Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 2 665 | labels stringlengths 4 554 | body stringlengths 3 235k | index stringclasses 6 values | text_combine stringlengths 96 235k | label stringclasses 2 values | text stringlengths 96 196k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
205,872 | 23,357,913,779 | IssuesEvent | 2022-08-10 09:05:02 | Gal-Doron/Baragon | https://api.github.com/repos/Gal-Doron/Baragon | opened | CVE-2020-24750 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2020-24750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon/commit/21e05aedc2dc15db5c3991ce71589fd5b8179836">21e05aedc2dc15db5c3991ce71589fd5b8179836</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.6 mishandles the interaction between serialization gadgets and typing, related to com.pastdev.httpcomponents.configuration.JndiConfiguration.
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750>CVE-2020-24750</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616</a></p>
<p>Release Date: 2020-09-17</p>
<p>Fix Resolution: 2.9.10.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2020-24750 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2020-24750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon/commit/21e05aedc2dc15db5c3991ce71589fd5b8179836">21e05aedc2dc15db5c3991ce71589fd5b8179836</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.6 mishandles the interaction between serialization gadgets and typing, related to com.pastdev.httpcomponents.configuration.JndiConfiguration.
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750>CVE-2020-24750</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616</a></p>
<p>Release Date: 2020-09-17</p>
<p>Fix Resolution: 2.9.10.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_infrastructure | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com pastdev httpcomponents configuration jndiconfiguration publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
652 | 2,822,948,701 | IssuesEvent | 2015-05-21 04:30:29 | angular/angular | https://api.github.com/repos/angular/angular | closed | Upgrade to jasmine 2.1 and report async errors | #development_infrastructure | Right now async errors to not report stack traces when tests fail. Makes it very hard to debug issues. | 1.0 | Upgrade to jasmine 2.1 and report async errors - Right now async errors to not report stack traces when tests fail. Makes it very hard to debug issues. | infrastructure | upgrade to jasmine and report async errors right now async errors to not report stack traces when tests fail makes it very hard to debug issues | 1 |
29,720 | 24,203,269,002 | IssuesEvent | 2022-09-24 21:48:51 | t3kt/raytk | https://api.github.com/repos/t3kt/raytk | closed | Pass parameters as separate uniforms | wontfix infrastructure | It may allow the GPU to better optimize things by treating them as constants internally. | 1.0 | Pass parameters as separate uniforms - It may allow the GPU to better optimize things by treating them as constants internally. | infrastructure | pass parameters as separate uniforms it may allow the gpu to better optimize things by treating them as constants internally | 1 |
27,314 | 7,934,024,090 | IssuesEvent | 2018-07-08 14:20:51 | openMVG/openMVG | https://api.github.com/repos/openMVG/openMVG | closed | There are some errors when using openmvg-develop as a library | build enhancement question | **I wrote this test code below.**
`#include <iostream>
#include "openMVG/sfm/sfm.hpp"
using namespace std;
int main(int argc, char **argv) {
std::cout << "Hello, OpenMVG" << std::endl;
return 0;
}`
`cmake_minimum_required(VERSION 3.0)
project(helloopenmvg)
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -std=c++11")
set(CMAKE_PREFIX_PATH "/home/owen/Libs/openMVG_develop_install")
include_directories("/usr/include/eigen3")
include_directories("/home/owen/Libs/openMVG_develop_install/include/openMVG")
find_package(OpenMVG REQUIRED)
include_directories(${OPENMVG_INCLUDE_DIRS})
add_executable(helloopenmvg main.cpp)
target_link_libraries(helloopenmvg ${OPENMVG_LIBRARIES})`
**But there are some errors when I build and execute the code. Please help me to handle this problem that had puzzled me for several days. Thank you very much in advance.**
/home/owen/SfM/useOpenMVG/Hello_1/HelloOpenMVG/build> make -j2 helloopenmvg
-- OpenMVG Find_Package
-- Found OpenMVG version: 1.3.0
-- Installed in: /home/owen/Libs/openMVG_develop_install
-- Used OpenMVG libraries: openMVG_camera;openMVG_exif;openMVG_features;openMVG_geodesy;openMVG_geometry;openMVG_graph;openMVG_image;openMVG_kvld;openMVG_lInftyComputerVision;openMVG_matching;openMVG_matching_image_collection;openMVG_multiview;openMVG_sfm;openMVG_system
-- Configuring done
-- Generating done
-- Build files have been written to: /home/owen/SfM/useOpenMVG/Hello_1/HelloOpenMVG/build
Scanning dependencies of target helloopenmvg
[ 50%] Building CXX object CMakeFiles/helloopenmvg.dir/main.cpp.o
[100%] Linking CXX executable helloopenmvg
/usr/bin/ld: cannot find -lopenMVG_camera
/usr/bin/ld: cannot find -lopenMVG_exif
/usr/bin/ld: cannot find -lopenMVG_features
/usr/bin/ld: cannot find -lopenMVG_geodesy
/usr/bin/ld: cannot find -lopenMVG_geometry
/usr/bin/ld: cannot find -lopenMVG_graph
/usr/bin/ld: cannot find -lopenMVG_image
/usr/bin/ld: cannot find -lopenMVG_kvld
/usr/bin/ld: cannot find -lopenMVG_lInftyComputerVision
/usr/bin/ld: cannot find -lopenMVG_matching
/usr/bin/ld: cannot find -lopenMVG_matching_image_collection
/usr/bin/ld: cannot find -lopenMVG_multiview
/usr/bin/ld: cannot find -lopenMVG_sfm
/usr/bin/ld: cannot find -lopenMVG_system
collect2: error: ld returned 1 exit status
CMakeFiles/helloopenmvg.dir/build.make:94: recipe for target 'helloopenmvg' failed
make[3]: *** [helloopenmvg] Error 1
CMakeFiles/Makefile2:67: recipe for target 'CMakeFiles/helloopenmvg.dir/all' failed
make[2]: *** [CMakeFiles/helloopenmvg.dir/all] Error 2
CMakeFiles/Makefile2:79: recipe for target 'CMakeFiles/helloopenmvg.dir/rule' failed
make[1]: *** [CMakeFiles/helloopenmvg.dir/rule] Error 2
Makefile:162: recipe for target 'helloopenmvg' failed
make: *** [helloopenmvg] Error 2
*** Failure: Exit code 2 ***
| 1.0 | There are some errors when using openmvg-develop as a library - **I wrote this test code below.**
`#include <iostream>
#include "openMVG/sfm/sfm.hpp"
using namespace std;
int main(int argc, char **argv) {
std::cout << "Hello, OpenMVG" << std::endl;
return 0;
}`
`cmake_minimum_required(VERSION 3.0)
project(helloopenmvg)
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -std=c++11")
set(CMAKE_PREFIX_PATH "/home/owen/Libs/openMVG_develop_install")
include_directories("/usr/include/eigen3")
include_directories("/home/owen/Libs/openMVG_develop_install/include/openMVG")
find_package(OpenMVG REQUIRED)
include_directories(${OPENMVG_INCLUDE_DIRS})
add_executable(helloopenmvg main.cpp)
target_link_libraries(helloopenmvg ${OPENMVG_LIBRARIES})`
**But there are some errors when I build and execute the code. Please help me to handle this problem that had puzzled me for several days. Thank you very much in advance.**
/home/owen/SfM/useOpenMVG/Hello_1/HelloOpenMVG/build> make -j2 helloopenmvg
-- OpenMVG Find_Package
-- Found OpenMVG version: 1.3.0
-- Installed in: /home/owen/Libs/openMVG_develop_install
-- Used OpenMVG libraries: openMVG_camera;openMVG_exif;openMVG_features;openMVG_geodesy;openMVG_geometry;openMVG_graph;openMVG_image;openMVG_kvld;openMVG_lInftyComputerVision;openMVG_matching;openMVG_matching_image_collection;openMVG_multiview;openMVG_sfm;openMVG_system
-- Configuring done
-- Generating done
-- Build files have been written to: /home/owen/SfM/useOpenMVG/Hello_1/HelloOpenMVG/build
Scanning dependencies of target helloopenmvg
[ 50%] Building CXX object CMakeFiles/helloopenmvg.dir/main.cpp.o
[100%] Linking CXX executable helloopenmvg
/usr/bin/ld: cannot find -lopenMVG_camera
/usr/bin/ld: cannot find -lopenMVG_exif
/usr/bin/ld: cannot find -lopenMVG_features
/usr/bin/ld: cannot find -lopenMVG_geodesy
/usr/bin/ld: cannot find -lopenMVG_geometry
/usr/bin/ld: cannot find -lopenMVG_graph
/usr/bin/ld: cannot find -lopenMVG_image
/usr/bin/ld: cannot find -lopenMVG_kvld
/usr/bin/ld: cannot find -lopenMVG_lInftyComputerVision
/usr/bin/ld: cannot find -lopenMVG_matching
/usr/bin/ld: cannot find -lopenMVG_matching_image_collection
/usr/bin/ld: cannot find -lopenMVG_multiview
/usr/bin/ld: cannot find -lopenMVG_sfm
/usr/bin/ld: cannot find -lopenMVG_system
collect2: error: ld returned 1 exit status
CMakeFiles/helloopenmvg.dir/build.make:94: recipe for target 'helloopenmvg' failed
make[3]: *** [helloopenmvg] Error 1
CMakeFiles/Makefile2:67: recipe for target 'CMakeFiles/helloopenmvg.dir/all' failed
make[2]: *** [CMakeFiles/helloopenmvg.dir/all] Error 2
CMakeFiles/Makefile2:79: recipe for target 'CMakeFiles/helloopenmvg.dir/rule' failed
make[1]: *** [CMakeFiles/helloopenmvg.dir/rule] Error 2
Makefile:162: recipe for target 'helloopenmvg' failed
make: *** [helloopenmvg] Error 2
*** Failure: Exit code 2 ***
| non_infrastructure | there are some errors when using openmvg develop as a library i wrote this test code below include include openmvg sfm sfm hpp using namespace std int main int argc char argv std cout hello openmvg std endl return cmake minimum required version project helloopenmvg set cmake cxx flags cmake cxx flags std c set cmake prefix path home owen libs openmvg develop install include directories usr include include directories home owen libs openmvg develop install include openmvg find package openmvg required include directories openmvg include dirs add executable helloopenmvg main cpp target link libraries helloopenmvg openmvg libraries but there are some errors when i build and execute the code please help me to handle this problem that had puzzled me for several days thank you very much in advance home owen sfm useopenmvg hello helloopenmvg build make helloopenmvg openmvg find package found openmvg version installed in home owen libs openmvg develop install used openmvg libraries openmvg camera openmvg exif openmvg features openmvg geodesy openmvg geometry openmvg graph openmvg image openmvg kvld openmvg linftycomputervision openmvg matching openmvg matching image collection openmvg multiview openmvg sfm openmvg system configuring done generating done build files have been written to home owen sfm useopenmvg hello helloopenmvg build scanning dependencies of target helloopenmvg building cxx object cmakefiles helloopenmvg dir main cpp o linking cxx executable helloopenmvg usr bin ld cannot find lopenmvg camera usr bin ld cannot find lopenmvg exif usr bin ld cannot find lopenmvg features usr bin ld cannot find lopenmvg geodesy usr bin ld cannot find lopenmvg geometry usr bin ld cannot find lopenmvg graph usr bin ld cannot find lopenmvg image usr bin ld cannot find lopenmvg kvld usr bin ld cannot find lopenmvg linftycomputervision usr bin ld cannot find lopenmvg matching usr bin ld cannot find lopenmvg matching image collection usr bin ld cannot find lopenmvg multiview usr bin ld cannot find lopenmvg sfm usr bin ld cannot find lopenmvg system error ld returned exit status cmakefiles helloopenmvg dir build make recipe for target helloopenmvg failed make error cmakefiles recipe for target cmakefiles helloopenmvg dir all failed make error cmakefiles recipe for target cmakefiles helloopenmvg dir rule failed make error makefile recipe for target helloopenmvg failed make error failure exit code | 0 |
32,477 | 26,727,107,724 | IssuesEvent | 2023-01-29 21:02:45 | it-for-us/todo | https://api.github.com/repos/it-for-us/todo | closed | Create deployment pipeline for frontend | infrastructure | - Pipeline will create a docker image and pushes to github container registry
- Pipeline will create a service, deployment and ingress rule on server side | 1.0 | Create deployment pipeline for frontend - - Pipeline will create a docker image and pushes to github container registry
- Pipeline will create a service, deployment and ingress rule on server side | infrastructure | create deployment pipeline for frontend pipeline will create a docker image and pushes to github container registry pipeline will create a service deployment and ingress rule on server side | 1 |
15,738 | 11,689,235,403 | IssuesEvent | 2020-03-05 15:45:35 | st-tu-dresden/inloop | https://api.github.com/repos/st-tu-dresden/inloop | closed | Clean up and update the Travis CI build configuration | enhancement infrastructure | - Migrate to newer dist (currently still at ubuntu 14.04 aka trusty)
- Add current Python versions
- Build config must not have warnings (see screenshot below)
- Get rid of duplication
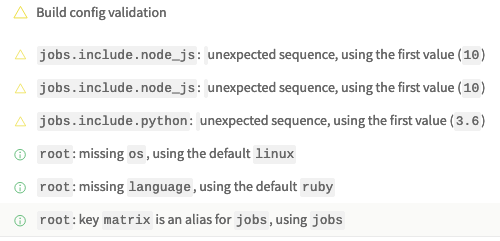
| 1.0 | Clean up and update the Travis CI build configuration - - Migrate to newer dist (currently still at ubuntu 14.04 aka trusty)
- Add current Python versions
- Build config must not have warnings (see screenshot below)
- Get rid of duplication
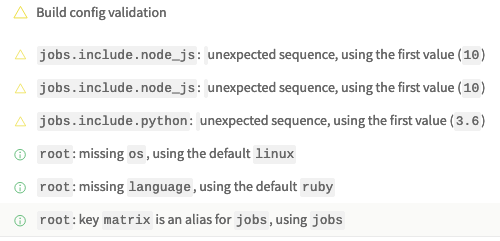
| infrastructure | clean up and update the travis ci build configuration migrate to newer dist currently still at ubuntu aka trusty add current python versions build config must not have warnings see screenshot below get rid of duplication | 1 |
20,062 | 10,450,850,840 | IssuesEvent | 2019-09-19 11:32:15 | liorzilberg/swagger-parser | https://api.github.com/repos/liorzilberg/swagger-parser | opened | CVE-2019-12086 (High) detected in jackson-databind-2.9.5.jar | security vulnerability | ## CVE-2019-12086 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/swagger-parser/modules/swagger-parser/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- swagger-core-1.5.21.jar (Root Library)
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/liorzilberg/swagger-parser/commits/9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b">9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint, the service has the mysql-connector-java jar (8.0.14 or earlier) in the classpath, and an attacker can host a crafted MySQL server reachable by the victim, an attacker can send a crafted JSON message that allows them to read arbitrary local files on the server. This occurs because of missing com.mysql.cj.jdbc.admin.MiniAdmin validation.
<p>Publish Date: 2019-05-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086>CVE-2019-12086</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086</a></p>
<p>Release Date: 2019-05-17</p>
<p>Fix Resolution: 2.9.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-12086 (High) detected in jackson-databind-2.9.5.jar - ## CVE-2019-12086 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/swagger-parser/modules/swagger-parser/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- swagger-core-1.5.21.jar (Root Library)
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/liorzilberg/swagger-parser/commits/9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b">9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint, the service has the mysql-connector-java jar (8.0.14 or earlier) in the classpath, and an attacker can host a crafted MySQL server reachable by the victim, an attacker can send a crafted JSON message that allows them to read arbitrary local files on the server. This occurs because of missing com.mysql.cj.jdbc.admin.MiniAdmin validation.
<p>Publish Date: 2019-05-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086>CVE-2019-12086</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086</a></p>
<p>Release Date: 2019-05-17</p>
<p>Fix Resolution: 2.9.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm swagger parser modules swagger parser pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy swagger core jar root library x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind x before when default typing is enabled either globally or for a specific property for an externally exposed json endpoint the service has the mysql connector java jar or earlier in the classpath and an attacker can host a crafted mysql server reachable by the victim an attacker can send a crafted json message that allows them to read arbitrary local files on the server this occurs because of missing com mysql cj jdbc admin miniadmin validation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
264,487 | 8,315,091,521 | IssuesEvent | 2018-09-25 02:59:33 | Atlantiss/NetherwingBugtracker | https://api.github.com/repos/Atlantiss/NetherwingBugtracker | closed | Mobs incombat positioning abuse. [Rogue] [Druid] [NPC] | - Core Mechanic Class: Druid Class: Rogue Exploit/Abuse - Priority NPC | [//]: # (Enclose links to things related to the bug using http://wowhead.com or any other TBC database.)
[//]: # (You can use screenshot ingame to visual the issue.)
[//]: # (Write your tickets according to the format:)
[//]: # ([Quest][Azuremyst Isle] Red Snapper - Very Tasty!)
[//]: # ([NPC] Magistrix Erona)
[//]: # ([Spell][Mage] Fireball)
[//]: # ([Npc][Drop] Ghostclaw Lynx)
[//]: # ([Web] Armory doesnt work)
**Description**: When you fighting mobs you can abuse mobs mechanic when they changing position to be in front of you (player). So I can use backstab staying in front of mob actualy. More in video.
**Current behaviour**: Server mechanic abuse.
**Expected behaviour**: -----.
**Server Revision**:
| 1.0 | Mobs incombat positioning abuse. [Rogue] [Druid] [NPC] - [//]: # (Enclose links to things related to the bug using http://wowhead.com or any other TBC database.)
[//]: # (You can use screenshot ingame to visual the issue.)
[//]: # (Write your tickets according to the format:)
[//]: # ([Quest][Azuremyst Isle] Red Snapper - Very Tasty!)
[//]: # ([NPC] Magistrix Erona)
[//]: # ([Spell][Mage] Fireball)
[//]: # ([Npc][Drop] Ghostclaw Lynx)
[//]: # ([Web] Armory doesnt work)
**Description**: When you fighting mobs you can abuse mobs mechanic when they changing position to be in front of you (player). So I can use backstab staying in front of mob actualy. More in video.
**Current behaviour**: Server mechanic abuse.
**Expected behaviour**: -----.
**Server Revision**:
| non_infrastructure | mobs incombat positioning abuse enclose links to things related to the bug using or any other tbc database you can use screenshot ingame to visual the issue write your tickets according to the format red snapper very tasty magistrix erona fireball ghostclaw lynx armory doesnt work description when you fighting mobs you can abuse mobs mechanic when they changing position to be in front of you player so i can use backstab staying in front of mob actualy more in video current behaviour server mechanic abuse expected behaviour server revision | 0 |
34,030 | 28,113,413,695 | IssuesEvent | 2023-03-31 08:57:44 | deckhouse/deckhouse | https://api.github.com/repos/deckhouse/deckhouse | closed | [node-manager] Status field artifacts when changing NodeGroup nodeType | type/bug status/needs-investigation area/cluster-and-infrastructure source/deckhouse-team | ### Preflight Checklist
- [X] I agree to follow the [Code of Conduct](https://github.com/deckhouse/deckhouse/blob/main/CODE_OF_CONDUCT.md) that this project adheres to.
- [X] I have searched the [issue tracker](https://github.com/deckhouse/deckhouse/issues) for an issue that matches the one I want to file, without success.
### Version
v1.44.4
### Expected Behavior
When changing the `spec.nodeType` of a node group from `CloudEphemeral` to `CloudStatic`, the `min`, `max`, `desired` and `instances` status fields should be missing.
### Actual Behavior
After changing `nodeType` from `CloudEphemeral` to `CloudStatic`, the `min`, `max`, `desired` and `instances` fields are displayed in NG status with zero (`0`) values.
### Steps To Reproduce
- Create NG with `spec.nodeType` = `CloudEphemeral`
- Change `spec.nodeType` to `CloudStatic`
- check NG status
### Proposed solution
Write a mutating webhook that removes unnecessary fields from the status
### Logs
_No response_ | 1.0 | [node-manager] Status field artifacts when changing NodeGroup nodeType - ### Preflight Checklist
- [X] I agree to follow the [Code of Conduct](https://github.com/deckhouse/deckhouse/blob/main/CODE_OF_CONDUCT.md) that this project adheres to.
- [X] I have searched the [issue tracker](https://github.com/deckhouse/deckhouse/issues) for an issue that matches the one I want to file, without success.
### Version
v1.44.4
### Expected Behavior
When changing the `spec.nodeType` of a node group from `CloudEphemeral` to `CloudStatic`, the `min`, `max`, `desired` and `instances` status fields should be missing.
### Actual Behavior
After changing `nodeType` from `CloudEphemeral` to `CloudStatic`, the `min`, `max`, `desired` and `instances` fields are displayed in NG status with zero (`0`) values.
### Steps To Reproduce
- Create NG with `spec.nodeType` = `CloudEphemeral`
- Change `spec.nodeType` to `CloudStatic`
- check NG status
### Proposed solution
Write a mutating webhook that removes unnecessary fields from the status
### Logs
_No response_ | infrastructure | status field artifacts when changing nodegroup nodetype preflight checklist i agree to follow the that this project adheres to i have searched the for an issue that matches the one i want to file without success version expected behavior when changing the spec nodetype of a node group from cloudephemeral to cloudstatic the min max desired and instances status fields should be missing actual behavior after changing nodetype from cloudephemeral to cloudstatic the min max desired and instances fields are displayed in ng status with zero values steps to reproduce create ng with spec nodetype cloudephemeral change spec nodetype to cloudstatic check ng status proposed solution write a mutating webhook that removes unnecessary fields from the status logs no response | 1 |
51,992 | 7,741,590,307 | IssuesEvent | 2018-05-29 06:34:24 | dustinRDF/food-roulette | https://api.github.com/repos/dustinRDF/food-roulette | closed | Create a Project Outline | Documentation | Create an outline that describes the development process that will be followed to create the application. | 1.0 | Create a Project Outline - Create an outline that describes the development process that will be followed to create the application. | non_infrastructure | create a project outline create an outline that describes the development process that will be followed to create the application | 0 |
10,787 | 8,721,869,890 | IssuesEvent | 2018-12-09 05:16:34 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Deterministic build fails to find ModifyVsixManifest tool | Area-Infrastructure | ```
build\Targets\RepoToolset\VisualStudio.targets(153,5): error MSB3073: The command ""C:\Users\vsagent\.nuget\packages\roslyntools.modifyvsixmanifest\1.0.0-beta2-63222-01\tools\ModifyVsixManifest.exe" --vsix="F:\vsagent\2\s\Binaries\VSSetup\Debug\Insertion\Roslyn.VisualStudio.Setup.vsix" --remove=//x:PackageManifest/x:Installation/@Experimental --add-attribute=//x:PackageManifest/x:Installation;SystemComponent;true" exited with code 3.
``` | 1.0 | Deterministic build fails to find ModifyVsixManifest tool - ```
build\Targets\RepoToolset\VisualStudio.targets(153,5): error MSB3073: The command ""C:\Users\vsagent\.nuget\packages\roslyntools.modifyvsixmanifest\1.0.0-beta2-63222-01\tools\ModifyVsixManifest.exe" --vsix="F:\vsagent\2\s\Binaries\VSSetup\Debug\Insertion\Roslyn.VisualStudio.Setup.vsix" --remove=//x:PackageManifest/x:Installation/@Experimental --add-attribute=//x:PackageManifest/x:Installation;SystemComponent;true" exited with code 3.
``` | infrastructure | deterministic build fails to find modifyvsixmanifest tool build targets repotoolset visualstudio targets error the command c users vsagent nuget packages roslyntools modifyvsixmanifest tools modifyvsixmanifest exe vsix f vsagent s binaries vssetup debug insertion roslyn visualstudio setup vsix remove x packagemanifest x installation experimental add attribute x packagemanifest x installation systemcomponent true exited with code | 1 |
18,338 | 12,942,026,079 | IssuesEvent | 2020-07-18 00:30:01 | galapagos-devs/Galapagos-Core | https://api.github.com/repos/galapagos-devs/Galapagos-Core | closed | Consistent `const` correctness. | enhancement galapagos infrastructure | We have gone through and made MOST of the metadata members `const` for the public API. We need to do the same for the private classes as well. All in all the whole codebase should be checked for improved `const` correctness.
It is better to do this earlier as the amount of work will only grow if we put it off. | 1.0 | Consistent `const` correctness. - We have gone through and made MOST of the metadata members `const` for the public API. We need to do the same for the private classes as well. All in all the whole codebase should be checked for improved `const` correctness.
It is better to do this earlier as the amount of work will only grow if we put it off. | infrastructure | consistent const correctness we have gone through and made most of the metadata members const for the public api we need to do the same for the private classes as well all in all the whole codebase should be checked for improved const correctness it is better to do this earlier as the amount of work will only grow if we put it off | 1 |
263,479 | 8,290,188,677 | IssuesEvent | 2018-09-19 16:36:30 | coq/coq | https://api.github.com/repos/coq/coq | opened | #8387 should be backported to v8.9 | priority: blocker | #### Version
v8.9
#### Description of the problem
https://github.com/coq/coq/pull/8387 should be backported to the v8.9 (and then most of #8374 on top of that) | 1.0 | #8387 should be backported to v8.9 - #### Version
v8.9
#### Description of the problem
https://github.com/coq/coq/pull/8387 should be backported to the v8.9 (and then most of #8374 on top of that) | non_infrastructure | should be backported to version description of the problem should be backported to the and then most of on top of that | 0 |
21,921 | 6,227,387,950 | IssuesEvent | 2017-07-10 20:39:44 | XceedBoucherS/TestImport5 | https://api.github.com/repos/XceedBoucherS/TestImport5 | closed | Feature Request: add DesignerWindowState property to ChildWindow | CodePlex | <b>brianlagunas[CodePlex]</b> <br />This still leaves the issue of the developer not able to hide it in design view. My childwindows are closed except for when I actually work on it. Most of the time, I am working on the actual windows which owns it, so it needs to be closed [the child window].
nbsp
Have a property to change the state in the designer is a better solution. Would it be possible to impliment an option like Microsoft implimented for the Height of the window? This would result in a something like this: d:DesignerWindowState=quotClosedquot.
nbsp
It would be great if that would be possible.
| 1.0 | Feature Request: add DesignerWindowState property to ChildWindow - <b>brianlagunas[CodePlex]</b> <br />This still leaves the issue of the developer not able to hide it in design view. My childwindows are closed except for when I actually work on it. Most of the time, I am working on the actual windows which owns it, so it needs to be closed [the child window].
nbsp
Have a property to change the state in the designer is a better solution. Would it be possible to impliment an option like Microsoft implimented for the Height of the window? This would result in a something like this: d:DesignerWindowState=quotClosedquot.
nbsp
It would be great if that would be possible.
| non_infrastructure | feature request add designerwindowstate property to childwindow brianlagunas this still leaves the issue of the developer not able to hide it in design view my childwindows are closed except for when i actually work on it most of the time i am working on the actual windows which owns it so it needs to be closed nbsp have a property to change the state in the designer is a better solution would it be possible to impliment an option like microsoft implimented for the height of the window this would result in a something like this d designerwindowstate quotclosedquot nbsp it would be great if that would be possible | 0 |
27,659 | 22,103,783,678 | IssuesEvent | 2022-06-01 15:28:32 | SonarSource/sonar-scanner-msbuild | https://api.github.com/repos/SonarSource/sonar-scanner-msbuild | closed | Add Package source mapping to nuget.config | Infrastructure | See https://devblogs.microsoft.com/nuget/introducing-package-source-mapping/
This feature is compatible with the following tools:
- [Visual Studio 2022 preview 4](https://visualstudio.microsoft.com/vs/preview/) and later
- [.NET SDK 6.0.100-rc.1](https://dotnet.microsoft.com/download/dotnet/6.0) and later
- [nuget.exe 6.0.0-preview.4](https://www.nuget.org/downloads) and later | 1.0 | Add Package source mapping to nuget.config - See https://devblogs.microsoft.com/nuget/introducing-package-source-mapping/
This feature is compatible with the following tools:
- [Visual Studio 2022 preview 4](https://visualstudio.microsoft.com/vs/preview/) and later
- [.NET SDK 6.0.100-rc.1](https://dotnet.microsoft.com/download/dotnet/6.0) and later
- [nuget.exe 6.0.0-preview.4](https://www.nuget.org/downloads) and later | infrastructure | add package source mapping to nuget config see this feature is compatible with the following tools and later and later and later | 1 |
15,229 | 11,423,301,641 | IssuesEvent | 2020-02-03 15:41:01 | patternfly/patternfly-react | https://api.github.com/repos/patternfly/patternfly-react | closed | CodeSandbox does not load | infrastructure | **Describe the issue. What is the expected and unexpected behavior?**
The Code Sandbox does not load
https://codesandbox.io/s/recursing-khorana-kmind
**Please provide the steps to reproduce. Feel free to link CodeSandbox or another tool.**
<!-- PatternFly-React Codesandbox template: https://codesandbox.io/s/recursing-khorana-kmind -->
click on the above link. The template example does not load.
**Is this a bug or enhancement? If this issue is a bug, is this issue blocking you or is there a work-around?**
bug
**What is your product and what release version are you targeting?**NA
cc @redallen | 1.0 | CodeSandbox does not load - **Describe the issue. What is the expected and unexpected behavior?**
The Code Sandbox does not load
https://codesandbox.io/s/recursing-khorana-kmind
**Please provide the steps to reproduce. Feel free to link CodeSandbox or another tool.**
<!-- PatternFly-React Codesandbox template: https://codesandbox.io/s/recursing-khorana-kmind -->
click on the above link. The template example does not load.
**Is this a bug or enhancement? If this issue is a bug, is this issue blocking you or is there a work-around?**
bug
**What is your product and what release version are you targeting?**NA
cc @redallen | infrastructure | codesandbox does not load describe the issue what is the expected and unexpected behavior the code sandbox does not load please provide the steps to reproduce feel free to link codesandbox or another tool click on the above link the template example does not load is this a bug or enhancement if this issue is a bug is this issue blocking you or is there a work around bug what is your product and what release version are you targeting na cc redallen | 1 |
106,979 | 16,742,794,035 | IssuesEvent | 2021-06-11 12:02:23 | joshnewton31080/JavaDemo | https://api.github.com/repos/joshnewton31080/JavaDemo | opened | CVE-2019-8331 (Medium) detected in bootstrap-3.3.7.min.js | security vulnerability | ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js</a></p>
<p>Path to dependency file: JavaDemo/src/main/webapp/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: JavaDemo/src/main/webapp/dfi/style_bootstrap.html,JavaDemo/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/joshnewton31080/JavaDemo/commit/a5b4f06490ac1cdfe26594565d128f037ac7297e">a5b4f06490ac1cdfe26594565d128f037ac7297e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.7","packageFilePaths":["/src/main/webapp/dfi/style_bootstrap.html","/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-8331","vulnerabilityDetails":"In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-8331 (Medium) detected in bootstrap-3.3.7.min.js - ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js</a></p>
<p>Path to dependency file: JavaDemo/src/main/webapp/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: JavaDemo/src/main/webapp/dfi/style_bootstrap.html,JavaDemo/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/joshnewton31080/JavaDemo/commit/a5b4f06490ac1cdfe26594565d128f037ac7297e">a5b4f06490ac1cdfe26594565d128f037ac7297e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.7","packageFilePaths":["/src/main/webapp/dfi/style_bootstrap.html","/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-8331","vulnerabilityDetails":"In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_infrastructure | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file javademo src main webapp dfi style bootstrap html path to vulnerable library javademo src main webapp dfi style bootstrap html javademo target easybuggy snapshot dfi style bootstrap html dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap bootstrap sass isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap bootstrap sass basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before and x before xss is possible in the tooltip or popover data template attribute vulnerabilityurl | 0 |
14,005 | 10,575,885,647 | IssuesEvent | 2019-10-07 16:38:12 | microsoft/WindowsTemplateStudio | https://api.github.com/repos/microsoft/WindowsTemplateStudio | closed | Improve testing of generated templates | Can Close Out Soon Infrastructure Testing meta | The current testing of templates is a long and slow process. There are a few scripts to enable running parallelizing of some test execution but we can (and should) do better.
Need to do more to fully scope this out but the goals are:
- make tests faster to run (to avoid excuses for not running them)
- make tests easier to run.
- avoid developers relying on automated test execution at PR (or post PR) time
- Make it easier to test small subsets of templates. This may require reviewing data-bound test generation (which is slow anyway)
| 1.0 | Improve testing of generated templates - The current testing of templates is a long and slow process. There are a few scripts to enable running parallelizing of some test execution but we can (and should) do better.
Need to do more to fully scope this out but the goals are:
- make tests faster to run (to avoid excuses for not running them)
- make tests easier to run.
- avoid developers relying on automated test execution at PR (or post PR) time
- Make it easier to test small subsets of templates. This may require reviewing data-bound test generation (which is slow anyway)
| infrastructure | improve testing of generated templates the current testing of templates is a long and slow process there are a few scripts to enable running parallelizing of some test execution but we can and should do better need to do more to fully scope this out but the goals are make tests faster to run to avoid excuses for not running them make tests easier to run avoid developers relying on automated test execution at pr or post pr time make it easier to test small subsets of templates this may require reviewing data bound test generation which is slow anyway | 1 |
107,054 | 16,749,668,311 | IssuesEvent | 2021-06-11 20:44:18 | talmax1124/creativeduoshopping-master | https://api.github.com/repos/talmax1124/creativeduoshopping-master | closed | CVE-2021-32640 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ws-7.4.5.tgz</b>, <b>ws-6.2.1.tgz</b>, <b>ws-5.2.2.tgz</b></p></summary>
<p>
<details><summary><b>ws-7.4.5.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.4.5.tgz">https://registry.npmjs.org/ws/-/ws-7.4.5.tgz</a></p>
<p>Path to dependency file: creativeduoshopping-master/package.json</p>
<p>Path to vulnerable library: creativeduoshopping-master/node_modules/engine.io-client/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- heroku-cli-7.0.9.tgz (Root Library)
- plugin-ci-1.9.12.tgz
- socket.io-client-2.4.0.tgz
- engine.io-client-3.5.2.tgz
- :x: **ws-7.4.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-6.2.1.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-6.2.1.tgz">https://registry.npmjs.org/ws/-/ws-6.2.1.tgz</a></p>
<p>Path to dependency file: creativeduoshopping-master/package.json</p>
<p>Path to vulnerable library: creativeduoshopping-master/node_modules/uncss/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- parcel-bundler-1.12.5.tgz (Root Library)
- htmlnano-0.2.9.tgz
- uncss-0.17.3.tgz
- jsdom-14.1.0.tgz
- :x: **ws-6.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-5.2.2.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-5.2.2.tgz">https://registry.npmjs.org/ws/-/ws-5.2.2.tgz</a></p>
<p>Path to dependency file: creativeduoshopping-master/package.json</p>
<p>Path to vulnerable library: creativeduoshopping-master/node_modules/ws/package.json,creativeduoshopping-master/frontend/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-2.1.8.tgz (Root Library)
- jest-23.6.0.tgz
- jest-cli-23.6.0.tgz
- jest-environment-jsdom-23.4.0.tgz
- jsdom-11.12.0.tgz
- :x: **ws-5.2.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/talmax1124/creativeduoshopping-master/commit/87c2e6e4b48a48e76ec6d8c0ad9a2aeb07b9df48">87c2e6e4b48a48e76ec6d8c0ad9a2aeb07b9df48</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: ws - 7.4.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-32640 (Medium) detected in multiple libraries - ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ws-7.4.5.tgz</b>, <b>ws-6.2.1.tgz</b>, <b>ws-5.2.2.tgz</b></p></summary>
<p>
<details><summary><b>ws-7.4.5.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.4.5.tgz">https://registry.npmjs.org/ws/-/ws-7.4.5.tgz</a></p>
<p>Path to dependency file: creativeduoshopping-master/package.json</p>
<p>Path to vulnerable library: creativeduoshopping-master/node_modules/engine.io-client/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- heroku-cli-7.0.9.tgz (Root Library)
- plugin-ci-1.9.12.tgz
- socket.io-client-2.4.0.tgz
- engine.io-client-3.5.2.tgz
- :x: **ws-7.4.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-6.2.1.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-6.2.1.tgz">https://registry.npmjs.org/ws/-/ws-6.2.1.tgz</a></p>
<p>Path to dependency file: creativeduoshopping-master/package.json</p>
<p>Path to vulnerable library: creativeduoshopping-master/node_modules/uncss/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- parcel-bundler-1.12.5.tgz (Root Library)
- htmlnano-0.2.9.tgz
- uncss-0.17.3.tgz
- jsdom-14.1.0.tgz
- :x: **ws-6.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-5.2.2.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-5.2.2.tgz">https://registry.npmjs.org/ws/-/ws-5.2.2.tgz</a></p>
<p>Path to dependency file: creativeduoshopping-master/package.json</p>
<p>Path to vulnerable library: creativeduoshopping-master/node_modules/ws/package.json,creativeduoshopping-master/frontend/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-2.1.8.tgz (Root Library)
- jest-23.6.0.tgz
- jest-cli-23.6.0.tgz
- jest-environment-jsdom-23.4.0.tgz
- jsdom-11.12.0.tgz
- :x: **ws-5.2.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/talmax1124/creativeduoshopping-master/commit/87c2e6e4b48a48e76ec6d8c0ad9a2aeb07b9df48">87c2e6e4b48a48e76ec6d8c0ad9a2aeb07b9df48</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: ws - 7.4.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries ws tgz ws tgz ws tgz ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file creativeduoshopping master package json path to vulnerable library creativeduoshopping master node modules engine io client node modules ws package json dependency hierarchy heroku cli tgz root library plugin ci tgz socket io client tgz engine io client tgz x ws tgz vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file creativeduoshopping master package json path to vulnerable library creativeduoshopping master node modules uncss node modules ws package json dependency hierarchy parcel bundler tgz root library htmlnano tgz uncss tgz jsdom tgz x ws tgz vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file creativeduoshopping master package json path to vulnerable library creativeduoshopping master node modules ws package json creativeduoshopping master frontend node modules ws package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz jest environment jsdom tgz jsdom tgz x ws tgz vulnerable library found in head commit a href found in base branch master vulnerability details ws is an open source websocket client and server library for node js a specially crafted value of the sec websocket protocol header can be used to significantly slow down a ws server the vulnerability has been fixed in ws in vulnerable versions of ws the issue can be mitigated by reducing the maximum allowed length of the request headers using the and or the options publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ws step up your open source security game with whitesource | 0 |
57,185 | 7,043,611,273 | IssuesEvent | 2017-12-31 09:33:55 | Jo-ravar/Tutorials | https://api.github.com/repos/Jo-ravar/Tutorials | reopened | [UI] Design a logo | Design | ### Issue Description
- Come up with your own logo designs and add screenshot here.
| 1.0 | [UI] Design a logo - ### Issue Description
- Come up with your own logo designs and add screenshot here.
| non_infrastructure | design a logo issue description come up with your own logo designs and add screenshot here | 0 |
357,171 | 25,176,337,458 | IssuesEvent | 2022-11-11 09:35:37 | chloeelim/pe | https://api.github.com/repos/chloeelim/pe | opened | Page breaks hindering reading UG | severity.VeryLow type.DocumentationBug | Diagrams shown on the next page when referenced in the previous page causing hindrance to reader even though better page breaks could have been added to address this issue.
<!--session: 1668152670490-7e6f3a4e-6e7c-4f76-9dc8-1f693dda9be8-->
<!--Version: Web v3.4.4--> | 1.0 | Page breaks hindering reading UG - Diagrams shown on the next page when referenced in the previous page causing hindrance to reader even though better page breaks could have been added to address this issue.
<!--session: 1668152670490-7e6f3a4e-6e7c-4f76-9dc8-1f693dda9be8-->
<!--Version: Web v3.4.4--> | non_infrastructure | page breaks hindering reading ug diagrams shown on the next page when referenced in the previous page causing hindrance to reader even though better page breaks could have been added to address this issue | 0 |
89,284 | 8,199,496,945 | IssuesEvent | 2018-08-31 20:26:48 | nabicht/SimpleTaskQueue | https://api.github.com/repos/nabicht/SimpleTaskQueue | opened | create a script to populate with tasks | testing | run a script that will pre-populate a running SimpleTaskQueue server with some tasks as a way to help with testing the UI. | 1.0 | create a script to populate with tasks - run a script that will pre-populate a running SimpleTaskQueue server with some tasks as a way to help with testing the UI. | non_infrastructure | create a script to populate with tasks run a script that will pre populate a running simpletaskqueue server with some tasks as a way to help with testing the ui | 0 |
32,543 | 26,775,226,602 | IssuesEvent | 2023-01-31 16:40:39 | w3f/polkadot-wiki | https://api.github.com/repos/w3f/polkadot-wiki | closed | Add documentation to README covering all active GitHub actions | Wiki Infrastructure | It would be useful to outline all the active GitHub actions and any details that are required for using them or time schedules by which they operate. This will help with knowledge sharing and keeping track of required updates or changes in the future. | 1.0 | Add documentation to README covering all active GitHub actions - It would be useful to outline all the active GitHub actions and any details that are required for using them or time schedules by which they operate. This will help with knowledge sharing and keeping track of required updates or changes in the future. | infrastructure | add documentation to readme covering all active github actions it would be useful to outline all the active github actions and any details that are required for using them or time schedules by which they operate this will help with knowledge sharing and keeping track of required updates or changes in the future | 1 |
17,673 | 12,500,257,859 | IssuesEvent | 2020-06-01 21:50:54 | BCDevOps/developer-experience | https://api.github.com/repos/BCDevOps/developer-experience | opened | INC0036853 Docker Image Registry full | Infrastructure | The platforms docker image registry has now hit 95% full. Here are the top 10 namespaces by usage.
wksv3k-tools is 272 GB
jik2hd-tools is 136 GB
empr-mds-tools is 124 GB
ifttgq-tools is 97 GB
devhub-tools is 95 GB
eazios-tools is 42 GB
q6qfzk-tools is 37 GB
lclb-cllc-tools is 37 GB
l9fjgg-tools is 34 GB
yuumcs-tools is 33 GB
It appears some projects make new tags for each PR build, and never clean them up. Leading to hundreds of tagged images that wont be pruned. | 1.0 | INC0036853 Docker Image Registry full - The platforms docker image registry has now hit 95% full. Here are the top 10 namespaces by usage.
wksv3k-tools is 272 GB
jik2hd-tools is 136 GB
empr-mds-tools is 124 GB
ifttgq-tools is 97 GB
devhub-tools is 95 GB
eazios-tools is 42 GB
q6qfzk-tools is 37 GB
lclb-cllc-tools is 37 GB
l9fjgg-tools is 34 GB
yuumcs-tools is 33 GB
It appears some projects make new tags for each PR build, and never clean them up. Leading to hundreds of tagged images that wont be pruned. | infrastructure | docker image registry full the platforms docker image registry has now hit full here are the top namespaces by usage tools is gb tools is gb empr mds tools is gb ifttgq tools is gb devhub tools is gb eazios tools is gb tools is gb lclb cllc tools is gb tools is gb yuumcs tools is gb it appears some projects make new tags for each pr build and never clean them up leading to hundreds of tagged images that wont be pruned | 1 |
57,519 | 3,082,701,114 | IssuesEvent | 2015-08-24 00:16:23 | magro/memcached-session-manager | https://api.github.com/repos/magro/memcached-session-manager | closed | Support locking with single node (without node-id) configuration | bug imported Milestone-1.6.1 Priority-Medium | _From [martin.grotzke](https://code.google.com/u/martin.grotzke/) on January 25, 2012 21:30:22_
This was requested/reported on the mailing list (<a href="http://groups.google.com/group/memcached-session-manager/browse_thread/thread/237168484a7b4217" rel="nofollow">http://groups.google.com/group/memcached-session-manager/browse_thread/thread/237168484a7b4217</a>):
With a single node configuration (without node id) it's not possible to enable locking. If tried the following exception is thrown:
2012-01-23T22:49:09+00:00 app[web.2]: WARNING: Could not load session with
id 7A218E2E0D4569248686ADB855FEAE74 from memcached.
2012-01-23T22:49:09+00:00 app[web.2]: Jan 23, 2012 10:49:09 PM
de.javakaffee.web.msm.MemcachedSessionService loadFromMemcached
2012-01-23T22:49:09+00:00 app[web.2]:
java.lang.UnsupportedOperationException: Not supported for single node
configuration without node id.
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.MemcachedSessionService.findSession(MemcachedSessionService.java:568)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.LockingStrategy.acquireLock(LockingStrategy.java:167)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.MemcachedSessionService.loadFromMemcached(MemcachedSessionService.java:998)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.LockingStrategy.lock(LockingStrategy.java:134)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.LockingStrategyAuto.onBeforeLoadFromMemcached(LockingStrategyAuto.java:133)
_Original issue: http://code.google.com/p/memcached-session-manager/issues/detail?id=119_ | 1.0 | Support locking with single node (without node-id) configuration - _From [martin.grotzke](https://code.google.com/u/martin.grotzke/) on January 25, 2012 21:30:22_
This was requested/reported on the mailing list (<a href="http://groups.google.com/group/memcached-session-manager/browse_thread/thread/237168484a7b4217" rel="nofollow">http://groups.google.com/group/memcached-session-manager/browse_thread/thread/237168484a7b4217</a>):
With a single node configuration (without node id) it's not possible to enable locking. If tried the following exception is thrown:
2012-01-23T22:49:09+00:00 app[web.2]: WARNING: Could not load session with
id 7A218E2E0D4569248686ADB855FEAE74 from memcached.
2012-01-23T22:49:09+00:00 app[web.2]: Jan 23, 2012 10:49:09 PM
de.javakaffee.web.msm.MemcachedSessionService loadFromMemcached
2012-01-23T22:49:09+00:00 app[web.2]:
java.lang.UnsupportedOperationException: Not supported for single node
configuration without node id.
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.MemcachedSessionService.findSession(MemcachedSessionService.java:568)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.LockingStrategy.acquireLock(LockingStrategy.java:167)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.MemcachedSessionService.loadFromMemcached(MemcachedSessionService.java:998)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.LockingStrategy.lock(LockingStrategy.java:134)
2012-01-23T22:49:09+00:00 app[web.2]: at
de.javakaffee.web.msm.LockingStrategyAuto.onBeforeLoadFromMemcached(LockingStrategyAuto.java:133)
_Original issue: http://code.google.com/p/memcached-session-manager/issues/detail?id=119_ | non_infrastructure | support locking with single node without node id configuration from on january this was requested reported on the mailing list with a single node configuration without node id it s not possible to enable locking if tried the following exception is thrown app warning could not load session with id from memcached app jan pm de javakaffee web msm memcachedsessionservice loadfrommemcached app java lang unsupportedoperationexception not supported for single node configuration without node id app at de javakaffee web msm memcachedsessionservice findsession memcachedsessionservice java app at de javakaffee web msm lockingstrategy acquirelock lockingstrategy java app at de javakaffee web msm memcachedsessionservice loadfrommemcached memcachedsessionservice java app at de javakaffee web msm lockingstrategy lock lockingstrategy java app at de javakaffee web msm lockingstrategyauto onbeforeloadfrommemcached lockingstrategyauto java original issue | 0 |
19,668 | 26,027,875,141 | IssuesEvent | 2022-12-21 17:59:59 | hashgraph/hedera-mirror-node | https://api.github.com/repos/hashgraph/hedera-mirror-node | closed | Automated release workflow fails at step Install JDK | bug regression process | ### Description
The automated release which works with the deprecated maven build system fails at step `Install SDK`:
```
Run actions/setup-java@v3
Installed distributions
Creating settings.xml with server-id: github
Writing to /home/runner/.m2/settings.xml
Error: No file in /home/runner/work/hedera-mirror-node/hedera-mirror-node matched to [**/pom.xml], make sure you have checked out the target repository
```
### Steps to reproduce
https://github.com/hashgraph/hedera-mirror-node/actions/runs/3751326043/jobs/6372181877
### Additional context
_No response_
### Hedera network
other
### Version
v0.72.0-SNAPSHOT
### Operating system
None | 1.0 | Automated release workflow fails at step Install JDK - ### Description
The automated release which works with the deprecated maven build system fails at step `Install SDK`:
```
Run actions/setup-java@v3
Installed distributions
Creating settings.xml with server-id: github
Writing to /home/runner/.m2/settings.xml
Error: No file in /home/runner/work/hedera-mirror-node/hedera-mirror-node matched to [**/pom.xml], make sure you have checked out the target repository
```
### Steps to reproduce
https://github.com/hashgraph/hedera-mirror-node/actions/runs/3751326043/jobs/6372181877
### Additional context
_No response_
### Hedera network
other
### Version
v0.72.0-SNAPSHOT
### Operating system
None | non_infrastructure | automated release workflow fails at step install jdk description the automated release which works with the deprecated maven build system fails at step install sdk run actions setup java installed distributions creating settings xml with server id github writing to home runner settings xml error no file in home runner work hedera mirror node hedera mirror node matched to make sure you have checked out the target repository steps to reproduce additional context no response hedera network other version snapshot operating system none | 0 |
17,347 | 12,305,283,781 | IssuesEvent | 2020-05-11 22:09:53 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | Saving changes at application close is not handled well in the GUI | bug interface/infrastructure | If you open a simulation in the GUI, make some changes, then attempt to close the application as a whole, you are presented (quite rightly) with a dialog asking whether you want to save the changes. If you close that dialog, rather than answer either "Yes" or "No", your simulation "disappears", but the application remains open. When you then again try to close the application, it too "disappears" but actually remains as a zombie background process. | 1.0 | Saving changes at application close is not handled well in the GUI - If you open a simulation in the GUI, make some changes, then attempt to close the application as a whole, you are presented (quite rightly) with a dialog asking whether you want to save the changes. If you close that dialog, rather than answer either "Yes" or "No", your simulation "disappears", but the application remains open. When you then again try to close the application, it too "disappears" but actually remains as a zombie background process. | infrastructure | saving changes at application close is not handled well in the gui if you open a simulation in the gui make some changes then attempt to close the application as a whole you are presented quite rightly with a dialog asking whether you want to save the changes if you close that dialog rather than answer either yes or no your simulation disappears but the application remains open when you then again try to close the application it too disappears but actually remains as a zombie background process | 1 |
676,887 | 23,141,370,749 | IssuesEvent | 2022-07-28 18:50:23 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | Script Canvas: Assigning values to variables can lead to crash | feature/scripting kind/bug sig/content triage/accepted priority/critical | **Describe the bug**
Assigning a value to a variable and saving seems to cause the engine to fall behind on a save. For example, if you make a function that simply takes in a string, sets an output string to the input string's value then returns the output string you will get the result you expect when you call the function and pass in "hello" (output = "hello"). If you change the output variable's value then change the value you pass into the function while saving and running with each step you will notice the expected output will fall behind.
Currently looking into simpler repro for this crash.
**Steps to reproduce**
Steps to reproduce the behavior:
1 - make a user function described above
2 - call the function in another graph with a print node to verify the output
3 - change input value to "hello". Save, Run. Verify "hello"
4 - change output variable value to "test". Save. Run. Verify "hello"
5 - clear output variable value. Save Run. Verify "hello"
6 - change input value to "world". Save. Run. Verify "world" <-will still output "hello"
**Expected behavior**
changing the input value will change the output value.
**Actual behavior**
the value you give to the input will fall behind by a save. i.e you provide "one" output comes out as "one". you provide "two" output comes out as "one". you provide "three" output comes out as "two".
If you continue to modify the values on variables and values on nodes while saving and running the editor eventually crashes.
[editorCallStack.txt](https://github.com/o3de/o3de/files/8279030/editorCallStack.txt)
**Found in Branch**
development
**Desktop/Device (please complete the following information):**
- Device: PC win 10
- nvidia 3070
- ryzen 5950
- 32GB ram
**Additional context**
Add any other context about the problem here. | 1.0 | Script Canvas: Assigning values to variables can lead to crash - **Describe the bug**
Assigning a value to a variable and saving seems to cause the engine to fall behind on a save. For example, if you make a function that simply takes in a string, sets an output string to the input string's value then returns the output string you will get the result you expect when you call the function and pass in "hello" (output = "hello"). If you change the output variable's value then change the value you pass into the function while saving and running with each step you will notice the expected output will fall behind.
Currently looking into simpler repro for this crash.
**Steps to reproduce**
Steps to reproduce the behavior:
1 - make a user function described above
2 - call the function in another graph with a print node to verify the output
3 - change input value to "hello". Save, Run. Verify "hello"
4 - change output variable value to "test". Save. Run. Verify "hello"
5 - clear output variable value. Save Run. Verify "hello"
6 - change input value to "world". Save. Run. Verify "world" <-will still output "hello"
**Expected behavior**
changing the input value will change the output value.
**Actual behavior**
the value you give to the input will fall behind by a save. i.e you provide "one" output comes out as "one". you provide "two" output comes out as "one". you provide "three" output comes out as "two".
If you continue to modify the values on variables and values on nodes while saving and running the editor eventually crashes.
[editorCallStack.txt](https://github.com/o3de/o3de/files/8279030/editorCallStack.txt)
**Found in Branch**
development
**Desktop/Device (please complete the following information):**
- Device: PC win 10
- nvidia 3070
- ryzen 5950
- 32GB ram
**Additional context**
Add any other context about the problem here. | non_infrastructure | script canvas assigning values to variables can lead to crash describe the bug assigning a value to a variable and saving seems to cause the engine to fall behind on a save for example if you make a function that simply takes in a string sets an output string to the input string s value then returns the output string you will get the result you expect when you call the function and pass in hello output hello if you change the output variable s value then change the value you pass into the function while saving and running with each step you will notice the expected output will fall behind currently looking into simpler repro for this crash steps to reproduce steps to reproduce the behavior make a user function described above call the function in another graph with a print node to verify the output change input value to hello save run verify hello change output variable value to test save run verify hello clear output variable value save run verify hello change input value to world save run verify world will still output hello expected behavior changing the input value will change the output value actual behavior the value you give to the input will fall behind by a save i e you provide one output comes out as one you provide two output comes out as one you provide three output comes out as two if you continue to modify the values on variables and values on nodes while saving and running the editor eventually crashes found in branch development desktop device please complete the following information device pc win nvidia ryzen ram additional context add any other context about the problem here | 0 |
315,700 | 23,592,820,402 | IssuesEvent | 2022-08-23 16:33:37 | uwcsc/codeybot | https://api.github.com/repos/uwcsc/codeybot | closed | Transfer setup information from README.md to SETUP.md | documentation | It would be more organized for all setup information to be found in SETUP.md, instead of it being split between README.md and SETUP.md. | 1.0 | Transfer setup information from README.md to SETUP.md - It would be more organized for all setup information to be found in SETUP.md, instead of it being split between README.md and SETUP.md. | non_infrastructure | transfer setup information from readme md to setup md it would be more organized for all setup information to be found in setup md instead of it being split between readme md and setup md | 0 |
27,508 | 21,799,795,371 | IssuesEvent | 2022-05-16 02:56:00 | C3ETH/c3eth-operations | https://api.github.com/repos/C3ETH/c3eth-operations | opened | Meeting [Team Checkin]: C3ETH Website Maintainers Team 13th May 2022 - 1000 to 1100 UTC | Meetup:Team Checkin Project:Activity Planning Operations:Infrastructure | # Meeting [Team Checkin]: C3ETH Website Maintainers Team 13th May 2022 - 1000 to 1100 UTC
## Topics
1. Website overview
2. Content Enhancement
3. General Site Cleanup
## Meeting Details:
### Attendees:
- Andre Cahyidi (@andrecahyadi)
- Jack O'Brien (@PardusEidolon)
### Apologies:
- Julius Mark Ibanez (@markibanez)
### Adgenda
1. General catch-up with each other.
2. Current website state (if any)
3. Site updates
4. New content to add
5. website enhacements/upgrades
### Discussion Summary:
#### Eastern Townhall website maintainers Meetup:
- General catchup and meet.
- Went through site anomolies with @andre.
- Shared [Giraffe Academy](https://www.youtube.com/watch?v=qtIqKaDlqXo&list=PLLAZ4kZ9dFpOnyRlyS-liKL5ReHDcj4G3)for hugo
- @andre going to learn hugo to help with the site maintenance | 1.0 | Meeting [Team Checkin]: C3ETH Website Maintainers Team 13th May 2022 - 1000 to 1100 UTC - # Meeting [Team Checkin]: C3ETH Website Maintainers Team 13th May 2022 - 1000 to 1100 UTC
## Topics
1. Website overview
2. Content Enhancement
3. General Site Cleanup
## Meeting Details:
### Attendees:
- Andre Cahyidi (@andrecahyadi)
- Jack O'Brien (@PardusEidolon)
### Apologies:
- Julius Mark Ibanez (@markibanez)
### Adgenda
1. General catch-up with each other.
2. Current website state (if any)
3. Site updates
4. New content to add
5. website enhacements/upgrades
### Discussion Summary:
#### Eastern Townhall website maintainers Meetup:
- General catchup and meet.
- Went through site anomolies with @andre.
- Shared [Giraffe Academy](https://www.youtube.com/watch?v=qtIqKaDlqXo&list=PLLAZ4kZ9dFpOnyRlyS-liKL5ReHDcj4G3)for hugo
- @andre going to learn hugo to help with the site maintenance | infrastructure | meeting website maintainers team may to utc meeting website maintainers team may to utc topics website overview content enhancement general site cleanup meeting details attendees andre cahyidi andrecahyadi jack o brien parduseidolon apologies julius mark ibanez markibanez adgenda general catch up with each other current website state if any site updates new content to add website enhacements upgrades discussion summary eastern townhall website maintainers meetup general catchup and meet went through site anomolies with andre shared hugo andre going to learn hugo to help with the site maintenance | 1 |
10,679 | 12,626,741,540 | IssuesEvent | 2020-06-14 18:01:31 | MoonchildProductions/UXP | https://api.github.com/repos/MoonchildProductions/UXP | opened | Implement ::slotted pseudo element | C: Layout - CSS Web Compatibility | **Spec:** https://drafts.csswg.org/css-scoping/#slotted-pseudo
***MDN:** https://developer.mozilla.org/en-US/docs/Web/CSS/::slotted
Reference Bugs:
WebKit: https://bugs.webkit.org/show_bug.cgi?id=149441
Gecko: https://bugzilla.mozilla.org/show_bug.cgi?id=1424605 (Servo Only)
Blocks #1361 | True | Implement ::slotted pseudo element - **Spec:** https://drafts.csswg.org/css-scoping/#slotted-pseudo
***MDN:** https://developer.mozilla.org/en-US/docs/Web/CSS/::slotted
Reference Bugs:
WebKit: https://bugs.webkit.org/show_bug.cgi?id=149441
Gecko: https://bugzilla.mozilla.org/show_bug.cgi?id=1424605 (Servo Only)
Blocks #1361 | non_infrastructure | implement slotted pseudo element spec mdn reference bugs webkit gecko servo only blocks | 0 |
3,985 | 4,750,984,232 | IssuesEvent | 2016-10-22 16:47:26 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | opened | Code coverage is broken | blocking-clean-ci Infrastructure | As can be seen in the latest report, it's only providing coverage for a single assembly out of 143 built.
http://dotnet-ci.cloudapp.net/job/dotnet_corefx/job/master/job/code_coverage_windows/Code_Coverage_Report/
It's at least partially related to https://github.com/dotnet/buildtools/issues/1144, but I expect there are issues beyond that, as when that issue was opened, the code coverage report was showing coverage for more than just one assembly.
cc: @karelz, @weshaggard, @MattGal, @mmitche | 1.0 | Code coverage is broken - As can be seen in the latest report, it's only providing coverage for a single assembly out of 143 built.
http://dotnet-ci.cloudapp.net/job/dotnet_corefx/job/master/job/code_coverage_windows/Code_Coverage_Report/
It's at least partially related to https://github.com/dotnet/buildtools/issues/1144, but I expect there are issues beyond that, as when that issue was opened, the code coverage report was showing coverage for more than just one assembly.
cc: @karelz, @weshaggard, @MattGal, @mmitche | infrastructure | code coverage is broken as can be seen in the latest report it s only providing coverage for a single assembly out of built it s at least partially related to but i expect there are issues beyond that as when that issue was opened the code coverage report was showing coverage for more than just one assembly cc karelz weshaggard mattgal mmitche | 1 |
28,132 | 23,036,534,334 | IssuesEvent | 2022-07-22 19:28:17 | memeLab/Jandig | https://api.github.com/repos/memeLab/Jandig | closed | Dependabot can't update vulnerable dependencies without a lockfile | bug infrastructure | **Describe the bug**
Dependabot can't update vulnerable dependencies without a lockfile. The currently installed version can't be determined. To resolve the issue add a supported lockfile (Pipfile.lock, pyproject.lock or poetry.lock).
It's blocking Dependabot from updating pillow on the last 20 days and will block other updates in the future.
| 1.0 | Dependabot can't update vulnerable dependencies without a lockfile - **Describe the bug**
Dependabot can't update vulnerable dependencies without a lockfile. The currently installed version can't be determined. To resolve the issue add a supported lockfile (Pipfile.lock, pyproject.lock or poetry.lock).
It's blocking Dependabot from updating pillow on the last 20 days and will block other updates in the future.
| infrastructure | dependabot can t update vulnerable dependencies without a lockfile describe the bug dependabot can t update vulnerable dependencies without a lockfile the currently installed version can t be determined to resolve the issue add a supported lockfile pipfile lock pyproject lock or poetry lock it s blocking dependabot from updating pillow on the last days and will block other updates in the future | 1 |
1,325 | 3,141,489,056 | IssuesEvent | 2015-09-12 16:55:10 | servo/servo | https://api.github.com/repos/servo/servo | closed | Stick to Windows-friendly filenames | A-infrastructure E-easy P-windows | e.g. The question mark in [`hello_a?foo#bar.html`](https://github.com/servo/servo/blob/master/tests/ref/hello_a%3Ffoo%23bar.html) is reported to cause problems. We also had issues with `aux.rs` in the past.
We should figure out the exact rules, then enforce them in `tidy.py`. | 1.0 | Stick to Windows-friendly filenames - e.g. The question mark in [`hello_a?foo#bar.html`](https://github.com/servo/servo/blob/master/tests/ref/hello_a%3Ffoo%23bar.html) is reported to cause problems. We also had issues with `aux.rs` in the past.
We should figure out the exact rules, then enforce them in `tidy.py`. | infrastructure | stick to windows friendly filenames e g the question mark in is reported to cause problems we also had issues with aux rs in the past we should figure out the exact rules then enforce them in tidy py | 1 |
30,697 | 13,298,679,817 | IssuesEvent | 2020-08-25 08:37:47 | woowacourse-teams/2020-doran-doran | https://api.github.com/repos/woowacourse-teams/2020-doran-doran | closed | 댓글 등록 시 위치가 없을 경우 스낵바로 고지한다. | :bug: Bug :dolphin: Front 👩👩👧👦 Service | ## 목적
위치를 확인할 수 없음을 사용자에게 알림
## 상세 작업내용
- [ ] 댓글 등록 시 위치 없음을 알림
## 주의사항
| 1.0 | 댓글 등록 시 위치가 없을 경우 스낵바로 고지한다. - ## 목적
위치를 확인할 수 없음을 사용자에게 알림
## 상세 작업내용
- [ ] 댓글 등록 시 위치 없음을 알림
## 주의사항
| non_infrastructure | 댓글 등록 시 위치가 없을 경우 스낵바로 고지한다 목적 위치를 확인할 수 없음을 사용자에게 알림 상세 작업내용 댓글 등록 시 위치 없음을 알림 주의사항 | 0 |
274,073 | 29,866,177,674 | IssuesEvent | 2023-06-20 04:12:38 | Chiencc/asuswrt-gt-ac5300 | https://api.github.com/repos/Chiencc/asuswrt-gt-ac5300 | closed | sqlite-amalgamation3.25.3: 12 vulnerabilities (highest severity is: 9.8) - autoclosed | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p></summary>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (sqlite-amalgamation3.25.3 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-19646](https://www.mend.io/vulnerability-database/CVE-2019-19646) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | sqlite-amalgamation3.25.3 | Direct | 3.31.0 | ❌ |
| [CVE-2020-11656](https://www.mend.io/vulnerability-database/CVE-2020-11656) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | sqlite-amalgamation3.25.3 | Direct | version-3.32.0 | ❌ |
| [CVE-2019-8457](https://www.mend.io/vulnerability-database/CVE-2019-8457) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | sqlite-amalgamation3.25.3 | Direct | 3.28.0 | ❌ |
| [CVE-2018-20505](https://www.mend.io/vulnerability-database/CVE-2018-20505) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | sqlite-amalgamation3.25.3 | Direct | 3.26.0 | ❌ |
| [CVE-2020-11655](https://www.mend.io/vulnerability-database/CVE-2020-11655) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.3 | ❌ |
| [CVE-2020-13630](https://www.mend.io/vulnerability-database/CVE-2020-13630) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.0 | sqlite-amalgamation3.25.3 | Direct | 3.32.0 | ❌ |
| [CVE-2019-16168](https://www.mend.io/vulnerability-database/CVE-2019-16168) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | sqlite-amalgamation3.25.3 | Direct | 3.30.0 | ❌ |
| [CVE-2020-13631](https://www.mend.io/vulnerability-database/CVE-2020-13631) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.0 | ❌ |
| [CVE-2020-13632](https://www.mend.io/vulnerability-database/CVE-2020-13632) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.0 | ❌ |
| [CVE-2020-13434](https://www.mend.io/vulnerability-database/CVE-2020-13434) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.1 | ❌ |
| [CVE-2020-13435](https://www.mend.io/vulnerability-database/CVE-2020-13435) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.1 | ❌ |
| [CVE-2019-19645](https://www.mend.io/vulnerability-database/CVE-2019-19645) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.31.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-19646</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
pragma.c in SQLite through 3.30.1 mishandles NOT NULL in an integrity_check PRAGMA command in certain cases of generated columns.
<p>Publish Date: 2019-12-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19646>CVE-2019-19646</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19646">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19646</a></p>
<p>Release Date: 2019-12-09</p>
<p>Fix Resolution: 3.31.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-11656</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SQLite through 3.31.1, the ALTER TABLE implementation has a use-after-free, as demonstrated by an ORDER BY clause that belongs to a compound SELECT statement.
<p>Publish Date: 2020-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11656>CVE-2020-11656</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-04-09</p>
<p>Fix Resolution: version-3.32.0 </p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-8457</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite3 from 3.6.0 to and including 3.27.2 is vulnerable to heap out-of-bound read in the rtreenode() function when handling invalid rtree tables.
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8457>CVE-2019-8457</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.sqlite.org/releaselog/3_28_0.html">https://www.sqlite.org/releaselog/3_28_0.html</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 3.28.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2018-20505</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite 3.25.2, when queries are run on a table with a malformed PRIMARY KEY, allows remote attackers to cause a denial of service (application crash) by leveraging the ability to run arbitrary SQL statements (such as in certain WebSQL use cases).
<p>Publish Date: 2019-04-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20505>CVE-2018-20505</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.sqlite.org/releaselog/3_26_0.html">https://www.sqlite.org/releaselog/3_26_0.html</a></p>
<p>Release Date: 2019-04-03</p>
<p>Fix Resolution: 3.26.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-11655</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite through 3.31.1 allows attackers to cause a denial of service (segmentation fault) via a malformed window-function query because the AggInfo object's initialization is mishandled.
<p>Publish Date: 2020-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11655>CVE-2020-11655</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-04-09</p>
<p>Fix Resolution: 3.32.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-13630</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
ext/fts3/fts3.c in SQLite before 3.32.0 has a use-after-free in fts3EvalNextRow, related to the snippet feature.
<p>Publish Date: 2020-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13630>CVE-2020-13630</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13630">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13630</a></p>
<p>Release Date: 2020-05-27</p>
<p>Fix Resolution: 3.32.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-16168</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SQLite through 3.29.0, whereLoopAddBtreeIndex in sqlite3.c can crash a browser or other application because of missing validation of a sqlite_stat1 sz field, aka a "severe division by zero in the query planner."
<p>Publish Date: 2019-09-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16168>CVE-2019-16168</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.sqlite.org/src/info/e4598ecbdd18bd82945f6029013296690e719a62">https://www.sqlite.org/src/info/e4598ecbdd18bd82945f6029013296690e719a62</a></p>
<p>Release Date: 2019-09-09</p>
<p>Fix Resolution: 3.30.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13631</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite before 3.32.0 allows a virtual table to be renamed to the name of one of its shadow tables, related to alter.c and build.c.
<p>Publish Date: 2020-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13631>CVE-2020-13631</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13631">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13631</a></p>
<p>Release Date: 2020-05-27</p>
<p>Fix Resolution: 3.32.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13632</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
ext/fts3/fts3_snippet.c in SQLite before 3.32.0 has a NULL pointer dereference via a crafted matchinfo() query.
<p>Publish Date: 2020-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13632>CVE-2020-13632</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13632">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13632</a></p>
<p>Release Date: 2020-05-27</p>
<p>Fix Resolution: 3.32.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13434</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite through 3.32.0 has an integer overflow in sqlite3_str_vappendf in printf.c.
<p>Publish Date: 2020-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13434>CVE-2020-13434</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13434">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13434</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: 3.32.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13435</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite through 3.32.0 has a segmentation fault in sqlite3ExprCodeTarget in expr.c.
<p>Publish Date: 2020-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13435>CVE-2020-13435</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13435">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13435</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: 3.32.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-19645</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
alter.c in SQLite through 3.30.1 allows attackers to trigger infinite recursion via certain types of self-referential views in conjunction with ALTER TABLE statements.
<p>Publish Date: 2019-12-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19645>CVE-2019-19645</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19645">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19645</a></p>
<p>Release Date: 2019-12-09</p>
<p>Fix Resolution: 3.31.0</p>
</p>
<p></p>
</details> | True | sqlite-amalgamation3.25.3: 12 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p></summary>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (sqlite-amalgamation3.25.3 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-19646](https://www.mend.io/vulnerability-database/CVE-2019-19646) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | sqlite-amalgamation3.25.3 | Direct | 3.31.0 | ❌ |
| [CVE-2020-11656](https://www.mend.io/vulnerability-database/CVE-2020-11656) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | sqlite-amalgamation3.25.3 | Direct | version-3.32.0 | ❌ |
| [CVE-2019-8457](https://www.mend.io/vulnerability-database/CVE-2019-8457) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | sqlite-amalgamation3.25.3 | Direct | 3.28.0 | ❌ |
| [CVE-2018-20505](https://www.mend.io/vulnerability-database/CVE-2018-20505) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | sqlite-amalgamation3.25.3 | Direct | 3.26.0 | ❌ |
| [CVE-2020-11655](https://www.mend.io/vulnerability-database/CVE-2020-11655) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.3 | ❌ |
| [CVE-2020-13630](https://www.mend.io/vulnerability-database/CVE-2020-13630) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.0 | sqlite-amalgamation3.25.3 | Direct | 3.32.0 | ❌ |
| [CVE-2019-16168](https://www.mend.io/vulnerability-database/CVE-2019-16168) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | sqlite-amalgamation3.25.3 | Direct | 3.30.0 | ❌ |
| [CVE-2020-13631](https://www.mend.io/vulnerability-database/CVE-2020-13631) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.0 | ❌ |
| [CVE-2020-13632](https://www.mend.io/vulnerability-database/CVE-2020-13632) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.0 | ❌ |
| [CVE-2020-13434](https://www.mend.io/vulnerability-database/CVE-2020-13434) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.1 | ❌ |
| [CVE-2020-13435](https://www.mend.io/vulnerability-database/CVE-2020-13435) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.32.1 | ❌ |
| [CVE-2019-19645](https://www.mend.io/vulnerability-database/CVE-2019-19645) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.5 | sqlite-amalgamation3.25.3 | Direct | 3.31.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-19646</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
pragma.c in SQLite through 3.30.1 mishandles NOT NULL in an integrity_check PRAGMA command in certain cases of generated columns.
<p>Publish Date: 2019-12-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19646>CVE-2019-19646</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19646">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19646</a></p>
<p>Release Date: 2019-12-09</p>
<p>Fix Resolution: 3.31.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-11656</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SQLite through 3.31.1, the ALTER TABLE implementation has a use-after-free, as demonstrated by an ORDER BY clause that belongs to a compound SELECT statement.
<p>Publish Date: 2020-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11656>CVE-2020-11656</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-04-09</p>
<p>Fix Resolution: version-3.32.0 </p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-8457</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite3 from 3.6.0 to and including 3.27.2 is vulnerable to heap out-of-bound read in the rtreenode() function when handling invalid rtree tables.
<p>Publish Date: 2019-05-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8457>CVE-2019-8457</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.sqlite.org/releaselog/3_28_0.html">https://www.sqlite.org/releaselog/3_28_0.html</a></p>
<p>Release Date: 2019-05-30</p>
<p>Fix Resolution: 3.28.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2018-20505</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite 3.25.2, when queries are run on a table with a malformed PRIMARY KEY, allows remote attackers to cause a denial of service (application crash) by leveraging the ability to run arbitrary SQL statements (such as in certain WebSQL use cases).
<p>Publish Date: 2019-04-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20505>CVE-2018-20505</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.sqlite.org/releaselog/3_26_0.html">https://www.sqlite.org/releaselog/3_26_0.html</a></p>
<p>Release Date: 2019-04-03</p>
<p>Fix Resolution: 3.26.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-11655</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite through 3.31.1 allows attackers to cause a denial of service (segmentation fault) via a malformed window-function query because the AggInfo object's initialization is mishandled.
<p>Publish Date: 2020-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11655>CVE-2020-11655</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-04-09</p>
<p>Fix Resolution: 3.32.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2020-13630</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
ext/fts3/fts3.c in SQLite before 3.32.0 has a use-after-free in fts3EvalNextRow, related to the snippet feature.
<p>Publish Date: 2020-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13630>CVE-2020-13630</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13630">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13630</a></p>
<p>Release Date: 2020-05-27</p>
<p>Fix Resolution: 3.32.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-16168</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SQLite through 3.29.0, whereLoopAddBtreeIndex in sqlite3.c can crash a browser or other application because of missing validation of a sqlite_stat1 sz field, aka a "severe division by zero in the query planner."
<p>Publish Date: 2019-09-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16168>CVE-2019-16168</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.sqlite.org/src/info/e4598ecbdd18bd82945f6029013296690e719a62">https://www.sqlite.org/src/info/e4598ecbdd18bd82945f6029013296690e719a62</a></p>
<p>Release Date: 2019-09-09</p>
<p>Fix Resolution: 3.30.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13631</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite before 3.32.0 allows a virtual table to be renamed to the name of one of its shadow tables, related to alter.c and build.c.
<p>Publish Date: 2020-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13631>CVE-2020-13631</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13631">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13631</a></p>
<p>Release Date: 2020-05-27</p>
<p>Fix Resolution: 3.32.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13632</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
ext/fts3/fts3_snippet.c in SQLite before 3.32.0 has a NULL pointer dereference via a crafted matchinfo() query.
<p>Publish Date: 2020-05-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13632>CVE-2020-13632</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13632">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13632</a></p>
<p>Release Date: 2020-05-27</p>
<p>Fix Resolution: 3.32.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13434</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite through 3.32.0 has an integer overflow in sqlite3_str_vappendf in printf.c.
<p>Publish Date: 2020-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13434>CVE-2020-13434</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13434">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13434</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: 3.32.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-13435</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQLite through 3.32.0 has a segmentation fault in sqlite3ExprCodeTarget in expr.c.
<p>Publish Date: 2020-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13435>CVE-2020-13435</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13435">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-13435</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: 3.32.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-19645</summary>
### Vulnerable Library - <b>sqlite-amalgamation3.25.3</b></p>
<p>
<p>SQLite is a C-language library that implements a small, fast, self-contained, high-reliability, full-featured, SQL database engine.</p>
<p>Library home page: <a href=https://www.sqlite.org/?wsslib=sqlite-amalgamation>https://www.sqlite.org/?wsslib=sqlite-amalgamation</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (2)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/release/src/router/sqlite/sqlite3.c</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
alter.c in SQLite through 3.30.1 allows attackers to trigger infinite recursion via certain types of self-referential views in conjunction with ALTER TABLE statements.
<p>Publish Date: 2019-12-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19645>CVE-2019-19645</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19645">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19645</a></p>
<p>Release Date: 2019-12-09</p>
<p>Fix Resolution: 3.31.0</p>
</p>
<p></p>
</details> | non_infrastructure | sqlite vulnerabilities highest severity is autoclosed vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href vulnerable source files release src router sqlite c release src router sqlite c vulnerabilities cve severity cvss dependency type fixed in sqlite version remediation available critical sqlite direct critical sqlite direct version critical sqlite direct high sqlite direct high sqlite direct high sqlite direct medium sqlite direct medium sqlite direct medium sqlite direct medium sqlite direct medium sqlite direct medium sqlite direct details cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details pragma c in sqlite through mishandles not null in an integrity check pragma command in certain cases of generated columns publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details in sqlite through the alter table implementation has a use after free as demonstrated by an order by clause that belongs to a compound select statement publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution version cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details from to and including is vulnerable to heap out of bound read in the rtreenode function when handling invalid rtree tables publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details sqlite when queries are run on a table with a malformed primary key allows remote attackers to cause a denial of service application crash by leveraging the ability to run arbitrary sql statements such as in certain websql use cases publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details sqlite through allows attackers to cause a denial of service segmentation fault via a malformed window function query because the agginfo object s initialization is mishandled publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details ext c in sqlite before has a use after free in related to the snippet feature publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details in sqlite through whereloopaddbtreeindex in c can crash a browser or other application because of missing validation of a sqlite sz field aka a severe division by zero in the query planner publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details sqlite before allows a virtual table to be renamed to the name of one of its shadow tables related to alter c and build c publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details ext snippet c in sqlite before has a null pointer dereference via a crafted matchinfo query publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details sqlite through has an integer overflow in str vappendf in printf c publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details sqlite through has a segmentation fault in in expr c publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library sqlite sqlite is a c language library that implements a small fast self contained high reliability full featured sql database engine library home page a href found in head commit a href found in base branch master vulnerable source files release src router sqlite c release src router sqlite c vulnerability details alter c in sqlite through allows attackers to trigger infinite recursion via certain types of self referential views in conjunction with alter table statements publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
40,111 | 20,592,011,454 | IssuesEvent | 2022-03-05 00:47:17 | cvc5/cvc5-projects | https://api.github.com/repos/cvc5/cvc5-projects | closed | QF_NRA: Unintuitive incompleteness on one inequality | performance | Commit: dac8b87
Weakening the solvable equality to `>=` results in an incompleteness, but not for `<=`. Is this expected behavior?
```
$ cvc5 -q known.smt2
sat
$ cat known.smt2
(declare-fun s () Real)
(declare-fun k () Real)
(assert (= (* s k) 1))
(check-sat)
$ cvc5 -q unknown.smt2
unknown
$ cat unknown.smt2
(declare-fun s () Real)
(declare-fun k () Real)
(assert (>= (* s k) 1))
(check-sat)
$ cvc5 -q known-2.smt2
sat
$ cat known-2.smt2
(declare-fun s () Real)
(declare-fun k () Real)
(assert (<= (* s k) 1))
(check-sat)
``` | True | QF_NRA: Unintuitive incompleteness on one inequality - Commit: dac8b87
Weakening the solvable equality to `>=` results in an incompleteness, but not for `<=`. Is this expected behavior?
```
$ cvc5 -q known.smt2
sat
$ cat known.smt2
(declare-fun s () Real)
(declare-fun k () Real)
(assert (= (* s k) 1))
(check-sat)
$ cvc5 -q unknown.smt2
unknown
$ cat unknown.smt2
(declare-fun s () Real)
(declare-fun k () Real)
(assert (>= (* s k) 1))
(check-sat)
$ cvc5 -q known-2.smt2
sat
$ cat known-2.smt2
(declare-fun s () Real)
(declare-fun k () Real)
(assert (<= (* s k) 1))
(check-sat)
``` | non_infrastructure | qf nra unintuitive incompleteness on one inequality commit weakening the solvable equality to results in an incompleteness but not for is this expected behavior q known sat cat known declare fun s real declare fun k real assert s k check sat q unknown unknown cat unknown declare fun s real declare fun k real assert s k check sat q known sat cat known declare fun s real declare fun k real assert s k check sat | 0 |
7,115 | 5,868,215,336 | IssuesEvent | 2017-05-14 10:30:43 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | [2.2.2] [2.3] [Windows] ownCloud still consuming excessive amount of CPU | Performance | ### Actual behaviour
Even after fixing #4967, ownCloud keeps eating an entire CPU core for me at times, which I think it already did in 2.1.1 from time to time, so it might be a problem not caught by the fix for #4967.
I'm running ownCloud on a dual-core CPU, so it becomes obvious that something is wrong as soon as another application maxes out the other core. ownCloud's scan thread (which I assume is responsible for this high CPU usage) should run with a rather low priority as it is essentially a background service. This way, "normal" threads should be able to take over the CPU when they need it, meaning that the applications that I actually intend to use would be more responsive.
As the question already came up in #4967, Explorer overlays are disabled.
### Client configuration
Client version: 2.2.2-6192
Operating system: Windows 7 x64
OS language: German
Installation path of client: Default
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/35564531-2-2-2-2-3-windows-owncloud-still-consuming-excessive-amount-of-cpu?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github).
</bountysource-plugin> | True | [2.2.2] [2.3] [Windows] ownCloud still consuming excessive amount of CPU - ### Actual behaviour
Even after fixing #4967, ownCloud keeps eating an entire CPU core for me at times, which I think it already did in 2.1.1 from time to time, so it might be a problem not caught by the fix for #4967.
I'm running ownCloud on a dual-core CPU, so it becomes obvious that something is wrong as soon as another application maxes out the other core. ownCloud's scan thread (which I assume is responsible for this high CPU usage) should run with a rather low priority as it is essentially a background service. This way, "normal" threads should be able to take over the CPU when they need it, meaning that the applications that I actually intend to use would be more responsive.
As the question already came up in #4967, Explorer overlays are disabled.
### Client configuration
Client version: 2.2.2-6192
Operating system: Windows 7 x64
OS language: German
Installation path of client: Default
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/35564531-2-2-2-2-3-windows-owncloud-still-consuming-excessive-amount-of-cpu?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F216457&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_infrastructure | owncloud still consuming excessive amount of cpu actual behaviour even after fixing owncloud keeps eating an entire cpu core for me at times which i think it already did in from time to time so it might be a problem not caught by the fix for i m running owncloud on a dual core cpu so it becomes obvious that something is wrong as soon as another application maxes out the other core owncloud s scan thread which i assume is responsible for this high cpu usage should run with a rather low priority as it is essentially a background service this way normal threads should be able to take over the cpu when they need it meaning that the applications that i actually intend to use would be more responsive as the question already came up in explorer overlays are disabled client configuration client version operating system windows os language german installation path of client default want to back this issue we accept bounties via | 0 |
86,069 | 24,757,192,278 | IssuesEvent | 2022-10-21 19:00:10 | dotnet/arcade | https://api.github.com/repos/dotnet/arcade | closed | Build failed: dotnet-arcade-validation-official/main #20221020.3 | Build Failed | Build [#20221020.3](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=2026312) partiallySucceeded
## :warning: : internal / dotnet-arcade-validation-official partiallySucceeded
### Summary
**Finished** - Fri, 21 Oct 2022 01:54:40 GMT
**Duration** - 112 minutes
**Requested for** - Microsoft.VisualStudio.Services.TFS
**Reason** - schedule
### Details
#### Promote Arcade to '.NET Eng - Latest' channel
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2026312/logs/386) - The latest build on 'main' branch for the 'runtime' repository was not successful.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2026312/logs/386) - The latest build on 'main' branch for the 'installer' repository was not successful.
### Changes
- [3b22e4d5](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/3b22e4d532f19831f1125dadc809c2599884a6f9) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221020.1 (#3465)
- [eb8a489e](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/eb8a489e6bbf4d7a5dbbb5e7156584ebadaabaea) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.12 (#3464)
- [2dc2e2b9](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/2dc2e2b9e09e7475e44061a73c80fdaf0a93390f) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.11 (#3463)
- [1478cb0f](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/1478cb0f7a56d99d479aa5e237b0841ff0758554) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.8 (#3462)
- [5ab03ec5](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/5ab03ec5fbf7c61f6afd4df9f419cfe91c3c8620) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.2 (#3461)
- [ee09405a](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/ee09405a6d31c26c0f9c1c34c58a0b9e8a920b34) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.1 (#3460)
- [700fb83c](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/700fb83c7b334d4300e6cc97026dcc15c87e5cfc) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.11 (#3459)
- [98246285](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/98246285b490f8727d3fe5e9f616efeadf56bfe7) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.4 (#3458)
- [8ed44334](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/8ed44334cc75441e7efc96a97b46e16c44862450) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.3 (#3457)
- [4cb90182](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/4cb90182595f687e87252dcf47eb05f0086ac6f0) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.2 (#3456)
| 1.0 | Build failed: dotnet-arcade-validation-official/main #20221020.3 - Build [#20221020.3](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=2026312) partiallySucceeded
## :warning: : internal / dotnet-arcade-validation-official partiallySucceeded
### Summary
**Finished** - Fri, 21 Oct 2022 01:54:40 GMT
**Duration** - 112 minutes
**Requested for** - Microsoft.VisualStudio.Services.TFS
**Reason** - schedule
### Details
#### Promote Arcade to '.NET Eng - Latest' channel
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2026312/logs/386) - The latest build on 'main' branch for the 'runtime' repository was not successful.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2026312/logs/386) - The latest build on 'main' branch for the 'installer' repository was not successful.
### Changes
- [3b22e4d5](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/3b22e4d532f19831f1125dadc809c2599884a6f9) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221020.1 (#3465)
- [eb8a489e](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/eb8a489e6bbf4d7a5dbbb5e7156584ebadaabaea) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.12 (#3464)
- [2dc2e2b9](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/2dc2e2b9e09e7475e44061a73c80fdaf0a93390f) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.11 (#3463)
- [1478cb0f](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/1478cb0f7a56d99d479aa5e237b0841ff0758554) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.8 (#3462)
- [5ab03ec5](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/5ab03ec5fbf7c61f6afd4df9f419cfe91c3c8620) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.2 (#3461)
- [ee09405a](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/ee09405a6d31c26c0f9c1c34c58a0b9e8a920b34) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221019.1 (#3460)
- [700fb83c](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/700fb83c7b334d4300e6cc97026dcc15c87e5cfc) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.11 (#3459)
- [98246285](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/98246285b490f8727d3fe5e9f616efeadf56bfe7) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.4 (#3458)
- [8ed44334](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/8ed44334cc75441e7efc96a97b46e16c44862450) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.3 (#3457)
- [4cb90182](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/017fb734-e4b4-4cc1-a90f-98a09ac25cd5/commit/4cb90182595f687e87252dcf47eb05f0086ac6f0) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221018.2 (#3456)
| non_infrastructure | build failed dotnet arcade validation official main build partiallysucceeded warning internal dotnet arcade validation official partiallysucceeded summary finished fri oct gmt duration minutes requested for microsoft visualstudio services tfs reason schedule details promote arcade to net eng latest channel warning the latest build on main branch for the runtime repository was not successful warning the latest build on main branch for the installer repository was not successful changes dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build dotnet maestro update dependencies from build | 0 |
5,386 | 5,630,045,653 | IssuesEvent | 2017-04-05 11:06:57 | hzi-braunschweig/SORMAS-Open | https://api.github.com/repos/hzi-braunschweig/SORMAS-Open | closed | Caption fixes/renaming | Infrastructure sormas-api sormas-app | - [x] "Assignee reply -> "Comments on execution"
- [x] "Phone" -> "Phone number"
- [x] "Date of symptom onset" -> ???
EpiData
- [x] rename "Contact" to "Exposure" for all fields associated with animals
- [x] "Date of contact" -> "Date of last exposure"
- [x] "Place of contact" -> "Place of last exposure" | 1.0 | Caption fixes/renaming - - [x] "Assignee reply -> "Comments on execution"
- [x] "Phone" -> "Phone number"
- [x] "Date of symptom onset" -> ???
EpiData
- [x] rename "Contact" to "Exposure" for all fields associated with animals
- [x] "Date of contact" -> "Date of last exposure"
- [x] "Place of contact" -> "Place of last exposure" | infrastructure | caption fixes renaming assignee reply comments on execution phone phone number date of symptom onset epidata rename contact to exposure for all fields associated with animals date of contact date of last exposure place of contact place of last exposure | 1 |
78,599 | 15,586,042,032 | IssuesEvent | 2021-03-18 01:02:20 | tamirverthim/fitbit-api-example-java | https://api.github.com/repos/tamirverthim/fitbit-api-example-java | closed | CVE-2018-1272 (High) detected in spring-core-4.3.2.RELEASE.jar - autoclosed | security vulnerability | ## CVE-2018-1272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-4.3.2.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: fitbit-api-example-java/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/springframework/spring-core/4.3.2.RELEASE/spring-core-4.3.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-oauth2-2.0.10.RELEASE.jar (Root Library)
- :x: **spring-core-4.3.2.RELEASE.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.
<p>Publish Date: 2018-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1272>CVE-2018-1272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2018-1272">https://tanzu.vmware.com/security/cve-2018-1272</a></p>
<p>Release Date: 2018-04-06</p>
<p>Fix Resolution: org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-core","packageVersion":"4.3.2.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.security.oauth:spring-security-oauth2:2.0.10.RELEASE;org.springframework:spring-core:4.3.2.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2018-1272","vulnerabilityDetails":"Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1272","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-1272 (High) detected in spring-core-4.3.2.RELEASE.jar - autoclosed - ## CVE-2018-1272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-4.3.2.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: fitbit-api-example-java/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/springframework/spring-core/4.3.2.RELEASE/spring-core-4.3.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-oauth2-2.0.10.RELEASE.jar (Root Library)
- :x: **spring-core-4.3.2.RELEASE.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.
<p>Publish Date: 2018-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1272>CVE-2018-1272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2018-1272">https://tanzu.vmware.com/security/cve-2018-1272</a></p>
<p>Release Date: 2018-04-06</p>
<p>Fix Resolution: org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-core","packageVersion":"4.3.2.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.security.oauth:spring-security-oauth2:2.0.10.RELEASE;org.springframework:spring-core:4.3.2.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2018-1272","vulnerabilityDetails":"Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1272","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_infrastructure | cve high detected in spring core release jar autoclosed cve high severity vulnerability vulnerable library spring core release jar spring core library home page a href path to dependency file fitbit api example java pom xml path to vulnerable library root repository org springframework spring core release spring core release jar dependency hierarchy spring security release jar root library x spring core release jar vulnerable library vulnerability details spring framework versions prior to and versions prior to and older unsupported versions provide client side support for multipart requests when spring mvc or spring webflux server application server a receives input from a remote client and then uses that input to make a multipart request to another server server b it can be exposed to an attack where an extra multipart is inserted in the content of the request from server a causing server b to use the wrong value for a part it expects this could to lead privilege escalation for example if the part content represents a username or user roles publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring core release release org springframework spring web release release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework security oauth spring security release org springframework spring core release isminimumfixversionavailable true minimumfixversion org springframework spring core release release org springframework spring web release release basebranches vulnerabilityidentifier cve vulnerabilitydetails spring framework versions prior to and versions prior to and older unsupported versions provide client side support for multipart requests when spring mvc or spring webflux server application server a receives input from a remote client and then uses that input to make a multipart request to another server server b it can be exposed to an attack where an extra multipart is inserted in the content of the request from server a causing server b to use the wrong value for a part it expects this could to lead privilege escalation for example if the part content represents a username or user roles vulnerabilityurl | 0 |
497,141 | 14,362,543,157 | IssuesEvent | 2020-11-30 19:59:55 | openforis/collect-earth-online | https://api.github.com/repos/openforis/collect-earth-online | closed | Suggestions: joining/managing organizations | Feature Request Low Priority | -A user should be able to request joining an organization as either a member OR an admin (currently they are not able to specify desired role)
-A user who is a member of an organization should be able to see which members are admins
-A user should receive notification when their pending status is switched to confirmed member for an organization
-An organization's admin should receive notification when a user has requested membership | 1.0 | Suggestions: joining/managing organizations - -A user should be able to request joining an organization as either a member OR an admin (currently they are not able to specify desired role)
-A user who is a member of an organization should be able to see which members are admins
-A user should receive notification when their pending status is switched to confirmed member for an organization
-An organization's admin should receive notification when a user has requested membership | non_infrastructure | suggestions joining managing organizations a user should be able to request joining an organization as either a member or an admin currently they are not able to specify desired role a user who is a member of an organization should be able to see which members are admins a user should receive notification when their pending status is switched to confirmed member for an organization an organization s admin should receive notification when a user has requested membership | 0 |
24,095 | 16,836,052,808 | IssuesEvent | 2021-06-18 12:14:14 | SCALE-MS/scale-ms | https://api.github.com/repos/SCALE-MS/scale-ms | opened | Make sure RP Pilot and Tasks are appropriately shut down under HPC job schedulers | infrastructure restart scalems.radical.runtime | We expect to minimize idle HPC job time by maximizing the ability to resume partially executed workflows. Also, we are targeting large workflows that can't complete in allowable job times on many systems.
Thus we expect to request less Pilot runtime than is expected to be necessary.
We need to decide on the appropriate way to run out the job allocation time and canceling remaining tasks as a first-tier supported use case.
The new Raptor facilities allow for individual Tasks to have walltime limits. This will help, as long as we can set the limits dynamically according to the expected remaining time on the allocation.
This issue can be used to collect additional thoughts and discussion. | 1.0 | Make sure RP Pilot and Tasks are appropriately shut down under HPC job schedulers - We expect to minimize idle HPC job time by maximizing the ability to resume partially executed workflows. Also, we are targeting large workflows that can't complete in allowable job times on many systems.
Thus we expect to request less Pilot runtime than is expected to be necessary.
We need to decide on the appropriate way to run out the job allocation time and canceling remaining tasks as a first-tier supported use case.
The new Raptor facilities allow for individual Tasks to have walltime limits. This will help, as long as we can set the limits dynamically according to the expected remaining time on the allocation.
This issue can be used to collect additional thoughts and discussion. | infrastructure | make sure rp pilot and tasks are appropriately shut down under hpc job schedulers we expect to minimize idle hpc job time by maximizing the ability to resume partially executed workflows also we are targeting large workflows that can t complete in allowable job times on many systems thus we expect to request less pilot runtime than is expected to be necessary we need to decide on the appropriate way to run out the job allocation time and canceling remaining tasks as a first tier supported use case the new raptor facilities allow for individual tasks to have walltime limits this will help as long as we can set the limits dynamically according to the expected remaining time on the allocation this issue can be used to collect additional thoughts and discussion | 1 |
22,740 | 15,418,702,989 | IssuesEvent | 2021-03-05 09:10:05 | skypyproject/skypy | https://api.github.com/repos/skypyproject/skypy | closed | Inconsistent wavenumber units and power spectrum normalisations | bug infrastructure module: power spectrum | **Describe the bug**
The SkyPy implementation of the Eisenstein-Hu linear power spectrum is inconsistent with the wrappers around CAMB, CLASS in terms of the wavelength units and amplitude scaling.
**To Reproduce**
```python
>>> from astropy.cosmology import Planck18
>>> from matplotlib import pyplot as plt
>>> import numpy as np
>>> from skypy.power_spectrum import camb, classy, eisenstein_hu, growth_function
>>> k = np.logspace(-3, -1, 50)
>>> z, A_s, n_s = 0, 2.2E-9, 0.97
>>> p_camb = camb(k, z, Planck18, A_s, n_s)
>>> p_classy = classy(k, z, Planck18, A_s=A_s, n_s=n_s)
>>> p_eh = eisenstein_hu(k, A_s, n_s, Planck18)
>>> plt.plot(k, p_camb, label='CAMB')
>>> plt.plot(k, p_classy, label='CLASS')
>>> plt.plot(k, p_eh, label='Eisenstein-Hu')
>>> plt.loglog()
>>> plt.legend()
>>> plt.show()
```
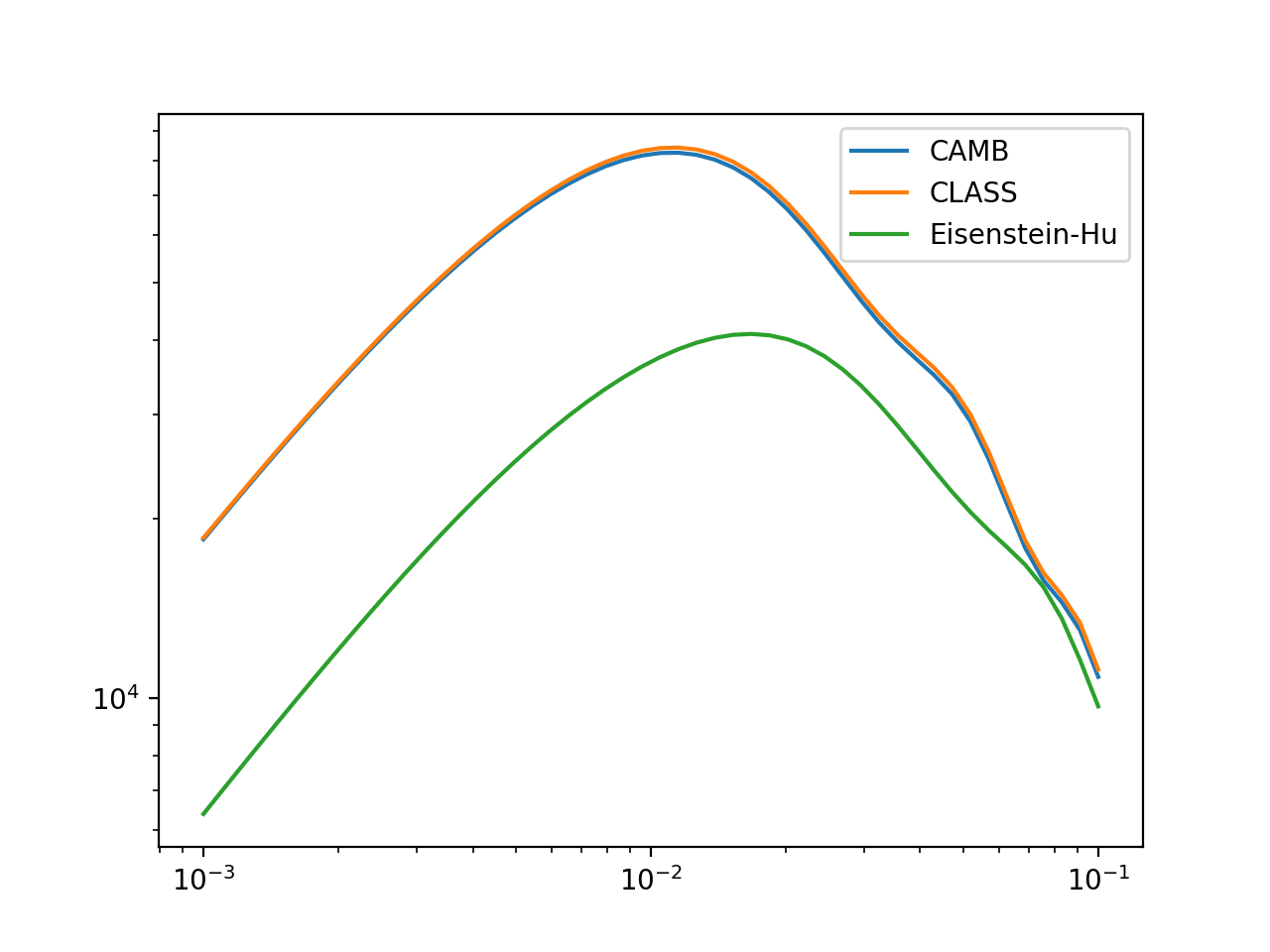
Here it is clear that the peak of the power spectrum is shifted horizontally, indicating that the different models are making different assumptions about the units of the wavenumber k. Also there is an overall amplitude offset.
```python
>>> d = growth_function(z, Planck18)
>>> plt.plot(k, p_camb, label='CAMB')
>>> plt.plot(k, p_classy, label='CLASS')
>>> plt.plot(k*Planck18.h, p_eh/(d*d), label='Eisenstein-Hu')
>>> plt.loglog()
>>> plt.legend()
>>> plt.show()
```
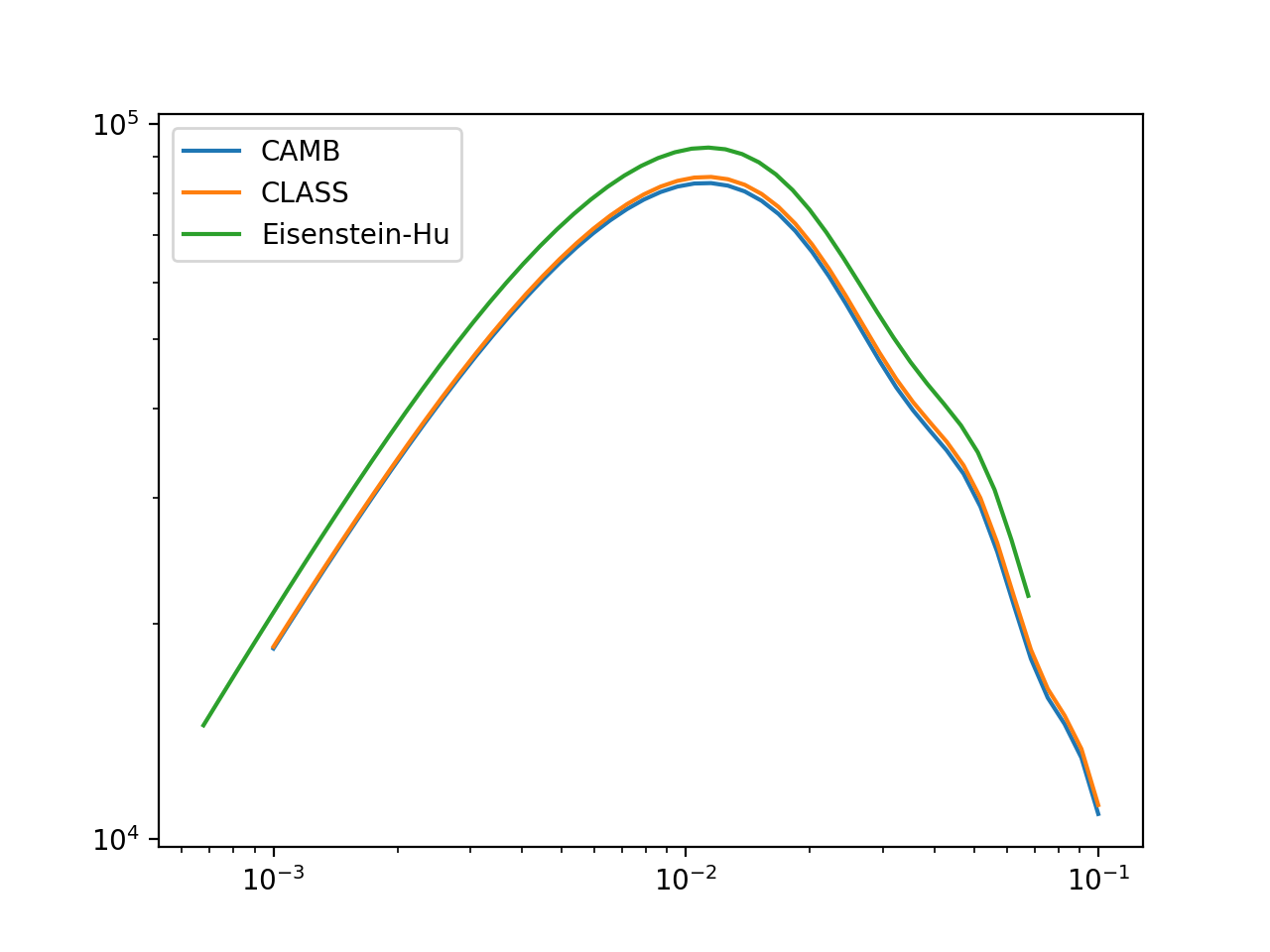
The second figure makes it clear that CAMB, CLASS and EH are not consistently assuming units of wavenumber to be Mpc (instead of Mpc/h; see [ADR-2](https://github.com/skypyproject/skypy/blob/main/docs/arch/adr-02.md)). Also the discrepancy in the normalisation could be a factor of the growth function at redshift zero squared although correcting for this does not give precise agreement.
**Expected behavior**
All power spectrum models should use the same wavenumber units and amplitude scaling conventions for consistency. I would suggest that modifying our implementation of EH to be consistent with the conventions used in CAMB/CLASS would make it more intuitive for users familiar with those codes, although I note that might go against our [ADR-2](https://github.com/skypyproject/skypy/blob/main/docs/arch/adr-02.md). Also (the option to) normalise based upon sigma_8 might be advantageous?
**Desktop (please complete the following information):**
- SkyPy `module/halos` branch
| 1.0 | Inconsistent wavenumber units and power spectrum normalisations - **Describe the bug**
The SkyPy implementation of the Eisenstein-Hu linear power spectrum is inconsistent with the wrappers around CAMB, CLASS in terms of the wavelength units and amplitude scaling.
**To Reproduce**
```python
>>> from astropy.cosmology import Planck18
>>> from matplotlib import pyplot as plt
>>> import numpy as np
>>> from skypy.power_spectrum import camb, classy, eisenstein_hu, growth_function
>>> k = np.logspace(-3, -1, 50)
>>> z, A_s, n_s = 0, 2.2E-9, 0.97
>>> p_camb = camb(k, z, Planck18, A_s, n_s)
>>> p_classy = classy(k, z, Planck18, A_s=A_s, n_s=n_s)
>>> p_eh = eisenstein_hu(k, A_s, n_s, Planck18)
>>> plt.plot(k, p_camb, label='CAMB')
>>> plt.plot(k, p_classy, label='CLASS')
>>> plt.plot(k, p_eh, label='Eisenstein-Hu')
>>> plt.loglog()
>>> plt.legend()
>>> plt.show()
```
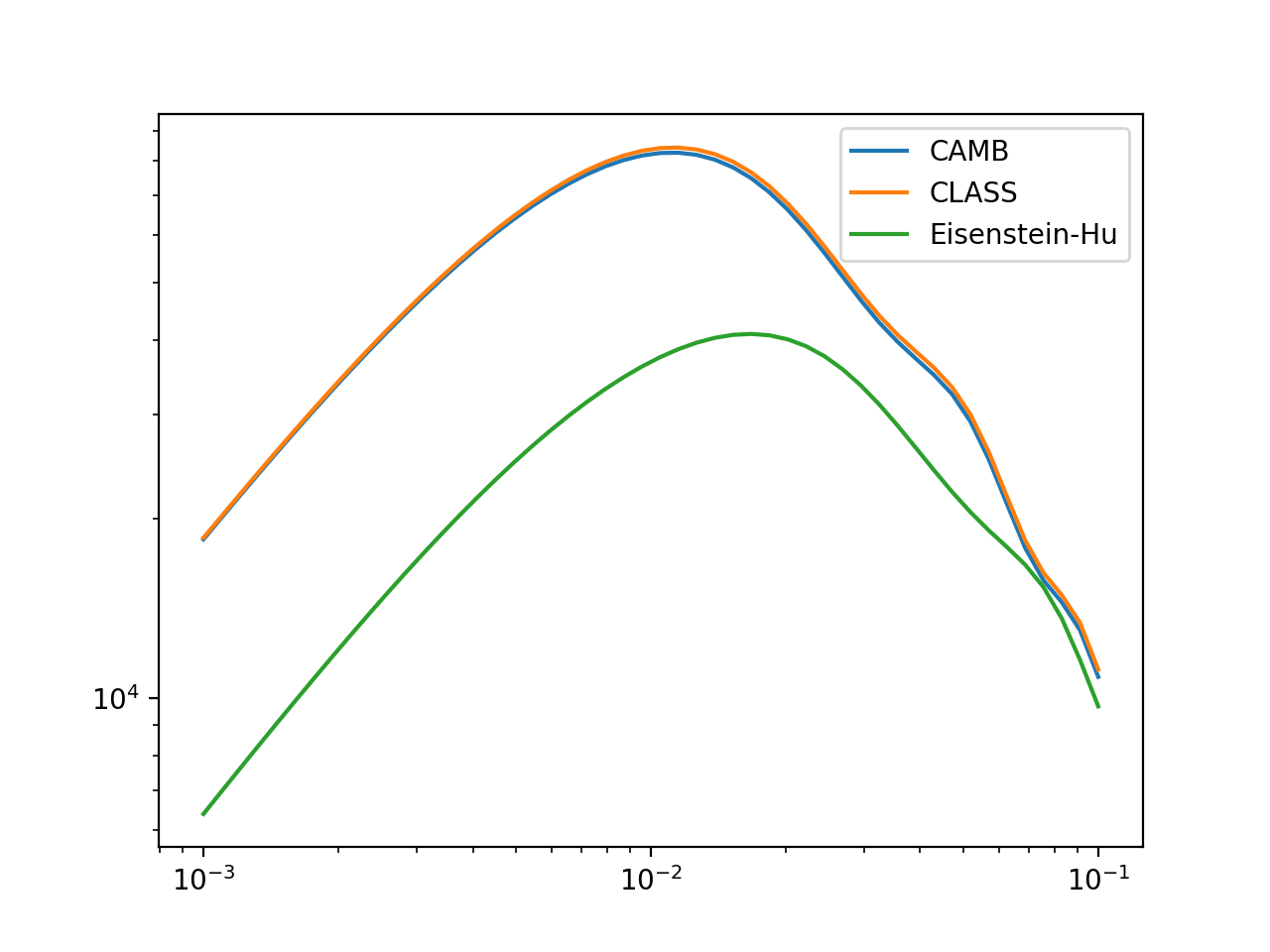
Here it is clear that the peak of the power spectrum is shifted horizontally, indicating that the different models are making different assumptions about the units of the wavenumber k. Also there is an overall amplitude offset.
```python
>>> d = growth_function(z, Planck18)
>>> plt.plot(k, p_camb, label='CAMB')
>>> plt.plot(k, p_classy, label='CLASS')
>>> plt.plot(k*Planck18.h, p_eh/(d*d), label='Eisenstein-Hu')
>>> plt.loglog()
>>> plt.legend()
>>> plt.show()
```
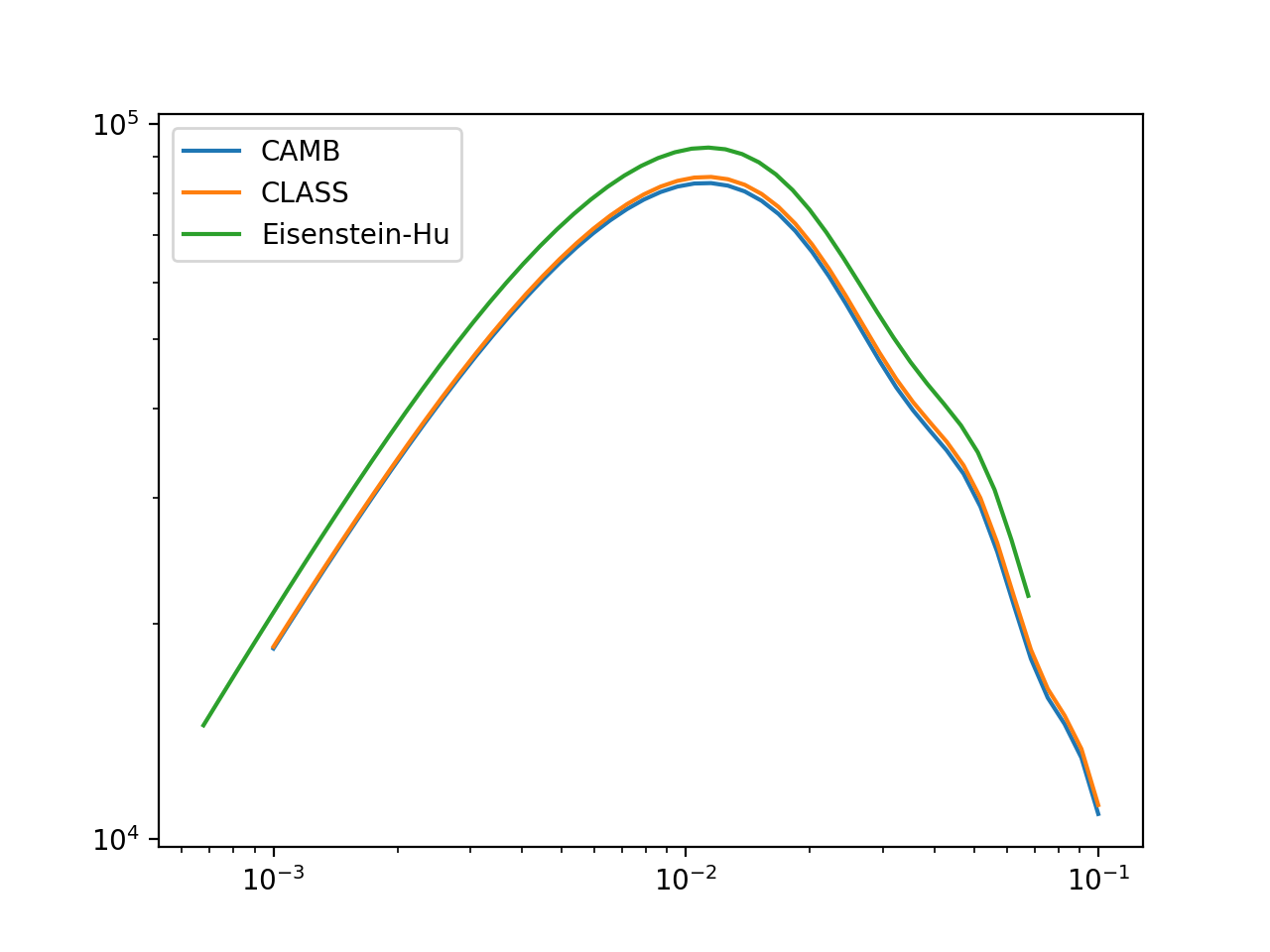
The second figure makes it clear that CAMB, CLASS and EH are not consistently assuming units of wavenumber to be Mpc (instead of Mpc/h; see [ADR-2](https://github.com/skypyproject/skypy/blob/main/docs/arch/adr-02.md)). Also the discrepancy in the normalisation could be a factor of the growth function at redshift zero squared although correcting for this does not give precise agreement.
**Expected behavior**
All power spectrum models should use the same wavenumber units and amplitude scaling conventions for consistency. I would suggest that modifying our implementation of EH to be consistent with the conventions used in CAMB/CLASS would make it more intuitive for users familiar with those codes, although I note that might go against our [ADR-2](https://github.com/skypyproject/skypy/blob/main/docs/arch/adr-02.md). Also (the option to) normalise based upon sigma_8 might be advantageous?
**Desktop (please complete the following information):**
- SkyPy `module/halos` branch
| infrastructure | inconsistent wavenumber units and power spectrum normalisations describe the bug the skypy implementation of the eisenstein hu linear power spectrum is inconsistent with the wrappers around camb class in terms of the wavelength units and amplitude scaling to reproduce python from astropy cosmology import from matplotlib import pyplot as plt import numpy as np from skypy power spectrum import camb classy eisenstein hu growth function k np logspace z a s n s p camb camb k z a s n s p classy classy k z a s a s n s n s p eh eisenstein hu k a s n s plt plot k p camb label camb plt plot k p classy label class plt plot k p eh label eisenstein hu plt loglog plt legend plt show here it is clear that the peak of the power spectrum is shifted horizontally indicating that the different models are making different assumptions about the units of the wavenumber k also there is an overall amplitude offset python d growth function z plt plot k p camb label camb plt plot k p classy label class plt plot k h p eh d d label eisenstein hu plt loglog plt legend plt show the second figure makes it clear that camb class and eh are not consistently assuming units of wavenumber to be mpc instead of mpc h see also the discrepancy in the normalisation could be a factor of the growth function at redshift zero squared although correcting for this does not give precise agreement expected behavior all power spectrum models should use the same wavenumber units and amplitude scaling conventions for consistency i would suggest that modifying our implementation of eh to be consistent with the conventions used in camb class would make it more intuitive for users familiar with those codes although i note that might go against our also the option to normalise based upon sigma might be advantageous desktop please complete the following information skypy module halos branch | 1 |
193,734 | 14,661,004,468 | IssuesEvent | 2020-12-29 01:59:30 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | google/badwolf-drivers: bwbolt/bolt_test.go; 17 LoC | fresh small test |
Found a possible issue in [google/badwolf-drivers](https://www.github.com/google/badwolf-drivers) at [bwbolt/bolt_test.go](https://github.com/google/badwolf-drivers/blob/e203770b1b3abfaeeb28912e33df8d14ca9030de/bwbolt/bolt_test.go#L390-L406)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable tr used in defer or goroutine at line 393
[Click here to see the code in its original context.](https://github.com/google/badwolf-drivers/blob/e203770b1b3abfaeeb28912e33df8d14ca9030de/bwbolt/bolt_test.go#L390-L406)
<details>
<summary>Click here to show the 17 line(s) of Go which triggered the analyzer.</summary>
```go
for _, tr := range trpls {
trps := make(chan *triple.Triple)
go func() {
err := g.TriplesForObject(ctx, tr.Object(), opts, trps)
if err != nil {
t.Fatalf("graph.PredicatesForObject(_, %q, _, _) failed with %v", tr.Object(), err)
}
}()
cnt := 0
for range trps {
cnt++
}
if cnt < 1 {
t.Errorf("graph.TripleForObject(_, %q, _, _) returned no object", tr.Object())
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: e203770b1b3abfaeeb28912e33df8d14ca9030de
| 1.0 | google/badwolf-drivers: bwbolt/bolt_test.go; 17 LoC -
Found a possible issue in [google/badwolf-drivers](https://www.github.com/google/badwolf-drivers) at [bwbolt/bolt_test.go](https://github.com/google/badwolf-drivers/blob/e203770b1b3abfaeeb28912e33df8d14ca9030de/bwbolt/bolt_test.go#L390-L406)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable tr used in defer or goroutine at line 393
[Click here to see the code in its original context.](https://github.com/google/badwolf-drivers/blob/e203770b1b3abfaeeb28912e33df8d14ca9030de/bwbolt/bolt_test.go#L390-L406)
<details>
<summary>Click here to show the 17 line(s) of Go which triggered the analyzer.</summary>
```go
for _, tr := range trpls {
trps := make(chan *triple.Triple)
go func() {
err := g.TriplesForObject(ctx, tr.Object(), opts, trps)
if err != nil {
t.Fatalf("graph.PredicatesForObject(_, %q, _, _) failed with %v", tr.Object(), err)
}
}()
cnt := 0
for range trps {
cnt++
}
if cnt < 1 {
t.Errorf("graph.TripleForObject(_, %q, _, _) returned no object", tr.Object())
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: e203770b1b3abfaeeb28912e33df8d14ca9030de
| non_infrastructure | google badwolf drivers bwbolt bolt test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable tr used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for tr range trpls trps make chan triple triple go func err g triplesforobject ctx tr object opts trps if err nil t fatalf graph predicatesforobject q failed with v tr object err cnt for range trps cnt if cnt t errorf graph tripleforobject q returned no object tr object leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
34,281 | 29,189,530,834 | IssuesEvent | 2023-05-19 18:32:14 | Qiskit-Extensions/quantum-serverless | https://api.github.com/repos/Qiskit-Extensions/quantum-serverless | closed | observability setup (monitoring and logging) | enhancement priority: high project: monitoring project: logging project: infrastructure | <!-- ⚠️ If you do not respect this template, your issue will be closed -->
<!-- ⚠️ Make sure to browse the opened and closed issues to confirm this idea does not exist. -->
### What is the expected enhancement?
A simple experience of accessing logs and metrics on executed jobs | 1.0 | observability setup (monitoring and logging) - <!-- ⚠️ If you do not respect this template, your issue will be closed -->
<!-- ⚠️ Make sure to browse the opened and closed issues to confirm this idea does not exist. -->
### What is the expected enhancement?
A simple experience of accessing logs and metrics on executed jobs | infrastructure | observability setup monitoring and logging what is the expected enhancement a simple experience of accessing logs and metrics on executed jobs | 1 |
415,336 | 12,127,900,055 | IssuesEvent | 2020-04-22 19:32:20 | kubeflow/kubeflow | https://api.github.com/repos/kubeflow/kubeflow | closed | Python SDK run_pipeline fails but pods are created | area/engprod kind/bug lifecycle/stale priority/p2 | /kind bug
**What steps did you take and what happened:**
I've run, via Python SDK, a `kfp.Client.run_pipeline` command with a valid `pipeline_id` but an invalid `experiment_id`.
The command failed with a 404 response, but **all the pods for the run were created**.
Furthermore, run's informations were not fetchable later from APIs (and UI ofc).
For pipelines that create Volumes and generally resources this is very bad
```
ApiException: (404)
Reason: Not Found
HTTP response headers: HTTPHeaderDict({'Content-Type': 'application/json', 'Trailer': 'Grpc-Trailer-Content-Type', 'Date': 'Tue, 12 Nov 2019 16:21:18 GMT', 'Transfer-Encoding': 'chunked'})
HTTP response body: {"error":"Failed to create a new run.: Failed to convert run model: Unable to convert resource references.: Failed to find the referred resource: Referred experiment not found.: ResourceNotFoundError: Experiment test-invalid-experiment not found.","message":"Failed to create a new run.: Failed to convert run model: Unable to convert resource references.: Failed to find the referred resource: Referred experiment not found.: ResourceNotFoundError: Experiment test-invalid-experiment not found.","code":5,"details":[{"@type":"type.googleapis.com/api.Error","error_message":"Experiment test-invalid-experiment not found.","error_details":"Failed to create a new run.: Failed to convert run model: Unable to convert resource references.: Failed to find the referred resource: Referred experiment not found.: ResourceNotFoundError: Experiment test-invalid-experiment not found."}]}
```
**What did you expect to happen:**
The command should not run the pipeline under the hood
**Anything else you would like to add:**
[Miscellaneous information that will assist in solving the issue.]
**Environment:**
- **Kubeflow version:** 0.7.0
- **Python SDK version:** 0.1.33
- kfctl version: v0.7.0-rc.8 (not important for the topic, imho)
- Kubernetes platform: gcloud
- Kubernetes version: v1.14.7-gke.14
- OS (e.g. from `/etc/os-release`): MacOS
| 1.0 | Python SDK run_pipeline fails but pods are created - /kind bug
**What steps did you take and what happened:**
I've run, via Python SDK, a `kfp.Client.run_pipeline` command with a valid `pipeline_id` but an invalid `experiment_id`.
The command failed with a 404 response, but **all the pods for the run were created**.
Furthermore, run's informations were not fetchable later from APIs (and UI ofc).
For pipelines that create Volumes and generally resources this is very bad
```
ApiException: (404)
Reason: Not Found
HTTP response headers: HTTPHeaderDict({'Content-Type': 'application/json', 'Trailer': 'Grpc-Trailer-Content-Type', 'Date': 'Tue, 12 Nov 2019 16:21:18 GMT', 'Transfer-Encoding': 'chunked'})
HTTP response body: {"error":"Failed to create a new run.: Failed to convert run model: Unable to convert resource references.: Failed to find the referred resource: Referred experiment not found.: ResourceNotFoundError: Experiment test-invalid-experiment not found.","message":"Failed to create a new run.: Failed to convert run model: Unable to convert resource references.: Failed to find the referred resource: Referred experiment not found.: ResourceNotFoundError: Experiment test-invalid-experiment not found.","code":5,"details":[{"@type":"type.googleapis.com/api.Error","error_message":"Experiment test-invalid-experiment not found.","error_details":"Failed to create a new run.: Failed to convert run model: Unable to convert resource references.: Failed to find the referred resource: Referred experiment not found.: ResourceNotFoundError: Experiment test-invalid-experiment not found."}]}
```
**What did you expect to happen:**
The command should not run the pipeline under the hood
**Anything else you would like to add:**
[Miscellaneous information that will assist in solving the issue.]
**Environment:**
- **Kubeflow version:** 0.7.0
- **Python SDK version:** 0.1.33
- kfctl version: v0.7.0-rc.8 (not important for the topic, imho)
- Kubernetes platform: gcloud
- Kubernetes version: v1.14.7-gke.14
- OS (e.g. from `/etc/os-release`): MacOS
| non_infrastructure | python sdk run pipeline fails but pods are created kind bug what steps did you take and what happened i ve run via python sdk a kfp client run pipeline command with a valid pipeline id but an invalid experiment id the command failed with a response but all the pods for the run were created furthermore run s informations were not fetchable later from apis and ui ofc for pipelines that create volumes and generally resources this is very bad apiexception reason not found http response headers httpheaderdict content type application json trailer grpc trailer content type date tue nov gmt transfer encoding chunked http response body error failed to create a new run failed to convert run model unable to convert resource references failed to find the referred resource referred experiment not found resourcenotfounderror experiment test invalid experiment not found message failed to create a new run failed to convert run model unable to convert resource references failed to find the referred resource referred experiment not found resourcenotfounderror experiment test invalid experiment not found code details what did you expect to happen the command should not run the pipeline under the hood anything else you would like to add environment kubeflow version python sdk version kfctl version rc not important for the topic imho kubernetes platform gcloud kubernetes version gke os e g from etc os release macos | 0 |
79,441 | 7,715,801,551 | IssuesEvent | 2018-05-23 08:48:05 | leo-project/notes | https://api.github.com/repos/leo-project/notes | closed | [1.3][benchmark] Checking the performance when accessing files sequentially | test v1.3 | ## Environment and Configuration
- OS: Ubuntu Server 14.04.3
- Erlang/OTP: 17.5
- LeoFS: 1.3.0
- CPU: Intel Xeon E5-2630 v3 @ 2.40GHz
- LeoFS' system
- number of leo_gateway: 1
- number of leo_storage: 5
- number of leo_manager: 2
## Report
https://github.com/leo-project/notes/tree/master/leofs/benchmark/leofs/1.3/1.3.0/front/20161011_fix50m_f4k_read_seq_2
| 1.0 | [1.3][benchmark] Checking the performance when accessing files sequentially - ## Environment and Configuration
- OS: Ubuntu Server 14.04.3
- Erlang/OTP: 17.5
- LeoFS: 1.3.0
- CPU: Intel Xeon E5-2630 v3 @ 2.40GHz
- LeoFS' system
- number of leo_gateway: 1
- number of leo_storage: 5
- number of leo_manager: 2
## Report
https://github.com/leo-project/notes/tree/master/leofs/benchmark/leofs/1.3/1.3.0/front/20161011_fix50m_f4k_read_seq_2
| non_infrastructure | checking the performance when accessing files sequentially environment and configuration os ubuntu server erlang otp leofs cpu intel xeon leofs system number of leo gateway number of leo storage number of leo manager report | 0 |
2,205 | 3,560,814,072 | IssuesEvent | 2016-01-23 10:14:18 | ForNeVeR/Tesla | https://api.github.com/repos/ForNeVeR/Tesla | opened | Bring Travis support back | infrastructure | While we're at rewriting Tesla from scratch, it wouldn't be bad to enable Travis builds again. But this time we will support them completely. | 1.0 | Bring Travis support back - While we're at rewriting Tesla from scratch, it wouldn't be bad to enable Travis builds again. But this time we will support them completely. | infrastructure | bring travis support back while we re at rewriting tesla from scratch it wouldn t be bad to enable travis builds again but this time we will support them completely | 1 |
97,330 | 3,988,913,153 | IssuesEvent | 2016-05-09 12:00:29 | dhowe/AdNauseam2 | https://api.github.com/repos/dhowe/AdNauseam2 | closed | Check that all text-ad filters work the same in Firefox and Opera | PRIORITY: Medium | First test the following text-ad filters in Chrome:
- Yahoo
- Bing
- Google
- Ask
Then test that the results are the same on Firefox and Opera
| 1.0 | Check that all text-ad filters work the same in Firefox and Opera - First test the following text-ad filters in Chrome:
- Yahoo
- Bing
- Google
- Ask
Then test that the results are the same on Firefox and Opera
| non_infrastructure | check that all text ad filters work the same in firefox and opera first test the following text ad filters in chrome yahoo bing google ask then test that the results are the same on firefox and opera | 0 |
15,788 | 6,038,809,918 | IssuesEvent | 2017-06-09 22:42:12 | SouthForkResearch/pyGNAT | https://api.github.com/repos/SouthForkResearch/pyGNAT | closed | Properly clear form and variables | bug Build Networks Tool | The Build Network form should have variables properly deleted when reset button is clicked or form is closed. Currently, after the reset button is clicked, or if the form is closed and reopened, you can just rerun it, even without changing variables. | 1.0 | Properly clear form and variables - The Build Network form should have variables properly deleted when reset button is clicked or form is closed. Currently, after the reset button is clicked, or if the form is closed and reopened, you can just rerun it, even without changing variables. | non_infrastructure | properly clear form and variables the build network form should have variables properly deleted when reset button is clicked or form is closed currently after the reset button is clicked or if the form is closed and reopened you can just rerun it even without changing variables | 0 |
112,558 | 14,265,993,941 | IssuesEvent | 2020-11-20 17:59:04 | ampproject/amphtml | https://api.github.com/repos/ampproject/amphtml | opened | Design Review 2020-12-09 16:30 UTC (Africa/Europe/western Asia) | Type: Design Review | Time: [2020-12-09 16:30 UTC](https://www.timeanddate.com/worldclock/meeting.html?year=2020&month=12&day=09&iv=0) ([add to Google Calendar](http://www.google.com/calendar/event?action=TEMPLATE&text=AMP%20Project%20Design%20Review&dates=20201209T163000Z/20201209T173000Z&details=https%3A%2F%2Fbit.ly%2Famp-dr))
Location: [Video conference via Google Meet](https://bit.ly/amp-dr)
The AMP community holds weekly engineering [design reviews](https://github.com/ampproject/amphtml/blob/master/contributing/design-reviews.md). **We encourage everyone in the community to participate in these design reviews.**
If you are interested in bringing your design to design review, read the [design review documentation](https://github.com/ampproject/amphtml/blob/master/contributing/design-reviews.md) and add a link to your design doc or issue by the Monday before your design review.
When attending a design review please read through the designs *before* the design review starts. This allows us to spend more time on discussion of the design.
We rotate our design review between times that work better for different parts of the world as described in our [design review documentation](https://github.com/ampproject/amphtml/blob/master/contributing/design-reviews.md), but you are welcome to attend any design review. If you cannot make any of the design reviews but have a design to discuss please let mrjoro@ know on [Slack](https://github.com/ampproject/amphtml/blob/master/CONTRIBUTING.md#discussion-channels) and we will find a time that works for you.
| 1.0 | Design Review 2020-12-09 16:30 UTC (Africa/Europe/western Asia) - Time: [2020-12-09 16:30 UTC](https://www.timeanddate.com/worldclock/meeting.html?year=2020&month=12&day=09&iv=0) ([add to Google Calendar](http://www.google.com/calendar/event?action=TEMPLATE&text=AMP%20Project%20Design%20Review&dates=20201209T163000Z/20201209T173000Z&details=https%3A%2F%2Fbit.ly%2Famp-dr))
Location: [Video conference via Google Meet](https://bit.ly/amp-dr)
The AMP community holds weekly engineering [design reviews](https://github.com/ampproject/amphtml/blob/master/contributing/design-reviews.md). **We encourage everyone in the community to participate in these design reviews.**
If you are interested in bringing your design to design review, read the [design review documentation](https://github.com/ampproject/amphtml/blob/master/contributing/design-reviews.md) and add a link to your design doc or issue by the Monday before your design review.
When attending a design review please read through the designs *before* the design review starts. This allows us to spend more time on discussion of the design.
We rotate our design review between times that work better for different parts of the world as described in our [design review documentation](https://github.com/ampproject/amphtml/blob/master/contributing/design-reviews.md), but you are welcome to attend any design review. If you cannot make any of the design reviews but have a design to discuss please let mrjoro@ know on [Slack](https://github.com/ampproject/amphtml/blob/master/CONTRIBUTING.md#discussion-channels) and we will find a time that works for you.
| non_infrastructure | design review utc africa europe western asia time location the amp community holds weekly engineering we encourage everyone in the community to participate in these design reviews if you are interested in bringing your design to design review read the and add a link to your design doc or issue by the monday before your design review when attending a design review please read through the designs before the design review starts this allows us to spend more time on discussion of the design we rotate our design review between times that work better for different parts of the world as described in our but you are welcome to attend any design review if you cannot make any of the design reviews but have a design to discuss please let mrjoro know on and we will find a time that works for you | 0 |
13,271 | 10,172,068,151 | IssuesEvent | 2019-08-08 09:48:42 | cockroachdb/docs | https://api.github.com/repos/cockroachdb/docs | closed | search results return empty for key kerberos terms | A-docs-infrastructure C-docs-improvement O-internal OT-sales-eng P-1 T-something-broken | searching the docs site for key terms like `kerberos`, `gssapi` or `kdc` all return "no results" even though these terms are used frequently in this docs page: https://www.cockroachlabs.com/docs/v19.1/gssapi_authentication.html | 1.0 | search results return empty for key kerberos terms - searching the docs site for key terms like `kerberos`, `gssapi` or `kdc` all return "no results" even though these terms are used frequently in this docs page: https://www.cockroachlabs.com/docs/v19.1/gssapi_authentication.html | infrastructure | search results return empty for key kerberos terms searching the docs site for key terms like kerberos gssapi or kdc all return no results even though these terms are used frequently in this docs page | 1 |
21,535 | 14,620,476,955 | IssuesEvent | 2020-12-22 19:47:48 | pytest-dev/pytest | https://api.github.com/repos/pytest-dev/pytest | opened | [infra] enable pre-commit.ci? | type: infrastructure | (internal issue)
I've been working on this for the last ~6 months or so and I think it's usable enough for pytest: https://pre-commit.ci
I wanted to make sure we had a discussion first before flipping it on though :)
Basically it will get us:
- a freed up CI worker
- autofixing of PRs (especially useful for the many drive-by PRs we get that don't set up the linting and/or commits that are made from the github UI)
- periodic autoupdate of the pre-commit configuration
- ~20 lines of github actions configuration _removed_
- much faster linting runs (a cold test run I just did was 1:40 vs 2:53 on github actions -- with everything cached it's ~1:10 and will only get faster as I make some planned improvements)
To enable, we'd just add the pytest repo to the pre-commit.ci app installation (it appears it's already installed on [pytest-randomly](https://results.pre-commit.ci/repo/github/55790864)) | 1.0 | [infra] enable pre-commit.ci? - (internal issue)
I've been working on this for the last ~6 months or so and I think it's usable enough for pytest: https://pre-commit.ci
I wanted to make sure we had a discussion first before flipping it on though :)
Basically it will get us:
- a freed up CI worker
- autofixing of PRs (especially useful for the many drive-by PRs we get that don't set up the linting and/or commits that are made from the github UI)
- periodic autoupdate of the pre-commit configuration
- ~20 lines of github actions configuration _removed_
- much faster linting runs (a cold test run I just did was 1:40 vs 2:53 on github actions -- with everything cached it's ~1:10 and will only get faster as I make some planned improvements)
To enable, we'd just add the pytest repo to the pre-commit.ci app installation (it appears it's already installed on [pytest-randomly](https://results.pre-commit.ci/repo/github/55790864)) | infrastructure | enable pre commit ci internal issue i ve been working on this for the last months or so and i think it s usable enough for pytest i wanted to make sure we had a discussion first before flipping it on though basically it will get us a freed up ci worker autofixing of prs especially useful for the many drive by prs we get that don t set up the linting and or commits that are made from the github ui periodic autoupdate of the pre commit configuration lines of github actions configuration removed much faster linting runs a cold test run i just did was vs on github actions with everything cached it s and will only get faster as i make some planned improvements to enable we d just add the pytest repo to the pre commit ci app installation it appears it s already installed on | 1 |
44,990 | 9,663,707,679 | IssuesEvent | 2019-05-21 01:58:46 | ladesign/ladesign.github.io | https://api.github.com/repos/ladesign/ladesign.github.io | opened | VS Code使用ESlint及Prettier插件實現保存時自動依ESlint標準格式化 | Develop Tools VS Code | 安裝ESLint插件:
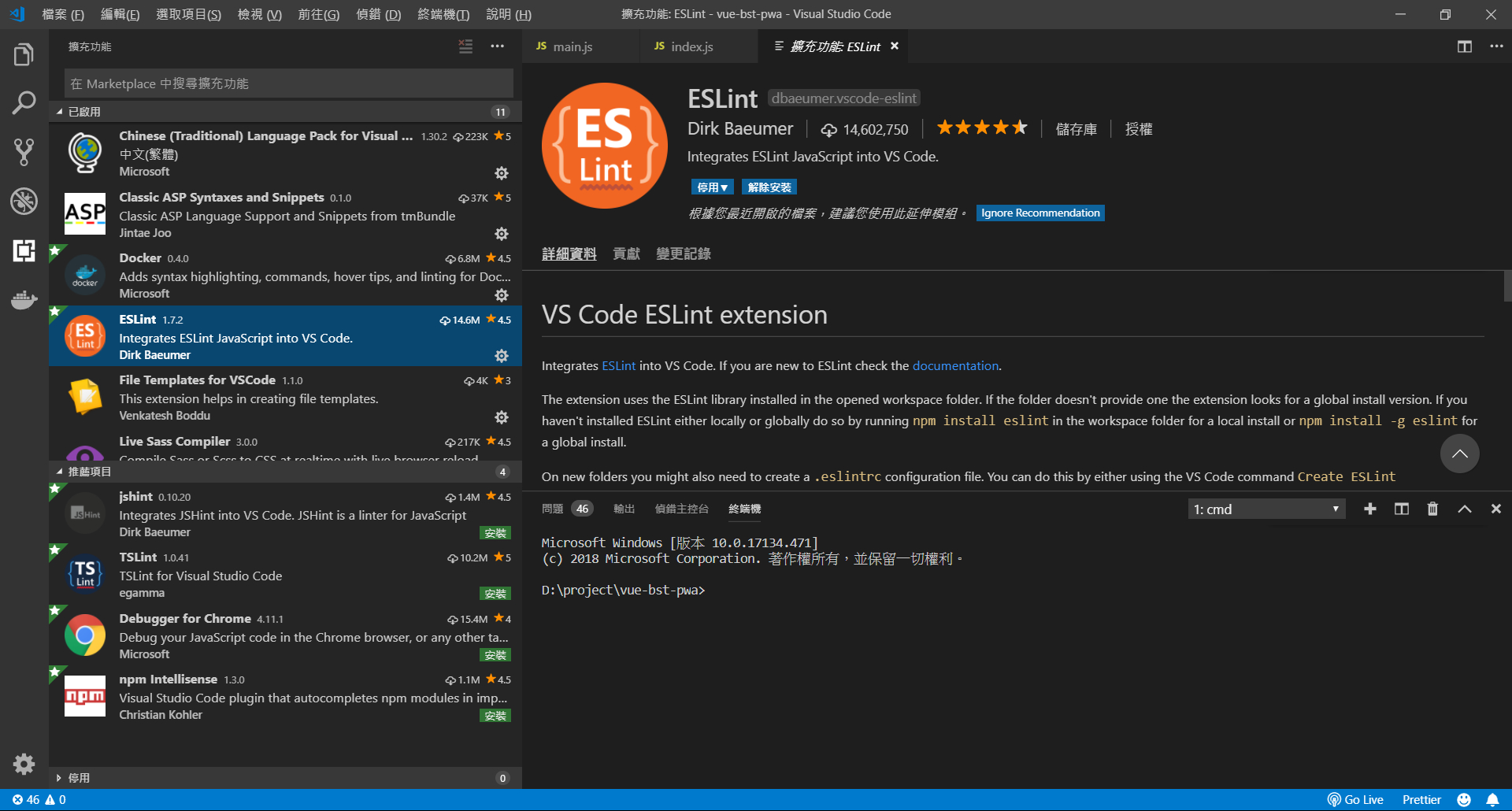
針對當前項目常見ESLint警告訊息配置:
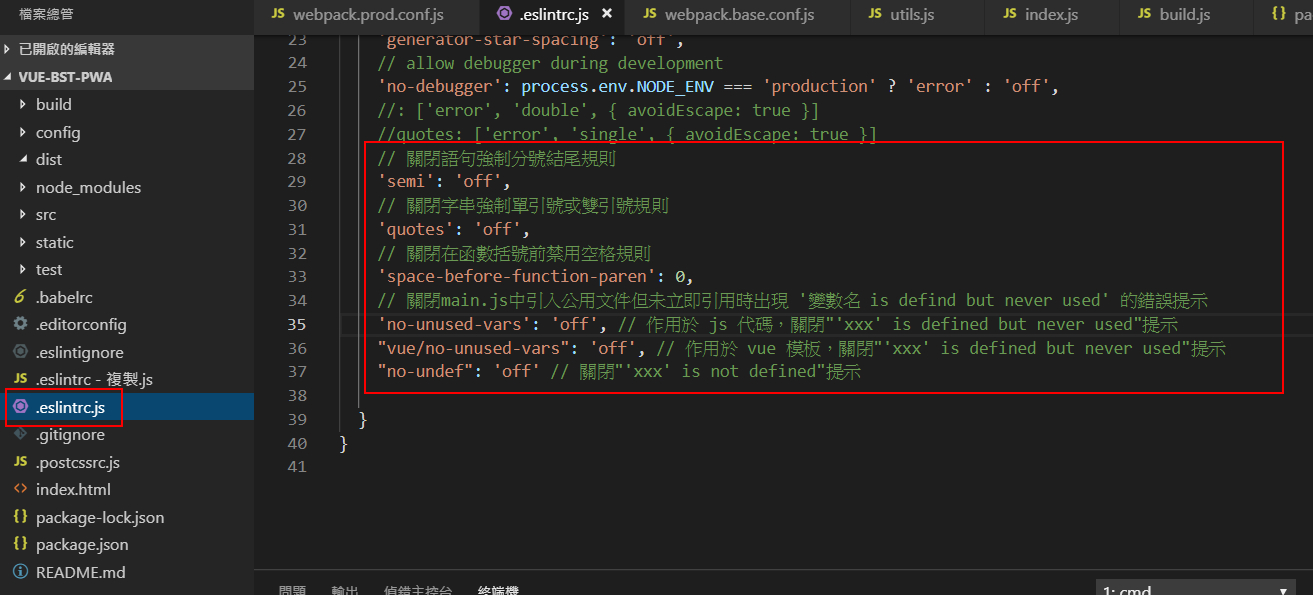
安裝Prettier-Code formatter插件:

確認prettier與eslint整合有勾選:
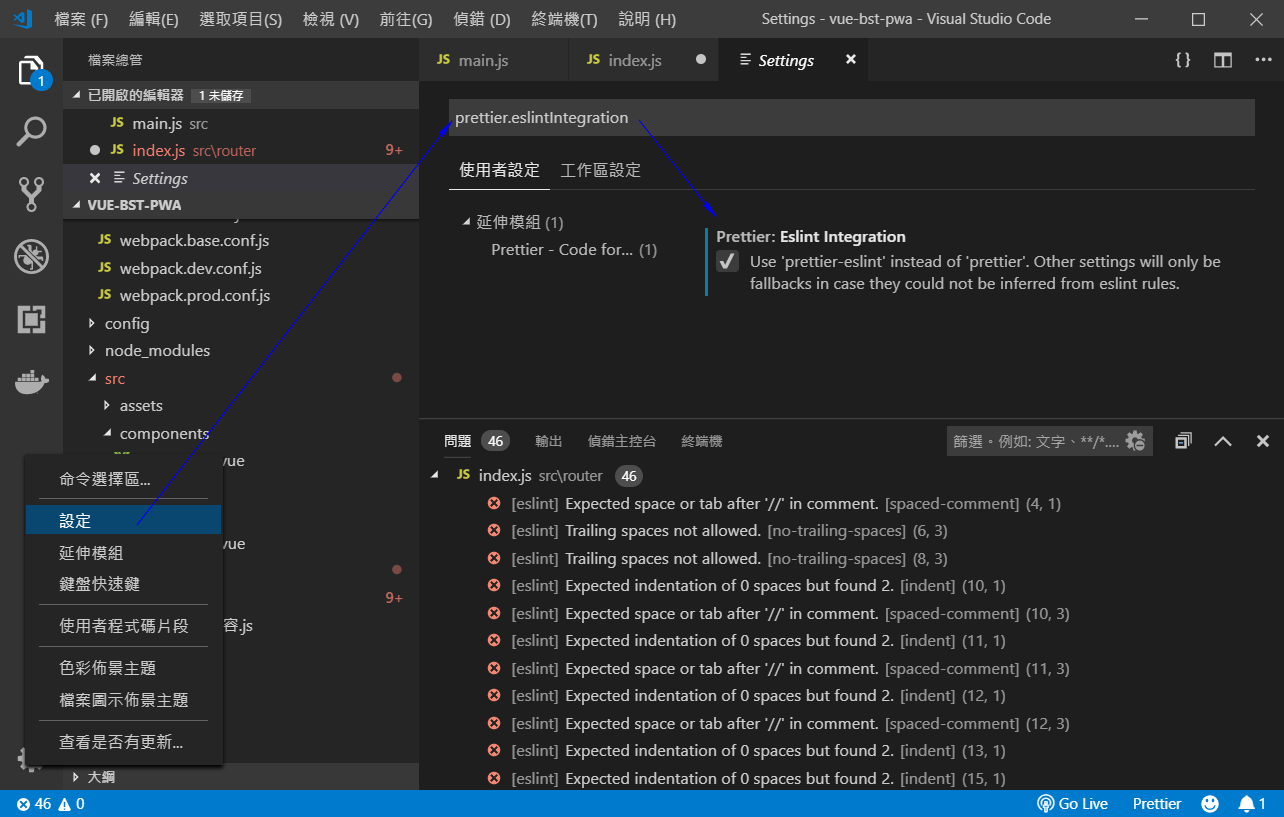
VS Code插件環境設置,實現存檔時自動格式化:
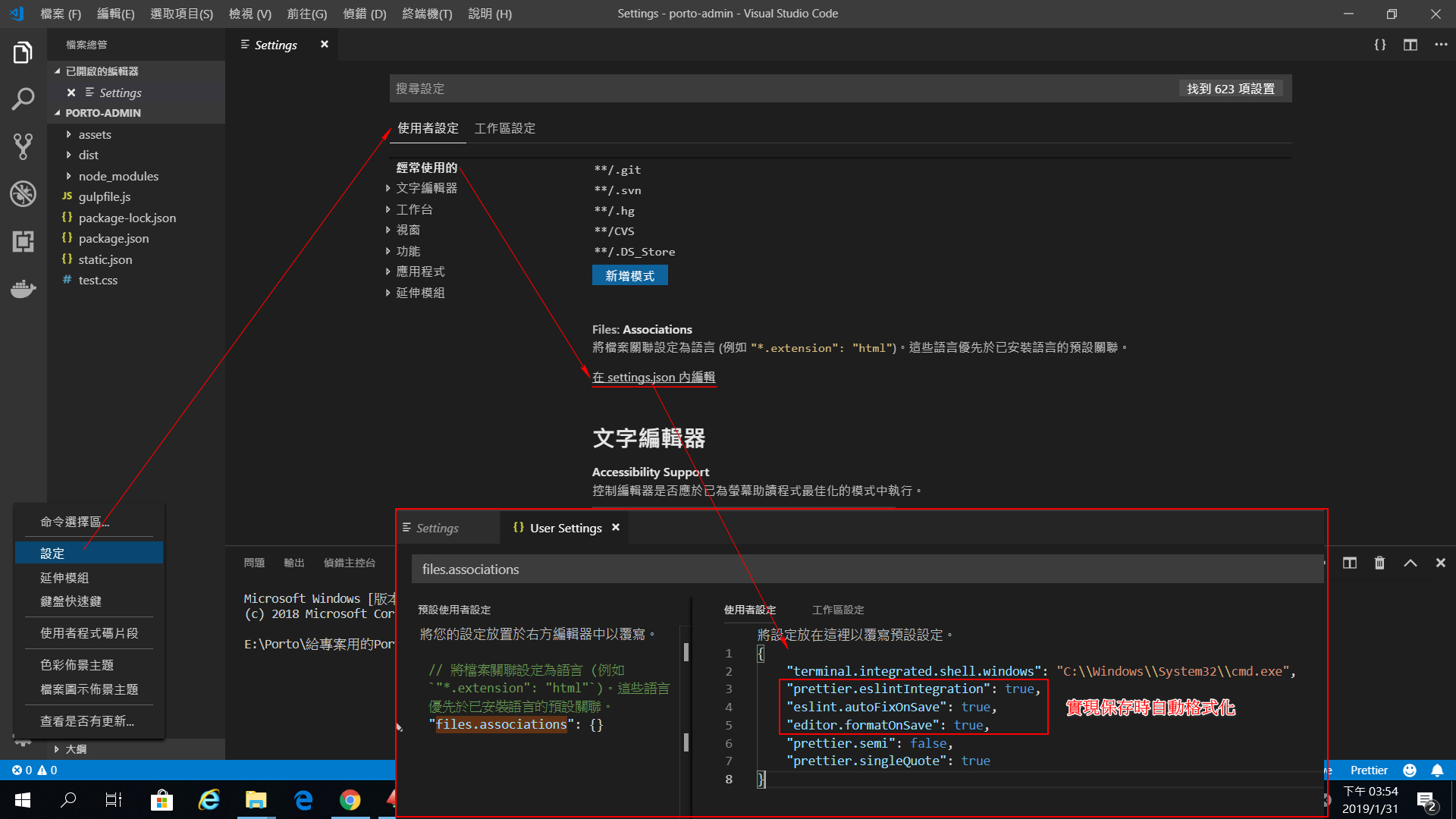
存檔自動格式化時格式跑掉時:
![Uploading 存檔自動格式化時格式跑掉.jpg…]()
根據自己的喜好設定Prettier格式化風格:
| 1.0 | VS Code使用ESlint及Prettier插件實現保存時自動依ESlint標準格式化 - 安裝ESLint插件:
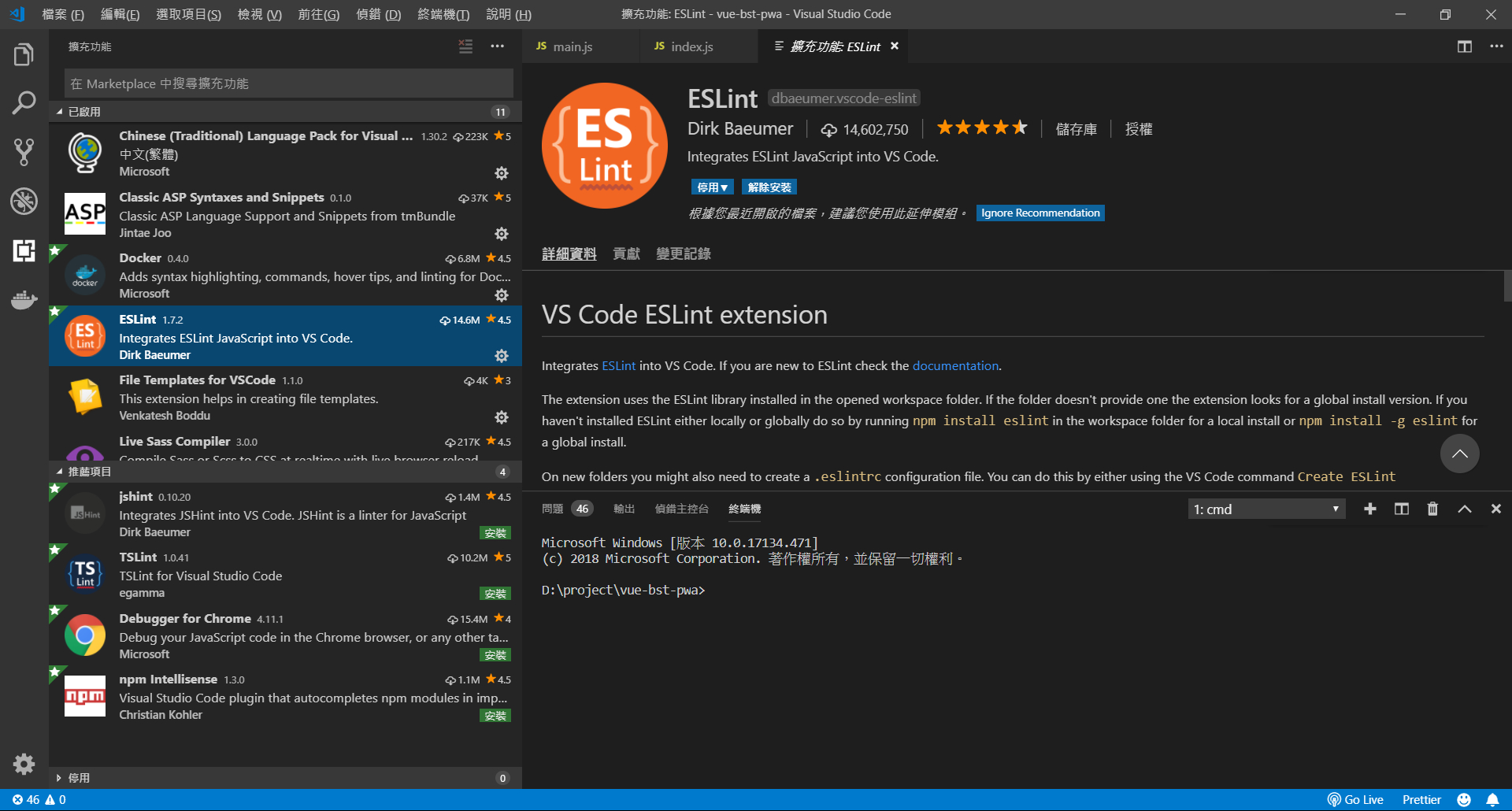
針對當前項目常見ESLint警告訊息配置:
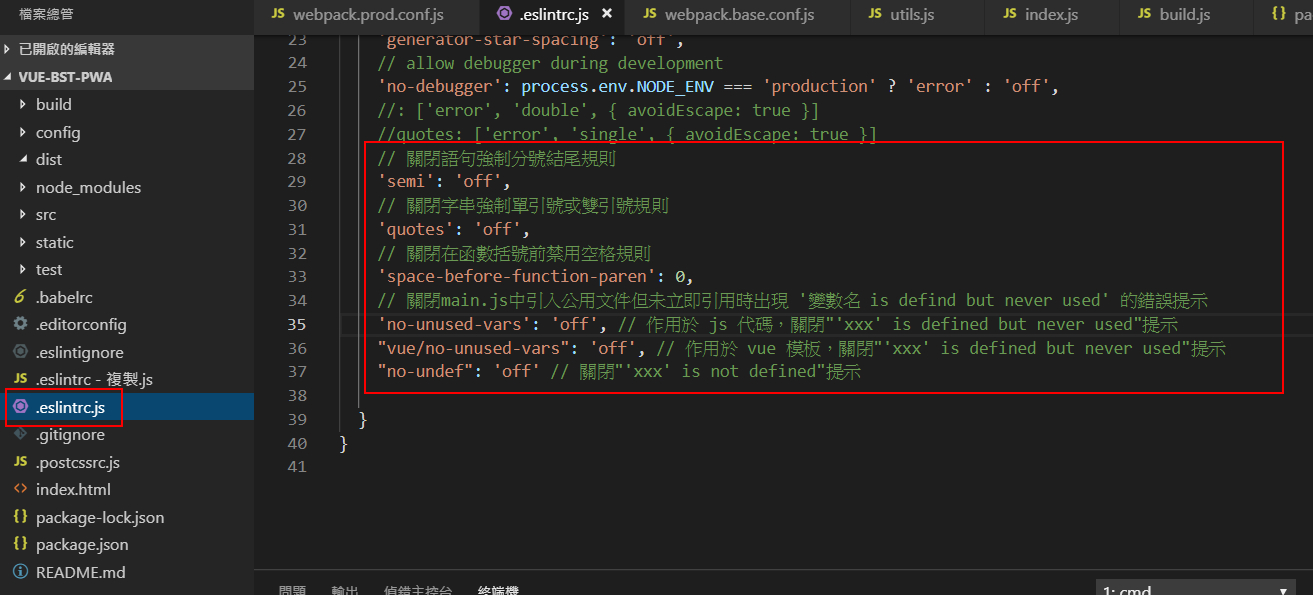
安裝Prettier-Code formatter插件:

確認prettier與eslint整合有勾選:
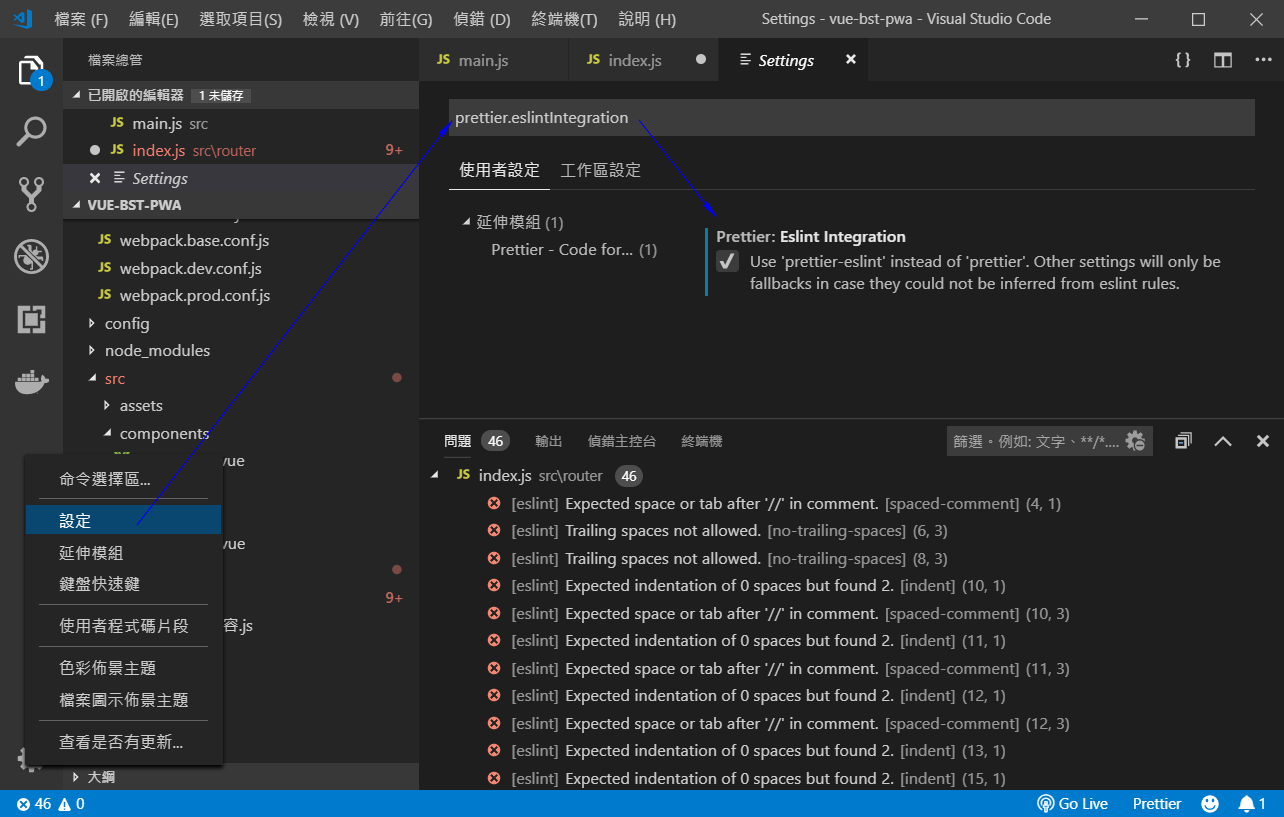
VS Code插件環境設置,實現存檔時自動格式化:
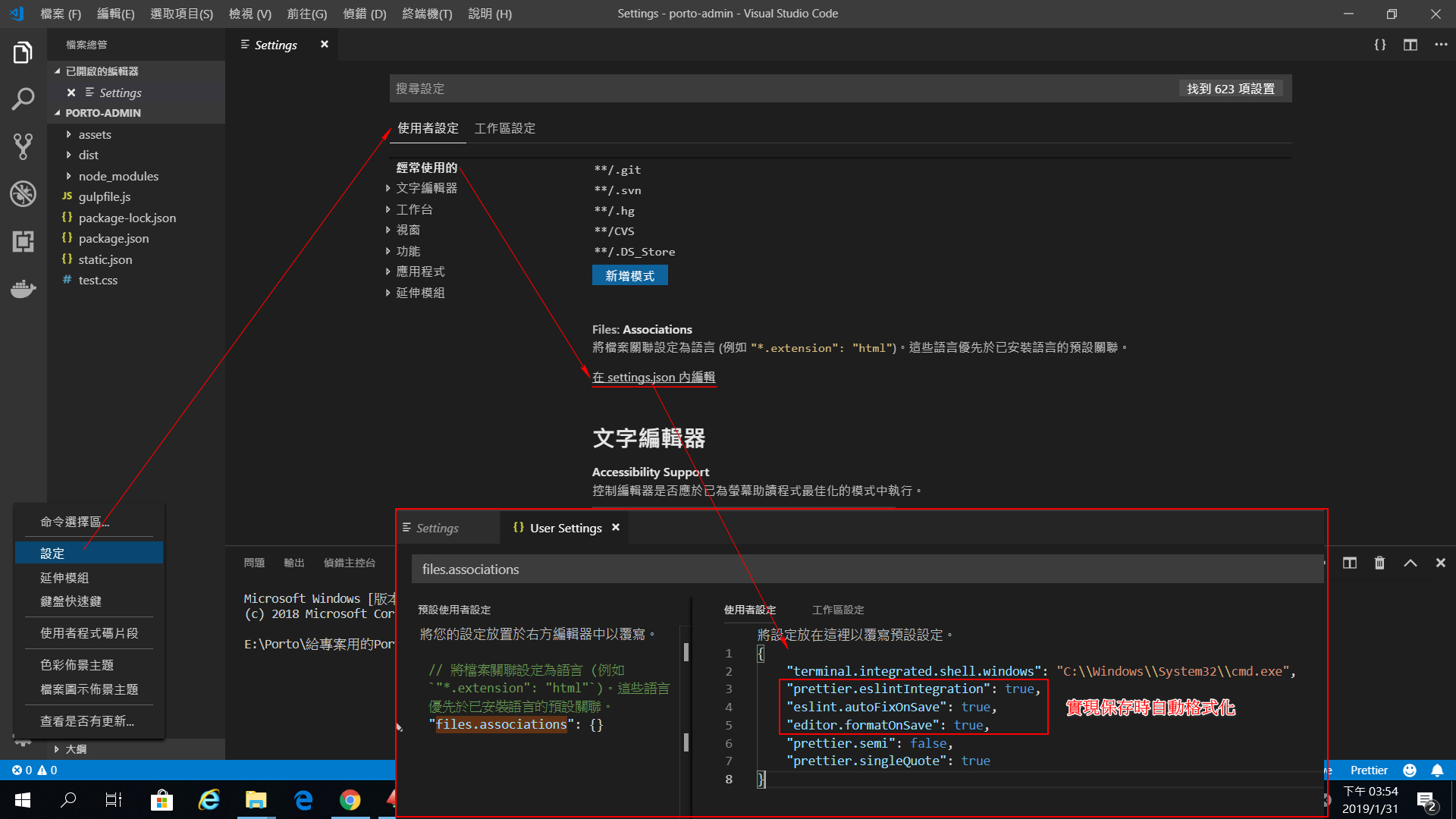
存檔自動格式化時格式跑掉時:
![Uploading 存檔自動格式化時格式跑掉.jpg…]()
根據自己的喜好設定Prettier格式化風格:
| non_infrastructure | vs code使用eslint及prettier插件實現保存時自動依eslint標準格式化 安裝eslint插件: 針對當前項目常見eslint警告訊息配置: 安裝prettier code formatter插件: 確認prettier與eslint整合有勾選: vs code插件環境設置,實現存檔時自動格式化: 存檔自動格式化時格式跑掉時: 根據自己的喜好設定prettier格式化風格: | 0 |
11,014 | 8,871,582,984 | IssuesEvent | 2019-01-11 13:06:43 | coq/coq | https://api.github.com/repos/coq/coq | closed | CI should check META.coq.in | kind: enhancement kind: infrastructure resolved: won't fix | #### Version
8.10+alpha
#### Description of the problem
There is no sanity check of META.coq.in, as far as I can tell, and no doc on when it should be updated. I am not entirely sure what should or should not go in this file, e.g., there's still natsyntax even though numeral notations removed the nat syntax plugin, and I added an entry for string notations, but there's no entry for numeral notations.
cc @ejgallego | 1.0 | CI should check META.coq.in - #### Version
8.10+alpha
#### Description of the problem
There is no sanity check of META.coq.in, as far as I can tell, and no doc on when it should be updated. I am not entirely sure what should or should not go in this file, e.g., there's still natsyntax even though numeral notations removed the nat syntax plugin, and I added an entry for string notations, but there's no entry for numeral notations.
cc @ejgallego | infrastructure | ci should check meta coq in version alpha description of the problem there is no sanity check of meta coq in as far as i can tell and no doc on when it should be updated i am not entirely sure what should or should not go in this file e g there s still natsyntax even though numeral notations removed the nat syntax plugin and i added an entry for string notations but there s no entry for numeral notations cc ejgallego | 1 |
13,951 | 10,560,900,721 | IssuesEvent | 2019-10-04 14:48:14 | ionide/ionide-vscode-fsharp | https://api.github.com/repos/ionide/ionide-vscode-fsharp | closed | Can't build ionide | infrastructure | Hi, I have this error a long time even after i reinstalled `High Sierra`.
I got `mono 5.8.0.129`, `dotnet 2.1.4` und `yarn 1.5.1`
```
> git clone https://github.com/ionide/ionide-vscode-fsharp.git
> cd ionide-vscode-fsharp
> yarn install
Done in 8.86s.
> dotnet restore master [20c3ba5]
shasum: /Users/fb/Documents/Github/ionide-vscode-fsharp/.paket/../paket-files/paket.restore.cached:
Paket version 5.142.0
Checking for uncommitted changes in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar
Checking for commits made in detached HEAD state in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar
Setting /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar to a715e9bda68f2a43e9d1e63c39e16b1c54f7a3e5
Checking for uncommitted changes in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp-editing/Forge
Checking for uncommitted changes in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp/FsAutoComplete
Checking for commits made in detached HEAD state in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp-editing/Forge
Checking for commits made in detached HEAD state in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp/FsAutoComplete
Setting /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp-editing/Forge to e52144c34b34b79cb095bb268efeb1e6eeebea42
Setting /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp/FsAutoComplete to 9ad3fc12d9266d2bcbf9c99a15643e79db841206
Performance:
- Disk IO: 22 milliseconds
- Runtime: 4 seconds
Paket failed with
-> Checkout to /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar failed.
Message: Updating the git cache at /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar failed.
Message: Could not run "git tag -f paket/lock a715e9bda68f2a43e9d1e63c39e16b1c54f7a3e5".
```
And then the error
```
/Users/fb/Documents/Github/ionide-vscode-fsharp/.paket/Paket.Restore.targets(74,5): error MSB3073: The command "/Library/Frameworks/Mono.framework/Commands/mono --runtime=v4.0.30319 "/Users/fb/Documents/Github/ionide-vscode-fsharp/.paket/../paket.exe" restore" exited with code 1. [/Users/fb/Documents/Github/ionide-vscode-fsharp/src/Ionide.FSharp.fsproj]
```
and a warning
```
/usr/local/share/dotnet/sdk/2.1.4/NuGet.targets(103,5): warning : Unable to find a project to restore! [/Users/fb/Documents/Github/ionide-vscode-fsharp/ionide-fsharp-vscode.sln]
``` | 1.0 | Can't build ionide - Hi, I have this error a long time even after i reinstalled `High Sierra`.
I got `mono 5.8.0.129`, `dotnet 2.1.4` und `yarn 1.5.1`
```
> git clone https://github.com/ionide/ionide-vscode-fsharp.git
> cd ionide-vscode-fsharp
> yarn install
Done in 8.86s.
> dotnet restore master [20c3ba5]
shasum: /Users/fb/Documents/Github/ionide-vscode-fsharp/.paket/../paket-files/paket.restore.cached:
Paket version 5.142.0
Checking for uncommitted changes in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar
Checking for commits made in detached HEAD state in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar
Setting /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar to a715e9bda68f2a43e9d1e63c39e16b1c54f7a3e5
Checking for uncommitted changes in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp-editing/Forge
Checking for uncommitted changes in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp/FsAutoComplete
Checking for commits made in detached HEAD state in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp-editing/Forge
Checking for commits made in detached HEAD state in /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp/FsAutoComplete
Setting /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp-editing/Forge to e52144c34b34b79cb095bb268efeb1e6eeebea42
Setting /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/fsharp/FsAutoComplete to 9ad3fc12d9266d2bcbf9c99a15643e79db841206
Performance:
- Disk IO: 22 milliseconds
- Runtime: 4 seconds
Paket failed with
-> Checkout to /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar failed.
Message: Updating the git cache at /Users/fb/Documents/Github/ionide-vscode-fsharp/paket-files/github.com/ionide/ionide-fsgrammar failed.
Message: Could not run "git tag -f paket/lock a715e9bda68f2a43e9d1e63c39e16b1c54f7a3e5".
```
And then the error
```
/Users/fb/Documents/Github/ionide-vscode-fsharp/.paket/Paket.Restore.targets(74,5): error MSB3073: The command "/Library/Frameworks/Mono.framework/Commands/mono --runtime=v4.0.30319 "/Users/fb/Documents/Github/ionide-vscode-fsharp/.paket/../paket.exe" restore" exited with code 1. [/Users/fb/Documents/Github/ionide-vscode-fsharp/src/Ionide.FSharp.fsproj]
```
and a warning
```
/usr/local/share/dotnet/sdk/2.1.4/NuGet.targets(103,5): warning : Unable to find a project to restore! [/Users/fb/Documents/Github/ionide-vscode-fsharp/ionide-fsharp-vscode.sln]
``` | infrastructure | can t build ionide hi i have this error a long time even after i reinstalled high sierra i got mono dotnet und yarn git clone cd ionide vscode fsharp yarn install done in dotnet restore master shasum users fb documents github ionide vscode fsharp paket paket files paket restore cached paket version checking for uncommitted changes in users fb documents github ionide vscode fsharp paket files github com ionide ionide fsgrammar checking for commits made in detached head state in users fb documents github ionide vscode fsharp paket files github com ionide ionide fsgrammar setting users fb documents github ionide vscode fsharp paket files github com ionide ionide fsgrammar to checking for uncommitted changes in users fb documents github ionide vscode fsharp paket files github com fsharp editing forge checking for uncommitted changes in users fb documents github ionide vscode fsharp paket files github com fsharp fsautocomplete checking for commits made in detached head state in users fb documents github ionide vscode fsharp paket files github com fsharp editing forge checking for commits made in detached head state in users fb documents github ionide vscode fsharp paket files github com fsharp fsautocomplete setting users fb documents github ionide vscode fsharp paket files github com fsharp editing forge to setting users fb documents github ionide vscode fsharp paket files github com fsharp fsautocomplete to performance disk io milliseconds runtime seconds paket failed with checkout to users fb documents github ionide vscode fsharp paket files github com ionide ionide fsgrammar failed message updating the git cache at users fb documents github ionide vscode fsharp paket files github com ionide ionide fsgrammar failed message could not run git tag f paket lock and then the error users fb documents github ionide vscode fsharp paket paket restore targets error the command library frameworks mono framework commands mono runtime users fb documents github ionide vscode fsharp paket paket exe restore exited with code and a warning usr local share dotnet sdk nuget targets warning unable to find a project to restore | 1 |
372,290 | 11,012,359,980 | IssuesEvent | 2019-12-04 18:06:11 | DrylandEcology/SOILWAT2 | https://api.github.com/repos/DrylandEcology/SOILWAT2 | closed | Update SOILWAT2 to be compatible with gridded_code branch of STEPWAT2 | Bugfix high priority | While updating STEPWAT2's gridded code I changed the variable Globals to a pointer. There is one reference to Globals in setGlobalSTEPWAT2_OutputVariables() in SW_Output_outarray.c that needs to be updated.
```
Globals.runModelYears to Globals->runModelYears
``` | 1.0 | Update SOILWAT2 to be compatible with gridded_code branch of STEPWAT2 - While updating STEPWAT2's gridded code I changed the variable Globals to a pointer. There is one reference to Globals in setGlobalSTEPWAT2_OutputVariables() in SW_Output_outarray.c that needs to be updated.
```
Globals.runModelYears to Globals->runModelYears
``` | non_infrastructure | update to be compatible with gridded code branch of while updating s gridded code i changed the variable globals to a pointer there is one reference to globals in outputvariables in sw output outarray c that needs to be updated globals runmodelyears to globals runmodelyears | 0 |
25,269 | 7,661,435,920 | IssuesEvent | 2018-05-11 14:14:20 | p-society/goals | https://api.github.com/repos/p-society/goals | closed | Turn p-society into a Mozilla campus club | community building cool and awesome work in progress | This is a work in progress and I am in talks with Mozilla.
People responsible @palash25 and @iamravitejag | 1.0 | Turn p-society into a Mozilla campus club - This is a work in progress and I am in talks with Mozilla.
People responsible @palash25 and @iamravitejag | non_infrastructure | turn p society into a mozilla campus club this is a work in progress and i am in talks with mozilla people responsible and iamravitejag | 0 |
20,539 | 14,002,344,010 | IssuesEvent | 2020-10-28 14:41:13 | pharo-spec/Spec | https://api.github.com/repos/pharo-spec/Spec | closed | Split tests in multiple packages | Cleaning Infrastructure | Currently, all tests are in one package. Do we really want only one? | 1.0 | Split tests in multiple packages - Currently, all tests are in one package. Do we really want only one? | infrastructure | split tests in multiple packages currently all tests are in one package do we really want only one | 1 |
283,767 | 30,913,543,186 | IssuesEvent | 2023-08-05 02:11:24 | hshivhare67/kernel_v4.19.72 | https://api.github.com/repos/hshivhare67/kernel_v4.19.72 | reopened | CVE-2023-1078 (High) detected in linuxlinux-4.19.282 | Mend: dependency security vulnerability | ## CVE-2023-1078 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/hshivhare67/kernel_v4.19.72/commit/139c4e073703974ca0b05255c4cff6dcd52a8e31">139c4e073703974ca0b05255c4cff6dcd52a8e31</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/rds/message.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/rds/message.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux Kernel in RDS (Reliable Datagram Sockets) protocol. The rds_rm_zerocopy_callback() uses list_entry() on the head of a list causing a type confusion. Local user can trigger this with rds_message_put(). Type confusion leads to `struct rds_msg_zcopy_info *info` actually points to something else that is potentially controlled by local user. It is known how to trigger this, which causes an out of bounds access, and a lock corruption.
<p>Publish Date: 2023-03-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1078>CVE-2023-1078</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-1078">https://www.linuxkernelcves.com/cves/CVE-2023-1078</a></p>
<p>Release Date: 2023-02-28</p>
<p>Fix Resolution: v4.19.273,v5.4.232,v5.10.168,v5.15.94,v6.1.12,v6.2-rc8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-1078 (High) detected in linuxlinux-4.19.282 - ## CVE-2023-1078 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/hshivhare67/kernel_v4.19.72/commit/139c4e073703974ca0b05255c4cff6dcd52a8e31">139c4e073703974ca0b05255c4cff6dcd52a8e31</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/rds/message.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/rds/message.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux Kernel in RDS (Reliable Datagram Sockets) protocol. The rds_rm_zerocopy_callback() uses list_entry() on the head of a list causing a type confusion. Local user can trigger this with rds_message_put(). Type confusion leads to `struct rds_msg_zcopy_info *info` actually points to something else that is potentially controlled by local user. It is known how to trigger this, which causes an out of bounds access, and a lock corruption.
<p>Publish Date: 2023-03-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1078>CVE-2023-1078</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-1078">https://www.linuxkernelcves.com/cves/CVE-2023-1078</a></p>
<p>Release Date: 2023-02-28</p>
<p>Fix Resolution: v4.19.273,v5.4.232,v5.10.168,v5.15.94,v6.1.12,v6.2-rc8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files net rds message c net rds message c vulnerability details a flaw was found in the linux kernel in rds reliable datagram sockets protocol the rds rm zerocopy callback uses list entry on the head of a list causing a type confusion local user can trigger this with rds message put type confusion leads to struct rds msg zcopy info info actually points to something else that is potentially controlled by local user it is known how to trigger this which causes an out of bounds access and a lock corruption publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
119,670 | 17,627,540,055 | IssuesEvent | 2021-08-19 01:02:02 | doc-ai/tensorflow | https://api.github.com/repos/doc-ai/tensorflow | opened | CVE-2021-37641 (High) detected in tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-37641 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>Path to vulnerable library: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. In affected versions if the arguments to `tf.raw_ops.RaggedGather` don't determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/ragged_gather_op.cc#L70) directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least 1 (i.e., it is not a scalar). Furthermore, the implementation does not check that the list given by `params_nested_splits` is not an empty list of tensors. We have patched the issue in GitHub commit a2b743f6017d7b97af1fe49087ae15f0ac634373. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-08-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37641>CVE-2021-37641</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-9c8h-vvrj-w2p8">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-9c8h-vvrj-w2p8</a></p>
<p>Release Date: 2021-08-12</p>
<p>Fix Resolution: tensorflow - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-cpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-gpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0b1","packageFilePaths":["/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0b1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-cpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-gpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-37641","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. In affected versions if the arguments to `tf.raw_ops.RaggedGather` don\u0027t determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/ragged_gather_op.cc#L70) directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least 1 (i.e., it is not a scalar). Furthermore, the implementation does not check that the list given by `params_nested_splits` is not an empty list of tensors. We have patched the issue in GitHub commit a2b743f6017d7b97af1fe49087ae15f0ac634373. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37641","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-37641 (High) detected in tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl - ## CVE-2021-37641 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/29/6c/2c9a5c4d095c63c2fb37d20def0e4f92685f7aee9243d6aae25862694fd1/tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>Path to vulnerable library: tensorflow/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0b1-cp36-cp36m-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. In affected versions if the arguments to `tf.raw_ops.RaggedGather` don't determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/ragged_gather_op.cc#L70) directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least 1 (i.e., it is not a scalar). Furthermore, the implementation does not check that the list given by `params_nested_splits` is not an empty list of tensors. We have patched the issue in GitHub commit a2b743f6017d7b97af1fe49087ae15f0ac634373. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-08-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37641>CVE-2021-37641</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-9c8h-vvrj-w2p8">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-9c8h-vvrj-w2p8</a></p>
<p>Release Date: 2021-08-12</p>
<p>Fix Resolution: tensorflow - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-cpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-gpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0b1","packageFilePaths":["/tensorflow/lite/micro/examples/magic_wand/train/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0b1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-cpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0, tensorflow-gpu - 2.3.4, 2.4.3, 2.5.1, 2.6.0"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-37641","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. In affected versions if the arguments to `tf.raw_ops.RaggedGather` don\u0027t determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/ragged_gather_op.cc#L70) directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least 1 (i.e., it is not a scalar). Furthermore, the implementation does not check that the list given by `params_nested_splits` is not an empty list of tensors. We have patched the issue in GitHub commit a2b743f6017d7b97af1fe49087ae15f0ac634373. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37641","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_infrastructure | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file tensorflow tensorflow lite micro examples magic wand train requirements txt path to vulnerable library tensorflow tensorflow lite micro examples magic wand train requirements txt dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an end to end open source platform for machine learning in affected versions if the arguments to tf raw ops raggedgather don t determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers the directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least i e it is not a scalar furthermore the implementation does not check that the list given by params nested splits is not an empty list of tensors we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree tensorflow isminimumfixversionavailable true minimumfixversion tensorflow tensorflow cpu tensorflow gpu basebranches vulnerabilityidentifier cve vulnerabilitydetails tensorflow is an end to end open source platform for machine learning in affected versions if the arguments to tf raw ops raggedgather don determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers the directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least i e it is not a scalar furthermore the implementation does not check that the list given by params nested splits is not an empty list of tensors we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range vulnerabilityurl | 0 |
91,070 | 11,461,804,340 | IssuesEvent | 2020-02-07 12:49:16 | angular-ui/ui-router | https://api.github.com/repos/angular-ui/ui-router | closed | Run Time State Setting | design stale | Not sure if I'm missing something in the docs, but I can't find anyway of doing this. I want to write a directive with a options of passing in a base path, ie
```
<div my-directive basepath="/some/path/"></div>
```
Then have my directive have a ui-router which appends all it's states to this path.
This doesn't seem possible at the moment as the states are created in the config step and there doesn't appear to be anyway of changing these. If the state urls could be looped through and updated, I could do this when the directive is first created and update the states.
Use cases for this are re-usable modules which bring there own routes. They would only really be re-usable if they could be appended to a specific state.
(I thought this kind of thing maybe possible after listening to Dean Sofer on JS Jabber - excellent module btw..)
| 1.0 | Run Time State Setting - Not sure if I'm missing something in the docs, but I can't find anyway of doing this. I want to write a directive with a options of passing in a base path, ie
```
<div my-directive basepath="/some/path/"></div>
```
Then have my directive have a ui-router which appends all it's states to this path.
This doesn't seem possible at the moment as the states are created in the config step and there doesn't appear to be anyway of changing these. If the state urls could be looped through and updated, I could do this when the directive is first created and update the states.
Use cases for this are re-usable modules which bring there own routes. They would only really be re-usable if they could be appended to a specific state.
(I thought this kind of thing maybe possible after listening to Dean Sofer on JS Jabber - excellent module btw..)
| non_infrastructure | run time state setting not sure if i m missing something in the docs but i can t find anyway of doing this i want to write a directive with a options of passing in a base path ie then have my directive have a ui router which appends all it s states to this path this doesn t seem possible at the moment as the states are created in the config step and there doesn t appear to be anyway of changing these if the state urls could be looped through and updated i could do this when the directive is first created and update the states use cases for this are re usable modules which bring there own routes they would only really be re usable if they could be appended to a specific state i thought this kind of thing maybe possible after listening to dean sofer on js jabber excellent module btw | 0 |
158,581 | 12,419,113,494 | IssuesEvent | 2020-05-23 04:02:25 | lokka30/LevelledMobs | https://api.github.com/repos/lokka30/LevelledMobs | closed | Cache the settings file! | done but needs testing request | Every time a mob spawns the settings file needs to be accessed a few times. Probably want to implement a settings cache and allow administrators to reload the cache when necessary. | 1.0 | Cache the settings file! - Every time a mob spawns the settings file needs to be accessed a few times. Probably want to implement a settings cache and allow administrators to reload the cache when necessary. | non_infrastructure | cache the settings file every time a mob spawns the settings file needs to be accessed a few times probably want to implement a settings cache and allow administrators to reload the cache when necessary | 0 |
26,089 | 19,659,374,781 | IssuesEvent | 2022-01-10 15:35:00 | twosixlabs/armory | https://api.github.com/repos/twosixlabs/armory | closed | fix sabot json corruption of performer configs | bug infrastructure configuration files | Sabot currently embeds the performer configuration as DynamoDB object. The numeric handling in DynamoDB does no distinguish between floats and ints yielding bad conversions such as `5` becomes `5.0` which violates type expectations of Python/Armory.
Since these configurations are queried as opaque blobs from the DB, there is no value in having dynamo treat them as well-formed json. Sabot should track these as either:
- opaque bytes completely uninterpreted by the DB, or
- S3 file refs with no config text in the DB
the sabot tools should behave identically to current regardless of the backing store used. | 1.0 | fix sabot json corruption of performer configs - Sabot currently embeds the performer configuration as DynamoDB object. The numeric handling in DynamoDB does no distinguish between floats and ints yielding bad conversions such as `5` becomes `5.0` which violates type expectations of Python/Armory.
Since these configurations are queried as opaque blobs from the DB, there is no value in having dynamo treat them as well-formed json. Sabot should track these as either:
- opaque bytes completely uninterpreted by the DB, or
- S3 file refs with no config text in the DB
the sabot tools should behave identically to current regardless of the backing store used. | infrastructure | fix sabot json corruption of performer configs sabot currently embeds the performer configuration as dynamodb object the numeric handling in dynamodb does no distinguish between floats and ints yielding bad conversions such as becomes which violates type expectations of python armory since these configurations are queried as opaque blobs from the db there is no value in having dynamo treat them as well formed json sabot should track these as either opaque bytes completely uninterpreted by the db or file refs with no config text in the db the sabot tools should behave identically to current regardless of the backing store used | 1 |
330,178 | 28,356,617,463 | IssuesEvent | 2023-04-12 07:50:03 | microcks/microcks | https://api.github.com/repos/microcks/microcks | opened | Allow resolution of external references on AsyncAPI file | component/tests kind/enhancement component/importer | ### Reason/Context
As of today, we have a reference resolution mechanism that is used on import time for AsyncAPI spec file. This has been added in #306 in order to support Avro schema references. It also has been used later on for gRPC support addition (one protobuf file may referenced other external protobuf files).
referencing JSON Schema files from OpenAPI files is now a very common practice (though I personally think that you then have to be very cautious on how you manage versioning of everything 😉 )
### Description
For unknown reasons, it hasn't been fully applied to AsyncAPI support yet as it has already been done for OpenAPI (see #548)
We should add this full reference resolution mechanism for AsyncAPI.
### Implementation ideas
It means that references will be discovered at import time but I see options on how to implement it:
1. Do not modify AsyncAPI file and add extra contracts for JSON Schema to keep everything "as is". This means that during tests we'll have to dereference everything and create an inlined OpenAPI spec in order to ease validation,
2. Dereference everything at import time and modify AsyncAPI file. This means that we'll not have to touch everything during tests and it'll speed up things. However, the user could be lost seeing the import result mentioning only 1 OpenAPI file,
3. Dereference everything at import time and modify AsyncAPI file, but also add extra contracts for JSON Schema to prove we discovered everything.
We'll implement `#3` that is the way things have been implemented in #548.
| 1.0 | Allow resolution of external references on AsyncAPI file - ### Reason/Context
As of today, we have a reference resolution mechanism that is used on import time for AsyncAPI spec file. This has been added in #306 in order to support Avro schema references. It also has been used later on for gRPC support addition (one protobuf file may referenced other external protobuf files).
referencing JSON Schema files from OpenAPI files is now a very common practice (though I personally think that you then have to be very cautious on how you manage versioning of everything 😉 )
### Description
For unknown reasons, it hasn't been fully applied to AsyncAPI support yet as it has already been done for OpenAPI (see #548)
We should add this full reference resolution mechanism for AsyncAPI.
### Implementation ideas
It means that references will be discovered at import time but I see options on how to implement it:
1. Do not modify AsyncAPI file and add extra contracts for JSON Schema to keep everything "as is". This means that during tests we'll have to dereference everything and create an inlined OpenAPI spec in order to ease validation,
2. Dereference everything at import time and modify AsyncAPI file. This means that we'll not have to touch everything during tests and it'll speed up things. However, the user could be lost seeing the import result mentioning only 1 OpenAPI file,
3. Dereference everything at import time and modify AsyncAPI file, but also add extra contracts for JSON Schema to prove we discovered everything.
We'll implement `#3` that is the way things have been implemented in #548.
| non_infrastructure | allow resolution of external references on asyncapi file reason context as of today we have a reference resolution mechanism that is used on import time for asyncapi spec file this has been added in in order to support avro schema references it also has been used later on for grpc support addition one protobuf file may referenced other external protobuf files referencing json schema files from openapi files is now a very common practice though i personally think that you then have to be very cautious on how you manage versioning of everything 😉 description for unknown reasons it hasn t been fully applied to asyncapi support yet as it has already been done for openapi see we should add this full reference resolution mechanism for asyncapi implementation ideas it means that references will be discovered at import time but i see options on how to implement it do not modify asyncapi file and add extra contracts for json schema to keep everything as is this means that during tests we ll have to dereference everything and create an inlined openapi spec in order to ease validation dereference everything at import time and modify asyncapi file this means that we ll not have to touch everything during tests and it ll speed up things however the user could be lost seeing the import result mentioning only openapi file dereference everything at import time and modify asyncapi file but also add extra contracts for json schema to prove we discovered everything we ll implement that is the way things have been implemented in | 0 |
22,303 | 15,091,408,254 | IssuesEvent | 2021-02-06 15:23:04 | crystal-lang/crystal | https://api.github.com/repos/crystal-lang/crystal | closed | Docs tarball missing for Github releases | topic:infrastructure | The tarball with the API docs is missing for 0.36.0 and 0.36.1 releases. Is this on purpose or just got lost in the release process? | 1.0 | Docs tarball missing for Github releases - The tarball with the API docs is missing for 0.36.0 and 0.36.1 releases. Is this on purpose or just got lost in the release process? | infrastructure | docs tarball missing for github releases the tarball with the api docs is missing for and releases is this on purpose or just got lost in the release process | 1 |
20,222 | 13,765,753,564 | IssuesEvent | 2020-10-07 13:47:42 | wireapp/wire-webapp | https://api.github.com/repos/wireapp/wire-webapp | closed | TypeScript Migration | comp: infrastructure prio: medium size: xxl type: refactoring 🛠 | ## Source code
[`src/script/`](https://github.com/wireapp/wire-webapp/tree/dev/src/script)
- [x] [`backup/Error.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/backup/Error.js) (78 lines)
- [x] [`components/accentColorPicker.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/accentColorPicker.js) (46 lines)
- [x] [`components/deviceRemove.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/deviceRemove.js) (88 lines)
- [x] [`components/ephemeralTimer.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/ephemeralTimer.js) (42 lines)
- [x] [`components/fullSearch.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/fullSearch.js) (176 lines)
- [x] [`components/groupList.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/groupList.js) (55 lines)
- [x] [`components/guestModeToggle.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/guestModeToggle.js) (43 lines)
- [x] [`components/icons.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/icons.js) (28 lines)
- [x] [`components/image.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/image.js) (71 lines)
- [x] [`components/infoToggle.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/infoToggle.js) (49 lines)
- [x] [`components/inputLevel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/inputLevel.js) (48 lines)
- [x] [`components/mentionSuggestions.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/mentionSuggestions.js) (203 lines)
- [x] [`components/message.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/message.js) (651 lines)
- [X] [`components/messageQuote.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/messageQuote.js) (191 lines)
- [x] [`components/messageTimerButton.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/messageTimerButton.js) (89 lines)
- [x] [`components/panel/userActions.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/panel/userActions.js) (190 lines)
- [x] [`components/participantAvatar.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/participantAvatar.js) (244 lines)
- [x] [`components/receiptModeToggle.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/receiptModeToggle.js) (46 lines)
- [x] [`components/serviceList.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/serviceList.js) (61 lines)
- [x] [`components/topPeople.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/topPeople.js) (51 lines)
- [x] [`components/userInput.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/userInput.js) (111 lines)
- [x] [`conversation/ClientMismatchHandler.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ClientMismatchHandler.js) (228 lines)
- [x] [`conversation/ConversationEphemeralHandler.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ConversationEphemeralHandler.js) (301 lines)
- [x] [`conversation/ConversationMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ConversationMapper.js) (473 lines)
- [x] [`conversation/ConversationRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ConversationRepository.js) (4282 lines)
- [x] [`conversation/EventMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/EventMapper.js) (869 lines)
- [x] [`cryptography/CryptographyMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/cryptography/CryptographyMapper.js) (525 lines)
- [x] [`cryptography/CryptographyRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/cryptography/CryptographyRepository.js) (498 lines)
- [x] [`entity/Conversation.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/entity/Conversation.js) (819 lines)
- [x] [`entity/User.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/entity/User.js) (257 lines)
- [x] [`error/AccessTokenError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/AccessTokenError.js) (47 lines)
- [x] [`error/AuthError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/AuthError.js) (47 lines)
- [x] [`error/BackendClientError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/BackendClientError.js) (100 lines)
- [x] [`error/BaseError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/BaseError.js) (54 lines)
- [x] [`error/CallError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/CallError.js) (65 lines)
- [x] [`error/ClientError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ClientError.js) (55 lines)
- [x] [`error/ConnectError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ConnectError.js) (45 lines)
- [x] [`error/ConnectionError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ConnectionError.js) (37 lines)
- [x] [`error/ConversationError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ConversationError.js) (63 lines)
- [x] [`error/CryptographyError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/CryptographyError.js) (53 lines)
- [x] [`error/EventError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/EventError.js) (59 lines)
- [x] [`error/LinkPreviewError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/LinkPreviewError.js) (47 lines)
- [x] [`error/MediaError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/MediaError.js) (49 lines)
- [x] [`error/PermissionError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/PermissionError.js) (42 lines)
- [x] [`error/StorageError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/StorageError.js) (57 lines)
- [x] [`error/TeamError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/TeamError.js) (41 lines)
- [x] [`error/UserError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/UserError.js) (51 lines)
- [x] [`event/EventRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/EventRepository.js) (944 lines)
- [x] [`event/EventService.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/EventService.js) (461 lines)
- [x] [`event/EventServiceNoCompound.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/EventServiceNoCompound.js) (99 lines)
- [x] [`event/preprocessor/QuotedMessageMiddleware.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/preprocessor/QuotedMessageMiddleware.js) (162 lines)
- [x] [`event/preprocessor/ReceiptsMiddleware.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/preprocessor/ReceiptsMiddleware.js) (112 lines)
- [x] [`event/preprocessor/ServiceMiddleware.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/preprocessor/ServiceMiddleware.js) (86 lines)
- [x] [`links/LinkPreviewRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/links/LinkPreviewRepository.js) (172 lines)
- [x] [`localization/Localizer.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/localization/Localizer.js) (99 lines)
- [x] [`locations.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/locations.js) (26 lines)
- [x] [`main/app.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/main/app.js) (943 lines)
- [x] [`media/MediaEmbeds.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/media/MediaEmbeds.js) (296 lines)
- [x] [`media/MediaParser.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/media/MediaParser.js) (59 lines)
- [x] [`search/SearchRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/search/SearchRepository.js) (195 lines)
- [x] [`team/TeamMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/team/TeamMapper.js) (98 lines)
- [x] [`team/TeamRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/team/TeamRepository.js) (347 lines)
- [x] [`telemetry/app_init/AppInitStatistics.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/telemetry/app_init/AppInitStatistics.js) (74 lines)
- [x] [`telemetry/app_init/AppInitTelemetry.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/telemetry/app_init/AppInitTelemetry.js) (70 lines)
- [x] [`telemetry/app_init/AppInitTimings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/telemetry/app_init/AppInitTimings.js) (74 lines)
- [x] [`ui/AvailabilityContextMenu.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/AvailabilityContextMenu.js) (49 lines)
- [x] [`ui/ContextMenu.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/ContextMenu.js) (182 lines)
- [x] [`ui/Modal.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/Modal.js) (126 lines)
- [x] [`ui/Shortcut.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/Shortcut.js) (213 lines)
- [x] [`ui/WindowHandler.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/WindowHandler.js) (50 lines)
- [x] [`ui/overlayedObserver.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/overlayedObserver.js) (87 lines)
- [x] [`ui/viewportObserver.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/viewportObserver.js) (88 lines)
- [x] [`util/DebugUtil.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/util/DebugUtil.js) (489 lines)
- [x] [`util/PeerConnectionUtil.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/util/PeerConnectionUtil.js) (51 lines)
- [x] [`util/objectUtil.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/util/objectUtil.js) (48 lines)
- [x] [`view_model/ActionsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ActionsViewModel.js) (343 lines)
- [x] [`view_model/ContentViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ContentViewModel.js) (363 lines)
- [x] [`view_model/FaviconViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/FaviconViewModel.js) (60 lines)
- [x] [`view_model/ImageDetailViewViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ImageDetailViewViewModel.js) (204 lines)
- [x] [`view_model/ListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ListViewModel.js) (492 lines)
- [x] [`view_model/LoadingViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/LoadingViewModel.js) (79 lines)
- [x] [`view_model/MainViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/MainViewModel.js) (226 lines)
- [x] [`view_model/ModalsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ModalsViewModel.js) (298 lines)
- [x] [`view_model/PanelViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/PanelViewModel.js) (267 lines)
- [x] [`view_model/ThemeViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ThemeViewModel.js) (47 lines)
- [x] [`view_model/WarningsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/WarningsViewModel.js) (173 lines)
- [x] [`view_model/WindowTitleViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/WindowTitleViewModel.js) (135 lines)
- [x] [`view_model/bindings/CommonBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/CommonBindings.js) (678 lines)
- [x] [`view_model/bindings/ConversationListBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/ConversationListBindings.js) (54 lines)
- [x] [`view_model/bindings/ListBackgroundBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/ListBackgroundBindings.js) (44 lines)
- [x] [`view_model/bindings/MessageListBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/MessageListBindings.js) (232 lines)
- [x] [`view_model/bindings/VideoCallingBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/VideoCallingBindings.js) (36 lines)
- [x] [`view_model/content/CollectionDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/CollectionDetailsViewModel.js) (156 lines)
- [x] [`view_model/content/CollectionViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/CollectionViewModel.js) (156 lines)
- [x] [`view_model/content/ConnectRequestsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/ConnectRequestsViewModel.js) (84 lines)
- [x] [`view_model/content/EmojiInputViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/EmojiInputViewModel.js) (441 lines)
- [x] [`view_model/content/GiphyViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/GiphyViewModel.js) (198 lines)
- [x] [`view_model/content/GroupCreationViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/GroupCreationViewModel.js) (251 lines)
- [x] [`view_model/content/HistoryExportViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/HistoryExportViewModel.js) (166 lines)
- [x] [`view_model/content/HistoryImportViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/HistoryImportViewModel.js) (146 lines)
- [x] [`view_model/content/InputBarViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/InputBarViewModel.js) (898 lines)
- [x] [`view_model/content/MessageListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/MessageListViewModel.js) (646 lines)
- [x] [`view_model/content/PreferencesAVViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesAVViewModel.js) (268 lines)
- [x] [`view_model/content/PreferencesAboutViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesAboutViewModel.js) (53 lines)
- [x] [`view_model/content/PreferencesAccountViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesAccountViewModel.js) (441 lines)
- [x] [`view_model/content/PreferencesDeviceDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesDeviceDetailsViewModel.js) (109 lines)
- [x] [`view_model/content/PreferencesDevicesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesDevicesViewModel.js) (78 lines)
- [x] [`view_model/content/PreferencesOptionsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesOptionsViewModel.js) (124 lines)
- [x] [`view_model/content/TitleBarViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/TitleBarViewModel.js) (160 lines)
- [x] [`view_model/list/ArchiveViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/ArchiveViewModel.js) (63 lines)
- [x] [`view_model/list/ConversationListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/ConversationListViewModel.js) (259 lines)
- [x] [`view_model/list/PreferencesListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/PreferencesListViewModel.js) (94 lines)
- [x] [`view_model/list/StartUIViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/StartUIViewModel.js) (388 lines)
- [x] [`view_model/list/TakeoverViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/TakeoverViewModel.js) (72 lines)
- [x] [`view_model/list/TemporaryGuestViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/TemporaryGuestViewModel.js) (71 lines)
- [x] [`view_model/panel/AddParticipantsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/AddParticipantsViewModel.js) (187 lines)
- [x] [`view_model/panel/ConversationDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/ConversationDetailsViewModel.js) (417 lines)
- [x] [`view_model/panel/GroupParticipantServiceViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/GroupParticipantServiceViewModel.js) (95 lines)
- [x] [`view_model/panel/GroupParticipantUserViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/GroupParticipantUserViewModel.js) (105 lines)
- [x] [`view_model/panel/GuestsAndServicesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/GuestsAndServicesViewModel.js) (157 lines)
- [x] [`view_model/panel/MessageDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/MessageDetailsViewModel.js) (177 lines)
- [x] [`view_model/panel/NotificationsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/NotificationsViewModel.js) (53 lines)
- [x] [`view_model/panel/ParticipantDevicesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/ParticipantDevicesViewModel.js) (55 lines)
- [x] [`view_model/panel/TimedMessagesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/TimedMessagesViewModel.js) (80 lines) | 1.0 | TypeScript Migration - ## Source code
[`src/script/`](https://github.com/wireapp/wire-webapp/tree/dev/src/script)
- [x] [`backup/Error.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/backup/Error.js) (78 lines)
- [x] [`components/accentColorPicker.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/accentColorPicker.js) (46 lines)
- [x] [`components/deviceRemove.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/deviceRemove.js) (88 lines)
- [x] [`components/ephemeralTimer.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/ephemeralTimer.js) (42 lines)
- [x] [`components/fullSearch.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/fullSearch.js) (176 lines)
- [x] [`components/groupList.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/groupList.js) (55 lines)
- [x] [`components/guestModeToggle.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/guestModeToggle.js) (43 lines)
- [x] [`components/icons.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/icons.js) (28 lines)
- [x] [`components/image.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/image.js) (71 lines)
- [x] [`components/infoToggle.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/infoToggle.js) (49 lines)
- [x] [`components/inputLevel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/inputLevel.js) (48 lines)
- [x] [`components/mentionSuggestions.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/mentionSuggestions.js) (203 lines)
- [x] [`components/message.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/message.js) (651 lines)
- [X] [`components/messageQuote.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/messageQuote.js) (191 lines)
- [x] [`components/messageTimerButton.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/messageTimerButton.js) (89 lines)
- [x] [`components/panel/userActions.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/panel/userActions.js) (190 lines)
- [x] [`components/participantAvatar.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/participantAvatar.js) (244 lines)
- [x] [`components/receiptModeToggle.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/receiptModeToggle.js) (46 lines)
- [x] [`components/serviceList.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/serviceList.js) (61 lines)
- [x] [`components/topPeople.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/topPeople.js) (51 lines)
- [x] [`components/userInput.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/components/userInput.js) (111 lines)
- [x] [`conversation/ClientMismatchHandler.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ClientMismatchHandler.js) (228 lines)
- [x] [`conversation/ConversationEphemeralHandler.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ConversationEphemeralHandler.js) (301 lines)
- [x] [`conversation/ConversationMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ConversationMapper.js) (473 lines)
- [x] [`conversation/ConversationRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/ConversationRepository.js) (4282 lines)
- [x] [`conversation/EventMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/conversation/EventMapper.js) (869 lines)
- [x] [`cryptography/CryptographyMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/cryptography/CryptographyMapper.js) (525 lines)
- [x] [`cryptography/CryptographyRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/cryptography/CryptographyRepository.js) (498 lines)
- [x] [`entity/Conversation.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/entity/Conversation.js) (819 lines)
- [x] [`entity/User.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/entity/User.js) (257 lines)
- [x] [`error/AccessTokenError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/AccessTokenError.js) (47 lines)
- [x] [`error/AuthError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/AuthError.js) (47 lines)
- [x] [`error/BackendClientError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/BackendClientError.js) (100 lines)
- [x] [`error/BaseError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/BaseError.js) (54 lines)
- [x] [`error/CallError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/CallError.js) (65 lines)
- [x] [`error/ClientError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ClientError.js) (55 lines)
- [x] [`error/ConnectError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ConnectError.js) (45 lines)
- [x] [`error/ConnectionError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ConnectionError.js) (37 lines)
- [x] [`error/ConversationError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/ConversationError.js) (63 lines)
- [x] [`error/CryptographyError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/CryptographyError.js) (53 lines)
- [x] [`error/EventError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/EventError.js) (59 lines)
- [x] [`error/LinkPreviewError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/LinkPreviewError.js) (47 lines)
- [x] [`error/MediaError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/MediaError.js) (49 lines)
- [x] [`error/PermissionError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/PermissionError.js) (42 lines)
- [x] [`error/StorageError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/StorageError.js) (57 lines)
- [x] [`error/TeamError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/TeamError.js) (41 lines)
- [x] [`error/UserError.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/error/UserError.js) (51 lines)
- [x] [`event/EventRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/EventRepository.js) (944 lines)
- [x] [`event/EventService.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/EventService.js) (461 lines)
- [x] [`event/EventServiceNoCompound.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/EventServiceNoCompound.js) (99 lines)
- [x] [`event/preprocessor/QuotedMessageMiddleware.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/preprocessor/QuotedMessageMiddleware.js) (162 lines)
- [x] [`event/preprocessor/ReceiptsMiddleware.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/preprocessor/ReceiptsMiddleware.js) (112 lines)
- [x] [`event/preprocessor/ServiceMiddleware.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/event/preprocessor/ServiceMiddleware.js) (86 lines)
- [x] [`links/LinkPreviewRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/links/LinkPreviewRepository.js) (172 lines)
- [x] [`localization/Localizer.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/localization/Localizer.js) (99 lines)
- [x] [`locations.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/locations.js) (26 lines)
- [x] [`main/app.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/main/app.js) (943 lines)
- [x] [`media/MediaEmbeds.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/media/MediaEmbeds.js) (296 lines)
- [x] [`media/MediaParser.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/media/MediaParser.js) (59 lines)
- [x] [`search/SearchRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/search/SearchRepository.js) (195 lines)
- [x] [`team/TeamMapper.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/team/TeamMapper.js) (98 lines)
- [x] [`team/TeamRepository.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/team/TeamRepository.js) (347 lines)
- [x] [`telemetry/app_init/AppInitStatistics.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/telemetry/app_init/AppInitStatistics.js) (74 lines)
- [x] [`telemetry/app_init/AppInitTelemetry.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/telemetry/app_init/AppInitTelemetry.js) (70 lines)
- [x] [`telemetry/app_init/AppInitTimings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/telemetry/app_init/AppInitTimings.js) (74 lines)
- [x] [`ui/AvailabilityContextMenu.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/AvailabilityContextMenu.js) (49 lines)
- [x] [`ui/ContextMenu.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/ContextMenu.js) (182 lines)
- [x] [`ui/Modal.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/Modal.js) (126 lines)
- [x] [`ui/Shortcut.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/Shortcut.js) (213 lines)
- [x] [`ui/WindowHandler.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/WindowHandler.js) (50 lines)
- [x] [`ui/overlayedObserver.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/overlayedObserver.js) (87 lines)
- [x] [`ui/viewportObserver.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/ui/viewportObserver.js) (88 lines)
- [x] [`util/DebugUtil.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/util/DebugUtil.js) (489 lines)
- [x] [`util/PeerConnectionUtil.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/util/PeerConnectionUtil.js) (51 lines)
- [x] [`util/objectUtil.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/util/objectUtil.js) (48 lines)
- [x] [`view_model/ActionsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ActionsViewModel.js) (343 lines)
- [x] [`view_model/ContentViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ContentViewModel.js) (363 lines)
- [x] [`view_model/FaviconViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/FaviconViewModel.js) (60 lines)
- [x] [`view_model/ImageDetailViewViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ImageDetailViewViewModel.js) (204 lines)
- [x] [`view_model/ListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ListViewModel.js) (492 lines)
- [x] [`view_model/LoadingViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/LoadingViewModel.js) (79 lines)
- [x] [`view_model/MainViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/MainViewModel.js) (226 lines)
- [x] [`view_model/ModalsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ModalsViewModel.js) (298 lines)
- [x] [`view_model/PanelViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/PanelViewModel.js) (267 lines)
- [x] [`view_model/ThemeViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/ThemeViewModel.js) (47 lines)
- [x] [`view_model/WarningsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/WarningsViewModel.js) (173 lines)
- [x] [`view_model/WindowTitleViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/WindowTitleViewModel.js) (135 lines)
- [x] [`view_model/bindings/CommonBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/CommonBindings.js) (678 lines)
- [x] [`view_model/bindings/ConversationListBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/ConversationListBindings.js) (54 lines)
- [x] [`view_model/bindings/ListBackgroundBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/ListBackgroundBindings.js) (44 lines)
- [x] [`view_model/bindings/MessageListBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/MessageListBindings.js) (232 lines)
- [x] [`view_model/bindings/VideoCallingBindings.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/bindings/VideoCallingBindings.js) (36 lines)
- [x] [`view_model/content/CollectionDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/CollectionDetailsViewModel.js) (156 lines)
- [x] [`view_model/content/CollectionViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/CollectionViewModel.js) (156 lines)
- [x] [`view_model/content/ConnectRequestsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/ConnectRequestsViewModel.js) (84 lines)
- [x] [`view_model/content/EmojiInputViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/EmojiInputViewModel.js) (441 lines)
- [x] [`view_model/content/GiphyViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/GiphyViewModel.js) (198 lines)
- [x] [`view_model/content/GroupCreationViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/GroupCreationViewModel.js) (251 lines)
- [x] [`view_model/content/HistoryExportViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/HistoryExportViewModel.js) (166 lines)
- [x] [`view_model/content/HistoryImportViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/HistoryImportViewModel.js) (146 lines)
- [x] [`view_model/content/InputBarViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/InputBarViewModel.js) (898 lines)
- [x] [`view_model/content/MessageListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/MessageListViewModel.js) (646 lines)
- [x] [`view_model/content/PreferencesAVViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesAVViewModel.js) (268 lines)
- [x] [`view_model/content/PreferencesAboutViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesAboutViewModel.js) (53 lines)
- [x] [`view_model/content/PreferencesAccountViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesAccountViewModel.js) (441 lines)
- [x] [`view_model/content/PreferencesDeviceDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesDeviceDetailsViewModel.js) (109 lines)
- [x] [`view_model/content/PreferencesDevicesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesDevicesViewModel.js) (78 lines)
- [x] [`view_model/content/PreferencesOptionsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/PreferencesOptionsViewModel.js) (124 lines)
- [x] [`view_model/content/TitleBarViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/content/TitleBarViewModel.js) (160 lines)
- [x] [`view_model/list/ArchiveViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/ArchiveViewModel.js) (63 lines)
- [x] [`view_model/list/ConversationListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/ConversationListViewModel.js) (259 lines)
- [x] [`view_model/list/PreferencesListViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/PreferencesListViewModel.js) (94 lines)
- [x] [`view_model/list/StartUIViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/StartUIViewModel.js) (388 lines)
- [x] [`view_model/list/TakeoverViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/TakeoverViewModel.js) (72 lines)
- [x] [`view_model/list/TemporaryGuestViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/list/TemporaryGuestViewModel.js) (71 lines)
- [x] [`view_model/panel/AddParticipantsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/AddParticipantsViewModel.js) (187 lines)
- [x] [`view_model/panel/ConversationDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/ConversationDetailsViewModel.js) (417 lines)
- [x] [`view_model/panel/GroupParticipantServiceViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/GroupParticipantServiceViewModel.js) (95 lines)
- [x] [`view_model/panel/GroupParticipantUserViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/GroupParticipantUserViewModel.js) (105 lines)
- [x] [`view_model/panel/GuestsAndServicesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/GuestsAndServicesViewModel.js) (157 lines)
- [x] [`view_model/panel/MessageDetailsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/MessageDetailsViewModel.js) (177 lines)
- [x] [`view_model/panel/NotificationsViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/NotificationsViewModel.js) (53 lines)
- [x] [`view_model/panel/ParticipantDevicesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/ParticipantDevicesViewModel.js) (55 lines)
- [x] [`view_model/panel/TimedMessagesViewModel.js`](https://github.com/wireapp/wire-webapp/tree/dev/src/script/view_model/panel/TimedMessagesViewModel.js) (80 lines) | infrastructure | typescript migration source code lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines lines | 1 |
9,433 | 3,908,955,252 | IssuesEvent | 2016-04-19 17:35:02 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Hidden tooltip | No Code Attached Yet | #### Steps to reproduce the issue
Go to Components>Messaging and select My settings from the toolbar
#### Expected result
Modal window with visible tooltips
#### Actual result
Modal window with top tooltip for "Lock Inbox" invisible
#### System information (as much as possible)
#### Additional comments
| 1.0 | Hidden tooltip - #### Steps to reproduce the issue
Go to Components>Messaging and select My settings from the toolbar
#### Expected result
Modal window with visible tooltips
#### Actual result
Modal window with top tooltip for "Lock Inbox" invisible
#### System information (as much as possible)
#### Additional comments
| non_infrastructure | hidden tooltip steps to reproduce the issue go to components messaging and select my settings from the toolbar expected result modal window with visible tooltips actual result modal window with top tooltip for lock inbox invisible system information as much as possible additional comments | 0 |
33,086 | 27,213,438,976 | IssuesEvent | 2023-02-20 18:46:57 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | closed | Issues with installation | type: bug work: infrastructure status: ready restricted: maintainers | I tried following [the docs](http://docs.mathesar.org/installation/docker-compose/) on my Mac. I wiped out all Docker images and containers before I started.
My Docker version: 20.10.8, build 3967b7d
My docker-compose version 1.29.2, build 5becea4c
### Issue 1: It failed.
`sudo docker compose --profile prod up -d --wait` failed and the script exited with ``unknown flag: --wait`
I had no idea what to do next or how to troubleshoot. Therefore I couldn't finish the install and can't provide feedback for the remaining steps.
**Edited to add**: I later found the Troubleshooting section that explains what Docker versions to use. This should be in requirements, and we should have minimum requirements clearly stated. #2504 addresses this somewhat. We may also want to check Docker versions ourselves and refuse to install if we don't have the right versions, because it's disconcerting for the script to exit without any indication about what's wrong.
I'll test with updated Docker versions tomorrow.
### Issue 2: Admin user is not validated
I accidentally hit Enter without entering a username when it asked me for an admin user. It then asked me for a password.
The script should make sure that the username actually exists and prompt the user for a username if it doesn't.
### Issue 3: Secret generation
```
Generating secret key...
tr: Illegal byte sequence
Secret key generated successfully.
```
I'm not sure what `tr: Illegal byte sequence` is but it made me worry.
### Issue 4: Config file location should be configurable.
This is the following step:
```
We begin by creating a directory on your system where we can put some files for
Mathesar to use.
```
It's fine to have a default, but the user should be able to change it.
### Issue 6: Usernames should have default values
This applies to both system database username and admin username. The user should be able to change them.
I'm also wondering if we should offer to auto-generate passwords (again, the user should be able to override).
### Issue 7: Install script docs are too verbose.
When I run the install script, the documentation is extremely verbose. Especially when I first run the script, it prints 2 terminal screens worth of stuff and it's overwhelming. I don't know what's important and what's just explanatory.
For example, the secret key steps says:
```
********************************************************************************
In order to keep Mathesar's web server secure, we'll randomly generate a secret
key. It's not necessary for you to know this secret, since it's just for
internal Mathesar use.
Generating secret key...
tr: Illegal byte sequence
Secret key generated successfully.
********************************************************************************
```
This is a lot to take in, especially for people unfamiliar with Mathesar. I do like the docs, but not the location. I would move the explanations of what's happening to the docs site, and make the output just:
```
Generating secret key...
Secret key generated successfully.
```
The docs site can have a "explanation of what the install script does" section and move the longer stuff like this there:
```
In order to keep Mathesar's web server secure, we'll randomly generate a secret
key. It's not necessary for you to know this secret, since it's just for
internal Mathesar use.
```
This applies to other steps too.
**Edited to add**: Here's [a screenshot](https://user-images.githubusercontent.com/35857179/161526235-5ee0d592-0105-4a57-aa53-b1048dca6aad.png) of NocoDB's installation process (from [this page](https://docs.nocodb.com/getting-started/installation)). Much less overwhelming!
### Issue 8: Postgres port
One of the steps says:
```
If you have a PostgreSQL database already running on this machine you may need
to choose a custom port for Mathesar's database to avoid conflict. If you're not
sure, just press ENTER to use the default port of 5432.
```
Isn't the DB going to be running in a container? Why would there be a second DB in the container with the same port?
### Issue 9: Final message
I didn't get this far, but the script says:
```
If running locally, you can access Mathesar by navigating to http://localhost
in your web browser.
```
This is weird because we ask for a domain earlier in the process. We should adapt this message to whether they set up a domain. | 1.0 | Issues with installation - I tried following [the docs](http://docs.mathesar.org/installation/docker-compose/) on my Mac. I wiped out all Docker images and containers before I started.
My Docker version: 20.10.8, build 3967b7d
My docker-compose version 1.29.2, build 5becea4c
### Issue 1: It failed.
`sudo docker compose --profile prod up -d --wait` failed and the script exited with ``unknown flag: --wait`
I had no idea what to do next or how to troubleshoot. Therefore I couldn't finish the install and can't provide feedback for the remaining steps.
**Edited to add**: I later found the Troubleshooting section that explains what Docker versions to use. This should be in requirements, and we should have minimum requirements clearly stated. #2504 addresses this somewhat. We may also want to check Docker versions ourselves and refuse to install if we don't have the right versions, because it's disconcerting for the script to exit without any indication about what's wrong.
I'll test with updated Docker versions tomorrow.
### Issue 2: Admin user is not validated
I accidentally hit Enter without entering a username when it asked me for an admin user. It then asked me for a password.
The script should make sure that the username actually exists and prompt the user for a username if it doesn't.
### Issue 3: Secret generation
```
Generating secret key...
tr: Illegal byte sequence
Secret key generated successfully.
```
I'm not sure what `tr: Illegal byte sequence` is but it made me worry.
### Issue 4: Config file location should be configurable.
This is the following step:
```
We begin by creating a directory on your system where we can put some files for
Mathesar to use.
```
It's fine to have a default, but the user should be able to change it.
### Issue 6: Usernames should have default values
This applies to both system database username and admin username. The user should be able to change them.
I'm also wondering if we should offer to auto-generate passwords (again, the user should be able to override).
### Issue 7: Install script docs are too verbose.
When I run the install script, the documentation is extremely verbose. Especially when I first run the script, it prints 2 terminal screens worth of stuff and it's overwhelming. I don't know what's important and what's just explanatory.
For example, the secret key steps says:
```
********************************************************************************
In order to keep Mathesar's web server secure, we'll randomly generate a secret
key. It's not necessary for you to know this secret, since it's just for
internal Mathesar use.
Generating secret key...
tr: Illegal byte sequence
Secret key generated successfully.
********************************************************************************
```
This is a lot to take in, especially for people unfamiliar with Mathesar. I do like the docs, but not the location. I would move the explanations of what's happening to the docs site, and make the output just:
```
Generating secret key...
Secret key generated successfully.
```
The docs site can have a "explanation of what the install script does" section and move the longer stuff like this there:
```
In order to keep Mathesar's web server secure, we'll randomly generate a secret
key. It's not necessary for you to know this secret, since it's just for
internal Mathesar use.
```
This applies to other steps too.
**Edited to add**: Here's [a screenshot](https://user-images.githubusercontent.com/35857179/161526235-5ee0d592-0105-4a57-aa53-b1048dca6aad.png) of NocoDB's installation process (from [this page](https://docs.nocodb.com/getting-started/installation)). Much less overwhelming!
### Issue 8: Postgres port
One of the steps says:
```
If you have a PostgreSQL database already running on this machine you may need
to choose a custom port for Mathesar's database to avoid conflict. If you're not
sure, just press ENTER to use the default port of 5432.
```
Isn't the DB going to be running in a container? Why would there be a second DB in the container with the same port?
### Issue 9: Final message
I didn't get this far, but the script says:
```
If running locally, you can access Mathesar by navigating to http://localhost
in your web browser.
```
This is weird because we ask for a domain earlier in the process. We should adapt this message to whether they set up a domain. | infrastructure | issues with installation i tried following on my mac i wiped out all docker images and containers before i started my docker version build my docker compose version build issue it failed sudo docker compose profile prod up d wait failed and the script exited with unknown flag wait i had no idea what to do next or how to troubleshoot therefore i couldn t finish the install and can t provide feedback for the remaining steps edited to add i later found the troubleshooting section that explains what docker versions to use this should be in requirements and we should have minimum requirements clearly stated addresses this somewhat we may also want to check docker versions ourselves and refuse to install if we don t have the right versions because it s disconcerting for the script to exit without any indication about what s wrong i ll test with updated docker versions tomorrow issue admin user is not validated i accidentally hit enter without entering a username when it asked me for an admin user it then asked me for a password the script should make sure that the username actually exists and prompt the user for a username if it doesn t issue secret generation generating secret key tr illegal byte sequence secret key generated successfully i m not sure what tr illegal byte sequence is but it made me worry issue config file location should be configurable this is the following step we begin by creating a directory on your system where we can put some files for mathesar to use it s fine to have a default but the user should be able to change it issue usernames should have default values this applies to both system database username and admin username the user should be able to change them i m also wondering if we should offer to auto generate passwords again the user should be able to override issue install script docs are too verbose when i run the install script the documentation is extremely verbose especially when i first run the script it prints terminal screens worth of stuff and it s overwhelming i don t know what s important and what s just explanatory for example the secret key steps says in order to keep mathesar s web server secure we ll randomly generate a secret key it s not necessary for you to know this secret since it s just for internal mathesar use generating secret key tr illegal byte sequence secret key generated successfully this is a lot to take in especially for people unfamiliar with mathesar i do like the docs but not the location i would move the explanations of what s happening to the docs site and make the output just generating secret key secret key generated successfully the docs site can have a explanation of what the install script does section and move the longer stuff like this there in order to keep mathesar s web server secure we ll randomly generate a secret key it s not necessary for you to know this secret since it s just for internal mathesar use this applies to other steps too edited to add here s of nocodb s installation process from much less overwhelming issue postgres port one of the steps says if you have a postgresql database already running on this machine you may need to choose a custom port for mathesar s database to avoid conflict if you re not sure just press enter to use the default port of isn t the db going to be running in a container why would there be a second db in the container with the same port issue final message i didn t get this far but the script says if running locally you can access mathesar by navigating to in your web browser this is weird because we ask for a domain earlier in the process we should adapt this message to whether they set up a domain | 1 |
821,733 | 30,833,661,608 | IssuesEvent | 2023-08-02 05:16:26 | OSU-Sustainability-Office/energy-dashboard | https://api.github.com/repos/OSU-Sustainability-Office/energy-dashboard | closed | Can upgrade SAM cli on github actions again | priority-low | We previously deprecated the SAM cli version in github actions due to an error (https://github.com/aws/aws-sam-cli/issues/4527), but apparently this is fixed on the newest version of SAM cli: https://github.com/aws/aws-sam-cli/issues/4527#issuecomment-1372630340. | 1.0 | Can upgrade SAM cli on github actions again - We previously deprecated the SAM cli version in github actions due to an error (https://github.com/aws/aws-sam-cli/issues/4527), but apparently this is fixed on the newest version of SAM cli: https://github.com/aws/aws-sam-cli/issues/4527#issuecomment-1372630340. | non_infrastructure | can upgrade sam cli on github actions again we previously deprecated the sam cli version in github actions due to an error but apparently this is fixed on the newest version of sam cli | 0 |
768,219 | 26,958,476,904 | IssuesEvent | 2023-02-08 16:26:16 | ProjectCentreLimited/TOMs | https://api.github.com/repos/ProjectCentreLimited/TOMs | closed | Map tile printing causes TOM to crash | need investigation High priority | Hi,
Just to make you aware that TOMs crashes for two users (so far) when trying to print map tiles:
| 1.0 | Map tile printing causes TOM to crash - Hi,
Just to make you aware that TOMs crashes for two users (so far) when trying to print map tiles:
| non_infrastructure | map tile printing causes tom to crash hi just to make you aware that toms crashes for two users so far when trying to print map tiles | 0 |
4,884 | 5,315,958,768 | IssuesEvent | 2017-02-13 18:39:32 | sastafford/marklogic-spring-batch | https://api.github.com/repos/sastafford/marklogic-spring-batch | closed | Log out the number of documents processed by the job | infrastructure | As a user
I want to TITLE
So that I can track the progress of the job | 1.0 | Log out the number of documents processed by the job - As a user
I want to TITLE
So that I can track the progress of the job | infrastructure | log out the number of documents processed by the job as a user i want to title so that i can track the progress of the job | 1 |
178,412 | 21,509,390,954 | IssuesEvent | 2022-04-28 01:35:59 | bharathirajatut/vulnerable-node | https://api.github.com/repos/bharathirajatut/vulnerable-node | closed | WS-2017-0247 (Low) detected in ms-0.7.1.tgz, ms-0.7.2.tgz - autoclosed | security vulnerability | ## WS-2017-0247 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ms-0.7.1.tgz</b>, <b>ms-0.7.2.tgz</b></p></summary>
<p>
<details><summary><b>ms-0.7.1.tgz</b></p></summary>
<p>Tiny ms conversion utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/ms/-/ms-0.7.1.tgz">https://registry.npmjs.org/ms/-/ms-0.7.1.tgz</a></p>
<p>Path to dependency file: vulnerable-node/package.json</p>
<p>Path to vulnerable library: vulnerable-node/node_modules/ms/package.json</p>
<p>
Dependency Hierarchy:
- debug-2.2.0.tgz (Root Library)
- :x: **ms-0.7.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ms-0.7.2.tgz</b></p></summary>
<p>Tiny milisecond conversion utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/ms/-/ms-0.7.2.tgz">https://registry.npmjs.org/ms/-/ms-0.7.2.tgz</a></p>
<p>Path to dependency file: vulnerable-node/package.json</p>
<p>Path to vulnerable library: vulnerable-node/node_modules/serve-favicon/node_modules/ms/package.json</p>
<p>
Dependency Hierarchy:
- serve-favicon-2.3.2.tgz (Root Library)
- :x: **ms-0.7.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/bharathirajatut/vulnerable-node/commit/51923322f8aee61b74043f78937dc1887d9565d4">51923322f8aee61b74043f78937dc1887d9565d4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).
<p>Publish Date: 2017-04-12
<p>URL: <a href=https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef>WS-2017-0247</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>3.4</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/ms/pull/89">https://github.com/vercel/ms/pull/89</a></p>
<p>Release Date: 2017-04-12</p>
<p>Fix Resolution: 2.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2017-0247 (Low) detected in ms-0.7.1.tgz, ms-0.7.2.tgz - autoclosed - ## WS-2017-0247 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ms-0.7.1.tgz</b>, <b>ms-0.7.2.tgz</b></p></summary>
<p>
<details><summary><b>ms-0.7.1.tgz</b></p></summary>
<p>Tiny ms conversion utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/ms/-/ms-0.7.1.tgz">https://registry.npmjs.org/ms/-/ms-0.7.1.tgz</a></p>
<p>Path to dependency file: vulnerable-node/package.json</p>
<p>Path to vulnerable library: vulnerable-node/node_modules/ms/package.json</p>
<p>
Dependency Hierarchy:
- debug-2.2.0.tgz (Root Library)
- :x: **ms-0.7.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ms-0.7.2.tgz</b></p></summary>
<p>Tiny milisecond conversion utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/ms/-/ms-0.7.2.tgz">https://registry.npmjs.org/ms/-/ms-0.7.2.tgz</a></p>
<p>Path to dependency file: vulnerable-node/package.json</p>
<p>Path to vulnerable library: vulnerable-node/node_modules/serve-favicon/node_modules/ms/package.json</p>
<p>
Dependency Hierarchy:
- serve-favicon-2.3.2.tgz (Root Library)
- :x: **ms-0.7.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/bharathirajatut/vulnerable-node/commit/51923322f8aee61b74043f78937dc1887d9565d4">51923322f8aee61b74043f78937dc1887d9565d4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).
<p>Publish Date: 2017-04-12
<p>URL: <a href=https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef>WS-2017-0247</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>3.4</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/ms/pull/89">https://github.com/vercel/ms/pull/89</a></p>
<p>Release Date: 2017-04-12</p>
<p>Fix Resolution: 2.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | ws low detected in ms tgz ms tgz autoclosed ws low severity vulnerability vulnerable libraries ms tgz ms tgz ms tgz tiny ms conversion utility library home page a href path to dependency file vulnerable node package json path to vulnerable library vulnerable node node modules ms package json dependency hierarchy debug tgz root library x ms tgz vulnerable library ms tgz tiny milisecond conversion utility library home page a href path to dependency file vulnerable node package json path to vulnerable library vulnerable node node modules serve favicon node modules ms package json dependency hierarchy serve favicon tgz root library x ms tgz vulnerable library found in head commit a href found in base branch master vulnerability details affected versions of this package are vulnerable to regular expression denial of service redos publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
74,167 | 7,388,063,955 | IssuesEvent | 2018-03-16 00:17:50 | Azure/azure-iot-sdk-csharp | https://api.github.com/repos/Azure/azure-iot-sdk-csharp | closed | Tracking issues with E2E port to NetStandard | help wanted test bug | Missing items discovered after adding the new E2E test project:
- [x] Azure EventHubs and ServiceBus changed API surface. We need to either port our code to use the new NuGet packages or branch and have 2 different implementations for .Net Framework vs .Net Core.
- [ ] Remove usage of obsolete SDK APIs in favor of the new SDK APIs.
To get started, search for TODOs with this issue# in them within our code base.
| 1.0 | Tracking issues with E2E port to NetStandard - Missing items discovered after adding the new E2E test project:
- [x] Azure EventHubs and ServiceBus changed API surface. We need to either port our code to use the new NuGet packages or branch and have 2 different implementations for .Net Framework vs .Net Core.
- [ ] Remove usage of obsolete SDK APIs in favor of the new SDK APIs.
To get started, search for TODOs with this issue# in them within our code base.
| non_infrastructure | tracking issues with port to netstandard missing items discovered after adding the new test project azure eventhubs and servicebus changed api surface we need to either port our code to use the new nuget packages or branch and have different implementations for net framework vs net core remove usage of obsolete sdk apis in favor of the new sdk apis to get started search for todos with this issue in them within our code base | 0 |
180,542 | 21,625,787,619 | IssuesEvent | 2022-05-05 01:49:28 | eldorplus/docker-web-ui | https://api.github.com/repos/eldorplus/docker-web-ui | opened | CVE-2022-27777 (Medium) detected in actionview-5.0.0.gem | security vulnerability | ## CVE-2022-27777 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-5.0.0.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-5.0.0.gem">https://rubygems.org/gems/actionview-5.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/actionview-5.0.0.gem</p>
<p>
Dependency Hierarchy:
- coffee-rails-4.2.1.gem (Root Library)
- railties-5.0.0.gem
- actionpack-5.0.0.gem
- :x: **actionview-5.0.0.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a possible XSS vulnerability in Action View tag helpers. Passing
untrusted input as hash keys can lead to a possible XSS vulnerability.
Fixed Versions: 7.0.2.4, 6.1.5.1, 6.0.4.8, 5.2.7.1
<p>Publish Date: 2022-03-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27777>CVE-2022-27777</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-ch3h-j2vf-95pv">https://github.com/advisories/GHSA-ch3h-j2vf-95pv</a></p>
<p>Release Date: 2022-03-24</p>
<p>Fix Resolution: actionview - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-27777 (Medium) detected in actionview-5.0.0.gem - ## CVE-2022-27777 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-5.0.0.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-5.0.0.gem">https://rubygems.org/gems/actionview-5.0.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.3.0/cache/actionview-5.0.0.gem</p>
<p>
Dependency Hierarchy:
- coffee-rails-4.2.1.gem (Root Library)
- railties-5.0.0.gem
- actionpack-5.0.0.gem
- :x: **actionview-5.0.0.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a possible XSS vulnerability in Action View tag helpers. Passing
untrusted input as hash keys can lead to a possible XSS vulnerability.
Fixed Versions: 7.0.2.4, 6.1.5.1, 6.0.4.8, 5.2.7.1
<p>Publish Date: 2022-03-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27777>CVE-2022-27777</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-ch3h-j2vf-95pv">https://github.com/advisories/GHSA-ch3h-j2vf-95pv</a></p>
<p>Release Date: 2022-03-24</p>
<p>Fix Resolution: actionview - 5.2.7.1,6.0.4.8,6.1.5.1,7.0.2.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in actionview gem cve medium severity vulnerability vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href path to dependency file gemfile lock path to vulnerable library var lib gems cache actionview gem dependency hierarchy coffee rails gem root library railties gem actionpack gem x actionview gem vulnerable library vulnerability details there is a possible xss vulnerability in action view tag helpers passing untrusted input as hash keys can lead to a possible xss vulnerability fixed versions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionview step up your open source security game with whitesource | 0 |
6,569 | 6,516,540,330 | IssuesEvent | 2017-08-27 10:44:00 | ColinDuquesnoy/MellowPlayer | https://api.github.com/repos/ColinDuquesnoy/MellowPlayer | opened | Use openSUSE Build Service to provide distribution specific packages | infrastructure linux packaging | Since AppImage won't work for all services (see #106), it would be wise to create distribution specific packages. openSUSE Build Service looks like a good candidate for automating package creation for supported distributions.
**A GNU/Linux distribution is supported if it provides Qt >= 5.9 .**
Supported distributions:
- OpenSuse Tumbleweed
- OpenSuse Leap
- Debian SID
- Archlinux (there is already an AUR package)
- KaOS (the distribution provides a working version out of the box).
Distributions that will be supported in the future:
- Ubuntu 17.10
Distributions to investigate:
- Fedora 25
- Gentoo
- Slackware
Let us know if you know your distribution supports Qt >= 5.9 and is not included in the above list.
| 1.0 | Use openSUSE Build Service to provide distribution specific packages - Since AppImage won't work for all services (see #106), it would be wise to create distribution specific packages. openSUSE Build Service looks like a good candidate for automating package creation for supported distributions.
**A GNU/Linux distribution is supported if it provides Qt >= 5.9 .**
Supported distributions:
- OpenSuse Tumbleweed
- OpenSuse Leap
- Debian SID
- Archlinux (there is already an AUR package)
- KaOS (the distribution provides a working version out of the box).
Distributions that will be supported in the future:
- Ubuntu 17.10
Distributions to investigate:
- Fedora 25
- Gentoo
- Slackware
Let us know if you know your distribution supports Qt >= 5.9 and is not included in the above list.
| infrastructure | use opensuse build service to provide distribution specific packages since appimage won t work for all services see it would be wise to create distribution specific packages opensuse build service looks like a good candidate for automating package creation for supported distributions a gnu linux distribution is supported if it provides qt supported distributions opensuse tumbleweed opensuse leap debian sid archlinux there is already an aur package kaos the distribution provides a working version out of the box distributions that will be supported in the future ubuntu distributions to investigate fedora gentoo slackware let us know if you know your distribution supports qt and is not included in the above list | 1 |
22,925 | 15,680,497,324 | IssuesEvent | 2021-03-25 03:01:43 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Mircosoft.apnetcore.Identity v2.2 package not run in core 5 | :heavy_check_mark: Resolution: Answered area-infrastructure | <!--
More information on our issue management policies can be found here: https://aka.ms/aspnet/issue-policies
Please keep in mind that the GitHub issue tracker is not intended as a general support forum, but for reporting **non-security** bugs and feature requests.
If you believe you have an issue that affects the SECURITY of the platform, please do NOT create an issue and instead email your issue details to secure@microsoft.com. Your report may be eligible for our [bug bounty](https://www.microsoft.com/en-us/msrc/bounty-dot-net-core) but ONLY if it is reported through email.
For other types of questions, consider using [StackOverflow](https://stackoverflow.com).
-->
### Describe the bug
A clear and concise description of what the bug is.
### To Reproduce
<!--
We ❤ code! Point us to a minimalistic repro project hosted in a GitHub repo.
For a repro project, create a new ASP.NET Core project using the template of your your choice, apply the minimum required code to result in the issue you're observing.
We will close this issue if:
- the repro project you share with us is complex. We can't investigate custom projects, so don't point us to such, please.
- if we will not be able to repro the behavior you're reporting
-->
### Exceptions (if any)
<!--
Include the exception you get when facing this issue
-->
### Further technical details
- ASP.NET Core version
- Include the output of `dotnet --info`
- The IDE (VS / VS Code/ VS4Mac) you're running on, and its version
| 1.0 | Mircosoft.apnetcore.Identity v2.2 package not run in core 5 - <!--
More information on our issue management policies can be found here: https://aka.ms/aspnet/issue-policies
Please keep in mind that the GitHub issue tracker is not intended as a general support forum, but for reporting **non-security** bugs and feature requests.
If you believe you have an issue that affects the SECURITY of the platform, please do NOT create an issue and instead email your issue details to secure@microsoft.com. Your report may be eligible for our [bug bounty](https://www.microsoft.com/en-us/msrc/bounty-dot-net-core) but ONLY if it is reported through email.
For other types of questions, consider using [StackOverflow](https://stackoverflow.com).
-->
### Describe the bug
A clear and concise description of what the bug is.
### To Reproduce
<!--
We ❤ code! Point us to a minimalistic repro project hosted in a GitHub repo.
For a repro project, create a new ASP.NET Core project using the template of your your choice, apply the minimum required code to result in the issue you're observing.
We will close this issue if:
- the repro project you share with us is complex. We can't investigate custom projects, so don't point us to such, please.
- if we will not be able to repro the behavior you're reporting
-->
### Exceptions (if any)
<!--
Include the exception you get when facing this issue
-->
### Further technical details
- ASP.NET Core version
- Include the output of `dotnet --info`
- The IDE (VS / VS Code/ VS4Mac) you're running on, and its version
| infrastructure | mircosoft apnetcore identity package not run in core more information on our issue management policies can be found here please keep in mind that the github issue tracker is not intended as a general support forum but for reporting non security bugs and feature requests if you believe you have an issue that affects the security of the platform please do not create an issue and instead email your issue details to secure microsoft com your report may be eligible for our but only if it is reported through email for other types of questions consider using describe the bug a clear and concise description of what the bug is to reproduce we ❤ code point us to a minimalistic repro project hosted in a github repo for a repro project create a new asp net core project using the template of your your choice apply the minimum required code to result in the issue you re observing we will close this issue if the repro project you share with us is complex we can t investigate custom projects so don t point us to such please if we will not be able to repro the behavior you re reporting exceptions if any include the exception you get when facing this issue further technical details asp net core version include the output of dotnet info the ide vs vs code you re running on and its version | 1 |
288,801 | 31,930,903,636 | IssuesEvent | 2023-09-19 07:21:07 | Trinadh465/linux-4.1.15_CVE-2023-4128 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2023-4128 | opened | CVE-2023-0047 (Medium) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2023-0047 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2023-4128/commit/0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8">0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/oom_kill.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/oom_kill.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
CVE-2023-0047 kernel: Out of memory in local cgroup's memory may cause denial of service outside its area
<p>Publish Date: 2023-01-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0047>CVE-2023-0047</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-0047">https://www.linuxkernelcves.com/cves/CVE-2023-0047</a></p>
<p>Release Date: 2023-01-04</p>
<p>Fix Resolution: v4.9.291,v4.14.256,v4.19.218,v5.4.160,v5.10.80,v5.14.19,v5.15.3,v5.16-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-0047 (Medium) detected in linuxlinux-4.6 - ## CVE-2023-0047 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2023-4128/commit/0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8">0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/oom_kill.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/oom_kill.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
CVE-2023-0047 kernel: Out of memory in local cgroup's memory may cause denial of service outside its area
<p>Publish Date: 2023-01-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0047>CVE-2023-0047</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-0047">https://www.linuxkernelcves.com/cves/CVE-2023-0047</a></p>
<p>Release Date: 2023-01-04</p>
<p>Fix Resolution: v4.9.291,v4.14.256,v4.19.218,v5.4.160,v5.10.80,v5.14.19,v5.15.3,v5.16-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files mm oom kill c mm oom kill c vulnerability details cve kernel out of memory in local cgroup s memory may cause denial of service outside its area publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
10,498 | 8,589,329,660 | IssuesEvent | 2018-11-14 16:11:58 | flathub/flathub | https://api.github.com/repos/flathub/flathub | reopened | Move CDN log endpoint to separate machine | infrastructure | Currently the Fastly CDN logs are streamed to an rsyslog instance running on the front.flathub.org VM. This is running on the hub.flathub.org machine that's getting overloaded. The logs should be streamed to a separate machine. A packet host at stats.flathub.org has been setup for this purpose. | 1.0 | Move CDN log endpoint to separate machine - Currently the Fastly CDN logs are streamed to an rsyslog instance running on the front.flathub.org VM. This is running on the hub.flathub.org machine that's getting overloaded. The logs should be streamed to a separate machine. A packet host at stats.flathub.org has been setup for this purpose. | infrastructure | move cdn log endpoint to separate machine currently the fastly cdn logs are streamed to an rsyslog instance running on the front flathub org vm this is running on the hub flathub org machine that s getting overloaded the logs should be streamed to a separate machine a packet host at stats flathub org has been setup for this purpose | 1 |
149,986 | 13,306,930,269 | IssuesEvent | 2020-08-25 21:08:07 | fga-eps-mds/2020-1-Grupo-4 | https://api.github.com/repos/fga-eps-mds/2020-1-Grupo-4 | closed | Visualizar trabalhos de grupos anteriores | documentation good first issue organization study | **Descrição**
Analisar padrão de trabalho de semestres anteriores.
**Sugestão de grupos**
- Acacia;
- Ada;
- Dulce;
- Dr-Down.
**Tarefas**
- Os integrantes usarem projetos de sucesso como exemplo para documentação e desenvolvimento do nosso projeto.
**Critério de Aceitação:
- [x] Introduzir aos integrantes que, projetos anteriores, são uma excelente fonte de pesquisa no desenrolar do nosso projeto. | 1.0 | Visualizar trabalhos de grupos anteriores - **Descrição**
Analisar padrão de trabalho de semestres anteriores.
**Sugestão de grupos**
- Acacia;
- Ada;
- Dulce;
- Dr-Down.
**Tarefas**
- Os integrantes usarem projetos de sucesso como exemplo para documentação e desenvolvimento do nosso projeto.
**Critério de Aceitação:
- [x] Introduzir aos integrantes que, projetos anteriores, são uma excelente fonte de pesquisa no desenrolar do nosso projeto. | non_infrastructure | visualizar trabalhos de grupos anteriores descrição analisar padrão de trabalho de semestres anteriores sugestão de grupos acacia ada dulce dr down tarefas os integrantes usarem projetos de sucesso como exemplo para documentação e desenvolvimento do nosso projeto critério de aceitação introduzir aos integrantes que projetos anteriores são uma excelente fonte de pesquisa no desenrolar do nosso projeto | 0 |
181,797 | 30,743,868,395 | IssuesEvent | 2023-07-28 13:37:01 | mui/mui-x | https://api.github.com/repos/mui/mui-x | closed | [pickers] Integral support for for reduced motion | accessibility component: pickers design: ux | ### Duplicates
- [X] I have searched the existing issues
### Latest version
- [X] I have tested the latest version
### Steps to reproduce 🕹
Link to live example: https://mui.com/x/react-date-pickers/getting-started/
Steps:
1. Make sure reduced motion is enabled on your OS or browser.
2. Open the date picker and move the month around
### Current behavior 😯
I see animation, and become disoriented. People with more severe motion sensitivity may experience headaches and/or nausia.
### Expected behavior 🤔
No animation when `prefers-reduced-motion` is set.
### Context 🔦
I think this is basic accessibility, and our project needs to meet certain accessibility standards.
We could workaround it, but I feel if a library provides animations pretty much hardcoded, it's on them to deal with disabling them when the browser/OS requests to do so.
### Your environment 🌎
Not applicable
### Order ID or Support key 💳 (optional)
_No response_ | 1.0 | [pickers] Integral support for for reduced motion - ### Duplicates
- [X] I have searched the existing issues
### Latest version
- [X] I have tested the latest version
### Steps to reproduce 🕹
Link to live example: https://mui.com/x/react-date-pickers/getting-started/
Steps:
1. Make sure reduced motion is enabled on your OS or browser.
2. Open the date picker and move the month around
### Current behavior 😯
I see animation, and become disoriented. People with more severe motion sensitivity may experience headaches and/or nausia.
### Expected behavior 🤔
No animation when `prefers-reduced-motion` is set.
### Context 🔦
I think this is basic accessibility, and our project needs to meet certain accessibility standards.
We could workaround it, but I feel if a library provides animations pretty much hardcoded, it's on them to deal with disabling them when the browser/OS requests to do so.
### Your environment 🌎
Not applicable
### Order ID or Support key 💳 (optional)
_No response_ | non_infrastructure | integral support for for reduced motion duplicates i have searched the existing issues latest version i have tested the latest version steps to reproduce 🕹 link to live example steps make sure reduced motion is enabled on your os or browser open the date picker and move the month around current behavior 😯 i see animation and become disoriented people with more severe motion sensitivity may experience headaches and or nausia expected behavior 🤔 no animation when prefers reduced motion is set context 🔦 i think this is basic accessibility and our project needs to meet certain accessibility standards we could workaround it but i feel if a library provides animations pretty much hardcoded it s on them to deal with disabling them when the browser os requests to do so your environment 🌎 not applicable order id or support key 💳 optional no response | 0 |
12,530 | 9,814,774,184 | IssuesEvent | 2019-06-13 11:00:13 | spring-cloud/spring-cloud-dataflow-acceptance-tests | https://api.github.com/repos/spring-cloud/spring-cloud-dataflow-acceptance-tests | closed | Add redis exclude flag to support SCDF 2.x | infrastructure | Since redis based metric repository is no longer used, we need to add a flag to exclude redis configuration when setting up the SCDF server in acceptance tests. | 1.0 | Add redis exclude flag to support SCDF 2.x - Since redis based metric repository is no longer used, we need to add a flag to exclude redis configuration when setting up the SCDF server in acceptance tests. | infrastructure | add redis exclude flag to support scdf x since redis based metric repository is no longer used we need to add a flag to exclude redis configuration when setting up the scdf server in acceptance tests | 1 |
703,361 | 24,155,257,143 | IssuesEvent | 2022-09-22 07:05:02 | mizdra/happy-css-modules | https://api.github.com/repos/mizdra/happy-css-modules | closed | Ignore http/https imports | Type: Feature Priority: High | It seems that http/https import cannot be resolved and may result in an error.
https://github.com/mizdra/happy-css-modules/blob/a14cc666690e7e94279c81552be3fb516b30801c/src/transformer/less-transformer.test.ts#L125
| 1.0 | Ignore http/https imports - It seems that http/https import cannot be resolved and may result in an error.
https://github.com/mizdra/happy-css-modules/blob/a14cc666690e7e94279c81552be3fb516b30801c/src/transformer/less-transformer.test.ts#L125
| non_infrastructure | ignore http https imports it seems that http https import cannot be resolved and may result in an error | 0 |
21,119 | 16,567,042,260 | IssuesEvent | 2021-05-29 16:27:13 | lethal-guitar/RigelEngine | https://api.github.com/repos/lethal-guitar/RigelEngine | closed | Deal with stereo/mono | usability | All of the game's original audio assets are in mono, but replacement music is likely to be in stereo. This means we should request stereo when opening the audio device, but that would also mean that we always need to convert sounds/AdLib music, even if all other audio parameters match. That might be a little wasteful in case no replacement assets are used - should test on Raspberry Pi Zero to see the impact.
Could also add a `--mono-audio` cli option.. | True | Deal with stereo/mono - All of the game's original audio assets are in mono, but replacement music is likely to be in stereo. This means we should request stereo when opening the audio device, but that would also mean that we always need to convert sounds/AdLib music, even if all other audio parameters match. That might be a little wasteful in case no replacement assets are used - should test on Raspberry Pi Zero to see the impact.
Could also add a `--mono-audio` cli option.. | non_infrastructure | deal with stereo mono all of the game s original audio assets are in mono but replacement music is likely to be in stereo this means we should request stereo when opening the audio device but that would also mean that we always need to convert sounds adlib music even if all other audio parameters match that might be a little wasteful in case no replacement assets are used should test on raspberry pi zero to see the impact could also add a mono audio cli option | 0 |
263,352 | 8,288,358,591 | IssuesEvent | 2018-09-19 11:45:29 | ArweaveTeam/arweave | https://api.github.com/repos/ArweaveTeam/arweave | closed | Infrequent POST /block errors | Priority: Normal Status: Done Type: Bug | Tests showed infrequent errors when posting blocks:
```
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: =ERROR REPORT==== 13-Sep-2018::06:22:59 ===
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: Error in process <0.32711.1> with exit value:
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {function_clause,[{lists,last,[undefined],[{file,"lists.erl"},{line,228}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {ar_block,'-generate_block_from_shadow/2-fun-2-',2,
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: [{file,"src/ar_block.erl"},{line,498}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {lists,dropwhile,2,[{file,"lists.erl"},{line,1396}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {ar_block,generate_block_from_shadow,2,
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: [{file,"src/ar_block.erl"},{line,497}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {ar_http_iface,'-handle/3-fun-1-',4,
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: [{file,"src/ar_http_iface.erl"},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {line,230}]}]}
``` | 1.0 | Infrequent POST /block errors - Tests showed infrequent errors when posting blocks:
```
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: =ERROR REPORT==== 13-Sep-2018::06:22:59 ===
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: Error in process <0.32711.1> with exit value:
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {function_clause,[{lists,last,[undefined],[{file,"lists.erl"},{line,228}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {ar_block,'-generate_block_from_shadow/2-fun-2-',2,
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: [{file,"src/ar_block.erl"},{line,498}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {lists,dropwhile,2,[{file,"lists.erl"},{line,1396}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {ar_block,generate_block_from_shadow,2,
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: [{file,"src/ar_block.erl"},{line,497}]},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {ar_http_iface,'-handle/3-fun-1-',4,
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: [{file,"src/ar_http_iface.erl"},
Sep 13 08:22:59 aws-oregon-1 session_2018-09-12_16-27-13.log: {line,230}]}]}
``` | non_infrastructure | infrequent post block errors tests showed infrequent errors when posting blocks sep aws oregon session log error report sep sep aws oregon session log error in process with exit value sep aws oregon session log function clause sep aws oregon session log ar block generate block from shadow fun sep aws oregon session log sep aws oregon session log lists dropwhile sep aws oregon session log ar block generate block from shadow sep aws oregon session log sep aws oregon session log ar http iface handle fun sep aws oregon session log file src ar http iface erl sep aws oregon session log line | 0 |
87,176 | 10,534,116,892 | IssuesEvent | 2019-10-01 14:16:38 | Requisitos-de-Software/2019.2-Shazam | https://api.github.com/repos/Requisitos-de-Software/2019.2-Shazam | closed | Subir e atualizar versão do documento de priorização MoSCoW no gh-pages | documentation priorization | Subir o documento para o repositório e versionar com a alteração, data da realização e responsáveis. | 1.0 | Subir e atualizar versão do documento de priorização MoSCoW no gh-pages - Subir o documento para o repositório e versionar com a alteração, data da realização e responsáveis. | non_infrastructure | subir e atualizar versão do documento de priorização moscow no gh pages subir o documento para o repositório e versionar com a alteração data da realização e responsáveis | 0 |
22,548 | 15,266,046,075 | IssuesEvent | 2021-02-22 08:16:31 | epfl-si/xaas-admin | https://api.github.com/repos/epfl-si/xaas-admin | opened | Check Service Manager existence | Infrastructure | Certains services manager peuvent au bout d'un moment quitter l'EPFL donc il faudrait :
- [ ] gérer ceci en le notifiant aux admins du service VSISSP
- [ ] Update l'admin du groupe dans https://groups.epfl.ch s'il change | 1.0 | Check Service Manager existence - Certains services manager peuvent au bout d'un moment quitter l'EPFL donc il faudrait :
- [ ] gérer ceci en le notifiant aux admins du service VSISSP
- [ ] Update l'admin du groupe dans https://groups.epfl.ch s'il change | infrastructure | check service manager existence certains services manager peuvent au bout d un moment quitter l epfl donc il faudrait gérer ceci en le notifiant aux admins du service vsissp update l admin du groupe dans s il change | 1 |
5,851 | 6,010,080,928 | IssuesEvent | 2017-06-06 12:20:24 | wellcometrust/platform-api | https://api.github.com/repos/wellcometrust/platform-api | closed | Transformer is spamming the SQS queue | bug infrastructure | We keep seeing the transformer stop with the single word “Killed” in the CloudWatch logs.
I suspect [memory use is to blame](http://docs.aws.amazon.com/AmazonECS/latest/developerguide/task_definition_parameters.html):
> If your container attempts to exceed the memory specified here, the container is killed.
The effect is to stuff the ID minter queue repeatedly (1.7m items and counting), because every time it restarts it picks up the whole table. This is probably bad. | 1.0 | Transformer is spamming the SQS queue - We keep seeing the transformer stop with the single word “Killed” in the CloudWatch logs.
I suspect [memory use is to blame](http://docs.aws.amazon.com/AmazonECS/latest/developerguide/task_definition_parameters.html):
> If your container attempts to exceed the memory specified here, the container is killed.
The effect is to stuff the ID minter queue repeatedly (1.7m items and counting), because every time it restarts it picks up the whole table. This is probably bad. | infrastructure | transformer is spamming the sqs queue we keep seeing the transformer stop with the single word “killed” in the cloudwatch logs i suspect if your container attempts to exceed the memory specified here the container is killed the effect is to stuff the id minter queue repeatedly items and counting because every time it restarts it picks up the whole table this is probably bad | 1 |
6,935 | 6,667,839,853 | IssuesEvent | 2017-10-03 13:59:07 | twosigma/beakerx | https://api.github.com/repos/twosigma/beakerx | closed | two copies of custom.css | Bug Infrastructure | see https://github.com/twosigma/beakerx/pull/6047/files
i think the one in static is the real one, should delete the other. | 1.0 | two copies of custom.css - see https://github.com/twosigma/beakerx/pull/6047/files
i think the one in static is the real one, should delete the other. | infrastructure | two copies of custom css see i think the one in static is the real one should delete the other | 1 |
136,132 | 18,722,341,651 | IssuesEvent | 2021-11-03 13:11:39 | KDWSS/dd-trace-java | https://api.github.com/repos/KDWSS/dd-trace-java | opened | CVE-2011-2894 (Medium) detected in spring-core-3.0.5.RELEASE.jar, spring-context-3.0.5.RELEASE.jar | security vulnerability | ## CVE-2011-2894 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-core-3.0.5.RELEASE.jar</b>, <b>spring-context-3.0.5.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-core-3.0.5.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-core/3.0.5.RELEASE/1633e94943d57746ef76910489f1cd71fe667e04/spring-core-3.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-1.1.0.RELEASE.jar (Root Library)
- spring-amqp-1.1.0.RELEASE.jar
- :x: **spring-core-3.0.5.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-context-3.0.5.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-context/3.0.5.RELEASE/6b05e397566cc7750d2d25f81a7441fe1aeecb75/spring-context-3.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-1.1.0.RELEASE.jar (Root Library)
- spring-tx-3.0.5.RELEASE.jar
- :x: **spring-context-3.0.5.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework 3.0.0 through 3.0.5, Spring Security 3.0.0 through 3.0.5 and 2.0.0 through 2.0.6, and possibly other versions deserialize objects from untrusted sources, which allows remote attackers to bypass intended security restrictions and execute untrusted code by (1) serializing a java.lang.Proxy instance and using InvocationHandler, or (2) accessing internal AOP interfaces, as demonstrated using deserialization of a DefaultListableBeanFactory instance to execute arbitrary commands via the java.lang.Runtime class.
<p>Publish Date: 2011-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2894>CVE-2011-2894</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-2894">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-2894</a></p>
<p>Release Date: 2011-10-04</p>
<p>Fix Resolution: org.springframework.security:spring-security-core:2.0.7.RELEASE,3.0.5.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-core","packageVersion":"3.0.5.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.amqp:spring-rabbit:1.1.0.RELEASE;org.springframework.amqp:spring-amqp:1.1.0.RELEASE;org.springframework:spring-core:3.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.security:spring-security-core:2.0.7.RELEASE,3.0.5.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-context","packageVersion":"3.0.5.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.amqp:spring-rabbit:1.1.0.RELEASE;org.springframework:spring-tx:3.0.5.RELEASE;org.springframework:spring-context:3.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.security:spring-security-core:2.0.7.RELEASE,3.0.5.RELEASE"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2011-2894","vulnerabilityDetails":"Spring Framework 3.0.0 through 3.0.5, Spring Security 3.0.0 through 3.0.5 and 2.0.0 through 2.0.6, and possibly other versions deserialize objects from untrusted sources, which allows remote attackers to bypass intended security restrictions and execute untrusted code by (1) serializing a java.lang.Proxy instance and using InvocationHandler, or (2) accessing internal AOP interfaces, as demonstrated using deserialization of a DefaultListableBeanFactory instance to execute arbitrary commands via the java.lang.Runtime class.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2894","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | True | CVE-2011-2894 (Medium) detected in spring-core-3.0.5.RELEASE.jar, spring-context-3.0.5.RELEASE.jar - ## CVE-2011-2894 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-core-3.0.5.RELEASE.jar</b>, <b>spring-context-3.0.5.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-core-3.0.5.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-core/3.0.5.RELEASE/1633e94943d57746ef76910489f1cd71fe667e04/spring-core-3.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-1.1.0.RELEASE.jar (Root Library)
- spring-amqp-1.1.0.RELEASE.jar
- :x: **spring-core-3.0.5.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-context-3.0.5.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-context/3.0.5.RELEASE/6b05e397566cc7750d2d25f81a7441fe1aeecb75/spring-context-3.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-1.1.0.RELEASE.jar (Root Library)
- spring-tx-3.0.5.RELEASE.jar
- :x: **spring-context-3.0.5.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework 3.0.0 through 3.0.5, Spring Security 3.0.0 through 3.0.5 and 2.0.0 through 2.0.6, and possibly other versions deserialize objects from untrusted sources, which allows remote attackers to bypass intended security restrictions and execute untrusted code by (1) serializing a java.lang.Proxy instance and using InvocationHandler, or (2) accessing internal AOP interfaces, as demonstrated using deserialization of a DefaultListableBeanFactory instance to execute arbitrary commands via the java.lang.Runtime class.
<p>Publish Date: 2011-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2894>CVE-2011-2894</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-2894">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-2894</a></p>
<p>Release Date: 2011-10-04</p>
<p>Fix Resolution: org.springframework.security:spring-security-core:2.0.7.RELEASE,3.0.5.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-core","packageVersion":"3.0.5.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.amqp:spring-rabbit:1.1.0.RELEASE;org.springframework.amqp:spring-amqp:1.1.0.RELEASE;org.springframework:spring-core:3.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.security:spring-security-core:2.0.7.RELEASE,3.0.5.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-context","packageVersion":"3.0.5.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/rabbitmq-amqp-2.7/rabbitmq-amqp-2.7.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.amqp:spring-rabbit:1.1.0.RELEASE;org.springframework:spring-tx:3.0.5.RELEASE;org.springframework:spring-context:3.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.security:spring-security-core:2.0.7.RELEASE,3.0.5.RELEASE"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2011-2894","vulnerabilityDetails":"Spring Framework 3.0.0 through 3.0.5, Spring Security 3.0.0 through 3.0.5 and 2.0.0 through 2.0.6, and possibly other versions deserialize objects from untrusted sources, which allows remote attackers to bypass intended security restrictions and execute untrusted code by (1) serializing a java.lang.Proxy instance and using InvocationHandler, or (2) accessing internal AOP interfaces, as demonstrated using deserialization of a DefaultListableBeanFactory instance to execute arbitrary commands via the java.lang.Runtime class.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2894","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | non_infrastructure | cve medium detected in spring core release jar spring context release jar cve medium severity vulnerability vulnerable libraries spring core release jar spring context release jar spring core release jar spring framework parent path to dependency file dd trace java dd java agent instrumentation rabbitmq amqp rabbitmq amqp gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring core release spring core release jar dependency hierarchy spring rabbit release jar root library spring amqp release jar x spring core release jar vulnerable library spring context release jar spring framework parent path to dependency file dd trace java dd java agent instrumentation rabbitmq amqp rabbitmq amqp gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring context release spring context release jar dependency hierarchy spring rabbit release jar root library spring tx release jar x spring context release jar vulnerable library found in head commit a href found in base branch master vulnerability details spring framework through spring security through and through and possibly other versions deserialize objects from untrusted sources which allows remote attackers to bypass intended security restrictions and execute untrusted code by serializing a java lang proxy instance and using invocationhandler or accessing internal aop interfaces as demonstrated using deserialization of a defaultlistablebeanfactory instance to execute arbitrary commands via the java lang runtime class publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security core release release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework amqp spring rabbit release org springframework amqp spring amqp release org springframework spring core release isminimumfixversionavailable true minimumfixversion org springframework security spring security core release release packagetype java groupid org springframework packagename spring context packageversion release packagefilepaths istransitivedependency true dependencytree org springframework amqp spring rabbit release org springframework spring tx release org springframework spring context release isminimumfixversionavailable true minimumfixversion org springframework security spring security core release release basebranches vulnerabilityidentifier cve vulnerabilitydetails spring framework through spring security through and through and possibly other versions deserialize objects from untrusted sources which allows remote attackers to bypass intended security restrictions and execute untrusted code by serializing a java lang proxy instance and using invocationhandler or accessing internal aop interfaces as demonstrated using deserialization of a defaultlistablebeanfactory instance to execute arbitrary commands via the java lang runtime class vulnerabilityurl | 0 |
20,182 | 13,749,118,342 | IssuesEvent | 2020-10-06 10:00:55 | blockframes/blockframes | https://api.github.com/repos/blockframes/blockframes | closed | Update `onFileDelete` backend function | Infrastructure Low priority TODO | Currently the `onFileDelete` backend function is made to only process raster images.
If the file is not an image the function just terminate.
In the future we might need to perform some task on deletion for other file type, we should then tape into this function to do the job.
| 1.0 | Update `onFileDelete` backend function - Currently the `onFileDelete` backend function is made to only process raster images.
If the file is not an image the function just terminate.
In the future we might need to perform some task on deletion for other file type, we should then tape into this function to do the job.
| infrastructure | update onfiledelete backend function currently the onfiledelete backend function is made to only process raster images if the file is not an image the function just terminate in the future we might need to perform some task on deletion for other file type we should then tape into this function to do the job | 1 |
33,713 | 27,743,239,195 | IssuesEvent | 2023-03-15 15:30:57 | Tonomy-Foundation/Tonomy-Communication | https://api.github.com/repos/Tonomy-Foundation/Tonomy-Communication | opened | Docker build is failing | infrastructure | Steps to reproduce
`docker buildx build .`
Expected that the doctor container built correctly
What happens is that the doctor container fails on `yarn install`
```
#0 68.29 [2/4] Fetching packages...
#0 87.05 info No lockfile found.
#0 87.08 error An unexpected error occurred: "Failed to replace env in config: ${NPM_TOKEN}".
#0 87.08 info If you think this is a bug, please open a bug report with the information provided in "/app/yarn-error.log".
#0 87.08 info Visit https://yarnpkg.com/en/docs/cli/install for documentation about this command.
``` | 1.0 | Docker build is failing - Steps to reproduce
`docker buildx build .`
Expected that the doctor container built correctly
What happens is that the doctor container fails on `yarn install`
```
#0 68.29 [2/4] Fetching packages...
#0 87.05 info No lockfile found.
#0 87.08 error An unexpected error occurred: "Failed to replace env in config: ${NPM_TOKEN}".
#0 87.08 info If you think this is a bug, please open a bug report with the information provided in "/app/yarn-error.log".
#0 87.08 info Visit https://yarnpkg.com/en/docs/cli/install for documentation about this command.
``` | infrastructure | docker build is failing steps to reproduce docker buildx build expected that the doctor container built correctly what happens is that the doctor container fails on yarn install fetching packages info no lockfile found error an unexpected error occurred failed to replace env in config npm token info if you think this is a bug please open a bug report with the information provided in app yarn error log info visit for documentation about this command | 1 |
57,902 | 7,106,274,040 | IssuesEvent | 2018-01-16 16:08:42 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Down arrow getting displayed for the matching indices doesn't contain any time field message. | :Design :Management bug | **Kibana version**: 7.0.0-alpha1 (master)
**Elasticsearch version**: 7.0.0-alpha1 (master)
**Server OS version**: darwin_x_86_64
**Browser version**: chrome latest
**Browser OS version**: OS X
**Original install method (e.g. download page, yum, from source, etc.)**: from staging
**Description of the problem including expected versus actual behavior**: When you try to create index pattern for indices without timefield - Kibana is correctly displaying the message that they don't contain timefield but with a down arrow.
Just a nit really. Please feel free to ignore if it's intended.
<img width="1280" alt="time_indices_down_arrow" src="https://user-images.githubusercontent.com/7074629/34715639-4b73c0d8-f4fb-11e7-8c9a-944b96d18ef8.png">
| 1.0 | Down arrow getting displayed for the matching indices doesn't contain any time field message. - **Kibana version**: 7.0.0-alpha1 (master)
**Elasticsearch version**: 7.0.0-alpha1 (master)
**Server OS version**: darwin_x_86_64
**Browser version**: chrome latest
**Browser OS version**: OS X
**Original install method (e.g. download page, yum, from source, etc.)**: from staging
**Description of the problem including expected versus actual behavior**: When you try to create index pattern for indices without timefield - Kibana is correctly displaying the message that they don't contain timefield but with a down arrow.
Just a nit really. Please feel free to ignore if it's intended.
<img width="1280" alt="time_indices_down_arrow" src="https://user-images.githubusercontent.com/7074629/34715639-4b73c0d8-f4fb-11e7-8c9a-944b96d18ef8.png">
| non_infrastructure | down arrow getting displayed for the matching indices doesn t contain any time field message kibana version master elasticsearch version master server os version darwin x browser version chrome latest browser os version os x original install method e g download page yum from source etc from staging description of the problem including expected versus actual behavior when you try to create index pattern for indices without timefield kibana is correctly displaying the message that they don t contain timefield but with a down arrow just a nit really please feel free to ignore if it s intended img width alt time indices down arrow src | 0 |
24,166 | 16,985,401,711 | IssuesEvent | 2021-06-30 13:53:34 | pytest-dev/pytest | https://api.github.com/repos/pytest-dev/pytest | closed | Filter [bot] names in release automation | status: easy type: infrastructure | Not related to the release itself, but we should probably remove `[bot]` names here.
_Originally posted by @The-Compiler in https://github.com/pytest-dev/pytest/pull/8814#r660067534_ | 1.0 | Filter [bot] names in release automation - Not related to the release itself, but we should probably remove `[bot]` names here.
_Originally posted by @The-Compiler in https://github.com/pytest-dev/pytest/pull/8814#r660067534_ | infrastructure | filter names in release automation not related to the release itself but we should probably remove names here originally posted by the compiler in | 1 |
606,432 | 18,762,355,860 | IssuesEvent | 2021-11-05 18:03:13 | garden-io/garden | https://api.github.com/repos/garden-io/garden | closed | Garden breaks with kubernetes 1.22 clusters | bug priority:high | ## Bug
### Current Behavior
Any `kubernetes` module, even with simple manifests (such as configmaps or secrets) is not possible to deploy due `Ingress` resources using the old `extensions/v1beta1` (with some values redacted)
```
✖ registries → Deploying version v-61b81356a7...
Failed deploying service 'registries' (from module 'registries'). Here is the output:
━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━
Command "/root/.garden/tools/kubectl/11ac0bbd21058c50/kubectl --context=lumiquote-dev apply --prune --selector service=registries --output=json -f -" failed with code 1:
error: error retrieving RESTMappings to prune: invalid resource extensions/v1beta1, Kind=Ingress, Namespaced=true: no matches for kind "Ingress" in version "extensions/v1beta1"
Here are the last 100 lines of the output:
"encryptedData": {
".dockerconfigjson": "redacted"
},
"template": {
"metadata": {
"annotations": {
"sealedsecrets.bitnami.com/cluster-wide": "true"
},
"creationTimestamp": null,
"name": "gitlab"
},
"type": "kubernetes.io/dockerconfigjson"
}
}
},
{
"apiVersion": "bitnami.com/v1alpha1",
"kind": "SealedSecret",
"metadata": {
"annotations": {
"garden.io/manifest-hash": "90a0ab304a1ee187d2af40c4fc4e63fc2edf60b5fdbd14dd29a58038ede2de6e",
"kubectl.kubernetes.io/last-applied-configuration": "{\"apiVersion\":\"bitnami.com/v1alpha1\",\"kind\":\"SealedSecret\",\"metadata\":{\"annotations\":{\"garden.io/manifest-hash\":\"90a0ab304a1ee187d2af40c4fc4e63fc2edf60b5fdbd14dd29a58038ede2de6e\",\"sealedsecrets.bitnami.com/cluster-wide\":\"true\",\"service\":\"registries\"},\"creationTimestamp\":null,\"labels\":{\"service\":\"registries\"},\"name\":\"azurecr\",\"namespace\":\"ci-123549441-810e4035\"},\"spec\":{\"encryptedData\":{\".dockerconfigjson\":\"redacted\"},\"template\":{\"data\":null,\"metadata\":{\"annotations\":{\"sealedsecrets.bitnami.com/cluster-wide\":\"true\"},\"creationTimestamp\":null,\"name\":\"azurecr\"},\"type\":\"kubernetes.io/dockerconfigjson\"}}}
",
"sealedsecrets.bitnami.com/cluster-wide": "true",
"service": "registries"
},
"creationTimestamp": "2021-10-29T06:39:31Z",
"generation": 1,
"labels": {
"service": "registries"
},
"managedFields": [
{
"apiVersion": "bitnami.com/v1alpha1",
"fieldsType": "FieldsV1",
"fieldsV1": {
"f:metadata": {
"f:annotations": {
".": {},
"f:garden.io/manifest-hash": {},
"f:kubectl.kubernetes.io/last-applied-configuration": {},
"f:sealedsecrets.bitnami.com/cluster-wide": {},
"f:service": {}
},
"f:labels": {
".": {},
"f:service": {}
}
},
"f:spec": {
".": {},
"f:encryptedData": {
".": {},
"f:.dockerconfigjson": {}
},
"f:template": {
".": {},
"f:data": {},
"f:metadata": {
".": {},
"f:annotations": {
".": {},
"f:sealedsecrets.bitnami.com/cluster-wide": {}
},
"f:creationTimestamp": {},
"f:name": {}
},
"f:type": {}
}
}
},
"manager": "kubectl-client-side-apply",
"operation": "Update",
"time": "2021-10-29T06:39:31Z"
}
],
"name": "azurecr",
"namespace": "ci-123549441-810e4035",
"resourceVersion": "200654175",
"uid": "04a38b06-4c2b-4146-b95c-e034022097bc"
},
"spec": {
"encryptedData": {
".dockerconfigjson": "{redacted}"
},
"template": {
"data": null,
"metadata": {
"annotations": {
"sealedsecrets.bitnami.com/cluster-wide": "true"
},
"creationTimestamp": null,
"name": "azurecr"
},
"type": "kubernetes.io/dockerconfigjson"
}
}
}
]
}
error: error retrieving RESTMappings to prune: invalid resource extensions/v1beta1, Kind=Ingress, Namespaced=true: no matches for kind "Ingress" in version "extensions/v1beta1"
```
### Expected behavior
Deploys the thing :)
### Workaround
Stop using garden `kubernetes` modules **and** `container` modules with services. Instead, just stuff everything into your own helm chart. That seems to work. (Garden is still able to build containers with the `container` module).
### Your environment
<!-- PLEASE FILL THIS OUT -->
* **OS:** Linux (gitlab runners)
* **How I'm running Kubernetes:** AKS 1.22.2
<!-- Please run and copy and paste the results -->
`garden version`
0.12.25 and later | 1.0 | Garden breaks with kubernetes 1.22 clusters - ## Bug
### Current Behavior
Any `kubernetes` module, even with simple manifests (such as configmaps or secrets) is not possible to deploy due `Ingress` resources using the old `extensions/v1beta1` (with some values redacted)
```
✖ registries → Deploying version v-61b81356a7...
Failed deploying service 'registries' (from module 'registries'). Here is the output:
━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━
Command "/root/.garden/tools/kubectl/11ac0bbd21058c50/kubectl --context=lumiquote-dev apply --prune --selector service=registries --output=json -f -" failed with code 1:
error: error retrieving RESTMappings to prune: invalid resource extensions/v1beta1, Kind=Ingress, Namespaced=true: no matches for kind "Ingress" in version "extensions/v1beta1"
Here are the last 100 lines of the output:
"encryptedData": {
".dockerconfigjson": "redacted"
},
"template": {
"metadata": {
"annotations": {
"sealedsecrets.bitnami.com/cluster-wide": "true"
},
"creationTimestamp": null,
"name": "gitlab"
},
"type": "kubernetes.io/dockerconfigjson"
}
}
},
{
"apiVersion": "bitnami.com/v1alpha1",
"kind": "SealedSecret",
"metadata": {
"annotations": {
"garden.io/manifest-hash": "90a0ab304a1ee187d2af40c4fc4e63fc2edf60b5fdbd14dd29a58038ede2de6e",
"kubectl.kubernetes.io/last-applied-configuration": "{\"apiVersion\":\"bitnami.com/v1alpha1\",\"kind\":\"SealedSecret\",\"metadata\":{\"annotations\":{\"garden.io/manifest-hash\":\"90a0ab304a1ee187d2af40c4fc4e63fc2edf60b5fdbd14dd29a58038ede2de6e\",\"sealedsecrets.bitnami.com/cluster-wide\":\"true\",\"service\":\"registries\"},\"creationTimestamp\":null,\"labels\":{\"service\":\"registries\"},\"name\":\"azurecr\",\"namespace\":\"ci-123549441-810e4035\"},\"spec\":{\"encryptedData\":{\".dockerconfigjson\":\"redacted\"},\"template\":{\"data\":null,\"metadata\":{\"annotations\":{\"sealedsecrets.bitnami.com/cluster-wide\":\"true\"},\"creationTimestamp\":null,\"name\":\"azurecr\"},\"type\":\"kubernetes.io/dockerconfigjson\"}}}
",
"sealedsecrets.bitnami.com/cluster-wide": "true",
"service": "registries"
},
"creationTimestamp": "2021-10-29T06:39:31Z",
"generation": 1,
"labels": {
"service": "registries"
},
"managedFields": [
{
"apiVersion": "bitnami.com/v1alpha1",
"fieldsType": "FieldsV1",
"fieldsV1": {
"f:metadata": {
"f:annotations": {
".": {},
"f:garden.io/manifest-hash": {},
"f:kubectl.kubernetes.io/last-applied-configuration": {},
"f:sealedsecrets.bitnami.com/cluster-wide": {},
"f:service": {}
},
"f:labels": {
".": {},
"f:service": {}
}
},
"f:spec": {
".": {},
"f:encryptedData": {
".": {},
"f:.dockerconfigjson": {}
},
"f:template": {
".": {},
"f:data": {},
"f:metadata": {
".": {},
"f:annotations": {
".": {},
"f:sealedsecrets.bitnami.com/cluster-wide": {}
},
"f:creationTimestamp": {},
"f:name": {}
},
"f:type": {}
}
}
},
"manager": "kubectl-client-side-apply",
"operation": "Update",
"time": "2021-10-29T06:39:31Z"
}
],
"name": "azurecr",
"namespace": "ci-123549441-810e4035",
"resourceVersion": "200654175",
"uid": "04a38b06-4c2b-4146-b95c-e034022097bc"
},
"spec": {
"encryptedData": {
".dockerconfigjson": "{redacted}"
},
"template": {
"data": null,
"metadata": {
"annotations": {
"sealedsecrets.bitnami.com/cluster-wide": "true"
},
"creationTimestamp": null,
"name": "azurecr"
},
"type": "kubernetes.io/dockerconfigjson"
}
}
}
]
}
error: error retrieving RESTMappings to prune: invalid resource extensions/v1beta1, Kind=Ingress, Namespaced=true: no matches for kind "Ingress" in version "extensions/v1beta1"
```
### Expected behavior
Deploys the thing :)
### Workaround
Stop using garden `kubernetes` modules **and** `container` modules with services. Instead, just stuff everything into your own helm chart. That seems to work. (Garden is still able to build containers with the `container` module).
### Your environment
<!-- PLEASE FILL THIS OUT -->
* **OS:** Linux (gitlab runners)
* **How I'm running Kubernetes:** AKS 1.22.2
<!-- Please run and copy and paste the results -->
`garden version`
0.12.25 and later | non_infrastructure | garden breaks with kubernetes clusters bug current behavior any kubernetes module even with simple manifests such as configmaps or secrets is not possible to deploy due ingress resources using the old extensions with some values redacted ✖ registries → deploying version v failed deploying service registries from module registries here is the output ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ command root garden tools kubectl kubectl context lumiquote dev apply prune selector service registries output json f failed with code error error retrieving restmappings to prune invalid resource extensions kind ingress namespaced true no matches for kind ingress in version extensions here are the last lines of the output encrypteddata dockerconfigjson redacted template metadata annotations sealedsecrets bitnami com cluster wide true creationtimestamp null name gitlab type kubernetes io dockerconfigjson apiversion bitnami com kind sealedsecret metadata annotations garden io manifest hash kubectl kubernetes io last applied configuration apiversion bitnami com kind sealedsecret metadata annotations garden io manifest hash sealedsecrets bitnami com cluster wide true service registries creationtimestamp null labels service registries name azurecr namespace ci spec encrypteddata dockerconfigjson redacted template data null metadata annotations sealedsecrets bitnami com cluster wide true creationtimestamp null name azurecr type kubernetes io dockerconfigjson sealedsecrets bitnami com cluster wide true service registries creationtimestamp generation labels service registries managedfields apiversion bitnami com fieldstype f metadata f annotations f garden io manifest hash f kubectl kubernetes io last applied configuration f sealedsecrets bitnami com cluster wide f service f labels f service f spec f encrypteddata f dockerconfigjson f template f data f metadata f annotations f sealedsecrets bitnami com cluster wide f creationtimestamp f name f type manager kubectl client side apply operation update time name azurecr namespace ci resourceversion uid spec encrypteddata dockerconfigjson redacted template data null metadata annotations sealedsecrets bitnami com cluster wide true creationtimestamp null name azurecr type kubernetes io dockerconfigjson error error retrieving restmappings to prune invalid resource extensions kind ingress namespaced true no matches for kind ingress in version extensions expected behavior deploys the thing workaround stop using garden kubernetes modules and container modules with services instead just stuff everything into your own helm chart that seems to work garden is still able to build containers with the container module your environment os linux gitlab runners how i m running kubernetes aks garden version and later | 0 |
27,314 | 21,606,788,300 | IssuesEvent | 2022-05-04 04:54:04 | jamandujanoa/WASA | https://api.github.com/repos/jamandujanoa/WASA | opened | Ensure all Azure environments that connect to your production environment apply your organization policy and IT governance controls for security | WARP-Import WAF-Assessment Security Health Modeling & Monitoring Resource and Infrastructure Level Monitoring | <a href="https://docs.microsoft.com/azure/security/fundamentals/identity-management-best-practices#manage-connected-tenants">Ensure all Azure environments that connect to your production environment apply your organization policy and IT governance controls for security</a>
<p><b>Why Consider This?</b></p>
Does your security team have visibility of all existing subscriptions and cloud environments? How do they discover new ones? Ensure the security organization is aware of all enrollments/subscriptions connected to the existing environment and is able to monitor those resources as part of your overall enterprise security posture.
<p><b>Context</b></p>
<p><span>The security team should have access to all Azure or connected enterprise assets to aid in risk assessment and to assure regulatory requirements are being followed.</span></p><p><span>The organizations cloud infrastructure should be well documented, with security team access to all resources required for monitoring and insight. Frequent scans of the cloud connected assets should be performed to ensure no additional subscriptions or tenants have been added outside of organizational controls. Guidance provided by Microsoft should be regularly reviewed to ensure any best practice guidance related to security team access is reviewed and followed.</span></p>
<p><b>Suggested Actions</b></p>
<p><span>Ensure all Azure environments that connect to your production environment apply your organization policy and IT governance controls for security</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/security/fundamentals/identity-management-best-practices#manage-connected-tenants" target="_blank"><span>Manage connected tenants</span></a><span /></p> | 1.0 | Ensure all Azure environments that connect to your production environment apply your organization policy and IT governance controls for security - <a href="https://docs.microsoft.com/azure/security/fundamentals/identity-management-best-practices#manage-connected-tenants">Ensure all Azure environments that connect to your production environment apply your organization policy and IT governance controls for security</a>
<p><b>Why Consider This?</b></p>
Does your security team have visibility of all existing subscriptions and cloud environments? How do they discover new ones? Ensure the security organization is aware of all enrollments/subscriptions connected to the existing environment and is able to monitor those resources as part of your overall enterprise security posture.
<p><b>Context</b></p>
<p><span>The security team should have access to all Azure or connected enterprise assets to aid in risk assessment and to assure regulatory requirements are being followed.</span></p><p><span>The organizations cloud infrastructure should be well documented, with security team access to all resources required for monitoring and insight. Frequent scans of the cloud connected assets should be performed to ensure no additional subscriptions or tenants have been added outside of organizational controls. Guidance provided by Microsoft should be regularly reviewed to ensure any best practice guidance related to security team access is reviewed and followed.</span></p>
<p><b>Suggested Actions</b></p>
<p><span>Ensure all Azure environments that connect to your production environment apply your organization policy and IT governance controls for security</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/security/fundamentals/identity-management-best-practices#manage-connected-tenants" target="_blank"><span>Manage connected tenants</span></a><span /></p> | infrastructure | ensure all azure environments that connect to your production environment apply your organization policy and it governance controls for security why consider this does your security team have visibility of all existing subscriptions and cloud environments how do they discover new ones ensure the security organization is aware of all enrollments subscriptions connected to the existing environment and is able to monitor those resources as part of your overall enterprise security posture context the security team should have access to all azure or connected enterprise assets to aid in risk assessment and to assure regulatory requirements are being followed the organizations cloud infrastructure should be well documented with security team access to all resources required for monitoring and insight frequent scans of the cloud connected assets should be performed to ensure no additional subscriptions or tenants have been added outside of organizational controls guidance provided by microsoft should be regularly reviewed to ensure any best practice guidance related to security team access is reviewed and followed suggested actions ensure all azure environments that connect to your production environment apply your organization policy and it governance controls for security learn more manage connected tenants | 1 |
15,285 | 11,448,613,233 | IssuesEvent | 2020-02-06 04:07:47 | battlecode/battlecode20 | https://api.github.com/repos/battlecode/battlecode20 | opened | Some resumes aren't in bucket, tho db claims the users have uploaded | backend critical frontend infrastructure | Smells like a similar issue we had with compilation...
(in particular these are user ids 2708, 2916, 2953, 3282, 3284) | 1.0 | Some resumes aren't in bucket, tho db claims the users have uploaded - Smells like a similar issue we had with compilation...
(in particular these are user ids 2708, 2916, 2953, 3282, 3284) | infrastructure | some resumes aren t in bucket tho db claims the users have uploaded smells like a similar issue we had with compilation in particular these are user ids | 1 |
146,474 | 23,073,157,033 | IssuesEvent | 2022-07-25 20:11:17 | lexml/lexml-eta | https://api.github.com/repos/lexml/lexml-eta | closed | Verificar possibilidade de uso da fonte Gentium Basic para textos da emenda | design | Se possível, utilizar a fonte Gentium Basic (mesma utilizada na impressão do PDF) para os textos serifados.
https://www.1001fonts.com/gentium-basic-font.html
Caso não seja possível, trocar para a Times New Roman. | 1.0 | Verificar possibilidade de uso da fonte Gentium Basic para textos da emenda - Se possível, utilizar a fonte Gentium Basic (mesma utilizada na impressão do PDF) para os textos serifados.
https://www.1001fonts.com/gentium-basic-font.html
Caso não seja possível, trocar para a Times New Roman. | non_infrastructure | verificar possibilidade de uso da fonte gentium basic para textos da emenda se possível utilizar a fonte gentium basic mesma utilizada na impressão do pdf para os textos serifados caso não seja possível trocar para a times new roman | 0 |
139,585 | 12,875,761,068 | IssuesEvent | 2020-07-11 00:35:50 | ethereum/web3.js | https://api.github.com/repos/ethereum/web3.js | closed | Create some sort of document for typing | 2.x Stale documentation types | I was thinking that we should create some sort of document so that contributors can update typing modules as per said instructions. This will save much time when reviewing any PR.
As, When to use `any` and If some type got used in many places then, it should be added to web3-core.
Also, someone should not create any unnecessary dependency, when updating typings.
We can add this in contributors sections.
What do you say @joshstevens19 and @nivida? | 1.0 | Create some sort of document for typing - I was thinking that we should create some sort of document so that contributors can update typing modules as per said instructions. This will save much time when reviewing any PR.
As, When to use `any` and If some type got used in many places then, it should be added to web3-core.
Also, someone should not create any unnecessary dependency, when updating typings.
We can add this in contributors sections.
What do you say @joshstevens19 and @nivida? | non_infrastructure | create some sort of document for typing i was thinking that we should create some sort of document so that contributors can update typing modules as per said instructions this will save much time when reviewing any pr as when to use any and if some type got used in many places then it should be added to core also someone should not create any unnecessary dependency when updating typings we can add this in contributors sections what do you say and nivida | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.