Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 2 665 | labels stringlengths 4 554 | body stringlengths 3 235k | index stringclasses 6 values | text_combine stringlengths 96 235k | label stringclasses 2 values | text stringlengths 96 196k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
215,690 | 16,700,293,625 | IssuesEvent | 2021-06-09 00:39:17 | QubesOS/updates-status | https://api.github.com/repos/QubesOS/updates-status | closed | linux-kernel v5.10.38-1 (r4.1) | r4.1-dom0-cur-test | Update of linux-kernel to v5.10.38-1 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-linux-kernel/commit/4c1c649efbbc0ae3fe90c2f500208ff0fef063b7
[Changes since previous version](https://github.com/QubesOS/qubes-linux-kernel/compare/v5.10.21-1...v5.10.38-1):
QubesOS/qubes-linux-kernel@4c1c649 Drop patch included upstream already
QubesOS/qubes-linux-kernel@1562fbb Update to kernel-5.10.38
QubesOS/qubes-linux-kernel@c844830 spec: fix detecting default kernel flavor
QubesOS/qubes-linux-kernel@621760c Clean up Makefile
QubesOS/qubes-linux-kernel@76dcaba Switch from wget to curl
QubesOS/qubes-linux-kernel@0f3fa06 Merge remote-tracking branch 'origin/pr/391' into stable-5.10
QubesOS/qubes-linux-kernel@209c552 Revert two commits breaking watching hotplug-status xenstore node
QubesOS/qubes-linux-kernel@3aa44b1 Update to kernel-5.10.37
QubesOS/qubes-linux-kernel@2eb57e1 version 5.10.35-1
QubesOS/qubes-linux-kernel@b93b6c6 Apply a fix for a crash in gntdev_mmap
QubesOS/qubes-linux-kernel@40b207b Update to kernel-5.10.33
QubesOS/qubes-linux-kernel@d854b16 version 5.10.28-1
QubesOS/qubes-linux-kernel@d8d13ca Merge remote-tracking branch 'origin/pr/374' into stable-5.10
QubesOS/qubes-linux-kernel@cafd0f7 makefile: don't use PACKAGE variable
QubesOS/qubes-linux-kernel@db693fb Update to kernel-5.10.27
QubesOS/qubes-linux-kernel@2c3a361 Re-enable EFI pstore backend
QubesOS/qubes-linux-kernel@465f0fa Update to kernel-5.10.25
Referenced issues:
QubesOS/qubes-issues#6397
If you're release manager, you can issue GPG-inline signed command:
* `Upload linux-kernel 4c1c649efbbc0ae3fe90c2f500208ff0fef063b7 r4.1 current repo` (available 7 days from now)
* `Upload linux-kernel 4c1c649efbbc0ae3fe90c2f500208ff0fef063b7 r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload linux-kernel 4c1c649efbbc0ae3fe90c2f500208ff0fef063b7 r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| 1.0 | linux-kernel v5.10.38-1 (r4.1) - Update of linux-kernel to v5.10.38-1 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-linux-kernel/commit/4c1c649efbbc0ae3fe90c2f500208ff0fef063b7
[Changes since previous version](https://github.com/QubesOS/qubes-linux-kernel/compare/v5.10.21-1...v5.10.38-1):
QubesOS/qubes-linux-kernel@4c1c649 Drop patch included upstream already
QubesOS/qubes-linux-kernel@1562fbb Update to kernel-5.10.38
QubesOS/qubes-linux-kernel@c844830 spec: fix detecting default kernel flavor
QubesOS/qubes-linux-kernel@621760c Clean up Makefile
QubesOS/qubes-linux-kernel@76dcaba Switch from wget to curl
QubesOS/qubes-linux-kernel@0f3fa06 Merge remote-tracking branch 'origin/pr/391' into stable-5.10
QubesOS/qubes-linux-kernel@209c552 Revert two commits breaking watching hotplug-status xenstore node
QubesOS/qubes-linux-kernel@3aa44b1 Update to kernel-5.10.37
QubesOS/qubes-linux-kernel@2eb57e1 version 5.10.35-1
QubesOS/qubes-linux-kernel@b93b6c6 Apply a fix for a crash in gntdev_mmap
QubesOS/qubes-linux-kernel@40b207b Update to kernel-5.10.33
QubesOS/qubes-linux-kernel@d854b16 version 5.10.28-1
QubesOS/qubes-linux-kernel@d8d13ca Merge remote-tracking branch 'origin/pr/374' into stable-5.10
QubesOS/qubes-linux-kernel@cafd0f7 makefile: don't use PACKAGE variable
QubesOS/qubes-linux-kernel@db693fb Update to kernel-5.10.27
QubesOS/qubes-linux-kernel@2c3a361 Re-enable EFI pstore backend
QubesOS/qubes-linux-kernel@465f0fa Update to kernel-5.10.25
Referenced issues:
QubesOS/qubes-issues#6397
If you're release manager, you can issue GPG-inline signed command:
* `Upload linux-kernel 4c1c649efbbc0ae3fe90c2f500208ff0fef063b7 r4.1 current repo` (available 7 days from now)
* `Upload linux-kernel 4c1c649efbbc0ae3fe90c2f500208ff0fef063b7 r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload linux-kernel 4c1c649efbbc0ae3fe90c2f500208ff0fef063b7 r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| non_infrastructure | linux kernel update of linux kernel to for qubes see comments below for details built from qubesos qubes linux kernel drop patch included upstream already qubesos qubes linux kernel update to kernel qubesos qubes linux kernel spec fix detecting default kernel flavor qubesos qubes linux kernel clean up makefile qubesos qubes linux kernel switch from wget to curl qubesos qubes linux kernel merge remote tracking branch origin pr into stable qubesos qubes linux kernel revert two commits breaking watching hotplug status xenstore node qubesos qubes linux kernel update to kernel qubesos qubes linux kernel version qubesos qubes linux kernel apply a fix for a crash in gntdev mmap qubesos qubes linux kernel update to kernel qubesos qubes linux kernel version qubesos qubes linux kernel merge remote tracking branch origin pr into stable qubesos qubes linux kernel makefile don t use package variable qubesos qubes linux kernel update to kernel qubesos qubes linux kernel re enable efi pstore backend qubesos qubes linux kernel update to kernel referenced issues qubesos qubes issues if you re release manager you can issue gpg inline signed command upload linux kernel current repo available days from now upload linux kernel current dists repo you can choose subset of distributions like vm vm available days from now upload linux kernel security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it | 0 |
380,644 | 26,427,222,033 | IssuesEvent | 2023-01-14 10:36:15 | unikraft/docs | https://api.github.com/repos/unikraft/docs | closed | Add documentation on contributing to documentation | documentation | The [`Contributing` section](https://unikraft.org/docs/contributing/) (in [`contributing/` directory](https://github.com/unikraft/docs/tree/main/content/en/docs/contributing) in the repository) doesn't have a section detailing how to contribute to this `docs/` repository:
- How can the documentation be build locally?
- What are the guidelines for adding / improving documentation? What are the Markdown rules (as enforced by the [`super-linter` workflow configuration rules](https://github.com/unikraft/docs/tree/main/.github/workflows)?
- How to format a commit? | 1.0 | Add documentation on contributing to documentation - The [`Contributing` section](https://unikraft.org/docs/contributing/) (in [`contributing/` directory](https://github.com/unikraft/docs/tree/main/content/en/docs/contributing) in the repository) doesn't have a section detailing how to contribute to this `docs/` repository:
- How can the documentation be build locally?
- What are the guidelines for adding / improving documentation? What are the Markdown rules (as enforced by the [`super-linter` workflow configuration rules](https://github.com/unikraft/docs/tree/main/.github/workflows)?
- How to format a commit? | non_infrastructure | add documentation on contributing to documentation the in in the repository doesn t have a section detailing how to contribute to this docs repository how can the documentation be build locally what are the guidelines for adding improving documentation what are the markdown rules as enforced by the how to format a commit | 0 |
30,820 | 25,096,460,716 | IssuesEvent | 2022-11-08 10:29:55 | RasaHQ/rasa | https://api.github.com/repos/RasaHQ/rasa | closed | Add full integration tests to CI | type:maintenance :wrench: area:rasa-oss :ferris_wheel: area:rasa-oss/infrastructure :bullettrain_front: priority:high effort:atom-squad/4 | **Description of Problem**: We currently don't have full end-to-end tests for Rasa Open Source which tests the whole setup of
* receiving a message
* respond to the message
* integration with action server
* forwarding messages via the `EventBroker`
* storing any conversation events in the `TrackerStore`
**Overview of the Solution**: The integration tests should ideally be as close as possible to a Rasa X production setup, which means using
* Postgres as `TrackerStore`
* a `RedisLockStore` as lockstore
* `RabbitMQ` as `EventBroker`
**Definition of Done**:
* [ ] Tests are added
* [ ] Tests can be executed locally (or it's described how to do so)
* [ ] Tests are executed as part of the CI | 1.0 | Add full integration tests to CI - **Description of Problem**: We currently don't have full end-to-end tests for Rasa Open Source which tests the whole setup of
* receiving a message
* respond to the message
* integration with action server
* forwarding messages via the `EventBroker`
* storing any conversation events in the `TrackerStore`
**Overview of the Solution**: The integration tests should ideally be as close as possible to a Rasa X production setup, which means using
* Postgres as `TrackerStore`
* a `RedisLockStore` as lockstore
* `RabbitMQ` as `EventBroker`
**Definition of Done**:
* [ ] Tests are added
* [ ] Tests can be executed locally (or it's described how to do so)
* [ ] Tests are executed as part of the CI | infrastructure | add full integration tests to ci description of problem we currently don t have full end to end tests for rasa open source which tests the whole setup of receiving a message respond to the message integration with action server forwarding messages via the eventbroker storing any conversation events in the trackerstore overview of the solution the integration tests should ideally be as close as possible to a rasa x production setup which means using postgres as trackerstore a redislockstore as lockstore rabbitmq as eventbroker definition of done tests are added tests can be executed locally or it s described how to do so tests are executed as part of the ci | 1 |
430,604 | 12,463,691,181 | IssuesEvent | 2020-05-28 11:05:04 | RaenonX/Jelly-Bot | https://api.github.com/repos/RaenonX/Jelly-Bot | closed | Unable to create new channel data | Priority: 9 Tag: Bot Tag: Stats Tag: System Tag: Website Type: Bug | ## Description
As title.
Unable to register the newly joined channel. (Seems so)
Message stats page returned weird stats.
## Expected Behavior
N/A
## Current Status
Not fixed.
## How to reproduce
1. Create a group with a few messages
2. Add the bot into the group
3. Send a few messages
## Origin
N/A
## Notes
May be caused by the name not being stored into the user name cache.
May be caused by no default profile created.
## Solution
Not yet resolved. Fixing commit to be mentioned after this had been fixed.
| 1.0 | Unable to create new channel data - ## Description
As title.
Unable to register the newly joined channel. (Seems so)
Message stats page returned weird stats.
## Expected Behavior
N/A
## Current Status
Not fixed.
## How to reproduce
1. Create a group with a few messages
2. Add the bot into the group
3. Send a few messages
## Origin
N/A
## Notes
May be caused by the name not being stored into the user name cache.
May be caused by no default profile created.
## Solution
Not yet resolved. Fixing commit to be mentioned after this had been fixed.
| non_infrastructure | unable to create new channel data description as title unable to register the newly joined channel seems so message stats page returned weird stats expected behavior n a current status not fixed how to reproduce create a group with a few messages add the bot into the group send a few messages origin n a notes may be caused by the name not being stored into the user name cache may be caused by no default profile created solution not yet resolved fixing commit to be mentioned after this had been fixed | 0 |
31,126 | 25,347,365,330 | IssuesEvent | 2022-11-19 11:04:23 | bounswe/bounswe2022group7 | https://api.github.com/repos/bounswe/bounswe2022group7 | opened | [CI/CD] Fix Android CI not running on Pull Requests | Type: Bug Status: In Progress Difficulty: Easy Target: Infrastructure | Currently our [Android CI](https://github.com/bounswe/bounswe2022group7/actions/workflows/Android-CI.yml) is not running properly on Pull Requests. So to ensure that each change works without major problems/passing tests, I need research the reasoning and fix the implementation of the workflow.
**Deadline: 23.59 2022-11-21**
**Reviewer: ** | 1.0 | [CI/CD] Fix Android CI not running on Pull Requests - Currently our [Android CI](https://github.com/bounswe/bounswe2022group7/actions/workflows/Android-CI.yml) is not running properly on Pull Requests. So to ensure that each change works without major problems/passing tests, I need research the reasoning and fix the implementation of the workflow.
**Deadline: 23.59 2022-11-21**
**Reviewer: ** | infrastructure | fix android ci not running on pull requests currently our is not running properly on pull requests so to ensure that each change works without major problems passing tests i need research the reasoning and fix the implementation of the workflow deadline reviewer | 1 |
23,030 | 15,772,331,851 | IssuesEvent | 2021-03-31 21:39:25 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | linker bump breaks AOTing on iOS and Android when EnableAggressiveTrimming=true | area-Infrastructure disabled-test in pr os-android os-ios | The linker bump in https://github.com/dotnet/runtime/pull/49577 seems to break AOT when EnableAggressiveTrimming=true. This originally was found in `Android.Device_Emulator.Aot.Test`, but also applies to all test projects.
```
Can't find custom attr constructor image: /Users/alexander/dev/runtime/artifacts/bin/Android.Device_Emulator.Aot.Test/net6.0-Debug/android-x64/publish/Microsoft.DotNet.XHarness.TestRunners.Common.dll mtoken: 0x0a000064 due to: Could not load file or assembly 'System.Runtime, Version=4.2.2.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a' or one of its dependencies.
* Assertion at /Users/alexander/dev/runtime/src/mono/mono/metadata/assembly.c:2116, condition `is_ok (error)' not met, function:mono_assembly_load_friends, Could not load file or assembly 'System.Runtime, Version=4.2.2.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a' or one of its dependencies.
```
Disabled the project temporarily. | 1.0 | linker bump breaks AOTing on iOS and Android when EnableAggressiveTrimming=true - The linker bump in https://github.com/dotnet/runtime/pull/49577 seems to break AOT when EnableAggressiveTrimming=true. This originally was found in `Android.Device_Emulator.Aot.Test`, but also applies to all test projects.
```
Can't find custom attr constructor image: /Users/alexander/dev/runtime/artifacts/bin/Android.Device_Emulator.Aot.Test/net6.0-Debug/android-x64/publish/Microsoft.DotNet.XHarness.TestRunners.Common.dll mtoken: 0x0a000064 due to: Could not load file or assembly 'System.Runtime, Version=4.2.2.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a' or one of its dependencies.
* Assertion at /Users/alexander/dev/runtime/src/mono/mono/metadata/assembly.c:2116, condition `is_ok (error)' not met, function:mono_assembly_load_friends, Could not load file or assembly 'System.Runtime, Version=4.2.2.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a' or one of its dependencies.
```
Disabled the project temporarily. | infrastructure | linker bump breaks aoting on ios and android when enableaggressivetrimming true the linker bump in seems to break aot when enableaggressivetrimming true this originally was found in android device emulator aot test but also applies to all test projects can t find custom attr constructor image users alexander dev runtime artifacts bin android device emulator aot test debug android publish microsoft dotnet xharness testrunners common dll mtoken due to could not load file or assembly system runtime version culture neutral publickeytoken or one of its dependencies assertion at users alexander dev runtime src mono mono metadata assembly c condition is ok error not met function mono assembly load friends could not load file or assembly system runtime version culture neutral publickeytoken or one of its dependencies disabled the project temporarily | 1 |
7,611 | 7,018,528,927 | IssuesEvent | 2017-12-21 14:04:57 | hzi-braunschweig/SORMAS-Open | https://api.github.com/repos/hzi-braunschweig/SORMAS-Open | closed | Improve mass data performance of UI [1] | 10239 accepted important Infrastructure sormas-ui | - [x] use index dto for cases list
- [x] use index dto for events list -> check why most events are not shown
- [x] use index dto for tasks list
- [x] refactor index dto for samples list
- [x] refactor index dto for contacts list
- [x] write unit tests for all index dtos
General approach
- [x] add buildCaption method to Dtos (api) with required parameters to build the caption
- [x] use this method for the toString methods (dto and entity)
- [x] add constructor to ReferenceDtos that uses the buildCaption method
- [x] add all requried fields to build the ReferenceDtos to IndexDtos and create them in the constructor
- [x] generate remaining columns (that are too complex) directly inside the generated properties
- [x] IndexDtos should not extend EntityDto, instead add UUID as new parameter | 1.0 | Improve mass data performance of UI [1] - - [x] use index dto for cases list
- [x] use index dto for events list -> check why most events are not shown
- [x] use index dto for tasks list
- [x] refactor index dto for samples list
- [x] refactor index dto for contacts list
- [x] write unit tests for all index dtos
General approach
- [x] add buildCaption method to Dtos (api) with required parameters to build the caption
- [x] use this method for the toString methods (dto and entity)
- [x] add constructor to ReferenceDtos that uses the buildCaption method
- [x] add all requried fields to build the ReferenceDtos to IndexDtos and create them in the constructor
- [x] generate remaining columns (that are too complex) directly inside the generated properties
- [x] IndexDtos should not extend EntityDto, instead add UUID as new parameter | infrastructure | improve mass data performance of ui use index dto for cases list use index dto for events list check why most events are not shown use index dto for tasks list refactor index dto for samples list refactor index dto for contacts list write unit tests for all index dtos general approach add buildcaption method to dtos api with required parameters to build the caption use this method for the tostring methods dto and entity add constructor to referencedtos that uses the buildcaption method add all requried fields to build the referencedtos to indexdtos and create them in the constructor generate remaining columns that are too complex directly inside the generated properties indexdtos should not extend entitydto instead add uuid as new parameter | 1 |
29,893 | 24,374,984,436 | IssuesEvent | 2022-10-03 23:31:29 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | Export of met and soil input data | newfeature interface/infrastructure | For some purposes it would be useful to have an option to export met and soil data in a spreadsheet format, e.g. .csv or .xlsx. Maybe others would also like to export other inputs. We have export options for outputs, but not yet for inputs as far as I can see, apart from as a summary file as text or printed. It would be appreciated if our option for this could be expanded.
| 1.0 | Export of met and soil input data - For some purposes it would be useful to have an option to export met and soil data in a spreadsheet format, e.g. .csv or .xlsx. Maybe others would also like to export other inputs. We have export options for outputs, but not yet for inputs as far as I can see, apart from as a summary file as text or printed. It would be appreciated if our option for this could be expanded.
| infrastructure | export of met and soil input data for some purposes it would be useful to have an option to export met and soil data in a spreadsheet format e g csv or xlsx maybe others would also like to export other inputs we have export options for outputs but not yet for inputs as far as i can see apart from as a summary file as text or printed it would be appreciated if our option for this could be expanded | 1 |
32,126 | 26,457,880,350 | IssuesEvent | 2023-01-16 15:28:20 | Subterfuge-Revived/Remake-Core | https://api.github.com/repos/Subterfuge-Revived/Remake-Core | closed | Convert gRPC server to REST | enhancement infrastructure | ## Enhancement Description
The current gRPC implementation is limiting and cannot be accessed by web browsers. It also requires any other developers who want to interface with the game to understand gRPC.
Remove this massive overhead and turn the server into a REST API instead.
## Solution
Use C# .NET API to turn the server into a REST API instead of a gRPC server.
Implement JWT Authentication, Logging, and implement API Controllers for each of the various services.
I am currently working on this.
| 1.0 | Convert gRPC server to REST - ## Enhancement Description
The current gRPC implementation is limiting and cannot be accessed by web browsers. It also requires any other developers who want to interface with the game to understand gRPC.
Remove this massive overhead and turn the server into a REST API instead.
## Solution
Use C# .NET API to turn the server into a REST API instead of a gRPC server.
Implement JWT Authentication, Logging, and implement API Controllers for each of the various services.
I am currently working on this.
| infrastructure | convert grpc server to rest enhancement description the current grpc implementation is limiting and cannot be accessed by web browsers it also requires any other developers who want to interface with the game to understand grpc remove this massive overhead and turn the server into a rest api instead solution use c net api to turn the server into a rest api instead of a grpc server implement jwt authentication logging and implement api controllers for each of the various services i am currently working on this | 1 |
8,133 | 7,245,253,214 | IssuesEvent | 2018-02-14 17:27:59 | AdguardTeam/AdguardFilters | https://api.github.com/repos/AdguardTeam/AdguardFilters | closed | uBO version of Adguard filters | Infrastructure | Hi @gorhill, as I see you're considering adding AG English filter to uBO stock lists: https://github.com/gorhill/uBlock/issues/2624
We'd like to make some preparations from our side. We have different "versions" of all AG filters for different platforms. For instance, this is the version for Chromium extension -- https://filters.adtidy.org/extension/chromium/filters/2.txt and this is for Android app -- https://filters.adtidy.org/android/filters/2.txt
I suppose it would be better if we prepare a version for uBO specifically, and cover possible incompatibilities there. Something like `/ublock/filters/2.txt`. With the [hints support](https://github.com/AdguardTeam/AdguardFilters/issues/3708#issuecomment-303155314) it'd be quite easy to do.
@gorhill is there anything you see which should be handled right now? Nested `:has` or `:not(:has)` for instance. | 1.0 | uBO version of Adguard filters - Hi @gorhill, as I see you're considering adding AG English filter to uBO stock lists: https://github.com/gorhill/uBlock/issues/2624
We'd like to make some preparations from our side. We have different "versions" of all AG filters for different platforms. For instance, this is the version for Chromium extension -- https://filters.adtidy.org/extension/chromium/filters/2.txt and this is for Android app -- https://filters.adtidy.org/android/filters/2.txt
I suppose it would be better if we prepare a version for uBO specifically, and cover possible incompatibilities there. Something like `/ublock/filters/2.txt`. With the [hints support](https://github.com/AdguardTeam/AdguardFilters/issues/3708#issuecomment-303155314) it'd be quite easy to do.
@gorhill is there anything you see which should be handled right now? Nested `:has` or `:not(:has)` for instance. | infrastructure | ubo version of adguard filters hi gorhill as i see you re considering adding ag english filter to ubo stock lists we d like to make some preparations from our side we have different versions of all ag filters for different platforms for instance this is the version for chromium extension and this is for android app i suppose it would be better if we prepare a version for ubo specifically and cover possible incompatibilities there something like ublock filters txt with the it d be quite easy to do gorhill is there anything you see which should be handled right now nested has or not has for instance | 1 |
13,892 | 4,787,256,395 | IssuesEvent | 2016-10-29 22:05:11 | dsherret/ts-type-info | https://api.github.com/repos/dsherret/ts-type-info | opened | Replace typeChecker.typeToString with own implementation | code improvement | The implementation of `typeChecker.typeToString` keeps changing within typescript's code. It would be better for this library to have it's own type to string so that it's not dependent on whatever the typescript team decides to do. | 1.0 | Replace typeChecker.typeToString with own implementation - The implementation of `typeChecker.typeToString` keeps changing within typescript's code. It would be better for this library to have it's own type to string so that it's not dependent on whatever the typescript team decides to do. | non_infrastructure | replace typechecker typetostring with own implementation the implementation of typechecker typetostring keeps changing within typescript s code it would be better for this library to have it s own type to string so that it s not dependent on whatever the typescript team decides to do | 0 |
32,204 | 26,527,815,860 | IssuesEvent | 2023-01-19 10:07:11 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Can't add Tested tag to active review to satisty Commit-Message-Has-TEST | area-infrastructure | I have an active review that I'm trying to submit. https://dart-review.googlesource.com/c/sdk/+/264640
I created the review by creating a PR and letting copybara create the review (first dart review and didn't know if this was the proper method).
I need to satisfy the Commit-Message-Has-TEST submit requirement, but when I try to add a TEST or Tested: to the gerrit commit message, I get an error
```
Error 403: modifying commit message not permitted
Endpoint: /changes/*~*/message
```
I do have a Tested line on the original PR https://github.com/dart-lang/sdk/pull/50240, but that doesn't seem to be pulled in to gerrit. How do I add a TEST or Tested to the gerrit review? | 1.0 | Can't add Tested tag to active review to satisty Commit-Message-Has-TEST - I have an active review that I'm trying to submit. https://dart-review.googlesource.com/c/sdk/+/264640
I created the review by creating a PR and letting copybara create the review (first dart review and didn't know if this was the proper method).
I need to satisfy the Commit-Message-Has-TEST submit requirement, but when I try to add a TEST or Tested: to the gerrit commit message, I get an error
```
Error 403: modifying commit message not permitted
Endpoint: /changes/*~*/message
```
I do have a Tested line on the original PR https://github.com/dart-lang/sdk/pull/50240, but that doesn't seem to be pulled in to gerrit. How do I add a TEST or Tested to the gerrit review? | infrastructure | can t add tested tag to active review to satisty commit message has test i have an active review that i m trying to submit i created the review by creating a pr and letting copybara create the review first dart review and didn t know if this was the proper method i need to satisfy the commit message has test submit requirement but when i try to add a test or tested to the gerrit commit message i get an error error modifying commit message not permitted endpoint changes message i do have a tested line on the original pr but that doesn t seem to be pulled in to gerrit how do i add a test or tested to the gerrit review | 1 |
3,721 | 4,511,477,594 | IssuesEvent | 2016-09-03 02:38:42 | JMRI/JMRI | https://api.github.com/repos/JMRI/JMRI | closed | Tests timeout on appveyor. | dev/test/publish infrastructure WIP | We are getting a number of test failures due to timeouts on AppVeyor. These failures are most likely caused by a GUI test failing and leaving a modal window or dialog open and being killed when the build timeout is exceeded.
The most likely cause of the GUI failure is the size of the available headless desktops. (Comments on the AppVeyor forums [suggest these default to a very small size](http://help.appveyor.com/discussions/problems/3906-selenium-testing-screen-size) like 480 x 640).
What size should these be made to be? The same as Travis CI? | 1.0 | Tests timeout on appveyor. - We are getting a number of test failures due to timeouts on AppVeyor. These failures are most likely caused by a GUI test failing and leaving a modal window or dialog open and being killed when the build timeout is exceeded.
The most likely cause of the GUI failure is the size of the available headless desktops. (Comments on the AppVeyor forums [suggest these default to a very small size](http://help.appveyor.com/discussions/problems/3906-selenium-testing-screen-size) like 480 x 640).
What size should these be made to be? The same as Travis CI? | infrastructure | tests timeout on appveyor we are getting a number of test failures due to timeouts on appveyor these failures are most likely caused by a gui test failing and leaving a modal window or dialog open and being killed when the build timeout is exceeded the most likely cause of the gui failure is the size of the available headless desktops comments on the appveyor forums like x what size should these be made to be the same as travis ci | 1 |
4,904 | 5,328,705,398 | IssuesEvent | 2017-02-15 12:56:15 | numahealth/Asknuma | https://api.github.com/repos/numahealth/Asknuma | closed | Feedback form ?changing styling of User's Back-end | Amending Infrastructure bug | See the mobile view of the back-end in the messaging console.
The text seems to be out of its wrapper.
<img width="393" alt="screen shot 2017-02-08 at 19 08 05" src="https://cloud.githubusercontent.com/assets/25155149/22752928/2185bffe-ee32-11e6-8aa9-92ce244c363f.png">
Is the feedback icon causing this?
| 1.0 | Feedback form ?changing styling of User's Back-end - See the mobile view of the back-end in the messaging console.
The text seems to be out of its wrapper.
<img width="393" alt="screen shot 2017-02-08 at 19 08 05" src="https://cloud.githubusercontent.com/assets/25155149/22752928/2185bffe-ee32-11e6-8aa9-92ce244c363f.png">
Is the feedback icon causing this?
| infrastructure | feedback form changing styling of user s back end see the mobile view of the back end in the messaging console the text seems to be out of its wrapper img width alt screen shot at src is the feedback icon causing this | 1 |
62,721 | 6,808,392,113 | IssuesEvent | 2017-11-04 02:03:57 | servo/servo | https://api.github.com/repos/servo/servo | closed | WPT tests runner Python error | A-testing | When I run `./mach test-wpt tests/wpt/web-platform-tests/fetch/http-cache`
I get
```
File "/servo/tests/wpt/grouping_formatter.py", line 108, in suite_start
self.number_of_tests = sum(len(tests) for tests in data["tests"].itervalues())
AttributeError: 'list' object has no attribute 'itervalues'
```
removing the call to `itervalues` at https://github.com/servo/servo/blob/e13f5a656af682add10cdc41fb8e625c04b60347/tests/wpt/grouping_formatter.py#L108 fixed it for me locally. Seems like the data is now a list, and not a dict?
Is this worth a PR or I am just getting something wrong in my local setup? | 1.0 | WPT tests runner Python error - When I run `./mach test-wpt tests/wpt/web-platform-tests/fetch/http-cache`
I get
```
File "/servo/tests/wpt/grouping_formatter.py", line 108, in suite_start
self.number_of_tests = sum(len(tests) for tests in data["tests"].itervalues())
AttributeError: 'list' object has no attribute 'itervalues'
```
removing the call to `itervalues` at https://github.com/servo/servo/blob/e13f5a656af682add10cdc41fb8e625c04b60347/tests/wpt/grouping_formatter.py#L108 fixed it for me locally. Seems like the data is now a list, and not a dict?
Is this worth a PR or I am just getting something wrong in my local setup? | non_infrastructure | wpt tests runner python error when i run mach test wpt tests wpt web platform tests fetch http cache i get file servo tests wpt grouping formatter py line in suite start self number of tests sum len tests for tests in data itervalues attributeerror list object has no attribute itervalues removing the call to itervalues at fixed it for me locally seems like the data is now a list and not a dict is this worth a pr or i am just getting something wrong in my local setup | 0 |
16,082 | 11,824,945,760 | IssuesEvent | 2020-03-21 09:54:08 | mchrapek/studia-projekt-zespolowy-backend | https://api.github.com/repos/mchrapek/studia-projekt-zespolowy-backend | closed | Dodanie serwisu z katalogiem wycieczek | core function infrastructure | [Kryteria akceptacji]
Dodanie serwisu obsługującego katalog wycieczek.
Rejestracja serwisu w gateway. | 1.0 | Dodanie serwisu z katalogiem wycieczek - [Kryteria akceptacji]
Dodanie serwisu obsługującego katalog wycieczek.
Rejestracja serwisu w gateway. | infrastructure | dodanie serwisu z katalogiem wycieczek dodanie serwisu obsługującego katalog wycieczek rejestracja serwisu w gateway | 1 |
698,733 | 23,990,832,690 | IssuesEvent | 2022-09-14 00:49:09 | MathMarEcol/WSMPA2 | https://api.github.com/repos/MathMarEcol/WSMPA2 | closed | Paragraphs describing example scenarios | NPI - TODO High Priority | Gary to provide some descriptive paragraphs of the 4 example scenarios for the help tab | 1.0 | Paragraphs describing example scenarios - Gary to provide some descriptive paragraphs of the 4 example scenarios for the help tab | non_infrastructure | paragraphs describing example scenarios gary to provide some descriptive paragraphs of the example scenarios for the help tab | 0 |
48,150 | 13,067,479,726 | IssuesEvent | 2020-07-31 00:35:27 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | [WaveCalibrator] SLC FADC clipping level is off by one (Trac #1863) | Migrated from Trac combo core defect | The each element of the SLC charge stamp is packed into 9 bits, dropping the LSB if the peak is greater than 512. This makes the charge stamps for high-amplitude SLC hits even by construction, which means that they clip at 1022 instead of 1023. Credit goes to @mzhu and @mrongen for finding this:
https://icecube-spno.slack.com/archives/software/p1475242504000696
WaveCalibrator should mark these bins as clipped so that they can be properly ignored in downstream reconstructions
Migrated from https://code.icecube.wisc.edu/ticket/1863
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:24",
"description": "The each element of the SLC charge stamp is packed into 9 bits, dropping the LSB if the peak is greater than 512. This makes the charge stamps for high-amplitude SLC hits even by construction, which means that they clip at 1022 instead of 1023. Credit goes to @mzhu and @mrongen for finding this:\n\nhttps://icecube-spno.slack.com/archives/software/p1475242504000696\n\nWaveCalibrator should mark these bins as clipped so that they can be properly ignored in downstream reconstructions",
"reporter": "jvansanten",
"cc": "",
"resolution": "fixed",
"_ts": "1550067204154158",
"component": "combo core",
"summary": "[WaveCalibrator] SLC FADC clipping level is off by one",
"priority": "critical",
"keywords": "",
"time": "2016-09-30T14:50:57",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
| 1.0 | [WaveCalibrator] SLC FADC clipping level is off by one (Trac #1863) - The each element of the SLC charge stamp is packed into 9 bits, dropping the LSB if the peak is greater than 512. This makes the charge stamps for high-amplitude SLC hits even by construction, which means that they clip at 1022 instead of 1023. Credit goes to @mzhu and @mrongen for finding this:
https://icecube-spno.slack.com/archives/software/p1475242504000696
WaveCalibrator should mark these bins as clipped so that they can be properly ignored in downstream reconstructions
Migrated from https://code.icecube.wisc.edu/ticket/1863
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:24",
"description": "The each element of the SLC charge stamp is packed into 9 bits, dropping the LSB if the peak is greater than 512. This makes the charge stamps for high-amplitude SLC hits even by construction, which means that they clip at 1022 instead of 1023. Credit goes to @mzhu and @mrongen for finding this:\n\nhttps://icecube-spno.slack.com/archives/software/p1475242504000696\n\nWaveCalibrator should mark these bins as clipped so that they can be properly ignored in downstream reconstructions",
"reporter": "jvansanten",
"cc": "",
"resolution": "fixed",
"_ts": "1550067204154158",
"component": "combo core",
"summary": "[WaveCalibrator] SLC FADC clipping level is off by one",
"priority": "critical",
"keywords": "",
"time": "2016-09-30T14:50:57",
"milestone": "",
"owner": "jvansanten",
"type": "defect"
}
```
| non_infrastructure | slc fadc clipping level is off by one trac the each element of the slc charge stamp is packed into bits dropping the lsb if the peak is greater than this makes the charge stamps for high amplitude slc hits even by construction which means that they clip at instead of credit goes to mzhu and mrongen for finding this wavecalibrator should mark these bins as clipped so that they can be properly ignored in downstream reconstructions migrated from json status closed changetime description the each element of the slc charge stamp is packed into bits dropping the lsb if the peak is greater than this makes the charge stamps for high amplitude slc hits even by construction which means that they clip at instead of credit goes to mzhu and mrongen for finding this n n should mark these bins as clipped so that they can be properly ignored in downstream reconstructions reporter jvansanten cc resolution fixed ts component combo core summary slc fadc clipping level is off by one priority critical keywords time milestone owner jvansanten type defect | 0 |
55,506 | 7,997,874,551 | IssuesEvent | 2018-07-21 02:18:57 | gravitational/teleport | https://api.github.com/repos/gravitational/teleport | opened | Document diag-addr and some key endpoints | documentation | ## Description
It is worth documenting our diag-addr endpoint as it's used in Kubernetes deployments and prometheus endpoint is used in production to check health of components:
New readyz endpoint is added to existing
/metrics and /healthz endpoints activated by
diag addr-flag:
`teleport start --diag-addr=127.0.0.1:1234`
Readyz endpoint will report 503 if node or
proxy failed to connect to the cluster and 200 OK
otherwise.
Additional prometheus gagues report connection
count for trusted and remote clusters:
```
remote_clusters{cluster="one"} 1
remote_clusters{cluster="two"} 1
trusted_clusters{cluster="one",state="connected"} 0
trusted_clusters{cluster="one",state="connecting"} 0
trusted_clusters{cluster="one",state="disconnected"} 0
trusted_clusters{cluster="one",state="discovered"} 1
trusted_clusters{cluster="one",state="discovering"} 0
``` | 1.0 | Document diag-addr and some key endpoints - ## Description
It is worth documenting our diag-addr endpoint as it's used in Kubernetes deployments and prometheus endpoint is used in production to check health of components:
New readyz endpoint is added to existing
/metrics and /healthz endpoints activated by
diag addr-flag:
`teleport start --diag-addr=127.0.0.1:1234`
Readyz endpoint will report 503 if node or
proxy failed to connect to the cluster and 200 OK
otherwise.
Additional prometheus gagues report connection
count for trusted and remote clusters:
```
remote_clusters{cluster="one"} 1
remote_clusters{cluster="two"} 1
trusted_clusters{cluster="one",state="connected"} 0
trusted_clusters{cluster="one",state="connecting"} 0
trusted_clusters{cluster="one",state="disconnected"} 0
trusted_clusters{cluster="one",state="discovered"} 1
trusted_clusters{cluster="one",state="discovering"} 0
``` | non_infrastructure | document diag addr and some key endpoints description it is worth documenting our diag addr endpoint as it s used in kubernetes deployments and prometheus endpoint is used in production to check health of components new readyz endpoint is added to existing metrics and healthz endpoints activated by diag addr flag teleport start diag addr readyz endpoint will report if node or proxy failed to connect to the cluster and ok otherwise additional prometheus gagues report connection count for trusted and remote clusters remote clusters cluster one remote clusters cluster two trusted clusters cluster one state connected trusted clusters cluster one state connecting trusted clusters cluster one state disconnected trusted clusters cluster one state discovered trusted clusters cluster one state discovering | 0 |
15,070 | 11,339,569,774 | IssuesEvent | 2020-01-23 02:32:53 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Switch to MIT license | Area-Infrastructure | I suggest that Roslyn's license should be changed to a MIT license. This would [alleviate legal problems for developers](https://github.com/dotnet/fsharp/issues/1727) and be consistent with the rest of .NET Core. | 1.0 | Switch to MIT license - I suggest that Roslyn's license should be changed to a MIT license. This would [alleviate legal problems for developers](https://github.com/dotnet/fsharp/issues/1727) and be consistent with the rest of .NET Core. | infrastructure | switch to mit license i suggest that roslyn s license should be changed to a mit license this would and be consistent with the rest of net core | 1 |
78,482 | 22,286,270,082 | IssuesEvent | 2022-06-11 17:24:21 | apache/jena | https://api.github.com/repos/apache/jena | opened | Delivery Fuseki UI as a jar file | Fuseki UI build | Currently (4.5.0) the Fuseki UI is built in `jena-fuseki-ui` then pulled into `jena-fuseki-webapp`.
This issue is to change to delivering the UI in the `jena-fuseki-ui` artifact jar file. The change is a step towards having the UI available in Fuseki Main.
This is issue is not changing the way the UI is delivered to `apache-jena-fuseki`, where is the `webapp` directory, and delivered to `jena-fuseki-war`.
| 1.0 | Delivery Fuseki UI as a jar file - Currently (4.5.0) the Fuseki UI is built in `jena-fuseki-ui` then pulled into `jena-fuseki-webapp`.
This issue is to change to delivering the UI in the `jena-fuseki-ui` artifact jar file. The change is a step towards having the UI available in Fuseki Main.
This is issue is not changing the way the UI is delivered to `apache-jena-fuseki`, where is the `webapp` directory, and delivered to `jena-fuseki-war`.
| non_infrastructure | delivery fuseki ui as a jar file currently the fuseki ui is built in jena fuseki ui then pulled into jena fuseki webapp this issue is to change to delivering the ui in the jena fuseki ui artifact jar file the change is a step towards having the ui available in fuseki main this is issue is not changing the way the ui is delivered to apache jena fuseki where is the webapp directory and delivered to jena fuseki war | 0 |
20,452 | 6,041,080,163 | IssuesEvent | 2017-06-10 20:32:30 | HopefulLlama/UnitTestSCAD | https://api.github.com/repos/HopefulLlama/UnitTestSCAD | closed | Fix "no-return-assign" issue in src/tester/Assertions.js | codeclimate technical | Return statement should not contain assignment.
https://codeclimate.com/github/HopefulLlama/UnitTestSCAD/src/tester/Assertions.js#issue_593b221e9711610001000034 | 1.0 | Fix "no-return-assign" issue in src/tester/Assertions.js - Return statement should not contain assignment.
https://codeclimate.com/github/HopefulLlama/UnitTestSCAD/src/tester/Assertions.js#issue_593b221e9711610001000034 | non_infrastructure | fix no return assign issue in src tester assertions js return statement should not contain assignment | 0 |
184,219 | 14,281,549,077 | IssuesEvent | 2020-11-23 08:15:03 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | netbox.openconfig_interfaces fails: '<' not supported between instances of 'dict' and 'dict' | Aluminium Bug Needs Testcase Severity: Medium | ### Description of Issue/Question
In my setup netbox.get_interfaces works. Now I tried netbox.openconfig_interfaces. This fails with:
Passed invalid arguments to netbox.openconfig_interfaces: '<' not supported between instances of 'dict' and 'dict'
### Setup
Plain setup of salt-2019.2.0-rc2, netbox with python 3.6
### Steps to Reproduce Issue
salt -l debug nms3 netbox.openconfig_interfaces device_name='switch03'
(...)
[DEBUG ] return event: {'nms3': {'ret': "Passed invalid arguments to netbox.openconfig_interfaces: '<' not supported between instances of 'dict' and 'dict' .. versionadded:: 2019.2.0\n\n Return a dictionary structured as standardised in the\n `openconfig-interfaces <http://ops.openconfig.net/branches/master/openconfig-interfaces.html>`_\n YANG model, containing physical and configuration data available in Netbox,\n e.g., IP addresses, MTU, enabled / disabled, etc.\n\n device_name: ``None``\n The name of the device to query the interface data for. If not provided,\n will use the Minion ID.\n\n CLI Example:\n\n .. code-block:: bash\n\n salt '*' netbox.openconfig_interfaces\n salt '*' netbox.openconfig_interfaces device_name=cr1.thn.lon\n ", 'out': 'nested', 'retcode': 1, 'jid': '20190225154145768780'}}
[DEBUG ] LazyLoaded nested.output
nms3:
Passed invalid arguments to netbox.openconfig_interfaces: '<' not supported between instances of 'dict' and 'dict'
(...)
### Versions Report
Salt Version:
Salt: 2019.2.0rc2
Dependency Versions:
cffi: 1.12.1
cherrypy: Not Installed
dateutil: 2.6.1
docker-py: Not Installed
gitdb: 2.0.3
gitpython: 2.1.8
ioflo: Not Installed
Jinja2: 2.10
libgit2: Not Installed
libnacl: Not Installed
M2Crypto: Not Installed
Mako: Not Installed
msgpack-pure: Not Installed
msgpack-python: 0.5.6
mysql-python: Not Installed
pycparser: 2.19
pycrypto: 3.7.2
pycryptodome: Not Installed
pygit2: Not Installed
Python: 3.6.7 (default, Oct 22 2018, 11:32:17)
python-gnupg: 0.4.1
PyYAML: 3.12
PyZMQ: 16.0.2
RAET: Not Installed
smmap: 2.0.3
timelib: Not Installed
Tornado: 4.5.3
ZMQ: 4.2.5
System Versions:
dist: Ubuntu 18.04 bionic
locale: UTF-8
machine: x86_64
release: 4.15.0-45-generic
system: Linux
version: Ubuntu 18.04 bionic | 1.0 | netbox.openconfig_interfaces fails: '<' not supported between instances of 'dict' and 'dict' - ### Description of Issue/Question
In my setup netbox.get_interfaces works. Now I tried netbox.openconfig_interfaces. This fails with:
Passed invalid arguments to netbox.openconfig_interfaces: '<' not supported between instances of 'dict' and 'dict'
### Setup
Plain setup of salt-2019.2.0-rc2, netbox with python 3.6
### Steps to Reproduce Issue
salt -l debug nms3 netbox.openconfig_interfaces device_name='switch03'
(...)
[DEBUG ] return event: {'nms3': {'ret': "Passed invalid arguments to netbox.openconfig_interfaces: '<' not supported between instances of 'dict' and 'dict' .. versionadded:: 2019.2.0\n\n Return a dictionary structured as standardised in the\n `openconfig-interfaces <http://ops.openconfig.net/branches/master/openconfig-interfaces.html>`_\n YANG model, containing physical and configuration data available in Netbox,\n e.g., IP addresses, MTU, enabled / disabled, etc.\n\n device_name: ``None``\n The name of the device to query the interface data for. If not provided,\n will use the Minion ID.\n\n CLI Example:\n\n .. code-block:: bash\n\n salt '*' netbox.openconfig_interfaces\n salt '*' netbox.openconfig_interfaces device_name=cr1.thn.lon\n ", 'out': 'nested', 'retcode': 1, 'jid': '20190225154145768780'}}
[DEBUG ] LazyLoaded nested.output
nms3:
Passed invalid arguments to netbox.openconfig_interfaces: '<' not supported between instances of 'dict' and 'dict'
(...)
### Versions Report
Salt Version:
Salt: 2019.2.0rc2
Dependency Versions:
cffi: 1.12.1
cherrypy: Not Installed
dateutil: 2.6.1
docker-py: Not Installed
gitdb: 2.0.3
gitpython: 2.1.8
ioflo: Not Installed
Jinja2: 2.10
libgit2: Not Installed
libnacl: Not Installed
M2Crypto: Not Installed
Mako: Not Installed
msgpack-pure: Not Installed
msgpack-python: 0.5.6
mysql-python: Not Installed
pycparser: 2.19
pycrypto: 3.7.2
pycryptodome: Not Installed
pygit2: Not Installed
Python: 3.6.7 (default, Oct 22 2018, 11:32:17)
python-gnupg: 0.4.1
PyYAML: 3.12
PyZMQ: 16.0.2
RAET: Not Installed
smmap: 2.0.3
timelib: Not Installed
Tornado: 4.5.3
ZMQ: 4.2.5
System Versions:
dist: Ubuntu 18.04 bionic
locale: UTF-8
machine: x86_64
release: 4.15.0-45-generic
system: Linux
version: Ubuntu 18.04 bionic | non_infrastructure | netbox openconfig interfaces fails not supported between instances of dict and dict description of issue question in my setup netbox get interfaces works now i tried netbox openconfig interfaces this fails with passed invalid arguments to netbox openconfig interfaces not supported between instances of dict and dict setup plain setup of salt netbox with python steps to reproduce issue salt l debug netbox openconfig interfaces device name return event ret passed invalid arguments to netbox openconfig interfaces not supported between instances of dict and dict versionadded n n return a dictionary structured as standardised in the n openconfig interfaces yang model containing physical and configuration data available in netbox n e g ip addresses mtu enabled disabled etc n n device name none n the name of the device to query the interface data for if not provided n will use the minion id n n cli example n n code block bash n n salt netbox openconfig interfaces n salt netbox openconfig interfaces device name thn lon n out nested retcode jid lazyloaded nested output passed invalid arguments to netbox openconfig interfaces not supported between instances of dict and dict versions report salt version salt dependency versions cffi cherrypy not installed dateutil docker py not installed gitdb gitpython ioflo not installed not installed libnacl not installed not installed mako not installed msgpack pure not installed msgpack python mysql python not installed pycparser pycrypto pycryptodome not installed not installed python default oct python gnupg pyyaml pyzmq raet not installed smmap timelib not installed tornado zmq system versions dist ubuntu bionic locale utf machine release generic system linux version ubuntu bionic | 0 |
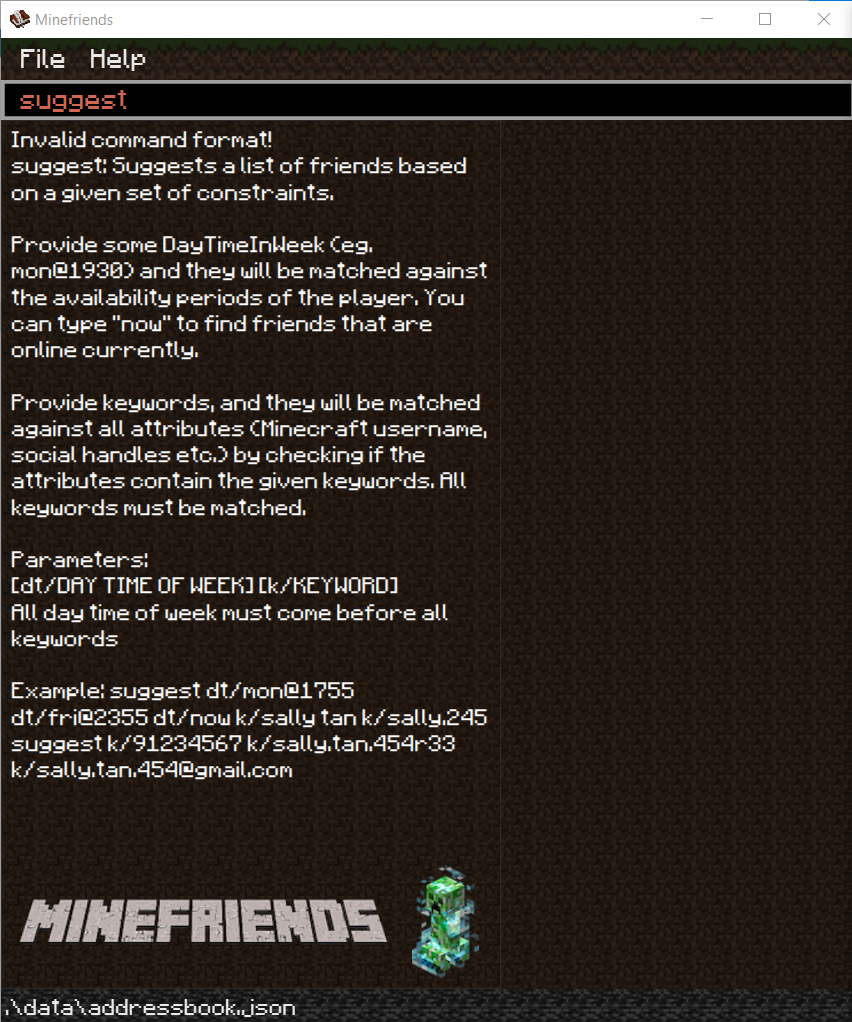
346,573 | 24,887,018,428 | IssuesEvent | 2022-10-28 08:39:53 | sharmaine1028/ped | https://api.github.com/repos/sharmaine1028/ped | opened | Some commands in user guide does not work | severity.Medium type.DocumentationBug | In the user guide, parameters in `[]` is said to be optional.
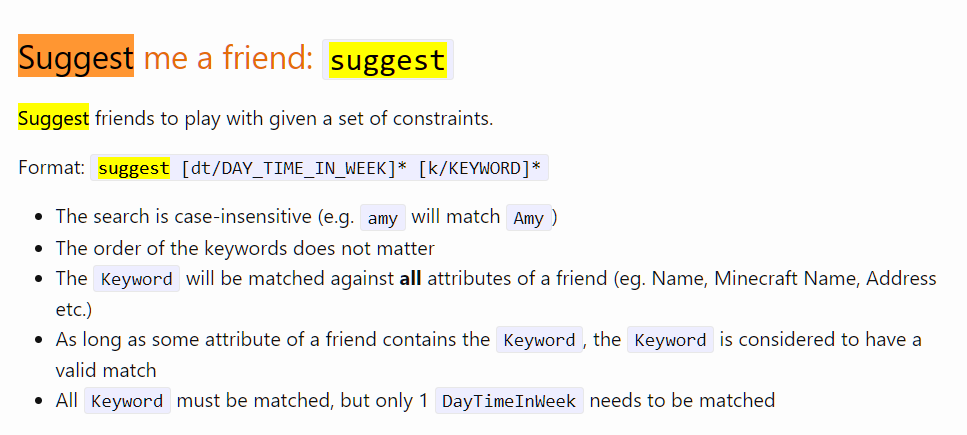
By that logic, the command `suggest` should work . However, I receive this error message when I try to type in just the command `suggest`
<!--session: 1666943903121-2ea44a57-8552-4fab-a01f-bc3d8251b6ce-->
<!--Version: Web v3.4.4--> | 1.0 | Some commands in user guide does not work - In the user guide, parameters in `[]` is said to be optional.
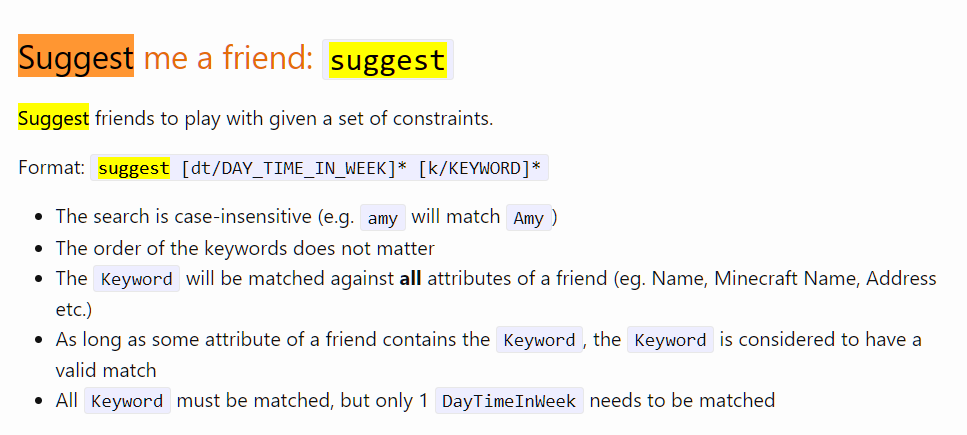
By that logic, the command `suggest` should work . However, I receive this error message when I try to type in just the command `suggest`
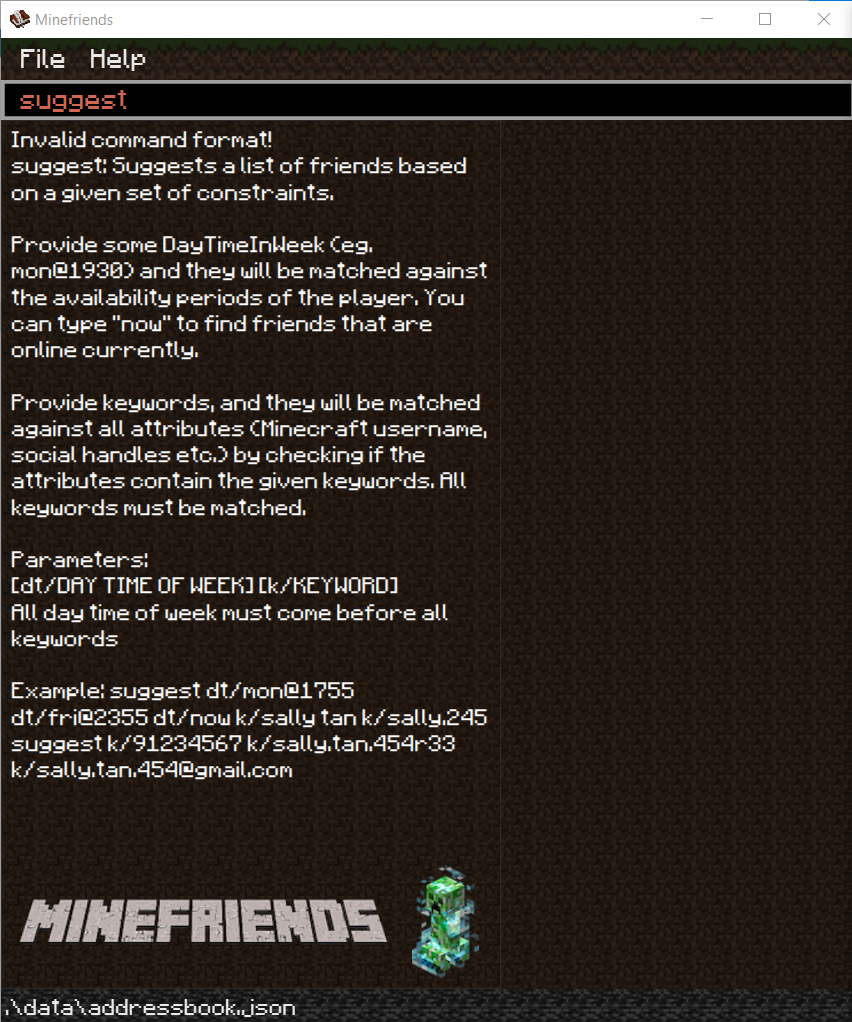
<!--session: 1666943903121-2ea44a57-8552-4fab-a01f-bc3d8251b6ce-->
<!--Version: Web v3.4.4--> | non_infrastructure | some commands in user guide does not work in the user guide parameters in is said to be optional by that logic the command suggest should work however i receive this error message when i try to type in just the command suggest | 0 |
27,962 | 22,645,157,174 | IssuesEvent | 2022-07-01 08:01:01 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Re-enable rich nav on PRs once perf issue is fixed | Area-Infrastructure Test | >I think it would be best to just disable completely on PRs and perhaps keep an eye on it for rolling builds so that we can see if the regression gets fixed.
I'm fine with disabling as well, can we file an issue assigned to richnav, and have them re-enable it on PRs once the regression is fixed?
_Originally posted by @dibarbet in https://github.com/dotnet/roslyn/issues/54662#issuecomment-875847652_
Tracking issue for RichNav (internal only): https://devdiv.visualstudio.com/DevDiv/_workitems/edit/1353111 | 1.0 | Re-enable rich nav on PRs once perf issue is fixed - >I think it would be best to just disable completely on PRs and perhaps keep an eye on it for rolling builds so that we can see if the regression gets fixed.
I'm fine with disabling as well, can we file an issue assigned to richnav, and have them re-enable it on PRs once the regression is fixed?
_Originally posted by @dibarbet in https://github.com/dotnet/roslyn/issues/54662#issuecomment-875847652_
Tracking issue for RichNav (internal only): https://devdiv.visualstudio.com/DevDiv/_workitems/edit/1353111 | infrastructure | re enable rich nav on prs once perf issue is fixed i think it would be best to just disable completely on prs and perhaps keep an eye on it for rolling builds so that we can see if the regression gets fixed i m fine with disabling as well can we file an issue assigned to richnav and have them re enable it on prs once the regression is fixed originally posted by dibarbet in tracking issue for richnav internal only | 1 |
35,575 | 31,841,686,498 | IssuesEvent | 2023-09-14 16:46:41 | spring-projects/spring-batch | https://api.github.com/repos/spring-projects/spring-batch | closed | Missing setter for strict field in DelimitedBuilder | in: infrastructure type: bug for: backport-to-5.0.x | **[tobecat](https://jira.spring.io/secure/ViewProfile.jspa?name=tobecat)** opened **[BATCH-2798](https://jira.spring.io/browse/BATCH-2798?redirect=false)** and commented
In static class DelimitedBuilder (FlatFileItemReaderBuilder Class), there is no method to set strict to DelimitedLineTokenizer. It is always true.
Please Add method for set strict flag.
public DelimitedBuilder \<T> strict(boolean strict) {
this.strict = strict;
return this;
}
---
No further details from [BATCH-2798](https://jira.spring.io/browse/BATCH-2798?redirect=false) | 1.0 | Missing setter for strict field in DelimitedBuilder - **[tobecat](https://jira.spring.io/secure/ViewProfile.jspa?name=tobecat)** opened **[BATCH-2798](https://jira.spring.io/browse/BATCH-2798?redirect=false)** and commented
In static class DelimitedBuilder (FlatFileItemReaderBuilder Class), there is no method to set strict to DelimitedLineTokenizer. It is always true.
Please Add method for set strict flag.
public DelimitedBuilder \<T> strict(boolean strict) {
this.strict = strict;
return this;
}
---
No further details from [BATCH-2798](https://jira.spring.io/browse/BATCH-2798?redirect=false) | infrastructure | missing setter for strict field in delimitedbuilder opened and commented in static class delimitedbuilder flatfileitemreaderbuilder class there is no method to set strict to delimitedlinetokenizer it is always true please add method for set strict flag public delimitedbuilder strict boolean strict this strict strict return this no further details from | 1 |
278,545 | 24,160,516,628 | IssuesEvent | 2022-09-22 11:14:54 | eclipse-openj9/openj9 | https://api.github.com/repos/eclipse-openj9/openj9 | closed | JDK17 aarch64_mac SC_Softmx_Increase_0_FAILED - net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest | test failure arch:aarch64 os:macos | Failure link
------------
From [an internal build](https://hyc-runtimes-jenkins.swg-devops.com/job/Test_openjdk17_j9_extended.system_aarch64_mac_testList_0/3/)(`macaarch64rt3`):
```
openjdk version "17.0.4-ea" 2022-07-19
IBM Semeru Runtime Open Edition 17.0.4.0-m2 (build 17.0.4-ea+7)
Eclipse OpenJ9 VM 17.0.4.0-m2 (build openj9-0.33.0-m2, JRE 17 Mac OS X aarch64-64-Bit 20220718_88 (JIT enabled, AOT enabled)
OpenJ9 - e7fc0d2f1
OMR - e25299388
JCL - 05652b1ac23 based on jdk-17.0.4+7)
```
[Rerun in Grinder](https://hyc-runtimes-jenkins.swg-devops.com/job/Grinder/parambuild/?SDK_RESOURCE=upstream&TARGET=-f+parallelList.mk+testList_0&TEST_FLAG=&UPSTREAM_TEST_JOB_NAME=Test_openjdk17_j9_extended.system_aarch64_mac&DOCKER_REQUIRED=false&ACTIVE_NODE_TIMEOUT=0&VENDOR_TEST_DIRS=&EXTRA_DOCKER_ARGS=&TKG_OWNER_BRANCH=adoptium%3Amaster&OPENJ9_SYSTEMTEST_OWNER_BRANCH=eclipse%3Amaster&PLATFORM=aarch64_mac&GENERATE_JOBS=false&KEEP_REPORTDIR=false&PERSONAL_BUILD=false&ADOPTOPENJDK_REPO=https%3A%2F%2Fgithub.com%2Fadoptium%2Faqa-tests.git&LABEL=&EXTRA_OPTIONS=&CUSTOMIZED_SDK_URL=+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-testimage_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-jre_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-debugimage_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-jdk_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz&BUILD_IDENTIFIER=&ADOPTOPENJDK_BRANCH=master&LIGHT_WEIGHT_CHECKOUT=true&USE_JRE=false&ARTIFACTORY_SERVER=na.artifactory.swg-devops&KEEP_WORKSPACE=false&USER_CREDENTIALS_ID=&JDK_VERSION=17&ITERATIONS=1&VENDOR_TEST_REPOS=&JDK_REPO=https%3A%2F%2Fgithub.com%2Fibmruntimes%2Fopenj9-openjdk-jdk17&RELEASE_TAG=v0.33.0-release&OPENJ9_BRANCH=v0.33.0-release&OPENJ9_SHA=&JCK_GIT_REPO=&VENDOR_TEST_BRANCHES=&OPENJ9_REPO=https%3A%2F%2Fgithub.com%2Feclipse-openj9%2Fopenj9.git&UPSTREAM_JOB_NAME=&CLOUD_PROVIDER=&CUSTOM_TARGET=&VENDOR_TEST_SHAS=&JDK_BRANCH=v0.33.0-release&LABEL_ADDITION=&ARTIFACTORY_REPO=&ARTIFACTORY_ROOT_DIR=&UPSTREAM_TEST_JOB_NUMBER=3&DOCKERIMAGE_TAG=&JDK_IMPL=openj9&TEST_TIME=&SSH_AGENT_CREDENTIAL=83181e25-eea4-4f55-8b3e-e79615733226&AUTO_DETECT=true&SLACK_CHANNEL=&DYNAMIC_COMPILE=false&ADOPTOPENJDK_SYSTEMTEST_OWNER_BRANCH=adoptium%3Amaster&CUSTOMIZED_SDK_URL_CREDENTIAL_ID=4e18ffe7-b1b1-4272-9979-99769b68bcc2&ARCHIVE_TEST_RESULTS=false&NUM_MACHINES=&OPENJDK_SHA=&TRSS_URL=http%3A%2F%2Ftrss1.fyre.ibm.com&USE_TESTENV_PROPERTIES=false&BUILD_LIST=system&UPSTREAM_JOB_NUMBER=&STF_OWNER_BRANCH=adoptium%3Amaster&TIME_LIMIT=20&JVM_OPTIONS=&PARALLEL=None) - Change TARGET to run only the failed test targets.
Optional info
-------------
Failure output (captured from console output)
---------------------------------------------
```
9.Jvm2.stdout
23:13:45.136 - Starting thread. Suite=0 thread=6
23:13:46.345 - First failure detected by thread: load-0. Not creating dumps as no dump generation is requested for this load test
23:13:46.380 - suite.getInventory().getInventoryFileRef(): openj9.test.load/config/inventories/mix/sharedclasses-mix.xml
23:13:46.380 - suite.isCreateDump() : false
23:13:46.409 - Test failed
Failure num. = 1
Test number = 88
Test details = 'JUnit[net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest]'
Suite number = 0
Thread number = 0
>>> Captured test output >>>
testStarted : testAllFileSystemsAreRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
testFailure: testAllFileSystemsAreRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest): Unable to match all memory FileSystems in the list of available providers expected:<1000> but was:<0>
junit.framework.AssertionFailedError: Unable to match all memory FileSystems in the list of available providers expected:<1000> but was:<0>
at junit.framework.Assert.fail(Assert.java:57)
at junit.framework.Assert.failNotEquals(Assert.java:329)
at junit.framework.Assert.assertEquals(Assert.java:78)
at junit.framework.Assert.assertEquals(Assert.java:234)
at junit.framework.TestCase.assertEquals(TestCase.java:401)
at net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest.testAllFileSystemsAreRegistered(FileSystemsTest.java:119)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at junit.framework.TestCase.runTest(TestCase.java:176)
at junit.framework.TestCase.runBare(TestCase.java:141)
at junit.framework.TestResult$1.protect(TestResult.java:122)
at junit.framework.TestResult.runProtected(TestResult.java:142)
at junit.framework.TestResult.run(TestResult.java:125)
at junit.framework.TestCase.run(TestCase.java:129)
at junit.framework.TestSuite.runTest(TestSuite.java:252)
at junit.framework.TestSuite.run(TestSuite.java:247)
at org.junit.internal.runners.JUnit38ClassRunner.run(JUnit38ClassRunner.java:86)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at net.adoptopenjdk.loadTest.adaptors.JUnitAdaptor.executeTest(JUnitAdaptor.java:130)
at net.adoptopenjdk.loadTest.LoadTestRunner$2.run(LoadTestRunner.java:182)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1136)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:635)
at java.base/java.lang.Thread.run(Thread.java:858)
testFinished: testAllFileSystemsAreRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
testStarted : testFileSystemIsRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
testFailure: testFileSystemIsRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest): Unable to find intial provider 'memory0'
junit.framework.AssertionFailedError: Unable to find intial provider 'memory0'
at junit.framework.Assert.fail(Assert.java:57)
at junit.framework.Assert.assertTrue(Assert.java:22)
at junit.framework.TestCase.assertTrue(TestCase.java:192)
at net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest.testFileSystemIsRegistered(FileSystemsTest.java:78)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at junit.framework.TestCase.runTest(TestCase.java:176)
at junit.framework.TestCase.runBare(TestCase.java:141)
at junit.framework.TestResult$1.protect(TestResult.java:122)
at junit.framework.TestResult.runProtected(TestResult.java:142)
at junit.framework.TestResult.run(TestResult.java:125)
at junit.framework.TestCase.run(TestCase.java:129)
at junit.framework.TestSuite.runTest(TestSuite.java:252)
at junit.framework.TestSuite.run(TestSuite.java:247)
at org.junit.internal.runners.JUnit38ClassRunner.run(JUnit38ClassRunner.java:86)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at net.adoptopenjdk.loadTest.adaptors.JUnitAdaptor.executeTest(JUnitAdaptor.java:130)
at net.adoptopenjdk.loadTest.LoadTestRunner$2.run(LoadTestRunner.java:182)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1136)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:635)
at java.base/java.lang.Thread.run(Thread.java:858)
testFinished: testFileSystemIsRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
JUnit Test Results for: net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest
Ran : 2
Passed : 0
Failed : 2
Ignored: 0
Result : FAILED
<<<
23:13:46.667 - Test failed. Details recorded in execution log.
```
| 1.0 | JDK17 aarch64_mac SC_Softmx_Increase_0_FAILED - net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest - Failure link
------------
From [an internal build](https://hyc-runtimes-jenkins.swg-devops.com/job/Test_openjdk17_j9_extended.system_aarch64_mac_testList_0/3/)(`macaarch64rt3`):
```
openjdk version "17.0.4-ea" 2022-07-19
IBM Semeru Runtime Open Edition 17.0.4.0-m2 (build 17.0.4-ea+7)
Eclipse OpenJ9 VM 17.0.4.0-m2 (build openj9-0.33.0-m2, JRE 17 Mac OS X aarch64-64-Bit 20220718_88 (JIT enabled, AOT enabled)
OpenJ9 - e7fc0d2f1
OMR - e25299388
JCL - 05652b1ac23 based on jdk-17.0.4+7)
```
[Rerun in Grinder](https://hyc-runtimes-jenkins.swg-devops.com/job/Grinder/parambuild/?SDK_RESOURCE=upstream&TARGET=-f+parallelList.mk+testList_0&TEST_FLAG=&UPSTREAM_TEST_JOB_NAME=Test_openjdk17_j9_extended.system_aarch64_mac&DOCKER_REQUIRED=false&ACTIVE_NODE_TIMEOUT=0&VENDOR_TEST_DIRS=&EXTRA_DOCKER_ARGS=&TKG_OWNER_BRANCH=adoptium%3Amaster&OPENJ9_SYSTEMTEST_OWNER_BRANCH=eclipse%3Amaster&PLATFORM=aarch64_mac&GENERATE_JOBS=false&KEEP_REPORTDIR=false&PERSONAL_BUILD=false&ADOPTOPENJDK_REPO=https%3A%2F%2Fgithub.com%2Fadoptium%2Faqa-tests.git&LABEL=&EXTRA_OPTIONS=&CUSTOMIZED_SDK_URL=+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-testimage_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-jre_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-debugimage_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz+https%3A%2F%2Fna.artifactory.swg-devops.com%2Fartifactory%2Fsys-rt-generic-local%2Fhyc-runtimes-jenkins.swg-devops.com%2Fbuild-scripts%2Fjobs%2Fjdk17u%2Fjdk17u-mac-aarch64-openj9%2F88%2Fibm-semeru-open-jdk_aarch64_mac_17.0.4_7_openj9-0.33.0-m2.tar.gz&BUILD_IDENTIFIER=&ADOPTOPENJDK_BRANCH=master&LIGHT_WEIGHT_CHECKOUT=true&USE_JRE=false&ARTIFACTORY_SERVER=na.artifactory.swg-devops&KEEP_WORKSPACE=false&USER_CREDENTIALS_ID=&JDK_VERSION=17&ITERATIONS=1&VENDOR_TEST_REPOS=&JDK_REPO=https%3A%2F%2Fgithub.com%2Fibmruntimes%2Fopenj9-openjdk-jdk17&RELEASE_TAG=v0.33.0-release&OPENJ9_BRANCH=v0.33.0-release&OPENJ9_SHA=&JCK_GIT_REPO=&VENDOR_TEST_BRANCHES=&OPENJ9_REPO=https%3A%2F%2Fgithub.com%2Feclipse-openj9%2Fopenj9.git&UPSTREAM_JOB_NAME=&CLOUD_PROVIDER=&CUSTOM_TARGET=&VENDOR_TEST_SHAS=&JDK_BRANCH=v0.33.0-release&LABEL_ADDITION=&ARTIFACTORY_REPO=&ARTIFACTORY_ROOT_DIR=&UPSTREAM_TEST_JOB_NUMBER=3&DOCKERIMAGE_TAG=&JDK_IMPL=openj9&TEST_TIME=&SSH_AGENT_CREDENTIAL=83181e25-eea4-4f55-8b3e-e79615733226&AUTO_DETECT=true&SLACK_CHANNEL=&DYNAMIC_COMPILE=false&ADOPTOPENJDK_SYSTEMTEST_OWNER_BRANCH=adoptium%3Amaster&CUSTOMIZED_SDK_URL_CREDENTIAL_ID=4e18ffe7-b1b1-4272-9979-99769b68bcc2&ARCHIVE_TEST_RESULTS=false&NUM_MACHINES=&OPENJDK_SHA=&TRSS_URL=http%3A%2F%2Ftrss1.fyre.ibm.com&USE_TESTENV_PROPERTIES=false&BUILD_LIST=system&UPSTREAM_JOB_NUMBER=&STF_OWNER_BRANCH=adoptium%3Amaster&TIME_LIMIT=20&JVM_OPTIONS=&PARALLEL=None) - Change TARGET to run only the failed test targets.
Optional info
-------------
Failure output (captured from console output)
---------------------------------------------
```
9.Jvm2.stdout
23:13:45.136 - Starting thread. Suite=0 thread=6
23:13:46.345 - First failure detected by thread: load-0. Not creating dumps as no dump generation is requested for this load test
23:13:46.380 - suite.getInventory().getInventoryFileRef(): openj9.test.load/config/inventories/mix/sharedclasses-mix.xml
23:13:46.380 - suite.isCreateDump() : false
23:13:46.409 - Test failed
Failure num. = 1
Test number = 88
Test details = 'JUnit[net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest]'
Suite number = 0
Thread number = 0
>>> Captured test output >>>
testStarted : testAllFileSystemsAreRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
testFailure: testAllFileSystemsAreRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest): Unable to match all memory FileSystems in the list of available providers expected:<1000> but was:<0>
junit.framework.AssertionFailedError: Unable to match all memory FileSystems in the list of available providers expected:<1000> but was:<0>
at junit.framework.Assert.fail(Assert.java:57)
at junit.framework.Assert.failNotEquals(Assert.java:329)
at junit.framework.Assert.assertEquals(Assert.java:78)
at junit.framework.Assert.assertEquals(Assert.java:234)
at junit.framework.TestCase.assertEquals(TestCase.java:401)
at net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest.testAllFileSystemsAreRegistered(FileSystemsTest.java:119)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at junit.framework.TestCase.runTest(TestCase.java:176)
at junit.framework.TestCase.runBare(TestCase.java:141)
at junit.framework.TestResult$1.protect(TestResult.java:122)
at junit.framework.TestResult.runProtected(TestResult.java:142)
at junit.framework.TestResult.run(TestResult.java:125)
at junit.framework.TestCase.run(TestCase.java:129)
at junit.framework.TestSuite.runTest(TestSuite.java:252)
at junit.framework.TestSuite.run(TestSuite.java:247)
at org.junit.internal.runners.JUnit38ClassRunner.run(JUnit38ClassRunner.java:86)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at net.adoptopenjdk.loadTest.adaptors.JUnitAdaptor.executeTest(JUnitAdaptor.java:130)
at net.adoptopenjdk.loadTest.LoadTestRunner$2.run(LoadTestRunner.java:182)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1136)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:635)
at java.base/java.lang.Thread.run(Thread.java:858)
testFinished: testAllFileSystemsAreRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
testStarted : testFileSystemIsRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
testFailure: testFileSystemIsRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest): Unable to find intial provider 'memory0'
junit.framework.AssertionFailedError: Unable to find intial provider 'memory0'
at junit.framework.Assert.fail(Assert.java:57)
at junit.framework.Assert.assertTrue(Assert.java:22)
at junit.framework.TestCase.assertTrue(TestCase.java:192)
at net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest.testFileSystemIsRegistered(FileSystemsTest.java:78)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:568)
at junit.framework.TestCase.runTest(TestCase.java:176)
at junit.framework.TestCase.runBare(TestCase.java:141)
at junit.framework.TestResult$1.protect(TestResult.java:122)
at junit.framework.TestResult.runProtected(TestResult.java:142)
at junit.framework.TestResult.run(TestResult.java:125)
at junit.framework.TestCase.run(TestCase.java:129)
at junit.framework.TestSuite.runTest(TestSuite.java:252)
at junit.framework.TestSuite.run(TestSuite.java:247)
at org.junit.internal.runners.JUnit38ClassRunner.run(JUnit38ClassRunner.java:86)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at net.adoptopenjdk.loadTest.adaptors.JUnitAdaptor.executeTest(JUnitAdaptor.java:130)
at net.adoptopenjdk.loadTest.LoadTestRunner$2.run(LoadTestRunner.java:182)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1136)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:635)
at java.base/java.lang.Thread.run(Thread.java:858)
testFinished: testFileSystemIsRegistered(net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest)
JUnit Test Results for: net.adoptopenjdk.test.nio2.filesystem.FileSystemsTest
Ran : 2
Passed : 0
Failed : 2
Ignored: 0
Result : FAILED
<<<
23:13:46.667 - Test failed. Details recorded in execution log.
```
| non_infrastructure | mac sc softmx increase failed net adoptopenjdk test filesystem filesystemstest failure link from openjdk version ea ibm semeru runtime open edition build ea eclipse vm build jre mac os x bit jit enabled aot enabled omr jcl based on jdk change target to run only the failed test targets optional info failure output captured from console output stdout starting thread suite thread first failure detected by thread load not creating dumps as no dump generation is requested for this load test suite getinventory getinventoryfileref test load config inventories mix sharedclasses mix xml suite iscreatedump false test failed failure num test number test details junit suite number thread number captured test output teststarted testallfilesystemsareregistered net adoptopenjdk test filesystem filesystemstest testfailure testallfilesystemsareregistered net adoptopenjdk test filesystem filesystemstest unable to match all memory filesystems in the list of available providers expected but was junit framework assertionfailederror unable to match all memory filesystems in the list of available providers expected but was at junit framework assert fail assert java at junit framework assert failnotequals assert java at junit framework assert assertequals assert java at junit framework assert assertequals assert java at junit framework testcase assertequals testcase java at net adoptopenjdk test filesystem filesystemstest testallfilesystemsareregistered filesystemstest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at junit framework testcase runtest testcase java at junit framework testcase runbare testcase java at junit framework testresult protect testresult java at junit framework testresult runprotected testresult java at junit framework testresult run testresult java at junit framework testcase run testcase java at junit framework testsuite runtest testsuite java at junit framework testsuite run testsuite java at org junit internal runners run java at org junit runners suite runchild suite java at org junit runners suite runchild suite java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org junit runner junitcore run junitcore java at org junit runner junitcore run junitcore java at net adoptopenjdk loadtest adaptors junitadaptor executetest junitadaptor java at net adoptopenjdk loadtest loadtestrunner run loadtestrunner java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java testfinished testallfilesystemsareregistered net adoptopenjdk test filesystem filesystemstest teststarted testfilesystemisregistered net adoptopenjdk test filesystem filesystemstest testfailure testfilesystemisregistered net adoptopenjdk test filesystem filesystemstest unable to find intial provider junit framework assertionfailederror unable to find intial provider at junit framework assert fail assert java at junit framework assert asserttrue assert java at junit framework testcase asserttrue testcase java at net adoptopenjdk test filesystem filesystemstest testfilesystemisregistered filesystemstest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at junit framework testcase runtest testcase java at junit framework testcase runbare testcase java at junit framework testresult protect testresult java at junit framework testresult runprotected testresult java at junit framework testresult run testresult java at junit framework testcase run testcase java at junit framework testsuite runtest testsuite java at junit framework testsuite run testsuite java at org junit internal runners run java at org junit runners suite runchild suite java at org junit runners suite runchild suite java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org junit runner junitcore run junitcore java at org junit runner junitcore run junitcore java at net adoptopenjdk loadtest adaptors junitadaptor executetest junitadaptor java at net adoptopenjdk loadtest loadtestrunner run loadtestrunner java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java testfinished testfilesystemisregistered net adoptopenjdk test filesystem filesystemstest junit test results for net adoptopenjdk test filesystem filesystemstest ran passed failed ignored result failed test failed details recorded in execution log | 0 |
66,658 | 12,810,604,975 | IssuesEvent | 2020-07-03 19:16:27 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [ 4.0.0 b2-dev]Install from Web - Joomla version compatibility. | J4 Issue No Code Attached Yet | ### Steps to reproduce the issue
### Expected result
Show compatibility for Joomla Extensions / only display compatible extensions.

### Actual result
Install from web not showing Joomla version compatibility for extensions.

### System information (as much as possible)
### Additional comments
| 1.0 | [ 4.0.0 b2-dev]Install from Web - Joomla version compatibility. - ### Steps to reproduce the issue
### Expected result
Show compatibility for Joomla Extensions / only display compatible extensions.

### Actual result
Install from web not showing Joomla version compatibility for extensions.

### System information (as much as possible)
### Additional comments
| non_infrastructure | install from web joomla version compatibility steps to reproduce the issue expected result show compatibility for joomla extensions only display compatible extensions actual result install from web not showing joomla version compatibility for extensions system information as much as possible additional comments | 0 |
305,094 | 9,359,264,248 | IssuesEvent | 2019-04-02 06:15:36 | medic/medic | https://api.github.com/repos/medic/medic | closed | Integration tests labeled as "passing" by travis even when not all E2E tests run | Help wanted Priority: 2 - Medium Type: Technical issue | Here is a build labeled as passing by Travis: https://travis-ci.org/medic/medic/builds/484489080?utm_source=github_status&utm_medium=notification
In the logs for the integration suite, I see:
```
Ran 147 of 199 specs
147 specs, 1 failure
Finished in 200.341 seconds
An error was thrown in an afterAll
AfterAll Expected $[0] = '_id,form,patient_id,reported_date,from,contact.name,contact.parent.name,contact.parent.parent.name,contact.parent.parent.parent.name,bar,baz,foo,smang.smong,wd_array,wd_emptyString,wd_false,wd_naughtyArray,wd_naughtyString,wd_null,wd_zero' to equal '_id,form,patient_id,reported_date,from,contact.name,contact.parent.name,contact.parent.parent.name,contact.parent.parent.parent.name,bar,baz,foo,smang.smong'.
Expected $[1] = '"export-data-2-test-doc-3","b","abc125",1517616000000,,,,,,,"bazVal",,,,,,,,,' to equal '"export-data-2-test-doc-3","b","abc125",1517616000000,,,,,,,"bazVal",,'.
>> 15:32:21.411 INFO [ActiveSessions$1.onStop] - Removing session e364978fac8e4d420bbf8e1456f82bc6 (org.openqa.selenium.chrome.ChromeDriverService)
[15:32:21] I/launcher - 0 instance(s) of WebDriver still running
[15:32:21] I/launcher - chrome #01 passed
Closing report
```
The suite took only 5 minutes to run and typically takes about 8 minutes. | 1.0 | Integration tests labeled as "passing" by travis even when not all E2E tests run - Here is a build labeled as passing by Travis: https://travis-ci.org/medic/medic/builds/484489080?utm_source=github_status&utm_medium=notification
In the logs for the integration suite, I see:
```
Ran 147 of 199 specs
147 specs, 1 failure
Finished in 200.341 seconds
An error was thrown in an afterAll
AfterAll Expected $[0] = '_id,form,patient_id,reported_date,from,contact.name,contact.parent.name,contact.parent.parent.name,contact.parent.parent.parent.name,bar,baz,foo,smang.smong,wd_array,wd_emptyString,wd_false,wd_naughtyArray,wd_naughtyString,wd_null,wd_zero' to equal '_id,form,patient_id,reported_date,from,contact.name,contact.parent.name,contact.parent.parent.name,contact.parent.parent.parent.name,bar,baz,foo,smang.smong'.
Expected $[1] = '"export-data-2-test-doc-3","b","abc125",1517616000000,,,,,,,"bazVal",,,,,,,,,' to equal '"export-data-2-test-doc-3","b","abc125",1517616000000,,,,,,,"bazVal",,'.
>> 15:32:21.411 INFO [ActiveSessions$1.onStop] - Removing session e364978fac8e4d420bbf8e1456f82bc6 (org.openqa.selenium.chrome.ChromeDriverService)
[15:32:21] I/launcher - 0 instance(s) of WebDriver still running
[15:32:21] I/launcher - chrome #01 passed
Closing report
```
The suite took only 5 minutes to run and typically takes about 8 minutes. | non_infrastructure | integration tests labeled as passing by travis even when not all tests run here is a build labeled as passing by travis in the logs for the integration suite i see ran of specs specs failure finished in seconds an error was thrown in an afterall afterall expected id form patient id reported date from contact name contact parent name contact parent parent name contact parent parent parent name bar baz foo smang smong wd array wd emptystring wd false wd naughtyarray wd naughtystring wd null wd zero to equal id form patient id reported date from contact name contact parent name contact parent parent name contact parent parent parent name bar baz foo smang smong expected export data test doc b bazval to equal export data test doc b bazval info removing session org openqa selenium chrome chromedriverservice i launcher instance s of webdriver still running i launcher chrome passed closing report the suite took only minutes to run and typically takes about minutes | 0 |
148,980 | 19,562,638,487 | IssuesEvent | 2022-01-03 18:27:04 | ibm-cio-vulnerability-scanning/insomnia | https://api.github.com/repos/ibm-cio-vulnerability-scanning/insomnia | opened | CVE-2021-23337 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.20.tgz</b>, <b>lodash-4.17.19.tgz</b>, <b>lodash-4.17.15.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.20.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz</a></p>
<p>Path to dependency file: /packages/insomnia-inso/package.json</p>
<p>Path to vulnerable library: /packages/insomnia-inso/node_modules/@stoplight/spectral/node_modules/lodash/package.json,/packages/openapi-2-kong/node_modules/request-promise-core/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/@babel/plugin-proposal-optional-chaining/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/request-promise-core/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/@babel/plugin-transform-runtime/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- jest-26.6.3.tgz (Root Library)
- jest-cli-26.6.3.tgz
- jest-config-26.6.3.tgz
- jest-environment-jsdom-26.6.2.tgz
- jsdom-16.4.0.tgz
- request-promise-native-1.0.9.tgz
- request-promise-core-1.1.4.tgz
- :x: **lodash-4.17.20.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.19.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.19.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.19.tgz</a></p>
<p>Path to dependency file: /packages/insomnia-smoke-test/package.json</p>
<p>Path to vulnerable library: /packages/insomnia-smoke-test/node_modules/lodash/package.json,/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.10.5.tgz (Root Library)
- :x: **lodash-4.17.19.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: /packages/openapi-2-kong/package.json</p>
<p>Path to vulnerable library: /packages/openapi-2-kong/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- core-7.7.7.tgz (Root Library)
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ibm-cio-vulnerability-scanning/insomnia/commit/66be0bf823b886e28f10e13043b244516268423b">66be0bf823b886e28f10e13043b244516268423b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23337 (High) detected in multiple libraries - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.20.tgz</b>, <b>lodash-4.17.19.tgz</b>, <b>lodash-4.17.15.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.20.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.20.tgz</a></p>
<p>Path to dependency file: /packages/insomnia-inso/package.json</p>
<p>Path to vulnerable library: /packages/insomnia-inso/node_modules/@stoplight/spectral/node_modules/lodash/package.json,/packages/openapi-2-kong/node_modules/request-promise-core/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/@babel/plugin-proposal-optional-chaining/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/request-promise-core/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/@babel/plugin-transform-runtime/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- jest-26.6.3.tgz (Root Library)
- jest-cli-26.6.3.tgz
- jest-config-26.6.3.tgz
- jest-environment-jsdom-26.6.2.tgz
- jsdom-16.4.0.tgz
- request-promise-native-1.0.9.tgz
- request-promise-core-1.1.4.tgz
- :x: **lodash-4.17.20.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.19.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.19.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.19.tgz</a></p>
<p>Path to dependency file: /packages/insomnia-smoke-test/package.json</p>
<p>Path to vulnerable library: /packages/insomnia-smoke-test/node_modules/lodash/package.json,/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.10.5.tgz (Root Library)
- :x: **lodash-4.17.19.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: /packages/openapi-2-kong/package.json</p>
<p>Path to vulnerable library: /packages/openapi-2-kong/node_modules/lodash/package.json,/packages/insomnia-components/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- core-7.7.7.tgz (Root Library)
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ibm-cio-vulnerability-scanning/insomnia/commit/66be0bf823b886e28f10e13043b244516268423b">66be0bf823b886e28f10e13043b244516268423b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file packages insomnia inso package json path to vulnerable library packages insomnia inso node modules stoplight spectral node modules lodash package json packages openapi kong node modules request promise core node modules lodash package json packages insomnia components node modules babel plugin proposal optional chaining node modules lodash package json packages insomnia components node modules request promise core node modules lodash package json packages insomnia components node modules babel plugin transform runtime node modules lodash package json dependency hierarchy jest tgz root library jest cli tgz jest config tgz jest environment jsdom tgz jsdom tgz request promise native tgz request promise core tgz x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file packages insomnia smoke test package json path to vulnerable library packages insomnia smoke test node modules lodash package json node modules lodash package json dependency hierarchy cli tgz root library x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file packages openapi kong package json path to vulnerable library packages openapi kong node modules lodash package json packages insomnia components node modules lodash package json dependency hierarchy core tgz root library x lodash tgz vulnerable library found in head commit a href vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash step up your open source security game with whitesource | 0 |
18,641 | 13,057,781,677 | IssuesEvent | 2020-07-30 07:58:09 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Support dotnet pack on libraries projects | area-Infrastructure-libraries | `dotnet pack` currently does nothing when invoked on an library project. We should be able to route `dotnet pack` invoked on the source project to the pkgproj and invoke its build target.
In addition to that it would be nice if the pkgproj build output doesn't point to the `nuspec` but to the `nupkg` instead (same what NuGet does). //update: already done by @ericstj: https://github.com/dotnet/arcade/commit/b0b76b68f059c3f94aba2818ae0da601adcc7096
Long term, we should consider getting rid of `pkgproj`s and enable `dotnet pack` natively on our source projects. This probably involves extending the existing NuGet infrastructure, presumably with a new msbuild sdk similar to the existing [Microsoft.DotNet.Build.Tasks.Packaging](https://github.com/dotnet/arcade/tree/master/src/Microsoft.DotNet.Build.Tasks.Packaging) infra package. Related: https://github.com/dotnet/arcade/issues/1033
See https://github.com/dotnet/runtime/issues/37961 for exposing a single entry point for generating the library package.
cc @joperezr @ericstj @Anipik | 1.0 | Support dotnet pack on libraries projects - `dotnet pack` currently does nothing when invoked on an library project. We should be able to route `dotnet pack` invoked on the source project to the pkgproj and invoke its build target.
In addition to that it would be nice if the pkgproj build output doesn't point to the `nuspec` but to the `nupkg` instead (same what NuGet does). //update: already done by @ericstj: https://github.com/dotnet/arcade/commit/b0b76b68f059c3f94aba2818ae0da601adcc7096
Long term, we should consider getting rid of `pkgproj`s and enable `dotnet pack` natively on our source projects. This probably involves extending the existing NuGet infrastructure, presumably with a new msbuild sdk similar to the existing [Microsoft.DotNet.Build.Tasks.Packaging](https://github.com/dotnet/arcade/tree/master/src/Microsoft.DotNet.Build.Tasks.Packaging) infra package. Related: https://github.com/dotnet/arcade/issues/1033
See https://github.com/dotnet/runtime/issues/37961 for exposing a single entry point for generating the library package.
cc @joperezr @ericstj @Anipik | infrastructure | support dotnet pack on libraries projects dotnet pack currently does nothing when invoked on an library project we should be able to route dotnet pack invoked on the source project to the pkgproj and invoke its build target in addition to that it would be nice if the pkgproj build output doesn t point to the nuspec but to the nupkg instead same what nuget does update already done by ericstj long term we should consider getting rid of pkgproj s and enable dotnet pack natively on our source projects this probably involves extending the existing nuget infrastructure presumably with a new msbuild sdk similar to the existing infra package related see for exposing a single entry point for generating the library package cc joperezr ericstj anipik | 1 |
25,041 | 18,062,964,707 | IssuesEvent | 2021-09-20 15:46:38 | sciencehistory/scihist_digicoll | https://api.github.com/repos/sciencehistory/scihist_digicoll | closed | add additional github projects to zenhub | infrastructure | All our github projects (terraform, ansible, archivespace-scripts) should be on our zenhub board.
Make sure issues show up in "Inbox" when they are created and show up on Zenhub board generally.
Pretty sure it's possible for zenhub to cover more than one github project, but I don't know how to set it up. | 1.0 | add additional github projects to zenhub - All our github projects (terraform, ansible, archivespace-scripts) should be on our zenhub board.
Make sure issues show up in "Inbox" when they are created and show up on Zenhub board generally.
Pretty sure it's possible for zenhub to cover more than one github project, but I don't know how to set it up. | infrastructure | add additional github projects to zenhub all our github projects terraform ansible archivespace scripts should be on our zenhub board make sure issues show up in inbox when they are created and show up on zenhub board generally pretty sure it s possible for zenhub to cover more than one github project but i don t know how to set it up | 1 |
389,597 | 26,823,995,164 | IssuesEvent | 2023-02-02 11:31:06 | hazelcast/hazelcast-go-client | https://api.github.com/repos/hazelcast/hazelcast-go-client | closed | Custom serializer lookup fails when pointers are used for registering | Type: Enhancement Type: Documentation Priority: Medium Estimation: S Source: Internal | In the example and documentation of custom serialization, pointers are passed for registering the serializers but in this case, `lookUpCustomSerializer()` method fails and Global serialization is used instead.
To reproduce this issue, put a breaking point at https://github.com/hazelcast/hazelcast-go-client/blob/master/internal/serialization/serialization.go#L267 and run the custom serialization example https://github.com/hazelcast/hazelcast-go-client/blob/master/examples/serialization/custom/main.go
Following files needs to be updated:
- https://github.com/hazelcast/hazelcast-go-client/blob/master/examples/serialization/custom/main.go
- https://github.com/hazelcast/hazelcast-go-client/blob/master/serialization/doc.go#L241
- https://github.com/hazelcast/hazelcast-go-client/blob/master/serialization/example_custom_serialization_test.go | 1.0 | Custom serializer lookup fails when pointers are used for registering - In the example and documentation of custom serialization, pointers are passed for registering the serializers but in this case, `lookUpCustomSerializer()` method fails and Global serialization is used instead.
To reproduce this issue, put a breaking point at https://github.com/hazelcast/hazelcast-go-client/blob/master/internal/serialization/serialization.go#L267 and run the custom serialization example https://github.com/hazelcast/hazelcast-go-client/blob/master/examples/serialization/custom/main.go
Following files needs to be updated:
- https://github.com/hazelcast/hazelcast-go-client/blob/master/examples/serialization/custom/main.go
- https://github.com/hazelcast/hazelcast-go-client/blob/master/serialization/doc.go#L241
- https://github.com/hazelcast/hazelcast-go-client/blob/master/serialization/example_custom_serialization_test.go | non_infrastructure | custom serializer lookup fails when pointers are used for registering in the example and documentation of custom serialization pointers are passed for registering the serializers but in this case lookupcustomserializer method fails and global serialization is used instead to reproduce this issue put a breaking point at and run the custom serialization example following files needs to be updated | 0 |
34,317 | 29,480,281,283 | IssuesEvent | 2023-06-02 04:40:37 | rusefi/rusefi | https://api.github.com/repos/rusefi/rusefi | closed | check for stlink step is hanging | INFRASTRUCTURE | how is that possible?
```
- name: Check for STLINK
run: lsusb | grep 'ST-LINK\|STLINK'
```

https://github.com/rusefi/rusefi/actions/runs/5145343519/jobs/9262858043 | 1.0 | check for stlink step is hanging - how is that possible?
```
- name: Check for STLINK
run: lsusb | grep 'ST-LINK\|STLINK'
```

https://github.com/rusefi/rusefi/actions/runs/5145343519/jobs/9262858043 | infrastructure | check for stlink step is hanging how is that possible name check for stlink run lsusb grep st link stlink | 1 |
21,703 | 14,729,346,883 | IssuesEvent | 2021-01-06 11:18:37 | RasaHQ/rasa-x-helm | https://api.github.com/repos/RasaHQ/rasa-x-helm | closed | Add CHANGELOG | area:rasa-x/infrastructure :steam_locomotive: priority:normal type:enhancement :sparkles: | Add a workflow that generates a changelog for release.
Things that have to be done:
- generate a file with changelog entries
- attach changelog entries to a GH release
- add information to README file on how to create a changelog entry | 1.0 | Add CHANGELOG - Add a workflow that generates a changelog for release.
Things that have to be done:
- generate a file with changelog entries
- attach changelog entries to a GH release
- add information to README file on how to create a changelog entry | infrastructure | add changelog add a workflow that generates a changelog for release things that have to be done generate a file with changelog entries attach changelog entries to a gh release add information to readme file on how to create a changelog entry | 1 |
148,676 | 19,541,002,581 | IssuesEvent | 2021-12-31 23:02:27 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | ArgumentOutOfRangeException at System.Net.Security.SslStream.ProcessBlob | area-System.Net.Security os-linux in pr | ### Description
I'm getting recurring but non consistent exceptions in couple of my environments running the same code under the Docker image `mcr.microsoft.com/dotnet/aspnet:6.0-bullseye-slim`
This only happened in environments where I have an SSL certificate provisioned by `certbot`, but I don't know if its related. Certificate is signed and up to date.
### Reproduction Steps
not consistent
### Expected behavior
No errors on Kestrel level
### Actual behavior
```cs
Microsoft.AspNetCore.Server.Kestrel: Unhandled exception while processing 0HMDG00D520FK.
System.ArgumentOutOfRangeException: Specified argument was out of the range of valid values.
at System.Net.Security.SslStream.ProcessBlob(Int32 frameSize)
at System.Net.Security.SslStream.ReceiveBlobAsync[TIOAdapter](TIOAdapter adapter)
at System.Net.Security.SslStream.ForceAuthenticationAsync[TIOAdapter](TIOAdapter adapter, Boolean receiveFirst, Byte[] reAuthenticationData, Boolean isApm)
at Microsoft.AspNetCore.Server.Kestrel.Https.Internal.HttpsConnectionMiddleware.OnConnectionAsync(ConnectionContext context)
at Microsoft.AspNetCore.Server.Kestrel.Core.Internal.Infrastructure.KestrelConnection`1.ExecuteAsync()
```
### Regression?
Did not observe this in dotnet 5 or core 3.1 that I run beforehand
### Known Workarounds
_No response_
### Configuration
Dotnet `6.0.100`
OS is `Ubuntu 18.0.4` `x86_64 , running Docker image `mcr.microsoft.com/dotnet/aspnet:6.0-bullseye-slim`
### Other information
_No response_ | True | ArgumentOutOfRangeException at System.Net.Security.SslStream.ProcessBlob - ### Description
I'm getting recurring but non consistent exceptions in couple of my environments running the same code under the Docker image `mcr.microsoft.com/dotnet/aspnet:6.0-bullseye-slim`
This only happened in environments where I have an SSL certificate provisioned by `certbot`, but I don't know if its related. Certificate is signed and up to date.
### Reproduction Steps
not consistent
### Expected behavior
No errors on Kestrel level
### Actual behavior
```cs
Microsoft.AspNetCore.Server.Kestrel: Unhandled exception while processing 0HMDG00D520FK.
System.ArgumentOutOfRangeException: Specified argument was out of the range of valid values.
at System.Net.Security.SslStream.ProcessBlob(Int32 frameSize)
at System.Net.Security.SslStream.ReceiveBlobAsync[TIOAdapter](TIOAdapter adapter)
at System.Net.Security.SslStream.ForceAuthenticationAsync[TIOAdapter](TIOAdapter adapter, Boolean receiveFirst, Byte[] reAuthenticationData, Boolean isApm)
at Microsoft.AspNetCore.Server.Kestrel.Https.Internal.HttpsConnectionMiddleware.OnConnectionAsync(ConnectionContext context)
at Microsoft.AspNetCore.Server.Kestrel.Core.Internal.Infrastructure.KestrelConnection`1.ExecuteAsync()
```
### Regression?
Did not observe this in dotnet 5 or core 3.1 that I run beforehand
### Known Workarounds
_No response_
### Configuration
Dotnet `6.0.100`
OS is `Ubuntu 18.0.4` `x86_64 , running Docker image `mcr.microsoft.com/dotnet/aspnet:6.0-bullseye-slim`
### Other information
_No response_ | non_infrastructure | argumentoutofrangeexception at system net security sslstream processblob description i m getting recurring but non consistent exceptions in couple of my environments running the same code under the docker image mcr microsoft com dotnet aspnet bullseye slim this only happened in environments where i have an ssl certificate provisioned by certbot but i don t know if its related certificate is signed and up to date reproduction steps not consistent expected behavior no errors on kestrel level actual behavior cs microsoft aspnetcore server kestrel unhandled exception while processing system argumentoutofrangeexception specified argument was out of the range of valid values at system net security sslstream processblob framesize at system net security sslstream receiveblobasync tioadapter adapter at system net security sslstream forceauthenticationasync tioadapter adapter boolean receivefirst byte reauthenticationdata boolean isapm at microsoft aspnetcore server kestrel https internal httpsconnectionmiddleware onconnectionasync connectioncontext context at microsoft aspnetcore server kestrel core internal infrastructure kestrelconnection executeasync regression did not observe this in dotnet or core that i run beforehand known workarounds no response configuration dotnet os is ubuntu running docker image mcr microsoft com dotnet aspnet bullseye slim other information no response | 0 |
27,783 | 22,337,727,064 | IssuesEvent | 2022-06-14 20:17:51 | bootstrapworld/curriculum | https://api.github.com/repos/bootstrapworld/curriculum | opened | Have build system generate print-ready cover files for lulu | Not urgent Infrastructure | Generating the covers is extremely labor intensive, as Lulu has a ton of specifications that must be met by hand. Investigate whether `pdfjs` could possibly just automate the whole thing. | 1.0 | Have build system generate print-ready cover files for lulu - Generating the covers is extremely labor intensive, as Lulu has a ton of specifications that must be met by hand. Investigate whether `pdfjs` could possibly just automate the whole thing. | infrastructure | have build system generate print ready cover files for lulu generating the covers is extremely labor intensive as lulu has a ton of specifications that must be met by hand investigate whether pdfjs could possibly just automate the whole thing | 1 |
2,051 | 3,488,181,451 | IssuesEvent | 2016-01-02 18:15:17 | spz-signup/spz-signup | https://api.github.com/repos/spz-signup/spz-signup | closed | Move away from Persona | infrastructure security | Persona is dead (unfortunately), better move away from it until it is too late and things will break.
http://www.stavros.io/posts/open-letter-mozilla-bring-back-persona/ | 1.0 | Move away from Persona - Persona is dead (unfortunately), better move away from it until it is too late and things will break.
http://www.stavros.io/posts/open-letter-mozilla-bring-back-persona/ | infrastructure | move away from persona persona is dead unfortunately better move away from it until it is too late and things will break | 1 |
172,242 | 21,043,287,277 | IssuesEvent | 2022-03-31 14:03:53 | TreyM-WSS/WhiteSource-Demo | https://api.github.com/repos/TreyM-WSS/WhiteSource-Demo | opened | CVE-2022-27772 (Medium) detected in spring-boot-1.4.0.RELEASE.jar | security vulnerability | ## CVE-2022-27772 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-1.4.0.RELEASE.jar</b></p></summary>
<p>Spring Boot</p>
<p>Library home page: <a href="http://projects.spring.io/spring-boot/">http://projects.spring.io/spring-boot/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot/1.4.0.RELEASE/spring-boot-1.4.0.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- spring-boot-starter-1.4.0.RELEASE.jar
- :x: **spring-boot-1.4.0.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** UNSUPPORTED WHEN ASSIGNED ** spring-boot versions prior to version v2.2.11.RELEASE was vulnerable to temporary directory hijacking. This vulnerability impacted the org.springframework.boot.web.server.AbstractConfigurableWebServerFactory.createTempDir method. NOTE: This vulnerability only affects products and/or versions that are no longer supported by the maintainer.
<p>Publish Date: 2022-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27772>CVE-2022-27772</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/JLLeitschuh/security-research/security/advisories/GHSA-cm59-pr5q-cw85">https://github.com/JLLeitschuh/security-research/security/advisories/GHSA-cm59-pr5q-cw85</a></p>
<p>Release Date: 2022-03-30</p>
<p>Fix Resolution: org.springframework.boot:spring-boot:2.2.11.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework.boot","packageName":"spring-boot","packageVersion":"1.4.0.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.4.0.RELEASE;org.springframework.boot:spring-boot-starter:1.4.0.RELEASE;org.springframework.boot:spring-boot:1.4.0.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.boot:spring-boot:2.2.11.RELEASE","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-27772","vulnerabilityDetails":"** UNSUPPORTED WHEN ASSIGNED ** spring-boot versions prior to version v2.2.11.RELEASE was vulnerable to temporary directory hijacking. This vulnerability impacted the org.springframework.boot.web.server.AbstractConfigurableWebServerFactory.createTempDir method. NOTE: This vulnerability only affects products and/or versions that are no longer supported by the maintainer.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27772","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-27772 (Medium) detected in spring-boot-1.4.0.RELEASE.jar - ## CVE-2022-27772 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-1.4.0.RELEASE.jar</b></p></summary>
<p>Spring Boot</p>
<p>Library home page: <a href="http://projects.spring.io/spring-boot/">http://projects.spring.io/spring-boot/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/boot/spring-boot/1.4.0.RELEASE/spring-boot-1.4.0.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- spring-boot-starter-1.4.0.RELEASE.jar
- :x: **spring-boot-1.4.0.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** UNSUPPORTED WHEN ASSIGNED ** spring-boot versions prior to version v2.2.11.RELEASE was vulnerable to temporary directory hijacking. This vulnerability impacted the org.springframework.boot.web.server.AbstractConfigurableWebServerFactory.createTempDir method. NOTE: This vulnerability only affects products and/or versions that are no longer supported by the maintainer.
<p>Publish Date: 2022-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27772>CVE-2022-27772</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/JLLeitschuh/security-research/security/advisories/GHSA-cm59-pr5q-cw85">https://github.com/JLLeitschuh/security-research/security/advisories/GHSA-cm59-pr5q-cw85</a></p>
<p>Release Date: 2022-03-30</p>
<p>Fix Resolution: org.springframework.boot:spring-boot:2.2.11.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework.boot","packageName":"spring-boot","packageVersion":"1.4.0.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.4.0.RELEASE;org.springframework.boot:spring-boot-starter:1.4.0.RELEASE;org.springframework.boot:spring-boot:1.4.0.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework.boot:spring-boot:2.2.11.RELEASE","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-27772","vulnerabilityDetails":"** UNSUPPORTED WHEN ASSIGNED ** spring-boot versions prior to version v2.2.11.RELEASE was vulnerable to temporary directory hijacking. This vulnerability impacted the org.springframework.boot.web.server.AbstractConfigurableWebServerFactory.createTempDir method. NOTE: This vulnerability only affects products and/or versions that are no longer supported by the maintainer.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-27772","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_infrastructure | cve medium detected in spring boot release jar cve medium severity vulnerability vulnerable library spring boot release jar spring boot library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework boot spring boot release spring boot release jar dependency hierarchy spring boot starter web release jar root library spring boot starter release jar x spring boot release jar vulnerable library found in base branch master vulnerability details unsupported when assigned spring boot versions prior to version release was vulnerable to temporary directory hijacking this vulnerability impacted the org springframework boot web server abstractconfigurablewebserverfactory createtempdir method note this vulnerability only affects products and or versions that are no longer supported by the maintainer publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework boot spring boot release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter release org springframework boot spring boot release isminimumfixversionavailable true minimumfixversion org springframework boot spring boot release isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails unsupported when assigned spring boot versions prior to version release was vulnerable to temporary directory hijacking this vulnerability impacted the org springframework boot web server abstractconfigurablewebserverfactory createtempdir method note this vulnerability only affects products and or versions that are no longer supported by the maintainer vulnerabilityurl | 0 |
49,126 | 6,148,210,738 | IssuesEvent | 2017-06-27 17:19:47 | phetsims/tasks | https://api.github.com/repos/phetsims/tasks | closed | Artwork for Coulomb's Law | design:artwork priority:3-medium | @clmccutchan we're working on a new sim called Coulomb's Law. It will be somewhat similar to [Gravity Force Lab](https://phet.colorado.edu/sims/html/gravity-force-lab/latest/gravity-force-lab_en.html), as they're both inverse square laws. In Gravity Force Lab, there are figures that pull against the masses so that they don't accelerate towards one another.

In Coulomb's Law, we'll be dealing with attractive and repulsive forces, so we'll need artwork for figures that are able to push and pull against the charges. Somewhat recently, we updated the pushers in [Forces and Motion: Basics](https://phet.colorado.edu/sims/html/forces-and-motion-basics/latest/forces-and-motion-basics_en.html) (pushers are in screens 2-4). We would like to create pullers in the same style to use in Coulomb's Law. I will email you the .ai file for the pushers.
I think it may be helpful if we could schedule a short Zoom chat sometime next week. We can coordinate via email to set up a time.
| 1.0 | Artwork for Coulomb's Law - @clmccutchan we're working on a new sim called Coulomb's Law. It will be somewhat similar to [Gravity Force Lab](https://phet.colorado.edu/sims/html/gravity-force-lab/latest/gravity-force-lab_en.html), as they're both inverse square laws. In Gravity Force Lab, there are figures that pull against the masses so that they don't accelerate towards one another.

In Coulomb's Law, we'll be dealing with attractive and repulsive forces, so we'll need artwork for figures that are able to push and pull against the charges. Somewhat recently, we updated the pushers in [Forces and Motion: Basics](https://phet.colorado.edu/sims/html/forces-and-motion-basics/latest/forces-and-motion-basics_en.html) (pushers are in screens 2-4). We would like to create pullers in the same style to use in Coulomb's Law. I will email you the .ai file for the pushers.
I think it may be helpful if we could schedule a short Zoom chat sometime next week. We can coordinate via email to set up a time.
| non_infrastructure | artwork for coulomb s law clmccutchan we re working on a new sim called coulomb s law it will be somewhat similar to as they re both inverse square laws in gravity force lab there are figures that pull against the masses so that they don t accelerate towards one another in coulomb s law we ll be dealing with attractive and repulsive forces so we ll need artwork for figures that are able to push and pull against the charges somewhat recently we updated the pushers in pushers are in screens we would like to create pullers in the same style to use in coulomb s law i will email you the ai file for the pushers i think it may be helpful if we could schedule a short zoom chat sometime next week we can coordinate via email to set up a time | 0 |
15,129 | 11,360,992,198 | IssuesEvent | 2020-01-26 11:48:50 | Zilliqa/scilla | https://api.github.com/repos/Zilliqa/scilla | closed | Scilla v0.5.1 tarball does not contain dependencies | infrastructure | I am trying to compile the latest scilla release. on Ubuntu 18.04 (via Windows Subsystem for linux)
but I get;
`
CMake Error: The source directory "/home/as1ndu/scilla-0.5.1/deps/libff/src" does not appear to contain CMakeLists.txt.
`
This `CMakeLists.txt` file doesn't seem to exist in the entire scilla codebase. What am I missing?
| 1.0 | Scilla v0.5.1 tarball does not contain dependencies - I am trying to compile the latest scilla release. on Ubuntu 18.04 (via Windows Subsystem for linux)
but I get;
`
CMake Error: The source directory "/home/as1ndu/scilla-0.5.1/deps/libff/src" does not appear to contain CMakeLists.txt.
`
This `CMakeLists.txt` file doesn't seem to exist in the entire scilla codebase. What am I missing?
| infrastructure | scilla tarball does not contain dependencies i am trying to compile the latest scilla release on ubuntu via windows subsystem for linux but i get cmake error the source directory home scilla deps libff src does not appear to contain cmakelists txt this cmakelists txt file doesn t seem to exist in the entire scilla codebase what am i missing | 1 |
20,496 | 13,942,197,357 | IssuesEvent | 2020-10-22 20:37:54 | alaoweb/2020.alaoweb.org | https://api.github.com/repos/alaoweb/2020.alaoweb.org | closed | Open Website on Friday Before Conference Week | infrastructure | - [ ] Distribute conference site password to Attendees list
- [ ] Update Netlify 'Production Builds' to enable basic authentication
- [ ] Enable session and poster content on site
- [ ] Test authentication, session video playback, etc... | 1.0 | Open Website on Friday Before Conference Week - - [ ] Distribute conference site password to Attendees list
- [ ] Update Netlify 'Production Builds' to enable basic authentication
- [ ] Enable session and poster content on site
- [ ] Test authentication, session video playback, etc... | infrastructure | open website on friday before conference week distribute conference site password to attendees list update netlify production builds to enable basic authentication enable session and poster content on site test authentication session video playback etc | 1 |
292,110 | 8,953,283,230 | IssuesEvent | 2019-01-25 18:59:30 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | "Reset Defaults" in graphics settings not reset sliders | Fixed Medium Priority | reset works only with check boxes, not sliders.
Same on release and master versions.
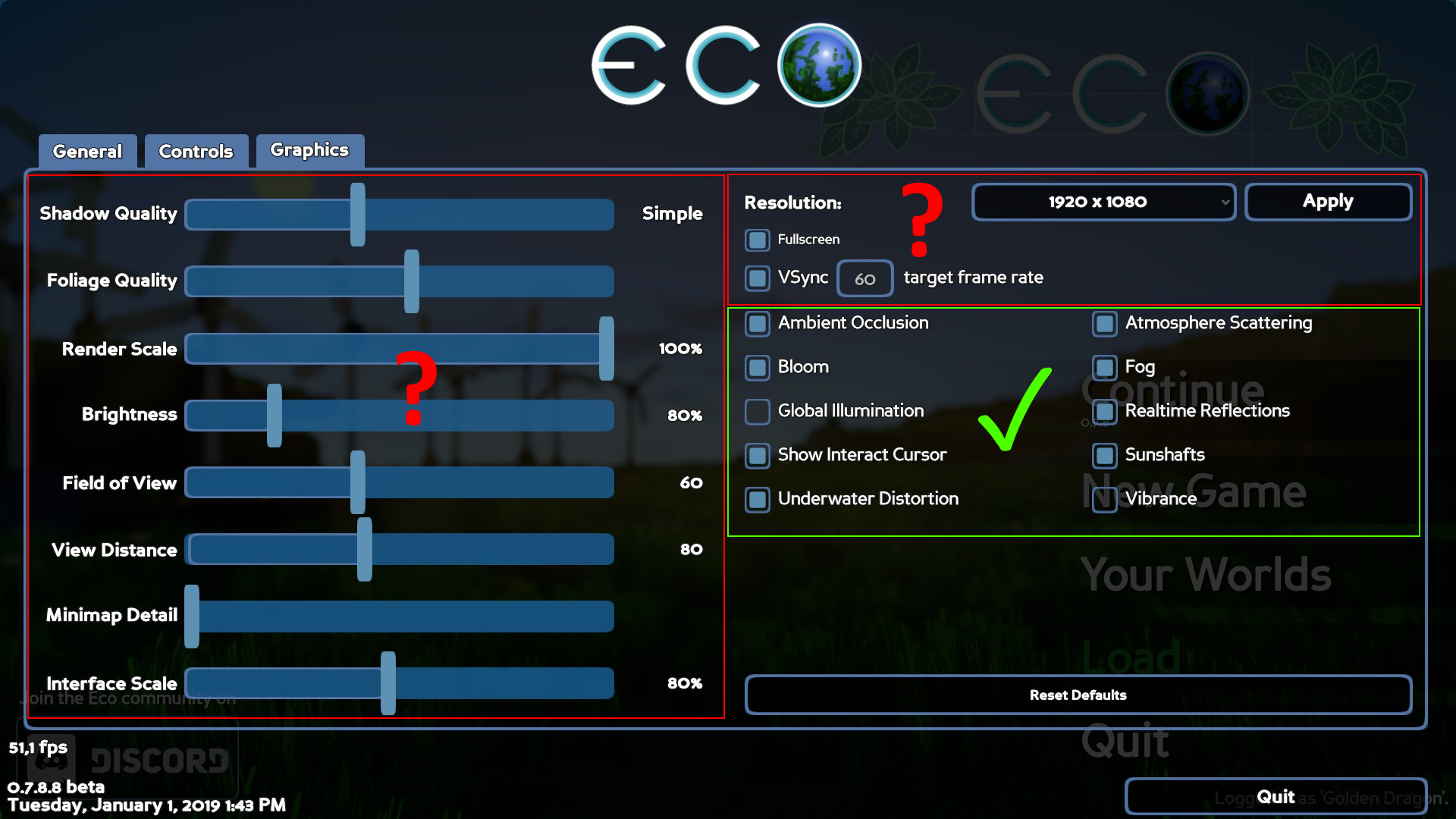
| 1.0 | "Reset Defaults" in graphics settings not reset sliders - reset works only with check boxes, not sliders.
Same on release and master versions.
| non_infrastructure | reset defaults in graphics settings not reset sliders reset works only with check boxes not sliders same on release and master versions | 0 |
806 | 2,918,934,230 | IssuesEvent | 2015-06-24 11:20:50 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Using roslyn in mac | Area-Infrastructure Portability | Hello, I'm new to C#/roslyn.
I want to look through parsing parts of roslyn.
I followed instructions here (https://github.com/dotnet/roslyn/blob/master/docs/infrastructure/cross-platform.md) and it succeeded.
However, I cannot execute .exe file in mac.
What would be the next step?
Also, I can't get how to run .csproj projects. (I tried Xamarin studio but it failed)
| 1.0 | Using roslyn in mac - Hello, I'm new to C#/roslyn.
I want to look through parsing parts of roslyn.
I followed instructions here (https://github.com/dotnet/roslyn/blob/master/docs/infrastructure/cross-platform.md) and it succeeded.
However, I cannot execute .exe file in mac.
What would be the next step?
Also, I can't get how to run .csproj projects. (I tried Xamarin studio but it failed)
| infrastructure | using roslyn in mac hello i m new to c roslyn i want to look through parsing parts of roslyn i followed instructions here and it succeeded however i cannot execute exe file in mac what would be the next step also i can t get how to run csproj projects i tried xamarin studio but it failed | 1 |
25,095 | 18,105,091,796 | IssuesEvent | 2021-09-22 18:18:13 | emory-libraries/blacklight-catalog | https://api.github.com/repos/emory-libraries/blacklight-catalog | opened | SPIKE: Investigate issues with page load time performance and provide suggestions for improvement | Application Development Infrastructure | The page load time for search.libraries.emory.edu and blackcat-test.library.emory.edu have become slower to load over the last month or so. The average page load time is about 7 seconds (slightly better for blackcat-arch) and the desired page load time should be under 5 seconds. For comparison of other Blacklight catalog products the following is used for benchmarking:
- [Temple University Library Search](https://librarysearch.temple.edu/catalog) - less than 2 seconds (no search initiated and not logged in)
- [Stanford Searchworks](https://searchworks.stanford.edu/) - less than 2 seconds (no search initiated and not logged in)
- [ ] I would like for the infrastructure and possibly application development team to research any errors or issues that might be indicative of a performance issue on the home page for either environment (production or test)
- [ ] If there are no errors or issues apparent, I would like for both teams to investigate how we might improve page load times including looking at connections to Solr, our AWS setup, API's to Alma, or facets that appear on the home page as possible reasons why our page times are so much slower than Temple or Stanford.
- [ ] Document all findings within this ticket along with a recommendation to improve performance.
| 1.0 | SPIKE: Investigate issues with page load time performance and provide suggestions for improvement - The page load time for search.libraries.emory.edu and blackcat-test.library.emory.edu have become slower to load over the last month or so. The average page load time is about 7 seconds (slightly better for blackcat-arch) and the desired page load time should be under 5 seconds. For comparison of other Blacklight catalog products the following is used for benchmarking:
- [Temple University Library Search](https://librarysearch.temple.edu/catalog) - less than 2 seconds (no search initiated and not logged in)
- [Stanford Searchworks](https://searchworks.stanford.edu/) - less than 2 seconds (no search initiated and not logged in)
- [ ] I would like for the infrastructure and possibly application development team to research any errors or issues that might be indicative of a performance issue on the home page for either environment (production or test)
- [ ] If there are no errors or issues apparent, I would like for both teams to investigate how we might improve page load times including looking at connections to Solr, our AWS setup, API's to Alma, or facets that appear on the home page as possible reasons why our page times are so much slower than Temple or Stanford.
- [ ] Document all findings within this ticket along with a recommendation to improve performance.
| infrastructure | spike investigate issues with page load time performance and provide suggestions for improvement the page load time for search libraries emory edu and blackcat test library emory edu have become slower to load over the last month or so the average page load time is about seconds slightly better for blackcat arch and the desired page load time should be under seconds for comparison of other blacklight catalog products the following is used for benchmarking less than seconds no search initiated and not logged in less than seconds no search initiated and not logged in i would like for the infrastructure and possibly application development team to research any errors or issues that might be indicative of a performance issue on the home page for either environment production or test if there are no errors or issues apparent i would like for both teams to investigate how we might improve page load times including looking at connections to solr our aws setup api s to alma or facets that appear on the home page as possible reasons why our page times are so much slower than temple or stanford document all findings within this ticket along with a recommendation to improve performance | 1 |
10,800 | 8,728,252,771 | IssuesEvent | 2018-12-10 16:54:45 | spacetelescope/notebooks | https://api.github.com/repos/spacetelescope/notebooks | opened | Show a per-notebook table of contents | Infrastructure | Right now to get a table of contents, the notebook creator has to do so manually with built-in HTML links. This can be distracting, is brittle (a later modifier may not think to update the TOC), and isn't guaranteed to be compatible with future browser interfaces (e.g. Jupyter Lab).
A safer bet is to have a generated TOC that infers the structure from the form of the headers. I'm taking inspiration from the sphinx-based approach to building notebooks:

(from http://www.astropy.org/astropy-tutorials/rst-tutorials/UVES.html)
There are two possible implementation paths I see:
1. Have some javascript that at-page-load figures out the structure from the headers and generates the TOC on the fly. (Probably a bit simpler, but requires javascript/at-load-time modification of the page)
2. Add the TOC to the jinja2 template for the pages. This would need to either get passed in the header-structure, or need some extra logic in `nbpages` to read a "first round" HTML for headers which then gets re-processed. (static in the page, but probably a bit more complex to code up).
I think the fastest approach might be to start with 1, and then try to implement 2 when there's a bit more time.
Assigning myself, although if anyone else wants to take a crack at it I'm all ears! | 1.0 | Show a per-notebook table of contents - Right now to get a table of contents, the notebook creator has to do so manually with built-in HTML links. This can be distracting, is brittle (a later modifier may not think to update the TOC), and isn't guaranteed to be compatible with future browser interfaces (e.g. Jupyter Lab).
A safer bet is to have a generated TOC that infers the structure from the form of the headers. I'm taking inspiration from the sphinx-based approach to building notebooks:

(from http://www.astropy.org/astropy-tutorials/rst-tutorials/UVES.html)
There are two possible implementation paths I see:
1. Have some javascript that at-page-load figures out the structure from the headers and generates the TOC on the fly. (Probably a bit simpler, but requires javascript/at-load-time modification of the page)
2. Add the TOC to the jinja2 template for the pages. This would need to either get passed in the header-structure, or need some extra logic in `nbpages` to read a "first round" HTML for headers which then gets re-processed. (static in the page, but probably a bit more complex to code up).
I think the fastest approach might be to start with 1, and then try to implement 2 when there's a bit more time.
Assigning myself, although if anyone else wants to take a crack at it I'm all ears! | infrastructure | show a per notebook table of contents right now to get a table of contents the notebook creator has to do so manually with built in html links this can be distracting is brittle a later modifier may not think to update the toc and isn t guaranteed to be compatible with future browser interfaces e g jupyter lab a safer bet is to have a generated toc that infers the structure from the form of the headers i m taking inspiration from the sphinx based approach to building notebooks from there are two possible implementation paths i see have some javascript that at page load figures out the structure from the headers and generates the toc on the fly probably a bit simpler but requires javascript at load time modification of the page add the toc to the template for the pages this would need to either get passed in the header structure or need some extra logic in nbpages to read a first round html for headers which then gets re processed static in the page but probably a bit more complex to code up i think the fastest approach might be to start with and then try to implement when there s a bit more time assigning myself although if anyone else wants to take a crack at it i m all ears | 1 |
336,681 | 30,214,847,813 | IssuesEvent | 2023-07-05 14:56:31 | istio/istio | https://api.github.com/repos/istio/istio | closed | build-base-images and release-builder specify creation and use of two different build instances | area/test and release lifecycle/staleproof | ### Bug Description
Looking in the logs for the base image check and build if vulnerable I see:
```
2022-04-11T19:01:28.498747Z info Running command: docker buildx create --name multi-arch --platform linux/amd64,linux/arm64 --use
multi-arch
2022-04-11T19:01:28.624854Z info Running command: tools/build-base-images.sh
+ source /tmp/tmp.8PdYWO48P3/build/work/src/istio.io/istio/prow/lib.sh
+ buildx-create
+ export DOCKER_CLI_EXPERIMENTAL=enabled
+ DOCKER_CLI_EXPERIMENTAL=enabled
+ docker buildx ls
+ grep -q container-builder
+ docker buildx create --driver-opt network=host,image=gcr.io/istio-testing/buildkit:v0.9.2 --name container-builder --buildkitd-flags=--debug
container-builder
+ docker buildx inspect --bootstrap container-builder
#1 [internal] booting buildkit
#1 pulling image gcr.io/istio-testing/buildkit:v0.9.2
#1 pulling image gcr.io/istio-testing/buildkit:v0.9.2 4.1s done
#1 creating container buildx_buildkit_container-builder0
#1 creating container buildx_buildkit_container-builder0 1.1s done
#1 DONE 5.2s
Name: container-builder
Driver: docker-container
Nodes:
Name: container-builder0
Endpoint: unix:///var/run/docker.sock
Status: running
Flags: --debug
Platforms: linux/amd64, linux/arm64, linux/riscv64, linux/ppc64le, linux/s390x, linux/386, linux/mips64le, linux/mips64, linux/arm/v7, linux/arm/v6
+ docker buildx use container-builder
```
It looks the `release-builder` code creates one builder instance to use and then we later create another and use it within the build-base-images script.
### Version
```prose
main branch of istio/release-builder and istio/istio.
```
### Additional Information
_No response_ | 1.0 | build-base-images and release-builder specify creation and use of two different build instances - ### Bug Description
Looking in the logs for the base image check and build if vulnerable I see:
```
2022-04-11T19:01:28.498747Z info Running command: docker buildx create --name multi-arch --platform linux/amd64,linux/arm64 --use
multi-arch
2022-04-11T19:01:28.624854Z info Running command: tools/build-base-images.sh
+ source /tmp/tmp.8PdYWO48P3/build/work/src/istio.io/istio/prow/lib.sh
+ buildx-create
+ export DOCKER_CLI_EXPERIMENTAL=enabled
+ DOCKER_CLI_EXPERIMENTAL=enabled
+ docker buildx ls
+ grep -q container-builder
+ docker buildx create --driver-opt network=host,image=gcr.io/istio-testing/buildkit:v0.9.2 --name container-builder --buildkitd-flags=--debug
container-builder
+ docker buildx inspect --bootstrap container-builder
#1 [internal] booting buildkit
#1 pulling image gcr.io/istio-testing/buildkit:v0.9.2
#1 pulling image gcr.io/istio-testing/buildkit:v0.9.2 4.1s done
#1 creating container buildx_buildkit_container-builder0
#1 creating container buildx_buildkit_container-builder0 1.1s done
#1 DONE 5.2s
Name: container-builder
Driver: docker-container
Nodes:
Name: container-builder0
Endpoint: unix:///var/run/docker.sock
Status: running
Flags: --debug
Platforms: linux/amd64, linux/arm64, linux/riscv64, linux/ppc64le, linux/s390x, linux/386, linux/mips64le, linux/mips64, linux/arm/v7, linux/arm/v6
+ docker buildx use container-builder
```
It looks the `release-builder` code creates one builder instance to use and then we later create another and use it within the build-base-images script.
### Version
```prose
main branch of istio/release-builder and istio/istio.
```
### Additional Information
_No response_ | non_infrastructure | build base images and release builder specify creation and use of two different build instances bug description looking in the logs for the base image check and build if vulnerable i see info running command docker buildx create name multi arch platform linux linux use multi arch info running command tools build base images sh source tmp tmp build work src istio io istio prow lib sh buildx create export docker cli experimental enabled docker cli experimental enabled docker buildx ls grep q container builder docker buildx create driver opt network host image gcr io istio testing buildkit name container builder buildkitd flags debug container builder docker buildx inspect bootstrap container builder booting buildkit pulling image gcr io istio testing buildkit pulling image gcr io istio testing buildkit done creating container buildx buildkit container creating container buildx buildkit container done done name container builder driver docker container nodes name container endpoint unix var run docker sock status running flags debug platforms linux linux linux linux linux linux linux linux linux arm linux arm docker buildx use container builder it looks the release builder code creates one builder instance to use and then we later create another and use it within the build base images script version prose main branch of istio release builder and istio istio additional information no response | 0 |
262,625 | 8,272,226,442 | IssuesEvent | 2018-09-16 17:54:16 | javaee/glassfish | https://api.github.com/repos/javaee/glassfish | closed | Config to disable automatic timer migration on instance stop/crash | Component: ejb_container ERR: Assignee Priority: Major Type: Improvement | Right now, there is no configuration to disable automatic timer migration on
instance stop if GMS is enabled. It would be nice to have that feature so that
user can have choice of using automatic migration of timer or migrate-timers CLI.
#### Environment
Operating System: Linux
Platform: Linux
#### Affected Versions
[3.1] | 1.0 | Config to disable automatic timer migration on instance stop/crash - Right now, there is no configuration to disable automatic timer migration on
instance stop if GMS is enabled. It would be nice to have that feature so that
user can have choice of using automatic migration of timer or migrate-timers CLI.
#### Environment
Operating System: Linux
Platform: Linux
#### Affected Versions
[3.1] | non_infrastructure | config to disable automatic timer migration on instance stop crash right now there is no configuration to disable automatic timer migration on instance stop if gms is enabled it would be nice to have that feature so that user can have choice of using automatic migration of timer or migrate timers cli environment operating system linux platform linux affected versions | 0 |
34,632 | 30,233,925,882 | IssuesEvent | 2023-07-06 08:55:40 | ministryofjustice/data-platform | https://api.github.com/repos/ministryofjustice/data-platform | closed | Continue Experimenting with Data Catalogue POC - CKAN | Data Platform Core Infrastructure | ## User Story
We would like to experiment with adding public and potential AP datasets into our candidates to see if we can arrive at a state that allows user research.
## User Type(s)
Developers and Data Engineers
## Value
We want to put candidates in a state where other people can start testing them.
## Questions / Assumptions / Hypothesis
<!-- Additional information to explain approach taken
### Hypothesis
If we... [do a thing]
Then... [this will happ]
### Proposal
A proposal that is something testable, don't worry whether it works or not, it's a place for ideas.
-->
## Definition of done
<!-- Checklist for definition of done and acceptance criteria, for example: -->
- [ ] Ingest a public datasource
- [ ] Ingest an AP datasource
- [ ] Timeboxed to 3 days
- [ ] tests are green
- [ ] Follow-on stories raised
## Reference
[How to write good user stories](https://www.gov.uk/service-manual/agile-delivery/writing-user-stories)
| 1.0 | Continue Experimenting with Data Catalogue POC - CKAN - ## User Story
We would like to experiment with adding public and potential AP datasets into our candidates to see if we can arrive at a state that allows user research.
## User Type(s)
Developers and Data Engineers
## Value
We want to put candidates in a state where other people can start testing them.
## Questions / Assumptions / Hypothesis
<!-- Additional information to explain approach taken
### Hypothesis
If we... [do a thing]
Then... [this will happ]
### Proposal
A proposal that is something testable, don't worry whether it works or not, it's a place for ideas.
-->
## Definition of done
<!-- Checklist for definition of done and acceptance criteria, for example: -->
- [ ] Ingest a public datasource
- [ ] Ingest an AP datasource
- [ ] Timeboxed to 3 days
- [ ] tests are green
- [ ] Follow-on stories raised
## Reference
[How to write good user stories](https://www.gov.uk/service-manual/agile-delivery/writing-user-stories)
| infrastructure | continue experimenting with data catalogue poc ckan user story we would like to experiment with adding public and potential ap datasets into our candidates to see if we can arrive at a state that allows user research user type s developers and data engineers value we want to put candidates in a state where other people can start testing them questions assumptions hypothesis additional information to explain approach taken hypothesis if we then proposal a proposal that is something testable don t worry whether it works or not it s a place for ideas definition of done ingest a public datasource ingest an ap datasource timeboxed to days tests are green follow on stories raised reference | 1 |
27,846 | 22,442,085,888 | IssuesEvent | 2022-06-21 02:30:47 | ZcashFoundation/zebra | https://api.github.com/repos/ZcashFoundation/zebra | closed | Add a CI job which compiles each Zebra crate individually | A-rust A-infrastructure A-devops C-enhancement P-Medium :zap: | ## Motivation
Sometimes we add code that needs a feature to a Zebra crate, then activate that feature in `zebrad`. But we forget to activate the feature in the crate that actually contains the code.
For an example, see PR #1365, where individual crates use features in their dependencies, but don't declare those features in their `Cargo.toml`.
## Design
- [ ] Build each Zebra crate individually in a CI job, including Zebra's custom Tower crates
- [ ] Fail the PR if any build fails.
We should add a new CI job, so that we don't slow down existing jobs.
Example script:
```sh
for crate in tower* zebra*; do
pushd "$crate"
cargo build
popd
done
```
## Related Work
- #4550
## Alternatives
<details>
Continue to occasionally break crates when they're used individually.
We can implement theses checks using `cargo-hack --workspace`:
- Build all targets (library, binary, example, test, and benchmark)
- Build the `--feature-powerset`
</details>
## Follow Up Tasks
<details>
- [ ] Also test if the crate is packaged succesfully (`cargo package`)
- [ ] Also test if it compiles/packages with the MSRV (and specify one if it doesn't)
</details> | 1.0 | Add a CI job which compiles each Zebra crate individually - ## Motivation
Sometimes we add code that needs a feature to a Zebra crate, then activate that feature in `zebrad`. But we forget to activate the feature in the crate that actually contains the code.
For an example, see PR #1365, where individual crates use features in their dependencies, but don't declare those features in their `Cargo.toml`.
## Design
- [ ] Build each Zebra crate individually in a CI job, including Zebra's custom Tower crates
- [ ] Fail the PR if any build fails.
We should add a new CI job, so that we don't slow down existing jobs.
Example script:
```sh
for crate in tower* zebra*; do
pushd "$crate"
cargo build
popd
done
```
## Related Work
- #4550
## Alternatives
<details>
Continue to occasionally break crates when they're used individually.
We can implement theses checks using `cargo-hack --workspace`:
- Build all targets (library, binary, example, test, and benchmark)
- Build the `--feature-powerset`
</details>
## Follow Up Tasks
<details>
- [ ] Also test if the crate is packaged succesfully (`cargo package`)
- [ ] Also test if it compiles/packages with the MSRV (and specify one if it doesn't)
</details> | infrastructure | add a ci job which compiles each zebra crate individually motivation sometimes we add code that needs a feature to a zebra crate then activate that feature in zebrad but we forget to activate the feature in the crate that actually contains the code for an example see pr where individual crates use features in their dependencies but don t declare those features in their cargo toml design build each zebra crate individually in a ci job including zebra s custom tower crates fail the pr if any build fails we should add a new ci job so that we don t slow down existing jobs example script sh for crate in tower zebra do pushd crate cargo build popd done related work alternatives continue to occasionally break crates when they re used individually we can implement theses checks using cargo hack workspace build all targets library binary example test and benchmark build the feature powerset follow up tasks also test if the crate is packaged succesfully cargo package also test if it compiles packages with the msrv and specify one if it doesn t | 1 |
269,134 | 28,960,011,566 | IssuesEvent | 2023-05-10 01:08:06 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | reopened | CVE-2014-0038 (High) detected in linuxv3.0 | Mend: dependency security vulnerability | ## CVE-2014-0038 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (0)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The compat_sys_recvmmsg function in net/compat.c in the Linux kernel before 3.13.2, when CONFIG_X86_X32 is enabled, allows local users to gain privileges via a recvmmsg system call with a crafted timeout pointer parameter.
<p>Publish Date: 2014-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0038>CVE-2014-0038</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-0038">https://nvd.nist.gov/vuln/detail/CVE-2014-0038</a></p>
<p>Release Date: 2014-02-06</p>
<p>Fix Resolution: 3.13.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2014-0038 (High) detected in linuxv3.0 - ## CVE-2014-0038 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (0)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The compat_sys_recvmmsg function in net/compat.c in the Linux kernel before 3.13.2, when CONFIG_X86_X32 is enabled, allows local users to gain privileges via a recvmmsg system call with a crafted timeout pointer parameter.
<p>Publish Date: 2014-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0038>CVE-2014-0038</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-0038">https://nvd.nist.gov/vuln/detail/CVE-2014-0038</a></p>
<p>Release Date: 2014-02-06</p>
<p>Fix Resolution: 3.13.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in cve high severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details the compat sys recvmmsg function in net compat c in the linux kernel before when config is enabled allows local users to gain privileges via a recvmmsg system call with a crafted timeout pointer parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
8,707 | 7,573,548,771 | IssuesEvent | 2018-04-23 18:06:54 | Dallas-Makerspace/tracker | https://api.github.com/repos/Dallas-Makerspace/tracker | closed | (Feat) Pre-prod and Prod LX compute Nodes | CR/enhancement Committee/Infrastructure Committee/VCC Priority/MEDIUM System/Community Grid System/Load Balencer wontfix | * **Acceptance Criteria**
- Should add pprlxcompute-* to swarm cluster with label `local.dms.environment==preprod`
- Should add prlxcompute-* to swarm cluster with label `local.dms.environment==prod`
- Should update edge.dms.local to have pass thru load balancing between each for 80/tcp and 443/tcp
- Should update edge.dms.local to have allow external access via `uat.dallas.ms` to `uat.communitygrid`
- Should update edge.dms.local to have allow external access via `apps.dallas.ms` to `apps.communitygrid`
- Should update edge.dms.local to have allow external access via `api.dallas.ms` to `api.communitygrid`
- Should update edge.dms.local to have api.dallas.ms route to `api.communitygrid` with `X-ENV` Header | 1.0 | (Feat) Pre-prod and Prod LX compute Nodes - * **Acceptance Criteria**
- Should add pprlxcompute-* to swarm cluster with label `local.dms.environment==preprod`
- Should add prlxcompute-* to swarm cluster with label `local.dms.environment==prod`
- Should update edge.dms.local to have pass thru load balancing between each for 80/tcp and 443/tcp
- Should update edge.dms.local to have allow external access via `uat.dallas.ms` to `uat.communitygrid`
- Should update edge.dms.local to have allow external access via `apps.dallas.ms` to `apps.communitygrid`
- Should update edge.dms.local to have allow external access via `api.dallas.ms` to `api.communitygrid`
- Should update edge.dms.local to have api.dallas.ms route to `api.communitygrid` with `X-ENV` Header | infrastructure | feat pre prod and prod lx compute nodes acceptance criteria should add pprlxcompute to swarm cluster with label local dms environment preprod should add prlxcompute to swarm cluster with label local dms environment prod should update edge dms local to have pass thru load balancing between each for tcp and tcp should update edge dms local to have allow external access via uat dallas ms to uat communitygrid should update edge dms local to have allow external access via apps dallas ms to apps communitygrid should update edge dms local to have allow external access via api dallas ms to api communitygrid should update edge dms local to have api dallas ms route to api communitygrid with x env header | 1 |
179,497 | 21,571,551,864 | IssuesEvent | 2022-05-02 08:50:29 | vital-ws/modern-monorepo-boilerplate | https://api.github.com/repos/vital-ws/modern-monorepo-boilerplate | closed | lerna-3.22.1.tgz: 19 vulnerabilities (highest severity is: 9.8) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lerna-3.22.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-23369](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23369) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.7.6.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-44906](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | minimist-1.2.5.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23383](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.7.6.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-7774](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | y18n-4.0.0.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-37701](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-37712](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-37713](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-32804](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-32803](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-28469](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-5.1.1.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-33623](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Transitive | 4.0.0 | ✅ |
| [CVE-2021-33502](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | normalize-url-3.3.0.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-27290](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | ssri-6.0.1.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-7788](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.5.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-23337](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | lodash-4.17.20.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2022-0235](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.1.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23425](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | trim-off-newlines-1.0.1.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-28500](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | lodash-4.17.20.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-23362](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | hosted-git-info-2.8.8.tgz | Transitive | 4.0.0 | ✅ |
## Details
> Partial details (11 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23369</summary>
### Vulnerable Library - <b>handlebars-4.7.6.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- conventional-changelog-writer-4.0.17.tgz
- :x: **handlebars-4.7.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Remote Code Execution (RCE) when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23369>CVE-2021-23369</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution (handlebars): 4.7.7</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44906</summary>
### Vulnerable Library - <b>minimist-1.2.5.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- get-pkg-repo-1.4.0.tgz
- meow-3.7.0.tgz
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23383</summary>
### Vulnerable Library - <b>handlebars-4.7.6.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- conventional-changelog-writer-4.0.17.tgz
- :x: **handlebars-4.7.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383>CVE-2021-23383</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution (handlebars): 4.7.7</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-4.0.0.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz">https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- npm-registry-fetch-4.0.0.tgz
- make-fetch-happen-5.0.2.tgz
- cacache-12.0.4.tgz
- :x: **y18n-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n = require('y18n')(); y18n.setLocale('__proto__'); y18n.updateLocale({polluted: true}); console.log(polluted); // true
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 4.0.1</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37701</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\` and `/` characters as path separators, however `\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701>CVE-2021-37701</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc">https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.16</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37712</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 "short path" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712>CVE-2021-37712</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p">https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37713</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\path`. If the drive letter does not match the extraction target, for example `D:\extraction\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713>CVE-2021-37713</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh">https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-32804</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 4.4.14</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-32803</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803>CVE-2021-32803</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw">https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 4.4.15</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-5.1.1.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- info-3.21.0.tgz
- command-3.21.0.tgz
- project-3.21.0.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33623</summary>
### Vulnerable Libraries - <b>trim-newlines-3.0.0.tgz</b>, <b>trim-newlines-1.0.0.tgz</b></p>
<p>
### <b>trim-newlines-3.0.0.tgz</b></p>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- conventional-commits-parser-3.1.0.tgz
- meow-7.1.1.tgz
- :x: **trim-newlines-3.0.0.tgz** (Vulnerable Library)
### <b>trim-newlines-1.0.0.tgz</b></p>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- get-pkg-repo-1.4.0.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution (trim-newlines): 3.0.1</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p><p>Fix Resolution (trim-newlines): 3.0.1</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23369","vulnerabilityDetails":"The package handlebars before 4.7.7 are vulnerable to Remote Code Execution (RCE) when selecting certain compiling options to compile templates coming from an untrusted source.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23369","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"lerna:3.22.1;@lerna/version:3.22.1;@lerna/conventional-commits:3.22.0;conventional-changelog-core:3.2.3;get-pkg-repo:1.4.0;meow:3.7.0;minimist:1.2.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 1.2.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23383","vulnerabilityDetails":"The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7774","vulnerabilityDetails":"This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n \u003d require(\u0027y18n\u0027)(); y18n.setLocale(\u0027__proto__\u0027); y18n.updateLocale({polluted: true}); console.log(polluted); // true","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-37701","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\\` and `/` characters as path separators, however `\\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-37712","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 \"short path\" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-37713","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\\path`. If the drive letter does not match the extraction target, for example `D:\\extraction\\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32804","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32803","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28469","vulnerabilityDetails":"This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false},{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33623","vulnerabilityDetails":"The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33502","vulnerabilityDetails":"The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-27290","vulnerabilityDetails":"ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7788","vulnerabilityDetails":"This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"2.6.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"lerna:3.22.1;@lerna/version:3.22.1;@lerna/github-client:3.22.0;@octokit/rest:16.43.2;@octokit/request:5.4.9;node-fetch:2.6.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"node-fetch - 2.6.7,3.1.1","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0235","vulnerabilityDetails":"node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23425","vulnerabilityDetails":"All versions of package trim-off-newlines are vulnerable to Regular Expression Denial of Service (ReDoS) via string processing.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23425","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.\n WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23362","vulnerabilityDetails":"The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | lerna-3.22.1.tgz: 19 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lerna-3.22.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-23369](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23369) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.7.6.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-44906](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | minimist-1.2.5.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23383](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | handlebars-4.7.6.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-7774](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | y18n-4.0.0.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-37701](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-37712](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-37713](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-32804](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-32803](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tar-4.4.13.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-28469](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-5.1.1.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-33623](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Transitive | 4.0.0 | ✅ |
| [CVE-2021-33502](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | normalize-url-3.3.0.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-27290](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | ssri-6.0.1.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-7788](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.5.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-23337](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | lodash-4.17.20.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2022-0235](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.1.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23425](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | trim-off-newlines-1.0.1.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2020-28500](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | lodash-4.17.20.tgz | Transitive | 4.0.0 | ✅ |
| [CVE-2021-23362](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | hosted-git-info-2.8.8.tgz | Transitive | 4.0.0 | ✅ |
## Details
> Partial details (11 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23369</summary>
### Vulnerable Library - <b>handlebars-4.7.6.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- conventional-changelog-writer-4.0.17.tgz
- :x: **handlebars-4.7.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Remote Code Execution (RCE) when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23369>CVE-2021-23369</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23369</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution (handlebars): 4.7.7</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-44906</summary>
### Vulnerable Library - <b>minimist-1.2.5.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- get-pkg-repo-1.4.0.tgz
- meow-3.7.0.tgz
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23383</summary>
### Vulnerable Library - <b>handlebars-4.7.6.tgz</b></p>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.7.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- conventional-changelog-writer-4.0.17.tgz
- :x: **handlebars-4.7.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383>CVE-2021-23383</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution (handlebars): 4.7.7</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-4.0.0.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz">https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- npm-registry-fetch-4.0.0.tgz
- make-fetch-happen-5.0.2.tgz
- cacache-12.0.4.tgz
- :x: **y18n-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n = require('y18n')(); y18n.setLocale('__proto__'); y18n.updateLocale({polluted: true}); console.log(polluted); // true
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 4.0.1</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37701</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\` and `/` characters as path separators, however `\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701>CVE-2021-37701</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc">https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.16</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37712</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 "short path" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712>CVE-2021-37712</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p">https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37713</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\path`. If the drive letter does not match the extraction target, for example `D:\extraction\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713>CVE-2021-37713</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh">https://github.com/npm/node-tar/security/advisories/GHSA-5955-9wpr-37jh</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-32804</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 4.4.14</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-32803</summary>
### Vulnerable Library - <b>tar-4.4.13.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- publish-3.22.1.tgz
- run-lifecycle-3.16.2.tgz
- npm-lifecycle-3.1.5.tgz
- node-gyp-5.1.1.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803>CVE-2021-32803</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw">https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 4.4.15</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-5.1.1.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- info-3.21.0.tgz
- command-3.21.0.tgz
- project-3.21.0.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33623</summary>
### Vulnerable Libraries - <b>trim-newlines-3.0.0.tgz</b>, <b>trim-newlines-1.0.0.tgz</b></p>
<p>
### <b>trim-newlines-3.0.0.tgz</b></p>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- conventional-commits-parser-3.1.0.tgz
- meow-7.1.1.tgz
- :x: **trim-newlines-3.0.0.tgz** (Vulnerable Library)
### <b>trim-newlines-1.0.0.tgz</b></p>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- conventional-commits-3.22.0.tgz
- conventional-changelog-core-3.2.3.tgz
- get-pkg-repo-1.4.0.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vital-ws/modern-monorepo-boilerplate/commit/e80381378da65ac8618d77dac77b8572f2bf2064">e80381378da65ac8618d77dac77b8572f2bf2064</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution (trim-newlines): 3.0.1</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p><p>Fix Resolution (trim-newlines): 3.0.1</p>
<p>Direct dependency fix Resolution (lerna): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23369","vulnerabilityDetails":"The package handlebars before 4.7.7 are vulnerable to Remote Code Execution (RCE) when selecting certain compiling options to compile templates coming from an untrusted source.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23369","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"lerna:3.22.1;@lerna/version:3.22.1;@lerna/conventional-commits:3.22.0;conventional-changelog-core:3.2.3;get-pkg-repo:1.4.0;meow:3.7.0;minimist:1.2.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 1.2.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44906","vulnerabilityDetails":"Minimist \u003c\u003d1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23383","vulnerabilityDetails":"The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7774","vulnerabilityDetails":"This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n \u003d require(\u0027y18n\u0027)(); y18n.setLocale(\u0027__proto__\u0027); y18n.updateLocale({polluted: true}); console.log(polluted); // true","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-37701","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\\` and `/` characters as path separators, however `\\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-37712","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 \"short path\" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37712","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-37713","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:some\\path`. If the drive letter does not match the extraction target, for example `D:\\extraction\\dir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37713","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32804","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32803","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28469","vulnerabilityDetails":"This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false},{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33623","vulnerabilityDetails":"The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33502","vulnerabilityDetails":"The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-27290","vulnerabilityDetails":"ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7788","vulnerabilityDetails":"This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-fetch","packageVersion":"2.6.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"lerna:3.22.1;@lerna/version:3.22.1;@lerna/github-client:3.22.0;@octokit/rest:16.43.2;@octokit/request:5.4.9;node-fetch:2.6.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"node-fetch - 2.6.7,3.1.1","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0235","vulnerabilityDetails":"node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23425","vulnerabilityDetails":"All versions of package trim-off-newlines are vulnerable to Regular Expression Denial of Service (ReDoS) via string processing.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23425","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.\n WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lerna","packageVersion":"3.22.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lerna:3.22.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23362","vulnerabilityDetails":"The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_infrastructure | lerna tgz vulnerabilities highest severity is autoclosed vulnerable library lerna tgz path to dependency file package json path to vulnerable library node modules tar package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high handlebars tgz transitive high minimist tgz transitive n a high handlebars tgz transitive high tgz transitive high tar tgz transitive high tar tgz transitive high tar tgz transitive high tar tgz transitive high tar tgz transitive high glob parent tgz transitive high multiple transitive high normalize url tgz transitive high ssri tgz transitive high ini tgz transitive high lodash tgz transitive medium node fetch tgz transitive n a medium trim off newlines tgz transitive medium lodash tgz transitive medium hosted git info tgz transitive details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules handlebars package json dependency hierarchy lerna tgz root library version tgz conventional commits tgz conventional changelog core tgz conventional changelog writer tgz x handlebars tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package handlebars before are vulnerable to remote code execution rce when selecting certain compiling options to compile templates coming from an untrusted source publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules minimist package json dependency hierarchy lerna tgz root library version tgz conventional commits tgz conventional changelog core tgz get pkg repo tgz meow tgz x minimist tgz vulnerable library found in head commit a href found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist cve vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file package json path to vulnerable library node modules handlebars package json dependency hierarchy lerna tgz root library version tgz conventional commits tgz conventional changelog core tgz conventional changelog writer tgz x handlebars tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package handlebars before are vulnerable to prototype pollution when selecting certain compiling options to compile templates coming from an untrusted source publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library tgz the bare bones internationalization library used by yargs library home page a href path to dependency file package json path to vulnerable library node modules package json dependency hierarchy lerna tgz root library publish tgz npm registry fetch tgz make fetch happen tgz cacache tgz x tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package before and poc by const require setlocale proto updatelocale polluted true console log polluted true publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules tar package json dependency hierarchy lerna tgz root library publish tgz run lifecycle tgz npm lifecycle tgz node gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems the cache checking logic used both and characters as path separators however is a valid filename character on posix systems by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite additionally a similar confusion could arise on case insensitive filesystems if a tar archive contained a directory at foo followed by a symbolic link named foo then on case insensitive file systems the creation of the symbolic link would remove the directory from the filesystem but not from the internal directory cache as it would not be treated as a cache hit a subsequent file entry within the foo directory would then be placed in the target of the symbolic link thinking that the directory had already been created these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules tar package json dependency hierarchy lerna tgz root library publish tgz run lifecycle tgz npm lifecycle tgz node gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value additionally on windows systems long path portions would resolve to the same file system entities as their short path counterparts a specially crafted tar archive could thus include a directory with one form of the path followed by a symbolic link with a different string that resolves to the same file system entity followed by a file using the first form by first creating a directory and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules tar package json dependency hierarchy lerna tgz root library publish tgz run lifecycle tgz npm lifecycle tgz node gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted this is in part accomplished by sanitizing absolute paths of entries within the archive skipping archive entries that contain path portions and resolving the sanitized paths against the extraction target directory this logic was insufficient on windows systems when extracting tar files that contained a path that was not an absolute path but specified a drive letter different from the extraction target such as c some path if the drive letter does not match the extraction target for example d extraction dir then the result of path resolve extractiondirectory entrypath would resolve against the current working directory on the c drive rather than the extraction target directory additionally a portion of the path could occur immediately after the drive letter such as c foo and was not properly sanitized by the logic that checked for within the normalized and split portions of the path this only affects users of node tar on windows systems these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar there is no reasonable way to work around this issue without performing the same path normalization procedures that node tar now does users are encouraged to upgrade to the latest patched versions of node tar rather than attempt to sanitize paths themselves publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules tar package json dependency hierarchy lerna tgz root library publish tgz run lifecycle tgz npm lifecycle tgz node gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has a arbitrary file creation overwrite vulnerability due to insufficient absolute path sanitization node tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the preservepaths flag is not set to true this is achieved by stripping the absolute path root from any absolute file paths contained in a tar file for example home user bashrc would turn into home user bashrc this logic was insufficient when file paths contained repeated path roots such as home user bashrc node tar would only strip a single path root from such paths when given an absolute file path with repeating path roots the resulting path e g home user bashrc would still resolve to an absolute path thus allowing arbitrary file creation and overwrite this issue was addressed in releases and users may work around this vulnerability without upgrading by creating a custom onentry method which sanitizes the entry path or a filter method which removes entries with absolute paths see referenced github advisory for details be aware of cve which fixes a similar bug in later versions of tar publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules tar package json dependency hierarchy lerna tgz root library publish tgz run lifecycle tgz npm lifecycle tgz node gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite vulnerability via insufficient symlink protection node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory this order of operations resulted in the directory being created and added to the node tar directory cache when a directory is present in the directory cache subsequent calls to mkdir for that directory are skipped however this is also where node tar checks for symlinks occur by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite this issue was addressed in releases and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file package json path to vulnerable library node modules glob parent package json dependency hierarchy lerna tgz root library info tgz command tgz project tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue cve vulnerable libraries trim newlines tgz trim newlines tgz trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file package json path to vulnerable library node modules trim newlines package json dependency hierarchy lerna tgz root library version tgz conventional commits tgz conventional changelog core tgz conventional commits parser tgz meow tgz x trim newlines tgz vulnerable library trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file package json path to vulnerable library node modules trim newlines package json dependency hierarchy lerna tgz root library version tgz conventional commits tgz conventional changelog core tgz get pkg repo tgz meow tgz x trim newlines tgz vulnerable library found in head commit a href found in base branch master vulnerability details the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution trim newlines direct dependency fix resolution lerna fix resolution trim newlines direct dependency fix resolution lerna rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package handlebars before are vulnerable to remote code execution rce when selecting certain compiling options to compile templates coming from an untrusted source vulnerabilityurl istransitivedependency true dependencytree lerna lerna version lerna conventional commits conventional changelog core get pkg repo meow minimist isminimumfixversionavailable true minimumfixversion minimist isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist is vulnerable to prototype pollution via file index js function setkey lines vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package handlebars before are vulnerable to prototype pollution when selecting certain compiling options to compile templates coming from an untrusted source vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package before and poc by const require setlocale proto updatelocale polluted true console log polluted true vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems the cache checking logic used both and characters as path separators however is a valid filename character on posix systems by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite additionally a similar confusion could arise on case insensitive filesystems if a tar archive contained a directory at foo followed by a symbolic link named foo then on case insensitive file systems the creation of the symbolic link would remove the directory from the filesystem but not from the internal directory cache as it would not be treated as a cache hit a subsequent file entry within the foo directory would then be placed in the target of the symbolic link thinking that the directory had already been created these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value additionally on windows systems long path portions would resolve to the same file system entities as their short path counterparts a specially crafted tar archive could thus include a directory with one form of the path followed by a symbolic link with a different string that resolves to the same file system entity followed by a file using the first form by first creating a directory and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted this is in part accomplished by sanitizing absolute paths of entries within the archive skipping archive entries that contain path portions and resolving the sanitized paths against the extraction target directory this logic was insufficient on windows systems when extracting tar files that contained a path that was not an absolute path but specified a drive letter different from the extraction target such as c some path if the drive letter does not match the extraction target for example d extraction dir then the result of path resolve extractiondirectory entrypath would resolve against the current working directory on the c drive rather than the extraction target directory additionally a portion of the path could occur immediately after the drive letter such as c foo and was not properly sanitized by the logic that checked for within the normalized and split portions of the path this only affects users of node tar on windows systems these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar there is no reasonable way to work around this issue without performing the same path normalization procedures that node tar now does users are encouraged to upgrade to the latest patched versions of node tar rather than attempt to sanitize paths themselves vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the npm package tar aka node tar before versions and has a arbitrary file creation overwrite vulnerability due to insufficient absolute path sanitization node tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the preservepaths flag is not set to true this is achieved by stripping the absolute path root from any absolute file paths contained in a tar file for example home user bashrc would turn into home user bashrc this logic was insufficient when file paths contained repeated path roots such as home user bashrc node tar would only strip a single path root from such paths when given an absolute file path with repeating path roots the resulting path e g home user bashrc would still resolve to an absolute path thus allowing arbitrary file creation and overwrite this issue was addressed in releases and users may work around this vulnerability without upgrading by creating a custom onentry method which sanitizes the entry path or a filter method which removes entries with absolute paths see referenced github advisory for details be aware of cve which fixes a similar bug in later versions of tar vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the npm package tar aka node tar before versions and has an arbitrary file creation overwrite vulnerability via insufficient symlink protection node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory this order of operations resulted in the directory being created and added to the node tar directory cache when a directory is present in the directory cache subsequent calls to mkdir for that directory are skipped however this is also where node tar checks for symlinks occur by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite this issue was addressed in releases and vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename lerna packageversion packagefilepaths istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the normalize url package before x before and x before for node js has a redos regular expression denial of service issue because it has exponential performance for data urls vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails ssri fixed in processes sris using a regular expression which is vulnerable to a denial of service malicious sris could take an extremely long time to process leading to denial of service this issue only affects consumers using the strict option vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to command injection via the template function vulnerabilityurl istransitivedependency true dependencytree lerna lerna version lerna github client octokit rest octokit request node fetch isminimumfixversionavailable true minimumfixversion node fetch isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails node fetch is vulnerable to exposure of sensitive information to an unauthorized actor vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails all versions of package trim off newlines are vulnerable to regular expression denial of service redos via string processing vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions n whitesource note after conducting further research whitesource has determined that cve only affects environments with versions to of lodash vulnerabilityurl istransitivedependency false dependencytree lerna isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package hosted git info before are vulnerable to regular expression denial of service redos via regular expression shortcutmatch in the fromurl function in index js the affected regular expression exhibits polynomial worst case time complexity vulnerabilityurl | 0 |
62,546 | 8,621,664,247 | IssuesEvent | 2018-11-20 17:58:17 | matplotlib/matplotlib | https://api.github.com/repos/matplotlib/matplotlib | closed | plt.table kwarg fontsize does not work | Documentation | ### Bug report
No way to change the fontsize of tables (matplotlib.pyplot.table )
**Bug summary**
The kwarg fontsize for matplotlib.pyplot.table does not set the fontsize, nor does looping through each cell and setting cell's fontsize.
<!--A short 1-2 sentences that succinctly describes the bug-->
**Code for reproduction**
<!--A minimum code snippet required to reproduce the bug, also minimizing the number of dependencies required-->
```python
#import numpy as np
import matplotlib.pyplot as plt
%matplotlib inline
data = [[ 66386, 174296, 75131, 577908, 32015],
[ 58230, 381139, 78045, 99308, 160454],
[ 89135, 80552, 152558, 497981, 603535],
[ 78415, 81858, 150656, 193263, 69638],
[139361, 331509, 343164, 781380, 52269]]
columns = ('Freeze', 'Wind', 'Flood', 'Quake', 'Hail')
rows = ['%d year' % x for x in (100, 50, 20, 10, 5)]
values = np.arange(0, 2500, 500)
value_increment = 1000
# Get some pastel shades for the colors
colors = plt.cm.BuPu(np.linspace(0, 0.5, len(rows)))
n_rows = len(data)
index = np.arange(len(columns)) + 0.3
bar_width = 0.4
# Initialize the vertical-offset for the stacked bar chart.
y_offset = np.zeros(len(columns))
# Plot bars and create text labels for the table
cell_text = []
for row in range(n_rows):
plt.bar(index, data[row], bar_width, bottom=y_offset, color=colors[row])
y_offset = y_offset + data[row]
cell_text.append(['%1.1f' % (x / 1000.0) for x in y_offset])
# Add a table at the bottom of the axes
the_table = plt.table(cellText=cell_text,
rowLabels=rows,
rowColours=colors,
colLabels=columns,
loc='bottom',
**fontsize = 30)**
# Adjust layout to make room for the table:
plt.subplots_adjust(left=0.2, bottom=.1)
plt.show()
<img width="518" alt="screen shot 2018-11-18 at 4 40 09 am" src="https://user-images.githubusercontent.com/10767779/48671898-10cf4280-eaec-11e8-94ba-19ef31681855.png">
```
**Actual outcome**
<img width="518" alt="screen shot 2018-11-18 at 4 40 09 am" src="https://user-images.githubusercontent.com/10767779/48671941-905d1180-eaec-11e8-84cc-62c5395812f7.png">
```
```
**Expected outcome**
<!--A description of the expected outcome from the code snippet--> The font in the table should be much bigger
**Matplotlib version**
<!--Please specify your platform and versions of the relevant libraries you are using:-->
* Operating system: OSX 10.13.6
* Matplotlib version:
* Matplotlib backend (`print(matplotlib.get_backend())`): module://ipykernel.pylab.backend_inline
* Python version: 3.6x
* Jupyter version (if applicable):
* Other libraries:
<!--Please tell us how you installed matplotlib and python e.g., from source, pip, conda--> conda
<!--If you installed from conda, please specify which channel you used if not the default-->
| 1.0 | plt.table kwarg fontsize does not work - ### Bug report
No way to change the fontsize of tables (matplotlib.pyplot.table )
**Bug summary**
The kwarg fontsize for matplotlib.pyplot.table does not set the fontsize, nor does looping through each cell and setting cell's fontsize.
<!--A short 1-2 sentences that succinctly describes the bug-->
**Code for reproduction**
<!--A minimum code snippet required to reproduce the bug, also minimizing the number of dependencies required-->
```python
#import numpy as np
import matplotlib.pyplot as plt
%matplotlib inline
data = [[ 66386, 174296, 75131, 577908, 32015],
[ 58230, 381139, 78045, 99308, 160454],
[ 89135, 80552, 152558, 497981, 603535],
[ 78415, 81858, 150656, 193263, 69638],
[139361, 331509, 343164, 781380, 52269]]
columns = ('Freeze', 'Wind', 'Flood', 'Quake', 'Hail')
rows = ['%d year' % x for x in (100, 50, 20, 10, 5)]
values = np.arange(0, 2500, 500)
value_increment = 1000
# Get some pastel shades for the colors
colors = plt.cm.BuPu(np.linspace(0, 0.5, len(rows)))
n_rows = len(data)
index = np.arange(len(columns)) + 0.3
bar_width = 0.4
# Initialize the vertical-offset for the stacked bar chart.
y_offset = np.zeros(len(columns))
# Plot bars and create text labels for the table
cell_text = []
for row in range(n_rows):
plt.bar(index, data[row], bar_width, bottom=y_offset, color=colors[row])
y_offset = y_offset + data[row]
cell_text.append(['%1.1f' % (x / 1000.0) for x in y_offset])
# Add a table at the bottom of the axes
the_table = plt.table(cellText=cell_text,
rowLabels=rows,
rowColours=colors,
colLabels=columns,
loc='bottom',
**fontsize = 30)**
# Adjust layout to make room for the table:
plt.subplots_adjust(left=0.2, bottom=.1)
plt.show()
<img width="518" alt="screen shot 2018-11-18 at 4 40 09 am" src="https://user-images.githubusercontent.com/10767779/48671898-10cf4280-eaec-11e8-94ba-19ef31681855.png">
```
**Actual outcome**
<img width="518" alt="screen shot 2018-11-18 at 4 40 09 am" src="https://user-images.githubusercontent.com/10767779/48671941-905d1180-eaec-11e8-84cc-62c5395812f7.png">
```
```
**Expected outcome**
<!--A description of the expected outcome from the code snippet--> The font in the table should be much bigger
**Matplotlib version**
<!--Please specify your platform and versions of the relevant libraries you are using:-->
* Operating system: OSX 10.13.6
* Matplotlib version:
* Matplotlib backend (`print(matplotlib.get_backend())`): module://ipykernel.pylab.backend_inline
* Python version: 3.6x
* Jupyter version (if applicable):
* Other libraries:
<!--Please tell us how you installed matplotlib and python e.g., from source, pip, conda--> conda
<!--If you installed from conda, please specify which channel you used if not the default-->
| non_infrastructure | plt table kwarg fontsize does not work bug report no way to change the fontsize of tables matplotlib pyplot table bug summary the kwarg fontsize for matplotlib pyplot table does not set the fontsize nor does looping through each cell and setting cell s fontsize code for reproduction python import numpy as np import matplotlib pyplot as plt matplotlib inline data columns freeze wind flood quake hail rows values np arange value increment get some pastel shades for the colors colors plt cm bupu np linspace len rows n rows len data index np arange len columns bar width initialize the vertical offset for the stacked bar chart y offset np zeros len columns plot bars and create text labels for the table cell text for row in range n rows plt bar index data bar width bottom y offset color colors y offset y offset data cell text append add a table at the bottom of the axes the table plt table celltext cell text rowlabels rows rowcolours colors collabels columns loc bottom fontsize adjust layout to make room for the table plt subplots adjust left bottom plt show img width alt screen shot at am src actual outcome img width alt screen shot at am src expected outcome the font in the table should be much bigger matplotlib version operating system osx matplotlib version matplotlib backend print matplotlib get backend module ipykernel pylab backend inline python version jupyter version if applicable other libraries conda | 0 |
386,938 | 26,708,002,374 | IssuesEvent | 2023-01-27 20:07:31 | JoranSlingerland/StockTracker | https://api.github.com/repos/JoranSlingerland/StockTracker | closed | Add better docstrings | documentation wontfix | add docstrings to all modules in the below format:
````python
def add(num1, num2):
"""
Add up two integer numbers.
This function simply wraps the ``+`` operator, and does not
do anything interesting, except for illustrating what
the docstring of a very simple function looks like.
Parameters
----------
num1 : int
First number to add.
num2 : int
Second number to add.
Returns
-------
int
The sum of ``num1`` and ``num2``.
See Also
--------
subtract : Subtract one integer from another.
Examples
--------
>>> add(2, 2)
4
>>> add(25, 0)
25
>>> add(10, -10)
0
"""
return num1 + num2
```` | 1.0 | Add better docstrings - add docstrings to all modules in the below format:
````python
def add(num1, num2):
"""
Add up two integer numbers.
This function simply wraps the ``+`` operator, and does not
do anything interesting, except for illustrating what
the docstring of a very simple function looks like.
Parameters
----------
num1 : int
First number to add.
num2 : int
Second number to add.
Returns
-------
int
The sum of ``num1`` and ``num2``.
See Also
--------
subtract : Subtract one integer from another.
Examples
--------
>>> add(2, 2)
4
>>> add(25, 0)
25
>>> add(10, -10)
0
"""
return num1 + num2
```` | non_infrastructure | add better docstrings add docstrings to all modules in the below format python def add add up two integer numbers this function simply wraps the operator and does not do anything interesting except for illustrating what the docstring of a very simple function looks like parameters int first number to add int second number to add returns int the sum of and see also subtract subtract one integer from another examples add add add return | 0 |
11,339 | 9,312,371,110 | IssuesEvent | 2019-03-26 00:55:07 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | How do you add a node type to an OnPremise Cluster? | assigned-to-author doc-enhancement service-fabric/svc triaged | How do you add a node type to an OnPremise Cluster?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: a6803a0f-eda8-acf7-c598-d4679833de08
* Version Independent ID: f441710f-8f4e-d46c-5eab-132940f4445f
* Content: [Add a node type to an Azure Service Fabric cluster](https://docs.microsoft.com/en-us/azure/service-fabric/virtual-machine-scale-set-scale-node-type-scale-out)
* Content Source: [articles/service-fabric/virtual-machine-scale-set-scale-node-type-scale-out.md](https://github.com/Microsoft/azure-docs/blob/master/articles/service-fabric/virtual-machine-scale-set-scale-node-type-scale-out.md)
* Service: **service-fabric**
* GitHub Login: @aljo-microsoft
* Microsoft Alias: **aljo** | 1.0 | How do you add a node type to an OnPremise Cluster? - How do you add a node type to an OnPremise Cluster?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: a6803a0f-eda8-acf7-c598-d4679833de08
* Version Independent ID: f441710f-8f4e-d46c-5eab-132940f4445f
* Content: [Add a node type to an Azure Service Fabric cluster](https://docs.microsoft.com/en-us/azure/service-fabric/virtual-machine-scale-set-scale-node-type-scale-out)
* Content Source: [articles/service-fabric/virtual-machine-scale-set-scale-node-type-scale-out.md](https://github.com/Microsoft/azure-docs/blob/master/articles/service-fabric/virtual-machine-scale-set-scale-node-type-scale-out.md)
* Service: **service-fabric**
* GitHub Login: @aljo-microsoft
* Microsoft Alias: **aljo** | non_infrastructure | how do you add a node type to an onpremise cluster how do you add a node type to an onpremise cluster document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service service fabric github login aljo microsoft microsoft alias aljo | 0 |
32,919 | 27,091,548,434 | IssuesEvent | 2023-02-14 21:33:21 | OpenLiberty/openliberty.io | https://api.github.com/repos/OpenLiberty/openliberty.io | closed | Investigate if ephemeral storage can be tuned lower | infrastructure | Ephemeral storage was increased to 1.5GB in the initial construction of the pipelines.
Code Engine requires that the ephemeral storage be less than the memory allocation. ([link](https://cloud.ibm.com/docs/codeengine?topic=codeengine-limits#:~:text=The%20ephemeral%20storage%20in%20Code,combinations%20of%20vCPU%20and%20memory.)) This means that the deployments could have over allocation of vCPU/Mem sizes only to increase the ephemeral storage amount.
In the past, the website war file was being expanded during Open Liberty startup. We have since moved to packaging a expanded war in the container images. In theory, this should mean less need for ephemeral storage as the runtime does not need as much storage to expand the war file.
Test to see if a full website application can run on lower than 1.5GB ephemeral storage.
Here is a [link](https://github.com/OpenLiberty/code-engine-toolchain/blob/9aff569ead838f774a230e4033e580e985a2c016/.tekton/tasks/task-deploy-to-code-engine.yml#L39-L41) to how the openliberty.io toolchains set the ephemeral storage. | 1.0 | Investigate if ephemeral storage can be tuned lower - Ephemeral storage was increased to 1.5GB in the initial construction of the pipelines.
Code Engine requires that the ephemeral storage be less than the memory allocation. ([link](https://cloud.ibm.com/docs/codeengine?topic=codeengine-limits#:~:text=The%20ephemeral%20storage%20in%20Code,combinations%20of%20vCPU%20and%20memory.)) This means that the deployments could have over allocation of vCPU/Mem sizes only to increase the ephemeral storage amount.
In the past, the website war file was being expanded during Open Liberty startup. We have since moved to packaging a expanded war in the container images. In theory, this should mean less need for ephemeral storage as the runtime does not need as much storage to expand the war file.
Test to see if a full website application can run on lower than 1.5GB ephemeral storage.
Here is a [link](https://github.com/OpenLiberty/code-engine-toolchain/blob/9aff569ead838f774a230e4033e580e985a2c016/.tekton/tasks/task-deploy-to-code-engine.yml#L39-L41) to how the openliberty.io toolchains set the ephemeral storage. | infrastructure | investigate if ephemeral storage can be tuned lower ephemeral storage was increased to in the initial construction of the pipelines code engine requires that the ephemeral storage be less than the memory allocation this means that the deployments could have over allocation of vcpu mem sizes only to increase the ephemeral storage amount in the past the website war file was being expanded during open liberty startup we have since moved to packaging a expanded war in the container images in theory this should mean less need for ephemeral storage as the runtime does not need as much storage to expand the war file test to see if a full website application can run on lower than ephemeral storage here is a to how the openliberty io toolchains set the ephemeral storage | 1 |
24,678 | 17,602,917,678 | IssuesEvent | 2021-08-17 13:54:45 | dotnet/xharness | https://api.github.com/repos/dotnet/xharness | opened | iOS app installation takes long on some machines | bug apple infrastructure | ### Problem
Looks like the installation itself took 14 minutes and the job was killed in the later stage by the Helix client:
```
...
[13:21:50] dbug: Xamarin.Hosting: Booting iPhone X (iOS 13.5) - created by XHarness...
[13:21:53] dbug: Xamarin.Hosting: Booted iPhone X (iOS 13.5) - created by XHarness successfully.
[13:21:53] dbug: Xamarin.Hosting: Installing /tmp/helix/working/B1230989/w/AB490967/e/System.Numerics.Vectors.Tests.app with Bundle Identifier net.dot.System.Numerics.Vectors.Tests on 'iOS 13.5 (17F61) - iPhone X'...
[13:35:17] dbug: Xamarin.Hosting: Installed 'net.dot.System.Numerics.Vectors.Tests' from /tmp/helix/working/B1230989/w/AB490967/e/System.Numerics.Vectors.Tests.app
[13:35:33] dbug: Xamarin.Hosting: Can't process potentially bad load commands, because the app is signed.
[13:35:33] dbug: Xamarin.Hosting: The bundle id net.dot.System.Numerics.Vectors.Tests was successfully installed.
[13:35:40] dbug: Xamarin.Hosting: Shutdown iPhone X (iOS 13.5) - created by XHarness successfully.
[13:35:40] dbug: Process mlaunch exited with 0
[13:35:40] info: Application 'System.Numerics.Vectors.Tests' was installed successfully on 'iPhone X (iOS 13.5) - created by XHarness'
XHarness exit code: 0
++ set +e
++ result=0
++ xharness apple just-test -t=ios-simulator-64 --device=9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98 -o=/tmp/helix/working/B1230989/w/AB490967/uploads --app=net.dot.System.Numerics.Vectors.Tests --launch-timeout=00:05:00 --timeout=00:05:00 -v
++ dotnet exec /tmp/helix/working/B1230989/p/microsoft.dotnet.xharness.cli/1.0.0-prerelease.21378.1/tools/net6.0/any/Microsoft.DotNet.XHarness.CLI.dll apple just-test -t=ios-simulator-64 --device=9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98 -o=/tmp/helix/working/B1230989/w/AB490967/uploads --app=net.dot.System.Numerics.Vectors.Tests --launch-timeout=00:05:00 --timeout=00:05:00 -v
XHarness command issued: apple just-test -t=ios-simulator-64 --device=9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98 -o=/tmp/helix/working/B1230989/w/AB490967/uploads --app=net.dot.System.Numerics.Vectors.Tests --launch-timeout=00:05:00 --timeout=00:05:00 -v
[13:35:47] info: Preparing run for ios-simulator-64 targeting 9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98
[13:35:47] info: Looking for available ios-simulator-64 simulators..
[13:35:47] dbug: Looking for available ios-simulator-64 simulators. Storing logs into list-ios-simulator-64-20210809_133547.log
/tmp/helix/working/B1230989/p/scripts/ec1a06bd816c49f49069ab2919012a09/execute.sh: line 13: 28858 Killed: 9 ./xharness-helix-job.apple.sh --app "System.Numerics.Vectors.Tests.app" --target "ios-simulator-64" --timeout "00:05:00" --launch-timeout "00:05:00" --includes-test-runner --expected-exit-code "0"
+ export _commandExitCode=137
```
### Proposal
We should set a shorter timeout for installation and let Helix SDK reboot the machine. | 1.0 | iOS app installation takes long on some machines - ### Problem
Looks like the installation itself took 14 minutes and the job was killed in the later stage by the Helix client:
```
...
[13:21:50] dbug: Xamarin.Hosting: Booting iPhone X (iOS 13.5) - created by XHarness...
[13:21:53] dbug: Xamarin.Hosting: Booted iPhone X (iOS 13.5) - created by XHarness successfully.
[13:21:53] dbug: Xamarin.Hosting: Installing /tmp/helix/working/B1230989/w/AB490967/e/System.Numerics.Vectors.Tests.app with Bundle Identifier net.dot.System.Numerics.Vectors.Tests on 'iOS 13.5 (17F61) - iPhone X'...
[13:35:17] dbug: Xamarin.Hosting: Installed 'net.dot.System.Numerics.Vectors.Tests' from /tmp/helix/working/B1230989/w/AB490967/e/System.Numerics.Vectors.Tests.app
[13:35:33] dbug: Xamarin.Hosting: Can't process potentially bad load commands, because the app is signed.
[13:35:33] dbug: Xamarin.Hosting: The bundle id net.dot.System.Numerics.Vectors.Tests was successfully installed.
[13:35:40] dbug: Xamarin.Hosting: Shutdown iPhone X (iOS 13.5) - created by XHarness successfully.
[13:35:40] dbug: Process mlaunch exited with 0
[13:35:40] info: Application 'System.Numerics.Vectors.Tests' was installed successfully on 'iPhone X (iOS 13.5) - created by XHarness'
XHarness exit code: 0
++ set +e
++ result=0
++ xharness apple just-test -t=ios-simulator-64 --device=9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98 -o=/tmp/helix/working/B1230989/w/AB490967/uploads --app=net.dot.System.Numerics.Vectors.Tests --launch-timeout=00:05:00 --timeout=00:05:00 -v
++ dotnet exec /tmp/helix/working/B1230989/p/microsoft.dotnet.xharness.cli/1.0.0-prerelease.21378.1/tools/net6.0/any/Microsoft.DotNet.XHarness.CLI.dll apple just-test -t=ios-simulator-64 --device=9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98 -o=/tmp/helix/working/B1230989/w/AB490967/uploads --app=net.dot.System.Numerics.Vectors.Tests --launch-timeout=00:05:00 --timeout=00:05:00 -v
XHarness command issued: apple just-test -t=ios-simulator-64 --device=9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98 -o=/tmp/helix/working/B1230989/w/AB490967/uploads --app=net.dot.System.Numerics.Vectors.Tests --launch-timeout=00:05:00 --timeout=00:05:00 -v
[13:35:47] info: Preparing run for ios-simulator-64 targeting 9D5D65A3-87CF-4933-9B79-0D1B0B8F3A98
[13:35:47] info: Looking for available ios-simulator-64 simulators..
[13:35:47] dbug: Looking for available ios-simulator-64 simulators. Storing logs into list-ios-simulator-64-20210809_133547.log
/tmp/helix/working/B1230989/p/scripts/ec1a06bd816c49f49069ab2919012a09/execute.sh: line 13: 28858 Killed: 9 ./xharness-helix-job.apple.sh --app "System.Numerics.Vectors.Tests.app" --target "ios-simulator-64" --timeout "00:05:00" --launch-timeout "00:05:00" --includes-test-runner --expected-exit-code "0"
+ export _commandExitCode=137
```
### Proposal
We should set a shorter timeout for installation and let Helix SDK reboot the machine. | infrastructure | ios app installation takes long on some machines problem looks like the installation itself took minutes and the job was killed in the later stage by the helix client dbug xamarin hosting booting iphone x ios created by xharness dbug xamarin hosting booted iphone x ios created by xharness successfully dbug xamarin hosting installing tmp helix working w e system numerics vectors tests app with bundle identifier net dot system numerics vectors tests on ios iphone x dbug xamarin hosting installed net dot system numerics vectors tests from tmp helix working w e system numerics vectors tests app dbug xamarin hosting can t process potentially bad load commands because the app is signed dbug xamarin hosting the bundle id net dot system numerics vectors tests was successfully installed dbug xamarin hosting shutdown iphone x ios created by xharness successfully dbug process mlaunch exited with info application system numerics vectors tests was installed successfully on iphone x ios created by xharness xharness exit code set e result xharness apple just test t ios simulator device o tmp helix working w uploads app net dot system numerics vectors tests launch timeout timeout v dotnet exec tmp helix working p microsoft dotnet xharness cli prerelease tools any microsoft dotnet xharness cli dll apple just test t ios simulator device o tmp helix working w uploads app net dot system numerics vectors tests launch timeout timeout v xharness command issued apple just test t ios simulator device o tmp helix working w uploads app net dot system numerics vectors tests launch timeout timeout v info preparing run for ios simulator targeting info looking for available ios simulator simulators dbug looking for available ios simulator simulators storing logs into list ios simulator log tmp helix working p scripts execute sh line killed xharness helix job apple sh app system numerics vectors tests app target ios simulator timeout launch timeout includes test runner expected exit code export commandexitcode proposal we should set a shorter timeout for installation and let helix sdk reboot the machine | 1 |
12,840 | 9,977,308,952 | IssuesEvent | 2019-07-09 16:56:31 | maidsafe/safe-build-infrastructure | https://api.github.com/repos/maidsafe/safe-build-infrastructure | closed | Remove HAProxy Restart from Reprovision | bug infrastructure | During the deployment process, after the first playbook runs to configure HAProxy, the service seems to go down completely and you can't access the environment until after the SSL configuration is re-applied. Need to identify where this happens and remove it. | 1.0 | Remove HAProxy Restart from Reprovision - During the deployment process, after the first playbook runs to configure HAProxy, the service seems to go down completely and you can't access the environment until after the SSL configuration is re-applied. Need to identify where this happens and remove it. | infrastructure | remove haproxy restart from reprovision during the deployment process after the first playbook runs to configure haproxy the service seems to go down completely and you can t access the environment until after the ssl configuration is re applied need to identify where this happens and remove it | 1 |
86,751 | 10,800,238,111 | IssuesEvent | 2019-11-06 13:51:48 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | Identify points of entry to access Decision Review page | Epic design research vsa-benefits vsa-decision-reviews | ## User Story or Problem Statement
As a designer, I need to identify how a Veteran can easily access the Decision Review page on VA.gov so that they can submit a Higher Level Review for my existing claim.
## Goal
Easy and direct access to the Decision Review page from multiple locations on VA.gov
## Acceptance Criteria
Scenario: System user wants to file an appeal for their disability claim decision
- GIVEN a Veteran has received a claim decision
- WHEN the user needs to request a Decision Review
- THEN the system will multiple points of entry where the user can access the Decision Review page to file their claim appeal
## Definition of Done
- [ ]
- [ ]
- [ ]
- [ ]
- [ ] *This relates to epic ticket #1053 *Check the box below when this has been completed and comment "done"._ | 1.0 | Identify points of entry to access Decision Review page - ## User Story or Problem Statement
As a designer, I need to identify how a Veteran can easily access the Decision Review page on VA.gov so that they can submit a Higher Level Review for my existing claim.
## Goal
Easy and direct access to the Decision Review page from multiple locations on VA.gov
## Acceptance Criteria
Scenario: System user wants to file an appeal for their disability claim decision
- GIVEN a Veteran has received a claim decision
- WHEN the user needs to request a Decision Review
- THEN the system will multiple points of entry where the user can access the Decision Review page to file their claim appeal
## Definition of Done
- [ ]
- [ ]
- [ ]
- [ ]
- [ ] *This relates to epic ticket #1053 *Check the box below when this has been completed and comment "done"._ | non_infrastructure | identify points of entry to access decision review page user story or problem statement as a designer i need to identify how a veteran can easily access the decision review page on va gov so that they can submit a higher level review for my existing claim goal easy and direct access to the decision review page from multiple locations on va gov acceptance criteria scenario system user wants to file an appeal for their disability claim decision given a veteran has received a claim decision when the user needs to request a decision review then the system will multiple points of entry where the user can access the decision review page to file their claim appeal definition of done this relates to epic ticket check the box below when this has been completed and comment done | 0 |
15,106 | 11,354,975,713 | IssuesEvent | 2020-01-24 18:55:12 | zachsanchez113/tableau | https://api.github.com/repos/zachsanchez113/tableau | closed | Configure IAM to grant everybody access to server | infrastructure | - Add keys to server for all members of team
- Create local users for all members of team
- Associate keys with users
- Create `sudo` policy
- Get rid of defaut `bitnami` user | 1.0 | Configure IAM to grant everybody access to server - - Add keys to server for all members of team
- Create local users for all members of team
- Associate keys with users
- Create `sudo` policy
- Get rid of defaut `bitnami` user | infrastructure | configure iam to grant everybody access to server add keys to server for all members of team create local users for all members of team associate keys with users create sudo policy get rid of defaut bitnami user | 1 |
817,074 | 30,624,235,797 | IssuesEvent | 2023-07-24 10:19:34 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.mi.com - site is not usable | browser-firefox priority-important engine-gecko | <!-- @browser: Firefox 115.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/115.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/124840 -->
**URL**: https://www.mi.com
**Browser / Version**: Firefox 115.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Edge
**Problem type**: Site is not usable
**Description**: Page not loading correctly
**Steps to Reproduce**:
The text is very big and the design completely broken in Firefox. Changing the size of the web does nothing. In Edge and Brave for Android works well.
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2023/7/643699c0-a05e-40db-b7c1-c1afdd298cc3.jpg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.mi.com - site is not usable - <!-- @browser: Firefox 115.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/115.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/124840 -->
**URL**: https://www.mi.com
**Browser / Version**: Firefox 115.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Edge
**Problem type**: Site is not usable
**Description**: Page not loading correctly
**Steps to Reproduce**:
The text is very big and the design completely broken in Firefox. Changing the size of the web does nothing. In Edge and Brave for Android works well.
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2023/7/643699c0-a05e-40db-b7c1-c1afdd298cc3.jpg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_infrastructure | site is not usable url browser version firefox operating system windows tested another browser yes edge problem type site is not usable description page not loading correctly steps to reproduce the text is very big and the design completely broken in firefox changing the size of the web does nothing in edge and brave for android works well view the screenshot img alt screenshot src browser configuration none from with ❤️ | 0 |
25,094 | 18,105,087,892 | IssuesEvent | 2021-09-22 18:17:58 | dotnet/fsharp | https://api.github.com/repos/dotnet/fsharp | closed | Fix dependencies on Microsoft.VisualStudio.Shell.Immutable.*.0.dll | Area-Infrastructure | Currently `FSharp.ProjectSystem.FSharp.dll` depends on `Microsoft.VisualStudio.Shell.Immutable.*.0.dll` which is **not** distributed with `VisualFSharpFull.vsix`, but that assembly is scheduled to be removed from the base VS install. The possibilities for fixing this are:
1. Migrate to consuming `Microsoft.VisualStudio.Shell.Framework.dll`; all types should be available from there. **Preferred.**
2. Include the `Microsoft.VisualStudio.Shell.Immutable.*.0.dll` assemblies in the VSIX. This would be the easier option, but is more likely to cause problems.
See internal bug [280708](https://devdiv.visualstudio.com/DevDiv/_workitems/edit/280708). | 1.0 | Fix dependencies on Microsoft.VisualStudio.Shell.Immutable.*.0.dll - Currently `FSharp.ProjectSystem.FSharp.dll` depends on `Microsoft.VisualStudio.Shell.Immutable.*.0.dll` which is **not** distributed with `VisualFSharpFull.vsix`, but that assembly is scheduled to be removed from the base VS install. The possibilities for fixing this are:
1. Migrate to consuming `Microsoft.VisualStudio.Shell.Framework.dll`; all types should be available from there. **Preferred.**
2. Include the `Microsoft.VisualStudio.Shell.Immutable.*.0.dll` assemblies in the VSIX. This would be the easier option, but is more likely to cause problems.
See internal bug [280708](https://devdiv.visualstudio.com/DevDiv/_workitems/edit/280708). | infrastructure | fix dependencies on microsoft visualstudio shell immutable dll currently fsharp projectsystem fsharp dll depends on microsoft visualstudio shell immutable dll which is not distributed with visualfsharpfull vsix but that assembly is scheduled to be removed from the base vs install the possibilities for fixing this are migrate to consuming microsoft visualstudio shell framework dll all types should be available from there preferred include the microsoft visualstudio shell immutable dll assemblies in the vsix this would be the easier option but is more likely to cause problems see internal bug | 1 |
1,086 | 3,030,624,461 | IssuesEvent | 2015-08-04 18:25:16 | google/trace-viewer | https://api.github.com/repos/google/trace-viewer | closed | python tests fail on windows | Infrastructure | After https://codereview.appspot.com/251100043/, there are still 3 failing tests. I'm not sure how to handle c:\ getting stuck on the absolute paths in Windows. Output:
======================================================================
ERROR: testInlineStylesheetURLs (tvcm.html_module_unittest.HTMLModuleTests)
----------------------------------------------------------------------
Traceback (most recent call last):
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\html_module_unittest.py", line 359, in testInlineStylesheetURLs
my_component.AppendDirectlyDependentFilenamesTo(computed_deps)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\html_module.py", line 89, in AppendDirectlyDependentFilenamesTo
self.loader, module_dirname, contents)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 34, in __init__
self._Load(containing_dirname)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 88, in _Load
self._images = [resolve_url(x) for x in matches]
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 84, in resolve_url
image = self.loader.LoadImage(abs_path)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 186, in LoadImage
raise module.DepsException("url('%s') did not exist" % abs_path)
DepsException: While loading:
a.b.my_component
Got: url('c:\tmp\a\something.jpg') did not exist
======================================================================
ERROR: testGetAllDependentFilenamesRecursive (tvcm.module_unittest.ModuleIntegrationTests)
----------------------------------------------------------------------
Traceback (most recent call last):
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\module_unittest.py", line 118, in testGetAllDependentFilenamesRecursive
my_module = loader.LoadModule(module_name='z.foo')
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 140, in LoadModule
m.Load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\html_module.py", line 38, in Load
super(HTMLModule, self).Load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\module.py", line 187, in Load
style_sheet = self.loader.LoadStyleSheet(name)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 177, in LoadStyleSheet
style_sheet.load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 129, in load
self._InitParsedStyleSheetIfNeeded()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 136, in _InitParsedStyleSheetIfNeeded
self.loader, module_dirname, self.contents)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 34, in __init__
self._Load(containing_dirname)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 88, in _Load
self._images = [resolve_url(x) for x in matches]
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 84, in resolve_url
image = self.loader.LoadImage(abs_path)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 186, in LoadImage
raise module.DepsException("url('%s') did not exist" % abs_path)
DepsException: While loading:
z.foo
z.foo.css
Got: url('c:\x\y\z\foo.jpeg') did not exist
======================================================================
ERROR: testImages (tvcm.style_sheet_unittest.StyleSheetUnittest)
----------------------------------------------------------------------
Traceback (most recent call last):
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet_unittest.py", line 29, in testImages
foo_x = loader.LoadStyleSheet('foo.x')
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 177, in LoadStyleSheet
style_sheet.load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 129, in load
self._InitParsedStyleSheetIfNeeded()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 136, in _InitParsedStyleSheetIfNeeded
self.loader, module_dirname, self.contents)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 34, in __init__
self._Load(containing_dirname)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 88, in _Load
self._images = [resolve_url(x) for x in matches]
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 84, in resolve_url
image = self.loader.LoadImage(abs_path)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 186, in LoadImage
raise module.DepsException("url('%s') did not exist" % abs_path)
DepsException: While loading:
foo.x.css
Got: url('c:\src\images\bar.jpeg') did not exist
----------------------------------------------------------------------
Ran 87 tests in 11.067s
FAILED (errors=3, skipped=22)
| 1.0 | python tests fail on windows - After https://codereview.appspot.com/251100043/, there are still 3 failing tests. I'm not sure how to handle c:\ getting stuck on the absolute paths in Windows. Output:
======================================================================
ERROR: testInlineStylesheetURLs (tvcm.html_module_unittest.HTMLModuleTests)
----------------------------------------------------------------------
Traceback (most recent call last):
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\html_module_unittest.py", line 359, in testInlineStylesheetURLs
my_component.AppendDirectlyDependentFilenamesTo(computed_deps)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\html_module.py", line 89, in AppendDirectlyDependentFilenamesTo
self.loader, module_dirname, contents)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 34, in __init__
self._Load(containing_dirname)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 88, in _Load
self._images = [resolve_url(x) for x in matches]
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 84, in resolve_url
image = self.loader.LoadImage(abs_path)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 186, in LoadImage
raise module.DepsException("url('%s') did not exist" % abs_path)
DepsException: While loading:
a.b.my_component
Got: url('c:\tmp\a\something.jpg') did not exist
======================================================================
ERROR: testGetAllDependentFilenamesRecursive (tvcm.module_unittest.ModuleIntegrationTests)
----------------------------------------------------------------------
Traceback (most recent call last):
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\module_unittest.py", line 118, in testGetAllDependentFilenamesRecursive
my_module = loader.LoadModule(module_name='z.foo')
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 140, in LoadModule
m.Load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\html_module.py", line 38, in Load
super(HTMLModule, self).Load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\module.py", line 187, in Load
style_sheet = self.loader.LoadStyleSheet(name)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 177, in LoadStyleSheet
style_sheet.load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 129, in load
self._InitParsedStyleSheetIfNeeded()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 136, in _InitParsedStyleSheetIfNeeded
self.loader, module_dirname, self.contents)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 34, in __init__
self._Load(containing_dirname)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 88, in _Load
self._images = [resolve_url(x) for x in matches]
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 84, in resolve_url
image = self.loader.LoadImage(abs_path)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 186, in LoadImage
raise module.DepsException("url('%s') did not exist" % abs_path)
DepsException: While loading:
z.foo
z.foo.css
Got: url('c:\x\y\z\foo.jpeg') did not exist
======================================================================
ERROR: testImages (tvcm.style_sheet_unittest.StyleSheetUnittest)
----------------------------------------------------------------------
Traceback (most recent call last):
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet_unittest.py", line 29, in testImages
foo_x = loader.LoadStyleSheet('foo.x')
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 177, in LoadStyleSheet
style_sheet.load()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 129, in load
self._InitParsedStyleSheetIfNeeded()
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 136, in _InitParsedStyleSheetIfNeeded
self.loader, module_dirname, self.contents)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 34, in __init__
self._Load(containing_dirname)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 88, in _Load
self._images = [resolve_url(x) for x in matches]
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\style_sheet.py", line 84, in resolve_url
image = self.loader.LoadImage(abs_path)
File "c:\github\trace-viewer\tracing\third_party\tvcm\tvcm\resource_loader.py", line 186, in LoadImage
raise module.DepsException("url('%s') did not exist" % abs_path)
DepsException: While loading:
foo.x.css
Got: url('c:\src\images\bar.jpeg') did not exist
----------------------------------------------------------------------
Ran 87 tests in 11.067s
FAILED (errors=3, skipped=22)
| infrastructure | python tests fail on windows after there are still failing tests i m not sure how to handle c getting stuck on the absolute paths in windows output error testinlinestylesheeturls tvcm html module unittest htmlmoduletests traceback most recent call last file c github trace viewer tracing third party tvcm tvcm html module unittest py line in testinlinestylesheeturls my component appenddirectlydependentfilenamesto computed deps file c github trace viewer tracing third party tvcm tvcm html module py line in appenddirectlydependentfilenamesto self loader module dirname contents file c github trace viewer tracing third party tvcm tvcm style sheet py line in init self load containing dirname file c github trace viewer tracing third party tvcm tvcm style sheet py line in load self images file c github trace viewer tracing third party tvcm tvcm style sheet py line in resolve url image self loader loadimage abs path file c github trace viewer tracing third party tvcm tvcm resource loader py line in loadimage raise module depsexception url s did not exist abs path depsexception while loading a b my component got url c tmp a something jpg did not exist error testgetalldependentfilenamesrecursive tvcm module unittest moduleintegrationtests traceback most recent call last file c github trace viewer tracing third party tvcm tvcm module unittest py line in testgetalldependentfilenamesrecursive my module loader loadmodule module name z foo file c github trace viewer tracing third party tvcm tvcm resource loader py line in loadmodule m load file c github trace viewer tracing third party tvcm tvcm html module py line in load super htmlmodule self load file c github trace viewer tracing third party tvcm tvcm module py line in load style sheet self loader loadstylesheet name file c github trace viewer tracing third party tvcm tvcm resource loader py line in loadstylesheet style sheet load file c github trace viewer tracing third party tvcm tvcm style sheet py line in load self initparsedstylesheetifneeded file c github trace viewer tracing third party tvcm tvcm style sheet py line in initparsedstylesheetifneeded self loader module dirname self contents file c github trace viewer tracing third party tvcm tvcm style sheet py line in init self load containing dirname file c github trace viewer tracing third party tvcm tvcm style sheet py line in load self images file c github trace viewer tracing third party tvcm tvcm style sheet py line in resolve url image self loader loadimage abs path file c github trace viewer tracing third party tvcm tvcm resource loader py line in loadimage raise module depsexception url s did not exist abs path depsexception while loading z foo z foo css got url c x y z foo jpeg did not exist error testimages tvcm style sheet unittest stylesheetunittest traceback most recent call last file c github trace viewer tracing third party tvcm tvcm style sheet unittest py line in testimages foo x loader loadstylesheet foo x file c github trace viewer tracing third party tvcm tvcm resource loader py line in loadstylesheet style sheet load file c github trace viewer tracing third party tvcm tvcm style sheet py line in load self initparsedstylesheetifneeded file c github trace viewer tracing third party tvcm tvcm style sheet py line in initparsedstylesheetifneeded self loader module dirname self contents file c github trace viewer tracing third party tvcm tvcm style sheet py line in init self load containing dirname file c github trace viewer tracing third party tvcm tvcm style sheet py line in load self images file c github trace viewer tracing third party tvcm tvcm style sheet py line in resolve url image self loader loadimage abs path file c github trace viewer tracing third party tvcm tvcm resource loader py line in loadimage raise module depsexception url s did not exist abs path depsexception while loading foo x css got url c src images bar jpeg did not exist ran tests in failed errors skipped | 1 |
36,762 | 6,548,826,243 | IssuesEvent | 2017-09-05 02:09:10 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Update DNS documentation | kind/documentation sig/network team/cluster (deprecated - do not use) | In file: docs/admin/dns.md
Reword to say that it is required not optional.
Remove text about issues which are resolved at head.
Mention new record types, if any.
Consider whether user-guide is a better place for this content.
| 1.0 | Update DNS documentation - In file: docs/admin/dns.md
Reword to say that it is required not optional.
Remove text about issues which are resolved at head.
Mention new record types, if any.
Consider whether user-guide is a better place for this content.
| non_infrastructure | update dns documentation in file docs admin dns md reword to say that it is required not optional remove text about issues which are resolved at head mention new record types if any consider whether user guide is a better place for this content | 0 |
2,977 | 2,535,086,075 | IssuesEvent | 2015-01-25 17:40:25 | tgstation/-tg-station | https://api.github.com/repos/tgstation/-tg-station | closed | Aubrie Allen stammers, "<p-p-pan-n c-c-cl-l-l-las-ss-s-s='san-n-n-ns-s-s'><s-s-sp-pan-n-n-n c-cl-l-lass-s='jok-ker-rm-m-man-n'>H-H-H-Hm-mm.</s-s-sp-pan-n></s-sp-pan-n>" | Bug Priority: High | Stammering interfers with other speech span classes. | 1.0 | Aubrie Allen stammers, "<p-p-pan-n c-c-cl-l-l-las-ss-s-s='san-n-n-ns-s-s'><s-s-sp-pan-n-n-n c-cl-l-lass-s='jok-ker-rm-m-man-n'>H-H-H-Hm-mm.</s-s-sp-pan-n></s-sp-pan-n>" - Stammering interfers with other speech span classes. | non_infrastructure | aubrie allen stammers h h h hm mm stammering interfers with other speech span classes | 0 |
167,834 | 26,558,191,137 | IssuesEvent | 2023-01-20 13:50:31 | phetsims/rosetta | https://api.github.com/repos/phetsims/rosetta | closed | Change copy English value icon? | design:general status:ready-for-review | @oliver-phet, @DianaTavares, what do you think a better icon would be for the copy English value icon? I am using https://icons.getbootstrap.com/.
In the test for Rosetta 2.0 (https://github.com/phetsims/qa/issues/869), @DianaTavares noted that it would be helpful to have a button to copy the English value to the clipboard so that it could be easily pasted into Google Translate.
I think this could be done with the [Clipboard API](https://developer.mozilla.org/en-US/docs/Web/API/Clipboard_API) easily enough. And we could add this feature in a future release.
However, the current button has an icon that looks a lot like a button for copying to the clipboard:

We should probably change this icon *before* Rosetta 2.0 is released to avoid confusion with a future copy to clipboard button. | 1.0 | Change copy English value icon? - @oliver-phet, @DianaTavares, what do you think a better icon would be for the copy English value icon? I am using https://icons.getbootstrap.com/.
In the test for Rosetta 2.0 (https://github.com/phetsims/qa/issues/869), @DianaTavares noted that it would be helpful to have a button to copy the English value to the clipboard so that it could be easily pasted into Google Translate.
I think this could be done with the [Clipboard API](https://developer.mozilla.org/en-US/docs/Web/API/Clipboard_API) easily enough. And we could add this feature in a future release.
However, the current button has an icon that looks a lot like a button for copying to the clipboard:

We should probably change this icon *before* Rosetta 2.0 is released to avoid confusion with a future copy to clipboard button. | non_infrastructure | change copy english value icon oliver phet dianatavares what do you think a better icon would be for the copy english value icon i am using in the test for rosetta dianatavares noted that it would be helpful to have a button to copy the english value to the clipboard so that it could be easily pasted into google translate i think this could be done with the easily enough and we could add this feature in a future release however the current button has an icon that looks a lot like a button for copying to the clipboard we should probably change this icon before rosetta is released to avoid confusion with a future copy to clipboard button | 0 |
27,798 | 22,345,528,427 | IssuesEvent | 2022-06-15 07:26:43 | informalsystems/ibc-rs | https://api.github.com/repos/informalsystems/ibc-rs | closed | lib-gm incorrectly references gaiad binary | good first issue testing infrastructure | https://github.com/informalsystems/ibc-rs/blob/3aed2d9636d6aff5735a8a3062733279d2fb5777/scripts/gm/bin/lib-gm#L1075
Possible solution:
```
TM="$($GAIAD_BINARY | grep -q 'unsafe' || echo "tendermint")"
```
This solution uses the correct binary for the specific chain. `gaiad` might not even be installed for the user. | 1.0 | lib-gm incorrectly references gaiad binary - https://github.com/informalsystems/ibc-rs/blob/3aed2d9636d6aff5735a8a3062733279d2fb5777/scripts/gm/bin/lib-gm#L1075
Possible solution:
```
TM="$($GAIAD_BINARY | grep -q 'unsafe' || echo "tendermint")"
```
This solution uses the correct binary for the specific chain. `gaiad` might not even be installed for the user. | infrastructure | lib gm incorrectly references gaiad binary possible solution tm gaiad binary grep q unsafe echo tendermint this solution uses the correct binary for the specific chain gaiad might not even be installed for the user | 1 |
504,083 | 14,612,790,622 | IssuesEvent | 2020-12-22 06:56:08 | Fl45h13-SS13/Fl45h13_Bay | https://api.github.com/repos/Fl45h13-SS13/Fl45h13_Bay | opened | Вывести некоторые функции во внешнюю библиотеку | priority: low type: feature | <!-- Это общий шаблон для создания issue. Все данные необходимо вписывать ниже заголовка, но до комментария следующего раздела -->
<!-- Этот раздел должен содержать описание предложения, либо же описание и шаги для воспроизведения ошибки -->
## Описание
- Освещение
- Атмос
- Логгирование
- SQL
За основу можно взять rust_g. | 1.0 | Вывести некоторые функции во внешнюю библиотеку - <!-- Это общий шаблон для создания issue. Все данные необходимо вписывать ниже заголовка, но до комментария следующего раздела -->
<!-- Этот раздел должен содержать описание предложения, либо же описание и шаги для воспроизведения ошибки -->
## Описание
- Освещение
- Атмос
- Логгирование
- SQL
За основу можно взять rust_g. | non_infrastructure | вывести некоторые функции во внешнюю библиотеку описание освещение атмос логгирование sql за основу можно взять rust g | 0 |
228,054 | 25,153,529,509 | IssuesEvent | 2022-11-10 11:50:54 | valtech-ch/microservice-kubernetes-cluster | https://api.github.com/repos/valtech-ch/microservice-kubernetes-cluster | reopened | CVE-2022-25857 (High) detected in snakeyaml-1.30.jar | security vulnerability | ## CVE-2022-25857 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.30.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="https://bitbucket.org/snakeyaml/snakeyaml">https://bitbucket.org/snakeyaml/snakeyaml</a></p>
<p>Path to dependency file: /persistence/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-aop-2.7.5.jar (Root Library)
- spring-boot-starter-2.7.5.jar
- :x: **snakeyaml-1.30.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/valtech-ch/microservice-kubernetes-cluster/commit/335a4047c89f52dfe860e93daefb32dc86a521a2">335a4047c89f52dfe860e93daefb32dc86a521a2</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package org.yaml:snakeyaml from 0 and before 1.31 are vulnerable to Denial of Service (DoS) due missing to nested depth limitation for collections.
<p>Publish Date: 2022-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25857>CVE-2022-25857</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857</a></p>
<p>Release Date: 2022-08-30</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-25857 (High) detected in snakeyaml-1.30.jar - ## CVE-2022-25857 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.30.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="https://bitbucket.org/snakeyaml/snakeyaml">https://bitbucket.org/snakeyaml/snakeyaml</a></p>
<p>Path to dependency file: /persistence/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.30/8fde7fe2586328ac3c68db92045e1c8759125000/snakeyaml-1.30.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-aop-2.7.5.jar (Root Library)
- spring-boot-starter-2.7.5.jar
- :x: **snakeyaml-1.30.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/valtech-ch/microservice-kubernetes-cluster/commit/335a4047c89f52dfe860e93daefb32dc86a521a2">335a4047c89f52dfe860e93daefb32dc86a521a2</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package org.yaml:snakeyaml from 0 and before 1.31 are vulnerable to Denial of Service (DoS) due missing to nested depth limitation for collections.
<p>Publish Date: 2022-08-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25857>CVE-2022-25857</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25857</a></p>
<p>Release Date: 2022-08-30</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in snakeyaml jar cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file persistence build gradle path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy spring boot starter aop jar root library spring boot starter jar x snakeyaml jar vulnerable library found in head commit a href found in base branch develop vulnerability details the package org yaml snakeyaml from and before are vulnerable to denial of service dos due missing to nested depth limitation for collections publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml step up your open source security game with mend | 0 |
163,795 | 13,927,533,818 | IssuesEvent | 2020-10-21 19:59:19 | getsentry/sentry | https://api.github.com/repos/getsentry/sentry | closed | Trailing slash in URL breaks U2F. | Component: Documentation | Testing latest master (I believe, listed as 8.23.0.dev0) if we run with a trailing slash in the configured URL, then U2F fails thinking it's an URL mismatch:
(company-internal domain replaced by `our.site` below, and some IPs changed)
```
ValueError: Invalid facet! Was: u'https://our.site', expecting one of: [u'https://our.site/']
```
Notice that the only difference is the trailing slash.
For more context:
```
17:59:34 [INFO] sentry.superuser: superuser.request (user_id=1 url=u'https://our.site/api/0/users/me/authenticators/u2f/enroll/' method=u'POST' ip_address=u'10.123.123.123')
Traceback (most recent call last):
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/base.py", line 87, in handle_exception
response = super(Endpoint, self).handle_exception(exc)
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/base.py", line 170, in dispatch
response = handler(request, *args, **kwargs)
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/decorators.py", line 28, in wrapped
return func(self, request, *args, **kwargs)
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/endpoints/user_authenticator_enroll.py", line 182, in post
serializer.data['deviceName']
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/models/authenticator.py", line 554, in try_enroll
binding, cert = u2f.complete_register(enrollment_data, response_data, self.u2f_facets)
File "/usr/local/lib/python2.7/site-packages/u2flib_server/u2f.py", line 64, in complete_register
valid_facets)
File "/usr/local/lib/python2.7/site-packages/u2flib_server/u2f_v2.py", line 203, in complete_register
"navigator.id.finishEnrollment", valid_facets)
File "/usr/local/lib/python2.7/site-packages/u2flib_server/u2f_v2.py", line 184, in _validate_client_data
client_data.origin, valid_facets))
ValueError: Invalid facet! Was: u'https://our.site', expecting one of: [u'https://our.site/']
10.123.123.123 - - [05/Jun/2018:17:59:34 +0000] "POST /api/0/users/me/authenticators/u2f/enroll/ HTTP/1.1" 500 576 "https://our.site/settings/account/security/u2f/enroll/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_13_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/66.0.3359.181 Safari/537.36"
```
Changing the URL through the admin interface and restarting web server resolved the issue. It's an easy fix, but it's not obvious what's going on until checking the locks. | 1.0 | Trailing slash in URL breaks U2F. - Testing latest master (I believe, listed as 8.23.0.dev0) if we run with a trailing slash in the configured URL, then U2F fails thinking it's an URL mismatch:
(company-internal domain replaced by `our.site` below, and some IPs changed)
```
ValueError: Invalid facet! Was: u'https://our.site', expecting one of: [u'https://our.site/']
```
Notice that the only difference is the trailing slash.
For more context:
```
17:59:34 [INFO] sentry.superuser: superuser.request (user_id=1 url=u'https://our.site/api/0/users/me/authenticators/u2f/enroll/' method=u'POST' ip_address=u'10.123.123.123')
Traceback (most recent call last):
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/base.py", line 87, in handle_exception
response = super(Endpoint, self).handle_exception(exc)
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/base.py", line 170, in dispatch
response = handler(request, *args, **kwargs)
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/decorators.py", line 28, in wrapped
return func(self, request, *args, **kwargs)
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/api/endpoints/user_authenticator_enroll.py", line 182, in post
serializer.data['deviceName']
File "/usr/local/lib/python2.7/site-packages/sentry-8.23.0.dev0-py2.7.egg/sentry/models/authenticator.py", line 554, in try_enroll
binding, cert = u2f.complete_register(enrollment_data, response_data, self.u2f_facets)
File "/usr/local/lib/python2.7/site-packages/u2flib_server/u2f.py", line 64, in complete_register
valid_facets)
File "/usr/local/lib/python2.7/site-packages/u2flib_server/u2f_v2.py", line 203, in complete_register
"navigator.id.finishEnrollment", valid_facets)
File "/usr/local/lib/python2.7/site-packages/u2flib_server/u2f_v2.py", line 184, in _validate_client_data
client_data.origin, valid_facets))
ValueError: Invalid facet! Was: u'https://our.site', expecting one of: [u'https://our.site/']
10.123.123.123 - - [05/Jun/2018:17:59:34 +0000] "POST /api/0/users/me/authenticators/u2f/enroll/ HTTP/1.1" 500 576 "https://our.site/settings/account/security/u2f/enroll/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_13_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/66.0.3359.181 Safari/537.36"
```
Changing the URL through the admin interface and restarting web server resolved the issue. It's an easy fix, but it's not obvious what's going on until checking the locks. | non_infrastructure | trailing slash in url breaks testing latest master i believe listed as if we run with a trailing slash in the configured url then fails thinking it s an url mismatch company internal domain replaced by our site below and some ips changed valueerror invalid facet was u expecting one of notice that the only difference is the trailing slash for more context sentry superuser superuser request user id url u method u post ip address u traceback most recent call last file usr local lib site packages sentry egg sentry api base py line in handle exception response super endpoint self handle exception exc file usr local lib site packages sentry egg sentry api base py line in dispatch response handler request args kwargs file usr local lib site packages sentry egg sentry api decorators py line in wrapped return func self request args kwargs file usr local lib site packages sentry egg sentry api endpoints user authenticator enroll py line in post serializer data file usr local lib site packages sentry egg sentry models authenticator py line in try enroll binding cert complete register enrollment data response data self facets file usr local lib site packages server py line in complete register valid facets file usr local lib site packages server py line in complete register navigator id finishenrollment valid facets file usr local lib site packages server py line in validate client data client data origin valid facets valueerror invalid facet was u expecting one of post api users me authenticators enroll http mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari changing the url through the admin interface and restarting web server resolved the issue it s an easy fix but it s not obvious what s going on until checking the locks | 0 |
4,007 | 4,763,422,329 | IssuesEvent | 2016-10-25 14:25:44 | camptocamp/c2cgeoportal | https://api.github.com/repos/camptocamp/c2cgeoportal | closed | Investigate about template parsing errors... | Infrastructure Ongoing | Example errors:
```
.build/venv/bin/pot-create --config lingua-client.cfg --output nyon/locale/nyon-client.pot nyon/templates/edit.html nyon/templates/desktop.html nyon/templates/routing.html nyon/templates/api/apihelp_old.html nyon/templates/api/xapihelp.html nyon/templates/api/apihelp.html nyon/templates/mobile.html nyon/static-ngeo/js/nyonmodule.js nyon/static-ngeo/js/mobile.js .build/config.yaml development.ini
Error parsing ./nyon/templates/desktop.html at line 3 column 102
Error parsing ./nyon/templates/mobile.html at line 6 column 74
```
But the script don't failed. | 1.0 | Investigate about template parsing errors... - Example errors:
```
.build/venv/bin/pot-create --config lingua-client.cfg --output nyon/locale/nyon-client.pot nyon/templates/edit.html nyon/templates/desktop.html nyon/templates/routing.html nyon/templates/api/apihelp_old.html nyon/templates/api/xapihelp.html nyon/templates/api/apihelp.html nyon/templates/mobile.html nyon/static-ngeo/js/nyonmodule.js nyon/static-ngeo/js/mobile.js .build/config.yaml development.ini
Error parsing ./nyon/templates/desktop.html at line 3 column 102
Error parsing ./nyon/templates/mobile.html at line 6 column 74
```
But the script don't failed. | infrastructure | investigate about template parsing errors example errors build venv bin pot create config lingua client cfg output nyon locale nyon client pot nyon templates edit html nyon templates desktop html nyon templates routing html nyon templates api apihelp old html nyon templates api xapihelp html nyon templates api apihelp html nyon templates mobile html nyon static ngeo js nyonmodule js nyon static ngeo js mobile js build config yaml development ini error parsing nyon templates desktop html at line column error parsing nyon templates mobile html at line column but the script don t failed | 1 |
23,646 | 16,489,452,443 | IssuesEvent | 2021-05-25 00:06:56 | learning-unlimited/ESP-Website | https://api.github.com/repos/learning-unlimited/ESP-Website | closed | Images and Theme folders not symlinked with defaults on older sites | Error Infrastructure | As described in the email thread.... The newer sites have symlinked images/ and styles/ to default_images/ and default_styles/, so they get all new/updated files. However, with Yale and some older sites, which were set up when we still used Dropbox, have full copies of esp/public/media/, possibly with modifications, and don't automatically get updated. Looks like we forgot to account for this for at least the last two stable releases.
The easiest things to do would either be change these sites over to using symlinks, or to copy the repository's versions of these files to the custom location. This would work fine for most sites, but I'd be afraid to do it for Stanford and Chicago and any other sites not using generic templates. For those, we should probably just copy over new files, and for modified files, we can either (a) figure out which files haven't been customized, and copy over the correct versions; or (b) not fix anything.
| 1.0 | Images and Theme folders not symlinked with defaults on older sites - As described in the email thread.... The newer sites have symlinked images/ and styles/ to default_images/ and default_styles/, so they get all new/updated files. However, with Yale and some older sites, which were set up when we still used Dropbox, have full copies of esp/public/media/, possibly with modifications, and don't automatically get updated. Looks like we forgot to account for this for at least the last two stable releases.
The easiest things to do would either be change these sites over to using symlinks, or to copy the repository's versions of these files to the custom location. This would work fine for most sites, but I'd be afraid to do it for Stanford and Chicago and any other sites not using generic templates. For those, we should probably just copy over new files, and for modified files, we can either (a) figure out which files haven't been customized, and copy over the correct versions; or (b) not fix anything.
| infrastructure | images and theme folders not symlinked with defaults on older sites as described in the email thread the newer sites have symlinked images and styles to default images and default styles so they get all new updated files however with yale and some older sites which were set up when we still used dropbox have full copies of esp public media possibly with modifications and don t automatically get updated looks like we forgot to account for this for at least the last two stable releases the easiest things to do would either be change these sites over to using symlinks or to copy the repository s versions of these files to the custom location this would work fine for most sites but i d be afraid to do it for stanford and chicago and any other sites not using generic templates for those we should probably just copy over new files and for modified files we can either a figure out which files haven t been customized and copy over the correct versions or b not fix anything | 1 |
312,170 | 9,544,258,214 | IssuesEvent | 2019-05-01 13:40:18 | TaiBIF/camera-trap-api | https://api.github.com/repos/TaiBIF/camera-trap-api | closed | 4.10 編輯模式 (操作相關_滑鼠右鍵) 複製一列並貼上/刪除列 | previous priority | - [x] `POST /media/annotation/:id/token/:index/replicate`
直接複製 _id === :id 的第 :index 個 token,插入到 annotation.tokens 的最後一個元素
- [x] 插入下一行的操作實際上要調整 tokens 的順序
i. e. 假設有 tokens 0, 1, 2,複製第 0 個的結果會插入到 1 的位置,剩下的 token 在 array 中向後順移,index 變為 2,3。新的 tokens array 是 0, 1 (new, replicated from 0), 2(原本的1), 3(原本的2)
- [x] `POST /media/annotation/:id/token/:index/delete`
直接刪除 _id === :id 的第 :index 個 token。當 tokens.length == 1 時不會再刪除。
- [x] 刪除後調整 tokens 的順序
i. e. 假設有 tokens 0, 1, 2,刪除第 1 個的結果,原 token index > 1 的元素在 array 中向前順移。新的 tokens array 是 0, 1 (原本的2)
- [ ] 權限管理 | 1.0 | 4.10 編輯模式 (操作相關_滑鼠右鍵) 複製一列並貼上/刪除列 - - [x] `POST /media/annotation/:id/token/:index/replicate`
直接複製 _id === :id 的第 :index 個 token,插入到 annotation.tokens 的最後一個元素
- [x] 插入下一行的操作實際上要調整 tokens 的順序
i. e. 假設有 tokens 0, 1, 2,複製第 0 個的結果會插入到 1 的位置,剩下的 token 在 array 中向後順移,index 變為 2,3。新的 tokens array 是 0, 1 (new, replicated from 0), 2(原本的1), 3(原本的2)
- [x] `POST /media/annotation/:id/token/:index/delete`
直接刪除 _id === :id 的第 :index 個 token。當 tokens.length == 1 時不會再刪除。
- [x] 刪除後調整 tokens 的順序
i. e. 假設有 tokens 0, 1, 2,刪除第 1 個的結果,原 token index > 1 的元素在 array 中向前順移。新的 tokens array 是 0, 1 (原本的2)
- [ ] 權限管理 | non_infrastructure | 編輯模式 操作相關 滑鼠右鍵 複製一列並貼上 刪除列 post media annotation id token index replicate 直接複製 id id 的第 index 個 token,插入到 annotation tokens 的最後一個元素 插入下一行的操作實際上要調整 tokens 的順序 i e 假設有 tokens ,複製第 個的結果會插入到 的位置,剩下的 token 在 array 中向後順移,index 變為 。新的 tokens array 是 new replicated from post media annotation id token index delete 直接刪除 id id 的第 index 個 token。當 tokens length 時不會再刪除。 刪除後調整 tokens 的順序 i e 假設有 tokens ,刪除第 個的結果,原 token index 的元素在 array 中向前順移。新的 tokens array 是 權限管理 | 0 |
20,676 | 14,099,371,023 | IssuesEvent | 2020-11-06 01:12:57 | noahtalerman/test-issues-kolide | https://api.github.com/repos/noahtalerman/test-issues-kolide | opened | [CLOSED] build all branches, using master as latest | Component: Development Infrastructure | <a href="https://github.com/groob"><img src="https://avatars3.githubusercontent.com/u/1526945?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [groob](https://github.com/groob)**
_Wednesday Sep 21, 2016 at 21:16 GMT_
_Originally opened as https://github.com/kolide/fleet/pull/226_
----
Update circle config to build a docker container on merges to master as well.
----
_**[groob](https://github.com/groob)** included the following code: https://github.com/kolide/fleet/pull/226/commits_
| 1.0 | [CLOSED] build all branches, using master as latest - <a href="https://github.com/groob"><img src="https://avatars3.githubusercontent.com/u/1526945?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [groob](https://github.com/groob)**
_Wednesday Sep 21, 2016 at 21:16 GMT_
_Originally opened as https://github.com/kolide/fleet/pull/226_
----
Update circle config to build a docker container on merges to master as well.
----
_**[groob](https://github.com/groob)** included the following code: https://github.com/kolide/fleet/pull/226/commits_
| infrastructure | build all branches using master as latest issue by wednesday sep at gmt originally opened as update circle config to build a docker container on merges to master as well included the following code | 1 |
136,829 | 12,735,886,227 | IssuesEvent | 2020-06-25 15:59:59 | handsontable/hyperformula | https://api.github.com/repos/handsontable/hyperformula | closed | Add `@throws` to TSDocs | Documentation Verified | ### Description
It would be great if at some point someone could review all public API methods and add `@throws` with the link to the exported error class and a short description when it happens.
I suppose it would be easier for someone who is familiar with the code. There are some check deep in the `crudOperations` module that are propagated to the end developer. If some errors are not exported, please do so #261.
### Example: addNamedExpression
```ts
/**
* Adds a specified named expression.
*
* Note that this method may trigger dependency graph recalculation.
*
* @param {string} expressionName - a name of the expression to be added
* @param {RawCellContent} expression - the expression
*
* @fires [[namedExpressionAdded]] always, unless [[batch]] mode is used
* @fires [[valuesUpdated]] if recalculation was triggered by this change
*
* @throws [[NamedExpressionNameIsAlreadyTaken]] when the named expression already exists
* @throws [[NamedExpressionNameIsInvalid]] when the name does not meet condition for a valid name
*
* @category Named Expression
*/
public addNamedExpression(expressionName: string, expression: RawCellContent): ExportedChange[] {
``` | 1.0 | Add `@throws` to TSDocs - ### Description
It would be great if at some point someone could review all public API methods and add `@throws` with the link to the exported error class and a short description when it happens.
I suppose it would be easier for someone who is familiar with the code. There are some check deep in the `crudOperations` module that are propagated to the end developer. If some errors are not exported, please do so #261.
### Example: addNamedExpression
```ts
/**
* Adds a specified named expression.
*
* Note that this method may trigger dependency graph recalculation.
*
* @param {string} expressionName - a name of the expression to be added
* @param {RawCellContent} expression - the expression
*
* @fires [[namedExpressionAdded]] always, unless [[batch]] mode is used
* @fires [[valuesUpdated]] if recalculation was triggered by this change
*
* @throws [[NamedExpressionNameIsAlreadyTaken]] when the named expression already exists
* @throws [[NamedExpressionNameIsInvalid]] when the name does not meet condition for a valid name
*
* @category Named Expression
*/
public addNamedExpression(expressionName: string, expression: RawCellContent): ExportedChange[] {
``` | non_infrastructure | add throws to tsdocs description it would be great if at some point someone could review all public api methods and add throws with the link to the exported error class and a short description when it happens i suppose it would be easier for someone who is familiar with the code there are some check deep in the crudoperations module that are propagated to the end developer if some errors are not exported please do so example addnamedexpression ts adds a specified named expression note that this method may trigger dependency graph recalculation param string expressionname a name of the expression to be added param rawcellcontent expression the expression fires always unless mode is used fires if recalculation was triggered by this change throws when the named expression already exists throws when the name does not meet condition for a valid name category named expression public addnamedexpression expressionname string expression rawcellcontent exportedchange | 0 |
10,954 | 8,837,887,560 | IssuesEvent | 2019-01-05 10:57:21 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | Ubuntu 18.04 x64 build failing | area-Infrastructure bug os-linux | On the current tip, I am seeing build failures on Linux x64.
The `./build.sh` script output ends with a message
```
Build failed (exit code '139'). See log: /home/stmaclea/git/corefx/eng/common/../../artifacts/log/Debug/Build.binlog
```
The `Build.binlog` is a binary file and does not seem to contain useful information.
Early in the console output there are a series of warnings
```
~/git/corefx$ ./build.sh
Downloading 'https://dot.net/v1/dotnet-install.sh'
dotnet-install: Downloading link: https://dotnetcli.azureedge.net/dotnet/Sdk/2.1.401/dotnet-sdk-2.1.401-linux-x64.tar.gz
dotnet-install: Extracting zip from https://dotnetcli.azureedge.net/dotnet/Sdk/2.1.401/dotnet-sdk-2.1.401-linux-x64.tar.gz
dotnet-install: Adding to current process PATH: `/home/stmaclea/git/corefx/.dotnet`. Note: This change will be visible only when sourcing script.
dotnet-install: Installation finished successfully.
/home/stmaclea/git/corefx/.dotnet/sdk/2.1.401/MSBuild.dll /nologo -maxcpucount /m -verbosity:m /v:minimal /bl:/home/stmaclea/git/corefx/eng/common/../../artifacts/log/Debug/ToolsetRestore.binlog /clp:Summary /clp:None /nr:true /p:__ToolsetLocationOutputFile=/home/stmaclea/git/corefx/eng/common/../../artifacts/toolset/1.0.0-beta.18565.8.txt /t:__WriteToolsetLocation /home/stmaclea/git/corefx/eng/common/../../artifacts/toolset/restore.proj
Build succeeded.
0 Warning(s)
0 Error(s)
Time Elapsed 00:00:00.23
/home/stmaclea/git/corefx/.dotnet/sdk/2.1.401/MSBuild.dll /nologo -maxcpucount /m -verbosity:m /v:minimal /bl:/home/stmaclea/git/corefx/eng/common/../../artifacts/log/Debug/Build.binlog /clp:Summary /nr:true /p:Configuration=Debug /p:Projects=/home/stmaclea/git/corefx/eng/common/../../*.sln /p:RepoRoot=/home/stmaclea/git/corefx/eng/common/../.. /p:Restore=true /p:Build=true /p:Rebuild=false /p:Test=false /p:Pack=false /p:IntegrationTest=false /p:PerformanceTest=false /p:Sign=false /p:Publish=false /p:ContinuousIntegrationBuild=false /home/stmaclea/.nuget/packages/microsoft.dotnet.arcade.sdk/1.0.0-beta.18565.8/tools/Build.proj
Restoring packages for /home/stmaclea/.nuget/packages/microsoft.dotnet.arcade.sdk/1.0.0-beta.18565.8/tools/Tools.proj...
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/toolset/Common/Tools.proj.nuget.g.props.
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/toolset/Common/Tools.proj.nuget.g.targets.
Restore completed in 231.43 ms for /home/stmaclea/.nuget/packages/microsoft.dotnet.arcade.sdk/1.0.0-beta.18565.8/tools/Tools.proj.
Restoring packages for /home/stmaclea/git/corefx/external/netstandard/netstandard.depproj...
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/obj/netstandard/netstandard/netstandard.depproj.nuget.g.props.
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/obj/netstandard/netstandard/netstandard.depproj.nuget.g.targets.
Restore completed in 31.45 ms for /home/stmaclea/git/corefx/external/netstandard/netstandard.depproj.
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : The type initializer for 'LibGit2Sharp.Core.NativeMethods' threw an exception. [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at LibGit2Sharp.Core.NativeMethods.git_buf_free(GitBuf buf) [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at LibGit2Sharp.Core.Proxy.ConvertPath(Func`2 pathRetriever) [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at LibGit2Sharp.Repository.Discover(String startingPath) [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at Microsoft.Build.Tasks.Git.GitOperations.LocateRepository(String directory) in /_/src/Microsoft.Build.Tasks.Git.Operations/GitOperations.cs:line 26 [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at Microsoft.Build.Tasks.Git.RepositoryTasks.LocateRepository(LocateRepository task) in /_/src/Microsoft.Build.Tasks.Git.Operations/RepositoryTasks.cs:line 58 [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.sourcelink.common/1.0.0-beta-63401-01/build/Microsoft.SourceLink.Common.targets(53,5): warning : Source control information is not available - the generated source link is empty. [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
```
| 1.0 | Ubuntu 18.04 x64 build failing - On the current tip, I am seeing build failures on Linux x64.
The `./build.sh` script output ends with a message
```
Build failed (exit code '139'). See log: /home/stmaclea/git/corefx/eng/common/../../artifacts/log/Debug/Build.binlog
```
The `Build.binlog` is a binary file and does not seem to contain useful information.
Early in the console output there are a series of warnings
```
~/git/corefx$ ./build.sh
Downloading 'https://dot.net/v1/dotnet-install.sh'
dotnet-install: Downloading link: https://dotnetcli.azureedge.net/dotnet/Sdk/2.1.401/dotnet-sdk-2.1.401-linux-x64.tar.gz
dotnet-install: Extracting zip from https://dotnetcli.azureedge.net/dotnet/Sdk/2.1.401/dotnet-sdk-2.1.401-linux-x64.tar.gz
dotnet-install: Adding to current process PATH: `/home/stmaclea/git/corefx/.dotnet`. Note: This change will be visible only when sourcing script.
dotnet-install: Installation finished successfully.
/home/stmaclea/git/corefx/.dotnet/sdk/2.1.401/MSBuild.dll /nologo -maxcpucount /m -verbosity:m /v:minimal /bl:/home/stmaclea/git/corefx/eng/common/../../artifacts/log/Debug/ToolsetRestore.binlog /clp:Summary /clp:None /nr:true /p:__ToolsetLocationOutputFile=/home/stmaclea/git/corefx/eng/common/../../artifacts/toolset/1.0.0-beta.18565.8.txt /t:__WriteToolsetLocation /home/stmaclea/git/corefx/eng/common/../../artifacts/toolset/restore.proj
Build succeeded.
0 Warning(s)
0 Error(s)
Time Elapsed 00:00:00.23
/home/stmaclea/git/corefx/.dotnet/sdk/2.1.401/MSBuild.dll /nologo -maxcpucount /m -verbosity:m /v:minimal /bl:/home/stmaclea/git/corefx/eng/common/../../artifacts/log/Debug/Build.binlog /clp:Summary /nr:true /p:Configuration=Debug /p:Projects=/home/stmaclea/git/corefx/eng/common/../../*.sln /p:RepoRoot=/home/stmaclea/git/corefx/eng/common/../.. /p:Restore=true /p:Build=true /p:Rebuild=false /p:Test=false /p:Pack=false /p:IntegrationTest=false /p:PerformanceTest=false /p:Sign=false /p:Publish=false /p:ContinuousIntegrationBuild=false /home/stmaclea/.nuget/packages/microsoft.dotnet.arcade.sdk/1.0.0-beta.18565.8/tools/Build.proj
Restoring packages for /home/stmaclea/.nuget/packages/microsoft.dotnet.arcade.sdk/1.0.0-beta.18565.8/tools/Tools.proj...
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/toolset/Common/Tools.proj.nuget.g.props.
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/toolset/Common/Tools.proj.nuget.g.targets.
Restore completed in 231.43 ms for /home/stmaclea/.nuget/packages/microsoft.dotnet.arcade.sdk/1.0.0-beta.18565.8/tools/Tools.proj.
Restoring packages for /home/stmaclea/git/corefx/external/netstandard/netstandard.depproj...
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/obj/netstandard/netstandard/netstandard.depproj.nuget.g.props.
Generating MSBuild file /home/stmaclea/git/corefx/artifacts/obj/netstandard/netstandard/netstandard.depproj.nuget.g.targets.
Restore completed in 31.45 ms for /home/stmaclea/git/corefx/external/netstandard/netstandard.depproj.
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : The type initializer for 'LibGit2Sharp.Core.NativeMethods' threw an exception. [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at LibGit2Sharp.Core.NativeMethods.git_buf_free(GitBuf buf) [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at LibGit2Sharp.Core.Proxy.ConvertPath(Func`2 pathRetriever) [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at LibGit2Sharp.Repository.Discover(String startingPath) [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at Microsoft.Build.Tasks.Git.GitOperations.LocateRepository(String directory) in /_/src/Microsoft.Build.Tasks.Git.Operations/GitOperations.cs:line 26 [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.build.tasks.git/1.0.0-beta-63401-01/build/Microsoft.Build.Tasks.Git.targets(20,5): warning : at Microsoft.Build.Tasks.Git.RepositoryTasks.LocateRepository(LocateRepository task) in /_/src/Microsoft.Build.Tasks.Git.Operations/RepositoryTasks.cs:line 58 [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
/home/stmaclea/.nuget/packages/microsoft.sourcelink.common/1.0.0-beta-63401-01/build/Microsoft.SourceLink.Common.targets(53,5): warning : Source control information is not available - the generated source link is empty. [/home/stmaclea/git/corefx/external/netstandard/netstandard.depproj]
```
| infrastructure | ubuntu build failing on the current tip i am seeing build failures on linux the build sh script output ends with a message build failed exit code see log home stmaclea git corefx eng common artifacts log debug build binlog the build binlog is a binary file and does not seem to contain useful information early in the console output there are a series of warnings git corefx build sh downloading dotnet install downloading link dotnet install extracting zip from dotnet install adding to current process path home stmaclea git corefx dotnet note this change will be visible only when sourcing script dotnet install installation finished successfully home stmaclea git corefx dotnet sdk msbuild dll nologo maxcpucount m verbosity m v minimal bl home stmaclea git corefx eng common artifacts log debug toolsetrestore binlog clp summary clp none nr true p toolsetlocationoutputfile home stmaclea git corefx eng common artifacts toolset beta txt t writetoolsetlocation home stmaclea git corefx eng common artifacts toolset restore proj build succeeded warning s error s time elapsed home stmaclea git corefx dotnet sdk msbuild dll nologo maxcpucount m verbosity m v minimal bl home stmaclea git corefx eng common artifacts log debug build binlog clp summary nr true p configuration debug p projects home stmaclea git corefx eng common sln p reporoot home stmaclea git corefx eng common p restore true p build true p rebuild false p test false p pack false p integrationtest false p performancetest false p sign false p publish false p continuousintegrationbuild false home stmaclea nuget packages microsoft dotnet arcade sdk beta tools build proj restoring packages for home stmaclea nuget packages microsoft dotnet arcade sdk beta tools tools proj generating msbuild file home stmaclea git corefx artifacts toolset common tools proj nuget g props generating msbuild file home stmaclea git corefx artifacts toolset common tools proj nuget g targets restore completed in ms for home stmaclea nuget packages microsoft dotnet arcade sdk beta tools tools proj restoring packages for home stmaclea git corefx external netstandard netstandard depproj generating msbuild file home stmaclea git corefx artifacts obj netstandard netstandard netstandard depproj nuget g props generating msbuild file home stmaclea git corefx artifacts obj netstandard netstandard netstandard depproj nuget g targets restore completed in ms for home stmaclea git corefx external netstandard netstandard depproj home stmaclea nuget packages microsoft build tasks git beta build microsoft build tasks git targets warning the type initializer for core nativemethods threw an exception home stmaclea nuget packages microsoft build tasks git beta build microsoft build tasks git targets warning at core nativemethods git buf free gitbuf buf home stmaclea nuget packages microsoft build tasks git beta build microsoft build tasks git targets warning at core proxy convertpath func pathretriever home stmaclea nuget packages microsoft build tasks git beta build microsoft build tasks git targets warning at repository discover string startingpath home stmaclea nuget packages microsoft build tasks git beta build microsoft build tasks git targets warning at microsoft build tasks git gitoperations locaterepository string directory in src microsoft build tasks git operations gitoperations cs line home stmaclea nuget packages microsoft build tasks git beta build microsoft build tasks git targets warning at microsoft build tasks git repositorytasks locaterepository locaterepository task in src microsoft build tasks git operations repositorytasks cs line home stmaclea nuget packages microsoft sourcelink common beta build microsoft sourcelink common targets warning source control information is not available the generated source link is empty | 1 |
29,511 | 24,053,315,654 | IssuesEvent | 2022-09-16 14:35:57 | cu-mkp/m-k-manuscript-data | https://api.github.com/repos/cu-mkp/m-k-manuscript-data | opened | check multcloud backup | infrastructure | From email notifications, last backup seems to have been 7/31/2022 -- check that this is still working | 1.0 | check multcloud backup - From email notifications, last backup seems to have been 7/31/2022 -- check that this is still working | infrastructure | check multcloud backup from email notifications last backup seems to have been check that this is still working | 1 |
3,555 | 4,396,996,220 | IssuesEvent | 2016-08-10 06:03:10 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Signed build machines need upgrading to VS2015.3 | Area-Infrastructure | Our signed build machines need to be upgraded to VS2015.3.
There are 27 InteractiveWindow.UnitTests that have been disabled as the Clipboard functionality has changed between Update 2 and Update 3.
Since the GAC overrides other assembly loading (including loading from NuGet packages) we cannot work around the issue on machines where Update 3 is not installed. | 1.0 | Signed build machines need upgrading to VS2015.3 - Our signed build machines need to be upgraded to VS2015.3.
There are 27 InteractiveWindow.UnitTests that have been disabled as the Clipboard functionality has changed between Update 2 and Update 3.
Since the GAC overrides other assembly loading (including loading from NuGet packages) we cannot work around the issue on machines where Update 3 is not installed. | infrastructure | signed build machines need upgrading to our signed build machines need to be upgraded to there are interactivewindow unittests that have been disabled as the clipboard functionality has changed between update and update since the gac overrides other assembly loading including loading from nuget packages we cannot work around the issue on machines where update is not installed | 1 |
305,663 | 9,374,968,794 | IssuesEvent | 2019-04-04 01:49:08 | Qiskit/qiskit-terra | https://api.github.com/repos/Qiskit/qiskit-terra | closed | Opaque gate definitions give an error in CircuitBackend | bug enhancement priority: medium | Defining a general opaque gate raises an error when unrolling into a circuit.
## Expected Behavior
Either an opaque gate should be taken as-is and be left alone, or when it is defined in the basis it should be left alone when reading in OpenQASM.
## Current Behavior
My OpenQASM code
```
OPENQASM 2.0;
include "qelib1.inc";
opaque mygate q1, q2, q3;
qreg q[3];
creg c[2];
mygate q[0], q[1], q[2];
measure q[0] -> c[0];
measure q[1] -> c[1];
```
and parsing code
```py
from sys import argv
from pathlib import Path
import matplotlib
matplotlib.use('TkAgg') # OSX workaround
from qiskit.qasm import Qasm
from qiskit.unroll import Unroller, CircuitBackend
from qiskit.tools.visualization import circuit_drawer
if len(argv) != 2:
raise RuntimeError("Exactly 1 argument is required.")
print(f"Opening {argv[1]}")
path = Path(argv[1]).resolve(strict=True)
qasm = Qasm(filename=str(path)).parse()
circuit = Unroller(qasm, CircuitBackend(
basis=["u1","u2","u3","id","cx","x","y","z","h","s","t","rx","ry","rz"])).execute()
im = circuit_drawer(circuit)
im.save(path.with_suffix('.png'))
```
When reading in OpenQASM with an opaque gate definition I get the error
```
Opening quantum-simulation.qasm
Traceback (most recent call last):
File "qasm-to-img.py", line 18, in <module>
basis=["u1","u2","u3","id","cx","x","y","z","h","s","t","rx","ry","rz"])).execute()
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 280, in execute
self._process_node(self.ast)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 187, in _process_node
self._process_children(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 182, in _process_children
self._process_node(kid)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 222, in _process_node
self._process_custom_unitary(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 111, in _process_custom_unitary
self.arg_stack[0:-1])
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_circuitbackend.py", line 211, in start_gate
raise BackendError("opaque gate %s not in basis" % name)
qiskit.unroll._backenderror.BackendError: 'opaque gate mygate not in basis'
```
So I did the obvious, and added `mygate` to the basis of the CircuitBackend constructor. But this still gives an error:
```
Opening quantum-simulation.qasm
Traceback (most recent call last):
File "qasm-to-img.py", line 18, in <module>
basis=["u1","u2","u3","id","cx","x","y","z","h","s","t","rx","ry","rz","mygate"])).execute()
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 280, in execute
self._process_node(self.ast)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 187, in _process_node
self._process_children(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 182, in _process_children
self._process_node(kid)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 222, in _process_node
self._process_custom_unitary(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 111, in _process_custom_unitary
self.arg_stack[0:-1])
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_circuitbackend.py", line 260, in start_gate
name)
qiskit.unroll._backenderror.BackendError: 'gate mygate not in standard extensions'
```
It seems that QISKit is insisting on unrolling opaque gates into an explicit circuit description, even though they are defined as opaque. (Even I don't know what `mygate` is.)
## Possible Solution
It seems that there is some code for detecting opaque gates in the CircuitBackend, but it still only expects gates from the standard library. Instead there should be support of opaque gates in a QuantumCircuit object.
Another design decision is whether to allow opaque gates to exist outside of the defined basis.
## Steps to Reproduce (for bugs)
1. Make a file `quantum-simulation.qasm` with the OpenQASM code above
2. Make a file `qasm-to-img.py` with the python code above
3. Install qiskit and pillow dependencies. (e.g. `pip install qiskit pillow`)
4. Run `python qasm-to-img.py quantum-simulation.qasm`
## Context
I'm trying to generate images of quantum circuits using OpenQASM. The circuit is supposed to represent some general quantum circuit for some arbitrary unitary U followed by some measurements.
## Your Environment
* Version used: qiskit 0.4.10
* Environment name and version (e.g. Python 3.6.1): 3.6.4
* Operating System and version: macOS 10.13 | 1.0 | Opaque gate definitions give an error in CircuitBackend - Defining a general opaque gate raises an error when unrolling into a circuit.
## Expected Behavior
Either an opaque gate should be taken as-is and be left alone, or when it is defined in the basis it should be left alone when reading in OpenQASM.
## Current Behavior
My OpenQASM code
```
OPENQASM 2.0;
include "qelib1.inc";
opaque mygate q1, q2, q3;
qreg q[3];
creg c[2];
mygate q[0], q[1], q[2];
measure q[0] -> c[0];
measure q[1] -> c[1];
```
and parsing code
```py
from sys import argv
from pathlib import Path
import matplotlib
matplotlib.use('TkAgg') # OSX workaround
from qiskit.qasm import Qasm
from qiskit.unroll import Unroller, CircuitBackend
from qiskit.tools.visualization import circuit_drawer
if len(argv) != 2:
raise RuntimeError("Exactly 1 argument is required.")
print(f"Opening {argv[1]}")
path = Path(argv[1]).resolve(strict=True)
qasm = Qasm(filename=str(path)).parse()
circuit = Unroller(qasm, CircuitBackend(
basis=["u1","u2","u3","id","cx","x","y","z","h","s","t","rx","ry","rz"])).execute()
im = circuit_drawer(circuit)
im.save(path.with_suffix('.png'))
```
When reading in OpenQASM with an opaque gate definition I get the error
```
Opening quantum-simulation.qasm
Traceback (most recent call last):
File "qasm-to-img.py", line 18, in <module>
basis=["u1","u2","u3","id","cx","x","y","z","h","s","t","rx","ry","rz"])).execute()
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 280, in execute
self._process_node(self.ast)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 187, in _process_node
self._process_children(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 182, in _process_children
self._process_node(kid)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 222, in _process_node
self._process_custom_unitary(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 111, in _process_custom_unitary
self.arg_stack[0:-1])
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_circuitbackend.py", line 211, in start_gate
raise BackendError("opaque gate %s not in basis" % name)
qiskit.unroll._backenderror.BackendError: 'opaque gate mygate not in basis'
```
So I did the obvious, and added `mygate` to the basis of the CircuitBackend constructor. But this still gives an error:
```
Opening quantum-simulation.qasm
Traceback (most recent call last):
File "qasm-to-img.py", line 18, in <module>
basis=["u1","u2","u3","id","cx","x","y","z","h","s","t","rx","ry","rz","mygate"])).execute()
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 280, in execute
self._process_node(self.ast)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 187, in _process_node
self._process_children(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 182, in _process_children
self._process_node(kid)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 222, in _process_node
self._process_custom_unitary(node)
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_unroller.py", line 111, in _process_custom_unitary
self.arg_stack[0:-1])
File "/Users/eddie/dev/quasci.com/img/circuits/.venv/lib/python3.6/site-packages/qiskit/unroll/_circuitbackend.py", line 260, in start_gate
name)
qiskit.unroll._backenderror.BackendError: 'gate mygate not in standard extensions'
```
It seems that QISKit is insisting on unrolling opaque gates into an explicit circuit description, even though they are defined as opaque. (Even I don't know what `mygate` is.)
## Possible Solution
It seems that there is some code for detecting opaque gates in the CircuitBackend, but it still only expects gates from the standard library. Instead there should be support of opaque gates in a QuantumCircuit object.
Another design decision is whether to allow opaque gates to exist outside of the defined basis.
## Steps to Reproduce (for bugs)
1. Make a file `quantum-simulation.qasm` with the OpenQASM code above
2. Make a file `qasm-to-img.py` with the python code above
3. Install qiskit and pillow dependencies. (e.g. `pip install qiskit pillow`)
4. Run `python qasm-to-img.py quantum-simulation.qasm`
## Context
I'm trying to generate images of quantum circuits using OpenQASM. The circuit is supposed to represent some general quantum circuit for some arbitrary unitary U followed by some measurements.
## Your Environment
* Version used: qiskit 0.4.10
* Environment name and version (e.g. Python 3.6.1): 3.6.4
* Operating System and version: macOS 10.13 | non_infrastructure | opaque gate definitions give an error in circuitbackend defining a general opaque gate raises an error when unrolling into a circuit expected behavior either an opaque gate should be taken as is and be left alone or when it is defined in the basis it should be left alone when reading in openqasm current behavior my openqasm code openqasm include inc opaque mygate qreg q creg c mygate q q q measure q c measure q c and parsing code py from sys import argv from pathlib import path import matplotlib matplotlib use tkagg osx workaround from qiskit qasm import qasm from qiskit unroll import unroller circuitbackend from qiskit tools visualization import circuit drawer if len argv raise runtimeerror exactly argument is required print f opening argv path path argv resolve strict true qasm qasm filename str path parse circuit unroller qasm circuitbackend basis execute im circuit drawer circuit im save path with suffix png when reading in openqasm with an opaque gate definition i get the error opening quantum simulation qasm traceback most recent call last file qasm to img py line in basis execute file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in execute self process node self ast file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process node self process children node file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process children self process node kid file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process node self process custom unitary node file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process custom unitary self arg stack file users eddie dev quasci com img circuits venv lib site packages qiskit unroll circuitbackend py line in start gate raise backenderror opaque gate s not in basis name qiskit unroll backenderror backenderror opaque gate mygate not in basis so i did the obvious and added mygate to the basis of the circuitbackend constructor but this still gives an error opening quantum simulation qasm traceback most recent call last file qasm to img py line in basis execute file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in execute self process node self ast file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process node self process children node file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process children self process node kid file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process node self process custom unitary node file users eddie dev quasci com img circuits venv lib site packages qiskit unroll unroller py line in process custom unitary self arg stack file users eddie dev quasci com img circuits venv lib site packages qiskit unroll circuitbackend py line in start gate name qiskit unroll backenderror backenderror gate mygate not in standard extensions it seems that qiskit is insisting on unrolling opaque gates into an explicit circuit description even though they are defined as opaque even i don t know what mygate is possible solution it seems that there is some code for detecting opaque gates in the circuitbackend but it still only expects gates from the standard library instead there should be support of opaque gates in a quantumcircuit object another design decision is whether to allow opaque gates to exist outside of the defined basis steps to reproduce for bugs make a file quantum simulation qasm with the openqasm code above make a file qasm to img py with the python code above install qiskit and pillow dependencies e g pip install qiskit pillow run python qasm to img py quantum simulation qasm context i m trying to generate images of quantum circuits using openqasm the circuit is supposed to represent some general quantum circuit for some arbitrary unitary u followed by some measurements your environment version used qiskit environment name and version e g python operating system and version macos | 0 |
22,924 | 4,858,243,267 | IssuesEvent | 2016-11-13 01:26:21 | craftworkgames/MonoGame.Extended | https://api.github.com/repos/craftworkgames/MonoGame.Extended | closed | Build with it or build on top of it? | documentation feature request help wanted up-for-grabs | I have been using MG.Extended for a while, and it helped me alot then. I want to contribute more but I don't know which way the project is going. Until now, I use some classes of the library to make small things, but what about when it comes to scenes and bigger things? When creating scenes and more "connected systems", a good time will be spent setting everything up and running successfull. To avoid that, we can create a template just like MG does (this already [was suggested](https://github.com/craftworkgames/MonoGame.Extended/issues/106)). But the point is, we go this way, or continue creating separated classes to implement on the games? Or maybe both?
If we choose to create a template, some things that could be already done:
- The NuGet packages and Content.mgcb with the DLLs
- Some viewport adapter working
- A scene that displays a map (maybe with Tiled) and the camera
- Maybe a sprite base class to animate sprites?
- Mouse and keyboard manager classes (already configurated within the game loop)
- The same to the FPS display
I believe this is the most basic a game can have, and the most annoying (or maybe hard?) things a beginner faces when start development with MonoGame.
| 1.0 | Build with it or build on top of it? - I have been using MG.Extended for a while, and it helped me alot then. I want to contribute more but I don't know which way the project is going. Until now, I use some classes of the library to make small things, but what about when it comes to scenes and bigger things? When creating scenes and more "connected systems", a good time will be spent setting everything up and running successfull. To avoid that, we can create a template just like MG does (this already [was suggested](https://github.com/craftworkgames/MonoGame.Extended/issues/106)). But the point is, we go this way, or continue creating separated classes to implement on the games? Or maybe both?
If we choose to create a template, some things that could be already done:
- The NuGet packages and Content.mgcb with the DLLs
- Some viewport adapter working
- A scene that displays a map (maybe with Tiled) and the camera
- Maybe a sprite base class to animate sprites?
- Mouse and keyboard manager classes (already configurated within the game loop)
- The same to the FPS display
I believe this is the most basic a game can have, and the most annoying (or maybe hard?) things a beginner faces when start development with MonoGame.
| non_infrastructure | build with it or build on top of it i have been using mg extended for a while and it helped me alot then i want to contribute more but i don t know which way the project is going until now i use some classes of the library to make small things but what about when it comes to scenes and bigger things when creating scenes and more connected systems a good time will be spent setting everything up and running successfull to avoid that we can create a template just like mg does this already but the point is we go this way or continue creating separated classes to implement on the games or maybe both if we choose to create a template some things that could be already done the nuget packages and content mgcb with the dlls some viewport adapter working a scene that displays a map maybe with tiled and the camera maybe a sprite base class to animate sprites mouse and keyboard manager classes already configurated within the game loop the same to the fps display i believe this is the most basic a game can have and the most annoying or maybe hard things a beginner faces when start development with monogame | 0 |
176,073 | 28,024,075,060 | IssuesEvent | 2023-03-28 07:58:38 | beyondDevelops/AnimalTalk | https://api.github.com/repos/beyondDevelops/AnimalTalk | opened | [issue] width 390 미만일 경우 앨범형 미지원 구현 | design component | ## 👨💻 무엇을 하실 건지 설명해주세요!
- width 390px 미만일 경우 앨범형을 미지원하도록 구현하여야 합니다.
<img width="364" alt="image" src="https://user-images.githubusercontent.com/90930391/228167974-0246dc2f-af15-436f-8843-3c0c87356483.png">
- 이유는 기존 flex-wrap으로 떨어지게 하였을 때 이미지의 width와 미일치하면 우측 공백이 크게 발생합니다.
- grid-cols-2로 적용한 경우, width에 따라 이미지가 겹치는 등의 현상이 발생하였습니다.
- 모바일 기기마다 width 값이 매우 다양하기 때문에 모든 경우에 대해 대비할 수는 없는 한계가 있습니다.
- 따라서 390px 미만의 길이를 가지는 모바일 기기에 대해서는 앨범형을 미지원하는 방향으로 기능을 제한할 필요성이 있다고 생각합니다.
## 🤔 구현방법 및 예상 동작
-
## ⭐ 특이사항
-
| 1.0 | [issue] width 390 미만일 경우 앨범형 미지원 구현 - ## 👨💻 무엇을 하실 건지 설명해주세요!
- width 390px 미만일 경우 앨범형을 미지원하도록 구현하여야 합니다.
<img width="364" alt="image" src="https://user-images.githubusercontent.com/90930391/228167974-0246dc2f-af15-436f-8843-3c0c87356483.png">
- 이유는 기존 flex-wrap으로 떨어지게 하였을 때 이미지의 width와 미일치하면 우측 공백이 크게 발생합니다.
- grid-cols-2로 적용한 경우, width에 따라 이미지가 겹치는 등의 현상이 발생하였습니다.
- 모바일 기기마다 width 값이 매우 다양하기 때문에 모든 경우에 대해 대비할 수는 없는 한계가 있습니다.
- 따라서 390px 미만의 길이를 가지는 모바일 기기에 대해서는 앨범형을 미지원하는 방향으로 기능을 제한할 필요성이 있다고 생각합니다.
## 🤔 구현방법 및 예상 동작
-
## ⭐ 특이사항
-
| non_infrastructure | width 미만일 경우 앨범형 미지원 구현 👨💻 무엇을 하실 건지 설명해주세요 width 미만일 경우 앨범형을 미지원하도록 구현하여야 합니다 img width alt image src 이유는 기존 flex wrap으로 떨어지게 하였을 때 이미지의 width와 미일치하면 우측 공백이 크게 발생합니다 grid cols 적용한 경우 width에 따라 이미지가 겹치는 등의 현상이 발생하였습니다 모바일 기기마다 width 값이 매우 다양하기 때문에 모든 경우에 대해 대비할 수는 없는 한계가 있습니다 따라서 미만의 길이를 가지는 모바일 기기에 대해서는 앨범형을 미지원하는 방향으로 기능을 제한할 필요성이 있다고 생각합니다 🤔 구현방법 및 예상 동작 ⭐ 특이사항 | 0 |
80,963 | 30,633,697,691 | IssuesEvent | 2023-07-24 16:08:22 | vector-im/element-call | https://api.github.com/repos/vector-im/element-call | reopened | Splitbrain caused by new user joining a call | T-Defect | ### Steps to reproduce
Tracker bug for a flavour of splitbrain issue we're seeing that looks to usually be caused by a set of people have a room they use for calls, then a new person joining that room for a call, at which point the new person doesn't see the existing group call in the room and creates a new one.
### Outcome
#### What did you expect?
#### What happened instead?
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Will you send logs?
Yes | 1.0 | Splitbrain caused by new user joining a call - ### Steps to reproduce
Tracker bug for a flavour of splitbrain issue we're seeing that looks to usually be caused by a set of people have a room they use for calls, then a new person joining that room for a call, at which point the new person doesn't see the existing group call in the room and creates a new one.
### Outcome
#### What did you expect?
#### What happened instead?
### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
_No response_
### Will you send logs?
Yes | non_infrastructure | splitbrain caused by new user joining a call steps to reproduce tracker bug for a flavour of splitbrain issue we re seeing that looks to usually be caused by a set of people have a room they use for calls then a new person joining that room for a call at which point the new person doesn t see the existing group call in the room and creates a new one outcome what did you expect what happened instead operating system no response browser information no response url for webapp no response will you send logs yes | 0 |
746,898 | 26,050,104,091 | IssuesEvent | 2022-12-22 17:46:01 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | `Samsung Mobile` folder being added into Brave on install that includes several bookmarks | bug feature/bookmarks priority/P2 QA/Yes release-notes/exclude OS/Android | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description <!-- Provide a brief description of the issue -->
When installing `Brave` on `Samsung` devices, it looks like a `Samsung Mobile` folder is created that includes the following bookmarks:
```
* Google - https://www.google.com
* Samsung - https://www.samsung.com
* Samsung Manual - https://www.samsung.com
```
We shouldn't be adding any default bookmarks into `Brave`, especially bookmarks that Brave didn't explicitly add.
## Steps to reproduce <!-- Please add a series of steps to reproduce the issue -->
1. install `1.48.60 Chromium: 108.0.5359.128`
2. go into bookmarks and notice there's a `Samsung Mobile` folder
## Actual result <!-- Please add screenshots if needed -->
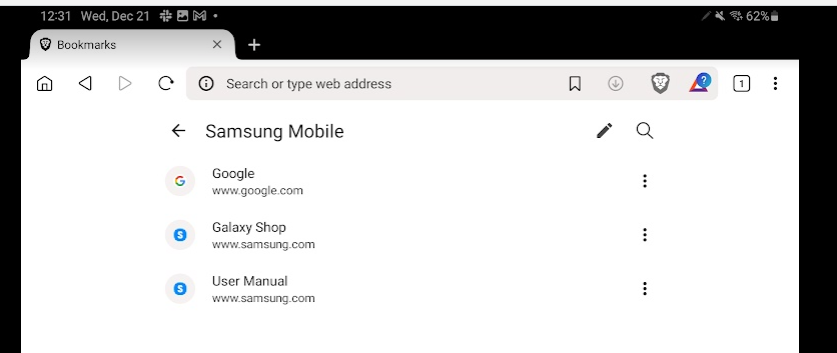
## Expected result
We shouldn't be adding any default bookmarks into `Brave`, especially bookmarks that Brave didn't explicitly add.
## Issue reproduces how often <!-- [Easily reproduced/Intermittent issue/No steps to reproduce] -->
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current Play Store version? `No`
- Can you reproduce this issue with the current Play Store Beta version? `Yes`
- Can you reproduce this issue with the current Play Store Nightly version? `Yes`
## Device details
- Install type (ARM, x86): `ARM`
- Device type (Phone, Tablet, Phablet): `Mobile` & `Tablet` (Samsung S10+ & Samsung Tab S8 Ultra)
- Android version: `Android 13`
## Brave version
```
Brave | 1.48.60 Chromium: 108.0.5359.128 (Official Build) canary (32-bit)
--- | ---
Revision | 1cd27afdb8e5d057070c0961e04c490d2aca1aa0-refs/branch-heads/5359@{#1185}
OS | Android 13; Build/TP1A.220624.014
```
```
Brave | 1.47.136 Chromium: 108.0.5359.128 (Official Build) beta (32-bit)
--- | ---
Revision | 1cd27afdb8e5d057070c0961e04c490d2aca1aa0-refs/branch-heads/5359@{#1185}
OS | Android 13; Build/TP1A.220624.014
```
### Website problems only
- Does the issue resolve itself when disabling Brave Shields? `N/A`
- Does the issue resolve itself when disabling Brave Rewards? `N/A`
- Is the issue reproducible on the latest version of Chrome? `N/A`
### Additional information
<!-- Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue -->
| 1.0 | `Samsung Mobile` folder being added into Brave on install that includes several bookmarks - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description <!-- Provide a brief description of the issue -->
When installing `Brave` on `Samsung` devices, it looks like a `Samsung Mobile` folder is created that includes the following bookmarks:
```
* Google - https://www.google.com
* Samsung - https://www.samsung.com
* Samsung Manual - https://www.samsung.com
```
We shouldn't be adding any default bookmarks into `Brave`, especially bookmarks that Brave didn't explicitly add.
## Steps to reproduce <!-- Please add a series of steps to reproduce the issue -->
1. install `1.48.60 Chromium: 108.0.5359.128`
2. go into bookmarks and notice there's a `Samsung Mobile` folder
## Actual result <!-- Please add screenshots if needed -->
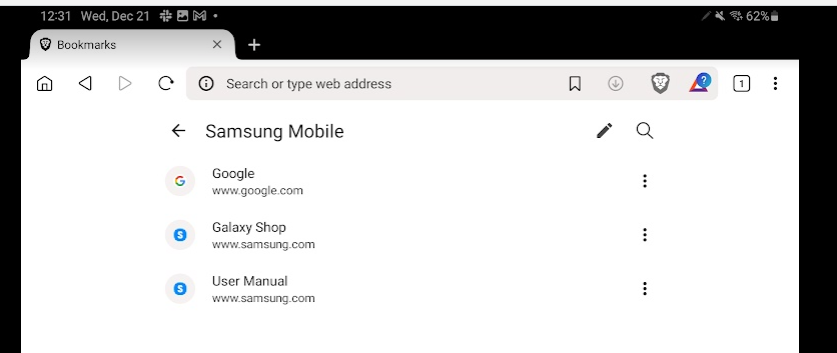
## Expected result
We shouldn't be adding any default bookmarks into `Brave`, especially bookmarks that Brave didn't explicitly add.
## Issue reproduces how often <!-- [Easily reproduced/Intermittent issue/No steps to reproduce] -->
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current Play Store version? `No`
- Can you reproduce this issue with the current Play Store Beta version? `Yes`
- Can you reproduce this issue with the current Play Store Nightly version? `Yes`
## Device details
- Install type (ARM, x86): `ARM`
- Device type (Phone, Tablet, Phablet): `Mobile` & `Tablet` (Samsung S10+ & Samsung Tab S8 Ultra)
- Android version: `Android 13`
## Brave version
```
Brave | 1.48.60 Chromium: 108.0.5359.128 (Official Build) canary (32-bit)
--- | ---
Revision | 1cd27afdb8e5d057070c0961e04c490d2aca1aa0-refs/branch-heads/5359@{#1185}
OS | Android 13; Build/TP1A.220624.014
```
```
Brave | 1.47.136 Chromium: 108.0.5359.128 (Official Build) beta (32-bit)
--- | ---
Revision | 1cd27afdb8e5d057070c0961e04c490d2aca1aa0-refs/branch-heads/5359@{#1185}
OS | Android 13; Build/TP1A.220624.014
```
### Website problems only
- Does the issue resolve itself when disabling Brave Shields? `N/A`
- Does the issue resolve itself when disabling Brave Rewards? `N/A`
- Is the issue reproducible on the latest version of Chrome? `N/A`
### Additional information
<!-- Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue -->
| non_infrastructure | samsung mobile folder being added into brave on install that includes several bookmarks have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will only be reopened after sufficient info is provided description when installing brave on samsung devices it looks like a samsung mobile folder is created that includes the following bookmarks google samsung samsung manual we shouldn t be adding any default bookmarks into brave especially bookmarks that brave didn t explicitly add steps to reproduce install chromium go into bookmarks and notice there s a samsung mobile folder actual result expected result we shouldn t be adding any default bookmarks into brave especially bookmarks that brave didn t explicitly add issue reproduces how often version channel information can you reproduce this issue with the current play store version no can you reproduce this issue with the current play store beta version yes can you reproduce this issue with the current play store nightly version yes device details install type arm arm device type phone tablet phablet mobile tablet samsung samsung tab ultra android version android brave version brave chromium official build canary bit revision refs branch heads os android build brave chromium official build beta bit revision refs branch heads os android build website problems only does the issue resolve itself when disabling brave shields n a does the issue resolve itself when disabling brave rewards n a is the issue reproducible on the latest version of chrome n a additional information | 0 |
437,907 | 12,604,447,714 | IssuesEvent | 2020-06-11 14:59:01 | ixofoundation/ixo-blockchain | https://api.github.com/repos/ixofoundation/ixo-blockchain | closed | General: Charge Transaction Fees (Gas) | priority | The ixo blockchain uses a custom `IxoTx` (instead of `StdTx`) and custom `AnteHandler`s. These currently do not implement the charging of transaction fees. | 1.0 | General: Charge Transaction Fees (Gas) - The ixo blockchain uses a custom `IxoTx` (instead of `StdTx`) and custom `AnteHandler`s. These currently do not implement the charging of transaction fees. | non_infrastructure | general charge transaction fees gas the ixo blockchain uses a custom ixotx instead of stdtx and custom antehandler s these currently do not implement the charging of transaction fees | 0 |
22,394 | 15,164,734,601 | IssuesEvent | 2021-02-12 14:09:08 | ILLIXR/ILLIXR | https://api.github.com/repos/ILLIXR/ILLIXR | closed | Add PortAudio dependencies for audio_pipeline to install scripts | infrastructure | Ubuntu packages:
- `libportaudio2`
- `libportaudiocpp0` | 1.0 | Add PortAudio dependencies for audio_pipeline to install scripts - Ubuntu packages:
- `libportaudio2`
- `libportaudiocpp0` | infrastructure | add portaudio dependencies for audio pipeline to install scripts ubuntu packages | 1 |
96 | 2,506,126,902 | IssuesEvent | 2015-01-12 06:28:54 | bit3/contao-meta-palettes | https://api.github.com/repos/bit3/contao-meta-palettes | closed | Class 'ContaoCommunityAlliance\DcGeneral\Contao\Dca\Builder\Legacy\DcaReadingDataDefinitionBuilder' not found | Defect | See https://github.com/bit3/contao-theme-plus/issues/89 | 1.0 | Class 'ContaoCommunityAlliance\DcGeneral\Contao\Dca\Builder\Legacy\DcaReadingDataDefinitionBuilder' not found - See https://github.com/bit3/contao-theme-plus/issues/89 | non_infrastructure | class contaocommunityalliance dcgeneral contao dca builder legacy dcareadingdatadefinitionbuilder not found see | 0 |
27,615 | 21,995,770,831 | IssuesEvent | 2022-05-26 06:06:24 | cpp-lln-lab/CPP_SPM | https://api.github.com/repos/cpp-lln-lab/CPP_SPM | closed | parallelize system tests | infrastructure :ladder: test | Currently are running serially:
- MoAE demos with different options
- then the `facerep` *
Better run those in parallel.
* that fails for now because the data needs to be downloaded first, because it is not possible to download data within a matlab github action apparently | 1.0 | parallelize system tests - Currently are running serially:
- MoAE demos with different options
- then the `facerep` *
Better run those in parallel.
* that fails for now because the data needs to be downloaded first, because it is not possible to download data within a matlab github action apparently | infrastructure | parallelize system tests currently are running serially moae demos with different options then the facerep better run those in parallel that fails for now because the data needs to be downloaded first because it is not possible to download data within a matlab github action apparently | 1 |
416,820 | 28,102,093,708 | IssuesEvent | 2023-03-30 20:22:15 | MayorMonty/cpsc-4160 | https://api.github.com/repos/MayorMonty/cpsc-4160 | closed | Milestone #1 - Documentation & Update Post | documentation | Create update in `final/milestones` talking about the work we accomplished in this milestone and the technical decisions made
| 1.0 | Milestone #1 - Documentation & Update Post - Create update in `final/milestones` talking about the work we accomplished in this milestone and the technical decisions made
| non_infrastructure | milestone documentation update post create update in final milestones talking about the work we accomplished in this milestone and the technical decisions made | 0 |
29,745 | 24,233,397,780 | IssuesEvent | 2022-09-26 20:25:53 | kurkle/chartjs-chart-treemap | https://api.github.com/repos/kurkle/chartjs-chart-treemap | opened | Transfer coverage from CI to Sonar | infrastructure | Coverage is build again in Sonar job.
It can be transferred between jobs using [actions/upload-artifact](https://github.com/actions/upload-artifact) and [actions/download-artifact](https://github.com/actions/download-artifact) | 1.0 | Transfer coverage from CI to Sonar - Coverage is build again in Sonar job.
It can be transferred between jobs using [actions/upload-artifact](https://github.com/actions/upload-artifact) and [actions/download-artifact](https://github.com/actions/download-artifact) | infrastructure | transfer coverage from ci to sonar coverage is build again in sonar job it can be transferred between jobs using and | 1 |
46,588 | 7,268,051,253 | IssuesEvent | 2018-02-20 08:40:39 | symfony/symfony-docs | https://api.github.com/repos/symfony/symfony-docs | closed | Added support for getting default values in Accept headers | HttpFoundation Missing Documentation hasPR | This is a common need for content negotiation, so if this is not documented yet, we should add a simple example about it. See https://github.com/symfony/symfony/pull/26036 | 1.0 | Added support for getting default values in Accept headers - This is a common need for content negotiation, so if this is not documented yet, we should add a simple example about it. See https://github.com/symfony/symfony/pull/26036 | non_infrastructure | added support for getting default values in accept headers this is a common need for content negotiation so if this is not documented yet we should add a simple example about it see | 0 |
34,452 | 29,950,538,896 | IssuesEvent | 2023-06-23 00:21:16 | Flutter-Bounty-Hunters/dart-rss | https://api.github.com/repos/Flutter-Bounty-Hunters/dart-rss | opened | Prevent GitHub from auto-targeting webfeed repo | area_infrastructure refactor | Every time I open a PR, GitHub tries to target the master branch of the webfeed project, instead of targeting the main branch of this project.
Fix this. | 1.0 | Prevent GitHub from auto-targeting webfeed repo - Every time I open a PR, GitHub tries to target the master branch of the webfeed project, instead of targeting the main branch of this project.
Fix this. | infrastructure | prevent github from auto targeting webfeed repo every time i open a pr github tries to target the master branch of the webfeed project instead of targeting the main branch of this project fix this | 1 |
6,278 | 5,345,646,889 | IssuesEvent | 2017-02-17 17:29:29 | seznam/euphoria | https://api.github.com/repos/seznam/euphoria | opened | Flink executor: Make use of ProcessFunction | Flink performance | Recently released Flink 1.2.0 introduced a low-level API for streaming that gives access to all internal parts of the engine (data, state, timers).
> The ProcessFunction can be thought of as a FlatMapFunction with access to keyed state and timers. It handles events be being invoked for each event received in the input stream(s).
More details described at https://ci.apache.org/projects/flink/flink-docs-release-1.2/dev/stream/process_function.html
It seems it's a good opportunity to optimize current state of `windowing` in Flink stream executor in a way that all wrapping class from package `cz.seznam.euphoria.flink.streaming.windowing` can be discarded and replaced by custom `WindowOperator` implementation relying on Euphoria-core `windowing and triggers` only. | True | Flink executor: Make use of ProcessFunction - Recently released Flink 1.2.0 introduced a low-level API for streaming that gives access to all internal parts of the engine (data, state, timers).
> The ProcessFunction can be thought of as a FlatMapFunction with access to keyed state and timers. It handles events be being invoked for each event received in the input stream(s).
More details described at https://ci.apache.org/projects/flink/flink-docs-release-1.2/dev/stream/process_function.html
It seems it's a good opportunity to optimize current state of `windowing` in Flink stream executor in a way that all wrapping class from package `cz.seznam.euphoria.flink.streaming.windowing` can be discarded and replaced by custom `WindowOperator` implementation relying on Euphoria-core `windowing and triggers` only. | non_infrastructure | flink executor make use of processfunction recently released flink introduced a low level api for streaming that gives access to all internal parts of the engine data state timers the processfunction can be thought of as a flatmapfunction with access to keyed state and timers it handles events be being invoked for each event received in the input stream s more details described at it seems it s a good opportunity to optimize current state of windowing in flink stream executor in a way that all wrapping class from package cz seznam euphoria flink streaming windowing can be discarded and replaced by custom windowoperator implementation relying on euphoria core windowing and triggers only | 0 |
84,368 | 3,663,965,085 | IssuesEvent | 2016-02-19 09:27:28 | Captianrock/android_PV | https://api.github.com/repos/Captianrock/android_PV | opened | Communication between Xposed and Android App | Medium Priority New Feature | - Android app activity and Xposed strangely independent. Needs to be communicating with each other. | 1.0 | Communication between Xposed and Android App - - Android app activity and Xposed strangely independent. Needs to be communicating with each other. | non_infrastructure | communication between xposed and android app android app activity and xposed strangely independent needs to be communicating with each other | 0 |
37,738 | 8,357,129,566 | IssuesEvent | 2018-10-02 20:35:54 | kobotoolbox/kpi | https://api.github.com/repos/kobotoolbox/kpi | closed | Only mark form as needing redeployment if form contents changes | UI & UX coded | Any change to the project's settings (including name, description, or other details) marks the form as requiring to be redeployed -- even though the form itself hasn't changed.
Expected behavior: Unless the form itself is changed, don't prompt the user to redeploy.
Supersedes #1469. | 1.0 | Only mark form as needing redeployment if form contents changes - Any change to the project's settings (including name, description, or other details) marks the form as requiring to be redeployed -- even though the form itself hasn't changed.
Expected behavior: Unless the form itself is changed, don't prompt the user to redeploy.
Supersedes #1469. | non_infrastructure | only mark form as needing redeployment if form contents changes any change to the project s settings including name description or other details marks the form as requiring to be redeployed even though the form itself hasn t changed expected behavior unless the form itself is changed don t prompt the user to redeploy supersedes | 0 |
11,134 | 8,955,907,226 | IssuesEvent | 2019-01-26 12:50:23 | ReliSA/CRCE | https://api.github.com/repos/ReliSA/CRCE | opened | merge the results of dockerization and modules-to-core into "dev" | branch:dev infrastructure | Once the two infrastructural changes are done, in the forked project/repo, merge them back here. | 1.0 | merge the results of dockerization and modules-to-core into "dev" - Once the two infrastructural changes are done, in the forked project/repo, merge them back here. | infrastructure | merge the results of dockerization and modules to core into dev once the two infrastructural changes are done in the forked project repo merge them back here | 1 |
10,651 | 8,665,226,834 | IssuesEvent | 2018-11-28 22:36:46 | SalesforceFoundation/Cumulus | https://api.github.com/repos/SalesforceFoundation/Cumulus | closed | As an NPSP developer, I would like a set of manual test cases to be run once per release. | accepted ci/infrastructure/devops test | Document some common failure prone user flows in a test org with uncommon features activated that can be run once per release as a smoke test.
| 1.0 | As an NPSP developer, I would like a set of manual test cases to be run once per release. - Document some common failure prone user flows in a test org with uncommon features activated that can be run once per release as a smoke test.
| infrastructure | as an npsp developer i would like a set of manual test cases to be run once per release document some common failure prone user flows in a test org with uncommon features activated that can be run once per release as a smoke test | 1 |
143,664 | 19,211,138,719 | IssuesEvent | 2021-12-07 02:09:46 | turkdevops/weblate | https://api.github.com/repos/turkdevops/weblate | closed | CVE-2018-14040 (Medium) detected in bootstrap-3.3.4.min.js - autoclosed | security vulnerability | ## CVE-2018-14040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: weblate/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/starter-template/index.html</p>
<p>Path to vulnerable library: /scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/starter-template/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/navbar-static-top/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/cover/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/non-responsive/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/offcanvas/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/navbar/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/jumbotron/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/blog/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/dashboard/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/carousel/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/theme/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/sticky-footer-navbar/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/tooltip-viewport/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/navbar-fixed-top/../../dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/weblate/commit/3aa9343e44c1c7fd2f515bd352399f25838354a4">3aa9343e44c1c7fd2f515bd352399f25838354a4</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-14040 (Medium) detected in bootstrap-3.3.4.min.js - autoclosed - ## CVE-2018-14040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: weblate/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/starter-template/index.html</p>
<p>Path to vulnerable library: /scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/starter-template/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/navbar-static-top/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/cover/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/non-responsive/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/offcanvas/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/navbar/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/jumbotron/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/blog/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/dashboard/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/carousel/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/theme/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/sticky-footer-navbar/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/tooltip-viewport/../../dist/js/bootstrap.min.js,/scripts/yarn/node_modules/bootstrap-rtl/examples/originals/examples/navbar-fixed-top/../../dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/weblate/commit/3aa9343e44c1c7fd2f515bd352399f25838354a4">3aa9343e44c1c7fd2f515bd352399f25838354a4</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in bootstrap min js autoclosed cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file weblate scripts yarn node modules bootstrap rtl examples originals examples starter template index html path to vulnerable library scripts yarn node modules bootstrap rtl examples originals examples starter template dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples navbar static top dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples cover dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples non responsive dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples offcanvas dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples navbar dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples jumbotron dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples blog dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples dashboard dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples carousel dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples theme dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples sticky footer navbar dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples tooltip viewport dist js bootstrap min js scripts yarn node modules bootstrap rtl examples originals examples navbar fixed top dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap step up your open source security game with whitesource | 0 |
3,956 | 4,730,474,978 | IssuesEvent | 2016-10-18 21:44:12 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | opened | `windows-determinism` is broken on dev15-rc | Area-Infrastructure Urgency-Now | #14445 broke the windows determinism build for dev15-rc, starting with https://ci.dot.net/job/dotnet_roslyn/job/dev15-rc/job/windows_determinism/13/.
| 1.0 | `windows-determinism` is broken on dev15-rc - #14445 broke the windows determinism build for dev15-rc, starting with https://ci.dot.net/job/dotnet_roslyn/job/dev15-rc/job/windows_determinism/13/.
| infrastructure | windows determinism is broken on rc broke the windows determinism build for rc starting with | 1 |
3,170 | 4,118,287,094 | IssuesEvent | 2016-06-08 10:50:15 | seqan/lambda | https://api.github.com/repos/seqan/lambda | closed | reduce compile time and binary size | infrastructure | - [x] use dynamic score matrix
- [x] strip binaries on gcc
- [x] scoring optimizations for linear gap costs hidden behind extra macro and deactivated by default
- [x] removed SimpleScore for aminoacid searches | 1.0 | reduce compile time and binary size - - [x] use dynamic score matrix
- [x] strip binaries on gcc
- [x] scoring optimizations for linear gap costs hidden behind extra macro and deactivated by default
- [x] removed SimpleScore for aminoacid searches | infrastructure | reduce compile time and binary size use dynamic score matrix strip binaries on gcc scoring optimizations for linear gap costs hidden behind extra macro and deactivated by default removed simplescore for aminoacid searches | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.