Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
151,173 | 12,016,494,834 | IssuesEvent | 2020-04-10 16:13:29 | mathjax/MathJax | https://api.github.com/repos/mathjax/MathJax | closed | Spacing after \setminus too large | Accepted Fixed Merged Test Needed v3 | $A\setminus B$ produces excessive space before the B.
Live page with example: https://logrus.math.tecnico.ulisboa.pt/test (MathJax 3.0.1)
Counterexample: https://cdi1tp.math.tecnico.ulisboa.pt/solucoes/T1B20181110 (MathJax 2.7.x)

Observed in current versions of Firefox and Chromium on Linux.
| 1.0 | Spacing after \setminus too large - $A\setminus B$ produces excessive space before the B.
Live page with example: https://logrus.math.tecnico.ulisboa.pt/test (MathJax 3.0.1)
Counterexample: https://cdi1tp.math.tecnico.ulisboa.pt/solucoes/T1B20181110 (MathJax 2.7.x)

Observed in current versions of Firefox and Chromium on Linux.
| non_priority | spacing after setminus too large a setminus b produces excessive space before the b live page with example mathjax counterexample mathjax x observed in current versions of firefox and chromium on linux | 0 |
82,212 | 10,275,531,701 | IssuesEvent | 2019-08-24 08:42:35 | cookiecutter/cookiecutter | https://api.github.com/repos/cookiecutter/cookiecutter | closed | Remove dead projects from "Similar projects" | documentation | * Cookiecutter version: Any
* Python version: All
* Operating System: All
### Description:
The similar projects list has projects with dead links. Or in the case of Pyramid's pcreate, have been superseded by Cookiecutter. Remove them from the list. | 1.0 | Remove dead projects from "Similar projects" - * Cookiecutter version: Any
* Python version: All
* Operating System: All
### Description:
The similar projects list has projects with dead links. Or in the case of Pyramid's pcreate, have been superseded by Cookiecutter. Remove them from the list. | non_priority | remove dead projects from similar projects cookiecutter version any python version all operating system all description the similar projects list has projects with dead links or in the case of pyramid s pcreate have been superseded by cookiecutter remove them from the list | 0 |
108,202 | 16,762,815,080 | IssuesEvent | 2021-06-14 03:16:08 | gms-ws-sandbox/nibrs-pr-test | https://api.github.com/repos/gms-ws-sandbox/nibrs-pr-test | opened | CVE-2019-11284 (High) detected in reactor-netty-0.8.8.RELEASE.jar | security vulnerability | ## CVE-2019-11284 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>reactor-netty-0.8.8.RELEASE.jar</b></p></summary>
<p>Reactive Streams Netty driver</p>
<p>Library home page: <a href="https://github.com/reactor/reactor-netty">https://github.com/reactor/reactor-netty</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/projectreactor/netty/reactor-netty/0.8.8.RELEASE/reactor-netty-0.8.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-webflux-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-reactor-netty-2.1.5.RELEASE.jar
- :x: **reactor-netty-0.8.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs-pr-test/commit/860cc22f54e17594e32e303f0716fb065202fff5">860cc22f54e17594e32e303f0716fb065202fff5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Reactor Netty, versions prior to 0.8.11, passes headers through redirects, including authorization ones. A remote unauthenticated malicious user may gain access to credentials for a different server than they have access to.
<p>Publish Date: 2019-10-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11284>CVE-2019-11284</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11284">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11284</a></p>
<p>Release Date: 2019-10-17</p>
<p>Fix Resolution: 0.8.11</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.projectreactor.netty","packageName":"reactor-netty","packageVersion":"0.8.8.RELEASE","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-webflux:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter-reactor-netty:2.1.5.RELEASE;io.projectreactor.netty:reactor-netty:0.8.8.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.8.11"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11284","vulnerabilityDetails":"Pivotal Reactor Netty, versions prior to 0.8.11, passes headers through redirects, including authorization ones. A remote unauthenticated malicious user may gain access to credentials for a different server than they have access to.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11284","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-11284 (High) detected in reactor-netty-0.8.8.RELEASE.jar - ## CVE-2019-11284 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>reactor-netty-0.8.8.RELEASE.jar</b></p></summary>
<p>Reactive Streams Netty driver</p>
<p>Library home page: <a href="https://github.com/reactor/reactor-netty">https://github.com/reactor/reactor-netty</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/projectreactor/netty/reactor-netty/0.8.8.RELEASE/reactor-netty-0.8.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-webflux-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-reactor-netty-2.1.5.RELEASE.jar
- :x: **reactor-netty-0.8.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs-pr-test/commit/860cc22f54e17594e32e303f0716fb065202fff5">860cc22f54e17594e32e303f0716fb065202fff5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Reactor Netty, versions prior to 0.8.11, passes headers through redirects, including authorization ones. A remote unauthenticated malicious user may gain access to credentials for a different server than they have access to.
<p>Publish Date: 2019-10-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11284>CVE-2019-11284</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11284">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11284</a></p>
<p>Release Date: 2019-10-17</p>
<p>Fix Resolution: 0.8.11</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.projectreactor.netty","packageName":"reactor-netty","packageVersion":"0.8.8.RELEASE","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-webflux:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter-reactor-netty:2.1.5.RELEASE;io.projectreactor.netty:reactor-netty:0.8.8.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.8.11"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11284","vulnerabilityDetails":"Pivotal Reactor Netty, versions prior to 0.8.11, passes headers through redirects, including authorization ones. A remote unauthenticated malicious user may gain access to credentials for a different server than they have access to.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11284","cvss3Severity":"high","cvss3Score":"8.6","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in reactor netty release jar cve high severity vulnerability vulnerable library reactor netty release jar reactive streams netty driver library home page a href path to dependency file nibrs pr test tools nibrs summary report common pom xml path to vulnerable library home wss scanner repository io projectreactor netty reactor netty release reactor netty release jar dependency hierarchy spring boot starter webflux release jar root library spring boot starter reactor netty release jar x reactor netty release jar vulnerable library found in head commit a href found in base branch master vulnerability details pivotal reactor netty versions prior to passes headers through redirects including authorization ones a remote unauthenticated malicious user may gain access to credentials for a different server than they have access to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter webflux release org springframework boot spring boot starter reactor netty release io projectreactor netty reactor netty release isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails pivotal reactor netty versions prior to passes headers through redirects including authorization ones a remote unauthenticated malicious user may gain access to credentials for a different server than they have access to vulnerabilityurl | 0 |
172,155 | 14,350,974,102 | IssuesEvent | 2020-11-29 23:17:45 | MazamaScience/RAWSmet | https://api.github.com/repos/MazamaScience/RAWSmet | closed | add a Developer_Style_Guide.Rmd vignette | documentation | For anyone in the future who might want to modify or enhance the code in this package, it will be useful to have a good understanding of how and why things are named as they are. To support consistency, we should provide a style guide for developers.
Please copy the following file to the vignettes/ directory and modify it as needed to reflect the "objects" and functions in the **RAWSmet** package:
https://github.com/MazamaScience/MazamaSpatialUtils/blob/master/vignettes/Developer_Style_Guide.Rmd | 1.0 | add a Developer_Style_Guide.Rmd vignette - For anyone in the future who might want to modify or enhance the code in this package, it will be useful to have a good understanding of how and why things are named as they are. To support consistency, we should provide a style guide for developers.
Please copy the following file to the vignettes/ directory and modify it as needed to reflect the "objects" and functions in the **RAWSmet** package:
https://github.com/MazamaScience/MazamaSpatialUtils/blob/master/vignettes/Developer_Style_Guide.Rmd | non_priority | add a developer style guide rmd vignette for anyone in the future who might want to modify or enhance the code in this package it will be useful to have a good understanding of how and why things are named as they are to support consistency we should provide a style guide for developers please copy the following file to the vignettes directory and modify it as needed to reflect the objects and functions in the rawsmet package | 0 |
173,919 | 27,543,908,997 | IssuesEvent | 2023-03-07 10:24:42 | pace-neutrons/Horace | https://api.github.com/repos/pace-neutrons/Horace | closed | Define performance tests | Design Testing | The system test plan notes that a set of full performance tests should be defined.
This ticket will define what those test are:
- what data (small and large data sets)
- what processes
- which systems to run on
Output:
- detailed description of the test cases and test data
- where the test data can be obtained | 1.0 | Define performance tests - The system test plan notes that a set of full performance tests should be defined.
This ticket will define what those test are:
- what data (small and large data sets)
- what processes
- which systems to run on
Output:
- detailed description of the test cases and test data
- where the test data can be obtained | non_priority | define performance tests the system test plan notes that a set of full performance tests should be defined this ticket will define what those test are what data small and large data sets what processes which systems to run on output detailed description of the test cases and test data where the test data can be obtained | 0 |
167,411 | 13,024,535,288 | IssuesEvent | 2020-07-27 12:02:44 | microsoft/botbuilder-python | https://api.github.com/repos/microsoft/botbuilder-python | closed | [PORT] add TestFlow.AssertNoReply and tests | BF Agility R10 testing framework | > Port this change from botbuilder-dotnet/master branch:
https://github.com/microsoft/botbuilder-dotnet/pull/3125
To make sure the bot really ends.
Unexpected replies once happend in VA-Skill interactions in solutions project.
| 1.0 | [PORT] add TestFlow.AssertNoReply and tests - > Port this change from botbuilder-dotnet/master branch:
https://github.com/microsoft/botbuilder-dotnet/pull/3125
To make sure the bot really ends.
Unexpected replies once happend in VA-Skill interactions in solutions project.
| non_priority | add testflow assertnoreply and tests port this change from botbuilder dotnet master branch to make sure the bot really ends unexpected replies once happend in va skill interactions in solutions project | 0 |
61,843 | 15,096,418,126 | IssuesEvent | 2021-02-07 15:00:52 | rclone/rclone | https://api.github.com/repos/rclone/rclone | closed | Support for Apple Silicon M1 chipset | Needs Go 1.16 OS: Mac build enhancement | #### Output of `rclone version`
Not applicable
#### Describe the issue
Apple has a new chipset called the M1 which runs ARM instead of x86. What is the plan for adding support for rclone on this chipset?
[https://en.wikipedia.org/wiki/Apple_M1](https://en.wikipedia.org/wiki/Apple_M1)
| 1.0 | Support for Apple Silicon M1 chipset - #### Output of `rclone version`
Not applicable
#### Describe the issue
Apple has a new chipset called the M1 which runs ARM instead of x86. What is the plan for adding support for rclone on this chipset?
[https://en.wikipedia.org/wiki/Apple_M1](https://en.wikipedia.org/wiki/Apple_M1)
| non_priority | support for apple silicon chipset output of rclone version not applicable describe the issue apple has a new chipset called the which runs arm instead of what is the plan for adding support for rclone on this chipset | 0 |
39,570 | 5,240,907,572 | IssuesEvent | 2017-01-31 14:27:20 | ValveSoftware/Source-1-Games | https://api.github.com/repos/ValveSoftware/Source-1-Games | closed | [CS:S] the main branch and the prerelease branch srcds.exe wont launch | Counter-Strike: Source Need Retest Reviewed Windows | had me and a friend download the cs:s dedicated server and i'm sure the windows loading thing appears and disappears for us and it doesn't appear in the processes on windows task manager when we try to launch it, no errors occurred as far as we know.
| 1.0 | [CS:S] the main branch and the prerelease branch srcds.exe wont launch - had me and a friend download the cs:s dedicated server and i'm sure the windows loading thing appears and disappears for us and it doesn't appear in the processes on windows task manager when we try to launch it, no errors occurred as far as we know.
| non_priority | the main branch and the prerelease branch srcds exe wont launch had me and a friend download the cs s dedicated server and i m sure the windows loading thing appears and disappears for us and it doesn t appear in the processes on windows task manager when we try to launch it no errors occurred as far as we know | 0 |
113,680 | 17,150,869,302 | IssuesEvent | 2021-07-13 20:24:50 | snowdensb/braindump | https://api.github.com/repos/snowdensb/braindump | opened | CVE-2019-11358 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.2.4.tgz</b>, <b>jquery-2.1.4.min.js</b>, <b>jquery-1.11.1.min.js</b>, <b>jquery-1.10.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.2.4.tgz</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://registry.npmjs.org/jquery/-/jquery-2.2.4.tgz">https://registry.npmjs.org/jquery/-/jquery-2.2.4.tgz</a></p>
<p>Path to dependency file: braindump/package.json</p>
<p>Path to vulnerable library: braindump/node_modules/jquery</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to dependency file: braindump/node_modules/bootstrap-tagsinput/examples/index.html</p>
<p>Path to vulnerable library: braindump/node_modules/bootstrap-tagsinput/examples/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to dependency file: braindump/node_modules/bootstrap-tagsinput/examples/bootstrap-2.3.2.html</p>
<p>Path to vulnerable library: braindump/node_modules/bootstrap-tagsinput/examples/bootstrap-2.3.2.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.10.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.1/jquery.min.js</a></p>
<p>Path to dependency file: braindump/node_modules/bootstrap-tabcollapse/example/example.html</p>
<p>Path to vulnerable library: braindump/node_modules/bootstrap-tabcollapse/example/lib/js/jquery-1.10.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/braindump/commit/815ae0afebcf867f02143f3ab9cf88b1d4dacdec">815ae0afebcf867f02143f3ab9cf88b1d4dacdec</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"jquery","packageVersion":"2.2.4","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"jquery:2.2.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"2.1.4","packageFilePaths":["/node_modules/bootstrap-tagsinput/examples/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:2.1.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.11.1","packageFilePaths":["/node_modules/bootstrap-tagsinput/examples/bootstrap-2.3.2.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.11.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.1","packageFilePaths":["/node_modules/bootstrap-tabcollapse/example/example.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11358","vulnerabilityDetails":"jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-11358 (Medium) detected in multiple libraries - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.2.4.tgz</b>, <b>jquery-2.1.4.min.js</b>, <b>jquery-1.11.1.min.js</b>, <b>jquery-1.10.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.2.4.tgz</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://registry.npmjs.org/jquery/-/jquery-2.2.4.tgz">https://registry.npmjs.org/jquery/-/jquery-2.2.4.tgz</a></p>
<p>Path to dependency file: braindump/package.json</p>
<p>Path to vulnerable library: braindump/node_modules/jquery</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to dependency file: braindump/node_modules/bootstrap-tagsinput/examples/index.html</p>
<p>Path to vulnerable library: braindump/node_modules/bootstrap-tagsinput/examples/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to dependency file: braindump/node_modules/bootstrap-tagsinput/examples/bootstrap-2.3.2.html</p>
<p>Path to vulnerable library: braindump/node_modules/bootstrap-tagsinput/examples/bootstrap-2.3.2.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.10.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.1/jquery.min.js</a></p>
<p>Path to dependency file: braindump/node_modules/bootstrap-tabcollapse/example/example.html</p>
<p>Path to vulnerable library: braindump/node_modules/bootstrap-tabcollapse/example/lib/js/jquery-1.10.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/braindump/commit/815ae0afebcf867f02143f3ab9cf88b1d4dacdec">815ae0afebcf867f02143f3ab9cf88b1d4dacdec</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"jquery","packageVersion":"2.2.4","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"jquery:2.2.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"2.1.4","packageFilePaths":["/node_modules/bootstrap-tagsinput/examples/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:2.1.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.11.1","packageFilePaths":["/node_modules/bootstrap-tagsinput/examples/bootstrap-2.3.2.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.11.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.1","packageFilePaths":["/node_modules/bootstrap-tabcollapse/example/example.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11358","vulnerabilityDetails":"jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries jquery tgz jquery min js jquery min js jquery min js jquery tgz javascript library for dom operations library home page a href path to dependency file braindump package json path to vulnerable library braindump node modules jquery dependency hierarchy x jquery tgz vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file braindump node modules bootstrap tagsinput examples index html path to vulnerable library braindump node modules bootstrap tagsinput examples index html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file braindump node modules bootstrap tagsinput examples bootstrap html path to vulnerable library braindump node modules bootstrap tagsinput examples bootstrap html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file braindump node modules bootstrap tabcollapse example example html path to vulnerable library braindump node modules bootstrap tabcollapse example lib js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion packagetype javascript packagename jquery packageversion packagefilepaths istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion packagetype javascript packagename jquery packageversion packagefilepaths istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion packagetype javascript packagename jquery packageversion packagefilepaths istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype vulnerabilityurl | 0 |
97,421 | 20,255,785,562 | IssuesEvent | 2022-02-14 23:02:41 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | insights: persisted global capture groups loading state should match normal loading state | bug team/code-insights backend capture-groups-insight insights-capture-groups-v2 |
Both of these insights have not run yet, but they show different states:
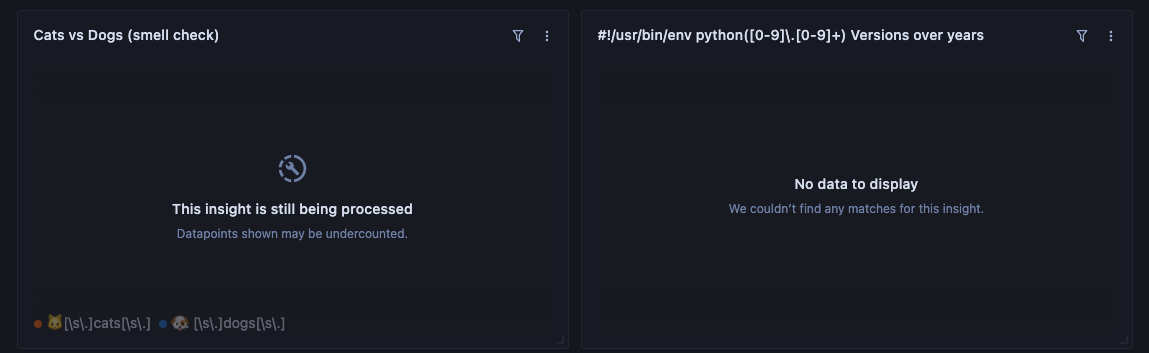
Right side: capture group that hasn't run yet. Left side: normal global search insights.
We should show the same loading state for both, that the capture group insight is processing, *not* "no data to display." This will mislead users to thinking their query was wrong because they would expect both to show the loading state.
I realize there may be some backend complexity in how we expose loading state from compute. | 1.0 | insights: persisted global capture groups loading state should match normal loading state -
Both of these insights have not run yet, but they show different states:
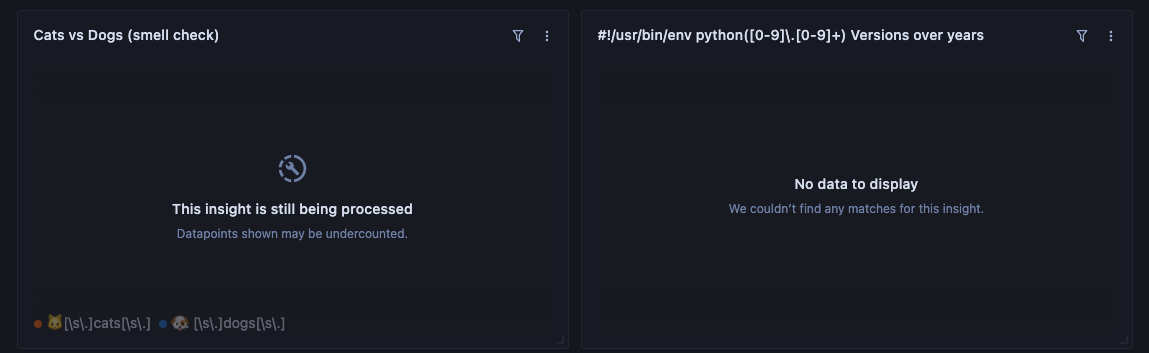
Right side: capture group that hasn't run yet. Left side: normal global search insights.
We should show the same loading state for both, that the capture group insight is processing, *not* "no data to display." This will mislead users to thinking their query was wrong because they would expect both to show the loading state.
I realize there may be some backend complexity in how we expose loading state from compute. | non_priority | insights persisted global capture groups loading state should match normal loading state both of these insights have not run yet but they show different states right side capture group that hasn t run yet left side normal global search insights we should show the same loading state for both that the capture group insight is processing not no data to display this will mislead users to thinking their query was wrong because they would expect both to show the loading state i realize there may be some backend complexity in how we expose loading state from compute | 0 |
55,434 | 23,469,225,467 | IssuesEvent | 2022-08-16 19:56:38 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Create Web App for Traffic Engineering Areas | Service: Geo Workgroup: TDS | <!-- Email -->
<!-- nathan.aubert@austintexas.gov -->
> What application are you using?
ArcGIS
> Describe the problem.
Our team has a map that we use to show areas which has changed. Both the people listed and the Council Districts have been updated. We would like a version which is updated or allows us to update as people transition into/out of the team.
> How soon do you need this?
Flexible — An extended timeline is OK
> Requested By
Nathan A.
[Attachment](https://api.knack.com/v1/applications/595d00ebd315cc4cb98daff4/download/asset/62d0728fe49830001e2d09b7/engineer_areas_11x17_12102019.mxd) (916.0kb)
Request ID: DTS22-104635
| 1.0 | Create Web App for Traffic Engineering Areas - <!-- Email -->
<!-- nathan.aubert@austintexas.gov -->
> What application are you using?
ArcGIS
> Describe the problem.
Our team has a map that we use to show areas which has changed. Both the people listed and the Council Districts have been updated. We would like a version which is updated or allows us to update as people transition into/out of the team.
> How soon do you need this?
Flexible — An extended timeline is OK
> Requested By
Nathan A.
[Attachment](https://api.knack.com/v1/applications/595d00ebd315cc4cb98daff4/download/asset/62d0728fe49830001e2d09b7/engineer_areas_11x17_12102019.mxd) (916.0kb)
Request ID: DTS22-104635
| non_priority | create web app for traffic engineering areas what application are you using arcgis describe the problem our team has a map that we use to show areas which has changed both the people listed and the council districts have been updated we would like a version which is updated or allows us to update as people transition into out of the team how soon do you need this flexible — an extended timeline is ok requested by nathan a request id | 0 |
94,790 | 11,911,348,558 | IssuesEvent | 2020-03-31 08:28:30 | ember-learn/ember-styleguide | https://api.github.com/repos/ember-learn/ember-styleguide | closed | Part 3: Create Issues based on analysis from parts 1 and 2. | Website Redesign RFC | At this point, the documentation should exist that identifies components needed for each page. | 1.0 | Part 3: Create Issues based on analysis from parts 1 and 2. - At this point, the documentation should exist that identifies components needed for each page. | non_priority | part create issues based on analysis from parts and at this point the documentation should exist that identifies components needed for each page | 0 |
290,584 | 21,890,277,035 | IssuesEvent | 2022-05-20 00:15:28 | LGomez96/LIM017-md-links | https://api.github.com/repos/LGomez96/LIM017-md-links | closed | Desacoplar file system | documentation good first issue | quiero guardar en un solo archivo separado las funciones que usaré de esta librería para importarlas donde las necesite | 1.0 | Desacoplar file system - quiero guardar en un solo archivo separado las funciones que usaré de esta librería para importarlas donde las necesite | non_priority | desacoplar file system quiero guardar en un solo archivo separado las funciones que usaré de esta librería para importarlas donde las necesite | 0 |
49,674 | 13,187,249,559 | IssuesEvent | 2020-08-13 02:49:14 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | [I3OmDb] Not compiling for icerec/V05-00-02 (Trac #1853) | Incomplete Migration Migrated from Trac combo reconstruction defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1853">https://code.icecube.wisc.edu/ticket/1853</a>, reported by maryon and owned by joertlin</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:24",
"description": "Does not compile for me when using clang however gcc works. Forward declaration wrongly executed.\n\n{{{\n[ 88%] Building CXX object STTools/CMakeFiles/STTools-pybindings.dir/private/pybindings/algorithms/seededRT/I3SeededRTConfigurationService.cxx.o\nIn file included from /home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/private/I3OmDb/I3OmDbFactory.cxx:2:\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:1280:8: error: 'Om_s' redeclared with 'private' access\nstruct Om_s \n ^\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:977:8: note: previously declared 'public' here\nstruct Om_s;\n ^\n1 error generated.\nmake[2]: *** [I3Db/CMakeFiles/I3Db.dir/private/I3OmDb/I3OmDbFactory.cxx.o] Error 1\nmake[2]: Target `I3Db/CMakeFiles/I3Db.dir/build' not remade because of errors.\nmake[1]: *** [I3Db/CMakeFiles/I3Db.dir/all] Error 2\n}}}\n",
"reporter": "maryon",
"cc": "",
"resolution": "fixed",
"_ts": "1550067204154158",
"component": "combo reconstruction",
"summary": "[I3OmDb] Not compiling for icerec/V05-00-02",
"priority": "blocker",
"keywords": "I3OmDb icerec",
"time": "2016-09-09T11:50:36",
"milestone": "",
"owner": "joertlin",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [I3OmDb] Not compiling for icerec/V05-00-02 (Trac #1853) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1853">https://code.icecube.wisc.edu/ticket/1853</a>, reported by maryon and owned by joertlin</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:13:24",
"description": "Does not compile for me when using clang however gcc works. Forward declaration wrongly executed.\n\n{{{\n[ 88%] Building CXX object STTools/CMakeFiles/STTools-pybindings.dir/private/pybindings/algorithms/seededRT/I3SeededRTConfigurationService.cxx.o\nIn file included from /home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/private/I3OmDb/I3OmDbFactory.cxx:2:\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:1280:8: error: 'Om_s' redeclared with 'private' access\nstruct Om_s \n ^\n/home/maryon/software/meta-projects/icerec/V05-00-02/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:977:8: note: previously declared 'public' here\nstruct Om_s;\n ^\n1 error generated.\nmake[2]: *** [I3Db/CMakeFiles/I3Db.dir/private/I3OmDb/I3OmDbFactory.cxx.o] Error 1\nmake[2]: Target `I3Db/CMakeFiles/I3Db.dir/build' not remade because of errors.\nmake[1]: *** [I3Db/CMakeFiles/I3Db.dir/all] Error 2\n}}}\n",
"reporter": "maryon",
"cc": "",
"resolution": "fixed",
"_ts": "1550067204154158",
"component": "combo reconstruction",
"summary": "[I3OmDb] Not compiling for icerec/V05-00-02",
"priority": "blocker",
"keywords": "I3OmDb icerec",
"time": "2016-09-09T11:50:36",
"milestone": "",
"owner": "joertlin",
"type": "defect"
}
```
</p>
</details>
| non_priority | not compiling for icerec trac migrated from json status closed changetime description does not compile for me when using clang however gcc works forward declaration wrongly executed n n n building cxx object sttools cmakefiles sttools pybindings dir private pybindings algorithms seededrt cxx o nin file included from home maryon software meta projects icerec src private cxx n home maryon software meta projects icerec src public h error om s redeclared with private access nstruct om s n n home maryon software meta projects icerec src public h note previously declared public here nstruct om s n error generated nmake error nmake target cmakefiles dir build not remade because of errors nmake error n n reporter maryon cc resolution fixed ts component combo reconstruction summary not compiling for icerec priority blocker keywords icerec time milestone owner joertlin type defect | 0 |
26,932 | 5,299,995,292 | IssuesEvent | 2017-02-10 02:28:18 | systemd/systemd | https://api.github.com/repos/systemd/systemd | closed | document or imply that settings such as RestrictAddressFamily= should be combined with SystemCallArchitectures=native | documentation has-pr pid1 | As discussed in #5254. | 1.0 | document or imply that settings such as RestrictAddressFamily= should be combined with SystemCallArchitectures=native - As discussed in #5254. | non_priority | document or imply that settings such as restrictaddressfamily should be combined with systemcallarchitectures native as discussed in | 0 |
222,581 | 17,083,601,882 | IssuesEvent | 2021-07-08 08:58:30 | ridgei/large_scale_ablation | https://api.github.com/repos/ridgei/large_scale_ablation | opened | make a draft research proposal draft | documentation | ## Summary
make a draft research proposal
## Goal
submit to Kimura-san
## Todo
- [ ] make a draft research proposal by Takemoto
- [ ] review and modify by Okuda-san
- [ ] submit to Kimura-san
## Deadline
07/16
## Parent issue
None
## References
None
## Notes
None
| 1.0 | make a draft research proposal draft - ## Summary
make a draft research proposal
## Goal
submit to Kimura-san
## Todo
- [ ] make a draft research proposal by Takemoto
- [ ] review and modify by Okuda-san
- [ ] submit to Kimura-san
## Deadline
07/16
## Parent issue
None
## References
None
## Notes
None
| non_priority | make a draft research proposal draft summary make a draft research proposal goal submit to kimura san todo make a draft research proposal by takemoto review and modify by okuda san submit to kimura san deadline parent issue none references none notes none | 0 |
106,483 | 9,160,103,925 | IssuesEvent | 2019-03-01 05:57:57 | xcat2/xcat2-task-management | https://api.github.com/repos/xcat2/xcat2-task-management | closed | offer a osimage definition to set up ppc build server docker host | sprint3 test | what to do:
* [ ] offer a osimage definition to leverage xcat_inventory to set up ppc build server docker host
* [ ] update doc [How to set up a ppc build server docker host from stracth](https://github.ibm.com/xcat2/team_process/blob/master/FVT/docs/The_steps_of_ppc_build_server_docker_host_setup.md) | 1.0 | offer a osimage definition to set up ppc build server docker host - what to do:
* [ ] offer a osimage definition to leverage xcat_inventory to set up ppc build server docker host
* [ ] update doc [How to set up a ppc build server docker host from stracth](https://github.ibm.com/xcat2/team_process/blob/master/FVT/docs/The_steps_of_ppc_build_server_docker_host_setup.md) | non_priority | offer a osimage definition to set up ppc build server docker host what to do offer a osimage definition to leverage xcat inventory to set up ppc build server docker host update doc | 0 |
53,861 | 6,762,035,899 | IssuesEvent | 2017-10-25 05:54:40 | kbenoit/quanteda | https://api.github.com/repos/kbenoit/quanteda | closed | What the best way to do lemmatization? | design | I have tried to do lemmatization myself after seeing https://stackoverflow.com/questions/46731429/quanteda-fastest-way-to-replace-tokens-with-lemma-from-dictionary/46742533#46742533.
`tokens_lookup` takes 114.234 sec only with 2000 docs, while `tokens_convert` is 0.067 sec (738 times faster!). We need to think.
```r
require(quanteda)
load("/home/kohei/Documents/Brexit/Analysis/data_tokens_guardian.RData")
toks <- head(data_tokens_guardian, 2000)
# http://www.lexiconista.com/Datasets/lemmatization-en.zip
data <- read.csv("/home/kohei/Documents/Dictionary/Lemma list/lemmatization-en.txt", sep = '\t', as.is = TRUE,
header = FALSE)
system.time(
dict <- dictionary(split(data[,2], data[,1]))
)
# user system elapsed
# 67.772 1.376 69.394
length(dict) # 26058
system.time(
toks_lemma <- tokens_lookup(toks, dict, valuetype = 'fixed', exclusive = FALSE, capkeys = FALSE)
)
# user system elapsed
# 43.888 3.656 44.840
tokens_convert <- function(x, from, to) {
type <- attr(x, 'types')
type_new <- to[match(type, from)]
type_new <- ifelse(is.na(type_new), type, type_new)
attr(x, 'types') <- type_new
quanteda:::tokens_recompile(x)
}
system.time(
toks_lemma2 <- tokens_convert(toks, from = data[,2], to = data[,1])
)
# user system elapsed
# 0.072 0.004 0.067
``` | 1.0 | What the best way to do lemmatization? - I have tried to do lemmatization myself after seeing https://stackoverflow.com/questions/46731429/quanteda-fastest-way-to-replace-tokens-with-lemma-from-dictionary/46742533#46742533.
`tokens_lookup` takes 114.234 sec only with 2000 docs, while `tokens_convert` is 0.067 sec (738 times faster!). We need to think.
```r
require(quanteda)
load("/home/kohei/Documents/Brexit/Analysis/data_tokens_guardian.RData")
toks <- head(data_tokens_guardian, 2000)
# http://www.lexiconista.com/Datasets/lemmatization-en.zip
data <- read.csv("/home/kohei/Documents/Dictionary/Lemma list/lemmatization-en.txt", sep = '\t', as.is = TRUE,
header = FALSE)
system.time(
dict <- dictionary(split(data[,2], data[,1]))
)
# user system elapsed
# 67.772 1.376 69.394
length(dict) # 26058
system.time(
toks_lemma <- tokens_lookup(toks, dict, valuetype = 'fixed', exclusive = FALSE, capkeys = FALSE)
)
# user system elapsed
# 43.888 3.656 44.840
tokens_convert <- function(x, from, to) {
type <- attr(x, 'types')
type_new <- to[match(type, from)]
type_new <- ifelse(is.na(type_new), type, type_new)
attr(x, 'types') <- type_new
quanteda:::tokens_recompile(x)
}
system.time(
toks_lemma2 <- tokens_convert(toks, from = data[,2], to = data[,1])
)
# user system elapsed
# 0.072 0.004 0.067
``` | non_priority | what the best way to do lemmatization i have tried to do lemmatization myself after seeing tokens lookup takes sec only with docs while tokens convert is sec times faster we need to think r require quanteda load home kohei documents brexit analysis data tokens guardian rdata toks head data tokens guardian data read csv home kohei documents dictionary lemma list lemmatization en txt sep t as is true header false system time dict dictionary split data data user system elapsed length dict system time toks lemma tokens lookup toks dict valuetype fixed exclusive false capkeys false user system elapsed tokens convert function x from to type attr x types type new to type new ifelse is na type new type type new attr x types type new quanteda tokens recompile x system time toks tokens convert toks from data to data user system elapsed | 0 |
20,074 | 11,382,042,453 | IssuesEvent | 2020-01-29 00:18:44 | badges/shields | https://api.github.com/repos/badges/shields | closed | MavenMetadata Service Test Failing | keep-service-tests-green service-badge | :clock11: **When did the problem start?**
~ 15th of January
<!-- Indicate when the problem started -->
:camera: **Live badge**
<!-- Provide a link to the live badge in plain text and markdown. -->
https://img.shields.io/maven-metadata/v?metadataUrl=https%3A%2F%2Frepo1.maven.org%2Fmaven2%2Fcom%2Fgoogle%2Fcode%2Fgson%2Fgson%2Fmaven-metadata.xml

:wrench: **Is the live badge working?**
Yes
<!-- Indicate whether or not the live badge is working. -->
:link: **CircleCI link**
https://circleci.com/gh/badges/daily-tests/854
<!-- Provide a link to the failing test in CircleCI. -->
:beetle: **Stack trace**
```
MavenMetadata [live] valid maven-metadata.xml uri [ GET /v.json?metadataUrl=http://central.maven.org/maven2/com/google/code/gson/gson/maven-metadata.xml ] - [ GET /v.json?metadataUrl=http://central.maven.org/maven2/com/google/code/gson/gson/maven-metadata.xml ]
ValidationError: message mismatch: "value" with value "inaccessible" fails to match the required pattern: /^v\d+(\.\d+)?(\.\d+)?$/
```
:bulb: **Possible solution**
Seems there's been some changes to Maven Central requiring HTTPS, so we just need to update our test targets accordingly (and probably the badge examples too)
https://blog.sonatype.com/central-repository-moving-to-https
<!--- Optional: only if you have suggestions on a fix/reason for the bug -->
<!-- Love Shields? Please consider donating $10 to sustain our activities:
👉 https://opencollective.com/shields -->
| 2.0 | MavenMetadata Service Test Failing - :clock11: **When did the problem start?**
~ 15th of January
<!-- Indicate when the problem started -->
:camera: **Live badge**
<!-- Provide a link to the live badge in plain text and markdown. -->
https://img.shields.io/maven-metadata/v?metadataUrl=https%3A%2F%2Frepo1.maven.org%2Fmaven2%2Fcom%2Fgoogle%2Fcode%2Fgson%2Fgson%2Fmaven-metadata.xml

:wrench: **Is the live badge working?**
Yes
<!-- Indicate whether or not the live badge is working. -->
:link: **CircleCI link**
https://circleci.com/gh/badges/daily-tests/854
<!-- Provide a link to the failing test in CircleCI. -->
:beetle: **Stack trace**
```
MavenMetadata [live] valid maven-metadata.xml uri [ GET /v.json?metadataUrl=http://central.maven.org/maven2/com/google/code/gson/gson/maven-metadata.xml ] - [ GET /v.json?metadataUrl=http://central.maven.org/maven2/com/google/code/gson/gson/maven-metadata.xml ]
ValidationError: message mismatch: "value" with value "inaccessible" fails to match the required pattern: /^v\d+(\.\d+)?(\.\d+)?$/
```
:bulb: **Possible solution**
Seems there's been some changes to Maven Central requiring HTTPS, so we just need to update our test targets accordingly (and probably the badge examples too)
https://blog.sonatype.com/central-repository-moving-to-https
<!--- Optional: only if you have suggestions on a fix/reason for the bug -->
<!-- Love Shields? Please consider donating $10 to sustain our activities:
👉 https://opencollective.com/shields -->
| non_priority | mavenmetadata service test failing when did the problem start of january camera live badge wrench is the live badge working yes link circleci link beetle stack trace mavenmetadata valid maven metadata xml uri validationerror message mismatch value with value inaccessible fails to match the required pattern v d d d bulb possible solution seems there s been some changes to maven central requiring https so we just need to update our test targets accordingly and probably the badge examples too love shields please consider donating to sustain our activities 👉 | 0 |
172,727 | 27,318,467,709 | IssuesEvent | 2023-02-24 17:34:53 | dotnet/machinelearning-modelbuilder | https://api.github.com/repos/dotnet/machinelearning-modelbuilder | opened | Redesign Model Builder Scenario Screen | Needs Design Needs PM | **Is your feature request related to a problem? Please describe.**
As we've expanded the number of scenarios in Model Builder, the screen has become cluttered and some scenarios require scrolling because the current tile design takes up too much space for each of the tiles.
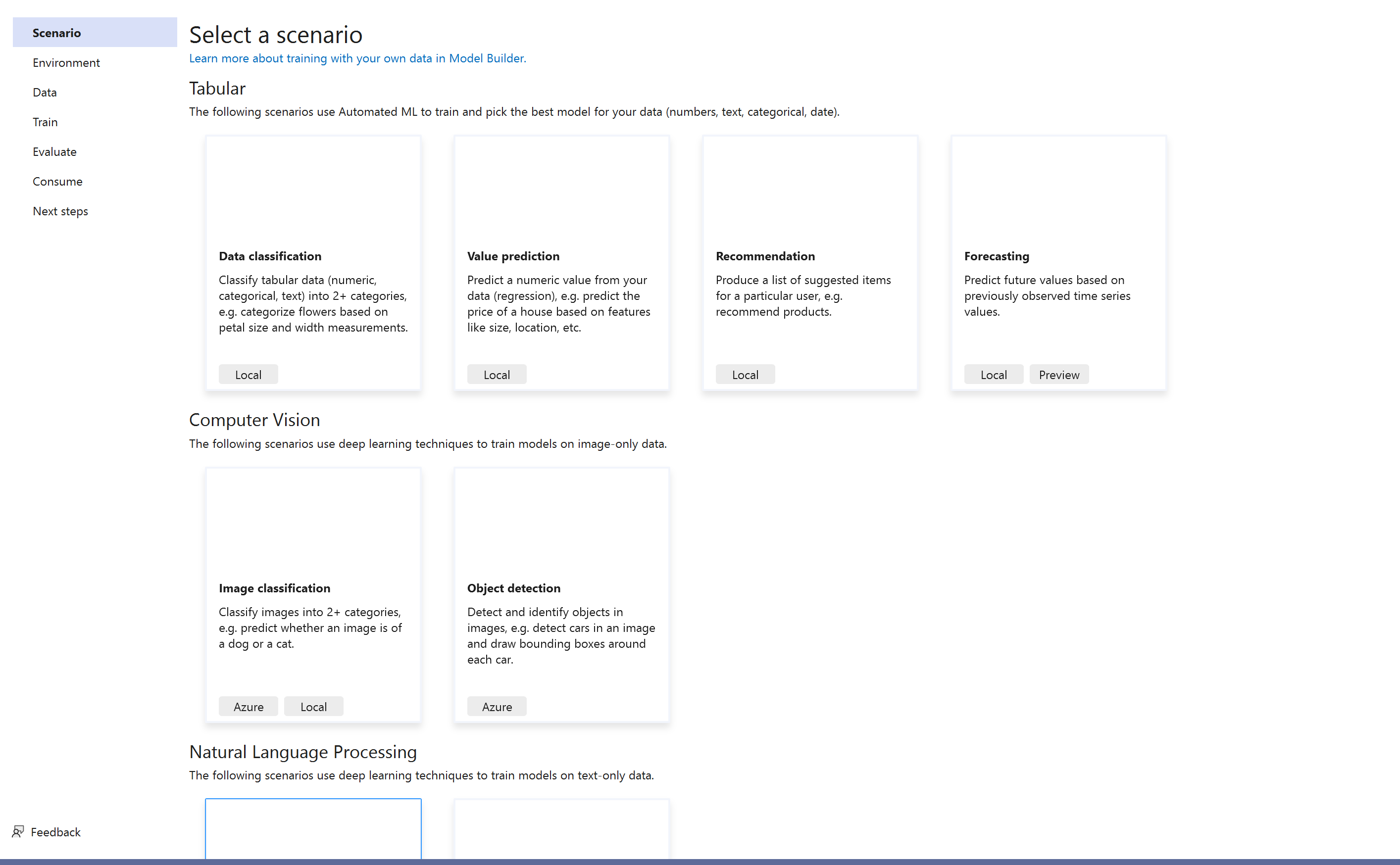
**Describe the solution you'd like**
Work with design team to come up with a more discoverable scenario screen.
**Describe alternatives you've considered**
N/A
**Additional context**
N/A
| 1.0 | Redesign Model Builder Scenario Screen - **Is your feature request related to a problem? Please describe.**
As we've expanded the number of scenarios in Model Builder, the screen has become cluttered and some scenarios require scrolling because the current tile design takes up too much space for each of the tiles.
**Describe the solution you'd like**
Work with design team to come up with a more discoverable scenario screen.
**Describe alternatives you've considered**
N/A
**Additional context**
N/A
| non_priority | redesign model builder scenario screen is your feature request related to a problem please describe as we ve expanded the number of scenarios in model builder the screen has become cluttered and some scenarios require scrolling because the current tile design takes up too much space for each of the tiles describe the solution you d like work with design team to come up with a more discoverable scenario screen describe alternatives you ve considered n a additional context n a | 0 |
326,352 | 24,080,415,557 | IssuesEvent | 2022-09-19 05:48:10 | codestates-seb/seb39_main_001 | https://api.github.com/repos/codestates-seb/seb39_main_001 | opened | [API 수정] | documentation BE | - [ ] PATCH /boards/{board-id}/{user-id}
- [ ] DELETE /boards/{board-id}/{user-id}
- [ ] POST /applications/{board-id}/{user-id}?position=
- [ ] POST /questions/{board-id}/{user-id}
- [ ] PATCH /questions/{question-id}/{user-id}
- [ ] POST /boards/{user-id}
- [ ] POST /bookmarks/{board-id}/{user-id}
- [ ] DELETE /bookmarks/{board-id}/{user-id}
- [ ] POST /answers/{question-id}/{user-id}
- [ ] PATCH /answers/{answer-id}/{user-id}
- [ ] DELETE /answers/{answer-id}/{user-id}
- [ ] DELETE /questions/{question-id}/{user-id}
| 1.0 | [API 수정] - - [ ] PATCH /boards/{board-id}/{user-id}
- [ ] DELETE /boards/{board-id}/{user-id}
- [ ] POST /applications/{board-id}/{user-id}?position=
- [ ] POST /questions/{board-id}/{user-id}
- [ ] PATCH /questions/{question-id}/{user-id}
- [ ] POST /boards/{user-id}
- [ ] POST /bookmarks/{board-id}/{user-id}
- [ ] DELETE /bookmarks/{board-id}/{user-id}
- [ ] POST /answers/{question-id}/{user-id}
- [ ] PATCH /answers/{answer-id}/{user-id}
- [ ] DELETE /answers/{answer-id}/{user-id}
- [ ] DELETE /questions/{question-id}/{user-id}
| non_priority | patch boards board id user id delete boards board id user id post applications board id user id position post questions board id user id patch questions question id user id post boards user id post bookmarks board id user id delete bookmarks board id user id post answers question id user id patch answers answer id user id delete answers answer id user id delete questions question id user id | 0 |
98,628 | 8,682,353,025 | IssuesEvent | 2018-12-02 07:12:24 | AOSC-Dev/aosc-os-abbs | https://api.github.com/repos/AOSC-Dev/aosc-os-abbs | reopened | ghostscript: multiple vulnerabilities | security to-testing | **CVE IDs:** CVE-2018-17961, CVE-2018-18073, CVE-2018-18284
**Other security advisory IDs:** USN-3803-1, DSA-4336-1, MGASA-2018-0408, ASA-201811-3
**Descriptions:**
Tavis Ormandy discovered multiple security issues in Ghostscript. If a user
or automated system were tricked into processing a specially crafted file,
a remote attacker could possibly use these issues to access arbitrary
files, execute arbitrary code, or cause a denial of service.
**Patches:** from Ubuntu, *update to Ghostscript 9.25 first!*
**Architectural progress:**
<!-- Please remove any architecture to which the security vulnerabilities do not apply. -->
- [x] AMD64 `amd64`
- [x] 32-bit Optional Environment `optenv32`
- [ ] AArch64 `arm64`
- [ ] ARMv7 `armel`
- [ ] PowerPC 64-bit BE `ppc64`
- [ ] PowerPC 32-bit BE `powerpc`
- [ ] RISC-V 64-bit `riscv64`
| 1.0 | ghostscript: multiple vulnerabilities - **CVE IDs:** CVE-2018-17961, CVE-2018-18073, CVE-2018-18284
**Other security advisory IDs:** USN-3803-1, DSA-4336-1, MGASA-2018-0408, ASA-201811-3
**Descriptions:**
Tavis Ormandy discovered multiple security issues in Ghostscript. If a user
or automated system were tricked into processing a specially crafted file,
a remote attacker could possibly use these issues to access arbitrary
files, execute arbitrary code, or cause a denial of service.
**Patches:** from Ubuntu, *update to Ghostscript 9.25 first!*
**Architectural progress:**
<!-- Please remove any architecture to which the security vulnerabilities do not apply. -->
- [x] AMD64 `amd64`
- [x] 32-bit Optional Environment `optenv32`
- [ ] AArch64 `arm64`
- [ ] ARMv7 `armel`
- [ ] PowerPC 64-bit BE `ppc64`
- [ ] PowerPC 32-bit BE `powerpc`
- [ ] RISC-V 64-bit `riscv64`
| non_priority | ghostscript multiple vulnerabilities cve ids cve cve cve other security advisory ids usn dsa mgasa asa descriptions tavis ormandy discovered multiple security issues in ghostscript if a user or automated system were tricked into processing a specially crafted file a remote attacker could possibly use these issues to access arbitrary files execute arbitrary code or cause a denial of service patches from ubuntu update to ghostscript first architectural progress bit optional environment armel powerpc bit be powerpc bit be powerpc risc v bit | 0 |
45,697 | 5,725,607,231 | IssuesEvent | 2017-04-20 16:57:43 | miw-upm/SPRING.tpv | https://api.github.com/repos/miw-upm/SPRING.tpv | closed | Database Seeder | high test | ### Poblador de BD a partir de Yaml
- Una sola carga inicial para todos los test
- Disponible en el API. Se permite elegir el fichero de precarga
> Tiempo estimado: **5h**. Tiempo real: **??h**
[Wiki](url)
| 1.0 | Database Seeder - ### Poblador de BD a partir de Yaml
- Una sola carga inicial para todos los test
- Disponible en el API. Se permite elegir el fichero de precarga
> Tiempo estimado: **5h**. Tiempo real: **??h**
[Wiki](url)
| non_priority | database seeder poblador de bd a partir de yaml una sola carga inicial para todos los test disponible en el api se permite elegir el fichero de precarga tiempo estimado tiempo real h url | 0 |
3,307 | 2,666,937,760 | IssuesEvent | 2015-03-22 02:30:06 | danshannon/javastravav3api | https://api.github.com/repos/danshannon/javastravav3api | closed | get segment effort returns activity without resource_state | has issue test has workaround Strava issue | `HTTP GET https://www.strava.com/api/v3/segment_efforts/5591276015`
returns `"activity":{"id":237374614}`
Should return `"activity":{"id":237374614, "resource_state":1}` to indicate that this is a META representation of the activity. | 1.0 | get segment effort returns activity without resource_state - `HTTP GET https://www.strava.com/api/v3/segment_efforts/5591276015`
returns `"activity":{"id":237374614}`
Should return `"activity":{"id":237374614, "resource_state":1}` to indicate that this is a META representation of the activity. | non_priority | get segment effort returns activity without resource state http get returns activity id should return activity id resource state to indicate that this is a meta representation of the activity | 0 |
36,265 | 5,040,792,297 | IssuesEvent | 2016-12-19 07:41:53 | db0sch/mnmlist | https://api.github.com/repos/db0sch/mnmlist | closed | Testing // Sign up & Sign In | primary ready testing | Write feature specs (which acts as a user on the browser) for sign up, sign in, problem with sign up and sign in.
Editing password, username, fisrt_name, and last_name... etc. | 1.0 | Testing // Sign up & Sign In - Write feature specs (which acts as a user on the browser) for sign up, sign in, problem with sign up and sign in.
Editing password, username, fisrt_name, and last_name... etc. | non_priority | testing sign up sign in write feature specs which acts as a user on the browser for sign up sign in problem with sign up and sign in editing password username fisrt name and last name etc | 0 |
152,255 | 13,449,790,587 | IssuesEvent | 2020-09-08 17:27:50 | Frankkwizera/films-webapp | https://api.github.com/repos/Frankkwizera/films-webapp | opened | Add project readme | documentation | Google how project readme files are written and write one for this repository | 1.0 | Add project readme - Google how project readme files are written and write one for this repository | non_priority | add project readme google how project readme files are written and write one for this repository | 0 |
216,655 | 24,287,825,724 | IssuesEvent | 2022-09-29 01:04:09 | DavidSpek/pipelines | https://api.github.com/repos/DavidSpek/pipelines | opened | CVE-2022-21797 (High) detected in joblib-0.14.1-py2.py3-none-any.whl | security vulnerability | ## CVE-2022-21797 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>joblib-0.14.1-py2.py3-none-any.whl</b></p></summary>
<p>Lightweight pipelining: using Python functions as pipeline jobs.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/28/5c/cf6a2b65a321c4a209efcdf64c2689efae2cb62661f8f6f4bb28547cf1bf/joblib-0.14.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/28/5c/cf6a2b65a321c4a209efcdf64c2689efae2cb62661f8f6f4bb28547cf1bf/joblib-0.14.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /backend/requirements.txt</p>
<p>Path to vulnerable library: /backend/requirements.txt,/backend/src/apiserver/visualization/requirements.txt,/test/sample-test/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **joblib-0.14.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package joblib from 0 and before 1.2.0 are vulnerable to Arbitrary Code Execution via the pre_dispatch flag in Parallel() class due to the eval() statement.
<p>Publish Date: 2022-09-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21797>CVE-2022-21797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-09-26</p>
<p>Fix Resolution: joblib - 1.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-21797 (High) detected in joblib-0.14.1-py2.py3-none-any.whl - ## CVE-2022-21797 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>joblib-0.14.1-py2.py3-none-any.whl</b></p></summary>
<p>Lightweight pipelining: using Python functions as pipeline jobs.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/28/5c/cf6a2b65a321c4a209efcdf64c2689efae2cb62661f8f6f4bb28547cf1bf/joblib-0.14.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/28/5c/cf6a2b65a321c4a209efcdf64c2689efae2cb62661f8f6f4bb28547cf1bf/joblib-0.14.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /backend/requirements.txt</p>
<p>Path to vulnerable library: /backend/requirements.txt,/backend/src/apiserver/visualization/requirements.txt,/test/sample-test/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **joblib-0.14.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package joblib from 0 and before 1.2.0 are vulnerable to Arbitrary Code Execution via the pre_dispatch flag in Parallel() class due to the eval() statement.
<p>Publish Date: 2022-09-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21797>CVE-2022-21797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-09-26</p>
<p>Fix Resolution: joblib - 1.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in joblib none any whl cve high severity vulnerability vulnerable library joblib none any whl lightweight pipelining using python functions as pipeline jobs library home page a href path to dependency file backend requirements txt path to vulnerable library backend requirements txt backend src apiserver visualization requirements txt test sample test requirements txt dependency hierarchy x joblib none any whl vulnerable library found in base branch master vulnerability details the package joblib from and before are vulnerable to arbitrary code execution via the pre dispatch flag in parallel class due to the eval statement publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution joblib step up your open source security game with mend | 0 |
105,006 | 22,820,493,705 | IssuesEvent | 2022-07-12 01:26:48 | arduino/arduino-ide | https://api.github.com/repos/arduino/arduino-ide | closed | Text colour clash. | topic: code type: imperfection topic: theme | **Describe the bug**
The _Dark (Theia)_ theme renders the intelli-sense info unreadable.
**To Reproduce**
Steps to reproduce the behavior:
1. Set theme to _Dark (Theia)_.
2. Try to read the intellisense/quick-info.
**Expected behavior**
The contrast between text and background is high enough to be readable.
**Screenshots**

Desktop (please complete the following information):
- Edition Windows 10 Home
- Version 21H1
- OS build 19043.1288
- Experience Windows Feature Experience Pack 120.2212.3920.0
Additional context
IDE:
- Version 2.0.0-beta.12
- Date 2021-10-07T07:55:54.325Z
- CLI Version 0.19.1 alpha [718bbbf2]
| 1.0 | Text colour clash. - **Describe the bug**
The _Dark (Theia)_ theme renders the intelli-sense info unreadable.
**To Reproduce**
Steps to reproduce the behavior:
1. Set theme to _Dark (Theia)_.
2. Try to read the intellisense/quick-info.
**Expected behavior**
The contrast between text and background is high enough to be readable.
**Screenshots**

Desktop (please complete the following information):
- Edition Windows 10 Home
- Version 21H1
- OS build 19043.1288
- Experience Windows Feature Experience Pack 120.2212.3920.0
Additional context
IDE:
- Version 2.0.0-beta.12
- Date 2021-10-07T07:55:54.325Z
- CLI Version 0.19.1 alpha [718bbbf2]
| non_priority | text colour clash describe the bug the dark theia theme renders the intelli sense info unreadable to reproduce steps to reproduce the behavior set theme to dark theia try to read the intellisense quick info expected behavior the contrast between text and background is high enough to be readable screenshots desktop please complete the following information edition windows home version os build experience windows feature experience pack additional context ide version beta date cli version alpha | 0 |
308,959 | 26,640,658,918 | IssuesEvent | 2023-01-25 04:17:04 | galaxyproject/galaxy | https://api.github.com/repos/galaxyproject/galaxy | opened | New datatypes page renders an empty table | kind/bug area/UI-UX release-testing-23.0 | **Describe the bug**
Testing #14464.
The `/datatypes` page should show a list of available datatypes but on Ubuntu/Chrome I got a long table of blank rows (screenshot below). I don't see any console or request errors. Hard-refresh did not fix.
The request to https://usegalaxy.org/api/datatypes?extension_only=true appears to be successful, returning a list of datatype strings:
```js
["ab1","affybatch","agilentbrukeryep.d.tar","agilentmasshunter.d.tar", ... ]
```
**Galaxy Version and/or server at which you observed the bug**
23.0
**To Reproduce**
Steps to reproduce the behaviour:
1. Visit https://usegalaxy.org/datatypes
**Expected behaviour**
The table should be populated with available datatypes.
**Screenshots**
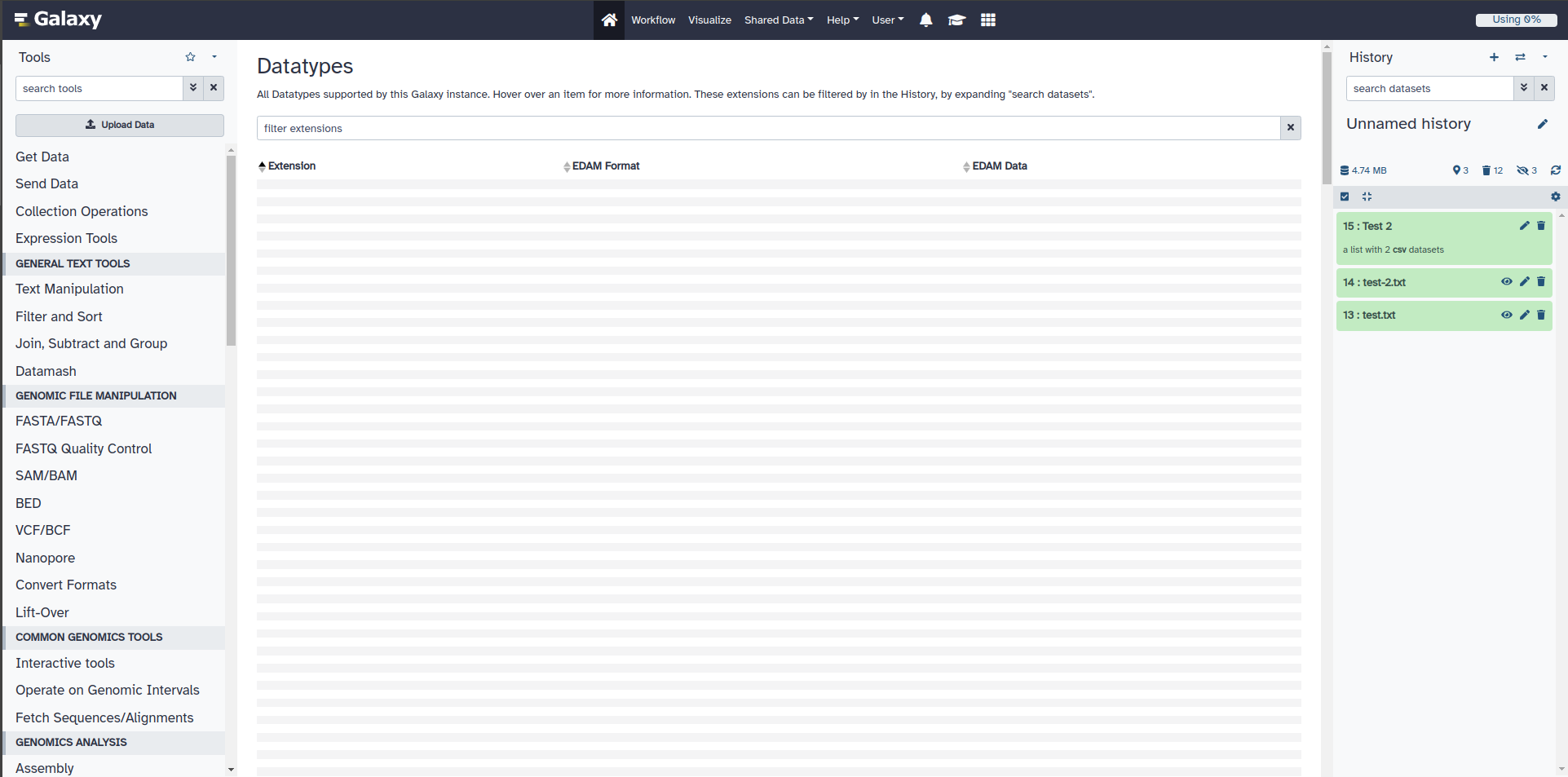
| 1.0 | New datatypes page renders an empty table - **Describe the bug**
Testing #14464.
The `/datatypes` page should show a list of available datatypes but on Ubuntu/Chrome I got a long table of blank rows (screenshot below). I don't see any console or request errors. Hard-refresh did not fix.
The request to https://usegalaxy.org/api/datatypes?extension_only=true appears to be successful, returning a list of datatype strings:
```js
["ab1","affybatch","agilentbrukeryep.d.tar","agilentmasshunter.d.tar", ... ]
```
**Galaxy Version and/or server at which you observed the bug**
23.0
**To Reproduce**
Steps to reproduce the behaviour:
1. Visit https://usegalaxy.org/datatypes
**Expected behaviour**
The table should be populated with available datatypes.
**Screenshots**
| non_priority | new datatypes page renders an empty table describe the bug testing the datatypes page should show a list of available datatypes but on ubuntu chrome i got a long table of blank rows screenshot below i don t see any console or request errors hard refresh did not fix the request to appears to be successful returning a list of datatype strings js galaxy version and or server at which you observed the bug to reproduce steps to reproduce the behaviour visit expected behaviour the table should be populated with available datatypes screenshots | 0 |
1,859 | 3,409,845,869 | IssuesEvent | 2015-12-04 17:25:26 | ChandraCXC/iris | https://api.github.com/repos/ChandraCXC/iris | closed | Prototype Approach for Integration Testing | story:test-infrastructure | We are not yet sure what the integration test setup is going to look like. Note that this is just to prototype and be sure we have a valid approach for setting up SAMP and SHERPA-SAMP. | 1.0 | Prototype Approach for Integration Testing - We are not yet sure what the integration test setup is going to look like. Note that this is just to prototype and be sure we have a valid approach for setting up SAMP and SHERPA-SAMP. | non_priority | prototype approach for integration testing we are not yet sure what the integration test setup is going to look like note that this is just to prototype and be sure we have a valid approach for setting up samp and sherpa samp | 0 |
75,214 | 25,590,112,856 | IssuesEvent | 2022-12-01 12:21:58 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | EDUs with room id field cause notifications | T-Defect A-Notifications X-Needs-Investigation | ### Description
Incoming EDUs over /sync can produce notifications if they contain the room_id field
Conduit:
```
{
"ephemeral": {
"events": [
{
"type": "m.receipt",
"content": {
"$zLsGHlRy8UIQnfoBCqagxOVz79DDb2y56XketZhxdw8": {
"m.read": {
"@tulir:maunium.net": {
"ts": 1620812476643
}
}
}
},
"room_id": "!EgoVrPyOnPSVXERlxj:gruenhage.xyz"
}
]
}
}
```
Synapse:
```
{
"ephemeral": {
"events": [
{
"type": "m.receipt",
"content": {
"$inJlQ2wHie4DHUbNCbFRVCxInkCe5GFTqFbPwAEAbx8": {
"m.read": {
"@ace:kittenface.studio": {
"ts": 1620812386378
}
}
}
}
}
]
}
}
```
I assume the presence of the room_id key triggers Element to apply a push rule to the event.
You can see here in the spec that receipt events should contain a room id: https://matrix.org/docs/spec/client_server/r0.6.1#m-receipt
You can also see it in the example response to /sync: https://matrix.org/docs/spec/client_server/r0.6.1#get-matrix-client-r0-sync (but the /sync definition for `Event` doesn't list the room_id field, so maybe it's a gray zone).
I think Element should not play notifications sounds for EDUs in any case
Version: Element Web staging
| 1.0 | EDUs with room id field cause notifications - ### Description
Incoming EDUs over /sync can produce notifications if they contain the room_id field
Conduit:
```
{
"ephemeral": {
"events": [
{
"type": "m.receipt",
"content": {
"$zLsGHlRy8UIQnfoBCqagxOVz79DDb2y56XketZhxdw8": {
"m.read": {
"@tulir:maunium.net": {
"ts": 1620812476643
}
}
}
},
"room_id": "!EgoVrPyOnPSVXERlxj:gruenhage.xyz"
}
]
}
}
```
Synapse:
```
{
"ephemeral": {
"events": [
{
"type": "m.receipt",
"content": {
"$inJlQ2wHie4DHUbNCbFRVCxInkCe5GFTqFbPwAEAbx8": {
"m.read": {
"@ace:kittenface.studio": {
"ts": 1620812386378
}
}
}
}
}
]
}
}
```
I assume the presence of the room_id key triggers Element to apply a push rule to the event.
You can see here in the spec that receipt events should contain a room id: https://matrix.org/docs/spec/client_server/r0.6.1#m-receipt
You can also see it in the example response to /sync: https://matrix.org/docs/spec/client_server/r0.6.1#get-matrix-client-r0-sync (but the /sync definition for `Event` doesn't list the room_id field, so maybe it's a gray zone).
I think Element should not play notifications sounds for EDUs in any case
Version: Element Web staging
| non_priority | edus with room id field cause notifications description incoming edus over sync can produce notifications if they contain the room id field conduit ephemeral events type m receipt content m read tulir maunium net ts room id egovrpyonpsvxerlxj gruenhage xyz synapse ephemeral events type m receipt content m read ace kittenface studio ts i assume the presence of the room id key triggers element to apply a push rule to the event you can see here in the spec that receipt events should contain a room id you can also see it in the example response to sync but the sync definition for event doesn t list the room id field so maybe it s a gray zone i think element should not play notifications sounds for edus in any case version element web staging | 0 |
37,990 | 8,393,559,213 | IssuesEvent | 2018-10-09 20:54:41 | phy25/tweetpi | https://api.github.com/repos/phy25/tweetpi | closed | Code Review by lyhuang@bu.edu | bug code review | **Code Review by lyhuang@bu.edu**
Congratulation on your finishing minipj1. However, you still have some problems. I can not run your code through your readme. Your code can **ONLY** be used on LINUX. On windows, when I use:
`TweetPI.py annotatedvideo --timeline POTUS --limit 50 --options '{"twitter_consumer_key":"...", "twitter_consumer_secret":"...", "twitter_access_token":"...", "twitter_access_secret":"...", "google_key_json":"gapi.json"}'`
I put everything in and nothing happens when I run the command(Even no errors!!!).
Default setting is important so that I can check if your code works in least time.
Basically, your code meets the MVP of this task. It can generate video from twitter pictures automatically and provide labels for them.
Advantages:
1. Your API has many functions to use. I believe users can benefit a lot from your API.
2. You have considered many conditions including:
- No json file or keys
- Twitter API fails
- No enough arguments
- FFMPEG API fails
- Photo sizes not adapted to ffmpeg
3. Users can user many functions in your API such as setting font color, size, from users’ homeline etc, which is good for those who have many requirements.
4. Naming convention is good for reader to know what the variable is as soon as possible.
However, there is still many disadvantages that I suggest to adjust.
1. First, if someone runs on windows, the code will not raise any errors, please write an environment check or adjust your code on windows system.
2. Second, too many arguments make users confused especially when they are required arguments. I need to type secrets and keys EVERY TIME I run your code, which is not user-friendly to those who just want to use as soon as possible. I strongly recommend you read keys and secrets in a given txt file or let users adjust in the code so that users do not need to type every time.
3. Third, too many functions with fewest tutorials is not recommended. I can’t even know how to use such a great number of arguments. Please write more in your tutorial.
4. Forth, Using as a library is so confused because I don’t know even know the name of your classes and their functions, could you please provide more guide to use as a library of your code?
5. Fifth, you can not deal with too many pictures situation, it is important because users may be confused if they can not get videos in a short period.
6. Sixth, default settings are important. For a starter, it is easiest and fastest way to access your API through simplest command with fewest or none parameters. I spend many times on learning to use your API, which I think is not user-friendly.
Other Details:
1. It is not a good idea to write all functions in a file. This may make your code confusing and look messing. To separate your class into different files may be a good idea.
2. More comments should be added otherwise readers may be confused.
3. Too many commits may confuse yourself. You have committed over 60 times in all the branches. This may make yourself confused when errors are found. If you setup automatic push in IDE, I strongly recommend you set a long time period.
| 1.0 | Code Review by lyhuang@bu.edu - **Code Review by lyhuang@bu.edu**
Congratulation on your finishing minipj1. However, you still have some problems. I can not run your code through your readme. Your code can **ONLY** be used on LINUX. On windows, when I use:
`TweetPI.py annotatedvideo --timeline POTUS --limit 50 --options '{"twitter_consumer_key":"...", "twitter_consumer_secret":"...", "twitter_access_token":"...", "twitter_access_secret":"...", "google_key_json":"gapi.json"}'`
I put everything in and nothing happens when I run the command(Even no errors!!!).
Default setting is important so that I can check if your code works in least time.
Basically, your code meets the MVP of this task. It can generate video from twitter pictures automatically and provide labels for them.
Advantages:
1. Your API has many functions to use. I believe users can benefit a lot from your API.
2. You have considered many conditions including:
- No json file or keys
- Twitter API fails
- No enough arguments
- FFMPEG API fails
- Photo sizes not adapted to ffmpeg
3. Users can user many functions in your API such as setting font color, size, from users’ homeline etc, which is good for those who have many requirements.
4. Naming convention is good for reader to know what the variable is as soon as possible.
However, there is still many disadvantages that I suggest to adjust.
1. First, if someone runs on windows, the code will not raise any errors, please write an environment check or adjust your code on windows system.
2. Second, too many arguments make users confused especially when they are required arguments. I need to type secrets and keys EVERY TIME I run your code, which is not user-friendly to those who just want to use as soon as possible. I strongly recommend you read keys and secrets in a given txt file or let users adjust in the code so that users do not need to type every time.
3. Third, too many functions with fewest tutorials is not recommended. I can’t even know how to use such a great number of arguments. Please write more in your tutorial.
4. Forth, Using as a library is so confused because I don’t know even know the name of your classes and their functions, could you please provide more guide to use as a library of your code?
5. Fifth, you can not deal with too many pictures situation, it is important because users may be confused if they can not get videos in a short period.
6. Sixth, default settings are important. For a starter, it is easiest and fastest way to access your API through simplest command with fewest or none parameters. I spend many times on learning to use your API, which I think is not user-friendly.
Other Details:
1. It is not a good idea to write all functions in a file. This may make your code confusing and look messing. To separate your class into different files may be a good idea.
2. More comments should be added otherwise readers may be confused.
3. Too many commits may confuse yourself. You have committed over 60 times in all the branches. This may make yourself confused when errors are found. If you setup automatic push in IDE, I strongly recommend you set a long time period.
| non_priority | code review by lyhuang bu edu code review by lyhuang bu edu congratulation on your finishing however you still have some problems i can not run your code through your readme your code can only be used on linux on windows when i use tweetpi py annotatedvideo timeline potus limit options twitter consumer key twitter consumer secret twitter access token twitter access secret google key json gapi json i put everything in and nothing happens when i run the command even no errors default setting is important so that i can check if your code works in least time basically your code meets the mvp of this task it can generate video from twitter pictures automatically and provide labels for them advantages your api has many functions to use i believe users can benefit a lot from your api you have considered many conditions including no json file or keys twitter api fails no enough arguments ffmpeg api fails photo sizes not adapted to ffmpeg users can user many functions in your api such as setting font color size from users’ homeline etc which is good for those who have many requirements naming convention is good for reader to know what the variable is as soon as possible however there is still many disadvantages that i suggest to adjust first if someone runs on windows the code will not raise any errors please write an environment check or adjust your code on windows system second too many arguments make users confused especially when they are required arguments i need to type secrets and keys every time i run your code which is not user friendly to those who just want to use as soon as possible i strongly recommend you read keys and secrets in a given txt file or let users adjust in the code so that users do not need to type every time third too many functions with fewest tutorials is not recommended i can’t even know how to use such a great number of arguments please write more in your tutorial forth using as a library is so confused because i don’t know even know the name of your classes and their functions could you please provide more guide to use as a library of your code fifth you can not deal with too many pictures situation it is important because users may be confused if they can not get videos in a short period sixth default settings are important for a starter it is easiest and fastest way to access your api through simplest command with fewest or none parameters i spend many times on learning to use your api which i think is not user friendly other details it is not a good idea to write all functions in a file this may make your code confusing and look messing to separate your class into different files may be a good idea more comments should be added otherwise readers may be confused too many commits may confuse yourself you have committed over times in all the branches this may make yourself confused when errors are found if you setup automatic push in ide i strongly recommend you set a long time period | 0 |
8,010 | 11,266,878,720 | IssuesEvent | 2020-01-14 00:13:52 | proot-me/gsoc | https://api.github.com/repos/proot-me/gsoc | closed | Project template | requirement | > Each project on the Ideas list should include: a) a project title/description b) more detailed description of the project (2-5 sentences) c) expected outcomes d) skills required/preferred e) possible mentors. And if possible, an easy, medium or hard rating of each project.
> Don’t be vague about the ideas. Be sure to write a few sentences describing what you need accomplished and not just an overall theoretical version of what you might want.
See: https://google.github.io/gsocguides/mentor/defining-a-project-ideas-list | 1.0 | Project template - > Each project on the Ideas list should include: a) a project title/description b) more detailed description of the project (2-5 sentences) c) expected outcomes d) skills required/preferred e) possible mentors. And if possible, an easy, medium or hard rating of each project.
> Don’t be vague about the ideas. Be sure to write a few sentences describing what you need accomplished and not just an overall theoretical version of what you might want.
See: https://google.github.io/gsocguides/mentor/defining-a-project-ideas-list | non_priority | project template each project on the ideas list should include a a project title description b more detailed description of the project sentences c expected outcomes d skills required preferred e possible mentors and if possible an easy medium or hard rating of each project don’t be vague about the ideas be sure to write a few sentences describing what you need accomplished and not just an overall theoretical version of what you might want see | 0 |
5,871 | 3,294,911,300 | IssuesEvent | 2015-10-31 13:37:21 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Not a bug but a suggestion for MODAL Image selection | No Code Attached Yet | #### Steps to reproduce the issue
The current use of bootstrap wells etc in a modal for the top and the bottom can be confusing to users since the upload and navigations are hidden without scrolling etc. I would like to suggest making the top thumbnail list or grid well fixed and the bottom upload a photo fixed as well. Here is my suggestion.
#### Expected result
.browser {
height: 325px;
width: 100%;
overflow: auto;
position: relative;
margin: 40px 0 40px 0;
padding: 40px 0;
}
.well {
margin: 0px;
position: fixed;
top: 0;
width: 94%;
z-index: 2;
}
#### Actual result
#### System information (as much as possible)
#### Additional comments | 1.0 | Not a bug but a suggestion for MODAL Image selection - #### Steps to reproduce the issue
The current use of bootstrap wells etc in a modal for the top and the bottom can be confusing to users since the upload and navigations are hidden without scrolling etc. I would like to suggest making the top thumbnail list or grid well fixed and the bottom upload a photo fixed as well. Here is my suggestion.
#### Expected result
.browser {
height: 325px;
width: 100%;
overflow: auto;
position: relative;
margin: 40px 0 40px 0;
padding: 40px 0;
}
.well {
margin: 0px;
position: fixed;
top: 0;
width: 94%;
z-index: 2;
}
#### Actual result
#### System information (as much as possible)
#### Additional comments | non_priority | not a bug but a suggestion for modal image selection steps to reproduce the issue the current use of bootstrap wells etc in a modal for the top and the bottom can be confusing to users since the upload and navigations are hidden without scrolling etc i would like to suggest making the top thumbnail list or grid well fixed and the bottom upload a photo fixed as well here is my suggestion expected result browser height width overflow auto position relative margin padding well margin position fixed top width z index actual result system information as much as possible additional comments | 0 |
20,263 | 6,019,351,744 | IssuesEvent | 2017-06-07 14:21:29 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | Remove legacy devhub index page | component: code quality component: devhub triaged | Our new devhub pages landed with mozilla/addons-frontend#1021 but our old index page is still in our code.
* [ ] Remove `devhub/index.html` - or replace it by the new index.html
* [ ] Add migration to remove waffle flag.
* [ ] Find unused css and images and remove them | 1.0 | Remove legacy devhub index page - Our new devhub pages landed with mozilla/addons-frontend#1021 but our old index page is still in our code.
* [ ] Remove `devhub/index.html` - or replace it by the new index.html
* [ ] Add migration to remove waffle flag.
* [ ] Find unused css and images and remove them | non_priority | remove legacy devhub index page our new devhub pages landed with mozilla addons frontend but our old index page is still in our code remove devhub index html or replace it by the new index html add migration to remove waffle flag find unused css and images and remove them | 0 |
5,836 | 5,190,706,266 | IssuesEvent | 2017-01-21 12:32:25 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | XLA: random numbers are the same across `session.run` calls | type:bug/performance | Not sure if that's intended, but that changes behavior of training pipelines:
```
from tensorflow.contrib.compiler import jit
jit_scope = jit.experimental_jit_scope
with jit_scope(compile_ops=True):
x = tf.random_uniform(())
sess = tf.Session()
print(sess.run(x))
print(sess.run(x))
```
Output:
```
0.768917
0.768917
``` | True | XLA: random numbers are the same across `session.run` calls - Not sure if that's intended, but that changes behavior of training pipelines:
```
from tensorflow.contrib.compiler import jit
jit_scope = jit.experimental_jit_scope
with jit_scope(compile_ops=True):
x = tf.random_uniform(())
sess = tf.Session()
print(sess.run(x))
print(sess.run(x))
```
Output:
```
0.768917
0.768917
``` | non_priority | xla random numbers are the same across session run calls not sure if that s intended but that changes behavior of training pipelines from tensorflow contrib compiler import jit jit scope jit experimental jit scope with jit scope compile ops true x tf random uniform sess tf session print sess run x print sess run x output | 0 |
179,921 | 21,606,571,012 | IssuesEvent | 2022-05-04 04:25:52 | testdemo1227/Demo-WebGoat1 | https://api.github.com/repos/testdemo1227/Demo-WebGoat1 | opened | jquery-1.10.2.min.js: 4 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.10.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-11023](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jquery - 3.5.0;jquery-rails - 4.4.0 | ❌ |
| [CVE-2020-11022](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - v3.0.0 | ❌ |
| [CVE-2019-11358](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11023</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-11358</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - 3.5.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11022","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v3.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-9251","vulnerabilityDetails":"jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11358","vulnerabilityDetails":"jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | True | jquery-1.10.2.min.js: 4 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.10.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-11023](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jquery - 3.5.0;jquery-rails - 4.4.0 | ❌ |
| [CVE-2020-11022](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - v3.0.0 | ❌ |
| [CVE-2019-11358](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11023</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-11358</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /newDesign/assets/js/jquery-1.10.2.min.js,/src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/testdemo1227/Demo-WebGoat1/commit/4bc811a006e2ea4234387fe41dc021407d92aae0">4bc811a006e2ea4234387fe41dc021407d92aae0</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - 3.5.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11022","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v3.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-9251","vulnerabilityDetails":"jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.10.2","packageFilePaths":["/newDesign/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.10.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11358","vulnerabilityDetails":"jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | non_priority | jquery min js vulnerabilities highest severity is vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library newdesign assets js jquery min js src main webapp js jquery jquery min js newdesign assets js jquery min js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium jquery min js direct jquery jquery rails medium jquery min js direct jquery medium jquery min js direct jquery medium jquery min js direct details cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library newdesign assets js jquery min js src main webapp js jquery jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery jquery rails step up your open source security game with whitesource cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library newdesign assets js jquery min js src main webapp js jquery jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library newdesign assets js jquery min js src main webapp js jquery jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library newdesign assets js jquery min js src main webapp js jquery jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery jquery rails isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed vulnerabilityurl istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype vulnerabilityurl | 0 |
156,421 | 13,648,717,424 | IssuesEvent | 2020-09-26 10:44:48 | wolfgangB33r/tabshop-android-issues | https://api.github.com/repos/wolfgangB33r/tabshop-android-issues | closed | Add printer setup instructions to TabShop help page | documentation | Setup documentation is needed to explain how to print invoices on a network printer or how to connect a Bluetooth Thermo printer.
Also some information about the ESC/POS commands is useful. | 1.0 | Add printer setup instructions to TabShop help page - Setup documentation is needed to explain how to print invoices on a network printer or how to connect a Bluetooth Thermo printer.
Also some information about the ESC/POS commands is useful. | non_priority | add printer setup instructions to tabshop help page setup documentation is needed to explain how to print invoices on a network printer or how to connect a bluetooth thermo printer also some information about the esc pos commands is useful | 0 |
313,597 | 23,484,011,341 | IssuesEvent | 2022-08-17 13:04:47 | dipzza/ultrastar-song2txt | https://api.github.com/repos/dipzza/ultrastar-song2txt | opened | Determine metrics to evaluate the pitch aplication. | documentation | Related to #11.
The most important behavior for the application is that the predicted pitches with high enough confidence are correct, if not the user would have to check the tones manually anyways. As the intention is to automate the process, is much more useful to get 60% right 40% unknown that 70% right 10% wrong 20% unknown for example.
To evaluate this behavior the classic Accuracy metric is useful, as well as precision and recall for multi-class classification (each note being a class) and we could favor precision in the precision-recall tradeoff.
Evaluation with metrics designed for pitch estimation could be useful to see if predictions are closer to be correct even if they are not exact, but it runs the risk of reevaluating the used techniques and not the final output of the application for little value. Nonetheless, raw pitch accuracy or some of the metrics defined here https://archives.ismir.net/ismir2019/paper/000090.pdf may be worth to take a look at.
Metrics usually used for linear regression may provide the information we are looking for aside from accuracy. MAE (mean squared error) for example heavily penalizes large differences between the predicted value and the ground truth, which is a desired behavior, as a semitone error may be overlooked, but a large enough difference is catastrophic. | 1.0 | Determine metrics to evaluate the pitch aplication. - Related to #11.
The most important behavior for the application is that the predicted pitches with high enough confidence are correct, if not the user would have to check the tones manually anyways. As the intention is to automate the process, is much more useful to get 60% right 40% unknown that 70% right 10% wrong 20% unknown for example.
To evaluate this behavior the classic Accuracy metric is useful, as well as precision and recall for multi-class classification (each note being a class) and we could favor precision in the precision-recall tradeoff.
Evaluation with metrics designed for pitch estimation could be useful to see if predictions are closer to be correct even if they are not exact, but it runs the risk of reevaluating the used techniques and not the final output of the application for little value. Nonetheless, raw pitch accuracy or some of the metrics defined here https://archives.ismir.net/ismir2019/paper/000090.pdf may be worth to take a look at.
Metrics usually used for linear regression may provide the information we are looking for aside from accuracy. MAE (mean squared error) for example heavily penalizes large differences between the predicted value and the ground truth, which is a desired behavior, as a semitone error may be overlooked, but a large enough difference is catastrophic. | non_priority | determine metrics to evaluate the pitch aplication related to the most important behavior for the application is that the predicted pitches with high enough confidence are correct if not the user would have to check the tones manually anyways as the intention is to automate the process is much more useful to get right unknown that right wrong unknown for example to evaluate this behavior the classic accuracy metric is useful as well as precision and recall for multi class classification each note being a class and we could favor precision in the precision recall tradeoff evaluation with metrics designed for pitch estimation could be useful to see if predictions are closer to be correct even if they are not exact but it runs the risk of reevaluating the used techniques and not the final output of the application for little value nonetheless raw pitch accuracy or some of the metrics defined here may be worth to take a look at metrics usually used for linear regression may provide the information we are looking for aside from accuracy mae mean squared error for example heavily penalizes large differences between the predicted value and the ground truth which is a desired behavior as a semitone error may be overlooked but a large enough difference is catastrophic | 0 |
122,406 | 17,703,856,507 | IssuesEvent | 2021-08-25 03:59:02 | Chiencc/Sample_Webgoat | https://api.github.com/repos/Chiencc/Sample_Webgoat | opened | CVE-2017-15095 (High) detected in jackson-databind-2.6.3.jar | security vulnerability | ## CVE-2017-15095 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Sample_Webgoat_depth_0/SourceCode/webgoat-standalone/webgoat-standalone/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.3/jackson-databind-2.6.3.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-7.1.jar (Root Library)
- :x: **jackson-databind-2.6.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/Sample_Webgoat/commit/8c8daafbebc152c1aabb39157cf71791044ee1af">8c8daafbebc152c1aabb39157cf71791044ee1af</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A deserialization flaw was discovered in the jackson-databind in versions before 2.8.10 and 2.9.1, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper. This issue extends the previous flaw CVE-2017-7525 by blacklisting more classes that could be used maliciously.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15095>CVE-2017-15095</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15095">https://nvd.nist.gov/vuln/detail/CVE-2017-15095</a></p>
<p>Release Date: 2018-02-06</p>
<p>Fix Resolution: 2.8.10,2.9.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-15095 (High) detected in jackson-databind-2.6.3.jar - ## CVE-2017-15095 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Sample_Webgoat_depth_0/SourceCode/webgoat-standalone/webgoat-standalone/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.3/jackson-databind-2.6.3.jar</p>
<p>
Dependency Hierarchy:
- webgoat-container-7.1.jar (Root Library)
- :x: **jackson-databind-2.6.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/Sample_Webgoat/commit/8c8daafbebc152c1aabb39157cf71791044ee1af">8c8daafbebc152c1aabb39157cf71791044ee1af</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A deserialization flaw was discovered in the jackson-databind in versions before 2.8.10 and 2.9.1, which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readValue method of the ObjectMapper. This issue extends the previous flaw CVE-2017-7525 by blacklisting more classes that could be used maliciously.
<p>Publish Date: 2018-02-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15095>CVE-2017-15095</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15095">https://nvd.nist.gov/vuln/detail/CVE-2017-15095</a></p>
<p>Release Date: 2018-02-06</p>
<p>Fix Resolution: 2.8.10,2.9.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file sample webgoat depth sourcecode webgoat standalone webgoat standalone pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy webgoat container jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a deserialization flaw was discovered in the jackson databind in versions before and which could allow an unauthenticated user to perform code execution by sending the maliciously crafted input to the readvalue method of the objectmapper this issue extends the previous flaw cve by blacklisting more classes that could be used maliciously publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
154,042 | 19,710,768,632 | IssuesEvent | 2022-01-13 04:53:28 | ChoeMinji/react-17.0.2 | https://api.github.com/repos/ChoeMinji/react-17.0.2 | opened | CVE-2017-16138 (High) detected in multiple libraries | security vulnerability | ## CVE-2017-16138 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>mime-1.3.4.tgz</b>, <b>mime-1.3.6.tgz</b>, <b>mime-1.2.11.tgz</b></p></summary>
<p>
<details><summary><b>mime-1.3.4.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.3.4.tgz">https://registry.npmjs.org/mime/-/mime-1.3.4.tgz</a></p>
<p>Path to dependency file: /fixtures/fiber-debugger/package.json</p>
<p>Path to vulnerable library: /fixtures/fiber-debugger/node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.2.tgz (Root Library)
- send-0.15.1.tgz
- :x: **mime-1.3.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>mime-1.3.6.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.3.6.tgz">https://registry.npmjs.org/mime/-/mime-1.3.6.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **mime-1.3.6.tgz** (Vulnerable Library)
</details>
<details><summary><b>mime-1.2.11.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.2.11.tgz">https://registry.npmjs.org/mime/-/mime-1.2.11.tgz</a></p>
<p>Path to dependency file: /fixtures/fiber-debugger/package.json</p>
<p>Path to vulnerable library: /fixtures/fiber-debugger/node_modules/url-loader/node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-0.9.5.tgz (Root Library)
- url-loader-0.5.7.tgz
- :x: **mime-1.2.11.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/react-17.0.2/commit/4669645897ed4ebcd4ee037f4dabb509ed4754c7">4669645897ed4ebcd4ee037f4dabb509ed4754c7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The mime module < 1.4.1, 2.0.1, 2.0.2 is vulnerable to regular expression denial of service when a mime lookup is performed on untrusted user input.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16138>CVE-2017-16138</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 1.4.1,2.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-16138 (High) detected in multiple libraries - ## CVE-2017-16138 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>mime-1.3.4.tgz</b>, <b>mime-1.3.6.tgz</b>, <b>mime-1.2.11.tgz</b></p></summary>
<p>
<details><summary><b>mime-1.3.4.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.3.4.tgz">https://registry.npmjs.org/mime/-/mime-1.3.4.tgz</a></p>
<p>Path to dependency file: /fixtures/fiber-debugger/package.json</p>
<p>Path to vulnerable library: /fixtures/fiber-debugger/node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- express-4.15.2.tgz (Root Library)
- send-0.15.1.tgz
- :x: **mime-1.3.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>mime-1.3.6.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.3.6.tgz">https://registry.npmjs.org/mime/-/mime-1.3.6.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **mime-1.3.6.tgz** (Vulnerable Library)
</details>
<details><summary><b>mime-1.2.11.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.2.11.tgz">https://registry.npmjs.org/mime/-/mime-1.2.11.tgz</a></p>
<p>Path to dependency file: /fixtures/fiber-debugger/package.json</p>
<p>Path to vulnerable library: /fixtures/fiber-debugger/node_modules/url-loader/node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-0.9.5.tgz (Root Library)
- url-loader-0.5.7.tgz
- :x: **mime-1.2.11.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/react-17.0.2/commit/4669645897ed4ebcd4ee037f4dabb509ed4754c7">4669645897ed4ebcd4ee037f4dabb509ed4754c7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The mime module < 1.4.1, 2.0.1, 2.0.2 is vulnerable to regular expression denial of service when a mime lookup is performed on untrusted user input.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16138>CVE-2017-16138</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16138</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 1.4.1,2.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries mime tgz mime tgz mime tgz mime tgz a comprehensive library for mime type mapping library home page a href path to dependency file fixtures fiber debugger package json path to vulnerable library fixtures fiber debugger node modules mime package json dependency hierarchy express tgz root library send tgz x mime tgz vulnerable library mime tgz a comprehensive library for mime type mapping library home page a href dependency hierarchy x mime tgz vulnerable library mime tgz a comprehensive library for mime type mapping library home page a href path to dependency file fixtures fiber debugger package json path to vulnerable library fixtures fiber debugger node modules url loader node modules mime package json dependency hierarchy react scripts tgz root library url loader tgz x mime tgz vulnerable library found in head commit a href found in base branch master vulnerability details the mime module is vulnerable to regular expression denial of service when a mime lookup is performed on untrusted user input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
126,509 | 26,869,318,656 | IssuesEvent | 2023-02-04 08:44:52 | lukebrogan/WebGoat | https://api.github.com/repos/lukebrogan/WebGoat | opened | Code Security Report: 45 high severity findings, 156 total findings | code security findings | # Code Security Report
**Latest Scan:** 2023-02-04 08:43am
**Total Findings:** 156
**Tested Project Files:** 424
**Detected Programming Languages:** 2
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: Java
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|SQL Injection|26|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Path/Directory Traversal|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Cross-Site Scripting|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Deserialization of Untrusted Data|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Server Side Request Forgery|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Hardcoded Password/Credentials|11|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|XML External Entity (XXE) Injection|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Heap Inspection|33|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-676](https://cwe.mitre.org/data/definitions/676.html)|Miscellaneous Dangerous Functions|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Console Output|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Error Messages Information Exposure|46|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-916](https://cwe.mitre.org/data/definitions/916.html)|Weak Hash Strength|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Cookie Injection|2|
### Details
> The below list presents the 20 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://saas.mend.io/sast/#/scans/d643c714-feee-4b72-8b10-0b3149c6dc8c/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>SQL Injection (CWE-89) : 20</summary>
#### Findings
<details>
<summary>mitigation/Servers.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/mitigation/Servers.java#L66-L71
</details>
<details>
<summary>advanced/SqlInjectionLesson6a.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66-L71
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/mitigation/SqlOnlyInputValidationOnKeywords.java#L57
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L71
</details>
</details>
<details>
<summary>advanced/SqlInjectionLesson6a.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66-L71
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/mitigation/SqlOnlyInputValidation.java#L51
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L71
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson10.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L66-L71
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L64
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L71
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson5a.java:64</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59-L64
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L56
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L64
</details>
</details>
<details>
<summary>advanced/SqlInjectionChallenge.java:69</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionChallenge.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionChallenge.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionChallenge.java#L69
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson4.java:60</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L55-L60
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L55
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L58
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L60
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson9.java:76</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L71-L76
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L61
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L64
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L76
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson2.java:65</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson2.java#L60-L65
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L60
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L63
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson5a.java:64</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59-L64
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L56
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L64
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson3.java:63</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L58-L63
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L54
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L57
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L63
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson5a.java:64</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59-L64
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L56
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L64
</details>
</details>
<details>
<summary>challenge5/Assignment5.java:59</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
</details>
<details>
<summary>introduction/SqlInjectionLesson3.java:63</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L58-L63
</details>
<details>
<summary>introduction/SqlInjectionLesson9.java:76</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L71-L76
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L61
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L64
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L76
</details>
</details>
<details>
<summary>challenge5/Assignment5.java:59</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L60
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L63
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
</details>
## Language: JavaScript / Node.js
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|DOM Based Cross-Site Scripting|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|2|
### Details
> The below list presents the 3 high vulnerability findings that need your attention. To view information on these findings, navigate to the [Mend SAST Application](https://saas.mend.io/sast/#/scans/d643c714-feee-4b72-8b10-0b3149c6dc8c/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>DOM Based Cross-Site Scripting (CWE-79) : 3</summary>
#### Findings
<details>
<summary>js/quiz.js:34</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29-L34
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L18
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L20
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L21
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L23
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L24
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L25
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L34
</details>
</details>
<details>
<summary>js/quiz.js:34</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29-L34
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L18
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L20
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L21
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L23
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L24
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L25
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L34
</details>
</details>
<details>
<summary>js/quiz.js:34</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29-L34
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L18
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L20
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L21
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L23
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L24
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L34
</details>
</details>
</details>
| 1.0 | Code Security Report: 45 high severity findings, 156 total findings - # Code Security Report
**Latest Scan:** 2023-02-04 08:43am
**Total Findings:** 156
**Tested Project Files:** 424
**Detected Programming Languages:** 2
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: Java
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|SQL Injection|26|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Path/Directory Traversal|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Cross-Site Scripting|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Deserialization of Untrusted Data|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Server Side Request Forgery|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Hardcoded Password/Credentials|11|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|XML External Entity (XXE) Injection|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Heap Inspection|33|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-676](https://cwe.mitre.org/data/definitions/676.html)|Miscellaneous Dangerous Functions|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Console Output|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Error Messages Information Exposure|46|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-916](https://cwe.mitre.org/data/definitions/916.html)|Weak Hash Strength|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Cookie Injection|2|
### Details
> The below list presents the 20 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://saas.mend.io/sast/#/scans/d643c714-feee-4b72-8b10-0b3149c6dc8c/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>SQL Injection (CWE-89) : 20</summary>
#### Findings
<details>
<summary>mitigation/Servers.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/mitigation/Servers.java#L66-L71
</details>
<details>
<summary>advanced/SqlInjectionLesson6a.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66-L71
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/mitigation/SqlOnlyInputValidationOnKeywords.java#L57
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L71
</details>
</details>
<details>
<summary>advanced/SqlInjectionLesson6a.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66-L71
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/mitigation/SqlOnlyInputValidation.java#L51
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionLesson6a.java#L71
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson10.java:71</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L66-L71
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L64
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson10.java#L71
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson5a.java:64</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59-L64
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L56
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L64
</details>
</details>
<details>
<summary>advanced/SqlInjectionChallenge.java:69</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionChallenge.java#L64-L69
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionChallenge.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/advanced/SqlInjectionChallenge.java#L69
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson4.java:60</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L55-L60
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L55
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L58
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson4.java#L60
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson9.java:76</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L71-L76
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L61
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L64
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L76
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson2.java:65</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson2.java#L60-L65
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L60
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L63
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson5a.java:64</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59-L64
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L56
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L64
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson3.java:63</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L58-L63
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L54
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L57
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L63
</details>
</details>
<details>
<summary>introduction/SqlInjectionLesson5a.java:64</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59-L64
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L56
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L59
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L62
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson5a.java#L64
</details>
</details>
<details>
<summary>challenge5/Assignment5.java:59</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
</details>
<details>
<summary>introduction/SqlInjectionLesson3.java:63</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson3.java#L58-L63
</details>
<details>
<summary>introduction/SqlInjectionLesson9.java:76</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L71-L76
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L61
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L64
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L66
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson9.java#L76
</details>
</details>
<details>
<summary>challenge5/Assignment5.java:59</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
</details>
<details>
<summary>introduction/SqlInjectionLesson8.java:78</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L73-L78
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L60
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L63
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L65
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/java/org/owasp/webgoat/lessons/sqlinjection/introduction/SqlInjectionLesson8.java#L78
</details>
</details>
</details>
## Language: JavaScript / Node.js
| Severity | CWE | Vulnerability Type | Count |
|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|DOM Based Cross-Site Scripting|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Weak Pseudo-Random|2|
### Details
> The below list presents the 3 high vulnerability findings that need your attention. To view information on these findings, navigate to the [Mend SAST Application](https://saas.mend.io/sast/#/scans/d643c714-feee-4b72-8b10-0b3149c6dc8c/details).
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20>DOM Based Cross-Site Scripting (CWE-79) : 3</summary>
#### Findings
<details>
<summary>js/quiz.js:34</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29-L34
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L18
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L20
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L21
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L23
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L24
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L25
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L34
</details>
</details>
<details>
<summary>js/quiz.js:34</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29-L34
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L18
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L20
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L21
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L23
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L24
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L25
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L34
</details>
</details>
<details>
<summary>js/quiz.js:34</summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29-L34
<details>
<summary> Trace </summary>
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L18
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L20
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L21
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L23
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L24
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L29
https://github.com/lukebrogan/WebGoat/blob/e50ad86a16eb0b10c53e398650e38965362b899a/src/main/resources/webgoat/static/js/quiz.js#L34
</details>
</details>
</details>
| non_priority | code security report high severity findings total findings code security report latest scan total findings tested project files detected programming languages check this box to manually trigger a scan language java severity cwe vulnerability type count high injection high traversal high scripting high of untrusted data high side request forgery medium password credentials medium external entity xxe injection medium pseudo random medium inspection medium dangerous functions medium output medium messages information exposure low hash strength low injection details the below list presents the most relevant findings that need your attention to view information on the remaining findings navigate to the sql injection cwe findings mitigation servers java advanced java trace advanced java trace introduction java trace introduction java trace advanced sqlinjectionchallenge java trace introduction java trace introduction java trace introduction java introduction java trace introduction java trace introduction java trace introduction java trace introduction java trace introduction java trace java introduction java introduction java trace java introduction java trace language javascript node js severity cwe vulnerability type count high based cross site scripting medium pseudo random details the below list presents the high vulnerability findings that need your attention to view information on these findings navigate to the dom based cross site scripting cwe findings js quiz js trace js quiz js trace js quiz js trace | 0 |
285,051 | 24,639,618,626 | IssuesEvent | 2022-10-17 10:33:59 | mantidproject/mantid | https://api.github.com/repos/mantidproject/mantid | closed | Windows Plotting Smoke Tests :chart_with_upwards_trend: :bar_chart: | Windows Only Manual Tests |
**Before testing**:
- Check this testing issue relates to the OS you will test on.
- If unassigned, please assign yourself as for a normal Github issue.
- Please run these tests on the release package of Mantid; **not a locally built version**.
**Afterwards**:
- Comment below with any issues you came across.
- If no major issues were found, please **close this testing issue**.
- Check the main issue for this OS for other unassigned smoke tests.
If you have any questions please contact the creator of this issue.
:chart_with_upwards_trend: :bar_chart:
* 1D plotting:[instructions](http://docs.mantidproject.org/nightly/tutorials/mantid_basic_course/loading_and_displaying_data/03_displaying_1D_data.html#displaying-1d-data)
- [x] Simple plot
- [x] Another way to plot
- [x] Adding curves to existing plots
- [x] Also, test out [waterfall](https://docs.mantidproject.org/nightly/plotting/WaterfallPlotsHelp.html#waterfall-plots) and [tiled]( https://docs.mantidproject.org/nightly/plotting/1DPlotsHelp.html#tiled-plots)
- [x] Check Toolbar buttons
* 2D plotting: [instructions](http://docs.mantidproject.org/nightly/tutorials/mantid_basic_course/loading_and_displaying_data/04_displaying_2D_data.html#displaying-2d-data)
- [x] Plot all spectra
- [x] Change colour map
- [x] [Contour plot](https://docs.mantidproject.org/nightly/plotting/ColorfillPlotsHelp.html#contour-plots) (under 3D menu)
- [x] Check Toolbar buttons
* [3D plotting](https://docs.mantidproject.org/nightly/plotting/3DPlotsHelp.html):
- Load some data eg `LOQ7041` from the ISIS sample data
- [x] 3D surface
- [x] 3D wire frame
- [x] Check Toolbar buttons
## Sliceviewer
- [x] Overly long instructions (don't spend long!) and data [here](https://developer.mantidproject.org/Testing/SliceViewer/SliceViewer.html). In particular try editing the data in a workspace while it is open in Sliceviewer! | 1.0 | Windows Plotting Smoke Tests :chart_with_upwards_trend: :bar_chart: -
**Before testing**:
- Check this testing issue relates to the OS you will test on.
- If unassigned, please assign yourself as for a normal Github issue.
- Please run these tests on the release package of Mantid; **not a locally built version**.
**Afterwards**:
- Comment below with any issues you came across.
- If no major issues were found, please **close this testing issue**.
- Check the main issue for this OS for other unassigned smoke tests.
If you have any questions please contact the creator of this issue.
:chart_with_upwards_trend: :bar_chart:
* 1D plotting:[instructions](http://docs.mantidproject.org/nightly/tutorials/mantid_basic_course/loading_and_displaying_data/03_displaying_1D_data.html#displaying-1d-data)
- [x] Simple plot
- [x] Another way to plot
- [x] Adding curves to existing plots
- [x] Also, test out [waterfall](https://docs.mantidproject.org/nightly/plotting/WaterfallPlotsHelp.html#waterfall-plots) and [tiled]( https://docs.mantidproject.org/nightly/plotting/1DPlotsHelp.html#tiled-plots)
- [x] Check Toolbar buttons
* 2D plotting: [instructions](http://docs.mantidproject.org/nightly/tutorials/mantid_basic_course/loading_and_displaying_data/04_displaying_2D_data.html#displaying-2d-data)
- [x] Plot all spectra
- [x] Change colour map
- [x] [Contour plot](https://docs.mantidproject.org/nightly/plotting/ColorfillPlotsHelp.html#contour-plots) (under 3D menu)
- [x] Check Toolbar buttons
* [3D plotting](https://docs.mantidproject.org/nightly/plotting/3DPlotsHelp.html):
- Load some data eg `LOQ7041` from the ISIS sample data
- [x] 3D surface
- [x] 3D wire frame
- [x] Check Toolbar buttons
## Sliceviewer
- [x] Overly long instructions (don't spend long!) and data [here](https://developer.mantidproject.org/Testing/SliceViewer/SliceViewer.html). In particular try editing the data in a workspace while it is open in Sliceviewer! | non_priority | windows plotting smoke tests chart with upwards trend bar chart before testing check this testing issue relates to the os you will test on if unassigned please assign yourself as for a normal github issue please run these tests on the release package of mantid not a locally built version afterwards comment below with any issues you came across if no major issues were found please close this testing issue check the main issue for this os for other unassigned smoke tests if you have any questions please contact the creator of this issue chart with upwards trend bar chart plotting simple plot another way to plot adding curves to existing plots also test out and check toolbar buttons plotting plot all spectra change colour map under menu check toolbar buttons load some data eg from the isis sample data surface wire frame check toolbar buttons sliceviewer overly long instructions don t spend long and data in particular try editing the data in a workspace while it is open in sliceviewer | 0 |
160,862 | 25,246,476,944 | IssuesEvent | 2022-11-15 11:28:21 | mdn/yari | https://api.github.com/repos/mdn/yari | closed | Navigation bar is not sticky | enhancement 🧑🤝🧑 community 🐌 idle redesign | MDN URL: https://developer.mozilla.org/en-US/docs/MDN/Contribute/Feedback
#### What information was incorrect, unhelpful, or incomplete?
Hi Team,
When we are trying to study anything content is good but your navigation bar is not
sticky. If your navigation bar would be sticky then we could not scroll up again and again.
We can save our time and we can easily reach out to our desired topic.
By the way Your website is very helpful for us :).
Thanks,
Satyam
#### Specific section or headline?
#### What did you expect to see?
#### Did you test this? If so, how?
<!-- Do not make changes below this line -->
<details>
<summary>MDN Content page report details</summary>
* Folder: `en-us/mdn/contribute/feedback`
* MDN URL: https://developer.mozilla.org/en-US/docs/MDN/Contribute/Feedback
* GitHub URL: https://github.com/mdn/content/blob/main/files/en-us/mdn/contribute/feedback/index.md
* Last commit: https://github.com/mdn/content/commit/072ff0c2bdfa29c02861450b6a91ff93f46e2218
* Document last modified: 2022-02-18T09:11:14.000Z
</details> | 1.0 | Navigation bar is not sticky - MDN URL: https://developer.mozilla.org/en-US/docs/MDN/Contribute/Feedback
#### What information was incorrect, unhelpful, or incomplete?
Hi Team,
When we are trying to study anything content is good but your navigation bar is not
sticky. If your navigation bar would be sticky then we could not scroll up again and again.
We can save our time and we can easily reach out to our desired topic.
By the way Your website is very helpful for us :).
Thanks,
Satyam
#### Specific section or headline?
#### What did you expect to see?
#### Did you test this? If so, how?
<!-- Do not make changes below this line -->
<details>
<summary>MDN Content page report details</summary>
* Folder: `en-us/mdn/contribute/feedback`
* MDN URL: https://developer.mozilla.org/en-US/docs/MDN/Contribute/Feedback
* GitHub URL: https://github.com/mdn/content/blob/main/files/en-us/mdn/contribute/feedback/index.md
* Last commit: https://github.com/mdn/content/commit/072ff0c2bdfa29c02861450b6a91ff93f46e2218
* Document last modified: 2022-02-18T09:11:14.000Z
</details> | non_priority | navigation bar is not sticky mdn url what information was incorrect unhelpful or incomplete hi team when we are trying to study anything content is good but your navigation bar is not sticky if your navigation bar would be sticky then we could not scroll up again and again we can save our time and we can easily reach out to our desired topic by the way your website is very helpful for us thanks satyam specific section or headline what did you expect to see did you test this if so how mdn content page report details folder en us mdn contribute feedback mdn url github url last commit document last modified | 0 |
10,882 | 12,876,370,748 | IssuesEvent | 2020-07-11 04:22:27 | ProgVal/Limnoria | https://api.github.com/repos/ProgVal/Limnoria | closed | UnicodeDecodeError with some Akas | Bug Python 2 compatibility | give is an aka alias:
```
.aka add give "echo $1, [$*]"
```
Giving something like 'list' works fine, but giving the weather in finnish:
```
.give Bane wunderground
```
Result:
```
supybot Uncaught exception in ['echo'].
Traceback (most recent call last):
File "/usr/lib/python2.7/site-packages/supybot/callbacks.py", line 1267, in _callCommand
self.callCommand(command, irc, msg, *args, **kwargs)
File "/usr/lib/python2.7/site-packages/supybot/utils/python.py", line 91, in g
f(self, *args, **kwargs)
File "/usr/lib/python2.7/site-packages/supybot/callbacks.py", line 1248, in callCommand
method(irc, msg, *args, **kwargs)
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 1071, in newf
state = spec(irc, msg, args, stateAttrs={'cb': self, 'log': self.log})
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 1057, in __call__
context(irc, msg, args, state)
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 837, in __call__
self.converter(irc, msg, args, state, *self.args)
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 715, in getText
state.args.append(' '.join(args))
UnicodeDecodeError: 'ascii' codec can't decode byte 0xc3 in position 67: ordinal not in range(128)
```
'args' with '.give Bane wunderground':
``` Python
[u'Bane,', '\x02Salo, Suomi\x02 :: Ukkosta :: \x030825C\x03 | \x02Maanantai\x02: Osittain pilvist\xc3\xa4. Ylin l\xc3\xa4mp\xc3\xb6tila 27\xc2\xbaC. Tuuli ESE, nopeus 15\xe2\x88\x9230 km/h. \x02Maanantaiy\xc3\xb6\x02: Aluksi ukkosta. Alin l\xc3\xa4mp\xc3\xb6tila 10\xc2\xbaC. Tuuli SSW, nopeus 15\xe2\x88\x9225 km/h. Sateen mahd: 50%.']
```
'echo [wunderground]' works fine, here's 'args' list with it:
``` Python
['\x02Salo, Suomi\x02 :: Ukkosta :: \x030825C\x03 | \x02Maanantai\x02: Osittain pilvist\xc3\xa4. Ylin l\xc3\xa4mp\xc3\xb6tila 27\xc2\xbaC. Tuuli ESE, nopeus 15\xe2\x88\x9230 km/h. \x02Maanantaiy\xc3\xb6\x02: Aluksi ukkosta. Alin l\xc3\xa4mp\xc3\xb6tila 10\xc2\xbaC. Tuuli SSW, nopeus 15\xe2\x88\x9225 km/h. Sateen mahd: 50%.']
```
| True | UnicodeDecodeError with some Akas - give is an aka alias:
```
.aka add give "echo $1, [$*]"
```
Giving something like 'list' works fine, but giving the weather in finnish:
```
.give Bane wunderground
```
Result:
```
supybot Uncaught exception in ['echo'].
Traceback (most recent call last):
File "/usr/lib/python2.7/site-packages/supybot/callbacks.py", line 1267, in _callCommand
self.callCommand(command, irc, msg, *args, **kwargs)
File "/usr/lib/python2.7/site-packages/supybot/utils/python.py", line 91, in g
f(self, *args, **kwargs)
File "/usr/lib/python2.7/site-packages/supybot/callbacks.py", line 1248, in callCommand
method(irc, msg, *args, **kwargs)
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 1071, in newf
state = spec(irc, msg, args, stateAttrs={'cb': self, 'log': self.log})
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 1057, in __call__
context(irc, msg, args, state)
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 837, in __call__
self.converter(irc, msg, args, state, *self.args)
File "/usr/lib/python2.7/site-packages/supybot/commands.py", line 715, in getText
state.args.append(' '.join(args))
UnicodeDecodeError: 'ascii' codec can't decode byte 0xc3 in position 67: ordinal not in range(128)
```
'args' with '.give Bane wunderground':
``` Python
[u'Bane,', '\x02Salo, Suomi\x02 :: Ukkosta :: \x030825C\x03 | \x02Maanantai\x02: Osittain pilvist\xc3\xa4. Ylin l\xc3\xa4mp\xc3\xb6tila 27\xc2\xbaC. Tuuli ESE, nopeus 15\xe2\x88\x9230 km/h. \x02Maanantaiy\xc3\xb6\x02: Aluksi ukkosta. Alin l\xc3\xa4mp\xc3\xb6tila 10\xc2\xbaC. Tuuli SSW, nopeus 15\xe2\x88\x9225 km/h. Sateen mahd: 50%.']
```
'echo [wunderground]' works fine, here's 'args' list with it:
``` Python
['\x02Salo, Suomi\x02 :: Ukkosta :: \x030825C\x03 | \x02Maanantai\x02: Osittain pilvist\xc3\xa4. Ylin l\xc3\xa4mp\xc3\xb6tila 27\xc2\xbaC. Tuuli ESE, nopeus 15\xe2\x88\x9230 km/h. \x02Maanantaiy\xc3\xb6\x02: Aluksi ukkosta. Alin l\xc3\xa4mp\xc3\xb6tila 10\xc2\xbaC. Tuuli SSW, nopeus 15\xe2\x88\x9225 km/h. Sateen mahd: 50%.']
```
| non_priority | unicodedecodeerror with some akas give is an aka alias aka add give echo giving something like list works fine but giving the weather in finnish give bane wunderground result supybot uncaught exception in traceback most recent call last file usr lib site packages supybot callbacks py line in callcommand self callcommand command irc msg args kwargs file usr lib site packages supybot utils python py line in g f self args kwargs file usr lib site packages supybot callbacks py line in callcommand method irc msg args kwargs file usr lib site packages supybot commands py line in newf state spec irc msg args stateattrs cb self log self log file usr lib site packages supybot commands py line in call context irc msg args state file usr lib site packages supybot commands py line in call self converter irc msg args state self args file usr lib site packages supybot commands py line in gettext state args append join args unicodedecodeerror ascii codec can t decode byte in position ordinal not in range args with give bane wunderground python echo works fine here s args list with it python | 0 |
139,656 | 31,722,256,437 | IssuesEvent | 2023-09-10 14:44:09 | llvm/llvm-project | https://api.github.com/repos/llvm/llvm-project | closed | Code Generation Failure and Crash | clang:codegen bugzilla | | | |
| --- | --- |
| Bugzilla Link | [51269](https://llvm.org/bz51269) |
| Version | 12.0 |
| OS | Linux |
| Attachments | [Preprocessed source(s)](https://user-images.githubusercontent.com/60944935/143762381-1133ca1a-1c65-4c3f-826b-b50e02965f85.gz), [run script(s)](https://user-images.githubusercontent.com/60944935/143762382-71308e15-1d25-49ee-b7e7-5dca69990878.gz), [bc file](https://user-images.githubusercontent.com/60944935/143762383-00d55f8b-bbf9-414f-971b-4bcb94013291.gz), [reduced and simplified bc file.](https://user-images.githubusercontent.com/60944935/143762384-abd2e864-8166-441d-a55b-0ba2c5ed1373.gz) |
| Reporter | LLVM Bugzilla Contributor |
| CC | @aaronpuchert,@kamleshbhalui,@zygoloid |
## Extended Description
PLEASE submit a bug report to https://bugs.llvm.org/ and include the crash backtrace, preprocessed source, and associated run script.
Stack dump:
0. Program arguments: /mnt/share/toolchains/linux-x86_64/clang/bin/clang -fheinous-gnu-extensions -fstack-check -fstack-protector-all -g -fno-omit-frame-pointer -fsanitize=memory,undefined -fsanitize-memory-track-origins -fsanitize-memory-use-after-dtor -fno-optimize-sibling-calls -fsanitize-recover=all -fsanitize-blacklist=/mnt/jlsws2/dev/orthrus/master/src/tools/toolchain/sanitizer/inc/ortsanitizer-orthrus-build-clang-sanitizer-memory.blacklist -DHAVE_CONFIG_H -I. -I/mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/build/phase3/speex/orthrus-speex/build/speex/speex-1.2rc1/libspeex -I.. -I/mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/build/phase3/speex/orthrus-speex/build/speex/speex-1.2rc1/include -I../include -I.. -I/mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/stage/libogg/include -O3 -g -fPIC -fvisibility=hidden -MT lsp.lo -MD -MP -MF .deps/lsp.Tpo -c /mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/build/phase3/speex/orthrus-speex/build/speex/speex-1.2rc1/libspeex/lsp.c
1. <eof> parser at end of file
2. Code generation
#​0 0x00007f99476b507d llvm::sys::PrintStackTrace(llvm::raw_ostream&, int) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xcfb07d)
#​1 0x00007f99476b2d84 llvm::sys::RunSignalHandlers() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xcf8d84)
#​2 0x00007f99475d61c8 CrashRecoverySignalHandler(int) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xc1c1c8)
#​3 0x00007f9951068630 __restore_rt (/lib64/libpthread.so.0+0xf630)
#​4 0x00007f994800aa30 llvm::DIE::getUnitDie() const (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x1650a30)
#​5 0x00007f994802993c llvm::DwarfDebug::finishEntityDefinitions() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x166f93c)
#​6 0x00007f9948042375 llvm::DwarfDebug::finalizeModuleInfo() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x1688375)
#​7 0x00007f99480454b8 llvm::DwarfDebug::endModule() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x168b4b8)
#​8 0x00007f9947ff4299 llvm::AsmPrinter::doFinalization(llvm::Module&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x163a299)
#​9 0x00007f99477f6b6d llvm::FPPassManager::doFinalization(llvm::Module&) (.localalias) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xe3cb6d)
#​10 0x00007f9947802bd0 llvm::legacy::PassManagerImpl::run(llvm::Module&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xe48bd0)
#​11 0x00007f994f00e4af clang::EmitBackendOutput(clang::DiagnosticsEngine&, clang::HeaderSearchOptions const&, clang::CodeGenOptions const&, clang::TargetOptions const&, clang::LangOptions const&, llvm::DataLayout const&, llvm::Module*, clang::BackendAction, std::unique_ptr<llvm::raw_pwrite_stream, std::default_delete<llvm::raw_pwrite_stream> >) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x19404af)
#​12 0x00007f994f378a74 clang::BackendConsumer::HandleTranslationUnit(clang::ASTContext&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x1caaa74)
#​13 0x00007f994e0b2949 clang::ParseAST(clang::Sema&, bool, bool) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x9e4949)
#​14 0x00007f994fae4139 clang::FrontendAction::Execute() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x2416139)
#​15 0x00007f994fa7c86b clang::CompilerInstance::ExecuteAction(clang::FrontendAction&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x23ae86b)
#​16 0x00007f994fb5fd08 clang::ExecuteCompilerInvocation(clang::CompilerInstance*) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x2491d08)
#​17 0x0000555e1061417d cc1_main(llvm::ArrayRef<char const*>, char const*, void*) (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0x1417d)
#​18 0x0000555e10611777 ExecuteCC1Tool(llvm::SmallVectorImpl<char const*>&) (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0x11777)
#​19 0x00007f994f747d05 void llvm::function_ref<void ()>::callback_fn<clang::driver::CC1Command::Execute(llvm::ArrayRef<llvm::Optional<llvm::StringRef> >, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> >*, bool*) const::'lambda'()>(long) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x2079d05)
#​20 0x00007f99475d62d3 llvm::CrashRecoveryContext::RunSafely(llvm::function_ref<void ()>) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xc1c2d3)
#​21 0x00007f994f748e55 clang::driver::CC1Command::Execute(llvm::ArrayRef<llvm::Optional<llvm::StringRef> >, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> >*, bool*) const (.part.0) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x207ae55)
#​22 0x00007f994f71ca57 clang::driver::Compilation::ExecuteCommand(clang::driver::Command const&, clang::driver::Command const*&) const (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x204ea57)
#​23 0x00007f994f71d449 clang::driver::Compilation::ExecuteJobs(clang::driver::JobList const&, llvm::SmallVectorImpl<std::pair<int, clang::driver::Command const*> >&) const (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x204f449)
#​24 0x00007f994f72d129 clang::driver::Driver::ExecuteCompilation(clang::driver::Compilation&, llvm::SmallVectorImpl<std::pair<int, clang::driver::Command const*> >&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x205f129)
#​25 0x0000555e1060f4d4 main (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0xf4d4)
#​26 0x00007f99460f5555 __libc_start_main (/lib64/libc.so.6+0x22555)
#​27 0x0000555e106110ad _start (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0x110ad)
clang-12: error: clang frontend command failed with exit code 139 (use -v to see invocation)
clang version 12.0.1
Target: x86_64-unknown-linux-gnu
Thread model: posix
InstalledDir: /mnt/share/toolchains/linux-x86_64/clang/bin
clang-12: note: diagnostic msg:
********************
PLEASE ATTACH THE FOLLOWING FILES TO THE BUG REPORT:
Preprocessed source(s) and associated run script(s) are located at:
clang-12: note: diagnostic msg: /tmp/lsp-f48f4a.c
clang-12: note: diagnostic msg: /tmp/lsp-f48f4a.sh
clang-12: note: diagnostic msg: | 1.0 | Code Generation Failure and Crash - | | |
| --- | --- |
| Bugzilla Link | [51269](https://llvm.org/bz51269) |
| Version | 12.0 |
| OS | Linux |
| Attachments | [Preprocessed source(s)](https://user-images.githubusercontent.com/60944935/143762381-1133ca1a-1c65-4c3f-826b-b50e02965f85.gz), [run script(s)](https://user-images.githubusercontent.com/60944935/143762382-71308e15-1d25-49ee-b7e7-5dca69990878.gz), [bc file](https://user-images.githubusercontent.com/60944935/143762383-00d55f8b-bbf9-414f-971b-4bcb94013291.gz), [reduced and simplified bc file.](https://user-images.githubusercontent.com/60944935/143762384-abd2e864-8166-441d-a55b-0ba2c5ed1373.gz) |
| Reporter | LLVM Bugzilla Contributor |
| CC | @aaronpuchert,@kamleshbhalui,@zygoloid |
## Extended Description
PLEASE submit a bug report to https://bugs.llvm.org/ and include the crash backtrace, preprocessed source, and associated run script.
Stack dump:
0. Program arguments: /mnt/share/toolchains/linux-x86_64/clang/bin/clang -fheinous-gnu-extensions -fstack-check -fstack-protector-all -g -fno-omit-frame-pointer -fsanitize=memory,undefined -fsanitize-memory-track-origins -fsanitize-memory-use-after-dtor -fno-optimize-sibling-calls -fsanitize-recover=all -fsanitize-blacklist=/mnt/jlsws2/dev/orthrus/master/src/tools/toolchain/sanitizer/inc/ortsanitizer-orthrus-build-clang-sanitizer-memory.blacklist -DHAVE_CONFIG_H -I. -I/mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/build/phase3/speex/orthrus-speex/build/speex/speex-1.2rc1/libspeex -I.. -I/mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/build/phase3/speex/orthrus-speex/build/speex/speex-1.2rc1/include -I../include -I.. -I/mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/stage/libogg/include -O3 -g -fPIC -fvisibility=hidden -MT lsp.lo -MD -MP -MF .deps/lsp.Tpo -c /mnt/jlsws2/dev/orthrus/master/build/centos7-64-sanitizer-clang-memory/build/phase3/speex/orthrus-speex/build/speex/speex-1.2rc1/libspeex/lsp.c
1. <eof> parser at end of file
2. Code generation
#​0 0x00007f99476b507d llvm::sys::PrintStackTrace(llvm::raw_ostream&, int) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xcfb07d)
#​1 0x00007f99476b2d84 llvm::sys::RunSignalHandlers() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xcf8d84)
#​2 0x00007f99475d61c8 CrashRecoverySignalHandler(int) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xc1c1c8)
#​3 0x00007f9951068630 __restore_rt (/lib64/libpthread.so.0+0xf630)
#​4 0x00007f994800aa30 llvm::DIE::getUnitDie() const (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x1650a30)
#​5 0x00007f994802993c llvm::DwarfDebug::finishEntityDefinitions() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x166f93c)
#​6 0x00007f9948042375 llvm::DwarfDebug::finalizeModuleInfo() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x1688375)
#​7 0x00007f99480454b8 llvm::DwarfDebug::endModule() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x168b4b8)
#​8 0x00007f9947ff4299 llvm::AsmPrinter::doFinalization(llvm::Module&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0x163a299)
#​9 0x00007f99477f6b6d llvm::FPPassManager::doFinalization(llvm::Module&) (.localalias) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xe3cb6d)
#​10 0x00007f9947802bd0 llvm::legacy::PassManagerImpl::run(llvm::Module&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xe48bd0)
#​11 0x00007f994f00e4af clang::EmitBackendOutput(clang::DiagnosticsEngine&, clang::HeaderSearchOptions const&, clang::CodeGenOptions const&, clang::TargetOptions const&, clang::LangOptions const&, llvm::DataLayout const&, llvm::Module*, clang::BackendAction, std::unique_ptr<llvm::raw_pwrite_stream, std::default_delete<llvm::raw_pwrite_stream> >) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x19404af)
#​12 0x00007f994f378a74 clang::BackendConsumer::HandleTranslationUnit(clang::ASTContext&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x1caaa74)
#​13 0x00007f994e0b2949 clang::ParseAST(clang::Sema&, bool, bool) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x9e4949)
#​14 0x00007f994fae4139 clang::FrontendAction::Execute() (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x2416139)
#​15 0x00007f994fa7c86b clang::CompilerInstance::ExecuteAction(clang::FrontendAction&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x23ae86b)
#​16 0x00007f994fb5fd08 clang::ExecuteCompilerInvocation(clang::CompilerInstance*) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x2491d08)
#​17 0x0000555e1061417d cc1_main(llvm::ArrayRef<char const*>, char const*, void*) (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0x1417d)
#​18 0x0000555e10611777 ExecuteCC1Tool(llvm::SmallVectorImpl<char const*>&) (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0x11777)
#​19 0x00007f994f747d05 void llvm::function_ref<void ()>::callback_fn<clang::driver::CC1Command::Execute(llvm::ArrayRef<llvm::Optional<llvm::StringRef> >, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> >*, bool*) const::'lambda'()>(long) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x2079d05)
#​20 0x00007f99475d62d3 llvm::CrashRecoveryContext::RunSafely(llvm::function_ref<void ()>) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libLLVM-12.so+0xc1c2d3)
#​21 0x00007f994f748e55 clang::driver::CC1Command::Execute(llvm::ArrayRef<llvm::Optional<llvm::StringRef> >, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> >*, bool*) const (.part.0) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x207ae55)
#​22 0x00007f994f71ca57 clang::driver::Compilation::ExecuteCommand(clang::driver::Command const&, clang::driver::Command const*&) const (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x204ea57)
#​23 0x00007f994f71d449 clang::driver::Compilation::ExecuteJobs(clang::driver::JobList const&, llvm::SmallVectorImpl<std::pair<int, clang::driver::Command const*> >&) const (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x204f449)
#​24 0x00007f994f72d129 clang::driver::Driver::ExecuteCompilation(clang::driver::Compilation&, llvm::SmallVectorImpl<std::pair<int, clang::driver::Command const*> >&) (/mnt/share/toolchains/linux-x86_64/toolchains-staged/clang-12.0.1-centos6-64/bin/../lib/libclang-cpp.so.12+0x205f129)
#​25 0x0000555e1060f4d4 main (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0xf4d4)
#​26 0x00007f99460f5555 __libc_start_main (/lib64/libc.so.6+0x22555)
#​27 0x0000555e106110ad _start (/mnt/share/toolchains/linux-x86_64/clang/bin/clang+0x110ad)
clang-12: error: clang frontend command failed with exit code 139 (use -v to see invocation)
clang version 12.0.1
Target: x86_64-unknown-linux-gnu
Thread model: posix
InstalledDir: /mnt/share/toolchains/linux-x86_64/clang/bin
clang-12: note: diagnostic msg:
********************
PLEASE ATTACH THE FOLLOWING FILES TO THE BUG REPORT:
Preprocessed source(s) and associated run script(s) are located at:
clang-12: note: diagnostic msg: /tmp/lsp-f48f4a.c
clang-12: note: diagnostic msg: /tmp/lsp-f48f4a.sh
clang-12: note: diagnostic msg: | non_priority | code generation failure and crash bugzilla link version os linux attachments reporter llvm bugzilla contributor cc aaronpuchert kamleshbhalui zygoloid extended description please submit a bug report to and include the crash backtrace preprocessed source and associated run script stack dump program arguments mnt share toolchains linux clang bin clang fheinous gnu extensions fstack check fstack protector all g fno omit frame pointer fsanitize memory undefined fsanitize memory track origins fsanitize memory use after dtor fno optimize sibling calls fsanitize recover all fsanitize blacklist mnt dev orthrus master src tools toolchain sanitizer inc ortsanitizer orthrus build clang sanitizer memory blacklist dhave config h i i mnt dev orthrus master build sanitizer clang memory build speex orthrus speex build speex speex libspeex i i mnt dev orthrus master build sanitizer clang memory build speex orthrus speex build speex speex include i include i i mnt dev orthrus master build sanitizer clang memory stage libogg include g fpic fvisibility hidden mt lsp lo md mp mf deps lsp tpo c mnt dev orthrus master build sanitizer clang memory build speex orthrus speex build speex speex libspeex lsp c parser at end of file code generation llvm sys printstacktrace llvm raw ostream int mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm sys runsignalhandlers mnt share toolchains linux toolchains staged clang bin lib libllvm so crashrecoverysignalhandler int mnt share toolchains linux toolchains staged clang bin lib libllvm so restore rt libpthread so llvm die getunitdie const mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm dwarfdebug finishentitydefinitions mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm dwarfdebug finalizemoduleinfo mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm dwarfdebug endmodule mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm asmprinter dofinalization llvm module mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm fppassmanager dofinalization llvm module localalias mnt share toolchains linux toolchains staged clang bin lib libllvm so llvm legacy passmanagerimpl run llvm module mnt share toolchains linux toolchains staged clang bin lib libllvm so clang emitbackendoutput clang diagnosticsengine clang headersearchoptions const clang codegenoptions const clang targetoptions const clang langoptions const llvm datalayout const llvm module clang backendaction std unique ptr mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang backendconsumer handletranslationunit clang astcontext mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang parseast clang sema bool bool mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang frontendaction execute mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang compilerinstance executeaction clang frontendaction mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang executecompilerinvocation clang compilerinstance mnt share toolchains linux toolchains staged clang bin lib libclang cpp so main llvm arrayref char const void mnt share toolchains linux clang bin clang llvm smallvectorimpl mnt share toolchains linux clang bin clang void llvm function ref callback fn std basic string std allocator bool const lambda long mnt share toolchains linux toolchains staged clang bin lib libclang cpp so llvm crashrecoverycontext runsafely llvm function ref mnt share toolchains linux toolchains staged clang bin lib libllvm so clang driver execute llvm arrayref std basic string std allocator bool const part mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang driver compilation executecommand clang driver command const clang driver command const const mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang driver compilation executejobs clang driver joblist const llvm smallvectorimpl const mnt share toolchains linux toolchains staged clang bin lib libclang cpp so clang driver driver executecompilation clang driver compilation llvm smallvectorimpl mnt share toolchains linux toolchains staged clang bin lib libclang cpp so main mnt share toolchains linux clang bin clang libc start main libc so start mnt share toolchains linux clang bin clang clang error clang frontend command failed with exit code use v to see invocation clang version target unknown linux gnu thread model posix installeddir mnt share toolchains linux clang bin clang note diagnostic msg please attach the following files to the bug report preprocessed source s and associated run script s are located at clang note diagnostic msg tmp lsp c clang note diagnostic msg tmp lsp sh clang note diagnostic msg | 0 |
175,207 | 27,808,020,400 | IssuesEvent | 2023-03-17 22:17:48 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Chip: add ability to put delete icon before label OR allow elements inside chip to accept gestures | new feature framework f: material design | ## Use case
I have a chip that, when tapped, changes its avatar to delete icon. I can neither make avatar tappable nor put the delete icon before the label. For now I'm stuck with having avatar after the label.
Chip is great and has a lot of useful functionality, so I wouldn't like to build my own implementation just for the icon position.
## Proposal
Add ability to put delete icon before label in chip OR allow elements inside chip to accept gestures
| 1.0 | Chip: add ability to put delete icon before label OR allow elements inside chip to accept gestures - ## Use case
I have a chip that, when tapped, changes its avatar to delete icon. I can neither make avatar tappable nor put the delete icon before the label. For now I'm stuck with having avatar after the label.
Chip is great and has a lot of useful functionality, so I wouldn't like to build my own implementation just for the icon position.
## Proposal
Add ability to put delete icon before label in chip OR allow elements inside chip to accept gestures
| non_priority | chip add ability to put delete icon before label or allow elements inside chip to accept gestures use case i have a chip that when tapped changes its avatar to delete icon i can neither make avatar tappable nor put the delete icon before the label for now i m stuck with having avatar after the label chip is great and has a lot of useful functionality so i wouldn t like to build my own implementation just for the icon position proposal add ability to put delete icon before label in chip or allow elements inside chip to accept gestures | 0 |
156,840 | 24,626,000,736 | IssuesEvent | 2022-10-16 14:27:12 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | EF generating invalid query - using pluralised table name, despite snapshot explicitly specifying (correctly) | closed-by-design customer-reported |
```
System.Data.SqlClient.SqlException (0x80131904): Invalid object name 'Credentials'.
at System.Data.SqlClient.SqlConnection.OnError(SqlException exception, Boolean breakConnection, Action`1 wrapCloseInAction)
at System.Data.SqlClient.TdsParser.ThrowExceptionAndWarning(TdsParserStateObject stateObj, Boolean callerHasConnectionLock, Boolean asyncClose)
at System.Data.SqlClient.TdsParser.TryRun(RunBehavior runBehavior, SqlCommand cmdHandler, SqlDataReader dataStream, BulkCopySimpleResultSet bulkCopyHandler, TdsParserStateObject stateObj, Boolean& dataReady)
at System.Data.SqlClient.SqlDataReader.TryConsumeMetaData()
at System.Data.SqlClient.SqlDataReader.get_MetaData()
at System.Data.SqlClient.SqlCommand.FinishExecuteReader(SqlDataReader ds, RunBehavior runBehavior, String resetOptionsString)
at System.Data.SqlClient.SqlCommand.RunExecuteReaderTds(CommandBehavior cmdBehavior, RunBehavior runBehavior, Boolean returnStream, Boolean async, Int32 timeout, Task& task, Boolean asyncWrite, SqlDataReader ds)
at System.Data.SqlClient.SqlCommand.ExecuteReader(CommandBehavior behavior)
at Microsoft.EntityFrameworkCore.Storage.Internal.RelationalCommand.Execute(IRelationalConnection connection, DbCommandMethod executeMethod, IReadOnlyDictionary`2 parameterValues)
at Microsoft.EntityFrameworkCore.Storage.Internal.RelationalCommand.ExecuteReader(IRelationalConnection connection, IReadOnlyDictionary`2 parameterValues)
at Microsoft.EntityFrameworkCore.Query.Internal.QueryingEnumerable`1.Enumerator.BufferlessMoveNext(DbContext _, Boolean buffer)
at Microsoft.EntityFrameworkCore.SqlServer.Storage.Internal.SqlServerExecutionStrategy.Execute[TState,TResult](TState state, Func`3 operation, Func`3 verifySucceeded)
at Microsoft.EntityFrameworkCore.Query.Internal.QueryingEnumerable`1.Enumerator.MoveNext()
at System.Linq.Enumerable.SingleOrDefault[TSource](IEnumerable`1 source)
at Microsoft.EntityFrameworkCore.Query.Internal.LinqOperatorProvider.ResultEnumerable`1.GetEnumerator()
at Microsoft.EntityFrameworkCore.Query.Internal.LinqOperatorProvider.ExceptionInterceptor`1.EnumeratorExceptionInterceptor.MoveNext()
at System.Linq.Enumerable.TryGetFirst[TSource](IEnumerable`1 source, Boolean& found)
at System.Linq.Enumerable.First[TSource](IEnumerable`1 source)
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.<>c__DisplayClass15_1`1.<CompileQueryCore>b__0(QueryContext qc)
at System.Linq.Queryable.SingleOrDefault[TSource](IQueryable`1 source)
```
### Steps to reproduce
Relevant part of snapshot:
```c#
modelBuilder.Entity("REDACTED.Storage.Model.Credential", b =>
{
b.Property<string>("Key")
.ValueGeneratedOnAdd();
b.Property<string>("Json");
b.Property<Guid>("UserId");
b.HasKey("Key");
b.HasIndex("UserId");
b.ToTable("Credential");
});
```
User code:
```c#
var match = _context.Set<Credential>()
.Where(c => c.Key == credentialKey)
.Select(c => c.Json)
.SingleOrDefault();
```
Generated SQL:
```sql
SELECT TOP(2) [c].[Json]
FROM [Credentials] AS [c]
WHERE [c].[Key] = @__credentialKey_0
```
Note - the only reference to `"Credentials"` is the name of the navigation property pointing to the `Credential` entity:
```c#
modelBuilder.Entity("REDACTED.Storage.Model.Credential", b =>
{
b.HasOne("REDACTED.Storage.Model.User", "User")
.WithMany("Credentials")
.HasForeignKey("UserId")
.OnDelete(DeleteBehavior.Cascade);
});
```
### Further technical details
EF Core version: `Microsoft.EntityFrameworkCore, Version=2.2.4.0, Culture=neutral, PublicKeyToken=adb9793829ddae60`
Database Provider: `Microsoft.EntityFrameworkCore.SqlServer`
Operating system: `Azure App Service`
Weird things:
- The table was created successfully via migration, with the correct name
- This same process works fine locally (same code version, same deploy)
- Other tables and queries work fine immediately prior to this one
Is there anything I can do to diagnose? | 1.0 | EF generating invalid query - using pluralised table name, despite snapshot explicitly specifying (correctly) -
```
System.Data.SqlClient.SqlException (0x80131904): Invalid object name 'Credentials'.
at System.Data.SqlClient.SqlConnection.OnError(SqlException exception, Boolean breakConnection, Action`1 wrapCloseInAction)
at System.Data.SqlClient.TdsParser.ThrowExceptionAndWarning(TdsParserStateObject stateObj, Boolean callerHasConnectionLock, Boolean asyncClose)
at System.Data.SqlClient.TdsParser.TryRun(RunBehavior runBehavior, SqlCommand cmdHandler, SqlDataReader dataStream, BulkCopySimpleResultSet bulkCopyHandler, TdsParserStateObject stateObj, Boolean& dataReady)
at System.Data.SqlClient.SqlDataReader.TryConsumeMetaData()
at System.Data.SqlClient.SqlDataReader.get_MetaData()
at System.Data.SqlClient.SqlCommand.FinishExecuteReader(SqlDataReader ds, RunBehavior runBehavior, String resetOptionsString)
at System.Data.SqlClient.SqlCommand.RunExecuteReaderTds(CommandBehavior cmdBehavior, RunBehavior runBehavior, Boolean returnStream, Boolean async, Int32 timeout, Task& task, Boolean asyncWrite, SqlDataReader ds)
at System.Data.SqlClient.SqlCommand.ExecuteReader(CommandBehavior behavior)
at Microsoft.EntityFrameworkCore.Storage.Internal.RelationalCommand.Execute(IRelationalConnection connection, DbCommandMethod executeMethod, IReadOnlyDictionary`2 parameterValues)
at Microsoft.EntityFrameworkCore.Storage.Internal.RelationalCommand.ExecuteReader(IRelationalConnection connection, IReadOnlyDictionary`2 parameterValues)
at Microsoft.EntityFrameworkCore.Query.Internal.QueryingEnumerable`1.Enumerator.BufferlessMoveNext(DbContext _, Boolean buffer)
at Microsoft.EntityFrameworkCore.SqlServer.Storage.Internal.SqlServerExecutionStrategy.Execute[TState,TResult](TState state, Func`3 operation, Func`3 verifySucceeded)
at Microsoft.EntityFrameworkCore.Query.Internal.QueryingEnumerable`1.Enumerator.MoveNext()
at System.Linq.Enumerable.SingleOrDefault[TSource](IEnumerable`1 source)
at Microsoft.EntityFrameworkCore.Query.Internal.LinqOperatorProvider.ResultEnumerable`1.GetEnumerator()
at Microsoft.EntityFrameworkCore.Query.Internal.LinqOperatorProvider.ExceptionInterceptor`1.EnumeratorExceptionInterceptor.MoveNext()
at System.Linq.Enumerable.TryGetFirst[TSource](IEnumerable`1 source, Boolean& found)
at System.Linq.Enumerable.First[TSource](IEnumerable`1 source)
at Microsoft.EntityFrameworkCore.Query.Internal.QueryCompiler.<>c__DisplayClass15_1`1.<CompileQueryCore>b__0(QueryContext qc)
at System.Linq.Queryable.SingleOrDefault[TSource](IQueryable`1 source)
```
### Steps to reproduce
Relevant part of snapshot:
```c#
modelBuilder.Entity("REDACTED.Storage.Model.Credential", b =>
{
b.Property<string>("Key")
.ValueGeneratedOnAdd();
b.Property<string>("Json");
b.Property<Guid>("UserId");
b.HasKey("Key");
b.HasIndex("UserId");
b.ToTable("Credential");
});
```
User code:
```c#
var match = _context.Set<Credential>()
.Where(c => c.Key == credentialKey)
.Select(c => c.Json)
.SingleOrDefault();
```
Generated SQL:
```sql
SELECT TOP(2) [c].[Json]
FROM [Credentials] AS [c]
WHERE [c].[Key] = @__credentialKey_0
```
Note - the only reference to `"Credentials"` is the name of the navigation property pointing to the `Credential` entity:
```c#
modelBuilder.Entity("REDACTED.Storage.Model.Credential", b =>
{
b.HasOne("REDACTED.Storage.Model.User", "User")
.WithMany("Credentials")
.HasForeignKey("UserId")
.OnDelete(DeleteBehavior.Cascade);
});
```
### Further technical details
EF Core version: `Microsoft.EntityFrameworkCore, Version=2.2.4.0, Culture=neutral, PublicKeyToken=adb9793829ddae60`
Database Provider: `Microsoft.EntityFrameworkCore.SqlServer`
Operating system: `Azure App Service`
Weird things:
- The table was created successfully via migration, with the correct name
- This same process works fine locally (same code version, same deploy)
- Other tables and queries work fine immediately prior to this one
Is there anything I can do to diagnose? | non_priority | ef generating invalid query using pluralised table name despite snapshot explicitly specifying correctly system data sqlclient sqlexception invalid object name credentials at system data sqlclient sqlconnection onerror sqlexception exception boolean breakconnection action wrapcloseinaction at system data sqlclient tdsparser throwexceptionandwarning tdsparserstateobject stateobj boolean callerhasconnectionlock boolean asyncclose at system data sqlclient tdsparser tryrun runbehavior runbehavior sqlcommand cmdhandler sqldatareader datastream bulkcopysimpleresultset bulkcopyhandler tdsparserstateobject stateobj boolean dataready at system data sqlclient sqldatareader tryconsumemetadata at system data sqlclient sqldatareader get metadata at system data sqlclient sqlcommand finishexecutereader sqldatareader ds runbehavior runbehavior string resetoptionsstring at system data sqlclient sqlcommand runexecutereadertds commandbehavior cmdbehavior runbehavior runbehavior boolean returnstream boolean async timeout task task boolean asyncwrite sqldatareader ds at system data sqlclient sqlcommand executereader commandbehavior behavior at microsoft entityframeworkcore storage internal relationalcommand execute irelationalconnection connection dbcommandmethod executemethod ireadonlydictionary parametervalues at microsoft entityframeworkcore storage internal relationalcommand executereader irelationalconnection connection ireadonlydictionary parametervalues at microsoft entityframeworkcore query internal queryingenumerable enumerator bufferlessmovenext dbcontext boolean buffer at microsoft entityframeworkcore sqlserver storage internal sqlserverexecutionstrategy execute tstate state func operation func verifysucceeded at microsoft entityframeworkcore query internal queryingenumerable enumerator movenext at system linq enumerable singleordefault ienumerable source at microsoft entityframeworkcore query internal linqoperatorprovider resultenumerable getenumerator at microsoft entityframeworkcore query internal linqoperatorprovider exceptioninterceptor enumeratorexceptioninterceptor movenext at system linq enumerable trygetfirst ienumerable source boolean found at system linq enumerable first ienumerable source at microsoft entityframeworkcore query internal querycompiler c b querycontext qc at system linq queryable singleordefault iqueryable source steps to reproduce relevant part of snapshot c modelbuilder entity redacted storage model credential b b property key valuegeneratedonadd b property json b property userid b haskey key b hasindex userid b totable credential user code c var match context set where c c key credentialkey select c c json singleordefault generated sql sql select top from as where credentialkey note the only reference to credentials is the name of the navigation property pointing to the credential entity c modelbuilder entity redacted storage model credential b b hasone redacted storage model user user withmany credentials hasforeignkey userid ondelete deletebehavior cascade further technical details ef core version microsoft entityframeworkcore version culture neutral publickeytoken database provider microsoft entityframeworkcore sqlserver operating system azure app service weird things the table was created successfully via migration with the correct name this same process works fine locally same code version same deploy other tables and queries work fine immediately prior to this one is there anything i can do to diagnose | 0 |
55,473 | 7,989,003,329 | IssuesEvent | 2018-07-19 13:00:45 | Hackerfleet/hfos | https://api.github.com/repos/Hackerfleet/hfos | opened | Add context sensitive help | documentation enhancement frontend | Add a state-contextual help or something to get detailed help.
This should be a link to documentation relevant to what the user is currently doing.
The link should be accessible via a small ? icon somewhere central (not the help menu, but maybe there as well ;) and keyboard shortcut (ctrl-f1)
The documentation (stubs) might be autogenerated by inspecting module's frontend bits for easy development. | 1.0 | Add context sensitive help - Add a state-contextual help or something to get detailed help.
This should be a link to documentation relevant to what the user is currently doing.
The link should be accessible via a small ? icon somewhere central (not the help menu, but maybe there as well ;) and keyboard shortcut (ctrl-f1)
The documentation (stubs) might be autogenerated by inspecting module's frontend bits for easy development. | non_priority | add context sensitive help add a state contextual help or something to get detailed help this should be a link to documentation relevant to what the user is currently doing the link should be accessible via a small icon somewhere central not the help menu but maybe there as well and keyboard shortcut ctrl the documentation stubs might be autogenerated by inspecting module s frontend bits for easy development | 0 |
70,683 | 30,722,319,360 | IssuesEvent | 2023-07-27 16:50:03 | hashicorp/terraform-provider-azurerm | https://api.github.com/repos/hashicorp/terraform-provider-azurerm | closed | Can't create read replica using terraform resource azurerm_cosmosdb_postgresql_cluster | bug service/cosmosdb v/3.x | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment and review the [contribution guide](https://github.com/hashicorp/terraform-provider-azurerm/blob/main/contributing/README.md) to help.
<!--- Thank you for keeping this note for the community --->
### Terraform Version
1.2.9
### AzureRM Provider Version
3.63.0
### Affected Resource(s)/Data Source(s)
azurerm_cosmosdb_postgresql_cluster
### Terraform Configuration Files
```hcl
terraform {
required_providers {
local = {
source = "hashicorp/local"
}
azurerm = {
source = "hashicorp/azurerm"
version = "= 3.63.0"
}
random = {
source = "hashicorp/random"
version = "~> 3.4.3"
}
azapi = {
source = "azure/azapi"
version = ">= 0.6.0"
}
azuread = {
source = "hashicorp/azuread"
version = "~> 2.15.0"
}
ec = {
source = "elastic/ec"
version = "= 0.7.0"
}
external = {
source = "hashicorp/external"
version = "= 2.3.1"
}
elasticstack = {
source = "elastic/elasticstack"
version = "= 0.6.1"
}
}
required_version = ">= 1.0"
}
```
### Debug Output/Panic Output
```shell
Various errors:
1.
╷
│ Error: Missing required argument
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 34, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 34: source_resource_id = azurerm_cosmosdb_postgresql_cluster.primary_replica.id
│
│ "source_resource_id": all of `point_in_time_in_utc,source_location,source_resource_id` must be specified
╵
2.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="The source cluster is not ready for restore yet."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="The source cluster is not ready for restore yet."
╵
3.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="pointInTimeUTC cannot be before 2023-07-10T19:43:44Z. If you need to restore your cluster to a point within last 35 days, open a support request."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="pointInTimeUTC cannot be before 2023-07-10T19:43:44Z. If you need to restore your cluster to a point within last 35 days, open a support request."
╵
4.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="Restoring a new cluster from a source cluster in another location is not supported yet."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="Restoring a new cluster from a source cluster in another location is not supported yet."
5.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="pointInTimeUTC cannot be in the future."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="pointInTimeUTC cannot be in the future."
╵
```
### Expected Behaviour
Read replica should be created for the CosmosDB Postgresql cluster.
I tried using the REST API instead and found it can work properly:
[cosmosdb_postgresql_cluster](https://learn.microsoft.com/en-us/rest/api/postgresqlhsc/clusters/create?tabs=Python#create-a-new-cluster-as-a-read-replica)
### Actual Behaviour
Failure with the various error messages mentioned in the debug output.
### Steps to Reproduce
terraform plan -out main.tfplan -var-file="./postgre.tfvars"
terraform apply "main.tfplan"
### Important Factoids
N/A
### References
_No response_ | 1.0 | Can't create read replica using terraform resource azurerm_cosmosdb_postgresql_cluster - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment and review the [contribution guide](https://github.com/hashicorp/terraform-provider-azurerm/blob/main/contributing/README.md) to help.
<!--- Thank you for keeping this note for the community --->
### Terraform Version
1.2.9
### AzureRM Provider Version
3.63.0
### Affected Resource(s)/Data Source(s)
azurerm_cosmosdb_postgresql_cluster
### Terraform Configuration Files
```hcl
terraform {
required_providers {
local = {
source = "hashicorp/local"
}
azurerm = {
source = "hashicorp/azurerm"
version = "= 3.63.0"
}
random = {
source = "hashicorp/random"
version = "~> 3.4.3"
}
azapi = {
source = "azure/azapi"
version = ">= 0.6.0"
}
azuread = {
source = "hashicorp/azuread"
version = "~> 2.15.0"
}
ec = {
source = "elastic/ec"
version = "= 0.7.0"
}
external = {
source = "hashicorp/external"
version = "= 2.3.1"
}
elasticstack = {
source = "elastic/elasticstack"
version = "= 0.6.1"
}
}
required_version = ">= 1.0"
}
```
### Debug Output/Panic Output
```shell
Various errors:
1.
╷
│ Error: Missing required argument
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 34, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 34: source_resource_id = azurerm_cosmosdb_postgresql_cluster.primary_replica.id
│
│ "source_resource_id": all of `point_in_time_in_utc,source_location,source_resource_id` must be specified
╵
2.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="The source cluster is not ready for restore yet."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="The source cluster is not ready for restore yet."
╵
3.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="pointInTimeUTC cannot be before 2023-07-10T19:43:44Z. If you need to restore your cluster to a point within last 35 days, open a support request."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="pointInTimeUTC cannot be before 2023-07-10T19:43:44Z. If you need to restore your cluster to a point within last 35 days, open a support request."
╵
4.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="Restoring a new cluster from a source cluster in another location is not supported yet."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="Restoring a new cluster from a source cluster in another location is not supported yet."
5.
╷
│ Error: creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request" Message="pointInTimeUTC cannot be in the future."
│
│ with azurerm_cosmosdb_postgresql_cluster.read_replica,
│ on main.tf line 23, in resource "azurerm_cosmosdb_postgresql_cluster" "read_replica":
│ 23: resource "azurerm_cosmosdb_postgresql_cluster" "read_replica" {
│
│ creating Server Groupsv 2 (Subscription: "aaaaaaaa-aaaa-aaaa-aaaa-aaaaaaaaaaaa"
│ Resource Group Name: "peterli07102023"
│ Server Groupsv 2 Name: "peterlitest0710secondary"): performing Create: clusters.ClustersClient#Create: Failure sending request: StatusCode=0 -- Original Error: Code="bad_request"
│ Message="pointInTimeUTC cannot be in the future."
╵
```
### Expected Behaviour
Read replica should be created for the CosmosDB Postgresql cluster.
I tried using the REST API instead and found it can work properly:
[cosmosdb_postgresql_cluster](https://learn.microsoft.com/en-us/rest/api/postgresqlhsc/clusters/create?tabs=Python#create-a-new-cluster-as-a-read-replica)
### Actual Behaviour
Failure with the various error messages mentioned in the debug output.
### Steps to Reproduce
terraform plan -out main.tfplan -var-file="./postgre.tfvars"
terraform apply "main.tfplan"
### Important Factoids
N/A
### References
_No response_ | non_priority | can t create read replica using terraform resource azurerm cosmosdb postgresql cluster is there an existing issue for this i have searched the existing issues community note please vote on this issue by adding a thumbsup to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment and review the to help terraform version azurerm provider version affected resource s data source s azurerm cosmosdb postgresql cluster terraform configuration files hcl terraform required providers local source hashicorp local azurerm source hashicorp azurerm version random source hashicorp random version azapi source azure azapi version azuread source hashicorp azuread version ec source elastic ec version external source hashicorp external version elasticstack source elastic elasticstack version required version debug output panic output shell various errors ╷ │ error missing required argument │ │ with azurerm cosmosdb postgresql cluster read replica │ on main tf line in resource azurerm cosmosdb postgresql cluster read replica │ source resource id azurerm cosmosdb postgresql cluster primary replica id │ │ source resource id all of point in time in utc source location source resource id must be specified ╵ ╷ │ error creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request message the source cluster is not ready for restore yet │ │ with azurerm cosmosdb postgresql cluster read replica │ on main tf line in resource azurerm cosmosdb postgresql cluster read replica │ resource azurerm cosmosdb postgresql cluster read replica │ │ creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request │ message the source cluster is not ready for restore yet ╵ ╷ │ error creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request message pointintimeutc cannot be before if you need to restore your cluster to a point within last days open a support request │ │ with azurerm cosmosdb postgresql cluster read replica │ on main tf line in resource azurerm cosmosdb postgresql cluster read replica │ resource azurerm cosmosdb postgresql cluster read replica │ │ creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request │ message pointintimeutc cannot be before if you need to restore your cluster to a point within last days open a support request ╵ ╷ │ error creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request message restoring a new cluster from a source cluster in another location is not supported yet │ │ with azurerm cosmosdb postgresql cluster read replica │ on main tf line in resource azurerm cosmosdb postgresql cluster read replica │ resource azurerm cosmosdb postgresql cluster read replica │ │ creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request │ message restoring a new cluster from a source cluster in another location is not supported yet ╷ │ error creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request message pointintimeutc cannot be in the future │ │ with azurerm cosmosdb postgresql cluster read replica │ on main tf line in resource azurerm cosmosdb postgresql cluster read replica │ resource azurerm cosmosdb postgresql cluster read replica │ │ creating server groupsv subscription aaaaaaaa aaaa aaaa aaaa aaaaaaaaaaaa │ resource group name │ server groupsv name performing create clusters clustersclient create failure sending request statuscode original error code bad request │ message pointintimeutc cannot be in the future ╵ expected behaviour read replica should be created for the cosmosdb postgresql cluster i tried using the rest api instead and found it can work properly actual behaviour failure with the various error messages mentioned in the debug output steps to reproduce terraform plan out main tfplan var file postgre tfvars terraform apply main tfplan important factoids n a references no response | 0 |
20,557 | 4,567,727,448 | IssuesEvent | 2016-09-15 12:17:43 | dwclark/http-builder-ng | https://api.github.com/repos/dwclark/http-builder-ng | closed | Java examples | documentation enhancement | All.the examples are for Groovy but the library should be usable from standard Java - add some documentation and examples of Java use. | 1.0 | Java examples - All.the examples are for Groovy but the library should be usable from standard Java - add some documentation and examples of Java use. | non_priority | java examples all the examples are for groovy but the library should be usable from standard java add some documentation and examples of java use | 0 |
46,590 | 5,823,921,747 | IssuesEvent | 2017-05-07 07:36:24 | FACN1/VolunteerApp | https://api.github.com/repos/FACN1/VolunteerApp | closed | user story not accomplished | user-testing | In the user stories, you have:: "Visit the home page and have a brief explanation about what the site is about"
I personally don't feel that this was accomplished, an Arabic user would strongly get the impression that the site is about Earth day or something from the imagery and Arabic writing.
Even if the site is supposed to be for general use of volunteering, it's not clear what exactly is going on, another user story says "Click on a button on the home page that shows me a list of organizations". Considering all the organizations are 1, I don't think this was accomplished. Are they number #1 at something? Do they represent several other organizations? Do they they represent the closest place for someone living in IndONEsia?...ok, maybe I tried too hard on that one, still, you're relying on volunteers, so you should take better care of considering your users, afterall, your site relies on being considerate of others | 1.0 | user story not accomplished - In the user stories, you have:: "Visit the home page and have a brief explanation about what the site is about"
I personally don't feel that this was accomplished, an Arabic user would strongly get the impression that the site is about Earth day or something from the imagery and Arabic writing.
Even if the site is supposed to be for general use of volunteering, it's not clear what exactly is going on, another user story says "Click on a button on the home page that shows me a list of organizations". Considering all the organizations are 1, I don't think this was accomplished. Are they number #1 at something? Do they represent several other organizations? Do they they represent the closest place for someone living in IndONEsia?...ok, maybe I tried too hard on that one, still, you're relying on volunteers, so you should take better care of considering your users, afterall, your site relies on being considerate of others | non_priority | user story not accomplished in the user stories you have visit the home page and have a brief explanation about what the site is about i personally don t feel that this was accomplished an arabic user would strongly get the impression that the site is about earth day or something from the imagery and arabic writing even if the site is supposed to be for general use of volunteering it s not clear what exactly is going on another user story says click on a button on the home page that shows me a list of organizations considering all the organizations are i don t think this was accomplished are they number at something do they represent several other organizations do they they represent the closest place for someone living in indonesia ok maybe i tried too hard on that one still you re relying on volunteers so you should take better care of considering your users afterall your site relies on being considerate of others | 0 |
175,530 | 27,875,694,454 | IssuesEvent | 2023-03-21 15:56:06 | ECE-458-Books/ece458books | https://api.github.com/repos/ECE-458-Books/ece458books | closed | Disable "Submit" button until something has been added to be able to submit | frontend ui/ux/visual design | Currently on the book add page for example, the submit button is clickable before any books have been added, and looking at the chrome console it does send a request to the backend with an empty number of books. Does not make sense to be sending unnecessary empty requests to the backend, so disable this submit button until a book has been added. This is on all the pages with a submit button | 1.0 | Disable "Submit" button until something has been added to be able to submit - Currently on the book add page for example, the submit button is clickable before any books have been added, and looking at the chrome console it does send a request to the backend with an empty number of books. Does not make sense to be sending unnecessary empty requests to the backend, so disable this submit button until a book has been added. This is on all the pages with a submit button | non_priority | disable submit button until something has been added to be able to submit currently on the book add page for example the submit button is clickable before any books have been added and looking at the chrome console it does send a request to the backend with an empty number of books does not make sense to be sending unnecessary empty requests to the backend so disable this submit button until a book has been added this is on all the pages with a submit button | 0 |
30,453 | 8,551,805,694 | IssuesEvent | 2018-11-07 19:08:05 | deltachat/deltachat-core | https://api.github.com/repos/deltachat/deltachat-core | closed | Consider building libsasl2 ourselves | build | Linking against the system version of `libsasl2` can sometimes be problematic. My current use case is simply trying to build `deltachat-core` on Travis, which we need in order to test `deltachat-node` properly. Apparently `libsasl2-dev` doesn't have a `.pc` file for Ubuntu 14.04 (which is what Travis uses) so resulting in problems when running `meson`:

Full log here: https://travis-ci.org/ralphtheninja/deltachat-node/builds/408001419
A solution would be to pull in `libsasl2` into our source tree via e.g. a git submodule. | 1.0 | Consider building libsasl2 ourselves - Linking against the system version of `libsasl2` can sometimes be problematic. My current use case is simply trying to build `deltachat-core` on Travis, which we need in order to test `deltachat-node` properly. Apparently `libsasl2-dev` doesn't have a `.pc` file for Ubuntu 14.04 (which is what Travis uses) so resulting in problems when running `meson`:

Full log here: https://travis-ci.org/ralphtheninja/deltachat-node/builds/408001419
A solution would be to pull in `libsasl2` into our source tree via e.g. a git submodule. | non_priority | consider building ourselves linking against the system version of can sometimes be problematic my current use case is simply trying to build deltachat core on travis which we need in order to test deltachat node properly apparently dev doesn t have a pc file for ubuntu which is what travis uses so resulting in problems when running meson full log here a solution would be to pull in into our source tree via e g a git submodule | 0 |
133,868 | 18,977,189,451 | IssuesEvent | 2021-11-20 07:10:27 | four-four-four/DAMOA-Frontend | https://api.github.com/repos/four-four-four/DAMOA-Frontend | opened | [디자인] Vue Bootstrap 템플릿 적용 | Design 0xe82de | ## Description
> Vue Bootstrap 템플릿으로 기존 프로젝트를 대체합니다. 추후에는 템플릿 기반으로 기능을 개발합니다.
## Details
- 템플릿 반영 후 정상적으로 적용되었는지 확인
## Progress
- [ ] 템플릿 선정
- [ ] 템플릿 적용
- [ ] 테스트 | 1.0 | [디자인] Vue Bootstrap 템플릿 적용 - ## Description
> Vue Bootstrap 템플릿으로 기존 프로젝트를 대체합니다. 추후에는 템플릿 기반으로 기능을 개발합니다.
## Details
- 템플릿 반영 후 정상적으로 적용되었는지 확인
## Progress
- [ ] 템플릿 선정
- [ ] 템플릿 적용
- [ ] 테스트 | non_priority | vue bootstrap 템플릿 적용 description vue bootstrap 템플릿으로 기존 프로젝트를 대체합니다 추후에는 템플릿 기반으로 기능을 개발합니다 details 템플릿 반영 후 정상적으로 적용되었는지 확인 progress 템플릿 선정 템플릿 적용 테스트 | 0 |
124,194 | 17,772,487,325 | IssuesEvent | 2021-08-30 15:07:32 | kapseliboi/core | https://api.github.com/repos/kapseliboi/core | opened | CVE-2018-1000620 (High) detected in cryptiles-2.0.5.tgz, cryptiles-3.1.2.tgz | security vulnerability | ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>cryptiles-2.0.5.tgz</b>, <b>cryptiles-3.1.2.tgz</b></p></summary>
<p>
<details><summary><b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>
Dependency Hierarchy:
- coveralls-2.13.3.tgz (Root Library)
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>cryptiles-3.1.2.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz</a></p>
<p>
Dependency Hierarchy:
- request-2.83.0.tgz (Root Library)
- hawk-6.0.2.tgz
- :x: **cryptiles-3.1.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/core/commit/e874360a594fee39a58bef623926d2a19086771d">e874360a594fee39a58bef623926d2a19086771d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-1000620 (High) detected in cryptiles-2.0.5.tgz, cryptiles-3.1.2.tgz - ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>cryptiles-2.0.5.tgz</b>, <b>cryptiles-3.1.2.tgz</b></p></summary>
<p>
<details><summary><b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>
Dependency Hierarchy:
- coveralls-2.13.3.tgz (Root Library)
- request-2.79.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>cryptiles-3.1.2.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-3.1.2.tgz</a></p>
<p>
Dependency Hierarchy:
- request-2.83.0.tgz (Root Library)
- hawk-6.0.2.tgz
- :x: **cryptiles-3.1.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/core/commit/e874360a594fee39a58bef623926d2a19086771d">e874360a594fee39a58bef623926d2a19086771d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in cryptiles tgz cryptiles tgz cve high severity vulnerability vulnerable libraries cryptiles tgz cryptiles tgz cryptiles tgz general purpose crypto utilities library home page a href dependency hierarchy coveralls tgz root library request tgz hawk tgz x cryptiles tgz vulnerable library cryptiles tgz general purpose crypto utilities library home page a href dependency hierarchy request tgz root library hawk tgz x cryptiles tgz vulnerable library found in head commit a href found in base branch master vulnerability details eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
65,072 | 8,786,965,569 | IssuesEvent | 2018-12-20 17:08:48 | NeutrinosPlatform/cordova-plugin-document-scanner | https://api.github.com/repos/NeutrinosPlatform/cordova-plugin-document-scanner | closed | Android Crash | bug change documentation enhancement | document-scanner version 1.1.1
Crashing in an app with the following code:
```
scanDocument() {
// scan document using document-scanner from the camera
scan.scanDoc(1, (imgUri) => {
this.claimDocImage.imagePath = normalizeURL(imgUri);
}, (err) => {
console.error(err);
});
}
```
```
--------- beginning of crash
05-08 14:01:23.852 28011-28011/com.eightysixdegrees.antellogistics E/AndroidRuntime: FATAL EXCEPTION: main
Process: com.eightysixdegrees.antellogistics, PID: 28011
java.lang.UnsatisfiedLinkError: dalvik.system.PathClassLoader[DexPathList[[zip file "/data/app/com.eightysixdegrees.antellogistics-h9hhwnZVYDRxsfP_9H8p1g==/base.apk"],nativeLibraryDirectories=[/data/app/com.eightysixdegrees.antellogistics-h9hhwnZVYDRxsfP_9H8p1g==/lib/arm64, /data/app/com.eightysixdegrees.antellogistics-h9hhwnZVYDRxsfP_9H8p1g==/base.apk!/lib/arm64-v8a, /system/lib64]]] couldn't find "libopencv_java3.so"
at java.lang.Runtime.loadLibrary0(Runtime.java:1011)
at java.lang.System.loadLibrary(System.java:1657)
at com.scanlibrary.Loader.load(Loader.java:14)
at com.scanlibrary.ScanActivity.<clinit>(ScanActivity.java:125)
at java.lang.Class.newInstance(Native Method)
at android.app.Instrumentation.newActivity(Instrumentation.java:1174)
at android.app.ActivityThread.performLaunchActivity(ActivityThread.java:2669)
at android.app.ActivityThread.handleLaunchActivity(ActivityThread.java:2856)
at android.app.ActivityThread.-wrap11(Unknown Source:0)
at android.app.ActivityThread$H.handleMessage(ActivityThread.java:1589)
at android.os.Handler.dispatchMessage(Handler.java:106)
at android.os.Looper.loop(Looper.java:164)
at android.app.ActivityThread.main(ActivityThread.java:6494)
at java.lang.reflect.Method.invoke(Native Method)
at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:438)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:807)
```
Info:
```
global packages:
cordova (Cordova CLI) : 8.0.0
local packages:
@ionic/app-scripts : 3.1.8
Cordova Platforms : android 7.1.0 ios 4.5.4
Ionic Framework : ionic-angular 3.9.2
System:
ios-deploy : 1.9.2
ios-sim : 6.1.2
Node : v8.11.1
npm : 5.8.0
OS : macOS High Sierra
Xcode : Xcode 9.3 Build version 9E145
```
| 1.0 | Android Crash - document-scanner version 1.1.1
Crashing in an app with the following code:
```
scanDocument() {
// scan document using document-scanner from the camera
scan.scanDoc(1, (imgUri) => {
this.claimDocImage.imagePath = normalizeURL(imgUri);
}, (err) => {
console.error(err);
});
}
```
```
--------- beginning of crash
05-08 14:01:23.852 28011-28011/com.eightysixdegrees.antellogistics E/AndroidRuntime: FATAL EXCEPTION: main
Process: com.eightysixdegrees.antellogistics, PID: 28011
java.lang.UnsatisfiedLinkError: dalvik.system.PathClassLoader[DexPathList[[zip file "/data/app/com.eightysixdegrees.antellogistics-h9hhwnZVYDRxsfP_9H8p1g==/base.apk"],nativeLibraryDirectories=[/data/app/com.eightysixdegrees.antellogistics-h9hhwnZVYDRxsfP_9H8p1g==/lib/arm64, /data/app/com.eightysixdegrees.antellogistics-h9hhwnZVYDRxsfP_9H8p1g==/base.apk!/lib/arm64-v8a, /system/lib64]]] couldn't find "libopencv_java3.so"
at java.lang.Runtime.loadLibrary0(Runtime.java:1011)
at java.lang.System.loadLibrary(System.java:1657)
at com.scanlibrary.Loader.load(Loader.java:14)
at com.scanlibrary.ScanActivity.<clinit>(ScanActivity.java:125)
at java.lang.Class.newInstance(Native Method)
at android.app.Instrumentation.newActivity(Instrumentation.java:1174)
at android.app.ActivityThread.performLaunchActivity(ActivityThread.java:2669)
at android.app.ActivityThread.handleLaunchActivity(ActivityThread.java:2856)
at android.app.ActivityThread.-wrap11(Unknown Source:0)
at android.app.ActivityThread$H.handleMessage(ActivityThread.java:1589)
at android.os.Handler.dispatchMessage(Handler.java:106)
at android.os.Looper.loop(Looper.java:164)
at android.app.ActivityThread.main(ActivityThread.java:6494)
at java.lang.reflect.Method.invoke(Native Method)
at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:438)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:807)
```
Info:
```
global packages:
cordova (Cordova CLI) : 8.0.0
local packages:
@ionic/app-scripts : 3.1.8
Cordova Platforms : android 7.1.0 ios 4.5.4
Ionic Framework : ionic-angular 3.9.2
System:
ios-deploy : 1.9.2
ios-sim : 6.1.2
Node : v8.11.1
npm : 5.8.0
OS : macOS High Sierra
Xcode : Xcode 9.3 Build version 9E145
```
| non_priority | android crash document scanner version crashing in an app with the following code scandocument scan document using document scanner from the camera scan scandoc imguri this claimdocimage imagepath normalizeurl imguri err console error err beginning of crash com eightysixdegrees antellogistics e androidruntime fatal exception main process com eightysixdegrees antellogistics pid java lang unsatisfiedlinkerror dalvik system pathclassloader nativelibrarydirectories couldn t find libopencv so at java lang runtime runtime java at java lang system loadlibrary system java at com scanlibrary loader load loader java at com scanlibrary scanactivity scanactivity java at java lang class newinstance native method at android app instrumentation newactivity instrumentation java at android app activitythread performlaunchactivity activitythread java at android app activitythread handlelaunchactivity activitythread java at android app activitythread unknown source at android app activitythread h handlemessage activitythread java at android os handler dispatchmessage handler java at android os looper loop looper java at android app activitythread main activitythread java at java lang reflect method invoke native method at com android internal os runtimeinit methodandargscaller run runtimeinit java at com android internal os zygoteinit main zygoteinit java info global packages cordova cordova cli local packages ionic app scripts cordova platforms android ios ionic framework ionic angular system ios deploy ios sim node npm os macos high sierra xcode xcode build version | 0 |
227,424 | 18,063,123,301 | IssuesEvent | 2021-09-20 15:56:10 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Few of the kubernetes tests are failing due to build failures | sig/storage sig/apps kind/failing-test triage/accepted | <!-- Please only use this template for submitting reports about continuously failing tests or jobs in Kubernetes CI -->
#### Which jobs are failing:
Following kubernetes tests are failing
make test WHAT=k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins
make test WHAT=k8s.io/kubernetes/pkg/controller/job
#### Which test(s) are failing:
Sample failure error trace
```
[root@karthik-workspace kubernetes]# make test WHAT=k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins
+++ [0917 10:23:04] Running tests without code coverage and with -race
# k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins
vendor/k8s.io/csi-translation-lib/plugins/in_tree_volume_test.go:683:4: (*testing.common).Errorf does not support error-wrapping directive %w
FAIL k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins [build failed]
FAIL
make: *** [Makefile:184: test] Error 1
```
Full Test report can be found [here](https://prow.ppc64le-cloud.org/view/gs/ppc64le-kubernetes/logs/periodic-kubernetes-containerd-conformance-test-ppc64le/1438805878072414208)
#### Since when has it been failing:
#### Testgrid link:
#### Reason for failure:
Incorrect format specifiers used in Errorf in test logging
#### Anything else we need to know:
| 1.0 | Few of the kubernetes tests are failing due to build failures - <!-- Please only use this template for submitting reports about continuously failing tests or jobs in Kubernetes CI -->
#### Which jobs are failing:
Following kubernetes tests are failing
make test WHAT=k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins
make test WHAT=k8s.io/kubernetes/pkg/controller/job
#### Which test(s) are failing:
Sample failure error trace
```
[root@karthik-workspace kubernetes]# make test WHAT=k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins
+++ [0917 10:23:04] Running tests without code coverage and with -race
# k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins
vendor/k8s.io/csi-translation-lib/plugins/in_tree_volume_test.go:683:4: (*testing.common).Errorf does not support error-wrapping directive %w
FAIL k8s.io/kubernetes/vendor/k8s.io/csi-translation-lib/plugins [build failed]
FAIL
make: *** [Makefile:184: test] Error 1
```
Full Test report can be found [here](https://prow.ppc64le-cloud.org/view/gs/ppc64le-kubernetes/logs/periodic-kubernetes-containerd-conformance-test-ppc64le/1438805878072414208)
#### Since when has it been failing:
#### Testgrid link:
#### Reason for failure:
Incorrect format specifiers used in Errorf in test logging
#### Anything else we need to know:
| non_priority | few of the kubernetes tests are failing due to build failures which jobs are failing following kubernetes tests are failing make test what io kubernetes vendor io csi translation lib plugins make test what io kubernetes pkg controller job which test s are failing sample failure error trace make test what io kubernetes vendor io csi translation lib plugins running tests without code coverage and with race io kubernetes vendor io csi translation lib plugins vendor io csi translation lib plugins in tree volume test go testing common errorf does not support error wrapping directive w fail io kubernetes vendor io csi translation lib plugins fail make error full test report can be found since when has it been failing testgrid link reason for failure incorrect format specifiers used in errorf in test logging anything else we need to know | 0 |
35,080 | 7,548,704,257 | IssuesEvent | 2018-04-18 12:09:49 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | panel component animation 'collapsed model' driven bug | defect | Bug report
code here:
<p-panel [(collapsed)]="show">
show = false;
**Current behavior**
I use a variable to control the collapsed status of panel component, but the animation of unfolding has some problem: it completely unfolds at first and gradually unfolds again later, which appears that a line of border drop down after unfold.
**Expected behavior**
it should be like what the demo shows.
**Minimal reproduction of the problem with instructions**
<!--
If the current behavior is a bug or you can illustrate your feature request better with an example,
please provide the *STEPS TO REPRODUCE* and if possible a *MINIMAL DEMO* of the problem via
https://plnkr.co or similar (you can use this template as a starting point: http://plnkr.co/edit/tpl:AvJOMERrnz94ekVua0u5).
-->
**What is the motivation / use case for changing the behavior?**
Collapsed status should be model driven.
**Please tell us about your environment:**
win7
* **Angular version:** 2.0.X
5.1.0
* **PrimeNG version:** 2.0.X
5.2.0
* **Browser:** [all | Chrome XX | Firefox XX | IE XX | Safari XX | Mobile Chrome XX | Android X.X Web Browser | iOS XX Safari | iOS XX UIWebView | iOS XX WKWebView ]
all
* **Language:** [all | TypeScript X.X | ES6/7 | ES5]
TypeScript 2.5.3
* **Node (for AoT issues):** `node --version` =
8.9.3 | 1.0 | panel component animation 'collapsed model' driven bug - Bug report
code here:
<p-panel [(collapsed)]="show">
show = false;
**Current behavior**
I use a variable to control the collapsed status of panel component, but the animation of unfolding has some problem: it completely unfolds at first and gradually unfolds again later, which appears that a line of border drop down after unfold.
**Expected behavior**
it should be like what the demo shows.
**Minimal reproduction of the problem with instructions**
<!--
If the current behavior is a bug or you can illustrate your feature request better with an example,
please provide the *STEPS TO REPRODUCE* and if possible a *MINIMAL DEMO* of the problem via
https://plnkr.co or similar (you can use this template as a starting point: http://plnkr.co/edit/tpl:AvJOMERrnz94ekVua0u5).
-->
**What is the motivation / use case for changing the behavior?**
Collapsed status should be model driven.
**Please tell us about your environment:**
win7
* **Angular version:** 2.0.X
5.1.0
* **PrimeNG version:** 2.0.X
5.2.0
* **Browser:** [all | Chrome XX | Firefox XX | IE XX | Safari XX | Mobile Chrome XX | Android X.X Web Browser | iOS XX Safari | iOS XX UIWebView | iOS XX WKWebView ]
all
* **Language:** [all | TypeScript X.X | ES6/7 | ES5]
TypeScript 2.5.3
* **Node (for AoT issues):** `node --version` =
8.9.3 | non_priority | panel component animation collapsed model driven bug bug report code here show false current behavior i use a variable to control the collapsed status of panel component but the animation of unfolding has some problem it completely unfolds at first and gradually unfolds again later which appears that a line of border drop down after unfold expected behavior it should be like what the demo shows minimal reproduction of the problem with instructions if the current behavior is a bug or you can illustrate your feature request better with an example please provide the steps to reproduce and if possible a minimal demo of the problem via or similar you can use this template as a starting point what is the motivation use case for changing the behavior collapsed status should be model driven please tell us about your environment angular version x primeng version x browser all language typescript node for aot issues node version | 0 |
140,392 | 18,901,290,588 | IssuesEvent | 2021-11-16 01:24:53 | dmyers87/seeds-packets | https://api.github.com/repos/dmyers87/seeds-packets | opened | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz | security vulnerability | ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>Path to dependency file: seeds-packets/package.json</p>
<p>Path to vulnerable library: seeds-packets/node_modules/json-schema,seeds-packets/packets/seedlings/node_modules/json-schema</p>
<p>
Dependency Hierarchy:
- node-sass-4.14.1.tgz (Root Library)
- request-2.88.2.tgz
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"json-schema","packageVersion":"0.2.3","packageFilePaths":["/package.json","/packets/seedlings/package.json"],"isTransitiveDependency":true,"dependencyTree":"node-sass:4.14.1;request:2.88.2;http-signature:1.2.0;jsprim:1.4.1;json-schema:0.2.3","isMinimumFixVersionAvailable":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-3918","vulnerabilityDetails":"json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (\u0027Prototype Pollution\u0027)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>Path to dependency file: seeds-packets/package.json</p>
<p>Path to vulnerable library: seeds-packets/node_modules/json-schema,seeds-packets/packets/seedlings/node_modules/json-schema</p>
<p>
Dependency Hierarchy:
- node-sass-4.14.1.tgz (Root Library)
- request-2.88.2.tgz
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"json-schema","packageVersion":"0.2.3","packageFilePaths":["/package.json","/packets/seedlings/package.json"],"isTransitiveDependency":true,"dependencyTree":"node-sass:4.14.1;request:2.88.2;http-signature:1.2.0;jsprim:1.4.1;json-schema:0.2.3","isMinimumFixVersionAvailable":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-3918","vulnerabilityDetails":"json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (\u0027Prototype Pollution\u0027)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in json schema tgz cve high severity vulnerability vulnerable library json schema tgz json schema validation and specifications library home page a href path to dependency file seeds packets package json path to vulnerable library seeds packets node modules json schema seeds packets packets seedlings node modules json schema dependency hierarchy node sass tgz root library request tgz http signature tgz jsprim tgz x json schema tgz vulnerable library found in base branch develop vulnerability details json schema is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree node sass request http signature jsprim json schema isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails json schema is vulnerable to improperly controlled modification of object prototype attributes pollution vulnerabilityurl | 0 |
201,959 | 23,048,136,450 | IssuesEvent | 2022-07-24 08:00:01 | ofirghc/easybuggy4django | https://api.github.com/repos/ofirghc/easybuggy4django | opened | requests-2.18.4-py2.py3-none-any.whl: 1 vulnerabilities (highest severity is: 5.0) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>requests-2.18.4-py2.py3-none-any.whl</b></p></summary>
<p>Python HTTP for Humans.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django</p>
<p>Path to vulnerable library: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django,/requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ofirghc/easybuggy4django/commit/acd9a84f150d1ed66178e1f4d333b905621e8082">acd9a84f150d1ed66178e1f4d333b905621e8082</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2018-18074](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-18074) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | requests-2.18.4-py2.py3-none-any.whl | Direct | Replace or update the following files: sessions.py, test_requests.py | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-18074</summary>
### Vulnerable Library - <b>requests-2.18.4-py2.py3-none-any.whl</b></p>
<p>Python HTTP for Humans.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django</p>
<p>Path to vulnerable library: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **requests-2.18.4-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ofirghc/easybuggy4django/commit/acd9a84f150d1ed66178e1f4d333b905621e8082">acd9a84f150d1ed66178e1f4d333b905621e8082</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Requests package before 2.20.0 for Python sends an HTTP Authorization header to an http URI upon receiving a same-hostname https-to-http redirect, which makes it easier for remote attackers to discover credentials by sniffing the network.
<p>Publish Date: 2018-10-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-18074>CVE-2018-18074</a></p>
</p>
<p></p>
### CVSS 2 Score Details (<b>5.0</b>)
<p>
Base Score Metrics not available</p>
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Change files</p>
<p>Release Date: 2018-09-14</p>
<p>Fix Resolution: Replace or update the following files: sessions.py, test_requests.py</p>
</p>
<p></p>
</details> | True | requests-2.18.4-py2.py3-none-any.whl: 1 vulnerabilities (highest severity is: 5.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>requests-2.18.4-py2.py3-none-any.whl</b></p></summary>
<p>Python HTTP for Humans.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django</p>
<p>Path to vulnerable library: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django,/requirements.txt</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ofirghc/easybuggy4django/commit/acd9a84f150d1ed66178e1f4d333b905621e8082">acd9a84f150d1ed66178e1f4d333b905621e8082</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2018-18074](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-18074) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | requests-2.18.4-py2.py3-none-any.whl | Direct | Replace or update the following files: sessions.py, test_requests.py | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-18074</summary>
### Vulnerable Library - <b>requests-2.18.4-py2.py3-none-any.whl</b></p>
<p>Python HTTP for Humans.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/49/df/50aa1999ab9bde74656c2919d9c0c085fd2b3775fd3eca826012bef76d8c/requests-2.18.4-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django</p>
<p>Path to vulnerable library: /C:/Users/OfirNir/AppData/Local/Temp/ws-scm/easybuggy4django,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **requests-2.18.4-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ofirghc/easybuggy4django/commit/acd9a84f150d1ed66178e1f4d333b905621e8082">acd9a84f150d1ed66178e1f4d333b905621e8082</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Requests package before 2.20.0 for Python sends an HTTP Authorization header to an http URI upon receiving a same-hostname https-to-http redirect, which makes it easier for remote attackers to discover credentials by sniffing the network.
<p>Publish Date: 2018-10-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-18074>CVE-2018-18074</a></p>
</p>
<p></p>
### CVSS 2 Score Details (<b>5.0</b>)
<p>
Base Score Metrics not available</p>
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Change files</p>
<p>Release Date: 2018-09-14</p>
<p>Fix Resolution: Replace or update the following files: sessions.py, test_requests.py</p>
</p>
<p></p>
</details> | non_priority | requests none any whl vulnerabilities highest severity is vulnerable library requests none any whl python http for humans library home page a href path to dependency file c users ofirnir appdata local temp ws scm path to vulnerable library c users ofirnir appdata local temp ws scm requirements txt found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium requests none any whl direct replace or update the following files sessions py test requests py details cve vulnerable library requests none any whl python http for humans library home page a href path to dependency file c users ofirnir appdata local temp ws scm path to vulnerable library c users ofirnir appdata local temp ws scm requirements txt dependency hierarchy x requests none any whl vulnerable library found in head commit a href found in base branch main vulnerability details the requests package before for python sends an http authorization header to an http uri upon receiving a same hostname https to http redirect which makes it easier for remote attackers to discover credentials by sniffing the network publish date url a href cvss score details base score metrics not available suggested fix type change files release date fix resolution replace or update the following files sessions py test requests py | 0 |
12,801 | 15,074,801,811 | IssuesEvent | 2021-02-05 00:35:51 | FoundationGames/Sandwichable | https://api.github.com/repos/FoundationGames/Sandwichable | closed | AppleSkin mod does not show the saturation that sandwiches can add | Fixed In Development compatibility | Hi there, I found AppleSkin mod does not show the saturation that sandwiches can add, so I cannot see clearly how much saturation the sandwiches I made is. Is it because the code doesn't define a prepared sandwich as food (so that AppleSkin mod cannot understand)? | True | AppleSkin mod does not show the saturation that sandwiches can add - Hi there, I found AppleSkin mod does not show the saturation that sandwiches can add, so I cannot see clearly how much saturation the sandwiches I made is. Is it because the code doesn't define a prepared sandwich as food (so that AppleSkin mod cannot understand)? | non_priority | appleskin mod does not show the saturation that sandwiches can add hi there i found appleskin mod does not show the saturation that sandwiches can add so i cannot see clearly how much saturation the sandwiches i made is is it because the code doesn t define a prepared sandwich as food so that appleskin mod cannot understand | 0 |
27,668 | 13,348,809,448 | IssuesEvent | 2020-08-29 20:34:46 | OpenRA/OpenRA | https://api.github.com/repos/OpenRA/OpenRA | closed | Instructing group of rocket soliders to hit inaccessible target causes game to slow significantly | Bug Performance | Instructing group of rocket soliders to hit inaccessible target causes game to slow significantly
| True | Instructing group of rocket soliders to hit inaccessible target causes game to slow significantly - Instructing group of rocket soliders to hit inaccessible target causes game to slow significantly
| non_priority | instructing group of rocket soliders to hit inaccessible target causes game to slow significantly instructing group of rocket soliders to hit inaccessible target causes game to slow significantly | 0 |
18,833 | 24,736,608,632 | IssuesEvent | 2022-10-20 22:43:36 | MPMG-DCC-UFMG/C01 | https://api.github.com/repos/MPMG-DCC-UFMG/C01 | closed | Tradução dos testes do módulo `step-by-step` | [1] Bug [0] Desenvolvimento [2] Média Prioridade [3] Processamento Dinâmico | ## Comportamento Esperado
Espera-se que os testes do módulo de passos com processamento dinâmico esteja usando Playwright ao invés de Pyppeteer.
## Comportamento Atual
Os testes desse módulo usam a biblioteca Pyppeteer. Além disso, contam com a existência de casos de testes antigos que foram deletados do módulo step-by-step.
## Passos para reproduzir o erro
Executar pytest tests e observar os erros gerados.
## Especificações da Coleta
Não se aplica
## Sistema (caso necessário)
- MP ou local: local
- Branch específica: dev
- Sistema diferente: sistema distribuído com playwright
## Screenshots (caso necessário)
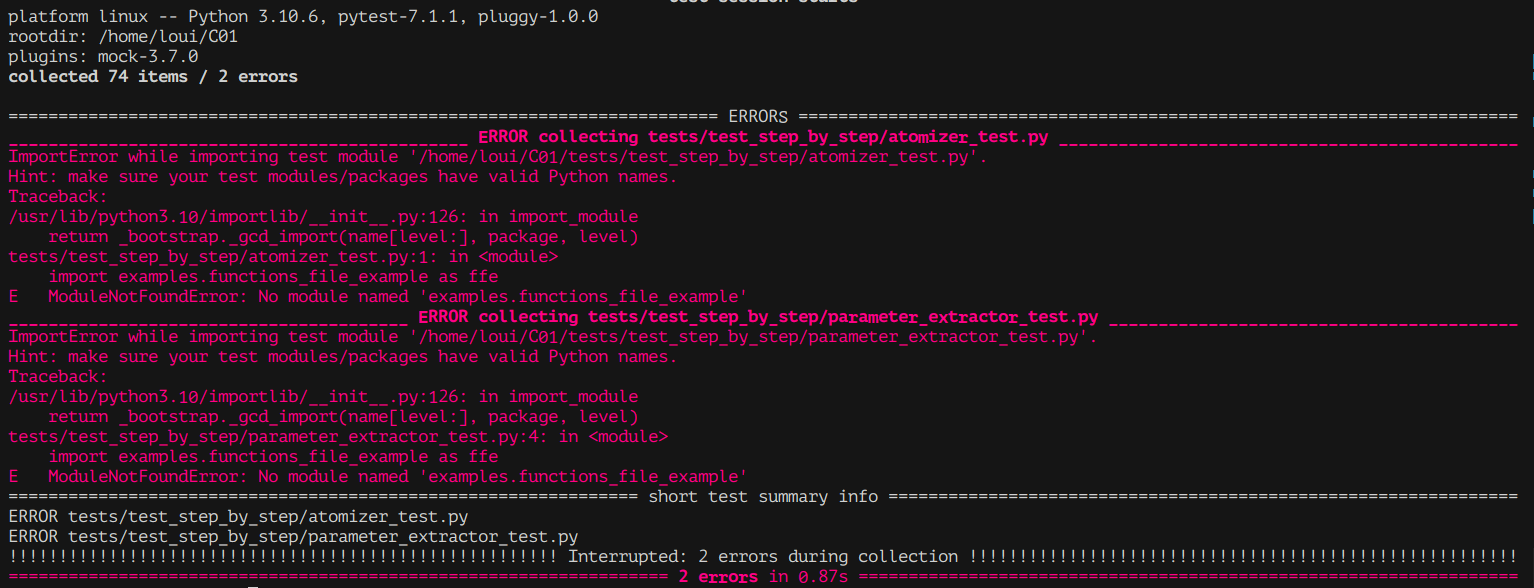
| 1.0 | Tradução dos testes do módulo `step-by-step` - ## Comportamento Esperado
Espera-se que os testes do módulo de passos com processamento dinâmico esteja usando Playwright ao invés de Pyppeteer.
## Comportamento Atual
Os testes desse módulo usam a biblioteca Pyppeteer. Além disso, contam com a existência de casos de testes antigos que foram deletados do módulo step-by-step.
## Passos para reproduzir o erro
Executar pytest tests e observar os erros gerados.
## Especificações da Coleta
Não se aplica
## Sistema (caso necessário)
- MP ou local: local
- Branch específica: dev
- Sistema diferente: sistema distribuído com playwright
## Screenshots (caso necessário)
| non_priority | tradução dos testes do módulo step by step comportamento esperado espera se que os testes do módulo de passos com processamento dinâmico esteja usando playwright ao invés de pyppeteer comportamento atual os testes desse módulo usam a biblioteca pyppeteer além disso contam com a existência de casos de testes antigos que foram deletados do módulo step by step passos para reproduzir o erro executar pytest tests e observar os erros gerados especificações da coleta não se aplica sistema caso necessário mp ou local local branch específica dev sistema diferente sistema distribuído com playwright screenshots caso necessário | 0 |
122,622 | 12,156,509,122 | IssuesEvent | 2020-04-25 17:38:23 | danielkelshaw/PyUAVSIM | https://api.github.com/repos/danielkelshaw/PyUAVSIM | closed | Improve Code Documentation | documentation | At the moment the code is very barebones in terms of documentation - it could be quite challenging for a third party to understand what is going on. It would be beneficial to improve the level of documentation throughout the code. | 1.0 | Improve Code Documentation - At the moment the code is very barebones in terms of documentation - it could be quite challenging for a third party to understand what is going on. It would be beneficial to improve the level of documentation throughout the code. | non_priority | improve code documentation at the moment the code is very barebones in terms of documentation it could be quite challenging for a third party to understand what is going on it would be beneficial to improve the level of documentation throughout the code | 0 |
240,760 | 18,373,574,392 | IssuesEvent | 2021-10-11 05:06:02 | jupyter/notebook | https://api.github.com/repos/jupyter/notebook | closed | [DOCS] Notebook examples not rendering properly | documentation | ### Description
Between version `v5.7.6` and the `stable`, the notebook examples section has become broken. For example:
- [The working version on `v5.7.6`](https://jupyter-notebook.readthedocs.io/en/5.7.6/examples/Notebook/Notebook%20Basics.html)

- [The broken version on `stable`](https://jupyter-notebook.readthedocs.io/en/stable/examples/Notebook/Notebook%20Basics.html)

It looks like the notebook `.ipynb` files are being parsed as raw text, rather than parsed properly by `nbsphinx`.
I tried getting a dev environment set up to debug this, but `pip install .` wasn't working because I ran into the error `error: [Errno 2] No such file or directory: 'bower'`. So opening this issue to track it.
The notebook examples are at the link below, and I suspect the fix will need to be somewhere around there, or in the Sphinx configuration:
https://github.com/jupyter/notebook/tree/master/docs/source/examples/Notebook
Originally reported in https://discourse.jupyter.org/t/error-in-jupyter-readthedocs-page-rendering/11038 | 1.0 | [DOCS] Notebook examples not rendering properly - ### Description
Between version `v5.7.6` and the `stable`, the notebook examples section has become broken. For example:
- [The working version on `v5.7.6`](https://jupyter-notebook.readthedocs.io/en/5.7.6/examples/Notebook/Notebook%20Basics.html)

- [The broken version on `stable`](https://jupyter-notebook.readthedocs.io/en/stable/examples/Notebook/Notebook%20Basics.html)

It looks like the notebook `.ipynb` files are being parsed as raw text, rather than parsed properly by `nbsphinx`.
I tried getting a dev environment set up to debug this, but `pip install .` wasn't working because I ran into the error `error: [Errno 2] No such file or directory: 'bower'`. So opening this issue to track it.
The notebook examples are at the link below, and I suspect the fix will need to be somewhere around there, or in the Sphinx configuration:
https://github.com/jupyter/notebook/tree/master/docs/source/examples/Notebook
Originally reported in https://discourse.jupyter.org/t/error-in-jupyter-readthedocs-page-rendering/11038 | non_priority | notebook examples not rendering properly description between version and the stable the notebook examples section has become broken for example it looks like the notebook ipynb files are being parsed as raw text rather than parsed properly by nbsphinx i tried getting a dev environment set up to debug this but pip install wasn t working because i ran into the error error no such file or directory bower so opening this issue to track it the notebook examples are at the link below and i suspect the fix will need to be somewhere around there or in the sphinx configuration originally reported in | 0 |
76,159 | 7,520,135,742 | IssuesEvent | 2018-04-12 13:43:57 | arquillian/ike-prow-plugins | https://api.github.com/repos/arquillian/ike-prow-plugins | closed | Add soft matcher and additional custom assertion | type/test-suite | - [ ] implement soft matcher that will behave as a soft assertion in AssertJ
- [ ] add a custom assertion for `PermissionStatus` object | 1.0 | Add soft matcher and additional custom assertion - - [ ] implement soft matcher that will behave as a soft assertion in AssertJ
- [ ] add a custom assertion for `PermissionStatus` object | non_priority | add soft matcher and additional custom assertion implement soft matcher that will behave as a soft assertion in assertj add a custom assertion for permissionstatus object | 0 |
285,168 | 24,646,994,068 | IssuesEvent | 2022-10-17 15:31:24 | KinsonDigital/Velaptor | https://api.github.com/repos/KinsonDigital/Velaptor | opened | 🧪QA Testing | 🧪qa testing | ### Complete The Item Below
- [X] I have linked all issues that will be tested for this release.
### Version Being Tested
asdf
### Issues To Test
_No response_
### Relevant Information
QA Testing Application:
- [VelaptorTesting-v1.0.0-preview.10.zip](https://github.com/KinsonDigital/Velaptor/files/9802135/VelaptorTesting-v1.0.0-preview.10.zip)
### QA Testing Dependencies
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | 🧪QA Testing - ### Complete The Item Below
- [X] I have linked all issues that will be tested for this release.
### Version Being Tested
asdf
### Issues To Test
_No response_
### Relevant Information
QA Testing Application:
- [VelaptorTesting-v1.0.0-preview.10.zip](https://github.com/KinsonDigital/Velaptor/files/9802135/VelaptorTesting-v1.0.0-preview.10.zip)
### QA Testing Dependencies
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | non_priority | 🧪qa testing complete the item below i have linked all issues that will be tested for this release version being tested asdf issues to test no response relevant information qa testing application qa testing dependencies no response code of conduct i agree to follow this project s code of conduct | 0 |
72,709 | 24,251,796,334 | IssuesEvent | 2022-09-27 14:42:01 | matrix-org/synapse | https://api.github.com/repos/matrix-org/synapse | closed | 'Cropped' thumbnails undershoot rather than overshoot the requested size (SYN-505) | A-Media-Repository T-Defect | Submitted by @​matthew:matrix.org
(Imported from https://matrix.org/jira/browse/SYN-505) | 1.0 | 'Cropped' thumbnails undershoot rather than overshoot the requested size (SYN-505) - Submitted by @​matthew:matrix.org
(Imported from https://matrix.org/jira/browse/SYN-505) | non_priority | cropped thumbnails undershoot rather than overshoot the requested size syn submitted by matthew matrix org imported from | 0 |
249,076 | 26,884,614,931 | IssuesEvent | 2023-02-06 01:12:43 | nidhi7598/linux-3.0.35_CVE-2018-13405 | https://api.github.com/repos/nidhi7598/linux-3.0.35_CVE-2018-13405 | opened | CVE-2021-45868 (Medium) detected in linux-stable-rtv3.8.6 | security vulnerability | ## CVE-2021-45868 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/quota/quota_tree.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/quota/quota_tree.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/quota/quota_tree.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel before 5.15.3, fs/quota/quota_tree.c does not validate the block number in the quota tree (on disk). This can, for example, lead to a kernel/locking/rwsem.c use-after-free if there is a corrupted quota file.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45868>CVE-2021-45868</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-45868">https://www.linuxkernelcves.com/cves/CVE-2021-45868</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: v4.4.293,v4.9.291,v4.14.256,v4.19.218,v5.4.160,v5.10.80,v5.14.19,v5.15.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-45868 (Medium) detected in linux-stable-rtv3.8.6 - ## CVE-2021-45868 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/quota/quota_tree.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/quota/quota_tree.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/quota/quota_tree.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel before 5.15.3, fs/quota/quota_tree.c does not validate the block number in the quota tree (on disk). This can, for example, lead to a kernel/locking/rwsem.c use-after-free if there is a corrupted quota file.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45868>CVE-2021-45868</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-45868">https://www.linuxkernelcves.com/cves/CVE-2021-45868</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: v4.4.293,v4.9.291,v4.14.256,v4.19.218,v5.4.160,v5.10.80,v5.14.19,v5.15.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files fs quota quota tree c fs quota quota tree c fs quota quota tree c vulnerability details in the linux kernel before fs quota quota tree c does not validate the block number in the quota tree on disk this can for example lead to a kernel locking rwsem c use after free if there is a corrupted quota file publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
400,423 | 27,284,247,119 | IssuesEvent | 2023-02-23 12:22:06 | tauri-apps/tauri-docs | https://api.github.com/repos/tauri-apps/tauri-docs | closed | [docs] Method for debugging in IntelliJ | type: documentation | I see in the documents there some method to debug with breakpoints in VSCode, however, I do not see anything regarding IntelliJ or CLion. Is there a well known method for running tauri in debug mode within IntelliJ using their configurations? I am at a point now where this is greatly needed over println everywhere. | 1.0 | [docs] Method for debugging in IntelliJ - I see in the documents there some method to debug with breakpoints in VSCode, however, I do not see anything regarding IntelliJ or CLion. Is there a well known method for running tauri in debug mode within IntelliJ using their configurations? I am at a point now where this is greatly needed over println everywhere. | non_priority | method for debugging in intellij i see in the documents there some method to debug with breakpoints in vscode however i do not see anything regarding intellij or clion is there a well known method for running tauri in debug mode within intellij using their configurations i am at a point now where this is greatly needed over println everywhere | 0 |
83,185 | 7,867,662,022 | IssuesEvent | 2018-06-23 11:43:50 | CodeWarriorsOrganization/CodeWarriorsFinalYearProject | https://api.github.com/repos/CodeWarriorsOrganization/CodeWarriorsFinalYearProject | closed | CW0013/T0013.5 - Create Test Cases (Priority 2) | test cases | ### User Story :
> AS a player,
> I NEED the game to contain at least 3 players
### Task :
> **Create Test Cases** | 1.0 | CW0013/T0013.5 - Create Test Cases (Priority 2) - ### User Story :
> AS a player,
> I NEED the game to contain at least 3 players
### Task :
> **Create Test Cases** | non_priority | create test cases priority user story as a player i need the game to contain at least players task create test cases | 0 |
55,162 | 6,890,326,526 | IssuesEvent | 2017-11-22 13:39:43 | Microsoft/WSL | https://api.github.com/repos/Microsoft/WSL | closed | Unable to install extra packages on Bash | bydesign | I have been following this documentation in order to install Docker on Bash:
https://docs.docker.com/engine/installation/linux/docker-ce/ubuntu/#uninstall-old-versions
When I get to the step that asks me to install the extra packages:
`sudo apt-get install linux-image-extra-$(uname -r) linux-image-extra-virtual`
it says:
```
Reading package lists... Done
Building dependency tree
Reading state information... Done
E: Unable to locate package linux-image-extra-4.4.0-43-Microsoft
E: Couldn't find any package by regex 'linux-image-extra-4.4.0-43-Microsoft'
```
| 1.0 | Unable to install extra packages on Bash - I have been following this documentation in order to install Docker on Bash:
https://docs.docker.com/engine/installation/linux/docker-ce/ubuntu/#uninstall-old-versions
When I get to the step that asks me to install the extra packages:
`sudo apt-get install linux-image-extra-$(uname -r) linux-image-extra-virtual`
it says:
```
Reading package lists... Done
Building dependency tree
Reading state information... Done
E: Unable to locate package linux-image-extra-4.4.0-43-Microsoft
E: Couldn't find any package by regex 'linux-image-extra-4.4.0-43-Microsoft'
```
| non_priority | unable to install extra packages on bash i have been following this documentation in order to install docker on bash when i get to the step that asks me to install the extra packages sudo apt get install linux image extra uname r linux image extra virtual it says reading package lists done building dependency tree reading state information done e unable to locate package linux image extra microsoft e couldn t find any package by regex linux image extra microsoft | 0 |
260,510 | 22,627,014,267 | IssuesEvent | 2022-06-30 11:36:52 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | opened | Intermittent UI test failure - < BookmarksTest.multipleBookmarkDeletionsTest> | b:crash eng:intermittent-test eng:ui-test | ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/8385706074016920331/executions/bs.82e8a2f7d51fa3da/test-cases)
### Stacktrace:
06-29 11:14:58.920: I/ActivityManager(478): Process org.mozilla.fenix.debug:gpu (pid 12247) has died: fg BTOP
06-29 11:14:58.921: W/ActivityManager(478): Scheduling restart of crashed service org.mozilla.fenix.debug/org.mozilla.gecko.process.GeckoChildProcessServices$gpu in 1000ms for connection
06-29 11:14:58.923: I/libprocessgroup(478): Successfully killed process cgroup uid 10152 pid 12247 in 0ms
06-29 11:14:58.926: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.959: W/WindowManager(478): removeWindowToken: Attempted to remove non-existing token: android.os.Binder@406d831
06-29 11:14:58.959: I/WindowManager(478): WIN DEATH: Window{56c5020 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity}
06-29 11:14:58.941: I/chatty(1861): uid=1041(audioserver) writer identical 1 line
06-29 11:14:58.956: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.960: W/InputDispatcher(478): Attempted to unregister already unregistered input channel '56c5020 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity (server)'
06-29 11:14:58.963: I/ActivityManager(478): Process org.mozilla.fenix.debug (pid 11601) has died: fg TOP
06-29 11:14:58.963: I/libprocessgroup(478): Successfully killed process cgroup uid 10152 pid 11601 in 0ms
06-29 11:14:58.971: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.976: W/ActivityTaskManager(478): Force removing ActivityRecord{7f41295 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9}: app died, no saved state
06-29 11:14:58.978: W/ActivityManager(478): Crash of app org.mozilla.fenix.debug running instrumentation ComponentInfo{org.mozilla.fenix.debug.test/androidx.test.runner.AndroidJUnitRunner}
06-29 11:14:58.983: I/ActivityManager(478): Force stopping org.mozilla.fenix.debug appid=10152 user=0: finished inst
06-29 11:14:58.984: I/ActivityManager(478): Killing 12032:org.mozilla.fenix.debug:tab20/u0a152 (adj 0): stop org.mozilla.fenix.debug due to finished inst
06-29 11:14:58.985: W/Binder(11539): Caught a RuntimeException from the binder stub implementation.
06-29 11:14:58.985: W/Binder(11539): java.lang.SecurityException: Calling from not trusted UID!
06-29 11:14:58.985: W/Binder(11539): at android.app.UiAutomationConnection.throwIfCalledByNotTrustedUidLocked(UiAutomationConnection.java:525)
06-29 11:14:58.985: W/Binder(11539): at android.app.UiAutomationConnection.shutdown(UiAutomationConnection.java:429)
06-29 11:14:58.985: W/Binder(11539): at android.app.IUiAutomationConnection$Stub.onTransact(IUiAutomationConnection.java:390)
06-29 11:14:58.985: W/Binder(11539): at android.os.Binder.execTransactInternal(Binder.java:1159)
06-29 11:14:58.985: W/Binder(11539): at android.os.Binder.execTransact(Binder.java:1123)
06-29 11:14:58.985: I/WindowManager(478): Force finishing activity ActivityRecord{7f41295 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9 f} isExiting}
06-29 11:14:58.985: W/ActivityTaskManager(478): Duplicate finish request for r=ActivityRecord{7f41295 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9 f} isExiting}
06-29 11:14:58.986: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.999: W/WindowManager(478): Cannot find window which accessibility connection is added to
06-29 11:14:59.007: W/ActivityManager(478): setHasOverlayUi called on unknown pid: 11601
06-29 11:14:59.001: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:59.013: I/BackdropActivity(10696): onResume()
06-29 11:14:59.015: I/ActivityTaskManager(478): Activity requesting to dismiss Keyguard: ActivityRecord{6711e55 u0 com.google.android.apps.mtaas.backdrop/.BackdropActivity t8}
06-29 11:14:59.016: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:59.019: D/AndroidRuntime(11539): Shutting down VM
### Build: 6/29 Main
### Notes: Similar with #24047
| 2.0 | Intermittent UI test failure - < BookmarksTest.multipleBookmarkDeletionsTest> - ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/8385706074016920331/executions/bs.82e8a2f7d51fa3da/test-cases)
### Stacktrace:
06-29 11:14:58.920: I/ActivityManager(478): Process org.mozilla.fenix.debug:gpu (pid 12247) has died: fg BTOP
06-29 11:14:58.921: W/ActivityManager(478): Scheduling restart of crashed service org.mozilla.fenix.debug/org.mozilla.gecko.process.GeckoChildProcessServices$gpu in 1000ms for connection
06-29 11:14:58.923: I/libprocessgroup(478): Successfully killed process cgroup uid 10152 pid 12247 in 0ms
06-29 11:14:58.926: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.959: W/WindowManager(478): removeWindowToken: Attempted to remove non-existing token: android.os.Binder@406d831
06-29 11:14:58.959: I/WindowManager(478): WIN DEATH: Window{56c5020 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity}
06-29 11:14:58.941: I/chatty(1861): uid=1041(audioserver) writer identical 1 line
06-29 11:14:58.956: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.960: W/InputDispatcher(478): Attempted to unregister already unregistered input channel '56c5020 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity (server)'
06-29 11:14:58.963: I/ActivityManager(478): Process org.mozilla.fenix.debug (pid 11601) has died: fg TOP
06-29 11:14:58.963: I/libprocessgroup(478): Successfully killed process cgroup uid 10152 pid 11601 in 0ms
06-29 11:14:58.971: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.976: W/ActivityTaskManager(478): Force removing ActivityRecord{7f41295 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9}: app died, no saved state
06-29 11:14:58.978: W/ActivityManager(478): Crash of app org.mozilla.fenix.debug running instrumentation ComponentInfo{org.mozilla.fenix.debug.test/androidx.test.runner.AndroidJUnitRunner}
06-29 11:14:58.983: I/ActivityManager(478): Force stopping org.mozilla.fenix.debug appid=10152 user=0: finished inst
06-29 11:14:58.984: I/ActivityManager(478): Killing 12032:org.mozilla.fenix.debug:tab20/u0a152 (adj 0): stop org.mozilla.fenix.debug due to finished inst
06-29 11:14:58.985: W/Binder(11539): Caught a RuntimeException from the binder stub implementation.
06-29 11:14:58.985: W/Binder(11539): java.lang.SecurityException: Calling from not trusted UID!
06-29 11:14:58.985: W/Binder(11539): at android.app.UiAutomationConnection.throwIfCalledByNotTrustedUidLocked(UiAutomationConnection.java:525)
06-29 11:14:58.985: W/Binder(11539): at android.app.UiAutomationConnection.shutdown(UiAutomationConnection.java:429)
06-29 11:14:58.985: W/Binder(11539): at android.app.IUiAutomationConnection$Stub.onTransact(IUiAutomationConnection.java:390)
06-29 11:14:58.985: W/Binder(11539): at android.os.Binder.execTransactInternal(Binder.java:1159)
06-29 11:14:58.985: W/Binder(11539): at android.os.Binder.execTransact(Binder.java:1123)
06-29 11:14:58.985: I/WindowManager(478): Force finishing activity ActivityRecord{7f41295 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9 f} isExiting}
06-29 11:14:58.985: W/ActivityTaskManager(478): Duplicate finish request for r=ActivityRecord{7f41295 u0 org.mozilla.fenix.debug/org.mozilla.fenix.HomeActivity t9 f} isExiting}
06-29 11:14:58.986: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:58.999: W/WindowManager(478): Cannot find window which accessibility connection is added to
06-29 11:14:59.007: W/ActivityManager(478): setHasOverlayUi called on unknown pid: 11601
06-29 11:14:59.001: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:59.013: I/BackdropActivity(10696): onResume()
06-29 11:14:59.015: I/ActivityTaskManager(478): Activity requesting to dismiss Keyguard: ActivityRecord{6711e55 u0 com.google.android.apps.mtaas.backdrop/.BackdropActivity t8}
06-29 11:14:59.016: W/audio_hw_generic(1861): Hardware backing HAL too slow, could only write 0 of 661 frames
06-29 11:14:59.019: D/AndroidRuntime(11539): Shutting down VM
### Build: 6/29 Main
### Notes: Similar with #24047
| non_priority | intermittent ui test failure firebase test run stacktrace i activitymanager process org mozilla fenix debug gpu pid has died fg btop w activitymanager scheduling restart of crashed service org mozilla fenix debug org mozilla gecko process geckochildprocessservices gpu in for connection i libprocessgroup successfully killed process cgroup uid pid in w audio hw generic hardware backing hal too slow could only write of frames w windowmanager removewindowtoken attempted to remove non existing token android os binder i windowmanager win death window org mozilla fenix debug org mozilla fenix homeactivity i chatty uid audioserver writer identical line w audio hw generic hardware backing hal too slow could only write of frames w inputdispatcher attempted to unregister already unregistered input channel org mozilla fenix debug org mozilla fenix homeactivity server i activitymanager process org mozilla fenix debug pid has died fg top i libprocessgroup successfully killed process cgroup uid pid in w audio hw generic hardware backing hal too slow could only write of frames w activitytaskmanager force removing activityrecord org mozilla fenix debug org mozilla fenix homeactivity app died no saved state w activitymanager crash of app org mozilla fenix debug running instrumentation componentinfo org mozilla fenix debug test androidx test runner androidjunitrunner i activitymanager force stopping org mozilla fenix debug appid user finished inst i activitymanager killing org mozilla fenix debug adj stop org mozilla fenix debug due to finished inst w binder caught a runtimeexception from the binder stub implementation w binder java lang securityexception calling from not trusted uid w binder at android app uiautomationconnection throwifcalledbynottrusteduidlocked uiautomationconnection java w binder at android app uiautomationconnection shutdown uiautomationconnection java w binder at android app iuiautomationconnection stub ontransact iuiautomationconnection java w binder at android os binder exectransactinternal binder java w binder at android os binder exectransact binder java i windowmanager force finishing activity activityrecord org mozilla fenix debug org mozilla fenix homeactivity f isexiting w activitytaskmanager duplicate finish request for r activityrecord org mozilla fenix debug org mozilla fenix homeactivity f isexiting w audio hw generic hardware backing hal too slow could only write of frames w windowmanager cannot find window which accessibility connection is added to w activitymanager sethasoverlayui called on unknown pid w audio hw generic hardware backing hal too slow could only write of frames i backdropactivity onresume i activitytaskmanager activity requesting to dismiss keyguard activityrecord com google android apps mtaas backdrop backdropactivity w audio hw generic hardware backing hal too slow could only write of frames d androidruntime shutting down vm build main notes similar with | 0 |
64,831 | 18,943,027,011 | IssuesEvent | 2021-11-18 06:43:45 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Composer keyboard focus is easily lost | T-Defect | ### Steps to reproduce
I've noticed that recently I start and try typing in element-desktop (not sure if that's any different in web :shrug: ) the cursor is never inside the composer when I expect it to. This probably happened about 100 times today.
This is happening when clicking the "down to bottom"-arrow button, even when the composer was focused before. It's also happening when clicking on random non-clickable areas in the timeline.
Some more notes here:
* It seems like previously hitting any non-shortcut key would focus the composer: https://github.com/vector-im/element-web/issues/5775#issuecomment-613354924 This definitely isn't happening anymore
* Trying to use tab to get the cursor back into the input field is not working. It keeps cycling through items in the timeline, potentially way offscreen where you last were, resetting your scroll-position.
### Outcome
#### What did you expect?
I would like to be able to type messages at pretty much all times.
#### What happened instead?
The cursor is almost never in the input field.
### Operating system
Arch Linux
### Application version
1.9.4
### How did you install the app?
archlinux-package
### Homeserver
bubu1.eu
### Will you send logs?
No | 1.0 | Composer keyboard focus is easily lost - ### Steps to reproduce
I've noticed that recently I start and try typing in element-desktop (not sure if that's any different in web :shrug: ) the cursor is never inside the composer when I expect it to. This probably happened about 100 times today.
This is happening when clicking the "down to bottom"-arrow button, even when the composer was focused before. It's also happening when clicking on random non-clickable areas in the timeline.
Some more notes here:
* It seems like previously hitting any non-shortcut key would focus the composer: https://github.com/vector-im/element-web/issues/5775#issuecomment-613354924 This definitely isn't happening anymore
* Trying to use tab to get the cursor back into the input field is not working. It keeps cycling through items in the timeline, potentially way offscreen where you last were, resetting your scroll-position.
### Outcome
#### What did you expect?
I would like to be able to type messages at pretty much all times.
#### What happened instead?
The cursor is almost never in the input field.
### Operating system
Arch Linux
### Application version
1.9.4
### How did you install the app?
archlinux-package
### Homeserver
bubu1.eu
### Will you send logs?
No | non_priority | composer keyboard focus is easily lost steps to reproduce i ve noticed that recently i start and try typing in element desktop not sure if that s any different in web shrug the cursor is never inside the composer when i expect it to this probably happened about times today this is happening when clicking the down to bottom arrow button even when the composer was focused before it s also happening when clicking on random non clickable areas in the timeline some more notes here it seems like previously hitting any non shortcut key would focus the composer this definitely isn t happening anymore trying to use tab to get the cursor back into the input field is not working it keeps cycling through items in the timeline potentially way offscreen where you last were resetting your scroll position outcome what did you expect i would like to be able to type messages at pretty much all times what happened instead the cursor is almost never in the input field operating system arch linux application version how did you install the app archlinux package homeserver eu will you send logs no | 0 |
314,426 | 23,521,470,617 | IssuesEvent | 2022-08-19 06:29:46 | ETTSU-StarTail/shapeshifter | https://api.github.com/repos/ETTSU-StarTail/shapeshifter | opened | [TASK]: 移行プロジェクトの詳細実装 | documentation enhancement | **タスクの意図**
移行プロジェクトの詳細表示を実装
**注意**
ドキュメント作成なら documentation タグのみを、機能作成・追加・改修であるなら enhancement タグのみを付ける。
| 1.0 | [TASK]: 移行プロジェクトの詳細実装 - **タスクの意図**
移行プロジェクトの詳細表示を実装
**注意**
ドキュメント作成なら documentation タグのみを、機能作成・追加・改修であるなら enhancement タグのみを付ける。
| non_priority | 移行プロジェクトの詳細実装 タスクの意図 移行プロジェクトの詳細表示を実装 注意 ドキュメント作成なら documentation タグのみを、機能作成・追加・改修であるなら enhancement タグのみを付ける。 | 0 |
224,767 | 17,774,101,258 | IssuesEvent | 2021-08-30 16:54:49 | ignitionrobotics/ign-gazebo | https://api.github.com/repos/ignitionrobotics/ign-gazebo | closed | New thermal camera test failure for Edifice | bug tests | <!-- If you're not sure whether your problem is a bug, please ask a question at
http://answers.gazebosim.org instead.-->
## Environment
* OS Version: Ubuntu 18.04
* Source or binary build? Source, commit https://github.com/ignitionrobotics/ign-gazebo/commit/6c91ff9e8e99e439307dfbd32607c5ab20f329d9
## Description
* Expected behavior: The `INTEGRATION_thermal_sensor_system` test (`ThermalSensorTest.ThermalSensorSystemInvalidConfig`) should pass
* Actual behavior: The test fails
## Steps to reproduce
<!-- Provide steps so we can try to reproduce this issue -->
1. Clone the repo: `git clone https://github.com/ignitionrobotics/ign-gazebo.git`
2. Complete the build so that tests are available:
```
cd ign-gazebo
mkdir build
cd build
cmake ..
make
```
3. Run the thermal sensor integration test:
```
# the following steps assume you are already in the ign-rendering/build directory
cd bin
./INTEGRATION_thermal_sensor_system
```
## Output
```
[Msg] Setting ambient temperature to 310 Kelvin and gradient to -0.0065 K/m. The resulting temperature range is: 0.750384 Kelvin.
[Wrn] [RenderUtil.cc:1048] Unable to set thermal camera temperature linear resolution. Value must be greater than 0. Using the default value: 3.
[Wrn] [RenderUtil.cc:1061] Unable to set thermal camera temperature range.Max temperature must be greater or equal to min. Using the default values : [-inf, inf].
/home/addisu/ws/edifice/src/ign-gazebo/test/integration/thermal_sensor_system.cc:197: Failure
Value of: received
Actual: false
Expected: true
/home/addisu/ws/edifice/src/ign-gazebo/test/integration/thermal_sensor_system.cc:198: Failure
Expected: (nullptr) != (g_image), actual: (nullptr) vs NULL
[Dbg] [Sensors.cc:309] SensorsPrivate::Stop
[Dbg] [Sensors.cc:295] SensorsPrivate::RenderThread stopped
[Dbg] [SimulationRunner.cc:499] Exiting postupdate worker thread (1)
[Dbg] [SimulationRunner.cc:499] Exiting postupdate worker thread (2)
[Dbg] [SimulationRunner.cc:499] Exiting postupdate worker thread (0)
[Dbg] [Sensors.cc:309] SensorsPrivate::Stop
[ FAILED ] ThermalSensorTest.ThermalSensorSystemInvalidConfig (3176 ms)
``` | 1.0 | New thermal camera test failure for Edifice - <!-- If you're not sure whether your problem is a bug, please ask a question at
http://answers.gazebosim.org instead.-->
## Environment
* OS Version: Ubuntu 18.04
* Source or binary build? Source, commit https://github.com/ignitionrobotics/ign-gazebo/commit/6c91ff9e8e99e439307dfbd32607c5ab20f329d9
## Description
* Expected behavior: The `INTEGRATION_thermal_sensor_system` test (`ThermalSensorTest.ThermalSensorSystemInvalidConfig`) should pass
* Actual behavior: The test fails
## Steps to reproduce
<!-- Provide steps so we can try to reproduce this issue -->
1. Clone the repo: `git clone https://github.com/ignitionrobotics/ign-gazebo.git`
2. Complete the build so that tests are available:
```
cd ign-gazebo
mkdir build
cd build
cmake ..
make
```
3. Run the thermal sensor integration test:
```
# the following steps assume you are already in the ign-rendering/build directory
cd bin
./INTEGRATION_thermal_sensor_system
```
## Output
```
[Msg] Setting ambient temperature to 310 Kelvin and gradient to -0.0065 K/m. The resulting temperature range is: 0.750384 Kelvin.
[Wrn] [RenderUtil.cc:1048] Unable to set thermal camera temperature linear resolution. Value must be greater than 0. Using the default value: 3.
[Wrn] [RenderUtil.cc:1061] Unable to set thermal camera temperature range.Max temperature must be greater or equal to min. Using the default values : [-inf, inf].
/home/addisu/ws/edifice/src/ign-gazebo/test/integration/thermal_sensor_system.cc:197: Failure
Value of: received
Actual: false
Expected: true
/home/addisu/ws/edifice/src/ign-gazebo/test/integration/thermal_sensor_system.cc:198: Failure
Expected: (nullptr) != (g_image), actual: (nullptr) vs NULL
[Dbg] [Sensors.cc:309] SensorsPrivate::Stop
[Dbg] [Sensors.cc:295] SensorsPrivate::RenderThread stopped
[Dbg] [SimulationRunner.cc:499] Exiting postupdate worker thread (1)
[Dbg] [SimulationRunner.cc:499] Exiting postupdate worker thread (2)
[Dbg] [SimulationRunner.cc:499] Exiting postupdate worker thread (0)
[Dbg] [Sensors.cc:309] SensorsPrivate::Stop
[ FAILED ] ThermalSensorTest.ThermalSensorSystemInvalidConfig (3176 ms)
``` | non_priority | new thermal camera test failure for edifice if you re not sure whether your problem is a bug please ask a question at instead environment os version ubuntu source or binary build source commit description expected behavior the integration thermal sensor system test thermalsensortest thermalsensorsysteminvalidconfig should pass actual behavior the test fails steps to reproduce clone the repo git clone complete the build so that tests are available cd ign gazebo mkdir build cd build cmake make run the thermal sensor integration test the following steps assume you are already in the ign rendering build directory cd bin integration thermal sensor system output setting ambient temperature to kelvin and gradient to k m the resulting temperature range is kelvin unable to set thermal camera temperature linear resolution value must be greater than using the default value unable to set thermal camera temperature range max temperature must be greater or equal to min using the default values home addisu ws edifice src ign gazebo test integration thermal sensor system cc failure value of received actual false expected true home addisu ws edifice src ign gazebo test integration thermal sensor system cc failure expected nullptr g image actual nullptr vs null sensorsprivate stop sensorsprivate renderthread stopped exiting postupdate worker thread exiting postupdate worker thread exiting postupdate worker thread sensorsprivate stop thermalsensortest thermalsensorsysteminvalidconfig ms | 0 |
129,976 | 12,421,501,630 | IssuesEvent | 2020-05-23 17:09:59 | WassimBenzarti/colab-ssh-connector | https://api.github.com/repos/WassimBenzarti/colab-ssh-connector | closed | Spurious IndexError | documentation | Occasionally I'm getting this IndexError when running `launch_ssh('<secret>', '<secret>')
/usr/local/lib/python3.6/dist-packages/colab_ssh/launch_ssh.py in launch_ssh(token, password, publish)
47 publish_host(info[0].decode().strip())
48
---> 49 if info[0]:
50 # Extract the host and port
51 host_and_port = re.match(r'.*://(.*):(\d+)\n', info[0].decode())
IndexError: list index out of range
| 1.0 | Spurious IndexError - Occasionally I'm getting this IndexError when running `launch_ssh('<secret>', '<secret>')
/usr/local/lib/python3.6/dist-packages/colab_ssh/launch_ssh.py in launch_ssh(token, password, publish)
47 publish_host(info[0].decode().strip())
48
---> 49 if info[0]:
50 # Extract the host and port
51 host_and_port = re.match(r'.*://(.*):(\d+)\n', info[0].decode())
IndexError: list index out of range
| non_priority | spurious indexerror occasionally i m getting this indexerror when running launch ssh usr local lib dist packages colab ssh launch ssh py in launch ssh token password publish publish host info decode strip if info extract the host and port host and port re match r d n info decode indexerror list index out of range | 0 |
22,021 | 18,288,238,012 | IssuesEvent | 2021-10-05 12:45:35 | maykinmedia/archiefvernietigingscomponent | https://api.github.com/repos/maykinmedia/archiefvernietigingscomponent | closed | Als proceseigenaar wil ik het controleren van de vernietigingslijst door een andere medewerker laten uitvoeren | proces en usability | De verwachting is dat de proceseigenaar niet zelf de controle van de te vernietigen zaken zal uitvoeren, maar dit zal willen laten doen door een medewerker van zijn afdeling/proces. | True | Als proceseigenaar wil ik het controleren van de vernietigingslijst door een andere medewerker laten uitvoeren - De verwachting is dat de proceseigenaar niet zelf de controle van de te vernietigen zaken zal uitvoeren, maar dit zal willen laten doen door een medewerker van zijn afdeling/proces. | non_priority | als proceseigenaar wil ik het controleren van de vernietigingslijst door een andere medewerker laten uitvoeren de verwachting is dat de proceseigenaar niet zelf de controle van de te vernietigen zaken zal uitvoeren maar dit zal willen laten doen door een medewerker van zijn afdeling proces | 0 |
93,420 | 8,415,091,814 | IssuesEvent | 2018-10-13 10:50:06 | sriyazahmed/fxLabsProd2UAT05Sep | https://api.github.com/repos/sriyazahmed/fxLabsProd2UAT05Sep | reopened | FxLabUATTest05sep : AccountsTC0O2CreateAccount | FxLabUATTest05sep | Project : FxLabUATTest05sep
Job : UAT
Env : UAT
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MDk5MGVmODAtY2JjMi00NmZlLTg4Y2MtNzM4ZjY1ZmExODJk; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Wed, 26 Sep 2018 10:47:17 GMT]}
Endpoint : http://13.56.210.25/api/v1/accounts
Request :
{
"org" : { },
"name" : "AccountsTC0O2CreateAccount+Johnston",
"accountType" : "Git",
"accessKey" : "AccountsTC0O2CreateAccount+Johnston",
"secretKey" : "AccountsTC0O2CreateAccount+Johnston"
}
Response :
{
"requestId" : "None",
"requestTime" : "2018-09-26T10:47:18.417+0000",
"errors" : false,
"messages" : [ ],
"data" : {
"id" : "8a808019661572000166157d809103c1",
"createdBy" : "4028b881620688c001620689a3210010",
"createdDate" : "2018-09-26T10:47:18.417+0000",
"modifiedBy" : "4028b881620688c001620689a3210010",
"modifiedDate" : "2018-09-26T10:47:18.417+0000",
"version" : null,
"inactive" : false,
"name" : "AccountsTC0O2CreateAccount+Johnston",
"region" : null,
"accessKey" : "AccountsTC0O2CreateAccount+Johnston",
"secretKey" : null,
"org" : {
"id" : "4028b881620688c001620689a3210000",
"createdBy" : null,
"createdDate" : null,
"modifiedBy" : null,
"modifiedDate" : null,
"version" : null,
"inactive" : false,
"name" : null
},
"accountType" : "Git",
"prop1" : null,
"prop2" : null,
"prop3" : null,
"allowedRegions" : null
},
"totalPages" : 0,
"totalElements" : 0
}
Logs :
Assertion [@Response.data.name == @Request.name] resolved-to [AccountsTC0O2CreateAccount+Johnston == AccountsTC0O2CreateAccount+Johnston] result [Passed]Assertion [@Response.errors == false] resolved-to [false == false] result [Passed]Assertion [@Response.data.account.id == @Request.account.id] resolved-to [ == ] result [Passed]Assertion [@Response.data.url == @Request.url] resolved-to [ == ] result [Passed]Assertion [@ResponseTime <= 1000] resolved-to [1406 <= 1000] result [Failed]Assertion [@ResponseSize <= 1024] resolved-to [767 <= 1024] result [Passed]Assertion [@StatusCode == 200] resolved-to [200 == 200] result [Passed]
--- FX Bot --- | 1.0 | FxLabUATTest05sep : AccountsTC0O2CreateAccount - Project : FxLabUATTest05sep
Job : UAT
Env : UAT
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MDk5MGVmODAtY2JjMi00NmZlLTg4Y2MtNzM4ZjY1ZmExODJk; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Wed, 26 Sep 2018 10:47:17 GMT]}
Endpoint : http://13.56.210.25/api/v1/accounts
Request :
{
"org" : { },
"name" : "AccountsTC0O2CreateAccount+Johnston",
"accountType" : "Git",
"accessKey" : "AccountsTC0O2CreateAccount+Johnston",
"secretKey" : "AccountsTC0O2CreateAccount+Johnston"
}
Response :
{
"requestId" : "None",
"requestTime" : "2018-09-26T10:47:18.417+0000",
"errors" : false,
"messages" : [ ],
"data" : {
"id" : "8a808019661572000166157d809103c1",
"createdBy" : "4028b881620688c001620689a3210010",
"createdDate" : "2018-09-26T10:47:18.417+0000",
"modifiedBy" : "4028b881620688c001620689a3210010",
"modifiedDate" : "2018-09-26T10:47:18.417+0000",
"version" : null,
"inactive" : false,
"name" : "AccountsTC0O2CreateAccount+Johnston",
"region" : null,
"accessKey" : "AccountsTC0O2CreateAccount+Johnston",
"secretKey" : null,
"org" : {
"id" : "4028b881620688c001620689a3210000",
"createdBy" : null,
"createdDate" : null,
"modifiedBy" : null,
"modifiedDate" : null,
"version" : null,
"inactive" : false,
"name" : null
},
"accountType" : "Git",
"prop1" : null,
"prop2" : null,
"prop3" : null,
"allowedRegions" : null
},
"totalPages" : 0,
"totalElements" : 0
}
Logs :
Assertion [@Response.data.name == @Request.name] resolved-to [AccountsTC0O2CreateAccount+Johnston == AccountsTC0O2CreateAccount+Johnston] result [Passed]Assertion [@Response.errors == false] resolved-to [false == false] result [Passed]Assertion [@Response.data.account.id == @Request.account.id] resolved-to [ == ] result [Passed]Assertion [@Response.data.url == @Request.url] resolved-to [ == ] result [Passed]Assertion [@ResponseTime <= 1000] resolved-to [1406 <= 1000] result [Failed]Assertion [@ResponseSize <= 1024] resolved-to [767 <= 1024] result [Passed]Assertion [@StatusCode == 200] resolved-to [200 == 200] result [Passed]
--- FX Bot --- | non_priority | project job uat env uat region fxlabs us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request org name johnston accounttype git accesskey johnston secretkey johnston response requestid none requesttime errors false messages data id createdby createddate modifiedby modifieddate version null inactive false name johnston region null accesskey johnston secretkey null org id createdby null createddate null modifiedby null modifieddate null version null inactive false name null accounttype git null null null allowedregions null totalpages totalelements logs assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result fx bot | 0 |
97,381 | 8,653,074,581 | IssuesEvent | 2018-11-27 09:53:34 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | reopened | new tested 27 : ApiV1JobsGetQueryParamPagesizeEmptyValue | new tested 27 | Project : new tested 27
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=YzA4YmE0M2EtOTBjNi00NzcxLWFmMjctZWI2MTEwMDM5OTM2; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 27 Nov 2018 09:50:59 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/jobs?pageSize=
Request :
Response :
{
"timestamp" : "2018-11-27T09:50:59.858+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/jobs"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 500] resolved-to [404 != 500] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]Assertion [@StatusCode != 200] resolved-to [404 != 200] result [Passed]
--- FX Bot --- | 1.0 | new tested 27 : ApiV1JobsGetQueryParamPagesizeEmptyValue - Project : new tested 27
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=YzA4YmE0M2EtOTBjNi00NzcxLWFmMjctZWI2MTEwMDM5OTM2; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 27 Nov 2018 09:50:59 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/jobs?pageSize=
Request :
Response :
{
"timestamp" : "2018-11-27T09:50:59.858+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/jobs"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 500] resolved-to [404 != 500] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]Assertion [@StatusCode != 200] resolved-to [404 != 200] result [Passed]
--- FX Bot --- | non_priority | new tested project new tested job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api jobs logs assertion resolved to result assertion resolved to result assertion resolved to result assertion resolved to result fx bot | 0 |
145,765 | 11,706,901,936 | IssuesEvent | 2020-03-08 01:46:23 | QubesOS/updates-status | https://api.github.com/repos/QubesOS/updates-status | closed | linux-kernel v5.4.21-1 (r4.1) | r4.1-dom0-cur-test | Update of linux-kernel to v5.4.21-1 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-linux-kernel/commit/ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a
[Changes since previous version](https://github.com/QubesOS/qubes-linux-kernel/compare/v4.19.100-1...v5.4.21-1):
QubesOS/qubes-linux-kernel@ea8d8f4 Update to kernel-5.4.21
QubesOS/qubes-linux-kernel@d03bb55 Increase modules.img sparse size
QubesOS/qubes-linux-kernel@a776d31 get-latest-config: use keys under builder-rpm
QubesOS/qubes-linux-kernel@b065f33 Drop -latest suffix for LTS kernel
QubesOS/qubes-linux-kernel@af7128d Update to kernel-5.4.5
QubesOS/qubes-linux-kernel@b5170f8 update WireGuard from 20191212 to 20191219
QubesOS/qubes-linux-kernel@1252f79 Update to kernel-5.4.3
QubesOS/qubes-linux-kernel@9f28598 update WireGuard from 20191127 to 20191212
QubesOS/qubes-linux-kernel@1554c07 Add BR: python3-devel for pathfix.py script
QubesOS/qubes-linux-kernel@8ee5779 Update to kernel-5.4.2
QubesOS/qubes-linux-kernel@366e681 get latest config: exit with clean and disable getting rc by default
QubesOS/qubes-linux-kernel@f841402 Merge remote-tracking branch 'origin/pr/128'
QubesOS/qubes-linux-kernel@8aca753 (re-)sign all the modules after processing debuginfo
QubesOS/qubes-linux-kernel@a5e7326 update WireGuard from 20191012 to 20191127
QubesOS/qubes-linux-kernel@5d68948 version 5.4.1-2
QubesOS/qubes-linux-kernel@1cc6951 config-qubes: allow signed modules as Fedora set it
QubesOS/qubes-linux-kernel@22b6866 Update to version 5.4.1
QubesOS/qubes-linux-kernel@7b1c020 Update Fedora keys for config updater script (add 32, remove 30 and 31)
QubesOS/qubes-linux-kernel@9fc4062 Merge remote-tracking branch 'origin/pr/119'
QubesOS/qubes-linux-kernel@fb9b485 spec: mangle /usr/bin/python shebangs to /usr/bin/python3
QubesOS/qubes-linux-kernel@ddf7602 Update to kernel-5.3.12
QubesOS/qubes-linux-kernel@18d5d66 Update to kernel-5.3.11
QubesOS/qubes-linux-kernel@ea53bfe Merge remote-tracking branch 'origin/pr/113'
QubesOS/qubes-linux-kernel@71964cd Update to kernel-5.3.9
QubesOS/qubes-linux-kernel@cddf334 update WireGuard from 20190913 to 20191012
QubesOS/qubes-linux-kernel@beccd92 Update to kernel-5.3.8
QubesOS/qubes-linux-kernel@17b7186 Make makefile and spec compatible with rc versions
QubesOS/qubes-linux-kernel@24ee349 Add Linus's signing key
QubesOS/qubes-linux-kernel@87ba67c Update to kernel-5.3.7
QubesOS/qubes-linux-kernel@9cf5108 Update to kernel-5.3.6
QubesOS/qubes-linux-kernel@8f82b34 Update to kernel-5.3.2
QubesOS/qubes-linux-kernel@383118a change WireGuard version from 20190702 to 20190913
QubesOS/qubes-linux-kernel@9a3ca00 Update to kernel-5.2.16
QubesOS/qubes-linux-kernel@c7cfdfe Merge remote-tracking branch 'origin/pr/91'
QubesOS/qubes-linux-kernel@1d50db3 rpm: set default kernel version based on package flavor
QubesOS/qubes-linux-kernel@9aac829 Update to kernel-5.2.14
QubesOS/qubes-linux-kernel@4e4cdf6 Update to kernel-5.2.13
QubesOS/qubes-linux-kernel@61485da Update to kernel-5.2.11
QubesOS/qubes-linux-kernel@c270f52 Update to kernel-5.2.9
QubesOS/qubes-linux-kernel@8b2aed9 version 5.2.7-1
QubesOS/qubes-linux-kernel@d9f5315 Drop AFTER_LINK patch
QubesOS/qubes-linux-kernel@150288e Update to kernel-5.2.3
QubesOS/qubes-linux-kernel@9ec4071 Update WireGuard to 0.0.20190702
QubesOS/qubes-linux-kernel@a40377d Update to kernel-5.1.17
QubesOS/qubes-linux-kernel@bd26af6 Update to kernel-5.1.16
QubesOS/qubes-linux-kernel@11d6f25 Update to kernel-5.1.15
QubesOS/qubes-linux-kernel@1574118 Update to kernel-5.1.13
QubesOS/qubes-linux-kernel@5adbe65 Update to kernel-5.1.9
QubesOS/qubes-linux-kernel@4f870c8 version 5.1.7-2
QubesOS/qubes-linux-kernel@d48c5ba Update to kernel-5.1.7
QubesOS/qubes-linux-kernel@e3a3420 Disable GCC plugins for out of tree kernel modules
QubesOS/qubes-linux-kernel@d1ad508 Update to kernel-5.1.6
QubesOS/qubes-linux-kernel@7108c83 Simplify WG_SIG_FILE set
QubesOS/qubes-linux-kernel@c6e1265 gitignore: add WireGuard
QubesOS/qubes-linux-kernel@7906851 build wireguard module (after gpg check)
QubesOS/qubes-linux-kernel@ef094d5 version 5.1.2-1
QubesOS/qubes-linux-kernel@c4c75cb Fix setting default kernel for VM
QubesOS/qubes-linux-kernel@98cd4d1 config: disable SELinux
QubesOS/qubes-linux-kernel@c68ee34 Update to kernel-5.1.1
QubesOS/qubes-linux-kernel@732780e get-fedora-latest-config: sort result when repoquerying kernel-core
QubesOS/qubes-linux-kernel@d08d1bf Update to kernel-5.0.11
QubesOS/qubes-linux-kernel@598d75d Update to kernel-5.0.9
QubesOS/qubes-linux-kernel@a48e051 get-fedora-latest-config: enable only fedora and fedora-updates when downloading the rpm
QubesOS/qubes-linux-kernel@5a1a029 get-fedora-latest-config: download relatively to current directory
QubesOS/qubes-linux-kernel@a5a4ae6 Support a build without u2mfn module
QubesOS/qubes-linux-kernel@1ffeed9 Update to kernel-5.0.7
QubesOS/qubes-linux-kernel@62c107b Update to kernel-5.0.5
QubesOS/qubes-linux-kernel@b16cc10 get-fedora-latest-config: enable only Fedora repos
QubesOS/qubes-linux-kernel@f2ddd7a Refactor: handle getting default latest stable Fedora
QubesOS/qubes-linux-kernel@9290c06 Add Fedora 31 primary key
QubesOS/qubes-linux-kernel@cfc9a4c version 5.0.2-1
QubesOS/qubes-linux-kernel@17bbb7d Merge remote-tracking branch 'origin/pr/28'
QubesOS/qubes-linux-kernel@1fe8359 rpm: one more typo fix
QubesOS/qubes-linux-kernel@047a30a version 4.20.16-2
QubesOS/qubes-linux-kernel@50b7baa rpm: typo fix
QubesOS/qubes-linux-kernel@fd14ac9 rpm: build modules.img at package build time only on new system
QubesOS/qubes-linux-kernel@1bedd11 Update patches
QubesOS/qubes-linux-kernel@0643a07 Update config with respect to upstream
QubesOS/qubes-linux-kernel@b935b16 get-fedora-latest-config: allow fetching config from rawhide repository
QubesOS/qubes-linux-kernel@924b8ab get-fedora-latest-config: don't hardcode Fedora version in regex rpm
QubesOS/qubes-linux-kernel@fe376be keys: add Fedora 30 primary key
QubesOS/qubes-linux-kernel@80fa61e get-sources: handle kernel-5.x
QubesOS/qubes-linux-kernel@00bbcc6 version 4.20.16-1
QubesOS/qubes-linux-kernel@c2a2c69 Merge remote-tracking branch 'origin/pr/27'
QubesOS/qubes-linux-kernel@61b9336 plymouth: ignore serial console hvc0 in UEFI
QubesOS/qubes-linux-kernel@a44160b Ensure the rebuild of grub.cfg with plymouth.ignore-serial-consoles
QubesOS/qubes-linux-kernel@e69b02b plymouth-ignore-serial-consoles: adjusting the method from marmarek suggestion
QubesOS/qubes-linux-kernel@af67412 plymouth: ignore serial console hvc0
QubesOS/qubes-linux-kernel@c8f70c1 Update to kernel-4.20.14
QubesOS/qubes-linux-kernel@9cfa9a9 Include default-kernelopts-common.txt with kernel-specific default options
QubesOS/qubes-linux-kernel@43235dd Improve reproducibility of initramfs
QubesOS/qubes-linux-kernel@eb4c9ed Build modules.img at module build time
QubesOS/qubes-linux-kernel@c2f7109 version 4.20.3-1
QubesOS/qubes-linux-kernel@c168934 Update to kernel-4.20.3 and config from Fedora's config 4.19.15-300
Referenced issues:
QubesOS/qubes-issues#4736
QubesOS/qubes-issues#4839
QubesOS/qubes-issues#3849
QubesOS/qubes-issues#4280
QubesOS/qubes-issues#5497
QubesOS/qubes-issues#2844
QubesOS/qubes-issues#5309
If you're release manager, you can issue GPG-inline signed command:
* `Upload linux-kernel ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a r4.1 current repo` (available 7 days from now)
* `Upload linux-kernel ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload linux-kernel ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| 1.0 | linux-kernel v5.4.21-1 (r4.1) - Update of linux-kernel to v5.4.21-1 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-linux-kernel/commit/ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a
[Changes since previous version](https://github.com/QubesOS/qubes-linux-kernel/compare/v4.19.100-1...v5.4.21-1):
QubesOS/qubes-linux-kernel@ea8d8f4 Update to kernel-5.4.21
QubesOS/qubes-linux-kernel@d03bb55 Increase modules.img sparse size
QubesOS/qubes-linux-kernel@a776d31 get-latest-config: use keys under builder-rpm
QubesOS/qubes-linux-kernel@b065f33 Drop -latest suffix for LTS kernel
QubesOS/qubes-linux-kernel@af7128d Update to kernel-5.4.5
QubesOS/qubes-linux-kernel@b5170f8 update WireGuard from 20191212 to 20191219
QubesOS/qubes-linux-kernel@1252f79 Update to kernel-5.4.3
QubesOS/qubes-linux-kernel@9f28598 update WireGuard from 20191127 to 20191212
QubesOS/qubes-linux-kernel@1554c07 Add BR: python3-devel for pathfix.py script
QubesOS/qubes-linux-kernel@8ee5779 Update to kernel-5.4.2
QubesOS/qubes-linux-kernel@366e681 get latest config: exit with clean and disable getting rc by default
QubesOS/qubes-linux-kernel@f841402 Merge remote-tracking branch 'origin/pr/128'
QubesOS/qubes-linux-kernel@8aca753 (re-)sign all the modules after processing debuginfo
QubesOS/qubes-linux-kernel@a5e7326 update WireGuard from 20191012 to 20191127
QubesOS/qubes-linux-kernel@5d68948 version 5.4.1-2
QubesOS/qubes-linux-kernel@1cc6951 config-qubes: allow signed modules as Fedora set it
QubesOS/qubes-linux-kernel@22b6866 Update to version 5.4.1
QubesOS/qubes-linux-kernel@7b1c020 Update Fedora keys for config updater script (add 32, remove 30 and 31)
QubesOS/qubes-linux-kernel@9fc4062 Merge remote-tracking branch 'origin/pr/119'
QubesOS/qubes-linux-kernel@fb9b485 spec: mangle /usr/bin/python shebangs to /usr/bin/python3
QubesOS/qubes-linux-kernel@ddf7602 Update to kernel-5.3.12
QubesOS/qubes-linux-kernel@18d5d66 Update to kernel-5.3.11
QubesOS/qubes-linux-kernel@ea53bfe Merge remote-tracking branch 'origin/pr/113'
QubesOS/qubes-linux-kernel@71964cd Update to kernel-5.3.9
QubesOS/qubes-linux-kernel@cddf334 update WireGuard from 20190913 to 20191012
QubesOS/qubes-linux-kernel@beccd92 Update to kernel-5.3.8
QubesOS/qubes-linux-kernel@17b7186 Make makefile and spec compatible with rc versions
QubesOS/qubes-linux-kernel@24ee349 Add Linus's signing key
QubesOS/qubes-linux-kernel@87ba67c Update to kernel-5.3.7
QubesOS/qubes-linux-kernel@9cf5108 Update to kernel-5.3.6
QubesOS/qubes-linux-kernel@8f82b34 Update to kernel-5.3.2
QubesOS/qubes-linux-kernel@383118a change WireGuard version from 20190702 to 20190913
QubesOS/qubes-linux-kernel@9a3ca00 Update to kernel-5.2.16
QubesOS/qubes-linux-kernel@c7cfdfe Merge remote-tracking branch 'origin/pr/91'
QubesOS/qubes-linux-kernel@1d50db3 rpm: set default kernel version based on package flavor
QubesOS/qubes-linux-kernel@9aac829 Update to kernel-5.2.14
QubesOS/qubes-linux-kernel@4e4cdf6 Update to kernel-5.2.13
QubesOS/qubes-linux-kernel@61485da Update to kernel-5.2.11
QubesOS/qubes-linux-kernel@c270f52 Update to kernel-5.2.9
QubesOS/qubes-linux-kernel@8b2aed9 version 5.2.7-1
QubesOS/qubes-linux-kernel@d9f5315 Drop AFTER_LINK patch
QubesOS/qubes-linux-kernel@150288e Update to kernel-5.2.3
QubesOS/qubes-linux-kernel@9ec4071 Update WireGuard to 0.0.20190702
QubesOS/qubes-linux-kernel@a40377d Update to kernel-5.1.17
QubesOS/qubes-linux-kernel@bd26af6 Update to kernel-5.1.16
QubesOS/qubes-linux-kernel@11d6f25 Update to kernel-5.1.15
QubesOS/qubes-linux-kernel@1574118 Update to kernel-5.1.13
QubesOS/qubes-linux-kernel@5adbe65 Update to kernel-5.1.9
QubesOS/qubes-linux-kernel@4f870c8 version 5.1.7-2
QubesOS/qubes-linux-kernel@d48c5ba Update to kernel-5.1.7
QubesOS/qubes-linux-kernel@e3a3420 Disable GCC plugins for out of tree kernel modules
QubesOS/qubes-linux-kernel@d1ad508 Update to kernel-5.1.6
QubesOS/qubes-linux-kernel@7108c83 Simplify WG_SIG_FILE set
QubesOS/qubes-linux-kernel@c6e1265 gitignore: add WireGuard
QubesOS/qubes-linux-kernel@7906851 build wireguard module (after gpg check)
QubesOS/qubes-linux-kernel@ef094d5 version 5.1.2-1
QubesOS/qubes-linux-kernel@c4c75cb Fix setting default kernel for VM
QubesOS/qubes-linux-kernel@98cd4d1 config: disable SELinux
QubesOS/qubes-linux-kernel@c68ee34 Update to kernel-5.1.1
QubesOS/qubes-linux-kernel@732780e get-fedora-latest-config: sort result when repoquerying kernel-core
QubesOS/qubes-linux-kernel@d08d1bf Update to kernel-5.0.11
QubesOS/qubes-linux-kernel@598d75d Update to kernel-5.0.9
QubesOS/qubes-linux-kernel@a48e051 get-fedora-latest-config: enable only fedora and fedora-updates when downloading the rpm
QubesOS/qubes-linux-kernel@5a1a029 get-fedora-latest-config: download relatively to current directory
QubesOS/qubes-linux-kernel@a5a4ae6 Support a build without u2mfn module
QubesOS/qubes-linux-kernel@1ffeed9 Update to kernel-5.0.7
QubesOS/qubes-linux-kernel@62c107b Update to kernel-5.0.5
QubesOS/qubes-linux-kernel@b16cc10 get-fedora-latest-config: enable only Fedora repos
QubesOS/qubes-linux-kernel@f2ddd7a Refactor: handle getting default latest stable Fedora
QubesOS/qubes-linux-kernel@9290c06 Add Fedora 31 primary key
QubesOS/qubes-linux-kernel@cfc9a4c version 5.0.2-1
QubesOS/qubes-linux-kernel@17bbb7d Merge remote-tracking branch 'origin/pr/28'
QubesOS/qubes-linux-kernel@1fe8359 rpm: one more typo fix
QubesOS/qubes-linux-kernel@047a30a version 4.20.16-2
QubesOS/qubes-linux-kernel@50b7baa rpm: typo fix
QubesOS/qubes-linux-kernel@fd14ac9 rpm: build modules.img at package build time only on new system
QubesOS/qubes-linux-kernel@1bedd11 Update patches
QubesOS/qubes-linux-kernel@0643a07 Update config with respect to upstream
QubesOS/qubes-linux-kernel@b935b16 get-fedora-latest-config: allow fetching config from rawhide repository
QubesOS/qubes-linux-kernel@924b8ab get-fedora-latest-config: don't hardcode Fedora version in regex rpm
QubesOS/qubes-linux-kernel@fe376be keys: add Fedora 30 primary key
QubesOS/qubes-linux-kernel@80fa61e get-sources: handle kernel-5.x
QubesOS/qubes-linux-kernel@00bbcc6 version 4.20.16-1
QubesOS/qubes-linux-kernel@c2a2c69 Merge remote-tracking branch 'origin/pr/27'
QubesOS/qubes-linux-kernel@61b9336 plymouth: ignore serial console hvc0 in UEFI
QubesOS/qubes-linux-kernel@a44160b Ensure the rebuild of grub.cfg with plymouth.ignore-serial-consoles
QubesOS/qubes-linux-kernel@e69b02b plymouth-ignore-serial-consoles: adjusting the method from marmarek suggestion
QubesOS/qubes-linux-kernel@af67412 plymouth: ignore serial console hvc0
QubesOS/qubes-linux-kernel@c8f70c1 Update to kernel-4.20.14
QubesOS/qubes-linux-kernel@9cfa9a9 Include default-kernelopts-common.txt with kernel-specific default options
QubesOS/qubes-linux-kernel@43235dd Improve reproducibility of initramfs
QubesOS/qubes-linux-kernel@eb4c9ed Build modules.img at module build time
QubesOS/qubes-linux-kernel@c2f7109 version 4.20.3-1
QubesOS/qubes-linux-kernel@c168934 Update to kernel-4.20.3 and config from Fedora's config 4.19.15-300
Referenced issues:
QubesOS/qubes-issues#4736
QubesOS/qubes-issues#4839
QubesOS/qubes-issues#3849
QubesOS/qubes-issues#4280
QubesOS/qubes-issues#5497
QubesOS/qubes-issues#2844
QubesOS/qubes-issues#5309
If you're release manager, you can issue GPG-inline signed command:
* `Upload linux-kernel ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a r4.1 current repo` (available 7 days from now)
* `Upload linux-kernel ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload linux-kernel ea8d8f46bb86ff6d4e4a24ff8cc0856bd765d13a r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| non_priority | linux kernel update of linux kernel to for qubes see comments below for details built from qubesos qubes linux kernel update to kernel qubesos qubes linux kernel increase modules img sparse size qubesos qubes linux kernel get latest config use keys under builder rpm qubesos qubes linux kernel drop latest suffix for lts kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update wireguard from to qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update wireguard from to qubesos qubes linux kernel add br devel for pathfix py script qubesos qubes linux kernel update to kernel qubesos qubes linux kernel get latest config exit with clean and disable getting rc by default qubesos qubes linux kernel merge remote tracking branch origin pr qubesos qubes linux kernel re sign all the modules after processing debuginfo qubesos qubes linux kernel update wireguard from to qubesos qubes linux kernel version qubesos qubes linux kernel config qubes allow signed modules as fedora set it qubesos qubes linux kernel update to version qubesos qubes linux kernel update fedora keys for config updater script add remove and qubesos qubes linux kernel merge remote tracking branch origin pr qubesos qubes linux kernel spec mangle usr bin python shebangs to usr bin qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel merge remote tracking branch origin pr qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update wireguard from to qubesos qubes linux kernel update to kernel qubesos qubes linux kernel make makefile and spec compatible with rc versions qubesos qubes linux kernel add linus s signing key qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel change wireguard version from to qubesos qubes linux kernel update to kernel qubesos qubes linux kernel merge remote tracking branch origin pr qubesos qubes linux kernel rpm set default kernel version based on package flavor qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel version qubesos qubes linux kernel drop after link patch qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update wireguard to qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel version qubesos qubes linux kernel update to kernel qubesos qubes linux kernel disable gcc plugins for out of tree kernel modules qubesos qubes linux kernel update to kernel qubesos qubes linux kernel simplify wg sig file set qubesos qubes linux kernel gitignore add wireguard qubesos qubes linux kernel build wireguard module after gpg check qubesos qubes linux kernel version qubesos qubes linux kernel fix setting default kernel for vm qubesos qubes linux kernel config disable selinux qubesos qubes linux kernel update to kernel qubesos qubes linux kernel get fedora latest config sort result when repoquerying kernel core qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel get fedora latest config enable only fedora and fedora updates when downloading the rpm qubesos qubes linux kernel get fedora latest config download relatively to current directory qubesos qubes linux kernel support a build without module qubesos qubes linux kernel update to kernel qubesos qubes linux kernel update to kernel qubesos qubes linux kernel get fedora latest config enable only fedora repos qubesos qubes linux kernel refactor handle getting default latest stable fedora qubesos qubes linux kernel add fedora primary key qubesos qubes linux kernel version qubesos qubes linux kernel merge remote tracking branch origin pr qubesos qubes linux kernel rpm one more typo fix qubesos qubes linux kernel version qubesos qubes linux kernel rpm typo fix qubesos qubes linux kernel rpm build modules img at package build time only on new system qubesos qubes linux kernel update patches qubesos qubes linux kernel update config with respect to upstream qubesos qubes linux kernel get fedora latest config allow fetching config from rawhide repository qubesos qubes linux kernel get fedora latest config don t hardcode fedora version in regex rpm qubesos qubes linux kernel keys add fedora primary key qubesos qubes linux kernel get sources handle kernel x qubesos qubes linux kernel version qubesos qubes linux kernel merge remote tracking branch origin pr qubesos qubes linux kernel plymouth ignore serial console in uefi qubesos qubes linux kernel ensure the rebuild of grub cfg with plymouth ignore serial consoles qubesos qubes linux kernel plymouth ignore serial consoles adjusting the method from marmarek suggestion qubesos qubes linux kernel plymouth ignore serial console qubesos qubes linux kernel update to kernel qubesos qubes linux kernel include default kernelopts common txt with kernel specific default options qubesos qubes linux kernel improve reproducibility of initramfs qubesos qubes linux kernel build modules img at module build time qubesos qubes linux kernel version qubesos qubes linux kernel update to kernel and config from fedora s config referenced issues qubesos qubes issues qubesos qubes issues qubesos qubes issues qubesos qubes issues qubesos qubes issues qubesos qubes issues qubesos qubes issues if you re release manager you can issue gpg inline signed command upload linux kernel current repo available days from now upload linux kernel current dists repo you can choose subset of distributions like vm vm available days from now upload linux kernel security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it | 0 |
214,877 | 24,121,685,784 | IssuesEvent | 2022-09-20 19:19:33 | bitovi/bitops | https://api.github.com/repos/bitovi/bitops | opened | Docker image signing | enhancement feature security | Implement Docker image signing before uploading artifacts to Docker Hub so the users could validate that the images are coming from us. This would add to the software supply chain security.
- [ ] Signing
- [ ] CI/CD
- [ ] Documentation
### Resources
- https://docs.docker.com/engine/security/trust/
- https://www.howtogeek.com/devops/how-to-sign-your-docker-images-to-increase-trust/
| True | Docker image signing - Implement Docker image signing before uploading artifacts to Docker Hub so the users could validate that the images are coming from us. This would add to the software supply chain security.
- [ ] Signing
- [ ] CI/CD
- [ ] Documentation
### Resources
- https://docs.docker.com/engine/security/trust/
- https://www.howtogeek.com/devops/how-to-sign-your-docker-images-to-increase-trust/
| non_priority | docker image signing implement docker image signing before uploading artifacts to docker hub so the users could validate that the images are coming from us this would add to the software supply chain security signing ci cd documentation resources | 0 |
134,210 | 19,098,217,847 | IssuesEvent | 2021-11-29 19:06:26 | UnB-KnEDLe/viabilidade-tecnica | https://api.github.com/repos/UnB-KnEDLe/viabilidade-tecnica | closed | Adicionar campo default para campos não existentes | 0 time: Designer | Otimizar os campos dos membros para aceitar itens genéricos. | 1.0 | Adicionar campo default para campos não existentes - Otimizar os campos dos membros para aceitar itens genéricos. | non_priority | adicionar campo default para campos não existentes otimizar os campos dos membros para aceitar itens genéricos | 0 |
3,531 | 6,570,735,297 | IssuesEvent | 2017-09-10 03:37:37 | Great-Hill-Corporation/quickBlocks | https://api.github.com/repos/Great-Hill-Corporation/quickBlocks | closed | Default files for ethprice and ethname | apps-ethPrice status-inprocess tools-ethName type-enhancement | It is probably better to copy in files to ethprice and ethName than create them on the fly. (1) faster, (2) easier to change | 1.0 | Default files for ethprice and ethname - It is probably better to copy in files to ethprice and ethName than create them on the fly. (1) faster, (2) easier to change | non_priority | default files for ethprice and ethname it is probably better to copy in files to ethprice and ethname than create them on the fly faster easier to change | 0 |
26,599 | 20,272,285,069 | IssuesEvent | 2022-02-15 17:12:56 | openfeatureflags/.github | https://api.github.com/repos/openfeatureflags/.github | closed | GitHub organization bootstrap | chore infrastructure | - [x] - Create GitHub organization
- [x] - CoC, READMEs
- [x] - Initial contributing guide
- [x] - Specification repository
- [x] - List of interested parties
Detached - Governance document | 1.0 | GitHub organization bootstrap - - [x] - Create GitHub organization
- [x] - CoC, READMEs
- [x] - Initial contributing guide
- [x] - Specification repository
- [x] - List of interested parties
Detached - Governance document | non_priority | github organization bootstrap create github organization coc readmes initial contributing guide specification repository list of interested parties detached governance document | 0 |
234,822 | 19,270,355,333 | IssuesEvent | 2021-12-10 04:01:42 | mattermost/focalboard | https://api.github.com/repos/mattermost/focalboard | closed | Write Focalboard E2E with Cypress: "MM-T4274 Create an Empty Board" | Help Wanted Area/E2E Tests Difficulty/1:Easy Tech/Automation |
<article>
<h1>MM-T4274 Create an Empty Board</h1>
<div>
<div>
<h3>Steps #1</h3>Click on the "+" icon at the top of the sidebar<h3>Expected</h3>"Create a Board" screen opens in the center view with template options<hr><h3>Steps #2</h3>Click on "Start with an Empty Board"<h3>Expected</h3>Board titled "Untitled Board" is created and opened<hr><h3>Steps #3</h3>Click on "Untitled Board" and type "Testing" and hit Enter<h3>Expected</h3>Title of the board updates to "Testing"<hr>
</div>
</div>
</article>
**Test code arrangement:**
```
it('MM-T4274 Create an Empty Board', () => {
// code
});
```
Note:
1. Use [queries from testing-library](https://testing-library.com/docs/dom-testing-library/api-queries) whenever possible. We share the same philosophy as the [testing-library](https://testing-library.com/) when doing UI automation like "Interact with your app the same way as your users" and so, please follow their guidelines especially when querying an element.
If you're interested, please comment here and come [join our "Contributors" community channel](https://community.mattermost.com/core/channels/tickets) on our daily build server, where you can discuss questions with community members and the Mattermost core team. For technical advice or questions, please [join our "Focalboard" community channel](https://community.mattermost.com/core/channels/focalboard).
For new contributors, please see our [guide](https://github.com/mattermost/focalboard#running-and-testing-the-server).
| 1.0 | Write Focalboard E2E with Cypress: "MM-T4274 Create an Empty Board" -
<article>
<h1>MM-T4274 Create an Empty Board</h1>
<div>
<div>
<h3>Steps #1</h3>Click on the "+" icon at the top of the sidebar<h3>Expected</h3>"Create a Board" screen opens in the center view with template options<hr><h3>Steps #2</h3>Click on "Start with an Empty Board"<h3>Expected</h3>Board titled "Untitled Board" is created and opened<hr><h3>Steps #3</h3>Click on "Untitled Board" and type "Testing" and hit Enter<h3>Expected</h3>Title of the board updates to "Testing"<hr>
</div>
</div>
</article>
**Test code arrangement:**
```
it('MM-T4274 Create an Empty Board', () => {
// code
});
```
Note:
1. Use [queries from testing-library](https://testing-library.com/docs/dom-testing-library/api-queries) whenever possible. We share the same philosophy as the [testing-library](https://testing-library.com/) when doing UI automation like "Interact with your app the same way as your users" and so, please follow their guidelines especially when querying an element.
If you're interested, please comment here and come [join our "Contributors" community channel](https://community.mattermost.com/core/channels/tickets) on our daily build server, where you can discuss questions with community members and the Mattermost core team. For technical advice or questions, please [join our "Focalboard" community channel](https://community.mattermost.com/core/channels/focalboard).
For new contributors, please see our [guide](https://github.com/mattermost/focalboard#running-and-testing-the-server).
| non_priority | write focalboard with cypress mm create an empty board mm create an empty board steps click on the icon at the top of the sidebar expected create a board screen opens in the center view with template options steps click on start with an empty board expected board titled untitled board is created and opened steps click on untitled board and type testing and hit enter expected title of the board updates to testing test code arrangement it mm create an empty board code note use whenever possible we share the same philosophy as the when doing ui automation like interact with your app the same way as your users and so please follow their guidelines especially when querying an element if you re interested please comment here and come on our daily build server where you can discuss questions with community members and the mattermost core team for technical advice or questions please for new contributors please see our | 0 |
236,782 | 19,574,206,167 | IssuesEvent | 2022-01-04 13:41:38 | chipsalliance/sv-tests | https://api.github.com/repos/chipsalliance/sv-tests | closed | Dashboard runner false-fail with NUL characters | bug tests | Many dozens of Verilator tests false-fail due to "NUL", indicating something wrong with the running system. (These all passed at one point). Maybe it's out of disk space?
e.g.
https://symbiflow.github.io/sv-tests-results/#Verilator|7.9.4|associative-arrays-first
https://symbiflow.github.io/sv-tests-results/#Verilator|7.12.1|array-locator-methods-find
```
make[1]: Entering directory '/tmpfs/tmp/tmpl0s9xbp0/vbuild'
Vtop.mk:13: warning: NUL character seen; rest of line ignored
/home/runner/work/conda-eda/conda-eda/workdir/conda-env/conda-bld/verilator-uhdm_1625528243349/_build_env/bin/x86_64-conda-linux-gnu-c++ -fvisibility-inlines-hidden -std=c++17 -fmessage-length=0 -march=nocona -mtune=haswell -ftree-vectorize -fPIC -fstack-protector-strong -fno-plt -O2 -ffunction-sections -pipe -isystem /home/kbuilder/miniconda/envs/sv-test-env/include -DNDEBUG -D_FORTIFY_SOURCE=2 -O2 -isystem /home/kbuilder/miniconda/envs/sv-test-env/include -I. -MMD -I/home/kbuilder/miniconda/envs/sv-test-env/share/verilator/include -I/home/kbuilder/miniconda/envs/sv-test-env/share/verilator/include/vltstd -DVM_COVERAGE=0 -DVM_SC=0 -DVM_TRACE=0 -DVM_TRACE_FST=0 -faligned-new -fcf-protection=none -Wno-bool-operation -Wno-sign-compare -Wno-uninitialized -Wno-unused-but-set-variable -Wno-unused-parameter -Wno-unused-variable -Wno-shadow -std=gnu++14 -Os -c -o vmain.o ../vmain.cpp
make[1]: /home/runner/work/conda-eda/conda-eda/workdir/conda-env/conda-bld/verilator-uhdm_1625528243349/_build_env/bin/x86_64-conda-linux-gnu-c++: Command not found
Vtop.mk:59: recipe for target 'vmain.o' failed
``` | 1.0 | Dashboard runner false-fail with NUL characters - Many dozens of Verilator tests false-fail due to "NUL", indicating something wrong with the running system. (These all passed at one point). Maybe it's out of disk space?
e.g.
https://symbiflow.github.io/sv-tests-results/#Verilator|7.9.4|associative-arrays-first
https://symbiflow.github.io/sv-tests-results/#Verilator|7.12.1|array-locator-methods-find
```
make[1]: Entering directory '/tmpfs/tmp/tmpl0s9xbp0/vbuild'
Vtop.mk:13: warning: NUL character seen; rest of line ignored
/home/runner/work/conda-eda/conda-eda/workdir/conda-env/conda-bld/verilator-uhdm_1625528243349/_build_env/bin/x86_64-conda-linux-gnu-c++ -fvisibility-inlines-hidden -std=c++17 -fmessage-length=0 -march=nocona -mtune=haswell -ftree-vectorize -fPIC -fstack-protector-strong -fno-plt -O2 -ffunction-sections -pipe -isystem /home/kbuilder/miniconda/envs/sv-test-env/include -DNDEBUG -D_FORTIFY_SOURCE=2 -O2 -isystem /home/kbuilder/miniconda/envs/sv-test-env/include -I. -MMD -I/home/kbuilder/miniconda/envs/sv-test-env/share/verilator/include -I/home/kbuilder/miniconda/envs/sv-test-env/share/verilator/include/vltstd -DVM_COVERAGE=0 -DVM_SC=0 -DVM_TRACE=0 -DVM_TRACE_FST=0 -faligned-new -fcf-protection=none -Wno-bool-operation -Wno-sign-compare -Wno-uninitialized -Wno-unused-but-set-variable -Wno-unused-parameter -Wno-unused-variable -Wno-shadow -std=gnu++14 -Os -c -o vmain.o ../vmain.cpp
make[1]: /home/runner/work/conda-eda/conda-eda/workdir/conda-env/conda-bld/verilator-uhdm_1625528243349/_build_env/bin/x86_64-conda-linux-gnu-c++: Command not found
Vtop.mk:59: recipe for target 'vmain.o' failed
``` | non_priority | dashboard runner false fail with nul characters many dozens of verilator tests false fail due to nul indicating something wrong with the running system these all passed at one point maybe it s out of disk space e g make entering directory tmpfs tmp vbuild vtop mk warning nul character seen rest of line ignored home runner work conda eda conda eda workdir conda env conda bld verilator uhdm build env bin conda linux gnu c fvisibility inlines hidden std c fmessage length march nocona mtune haswell ftree vectorize fpic fstack protector strong fno plt ffunction sections pipe isystem home kbuilder miniconda envs sv test env include dndebug d fortify source isystem home kbuilder miniconda envs sv test env include i mmd i home kbuilder miniconda envs sv test env share verilator include i home kbuilder miniconda envs sv test env share verilator include vltstd dvm coverage dvm sc dvm trace dvm trace fst faligned new fcf protection none wno bool operation wno sign compare wno uninitialized wno unused but set variable wno unused parameter wno unused variable wno shadow std gnu os c o vmain o vmain cpp make home runner work conda eda conda eda workdir conda env conda bld verilator uhdm build env bin conda linux gnu c command not found vtop mk recipe for target vmain o failed | 0 |
198,419 | 22,640,564,896 | IssuesEvent | 2022-07-01 01:15:54 | NCIOCPL/cgov-digital-platform | https://api.github.com/repos/NCIOCPL/cgov-digital-platform | closed | CSRF prevention on forms and page loads | Security | Several admin pages were flagged as being vulnerable to CSRF attacks. From what I've seen so far these were the standard content type admin pages.
## Scan Information
**Description**
CSRF is a very common vulnerability. It's an attack which forces a user to execute unwanted actions on a web application in which the user is currently authenticated.
**Impact**
Depending on the application, an attacker can mount any of the actions that can be done by the user such as adding a user, modifying content, deleting data. All the functionality that’s available to the victim can be used by the attacker. Only exception to this rule is a page that requires extra information that only the legitimate user can know (such as user’s password).
**Remedy**
Send additional information in each HTTP request that can be used to determine whether the request came from an authorized source. This "validation token" should be hard to guess for attacker who does not already have access to the user's account. If a request is missing a validation token or the token does not match the expected value, the server should reject the request.
If you are posting form in ajax request, custom HTTP headers can be used to prevent CSRF because the browser prevents sites from sending custom HTTP headers to another site but allows sites to send custom HTTP headers to themselves using XMLHttpRequest.
## Links
- [OWASP](https://owasp.org/www-community/attacks/csrf)
- [Drupal](https://www.drupal.org/docs/8/api/routing-system/access-checking-on-routes/csrf-access-checking) | True | CSRF prevention on forms and page loads - Several admin pages were flagged as being vulnerable to CSRF attacks. From what I've seen so far these were the standard content type admin pages.
## Scan Information
**Description**
CSRF is a very common vulnerability. It's an attack which forces a user to execute unwanted actions on a web application in which the user is currently authenticated.
**Impact**
Depending on the application, an attacker can mount any of the actions that can be done by the user such as adding a user, modifying content, deleting data. All the functionality that’s available to the victim can be used by the attacker. Only exception to this rule is a page that requires extra information that only the legitimate user can know (such as user’s password).
**Remedy**
Send additional information in each HTTP request that can be used to determine whether the request came from an authorized source. This "validation token" should be hard to guess for attacker who does not already have access to the user's account. If a request is missing a validation token or the token does not match the expected value, the server should reject the request.
If you are posting form in ajax request, custom HTTP headers can be used to prevent CSRF because the browser prevents sites from sending custom HTTP headers to another site but allows sites to send custom HTTP headers to themselves using XMLHttpRequest.
## Links
- [OWASP](https://owasp.org/www-community/attacks/csrf)
- [Drupal](https://www.drupal.org/docs/8/api/routing-system/access-checking-on-routes/csrf-access-checking) | non_priority | csrf prevention on forms and page loads several admin pages were flagged as being vulnerable to csrf attacks from what i ve seen so far these were the standard content type admin pages scan information description csrf is a very common vulnerability it s an attack which forces a user to execute unwanted actions on a web application in which the user is currently authenticated impact depending on the application an attacker can mount any of the actions that can be done by the user such as adding a user modifying content deleting data all the functionality that’s available to the victim can be used by the attacker only exception to this rule is a page that requires extra information that only the legitimate user can know such as user’s password remedy send additional information in each http request that can be used to determine whether the request came from an authorized source this validation token should be hard to guess for attacker who does not already have access to the user s account if a request is missing a validation token or the token does not match the expected value the server should reject the request if you are posting form in ajax request custom http headers can be used to prevent csrf because the browser prevents sites from sending custom http headers to another site but allows sites to send custom http headers to themselves using xmlhttprequest links | 0 |
92,866 | 11,716,565,616 | IssuesEvent | 2020-03-09 15:50:17 | phetsims/ph-scale | https://api.github.com/repos/phetsims/ph-scale | closed | instrumentation of microScreen.model.pHMeter | design:phet-io | Something I noticed while working on another issue...
Instrumentation of the pH meter mode in _Macro_ screen looks like this:
```
-phScale
-microScreen
-model
-pHMeter
valueProperty
-probe
positionProperty
```
There are 3 problems here:
- [ ] `valueProperty` is never updated, always `null`
- [ ] this meter doesn't have a separate movable probe, so both `probe` and `positionProperty` are irrelevant
I think the structure should look like this, where `*pHProperty` is a link to `solution.pHProperty`.
```
-phScale
-microScreen
-model
-pHMeter
*pHProperty
```
@arouinfar do you agree? | 1.0 | instrumentation of microScreen.model.pHMeter - Something I noticed while working on another issue...
Instrumentation of the pH meter mode in _Macro_ screen looks like this:
```
-phScale
-microScreen
-model
-pHMeter
valueProperty
-probe
positionProperty
```
There are 3 problems here:
- [ ] `valueProperty` is never updated, always `null`
- [ ] this meter doesn't have a separate movable probe, so both `probe` and `positionProperty` are irrelevant
I think the structure should look like this, where `*pHProperty` is a link to `solution.pHProperty`.
```
-phScale
-microScreen
-model
-pHMeter
*pHProperty
```
@arouinfar do you agree? | non_priority | instrumentation of microscreen model phmeter something i noticed while working on another issue instrumentation of the ph meter mode in macro screen looks like this phscale microscreen model phmeter valueproperty probe positionproperty there are problems here valueproperty is never updated always null this meter doesn t have a separate movable probe so both probe and positionproperty are irrelevant i think the structure should look like this where phproperty is a link to solution phproperty phscale microscreen model phmeter phproperty arouinfar do you agree | 0 |
73,761 | 15,282,040,021 | IssuesEvent | 2021-02-23 09:01:54 | hazelcast/hazelcast-jet | https://api.github.com/repos/hazelcast/hazelcast-jet | opened | Vulnerabilities in Apache Commons Compress used by Jet 4.3 | security | Jet uses Apache Commons Compress `1.8.1` which includes following vulnerabilities:
- CVE-2018-11771 - https://nvd.nist.gov/vuln/detail/CVE-2018-11771 (fixed in 1.18) | True | Vulnerabilities in Apache Commons Compress used by Jet 4.3 - Jet uses Apache Commons Compress `1.8.1` which includes following vulnerabilities:
- CVE-2018-11771 - https://nvd.nist.gov/vuln/detail/CVE-2018-11771 (fixed in 1.18) | non_priority | vulnerabilities in apache commons compress used by jet jet uses apache commons compress which includes following vulnerabilities cve fixed in | 0 |
317,704 | 27,258,807,583 | IssuesEvent | 2023-02-22 13:31:52 | pymc-labs/pymc-marketing | https://api.github.com/repos/pymc-labs/pymc-marketing | opened | TestBetaGeo `setup_class` is too slow | CLV tests | The `setup_class` of TestBetaGeo is too slow as it performs MCMC sampling on a synthetic dataset. We should make this a fixture of tests that actually need it (if there's more than one), and possibly mark them with `@pytest.mark.slow` so that they are not ran locally by default.
https://github.com/pymc-labs/pymc-marketing/blob/7ebc19465ad6daf62fbcb56d1b91fc40d09da7a0/tests/clv/models/test_beta_geo.py#L50
For other tests I have faked posterior draws by doing prior sampling with narrow priors around the "expected" values. This allows us to check the summary methods work as expected without doing slow mcmc sampling.
CC @larryshamalama | 1.0 | TestBetaGeo `setup_class` is too slow - The `setup_class` of TestBetaGeo is too slow as it performs MCMC sampling on a synthetic dataset. We should make this a fixture of tests that actually need it (if there's more than one), and possibly mark them with `@pytest.mark.slow` so that they are not ran locally by default.
https://github.com/pymc-labs/pymc-marketing/blob/7ebc19465ad6daf62fbcb56d1b91fc40d09da7a0/tests/clv/models/test_beta_geo.py#L50
For other tests I have faked posterior draws by doing prior sampling with narrow priors around the "expected" values. This allows us to check the summary methods work as expected without doing slow mcmc sampling.
CC @larryshamalama | non_priority | testbetageo setup class is too slow the setup class of testbetageo is too slow as it performs mcmc sampling on a synthetic dataset we should make this a fixture of tests that actually need it if there s more than one and possibly mark them with pytest mark slow so that they are not ran locally by default for other tests i have faked posterior draws by doing prior sampling with narrow priors around the expected values this allows us to check the summary methods work as expected without doing slow mcmc sampling cc larryshamalama | 0 |
69,084 | 17,568,884,249 | IssuesEvent | 2021-08-14 08:52:29 | komascript/makelabels | https://api.github.com/repos/komascript/makelabels | closed | `l3build doc` failes because of missing `makefiles*-example.pdf` | build | There seem to be something wrong with the build process using `l3build doc`. The first try (after `l3build clean`) fails, because of missing `makefiles-example.pdf` and `makefiles-envlab-example.pdf`. Both files are generated but not copied to `build/doc`. Next run of `l3build doc` is successful, because it copies `makefiles-example.pdf` and `makefiles-envlab-example.pdf` from the working directory to `build/doc` before running LaTeX.
If someone could explain, how to explain `l3build` to copy `makefiles-example.pdf` and `makefiles-envlab-example.pdf` after they have been typeset but before typesetting `makefiles.dtx`, I would be glad. I think, it is a small mistake, but currently I'm too tired to find it. | 1.0 | `l3build doc` failes because of missing `makefiles*-example.pdf` - There seem to be something wrong with the build process using `l3build doc`. The first try (after `l3build clean`) fails, because of missing `makefiles-example.pdf` and `makefiles-envlab-example.pdf`. Both files are generated but not copied to `build/doc`. Next run of `l3build doc` is successful, because it copies `makefiles-example.pdf` and `makefiles-envlab-example.pdf` from the working directory to `build/doc` before running LaTeX.
If someone could explain, how to explain `l3build` to copy `makefiles-example.pdf` and `makefiles-envlab-example.pdf` after they have been typeset but before typesetting `makefiles.dtx`, I would be glad. I think, it is a small mistake, but currently I'm too tired to find it. | non_priority | doc failes because of missing makefiles example pdf there seem to be something wrong with the build process using doc the first try after clean fails because of missing makefiles example pdf and makefiles envlab example pdf both files are generated but not copied to build doc next run of doc is successful because it copies makefiles example pdf and makefiles envlab example pdf from the working directory to build doc before running latex if someone could explain how to explain to copy makefiles example pdf and makefiles envlab example pdf after they have been typeset but before typesetting makefiles dtx i would be glad i think it is a small mistake but currently i m too tired to find it | 0 |
32,721 | 13,916,675,106 | IssuesEvent | 2020-10-21 04:00:27 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Wrong description - Large (Nested Virtualization) | Pri2 awaiting-product-team-response cxp lab-services/svc product-question triaged | Large (Nested Virtualization) | 8 Cores 32 GB RAM
### Comments
The vm is Large (Nested Virtualization) | 8 Cores 32 GB RAM instead of Large (Nested Virtualization) | 8 Cores 16 GB RAM
I don't know with VM is associated with this configuration
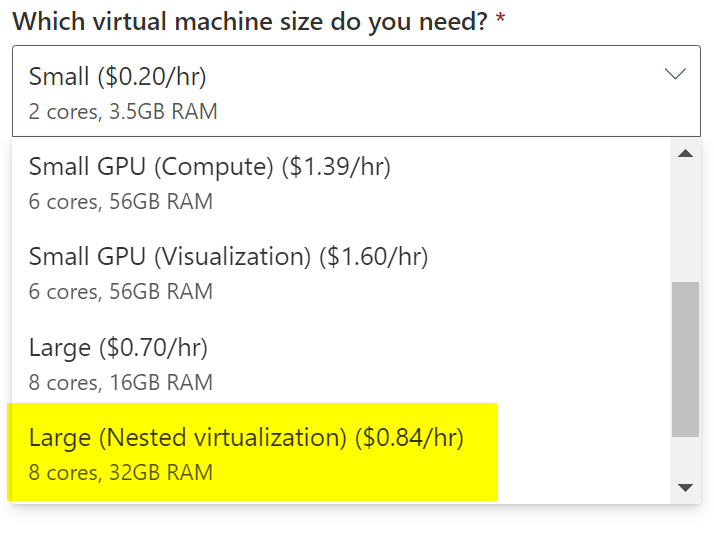
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 191dec24-ed36-2aea-3384-dfeb69c6d1c8
* Version Independent ID: c3cc622e-c92e-feb0-2835-551ddd601cf3
* Content: [Azure Lab Services - Administrator guide - Azure Lab Services](https://docs.microsoft.com/en-us/azure/lab-services/administrator-guide#vm-sizing)
* Content Source: [articles/lab-services/administrator-guide.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/lab-services/administrator-guide.md)
* Service: **lab-services**
* GitHub Login: @Juliako
* Microsoft Alias: **juliako** | 1.0 | Wrong description - Large (Nested Virtualization) - Large (Nested Virtualization) | 8 Cores 32 GB RAM
### Comments
The vm is Large (Nested Virtualization) | 8 Cores 32 GB RAM instead of Large (Nested Virtualization) | 8 Cores 16 GB RAM
I don't know with VM is associated with this configuration
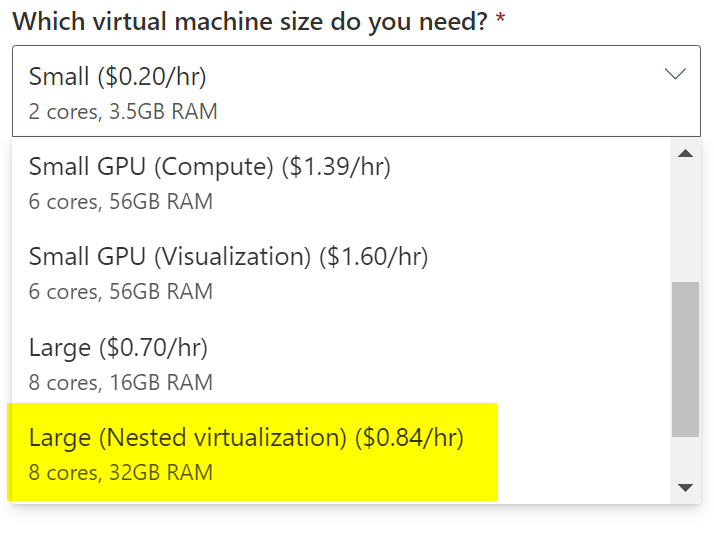
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 191dec24-ed36-2aea-3384-dfeb69c6d1c8
* Version Independent ID: c3cc622e-c92e-feb0-2835-551ddd601cf3
* Content: [Azure Lab Services - Administrator guide - Azure Lab Services](https://docs.microsoft.com/en-us/azure/lab-services/administrator-guide#vm-sizing)
* Content Source: [articles/lab-services/administrator-guide.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/lab-services/administrator-guide.md)
* Service: **lab-services**
* GitHub Login: @Juliako
* Microsoft Alias: **juliako** | non_priority | wrong description large nested virtualization large nested virtualization cores gb ram comments the vm is large nested virtualization cores gb ram instead of large nested virtualization cores gb ram i don t know with vm is associated with this configuration document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service lab services github login juliako microsoft alias juliako | 0 |
74,517 | 14,266,441,836 | IssuesEvent | 2020-11-20 18:42:45 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | ability to remove up/down arrows from a number field | No Code Attached Yet | ### Is your feature request related to a problem? Please describe.
Currently all rendered number fields have the up/down arrows on them. The arrows can be removed by CSS if needed but this is template/css based.
**With Arrows**

**Without arrows**

### Describe the solution you'd like
I would like an option that you can configure in the field configuation so this option was not template/css dependant.
Maybe call the new option `arrows="false"`
```xml
<field
name="id"
type="number"
label="JGLOBAL_FIELD_ID_LABEL"
description="JGLOBAL_FIELD_ID_DESC"
default="0"
class="readonly"
size="10"
readonly="true"
arrows="false"
/>
```
### Additional context
You can use the following css to remove the arrows:
```css
style="appearance: textfield"
```
There is not an option I have found https://docs.joomla.org/Number_form_field_type | 1.0 | ability to remove up/down arrows from a number field - ### Is your feature request related to a problem? Please describe.
Currently all rendered number fields have the up/down arrows on them. The arrows can be removed by CSS if needed but this is template/css based.
**With Arrows**

**Without arrows**

### Describe the solution you'd like
I would like an option that you can configure in the field configuation so this option was not template/css dependant.
Maybe call the new option `arrows="false"`
```xml
<field
name="id"
type="number"
label="JGLOBAL_FIELD_ID_LABEL"
description="JGLOBAL_FIELD_ID_DESC"
default="0"
class="readonly"
size="10"
readonly="true"
arrows="false"
/>
```
### Additional context
You can use the following css to remove the arrows:
```css
style="appearance: textfield"
```
There is not an option I have found https://docs.joomla.org/Number_form_field_type | non_priority | ability to remove up down arrows from a number field is your feature request related to a problem please describe currently all rendered number fields have the up down arrows on them the arrows can be removed by css if needed but this is template css based with arrows without arrows describe the solution you d like i would like an option that you can configure in the field configuation so this option was not template css dependant maybe call the new option arrows false xml field name id type number label jglobal field id label description jglobal field id desc default class readonly size readonly true arrows false additional context you can use the following css to remove the arrows css style appearance textfield there is not an option i have found | 0 |
326,183 | 24,074,806,153 | IssuesEvent | 2022-09-18 16:58:12 | RobbieWagner/Snowstorm | https://api.github.com/repos/RobbieWagner/Snowstorm | closed | Display buttons for tutorials | documentation enhancement | Instead of a single tutorial that displays when the user starts doing certain tasks (interacting with things), have buttons display the keys to press/actions to perform | 1.0 | Display buttons for tutorials - Instead of a single tutorial that displays when the user starts doing certain tasks (interacting with things), have buttons display the keys to press/actions to perform | non_priority | display buttons for tutorials instead of a single tutorial that displays when the user starts doing certain tasks interacting with things have buttons display the keys to press actions to perform | 0 |
446,979 | 31,565,582,930 | IssuesEvent | 2023-09-03 19:36:57 | phren-ke/spa | https://api.github.com/repos/phren-ke/spa | closed | About us | documentation good first issue | ### About Us Description
Have a title saying "About Us"
Write a captivating message about us that shows why the services are better than others.
Describe in about 1 or 2 paragraphs
| 1.0 | About us - ### About Us Description
Have a title saying "About Us"
Write a captivating message about us that shows why the services are better than others.
Describe in about 1 or 2 paragraphs
| non_priority | about us about us description have a title saying about us write a captivating message about us that shows why the services are better than others describe in about or paragraphs | 0 |
380,509 | 26,422,664,447 | IssuesEvent | 2023-01-13 22:22:38 | fga-eps-mds/2022-2-BOTO | https://api.github.com/repos/fga-eps-mds/2022-2-BOTO | opened | Documentação de como é feito o teste | documentation | #### Objetivo?
Documentar como é feito o teste unitario e enviar as informações que a professora quer na issue que tem que marcar ela
#### Tarefas // Criterios de aceitação
- [ ] Documentar como é feito o teste
- [ ] Criar a issue com a professora com as informações pedidas no telegram
#### Comentários
----------------
| 1.0 | Documentação de como é feito o teste - #### Objetivo?
Documentar como é feito o teste unitario e enviar as informações que a professora quer na issue que tem que marcar ela
#### Tarefas // Criterios de aceitação
- [ ] Documentar como é feito o teste
- [ ] Criar a issue com a professora com as informações pedidas no telegram
#### Comentários
----------------
| non_priority | documentação de como é feito o teste objetivo documentar como é feito o teste unitario e enviar as informações que a professora quer na issue que tem que marcar ela tarefas criterios de aceitação documentar como é feito o teste criar a issue com a professora com as informações pedidas no telegram comentários | 0 |
311,976 | 23,412,265,609 | IssuesEvent | 2022-08-12 18:55:57 | timoast/signac | https://api.github.com/repos/timoast/signac | closed | ATAC imputation? | documentation | Hello,
I appreciate this wonderful tool! I am fairly new to scATACseq analysis, so forgive me if if my question is naive. I have 1 multiome dataset and 1 CITEseq dataset. I’d like to follow the steps on the “RNA imputation” part of this vignette: https://satijalab.org/signac/articles/integrate_atac.html#rna-imputation-1 , except I would like to impute ATAC for the CITEseq dataset. Below is the code I’ve tried, and while the data does transfer, I’m not able to do any downstream analysis with my newly added “predicted_ATAC” slot in the CITEseq dataset. Am I missing something or is this kind of imputation not possible? Thanks in advance for any insight.
My code:
````
DefaultAssay(multiome) <- "RNA"
DefaultAssay(cite) <- "RNA"
multiome <- RunSPCA(multiome, assay = "RNA", graph = "wsnn")
#Computing a cached neighbor index
multiome <- FindNeighbors(
object = multiome,
reduction = "spca",
dims = 1:50,
graph.name = "spca.annoy.neighbors",
k.param = 50,
cache.index = TRUE,
return.neighbor = TRUE,
l2.norm = TRUE
)
#Query dataset processing
#Find anchors between the query and reference
anchors <- list()
anchors <- FindTransferAnchors(
reference = multiome,
query = cite,
k.filter = NA,
reference.reduction = "spca",
reference.neighbors = "spca.annoy.neighbors",
dims = 1:50
)
atac <- TransferData(
anchorset = anchors,
refdata = GetAssayData(multiome[["peaks"]], slot = "data"),
weight.reduction = cite[["pca"]],
dims = 1:50
)
cite[["predicted_ATAC"]] <- atac
cite[["predicted_ATAC"]] <- as.ChromatinAssay(cite[["predicted_ATAC"]])
```` | 1.0 | ATAC imputation? - Hello,
I appreciate this wonderful tool! I am fairly new to scATACseq analysis, so forgive me if if my question is naive. I have 1 multiome dataset and 1 CITEseq dataset. I’d like to follow the steps on the “RNA imputation” part of this vignette: https://satijalab.org/signac/articles/integrate_atac.html#rna-imputation-1 , except I would like to impute ATAC for the CITEseq dataset. Below is the code I’ve tried, and while the data does transfer, I’m not able to do any downstream analysis with my newly added “predicted_ATAC” slot in the CITEseq dataset. Am I missing something or is this kind of imputation not possible? Thanks in advance for any insight.
My code:
````
DefaultAssay(multiome) <- "RNA"
DefaultAssay(cite) <- "RNA"
multiome <- RunSPCA(multiome, assay = "RNA", graph = "wsnn")
#Computing a cached neighbor index
multiome <- FindNeighbors(
object = multiome,
reduction = "spca",
dims = 1:50,
graph.name = "spca.annoy.neighbors",
k.param = 50,
cache.index = TRUE,
return.neighbor = TRUE,
l2.norm = TRUE
)
#Query dataset processing
#Find anchors between the query and reference
anchors <- list()
anchors <- FindTransferAnchors(
reference = multiome,
query = cite,
k.filter = NA,
reference.reduction = "spca",
reference.neighbors = "spca.annoy.neighbors",
dims = 1:50
)
atac <- TransferData(
anchorset = anchors,
refdata = GetAssayData(multiome[["peaks"]], slot = "data"),
weight.reduction = cite[["pca"]],
dims = 1:50
)
cite[["predicted_ATAC"]] <- atac
cite[["predicted_ATAC"]] <- as.ChromatinAssay(cite[["predicted_ATAC"]])
```` | non_priority | atac imputation hello i appreciate this wonderful tool i am fairly new to scatacseq analysis so forgive me if if my question is naive i have multiome dataset and citeseq dataset i’d like to follow the steps on the “rna imputation” part of this vignette except i would like to impute atac for the citeseq dataset below is the code i’ve tried and while the data does transfer i’m not able to do any downstream analysis with my newly added “predicted atac” slot in the citeseq dataset am i missing something or is this kind of imputation not possible thanks in advance for any insight my code defaultassay multiome rna defaultassay cite rna multiome runspca multiome assay rna graph wsnn computing a cached neighbor index multiome findneighbors object multiome reduction spca dims graph name spca annoy neighbors k param cache index true return neighbor true norm true query dataset processing find anchors between the query and reference anchors list anchors findtransferanchors reference multiome query cite k filter na reference reduction spca reference neighbors spca annoy neighbors dims atac transferdata anchorset anchors refdata getassaydata multiome slot data weight reduction cite dims cite atac cite as chromatinassay cite | 0 |
168,855 | 20,825,726,170 | IssuesEvent | 2022-03-18 20:35:54 | vincenzodistasio97/main | https://api.github.com/repos/vincenzodistasio97/main | opened | pm2-4.2.3.tgz: 22 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pm2-4.2.3.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-21388](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21388) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-26245](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26245) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-26300](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26300) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-23406](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23406) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | multiple | Transitive | 5.0.0 | ❌ |
| [CVE-2021-28918](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | netmask-1.0.6.tgz | Transitive | 4.5.6 | ❌ |
| [CVE-2020-26274](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26274) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-7752](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7752) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-21315](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21315) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-28469](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-5.1.0.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-23343](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | path-parse-1.0.6.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-3749](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | axios-0.19.2.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2020-8203](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.4 | lodash-4.17.14.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-7778](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7778) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-7788](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.5.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-23337](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | lodash-4.17.14.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2022-0144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0144) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.1 | shelljs-0.8.3.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2022-0155](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | follow-redirects-1.5.10.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2022-0536](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | follow-redirects-1.5.10.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2020-28168](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28168) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | axios-0.19.2.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2020-28500](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | lodash-4.17.14.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-32640](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | multiple | Transitive | 4.3.0 | ❌ |
| [CVE-2021-29418](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29418) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | netmask-1.0.6.tgz | Transitive | 4.5.6 | ❌ |
## Details
> Partial details (15 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21388</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
systeminformation is an open source system and OS information library for node.js. A command injection vulnerability has been discovered in versions of systeminformation prior to 5.6.4. The issue has been fixed with a parameter check on user input. Please upgrade to version >= 5.6.4. If you cannot upgrade, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() and other commands. Only allow strings, reject any arrays. String sanitation works as expected.
<p>Publish Date: 2021-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21388>CVE-2021-21388</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/pull/492">https://github.com/sebhildebrandt/systeminformation/pull/492</a></p>
<p>Release Date: 2021-04-29</p>
<p>Fix Resolution (systeminformation): 4.34.11</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26245</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
npm package systeminformation before version 4.30.5 is vulnerable to Prototype Pollution leading to Command Injection. The issue was fixed with a rewrite of shell sanitations to avoid prototyper pollution problems. The issue is fixed in version 4.30.5. If you cannot upgrade, be sure to check or sanitize service parameter strings that are passed to si.inetChecksite().
<p>Publish Date: 2020-11-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26245>CVE-2020-26245</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-4v2w-h9jm-mqjg">https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-4v2w-h9jm-mqjg</a></p>
<p>Release Date: 2020-11-27</p>
<p>Fix Resolution (systeminformation): 4.30.5</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26300</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
systeminformation is an npm package that provides system and OS information library for node.js. In systeminformation before version 4.26.2 there is a command injection vulnerability. Problem was fixed in version 4.26.2 with a shell string sanitation fix.
<p>Publish Date: 2021-09-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26300>CVE-2020-26300</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fj59-f6c3-3vw4">https://github.com/advisories/GHSA-fj59-f6c3-3vw4</a></p>
<p>Release Date: 2021-09-09</p>
<p>Fix Resolution (systeminformation): 4.26.2</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23406</summary>
### Vulnerable Libraries - <b>pac-resolver-3.0.0.tgz</b>, <b>degenerator-1.0.4.tgz</b></p>
<p>
### <b>pac-resolver-3.0.0.tgz</b></p>
<p>Generates an asynchronous resolver function from a PAC file</p>
<p>Library home page: <a href="https://registry.npmjs.org/pac-resolver/-/pac-resolver-3.0.0.tgz">https://registry.npmjs.org/pac-resolver/-/pac-resolver-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pac-resolver/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- agent-0.5.26.tgz
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- :x: **pac-resolver-3.0.0.tgz** (Vulnerable Library)
### <b>degenerator-1.0.4.tgz</b></p>
<p>Turns sync functions into async generator functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/degenerator/-/degenerator-1.0.4.tgz">https://registry.npmjs.org/degenerator/-/degenerator-1.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/degenerator/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- agent-0.5.26.tgz
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- pac-resolver-3.0.0.tgz
- :x: **degenerator-1.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package pac-resolver before 5.0.0. This can occur when used with untrusted input, due to unsafe PAC file handling. **NOTE:** The fix for this vulnerability is applied in the node-degenerator library, a dependency written by the same maintainer.
<p>Publish Date: 2021-08-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23406>CVE-2021-23406</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9j49-mfvp-vmhm">https://github.com/advisories/GHSA-9j49-mfvp-vmhm</a></p>
<p>Release Date: 2021-08-24</p>
<p>Fix Resolution (pac-resolver): 5.0.0</p>
<p>Direct dependency fix Resolution (pm2): 5.0.0</p><p>Fix Resolution (degenerator): 3.0.1</p>
<p>Direct dependency fix Resolution (pm2): 5.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-28918</summary>
### Vulnerable Library - <b>netmask-1.0.6.tgz</b></p>
<p>Parse and lookup IP network blocks</p>
<p>Library home page: <a href="https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz">https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/netmask/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- agent-0.5.26.tgz
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- pac-resolver-3.0.0.tgz
- :x: **netmask-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.
<p>Publish Date: 2021-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918>CVE-2021-28918</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pch5-whg9-qr2r">https://github.com/advisories/GHSA-pch5-whg9-qr2r</a></p>
<p>Release Date: 2021-04-01</p>
<p>Fix Resolution (netmask): 2.0.1</p>
<p>Direct dependency fix Resolution (pm2): 4.5.6</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26274</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In systeminformation (npm package) before version 4.31.1 there is a command injection vulnerability. The problem was fixed in version 4.31.1 with a shell string sanitation fix.
<p>Publish Date: 2020-12-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26274>CVE-2020-26274</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/package/systeminformation/v/4.31.0">https://www.npmjs.com/package/systeminformation/v/4.31.0</a></p>
<p>Release Date: 2020-12-16</p>
<p>Fix Resolution (systeminformation): 4.31.1</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7752</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package systeminformation before 4.27.11. This package is vulnerable to Command Injection. The attacker can concatenate curl's parameters to overwrite Javascript files and then execute any OS commands.
<p>Publish Date: 2020-10-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7752>CVE-2020-7752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7752">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7752</a></p>
<p>Release Date: 2020-10-26</p>
<p>Fix Resolution (systeminformation): 4.27.11</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21315</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The System Information Library for Node.JS (npm package "systeminformation") is an open source collection of functions to retrieve detailed hardware, system and OS information. In systeminformation before version 5.3.1 there is a command injection vulnerability. Problem was fixed in version 5.3.1. As a workaround instead of upgrading, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() ... do only allow strings, reject any arrays. String sanitation works as expected.
<p>Publish Date: 2021-02-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21315>CVE-2021-21315</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-2m8v-572m-ff2v">https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-2m8v-572m-ff2v</a></p>
<p>Release Date: 2021-02-16</p>
<p>Fix Resolution (systeminformation): 4.34.11</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-5.1.0.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- chokidar-3.3.1.tgz
- :x: **glob-parent-5.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23343</summary>
### Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/path-parse/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- shelljs-0.8.3.tgz
- rechoir-0.6.2.tgz
- resolve-1.15.1.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jbgutierrez/path-parse/issues/8">https://github.com/jbgutierrez/path-parse/issues/8</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution (path-parse): 1.0.7</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3749</summary>
### Vulnerable Library - <b>axios-0.19.2.tgz</b></p>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.19.2.tgz">https://registry.npmjs.org/axios/-/axios-0.19.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- js-api-0.5.60.tgz
- :x: **axios-0.19.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
axios is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749>CVE-2021-3749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/axios/axios/releases/tag/v0.21.2">https://github.com/axios/axios/releases/tag/v0.21.2</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (axios): 0.20.0</p>
<p>Direct dependency fix Resolution (pm2): 4.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8203</summary>
### Vulnerable Library - <b>lodash-4.17.14.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pm2/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **lodash-4.17.14.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution (lodash): 4.17.19</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7778</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package systeminformation before 4.30.2. The attacker can overwrite the properties and functions of an object, which can lead to executing OS commands.
<p>Publish Date: 2020-11-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7778>CVE-2020-7778</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/releases/tag/v4.30.2">https://github.com/sebhildebrandt/systeminformation/releases/tag/v4.30.2</a></p>
<p>Release Date: 2020-11-26</p>
<p>Fix Resolution (systeminformation): 4.30.2</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7788</summary>
### Vulnerable Library - <b>ini-1.3.5.tgz</b></p>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.5.tgz">https://registry.npmjs.org/ini/-/ini-1.3.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- vizion-2.0.2.tgz
- :x: **ini-1.3.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (ini): 1.3.6</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23337</summary>
### Vulnerable Library - <b>lodash-4.17.14.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pm2/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **lodash-4.17.14.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-21388","vulnerabilityDetails":"systeminformation is an open source system and OS information library for node.js. A command injection vulnerability has been discovered in versions of systeminformation prior to 5.6.4. The issue has been fixed with a parameter check on user input. Please upgrade to version \u003e\u003d 5.6.4. If you cannot upgrade, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() and other commands. Only allow strings, reject any arrays. String sanitation works as expected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21388","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26245","vulnerabilityDetails":"npm package systeminformation before version 4.30.5 is vulnerable to Prototype Pollution leading to Command Injection. The issue was fixed with a rewrite of shell sanitations to avoid prototyper pollution problems. The issue is fixed in version 4.30.5. If you cannot upgrade, be sure to check or sanitize service parameter strings that are passed to si.inetChecksite().","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26245","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26300","vulnerabilityDetails":"systeminformation is an npm package that provides system and OS information library for node.js. In systeminformation before version 4.26.2 there is a command injection vulnerability. Problem was fixed in version 4.26.2 with a shell string sanitation fix.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26300","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.0.0","isBinary":false},{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23406","vulnerabilityDetails":"This affects the package pac-resolver before 5.0.0. This can occur when used with untrusted input, due to unsafe PAC file handling. **NOTE:** The fix for this vulnerability is applied in the node-degenerator library, a dependency written by the same maintainer.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23406","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.5.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-28918","vulnerabilityDetails":"Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26274","vulnerabilityDetails":"In systeminformation (npm package) before version 4.31.1 there is a command injection vulnerability. The problem was fixed in version 4.31.1 with a shell string sanitation fix.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26274","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7752","vulnerabilityDetails":"This affects the package systeminformation before 4.27.11. This package is vulnerable to Command Injection. The attacker can concatenate curl\u0027s parameters to overwrite Javascript files and then execute any OS commands.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7752","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-21315","vulnerabilityDetails":"The System Information Library for Node.JS (npm package \"systeminformation\") is an open source collection of functions to retrieve detailed hardware, system and OS information. In systeminformation before version 5.3.1 there is a command injection vulnerability. Problem was fixed in version 5.3.1. As a workaround instead of upgrading, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() ... do only allow strings, reject any arrays. String sanitation works as expected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21315","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28469","vulnerabilityDetails":"This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23343","vulnerabilityDetails":"All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-3749","vulnerabilityDetails":"axios is vulnerable to Inefficient Regular Expression Complexity","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8203","vulnerabilityDetails":"Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7778","vulnerabilityDetails":"This affects the package systeminformation before 4.30.2. The attacker can overwrite the properties and functions of an object, which can lead to executing OS commands.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7778","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7788","vulnerabilityDetails":"This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0144","vulnerabilityDetails":"shelljs is vulnerable to Improper Privilege Management","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0144","cvss3Severity":"high","cvss3Score":"7.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0155","vulnerabilityDetails":"follow-redirects is vulnerable to Exposure of Private Personal Information to an Unauthorized Actor","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0536","vulnerabilityDetails":"Exposure of Sensitive Information to an Unauthorized Actor in NPM follow-redirects prior to 1.14.8.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28168","vulnerabilityDetails":"Axios NPM package 0.21.0 contains a Server-Side Request Forgery (SSRF) vulnerability where an attacker is able to bypass a proxy by providing a URL that responds with a redirect to a restricted host or IP address.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28168","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.\n WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false},{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32640","vulnerabilityDetails":"ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size\u003dsize`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.5.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-29418","vulnerabilityDetails":"The netmask package before 2.0.1 for Node.js mishandles certain unexpected characters in an IP address string, such as an octal digit of 9. This (in some situations) allows attackers to bypass access control that is based on IP addresses. NOTE: this issue exists because of an incomplete fix for CVE-2021-28918.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29418","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | True | pm2-4.2.3.tgz: 22 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pm2-4.2.3.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-21388](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21388) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-26245](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26245) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-26300](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26300) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-23406](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23406) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | multiple | Transitive | 5.0.0 | ❌ |
| [CVE-2021-28918](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | netmask-1.0.6.tgz | Transitive | 4.5.6 | ❌ |
| [CVE-2020-26274](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26274) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-7752](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7752) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-21315](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21315) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-28469](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | glob-parent-5.1.0.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-23343](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | path-parse-1.0.6.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-3749](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | axios-0.19.2.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2020-8203](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.4 | lodash-4.17.14.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-7778](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7778) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | systeminformation-4.23.1.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2020-7788](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.5.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-23337](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | lodash-4.17.14.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2022-0144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0144) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.1 | shelljs-0.8.3.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2022-0155](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | follow-redirects-1.5.10.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2022-0536](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | follow-redirects-1.5.10.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2020-28168](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28168) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | axios-0.19.2.tgz | Transitive | 4.4.0 | ❌ |
| [CVE-2020-28500](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | lodash-4.17.14.tgz | Transitive | 4.3.0 | ❌ |
| [CVE-2021-32640](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | multiple | Transitive | 4.3.0 | ❌ |
| [CVE-2021-29418](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29418) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | netmask-1.0.6.tgz | Transitive | 4.5.6 | ❌ |
## Details
> Partial details (15 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21388</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
systeminformation is an open source system and OS information library for node.js. A command injection vulnerability has been discovered in versions of systeminformation prior to 5.6.4. The issue has been fixed with a parameter check on user input. Please upgrade to version >= 5.6.4. If you cannot upgrade, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() and other commands. Only allow strings, reject any arrays. String sanitation works as expected.
<p>Publish Date: 2021-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21388>CVE-2021-21388</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/pull/492">https://github.com/sebhildebrandt/systeminformation/pull/492</a></p>
<p>Release Date: 2021-04-29</p>
<p>Fix Resolution (systeminformation): 4.34.11</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26245</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
npm package systeminformation before version 4.30.5 is vulnerable to Prototype Pollution leading to Command Injection. The issue was fixed with a rewrite of shell sanitations to avoid prototyper pollution problems. The issue is fixed in version 4.30.5. If you cannot upgrade, be sure to check or sanitize service parameter strings that are passed to si.inetChecksite().
<p>Publish Date: 2020-11-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26245>CVE-2020-26245</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-4v2w-h9jm-mqjg">https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-4v2w-h9jm-mqjg</a></p>
<p>Release Date: 2020-11-27</p>
<p>Fix Resolution (systeminformation): 4.30.5</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26300</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
systeminformation is an npm package that provides system and OS information library for node.js. In systeminformation before version 4.26.2 there is a command injection vulnerability. Problem was fixed in version 4.26.2 with a shell string sanitation fix.
<p>Publish Date: 2021-09-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26300>CVE-2020-26300</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fj59-f6c3-3vw4">https://github.com/advisories/GHSA-fj59-f6c3-3vw4</a></p>
<p>Release Date: 2021-09-09</p>
<p>Fix Resolution (systeminformation): 4.26.2</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23406</summary>
### Vulnerable Libraries - <b>pac-resolver-3.0.0.tgz</b>, <b>degenerator-1.0.4.tgz</b></p>
<p>
### <b>pac-resolver-3.0.0.tgz</b></p>
<p>Generates an asynchronous resolver function from a PAC file</p>
<p>Library home page: <a href="https://registry.npmjs.org/pac-resolver/-/pac-resolver-3.0.0.tgz">https://registry.npmjs.org/pac-resolver/-/pac-resolver-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pac-resolver/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- agent-0.5.26.tgz
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- :x: **pac-resolver-3.0.0.tgz** (Vulnerable Library)
### <b>degenerator-1.0.4.tgz</b></p>
<p>Turns sync functions into async generator functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/degenerator/-/degenerator-1.0.4.tgz">https://registry.npmjs.org/degenerator/-/degenerator-1.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/degenerator/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- agent-0.5.26.tgz
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- pac-resolver-3.0.0.tgz
- :x: **degenerator-1.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package pac-resolver before 5.0.0. This can occur when used with untrusted input, due to unsafe PAC file handling. **NOTE:** The fix for this vulnerability is applied in the node-degenerator library, a dependency written by the same maintainer.
<p>Publish Date: 2021-08-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23406>CVE-2021-23406</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9j49-mfvp-vmhm">https://github.com/advisories/GHSA-9j49-mfvp-vmhm</a></p>
<p>Release Date: 2021-08-24</p>
<p>Fix Resolution (pac-resolver): 5.0.0</p>
<p>Direct dependency fix Resolution (pm2): 5.0.0</p><p>Fix Resolution (degenerator): 3.0.1</p>
<p>Direct dependency fix Resolution (pm2): 5.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-28918</summary>
### Vulnerable Library - <b>netmask-1.0.6.tgz</b></p>
<p>Parse and lookup IP network blocks</p>
<p>Library home page: <a href="https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz">https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/netmask/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- agent-0.5.26.tgz
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- pac-resolver-3.0.0.tgz
- :x: **netmask-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.
<p>Publish Date: 2021-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918>CVE-2021-28918</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pch5-whg9-qr2r">https://github.com/advisories/GHSA-pch5-whg9-qr2r</a></p>
<p>Release Date: 2021-04-01</p>
<p>Fix Resolution (netmask): 2.0.1</p>
<p>Direct dependency fix Resolution (pm2): 4.5.6</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-26274</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In systeminformation (npm package) before version 4.31.1 there is a command injection vulnerability. The problem was fixed in version 4.31.1 with a shell string sanitation fix.
<p>Publish Date: 2020-12-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26274>CVE-2020-26274</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/package/systeminformation/v/4.31.0">https://www.npmjs.com/package/systeminformation/v/4.31.0</a></p>
<p>Release Date: 2020-12-16</p>
<p>Fix Resolution (systeminformation): 4.31.1</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7752</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package systeminformation before 4.27.11. This package is vulnerable to Command Injection. The attacker can concatenate curl's parameters to overwrite Javascript files and then execute any OS commands.
<p>Publish Date: 2020-10-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7752>CVE-2020-7752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7752">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7752</a></p>
<p>Release Date: 2020-10-26</p>
<p>Fix Resolution (systeminformation): 4.27.11</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-21315</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The System Information Library for Node.JS (npm package "systeminformation") is an open source collection of functions to retrieve detailed hardware, system and OS information. In systeminformation before version 5.3.1 there is a command injection vulnerability. Problem was fixed in version 5.3.1. As a workaround instead of upgrading, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() ... do only allow strings, reject any arrays. String sanitation works as expected.
<p>Publish Date: 2021-02-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21315>CVE-2021-21315</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-2m8v-572m-ff2v">https://github.com/sebhildebrandt/systeminformation/security/advisories/GHSA-2m8v-572m-ff2v</a></p>
<p>Release Date: 2021-02-16</p>
<p>Fix Resolution (systeminformation): 4.34.11</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-28469</summary>
### Vulnerable Library - <b>glob-parent-5.1.0.tgz</b></p>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- chokidar-3.3.1.tgz
- :x: **glob-parent-5.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23343</summary>
### Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/path-parse/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- shelljs-0.8.3.tgz
- rechoir-0.6.2.tgz
- resolve-1.15.1.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jbgutierrez/path-parse/issues/8">https://github.com/jbgutierrez/path-parse/issues/8</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution (path-parse): 1.0.7</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3749</summary>
### Vulnerable Library - <b>axios-0.19.2.tgz</b></p>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.19.2.tgz">https://registry.npmjs.org/axios/-/axios-0.19.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- js-api-0.5.60.tgz
- :x: **axios-0.19.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
axios is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749>CVE-2021-3749</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/axios/axios/releases/tag/v0.21.2">https://github.com/axios/axios/releases/tag/v0.21.2</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (axios): 0.20.0</p>
<p>Direct dependency fix Resolution (pm2): 4.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8203</summary>
### Vulnerable Library - <b>lodash-4.17.14.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pm2/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **lodash-4.17.14.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution (lodash): 4.17.19</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7778</summary>
### Vulnerable Library - <b>systeminformation-4.23.1.tgz</b></p>
<p>Simple system and OS information library</p>
<p>Library home page: <a href="https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz">https://registry.npmjs.org/systeminformation/-/systeminformation-4.23.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/systeminformation/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **systeminformation-4.23.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package systeminformation before 4.30.2. The attacker can overwrite the properties and functions of an object, which can lead to executing OS commands.
<p>Publish Date: 2020-11-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7778>CVE-2020-7778</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sebhildebrandt/systeminformation/releases/tag/v4.30.2">https://github.com/sebhildebrandt/systeminformation/releases/tag/v4.30.2</a></p>
<p>Release Date: 2020-11-26</p>
<p>Fix Resolution (systeminformation): 4.30.2</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7788</summary>
### Vulnerable Library - <b>ini-1.3.5.tgz</b></p>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.5.tgz">https://registry.npmjs.org/ini/-/ini-1.3.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- vizion-2.0.2.tgz
- :x: **ini-1.3.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (ini): 1.3.6</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23337</summary>
### Vulnerable Library - <b>lodash-4.17.14.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.14.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pm2/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- pm2-4.2.3.tgz (Root Library)
- :x: **lodash-4.17.14.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/main/commit/ecb3574ba0c4685d9a34e0b4904ed81d76026f9b">ecb3574ba0c4685d9a34e0b4904ed81d76026f9b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (pm2): 4.3.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-21388","vulnerabilityDetails":"systeminformation is an open source system and OS information library for node.js. A command injection vulnerability has been discovered in versions of systeminformation prior to 5.6.4. The issue has been fixed with a parameter check on user input. Please upgrade to version \u003e\u003d 5.6.4. If you cannot upgrade, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() and other commands. Only allow strings, reject any arrays. String sanitation works as expected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21388","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26245","vulnerabilityDetails":"npm package systeminformation before version 4.30.5 is vulnerable to Prototype Pollution leading to Command Injection. The issue was fixed with a rewrite of shell sanitations to avoid prototyper pollution problems. The issue is fixed in version 4.30.5. If you cannot upgrade, be sure to check or sanitize service parameter strings that are passed to si.inetChecksite().","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26245","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26300","vulnerabilityDetails":"systeminformation is an npm package that provides system and OS information library for node.js. In systeminformation before version 4.26.2 there is a command injection vulnerability. Problem was fixed in version 4.26.2 with a shell string sanitation fix.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26300","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.0.0","isBinary":false},{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.0.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23406","vulnerabilityDetails":"This affects the package pac-resolver before 5.0.0. This can occur when used with untrusted input, due to unsafe PAC file handling. **NOTE:** The fix for this vulnerability is applied in the node-degenerator library, a dependency written by the same maintainer.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23406","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.5.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-28918","vulnerabilityDetails":"Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-26274","vulnerabilityDetails":"In systeminformation (npm package) before version 4.31.1 there is a command injection vulnerability. The problem was fixed in version 4.31.1 with a shell string sanitation fix.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26274","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7752","vulnerabilityDetails":"This affects the package systeminformation before 4.27.11. This package is vulnerable to Command Injection. The attacker can concatenate curl\u0027s parameters to overwrite Javascript files and then execute any OS commands.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7752","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-21315","vulnerabilityDetails":"The System Information Library for Node.JS (npm package \"systeminformation\") is an open source collection of functions to retrieve detailed hardware, system and OS information. In systeminformation before version 5.3.1 there is a command injection vulnerability. Problem was fixed in version 5.3.1. As a workaround instead of upgrading, be sure to check or sanitize service parameters that are passed to si.inetLatency(), si.inetChecksite(), si.services(), si.processLoad() ... do only allow strings, reject any arrays. String sanitation works as expected.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21315","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28469","vulnerabilityDetails":"This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23343","vulnerabilityDetails":"All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-3749","vulnerabilityDetails":"axios is vulnerable to Inefficient Regular Expression Complexity","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8203","vulnerabilityDetails":"Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7778","vulnerabilityDetails":"This affects the package systeminformation before 4.30.2. The attacker can overwrite the properties and functions of an object, which can lead to executing OS commands.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7778","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7788","vulnerabilityDetails":"This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0144","vulnerabilityDetails":"shelljs is vulnerable to Improper Privilege Management","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0144","cvss3Severity":"high","cvss3Score":"7.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0155","vulnerabilityDetails":"follow-redirects is vulnerable to Exposure of Private Personal Information to an Unauthorized Actor","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0155","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-0536","vulnerabilityDetails":"Exposure of Sensitive Information to an Unauthorized Actor in NPM follow-redirects prior to 1.14.8.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0536","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28168","vulnerabilityDetails":"Axios NPM package 0.21.0 contains a Server-Side Request Forgery (SSRF) vulnerability where an attacker is able to bypass a proxy by providing a URL that responds with a redirect to a restricted host or IP address.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28168","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.\n WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false},{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32640","vulnerabilityDetails":"ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size\u003dsize`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"pm2","packageVersion":"4.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"pm2:4.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.5.6","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-29418","vulnerabilityDetails":"The netmask package before 2.0.1 for Node.js mishandles certain unexpected characters in an IP address string, such as an octal digit of 9. This (in some situations) allows attackers to bypass access control that is based on IP addresses. NOTE: this issue exists because of an incomplete fix for CVE-2021-28918.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29418","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | non_priority | tgz vulnerabilities highest severity is vulnerable library tgz path to dependency file package json path to vulnerable library node modules systeminformation package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high systeminformation tgz transitive high systeminformation tgz transitive high systeminformation tgz transitive high multiple transitive high netmask tgz transitive high systeminformation tgz transitive high systeminformation tgz transitive high systeminformation tgz transitive high glob parent tgz transitive high path parse tgz transitive high axios tgz transitive high lodash tgz transitive high systeminformation tgz transitive high ini tgz transitive high lodash tgz transitive high shelljs tgz transitive medium follow redirects tgz transitive medium follow redirects tgz transitive medium axios tgz transitive medium lodash tgz transitive medium multiple transitive medium netmask tgz transitive details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details systeminformation is an open source system and os information library for node js a command injection vulnerability has been discovered in versions of systeminformation prior to the issue has been fixed with a parameter check on user input please upgrade to version if you cannot upgrade be sure to check or sanitize service parameters that are passed to si inetlatency si inetchecksite si services si processload and other commands only allow strings reject any arrays string sanitation works as expected publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details npm package systeminformation before version is vulnerable to prototype pollution leading to command injection the issue was fixed with a rewrite of shell sanitations to avoid prototyper pollution problems the issue is fixed in version if you cannot upgrade be sure to check or sanitize service parameter strings that are passed to si inetchecksite publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details systeminformation is an npm package that provides system and os information library for node js in systeminformation before version there is a command injection vulnerability problem was fixed in version with a shell string sanitation fix publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable libraries pac resolver tgz degenerator tgz pac resolver tgz generates an asynchronous resolver function from a pac file library home page a href path to dependency file package json path to vulnerable library node modules pac resolver package json dependency hierarchy tgz root library agent tgz proxy agent tgz pac proxy agent tgz x pac resolver tgz vulnerable library degenerator tgz turns sync functions into async generator functions library home page a href path to dependency file package json path to vulnerable library node modules degenerator package json dependency hierarchy tgz root library agent tgz proxy agent tgz pac proxy agent tgz pac resolver tgz x degenerator tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package pac resolver before this can occur when used with untrusted input due to unsafe pac file handling note the fix for this vulnerability is applied in the node degenerator library a dependency written by the same maintainer publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pac resolver direct dependency fix resolution fix resolution degenerator direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library netmask tgz parse and lookup ip network blocks library home page a href path to dependency file package json path to vulnerable library node modules netmask package json dependency hierarchy tgz root library agent tgz proxy agent tgz pac proxy agent tgz pac resolver tgz x netmask tgz vulnerable library found in head commit a href found in base branch master vulnerability details improper input validation of octal strings in netmask npm package and below allows unauthenticated remote attackers to perform indeterminate ssrf rfi and lfi attacks on many of the dependent packages a remote unauthenticated attacker can bypass packages relying on netmask to filter ips and reach critical vpn or lan hosts publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution netmask direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details in systeminformation npm package before version there is a command injection vulnerability the problem was fixed in version with a shell string sanitation fix publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package systeminformation before this package is vulnerable to command injection the attacker can concatenate curl s parameters to overwrite javascript files and then execute any os commands publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details the system information library for node js npm package systeminformation is an open source collection of functions to retrieve detailed hardware system and os information in systeminformation before version there is a command injection vulnerability problem was fixed in version as a workaround instead of upgrading be sure to check or sanitize service parameters that are passed to si inetlatency si inetchecksite si services si processload do only allow strings reject any arrays string sanitation works as expected publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file package json path to vulnerable library node modules glob parent package json dependency hierarchy tgz root library chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library path parse tgz node js path parse ponyfill library home page a href path to dependency file package json path to vulnerable library node modules path parse package json dependency hierarchy tgz root library shelljs tgz rechoir tgz resolve tgz x path parse tgz vulnerable library found in head commit a href found in base branch master vulnerability details all versions of package path parse are vulnerable to regular expression denial of service redos via splitdevicere splittailre and splitpathre regular expressions redos exhibits polynomial worst case time complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution path parse direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library axios tgz promise based http client for the browser and node js library home page a href path to dependency file package json path to vulnerable library node modules axios package json dependency hierarchy tgz root library js api tgz x axios tgz vulnerable library found in head commit a href found in base branch master vulnerability details axios is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution axios direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file package json path to vulnerable library node modules node modules lodash package json dependency hierarchy tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details prototype pollution attack when using zipobjectdeep in lodash before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library systeminformation tgz simple system and os information library library home page a href path to dependency file package json path to vulnerable library node modules systeminformation package json dependency hierarchy tgz root library x systeminformation tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package systeminformation before the attacker can overwrite the properties and functions of an object which can lead to executing os commands publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution systeminformation direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library ini tgz an ini encoder decoder for node library home page a href path to dependency file package json path to vulnerable library node modules ini package json dependency hierarchy tgz root library vizion tgz x ini tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ini direct dependency fix resolution step up your open source security game with whitesource cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file package json path to vulnerable library node modules node modules lodash package json dependency hierarchy tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash direct dependency fix resolution step up your open source security game with whitesource istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails systeminformation is an open source system and os information library for node js a command injection vulnerability has been discovered in versions of systeminformation prior to the issue has been fixed with a parameter check on user input please upgrade to version if you cannot upgrade be sure to check or sanitize service parameters that are passed to si inetlatency si inetchecksite si services si processload and other commands only allow strings reject any arrays string sanitation works as expected vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails npm package systeminformation before version is vulnerable to prototype pollution leading to command injection the issue was fixed with a rewrite of shell sanitations to avoid prototyper pollution problems the issue is fixed in version if you cannot upgrade be sure to check or sanitize service parameter strings that are passed to si inetchecksite vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails systeminformation is an npm package that provides system and os information library for node js in systeminformation before version there is a command injection vulnerability problem was fixed in version with a shell string sanitation fix vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename packageversion packagefilepaths istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package pac resolver before this can occur when used with untrusted input due to unsafe pac file handling note the fix for this vulnerability is applied in the node degenerator library a dependency written by the same maintainer vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails improper input validation of octal strings in netmask npm package and below allows unauthenticated remote attackers to perform indeterminate ssrf rfi and lfi attacks on many of the dependent packages a remote unauthenticated attacker can bypass packages relying on netmask to filter ips and reach critical vpn or lan hosts vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in systeminformation npm package before version there is a command injection vulnerability the problem was fixed in version with a shell string sanitation fix vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package systeminformation before this package is vulnerable to command injection the attacker can concatenate curl parameters to overwrite javascript files and then execute any os commands vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the system information library for node js npm package systeminformation is an open source collection of functions to retrieve detailed hardware system and os information in systeminformation before version there is a command injection vulnerability problem was fixed in version as a workaround instead of upgrading be sure to check or sanitize service parameters that are passed to si inetlatency si inetchecksite si services si processload do only allow strings reject any arrays string sanitation works as expected vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails all versions of package path parse are vulnerable to regular expression denial of service redos via splitdevicere splittailre and splitpathre regular expressions redos exhibits polynomial worst case time complexity vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails axios is vulnerable to inefficient regular expression complexity vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails prototype pollution attack when using zipobjectdeep in lodash before vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package systeminformation before the attacker can overwrite the properties and functions of an object which can lead to executing os commands vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to command injection via the template function vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails shelljs is vulnerable to improper privilege management vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails follow redirects is vulnerable to exposure of private personal information to an unauthorized actor vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails exposure of sensitive information to an unauthorized actor in npm follow redirects prior to vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails axios npm package contains a server side request forgery ssrf vulnerability where an attacker is able to bypass a proxy by providing a url that responds with a redirect to a restricted host or ip address vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions n whitesource note after conducting further research whitesource has determined that cve only affects environments with versions to of lodash vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false packagetype javascript node js packagename packageversion packagefilepaths istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails ws is an open source websocket client and server library for node js a specially crafted value of the sec websocket protocol header can be used to significantly slow down a ws server the vulnerability has been fixed in ws in vulnerable versions of ws the issue can be mitigated by reducing the maximum allowed length of the request headers using the and or the options vulnerabilityurl istransitivedependency false dependencytree isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the netmask package before for node js mishandles certain unexpected characters in an ip address string such as an octal digit of this in some situations allows attackers to bypass access control that is based on ip addresses note this issue exists because of an incomplete fix for cve vulnerabilityurl | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.