Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
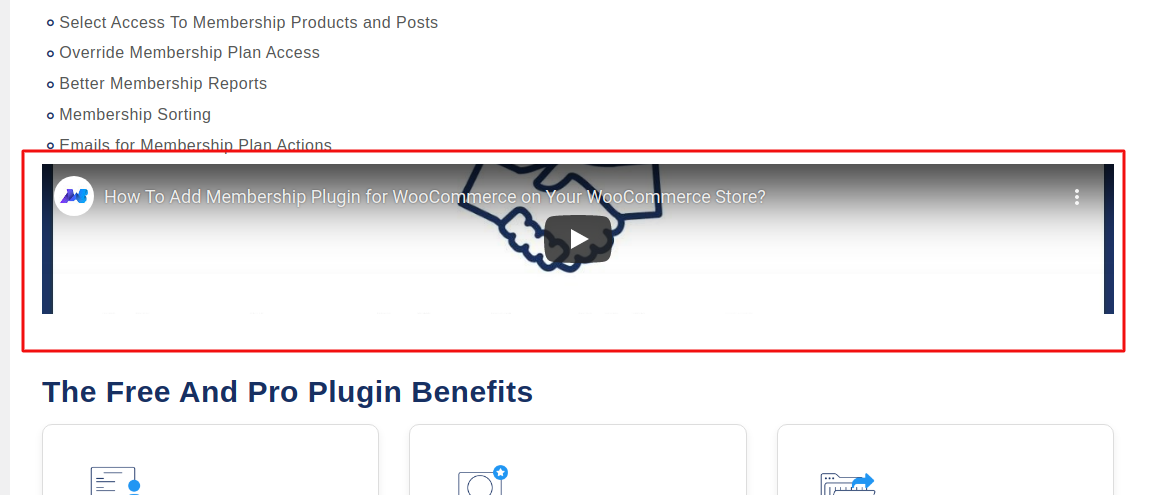
130,721 | 18,111,315,198 | IssuesEvent | 2021-09-23 04:38:47 | Makewebbetter/membership-for-woocommerce | https://api.github.com/repos/Makewebbetter/membership-for-woocommerce | closed | Video is not visible correctly on overview page. | design issue | WordPress version: 5.8.1
WooCommerce version: 5.6.0
Area Path: Admin panel-> MakeWebBetter-> Membership For WooCommerce-> Overview
Version: 1.2.0
Description: Video is not visible correctly on the overview page.
| 1.0 | Video is not visible correctly on overview page. - WordPress version: 5.8.1
WooCommerce version: 5.6.0
Area Path: Admin panel-> MakeWebBetter-> Membership For WooCommerce-> Overview
Version: 1.2.0
Description: Video is not visible correctly on the overview page.
| non_priority | video is not visible correctly on overview page wordpress version woocommerce version area path admin panel makewebbetter membership for woocommerce overview version description video is not visible correctly on the overview page | 0 |
332,426 | 29,418,252,377 | IssuesEvent | 2023-05-31 00:03:03 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | [Flaky Test] inserts blocks by dragging and dropping from the global inserter | [Status] Stale [Type] Flaky Test | <!-- __META_DATA__:{} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
inserts blocks by dragging and dropping from the global inserter
## Test path
`/test/e2e/specs/editor/various/inserting-blocks.spec.js`
## Errors
<!-- __TEST_RESULTS_LIST__ -->
<!-- __TEST_RESULT__ --><time datetime="2022-11-03T15:22:22.338Z"><code>[2022-11-03T15:22:22.338Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3386732307"><code>add/experimental-duplicate-of-list-view</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-11-03T15:54:19.298Z"><code>[2022-11-03T15:54:19.298Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3386934804"><code>add/list-view-to-navigation-block</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2023-03-07T04:29:16.824Z"><code>[2023-03-07T04:29:16.824Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/4350501759"><code>add/template-description-in-navigation-sidebar</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2023-03-28T03:59:17.575Z"><code>[2023-03-28T03:59:17.575Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/4538940826"><code>rnmobile/add-reassure-pt-2</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><details>
<summary>
<time datetime="2023-04-27T08:47:04.627Z"><code>[2023-04-27T08:47:04.627Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/4817449961"><code>trunk</code></a>.
</summary>
```
Error: expect(received).toBe(expected) // Object.is equality
- Expected - 6
+ Received + 6
- <!-- wp:paragraph -->
- <p>Dummy text</p>
+ <!-- wp:heading -->
+ <h2 class="wp-block-heading"></h2>
- <!-- /wp:paragraph -->
+ <!-- /wp:heading -->
- <!-- wp:heading -->
- <h2 class="wp-block-heading"></h2>
+ <!-- wp:paragraph -->
+ <p>Dummy text</p>
- <!-- /wp:heading -->
+ <!-- /wp:paragraph -->
Call Log:
- Timeout 5000ms exceeded while waiting on the predicate
at /home/runner/work/gutenberg/gutenberg/test/e2e/specs/editor/various/inserting-blocks.spec.js:95:3
```
</details><!-- /__TEST_RESULT__ -->
<!-- /__TEST_RESULTS_LIST__ -->
| 1.0 | [Flaky Test] inserts blocks by dragging and dropping from the global inserter - <!-- __META_DATA__:{} -->
**Flaky test detected. This is an auto-generated issue by GitHub Actions. Please do NOT edit this manually.**
## Test title
inserts blocks by dragging and dropping from the global inserter
## Test path
`/test/e2e/specs/editor/various/inserting-blocks.spec.js`
## Errors
<!-- __TEST_RESULTS_LIST__ -->
<!-- __TEST_RESULT__ --><time datetime="2022-11-03T15:22:22.338Z"><code>[2022-11-03T15:22:22.338Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3386732307"><code>add/experimental-duplicate-of-list-view</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2022-11-03T15:54:19.298Z"><code>[2022-11-03T15:54:19.298Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/3386934804"><code>add/list-view-to-navigation-block</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2023-03-07T04:29:16.824Z"><code>[2023-03-07T04:29:16.824Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/4350501759"><code>add/template-description-in-navigation-sidebar</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><time datetime="2023-03-28T03:59:17.575Z"><code>[2023-03-28T03:59:17.575Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/4538940826"><code>rnmobile/add-reassure-pt-2</code></a>.<!-- /__TEST_RESULT__ -->
<br/>
<!-- __TEST_RESULT__ --><details>
<summary>
<time datetime="2023-04-27T08:47:04.627Z"><code>[2023-04-27T08:47:04.627Z]</code></time> Test passed after 1 failed attempt on <a href="https://github.com/WordPress/gutenberg/actions/runs/4817449961"><code>trunk</code></a>.
</summary>
```
Error: expect(received).toBe(expected) // Object.is equality
- Expected - 6
+ Received + 6
- <!-- wp:paragraph -->
- <p>Dummy text</p>
+ <!-- wp:heading -->
+ <h2 class="wp-block-heading"></h2>
- <!-- /wp:paragraph -->
+ <!-- /wp:heading -->
- <!-- wp:heading -->
- <h2 class="wp-block-heading"></h2>
+ <!-- wp:paragraph -->
+ <p>Dummy text</p>
- <!-- /wp:heading -->
+ <!-- /wp:paragraph -->
Call Log:
- Timeout 5000ms exceeded while waiting on the predicate
at /home/runner/work/gutenberg/gutenberg/test/e2e/specs/editor/various/inserting-blocks.spec.js:95:3
```
</details><!-- /__TEST_RESULT__ -->
<!-- /__TEST_RESULTS_LIST__ -->
| non_priority | inserts blocks by dragging and dropping from the global inserter flaky test detected this is an auto generated issue by github actions please do not edit this manually test title inserts blocks by dragging and dropping from the global inserter test path test specs editor various inserting blocks spec js errors test passed after failed attempt on test passed after failed attempt on test passed after failed attempt on test passed after failed attempt on test passed after failed attempt on a href error expect received tobe expected object is equality expected received dummy text dummy text call log timeout exceeded while waiting on the predicate at home runner work gutenberg gutenberg test specs editor various inserting blocks spec js | 0 |
102,745 | 8,853,229,217 | IssuesEvent | 2019-01-08 20:42:23 | doctrine/mongodb-odm | https://api.github.com/repos/doctrine/mongodb-odm | closed | Protected properties in MappedSuperClass | needs test | I had my Documents using Annotation Mappings, have my "BaseDocument" with protected properties.
Everything worked well with Annotations.
I recently changed to XML mapping, and now the properties in my "BaseDocument" are undefined (`$id` property).
May be related to https://github.com/doctrine/mongodb-odm/issues/918 I guess, but why protected properties would work with Annotations mapping and not with XML mapping ?
I can't try to change my protected properties to private right now, but it seems the problems came from changing from Annotation to XML.
Will be able to put more info in few hours, if needed. | 1.0 | Protected properties in MappedSuperClass - I had my Documents using Annotation Mappings, have my "BaseDocument" with protected properties.
Everything worked well with Annotations.
I recently changed to XML mapping, and now the properties in my "BaseDocument" are undefined (`$id` property).
May be related to https://github.com/doctrine/mongodb-odm/issues/918 I guess, but why protected properties would work with Annotations mapping and not with XML mapping ?
I can't try to change my protected properties to private right now, but it seems the problems came from changing from Annotation to XML.
Will be able to put more info in few hours, if needed. | non_priority | protected properties in mappedsuperclass i had my documents using annotation mappings have my basedocument with protected properties everything worked well with annotations i recently changed to xml mapping and now the properties in my basedocument are undefined id property may be related to i guess but why protected properties would work with annotations mapping and not with xml mapping i can t try to change my protected properties to private right now but it seems the problems came from changing from annotation to xml will be able to put more info in few hours if needed | 0 |
13,896 | 3,368,155,362 | IssuesEvent | 2015-11-22 19:23:52 | PiratesDen/Potp | https://api.github.com/repos/PiratesDen/Potp | opened | Implement the data structure for testing informed | INFORMED TEST | Implement the data structure for testing informed as a list of current happiness and next move happiness. each comparison should exist on its own line for human readability. | 1.0 | Implement the data structure for testing informed - Implement the data structure for testing informed as a list of current happiness and next move happiness. each comparison should exist on its own line for human readability. | non_priority | implement the data structure for testing informed implement the data structure for testing informed as a list of current happiness and next move happiness each comparison should exist on its own line for human readability | 0 |
59,721 | 6,661,892,170 | IssuesEvent | 2017-10-02 10:40:13 | Kademi/kademi-dev | https://api.github.com/repos/Kademi/kademi-dev | closed | Email Shows Wrong Content | bug Ready to Test QA | This email , in title " Lead viewed link " , that send when the lead open link which sent to him in other email , show wrong content
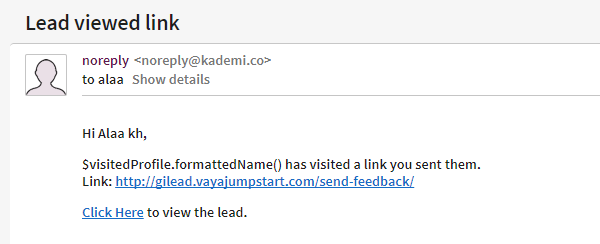
| 1.0 | Email Shows Wrong Content - This email , in title " Lead viewed link " , that send when the lead open link which sent to him in other email , show wrong content
| non_priority | email shows wrong content this email in title lead viewed link that send when the lead open link which sent to him in other email show wrong content | 0 |
162,340 | 13,886,603,385 | IssuesEvent | 2020-10-19 01:18:05 | msandfor/10-Easy-Steps | https://api.github.com/repos/msandfor/10-Easy-Steps | closed | [Hacktoberfest]: Edit Kent C Dodds in the Mentors Section | beginner beginner-friendly documentation :memo: first-contribution good first issue hacktoberfest :children_crossing: help wanted :hand: up-for-grabs | 🆕🐥☝ Beginners Only:
This issue is reserved for people who are new to Open Source. We know that the process of creating a pull request is the biggest barrier for new contributors. This issue is for you 💝
To do:
* Edit Kent C Dodds Comment in the Mentors Section
* See below for link to step-by-step tutorial
* Go down to mentors section
Edit the Comments section to replace *Be Kind* with *Improving the world w/ quality software · Husband, Father, Latter-day Saint, Teacher, OSS*
* Add your details in the contributors section at the bottom of the page using the same formatting as the last one
📋 *Step by Step*
[Step-By-Step Tutorial](https://github.com/msandfor/10-Easy-Steps/blob/master/docs/GitHub-browser-tutorial.md)
Remember to observe the [Code of Conduct](https://github.com/msandfor/10-Easy-Steps/blob/master/code_of_conduct.md) - by which we mean, in short - Be Kind, Be Positive, Be Helpful
| 1.0 | [Hacktoberfest]: Edit Kent C Dodds in the Mentors Section - 🆕🐥☝ Beginners Only:
This issue is reserved for people who are new to Open Source. We know that the process of creating a pull request is the biggest barrier for new contributors. This issue is for you 💝
To do:
* Edit Kent C Dodds Comment in the Mentors Section
* See below for link to step-by-step tutorial
* Go down to mentors section
Edit the Comments section to replace *Be Kind* with *Improving the world w/ quality software · Husband, Father, Latter-day Saint, Teacher, OSS*
* Add your details in the contributors section at the bottom of the page using the same formatting as the last one
📋 *Step by Step*
[Step-By-Step Tutorial](https://github.com/msandfor/10-Easy-Steps/blob/master/docs/GitHub-browser-tutorial.md)
Remember to observe the [Code of Conduct](https://github.com/msandfor/10-Easy-Steps/blob/master/code_of_conduct.md) - by which we mean, in short - Be Kind, Be Positive, Be Helpful
| non_priority | edit kent c dodds in the mentors section 🆕🐥☝ beginners only this issue is reserved for people who are new to open source we know that the process of creating a pull request is the biggest barrier for new contributors this issue is for you 💝 to do edit kent c dodds comment in the mentors section see below for link to step by step tutorial go down to mentors section edit the comments section to replace be kind with improving the world w quality software · husband father latter day saint teacher oss add your details in the contributors section at the bottom of the page using the same formatting as the last one 📋 step by step remember to observe the by which we mean in short be kind be positive be helpful | 0 |
133,308 | 10,807,863,963 | IssuesEvent | 2019-11-07 09:22:49 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | opened | Add more UI tests for rustdoc | A-doctests T-rustdoc | It is linked to https://github.com/rust-lang/rust/issues/60033.
This is the tests we need to add (the list is non-exhaustive):
* [ ] a UI test for **each** setting
* [ ] click on element in the sidebar hidden by default to be sure it gets fully un-collapsed and scrolled to
* [ ] make tests for each shortcut
* [ ] make tests for source code navigation (through files in the first time should be enough)
* [ ] run all the previous tests in mobile mode | 1.0 | Add more UI tests for rustdoc - It is linked to https://github.com/rust-lang/rust/issues/60033.
This is the tests we need to add (the list is non-exhaustive):
* [ ] a UI test for **each** setting
* [ ] click on element in the sidebar hidden by default to be sure it gets fully un-collapsed and scrolled to
* [ ] make tests for each shortcut
* [ ] make tests for source code navigation (through files in the first time should be enough)
* [ ] run all the previous tests in mobile mode | non_priority | add more ui tests for rustdoc it is linked to this is the tests we need to add the list is non exhaustive a ui test for each setting click on element in the sidebar hidden by default to be sure it gets fully un collapsed and scrolled to make tests for each shortcut make tests for source code navigation through files in the first time should be enough run all the previous tests in mobile mode | 0 |
114,967 | 17,268,557,718 | IssuesEvent | 2021-07-22 16:33:54 | harrinry/gocd-build-status-notifier | https://api.github.com/repos/harrinry/gocd-build-status-notifier | opened | CVE-2017-7525 (High) detected in jackson-databind-2.5.3.jar | security vulnerability | ## CVE-2017-7525 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.5.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: gocd-build-status-notifier/gitlab-mr-status/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.5.3/c37875ff66127d93e5f672708cb2dcc14c8232ab/jackson-databind-2.5.3.jar</p>
<p>
Dependency Hierarchy:
- java-gitlab-api-4.1.0.jar (Root Library)
- :x: **jackson-databind-2.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/gocd-build-status-notifier/commit/039d60b34386e06662f779ce1a97720d950bae52">039d60b34386e06662f779ce1a97720d950bae52</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A deserialization flaw was discovered in the jackson-databind, versions before 2.6.7.1, 2.7.9.1 and 2.8.9, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7525>CVE-2017-7525</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525</a></p>
<p>Release Date: 2018-02-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.1,2.7.9.1,2.8.9</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.5.3","packageFilePaths":["/gitlab-mr-status/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.gitlab:java-gitlab-api:4.1.0;com.fasterxml.jackson.core:jackson-databind:2.5.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.6.7.1,2.7.9.1,2.8.9"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-7525","vulnerabilityDetails":"A deserialization flaw was discovered in the jackson-databind, versions before 2.6.7.1, 2.7.9.1 and 2.8.9, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7525","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-7525 (High) detected in jackson-databind-2.5.3.jar - ## CVE-2017-7525 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.5.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: gocd-build-status-notifier/gitlab-mr-status/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.5.3/c37875ff66127d93e5f672708cb2dcc14c8232ab/jackson-databind-2.5.3.jar</p>
<p>
Dependency Hierarchy:
- java-gitlab-api-4.1.0.jar (Root Library)
- :x: **jackson-databind-2.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/gocd-build-status-notifier/commit/039d60b34386e06662f779ce1a97720d950bae52">039d60b34386e06662f779ce1a97720d950bae52</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A deserialization flaw was discovered in the jackson-databind, versions before 2.6.7.1, 2.7.9.1 and 2.8.9, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7525>CVE-2017-7525</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7525</a></p>
<p>Release Date: 2018-02-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.1,2.7.9.1,2.8.9</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.5.3","packageFilePaths":["/gitlab-mr-status/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.gitlab:java-gitlab-api:4.1.0;com.fasterxml.jackson.core:jackson-databind:2.5.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.6.7.1,2.7.9.1,2.8.9"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-7525","vulnerabilityDetails":"A deserialization flaw was discovered in the jackson-databind, versions before 2.6.7.1, 2.7.9.1 and 2.8.9, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7525","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file gocd build status notifier gitlab mr status build gradle path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy java gitlab api jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a deserialization flaw was discovered in the jackson databind versions before and which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readvalue method of the objectmapper publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org gitlab java gitlab api com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind basebranches vulnerabilityidentifier cve vulnerabilitydetails a deserialization flaw was discovered in the jackson databind versions before and which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readvalue method of the objectmapper vulnerabilityurl | 0 |
103,274 | 8,893,762,232 | IssuesEvent | 2019-01-16 00:49:57 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | Test failure: System.Drawing.Tests.Graphics_DrawLineTests/DrawLines_PointFs | area-System.Drawing test-run-core | Opened on behalf of @Sunny-pu
The test `System.Drawing.Tests.Graphics_DrawLineTests/DrawLines_PointFs` has failed.
Assert.Equal() Failure
Expected: Byte[] [85, 64, 216, 170, 199, ...]
Actual: Byte[] [142, 194, 251, 180, 222, ...]
Stack Trace:
at System.Drawing.Tests.DrawingTest.ValidateImageContent(Image image, Byte[] expectedHash) in /root/corefx-1753603/src/System.Drawing.Common/tests/DrawingTest.cs:line 21
at System.Drawing.Tests.Graphics_DrawLineTests.DrawLines_PointFs() in /root/corefx-1753603/src/System.Drawing.Common/tests/Graphics_DrawLineTests.cs:line 33
Build : Master - 20180607.01 (Core Tests)
Failing configurations:
- SLES.12.Amd64-x64
- Release
- RedHat.69.Amd64-x64
- Release
Details: https://mc.dot.net/#/product/netcore/master/source/official~2Fcorefx~2Fmaster~2F/type/test~2Ffunctional~2Fcli~2F/build/20180607.01/workItem/System.Drawing.Common.Tests/analysis/xunit/System.Drawing.Tests.Graphics_DrawLineTests~2FDrawLines_PointFs | 1.0 | Test failure: System.Drawing.Tests.Graphics_DrawLineTests/DrawLines_PointFs - Opened on behalf of @Sunny-pu
The test `System.Drawing.Tests.Graphics_DrawLineTests/DrawLines_PointFs` has failed.
Assert.Equal() Failure
Expected: Byte[] [85, 64, 216, 170, 199, ...]
Actual: Byte[] [142, 194, 251, 180, 222, ...]
Stack Trace:
at System.Drawing.Tests.DrawingTest.ValidateImageContent(Image image, Byte[] expectedHash) in /root/corefx-1753603/src/System.Drawing.Common/tests/DrawingTest.cs:line 21
at System.Drawing.Tests.Graphics_DrawLineTests.DrawLines_PointFs() in /root/corefx-1753603/src/System.Drawing.Common/tests/Graphics_DrawLineTests.cs:line 33
Build : Master - 20180607.01 (Core Tests)
Failing configurations:
- SLES.12.Amd64-x64
- Release
- RedHat.69.Amd64-x64
- Release
Details: https://mc.dot.net/#/product/netcore/master/source/official~2Fcorefx~2Fmaster~2F/type/test~2Ffunctional~2Fcli~2F/build/20180607.01/workItem/System.Drawing.Common.Tests/analysis/xunit/System.Drawing.Tests.Graphics_DrawLineTests~2FDrawLines_PointFs | non_priority | test failure system drawing tests graphics drawlinetests drawlines pointfs opened on behalf of sunny pu the test system drawing tests graphics drawlinetests drawlines pointfs has failed assert equal failure expected byte actual byte stack trace at system drawing tests drawingtest validateimagecontent image image byte expectedhash in root corefx src system drawing common tests drawingtest cs line at system drawing tests graphics drawlinetests drawlines pointfs in root corefx src system drawing common tests graphics drawlinetests cs line build master core tests failing configurations sles release redhat release details | 0 |
278,837 | 24,180,413,293 | IssuesEvent | 2022-09-23 08:21:32 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: restore2TB/nodes=32 failed [raft recv oom, reproducible] | C-test-failure O-robot S-3 O-roachtest branch-master T-kv-replication | roachtest.restore2TB/nodes=32 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4924120&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4924120&tab=artifacts#/restore2TB/nodes=32) on master @ [1fdbb16fa206c5fd77c3aa111ec40916edfb55df](https://github.com/cockroachdb/cockroach/commits/1fdbb16fa206c5fd77c3aa111ec40916edfb55df):
```
| main/pkg/cmd/roachtest/monitor.go:105
| golang.org/x/sync/errgroup.(*Group).Go.func1
| golang.org/x/sync/errgroup/external/org_golang_x_sync/errgroup/errgroup.go:57
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1581
Wraps: (2) output in run_090427.112984326_n1_cockroach_sql
Wraps: (3) ./cockroach sql --insecure -e "
| RESTORE csv.bank FROM
| 'gs://cockroach-fixtures/workload/bank/version=1.0.0,payload-bytes=10240,ranges=0,rows=65104166,seed=1/bank?AUTH=implicit'
| WITH into_db = 'restore2tb'" returned
| stderr:
|
| stdout:
Wraps: (4) secondary error attachment
| UNCLASSIFIED_PROBLEM: context canceled
| (1) UNCLASSIFIED_PROBLEM
| Wraps: (2) Node 1. Command with error:
| | ``````
| | ./cockroach sql --insecure -e "
| | RESTORE csv.bank FROM
| | 'gs://cockroach-fixtures/workload/bank/version=1.0.0,payload-bytes=10240,ranges=0,rows=65104166,seed=1/bank?AUTH=implicit'
| | WITH into_db = 'restore2tb'"
| | ``````
| Wraps: (3) context canceled
| Error types: (1) errors.Unclassified (2) *hintdetail.withDetail (3) *errors.errorString
Wraps: (5) context canceled
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *secondary.withSecondaryError (5) *errors.errorString
monitor.go:127,restore.go:453,test_runner.go:875: monitor failure: monitor task failed: dial tcp 35.229.83.139:26257: connect: connection refused
(1) attached stack trace
-- stack trace:
| main.(*monitorImpl).WaitE
| main/pkg/cmd/roachtest/monitor.go:115
| main.(*monitorImpl).Wait
| main/pkg/cmd/roachtest/monitor.go:123
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.registerRestore.func1
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/restore.go:453
| [...repeated from below...]
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
-- stack trace:
| main.(*monitorImpl).wait.func2
| main/pkg/cmd/roachtest/monitor.go:171
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1581
Wraps: (4) monitor task failed
Wraps: (5) dial tcp 35.229.83.139:26257
Wraps: (6) connect
Wraps: (7) connection refused
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.withPrefix (5) *net.OpError (6) *os.SyscallError (7) syscall.Errno
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/bulk-io
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*restore2TB/nodes=32.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-15827 | 2.0 | roachtest: restore2TB/nodes=32 failed [raft recv oom, reproducible] - roachtest.restore2TB/nodes=32 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4924120&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4924120&tab=artifacts#/restore2TB/nodes=32) on master @ [1fdbb16fa206c5fd77c3aa111ec40916edfb55df](https://github.com/cockroachdb/cockroach/commits/1fdbb16fa206c5fd77c3aa111ec40916edfb55df):
```
| main/pkg/cmd/roachtest/monitor.go:105
| golang.org/x/sync/errgroup.(*Group).Go.func1
| golang.org/x/sync/errgroup/external/org_golang_x_sync/errgroup/errgroup.go:57
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1581
Wraps: (2) output in run_090427.112984326_n1_cockroach_sql
Wraps: (3) ./cockroach sql --insecure -e "
| RESTORE csv.bank FROM
| 'gs://cockroach-fixtures/workload/bank/version=1.0.0,payload-bytes=10240,ranges=0,rows=65104166,seed=1/bank?AUTH=implicit'
| WITH into_db = 'restore2tb'" returned
| stderr:
|
| stdout:
Wraps: (4) secondary error attachment
| UNCLASSIFIED_PROBLEM: context canceled
| (1) UNCLASSIFIED_PROBLEM
| Wraps: (2) Node 1. Command with error:
| | ``````
| | ./cockroach sql --insecure -e "
| | RESTORE csv.bank FROM
| | 'gs://cockroach-fixtures/workload/bank/version=1.0.0,payload-bytes=10240,ranges=0,rows=65104166,seed=1/bank?AUTH=implicit'
| | WITH into_db = 'restore2tb'"
| | ``````
| Wraps: (3) context canceled
| Error types: (1) errors.Unclassified (2) *hintdetail.withDetail (3) *errors.errorString
Wraps: (5) context canceled
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *secondary.withSecondaryError (5) *errors.errorString
monitor.go:127,restore.go:453,test_runner.go:875: monitor failure: monitor task failed: dial tcp 35.229.83.139:26257: connect: connection refused
(1) attached stack trace
-- stack trace:
| main.(*monitorImpl).WaitE
| main/pkg/cmd/roachtest/monitor.go:115
| main.(*monitorImpl).Wait
| main/pkg/cmd/roachtest/monitor.go:123
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.registerRestore.func1
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/restore.go:453
| [...repeated from below...]
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
-- stack trace:
| main.(*monitorImpl).wait.func2
| main/pkg/cmd/roachtest/monitor.go:171
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1581
Wraps: (4) monitor task failed
Wraps: (5) dial tcp 35.229.83.139:26257
Wraps: (6) connect
Wraps: (7) connection refused
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.withPrefix (5) *net.OpError (6) *os.SyscallError (7) syscall.Errno
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/bulk-io
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*restore2TB/nodes=32.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-15827 | non_priority | roachtest nodes failed roachtest nodes with on master main pkg cmd roachtest monitor go golang org x sync errgroup group go golang org x sync errgroup external org golang x sync errgroup errgroup go runtime goexit goroot src runtime asm s wraps output in run cockroach sql wraps cockroach sql insecure e restore csv bank from gs cockroach fixtures workload bank version payload bytes ranges rows seed bank auth implicit with into db returned stderr stdout wraps secondary error attachment unclassified problem context canceled unclassified problem wraps node command with error cockroach sql insecure e restore csv bank from gs cockroach fixtures workload bank version payload bytes ranges rows seed bank auth implicit with into db wraps context canceled error types errors unclassified hintdetail withdetail errors errorstring wraps context canceled error types withstack withstack errutil withprefix cluster withcommanddetails secondary withsecondaryerror errors errorstring monitor go restore go test runner go monitor failure monitor task failed dial tcp connect connection refused attached stack trace stack trace main monitorimpl waite main pkg cmd roachtest monitor go main monitorimpl wait main pkg cmd roachtest monitor go github com cockroachdb cockroach pkg cmd roachtest tests registerrestore github com cockroachdb cockroach pkg cmd roachtest tests restore go wraps monitor failure wraps attached stack trace stack trace main monitorimpl wait main pkg cmd roachtest monitor go runtime goexit goroot src runtime asm s wraps monitor task failed wraps dial tcp wraps connect wraps connection refused error types withstack withstack errutil withprefix withstack withstack errutil withprefix net operror os syscallerror syscall errno help see see cc cockroachdb bulk io jira issue crdb | 0 |
268,501 | 28,566,037,875 | IssuesEvent | 2023-04-21 02:14:31 | Satheesh575555/packages_apps_Settings_AOSP10_r33_CVE-2020-0416 | https://api.github.com/repos/Satheesh575555/packages_apps_Settings_AOSP10_r33_CVE-2020-0416 | closed | CVE-2020-0416 (High) detected in multiple libraries - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-0416 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>Settingsandroid-11.0.0_r47</b>, <b>Settingsandroid-11.0.0_r47</b>, <b>Settingsandroid-11.0.0_r47</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In multiple settings screens, there are possible tapjacking attacks due to an insecure default value. This could lead to local escalation of privilege and permissions with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-155288585
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0416>CVE-2020-0416</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-0416 (High) detected in multiple libraries - autoclosed - ## CVE-2020-0416 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>Settingsandroid-11.0.0_r47</b>, <b>Settingsandroid-11.0.0_r47</b>, <b>Settingsandroid-11.0.0_r47</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In multiple settings screens, there are possible tapjacking attacks due to an insecure default value. This could lead to local escalation of privilege and permissions with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-155288585
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0416>CVE-2020-0416</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries autoclosed cve high severity vulnerability vulnerable libraries settingsandroid settingsandroid settingsandroid vulnerability details in multiple settings screens there are possible tapjacking attacks due to an insecure default value this could lead to local escalation of privilege and permissions with no additional execution privileges needed user interaction is needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
24,695 | 5,097,168,285 | IssuesEvent | 2017-01-03 20:35:50 | reflectoring/coderadar | https://api.github.com/repos/reflectoring/coderadar | closed | Create contribution info | documentation | Create a document containing contribution infos for potential contributors. | 1.0 | Create contribution info - Create a document containing contribution infos for potential contributors. | non_priority | create contribution info create a document containing contribution infos for potential contributors | 0 |
47,223 | 24,913,163,901 | IssuesEvent | 2022-10-30 04:20:07 | IGCIT/Intel-GPU-Community-Issue-Tracker-IGCIT | https://api.github.com/repos/IGCIT/Intel-GPU-Community-Issue-Tracker-IGCIT | reopened | Mass Effect Legendary Edition - Frametime issues | Info: Needs Replication Type: Bad Performance | ### Checklist [README]
- [X] Device is not undervolted nor overclocked
- [X] Device is using the [latest drivers](https://github.com/IGCIT/Intel-GPU-Community-Issue-Tracker-IGCIT/wiki/Intel-driver-updates-and-changelogs)
- [X] Game is not cracked, modded and use the latest patch
### Game / Application [Required]
Mass Effect Legendary Edition
### Game Platform [Required]
- [ ] Steam
- [ ] Origin
- [ ] Microsoft Store
- [ ] GOG Galaxy
- [ ] Ubisoft Connect
- [ ] Battle.net
- [ ] Epic Games
- [ ] Rockstar Games Launcher
- [X] EA app
- [ ] Other (please specify)
### Other game platform
_No response_
### Processor / Processor Number [Required]
i9-13900K
### Graphic Card [Required]
Intel ARC A770 LE
### GPU Driver Version [Required]
- [X] 31.0.101.3491 (*latest*)
- [ ] 31.0.101.3490
- [ ] 31.0.101.3430
- [ ] 31.0.101.3276
- [ ] 30.0.101.3268
- [ ] 30.0.101.3259
- [ ] 30.0.101.1743
### Rendering API [Required]
- [ ] Vulkan
- [ ] OpenGL
- [ ] DirectX12
- [X] DirectX11
- [ ] DirectX10
- [ ] DirectX9
### Windows Build Number [Required]
- [X] Windows 11 22H2
- [ ] Windows 11 21H1 (*October 2021 Update*)
- [ ] Windows 10 21H2 (*November 2021 Update*)
- [ ] Windows 10 21H1 (*May 2021 Update*)
- [ ] Windows 10 20H2 (*October 2020 Update*)
- [ ] Other (Please specify)
### Other Windows build number
_No response_
### Intel System Support Utility report
[intel-ssu.txt](https://github.com/IGCIT/Intel-GPU-Community-Issue-Tracker-IGCIT/files/9856691/intel-ssu.txt)
### Description and steps to reproduce [Required]
Start gameplay
Running highest settings
Framerate in general is very good in this game, but it has frequent dips which make it feel stuttery. Imposing a framerate limiter to 120fps (or lower) will mitigate this issue somewhat, but it is still perceptible at 120hz.
### Game graphic quality [Required]
- [ ] Low
- [ ] Medium
- [ ] High
- [X] Ultra
### Game resolution [Required]
2560x1440
### Game VSync [Required]
Off
### Game display mode [Required]
- [X] Fullscreen
- [ ] Windowed
- [ ] Borderless Windowed
### Detailed game settings [Required]

### Device / Platform name
_No response_
### Crash dumps [Required]
N/A - There is no crash occuring.
### Save game
_No response_
### Game custom logs
This is an example of turning around in a hallway

| True | Mass Effect Legendary Edition - Frametime issues - ### Checklist [README]
- [X] Device is not undervolted nor overclocked
- [X] Device is using the [latest drivers](https://github.com/IGCIT/Intel-GPU-Community-Issue-Tracker-IGCIT/wiki/Intel-driver-updates-and-changelogs)
- [X] Game is not cracked, modded and use the latest patch
### Game / Application [Required]
Mass Effect Legendary Edition
### Game Platform [Required]
- [ ] Steam
- [ ] Origin
- [ ] Microsoft Store
- [ ] GOG Galaxy
- [ ] Ubisoft Connect
- [ ] Battle.net
- [ ] Epic Games
- [ ] Rockstar Games Launcher
- [X] EA app
- [ ] Other (please specify)
### Other game platform
_No response_
### Processor / Processor Number [Required]
i9-13900K
### Graphic Card [Required]
Intel ARC A770 LE
### GPU Driver Version [Required]
- [X] 31.0.101.3491 (*latest*)
- [ ] 31.0.101.3490
- [ ] 31.0.101.3430
- [ ] 31.0.101.3276
- [ ] 30.0.101.3268
- [ ] 30.0.101.3259
- [ ] 30.0.101.1743
### Rendering API [Required]
- [ ] Vulkan
- [ ] OpenGL
- [ ] DirectX12
- [X] DirectX11
- [ ] DirectX10
- [ ] DirectX9
### Windows Build Number [Required]
- [X] Windows 11 22H2
- [ ] Windows 11 21H1 (*October 2021 Update*)
- [ ] Windows 10 21H2 (*November 2021 Update*)
- [ ] Windows 10 21H1 (*May 2021 Update*)
- [ ] Windows 10 20H2 (*October 2020 Update*)
- [ ] Other (Please specify)
### Other Windows build number
_No response_
### Intel System Support Utility report
[intel-ssu.txt](https://github.com/IGCIT/Intel-GPU-Community-Issue-Tracker-IGCIT/files/9856691/intel-ssu.txt)
### Description and steps to reproduce [Required]
Start gameplay
Running highest settings
Framerate in general is very good in this game, but it has frequent dips which make it feel stuttery. Imposing a framerate limiter to 120fps (or lower) will mitigate this issue somewhat, but it is still perceptible at 120hz.
### Game graphic quality [Required]
- [ ] Low
- [ ] Medium
- [ ] High
- [X] Ultra
### Game resolution [Required]
2560x1440
### Game VSync [Required]
Off
### Game display mode [Required]
- [X] Fullscreen
- [ ] Windowed
- [ ] Borderless Windowed
### Detailed game settings [Required]

### Device / Platform name
_No response_
### Crash dumps [Required]
N/A - There is no crash occuring.
### Save game
_No response_
### Game custom logs
This is an example of turning around in a hallway

| non_priority | mass effect legendary edition frametime issues checklist device is not undervolted nor overclocked device is using the game is not cracked modded and use the latest patch game application mass effect legendary edition game platform steam origin microsoft store gog galaxy ubisoft connect battle net epic games rockstar games launcher ea app other please specify other game platform no response processor processor number graphic card intel arc le gpu driver version latest rendering api vulkan opengl windows build number windows windows october update windows november update windows may update windows october update other please specify other windows build number no response intel system support utility report description and steps to reproduce start gameplay running highest settings framerate in general is very good in this game but it has frequent dips which make it feel stuttery imposing a framerate limiter to or lower will mitigate this issue somewhat but it is still perceptible at game graphic quality low medium high ultra game resolution game vsync off game display mode fullscreen windowed borderless windowed detailed game settings device platform name no response crash dumps n a there is no crash occuring save game no response game custom logs this is an example of turning around in a hallway | 0 |
53,076 | 6,677,610,730 | IssuesEvent | 2017-10-05 11:12:42 | liqd/a4-advocate-europe | https://api.github.com/repos/liqd/a4-advocate-europe | opened | Account settings: two bios are too much! | bug design | <img width="580" alt="bildschirmfoto 2017-10-05 um 11 54 02" src="https://user-images.githubusercontent.com/22769111/31224555-b8b5fdfa-a9ce-11e7-834c-bba7b93c830b.png">
Instead of two fields there should only be one, but one that's more open to the user's priorities.
The label could say something like:
**Tell us about you**
_For example your background, your interests, your motivation for change in Europe (144 chars)_
| 1.0 | Account settings: two bios are too much! - <img width="580" alt="bildschirmfoto 2017-10-05 um 11 54 02" src="https://user-images.githubusercontent.com/22769111/31224555-b8b5fdfa-a9ce-11e7-834c-bba7b93c830b.png">
Instead of two fields there should only be one, but one that's more open to the user's priorities.
The label could say something like:
**Tell us about you**
_For example your background, your interests, your motivation for change in Europe (144 chars)_
| non_priority | account settings two bios are too much img width alt bildschirmfoto um src instead of two fields there should only be one but one that s more open to the user s priorities the label could say something like tell us about you for example your background your interests your motivation for change in europe chars | 0 |
34,613 | 16,616,550,225 | IssuesEvent | 2021-06-02 17:26:58 | cBioPortal/cbioportal | https://api.github.com/repos/cBioPortal/cbioportal | closed | Performance investigations | performance | - [ ] Try to correlate downtime with specific incidents in monitoring and ultimately specific user activity
- [ ] The waits in the db are all blue, "sending data" latency. What is the right way to address this? | True | Performance investigations - - [ ] Try to correlate downtime with specific incidents in monitoring and ultimately specific user activity
- [ ] The waits in the db are all blue, "sending data" latency. What is the right way to address this? | non_priority | performance investigations try to correlate downtime with specific incidents in monitoring and ultimately specific user activity the waits in the db are all blue sending data latency what is the right way to address this | 0 |
91,006 | 10,706,775,418 | IssuesEvent | 2019-10-24 16:01:31 | EducationalTestingService/skll | https://api.github.com/repos/EducationalTestingService/skll | closed | Update release process documentation | documentation | We will need to update the release process because of:
- new version of conda
- moving the SKLL package to the ETS organization anaconda.org account
| 1.0 | Update release process documentation - We will need to update the release process because of:
- new version of conda
- moving the SKLL package to the ETS organization anaconda.org account
| non_priority | update release process documentation we will need to update the release process because of new version of conda moving the skll package to the ets organization anaconda org account | 0 |
83,313 | 10,340,552,655 | IssuesEvent | 2019-09-03 22:21:19 | CyberTropic/StellarGaze | https://api.github.com/repos/CyberTropic/StellarGaze | closed | CSS tweaks | CSS design interface | - [x] review alerts (all scenarios)
- [x] login/reg alerts (all scenarios)
- [x] review comment box stylize
- [x] color review stars (not bright red)
- [x] review alerts change more info card icon positioning on media query <780px more aligned
- [x] style Favorites page, emphasize username | 1.0 | CSS tweaks - - [x] review alerts (all scenarios)
- [x] login/reg alerts (all scenarios)
- [x] review comment box stylize
- [x] color review stars (not bright red)
- [x] review alerts change more info card icon positioning on media query <780px more aligned
- [x] style Favorites page, emphasize username | non_priority | css tweaks review alerts all scenarios login reg alerts all scenarios review comment box stylize color review stars not bright red review alerts change more info card icon positioning on media query more aligned style favorites page emphasize username | 0 |
339,510 | 30,452,492,429 | IssuesEvent | 2023-07-16 13:24:19 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | [RC 6] Hover in node inspector have strange behavior | bug topic:editor needs testing topic:input topic:gui | ### Godot version
4.0.rc6
### System information
macOS 12.3.1, macOS 12.6.5
### Issue description
When hovering the node inspector, the state can stay as hovered even if the mouse left it; it results in showing the hover background.
https://user-images.githubusercontent.com/1923206/221655801-20b850a0-2c07-4c53-b8ef-f1a5a9c4e3ea.mp4
### Steps to reproduce
Hover some items in the node inspector.
### Minimal reproduction project
Any project can reproduce it. | 1.0 | [RC 6] Hover in node inspector have strange behavior - ### Godot version
4.0.rc6
### System information
macOS 12.3.1, macOS 12.6.5
### Issue description
When hovering the node inspector, the state can stay as hovered even if the mouse left it; it results in showing the hover background.
https://user-images.githubusercontent.com/1923206/221655801-20b850a0-2c07-4c53-b8ef-f1a5a9c4e3ea.mp4
### Steps to reproduce
Hover some items in the node inspector.
### Minimal reproduction project
Any project can reproduce it. | non_priority | hover in node inspector have strange behavior godot version system information macos macos issue description when hovering the node inspector the state can stay as hovered even if the mouse left it it results in showing the hover background steps to reproduce hover some items in the node inspector minimal reproduction project any project can reproduce it | 0 |
111,712 | 9,539,638,743 | IssuesEvent | 2019-04-30 17:28:07 | NuGet/Home | https://api.github.com/repos/NuGet/Home | closed | Analyze test failure DependencyGraphRestoreUtility_LegacyPackageRef_Restore_BuildTransitive | Area:Test Sprint 152 | Disabled one unit test `DependencyGraphRestoreUtility_LegacyPackageRef_Restore_BuildTransitive` which is consistenly failing in CI but passing locally.
https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=2365490&view=logs | 1.0 | Analyze test failure DependencyGraphRestoreUtility_LegacyPackageRef_Restore_BuildTransitive - Disabled one unit test `DependencyGraphRestoreUtility_LegacyPackageRef_Restore_BuildTransitive` which is consistenly failing in CI but passing locally.
https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=2365490&view=logs | non_priority | analyze test failure dependencygraphrestoreutility legacypackageref restore buildtransitive disabled one unit test dependencygraphrestoreutility legacypackageref restore buildtransitive which is consistenly failing in ci but passing locally | 0 |
236,611 | 18,103,662,404 | IssuesEvent | 2021-09-22 16:41:54 | neuronetio/gantt-schedule-timeline-calendar | https://api.github.com/repos/neuronetio/gantt-schedule-timeline-calendar | closed | Documentation for Plugins | 📃 Documentation | Currently, we are using a trial license to evaluate, if this component solves all our functional needs.
Is there a documentation for plugins? I only see this empty page: https://gantt-schedule-timeline-calendar.neuronet.io/documentation/configuration/plugins
1. We would like to know what functions are already supported by your component out of the box.
2. You are writing in the feature list "You can make your own plugins". Is there a small example or guide how a new plugin can be developed and added? I expect, that we have to extend its functionality.
Thanks you. | 1.0 | Documentation for Plugins - Currently, we are using a trial license to evaluate, if this component solves all our functional needs.
Is there a documentation for plugins? I only see this empty page: https://gantt-schedule-timeline-calendar.neuronet.io/documentation/configuration/plugins
1. We would like to know what functions are already supported by your component out of the box.
2. You are writing in the feature list "You can make your own plugins". Is there a small example or guide how a new plugin can be developed and added? I expect, that we have to extend its functionality.
Thanks you. | non_priority | documentation for plugins currently we are using a trial license to evaluate if this component solves all our functional needs is there a documentation for plugins i only see this empty page we would like to know what functions are already supported by your component out of the box you are writing in the feature list you can make your own plugins is there a small example or guide how a new plugin can be developed and added i expect that we have to extend its functionality thanks you | 0 |
21,011 | 14,274,345,597 | IssuesEvent | 2020-11-22 03:18:45 | google/iree | https://api.github.com/repos/google/iree | opened | Have a iree_runtime_size_benchmark target and track its size | help wanted infrastructure runtime triage-required | We should be able to have a minimal target that pulls in the dylib backend, no flags, no logging, etc and just uses iree_vm_invoke to call a model, similar to the existing iree/vm/bytecode_module_size_benchmark. The intent is to see what the impact of a standalone IREE build is to a user's application size. Even better would be another standard_library_size_benchmark that was just main() and pulled in a few things that we can reasonably expect any integrator to already have (like printf, std::string/std::vector as used by our current C++ code, etc). Diffing those two will give us the delta IREE adds to an average application.
@hanhanW I feel like you were playing with some benchmark tracking stuff at some point - could we potentially feed the byte size values to the same thing as time values and get size-over-time tracking? | 1.0 | Have a iree_runtime_size_benchmark target and track its size - We should be able to have a minimal target that pulls in the dylib backend, no flags, no logging, etc and just uses iree_vm_invoke to call a model, similar to the existing iree/vm/bytecode_module_size_benchmark. The intent is to see what the impact of a standalone IREE build is to a user's application size. Even better would be another standard_library_size_benchmark that was just main() and pulled in a few things that we can reasonably expect any integrator to already have (like printf, std::string/std::vector as used by our current C++ code, etc). Diffing those two will give us the delta IREE adds to an average application.
@hanhanW I feel like you were playing with some benchmark tracking stuff at some point - could we potentially feed the byte size values to the same thing as time values and get size-over-time tracking? | non_priority | have a iree runtime size benchmark target and track its size we should be able to have a minimal target that pulls in the dylib backend no flags no logging etc and just uses iree vm invoke to call a model similar to the existing iree vm bytecode module size benchmark the intent is to see what the impact of a standalone iree build is to a user s application size even better would be another standard library size benchmark that was just main and pulled in a few things that we can reasonably expect any integrator to already have like printf std string std vector as used by our current c code etc diffing those two will give us the delta iree adds to an average application hanhanw i feel like you were playing with some benchmark tracking stuff at some point could we potentially feed the byte size values to the same thing as time values and get size over time tracking | 0 |
336,415 | 24,497,791,985 | IssuesEvent | 2022-10-10 10:10:26 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | Document Import From Derivation | 9.needs: documentation | ## Problem
Currently the "Import From Derivation" (IFD) pattern is only documented in the NixOS Wiki, and therefore not curated by Nixpkgs maintainers. Even the [manual refers to the Wiki](https://nixos.org/manual/nixpkgs/unstable/#javascript-outside-nixpkgs).
This means, there is no authoritative reference on the concept.
## Checklist
<!-- make sure this issue is not redundant or obsolete -->
- [x] checked [latest Nixpkgs manual] \([source][nixpkgs-source]) and [latest NixOS manual] \([source][nixos-source])
- [x] checked [open documentation issues] for possible duplicates
- [x] checked [open documentation pull requests] for possible solutions
[latest Nixpkgs manual]: https://nixos.org/manual/nixpkgs/unstable/
[latest NixOS manual]: https://nixos.org/manual/nixos/unstable/
[nixpkgs-source]: https://github.com/NixOS/nixpkgs/tree/master/doc
[nixos-source]: https://github.com/NixOS/nixpkgs/tree/master/nixos/doc/manual
[open documentation issues]: https://github.com/NixOS/nixpkgs/issues?q=is%3Aissue+is%3Aopen+label%3A%229.needs%3A+documentation%22
[open documentation pull requests]: https://github.com/NixOS/nixpkgs/pulls?q=is%3Aopen+is%3Apr+label%3A%228.has%3A+documentation%22%2C%226.topic%3A+documentation%22
## Proposal
Document IFD and Nixpkgs' policy in the Nixpkgs manual in full detail.
Related:
- [Nix manual: `allow-import-from-derivation`](https://nixos.org/manual/nix/unstable/command-ref/conf-file.html#conf-allow-import-from-derivation)
- [NixOS Wiki: Import From Derivation](https://nixos.wiki/wiki/Import_From_Derivation)
Related discussions involving IFD:
- https://github.com/NixOS/nixpkgs/pull/188354#discussion_r957656189
- https://github.com/NixOS/nix/issues/954
- https://github.com/NixOS/nixpkgs/pull/112083 | 1.0 | Document Import From Derivation - ## Problem
Currently the "Import From Derivation" (IFD) pattern is only documented in the NixOS Wiki, and therefore not curated by Nixpkgs maintainers. Even the [manual refers to the Wiki](https://nixos.org/manual/nixpkgs/unstable/#javascript-outside-nixpkgs).
This means, there is no authoritative reference on the concept.
## Checklist
<!-- make sure this issue is not redundant or obsolete -->
- [x] checked [latest Nixpkgs manual] \([source][nixpkgs-source]) and [latest NixOS manual] \([source][nixos-source])
- [x] checked [open documentation issues] for possible duplicates
- [x] checked [open documentation pull requests] for possible solutions
[latest Nixpkgs manual]: https://nixos.org/manual/nixpkgs/unstable/
[latest NixOS manual]: https://nixos.org/manual/nixos/unstable/
[nixpkgs-source]: https://github.com/NixOS/nixpkgs/tree/master/doc
[nixos-source]: https://github.com/NixOS/nixpkgs/tree/master/nixos/doc/manual
[open documentation issues]: https://github.com/NixOS/nixpkgs/issues?q=is%3Aissue+is%3Aopen+label%3A%229.needs%3A+documentation%22
[open documentation pull requests]: https://github.com/NixOS/nixpkgs/pulls?q=is%3Aopen+is%3Apr+label%3A%228.has%3A+documentation%22%2C%226.topic%3A+documentation%22
## Proposal
Document IFD and Nixpkgs' policy in the Nixpkgs manual in full detail.
Related:
- [Nix manual: `allow-import-from-derivation`](https://nixos.org/manual/nix/unstable/command-ref/conf-file.html#conf-allow-import-from-derivation)
- [NixOS Wiki: Import From Derivation](https://nixos.wiki/wiki/Import_From_Derivation)
Related discussions involving IFD:
- https://github.com/NixOS/nixpkgs/pull/188354#discussion_r957656189
- https://github.com/NixOS/nix/issues/954
- https://github.com/NixOS/nixpkgs/pull/112083 | non_priority | document import from derivation problem currently the import from derivation ifd pattern is only documented in the nixos wiki and therefore not curated by nixpkgs maintainers even the this means there is no authoritative reference on the concept checklist checked and checked for possible duplicates checked for possible solutions proposal document ifd and nixpkgs policy in the nixpkgs manual in full detail related related discussions involving ifd | 0 |
319,079 | 27,346,526,310 | IssuesEvent | 2023-02-27 05:40:58 | heshammourad/vexillology-contests | https://api.github.com/repos/heshammourad/vexillology-contests | closed | Prompt for refreshes when countdown expires | enhancement contest migration | Make the process of transitioning from voting to results easier by:
- Add a message after the countdown expires saying: "Voting is concluded. Click here to see results."
- Replace the generic error message when voting is rejected with a similar message.
This can be accomplished by adding a callback to the countdown, which will be called after expiry to delete the `contest` data from the local store. | 1.0 | Prompt for refreshes when countdown expires - Make the process of transitioning from voting to results easier by:
- Add a message after the countdown expires saying: "Voting is concluded. Click here to see results."
- Replace the generic error message when voting is rejected with a similar message.
This can be accomplished by adding a callback to the countdown, which will be called after expiry to delete the `contest` data from the local store. | non_priority | prompt for refreshes when countdown expires make the process of transitioning from voting to results easier by add a message after the countdown expires saying voting is concluded click here to see results replace the generic error message when voting is rejected with a similar message this can be accomplished by adding a callback to the countdown which will be called after expiry to delete the contest data from the local store | 0 |
240,441 | 18,353,241,610 | IssuesEvent | 2021-10-08 14:51:49 | TheThingsIndustries/generic-node-docs | https://api.github.com/repos/TheThingsIndustries/generic-node-docs | closed | Software architecture diagram | documentation | <!--
Thanks for submitting this documentation request. Please fill the template
below, otherwise we will not be able to process this request.
-->
#### Summary
<!-- Summarize the request in a few sentences: -->
Need to add a diagram of the software architecture.
#### Why do we need this ?
<!-- Please explain the motivation, for whom, etc. -->
To explain to new comers how to use the GNSE software.
#### What is already there? What do you see now?
<!--
Please add any relevant documentation articles and resources. Screenshots if necessary.
-->
Application explanations.
#### What is missing? What do you want to see?
<!-- Please add documentation sources (forum links, outside sources...), mock-ups if applicable -->
Software architecture and Software diagram.
#### How do you propose to document this?
<!-- Please think about how this could be fixed. -->
Create SW arcticture PNG.
#### Can you do this yourself and submit a Pull Request?
<!-- You can also @mention experts if you need help with this. -->
All.
| 1.0 | Software architecture diagram - <!--
Thanks for submitting this documentation request. Please fill the template
below, otherwise we will not be able to process this request.
-->
#### Summary
<!-- Summarize the request in a few sentences: -->
Need to add a diagram of the software architecture.
#### Why do we need this ?
<!-- Please explain the motivation, for whom, etc. -->
To explain to new comers how to use the GNSE software.
#### What is already there? What do you see now?
<!--
Please add any relevant documentation articles and resources. Screenshots if necessary.
-->
Application explanations.
#### What is missing? What do you want to see?
<!-- Please add documentation sources (forum links, outside sources...), mock-ups if applicable -->
Software architecture and Software diagram.
#### How do you propose to document this?
<!-- Please think about how this could be fixed. -->
Create SW arcticture PNG.
#### Can you do this yourself and submit a Pull Request?
<!-- You can also @mention experts if you need help with this. -->
All.
| non_priority | software architecture diagram thanks for submitting this documentation request please fill the template below otherwise we will not be able to process this request summary need to add a diagram of the software architecture why do we need this to explain to new comers how to use the gnse software what is already there what do you see now please add any relevant documentation articles and resources screenshots if necessary application explanations what is missing what do you want to see software architecture and software diagram how do you propose to document this create sw arcticture png can you do this yourself and submit a pull request all | 0 |
31,639 | 15,026,308,764 | IssuesEvent | 2021-02-01 22:27:13 | DynamoRIO/dynamorio | https://api.github.com/repos/DynamoRIO/dynamorio | closed | [AArch64] Inline instr counting for trace_after_instrs in drcachesim | Component-DrCacheSim OpSys-AArch64 OpSys-ARM Performance | Today for AArch64, instr counting for the `-trace_after_instrs` option in drcachesim is not inlined. Instead it's done using a clean call. https://github.com/DynamoRIO/dynamorio/blob/5cbe8113c919b557f7bfc3daafffc9b1fef7938c/clients/drcachesim/tracer/tracer.cpp#L1430
We should inline it for better performance. | True | [AArch64] Inline instr counting for trace_after_instrs in drcachesim - Today for AArch64, instr counting for the `-trace_after_instrs` option in drcachesim is not inlined. Instead it's done using a clean call. https://github.com/DynamoRIO/dynamorio/blob/5cbe8113c919b557f7bfc3daafffc9b1fef7938c/clients/drcachesim/tracer/tracer.cpp#L1430
We should inline it for better performance. | non_priority | inline instr counting for trace after instrs in drcachesim today for instr counting for the trace after instrs option in drcachesim is not inlined instead it s done using a clean call we should inline it for better performance | 0 |
39,655 | 20,120,724,607 | IssuesEvent | 2022-02-08 01:49:11 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | [animation] swipe-to-pop-navigator animation is janky (but can be fixed if you put a CircularProgressIndicator in the view) | created via performance template | ## Details
This is the code. A very simple list view
https://gist.github.com/linhewinner/7868481e512780ba793775bb818b871f
This is a demonstration of the jank. As you can see "Demo Details 1" is janky while "Demo Details 0" is not janky:
https://user-images.githubusercontent.com/97132583/152900793-28d7ee27-a18c-4dcd-bdb4-2a399caf27eb.MP4
When the jank happens, DevTools Profiler is well under 8ms every frame.
The weird thing is that if you put a CircularProgressIndicator in the view hierarchy, the jank goes away.
I also experimented with replacing the CircularProgressIndicator with a StatefulComponent that just updates itself every 16ms. That also fixes the jank.
I switched to flutter master, and see the exact same behavior.
<!--
1. This is the code. A very simple list view
2. Please attach a small application (ideally just one main.dart file) that
reproduces the problem. You could use https://gist.github.com/ for this.
3. Switch flutter to master channel and run this app on a physical device
using profile mode with Skia tracing enabled, as follows:
flutter channel master
flutter run --profile --trace-skia
The bleeding edge master channel is encouraged here because Flutter is
constantly fixing bugs and improving its performance. Your problem in an
older Flutter version may have already been solved in the master channel.
4. Record a video of the performance issue using another phone so we
can have an intuitive understanding of what happened. Don’t use
"adb screenrecord", as that affects the performance of the profile run.
5. Open Observatory and save a timeline trace of the performance issue
so we know which functions might be causing it. See "How to Collect
and Read Timeline Traces" on this blog post:
https://medium.com/flutter/profiling-flutter-applications-using-the-timeline-a1a434964af3#a499
Make sure the performance overlay is turned OFF when recording the
trace as that may affect the performance of the profile run.
(Pressing ‘P’ on the command line toggles the overlay.)
-->
<!--
Please tell us which target platform(s) the problem occurs (Android / iOS / Web / macOS / Linux / Windows)
Which target OS version, for Web, browser, is the test system running?
Does the problem occur on emulator/simulator as well as on physical devices?
-->
**Target Platform:** iOS
**Target OS version/browser:** iOS 14
**Devices:** iPhone 13 Pro
## Logs
<details>
<summary>Logs</summary>
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
Analyzing [REDACTED]...
No issues found! (ran in 3.5s)
```
<!-- Finally, paste the output of running `flutter doctor -v` here, with your device plugged in. -->
```
linhe@/Users/linhe/[REDACTED] flutter doctor -v
[✓] Flutter (Channel stable, 2.8.1, on macOS 12.1 21C52 darwin-x64, locale en-US)
• Flutter version 2.8.1 at /Users/linhe/development/flutter
• Upstream repository https://github.com/flutter/flutter.git
• Framework revision 77d935af4d (8 weeks ago), 2021-12-16 08:37:33 -0800
• Engine revision 890a5fca2e
• Dart version 2.15.1
[✓] Android toolchain - develop for Android devices (Android SDK version 32.1.0-rc1)
• Android SDK at /Users/linhe/Library/Android/sdk
• Platform android-32, build-tools 32.1.0-rc1
• Java binary at: /Applications/Android Studio.app/Contents/jre/Contents/Home/bin/java
• Java version OpenJDK Runtime Environment (build 11.0.11+0-b60-7590822)
• All Android licenses accepted.
[✓] Xcode - develop for iOS and macOS (Xcode 13.2.1)
• Xcode at /Applications/Xcode.app/Contents/Developer
• CocoaPods version 1.11.2
[✓] Chrome - develop for the web
• Chrome at /Applications/Google Chrome.app/Contents/MacOS/Google Chrome
[✓] Android Studio (version 2021.1)
• Android Studio at /Applications/Android Studio.app/Contents
• Flutter plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/9212-flutter
• Dart plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/6351-dart
• Java version OpenJDK Runtime Environment (build 11.0.11+0-b60-7590822)
[✓] VS Code (version 1.64.0)
• VS Code at /Applications/Visual Studio Code.app/Contents
• Flutter extension version 3.34.0
[✓] Connected device (3 available)
• Lin’s iPhone (mobile) • 00008110-0002393C3E7A801E • ios • iOS 15.2.1 19C63
• iPhone 13 (mobile) • F291AF0C-5B8C-434C-955E-A08AB84C3786 • ios • com.apple.CoreSimulator.SimRuntime.iOS-15-2 (simulator)
• Chrome (web) • chrome • web-javascript • Google Chrome 98.0.4758.80
• No issues found!
```
</details>
| True | [animation] swipe-to-pop-navigator animation is janky (but can be fixed if you put a CircularProgressIndicator in the view) - ## Details
This is the code. A very simple list view
https://gist.github.com/linhewinner/7868481e512780ba793775bb818b871f
This is a demonstration of the jank. As you can see "Demo Details 1" is janky while "Demo Details 0" is not janky:
https://user-images.githubusercontent.com/97132583/152900793-28d7ee27-a18c-4dcd-bdb4-2a399caf27eb.MP4
When the jank happens, DevTools Profiler is well under 8ms every frame.
The weird thing is that if you put a CircularProgressIndicator in the view hierarchy, the jank goes away.
I also experimented with replacing the CircularProgressIndicator with a StatefulComponent that just updates itself every 16ms. That also fixes the jank.
I switched to flutter master, and see the exact same behavior.
<!--
1. This is the code. A very simple list view
2. Please attach a small application (ideally just one main.dart file) that
reproduces the problem. You could use https://gist.github.com/ for this.
3. Switch flutter to master channel and run this app on a physical device
using profile mode with Skia tracing enabled, as follows:
flutter channel master
flutter run --profile --trace-skia
The bleeding edge master channel is encouraged here because Flutter is
constantly fixing bugs and improving its performance. Your problem in an
older Flutter version may have already been solved in the master channel.
4. Record a video of the performance issue using another phone so we
can have an intuitive understanding of what happened. Don’t use
"adb screenrecord", as that affects the performance of the profile run.
5. Open Observatory and save a timeline trace of the performance issue
so we know which functions might be causing it. See "How to Collect
and Read Timeline Traces" on this blog post:
https://medium.com/flutter/profiling-flutter-applications-using-the-timeline-a1a434964af3#a499
Make sure the performance overlay is turned OFF when recording the
trace as that may affect the performance of the profile run.
(Pressing ‘P’ on the command line toggles the overlay.)
-->
<!--
Please tell us which target platform(s) the problem occurs (Android / iOS / Web / macOS / Linux / Windows)
Which target OS version, for Web, browser, is the test system running?
Does the problem occur on emulator/simulator as well as on physical devices?
-->
**Target Platform:** iOS
**Target OS version/browser:** iOS 14
**Devices:** iPhone 13 Pro
## Logs
<details>
<summary>Logs</summary>
<!--
Run `flutter analyze` and attach any output of that command below.
If there are any analysis errors, try resolving them before filing this issue.
-->
```
Analyzing [REDACTED]...
No issues found! (ran in 3.5s)
```
<!-- Finally, paste the output of running `flutter doctor -v` here, with your device plugged in. -->
```
linhe@/Users/linhe/[REDACTED] flutter doctor -v
[✓] Flutter (Channel stable, 2.8.1, on macOS 12.1 21C52 darwin-x64, locale en-US)
• Flutter version 2.8.1 at /Users/linhe/development/flutter
• Upstream repository https://github.com/flutter/flutter.git
• Framework revision 77d935af4d (8 weeks ago), 2021-12-16 08:37:33 -0800
• Engine revision 890a5fca2e
• Dart version 2.15.1
[✓] Android toolchain - develop for Android devices (Android SDK version 32.1.0-rc1)
• Android SDK at /Users/linhe/Library/Android/sdk
• Platform android-32, build-tools 32.1.0-rc1
• Java binary at: /Applications/Android Studio.app/Contents/jre/Contents/Home/bin/java
• Java version OpenJDK Runtime Environment (build 11.0.11+0-b60-7590822)
• All Android licenses accepted.
[✓] Xcode - develop for iOS and macOS (Xcode 13.2.1)
• Xcode at /Applications/Xcode.app/Contents/Developer
• CocoaPods version 1.11.2
[✓] Chrome - develop for the web
• Chrome at /Applications/Google Chrome.app/Contents/MacOS/Google Chrome
[✓] Android Studio (version 2021.1)
• Android Studio at /Applications/Android Studio.app/Contents
• Flutter plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/9212-flutter
• Dart plugin can be installed from:
🔨 https://plugins.jetbrains.com/plugin/6351-dart
• Java version OpenJDK Runtime Environment (build 11.0.11+0-b60-7590822)
[✓] VS Code (version 1.64.0)
• VS Code at /Applications/Visual Studio Code.app/Contents
• Flutter extension version 3.34.0
[✓] Connected device (3 available)
• Lin’s iPhone (mobile) • 00008110-0002393C3E7A801E • ios • iOS 15.2.1 19C63
• iPhone 13 (mobile) • F291AF0C-5B8C-434C-955E-A08AB84C3786 • ios • com.apple.CoreSimulator.SimRuntime.iOS-15-2 (simulator)
• Chrome (web) • chrome • web-javascript • Google Chrome 98.0.4758.80
• No issues found!
```
</details>
| non_priority | swipe to pop navigator animation is janky but can be fixed if you put a circularprogressindicator in the view details this is the code a very simple list view this is a demonstration of the jank as you can see demo details is janky while demo details is not janky when the jank happens devtools profiler is well under every frame the weird thing is that if you put a circularprogressindicator in the view hierarchy the jank goes away i also experimented with replacing the circularprogressindicator with a statefulcomponent that just updates itself every that also fixes the jank i switched to flutter master and see the exact same behavior this is the code a very simple list view please attach a small application ideally just one main dart file that reproduces the problem you could use for this switch flutter to master channel and run this app on a physical device using profile mode with skia tracing enabled as follows flutter channel master flutter run profile trace skia the bleeding edge master channel is encouraged here because flutter is constantly fixing bugs and improving its performance your problem in an older flutter version may have already been solved in the master channel record a video of the performance issue using another phone so we can have an intuitive understanding of what happened don’t use adb screenrecord as that affects the performance of the profile run open observatory and save a timeline trace of the performance issue so we know which functions might be causing it see how to collect and read timeline traces on this blog post make sure the performance overlay is turned off when recording the trace as that may affect the performance of the profile run pressing ‘p’ on the command line toggles the overlay please tell us which target platform s the problem occurs android ios web macos linux windows which target os version for web browser is the test system running does the problem occur on emulator simulator as well as on physical devices target platform ios target os version browser ios devices iphone pro logs logs run flutter analyze and attach any output of that command below if there are any analysis errors try resolving them before filing this issue analyzing no issues found ran in linhe users linhe flutter doctor v flutter channel stable on macos darwin locale en us • flutter version at users linhe development flutter • upstream repository • framework revision weeks ago • engine revision • dart version android toolchain develop for android devices android sdk version • android sdk at users linhe library android sdk • platform android build tools • java binary at applications android studio app contents jre contents home bin java • java version openjdk runtime environment build • all android licenses accepted xcode develop for ios and macos xcode • xcode at applications xcode app contents developer • cocoapods version chrome develop for the web • chrome at applications google chrome app contents macos google chrome android studio version • android studio at applications android studio app contents • flutter plugin can be installed from 🔨 • dart plugin can be installed from 🔨 • java version openjdk runtime environment build vs code version • vs code at applications visual studio code app contents • flutter extension version connected device available • lin’s iphone mobile • • ios • ios • iphone mobile • • ios • com apple coresimulator simruntime ios simulator • chrome web • chrome • web javascript • google chrome • no issues found | 0 |
34,997 | 30,668,356,325 | IssuesEvent | 2023-07-25 20:09:23 | FuelLabs/fuel-indexer | https://api.github.com/repos/FuelLabs/fuel-indexer | opened | Create data dashboard for `fuel-explorer` | infrastructure explorer | - The explorer will be an owned and operated production Fuel service
- We will want some way of monitoring it
- So far we're just using Grafana for general service performance metrics
- We need to add some other views:
- View-1
- General service performance (we already have this)
- View-2
- Index stats (for the literal explorer data)
- View-3
- Log stats from opensearch (we can't add these to the indexer service because this would be for the explorer (an indexer) not the general Fuel indexer service)
Additional context:
- This require hooking Grafana into AWS RDS
- This would require also hooking Grafana into Opensearch (ideally) | 1.0 | Create data dashboard for `fuel-explorer` - - The explorer will be an owned and operated production Fuel service
- We will want some way of monitoring it
- So far we're just using Grafana for general service performance metrics
- We need to add some other views:
- View-1
- General service performance (we already have this)
- View-2
- Index stats (for the literal explorer data)
- View-3
- Log stats from opensearch (we can't add these to the indexer service because this would be for the explorer (an indexer) not the general Fuel indexer service)
Additional context:
- This require hooking Grafana into AWS RDS
- This would require also hooking Grafana into Opensearch (ideally) | non_priority | create data dashboard for fuel explorer the explorer will be an owned and operated production fuel service we will want some way of monitoring it so far we re just using grafana for general service performance metrics we need to add some other views view general service performance we already have this view index stats for the literal explorer data view log stats from opensearch we can t add these to the indexer service because this would be for the explorer an indexer not the general fuel indexer service additional context this require hooking grafana into aws rds this would require also hooking grafana into opensearch ideally | 0 |
47,500 | 13,056,210,918 | IssuesEvent | 2020-07-30 04:00:20 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | non-english locales can cause errors in 'greps' in cmake files (Trac #644) | Migrated from Trac cmake defect | The following doesn't catch a no-match because a no-match is not an error. It's a no-match.
Fix is to test for an empty variable, then set it to zero.
```text
#
# Get SVN_REVISION from svn info
#
option(USE_SVN_REVISION_FLAGS "Add compiled-in svn revision information." ON)
if(NOT HAVE_SVN_REVISION)
set(HAVE_SVN_REVISION TRUE CACHE INTERNAL "flag")
execute_process(COMMAND ${SVN_EXECUTABLE} info ${CMAKE_SOURCE_DIR}
COMMAND awk "/^Revision:/ { printf $2 }"
OUTPUT_VARIABLE SVN_REVISION
ERROR_VARIABLE SVN_REVISION_ERROR)
if (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)
message(STATUS "******\tUnable to determine svn revision (does svn info not accept '--xml'?)")
set(SVN_REVISION "0")
endif (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)
if(NOT USE_SVN_REVISION_FLAGS)
message(STATUS " \tNot compiling in svn revision information. Hope you aren't running simprod")
set(SVN_REVISION "0")
endif(NOT USE_SVN_REVISION_FLAGS)
boost_report_value(SVN_REVISION)
set(SVN_REVISION ${SVN_REVISION} CACHE INTERNAL "svn revision")
endif(NOT HAVE_SVN_REVISION)
```
This was reported via email:
```text
On 07/24/2011 06:41 PM, Nathan Whitehorn wrote:
> Wow. That's a subtle one. Maybe we should make this fill itself in using
> SVN keyword expansion instead? That would protect us against features
> like this...
> -Nathan
>
> On 07/24/11 17:39, Juan Carlos Díaz Vélez wrote:
>> Ah, yes. Thank you. My LANG variable was set to Spanish and apparently
>> the newest update to subversion includes multilingual support.
>> config.cmake wasn't able to find "Revision" since subersion was
>> returning "Revisión".
>>
>> Thanks,
>>
>> Juan Carlos
```
Migrated from https://code.icecube.wisc.edu/ticket/644
```json
{
"status": "closed",
"changetime": "2014-11-23T03:37:57",
"description": "The following doesn't catch a no-match because a no-match is not an error. It's a no-match.\n\nFix is to test for an empty variable, then set it to zero.\n\n{{{\n\n#\n# Get SVN_REVISION from svn info\n#\noption(USE_SVN_REVISION_FLAGS \"Add compiled-in svn revision information.\" ON)\n\nif(NOT HAVE_SVN_REVISION)\n set(HAVE_SVN_REVISION TRUE CACHE INTERNAL \"flag\")\n execute_process(COMMAND ${SVN_EXECUTABLE} info ${CMAKE_SOURCE_DIR}\n COMMAND awk \"/^Revision:/ { printf $2 }\"\n OUTPUT_VARIABLE SVN_REVISION\n ERROR_VARIABLE SVN_REVISION_ERROR)\n\n if (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)\n message(STATUS \"******\\tUnable to determine svn revision (does svn info not accept '--xml'?)\")\n set(SVN_REVISION \"0\")\n endif (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)\n\n if(NOT USE_SVN_REVISION_FLAGS)\n message(STATUS \" \\tNot compiling in svn revision information. Hope you aren't running simprod\")\n set(SVN_REVISION \"0\")\n endif(NOT USE_SVN_REVISION_FLAGS)\n\n boost_report_value(SVN_REVISION)\n set(SVN_REVISION ${SVN_REVISION} CACHE INTERNAL \"svn revision\")\n\nendif(NOT HAVE_SVN_REVISION)\n}}}\n\nThis was reported via email:\n{{{\nOn 07/24/2011 06:41 PM, Nathan Whitehorn wrote:\n> Wow. That's a subtle one. Maybe we should make this fill itself in using\n> SVN keyword expansion instead? That would protect us against features\n> like this...\n> -Nathan\n> \n> On 07/24/11 17:39, Juan Carlos D\u00edaz V\u00e9lez wrote:\n>> Ah, yes. Thank you. My LANG variable was set to Spanish and apparently\n>> the newest update to subversion includes multilingual support.\n>> config.cmake wasn't able to find \"Revision\" since subersion was\n>> returning \"Revisi\u00f3n\".\n>>\n>> Thanks,\n>>\n>> Juan Carlos\n}}}",
"reporter": "nega",
"cc": "juancarlos, nwhitehorn",
"resolution": "fixed",
"_ts": "1416713877111216",
"component": "cmake",
"summary": "non-english locales can cause errors in 'greps' in cmake files",
"priority": "normal",
"keywords": "",
"time": "2011-07-29T00:10:54",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
| 1.0 | non-english locales can cause errors in 'greps' in cmake files (Trac #644) - The following doesn't catch a no-match because a no-match is not an error. It's a no-match.
Fix is to test for an empty variable, then set it to zero.
```text
#
# Get SVN_REVISION from svn info
#
option(USE_SVN_REVISION_FLAGS "Add compiled-in svn revision information." ON)
if(NOT HAVE_SVN_REVISION)
set(HAVE_SVN_REVISION TRUE CACHE INTERNAL "flag")
execute_process(COMMAND ${SVN_EXECUTABLE} info ${CMAKE_SOURCE_DIR}
COMMAND awk "/^Revision:/ { printf $2 }"
OUTPUT_VARIABLE SVN_REVISION
ERROR_VARIABLE SVN_REVISION_ERROR)
if (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)
message(STATUS "******\tUnable to determine svn revision (does svn info not accept '--xml'?)")
set(SVN_REVISION "0")
endif (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)
if(NOT USE_SVN_REVISION_FLAGS)
message(STATUS " \tNot compiling in svn revision information. Hope you aren't running simprod")
set(SVN_REVISION "0")
endif(NOT USE_SVN_REVISION_FLAGS)
boost_report_value(SVN_REVISION)
set(SVN_REVISION ${SVN_REVISION} CACHE INTERNAL "svn revision")
endif(NOT HAVE_SVN_REVISION)
```
This was reported via email:
```text
On 07/24/2011 06:41 PM, Nathan Whitehorn wrote:
> Wow. That's a subtle one. Maybe we should make this fill itself in using
> SVN keyword expansion instead? That would protect us against features
> like this...
> -Nathan
>
> On 07/24/11 17:39, Juan Carlos Díaz Vélez wrote:
>> Ah, yes. Thank you. My LANG variable was set to Spanish and apparently
>> the newest update to subversion includes multilingual support.
>> config.cmake wasn't able to find "Revision" since subersion was
>> returning "Revisión".
>>
>> Thanks,
>>
>> Juan Carlos
```
Migrated from https://code.icecube.wisc.edu/ticket/644
```json
{
"status": "closed",
"changetime": "2014-11-23T03:37:57",
"description": "The following doesn't catch a no-match because a no-match is not an error. It's a no-match.\n\nFix is to test for an empty variable, then set it to zero.\n\n{{{\n\n#\n# Get SVN_REVISION from svn info\n#\noption(USE_SVN_REVISION_FLAGS \"Add compiled-in svn revision information.\" ON)\n\nif(NOT HAVE_SVN_REVISION)\n set(HAVE_SVN_REVISION TRUE CACHE INTERNAL \"flag\")\n execute_process(COMMAND ${SVN_EXECUTABLE} info ${CMAKE_SOURCE_DIR}\n COMMAND awk \"/^Revision:/ { printf $2 }\"\n OUTPUT_VARIABLE SVN_REVISION\n ERROR_VARIABLE SVN_REVISION_ERROR)\n\n if (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)\n message(STATUS \"******\\tUnable to determine svn revision (does svn info not accept '--xml'?)\")\n set(SVN_REVISION \"0\")\n endif (SVN_REVISION_ERROR OR NOT SVN_EXECUTABLE)\n\n if(NOT USE_SVN_REVISION_FLAGS)\n message(STATUS \" \\tNot compiling in svn revision information. Hope you aren't running simprod\")\n set(SVN_REVISION \"0\")\n endif(NOT USE_SVN_REVISION_FLAGS)\n\n boost_report_value(SVN_REVISION)\n set(SVN_REVISION ${SVN_REVISION} CACHE INTERNAL \"svn revision\")\n\nendif(NOT HAVE_SVN_REVISION)\n}}}\n\nThis was reported via email:\n{{{\nOn 07/24/2011 06:41 PM, Nathan Whitehorn wrote:\n> Wow. That's a subtle one. Maybe we should make this fill itself in using\n> SVN keyword expansion instead? That would protect us against features\n> like this...\n> -Nathan\n> \n> On 07/24/11 17:39, Juan Carlos D\u00edaz V\u00e9lez wrote:\n>> Ah, yes. Thank you. My LANG variable was set to Spanish and apparently\n>> the newest update to subversion includes multilingual support.\n>> config.cmake wasn't able to find \"Revision\" since subersion was\n>> returning \"Revisi\u00f3n\".\n>>\n>> Thanks,\n>>\n>> Juan Carlos\n}}}",
"reporter": "nega",
"cc": "juancarlos, nwhitehorn",
"resolution": "fixed",
"_ts": "1416713877111216",
"component": "cmake",
"summary": "non-english locales can cause errors in 'greps' in cmake files",
"priority": "normal",
"keywords": "",
"time": "2011-07-29T00:10:54",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
| non_priority | non english locales can cause errors in greps in cmake files trac the following doesn t catch a no match because a no match is not an error it s a no match fix is to test for an empty variable then set it to zero text get svn revision from svn info option use svn revision flags add compiled in svn revision information on if not have svn revision set have svn revision true cache internal flag execute process command svn executable info cmake source dir command awk revision printf output variable svn revision error variable svn revision error if svn revision error or not svn executable message status tunable to determine svn revision does svn info not accept xml set svn revision endif svn revision error or not svn executable if not use svn revision flags message status tnot compiling in svn revision information hope you aren t running simprod set svn revision endif not use svn revision flags boost report value svn revision set svn revision svn revision cache internal svn revision endif not have svn revision this was reported via email text on pm nathan whitehorn wrote wow that s a subtle one maybe we should make this fill itself in using svn keyword expansion instead that would protect us against features like this nathan on juan carlos díaz vélez wrote ah yes thank you my lang variable was set to spanish and apparently the newest update to subversion includes multilingual support config cmake wasn t able to find revision since subersion was returning revisión thanks juan carlos migrated from json status closed changetime description the following doesn t catch a no match because a no match is not an error it s a no match n nfix is to test for an empty variable then set it to zero n n n n n get svn revision from svn info n noption use svn revision flags add compiled in svn revision information on n nif not have svn revision n set have svn revision true cache internal flag n execute process command svn executable info cmake source dir n command awk revision printf n output variable svn revision n error variable svn revision error n n if svn revision error or not svn executable n message status tunable to determine svn revision does svn info not accept xml n set svn revision n endif svn revision error or not svn executable n n if not use svn revision flags n message status tnot compiling in svn revision information hope you aren t running simprod n set svn revision n endif not use svn revision flags n n boost report value svn revision n set svn revision svn revision cache internal svn revision n nendif not have svn revision n n nthis was reported via email n non pm nathan whitehorn wrote n wow that s a subtle one maybe we should make this fill itself in using n svn keyword expansion instead that would protect us against features n like this n nathan n n on juan carlos d v wrote n ah yes thank you my lang variable was set to spanish and apparently n the newest update to subversion includes multilingual support n config cmake wasn t able to find revision since subersion was n returning revisi n n thanks n n juan carlos n reporter nega cc juancarlos nwhitehorn resolution fixed ts component cmake summary non english locales can cause errors in greps in cmake files priority normal keywords time milestone owner nega type defect | 0 |
276,649 | 24,008,490,909 | IssuesEvent | 2022-09-14 16:37:22 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Manual test run on macOS (Intel) for 1.43.x - Release #4 | tests OS/macOS QA/Yes release-notes/exclude OS/Desktop | ### Installer
- [x] Check signature:
- [x] If macOS, using x64 binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
- [x] If macOS, using universal binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
### `105.0.5195.127` Related Checks:
- [ ] Ensure that Chromast is still working and you're able to stream media from the mobile device (quick spot check)
### Widevine
- [x] Verify `Widevine Notification` is shown when you visit Netflix for the first time
- [x] Test that you can stream on Netflix on a fresh profile after installing Widevine
- [x] If macOS, run the above Widevine tests for both `x64` and `universal` builds
### Rewards
- [x] Verify that you are able to successfully join Rewards on a fresh profile
### TLS Pinning
- [x] Visit https://ssl-pinning.someblog.org/ and verify a pinning error is displayed
- [x] Visit https://pinning-test.badssl.com/ and verify a pinning error is **not** displayed
### Upgrade
- [x] Make sure that data from the last version appears in the new version OK
- [x] Ensure that `brave://version` lists the expected Brave & Chromium versions
- [x] With data from the last version, verify that
- [x] Bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] Cookies are preserved
- [x] Installed extensions are retained and work correctly
- [x] Opened tabs can be reloaded
- [x] Stored passwords are preserved
- [x] Sync chain created in previous version is retained
- [x] Social media blocking buttons changes are retained
- [x] Rewards
- [x] BAT balance is retained
- [x] Auto-contribute list is retained
- [x] Both Tips and Monthly Contributions are retained
- [x] Panel transactions list is retained
- [x] Changes to rewards settings are retained
- [x] Ensure that Auto Contribute is not being enabled when upgrading to a new version if AC was disabled
- [x] Ads
- [x] Both `Estimated pending rewards` & `Ad notifications received this month` are retained
- [x] Changes to ads settings are retained
- [x] Ensure that ads are not being enabled when upgrading to a new version if they were disabled
- [x] Ensure that ads are not disabled when upgrading to a new version if they were enabled | 1.0 | Manual test run on macOS (Intel) for 1.43.x - Release #4 - ### Installer
- [x] Check signature:
- [x] If macOS, using x64 binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
- [x] If macOS, using universal binary run `spctl --assess --verbose` for the installed version and make sure it returns `accepted`
### `105.0.5195.127` Related Checks:
- [ ] Ensure that Chromast is still working and you're able to stream media from the mobile device (quick spot check)
### Widevine
- [x] Verify `Widevine Notification` is shown when you visit Netflix for the first time
- [x] Test that you can stream on Netflix on a fresh profile after installing Widevine
- [x] If macOS, run the above Widevine tests for both `x64` and `universal` builds
### Rewards
- [x] Verify that you are able to successfully join Rewards on a fresh profile
### TLS Pinning
- [x] Visit https://ssl-pinning.someblog.org/ and verify a pinning error is displayed
- [x] Visit https://pinning-test.badssl.com/ and verify a pinning error is **not** displayed
### Upgrade
- [x] Make sure that data from the last version appears in the new version OK
- [x] Ensure that `brave://version` lists the expected Brave & Chromium versions
- [x] With data from the last version, verify that
- [x] Bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] Cookies are preserved
- [x] Installed extensions are retained and work correctly
- [x] Opened tabs can be reloaded
- [x] Stored passwords are preserved
- [x] Sync chain created in previous version is retained
- [x] Social media blocking buttons changes are retained
- [x] Rewards
- [x] BAT balance is retained
- [x] Auto-contribute list is retained
- [x] Both Tips and Monthly Contributions are retained
- [x] Panel transactions list is retained
- [x] Changes to rewards settings are retained
- [x] Ensure that Auto Contribute is not being enabled when upgrading to a new version if AC was disabled
- [x] Ads
- [x] Both `Estimated pending rewards` & `Ad notifications received this month` are retained
- [x] Changes to ads settings are retained
- [x] Ensure that ads are not being enabled when upgrading to a new version if they were disabled
- [x] Ensure that ads are not disabled when upgrading to a new version if they were enabled | non_priority | manual test run on macos intel for x release installer check signature if macos using binary run spctl assess verbose for the installed version and make sure it returns accepted if macos using universal binary run spctl assess verbose for the installed version and make sure it returns accepted related checks ensure that chromast is still working and you re able to stream media from the mobile device quick spot check widevine verify widevine notification is shown when you visit netflix for the first time test that you can stream on netflix on a fresh profile after installing widevine if macos run the above widevine tests for both and universal builds rewards verify that you are able to successfully join rewards on a fresh profile tls pinning visit and verify a pinning error is displayed visit and verify a pinning error is not displayed upgrade make sure that data from the last version appears in the new version ok ensure that brave version lists the expected brave chromium versions with data from the last version verify that bookmarks on the bookmark toolbar and bookmark folders can be opened cookies are preserved installed extensions are retained and work correctly opened tabs can be reloaded stored passwords are preserved sync chain created in previous version is retained social media blocking buttons changes are retained rewards bat balance is retained auto contribute list is retained both tips and monthly contributions are retained panel transactions list is retained changes to rewards settings are retained ensure that auto contribute is not being enabled when upgrading to a new version if ac was disabled ads both estimated pending rewards ad notifications received this month are retained changes to ads settings are retained ensure that ads are not being enabled when upgrading to a new version if they were disabled ensure that ads are not disabled when upgrading to a new version if they were enabled | 0 |
112,290 | 24,250,394,578 | IssuesEvent | 2022-09-27 13:49:20 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Having NPC's health interface open when your character has nausea and vomits closes the interface but still keeps the character grabbed | Bug Code Networking | ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [ ] My issue happened while using mods.
### What happened?
Noticed in multiplayer, in singleplayer you don't have access to NPC health interfaces. But this should also happen when checking the health of bots and other players.
As the title says if you vomit while you are checking a outpost NPC the health interface closes but you are still grabbed to the NPC
It should instead also lose the grab or then re-open the health interface while your character is done vomiting
### Reproduction steps
1. Start multiplayer campaign
2. Drink Ethanol until you start vomiting
3. Find a NPC and access their health interface
4. Wait until your character vomits
5. Notice that the health interface closes but you are still grabbing the NPC
### Bug prevalence
Happens every time I play
### Version
0.19.5.0 (unstable)
### -
Branch: dev Commit: https://github.com/Regalis11/Barotrauma-development/commit/ca8b2264ff5b03ff831f1f525e347ab08990655b
### Which operating system did you encounter this bug on?
Windows
### Relevant error messages and crash reports
_No response_ | 1.0 | Having NPC's health interface open when your character has nausea and vomits closes the interface but still keeps the character grabbed - ### Disclaimers
- [X] I have searched the issue tracker to check if the issue has already been reported.
- [ ] My issue happened while using mods.
### What happened?
Noticed in multiplayer, in singleplayer you don't have access to NPC health interfaces. But this should also happen when checking the health of bots and other players.
As the title says if you vomit while you are checking a outpost NPC the health interface closes but you are still grabbed to the NPC
It should instead also lose the grab or then re-open the health interface while your character is done vomiting
### Reproduction steps
1. Start multiplayer campaign
2. Drink Ethanol until you start vomiting
3. Find a NPC and access their health interface
4. Wait until your character vomits
5. Notice that the health interface closes but you are still grabbing the NPC
### Bug prevalence
Happens every time I play
### Version
0.19.5.0 (unstable)
### -
Branch: dev Commit: https://github.com/Regalis11/Barotrauma-development/commit/ca8b2264ff5b03ff831f1f525e347ab08990655b
### Which operating system did you encounter this bug on?
Windows
### Relevant error messages and crash reports
_No response_ | non_priority | having npc s health interface open when your character has nausea and vomits closes the interface but still keeps the character grabbed disclaimers i have searched the issue tracker to check if the issue has already been reported my issue happened while using mods what happened noticed in multiplayer in singleplayer you don t have access to npc health interfaces but this should also happen when checking the health of bots and other players as the title says if you vomit while you are checking a outpost npc the health interface closes but you are still grabbed to the npc it should instead also lose the grab or then re open the health interface while your character is done vomiting reproduction steps start multiplayer campaign drink ethanol until you start vomiting find a npc and access their health interface wait until your character vomits notice that the health interface closes but you are still grabbing the npc bug prevalence happens every time i play version unstable branch dev commit which operating system did you encounter this bug on windows relevant error messages and crash reports no response | 0 |
25,865 | 6,717,291,940 | IssuesEvent | 2017-10-14 19:23:16 | andy5995/rmw | https://api.github.com/repos/andy5995/rmw | opened | review the output messages | code enhancement Hacktoberfest help wanted pri:normal | Would anyone like to review and possibly improve the messages (how they appear, or code related to them) output by the program?
* messages when files are `rmw'ed`
* error messages (or how the functions are called)
* messages when files are restored | 1.0 | review the output messages - Would anyone like to review and possibly improve the messages (how they appear, or code related to them) output by the program?
* messages when files are `rmw'ed`
* error messages (or how the functions are called)
* messages when files are restored | non_priority | review the output messages would anyone like to review and possibly improve the messages how they appear or code related to them output by the program messages when files are rmw ed error messages or how the functions are called messages when files are restored | 0 |
382,092 | 26,484,702,072 | IssuesEvent | 2023-01-17 17:04:39 | NOAA-EMC/NCEPLIBS-w3emc | https://api.github.com/repos/NOAA-EMC/NCEPLIBS-w3emc | closed | Update readme with Alex as code manager... | documentation | Assigning Alex as a code manager instead of Kyle. ;-) | 1.0 | Update readme with Alex as code manager... - Assigning Alex as a code manager instead of Kyle. ;-) | non_priority | update readme with alex as code manager assigning alex as a code manager instead of kyle | 0 |
13,835 | 16,557,439,166 | IssuesEvent | 2021-05-28 15:25:57 | fourMs/MGT-python | https://api.github.com/repos/fourMs/MGT-python | opened | ffmpeg_cmd and ffmpeg_cmd_async should raise exception if something goes wrong | bug compatibility enhancement | ...instead of misleadingly printing 'Progress 100%'. The exception should print stderr. | True | ffmpeg_cmd and ffmpeg_cmd_async should raise exception if something goes wrong - ...instead of misleadingly printing 'Progress 100%'. The exception should print stderr. | non_priority | ffmpeg cmd and ffmpeg cmd async should raise exception if something goes wrong instead of misleadingly printing progress the exception should print stderr | 0 |
175,086 | 13,532,492,570 | IssuesEvent | 2020-09-16 00:17:12 | asgiom/cr8-brm-mobile-issues | https://api.github.com/repos/asgiom/cr8-brm-mobile-issues | closed | [BUG]Adding a contact forwards to send page | bug test | **Describe the bug**
If you add a contact you get redirect to the send page, while you should be taken to the contact list.
**To Reproduce**
Steps to reproduce the behavior:
1. Add a contact
2. See error
**Expected behavior**
After adding a contact you should be taken to the contact list.
**Smartphone (please complete the following information):**
- Device: Note8
- OS: Android
- OS Version 10
- App Version 0.5.2
**Additional context**
Add any other context about the problem here.
| 1.0 | [BUG]Adding a contact forwards to send page - **Describe the bug**
If you add a contact you get redirect to the send page, while you should be taken to the contact list.
**To Reproduce**
Steps to reproduce the behavior:
1. Add a contact
2. See error
**Expected behavior**
After adding a contact you should be taken to the contact list.
**Smartphone (please complete the following information):**
- Device: Note8
- OS: Android
- OS Version 10
- App Version 0.5.2
**Additional context**
Add any other context about the problem here.
| non_priority | adding a contact forwards to send page describe the bug if you add a contact you get redirect to the send page while you should be taken to the contact list to reproduce steps to reproduce the behavior add a contact see error expected behavior after adding a contact you should be taken to the contact list smartphone please complete the following information device os android os version app version additional context add any other context about the problem here | 0 |
248,200 | 18,858,046,694 | IssuesEvent | 2021-11-12 09:19:30 | pss-coder/pe | https://api.github.com/repos/pss-coder/pe | opened | Model Component weird multiplicity | type.DocumentationBug severity.Medium | What does the *a and *f mean ?? Though you included what the 'a' and 'f' mean I think would be better to describe what it means since it is not your usual multiplicity.

<!--session: 1636704585877-8b82bb88-bedf-4d7a-ab66-f744764ccb3b-->
<!--Version: Web v3.4.1--> | 1.0 | Model Component weird multiplicity - What does the *a and *f mean ?? Though you included what the 'a' and 'f' mean I think would be better to describe what it means since it is not your usual multiplicity.

<!--session: 1636704585877-8b82bb88-bedf-4d7a-ab66-f744764ccb3b-->
<!--Version: Web v3.4.1--> | non_priority | model component weird multiplicity what does the a and f mean though you included what the a and f mean i think would be better to describe what it means since it is not your usual multiplicity | 0 |
116,287 | 17,360,112,335 | IssuesEvent | 2021-07-29 19:19:07 | lukebroganws/JS-Demo | https://api.github.com/repos/lukebroganws/JS-Demo | opened | WS-2017-0266 (Low) detected in http-signature-0.10.1.tgz | security vulnerability | ## WS-2017-0266 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-signature-0.10.1.tgz</b></p></summary>
<p>Reference implementation of Joyent's HTTP Signature scheme.</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz">https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/zaproxy/node_modules/http-signature/package.json</p>
<p>
Dependency Hierarchy:
- zaproxy-0.2.0.tgz (Root Library)
- request-2.36.0.tgz
- :x: **http-signature-0.10.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/JS-Demo/commit/ad02c7350709424606f9242b8b5a7eb8a9d174c0">ad02c7350709424606f9242b8b5a7eb8a9d174c0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected versions (before 1.0.0) of the http-signature package are vulnerable to Timing Attacks.
<p>Publish Date: 2015-01-22
<p>URL: <a href=https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56>WS-2017-0266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/joyent/node-http-signature/pull/36">https://github.com/joyent/node-http-signature/pull/36</a></p>
<p>Release Date: 2017-01-31</p>
<p>Fix Resolution: 1.0.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"http-signature","packageVersion":"0.10.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"zaproxy:0.2.0;request:2.36.0;http-signature:0.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2017-0266","vulnerabilityDetails":"Affected versions (before 1.0.0) of the http-signature package are vulnerable to Timing Attacks.","vulnerabilityUrl":"https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56","cvss3Severity":"low","cvss3Score":"3.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"Required","AV":"Adjacent","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2017-0266 (Low) detected in http-signature-0.10.1.tgz - ## WS-2017-0266 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-signature-0.10.1.tgz</b></p></summary>
<p>Reference implementation of Joyent's HTTP Signature scheme.</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz">https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/zaproxy/node_modules/http-signature/package.json</p>
<p>
Dependency Hierarchy:
- zaproxy-0.2.0.tgz (Root Library)
- request-2.36.0.tgz
- :x: **http-signature-0.10.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/JS-Demo/commit/ad02c7350709424606f9242b8b5a7eb8a9d174c0">ad02c7350709424606f9242b8b5a7eb8a9d174c0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected versions (before 1.0.0) of the http-signature package are vulnerable to Timing Attacks.
<p>Publish Date: 2015-01-22
<p>URL: <a href=https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56>WS-2017-0266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/joyent/node-http-signature/pull/36">https://github.com/joyent/node-http-signature/pull/36</a></p>
<p>Release Date: 2017-01-31</p>
<p>Fix Resolution: 1.0.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"http-signature","packageVersion":"0.10.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"zaproxy:0.2.0;request:2.36.0;http-signature:0.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2017-0266","vulnerabilityDetails":"Affected versions (before 1.0.0) of the http-signature package are vulnerable to Timing Attacks.","vulnerabilityUrl":"https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56","cvss3Severity":"low","cvss3Score":"3.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"Required","AV":"Adjacent","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws low detected in http signature tgz ws low severity vulnerability vulnerable library http signature tgz reference implementation of joyent s http signature scheme library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules zaproxy node modules http signature package json dependency hierarchy zaproxy tgz root library request tgz x http signature tgz vulnerable library found in head commit a href found in base branch master vulnerability details affected versions before of the http signature package are vulnerable to timing attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree zaproxy request http signature isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier ws vulnerabilitydetails affected versions before of the http signature package are vulnerable to timing attacks vulnerabilityurl | 0 |
49,609 | 12,391,433,242 | IssuesEvent | 2020-05-20 12:29:19 | alpheios-project/alpheios-core | https://api.github.com/repos/alpheios-project/alpheios-core | closed | make default max size of popup smaller | components enhancement waiting_build waiting_verification | I think we should make the max default size of the popup smaller than it is, now that we have added the ability for people to configure this (via #263). Currently the default is 1200px which produces a really big popup when definitions or credit text is long.
I think the medium width of 800px would probably work. | 1.0 | make default max size of popup smaller - I think we should make the max default size of the popup smaller than it is, now that we have added the ability for people to configure this (via #263). Currently the default is 1200px which produces a really big popup when definitions or credit text is long.
I think the medium width of 800px would probably work. | non_priority | make default max size of popup smaller i think we should make the max default size of the popup smaller than it is now that we have added the ability for people to configure this via currently the default is which produces a really big popup when definitions or credit text is long i think the medium width of would probably work | 0 |
230,739 | 17,643,987,937 | IssuesEvent | 2021-08-20 01:23:54 | felipebaltazar/FeatureFlag.Management | https://api.github.com/repos/felipebaltazar/FeatureFlag.Management | opened | [Improvement] Update demo app to use a DI container | documentation enhancement | ## Description
We need to update the sample app to use a better approach about manager instance resolution.
## Tasks
- [ ] Implement Tiny IOC on the demo app
- [ ] Remove singletons
- [ ] Update docs | 1.0 | [Improvement] Update demo app to use a DI container - ## Description
We need to update the sample app to use a better approach about manager instance resolution.
## Tasks
- [ ] Implement Tiny IOC on the demo app
- [ ] Remove singletons
- [ ] Update docs | non_priority | update demo app to use a di container description we need to update the sample app to use a better approach about manager instance resolution tasks implement tiny ioc on the demo app remove singletons update docs | 0 |
199,205 | 15,028,150,966 | IssuesEvent | 2021-02-02 02:25:32 | flutter/flutter | https://api.github.com/repos/flutter/flutter | reopened | Gold flake: gold client not ready | a: tests framework passed secondary triage team team: flakes team: infra | Originating from #49956
This passed on a re-run.
https://cirrus-ci.com/task/6635508625309696
```
mp/flutter sdk/packages/flutter/test/cupertino/text_field_test.dart: Cupertino cursor golden (TargetPlatform.macOS)
══╡ EXCEPTION CAUGHT BY FLUTTER TEST FRAMEWORK ╞════════════════════════════════════════════════════
The following _Exception was thrown while running async test code:
Exception: Unexpected Gold tryjobAdd failure.
Tryjob execution for golden file test cupertino.text_field_cursor_test.cupertino_macos.1.png failed
for
a reason unrelated to pixel comparison.
Debug information for Gold:
stdout:
stderr: ERROR: logging before flag.Parse: I0204 01:11:34.738559 64806 auth.go:364] auth.go:364
Read from file /private/tmp/flutter
sdk/bin/cache/pkg/skia_goldens4761/packages/flutter/test/cupertino/serviceAccount.json
Error running command: ''gold client not ready: Gold results fields invalid: Received nil pointer
for GoldResult. At jsonio.go:197 goldclient.go:468 goldclient.go:301 goldclient.go:291
cmd_imgtest.go:338 command.go:835 command.go:919 main.go:42 proc.go:203 asm_amd64.s:1357''
When the exception was thrown, this was the stack:
#0 SkiaGoldClient.tryjobAdd (package:flutter_goldens_client/skia_client.dart:371:9)
<asynchronous suspension>
#1 _AuthorizedFlutterPreSubmitComparator.compare (package:flutter_goldens/flutter_goldens.dart:374:23)
<asynchronous suspension>
#2 MatchesGoldenFile.matchAsync.<anonymous closure> (package:flutter_test/src/_matchers_io.dart:82:57)
<asynchronous suspension>
#3 AutomatedTestWidgetsFlutterBinding.runAsync.<anonymous closure> (package:flutter_test/src/binding.dart:924:22)
#6 AutomatedTestWidgetsFlutterBinding.runAsync (package:flutter_test/src/binding.dart:922:26)
#7 MatchesGoldenFile.matchAsync (package:flutter_test/src/_matchers_io.dart:72:20)
#9 MatchesGoldenFile.matchAsync (package:flutter_test/src/_matchers_io.dart:52:28)
#10 _expect (package:test_api/src/frontend/expect.dart:116:26)
#11 expectLater (package:test_api/src/frontend/expect.dart:75:5)
#12 expectLater (package:flutter_test/src/widget_tester.dart:385:10)
#13 main.<anonymous closure> (file:///private/tmp/flutter%20sdk/packages/flutter/test/cupertino/text_field_test.dart:523:11)
#26 AutomatedTestWidgetsFlutterBinding.runTest.<anonymous closure> (package:flutter_test/src/binding.dart:1102:17)
#28 AutomatedTestWidgetsFlutterBinding.runTest.<anonymous closure> (package:flutter_test/src/binding.dart:1090:35)
(elided 31 frames from class _FakeAsync, dart:async, dart:async-patch, and package:stack_trace)
════════════════════════════════════════════════════════════════════════════════════════════════════
``` | 1.0 | Gold flake: gold client not ready - Originating from #49956
This passed on a re-run.
https://cirrus-ci.com/task/6635508625309696
```
mp/flutter sdk/packages/flutter/test/cupertino/text_field_test.dart: Cupertino cursor golden (TargetPlatform.macOS)
══╡ EXCEPTION CAUGHT BY FLUTTER TEST FRAMEWORK ╞════════════════════════════════════════════════════
The following _Exception was thrown while running async test code:
Exception: Unexpected Gold tryjobAdd failure.
Tryjob execution for golden file test cupertino.text_field_cursor_test.cupertino_macos.1.png failed
for
a reason unrelated to pixel comparison.
Debug information for Gold:
stdout:
stderr: ERROR: logging before flag.Parse: I0204 01:11:34.738559 64806 auth.go:364] auth.go:364
Read from file /private/tmp/flutter
sdk/bin/cache/pkg/skia_goldens4761/packages/flutter/test/cupertino/serviceAccount.json
Error running command: ''gold client not ready: Gold results fields invalid: Received nil pointer
for GoldResult. At jsonio.go:197 goldclient.go:468 goldclient.go:301 goldclient.go:291
cmd_imgtest.go:338 command.go:835 command.go:919 main.go:42 proc.go:203 asm_amd64.s:1357''
When the exception was thrown, this was the stack:
#0 SkiaGoldClient.tryjobAdd (package:flutter_goldens_client/skia_client.dart:371:9)
<asynchronous suspension>
#1 _AuthorizedFlutterPreSubmitComparator.compare (package:flutter_goldens/flutter_goldens.dart:374:23)
<asynchronous suspension>
#2 MatchesGoldenFile.matchAsync.<anonymous closure> (package:flutter_test/src/_matchers_io.dart:82:57)
<asynchronous suspension>
#3 AutomatedTestWidgetsFlutterBinding.runAsync.<anonymous closure> (package:flutter_test/src/binding.dart:924:22)
#6 AutomatedTestWidgetsFlutterBinding.runAsync (package:flutter_test/src/binding.dart:922:26)
#7 MatchesGoldenFile.matchAsync (package:flutter_test/src/_matchers_io.dart:72:20)
#9 MatchesGoldenFile.matchAsync (package:flutter_test/src/_matchers_io.dart:52:28)
#10 _expect (package:test_api/src/frontend/expect.dart:116:26)
#11 expectLater (package:test_api/src/frontend/expect.dart:75:5)
#12 expectLater (package:flutter_test/src/widget_tester.dart:385:10)
#13 main.<anonymous closure> (file:///private/tmp/flutter%20sdk/packages/flutter/test/cupertino/text_field_test.dart:523:11)
#26 AutomatedTestWidgetsFlutterBinding.runTest.<anonymous closure> (package:flutter_test/src/binding.dart:1102:17)
#28 AutomatedTestWidgetsFlutterBinding.runTest.<anonymous closure> (package:flutter_test/src/binding.dart:1090:35)
(elided 31 frames from class _FakeAsync, dart:async, dart:async-patch, and package:stack_trace)
════════════════════════════════════════════════════════════════════════════════════════════════════
``` | non_priority | gold flake gold client not ready originating from this passed on a re run mp flutter sdk packages flutter test cupertino text field test dart cupertino cursor golden targetplatform macos ══╡ exception caught by flutter test framework ╞════════════════════════════════════════════════════ the following exception was thrown while running async test code exception unexpected gold tryjobadd failure tryjob execution for golden file test cupertino text field cursor test cupertino macos png failed for a reason unrelated to pixel comparison debug information for gold stdout stderr error logging before flag parse auth go auth go read from file private tmp flutter sdk bin cache pkg skia packages flutter test cupertino serviceaccount json error running command gold client not ready gold results fields invalid received nil pointer for goldresult at jsonio go goldclient go goldclient go goldclient go cmd imgtest go command go command go main go proc go asm s when the exception was thrown this was the stack skiagoldclient tryjobadd package flutter goldens client skia client dart authorizedflutterpresubmitcomparator compare package flutter goldens flutter goldens dart matchesgoldenfile matchasync package flutter test src matchers io dart automatedtestwidgetsflutterbinding runasync package flutter test src binding dart automatedtestwidgetsflutterbinding runasync package flutter test src binding dart matchesgoldenfile matchasync package flutter test src matchers io dart matchesgoldenfile matchasync package flutter test src matchers io dart expect package test api src frontend expect dart expectlater package test api src frontend expect dart expectlater package flutter test src widget tester dart main file private tmp flutter packages flutter test cupertino text field test dart automatedtestwidgetsflutterbinding runtest package flutter test src binding dart automatedtestwidgetsflutterbinding runtest package flutter test src binding dart elided frames from class fakeasync dart async dart async patch and package stack trace ════════════════════════════════════════════════════════════════════════════════════════════════════ | 0 |
4,782 | 3,449,144,986 | IssuesEvent | 2015-12-16 12:09:52 | debugworkbench/hydragon | https://api.github.com/repos/debugworkbench/hydragon | closed | Consolidate the three tsconfig(s) back to two | build | Currently there's `main-tsconfig.json`, `renderer-tsconfig.json`, and `tsconfig.json`. The third one only exists because VSCode needs it and keeping that one up to date is a bit annoying. So, move `main-tsconfig.json` and `renderer-tsconfig.json` back to the directories they came from and renamed them back to `tsconfig.json` so VSCode can process them. | 1.0 | Consolidate the three tsconfig(s) back to two - Currently there's `main-tsconfig.json`, `renderer-tsconfig.json`, and `tsconfig.json`. The third one only exists because VSCode needs it and keeping that one up to date is a bit annoying. So, move `main-tsconfig.json` and `renderer-tsconfig.json` back to the directories they came from and renamed them back to `tsconfig.json` so VSCode can process them. | non_priority | consolidate the three tsconfig s back to two currently there s main tsconfig json renderer tsconfig json and tsconfig json the third one only exists because vscode needs it and keeping that one up to date is a bit annoying so move main tsconfig json and renderer tsconfig json back to the directories they came from and renamed them back to tsconfig json so vscode can process them | 0 |
31,597 | 11,957,130,654 | IssuesEvent | 2020-04-04 13:19:33 | amorvincitomnia/thehand | https://api.github.com/repos/amorvincitomnia/thehand | closed | CVE-2019-11358 (Medium) detected in jquery-2.2.0.min.js | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.2.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.0/jquery.min.js</a></p>
<p>Path to vulnerable library: /thehand/public/javascripts/jquery-2.2.0.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.0.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amorvincitomnia/thehand/commit/af8b399de41c0369e92cd59114c929911783e069">af8b399de41c0369e92cd59114c929911783e069</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-11358 (Medium) detected in jquery-2.2.0.min.js - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.2.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.0/jquery.min.js</a></p>
<p>Path to vulnerable library: /thehand/public/javascripts/jquery-2.2.0.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.0.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amorvincitomnia/thehand/commit/af8b399de41c0369e92cd59114c929911783e069">af8b399de41c0369e92cd59114c929911783e069</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library thehand public javascripts jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
8,725 | 7,595,332,773 | IssuesEvent | 2018-04-27 04:45:07 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | Links to model documentation missing for Next Gen Web site | bug interface/infrastructure | Currently there is just a blank page | 1.0 | Links to model documentation missing for Next Gen Web site - Currently there is just a blank page | non_priority | links to model documentation missing for next gen web site currently there is just a blank page | 0 |
9,210 | 7,613,843,111 | IssuesEvent | 2018-05-01 23:04:25 | swagger-api/swagger-js | https://api.github.com/repos/swagger-api/swagger-js | closed | Prototype Pollution Vulnerability | P1 cat: security | A security issue exists in one of the dependencies (deep-extends) used by the project.
More information about the problem can be found [here](https://snyk.io/test/npm/swagger-client/3.7.2?severity=high&severity=medium&severity=low).
This fix is important once this vulnerability was detected by nsp and it is breaking a lot of building scripts (that is my case). | True | Prototype Pollution Vulnerability - A security issue exists in one of the dependencies (deep-extends) used by the project.
More information about the problem can be found [here](https://snyk.io/test/npm/swagger-client/3.7.2?severity=high&severity=medium&severity=low).
This fix is important once this vulnerability was detected by nsp and it is breaking a lot of building scripts (that is my case). | non_priority | prototype pollution vulnerability a security issue exists in one of the dependencies deep extends used by the project more information about the problem can be found this fix is important once this vulnerability was detected by nsp and it is breaking a lot of building scripts that is my case | 0 |
53,031 | 13,260,072,691 | IssuesEvent | 2020-08-20 17:38:52 | jkoan/test-navit | https://api.github.com/repos/jkoan/test-navit | closed | osm2navit segfaults (Trac #32) | Incomplete Migration Migrated from Trac cp15 defect/bug tools | Migrated from http://trac.navit-project.org/ticket/32
```json
{
"status": "closed",
"changetime": "2008-08-20T15:43:48",
"_ts": "1219247028000000",
"description": "\n{{{\n(gdb) c\nContinuing.\n\nProgram received signal SIGSEGV, Segmentation fault.\n0x08049cc8 in node_item_get (id=200542) at osm2navit.c:445\n445 int p=count/2;\n(gdb) bt\n#0 0x08049cc8 in node_item_get (id=200542) at osm2navit.c:445\n#1 0x08049f1f in parse_nd (p=0xbf9f12e4 \"<nd ref=\\\"200542\\\" />\\n\") at osm2navit.c:581\n#2 0x0804ac93 in phase1 (in=0xb7e57440, out_ways=0x80e5a00, out_nodes=0x80e5b68) at osm2navit.c:669\n#3 0x0804cdf0 in main (argc=Cannot access memory at address 0x0\n) at osm2navit.c:1656\n}}}\n\n{{{\n> free -m\n total used free shared buffers cached\nMem: 1002 982 20 0 57 61\n-/+ buffers/cache: 862 139\nSwap: 2933 1678 1255\n\n df -h\nSys. de fich. Tail. Occ. Disp. %Occ. Mont\u00e9 sur\n/dev/sda5 8,7G 7,5G 775M 91% /\nudev 502M 96K 502M 1% /dev\n/dev/sda7 16G 11G 4,6G 71% /home\n}}}\n\n\n\n{{{\nPROGRESS1: Processed 106712711 nodes (79310126 out) 1 ways 0 relations 0 tiles\n./nvt_pro.sh: line 6: 4523 Relais bris\u00e9 (pipe) bzcat planet-latest.osm.bz2\n 4524 Erreur de segmentation | ./osm2navit $output\n}}}\n\n\n",
"reporter": "KaZeR",
"cc": "",
"resolution": "fixed",
"time": "2007-11-28T09:03:39",
"component": "tools",
"summary": "osm2navit segfaults",
"priority": "major",
"keywords": "",
"version": "0.0.3",
"milestone": "version 0.1.0",
"owner": "cp15",
"type": "defect/bug",
"severity": ""
}
```
| 1.0 | osm2navit segfaults (Trac #32) - Migrated from http://trac.navit-project.org/ticket/32
```json
{
"status": "closed",
"changetime": "2008-08-20T15:43:48",
"_ts": "1219247028000000",
"description": "\n{{{\n(gdb) c\nContinuing.\n\nProgram received signal SIGSEGV, Segmentation fault.\n0x08049cc8 in node_item_get (id=200542) at osm2navit.c:445\n445 int p=count/2;\n(gdb) bt\n#0 0x08049cc8 in node_item_get (id=200542) at osm2navit.c:445\n#1 0x08049f1f in parse_nd (p=0xbf9f12e4 \"<nd ref=\\\"200542\\\" />\\n\") at osm2navit.c:581\n#2 0x0804ac93 in phase1 (in=0xb7e57440, out_ways=0x80e5a00, out_nodes=0x80e5b68) at osm2navit.c:669\n#3 0x0804cdf0 in main (argc=Cannot access memory at address 0x0\n) at osm2navit.c:1656\n}}}\n\n{{{\n> free -m\n total used free shared buffers cached\nMem: 1002 982 20 0 57 61\n-/+ buffers/cache: 862 139\nSwap: 2933 1678 1255\n\n df -h\nSys. de fich. Tail. Occ. Disp. %Occ. Mont\u00e9 sur\n/dev/sda5 8,7G 7,5G 775M 91% /\nudev 502M 96K 502M 1% /dev\n/dev/sda7 16G 11G 4,6G 71% /home\n}}}\n\n\n\n{{{\nPROGRESS1: Processed 106712711 nodes (79310126 out) 1 ways 0 relations 0 tiles\n./nvt_pro.sh: line 6: 4523 Relais bris\u00e9 (pipe) bzcat planet-latest.osm.bz2\n 4524 Erreur de segmentation | ./osm2navit $output\n}}}\n\n\n",
"reporter": "KaZeR",
"cc": "",
"resolution": "fixed",
"time": "2007-11-28T09:03:39",
"component": "tools",
"summary": "osm2navit segfaults",
"priority": "major",
"keywords": "",
"version": "0.0.3",
"milestone": "version 0.1.0",
"owner": "cp15",
"type": "defect/bug",
"severity": ""
}
```
| non_priority | segfaults trac migrated from json status closed changetime ts description n n gdb c ncontinuing n nprogram received signal sigsegv segmentation fault in node item get id at c int p count n gdb bt n in node item get id at c n in parse nd p n at c n in in out ways out nodes at c n in main argc cannot access memory at address n at c n n n n free m n total used free shared buffers cached nmem n buffers cache nswap n n df h nsys de fich tail occ disp occ mont sur n dev nudev dev n dev home n n n n n processed nodes out ways relations tiles n nvt pro sh line relais bris pipe bzcat planet latest osm n erreur de segmentation output n n n n reporter kazer cc resolution fixed time component tools summary segfaults priority major keywords version milestone version owner type defect bug severity | 0 |
66,101 | 19,984,862,763 | IssuesEvent | 2022-01-30 13:58:50 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | If a web session is closed without signing out, messages received afterwards will be unable to be decrypted | T-Defect | ### Steps to reproduce
I've noticed that if the user closes a web session and loses the session completely (eg it was in an incognito/private window, or the user cleared all cookies), that session will still be considered "active" by Matrix. And there are scenarios where this can cause messages to be indecipherable.
From what I've tested, the following steps will **consistently reproduce this bug** (I added a screenshot of the process below that should help as well):
1. User 1 and User 2 are in a room together
2. User 2 signs out of all sessions, including their current one
3. User 2 signs into Element Web in an incognito/private session, and verifies using their security phrase
4. User 1 and User 2 exchange some messages
5. User 2 closes their incognito session, without signing out of their Element Web session
6. User 1 sends a message to User 2 while they are signed out
7. User 2 signs into Element Desktop and verifies using their security phrase
8. User 1 and User 2 exchange a few messages
9. User 2 signs out of Element Desktop
10. User 1 sends a message to User 2 while they are signed out
11. User 2 signs into Element Desktop and verifies using their security phrase
12. User 2 will be unable to decrypt User 1's last message

Note that nothing User 2 does seems to help, like restoring keys from secure backup, or re-requesting keys for the message, or signing out of the old web session from element desktop and then re-requesting keys for the message. Also note that interestingly, the first time User 2 signs into Element Desktop, they can view the messages they received while they were gone. It's only when User 2 signs in a second time, that they can't decrypt any messages received while gone.
Now I can understand that this is probably very tricky to solve, because there's no way for Matrix to tell the difference between a web session that can be restored (eg you closed the browser but the cookies are still stored) and a web session that is lost (eg you cleared all cookies). However, I still feel like there should be a way for users to decrypt their messages without requesting keys from other "active" sessions. This may be related to https://github.com/vector-im/element-web/issues/3822 and [Matrix Olm unwedging proposal](https://github.com/uhoreg/matrix-doc/blob/olm_unwedging/proposals/1719-olm_unwedging.md).
I am not too familiar with the double-ratchet protocol and olm sessions, but one idea I had: if a user signs into a new (verified) session and there are other "active" sessions that cannot currently respond to key requests, then we fall back to the trust from identity keys (as mentioned in https://github.com/vector-im/element-web/issues/3822). But if one of those other active sessions comes back online, it can **upgrade** the user's current session to full trust with shared ratchet state.
I'm not sure if this "upgrade" step is possible, but even if so, I think we should still consider at least allowing the user to decrypt their messages, even if it means falling back to the trust from identity keys. Consider the following: if User 2 in the scenario above had simply signed out of their web session in the first place, then they would have no issues with decrypting subsequent messages. So in a sense, User 2 is being _punished_ for closing the window instead of signing out of their web session. Considering entire chains of messages can be lost from such a small action (see below), this seems like a bit harsh.

### Outcome
#### What did you expect?
Messages received while offline should be able to be decrypted.
#### What happened instead?
Messages received are impossible to decrypt.
### Operating system
Windows
### Browser information
Ungoogled Chromium Version 96.0.4664.45
### URL for webapp
app.element.io
### Application version
Element version: 1.9.9 Olm version: 3.2.8
### Homeserver
matrix.org
### Will you send logs?
Yes | 1.0 | If a web session is closed without signing out, messages received afterwards will be unable to be decrypted - ### Steps to reproduce
I've noticed that if the user closes a web session and loses the session completely (eg it was in an incognito/private window, or the user cleared all cookies), that session will still be considered "active" by Matrix. And there are scenarios where this can cause messages to be indecipherable.
From what I've tested, the following steps will **consistently reproduce this bug** (I added a screenshot of the process below that should help as well):
1. User 1 and User 2 are in a room together
2. User 2 signs out of all sessions, including their current one
3. User 2 signs into Element Web in an incognito/private session, and verifies using their security phrase
4. User 1 and User 2 exchange some messages
5. User 2 closes their incognito session, without signing out of their Element Web session
6. User 1 sends a message to User 2 while they are signed out
7. User 2 signs into Element Desktop and verifies using their security phrase
8. User 1 and User 2 exchange a few messages
9. User 2 signs out of Element Desktop
10. User 1 sends a message to User 2 while they are signed out
11. User 2 signs into Element Desktop and verifies using their security phrase
12. User 2 will be unable to decrypt User 1's last message

Note that nothing User 2 does seems to help, like restoring keys from secure backup, or re-requesting keys for the message, or signing out of the old web session from element desktop and then re-requesting keys for the message. Also note that interestingly, the first time User 2 signs into Element Desktop, they can view the messages they received while they were gone. It's only when User 2 signs in a second time, that they can't decrypt any messages received while gone.
Now I can understand that this is probably very tricky to solve, because there's no way for Matrix to tell the difference between a web session that can be restored (eg you closed the browser but the cookies are still stored) and a web session that is lost (eg you cleared all cookies). However, I still feel like there should be a way for users to decrypt their messages without requesting keys from other "active" sessions. This may be related to https://github.com/vector-im/element-web/issues/3822 and [Matrix Olm unwedging proposal](https://github.com/uhoreg/matrix-doc/blob/olm_unwedging/proposals/1719-olm_unwedging.md).
I am not too familiar with the double-ratchet protocol and olm sessions, but one idea I had: if a user signs into a new (verified) session and there are other "active" sessions that cannot currently respond to key requests, then we fall back to the trust from identity keys (as mentioned in https://github.com/vector-im/element-web/issues/3822). But if one of those other active sessions comes back online, it can **upgrade** the user's current session to full trust with shared ratchet state.
I'm not sure if this "upgrade" step is possible, but even if so, I think we should still consider at least allowing the user to decrypt their messages, even if it means falling back to the trust from identity keys. Consider the following: if User 2 in the scenario above had simply signed out of their web session in the first place, then they would have no issues with decrypting subsequent messages. So in a sense, User 2 is being _punished_ for closing the window instead of signing out of their web session. Considering entire chains of messages can be lost from such a small action (see below), this seems like a bit harsh.

### Outcome
#### What did you expect?
Messages received while offline should be able to be decrypted.
#### What happened instead?
Messages received are impossible to decrypt.
### Operating system
Windows
### Browser information
Ungoogled Chromium Version 96.0.4664.45
### URL for webapp
app.element.io
### Application version
Element version: 1.9.9 Olm version: 3.2.8
### Homeserver
matrix.org
### Will you send logs?
Yes | non_priority | if a web session is closed without signing out messages received afterwards will be unable to be decrypted steps to reproduce i ve noticed that if the user closes a web session and loses the session completely eg it was in an incognito private window or the user cleared all cookies that session will still be considered active by matrix and there are scenarios where this can cause messages to be indecipherable from what i ve tested the following steps will consistently reproduce this bug i added a screenshot of the process below that should help as well user and user are in a room together user signs out of all sessions including their current one user signs into element web in an incognito private session and verifies using their security phrase user and user exchange some messages user closes their incognito session without signing out of their element web session user sends a message to user while they are signed out user signs into element desktop and verifies using their security phrase user and user exchange a few messages user signs out of element desktop user sends a message to user while they are signed out user signs into element desktop and verifies using their security phrase user will be unable to decrypt user s last message note that nothing user does seems to help like restoring keys from secure backup or re requesting keys for the message or signing out of the old web session from element desktop and then re requesting keys for the message also note that interestingly the first time user signs into element desktop they can view the messages they received while they were gone it s only when user signs in a second time that they can t decrypt any messages received while gone now i can understand that this is probably very tricky to solve because there s no way for matrix to tell the difference between a web session that can be restored eg you closed the browser but the cookies are still stored and a web session that is lost eg you cleared all cookies however i still feel like there should be a way for users to decrypt their messages without requesting keys from other active sessions this may be related to and i am not too familiar with the double ratchet protocol and olm sessions but one idea i had if a user signs into a new verified session and there are other active sessions that cannot currently respond to key requests then we fall back to the trust from identity keys as mentioned in but if one of those other active sessions comes back online it can upgrade the user s current session to full trust with shared ratchet state i m not sure if this upgrade step is possible but even if so i think we should still consider at least allowing the user to decrypt their messages even if it means falling back to the trust from identity keys consider the following if user in the scenario above had simply signed out of their web session in the first place then they would have no issues with decrypting subsequent messages so in a sense user is being punished for closing the window instead of signing out of their web session considering entire chains of messages can be lost from such a small action see below this seems like a bit harsh outcome what did you expect messages received while offline should be able to be decrypted what happened instead messages received are impossible to decrypt operating system windows browser information ungoogled chromium version url for webapp app element io application version element version olm version homeserver matrix org will you send logs yes | 0 |
97,946 | 12,270,433,819 | IssuesEvent | 2020-05-07 15:29:52 | Opentrons/opentrons | https://api.github.com/repos/Opentrons/opentrons | opened | EPIC - PD: TC State Step Form | :spider: SPDDRS Epic protocol designer | For reference:
Thermocycler form field values:
```
{|
thermocyclerFormType: 'thermocyclerState' | 'thermocyclerProfile',
moduleId: string,
blockIsActive: boolean,
blockTargetTemp: number | null,
lidIsActive: boolean,
lidTargetTemp: number | null,
lidOpen: boolean | null // if false, closed. If null, it's the initial unknown state
// TODO later we will add the TC Profile fields here
|}
```
---
Module state type (`ThermocyclerModuleState` in `RobotState`)
```
{|
type: TEMPERATURE_MODULE_TYPE,
blockIsActive: boolean,
blockTargetTemp: number | null,
lidIsActive: boolean,
lidTargetTemp: number | null,
lidOpen = boolean | null
|}
```
The initial module state (`ThermocyclerModuleState` in `RobotState`) is:
```
{
type: TEMPERATURE_MODULE_TYPE,
blockIsActive = false,
blockTargetTemp = null,
lidIsActive = false,
lidTargetTemp = null,
lidOpen = false // NOTE: we may make this initally `null` later
}
``` | 1.0 | EPIC - PD: TC State Step Form - For reference:
Thermocycler form field values:
```
{|
thermocyclerFormType: 'thermocyclerState' | 'thermocyclerProfile',
moduleId: string,
blockIsActive: boolean,
blockTargetTemp: number | null,
lidIsActive: boolean,
lidTargetTemp: number | null,
lidOpen: boolean | null // if false, closed. If null, it's the initial unknown state
// TODO later we will add the TC Profile fields here
|}
```
---
Module state type (`ThermocyclerModuleState` in `RobotState`)
```
{|
type: TEMPERATURE_MODULE_TYPE,
blockIsActive: boolean,
blockTargetTemp: number | null,
lidIsActive: boolean,
lidTargetTemp: number | null,
lidOpen = boolean | null
|}
```
The initial module state (`ThermocyclerModuleState` in `RobotState`) is:
```
{
type: TEMPERATURE_MODULE_TYPE,
blockIsActive = false,
blockTargetTemp = null,
lidIsActive = false,
lidTargetTemp = null,
lidOpen = false // NOTE: we may make this initally `null` later
}
``` | non_priority | epic pd tc state step form for reference thermocycler form field values thermocyclerformtype thermocyclerstate thermocyclerprofile moduleid string blockisactive boolean blocktargettemp number null lidisactive boolean lidtargettemp number null lidopen boolean null if false closed if null it s the initial unknown state todo later we will add the tc profile fields here module state type thermocyclermodulestate in robotstate type temperature module type blockisactive boolean blocktargettemp number null lidisactive boolean lidtargettemp number null lidopen boolean null the initial module state thermocyclermodulestate in robotstate is type temperature module type blockisactive false blocktargettemp null lidisactive false lidtargettemp null lidopen false note we may make this initally null later | 0 |
66,308 | 12,745,725,455 | IssuesEvent | 2020-06-26 14:43:59 | harshkumarkhatri/gymaale_pycharm | https://api.github.com/repos/harshkumarkhatri/gymaale_pycharm | opened | Notification system | StudentCode-in | The project currently does not a section where the users can get a notification about new gyms or trainers being added or new blogs being published.
Your task is to add a notification section where all the notifications will be visible to the user and will change color whenever a new notification will be there. | 1.0 | Notification system - The project currently does not a section where the users can get a notification about new gyms or trainers being added or new blogs being published.
Your task is to add a notification section where all the notifications will be visible to the user and will change color whenever a new notification will be there. | non_priority | notification system the project currently does not a section where the users can get a notification about new gyms or trainers being added or new blogs being published your task is to add a notification section where all the notifications will be visible to the user and will change color whenever a new notification will be there | 0 |
90,220 | 10,675,558,548 | IssuesEvent | 2019-10-21 11:58:48 | NSInductus/CC_Proyecto | https://api.github.com/repos/NSInductus/CC_Proyecto | closed | Documentar los pasos realizados durante el hito 0 | documentation | Añadir como he configurado github, la seguridad extra, etc... | 1.0 | Documentar los pasos realizados durante el hito 0 - Añadir como he configurado github, la seguridad extra, etc... | non_priority | documentar los pasos realizados durante el hito añadir como he configurado github la seguridad extra etc | 0 |
156,677 | 24,625,061,467 | IssuesEvent | 2022-10-16 12:12:31 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | Query: compilation error for complex query with group by and correlated subquery | closed-by-design area-query | query:
```cs
var query = ctx.Parents
.Select(p => new
{
ParentId = p.Id,
Bars = p.Children
.Select(c => c.Group)
.GroupBy(g => g)
.Select(g => new
{
Group = g.Key,
GroupCount = g.Count()
})
}).ToList();
```
throws:
```
Unhandled Exception: System.ArgumentException: Expression of type 'System.Collections.Generic.IEnumerable`1[Microsoft.EntityFrameworkCore.Storage.ValueBuffer]' cannot be used for parameter of type 'Microsoft.EntityFrameworkCore.Query.Internal.ShaperCommandContext' of method 'System.Collections.Generic.IEnumerable`1[Microsoft.EntityFrameworkCore.Storage.ValueBuffer] _ShapedQuery[ValueBuffer](Microsoft.EntityFrameworkCore.Query.QueryContext, Microsoft.EntityFrameworkCore.Query.Internal.ShaperCommandContext, Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.Internal.IShaper`1[Microsoft.EntityFrameworkCore.Storage.ValueBuffer])'
Parameter name: arg1
at System.Dynamic.Utils.ExpressionUtils.ValidateOneArgument(MethodBase method, ExpressionType nodeKind, Expression arguments, ParameterInfo pi, String methodParamName, String argumentParamName, Int32 index)
at System.Linq.Expressions.Expression.Call(MethodInfo method, Expression arg0, Expression arg1, Expression arg2)
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.GroupByAggregateTranslatingExpressionVisitor.CanTranslate(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 459
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.GroupByAggregateTranslatingExpressionVisitor.Translate(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 313
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.Visit(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 161
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 1166
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 1130
at Remotion.Linq.QueryModelVisitorBase.VisitQueryModel(QueryModel queryModel)
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 758
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 292
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.ProjectionExpressionVisitor.VisitSubQuery(SubQueryExpression expression) in D:\git\EntityFrameworkCore\src\EFCore\Query\ExpressionVisitors\ProjectionExpressionVisitor.cs:line 192
at System.Linq.Expressions.ExpressionVisitor.Visit(Expression node)
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.Visit(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 215
at System.Linq.Expressions.ExpressionVisitor.VisitAndConvert[T](ReadOnlyCollection`1 nodes, String callerName)
at Remotion.Linq.Parsing.RelinqExpressionVisitor.VisitNew(NewExpression expression)
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.VisitNew(NewExpression newExpression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 123
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.Visit(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 187
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 1166
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 1130
at Remotion.Linq.QueryModelVisitorBase.VisitQueryModel(QueryModel queryModel)
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 758
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 292
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.CreateQueryExecutor[TResult](QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 175
at Microsoft.EntityFrameworkCore.Storage.Database.CompileQuery[TResult](QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Storage\Database.cs:line 70
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.CompileQueryCore[TResult](Expression query, IQueryModelGenerator queryModelGenerator, IDatabase database, IDiagnosticsLogger`1 logger, Type contextType) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\QueryCompiler.cs:line 151
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.<>c__DisplayClass13_0`1.<Execute>b__0() in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\QueryCompiler.cs:line 91
at Microsoft.EntityFrameworkCore.Query.Internal.CompiledQueryCache.GetOrAddQueryCore[TFunc](Object cacheKey, Func`1 compiler) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\CompiledQueryCache.cs:line 69
at Microsoft.EntityFrameworkCore.Query.Internal.CompiledQueryCache.GetOrAddQuery[TResult](Object cacheKey, Func`1 compiler) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\CompiledQueryCache.cs:line 44
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.Execute[TResult](Expression query) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\QueryCompiler.cs:line 87
at Microsoft.EntityFrameworkCore.Query.Internal.EntityQueryProvider.Execute[TResult](Expression expression) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\EntityQueryProvider.cs:line 62
at Remotion.Linq.QueryableBase`1.GetEnumerator()
at System.Collections.Generic.List`1.AddEnumerable(IEnumerable`1 enumerable)
at System.Linq.Enumerable.ToList[TSource](IEnumerable`1 source)
``` | 1.0 | Query: compilation error for complex query with group by and correlated subquery - query:
```cs
var query = ctx.Parents
.Select(p => new
{
ParentId = p.Id,
Bars = p.Children
.Select(c => c.Group)
.GroupBy(g => g)
.Select(g => new
{
Group = g.Key,
GroupCount = g.Count()
})
}).ToList();
```
throws:
```
Unhandled Exception: System.ArgumentException: Expression of type 'System.Collections.Generic.IEnumerable`1[Microsoft.EntityFrameworkCore.Storage.ValueBuffer]' cannot be used for parameter of type 'Microsoft.EntityFrameworkCore.Query.Internal.ShaperCommandContext' of method 'System.Collections.Generic.IEnumerable`1[Microsoft.EntityFrameworkCore.Storage.ValueBuffer] _ShapedQuery[ValueBuffer](Microsoft.EntityFrameworkCore.Query.QueryContext, Microsoft.EntityFrameworkCore.Query.Internal.ShaperCommandContext, Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.Internal.IShaper`1[Microsoft.EntityFrameworkCore.Storage.ValueBuffer])'
Parameter name: arg1
at System.Dynamic.Utils.ExpressionUtils.ValidateOneArgument(MethodBase method, ExpressionType nodeKind, Expression arguments, ParameterInfo pi, String methodParamName, String argumentParamName, Int32 index)
at System.Linq.Expressions.Expression.Call(MethodInfo method, Expression arg0, Expression arg1, Expression arg2)
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.GroupByAggregateTranslatingExpressionVisitor.CanTranslate(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 459
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.GroupByAggregateTranslatingExpressionVisitor.Translate(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 313
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.Visit(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 161
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 1166
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 1130
at Remotion.Linq.QueryModelVisitorBase.VisitQueryModel(QueryModel queryModel)
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 758
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 292
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.ProjectionExpressionVisitor.VisitSubQuery(SubQueryExpression expression) in D:\git\EntityFrameworkCore\src\EFCore\Query\ExpressionVisitors\ProjectionExpressionVisitor.cs:line 192
at System.Linq.Expressions.ExpressionVisitor.Visit(Expression node)
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.Visit(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 215
at System.Linq.Expressions.ExpressionVisitor.VisitAndConvert[T](ReadOnlyCollection`1 nodes, String callerName)
at Remotion.Linq.Parsing.RelinqExpressionVisitor.VisitNew(NewExpression expression)
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.VisitNew(NewExpression newExpression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 123
at Microsoft.EntityFrameworkCore.Query.ExpressionVisitors.RelationalProjectionExpressionVisitor.Visit(Expression expression) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\ExpressionVisitors\RelationalProjectionExpressionVisitor.cs:line 187
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 1166
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitSelectClause(SelectClause selectClause, QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 1130
at Remotion.Linq.QueryModelVisitorBase.VisitQueryModel(QueryModel queryModel)
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 758
at Microsoft.EntityFrameworkCore.Query.RelationalQueryModelVisitor.VisitQueryModel(QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore.Relational\Query\RelationalQueryModelVisitor.cs:line 292
at Microsoft.EntityFrameworkCore.Query.EntityQueryModelVisitor.CreateQueryExecutor[TResult](QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Query\EntityQueryModelVisitor.cs:line 175
at Microsoft.EntityFrameworkCore.Storage.Database.CompileQuery[TResult](QueryModel queryModel) in D:\git\EntityFrameworkCore\src\EFCore\Storage\Database.cs:line 70
--- End of stack trace from previous location where exception was thrown ---
at System.Runtime.ExceptionServices.ExceptionDispatchInfo.Throw()
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.CompileQueryCore[TResult](Expression query, IQueryModelGenerator queryModelGenerator, IDatabase database, IDiagnosticsLogger`1 logger, Type contextType) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\QueryCompiler.cs:line 151
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.<>c__DisplayClass13_0`1.<Execute>b__0() in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\QueryCompiler.cs:line 91
at Microsoft.EntityFrameworkCore.Query.Internal.CompiledQueryCache.GetOrAddQueryCore[TFunc](Object cacheKey, Func`1 compiler) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\CompiledQueryCache.cs:line 69
at Microsoft.EntityFrameworkCore.Query.Internal.CompiledQueryCache.GetOrAddQuery[TResult](Object cacheKey, Func`1 compiler) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\CompiledQueryCache.cs:line 44
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.Execute[TResult](Expression query) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\QueryCompiler.cs:line 87
at Microsoft.EntityFrameworkCore.Query.Internal.EntityQueryProvider.Execute[TResult](Expression expression) in D:\git\EntityFrameworkCore\src\EFCore\Query\Internal\EntityQueryProvider.cs:line 62
at Remotion.Linq.QueryableBase`1.GetEnumerator()
at System.Collections.Generic.List`1.AddEnumerable(IEnumerable`1 enumerable)
at System.Linq.Enumerable.ToList[TSource](IEnumerable`1 source)
``` | non_priority | query compilation error for complex query with group by and correlated subquery query cs var query ctx parents select p new parentid p id bars p children select c c group groupby g g select g new group g key groupcount g count tolist throws unhandled exception system argumentexception expression of type system collections generic ienumerable cannot be used for parameter of type microsoft entityframeworkcore query internal shapercommandcontext of method system collections generic ienumerable shapedquery microsoft entityframeworkcore query querycontext microsoft entityframeworkcore query internal shapercommandcontext microsoft entityframeworkcore query expressionvisitors internal ishaper parameter name at system dynamic utils expressionutils validateoneargument methodbase method expressiontype nodekind expression arguments parameterinfo pi string methodparamname string argumentparamname index at system linq expressions expression call methodinfo method expression expression expression at microsoft entityframeworkcore query expressionvisitors relationalprojectionexpressionvisitor groupbyaggregatetranslatingexpressionvisitor cantranslate expression expression in d git entityframeworkcore src efcore relational query expressionvisitors relationalprojectionexpressionvisitor cs line at microsoft entityframeworkcore query expressionvisitors relationalprojectionexpressionvisitor groupbyaggregatetranslatingexpressionvisitor translate expression expression in d git entityframeworkcore src efcore relational query expressionvisitors relationalprojectionexpressionvisitor cs line at microsoft entityframeworkcore query expressionvisitors relationalprojectionexpressionvisitor visit expression expression in d git entityframeworkcore src efcore relational query expressionvisitors relationalprojectionexpressionvisitor cs line at microsoft entityframeworkcore query entityquerymodelvisitor visitselectclause selectclause selectclause querymodel querymodel in d git entityframeworkcore src efcore query entityquerymodelvisitor cs line at microsoft entityframeworkcore query relationalquerymodelvisitor visitselectclause selectclause selectclause querymodel querymodel in d git entityframeworkcore src efcore relational query relationalquerymodelvisitor cs line at remotion linq querymodelvisitorbase visitquerymodel querymodel querymodel at microsoft entityframeworkcore query entityquerymodelvisitor visitquerymodel querymodel querymodel in d git entityframeworkcore src efcore query entityquerymodelvisitor cs line at microsoft entityframeworkcore query relationalquerymodelvisitor visitquerymodel querymodel querymodel in d git entityframeworkcore src efcore relational query relationalquerymodelvisitor cs line at microsoft entityframeworkcore query expressionvisitors projectionexpressionvisitor visitsubquery subqueryexpression expression in d git entityframeworkcore src efcore query expressionvisitors projectionexpressionvisitor cs line at system linq expressions expressionvisitor visit expression node at microsoft entityframeworkcore query expressionvisitors relationalprojectionexpressionvisitor visit expression expression in d git entityframeworkcore src efcore relational query expressionvisitors relationalprojectionexpressionvisitor cs line at system linq expressions expressionvisitor visitandconvert readonlycollection nodes string callername at remotion linq parsing relinqexpressionvisitor visitnew newexpression expression at microsoft entityframeworkcore query expressionvisitors relationalprojectionexpressionvisitor visitnew newexpression newexpression in d git entityframeworkcore src efcore relational query expressionvisitors relationalprojectionexpressionvisitor cs line at microsoft entityframeworkcore query expressionvisitors relationalprojectionexpressionvisitor visit expression expression in d git entityframeworkcore src efcore relational query expressionvisitors relationalprojectionexpressionvisitor cs line at microsoft entityframeworkcore query entityquerymodelvisitor visitselectclause selectclause selectclause querymodel querymodel in d git entityframeworkcore src efcore query entityquerymodelvisitor cs line at microsoft entityframeworkcore query relationalquerymodelvisitor visitselectclause selectclause selectclause querymodel querymodel in d git entityframeworkcore src efcore relational query relationalquerymodelvisitor cs line at remotion linq querymodelvisitorbase visitquerymodel querymodel querymodel at microsoft entityframeworkcore query entityquerymodelvisitor visitquerymodel querymodel querymodel in d git entityframeworkcore src efcore query entityquerymodelvisitor cs line at microsoft entityframeworkcore query relationalquerymodelvisitor visitquerymodel querymodel querymodel in d git entityframeworkcore src efcore relational query relationalquerymodelvisitor cs line at microsoft entityframeworkcore query entityquerymodelvisitor createqueryexecutor querymodel querymodel in d git entityframeworkcore src efcore query entityquerymodelvisitor cs line at microsoft entityframeworkcore storage database compilequery querymodel querymodel in d git entityframeworkcore src efcore storage database cs line end of stack trace from previous location where exception was thrown at system runtime exceptionservices exceptiondispatchinfo throw at microsoft entityframeworkcore query internal querycompiler compilequerycore expression query iquerymodelgenerator querymodelgenerator idatabase database idiagnosticslogger logger type contexttype in d git entityframeworkcore src efcore query internal querycompiler cs line at microsoft entityframeworkcore query internal querycompiler c b in d git entityframeworkcore src efcore query internal querycompiler cs line at microsoft entityframeworkcore query internal compiledquerycache getoraddquerycore object cachekey func compiler in d git entityframeworkcore src efcore query internal compiledquerycache cs line at microsoft entityframeworkcore query internal compiledquerycache getoraddquery object cachekey func compiler in d git entityframeworkcore src efcore query internal compiledquerycache cs line at microsoft entityframeworkcore query internal querycompiler execute expression query in d git entityframeworkcore src efcore query internal querycompiler cs line at microsoft entityframeworkcore query internal entityqueryprovider execute expression expression in d git entityframeworkcore src efcore query internal entityqueryprovider cs line at remotion linq queryablebase getenumerator at system collections generic list addenumerable ienumerable enumerable at system linq enumerable tolist ienumerable source | 0 |
371,366 | 25,949,324,363 | IssuesEvent | 2022-12-17 11:22:58 | fbourgeois24/GesMat-bugtracker | https://api.github.com/repos/fbourgeois24/GesMat-bugtracker | closed | Créer un wiki à la place du readme | documentation | - [x] Rajouter dans la mise à jour de renvoyer 'error_code' <int> | 1.0 | Créer un wiki à la place du readme - - [x] Rajouter dans la mise à jour de renvoyer 'error_code' <int> | non_priority | créer un wiki à la place du readme rajouter dans la mise à jour de renvoyer error code | 0 |
53,163 | 13,789,434,718 | IssuesEvent | 2020-10-09 08:52:33 | anyulled/mws-restaurant-stage-1 | https://api.github.com/repos/anyulled/mws-restaurant-stage-1 | opened | CVE-2019-20149 (High) detected in kind-of-6.0.2.tgz | security vulnerability | ## CVE-2019-20149 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kind-of-6.0.2.tgz</b></p></summary>
<p>Get the native type of a value.</p>
<p>Library home page: <a href="https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz">https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz</a></p>
<p>Path to dependency file: mws-restaurant-stage-1/package.json</p>
<p>Path to vulnerable library: mws-restaurant-stage-1/node_modules/micromatch/node_modules/kind-of/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.24.4.tgz (Root Library)
- micromatch-2.3.11.tgz
- braces-1.8.5.tgz
- expand-range-1.8.2.tgz
- fill-range-2.2.4.tgz
- randomatic-3.0.0.tgz
- :x: **kind-of-6.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/anyulled/mws-restaurant-stage-1/commit/302bbf347526c27d54b90c73c0a13f471ed35ab0">302bbf347526c27d54b90c73c0a13f471ed35ab0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ctorName in index.js in kind-of v6.0.2 allows external user input to overwrite certain internal attributes via a conflicting name, as demonstrated by 'constructor': {'name':'Symbol'}. Hence, a crafted payload can overwrite this builtin attribute to manipulate the type detection result.
<p>Publish Date: 2019-12-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20149>CVE-2019-20149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149</a></p>
<p>Release Date: 2019-12-30</p>
<p>Fix Resolution: 6.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-20149 (High) detected in kind-of-6.0.2.tgz - ## CVE-2019-20149 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kind-of-6.0.2.tgz</b></p></summary>
<p>Get the native type of a value.</p>
<p>Library home page: <a href="https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz">https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz</a></p>
<p>Path to dependency file: mws-restaurant-stage-1/package.json</p>
<p>Path to vulnerable library: mws-restaurant-stage-1/node_modules/micromatch/node_modules/kind-of/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.24.4.tgz (Root Library)
- micromatch-2.3.11.tgz
- braces-1.8.5.tgz
- expand-range-1.8.2.tgz
- fill-range-2.2.4.tgz
- randomatic-3.0.0.tgz
- :x: **kind-of-6.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/anyulled/mws-restaurant-stage-1/commit/302bbf347526c27d54b90c73c0a13f471ed35ab0">302bbf347526c27d54b90c73c0a13f471ed35ab0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ctorName in index.js in kind-of v6.0.2 allows external user input to overwrite certain internal attributes via a conflicting name, as demonstrated by 'constructor': {'name':'Symbol'}. Hence, a crafted payload can overwrite this builtin attribute to manipulate the type detection result.
<p>Publish Date: 2019-12-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20149>CVE-2019-20149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149</a></p>
<p>Release Date: 2019-12-30</p>
<p>Fix Resolution: 6.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in kind of tgz cve high severity vulnerability vulnerable library kind of tgz get the native type of a value library home page a href path to dependency file mws restaurant stage package json path to vulnerable library mws restaurant stage node modules micromatch node modules kind of package json dependency hierarchy browser sync tgz root library micromatch tgz braces tgz expand range tgz fill range tgz randomatic tgz x kind of tgz vulnerable library found in head commit a href found in base branch master vulnerability details ctorname in index js in kind of allows external user input to overwrite certain internal attributes via a conflicting name as demonstrated by constructor name symbol hence a crafted payload can overwrite this builtin attribute to manipulate the type detection result publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
119,727 | 10,062,228,625 | IssuesEvent | 2019-07-23 00:11:31 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | K8s metadata - behavior of MaxRancherVersion and MinRancherVersion | [zube]: To Test kind/bug-qa team/ca | Bug
set the metadata such that for k8s version `v1.13.7-rancher1-1`:
```
"v1.13": {
MinRancherVersion: "2.3.3",
MaxRancherVersion: "2.3.3",
MaxRKEVersion: "0.2.2",
},
```
Expected Results:
We expected to see the k8s `v1.13.7-rancher1-1` shows only in Rancher `rancher:v2.3.3`
Results:
in fact `v1.13.7-rancher1-1` shows in other Rancher versions:
- rancher:v2.3.4
- rancher:v2.3.2
- rancher:v2.4.0
Question:
How to configure to make `v1.13.7-rancher1-1` shows only in Rancher `rancher:v2.3.3`?
Is it possible?
More Info:
- tested with the following config, but still not work as expected
```
"v1.13": {
MaxRancherVersion: "2.3.3",
MaxRKEVersion: "0.2.2",
},
"v1.13.7-rancher1-1": {
MinRancherVersion: "2.3.3",
MaxRKEVersion: "0.2.2",
},
```
New finding:
- it turns out it will not work if setting the min and max the same value
| 1.0 | K8s metadata - behavior of MaxRancherVersion and MinRancherVersion - Bug
set the metadata such that for k8s version `v1.13.7-rancher1-1`:
```
"v1.13": {
MinRancherVersion: "2.3.3",
MaxRancherVersion: "2.3.3",
MaxRKEVersion: "0.2.2",
},
```
Expected Results:
We expected to see the k8s `v1.13.7-rancher1-1` shows only in Rancher `rancher:v2.3.3`
Results:
in fact `v1.13.7-rancher1-1` shows in other Rancher versions:
- rancher:v2.3.4
- rancher:v2.3.2
- rancher:v2.4.0
Question:
How to configure to make `v1.13.7-rancher1-1` shows only in Rancher `rancher:v2.3.3`?
Is it possible?
More Info:
- tested with the following config, but still not work as expected
```
"v1.13": {
MaxRancherVersion: "2.3.3",
MaxRKEVersion: "0.2.2",
},
"v1.13.7-rancher1-1": {
MinRancherVersion: "2.3.3",
MaxRKEVersion: "0.2.2",
},
```
New finding:
- it turns out it will not work if setting the min and max the same value
| non_priority | metadata behavior of maxrancherversion and minrancherversion bug set the metadata such that for version minrancherversion maxrancherversion maxrkeversion expected results we expected to see the shows only in rancher rancher results in fact shows in other rancher versions rancher rancher rancher question how to configure to make shows only in rancher rancher is it possible more info tested with the following config but still not work as expected maxrancherversion maxrkeversion minrancherversion maxrkeversion new finding it turns out it will not work if setting the min and max the same value | 0 |
289,268 | 31,931,326,921 | IssuesEvent | 2023-09-19 07:38:24 | Trinadh465/linux-4.1.15_CVE-2023-4128 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2023-4128 | opened | CVE-2016-10154 (Medium) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2016-10154 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2023-4128/commit/0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8">0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/cifs/smbencrypt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The smbhash function in fs/cifs/smbencrypt.c in the Linux kernel 4.9.x before 4.9.1 interacts incorrectly with the CONFIG_VMAP_STACK option, which allows local users to cause a denial of service (system crash or memory corruption) or possibly have unspecified other impact by leveraging use of more than one virtual page for a scatterlist.
<p>Publish Date: 2017-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10154>CVE-2016-10154</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-10154">https://nvd.nist.gov/vuln/detail/CVE-2016-10154</a></p>
<p>Release Date: 2017-02-06</p>
<p>Fix Resolution: 4.9.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-10154 (Medium) detected in linuxlinux-4.6 - ## CVE-2016-10154 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2023-4128/commit/0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8">0c6c8d8c809f697cd5fc581c6c08e9ad646c55a8</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/cifs/smbencrypt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The smbhash function in fs/cifs/smbencrypt.c in the Linux kernel 4.9.x before 4.9.1 interacts incorrectly with the CONFIG_VMAP_STACK option, which allows local users to cause a denial of service (system crash or memory corruption) or possibly have unspecified other impact by leveraging use of more than one virtual page for a scatterlist.
<p>Publish Date: 2017-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10154>CVE-2016-10154</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-10154">https://nvd.nist.gov/vuln/detail/CVE-2016-10154</a></p>
<p>Release Date: 2017-02-06</p>
<p>Fix Resolution: 4.9.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files fs cifs smbencrypt c vulnerability details the smbhash function in fs cifs smbencrypt c in the linux kernel x before interacts incorrectly with the config vmap stack option which allows local users to cause a denial of service system crash or memory corruption or possibly have unspecified other impact by leveraging use of more than one virtual page for a scatterlist publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
159,543 | 12,479,485,927 | IssuesEvent | 2020-05-29 18:21:36 | jpmorganchase/nbcelltests | https://api.github.com/repos/jpmorganchase/nbcelltests | opened | Handling of newlines, %cell (and probably more) within cell and/or test source is likely to be broken | cell tests | Referring to nbcelltests/test.py. Tricky to say what all issues are as code is built up in a string, but it _looks_ suspicious in places. Should be straightforward to write tests for various cases and then fix. Or could just wait until re-doing that code. | 1.0 | Handling of newlines, %cell (and probably more) within cell and/or test source is likely to be broken - Referring to nbcelltests/test.py. Tricky to say what all issues are as code is built up in a string, but it _looks_ suspicious in places. Should be straightforward to write tests for various cases and then fix. Or could just wait until re-doing that code. | non_priority | handling of newlines cell and probably more within cell and or test source is likely to be broken referring to nbcelltests test py tricky to say what all issues are as code is built up in a string but it looks suspicious in places should be straightforward to write tests for various cases and then fix or could just wait until re doing that code | 0 |
18,712 | 3,398,860,789 | IssuesEvent | 2015-12-02 07:37:53 | Roy2014Kimi/JI3U47XFP7X25PCEAD3LMVXQ | https://api.github.com/repos/Roy2014Kimi/JI3U47XFP7X25PCEAD3LMVXQ | closed | kfoX3a1C9bh+eDp29qY1/f+8uGfuG+9ioAUh7cqJVg1KvpL16RymJz7RhGcU2Mw0DLCJPrCzbfesmkql3Pt3N6lbHJW3K534iDe0J3jUry/FRWTtHgriD21TSOjd5h1IGyurKUaIrGb/iNk3Jxa0PQMgX8GFkCx5RueLJXbiWFw= | design | jr5ajgGZeNNuy+NJysHwH9THbOL4mXDjnxHkli/9seejiaxqZt0c2OPem9Zd23VD+wBH9n7C8rxuLnR7Uv9vZ2nWriUzMzJLx0RRNWebvm8OLzpRlTG8O4URAdPVyLguV4jSM63k9M1cCJB6tozO5leI0jOt5PTNXAiQeraMzuZXiNIzreT0zVwIkHq2jM7mV4jSM63k9M1cCJB6tozO5vN4hHx8DzfSl2Ue7uCoCX8ogY3cAaAh/BiRvwEgWGkxNTOLpmAXG0HmHumGWRL5XB7Sj3m43kzFzxB9H1uEvmXiL1n7RkT15jPsrXnuV3g/CUkzZDOLm0T3z1DXqoK6p38Um6QpdChkwRXOyE2VTWu4AdCZrbWTd+ndua7AsoTsfudg3SfainhQLm33bhdS48uVE0jK/+ziVhTVvw1ie+EbT1USPTJZW77RaZvjfO7GHs4R5xapcY1NCHjWaY+IH0X0xyiEOvMEI53gN1snzIoW/8Q38vhdBH9G9f796FnTnipIKglsnypdgNz7fdNJd6PCNG8SSxH6KEfkJCYIhPHHxfcEQ3n+DWj3yTGNckCFuAHQma21k3fp3bmuwLKE7PIq4UdcVV+pkITDIRmUiJbLlRNIyv/s4lYU1b8NYnvhoA2berl1plLZUXB+qYmhhe0xee1wkvaq4rWi12XEEo1F9McohDrzBCOd4DdbJ8yKK2lAMXrxrFOZo/SRvEGJhJ4qSCoJbJ8qXYDc+33TSXdsfR4UifKLg2KXZR6hCMGgoYyQ7XKs1+0b5ponKvfuaKyD+K961sZQzR8O9nqOtfY4AfKD3yK12BznUGphgSnsjPMibvZhJ53CWah3xlWAqvOLNtFwHOl3SLWdOVGyfU7rKZDQ1YdQqL4qMnSdt0EYuAHQma21k3fp3bmuwLKE7H7nYN0n2op4UC5t924XUuPLlRNIyv/s4lYU1b8NYnvhAk73IhNzE/GR4fpN/tU+95BRxo7ou9FOgEWlOAispzK4AdCZrbWTd+ndua7AsoTswNWGt+mPfLR5K+G4RAuqT8uVE0jK/+ziVhTVvw1ie+HYVoGb/3QjYF+PZOH7PPyZEAx6ug3RktXZrzi1ruKRMqJlZJheYZPXB/9eq7F3jR7JlusN5zJ6qbVvvWxNSSnCw4JJVS4vUgmjb3ZrTxpoPA== | 1.0 | kfoX3a1C9bh+eDp29qY1/f+8uGfuG+9ioAUh7cqJVg1KvpL16RymJz7RhGcU2Mw0DLCJPrCzbfesmkql3Pt3N6lbHJW3K534iDe0J3jUry/FRWTtHgriD21TSOjd5h1IGyurKUaIrGb/iNk3Jxa0PQMgX8GFkCx5RueLJXbiWFw= - jr5ajgGZeNNuy+NJysHwH9THbOL4mXDjnxHkli/9seejiaxqZt0c2OPem9Zd23VD+wBH9n7C8rxuLnR7Uv9vZ2nWriUzMzJLx0RRNWebvm8OLzpRlTG8O4URAdPVyLguV4jSM63k9M1cCJB6tozO5leI0jOt5PTNXAiQeraMzuZXiNIzreT0zVwIkHq2jM7mV4jSM63k9M1cCJB6tozO5vN4hHx8DzfSl2Ue7uCoCX8ogY3cAaAh/BiRvwEgWGkxNTOLpmAXG0HmHumGWRL5XB7Sj3m43kzFzxB9H1uEvmXiL1n7RkT15jPsrXnuV3g/CUkzZDOLm0T3z1DXqoK6p38Um6QpdChkwRXOyE2VTWu4AdCZrbWTd+ndua7AsoTsfudg3SfainhQLm33bhdS48uVE0jK/+ziVhTVvw1ie+EbT1USPTJZW77RaZvjfO7GHs4R5xapcY1NCHjWaY+IH0X0xyiEOvMEI53gN1snzIoW/8Q38vhdBH9G9f796FnTnipIKglsnypdgNz7fdNJd6PCNG8SSxH6KEfkJCYIhPHHxfcEQ3n+DWj3yTGNckCFuAHQma21k3fp3bmuwLKE7PIq4UdcVV+pkITDIRmUiJbLlRNIyv/s4lYU1b8NYnvhoA2berl1plLZUXB+qYmhhe0xee1wkvaq4rWi12XEEo1F9McohDrzBCOd4DdbJ8yKK2lAMXrxrFOZo/SRvEGJhJ4qSCoJbJ8qXYDc+33TSXdsfR4UifKLg2KXZR6hCMGgoYyQ7XKs1+0b5ponKvfuaKyD+K961sZQzR8O9nqOtfY4AfKD3yK12BznUGphgSnsjPMibvZhJ53CWah3xlWAqvOLNtFwHOl3SLWdOVGyfU7rKZDQ1YdQqL4qMnSdt0EYuAHQma21k3fp3bmuwLKE7H7nYN0n2op4UC5t924XUuPLlRNIyv/s4lYU1b8NYnvhAk73IhNzE/GR4fpN/tU+95BRxo7ou9FOgEWlOAispzK4AdCZrbWTd+ndua7AsoTswNWGt+mPfLR5K+G4RAuqT8uVE0jK/+ziVhTVvw1ie+HYVoGb/3QjYF+PZOH7PPyZEAx6ug3RktXZrzi1ruKRMqJlZJheYZPXB/9eq7F3jR7JlusN5zJ6qbVvvWxNSSnCw4JJVS4vUgmjb3ZrTxpoPA== | non_priority | f pkitdirmuijbllrniyv tu hyvogb | 0 |
57,857 | 11,799,530,249 | IssuesEvent | 2020-03-18 16:02:23 | microsoft/Azure-Kinect-Sensor-SDK | https://api.github.com/repos/microsoft/Azure-Kinect-Sensor-SDK | closed | same k4a_image_format_t format() function works fine for depth image, get error for color image | Bug Code Sample Triage Needed | This piece of code, works fine for k4a_capture_get_depth_image(), but change it to k4a_capture_get_color_image() will get the error below.
//------------------------Code :
#pragma comment(lib, "k4a.lib")
#include <k4a/k4a.h>
#include <opencv2/opencv.hpp>
// #include <opencv2/highgui.hpp>
// #include <opencv2/highgui/highgui.hpp>
using namespace cv;
#include <stdio.h>
#include <stdlib.h>
int main()
{
uint32_t count = k4a_device_get_installed_count();
if (count == 0)
{
printf("No k4a devices attached!\n");
return 1;
}
// Open the first plugged in Kinect device
k4a_device_t device = NULL;
if (K4A_FAILED(k4a_device_open(K4A_DEVICE_DEFAULT, &device)))
{
printf("Failed to open k4a device!\n");
return 1;
}
// Get the size of the serial number
size_t serial_size = 0;
k4a_device_get_serialnum(device, NULL, &serial_size);
// Allocate memory for the serial, then acquire it
char *serial = (char*)(malloc(serial_size));
k4a_device_get_serialnum(device, serial, &serial_size);
printf("Opened device: %s\n", serial);
free(serial);
// Configure a stream of 4096x3072 BRGA color data at 15 frames per second
k4a_device_configuration_t config = K4A_DEVICE_CONFIG_INIT_DISABLE_ALL;
config.camera_fps = K4A_FRAMES_PER_SECOND_15;
config.color_format = K4A_IMAGE_FORMAT_COLOR_BGRA32;
config.color_resolution = K4A_COLOR_RESOLUTION_720P;
config.depth_mode = K4A_DEPTH_MODE_NFOV_UNBINNED;
// Start the camera with the given configuration
if (K4A_FAILED(k4a_device_start_cameras(device, &config)))
{
printf("Failed to start cameras!\n");
k4a_device_close(device);
return 1;
}
std::cout<< "started camera" <<std::endl;
k4a_capture_t capture = NULL;
k4a_wait_result_t result = k4a_device_get_capture(device, &capture, K4A_WAIT_INFINITE );
k4a_image_t color_image = k4a_capture_get_color_image(capture);
if (color_image != NULL)
{
printf("color image got\n");
}
k4a_image_format_t format = k4a_image_get_format(color_image);
int rows = k4a_image_get_height_pixels(color_image);
std::cout<< rows <<std::endl;
int cols = k4a_image_get_width_pixels(color_image);
int stride = k4a_image_get_stride_bytes(color_image);
uint8_t* buffer = k4a_image_get_buffer(color_image);
cv::Mat colorMat(rows , cols, CV_8UC4, (void*)buffer, cv::Mat::AUTO_STEP);
cv::imshow("Image", colorMat);
cv::waitKey(0);
k4a_capture_release(capture);
// Camera capture and application specific code would go here
// Shut down the camera when finished with application logic
k4a_device_stop_cameras(device);
k4a_device_close(device);
return 0;
}
//-------------------------
error :
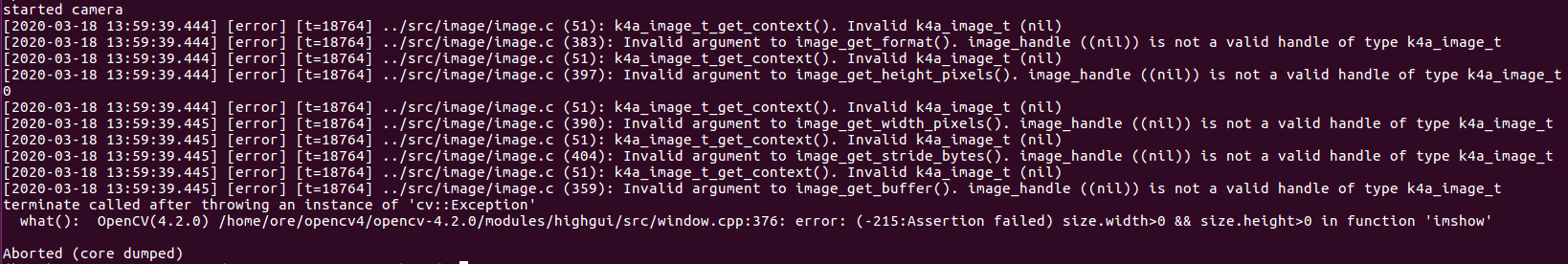
Thanks. | 1.0 | same k4a_image_format_t format() function works fine for depth image, get error for color image - This piece of code, works fine for k4a_capture_get_depth_image(), but change it to k4a_capture_get_color_image() will get the error below.
//------------------------Code :
#pragma comment(lib, "k4a.lib")
#include <k4a/k4a.h>
#include <opencv2/opencv.hpp>
// #include <opencv2/highgui.hpp>
// #include <opencv2/highgui/highgui.hpp>
using namespace cv;
#include <stdio.h>
#include <stdlib.h>
int main()
{
uint32_t count = k4a_device_get_installed_count();
if (count == 0)
{
printf("No k4a devices attached!\n");
return 1;
}
// Open the first plugged in Kinect device
k4a_device_t device = NULL;
if (K4A_FAILED(k4a_device_open(K4A_DEVICE_DEFAULT, &device)))
{
printf("Failed to open k4a device!\n");
return 1;
}
// Get the size of the serial number
size_t serial_size = 0;
k4a_device_get_serialnum(device, NULL, &serial_size);
// Allocate memory for the serial, then acquire it
char *serial = (char*)(malloc(serial_size));
k4a_device_get_serialnum(device, serial, &serial_size);
printf("Opened device: %s\n", serial);
free(serial);
// Configure a stream of 4096x3072 BRGA color data at 15 frames per second
k4a_device_configuration_t config = K4A_DEVICE_CONFIG_INIT_DISABLE_ALL;
config.camera_fps = K4A_FRAMES_PER_SECOND_15;
config.color_format = K4A_IMAGE_FORMAT_COLOR_BGRA32;
config.color_resolution = K4A_COLOR_RESOLUTION_720P;
config.depth_mode = K4A_DEPTH_MODE_NFOV_UNBINNED;
// Start the camera with the given configuration
if (K4A_FAILED(k4a_device_start_cameras(device, &config)))
{
printf("Failed to start cameras!\n");
k4a_device_close(device);
return 1;
}
std::cout<< "started camera" <<std::endl;
k4a_capture_t capture = NULL;
k4a_wait_result_t result = k4a_device_get_capture(device, &capture, K4A_WAIT_INFINITE );
k4a_image_t color_image = k4a_capture_get_color_image(capture);
if (color_image != NULL)
{
printf("color image got\n");
}
k4a_image_format_t format = k4a_image_get_format(color_image);
int rows = k4a_image_get_height_pixels(color_image);
std::cout<< rows <<std::endl;
int cols = k4a_image_get_width_pixels(color_image);
int stride = k4a_image_get_stride_bytes(color_image);
uint8_t* buffer = k4a_image_get_buffer(color_image);
cv::Mat colorMat(rows , cols, CV_8UC4, (void*)buffer, cv::Mat::AUTO_STEP);
cv::imshow("Image", colorMat);
cv::waitKey(0);
k4a_capture_release(capture);
// Camera capture and application specific code would go here
// Shut down the camera when finished with application logic
k4a_device_stop_cameras(device);
k4a_device_close(device);
return 0;
}
//-------------------------
error :
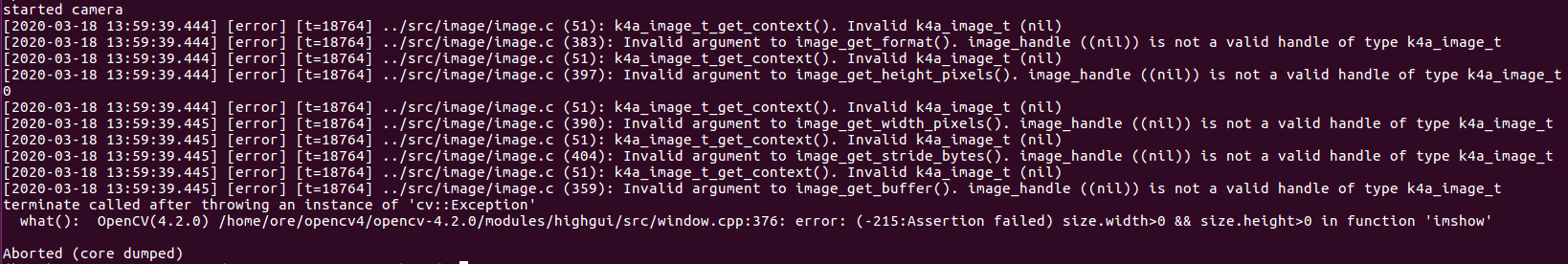
Thanks. | non_priority | same image format t format function works fine for depth image get error for color image this piece of code works fine for capture get depth image but change it to capture get color image will get the error below code pragma comment lib lib include include include include using namespace cv include include int main t count device get installed count if count printf no devices attached n return open the first plugged in kinect device device t device null if failed device open device default device printf failed to open device n return get the size of the serial number size t serial size device get serialnum device null serial size allocate memory for the serial then acquire it char serial char malloc serial size device get serialnum device serial serial size printf opened device s n serial free serial configure a stream of brga color data at frames per second device configuration t config device config init disable all config camera fps frames per second config color format image format color config color resolution color resolution config depth mode depth mode nfov unbinned start the camera with the given configuration if failed device start cameras device config printf failed to start cameras n device close device return std cout started camera std endl capture t capture null wait result t result device get capture device capture wait infinite image t color image capture get color image capture if color image null printf color image got n image format t format image get format color image int rows image get height pixels color image std cout rows std endl int cols image get width pixels color image int stride image get stride bytes color image t buffer image get buffer color image cv mat colormat rows cols cv void buffer cv mat auto step cv imshow image colormat cv waitkey capture release capture camera capture and application specific code would go here shut down the camera when finished with application logic device stop cameras device device close device return error thanks | 0 |
12,306 | 2,690,391,736 | IssuesEvent | 2015-03-31 15:51:57 | SeattleTestbed/nodemanager | https://api.github.com/repos/SeattleTestbed/nodemanager | closed | repeated NMClient timeout exceptions from node 128.28.84.154.71 | C: node manager P: minor T: defect | Planet lab Node with IP 128.84.154.71 repeatably times out when attempted to be contacted including ssh. This has been occurring for weeks now. Maybe we should have a check for this sort of behavior and mark the node inactive if it repeated causes errors over a period of time. | 1.0 | repeated NMClient timeout exceptions from node 128.28.84.154.71 - Planet lab Node with IP 128.84.154.71 repeatably times out when attempted to be contacted including ssh. This has been occurring for weeks now. Maybe we should have a check for this sort of behavior and mark the node inactive if it repeated causes errors over a period of time. | non_priority | repeated nmclient timeout exceptions from node planet lab node with ip repeatably times out when attempted to be contacted including ssh this has been occurring for weeks now maybe we should have a check for this sort of behavior and mark the node inactive if it repeated causes errors over a period of time | 0 |
51,999 | 6,206,470,448 | IssuesEvent | 2017-07-06 18:30:16 | chain/chain | https://api.github.com/repos/chain/chain | closed | net/raft: unit test raft snapshots | testing | Currently, we don't have any unit tests covering raft snapshots. We only trigger snapshots every 10,000 raft entries, so most (all?) of our tests never trigger a snapshot. With the test State implementation from #1336, we can write a net/raft unit test that triggers snapshots more frequently. This kind of unit test could detect a regression of the crash from #1284.
`snapCount` and `nSnapCatchupEntries` are constants right now. We might need to copy those values into the Service struct so that the unit test can configure them with very low values to force frequent snapshots. | 1.0 | net/raft: unit test raft snapshots - Currently, we don't have any unit tests covering raft snapshots. We only trigger snapshots every 10,000 raft entries, so most (all?) of our tests never trigger a snapshot. With the test State implementation from #1336, we can write a net/raft unit test that triggers snapshots more frequently. This kind of unit test could detect a regression of the crash from #1284.
`snapCount` and `nSnapCatchupEntries` are constants right now. We might need to copy those values into the Service struct so that the unit test can configure them with very low values to force frequent snapshots. | non_priority | net raft unit test raft snapshots currently we don t have any unit tests covering raft snapshots we only trigger snapshots every raft entries so most all of our tests never trigger a snapshot with the test state implementation from we can write a net raft unit test that triggers snapshots more frequently this kind of unit test could detect a regression of the crash from snapcount and nsnapcatchupentries are constants right now we might need to copy those values into the service struct so that the unit test can configure them with very low values to force frequent snapshots | 0 |
155,617 | 19,802,912,469 | IssuesEvent | 2022-01-19 01:11:03 | tidharm/ksa | https://api.github.com/repos/tidharm/ksa | opened | CVE-2020-13933 (High) detected in shiro-core-1.2.0.jar | security vulnerability | ## CVE-2020-13933 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shiro-core-1.2.0.jar</b></p></summary>
<p>Apache Shiro is a powerful and flexible open-source security framework that cleanly handles
authentication, authorization, enterprise session management, single sign-on and cryptography services.</p>
<p>Library home page: <a href="http://shiro.apache.org/">http://shiro.apache.org/</a></p>
<p>Path to dependency file: /ksa-web-root/ksa-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/canner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/ksa/ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **shiro-core-1.2.0.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Shiro before 1.6.0, when using Apache Shiro, a specially crafted HTTP request may cause an authentication bypass.
<p>Publish Date: 2020-08-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13933>CVE-2020-13933</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-13933">https://nvd.nist.gov/vuln/detail/CVE-2020-13933</a></p>
<p>Release Date: 2020-08-17</p>
<p>Fix Resolution: org.apache.shiro:shiro-core - 1.6.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.shiro","packageName":"shiro-core","packageVersion":"1.2.0","packageFilePaths":["/ksa-web-root/ksa-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.shiro:shiro-core:1.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.shiro:shiro-core - 1.6.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-13933","vulnerabilityDetails":"Apache Shiro before 1.6.0, when using Apache Shiro, a specially crafted HTTP request may cause an authentication bypass.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13933","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-13933 (High) detected in shiro-core-1.2.0.jar - ## CVE-2020-13933 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shiro-core-1.2.0.jar</b></p></summary>
<p>Apache Shiro is a powerful and flexible open-source security framework that cleanly handles
authentication, authorization, enterprise session management, single sign-on and cryptography services.</p>
<p>Library home page: <a href="http://shiro.apache.org/">http://shiro.apache.org/</a></p>
<p>Path to dependency file: /ksa-web-root/ksa-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/canner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/ksa/ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar,/home/wss-scanner/.m2/repository/org/apache/shiro/shiro-core/1.2.0/shiro-core-1.2.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **shiro-core-1.2.0.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Shiro before 1.6.0, when using Apache Shiro, a specially crafted HTTP request may cause an authentication bypass.
<p>Publish Date: 2020-08-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13933>CVE-2020-13933</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-13933">https://nvd.nist.gov/vuln/detail/CVE-2020-13933</a></p>
<p>Release Date: 2020-08-17</p>
<p>Fix Resolution: org.apache.shiro:shiro-core - 1.6.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.shiro","packageName":"shiro-core","packageVersion":"1.2.0","packageFilePaths":["/ksa-web-root/ksa-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.apache.shiro:shiro-core:1.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.shiro:shiro-core - 1.6.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-13933","vulnerabilityDetails":"Apache Shiro before 1.6.0, when using Apache Shiro, a specially crafted HTTP request may cause an authentication bypass.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13933","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in shiro core jar cve high severity vulnerability vulnerable library shiro core jar apache shiro is a powerful and flexible open source security framework that cleanly handles authentication authorization enterprise session management single sign on and cryptography services library home page a href path to dependency file ksa web root ksa web pom xml path to vulnerable library home wss scanner repository org apache shiro shiro core shiro core jar canner repository org apache shiro shiro core shiro core jar ksa ksa web root ksa web target root web inf lib shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar home wss scanner repository org apache shiro shiro core shiro core jar dependency hierarchy x shiro core jar vulnerable library found in base branch master vulnerability details apache shiro before when using apache shiro a specially crafted http request may cause an authentication bypass publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache shiro shiro core rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org apache shiro shiro core isminimumfixversionavailable true minimumfixversion org apache shiro shiro core isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails apache shiro before when using apache shiro a specially crafted http request may cause an authentication bypass vulnerabilityurl | 0 |
36,590 | 9,842,235,069 | IssuesEvent | 2019-06-18 08:50:45 | spack/spack | https://api.github.com/repos/spack/spack | opened | Installation issue: Nettle | build-error | ### Steps to reproduce the issue
```console
$ spack install nettle %gcc@4.8.5
...
==> Error: ProcessError: Command exited with status 2:
'make' '-j80'
3 errors found in build log:
643 && true
644 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT dsa-sha256-sign.o -MD -MP -MF dsa-sha256-sign.o.d -c dsa-sha256-sign.c \
645 && true
646 rsa-sign-tr.c: In function 'sec_equal':
647 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT dsa-sha256-verify.o -MD -MP -MF dsa-sha256-verify.o.d -c dsa-sha256-verify.c \
648 && true
>> 649 rsa-sign-tr.c:243:3: error: 'for' loop initial declarations are only allowed in C99 mode
650 for (size_t i = 0; i < limbs; i++)
651 ^
652 rsa-sign-tr.c:243:3: note: use option -std=c99 or -std=gnu99 to compile your code
653 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT dsa2sexp.o -MD -MP -MF dsa2sexp.o.d -c dsa2sexp.c \
654 && true
655 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT sexp2dsa.o -MD -MP -MF sexp2dsa.o.d -c sexp2dsa.c \
656 && true
>> 657 make[1]: *** [rsa-sign-tr.o] Error 1
658 make[1]: *** Waiting for unfinished jobs....
659 make[1]: Leaving directory `/tmp/root/spack-stage/spack-stage-sHHgXL/nettle-3.4.1'
>> 660 make: *** [all] Error 2
```
### Platform and user environment
Please report your OS here:
```commandline
$ uname -a
Linux maxlogin2 3.10.0-957.10.1.el7.x86_64 #1 SMP Mon Mar 18 15:06:45 UTC 2019 x86_64 x86_64 x86_64 GNU/Linux
```
### Additional information
My target application is CP2K using Nettle as a dependency.
```console
$ ./spack spec --install-status nettle %gcc@4.8.5
Input spec
--------------------------------
- nettle%gcc@4.8.5
Concretized
--------------------------------
- nettle@3.4.1%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^gmp@6.1.2%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^autoconf@2.69%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^m4@1.4.18%gcc@4.8.5 patches=3877ab548f88597ab2327a2230ee048d2d07ace1062efe81fc92e91b7f39cd00,c0a408fbffb7255fcc75e26bd8edab116fc81d216bfd18b473668b7739a4158e,fc9b61654a3ba1a8d6cd78ce087e7c96366c290bc8d2c299f09828d793b853c8 +sigsegv arch=linux-centos7-x86_64
[+] ^libsigsegv@2.11%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^perl@5.26.2%gcc@4.8.5+cpanm patches=0eac10ed90aeb0459ad8851f88081d439a4e41978e586ec743069e8b059370ac +shared+threads arch=linux-centos7-x86_64
[+] ^gdbm@1.18.1%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^readline@7.0%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^ncurses@6.1%gcc@4.8.5~symlinks~termlib arch=linux-centos7-x86_64
[+] ^pkgconf@1.6.0%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^automake@1.16.1%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^libtool@2.4.6%gcc@4.8.5 arch=linux-centos7-x86_64
```
You might want to run this command on the `config.log` or any other similar file
found in the stage directory:
```console
./spack location -s nettle
/opt/software/uoa/2019/spack/var/spack/stage/nettle-3.4.1-dzgj2ckkldnwi4e23k6s6zmbanbucbm3
```
```console
$ ./spack -d install -j 1 nettle
...
==> [2019-06-18-09:43:00.288740] Error: ProcessError: Command exited with status 2:
'make'
3 errors found in build log:
565 && true
566 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT rsa-sign.o -MD -MP -MF rsa-sign.o.d -c rsa-sign.c \
567 && true
568 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT rsa-sign-tr.o -MD -MP -MF rsa-sign-tr.o.d -c rsa-sign-tr.c \
569 && true
570 rsa-sign-tr.c: In function 'sec_equal':
>> 571 rsa-sign-tr.c:243:3: error: 'for' loop initial declarations are only allowed in C99 mode
572 for (size_t i = 0; i < limbs; i++)
573 ^
574 rsa-sign-tr.c:243:3: note: use option -std=c99 or -std=gnu99 to compile your code
>> 575 make[1]: *** [rsa-sign-tr.o] Error 1
576 make[1]: Leaving directory `/tmp/root/spack-stage/spack-stage-4Jz1N8/nettle-3.4.1'
>> 577 make: *** [all] Error 2
See build log for details:
/opt/software/uoa/2019/spack/var/spack/stage/nettle-3.4.1-dzgj2ckkldnwi4e23k6s6zmbanbucbm3/spack-build.out
Traceback (most recent call last):
File "/opt/software/uoa/2019/spack/lib/spack/spack/build_environment.py", line 765, in child_process
return_value = function()
File "/opt/software/uoa/2019/spack/lib/spack/spack/package.py", line 1567, in build_process
phase(self.spec, self.prefix)
File "/opt/software/uoa/2019/spack/lib/spack/spack/package.py", line 99, in phase_wrapper
phase(spec, prefix)
File "/opt/software/uoa/2019/spack/lib/spack/spack/build_systems/autotools.py", line 263, in build
inspect.getmodule(self).make(*self.build_targets)
File "/opt/software/uoa/2019/spack/lib/spack/spack/build_environment.py", line 131, in __call__
return super(MakeExecutable, self).__call__(*args, **kwargs)
File "/opt/software/uoa/2019/spack/lib/spack/spack/util/executable.py", line 189, in __call__
proc.returncode, long_msg)
ProcessError: Command exited with status 2:
'make'
``` | 1.0 | Installation issue: Nettle - ### Steps to reproduce the issue
```console
$ spack install nettle %gcc@4.8.5
...
==> Error: ProcessError: Command exited with status 2:
'make' '-j80'
3 errors found in build log:
643 && true
644 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT dsa-sha256-sign.o -MD -MP -MF dsa-sha256-sign.o.d -c dsa-sha256-sign.c \
645 && true
646 rsa-sign-tr.c: In function 'sec_equal':
647 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT dsa-sha256-verify.o -MD -MP -MF dsa-sha256-verify.o.d -c dsa-sha256-verify.c \
648 && true
>> 649 rsa-sign-tr.c:243:3: error: 'for' loop initial declarations are only allowed in C99 mode
650 for (size_t i = 0; i < limbs; i++)
651 ^
652 rsa-sign-tr.c:243:3: note: use option -std=c99 or -std=gnu99 to compile your code
653 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT dsa2sexp.o -MD -MP -MF dsa2sexp.o.d -c dsa2sexp.c \
654 && true
655 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT sexp2dsa.o -MD -MP -MF sexp2dsa.o.d -c sexp2dsa.c \
656 && true
>> 657 make[1]: *** [rsa-sign-tr.o] Error 1
658 make[1]: *** Waiting for unfinished jobs....
659 make[1]: Leaving directory `/tmp/root/spack-stage/spack-stage-sHHgXL/nettle-3.4.1'
>> 660 make: *** [all] Error 2
```
### Platform and user environment
Please report your OS here:
```commandline
$ uname -a
Linux maxlogin2 3.10.0-957.10.1.el7.x86_64 #1 SMP Mon Mar 18 15:06:45 UTC 2019 x86_64 x86_64 x86_64 GNU/Linux
```
### Additional information
My target application is CP2K using Nettle as a dependency.
```console
$ ./spack spec --install-status nettle %gcc@4.8.5
Input spec
--------------------------------
- nettle%gcc@4.8.5
Concretized
--------------------------------
- nettle@3.4.1%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^gmp@6.1.2%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^autoconf@2.69%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^m4@1.4.18%gcc@4.8.5 patches=3877ab548f88597ab2327a2230ee048d2d07ace1062efe81fc92e91b7f39cd00,c0a408fbffb7255fcc75e26bd8edab116fc81d216bfd18b473668b7739a4158e,fc9b61654a3ba1a8d6cd78ce087e7c96366c290bc8d2c299f09828d793b853c8 +sigsegv arch=linux-centos7-x86_64
[+] ^libsigsegv@2.11%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^perl@5.26.2%gcc@4.8.5+cpanm patches=0eac10ed90aeb0459ad8851f88081d439a4e41978e586ec743069e8b059370ac +shared+threads arch=linux-centos7-x86_64
[+] ^gdbm@1.18.1%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^readline@7.0%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^ncurses@6.1%gcc@4.8.5~symlinks~termlib arch=linux-centos7-x86_64
[+] ^pkgconf@1.6.0%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^automake@1.16.1%gcc@4.8.5 arch=linux-centos7-x86_64
[+] ^libtool@2.4.6%gcc@4.8.5 arch=linux-centos7-x86_64
```
You might want to run this command on the `config.log` or any other similar file
found in the stage directory:
```console
./spack location -s nettle
/opt/software/uoa/2019/spack/var/spack/stage/nettle-3.4.1-dzgj2ckkldnwi4e23k6s6zmbanbucbm3
```
```console
$ ./spack -d install -j 1 nettle
...
==> [2019-06-18-09:43:00.288740] Error: ProcessError: Command exited with status 2:
'make'
3 errors found in build log:
565 && true
566 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT rsa-sign.o -MD -MP -MF rsa-sign.o.d -c rsa-sign.c \
567 && true
568 /opt/software/uoa/2019/spack/lib/spack/env/gcc/gcc -I. -DHAVE_CONFIG_H -g -O2 -ggdb3 -Wno-pointer-sign -Wall -W -Wmissing-prototypes -Wmissing-declarations -Wstrict-prototypes -Wpointer-arith -Wbad-function-cast -Wne
sted-externs -fpic -MT rsa-sign-tr.o -MD -MP -MF rsa-sign-tr.o.d -c rsa-sign-tr.c \
569 && true
570 rsa-sign-tr.c: In function 'sec_equal':
>> 571 rsa-sign-tr.c:243:3: error: 'for' loop initial declarations are only allowed in C99 mode
572 for (size_t i = 0; i < limbs; i++)
573 ^
574 rsa-sign-tr.c:243:3: note: use option -std=c99 or -std=gnu99 to compile your code
>> 575 make[1]: *** [rsa-sign-tr.o] Error 1
576 make[1]: Leaving directory `/tmp/root/spack-stage/spack-stage-4Jz1N8/nettle-3.4.1'
>> 577 make: *** [all] Error 2
See build log for details:
/opt/software/uoa/2019/spack/var/spack/stage/nettle-3.4.1-dzgj2ckkldnwi4e23k6s6zmbanbucbm3/spack-build.out
Traceback (most recent call last):
File "/opt/software/uoa/2019/spack/lib/spack/spack/build_environment.py", line 765, in child_process
return_value = function()
File "/opt/software/uoa/2019/spack/lib/spack/spack/package.py", line 1567, in build_process
phase(self.spec, self.prefix)
File "/opt/software/uoa/2019/spack/lib/spack/spack/package.py", line 99, in phase_wrapper
phase(spec, prefix)
File "/opt/software/uoa/2019/spack/lib/spack/spack/build_systems/autotools.py", line 263, in build
inspect.getmodule(self).make(*self.build_targets)
File "/opt/software/uoa/2019/spack/lib/spack/spack/build_environment.py", line 131, in __call__
return super(MakeExecutable, self).__call__(*args, **kwargs)
File "/opt/software/uoa/2019/spack/lib/spack/spack/util/executable.py", line 189, in __call__
proc.returncode, long_msg)
ProcessError: Command exited with status 2:
'make'
``` | non_priority | installation issue nettle steps to reproduce the issue console spack install nettle gcc error processerror command exited with status make errors found in build log true opt software uoa spack lib spack env gcc gcc i dhave config h g wno pointer sign wall w wmissing prototypes wmissing declarations wstrict prototypes wpointer arith wbad function cast wne sted externs fpic mt dsa sign o md mp mf dsa sign o d c dsa sign c true rsa sign tr c in function sec equal opt software uoa spack lib spack env gcc gcc i dhave config h g wno pointer sign wall w wmissing prototypes wmissing declarations wstrict prototypes wpointer arith wbad function cast wne sted externs fpic mt dsa verify o md mp mf dsa verify o d c dsa verify c true rsa sign tr c error for loop initial declarations are only allowed in mode for size t i i limbs i rsa sign tr c note use option std or std to compile your code opt software uoa spack lib spack env gcc gcc i dhave config h g wno pointer sign wall w wmissing prototypes wmissing declarations wstrict prototypes wpointer arith wbad function cast wne sted externs fpic mt o md mp mf o d c c true opt software uoa spack lib spack env gcc gcc i dhave config h g wno pointer sign wall w wmissing prototypes wmissing declarations wstrict prototypes wpointer arith wbad function cast wne sted externs fpic mt o md mp mf o d c c true make error make waiting for unfinished jobs make leaving directory tmp root spack stage spack stage shhgxl nettle make error platform and user environment please report your os here commandline uname a linux smp mon mar utc gnu linux additional information my target application is using nettle as a dependency console spack spec install status nettle gcc input spec nettle gcc concretized nettle gcc arch linux gmp gcc arch linux autoconf gcc arch linux gcc patches sigsegv arch linux libsigsegv gcc arch linux perl gcc cpanm patches shared threads arch linux gdbm gcc arch linux readline gcc arch linux ncurses gcc symlinks termlib arch linux pkgconf gcc arch linux automake gcc arch linux libtool gcc arch linux you might want to run this command on the config log or any other similar file found in the stage directory console spack location s nettle opt software uoa spack var spack stage nettle console spack d install j nettle error processerror command exited with status make errors found in build log true opt software uoa spack lib spack env gcc gcc i dhave config h g wno pointer sign wall w wmissing prototypes wmissing declarations wstrict prototypes wpointer arith wbad function cast wne sted externs fpic mt rsa sign o md mp mf rsa sign o d c rsa sign c true opt software uoa spack lib spack env gcc gcc i dhave config h g wno pointer sign wall w wmissing prototypes wmissing declarations wstrict prototypes wpointer arith wbad function cast wne sted externs fpic mt rsa sign tr o md mp mf rsa sign tr o d c rsa sign tr c true rsa sign tr c in function sec equal rsa sign tr c error for loop initial declarations are only allowed in mode for size t i i limbs i rsa sign tr c note use option std or std to compile your code make error make leaving directory tmp root spack stage spack stage nettle make error see build log for details opt software uoa spack var spack stage nettle spack build out traceback most recent call last file opt software uoa spack lib spack spack build environment py line in child process return value function file opt software uoa spack lib spack spack package py line in build process phase self spec self prefix file opt software uoa spack lib spack spack package py line in phase wrapper phase spec prefix file opt software uoa spack lib spack spack build systems autotools py line in build inspect getmodule self make self build targets file opt software uoa spack lib spack spack build environment py line in call return super makeexecutable self call args kwargs file opt software uoa spack lib spack spack util executable py line in call proc returncode long msg processerror command exited with status make | 0 |
94,693 | 16,020,376,534 | IssuesEvent | 2021-04-20 21:59:23 | joshnewton31080/easybuggy | https://api.github.com/repos/joshnewton31080/easybuggy | closed | CVE-2009-2625 (Medium) detected in xercesImpl-2.8.0.jar - autoclosed | security vulnerability | ## CVE-2009-2625 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: easybuggy/pom.xml</p>
<p>Path to vulnerable library: easybuggy/target/easybuggy-1-SNAPSHOT/WEB-INF/lib/xercesImpl-2.8.0.jar,/home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar,easybuggy/.extract/webapps/ROOT/WEB-INF/lib/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/joshnewton31080/easybuggy/commit/be37261abafd3c9fca38848d72e776deddfd13cb">be37261abafd3c9fca38848d72e776deddfd13cb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.
<p>Publish Date: 2009-08-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625>CVE-2009-2625</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://www.securitytracker.com/id?1022680">http://www.securitytracker.com/id?1022680</a></p>
<p>Release Date: 2017-12-31</p>
<p>Fix Resolution: The vendor has issued a fix for Windows, Solaris, and Linux:
* JDK and JRE 6 Update 15 or later
* JDK and JRE 5.0 Update 20 or later
Java SE releases are available at:
JDK and JRE 6 Update 15:
http://java.sun.com/javase/downloads/index.jsp
JRE 6 Update 15:
http://java.com/
through the Java Update tool for Microsoft Windows users.
JDK 6 Update 15 for Solaris is available in the following patches:
* Java SE 6 Update 15 (as delivered in patch 125136-16)
* Java SE 6 Update 15 (as delivered in patch 125137-16 (64bit))
* Java SE 6_x86 Update 15 (as delivered in patch 125138-16)
* Java SE 6_x86 Update 15 (as delivered in patch 125139-16 (64bit))
JDK and JRE 5.0 Update 20:
http://java.sun.com/javase/downloads/index_jdk5.jsp
JDK 5.0 Update 20 for Solaris is available in the following patches:
* J2SE 5.0 Update 18 (as delivered in patch 118666-21)
* J2SE 5.0 Update 18 (as delivered in patch 118667-21 (64bit))
* J2SE 5.0_x86 Update 18 (as delivered in patch 118668-21)
* J2SE 5.0_x86 Update 18 (as delivered in patch 118669-21 (64bit))
Java SE for Business releases are available at:
http://www.sun.com/software/javaseforbusiness/getit_download.jsp
Note: When installing a new version of the product from a source other than a Solaris patch, it is recommended that the old affected versions be removed from your system. To remove old affected versions on the Windows platform, please see:
http://www.java.com/en/download/help/5000010800.xml
The vendor's advisory is available at:
http://sunsolve.sun.com/search/document.do?assetkey=1-66-263489-1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"xerces","packageName":"xercesImpl","packageVersion":"2.8.0","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"xerces:xercesImpl:2.8.0","isMinimumFixVersionAvailable":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2009-2625","vulnerabilityDetails":"XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | True | CVE-2009-2625 (Medium) detected in xercesImpl-2.8.0.jar - autoclosed - ## CVE-2009-2625 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: easybuggy/pom.xml</p>
<p>Path to vulnerable library: easybuggy/target/easybuggy-1-SNAPSHOT/WEB-INF/lib/xercesImpl-2.8.0.jar,/home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar,easybuggy/.extract/webapps/ROOT/WEB-INF/lib/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/joshnewton31080/easybuggy/commit/be37261abafd3c9fca38848d72e776deddfd13cb">be37261abafd3c9fca38848d72e776deddfd13cb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.
<p>Publish Date: 2009-08-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625>CVE-2009-2625</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://www.securitytracker.com/id?1022680">http://www.securitytracker.com/id?1022680</a></p>
<p>Release Date: 2017-12-31</p>
<p>Fix Resolution: The vendor has issued a fix for Windows, Solaris, and Linux:
* JDK and JRE 6 Update 15 or later
* JDK and JRE 5.0 Update 20 or later
Java SE releases are available at:
JDK and JRE 6 Update 15:
http://java.sun.com/javase/downloads/index.jsp
JRE 6 Update 15:
http://java.com/
through the Java Update tool for Microsoft Windows users.
JDK 6 Update 15 for Solaris is available in the following patches:
* Java SE 6 Update 15 (as delivered in patch 125136-16)
* Java SE 6 Update 15 (as delivered in patch 125137-16 (64bit))
* Java SE 6_x86 Update 15 (as delivered in patch 125138-16)
* Java SE 6_x86 Update 15 (as delivered in patch 125139-16 (64bit))
JDK and JRE 5.0 Update 20:
http://java.sun.com/javase/downloads/index_jdk5.jsp
JDK 5.0 Update 20 for Solaris is available in the following patches:
* J2SE 5.0 Update 18 (as delivered in patch 118666-21)
* J2SE 5.0 Update 18 (as delivered in patch 118667-21 (64bit))
* J2SE 5.0_x86 Update 18 (as delivered in patch 118668-21)
* J2SE 5.0_x86 Update 18 (as delivered in patch 118669-21 (64bit))
Java SE for Business releases are available at:
http://www.sun.com/software/javaseforbusiness/getit_download.jsp
Note: When installing a new version of the product from a source other than a Solaris patch, it is recommended that the old affected versions be removed from your system. To remove old affected versions on the Windows platform, please see:
http://www.java.com/en/download/help/5000010800.xml
The vendor's advisory is available at:
http://sunsolve.sun.com/search/document.do?assetkey=1-66-263489-1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"xerces","packageName":"xercesImpl","packageVersion":"2.8.0","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"xerces:xercesImpl:2.8.0","isMinimumFixVersionAvailable":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2009-2625","vulnerabilityDetails":"XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in xercesimpl jar autoclosed cve medium severity vulnerability vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file easybuggy pom xml path to vulnerable library easybuggy target easybuggy snapshot web inf lib xercesimpl jar home wss scanner repository xerces xercesimpl xercesimpl jar easybuggy extract webapps root web inf lib xercesimpl jar dependency hierarchy x xercesimpl jar vulnerable library found in head commit a href found in base branch main vulnerability details xmlscanner java in apache java as used in sun java runtime environment jre in jdk and jre before update and jdk and jre before update and in other products allows remote attackers to cause a denial of service infinite loop and application hang via malformed xml input as demonstrated by the codenomicon xml fuzzing framework publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution the vendor has issued a fix for windows solaris and linux jdk and jre update or later jdk and jre update or later java se releases are available at jdk and jre update jre update through the java update tool for microsoft windows users jdk update for solaris is available in the following patches java se update as delivered in patch java se update as delivered in patch java se update as delivered in patch java se update as delivered in patch jdk and jre update jdk update for solaris is available in the following patches update as delivered in patch update as delivered in patch update as delivered in patch update as delivered in patch java se for business releases are available at note when installing a new version of the product from a source other than a solaris patch it is recommended that the old affected versions be removed from your system to remove old affected versions on the windows platform please see the vendor s advisory is available at isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree xerces xercesimpl isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails xmlscanner java in apache java as used in sun java runtime environment jre in jdk and jre before update and jdk and jre before update and in other products allows remote attackers to cause a denial of service infinite loop and application hang via malformed xml input as demonstrated by the codenomicon xml fuzzing framework vulnerabilityurl | 0 |
369,539 | 25,856,041,489 | IssuesEvent | 2022-12-13 13:50:47 | firebase/flutterfire | https://api.github.com/repos/firebase/flutterfire | closed | [📚] Example code does not work | type: documentation good first issue plugin: ui | Using the latest Flutter release, I tried the example code here:
https://pub.dev/packages/firebase_ui_auth
I get the following errors:
```
lib/main.dart:8:24: Error: 'EmailAuthProvider' is imported from both 'package:firebase_auth_platform_interface/src/providers/email_auth.dart' and 'package:firebase_ui_auth/src/providers/email_auth_provider.dart'.
const providers = [EmailAuthProvider()];
^^^^^^^^^^^^^^^^^
lib/main.dart:15:24: Error: The argument type 'List<dynamic>' can't be assigned to the parameter type 'List<AuthProvider<AuthListener, AuthCredential>>?'.
- 'List' is from 'dart:core'.
- 'AuthProvider' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthListener' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthCredential' is from 'package:firebase_auth_platform_interface/src/auth_credential.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_platform_interface-6.11.4/lib/src/auth_credential.dart').
providers: providers,
^
lib/main.dart:25:24: Error: The argument type 'List<dynamic>' can't be assigned to the parameter type 'List<AuthProvider<AuthListener, AuthCredential>>?'.
- 'List' is from 'dart:core'.
- 'AuthProvider' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthListener' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthCredential' is from 'package:firebase_auth_platform_interface/src/auth_credential.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_platform_interface-6.11.4/lib/src/auth_credential.dart').
providers: providers,
^
``` | 1.0 | [📚] Example code does not work - Using the latest Flutter release, I tried the example code here:
https://pub.dev/packages/firebase_ui_auth
I get the following errors:
```
lib/main.dart:8:24: Error: 'EmailAuthProvider' is imported from both 'package:firebase_auth_platform_interface/src/providers/email_auth.dart' and 'package:firebase_ui_auth/src/providers/email_auth_provider.dart'.
const providers = [EmailAuthProvider()];
^^^^^^^^^^^^^^^^^
lib/main.dart:15:24: Error: The argument type 'List<dynamic>' can't be assigned to the parameter type 'List<AuthProvider<AuthListener, AuthCredential>>?'.
- 'List' is from 'dart:core'.
- 'AuthProvider' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthListener' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthCredential' is from 'package:firebase_auth_platform_interface/src/auth_credential.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_platform_interface-6.11.4/lib/src/auth_credential.dart').
providers: providers,
^
lib/main.dart:25:24: Error: The argument type 'List<dynamic>' can't be assigned to the parameter type 'List<AuthProvider<AuthListener, AuthCredential>>?'.
- 'List' is from 'dart:core'.
- 'AuthProvider' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthListener' is from 'package:firebase_ui_auth/src/providers/auth_provider.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_ui_auth-1.1.2/lib/src/providers/auth_provider.dart').
- 'AuthCredential' is from 'package:firebase_auth_platform_interface/src/auth_credential.dart' ('/opt/flutter/.pub-cache/hosted/pub.dartlang.org/firebase_auth_platform_interface-6.11.4/lib/src/auth_credential.dart').
providers: providers,
^
``` | non_priority | example code does not work using the latest flutter release i tried the example code here i get the following errors lib main dart error emailauthprovider is imported from both package firebase auth platform interface src providers email auth dart and package firebase ui auth src providers email auth provider dart const providers lib main dart error the argument type list can t be assigned to the parameter type list list is from dart core authprovider is from package firebase ui auth src providers auth provider dart opt flutter pub cache hosted pub dartlang org firebase ui auth lib src providers auth provider dart authlistener is from package firebase ui auth src providers auth provider dart opt flutter pub cache hosted pub dartlang org firebase ui auth lib src providers auth provider dart authcredential is from package firebase auth platform interface src auth credential dart opt flutter pub cache hosted pub dartlang org firebase auth platform interface lib src auth credential dart providers providers lib main dart error the argument type list can t be assigned to the parameter type list list is from dart core authprovider is from package firebase ui auth src providers auth provider dart opt flutter pub cache hosted pub dartlang org firebase ui auth lib src providers auth provider dart authlistener is from package firebase ui auth src providers auth provider dart opt flutter pub cache hosted pub dartlang org firebase ui auth lib src providers auth provider dart authcredential is from package firebase auth platform interface src auth credential dart opt flutter pub cache hosted pub dartlang org firebase auth platform interface lib src auth credential dart providers providers | 0 |
31,646 | 6,573,643,630 | IssuesEvent | 2017-09-11 09:34:27 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | closed | Clone of assignmentExpression.Left in Preconverter is changing runtime behavior | defect | In case when left part of assignment expression has "side effects", expression like
`data[i++] += 1` is translated to something like `data[i++] = data[i++] + 1` and can cause weird runtime errors.
### Steps To Reproduce
https://deck.net/8fcea6a0ad63ef4caeeda143580f3feb
```c#
public class Program
{
public static void Main()
{
int[] data = {10,20,30};
int i = 0;
data[i++] += 1;
Console.WriteLine("data[0] = " + data[0]);
Console.WriteLine("data[1] = " + data[1]);
Console.WriteLine("i = " + i);
}
}
```
### Expected Result
```js
data[0] = 11
data[1] = 20
i = 1
```
### Actual Result
```js
data[0] = 21
data[1] = 20
i = 2
```
| 1.0 | Clone of assignmentExpression.Left in Preconverter is changing runtime behavior - In case when left part of assignment expression has "side effects", expression like
`data[i++] += 1` is translated to something like `data[i++] = data[i++] + 1` and can cause weird runtime errors.
### Steps To Reproduce
https://deck.net/8fcea6a0ad63ef4caeeda143580f3feb
```c#
public class Program
{
public static void Main()
{
int[] data = {10,20,30};
int i = 0;
data[i++] += 1;
Console.WriteLine("data[0] = " + data[0]);
Console.WriteLine("data[1] = " + data[1]);
Console.WriteLine("i = " + i);
}
}
```
### Expected Result
```js
data[0] = 11
data[1] = 20
i = 1
```
### Actual Result
```js
data[0] = 21
data[1] = 20
i = 2
```
| non_priority | clone of assignmentexpression left in preconverter is changing runtime behavior in case when left part of assignment expression has side effects expression like data is translated to something like data data and can cause weird runtime errors steps to reproduce c public class program public static void main int data int i data console writeline data data console writeline data data console writeline i i expected result js data data i actual result js data data i | 0 |
25,163 | 5,140,753,995 | IssuesEvent | 2017-01-12 07:02:20 | TheLocehiliosan/yadm | https://api.github.com/repos/TheLocehiliosan/yadm | closed | `yadm config` doesn't appear to work | documentation | This is what I'm seeing:
```bash
[karma0:~] % yadm config user.name Bobby
[karma0:~] % yadm config user.email karma0@gmail.com
[karma0:~] % yadm commit -am "Initializing"
*** Please tell me who you are.
Run
git config --global user.email "you@example.com"
git config --global user.name "Your Name"
to set your account's default identity.
Omit --global to set the identity only in this repository.
fatal: empty ident name (for <(null)>) not allowed
```
| 1.0 | `yadm config` doesn't appear to work - This is what I'm seeing:
```bash
[karma0:~] % yadm config user.name Bobby
[karma0:~] % yadm config user.email karma0@gmail.com
[karma0:~] % yadm commit -am "Initializing"
*** Please tell me who you are.
Run
git config --global user.email "you@example.com"
git config --global user.name "Your Name"
to set your account's default identity.
Omit --global to set the identity only in this repository.
fatal: empty ident name (for <(null)>) not allowed
```
| non_priority | yadm config doesn t appear to work this is what i m seeing bash yadm config user name bobby yadm config user email gmail com yadm commit am initializing please tell me who you are run git config global user email you example com git config global user name your name to set your account s default identity omit global to set the identity only in this repository fatal empty ident name for not allowed | 0 |
231,815 | 18,797,018,823 | IssuesEvent | 2021-11-09 00:03:22 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: schemachange/database-version-upgrade failed | C-test-failure O-robot O-roachtest branch-master release-blocker T-sql-schema | roachtest.schemachange/database-version-upgrade [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3674519&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3674519&tab=artifacts#/schemachange/database-version-upgrade) on master @ [05d36621ae805e644d98ef6b35d453ae16255ccc](https://github.com/cockroachdb/cockroach/commits/05d36621ae805e644d98ef6b35d453ae16255ccc):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/schemachange/database-version-upgrade/run_1
cluster.go:1855,schema_change_database_version_upgrade.go:51,versionupgrade.go:213,schema_change_database_version_upgrade.go:281,schema_change_database_version_upgrade.go:41,test_runner.go:777: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --binary=v21.2.0-beta.2/cockroach --encrypt=false --sequential=false teamcity-3674519-1635924358-91-n3cpu4:1-3 returned: exit status 7
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --binary=v21.2.0-beta.2/cockroach --encrypt=false --sequential=false teamcity-3674519-1635924358-91-n3cpu4:1-3 returned
| stderr:
|
| stdout:
| <... some data truncated by circular buffer; go to artifacts for details ...>
| c9(0x1a0f940, 0xc0005ab980, 0x1, 0x4, 0xc00035fa10, 0xc00035fa38)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:472 +0x1d5
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !main.wrap.func1(0x1a0f940, 0xc0005ab980, 0x1, 0x4)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:122 +0x6b
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !github.com/spf13/cobra.(*Command).execute(0x1a0f940, 0xc0005ab940, 0x4, 0x4, 0x1a0f940, 0xc0005ab940)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:856 +0x2c2
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !github.com/spf13/cobra.(*Command).ExecuteC(0x1a0f6c0, 0x0, 0x0, 0xc0004588c0)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:960 +0x375
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !github.com/spf13/cobra.(*Command).Execute(...)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:897
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !main.main()
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1282 +0x2619
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !****************************************************************************
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !This node experienced a fatal error (printed above), and as a result the
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !process is terminating.
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !Fatal errors can occur due to faulty hardware (disks, memory, clocks) or a
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !problem in CockroachDB. With your help, the support team at Cockroach Labs
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !will try to determine the root cause, recommend next steps, and we can
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !improve CockroachDB based on your report.
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !Please submit a crash report by following the instructions here:
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! https://github.com/cockroachdb/cockroach/issues/new/choose
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !If you would rather not post publicly, please contact us directly at:
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! support@cockroachlabs.com
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !The Cockroach Labs team appreciates your feedback.
Wraps: (2) exit status 7
Error types: (1) *cluster.WithCommandDetails (2) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
|
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-schema
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*schemachange/database-version-upgrade.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: schemachange/database-version-upgrade failed - roachtest.schemachange/database-version-upgrade [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3674519&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3674519&tab=artifacts#/schemachange/database-version-upgrade) on master @ [05d36621ae805e644d98ef6b35d453ae16255ccc](https://github.com/cockroachdb/cockroach/commits/05d36621ae805e644d98ef6b35d453ae16255ccc):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/schemachange/database-version-upgrade/run_1
cluster.go:1855,schema_change_database_version_upgrade.go:51,versionupgrade.go:213,schema_change_database_version_upgrade.go:281,schema_change_database_version_upgrade.go:41,test_runner.go:777: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --binary=v21.2.0-beta.2/cockroach --encrypt=false --sequential=false teamcity-3674519-1635924358-91-n3cpu4:1-3 returned: exit status 7
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --binary=v21.2.0-beta.2/cockroach --encrypt=false --sequential=false teamcity-3674519-1635924358-91-n3cpu4:1-3 returned
| stderr:
|
| stdout:
| <... some data truncated by circular buffer; go to artifacts for details ...>
| c9(0x1a0f940, 0xc0005ab980, 0x1, 0x4, 0xc00035fa10, 0xc00035fa38)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:472 +0x1d5
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !main.wrap.func1(0x1a0f940, 0xc0005ab980, 0x1, 0x4)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:122 +0x6b
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !github.com/spf13/cobra.(*Command).execute(0x1a0f940, 0xc0005ab940, 0x4, 0x4, 0x1a0f940, 0xc0005ab940)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:856 +0x2c2
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !github.com/spf13/cobra.(*Command).ExecuteC(0x1a0f6c0, 0x0, 0x0, 0xc0004588c0)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:960 +0x375
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !github.com/spf13/cobra.(*Command).Execute(...)
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:897
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !main.main()
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1282 +0x2619
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !****************************************************************************
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !This node experienced a fatal error (printed above), and as a result the
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !process is terminating.
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !Fatal errors can occur due to faulty hardware (disks, memory, clocks) or a
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !problem in CockroachDB. With your help, the support team at Cockroach Labs
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !will try to determine the root cause, recommend next steps, and we can
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !improve CockroachDB based on your report.
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !Please submit a crash report by following the instructions here:
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! https://github.com/cockroachdb/cockroach/issues/new/choose
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !If you would rather not post publicly, please contact us directly at:
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 ! support@cockroachlabs.com
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !
| F211103 13:46:16.118335 1 roachprod/install/cluster_synced.go:1678 [-] 2 !The Cockroach Labs team appreciates your feedback.
Wraps: (2) exit status 7
Error types: (1) *cluster.WithCommandDetails (2) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
|
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-schema
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*schemachange/database-version-upgrade.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest schemachange database version upgrade failed roachtest schemachange database version upgrade with on master the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts schemachange database version upgrade run cluster go schema change database version upgrade go versionupgrade go schema change database version upgrade go schema change database version upgrade go test runner go home agent work go src github com cockroachdb cockroach bin roachprod start binary beta cockroach encrypt false sequential false teamcity returned exit status home agent work go src github com cockroachdb cockroach bin roachprod start binary beta cockroach encrypt false sequential false teamcity returned stderr stdout roachprod install cluster synced go home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go roachprod install cluster synced go main wrap roachprod install cluster synced go home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go roachprod install cluster synced go github com cobra command execute roachprod install cluster synced go home agent work go src github com cockroachdb cockroach vendor github com cobra command go roachprod install cluster synced go github com cobra command executec roachprod install cluster synced go home agent work go src github com cockroachdb cockroach vendor github com cobra command go roachprod install cluster synced go github com cobra command execute roachprod install cluster synced go home agent work go src github com cockroachdb cockroach vendor github com cobra command go roachprod install cluster synced go main main roachprod install cluster synced go home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go this node experienced a fatal error printed above and as a result the roachprod install cluster synced go process is terminating roachprod install cluster synced go roachprod install cluster synced go fatal errors can occur due to faulty hardware disks memory clocks or a roachprod install cluster synced go problem in cockroachdb with your help the support team at cockroach labs roachprod install cluster synced go will try to determine the root cause recommend next steps and we can roachprod install cluster synced go improve cockroachdb based on your report roachprod install cluster synced go roachprod install cluster synced go please submit a crash report by following the instructions here roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go if you would rather not post publicly please contact us directly at roachprod install cluster synced go roachprod install cluster synced go support cockroachlabs com roachprod install cluster synced go roachprod install cluster synced go the cockroach labs team appreciates your feedback wraps exit status error types cluster withcommanddetails exec exiterror help see see cc cockroachdb sql schema | 0 |
61,321 | 14,969,923,620 | IssuesEvent | 2021-01-27 18:51:08 | Unidata/netcdf-c | https://api.github.com/repos/Unidata/netcdf-c | opened | nczarr failures w/ Visual Studio, Windows 10 | arch/32-bit arch/64-bit area/build/cmake platform/windows | In preparation for the `4.8.0` release, I am testing with Visual Studio 2017 on Windows, using the MSYS shell to provide 'bash'. I am seeing the following failures:
## 64-bit tests
* `nc_test4/tst_filter`
* `nczarr_test/tst_nccopyz`
## 32-bit tests
* `nc_test4/test_filter`
* `ncdap_tst_remote3`
* `nczarr_test/run_ut_map`
* `nczarr_test/run_ut_mapapi`
* `nczarr_test/tst_nccopyz`
Further details added below as I work through this. | 1.0 | nczarr failures w/ Visual Studio, Windows 10 - In preparation for the `4.8.0` release, I am testing with Visual Studio 2017 on Windows, using the MSYS shell to provide 'bash'. I am seeing the following failures:
## 64-bit tests
* `nc_test4/tst_filter`
* `nczarr_test/tst_nccopyz`
## 32-bit tests
* `nc_test4/test_filter`
* `ncdap_tst_remote3`
* `nczarr_test/run_ut_map`
* `nczarr_test/run_ut_mapapi`
* `nczarr_test/tst_nccopyz`
Further details added below as I work through this. | non_priority | nczarr failures w visual studio windows in preparation for the release i am testing with visual studio on windows using the msys shell to provide bash i am seeing the following failures bit tests nc tst filter nczarr test tst nccopyz bit tests nc test filter ncdap tst nczarr test run ut map nczarr test run ut mapapi nczarr test tst nccopyz further details added below as i work through this | 0 |
12,852 | 3,097,835,055 | IssuesEvent | 2015-08-28 06:39:42 | Mobicents/RestComm | https://api.github.com/repos/Mobicents/RestComm | opened | Remember IDE status modules etc. per user/project | Visual App Designer | When a user re-opens a project he has already worked on it would be nice to remember which modules where open. Other IDE settings may also me remembered too.
The question is whether the 'remembering' will be per user, per project or per user-project. | 1.0 | Remember IDE status modules etc. per user/project - When a user re-opens a project he has already worked on it would be nice to remember which modules where open. Other IDE settings may also me remembered too.
The question is whether the 'remembering' will be per user, per project or per user-project. | non_priority | remember ide status modules etc per user project when a user re opens a project he has already worked on it would be nice to remember which modules where open other ide settings may also me remembered too the question is whether the remembering will be per user per project or per user project | 0 |
255,996 | 19,349,944,612 | IssuesEvent | 2021-12-15 14:44:14 | alphagov/govuk-prototype-kit | https://api.github.com/repos/alphagov/govuk-prototype-kit | closed | Update guidance to updating Prototype Kit to v12.0.0 | documentation 🕔 hours | ## What
Update guidance for [updating your Prototype Kit](https://govuk-prototype-kit.herokuapp.com/docs/updating-the-kit) following the v12 release.
## Tasks
- [x] Draft amends to content
- [x] Team review of content
- [x] Publish content on 15 December | 1.0 | Update guidance to updating Prototype Kit to v12.0.0 - ## What
Update guidance for [updating your Prototype Kit](https://govuk-prototype-kit.herokuapp.com/docs/updating-the-kit) following the v12 release.
## Tasks
- [x] Draft amends to content
- [x] Team review of content
- [x] Publish content on 15 December | non_priority | update guidance to updating prototype kit to what update guidance for following the release tasks draft amends to content team review of content publish content on december | 0 |
184,167 | 31,833,649,752 | IssuesEvent | 2023-09-14 12:16:55 | engrenage13/Anovel | https://api.github.com/repos/engrenage13/Anovel | opened | Refonte de la page d'après jeu | UI & design upgrade Archipel BattleShip | ## Objectifs
- + de clarté
- Supprimer les éléments ajoutés "pour faire joli"
- optimisée pour 1 à `x` joueurs
- Tableaux de stats (commun et individuels).
- Une seule page pour Archipel et la bataille navale. | 1.0 | Refonte de la page d'après jeu - ## Objectifs
- + de clarté
- Supprimer les éléments ajoutés "pour faire joli"
- optimisée pour 1 à `x` joueurs
- Tableaux de stats (commun et individuels).
- Une seule page pour Archipel et la bataille navale. | non_priority | refonte de la page d après jeu objectifs de clarté supprimer les éléments ajoutés pour faire joli optimisée pour à x joueurs tableaux de stats commun et individuels une seule page pour archipel et la bataille navale | 0 |
28,093 | 5,430,470,725 | IssuesEvent | 2017-03-03 21:20:33 | OAI/OpenAPI-Specification | https://api.github.com/repos/OAI/OpenAPI-Specification | closed | Break up the spec into a set of documents | Documentation OpenAPI.Next Proposal | Such that it can be displayed on a site like https://readthedocs.org/ or built into a doc set with a generated index.
This is a more significant change than that proposed by #464, but its a long spec and hard to digest currently.
| 1.0 | Break up the spec into a set of documents - Such that it can be displayed on a site like https://readthedocs.org/ or built into a doc set with a generated index.
This is a more significant change than that proposed by #464, but its a long spec and hard to digest currently.
| non_priority | break up the spec into a set of documents such that it can be displayed on a site like or built into a doc set with a generated index this is a more significant change than that proposed by but its a long spec and hard to digest currently | 0 |
20,814 | 10,554,457,686 | IssuesEvent | 2019-10-03 19:30:51 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Include the "Five steps to securing your identity infrastructure" article | Pri1 cxp doc-enhancement security-fundamentals/subsvc security/svc triaged | Five steps to securing your identity infrastructure
https://docs.microsoft.com/en-us/azure/security/fundamentals/steps-secure-identity
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d3e80266-d60e-c46d-38a1-83cfd677f299
* Version Independent ID: c255951e-acda-184a-996b-b3df4a18913a
* Content: [Security best practices and patterns - Microsoft Azure](https://docs.microsoft.com/en-us/azure/security/fundamentals/best-practices-and-patterns#feedback)
* Content Source: [articles/security/fundamentals/best-practices-and-patterns.md](https://github.com/Microsoft/azure-docs/blob/master/articles/security/fundamentals/best-practices-and-patterns.md)
* Service: **security**
* Sub-service: **security-fundamentals**
* GitHub Login: @TerryLanfear
* Microsoft Alias: **terrylan** | True | Include the "Five steps to securing your identity infrastructure" article - Five steps to securing your identity infrastructure
https://docs.microsoft.com/en-us/azure/security/fundamentals/steps-secure-identity
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d3e80266-d60e-c46d-38a1-83cfd677f299
* Version Independent ID: c255951e-acda-184a-996b-b3df4a18913a
* Content: [Security best practices and patterns - Microsoft Azure](https://docs.microsoft.com/en-us/azure/security/fundamentals/best-practices-and-patterns#feedback)
* Content Source: [articles/security/fundamentals/best-practices-and-patterns.md](https://github.com/Microsoft/azure-docs/blob/master/articles/security/fundamentals/best-practices-and-patterns.md)
* Service: **security**
* Sub-service: **security-fundamentals**
* GitHub Login: @TerryLanfear
* Microsoft Alias: **terrylan** | non_priority | include the five steps to securing your identity infrastructure article five steps to securing your identity infrastructure document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id acda content content source service security sub service security fundamentals github login terrylanfear microsoft alias terrylan | 0 |
252,467 | 19,027,407,132 | IssuesEvent | 2021-11-24 06:27:45 | DocNow/twarc-csv | https://api.github.com/repos/DocNow/twarc-csv | closed | DataFrameConverter to single tweet | documentation | I have a large set of tweets, and I would like to wrangle and write them to file as I go. DataFrameConverter would be ideal for this, but if I try to pass a tweet to it, I get an error message: `TypeError: process() missing 1 required positional argument: 'objects'`. I followed these instructions:
```
from twarc_csv import DataFrameConverter
json_objects = [...]
df = DataFrameConverter.process(json_objects)
```
passing converter a tweet or a page scraped as described in examples.
What am I doing wrong or can I not use this at all as I would like to?
| 1.0 | DataFrameConverter to single tweet - I have a large set of tweets, and I would like to wrangle and write them to file as I go. DataFrameConverter would be ideal for this, but if I try to pass a tweet to it, I get an error message: `TypeError: process() missing 1 required positional argument: 'objects'`. I followed these instructions:
```
from twarc_csv import DataFrameConverter
json_objects = [...]
df = DataFrameConverter.process(json_objects)
```
passing converter a tweet or a page scraped as described in examples.
What am I doing wrong or can I not use this at all as I would like to?
| non_priority | dataframeconverter to single tweet i have a large set of tweets and i would like to wrangle and write them to file as i go dataframeconverter would be ideal for this but if i try to pass a tweet to it i get an error message typeerror process missing required positional argument objects i followed these instructions from twarc csv import dataframeconverter json objects df dataframeconverter process json objects passing converter a tweet or a page scraped as described in examples what am i doing wrong or can i not use this at all as i would like to | 0 |
284,536 | 30,913,643,163 | IssuesEvent | 2023-08-05 02:28:54 | panasalap/linux-4.19.72_Fix | https://api.github.com/repos/panasalap/linux-4.19.72_Fix | reopened | CVE-2020-28974 (Medium) detected in linux-yoctov5.4.51 | Mend: dependency security vulnerability | ## CVE-2020-28974 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/fc232d9ef12e2320ea3e8cb3de916a34aad68b6a">fc232d9ef12e2320ea3e8cb3de916a34aad68b6a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/tty/vt/vt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A slab-out-of-bounds read in fbcon in the Linux kernel before 5.9.7 could be used by local attackers to read privileged information or potentially crash the kernel, aka CID-3c4e0dff2095. This occurs because KD_FONT_OP_COPY in drivers/tty/vt/vt.c can be used for manipulations such as font height.
<p>Publish Date: 2020-11-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28974>CVE-2020-28974</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.9.7">https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.9.7</a></p>
<p>Release Date: 2020-11-20</p>
<p>Fix Resolution: v5.9.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28974 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2020-28974 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/fc232d9ef12e2320ea3e8cb3de916a34aad68b6a">fc232d9ef12e2320ea3e8cb3de916a34aad68b6a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/tty/vt/vt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A slab-out-of-bounds read in fbcon in the Linux kernel before 5.9.7 could be used by local attackers to read privileged information or potentially crash the kernel, aka CID-3c4e0dff2095. This occurs because KD_FONT_OP_COPY in drivers/tty/vt/vt.c can be used for manipulations such as font height.
<p>Publish Date: 2020-11-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-28974>CVE-2020-28974</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.9.7">https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.9.7</a></p>
<p>Release Date: 2020-11-20</p>
<p>Fix Resolution: v5.9.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers tty vt vt c vulnerability details a slab out of bounds read in fbcon in the linux kernel before could be used by local attackers to read privileged information or potentially crash the kernel aka cid this occurs because kd font op copy in drivers tty vt vt c can be used for manipulations such as font height publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
224,468 | 17,189,626,049 | IssuesEvent | 2021-07-16 09:04:22 | RHEAGROUP/DEH-ECOSIMPRO | https://api.github.com/repos/RHEAGROUP/DEH-ECOSIMPRO | closed | Release document for 1.4.0 | 0.5sp DEHP-ECOSIM documentation | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am running the latest version of the DEHP-EcosimPro
- [x] I have searched [open](https://github.com/RHEAGROUP/DEHP-ECOSIMPRO/issues) and [closed](https://github.com/RHEAGROUP/DEHP-ECOSIMPRO/issues?q=is%3Aissue+is%3Aclosed) issues to ensure it has not already been reported
### Description
<!-- A description of the bug or feature -->
- [x] SVR
- [x] SUM
- [x] SReID
### Steps to Reproduce
<!-- List of steps, sample code, failing test or link to a project that reproduces the behavior -->
### System Configuration
<!-- Tell us about the environment where you are experiencing the bug -->
- DEHPCommon version:
- Environment (Operating system, version and so on):
- .NET Framework version:
- Additional information:
<!-- Thanks for reporting the issue to DEHP-EcosimPro! --> | 1.0 | Release document for 1.4.0 - ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am running the latest version of the DEHP-EcosimPro
- [x] I have searched [open](https://github.com/RHEAGROUP/DEHP-ECOSIMPRO/issues) and [closed](https://github.com/RHEAGROUP/DEHP-ECOSIMPRO/issues?q=is%3Aissue+is%3Aclosed) issues to ensure it has not already been reported
### Description
<!-- A description of the bug or feature -->
- [x] SVR
- [x] SUM
- [x] SReID
### Steps to Reproduce
<!-- List of steps, sample code, failing test or link to a project that reproduces the behavior -->
### System Configuration
<!-- Tell us about the environment where you are experiencing the bug -->
- DEHPCommon version:
- Environment (Operating system, version and so on):
- .NET Framework version:
- Additional information:
<!-- Thanks for reporting the issue to DEHP-EcosimPro! --> | non_priority | release document for prerequisites i have written a descriptive issue title i have verified that i am running the latest version of the dehp ecosimpro i have searched and issues to ensure it has not already been reported description svr sum sreid steps to reproduce system configuration dehpcommon version environment operating system version and so on net framework version additional information | 0 |
934 | 3,244,665,093 | IssuesEvent | 2015-10-16 04:40:09 | aodn/content | https://api.github.com/repos/aodn/content | opened | ANMN layers misleading legend | configuration web map service | **Steps to reproduce:**
Add any of the following collections
IMOS - Australian National Mooring Network (ANMN) Facility - Current velocity time-series
IMOS - Australian National Mooring Network (ANMN) Facility - WQM and CTD burst averaged data products
IMOS - SRS Satellite Altimetry Calibration and Validation Sub-Facility
IMOS - ANMN National Reference Stations - Maria and North Stradbroke Islands - Near real-time meteorology and sea surface temperature
IMOS - ANMN National Reference Stations - Maria and North Stradbroke Islands - Near real-time water quality
IMOS - ABOS Southern Ocean Flux Station (SOFS) - Surface properties (delayed mode)
IMOS - ANMN National Reference Stations - Maria and North Stradbroke Islands - Near real-time wave height
On step 2 look at the layer tab
**What should happen:**
Symbol has a label indicating location of mooring or that it is a mooring?
**What does happen:**
They all say Phytoplankton location
@mhidas perhaps you can comment on this one too?
| 1.0 | ANMN layers misleading legend - **Steps to reproduce:**
Add any of the following collections
IMOS - Australian National Mooring Network (ANMN) Facility - Current velocity time-series
IMOS - Australian National Mooring Network (ANMN) Facility - WQM and CTD burst averaged data products
IMOS - SRS Satellite Altimetry Calibration and Validation Sub-Facility
IMOS - ANMN National Reference Stations - Maria and North Stradbroke Islands - Near real-time meteorology and sea surface temperature
IMOS - ANMN National Reference Stations - Maria and North Stradbroke Islands - Near real-time water quality
IMOS - ABOS Southern Ocean Flux Station (SOFS) - Surface properties (delayed mode)
IMOS - ANMN National Reference Stations - Maria and North Stradbroke Islands - Near real-time wave height
On step 2 look at the layer tab
**What should happen:**
Symbol has a label indicating location of mooring or that it is a mooring?
**What does happen:**
They all say Phytoplankton location
@mhidas perhaps you can comment on this one too?
| non_priority | anmn layers misleading legend steps to reproduce add any of the following collections imos australian national mooring network anmn facility current velocity time series imos australian national mooring network anmn facility wqm and ctd burst averaged data products imos srs satellite altimetry calibration and validation sub facility imos anmn national reference stations maria and north stradbroke islands near real time meteorology and sea surface temperature imos anmn national reference stations maria and north stradbroke islands near real time water quality imos abos southern ocean flux station sofs surface properties delayed mode imos anmn national reference stations maria and north stradbroke islands near real time wave height on step look at the layer tab what should happen symbol has a label indicating location of mooring or that it is a mooring what does happen they all say phytoplankton location mhidas perhaps you can comment on this one too | 0 |
40,523 | 20,958,901,315 | IssuesEvent | 2022-03-27 13:57:55 | pandas-dev/pandas | https://api.github.com/repos/pandas-dev/pandas | opened | groupby on an unsorted index slows to a crawl. works fine if index is sorted. | Performance Needs Triage | ### Pandas version checks
- [X] I have checked that this issue has not already been reported.
- [X] I have confirmed this issue exists on the [latest version](https://pandas.pydata.org/docs/whatsnew/index.html) of pandas.
- [X] I have confirmed this issue exists on the main branch of pandas.
### Reproducible Example
import numpy as np
import pandas as pd
nkeys, nrows, ncols = 50, 5000, 10
tickers = ["X%04d" % i for i in range(nkeys)]
columns = ["C%d" % i for i in range(ncols)]
sample = pd.DataFrame(np.zeros((nrows, ncols)), columns=columns)
tickers = tickers[::-1] # to reverse the tickers
data = {t: sample for t in tickers}
rawdata = pd.concat(data, names=["ticker"])
rawdata = rawdata.reset_index().drop(columns="level_1")
indexed = rawdata.set_index('ticker')
indexed.groupby('ticker').apply(lambda x:x)
### Installed Versions
<details>
INSTALLED VERSIONS
------------------
commit : 06d230151e6f18fdb8139d09abf539867a8cd481
python : 3.8.8.final.0
python-bits : 64
OS : Windows
OS-release : 10
Version : 10.0.22000
machine : AMD64
processor : Intel64 Family 6 Model 158 Stepping 13, GenuineIntel
byteorder : little
LC_ALL : en_US.UTF-8
LANG : en_US.UTF-8
LOCALE : English_United States.1252
pandas : 1.4.1
numpy : 1.20.1
pytz : 2021.1
dateutil : 2.8.1
pip : 21.0.1
setuptools : 52.0.0.post20210125
Cython : 0.29.23
pytest : 6.2.3
hypothesis : None
sphinx : 4.0.1
blosc : None
feather : None
xlsxwriter : 1.3.8
lxml.etree : 4.6.3
html5lib : 1.1
pymysql : 1.0.2
psycopg2 : None
jinja2 : 2.11.3
IPython : 7.22.0
pandas_datareader: 0.10.0
bs4 : 4.9.3
bottleneck : 1.3.2
fastparquet : None
fsspec : 0.9.0
gcsfs : None
matplotlib : 3.3.4
numba : 0.53.1
numexpr : 2.7.3
odfpy : None
openpyxl : 3.0.7
pandas_gbq : None
pyarrow : 7.0.0
pyreadstat : None
pyxlsb : None
s3fs : 0.4.2
scipy : 1.6.2
sqlalchemy : 1.4.7
tables : 3.6.1
tabulate : None
xarray : None
xlrd : 2.0.1
xlwt : 1.3.0
zstandard : None
</details>
### Prior Performance
When indexed is sorted runs under 100 ms.
When not indexed (ie ticker as column) also runs under 100 ms.
Just remove the following code to check :
tickers = tickers[::-1]
| True | groupby on an unsorted index slows to a crawl. works fine if index is sorted. - ### Pandas version checks
- [X] I have checked that this issue has not already been reported.
- [X] I have confirmed this issue exists on the [latest version](https://pandas.pydata.org/docs/whatsnew/index.html) of pandas.
- [X] I have confirmed this issue exists on the main branch of pandas.
### Reproducible Example
import numpy as np
import pandas as pd
nkeys, nrows, ncols = 50, 5000, 10
tickers = ["X%04d" % i for i in range(nkeys)]
columns = ["C%d" % i for i in range(ncols)]
sample = pd.DataFrame(np.zeros((nrows, ncols)), columns=columns)
tickers = tickers[::-1] # to reverse the tickers
data = {t: sample for t in tickers}
rawdata = pd.concat(data, names=["ticker"])
rawdata = rawdata.reset_index().drop(columns="level_1")
indexed = rawdata.set_index('ticker')
indexed.groupby('ticker').apply(lambda x:x)
### Installed Versions
<details>
INSTALLED VERSIONS
------------------
commit : 06d230151e6f18fdb8139d09abf539867a8cd481
python : 3.8.8.final.0
python-bits : 64
OS : Windows
OS-release : 10
Version : 10.0.22000
machine : AMD64
processor : Intel64 Family 6 Model 158 Stepping 13, GenuineIntel
byteorder : little
LC_ALL : en_US.UTF-8
LANG : en_US.UTF-8
LOCALE : English_United States.1252
pandas : 1.4.1
numpy : 1.20.1
pytz : 2021.1
dateutil : 2.8.1
pip : 21.0.1
setuptools : 52.0.0.post20210125
Cython : 0.29.23
pytest : 6.2.3
hypothesis : None
sphinx : 4.0.1
blosc : None
feather : None
xlsxwriter : 1.3.8
lxml.etree : 4.6.3
html5lib : 1.1
pymysql : 1.0.2
psycopg2 : None
jinja2 : 2.11.3
IPython : 7.22.0
pandas_datareader: 0.10.0
bs4 : 4.9.3
bottleneck : 1.3.2
fastparquet : None
fsspec : 0.9.0
gcsfs : None
matplotlib : 3.3.4
numba : 0.53.1
numexpr : 2.7.3
odfpy : None
openpyxl : 3.0.7
pandas_gbq : None
pyarrow : 7.0.0
pyreadstat : None
pyxlsb : None
s3fs : 0.4.2
scipy : 1.6.2
sqlalchemy : 1.4.7
tables : 3.6.1
tabulate : None
xarray : None
xlrd : 2.0.1
xlwt : 1.3.0
zstandard : None
</details>
### Prior Performance
When indexed is sorted runs under 100 ms.
When not indexed (ie ticker as column) also runs under 100 ms.
Just remove the following code to check :
tickers = tickers[::-1]
| non_priority | groupby on an unsorted index slows to a crawl works fine if index is sorted pandas version checks i have checked that this issue has not already been reported i have confirmed this issue exists on the of pandas i have confirmed this issue exists on the main branch of pandas reproducible example import numpy as np import pandas as pd nkeys nrows ncols tickers columns sample pd dataframe np zeros nrows ncols columns columns tickers tickers to reverse the tickers data t sample for t in tickers rawdata pd concat data names rawdata rawdata reset index drop columns level indexed rawdata set index ticker indexed groupby ticker apply lambda x x installed versions installed versions commit python final python bits os windows os release version machine processor family model stepping genuineintel byteorder little lc all en us utf lang en us utf locale english united states pandas numpy pytz dateutil pip setuptools cython pytest hypothesis none sphinx blosc none feather none xlsxwriter lxml etree pymysql none ipython pandas datareader bottleneck fastparquet none fsspec gcsfs none matplotlib numba numexpr odfpy none openpyxl pandas gbq none pyarrow pyreadstat none pyxlsb none scipy sqlalchemy tables tabulate none xarray none xlrd xlwt zstandard none prior performance when indexed is sorted runs under ms when not indexed ie ticker as column also runs under ms just remove the following code to check tickers tickers | 0 |
343,794 | 30,689,975,049 | IssuesEvent | 2023-07-26 14:36:29 | soujava/vagas-java | https://api.github.com/repos/soujava/vagas-java | closed | [Remoto] Desenvolvedor(a) Backend Java | Improving | Sênior Júnior CLT Pleno Remoto DevOps Spring Docker NoSQL Kotlin Testes Unitários Java Google Cloud Consultoria job opportunity Stale | ## Descrição da vaga
Tem experiência com sistemas distribuídos em Java e gostaria de trabalhar da sua casa implementando sistemas que serão usados por milhões de pessoas em uma empresa que valoriza e dá autonomia aos profissionais?
Você poderá trabalhar de qualquer lugar do Brasil, em regime 100% remoto CLT.
Há equipes atendendo a diferentes negócios e com tecnologias distintas, como bancos digitais, pagamentos e cartões, grandes e-commerces, envolvendo usos de linguagens diferentes da JVM, como Java, Kotlin e Clojure, sempre com arquiteturas reativas modernas de microsserviços.
## Local
Remoto
## Benefícios
- Salário entre R$ 5.500 e R$ 16.500 (dependendo de como você for avaliado) ;
- R$ 1.100 em vale-refeição ou vale-alimentação (você escolhe) com um pagamento extra em dezembro ;
- Plano de saúde SulAmérica ou Unimed integral (com desconto de 50% para dependentes);
- Plano odontológico SulAmérica;
- Seguro de vida;
- Auxílio creche;
- Aulas de inglês na Cambly;
- Auxílio equipamento (notebook, cadeira etc) de R$ 4.000,00;
- Bônus anual entre 1 e 3 salários com base no desempenho da empresa
## Diferenciais
- Trabalhar remotamente, com qualidade de vida, interagindo com tecnologias de ponta, definindo a arquitetura e participando na construção de sistemas que serão usados por milhões de pessoas;
- Ter autonomia e incentivo ao crescimento profissional, tendo tempo de prototipar com o time diferentes tecnologias para ver qual atende melhor às necessidades do cliente.
## Requisitos
#### Obrigatórios:
- Espírito de trabalho em equipe, comprometimento e vontade de pôr a mão na massa;
- Capacidade de aprender rapidamente tecnologias emergentes mediante ao consumo de livros, documentação técnica, vídeos ou palestras;
- Domínio de orientação a objetos, Java SE 8 (incluindo lambda) e suas APIs principais (java.lang, Collections, streams, etc);
- Conhecimento e consciência da necessidade de testes unitários, de integração e aceitação;
- Sólidos conhecimentos em bancos de dados relacionais;
- Familiaridade com Docker
#### Desejáveis:
- Sólidos conhecimentos em arquitetura reativa;
- Sólidos conhecimentos de pelo menos um ambiente de cloud;
- Ampla experiência com integrações de sistemas, arquitetura de microsserviços e DDD;
- Conhecimento prático de técnicas para escalar serviços e resolver problemas de performance;
- Experiência com Kotlin, Clojure e/ou com as versões mais recentes do Java SE;
- Experiência com Spring WebFlux;
- Experiência com Google Cloud Platform;
- Experiência com Kubernetes;
- Experiência com bancos NoSQL;
- Conhecimentos de segurança;
- Conhecimentos de entrega contínua e automação de infraestrutura em geral
## Contratação
Você será contratado em regime CLT
## Nossa empresa
A empresa é uma consultoria que existe há 10 anos e foca apenas em projetos de longa duração que tragam impacto positivo para a sociedade e que ajudem os desenvolvedores a evoluir. Além disso, acredita em desenvolvimento ágil, DevOps e trabalho remoto e segue um modelo completamente diferente do body shop - você não está condicionado ao projeto em que iniciará nem se o cliente manterá o projeto ou não. Algumas práticas do dia a dia mostram que você realmente é parte da empresa, como por exemplo os projetos possuírem code review de pessoas externas àquela conta.
## Como se candidatar
Basta entrar no seguinte link: [http://bit.ly/2XFoLVo](http://bit.ly/2XFoLVo), preencher nome e email e te enviaremos as instruções.
## Tempo médio de feedbacks
Costumamos enviar feedbacks em até 6 dias úteis após cada processo.
Caso não haja resposta, basta responder ao email de conclusão da etapa.
#### Alocação
- Remoto
#### Regime
- CLT
#### Nível
- Júnior
- Pleno
- Sênior
- Especialista
| 1.0 | [Remoto] Desenvolvedor(a) Backend Java | Improving - ## Descrição da vaga
Tem experiência com sistemas distribuídos em Java e gostaria de trabalhar da sua casa implementando sistemas que serão usados por milhões de pessoas em uma empresa que valoriza e dá autonomia aos profissionais?
Você poderá trabalhar de qualquer lugar do Brasil, em regime 100% remoto CLT.
Há equipes atendendo a diferentes negócios e com tecnologias distintas, como bancos digitais, pagamentos e cartões, grandes e-commerces, envolvendo usos de linguagens diferentes da JVM, como Java, Kotlin e Clojure, sempre com arquiteturas reativas modernas de microsserviços.
## Local
Remoto
## Benefícios
- Salário entre R$ 5.500 e R$ 16.500 (dependendo de como você for avaliado) ;
- R$ 1.100 em vale-refeição ou vale-alimentação (você escolhe) com um pagamento extra em dezembro ;
- Plano de saúde SulAmérica ou Unimed integral (com desconto de 50% para dependentes);
- Plano odontológico SulAmérica;
- Seguro de vida;
- Auxílio creche;
- Aulas de inglês na Cambly;
- Auxílio equipamento (notebook, cadeira etc) de R$ 4.000,00;
- Bônus anual entre 1 e 3 salários com base no desempenho da empresa
## Diferenciais
- Trabalhar remotamente, com qualidade de vida, interagindo com tecnologias de ponta, definindo a arquitetura e participando na construção de sistemas que serão usados por milhões de pessoas;
- Ter autonomia e incentivo ao crescimento profissional, tendo tempo de prototipar com o time diferentes tecnologias para ver qual atende melhor às necessidades do cliente.
## Requisitos
#### Obrigatórios:
- Espírito de trabalho em equipe, comprometimento e vontade de pôr a mão na massa;
- Capacidade de aprender rapidamente tecnologias emergentes mediante ao consumo de livros, documentação técnica, vídeos ou palestras;
- Domínio de orientação a objetos, Java SE 8 (incluindo lambda) e suas APIs principais (java.lang, Collections, streams, etc);
- Conhecimento e consciência da necessidade de testes unitários, de integração e aceitação;
- Sólidos conhecimentos em bancos de dados relacionais;
- Familiaridade com Docker
#### Desejáveis:
- Sólidos conhecimentos em arquitetura reativa;
- Sólidos conhecimentos de pelo menos um ambiente de cloud;
- Ampla experiência com integrações de sistemas, arquitetura de microsserviços e DDD;
- Conhecimento prático de técnicas para escalar serviços e resolver problemas de performance;
- Experiência com Kotlin, Clojure e/ou com as versões mais recentes do Java SE;
- Experiência com Spring WebFlux;
- Experiência com Google Cloud Platform;
- Experiência com Kubernetes;
- Experiência com bancos NoSQL;
- Conhecimentos de segurança;
- Conhecimentos de entrega contínua e automação de infraestrutura em geral
## Contratação
Você será contratado em regime CLT
## Nossa empresa
A empresa é uma consultoria que existe há 10 anos e foca apenas em projetos de longa duração que tragam impacto positivo para a sociedade e que ajudem os desenvolvedores a evoluir. Além disso, acredita em desenvolvimento ágil, DevOps e trabalho remoto e segue um modelo completamente diferente do body shop - você não está condicionado ao projeto em que iniciará nem se o cliente manterá o projeto ou não. Algumas práticas do dia a dia mostram que você realmente é parte da empresa, como por exemplo os projetos possuírem code review de pessoas externas àquela conta.
## Como se candidatar
Basta entrar no seguinte link: [http://bit.ly/2XFoLVo](http://bit.ly/2XFoLVo), preencher nome e email e te enviaremos as instruções.
## Tempo médio de feedbacks
Costumamos enviar feedbacks em até 6 dias úteis após cada processo.
Caso não haja resposta, basta responder ao email de conclusão da etapa.
#### Alocação
- Remoto
#### Regime
- CLT
#### Nível
- Júnior
- Pleno
- Sênior
- Especialista
| non_priority | desenvolvedor a backend java improving descrição da vaga tem experiência com sistemas distribuídos em java e gostaria de trabalhar da sua casa implementando sistemas que serão usados por milhões de pessoas em uma empresa que valoriza e dá autonomia aos profissionais você poderá trabalhar de qualquer lugar do brasil em regime remoto clt há equipes atendendo a diferentes negócios e com tecnologias distintas como bancos digitais pagamentos e cartões grandes e commerces envolvendo usos de linguagens diferentes da jvm como java kotlin e clojure sempre com arquiteturas reativas modernas de microsserviços local remoto benefícios salário entre r e r dependendo de como você for avaliado r em vale refeição ou vale alimentação você escolhe com um pagamento extra em dezembro plano de saúde sulamérica ou unimed integral com desconto de para dependentes plano odontológico sulamérica seguro de vida auxílio creche aulas de inglês na cambly auxílio equipamento notebook cadeira etc de r bônus anual entre e salários com base no desempenho da empresa diferenciais trabalhar remotamente com qualidade de vida interagindo com tecnologias de ponta definindo a arquitetura e participando na construção de sistemas que serão usados por milhões de pessoas ter autonomia e incentivo ao crescimento profissional tendo tempo de prototipar com o time diferentes tecnologias para ver qual atende melhor às necessidades do cliente requisitos obrigatórios espírito de trabalho em equipe comprometimento e vontade de pôr a mão na massa capacidade de aprender rapidamente tecnologias emergentes mediante ao consumo de livros documentação técnica vídeos ou palestras domínio de orientação a objetos java se incluindo lambda e suas apis principais java lang collections streams etc conhecimento e consciência da necessidade de testes unitários de integração e aceitação sólidos conhecimentos em bancos de dados relacionais familiaridade com docker desejáveis sólidos conhecimentos em arquitetura reativa sólidos conhecimentos de pelo menos um ambiente de cloud ampla experiência com integrações de sistemas arquitetura de microsserviços e ddd conhecimento prático de técnicas para escalar serviços e resolver problemas de performance experiência com kotlin clojure e ou com as versões mais recentes do java se experiência com spring webflux experiência com google cloud platform experiência com kubernetes experiência com bancos nosql conhecimentos de segurança conhecimentos de entrega contínua e automação de infraestrutura em geral contratação você será contratado em regime clt nossa empresa a empresa é uma consultoria que existe há anos e foca apenas em projetos de longa duração que tragam impacto positivo para a sociedade e que ajudem os desenvolvedores a evoluir além disso acredita em desenvolvimento ágil devops e trabalho remoto e segue um modelo completamente diferente do body shop você não está condicionado ao projeto em que iniciará nem se o cliente manterá o projeto ou não algumas práticas do dia a dia mostram que você realmente é parte da empresa como por exemplo os projetos possuírem code review de pessoas externas àquela conta como se candidatar basta entrar no seguinte link preencher nome e email e te enviaremos as instruções tempo médio de feedbacks costumamos enviar feedbacks em até dias úteis após cada processo caso não haja resposta basta responder ao email de conclusão da etapa alocação remoto regime clt nível júnior pleno sênior especialista | 0 |
73,965 | 7,370,985,048 | IssuesEvent | 2018-03-13 10:15:33 | red/red | https://api.github.com/repos/red/red | closed | PRIN / PRINT doesn't output anything after compilation on Windows targets | GUI status.built status.tested type.bug | ### Expected behavior
Script prints `something` in shell console.
### Actual behavior
No output (checked on Wine, Win7 and Win10).
Wine chokes with following exception:
```
*** Runtime Error err:seh:raise_exception Unhandled exception code c0000005 flags 0 addr 0x416191
```
### Steps to reproduce the problem
```Red
Red [Needs: View]
print "something"
```
Compile the script above for `Windows` or `WindowsXP` targets and execute it from shell. Same script works as expected for `Linux` (with `Needs: View` omitted for obvious reasons) and `MSDOS` targets.
### Red version and build date, operating system with version.
I think it applies to latest ones too.
```Red
>> about
Red for Windows version 0.6.3 built 25-Jan-2018/23:52:32+05:00
``` | 1.0 | PRIN / PRINT doesn't output anything after compilation on Windows targets - ### Expected behavior
Script prints `something` in shell console.
### Actual behavior
No output (checked on Wine, Win7 and Win10).
Wine chokes with following exception:
```
*** Runtime Error err:seh:raise_exception Unhandled exception code c0000005 flags 0 addr 0x416191
```
### Steps to reproduce the problem
```Red
Red [Needs: View]
print "something"
```
Compile the script above for `Windows` or `WindowsXP` targets and execute it from shell. Same script works as expected for `Linux` (with `Needs: View` omitted for obvious reasons) and `MSDOS` targets.
### Red version and build date, operating system with version.
I think it applies to latest ones too.
```Red
>> about
Red for Windows version 0.6.3 built 25-Jan-2018/23:52:32+05:00
``` | non_priority | prin print doesn t output anything after compilation on windows targets expected behavior script prints something in shell console actual behavior no output checked on wine and wine chokes with following exception runtime error err seh raise exception unhandled exception code flags addr steps to reproduce the problem red red print something compile the script above for windows or windowsxp targets and execute it from shell same script works as expected for linux with needs view omitted for obvious reasons and msdos targets red version and build date operating system with version i think it applies to latest ones too red about red for windows version built jan | 0 |
64,617 | 15,964,983,436 | IssuesEvent | 2021-04-16 07:07:42 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug] Multi-select dropdown widget doesn't show selected options count | Bug Dropdown Widget Low Low effort UI Building Pod Widgets | The multi-select dropdown widget is supposed to show the names of a few selected options and then truncate the rest to show a count when there's not enough space.
1. This is how it looks today.
<img width="246" alt="Screen Shot 2021-04-15 at 7 53 56 PM" src="https://user-images.githubusercontent.com/30255708/114886059-dab15c80-9e24-11eb-9d45-ddf7cd069962.png">
2. This is how it is supposed to look
<img width="398" alt="Screen Shot 2021-04-15 at 7 55 32 PM" src="https://user-images.githubusercontent.com/30255708/114886064-dbe28980-9e24-11eb-8277-aee3143035bb.png">
Link to Figma: https://www.figma.com/file/moGQyQffFfyUhHUMO9xqn3/Appsmith-v1.0-Final?node-id=8229%3A6383
| 1.0 | [Bug] Multi-select dropdown widget doesn't show selected options count - The multi-select dropdown widget is supposed to show the names of a few selected options and then truncate the rest to show a count when there's not enough space.
1. This is how it looks today.
<img width="246" alt="Screen Shot 2021-04-15 at 7 53 56 PM" src="https://user-images.githubusercontent.com/30255708/114886059-dab15c80-9e24-11eb-9d45-ddf7cd069962.png">
2. This is how it is supposed to look
<img width="398" alt="Screen Shot 2021-04-15 at 7 55 32 PM" src="https://user-images.githubusercontent.com/30255708/114886064-dbe28980-9e24-11eb-8277-aee3143035bb.png">
Link to Figma: https://www.figma.com/file/moGQyQffFfyUhHUMO9xqn3/Appsmith-v1.0-Final?node-id=8229%3A6383
| non_priority | multi select dropdown widget doesn t show selected options count the multi select dropdown widget is supposed to show the names of a few selected options and then truncate the rest to show a count when there s not enough space this is how it looks today img width alt screen shot at pm src this is how it is supposed to look img width alt screen shot at pm src link to figma | 0 |
43,532 | 13,018,829,289 | IssuesEvent | 2020-07-26 19:18:38 | Ramithags/StockExchange | https://api.github.com/repos/Ramithags/StockExchange | closed | CVE-2020-14195 (High) detected in jackson-databind-2.9.6.jar | security vulnerability | ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/StockExchange/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.5.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Ramithags/StockExchange/commit/0a932eaf07b9e100b7bbe0124d67cc49a267eab4">0a932eaf07b9e100b7bbe0124d67cc49a267eab4</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-14195 (High) detected in jackson-databind-2.9.6.jar - ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/StockExchange/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.5.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Ramithags/StockExchange/commit/0a932eaf07b9e100b7bbe0124d67cc49a267eab4">0a932eaf07b9e100b7bbe0124d67cc49a267eab4</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm stockexchange pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
48,011 | 10,195,586,179 | IssuesEvent | 2019-08-12 18:30:50 | clormor/hacker-rank-java | https://api.github.com/repos/clormor/hacker-rank-java | opened | Fix "method_complexity" issue in src/main/java/io/github/clormor/hackerrank/ai/BotSavesPrincess.java | code-climate | Method `locateTarget` has a Cognitive Complexity of 6 (exceeds 5 allowed). Consider refactoring.
https://codeclimate.com/github/clormor/hacker-rank-java/src/main/java/io/github/clormor/hackerrank/ai/BotSavesPrincess.java#issue_5d51a46cf17d0c0001000027 | 1.0 | Fix "method_complexity" issue in src/main/java/io/github/clormor/hackerrank/ai/BotSavesPrincess.java - Method `locateTarget` has a Cognitive Complexity of 6 (exceeds 5 allowed). Consider refactoring.
https://codeclimate.com/github/clormor/hacker-rank-java/src/main/java/io/github/clormor/hackerrank/ai/BotSavesPrincess.java#issue_5d51a46cf17d0c0001000027 | non_priority | fix method complexity issue in src main java io github clormor hackerrank ai botsavesprincess java method locatetarget has a cognitive complexity of exceeds allowed consider refactoring | 0 |
284,632 | 30,913,656,374 | IssuesEvent | 2023-08-05 02:31:06 | Nivaskumark/kernel_v4.19.72_old | https://api.github.com/repos/Nivaskumark/kernel_v4.19.72_old | reopened | CVE-2022-20227 (Medium) detected in linux-yoctov5.4.51 | Mend: dependency security vulnerability | ## CVE-2022-20227 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In USB driver, there is a possible out of bounds read due to a heap buffer overflow. This could lead to local information disclosure with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-216825460References: Upstream kernel
<p>Publish Date: 2022-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20227>CVE-2022-20227</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/kernel/common/+/fb4ff0f96de37">https://android.googlesource.com/kernel/common/+/fb4ff0f96de37</a></p>
<p>Release Date: 2022-07-13</p>
<p>Fix Resolution: android-12.1.0_r0.35</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-20227 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2022-20227 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In USB driver, there is a possible out of bounds read due to a heap buffer overflow. This could lead to local information disclosure with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-216825460References: Upstream kernel
<p>Publish Date: 2022-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20227>CVE-2022-20227</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/kernel/common/+/fb4ff0f96de37">https://android.googlesource.com/kernel/common/+/fb4ff0f96de37</a></p>
<p>Release Date: 2022-07-13</p>
<p>Fix Resolution: android-12.1.0_r0.35</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in base branch master vulnerable source files vulnerability details in usb driver there is a possible out of bounds read due to a heap buffer overflow this could lead to local information disclosure with user execution privileges needed user interaction is not needed for exploitation product androidversions android kernelandroid id a upstream kernel publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend | 0 |
25,723 | 12,294,046,004 | IssuesEvent | 2020-05-10 21:51:06 | TeamNewPipe/NewPipe | https://api.github.com/repos/TeamNewPipe/NewPipe | closed | Add support banned.video | enhancement new service | <!-- Hey. Our contribution guidelines (https://github.com/TeamNewPipe/NewPipe/blob/HEAD/.github/CONTRIBUTING.md) might be an appropriate
document to read before you fill out the request :) -->
<!-- The comments between these brackets won't show up in the submitted issue (as you can see in the preview). -->
#### Describe the feature you want
<!-- A clear and concise description of what you want to happen. PLEASE MAKE SURE it is one feature ONLY. You should open separate issues for separate feature requests, because those issues will be used to track their status.
Example: *I think it would be nice if you add feature Y which makes X possible.*
Optionally, also describe alternatives you've considered.
Example: *Z is also a good alternative. Not as good as Y, but at least...* or *I considered Z, but that didn't turn out to be a good idea because...* -->
Add support for site `https://banned.video/`
<!-- Write below this -->
#### Is your feature request related to a problem? Please describe it
<!-- A clear and concise description of what the problem is. Maybe the developers could brainstorm and come up with a better solution to your problem. If they exist, link to related Issues and/or PRs for developers to keep track easier.
Example: *I want to do X, but there is no way to do it.* -->
<!-- Write below this -->
#### Additional context
<!-- Add any other context, like screenshots, about the feature request here.
Example: *Here's a photo of my cat!* -->
<!-- Write below this -->
#### How will you/everyone benefit from this feature?
<!-- Convince us! How does it change your NewPipe experience and/or your life?
The better this paragraph is, the more likely a developer will think about working on it.
Example: *This feature will help us colonize the galaxy! -->
<!-- Write below this -->
| 1.0 | Add support banned.video - <!-- Hey. Our contribution guidelines (https://github.com/TeamNewPipe/NewPipe/blob/HEAD/.github/CONTRIBUTING.md) might be an appropriate
document to read before you fill out the request :) -->
<!-- The comments between these brackets won't show up in the submitted issue (as you can see in the preview). -->
#### Describe the feature you want
<!-- A clear and concise description of what you want to happen. PLEASE MAKE SURE it is one feature ONLY. You should open separate issues for separate feature requests, because those issues will be used to track their status.
Example: *I think it would be nice if you add feature Y which makes X possible.*
Optionally, also describe alternatives you've considered.
Example: *Z is also a good alternative. Not as good as Y, but at least...* or *I considered Z, but that didn't turn out to be a good idea because...* -->
Add support for site `https://banned.video/`
<!-- Write below this -->
#### Is your feature request related to a problem? Please describe it
<!-- A clear and concise description of what the problem is. Maybe the developers could brainstorm and come up with a better solution to your problem. If they exist, link to related Issues and/or PRs for developers to keep track easier.
Example: *I want to do X, but there is no way to do it.* -->
<!-- Write below this -->
#### Additional context
<!-- Add any other context, like screenshots, about the feature request here.
Example: *Here's a photo of my cat!* -->
<!-- Write below this -->
#### How will you/everyone benefit from this feature?
<!-- Convince us! How does it change your NewPipe experience and/or your life?
The better this paragraph is, the more likely a developer will think about working on it.
Example: *This feature will help us colonize the galaxy! -->
<!-- Write below this -->
| non_priority | add support banned video hey our contribution guidelines might be an appropriate document to read before you fill out the request describe the feature you want a clear and concise description of what you want to happen please make sure it is one feature only you should open separate issues for separate feature requests because those issues will be used to track their status example i think it would be nice if you add feature y which makes x possible optionally also describe alternatives you ve considered example z is also a good alternative not as good as y but at least or i considered z but that didn t turn out to be a good idea because add support for site is your feature request related to a problem please describe it a clear and concise description of what the problem is maybe the developers could brainstorm and come up with a better solution to your problem if they exist link to related issues and or prs for developers to keep track easier example i want to do x but there is no way to do it additional context add any other context like screenshots about the feature request here example here s a photo of my cat how will you everyone benefit from this feature convince us how does it change your newpipe experience and or your life the better this paragraph is the more likely a developer will think about working on it example this feature will help us colonize the galaxy | 0 |
36,554 | 8,132,092,272 | IssuesEvent | 2018-08-18 06:57:12 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] Router bug: contacts | J4 Issue No Code Attached Yet | This report is limited to com_contacts but it could also touch some other components in core.
### Steps to reproduce the issue
Use latest 4.0-dev
Tested on a multilingual site.
Create a contact category tagged to each language.
Create a contact in each of these categories, tagged to the same language.
I have as menu item type "List Contacts in a category"
`/index.php/en/contact-category-en-gb`
The link on that page displaying the contact is
`/index.php/en/contact-category-en-gb/mycontact` // see below direct menu item. this url is a double with the one below (it should be `/index.php/en/my-contact`). Alias of that single contact is `mycontact`
// I do also have a direct menu item to that contact (alias of the menu item is `my_contact`)
When I use this last one (`/index.php/en/my-contact`), the category link above the contact gives
`/index.php/en/my-contact?view=category&id=14` instead of the existing `/index.php/en/contact-category-en-gb`
| 1.0 | [4.0] Router bug: contacts - This report is limited to com_contacts but it could also touch some other components in core.
### Steps to reproduce the issue
Use latest 4.0-dev
Tested on a multilingual site.
Create a contact category tagged to each language.
Create a contact in each of these categories, tagged to the same language.
I have as menu item type "List Contacts in a category"
`/index.php/en/contact-category-en-gb`
The link on that page displaying the contact is
`/index.php/en/contact-category-en-gb/mycontact` // see below direct menu item. this url is a double with the one below (it should be `/index.php/en/my-contact`). Alias of that single contact is `mycontact`
// I do also have a direct menu item to that contact (alias of the menu item is `my_contact`)
When I use this last one (`/index.php/en/my-contact`), the category link above the contact gives
`/index.php/en/my-contact?view=category&id=14` instead of the existing `/index.php/en/contact-category-en-gb`
| non_priority | router bug contacts this report is limited to com contacts but it could also touch some other components in core steps to reproduce the issue use latest dev tested on a multilingual site create a contact category tagged to each language create a contact in each of these categories tagged to the same language i have as menu item type list contacts in a category index php en contact category en gb the link on that page displaying the contact is index php en contact category en gb mycontact see below direct menu item this url is a double with the one below it should be index php en my contact alias of that single contact is mycontact i do also have a direct menu item to that contact alias of the menu item is my contact when i use this last one index php en my contact the category link above the contact gives index php en my contact view category id instead of the existing index php en contact category en gb | 0 |
190,467 | 14,546,897,928 | IssuesEvent | 2020-12-15 22:00:00 | gigantum/gigantum-client | https://api.github.com/repos/gigantum/gigantum-client | opened | Add test case for merge conflicts | test-harness | ## Description
This test case is a long workflow that tests basic merge conflict behavior ('mine', 'theirs', 'abort')
A test fixture should remove the created project and docker image from the host during tear down. It should be robust to the project not existing locally in case a failure occurs at any point in the test.
Steps should be in 1 test class and broken into methods in logical groupings.
The test case should delete the project from the server if it is successfully published. This should happen in a fixture in case the test fails so published projects do not accumulate.
## Steps
**Create Project and add file**
- Log in as user 1
- Click on "Create New"
- Enter a unique random name and description
- Click "Continue"
- Select the "Python3 Minimal" Base
- Click "Create Project"
- Monitor container status to go through building -> stopped state
- Click on the "Code" data tab and drag and drop a text file with the contents `user1:created`
**Publish**
- Click the publish button
- Select "private" in the modal and publish the project
- Wait for publish process to complete
- Open the collaborator modal and add user 2 as an admin
**Switch users and import**
- Click on the logout button
- Log in as user 2
- Navigate to the "Gigantum Hub" tab
- Click the "import button" and wait for import and build to complete
**Update files and sync**
- Verify the contents of the file to be `user1:created`
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user2:modified1`
- Click on the sync button and wait for the sync process to complete
**Switch users**
- Click on the logout button
- Log in as user 1
**Update file and sync -> Conflict, Abort**
- Verify the contents of the file to be `user1:created` still
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user1:modified1`
- Click on the sync button
- Verify the merge conflict modal appears
- Click on the "abort" button
- Verify the modal closes
- Verify the contents of the file to be `user1:modified1` still
**Resolve Conflict - Theirs**
- Click on the sync button again
- Verify the merge conflict modal appears again
- Click on the "theirs" button
- Verify the modal closes. wait for sync to complete.
- Verify the contents of the file to be `user2:modified1`
**Create another conflict**
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user1:modified2`
- Click on the sync button. No conflict modal should appear. Wait for sync to complete.
**Switch users**
- Click on the logout button
- Log in as user 2
**Update file and sync -> Conflict, Mine**
- Verify the contents of the file to be `user2:modified1` still
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user2:modified2`
- Click on the sync button
- Verify the merge conflict modal appears
- Click on the "mine" button
- Verify the modal closes and wait for the sync to complete
- Verify the contents of the file to be `user2:modified2`
**Switch users**
- Click on the logout button
- Log in as user 1
**sync and verify resolution**
- Verify the contents of the file to be `user1:modified2`
- Click on the sync button
- Verify no conflict occurs and wait for sync to complete
- Verify the contents of the file to be `user2:modified2`
| 1.0 | Add test case for merge conflicts - ## Description
This test case is a long workflow that tests basic merge conflict behavior ('mine', 'theirs', 'abort')
A test fixture should remove the created project and docker image from the host during tear down. It should be robust to the project not existing locally in case a failure occurs at any point in the test.
Steps should be in 1 test class and broken into methods in logical groupings.
The test case should delete the project from the server if it is successfully published. This should happen in a fixture in case the test fails so published projects do not accumulate.
## Steps
**Create Project and add file**
- Log in as user 1
- Click on "Create New"
- Enter a unique random name and description
- Click "Continue"
- Select the "Python3 Minimal" Base
- Click "Create Project"
- Monitor container status to go through building -> stopped state
- Click on the "Code" data tab and drag and drop a text file with the contents `user1:created`
**Publish**
- Click the publish button
- Select "private" in the modal and publish the project
- Wait for publish process to complete
- Open the collaborator modal and add user 2 as an admin
**Switch users and import**
- Click on the logout button
- Log in as user 2
- Navigate to the "Gigantum Hub" tab
- Click the "import button" and wait for import and build to complete
**Update files and sync**
- Verify the contents of the file to be `user1:created`
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user2:modified1`
- Click on the sync button and wait for the sync process to complete
**Switch users**
- Click on the logout button
- Log in as user 1
**Update file and sync -> Conflict, Abort**
- Verify the contents of the file to be `user1:created` still
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user1:modified1`
- Click on the sync button
- Verify the merge conflict modal appears
- Click on the "abort" button
- Verify the modal closes
- Verify the contents of the file to be `user1:modified1` still
**Resolve Conflict - Theirs**
- Click on the sync button again
- Verify the merge conflict modal appears again
- Click on the "theirs" button
- Verify the modal closes. wait for sync to complete.
- Verify the contents of the file to be `user2:modified1`
**Create another conflict**
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user1:modified2`
- Click on the sync button. No conflict modal should appear. Wait for sync to complete.
**Switch users**
- Click on the logout button
- Log in as user 2
**Update file and sync -> Conflict, Mine**
- Verify the contents of the file to be `user2:modified1` still
- Click on the "Code" tab and drag and drop a text file with the same name as previously used, but change the contents to `user2:modified2`
- Click on the sync button
- Verify the merge conflict modal appears
- Click on the "mine" button
- Verify the modal closes and wait for the sync to complete
- Verify the contents of the file to be `user2:modified2`
**Switch users**
- Click on the logout button
- Log in as user 1
**sync and verify resolution**
- Verify the contents of the file to be `user1:modified2`
- Click on the sync button
- Verify no conflict occurs and wait for sync to complete
- Verify the contents of the file to be `user2:modified2`
| non_priority | add test case for merge conflicts description this test case is a long workflow that tests basic merge conflict behavior mine theirs abort a test fixture should remove the created project and docker image from the host during tear down it should be robust to the project not existing locally in case a failure occurs at any point in the test steps should be in test class and broken into methods in logical groupings the test case should delete the project from the server if it is successfully published this should happen in a fixture in case the test fails so published projects do not accumulate steps create project and add file log in as user click on create new enter a unique random name and description click continue select the minimal base click create project monitor container status to go through building stopped state click on the code data tab and drag and drop a text file with the contents created publish click the publish button select private in the modal and publish the project wait for publish process to complete open the collaborator modal and add user as an admin switch users and import click on the logout button log in as user navigate to the gigantum hub tab click the import button and wait for import and build to complete update files and sync verify the contents of the file to be created click on the code tab and drag and drop a text file with the same name as previously used but change the contents to click on the sync button and wait for the sync process to complete switch users click on the logout button log in as user update file and sync conflict abort verify the contents of the file to be created still click on the code tab and drag and drop a text file with the same name as previously used but change the contents to click on the sync button verify the merge conflict modal appears click on the abort button verify the modal closes verify the contents of the file to be still resolve conflict theirs click on the sync button again verify the merge conflict modal appears again click on the theirs button verify the modal closes wait for sync to complete verify the contents of the file to be create another conflict click on the code tab and drag and drop a text file with the same name as previously used but change the contents to click on the sync button no conflict modal should appear wait for sync to complete switch users click on the logout button log in as user update file and sync conflict mine verify the contents of the file to be still click on the code tab and drag and drop a text file with the same name as previously used but change the contents to click on the sync button verify the merge conflict modal appears click on the mine button verify the modal closes and wait for the sync to complete verify the contents of the file to be switch users click on the logout button log in as user sync and verify resolution verify the contents of the file to be click on the sync button verify no conflict occurs and wait for sync to complete verify the contents of the file to be | 0 |
14,461 | 24,915,231,267 | IssuesEvent | 2022-10-30 10:17:04 | cskefu/cskefu | https://api.github.com/repos/cskefu/cskefu | closed | Setup 春松客服贡献者协议:DCO or CLA | requirement |
Use contributor-assistant, https://github.com/contributor-assistant/github-action.
Decide which form to use: DCO or CLA.
| 1.0 | Setup 春松客服贡献者协议:DCO or CLA -
Use contributor-assistant, https://github.com/contributor-assistant/github-action.
Decide which form to use: DCO or CLA.
| non_priority | setup 春松客服贡献者协议:dco or cla use contributor assistant decide which form to use dco or cla | 0 |
253,874 | 21,711,175,678 | IssuesEvent | 2022-05-10 14:00:00 | Azordev/various-tasks | https://api.github.com/repos/Azordev/various-tasks | closed | Component Unit Test #3 | EE-1 Under Review Test | ## Explanation
In SP we need to create unit tests for some components, in this task you will see collected 5 components that do not have unit tests and need to be added, each component must meet the following tests:
- Snapshot
- Is render correctly
- Functionality tests if apply
- Negative tests if apply
The components that are being mentioned are inside **/src/components**, first you should go to **src/components,** and then follow the path that the checklist says: for example **src/components/Modals/EmailCaptureSubmitBtn**
### Checklist
- [ ] Modals/BtnCloseEmailModalWrapper has the tests mentioned in the explanation
- [ ] Modals/EmailCaptureModal has the tests mentioned in the explanation
- [ ] Modals/Modal has the tests mentioned in the explanation
- [ ] Modals/EmailCaptureContent has the tests mentioned in the explanation
- [ ] Modals/EmailCaptureSubmitBtn has the tests mentioned in the explanation
| 1.0 | Component Unit Test #3 - ## Explanation
In SP we need to create unit tests for some components, in this task you will see collected 5 components that do not have unit tests and need to be added, each component must meet the following tests:
- Snapshot
- Is render correctly
- Functionality tests if apply
- Negative tests if apply
The components that are being mentioned are inside **/src/components**, first you should go to **src/components,** and then follow the path that the checklist says: for example **src/components/Modals/EmailCaptureSubmitBtn**
### Checklist
- [ ] Modals/BtnCloseEmailModalWrapper has the tests mentioned in the explanation
- [ ] Modals/EmailCaptureModal has the tests mentioned in the explanation
- [ ] Modals/Modal has the tests mentioned in the explanation
- [ ] Modals/EmailCaptureContent has the tests mentioned in the explanation
- [ ] Modals/EmailCaptureSubmitBtn has the tests mentioned in the explanation
| non_priority | component unit test explanation in sp we need to create unit tests for some components in this task you will see collected components that do not have unit tests and need to be added each component must meet the following tests snapshot is render correctly functionality tests if apply negative tests if apply the components that are being mentioned are inside src components first you should go to src components and then follow the path that the checklist says for example src components modals emailcapturesubmitbtn checklist modals btncloseemailmodalwrapper has the tests mentioned in the explanation modals emailcapturemodal has the tests mentioned in the explanation modals modal has the tests mentioned in the explanation modals emailcapturecontent has the tests mentioned in the explanation modals emailcapturesubmitbtn has the tests mentioned in the explanation | 0 |
94,036 | 27,101,095,484 | IssuesEvent | 2023-02-15 08:43:44 | PaddlePaddle/Paddle | https://api.github.com/repos/PaddlePaddle/Paddle | opened | 请问,有或者能提供arm架构下gpu版的paddle的docker安装的镜像吗 | status/new-issue type/build | ### 问题描述 Issue Description
希望在国产机器上使用paddle和paddlenlp,但是苦于您的官网上没有提供相应的docker镜像,所以希望您能给与一些解决办法或增加相应的docker镜像安装方式,谢谢
### 版本&环境信息 Version & Environment Information
服务器信息:
cpu Huawei Kunpeng 920
gpu Riser1&2 1*16X+ 1*8X(PCIE4.0)双宽GPU * 2
具体版本:
python 3.8
paddle2onnx 1.0.5
paddlenlp 2.4.0
paddlepaddle-gpu 2.3.2.post112
onnxruntime 1.13.1 | 1.0 | 请问,有或者能提供arm架构下gpu版的paddle的docker安装的镜像吗 - ### 问题描述 Issue Description
希望在国产机器上使用paddle和paddlenlp,但是苦于您的官网上没有提供相应的docker镜像,所以希望您能给与一些解决办法或增加相应的docker镜像安装方式,谢谢
### 版本&环境信息 Version & Environment Information
服务器信息:
cpu Huawei Kunpeng 920
gpu Riser1&2 1*16X+ 1*8X(PCIE4.0)双宽GPU * 2
具体版本:
python 3.8
paddle2onnx 1.0.5
paddlenlp 2.4.0
paddlepaddle-gpu 2.3.2.post112
onnxruntime 1.13.1 | non_priority | 请问,有或者能提供arm架构下gpu版的paddle的docker安装的镜像吗 问题描述 issue description 希望在国产机器上使用paddle和paddlenlp,但是苦于您的官网上没有提供相应的docker镜像,所以希望您能给与一些解决办法或增加相应的docker镜像安装方式,谢谢 版本 环境信息 version environment information 服务器信息: cpu huawei kunpeng gpu 双宽gpu 具体版本: python paddlenlp paddlepaddle gpu onnxruntime | 0 |
16,637 | 5,266,021,685 | IssuesEvent | 2017-02-04 07:32:41 | jadedtdt/MusicBot | https://api.github.com/repos/jadedtdt/MusicBot | closed | improve random user selection for APL | code-improvement | rather than randomly select from the master list of IDs, get the list of ids in the channel and pick from that | 1.0 | improve random user selection for APL - rather than randomly select from the master list of IDs, get the list of ids in the channel and pick from that | non_priority | improve random user selection for apl rather than randomly select from the master list of ids get the list of ids in the channel and pick from that | 0 |
112,068 | 24,232,639,808 | IssuesEvent | 2022-09-26 19:44:26 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | RFC 619: Move ✨policies's background jobs ✨ to the Policies service | team/code-intelligence code-intelligence-platform rfc-619 team/language-platform-and-navigation code-intel-ongoing-backlog | Move ✨policies's background jobs ✨ to the Policies service as part of our ongoing efforts to implement RFC 619 Code Intelligence Platform. | 3.0 | RFC 619: Move ✨policies's background jobs ✨ to the Policies service - Move ✨policies's background jobs ✨ to the Policies service as part of our ongoing efforts to implement RFC 619 Code Intelligence Platform. | non_priority | rfc move ✨policies s background jobs ✨ to the policies service move ✨policies s background jobs ✨ to the policies service as part of our ongoing efforts to implement rfc code intelligence platform | 0 |
143,609 | 11,570,874,023 | IssuesEvent | 2020-02-20 20:21:51 | phac-nml/irida | https://api.github.com/repos/phac-nml/irida | closed | ClientsControllerTest failing after hotfix | bug test | ## Describe the bug
`ClientsControllerTest.testGetAjaxClientList` is failing due to the hotfix lower casing the search terms coming in to the new ant tables.
## Steps to reproduce the problem
What were you doing when you encountered the problem?
1. ran `mvn test`
2. `ClientsControllerTest.testGetAjaxClientList` failed
3.
## Expected behaviour
`ClientsControllerTest.testGetAjaxClientList` pass
## Additional context
It's a null pointer due to the change to ant design on the clients table. It looks like no search term is being sent to the tablerequest. | 1.0 | ClientsControllerTest failing after hotfix - ## Describe the bug
`ClientsControllerTest.testGetAjaxClientList` is failing due to the hotfix lower casing the search terms coming in to the new ant tables.
## Steps to reproduce the problem
What were you doing when you encountered the problem?
1. ran `mvn test`
2. `ClientsControllerTest.testGetAjaxClientList` failed
3.
## Expected behaviour
`ClientsControllerTest.testGetAjaxClientList` pass
## Additional context
It's a null pointer due to the change to ant design on the clients table. It looks like no search term is being sent to the tablerequest. | non_priority | clientscontrollertest failing after hotfix describe the bug clientscontrollertest testgetajaxclientlist is failing due to the hotfix lower casing the search terms coming in to the new ant tables steps to reproduce the problem what were you doing when you encountered the problem ran mvn test clientscontrollertest testgetajaxclientlist failed expected behaviour clientscontrollertest testgetajaxclientlist pass additional context it s a null pointer due to the change to ant design on the clients table it looks like no search term is being sent to the tablerequest | 0 |
199,231 | 15,029,876,990 | IssuesEvent | 2021-02-02 06:27:38 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: pebble/ycsb/size=1024 failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).pebble/ycsb/size=1024 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2635591&tab=buildLog) on [master@0e6727832d58faf0f900601cd6fa6807e0a2ba75](https://github.com/cockroachdb/cockroach/commits/0e6727832d58faf0f900601cd6fa6807e0a2ba75):
```
The test failed on branch=master, cloud=aws:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/pebble/ycsb/size=1024/run_1
pebble.go:45,pebble.go:71,pebble.go:111,test_runner.go:767: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2635591-1612245917-01-n5cpu16:1-5 -- rm -fr $(dirname {store-dir})/bench && tar xPf $(dirname {store-dir})/data.tar && ./pebble bench ycsb $(dirname {store-dir})/bench --workload=A --concurrency=256 --values=1024 --keys=zipf --initial-keys=0 --prepopulated-keys=10000000 --cache=4294967296 --duration=10m0s > ycsb.log 2>&1 returned: exit status 10
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2635591-1612245917-01-n5cpu16:1-5 -- rm -fr $(dirname {store-dir})/bench && tar xPf $(dirname {store-dir})/data.tar && ./pebble bench ycsb $(dirname {store-dir})/bench --workload=A --concurrency=256 --values=1024 --keys=zipf --initial-keys=0 --prepopulated-keys=10000000 --cache=4294967296 --duration=10m0s > ycsb.log 2>&1 returned
| stderr:
|
| stdout:
| teamcity-2635591-1612245917-01-n5cpu16: rm -fr $(dirname {store-dir...................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................
| 1:
| 2:
| SSH_PROBLEM: exit status 255
| 3:
| 4:
| 5:
| SSH_PROBLEM: exit status 255
| Error: SSH_PROBLEM: exit status 255
| (1) SSH_PROBLEM
| Wraps: (2) Node 2. Command with error:
| | ```
| | rm -fr $(dirname {store-dir})/bench && tar xPf $(dirname {store-dir})/data.tar && ./pebble bench ycsb $(dirname {store-dir})/bench --workload=A --concurrency=256 --values=1024 --keys=zipf --initial-keys=0 --prepopulated-keys=10000000 --cache=4294967296 --duration=10m0s > ycsb.log 2>&1
| | ```
| Wraps: (3) exit status 255
| Error types: (1) errors.SSH (2) *hintdetail.withDetail (3) *exec.ExitError
Wraps: (2) exit status 10
Error types: (1) *main.withCommandDetails (2) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/pebble/ycsb/size=1024](https://teamcity.cockroachdb.com/viewLog.html?buildId=2635591&tab=artifacts#/pebble/ycsb/size=1024)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Apebble%2Fycsb%2Fsize%3D1024.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: pebble/ycsb/size=1024 failed - [(roachtest).pebble/ycsb/size=1024 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2635591&tab=buildLog) on [master@0e6727832d58faf0f900601cd6fa6807e0a2ba75](https://github.com/cockroachdb/cockroach/commits/0e6727832d58faf0f900601cd6fa6807e0a2ba75):
```
The test failed on branch=master, cloud=aws:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/pebble/ycsb/size=1024/run_1
pebble.go:45,pebble.go:71,pebble.go:111,test_runner.go:767: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2635591-1612245917-01-n5cpu16:1-5 -- rm -fr $(dirname {store-dir})/bench && tar xPf $(dirname {store-dir})/data.tar && ./pebble bench ycsb $(dirname {store-dir})/bench --workload=A --concurrency=256 --values=1024 --keys=zipf --initial-keys=0 --prepopulated-keys=10000000 --cache=4294967296 --duration=10m0s > ycsb.log 2>&1 returned: exit status 10
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2635591-1612245917-01-n5cpu16:1-5 -- rm -fr $(dirname {store-dir})/bench && tar xPf $(dirname {store-dir})/data.tar && ./pebble bench ycsb $(dirname {store-dir})/bench --workload=A --concurrency=256 --values=1024 --keys=zipf --initial-keys=0 --prepopulated-keys=10000000 --cache=4294967296 --duration=10m0s > ycsb.log 2>&1 returned
| stderr:
|
| stdout:
| teamcity-2635591-1612245917-01-n5cpu16: rm -fr $(dirname {store-dir...................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................
| 1:
| 2:
| SSH_PROBLEM: exit status 255
| 3:
| 4:
| 5:
| SSH_PROBLEM: exit status 255
| Error: SSH_PROBLEM: exit status 255
| (1) SSH_PROBLEM
| Wraps: (2) Node 2. Command with error:
| | ```
| | rm -fr $(dirname {store-dir})/bench && tar xPf $(dirname {store-dir})/data.tar && ./pebble bench ycsb $(dirname {store-dir})/bench --workload=A --concurrency=256 --values=1024 --keys=zipf --initial-keys=0 --prepopulated-keys=10000000 --cache=4294967296 --duration=10m0s > ycsb.log 2>&1
| | ```
| Wraps: (3) exit status 255
| Error types: (1) errors.SSH (2) *hintdetail.withDetail (3) *exec.ExitError
Wraps: (2) exit status 10
Error types: (1) *main.withCommandDetails (2) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/pebble/ycsb/size=1024](https://teamcity.cockroachdb.com/viewLog.html?buildId=2635591&tab=artifacts#/pebble/ycsb/size=1024)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Apebble%2Fycsb%2Fsize%3D1024.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | roachtest pebble ycsb size failed on the test failed on branch master cloud aws test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts pebble ycsb size run pebble go pebble go pebble go test runner go home agent work go src github com cockroachdb cockroach bin roachprod run teamcity rm fr dirname store dir bench tar xpf dirname store dir data tar pebble bench ycsb dirname store dir bench workload a concurrency values keys zipf initial keys prepopulated keys cache duration ycsb log returned exit status home agent work go src github com cockroachdb cockroach bin roachprod run teamcity rm fr dirname store dir bench tar xpf dirname store dir data tar pebble bench ycsb dirname store dir bench workload a concurrency values keys zipf initial keys prepopulated keys cache duration ycsb log returned stderr stdout teamcity rm fr dirname store dir ssh problem exit status ssh problem exit status error ssh problem exit status ssh problem wraps node command with error rm fr dirname store dir bench tar xpf dirname store dir data tar pebble bench ycsb dirname store dir bench workload a concurrency values keys zipf initial keys prepopulated keys cache duration ycsb log wraps exit status error types errors ssh hintdetail withdetail exec exiterror wraps exit status error types main withcommanddetails exec exiterror more artifacts powered by | 0 |
25,445 | 6,663,141,657 | IssuesEvent | 2017-10-02 15:24:39 | iiitv/ChefLib | https://api.github.com/repos/iiitv/ChefLib | closed | LIKECS01 (COOK86) [C++] | code/new Hacktoberfest lang-cpp lunchtime | - [x] Issue Title is in form `Problem Code (Contest Code) [Language]`
- [x] I ensure I'm Eligible as per [ECR](https://github.com/iiitv/ChefLib/blob/master/README.md#ecr).
- [ ] I got AC for this problem when the contest was live. (Not necessary, but appreciable).
- [x] I have checked that my solution is passing on Problem (in case you make some changes).
- [x] I will send my PR only after I'm assigned to this issue by any maintainer.
- [x] I ensure that I'm not assigned to more than 2 issues.
- [x] Assign this issue to me (I want to work on this).
##### It's not necessary for all for points to be checked, we will look at what is required once you open an issue.
| 1.0 | LIKECS01 (COOK86) [C++] - - [x] Issue Title is in form `Problem Code (Contest Code) [Language]`
- [x] I ensure I'm Eligible as per [ECR](https://github.com/iiitv/ChefLib/blob/master/README.md#ecr).
- [ ] I got AC for this problem when the contest was live. (Not necessary, but appreciable).
- [x] I have checked that my solution is passing on Problem (in case you make some changes).
- [x] I will send my PR only after I'm assigned to this issue by any maintainer.
- [x] I ensure that I'm not assigned to more than 2 issues.
- [x] Assign this issue to me (I want to work on this).
##### It's not necessary for all for points to be checked, we will look at what is required once you open an issue.
| non_priority | issue title is in form problem code contest code i ensure i m eligible as per i got ac for this problem when the contest was live not necessary but appreciable i have checked that my solution is passing on problem in case you make some changes i will send my pr only after i m assigned to this issue by any maintainer i ensure that i m not assigned to more than issues assign this issue to me i want to work on this it s not necessary for all for points to be checked we will look at what is required once you open an issue | 0 |
280,460 | 30,826,278,186 | IssuesEvent | 2023-08-01 20:20:39 | GHCbflam1/Easy-Buggy | https://api.github.com/repos/GHCbflam1/Easy-Buggy | opened | CVE-2017-3589 (Low) detected in mysql-connector-java-5.1.25.jar | Mend: dependency security vulnerability | ## CVE-2017-3589 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GHCbflam1/Easy-Buggy/commit/b478faf89f68b8e991cf688bde9520087add7126">b478faf89f68b8e991cf688bde9520087add7126</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3589>CVE-2017-3589</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.42</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2017-3589 (Low) detected in mysql-connector-java-5.1.25.jar - ## CVE-2017-3589 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GHCbflam1/Easy-Buggy/commit/b478faf89f68b8e991cf688bde9520087add7126">b478faf89f68b8e991cf688bde9520087add7126</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-3589>CVE-2017-3589</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.42</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve low detected in mysql connector java jar cve low severity vulnerability vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch master vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data cvss base score integrity impacts cvss vector cvss av l ac l pr l ui n s u c n i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
50,282 | 13,505,930,244 | IssuesEvent | 2020-09-14 01:16:37 | LevyForchh/workflow2 | https://api.github.com/repos/LevyForchh/workflow2 | opened | CVE-2020-15169 (Medium) detected in actionview-4.2.11.1.gem | security vulnerability | ## CVE-2020-15169 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-4.2.11.1.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-4.2.11.1.gem">https://rubygems.org/gems/actionview-4.2.11.1.gem</a></p>
<p>Path to dependency file: workflow2/workflow_db/database/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.5.0/cache/actionview-4.2.11.1.gem</p>
<p>
Dependency Hierarchy:
- rails-4.2.11.1.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-4.2.11.1.gem
- :x: **actionview-4.2.11.1.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Action View before versions 5.2.4.4 and 6.0.3.3 there is a potential Cross-Site Scripting (XSS) vulnerability in Action View's translation helpers. Views that allow the user to control the default (not found) value of the `t` and `translate` helpers could be susceptible to XSS attacks. When an HTML-unsafe string is passed as the default for a missing translation key named html or ending in _html, the default string is incorrectly marked as HTML-safe and not escaped. This is patched in versions 6.0.3.3 and 5.2.4.4. A workaround without upgrading is proposed in the source advisory.
<p>Publish Date: 2020-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15169>CVE-2020-15169</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://rubygems.org/gems/actionview/versions/6.0.3.3">https://rubygems.org/gems/actionview/versions/6.0.3.3</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 6.0.3.3, 5.2.4.4</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Ruby","packageName":"actionview","packageVersion":"4.2.11.1","isTransitiveDependency":true,"dependencyTree":"rails:4.2.11.1;sprockets-rails:3.2.1;actionpack:4.2.11.1;actionview:4.2.11.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.0.3.3, 5.2.4.4"}],"vulnerabilityIdentifier":"CVE-2020-15169","vulnerabilityDetails":"In Action View before versions 5.2.4.4 and 6.0.3.3 there is a potential Cross-Site Scripting (XSS) vulnerability in Action View\u0027s translation helpers. Views that allow the user to control the default (not found) value of the `t` and `translate` helpers could be susceptible to XSS attacks. When an HTML-unsafe string is passed as the default for a missing translation key named html or ending in _html, the default string is incorrectly marked as HTML-safe and not escaped. This is patched in versions 6.0.3.3 and 5.2.4.4. A workaround without upgrading is proposed in the source advisory.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15169","cvss3Severity":"medium","cvss3Score":"5.4","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-15169 (Medium) detected in actionview-4.2.11.1.gem - ## CVE-2020-15169 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionview-4.2.11.1.gem</b></p></summary>
<p>Simple, battle-tested conventions and helpers for building web pages.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionview-4.2.11.1.gem">https://rubygems.org/gems/actionview-4.2.11.1.gem</a></p>
<p>Path to dependency file: workflow2/workflow_db/database/Gemfile.lock</p>
<p>Path to vulnerable library: /var/lib/gems/2.5.0/cache/actionview-4.2.11.1.gem</p>
<p>
Dependency Hierarchy:
- rails-4.2.11.1.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-4.2.11.1.gem
- :x: **actionview-4.2.11.1.gem** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Action View before versions 5.2.4.4 and 6.0.3.3 there is a potential Cross-Site Scripting (XSS) vulnerability in Action View's translation helpers. Views that allow the user to control the default (not found) value of the `t` and `translate` helpers could be susceptible to XSS attacks. When an HTML-unsafe string is passed as the default for a missing translation key named html or ending in _html, the default string is incorrectly marked as HTML-safe and not escaped. This is patched in versions 6.0.3.3 and 5.2.4.4. A workaround without upgrading is proposed in the source advisory.
<p>Publish Date: 2020-07-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15169>CVE-2020-15169</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://rubygems.org/gems/actionview/versions/6.0.3.3">https://rubygems.org/gems/actionview/versions/6.0.3.3</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 6.0.3.3, 5.2.4.4</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Ruby","packageName":"actionview","packageVersion":"4.2.11.1","isTransitiveDependency":true,"dependencyTree":"rails:4.2.11.1;sprockets-rails:3.2.1;actionpack:4.2.11.1;actionview:4.2.11.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.0.3.3, 5.2.4.4"}],"vulnerabilityIdentifier":"CVE-2020-15169","vulnerabilityDetails":"In Action View before versions 5.2.4.4 and 6.0.3.3 there is a potential Cross-Site Scripting (XSS) vulnerability in Action View\u0027s translation helpers. Views that allow the user to control the default (not found) value of the `t` and `translate` helpers could be susceptible to XSS attacks. When an HTML-unsafe string is passed as the default for a missing translation key named html or ending in _html, the default string is incorrectly marked as HTML-safe and not escaped. This is patched in versions 6.0.3.3 and 5.2.4.4. A workaround without upgrading is proposed in the source advisory.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15169","cvss3Severity":"medium","cvss3Score":"5.4","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in actionview gem cve medium severity vulnerability vulnerable library actionview gem simple battle tested conventions and helpers for building web pages library home page a href path to dependency file workflow db database gemfile lock path to vulnerable library var lib gems cache actionview gem dependency hierarchy rails gem root library sprockets rails gem actionpack gem x actionview gem vulnerable library vulnerability details in action view before versions and there is a potential cross site scripting xss vulnerability in action view s translation helpers views that allow the user to control the default not found value of the t and translate helpers could be susceptible to xss attacks when an html unsafe string is passed as the default for a missing translation key named html or ending in html the default string is incorrectly marked as html safe and not escaped this is patched in versions and a workaround without upgrading is proposed in the source advisory publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails in action view before versions and there is a potential cross site scripting xss vulnerability in action view translation helpers views that allow the user to control the default not found value of the t and translate helpers could be susceptible to xss attacks when an html unsafe string is passed as the default for a missing translation key named html or ending in html the default string is incorrectly marked as html safe and not escaped this is patched in versions and a workaround without upgrading is proposed in the source advisory vulnerabilityurl | 0 |
47,969 | 10,188,156,257 | IssuesEvent | 2019-08-11 08:01:16 | fish-stack/AlgoMath | https://api.github.com/repos/fish-stack/AlgoMath | opened | 1. 两数之和 | Java LeetCode Map 简单 | 给定一个整数数组 nums 和一个目标值 target,请你在该数组中找出和为目标值的那 两个 整数,并返回他们的数组下标。
你可以假设每种输入只会对应一个答案。但是,你不能重复利用这个数组中同样的元素。
示例:
```
给定 nums = [2, 7, 11, 15], target = 9
因为 nums[0] + nums[1] = 2 + 7 = 9
所以返回 [0, 1]
``` | 1.0 | 1. 两数之和 - 给定一个整数数组 nums 和一个目标值 target,请你在该数组中找出和为目标值的那 两个 整数,并返回他们的数组下标。
你可以假设每种输入只会对应一个答案。但是,你不能重复利用这个数组中同样的元素。
示例:
```
给定 nums = [2, 7, 11, 15], target = 9
因为 nums[0] + nums[1] = 2 + 7 = 9
所以返回 [0, 1]
``` | non_priority | 两数之和 给定一个整数数组 nums 和一个目标值 target,请你在该数组中找出和为目标值的那 两个 整数,并返回他们的数组下标。 你可以假设每种输入只会对应一个答案。但是,你不能重复利用这个数组中同样的元素。 示例 给定 nums target 因为 nums nums 所以返回 | 0 |
14,582 | 9,358,673,019 | IssuesEvent | 2019-04-02 03:27:50 | sesong11/zboot | https://api.github.com/repos/sesong11/zboot | opened | CVE-2018-19360 High Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2018-19360 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>path: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
<p>Library home page: <a href=http://github.com/FasterXML/jackson>http://github.com/FasterXML/jackson</a></p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.5.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the axis2-transport-jms class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360>CVE-2018-19360</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19360 High Severity Vulnerability detected by WhiteSource - ## CVE-2018-19360 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>path: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
<p>Library home page: <a href=http://github.com/FasterXML/jackson>http://github.com/FasterXML/jackson</a></p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.5.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the axis2-transport-jms class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360>CVE-2018-19360</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19360</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path root repository com fasterxml jackson core jackson databind jackson databind jar library home page a href dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the transport jms class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
140,489 | 21,104,032,347 | IssuesEvent | 2022-04-04 16:55:52 | CA-Data/Open-Data-Portal | https://api.github.com/repos/CA-Data/Open-Data-Portal | opened | Data preview - A-table-002 | P1 Engineering UX Visual Design QA/TESTING | Preview works only for csv file. Preview for non-csv files **does not work**.
Discuss how to handle non-csv files (add them in; do not display link, etc) | 1.0 | Data preview - A-table-002 - Preview works only for csv file. Preview for non-csv files **does not work**.
Discuss how to handle non-csv files (add them in; do not display link, etc) | non_priority | data preview a table preview works only for csv file preview for non csv files does not work discuss how to handle non csv files add them in do not display link etc | 0 |
26,220 | 26,569,566,511 | IssuesEvent | 2023-01-21 01:21:12 | jstanden/cerb | https://api.github.com/repos/jstanden/cerb | closed | [Enhancement Request] Need a way to differentiate Profile Widgets by target | feature-request usability | The new profile widgets are great, but in Search -> Profile Widgets, when you search for "org", there are five widgets that are all visually identical in the worklist, though they target different object types. Is there any way to mark / flag those in such a way that they can be differentiated there?
I know the workaround / preferred method would be to just edit the widget from the actual profile page, but it's a point of confusion. | True | [Enhancement Request] Need a way to differentiate Profile Widgets by target - The new profile widgets are great, but in Search -> Profile Widgets, when you search for "org", there are five widgets that are all visually identical in the worklist, though they target different object types. Is there any way to mark / flag those in such a way that they can be differentiated there?
I know the workaround / preferred method would be to just edit the widget from the actual profile page, but it's a point of confusion. | non_priority | need a way to differentiate profile widgets by target the new profile widgets are great but in search profile widgets when you search for org there are five widgets that are all visually identical in the worklist though they target different object types is there any way to mark flag those in such a way that they can be differentiated there i know the workaround preferred method would be to just edit the widget from the actual profile page but it s a point of confusion | 0 |
121,348 | 12,123,688,905 | IssuesEvent | 2020-04-22 13:07:24 | tektoncd/website | https://api.github.com/repos/tektoncd/website | closed | Relative Links are Broken. | kind/documentation | # Expected Behavior
I accept that when I click on [Tekton Pipeline Link](https://github.com/tektoncd/dashboard/releases) it should give me some type of documentation.
# Actual Behavior
It sends me to the github documentation
# Steps to Reproduce the Problem
1. Go to https://tekton.dev/docs/pipelines/
2. Click on pipeline metric
3. It should send you to https://tekton.dev/docs/pipelines/metrics
# Additional Info
I think the scraper should change the absolute link to the relative link if the relative link does not return a 400 type error.
| 1.0 | Relative Links are Broken. - # Expected Behavior
I accept that when I click on [Tekton Pipeline Link](https://github.com/tektoncd/dashboard/releases) it should give me some type of documentation.
# Actual Behavior
It sends me to the github documentation
# Steps to Reproduce the Problem
1. Go to https://tekton.dev/docs/pipelines/
2. Click on pipeline metric
3. It should send you to https://tekton.dev/docs/pipelines/metrics
# Additional Info
I think the scraper should change the absolute link to the relative link if the relative link does not return a 400 type error.
| non_priority | relative links are broken expected behavior i accept that when i click on it should give me some type of documentation actual behavior it sends me to the github documentation steps to reproduce the problem go to click on pipeline metric it should send you to additional info i think the scraper should change the absolute link to the relative link if the relative link does not return a type error | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.