Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
45,719 | 13,132,167,890 | IssuesEvent | 2020-08-06 18:23:23 | jgeraigery/imhotep | https://api.github.com/repos/jgeraigery/imhotep | closed | CVE-2019-14540 (High) detected in jackson-databind-2.2.3.jar, jackson-databind-2.6.7.1.jar | security vulnerability | ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.2.3.jar</b>, <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.2.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /tmp/ws-scm/imhotep/imhotep-archive/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.2.3/jackson-databind-2.2.3.jar</p>
<p>
Dependency Hierarchy:
- hadoop-client-2.6.0-cdh5.4.11.jar (Root Library)
- hadoop-aws-2.6.0-cdh5.4.11.jar
- :x: **jackson-databind-2.2.3.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/imhotep/imhotep-server/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.7.1/jackson-databind-2.6.7.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.7.1.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/imhotep/commit/bf965e8cec478527a7e53b2ad0369a14e2a7162e">bf965e8cec478527a7e53b2ad0369a14e2a7162e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.2.3","isTransitiveDependency":true,"dependencyTree":"org.apache.hadoop:hadoop-client:2.6.0-cdh5.4.11;org.apache.hadoop:hadoop-aws:2.6.0-cdh5.4.11;com.fasterxml.jackson.core:jackson-databind:2.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.7.1","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1"}],"vulnerabilityIdentifier":"CVE-2019-14540","vulnerabilityDetails":"A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-14540 (High) detected in jackson-databind-2.2.3.jar, jackson-databind-2.6.7.1.jar - ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.2.3.jar</b>, <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.2.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to dependency file: /tmp/ws-scm/imhotep/imhotep-archive/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.2.3/jackson-databind-2.2.3.jar</p>
<p>
Dependency Hierarchy:
- hadoop-client-2.6.0-cdh5.4.11.jar (Root Library)
- hadoop-aws-2.6.0-cdh5.4.11.jar
- :x: **jackson-databind-2.2.3.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/imhotep/imhotep-server/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.7.1/jackson-databind-2.6.7.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.7.1.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/imhotep/commit/bf965e8cec478527a7e53b2ad0369a14e2a7162e">bf965e8cec478527a7e53b2ad0369a14e2a7162e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.2.3","isTransitiveDependency":true,"dependencyTree":"org.apache.hadoop:hadoop-client:2.6.0-cdh5.4.11;org.apache.hadoop:hadoop-aws:2.6.0-cdh5.4.11;com.fasterxml.jackson.core:jackson-databind:2.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.7.1","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1"}],"vulnerabilityIdentifier":"CVE-2019-14540","vulnerabilityDetails":"A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file tmp ws scm imhotep imhotep archive pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy hadoop client jar root library hadoop aws jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm imhotep imhotep server pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig vulnerabilityurl | 0 |
4,372 | 4,323,164,598 | IssuesEvent | 2016-07-25 16:08:35 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | opened | IDE analyzers shouldn't execute on closed files by default | Area-IDE Bug Tenet-Performance Urgency-Soon | IDE analyzers, such as simplify type name (are there more?), are currently executing on closed files as it reports descriptors with non-hidden severity. IDE diagnostic engine currently decides whether or not to run analyzers on closed files based on whether or not the analyzer reports any non-hidden diagnostics - and this has severe performance impact when full solution analysis is enabled as these analyzers are very expensive to run on closed files.
https://github.com/dotnet/roslyn/issues/12713 tracks adding an explicit tools option to configure closed file execution for analyzers in IDE. Until that has been implemented (which seems likely to be post preview 4), we should change IDE analyzers to only report hidden diagnostic descriptors so they don't end up running for closed files. | True | IDE analyzers shouldn't execute on closed files by default - IDE analyzers, such as simplify type name (are there more?), are currently executing on closed files as it reports descriptors with non-hidden severity. IDE diagnostic engine currently decides whether or not to run analyzers on closed files based on whether or not the analyzer reports any non-hidden diagnostics - and this has severe performance impact when full solution analysis is enabled as these analyzers are very expensive to run on closed files.
https://github.com/dotnet/roslyn/issues/12713 tracks adding an explicit tools option to configure closed file execution for analyzers in IDE. Until that has been implemented (which seems likely to be post preview 4), we should change IDE analyzers to only report hidden diagnostic descriptors so they don't end up running for closed files. | non_priority | ide analyzers shouldn t execute on closed files by default ide analyzers such as simplify type name are there more are currently executing on closed files as it reports descriptors with non hidden severity ide diagnostic engine currently decides whether or not to run analyzers on closed files based on whether or not the analyzer reports any non hidden diagnostics and this has severe performance impact when full solution analysis is enabled as these analyzers are very expensive to run on closed files tracks adding an explicit tools option to configure closed file execution for analyzers in ide until that has been implemented which seems likely to be post preview we should change ide analyzers to only report hidden diagnostic descriptors so they don t end up running for closed files | 0 |
19,495 | 27,074,949,882 | IssuesEvent | 2023-02-14 09:56:19 | Sansui233/logseq-bonofix-theme | https://api.github.com/repos/Sansui233/logseq-bonofix-theme | closed | Bonofix使用透明度颜色用于混合 导致Awesome UI的属性icon出现重叠与边框的Bug | compatibility | 现象:使用Awesome UI时,Bonofix的属性icon出现重叠与多余方框。
> Default theme:
> <img width="572" alt="image" src="https://user-images.githubusercontent.com/96460796/218246263-0d9004f9-adf6-4d89-98b0-a701a7e24e6e.png">
> Bonofix theme:
> <img width="564" alt="image" src="https://user-images.githubusercontent.com/96460796/218246592-b27cee04-48e7-4e1d-abd7-70262cd76702.png">
Awesome UI作者表示是Bonofix所用的颜色使用了透明度导致:
> in the case of "Bonofix" - bg color is using transparency:
>
> 
>
> contact author to somehow solve it - https://github.com/Sansui233/logseq-bonofix-theme/issues
> Gitbreast: I see(a little bit), Bonofix uses a color with transparency to mix with default theme's color to get Bonofix's color, right? I'll issue it to Bonofix.
_Originally posted by @Gitbreast in https://github.com/yoyurec/logseq-awesome-ui/issues/45#issuecomment-1426708420_
Dev theme也有类似问题但原因不一样,好像是没用logseq的变量名而导致:https://github.com/pengx17/logseq-dev-theme/pull/87
是否直接使用混合后的非透明度颜色的值,这个Bug就会解决? | True | Bonofix使用透明度颜色用于混合 导致Awesome UI的属性icon出现重叠与边框的Bug - 现象:使用Awesome UI时,Bonofix的属性icon出现重叠与多余方框。
> Default theme:
> <img width="572" alt="image" src="https://user-images.githubusercontent.com/96460796/218246263-0d9004f9-adf6-4d89-98b0-a701a7e24e6e.png">
> Bonofix theme:
> <img width="564" alt="image" src="https://user-images.githubusercontent.com/96460796/218246592-b27cee04-48e7-4e1d-abd7-70262cd76702.png">
Awesome UI作者表示是Bonofix所用的颜色使用了透明度导致:
> in the case of "Bonofix" - bg color is using transparency:
>
> 
>
> contact author to somehow solve it - https://github.com/Sansui233/logseq-bonofix-theme/issues
> Gitbreast: I see(a little bit), Bonofix uses a color with transparency to mix with default theme's color to get Bonofix's color, right? I'll issue it to Bonofix.
_Originally posted by @Gitbreast in https://github.com/yoyurec/logseq-awesome-ui/issues/45#issuecomment-1426708420_
Dev theme也有类似问题但原因不一样,好像是没用logseq的变量名而导致:https://github.com/pengx17/logseq-dev-theme/pull/87
是否直接使用混合后的非透明度颜色的值,这个Bug就会解决? | non_priority | bonofix使用透明度颜色用于混合 导致awesome ui的属性icon出现重叠与边框的bug 现象:使用awesome ui时,bonofix的属性icon出现重叠与多余方框。 default theme img width alt image src bonofix theme img width alt image src awesome ui作者表示是bonofix所用的颜色使用了透明度导致: in the case of bonofix bg color is using transparency contact author to somehow solve it gitbreast i see a little bit bonofix uses a color with transparency to mix with default theme s color to get bonofix s color right i ll issue it to bonofix originally posted by gitbreast in dev theme也有类似问题但原因不一样,好像是没用logseq的变量名而导致: 是否直接使用混合后的非透明度颜色的值,这个bug就会解决? | 0 |
194,029 | 15,395,323,958 | IssuesEvent | 2021-03-03 19:04:13 | grommet/grommet | https://api.github.com/repos/grommet/grommet | closed | Button active and hover themes not working | documentation :memo: waiting | It looks like button theming is not working correctly as of v2.14.0.
### Expected Behavior
Buttons should be themable by `button.active.primary.extend`, `button.hover.primary.extend` etc as shown in [base.d.ts#L323](https://github.com/grommet/grommet/blob/master/src/js/themes/base.d.ts#L323). The custom button in the [storybook](https://storybook.grommet.io/?path=/story/button--custom) is not using this new theme format.
### Actual Behavior
When using the new format with `button.active.primary` instead of `button.primary.active` the theme has no effect.
| 1.0 | Button active and hover themes not working - It looks like button theming is not working correctly as of v2.14.0.
### Expected Behavior
Buttons should be themable by `button.active.primary.extend`, `button.hover.primary.extend` etc as shown in [base.d.ts#L323](https://github.com/grommet/grommet/blob/master/src/js/themes/base.d.ts#L323). The custom button in the [storybook](https://storybook.grommet.io/?path=/story/button--custom) is not using this new theme format.
### Actual Behavior
When using the new format with `button.active.primary` instead of `button.primary.active` the theme has no effect.
| non_priority | button active and hover themes not working it looks like button theming is not working correctly as of expected behavior buttons should be themable by button active primary extend button hover primary extend etc as shown in the custom button in the is not using this new theme format actual behavior when using the new format with button active primary instead of button primary active the theme has no effect | 0 |
46,298 | 11,811,846,624 | IssuesEvent | 2020-03-19 18:58:36 | apache/incubator-mxnet | https://api.github.com/repos/apache/incubator-mxnet | closed | CI Build Failures: unix-gpu TensorRT | Bug Build CI | http://jenkins.mxnet-ci.amazon-ml.com/blue/organizations/jenkins/mxnet-validation%2Funix-gpu/detail/PR-14959/2/pipeline.
TensorRT build fails with:
```
-- Could NOT find TENSORRT (missing: TENSORRT_INCLUDE_DIR TENSORRT_LIBRARY)
ERRORCannot find TensorRT library.
CMake Error: The following variables are used in this project, but they are set to NOTFOUND.
Please set them or make sure they are set and tested correctly in the CMake files:
/work/mxnet/3rdparty/onnx-tensorrt/TENSORRT_INCLUDE_DIR
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
-- Configuring incomplete, errors occurred!
See also "/work/mxnet/3rdparty/onnx-tensorrt/build/CMakeFiles/CMakeOutput.log".
See also "/work/mxnet/3rdparty/onnx-tensorrt/build/CMakeFiles/CMakeError.log".
TENSORRT_INCLUDE_DIR
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
TENSORRT_LIBRARY_INFER
linked by target "nvonnxparser_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_plugin" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
TENSORRT_LIBRARY_INFER_PLUGIN
linked by target "nvonnxparser_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_plugin" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
build.py: 2019-05-15 08:02:20,417Z INFO Waiting for status of container cc30cac8c8bd for 600 s.
build.py: 2019-05-15 08:02:22,337Z INFO Container exit status: {'Error': None, 'StatusCode': 1}
build.py: 2019-05-15 08:02:22,337Z ERROR Container exited with an error 😞
``` | 1.0 | CI Build Failures: unix-gpu TensorRT - http://jenkins.mxnet-ci.amazon-ml.com/blue/organizations/jenkins/mxnet-validation%2Funix-gpu/detail/PR-14959/2/pipeline.
TensorRT build fails with:
```
-- Could NOT find TENSORRT (missing: TENSORRT_INCLUDE_DIR TENSORRT_LIBRARY)
ERRORCannot find TensorRT library.
CMake Error: The following variables are used in this project, but they are set to NOTFOUND.
Please set them or make sure they are set and tested correctly in the CMake files:
/work/mxnet/3rdparty/onnx-tensorrt/TENSORRT_INCLUDE_DIR
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
-- Configuring incomplete, errors occurred!
See also "/work/mxnet/3rdparty/onnx-tensorrt/build/CMakeFiles/CMakeOutput.log".
See also "/work/mxnet/3rdparty/onnx-tensorrt/build/CMakeFiles/CMakeError.log".
TENSORRT_INCLUDE_DIR
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
used as include directory in directory /work/mxnet/3rdparty/onnx-tensorrt
TENSORRT_LIBRARY_INFER
linked by target "nvonnxparser_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_plugin" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
TENSORRT_LIBRARY_INFER_PLUGIN
linked by target "nvonnxparser_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_plugin" in directory /work/mxnet/3rdparty/onnx-tensorrt
linked by target "nvonnxparser_runtime_static" in directory /work/mxnet/3rdparty/onnx-tensorrt
build.py: 2019-05-15 08:02:20,417Z INFO Waiting for status of container cc30cac8c8bd for 600 s.
build.py: 2019-05-15 08:02:22,337Z INFO Container exit status: {'Error': None, 'StatusCode': 1}
build.py: 2019-05-15 08:02:22,337Z ERROR Container exited with an error 😞
``` | non_priority | ci build failures unix gpu tensorrt tensorrt build fails with could not find tensorrt missing tensorrt include dir tensorrt library errorcannot find tensorrt library cmake error the following variables are used in this project but they are set to notfound please set them or make sure they are set and tested correctly in the cmake files work mxnet onnx tensorrt tensorrt include dir used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt configuring incomplete errors occurred see also work mxnet onnx tensorrt build cmakefiles cmakeoutput log see also work mxnet onnx tensorrt build cmakefiles cmakeerror log tensorrt include dir used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt used as include directory in directory work mxnet onnx tensorrt tensorrt library infer linked by target nvonnxparser static in directory work mxnet onnx tensorrt linked by target nvonnxparser in directory work mxnet onnx tensorrt linked by target nvonnxparser runtime in directory work mxnet onnx tensorrt linked by target nvonnxparser plugin in directory work mxnet onnx tensorrt linked by target nvonnxparser runtime static in directory work mxnet onnx tensorrt tensorrt library infer plugin linked by target nvonnxparser static in directory work mxnet onnx tensorrt linked by target nvonnxparser in directory work mxnet onnx tensorrt linked by target nvonnxparser runtime in directory work mxnet onnx tensorrt linked by target nvonnxparser plugin in directory work mxnet onnx tensorrt linked by target nvonnxparser runtime static in directory work mxnet onnx tensorrt build py info waiting for status of container for s build py info container exit status error none statuscode build py error container exited with an error 😞 | 0 |
241,649 | 20,154,352,236 | IssuesEvent | 2022-02-09 15:12:44 | hibernate/hibernate-reactive | https://api.github.com/repos/hibernate/hibernate-reactive | reopened | UnsupportedOperationException on CI with MySql when credentials are wrong | testing | I've updated the test WrongCredentialsTest so that it runs for every datastore. It seems to work fine locally but when it runs on CI with MySQL and the latest ORM Snapshot it throws an UnsupportedOperationException instead of the expected one:
```
java.lang.UnsupportedOperationException: Unsupported authentication method: sha256_password
```
I cannot replicate this issue locally and I'm not sure what causing it on CI.
This is the test class:
https://github.com/DavideD/hibernate-reactive/blob/d131bb2b38662b3bc64ee88faae42a9c223e5a70/hibernate-reactive-core/src/test/java/org/hibernate/reactive/WrongCredentialsTest.java
On CI it seems to happen with the latest ORM snapshot but I don't think it's related.
Here's the failed workflow: https://github.com/hibernate/hibernate-reactive/runs/1687501809?check_suite_focus=true#step:5:314
See also: https://github.com/eclipse-vertx/vertx-sql-client/issues/1132 | 1.0 | UnsupportedOperationException on CI with MySql when credentials are wrong - I've updated the test WrongCredentialsTest so that it runs for every datastore. It seems to work fine locally but when it runs on CI with MySQL and the latest ORM Snapshot it throws an UnsupportedOperationException instead of the expected one:
```
java.lang.UnsupportedOperationException: Unsupported authentication method: sha256_password
```
I cannot replicate this issue locally and I'm not sure what causing it on CI.
This is the test class:
https://github.com/DavideD/hibernate-reactive/blob/d131bb2b38662b3bc64ee88faae42a9c223e5a70/hibernate-reactive-core/src/test/java/org/hibernate/reactive/WrongCredentialsTest.java
On CI it seems to happen with the latest ORM snapshot but I don't think it's related.
Here's the failed workflow: https://github.com/hibernate/hibernate-reactive/runs/1687501809?check_suite_focus=true#step:5:314
See also: https://github.com/eclipse-vertx/vertx-sql-client/issues/1132 | non_priority | unsupportedoperationexception on ci with mysql when credentials are wrong i ve updated the test wrongcredentialstest so that it runs for every datastore it seems to work fine locally but when it runs on ci with mysql and the latest orm snapshot it throws an unsupportedoperationexception instead of the expected one java lang unsupportedoperationexception unsupported authentication method password i cannot replicate this issue locally and i m not sure what causing it on ci this is the test class on ci it seems to happen with the latest orm snapshot but i don t think it s related here s the failed workflow see also | 0 |
68,011 | 13,060,442,668 | IssuesEvent | 2020-07-30 12:26:42 | hypergraph-xyz/desktop | https://api.github.com/repos/hypergraph-xyz/desktop | closed | Tab Index | code feature | - [x] Ensure all elements have a tab index that makes sense
- [x] Ensure all elements have a visible active state. | 1.0 | Tab Index - - [x] Ensure all elements have a tab index that makes sense
- [x] Ensure all elements have a visible active state. | non_priority | tab index ensure all elements have a tab index that makes sense ensure all elements have a visible active state | 0 |
3,596 | 4,542,298,354 | IssuesEvent | 2016-09-09 20:43:02 | twschiller/open-synthesis | https://api.github.com/repos/twschiller/open-synthesis | opened | Security scan infrastructure | devops help wanted security | Preliminary automatic scan with [OWASP ZAP](https://github.com/zaproxy/zaproxy) showed no major issues. However, we should set up infrastructure (e.g., Docker) for running scans regularly. | True | Security scan infrastructure - Preliminary automatic scan with [OWASP ZAP](https://github.com/zaproxy/zaproxy) showed no major issues. However, we should set up infrastructure (e.g., Docker) for running scans regularly. | non_priority | security scan infrastructure preliminary automatic scan with showed no major issues however we should set up infrastructure e g docker for running scans regularly | 0 |
5,541 | 7,201,739,914 | IssuesEvent | 2018-02-05 23:58:21 | USEPA/e-manifest | https://api.github.com/repos/USEPA/e-manifest | closed | Hide RQ fields when waste is non-hazardous | Awaiting Approval EM-826 Services and Signatures 6 bug | As a generator, the RQ and RQ description fields are displaying when the waste is non-hazardous and the manifest is in the "Scheduled" status. The fields are also displaying on the View and CoR page for all users. | 1.0 | Hide RQ fields when waste is non-hazardous - As a generator, the RQ and RQ description fields are displaying when the waste is non-hazardous and the manifest is in the "Scheduled" status. The fields are also displaying on the View and CoR page for all users. | non_priority | hide rq fields when waste is non hazardous as a generator the rq and rq description fields are displaying when the waste is non hazardous and the manifest is in the scheduled status the fields are also displaying on the view and cor page for all users | 0 |
385,983 | 26,661,817,283 | IssuesEvent | 2023-01-25 21:53:38 | johnmck95/mtbTG | https://api.github.com/repos/johnmck95/mtbTG | opened | Populate Help Page with Content | feautre documentation | - [ ] Write descriptions for all headings
- [ ] Create images in Canva to help explain concepts
- [ ] Decided if it's worth including the search feature, and either hook it up or remove it. | 1.0 | Populate Help Page with Content - - [ ] Write descriptions for all headings
- [ ] Create images in Canva to help explain concepts
- [ ] Decided if it's worth including the search feature, and either hook it up or remove it. | non_priority | populate help page with content write descriptions for all headings create images in canva to help explain concepts decided if it s worth including the search feature and either hook it up or remove it | 0 |
109,939 | 13,879,629,550 | IssuesEvent | 2020-10-17 15:17:05 | kambiz-frounchi/Foodie | https://api.github.com/repos/kambiz-frounchi/Foodie | opened | Define mongodb schemas | design | This story defines the mongodb schemas.
At first glance these are the schemas that come to mind:
1. **recipe**:
- name (string)
- image (string to the image path?)
- time (enum)
- difficultyLevel (enum)
- category (enum)
- ingredients (array of ingredients (strings))
- tags (array of tags (strings))
2. **feed**:
- recipes (array of recipe objects)
3. **user**:
- status
- recipes (array of recipes only pertaining to this user)
| 1.0 | Define mongodb schemas - This story defines the mongodb schemas.
At first glance these are the schemas that come to mind:
1. **recipe**:
- name (string)
- image (string to the image path?)
- time (enum)
- difficultyLevel (enum)
- category (enum)
- ingredients (array of ingredients (strings))
- tags (array of tags (strings))
2. **feed**:
- recipes (array of recipe objects)
3. **user**:
- status
- recipes (array of recipes only pertaining to this user)
| non_priority | define mongodb schemas this story defines the mongodb schemas at first glance these are the schemas that come to mind recipe name string image string to the image path time enum difficultylevel enum category enum ingredients array of ingredients strings tags array of tags strings feed recipes array of recipe objects user status recipes array of recipes only pertaining to this user | 0 |
421,801 | 28,359,396,190 | IssuesEvent | 2023-04-12 09:39:17 | cloudflare/cloudflare-docs | https://api.github.com/repos/cloudflare/cloudflare-docs | closed | Pages: architecture target for custom build executables? | documentation product:pages | ### Expected Behavior
The docs have a lot of information about what tooling is available in the build env, but it doesn't specify the OS / architecture / shell. I'm trying to use a Rust built executable as my build step (it's committed to my repo), but I get an error when I try to run it on the server.
I'm building on an ARM Mac, so I probably need to compile it for some sort of x86 linux environment? I can figure this out by trial an error, but I'm new to cross compiling Rust and it will take me some time to figure out... so it'd be nice to have the answer available in the docs. Or, if it's the case, to know it's not supported.
### Actual Behavior
Is it possible to run custom executables as the build command? If so, what OS/architecture should we target?
### Section that requires update
https://developers.cloudflare.com/pages/platform/build-configuration
### Additional information
The error I get is `./scripts/build_script: 1: ./scripts/build_script: Syntax error: word unexpected (expecting ")")` which I believe is the error that you receive if you have an executable built for the wrong architecture or with the wrong shell assumptions. | 1.0 | Pages: architecture target for custom build executables? - ### Expected Behavior
The docs have a lot of information about what tooling is available in the build env, but it doesn't specify the OS / architecture / shell. I'm trying to use a Rust built executable as my build step (it's committed to my repo), but I get an error when I try to run it on the server.
I'm building on an ARM Mac, so I probably need to compile it for some sort of x86 linux environment? I can figure this out by trial an error, but I'm new to cross compiling Rust and it will take me some time to figure out... so it'd be nice to have the answer available in the docs. Or, if it's the case, to know it's not supported.
### Actual Behavior
Is it possible to run custom executables as the build command? If so, what OS/architecture should we target?
### Section that requires update
https://developers.cloudflare.com/pages/platform/build-configuration
### Additional information
The error I get is `./scripts/build_script: 1: ./scripts/build_script: Syntax error: word unexpected (expecting ")")` which I believe is the error that you receive if you have an executable built for the wrong architecture or with the wrong shell assumptions. | non_priority | pages architecture target for custom build executables expected behavior the docs have a lot of information about what tooling is available in the build env but it doesn t specify the os architecture shell i m trying to use a rust built executable as my build step it s committed to my repo but i get an error when i try to run it on the server i m building on an arm mac so i probably need to compile it for some sort of linux environment i can figure this out by trial an error but i m new to cross compiling rust and it will take me some time to figure out so it d be nice to have the answer available in the docs or if it s the case to know it s not supported actual behavior is it possible to run custom executables as the build command if so what os architecture should we target section that requires update additional information the error i get is scripts build script scripts build script syntax error word unexpected expecting which i believe is the error that you receive if you have an executable built for the wrong architecture or with the wrong shell assumptions | 0 |
182,973 | 21,678,646,516 | IssuesEvent | 2022-05-09 02:23:58 | turkdevops/thread-loader | https://api.github.com/repos/turkdevops/thread-loader | closed | CVE-2020-7774 (High) detected in y18n-4.0.0.tgz - autoclosed | security vulnerability | ## CVE-2020-7774 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>y18n-4.0.0.tgz</b></p></summary>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz">https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- cli-11.0.0.tgz (Root Library)
- yargs-15.4.1.tgz
- :x: **y18n-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/thread-loader/commit/751b60aa5b87b55382bde58feeb3dbfbe2433fad">751b60aa5b87b55382bde58feeb3dbfbe2433fad</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n = require('y18n')(); y18n.setLocale('__proto__'); y18n.updateLocale({polluted: true}); console.log(polluted); // true
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 4.0.1</p>
<p>Direct dependency fix Resolution (@commitlint/cli): 12.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7774 (High) detected in y18n-4.0.0.tgz - autoclosed - ## CVE-2020-7774 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>y18n-4.0.0.tgz</b></p></summary>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz">https://registry.npmjs.org/y18n/-/y18n-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- cli-11.0.0.tgz (Root Library)
- yargs-15.4.1.tgz
- :x: **y18n-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/thread-loader/commit/751b60aa5b87b55382bde58feeb3dbfbe2433fad">751b60aa5b87b55382bde58feeb3dbfbe2433fad</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n = require('y18n')(); y18n.setLocale('__proto__'); y18n.updateLocale({polluted: true}); console.log(polluted); // true
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 4.0.1</p>
<p>Direct dependency fix Resolution (@commitlint/cli): 12.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tgz autoclosed cve high severity vulnerability vulnerable library tgz the bare bones internationalization library used by yargs library home page a href path to dependency file package json path to vulnerable library node modules package json dependency hierarchy cli tgz root library yargs tgz x tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package before and poc by const require setlocale proto updatelocale polluted true console log polluted true publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution direct dependency fix resolution commitlint cli step up your open source security game with whitesource | 0 |
29,329 | 4,489,720,470 | IssuesEvent | 2016-08-30 12:07:53 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | Test: Should allow adjusting font weight | testplan-item | Test for #381 (came in via PR #10515)
- [x] Any OS **dbaeumer**
Complexity 1
Adds two new settings `editor.fontWeight` and `terminal.integrated.fontWeight`. If `terminal.integrated.fontWeight` is missing, `editor.fontWeight` will be picked up by the terminal.
Please check that you can change the editor's and the terminal's font weight. | 1.0 | Test: Should allow adjusting font weight - Test for #381 (came in via PR #10515)
- [x] Any OS **dbaeumer**
Complexity 1
Adds two new settings `editor.fontWeight` and `terminal.integrated.fontWeight`. If `terminal.integrated.fontWeight` is missing, `editor.fontWeight` will be picked up by the terminal.
Please check that you can change the editor's and the terminal's font weight. | non_priority | test should allow adjusting font weight test for came in via pr any os dbaeumer complexity adds two new settings editor fontweight and terminal integrated fontweight if terminal integrated fontweight is missing editor fontweight will be picked up by the terminal please check that you can change the editor s and the terminal s font weight | 0 |
46,855 | 19,530,618,864 | IssuesEvent | 2021-12-30 16:05:42 | dyc3/opentogethertube | https://api.github.com/repos/dyc3/opentogethertube | opened | Dailymotion put video ads in their iframe player and it causes UX issues. | bug client service/dailymotion regression | ### Current Behavior
Example:

### Expected Behavior
Dailymotion videos should play without ads or the client should be able to tell the server that there is an ad.
### Steps To Reproduce
1. queue up and play the "test dailymotion 0" video
### Environment
- [X] This happens on the official site, opentogethertube.com
- [X] This happens using a self-hosted version.
- [ ] I'm using the docker image.
### Anything else?
_No response_ | 1.0 | Dailymotion put video ads in their iframe player and it causes UX issues. - ### Current Behavior
Example:

### Expected Behavior
Dailymotion videos should play without ads or the client should be able to tell the server that there is an ad.
### Steps To Reproduce
1. queue up and play the "test dailymotion 0" video
### Environment
- [X] This happens on the official site, opentogethertube.com
- [X] This happens using a self-hosted version.
- [ ] I'm using the docker image.
### Anything else?
_No response_ | non_priority | dailymotion put video ads in their iframe player and it causes ux issues current behavior example expected behavior dailymotion videos should play without ads or the client should be able to tell the server that there is an ad steps to reproduce queue up and play the test dailymotion video environment this happens on the official site opentogethertube com this happens using a self hosted version i m using the docker image anything else no response | 0 |
71,013 | 23,409,534,913 | IssuesEvent | 2022-08-12 15:57:57 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | [BUG]: Dismissible alert on the benefit letter download page doesn't work and isn't uniquely labelled | bug frontend 508/Accessibility 508-defect-1 508-defect-3 Letters benefits-crew benefits-team-1 | ## What happened?
The dismissible alert "Download your VA Letters on your mobile device" does not respond to keyboard (space and enter) and mouse (click). The button's label is also generic "Close notification."
@bkjohnson caught the following issue in the app code:
```js
onClose={() => {
setIsHidden(true);
sessionStorage.setItem(STORAGE_KEY, 'hidden');
}}
```
This can be fixed by changing it to:
```js
onCloseEvent={() => dismissNotification(notification.id)}
```
## Specs:
- Device: Macbook
- Browser: Chrome and safari
## Steps to Reproduce
- URL: https://staging.va.gov/records/download-va-letters/
## Desired behavior
- This should respond to `space`, `enter`, and `click`
- This can be uniquely labelled by either using:
- Updating the `aria-label` e.g. aria-label="Close download VA letters notification"
- Using `aria-describedby` to let the heading describe the button
## Acceptance Criteria
- [ ] Button responds to `space`, `enter`, and `click`
- [ ] Button label is unique
## How to configure this issue
- [x] **Attached to a Milestone** (when will this be completed?)
- [x] **Attached to Epic** (what body of work is this a part of? possibly `Ongoing Maintenance`)
- [x] **Labeled with Team** (`product support`, `analytics-insights`, `operations`, `triage`, `tools-improvements`)
- [x] **Labeled with Practice Area** (`backend`, `frontend`, `devops`, `design`, `research`, `product`, `ia`, `qa`, `analytics`, `contact center`, `research`, `accessibility`, `content`)
- [x] **Labeled with `Bug`**
| 2.0 | [BUG]: Dismissible alert on the benefit letter download page doesn't work and isn't uniquely labelled - ## What happened?
The dismissible alert "Download your VA Letters on your mobile device" does not respond to keyboard (space and enter) and mouse (click). The button's label is also generic "Close notification."
@bkjohnson caught the following issue in the app code:
```js
onClose={() => {
setIsHidden(true);
sessionStorage.setItem(STORAGE_KEY, 'hidden');
}}
```
This can be fixed by changing it to:
```js
onCloseEvent={() => dismissNotification(notification.id)}
```
## Specs:
- Device: Macbook
- Browser: Chrome and safari
## Steps to Reproduce
- URL: https://staging.va.gov/records/download-va-letters/
## Desired behavior
- This should respond to `space`, `enter`, and `click`
- This can be uniquely labelled by either using:
- Updating the `aria-label` e.g. aria-label="Close download VA letters notification"
- Using `aria-describedby` to let the heading describe the button
## Acceptance Criteria
- [ ] Button responds to `space`, `enter`, and `click`
- [ ] Button label is unique
## How to configure this issue
- [x] **Attached to a Milestone** (when will this be completed?)
- [x] **Attached to Epic** (what body of work is this a part of? possibly `Ongoing Maintenance`)
- [x] **Labeled with Team** (`product support`, `analytics-insights`, `operations`, `triage`, `tools-improvements`)
- [x] **Labeled with Practice Area** (`backend`, `frontend`, `devops`, `design`, `research`, `product`, `ia`, `qa`, `analytics`, `contact center`, `research`, `accessibility`, `content`)
- [x] **Labeled with `Bug`**
| non_priority | dismissible alert on the benefit letter download page doesn t work and isn t uniquely labelled what happened the dismissible alert download your va letters on your mobile device does not respond to keyboard space and enter and mouse click the button s label is also generic close notification bkjohnson caught the following issue in the app code js onclose setishidden true sessionstorage setitem storage key hidden this can be fixed by changing it to js oncloseevent dismissnotification notification id specs device macbook browser chrome and safari steps to reproduce url desired behavior this should respond to space enter and click this can be uniquely labelled by either using updating the aria label e g aria label close download va letters notification using aria describedby to let the heading describe the button acceptance criteria button responds to space enter and click button label is unique how to configure this issue attached to a milestone when will this be completed attached to epic what body of work is this a part of possibly ongoing maintenance labeled with team product support analytics insights operations triage tools improvements labeled with practice area backend frontend devops design research product ia qa analytics contact center research accessibility content labeled with bug | 0 |
266,514 | 20,156,148,732 | IssuesEvent | 2022-02-09 16:37:55 | awslabs/aws-lambda-powertools-python | https://api.github.com/repos/awslabs/aws-lambda-powertools-python | closed | docs: fix examples in tutorial and api gw handler | documentation status/staged-next-release | **What were you initially searching for in the docs?**
- Working code examples.
**Is this related to an existing part of the documentation? Please share a link**
- api gw handler (https://awslabs.github.io/aws-lambda-powertools-python/latest/core/event_handler/api_gateway/)
- appsync handler (https://awslabs.github.io/aws-lambda-powertools-python/latest/core/event_handler/appsync/)
- tutorials (https://awslabs.github.io/aws-lambda-powertools-python/latest/tutorial/)
- feature flag (https://awslabs.github.io/aws-lambda-powertools-python/latest/utilities/feature_flags/)
**Describe how we could make it clearer**
- Fix code examples
**If you have a proposed update, please share it here**
List of things to fix:
- fix line number highlights
- fix missing imports
- fix syntax error
- fix indents
- fix example code rendering
Indent issue example:
<img width="1079" alt="Screen Shot 2022-02-07 at 10 17 20 PM" src="https://user-images.githubusercontent.com/5442469/152929369-48b671da-83b5-437e-a53a-4fcfdf7d125d.png">
Syntax Error example:
<img width="1091" alt="Screen Shot 2022-02-07 at 10 20 59 PM" src="https://user-images.githubusercontent.com/5442469/152929738-d35a7355-316f-4a26-9da4-70cce33548c3.png">
Missing import example for `json` example:
<img width="1062" alt="Screen Shot 2022-02-07 at 10 22 54 PM" src="https://user-images.githubusercontent.com/5442469/152930018-c21137d4-382e-45a6-857d-9c298c9b2a5d.png">
Code rendering example:
<img width="1100" alt="Screen Shot 2022-02-07 at 10 23 59 PM" src="https://user-images.githubusercontent.com/5442469/152930156-99084509-a9ba-409a-8e08-5397f4840530.png">
PR:
- https://github.com/awslabs/aws-lambda-powertools-python/pull/1004
| 1.0 | docs: fix examples in tutorial and api gw handler - **What were you initially searching for in the docs?**
- Working code examples.
**Is this related to an existing part of the documentation? Please share a link**
- api gw handler (https://awslabs.github.io/aws-lambda-powertools-python/latest/core/event_handler/api_gateway/)
- appsync handler (https://awslabs.github.io/aws-lambda-powertools-python/latest/core/event_handler/appsync/)
- tutorials (https://awslabs.github.io/aws-lambda-powertools-python/latest/tutorial/)
- feature flag (https://awslabs.github.io/aws-lambda-powertools-python/latest/utilities/feature_flags/)
**Describe how we could make it clearer**
- Fix code examples
**If you have a proposed update, please share it here**
List of things to fix:
- fix line number highlights
- fix missing imports
- fix syntax error
- fix indents
- fix example code rendering
Indent issue example:
<img width="1079" alt="Screen Shot 2022-02-07 at 10 17 20 PM" src="https://user-images.githubusercontent.com/5442469/152929369-48b671da-83b5-437e-a53a-4fcfdf7d125d.png">
Syntax Error example:
<img width="1091" alt="Screen Shot 2022-02-07 at 10 20 59 PM" src="https://user-images.githubusercontent.com/5442469/152929738-d35a7355-316f-4a26-9da4-70cce33548c3.png">
Missing import example for `json` example:
<img width="1062" alt="Screen Shot 2022-02-07 at 10 22 54 PM" src="https://user-images.githubusercontent.com/5442469/152930018-c21137d4-382e-45a6-857d-9c298c9b2a5d.png">
Code rendering example:
<img width="1100" alt="Screen Shot 2022-02-07 at 10 23 59 PM" src="https://user-images.githubusercontent.com/5442469/152930156-99084509-a9ba-409a-8e08-5397f4840530.png">
PR:
- https://github.com/awslabs/aws-lambda-powertools-python/pull/1004
| non_priority | docs fix examples in tutorial and api gw handler what were you initially searching for in the docs working code examples is this related to an existing part of the documentation please share a link api gw handler appsync handler tutorials feature flag describe how we could make it clearer fix code examples if you have a proposed update please share it here list of things to fix fix line number highlights fix missing imports fix syntax error fix indents fix example code rendering indent issue example img width alt screen shot at pm src syntax error example img width alt screen shot at pm src missing import example for json example img width alt screen shot at pm src code rendering example img width alt screen shot at pm src pr | 0 |
12,693 | 9,917,409,110 | IssuesEvent | 2019-06-29 00:15:47 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | opened | Port ResultProviders tests to support .NET Core | Area-Infrastructure Interactive-Debugging Test-Gap | There happen issues with Expression Evaluator working with .NET Core applications. These issue could be caused either by Roslyn or by Debugger or by CoreClr.
Roslyn Result Provider tests now are .NET Framework dependent. They are not running against .NET Core. So, it is hard to investigate EE + .NET Core issues. | 1.0 | Port ResultProviders tests to support .NET Core - There happen issues with Expression Evaluator working with .NET Core applications. These issue could be caused either by Roslyn or by Debugger or by CoreClr.
Roslyn Result Provider tests now are .NET Framework dependent. They are not running against .NET Core. So, it is hard to investigate EE + .NET Core issues. | non_priority | port resultproviders tests to support net core there happen issues with expression evaluator working with net core applications these issue could be caused either by roslyn or by debugger or by coreclr roslyn result provider tests now are net framework dependent they are not running against net core so it is hard to investigate ee net core issues | 0 |
334,726 | 29,953,071,629 | IssuesEvent | 2023-06-23 04:16:26 | Rhovas/Interpreter | https://api.github.com/repos/Rhovas/Interpreter | closed | Improve test coverage for easily-testable cases | testing parser evaluator analyzer typing | Following the Kotest migration, it should be much easier to add new test cases and catchup on coverage skipped previously (e.g. classes and error conditions). There are no strict goals for test coverage, however in most cases it should be easy to add missing cases to at least have good branch coverage.
- [x] Parser
- [x] Analyzer
- [x] Evaluator
- [x] Environment (Type) | 1.0 | Improve test coverage for easily-testable cases - Following the Kotest migration, it should be much easier to add new test cases and catchup on coverage skipped previously (e.g. classes and error conditions). There are no strict goals for test coverage, however in most cases it should be easy to add missing cases to at least have good branch coverage.
- [x] Parser
- [x] Analyzer
- [x] Evaluator
- [x] Environment (Type) | non_priority | improve test coverage for easily testable cases following the kotest migration it should be much easier to add new test cases and catchup on coverage skipped previously e g classes and error conditions there are no strict goals for test coverage however in most cases it should be easy to add missing cases to at least have good branch coverage parser analyzer evaluator environment type | 0 |
288,149 | 31,857,047,738 | IssuesEvent | 2023-09-15 08:14:38 | nidhi7598/linux-4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-4.19.72_CVE-2022-3564 | closed | CVE-2020-12652 (Medium) detected in linuxlinux-4.19.294 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-12652 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.19.72_CVE-2022-3564/commit/454c7dacf6fa9a6de86d4067f5a08f25cffa519b">454c7dacf6fa9a6de86d4067f5a08f25cffa519b</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/message/fusion/mptctl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/message/fusion/mptctl.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The __mptctl_ioctl function in drivers/message/fusion/mptctl.c in the Linux kernel before 5.4.14 allows local users to hold an incorrect lock during the ioctl operation and trigger a race condition, i.e., a "double fetch" vulnerability, aka CID-28d76df18f0a. NOTE: the vendor states "The security impact of this bug is not as bad as it could have been because these operations are all privileged and root already has enormous destructive power."
<p>Publish Date: 2020-05-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-12652>CVE-2020-12652</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.4.14">https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.4.14</a></p>
<p>Release Date: 2020-06-13</p>
<p>Fix Resolution: 5.4.14</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-12652 (Medium) detected in linuxlinux-4.19.294 - autoclosed - ## CVE-2020-12652 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.19.72_CVE-2022-3564/commit/454c7dacf6fa9a6de86d4067f5a08f25cffa519b">454c7dacf6fa9a6de86d4067f5a08f25cffa519b</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/message/fusion/mptctl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/message/fusion/mptctl.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The __mptctl_ioctl function in drivers/message/fusion/mptctl.c in the Linux kernel before 5.4.14 allows local users to hold an incorrect lock during the ioctl operation and trigger a race condition, i.e., a "double fetch" vulnerability, aka CID-28d76df18f0a. NOTE: the vendor states "The security impact of this bug is not as bad as it could have been because these operations are all privileged and root already has enormous destructive power."
<p>Publish Date: 2020-05-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-12652>CVE-2020-12652</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.4.14">https://cdn.kernel.org/pub/linux/kernel/v5.x/ChangeLog-5.4.14</a></p>
<p>Release Date: 2020-06-13</p>
<p>Fix Resolution: 5.4.14</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux autoclosed cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files drivers message fusion mptctl c drivers message fusion mptctl c vulnerability details the mptctl ioctl function in drivers message fusion mptctl c in the linux kernel before allows local users to hold an incorrect lock during the ioctl operation and trigger a race condition i e a double fetch vulnerability aka cid note the vendor states the security impact of this bug is not as bad as it could have been because these operations are all privileged and root already has enormous destructive power publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
12,507 | 14,961,991,158 | IssuesEvent | 2021-01-27 08:38:40 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | Make auth server login screens error toasts more visible | Auth server Feature request P1 Process: Fixed Process: Tested dev | Right now when a user is not found or a password is expired the login screen (participant manager) shows a red toast at the bottom of the screen. It is currently difficult to see and notice. To make it easier to see:
1. Increase toast duration (currently it looks like 1 second, so perhaps 5 seconds would be good)
1. Move toast to the space between "sign in" and "email" if there is room (this is lower priority than making the duration longer as I imagine this is more work than changing the timer on the toast)
This same issue occurs in Android - the error message is often below the bottom of the screen and so goes unnoticed by the user. | 2.0 | Make auth server login screens error toasts more visible - Right now when a user is not found or a password is expired the login screen (participant manager) shows a red toast at the bottom of the screen. It is currently difficult to see and notice. To make it easier to see:
1. Increase toast duration (currently it looks like 1 second, so perhaps 5 seconds would be good)
1. Move toast to the space between "sign in" and "email" if there is room (this is lower priority than making the duration longer as I imagine this is more work than changing the timer on the toast)
This same issue occurs in Android - the error message is often below the bottom of the screen and so goes unnoticed by the user. | non_priority | make auth server login screens error toasts more visible right now when a user is not found or a password is expired the login screen participant manager shows a red toast at the bottom of the screen it is currently difficult to see and notice to make it easier to see increase toast duration currently it looks like second so perhaps seconds would be good move toast to the space between sign in and email if there is room this is lower priority than making the duration longer as i imagine this is more work than changing the timer on the toast this same issue occurs in android the error message is often below the bottom of the screen and so goes unnoticed by the user | 0 |
140,149 | 12,888,263,153 | IssuesEvent | 2020-07-13 12:44:32 | ibm-garage-ref-storefront/planning | https://api.github.com/repos/ibm-garage-ref-storefront/planning | closed | Add to the site docs for how to work with customized pipelines and automate their release | documentation | On this section
https://cloudnativereference.dev/related-repositories/pipelines
Answer the following questions:
- How can the user use our custom pipelines to get started?
- Allow the user to introspect and really understand how these decoupled kabanero tasks can be reused with our custom pipelines. | 1.0 | Add to the site docs for how to work with customized pipelines and automate their release - On this section
https://cloudnativereference.dev/related-repositories/pipelines
Answer the following questions:
- How can the user use our custom pipelines to get started?
- Allow the user to introspect and really understand how these decoupled kabanero tasks can be reused with our custom pipelines. | non_priority | add to the site docs for how to work with customized pipelines and automate their release on this section answer the following questions how can the user use our custom pipelines to get started allow the user to introspect and really understand how these decoupled kabanero tasks can be reused with our custom pipelines | 0 |
57,465 | 24,123,750,096 | IssuesEvent | 2022-09-20 21:18:39 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Index Patterns - Define API for determining dependencies on a given index pattern | loe:week Feature:Data Views Team:AppServicesSv impact:low | It would be helpful if there was an API for communicating which saved objects had a dependency on a particular index pattern. Saved object references address the vast majority of uses cases but TSVB and perhaps a couple of others use index patterns in a non standard way.
There are two places where this could be used - as an additional tab on the index pattern management and in the index pattern field editor when fields are being changed or removed.
For this issue, lets just DEFINE the API, perhaps creating an RFC.
This work should start based on the the saved object relationship view and consider extending from there -
<img width="940" alt="Screen Shot 2021-04-21 at 10 14 05 PM" src="https://user-images.githubusercontent.com/216176/115650547-06ce5100-a2ef-11eb-8cae-2b385bd41199.png">
API should initially be used in index pattern management
| 1.0 | Index Patterns - Define API for determining dependencies on a given index pattern - It would be helpful if there was an API for communicating which saved objects had a dependency on a particular index pattern. Saved object references address the vast majority of uses cases but TSVB and perhaps a couple of others use index patterns in a non standard way.
There are two places where this could be used - as an additional tab on the index pattern management and in the index pattern field editor when fields are being changed or removed.
For this issue, lets just DEFINE the API, perhaps creating an RFC.
This work should start based on the the saved object relationship view and consider extending from there -
<img width="940" alt="Screen Shot 2021-04-21 at 10 14 05 PM" src="https://user-images.githubusercontent.com/216176/115650547-06ce5100-a2ef-11eb-8cae-2b385bd41199.png">
API should initially be used in index pattern management
| non_priority | index patterns define api for determining dependencies on a given index pattern it would be helpful if there was an api for communicating which saved objects had a dependency on a particular index pattern saved object references address the vast majority of uses cases but tsvb and perhaps a couple of others use index patterns in a non standard way there are two places where this could be used as an additional tab on the index pattern management and in the index pattern field editor when fields are being changed or removed for this issue lets just define the api perhaps creating an rfc this work should start based on the the saved object relationship view and consider extending from there img width alt screen shot at pm src api should initially be used in index pattern management | 0 |
14,978 | 8,722,412,394 | IssuesEvent | 2018-12-09 12:16:39 | pytest-dev/pytest | https://api.github.com/repos/pytest-dev/pytest | closed | Performance issue with large tracebacks (recursion) | type: performance | With this code:
``` python
import re
def test_re_recursion():
re.compile('(' * 500)
```
pytest takes 16 seconds to run. With `--tb=native` the same test finishes instantly.
I tried with pytest 2.8.2 on Archlinux on Python 3.5.
I did a quick profile run - by cumulative time:
```
ncalls tottime percall cumtime percall filename:lineno(function)
163/1 0.012 0.000 26.909 26.909 {built-in method builtins.exec}
1 0.000 0.000 26.909 26.909 /usr/bin/py.test:3(<module>)
185/51 0.000 0.000 26.683 0.523 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:335(_hookexec)
185/51 0.000 0.000 26.683 0.523 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:332(<lambda>)
231/51 0.001 0.000 26.683 0.523 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:586(execute)
1 0.000 0.000 26.682 26.682 /usr/lib/python3.5/site-packages/_pytest/config.py:28(main)
73/2 0.000 0.000 26.682 13.341 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:722(__call__)
1 0.000 0.000 26.648 26.648 /usr/lib/python3.5/site-packages/_pytest/main.py:114(pytest_cmdline_main)
1 0.000 0.000 26.648 26.648 /usr/lib/python3.5/site-packages/_pytest/main.py:79(wrap_session)
46/5 0.000 0.000 26.644 5.329 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:237(_wrapped_call)
46/5 0.000 0.000 26.589 5.318 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:262(__init__)
1 0.000 0.000 26.556 26.556 /usr/lib/python3.5/site-packages/_pytest/main.py:117(_main)
1 0.000 0.000 26.553 26.553 /usr/lib/python3.5/site-packages/_pytest/main.py:131(pytest_runtestloop)
1 0.000 0.000 26.552 26.552 /usr/lib/python3.5/site-packages/_pytest/runner.py:61(pytest_runtest_protocol)
1 0.000 0.000 26.552 26.552 /usr/lib/python3.5/site-packages/_pytest/runner.py:68(runtestprotocol)
3 0.000 0.000 26.552 8.851 /usr/lib/python3.5/site-packages/_pytest/runner.py:118(call_and_report)
3 0.000 0.000 26.545 8.848 /usr/lib/python3.5/site-packages/_pytest/runner.py:204(pytest_runtest_makereport)
1 0.000 0.000 26.545 26.545 /usr/lib/python3.5/site-packages/_pytest/python.py:727(repr_failure)
1 0.000 0.000 26.545 26.545 /usr/lib/python3.5/site-packages/_pytest/python.py:720(_repr_failure_py)
1 0.001 0.001 26.545 26.545 /usr/lib/python3.5/site-packages/_pytest/main.py:389(_repr_failure_py)
1 0.000 0.000 26.526 26.526 /usr/lib/python3.5/site-packages/py/_code/code.py:393(getrepr)
1 0.000 0.000 26.526 26.526 /usr/lib/python3.5/site-packages/py/_code/code.py:589(repr_excinfo)
1 0.006 0.006 26.526 26.526 /usr/lib/python3.5/site-packages/py/_code/code.py:569(repr_traceback)
917 0.011 0.000 25.875 0.028 /usr/lib/python3.5/site-packages/py/_code/code.py:527(repr_traceback_entry)
917 0.016 0.000 25.713 0.028 /usr/lib/python3.5/site-packages/py/_code/code.py:454(_getentrysource)
917 0.016 0.000 25.688 0.028 /usr/lib/python3.5/site-packages/py/_code/code.py:188(getsource)
919 0.008 0.000 25.347 0.028 /usr/lib/python3.5/site-packages/py/_code/source.py:342(getstatementrange_ast)
919 3.725 0.004 25.325 0.028 /usr/lib/python3.5/site-packages/py/_code/source.py:319(get_statement_startend2)
5558450 3.477 0.000 19.355 0.000 /usr/lib/python3.5/ast.py:207(walk)
5557531 1.981 0.000 15.525 0.000 {method 'extend' of 'collections.deque' objects}
11114143 6.945 0.000 13.545 0.000 /usr/lib/python3.5/ast.py:177(iter_child_nodes)
13446880 3.780 0.000 5.031 0.000 /usr/lib/python3.5/ast.py:165(iter_fields)
24514212 2.897 0.000 2.897 0.000 {built-in method builtins.isinstance}
9228325/9228317 2.039 0.000 2.039 0.000 {built-in method builtins.getattr}
...
```
by total time:
```
ncalls tottime percall cumtime percall filename:lineno(function)
11114143 6.945 0.000 13.545 0.000 /usr/lib/python3.5/ast.py:177(iter_child_nodes)
13446880 3.780 0.000 5.031 0.000 /usr/lib/python3.5/ast.py:165(iter_fields)
919 3.725 0.004 25.325 0.028 /usr/lib/python3.5/site-packages/py/_code/source.py:319(get_statement_startend2)
5558450 3.477 0.000 19.355 0.000 /usr/lib/python3.5/ast.py:207(walk)
24514212 2.897 0.000 2.897 0.000 {built-in method builtins.isinstance}
9228325/9228317 2.039 0.000 2.039 0.000 {built-in method builtins.getattr}
5557531 1.981 0.000 15.525 0.000 {method 'extend' of 'collections.deque' objects}
...
```
| True | Performance issue with large tracebacks (recursion) - With this code:
``` python
import re
def test_re_recursion():
re.compile('(' * 500)
```
pytest takes 16 seconds to run. With `--tb=native` the same test finishes instantly.
I tried with pytest 2.8.2 on Archlinux on Python 3.5.
I did a quick profile run - by cumulative time:
```
ncalls tottime percall cumtime percall filename:lineno(function)
163/1 0.012 0.000 26.909 26.909 {built-in method builtins.exec}
1 0.000 0.000 26.909 26.909 /usr/bin/py.test:3(<module>)
185/51 0.000 0.000 26.683 0.523 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:335(_hookexec)
185/51 0.000 0.000 26.683 0.523 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:332(<lambda>)
231/51 0.001 0.000 26.683 0.523 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:586(execute)
1 0.000 0.000 26.682 26.682 /usr/lib/python3.5/site-packages/_pytest/config.py:28(main)
73/2 0.000 0.000 26.682 13.341 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:722(__call__)
1 0.000 0.000 26.648 26.648 /usr/lib/python3.5/site-packages/_pytest/main.py:114(pytest_cmdline_main)
1 0.000 0.000 26.648 26.648 /usr/lib/python3.5/site-packages/_pytest/main.py:79(wrap_session)
46/5 0.000 0.000 26.644 5.329 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:237(_wrapped_call)
46/5 0.000 0.000 26.589 5.318 /usr/lib/python3.5/site-packages/_pytest/vendored_packages/pluggy.py:262(__init__)
1 0.000 0.000 26.556 26.556 /usr/lib/python3.5/site-packages/_pytest/main.py:117(_main)
1 0.000 0.000 26.553 26.553 /usr/lib/python3.5/site-packages/_pytest/main.py:131(pytest_runtestloop)
1 0.000 0.000 26.552 26.552 /usr/lib/python3.5/site-packages/_pytest/runner.py:61(pytest_runtest_protocol)
1 0.000 0.000 26.552 26.552 /usr/lib/python3.5/site-packages/_pytest/runner.py:68(runtestprotocol)
3 0.000 0.000 26.552 8.851 /usr/lib/python3.5/site-packages/_pytest/runner.py:118(call_and_report)
3 0.000 0.000 26.545 8.848 /usr/lib/python3.5/site-packages/_pytest/runner.py:204(pytest_runtest_makereport)
1 0.000 0.000 26.545 26.545 /usr/lib/python3.5/site-packages/_pytest/python.py:727(repr_failure)
1 0.000 0.000 26.545 26.545 /usr/lib/python3.5/site-packages/_pytest/python.py:720(_repr_failure_py)
1 0.001 0.001 26.545 26.545 /usr/lib/python3.5/site-packages/_pytest/main.py:389(_repr_failure_py)
1 0.000 0.000 26.526 26.526 /usr/lib/python3.5/site-packages/py/_code/code.py:393(getrepr)
1 0.000 0.000 26.526 26.526 /usr/lib/python3.5/site-packages/py/_code/code.py:589(repr_excinfo)
1 0.006 0.006 26.526 26.526 /usr/lib/python3.5/site-packages/py/_code/code.py:569(repr_traceback)
917 0.011 0.000 25.875 0.028 /usr/lib/python3.5/site-packages/py/_code/code.py:527(repr_traceback_entry)
917 0.016 0.000 25.713 0.028 /usr/lib/python3.5/site-packages/py/_code/code.py:454(_getentrysource)
917 0.016 0.000 25.688 0.028 /usr/lib/python3.5/site-packages/py/_code/code.py:188(getsource)
919 0.008 0.000 25.347 0.028 /usr/lib/python3.5/site-packages/py/_code/source.py:342(getstatementrange_ast)
919 3.725 0.004 25.325 0.028 /usr/lib/python3.5/site-packages/py/_code/source.py:319(get_statement_startend2)
5558450 3.477 0.000 19.355 0.000 /usr/lib/python3.5/ast.py:207(walk)
5557531 1.981 0.000 15.525 0.000 {method 'extend' of 'collections.deque' objects}
11114143 6.945 0.000 13.545 0.000 /usr/lib/python3.5/ast.py:177(iter_child_nodes)
13446880 3.780 0.000 5.031 0.000 /usr/lib/python3.5/ast.py:165(iter_fields)
24514212 2.897 0.000 2.897 0.000 {built-in method builtins.isinstance}
9228325/9228317 2.039 0.000 2.039 0.000 {built-in method builtins.getattr}
...
```
by total time:
```
ncalls tottime percall cumtime percall filename:lineno(function)
11114143 6.945 0.000 13.545 0.000 /usr/lib/python3.5/ast.py:177(iter_child_nodes)
13446880 3.780 0.000 5.031 0.000 /usr/lib/python3.5/ast.py:165(iter_fields)
919 3.725 0.004 25.325 0.028 /usr/lib/python3.5/site-packages/py/_code/source.py:319(get_statement_startend2)
5558450 3.477 0.000 19.355 0.000 /usr/lib/python3.5/ast.py:207(walk)
24514212 2.897 0.000 2.897 0.000 {built-in method builtins.isinstance}
9228325/9228317 2.039 0.000 2.039 0.000 {built-in method builtins.getattr}
5557531 1.981 0.000 15.525 0.000 {method 'extend' of 'collections.deque' objects}
...
```
| non_priority | performance issue with large tracebacks recursion with this code python import re def test re recursion re compile pytest takes seconds to run with tb native the same test finishes instantly i tried with pytest on archlinux on python i did a quick profile run by cumulative time ncalls tottime percall cumtime percall filename lineno function built in method builtins exec usr bin py test usr lib site packages pytest vendored packages pluggy py hookexec usr lib site packages pytest vendored packages pluggy py usr lib site packages pytest vendored packages pluggy py execute usr lib site packages pytest config py main usr lib site packages pytest vendored packages pluggy py call usr lib site packages pytest main py pytest cmdline main usr lib site packages pytest main py wrap session usr lib site packages pytest vendored packages pluggy py wrapped call usr lib site packages pytest vendored packages pluggy py init usr lib site packages pytest main py main usr lib site packages pytest main py pytest runtestloop usr lib site packages pytest runner py pytest runtest protocol usr lib site packages pytest runner py runtestprotocol usr lib site packages pytest runner py call and report usr lib site packages pytest runner py pytest runtest makereport usr lib site packages pytest python py repr failure usr lib site packages pytest python py repr failure py usr lib site packages pytest main py repr failure py usr lib site packages py code code py getrepr usr lib site packages py code code py repr excinfo usr lib site packages py code code py repr traceback usr lib site packages py code code py repr traceback entry usr lib site packages py code code py getentrysource usr lib site packages py code code py getsource usr lib site packages py code source py getstatementrange ast usr lib site packages py code source py get statement usr lib ast py walk method extend of collections deque objects usr lib ast py iter child nodes usr lib ast py iter fields built in method builtins isinstance built in method builtins getattr by total time ncalls tottime percall cumtime percall filename lineno function usr lib ast py iter child nodes usr lib ast py iter fields usr lib site packages py code source py get statement usr lib ast py walk built in method builtins isinstance built in method builtins getattr method extend of collections deque objects | 0 |
290,519 | 25,072,989,664 | IssuesEvent | 2022-11-07 13:35:45 | bankidz/bankidz-client | https://api.github.com/repos/bankidz/bankidz-client | closed | [FEATURE] 디자인 시스템 고도화 | Type: Test | # 🤖 기능 개요
<!-- 이슈에 할당된 기능이 무엇인지 간략하게 한 줄로 적습니다 -->
* storybook 뽕뽑기
### ✅ Implement TODO
<!-- 이슈에 할당된 TODO를 나름대로 항목화하여 적습니다 (PR할 때에는 모두 체크되어야함) -->
- [ ]
### 📚 Remarks
<!-- 기능 개발에 있어 비고사항이 있었다면 적기 -->
| 1.0 | [FEATURE] 디자인 시스템 고도화 - # 🤖 기능 개요
<!-- 이슈에 할당된 기능이 무엇인지 간략하게 한 줄로 적습니다 -->
* storybook 뽕뽑기
### ✅ Implement TODO
<!-- 이슈에 할당된 TODO를 나름대로 항목화하여 적습니다 (PR할 때에는 모두 체크되어야함) -->
- [ ]
### 📚 Remarks
<!-- 기능 개발에 있어 비고사항이 있었다면 적기 -->
| non_priority | 디자인 시스템 고도화 🤖 기능 개요 storybook 뽕뽑기 ✅ implement todo 📚 remarks | 0 |
33,350 | 14,078,403,360 | IssuesEvent | 2020-11-04 13:31:29 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | .env file location is incorrect | Pri2 cxp doc-bug lva-edge/subsvc media-services/svc triaged |
In section
https://docs.microsoft.com/en-us/azure/media-services/live-video-analytics-edge/event-based-video-recording-tutorial#set-up-your-development-environment
in step 6. the text should be fixed to
Copy the contents from the ~/clouddrive/lva-sample/edge-deployment/.env file. The text should look like:
Based on feedback from
https://github.com/MicrosoftDocs/azure-docs/issues/65373
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: bd4faa47-7e66-b3f5-1100-eeed4222fece
* Version Independent ID: 5de49fd7-8242-f5bd-0e1c-a2e24bae777d
* Content: [Event-based video recording to the cloud and playback from the cloud tutorial - Azure - Live Video Analytics on IoT Edge](https://docs.microsoft.com/en-us/azure/media-services/live-video-analytics-edge/event-based-video-recording-tutorial)
* Content Source: [articles/media-services/live-video-analytics-edge/event-based-video-recording-tutorial.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/media-services/live-video-analytics-edge/event-based-video-recording-tutorial.md)
* Service: **media-services**
* Sub-service: **lva-edge**
* GitHub Login: @Juliako
* Microsoft Alias: **juliako** | 1.0 | .env file location is incorrect -
In section
https://docs.microsoft.com/en-us/azure/media-services/live-video-analytics-edge/event-based-video-recording-tutorial#set-up-your-development-environment
in step 6. the text should be fixed to
Copy the contents from the ~/clouddrive/lva-sample/edge-deployment/.env file. The text should look like:
Based on feedback from
https://github.com/MicrosoftDocs/azure-docs/issues/65373
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: bd4faa47-7e66-b3f5-1100-eeed4222fece
* Version Independent ID: 5de49fd7-8242-f5bd-0e1c-a2e24bae777d
* Content: [Event-based video recording to the cloud and playback from the cloud tutorial - Azure - Live Video Analytics on IoT Edge](https://docs.microsoft.com/en-us/azure/media-services/live-video-analytics-edge/event-based-video-recording-tutorial)
* Content Source: [articles/media-services/live-video-analytics-edge/event-based-video-recording-tutorial.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/media-services/live-video-analytics-edge/event-based-video-recording-tutorial.md)
* Service: **media-services**
* Sub-service: **lva-edge**
* GitHub Login: @Juliako
* Microsoft Alias: **juliako** | non_priority | env file location is incorrect in section in step the text should be fixed to copy the contents from the clouddrive lva sample edge deployment env file the text should look like based on feedback from document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service media services sub service lva edge github login juliako microsoft alias juliako | 0 |
317,824 | 23,691,143,658 | IssuesEvent | 2022-08-29 10:54:59 | snyssen/ansible_role_compose_deploy | https://api.github.com/repos/snyssen/ansible_role_compose_deploy | opened | There is no documentation | documentation | I'm in a bit of a hurry right now so I can't add the documentation, but it will have to be done at some point. | 1.0 | There is no documentation - I'm in a bit of a hurry right now so I can't add the documentation, but it will have to be done at some point. | non_priority | there is no documentation i m in a bit of a hurry right now so i can t add the documentation but it will have to be done at some point | 0 |
46,514 | 13,055,925,255 | IssuesEvent | 2020-07-30 03:08:18 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | [steamshovel] Save frame is broken if filters are on (Trac #1347) | Incomplete Migration Migrated from Trac combo core defect | Migrated from https://code.icecube.wisc.edu/ticket/1347
```json
{
"status": "closed",
"changetime": "2015-09-17T19:04:23",
"description": "Save frame does not work as intended when the frame stream is filtered.",
"reporter": "hdembinski",
"cc": "dschultz",
"resolution": "fixed",
"_ts": "1442516663246308",
"component": "combo core",
"summary": "[steamshovel] Save frame is broken if filters are on",
"priority": "blocker",
"keywords": "",
"time": "2015-09-15T19:36:54",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| 1.0 | [steamshovel] Save frame is broken if filters are on (Trac #1347) - Migrated from https://code.icecube.wisc.edu/ticket/1347
```json
{
"status": "closed",
"changetime": "2015-09-17T19:04:23",
"description": "Save frame does not work as intended when the frame stream is filtered.",
"reporter": "hdembinski",
"cc": "dschultz",
"resolution": "fixed",
"_ts": "1442516663246308",
"component": "combo core",
"summary": "[steamshovel] Save frame is broken if filters are on",
"priority": "blocker",
"keywords": "",
"time": "2015-09-15T19:36:54",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| non_priority | save frame is broken if filters are on trac migrated from json status closed changetime description save frame does not work as intended when the frame stream is filtered reporter hdembinski cc dschultz resolution fixed ts component combo core summary save frame is broken if filters are on priority blocker keywords time milestone owner hdembinski type defect | 0 |
207,473 | 16,085,540,390 | IssuesEvent | 2021-04-26 10:46:07 | pyccel/pyccel | https://api.github.com/repos/pyccel/pyccel | closed | Supported Numpy functions guide. | documentation | list the following supported Numpy functions in `tutorial/numpy-functions`:
- [ ] norm
- [ ] real
- [ ] imag
- [ ] mod
- [ ] prod
- [ ] matmul
- [ ] mod
and Numpy types (cast functions) too:
- [ ] float
- [ ] double
- [ ] float32
- [ ] float64
- [ ] int
- [ ] int32
- [ ] int64
- [ ] complex128
- [ ] complex64
supported arguments and their data type/structure should be mentioned too. | 1.0 | Supported Numpy functions guide. - list the following supported Numpy functions in `tutorial/numpy-functions`:
- [ ] norm
- [ ] real
- [ ] imag
- [ ] mod
- [ ] prod
- [ ] matmul
- [ ] mod
and Numpy types (cast functions) too:
- [ ] float
- [ ] double
- [ ] float32
- [ ] float64
- [ ] int
- [ ] int32
- [ ] int64
- [ ] complex128
- [ ] complex64
supported arguments and their data type/structure should be mentioned too. | non_priority | supported numpy functions guide list the following supported numpy functions in tutorial numpy functions norm real imag mod prod matmul mod and numpy types cast functions too float double int supported arguments and their data type structure should be mentioned too | 0 |
18,720 | 13,168,406,088 | IssuesEvent | 2020-08-11 12:04:31 | topcoder-platform/qa-fun | https://api.github.com/repos/topcoder-platform/qa-fun | closed | [TCO20-REGIONAL] [Web-Chrome] Links with strange fonts at bottom of careers page | UX/Usability | Steps:
1. In [web-chrome] click on careers link down the bottom
2. Scroll down to Join our team links.
Expected result:
Links should be nice and compact.
Actual result:
Current links are very ugly. Font is too big and colour clashes with background.
Screenshot:
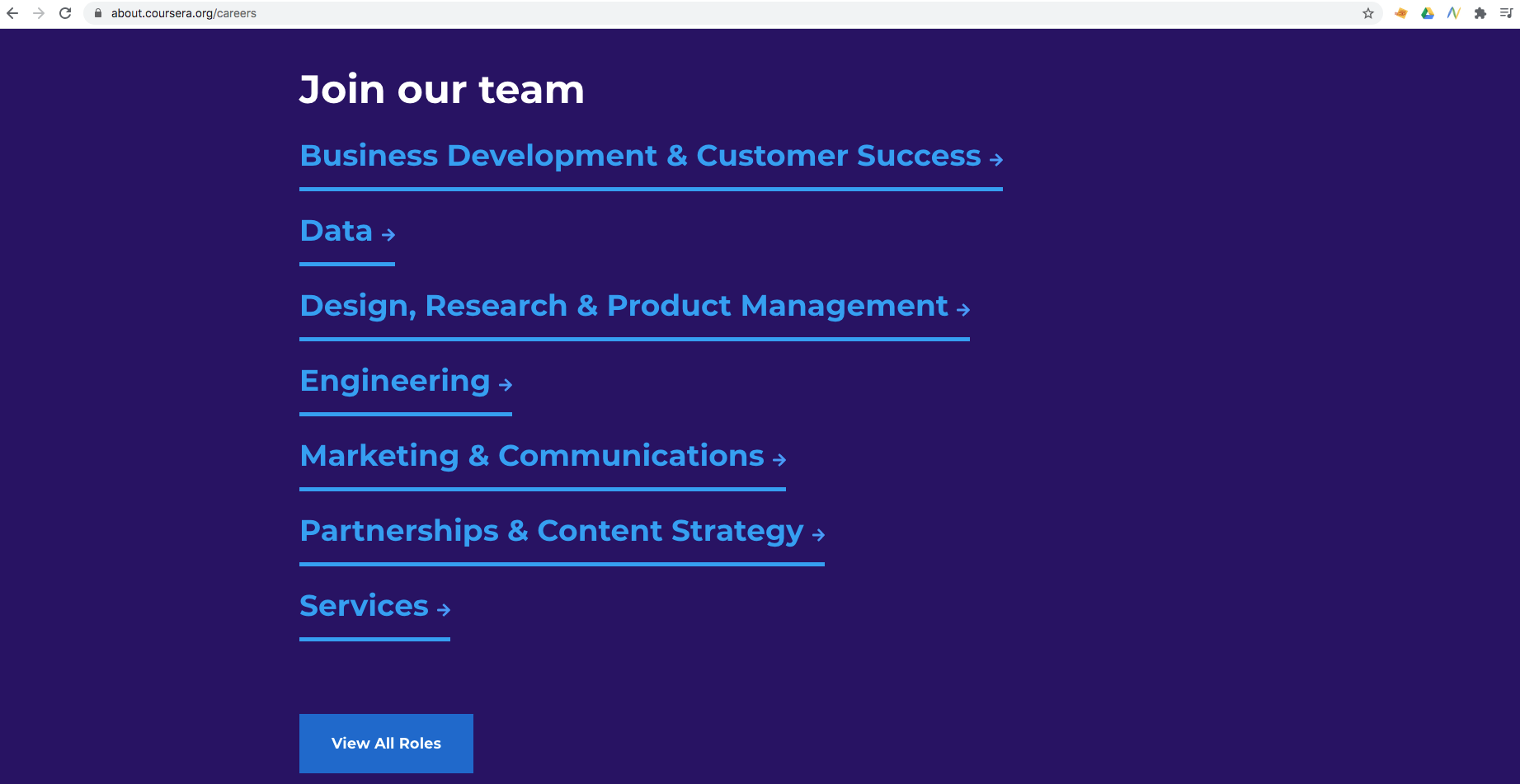
| True | [TCO20-REGIONAL] [Web-Chrome] Links with strange fonts at bottom of careers page - Steps:
1. In [web-chrome] click on careers link down the bottom
2. Scroll down to Join our team links.
Expected result:
Links should be nice and compact.
Actual result:
Current links are very ugly. Font is too big and colour clashes with background.
Screenshot:
| non_priority | links with strange fonts at bottom of careers page steps in click on careers link down the bottom scroll down to join our team links expected result links should be nice and compact actual result current links are very ugly font is too big and colour clashes with background screenshot | 0 |
18,873 | 11,096,971,892 | IssuesEvent | 2019-12-16 12:21:58 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | App Service stack for .NET Core | Pri3 app-service/svc cxp needs-more-info product-question triaged | Hi
I am creating Azure Web App, by default the the Runtime Stack is .NET, i am deploying a .NET Core app but the Runtime Stack is still set to .Net with version 3.5 on it.
i can find a powershell command to change the stack to .NET Core either.
How does the runtime stack get updated to .NET Core if i dont want to do it manually. | 1.0 | App Service stack for .NET Core - Hi
I am creating Azure Web App, by default the the Runtime Stack is .NET, i am deploying a .NET Core app but the Runtime Stack is still set to .Net with version 3.5 on it.
i can find a powershell command to change the stack to .NET Core either.
How does the runtime stack get updated to .NET Core if i dont want to do it manually. | non_priority | app service stack for net core hi i am creating azure web app by default the the runtime stack is net i am deploying a net core app but the runtime stack is still set to net with version on it i can find a powershell command to change the stack to net core either how does the runtime stack get updated to net core if i dont want to do it manually | 0 |
13,073 | 8,235,744,270 | IssuesEvent | 2018-09-09 08:49:57 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | closed | Disable Ctrl+MouseWheel zooming | fixed-with-brave-core needs-info suggestion usability wontfix | Disable "Ctrl+MouseWheel" to prevent unwanted zooming
- Platform macOS
- Brave Version 0.18.14
| True | Disable Ctrl+MouseWheel zooming - Disable "Ctrl+MouseWheel" to prevent unwanted zooming
- Platform macOS
- Brave Version 0.18.14
| non_priority | disable ctrl mousewheel zooming disable ctrl mousewheel to prevent unwanted zooming platform macos brave version | 0 |
182,043 | 14,099,666,163 | IssuesEvent | 2020-11-06 02:01:01 | MinaProtocol/mina | https://api.github.com/repos/MinaProtocol/mina | closed | Integration tests for bootstrapping | daemon medium tests | In order to achieve this, we will need to do some rearchitecting of our integration testing framework. The main things we would like to test:
- does a bootstrapping node successfully bootstrap in a good network scenario?
- does a bootstrapping node recover from faulty information?
- does a bootstrapping node recover from going offline too long? | 1.0 | Integration tests for bootstrapping - In order to achieve this, we will need to do some rearchitecting of our integration testing framework. The main things we would like to test:
- does a bootstrapping node successfully bootstrap in a good network scenario?
- does a bootstrapping node recover from faulty information?
- does a bootstrapping node recover from going offline too long? | non_priority | integration tests for bootstrapping in order to achieve this we will need to do some rearchitecting of our integration testing framework the main things we would like to test does a bootstrapping node successfully bootstrap in a good network scenario does a bootstrapping node recover from faulty information does a bootstrapping node recover from going offline too long | 0 |
2,841 | 2,773,308,895 | IssuesEvent | 2015-05-03 14:24:39 | ctavan/express-validator | https://api.github.com/repos/ctavan/express-validator | closed | Code Quality Configs | code-quality | * [x] Add .jshintrc (https://gist.github.com/rustybailey/8424351)
* [x] Add .editorconfig (like https://gist.github.com/rustybailey/e8bd17fe6a45ddf4fd07, but 2 spaces) to root.
* [x] Add jshint as dev dependency.
* [x] ~~Possibly add a .jscsrc~~ Not really necessary with a small codebase.
* [x] Add node 0.12 to travis.yml
* at the very least we should support what node-validator supports: https://github.com/chriso/validator.js/blob/master/.travis.yml
* [x] Add `license: "MIT"` to package.json
* [x] Add github-changes module to devDependencies and add the changelog command from #131 to npm scripts
* [x] Remove dead link to gist at the top of README
* [x] Bump node-validator to latest version | 1.0 | Code Quality Configs - * [x] Add .jshintrc (https://gist.github.com/rustybailey/8424351)
* [x] Add .editorconfig (like https://gist.github.com/rustybailey/e8bd17fe6a45ddf4fd07, but 2 spaces) to root.
* [x] Add jshint as dev dependency.
* [x] ~~Possibly add a .jscsrc~~ Not really necessary with a small codebase.
* [x] Add node 0.12 to travis.yml
* at the very least we should support what node-validator supports: https://github.com/chriso/validator.js/blob/master/.travis.yml
* [x] Add `license: "MIT"` to package.json
* [x] Add github-changes module to devDependencies and add the changelog command from #131 to npm scripts
* [x] Remove dead link to gist at the top of README
* [x] Bump node-validator to latest version | non_priority | code quality configs add jshintrc add editorconfig like but spaces to root add jshint as dev dependency possibly add a jscsrc not really necessary with a small codebase add node to travis yml at the very least we should support what node validator supports add license mit to package json add github changes module to devdependencies and add the changelog command from to npm scripts remove dead link to gist at the top of readme bump node validator to latest version | 0 |
448,743 | 31,811,057,741 | IssuesEvent | 2023-09-13 16:51:57 | vijayk3327/JavaScript-JQuery | https://api.github.com/repos/vijayk3327/JavaScript-JQuery | opened | How to Create Custom Banner Rotating Image with Text Slider Using JQuery and css3 | documentation question | In this post we are going to learn about How to Create Custom Banner Rotating Image with Text Slider Using JQuery and css3.
**[👉 Get source code live demo link:-](https://www.w3web.net/custom-rotating-image-with-text-slider-in-jquery-and-css3/)**
<img src="https://www.w3web.net/wp-content/uploads/2020/10/bannerRotateSlideJQ-min.gif"/>
**Step 1:- Create HTML File : banner-rotate_slide.html
banner-rotate_slide.html [HTML File]**
`<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1" />
<title>Untitled Document</title>
<script type="text/javascript" src="js/jquery-1.7.1.min.js"></script>
<script type="text/javascript" src="include/bannerRotateSlide.js"></script>
<link rel="stylesheet" href="include/bannerRotateSlide.css" type="text/css" media="all">
</head>
<body>
<div id="mainContainer">
<ul class="slideList">
<li><p>In this post we are going to learn about that how to edit row, saving row or removing row dynamically in Salesforce lightning component.</p>
<p>In this example we will customize the same component and achieve to the editing row, saving row and removing rows functionality of dynamically on Custom sObject by help of wrapper apex class and JavaScript Controller in lightning component...<span class="readMore"><a href="https://www.w3web.net/edit-save-and-remove-rows-dynamically-in-lightning-component/">Read more...</a></span></p></li>
<li>
<p>In this post we are going to learn about how to validate child component from parent component on click button using aura method in Salesforce lightning component.</p>
<p>Real time scenarios:- Create a custom and stylish form validation and validate child component from parent component using aura method in lightning component...<span class="readMore"><a href="https://www.w3web.net/how-to-validate-child-component-from-parent-component/">Read more...</a></span> </p>
</li>
<li>
<p><strong>Real time scenarios:-</strong> Write a trigger on parent object where create a <strong>custom field</strong> as Employee (Number type).</p>
<p>Or if user update the value of employee <strong>less then</strong> the total number of child records, in this case the child records should be <strong>exist only equal to </strong> employee size, rest records of child object should be automatic removed. <span class="readMore"><a href="https://www.w3web.net/update-count-of-child-record-based-on-parent-object-value/">Read more...</a></span></p>
</li>
<li>
<p>In this post we are going to learn about How to create roll-up summary trigger for <b>count child records</b> on custom object using Apex trigger in Salesforce.</p>
<p><strong>Real time scenarios:-</strong> Write a roll-up summary trigger for count child records on custom parent object. Create a custom field (Number Type) on parent object, <strong>calculate the total number</strong> of related <strong>child records</strong> <span class="readMore"><a href="https://www.w3web.net/roll-up-summary-trigger-on-custom-object/">Read more...</a></span></p>
</li>
</ul>
<ul class="sublist">
<li>
<div class="postImage">
<a href="https://www.w3web.net/edit-save-and-remove-rows-dynamically-in-lightning-component/">
<img src="https://www.w3web.net/wp-content/uploads/2020/07/editDeleteSave.png" />
</a>
</div>
</li>
<li>
<div class="postImage">
<a href="https://www.w3web.net/how-to-validate-child-component-from-parent-component/">
<img src="https://www.w3web.net/wp-content/uploads/2020/08/stylishFormValidation.png" width="200" height="150"/>
</a>
</div>
</li>
<li>
<div class="postImage">
<a href="https://www.w3web.net/roll-up-summary-trigger-on-custom-object/">
<img src="https://www.w3web.net/wp-content/uploads/2020/08/employeeSizeTrigger.png" width="200" height="150"/>
</a>
</div>
</li>
<li>
<div class="postImage">
<a href="https://www.w3web.net/roll-up-summary-trigger-on-custom-object/">
<img src="https://www.w3web.net/wp-content/uploads/2020/08/rollupSummary-trigger.png" width="200" height="150"/>
</a>
</div>
</li>
</ul>
</div>
<br/>
<!--Start RelatedTopics Section-->
<div style="border:1px #ddd solid; padding:10px; background:#eee; margin:40px 0;">
<p data-aura-rendered-by="435:0"><img src="https://www.w3web.net/wp-content/uploads/2021/05/thumbsUpLike.png" width="25" height="25" style="vertical-align:top; margin-right:10px;" data-aura-rendered-by="436:0"><strong data-aura-rendered-by="437:0"><span style="font-size:16px; font-style:italic; display:inline-block; margin-right:5px;">Don't forget to check out:-</span><a href="https://www.w3web.net/" target="_blank" rel="noopener noreferrer" style="text-decoration:none;" data-aura-rendered-by="440:0">An easy way to learn step-by-step online free Salesforce tutorial, To know more Click <span style="color:#ff8000; font-size:18px;" data-aura-rendered-by="442:0">Here..</span></a></strong></p>
<br/><br/>
<p data-aura-rendered-by="435:0"><img src="https://www.w3web.net/wp-content/uploads/2021/07/tickMarkIcon.png" width="25" height="25" style="vertical-align:top; margin-right:10px;" data-aura-rendered-by="436:0"><strong data-aura-rendered-by="437:0"><span style="font-size:17px; font-style:italic; display:inline-block; margin-right:5px; color:rgb(255 128 0);">You May Also Like →</span> </strong></p>
<div style="display:block; overflow:hidden;">
<div style="width: 50%; float:left; display:inline-block">
<ul style="list-style-type: square; font-size: 16px; margin: 0 0 0 54px; padding: 0;">
<li><a href="https://www.w3web.net/lwc-get-set-lightning-checkbox-value/" target="_blank" rel="noopener noreferrer">How to get selected checkbox value in lwc</a></li>
<li><a href="https://www.w3web.net/display-account-related-contacts-in-lwc/" target="_blank" rel="noopener noreferrer">how to display account related contacts based on AccountId in lwc</a></li>
<li><a href="https://www.w3web.net/create-lightning-datatable-row-actions-in-lwc/" target="_blank" rel="noopener noreferrer">how to create lightning datatable row actions in lwc</a></li>
<li><a href="https://www.w3web.net/if-and-else-condition-in-lwc/" target="_blank" rel="noopener noreferrer">how to use if and else condition in lwc</a></li>
<li><a href="https://www.w3web.net/get-selected-radio-button-value-and-checked-default-in-lwc/" target="_blank" rel="noopener noreferrer">how to display selected radio button value in lwc</a></li>
</ul>
</div>
<div style="width: 50%; float:left; display:inline-block">
<ul style="list-style-type: square; font-size: 16px; margin: 0 0 0 54px; padding: 0;">
<li><a href="https://www.w3web.net/display-account-related-contacts-lwc/" target="_blank" rel="noopener noreferrer">display account related contacts based on account name in lwc</a></li>
<li><a href="https://www.w3web.net/create-lightning-datatable-row-actions-in-lwc/" target="_blank" rel="noopener noreferrer">how to insert a record of account Using apex class in LWC</a></li>
<li><a href="https://www.w3web.net/fetch-picklist-values-dynamic-in-lwc/" target="_blank" rel="noopener noreferrer">how to get picklist values dynamically in lwc</a></li>
<li><a href="https://www.w3web.net/edit-save-and-remove-rows-dynamically-in-lightning-component/" target="_blank" rel="noopener noreferrer">how to edit/save row dynamically in lightning component</a></li>
<li><a href="https://www.w3web.net/update-parent-object-from-child/" target="_blank" rel="noopener noreferrer">update parent field from child using apex trigger</a></li>
</ul>
</div>
<div style="clear:both;"></div>
<br/>
<div class="youtubeIcon">
<a href="https://www.youtube.com/channel/UCW62gTen2zniILj9xE6LmOg" target="_blank" rel="noopener noreferrer"><img src="https://www.w3web.net/wp-content/uploads/2021/11/youtubeIcon.png" width="25" height="25" style="vertical-align:top; margin-right:10px;"/> <strong>TechW3web:-</strong> To know more, Use this <span style="color: #ff8000; font-weight: bold;">Link</span> </a>
</div>
</div>
</div>
<!--End RelatedTopics Section-->
</body>
</html>`
**Step 2:- Create JavaScript File : bannerRotateSlide.js
bannerRotateSlide.js [JavaScript File]
**
`$(document).ready(function(){
$('#mainContainer').autoslide();
});
$.fn.autoslide=function(){
var thisObj = $(this);
var ulmain = thisObj.find('ul:first');
$('ul.slideList li').not(':first').hide();
$('ul.sublist li').not(':first').hide();
$('#mainContainer').append('<div id="roundList"></div>');
$('ul.slideList li').each(function(i){
$('#roundList').append("<a href='#'>"+i+"</a>");
});
$('#roundList a:eq(0)').addClass('active');
var lastIndex = 0;
var animation= true;
$('#roundList a').click(function(event){
event.preventDefault();
var anchorTxt = $(this).text();
if(lastIndex!=anchorTxt)
{
if(animation)
{
animation=false;
$("ul.sublist li:eq("+lastIndex+")").hide(500);
$("ul.sublist li:eq("+anchorTxt+")").show(500);
$("ul.slideList li:eq("+lastIndex+")").fadeOut();
$("ul.slideList li:eq("+anchorTxt+")").fadeIn(10, function(){
lastIndex=anchorTxt;
animation= true;
});
$('#roundList a').removeClass('active');
$(this).addClass('active');
}
}
return false;
})
}`
**Step 3:- Create Style CSS : bannerRotateSlide.css
bannerRotateSlide.css [Style CSS File]**
`#mainContainer{ width:400px; margin:auto; font-family:Arial, Helvetica, sans-serif; position:relative;}
ul.slideList{ margin:0; padding:0; list-style:none; z-index:10;}
ul.slideList li { padding:5px; width:600px; position:absolute; border:1px #ccc solid; height:300px;}
#roundList{ font-size:11px; color:#000000; position:absolute; left:20px; top:280px; text-indent:25px;}
#roundList a{ float:left; width:10px; height:10px; border-radius:10px; display:inline-block; border:1px #ff0000 solid; margin:0 5px 0 0; overflow:hidden;}
#roundList a:hover, #roundList a.active{ background:#ff0000;}
ul.sublist{ margin:0; padding:0; list-style:none; position:relative;}
ul.sublist li{ width:240px; height:180px; overflow:hidden; position:absolute; right:-200px; top:145px;}
ul.sublist li img{ max-width:100%;}`
<img src="https://www.w3web.net/wp-content/uploads/2020/10/bannerRotateSlide.png"/>
**[👉 Get source code live demo link:-](https://www.w3web.net/custom-rotating-image-with-text-slider-in-jquery-and-css3/)** | 1.0 | How to Create Custom Banner Rotating Image with Text Slider Using JQuery and css3 - In this post we are going to learn about How to Create Custom Banner Rotating Image with Text Slider Using JQuery and css3.
**[👉 Get source code live demo link:-](https://www.w3web.net/custom-rotating-image-with-text-slider-in-jquery-and-css3/)**
<img src="https://www.w3web.net/wp-content/uploads/2020/10/bannerRotateSlideJQ-min.gif"/>
**Step 1:- Create HTML File : banner-rotate_slide.html
banner-rotate_slide.html [HTML File]**
`<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=iso-8859-1" />
<title>Untitled Document</title>
<script type="text/javascript" src="js/jquery-1.7.1.min.js"></script>
<script type="text/javascript" src="include/bannerRotateSlide.js"></script>
<link rel="stylesheet" href="include/bannerRotateSlide.css" type="text/css" media="all">
</head>
<body>
<div id="mainContainer">
<ul class="slideList">
<li><p>In this post we are going to learn about that how to edit row, saving row or removing row dynamically in Salesforce lightning component.</p>
<p>In this example we will customize the same component and achieve to the editing row, saving row and removing rows functionality of dynamically on Custom sObject by help of wrapper apex class and JavaScript Controller in lightning component...<span class="readMore"><a href="https://www.w3web.net/edit-save-and-remove-rows-dynamically-in-lightning-component/">Read more...</a></span></p></li>
<li>
<p>In this post we are going to learn about how to validate child component from parent component on click button using aura method in Salesforce lightning component.</p>
<p>Real time scenarios:- Create a custom and stylish form validation and validate child component from parent component using aura method in lightning component...<span class="readMore"><a href="https://www.w3web.net/how-to-validate-child-component-from-parent-component/">Read more...</a></span> </p>
</li>
<li>
<p><strong>Real time scenarios:-</strong> Write a trigger on parent object where create a <strong>custom field</strong> as Employee (Number type).</p>
<p>Or if user update the value of employee <strong>less then</strong> the total number of child records, in this case the child records should be <strong>exist only equal to </strong> employee size, rest records of child object should be automatic removed. <span class="readMore"><a href="https://www.w3web.net/update-count-of-child-record-based-on-parent-object-value/">Read more...</a></span></p>
</li>
<li>
<p>In this post we are going to learn about How to create roll-up summary trigger for <b>count child records</b> on custom object using Apex trigger in Salesforce.</p>
<p><strong>Real time scenarios:-</strong> Write a roll-up summary trigger for count child records on custom parent object. Create a custom field (Number Type) on parent object, <strong>calculate the total number</strong> of related <strong>child records</strong> <span class="readMore"><a href="https://www.w3web.net/roll-up-summary-trigger-on-custom-object/">Read more...</a></span></p>
</li>
</ul>
<ul class="sublist">
<li>
<div class="postImage">
<a href="https://www.w3web.net/edit-save-and-remove-rows-dynamically-in-lightning-component/">
<img src="https://www.w3web.net/wp-content/uploads/2020/07/editDeleteSave.png" />
</a>
</div>
</li>
<li>
<div class="postImage">
<a href="https://www.w3web.net/how-to-validate-child-component-from-parent-component/">
<img src="https://www.w3web.net/wp-content/uploads/2020/08/stylishFormValidation.png" width="200" height="150"/>
</a>
</div>
</li>
<li>
<div class="postImage">
<a href="https://www.w3web.net/roll-up-summary-trigger-on-custom-object/">
<img src="https://www.w3web.net/wp-content/uploads/2020/08/employeeSizeTrigger.png" width="200" height="150"/>
</a>
</div>
</li>
<li>
<div class="postImage">
<a href="https://www.w3web.net/roll-up-summary-trigger-on-custom-object/">
<img src="https://www.w3web.net/wp-content/uploads/2020/08/rollupSummary-trigger.png" width="200" height="150"/>
</a>
</div>
</li>
</ul>
</div>
<br/>
<!--Start RelatedTopics Section-->
<div style="border:1px #ddd solid; padding:10px; background:#eee; margin:40px 0;">
<p data-aura-rendered-by="435:0"><img src="https://www.w3web.net/wp-content/uploads/2021/05/thumbsUpLike.png" width="25" height="25" style="vertical-align:top; margin-right:10px;" data-aura-rendered-by="436:0"><strong data-aura-rendered-by="437:0"><span style="font-size:16px; font-style:italic; display:inline-block; margin-right:5px;">Don't forget to check out:-</span><a href="https://www.w3web.net/" target="_blank" rel="noopener noreferrer" style="text-decoration:none;" data-aura-rendered-by="440:0">An easy way to learn step-by-step online free Salesforce tutorial, To know more Click <span style="color:#ff8000; font-size:18px;" data-aura-rendered-by="442:0">Here..</span></a></strong></p>
<br/><br/>
<p data-aura-rendered-by="435:0"><img src="https://www.w3web.net/wp-content/uploads/2021/07/tickMarkIcon.png" width="25" height="25" style="vertical-align:top; margin-right:10px;" data-aura-rendered-by="436:0"><strong data-aura-rendered-by="437:0"><span style="font-size:17px; font-style:italic; display:inline-block; margin-right:5px; color:rgb(255 128 0);">You May Also Like →</span> </strong></p>
<div style="display:block; overflow:hidden;">
<div style="width: 50%; float:left; display:inline-block">
<ul style="list-style-type: square; font-size: 16px; margin: 0 0 0 54px; padding: 0;">
<li><a href="https://www.w3web.net/lwc-get-set-lightning-checkbox-value/" target="_blank" rel="noopener noreferrer">How to get selected checkbox value in lwc</a></li>
<li><a href="https://www.w3web.net/display-account-related-contacts-in-lwc/" target="_blank" rel="noopener noreferrer">how to display account related contacts based on AccountId in lwc</a></li>
<li><a href="https://www.w3web.net/create-lightning-datatable-row-actions-in-lwc/" target="_blank" rel="noopener noreferrer">how to create lightning datatable row actions in lwc</a></li>
<li><a href="https://www.w3web.net/if-and-else-condition-in-lwc/" target="_blank" rel="noopener noreferrer">how to use if and else condition in lwc</a></li>
<li><a href="https://www.w3web.net/get-selected-radio-button-value-and-checked-default-in-lwc/" target="_blank" rel="noopener noreferrer">how to display selected radio button value in lwc</a></li>
</ul>
</div>
<div style="width: 50%; float:left; display:inline-block">
<ul style="list-style-type: square; font-size: 16px; margin: 0 0 0 54px; padding: 0;">
<li><a href="https://www.w3web.net/display-account-related-contacts-lwc/" target="_blank" rel="noopener noreferrer">display account related contacts based on account name in lwc</a></li>
<li><a href="https://www.w3web.net/create-lightning-datatable-row-actions-in-lwc/" target="_blank" rel="noopener noreferrer">how to insert a record of account Using apex class in LWC</a></li>
<li><a href="https://www.w3web.net/fetch-picklist-values-dynamic-in-lwc/" target="_blank" rel="noopener noreferrer">how to get picklist values dynamically in lwc</a></li>
<li><a href="https://www.w3web.net/edit-save-and-remove-rows-dynamically-in-lightning-component/" target="_blank" rel="noopener noreferrer">how to edit/save row dynamically in lightning component</a></li>
<li><a href="https://www.w3web.net/update-parent-object-from-child/" target="_blank" rel="noopener noreferrer">update parent field from child using apex trigger</a></li>
</ul>
</div>
<div style="clear:both;"></div>
<br/>
<div class="youtubeIcon">
<a href="https://www.youtube.com/channel/UCW62gTen2zniILj9xE6LmOg" target="_blank" rel="noopener noreferrer"><img src="https://www.w3web.net/wp-content/uploads/2021/11/youtubeIcon.png" width="25" height="25" style="vertical-align:top; margin-right:10px;"/> <strong>TechW3web:-</strong> To know more, Use this <span style="color: #ff8000; font-weight: bold;">Link</span> </a>
</div>
</div>
</div>
<!--End RelatedTopics Section-->
</body>
</html>`
**Step 2:- Create JavaScript File : bannerRotateSlide.js
bannerRotateSlide.js [JavaScript File]
**
`$(document).ready(function(){
$('#mainContainer').autoslide();
});
$.fn.autoslide=function(){
var thisObj = $(this);
var ulmain = thisObj.find('ul:first');
$('ul.slideList li').not(':first').hide();
$('ul.sublist li').not(':first').hide();
$('#mainContainer').append('<div id="roundList"></div>');
$('ul.slideList li').each(function(i){
$('#roundList').append("<a href='#'>"+i+"</a>");
});
$('#roundList a:eq(0)').addClass('active');
var lastIndex = 0;
var animation= true;
$('#roundList a').click(function(event){
event.preventDefault();
var anchorTxt = $(this).text();
if(lastIndex!=anchorTxt)
{
if(animation)
{
animation=false;
$("ul.sublist li:eq("+lastIndex+")").hide(500);
$("ul.sublist li:eq("+anchorTxt+")").show(500);
$("ul.slideList li:eq("+lastIndex+")").fadeOut();
$("ul.slideList li:eq("+anchorTxt+")").fadeIn(10, function(){
lastIndex=anchorTxt;
animation= true;
});
$('#roundList a').removeClass('active');
$(this).addClass('active');
}
}
return false;
})
}`
**Step 3:- Create Style CSS : bannerRotateSlide.css
bannerRotateSlide.css [Style CSS File]**
`#mainContainer{ width:400px; margin:auto; font-family:Arial, Helvetica, sans-serif; position:relative;}
ul.slideList{ margin:0; padding:0; list-style:none; z-index:10;}
ul.slideList li { padding:5px; width:600px; position:absolute; border:1px #ccc solid; height:300px;}
#roundList{ font-size:11px; color:#000000; position:absolute; left:20px; top:280px; text-indent:25px;}
#roundList a{ float:left; width:10px; height:10px; border-radius:10px; display:inline-block; border:1px #ff0000 solid; margin:0 5px 0 0; overflow:hidden;}
#roundList a:hover, #roundList a.active{ background:#ff0000;}
ul.sublist{ margin:0; padding:0; list-style:none; position:relative;}
ul.sublist li{ width:240px; height:180px; overflow:hidden; position:absolute; right:-200px; top:145px;}
ul.sublist li img{ max-width:100%;}`
<img src="https://www.w3web.net/wp-content/uploads/2020/10/bannerRotateSlide.png"/>
**[👉 Get source code live demo link:-](https://www.w3web.net/custom-rotating-image-with-text-slider-in-jquery-and-css3/)** | non_priority | how to create custom banner rotating image with text slider using jquery and in this post we are going to learn about how to create custom banner rotating image with text slider using jquery and img src step create html file banner rotate slide html banner rotate slide html doctype html public dtd xhtml transitional en html xmlns untitled document in this post we are going to learn about that how to edit row saving row or removing row dynamically in salesforce lightning component in this example we will customize the same component and achieve to the editing row saving row and removing rows functionality of dynamically on custom sobject by help of wrapper apex class and javascript controller in lightning component in this post we are going to learn about how to validate child component from parent component on click button using aura method in salesforce lightning component real time scenarios create a custom and stylish form validation and validate child component from parent component using aura method in lightning component real time scenarios write a trigger on parent object where create a custom field as employee number type or if user update the value of employee less then the total number of child records in this case the child records should be exist only equal to employee size rest records of child object should be automatic removed in this post we are going to learn about how to create roll up summary trigger for count child records on custom object using apex trigger in salesforce real time scenarios write a roll up summary trigger for count child records on custom parent object create a custom field number type on parent object calculate the total number of related child records a href a href a href a href don t forget to check out an easy way to learn step by step online free salesforce tutorial to know more click here you may also like → how to get selected checkbox value in lwc how to display account related contacts based on accountid in lwc how to create lightning datatable row actions in lwc how to use if and else condition in lwc how to display selected radio button value in lwc display account related contacts based on account name in lwc how to insert a record of account using apex class in lwc how to get picklist values dynamically in lwc how to edit save row dynamically in lightning component update parent field from child using apex trigger to know more use this link step create javascript file bannerrotateslide js bannerrotateslide js document ready function maincontainer autoslide fn autoslide function var thisobj this var ulmain thisobj find ul first ul slidelist li not first hide ul sublist li not first hide maincontainer append ul slidelist li each function i roundlist append i roundlist a eq addclass active var lastindex var animation true roundlist a click function event event preventdefault var anchortxt this text if lastindex anchortxt if animation animation false ul sublist li eq lastindex hide ul sublist li eq anchortxt show ul slidelist li eq lastindex fadeout ul slidelist li eq anchortxt fadein function lastindex anchortxt animation true roundlist a removeclass active this addclass active return false step create style css bannerrotateslide css bannerrotateslide css maincontainer width margin auto font family arial helvetica sans serif position relative ul slidelist margin padding list style none z index ul slidelist li padding width position absolute border ccc solid height roundlist font size color position absolute left top text indent roundlist a float left width height border radius display inline block border solid margin overflow hidden roundlist a hover roundlist a active background ul sublist margin padding list style none position relative ul sublist li width height overflow hidden position absolute right top ul sublist li img max width img src | 0 |
231,839 | 17,758,872,073 | IssuesEvent | 2021-08-29 09:57:56 | BaguaSys/bagua | https://api.github.com/repos/BaguaSys/bagua | closed | comprehensive experimental results with all optimizations enabled | documentation benchmark | 16*8 V100 VGG16 speedup (100Gb, 25Gb, 10Gb) for
- Bagua gradient allreduce
- Bagua qadam
- Bagua bytegrad
- Bagua decentralized
- Bagua low precision decentralized
- Bagua Async
- PyTorch DDP
- Horovod
- BytePS
Enable all Bagua optimizations such as `bagua-net` and io caching. | 1.0 | comprehensive experimental results with all optimizations enabled - 16*8 V100 VGG16 speedup (100Gb, 25Gb, 10Gb) for
- Bagua gradient allreduce
- Bagua qadam
- Bagua bytegrad
- Bagua decentralized
- Bagua low precision decentralized
- Bagua Async
- PyTorch DDP
- Horovod
- BytePS
Enable all Bagua optimizations such as `bagua-net` and io caching. | non_priority | comprehensive experimental results with all optimizations enabled speedup for bagua gradient allreduce bagua qadam bagua bytegrad bagua decentralized bagua low precision decentralized bagua async pytorch ddp horovod byteps enable all bagua optimizations such as bagua net and io caching | 0 |
157,756 | 19,983,048,919 | IssuesEvent | 2022-01-30 07:43:16 | sultanabubaker/NPM_test | https://api.github.com/repos/sultanabubaker/NPM_test | closed | mocha-3.4.1.tgz: 6 vulnerabilities (highest severity is: 9.8) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-3.4.1.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz">https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-16042](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | growl-1.9.2.tgz | Transitive | 4.0.0 | ✅ |
| [WS-2018-0590](https://bugzilla.redhat.com/show_bug.cgi?id=1552148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.0 | diff-3.2.0.tgz | Transitive | 5.0.3 | ✅ |
| [CVE-2020-7598](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | minimist-0.0.8.tgz | Transitive | 6.2.3 | ✅ |
| [WS-2019-0425](https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | mocha-3.4.1.tgz | Direct | 6.0.0 | ✅ |
| [CVE-2017-16137](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | debug-2.6.0.tgz | Transitive | 4.0.0 | ✅ |
| [WS-2017-0247](https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.4 | ms-0.7.2.tgz | Transitive | 3.5.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16042</summary>
### Vulnerable Library - <b>growl-1.9.2.tgz</b></p>
<p>Growl unobtrusive notifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/growl/-/growl-1.9.2.tgz">https://registry.npmjs.org/growl/-/growl-1.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/growl/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- :x: **growl-1.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042>CVE-2017-16042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16042">https://nvd.nist.gov/vuln/detail/CVE-2017-16042</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution (growl): 1.10.2</p>
<p>Direct dependency fix Resolution (mocha): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16042","vulnerabilityDetails":"Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0590</summary>
### Vulnerable Library - <b>diff-3.2.0.tgz</b></p>
<p>A javascript text diff implementation.</p>
<p>Library home page: <a href="https://registry.npmjs.org/diff/-/diff-3.2.0.tgz">https://registry.npmjs.org/diff/-/diff-3.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/diff/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- :x: **diff-3.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.
<p>Publish Date: 2018-03-05
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1552148>WS-2018-0590</a></p>
</p>
<p></p>
### CVSS 2 Score Details (<b>7.0</b>)
<p>
Base Score Metrics not available</p>
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/kpdecker/jsdiff/commit/2aec4298639bf30fb88a00b356bf404d3551b8c0">https://github.com/kpdecker/jsdiff/commit/2aec4298639bf30fb88a00b356bf404d3551b8c0</a></p>
<p>Release Date: 2018-03-05</p>
<p>Fix Resolution (diff): 3.5.0</p>
<p>Direct dependency fix Resolution (mocha): 5.0.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.0.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0590","vulnerabilityDetails":"A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.","vulnerabilityUrl":"https://bugzilla.redhat.com/show_bug.cgi?id\u003d1552148","cvss2Severity":"high","cvss2Score":"7.0","extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7598</summary>
### Vulnerable Library - <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution (minimist): 0.2.1</p>
<p>Direct dependency fix Resolution (mocha): 6.2.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.2.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2019-0425</summary>
### Vulnerable Library - <b>mocha-3.4.1.tgz</b></p>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz">https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-3.4.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: 6.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2019-0425","vulnerabilityDetails":"Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.","vulnerabilityUrl":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16137</summary>
### Vulnerable Library - <b>debug-2.6.0.tgz</b></p>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-2.6.0.tgz">https://registry.npmjs.org/debug/-/debug-2.6.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- :x: **debug-2.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (debug): 2.6.9</p>
<p>Direct dependency fix Resolution (mocha): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16137","vulnerabilityDetails":"The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> WS-2017-0247</summary>
### Vulnerable Library - <b>ms-0.7.2.tgz</b></p>
<p>Tiny milisecond conversion utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/ms/-/ms-0.7.2.tgz">https://registry.npmjs.org/ms/-/ms-0.7.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/node_modules/ms/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- debug-2.6.0.tgz
- :x: **ms-0.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).
<p>Publish Date: 2017-04-12
<p>URL: <a href=https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef>WS-2017-0247</a></p>
</p>
<p></p>
### CVSS 2 Score Details (<b>3.4</b>)
<p>
Base Score Metrics not available</p>
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/ms/pull/89">https://github.com/vercel/ms/pull/89</a></p>
<p>Release Date: 2017-04-12</p>
<p>Fix Resolution (ms): 2.0.0</p>
<p>Direct dependency fix Resolution (mocha): 3.5.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.5.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2017-0247","vulnerabilityDetails":"Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).","vulnerabilityUrl":"https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef","cvss2Severity":"low","cvss2Score":"3.4","extraData":{}}</REMEDIATE> -->
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | mocha-3.4.1.tgz: 6 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-3.4.1.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz">https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-16042](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | growl-1.9.2.tgz | Transitive | 4.0.0 | ✅ |
| [WS-2018-0590](https://bugzilla.redhat.com/show_bug.cgi?id=1552148) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.0 | diff-3.2.0.tgz | Transitive | 5.0.3 | ✅ |
| [CVE-2020-7598](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | minimist-0.0.8.tgz | Transitive | 6.2.3 | ✅ |
| [WS-2019-0425](https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | mocha-3.4.1.tgz | Direct | 6.0.0 | ✅ |
| [CVE-2017-16137](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | debug-2.6.0.tgz | Transitive | 4.0.0 | ✅ |
| [WS-2017-0247](https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.4 | ms-0.7.2.tgz | Transitive | 3.5.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-16042</summary>
### Vulnerable Library - <b>growl-1.9.2.tgz</b></p>
<p>Growl unobtrusive notifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/growl/-/growl-1.9.2.tgz">https://registry.npmjs.org/growl/-/growl-1.9.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/growl/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- :x: **growl-1.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042>CVE-2017-16042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16042">https://nvd.nist.gov/vuln/detail/CVE-2017-16042</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution (growl): 1.10.2</p>
<p>Direct dependency fix Resolution (mocha): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16042","vulnerabilityDetails":"Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0590</summary>
### Vulnerable Library - <b>diff-3.2.0.tgz</b></p>
<p>A javascript text diff implementation.</p>
<p>Library home page: <a href="https://registry.npmjs.org/diff/-/diff-3.2.0.tgz">https://registry.npmjs.org/diff/-/diff-3.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/diff/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- :x: **diff-3.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.
<p>Publish Date: 2018-03-05
<p>URL: <a href=https://bugzilla.redhat.com/show_bug.cgi?id=1552148>WS-2018-0590</a></p>
</p>
<p></p>
### CVSS 2 Score Details (<b>7.0</b>)
<p>
Base Score Metrics not available</p>
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/kpdecker/jsdiff/commit/2aec4298639bf30fb88a00b356bf404d3551b8c0">https://github.com/kpdecker/jsdiff/commit/2aec4298639bf30fb88a00b356bf404d3551b8c0</a></p>
<p>Release Date: 2018-03-05</p>
<p>Fix Resolution (diff): 3.5.0</p>
<p>Direct dependency fix Resolution (mocha): 5.0.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.0.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0590","vulnerabilityDetails":"A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.","vulnerabilityUrl":"https://bugzilla.redhat.com/show_bug.cgi?id\u003d1552148","cvss2Severity":"high","cvss2Score":"7.0","extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7598</summary>
### Vulnerable Library - <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution (minimist): 0.2.1</p>
<p>Direct dependency fix Resolution (mocha): 6.2.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.2.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2019-0425</summary>
### Vulnerable Library - <b>mocha-3.4.1.tgz</b></p>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz">https://registry.npmjs.org/mocha/-/mocha-3.4.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-3.4.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: 6.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"6.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2019-0425","vulnerabilityDetails":"Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.","vulnerabilityUrl":"https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16137</summary>
### Vulnerable Library - <b>debug-2.6.0.tgz</b></p>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-2.6.0.tgz">https://registry.npmjs.org/debug/-/debug-2.6.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- :x: **debug-2.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (debug): 2.6.9</p>
<p>Direct dependency fix Resolution (mocha): 4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16137","vulnerabilityDetails":"The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> WS-2017-0247</summary>
### Vulnerable Library - <b>ms-0.7.2.tgz</b></p>
<p>Tiny milisecond conversion utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/ms/-/ms-0.7.2.tgz">https://registry.npmjs.org/ms/-/ms-0.7.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/node_modules/ms/package.json</p>
<p>
Dependency Hierarchy:
- mocha-3.4.1.tgz (Root Library)
- debug-2.6.0.tgz
- :x: **ms-0.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/NPM_test/commit/ebaa37fcd836520528512afb4b70905a12225d91">ebaa37fcd836520528512afb4b70905a12225d91</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).
<p>Publish Date: 2017-04-12
<p>URL: <a href=https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef>WS-2017-0247</a></p>
</p>
<p></p>
### CVSS 2 Score Details (<b>3.4</b>)
<p>
Base Score Metrics not available</p>
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/vercel/ms/pull/89">https://github.com/vercel/ms/pull/89</a></p>
<p>Release Date: 2017-04-12</p>
<p>Fix Resolution (ms): 2.0.0</p>
<p>Direct dependency fix Resolution (mocha): 3.5.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mocha","packageVersion":"3.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"mocha:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.5.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2017-0247","vulnerabilityDetails":"Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).","vulnerabilityUrl":"https://github.com/zeit/ms/commit/305f2ddcd4eff7cc7c518aca6bb2b2d2daad8fef","cvss2Severity":"low","cvss2Score":"3.4","extraData":{}}</REMEDIATE> -->
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | mocha tgz vulnerabilities highest severity is autoclosed vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file package json path to vulnerable library node modules mocha package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high growl tgz transitive ✅ high diff tgz transitive ✅ medium minimist tgz transitive ✅ medium mocha tgz direct ✅ medium debug tgz transitive ✅ low ms tgz transitive ✅ details cve vulnerable library growl tgz growl unobtrusive notifications library home page a href path to dependency file package json path to vulnerable library node modules growl package json dependency hierarchy mocha tgz root library x growl tgz vulnerable library found in head commit a href found in base branch main vulnerability details growl adds growl notification support to nodejs growl before does not properly sanitize input before passing it to exec allowing for arbitrary command execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution growl direct dependency fix resolution mocha rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails growl adds growl notification support to nodejs growl before does not properly sanitize input before passing it to exec allowing for arbitrary command execution vulnerabilityurl ws vulnerable library diff tgz a javascript text diff implementation library home page a href path to dependency file package json path to vulnerable library node modules diff package json dependency hierarchy mocha tgz root library x diff tgz vulnerable library found in head commit a href found in base branch main vulnerability details a vulnerability was found in diff before the affected versions of this package are vulnerable to regular expression denial of service redos attacks publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution diff direct dependency fix resolution mocha rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails a vulnerability was found in diff before the affected versions of this package are vulnerable to regular expression denial of service redos attacks vulnerabilityurl cve vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules mocha node modules minimist package json dependency hierarchy mocha tgz root library mkdirp tgz x minimist tgz vulnerable library found in head commit a href found in base branch main vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist direct dependency fix resolution mocha rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl ws vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file package json path to vulnerable library node modules mocha package json dependency hierarchy x mocha tgz vulnerable library found in head commit a href found in base branch main vulnerability details mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time vulnerabilityurl cve vulnerable library debug tgz small debugging utility library home page a href path to dependency file package json path to vulnerable library node modules mocha node modules debug package json dependency hierarchy mocha tgz root library x debug tgz vulnerable library found in head commit a href found in base branch main vulnerability details the debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter it takes around characters to block for seconds making this a low severity issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution debug direct dependency fix resolution mocha rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter it takes around characters to block for seconds making this a low severity issue vulnerabilityurl ws vulnerable library ms tgz tiny milisecond conversion utility library home page a href path to dependency file package json path to vulnerable library node modules mocha node modules ms package json dependency hierarchy mocha tgz root library debug tgz x ms tgz vulnerable library found in head commit a href found in base branch main vulnerability details affected versions of this package are vulnerable to regular expression denial of service redos publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution ms direct dependency fix resolution mocha rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree mocha isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails affected versions of this package are vulnerable to regular expression denial of service redos vulnerabilityurl rescue worker helmet automatic remediation is available for this issue | 0 |
271,196 | 29,351,406,277 | IssuesEvent | 2023-05-27 01:05:40 | snykiotcubedev/arangodb-3.7.6 | https://api.github.com/repos/snykiotcubedev/arangodb-3.7.6 | reopened | CVE-2019-6284 (Medium) detected in node-sass-4.14.1.tgz | Mend: dependency security vulnerability | ## CVE-2019-6284 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/arangodb-3.7.6/commit/fce8f85f1c2f070c8e6a8e76d17210a2117d3833">fce8f85f1c2f070c8e6a8e76d17210a2117d3833</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::alternatives in prelexer.hpp.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-6284>CVE-2019-6284</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-14</p>
<p>Fix Resolution: 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-6284 (Medium) detected in node-sass-4.14.1.tgz - ## CVE-2019-6284 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snykiotcubedev/arangodb-3.7.6/commit/fce8f85f1c2f070c8e6a8e76d17210a2117d3833">fce8f85f1c2f070c8e6a8e76d17210a2117d3833</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::alternatives in prelexer.hpp.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-6284>CVE-2019-6284</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-14</p>
<p>Fix Resolution: 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href dependency hierarchy x node sass tgz vulnerable library found in head commit a href found in base branch main vulnerability details in libsass a heap based buffer over read exists in sass prelexer alternatives in prelexer hpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
128,195 | 17,460,996,552 | IssuesEvent | 2021-08-06 10:24:55 | Altinn/altinn-studio | https://api.github.com/repos/Altinn/altinn-studio | closed | Alert service developer that someone else is working on the service (to avoid merge conflicts) | area/dashboard solution/studio/designer kind/user-story area/version-control | **Functional architect/designer:** @-mention
**Technical architect:** @-mention
**Description**
As a service developer I need to be alerted that someone else is working on the same service as me to reduce the risk of merge conflicts.
The alert shall be shown once another user has done changes to files in the users repository than the current user, meaning that the users repos is different from master or which ever branch the changes are made.
The alert shall be shown on the service developement pages and might reuse the layout as for the get latest alert. It shall also be possible to see which users who are working on the service, if possible you should see if it is in the "local" Altinn Studio repo, the changes are made or if the changes are done in a local code editor. (when latest pull is done for perhaps?)
If there is only one user working on the service, it shall not be shown an alert that others are working on the service.
For services that uses branches, it might be best to show this status per branch?
This issue needs to be consider together with how #335 have been solved.
**Sketch (if relevant)**
Need sketches of:
- How the alert of "someone else is working on the service" shall be shown
- Overview of which users are "working" on the service.
**Navigation from/to (if relevant)**
Shall be shown on the service development pages on a given service.
**Technical considerations**
Input (beyond tasks) on how the user story should be solved can be put here.
**Acceptance criterea**
- It shall be alerted when two or more service developers have different files from the branch that is in the central repo, that there are several users working on that service.
- It shall be possible to see which other users are working on the branch as defined above.
**Tasks**
- [ ] Sketch up how the alert shall be shown and how the overview is presented.
- [ ] Find out what is possible to see if a user has changed files on his local code editor.
- [ ]
| 1.0 | Alert service developer that someone else is working on the service (to avoid merge conflicts) - **Functional architect/designer:** @-mention
**Technical architect:** @-mention
**Description**
As a service developer I need to be alerted that someone else is working on the same service as me to reduce the risk of merge conflicts.
The alert shall be shown once another user has done changes to files in the users repository than the current user, meaning that the users repos is different from master or which ever branch the changes are made.
The alert shall be shown on the service developement pages and might reuse the layout as for the get latest alert. It shall also be possible to see which users who are working on the service, if possible you should see if it is in the "local" Altinn Studio repo, the changes are made or if the changes are done in a local code editor. (when latest pull is done for perhaps?)
If there is only one user working on the service, it shall not be shown an alert that others are working on the service.
For services that uses branches, it might be best to show this status per branch?
This issue needs to be consider together with how #335 have been solved.
**Sketch (if relevant)**
Need sketches of:
- How the alert of "someone else is working on the service" shall be shown
- Overview of which users are "working" on the service.
**Navigation from/to (if relevant)**
Shall be shown on the service development pages on a given service.
**Technical considerations**
Input (beyond tasks) on how the user story should be solved can be put here.
**Acceptance criterea**
- It shall be alerted when two or more service developers have different files from the branch that is in the central repo, that there are several users working on that service.
- It shall be possible to see which other users are working on the branch as defined above.
**Tasks**
- [ ] Sketch up how the alert shall be shown and how the overview is presented.
- [ ] Find out what is possible to see if a user has changed files on his local code editor.
- [ ]
| non_priority | alert service developer that someone else is working on the service to avoid merge conflicts functional architect designer mention technical architect mention description as a service developer i need to be alerted that someone else is working on the same service as me to reduce the risk of merge conflicts the alert shall be shown once another user has done changes to files in the users repository than the current user meaning that the users repos is different from master or which ever branch the changes are made the alert shall be shown on the service developement pages and might reuse the layout as for the get latest alert it shall also be possible to see which users who are working on the service if possible you should see if it is in the local altinn studio repo the changes are made or if the changes are done in a local code editor when latest pull is done for perhaps if there is only one user working on the service it shall not be shown an alert that others are working on the service for services that uses branches it might be best to show this status per branch this issue needs to be consider together with how have been solved sketch if relevant need sketches of how the alert of someone else is working on the service shall be shown overview of which users are working on the service navigation from to if relevant shall be shown on the service development pages on a given service technical considerations input beyond tasks on how the user story should be solved can be put here acceptance criterea it shall be alerted when two or more service developers have different files from the branch that is in the central repo that there are several users working on that service it shall be possible to see which other users are working on the branch as defined above tasks sketch up how the alert shall be shown and how the overview is presented find out what is possible to see if a user has changed files on his local code editor | 0 |
255,804 | 19,340,261,794 | IssuesEvent | 2021-12-15 03:04:19 | WordPress/Documentation-Issue-Tracker | https://api.github.com/repos/WordPress/Documentation-Issue-Tracker | opened | Update Template Editor Support Doc | user documentation enhancement 5.9 block editor tracking issue | Need to update this page https://wordpress.org/support/article/template-editor/ Off the top of my head, the following needs to be thought of:
- Add info about browsing templates/site editing flows (whether this doc makes sense or a new one is needed).
- Add in mention of new theme blocks one can use.
- Add demo/video of navigating between templates.
- Explain how one can add a custom template using the template editor via post/pages but not via browsing (yet). More here: https://github.com/WordPress/gutenberg/issues/36860#issuecomment-988969089 | 1.0 | Update Template Editor Support Doc - Need to update this page https://wordpress.org/support/article/template-editor/ Off the top of my head, the following needs to be thought of:
- Add info about browsing templates/site editing flows (whether this doc makes sense or a new one is needed).
- Add in mention of new theme blocks one can use.
- Add demo/video of navigating between templates.
- Explain how one can add a custom template using the template editor via post/pages but not via browsing (yet). More here: https://github.com/WordPress/gutenberg/issues/36860#issuecomment-988969089 | non_priority | update template editor support doc need to update this page off the top of my head the following needs to be thought of add info about browsing templates site editing flows whether this doc makes sense or a new one is needed add in mention of new theme blocks one can use add demo video of navigating between templates explain how one can add a custom template using the template editor via post pages but not via browsing yet more here | 0 |
330,084 | 24,246,166,604 | IssuesEvent | 2022-09-27 10:43:58 | mheob/config | https://api.github.com/repos/mheob/config | closed | [BUG]: CPM `@mheob/` scope is missing in the README usage | bug documentation cpm | ### Description of the bug
In the usage section of the README scripts are called without the `@mheob/` scope.
### Steps To Reproduce
See the README file.
### Additional Information
_No response_ | 1.0 | [BUG]: CPM `@mheob/` scope is missing in the README usage - ### Description of the bug
In the usage section of the README scripts are called without the `@mheob/` scope.
### Steps To Reproduce
See the README file.
### Additional Information
_No response_ | non_priority | cpm mheob scope is missing in the readme usage description of the bug in the usage section of the readme scripts are called without the mheob scope steps to reproduce see the readme file additional information no response | 0 |
273 | 2,562,433,741 | IssuesEvent | 2015-02-06 01:37:03 | geneontology/amigo | https://api.github.com/repos/geneontology/amigo | closed | Double check that multiple relations are handled correctly in visual context | bug (B: affects usability) | This means that the perl and JS widget correctly handle having multiple relations in the transitivity graph (e.g. when both is_a and regulates are available, regulates is chosen). | True | Double check that multiple relations are handled correctly in visual context - This means that the perl and JS widget correctly handle having multiple relations in the transitivity graph (e.g. when both is_a and regulates are available, regulates is chosen). | non_priority | double check that multiple relations are handled correctly in visual context this means that the perl and js widget correctly handle having multiple relations in the transitivity graph e g when both is a and regulates are available regulates is chosen | 0 |
20,235 | 10,479,679,127 | IssuesEvent | 2019-09-24 05:13:41 | bradykondek/disneyworldman | https://api.github.com/repos/bradykondek/disneyworldman | opened | CVE-2018-20677 (Medium) detected in bootstrap-3.2.0-3.3.0.js, bootstrap-3.2.0-3.3.0.min.js | security vulnerability | ## CVE-2018-20677 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-3.2.0-3.3.0.js</b>, <b>bootstrap-3.2.0-3.3.0.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-3.2.0-3.3.0.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /disneyworldman/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0-3.3.0.js** (Vulnerable Library)
</details>
<details><summary><b>bootstrap-3.2.0-3.3.0.min.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /disneyworldman/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0-3.3.0.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/bradykondek/disneyworldman/commit/f23daba353a0a7d726aa89d6a90422fc73c2e1aa">f23daba353a0a7d726aa89d6a90422fc73c2e1aa</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677>CVE-2018-20677</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-20677 (Medium) detected in bootstrap-3.2.0-3.3.0.js, bootstrap-3.2.0-3.3.0.min.js - ## CVE-2018-20677 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-3.2.0-3.3.0.js</b>, <b>bootstrap-3.2.0-3.3.0.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-3.2.0-3.3.0.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /disneyworldman/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0-3.3.0.js** (Vulnerable Library)
</details>
<details><summary><b>bootstrap-3.2.0-3.3.0.min.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.2.0-3.3.0/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /disneyworldman/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0-3.3.0.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/bradykondek/disneyworldman/commit/f23daba353a0a7d726aa89d6a90422fc73c2e1aa">f23daba353a0a7d726aa89d6a90422fc73c2e1aa</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677>CVE-2018-20677</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bootstrap js bootstrap min js cve medium severity vulnerability vulnerable libraries bootstrap js bootstrap min js bootstrap js google styled theme for bootstrap library home page a href path to vulnerable library disneyworldman js bootstrap js dependency hierarchy x bootstrap js vulnerable library bootstrap min js google styled theme for bootstrap library home page a href path to vulnerable library disneyworldman js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter step up your open source security game with whitesource | 0 |
113,156 | 9,630,226,112 | IssuesEvent | 2019-05-15 11:32:20 | jenkinsci/ecutest-plugin | https://api.github.com/repos/jenkinsci/ecutest-plugin | closed | Allow dynamic inline ECU-TEST instances in pipelines | ecu-test feature | In order to reduce maintenance efforts for multiple ECU-TEST installations in the Jenkins global tool configuration there should be a dynamic way for pipelines to define ECU-TEST installation configurations inline. The existing ECU-TEST build step must be extended to accept such installation configurations.
### Proposed method signatures
#### Define new installation
`ET.newInstance(String toolName, String installPath) : ETInstallation`
or
`ET.newInstance(String toolName, String installPath, ETToolProperty property) : ETInstallation`
#### Get configured installation
`ET.getInstance(String toolName) : ETInstallation`
#### Build steps
`startET(ETInstallation installation) : void`
or
`startET(ETInstallation installation, String workspaceDir, String settingsDir, int timeout, boolean debug) : void`
and
`stopET(ETInstallation installation) : void`
etc. | 1.0 | Allow dynamic inline ECU-TEST instances in pipelines - In order to reduce maintenance efforts for multiple ECU-TEST installations in the Jenkins global tool configuration there should be a dynamic way for pipelines to define ECU-TEST installation configurations inline. The existing ECU-TEST build step must be extended to accept such installation configurations.
### Proposed method signatures
#### Define new installation
`ET.newInstance(String toolName, String installPath) : ETInstallation`
or
`ET.newInstance(String toolName, String installPath, ETToolProperty property) : ETInstallation`
#### Get configured installation
`ET.getInstance(String toolName) : ETInstallation`
#### Build steps
`startET(ETInstallation installation) : void`
or
`startET(ETInstallation installation, String workspaceDir, String settingsDir, int timeout, boolean debug) : void`
and
`stopET(ETInstallation installation) : void`
etc. | non_priority | allow dynamic inline ecu test instances in pipelines in order to reduce maintenance efforts for multiple ecu test installations in the jenkins global tool configuration there should be a dynamic way for pipelines to define ecu test installation configurations inline the existing ecu test build step must be extended to accept such installation configurations proposed method signatures define new installation et newinstance string toolname string installpath etinstallation or et newinstance string toolname string installpath ettoolproperty property etinstallation get configured installation et getinstance string toolname etinstallation build steps startet etinstallation installation void or startet etinstallation installation string workspacedir string settingsdir int timeout boolean debug void and stopet etinstallation installation void etc | 0 |
8,905 | 8,460,719,584 | IssuesEvent | 2018-10-22 19:40:26 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | Use bundle release | area/service-catalog | AC:
- create first bundle GitHub release with one bundle - redis
- set the helm-broker repository url to that release | 1.0 | Use bundle release - AC:
- create first bundle GitHub release with one bundle - redis
- set the helm-broker repository url to that release | non_priority | use bundle release ac create first bundle github release with one bundle redis set the helm broker repository url to that release | 0 |
45,554 | 11,698,371,645 | IssuesEvent | 2020-03-06 13:46:23 | etclabscore/core-geth | https://api.github.com/repos/etclabscore/core-geth | closed | Publish docker image to hub.docker.com | M0-build 🏗 M1-ci 🙉 M9-deploy 🏄♀️ P5-sometimesoon 🌲 | Should publish an image regularly to the Docker registry for easy `docker pull`ing.
| 1.0 | Publish docker image to hub.docker.com - Should publish an image regularly to the Docker registry for easy `docker pull`ing.
| non_priority | publish docker image to hub docker com should publish an image regularly to the docker registry for easy docker pull ing | 0 |
154,245 | 12,197,730,873 | IssuesEvent | 2020-04-29 21:19:33 | istio/istio | https://api.github.com/repos/istio/istio | closed | sample custom gateway yaml need be updated | community/testing days kind/docs | https://preliminary.istio.io/docs/setup/install/istioctl/
Note that Helm values (spec.values.gateways.istio-ingressgateway/egressgateway) are shared by all ingress/egress gateways. If these must be customized per gateway, it is recommended to use a separate IstioOperator CR to generate a manifest for the user gateways, separate from the main Istio installation:
need to add `namespace: user-ingressgateway-ns` to align with the previous step. otherwise, it will create a new ilb-gateway in `istio-system` namespace
```
apiVersion: install.istio.io/v1alpha1
kind: IstioOperator
spec:
profile: empty
components:
ingressGateways:
- name: ilb-gateway
enabled: true
**namespace: user-ingressgateway-ns**
# Copy settings from istio-ingressgateway as needed.
values:
gateways:
istio-ingressgateway:
debug: error
``` | 1.0 | sample custom gateway yaml need be updated - https://preliminary.istio.io/docs/setup/install/istioctl/
Note that Helm values (spec.values.gateways.istio-ingressgateway/egressgateway) are shared by all ingress/egress gateways. If these must be customized per gateway, it is recommended to use a separate IstioOperator CR to generate a manifest for the user gateways, separate from the main Istio installation:
need to add `namespace: user-ingressgateway-ns` to align with the previous step. otherwise, it will create a new ilb-gateway in `istio-system` namespace
```
apiVersion: install.istio.io/v1alpha1
kind: IstioOperator
spec:
profile: empty
components:
ingressGateways:
- name: ilb-gateway
enabled: true
**namespace: user-ingressgateway-ns**
# Copy settings from istio-ingressgateway as needed.
values:
gateways:
istio-ingressgateway:
debug: error
``` | non_priority | sample custom gateway yaml need be updated note that helm values spec values gateways istio ingressgateway egressgateway are shared by all ingress egress gateways if these must be customized per gateway it is recommended to use a separate istiooperator cr to generate a manifest for the user gateways separate from the main istio installation need to add namespace user ingressgateway ns to align with the previous step otherwise it will create a new ilb gateway in istio system namespace apiversion install istio io kind istiooperator spec profile empty components ingressgateways name ilb gateway enabled true namespace user ingressgateway ns copy settings from istio ingressgateway as needed values gateways istio ingressgateway debug error | 0 |
263,003 | 19,862,012,101 | IssuesEvent | 2022-01-22 01:42:15 | sm3dev/michaelpwright-portfolio | https://api.github.com/repos/sm3dev/michaelpwright-portfolio | opened | Styling: Import Font Family: Work Sans | documentation enhancement | Import **Work Sans** font family with all weights
Reference: https://fonts.google.com/specimen/Work+Sans?query=work+sans#standard-styles | 1.0 | Styling: Import Font Family: Work Sans - Import **Work Sans** font family with all weights
Reference: https://fonts.google.com/specimen/Work+Sans?query=work+sans#standard-styles | non_priority | styling import font family work sans import work sans font family with all weights reference | 0 |
217,781 | 16,737,921,519 | IssuesEvent | 2021-06-11 05:55:18 | tendermint/liquidity | https://api.github.com/repos/tendermint/liquidity | closed | QA Liquidity Module Spec Markdown docs | documentation | The purpose of the issue is to QA the specification documentation for the Liquidity module. Documentation can be found [in the tendermint repo](https://github.com/tendermint/liquidity/blob/develop/x/liquidity/spec)
Outcomes will include
- Edits suggested in PR https://github.com/tendermint/liquidity/pull/201
- Comments that will outline areas for improvements and identify
- It may also include plans for remediation and how to write better documentation
| 1.0 | QA Liquidity Module Spec Markdown docs - The purpose of the issue is to QA the specification documentation for the Liquidity module. Documentation can be found [in the tendermint repo](https://github.com/tendermint/liquidity/blob/develop/x/liquidity/spec)
Outcomes will include
- Edits suggested in PR https://github.com/tendermint/liquidity/pull/201
- Comments that will outline areas for improvements and identify
- It may also include plans for remediation and how to write better documentation
| non_priority | qa liquidity module spec markdown docs the purpose of the issue is to qa the specification documentation for the liquidity module documentation can be found outcomes will include edits suggested in pr comments that will outline areas for improvements and identify it may also include plans for remediation and how to write better documentation | 0 |
87,072 | 15,755,946,958 | IssuesEvent | 2021-03-31 02:39:37 | benlazarine/troposphere | https://api.github.com/repos/benlazarine/troposphere | opened | CVE-2021-23358 (High) detected in underscore-1.9.1.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.9.1.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.9.1.tgz">https://registry.npmjs.org/underscore/-/underscore-1.9.1.tgz</a></p>
<p>Path to dependency file: troposphere/package.json</p>
<p>Path to vulnerable library: troposphere/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- :x: **underscore-1.9.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Execution via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23358 (High) detected in underscore-1.9.1.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.9.1.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.9.1.tgz">https://registry.npmjs.org/underscore/-/underscore-1.9.1.tgz</a></p>
<p>Path to dependency file: troposphere/package.json</p>
<p>Path to vulnerable library: troposphere/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- :x: **underscore-1.9.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Execution via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file troposphere package json path to vulnerable library troposphere node modules underscore package json dependency hierarchy x underscore tgz vulnerable library vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code execution via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore step up your open source security game with whitesource | 0 |
12,642 | 9,725,691,357 | IssuesEvent | 2019-05-30 09:24:27 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Cannot deploy application | container-service/svc cxp product-question triaged | Hi, I'm following your guide to install Windows container. When I run command: kubectl apply -f sample.yaml getting this error:
error: SchemaError(io.k8s.api.core.v1.AzureFileVolumeSource): invalid object doesn't have additional properties
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 6de70aec-9ebe-5655-6657-5c171de374b1
* Version Independent ID: c9eb35c8-8703-511b-987b-e2a441be2e47
* Content: [Preview - Create a Windows Server container on an Azure Kubernetes Service (AKS) cluster](https://docs.microsoft.com/en-us/azure/aks/windows-container-cli)
* Content Source: [articles/aks/windows-container-cli.md](https://github.com/Microsoft/azure-docs/blob/master/articles/aks/windows-container-cli.md)
* Service: **container-service**
* GitHub Login: @zr-msft
* Microsoft Alias: **zarhoads** | 1.0 | Cannot deploy application - Hi, I'm following your guide to install Windows container. When I run command: kubectl apply -f sample.yaml getting this error:
error: SchemaError(io.k8s.api.core.v1.AzureFileVolumeSource): invalid object doesn't have additional properties
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 6de70aec-9ebe-5655-6657-5c171de374b1
* Version Independent ID: c9eb35c8-8703-511b-987b-e2a441be2e47
* Content: [Preview - Create a Windows Server container on an Azure Kubernetes Service (AKS) cluster](https://docs.microsoft.com/en-us/azure/aks/windows-container-cli)
* Content Source: [articles/aks/windows-container-cli.md](https://github.com/Microsoft/azure-docs/blob/master/articles/aks/windows-container-cli.md)
* Service: **container-service**
* GitHub Login: @zr-msft
* Microsoft Alias: **zarhoads** | non_priority | cannot deploy application hi i m following your guide to install windows container when i run command kubectl apply f sample yaml getting this error error schemaerror io api core azurefilevolumesource invalid object doesn t have additional properties document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login zr msft microsoft alias zarhoads | 0 |
33,245 | 6,187,905,995 | IssuesEvent | 2017-07-04 08:50:36 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | Document lessons-learned re: CouchDB database compaction, view compaction/rebuilding/cleanup | Documentation Needs Triage | We recently learned a bunch of potentially-troubling things about how CouchDB manages disk space and on-disk view indexes. Since the upstream documentation isn't spectacular, document the limitations we discovered and come up with a set of best practices for managing disk space and index rebuilds.
| 1.0 | Document lessons-learned re: CouchDB database compaction, view compaction/rebuilding/cleanup - We recently learned a bunch of potentially-troubling things about how CouchDB manages disk space and on-disk view indexes. Since the upstream documentation isn't spectacular, document the limitations we discovered and come up with a set of best practices for managing disk space and index rebuilds.
| non_priority | document lessons learned re couchdb database compaction view compaction rebuilding cleanup we recently learned a bunch of potentially troubling things about how couchdb manages disk space and on disk view indexes since the upstream documentation isn t spectacular document the limitations we discovered and come up with a set of best practices for managing disk space and index rebuilds | 0 |
698 | 2,566,032,624 | IssuesEvent | 2015-02-08 02:22:53 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Not correct "Count Module positions" | No Code Attached Yet | #### Steps to reproduce the issue
Publish "Syndication Feeds Module" or "Similar Tags Module" in Protostar template in to the position-7 or position-8. Other modules unpublish from those positions.
If this module has empty results (= not displayed module), that module position can't be calculated (and must be ignored) by Joomla! 3.3.6.
#### Expected result
With blank/empty results of those modules (e.g. no RSS in article view), mean if is RSS module in position-7 or position-8 (left or right sides of template) is empty, that positions should not be displayed (calculated), But now Joomla! 3.3.6 is displaying empty module position-7 or position-8 as blank column, but that column of template should not be visible (in case you don't have other modules in that position).
#### Actual result
Blank columns if you have in Protostar template published (in positon-7,8) only RSS or Similar tags modules. But it is not bug of Protostar template, it is bug of Joomla when is calculating positions.
#### System information (as much as possible)
Database Version: 5.5.25a
Database Collation: utf8_general_ci
PHP Version: 5.4.4
Web Server: Apache/2.4.2 (Win32) OpenSSL/1.0.1c PHP/5.4.4
WebServer to PHP Interface: apache2handler
Joomla! Version: Joomla! 3.3.6 Stable [ Ember ] 01-October-2014 02:00 GMT
Joomla! Platform Version: Joomla Platform 13.1.0 Stable [ Curiosity ] 24-Apr-2013 00:00 GMT
User Agent: Mozilla/5.0 (Windows NT 5.1; rv:35.0) Gecko/20100101 Firefox/35.0
#### Additional comments
It is annoying to have empty columns in template (in case that RSS or similar tags modules have empty resaults and are only ones in that positions).
| 1.0 | Not correct "Count Module positions" - #### Steps to reproduce the issue
Publish "Syndication Feeds Module" or "Similar Tags Module" in Protostar template in to the position-7 or position-8. Other modules unpublish from those positions.
If this module has empty results (= not displayed module), that module position can't be calculated (and must be ignored) by Joomla! 3.3.6.
#### Expected result
With blank/empty results of those modules (e.g. no RSS in article view), mean if is RSS module in position-7 or position-8 (left or right sides of template) is empty, that positions should not be displayed (calculated), But now Joomla! 3.3.6 is displaying empty module position-7 or position-8 as blank column, but that column of template should not be visible (in case you don't have other modules in that position).
#### Actual result
Blank columns if you have in Protostar template published (in positon-7,8) only RSS or Similar tags modules. But it is not bug of Protostar template, it is bug of Joomla when is calculating positions.
#### System information (as much as possible)
Database Version: 5.5.25a
Database Collation: utf8_general_ci
PHP Version: 5.4.4
Web Server: Apache/2.4.2 (Win32) OpenSSL/1.0.1c PHP/5.4.4
WebServer to PHP Interface: apache2handler
Joomla! Version: Joomla! 3.3.6 Stable [ Ember ] 01-October-2014 02:00 GMT
Joomla! Platform Version: Joomla Platform 13.1.0 Stable [ Curiosity ] 24-Apr-2013 00:00 GMT
User Agent: Mozilla/5.0 (Windows NT 5.1; rv:35.0) Gecko/20100101 Firefox/35.0
#### Additional comments
It is annoying to have empty columns in template (in case that RSS or similar tags modules have empty resaults and are only ones in that positions).
| non_priority | not correct count module positions steps to reproduce the issue publish syndication feeds module or similar tags module in protostar template in to the position or position other modules unpublish from those positions if this module has empty results not displayed module that module position can t be calculated and must be ignored by joomla expected result with blank empty results of those modules e g no rss in article view mean if is rss module in position or position left or right sides of template is empty that positions should not be displayed calculated but now joomla is displaying empty module position or position as blank column but that column of template should not be visible in case you don t have other modules in that position actual result blank columns if you have in protostar template published in positon only rss or similar tags modules but it is not bug of protostar template it is bug of joomla when is calculating positions system information as much as possible database version database collation general ci php version web server apache openssl php webserver to php interface joomla version joomla stable october gmt joomla platform version joomla platform stable apr gmt user agent mozilla windows nt rv gecko firefox additional comments it is annoying to have empty columns in template in case that rss or similar tags modules have empty resaults and are only ones in that positions | 0 |
60,551 | 6,705,882,252 | IssuesEvent | 2017-10-12 03:16:24 | IF977/WhereIGo | https://api.github.com/repos/IF977/WhereIGo | opened | [2-1] Testes de avaliação de estabelecimento | testes | Itens a serem realizados:
- Criar testes de avaliação de estabelecimento com Rspec/Cucumber | 1.0 | [2-1] Testes de avaliação de estabelecimento - Itens a serem realizados:
- Criar testes de avaliação de estabelecimento com Rspec/Cucumber | non_priority | testes de avaliação de estabelecimento itens a serem realizados criar testes de avaliação de estabelecimento com rspec cucumber | 0 |
214,984 | 16,585,142,026 | IssuesEvent | 2021-05-31 17:48:12 | gii-is-psg2/PSG2-2021-G4-41 | https://api.github.com/repos/gii-is-psg2/PSG2-2021-G4-41 | closed | A4.4.a: Fill the technical report | documentation | ## To do:
- [x] A screenshot of the SLA generated in iTop, and its association to the maintenance service as created in the iTop tool.CMDB
- [x] The definition of the SLA document, including the terms of service and the service level targets.
- [x] A justification and rationale of the value provided for the guarantee in the SLA. | 1.0 | A4.4.a: Fill the technical report - ## To do:
- [x] A screenshot of the SLA generated in iTop, and its association to the maintenance service as created in the iTop tool.CMDB
- [x] The definition of the SLA document, including the terms of service and the service level targets.
- [x] A justification and rationale of the value provided for the guarantee in the SLA. | non_priority | a fill the technical report to do a screenshot of the sla generated in itop and its association to the maintenance service as created in the itop tool cmdb the definition of the sla document including the terms of service and the service level targets a justification and rationale of the value provided for the guarantee in the sla | 0 |
11,435 | 7,545,155,414 | IssuesEvent | 2018-04-17 20:41:39 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | HttpClient.Post sends separate TCP packets for Header and Body | area-System.Net.Http enhancement tenet-performance | This is a general issue with .net I am assuming.
Using Microsoft Message Analyzer, I can see that post data using the HttpClient is being sent in two tcp packets. One for the header, then one for the post body. This data could easily fit into one packet, however it is being split into two. I have explicitly turned on nagling and expect 100 continue off using the ServicePointManager, though, it doesn't seem to help.
```
public void TestRequest()
{
var uri = new Uri("http://www.webscantest.com/");
ServicePointManager.Expect100Continue = false;
ServicePointManager.UseNagleAlgorithm = true;
var p = ServicePointManager.FindServicePoint(uri);
p.Expect100Continue = false;
p.UseNagleAlgorithm = true;
HttpClient client = new HttpClient();
client.DefaultRequestHeaders.Add("Connection", "close");
var values = new Dictionary<string, string>
{
{ "thing1", "hello" },
{ "thing2", "world" }
};
var content = new FormUrlEncodedContent(values);
var response = client.PostAsync("http://www.webscantest.com/", content, CancellationToken.None).Result;
}
```
I raised this on [stackoverflow](https://stackoverflow.com/questions/49727720/c-sharp-httpclient-post-force-single-packet/49788340#49788340) and did some research to find the problem. | True | HttpClient.Post sends separate TCP packets for Header and Body - This is a general issue with .net I am assuming.
Using Microsoft Message Analyzer, I can see that post data using the HttpClient is being sent in two tcp packets. One for the header, then one for the post body. This data could easily fit into one packet, however it is being split into two. I have explicitly turned on nagling and expect 100 continue off using the ServicePointManager, though, it doesn't seem to help.
```
public void TestRequest()
{
var uri = new Uri("http://www.webscantest.com/");
ServicePointManager.Expect100Continue = false;
ServicePointManager.UseNagleAlgorithm = true;
var p = ServicePointManager.FindServicePoint(uri);
p.Expect100Continue = false;
p.UseNagleAlgorithm = true;
HttpClient client = new HttpClient();
client.DefaultRequestHeaders.Add("Connection", "close");
var values = new Dictionary<string, string>
{
{ "thing1", "hello" },
{ "thing2", "world" }
};
var content = new FormUrlEncodedContent(values);
var response = client.PostAsync("http://www.webscantest.com/", content, CancellationToken.None).Result;
}
```
I raised this on [stackoverflow](https://stackoverflow.com/questions/49727720/c-sharp-httpclient-post-force-single-packet/49788340#49788340) and did some research to find the problem. | non_priority | httpclient post sends separate tcp packets for header and body this is a general issue with net i am assuming using microsoft message analyzer i can see that post data using the httpclient is being sent in two tcp packets one for the header then one for the post body this data could easily fit into one packet however it is being split into two i have explicitly turned on nagling and expect continue off using the servicepointmanager though it doesn t seem to help public void testrequest var uri new uri servicepointmanager false servicepointmanager usenaglealgorithm true var p servicepointmanager findservicepoint uri p false p usenaglealgorithm true httpclient client new httpclient client defaultrequestheaders add connection close var values new dictionary hello world var content new formurlencodedcontent values var response client postasync content cancellationtoken none result i raised this on and did some research to find the problem | 0 |
9,969 | 8,758,339,698 | IssuesEvent | 2018-12-15 02:39:34 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Scale | app-service-web/svc cxp product-question triaged | How far do the different alternatives scale for one deployment?
CloudServices can take 10.000 cores per subscription.
What about service fabric (used to advertice with 1000 VMs, which is puny) and app services.
(Yes, I understand you can have lots of deployments, but comparing how many in one still gives value.)
---
#### Dokumentinformasjon
⚠ *Ikke rediger denne delen. Den kreves for koblingen docs.microsoft.com ➟ GitHub-problem.*
* ID: 02a4abb1-48c0-178e-a37e-290034b4dcae
* Version Independent ID: 61da6a8b-fa37-a499-ba79-0dd6b5346f2a
* Content: [Compare App Service, VM, Service Fabric, and Cloud Services - Azure](https://docs.microsoft.com/nb-no/azure/app-service/choose-web-site-cloud-service-vm)
* Content Source: [articles/app-service/choose-web-site-cloud-service-vm.md](https://github.com/Microsoft/azure-docs/blob/master/articles/app-service/choose-web-site-cloud-service-vm.md)
* Service: **app-service-web**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | 1.0 | Scale - How far do the different alternatives scale for one deployment?
CloudServices can take 10.000 cores per subscription.
What about service fabric (used to advertice with 1000 VMs, which is puny) and app services.
(Yes, I understand you can have lots of deployments, but comparing how many in one still gives value.)
---
#### Dokumentinformasjon
⚠ *Ikke rediger denne delen. Den kreves for koblingen docs.microsoft.com ➟ GitHub-problem.*
* ID: 02a4abb1-48c0-178e-a37e-290034b4dcae
* Version Independent ID: 61da6a8b-fa37-a499-ba79-0dd6b5346f2a
* Content: [Compare App Service, VM, Service Fabric, and Cloud Services - Azure](https://docs.microsoft.com/nb-no/azure/app-service/choose-web-site-cloud-service-vm)
* Content Source: [articles/app-service/choose-web-site-cloud-service-vm.md](https://github.com/Microsoft/azure-docs/blob/master/articles/app-service/choose-web-site-cloud-service-vm.md)
* Service: **app-service-web**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | non_priority | scale how far do the different alternatives scale for one deployment cloudservices can take cores per subscription what about service fabric used to advertice with vms which is puny and app services yes i understand you can have lots of deployments but comparing how many in one still gives value dokumentinformasjon ⚠ ikke rediger denne delen den kreves for koblingen docs microsoft com ➟ github problem id version independent id content content source service app service web github login cephalin microsoft alias cephalin | 0 |
151,581 | 12,043,779,942 | IssuesEvent | 2020-04-14 13:01:46 | odrotbohm/moduliths | https://api.github.com/repos/odrotbohm/moduliths | opened | Make @ModuleTest work more like a Spring bean | in: test support type: enhancement | We should default to the by-class lifecycle and enable constructor autowiring. | 1.0 | Make @ModuleTest work more like a Spring bean - We should default to the by-class lifecycle and enable constructor autowiring. | non_priority | make moduletest work more like a spring bean we should default to the by class lifecycle and enable constructor autowiring | 0 |
234,729 | 25,885,077,212 | IssuesEvent | 2022-12-14 14:02:02 | pustovitDmytro/npm-boilerplate | https://api.github.com/repos/pustovitDmytro/npm-boilerplate | closed | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - autoclosed | security vulnerability | ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/minimatch/package.json,/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- semantic-release-19.0.2.tgz (Root Library)
- npm-9.0.0.tgz
- npm-8.4.0.tgz
- glob-7.2.0.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/npm-boilerplate/commit/0888eee49d490c03a2d773287f1270e8a617d8ca">0888eee49d490c03a2d773287f1270e8a617d8ca</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - autoclosed - ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/minimatch/package.json,/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- semantic-release-19.0.2.tgz (Root Library)
- npm-9.0.0.tgz
- npm-8.4.0.tgz
- glob-7.2.0.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/pustovitDmytro/npm-boilerplate/commit/0888eee49d490c03a2d773287f1270e8a617d8ca">0888eee49d490c03a2d773287f1270e8a617d8ca</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in minimatch tgz autoclosed cve high severity vulnerability vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file package json path to vulnerable library node modules npm node modules minimatch package json node modules minimatch package json dependency hierarchy semantic release tgz root library npm tgz npm tgz glob tgz x minimatch tgz vulnerable library found in head commit a href found in base branch master vulnerability details a vulnerability was found in the minimatch package this flaw allows a regular expression denial of service redos when calling the braceexpand function with specific arguments resulting in a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimatch step up your open source security game with mend | 0 |
44,177 | 13,048,649,204 | IssuesEvent | 2020-07-29 12:54:06 | jgeraigery/gradle | https://api.github.com/repos/jgeraigery/gradle | opened | CVE-2020-5529 (High) detected in htmlunit-2.27.jar | security vulnerability | ## CVE-2020-5529 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>htmlunit-2.27.jar</b></p></summary>
<p>A headless browser intended for use in testing web-based applications.</p>
<p>Library home page: <a href="http://htmlunit.sourceforge.net">http://htmlunit.sourceforge.net</a></p>
<p>Path to dependency file: /tmp/ws-scm/gradle/subprojects/docs/src/snippets/play/multiproject/groovy/modules/user/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/net.sourceforge.htmlunit/htmlunit/2.27/aea70f853583b0eadcaa6a0429595973036cc745/htmlunit-2.27.jar</p>
<p>
Dependency Hierarchy:
- play-test_2.12-2.6.15.jar (Root Library)
- htmlunit-driver-2.27.jar
- :x: **htmlunit-2.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/gradle/commit/65bed555d82578998e80c7e348fe6a8698dbd75c">65bed555d82578998e80c7e348fe6a8698dbd75c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
HtmlUnit prior to 2.37.0 contains code execution vulnerabilities. HtmlUnit initializes Rhino engine improperly, hence a malicious JavScript code can execute arbitrary Java code on the application. Moreover, when embedded in Android application, Android-specific initialization of Rhino engine is done in an improper way, hence a malicious JavaScript code can execute arbitrary Java code on the application.
<p>Publish Date: 2020-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-5529>CVE-2020-5529</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/HtmlUnit/htmlunit/releases/tag/2.37.0">https://github.com/HtmlUnit/htmlunit/releases/tag/2.37.0</a></p>
<p>Release Date: 2020-02-11</p>
<p>Fix Resolution: net.sourceforge.htmlunit:htmlunit:2.37.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"net.sourceforge.htmlunit","packageName":"htmlunit","packageVersion":"2.27","isTransitiveDependency":true,"dependencyTree":"com.typesafe.play:play-test_2.12:2.6.15;org.seleniumhq.selenium:htmlunit-driver:2.27;net.sourceforge.htmlunit:htmlunit:2.27","isMinimumFixVersionAvailable":true,"minimumFixVersion":"net.sourceforge.htmlunit:htmlunit:2.37.0"}],"vulnerabilityIdentifier":"CVE-2020-5529","vulnerabilityDetails":"HtmlUnit prior to 2.37.0 contains code execution vulnerabilities. HtmlUnit initializes Rhino engine improperly, hence a malicious JavScript code can execute arbitrary Java code on the application. Moreover, when embedded in Android application, Android-specific initialization of Rhino engine is done in an improper way, hence a malicious JavaScript code can execute arbitrary Java code on the application.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-5529","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-5529 (High) detected in htmlunit-2.27.jar - ## CVE-2020-5529 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>htmlunit-2.27.jar</b></p></summary>
<p>A headless browser intended for use in testing web-based applications.</p>
<p>Library home page: <a href="http://htmlunit.sourceforge.net">http://htmlunit.sourceforge.net</a></p>
<p>Path to dependency file: /tmp/ws-scm/gradle/subprojects/docs/src/snippets/play/multiproject/groovy/modules/user/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/net.sourceforge.htmlunit/htmlunit/2.27/aea70f853583b0eadcaa6a0429595973036cc745/htmlunit-2.27.jar</p>
<p>
Dependency Hierarchy:
- play-test_2.12-2.6.15.jar (Root Library)
- htmlunit-driver-2.27.jar
- :x: **htmlunit-2.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/gradle/commit/65bed555d82578998e80c7e348fe6a8698dbd75c">65bed555d82578998e80c7e348fe6a8698dbd75c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
HtmlUnit prior to 2.37.0 contains code execution vulnerabilities. HtmlUnit initializes Rhino engine improperly, hence a malicious JavScript code can execute arbitrary Java code on the application. Moreover, when embedded in Android application, Android-specific initialization of Rhino engine is done in an improper way, hence a malicious JavaScript code can execute arbitrary Java code on the application.
<p>Publish Date: 2020-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-5529>CVE-2020-5529</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/HtmlUnit/htmlunit/releases/tag/2.37.0">https://github.com/HtmlUnit/htmlunit/releases/tag/2.37.0</a></p>
<p>Release Date: 2020-02-11</p>
<p>Fix Resolution: net.sourceforge.htmlunit:htmlunit:2.37.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"net.sourceforge.htmlunit","packageName":"htmlunit","packageVersion":"2.27","isTransitiveDependency":true,"dependencyTree":"com.typesafe.play:play-test_2.12:2.6.15;org.seleniumhq.selenium:htmlunit-driver:2.27;net.sourceforge.htmlunit:htmlunit:2.27","isMinimumFixVersionAvailable":true,"minimumFixVersion":"net.sourceforge.htmlunit:htmlunit:2.37.0"}],"vulnerabilityIdentifier":"CVE-2020-5529","vulnerabilityDetails":"HtmlUnit prior to 2.37.0 contains code execution vulnerabilities. HtmlUnit initializes Rhino engine improperly, hence a malicious JavScript code can execute arbitrary Java code on the application. Moreover, when embedded in Android application, Android-specific initialization of Rhino engine is done in an improper way, hence a malicious JavaScript code can execute arbitrary Java code on the application.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-5529","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in htmlunit jar cve high severity vulnerability vulnerable library htmlunit jar a headless browser intended for use in testing web based applications library home page a href path to dependency file tmp ws scm gradle subprojects docs src snippets play multiproject groovy modules user build gradle path to vulnerable library home wss scanner gradle caches modules files net sourceforge htmlunit htmlunit htmlunit jar dependency hierarchy play test jar root library htmlunit driver jar x htmlunit jar vulnerable library found in head commit a href vulnerability details htmlunit prior to contains code execution vulnerabilities htmlunit initializes rhino engine improperly hence a malicious javscript code can execute arbitrary java code on the application moreover when embedded in android application android specific initialization of rhino engine is done in an improper way hence a malicious javascript code can execute arbitrary java code on the application publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution net sourceforge htmlunit htmlunit isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails htmlunit prior to contains code execution vulnerabilities htmlunit initializes rhino engine improperly hence a malicious javscript code can execute arbitrary java code on the application moreover when embedded in android application android specific initialization of rhino engine is done in an improper way hence a malicious javascript code can execute arbitrary java code on the application vulnerabilityurl | 0 |
78,501 | 22,289,871,077 | IssuesEvent | 2022-06-12 07:34:08 | hannobraun/Fornjot | https://api.github.com/repos/hannobraun/Fornjot | opened | Some crates are missing from `default-members` in `Cargo.lock` | good first issue type: development topic: build | In the top-level `Cargo.lock` file, not all crates from the `crates/` directory are present in `default-members/`. This means that parts of the CI build (and the `justfile`) don't apply to them. Running `cargo test` from the repository root, for example, will not run tests from these crates.
This should be addressed. Everything from `crates/` should be in `default-members`. Labeling https://github.com/hannobraun/Fornjot/labels/good%20first%20issue, since this is a small change that doesn't require any specific knowledge about Fornjot. | 1.0 | Some crates are missing from `default-members` in `Cargo.lock` - In the top-level `Cargo.lock` file, not all crates from the `crates/` directory are present in `default-members/`. This means that parts of the CI build (and the `justfile`) don't apply to them. Running `cargo test` from the repository root, for example, will not run tests from these crates.
This should be addressed. Everything from `crates/` should be in `default-members`. Labeling https://github.com/hannobraun/Fornjot/labels/good%20first%20issue, since this is a small change that doesn't require any specific knowledge about Fornjot. | non_priority | some crates are missing from default members in cargo lock in the top level cargo lock file not all crates from the crates directory are present in default members this means that parts of the ci build and the justfile don t apply to them running cargo test from the repository root for example will not run tests from these crates this should be addressed everything from crates should be in default members labeling since this is a small change that doesn t require any specific knowledge about fornjot | 0 |
74,673 | 25,250,279,046 | IssuesEvent | 2022-11-15 14:13:12 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | "Error uploading one-time keys" on login | T-Defect | Surprising OTK upload error from IDB on a fresh login on an old account on plain Chrome...
```
Initialised rageshake.
rageshake.js?432e:65 To fix line numbers in Chrome: Meatball menu → Settings → Blackboxing → Add /rageshake\.js$
rageshake.js?432e:65 Using Web platform
/develop/config.riot.im.json?cachebuster=1587050412257:1 Failed to load resource: the server responded with a status of 404 ()
rageshake.js?432e:65 Loading skin...
rageshake.js?432e:65 Starting watcher for RoomList.orderAlphabetically@<null room> as ID 1587050412411_1_RoomList.orderAlphabetically_null
rageshake.js?432e:65 Starting watcher for RoomList.orderByImportance@<null room> as ID 1587050412411_2_RoomList.orderByImportance_null
rageshake.js?432e:65 Starting watcher for feature_custom_tags@<null room> as ID 1587050412411_3_feature_custom_tags_null
rageshake.js?432e:65 Starting watcher for TagPanel.disableTagPanel@<null room> as ID 1587050412413_4_TagPanel.disableTagPanel_null
rageshake.js?432e:65 Skin loaded!
rageshake.js?432e:65 Using WebAssembly Olm
rageshake.js?432e:65 set language to en
rageshake.js?432e:65 Vector starting at https://riot.im/develop/
rageshake.js?432e:65 Verifying homeserver configuration
rageshake.js?432e:65 Config uses a default_server_name - doing .well-known lookup
rageshake.js?432e:65 DEPRECATED CONFIG OPTION: In the future, default_server_name will not be accepted. Please use default_server_config instead.
consoleObj.<computed> @ rageshake.js?432e:65
rageshake.js?432e:65 Using homeserver config: ValidatedServerConfig
rageshake.js?432e:65 Updating SdkConfig with validated discovery information
rageshake.js?432e:65 Starting watcher for theme@<null room> as ID 1587050413162_5_theme_null
rageshake.js?432e:65 Starting watcher for use_system_theme@<null room> as ID 1587050413163_6_use_system_theme_null
rageshake.js?432e:65 No previous session found.
rageshake.js?432e:65 Doing guest login on https://matrix-client.matrix.org
The resource https://riot.im/develop/bundles/4579131589870492b0a9/error-view.js was preloaded using link preload but not used within a few seconds from the window's load event. Please make sure it has an appropriate `as` value and it is preloaded intentionally.
rageshake.js?432e:65 Registered as guest: @56438099644:matrix.org
rageshake.js?432e:65 setLoggedIn: mxid: @56438099644:matrix.org deviceId: guest_device guest: true hs: https://matrix-client.matrix.org softLogout: false
rageshake.js?432e:65 Removing indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 Removed indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 Removing indexeddb instance: matrix-js-sdk:riot-web-sync
logger.js?c9c0:46 Removed indexeddb instance: matrix-js-sdk:riot-web-sync
rageshake.js?432e:65 Deleted indexeddb data.
rageshake.js?432e:65 StorageManager: Checking storage consistency
rageshake.js?432e:65 StorageManager: Local storage supported? true
rageshake.js?432e:65 StorageManager: IndexedDB supported? true
rageshake.js?432e:65 StorageManager: Local storage contains data? false
rageshake.js?432e:65 StorageManager: Crypto initialised? null
rageshake.js?432e:65 StorageManager: Sync store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Crypto store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Storage consistency checks passed
rageshake.js?432e:65 Session persisted for @56438099644:matrix.org
rageshake.js?432e:65 Lifecycle: Starting MatrixClient
2rageshake.js?432e:65 Updating homeserver-configured integration managers...
rageshake.js?432e:65 Starting watcher for mjolnirRooms@<null room> as ID 1587050417527_7_mjolnirRooms_null
rageshake.js?432e:65 IndexedDBStore.startup: connecting to backend
rageshake.js?432e:65 MatrixClientPeg: waiting for MatrixClient store to initialise
rageshake.js?432e:65 Homeserver has no integration managers
rageshake.js?432e:65 StorageManager: Persistent? false
rageshake.js?432e:65 Homeserver has no integration managers
rageshake.js?432e:65 newscreen welcome
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connecting...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: awaiting connection...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: upgrading from 0
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connected
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading account data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading sync data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded account data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded sync data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded initial data
rageshake.js?432e:65 IndexedDBStore.startup: loading presence events
rageshake.js?432e:65 IndexedDBStore.startup: processing presence events
rageshake.js?432e:65 Crypto: Starting up crypto store...
rageshake.js?432e:65 connecting to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Upgrading IndexedDBCryptoStore from version 0 to 9
rageshake.js?432e:65 connected to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Crypto: initialising roomlist...
rageshake.js?432e:65 Crypto: initialising crypto object...
rageshake.js?432e:65 Crypto: initialising Olm...
rageshake.js?432e:65 Crypto: initialising Olm device...
rageshake.js?432e:65 Crypto: loading device list...
rageshake.js?432e:65 Crypto: fetching own devices...
rageshake.js?432e:65 Crypto: adding this device to the store...
rageshake.js?432e:65 Now tracking device list for @56438099644:matrix.org
rageshake.js?432e:65 Crypto: checking for key backup...
rageshake.js?432e:65 Checking key backup status...
rageshake.js?432e:65 Skipping key backup check since user is guest
webpack-internal:///1351:68 MatrixClientPeg: really starting MatrixClient
webpack-internal:///1351:68 MatrixClientPeg: MatrixClient started
webpack-internal:///1351:68 Attempting to get Jitsi conference information from homeserver
webpack-internal:///1351:68 Jitsi conference domain: jitsi.riot.im
webpack-internal:///1351:68 Saving device tracking data null
webpack-internal:///1351:68 Looking for queued outgoing room key requests
webpack-internal:///1351:68 No more outgoing room key requests
webpack-internal:///1351:68 Got TURN URIs: turn:turn.matrix.org:3478?transport=udp,turn:turn.matrix.org:3478?transport=tcp,turns:turn.matrix.org:443?transport=tcp refresh in 86400 secs
matrix-client.matrix.org/_matrix/client/r0/user/%4056438099644%3Amatrix.org/account_data/m.cross_signing.master:1 Failed to load resource: the server responded with a status of 403 ()
webpack-internal:///957:240 Uncaught (in promise) MatrixError
webpack-internal:///1351:68 Routing URL https://riot.im/develop/#/login
webpack-internal:///1351:68 newscreen login
webpack-internal:///1351:68 Initial sync performed - resetting device tracking state
webpack-internal:///1351:68 Now tracking device list for @56438099644:matrix.org
webpack-internal:///1351:68 MatrixClient sync state => PREPARED
webpack-internal:///1351:68 Updating room sorting algorithm: Object
webpack-internal:///1351:68 Generating initial room lists
webpack-internal:///1351:68 Starting key download for Array(1)
webpack-internal:///1351:68 MatrixClient sync state => SYNCING
webpack-internal:///1351:68 Saving device tracking data s1341180301_757269739_2496318_481996594_314915180_1172000_48052007_26369725_93042
webpack-internal:///1351:68 Setting up Mjolnir: after sync
webpack-internal:///1351:68 Updating Mjolnir ban lists to:
logger.js?c9c0:46 Persisting sync data up to s1341180301_757269739_2496318_481996594_314915180_1172000_48052007_26369725_93042
webpack-internal:///1351:68 got device keys for @56438099644:matrix.org: Object
webpack-internal:///1351:68 got cross-signing keys for @56438099644:matrix.org: Object
webpack-internal:///1351:68 Completed key download for @56438099644:matrix.org
webpack-internal:///1351:68 Device list for @56438099644:matrix.org now up to date
webpack-internal:///1351:68 Saving device tracking data s1341180301_757269739_2496318_481996594_314915180_1172000_48052007_26369725_93042
matrix-client.matrix.org/_matrix/client/r0/login:1 Failed to load resource: the server responded with a status of 403 ()
webpack-internal:///1351:68 Login failed MatrixError
matrix-client.matrix.org/_matrix/client/unstable/room_keys/version:1 Failed to load resource: the server responded with a status of 403 ()
webpack-internal:///957:240 Uncaught (in promise) MatrixError
rageshake.js?432e:65 Overrode homeserver setting with https://matrix-client.matrix.org/ from login response
rageshake.js?432e:65 Ending watcher ID 1587050417527_7_mjolnirRooms_null
rageshake.js?432e:65 stopping MatrixClient
rageshake.js?432e:65 SyncApi.stop
rageshake.js?432e:65 stopping OutgoingRoomKeyRequestManager
rageshake.js?432e:65 setLoggedIn: mxid: @matthewtest17:matrix.org deviceId: NOHYRLDQVZ guest: false hs: https://matrix-client.matrix.org/ softLogout: false
rageshake.js?432e:65 Sync no longer running: exiting
rageshake.js?432e:65 Removing indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 versionchange for indexeddb undefined: closing
rageshake.js?432e:65 Removed indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 Removing indexeddb instance: matrix-js-sdk:riot-web-sync
logger.js?c9c0:46 Removed indexeddb instance: matrix-js-sdk:riot-web-sync
rageshake.js?432e:65 Deleted indexeddb data.
rageshake.js?432e:65 StorageManager: Checking storage consistency
rageshake.js?432e:65 StorageManager: Local storage supported? true
rageshake.js?432e:65 StorageManager: IndexedDB supported? true
rageshake.js?432e:65 StorageManager: Local storage contains data? false
rageshake.js?432e:65 StorageManager: Crypto initialised? null
rageshake.js?432e:65 StorageManager: Sync store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Crypto store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Storage consistency checks passed
rageshake.js?432e:65 Session persisted for @matthewtest17:matrix.org
rageshake.js?432e:65 Lifecycle: Starting MatrixClient
rageshake.js?432e:65 Updating homeserver-configured integration managers...
rageshake.js?432e:65 Starting watcher for mjolnirRooms@<null room> as ID 1587050457003_8_mjolnirRooms_null
rageshake.js?432e:65 IndexedDBStore.startup: connecting to backend
rageshake.js?432e:65 MatrixClientPeg: waiting for MatrixClient store to initialise
rageshake.js?432e:65 Homeserver has no integration managers
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connecting...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: awaiting connection...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: upgrading from 0
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connected
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading account data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading sync data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded account data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded sync data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded initial data
rageshake.js?432e:65 IndexedDBStore.startup: loading presence events
rageshake.js?432e:65 IndexedDBStore.startup: processing presence events
rageshake.js?432e:65 Crypto: Starting up crypto store...
rageshake.js?432e:65 connecting to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Upgrading IndexedDBCryptoStore from version 0 to 9
rageshake.js?432e:65 connected to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Crypto: initialising roomlist...
rageshake.js?432e:65 Crypto: initialising crypto object...
rageshake.js?432e:65 Crypto: initialising Olm...
rageshake.js?432e:65 Crypto: initialising Olm device...
rageshake.js?432e:65 Crypto: loading device list...
rageshake.js?432e:65 Crypto: fetching own devices...
rageshake.js?432e:65 Crypto: adding this device to the store...
rageshake.js?432e:65 Now tracking device list for @matthewtest17:matrix.org
rageshake.js?432e:65 Crypto: checking for key backup...
rageshake.js?432e:65 Checking key backup status...
rageshake.js?432e:65 MatrixClientPeg: really starting MatrixClient
rageshake.js?432e:65 Getting saved sync token...
rageshake.js?432e:65 Getting push rules...
rageshake.js?432e:65 MatrixClientPeg: MatrixClient started
rageshake.js?432e:65 Attempting to get Jitsi conference information from homeserver
rageshake.js?432e:65 Got saved sync token
rageshake.js?432e:65 Getting saved sync...
rageshake.js?432e:65 Jitsi conference domain: jitsi.riot.im
rageshake.js?432e:65 Got reply from saved sync, exists? false
rageshake.js?432e:65 Saving device tracking data null
rageshake.js?432e:65 Looking for queued outgoing room key requests
rageshake.js?432e:65 No more outgoing room key requests
rageshake.js?432e:65 Got TURN URIs: turn:turn.matrix.org:3478?transport=udp,turn:turn.matrix.org:3478?transport=tcp,turns:turn.matrix.org:443?transport=tcp refresh in 86400 secs
rageshake.js?432e:65 Got push rules
rageshake.js?432e:65 Checking lazy load status...
rageshake.js?432e:65 Checking server lazy load support...
rageshake.js?432e:65 Creating and storing lazy load sync filter...
rageshake.js?432e:65 Error uploading one-time keys Error: Failed to execute 'transaction' on 'IDBDatabase': The database connection is closing.
at Backend.doTxn (webpack-internal:///111:817:26)
at IndexedDBCryptoStore.doTxn (webpack-internal:///109:607:26)
at OlmDevice.markKeysAsPublished (webpack-internal:///113:409:27)
at _uploadOneTimeKeys (webpack-internal:///112:1870:27)
``` | 1.0 | "Error uploading one-time keys" on login - Surprising OTK upload error from IDB on a fresh login on an old account on plain Chrome...
```
Initialised rageshake.
rageshake.js?432e:65 To fix line numbers in Chrome: Meatball menu → Settings → Blackboxing → Add /rageshake\.js$
rageshake.js?432e:65 Using Web platform
/develop/config.riot.im.json?cachebuster=1587050412257:1 Failed to load resource: the server responded with a status of 404 ()
rageshake.js?432e:65 Loading skin...
rageshake.js?432e:65 Starting watcher for RoomList.orderAlphabetically@<null room> as ID 1587050412411_1_RoomList.orderAlphabetically_null
rageshake.js?432e:65 Starting watcher for RoomList.orderByImportance@<null room> as ID 1587050412411_2_RoomList.orderByImportance_null
rageshake.js?432e:65 Starting watcher for feature_custom_tags@<null room> as ID 1587050412411_3_feature_custom_tags_null
rageshake.js?432e:65 Starting watcher for TagPanel.disableTagPanel@<null room> as ID 1587050412413_4_TagPanel.disableTagPanel_null
rageshake.js?432e:65 Skin loaded!
rageshake.js?432e:65 Using WebAssembly Olm
rageshake.js?432e:65 set language to en
rageshake.js?432e:65 Vector starting at https://riot.im/develop/
rageshake.js?432e:65 Verifying homeserver configuration
rageshake.js?432e:65 Config uses a default_server_name - doing .well-known lookup
rageshake.js?432e:65 DEPRECATED CONFIG OPTION: In the future, default_server_name will not be accepted. Please use default_server_config instead.
consoleObj.<computed> @ rageshake.js?432e:65
rageshake.js?432e:65 Using homeserver config: ValidatedServerConfig
rageshake.js?432e:65 Updating SdkConfig with validated discovery information
rageshake.js?432e:65 Starting watcher for theme@<null room> as ID 1587050413162_5_theme_null
rageshake.js?432e:65 Starting watcher for use_system_theme@<null room> as ID 1587050413163_6_use_system_theme_null
rageshake.js?432e:65 No previous session found.
rageshake.js?432e:65 Doing guest login on https://matrix-client.matrix.org
The resource https://riot.im/develop/bundles/4579131589870492b0a9/error-view.js was preloaded using link preload but not used within a few seconds from the window's load event. Please make sure it has an appropriate `as` value and it is preloaded intentionally.
rageshake.js?432e:65 Registered as guest: @56438099644:matrix.org
rageshake.js?432e:65 setLoggedIn: mxid: @56438099644:matrix.org deviceId: guest_device guest: true hs: https://matrix-client.matrix.org softLogout: false
rageshake.js?432e:65 Removing indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 Removed indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 Removing indexeddb instance: matrix-js-sdk:riot-web-sync
logger.js?c9c0:46 Removed indexeddb instance: matrix-js-sdk:riot-web-sync
rageshake.js?432e:65 Deleted indexeddb data.
rageshake.js?432e:65 StorageManager: Checking storage consistency
rageshake.js?432e:65 StorageManager: Local storage supported? true
rageshake.js?432e:65 StorageManager: IndexedDB supported? true
rageshake.js?432e:65 StorageManager: Local storage contains data? false
rageshake.js?432e:65 StorageManager: Crypto initialised? null
rageshake.js?432e:65 StorageManager: Sync store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Crypto store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Storage consistency checks passed
rageshake.js?432e:65 Session persisted for @56438099644:matrix.org
rageshake.js?432e:65 Lifecycle: Starting MatrixClient
2rageshake.js?432e:65 Updating homeserver-configured integration managers...
rageshake.js?432e:65 Starting watcher for mjolnirRooms@<null room> as ID 1587050417527_7_mjolnirRooms_null
rageshake.js?432e:65 IndexedDBStore.startup: connecting to backend
rageshake.js?432e:65 MatrixClientPeg: waiting for MatrixClient store to initialise
rageshake.js?432e:65 Homeserver has no integration managers
rageshake.js?432e:65 StorageManager: Persistent? false
rageshake.js?432e:65 Homeserver has no integration managers
rageshake.js?432e:65 newscreen welcome
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connecting...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: awaiting connection...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: upgrading from 0
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connected
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading account data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading sync data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded account data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded sync data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded initial data
rageshake.js?432e:65 IndexedDBStore.startup: loading presence events
rageshake.js?432e:65 IndexedDBStore.startup: processing presence events
rageshake.js?432e:65 Crypto: Starting up crypto store...
rageshake.js?432e:65 connecting to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Upgrading IndexedDBCryptoStore from version 0 to 9
rageshake.js?432e:65 connected to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Crypto: initialising roomlist...
rageshake.js?432e:65 Crypto: initialising crypto object...
rageshake.js?432e:65 Crypto: initialising Olm...
rageshake.js?432e:65 Crypto: initialising Olm device...
rageshake.js?432e:65 Crypto: loading device list...
rageshake.js?432e:65 Crypto: fetching own devices...
rageshake.js?432e:65 Crypto: adding this device to the store...
rageshake.js?432e:65 Now tracking device list for @56438099644:matrix.org
rageshake.js?432e:65 Crypto: checking for key backup...
rageshake.js?432e:65 Checking key backup status...
rageshake.js?432e:65 Skipping key backup check since user is guest
webpack-internal:///1351:68 MatrixClientPeg: really starting MatrixClient
webpack-internal:///1351:68 MatrixClientPeg: MatrixClient started
webpack-internal:///1351:68 Attempting to get Jitsi conference information from homeserver
webpack-internal:///1351:68 Jitsi conference domain: jitsi.riot.im
webpack-internal:///1351:68 Saving device tracking data null
webpack-internal:///1351:68 Looking for queued outgoing room key requests
webpack-internal:///1351:68 No more outgoing room key requests
webpack-internal:///1351:68 Got TURN URIs: turn:turn.matrix.org:3478?transport=udp,turn:turn.matrix.org:3478?transport=tcp,turns:turn.matrix.org:443?transport=tcp refresh in 86400 secs
matrix-client.matrix.org/_matrix/client/r0/user/%4056438099644%3Amatrix.org/account_data/m.cross_signing.master:1 Failed to load resource: the server responded with a status of 403 ()
webpack-internal:///957:240 Uncaught (in promise) MatrixError
webpack-internal:///1351:68 Routing URL https://riot.im/develop/#/login
webpack-internal:///1351:68 newscreen login
webpack-internal:///1351:68 Initial sync performed - resetting device tracking state
webpack-internal:///1351:68 Now tracking device list for @56438099644:matrix.org
webpack-internal:///1351:68 MatrixClient sync state => PREPARED
webpack-internal:///1351:68 Updating room sorting algorithm: Object
webpack-internal:///1351:68 Generating initial room lists
webpack-internal:///1351:68 Starting key download for Array(1)
webpack-internal:///1351:68 MatrixClient sync state => SYNCING
webpack-internal:///1351:68 Saving device tracking data s1341180301_757269739_2496318_481996594_314915180_1172000_48052007_26369725_93042
webpack-internal:///1351:68 Setting up Mjolnir: after sync
webpack-internal:///1351:68 Updating Mjolnir ban lists to:
logger.js?c9c0:46 Persisting sync data up to s1341180301_757269739_2496318_481996594_314915180_1172000_48052007_26369725_93042
webpack-internal:///1351:68 got device keys for @56438099644:matrix.org: Object
webpack-internal:///1351:68 got cross-signing keys for @56438099644:matrix.org: Object
webpack-internal:///1351:68 Completed key download for @56438099644:matrix.org
webpack-internal:///1351:68 Device list for @56438099644:matrix.org now up to date
webpack-internal:///1351:68 Saving device tracking data s1341180301_757269739_2496318_481996594_314915180_1172000_48052007_26369725_93042
matrix-client.matrix.org/_matrix/client/r0/login:1 Failed to load resource: the server responded with a status of 403 ()
webpack-internal:///1351:68 Login failed MatrixError
matrix-client.matrix.org/_matrix/client/unstable/room_keys/version:1 Failed to load resource: the server responded with a status of 403 ()
webpack-internal:///957:240 Uncaught (in promise) MatrixError
rageshake.js?432e:65 Overrode homeserver setting with https://matrix-client.matrix.org/ from login response
rageshake.js?432e:65 Ending watcher ID 1587050417527_7_mjolnirRooms_null
rageshake.js?432e:65 stopping MatrixClient
rageshake.js?432e:65 SyncApi.stop
rageshake.js?432e:65 stopping OutgoingRoomKeyRequestManager
rageshake.js?432e:65 setLoggedIn: mxid: @matthewtest17:matrix.org deviceId: NOHYRLDQVZ guest: false hs: https://matrix-client.matrix.org/ softLogout: false
rageshake.js?432e:65 Sync no longer running: exiting
rageshake.js?432e:65 Removing indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 versionchange for indexeddb undefined: closing
rageshake.js?432e:65 Removed indexeddb instance: matrix-js-sdk:crypto
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 Removing indexeddb instance: matrix-js-sdk:riot-web-sync
logger.js?c9c0:46 Removed indexeddb instance: matrix-js-sdk:riot-web-sync
rageshake.js?432e:65 Deleted indexeddb data.
rageshake.js?432e:65 StorageManager: Checking storage consistency
rageshake.js?432e:65 StorageManager: Local storage supported? true
rageshake.js?432e:65 StorageManager: IndexedDB supported? true
rageshake.js?432e:65 StorageManager: Local storage contains data? false
rageshake.js?432e:65 StorageManager: Crypto initialised? null
rageshake.js?432e:65 StorageManager: Sync store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Crypto store using IndexedDB contains data? false
rageshake.js?432e:65 StorageManager: Storage consistency checks passed
rageshake.js?432e:65 Session persisted for @matthewtest17:matrix.org
rageshake.js?432e:65 Lifecycle: Starting MatrixClient
rageshake.js?432e:65 Updating homeserver-configured integration managers...
rageshake.js?432e:65 Starting watcher for mjolnirRooms@<null room> as ID 1587050457003_8_mjolnirRooms_null
rageshake.js?432e:65 IndexedDBStore.startup: connecting to backend
rageshake.js?432e:65 MatrixClientPeg: waiting for MatrixClient store to initialise
rageshake.js?432e:65 Homeserver has no integration managers
rageshake.js?432e:65 IndexedDB worker is ready
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connecting...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: awaiting connection...
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: upgrading from 0
logger.js?c9c0:46 LocalIndexedDBStoreBackend.connect: connected
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading account data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loading sync data...
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded account data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded sync data
logger.js?c9c0:46 LocalIndexedDBStoreBackend: loaded initial data
rageshake.js?432e:65 IndexedDBStore.startup: loading presence events
rageshake.js?432e:65 IndexedDBStore.startup: processing presence events
rageshake.js?432e:65 Crypto: Starting up crypto store...
rageshake.js?432e:65 connecting to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Upgrading IndexedDBCryptoStore from version 0 to 9
rageshake.js?432e:65 connected to indexeddb matrix-js-sdk:crypto
rageshake.js?432e:65 Crypto: initialising roomlist...
rageshake.js?432e:65 Crypto: initialising crypto object...
rageshake.js?432e:65 Crypto: initialising Olm...
rageshake.js?432e:65 Crypto: initialising Olm device...
rageshake.js?432e:65 Crypto: loading device list...
rageshake.js?432e:65 Crypto: fetching own devices...
rageshake.js?432e:65 Crypto: adding this device to the store...
rageshake.js?432e:65 Now tracking device list for @matthewtest17:matrix.org
rageshake.js?432e:65 Crypto: checking for key backup...
rageshake.js?432e:65 Checking key backup status...
rageshake.js?432e:65 MatrixClientPeg: really starting MatrixClient
rageshake.js?432e:65 Getting saved sync token...
rageshake.js?432e:65 Getting push rules...
rageshake.js?432e:65 MatrixClientPeg: MatrixClient started
rageshake.js?432e:65 Attempting to get Jitsi conference information from homeserver
rageshake.js?432e:65 Got saved sync token
rageshake.js?432e:65 Getting saved sync...
rageshake.js?432e:65 Jitsi conference domain: jitsi.riot.im
rageshake.js?432e:65 Got reply from saved sync, exists? false
rageshake.js?432e:65 Saving device tracking data null
rageshake.js?432e:65 Looking for queued outgoing room key requests
rageshake.js?432e:65 No more outgoing room key requests
rageshake.js?432e:65 Got TURN URIs: turn:turn.matrix.org:3478?transport=udp,turn:turn.matrix.org:3478?transport=tcp,turns:turn.matrix.org:443?transport=tcp refresh in 86400 secs
rageshake.js?432e:65 Got push rules
rageshake.js?432e:65 Checking lazy load status...
rageshake.js?432e:65 Checking server lazy load support...
rageshake.js?432e:65 Creating and storing lazy load sync filter...
rageshake.js?432e:65 Error uploading one-time keys Error: Failed to execute 'transaction' on 'IDBDatabase': The database connection is closing.
at Backend.doTxn (webpack-internal:///111:817:26)
at IndexedDBCryptoStore.doTxn (webpack-internal:///109:607:26)
at OlmDevice.markKeysAsPublished (webpack-internal:///113:409:27)
at _uploadOneTimeKeys (webpack-internal:///112:1870:27)
``` | non_priority | error uploading one time keys on login surprising otk upload error from idb on a fresh login on an old account on plain chrome initialised rageshake rageshake js to fix line numbers in chrome meatball menu → settings → blackboxing → add rageshake js rageshake js using web platform develop config riot im json cachebuster failed to load resource the server responded with a status of rageshake js loading skin rageshake js starting watcher for roomlist orderalphabetically as id roomlist orderalphabetically null rageshake js starting watcher for roomlist orderbyimportance as id roomlist orderbyimportance null rageshake js starting watcher for feature custom tags as id feature custom tags null rageshake js starting watcher for tagpanel disabletagpanel as id tagpanel disabletagpanel null rageshake js skin loaded rageshake js using webassembly olm rageshake js set language to en rageshake js vector starting at rageshake js verifying homeserver configuration rageshake js config uses a default server name doing well known lookup rageshake js deprecated config option in the future default server name will not be accepted please use default server config instead consoleobj rageshake js rageshake js using homeserver config validatedserverconfig rageshake js updating sdkconfig with validated discovery information rageshake js starting watcher for theme as id theme null rageshake js starting watcher for use system theme as id use system theme null rageshake js no previous session found rageshake js doing guest login on the resource was preloaded using link preload but not used within a few seconds from the window s load event please make sure it has an appropriate as value and it is preloaded intentionally rageshake js registered as guest matrix org rageshake js setloggedin mxid matrix org deviceid guest device guest true hs softlogout false rageshake js removing indexeddb instance matrix js sdk crypto rageshake js removed indexeddb instance matrix js sdk crypto rageshake js indexeddb worker is ready logger js removing indexeddb instance matrix js sdk riot web sync logger js removed indexeddb instance matrix js sdk riot web sync rageshake js deleted indexeddb data rageshake js storagemanager checking storage consistency rageshake js storagemanager local storage supported true rageshake js storagemanager indexeddb supported true rageshake js storagemanager local storage contains data false rageshake js storagemanager crypto initialised null rageshake js storagemanager sync store using indexeddb contains data false rageshake js storagemanager crypto store using indexeddb contains data false rageshake js storagemanager storage consistency checks passed rageshake js session persisted for matrix org rageshake js lifecycle starting matrixclient js updating homeserver configured integration managers rageshake js starting watcher for mjolnirrooms as id mjolnirrooms null rageshake js indexeddbstore startup connecting to backend rageshake js matrixclientpeg waiting for matrixclient store to initialise rageshake js homeserver has no integration managers rageshake js storagemanager persistent false rageshake js homeserver has no integration managers rageshake js newscreen welcome rageshake js indexeddb worker is ready logger js localindexeddbstorebackend connect connecting logger js localindexeddbstorebackend connect awaiting connection logger js localindexeddbstorebackend connect upgrading from logger js localindexeddbstorebackend connect connected logger js localindexeddbstorebackend loading account data logger js localindexeddbstorebackend loading sync data logger js localindexeddbstorebackend loaded account data logger js localindexeddbstorebackend loaded sync data logger js localindexeddbstorebackend loaded initial data rageshake js indexeddbstore startup loading presence events rageshake js indexeddbstore startup processing presence events rageshake js crypto starting up crypto store rageshake js connecting to indexeddb matrix js sdk crypto rageshake js upgrading indexeddbcryptostore from version to rageshake js connected to indexeddb matrix js sdk crypto rageshake js crypto initialising roomlist rageshake js crypto initialising crypto object rageshake js crypto initialising olm rageshake js crypto initialising olm device rageshake js crypto loading device list rageshake js crypto fetching own devices rageshake js crypto adding this device to the store rageshake js now tracking device list for matrix org rageshake js crypto checking for key backup rageshake js checking key backup status rageshake js skipping key backup check since user is guest webpack internal matrixclientpeg really starting matrixclient webpack internal matrixclientpeg matrixclient started webpack internal attempting to get jitsi conference information from homeserver webpack internal jitsi conference domain jitsi riot im webpack internal saving device tracking data null webpack internal looking for queued outgoing room key requests webpack internal no more outgoing room key requests webpack internal got turn uris turn turn matrix org transport udp turn turn matrix org transport tcp turns turn matrix org transport tcp refresh in secs matrix client matrix org matrix client user org account data m cross signing master failed to load resource the server responded with a status of webpack internal uncaught in promise matrixerror webpack internal routing url webpack internal newscreen login webpack internal initial sync performed resetting device tracking state webpack internal now tracking device list for matrix org webpack internal matrixclient sync state prepared webpack internal updating room sorting algorithm object webpack internal generating initial room lists webpack internal starting key download for array webpack internal matrixclient sync state syncing webpack internal saving device tracking data webpack internal setting up mjolnir after sync webpack internal updating mjolnir ban lists to logger js persisting sync data up to webpack internal got device keys for matrix org object webpack internal got cross signing keys for matrix org object webpack internal completed key download for matrix org webpack internal device list for matrix org now up to date webpack internal saving device tracking data matrix client matrix org matrix client login failed to load resource the server responded with a status of webpack internal login failed matrixerror matrix client matrix org matrix client unstable room keys version failed to load resource the server responded with a status of webpack internal uncaught in promise matrixerror rageshake js overrode homeserver setting with from login response rageshake js ending watcher id mjolnirrooms null rageshake js stopping matrixclient rageshake js syncapi stop rageshake js stopping outgoingroomkeyrequestmanager rageshake js setloggedin mxid matrix org deviceid nohyrldqvz guest false hs softlogout false rageshake js sync no longer running exiting rageshake js removing indexeddb instance matrix js sdk crypto rageshake js versionchange for indexeddb undefined closing rageshake js removed indexeddb instance matrix js sdk crypto rageshake js indexeddb worker is ready logger js removing indexeddb instance matrix js sdk riot web sync logger js removed indexeddb instance matrix js sdk riot web sync rageshake js deleted indexeddb data rageshake js storagemanager checking storage consistency rageshake js storagemanager local storage supported true rageshake js storagemanager indexeddb supported true rageshake js storagemanager local storage contains data false rageshake js storagemanager crypto initialised null rageshake js storagemanager sync store using indexeddb contains data false rageshake js storagemanager crypto store using indexeddb contains data false rageshake js storagemanager storage consistency checks passed rageshake js session persisted for matrix org rageshake js lifecycle starting matrixclient rageshake js updating homeserver configured integration managers rageshake js starting watcher for mjolnirrooms as id mjolnirrooms null rageshake js indexeddbstore startup connecting to backend rageshake js matrixclientpeg waiting for matrixclient store to initialise rageshake js homeserver has no integration managers rageshake js indexeddb worker is ready logger js localindexeddbstorebackend connect connecting logger js localindexeddbstorebackend connect awaiting connection logger js localindexeddbstorebackend connect upgrading from logger js localindexeddbstorebackend connect connected logger js localindexeddbstorebackend loading account data logger js localindexeddbstorebackend loading sync data logger js localindexeddbstorebackend loaded account data logger js localindexeddbstorebackend loaded sync data logger js localindexeddbstorebackend loaded initial data rageshake js indexeddbstore startup loading presence events rageshake js indexeddbstore startup processing presence events rageshake js crypto starting up crypto store rageshake js connecting to indexeddb matrix js sdk crypto rageshake js upgrading indexeddbcryptostore from version to rageshake js connected to indexeddb matrix js sdk crypto rageshake js crypto initialising roomlist rageshake js crypto initialising crypto object rageshake js crypto initialising olm rageshake js crypto initialising olm device rageshake js crypto loading device list rageshake js crypto fetching own devices rageshake js crypto adding this device to the store rageshake js now tracking device list for matrix org rageshake js crypto checking for key backup rageshake js checking key backup status rageshake js matrixclientpeg really starting matrixclient rageshake js getting saved sync token rageshake js getting push rules rageshake js matrixclientpeg matrixclient started rageshake js attempting to get jitsi conference information from homeserver rageshake js got saved sync token rageshake js getting saved sync rageshake js jitsi conference domain jitsi riot im rageshake js got reply from saved sync exists false rageshake js saving device tracking data null rageshake js looking for queued outgoing room key requests rageshake js no more outgoing room key requests rageshake js got turn uris turn turn matrix org transport udp turn turn matrix org transport tcp turns turn matrix org transport tcp refresh in secs rageshake js got push rules rageshake js checking lazy load status rageshake js checking server lazy load support rageshake js creating and storing lazy load sync filter rageshake js error uploading one time keys error failed to execute transaction on idbdatabase the database connection is closing at backend dotxn webpack internal at indexeddbcryptostore dotxn webpack internal at olmdevice markkeysaspublished webpack internal at uploadonetimekeys webpack internal | 0 |
303,574 | 23,030,724,129 | IssuesEvent | 2022-07-22 13:41:13 | projectcontour/contour | https://api.github.com/repos/projectcontour/contour | closed | update "Introduction to Contour" link on projectcontour.io | help wanted good first issue area/documentation lifecycle/needs-triage doc-impact | The "Introduction to Contour" link on the projectcontour.io landing page points to a blog from 2019 that references Contour v0.10, this link should be updated to point to something newer, or perhaps we could drop that entire section as it seems somewhat redundant with other ways to navigate the site. | 1.0 | update "Introduction to Contour" link on projectcontour.io - The "Introduction to Contour" link on the projectcontour.io landing page points to a blog from 2019 that references Contour v0.10, this link should be updated to point to something newer, or perhaps we could drop that entire section as it seems somewhat redundant with other ways to navigate the site. | non_priority | update introduction to contour link on projectcontour io the introduction to contour link on the projectcontour io landing page points to a blog from that references contour this link should be updated to point to something newer or perhaps we could drop that entire section as it seems somewhat redundant with other ways to navigate the site | 0 |
331,546 | 24,312,301,423 | IssuesEvent | 2022-09-30 00:29:15 | timescale/docs | https://api.github.com/repos/timescale/docs | closed | Update Timescale Cloud / MST description in "Deployment options" page | documentation enhancement | # Describe change in content, appearance, or functionality
This page https://docs.timescale.com/timescaledb/latest/overview/deployment-options/ describes Timescale Cloud and MST using "old language". We recently reviewed the language for this in other docs pages—could we please change the copy here as well? 🙏 You can use the language here as inspiration: https://docs.google.com/document/d/1dsZ5ylNFnI4HTWxU7md2X-dzAHa-MTIYUbWCWMtd6lQ/edit.
# Subject matter expert (SME)
Reach out to me (Carlota) if you have questions or you need a review of the final copy! Thanks a lot.
| 1.0 | Update Timescale Cloud / MST description in "Deployment options" page - # Describe change in content, appearance, or functionality
This page https://docs.timescale.com/timescaledb/latest/overview/deployment-options/ describes Timescale Cloud and MST using "old language". We recently reviewed the language for this in other docs pages—could we please change the copy here as well? 🙏 You can use the language here as inspiration: https://docs.google.com/document/d/1dsZ5ylNFnI4HTWxU7md2X-dzAHa-MTIYUbWCWMtd6lQ/edit.
# Subject matter expert (SME)
Reach out to me (Carlota) if you have questions or you need a review of the final copy! Thanks a lot.
| non_priority | update timescale cloud mst description in deployment options page describe change in content appearance or functionality this page describes timescale cloud and mst using old language we recently reviewed the language for this in other docs pages—could we please change the copy here as well 🙏 you can use the language here as inspiration subject matter expert sme reach out to me carlota if you have questions or you need a review of the final copy thanks a lot | 0 |
26,618 | 5,276,915,737 | IssuesEvent | 2017-02-07 01:00:16 | mjavaly/Prairie | https://api.github.com/repos/mjavaly/Prairie | closed | Redo Annotations Wiki | documentation | Since redoing the mechanics of adding/editing annotations, the current wiki entry is out of date. | 1.0 | Redo Annotations Wiki - Since redoing the mechanics of adding/editing annotations, the current wiki entry is out of date. | non_priority | redo annotations wiki since redoing the mechanics of adding editing annotations the current wiki entry is out of date | 0 |
142,829 | 13,041,923,800 | IssuesEvent | 2020-07-28 21:19:54 | clabonte/codeprimer | https://api.github.com/repos/clabonte/codeprimer | closed | Document CodePrimer Data Model | documentation | Create a document to explain the data model on which CodePrimer is being built.
This is very important to help people understand how to turn this data model into various artifacts, being code, configuration or documentation | 1.0 | Document CodePrimer Data Model - Create a document to explain the data model on which CodePrimer is being built.
This is very important to help people understand how to turn this data model into various artifacts, being code, configuration or documentation | non_priority | document codeprimer data model create a document to explain the data model on which codeprimer is being built this is very important to help people understand how to turn this data model into various artifacts being code configuration or documentation | 0 |
699 | 2,856,939,693 | IssuesEvent | 2015-06-02 17:15:53 | symfony/symfony | https://api.github.com/repos/symfony/symfony | closed | Remove Deprecated Class+Interface from Map of Compiled Classes | SecurityBundle | In the security bundle's extension class for Symfony `v2.7.0` (and apparently still in `master` and `2.7` branches) there is still a reference to `Symfony\Component\Security\Core\SecurityContext` in a call to `addClassesToCompile()` on line 103 in file `src/Symfony/Bundle/SecurityBundle/DependencyInjection/SecurityExtension.php`.
Due to `SexurityContext` being included in the compiled `classes.map` and `classes.php`, two deprecated errors are thrown on every request (an extra one is thrown due to the inclusion of `SecurityContextInterface` which `SecurityContext` implements). | True | Remove Deprecated Class+Interface from Map of Compiled Classes - In the security bundle's extension class for Symfony `v2.7.0` (and apparently still in `master` and `2.7` branches) there is still a reference to `Symfony\Component\Security\Core\SecurityContext` in a call to `addClassesToCompile()` on line 103 in file `src/Symfony/Bundle/SecurityBundle/DependencyInjection/SecurityExtension.php`.
Due to `SexurityContext` being included in the compiled `classes.map` and `classes.php`, two deprecated errors are thrown on every request (an extra one is thrown due to the inclusion of `SecurityContextInterface` which `SecurityContext` implements). | non_priority | remove deprecated class interface from map of compiled classes in the security bundle s extension class for symfony and apparently still in master and branches there is still a reference to symfony component security core securitycontext in a call to addclassestocompile on line in file src symfony bundle securitybundle dependencyinjection securityextension php due to sexuritycontext being included in the compiled classes map and classes php two deprecated errors are thrown on every request an extra one is thrown due to the inclusion of securitycontextinterface which securitycontext implements | 0 |
243,825 | 20,592,053,598 | IssuesEvent | 2022-03-05 00:54:24 | backend-br/vagas | https://api.github.com/repos/backend-br/vagas | closed | [Porto Alegre] Dev Java na DBServer | TDD Java Testes automatizados Stale | ## **O que vamos construir juntos?**
Projeto Internacional que tem como produto principal ferramenta de gestão de ativos.
## **Requisitos para se candidatar a vaga:**
- Java;
- PHP;
- Angular
- Métodos ágeis;
- Inglês Intermediário/avançado;
## **Será legal se você tiver conhecimento em:**
- Liderança técnica.
_**Conheça nossas vagas em:**_ **https://jobs.kenoby.com/dbserver**
## **A DBServer**
Somos uma softwarehouse que constrói entregas sob medida. Há 28 anos trabalhamos com foco nas pessoas, guiados por nossos valores, crescendo lado a lado com nossos colaboradores. Nosso lema é fazer a coisa certa do jeito certo através do design e do build.
Nos últimos anos, iniciamos uma caminhada em direção a diversidade e a inclusão e após o lançamento do nosso Marco Ético temos agora um norteador dos princípios que irão trilhar a nossa trajetória.
Estamos orgulhosos de promover um ambiente de trabalho livre de discriminação. Acreditamos que a diversidade de experiências, perspectivas e histórico transforma nosso ambiente de trabalho. Estamos empenhados a construir esse legado com a sua parceria!
Conheça nosso Marco ético: http://www.dbserver.com.br/marcoetico/ | 1.0 | [Porto Alegre] Dev Java na DBServer - ## **O que vamos construir juntos?**
Projeto Internacional que tem como produto principal ferramenta de gestão de ativos.
## **Requisitos para se candidatar a vaga:**
- Java;
- PHP;
- Angular
- Métodos ágeis;
- Inglês Intermediário/avançado;
## **Será legal se você tiver conhecimento em:**
- Liderança técnica.
_**Conheça nossas vagas em:**_ **https://jobs.kenoby.com/dbserver**
## **A DBServer**
Somos uma softwarehouse que constrói entregas sob medida. Há 28 anos trabalhamos com foco nas pessoas, guiados por nossos valores, crescendo lado a lado com nossos colaboradores. Nosso lema é fazer a coisa certa do jeito certo através do design e do build.
Nos últimos anos, iniciamos uma caminhada em direção a diversidade e a inclusão e após o lançamento do nosso Marco Ético temos agora um norteador dos princípios que irão trilhar a nossa trajetória.
Estamos orgulhosos de promover um ambiente de trabalho livre de discriminação. Acreditamos que a diversidade de experiências, perspectivas e histórico transforma nosso ambiente de trabalho. Estamos empenhados a construir esse legado com a sua parceria!
Conheça nosso Marco ético: http://www.dbserver.com.br/marcoetico/ | non_priority | dev java na dbserver o que vamos construir juntos projeto internacional que tem como produto principal ferramenta de gestão de ativos requisitos para se candidatar a vaga java php angular métodos ágeis inglês intermediário avançado será legal se você tiver conhecimento em liderança técnica conheça nossas vagas em a dbserver somos uma softwarehouse que constrói entregas sob medida há anos trabalhamos com foco nas pessoas guiados por nossos valores crescendo lado a lado com nossos colaboradores nosso lema é fazer a coisa certa do jeito certo através do design e do build nos últimos anos iniciamos uma caminhada em direção a diversidade e a inclusão e após o lançamento do nosso marco ético temos agora um norteador dos princípios que irão trilhar a nossa trajetória estamos orgulhosos de promover um ambiente de trabalho livre de discriminação acreditamos que a diversidade de experiências perspectivas e histórico transforma nosso ambiente de trabalho estamos empenhados a construir esse legado com a sua parceria conheça nosso marco ético | 0 |
36,596 | 6,541,749,243 | IssuesEvent | 2017-09-01 21:38:00 | eslint/eslint | https://api.github.com/repos/eslint/eslint | closed | prefer-arrow-callback: allowUnboundThis description may be confusing | accepted beginner documentation rule | http://eslint.org/docs/rules/prefer-arrow-callback#allowunboundthis
I've read this paragraph several times and by comparison with the code example it seems a bit confusing:
1. "When set to `false`, this option allows the use of `this` without restriction...": does not the option apply more restrictions for using `this`?
2. "...checks for dynamically assigned `this` values...": does "checks" mean "prohibits" or "allows"?
3. "Normally, the rule will flag...": does "Normally" mean "true" or "false" for this option?
The code example is clear, but the description seems to be vague. | 1.0 | prefer-arrow-callback: allowUnboundThis description may be confusing - http://eslint.org/docs/rules/prefer-arrow-callback#allowunboundthis
I've read this paragraph several times and by comparison with the code example it seems a bit confusing:
1. "When set to `false`, this option allows the use of `this` without restriction...": does not the option apply more restrictions for using `this`?
2. "...checks for dynamically assigned `this` values...": does "checks" mean "prohibits" or "allows"?
3. "Normally, the rule will flag...": does "Normally" mean "true" or "false" for this option?
The code example is clear, but the description seems to be vague. | non_priority | prefer arrow callback allowunboundthis description may be confusing i ve read this paragraph several times and by comparison with the code example it seems a bit confusing when set to false this option allows the use of this without restriction does not the option apply more restrictions for using this checks for dynamically assigned this values does checks mean prohibits or allows normally the rule will flag does normally mean true or false for this option the code example is clear but the description seems to be vague | 0 |
50,991 | 6,142,363,719 | IssuesEvent | 2017-06-27 00:21:28 | NSW-OEH-EMS-KST/grid-garage | https://api.github.com/repos/NSW-OEH-EMS-KST/grid-garage | closed | raster-copy | bug tested and working | Failing when copying a raster from a file goedatabase to a TIF raster in an output folder.
Error message: "Failed to execute. Parameters are not valid., ERROR 000800: The value is not a member of TIFF | IMAGINE iMAGE | BMP |... ETC.."
See MXD in 'C:\Data\dirtydebug_keep_small\raster-copy' to replicate. | 1.0 | raster-copy - Failing when copying a raster from a file goedatabase to a TIF raster in an output folder.
Error message: "Failed to execute. Parameters are not valid., ERROR 000800: The value is not a member of TIFF | IMAGINE iMAGE | BMP |... ETC.."
See MXD in 'C:\Data\dirtydebug_keep_small\raster-copy' to replicate. | non_priority | raster copy failing when copying a raster from a file goedatabase to a tif raster in an output folder error message failed to execute parameters are not valid error the value is not a member of tiff imagine image bmp etc see mxd in c data dirtydebug keep small raster copy to replicate | 0 |
137,251 | 20,111,754,738 | IssuesEvent | 2022-02-07 15:40:12 | FreeCAD/FreeCAD | https://api.github.com/repos/FreeCAD/FreeCAD | opened | Add taper angle feature in pad and pocket | 🚜 PartDesign Feature | Issue imported from https://tracker.freecad.org/view.php?id=622
* **Reporter:** electronlibre
* **Date submitted:** 3/5/2012
* **FreeCAD version:** 0.12
* **Category:** Feature
* **Status:** confirmed
* **Tags:**
# Original report text
It would be nice to have a taper angle option in pad and pocket tools (Part design workbench), similar to that on Extrude (Part WB).
# Other bug information
* **Priority:** normal
* **Severity:** feature
* **Category:** Feature
* **Updated:** 2/6/2021
# Discussion from Mantis ticket
### Comment by Jriegel 2012-05-18 10:38
Patch applied to Assembly branch!
Works well!
To be done -> Use code in Pocket
---
### Comment by helo10 2012-06-08 11:26
in progress
---
### Comment by jrheinlaender 2013-01-13 14:32
V0.13 now has a PartDesign::Draft feature which allows to select faces and apply a draft angle to them.
This is not the same functionality as that requested, but will lead to the same result.
I am not sure whether we should put even more options into the Pad/Pocket features. When I modelled for customers from the German automative industry, they insisted on always having draft in a separate feature.
---
### Comment by Jriegel 2013-01-13 14:39
Draft can be done Pocket/Pad for easy and simple cases. If you want to have more control Pad/Pocket get for sure overloaded.
I think both make sense. A one angle solution in the basic features and a own feature for the more sophisticated (future) solutions..
I have generally no problem if there are overlapping features functionality.
May the better win!
| 1.0 | Add taper angle feature in pad and pocket - Issue imported from https://tracker.freecad.org/view.php?id=622
* **Reporter:** electronlibre
* **Date submitted:** 3/5/2012
* **FreeCAD version:** 0.12
* **Category:** Feature
* **Status:** confirmed
* **Tags:**
# Original report text
It would be nice to have a taper angle option in pad and pocket tools (Part design workbench), similar to that on Extrude (Part WB).
# Other bug information
* **Priority:** normal
* **Severity:** feature
* **Category:** Feature
* **Updated:** 2/6/2021
# Discussion from Mantis ticket
### Comment by Jriegel 2012-05-18 10:38
Patch applied to Assembly branch!
Works well!
To be done -> Use code in Pocket
---
### Comment by helo10 2012-06-08 11:26
in progress
---
### Comment by jrheinlaender 2013-01-13 14:32
V0.13 now has a PartDesign::Draft feature which allows to select faces and apply a draft angle to them.
This is not the same functionality as that requested, but will lead to the same result.
I am not sure whether we should put even more options into the Pad/Pocket features. When I modelled for customers from the German automative industry, they insisted on always having draft in a separate feature.
---
### Comment by Jriegel 2013-01-13 14:39
Draft can be done Pocket/Pad for easy and simple cases. If you want to have more control Pad/Pocket get for sure overloaded.
I think both make sense. A one angle solution in the basic features and a own feature for the more sophisticated (future) solutions..
I have generally no problem if there are overlapping features functionality.
May the better win!
| non_priority | add taper angle feature in pad and pocket issue imported from reporter electronlibre date submitted freecad version category feature status confirmed tags original report text it would be nice to have a taper angle option in pad and pocket tools part design workbench similar to that on extrude part wb other bug information priority normal severity feature category feature updated discussion from mantis ticket comment by jriegel patch applied to assembly branch works well to be done use code in pocket comment by in progress comment by jrheinlaender now has a partdesign draft feature which allows to select faces and apply a draft angle to them this is not the same functionality as that requested but will lead to the same result i am not sure whether we should put even more options into the pad pocket features when i modelled for customers from the german automative industry they insisted on always having draft in a separate feature comment by jriegel draft can be done pocket pad for easy and simple cases if you want to have more control pad pocket get for sure overloaded i think both make sense a one angle solution in the basic features and a own feature for the more sophisticated future solutions i have generally no problem if there are overlapping features functionality may the better win | 0 |
103,547 | 8,921,712,279 | IssuesEvent | 2019-01-21 10:50:04 | jordan528/rbac | https://api.github.com/repos/jordan528/rbac | closed | RBAC testing : ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac | RBAC testing | Project : RBAC testing
Job : Default
Env : Default
Category : RBAC
Tags : [OWASP - OTG-IDENT-001 , FX Top 10 - API Vulnerability]
Severity : Major
Region : local
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig
Request :
{
"createdBy" : "",
"createdDate" : "",
"genPolicy" : "Create",
"generators" : [ { } ],
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"openAPISpec" : "eiQEvoMC",
"project" : {
"account" : {
"accountType" : "Jira",
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"region" : "eiQEvoMC",
"version" : ""
},
"autoGenSuites" : "18709402",
"branch" : "eiQEvoMC",
"createdBy" : "",
"createdDate" : "",
"description" : "eiQEvoMC",
"genPolicy" : "None",
"id" : "",
"inactive" : false,
"lastCommit" : "eiQEvoMC",
"lastSync" : null,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"openAPISpec" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"props" : null,
"url" : "eiQEvoMC",
"version" : ""
},
"version" : ""
}
Response :
I/O error on POST request for "http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig": Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect; nested exception is org.apache.http.conn.HttpHostConnectException: Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect
Logs :
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : URL [http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Method [POST]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Request [{
"createdBy" : "",
"createdDate" : "",
"genPolicy" : "Create",
"generators" : [ { } ],
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"openAPISpec" : "eiQEvoMC",
"project" : {
"account" : {
"accountType" : "Jira",
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"region" : "eiQEvoMC",
"version" : ""
},
"autoGenSuites" : "18709402",
"branch" : "eiQEvoMC",
"createdBy" : "",
"createdDate" : "",
"description" : "eiQEvoMC",
"genPolicy" : "None",
"id" : "",
"inactive" : false,
"lastCommit" : "eiQEvoMC",
"lastSync" : null,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"openAPISpec" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"props" : null,
"url" : "eiQEvoMC",
"version" : ""
},
"version" : ""
}]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Request-Headers [{Content-Type=[application/json], Accept=[application/json]}]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Response [I/O error on POST request for "http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig": Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect; nested exception is org.apache.http.conn.HttpHostConnectException: Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Response-Headers [{}]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : StatusCode [500]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Time [2073]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Size [388]
2019-01-21 06:53:43 ERROR [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Assertion [@StatusCode == 401 OR @StatusCode == 403] resolved-to [500 == 401 OR 500 == 403] result [Failed]
--- FX Bot --- | 1.0 | RBAC testing : ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac - Project : RBAC testing
Job : Default
Env : Default
Category : RBAC
Tags : [OWASP - OTG-IDENT-001 , FX Top 10 - API Vulnerability]
Severity : Major
Region : local
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig
Request :
{
"createdBy" : "",
"createdDate" : "",
"genPolicy" : "Create",
"generators" : [ { } ],
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"openAPISpec" : "eiQEvoMC",
"project" : {
"account" : {
"accountType" : "Jira",
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"region" : "eiQEvoMC",
"version" : ""
},
"autoGenSuites" : "18709402",
"branch" : "eiQEvoMC",
"createdBy" : "",
"createdDate" : "",
"description" : "eiQEvoMC",
"genPolicy" : "None",
"id" : "",
"inactive" : false,
"lastCommit" : "eiQEvoMC",
"lastSync" : null,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"openAPISpec" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"props" : null,
"url" : "eiQEvoMC",
"version" : ""
},
"version" : ""
}
Response :
I/O error on POST request for "http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig": Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect; nested exception is org.apache.http.conn.HttpHostConnectException: Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect
Logs :
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : URL [http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Method [POST]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Request [{
"createdBy" : "",
"createdDate" : "",
"genPolicy" : "Create",
"generators" : [ { } ],
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"openAPISpec" : "eiQEvoMC",
"project" : {
"account" : {
"accountType" : "Jira",
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"region" : "eiQEvoMC",
"version" : ""
},
"autoGenSuites" : "18709402",
"branch" : "eiQEvoMC",
"createdBy" : "",
"createdDate" : "",
"description" : "eiQEvoMC",
"genPolicy" : "None",
"id" : "",
"inactive" : false,
"lastCommit" : "eiQEvoMC",
"lastSync" : null,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"openAPISpec" : "eiQEvoMC",
"org" : {
"createdBy" : "",
"createdDate" : "",
"id" : "",
"inactive" : false,
"modifiedBy" : "",
"modifiedDate" : "",
"name" : "eiQEvoMC",
"version" : ""
},
"props" : null,
"url" : "eiQEvoMC",
"version" : ""
},
"version" : ""
}]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Request-Headers [{Content-Type=[application/json], Accept=[application/json]}]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Response [I/O error on POST request for "http://localhost:8090/api/v1/projects/vWR8MH48/new/autocodeconfig": Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect; nested exception is org.apache.http.conn.HttpHostConnectException: Connect to localhost:8090 [localhost/127.0.0.1, localhost/0:0:0:0:0:0:0:1] failed: Connection refused: connect]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Response-Headers [{}]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : StatusCode [500]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Time [2073]
2019-01-21 06:53:43 DEBUG [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Size [388]
2019-01-21 06:53:43 ERROR [ApiV1ProjectsProjectidNewAutocodeconfigPostRoleUserDisallowedRbac] : Assertion [@StatusCode == 401 OR @StatusCode == 403] resolved-to [500 == 401 OR 500 == 403] result [Failed]
--- FX Bot --- | non_priority | rbac testing project rbac testing job default env default category rbac tags severity major region local result fail status code headers endpoint request createdby createddate genpolicy create generators id inactive false modifiedby modifieddate openapispec eiqevomc project account accounttype jira createdby createddate id inactive false modifiedby modifieddate name eiqevomc org createdby createddate id inactive false modifiedby modifieddate name eiqevomc version region eiqevomc version autogensuites branch eiqevomc createdby createddate description eiqevomc genpolicy none id inactive false lastcommit eiqevomc lastsync null modifiedby modifieddate name eiqevomc openapispec eiqevomc org createdby createddate id inactive false modifiedby modifieddate name eiqevomc version props null url eiqevomc version version response i o error on post request for connect to localhost failed connection refused connect nested exception is org apache http conn httphostconnectexception connect to localhost failed connection refused connect logs debug url debug method debug request createdby createddate genpolicy create generators id inactive false modifiedby modifieddate openapispec eiqevomc project account accounttype jira createdby createddate id inactive false modifiedby modifieddate name eiqevomc org createdby createddate id inactive false modifiedby modifieddate name eiqevomc version region eiqevomc version autogensuites branch eiqevomc createdby createddate description eiqevomc genpolicy none id inactive false lastcommit eiqevomc lastsync null modifiedby modifieddate name eiqevomc openapispec eiqevomc org createdby createddate id inactive false modifiedby modifieddate name eiqevomc version props null url eiqevomc version version debug request headers accept debug response failed connection refused connect nested exception is org apache http conn httphostconnectexception connect to localhost failed connection refused connect debug response headers debug statuscode debug time debug size error assertion resolved to result fx bot | 0 |
369,166 | 25,830,191,733 | IssuesEvent | 2022-12-12 15:35:36 | python-telegram-bot/python-telegram-bot | https://api.github.com/repos/python-telegram-bot/python-telegram-bot | opened | [DOCS] add references to Code Resources Wiki section? | enhancement documentation | ### What kind of feature are you missing? Where do you notice a shortcoming of PTB?
in #3398 I added `seealso` references to Wiki pages to close #31110. I think I could add more references - from docs to section with code resources.
For example, from `ReplyKeyboardMarkup` to "Keyboard Menus" section of [Code Snippets](https://github.com/python-telegram-bot/python-telegram-bot/wiki/Code-snippets).
### Describe the solution you'd like
If you are in favor of this, what do you think should be the link text? In other Wiki references the link text is the name of Wiki page, but here we might want to choose something different. The target of the link should in any case be not the page but a heading within it.
- "Code Snippets"
- "Code Snippets in Wiki"
- "Code Snippets: Keyboard Menus"
- "Keyboard Menus"
### Describe alternatives you've considered
_No response_
### Additional context
I think that as a beginning bot developer, I would like to have links to these snippets from docs. | 1.0 | [DOCS] add references to Code Resources Wiki section? - ### What kind of feature are you missing? Where do you notice a shortcoming of PTB?
in #3398 I added `seealso` references to Wiki pages to close #31110. I think I could add more references - from docs to section with code resources.
For example, from `ReplyKeyboardMarkup` to "Keyboard Menus" section of [Code Snippets](https://github.com/python-telegram-bot/python-telegram-bot/wiki/Code-snippets).
### Describe the solution you'd like
If you are in favor of this, what do you think should be the link text? In other Wiki references the link text is the name of Wiki page, but here we might want to choose something different. The target of the link should in any case be not the page but a heading within it.
- "Code Snippets"
- "Code Snippets in Wiki"
- "Code Snippets: Keyboard Menus"
- "Keyboard Menus"
### Describe alternatives you've considered
_No response_
### Additional context
I think that as a beginning bot developer, I would like to have links to these snippets from docs. | non_priority | add references to code resources wiki section what kind of feature are you missing where do you notice a shortcoming of ptb in i added seealso references to wiki pages to close i think i could add more references from docs to section with code resources for example from replykeyboardmarkup to keyboard menus section of describe the solution you d like if you are in favor of this what do you think should be the link text in other wiki references the link text is the name of wiki page but here we might want to choose something different the target of the link should in any case be not the page but a heading within it code snippets code snippets in wiki code snippets keyboard menus keyboard menus describe alternatives you ve considered no response additional context i think that as a beginning bot developer i would like to have links to these snippets from docs | 0 |
266,784 | 23,259,667,078 | IssuesEvent | 2022-08-04 12:29:43 | keycloak/keycloak | https://api.github.com/repos/keycloak/keycloak | opened | User Federation tests failures in the pipeline | area/testsuite kind/bug status/triage | ### Describe the bug
User Federation Tests / user_federation_tests / msad-kerberos
Link: https://keycloak-jenkins.com/job/universal-test-pipeline-server/1991/testReport/org.keycloak.testsuite.federation.kerberos/
```
javax.ws.rs.ProcessingException: RESTEASY004655: Unable to invoke request: java.lang.RuntimeException: javax.security.auth.login.LoginException: Clock skew too great (37)
at org.jboss.resteasy.client.jaxrs.engines.ManualClosingApacheHttpClient43Engine.invoke(ManualClosingApacheHttpClient43Engine.java:321)
at org.jboss.resteasy.client.jaxrs.internal.ClientInvocation.invoke(ClientInvocation.java:494)
at org.jboss.resteasy.client.jaxrs.internal.ClientInvocation.invoke(ClientInvocation.java:69)
at org.jboss.resteasy.client.jaxrs.internal.ClientInvocationBuilder.get(ClientInvocationBuilder.java:190)
at org.keycloak.testsuite.federation.kerberos.AbstractKerberosTest.spnegoLogin(AbstractKerberosTest.java:242)
at org.keycloak.testsuite.federation.kerberos.AbstractKerberosTest.assertSuccessfulSpnegoLogin(AbstractKerberosTest.java:190)
at org.keycloak.testsuite.federation.kerberos.AbstractKerberosTest.assertSuccessfulSpnegoLogin(AbstractKerberosTest.java:185)
at org.keycloak.testsuite.federation.kerberos.KerberosLdapTest.spnegoLoginTest(KerberosLdapTest.java:84)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.jboss.arquillian.junit.Arquillian$8$1.invokeMethod(Arquillian.java:325)
at org.jboss.arquillian.junit.MethodInvoker$1.invoke(MethodInvoker.java:18)
at org.jboss.arquillian.container.test.impl.execution.LocalTestExecuter.execute(LocalTestExecuter.java:57)
at org.keycloak.testsuite.arquillian.ModelTestExecutor.execute(ModelTestExecutor.java:50)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.invokeObservers(EventContextImpl.java:103)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:90)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:133)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:105)
at org.jboss.arquillian.core.impl.EventImpl.fire(EventImpl.java:62)
at org.jboss.arquillian.container.test.impl.execution.ClientTestExecuter.execute(ClientTestExecuter.java:50)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.invokeObservers(EventContextImpl.java:103)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:90)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createContext(ContainerEventController.java:128)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createTestContext(ContainerEventController.java:118)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createSuiteContext(TestContextHandler.java:69)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createTestContext(TestContextHandler.java:116)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createClassContext(TestContextHandler.java:83)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:133)
at org.jboss.arquillian.test.impl.EventTestRunnerAdaptor.test(EventTestRunnerAdaptor.java:139)
at org.jboss.arquillian.junit.MethodInvoker.invoke(MethodInvoker.java:15)
at org.jboss.arquillian.junit.Arquillian$8.evaluate(Arquillian.java:332)
at org.jboss.arquillian.junit.Arquillian$4.evaluate(Arquillian.java:204)
at org.jboss.arquillian.junit.Arquillian.multiExecute(Arquillian.java:350)
at org.jboss.arquillian.junit.Arquillian.access$200(Arquillian.java:54)
at org.jboss.arquillian.junit.Arquillian$5.evaluate(Arquillian.java:215)
at org.keycloak.testsuite.AssertEvents$1.evaluate(AssertEvents.java:73)
at org.jboss.arquillian.junit.Arquillian$7$1.invoke(Arquillian.java:279)
at org.jboss.arquillian.container.test.impl.execution.ClientBeforeAfterLifecycleEventExecuter.execute(ClientBeforeAfterLifecycleEventExecuter.java:88)
at org.jboss.arquillian.container.test.impl.execution.ClientBeforeAfterLifecycleEventExecuter.on(ClientBeforeAfterLifecycleEventExecuter.java:66)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.invokeObservers(EventContextImpl.java:103)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:90)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createContext(ContainerEventController.java:128)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createBeforeContext(ContainerEventController.java:114)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createSuiteContext(TestContextHandler.java:69)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createTestContext(TestContextHandler.java:116)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createClassContext(TestContextHandler.java:83)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:133)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:105)
at org.jboss.arquillian.test.impl.EventTestRunnerAdaptor.fireCustomLifecycle(EventTestRunnerAdaptor.java:159)
at org.jboss.arquillian.junit.Arquillian$7.evaluate(Arquillian.java:273)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.jboss.arquillian.junit.Arquillian$2.evaluate(Arquillian.java:166)
at org.jboss.arquillian.junit.Arquillian.multiExecute(Arquillian.java:350)
at org.jboss.arquillian.junit.Arquillian.access$200(Arquillian.java:54)
at org.jboss.arquillian.junit.Arquillian$3.evaluate(Arquillian.java:177)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:54)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:54)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.jboss.arquillian.junit.Arquillian.run(Arquillian.java:115)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:377)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeWithRerun(JUnit4Provider.java:284)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:248)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:167)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:456)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:169)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:595)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:581)
Caused by: java.lang.RuntimeException: javax.security.auth.login.LoginException: Clock skew too great (37)
at org.keycloak.testsuite.federation.kerberos.KeycloakSPNegoSchemeFactory$KeycloakSPNegoScheme.generateGSSToken(KeycloakSPNegoSchemeFactory.java:104)
at org.apache.http.impl.auth.SPNegoScheme.generateToken(SPNegoScheme.java:95)
at org.apache.http.impl.auth.GGSSchemeBase.authenticate(GGSSchemeBase.java:221)
at org.apache.http.impl.auth.SPNegoScheme.authenticate(SPNegoScheme.java:85)
at org.apache.http.impl.auth.HttpAuthenticator.doAuth(HttpAuthenticator.java:233)
at org.apache.http.impl.auth.HttpAuthenticator.generateAuthResponse(HttpAuthenticator.java:198)
at org.apache.http.impl.execchain.MainClientExec.execute(MainClientExec.java:262)
at org.apache.http.impl.execchain.ProtocolExec.execute(ProtocolExec.java:186)
at org.apache.http.impl.execchain.RetryExec.execute(RetryExec.java:89)
at org.apache.http.impl.execchain.RedirectExec.execute(RedirectExec.java:110)
at org.apache.http.impl.client.InternalHttpClient.doExecute(InternalHttpClient.java:185)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:83)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:56)
at org.jboss.resteasy.client.jaxrs.engines.ManualClosingApacheHttpClient43Engine.invoke(ManualClosingApacheHttpClient43Engine.java:302)
... 144 more
Caused by: javax.security.auth.login.LoginException: Clock skew too great (37)
at jdk.security.auth/com.sun.security.auth.module.Krb5LoginModule.attemptAuthentication(Krb5LoginModule.java:784)
at jdk.security.auth/com.sun.security.auth.module.Krb5LoginModule.login(Krb5LoginModule.java:592)
at java.base/javax.security.auth.login.LoginContext.invoke(LoginContext.java:726)
at java.base/javax.security.auth.login.LoginContext$4.run(LoginContext.java:665)
at java.base/javax.security.auth.login.LoginContext$4.run(LoginContext.java:663)
at java.base/java.security.AccessController.doPrivileged(Native Method)
at java.base/javax.security.auth.login.LoginContext.invokePriv(LoginContext.java:663)
at java.base/javax.security.auth.login.LoginContext.login(LoginContext.java:574)
at org.keycloak.federation.kerberos.impl.KerberosUsernamePasswordAuthenticator.authenticateSubject(KerberosUsernamePasswordAuthenticator.java:128)
at org.keycloak.testsuite.federation.kerberos.KeycloakSPNegoSchemeFactory$KeycloakSPNegoScheme.generateGSSToken(KeycloakSPNegoSchemeFactory.java:98)
... 157 more
Caused by: KrbException: Clock skew too great (37)
at java.security.jgss/sun.security.krb5.KrbAsRep.<init>(KrbAsRep.java:76)
at java.security.jgss/sun.security.krb5.KrbAsReqBuilder.send(KrbAsReqBuilder.java:345)
at java.security.jgss/sun.security.krb5.KrbAsReqBuilder.action(KrbAsReqBuilder.java:498)
at jdk.security.auth/com.sun.security.auth.module.Krb5LoginModule.attemptAuthentication(Krb5LoginModule.java:746)
... 166 more
Caused by: KrbException: Identifier doesn't match expected value (906)
at java.security.jgss/sun.security.krb5.internal.KDCRep.init(KDCRep.java:140)
at java.security.jgss/sun.security.krb5.internal.ASRep.init(ASRep.java:64)
at java.security.jgss/sun.security.krb5.internal.ASRep.<init>(ASRep.java:59)
at java.security.jgss/sun.security.krb5.KrbAsRep.<init>(KrbAsRep.java:60)
... 169 more
```
-------------------
It seems the bug is present in the pipeline for some time; occurs occasionally. AFAIK, it's related to the time synchronization on dedicated agents for UF tests.
@pdrozd Do you have any better solution than the manual setting? Thank you
### Version
999
### Expected behavior
_No response_
### Actual behavior
_No response_
### How to Reproduce?
Execute UF tests in the pipeline
### Anything else?
_No response_ | 1.0 | User Federation tests failures in the pipeline - ### Describe the bug
User Federation Tests / user_federation_tests / msad-kerberos
Link: https://keycloak-jenkins.com/job/universal-test-pipeline-server/1991/testReport/org.keycloak.testsuite.federation.kerberos/
```
javax.ws.rs.ProcessingException: RESTEASY004655: Unable to invoke request: java.lang.RuntimeException: javax.security.auth.login.LoginException: Clock skew too great (37)
at org.jboss.resteasy.client.jaxrs.engines.ManualClosingApacheHttpClient43Engine.invoke(ManualClosingApacheHttpClient43Engine.java:321)
at org.jboss.resteasy.client.jaxrs.internal.ClientInvocation.invoke(ClientInvocation.java:494)
at org.jboss.resteasy.client.jaxrs.internal.ClientInvocation.invoke(ClientInvocation.java:69)
at org.jboss.resteasy.client.jaxrs.internal.ClientInvocationBuilder.get(ClientInvocationBuilder.java:190)
at org.keycloak.testsuite.federation.kerberos.AbstractKerberosTest.spnegoLogin(AbstractKerberosTest.java:242)
at org.keycloak.testsuite.federation.kerberos.AbstractKerberosTest.assertSuccessfulSpnegoLogin(AbstractKerberosTest.java:190)
at org.keycloak.testsuite.federation.kerberos.AbstractKerberosTest.assertSuccessfulSpnegoLogin(AbstractKerberosTest.java:185)
at org.keycloak.testsuite.federation.kerberos.KerberosLdapTest.spnegoLoginTest(KerberosLdapTest.java:84)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.jboss.arquillian.junit.Arquillian$8$1.invokeMethod(Arquillian.java:325)
at org.jboss.arquillian.junit.MethodInvoker$1.invoke(MethodInvoker.java:18)
at org.jboss.arquillian.container.test.impl.execution.LocalTestExecuter.execute(LocalTestExecuter.java:57)
at org.keycloak.testsuite.arquillian.ModelTestExecutor.execute(ModelTestExecutor.java:50)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.invokeObservers(EventContextImpl.java:103)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:90)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:133)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:105)
at org.jboss.arquillian.core.impl.EventImpl.fire(EventImpl.java:62)
at org.jboss.arquillian.container.test.impl.execution.ClientTestExecuter.execute(ClientTestExecuter.java:50)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.invokeObservers(EventContextImpl.java:103)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:90)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createContext(ContainerEventController.java:128)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createTestContext(ContainerEventController.java:118)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createSuiteContext(TestContextHandler.java:69)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createTestContext(TestContextHandler.java:116)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createClassContext(TestContextHandler.java:83)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:133)
at org.jboss.arquillian.test.impl.EventTestRunnerAdaptor.test(EventTestRunnerAdaptor.java:139)
at org.jboss.arquillian.junit.MethodInvoker.invoke(MethodInvoker.java:15)
at org.jboss.arquillian.junit.Arquillian$8.evaluate(Arquillian.java:332)
at org.jboss.arquillian.junit.Arquillian$4.evaluate(Arquillian.java:204)
at org.jboss.arquillian.junit.Arquillian.multiExecute(Arquillian.java:350)
at org.jboss.arquillian.junit.Arquillian.access$200(Arquillian.java:54)
at org.jboss.arquillian.junit.Arquillian$5.evaluate(Arquillian.java:215)
at org.keycloak.testsuite.AssertEvents$1.evaluate(AssertEvents.java:73)
at org.jboss.arquillian.junit.Arquillian$7$1.invoke(Arquillian.java:279)
at org.jboss.arquillian.container.test.impl.execution.ClientBeforeAfterLifecycleEventExecuter.execute(ClientBeforeAfterLifecycleEventExecuter.java:88)
at org.jboss.arquillian.container.test.impl.execution.ClientBeforeAfterLifecycleEventExecuter.on(ClientBeforeAfterLifecycleEventExecuter.java:66)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.invokeObservers(EventContextImpl.java:103)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:90)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createContext(ContainerEventController.java:128)
at org.jboss.arquillian.container.test.impl.client.ContainerEventController.createBeforeContext(ContainerEventController.java:114)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createSuiteContext(TestContextHandler.java:69)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createTestContext(TestContextHandler.java:116)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.test.impl.TestContextHandler.createClassContext(TestContextHandler.java:83)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.jboss.arquillian.core.impl.ObserverImpl.invoke(ObserverImpl.java:86)
at org.jboss.arquillian.core.impl.EventContextImpl.proceed(EventContextImpl.java:95)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:133)
at org.jboss.arquillian.core.impl.ManagerImpl.fire(ManagerImpl.java:105)
at org.jboss.arquillian.test.impl.EventTestRunnerAdaptor.fireCustomLifecycle(EventTestRunnerAdaptor.java:159)
at org.jboss.arquillian.junit.Arquillian$7.evaluate(Arquillian.java:273)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.jboss.arquillian.junit.Arquillian$2.evaluate(Arquillian.java:166)
at org.jboss.arquillian.junit.Arquillian.multiExecute(Arquillian.java:350)
at org.jboss.arquillian.junit.Arquillian.access$200(Arquillian.java:54)
at org.jboss.arquillian.junit.Arquillian$3.evaluate(Arquillian.java:177)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:54)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:54)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.jboss.arquillian.junit.Arquillian.run(Arquillian.java:115)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:377)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeWithRerun(JUnit4Provider.java:284)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:248)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:167)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:456)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:169)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:595)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:581)
Caused by: java.lang.RuntimeException: javax.security.auth.login.LoginException: Clock skew too great (37)
at org.keycloak.testsuite.federation.kerberos.KeycloakSPNegoSchemeFactory$KeycloakSPNegoScheme.generateGSSToken(KeycloakSPNegoSchemeFactory.java:104)
at org.apache.http.impl.auth.SPNegoScheme.generateToken(SPNegoScheme.java:95)
at org.apache.http.impl.auth.GGSSchemeBase.authenticate(GGSSchemeBase.java:221)
at org.apache.http.impl.auth.SPNegoScheme.authenticate(SPNegoScheme.java:85)
at org.apache.http.impl.auth.HttpAuthenticator.doAuth(HttpAuthenticator.java:233)
at org.apache.http.impl.auth.HttpAuthenticator.generateAuthResponse(HttpAuthenticator.java:198)
at org.apache.http.impl.execchain.MainClientExec.execute(MainClientExec.java:262)
at org.apache.http.impl.execchain.ProtocolExec.execute(ProtocolExec.java:186)
at org.apache.http.impl.execchain.RetryExec.execute(RetryExec.java:89)
at org.apache.http.impl.execchain.RedirectExec.execute(RedirectExec.java:110)
at org.apache.http.impl.client.InternalHttpClient.doExecute(InternalHttpClient.java:185)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:83)
at org.apache.http.impl.client.CloseableHttpClient.execute(CloseableHttpClient.java:56)
at org.jboss.resteasy.client.jaxrs.engines.ManualClosingApacheHttpClient43Engine.invoke(ManualClosingApacheHttpClient43Engine.java:302)
... 144 more
Caused by: javax.security.auth.login.LoginException: Clock skew too great (37)
at jdk.security.auth/com.sun.security.auth.module.Krb5LoginModule.attemptAuthentication(Krb5LoginModule.java:784)
at jdk.security.auth/com.sun.security.auth.module.Krb5LoginModule.login(Krb5LoginModule.java:592)
at java.base/javax.security.auth.login.LoginContext.invoke(LoginContext.java:726)
at java.base/javax.security.auth.login.LoginContext$4.run(LoginContext.java:665)
at java.base/javax.security.auth.login.LoginContext$4.run(LoginContext.java:663)
at java.base/java.security.AccessController.doPrivileged(Native Method)
at java.base/javax.security.auth.login.LoginContext.invokePriv(LoginContext.java:663)
at java.base/javax.security.auth.login.LoginContext.login(LoginContext.java:574)
at org.keycloak.federation.kerberos.impl.KerberosUsernamePasswordAuthenticator.authenticateSubject(KerberosUsernamePasswordAuthenticator.java:128)
at org.keycloak.testsuite.federation.kerberos.KeycloakSPNegoSchemeFactory$KeycloakSPNegoScheme.generateGSSToken(KeycloakSPNegoSchemeFactory.java:98)
... 157 more
Caused by: KrbException: Clock skew too great (37)
at java.security.jgss/sun.security.krb5.KrbAsRep.<init>(KrbAsRep.java:76)
at java.security.jgss/sun.security.krb5.KrbAsReqBuilder.send(KrbAsReqBuilder.java:345)
at java.security.jgss/sun.security.krb5.KrbAsReqBuilder.action(KrbAsReqBuilder.java:498)
at jdk.security.auth/com.sun.security.auth.module.Krb5LoginModule.attemptAuthentication(Krb5LoginModule.java:746)
... 166 more
Caused by: KrbException: Identifier doesn't match expected value (906)
at java.security.jgss/sun.security.krb5.internal.KDCRep.init(KDCRep.java:140)
at java.security.jgss/sun.security.krb5.internal.ASRep.init(ASRep.java:64)
at java.security.jgss/sun.security.krb5.internal.ASRep.<init>(ASRep.java:59)
at java.security.jgss/sun.security.krb5.KrbAsRep.<init>(KrbAsRep.java:60)
... 169 more
```
-------------------
It seems the bug is present in the pipeline for some time; occurs occasionally. AFAIK, it's related to the time synchronization on dedicated agents for UF tests.
@pdrozd Do you have any better solution than the manual setting? Thank you
### Version
999
### Expected behavior
_No response_
### Actual behavior
_No response_
### How to Reproduce?
Execute UF tests in the pipeline
### Anything else?
_No response_ | non_priority | user federation tests failures in the pipeline describe the bug user federation tests user federation tests msad kerberos link javax ws rs processingexception unable to invoke request java lang runtimeexception javax security auth login loginexception clock skew too great at org jboss resteasy client jaxrs engines invoke java at org jboss resteasy client jaxrs internal clientinvocation invoke clientinvocation java at org jboss resteasy client jaxrs internal clientinvocation invoke clientinvocation java at org jboss resteasy client jaxrs internal clientinvocationbuilder get clientinvocationbuilder java at org keycloak testsuite federation kerberos abstractkerberostest spnegologin abstractkerberostest java at org keycloak testsuite federation kerberos abstractkerberostest assertsuccessfulspnegologin abstractkerberostest java at org keycloak testsuite federation kerberos abstractkerberostest assertsuccessfulspnegologin abstractkerberostest java at org keycloak testsuite federation kerberos kerberosldaptest spnegologintest kerberosldaptest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org jboss arquillian junit arquillian invokemethod arquillian java at org jboss arquillian junit methodinvoker invoke methodinvoker java at org jboss arquillian container test impl execution localtestexecuter execute localtestexecuter java at org keycloak testsuite arquillian modeltestexecutor execute modeltestexecutor java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl invokeobservers eventcontextimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian core impl managerimpl fire managerimpl java at org jboss arquillian core impl managerimpl fire managerimpl java at org jboss arquillian core impl eventimpl fire eventimpl java at org jboss arquillian container test impl execution clienttestexecuter execute clienttestexecuter java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl invokeobservers eventcontextimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian container test impl client containereventcontroller createcontext containereventcontroller java at org jboss arquillian container test impl client containereventcontroller createtestcontext containereventcontroller java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian test impl testcontexthandler createsuitecontext testcontexthandler java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian test impl testcontexthandler createtestcontext testcontexthandler java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian test impl testcontexthandler createclasscontext testcontexthandler java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian core impl managerimpl fire managerimpl java at org jboss arquillian test impl eventtestrunneradaptor test eventtestrunneradaptor java at org jboss arquillian junit methodinvoker invoke methodinvoker java at org jboss arquillian junit arquillian evaluate arquillian java at org jboss arquillian junit arquillian evaluate arquillian java at org jboss arquillian junit arquillian multiexecute arquillian java at org jboss arquillian junit arquillian access arquillian java at org jboss arquillian junit arquillian evaluate arquillian java at org keycloak testsuite assertevents evaluate assertevents java at org jboss arquillian junit arquillian invoke arquillian java at org jboss arquillian container test impl execution clientbeforeafterlifecycleeventexecuter execute clientbeforeafterlifecycleeventexecuter java at org jboss arquillian container test impl execution clientbeforeafterlifecycleeventexecuter on clientbeforeafterlifecycleeventexecuter java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl invokeobservers eventcontextimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian container test impl client containereventcontroller createcontext containereventcontroller java at org jboss arquillian container test impl client containereventcontroller createbeforecontext containereventcontroller java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian test impl testcontexthandler createsuitecontext testcontexthandler java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian test impl testcontexthandler createtestcontext testcontexthandler java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian test impl testcontexthandler createclasscontext testcontexthandler java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org jboss arquillian core impl observerimpl invoke observerimpl java at org jboss arquillian core impl eventcontextimpl proceed eventcontextimpl java at org jboss arquillian core impl managerimpl fire managerimpl java at org jboss arquillian core impl managerimpl fire managerimpl java at org jboss arquillian test impl eventtestrunneradaptor firecustomlifecycle eventtestrunneradaptor java at org jboss arquillian junit arquillian evaluate arquillian java at org junit runners evaluate java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org jboss arquillian junit arquillian evaluate arquillian java at org jboss arquillian junit arquillian multiexecute arquillian java at org jboss arquillian junit arquillian access arquillian java at org jboss arquillian junit arquillian evaluate arquillian java at org junit rules externalresource evaluate externalresource java at org junit rules externalresource evaluate externalresource java at org junit rules runrules evaluate runrules java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org jboss arquillian junit arquillian run arquillian java at org apache maven surefire execute java at org apache maven surefire executewithrerun java at org apache maven surefire executetestset java at org apache maven surefire invoke java at org apache maven surefire booter forkedbooter runsuitesinprocess forkedbooter java at org apache maven surefire booter forkedbooter execute forkedbooter java at org apache maven surefire booter forkedbooter run forkedbooter java at org apache maven surefire booter forkedbooter main forkedbooter java caused by java lang runtimeexception javax security auth login loginexception clock skew too great at org keycloak testsuite federation kerberos keycloakspnegoschemefactory keycloakspnegoscheme generategsstoken keycloakspnegoschemefactory java at org apache http impl auth spnegoscheme generatetoken spnegoscheme java at org apache http impl auth ggsschemebase authenticate ggsschemebase java at org apache http impl auth spnegoscheme authenticate spnegoscheme java at org apache http impl auth httpauthenticator doauth httpauthenticator java at org apache http impl auth httpauthenticator generateauthresponse httpauthenticator java at org apache http impl execchain mainclientexec execute mainclientexec java at org apache http impl execchain protocolexec execute protocolexec java at org apache http impl execchain retryexec execute retryexec java at org apache http impl execchain redirectexec execute redirectexec java at org apache http impl client internalhttpclient doexecute internalhttpclient java at org apache http impl client closeablehttpclient execute closeablehttpclient java at org apache http impl client closeablehttpclient execute closeablehttpclient java at org jboss resteasy client jaxrs engines invoke java more caused by javax security auth login loginexception clock skew too great at jdk security auth com sun security auth module attemptauthentication java at jdk security auth com sun security auth module login java at java base javax security auth login logincontext invoke logincontext java at java base javax security auth login logincontext run logincontext java at java base javax security auth login logincontext run logincontext java at java base java security accesscontroller doprivileged native method at java base javax security auth login logincontext invokepriv logincontext java at java base javax security auth login logincontext login logincontext java at org keycloak federation kerberos impl kerberosusernamepasswordauthenticator authenticatesubject kerberosusernamepasswordauthenticator java at org keycloak testsuite federation kerberos keycloakspnegoschemefactory keycloakspnegoscheme generategsstoken keycloakspnegoschemefactory java more caused by krbexception clock skew too great at java security jgss sun security krbasrep krbasrep java at java security jgss sun security krbasreqbuilder send krbasreqbuilder java at java security jgss sun security krbasreqbuilder action krbasreqbuilder java at jdk security auth com sun security auth module attemptauthentication java more caused by krbexception identifier doesn t match expected value at java security jgss sun security internal kdcrep init kdcrep java at java security jgss sun security internal asrep init asrep java at java security jgss sun security internal asrep asrep java at java security jgss sun security krbasrep krbasrep java more it seems the bug is present in the pipeline for some time occurs occasionally afaik it s related to the time synchronization on dedicated agents for uf tests pdrozd do you have any better solution than the manual setting thank you version expected behavior no response actual behavior no response how to reproduce execute uf tests in the pipeline anything else no response | 0 |
354,956 | 25,175,278,936 | IssuesEvent | 2022-11-11 08:41:15 | domoberzin/pe | https://api.github.com/repos/domoberzin/pe | opened | Deleting a contact deletes all of their assigned tasks | type.DocumentationBug severity.VeryLow | As stated in title, when I delete a contact with some tasks that are assigned to them, the tasks get deleted as well. However I am unable to find documentation of this behaviour in the UG.
<!--session: 1668152369213-3a5dd7dd-3795-4ca3-b475-d951537b6bde-->
<!--Version: Web v3.4.4--> | 1.0 | Deleting a contact deletes all of their assigned tasks - As stated in title, when I delete a contact with some tasks that are assigned to them, the tasks get deleted as well. However I am unable to find documentation of this behaviour in the UG.
<!--session: 1668152369213-3a5dd7dd-3795-4ca3-b475-d951537b6bde-->
<!--Version: Web v3.4.4--> | non_priority | deleting a contact deletes all of their assigned tasks as stated in title when i delete a contact with some tasks that are assigned to them the tasks get deleted as well however i am unable to find documentation of this behaviour in the ug | 0 |
133,767 | 12,553,200,247 | IssuesEvent | 2020-06-06 21:01:09 | PANDATD/pandassistant | https://api.github.com/repos/PANDATD/pandassistant | closed | still not support voice | bug documentation good first issue help wanted | hey still not support **_voice commonds_**
_we are implementing in future as per as possiable_
and minor bugs are there !
_we fix as per as possiable .._
| 1.0 | still not support voice - hey still not support **_voice commonds_**
_we are implementing in future as per as possiable_
and minor bugs are there !
_we fix as per as possiable .._
| non_priority | still not support voice hey still not support voice commonds we are implementing in future as per as possiable and minor bugs are there we fix as per as possiable | 0 |
86,406 | 10,491,768,207 | IssuesEvent | 2019-09-25 11:55:11 | GIScience/openrouteservice | https://api.github.com/repos/GIScience/openrouteservice | closed | Add app.config documentation to wiki | documentation infrastructure | It is currently almost impossible to understand how the app.config works. The comments within should be added to the wiki that a user understands how to configure running openrouteservice locally.
https://github.com/GIScience/openrouteservice/wiki/Configuration
Extract the information from https://github.com/GIScience/openrouteservice/blob/1d2837a9d24cfad6840646069234f4f61c40bb57/openrouteservice/src/main/resources/app.config.sample | 1.0 | Add app.config documentation to wiki - It is currently almost impossible to understand how the app.config works. The comments within should be added to the wiki that a user understands how to configure running openrouteservice locally.
https://github.com/GIScience/openrouteservice/wiki/Configuration
Extract the information from https://github.com/GIScience/openrouteservice/blob/1d2837a9d24cfad6840646069234f4f61c40bb57/openrouteservice/src/main/resources/app.config.sample | non_priority | add app config documentation to wiki it is currently almost impossible to understand how the app config works the comments within should be added to the wiki that a user understands how to configure running openrouteservice locally extract the information from | 0 |
49,583 | 13,454,373,765 | IssuesEvent | 2020-09-09 03:31:47 | ErezDasa/RB2 | https://api.github.com/repos/ErezDasa/RB2 | opened | CVE-2020-24616 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2020-24616 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/RB2/infra_github/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-config-2.0.3.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ErezDasa/RB2/commit/76c9fcc27c447880699d2960c8688c59736444af">76c9fcc27c447880699d2960c8688c59736444af</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.6 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPDataSource (aka Anteros-DBCP).
<p>Publish Date: 2020-08-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24616>CVE-2020-24616</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616</a></p>
<p>Release Date: 2020-08-25</p>
<p>Fix Resolution: 2.9.10.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-24616 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2020-24616 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/RB2/infra_github/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-config-2.0.3.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ErezDasa/RB2/commit/76c9fcc27c447880699d2960c8688c59736444af">76c9fcc27c447880699d2960c8688c59736444af</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.6 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPDataSource (aka Anteros-DBCP).
<p>Publish Date: 2020-08-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24616>CVE-2020-24616</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616</a></p>
<p>Release Date: 2020-08-25</p>
<p>Fix Resolution: 2.9.10.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm infra github pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring cloud starter config release jar root library x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to br com anteros dbcp anterosdbcpdatasource aka anteros dbcp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
106,558 | 16,684,262,248 | IssuesEvent | 2021-06-08 05:59:42 | brigadecore/brigade | https://api.github.com/repos/brigadecore/brigade | closed | Add yarn audit job | 2.0 good first issue security | We should add a job to our brigade.js to run `yarn audit`.
GitHub automatically scans for npm dependencies with known vulnerabilities, but it only seems to do this for master/main branches.
I'd like to get these same checks happening on our `v2` development branch on a regular basis. | True | Add yarn audit job - We should add a job to our brigade.js to run `yarn audit`.
GitHub automatically scans for npm dependencies with known vulnerabilities, but it only seems to do this for master/main branches.
I'd like to get these same checks happening on our `v2` development branch on a regular basis. | non_priority | add yarn audit job we should add a job to our brigade js to run yarn audit github automatically scans for npm dependencies with known vulnerabilities but it only seems to do this for master main branches i d like to get these same checks happening on our development branch on a regular basis | 0 |
4,493 | 3,870,171,486 | IssuesEvent | 2016-04-11 01:01:55 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 22995813: UINavigationController during peeking should use low height navigation bar | classification:ui/usability reproducible:always status:open | #### Description
Summary:
UINavigationController during peeking should use low height navigation bar, as if there is no status bar above it which is true during peeking. Currently even if returning true from prefersStatusBarHidden can not get low height navigation bar during peeking.
Steps to Reproduce:
1. Launch sample app
2. 3D Touch to peek & pop.
Sample code:
http://cl.ly/2U1l2w1v0O2r
-
Product Version: 9.0
Created: 2015-10-06T19:32:41.734940
Originated: 2015-10-06T14:32:00
Open Radar Link: http://www.openradar.me/22995813 | True | 22995813: UINavigationController during peeking should use low height navigation bar - #### Description
Summary:
UINavigationController during peeking should use low height navigation bar, as if there is no status bar above it which is true during peeking. Currently even if returning true from prefersStatusBarHidden can not get low height navigation bar during peeking.
Steps to Reproduce:
1. Launch sample app
2. 3D Touch to peek & pop.
Sample code:
http://cl.ly/2U1l2w1v0O2r
-
Product Version: 9.0
Created: 2015-10-06T19:32:41.734940
Originated: 2015-10-06T14:32:00
Open Radar Link: http://www.openradar.me/22995813 | non_priority | uinavigationcontroller during peeking should use low height navigation bar description summary uinavigationcontroller during peeking should use low height navigation bar as if there is no status bar above it which is true during peeking currently even if returning true from prefersstatusbarhidden can not get low height navigation bar during peeking steps to reproduce launch sample app touch to peek pop sample code product version created originated open radar link | 0 |
91,121 | 10,709,757,385 | IssuesEvent | 2019-10-24 23:16:38 | Nikronic/nikronic.github.io | https://api.github.com/repos/Nikronic/nikronic.github.io | closed | Design/Grammar/Word Fix/Improvement | Status: Assigned documentation enhancement good first issue hacktoberfest help wanted | I have hard-coded many parts as I am not a web developer and the code may seem ridiculous even I have used a template and googled a lot!
I would be grateful for any help about fixing issues related to design or any improvement or suggestion. :-) | 1.0 | Design/Grammar/Word Fix/Improvement - I have hard-coded many parts as I am not a web developer and the code may seem ridiculous even I have used a template and googled a lot!
I would be grateful for any help about fixing issues related to design or any improvement or suggestion. :-) | non_priority | design grammar word fix improvement i have hard coded many parts as i am not a web developer and the code may seem ridiculous even i have used a template and googled a lot i would be grateful for any help about fixing issues related to design or any improvement or suggestion | 0 |
208,902 | 15,948,343,152 | IssuesEvent | 2021-04-15 05:39:26 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: clock/jump/large_backward_disabled failed | C-test-failure O-roachtest O-robot branch-ricky-test-upgrade-roachprod release-blocker | roachtest.clock/jump/large_backward_disabled [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2883518&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=2883518&tab=artifacts#/clock/jump/large_backward_disabled) on ricky-test-upgrade-roachprod @ [54211ed8213a53ed455b859d3b157539618d6e8b](https://github.com/cockroachdb/cockroach/commits/54211ed8213a53ed455b859d3b157539618d6e8b):
```
The test failed on branch=ricky-test-upgrade-roachprod, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/clock/jump/large_backward_disabled/run_1
clock_jump_crash.go:31,clock_jump_crash.go:138,test_runner.go:768: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2883518-1618433186-32-n1cpu4:1 -- sed -i s/&tz/NULL/g bumptime.c returned: exit status 20
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2883518-1618433186-32-n1cpu4:1 -- sed -i s/&tz/NULL/g bumptime.c returned
| stderr:
|
| stdout:
| bash: tz/NULL/g: No such file or directory
| sed: -e expression #1, char 2: unterminated ``s' command
| Error: COMMAND_PROBLEM: exit status 127
| (1) COMMAND_PROBLEM
| Wraps: (2) Node 1. Command with error:
| | ``````
| | sed -i s/&tz/NULL/g bumptime.c
| | ``````
| Wraps: (3) exit status 127
| Error types: (1) errors.Cmd (2) *hintdetail.withDetail (3) *exec.ExitError
Wraps: (2) exit status 20
Error types: (1) *main.withCommandDetails (2) *exec.ExitError
```
<details><summary>Reproduce</summary>
<p>
<p>To reproduce, try:
```bash
# From https://go.crdb.dev/p/roachstress, perhaps edited lightly.
caffeinate ./roachstress.sh clock/jump/large_backward_disabled
```
</p>
</p>
</details>
/cc @cockroachdb/kv
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*clock/jump/large_backward_disabled.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 3.0 | roachtest: clock/jump/large_backward_disabled failed - roachtest.clock/jump/large_backward_disabled [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2883518&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=2883518&tab=artifacts#/clock/jump/large_backward_disabled) on ricky-test-upgrade-roachprod @ [54211ed8213a53ed455b859d3b157539618d6e8b](https://github.com/cockroachdb/cockroach/commits/54211ed8213a53ed455b859d3b157539618d6e8b):
```
The test failed on branch=ricky-test-upgrade-roachprod, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/clock/jump/large_backward_disabled/run_1
clock_jump_crash.go:31,clock_jump_crash.go:138,test_runner.go:768: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2883518-1618433186-32-n1cpu4:1 -- sed -i s/&tz/NULL/g bumptime.c returned: exit status 20
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2883518-1618433186-32-n1cpu4:1 -- sed -i s/&tz/NULL/g bumptime.c returned
| stderr:
|
| stdout:
| bash: tz/NULL/g: No such file or directory
| sed: -e expression #1, char 2: unterminated ``s' command
| Error: COMMAND_PROBLEM: exit status 127
| (1) COMMAND_PROBLEM
| Wraps: (2) Node 1. Command with error:
| | ``````
| | sed -i s/&tz/NULL/g bumptime.c
| | ``````
| Wraps: (3) exit status 127
| Error types: (1) errors.Cmd (2) *hintdetail.withDetail (3) *exec.ExitError
Wraps: (2) exit status 20
Error types: (1) *main.withCommandDetails (2) *exec.ExitError
```
<details><summary>Reproduce</summary>
<p>
<p>To reproduce, try:
```bash
# From https://go.crdb.dev/p/roachstress, perhaps edited lightly.
caffeinate ./roachstress.sh clock/jump/large_backward_disabled
```
</p>
</p>
</details>
/cc @cockroachdb/kv
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*clock/jump/large_backward_disabled.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest clock jump large backward disabled failed roachtest clock jump large backward disabled with on ricky test upgrade roachprod the test failed on branch ricky test upgrade roachprod cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts clock jump large backward disabled run clock jump crash go clock jump crash go test runner go home agent work go src github com cockroachdb cockroach bin roachprod run teamcity sed i s tz null g bumptime c returned exit status home agent work go src github com cockroachdb cockroach bin roachprod run teamcity sed i s tz null g bumptime c returned stderr stdout bash tz null g no such file or directory sed e expression char unterminated s command error command problem exit status command problem wraps node command with error sed i s tz null g bumptime c wraps exit status error types errors cmd hintdetail withdetail exec exiterror wraps exit status error types main withcommanddetails exec exiterror reproduce to reproduce try bash from perhaps edited lightly caffeinate roachstress sh clock jump large backward disabled cc cockroachdb kv | 0 |
25,185 | 24,857,536,434 | IssuesEvent | 2022-10-27 04:40:04 | home-climate-control/dz | https://api.github.com/repos/home-climate-control/dz | opened | Swing Console: Celsius/Fahrenheit switch breaks the layout | bug Swing usability Fahrenheit reactive | ### Expected Behavior
Switch from Celsius to Fahrenheit shouldn't change anything other than temperature display.
### Actual Behavior
Zone cell height is significantly reduced, and restored only when switched back to Celsius. | True | Swing Console: Celsius/Fahrenheit switch breaks the layout - ### Expected Behavior
Switch from Celsius to Fahrenheit shouldn't change anything other than temperature display.
### Actual Behavior
Zone cell height is significantly reduced, and restored only when switched back to Celsius. | non_priority | swing console celsius fahrenheit switch breaks the layout expected behavior switch from celsius to fahrenheit shouldn t change anything other than temperature display actual behavior zone cell height is significantly reduced and restored only when switched back to celsius | 0 |
242,814 | 26,277,835,091 | IssuesEvent | 2023-01-07 01:17:30 | tt9133github/kubernetes | https://api.github.com/repos/tt9133github/kubernetes | closed | CVE-2019-11840 (Medium) detected in github.com/thecodeteam/goscaleio-v0.1.0 - autoclosed | security vulnerability | ## CVE-2019-11840 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/thecodeteam/goscaleio-v0.1.0</b></p></summary>
<p>Archived repo for GoScaleIO</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/thecodeteam/goscaleio/@v/v0.1.0.zip">https://proxy.golang.org/github.com/thecodeteam/goscaleio/@v/v0.1.0.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/thecodeteam/goscaleio-v0.1.0** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in supplementary Go cryptography libraries, aka golang-googlecode-go-crypto, before 2019-03-20. A flaw was found in the amd64 implementation of golang.org/x/crypto/salsa20 and golang.org/x/crypto/salsa20/salsa. If more than 256 GiB of keystream is generated, or if the counter otherwise grows greater than 32 bits, the amd64 implementation will first generate incorrect output, and then cycle back to previously generated keystream. Repeated keystream bytes can lead to loss of confidentiality in encryption applications, or to predictability in CSPRNG applications.
<p>Publish Date: 2019-05-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11840>CVE-2019-11840</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1691529">https://bugzilla.redhat.com/show_bug.cgi?id=1691529</a></p>
<p>Fix Resolution: Upgrade to version golang.org/x/crypto v0.0.0-0.20190320223903-b7391e95e576 or greater</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-11840 (Medium) detected in github.com/thecodeteam/goscaleio-v0.1.0 - autoclosed - ## CVE-2019-11840 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/thecodeteam/goscaleio-v0.1.0</b></p></summary>
<p>Archived repo for GoScaleIO</p>
<p>Library home page: <a href="https://proxy.golang.org/github.com/thecodeteam/goscaleio/@v/v0.1.0.zip">https://proxy.golang.org/github.com/thecodeteam/goscaleio/@v/v0.1.0.zip</a></p>
<p>
Dependency Hierarchy:
- :x: **github.com/thecodeteam/goscaleio-v0.1.0** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in supplementary Go cryptography libraries, aka golang-googlecode-go-crypto, before 2019-03-20. A flaw was found in the amd64 implementation of golang.org/x/crypto/salsa20 and golang.org/x/crypto/salsa20/salsa. If more than 256 GiB of keystream is generated, or if the counter otherwise grows greater than 32 bits, the amd64 implementation will first generate incorrect output, and then cycle back to previously generated keystream. Repeated keystream bytes can lead to loss of confidentiality in encryption applications, or to predictability in CSPRNG applications.
<p>Publish Date: 2019-05-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11840>CVE-2019-11840</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1691529">https://bugzilla.redhat.com/show_bug.cgi?id=1691529</a></p>
<p>Fix Resolution: Upgrade to version golang.org/x/crypto v0.0.0-0.20190320223903-b7391e95e576 or greater</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in github com thecodeteam goscaleio autoclosed cve medium severity vulnerability vulnerable library github com thecodeteam goscaleio archived repo for goscaleio library home page a href dependency hierarchy x github com thecodeteam goscaleio vulnerable library vulnerability details an issue was discovered in supplementary go cryptography libraries aka golang googlecode go crypto before a flaw was found in the implementation of golang org x crypto and golang org x crypto salsa if more than gib of keystream is generated or if the counter otherwise grows greater than bits the implementation will first generate incorrect output and then cycle back to previously generated keystream repeated keystream bytes can lead to loss of confidentiality in encryption applications or to predictability in csprng applications publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href fix resolution upgrade to version golang org x crypto or greater step up your open source security game with mend | 0 |
319,571 | 23,779,614,224 | IssuesEvent | 2022-09-02 02:16:09 | pcuzner/odf-grafana | https://api.github.com/repos/pcuzner/odf-grafana | closed | Error while getting the grafana route URL | documentation | I am getting the following error while running `ansible-playbook deploy-grafana.yml`
I have installed all the packages as mentioned in the README.
```
TASK [grafana : Extract the grafana route URL] ***********************************************************************************************************************************************************************************************
Wednesday 24 August 2022 17:53:27 -0400 (0:00:10.725) 0:00:43.373 ******
fatal: [localhost]: FAILED! => {"msg": "You need to install \"jmespath\" prior to running json_query filter"}
PLAY RECAP ***********************************************************************************************************************************************************************************************************************************
localhost : ok=11 changed=9 unreachable=0 failed=1 skipped=4 rescued=0 ignored=0
``` | 1.0 | Error while getting the grafana route URL - I am getting the following error while running `ansible-playbook deploy-grafana.yml`
I have installed all the packages as mentioned in the README.
```
TASK [grafana : Extract the grafana route URL] ***********************************************************************************************************************************************************************************************
Wednesday 24 August 2022 17:53:27 -0400 (0:00:10.725) 0:00:43.373 ******
fatal: [localhost]: FAILED! => {"msg": "You need to install \"jmespath\" prior to running json_query filter"}
PLAY RECAP ***********************************************************************************************************************************************************************************************************************************
localhost : ok=11 changed=9 unreachable=0 failed=1 skipped=4 rescued=0 ignored=0
``` | non_priority | error while getting the grafana route url i am getting the following error while running ansible playbook deploy grafana yml i have installed all the packages as mentioned in the readme task wednesday august fatal failed msg you need to install jmespath prior to running json query filter play recap localhost ok changed unreachable failed skipped rescued ignored | 0 |
118,544 | 11,983,003,900 | IssuesEvent | 2020-04-07 13:49:45 | Concordia-Campus-Guide/Concordia-Campus-Guide | https://api.github.com/repos/Concordia-Campus-Guide/Concordia-Campus-Guide | opened | Quality Measurement Report | documentation | As a developer, I want to have a report metrics related to code duplication, code documentation, size, coupling and cohesion, so I can have an idea about the quality of code and the improvement that we have made since last sprint. | 1.0 | Quality Measurement Report - As a developer, I want to have a report metrics related to code duplication, code documentation, size, coupling and cohesion, so I can have an idea about the quality of code and the improvement that we have made since last sprint. | non_priority | quality measurement report as a developer i want to have a report metrics related to code duplication code documentation size coupling and cohesion so i can have an idea about the quality of code and the improvement that we have made since last sprint | 0 |
100,770 | 21,512,238,627 | IssuesEvent | 2022-04-28 06:24:44 | haproxy/haproxy | https://api.github.com/repos/haproxy/haproxy | closed | several defects found by coverity | type: code-report | ### Tool Name and Version
coverity
### Code Report
```plain
** CID 1488360: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488360: Error handling issues (CHECKED_RETURN)
/src/sock.c: 98 in sock_accept_conn()
92 (errno == ENOSYS || errno == EINVAL || errno == EBADF) &&
93 ((accept4_broken = 1))))
94 #endif
95 {
96 laddr = sizeof(*conn->src);
97 if ((cfd = accept(l->rx.fd, (struct sockaddr*)addr, &laddr)) != -1) {
>>> CID 1488360: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(cfd)" without checking return value. It wraps a library function that may fail and return an error code.
98 fd_set_nonblock(cfd);
99 if (master)
100 fd_set_cloexec(cfd);
101 }
102 }
103
** CID 1488359: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488359: Error handling issues (CHECKED_RETURN)
/src/fd.c: 791 in init_pollers_per_thread()
785
786 if (pipe(mypipe) < 0)
787 return 0;
788
789 poller_rd_pipe = mypipe[0];
790 poller_wr_pipe[tid] = mypipe[1];
>>> CID 1488359: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(poller_rd_pipe)" without checking return value. It wraps a library function that may fail and return an error code.
791 fd_set_nonblock(poller_rd_pipe);
792 fd_insert(poller_rd_pipe, poller_pipe_io_handler, poller_pipe_io_handler, tid_bit);
793 fd_insert(poller_wr_pipe[tid], poller_pipe_io_handler, poller_pipe_io_handler, tid_bit);
794 fd_want_recv(poller_rd_pipe);
795 fd_stop_both(poller_wr_pipe[tid]);
796 return 1;
** CID 1488358: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488358: Error handling issues (CHECKED_RETURN)
/src/dns.c: 73 in dns_connect_nameserver()
67 ns->counters->id, ns->id);
68 close(fd);
69 return -1;
70 }
71
72 /* Make the socket non blocking */
>>> CID 1488358: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(fd)" without checking return value. It wraps a library function that may fail and return an error code.
73 fd_set_nonblock(fd);
74
75 /* Add the fd in the fd list and update its parameters */
76 dgram->t.sock.fd = fd;
77 fd_insert(fd, dgram, dgram_fd_handler, MAX_THREADS_MASK);
78 fd_want_recv(fd);
** CID 1488357: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488357: Error handling issues (CHECKED_RETURN)
/src/sock.c: 100 in sock_accept_conn()
94 #endif
95 {
96 laddr = sizeof(*conn->src);
97 if ((cfd = accept(l->rx.fd, (struct sockaddr*)addr, &laddr)) != -1) {
98 fd_set_nonblock(cfd);
99 if (master)
>>> CID 1488357: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_cloexec(cfd)" without checking return value. It wraps a library function that may fail and return an error code.
100 fd_set_cloexec(cfd);
101 }
102 }
103
104 if (likely(cfd != -1)) {
105 if (unlikely(cfd >= global.maxsock)) {
** CID 1488356: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488356: Error handling issues (CHECKED_RETURN)
/src/log.c: 1670 in __do_send_log()
1664 return;
1665 } else {
1666 /* we don't want to receive anything on this socket */
1667 setsockopt(*plogfd, SOL_SOCKET, SO_RCVBUF, &zero, sizeof(zero));
1668 /* does nothing under Linux, maybe needed for others */
1669 shutdown(*plogfd, SHUT_RD);
>>> CID 1488356: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_cloexec(*plogfd)" without checking return value. It wraps a library function that may fail and return an error code.
1670 fd_set_cloexec(*plogfd);
1671 }
1672 }
1673
1674 msg_header = build_log_header(logsrv->format, level, facility, metadata, &nbelem);
1675 send:
** CID 1488355: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488355: Error handling issues (CHECKED_RETURN)
/src/proto_sockpair.c: 471 in sockpair_accept_conn()
465 struct proxy *p = l->bind_conf->frontend;
466 struct connection *conn = NULL;
467 int ret;
468 int cfd;
469
470 if ((cfd = recv_fd_uxst(l->rx.fd)) != -1)
>>> CID 1488355: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(cfd)" without checking return value. It wraps a library function that may fail and return an error code.
471 fd_set_nonblock(cfd);
472
473 if (likely(cfd != -1)) {
474 /* Perfect, the connection was accepted */
475 conn = conn_new(&l->obj_type);
476 if (!conn)
** CID 1488354: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488354: Error handling issues (CHECKED_RETURN)
/src/mworker.c: 424 in mworker_pipe_register_per_thread()
418 if (!(global.mode & MODE_MWORKER) || master)
419 return 1;
420
421 if (tid != 0)
422 return 1;
423
>>> CID 1488354: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(proc_self->ipc_fd[1])" without checking return value. It wraps a library function that may fail and return an error code.
424 fd_set_nonblock(proc_self->ipc_fd[1]);
425 /* In multi-tread, we need only one thread to process
426 * events on the pipe with master
427 */
428 fd_insert(proc_self->ipc_fd[1], fdtab[proc_self->ipc_fd[1]].owner, mworker_accept_wrapper, tid_bit);
429 fd_want_recv(proc_self->ipc_fd[1]);
```
### Additional Information
_No response_
### Output of `haproxy -vv`
```plain
no
```
| 1.0 | several defects found by coverity - ### Tool Name and Version
coverity
### Code Report
```plain
** CID 1488360: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488360: Error handling issues (CHECKED_RETURN)
/src/sock.c: 98 in sock_accept_conn()
92 (errno == ENOSYS || errno == EINVAL || errno == EBADF) &&
93 ((accept4_broken = 1))))
94 #endif
95 {
96 laddr = sizeof(*conn->src);
97 if ((cfd = accept(l->rx.fd, (struct sockaddr*)addr, &laddr)) != -1) {
>>> CID 1488360: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(cfd)" without checking return value. It wraps a library function that may fail and return an error code.
98 fd_set_nonblock(cfd);
99 if (master)
100 fd_set_cloexec(cfd);
101 }
102 }
103
** CID 1488359: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488359: Error handling issues (CHECKED_RETURN)
/src/fd.c: 791 in init_pollers_per_thread()
785
786 if (pipe(mypipe) < 0)
787 return 0;
788
789 poller_rd_pipe = mypipe[0];
790 poller_wr_pipe[tid] = mypipe[1];
>>> CID 1488359: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(poller_rd_pipe)" without checking return value. It wraps a library function that may fail and return an error code.
791 fd_set_nonblock(poller_rd_pipe);
792 fd_insert(poller_rd_pipe, poller_pipe_io_handler, poller_pipe_io_handler, tid_bit);
793 fd_insert(poller_wr_pipe[tid], poller_pipe_io_handler, poller_pipe_io_handler, tid_bit);
794 fd_want_recv(poller_rd_pipe);
795 fd_stop_both(poller_wr_pipe[tid]);
796 return 1;
** CID 1488358: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488358: Error handling issues (CHECKED_RETURN)
/src/dns.c: 73 in dns_connect_nameserver()
67 ns->counters->id, ns->id);
68 close(fd);
69 return -1;
70 }
71
72 /* Make the socket non blocking */
>>> CID 1488358: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(fd)" without checking return value. It wraps a library function that may fail and return an error code.
73 fd_set_nonblock(fd);
74
75 /* Add the fd in the fd list and update its parameters */
76 dgram->t.sock.fd = fd;
77 fd_insert(fd, dgram, dgram_fd_handler, MAX_THREADS_MASK);
78 fd_want_recv(fd);
** CID 1488357: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488357: Error handling issues (CHECKED_RETURN)
/src/sock.c: 100 in sock_accept_conn()
94 #endif
95 {
96 laddr = sizeof(*conn->src);
97 if ((cfd = accept(l->rx.fd, (struct sockaddr*)addr, &laddr)) != -1) {
98 fd_set_nonblock(cfd);
99 if (master)
>>> CID 1488357: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_cloexec(cfd)" without checking return value. It wraps a library function that may fail and return an error code.
100 fd_set_cloexec(cfd);
101 }
102 }
103
104 if (likely(cfd != -1)) {
105 if (unlikely(cfd >= global.maxsock)) {
** CID 1488356: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488356: Error handling issues (CHECKED_RETURN)
/src/log.c: 1670 in __do_send_log()
1664 return;
1665 } else {
1666 /* we don't want to receive anything on this socket */
1667 setsockopt(*plogfd, SOL_SOCKET, SO_RCVBUF, &zero, sizeof(zero));
1668 /* does nothing under Linux, maybe needed for others */
1669 shutdown(*plogfd, SHUT_RD);
>>> CID 1488356: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_cloexec(*plogfd)" without checking return value. It wraps a library function that may fail and return an error code.
1670 fd_set_cloexec(*plogfd);
1671 }
1672 }
1673
1674 msg_header = build_log_header(logsrv->format, level, facility, metadata, &nbelem);
1675 send:
** CID 1488355: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488355: Error handling issues (CHECKED_RETURN)
/src/proto_sockpair.c: 471 in sockpair_accept_conn()
465 struct proxy *p = l->bind_conf->frontend;
466 struct connection *conn = NULL;
467 int ret;
468 int cfd;
469
470 if ((cfd = recv_fd_uxst(l->rx.fd)) != -1)
>>> CID 1488355: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(cfd)" without checking return value. It wraps a library function that may fail and return an error code.
471 fd_set_nonblock(cfd);
472
473 if (likely(cfd != -1)) {
474 /* Perfect, the connection was accepted */
475 conn = conn_new(&l->obj_type);
476 if (!conn)
** CID 1488354: Error handling issues (CHECKED_RETURN)
________________________________________________________________________________________________________
*** CID 1488354: Error handling issues (CHECKED_RETURN)
/src/mworker.c: 424 in mworker_pipe_register_per_thread()
418 if (!(global.mode & MODE_MWORKER) || master)
419 return 1;
420
421 if (tid != 0)
422 return 1;
423
>>> CID 1488354: Error handling issues (CHECKED_RETURN)
>>> Calling "fd_set_nonblock(proc_self->ipc_fd[1])" without checking return value. It wraps a library function that may fail and return an error code.
424 fd_set_nonblock(proc_self->ipc_fd[1]);
425 /* In multi-tread, we need only one thread to process
426 * events on the pipe with master
427 */
428 fd_insert(proc_self->ipc_fd[1], fdtab[proc_self->ipc_fd[1]].owner, mworker_accept_wrapper, tid_bit);
429 fd_want_recv(proc_self->ipc_fd[1]);
```
### Additional Information
_No response_
### Output of `haproxy -vv`
```plain
no
```
| non_priority | several defects found by coverity tool name and version coverity code report plain cid error handling issues checked return cid error handling issues checked return src sock c in sock accept conn errno enosys errno einval errno ebadf broken endif laddr sizeof conn src if cfd accept l rx fd struct sockaddr addr laddr cid error handling issues checked return calling fd set nonblock cfd without checking return value it wraps a library function that may fail and return an error code fd set nonblock cfd if master fd set cloexec cfd cid error handling issues checked return cid error handling issues checked return src fd c in init pollers per thread if pipe mypipe return poller rd pipe mypipe poller wr pipe mypipe cid error handling issues checked return calling fd set nonblock poller rd pipe without checking return value it wraps a library function that may fail and return an error code fd set nonblock poller rd pipe fd insert poller rd pipe poller pipe io handler poller pipe io handler tid bit fd insert poller wr pipe poller pipe io handler poller pipe io handler tid bit fd want recv poller rd pipe fd stop both poller wr pipe return cid error handling issues checked return cid error handling issues checked return src dns c in dns connect nameserver ns counters id ns id close fd return make the socket non blocking cid error handling issues checked return calling fd set nonblock fd without checking return value it wraps a library function that may fail and return an error code fd set nonblock fd add the fd in the fd list and update its parameters dgram t sock fd fd fd insert fd dgram dgram fd handler max threads mask fd want recv fd cid error handling issues checked return cid error handling issues checked return src sock c in sock accept conn endif laddr sizeof conn src if cfd accept l rx fd struct sockaddr addr laddr fd set nonblock cfd if master cid error handling issues checked return calling fd set cloexec cfd without checking return value it wraps a library function that may fail and return an error code fd set cloexec cfd if likely cfd if unlikely cfd global maxsock cid error handling issues checked return cid error handling issues checked return src log c in do send log return else we don t want to receive anything on this socket setsockopt plogfd sol socket so rcvbuf zero sizeof zero does nothing under linux maybe needed for others shutdown plogfd shut rd cid error handling issues checked return calling fd set cloexec plogfd without checking return value it wraps a library function that may fail and return an error code fd set cloexec plogfd msg header build log header logsrv format level facility metadata nbelem send cid error handling issues checked return cid error handling issues checked return src proto sockpair c in sockpair accept conn struct proxy p l bind conf frontend struct connection conn null int ret int cfd if cfd recv fd uxst l rx fd cid error handling issues checked return calling fd set nonblock cfd without checking return value it wraps a library function that may fail and return an error code fd set nonblock cfd if likely cfd perfect the connection was accepted conn conn new l obj type if conn cid error handling issues checked return cid error handling issues checked return src mworker c in mworker pipe register per thread if global mode mode mworker master return if tid return cid error handling issues checked return calling fd set nonblock proc self ipc fd without checking return value it wraps a library function that may fail and return an error code fd set nonblock proc self ipc fd in multi tread we need only one thread to process events on the pipe with master fd insert proc self ipc fd fdtab owner mworker accept wrapper tid bit fd want recv proc self ipc fd additional information no response output of haproxy vv plain no | 0 |
88,326 | 17,567,470,384 | IssuesEvent | 2021-08-14 02:00:41 | microsoft/appcenter | https://api.github.com/repos/microsoft/appcenter | closed | Multiple Code Push keys for an 1 application | feature request codepush Stale | Current [implementation of code push](https://docs.microsoft.com/en-us/appcenter/distribution/codepush/rn-get-started) limits us to have 1 code push key per application. Our design is much more modular and we want to allow for independent reach native bundles within the same app so we can independently update them if/when required, instead of having to push a monolithic bundle.
Current code push SDK for iOS is setup to take the code push key from a plist variable. If this could instead be configured as the time of each initialization, we could easily support multiple code push keys - 1 for each react native initialization within an app.
| 1.0 | Multiple Code Push keys for an 1 application - Current [implementation of code push](https://docs.microsoft.com/en-us/appcenter/distribution/codepush/rn-get-started) limits us to have 1 code push key per application. Our design is much more modular and we want to allow for independent reach native bundles within the same app so we can independently update them if/when required, instead of having to push a monolithic bundle.
Current code push SDK for iOS is setup to take the code push key from a plist variable. If this could instead be configured as the time of each initialization, we could easily support multiple code push keys - 1 for each react native initialization within an app.
| non_priority | multiple code push keys for an application current limits us to have code push key per application our design is much more modular and we want to allow for independent reach native bundles within the same app so we can independently update them if when required instead of having to push a monolithic bundle current code push sdk for ios is setup to take the code push key from a plist variable if this could instead be configured as the time of each initialization we could easily support multiple code push keys for each react native initialization within an app | 0 |
157,741 | 13,721,937,664 | IssuesEvent | 2020-10-03 00:57:46 | rodgeraraujo/minus.css | https://api.github.com/repos/rodgeraraujo/minus.css | opened | New ideas or improvement of the existing ones | documentation enhancement good first issue hacktoberfest help wanted | If you have any new ideas or suggestions for improvement feel free to fork and contribute
But remember, this is a `small and minimalistic css framework`.
| 1.0 | New ideas or improvement of the existing ones - If you have any new ideas or suggestions for improvement feel free to fork and contribute
But remember, this is a `small and minimalistic css framework`.
| non_priority | new ideas or improvement of the existing ones if you have any new ideas or suggestions for improvement feel free to fork and contribute but remember this is a small and minimalistic css framework | 0 |
77,809 | 21,965,538,976 | IssuesEvent | 2022-05-24 19:53:34 | sandboxie-plus/Sandboxie | https://api.github.com/repos/sandboxie-plus/Sandboxie | closed | Show size of each Sandbox in GUI | Feature request ToDo added in next build Work in progress | ### Is your feature request related to a problem or use case?
It would be helpful to easily see how much disk space is used by each Sandbox.
### Describe the solution you'd like
Add a column to the Sandboxie GUI called Size, where it shows the amount of disk space used by each Box.
If querying file sizes might be resource-intensive or add wear and tear to the disk, you could make it refresh one of these ways:
1) manually - user has to click a button each time
2) at a 30-minute interval - easy to program but 99% of the time, the size won't change
3) intelligently - when Sandboxie notices that a disk-write has occurred inside a sandbox, it will refresh the Size column for just that Box. Don't refresh more than once per 5 seconds. Don't refresh if the Sandboxie GUI is not open & visible.
### Describe alternatives you've considered
_No response_ | 1.0 | Show size of each Sandbox in GUI - ### Is your feature request related to a problem or use case?
It would be helpful to easily see how much disk space is used by each Sandbox.
### Describe the solution you'd like
Add a column to the Sandboxie GUI called Size, where it shows the amount of disk space used by each Box.
If querying file sizes might be resource-intensive or add wear and tear to the disk, you could make it refresh one of these ways:
1) manually - user has to click a button each time
2) at a 30-minute interval - easy to program but 99% of the time, the size won't change
3) intelligently - when Sandboxie notices that a disk-write has occurred inside a sandbox, it will refresh the Size column for just that Box. Don't refresh more than once per 5 seconds. Don't refresh if the Sandboxie GUI is not open & visible.
### Describe alternatives you've considered
_No response_ | non_priority | show size of each sandbox in gui is your feature request related to a problem or use case it would be helpful to easily see how much disk space is used by each sandbox describe the solution you d like add a column to the sandboxie gui called size where it shows the amount of disk space used by each box if querying file sizes might be resource intensive or add wear and tear to the disk you could make it refresh one of these ways manually user has to click a button each time at a minute interval easy to program but of the time the size won t change intelligently when sandboxie notices that a disk write has occurred inside a sandbox it will refresh the size column for just that box don t refresh more than once per seconds don t refresh if the sandboxie gui is not open visible describe alternatives you ve considered no response | 0 |
226,154 | 17,314,219,466 | IssuesEvent | 2021-07-27 02:13:41 | rero/rero-ils | https://api.github.com/repos/rero/rero-ils | closed | Add a changelog autogeneration script | developers documentation enhancement p-Low stale | # Description
`CHANGES.rst` is now generated by https://github.com/github-changelog-generator/github-changelog-generator
Each time we want to update the release, we need to:
- generate the .md file (Markdown)
- transform it to .rst
- append after the header
- delete all text older that tag v0.1.0a16
These actions could be done via an automatic script. | 1.0 | Add a changelog autogeneration script - # Description
`CHANGES.rst` is now generated by https://github.com/github-changelog-generator/github-changelog-generator
Each time we want to update the release, we need to:
- generate the .md file (Markdown)
- transform it to .rst
- append after the header
- delete all text older that tag v0.1.0a16
These actions could be done via an automatic script. | non_priority | add a changelog autogeneration script description changes rst is now generated by each time we want to update the release we need to generate the md file markdown transform it to rst append after the header delete all text older that tag these actions could be done via an automatic script | 0 |
112,071 | 17,068,106,720 | IssuesEvent | 2021-07-07 09:51:22 | AlexRogalskiy/java4you | https://api.github.com/repos/AlexRogalskiy/java4you | opened | CVE-2020-28491 (High) detected in jackson-dataformat-cbor-2.6.7.jar | security vulnerability | ## CVE-2020-28491 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-dataformat-cbor-2.6.7.jar</b></p></summary>
<p>Support for reading and writing Concise Binary Object Representation
([CBOR](https://www.rfc-editor.org/info/rfc7049)
encoded data using Jackson abstractions (streaming API, data binding, tree model)</p>
<p>Path to dependency file: java4you/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/dataformat/jackson-dataformat-cbor/2.6.7/jackson-dataformat-cbor-2.6.7.jar</p>
<p>
Dependency Hierarchy:
- aws-java-sdk-dynamodb-1.11.946.jar (Root Library)
- aws-java-sdk-core-1.11.946.jar
- :x: **jackson-dataformat-cbor-2.6.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/java4you/commit/587cddeefe085812cffa745ecc4fd43a95cc1a79">587cddeefe085812cffa745ecc4fd43a95cc1a79</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package com.fasterxml.jackson.dataformat:jackson-dataformat-cbor from 0 and before 2.11.4, from 2.12.0-rc1 and before 2.12.1. Unchecked allocation of byte buffer can cause a java.lang.OutOfMemoryError exception.
<p>Publish Date: 2021-02-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28491>CVE-2020-28491</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28491">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28491</a></p>
<p>Release Date: 2021-02-18</p>
<p>Fix Resolution: com.fasterxml.jackson.dataformat:jackson-dataformat-cbor:2.11.4, com.fasterxml.jackson.dataformat:jackson-dataformat-cbor:2.12.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28491 (High) detected in jackson-dataformat-cbor-2.6.7.jar - ## CVE-2020-28491 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-dataformat-cbor-2.6.7.jar</b></p></summary>
<p>Support for reading and writing Concise Binary Object Representation
([CBOR](https://www.rfc-editor.org/info/rfc7049)
encoded data using Jackson abstractions (streaming API, data binding, tree model)</p>
<p>Path to dependency file: java4you/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/dataformat/jackson-dataformat-cbor/2.6.7/jackson-dataformat-cbor-2.6.7.jar</p>
<p>
Dependency Hierarchy:
- aws-java-sdk-dynamodb-1.11.946.jar (Root Library)
- aws-java-sdk-core-1.11.946.jar
- :x: **jackson-dataformat-cbor-2.6.7.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/java4you/commit/587cddeefe085812cffa745ecc4fd43a95cc1a79">587cddeefe085812cffa745ecc4fd43a95cc1a79</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package com.fasterxml.jackson.dataformat:jackson-dataformat-cbor from 0 and before 2.11.4, from 2.12.0-rc1 and before 2.12.1. Unchecked allocation of byte buffer can cause a java.lang.OutOfMemoryError exception.
<p>Publish Date: 2021-02-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28491>CVE-2020-28491</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28491">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28491</a></p>
<p>Release Date: 2021-02-18</p>
<p>Fix Resolution: com.fasterxml.jackson.dataformat:jackson-dataformat-cbor:2.11.4, com.fasterxml.jackson.dataformat:jackson-dataformat-cbor:2.12.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson dataformat cbor jar cve high severity vulnerability vulnerable library jackson dataformat cbor jar support for reading and writing concise binary object representation encoded data using jackson abstractions streaming api data binding tree model path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson dataformat jackson dataformat cbor jackson dataformat cbor jar dependency hierarchy aws java sdk dynamodb jar root library aws java sdk core jar x jackson dataformat cbor jar vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package com fasterxml jackson dataformat jackson dataformat cbor from and before from and before unchecked allocation of byte buffer can cause a java lang outofmemoryerror exception publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson dataformat jackson dataformat cbor com fasterxml jackson dataformat jackson dataformat cbor step up your open source security game with whitesource | 0 |
79,299 | 10,116,047,737 | IssuesEvent | 2019-07-31 00:07:48 | ampproject/amp.dev | https://api.github.com/repos/ampproject/amp.dev | opened | Create new reference document for `amp-story-page-attachment` | Category: Content Category: Documentation Type: Update | ## 📖 Missing or out-of-date documentation
**Describe the content that is missing or should be up dated**
`amp-story-page-attachmente` is a separate amp component from `amp-story`. It should be migrated to its own page and include a code samples and a top table with description, required script, ect.
https://amp.dev/documentation/components/amp-story/?format=websites#page-attachments
| 1.0 | Create new reference document for `amp-story-page-attachment` - ## 📖 Missing or out-of-date documentation
**Describe the content that is missing or should be up dated**
`amp-story-page-attachmente` is a separate amp component from `amp-story`. It should be migrated to its own page and include a code samples and a top table with description, required script, ect.
https://amp.dev/documentation/components/amp-story/?format=websites#page-attachments
| non_priority | create new reference document for amp story page attachment 📖 missing or out of date documentation describe the content that is missing or should be up dated amp story page attachmente is a separate amp component from amp story it should be migrated to its own page and include a code samples and a top table with description required script ect | 0 |
95,035 | 11,950,128,398 | IssuesEvent | 2020-04-03 14:43:32 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | How to prevent auto scroll down on tab2 when user scroll down on tab1? | d: stackoverflow f: material design f: scrolling framework | Hi, I am new to flutter and I have a problem that I couldn't solve.
I asked the question on [stackoverflow](https://stackoverflow.com/q/54647229/1027507) but I haven't found the solution. So I am asking at here.
I created a screen using `SliverAppBar`, `SliverPersistentHeader`, `TabView` and `ListView`.
If I scroll down in tab1, tab2 scrolling down automatically. So If I swith to tab2, list not starting from first item. How can I prevent this?
Simplified build function content of screen:
```dart
return Scaffold(
body: DefaultTabController(
length: 2,
child: NestedScrollView(
headerSliverBuilder: (BuildContext context, bool innerBoxIsScrolled) {
return <Widget>[
SliverAppBar(
expandedHeight: 120.0,
floating: false,
forceElevated: innerBoxIsScrolled,
backgroundColor: Colors.green,
pinned: true,
flexibleSpace: FlexibleSpaceBar(
collapseMode: CollapseMode.pin,
centerTitle: true,
title: Text(
spaceBarFlatName,
style: TextStyle(color: config.topBarTextColor),
textAlign: TextAlign.left,
overflow: TextOverflow.ellipsis,
softWrap: true,
maxLines: 1,
),
background: Container(
alignment: Alignment.topCenter,
child: Column(
mainAxisAlignment: MainAxisAlignment.spaceEvenly,
children: <Widget>[
Row(
children: <Widget>[
Text(
'${formatMoney(periodBalance.abs())}',
style: TextStyle(
color: config.topBarTextColor,
fontSize: 30.0,
fontWeight: FontWeight.bold),
),
Icon(FontAwesomeIcons.liraSign,
color: textColor, size: 24.0),
Text(" (Alacak)",
style: TextStyle(
color: config.topBarTextColor,
fontSize: 20.0,
),
)
],
mainAxisAlignment: MainAxisAlignment.center,
),
Container(width: 0,height: 0)
],
),
),
),
),
SliverPersistentHeader(
pinned: true,
delegate: _SliverAppBarDelegate(
TabBar(
tabs: [
Tab(child: Text("Borçlarım"),
Tab(child: Text("Ödemelerim"),
],
),
),
),
];
},
body: TabBarView(
children: [
Container(
child: ListView.builder(
scrollDirection: Axis.vertical,
shrinkWrap: true,
itemCount: debits.length,
//itemExtent: 1.0,
itemBuilder: (context, index) {
return DebitCard(debits[index]);
}),
),
Container(
child: ListView.builder(
scrollDirection: Axis.vertical,
shrinkWrap: true,
itemCount: receipts.length,
//itemExtent: 1.0,
itemBuilder: (context, index) {
return ReceiptCard(receipts[index]);
}),
),
]
),
),
),
);
```
**Initial state of the screen:**
<img src="https://user-images.githubusercontent.com/823338/52731908-f49a4f00-2fcf-11e9-81e6-adf3bba50754.jpeg" width="350">
**If I scroll tab1 shown as below:**
<img src="https://user-images.githubusercontent.com/823338/52731909-f532e580-2fcf-11e9-926c-912162595a2b.jpeg" width="350">
**Tab2 scrolling down automatically shown as below when I scroll tab1 which I don't want to be:**
<img src="https://user-images.githubusercontent.com/823338/52731910-f532e580-2fcf-11e9-9650-887993f0b626.jpeg" width="350">
I want when user switch to tab2, scroll should start in other words why tab2 scrolling automatically when I scroll on tab1?
------
```
$ flutter doctor -v
[✓] Flutter (Channel beta, v1.1.8, on Linux, locale en_US.UTF-8)
• Flutter version 1.1.8 at /opt/flutter-sdk/flutter
• Framework revision 985ccb6d14 (5 weeks ago), 2019-01-08 13:45:55 -0800
• Engine revision 7112b72cc2
• Dart version 2.1.1 (build 2.1.1-dev.0.1 ec86471ccc)
[✓] Android toolchain - develop for Android devices (Android SDK version 28.0.3)
• Android SDK at /opt/android-sdk
• Android NDK location not configured (optional; useful for native profiling support)
• Platform android-28, build-tools 28.0.3
• ANDROID_HOME = /opt/android-sdk
• Java binary at: /opt/android-studio/jre/bin/java
• Java version OpenJDK Runtime Environment (build 1.8.0_152-release-1248-b01)
• All Android licenses accepted.
[✓] Android Studio (version 3.3)
• Android Studio at /opt/android-studio
• Flutter plugin version 32.0.1
• Dart plugin version 182.5215
• Java version OpenJDK Runtime Environment (build 1.8.0_152-release-1248-b01)
[!] IntelliJ IDEA Ultimate Edition (version 2018.2)
• IntelliJ at /home/mesuutt/tmp/tools/idea-IU-182.4892.20
✗ Flutter plugin not installed; this adds Flutter specific functionality.
✗ Dart plugin not installed; this adds Dart specific functionality.
``` | 1.0 | How to prevent auto scroll down on tab2 when user scroll down on tab1? - Hi, I am new to flutter and I have a problem that I couldn't solve.
I asked the question on [stackoverflow](https://stackoverflow.com/q/54647229/1027507) but I haven't found the solution. So I am asking at here.
I created a screen using `SliverAppBar`, `SliverPersistentHeader`, `TabView` and `ListView`.
If I scroll down in tab1, tab2 scrolling down automatically. So If I swith to tab2, list not starting from first item. How can I prevent this?
Simplified build function content of screen:
```dart
return Scaffold(
body: DefaultTabController(
length: 2,
child: NestedScrollView(
headerSliverBuilder: (BuildContext context, bool innerBoxIsScrolled) {
return <Widget>[
SliverAppBar(
expandedHeight: 120.0,
floating: false,
forceElevated: innerBoxIsScrolled,
backgroundColor: Colors.green,
pinned: true,
flexibleSpace: FlexibleSpaceBar(
collapseMode: CollapseMode.pin,
centerTitle: true,
title: Text(
spaceBarFlatName,
style: TextStyle(color: config.topBarTextColor),
textAlign: TextAlign.left,
overflow: TextOverflow.ellipsis,
softWrap: true,
maxLines: 1,
),
background: Container(
alignment: Alignment.topCenter,
child: Column(
mainAxisAlignment: MainAxisAlignment.spaceEvenly,
children: <Widget>[
Row(
children: <Widget>[
Text(
'${formatMoney(periodBalance.abs())}',
style: TextStyle(
color: config.topBarTextColor,
fontSize: 30.0,
fontWeight: FontWeight.bold),
),
Icon(FontAwesomeIcons.liraSign,
color: textColor, size: 24.0),
Text(" (Alacak)",
style: TextStyle(
color: config.topBarTextColor,
fontSize: 20.0,
),
)
],
mainAxisAlignment: MainAxisAlignment.center,
),
Container(width: 0,height: 0)
],
),
),
),
),
SliverPersistentHeader(
pinned: true,
delegate: _SliverAppBarDelegate(
TabBar(
tabs: [
Tab(child: Text("Borçlarım"),
Tab(child: Text("Ödemelerim"),
],
),
),
),
];
},
body: TabBarView(
children: [
Container(
child: ListView.builder(
scrollDirection: Axis.vertical,
shrinkWrap: true,
itemCount: debits.length,
//itemExtent: 1.0,
itemBuilder: (context, index) {
return DebitCard(debits[index]);
}),
),
Container(
child: ListView.builder(
scrollDirection: Axis.vertical,
shrinkWrap: true,
itemCount: receipts.length,
//itemExtent: 1.0,
itemBuilder: (context, index) {
return ReceiptCard(receipts[index]);
}),
),
]
),
),
),
);
```
**Initial state of the screen:**
<img src="https://user-images.githubusercontent.com/823338/52731908-f49a4f00-2fcf-11e9-81e6-adf3bba50754.jpeg" width="350">
**If I scroll tab1 shown as below:**
<img src="https://user-images.githubusercontent.com/823338/52731909-f532e580-2fcf-11e9-926c-912162595a2b.jpeg" width="350">
**Tab2 scrolling down automatically shown as below when I scroll tab1 which I don't want to be:**
<img src="https://user-images.githubusercontent.com/823338/52731910-f532e580-2fcf-11e9-9650-887993f0b626.jpeg" width="350">
I want when user switch to tab2, scroll should start in other words why tab2 scrolling automatically when I scroll on tab1?
------
```
$ flutter doctor -v
[✓] Flutter (Channel beta, v1.1.8, on Linux, locale en_US.UTF-8)
• Flutter version 1.1.8 at /opt/flutter-sdk/flutter
• Framework revision 985ccb6d14 (5 weeks ago), 2019-01-08 13:45:55 -0800
• Engine revision 7112b72cc2
• Dart version 2.1.1 (build 2.1.1-dev.0.1 ec86471ccc)
[✓] Android toolchain - develop for Android devices (Android SDK version 28.0.3)
• Android SDK at /opt/android-sdk
• Android NDK location not configured (optional; useful for native profiling support)
• Platform android-28, build-tools 28.0.3
• ANDROID_HOME = /opt/android-sdk
• Java binary at: /opt/android-studio/jre/bin/java
• Java version OpenJDK Runtime Environment (build 1.8.0_152-release-1248-b01)
• All Android licenses accepted.
[✓] Android Studio (version 3.3)
• Android Studio at /opt/android-studio
• Flutter plugin version 32.0.1
• Dart plugin version 182.5215
• Java version OpenJDK Runtime Environment (build 1.8.0_152-release-1248-b01)
[!] IntelliJ IDEA Ultimate Edition (version 2018.2)
• IntelliJ at /home/mesuutt/tmp/tools/idea-IU-182.4892.20
✗ Flutter plugin not installed; this adds Flutter specific functionality.
✗ Dart plugin not installed; this adds Dart specific functionality.
``` | non_priority | how to prevent auto scroll down on when user scroll down on hi i am new to flutter and i have a problem that i couldn t solve i asked the question on but i haven t found the solution so i am asking at here i created a screen using sliverappbar sliverpersistentheader tabview and listview if i scroll down in scrolling down automatically so if i swith to list not starting from first item how can i prevent this simplified build function content of screen dart return scaffold body defaulttabcontroller length child nestedscrollview headersliverbuilder buildcontext context bool innerboxisscrolled return sliverappbar expandedheight floating false forceelevated innerboxisscrolled backgroundcolor colors green pinned true flexiblespace flexiblespacebar collapsemode collapsemode pin centertitle true title text spacebarflatname style textstyle color config topbartextcolor textalign textalign left overflow textoverflow ellipsis softwrap true maxlines background container alignment alignment topcenter child column mainaxisalignment mainaxisalignment spaceevenly children row children text formatmoney periodbalance abs style textstyle color config topbartextcolor fontsize fontweight fontweight bold icon fontawesomeicons lirasign color textcolor size text alacak style textstyle color config topbartextcolor fontsize mainaxisalignment mainaxisalignment center container width height sliverpersistentheader pinned true delegate sliverappbardelegate tabbar tabs tab child text borçlarım tab child text ödemelerim body tabbarview children container child listview builder scrolldirection axis vertical shrinkwrap true itemcount debits length itemextent itembuilder context index return debitcard debits container child listview builder scrolldirection axis vertical shrinkwrap true itemcount receipts length itemextent itembuilder context index return receiptcard receipts initial state of the screen if i scroll shown as below scrolling down automatically shown as below when i scroll which i don t want to be i want when user switch to scroll should start in other words why scrolling automatically when i scroll on flutter doctor v flutter channel beta on linux locale en us utf • flutter version at opt flutter sdk flutter • framework revision weeks ago • engine revision • dart version build dev android toolchain develop for android devices android sdk version • android sdk at opt android sdk • android ndk location not configured optional useful for native profiling support • platform android build tools • android home opt android sdk • java binary at opt android studio jre bin java • java version openjdk runtime environment build release • all android licenses accepted android studio version • android studio at opt android studio • flutter plugin version • dart plugin version • java version openjdk runtime environment build release intellij idea ultimate edition version • intellij at home mesuutt tmp tools idea iu ✗ flutter plugin not installed this adds flutter specific functionality ✗ dart plugin not installed this adds dart specific functionality | 0 |
35,572 | 31,841,155,404 | IssuesEvent | 2023-09-14 16:24:19 | dotnet/dotnet-docker | https://api.github.com/repos/dotnet/dotnet-docker | opened | Make VerifyComplexAppSample Test a [Theory] | bug area-infrastructure |
Looking at the VerifyComplexAppSample test, there are two concerns:
1. The `complexapp` sample Dockerfile uses the multi-platform tags and therefore won't build on Windows in .NET 8 due to https://github.com/dotnet/dotnet-docker/issues/4492:
https://github.com/dotnet/dotnet-docker/blob/c09ce8b720090c91933e4bd380bd1baa3c89f3d3/samples/complexapp/Dockerfile#L1-L3
2. The test is a `[Fact]`, and therefore runs once per leg but uses only one base image, the multi-platform image, which is Debian. The Dockerfile should be amended to support multiple different images and the test should be amended to test across supported operating systems like the other sample tests.
https://github.com/dotnet/dotnet-docker/blob/c09ce8b720090c91933e4bd380bd1baa3c89f3d3/tests/Microsoft.DotNet.Docker.Tests/SampleImageTests.cs#L92-L93 | 1.0 | Make VerifyComplexAppSample Test a [Theory] -
Looking at the VerifyComplexAppSample test, there are two concerns:
1. The `complexapp` sample Dockerfile uses the multi-platform tags and therefore won't build on Windows in .NET 8 due to https://github.com/dotnet/dotnet-docker/issues/4492:
https://github.com/dotnet/dotnet-docker/blob/c09ce8b720090c91933e4bd380bd1baa3c89f3d3/samples/complexapp/Dockerfile#L1-L3
2. The test is a `[Fact]`, and therefore runs once per leg but uses only one base image, the multi-platform image, which is Debian. The Dockerfile should be amended to support multiple different images and the test should be amended to test across supported operating systems like the other sample tests.
https://github.com/dotnet/dotnet-docker/blob/c09ce8b720090c91933e4bd380bd1baa3c89f3d3/tests/Microsoft.DotNet.Docker.Tests/SampleImageTests.cs#L92-L93 | non_priority | make verifycomplexappsample test a looking at the verifycomplexappsample test there are two concerns the complexapp sample dockerfile uses the multi platform tags and therefore won t build on windows in net due to the test is a and therefore runs once per leg but uses only one base image the multi platform image which is debian the dockerfile should be amended to support multiple different images and the test should be amended to test across supported operating systems like the other sample tests | 0 |
266,234 | 28,310,123,129 | IssuesEvent | 2023-04-10 14:41:53 | RG4421/openedr | https://api.github.com/repos/RG4421/openedr | closed | CVE-2020-11023 (Medium) detected in multiple libraries - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.1.min.js</b>, <b>jquery-1.11.1.min.js</b>, <b>jquery-3.1.0.min.js</b>, <b>jquery-3.1.0.js</b></p></summary>
<p>
<details><summary><b>jquery-2.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.1/jquery.min.js</a></p>
<p>Path to dependency file: /edrav2/eprj/jsonrpccpp/src/examples/index.html</p>
<p>Path to vulnerable library: /edrav2/eprj/jsonrpccpp/src/examples/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to dependency file: /edrav2/eprj/boost/libs/hana/benchmark/chart.html</p>
<p>Path to vulnerable library: /edrav2/eprj/boost/libs/hana/benchmark/chart.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.1.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.min.js</a></p>
<p>Path to dependency file: /edrav2/eprj/boost/libs/hof/doc/html/include/boost/hof/partial.html</p>
<p>Path to vulnerable library: /edrav2/eprj/boost/libs/hof/doc/html/_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/include/boost/hof/../../../_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/reference/../_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/doc/../_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/doc/src/../../_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/tutorial/../_static/jquery.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.0.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.1.0.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.js</a></p>
<p>Path to vulnerable library: /edrav2/eprj/boost/libs/hof/doc/html/_static/jquery-3.1.0.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/_static/jquery-3.1.0.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.0.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/RG4421/openedr/commit/f991dbd97bf34917a1d61c43ef4b41832708779c">f991dbd97bf34917a1d61c43ef4b41832708779c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
| True | CVE-2020-11023 (Medium) detected in multiple libraries - autoclosed - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.1.min.js</b>, <b>jquery-1.11.1.min.js</b>, <b>jquery-3.1.0.min.js</b>, <b>jquery-3.1.0.js</b></p></summary>
<p>
<details><summary><b>jquery-2.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.1/jquery.min.js</a></p>
<p>Path to dependency file: /edrav2/eprj/jsonrpccpp/src/examples/index.html</p>
<p>Path to vulnerable library: /edrav2/eprj/jsonrpccpp/src/examples/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to dependency file: /edrav2/eprj/boost/libs/hana/benchmark/chart.html</p>
<p>Path to vulnerable library: /edrav2/eprj/boost/libs/hana/benchmark/chart.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.1.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.min.js</a></p>
<p>Path to dependency file: /edrav2/eprj/boost/libs/hof/doc/html/include/boost/hof/partial.html</p>
<p>Path to vulnerable library: /edrav2/eprj/boost/libs/hof/doc/html/_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/include/boost/hof/../../../_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/reference/../_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/doc/../_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/_static/jquery.js,/edrav2/eprj/boost/libs/hof/doc/html/doc/src/../../_static/jquery.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/tutorial/../_static/jquery.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.0.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.1.0.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.0/jquery.js</a></p>
<p>Path to vulnerable library: /edrav2/eprj/boost/libs/hof/doc/html/_static/jquery-3.1.0.js,/edrav2/eprj/boost/libs/python/doc/html/numpy/_static/jquery-3.1.0.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.0.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/RG4421/openedr/commit/f991dbd97bf34917a1d61c43ef4b41832708779c">f991dbd97bf34917a1d61c43ef4b41832708779c</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in multiple libraries autoclosed cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js jquery js jquery min js javascript library for dom operations library home page a href path to dependency file eprj jsonrpccpp src examples index html path to vulnerable library eprj jsonrpccpp src examples index html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file eprj boost libs hana benchmark chart html path to vulnerable library eprj boost libs hana benchmark chart html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file eprj boost libs hof doc html include boost hof partial html path to vulnerable library eprj boost libs hof doc html static jquery js eprj boost libs hof doc html include boost hof static jquery js eprj boost libs python doc html numpy reference static jquery js eprj boost libs python doc html numpy static jquery js eprj boost libs python doc html numpy static jquery js eprj boost libs hof doc html doc static jquery js eprj boost libs hof doc html static jquery js eprj boost libs hof doc html doc src static jquery js eprj boost libs python doc html numpy tutorial static jquery js dependency hierarchy x jquery min js vulnerable library jquery js javascript library for dom operations library home page a href path to vulnerable library eprj boost libs hof doc html static jquery js eprj boost libs python doc html numpy static jquery js dependency hierarchy x jquery js vulnerable library found in head commit a href found in base branch main vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery jquery rails | 0 |
53,499 | 6,332,507,967 | IssuesEvent | 2017-07-26 12:50:55 | LeverylTeam/Leveryl | https://api.github.com/repos/LeverylTeam/Leveryl | closed | invetory get cleared when join | STATUS: Untested | <!--
RULES:
- Make sure that you are using the latest supported version before opening an issue.
- Test it on a clean test server, WITHOUT PLUGINS, to see if the issue still occurs. If not then it may be a plugin issue. Please also indicate the result of such tests.
- Search the issue tracker to check if anyone has already reported it, to avoid needlessly creating duplicate issues. Make sure you also check closed issues, as an issue you think is valid may already have been resolved.
- If your issue is related to a plugin, do not report here, contact the plugin's original author instead.
- Support requests are not bugs. Issues such as "How do I do this" are not bugs and will be closed. If you need help, please see here and do not misuse our issue tracker.
- No generic titles such as "Question", "Help", "Crash Report" etc. A good issue report provides a quick summary in the title. If you just got a crash report but you don't understand it, please look for a line starting with Message. It summarizes the bug.
- Information must be provided in the issue body, not in the title. No tags like [BUG] are allowed in the title, including [SOLVED] for solved issues.
- To express appreciation, objection, confusion or other supported reactions on pull requests, issues or comments on them, use GitHub reactions rather than posting an individual comment with an emoji only. This helps keeping the issue/pull request conversation clean and readable.
The Drill: https://github.com/LeverylTeam/Leveryl/blob/master/assets/joke.jpg
-->
### Issue description
Write a short description about the issue
### Steps to reproduce the issue
1. ...title says everything
2. ...not a plugin reason
3. ...
### OS and versions
* Leveryl Version: Leveryl 1.0.0 「EXPERIMENTAL」 implementing API version 3.0.0-ALPHA5 for Minecraft: PE v1.1.0.55 (protocol version 113)
* PHP Version: 7.0.3
* Server OS: linux
* Game version: PE / Win10
* Game OS:
### Plugins
Test on a clean server without plugins: is the issue reproducible without any plugins loaded?
If the issue is NOT reproducible without plugins, It's probably a Plugin Issue. Please ask the author of the plugin.
### Crashdump, backtrace or other files
Please add a CrashDump to help us resolve the issue. :)
| 1.0 | invetory get cleared when join - <!--
RULES:
- Make sure that you are using the latest supported version before opening an issue.
- Test it on a clean test server, WITHOUT PLUGINS, to see if the issue still occurs. If not then it may be a plugin issue. Please also indicate the result of such tests.
- Search the issue tracker to check if anyone has already reported it, to avoid needlessly creating duplicate issues. Make sure you also check closed issues, as an issue you think is valid may already have been resolved.
- If your issue is related to a plugin, do not report here, contact the plugin's original author instead.
- Support requests are not bugs. Issues such as "How do I do this" are not bugs and will be closed. If you need help, please see here and do not misuse our issue tracker.
- No generic titles such as "Question", "Help", "Crash Report" etc. A good issue report provides a quick summary in the title. If you just got a crash report but you don't understand it, please look for a line starting with Message. It summarizes the bug.
- Information must be provided in the issue body, not in the title. No tags like [BUG] are allowed in the title, including [SOLVED] for solved issues.
- To express appreciation, objection, confusion or other supported reactions on pull requests, issues or comments on them, use GitHub reactions rather than posting an individual comment with an emoji only. This helps keeping the issue/pull request conversation clean and readable.
The Drill: https://github.com/LeverylTeam/Leveryl/blob/master/assets/joke.jpg
-->
### Issue description
Write a short description about the issue
### Steps to reproduce the issue
1. ...title says everything
2. ...not a plugin reason
3. ...
### OS and versions
* Leveryl Version: Leveryl 1.0.0 「EXPERIMENTAL」 implementing API version 3.0.0-ALPHA5 for Minecraft: PE v1.1.0.55 (protocol version 113)
* PHP Version: 7.0.3
* Server OS: linux
* Game version: PE / Win10
* Game OS:
### Plugins
Test on a clean server without plugins: is the issue reproducible without any plugins loaded?
If the issue is NOT reproducible without plugins, It's probably a Plugin Issue. Please ask the author of the plugin.
### Crashdump, backtrace or other files
Please add a CrashDump to help us resolve the issue. :)
| non_priority | invetory get cleared when join rules make sure that you are using the latest supported version before opening an issue test it on a clean test server without plugins to see if the issue still occurs if not then it may be a plugin issue please also indicate the result of such tests search the issue tracker to check if anyone has already reported it to avoid needlessly creating duplicate issues make sure you also check closed issues as an issue you think is valid may already have been resolved if your issue is related to a plugin do not report here contact the plugin s original author instead support requests are not bugs issues such as how do i do this are not bugs and will be closed if you need help please see here and do not misuse our issue tracker no generic titles such as question help crash report etc a good issue report provides a quick summary in the title if you just got a crash report but you don t understand it please look for a line starting with message it summarizes the bug information must be provided in the issue body not in the title no tags like are allowed in the title including for solved issues to express appreciation objection confusion or other supported reactions on pull requests issues or comments on them use github reactions rather than posting an individual comment with an emoji only this helps keeping the issue pull request conversation clean and readable the drill issue description write a short description about the issue steps to reproduce the issue title says everything not a plugin reason os and versions leveryl version leveryl 「experimental」 implementing api version for minecraft pe protocol version php version server os linux game version pe game os plugins test on a clean server without plugins is the issue reproducible without any plugins loaded if the issue is not reproducible without plugins it s probably a plugin issue please ask the author of the plugin crashdump backtrace or other files please add a crashdump to help us resolve the issue | 0 |
320,079 | 23,801,004,108 | IssuesEvent | 2022-09-03 09:32:59 | CA-G12/reddit-clone | https://api.github.com/repos/CA-G12/reddit-clone | opened | User journey. | documentation to-do | # User Stories:
* User can sign up and login.
* User can view their own profiles as well as any other person's profiles.
* User don't need to be logged in to view the website, however you need to be logged in to post, comment, up-vote...etc.
* User should see all posts on the home page, ranked in descending order by votes.
* User should be able to click on a "Create Post" button and see a modal to create a new Post.
* User should be able delete their own posts.
* User should be able to create a comment on a Post. | 1.0 | User journey. - # User Stories:
* User can sign up and login.
* User can view their own profiles as well as any other person's profiles.
* User don't need to be logged in to view the website, however you need to be logged in to post, comment, up-vote...etc.
* User should see all posts on the home page, ranked in descending order by votes.
* User should be able to click on a "Create Post" button and see a modal to create a new Post.
* User should be able delete their own posts.
* User should be able to create a comment on a Post. | non_priority | user journey user stories user can sign up and login user can view their own profiles as well as any other person s profiles user don t need to be logged in to view the website however you need to be logged in to post comment up vote etc user should see all posts on the home page ranked in descending order by votes user should be able to click on a create post button and see a modal to create a new post user should be able delete their own posts user should be able to create a comment on a post | 0 |
105,092 | 13,161,995,272 | IssuesEvent | 2020-08-10 20:40:01 | IFRCGo/go-frontend | https://api.github.com/repos/IFRCGo/go-frontend | closed | Key Numbers - styling across the platform | UI - Design | UI styling for the top key numbers across the platform. The UI proposal should be upon acceptance be implemented by the front-end team. | 1.0 | Key Numbers - styling across the platform - UI styling for the top key numbers across the platform. The UI proposal should be upon acceptance be implemented by the front-end team. | non_priority | key numbers styling across the platform ui styling for the top key numbers across the platform the ui proposal should be upon acceptance be implemented by the front end team | 0 |
58,147 | 11,843,782,997 | IssuesEvent | 2020-03-24 03:30:08 | MicrosoftDocs/live-share | https://api.github.com/repos/MicrosoftDocs/live-share | closed | Live Share invokes executeCodeLensProvider over and over | area: language services bug feature-request vscode | - Latest Insiders, on Windows 10, Live Share 0.3.954
- Open empty window, or any folder
- "Set Log Level" > Trace
- Open "Log (Extension Host)"
- See that Live Share is apparently calling `vscode.executeCodeLensProvider` for no reason
```
[2018-11-14 11:37:01.204] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:01.204] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:01.206] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:01.206] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:01.207] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 4ms
[2018-11-14 11:37:02.523] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:02.523] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:02.523] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:02.526] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:02.526] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:02.526] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:03.193] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:03.193] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:03.193] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:03.195] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:03.195] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:03.197] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 4ms
[2018-11-14 11:37:04.241] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:04.241] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:04.241] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:04.243] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:04.243] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:04.244] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 4ms
[2018-11-14 11:37:05.447] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
```
Only a couple other extensions activated in an empty window, let me know how I can help debug. | 1.0 | Live Share invokes executeCodeLensProvider over and over - - Latest Insiders, on Windows 10, Live Share 0.3.954
- Open empty window, or any folder
- "Set Log Level" > Trace
- Open "Log (Extension Host)"
- See that Live Share is apparently calling `vscode.executeCodeLensProvider` for no reason
```
[2018-11-14 11:37:01.204] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:01.204] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:01.206] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:01.206] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:01.207] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 4ms
[2018-11-14 11:37:02.523] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:02.523] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:02.523] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:02.526] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:02.526] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:02.526] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:03.193] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:03.193] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:03.193] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:03.195] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:03.195] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:03.197] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 4ms
[2018-11-14 11:37:04.241] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:04.241] [exthost] [trace] ExtHostCommands#executeCommand vscode.executeCodeLensProvider
[2018-11-14 11:37:04.241] [exthost] [trace] ExtHostCommands#executeCommand _executeCodeLensProvider
[2018-11-14 11:37:04.243] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
[2018-11-14 11:37:04.243] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 0ms
[2018-11-14 11:37:04.244] [exthost] [trace] [ms-vsliveshare.vsliveshare] provider DONE after 4ms
[2018-11-14 11:37:05.447] [exthost] [trace] [ms-vsliveshare.vsliveshare] INVOKE provider 'e'
```
Only a couple other extensions activated in an empty window, let me know how I can help debug. | non_priority | live share invokes executecodelensprovider over and over latest insiders on windows live share open empty window or any folder set log level trace open log extension host see that live share is apparently calling vscode executecodelensprovider for no reason exthostcommands executecommand vscode executecodelensprovider exthostcommands executecommand executecodelensprovider invoke provider e provider done after provider done after invoke provider e exthostcommands executecommand vscode executecodelensprovider exthostcommands executecommand executecodelensprovider invoke provider e provider done after provider done after invoke provider e exthostcommands executecommand vscode executecodelensprovider exthostcommands executecommand executecodelensprovider invoke provider e provider done after provider done after invoke provider e exthostcommands executecommand vscode executecodelensprovider exthostcommands executecommand executecodelensprovider invoke provider e provider done after provider done after invoke provider e only a couple other extensions activated in an empty window let me know how i can help debug | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.