
*IMPORTANT* - This issue tracker is for *bugs* and *issues* only.
Please search the wiki and the mailing list archives before asking
questions on the mailing list.
https://github.com/zfsonlinux/zfs/wiki/Mailing-Lists
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Debian
Distribution Version | 9.9 (Stretch)
Linux Kernel | 4.9.0-9-amd64
Architecture | amd64
ZFS Version | 0.8.0-1
SPL Version | 0.8.0-1
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
When attempting to browse auto-mounting ZFS dataset snapshots (.zfs/snapshot directory) over a chrooted SFTP (OpenSSH’s `ChrootDirectory` directive), snapshot access fails with the following error:
`WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512`
Browsing snapshots in this manner works as intended if `ChrootDirectory` is not set (not a workable solution, due to needing to restrict SFTP client access to the filesystem), and also works correctly on FreeBSD (11.2-RELEASE, 12.0-RELEASE), presumably because of differing methods of auto-mounting snapshot access.
This appears to be extremely similar to #3778, and @behlendorf indicated various fixes landing in 0.6.x and 0.7.x, although perhaps it wasn’t fully resolved for all kinds of chroot? The error is clear, in that the `mount` operation is being called on the SFTP client’s view of the filesystem (where `/tank/backups/test01` appears as `/`), even though it should be resolved outside of the chroot.
I first ran into this issue on Ubuntu 18.04, running distro-provided zfs/spl 0.7.5, although attempted this reproduction on Debian with the latest 0.8.0 release to see whether the #3778 discussion/fixes were landed after Ubuntu’s version.
### Describe how to reproduce the problem
1. Create a new dataset for hosting restricted client content, e.g. `tank/backups/test01`, mounted at `/tank/backups/test01`.
2. Create some dummy files, and create a symlink at the top of the dataset, pointing to the hidden snapshots directory: `ln -s .zfs/snapshot snapshots`. **(The symlink is only so that SFTP clients don’t have to explicitly view hidden files, it’s not a prerequisite for reproducing the issue!)**
3. Create a few snapshots of the dataset: `zfs snapshot tank/backups/test01@one`, `zfs snapshot tank/backups/test01@two`.
4. Create a test user (e.g. test01) and configure OpenSSH to restrict access for that particular user, including ChrootDirectory, and restart `sshd`. E.g.:
```
Match User test01
ChrootDirectory /tank/backups/test01
ForceCommand internal-sftp -l INFO -u 022
PasswordAuthentication yes
```
5. Connect via SFTP as specified test user. Verify that dummy files and directories are successfully browsable.
6. Change into the `snapshots` symlink (.zfs/snapshot), and verify that snapshots list is accurate. **(The symlink is only so that SFTP clients don’t have to explicitly view hidden files, it’s not a prerequisite for reproducing the issue!)**
7. Attempt to enter one or more snapshot directories. No content will appear, and kernel log on host system will include one or more errors similar to above: `WARNING: Unable to automount /.zfs/snapshot/one/tank/backups/test01@one: 512`.
### Include any warning/errors/backtraces from the system logs
<!--
*IMPORTANT* - Please mark logs and text output from terminal commands
or else Github will not display them correctly.
An example is provided below.
Example:
```
this is an example how log text should be marked (wrap it with ```)
```
-->
```
[ 5061.371785] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5061.457781] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5061.464070] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5063.660823] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5063.747940] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
[ 5063.757878] WARNING: Unable to automount /.zfs/snapshot/2019-06-13T221233/tank/backups/test01@2019-06-13T221233: 512
``` | non_priority | snapshot automount zfs still fails under chroot openssh chrootdirectory thank you for reporting an issue important please search our issue tracker before making a new issue if you cannot find a similar issue then create a new issue important this issue tracker is for bugs and issues only please search the wiki and the mailing list archives before asking questions on the mailing list please fill in as much of the template as possible system information type version name distribution name debian distribution version stretch linux kernel architecture zfs version spl version commands to find zfs spl versions modinfo zfs grep iw version modinfo spl grep iw version describe the problem you re observing when attempting to browse auto mounting zfs dataset snapshots zfs snapshot directory over a chrooted sftp openssh’s chrootdirectory directive snapshot access fails with the following error warning unable to automount zfs snapshot tank backups browsing snapshots in this manner works as intended if chrootdirectory is not set not a workable solution due to needing to restrict sftp client access to the filesystem and also works correctly on freebsd release release presumably because of differing methods of auto mounting snapshot access this appears to be extremely similar to and behlendorf indicated various fixes landing in x and x although perhaps it wasn’t fully resolved for all kinds of chroot the error is clear in that the mount operation is being called on the sftp client’s view of the filesystem where tank backups appears as even though it should be resolved outside of the chroot i first ran into this issue on ubuntu running distro provided zfs spl although attempted this reproduction on debian with the latest release to see whether the discussion fixes were landed after ubuntu’s version describe how to reproduce the problem create a new dataset for hosting restricted client content e g tank backups mounted at tank backups create some dummy files and create a symlink at the top of the dataset pointing to the hidden snapshots directory ln s zfs snapshot snapshots the symlink is only so that sftp clients don’t have to explicitly view hidden files it’s not a prerequisite for reproducing the issue create a few snapshots of the dataset zfs snapshot tank backups one zfs snapshot tank backups two create a test user e g and configure openssh to restrict access for that particular user including chrootdirectory and restart sshd e g match user chrootdirectory tank backups forcecommand internal sftp l info u passwordauthentication yes connect via sftp as specified test user verify that dummy files and directories are successfully browsable change into the snapshots symlink zfs snapshot and verify that snapshots list is accurate the symlink is only so that sftp clients don’t have to explicitly view hidden files it’s not a prerequisite for reproducing the issue attempt to enter one or more snapshot directories no content will appear and kernel log on host system will include one or more errors similar to above warning unable to automount zfs snapshot one tank backups one include any warning errors backtraces from the system logs important please mark logs and text output from terminal commands or else github will not display them correctly an example is provided below example this is an example how log text should be marked wrap it with warning unable to automount zfs snapshot tank backups warning unable to automount zfs snapshot tank backups warning unable to automount zfs snapshot tank backups warning unable to automount zfs snapshot tank backups warning unable to automount zfs snapshot tank backups warning unable to automount zfs snapshot tank backups | 0 |
104,267 | 13,048,401,319 | IssuesEvent | 2020-07-29 12:28:42 | blockframes/blockframes | https://api.github.com/repos/blockframes/blockframes | closed | Movie Form UI | Design | ## Description
Le chantier avance bien, il faudrait qu'à la fin de ce sprint l'on puisse valider certaines pages et avoir une première version de toutes celles rattachées à Archipel Market. | 1.0 | Movie Form UI - ## Description
Le chantier avance bien, il faudrait qu'à la fin de ce sprint l'on puisse valider certaines pages et avoir une première version de toutes celles rattachées à Archipel Market. | non_priority | movie form ui description le chantier avance bien il faudrait qu à la fin de ce sprint l on puisse valider certaines pages et avoir une première version de toutes celles rattachées à archipel market | 0 |
37,358 | 15,266,110,042 | IssuesEvent | 2021-02-22 08:21:51 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Replace cycle for [azurerm_backup_protected_vm] when the backup item resource group name is uppercased from azure api | bug service/recovery-services upstream-microsoft | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
Terraform v0.12.29
provider.azurerm v2.21.0
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* azurerm_backup_protected_vm
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
resource "azurerm_backup_protected_vm" "main" {
count = var.azure_vm_backups_enabled == true ? 1 : 0
resource_group_name = var.stackSettings.azurerm_resource_group.name
recovery_vault_name = var.stackSettings.azurerm_recovery_services_vault.name
source_vm_id = azurerm_virtual_machine.main.id
backup_policy_id = var.stackSettings.azurerm_backup_policy_vm.id
}
```
### Debug Output
```
# module.core.module.server1.azurerm_backup_protected_vm.main[0] must be replaced
-/+ resource "azurerm_backup_protected_vm" "main" {
backup_policy_id = "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/abc123-rg/providers/Microsoft.RecoveryServices/vaults/abc123rv/backupPolicies/abc123-rp"
~ id = "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/abc123-rg/providers/Microsoft.RecoveryServices/vaults/abc123rv/backupFabrics/Azure/protectionContainers/IaasVMContainer;iaasvmcontainerv2;abc123-rg;abc123-vm0f11/protectedItems/VM;iaasvmcontainerv2;abc123-rg;abc123-vm0f11" -> (known after apply)
recovery_vault_name = "abc123rv"
resource_group_name = "abc123-rg"
~ source_vm_id = "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/ABC123-RG/providers/Microsoft.Compute/virtualMachines/abc123-vm0f11" -> "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/abc123-rg/providers/Microsoft.Compute/virtualMachines/abc123-vm0f11" # forces replacement
- tags = {} -> null
}
```
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
### Expected Behavior
No changes
### Actual Behavior
Terraform sees the uppercase version of the resource group and tries to replace every apply
### Steps to Reproduce
I have 3 VMs in a build, 2 have the uppercase version pinned to the item, 1 is lower case.
I have been unable to reproduce this state, and even manually deleting/recreating the items in azure portal will not remove the uppercase versions.
I have an active ticket with MS to figure out why this occurred.
They are stating the API may or may not return uppercase, so terraform may need to be adjusted for the condition where a backup source_vm_id may be uppercase in the API, but lowercase in the state.
| 2.0 | Replace cycle for [azurerm_backup_protected_vm] when the backup item resource group name is uppercased from azure api - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
Terraform v0.12.29
provider.azurerm v2.21.0
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* azurerm_backup_protected_vm
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
resource "azurerm_backup_protected_vm" "main" {
count = var.azure_vm_backups_enabled == true ? 1 : 0
resource_group_name = var.stackSettings.azurerm_resource_group.name
recovery_vault_name = var.stackSettings.azurerm_recovery_services_vault.name
source_vm_id = azurerm_virtual_machine.main.id
backup_policy_id = var.stackSettings.azurerm_backup_policy_vm.id
}
```
### Debug Output
```
# module.core.module.server1.azurerm_backup_protected_vm.main[0] must be replaced
-/+ resource "azurerm_backup_protected_vm" "main" {
backup_policy_id = "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/abc123-rg/providers/Microsoft.RecoveryServices/vaults/abc123rv/backupPolicies/abc123-rp"
~ id = "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/abc123-rg/providers/Microsoft.RecoveryServices/vaults/abc123rv/backupFabrics/Azure/protectionContainers/IaasVMContainer;iaasvmcontainerv2;abc123-rg;abc123-vm0f11/protectedItems/VM;iaasvmcontainerv2;abc123-rg;abc123-vm0f11" -> (known after apply)
recovery_vault_name = "abc123rv"
resource_group_name = "abc123-rg"
~ source_vm_id = "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/ABC123-RG/providers/Microsoft.Compute/virtualMachines/abc123-vm0f11" -> "/subscriptions/xxxxxxxxx-xxxx-xxxxxxx-xxxxxxxx/resourceGroups/abc123-rg/providers/Microsoft.Compute/virtualMachines/abc123-vm0f11" # forces replacement
- tags = {} -> null
}
```
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
### Expected Behavior
No changes
### Actual Behavior
Terraform sees the uppercase version of the resource group and tries to replace every apply
### Steps to Reproduce
I have 3 VMs in a build, 2 have the uppercase version pinned to the item, 1 is lower case.
I have been unable to reproduce this state, and even manually deleting/recreating the items in azure portal will not remove the uppercase versions.
I have an active ticket with MS to figure out why this occurred.
They are stating the API may or may not return uppercase, so terraform may need to be adjusted for the condition where a backup source_vm_id may be uppercase in the API, but lowercase in the state.
| non_priority | replace cycle for when the backup item resource group name is uppercased from azure api please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one of these scenarios we recommend opening an issue in the instead community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform and azurerm provider version terraform provider azurerm affected resource s azurerm backup protected vm terraform configuration files hcl resource azurerm backup protected vm main count var azure vm backups enabled true resource group name var stacksettings azurerm resource group name recovery vault name var stacksettings azurerm recovery services vault name source vm id azurerm virtual machine main id backup policy id var stacksettings azurerm backup policy vm id debug output module core module azurerm backup protected vm main must be replaced resource azurerm backup protected vm main backup policy id subscriptions xxxxxxxxx xxxx xxxxxxx xxxxxxxx resourcegroups rg providers microsoft recoveryservices vaults backuppolicies rp id subscriptions xxxxxxxxx xxxx xxxxxxx xxxxxxxx resourcegroups rg providers microsoft recoveryservices vaults backupfabrics azure protectioncontainers iaasvmcontainer rg protecteditems vm rg known after apply recovery vault name resource group name rg source vm id subscriptions xxxxxxxxx xxxx xxxxxxx xxxxxxxx resourcegroups rg providers microsoft compute virtualmachines subscriptions xxxxxxxxx xxxx xxxxxxx xxxxxxxx resourcegroups rg providers microsoft compute virtualmachines forces replacement tags null panic output expected behavior no changes actual behavior terraform sees the uppercase version of the resource group and tries to replace every apply steps to reproduce i have vms in a build have the uppercase version pinned to the item is lower case i have been unable to reproduce this state and even manually deleting recreating the items in azure portal will not remove the uppercase versions i have an active ticket with ms to figure out why this occurred they are stating the api may or may not return uppercase so terraform may need to be adjusted for the condition where a backup source vm id may be uppercase in the api but lowercase in the state | 0 |
86,228 | 10,729,582,991 | IssuesEvent | 2019-10-28 15:50:54 | patternfly/patternfly-org | https://api.github.com/repos/patternfly/patternfly-org | opened | Update Empty State design guidelines | PF4 design Guidelines | Update the empty state design guidelines to provide more detailed usage guidance. This should be based on the analysis done here: https://docs.google.com/presentation/d/14l3A2oLx6AEZIPijbWcBmaSRoqZfR2sLZqYgaO33tto/edit?usp=sharing | 1.0 | Update Empty State design guidelines - Update the empty state design guidelines to provide more detailed usage guidance. This should be based on the analysis done here: https://docs.google.com/presentation/d/14l3A2oLx6AEZIPijbWcBmaSRoqZfR2sLZqYgaO33tto/edit?usp=sharing | non_priority | update empty state design guidelines update the empty state design guidelines to provide more detailed usage guidance this should be based on the analysis done here | 0 |
59,385 | 14,380,126,664 | IssuesEvent | 2020-12-02 02:02:51 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Microsoft Security Advisory CVE-2019-0815: ASP.NET Core denial of service vulnerability | Security | # Microsoft Security Advisory CVE-2019-0815: ASP.NET Core denial of service vulnerability
## Executive Summary
Microsoft is releasing this security advisory to provide information about a vulnerability in public ASP.NET Core 2.2. This advisory also provides guidance on what developers can do to update their applications correctly.
Microsoft is aware of a security vulnerability in all public versions of ASP.NET Core where, if an application is hosted on Internet Information Server (IIS) a remote unauthenticated attacker can use a specially crafted request can cause a Denial of Service. The security update addresses the vulnerability by ensuring the IIS worker process does not crash in response to specially crafted requests.
## Announcement
The original announcement for this issue can be found at https://github.com/aspnet/Announcements/issues/352
## Affected Software
The vulnerability affects any Microsoft ASP.NET Core 2.2 applications if it is hosted on an IIS server running AspNetCoreModuleV2 (ANCM) prior to and including version 12.2.19024.2.
The vulnerability affects any Microsoft ASP.NET Core 1.0/1.1/2/1 application if they have explicitly opted into using the newer AspNetCoreModuleV2 (ANCM) prior to and including version 12.2.19024.2.
## Advisory FAQ
### How do I know if I am affected?
You are affected if **BOTH** criteria below are met.
1. The AspNetCoreModuleV2 module is used by your application
The modules attribute in the handler mapping section of the web.config of your application must exactly match the string `AspNetCoreModuleV2`.
```xml
<?xml version="1.0" encoding="utf-8"?>
<configuration>
<location path="." inheritInChildApplications="false">
<system.webServer>
<handlers>
<add name="aspNetCore" path="*" verb="*" modules="AspNetCoreModuleV2" resourceType="Unspecified" />
</handlers>
<aspNetCore processPath="dotnet" arguments=".\myapp.dll" stdoutLogEnabled="false" stdoutLogFile=".\logs\stdout" hostingModel="inprocess" />
</system.webServer>
</location>
</configuration>
```
2. The version of AspNetCoreModuleV2 module installed on your machine is less than or equal to 12.2.19024.2
Open a PowerShell prompt and run the following command
```ps1
(Get-Item "$env:ProgramFiles\IIS\Asp.Net Core Module\V2\aspnetcorev2.dll").VersionInfo
```
or use the Windows file properties dialog to check the version on C:\Program Files\IIS\Asp.Net Core Module\V2\aspnetcorev2.dll, where C: is your OS install drive.
How do I fix the issue?
Install the latest version of the ASP.NET Core Runtime & Hosting Bundle 2.2.
Then restart IIS by running
```cmd
net stop was /y
net start w3svc
```
from an elevated command line.
## Other Information
### Reporting Security Issues
If you have found a potential security issue in .NET Core, please email details to secure@microsoft.com. Reports may qualify for the .NET Core Bug Bounty. Details of the .NET Core Bug Bounty including Terms and Conditions are at [https://aka.ms/corebounty](https://aka.ms/corebounty).
### Support
You can ask questions about this issue on GitHub in the .NET Core or ASP.NET Core organizations. These are located at https://github.com/dotnet/ and https://github.com/aspnet/. The Announcements repo for each product (https://github.com/dotnet/Announcements and https://github.com/aspnet/Announcements) will contain this bulletin as an issue and will include a link to a discussion issue where you can ask questions.
### Disclaimer
The information provided in this advisory is provided "as is" without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
### External Links
[CVE-2019-0815](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-0815)
### Revisions
V1.0 (Apr 9 2019): Advisory published.
_Version 1.0_
_Last Updated 2019-04-09_
| True | Microsoft Security Advisory CVE-2019-0815: ASP.NET Core denial of service vulnerability - # Microsoft Security Advisory CVE-2019-0815: ASP.NET Core denial of service vulnerability
## Executive Summary
Microsoft is releasing this security advisory to provide information about a vulnerability in public ASP.NET Core 2.2. This advisory also provides guidance on what developers can do to update their applications correctly.
Microsoft is aware of a security vulnerability in all public versions of ASP.NET Core where, if an application is hosted on Internet Information Server (IIS) a remote unauthenticated attacker can use a specially crafted request can cause a Denial of Service. The security update addresses the vulnerability by ensuring the IIS worker process does not crash in response to specially crafted requests.
## Announcement
The original announcement for this issue can be found at https://github.com/aspnet/Announcements/issues/352
## Affected Software
The vulnerability affects any Microsoft ASP.NET Core 2.2 applications if it is hosted on an IIS server running AspNetCoreModuleV2 (ANCM) prior to and including version 12.2.19024.2.
The vulnerability affects any Microsoft ASP.NET Core 1.0/1.1/2/1 application if they have explicitly opted into using the newer AspNetCoreModuleV2 (ANCM) prior to and including version 12.2.19024.2.
## Advisory FAQ
### How do I know if I am affected?
You are affected if **BOTH** criteria below are met.
1. The AspNetCoreModuleV2 module is used by your application
The modules attribute in the handler mapping section of the web.config of your application must exactly match the string `AspNetCoreModuleV2`.
```xml
<?xml version="1.0" encoding="utf-8"?>
<configuration>
<location path="." inheritInChildApplications="false">
<system.webServer>
<handlers>
<add name="aspNetCore" path="*" verb="*" modules="AspNetCoreModuleV2" resourceType="Unspecified" />
</handlers>
<aspNetCore processPath="dotnet" arguments=".\myapp.dll" stdoutLogEnabled="false" stdoutLogFile=".\logs\stdout" hostingModel="inprocess" />
</system.webServer>
</location>
</configuration>
```
2. The version of AspNetCoreModuleV2 module installed on your machine is less than or equal to 12.2.19024.2
Open a PowerShell prompt and run the following command
```ps1
(Get-Item "$env:ProgramFiles\IIS\Asp.Net Core Module\V2\aspnetcorev2.dll").VersionInfo
```
or use the Windows file properties dialog to check the version on C:\Program Files\IIS\Asp.Net Core Module\V2\aspnetcorev2.dll, where C: is your OS install drive.
How do I fix the issue?
Install the latest version of the ASP.NET Core Runtime & Hosting Bundle 2.2.
Then restart IIS by running
```cmd
net stop was /y
net start w3svc
```
from an elevated command line.
## Other Information
### Reporting Security Issues
If you have found a potential security issue in .NET Core, please email details to secure@microsoft.com. Reports may qualify for the .NET Core Bug Bounty. Details of the .NET Core Bug Bounty including Terms and Conditions are at [https://aka.ms/corebounty](https://aka.ms/corebounty).
### Support
You can ask questions about this issue on GitHub in the .NET Core or ASP.NET Core organizations. These are located at https://github.com/dotnet/ and https://github.com/aspnet/. The Announcements repo for each product (https://github.com/dotnet/Announcements and https://github.com/aspnet/Announcements) will contain this bulletin as an issue and will include a link to a discussion issue where you can ask questions.
### Disclaimer
The information provided in this advisory is provided "as is" without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
### External Links
[CVE-2019-0815](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-0815)
### Revisions
V1.0 (Apr 9 2019): Advisory published.
_Version 1.0_
_Last Updated 2019-04-09_
| non_priority | microsoft security advisory cve asp net core denial of service vulnerability microsoft security advisory cve asp net core denial of service vulnerability executive summary microsoft is releasing this security advisory to provide information about a vulnerability in public asp net core this advisory also provides guidance on what developers can do to update their applications correctly microsoft is aware of a security vulnerability in all public versions of asp net core where if an application is hosted on internet information server iis a remote unauthenticated attacker can use a specially crafted request can cause a denial of service the security update addresses the vulnerability by ensuring the iis worker process does not crash in response to specially crafted requests announcement the original announcement for this issue can be found at affected software the vulnerability affects any microsoft asp net core applications if it is hosted on an iis server running ancm prior to and including version the vulnerability affects any microsoft asp net core application if they have explicitly opted into using the newer ancm prior to and including version advisory faq how do i know if i am affected you are affected if both criteria below are met the module is used by your application the modules attribute in the handler mapping section of the web config of your application must exactly match the string xml the version of module installed on your machine is less than or equal to open a powershell prompt and run the following command get item env programfiles iis asp net core module dll versioninfo or use the windows file properties dialog to check the version on c program files iis asp net core module dll where c is your os install drive how do i fix the issue install the latest version of the asp net core runtime hosting bundle then restart iis by running cmd net stop was y net start from an elevated command line other information reporting security issues if you have found a potential security issue in net core please email details to secure microsoft com reports may qualify for the net core bug bounty details of the net core bug bounty including terms and conditions are at support you can ask questions about this issue on github in the net core or asp net core organizations these are located at and the announcements repo for each product and will contain this bulletin as an issue and will include a link to a discussion issue where you can ask questions disclaimer the information provided in this advisory is provided as is without warranty of any kind microsoft disclaims all warranties either express or implied including the warranties of merchantability and fitness for a particular purpose in no event shall microsoft corporation or its suppliers be liable for any damages whatsoever including direct indirect incidental consequential loss of business profits or special damages even if microsoft corporation or its suppliers have been advised of the possibility of such damages some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply external links revisions apr advisory published version last updated | 0 |
124,093 | 17,772,460,057 | IssuesEvent | 2021-08-30 15:05:58 | kapseliboi/mimic | https://api.github.com/repos/kapseliboi/mimic | opened | WS-2013-0003 (Medium) detected in connect-2.7.2.tgz | security vulnerability | ## WS-2013-0003 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>connect-2.7.2.tgz</b></p></summary>
<p>High performance middleware framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/connect/-/connect-2.7.2.tgz">https://registry.npmjs.org/connect/-/connect-2.7.2.tgz</a></p>
<p>Path to dependency file: mimic/package.json</p>
<p>Path to vulnerable library: mimic/node_modules/node-osx-notifier/node_modules/connect/package.json</p>
<p>
Dependency Hierarchy:
- karma-osx-reporter-0.2.1.tgz (Root Library)
- node-osx-notifier-0.1.0.tgz
- express-3.0.6.tgz
- :x: **connect-2.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/mimic/commit/1b3df8b0fb992059d70591ed86206dbf53aec93d">1b3df8b0fb992059d70591ed86206dbf53aec93d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
senchalabs/connect prior to 2.8.1 is vulnerable to xss attack
<p>Publish Date: 2013-06-27
<p>URL: <a href=https://github.com/senchalabs/connect/commit/277e5aad6a95d00f55571a9a0e11f2fa190d8135>WS-2013-0003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/methodOverride_Middleware_Reflected_Cross-Site_Scripting">https://nodesecurity.io/advisories/methodOverride_Middleware_Reflected_Cross-Site_Scripting</a></p>
<p>Release Date: 2013-07-01</p>
<p>Fix Resolution: Update to the newest version of Connect or disable methodOverride. It is not possible to avoid the vulnerability if you have enabled this middleware in the top of your stack.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2013-0003 (Medium) detected in connect-2.7.2.tgz - ## WS-2013-0003 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>connect-2.7.2.tgz</b></p></summary>
<p>High performance middleware framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/connect/-/connect-2.7.2.tgz">https://registry.npmjs.org/connect/-/connect-2.7.2.tgz</a></p>
<p>Path to dependency file: mimic/package.json</p>
<p>Path to vulnerable library: mimic/node_modules/node-osx-notifier/node_modules/connect/package.json</p>
<p>
Dependency Hierarchy:
- karma-osx-reporter-0.2.1.tgz (Root Library)
- node-osx-notifier-0.1.0.tgz
- express-3.0.6.tgz
- :x: **connect-2.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/mimic/commit/1b3df8b0fb992059d70591ed86206dbf53aec93d">1b3df8b0fb992059d70591ed86206dbf53aec93d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
senchalabs/connect prior to 2.8.1 is vulnerable to xss attack
<p>Publish Date: 2013-06-27
<p>URL: <a href=https://github.com/senchalabs/connect/commit/277e5aad6a95d00f55571a9a0e11f2fa190d8135>WS-2013-0003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/methodOverride_Middleware_Reflected_Cross-Site_Scripting">https://nodesecurity.io/advisories/methodOverride_Middleware_Reflected_Cross-Site_Scripting</a></p>
<p>Release Date: 2013-07-01</p>
<p>Fix Resolution: Update to the newest version of Connect or disable methodOverride. It is not possible to avoid the vulnerability if you have enabled this middleware in the top of your stack.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in connect tgz ws medium severity vulnerability vulnerable library connect tgz high performance middleware framework library home page a href path to dependency file mimic package json path to vulnerable library mimic node modules node osx notifier node modules connect package json dependency hierarchy karma osx reporter tgz root library node osx notifier tgz express tgz x connect tgz vulnerable library found in head commit a href found in base branch master vulnerability details senchalabs connect prior to is vulnerable to xss attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution update to the newest version of connect or disable methodoverride it is not possible to avoid the vulnerability if you have enabled this middleware in the top of your stack step up your open source security game with whitesource | 0 |
204,833 | 15,557,148,975 | IssuesEvent | 2021-03-16 08:47:14 | Altinn/altinn-studio | https://api.github.com/repos/Altinn/altinn-studio | reopened | Upgrade apps to support v 4.0.0 | area/app-test kind/user-story solution/app-backend | ## Description
As a result of breaking change in #5852 a number of apps must be updated.
## Considerations
> Describe input (beyond tasks) on how the user story should be solved can be put here.
## Acceptance criteria
- [x] PR for apps in production
- [x] All test apps are patched
## Development tasks
- [x] Test appsused by bruksmønster
- [x] Create PRs for [the apps in production](https://altinn.github.io/docs/altinn-studio/launched-apps/) and under development (sirius, etc), and inform the owners so they can merge and test, and update other apps in their pipeline.
## Test
> Add test cases here as checkboxes that are being tested as part of the changes.
| 1.0 | Upgrade apps to support v 4.0.0 - ## Description
As a result of breaking change in #5852 a number of apps must be updated.
## Considerations
> Describe input (beyond tasks) on how the user story should be solved can be put here.
## Acceptance criteria
- [x] PR for apps in production
- [x] All test apps are patched
## Development tasks
- [x] Test appsused by bruksmønster
- [x] Create PRs for [the apps in production](https://altinn.github.io/docs/altinn-studio/launched-apps/) and under development (sirius, etc), and inform the owners so they can merge and test, and update other apps in their pipeline.
## Test
> Add test cases here as checkboxes that are being tested as part of the changes.
| non_priority | upgrade apps to support v description as a result of breaking change in a number of apps must be updated considerations describe input beyond tasks on how the user story should be solved can be put here acceptance criteria pr for apps in production all test apps are patched development tasks test appsused by bruksmønster create prs for and under development sirius etc and inform the owners so they can merge and test and update other apps in their pipeline test add test cases here as checkboxes that are being tested as part of the changes | 0 |
59,652 | 14,626,141,258 | IssuesEvent | 2020-12-23 09:49:31 | kubevirt/kubevirt | https://api.github.com/repos/kubevirt/kubevirt | closed | [Flaky CI] [rfe_id:694][crit:medium][vendor:cnv-qe@redhat.com][level:component]Networking VirtualMachineInstance with masquerade binding mechanism [test_id:1780][label:masquerade_binding_connectivity]should allow regular network connection with custom CIDR | kind/bug lifecycle/rotten sig/network triage/build-watcher | /kind bug
/triage build-officer
**What happened**:
```
/root/go/src/kubevirt.io/kubevirt/vendor/github.com/onsi/ginkgo/extensions/table/table_entry.go:43
Unexpected error:
<expect.TimeoutError>: 30000000000
expect: timer expired after 30 seconds
occurred
/root/go/src/kubevirt.io/kubevirt/tests/vmi_networking_test.go:773
```
https://prow.apps.ovirt.org/view/gcs/kubevirt-prow/pr-logs/pull/kubevirt_kubevirt/3803/pull-kubevirt-e2e-kind-k8s-1.17.0-ipv6/1282776410632491011 | 1.0 | [Flaky CI] [rfe_id:694][crit:medium][vendor:cnv-qe@redhat.com][level:component]Networking VirtualMachineInstance with masquerade binding mechanism [test_id:1780][label:masquerade_binding_connectivity]should allow regular network connection with custom CIDR - /kind bug
/triage build-officer
**What happened**:
```
/root/go/src/kubevirt.io/kubevirt/vendor/github.com/onsi/ginkgo/extensions/table/table_entry.go:43
Unexpected error:
<expect.TimeoutError>: 30000000000
expect: timer expired after 30 seconds
occurred
/root/go/src/kubevirt.io/kubevirt/tests/vmi_networking_test.go:773
```
https://prow.apps.ovirt.org/view/gcs/kubevirt-prow/pr-logs/pull/kubevirt_kubevirt/3803/pull-kubevirt-e2e-kind-k8s-1.17.0-ipv6/1282776410632491011 | non_priority | networking virtualmachineinstance with masquerade binding mechanism should allow regular network connection with custom cidr kind bug triage build officer what happened root go src kubevirt io kubevirt vendor github com onsi ginkgo extensions table table entry go unexpected error expect timer expired after seconds occurred root go src kubevirt io kubevirt tests vmi networking test go | 0 |
177,992 | 14,657,037,085 | IssuesEvent | 2020-12-28 14:44:19 | Frontend-Stars/angular-guideline | https://api.github.com/repos/Frontend-Stars/angular-guideline | opened | Render | dependency injection documentation | **Details:**
write article for describe how to work render in angular 2, add examples and best practices
[Link to Wiki](https://github.com/dmitry-nizovsky/angular-guideline/wiki/Render)
**Sub issues:**
- [Render: performance](https://github.com/dmitry-nizovsky/angular-guideline/projects/1#card-49880195)
- [Render: NgZone](https://github.com/dmitry-nizovsky/angular-guideline/projects/1#card-49880772) | 1.0 | Render - **Details:**
write article for describe how to work render in angular 2, add examples and best practices
[Link to Wiki](https://github.com/dmitry-nizovsky/angular-guideline/wiki/Render)
**Sub issues:**
- [Render: performance](https://github.com/dmitry-nizovsky/angular-guideline/projects/1#card-49880195)
- [Render: NgZone](https://github.com/dmitry-nizovsky/angular-guideline/projects/1#card-49880772) | non_priority | render details write article for describe how to work render in angular add examples and best practices sub issues | 0 |
98,040 | 12,287,392,438 | IssuesEvent | 2020-05-09 11:58:38 | reach4help/reach4help | https://api.github.com/repos/reach4help/reach4help | closed | UI of CAV Flow View #3: Requests | UI Design | Since the CAV UX is ready, we are able to start building the UI design of CAV View "Timeline". Referred by the attached image or this [link](https://www.figma.com/file/OiU7Tl4k1YFfqZQXxLaRrl/Reach4Help?node-id=1055%3A235)

<!--zenhub info: do not edit anything after this line, it will be automatically changed-->
--------
### [ZenHub Information](https://app.zenhub.com/workspaces/reach4help-5e8dcbfb14ac087f410cbabb/issues/reach4help/reach4help/456)
*This information is updated automatically. To modify it, please use ZenHub.*
**Belonging to Epics:**
* **[EPIC]** [#455 - CAV Flow View #3: Requests](https://github.com/reach4help/reach4help/issues/455)
<!--zenhub info end--> | 1.0 | UI of CAV Flow View #3: Requests - Since the CAV UX is ready, we are able to start building the UI design of CAV View "Timeline". Referred by the attached image or this [link](https://www.figma.com/file/OiU7Tl4k1YFfqZQXxLaRrl/Reach4Help?node-id=1055%3A235)

<!--zenhub info: do not edit anything after this line, it will be automatically changed-->
--------
### [ZenHub Information](https://app.zenhub.com/workspaces/reach4help-5e8dcbfb14ac087f410cbabb/issues/reach4help/reach4help/456)
*This information is updated automatically. To modify it, please use ZenHub.*
**Belonging to Epics:**
* **[EPIC]** [#455 - CAV Flow View #3: Requests](https://github.com/reach4help/reach4help/issues/455)
<!--zenhub info end--> | non_priority | ui of cav flow view requests since the cav ux is ready we are able to start building the ui design of cav view timeline referred by the attached image or this this information is updated automatically to modify it please use zenhub belonging to epics | 0 |
303,101 | 26,184,612,952 | IssuesEvent | 2023-01-02 21:19:10 | BoBAdministration/QA-Bug-Reports | https://api.github.com/repos/BoBAdministration/QA-Bug-Reports | closed | Egg Growth Speed is affected by Server Growth Choices | Fixed-PendingTesting | **Describe the Bug**
Eggs will grow slower or faster depending on the growth speed settings of servers.
**To Reproduce**
1. Set Server Growth Speed to Slow
2. Take any egg
3. Experience longer growth time once the egg reaches 1.0, requiring for you to wait an extended time for the egg to hatch.
4. Set Server Growth Speed to Normal
5. Take any egg
6. Experience normal egg growth time.
**Expected behavior**
Eggs grow at the same speed regardless of server growth choices.
**Actual behavior**
Eggs are affected by the server's growth speed.
**Screenshots & Video**
Egg growth speed after reaching 1.0, while unable to hatch. Server growth speed is set to slow.
**Branch Version**
Live
**Character Information**
Egg displays this modified speed on slow only after reaching 1.0.
**Additional Information**
N/A
| 1.0 | Egg Growth Speed is affected by Server Growth Choices - **Describe the Bug**
Eggs will grow slower or faster depending on the growth speed settings of servers.
**To Reproduce**
1. Set Server Growth Speed to Slow
2. Take any egg
3. Experience longer growth time once the egg reaches 1.0, requiring for you to wait an extended time for the egg to hatch.
4. Set Server Growth Speed to Normal
5. Take any egg
6. Experience normal egg growth time.
**Expected behavior**
Eggs grow at the same speed regardless of server growth choices.
**Actual behavior**
Eggs are affected by the server's growth speed.
**Screenshots & Video**
Egg growth speed after reaching 1.0, while unable to hatch. Server growth speed is set to slow.
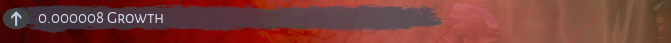
**Branch Version**
Live
**Character Information**
Egg displays this modified speed on slow only after reaching 1.0.
**Additional Information**
N/A
| non_priority | egg growth speed is affected by server growth choices describe the bug eggs will grow slower or faster depending on the growth speed settings of servers to reproduce set server growth speed to slow take any egg experience longer growth time once the egg reaches requiring for you to wait an extended time for the egg to hatch set server growth speed to normal take any egg experience normal egg growth time expected behavior eggs grow at the same speed regardless of server growth choices actual behavior eggs are affected by the server s growth speed screenshots video egg growth speed after reaching while unable to hatch server growth speed is set to slow branch version live character information egg displays this modified speed on slow only after reaching additional information n a | 0 |
96,100 | 19,899,788,207 | IssuesEvent | 2022-01-25 06:09:30 | flutter/website | https://api.github.com/repos/flutter/website | closed | [PAGE ISSUE]: 'Write your first Flutter app on the web' | p3-low e0-minutes codelab | ### Page URL
https://flutter.dev/docs/get-started/codelab-web/
### Page source
https://github.com/flutter/website/tree/main/src/docs/get-started/codelab-web.md
### Describe the problem
The codelab stills asks the user to switch to the beta channel whereas the web has been pushed into stable.
### Expected fix
Remove the steps to change to beta version of flutter
### Additional context
_No response_ | 1.0 | [PAGE ISSUE]: 'Write your first Flutter app on the web' - ### Page URL
https://flutter.dev/docs/get-started/codelab-web/
### Page source
https://github.com/flutter/website/tree/main/src/docs/get-started/codelab-web.md
### Describe the problem
The codelab stills asks the user to switch to the beta channel whereas the web has been pushed into stable.
### Expected fix
Remove the steps to change to beta version of flutter
### Additional context
_No response_ | non_priority | write your first flutter app on the web page url page source describe the problem the codelab stills asks the user to switch to the beta channel whereas the web has been pushed into stable expected fix remove the steps to change to beta version of flutter additional context no response | 0 |
67,863 | 7,065,748,884 | IssuesEvent | 2018-01-07 00:17:46 | vergecurrency/VERGE | https://api.github.com/repos/vergecurrency/VERGE | closed | Beta testing stealth, testnet | testing | I would like to be able to test the new code, but unsure of how to access the testnet.
"VERGE-qt -testnet" from command line should work, but how do I specify a different data directory? Which branch is the most current or relevant for testing stealth? What at the git commands to specify and pull a different branch?
| 1.0 | Beta testing stealth, testnet - I would like to be able to test the new code, but unsure of how to access the testnet.
"VERGE-qt -testnet" from command line should work, but how do I specify a different data directory? Which branch is the most current or relevant for testing stealth? What at the git commands to specify and pull a different branch?
| non_priority | beta testing stealth testnet i would like to be able to test the new code but unsure of how to access the testnet verge qt testnet from command line should work but how do i specify a different data directory which branch is the most current or relevant for testing stealth what at the git commands to specify and pull a different branch | 0 |
31,583 | 4,711,673,141 | IssuesEvent | 2016-10-14 14:31:53 | outscale/butterfly | https://api.github.com/repos/outscale/butterfly | closed | test: add/delete SG members | tests | Initial setup:
- Machine A security group: SG1
- Machine B security group: SG2
- SG1 members: A's IP
- SG2 members: B's IP
- SG1 rule: Allow all members of SG1 to access UDP port 8000
- SG2 rule: Allow all members of SG2 to access UDP port 9000
Tests that:
- machine A can't speak with B on UDP port 9000.
- machine B can't speak with A on UDP port 8000.
Change setup:
- SG1: members: add B's IP
- SG2: members: add A's IP
Test that:
- machine A can speak with B on UDP port 9000.
- machine B can speak with A on UDP port 8000.
Change setup:
- SG1: members: remove B's IP
- SG2: members: remove A's IP
Test that:
- machine A can't speak with B on UDP port 9000.
- machine B can't speak with A on UDP port 8000. | 1.0 | test: add/delete SG members - Initial setup:
- Machine A security group: SG1
- Machine B security group: SG2
- SG1 members: A's IP
- SG2 members: B's IP
- SG1 rule: Allow all members of SG1 to access UDP port 8000
- SG2 rule: Allow all members of SG2 to access UDP port 9000
Tests that:
- machine A can't speak with B on UDP port 9000.
- machine B can't speak with A on UDP port 8000.
Change setup:
- SG1: members: add B's IP
- SG2: members: add A's IP
Test that:
- machine A can speak with B on UDP port 9000.
- machine B can speak with A on UDP port 8000.
Change setup:
- SG1: members: remove B's IP
- SG2: members: remove A's IP
Test that:
- machine A can't speak with B on UDP port 9000.
- machine B can't speak with A on UDP port 8000. | non_priority | test add delete sg members initial setup machine a security group machine b security group members a s ip members b s ip rule allow all members of to access udp port rule allow all members of to access udp port tests that machine a can t speak with b on udp port machine b can t speak with a on udp port change setup members add b s ip members add a s ip test that machine a can speak with b on udp port machine b can speak with a on udp port change setup members remove b s ip members remove a s ip test that machine a can t speak with b on udp port machine b can t speak with a on udp port | 0 |
285,803 | 31,155,610,435 | IssuesEvent | 2023-08-16 12:57:35 | nidhi7598/linux-4.1.15_CVE-2018-5873 | https://api.github.com/repos/nidhi7598/linux-4.1.15_CVE-2018-5873 | opened | CVE-2016-9178 (Medium) detected in linuxlinux-4.1.52 | Mend: dependency security vulnerability | ## CVE-2016-9178 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The __get_user_asm_ex macro in arch/x86/include/asm/uaccess.h in the Linux kernel before 4.7.5 does not initialize a certain integer variable, which allows local users to obtain sensitive information from kernel stack memory by triggering failure of a get_user_ex call.
<p>Publish Date: 2016-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-9178>CVE-2016-9178</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9178">https://nvd.nist.gov/vuln/detail/CVE-2016-9178</a></p>
<p>Release Date: 2016-11-28</p>
<p>Fix Resolution: 4.7.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-9178 (Medium) detected in linuxlinux-4.1.52 - ## CVE-2016-9178 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The __get_user_asm_ex macro in arch/x86/include/asm/uaccess.h in the Linux kernel before 4.7.5 does not initialize a certain integer variable, which allows local users to obtain sensitive information from kernel stack memory by triggering failure of a get_user_ex call.
<p>Publish Date: 2016-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-9178>CVE-2016-9178</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9178">https://nvd.nist.gov/vuln/detail/CVE-2016-9178</a></p>
<p>Release Date: 2016-11-28</p>
<p>Fix Resolution: 4.7.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files vulnerability details the get user asm ex macro in arch include asm uaccess h in the linux kernel before does not initialize a certain integer variable which allows local users to obtain sensitive information from kernel stack memory by triggering failure of a get user ex call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
88,750 | 25,497,029,628 | IssuesEvent | 2022-11-27 20:04:14 | expo/expo | https://api.github.com/repos/expo/expo | closed | expo-dev-menu@1.2.1 vendors breaking with newrelic-react-native-agent@0.0.2 | stale Issue accepted Development Builds | ### Summary
Vendored packages classes inscide expo-dev-menu are duplicated when using newrelic-react-native-agent.
Is using vendored versions of react-native-{gesture-handler,reanimated,safe-area-context} a good practice ?
PS: Idk how to contact NewRelic developers neither submit them an issue, their repository github.com/newrelic/newrelic-react-native-agent is private
### Managed or bare workflow?
managed
### What platform(s) does this occur on?
Android
### Package versions
eas-cli@0.60.0
expo-dev-client@1.2.1
expo-updates@0.14.4
newrelic-react-native-agent@0.0.2
### Environment
expo-env-info 1.0.5 environment info:
System:
OS: macOS 12.5
Shell: 5.8.1 - /bin/zsh
Binaries:
Node: 16.15.1 - ~/.volta/tools/image/node/16.15.1/bin/node
Yarn: 1.22.19 - ~/.volta/tools/image/yarn/1.22.19/bin/yarn
npm: 8.11.0 - ~/.volta/tools/image/node/16.15.1/bin/npm
Managers:
CocoaPods: 1.11.3 - /opt/homebrew/bin/pod
SDKs:
iOS SDK:
Platforms: DriverKit 21.4, iOS 15.5, macOS 12.3, tvOS 15.4, watchOS 8.5
IDEs:
Android Studio: 2021.2 AI-212.5712.43.2112.8815526
Xcode: 13.4.1/13F100 - /usr/bin/xcodebuild
npmPackages:
expo: ^46.0.0 => 46.0.7
react: 18.0.0 => 18.0.0
react-dom: 18.0.0 => 18.0.0
react-native: 0.69.4 => 0.69.4
react-native-web: ~0.18.7 => 0.18.7
Expo Workflow: managed
### Reproducible demo
```
git clone https://github.com/90dy/issue-expo-newrelic
cd issue-expo-newrelic
yarn
eas build --profile preview --platform android --local
```
Working if you remove `newrelic-react-native-agent` plugin in app.json
### Stacktrace (if a crash is involved)
<details>
<summary>Show more</summary>
[...]
[RUN_GRADLEW] > Task :app:transformClassesWithNewrelicTransformForDebug
[RUN_GRADLEW] > Task :app:dexBuilderDebug
[RUN_GRADLEW] > Task :expo-dev-menu-interface:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :app:mergeExtDexDebug
[RUN_GRADLEW] > Task :expo-dev-menu-interface:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :app:mergeLibDexDebug
[RUN_GRADLEW] > Task :expo-error-recovery:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-error-recovery:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-error-recovery:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-file-system:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-file-system:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-file-system:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-font:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-font:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-font:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-json-utils:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-json-utils:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-json-utils:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-dev-menu:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-keep-awake:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-keep-awake:mergeDebugNativeLibs
[RUN_GRADLEW] NO-SOURCE
[RUN_GRADLEW] > Task :expo-keep-awake:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-manifests:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-manifests:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-modules-core:createNativeDepsDirectories UP-TO-DATE
[RUN_GRADLEW] > Task :expo-manifests:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-modules-core:prepareHermes UP-TO-DATE
[RUN_GRADLEW] > Task :expo-modules-core:extractReactNativeAARRelease
[RUN_GRADLEW] > Task :expo-modules-core:downloadFolly
[RUN_GRADLEW] Download https://github.com/facebook/folly/archive/v2021.06.28.00.tar.gz
[RUN_GRADLEW] > Task :expo-modules-core:downloadDoubleConversion
[RUN_GRADLEW] Download https://github.com/google/double-conversion/archive/v1.1.6.tar.gz
[RUN_GRADLEW] > Task :expo-modules-core:extractReactNativeAARDebug
[RUN_GRADLEW] > Task :expo-modules-core:prepareDoubleConversion
[RUN_GRADLEW] > Task :app:mergeProjectDexDebug FAILED
[RUN_GRADLEW] ERROR:/private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar: D8: Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] com.android.builder.dexing.DexArchiveMergerException: Error while merging dex archives:
[RUN_GRADLEW] Learn how to resolve the issue at https://developer.android.com/studio/build/dependencies#duplicate_classes.
[RUN_GRADLEW] Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] at com.android.builder.dexing.D8DexArchiveMerger.getExceptionToRethrow(D8DexArchiveMerger.java:151)
[RUN_GRADLEW] at com.android.builder.dexing.D8DexArchiveMerger.mergeDexArchives(D8DexArchiveMerger.java:138)
[RUN_GRADLEW] at com.android.build.gradle.internal.tasks.DexMergingWorkAction.merge(DexMergingTask.kt:859)
[RUN_GRADLEW] at com.android.build.gradle.internal.tasks.DexMergingWorkAction.run(DexMergingTask.kt:805)
[RUN_GRADLEW] at com.android.build.gradle.internal.profile.ProfileAwareWorkAction.execute(ProfileAwareWorkAction.kt:74)
[RUN_GRADLEW] at org.gradle.workers.internal.DefaultWorkerServer.execute(DefaultWorkerServer.java:63)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1$1.create(NoIsolationWorkerFactory.java:66)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1$1.create(NoIsolationWorkerFactory.java:62)
[RUN_GRADLEW] at org.gradle.internal.classloader.ClassLoaderUtils.executeInClassloader(ClassLoaderUtils.java:97)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1.lambda$execute$0(NoIsolationWorkerFactory.java:62)
[RUN_GRADLEW] at org.gradle.workers.internal.AbstractWorker$1.call(AbstractWorker.java:44)
[RUN_GRADLEW] at org.gradle.workers.internal.AbstractWorker$1.call(AbstractWorker.java:41)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$CallableBuildOperationWorker.execute(DefaultBuildOperationRunner.java:204)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$CallableBuildOperationWorker.execute(DefaultBuildOperationRunner.java:199)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$2.execute(DefaultBuildOperationRunner.java:66)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$2.execute(DefaultBuildOperationRunner.java:59)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner.execute(DefaultBuildOperationRunner.java:157)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner.execute(DefaultBuildOperationRunner.java:59)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner.call(DefaultBuildOperationRunner.java:53)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:73)
[RUN_GRADLEW] at org.gradle.workers.internal.AbstractWorker.executeWrappedInBuildOperation(AbstractWorker.java:41)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1.execute(NoIsolationWorkerFactory.java:59)
[RUN_GRADLEW] at org.gradle.workers.internal.DefaultWorkerExecutor.lambda$submitWork$2(DefaultWorkerExecutor.java:206)
[RUN_GRADLEW] at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
[RUN_GRADLEW] at org.gradle.internal.work.DefaultConditionalExecutionQueue$ExecutionRunner.runExecution(DefaultConditionalExecutionQueue.java:214)
[RUN_GRADLEW] at org.gradle.internal.work.DefaultConditionalExecutionQueue$ExecutionRunner.runBatch(DefaultConditionalExecutionQueue.java:164)
[RUN_GRADLEW] at org.gradle.internal.work.DefaultConditionalExecutionQueue$ExecutionRunner.run(DefaultConditionalExecutionQueue.java:131)
[RUN_GRADLEW] at java.base/java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515)
[RUN_GRADLEW] at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
[RUN_GRADLEW] at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
[RUN_GRADLEW] at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
[RUN_GRADLEW] at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
[RUN_GRADLEW] at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
[RUN_GRADLEW] at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:61)
[RUN_GRADLEW] at java.base/java.lang.Thread.run(Thread.java:829)
[RUN_GRADLEW] Caused by: com.android.tools.r8.CompilationFailedException: Compilation failed to complete, origin: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex
[RUN_GRADLEW] at Version.fakeStackEntry(Version_3.1.51.java:0)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:68)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:28)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:27)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.b(SourceFile:3)
[RUN_GRADLEW] at com.android.tools.r8.D8.run(D8.java:11)
[RUN_GRADLEW] at com.android.builder.dexing.D8DexArchiveMerger.mergeDexArchives(D8DexArchiveMerger.java:136)
[RUN_GRADLEW] ... 33 more
[RUN_GRADLEW] Caused by: com.android.tools.r8.internal.b: Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] at com.android.tools.r8.internal.il1.a(SourceFile:14)
[RUN_GRADLEW] at com.android.tools.r8.internal.il1.a(SourceFile:22)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.b(SourceFile:6)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.a(SourceFile:23)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.a(SourceFile:10)
[RUN_GRADLEW] at java.base/java.util.concurrent.ConcurrentHashMap.merge(ConcurrentHashMap.java:2048)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.a(SourceFile:6)
[RUN_GRADLEW] at com.android.tools.r8.graph.r2$a.f(SourceFile:4)
[RUN_GRADLEW] at com.android.tools.r8.dex.b.a(SourceFile:96)
[RUN_GRADLEW] at com.android.tools.r8.dex.b.a(SourceFile:21)
[RUN_GRADLEW] at com.android.tools.r8.D8.a(D8.java:21)
[RUN_GRADLEW] at com.android.tools.r8.D8.d(D8.java:11)
[RUN_GRADLEW] at com.android.tools.r8.D8.b(D8.java:1)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:24)
[RUN_GRADLEW] ... 36 more
[RUN_GRADLEW] > Task :expo-modules-core:downloadBoost
[RUN_GRADLEW] Download https://boostorg.jfrog.io/artifactory/main/release/1.76.0/source/boost_1_76_0.tar.gz
[RUN_GRADLEW] > Task :expo-modules-core:prepareFolly
[RUN_GRADLEW] w: Detected multiple Kotlin daemon sessions at build/kotlin/sessions
[RUN_GRADLEW] Deprecated Gradle features were used in this build, making it incompatible with Gradle 8.0.
[RUN_GRADLEW] You can use '--warning-mode all' to show the individual deprecation warnings and determine if they come from your own scripts or plugins.
[RUN_GRADLEW] See https://docs.gradle.org/7.3.3/userguide/command_line_interface.html#sec:command_line_warnings
[RUN_GRADLEW] Execution optimizations have been disabled for 1 invalid unit(s) of work during this build to ensure correctness.
[RUN_GRADLEW] Please consult deprecation warnings for more details.
[RUN_GRADLEW] 361 actionable tasks: 361 executed
[RUN_GRADLEW] FAILURE: Build failed with an exception.
[RUN_GRADLEW] * What went wrong:
[RUN_GRADLEW] Execution failed for task ':app:mergeProjectDexDebug'.
[RUN_GRADLEW] > A failure occurred while executing com.android.build.gradle.internal.tasks.DexMergingTaskDelegate
[RUN_GRADLEW] > There was a failure while executing work items
[RUN_GRADLEW] > A failure occurred while executing com.android.build.gradle.internal.tasks.DexMergingWorkAction
[RUN_GRADLEW] > com.android.builder.dexing.DexArchiveMergerException: Error while merging dex archives:
[RUN_GRADLEW] Learn how to resolve the issue at https://developer.android.com/studio/build/dependencies#duplicate_classes.
[RUN_GRADLEW] Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] * Try:
[RUN_GRADLEW] > Run with --stacktrace option to get the stack trace.
[RUN_GRADLEW] > Run with --info or --debug option to get more log output.
[RUN_GRADLEW] > Run with --scan to get full insights.
[RUN_GRADLEW] * Get more help at https://help.gradle.org
[RUN_GRADLEW] BUILD FAILED in 1m 45s
[RUN_GRADLEW] Error: Gradle build failed with unknown error. Please see logs for the "Run gradlew" phase.
Build failed
Gradle build failed with unknown error. Please see logs for the "Run gradlew" phase.
Error: npx exited with non-zero code: 1
error Command failed with exit code 1.
info Visit https://yarnpkg.com/en/docs/cli/run for documentation about this command.
</details>
| 1.0 | expo-dev-menu@1.2.1 vendors breaking with newrelic-react-native-agent@0.0.2 - ### Summary
Vendored packages classes inscide expo-dev-menu are duplicated when using newrelic-react-native-agent.
Is using vendored versions of react-native-{gesture-handler,reanimated,safe-area-context} a good practice ?
PS: Idk how to contact NewRelic developers neither submit them an issue, their repository github.com/newrelic/newrelic-react-native-agent is private
### Managed or bare workflow?
managed
### What platform(s) does this occur on?
Android
### Package versions
eas-cli@0.60.0
expo-dev-client@1.2.1
expo-updates@0.14.4
newrelic-react-native-agent@0.0.2
### Environment
expo-env-info 1.0.5 environment info:
System:
OS: macOS 12.5
Shell: 5.8.1 - /bin/zsh
Binaries:
Node: 16.15.1 - ~/.volta/tools/image/node/16.15.1/bin/node
Yarn: 1.22.19 - ~/.volta/tools/image/yarn/1.22.19/bin/yarn
npm: 8.11.0 - ~/.volta/tools/image/node/16.15.1/bin/npm
Managers:
CocoaPods: 1.11.3 - /opt/homebrew/bin/pod
SDKs:
iOS SDK:
Platforms: DriverKit 21.4, iOS 15.5, macOS 12.3, tvOS 15.4, watchOS 8.5
IDEs:
Android Studio: 2021.2 AI-212.5712.43.2112.8815526
Xcode: 13.4.1/13F100 - /usr/bin/xcodebuild
npmPackages:
expo: ^46.0.0 => 46.0.7
react: 18.0.0 => 18.0.0
react-dom: 18.0.0 => 18.0.0
react-native: 0.69.4 => 0.69.4
react-native-web: ~0.18.7 => 0.18.7
Expo Workflow: managed
### Reproducible demo
```
git clone https://github.com/90dy/issue-expo-newrelic
cd issue-expo-newrelic
yarn
eas build --profile preview --platform android --local
```
Working if you remove `newrelic-react-native-agent` plugin in app.json
### Stacktrace (if a crash is involved)
<details>
<summary>Show more</summary>
[...]
[RUN_GRADLEW] > Task :app:transformClassesWithNewrelicTransformForDebug
[RUN_GRADLEW] > Task :app:dexBuilderDebug
[RUN_GRADLEW] > Task :expo-dev-menu-interface:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :app:mergeExtDexDebug
[RUN_GRADLEW] > Task :expo-dev-menu-interface:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :app:mergeLibDexDebug
[RUN_GRADLEW] > Task :expo-error-recovery:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-error-recovery:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-error-recovery:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-file-system:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-file-system:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-file-system:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-font:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-font:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-font:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-json-utils:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-json-utils:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-json-utils:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-dev-menu:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-keep-awake:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-keep-awake:mergeDebugNativeLibs
[RUN_GRADLEW] NO-SOURCE
[RUN_GRADLEW] > Task :expo-keep-awake:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-manifests:mergeDebugJniLibFolders
[RUN_GRADLEW] > Task :expo-manifests:mergeDebugNativeLibs NO-SOURCE
[RUN_GRADLEW] > Task :expo-modules-core:createNativeDepsDirectories UP-TO-DATE
[RUN_GRADLEW] > Task :expo-manifests:copyDebugJniLibsProjectOnly
[RUN_GRADLEW] > Task :expo-modules-core:prepareHermes UP-TO-DATE
[RUN_GRADLEW] > Task :expo-modules-core:extractReactNativeAARRelease
[RUN_GRADLEW] > Task :expo-modules-core:downloadFolly
[RUN_GRADLEW] Download https://github.com/facebook/folly/archive/v2021.06.28.00.tar.gz
[RUN_GRADLEW] > Task :expo-modules-core:downloadDoubleConversion
[RUN_GRADLEW] Download https://github.com/google/double-conversion/archive/v1.1.6.tar.gz
[RUN_GRADLEW] > Task :expo-modules-core:extractReactNativeAARDebug
[RUN_GRADLEW] > Task :expo-modules-core:prepareDoubleConversion
[RUN_GRADLEW] > Task :app:mergeProjectDexDebug FAILED
[RUN_GRADLEW] ERROR:/private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar: D8: Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] com.android.builder.dexing.DexArchiveMergerException: Error while merging dex archives:
[RUN_GRADLEW] Learn how to resolve the issue at https://developer.android.com/studio/build/dependencies#duplicate_classes.
[RUN_GRADLEW] Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] at com.android.builder.dexing.D8DexArchiveMerger.getExceptionToRethrow(D8DexArchiveMerger.java:151)
[RUN_GRADLEW] at com.android.builder.dexing.D8DexArchiveMerger.mergeDexArchives(D8DexArchiveMerger.java:138)
[RUN_GRADLEW] at com.android.build.gradle.internal.tasks.DexMergingWorkAction.merge(DexMergingTask.kt:859)
[RUN_GRADLEW] at com.android.build.gradle.internal.tasks.DexMergingWorkAction.run(DexMergingTask.kt:805)
[RUN_GRADLEW] at com.android.build.gradle.internal.profile.ProfileAwareWorkAction.execute(ProfileAwareWorkAction.kt:74)
[RUN_GRADLEW] at org.gradle.workers.internal.DefaultWorkerServer.execute(DefaultWorkerServer.java:63)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1$1.create(NoIsolationWorkerFactory.java:66)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1$1.create(NoIsolationWorkerFactory.java:62)
[RUN_GRADLEW] at org.gradle.internal.classloader.ClassLoaderUtils.executeInClassloader(ClassLoaderUtils.java:97)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1.lambda$execute$0(NoIsolationWorkerFactory.java:62)
[RUN_GRADLEW] at org.gradle.workers.internal.AbstractWorker$1.call(AbstractWorker.java:44)
[RUN_GRADLEW] at org.gradle.workers.internal.AbstractWorker$1.call(AbstractWorker.java:41)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$CallableBuildOperationWorker.execute(DefaultBuildOperationRunner.java:204)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$CallableBuildOperationWorker.execute(DefaultBuildOperationRunner.java:199)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$2.execute(DefaultBuildOperationRunner.java:66)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner$2.execute(DefaultBuildOperationRunner.java:59)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner.execute(DefaultBuildOperationRunner.java:157)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner.execute(DefaultBuildOperationRunner.java:59)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationRunner.call(DefaultBuildOperationRunner.java:53)
[RUN_GRADLEW] at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:73)
[RUN_GRADLEW] at org.gradle.workers.internal.AbstractWorker.executeWrappedInBuildOperation(AbstractWorker.java:41)
[RUN_GRADLEW] at org.gradle.workers.internal.NoIsolationWorkerFactory$1.execute(NoIsolationWorkerFactory.java:59)
[RUN_GRADLEW] at org.gradle.workers.internal.DefaultWorkerExecutor.lambda$submitWork$2(DefaultWorkerExecutor.java:206)
[RUN_GRADLEW] at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
[RUN_GRADLEW] at org.gradle.internal.work.DefaultConditionalExecutionQueue$ExecutionRunner.runExecution(DefaultConditionalExecutionQueue.java:214)
[RUN_GRADLEW] at org.gradle.internal.work.DefaultConditionalExecutionQueue$ExecutionRunner.runBatch(DefaultConditionalExecutionQueue.java:164)
[RUN_GRADLEW] at org.gradle.internal.work.DefaultConditionalExecutionQueue$ExecutionRunner.run(DefaultConditionalExecutionQueue.java:131)
[RUN_GRADLEW] at java.base/java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:515)
[RUN_GRADLEW] at java.base/java.util.concurrent.FutureTask.run(FutureTask.java:264)
[RUN_GRADLEW] at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
[RUN_GRADLEW] at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
[RUN_GRADLEW] at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
[RUN_GRADLEW] at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
[RUN_GRADLEW] at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:61)
[RUN_GRADLEW] at java.base/java.lang.Thread.run(Thread.java:829)
[RUN_GRADLEW] Caused by: com.android.tools.r8.CompilationFailedException: Compilation failed to complete, origin: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex
[RUN_GRADLEW] at Version.fakeStackEntry(Version_3.1.51.java:0)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:68)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:28)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:27)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.b(SourceFile:3)
[RUN_GRADLEW] at com.android.tools.r8.D8.run(D8.java:11)
[RUN_GRADLEW] at com.android.builder.dexing.D8DexArchiveMerger.mergeDexArchives(D8DexArchiveMerger.java:136)
[RUN_GRADLEW] ... 33 more
[RUN_GRADLEW] Caused by: com.android.tools.r8.internal.b: Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] at com.android.tools.r8.internal.il1.a(SourceFile:14)
[RUN_GRADLEW] at com.android.tools.r8.internal.il1.a(SourceFile:22)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.b(SourceFile:6)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.a(SourceFile:23)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.a(SourceFile:10)
[RUN_GRADLEW] at java.base/java.util.concurrent.ConcurrentHashMap.merge(ConcurrentHashMap.java:2048)
[RUN_GRADLEW] at com.android.tools.r8.internal.lf1.a(SourceFile:6)
[RUN_GRADLEW] at com.android.tools.r8.graph.r2$a.f(SourceFile:4)
[RUN_GRADLEW] at com.android.tools.r8.dex.b.a(SourceFile:96)
[RUN_GRADLEW] at com.android.tools.r8.dex.b.a(SourceFile:21)
[RUN_GRADLEW] at com.android.tools.r8.D8.a(D8.java:21)
[RUN_GRADLEW] at com.android.tools.r8.D8.d(D8.java:11)
[RUN_GRADLEW] at com.android.tools.r8.D8.b(D8.java:1)
[RUN_GRADLEW] at com.android.tools.r8.internal.oO0.a(SourceFile:24)
[RUN_GRADLEW] ... 36 more
[RUN_GRADLEW] > Task :expo-modules-core:downloadBoost
[RUN_GRADLEW] Download https://boostorg.jfrog.io/artifactory/main/release/1.76.0/source/boost_1_76_0.tar.gz
[RUN_GRADLEW] > Task :expo-modules-core:prepareFolly
[RUN_GRADLEW] w: Detected multiple Kotlin daemon sessions at build/kotlin/sessions
[RUN_GRADLEW] Deprecated Gradle features were used in this build, making it incompatible with Gradle 8.0.
[RUN_GRADLEW] You can use '--warning-mode all' to show the individual deprecation warnings and determine if they come from your own scripts or plugins.
[RUN_GRADLEW] See https://docs.gradle.org/7.3.3/userguide/command_line_interface.html#sec:command_line_warnings
[RUN_GRADLEW] Execution optimizations have been disabled for 1 invalid unit(s) of work during this build to ensure correctness.
[RUN_GRADLEW] Please consult deprecation warnings for more details.
[RUN_GRADLEW] 361 actionable tasks: 361 executed
[RUN_GRADLEW] FAILURE: Build failed with an exception.
[RUN_GRADLEW] * What went wrong:
[RUN_GRADLEW] Execution failed for task ':app:mergeProjectDexDebug'.
[RUN_GRADLEW] > A failure occurred while executing com.android.build.gradle.internal.tasks.DexMergingTaskDelegate
[RUN_GRADLEW] > There was a failure while executing work items
[RUN_GRADLEW] > A failure occurred while executing com.android.build.gradle.internal.tasks.DexMergingWorkAction
[RUN_GRADLEW] > com.android.builder.dexing.DexArchiveMergerException: Error while merging dex archives:
[RUN_GRADLEW] Learn how to resolve the issue at https://developer.android.com/studio/build/dependencies#duplicate_classes.
[RUN_GRADLEW] Type devmenu.com.swmansion.common.GestureHandlerStateManager is defined multiple times: /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/5e7dbb4869e56e0e1a799a81f4a55a2e2fb653c6471f07002f1e3556a621f0e5_0.jar:classes.dex, /private/var/folders/_x/nmly3n_d43xd9j84qhnvdfxr0000gn/T/eas-build-local-nodejs/242dfbfa-b363-4c77-b713-573746bf4f44/build/android/app/build/intermediates/mixed_scope_dex_archive/debug/out/abf280864f159d56a3b1d73b5fdeb59fa0211fd5a8a38181c24112cdd2d7a10a_0.jar:classes.dex
[RUN_GRADLEW] * Try:
[RUN_GRADLEW] > Run with --stacktrace option to get the stack trace.
[RUN_GRADLEW] > Run with --info or --debug option to get more log output.
[RUN_GRADLEW] > Run with --scan to get full insights.
[RUN_GRADLEW] * Get more help at https://help.gradle.org
[RUN_GRADLEW] BUILD FAILED in 1m 45s
[RUN_GRADLEW] Error: Gradle build failed with unknown error. Please see logs for the "Run gradlew" phase.
Build failed
Gradle build failed with unknown error. Please see logs for the "Run gradlew" phase.
Error: npx exited with non-zero code: 1
error Command failed with exit code 1.
info Visit https://yarnpkg.com/en/docs/cli/run for documentation about this command.
</details>
| non_priority | expo dev menu vendors breaking with newrelic react native agent summary vendored packages classes inscide expo dev menu are duplicated when using newrelic react native agent is using vendored versions of react native gesture handler reanimated safe area context a good practice ps idk how to contact newrelic developers neither submit them an issue their repository github com newrelic newrelic react native agent is private managed or bare workflow managed what platform s does this occur on android package versions eas cli expo dev client expo updates newrelic react native agent environment expo env info environment info system os macos shell bin zsh binaries node volta tools image node bin node yarn volta tools image yarn bin yarn npm volta tools image node bin npm managers cocoapods opt homebrew bin pod sdks ios sdk platforms driverkit ios macos tvos watchos ides android studio ai xcode usr bin xcodebuild npmpackages expo react react dom react native react native web expo workflow managed reproducible demo git clone cd issue expo newrelic yarn eas build profile preview platform android local working if you remove newrelic react native agent plugin in app json stacktrace if a crash is involved show more task app transformclasseswithnewrelictransformfordebug task app dexbuilderdebug task expo dev menu interface mergedebugnativelibs no source task app mergeextdexdebug task expo dev menu interface copydebugjnilibsprojectonly task app mergelibdexdebug task expo error recovery mergedebugjnilibfolders task expo error recovery mergedebugnativelibs no source task expo error recovery copydebugjnilibsprojectonly task expo file system mergedebugjnilibfolders task expo file system mergedebugnativelibs no source task expo file system copydebugjnilibsprojectonly task expo font mergedebugjnilibfolders task expo font mergedebugnativelibs no source task expo font copydebugjnilibsprojectonly task expo json utils mergedebugjnilibfolders task expo json utils mergedebugnativelibs no source task expo json utils copydebugjnilibsprojectonly task expo dev menu copydebugjnilibsprojectonly task expo keep awake mergedebugjnilibfolders task expo keep awake mergedebugnativelibs no source task expo keep awake copydebugjnilibsprojectonly task expo manifests mergedebugjnilibfolders task expo manifests mergedebugnativelibs no source task expo modules core createnativedepsdirectories up to date task expo manifests copydebugjnilibsprojectonly task expo modules core preparehermes up to date task expo modules core extractreactnativeaarrelease task expo modules core downloadfolly download task expo modules core downloaddoubleconversion download task expo modules core extractreactnativeaardebug task expo modules core preparedoubleconversion task app mergeprojectdexdebug failed error private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar type devmenu com swmansion common gesturehandlerstatemanager is defined multiple times private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex com android builder dexing dexarchivemergerexception error while merging dex archives learn how to resolve the issue at type devmenu com swmansion common gesturehandlerstatemanager is defined multiple times private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex at com android builder dexing getexceptiontorethrow java at com android builder dexing mergedexarchives java at com android build gradle internal tasks dexmergingworkaction merge dexmergingtask kt at com android build gradle internal tasks dexmergingworkaction run dexmergingtask kt at com android build gradle internal profile profileawareworkaction execute profileawareworkaction kt at org gradle workers internal defaultworkerserver execute defaultworkerserver java at org gradle workers internal noisolationworkerfactory create noisolationworkerfactory java at org gradle workers internal noisolationworkerfactory create noisolationworkerfactory java at org gradle internal classloader classloaderutils executeinclassloader classloaderutils java at org gradle workers internal noisolationworkerfactory lambda execute noisolationworkerfactory java at org gradle workers internal abstractworker call abstractworker java at org gradle workers internal abstractworker call abstractworker java at org gradle internal operations defaultbuildoperationrunner callablebuildoperationworker execute defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationrunner callablebuildoperationworker execute defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationrunner execute defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationrunner execute defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationrunner execute defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationrunner execute defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationrunner call defaultbuildoperationrunner java at org gradle internal operations defaultbuildoperationexecutor call defaultbuildoperationexecutor java at org gradle workers internal abstractworker executewrappedinbuildoperation abstractworker java at org gradle workers internal noisolationworkerfactory execute noisolationworkerfactory java at org gradle workers internal defaultworkerexecutor lambda submitwork defaultworkerexecutor java at java base java util concurrent futuretask run futuretask java at org gradle internal work defaultconditionalexecutionqueue executionrunner runexecution defaultconditionalexecutionqueue java at org gradle internal work defaultconditionalexecutionqueue executionrunner runbatch defaultconditionalexecutionqueue java at org gradle internal work defaultconditionalexecutionqueue executionrunner run defaultconditionalexecutionqueue java at java base java util concurrent executors runnableadapter call executors java at java base java util concurrent futuretask run futuretask java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java base java lang thread run thread java caused by com android tools compilationfailedexception compilation failed to complete origin private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex at version fakestackentry version java at com android tools internal a sourcefile at com android tools internal a sourcefile at com android tools internal a sourcefile at com android tools internal b sourcefile at com android tools run java at com android builder dexing mergedexarchives java more caused by com android tools internal b type devmenu com swmansion common gesturehandlerstatemanager is defined multiple times private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex at com android tools internal a sourcefile at com android tools internal a sourcefile at com android tools internal b sourcefile at com android tools internal a sourcefile at com android tools internal a sourcefile at java base java util concurrent concurrenthashmap merge concurrenthashmap java at com android tools internal a sourcefile at com android tools graph a f sourcefile at com android tools dex b a sourcefile at com android tools dex b a sourcefile at com android tools a java at com android tools d java at com android tools b java at com android tools internal a sourcefile more task expo modules core downloadboost download task expo modules core preparefolly w detected multiple kotlin daemon sessions at build kotlin sessions deprecated gradle features were used in this build making it incompatible with gradle you can use warning mode all to show the individual deprecation warnings and determine if they come from your own scripts or plugins see execution optimizations have been disabled for invalid unit s of work during this build to ensure correctness please consult deprecation warnings for more details actionable tasks executed failure build failed with an exception what went wrong execution failed for task app mergeprojectdexdebug a failure occurred while executing com android build gradle internal tasks dexmergingtaskdelegate there was a failure while executing work items a failure occurred while executing com android build gradle internal tasks dexmergingworkaction com android builder dexing dexarchivemergerexception error while merging dex archives learn how to resolve the issue at type devmenu com swmansion common gesturehandlerstatemanager is defined multiple times private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex private var folders x t eas build local nodejs build android app build intermediates mixed scope dex archive debug out jar classes dex try run with stacktrace option to get the stack trace run with info or debug option to get more log output run with scan to get full insights get more help at build failed in error gradle build failed with unknown error please see logs for the run gradlew phase build failed gradle build failed with unknown error please see logs for the run gradlew phase error npx exited with non zero code error command failed with exit code info visit for documentation about this command | 0 |
11,630 | 13,683,299,349 | IssuesEvent | 2020-09-30 01:23:53 | scylladb/scylla | https://api.github.com/repos/scylladb/scylla | closed | Add MAX_WINDOW_SIZE_SECONDS to DTCS compaction settings | cassandra 3.x compatibility enhancement | *Installation details*
Allow DTCS compaction governance based on maximum window size rather than SSTable age.
Similar to https://issues.apache.org/jira/browse/CASSANDRA-10280 | True | Add MAX_WINDOW_SIZE_SECONDS to DTCS compaction settings - *Installation details*
Allow DTCS compaction governance based on maximum window size rather than SSTable age.
Similar to https://issues.apache.org/jira/browse/CASSANDRA-10280 | non_priority | add max window size seconds to dtcs compaction settings installation details allow dtcs compaction governance based on maximum window size rather than sstable age similar to | 0 |
140,650 | 32,042,091,278 | IssuesEvent | 2023-09-22 20:19:35 | devgpt-labs/devgpt-releases | https://api.github.com/repos/devgpt-labs/devgpt-releases | closed | Its not working its just loading loading and loading despite of me having pro version of the app | Bug Code Generation | Its loading since last 2 hours and forever | 1.0 | Its not working its just loading loading and loading despite of me having pro version of the app - Its loading since last 2 hours and forever | non_priority | its not working its just loading loading and loading despite of me having pro version of the app its loading since last hours and forever | 0 |
274,238 | 29,951,054,585 | IssuesEvent | 2023-06-23 01:09:25 | summercms/rust-template | https://api.github.com/repos/summercms/rust-template | opened | WS-2023-0196 (Medium) detected in memoffset-0.5.6.crate | Mend: dependency security vulnerability | ## WS-2023-0196 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>memoffset-0.5.6.crate</b></p></summary>
<p>offset_of functionality for Rust structs.</p>
<p>Library home page: <a href="https://crates.io/api/v1/crates/memoffset/0.5.6/download">https://crates.io/api/v1/crates/memoffset/0.5.6/download</a></p>
<p>
Dependency Hierarchy:
- config-0.1.0.crate (Root Library)
- solana-client-1.7.10.crate
- solana-vote-program-1.7.10.crate
- solana-metrics-1.7.10.crate
- solana-sdk-1.7.10.crate
- solana-crate-features-1.7.10.crate
- tokio-0.1.22.crate
- tokio-fs-0.1.7.crate
- tokio-threadpool-0.1.18.crate
- crossbeam-deque-0.7.4.crate
- crossbeam-epoch-0.8.2.crate
- :x: **memoffset-0.5.6.crate** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
memoffset allows reading uninitialized memory
<p>Publish Date: 2023-06-22
<p>URL: <a href=https://github.com/Gilnaa/memoffset/commit/576166bb63d238d97d5a4979d3484bc82c9bde3e>WS-2023-0196</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wfg4-322g-9vqv">https://github.com/advisories/GHSA-wfg4-322g-9vqv</a></p>
<p>Release Date: 2023-06-22</p>
<p>Fix Resolution: memoffset - 0.6.2
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2023-0196 (Medium) detected in memoffset-0.5.6.crate - ## WS-2023-0196 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>memoffset-0.5.6.crate</b></p></summary>
<p>offset_of functionality for Rust structs.</p>
<p>Library home page: <a href="https://crates.io/api/v1/crates/memoffset/0.5.6/download">https://crates.io/api/v1/crates/memoffset/0.5.6/download</a></p>
<p>
Dependency Hierarchy:
- config-0.1.0.crate (Root Library)
- solana-client-1.7.10.crate
- solana-vote-program-1.7.10.crate
- solana-metrics-1.7.10.crate
- solana-sdk-1.7.10.crate
- solana-crate-features-1.7.10.crate
- tokio-0.1.22.crate
- tokio-fs-0.1.7.crate
- tokio-threadpool-0.1.18.crate
- crossbeam-deque-0.7.4.crate
- crossbeam-epoch-0.8.2.crate
- :x: **memoffset-0.5.6.crate** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
memoffset allows reading uninitialized memory
<p>Publish Date: 2023-06-22
<p>URL: <a href=https://github.com/Gilnaa/memoffset/commit/576166bb63d238d97d5a4979d3484bc82c9bde3e>WS-2023-0196</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wfg4-322g-9vqv">https://github.com/advisories/GHSA-wfg4-322g-9vqv</a></p>
<p>Release Date: 2023-06-22</p>
<p>Fix Resolution: memoffset - 0.6.2
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in memoffset crate ws medium severity vulnerability vulnerable library memoffset crate offset of functionality for rust structs library home page a href dependency hierarchy config crate root library solana client crate solana vote program crate solana metrics crate solana sdk crate solana crate features crate tokio crate tokio fs crate tokio threadpool crate crossbeam deque crate crossbeam epoch crate x memoffset crate vulnerable library found in base branch master vulnerability details memoffset allows reading uninitialized memory publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution memoffset step up your open source security game with mend | 0 |
18,389 | 12,839,572,697 | IssuesEvent | 2020-07-07 19:31:59 | GoogleContainerTools/skaffold | https://api.github.com/repos/GoogleContainerTools/skaffold | opened | gLinux Skaffold outputs many deployment in progress events, which floods our logs | p1 usability | From cloud-code-vscode-internal created by [j-windsor](https://github.com/j-windsor): GoogleCloudPlatform/cloud-code-vscode-internal#2682
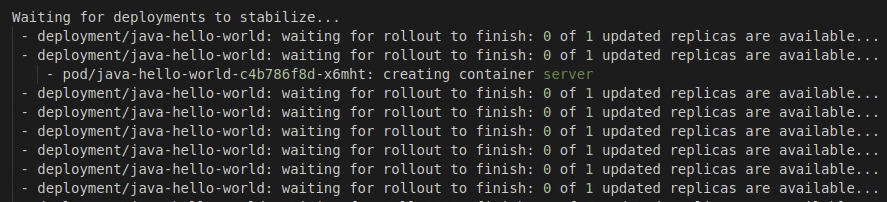
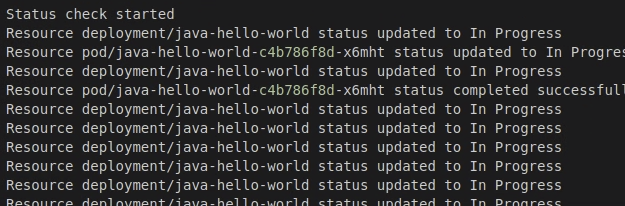
| True | gLinux Skaffold outputs many deployment in progress events, which floods our logs - From cloud-code-vscode-internal created by [j-windsor](https://github.com/j-windsor): GoogleCloudPlatform/cloud-code-vscode-internal#2682
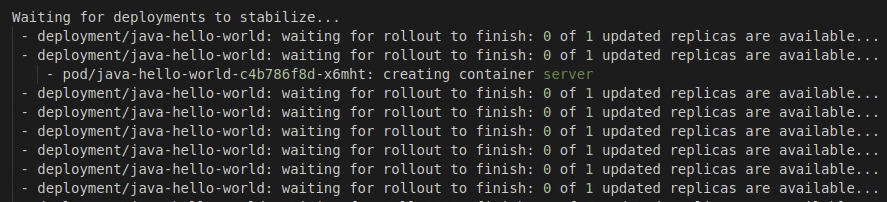
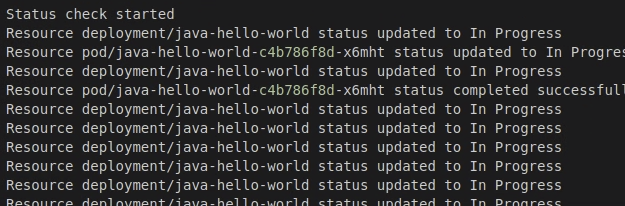
| non_priority | glinux skaffold outputs many deployment in progress events which floods our logs from cloud code vscode internal created by googlecloudplatform cloud code vscode internal | 0 |
38,547 | 5,191,255,907 | IssuesEvent | 2017-01-21 18:27:44 | ukdtom/WebTools.bundle | https://api.github.com/repos/ukdtom/WebTools.bundle | closed | UAS main screen | Cosmetic Prioritize Ready for testing | UAS main screen has a link towards Plex2CSV for a manual install
We need to change that into: https://github.com/ukdtom/ExportTools.bundle instead, since that will replace the other one, when the next version of PMS is released | 1.0 | UAS main screen - UAS main screen has a link towards Plex2CSV for a manual install
We need to change that into: https://github.com/ukdtom/ExportTools.bundle instead, since that will replace the other one, when the next version of PMS is released | non_priority | uas main screen uas main screen has a link towards for a manual install we need to change that into instead since that will replace the other one when the next version of pms is released | 0 |
134,702 | 19,306,317,023 | IssuesEvent | 2021-12-13 11:55:26 | OpenEnergyPlatform/oeplatform | https://api.github.com/repos/OpenEnergyPlatform/oeplatform | opened | Better navigation for 'textual' oeo viewer | enhancement design/layout | I would like to suggest to add some simple navigational elements to the "textual" oeo viewer. Like this it can be navigated easier and usability will increase. I made a scribble below on how it could look like when viewing a specific entity. Of course it would be great if the search bar would already be visible when landing here: https://openenergy-platform.org/ontology/oeo/
- _search bar_ lets users search for terms (this is already possible in the[ "visual" viewer](https://openenergy-platform.org/viewer/oeo/))
- _back button_ would navigate to the previous page viewed
- _oeo home_ would lead back to https://openenergy-platform.org/ontology/oeo/
I think the search bar would be the most important element and increase usability quickly.
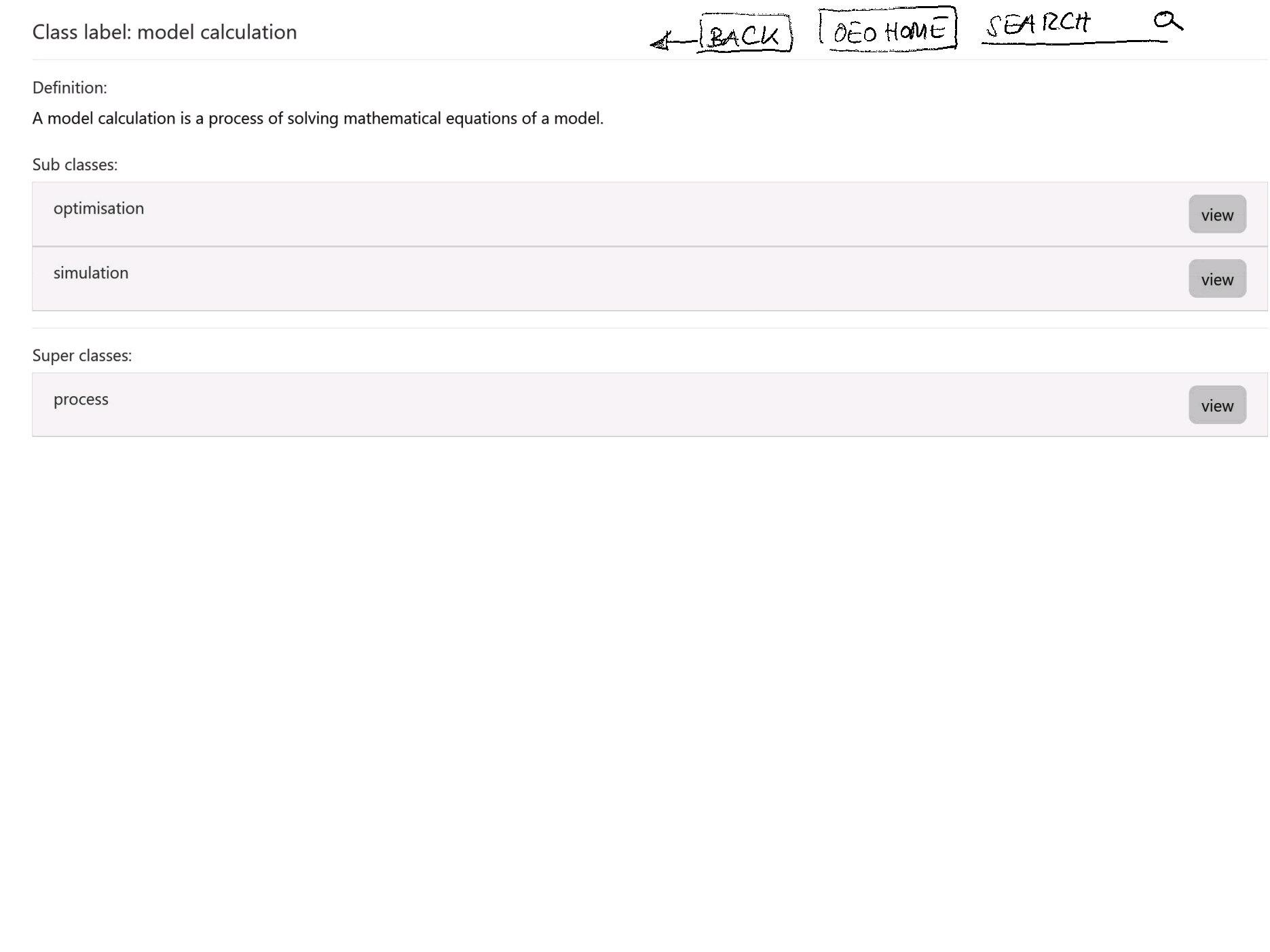
cc @l-emele @stap-m | 1.0 | Better navigation for 'textual' oeo viewer - I would like to suggest to add some simple navigational elements to the "textual" oeo viewer. Like this it can be navigated easier and usability will increase. I made a scribble below on how it could look like when viewing a specific entity. Of course it would be great if the search bar would already be visible when landing here: https://openenergy-platform.org/ontology/oeo/
- _search bar_ lets users search for terms (this is already possible in the[ "visual" viewer](https://openenergy-platform.org/viewer/oeo/))
- _back button_ would navigate to the previous page viewed
- _oeo home_ would lead back to https://openenergy-platform.org/ontology/oeo/
I think the search bar would be the most important element and increase usability quickly.
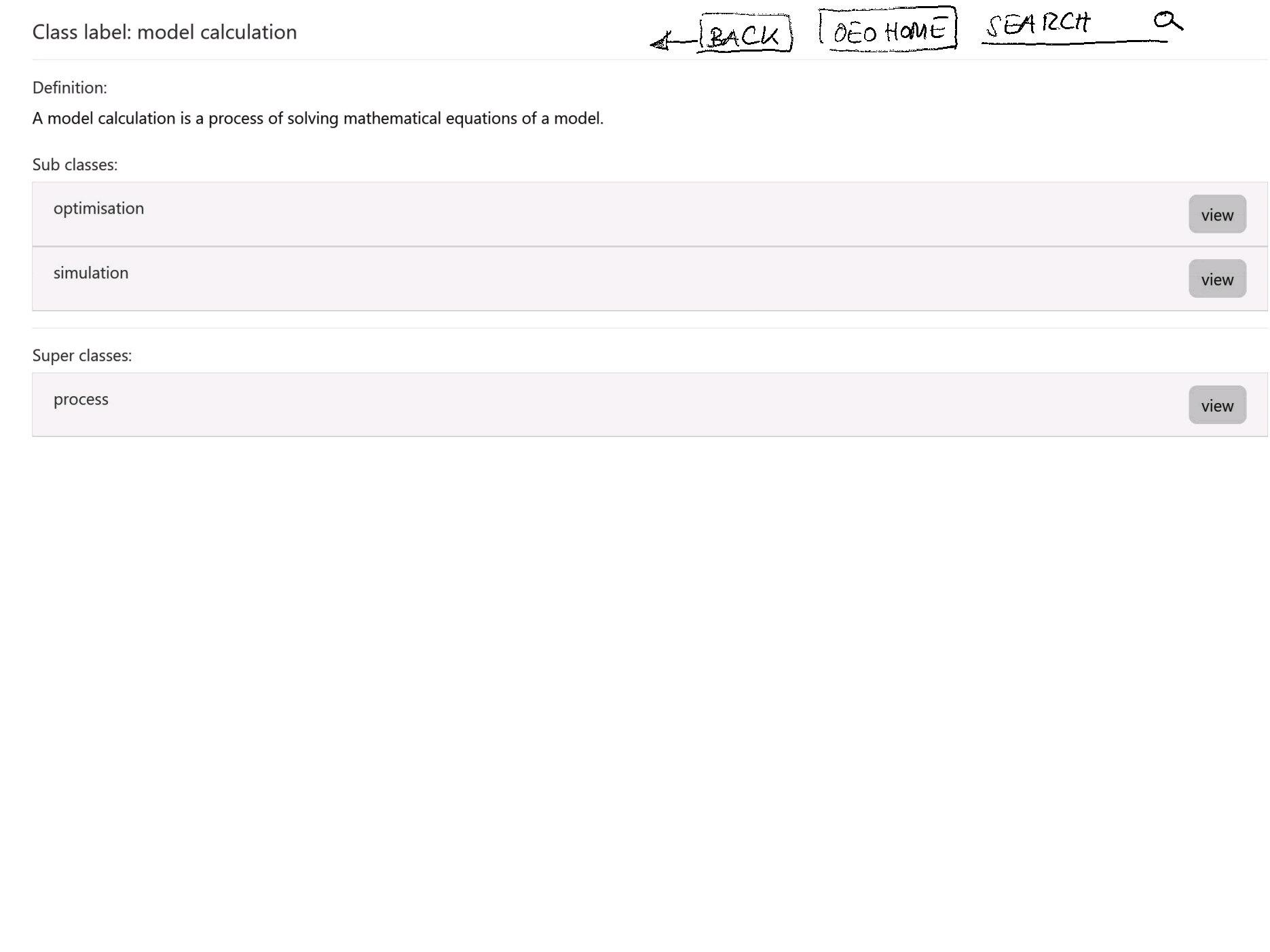
cc @l-emele @stap-m | non_priority | better navigation for textual oeo viewer i would like to suggest to add some simple navigational elements to the textual oeo viewer like this it can be navigated easier and usability will increase i made a scribble below on how it could look like when viewing a specific entity of course it would be great if the search bar would already be visible when landing here search bar lets users search for terms this is already possible in the back button would navigate to the previous page viewed oeo home would lead back to i think the search bar would be the most important element and increase usability quickly cc l emele stap m | 0 |
22,162 | 11,695,430,185 | IssuesEvent | 2020-03-06 07:29:47 | arcus-azure/arcus.messaging | https://api.github.com/repos/arcus-azure/arcus.messaging | closed | Provide Azure Service Bus plugin for interpreting correlation info from messages | area:correlation area:operations feature integration:service-bus | Provide Azure Service Bus plugin for interpreting correlation info for inbound messages and populate `ICorrelationInfo`, if possible.
This is just an idea and should first be analysed if it's possible and worth the effort.
For an example of what a Service Bus plugin is, see [SeanFeldman/ServiceBus.AttachmentPlugin](https://github.com/SeanFeldman/ServiceBus.AttachmentPlugin). | 1.0 | Provide Azure Service Bus plugin for interpreting correlation info from messages - Provide Azure Service Bus plugin for interpreting correlation info for inbound messages and populate `ICorrelationInfo`, if possible.
This is just an idea and should first be analysed if it's possible and worth the effort.
For an example of what a Service Bus plugin is, see [SeanFeldman/ServiceBus.AttachmentPlugin](https://github.com/SeanFeldman/ServiceBus.AttachmentPlugin). | non_priority | provide azure service bus plugin for interpreting correlation info from messages provide azure service bus plugin for interpreting correlation info for inbound messages and populate icorrelationinfo if possible this is just an idea and should first be analysed if it s possible and worth the effort for an example of what a service bus plugin is see | 0 |
146,845 | 11,758,644,639 | IssuesEvent | 2020-03-13 15:46:50 | juliema/aTRAM | https://api.github.com/repos/juliema/aTRAM | closed | add a setup test? | ready to test | would it be possible to add a little test so people can determine if python and libs are installed + bash and an assembler?
| 1.0 | add a setup test? - would it be possible to add a little test so people can determine if python and libs are installed + bash and an assembler?
| non_priority | add a setup test would it be possible to add a little test so people can determine if python and libs are installed bash and an assembler | 0 |
147,126 | 13,201,075,046 | IssuesEvent | 2020-08-14 09:26:19 | fac20/week-5-ELMP | https://api.github.com/repos/fac20/week-5-ELMP | opened | Would be great to have different error messages/codes for server errors | documentation | On submission, we have a 500 error coming back and the message is that our fortune is not well received, but we can't tell if this is coming from line 67 or line 73 of handlers.js. Is it possible to give them different error codes? | 1.0 | Would be great to have different error messages/codes for server errors - On submission, we have a 500 error coming back and the message is that our fortune is not well received, but we can't tell if this is coming from line 67 or line 73 of handlers.js. Is it possible to give them different error codes? | non_priority | would be great to have different error messages codes for server errors on submission we have a error coming back and the message is that our fortune is not well received but we can t tell if this is coming from line or line of handlers js is it possible to give them different error codes | 0 |
112,584 | 14,267,217,789 | IssuesEvent | 2020-11-20 20:04:34 | stoolball-england/stoolball-org-uk | https://api.github.com/repos/stoolball-england/stoolball-org-uk | opened | Review design for edit match result | design matches mvp | Includes print styles and required/optional fields.
- prominent link into the flow (eg on hover in match list, bottom of screen on mobile)
- before play
- batting scorecard (especially mobile)
- bowling scorecard (especially mobile)
- after play | 1.0 | Review design for edit match result - Includes print styles and required/optional fields.
- prominent link into the flow (eg on hover in match list, bottom of screen on mobile)
- before play
- batting scorecard (especially mobile)
- bowling scorecard (especially mobile)
- after play | non_priority | review design for edit match result includes print styles and required optional fields prominent link into the flow eg on hover in match list bottom of screen on mobile before play batting scorecard especially mobile bowling scorecard especially mobile after play | 0 |
2,115 | 4,240,718,109 | IssuesEvent | 2016-07-06 14:18:05 | cerana/cerana | https://api.github.com/repos/cerana/cerana | opened | Update service provider to use the daisy binary | provider - service | #### Issue Description
Have the service provider use the daisy binary to run services. Update accordingly to make that fit. Sort out the UID/GID allocation based on what that expects.
#### Related Tickets
#166 | 1.0 | Update service provider to use the daisy binary - #### Issue Description
Have the service provider use the daisy binary to run services. Update accordingly to make that fit. Sort out the UID/GID allocation based on what that expects.
#### Related Tickets
#166 | non_priority | update service provider to use the daisy binary issue description have the service provider use the daisy binary to run services update accordingly to make that fit sort out the uid gid allocation based on what that expects related tickets | 0 |
232,231 | 25,565,461,675 | IssuesEvent | 2022-11-30 14:00:33 | hygieia/api-audit | https://api.github.com/repos/hygieia/api-audit | closed | CVE-2021-43980 (Medium) detected in tomcat-embed-core-8.5.70.jar - autoclosed | security vulnerability | ## CVE-2021-43980 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.70.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.70/tomcat-embed-core-8.5.70.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.22.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.22.RELEASE.jar
- :x: **tomcat-embed-core-8.5.70.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/api-audit/commit/9c627a3dee72bf43b46a7cc41b8c073efba5cfab">9c627a3dee72bf43b46a7cc41b8c073efba5cfab</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The simplified implementation of blocking reads and writes introduced in Tomcat 10 and back-ported to Tomcat 9.0.47 onwards exposed a long standing (but extremely hard to trigger) concurrency bug in Apache Tomcat 10.1.0 to 10.1.0-M12, 10.0.0-M1 to 10.0.18, 9.0.0-M1 to 9.0.60 and 8.5.0 to 8.5.77 that could cause client connections to share an Http11Processor instance resulting in responses, or part responses, to be received by the wrong client.
<p>Publish Date: 2022-09-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43980>CVE-2021-43980</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3">https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3</a></p>
<p>Release Date: 2022-09-28</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 8.5.78</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.0.0.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-43980 (Medium) detected in tomcat-embed-core-8.5.70.jar - autoclosed - ## CVE-2021-43980 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.70.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.70/tomcat-embed-core-8.5.70.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.22.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.22.RELEASE.jar
- :x: **tomcat-embed-core-8.5.70.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/api-audit/commit/9c627a3dee72bf43b46a7cc41b8c073efba5cfab">9c627a3dee72bf43b46a7cc41b8c073efba5cfab</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The simplified implementation of blocking reads and writes introduced in Tomcat 10 and back-ported to Tomcat 9.0.47 onwards exposed a long standing (but extremely hard to trigger) concurrency bug in Apache Tomcat 10.1.0 to 10.1.0-M12, 10.0.0-M1 to 10.0.18, 9.0.0-M1 to 9.0.60 and 8.5.0 to 8.5.77 that could cause client connections to share an Http11Processor instance resulting in responses, or part responses, to be received by the wrong client.
<p>Publish Date: 2022-09-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43980>CVE-2021-43980</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3">https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3</a></p>
<p>Release Date: 2022-09-28</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 8.5.78</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.0.0.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tomcat embed core jar autoclosed cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details the simplified implementation of blocking reads and writes introduced in tomcat and back ported to tomcat onwards exposed a long standing but extremely hard to trigger concurrency bug in apache tomcat to to to and to that could cause client connections to share an instance resulting in responses or part responses to be received by the wrong client publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core direct dependency fix resolution org springframework boot spring boot starter web release step up your open source security game with mend | 0 |
273,619 | 23,771,618,282 | IssuesEvent | 2022-09-01 16:49:47 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Remove speedreader updater component (enabling theme support) | QA/Yes QA/Test-Plan-Specified release-notes feature/components OS/Android feature/speedreader OS/Desktop | The `Brave Speedreader Updater` component (`jicbkmdloagakknpihibphagfckhjdih`) only ships two data files in its CRX - `content-stylesheet.css` and `speedreader-updater.dat`.
The `.dat` file is completely unused, since Speedreader has been updated to no longer use the adblock list-based backend.
`content-stylesheet.css` is still used to override the style in `brave-core`, but it does so unconditionally even though there is already a speedreader stylesheet bundled inside `brave-core`. The stylesheet is now stable enough to not need to be updated dynamically, so it should be safe to remove this as well.
The stylesheet currently shipped by the component updater is fairly old and there is a PR (https://github.com/brave-experiments/SpeedReader/pull/36) to update it to match the current version in `brave-core`, enabling theme support. Merging this will make themes work without requiring the component at all.
Once this has enough roll-out, we should remove the speedreader component from `brave-core-crx-packager` as well. | 1.0 | Remove speedreader updater component (enabling theme support) - The `Brave Speedreader Updater` component (`jicbkmdloagakknpihibphagfckhjdih`) only ships two data files in its CRX - `content-stylesheet.css` and `speedreader-updater.dat`.
The `.dat` file is completely unused, since Speedreader has been updated to no longer use the adblock list-based backend.
`content-stylesheet.css` is still used to override the style in `brave-core`, but it does so unconditionally even though there is already a speedreader stylesheet bundled inside `brave-core`. The stylesheet is now stable enough to not need to be updated dynamically, so it should be safe to remove this as well.
The stylesheet currently shipped by the component updater is fairly old and there is a PR (https://github.com/brave-experiments/SpeedReader/pull/36) to update it to match the current version in `brave-core`, enabling theme support. Merging this will make themes work without requiring the component at all.
Once this has enough roll-out, we should remove the speedreader component from `brave-core-crx-packager` as well. | non_priority | remove speedreader updater component enabling theme support the brave speedreader updater component jicbkmdloagakknpihibphagfckhjdih only ships two data files in its crx content stylesheet css and speedreader updater dat the dat file is completely unused since speedreader has been updated to no longer use the adblock list based backend content stylesheet css is still used to override the style in brave core but it does so unconditionally even though there is already a speedreader stylesheet bundled inside brave core the stylesheet is now stable enough to not need to be updated dynamically so it should be safe to remove this as well the stylesheet currently shipped by the component updater is fairly old and there is a pr to update it to match the current version in brave core enabling theme support merging this will make themes work without requiring the component at all once this has enough roll out we should remove the speedreader component from brave core crx packager as well | 0 |
13,042 | 9,850,477,672 | IssuesEvent | 2019-06-19 08:16:47 | assistance-online/status | https://api.github.com/repos/assistance-online/status | opened | Release 2019.23 | AO api AO backend/core AO chauffeurs app AO identityservice AO webapplicatie | Planning
Deze update staat gepland om 10:30 uur. Zoals bij alle andere releases het verzoek om niet te factureren gedurende de update periode, deze zal naar verwachting voor 11:30 uur afgerond zijn.
Navolgend zal de DriverApp update uitgevoerd worden. De mi-databases zullen later op de middag opnieuw opgebouwd worden.
Wijzigingen:
• Grootste verandering in de afgelopen week/weken is nog niet direct zichtbaar, maar betreft de integratie met Allianz. Inmiddels hebben we alle berichtenstromen opgevangen en vinden er end-to-end testen plaats
• Naast Allianz is met behulp van Stephan Wiegers de finale ketentest voor SOS succesvol verlopen en zal ook SOS rechtstreeks opdrachten gaan aanbieden aan AO (deze week zijn ze hiermee gestart bij Bergnet)
• Binnen een dossier bestaat nu de mogelijkheid om niet alleen een Particuliere factuur toe te voegen, maar ook een factuur richting een niet particuliere debiteur
• Extra validatie in de flow van Transport zonder reparatiepoging (doordat de ingave van een eindbestemming niet werd afgedwongen bleven enkele dossiers hier hangen op Ter plaatse)
• Flow voor foutparkeerder aangepast zodat er geen zwevende dossiers meer ontstaan bij het afmelden van alleen de laadlocatie (zonder tussen of eindbestemming)
• Toevoegen van diverse parameters in vrachtbrief template
• Toevoegen LL/IM veld in chartermailtemplate
• Bugfix voor verspringing in lijsten (ontstaan door automatische update van component dat we hiervoor gebruiken)
• Verbetering voor automatische geocodeeractie
• Toevoegen van de optie om een link in de factuurmails mee te sturen. Sommige virusscanners lijken pdf’s van de mail te verwijderen, in de mailbody wordt nu een download link naar het bestand toegevoegd (in te richten via de mailtemplate)
• Retry mechaniek in de opbouw voor de MI gemaakt, zodat bij verstoringen het proces automatisch weer hervat wordt
• Dynamische vragenlijsten toegevoegd aan de MI database
• Bugfix voor fout met door elkaar lopende meldingen. Deze bestond uit 2 mogelijke oorzaken 1 ervan is opgepakt, de andere loopt in de huidige sprint mee. | 1.0 | Release 2019.23 - Planning
Deze update staat gepland om 10:30 uur. Zoals bij alle andere releases het verzoek om niet te factureren gedurende de update periode, deze zal naar verwachting voor 11:30 uur afgerond zijn.
Navolgend zal de DriverApp update uitgevoerd worden. De mi-databases zullen later op de middag opnieuw opgebouwd worden.
Wijzigingen:
• Grootste verandering in de afgelopen week/weken is nog niet direct zichtbaar, maar betreft de integratie met Allianz. Inmiddels hebben we alle berichtenstromen opgevangen en vinden er end-to-end testen plaats
• Naast Allianz is met behulp van Stephan Wiegers de finale ketentest voor SOS succesvol verlopen en zal ook SOS rechtstreeks opdrachten gaan aanbieden aan AO (deze week zijn ze hiermee gestart bij Bergnet)
• Binnen een dossier bestaat nu de mogelijkheid om niet alleen een Particuliere factuur toe te voegen, maar ook een factuur richting een niet particuliere debiteur
• Extra validatie in de flow van Transport zonder reparatiepoging (doordat de ingave van een eindbestemming niet werd afgedwongen bleven enkele dossiers hier hangen op Ter plaatse)
• Flow voor foutparkeerder aangepast zodat er geen zwevende dossiers meer ontstaan bij het afmelden van alleen de laadlocatie (zonder tussen of eindbestemming)
• Toevoegen van diverse parameters in vrachtbrief template
• Toevoegen LL/IM veld in chartermailtemplate
• Bugfix voor verspringing in lijsten (ontstaan door automatische update van component dat we hiervoor gebruiken)
• Verbetering voor automatische geocodeeractie
• Toevoegen van de optie om een link in de factuurmails mee te sturen. Sommige virusscanners lijken pdf’s van de mail te verwijderen, in de mailbody wordt nu een download link naar het bestand toegevoegd (in te richten via de mailtemplate)
• Retry mechaniek in de opbouw voor de MI gemaakt, zodat bij verstoringen het proces automatisch weer hervat wordt
• Dynamische vragenlijsten toegevoegd aan de MI database
• Bugfix voor fout met door elkaar lopende meldingen. Deze bestond uit 2 mogelijke oorzaken 1 ervan is opgepakt, de andere loopt in de huidige sprint mee. | non_priority | release planning deze update staat gepland om uur zoals bij alle andere releases het verzoek om niet te factureren gedurende de update periode deze zal naar verwachting voor uur afgerond zijn navolgend zal de driverapp update uitgevoerd worden de mi databases zullen later op de middag opnieuw opgebouwd worden wijzigingen • grootste verandering in de afgelopen week weken is nog niet direct zichtbaar maar betreft de integratie met allianz inmiddels hebben we alle berichtenstromen opgevangen en vinden er end to end testen plaats • naast allianz is met behulp van stephan wiegers de finale ketentest voor sos succesvol verlopen en zal ook sos rechtstreeks opdrachten gaan aanbieden aan ao deze week zijn ze hiermee gestart bij bergnet • binnen een dossier bestaat nu de mogelijkheid om niet alleen een particuliere factuur toe te voegen maar ook een factuur richting een niet particuliere debiteur • extra validatie in de flow van transport zonder reparatiepoging doordat de ingave van een eindbestemming niet werd afgedwongen bleven enkele dossiers hier hangen op ter plaatse • flow voor foutparkeerder aangepast zodat er geen zwevende dossiers meer ontstaan bij het afmelden van alleen de laadlocatie zonder tussen of eindbestemming • toevoegen van diverse parameters in vrachtbrief template • toevoegen ll im veld in chartermailtemplate • bugfix voor verspringing in lijsten ontstaan door automatische update van component dat we hiervoor gebruiken • verbetering voor automatische geocodeeractie • toevoegen van de optie om een link in de factuurmails mee te sturen sommige virusscanners lijken pdf’s van de mail te verwijderen in de mailbody wordt nu een download link naar het bestand toegevoegd in te richten via de mailtemplate • retry mechaniek in de opbouw voor de mi gemaakt zodat bij verstoringen het proces automatisch weer hervat wordt • dynamische vragenlijsten toegevoegd aan de mi database • bugfix voor fout met door elkaar lopende meldingen deze bestond uit mogelijke oorzaken ervan is opgepakt de andere loopt in de huidige sprint mee | 0 |
24,787 | 24,288,596,776 | IssuesEvent | 2022-09-29 02:19:03 | yirugi/sptest | https://api.github.com/repos/yirugi/sptest | opened | Y format for regression models | usability | <a href="https://github.itap.purdue.edu/hung17"><img src="https://avatars.github.itap.purdue.edu/u/3747?" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [hung17](https://github.itap.purdue.edu/hung17)**
_Monday Apr 25, 2022 at 20:05 GMT_
_Originally opened as https://github.itap.purdue.edu/ScientificSolutions/superpower_gui/issues/191_
----
**Describe the bug**
From Madeline's todo list in #184, the Y format for regression model needs to be updated.
**To Reproduce**
Steps to reproduce the behavior:
1. In the model specification, select "Regression", choose one of the distribution
2. Click Proceed button
3. In the Parameter Estimates tab, locate the Y format
**Error Message**
NA
**Expected behavior**
- Un/Standardized – Logistic, “Proportion” --> “Location” and “Scale”
- Un/Standardized – Poisson, “Rate” --> “Rate/Mean”
- Un/Standardized – Negative Binomial, “Mean” --> “Dispersion”, “SD” --> “Probability”
**Screenshots**
Un/Standardized – Logistic

Un/Standardized – Poisson

Un/Standardized – Negative Binomial

**System**
Version RC3.6 - published on 11 April 2022
Windows 10 Home (64-bit) 21H1
Google Chrome Version 100.0.4896.127 (Official Build) (32-bit)
| True | Y format for regression models - <a href="https://github.itap.purdue.edu/hung17"><img src="https://avatars.github.itap.purdue.edu/u/3747?" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [hung17](https://github.itap.purdue.edu/hung17)**
_Monday Apr 25, 2022 at 20:05 GMT_
_Originally opened as https://github.itap.purdue.edu/ScientificSolutions/superpower_gui/issues/191_
----
**Describe the bug**
From Madeline's todo list in #184, the Y format for regression model needs to be updated.
**To Reproduce**
Steps to reproduce the behavior:
1. In the model specification, select "Regression", choose one of the distribution
2. Click Proceed button
3. In the Parameter Estimates tab, locate the Y format
**Error Message**
NA
**Expected behavior**
- Un/Standardized – Logistic, “Proportion” --> “Location” and “Scale”
- Un/Standardized – Poisson, “Rate” --> “Rate/Mean”
- Un/Standardized – Negative Binomial, “Mean” --> “Dispersion”, “SD” --> “Probability”
**Screenshots**
Un/Standardized – Logistic

Un/Standardized – Poisson

Un/Standardized – Negative Binomial

**System**
Version RC3.6 - published on 11 April 2022
Windows 10 Home (64-bit) 21H1
Google Chrome Version 100.0.4896.127 (Official Build) (32-bit)
| non_priority | y format for regression models issue by monday apr at gmt originally opened as describe the bug from madeline s todo list in the y format for regression model needs to be updated to reproduce steps to reproduce the behavior in the model specification select regression choose one of the distribution click proceed button in the parameter estimates tab locate the y format error message na expected behavior un standardized – logistic “proportion” “location” and “scale” un standardized – poisson “rate” “rate mean” un standardized – negative binomial “mean” “dispersion” “sd” “probability” screenshots un standardized – logistic un standardized – poisson un standardized – negative binomial system version published on april windows home bit google chrome version official build bit | 0 |
249,637 | 26,968,332,994 | IssuesEvent | 2023-02-09 01:11:15 | Jsn2win/mergify_27ENG- | https://api.github.com/repos/Jsn2win/mergify_27ENG- | opened | CVE-2023-23931 (Medium) detected in cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl, cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2023-23931 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl</b>, <b>cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl</b></p></summary>
<p>
<details><summary><b>cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl</b></p></summary>
<p>cryptography is a package which provides cryptographic recipes and primitives to Python developers.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b2/26/7af637e6a7e87258b963f1731c5982fb31cd507f0d90d91836e446955d02/cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl">https://files.pythonhosted.org/packages/b2/26/7af637e6a7e87258b963f1731c5982fb31cd507f0d90d91836e446955d02/cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/mergify_27ENG-</p>
<p>Path to vulnerable library: /mergify_27ENG-</p>
<p>
Dependency Hierarchy:
- :x: **cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl** (Vulnerable Library)
</details>
<details><summary><b>cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl</b></p></summary>
<p>cryptography is a package which provides cryptographic recipes and primitives to Python developers.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/4c/a2/6565c5271a79e3c96d7a079053b4d8408a740d4bf365f0f5f244a807bd09/cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/4c/a2/6565c5271a79e3c96d7a079053b4d8408a740d4bf365f0f5f244a807bd09/cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/mergify_27ENG-</p>
<p>Path to vulnerable library: /mergify_27ENG-,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Jsn2win/mergify_27ENG-/commit/1badb2c85a0c3d00ce9ce53697d9d25fead7faf8">1badb2c85a0c3d00ce9ce53697d9d25fead7faf8</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
cryptography is a package designed to expose cryptographic primitives and recipes to Python developers. In affected versions `Cipher.update_into` would accept Python objects which implement the buffer protocol, but provide only immutable buffers. This would allow immutable objects (such as `bytes`) to be mutated, thus violating fundamental rules of Python and resulting in corrupted output. This now correctly raises an exception. This issue has been present since `update_into` was originally introduced in cryptography 1.8.
<p>Publish Date: 2023-02-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-23931>CVE-2023-23931</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-23931">https://www.cve.org/CVERecord?id=CVE-2023-23931</a></p>
<p>Release Date: 2023-02-07</p>
<p>Fix Resolution: cryptography - 39.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-23931 (Medium) detected in cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl, cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl - ## CVE-2023-23931 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl</b>, <b>cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl</b></p></summary>
<p>
<details><summary><b>cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl</b></p></summary>
<p>cryptography is a package which provides cryptographic recipes and primitives to Python developers.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/b2/26/7af637e6a7e87258b963f1731c5982fb31cd507f0d90d91836e446955d02/cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl">https://files.pythonhosted.org/packages/b2/26/7af637e6a7e87258b963f1731c5982fb31cd507f0d90d91836e446955d02/cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/mergify_27ENG-</p>
<p>Path to vulnerable library: /mergify_27ENG-</p>
<p>
Dependency Hierarchy:
- :x: **cryptography-3.4.7-cp36-abi3-manylinux2014_x86_64.whl** (Vulnerable Library)
</details>
<details><summary><b>cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl</b></p></summary>
<p>cryptography is a package which provides cryptographic recipes and primitives to Python developers.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/4c/a2/6565c5271a79e3c96d7a079053b4d8408a740d4bf365f0f5f244a807bd09/cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/4c/a2/6565c5271a79e3c96d7a079053b4d8408a740d4bf365f0f5f244a807bd09/cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/mergify_27ENG-</p>
<p>Path to vulnerable library: /mergify_27ENG-,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **cryptography-3.2.1-cp35-abi3-manylinux2010_x86_64.whl** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Jsn2win/mergify_27ENG-/commit/1badb2c85a0c3d00ce9ce53697d9d25fead7faf8">1badb2c85a0c3d00ce9ce53697d9d25fead7faf8</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
cryptography is a package designed to expose cryptographic primitives and recipes to Python developers. In affected versions `Cipher.update_into` would accept Python objects which implement the buffer protocol, but provide only immutable buffers. This would allow immutable objects (such as `bytes`) to be mutated, thus violating fundamental rules of Python and resulting in corrupted output. This now correctly raises an exception. This issue has been present since `update_into` was originally introduced in cryptography 1.8.
<p>Publish Date: 2023-02-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-23931>CVE-2023-23931</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-23931">https://www.cve.org/CVERecord?id=CVE-2023-23931</a></p>
<p>Release Date: 2023-02-07</p>
<p>Fix Resolution: cryptography - 39.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cryptography whl cryptography whl cve medium severity vulnerability vulnerable libraries cryptography whl cryptography whl cryptography whl cryptography is a package which provides cryptographic recipes and primitives to python developers library home page a href path to dependency file tmp ws scm mergify path to vulnerable library mergify dependency hierarchy x cryptography whl vulnerable library cryptography whl cryptography is a package which provides cryptographic recipes and primitives to python developers library home page a href path to dependency file tmp ws scm mergify path to vulnerable library mergify requirements txt dependency hierarchy x cryptography whl vulnerable library found in head commit a href found in base branch main vulnerability details cryptography is a package designed to expose cryptographic primitives and recipes to python developers in affected versions cipher update into would accept python objects which implement the buffer protocol but provide only immutable buffers this would allow immutable objects such as bytes to be mutated thus violating fundamental rules of python and resulting in corrupted output this now correctly raises an exception this issue has been present since update into was originally introduced in cryptography publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cryptography step up your open source security game with mend | 0 |
26,330 | 4,676,780,681 | IssuesEvent | 2016-10-07 13:10:36 | phingofficial/phing-issues-test | https://api.github.com/repos/phingofficial/phing-issues-test | opened | Win32FileSystem::resolveFile() broken (Trac #54) | defect Incomplete Migration Migrated from Trac | Migrated from https://www.phing.info/trac/ticket/54
```json
{
"status": "closed",
"changetime": "2009-09-22T21:44:32",
"description": "Win32FileSystem::resolveFile() sometimes returns the string \"path\" instead of the resolved path name.\n\nfix:\n\nin system/io/Win32FileSystem.php line 352,\nchange \"return path;\"\nto \"return $path;\"\n\nRegards,\n\nap.",
"reporter": "Andrew Prendergast",
"cc": "",
"resolution": "fixed",
"_ts": "1253655872000000",
"component": "",
"summary": "Win32FileSystem::resolveFile() broken",
"priority": "major",
"keywords": "",
"version": "2.2.0RC3",
"time": "2006-12-28T08:00:22",
"milestone": "",
"owner": "",
"type": "defect"
}
```
| 1.0 | Win32FileSystem::resolveFile() broken (Trac #54) - Migrated from https://www.phing.info/trac/ticket/54
```json
{
"status": "closed",
"changetime": "2009-09-22T21:44:32",
"description": "Win32FileSystem::resolveFile() sometimes returns the string \"path\" instead of the resolved path name.\n\nfix:\n\nin system/io/Win32FileSystem.php line 352,\nchange \"return path;\"\nto \"return $path;\"\n\nRegards,\n\nap.",
"reporter": "Andrew Prendergast",
"cc": "",
"resolution": "fixed",
"_ts": "1253655872000000",
"component": "",
"summary": "Win32FileSystem::resolveFile() broken",
"priority": "major",
"keywords": "",
"version": "2.2.0RC3",
"time": "2006-12-28T08:00:22",
"milestone": "",
"owner": "",
"type": "defect"
}
```
| non_priority | resolvefile broken trac migrated from json status closed changetime description resolvefile sometimes returns the string path instead of the resolved path name n nfix n nin system io php line nchange return path nto return path n nregards n nap reporter andrew prendergast cc resolution fixed ts component summary resolvefile broken priority major keywords version time milestone owner type defect | 0 |
221,150 | 24,590,748,487 | IssuesEvent | 2022-10-14 01:48:16 | postgres-ai/database-lab-engine | https://api.github.com/repos/postgres-ai/database-lab-engine | opened | CVE-2022-37601 (High) detected in loader-utils-1.4.0.tgz | security vulnerability | ## CVE-2022-37601 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>loader-utils-1.4.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>
Dependency Hierarchy:
- @postgres.ai/ce-file:packages/ce.tgz (Root Library)
- react-scripts-5.0.0.tgz
- babel-loader-8.2.3.tgz
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/postgres-ai/database-lab-engine/commit/b3ac62d12e3d43994ff7ad836e34da801ed665fb">b3ac62d12e3d43994ff7ad836e34da801ed665fb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in function parseQuery in parseQuery.js in webpack loader-utils 2.0.0 via the name variable in parseQuery.js.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-37601>CVE-2022-37601</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution: loader-utils - v2.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-37601 (High) detected in loader-utils-1.4.0.tgz - ## CVE-2022-37601 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>loader-utils-1.4.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>
Dependency Hierarchy:
- @postgres.ai/ce-file:packages/ce.tgz (Root Library)
- react-scripts-5.0.0.tgz
- babel-loader-8.2.3.tgz
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/postgres-ai/database-lab-engine/commit/b3ac62d12e3d43994ff7ad836e34da801ed665fb">b3ac62d12e3d43994ff7ad836e34da801ed665fb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in function parseQuery in parseQuery.js in webpack loader-utils 2.0.0 via the name variable in parseQuery.js.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-37601>CVE-2022-37601</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution: loader-utils - v2.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in loader utils tgz cve high severity vulnerability vulnerable library loader utils tgz utils for webpack loaders library home page a href dependency hierarchy postgres ai ce file packages ce tgz root library react scripts tgz babel loader tgz x loader utils tgz vulnerable library found in head commit a href found in base branch master vulnerability details prototype pollution vulnerability in function parsequery in parsequery js in webpack loader utils via the name variable in parsequery js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution loader utils step up your open source security game with mend | 0 |
300,693 | 22,692,638,607 | IssuesEvent | 2022-07-04 23:36:28 | FuelLabs/fuel-specs | https://api.github.com/repos/FuelLabs/fuel-specs | closed | Update sudo code to no longer use old color naming for asset_id | documentation | The sudo code in tx_validity.md has sudo code that names a param `col` which is from when "asset ID" used to be called "color". | 1.0 | Update sudo code to no longer use old color naming for asset_id - The sudo code in tx_validity.md has sudo code that names a param `col` which is from when "asset ID" used to be called "color". | non_priority | update sudo code to no longer use old color naming for asset id the sudo code in tx validity md has sudo code that names a param col which is from when asset id used to be called color | 0 |
107,123 | 16,751,633,612 | IssuesEvent | 2021-06-12 01:33:50 | gms-ws-demo/nibrs | https://api.github.com/repos/gms-ws-demo/nibrs | opened | CVE-2020-36189 (High) detected in multiple libraries | security vulnerability | ## CVE-2020-36189 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.5.jar</b>, <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.8.0.jar</b>, <b>jackson-databind-2.8.10.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-flatfile/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.0/jackson-databind-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- :x: **jackson-databind-2.8.0.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.10/jackson-databind-2.8.10.jar,nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/jackson-databind-2.8.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.10.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.DriverManagerConnectionSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189>CVE-2020-36189</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2996">https://github.com/FasterXML/jackson-databind/issues/2996</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.5","packageFilePaths":["/tools/nibrs-flatfile/pom.xml","/tools/nibrs-validate-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;com.fasterxml.jackson.core:jackson-databind:2.9.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-validation/pom.xml","/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter-json:2.1.5.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.0","packageFilePaths":["/tools/nibrs-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;com.fasterxml.jackson.core:jackson-databind:2.8.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.10","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.8.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-36189","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.DriverManagerConnectionSource.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-36189 (High) detected in multiple libraries - ## CVE-2020-36189 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.5.jar</b>, <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.8.0.jar</b>, <b>jackson-databind-2.8.10.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-flatfile/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.0/jackson-databind-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- :x: **jackson-databind-2.8.0.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.10/jackson-databind-2.8.10.jar,nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/jackson-databind-2.8.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.10.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.DriverManagerConnectionSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189>CVE-2020-36189</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2996">https://github.com/FasterXML/jackson-databind/issues/2996</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.5","packageFilePaths":["/tools/nibrs-flatfile/pom.xml","/tools/nibrs-validate-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;com.fasterxml.jackson.core:jackson-databind:2.9.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-validation/pom.xml","/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter-json:2.1.5.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.0","packageFilePaths":["/tools/nibrs-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;com.fasterxml.jackson.core:jackson-databind:2.8.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.10","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.8.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-36189","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.DriverManagerConnectionSource.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file nibrs tools nibrs flatfile pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy tika parsers jar root library x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file nibrs tools nibrs staging data pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar nibrs web nibrs web target nibrs web web inf lib jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar canner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file nibrs tools nibrs summary report common pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file nibrs tools nibrs common pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy tika parsers jar root library x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file nibrs tools nibrs fbi service pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar nibrs tools nibrs fbi service target nibrs fbi service web inf lib jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com newrelic agent deps ch qos logback core db drivermanagerconnectionsource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache tika tika parsers com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter json release com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree org apache tika tika parsers com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com newrelic agent deps ch qos logback core db drivermanagerconnectionsource vulnerabilityurl | 0 |
109,227 | 16,834,383,007 | IssuesEvent | 2021-06-18 09:57:57 | tunapanda/wikonnect | https://api.github.com/repos/tunapanda/wikonnect | closed | [BUG][SECURITY] User password cached in the browser after signup | security | ### Describe the bug:
An Ember record is created to hold the signup form values. Due to Ember store cache behavior, the initial values are merged with a successful user-created response. The new user-created profile data inclusive of the password are cached until either on tab reloads or user logouts.
The behavior currently causes issues with editing user profile immediately after signup
### Expected Behavior
Passwords should never be cached in the browser memory.
### Steps to reproduce
1) Visit https://app.wikonnect.org
2) Signup using email/username/password form
3) Inspect the Ember data store (using Ember inspector)
### Error Log / Stack Trace (where applicable)
### Tell us about your browser and operating system:
- Operating System:
- NodeJS Version:
- Ember Version:
### Screenshots where applicable
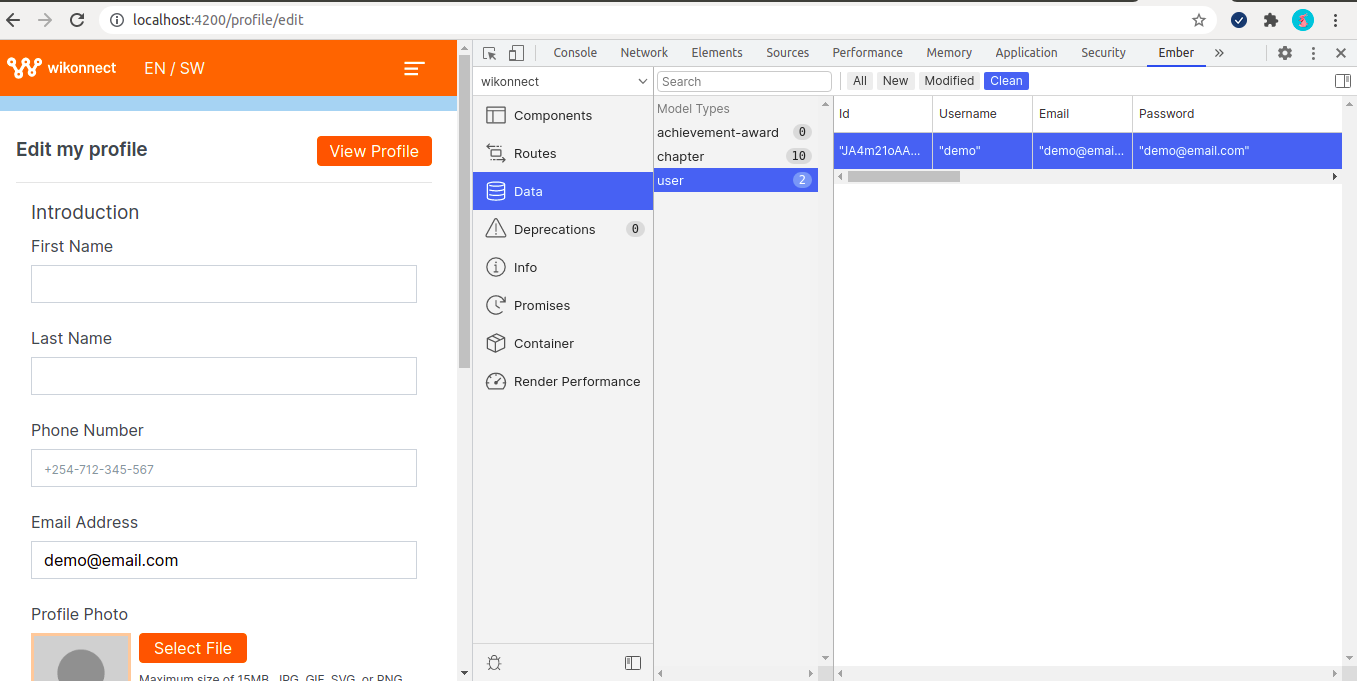
| True | [BUG][SECURITY] User password cached in the browser after signup - ### Describe the bug:
An Ember record is created to hold the signup form values. Due to Ember store cache behavior, the initial values are merged with a successful user-created response. The new user-created profile data inclusive of the password are cached until either on tab reloads or user logouts.
The behavior currently causes issues with editing user profile immediately after signup
### Expected Behavior
Passwords should never be cached in the browser memory.
### Steps to reproduce
1) Visit https://app.wikonnect.org
2) Signup using email/username/password form
3) Inspect the Ember data store (using Ember inspector)
### Error Log / Stack Trace (where applicable)
### Tell us about your browser and operating system:
- Operating System:
- NodeJS Version:
- Ember Version:
### Screenshots where applicable
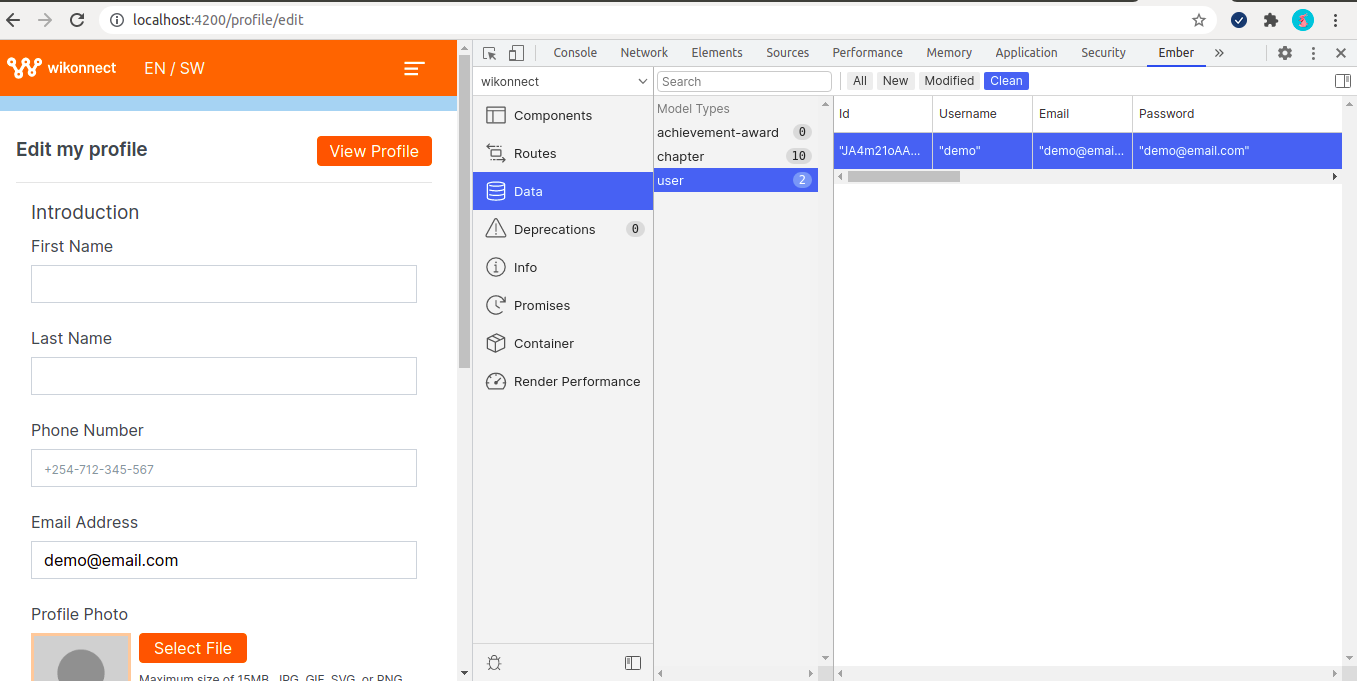
| non_priority | user password cached in the browser after signup describe the bug an ember record is created to hold the signup form values due to ember store cache behavior the initial values are merged with a successful user created response the new user created profile data inclusive of the password are cached until either on tab reloads or user logouts the behavior currently causes issues with editing user profile immediately after signup expected behavior passwords should never be cached in the browser memory steps to reproduce visit signup using email username password form inspect the ember data store using ember inspector error log stack trace where applicable tell us about your browser and operating system operating system nodejs version ember version screenshots where applicable | 0 |
402,625 | 27,377,133,969 | IssuesEvent | 2023-02-28 07:11:11 | jspm/generator | https://api.github.com/repos/jspm/generator | opened | Migrate jspm resolution rules doc into a local markdown | documentation | Currently the JSPM resolution rules are specified in a google docs:
https://docs.google.com/document/d/10SuVDUYTib8gkI8eeRyXZDY-j4zKR5Nd4bS9WcOy2Hw/edit#
We should move it to a markdown in this repo rather. | 1.0 | Migrate jspm resolution rules doc into a local markdown - Currently the JSPM resolution rules are specified in a google docs:
https://docs.google.com/document/d/10SuVDUYTib8gkI8eeRyXZDY-j4zKR5Nd4bS9WcOy2Hw/edit#
We should move it to a markdown in this repo rather. | non_priority | migrate jspm resolution rules doc into a local markdown currently the jspm resolution rules are specified in a google docs we should move it to a markdown in this repo rather | 0 |
236,272 | 18,091,011,121 | IssuesEvent | 2021-09-22 01:37:24 | KinsonDigital/Velaptor | https://api.github.com/repos/KinsonDigital/Velaptor | closed | 🚧Fix grammar issue in bug issue template | documentation | ### I have done the items below . . .
- [X] I have updated the title by replacing the '**_<title_**>' section.
### Description
In the _**Operating System**_ section of the _**Bug Issue Template**_, fix the grammar issue for the field title about the OS that the bug occurred on.
**It should be the value below:**
If you now what OS version the bug occurred on, enter the OS version here
**Incorrect Grammar Screenshot:**

### Acceptance Criteria
**This issue is finished when:**
- [x] Grammar issue fixed
### ToDo Items
- [x] Draft pull request created and linked to this issue
- [X] Priority label added to issue (**_low priority_**, **_medium priority_**, or **_high priority_**)
- [X] Issue linked to the proper project
- [X] Issue linked to proper milestone
- [X] ~Unit tests have been written and/or adjusted for code additions or changes~
- [X] ~All unit tests pass~
### Issue Dependencies
_No response_
### Related Work
_No response_ | 1.0 | 🚧Fix grammar issue in bug issue template - ### I have done the items below . . .
- [X] I have updated the title by replacing the '**_<title_**>' section.
### Description
In the _**Operating System**_ section of the _**Bug Issue Template**_, fix the grammar issue for the field title about the OS that the bug occurred on.
**It should be the value below:**
If you now what OS version the bug occurred on, enter the OS version here
**Incorrect Grammar Screenshot:**

### Acceptance Criteria
**This issue is finished when:**
- [x] Grammar issue fixed
### ToDo Items
- [x] Draft pull request created and linked to this issue
- [X] Priority label added to issue (**_low priority_**, **_medium priority_**, or **_high priority_**)
- [X] Issue linked to the proper project
- [X] Issue linked to proper milestone
- [X] ~Unit tests have been written and/or adjusted for code additions or changes~
- [X] ~All unit tests pass~
### Issue Dependencies
_No response_
### Related Work
_No response_ | non_priority | 🚧fix grammar issue in bug issue template i have done the items below i have updated the title by replacing the section description in the operating system section of the bug issue template fix the grammar issue for the field title about the os that the bug occurred on it should be the value below if you now what os version the bug occurred on enter the os version here incorrect grammar screenshot acceptance criteria this issue is finished when grammar issue fixed todo items draft pull request created and linked to this issue priority label added to issue low priority medium priority or high priority issue linked to the proper project issue linked to proper milestone unit tests have been written and or adjusted for code additions or changes all unit tests pass issue dependencies no response related work no response | 0 |
37,097 | 15,168,964,399 | IssuesEvent | 2021-02-12 20:18:13 | taskcluster/taskcluster | https://api.github.com/repos/taskcluster/taskcluster | closed | Add a put-url upload method | object-service | This should be similar to the current `s3` object type in the queue, but without S3-specific bits. Basically, caller specifies some metadata and gets back a URL to which they can make a PUT request.
Things to worry about:
* Some way to indicate to the caller whether they can or cannot have a non-identity content-encoding (GCS can [automatically decode a gzip encoding](https://cloud.google.com/storage/docs/transcoding) while AWS cannot)
* If possible, allow the caller to specify a hash (GCS and AWS both seem to use MD5?) that the cloud provider will verify
* The method should be idempotent, so for example if the upload fails and must be retried, a call to `uploadObject` with the same parameters should result in a newly signed URL for the same object
It's OK to make sub-optimal decisions here (such as "Content-Encoding must be identity"). Looking at the upload docs for GCS and AWS shows that they are not at all compatible, so we will likely have `s3-multipart` and `gcs-resumable` upload methods that allow the full expression of each cloud's functionality. | 1.0 | Add a put-url upload method - This should be similar to the current `s3` object type in the queue, but without S3-specific bits. Basically, caller specifies some metadata and gets back a URL to which they can make a PUT request.
Things to worry about:
* Some way to indicate to the caller whether they can or cannot have a non-identity content-encoding (GCS can [automatically decode a gzip encoding](https://cloud.google.com/storage/docs/transcoding) while AWS cannot)
* If possible, allow the caller to specify a hash (GCS and AWS both seem to use MD5?) that the cloud provider will verify
* The method should be idempotent, so for example if the upload fails and must be retried, a call to `uploadObject` with the same parameters should result in a newly signed URL for the same object
It's OK to make sub-optimal decisions here (such as "Content-Encoding must be identity"). Looking at the upload docs for GCS and AWS shows that they are not at all compatible, so we will likely have `s3-multipart` and `gcs-resumable` upload methods that allow the full expression of each cloud's functionality. | non_priority | add a put url upload method this should be similar to the current object type in the queue but without specific bits basically caller specifies some metadata and gets back a url to which they can make a put request things to worry about some way to indicate to the caller whether they can or cannot have a non identity content encoding gcs can while aws cannot if possible allow the caller to specify a hash gcs and aws both seem to use that the cloud provider will verify the method should be idempotent so for example if the upload fails and must be retried a call to uploadobject with the same parameters should result in a newly signed url for the same object it s ok to make sub optimal decisions here such as content encoding must be identity looking at the upload docs for gcs and aws shows that they are not at all compatible so we will likely have multipart and gcs resumable upload methods that allow the full expression of each cloud s functionality | 0 |
386,569 | 26,690,104,166 | IssuesEvent | 2023-01-27 03:30:36 | serilog/serilog | https://api.github.com/repos/serilog/serilog | closed | Wiki: "Home" doesn't follow recommendations | documentation | The [Home page](https://github.com/serilog/serilog/wiki) of the wiki uses a trailing period in its message template.
> ```cs
> var input = new { Latitude = 25, Longitude = 134 };
> var time = 34;
>
> log.Information("Processed {@SensorInput} in {TimeMS:000} ms.", input, time);
> ```
> ...
> The :000 segment following TimeMS is a standard .NET format string that affects how the property is rendered (not how it is captured). The standard console sink included with Serilog will render the above message as:
>
> `09:14:22 [Information] Processed { Latitude: 25, Longitude: 134 } in 034 ms.`
The wiki also has [recommendations on how message templates](https://github.com/serilog/serilog/wiki/Writing-Log-Events#message-template-recommendations) should be written:
> Sentences vs. Fragments - log event messages are fragments, not sentences; for consistency with other libraries that use Serilog, avoid a trailing period/full stop when possible.
The home page probably shouldn't have the trailing period.
I would submit a PR but GitHub doesn't support that for wikis? | 1.0 | Wiki: "Home" doesn't follow recommendations - The [Home page](https://github.com/serilog/serilog/wiki) of the wiki uses a trailing period in its message template.
> ```cs
> var input = new { Latitude = 25, Longitude = 134 };
> var time = 34;
>
> log.Information("Processed {@SensorInput} in {TimeMS:000} ms.", input, time);
> ```
> ...
> The :000 segment following TimeMS is a standard .NET format string that affects how the property is rendered (not how it is captured). The standard console sink included with Serilog will render the above message as:
>
> `09:14:22 [Information] Processed { Latitude: 25, Longitude: 134 } in 034 ms.`
The wiki also has [recommendations on how message templates](https://github.com/serilog/serilog/wiki/Writing-Log-Events#message-template-recommendations) should be written:
> Sentences vs. Fragments - log event messages are fragments, not sentences; for consistency with other libraries that use Serilog, avoid a trailing period/full stop when possible.
The home page probably shouldn't have the trailing period.
I would submit a PR but GitHub doesn't support that for wikis? | non_priority | wiki home doesn t follow recommendations the of the wiki uses a trailing period in its message template cs var input new latitude longitude var time log information processed sensorinput in timems ms input time the segment following timems is a standard net format string that affects how the property is rendered not how it is captured the standard console sink included with serilog will render the above message as processed latitude longitude in ms the wiki also has should be written sentences vs fragments log event messages are fragments not sentences for consistency with other libraries that use serilog avoid a trailing period full stop when possible the home page probably shouldn t have the trailing period i would submit a pr but github doesn t support that for wikis | 0 |
247,128 | 20,958,495,855 | IssuesEvent | 2022-03-27 12:53:39 | dnd-side-project/dnd-6th-5-backend | https://api.github.com/repos/dnd-side-project/dnd-6th-5-backend | closed | test : getOneUserPosts컨트롤러에 대한 유닛 테스트, 통합테스트 작성 | test | - [x] getOneUserPosts컨트롤러에 대한 유닛 테스트 작성
- [x] get user/:id/post api에 대한 통합 테스트 작성 | 1.0 | test : getOneUserPosts컨트롤러에 대한 유닛 테스트, 통합테스트 작성 - - [x] getOneUserPosts컨트롤러에 대한 유닛 테스트 작성
- [x] get user/:id/post api에 대한 통합 테스트 작성 | non_priority | test getoneuserposts컨트롤러에 대한 유닛 테스트 통합테스트 작성 getoneuserposts컨트롤러에 대한 유닛 테스트 작성 get user id post api에 대한 통합 테스트 작성 | 0 |
171,736 | 27,170,342,131 | IssuesEvent | 2023-02-17 18:48:31 | chanzuckerberg/single-cell-data-portal | https://api.github.com/repos/chanzuckerberg/single-cell-data-portal | opened | Hide marker genes with marker score <0.5 | design P1 gene expression | We have determined that marker genes with scores <0.5 are not very useful to users. To provide more valuable genes, we'd like to implement a cut off where no marker genes with scores <0.5 are surfaced in the marker score panel.
This ticket covers the following work:
- [ ] Implement cutoff
- [ ] if a cell type does not have any marker genes with scores >= 0.5 (design needed)
- [ ] Add a line to the documentation explaining this cutoff | 1.0 | Hide marker genes with marker score <0.5 - We have determined that marker genes with scores <0.5 are not very useful to users. To provide more valuable genes, we'd like to implement a cut off where no marker genes with scores <0.5 are surfaced in the marker score panel.
This ticket covers the following work:
- [ ] Implement cutoff
- [ ] if a cell type does not have any marker genes with scores >= 0.5 (design needed)
- [ ] Add a line to the documentation explaining this cutoff | non_priority | hide marker genes with marker score we have determined that marker genes with scores are not very useful to users to provide more valuable genes we d like to implement a cut off where no marker genes with scores are surfaced in the marker score panel this ticket covers the following work implement cutoff if a cell type does not have any marker genes with scores design needed add a line to the documentation explaining this cutoff | 0 |
2,537 | 4,891,018,956 | IssuesEvent | 2016-11-18 15:34:16 | OpenBCI/OpenBCI_GUI_v2.0 | https://api.github.com/repos/OpenBCI/OpenBCI_GUI_v2.0 | closed | Widget: EMG Responsiveness | finalize frontend in progress requirement | Improve the overall responsiveness of the EMG widget
- [X] Backend
- [X] Sliders
- [x] Stop circles from leaving window
- [x] Fix config window | 1.0 | Widget: EMG Responsiveness - Improve the overall responsiveness of the EMG widget
- [X] Backend
- [X] Sliders
- [x] Stop circles from leaving window
- [x] Fix config window | non_priority | widget emg responsiveness improve the overall responsiveness of the emg widget backend sliders stop circles from leaving window fix config window | 0 |
92,290 | 8,358,396,443 | IssuesEvent | 2018-10-03 02:34:44 | internetarchive/openlibrary | https://api.github.com/repos/internetarchive/openlibrary | opened | bundlesize fails on `make test` in docker image | docker tests | The css `bundlesize` tests fail inside the dev docker container.
on `make test`:
```
sh: 1: bundlesize: not found
npm ERR! Linux 4.4.0-135-generic
npm ERR! argv "/usr/bin/nodejs" "/usr/bin/npm" "run" "check-bundles"
npm ERR! node v4.2.6
npm ERR! npm v3.5.2
npm ERR! file sh
npm ERR! code ELIFECYCLE
npm ERR! errno ENOENT
npm ERR! syscall spawn
npm ERR! openlibrary@1.0.0 check-bundles: `npm run build-assets && bundlesize`
npm ERR! spawn ENOENT
npm ERR!
npm ERR! Failed at the openlibrary@1.0.0 check-bundles script 'npm run build-assets && bundlesize'.
npm ERR! Make sure you have the latest version of node.js and npm installed.
npm ERR! If you do, this is most likely a problem with the openlibrary package,
npm ERR! not with npm itself.
npm ERR! Tell the author that this fails on your system:
npm ERR! npm run build-assets && bundlesize
npm ERR! You can get information on how to open an issue for this project with:
npm ERR! npm bugs openlibrary
npm ERR! Or if that isn't available, you can get their info via:
npm ERR! npm owner ls openlibrary
npm ERR! There is likely additional logging output above.
npm ERR! Please include the following file with any support request:
npm ERR! /openlibrary/npm-debug.log
npm ERR! Test failed. See above for more details.
Makefile:98: recipe for target 'test' failed
make: *** [test] Error 1
```
Installing bundlesize globally with
`npm install bundlesize -g`
still fails, but with a different error:
```
make[1]: Leaving directory '/openlibrary'
/openlibrary/node_modules/bundlesize/index.js:3
const { inspect } = require('util')
^
SyntaxError: Unexpected token {
at exports.runInThisContext (vm.js:53:16)
at Module._compile (module.js:374:25)
at Object.Module._extensions..js (module.js:417:10)
at Module.load (module.js:344:32)
at Function.Module._load (module.js:301:12)
at Function.Module.runMain (module.js:442:10)
at startup (node.js:136:18)
at node.js:966:3
```
This is what I was seeing in 1136 (description)
The docker Xenial image has versions `(current: {"node":"4.2.6","npm":"3.5.2"})`
| 1.0 | bundlesize fails on `make test` in docker image - The css `bundlesize` tests fail inside the dev docker container.
on `make test`:
```
sh: 1: bundlesize: not found
npm ERR! Linux 4.4.0-135-generic
npm ERR! argv "/usr/bin/nodejs" "/usr/bin/npm" "run" "check-bundles"
npm ERR! node v4.2.6
npm ERR! npm v3.5.2
npm ERR! file sh
npm ERR! code ELIFECYCLE
npm ERR! errno ENOENT
npm ERR! syscall spawn
npm ERR! openlibrary@1.0.0 check-bundles: `npm run build-assets && bundlesize`
npm ERR! spawn ENOENT
npm ERR!
npm ERR! Failed at the openlibrary@1.0.0 check-bundles script 'npm run build-assets && bundlesize'.
npm ERR! Make sure you have the latest version of node.js and npm installed.
npm ERR! If you do, this is most likely a problem with the openlibrary package,
npm ERR! not with npm itself.
npm ERR! Tell the author that this fails on your system:
npm ERR! npm run build-assets && bundlesize
npm ERR! You can get information on how to open an issue for this project with:
npm ERR! npm bugs openlibrary
npm ERR! Or if that isn't available, you can get their info via:
npm ERR! npm owner ls openlibrary
npm ERR! There is likely additional logging output above.
npm ERR! Please include the following file with any support request:
npm ERR! /openlibrary/npm-debug.log
npm ERR! Test failed. See above for more details.
Makefile:98: recipe for target 'test' failed
make: *** [test] Error 1
```
Installing bundlesize globally with
`npm install bundlesize -g`
still fails, but with a different error:
```
make[1]: Leaving directory '/openlibrary'
/openlibrary/node_modules/bundlesize/index.js:3
const { inspect } = require('util')
^
SyntaxError: Unexpected token {
at exports.runInThisContext (vm.js:53:16)
at Module._compile (module.js:374:25)
at Object.Module._extensions..js (module.js:417:10)
at Module.load (module.js:344:32)
at Function.Module._load (module.js:301:12)
at Function.Module.runMain (module.js:442:10)
at startup (node.js:136:18)
at node.js:966:3
```
This is what I was seeing in 1136 (description)
The docker Xenial image has versions `(current: {"node":"4.2.6","npm":"3.5.2"})`
| non_priority | bundlesize fails on make test in docker image the css bundlesize tests fail inside the dev docker container on make test sh bundlesize not found npm err linux generic npm err argv usr bin nodejs usr bin npm run check bundles npm err node npm err npm npm err file sh npm err code elifecycle npm err errno enoent npm err syscall spawn npm err openlibrary check bundles npm run build assets bundlesize npm err spawn enoent npm err npm err failed at the openlibrary check bundles script npm run build assets bundlesize npm err make sure you have the latest version of node js and npm installed npm err if you do this is most likely a problem with the openlibrary package npm err not with npm itself npm err tell the author that this fails on your system npm err npm run build assets bundlesize npm err you can get information on how to open an issue for this project with npm err npm bugs openlibrary npm err or if that isn t available you can get their info via npm err npm owner ls openlibrary npm err there is likely additional logging output above npm err please include the following file with any support request npm err openlibrary npm debug log npm err test failed see above for more details makefile recipe for target test failed make error installing bundlesize globally with npm install bundlesize g still fails but with a different error make leaving directory openlibrary openlibrary node modules bundlesize index js const inspect require util syntaxerror unexpected token at exports runinthiscontext vm js at module compile module js at object module extensions js module js at module load module js at function module load module js at function module runmain module js at startup node js at node js this is what i was seeing in description the docker xenial image has versions current node npm | 0 |
6,349 | 4,233,324,797 | IssuesEvent | 2016-07-05 07:20:31 | MISP/MISP | https://api.github.com/repos/MISP/MISP | opened | Migrate Tag to Taxonomy | enhancement support usability | Feature request, or more a discussion point of finding the best way to do this.
For multiple things we still use the old tags for markings that are present in the taxonomies. It would be good for us to migrate from one system to the other.
An example is for example the TLP marking. We have a TAG called "TLP: Green" , and a taxonomy "tlp:green". How should we migrate everything cleanly?
- external python script - removing the old tag, and adding the new
- custom dirty php code updating the tags - removing tag, adding new, updating timestamps?
- general "migrate tag functionality"
Feedback is welcome
| True | Migrate Tag to Taxonomy - Feature request, or more a discussion point of finding the best way to do this.
For multiple things we still use the old tags for markings that are present in the taxonomies. It would be good for us to migrate from one system to the other.
An example is for example the TLP marking. We have a TAG called "TLP: Green" , and a taxonomy "tlp:green". How should we migrate everything cleanly?
- external python script - removing the old tag, and adding the new
- custom dirty php code updating the tags - removing tag, adding new, updating timestamps?
- general "migrate tag functionality"
Feedback is welcome
| non_priority | migrate tag to taxonomy feature request or more a discussion point of finding the best way to do this for multiple things we still use the old tags for markings that are present in the taxonomies it would be good for us to migrate from one system to the other an example is for example the tlp marking we have a tag called tlp green and a taxonomy tlp green how should we migrate everything cleanly external python script removing the old tag and adding the new custom dirty php code updating the tags removing tag adding new updating timestamps general migrate tag functionality feedback is welcome | 0 |
27,478 | 7,969,085,150 | IssuesEvent | 2018-07-16 07:41:44 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | opened | Candidate : Updated "SSN#" not be being updated in approved document from HR's end | Candidate Module Defect P1 Release#3 Build#13 Reopen on Release#3 Build10 | Steps To Replicate
Create a New Hire with W2 category
1. Login as Candidate
2. Sign the offer letter
3. Complete all the webforms by entering valid information
4. From the dash board screen >> Sign all the documents
5. Login as HR admin >> Reject only one document which has SSN in it
6. Login as candidate >> click on Getstarted >> user is navigated to "common details" form
7. change the SSN# and click on update
Experienced Behavior : Observed that the updated SSN # is not getting reflected in all the areas , It is updated in only rejected document
Expected Behavior : Ensure that the updated SSN # should get updated across all the areas where we have SSN# | 2.0 | Candidate : Updated "SSN#" not be being updated in approved document from HR's end - Steps To Replicate
Create a New Hire with W2 category
1. Login as Candidate
2. Sign the offer letter
3. Complete all the webforms by entering valid information
4. From the dash board screen >> Sign all the documents
5. Login as HR admin >> Reject only one document which has SSN in it
6. Login as candidate >> click on Getstarted >> user is navigated to "common details" form
7. change the SSN# and click on update
Experienced Behavior : Observed that the updated SSN # is not getting reflected in all the areas , It is updated in only rejected document
Expected Behavior : Ensure that the updated SSN # should get updated across all the areas where we have SSN# | non_priority | candidate updated ssn not be being updated in approved document from hr s end steps to replicate create a new hire with category login as candidate sign the offer letter complete all the webforms by entering valid information from the dash board screen sign all the documents login as hr admin reject only one document which has ssn in it login as candidate click on getstarted user is navigated to common details form change the ssn and click on update experienced behavior observed that the updated ssn is not getting reflected in all the areas it is updated in only rejected document expected behavior ensure that the updated ssn should get updated across all the areas where we have ssn | 0 |
264,802 | 20,033,331,726 | IssuesEvent | 2022-02-02 09:14:19 | eclipse/eclipsefuro | https://api.github.com/repos/eclipse/eclipsefuro | closed | Remove duplicate content in the documentation | documentation | Some of the documentation content is available in different pages. The FIDL docs have content that belongs to furo-cli and vice versa.
It makes no sense to maintain them multiple times.
There is also a chance to forget to update a "copy" of the content. | 1.0 | Remove duplicate content in the documentation - Some of the documentation content is available in different pages. The FIDL docs have content that belongs to furo-cli and vice versa.
It makes no sense to maintain them multiple times.
There is also a chance to forget to update a "copy" of the content. | non_priority | remove duplicate content in the documentation some of the documentation content is available in different pages the fidl docs have content that belongs to furo cli and vice versa it makes no sense to maintain them multiple times there is also a chance to forget to update a copy of the content | 0 |
7,682 | 10,853,931,968 | IssuesEvent | 2019-11-13 15:34:08 | LucaFalasca/Stoocky | https://api.github.com/repos/LucaFalasca/Stoocky | opened | Suggestion elements | Functional Requirement | The system shall suggest registered elements* added when the user tries to add a new element. | 1.0 | Suggestion elements - The system shall suggest registered elements* added when the user tries to add a new element. | non_priority | suggestion elements the system shall suggest registered elements added when the user tries to add a new element | 0 |
34,141 | 28,323,037,110 | IssuesEvent | 2023-04-11 03:58:55 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | UI Locks up when being shared via zoom | bug interface/infrastructure | I've been using the APSIM2021.07.08.6612 Windows build, and demonstrating it to a class of students via a Zoom (v5.7.1) screen (window) share.
The students have also screen shared from their computers.
The UI has locked up (won't open/close tree nodes, or do other actions like download/add soil) on a variety of computers (mine and student). This only happens when the window is being shared via zoom. It's intermittent - reminds me a bit of the behaviour of a single threaded browser app.
I'm not sure why Zoom is a particular problem. There has been no problem with the UI in other screen captures (eg OBS Studio).
Hopefully something that someone who is familiar with the UI components can figure out.
Cheers and well done on the new version!
Ben
| 1.0 | UI Locks up when being shared via zoom - I've been using the APSIM2021.07.08.6612 Windows build, and demonstrating it to a class of students via a Zoom (v5.7.1) screen (window) share.
The students have also screen shared from their computers.
The UI has locked up (won't open/close tree nodes, or do other actions like download/add soil) on a variety of computers (mine and student). This only happens when the window is being shared via zoom. It's intermittent - reminds me a bit of the behaviour of a single threaded browser app.
I'm not sure why Zoom is a particular problem. There has been no problem with the UI in other screen captures (eg OBS Studio).
Hopefully something that someone who is familiar with the UI components can figure out.
Cheers and well done on the new version!
Ben
| non_priority | ui locks up when being shared via zoom i ve been using the windows build and demonstrating it to a class of students via a zoom screen window share the students have also screen shared from their computers the ui has locked up won t open close tree nodes or do other actions like download add soil on a variety of computers mine and student this only happens when the window is being shared via zoom it s intermittent reminds me a bit of the behaviour of a single threaded browser app i m not sure why zoom is a particular problem there has been no problem with the ui in other screen captures eg obs studio hopefully something that someone who is familiar with the ui components can figure out cheers and well done on the new version ben | 0 |
90,812 | 8,272,811,511 | IssuesEvent | 2018-09-17 00:32:38 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed tests on release-2.1: roachtest/acceptance | C-test-failure O-robot | The following tests appear to have failed:
[#907833](https://teamcity.cockroachdb.com/viewLog.html?buildId=907833):
```
--- FAIL: roachtest/acceptance/cli/node-status (27.459s)
test.go:503,cli.go:79,cli.go:85,acceptance.go:59: expected [is_available is_live true true false false true true], but found [is_available is_live true true true true false false]:
--- FAIL: roachtest/acceptance/cli/node-status (27.459s)
test.go:503,cli.go:79,cli.go:85,acceptance.go:59: expected [is_available is_live true true false false true true], but found [is_available is_live true true true true false false]:
```
Please assign, take a look and update the issue accordingly.
| 1.0 | teamcity: failed tests on release-2.1: roachtest/acceptance - The following tests appear to have failed:
[#907833](https://teamcity.cockroachdb.com/viewLog.html?buildId=907833):
```
--- FAIL: roachtest/acceptance/cli/node-status (27.459s)
test.go:503,cli.go:79,cli.go:85,acceptance.go:59: expected [is_available is_live true true false false true true], but found [is_available is_live true true true true false false]:
--- FAIL: roachtest/acceptance/cli/node-status (27.459s)
test.go:503,cli.go:79,cli.go:85,acceptance.go:59: expected [is_available is_live true true false false true true], but found [is_available is_live true true true true false false]:
```
Please assign, take a look and update the issue accordingly.
| non_priority | teamcity failed tests on release roachtest acceptance the following tests appear to have failed fail roachtest acceptance cli node status test go cli go cli go acceptance go expected but found fail roachtest acceptance cli node status test go cli go cli go acceptance go expected but found please assign take a look and update the issue accordingly | 0 |
278,364 | 30,702,288,617 | IssuesEvent | 2023-07-27 01:17:46 | Trinadh465/linux-4.1.15_CVE-2023-28772 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2023-28772 | closed | CVE-2020-12770 (Medium) detected in linuxlinux-4.6 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-12770 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2023-28772/commit/943a37114977025aa089143316b489c8146cc673">943a37114977025aa089143316b489c8146cc673</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/scsi/sg.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/scsi/sg.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel through 5.6.11. sg_write lacks an sg_remove_request call in a certain failure case, aka CID-83c6f2390040.
<p>Publish Date: 2020-05-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-12770>CVE-2020-12770</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12770">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12770</a></p>
<p>Release Date: 2020-07-29</p>
<p>Fix Resolution: v5.7-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-12770 (Medium) detected in linuxlinux-4.6 - autoclosed - ## CVE-2020-12770 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2023-28772/commit/943a37114977025aa089143316b489c8146cc673">943a37114977025aa089143316b489c8146cc673</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/scsi/sg.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/scsi/sg.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel through 5.6.11. sg_write lacks an sg_remove_request call in a certain failure case, aka CID-83c6f2390040.
<p>Publish Date: 2020-05-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-12770>CVE-2020-12770</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12770">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-12770</a></p>
<p>Release Date: 2020-07-29</p>
<p>Fix Resolution: v5.7-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux autoclosed cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers scsi sg c drivers scsi sg c vulnerability details an issue was discovered in the linux kernel through sg write lacks an sg remove request call in a certain failure case aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
174,662 | 27,705,171,907 | IssuesEvent | 2023-03-14 10:42:40 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | Display the private shares as a list | Enhancement Design & UX feature:sharing | Follow up of https://github.com/owncloud/client/pull/4310#issuecomment-345999910
Maybe we could consider delimiting each entry (share) using a list with alternate colors (like the one in "Sync Protocol/Not Synced") to get rid of the rectangle that encloses the checkboxes now. I remember a mockup from some time ago:
<p align="center">
<img src="https://user-images.githubusercontent.com/2644445/33070389-222fa6ec-ceb8-11e7-9bb4-52cb343fc21d.png"/>
</p>
Additionally we could think of a way (icons, multi-line...) to avoid widening the dialog on such long names e.g. remote shares (currently displays the full federated share id + the string "`(remote)`")
## Screenshot for reference:
<p align="center">
<img src="https://user-images.githubusercontent.com/2644445/33069989-af6f5c34-ceb6-11e7-93b5-29359822499e.png"/>
</p> | 1.0 | Display the private shares as a list - Follow up of https://github.com/owncloud/client/pull/4310#issuecomment-345999910
Maybe we could consider delimiting each entry (share) using a list with alternate colors (like the one in "Sync Protocol/Not Synced") to get rid of the rectangle that encloses the checkboxes now. I remember a mockup from some time ago:
<p align="center">
<img src="https://user-images.githubusercontent.com/2644445/33070389-222fa6ec-ceb8-11e7-9bb4-52cb343fc21d.png"/>
</p>
Additionally we could think of a way (icons, multi-line...) to avoid widening the dialog on such long names e.g. remote shares (currently displays the full federated share id + the string "`(remote)`")
## Screenshot for reference:
<p align="center">
<img src="https://user-images.githubusercontent.com/2644445/33069989-af6f5c34-ceb6-11e7-93b5-29359822499e.png"/>
</p> | non_priority | display the private shares as a list follow up of maybe we could consider delimiting each entry share using a list with alternate colors like the one in sync protocol not synced to get rid of the rectangle that encloses the checkboxes now i remember a mockup from some time ago img src additionally we could think of a way icons multi line to avoid widening the dialog on such long names e g remote shares currently displays the full federated share id the string remote screenshot for reference img src | 0 |
370,439 | 25,907,125,655 | IssuesEvent | 2022-12-15 11:05:36 | pulp/pulp-oci-images | https://api.github.com/repos/pulp/pulp-oci-images | closed | Write multi-process container docs for signing service | Documentation prio-list | We need to document how to add the signing services to the multi-process container.
We should consider storing the scripts under /etc rather than /var/lib/pulp (to facilitate object storage eliminating /var/lib/pulp ). | 1.0 | Write multi-process container docs for signing service - We need to document how to add the signing services to the multi-process container.
We should consider storing the scripts under /etc rather than /var/lib/pulp (to facilitate object storage eliminating /var/lib/pulp ). | non_priority | write multi process container docs for signing service we need to document how to add the signing services to the multi process container we should consider storing the scripts under etc rather than var lib pulp to facilitate object storage eliminating var lib pulp | 0 |
12,815 | 3,091,801,719 | IssuesEvent | 2015-08-26 14:53:20 | education/classroom | https://api.github.com/repos/education/classroom | closed | Replace placeholder copy on create assignment page | bug design | Likely just an oversight:
<img width="996" alt="screen shot 2015-08-25 at 3 24 38 pm" src="https://cloud.githubusercontent.com/assets/123345/9469166/7748b1ec-4b3d-11e5-84b6-f268ddac308c.png">
| 1.0 | Replace placeholder copy on create assignment page - Likely just an oversight:
<img width="996" alt="screen shot 2015-08-25 at 3 24 38 pm" src="https://cloud.githubusercontent.com/assets/123345/9469166/7748b1ec-4b3d-11e5-84b6-f268ddac308c.png">
| non_priority | replace placeholder copy on create assignment page likely just an oversight img width alt screen shot at pm src | 0 |
51,689 | 21,779,147,302 | IssuesEvent | 2022-05-13 16:45:02 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Incorrect stub generated by the LibraryImportGenerator when pinning is used | area-System.Runtime.InteropServices in-pr | ### Description
I'm testing the **LibraryImportGenerator** and it would appear that the stub it generates is incorrect when a marshaller uses the two-stage marshalling feature and also provides a `GetPinnableReference` method returning a data type different from the one used by the `ToNativeValue` and `FromNativeValue` methods.
According to https://github.com/dotnet/runtime/blob/main/docs/design/libraries/LibraryImportGenerator/StructMarshalling.md that should not be a problem.
> If the TwoStageMarshalling feature is specified, the developer may also provide a ref-returning or readonly-ref-returning GetPinnableReference method. The GetPinnableReference method will be called before the ToNativeValue method is called. The ref returned by GetPinnableReference will be pinned with a fixed statement, but the pinned value will not be used (it acts exclusively as a side-effect). As a result, GetPinnableReference **can return a ref to any T** that can be used in a fixed statement (a C# unmanaged type).
### Reproduction Steps
The following code demonstrates the problem. It's incomplete, but enough to generate a marshalling stub.
``` C#
using System;
using System.Runtime.InteropServices;
[NativeMarshalling(typeof(TManagedMarshaller))]
public struct TManaged
{
}
public struct TOther
{
}
public struct TNative
{
}
[CustomTypeMarshaller(typeof(TManaged),
BufferSize = 10,
Features = CustomTypeMarshallerFeatures.TwoStageMarshalling | CustomTypeMarshallerFeatures.CallerAllocatedBuffer)]
public unsafe ref struct TManagedMarshaller
{
private Span<TOther> _buffer;
public TManagedMarshaller(TManaged managed)
: this(managed, Span<TOther>.Empty)
{
}
public TManagedMarshaller(TManaged managed, Span<TOther> buffer)
{
_buffer = buffer;
}
public ref TOther GetPinnableReference() => ref MemoryMarshal.GetReference(_buffer);
public TManaged ToManaged() => throw new NotImplementedException();
public TNative* ToNativeValue() => throw new NotImplementedException();
public void FromNativeValue(TNative* value) => throw new NotImplementedException();
}
partial class NativeMethods
{
[LibraryImport("TestLib")]
public static partial void Foo(TManaged value);
}
```
The code above generates the following stub where the data type of the variable in the fixed statement is `TNative` instead of `TOther`, which is the data type returned by `GetPinnableReference`.
``` C#
[System.CodeDom.Compiler.GeneratedCodeAttribute("Microsoft.Interop.LibraryImportGenerator", "7.0.6.25401")]
[System.Runtime.CompilerServices.SkipLocalsInitAttribute]
public static partial void Foo(global::Sandbox.TManaged value)
{
global::Sandbox.TNative* __value_gen_native;
//
// Setup
//
global::Sandbox.TManagedMarshaller __value_gen_native__marshaller = default;
//
// Marshal
//
global::Sandbox.TOther* __value_gen_native__marshaller__stackptr = stackalloc global::Sandbox.TOther[10];
__value_gen_native__marshaller = new(value, new System.Span<global::Sandbox.TOther>(__value_gen_native__marshaller__stackptr, 10));
fixed (global::Sandbox.TNative* __value_gen_native__ignored = __value_gen_native__marshaller)
{
__value_gen_native = __value_gen_native__marshaller.ToNativeValue();
{
__PInvoke__(__value_gen_native);
}
}
//
// Local P/Invoke
//
[System.Runtime.InteropServices.DllImportAttribute("TestLib", EntryPoint = "Foo", ExactSpelling = true)]
extern static unsafe void __PInvoke__(global::Sandbox.TNative* value);
}
```
### Expected behavior
The generated code should compile successfully.
### Actual behavior
The compiler produces the following error.
error CS0266: Cannot implicitly convert type 'Sandbox.TOther*' to 'Sandbox.TNative*'. An explicit conversion exists (are you missing a cast?)t?)
### Regression?
_No response_
### Known Workarounds
_No response_
### Configuration
**.NET SDK: Version:** 7.0.100-preview.5.22255.1
**OS Name:** Windows
**OS Version:** 10.0.19044
**OS Platform:** Windows
**RID:** win10-x64
### Other information
_No response_ | 1.0 | Incorrect stub generated by the LibraryImportGenerator when pinning is used - ### Description
I'm testing the **LibraryImportGenerator** and it would appear that the stub it generates is incorrect when a marshaller uses the two-stage marshalling feature and also provides a `GetPinnableReference` method returning a data type different from the one used by the `ToNativeValue` and `FromNativeValue` methods.
According to https://github.com/dotnet/runtime/blob/main/docs/design/libraries/LibraryImportGenerator/StructMarshalling.md that should not be a problem.
> If the TwoStageMarshalling feature is specified, the developer may also provide a ref-returning or readonly-ref-returning GetPinnableReference method. The GetPinnableReference method will be called before the ToNativeValue method is called. The ref returned by GetPinnableReference will be pinned with a fixed statement, but the pinned value will not be used (it acts exclusively as a side-effect). As a result, GetPinnableReference **can return a ref to any T** that can be used in a fixed statement (a C# unmanaged type).
### Reproduction Steps
The following code demonstrates the problem. It's incomplete, but enough to generate a marshalling stub.
``` C#
using System;
using System.Runtime.InteropServices;
[NativeMarshalling(typeof(TManagedMarshaller))]
public struct TManaged
{
}
public struct TOther
{
}
public struct TNative
{
}
[CustomTypeMarshaller(typeof(TManaged),
BufferSize = 10,
Features = CustomTypeMarshallerFeatures.TwoStageMarshalling | CustomTypeMarshallerFeatures.CallerAllocatedBuffer)]
public unsafe ref struct TManagedMarshaller
{
private Span<TOther> _buffer;
public TManagedMarshaller(TManaged managed)
: this(managed, Span<TOther>.Empty)
{
}
public TManagedMarshaller(TManaged managed, Span<TOther> buffer)
{
_buffer = buffer;
}
public ref TOther GetPinnableReference() => ref MemoryMarshal.GetReference(_buffer);
public TManaged ToManaged() => throw new NotImplementedException();
public TNative* ToNativeValue() => throw new NotImplementedException();
public void FromNativeValue(TNative* value) => throw new NotImplementedException();
}
partial class NativeMethods
{
[LibraryImport("TestLib")]
public static partial void Foo(TManaged value);
}
```
The code above generates the following stub where the data type of the variable in the fixed statement is `TNative` instead of `TOther`, which is the data type returned by `GetPinnableReference`.
``` C#
[System.CodeDom.Compiler.GeneratedCodeAttribute("Microsoft.Interop.LibraryImportGenerator", "7.0.6.25401")]
[System.Runtime.CompilerServices.SkipLocalsInitAttribute]
public static partial void Foo(global::Sandbox.TManaged value)
{
global::Sandbox.TNative* __value_gen_native;
//
// Setup
//
global::Sandbox.TManagedMarshaller __value_gen_native__marshaller = default;
//
// Marshal
//
global::Sandbox.TOther* __value_gen_native__marshaller__stackptr = stackalloc global::Sandbox.TOther[10];
__value_gen_native__marshaller = new(value, new System.Span<global::Sandbox.TOther>(__value_gen_native__marshaller__stackptr, 10));
fixed (global::Sandbox.TNative* __value_gen_native__ignored = __value_gen_native__marshaller)
{
__value_gen_native = __value_gen_native__marshaller.ToNativeValue();
{
__PInvoke__(__value_gen_native);
}
}
//
// Local P/Invoke
//
[System.Runtime.InteropServices.DllImportAttribute("TestLib", EntryPoint = "Foo", ExactSpelling = true)]
extern static unsafe void __PInvoke__(global::Sandbox.TNative* value);
}
```
### Expected behavior
The generated code should compile successfully.
### Actual behavior
The compiler produces the following error.
error CS0266: Cannot implicitly convert type 'Sandbox.TOther*' to 'Sandbox.TNative*'. An explicit conversion exists (are you missing a cast?)t?)
### Regression?
_No response_
### Known Workarounds
_No response_
### Configuration
**.NET SDK: Version:** 7.0.100-preview.5.22255.1
**OS Name:** Windows
**OS Version:** 10.0.19044
**OS Platform:** Windows
**RID:** win10-x64
### Other information
_No response_ | non_priority | incorrect stub generated by the libraryimportgenerator when pinning is used description i m testing the libraryimportgenerator and it would appear that the stub it generates is incorrect when a marshaller uses the two stage marshalling feature and also provides a getpinnablereference method returning a data type different from the one used by the tonativevalue and fromnativevalue methods according to that should not be a problem if the twostagemarshalling feature is specified the developer may also provide a ref returning or readonly ref returning getpinnablereference method the getpinnablereference method will be called before the tonativevalue method is called the ref returned by getpinnablereference will be pinned with a fixed statement but the pinned value will not be used it acts exclusively as a side effect as a result getpinnablereference can return a ref to any t that can be used in a fixed statement a c unmanaged type reproduction steps the following code demonstrates the problem it s incomplete but enough to generate a marshalling stub c using system using system runtime interopservices public struct tmanaged public struct tother public struct tnative customtypemarshaller typeof tmanaged buffersize features customtypemarshallerfeatures twostagemarshalling customtypemarshallerfeatures callerallocatedbuffer public unsafe ref struct tmanagedmarshaller private span buffer public tmanagedmarshaller tmanaged managed this managed span empty public tmanagedmarshaller tmanaged managed span buffer buffer buffer public ref tother getpinnablereference ref memorymarshal getreference buffer public tmanaged tomanaged throw new notimplementedexception public tnative tonativevalue throw new notimplementedexception public void fromnativevalue tnative value throw new notimplementedexception partial class nativemethods public static partial void foo tmanaged value the code above generates the following stub where the data type of the variable in the fixed statement is tnative instead of tother which is the data type returned by getpinnablereference c public static partial void foo global sandbox tmanaged value global sandbox tnative value gen native setup global sandbox tmanagedmarshaller value gen native marshaller default marshal global sandbox tother value gen native marshaller stackptr stackalloc global sandbox tother value gen native marshaller new value new system span value gen native marshaller stackptr fixed global sandbox tnative value gen native ignored value gen native marshaller value gen native value gen native marshaller tonativevalue pinvoke value gen native local p invoke extern static unsafe void pinvoke global sandbox tnative value expected behavior the generated code should compile successfully actual behavior the compiler produces the following error error cannot implicitly convert type sandbox tother to sandbox tnative an explicit conversion exists are you missing a cast t regression no response known workarounds no response configuration net sdk version preview os name windows os version os platform windows rid other information no response | 0 |
37,196 | 9,977,696,582 | IssuesEvent | 2019-07-09 17:56:56 | nodejs/node | https://api.github.com/repos/nodejs/node | closed | Cosmetic: Start menu item installed by Node 12 uses old/outdated node icon | build | Start menu item installed by Node 12 uses old/outdated node icon (last updated Aug 2015):

It should look more like this image (per current branding from Feb 2016):

| 1.0 | Cosmetic: Start menu item installed by Node 12 uses old/outdated node icon - Start menu item installed by Node 12 uses old/outdated node icon (last updated Aug 2015):

It should look more like this image (per current branding from Feb 2016):

| non_priority | cosmetic start menu item installed by node uses old outdated node icon start menu item installed by node uses old outdated node icon last updated aug it should look more like this image per current branding from feb | 0 |
112,109 | 9,554,052,488 | IssuesEvent | 2019-05-02 20:55:38 | mautic/mautic | https://api.github.com/repos/mautic/mautic | closed | Update needed on GoTo plugin before 14th August | Bug Plugin Ready To Test | | Q | A
| ---| ---
| Bug report? | x
| Feature request? |
| Enhancement? |
## Description:
> Dear LogMeIn GoTo Developer,
>
> Thank you for using the LogMeIn GoTo Developer Center. We want to make sure you are aware of important changes that will impact use of the Center and APIs. Please note that your action is required.
>
> To improve security for our API program, we are going to start to enforce a strict OAuth 2.0 authentication protocol.
>
> This change in authentication protocol is available now, however, the old protocol will also remain in place until August 14, 2018 to give you time to test and update your code to use the new authentication services available under https://api.getgo.com/oauth/v2.
>
> These changes affect the following APIs: GoToMeeting APIs, GoToWebinar APIs, GoToTraining APIs, GoToAssist APIs, GoToAssist SeeIt APIs and related Administrative APIs. GoToAssist Corporate APIs are not impacted by this change.
>
> Please review the OAuth Migration Guide (http://go.logmeininc.com/JG1QAO0rqF04Ymu3Hm006r0) for details. Please direct any questions to developer-support@logmein.com.
>
> Our number one priority continues to be delivering great service and a best-in-class experience to you, our valued customer. We are here to help should you have any questions!
>
> Thank you,
>
> The LogMeIn GoTo Developer team | 1.0 | Update needed on GoTo plugin before 14th August - | Q | A
| ---| ---
| Bug report? | x
| Feature request? |
| Enhancement? |
## Description:
> Dear LogMeIn GoTo Developer,
>
> Thank you for using the LogMeIn GoTo Developer Center. We want to make sure you are aware of important changes that will impact use of the Center and APIs. Please note that your action is required.
>
> To improve security for our API program, we are going to start to enforce a strict OAuth 2.0 authentication protocol.
>
> This change in authentication protocol is available now, however, the old protocol will also remain in place until August 14, 2018 to give you time to test and update your code to use the new authentication services available under https://api.getgo.com/oauth/v2.
>
> These changes affect the following APIs: GoToMeeting APIs, GoToWebinar APIs, GoToTraining APIs, GoToAssist APIs, GoToAssist SeeIt APIs and related Administrative APIs. GoToAssist Corporate APIs are not impacted by this change.
>
> Please review the OAuth Migration Guide (http://go.logmeininc.com/JG1QAO0rqF04Ymu3Hm006r0) for details. Please direct any questions to developer-support@logmein.com.
>
> Our number one priority continues to be delivering great service and a best-in-class experience to you, our valued customer. We are here to help should you have any questions!
>
> Thank you,
>
> The LogMeIn GoTo Developer team | non_priority | update needed on goto plugin before august q a bug report x feature request enhancement description dear logmein goto developer thank you for using the logmein goto developer center we want to make sure you are aware of important changes that will impact use of the center and apis please note that your action is required to improve security for our api program we are going to start to enforce a strict oauth authentication protocol this change in authentication protocol is available now however the old protocol will also remain in place until august to give you time to test and update your code to use the new authentication services available under https api getgo com oauth these changes affect the following apis gotomeeting apis gotowebinar apis gototraining apis gotoassist apis gotoassist seeit apis and related administrative apis gotoassist corporate apis are not impacted by this change please review the oauth migration guide for details please direct any questions to developer support logmein com our number one priority continues to be delivering great service and a best in class experience to you our valued customer we are here to help should you have any questions thank you the logmein goto developer team | 0 |
4,526 | 3,036,595,289 | IssuesEvent | 2015-08-06 12:56:03 | dotse/zonemaster-engine | https://api.github.com/repos/dotse/zonemaster-engine | opened | args.ns should only be a name server name | test code | args.ns should always be only the nameserver name, now it is often a mix of ns/address.
If there is an address, split it out to args.address.
Any change must also update the logging string so that the address is not forgotten,
"Nameserver {ns} did not..." -> "Nameserver {ns}/{address} did not..."
This also affects all the translation strings. | 1.0 | args.ns should only be a name server name - args.ns should always be only the nameserver name, now it is often a mix of ns/address.
If there is an address, split it out to args.address.
Any change must also update the logging string so that the address is not forgotten,
"Nameserver {ns} did not..." -> "Nameserver {ns}/{address} did not..."
This also affects all the translation strings. | non_priority | args ns should only be a name server name args ns should always be only the nameserver name now it is often a mix of ns address if there is an address split it out to args address any change must also update the logging string so that the address is not forgotten nameserver ns did not nameserver ns address did not this also affects all the translation strings | 0 |
35,171 | 14,628,152,802 | IssuesEvent | 2020-12-23 13:39:29 | Componolit/systematization-binary-vulnerabilities | https://api.github.com/repos/Componolit/systematization-binary-vulnerabilities | opened | CVE-YYYY-NNNN: <Short name> | Denial of Service IPv6 | # Description
> The function used to decapsulate RPL extension headers does not check the length value of an RPL extension header received, allowing attackers to put it into an infinite loop.
# Root cause
> An infinite loop exists in the uIP TCP/IP stack component when handling RPL extension headers of IPv6 network packets in rpl_remove_header in net/rpl/rpl-ext-header.c.
# Links
- [CVE Entry](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13986)
- [Report](https://www.forescout.com/company/resources/amnesia33-how-tcp-ip-stacks-breed-critical-vulnerabilities-in-iot-ot-and-it-devices/)
| 1.0 | CVE-YYYY-NNNN: <Short name> - # Description
> The function used to decapsulate RPL extension headers does not check the length value of an RPL extension header received, allowing attackers to put it into an infinite loop.
# Root cause
> An infinite loop exists in the uIP TCP/IP stack component when handling RPL extension headers of IPv6 network packets in rpl_remove_header in net/rpl/rpl-ext-header.c.
# Links
- [CVE Entry](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13986)
- [Report](https://www.forescout.com/company/resources/amnesia33-how-tcp-ip-stacks-breed-critical-vulnerabilities-in-iot-ot-and-it-devices/)
| non_priority | cve yyyy nnnn description the function used to decapsulate rpl extension headers does not check the length value of an rpl extension header received allowing attackers to put it into an infinite loop root cause an infinite loop exists in the uip tcp ip stack component when handling rpl extension headers of network packets in rpl remove header in net rpl rpl ext header c links | 0 |
26,928 | 20,912,063,246 | IssuesEvent | 2022-03-24 10:12:30 | lvaudor/glitter | https://api.github.com/repos/lvaudor/glitter | closed | Create an lvaudor R-universe | Infrastructure :hammer_and_wrench: | See "Enable your personal universe" on https://r-universe.dev/help/
With that we will have simpler installation instructions in the README. | 1.0 | Create an lvaudor R-universe - See "Enable your personal universe" on https://r-universe.dev/help/
With that we will have simpler installation instructions in the README. | non_priority | create an lvaudor r universe see enable your personal universe on with that we will have simpler installation instructions in the readme | 0 |
98,453 | 12,325,115,674 | IssuesEvent | 2020-05-13 14:38:12 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | ReorderableListview improvement needed | f: material design f: scrolling framework proposal | When using ReorderableListview, it works fine when you reorder upwards, but when you reorder downwards, the transition isn't triggered soon enough. I guess in case of downwards reorder, the top line instead of bottom line of the object below should be used to trigger. | 1.0 | ReorderableListview improvement needed - When using ReorderableListview, it works fine when you reorder upwards, but when you reorder downwards, the transition isn't triggered soon enough. I guess in case of downwards reorder, the top line instead of bottom line of the object below should be used to trigger. | non_priority | reorderablelistview improvement needed when using reorderablelistview it works fine when you reorder upwards but when you reorder downwards the transition isn t triggered soon enough i guess in case of downwards reorder the top line instead of bottom line of the object below should be used to trigger | 0 |
202,681 | 15,837,776,084 | IssuesEvent | 2021-04-06 21:18:09 | mvdh7/pytzer | https://api.github.com/repos/mvdh7/pytzer | closed | Document the Seawater coefficient library | documentation | It's the default, and parts of the documentation refer to it, but it is not itself documented yet | 1.0 | Document the Seawater coefficient library - It's the default, and parts of the documentation refer to it, but it is not itself documented yet | non_priority | document the seawater coefficient library it s the default and parts of the documentation refer to it but it is not itself documented yet | 0 |
63,266 | 7,709,286,187 | IssuesEvent | 2018-05-22 08:44:10 | greatnewcls/IQ4LK23ROQOKHZC3VKUTGRNI | https://api.github.com/repos/greatnewcls/IQ4LK23ROQOKHZC3VKUTGRNI | reopened | hKZI3uZkv/UiFurh4+AhXNmJQUZ3ehbcOzkL9fXbtiWoN5ahAeQnt+vU1SRlOI5mgxFTnHulmYUab1EYytWdOWq5zsJIGHiKMTvrV2XKXCM4W93nYAjlvoQsc0hdPY1P7AwMAgTCHtZJzbGzDXV0XYTGLt7pXwEefDWXwcr//Fg= | design | WgvrwxZzWNjhogB/LbiJLVzKV2uEbeQXps/zMKR8hqMx22itcnxuCUfW3697QhtI1Ek0t1MEnXGR6xONTLhVt+7WEFcm3GqUaCnToNBxS5HCwY1FPMOfMuBDdMAB3rQ7Q4nyIf99pVJ+fNJe+gY6KUidmRtwnJiqgCDcYrtL6/Wt/6+vklkdOLZsXYJsuGISQVKm4QJorJUn8hErmhrJCdUjzMTIAAmuoRx/1KGYDvy5TKraSmzfB6+2uS4Kd9kCpVluTF1iocxmX+PV4ho2bp6Hr7itDyGaIEYBWUPNevTbZgkOIY/6vsGEcs7LxidQqWTO4f76e+kINbW5r2cmkmgi0XanTnmm4X9vxqqdRWwAXczUGHHVQ+khTYIhW/nJFZlbebt/dl72ae3zTBpZCqr4a1OQqnmr1hbpYrLGUy9HrWxG3fS+FhbjjEUw/XkoHaocqygRHO0M3o17rL9dQ0tdXx3BYoLmgK5HjWEnSLJD3vhnMmkVHxi5I8dFH7dBtYEhTNB4MBDQB0TM+Mba+l/xjNch46bhkV++fh+xEggE+knWYrfsbWaH7DskYMcP2V7Le2x11rJx2UdeZbQ9/8rEH+76zBrQVfqJcyyRLR31nFSMYDLG9JxzhudMpJX9BPpJ1mK37G1mh+w7JGDHD39ESwrmDgqsB2hUYPG1m8zw1ljwG6R1bba201qiY6L+lmHn2tGvLVBnHhYmRYwLIvbLNZKZnPQsMxwlZ0RXjR0yqhAGe+Fb+980AU+2aQDp9ZxUjGAyxvScc4bnTKSV/QT6SdZit+xtZofsOyRgxw/zURIC9wcFFhmb8p2KGzDp28EpJxw6E6FOF7rifb0RWllsi3MAq4KJUvTKrNEzsbZGVQkCM/OAwPtIPjCr2Pz7jtwLUhqIC7Thj9k1Ppgh+uuBKc9tG3X4wcbPB7p3sHyRpRgSMQJzf3fEtivZ7wvdCW4SWUDE7nKbXR8Wq+2X4BcNFStdBYilRr0iCf823YVR3EUmeJY7B0DHyyyaIjm1Jvpl40LGyBPuI0RGklEWtG8FKPRWYTMryr/LDieRCvtjFcYVXI8nQKVih9IFoFfJfZQALVWvXqjOey/ftY4232i4/etrshNctL1ZXxtAfHHrjMCsQBM9V/Qe92c0++SwASSy+wiQV3pBJvoyCdErJA1eJxtC1cV/EDcvYj5lVkkE+knWYrfsbWaH7DskYMcPgNe1yRZ48BVIl1urhvuppImYVJJyTVEUz3bFzqT9OxjiwRRYvP1semePtMPDCCXHzxWqVKSmeLHK4ByTZnhKBRZ0KntVL6HN3poD3gNdDdRHKiPSdQ/D4VWePRuNE5nHHyZK055pfoQGwI4Iua7QCBZ0KntVL6HN3poD3gNdDdQxQDsBUFIxBEkwm0ebT1hzvYYbweiTa0JzWR8ESMgUdVGm5aklsXn4sOJtPSG7uHO3dw7MIQ6BF/OSfABQrBZs2GZgYRjL+6gAsbXNGijAks2NrYd2FRt/uq7OIubbD5XrYAfhr06EWOtHupeSorAMQhL23FuJ5aXfnyRfrOtQ2dKcik3U3v+UcO2GT6B0OQHnEBrtIdSvqNVwzEUCzzKB2zr25EmX3kAQ5s1pmP6VcU645+G0T3dAbpLickmRQF5ITMYeZI54AhNm9wbsPVG5ari/i453Ta5o/xK4Z6jECfzCZnTVu3NIYeUOk0U3tu/yx9N6nlSqlulShwxEYqQOQ91GaqqDisI6noLWQi+uRxTtL/0EmbZ4zEKxPqEG+86QA401G+dVnpYUPG6V4ng/4sEUWLz9bHpnj7TDwwglx1ar7IzG9WUuRL+cI8Qm8P5Fl2g4+hy1I9bNZBuxK2T64sEUWLz9bHpnj7TDwwglx/pfxPUu6xx5KmooKvR+0wXWQ4/xCxGv6AYdiaWBLR+t97Lk73Qlv3UarawsdWSJUvXhuiSYFDzltdc1k2YyQxDANLujbHVMWktyarf/nEwqORriBZNnkRDuK/g3q4x+ZtMOz3yeDt8bZhF4/NH/1qBDZO2zdD+1S/ByadwvIc4YYRw+PAQA+HTJRVmrGA2qymbjg1mkiMG4DybJ3f49UJErSEF1zQ0+7ii+aPkqVECuRSC3ZxNMmKdrFUh5zu51k5noSlEJvyOtdb7eWjhNw/Xd3xl3F4dNSJDzJjXa3kzw6SvlFns4+HI/LoHbAnErqU6OnbzqmTiQlGIZ+kYJTg5UP9FCPDt+hR4loo78etrqzmY/HLfBjiMfk/+JiqCqShsGwd0Vh6rvEfHtR7MDFFjCo0z9TgAST+oN+sUZ4Bt7Vi5XoPu+t/QXVty45HsdPqv4EZWFL2A3UhpT3VqpBYV1Kpb26ACsUOfx5L9XytuqgtZxHi8da8XgLlYhQq3oVW35uuE6+v8XWbtIyBzmjN7DJFylYj3hHGKd4D2uuSH2UaBWUX3KToEyMYVsI6MONeLBFFi8/Wx6Z4+0w8MIJceGhmXTrPAaMUW/Q/oS+dvDBr74sfqkCwqkxunqezvpPwT6SdZit+xtZofsOyRgxw+fXq+lavJBH8/SpeFgTJHjlTxUIEyQpCOlKqZxManS+zwXJwYfJIepCIZrdD7kB/ekpiaH/sQ+q5r6Sibiv+E/9ss1kpmc9CwzHCVnRFeNHSMigY6dCY1XSGpldehrwegnmKvlZor7qHEd3h/bhvMMqLKdp3Ja1RvqpWOrwj88nuLBFFi8/Wx6Z4+0w8MIJccVDv0tB6XV8GNJz/4h1R4Vy6cNNDKNG0zvJBatTiYLS1dr8Uft4en4ER2ZQrDjqMVxgoHTp+yUmXz9ffIrGMsrPjkJcPOwYVhdiFiNNgZJP4c4Qb6MFkjhyrZA15pm/2CMUst7Qni7LIio3CDxTVPsJyzDVynXLdI2zv3zSD2lQdncQwouC5iiMPLvS6WEmwJ3xgP6fT8E2LZkhoaADEADEmGADH+5xCjZFvVVu5yNHgwFdcpTy9CxEsMLNqnhMYtfB8q+VPEuTvbHgYx4rnHlQ3/yY4LYU0muav1yJpeWiHzv4myjshXqA4WWKeCNCZbZ3EMKLguYojDy70ulhJsCv2y4fEYeDiasbo7qVBCWJdIdtE2GL0F0gV2T+Y0SA72PkRxAuTgRIMHeE+VOHFR8rshdLK1Ap4a8nVsqs3FhwoWHmbts1hklZcY1oDV3h5/wAFQ/GtBwZKUQMxrVEaqbmOV68nV6tiky1aCwtW2fq18Hyr5U8S5O9seBjHiuceWMNIKdVGqtVAhicO6iU8eky99w2FfDLOe/govp/Fz8HbrpWvOze8Ie5hsP6Zv0LvKcArnNFhDqsswkWBBWhPolBeKNx6dDm493CFBulioDfQ+wYxnE02U3eq+QnwCwRcME+knWYrfsbWaH7DskYMcPKXVQa+o00pX2mexmfr/qvqewSxP5LjJCeaNYnAiF2zuBxIGNTUKjuOq6VCXKa8IaNxgBm483Ih4xbfN2Z2QJr6r1YjXrPBxExoR4FUSKQEJW2ukelAr+Fm0daLKoXP1liZ5AwLY2SPQd8YKdK6eNr79tPgm+oVzC/+6KWkT7PecyRsC4hlFnwqUtAQsWziR4WjFT75BjqBBHacoNi8I22WIcNevv2x78VSKuM1sVS/i+9BgVsLe7t4RwXtANGs6RQ974ZzJpFR8YuSPHRR+3QXd4NtKOtXRgWSHVwVX7wBGt4C8v4aV5SMdGiwVnZdzzEhDoVGjZaBocU9zMG5mvwf1LX/SfQ2ht0i4CqPreC1Suz21w4jOQly+A/8fVWx81LbMB8dfAjCMiuDyYJWGbEX2JIanNv3T4dX7BubNRjo4pJPqER1Qn2FtVqOuQGaSGL0kgcxATGGeZXN29k34axIQHwgKM3GxIrcQUp0n5SA3nrPWt0QWHAY6HAqod2CY2 | 1.0 | hKZI3uZkv/UiFurh4+AhXNmJQUZ3ehbcOzkL9fXbtiWoN5ahAeQnt+vU1SRlOI5mgxFTnHulmYUab1EYytWdOWq5zsJIGHiKMTvrV2XKXCM4W93nYAjlvoQsc0hdPY1P7AwMAgTCHtZJzbGzDXV0XYTGLt7pXwEefDWXwcr//Fg= - WgvrwxZzWNjhogB/LbiJLVzKV2uEbeQXps/zMKR8hqMx22itcnxuCUfW3697QhtI1Ek0t1MEnXGR6xONTLhVt+7WEFcm3GqUaCnToNBxS5HCwY1FPMOfMuBDdMAB3rQ7Q4nyIf99pVJ+fNJe+gY6KUidmRtwnJiqgCDcYrtL6/Wt/6+vklkdOLZsXYJsuGISQVKm4QJorJUn8hErmhrJCdUjzMTIAAmuoRx/1KGYDvy5TKraSmzfB6+2uS4Kd9kCpVluTF1iocxmX+PV4ho2bp6Hr7itDyGaIEYBWUPNevTbZgkOIY/6vsGEcs7LxidQqWTO4f76e+kINbW5r2cmkmgi0XanTnmm4X9vxqqdRWwAXczUGHHVQ+khTYIhW/nJFZlbebt/dl72ae3zTBpZCqr4a1OQqnmr1hbpYrLGUy9HrWxG3fS+FhbjjEUw/XkoHaocqygRHO0M3o17rL9dQ0tdXx3BYoLmgK5HjWEnSLJD3vhnMmkVHxi5I8dFH7dBtYEhTNB4MBDQB0TM+Mba+l/xjNch46bhkV++fh+xEggE+knWYrfsbWaH7DskYMcP2V7Le2x11rJx2UdeZbQ9/8rEH+76zBrQVfqJcyyRLR31nFSMYDLG9JxzhudMpJX9BPpJ1mK37G1mh+w7JGDHD39ESwrmDgqsB2hUYPG1m8zw1ljwG6R1bba201qiY6L+lmHn2tGvLVBnHhYmRYwLIvbLNZKZnPQsMxwlZ0RXjR0yqhAGe+Fb+980AU+2aQDp9ZxUjGAyxvScc4bnTKSV/QT6SdZit+xtZofsOyRgxw/zURIC9wcFFhmb8p2KGzDp28EpJxw6E6FOF7rifb0RWllsi3MAq4KJUvTKrNEzsbZGVQkCM/OAwPtIPjCr2Pz7jtwLUhqIC7Thj9k1Ppgh+uuBKc9tG3X4wcbPB7p3sHyRpRgSMQJzf3fEtivZ7wvdCW4SWUDE7nKbXR8Wq+2X4BcNFStdBYilRr0iCf823YVR3EUmeJY7B0DHyyyaIjm1Jvpl40LGyBPuI0RGklEWtG8FKPRWYTMryr/LDieRCvtjFcYVXI8nQKVih9IFoFfJfZQALVWvXqjOey/ftY4232i4/etrshNctL1ZXxtAfHHrjMCsQBM9V/Qe92c0++SwASSy+wiQV3pBJvoyCdErJA1eJxtC1cV/EDcvYj5lVkkE+knWYrfsbWaH7DskYMcPgNe1yRZ48BVIl1urhvuppImYVJJyTVEUz3bFzqT9OxjiwRRYvP1semePtMPDCCXHzxWqVKSmeLHK4ByTZnhKBRZ0KntVL6HN3poD3gNdDdRHKiPSdQ/D4VWePRuNE5nHHyZK055pfoQGwI4Iua7QCBZ0KntVL6HN3poD3gNdDdQxQDsBUFIxBEkwm0ebT1hzvYYbweiTa0JzWR8ESMgUdVGm5aklsXn4sOJtPSG7uHO3dw7MIQ6BF/OSfABQrBZs2GZgYRjL+6gAsbXNGijAks2NrYd2FRt/uq7OIubbD5XrYAfhr06EWOtHupeSorAMQhL23FuJ5aXfnyRfrOtQ2dKcik3U3v+UcO2GT6B0OQHnEBrtIdSvqNVwzEUCzzKB2zr25EmX3kAQ5s1pmP6VcU645+G0T3dAbpLickmRQF5ITMYeZI54AhNm9wbsPVG5ari/i453Ta5o/xK4Z6jECfzCZnTVu3NIYeUOk0U3tu/yx9N6nlSqlulShwxEYqQOQ91GaqqDisI6noLWQi+uRxTtL/0EmbZ4zEKxPqEG+86QA401G+dVnpYUPG6V4ng/4sEUWLz9bHpnj7TDwwglx1ar7IzG9WUuRL+cI8Qm8P5Fl2g4+hy1I9bNZBuxK2T64sEUWLz9bHpnj7TDwwglx/pfxPUu6xx5KmooKvR+0wXWQ4/xCxGv6AYdiaWBLR+t97Lk73Qlv3UarawsdWSJUvXhuiSYFDzltdc1k2YyQxDANLujbHVMWktyarf/nEwqORriBZNnkRDuK/g3q4x+ZtMOz3yeDt8bZhF4/NH/1qBDZO2zdD+1S/ByadwvIc4YYRw+PAQA+HTJRVmrGA2qymbjg1mkiMG4DybJ3f49UJErSEF1zQ0+7ii+aPkqVECuRSC3ZxNMmKdrFUh5zu51k5noSlEJvyOtdb7eWjhNw/Xd3xl3F4dNSJDzJjXa3kzw6SvlFns4+HI/LoHbAnErqU6OnbzqmTiQlGIZ+kYJTg5UP9FCPDt+hR4loo78etrqzmY/HLfBjiMfk/+JiqCqShsGwd0Vh6rvEfHtR7MDFFjCo0z9TgAST+oN+sUZ4Bt7Vi5XoPu+t/QXVty45HsdPqv4EZWFL2A3UhpT3VqpBYV1Kpb26ACsUOfx5L9XytuqgtZxHi8da8XgLlYhQq3oVW35uuE6+v8XWbtIyBzmjN7DJFylYj3hHGKd4D2uuSH2UaBWUX3KToEyMYVsI6MONeLBFFi8/Wx6Z4+0w8MIJceGhmXTrPAaMUW/Q/oS+dvDBr74sfqkCwqkxunqezvpPwT6SdZit+xtZofsOyRgxw+fXq+lavJBH8/SpeFgTJHjlTxUIEyQpCOlKqZxManS+zwXJwYfJIepCIZrdD7kB/ekpiaH/sQ+q5r6Sibiv+E/9ss1kpmc9CwzHCVnRFeNHSMigY6dCY1XSGpldehrwegnmKvlZor7qHEd3h/bhvMMqLKdp3Ja1RvqpWOrwj88nuLBFFi8/Wx6Z4+0w8MIJccVDv0tB6XV8GNJz/4h1R4Vy6cNNDKNG0zvJBatTiYLS1dr8Uft4en4ER2ZQrDjqMVxgoHTp+yUmXz9ffIrGMsrPjkJcPOwYVhdiFiNNgZJP4c4Qb6MFkjhyrZA15pm/2CMUst7Qni7LIio3CDxTVPsJyzDVynXLdI2zv3zSD2lQdncQwouC5iiMPLvS6WEmwJ3xgP6fT8E2LZkhoaADEADEmGADH+5xCjZFvVVu5yNHgwFdcpTy9CxEsMLNqnhMYtfB8q+VPEuTvbHgYx4rnHlQ3/yY4LYU0muav1yJpeWiHzv4myjshXqA4WWKeCNCZbZ3EMKLguYojDy70ulhJsCv2y4fEYeDiasbo7qVBCWJdIdtE2GL0F0gV2T+Y0SA72PkRxAuTgRIMHeE+VOHFR8rshdLK1Ap4a8nVsqs3FhwoWHmbts1hklZcY1oDV3h5/wAFQ/GtBwZKUQMxrVEaqbmOV68nV6tiky1aCwtW2fq18Hyr5U8S5O9seBjHiuceWMNIKdVGqtVAhicO6iU8eky99w2FfDLOe/govp/Fz8HbrpWvOze8Ie5hsP6Zv0LvKcArnNFhDqsswkWBBWhPolBeKNx6dDm493CFBulioDfQ+wYxnE02U3eq+QnwCwRcME+knWYrfsbWaH7DskYMcPKXVQa+o00pX2mexmfr/qvqewSxP5LjJCeaNYnAiF2zuBxIGNTUKjuOq6VCXKa8IaNxgBm483Ih4xbfN2Z2QJr6r1YjXrPBxExoR4FUSKQEJW2ukelAr+Fm0daLKoXP1liZ5AwLY2SPQd8YKdK6eNr79tPgm+oVzC/+6KWkT7PecyRsC4hlFnwqUtAQsWziR4WjFT75BjqBBHacoNi8I22WIcNevv2x78VSKuM1sVS/i+9BgVsLe7t4RwXtANGs6RQ974ZzJpFR8YuSPHRR+3QXd4NtKOtXRgWSHVwVX7wBGt4C8v4aV5SMdGiwVnZdzzEhDoVGjZaBocU9zMG5mvwf1LX/SfQ2ht0i4CqPreC1Suz21w4jOQly+A/8fVWx81LbMB8dfAjCMiuDyYJWGbEX2JIanNv3T4dX7BubNRjo4pJPqER1Qn2FtVqOuQGaSGL0kgcxATGGeZXN29k34axIQHwgKM3GxIrcQUp0n5SA3nrPWt0QWHAY6HAqod2CY2 | non_priority | fg wgvrwxzzwnjhogb fnje wt khtyihw njfzlbebt fhbjjeuw mba l fh xegge fb xtzofsoyrgxw swassy urxttl newqorribznnkrduk nh paqa hi hlfbjimfk on t q os xtzofsoyrgxw fxq spefgtjhjltxuieyqpcolkqzxmans ekpiah sq e wafq govp qnwcwrcme ovzc i a | 0 |
287,300 | 31,834,284,496 | IssuesEvent | 2023-09-14 12:38:40 | Trinadh465/linux-4.1.15_CVE-2022-3564 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2022-3564 | closed | CVE-2015-7885 (Low) detected in linuxlinux-4.6 - autoclosed | Mend: dependency security vulnerability | ## CVE-2015-7885 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2022-3564/commit/3e3e73fc07b87b414cc43712be62ebb4ac7de2e9">3e3e73fc07b87b414cc43712be62ebb4ac7de2e9</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/dgnc/dgnc_mgmt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/dgnc/dgnc_mgmt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The dgnc_mgmt_ioctl function in drivers/staging/dgnc/dgnc_mgmt.c in the Linux kernel through 4.3.3 does not initialize a certain structure member, which allows local users to obtain sensitive information from kernel memory via a crafted application.
<p>Publish Date: 2015-12-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-7885>CVE-2015-7885</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>2.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2015-7885">https://www.linuxkernelcves.com/cves/CVE-2015-7885</a></p>
<p>Release Date: 2015-12-28</p>
<p>Fix Resolution: v4.4-rc1,v3.12.53,v3.16.35</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-7885 (Low) detected in linuxlinux-4.6 - autoclosed - ## CVE-2015-7885 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2022-3564/commit/3e3e73fc07b87b414cc43712be62ebb4ac7de2e9">3e3e73fc07b87b414cc43712be62ebb4ac7de2e9</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/dgnc/dgnc_mgmt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/dgnc/dgnc_mgmt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The dgnc_mgmt_ioctl function in drivers/staging/dgnc/dgnc_mgmt.c in the Linux kernel through 4.3.3 does not initialize a certain structure member, which allows local users to obtain sensitive information from kernel memory via a crafted application.
<p>Publish Date: 2015-12-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-7885>CVE-2015-7885</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>2.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2015-7885">https://www.linuxkernelcves.com/cves/CVE-2015-7885</a></p>
<p>Release Date: 2015-12-28</p>
<p>Fix Resolution: v4.4-rc1,v3.12.53,v3.16.35</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve low detected in linuxlinux autoclosed cve low severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers staging dgnc dgnc mgmt c drivers staging dgnc dgnc mgmt c vulnerability details the dgnc mgmt ioctl function in drivers staging dgnc dgnc mgmt c in the linux kernel through does not initialize a certain structure member which allows local users to obtain sensitive information from kernel memory via a crafted application publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
100,821 | 30,785,761,266 | IssuesEvent | 2023-07-31 13:09:08 | haskell/haskell-language-server | https://api.github.com/repos/haskell/haskell-language-server | closed | Multi Cradle: No prefixes matched when editing Setup.hs | type: bug build tool: stack build tool: cabal | ### Your environment
Arch Linux
Cabal
Neovim (lsp-config)
### Steps to reproduce
1. Create new project
2. Change build-type to Custom
```
build-type: Custom
custom-setup
setup-depends:
base,
Cabal
```
3. Create a Setup.hs file and build
4. Open Setup.hs
### Expected behaviour
hls works seamlessly on Setup.hs
### Actual behaviour
hls output this error
```
Multi Cradle: No prefixes matched
pwd: /home/cha0s/testing
filepath: /home/cha0s/testing/Setup.hs
prefixes:
("app/Main.hs",Cabal {component = Just "testing:exe:testing"})
```
### Debug information
I found this [reddit](https://www.reddit.com/r/haskell/comments/wcny2p/hls_issues_in_stack_project/) post describing something similar but Stack is used instead.
The custom build script Setup.hs is the only file affected, the other seems to work fine.
| 2.0 | Multi Cradle: No prefixes matched when editing Setup.hs - ### Your environment
Arch Linux
Cabal
Neovim (lsp-config)
### Steps to reproduce
1. Create new project
2. Change build-type to Custom
```
build-type: Custom
custom-setup
setup-depends:
base,
Cabal
```
3. Create a Setup.hs file and build
4. Open Setup.hs
### Expected behaviour
hls works seamlessly on Setup.hs
### Actual behaviour
hls output this error
```
Multi Cradle: No prefixes matched
pwd: /home/cha0s/testing
filepath: /home/cha0s/testing/Setup.hs
prefixes:
("app/Main.hs",Cabal {component = Just "testing:exe:testing"})
```
### Debug information
I found this [reddit](https://www.reddit.com/r/haskell/comments/wcny2p/hls_issues_in_stack_project/) post describing something similar but Stack is used instead.
The custom build script Setup.hs is the only file affected, the other seems to work fine.
| non_priority | multi cradle no prefixes matched when editing setup hs your environment arch linux cabal neovim lsp config steps to reproduce create new project change build type to custom build type custom custom setup setup depends base cabal create a setup hs file and build open setup hs expected behaviour hls works seamlessly on setup hs actual behaviour hls output this error multi cradle no prefixes matched pwd home testing filepath home testing setup hs prefixes app main hs cabal component just testing exe testing debug information i found this post describing something similar but stack is used instead the custom build script setup hs is the only file affected the other seems to work fine | 0 |
68,227 | 17,195,565,184 | IssuesEvent | 2021-07-16 16:48:54 | deegree/deegree3 | https://api.github.com/repos/deegree/deegree3 | closed | Server migration of plaza.deegree.org | CI and build TMC discussion contributions welcome website wiki | The server plaza.deegree.org will be upgraded to a new machine (from EX-41 to EX-42 sponsored by FOSSGIS e.V.).
List of tasks:
- [x] create a private repository on https://github.com/deegree/infrastructure for all infrastructure code (docker compose)
- [x] decide on host name of new server
- [x] new server is created (requires support by FOSSGIS admins)
- [x] basic installation of Ubuntu 20 LTS @stephanr
- [x] setup accounts and login via SSH (fail2ban) @stephanr
- [x] setup Hetzner firewall and fw on local machine @stephanr
- [x] installation of official docker from docker.com @stephanr
- [x] create initial docker compose file with the infrastructure/services @copierrj
- [x] setup apache httpd/nginx/traeffic
- [x] setup the SSL certificate (lets encrypt) @stephanr
- [x] migrate api, documentation, schemas, the old wiki pages @stephanr
- [x] setup nexus using docker @copierrj
- [x] migrate nexus content @copierrj
- [x] migrate nexus from v2 to v3 @copierrj
- [x] setup jenkins using docker @tfr42
- [x] migrate jenkins content @tfr42
- [x] migrate deegree reference implementation (CITE, OGCRI) @dstenger, @stephanr
- [x] update reference implementation workspace (CITE, OGCRI) @dstenger, @stephanr
- [x] migrate deegree demo @tfr42
- [x] fix the remaining issues in the demo workspaces
- [x] complete backup of files from plaza and transfer to central
- [x] change DNS entries (requires OSGeo SAC team, see https://trac.osgeo.org/osgeo/ticket/2568)
see more information about the infrastructure in wiki https://github.com/deegree/deegree3/wiki/Infrastructure | 1.0 | Server migration of plaza.deegree.org - The server plaza.deegree.org will be upgraded to a new machine (from EX-41 to EX-42 sponsored by FOSSGIS e.V.).
List of tasks:
- [x] create a private repository on https://github.com/deegree/infrastructure for all infrastructure code (docker compose)
- [x] decide on host name of new server
- [x] new server is created (requires support by FOSSGIS admins)
- [x] basic installation of Ubuntu 20 LTS @stephanr
- [x] setup accounts and login via SSH (fail2ban) @stephanr
- [x] setup Hetzner firewall and fw on local machine @stephanr
- [x] installation of official docker from docker.com @stephanr
- [x] create initial docker compose file with the infrastructure/services @copierrj
- [x] setup apache httpd/nginx/traeffic
- [x] setup the SSL certificate (lets encrypt) @stephanr
- [x] migrate api, documentation, schemas, the old wiki pages @stephanr
- [x] setup nexus using docker @copierrj
- [x] migrate nexus content @copierrj
- [x] migrate nexus from v2 to v3 @copierrj
- [x] setup jenkins using docker @tfr42
- [x] migrate jenkins content @tfr42
- [x] migrate deegree reference implementation (CITE, OGCRI) @dstenger, @stephanr
- [x] update reference implementation workspace (CITE, OGCRI) @dstenger, @stephanr
- [x] migrate deegree demo @tfr42
- [x] fix the remaining issues in the demo workspaces
- [x] complete backup of files from plaza and transfer to central
- [x] change DNS entries (requires OSGeo SAC team, see https://trac.osgeo.org/osgeo/ticket/2568)
see more information about the infrastructure in wiki https://github.com/deegree/deegree3/wiki/Infrastructure | non_priority | server migration of plaza deegree org the server plaza deegree org will be upgraded to a new machine from ex to ex sponsored by fossgis e v list of tasks create a private repository on for all infrastructure code docker compose decide on host name of new server new server is created requires support by fossgis admins basic installation of ubuntu lts stephanr setup accounts and login via ssh stephanr setup hetzner firewall and fw on local machine stephanr installation of official docker from docker com stephanr create initial docker compose file with the infrastructure services copierrj setup apache httpd nginx traeffic setup the ssl certificate lets encrypt stephanr migrate api documentation schemas the old wiki pages stephanr setup nexus using docker copierrj migrate nexus content copierrj migrate nexus from to copierrj setup jenkins using docker migrate jenkins content migrate deegree reference implementation cite ogcri dstenger stephanr update reference implementation workspace cite ogcri dstenger stephanr migrate deegree demo fix the remaining issues in the demo workspaces complete backup of files from plaza and transfer to central change dns entries requires osgeo sac team see see more information about the infrastructure in wiki | 0 |
113,674 | 24,470,732,923 | IssuesEvent | 2022-10-07 19:37:21 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | [Accessibility]: Screen reader doesn't announce anything about pie chart content | bug webapp accessibility team/code-insights wcag/2.1 | Similar to https://github.com/sourcegraph/sourcegraph/issues/40873
I am unable to navigate into the chart to explore the groups and values with a screen reader. When drilling into the pie chart, the screen reader only announces "No visible title to interact" with no further elements that are explorable.
| 1.0 | [Accessibility]: Screen reader doesn't announce anything about pie chart content - Similar to https://github.com/sourcegraph/sourcegraph/issues/40873
I am unable to navigate into the chart to explore the groups and values with a screen reader. When drilling into the pie chart, the screen reader only announces "No visible title to interact" with no further elements that are explorable.
| non_priority | screen reader doesn t announce anything about pie chart content similar to i am unable to navigate into the chart to explore the groups and values with a screen reader when drilling into the pie chart the screen reader only announces no visible title to interact with no further elements that are explorable | 0 |
10,480 | 7,194,727,688 | IssuesEvent | 2018-02-04 09:05:55 | Shougo/deoplete.nvim | https://api.github.com/repos/Shougo/deoplete.nvim | closed | Dynamic completion candidates update? | enhancement performance | Different sources have different speeds. Some are very fast - like "buffer" and "around", some may take many seconds to gather candidates from, e.g. "tag" source. Can we show the completion candidates as they become avaliable from the source? I.e. when I start typing, I should instantly get completions from "buffer" and "around", and if I'm willing to wait for so many seconds - the candidates from "tag" would appear and the candidates list will be dynamically redrawn. | True | Dynamic completion candidates update? - Different sources have different speeds. Some are very fast - like "buffer" and "around", some may take many seconds to gather candidates from, e.g. "tag" source. Can we show the completion candidates as they become avaliable from the source? I.e. when I start typing, I should instantly get completions from "buffer" and "around", and if I'm willing to wait for so many seconds - the candidates from "tag" would appear and the candidates list will be dynamically redrawn. | non_priority | dynamic completion candidates update different sources have different speeds some are very fast like buffer and around some may take many seconds to gather candidates from e g tag source can we show the completion candidates as they become avaliable from the source i e when i start typing i should instantly get completions from buffer and around and if i m willing to wait for so many seconds the candidates from tag would appear and the candidates list will be dynamically redrawn | 0 |
39,150 | 5,220,158,710 | IssuesEvent | 2017-01-26 21:05:11 | metafizzy/isotope | https://api.github.com/repos/metafizzy/isotope | closed | hideItemElements / revealItemElements - issue | test case required | hello !
isotope is a very good tool and i use it since the first versions.
i use hideItemElements and revealItemElements so that to spend the less of time to display my items.
sorry for my english, i'm french....
i apply different filter sessions and my cache collection is finally...full of my items.
so i have just to hide or show the filtered items and that's why i use these two functionalities.
my problem : **i have holes in display** the layout method does'nt re-arrange ( just after a filter scenario )
**if i resize the browser window**, the visible items go up **but the item container lose the mansory layout**
what kind of method can i use dynamically to force the layout to re-arrange my items and to see the mansory layout play ?
Is there somebody with the same issue ? did you solve it ?
thank you for your attention, have a nice day,
alien, from south of france
| 1.0 | hideItemElements / revealItemElements - issue - hello !
isotope is a very good tool and i use it since the first versions.
i use hideItemElements and revealItemElements so that to spend the less of time to display my items.
sorry for my english, i'm french....
i apply different filter sessions and my cache collection is finally...full of my items.
so i have just to hide or show the filtered items and that's why i use these two functionalities.
my problem : **i have holes in display** the layout method does'nt re-arrange ( just after a filter scenario )
**if i resize the browser window**, the visible items go up **but the item container lose the mansory layout**
what kind of method can i use dynamically to force the layout to re-arrange my items and to see the mansory layout play ?
Is there somebody with the same issue ? did you solve it ?
thank you for your attention, have a nice day,
alien, from south of france
| non_priority | hideitemelements revealitemelements issue hello isotope is a very good tool and i use it since the first versions i use hideitemelements and revealitemelements so that to spend the less of time to display my items sorry for my english i m french i apply different filter sessions and my cache collection is finally full of my items so i have just to hide or show the filtered items and that s why i use these two functionalities my problem i have holes in display the layout method does nt re arrange just after a filter scenario if i resize the browser window the visible items go up but the item container lose the mansory layout what kind of method can i use dynamically to force the layout to re arrange my items and to see the mansory layout play is there somebody with the same issue did you solve it thank you for your attention have a nice day alien from south of france | 0 |
309,336 | 23,291,879,492 | IssuesEvent | 2022-08-06 01:23:06 | adafruit/Adafruit_CircuitPython_Requests | https://api.github.com/repos/adafruit/Adafruit_CircuitPython_Requests | opened | Move typing annotation definitions to `circuitpython_typing` | documentation good first issue | This library may improve from having some of the type annotations reworked and checked, as well as moved to `circuitpython_typing`. This might improve readability of the library. | 1.0 | Move typing annotation definitions to `circuitpython_typing` - This library may improve from having some of the type annotations reworked and checked, as well as moved to `circuitpython_typing`. This might improve readability of the library. | non_priority | move typing annotation definitions to circuitpython typing this library may improve from having some of the type annotations reworked and checked as well as moved to circuitpython typing this might improve readability of the library | 0 |
14,726 | 18,076,213,677 | IssuesEvent | 2021-09-21 10:10:23 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | System.Uri constructor returns an object that does is not equal to the input | bug area-System.Net tenet-compatibility in pr | <!--This is just a template - feel free to delete any and all of it and replace as appropriate.-->
### Description
Create a `Uri` that represents a `MAPI` item
Example code:
```c#
var input = "mapi16:///{S-1-5-0000000}/mail@example.com/곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가";
var uri = new Uri(input, UriKind.Absolute);
```
Expected:
`uri` should have the same value as `input`
Actual:
`uri` has this value: `mapi16:///{S-1-5-0000000}/mail@example.com/곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가/{S-1-5-0000000}/mail@example.com/곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가`
### Configuration
Code is running on .NET 5
### Regression?
This was working in both .NET Framework and UWP (.NET Core)
| True | System.Uri constructor returns an object that does is not equal to the input - <!--This is just a template - feel free to delete any and all of it and replace as appropriate.-->
### Description
Create a `Uri` that represents a `MAPI` item
Example code:
```c#
var input = "mapi16:///{S-1-5-0000000}/mail@example.com/곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가";
var uri = new Uri(input, UriKind.Absolute);
```
Expected:
`uri` should have the same value as `input`
Actual:
`uri` has this value: `mapi16:///{S-1-5-0000000}/mail@example.com/곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가/{S-1-5-0000000}/mail@example.com/곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가`
### Configuration
Code is running on .NET 5
### Regression?
This was working in both .NET Framework and UWP (.NET Core)
| non_priority | system uri constructor returns an object that does is not equal to the input description create a uri that represents a mapi item example code c var input s mail example com 곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가 var uri new uri input urikind absolute expected uri should have the same value as input actual uri has this value s mail example com 곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가 s mail example com 곯가가가공갫갡곤갘갖갯걆겹갹곓곌갂겥강걥겤걿갨가 configuration code is running on net regression this was working in both net framework and uwp net core | 0 |
35,195 | 7,644,981,385 | IssuesEvent | 2018-05-08 17:06:48 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | scipy.stats.multinomial.pmf is numerically incorrect. | defect scipy.stats | scipy.stats.multinomial.pmf appears to be numerically incorrect as per examples in code below.
```
import numpy as np
from scipy.stats import multinomial
from math import log, factorial
def multinomial_pmf(counts, probs):
x = np.prod(probs ** counts)
y = np.prod([factorial(i) for i in counts])
z = factorial(np.sum(counts))
return x * z / y
def multinomial_pmf_log(counts, probs):
xx = np.log(probs) * counts
counts = np.array(counts)
xx[np.where(counts == 0.)] = 0. # otherwise x will contain NaN even if count = 0
x = np.sum(xx)
y = np.sum([log(factorial(i)) for i in counts])
z = np.sum(np.log(np.arange(1, sum(counts) + 1)))
mult_prob = np.exp(x + z - y)
return mult_prob
counts = np.array([0,3,0,0,3,1])
p1 = np.array([9.495e-01, 3.261e-02, 1.123e-02, 4.170e-03, 2.165e-03, 3.633e-04])
p2 = np.array([9.289e-01, 6.639e-02, 0.0, 2.921e-03, 1.238e-03, 5.623e-04])
print('\n', multinomial.pmf(counts, np.sum(counts), p1))
print(multinomial_pmf(counts, p1))
print(multinomial_pmf_log(counts, p1))
print('\n', multinomial.pmf(counts, np.sum(counts), p2))
print(multinomial_pmf(counts, p2))
print(multinomial_pmf_log(counts, p2))
```
rsb0001148:bayescoalescentest helmutsimon$ python -c "import scipy; print(scipy.__version__)"
1.1.0
| 1.0 | scipy.stats.multinomial.pmf is numerically incorrect. - scipy.stats.multinomial.pmf appears to be numerically incorrect as per examples in code below.
```
import numpy as np
from scipy.stats import multinomial
from math import log, factorial
def multinomial_pmf(counts, probs):
x = np.prod(probs ** counts)
y = np.prod([factorial(i) for i in counts])
z = factorial(np.sum(counts))
return x * z / y
def multinomial_pmf_log(counts, probs):
xx = np.log(probs) * counts
counts = np.array(counts)
xx[np.where(counts == 0.)] = 0. # otherwise x will contain NaN even if count = 0
x = np.sum(xx)
y = np.sum([log(factorial(i)) for i in counts])
z = np.sum(np.log(np.arange(1, sum(counts) + 1)))
mult_prob = np.exp(x + z - y)
return mult_prob
counts = np.array([0,3,0,0,3,1])
p1 = np.array([9.495e-01, 3.261e-02, 1.123e-02, 4.170e-03, 2.165e-03, 3.633e-04])
p2 = np.array([9.289e-01, 6.639e-02, 0.0, 2.921e-03, 1.238e-03, 5.623e-04])
print('\n', multinomial.pmf(counts, np.sum(counts), p1))
print(multinomial_pmf(counts, p1))
print(multinomial_pmf_log(counts, p1))
print('\n', multinomial.pmf(counts, np.sum(counts), p2))
print(multinomial_pmf(counts, p2))
print(multinomial_pmf_log(counts, p2))
```
rsb0001148:bayescoalescentest helmutsimon$ python -c "import scipy; print(scipy.__version__)"
1.1.0
| non_priority | scipy stats multinomial pmf is numerically incorrect scipy stats multinomial pmf appears to be numerically incorrect as per examples in code below import numpy as np from scipy stats import multinomial from math import log factorial def multinomial pmf counts probs x np prod probs counts y np prod z factorial np sum counts return x z y def multinomial pmf log counts probs xx np log probs counts counts np array counts xx otherwise x will contain nan even if count x np sum xx y np sum z np sum np log np arange sum counts mult prob np exp x z y return mult prob counts np array np array np array print n multinomial pmf counts np sum counts print multinomial pmf counts print multinomial pmf log counts print n multinomial pmf counts np sum counts print multinomial pmf counts print multinomial pmf log counts bayescoalescentest helmutsimon python c import scipy print scipy version | 0 |
76,737 | 21,562,552,359 | IssuesEvent | 2022-05-01 11:37:01 | audacity/audacity | https://api.github.com/repos/audacity/audacity | closed | build: DISABLE_DYNAMIC_LOADING_LAME is not defined if libmp3lame is "system" | Build / CI Known Issue | If building with `-Daudacity_use_libmp3lame:STRING=system`, DISABLE_DYNAMIC_LOADING_LAME does not become defined because of a mistake (?) is src/CMakeLists.txt:
```cmake
if( NOT CMAKE_SYSTEM_NAME MATCHES "Windows|Darwin" )
if( "${${_OPT}use_lame}" STREQUAL "local" )
set( DISABLE_DYNAMIC_LOADING_LAME YES )
endif()
if( "${${_OPT}use_ffmpeg}" STREQUAL "linked" )
set( DISABLE_DYNAMIC_LOADING_FFMPEG YES )
endif()
endif()
```
Also note "linked" ffmpeg which was removed. | 1.0 | build: DISABLE_DYNAMIC_LOADING_LAME is not defined if libmp3lame is "system" - If building with `-Daudacity_use_libmp3lame:STRING=system`, DISABLE_DYNAMIC_LOADING_LAME does not become defined because of a mistake (?) is src/CMakeLists.txt:
```cmake
if( NOT CMAKE_SYSTEM_NAME MATCHES "Windows|Darwin" )
if( "${${_OPT}use_lame}" STREQUAL "local" )
set( DISABLE_DYNAMIC_LOADING_LAME YES )
endif()
if( "${${_OPT}use_ffmpeg}" STREQUAL "linked" )
set( DISABLE_DYNAMIC_LOADING_FFMPEG YES )
endif()
endif()
```
Also note "linked" ffmpeg which was removed. | non_priority | build disable dynamic loading lame is not defined if is system if building with daudacity use string system disable dynamic loading lame does not become defined because of a mistake is src cmakelists txt cmake if not cmake system name matches windows darwin if opt use lame strequal local set disable dynamic loading lame yes endif if opt use ffmpeg strequal linked set disable dynamic loading ffmpeg yes endif endif also note linked ffmpeg which was removed | 0 |
18,947 | 3,734,961,440 | IssuesEvent | 2016-03-08 09:54:47 | e107inc/e107 | https://api.github.com/repos/e107inc/e107 | closed | media manager - national characters in file name | testing required | When I uploaded picture via media manager with national character (German):
in import part: (seems fine)

after upload: (title and caption are incorrect, but photo is ok)

after import: (thumbnail wasn't working before, not related with this)

I can manually change texts, no problem.
But when I upload the same image via f.e menu image (in Page/Menu parts), there is problem with image name (it's the new image, not from media folder):

| 1.0 | media manager - national characters in file name - When I uploaded picture via media manager with national character (German):
in import part: (seems fine)

after upload: (title and caption are incorrect, but photo is ok)

after import: (thumbnail wasn't working before, not related with this)

I can manually change texts, no problem.
But when I upload the same image via f.e menu image (in Page/Menu parts), there is problem with image name (it's the new image, not from media folder):

| non_priority | media manager national characters in file name when i uploaded picture via media manager with national character german in import part seems fine after upload title and caption are incorrect but photo is ok after import thumbnail wasn t working before not related with this i can manually change texts no problem but when i upload the same image via f e menu image in page menu parts there is problem with image name it s the new image not from media folder | 0 |
139,602 | 31,713,488,141 | IssuesEvent | 2023-09-09 15:11:44 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | JIT: Bad codegen with try/finally | area-CodeGen-coreclr in-pr | ```csharp
// Generated by Fuzzlyn v1.6 on 2023-09-03 15:59:01
// Run on X64 Windows
// Seed: 11520325105937570553
// Reduced from 294.5 KiB to 0.7 KiB in 00:04:32
// Debug: Outputs False
// Release: Outputs True
public class Program
{
public static IRuntime s_rt;
public static void Main()
{
s_rt = new Runtime();
bool vr1 = default(bool);
try
{
long[] vr2 = default(long[]);
var vr3 = vr2[0];
bool vr4 = default(bool);
vr1 = !vr4;
}
finally
{
ref bool vr5 = ref vr1;
s_rt.WriteLine(vr5);
}
}
}
public interface IRuntime
{
void WriteLine<T>(T value);
}
public class Runtime : IRuntime
{
public void WriteLine<T>(T value) => System.Console.WriteLine(value);
}
```
| 1.0 | JIT: Bad codegen with try/finally - ```csharp
// Generated by Fuzzlyn v1.6 on 2023-09-03 15:59:01
// Run on X64 Windows
// Seed: 11520325105937570553
// Reduced from 294.5 KiB to 0.7 KiB in 00:04:32
// Debug: Outputs False
// Release: Outputs True
public class Program
{
public static IRuntime s_rt;
public static void Main()
{
s_rt = new Runtime();
bool vr1 = default(bool);
try
{
long[] vr2 = default(long[]);
var vr3 = vr2[0];
bool vr4 = default(bool);
vr1 = !vr4;
}
finally
{
ref bool vr5 = ref vr1;
s_rt.WriteLine(vr5);
}
}
}
public interface IRuntime
{
void WriteLine<T>(T value);
}
public class Runtime : IRuntime
{
public void WriteLine<T>(T value) => System.Console.WriteLine(value);
}
```
| non_priority | jit bad codegen with try finally csharp generated by fuzzlyn on run on windows seed reduced from kib to kib in debug outputs false release outputs true public class program public static iruntime s rt public static void main s rt new runtime bool default bool try long default long var bool default bool finally ref bool ref s rt writeline public interface iruntime void writeline t value public class runtime iruntime public void writeline t value system console writeline value | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.