Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
94,676 | 11,902,218,995 | IssuesEvent | 2020-03-30 13:40:07 | microsoft/ChakraCore | https://api.github.com/repos/microsoft/ChakraCore | closed | Wrong realization of 'minus operation' [maybe] of Date object | By Design | I run the following code in Characore-1.11.15 and get a very odd output. I do not know why the output is so strange. The two print should be same output, both 0. However, the first is -5 in ch. I think there must be something wrong in ch's realization.
The code:
```
var tmp = new Date() - new((2, function() { return Date })());
print(tmp);
var tmp1 = new Date() - new(Date);
print(tmp1);
print("BT_FLAG");
```
Output
```
-5
0
BT_FLAG
```
The result should be:
```
0
0
BT_FLAG
```
ISec Lab
2019.12.21 | 1.0 | Wrong realization of 'minus operation' [maybe] of Date object - I run the following code in Characore-1.11.15 and get a very odd output. I do not know why the output is so strange. The two print should be same output, both 0. However, the first is -5 in ch. I think there must be something wrong in ch's realization.
The code:
```
var tmp = new Date() - new((2, function() { return Date })());
print(tmp);
var tmp1 = new Date() - new(Date);
print(tmp1);
print("BT_FLAG");
```
Output
```
-5
0
BT_FLAG
```
The result should be:
```
0
0
BT_FLAG
```
ISec Lab
2019.12.21 | non_priority | wrong realization of minus operation of date object i run the following code in characore and get a very odd output i do not know why the output is so strange the two print should be same output both however the first is in ch i think there must be something wrong in ch s realization the code var tmp new date new function return date print tmp var new date new date print print bt flag output bt flag the result should be bt flag isec lab | 0 |
1,634 | 3,296,163,627 | IssuesEvent | 2015-11-01 16:38:20 | eslint/eslint | https://api.github.com/repos/eslint/eslint | closed | Add node 5 to build | accepted enhancement infrastructure | Add node 5.x version to travis build.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/27873308-add-node-5-to-build?utm_campaign=plugin&utm_content=tracker%2F282608&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F282608&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | Add node 5 to build - Add node 5.x version to travis build.
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/27873308-add-node-5-to-build?utm_campaign=plugin&utm_content=tracker%2F282608&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F282608&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_priority | add node to build add node x version to travis build want to back this issue we accept bounties via | 0 |
184,032 | 14,267,842,939 | IssuesEvent | 2020-11-20 21:15:24 | chamilo/chamilo-lms | https://api.github.com/repos/chamilo/chamilo-lms | closed | Datos de usuario que se muestran sin haberse autenticado en la plataforma | Bug Enhancement Requires testing/validation | **Describe el problema**
Si se accede a la página https://11.chamilo.org/main/inc/ajax/user_manager.ajax.php?a=get_user_popup&course_id=125&user_id=20
Directamente, mediante la URL, se muestra la fotografía del usuario, y en caso de ser profesor en la versión 1.11.10 se muestra también su nombre, sin necesidad de loguearse en la plataforma, y hasta puede ser indexado por buscadores.
**Cómo reproducir**
Ejemplos:
https://11.chamilo.org/main/inc/ajax/user_manager.ajax.php?a=get_user_popup&course_id=125&user_id=20
https://11.chamilo.org/main/inc/ajax/user_manager.ajax.php?a=get_user_popup&course_id=105&user_id=230
**Comportamiento esperado**
Esta información no debería ser accesible sin estar registrado.
**Servidor
- Versión de Chamilo: 1.11.10 y 1.11.12
| 1.0 | Datos de usuario que se muestran sin haberse autenticado en la plataforma - **Describe el problema**
Si se accede a la página https://11.chamilo.org/main/inc/ajax/user_manager.ajax.php?a=get_user_popup&course_id=125&user_id=20
Directamente, mediante la URL, se muestra la fotografía del usuario, y en caso de ser profesor en la versión 1.11.10 se muestra también su nombre, sin necesidad de loguearse en la plataforma, y hasta puede ser indexado por buscadores.
**Cómo reproducir**
Ejemplos:
https://11.chamilo.org/main/inc/ajax/user_manager.ajax.php?a=get_user_popup&course_id=125&user_id=20
https://11.chamilo.org/main/inc/ajax/user_manager.ajax.php?a=get_user_popup&course_id=105&user_id=230
**Comportamiento esperado**
Esta información no debería ser accesible sin estar registrado.
**Servidor
- Versión de Chamilo: 1.11.10 y 1.11.12
| non_priority | datos de usuario que se muestran sin haberse autenticado en la plataforma describe el problema si se accede a la página directamente mediante la url se muestra la fotografía del usuario y en caso de ser profesor en la versión se muestra también su nombre sin necesidad de loguearse en la plataforma y hasta puede ser indexado por buscadores cómo reproducir ejemplos comportamiento esperado esta información no debería ser accesible sin estar registrado servidor versión de chamilo y | 0 |
96,410 | 10,932,573,865 | IssuesEvent | 2019-11-23 18:42:57 | fga-eps-mds/2019.2-Acacia | https://api.github.com/repos/fga-eps-mds/2019.2-Acacia | closed | Documentação da Sprint 11 | documentation scrum master | **Descrição**
Eu, como scrum master, gostaria de documentar a sprint 9 para acompanhar o projeto e a equipe.
**Critérios de Aceitação**
- Deverá ter o planejamento, retrospectiva e revisão e análise do scrum master;
- Deverá apresentar dados dos indicadores e métricas da equipe(quadro de conhecimentos, burndown, burndown de riscos);
**Tarefas**
- [x] Documentar planejamento;
- [x] Documentar revisão;
- [x] Documentar métricas;
- [x] Documentar retrospectiva;
- [x] Documentar análise do scrum master | 1.0 | Documentação da Sprint 11 - **Descrição**
Eu, como scrum master, gostaria de documentar a sprint 9 para acompanhar o projeto e a equipe.
**Critérios de Aceitação**
- Deverá ter o planejamento, retrospectiva e revisão e análise do scrum master;
- Deverá apresentar dados dos indicadores e métricas da equipe(quadro de conhecimentos, burndown, burndown de riscos);
**Tarefas**
- [x] Documentar planejamento;
- [x] Documentar revisão;
- [x] Documentar métricas;
- [x] Documentar retrospectiva;
- [x] Documentar análise do scrum master | non_priority | documentação da sprint descrição eu como scrum master gostaria de documentar a sprint para acompanhar o projeto e a equipe critérios de aceitação deverá ter o planejamento retrospectiva e revisão e análise do scrum master deverá apresentar dados dos indicadores e métricas da equipe quadro de conhecimentos burndown burndown de riscos tarefas documentar planejamento documentar revisão documentar métricas documentar retrospectiva documentar análise do scrum master | 0 |
1,652 | 2,613,398,073 | IssuesEvent | 2015-02-27 20:43:24 | Datafable/gbif-dataset-metrics | https://api.github.com/repos/Datafable/gbif-dataset-metrics | closed | Document multimedia categories | documentation | At: https://github.com/peterdesmet/gbif-challenge/blob/master/documentation/media_type.md
* [ ] Title
* [ ] Description
* [ ] Rationale
* [ ] Services used
* [ ] Suggestions for further development
* [ ] Suggestions for GBIF | 1.0 | Document multimedia categories - At: https://github.com/peterdesmet/gbif-challenge/blob/master/documentation/media_type.md
* [ ] Title
* [ ] Description
* [ ] Rationale
* [ ] Services used
* [ ] Suggestions for further development
* [ ] Suggestions for GBIF | non_priority | document multimedia categories at title description rationale services used suggestions for further development suggestions for gbif | 0 |
9,687 | 25,040,660,704 | IssuesEvent | 2022-11-04 20:22:09 | Azure/azure-sdk | https://api.github.com/repos/Azure/azure-sdk | opened | Board Review: package name for HybridContainerService management plane SDK | architecture board-review | Thank you for starting the process for approval of the client library for your Azure service. Thorough review of your client library ensures that your APIs are consistent with the guidelines and the consumers of your client library have a consistently good experience when using Azure.
**The Architecture Board reviews [Track 2 libraries](https://azure.github.io/azure-sdk/general_introduction.html) only.** If your library does not meet this requirement, please reach out to [Architecture Board](adparch@microsoft.com) before creating the issue.
Please reference our [review process guidelines](https://azure.github.io/azure-sdk/policies_reviewprocess.html) to understand what is being asked for in the issue template.
**Before submitting, ensure you adjust the title of the issue appropriately.**
**Note that the required material must be included before a meeting can be scheduled.**
## Contacts and Timeline
* Service team responsible for the client library: MSK8s
* Main contacts: hav, jocelynb
* Expected stable release date for this library: 11/9/2022
## About the Service
* Link to documentation introducing/describing the service: https://learn.microsoft.com/en-us/azure/aks/hybrid/aks-hybrid-preview-overview
* Link to the service REST APIs: https://github.com/Azure/azure-rest-api-specs/tree/main/specification/hybridaks/resource-manager/Microsoft.HybridContainerService/preview/2022-05-01-preview
* Is the goal to release a Public Preview, Private Preview, or GA?
Public Preview
## About the client library
* Name of client library:
* .Net: `Azure.ResourceManager.HybridContainerService`
* Java: `com.azure.resourcemanager.hybridcontainerservice`
* Python: `azure.mgmt.hybridcontainerservice`
* Go: `sdk/resourcemanager/hybridcontainerservice/armhybridcontainerservice`
* JS: `@azure/arm-hybridcontainerservice` | 1.0 | Board Review: package name for HybridContainerService management plane SDK - Thank you for starting the process for approval of the client library for your Azure service. Thorough review of your client library ensures that your APIs are consistent with the guidelines and the consumers of your client library have a consistently good experience when using Azure.
**The Architecture Board reviews [Track 2 libraries](https://azure.github.io/azure-sdk/general_introduction.html) only.** If your library does not meet this requirement, please reach out to [Architecture Board](adparch@microsoft.com) before creating the issue.
Please reference our [review process guidelines](https://azure.github.io/azure-sdk/policies_reviewprocess.html) to understand what is being asked for in the issue template.
**Before submitting, ensure you adjust the title of the issue appropriately.**
**Note that the required material must be included before a meeting can be scheduled.**
## Contacts and Timeline
* Service team responsible for the client library: MSK8s
* Main contacts: hav, jocelynb
* Expected stable release date for this library: 11/9/2022
## About the Service
* Link to documentation introducing/describing the service: https://learn.microsoft.com/en-us/azure/aks/hybrid/aks-hybrid-preview-overview
* Link to the service REST APIs: https://github.com/Azure/azure-rest-api-specs/tree/main/specification/hybridaks/resource-manager/Microsoft.HybridContainerService/preview/2022-05-01-preview
* Is the goal to release a Public Preview, Private Preview, or GA?
Public Preview
## About the client library
* Name of client library:
* .Net: `Azure.ResourceManager.HybridContainerService`
* Java: `com.azure.resourcemanager.hybridcontainerservice`
* Python: `azure.mgmt.hybridcontainerservice`
* Go: `sdk/resourcemanager/hybridcontainerservice/armhybridcontainerservice`
* JS: `@azure/arm-hybridcontainerservice` | non_priority | board review package name for hybridcontainerservice management plane sdk thank you for starting the process for approval of the client library for your azure service thorough review of your client library ensures that your apis are consistent with the guidelines and the consumers of your client library have a consistently good experience when using azure the architecture board reviews only if your library does not meet this requirement please reach out to adparch microsoft com before creating the issue please reference our to understand what is being asked for in the issue template before submitting ensure you adjust the title of the issue appropriately note that the required material must be included before a meeting can be scheduled contacts and timeline service team responsible for the client library main contacts hav jocelynb expected stable release date for this library about the service link to documentation introducing describing the service link to the service rest apis is the goal to release a public preview private preview or ga public preview about the client library name of client library net azure resourcemanager hybridcontainerservice java com azure resourcemanager hybridcontainerservice python azure mgmt hybridcontainerservice go sdk resourcemanager hybridcontainerservice armhybridcontainerservice js azure arm hybridcontainerservice | 0 |
178,820 | 14,680,579,360 | IssuesEvent | 2020-12-31 10:30:34 | lisphilar/covid19-sir | https://api.github.com/repos/lisphilar/covid19-sir | closed | [New] Relationship of OxCGRT index and parameter values (short-term prediction) | brainstorming documentation enhancement | ## What we need to document?
I am referring to https://lisphilar.github.io/covid19-sir/usage_policy.html, in specific to the `(Experimental): Relationship of OxCGRT index and parameter values` section.
What all these results actually mean? Could you provide a more detailed documentation and analysis, about the OxCGRT index usage and how it affects the parameter values for each country, with examples and practical explanations?
- For example, what does that correlation table mean practically, how are these results interpreted and what's the results significance/impact on the general countries analyses?
- The scatter plot at the bottom for every country, depicting the relationship between the Reproductive number (Rt) and the OxCGRT stringency index, what does it mean practically? Does it mean that for example for higher index values, the Rt is lower?
The results have to be reworked/scaled, in order to display properly all the points around 0-100 zone and to ignore the high outliers.
- More detailed examples (preferably in notebook .ipynb format) should be provided about how the OxCGRT index and the policy measures affect specific countries (i.e. Japan, USA, India, Greece, Italy, Spain) and how such results are interpreted for each country.
- Why is this feature "Experimental"? Does it not fully work? Is there an open issue for that and active development being done? | 1.0 | [New] Relationship of OxCGRT index and parameter values (short-term prediction) - ## What we need to document?
I am referring to https://lisphilar.github.io/covid19-sir/usage_policy.html, in specific to the `(Experimental): Relationship of OxCGRT index and parameter values` section.
What all these results actually mean? Could you provide a more detailed documentation and analysis, about the OxCGRT index usage and how it affects the parameter values for each country, with examples and practical explanations?
- For example, what does that correlation table mean practically, how are these results interpreted and what's the results significance/impact on the general countries analyses?
- The scatter plot at the bottom for every country, depicting the relationship between the Reproductive number (Rt) and the OxCGRT stringency index, what does it mean practically? Does it mean that for example for higher index values, the Rt is lower?
The results have to be reworked/scaled, in order to display properly all the points around 0-100 zone and to ignore the high outliers.
- More detailed examples (preferably in notebook .ipynb format) should be provided about how the OxCGRT index and the policy measures affect specific countries (i.e. Japan, USA, India, Greece, Italy, Spain) and how such results are interpreted for each country.
- Why is this feature "Experimental"? Does it not fully work? Is there an open issue for that and active development being done? | non_priority | relationship of oxcgrt index and parameter values short term prediction what we need to document i am referring to in specific to the experimental relationship of oxcgrt index and parameter values section what all these results actually mean could you provide a more detailed documentation and analysis about the oxcgrt index usage and how it affects the parameter values for each country with examples and practical explanations for example what does that correlation table mean practically how are these results interpreted and what s the results significance impact on the general countries analyses the scatter plot at the bottom for every country depicting the relationship between the reproductive number rt and the oxcgrt stringency index what does it mean practically does it mean that for example for higher index values the rt is lower the results have to be reworked scaled in order to display properly all the points around zone and to ignore the high outliers more detailed examples preferably in notebook ipynb format should be provided about how the oxcgrt index and the policy measures affect specific countries i e japan usa india greece italy spain and how such results are interpreted for each country why is this feature experimental does it not fully work is there an open issue for that and active development being done | 0 |
26,426 | 5,253,289,873 | IssuesEvent | 2017-02-02 09:06:11 | nest/nest-simulator | https://api.github.com/repos/nest/nest-simulator | closed | Some examples do not run (properly) | C: Documentation I: No breaking change P: In progess S: Critical T: Bug | The following examples currently do not work:
```
/Users/plesser/NEST/code/src/examples/nest/ArtificialSynchrony.sli
/Users/plesser/NEST/code/src/examples/nest/balancedneuron-2.sli
/Users/plesser/NEST/code/src/examples/nest/hpc_benchmark.sli
```
I am working on a PR. The failure of the `ArtificialSynchrony` test is related to #643. The other two failures are related to the change from `iaf_neuron` to `iaf_psc_alpha`. Furthermore, response behavior off `hpc_benchmark.sli` seems off (very high firing rates, esp towards end). | 1.0 | Some examples do not run (properly) - The following examples currently do not work:
```
/Users/plesser/NEST/code/src/examples/nest/ArtificialSynchrony.sli
/Users/plesser/NEST/code/src/examples/nest/balancedneuron-2.sli
/Users/plesser/NEST/code/src/examples/nest/hpc_benchmark.sli
```
I am working on a PR. The failure of the `ArtificialSynchrony` test is related to #643. The other two failures are related to the change from `iaf_neuron` to `iaf_psc_alpha`. Furthermore, response behavior off `hpc_benchmark.sli` seems off (very high firing rates, esp towards end). | non_priority | some examples do not run properly the following examples currently do not work users plesser nest code src examples nest artificialsynchrony sli users plesser nest code src examples nest balancedneuron sli users plesser nest code src examples nest hpc benchmark sli i am working on a pr the failure of the artificialsynchrony test is related to the other two failures are related to the change from iaf neuron to iaf psc alpha furthermore response behavior off hpc benchmark sli seems off very high firing rates esp towards end | 0 |
316,907 | 23,654,260,067 | IssuesEvent | 2022-08-26 09:39:43 | paulithu/Website_2.0. | https://api.github.com/repos/paulithu/Website_2.0. | closed | Abschlusspräsentation | documentation | Die Finale Präsentation für den Vorstellung Termin erstellen.
Aufteilen der Folien/ Texte
Üben der Folien und Texte | 1.0 | Abschlusspräsentation - Die Finale Präsentation für den Vorstellung Termin erstellen.
Aufteilen der Folien/ Texte
Üben der Folien und Texte | non_priority | abschlusspräsentation die finale präsentation für den vorstellung termin erstellen aufteilen der folien texte üben der folien und texte | 0 |
175,883 | 14,543,991,062 | IssuesEvent | 2020-12-15 17:34:20 | atlp-rwanda/incredible-phantom-backend | https://api.github.com/repos/atlp-rwanda/incredible-phantom-backend | closed | Update production URL | documentation | ### Description
Update your production url in README. Also, language settings don't seem to work properly so, I want to think one of the open pull requests will fix the issue. | 1.0 | Update production URL - ### Description
Update your production url in README. Also, language settings don't seem to work properly so, I want to think one of the open pull requests will fix the issue. | non_priority | update production url description update your production url in readme also language settings don t seem to work properly so i want to think one of the open pull requests will fix the issue | 0 |
262,818 | 19,842,931,939 | IssuesEvent | 2022-01-21 00:39:13 | microsoft/Guan | https://api.github.com/repos/microsoft/Guan | closed | Work Item: Add Getting Started documentation | documentation | Add a Getting Started document that explains, in simple terms with examples, how to use Guan. | 1.0 | Work Item: Add Getting Started documentation - Add a Getting Started document that explains, in simple terms with examples, how to use Guan. | non_priority | work item add getting started documentation add a getting started document that explains in simple terms with examples how to use guan | 0 |
138,144 | 20,361,517,220 | IssuesEvent | 2022-02-20 19:00:06 | kaff-oregonstate/oregon-state-evacuation-app | https://api.github.com/repos/kaff-oregonstate/oregon-state-evacuation-app | opened | Implement timer in DuringDrill widget | enhancement design | - [ ] in Widget (not State), initialize a DateTime with DateTime.now() to save start time
- [ ] in State, write a function which gets difference (final - initial) between: (initial) new DateTime.now(), and (final) previously saved value
- [ ] have output of function be type that timer display widget can use as input (minutes:seconds format, String?)
- [ ] have timer display widget call function
There may be aspects of this feature I have not foreseen.
This may need to be optimized to not run 60 fps (Flutter default). | 1.0 | Implement timer in DuringDrill widget - - [ ] in Widget (not State), initialize a DateTime with DateTime.now() to save start time
- [ ] in State, write a function which gets difference (final - initial) between: (initial) new DateTime.now(), and (final) previously saved value
- [ ] have output of function be type that timer display widget can use as input (minutes:seconds format, String?)
- [ ] have timer display widget call function
There may be aspects of this feature I have not foreseen.
This may need to be optimized to not run 60 fps (Flutter default). | non_priority | implement timer in duringdrill widget in widget not state initialize a datetime with datetime now to save start time in state write a function which gets difference final initial between initial new datetime now and final previously saved value have output of function be type that timer display widget can use as input minutes seconds format string have timer display widget call function there may be aspects of this feature i have not foreseen this may need to be optimized to not run fps flutter default | 0 |
134,681 | 30,115,330,714 | IssuesEvent | 2023-06-30 11:00:26 | FerretDB/FerretDB | https://api.github.com/repos/FerretDB/FerretDB | opened | updateMany with filter with no result and upsert true yields errors instead of creating new document | code/bug not ready | ### FerretDB version
FerretDB v1.4.0
### Backend
PostgreSQL 15.3
### Environment
Docker using ghcr.io/ferretdb/ferretdb image
### What did you do?
```
ferretdb> db.restaurant.insertOne({ "_id" : 1, "name" : "Central Perk Cafe", "violations" : 3 });
{ acknowledged: true, insertedId: 1 }
ferretdb> db.restaurant.updateMany({ "violations": { "$gt": 3 } }, { "$set": { "found": true } }, { "upsert": true } );
MongoServerError: invalid key: "$gt" (key must not start with '$' sign)
```
### What did you expect to see?
same statement executed against mongodb:
```
test> db.restaurant.insertOne({ "_id" : 1, "name" : "Central Perk Cafe", "violations" : 3 });
{ acknowledged: true, insertedId: 1 }
test> db.restaurant.updateMany({ "violations": { "$gt": 3 } }, { "$set": { "found": true } }, { "upsert": true } );
{
acknowledged: true,
insertedId: ObjectId("649eb3347e069bee52c272fc"),
matchedCount: 0,
modifiedCount: 0,
upsertedCount: 1
}
test> db.restaurant.countDocuments()
2
```
### What did you see instead?
`MongoServerError: invalid key: "$gt" (key must not start with '$' sign)`
```
ferretdb_1 | {
ferretdb_1 | "Checksum": 0,
ferretdb_1 | "FlagBits": 0,
ferretdb_1 | "Sections": [
ferretdb_1 | {
ferretdb_1 | "Document": {
ferretdb_1 | "$k": [
ferretdb_1 | "ok",
ferretdb_1 | "errmsg",
ferretdb_1 | "code",
ferretdb_1 | "codeName"
ferretdb_1 | ],
ferretdb_1 | "ok": {
ferretdb_1 | "$f": 0
ferretdb_1 | },
ferretdb_1 | "errmsg": "invalid key: \"$gt\" (key must not start with '$' sign)",
ferretdb_1 | "code": 2,
ferretdb_1 | "codeName": "BadValue"
ferretdb_1 | },
ferretdb_1 | "Kind": 0
ferretdb_1 | }
ferretdb_1 | ]
ferretdb_1 | }
```
| 1.0 | updateMany with filter with no result and upsert true yields errors instead of creating new document - ### FerretDB version
FerretDB v1.4.0
### Backend
PostgreSQL 15.3
### Environment
Docker using ghcr.io/ferretdb/ferretdb image
### What did you do?
```
ferretdb> db.restaurant.insertOne({ "_id" : 1, "name" : "Central Perk Cafe", "violations" : 3 });
{ acknowledged: true, insertedId: 1 }
ferretdb> db.restaurant.updateMany({ "violations": { "$gt": 3 } }, { "$set": { "found": true } }, { "upsert": true } );
MongoServerError: invalid key: "$gt" (key must not start with '$' sign)
```
### What did you expect to see?
same statement executed against mongodb:
```
test> db.restaurant.insertOne({ "_id" : 1, "name" : "Central Perk Cafe", "violations" : 3 });
{ acknowledged: true, insertedId: 1 }
test> db.restaurant.updateMany({ "violations": { "$gt": 3 } }, { "$set": { "found": true } }, { "upsert": true } );
{
acknowledged: true,
insertedId: ObjectId("649eb3347e069bee52c272fc"),
matchedCount: 0,
modifiedCount: 0,
upsertedCount: 1
}
test> db.restaurant.countDocuments()
2
```
### What did you see instead?
`MongoServerError: invalid key: "$gt" (key must not start with '$' sign)`
```
ferretdb_1 | {
ferretdb_1 | "Checksum": 0,
ferretdb_1 | "FlagBits": 0,
ferretdb_1 | "Sections": [
ferretdb_1 | {
ferretdb_1 | "Document": {
ferretdb_1 | "$k": [
ferretdb_1 | "ok",
ferretdb_1 | "errmsg",
ferretdb_1 | "code",
ferretdb_1 | "codeName"
ferretdb_1 | ],
ferretdb_1 | "ok": {
ferretdb_1 | "$f": 0
ferretdb_1 | },
ferretdb_1 | "errmsg": "invalid key: \"$gt\" (key must not start with '$' sign)",
ferretdb_1 | "code": 2,
ferretdb_1 | "codeName": "BadValue"
ferretdb_1 | },
ferretdb_1 | "Kind": 0
ferretdb_1 | }
ferretdb_1 | ]
ferretdb_1 | }
```
| non_priority | updatemany with filter with no result and upsert true yields errors instead of creating new document ferretdb version ferretdb backend postgresql environment docker using ghcr io ferretdb ferretdb image what did you do ferretdb db restaurant insertone id name central perk cafe violations acknowledged true insertedid ferretdb db restaurant updatemany violations gt set found true upsert true mongoservererror invalid key gt key must not start with sign what did you expect to see same statement executed against mongodb test db restaurant insertone id name central perk cafe violations acknowledged true insertedid test db restaurant updatemany violations gt set found true upsert true acknowledged true insertedid objectid matchedcount modifiedcount upsertedcount test db restaurant countdocuments what did you see instead mongoservererror invalid key gt key must not start with sign ferretdb ferretdb checksum ferretdb flagbits ferretdb sections ferretdb ferretdb document ferretdb k ferretdb ok ferretdb errmsg ferretdb code ferretdb codename ferretdb ferretdb ok ferretdb f ferretdb ferretdb errmsg invalid key gt key must not start with sign ferretdb code ferretdb codename badvalue ferretdb ferretdb kind ferretdb ferretdb ferretdb | 0 |
168,287 | 26,627,621,684 | IssuesEvent | 2023-01-24 15:34:55 | hpi-swa-lab/BP2021RH1 | https://api.github.com/repos/hpi-swa-lab/BP2021RH1 | closed | Darstellung der Kategorien auf der Browseview überarbeiten | C-user-story P-8 C-design-prototype | Problemstellung: Aktuell wird die Browseview von dutzenden Kategorien überflutet, die sie unübersichtlich machen.
Aufgabe: Entwickeln von zwei Prototypen für übersichtlichere Darstellungen | 1.0 | Darstellung der Kategorien auf der Browseview überarbeiten - Problemstellung: Aktuell wird die Browseview von dutzenden Kategorien überflutet, die sie unübersichtlich machen.
Aufgabe: Entwickeln von zwei Prototypen für übersichtlichere Darstellungen | non_priority | darstellung der kategorien auf der browseview überarbeiten problemstellung aktuell wird die browseview von dutzenden kategorien überflutet die sie unübersichtlich machen aufgabe entwickeln von zwei prototypen für übersichtlichere darstellungen | 0 |
263,897 | 28,070,756,283 | IssuesEvent | 2023-03-29 18:52:54 | turkdevops/cirrus-ci-web | https://api.github.com/repos/turkdevops/cirrus-ci-web | closed | CVE-2021-42740 (High) detected in shell-quote-1.7.2.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p></summary>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/shell-quote</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- react-dev-utils-10.2.1.tgz
- :x: **shell-quote-1.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/cirrus-ci-web/commit/31e3781d9cd380020c335ba4f4897abf983dbc02">31e3781d9cd380020c335ba4f4897abf983dbc02</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution (shell-quote): 1.7.3</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-42740 (High) detected in shell-quote-1.7.2.tgz - autoclosed - ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p></summary>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.7.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/shell-quote</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- react-dev-utils-10.2.1.tgz
- :x: **shell-quote-1.7.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/cirrus-ci-web/commit/31e3781d9cd380020c335ba4f4897abf983dbc02">31e3781d9cd380020c335ba4f4897abf983dbc02</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution (shell-quote): 1.7.3</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in shell quote tgz autoclosed cve high severity vulnerability vulnerable library shell quote tgz quote and parse shell commands library home page a href path to dependency file package json path to vulnerable library node modules shell quote dependency hierarchy react scripts tgz root library react dev utils tgz x shell quote tgz vulnerable library found in head commit a href found in base branch master vulnerability details the shell quote package before for node js allows command injection an attacker can inject unescaped shell metacharacters through a regex designed to support windows drive letters if the output of this package is passed to a real shell as a quoted argument to a command with exec an attacker can inject arbitrary commands this is because the windows drive letter regex character class is a z instead of the correct a za z several shell metacharacters exist in the space between capital letter z and lower case letter a such as the backtick character publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution shell quote direct dependency fix resolution react scripts step up your open source security game with mend | 0 |
35,617 | 12,365,374,764 | IssuesEvent | 2020-05-18 08:44:11 | NatalyaDalid/NatRepository | https://api.github.com/repos/NatalyaDalid/NatRepository | closed | WS-2018-0021 (Medium) detected in bootstrap-3.1.1.min.js | security vulnerability | ## WS-2018-0021 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /NatRepository/webgoat-lessons/challenge/src/main/resources/js/bootstrap.min.js,/NatRepository/webgoat-container/src/main/resources/static/plugins/bootstrap/js/bootstrap.min.js,/NatRepository/webgoat-container/target/classes/static/plugins/bootstrap/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NatalyaDalid/NatRepository/commit/d5855b917e28b880e479d9131093e8937cf1b61c">d5855b917e28b880e479d9131093e8937cf1b61c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XSS in data-target in bootstrap (3.3.7 and before)
<p>Publish Date: 2017-09-29
<p>URL: <a href=https://github.com/twbs/bootstrap/issues/20184>WS-2018-0021</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-06-12</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.1.1","isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"vulnerabilityIdentifier":"WS-2018-0021","vulnerabilityDetails":"XSS in data-target in bootstrap (3.3.7 and before)","vulnerabilityUrl":"https://github.com/twbs/bootstrap/issues/20184","cvss2Severity":"medium","cvss2Score":"6.5","extraData":{}}</REMEDIATE> --> | True | WS-2018-0021 (Medium) detected in bootstrap-3.1.1.min.js - ## WS-2018-0021 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /NatRepository/webgoat-lessons/challenge/src/main/resources/js/bootstrap.min.js,/NatRepository/webgoat-container/src/main/resources/static/plugins/bootstrap/js/bootstrap.min.js,/NatRepository/webgoat-container/target/classes/static/plugins/bootstrap/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/NatalyaDalid/NatRepository/commit/d5855b917e28b880e479d9131093e8937cf1b61c">d5855b917e28b880e479d9131093e8937cf1b61c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XSS in data-target in bootstrap (3.3.7 and before)
<p>Publish Date: 2017-09-29
<p>URL: <a href=https://github.com/twbs/bootstrap/issues/20184>WS-2018-0021</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-06-12</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.1.1","isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"vulnerabilityIdentifier":"WS-2018-0021","vulnerabilityDetails":"XSS in data-target in bootstrap (3.3.7 and before)","vulnerabilityUrl":"https://github.com/twbs/bootstrap/issues/20184","cvss2Severity":"medium","cvss2Score":"6.5","extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in bootstrap min js ws medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library natrepository webgoat lessons challenge src main resources js bootstrap min js natrepository webgoat container src main resources static plugins bootstrap js bootstrap min js natrepository webgoat container target classes static plugins bootstrap js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href vulnerability details xss in data target in bootstrap and before publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails xss in data target in bootstrap and before vulnerabilityurl | 0 |
127,948 | 27,159,163,678 | IssuesEvent | 2023-02-17 10:24:04 | apache/netbeans | https://api.github.com/repos/apache/netbeans | opened | Gradle stores some settings into .gradle which are later marked by MS Java Ext pack as modified project | kind:bug VSCode Extension | ### Apache NetBeans version
Apache NetBeans 17 release candidate
### What happened
Created Gradle project with subprojects using VSNetBeans 16.0.301 and OCI tooling. This is done in coexistence with MS Java Ext Pack (JDT). Later MS Java reports as problem that Gradle project files was modified and needs to be reloaded to make it effective. It looks like some recent change or regression on NBLS side.
<img width="776" alt="Screenshot 2023-02-17 at 9 56 59" src="https://user-images.githubusercontent.com/26064232/219617972-142d7e36-a955-4579-85eb-120f6246cd62.png">
It is not shown when project is open for 2nd time, just after its creation when OCI powered Vulnerabilities audit completes.
Using VSNetBeans 16.0.301
### How to reproduce
_No response_
### Did this work correctly in an earlier version?
Apache NetBeans 15
### Operating System
macOS
### JDK
GraalVM 22.3.0 JDK17
### Apache NetBeans packaging
Apache VSNetBeans for VSCode
### Anything else
_No response_
### Are you willing to submit a pull request?
Yes
### Code of Conduct
Yes | 1.0 | Gradle stores some settings into .gradle which are later marked by MS Java Ext pack as modified project - ### Apache NetBeans version
Apache NetBeans 17 release candidate
### What happened
Created Gradle project with subprojects using VSNetBeans 16.0.301 and OCI tooling. This is done in coexistence with MS Java Ext Pack (JDT). Later MS Java reports as problem that Gradle project files was modified and needs to be reloaded to make it effective. It looks like some recent change or regression on NBLS side.
<img width="776" alt="Screenshot 2023-02-17 at 9 56 59" src="https://user-images.githubusercontent.com/26064232/219617972-142d7e36-a955-4579-85eb-120f6246cd62.png">
It is not shown when project is open for 2nd time, just after its creation when OCI powered Vulnerabilities audit completes.
Using VSNetBeans 16.0.301
### How to reproduce
_No response_
### Did this work correctly in an earlier version?
Apache NetBeans 15
### Operating System
macOS
### JDK
GraalVM 22.3.0 JDK17
### Apache NetBeans packaging
Apache VSNetBeans for VSCode
### Anything else
_No response_
### Are you willing to submit a pull request?
Yes
### Code of Conduct
Yes | non_priority | gradle stores some settings into gradle which are later marked by ms java ext pack as modified project apache netbeans version apache netbeans release candidate what happened created gradle project with subprojects using vsnetbeans and oci tooling this is done in coexistence with ms java ext pack jdt later ms java reports as problem that gradle project files was modified and needs to be reloaded to make it effective it looks like some recent change or regression on nbls side img width alt screenshot at src it is not shown when project is open for time just after its creation when oci powered vulnerabilities audit completes using vsnetbeans how to reproduce no response did this work correctly in an earlier version apache netbeans operating system macos jdk graalvm apache netbeans packaging apache vsnetbeans for vscode anything else no response are you willing to submit a pull request yes code of conduct yes | 0 |
163,833 | 13,928,344,884 | IssuesEvent | 2020-10-21 21:18:38 | HarshdipD/job-tracker | https://api.github.com/repos/HarshdipD/job-tracker | opened | Website for the extension | documentation enhancement good first issue | It's high time I have a website for the extension to describe what it does, and a link to the Chrome web store. Nothing fancy, just something to direct users to and from the Chrome web store.
An image of the extension in action, and a gif. It should also include links to my website, this GitHub repo if anyone wants to contribute and a donate button.
Good first issue if anyone wants to try something open-source and build or implement their web dev skills!
If you're interested, please comment in this thread and I can provide you with images, gifs, and other data to use.
Bootstrap 4.0 is to be used for CSS. | 1.0 | Website for the extension - It's high time I have a website for the extension to describe what it does, and a link to the Chrome web store. Nothing fancy, just something to direct users to and from the Chrome web store.
An image of the extension in action, and a gif. It should also include links to my website, this GitHub repo if anyone wants to contribute and a donate button.
Good first issue if anyone wants to try something open-source and build or implement their web dev skills!
If you're interested, please comment in this thread and I can provide you with images, gifs, and other data to use.
Bootstrap 4.0 is to be used for CSS. | non_priority | website for the extension it s high time i have a website for the extension to describe what it does and a link to the chrome web store nothing fancy just something to direct users to and from the chrome web store an image of the extension in action and a gif it should also include links to my website this github repo if anyone wants to contribute and a donate button good first issue if anyone wants to try something open source and build or implement their web dev skills if you re interested please comment in this thread and i can provide you with images gifs and other data to use bootstrap is to be used for css | 0 |
1,763 | 2,845,720,250 | IssuesEvent | 2015-05-29 06:19:47 | arangodb/arangodb | https://api.github.com/repos/arangodb/arangodb | closed | arangodump into client packages? | build Feature | It would be grat to create a dump from a client, where only arangodb-client package installed. | 1.0 | arangodump into client packages? - It would be grat to create a dump from a client, where only arangodb-client package installed. | non_priority | arangodump into client packages it would be grat to create a dump from a client where only arangodb client package installed | 0 |
77,185 | 15,500,343,486 | IssuesEvent | 2021-03-11 09:12:00 | gsylvie/madness | https://api.github.com/repos/gsylvie/madness | opened | CVE-2020-11988 (Medium) detected in xmlgraphics-commons-2.3.jar | security vulnerability | ## CVE-2020-11988 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlgraphics-commons-2.3.jar</b></p></summary>
<p>Apache XML Graphics Commons is a library that consists of several reusable
components used by Apache Batik and Apache FOP. Many of these components
can easily be used separately outside the domains of SVG and XSL-FO.</p>
<p>Path to dependency file: madness/ear/pom.xml</p>
<p>Path to vulnerable library: madness/ear/target/madness-ear-2019.02.01/xmlgraphics-commons-2.3.jar,/home/wss-scanner/.m2/repository/org/apache/xmlgraphics/xmlgraphics-commons/2.3/xmlgraphics-commons-2.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **xmlgraphics-commons-2.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gsylvie/madness/commit/432990e598eb33c3799ec7e073aab5455a260c8c">432990e598eb33c3799ec7e073aab5455a260c8c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache XmlGraphics Commons 2.4 is vulnerable to server-side request forgery, caused by improper input validation by the XMPParser. By using a specially-crafted argument, an attacker could exploit this vulnerability to cause the underlying server to make arbitrary GET requests.
<p>Publish Date: 2021-02-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11988>CVE-2020-11988</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://xmlgraphics.apache.org/security.html">https://xmlgraphics.apache.org/security.html</a></p>
<p>Release Date: 2021-02-24</p>
<p>Fix Resolution: org.apache.xmlgraphics:xmlgraphics-commons:commons-2_6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11988 (Medium) detected in xmlgraphics-commons-2.3.jar - ## CVE-2020-11988 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlgraphics-commons-2.3.jar</b></p></summary>
<p>Apache XML Graphics Commons is a library that consists of several reusable
components used by Apache Batik and Apache FOP. Many of these components
can easily be used separately outside the domains of SVG and XSL-FO.</p>
<p>Path to dependency file: madness/ear/pom.xml</p>
<p>Path to vulnerable library: madness/ear/target/madness-ear-2019.02.01/xmlgraphics-commons-2.3.jar,/home/wss-scanner/.m2/repository/org/apache/xmlgraphics/xmlgraphics-commons/2.3/xmlgraphics-commons-2.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **xmlgraphics-commons-2.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/gsylvie/madness/commit/432990e598eb33c3799ec7e073aab5455a260c8c">432990e598eb33c3799ec7e073aab5455a260c8c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache XmlGraphics Commons 2.4 is vulnerable to server-side request forgery, caused by improper input validation by the XMPParser. By using a specially-crafted argument, an attacker could exploit this vulnerability to cause the underlying server to make arbitrary GET requests.
<p>Publish Date: 2021-02-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11988>CVE-2020-11988</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://xmlgraphics.apache.org/security.html">https://xmlgraphics.apache.org/security.html</a></p>
<p>Release Date: 2021-02-24</p>
<p>Fix Resolution: org.apache.xmlgraphics:xmlgraphics-commons:commons-2_6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in xmlgraphics commons jar cve medium severity vulnerability vulnerable library xmlgraphics commons jar apache xml graphics commons is a library that consists of several reusable components used by apache batik and apache fop many of these components can easily be used separately outside the domains of svg and xsl fo path to dependency file madness ear pom xml path to vulnerable library madness ear target madness ear xmlgraphics commons jar home wss scanner repository org apache xmlgraphics xmlgraphics commons xmlgraphics commons jar dependency hierarchy x xmlgraphics commons jar vulnerable library found in head commit a href vulnerability details apache xmlgraphics commons is vulnerable to server side request forgery caused by improper input validation by the xmpparser by using a specially crafted argument an attacker could exploit this vulnerability to cause the underlying server to make arbitrary get requests publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache xmlgraphics xmlgraphics commons commons step up your open source security game with whitesource | 0 |
85,267 | 16,624,265,552 | IssuesEvent | 2021-06-03 07:35:52 | HydrolienF/Formiko | https://api.github.com/repos/HydrolienF/Formiko | closed | implement View #175 with GUI2D : ViewGUI | code reorganization doing done graphics | - [x] Game should work with all function of ViewGUI2d
- [x] ViewGUI need to be link to all Panel.
- [ ] To switch to an other panel it need to swap main panel in Fenetre to an other 1.
- [x] Any panel can be draw anytime. So we need to check that frame exist and add it if not.
- [x] launch of PanneauMenu kill cheat code listening, it shoundn't. | 1.0 | implement View #175 with GUI2D : ViewGUI - - [x] Game should work with all function of ViewGUI2d
- [x] ViewGUI need to be link to all Panel.
- [ ] To switch to an other panel it need to swap main panel in Fenetre to an other 1.
- [x] Any panel can be draw anytime. So we need to check that frame exist and add it if not.
- [x] launch of PanneauMenu kill cheat code listening, it shoundn't. | non_priority | implement view with viewgui game should work with all function of viewgui need to be link to all panel to switch to an other panel it need to swap main panel in fenetre to an other any panel can be draw anytime so we need to check that frame exist and add it if not launch of panneaumenu kill cheat code listening it shoundn t | 0 |
51,347 | 6,156,467,074 | IssuesEvent | 2017-06-28 16:46:19 | WormBase/website | https://api.github.com/repos/WormBase/website | closed | URLs for Disease Ontology (DO) Terms need to be changed | Under testing Webteam | @sibyl229 @Paul-Davis: The Disease Ontology site has proper URL's for their term pages now. I remember @Paul-Davis, when we first imported the DO a while ago, their pages were sparse. So we went with whatever they had.
Please update DO term URLs to the correct Disease Ontology web pages, for example, on the Alzheimer's page:
https://www.wormbase.org/resources/disease/DOID:10652#0--10
the DOID:10652 points to: http://disease-ontology.org/term/DOID%3A10652/
It should point to: http://www.disease-ontology.org/?id=DOID:10652
For the gene pages, looks like the DOID points to the WB disease report page, so this is fine:
for example, for aip-1,
https://www.wormbase.org/species/c_elegans/gene/WBGene00000097#07-9g-3
'aip is an experimental model for Alzheimer's disease (DOID:10652)", ID goes to our disease page, so this is fine.
Thanks! | 1.0 | URLs for Disease Ontology (DO) Terms need to be changed - @sibyl229 @Paul-Davis: The Disease Ontology site has proper URL's for their term pages now. I remember @Paul-Davis, when we first imported the DO a while ago, their pages were sparse. So we went with whatever they had.
Please update DO term URLs to the correct Disease Ontology web pages, for example, on the Alzheimer's page:
https://www.wormbase.org/resources/disease/DOID:10652#0--10
the DOID:10652 points to: http://disease-ontology.org/term/DOID%3A10652/
It should point to: http://www.disease-ontology.org/?id=DOID:10652
For the gene pages, looks like the DOID points to the WB disease report page, so this is fine:
for example, for aip-1,
https://www.wormbase.org/species/c_elegans/gene/WBGene00000097#07-9g-3
'aip is an experimental model for Alzheimer's disease (DOID:10652)", ID goes to our disease page, so this is fine.
Thanks! | non_priority | urls for disease ontology do terms need to be changed paul davis the disease ontology site has proper url s for their term pages now i remember paul davis when we first imported the do a while ago their pages were sparse so we went with whatever they had please update do term urls to the correct disease ontology web pages for example on the alzheimer s page the doid points to it should point to for the gene pages looks like the doid points to the wb disease report page so this is fine for example for aip aip is an experimental model for alzheimer s disease doid id goes to our disease page so this is fine thanks | 0 |
38,805 | 15,797,960,343 | IssuesEvent | 2021-04-02 17:44:23 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | autocomplete does not work after including p18f4550.h | Feature: Auto-complete Language Service Not Repro - Internal bug | **Type: LanguageService**
<!----- Input information below ----->
<!--
**Prior to filing an issue, please review:**
- Existing issues at https://github.com/Microsoft/vscode-cpptools/issues
- Our documentation at https://code.visualstudio.com/docs/languages/cpp
- FAQs at https://code.visualstudio.com/docs/cpp/faq-cpp
-->
**Describe the bug**
- OS and Version:
- VS Code Version:
- C/C++ Extension Version:
- Other extensions you installed (and if the issue persists after disabling them):
- Does this issue involve using SSH remote to run the extension on a remote machine?:
- A clear and concise description of what the bug is, including information about the workspace (i.e. is the workspace a single project or multiple projects, size of the project, etc).
**Steps to reproduce**
<!-- Provide clear steps to reproduce the behavior: -->
<!-- *The most actionable issue reports include a code sample including configuration files such as c_cpp_properties.json* -->
1. Add "#include <p18f4550.h>"
2. all the structs should be available for autocompletion
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
<!-- Please provide the following logs that show diagnostics and debugging information about the language server.
1. Logs from the command `C/C++: Log Diagnostics`
2. Logs from [the language server](https://code.visualstudio.com/docs/cpp/enable-logging-cpp#_enable-logging-for-the-language-server)
-->
<details>
<summary><strong>Logs</strong></summary>
<!-- Note: do not remove empty line after </summary> tag, otherwise the code blocks formatting won't show correctly. -->
```
Insert logs here.
```
</details>
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
**Additional context**
<!--
* Call Stacks: For bugs like crashes, deadlocks, infinite loops, etc. that we are not able to repro and for which the call stack may be useful, please attach a debugger and/or create a dmp and provide the call stacks. Windows binaries have symbols available in VS Code by setting your "symbolSearchPath" to "https://msdl.microsoft.com/download/symbols".
-->
| 1.0 | autocomplete does not work after including p18f4550.h - **Type: LanguageService**
<!----- Input information below ----->
<!--
**Prior to filing an issue, please review:**
- Existing issues at https://github.com/Microsoft/vscode-cpptools/issues
- Our documentation at https://code.visualstudio.com/docs/languages/cpp
- FAQs at https://code.visualstudio.com/docs/cpp/faq-cpp
-->
**Describe the bug**
- OS and Version:
- VS Code Version:
- C/C++ Extension Version:
- Other extensions you installed (and if the issue persists after disabling them):
- Does this issue involve using SSH remote to run the extension on a remote machine?:
- A clear and concise description of what the bug is, including information about the workspace (i.e. is the workspace a single project or multiple projects, size of the project, etc).
**Steps to reproduce**
<!-- Provide clear steps to reproduce the behavior: -->
<!-- *The most actionable issue reports include a code sample including configuration files such as c_cpp_properties.json* -->
1. Add "#include <p18f4550.h>"
2. all the structs should be available for autocompletion
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
<!-- Please provide the following logs that show diagnostics and debugging information about the language server.
1. Logs from the command `C/C++: Log Diagnostics`
2. Logs from [the language server](https://code.visualstudio.com/docs/cpp/enable-logging-cpp#_enable-logging-for-the-language-server)
-->
<details>
<summary><strong>Logs</strong></summary>
<!-- Note: do not remove empty line after </summary> tag, otherwise the code blocks formatting won't show correctly. -->
```
Insert logs here.
```
</details>
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
**Additional context**
<!--
* Call Stacks: For bugs like crashes, deadlocks, infinite loops, etc. that we are not able to repro and for which the call stack may be useful, please attach a debugger and/or create a dmp and provide the call stacks. Windows binaries have symbols available in VS Code by setting your "symbolSearchPath" to "https://msdl.microsoft.com/download/symbols".
-->
| non_priority | autocomplete does not work after including h type languageservice prior to filing an issue please review existing issues at our documentation at faqs at describe the bug os and version vs code version c c extension version other extensions you installed and if the issue persists after disabling them does this issue involve using ssh remote to run the extension on a remote machine a clear and concise description of what the bug is including information about the workspace i e is the workspace a single project or multiple projects size of the project etc steps to reproduce add include all the structs should be available for autocompletion expected behavior please provide the following logs that show diagnostics and debugging information about the language server logs from the command c c log diagnostics logs from logs tag otherwise the code blocks formatting won t show correctly insert logs here screenshots additional context call stacks for bugs like crashes deadlocks infinite loops etc that we are not able to repro and for which the call stack may be useful please attach a debugger and or create a dmp and provide the call stacks windows binaries have symbols available in vs code by setting your symbolsearchpath to | 0 |
339,210 | 24,613,942,743 | IssuesEvent | 2022-10-15 04:16:13 | temporalio/sdk-typescript | https://api.github.com/repos/temporalio/sdk-typescript | closed | [Bug] Docs Search Result Link 404 | bug documentation | ### What are you really trying to do?
<!--
Tell us at a high level what you're doing, to avoid XY problem (https://en.wikipedia.org/wiki/XY_problem)
-->
Using the docs, we want to search for classes and then share the link to the search result. The shared link should always work.
### Describe the bug
<!-- A clear and concise description of what the bug is. -->
Clicking on a search result from the docs search navigates to a URL that may contain uppercase characters. Opening this URL in a new tab goes to a 404 if it contains uppercase characters.
<!-- If applicable, add screenshots or code blocks to help explain your problem. You can also use [Loom](http://loom.com/) to do short, free video bug reports. -->
### Minimal Reproduction
<!--
Modify our hello world templates to demonstrate:
- TypeScript: https://github.com/temporalio/samples-typescript/tree/main/hello-world
- Go: https://github.com/temporalio/money-transfer-project-template-go
- Java: https://github.com/temporalio/money-transfer-project-template-java
- PHP: https://github.com/temporalio/samples-php#samples
-->
- Go to https://typescript.temporal.io/
- Click the Search button on the top right (Cmd+K)
- Search for `ApplicationFailure` and click the Class result
- The search result links to this URL: https://typescript.temporal.io/api/classes/common.applicationfailure/
- Open the URL in a new tab, or refresh the page
- The page is a 404
The correct URL for the search result should be https://typescript.temporal.io/api/classes/common.ApplicationFailure
### Environment/Versions
<!-- Please complete the following information where relevant. -->
- OS and processor: Intel Mac
- Temporal Version: N/A
- Are you using Docker or Kubernetes or building Temporal from source? N/A
### Additional context
<!-- Add any other context about the problem here. -->
This could be an issue with https://docusaurus.io/docs/search#using-algolia-docsearch or `docusaurus-plugin-typedoc`
| 1.0 | [Bug] Docs Search Result Link 404 - ### What are you really trying to do?
<!--
Tell us at a high level what you're doing, to avoid XY problem (https://en.wikipedia.org/wiki/XY_problem)
-->
Using the docs, we want to search for classes and then share the link to the search result. The shared link should always work.
### Describe the bug
<!-- A clear and concise description of what the bug is. -->
Clicking on a search result from the docs search navigates to a URL that may contain uppercase characters. Opening this URL in a new tab goes to a 404 if it contains uppercase characters.
<!-- If applicable, add screenshots or code blocks to help explain your problem. You can also use [Loom](http://loom.com/) to do short, free video bug reports. -->
### Minimal Reproduction
<!--
Modify our hello world templates to demonstrate:
- TypeScript: https://github.com/temporalio/samples-typescript/tree/main/hello-world
- Go: https://github.com/temporalio/money-transfer-project-template-go
- Java: https://github.com/temporalio/money-transfer-project-template-java
- PHP: https://github.com/temporalio/samples-php#samples
-->
- Go to https://typescript.temporal.io/
- Click the Search button on the top right (Cmd+K)
- Search for `ApplicationFailure` and click the Class result
- The search result links to this URL: https://typescript.temporal.io/api/classes/common.applicationfailure/
- Open the URL in a new tab, or refresh the page
- The page is a 404
The correct URL for the search result should be https://typescript.temporal.io/api/classes/common.ApplicationFailure
### Environment/Versions
<!-- Please complete the following information where relevant. -->
- OS and processor: Intel Mac
- Temporal Version: N/A
- Are you using Docker or Kubernetes or building Temporal from source? N/A
### Additional context
<!-- Add any other context about the problem here. -->
This could be an issue with https://docusaurus.io/docs/search#using-algolia-docsearch or `docusaurus-plugin-typedoc`
| non_priority | docs search result link what are you really trying to do tell us at a high level what you re doing to avoid xy problem using the docs we want to search for classes and then share the link to the search result the shared link should always work describe the bug clicking on a search result from the docs search navigates to a url that may contain uppercase characters opening this url in a new tab goes to a if it contains uppercase characters minimal reproduction modify our hello world templates to demonstrate typescript go java php go to click the search button on the top right cmd k search for applicationfailure and click the class result the search result links to this url open the url in a new tab or refresh the page the page is a the correct url for the search result should be environment versions os and processor intel mac temporal version n a are you using docker or kubernetes or building temporal from source n a additional context this could be an issue with or docusaurus plugin typedoc | 0 |
74,799 | 14,344,114,054 | IssuesEvent | 2020-11-28 12:56:56 | swyddfa/esbonio | https://api.github.com/repos/swyddfa/esbonio | closed | Look at adding a .vscodeignore file | devops vscode | It would be good to ensure we don't include anything that's not necessary in the packaged extension | 1.0 | Look at adding a .vscodeignore file - It would be good to ensure we don't include anything that's not necessary in the packaged extension | non_priority | look at adding a vscodeignore file it would be good to ensure we don t include anything that s not necessary in the packaged extension | 0 |
350,898 | 31,932,522,637 | IssuesEvent | 2023-09-19 08:23:56 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix elementwise.test_copysign | Sub Task Ivy API Experimental Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix elementwise.test_copysign - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5769275703/job/15641140910"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix elementwise test copysign jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 0 |
256,653 | 27,561,704,120 | IssuesEvent | 2023-03-07 22:41:08 | samqws-marketing/box_mojito | https://api.github.com/repos/samqws-marketing/box_mojito | closed | CVE-2016-1000345 (Medium) detected in bcprov-jdk15on-1.52.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2016-1000345 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.52.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /webapp/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.52/bcprov-jdk15on-1.52.jar</p>
<p>
Dependency Hierarchy:
- box-java-sdk-2.1.1.jar (Root Library)
- :x: **bcprov-jdk15on-1.52.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/box_mojito/commit/65290aeb818102fa2443a637efdccebebfed1eb9">65290aeb818102fa2443a637efdccebebfed1eb9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Bouncy Castle JCE Provider version 1.55 and earlier the DHIES/ECIES CBC mode vulnerable to padding oracle attack. For BC 1.55 and older, in an environment where timings can be easily observed, it is possible with enough observations to identify when the decryption is failing due to padding.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1000345>CVE-2016-1000345</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000345">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000345</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution (org.bouncycastle:bcprov-jdk15on): 1.56</p>
<p>Direct dependency fix Resolution (com.box:box-java-sdk): 2.25.1</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2016-1000345 (Medium) detected in bcprov-jdk15on-1.52.jar - autoclosed - ## CVE-2016-1000345 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.52.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: /webapp/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/bouncycastle/bcprov-jdk15on/1.52/bcprov-jdk15on-1.52.jar</p>
<p>
Dependency Hierarchy:
- box-java-sdk-2.1.1.jar (Root Library)
- :x: **bcprov-jdk15on-1.52.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/box_mojito/commit/65290aeb818102fa2443a637efdccebebfed1eb9">65290aeb818102fa2443a637efdccebebfed1eb9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Bouncy Castle JCE Provider version 1.55 and earlier the DHIES/ECIES CBC mode vulnerable to padding oracle attack. For BC 1.55 and older, in an environment where timings can be easily observed, it is possible with enough observations to identify when the decryption is failing due to padding.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1000345>CVE-2016-1000345</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000345">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000345</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution (org.bouncycastle:bcprov-jdk15on): 1.56</p>
<p>Direct dependency fix Resolution (com.box:box-java-sdk): 2.25.1</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in bcprov jar autoclosed cve medium severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file webapp pom xml path to vulnerable library home wss scanner repository org bouncycastle bcprov bcprov jar dependency hierarchy box java sdk jar root library x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details in the bouncy castle jce provider version and earlier the dhies ecies cbc mode vulnerable to padding oracle attack for bc and older in an environment where timings can be easily observed it is possible with enough observations to identify when the decryption is failing due to padding publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bcprov direct dependency fix resolution com box box java sdk check this box to open an automated fix pr | 0 |
322,587 | 27,619,575,489 | IssuesEvent | 2023-03-09 22:28:36 | RamenDR/ramen | https://api.github.com/repos/RamenDR/ramen | reopened | Ramen catalog fails to report healthy in drenv, potentially due to olm installation differences | good first issue test | This is a problem that was reported earlier by @nirs that the method to get ramen catalog and bundles installed via OLM on a minikube cluster as described [here](https://github.com/RamenDR/ramen/blob/main/docs/install.md#ramen-hub-operator) does not work.
Subsequent testing with and without drenv resulted in the following conclusion:
1. In a vanilla minikube cluster, if the steps are followed as laid out AND olm installed using [operator-sdk](https://olm.operatorframework.io/docs/getting-started/#installing-olm-in-your-cluster), the ramen bundle gets installed and the operator starts running
2. In drenv if the steps are followed, the pod created for the catalog source in the `ramen-system` namespace crashes with errors like so: `Error: open db-118615996: permission denied`
- this leads to the Subscription not resolving to fetch and install the bundle as the CatalogSource remains unhealthy with a TRANSIENT_FAILURE
3. In the same drenv created cluster, if operator-sdk was used to uninstall and then install olm again, the scheme as before starts working.
The issue seems to either be the version of olm installed by drenv (0.22) or the manner of installing the same (although steps seems to follow the upstream olm install procedure as laid out). This needs further investigation and a fix, in case operator-sdk is not going to be used to install olm.
Another alternative could be to try using the [install script](https://github.com/operator-framework/operator-lifecycle-manager/releases/tag/v0.23.1) provided part of the olm releases to install and ensure our catalog works. This also seems to be less work at our end to install, than go through installing various manifests one after the other. | 1.0 | Ramen catalog fails to report healthy in drenv, potentially due to olm installation differences - This is a problem that was reported earlier by @nirs that the method to get ramen catalog and bundles installed via OLM on a minikube cluster as described [here](https://github.com/RamenDR/ramen/blob/main/docs/install.md#ramen-hub-operator) does not work.
Subsequent testing with and without drenv resulted in the following conclusion:
1. In a vanilla minikube cluster, if the steps are followed as laid out AND olm installed using [operator-sdk](https://olm.operatorframework.io/docs/getting-started/#installing-olm-in-your-cluster), the ramen bundle gets installed and the operator starts running
2. In drenv if the steps are followed, the pod created for the catalog source in the `ramen-system` namespace crashes with errors like so: `Error: open db-118615996: permission denied`
- this leads to the Subscription not resolving to fetch and install the bundle as the CatalogSource remains unhealthy with a TRANSIENT_FAILURE
3. In the same drenv created cluster, if operator-sdk was used to uninstall and then install olm again, the scheme as before starts working.
The issue seems to either be the version of olm installed by drenv (0.22) or the manner of installing the same (although steps seems to follow the upstream olm install procedure as laid out). This needs further investigation and a fix, in case operator-sdk is not going to be used to install olm.
Another alternative could be to try using the [install script](https://github.com/operator-framework/operator-lifecycle-manager/releases/tag/v0.23.1) provided part of the olm releases to install and ensure our catalog works. This also seems to be less work at our end to install, than go through installing various manifests one after the other. | non_priority | ramen catalog fails to report healthy in drenv potentially due to olm installation differences this is a problem that was reported earlier by nirs that the method to get ramen catalog and bundles installed via olm on a minikube cluster as described does not work subsequent testing with and without drenv resulted in the following conclusion in a vanilla minikube cluster if the steps are followed as laid out and olm installed using the ramen bundle gets installed and the operator starts running in drenv if the steps are followed the pod created for the catalog source in the ramen system namespace crashes with errors like so error open db permission denied this leads to the subscription not resolving to fetch and install the bundle as the catalogsource remains unhealthy with a transient failure in the same drenv created cluster if operator sdk was used to uninstall and then install olm again the scheme as before starts working the issue seems to either be the version of olm installed by drenv or the manner of installing the same although steps seems to follow the upstream olm install procedure as laid out this needs further investigation and a fix in case operator sdk is not going to be used to install olm another alternative could be to try using the provided part of the olm releases to install and ensure our catalog works this also seems to be less work at our end to install than go through installing various manifests one after the other | 0 |
12,917 | 8,038,111,057 | IssuesEvent | 2018-07-30 14:33:40 | docker/for-win | https://api.github.com/repos/docker/for-win | closed | Docker won't start while Folding@Home or BOINC is Running | area/hyper-v area/startup area/windows 10 kind/performance lifecycle/stale status/0-triage | ### Expected behavior
Docker starts up
### Actual behavior
Docker won't start, with the error: `Docker hv-sock proxy (vsudd) is not reachable`
### Information
Docker fails to start up if [Folding@Home](http://folding.stanford.edu/) is running.
Exiting Folding@Home then starting Docker and re-launching F@H works.
### Steps to reproduce the behavior
1. Boot up with F@H and Docker both running on startup
| True | Docker won't start while Folding@Home or BOINC is Running - ### Expected behavior
Docker starts up
### Actual behavior
Docker won't start, with the error: `Docker hv-sock proxy (vsudd) is not reachable`
### Information
Docker fails to start up if [Folding@Home](http://folding.stanford.edu/) is running.
Exiting Folding@Home then starting Docker and re-launching F@H works.
### Steps to reproduce the behavior
1. Boot up with F@H and Docker both running on startup
| non_priority | docker won t start while folding home or boinc is running expected behavior docker starts up actual behavior docker won t start with the error docker hv sock proxy vsudd is not reachable information docker fails to start up if is running exiting folding home then starting docker and re launching f h works steps to reproduce the behavior boot up with f h and docker both running on startup | 0 |
290,098 | 21,843,135,217 | IssuesEvent | 2022-05-18 00:01:54 | AgnosticUI/agnosticui | https://api.github.com/repos/AgnosticUI/agnosticui | closed | Layouts Page | documentation v2 | Probably would go under the Advanced section.
If you visit the AgnosticUI Svelte examples [on d2](https://developtodesign.com/agnosticui-examples) (and click the Layouts tab there's a really nice set of CSS Grid examples.
I think these could be ported to the documentation as a page off of the Advanced section. Big idea is…
1. "So you're asking where the grid component and layout tools? Well..." `[and we continue with same as what's on the blog]`:
> Layout capabilities are already available on in modern browsers with CSS. [AgnosticUI](https://agnosticui.com/) users have these choices:
and so on...
3. Then we explain similar to the blog post that CSS Grid and Flexbox is all you need.
4. We show the flexbox utilities page example and link to the [utility classes page](https://www.agnosticui.com/docs/utilities.html) for more details
5. We use the same Layouts examples
| 1.0 | Layouts Page - Probably would go under the Advanced section.
If you visit the AgnosticUI Svelte examples [on d2](https://developtodesign.com/agnosticui-examples) (and click the Layouts tab there's a really nice set of CSS Grid examples.
I think these could be ported to the documentation as a page off of the Advanced section. Big idea is…
1. "So you're asking where the grid component and layout tools? Well..." `[and we continue with same as what's on the blog]`:
> Layout capabilities are already available on in modern browsers with CSS. [AgnosticUI](https://agnosticui.com/) users have these choices:
and so on...
3. Then we explain similar to the blog post that CSS Grid and Flexbox is all you need.
4. We show the flexbox utilities page example and link to the [utility classes page](https://www.agnosticui.com/docs/utilities.html) for more details
5. We use the same Layouts examples
| non_priority | layouts page probably would go under the advanced section if you visit the agnosticui svelte examples and click the layouts tab there s a really nice set of css grid examples i think these could be ported to the documentation as a page off of the advanced section big idea is… so you re asking where the grid component and layout tools well layout capabilities are already available on in modern browsers with css users have these choices and so on then we explain similar to the blog post that css grid and flexbox is all you need we show the flexbox utilities page example and link to the for more details we use the same layouts examples | 0 |
20,204 | 3,315,162,241 | IssuesEvent | 2015-11-06 10:28:17 | junichi11/cakephp3-netbeans | https://api.github.com/repos/junichi11/cakephp3-netbeans | closed | Trouble installing under NetBeans 8.1 | defect NB81 | #### Overview description
I am unable to install the plugin in NetBeans 8.1
#### Steps to reproduce
1. Downloaded the npm
2. Added to the Downloaded plug-ins and attempted to install
#### Actual results
NetBeans returns: Some plugins require plugin Web Common to be installed. The plugin Web Common is requested in implementation version 201510122201.
#### Expected results
The installed plugin
#### Version number of the plugin
0.2.0
#### Version information of NetBeans
NetBeans IDE 8.1 (Build 201510222201)
| 1.0 | Trouble installing under NetBeans 8.1 - #### Overview description
I am unable to install the plugin in NetBeans 8.1
#### Steps to reproduce
1. Downloaded the npm
2. Added to the Downloaded plug-ins and attempted to install
#### Actual results
NetBeans returns: Some plugins require plugin Web Common to be installed. The plugin Web Common is requested in implementation version 201510122201.
#### Expected results
The installed plugin
#### Version number of the plugin
0.2.0
#### Version information of NetBeans
NetBeans IDE 8.1 (Build 201510222201)
| non_priority | trouble installing under netbeans overview description i am unable to install the plugin in netbeans steps to reproduce downloaded the npm added to the downloaded plug ins and attempted to install actual results netbeans returns some plugins require plugin web common to be installed the plugin web common is requested in implementation version expected results the installed plugin version number of the plugin version information of netbeans netbeans ide build | 0 |
42,051 | 6,962,486,072 | IssuesEvent | 2017-12-08 13:57:03 | wagtail/wagtail | https://api.github.com/repos/wagtail/wagtail | opened | Possible to add tags with spaces when TAG_SPACES_ALLOWED = False | component:Frontend Documentation type:Bug | ### Issue Summary
It's possible to add spaces into tags with `TAG_SPACES_ALLOWED = False`.
### Steps to Reproduce
0. Set `TAG_SPACES_ALLOWED = False` in your settings
1. Open the editing interface for a document or a page with the default Wagtail tags input
2. Copy few words with a space inside into clipboard
3. Paste into the tag input
3. Hit the save/publish button
**Result:** Tag with a space will be saved into a database
We need to prevent copy-pasting when `TAG_SPACES_ALLOWED is False` on front-end and/or implement validation on back-end.
### Technical details
* Wagtail version: Wagtail 1.13.1
* Browser version: 62.0.3202.94 (64-bit, MacOS 10.13.1) | 1.0 | Possible to add tags with spaces when TAG_SPACES_ALLOWED = False - ### Issue Summary
It's possible to add spaces into tags with `TAG_SPACES_ALLOWED = False`.
### Steps to Reproduce
0. Set `TAG_SPACES_ALLOWED = False` in your settings
1. Open the editing interface for a document or a page with the default Wagtail tags input
2. Copy few words with a space inside into clipboard
3. Paste into the tag input
3. Hit the save/publish button
**Result:** Tag with a space will be saved into a database
We need to prevent copy-pasting when `TAG_SPACES_ALLOWED is False` on front-end and/or implement validation on back-end.
### Technical details
* Wagtail version: Wagtail 1.13.1
* Browser version: 62.0.3202.94 (64-bit, MacOS 10.13.1) | non_priority | possible to add tags with spaces when tag spaces allowed false issue summary it s possible to add spaces into tags with tag spaces allowed false steps to reproduce set tag spaces allowed false in your settings open the editing interface for a document or a page with the default wagtail tags input copy few words with a space inside into clipboard paste into the tag input hit the save publish button result tag with a space will be saved into a database we need to prevent copy pasting when tag spaces allowed is false on front end and or implement validation on back end technical details wagtail version wagtail browser version bit macos | 0 |
157,443 | 24,673,551,591 | IssuesEvent | 2022-10-18 15:18:06 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | Improve licenses page | f: material design proposal | - [ ] "Powered by Flutter" isn't localized. Consider localizing and making optional, OR removing altogether.
- [ ] UI renders inside an elevated card-Material that uses a non-standard background color. Consider rendering directly on background.
- [ ] Lack of `SafeArea`, content overlaps with on-screen controls. Easy fix. | 1.0 | Improve licenses page - - [ ] "Powered by Flutter" isn't localized. Consider localizing and making optional, OR removing altogether.
- [ ] UI renders inside an elevated card-Material that uses a non-standard background color. Consider rendering directly on background.
- [ ] Lack of `SafeArea`, content overlaps with on-screen controls. Easy fix. | non_priority | improve licenses page powered by flutter isn t localized consider localizing and making optional or removing altogether ui renders inside an elevated card material that uses a non standard background color consider rendering directly on background lack of safearea content overlaps with on screen controls easy fix | 0 |
66,507 | 20,252,204,232 | IssuesEvent | 2022-02-14 19:04:13 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | opened | Right panel thread view time stamp overlaps message text | T-Defect | ### Steps to reproduce
1. Where are you starting? What can you see?
Timeline open on a room with a preexisting thread consisting of multiple messages.
2. What do you click?
I click on the thread view button in the upper right.
### Outcome
#### What did you expect?
I expect to see the message with timestamps separated from the message text like in the timeline view of messages.
#### What happened instead?
The message timestamp slightly overlaps the message text as shown in the following image.

### Operating system
Debian 11
### Browser information
Version 98.0.4758.80 (Official Build) (64-bit)
### URL for webapp
Element version: 1.10.2 Olm version: 3.2.8
### Application version
Element version: 1.10.2 Olm version: 3.2.8
### Homeserver
Synapse 1.52.0
### Will you send logs?
No | 1.0 | Right panel thread view time stamp overlaps message text - ### Steps to reproduce
1. Where are you starting? What can you see?
Timeline open on a room with a preexisting thread consisting of multiple messages.
2. What do you click?
I click on the thread view button in the upper right.
### Outcome
#### What did you expect?
I expect to see the message with timestamps separated from the message text like in the timeline view of messages.
#### What happened instead?
The message timestamp slightly overlaps the message text as shown in the following image.

### Operating system
Debian 11
### Browser information
Version 98.0.4758.80 (Official Build) (64-bit)
### URL for webapp
Element version: 1.10.2 Olm version: 3.2.8
### Application version
Element version: 1.10.2 Olm version: 3.2.8
### Homeserver
Synapse 1.52.0
### Will you send logs?
No | non_priority | right panel thread view time stamp overlaps message text steps to reproduce where are you starting what can you see timeline open on a room with a preexisting thread consisting of multiple messages what do you click i click on the thread view button in the upper right outcome what did you expect i expect to see the message with timestamps separated from the message text like in the timeline view of messages what happened instead the message timestamp slightly overlaps the message text as shown in the following image operating system debian browser information version official build bit url for webapp element version olm version application version element version olm version homeserver synapse will you send logs no | 0 |
82,460 | 23,788,337,641 | IssuesEvent | 2022-09-02 12:21:40 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | sane-backends fails to cross-compile on aarch64 | 6.topic: cross-compilation 0.kind: build failure | ### Steps To Reproduce
Steps to reproduce the behavior:
1. `nix build nixpkgs#pkgsCross.aarch64-multiplatform.sane-backends`
### Build log
(this is the first error, the sane-desc problem would appear later in the build if we skip pieusb by setting BACKENDS=genesys for example).
```
pieusb_buffer.c: In function 'sanei_pieusb_buffer_create':
pieusb_buffer.c:201:2: error: #error mmap(2) not available, aborting
201 | #error mmap(2) not available, aborting
| ^~~~~
pieusb_buffer.c: In function 'sanei_pieusb_buffer_delete':
pieusb_buffer.c:241:2: error: #error mmap(2) not available, aborting
241 | #error mmap(2) not available, aborting
| ^~~~~
rm -f ricoh2-s.c
```
### Additional context
The `sane-desc` tool executed during the build procedure in `postInstall` is built for the target architecture, not for the build machine architecture.
The `pieusb` backend of sane uses autoconf's `HAVE_MMAP` which is never defined under cross-compilation (since it's checks the availability of the mmap syscall during the build-process on the build-machine). In consequence the build aborts.
### Metadata
```console
nix run nixpkgs#nix-info -- -m
- system: `"x86_64-linux"`
- host os: `Linux 5.10.132, NixOS, 22.05 (Quokka), 22.05.20220728.9370544`
- multi-user?: `yes`
- sandbox: `yes`
- version: `nix-env (Nix) 2.8.1`
- channels(yvesf): `""`
- nixpkgs: `/nix/var/nix/profiles/per-user/root/channels/nixos`
```
| 1.0 | sane-backends fails to cross-compile on aarch64 - ### Steps To Reproduce
Steps to reproduce the behavior:
1. `nix build nixpkgs#pkgsCross.aarch64-multiplatform.sane-backends`
### Build log
(this is the first error, the sane-desc problem would appear later in the build if we skip pieusb by setting BACKENDS=genesys for example).
```
pieusb_buffer.c: In function 'sanei_pieusb_buffer_create':
pieusb_buffer.c:201:2: error: #error mmap(2) not available, aborting
201 | #error mmap(2) not available, aborting
| ^~~~~
pieusb_buffer.c: In function 'sanei_pieusb_buffer_delete':
pieusb_buffer.c:241:2: error: #error mmap(2) not available, aborting
241 | #error mmap(2) not available, aborting
| ^~~~~
rm -f ricoh2-s.c
```
### Additional context
The `sane-desc` tool executed during the build procedure in `postInstall` is built for the target architecture, not for the build machine architecture.
The `pieusb` backend of sane uses autoconf's `HAVE_MMAP` which is never defined under cross-compilation (since it's checks the availability of the mmap syscall during the build-process on the build-machine). In consequence the build aborts.
### Metadata
```console
nix run nixpkgs#nix-info -- -m
- system: `"x86_64-linux"`
- host os: `Linux 5.10.132, NixOS, 22.05 (Quokka), 22.05.20220728.9370544`
- multi-user?: `yes`
- sandbox: `yes`
- version: `nix-env (Nix) 2.8.1`
- channels(yvesf): `""`
- nixpkgs: `/nix/var/nix/profiles/per-user/root/channels/nixos`
```
| non_priority | sane backends fails to cross compile on steps to reproduce steps to reproduce the behavior nix build nixpkgs pkgscross multiplatform sane backends build log this is the first error the sane desc problem would appear later in the build if we skip pieusb by setting backends genesys for example pieusb buffer c in function sanei pieusb buffer create pieusb buffer c error error mmap not available aborting error mmap not available aborting pieusb buffer c in function sanei pieusb buffer delete pieusb buffer c error error mmap not available aborting error mmap not available aborting rm f s c additional context the sane desc tool executed during the build procedure in postinstall is built for the target architecture not for the build machine architecture the pieusb backend of sane uses autoconf s have mmap which is never defined under cross compilation since it s checks the availability of the mmap syscall during the build process on the build machine in consequence the build aborts metadata console nix run nixpkgs nix info m system linux host os linux nixos quokka multi user yes sandbox yes version nix env nix channels yvesf nixpkgs nix var nix profiles per user root channels nixos | 0 |
15,819 | 9,102,155,099 | IssuesEvent | 2019-02-20 13:05:07 | actor-framework/actor-framework | https://api.github.com/repos/actor-framework/actor-framework | closed | Serialize outgoing messages in proxy instances | new feature performance | Currently, the BASP broker serializes all outgoing messages. This slows the multiplexer thread (also see #819), causing CAF to waste cycles in this thread it should rather spend doing I/O. By moving the serialization into the proxies and scheduling them as ordinary actors, we can offload a significant amount of work. | True | Serialize outgoing messages in proxy instances - Currently, the BASP broker serializes all outgoing messages. This slows the multiplexer thread (also see #819), causing CAF to waste cycles in this thread it should rather spend doing I/O. By moving the serialization into the proxies and scheduling them as ordinary actors, we can offload a significant amount of work. | non_priority | serialize outgoing messages in proxy instances currently the basp broker serializes all outgoing messages this slows the multiplexer thread also see causing caf to waste cycles in this thread it should rather spend doing i o by moving the serialization into the proxies and scheduling them as ordinary actors we can offload a significant amount of work | 0 |
56,489 | 6,520,723,098 | IssuesEvent | 2017-08-28 17:41:02 | eventespresso/event-espresso-core | https://api.github.com/repos/eventespresso/event-espresso-core | closed | Price modifier surcharge conflicts with promotional code | bug needs testing | > Before submitting your issue, please ensure that what you are reporting is specific to Event Espresso 4.
When submitting an issue, please follow this rough guideline for your report.
### Is this a bug report?
* [/] yes
* [ ] no
### What branch did this occur in?
Master
### What version of WordPress is on the site this issue happened?
4.7.3
### Outline the steps to reproduce
I have implemented a mandatory transaction fee for every transaction base on the code snippet from here:
https://github.com/eventespresso/ee-code-snippet-library/blob/master/checkout/bc_ee_apply_transaction_surcharge.php
It works perfectly except when an overall promotional code apply to transaction, the total price will calculate strangely. For example, if I put a 50% off promo code in, the Total will be 50% off (including the surcharge). However when I refresh the checkout page, the promote code will then only apply to everything except the surcharge. I believe the latter is the correct result, but why it is incorrect at first? I thought it might the priority of the applying the filter, but after a few test, not good outcome. Please find my code below:
```
function bc_ee_determine_whether_to_apply_surcharge() {
// CHANGE $surcharge_QST_ID VALUE TO MATCH THE ID OF YOUR QUESTION
$surcharge_QST_ID = 14;
if ( isset( $_REQUEST[ 'ee_reg_qstn' ] ) ) {
foreach ( $_REQUEST[ 'ee_reg_qstn' ] as $registrations ) {
if ( ! empty( $registrations ) ) {
foreach ( $registrations as $QST_ID => $response ) {
if ( $QST_ID === $surcharge_QST_ID ) {
switch ( $response ) {
// CHANGE THESE TO EXACTLY MATCH THE ANSWER OPTIONS FOR YOUR QUESTION
// THEN EDIT / ADD / DELETE THE FUNCTIONS BELOW
// WHOSE NAMES MATCH THESE OPTIONS
// YOU CAN ADD NEW OPTIONS, JUST MAKE SURE TO HAVE A CORRESPONDING
// FUNCTION FOR SETTING THE SURCHARGE DETAILS
case 'Ticket Transaction Fee' :
// apply the surcharge
add_filter( 'FHEE__bc_ee_apply_transaction_surcharge__apply_surcharge', '__return_true' );
// hook into function below to set surcharge details
add_filter( 'FHEE__bc_ee_apply_transaction_surcharge__surcharge_details', 'bc_ee_ticket_service_fee_surcharge_details' );
break;
}
}
}
}
}
}
}
add_action( 'AHEE__EE_System__core_loaded_and_ready', 'bc_ee_determine_whether_to_apply_surcharge', 1 );
/**
* EDIT THIS TO HOLD THE DETAILS FOR ONE OF YOUR ANSWER OPTIONS
* @return array
*/
function bc_ee_ticket_service_fee_surcharge_details() {
return array(
'name' => 'Ticket Transaction Fee',
'code' => 'ticket-transaction-fee',
'description' => 'service fee for online tickets',
'unit_price' => 3.00,
'taxable' => false,
);
}
/**
* DO NOT EDIT ANYTHING EXCEPT DEFAULT SURCHARGE DETAILS
*
* bc_ee_apply_transaction_surcharge
*
* @param \EE_Checkout $checkout
* @return \EE_Checkout
*/
function bc_ee_apply_transaction_surcharge( EE_Checkout $checkout ) {
// DEFAULT SURCHARGE DETAILS - EDIT THIS
$surcharge_details = apply_filters(
'FHEE__bc_ee_apply_transaction_surcharge__surcharge_details',
array(
// name for surcharge that will be displayed, ie: 'printing fee'
'name' => 'Ticket Transaction Fee',
// unique code used to identify surcharge in the db, ie: 'print-at-home-fee'
'code' => 'ticket-transaction-fee',
// 'fee for printing tickets'
'description' => 'service fee for online tickets',
// surcharge amount
'unit_price' => 3.00,
// whether or not tax is applied on top of the surcharge
'taxable' => false,
)
);
// STOP EDITING
// apply the surcharge ?
if ( ! apply_filters( 'FHEE__bc_ee_apply_transaction_surcharge__apply_surcharge', false ) ) {
return $checkout;
}
// verify checkout
if ( ! $checkout instanceof EE_Checkout ) {
return $checkout;
}
// verify cart
$cart = $checkout->cart;
if ( ! $cart instanceof EE_Cart ) {
return $checkout;
}
// verify grand total line item
$grand_total = $cart->get_grand_total();
if ( ! $grand_total instanceof EE_Line_Item ) {
return $checkout;
}
// has surcharge already been applied ?
$existing_surcharge = $grand_total->get_child_line_item( $surcharge_details[ 'code' ] );
if ( $existing_surcharge instanceof EE_Line_Item ) {
return $checkout;
}
EE_Registry::instance()->load_helper( 'Line_Item' );
$pre_tax_subtotal = EEH_Line_Item::get_pre_tax_subtotal( $grand_total );
$pre_tax_subtotal->add_child_line_item(
EE_Line_Item::new_instance( array(
'LIN_name' => $surcharge_details[ 'name' ],
'LIN_desc' => $surcharge_details[ 'description' ],
'LIN_unit_price' => (float) $surcharge_details[ 'unit_price' ],
'LIN_quantity' => 1,
'LIN_is_taxable' => $surcharge_details[ 'taxable' ],
'LIN_order' => 0,
'LIN_total' => (float) $surcharge_details[ 'unit_price' ],
'LIN_type' => EEM_Line_Item::type_line_item,
'LIN_code' => $surcharge_details[ 'code' ],
) )
);
$grand_total->recalculate_total_including_taxes();
return $checkout;
}
add_filter( 'FHEE__EED_Single_Page_Checkout___initialize_checkout__checkout', 'bc_ee_apply_transaction_surcharge');
```
### Please include any screenshots ar screencasts that can help illustrate the issue (if possible).
### Please include any links to the page(s) demonstrating this issue (if possible).
| 1.0 | Price modifier surcharge conflicts with promotional code - > Before submitting your issue, please ensure that what you are reporting is specific to Event Espresso 4.
When submitting an issue, please follow this rough guideline for your report.
### Is this a bug report?
* [/] yes
* [ ] no
### What branch did this occur in?
Master
### What version of WordPress is on the site this issue happened?
4.7.3
### Outline the steps to reproduce
I have implemented a mandatory transaction fee for every transaction base on the code snippet from here:
https://github.com/eventespresso/ee-code-snippet-library/blob/master/checkout/bc_ee_apply_transaction_surcharge.php
It works perfectly except when an overall promotional code apply to transaction, the total price will calculate strangely. For example, if I put a 50% off promo code in, the Total will be 50% off (including the surcharge). However when I refresh the checkout page, the promote code will then only apply to everything except the surcharge. I believe the latter is the correct result, but why it is incorrect at first? I thought it might the priority of the applying the filter, but after a few test, not good outcome. Please find my code below:
```
function bc_ee_determine_whether_to_apply_surcharge() {
// CHANGE $surcharge_QST_ID VALUE TO MATCH THE ID OF YOUR QUESTION
$surcharge_QST_ID = 14;
if ( isset( $_REQUEST[ 'ee_reg_qstn' ] ) ) {
foreach ( $_REQUEST[ 'ee_reg_qstn' ] as $registrations ) {
if ( ! empty( $registrations ) ) {
foreach ( $registrations as $QST_ID => $response ) {
if ( $QST_ID === $surcharge_QST_ID ) {
switch ( $response ) {
// CHANGE THESE TO EXACTLY MATCH THE ANSWER OPTIONS FOR YOUR QUESTION
// THEN EDIT / ADD / DELETE THE FUNCTIONS BELOW
// WHOSE NAMES MATCH THESE OPTIONS
// YOU CAN ADD NEW OPTIONS, JUST MAKE SURE TO HAVE A CORRESPONDING
// FUNCTION FOR SETTING THE SURCHARGE DETAILS
case 'Ticket Transaction Fee' :
// apply the surcharge
add_filter( 'FHEE__bc_ee_apply_transaction_surcharge__apply_surcharge', '__return_true' );
// hook into function below to set surcharge details
add_filter( 'FHEE__bc_ee_apply_transaction_surcharge__surcharge_details', 'bc_ee_ticket_service_fee_surcharge_details' );
break;
}
}
}
}
}
}
}
add_action( 'AHEE__EE_System__core_loaded_and_ready', 'bc_ee_determine_whether_to_apply_surcharge', 1 );
/**
* EDIT THIS TO HOLD THE DETAILS FOR ONE OF YOUR ANSWER OPTIONS
* @return array
*/
function bc_ee_ticket_service_fee_surcharge_details() {
return array(
'name' => 'Ticket Transaction Fee',
'code' => 'ticket-transaction-fee',
'description' => 'service fee for online tickets',
'unit_price' => 3.00,
'taxable' => false,
);
}
/**
* DO NOT EDIT ANYTHING EXCEPT DEFAULT SURCHARGE DETAILS
*
* bc_ee_apply_transaction_surcharge
*
* @param \EE_Checkout $checkout
* @return \EE_Checkout
*/
function bc_ee_apply_transaction_surcharge( EE_Checkout $checkout ) {
// DEFAULT SURCHARGE DETAILS - EDIT THIS
$surcharge_details = apply_filters(
'FHEE__bc_ee_apply_transaction_surcharge__surcharge_details',
array(
// name for surcharge that will be displayed, ie: 'printing fee'
'name' => 'Ticket Transaction Fee',
// unique code used to identify surcharge in the db, ie: 'print-at-home-fee'
'code' => 'ticket-transaction-fee',
// 'fee for printing tickets'
'description' => 'service fee for online tickets',
// surcharge amount
'unit_price' => 3.00,
// whether or not tax is applied on top of the surcharge
'taxable' => false,
)
);
// STOP EDITING
// apply the surcharge ?
if ( ! apply_filters( 'FHEE__bc_ee_apply_transaction_surcharge__apply_surcharge', false ) ) {
return $checkout;
}
// verify checkout
if ( ! $checkout instanceof EE_Checkout ) {
return $checkout;
}
// verify cart
$cart = $checkout->cart;
if ( ! $cart instanceof EE_Cart ) {
return $checkout;
}
// verify grand total line item
$grand_total = $cart->get_grand_total();
if ( ! $grand_total instanceof EE_Line_Item ) {
return $checkout;
}
// has surcharge already been applied ?
$existing_surcharge = $grand_total->get_child_line_item( $surcharge_details[ 'code' ] );
if ( $existing_surcharge instanceof EE_Line_Item ) {
return $checkout;
}
EE_Registry::instance()->load_helper( 'Line_Item' );
$pre_tax_subtotal = EEH_Line_Item::get_pre_tax_subtotal( $grand_total );
$pre_tax_subtotal->add_child_line_item(
EE_Line_Item::new_instance( array(
'LIN_name' => $surcharge_details[ 'name' ],
'LIN_desc' => $surcharge_details[ 'description' ],
'LIN_unit_price' => (float) $surcharge_details[ 'unit_price' ],
'LIN_quantity' => 1,
'LIN_is_taxable' => $surcharge_details[ 'taxable' ],
'LIN_order' => 0,
'LIN_total' => (float) $surcharge_details[ 'unit_price' ],
'LIN_type' => EEM_Line_Item::type_line_item,
'LIN_code' => $surcharge_details[ 'code' ],
) )
);
$grand_total->recalculate_total_including_taxes();
return $checkout;
}
add_filter( 'FHEE__EED_Single_Page_Checkout___initialize_checkout__checkout', 'bc_ee_apply_transaction_surcharge');
```
### Please include any screenshots ar screencasts that can help illustrate the issue (if possible).
### Please include any links to the page(s) demonstrating this issue (if possible).
| non_priority | price modifier surcharge conflicts with promotional code before submitting your issue please ensure that what you are reporting is specific to event espresso when submitting an issue please follow this rough guideline for your report is this a bug report yes no what branch did this occur in master what version of wordpress is on the site this issue happened outline the steps to reproduce i have implemented a mandatory transaction fee for every transaction base on the code snippet from here it works perfectly except when an overall promotional code apply to transaction the total price will calculate strangely for example if i put a off promo code in the total will be off including the surcharge however when i refresh the checkout page the promote code will then only apply to everything except the surcharge i believe the latter is the correct result but why it is incorrect at first i thought it might the priority of the applying the filter but after a few test not good outcome please find my code below function bc ee determine whether to apply surcharge change surcharge qst id value to match the id of your question surcharge qst id if isset request foreach request as registrations if empty registrations foreach registrations as qst id response if qst id surcharge qst id switch response change these to exactly match the answer options for your question then edit add delete the functions below whose names match these options you can add new options just make sure to have a corresponding function for setting the surcharge details case ticket transaction fee apply the surcharge add filter fhee bc ee apply transaction surcharge apply surcharge return true hook into function below to set surcharge details add filter fhee bc ee apply transaction surcharge surcharge details bc ee ticket service fee surcharge details break add action ahee ee system core loaded and ready bc ee determine whether to apply surcharge edit this to hold the details for one of your answer options return array function bc ee ticket service fee surcharge details return array name ticket transaction fee code ticket transaction fee description service fee for online tickets unit price taxable false do not edit anything except default surcharge details bc ee apply transaction surcharge param ee checkout checkout return ee checkout function bc ee apply transaction surcharge ee checkout checkout default surcharge details edit this surcharge details apply filters fhee bc ee apply transaction surcharge surcharge details array name for surcharge that will be displayed ie printing fee name ticket transaction fee unique code used to identify surcharge in the db ie print at home fee code ticket transaction fee fee for printing tickets description service fee for online tickets surcharge amount unit price whether or not tax is applied on top of the surcharge taxable false stop editing apply the surcharge if apply filters fhee bc ee apply transaction surcharge apply surcharge false return checkout verify checkout if checkout instanceof ee checkout return checkout verify cart cart checkout cart if cart instanceof ee cart return checkout verify grand total line item grand total cart get grand total if grand total instanceof ee line item return checkout has surcharge already been applied existing surcharge grand total get child line item surcharge details if existing surcharge instanceof ee line item return checkout ee registry instance load helper line item pre tax subtotal eeh line item get pre tax subtotal grand total pre tax subtotal add child line item ee line item new instance array lin name surcharge details lin desc surcharge details lin unit price float surcharge details lin quantity lin is taxable surcharge details lin order lin total float surcharge details lin type eem line item type line item lin code surcharge details grand total recalculate total including taxes return checkout add filter fhee eed single page checkout initialize checkout checkout bc ee apply transaction surcharge please include any screenshots ar screencasts that can help illustrate the issue if possible please include any links to the page s demonstrating this issue if possible | 0 |
30,625 | 6,198,214,847 | IssuesEvent | 2017-07-05 18:38:32 | contao/core-bundle | https://api.github.com/repos/contao/core-bundle | closed | Contao 4.4: new DCA picker does not work for non-admins | defect | ### Reproduction
1. Log-in as a non-admin user.
2. Create a new text element and write some text.
3. Select the text and choose _Edit/insert link_.
4. Click on the "browse" icon.
You will see the message "Forbidden - Invalid content element ID".
### Cause
The picker popup is opened with the following GET parameters:
```
array(5) {
["target"] => string(20) "tl_content.singleSRC"
["value"] => string(2) "10"
["context"] => string(4) "link"
["popup"] => string(1) "1"
["do"] => string(4) "page"
}
```
However, the function `tl_content::checkPermissions` requires an `id` parameter, containing the `id` of the article. Since this is missing, `tl_content::checkAccessToElement` is called with `NULL` for `$id` and thus the `AccessDeniedException` with `Invalid content element ID ` is thrown.
It still works for admins, since no such permissions are checked for admins of course. | 1.0 | Contao 4.4: new DCA picker does not work for non-admins - ### Reproduction
1. Log-in as a non-admin user.
2. Create a new text element and write some text.
3. Select the text and choose _Edit/insert link_.
4. Click on the "browse" icon.
You will see the message "Forbidden - Invalid content element ID".
### Cause
The picker popup is opened with the following GET parameters:
```
array(5) {
["target"] => string(20) "tl_content.singleSRC"
["value"] => string(2) "10"
["context"] => string(4) "link"
["popup"] => string(1) "1"
["do"] => string(4) "page"
}
```
However, the function `tl_content::checkPermissions` requires an `id` parameter, containing the `id` of the article. Since this is missing, `tl_content::checkAccessToElement` is called with `NULL` for `$id` and thus the `AccessDeniedException` with `Invalid content element ID ` is thrown.
It still works for admins, since no such permissions are checked for admins of course. | non_priority | contao new dca picker does not work for non admins reproduction log in as a non admin user create a new text element and write some text select the text and choose edit insert link click on the browse icon you will see the message forbidden invalid content element id cause the picker popup is opened with the following get parameters array string tl content singlesrc string string link string string page however the function tl content checkpermissions requires an id parameter containing the id of the article since this is missing tl content checkaccesstoelement is called with null for id and thus the accessdeniedexception with invalid content element id is thrown it still works for admins since no such permissions are checked for admins of course | 0 |
192,624 | 22,215,980,210 | IssuesEvent | 2022-06-08 01:43:26 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | reopened | CVE-2019-9857 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2019-9857 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/inotify/inotify_user.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/inotify/inotify_user.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel through 5.0.2, the function inotify_update_existing_watch() in fs/notify/inotify/inotify_user.c neglects to call fsnotify_put_mark() with IN_MASK_CREATE after fsnotify_find_mark(), which will cause a memory leak (aka refcount leak). Finally, this will cause a denial of service.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-9857>CVE-2019-9857</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2019-9857">https://www.linuxkernelcves.com/cves/CVE-2019-9857</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.1-rc2,v4.19.36,v5.0.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-9857 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2019-9857 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/inotify/inotify_user.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/inotify/inotify_user.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel through 5.0.2, the function inotify_update_existing_watch() in fs/notify/inotify/inotify_user.c neglects to call fsnotify_put_mark() with IN_MASK_CREATE after fsnotify_find_mark(), which will cause a memory leak (aka refcount leak). Finally, this will cause a denial of service.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-9857>CVE-2019-9857</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2019-9857">https://www.linuxkernelcves.com/cves/CVE-2019-9857</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.1-rc2,v4.19.36,v5.0.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files fs notify inotify inotify user c fs notify inotify inotify user c vulnerability details in the linux kernel through the function inotify update existing watch in fs notify inotify inotify user c neglects to call fsnotify put mark with in mask create after fsnotify find mark which will cause a memory leak aka refcount leak finally this will cause a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
6,046 | 4,127,839,026 | IssuesEvent | 2016-06-10 01:16:41 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Font Import Plug-in Discrepancy. | bug topic:editor usability | When a large path to a font file is present the options box is crammed into an unusable section on the window making it unusable. If this bug is present here it might also be present in other parts of the editor.
Visual of the Problem:

| True | Font Import Plug-in Discrepancy. - When a large path to a font file is present the options box is crammed into an unusable section on the window making it unusable. If this bug is present here it might also be present in other parts of the editor.
Visual of the Problem:

| non_priority | font import plug in discrepancy when a large path to a font file is present the options box is crammed into an unusable section on the window making it unusable if this bug is present here it might also be present in other parts of the editor visual of the problem | 0 |
288,011 | 24,881,271,570 | IssuesEvent | 2022-10-28 01:28:56 | rancher/rke2 | https://api.github.com/repos/rancher/rke2 | closed | Validate SLE Micro 5.3 | kind/test | Perform all standard new OS validations:
1. Sonobuoy conformance checks
2. SUC upgrade
3. Install Rancher as local management cluster
4. Perform a cluster-reset | 1.0 | Validate SLE Micro 5.3 - Perform all standard new OS validations:
1. Sonobuoy conformance checks
2. SUC upgrade
3. Install Rancher as local management cluster
4. Perform a cluster-reset | non_priority | validate sle micro perform all standard new os validations sonobuoy conformance checks suc upgrade install rancher as local management cluster perform a cluster reset | 0 |
5,802 | 30,727,495,672 | IssuesEvent | 2023-07-27 21:00:22 | cncf/tag-contributor-strategy | https://api.github.com/repos/cncf/tag-contributor-strategy | closed | Create a roadmap for the TAG | wg/governance wg/contribgrowth mentoring wg/maintainers-circle | In #329 we discussed how helpful having a roadmap is to encourage contributors and focus their efforts on high impact items. We should take our own advice and make one ourselves. Couple thoughts:
* Avoid making a wishlist. Limit to what we can realistically do with the current amount of time / velocity on projects.
* If needed call out what isn't on the roadmap that people may be looking for and wondering about.
* Prioritize or otherwise call out hard commitments for supporting the TOC.
* Make sure to include any time spent generally supporting projects, sometimes what we do doesn't fall into a "feature" type bucket but is still important. | True | Create a roadmap for the TAG - In #329 we discussed how helpful having a roadmap is to encourage contributors and focus their efforts on high impact items. We should take our own advice and make one ourselves. Couple thoughts:
* Avoid making a wishlist. Limit to what we can realistically do with the current amount of time / velocity on projects.
* If needed call out what isn't on the roadmap that people may be looking for and wondering about.
* Prioritize or otherwise call out hard commitments for supporting the TOC.
* Make sure to include any time spent generally supporting projects, sometimes what we do doesn't fall into a "feature" type bucket but is still important. | non_priority | create a roadmap for the tag in we discussed how helpful having a roadmap is to encourage contributors and focus their efforts on high impact items we should take our own advice and make one ourselves couple thoughts avoid making a wishlist limit to what we can realistically do with the current amount of time velocity on projects if needed call out what isn t on the roadmap that people may be looking for and wondering about prioritize or otherwise call out hard commitments for supporting the toc make sure to include any time spent generally supporting projects sometimes what we do doesn t fall into a feature type bucket but is still important | 0 |
32,235 | 13,784,183,377 | IssuesEvent | 2020-10-08 20:27:01 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | Issues with the fstream file in the database | Language Service more info needed | **Type: LanguageService**
I needed to create a program that can read or write from a file and even after naming the path, the terminal keeps stating that it's object types are undefined.
**Describe the bug**
- OS and Version: Windows 10 Pro version 2004
- VS Code Version: 1.49.3
- C/C++ Extension Version: v1.0.1
- Other extensions you installed (and if the issue persists after disabling them): A rather small set of other extensions that work in tandem to create Unity projects. (If I disabled them it would likely not change anything except whether or not I can use Unity.)
- Does this issue involve using SSH remote to run the extension on a remote machine?:
- The files for <fstream> keep stating they are undefined even after including them.
**Steps to reproduce**
The only step needed is to open a .cpp file and use `#include <fstream>`, and then put an object creation statement in main.
**Expected behavior**
I expected the program to let me state and use ifstream, ofstream, and fstream objects.
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
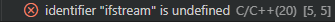
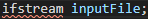 | 1.0 | Issues with the fstream file in the database - **Type: LanguageService**
I needed to create a program that can read or write from a file and even after naming the path, the terminal keeps stating that it's object types are undefined.
**Describe the bug**
- OS and Version: Windows 10 Pro version 2004
- VS Code Version: 1.49.3
- C/C++ Extension Version: v1.0.1
- Other extensions you installed (and if the issue persists after disabling them): A rather small set of other extensions that work in tandem to create Unity projects. (If I disabled them it would likely not change anything except whether or not I can use Unity.)
- Does this issue involve using SSH remote to run the extension on a remote machine?:
- The files for <fstream> keep stating they are undefined even after including them.
**Steps to reproduce**
The only step needed is to open a .cpp file and use `#include <fstream>`, and then put an object creation statement in main.
**Expected behavior**
I expected the program to let me state and use ifstream, ofstream, and fstream objects.
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
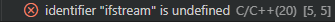
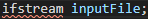 | non_priority | issues with the fstream file in the database type languageservice i needed to create a program that can read or write from a file and even after naming the path the terminal keeps stating that it s object types are undefined describe the bug os and version windows pro version vs code version c c extension version other extensions you installed and if the issue persists after disabling them a rather small set of other extensions that work in tandem to create unity projects if i disabled them it would likely not change anything except whether or not i can use unity does this issue involve using ssh remote to run the extension on a remote machine the files for keep stating they are undefined even after including them steps to reproduce the only step needed is to open a cpp file and use include and then put an object creation statement in main expected behavior i expected the program to let me state and use ifstream ofstream and fstream objects screenshots | 0 |
127,068 | 18,010,259,330 | IssuesEvent | 2021-09-16 07:46:25 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | opened | CVE-2020-27171 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2020-27171 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/bpf/verifier.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/bpf/verifier.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.11.8. kernel/bpf/verifier.c has an off-by-one error (with a resultant integer underflow) affecting out-of-bounds speculation on pointer arithmetic, leading to side-channel attacks that defeat Spectre mitigations and obtain sensitive information from kernel memory, aka CID-10d2bb2e6b1d.
<p>Publish Date: 2021-03-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-27171>CVE-2020-27171</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/10d2bb2e6b1d8c4576c56a748f697dbeb8388899">https://github.com/torvalds/linux/commit/10d2bb2e6b1d8c4576c56a748f697dbeb8388899</a></p>
<p>Release Date: 2021-03-17</p>
<p>Fix Resolution: Replace or update the following file: verifier.c</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-27171 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2020-27171 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/bpf/verifier.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/bpf/verifier.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.11.8. kernel/bpf/verifier.c has an off-by-one error (with a resultant integer underflow) affecting out-of-bounds speculation on pointer arithmetic, leading to side-channel attacks that defeat Spectre mitigations and obtain sensitive information from kernel memory, aka CID-10d2bb2e6b1d.
<p>Publish Date: 2021-03-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-27171>CVE-2020-27171</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/10d2bb2e6b1d8c4576c56a748f697dbeb8388899">https://github.com/torvalds/linux/commit/10d2bb2e6b1d8c4576c56a748f697dbeb8388899</a></p>
<p>Release Date: 2021-03-17</p>
<p>Fix Resolution: Replace or update the following file: verifier.c</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href vulnerable source files kernel bpf verifier c kernel bpf verifier c vulnerability details an issue was discovered in the linux kernel before kernel bpf verifier c has an off by one error with a resultant integer underflow affecting out of bounds speculation on pointer arithmetic leading to side channel attacks that defeat spectre mitigations and obtain sensitive information from kernel memory aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following file verifier c step up your open source security game with whitesource | 0 |
145,012 | 19,319,012,251 | IssuesEvent | 2021-12-14 01:49:49 | peterwkc85/selenium-jupiter | https://api.github.com/repos/peterwkc85/selenium-jupiter | opened | CVE-2019-14540 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /selenium-jupiter/build.gradle</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- docker-client-8.15.2.jar (Root Library)
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-14540 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-14540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /selenium-jupiter/build.gradle</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- docker-client-8.15.2.jar (Root Library)
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file selenium jupiter build gradle path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy docker client jar root library x jackson databind jar vulnerable library vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
7,150 | 3,081,270,311 | IssuesEvent | 2015-08-22 15:04:48 | RexOps/Rex | https://api.github.com/repos/RexOps/Rex | closed | Documentation for Rex::Transaction wrong | documentation easy-to-fix | The documentation says that the `on_rollback {}` code block should be called before the `transaction {}` block, but this is wrong, because then rex don't know that this specific `on_rollback` code belongs to which `transaction` code.
So the right documentation would be:
```perl
task "do-something", "server01", sub {
transaction {
on_rollback {
rmdir "/tmp/mydata";
};
mkdir "/tmp/mydata";
upload "files/myapp.tar.gz", "/tmp/mydata";
run "cd /tmp/mydata; tar xzf myapp.tar.gz";
if($? != 0) { die("Error extracting myapp.tar.gz"); }
};
};
``` | 1.0 | Documentation for Rex::Transaction wrong - The documentation says that the `on_rollback {}` code block should be called before the `transaction {}` block, but this is wrong, because then rex don't know that this specific `on_rollback` code belongs to which `transaction` code.
So the right documentation would be:
```perl
task "do-something", "server01", sub {
transaction {
on_rollback {
rmdir "/tmp/mydata";
};
mkdir "/tmp/mydata";
upload "files/myapp.tar.gz", "/tmp/mydata";
run "cd /tmp/mydata; tar xzf myapp.tar.gz";
if($? != 0) { die("Error extracting myapp.tar.gz"); }
};
};
``` | non_priority | documentation for rex transaction wrong the documentation says that the on rollback code block should be called before the transaction block but this is wrong because then rex don t know that this specific on rollback code belongs to which transaction code so the right documentation would be perl task do something sub transaction on rollback rmdir tmp mydata mkdir tmp mydata upload files myapp tar gz tmp mydata run cd tmp mydata tar xzf myapp tar gz if die error extracting myapp tar gz | 0 |
306,452 | 23,160,794,182 | IssuesEvent | 2022-07-29 17:30:12 | tskit-dev/tskit | https://api.github.com/repos/tskit-dev/tskit | closed | Export examples section needed | documentation | When we're next thinking about how to rejig the docs, we badly need to get a section where we can give some explanation and text about how to export data to VCF etc. The docstring for write_vcf is huge at the moment, and it would be much better structured (and we could say more, giving example etc) if it was done in an example-driven way like the msprime docs.
I'm not sure where this fits in the overall structure, though. | 1.0 | Export examples section needed - When we're next thinking about how to rejig the docs, we badly need to get a section where we can give some explanation and text about how to export data to VCF etc. The docstring for write_vcf is huge at the moment, and it would be much better structured (and we could say more, giving example etc) if it was done in an example-driven way like the msprime docs.
I'm not sure where this fits in the overall structure, though. | non_priority | export examples section needed when we re next thinking about how to rejig the docs we badly need to get a section where we can give some explanation and text about how to export data to vcf etc the docstring for write vcf is huge at the moment and it would be much better structured and we could say more giving example etc if it was done in an example driven way like the msprime docs i m not sure where this fits in the overall structure though | 0 |
441,475 | 30,785,578,104 | IssuesEvent | 2023-07-31 13:02:38 | hhuslamlab/website | https://api.github.com/repos/hhuslamlab/website | closed | HOW TO INSTALL JUPYTER NOTEBOOK ON UBUNTU? | documentation | Nele has tried to install JupyterNotebook but the normal `pip install` command doesn't work
What has worked for her instead are
``` shell=
sudo apt install epiphany jupyter-notebook
```
```shell=
sudo apt install jupyter-notebook
```
```shell=
sudo apt install python3-notebook jupyter jupyter-core python-ipykernel
```
She will send you the exact error message.
Source: https://askubuntu.com/questions/737094/jupyter-notebook-installation | 1.0 | HOW TO INSTALL JUPYTER NOTEBOOK ON UBUNTU? - Nele has tried to install JupyterNotebook but the normal `pip install` command doesn't work
What has worked for her instead are
``` shell=
sudo apt install epiphany jupyter-notebook
```
```shell=
sudo apt install jupyter-notebook
```
```shell=
sudo apt install python3-notebook jupyter jupyter-core python-ipykernel
```
She will send you the exact error message.
Source: https://askubuntu.com/questions/737094/jupyter-notebook-installation | non_priority | how to install jupyter notebook on ubuntu nele has tried to install jupyternotebook but the normal pip install command doesn t work what has worked for her instead are shell sudo apt install epiphany jupyter notebook shell sudo apt install jupyter notebook shell sudo apt install notebook jupyter jupyter core python ipykernel she will send you the exact error message source | 0 |
239,440 | 26,231,558,538 | IssuesEvent | 2023-01-05 00:58:52 | ibm-cio-vulnerability-scanning/insomnia | https://api.github.com/repos/ibm-cio-vulnerability-scanning/insomnia | opened | CVE-2022-23540 (High) detected in jsonwebtoken-5.7.0.tgz | security vulnerability | ## CVE-2022-23540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsonwebtoken-5.7.0.tgz</b></p></summary>
<p>JSON Web Token implementation (symmetric and asymmetric)</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonwebtoken/-/jsonwebtoken-5.7.0.tgz">https://registry.npmjs.org/jsonwebtoken/-/jsonwebtoken-5.7.0.tgz</a></p>
<p>
Dependency Hierarchy:
- jwt-authentication-0.4.0.tgz (Root Library)
- :x: **jsonwebtoken-5.7.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ibm-cio-vulnerability-scanning/insomnia/commit/6584b84b5580d875cdc382437add0bd24e27b39e">6584b84b5580d875cdc382437add0bd24e27b39e</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In versions `<=8.5.1` of `jsonwebtoken` library, lack of algorithm definition in the `jwt.verify()` function can lead to signature validation bypass due to defaulting to the `none` algorithm for signature verification. Users are affected if you do not specify algorithms in the `jwt.verify()` function. This issue has been fixed, please update to version 9.0.0 which removes the default support for the none algorithm in the `jwt.verify()` method. There will be no impact, if you update to version 9.0.0 and you don’t need to allow for the `none` algorithm. If you need 'none' algorithm, you have to explicitly specify that in `jwt.verify()` options.
<p>Publish Date: 2022-12-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23540>CVE-2022-23540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-23540">https://www.cve.org/CVERecord?id=CVE-2022-23540</a></p>
<p>Release Date: 2022-12-22</p>
<p>Fix Resolution: jsonwebtoken - 9.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-23540 (High) detected in jsonwebtoken-5.7.0.tgz - ## CVE-2022-23540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsonwebtoken-5.7.0.tgz</b></p></summary>
<p>JSON Web Token implementation (symmetric and asymmetric)</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonwebtoken/-/jsonwebtoken-5.7.0.tgz">https://registry.npmjs.org/jsonwebtoken/-/jsonwebtoken-5.7.0.tgz</a></p>
<p>
Dependency Hierarchy:
- jwt-authentication-0.4.0.tgz (Root Library)
- :x: **jsonwebtoken-5.7.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ibm-cio-vulnerability-scanning/insomnia/commit/6584b84b5580d875cdc382437add0bd24e27b39e">6584b84b5580d875cdc382437add0bd24e27b39e</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In versions `<=8.5.1` of `jsonwebtoken` library, lack of algorithm definition in the `jwt.verify()` function can lead to signature validation bypass due to defaulting to the `none` algorithm for signature verification. Users are affected if you do not specify algorithms in the `jwt.verify()` function. This issue has been fixed, please update to version 9.0.0 which removes the default support for the none algorithm in the `jwt.verify()` method. There will be no impact, if you update to version 9.0.0 and you don’t need to allow for the `none` algorithm. If you need 'none' algorithm, you have to explicitly specify that in `jwt.verify()` options.
<p>Publish Date: 2022-12-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23540>CVE-2022-23540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-23540">https://www.cve.org/CVERecord?id=CVE-2022-23540</a></p>
<p>Release Date: 2022-12-22</p>
<p>Fix Resolution: jsonwebtoken - 9.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jsonwebtoken tgz cve high severity vulnerability vulnerable library jsonwebtoken tgz json web token implementation symmetric and asymmetric library home page a href dependency hierarchy jwt authentication tgz root library x jsonwebtoken tgz vulnerable library found in head commit a href found in base branch develop vulnerability details in versions of jsonwebtoken library lack of algorithm definition in the jwt verify function can lead to signature validation bypass due to defaulting to the none algorithm for signature verification users are affected if you do not specify algorithms in the jwt verify function this issue has been fixed please update to version which removes the default support for the none algorithm in the jwt verify method there will be no impact if you update to version and you don’t need to allow for the none algorithm if you need none algorithm you have to explicitly specify that in jwt verify options publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jsonwebtoken step up your open source security game with mend | 0 |
13,350 | 2,754,354,338 | IssuesEvent | 2015-04-25 15:57:01 | Xety/Xeta | https://api.github.com/repos/Xety/Xeta | closed | Use pluralize translate function instead of conditions | Defect Language | Replace the condition by the function `__n()` :
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/article.ctp#L95
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/article.ctp#L100
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/article.ctp#L410
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/archive.ctp#L81
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/archive.ctp#L87
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/category.ctp#L70
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/category.ctp#L75
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/index.ctp#L85
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/index.ctp#L90
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/search.ctp#L67
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/search.ctp#L72
| 1.0 | Use pluralize translate function instead of conditions - Replace the condition by the function `__n()` :
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/article.ctp#L95
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/article.ctp#L100
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/article.ctp#L410
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/archive.ctp#L81
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/archive.ctp#L87
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/category.ctp#L70
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/category.ctp#L75
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/index.ctp#L85
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/index.ctp#L90
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/search.ctp#L67
https://github.com/Xety/Xeta/blob/master/src/Template/Blog/search.ctp#L72
| non_priority | use pluralize translate function instead of conditions replace the condition by the function n | 0 |
26,091 | 19,659,984,752 | IssuesEvent | 2022-01-10 16:06:13 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | Platform Infrastructure: Make Vets-API operational in EKS | operations VSP-Initiative infrastructure | ## Problem Statement
Maintaining two infrastructure delivery systems is hard. Vets-API must migrate away from BRD before sunsetting the platform's legacy delivery systems.
How might we transition Vets-API away from the legacy infrastructure?
How might we make it easier to deploy and maintain Vets-API?
How might we grant VFS and Platform Crew teams more autonomy and flexibility as it relates to the development and deployment of Vets-API (or other backend services)?
## Hypothesis or Bet
We believe that this will enable the platform to move Vets-API toward a micro-services backend architecture.
We believe that this will enable other teams to move more quickly in developing against Vets-API.
We believe that this will make it easier for other teams to develop against Vets-API.
## We will know we're done when... ("Definition of Done")
Vets-API & Reverse Proxy are fully functional in the EKS environment(s). Live traffic is flowing through these infrastructure components.
## Known Blockers/Dependencies
Dedicated engineering resources from developers/maintainers of the Vets-API application.
## Projected Launch Date
Q2 2022
## Launch Checklist
### Is this service / tool / feature...
### ... tested?
- [ ] Usability test (_TODO: link_) has been performed, to validate that new changes enable users to do what was intended and that these changes don't worsen quality elsewhere. If usability test isn't relevant for this change, document the reason for skipping it.
- [ ] ... and issues discovered in usability testing have been addressed.
* _Note on skipping: metrics that show the impact of before/after can be a substitute for usability testing._
- [ ] End-to-end [manual QA](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/quality-assurance/README.md) or [UAT](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/research/planning/what-is-uat.md) is complete, to validate there are no high-severity issues before launching
- [ ] _(if applicable)_ New functionality has thorough, automated tests running in CI/CD
### ... documented?
- [ ] New documentation is written pursuant to our [documentation style guide](https://vfs.atlassian.net/wiki/spaces/AP/pages/622264362/Style+guide)
- [ ] Product is included in the [List of VSP Products](https://docs.google.com/spreadsheets/d/1Fn2lD419WE3sTZJtN2Ensrjqaz0jH3WvLaBtn812Wjo/edit#gid=0)
* _List the existing product that this initiative fits within, or add a new product to this list._
- [ ] Internal-facing: there's a [Product Outline](https://vfs.atlassian.net/wiki/spaces/PMCP/pages/1924628490/Product+Outline+Template)
- [ ] External-facing: a [User Guide on Platform Website](https://vfs.atlassian.net/wiki/spaces/AP/pages/1477017691/Platform+website+guidelines) exists for this product/feature tool
- [ ] _(if applicable)_ Post to [#vsp-service-design](https://dsva.slack.com/channels/vsp-service-design) for external communication about this change (e.g. VSP Newsletter, customer-facing meetings)
### ... measurable
- [ ] _(if applicable)_ This change has clearly-defined success metrics, with instrumentation of those analytics where possible, or a reason documented for skipping it.
* For help, see: [Analytics team](https://depo-platform-documentation.scrollhelp.site/analytics-monitoring/Analytics-customer-support-guide.1586823275.html)
- [ ] This change has an accompanying [VSP Initiative Release Plan](https://github.com/department-of-veterans-affairs/va.gov-team/issues/new/choose).
### When you're ready to launch...
- [ ] Conduct a [go/no-go] (https://vfs.atlassian.net/wiki/spaces/AP/pages/1670938648/Platform+Crew+Office+Hours#Go%2FNo-Go) when you're almost ready to launch.
## Required Artifacts
### Documentation
* **`PRODUCT_NAME`**: _directory name used for your product documentation_
* **Product Outline**: _link to Product Outline_
* **User Guide**: _link to User Guide_
### Testing
* **Usability test**: _link to GitHub issue, or provide reason for skipping_
* **Manual QA**: _link to GitHub issue or documented results_
* **Automated tests**: _link to tests, or "N/A"_
### Measurement
* **Success metrics**: _link to where success metrics are measured, or where they're defined (Product Outline is OK), or provide reason for skipping_
* **Release plan**: _link to Release Plan ticket_
## TODOs
- [ ] Convert this issue to an epic
- [ ] Add your team's label to this epic
| 1.0 | Platform Infrastructure: Make Vets-API operational in EKS - ## Problem Statement
Maintaining two infrastructure delivery systems is hard. Vets-API must migrate away from BRD before sunsetting the platform's legacy delivery systems.
How might we transition Vets-API away from the legacy infrastructure?
How might we make it easier to deploy and maintain Vets-API?
How might we grant VFS and Platform Crew teams more autonomy and flexibility as it relates to the development and deployment of Vets-API (or other backend services)?
## Hypothesis or Bet
We believe that this will enable the platform to move Vets-API toward a micro-services backend architecture.
We believe that this will enable other teams to move more quickly in developing against Vets-API.
We believe that this will make it easier for other teams to develop against Vets-API.
## We will know we're done when... ("Definition of Done")
Vets-API & Reverse Proxy are fully functional in the EKS environment(s). Live traffic is flowing through these infrastructure components.
## Known Blockers/Dependencies
Dedicated engineering resources from developers/maintainers of the Vets-API application.
## Projected Launch Date
Q2 2022
## Launch Checklist
### Is this service / tool / feature...
### ... tested?
- [ ] Usability test (_TODO: link_) has been performed, to validate that new changes enable users to do what was intended and that these changes don't worsen quality elsewhere. If usability test isn't relevant for this change, document the reason for skipping it.
- [ ] ... and issues discovered in usability testing have been addressed.
* _Note on skipping: metrics that show the impact of before/after can be a substitute for usability testing._
- [ ] End-to-end [manual QA](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/quality-assurance/README.md) or [UAT](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/research/planning/what-is-uat.md) is complete, to validate there are no high-severity issues before launching
- [ ] _(if applicable)_ New functionality has thorough, automated tests running in CI/CD
### ... documented?
- [ ] New documentation is written pursuant to our [documentation style guide](https://vfs.atlassian.net/wiki/spaces/AP/pages/622264362/Style+guide)
- [ ] Product is included in the [List of VSP Products](https://docs.google.com/spreadsheets/d/1Fn2lD419WE3sTZJtN2Ensrjqaz0jH3WvLaBtn812Wjo/edit#gid=0)
* _List the existing product that this initiative fits within, or add a new product to this list._
- [ ] Internal-facing: there's a [Product Outline](https://vfs.atlassian.net/wiki/spaces/PMCP/pages/1924628490/Product+Outline+Template)
- [ ] External-facing: a [User Guide on Platform Website](https://vfs.atlassian.net/wiki/spaces/AP/pages/1477017691/Platform+website+guidelines) exists for this product/feature tool
- [ ] _(if applicable)_ Post to [#vsp-service-design](https://dsva.slack.com/channels/vsp-service-design) for external communication about this change (e.g. VSP Newsletter, customer-facing meetings)
### ... measurable
- [ ] _(if applicable)_ This change has clearly-defined success metrics, with instrumentation of those analytics where possible, or a reason documented for skipping it.
* For help, see: [Analytics team](https://depo-platform-documentation.scrollhelp.site/analytics-monitoring/Analytics-customer-support-guide.1586823275.html)
- [ ] This change has an accompanying [VSP Initiative Release Plan](https://github.com/department-of-veterans-affairs/va.gov-team/issues/new/choose).
### When you're ready to launch...
- [ ] Conduct a [go/no-go] (https://vfs.atlassian.net/wiki/spaces/AP/pages/1670938648/Platform+Crew+Office+Hours#Go%2FNo-Go) when you're almost ready to launch.
## Required Artifacts
### Documentation
* **`PRODUCT_NAME`**: _directory name used for your product documentation_
* **Product Outline**: _link to Product Outline_
* **User Guide**: _link to User Guide_
### Testing
* **Usability test**: _link to GitHub issue, or provide reason for skipping_
* **Manual QA**: _link to GitHub issue or documented results_
* **Automated tests**: _link to tests, or "N/A"_
### Measurement
* **Success metrics**: _link to where success metrics are measured, or where they're defined (Product Outline is OK), or provide reason for skipping_
* **Release plan**: _link to Release Plan ticket_
## TODOs
- [ ] Convert this issue to an epic
- [ ] Add your team's label to this epic
| non_priority | platform infrastructure make vets api operational in eks problem statement maintaining two infrastructure delivery systems is hard vets api must migrate away from brd before sunsetting the platform s legacy delivery systems how might we transition vets api away from the legacy infrastructure how might we make it easier to deploy and maintain vets api how might we grant vfs and platform crew teams more autonomy and flexibility as it relates to the development and deployment of vets api or other backend services hypothesis or bet we believe that this will enable the platform to move vets api toward a micro services backend architecture we believe that this will enable other teams to move more quickly in developing against vets api we believe that this will make it easier for other teams to develop against vets api we will know we re done when definition of done vets api reverse proxy are fully functional in the eks environment s live traffic is flowing through these infrastructure components known blockers dependencies dedicated engineering resources from developers maintainers of the vets api application projected launch date launch checklist is this service tool feature tested usability test todo link has been performed to validate that new changes enable users to do what was intended and that these changes don t worsen quality elsewhere if usability test isn t relevant for this change document the reason for skipping it and issues discovered in usability testing have been addressed note on skipping metrics that show the impact of before after can be a substitute for usability testing end to end or is complete to validate there are no high severity issues before launching if applicable new functionality has thorough automated tests running in ci cd documented new documentation is written pursuant to our product is included in the list the existing product that this initiative fits within or add a new product to this list internal facing there s a external facing a exists for this product feature tool if applicable post to for external communication about this change e g vsp newsletter customer facing meetings measurable if applicable this change has clearly defined success metrics with instrumentation of those analytics where possible or a reason documented for skipping it for help see this change has an accompanying when you re ready to launch conduct a when you re almost ready to launch required artifacts documentation product name directory name used for your product documentation product outline link to product outline user guide link to user guide testing usability test link to github issue or provide reason for skipping manual qa link to github issue or documented results automated tests link to tests or n a measurement success metrics link to where success metrics are measured or where they re defined product outline is ok or provide reason for skipping release plan link to release plan ticket todos convert this issue to an epic add your team s label to this epic | 0 |
210,973 | 16,413,753,383 | IssuesEvent | 2021-05-19 01:54:12 | django-cms/django-cms | https://api.github.com/repos/django-cms/django-cms | closed | TypeError: argument of type 'WindowsPath' is not iterable | component: documentation easy pickings | this error face me when I am trying install Django-cms manually
http://docs.django-cms.org/en/latest/how_to/install.html
I use Django 3.0 and django-cms-3.7.4

| 1.0 | TypeError: argument of type 'WindowsPath' is not iterable - this error face me when I am trying install Django-cms manually
http://docs.django-cms.org/en/latest/how_to/install.html
I use Django 3.0 and django-cms-3.7.4

| non_priority | typeerror argument of type windowspath is not iterable this error face me when i am trying install django cms manually i use django and django cms | 0 |
405,439 | 27,519,113,490 | IssuesEvent | 2023-03-06 13:59:42 | jphayek/Git-tp-finale | https://api.github.com/repos/jphayek/Git-tp-finale | closed | Branch Develop | documentation | Develop or any other branch is typically created by Admin to restrict developers to make any changes in master branch. As doing this without proper review and testing will break the working of application.
| 1.0 | Branch Develop - Develop or any other branch is typically created by Admin to restrict developers to make any changes in master branch. As doing this without proper review and testing will break the working of application.
| non_priority | branch develop develop or any other branch is typically created by admin to restrict developers to make any changes in master branch as doing this without proper review and testing will break the working of application | 0 |
49,045 | 13,437,213,896 | IssuesEvent | 2020-09-07 15:33:03 | ghosind/requester | https://api.github.com/repos/ghosind/requester | opened | CVE-2018-11694 (High) detected in node-sass-4.14.1.tgz, node-sass-v4.14.1 | security vulnerability | ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/requester/package.json</p>
<p>Path to vulnerable library: /requester/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ghosind/requester/commit/320f3ddc189b9ec59618944a9aa3995e62912f1b">320f3ddc189b9ec59618944a9aa3995e62912f1b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Functions::selector_append which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11694>CVE-2018-11694</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11694 (High) detected in node-sass-4.14.1.tgz, node-sass-v4.14.1 - ## CVE-2018-11694 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/requester/package.json</p>
<p>Path to vulnerable library: /requester/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ghosind/requester/commit/320f3ddc189b9ec59618944a9aa3995e62912f1b">320f3ddc189b9ec59618944a9aa3995e62912f1b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Functions::selector_append which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11694>CVE-2018-11694</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11694</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node sass tgz node sass cve high severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm requester package json path to vulnerable library requester node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href vulnerability details an issue was discovered in libsass through a null pointer dereference was found in the function sass functions selector append which could be leveraged by an attacker to cause a denial of service application crash or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
145,239 | 22,630,453,498 | IssuesEvent | 2022-06-30 14:15:53 | blockframes/blockframes | https://api.github.com/repos/blockframes/blockframes | closed | Tooltips still bugs | Bug Design - UI | In spite of many updates and corrections on tooltips. We still notice contrast problem. (light theme only)

| 1.0 | Tooltips still bugs - In spite of many updates and corrections on tooltips. We still notice contrast problem. (light theme only)

| non_priority | tooltips still bugs in spite of many updates and corrections on tooltips we still notice contrast problem light theme only | 0 |
428,931 | 30,017,110,652 | IssuesEvent | 2023-06-26 19:39:09 | josdem/playwright-applitools | https://api.github.com/repos/josdem/playwright-applitools | opened | Add a run tests workflow to the project | documentation enhancement | As a **user **, I want to create a workflow **so that** I can execute test cases and publish results to [Applitools](https://applitools.com/)
**Acceptance Criteria**
- I am able to run a workflow from GitHub actions
- Documentation is updated with workflow | 1.0 | Add a run tests workflow to the project - As a **user **, I want to create a workflow **so that** I can execute test cases and publish results to [Applitools](https://applitools.com/)
**Acceptance Criteria**
- I am able to run a workflow from GitHub actions
- Documentation is updated with workflow | non_priority | add a run tests workflow to the project as a user i want to create a workflow so that i can execute test cases and publish results to acceptance criteria i am able to run a workflow from github actions documentation is updated with workflow | 0 |
65,110 | 26,980,449,530 | IssuesEvent | 2023-02-09 12:44:22 | Ocelot-Social-Community/Ocelot-Social | https://api.github.com/repos/Ocelot-Social-Community/Ocelot-Social | closed | 🐛 [Bug] close mobile menu on all links and sub menu | bug service: webapp | <!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🐛 Bugreport
the mobile menu should be closed for all necessary links. especially in the sub menu!

| 1.0 | 🐛 [Bug] close mobile menu on all links and sub menu - <!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🐛 Bugreport
the mobile menu should be closed for all necessary links. especially in the sub menu!

| non_priority | 🐛 close mobile menu on all links and sub menu 🐛 bugreport the mobile menu should be closed for all necessary links especially in the sub menu | 0 |
43,744 | 23,355,817,471 | IssuesEvent | 2022-08-10 07:18:05 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | frontend_server JavaScript support for new invalidation strategy | new feature tool severe: performance passed first triage P5 | I did not remember if I filled a bug for this, but filling now so that we can keep track of it.
2.2/2.1 introduced a new invalidation strategy for incremental compilation that is faster for larger edits where the public API is unchanged. This is currently enabled for mobile/desktop but disabled for web since it doesn't work out of the box.
We need to research why that is, off the top of my head:
* Need to handle computing SCC when only given a single library.
* Need to persist summary components for DDC
* possibly need special rules for invalidating circular imports
Probably some more after that. | True | frontend_server JavaScript support for new invalidation strategy - I did not remember if I filled a bug for this, but filling now so that we can keep track of it.
2.2/2.1 introduced a new invalidation strategy for incremental compilation that is faster for larger edits where the public API is unchanged. This is currently enabled for mobile/desktop but disabled for web since it doesn't work out of the box.
We need to research why that is, off the top of my head:
* Need to handle computing SCC when only given a single library.
* Need to persist summary components for DDC
* possibly need special rules for invalidating circular imports
Probably some more after that. | non_priority | frontend server javascript support for new invalidation strategy i did not remember if i filled a bug for this but filling now so that we can keep track of it introduced a new invalidation strategy for incremental compilation that is faster for larger edits where the public api is unchanged this is currently enabled for mobile desktop but disabled for web since it doesn t work out of the box we need to research why that is off the top of my head need to handle computing scc when only given a single library need to persist summary components for ddc possibly need special rules for invalidating circular imports probably some more after that | 0 |
102,006 | 31,789,525,804 | IssuesEvent | 2023-09-13 01:22:47 | nodejs/node | https://api.github.com/repos/nodejs/node | closed | Use only one copy of llhttp ? | build feature request stale fetch | ### What is the problem this feature will solve?
Versions of Node using Undici (16, 18) are actually using two different copies of llhttp
### What is the feature you are proposing to solve the problem?
Would it make sense to use llhttp wasm that is bundled in Undici, instead of recompiling it ?
### What alternatives have you considered?
n/a it's a refactoring. | 1.0 | Use only one copy of llhttp ? - ### What is the problem this feature will solve?
Versions of Node using Undici (16, 18) are actually using two different copies of llhttp
### What is the feature you are proposing to solve the problem?
Would it make sense to use llhttp wasm that is bundled in Undici, instead of recompiling it ?
### What alternatives have you considered?
n/a it's a refactoring. | non_priority | use only one copy of llhttp what is the problem this feature will solve versions of node using undici are actually using two different copies of llhttp what is the feature you are proposing to solve the problem would it make sense to use llhttp wasm that is bundled in undici instead of recompiling it what alternatives have you considered n a it s a refactoring | 0 |
119,774 | 12,042,550,471 | IssuesEvent | 2020-04-14 10:46:33 | apjanke/octave-slf4o | https://api.github.com/repos/apjanke/octave-slf4o | closed | Add "Introduction" section to manual | documentation enhancement | The user manual (in doc/slf4o.texi.in) could use an "Introduction" section. Add one. | 1.0 | Add "Introduction" section to manual - The user manual (in doc/slf4o.texi.in) could use an "Introduction" section. Add one. | non_priority | add introduction section to manual the user manual in doc texi in could use an introduction section add one | 0 |
26,747 | 27,147,313,095 | IssuesEvent | 2023-02-16 21:06:36 | bevyengine/bevy | https://api.github.com/repos/bevyengine/bevy | closed | Infinite loop if states are inserted as Resources | C-Docs S-User-Error A-Core C-Usability | ## Bevy version
0.5
## Operating system & version
Debian GNU/Linux "buster"
## What you did
Ported a Bevy 0.4 program that had a modal state-driven UI. The current program state is represented as an enum. I didn't realize I needed to change `.insert_resource(State::new(MyState::Initial))` to `.add_state(MyState::Initial)`.
## What you expected to happen
One of:
1. The program launches as normal.
2. The program runs but the state can't be changed.
3. The program runs but nothing connected to a state works.
4. The program panics at startup.
## What actually happened
I get a blank screen. `gdb` shows all threads apparently idle. Hacking up Bevy to print messages when it starts and finishes running systems produces this output:
```
done running: "&bevy_ecs::schedule::state::State<gridded_demo::GridInteractionMode>::on_update::{{closure}}"
running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridInteractionMode>"
done running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridInteractionMode>"
running: "&bevy_ecs::schedule::state::State<gridded_demo::GridMode>::on_exit::{{closure}}"
done running: "&bevy_ecs::schedule::state::State<gridded_demo::GridMode>::on_exit::{{closure}}"
running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridMode>"
done running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridMode>"
running: "&bevy_ecs::schedule::state::State<gridded_demo::GridInteractionMode>::on_update::{{closure}}"
done running: "&bevy_ecs::schedule::state::State<gridded_demo::GridInteractionMode>::on_update::{{closure}}"
```
It looks like Bevy has gone into some kind of infinite loop checking if the state is up to date.
If I comment out all state-dependent systems, my screen is still blank (since the program does nothing) but my debugging output changes to show that other systems are running, for instance:
```
running: "&bevy_app::event::Events<bevy_input::touch::TouchInput>::update_system"
done running: "&bevy_app::event::Events<bevy_window::event::CloseWindow>::update_system"
done running: "&bevy_app::event::Events<bevy_window::event::WindowResized>::update_system"
done running: "&bevy_app::event::Events<bevy_input::touch::TouchInput>::update_system"
running: "&bevy_app::event::Events<bevy_input::mouse::MouseMotion>::update_system"
running: "&bevy_app::event::Events<bevy_app::app::AppExit>::update_system"
running: "&bevy_app::event::Events<bevy_input::mouse::MouseWheel>::update_system"
done running: "&bevy_app::event::Events<bevy_input::mouse::MouseMotion>::update_system"
done running: "&bevy_app::event::Events<bevy_input::mouse::MouseWheel>::update_system"
```
Changing `insert_resource` to `add_state` makes everything work (or at least fixes this problem :smile:) | True | Infinite loop if states are inserted as Resources - ## Bevy version
0.5
## Operating system & version
Debian GNU/Linux "buster"
## What you did
Ported a Bevy 0.4 program that had a modal state-driven UI. The current program state is represented as an enum. I didn't realize I needed to change `.insert_resource(State::new(MyState::Initial))` to `.add_state(MyState::Initial)`.
## What you expected to happen
One of:
1. The program launches as normal.
2. The program runs but the state can't be changed.
3. The program runs but nothing connected to a state works.
4. The program panics at startup.
## What actually happened
I get a blank screen. `gdb` shows all threads apparently idle. Hacking up Bevy to print messages when it starts and finishes running systems produces this output:
```
done running: "&bevy_ecs::schedule::state::State<gridded_demo::GridInteractionMode>::on_update::{{closure}}"
running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridInteractionMode>"
done running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridInteractionMode>"
running: "&bevy_ecs::schedule::state::State<gridded_demo::GridMode>::on_exit::{{closure}}"
done running: "&bevy_ecs::schedule::state::State<gridded_demo::GridMode>::on_exit::{{closure}}"
running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridMode>"
done running: "&bevy_ecs::schedule::state::should_run_adapter<gridded_demo::GridMode>"
running: "&bevy_ecs::schedule::state::State<gridded_demo::GridInteractionMode>::on_update::{{closure}}"
done running: "&bevy_ecs::schedule::state::State<gridded_demo::GridInteractionMode>::on_update::{{closure}}"
```
It looks like Bevy has gone into some kind of infinite loop checking if the state is up to date.
If I comment out all state-dependent systems, my screen is still blank (since the program does nothing) but my debugging output changes to show that other systems are running, for instance:
```
running: "&bevy_app::event::Events<bevy_input::touch::TouchInput>::update_system"
done running: "&bevy_app::event::Events<bevy_window::event::CloseWindow>::update_system"
done running: "&bevy_app::event::Events<bevy_window::event::WindowResized>::update_system"
done running: "&bevy_app::event::Events<bevy_input::touch::TouchInput>::update_system"
running: "&bevy_app::event::Events<bevy_input::mouse::MouseMotion>::update_system"
running: "&bevy_app::event::Events<bevy_app::app::AppExit>::update_system"
running: "&bevy_app::event::Events<bevy_input::mouse::MouseWheel>::update_system"
done running: "&bevy_app::event::Events<bevy_input::mouse::MouseMotion>::update_system"
done running: "&bevy_app::event::Events<bevy_input::mouse::MouseWheel>::update_system"
```
Changing `insert_resource` to `add_state` makes everything work (or at least fixes this problem :smile:) | non_priority | infinite loop if states are inserted as resources bevy version operating system version debian gnu linux buster what you did ported a bevy program that had a modal state driven ui the current program state is represented as an enum i didn t realize i needed to change insert resource state new mystate initial to add state mystate initial what you expected to happen one of the program launches as normal the program runs but the state can t be changed the program runs but nothing connected to a state works the program panics at startup what actually happened i get a blank screen gdb shows all threads apparently idle hacking up bevy to print messages when it starts and finishes running systems produces this output done running bevy ecs schedule state state on update closure running bevy ecs schedule state should run adapter done running bevy ecs schedule state should run adapter running bevy ecs schedule state state on exit closure done running bevy ecs schedule state state on exit closure running bevy ecs schedule state should run adapter done running bevy ecs schedule state should run adapter running bevy ecs schedule state state on update closure done running bevy ecs schedule state state on update closure it looks like bevy has gone into some kind of infinite loop checking if the state is up to date if i comment out all state dependent systems my screen is still blank since the program does nothing but my debugging output changes to show that other systems are running for instance running bevy app event events update system done running bevy app event events update system done running bevy app event events update system done running bevy app event events update system running bevy app event events update system running bevy app event events update system running bevy app event events update system done running bevy app event events update system done running bevy app event events update system changing insert resource to add state makes everything work or at least fixes this problem smile | 0 |
220,301 | 16,920,115,189 | IssuesEvent | 2021-06-25 03:26:51 | FreshRSS/FreshRSS | https://api.github.com/repos/FreshRSS/FreshRSS | closed | I USE The docker to build FRESHRSS, How could change my time zone | Docker Documentation :books: | I USE The docker to build FRESHRSS, How could change my time zone | 1.0 | I USE The docker to build FRESHRSS, How could change my time zone - I USE The docker to build FRESHRSS, How could change my time zone | non_priority | i use the docker to build freshrss how could change my time zone i use the docker to build freshrss how could change my time zone | 0 |
337,188 | 24,529,690,220 | IssuesEvent | 2022-10-11 15:28:58 | flame-engine/flame | https://api.github.com/repos/flame-engine/flame | closed | Bridge package docs: `flame_tiled` | enhancement good first issue documentation hacktoberfest bridge package docs | # Bridge package docs for `flame_tiled`
This bridge package should have its own documentation section on the docs site, similarly to `flame_audio` for example:
https://docs.flame-engine.org/main/flame_audio/flame_audio.html
For inspiration (and copy-pasting) you can have a look at the documentation for the package written in the `README.md` file and the documentation that the package is bridging too.
# Good to know
Make sure that you comment on the issue that you will be working on this before starting to program.
To set up the Flame environment you need to follow the instructions in our [contributing.md](https://github.com/flame-engine/flame/blob/main/CONTRIBUTING.md#environment-setup) doc, if you have any problems setting up your environment (or other issues of course) feel free to ask for help in the Flame channel on our [Discord server](https://discord.com/invite/pxrBmy4).
Since this is a documentation change, you need to be able to build the docs. You can do that by running `melos sphinxdoc` after you have followed the instructions in the contributing.md doc and also [installed Sphinx on your system](https://www.sphinx-doc.org/en/master/usage/installation.html). After you have built the docs you can open the `doc/_build/html/index.html` file in your web browser to see the changes.
Make sure to include a video of the example when you upload the PR so that it will be easier for us to review it. (You can attach videos directly in the PR, so no need to upload them somewhere else)
**Happy hacking!**
| 1.0 | Bridge package docs: `flame_tiled` - # Bridge package docs for `flame_tiled`
This bridge package should have its own documentation section on the docs site, similarly to `flame_audio` for example:
https://docs.flame-engine.org/main/flame_audio/flame_audio.html
For inspiration (and copy-pasting) you can have a look at the documentation for the package written in the `README.md` file and the documentation that the package is bridging too.
# Good to know
Make sure that you comment on the issue that you will be working on this before starting to program.
To set up the Flame environment you need to follow the instructions in our [contributing.md](https://github.com/flame-engine/flame/blob/main/CONTRIBUTING.md#environment-setup) doc, if you have any problems setting up your environment (or other issues of course) feel free to ask for help in the Flame channel on our [Discord server](https://discord.com/invite/pxrBmy4).
Since this is a documentation change, you need to be able to build the docs. You can do that by running `melos sphinxdoc` after you have followed the instructions in the contributing.md doc and also [installed Sphinx on your system](https://www.sphinx-doc.org/en/master/usage/installation.html). After you have built the docs you can open the `doc/_build/html/index.html` file in your web browser to see the changes.
Make sure to include a video of the example when you upload the PR so that it will be easier for us to review it. (You can attach videos directly in the PR, so no need to upload them somewhere else)
**Happy hacking!**
| non_priority | bridge package docs flame tiled bridge package docs for flame tiled this bridge package should have its own documentation section on the docs site similarly to flame audio for example for inspiration and copy pasting you can have a look at the documentation for the package written in the readme md file and the documentation that the package is bridging too good to know make sure that you comment on the issue that you will be working on this before starting to program to set up the flame environment you need to follow the instructions in our doc if you have any problems setting up your environment or other issues of course feel free to ask for help in the flame channel on our since this is a documentation change you need to be able to build the docs you can do that by running melos sphinxdoc after you have followed the instructions in the contributing md doc and also after you have built the docs you can open the doc build html index html file in your web browser to see the changes make sure to include a video of the example when you upload the pr so that it will be easier for us to review it you can attach videos directly in the pr so no need to upload them somewhere else happy hacking | 0 |
66,012 | 16,522,759,527 | IssuesEvent | 2021-05-26 16:11:32 | dartoos-dev/callor | https://api.github.com/repos/dartoos-dev/callor | closed | Migrating to null safety | build refactor | Steps for migration:
- [x] check dependency status: ```dart pub outdated --mode=null-safety```
- [x] update dependencies to null-safety releases, if they exist: ```dart pub upgrade --null-safety```
- [x] run Dart's migration tool ```dart migrate``` and fix the reported issues
[migration guide](https://dart.dev/null-safety/migration-guide) | 1.0 | Migrating to null safety - Steps for migration:
- [x] check dependency status: ```dart pub outdated --mode=null-safety```
- [x] update dependencies to null-safety releases, if they exist: ```dart pub upgrade --null-safety```
- [x] run Dart's migration tool ```dart migrate``` and fix the reported issues
[migration guide](https://dart.dev/null-safety/migration-guide) | non_priority | migrating to null safety steps for migration check dependency status dart pub outdated mode null safety update dependencies to null safety releases if they exist dart pub upgrade null safety run dart s migration tool dart migrate and fix the reported issues | 0 |
67,621 | 9,082,410,229 | IssuesEvent | 2019-02-17 12:06:57 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | File get_var() / eof_reached() problem | documentation platform:windows topic:core topic:porting | <!-- Please search existing issues for potential duplicates before filing yours:
https://github.com/godotengine/godot/issues?q=is%3Aissue
-->
**Godot version:**
<!-- Specify commit hash if non-official. -->
Godot 3 - Godot 2.1
**OS/device including version:**
<!-- Specify GPU model and drivers if graphics-related. -->
Win 7 32 y 64 bit
**Issue description:**
<!-- What happened, and what was expected. -->
What happened:
If I try to iterate in a file with **file.get_var()** until **eof_reached()** is true, no matters i put this condition up or down to **get_var()**... **eof_reached()** always is triggered after get_var is trying to get an non existinting var and returns **ERR_INVALID_DATA**.
The behavior that i expect is **eof_reached()** going "true" in the same moment that the last var was reached and getted, not in the moment that get_var() is trying to get the "total_numbers_of_var"+1, because the "LEN < 4" error is unskippable (and eof_reached becomes useless with get_var())
(I know other ways of parse the file without use eof_reached(), this issue is not asking for help to do that, is to report a behavior that i think is wrong and to know if behavior is expected)
**Steps to reproduce:**
Iterate a file getting all vars until eof_reached() is true (not do "for" loop or similar and don´t filter with any comparison, only get all vars until eof_reached() is true with while or similar), eof reached allways becomes true after get_var returns: decode_variant: Condition `len < 4`is true. returned: ERR_INVALID_DATA.
**Minimal reproduction project:**
<!-- Recommended as it greatly speeds up debugging. Drag and drop a zip archive to upload it. -->
| 1.0 | File get_var() / eof_reached() problem - <!-- Please search existing issues for potential duplicates before filing yours:
https://github.com/godotengine/godot/issues?q=is%3Aissue
-->
**Godot version:**
<!-- Specify commit hash if non-official. -->
Godot 3 - Godot 2.1
**OS/device including version:**
<!-- Specify GPU model and drivers if graphics-related. -->
Win 7 32 y 64 bit
**Issue description:**
<!-- What happened, and what was expected. -->
What happened:
If I try to iterate in a file with **file.get_var()** until **eof_reached()** is true, no matters i put this condition up or down to **get_var()**... **eof_reached()** always is triggered after get_var is trying to get an non existinting var and returns **ERR_INVALID_DATA**.
The behavior that i expect is **eof_reached()** going "true" in the same moment that the last var was reached and getted, not in the moment that get_var() is trying to get the "total_numbers_of_var"+1, because the "LEN < 4" error is unskippable (and eof_reached becomes useless with get_var())
(I know other ways of parse the file without use eof_reached(), this issue is not asking for help to do that, is to report a behavior that i think is wrong and to know if behavior is expected)
**Steps to reproduce:**
Iterate a file getting all vars until eof_reached() is true (not do "for" loop or similar and don´t filter with any comparison, only get all vars until eof_reached() is true with while or similar), eof reached allways becomes true after get_var returns: decode_variant: Condition `len < 4`is true. returned: ERR_INVALID_DATA.
**Minimal reproduction project:**
<!-- Recommended as it greatly speeds up debugging. Drag and drop a zip archive to upload it. -->
| non_priority | file get var eof reached problem please search existing issues for potential duplicates before filing yours godot version godot godot os device including version win y bit issue description what happened if i try to iterate in a file with file get var until eof reached is true no matters i put this condition up or down to get var eof reached always is triggered after get var is trying to get an non existinting var and returns err invalid data the behavior that i expect is eof reached going true in the same moment that the last var was reached and getted not in the moment that get var is trying to get the total numbers of var because the len error is unskippable and eof reached becomes useless with get var i know other ways of parse the file without use eof reached this issue is not asking for help to do that is to report a behavior that i think is wrong and to know if behavior is expected steps to reproduce iterate a file getting all vars until eof reached is true not do for loop or similar and don´t filter with any comparison only get all vars until eof reached is true with while or similar eof reached allways becomes true after get var returns decode variant condition len is true returned err invalid data minimal reproduction project | 0 |
330,669 | 24,272,174,067 | IssuesEvent | 2022-09-28 11:11:22 | owncloud/web | https://api.github.com/repos/owncloud/web | closed | [documentation] generate test report information | QA:team Topic:Documentation | ### Description
Currently `Watch the test report` section for testing is written under `Acceptance Test`
https://github.com/owncloud/web/blob/8cce5122bfd2501331f607f1a84d86db4e1c4221/docs/testing/testing.md?plain=1#L183
Generating reports process should be the same for both `e2e` and `acceptance` tests as both use cucumber. Thanks to `tests/e2e2cucumber/reportGenerator` we can build a report for acceptance tests too with the use of flag `--report-input` and providing the path of respective `report.json`
IMO the report generation information can be taken out from the acceptance section and generalized for both types of testing.
| 1.0 | [documentation] generate test report information - ### Description
Currently `Watch the test report` section for testing is written under `Acceptance Test`
https://github.com/owncloud/web/blob/8cce5122bfd2501331f607f1a84d86db4e1c4221/docs/testing/testing.md?plain=1#L183
Generating reports process should be the same for both `e2e` and `acceptance` tests as both use cucumber. Thanks to `tests/e2e2cucumber/reportGenerator` we can build a report for acceptance tests too with the use of flag `--report-input` and providing the path of respective `report.json`
IMO the report generation information can be taken out from the acceptance section and generalized for both types of testing.
| non_priority | generate test report information description currently watch the test report section for testing is written under acceptance test generating reports process should be the same for both and acceptance tests as both use cucumber thanks to tests reportgenerator we can build a report for acceptance tests too with the use of flag report input and providing the path of respective report json imo the report generation information can be taken out from the acceptance section and generalized for both types of testing | 0 |
66,465 | 27,457,615,954 | IssuesEvent | 2023-03-02 22:56:08 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | AGOL Web App Request: 2023 SXSW ATX Mobility Guide | Workgroup: OSE Type: Map Request Type: Data Service: Geo | - [ ]
#11405
#11409
#11406
#11407
#11408
#11410
#11411
#11412
#11413
#11443
#11478
#11479 | 1.0 | AGOL Web App Request: 2023 SXSW ATX Mobility Guide - - [ ]
#11405
#11409
#11406
#11407
#11408
#11410
#11411
#11412
#11413
#11443
#11478
#11479 | non_priority | agol web app request sxsw atx mobility guide | 0 |
108,895 | 16,822,740,466 | IssuesEvent | 2021-06-17 14:49:35 | idonthaveafifaaddiction/flink | https://api.github.com/repos/idonthaveafifaaddiction/flink | opened | CVE-2017-7656 (High) detected in jetty-http-9.3.20.v20170531.jar, jetty-server-9.3.20.v20170531.jar | security vulnerability | ## CVE-2017-7656 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jetty-http-9.3.20.v20170531.jar</b>, <b>jetty-server-9.3.20.v20170531.jar</b></p></summary>
<p>
<details><summary><b>jetty-http-9.3.20.v20170531.jar</b></p></summary>
<p>Administrative parent pom for Jetty modules</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.3.20.v20170531/jetty-http-9.3.20.v20170531.jar</p>
<p>
Dependency Hierarchy:
- hive-exec-3.1.2.jar (Root Library)
- hive-llap-tez-3.1.2.jar
- hive-common-3.1.2.jar
- :x: **jetty-http-9.3.20.v20170531.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-server-9.3.20.v20170531.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-server/9.3.20.v20170531/jetty-server-9.3.20.v20170531.jar</p>
<p>
Dependency Hierarchy:
- hive-exec-3.1.2.jar (Root Library)
- hive-llap-tez-3.1.2.jar
- hive-common-3.1.2.jar
- :x: **jetty-server-9.3.20.v20170531.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/flink/commit/d77b18bba5da590fb2e8e8aa13f2dcb0674d52be">d77b18bba5da590fb2e8e8aa13f2dcb0674d52be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Eclipse Jetty, versions 9.2.x and older, 9.3.x (all configurations), and 9.4.x (non-default configuration with RFC2616 compliance enabled), HTTP/0.9 is handled poorly. An HTTP/1 style request line (i.e. method space URI space version) that declares a version of HTTP/0.9 was accepted and treated as a 0.9 request. If deployed behind an intermediary that also accepted and passed through the 0.9 version (but did not act on it), then the response sent could be interpreted by the intermediary as HTTP/1 headers. This could be used to poison the cache if the server allowed the origin client to generate arbitrary content in the response.
<p>Publish Date: 2018-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7656>CVE-2017-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.eclipse.org/bugs/show_bug.cgi?id=535667">https://bugs.eclipse.org/bugs/show_bug.cgi?id=535667</a></p>
<p>Release Date: 2018-06-26</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-server:9.2.25.v20180606,9.3.24.v20180605,9.4.11.v20180605;org.eclipse.jetty:jetty-http:9.2.25.v20180606.,9.3.24.v20180605,9.4.11.v20180605</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.3.20.v20170531","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-exec:3.1.2;org.apache.hive:hive-llap-tez:3.1.2;org.apache.hive:hive-common:3.1.2;org.eclipse.jetty:jetty-http:9.3.20.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.2.25.v20180606,9.3.24.v20180605,9.4.11.v20180605;org.eclipse.jetty:jetty-http:9.2.25.v20180606.,9.3.24.v20180605,9.4.11.v20180605"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-server","packageVersion":"9.3.20.v20170531","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-exec:3.1.2;org.apache.hive:hive-llap-tez:3.1.2;org.apache.hive:hive-common:3.1.2;org.eclipse.jetty:jetty-server:9.3.20.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.2.25.v20180606,9.3.24.v20180605,9.4.11.v20180605;org.eclipse.jetty:jetty-http:9.2.25.v20180606.,9.3.24.v20180605,9.4.11.v20180605"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-7656","vulnerabilityDetails":"In Eclipse Jetty, versions 9.2.x and older, 9.3.x (all configurations), and 9.4.x (non-default configuration with RFC2616 compliance enabled), HTTP/0.9 is handled poorly. An HTTP/1 style request line (i.e. method space URI space version) that declares a version of HTTP/0.9 was accepted and treated as a 0.9 request. If deployed behind an intermediary that also accepted and passed through the 0.9 version (but did not act on it), then the response sent could be interpreted by the intermediary as HTTP/1 headers. This could be used to poison the cache if the server allowed the origin client to generate arbitrary content in the response.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7656","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-7656 (High) detected in jetty-http-9.3.20.v20170531.jar, jetty-server-9.3.20.v20170531.jar - ## CVE-2017-7656 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jetty-http-9.3.20.v20170531.jar</b>, <b>jetty-server-9.3.20.v20170531.jar</b></p></summary>
<p>
<details><summary><b>jetty-http-9.3.20.v20170531.jar</b></p></summary>
<p>Administrative parent pom for Jetty modules</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.3.20.v20170531/jetty-http-9.3.20.v20170531.jar</p>
<p>
Dependency Hierarchy:
- hive-exec-3.1.2.jar (Root Library)
- hive-llap-tez-3.1.2.jar
- hive-common-3.1.2.jar
- :x: **jetty-http-9.3.20.v20170531.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-server-9.3.20.v20170531.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-server/9.3.20.v20170531/jetty-server-9.3.20.v20170531.jar</p>
<p>
Dependency Hierarchy:
- hive-exec-3.1.2.jar (Root Library)
- hive-llap-tez-3.1.2.jar
- hive-common-3.1.2.jar
- :x: **jetty-server-9.3.20.v20170531.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/flink/commit/d77b18bba5da590fb2e8e8aa13f2dcb0674d52be">d77b18bba5da590fb2e8e8aa13f2dcb0674d52be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Eclipse Jetty, versions 9.2.x and older, 9.3.x (all configurations), and 9.4.x (non-default configuration with RFC2616 compliance enabled), HTTP/0.9 is handled poorly. An HTTP/1 style request line (i.e. method space URI space version) that declares a version of HTTP/0.9 was accepted and treated as a 0.9 request. If deployed behind an intermediary that also accepted and passed through the 0.9 version (but did not act on it), then the response sent could be interpreted by the intermediary as HTTP/1 headers. This could be used to poison the cache if the server allowed the origin client to generate arbitrary content in the response.
<p>Publish Date: 2018-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7656>CVE-2017-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugs.eclipse.org/bugs/show_bug.cgi?id=535667">https://bugs.eclipse.org/bugs/show_bug.cgi?id=535667</a></p>
<p>Release Date: 2018-06-26</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-server:9.2.25.v20180606,9.3.24.v20180605,9.4.11.v20180605;org.eclipse.jetty:jetty-http:9.2.25.v20180606.,9.3.24.v20180605,9.4.11.v20180605</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.3.20.v20170531","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-exec:3.1.2;org.apache.hive:hive-llap-tez:3.1.2;org.apache.hive:hive-common:3.1.2;org.eclipse.jetty:jetty-http:9.3.20.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.2.25.v20180606,9.3.24.v20180605,9.4.11.v20180605;org.eclipse.jetty:jetty-http:9.2.25.v20180606.,9.3.24.v20180605,9.4.11.v20180605"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-server","packageVersion":"9.3.20.v20170531","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-exec:3.1.2;org.apache.hive:hive-llap-tez:3.1.2;org.apache.hive:hive-common:3.1.2;org.eclipse.jetty:jetty-server:9.3.20.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.2.25.v20180606,9.3.24.v20180605,9.4.11.v20180605;org.eclipse.jetty:jetty-http:9.2.25.v20180606.,9.3.24.v20180605,9.4.11.v20180605"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-7656","vulnerabilityDetails":"In Eclipse Jetty, versions 9.2.x and older, 9.3.x (all configurations), and 9.4.x (non-default configuration with RFC2616 compliance enabled), HTTP/0.9 is handled poorly. An HTTP/1 style request line (i.e. method space URI space version) that declares a version of HTTP/0.9 was accepted and treated as a 0.9 request. If deployed behind an intermediary that also accepted and passed through the 0.9 version (but did not act on it), then the response sent could be interpreted by the intermediary as HTTP/1 headers. This could be used to poison the cache if the server allowed the origin client to generate arbitrary content in the response.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7656","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jetty http jar jetty server jar cve high severity vulnerability vulnerable libraries jetty http jar jetty server jar jetty http jar administrative parent pom for jetty modules library home page a href path to vulnerable library home wss scanner repository org eclipse jetty jetty http jetty http jar dependency hierarchy hive exec jar root library hive llap tez jar hive common jar x jetty http jar vulnerable library jetty server jar the core jetty server artifact library home page a href path to vulnerable library home wss scanner repository org eclipse jetty jetty server jetty server jar dependency hierarchy hive exec jar root library hive llap tez jar hive common jar x jetty server jar vulnerable library found in head commit a href found in base branch master vulnerability details in eclipse jetty versions x and older x all configurations and x non default configuration with compliance enabled http is handled poorly an http style request line i e method space uri space version that declares a version of http was accepted and treated as a request if deployed behind an intermediary that also accepted and passed through the version but did not act on it then the response sent could be interpreted by the intermediary as http headers this could be used to poison the cache if the server allowed the origin client to generate arbitrary content in the response publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org eclipse jetty jetty server org eclipse jetty jetty http isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache hive hive exec org apache hive hive llap tez org apache hive hive common org eclipse jetty jetty http isminimumfixversionavailable true minimumfixversion org eclipse jetty jetty server org eclipse jetty jetty http packagetype java groupid org eclipse jetty packagename jetty server packageversion packagefilepaths istransitivedependency true dependencytree org apache hive hive exec org apache hive hive llap tez org apache hive hive common org eclipse jetty jetty server isminimumfixversionavailable true minimumfixversion org eclipse jetty jetty server org eclipse jetty jetty http basebranches vulnerabilityidentifier cve vulnerabilitydetails in eclipse jetty versions x and older x all configurations and x non default configuration with compliance enabled http is handled poorly an http style request line i e method space uri space version that declares a version of http was accepted and treated as a request if deployed behind an intermediary that also accepted and passed through the version but did not act on it then the response sent could be interpreted by the intermediary as http headers this could be used to poison the cache if the server allowed the origin client to generate arbitrary content in the response vulnerabilityurl | 0 |
439,191 | 30,683,399,367 | IssuesEvent | 2023-07-26 10:38:50 | interledger/rafiki | https://api.github.com/repos/interledger/rafiki | opened | Add documentation for Auth Admin API | documentation | We should add the Auth Admin API to the rafiki.dev documentation.
This requires us to generate the graphql markdown types for the Auth Admin API schemas.
I imagine the documation page could look something like this:
<img width="298" alt="Screenshot 2023-07-26 at 13 37 24" src="https://github.com/interledger/rafiki/assets/15069181/89dff29a-9d4e-4385-acc6-93465973c8f3">
Tasks
- [ ] Add new page to the documentation for auth admin API
- [ ] Generate markdown doc files from the auth admin API schema
- [ ] Update Github actions to fail checks if auth admin API changes are made, but the documentation hasn't changed
| 1.0 | Add documentation for Auth Admin API - We should add the Auth Admin API to the rafiki.dev documentation.
This requires us to generate the graphql markdown types for the Auth Admin API schemas.
I imagine the documation page could look something like this:
<img width="298" alt="Screenshot 2023-07-26 at 13 37 24" src="https://github.com/interledger/rafiki/assets/15069181/89dff29a-9d4e-4385-acc6-93465973c8f3">
Tasks
- [ ] Add new page to the documentation for auth admin API
- [ ] Generate markdown doc files from the auth admin API schema
- [ ] Update Github actions to fail checks if auth admin API changes are made, but the documentation hasn't changed
| non_priority | add documentation for auth admin api we should add the auth admin api to the rafiki dev documentation this requires us to generate the graphql markdown types for the auth admin api schemas i imagine the documation page could look something like this img width alt screenshot at src tasks add new page to the documentation for auth admin api generate markdown doc files from the auth admin api schema update github actions to fail checks if auth admin api changes are made but the documentation hasn t changed | 0 |
328,843 | 24,200,851,308 | IssuesEvent | 2022-09-24 14:46:44 | bhuann/ICT2101-p3-07 | https://api.github.com/repos/bhuann/ICT2101-p3-07 | closed | Create low-fi prototype UI | documentation SRS | The low-fi wireframe prototypes of the website UI are created
- [x] Login page (Manager)
- [x] Login page (Staff)
- [x] Login page (IT Administrator)
- [x] Manager Landing page
- [x] Staff Landing page
- [x] IT Administrator Landing page
- [x] Manager Job Allocation page
- [x] View Job Calendar
- [x] Add Job Availability Form
- [x] Reject Job Allocation | 1.0 | Create low-fi prototype UI - The low-fi wireframe prototypes of the website UI are created
- [x] Login page (Manager)
- [x] Login page (Staff)
- [x] Login page (IT Administrator)
- [x] Manager Landing page
- [x] Staff Landing page
- [x] IT Administrator Landing page
- [x] Manager Job Allocation page
- [x] View Job Calendar
- [x] Add Job Availability Form
- [x] Reject Job Allocation | non_priority | create low fi prototype ui the low fi wireframe prototypes of the website ui are created login page manager login page staff login page it administrator manager landing page staff landing page it administrator landing page manager job allocation page view job calendar add job availability form reject job allocation | 0 |
22,405 | 7,166,918,356 | IssuesEvent | 2018-01-29 18:48:23 | ManageIQ/ui-components | https://api.github.com/repos/ManageIQ/ui-components | closed | Unable to build with Node 7.x stable (works with 6.x LTS) | bug build stale | Node 6.x is LTS is good, but 7.x stable doesn't run (at least on OS/X). Since it is the stable version and we are in Dev, it should probably also run in 7.x.
Child extract-text-webpack-plugin:
+ 1 hidden modules
ERROR in Missing binding ui-components/node_modules/node-sass/vendor/darwin-x64-51/binding.node
Node Sass could not find a binding for your current environment: OS X 64-bit with Node.js 7.x
Found bindings for the following environments:
- OS X 64-bit with Node.js 6.x
This usually happens because your environment has changed since running `npm install`.
Run `npm rebuild node-sass` to build the binding for your current environment. | 1.0 | Unable to build with Node 7.x stable (works with 6.x LTS) - Node 6.x is LTS is good, but 7.x stable doesn't run (at least on OS/X). Since it is the stable version and we are in Dev, it should probably also run in 7.x.
Child extract-text-webpack-plugin:
+ 1 hidden modules
ERROR in Missing binding ui-components/node_modules/node-sass/vendor/darwin-x64-51/binding.node
Node Sass could not find a binding for your current environment: OS X 64-bit with Node.js 7.x
Found bindings for the following environments:
- OS X 64-bit with Node.js 6.x
This usually happens because your environment has changed since running `npm install`.
Run `npm rebuild node-sass` to build the binding for your current environment. | non_priority | unable to build with node x stable works with x lts node x is lts is good but x stable doesn t run at least on os x since it is the stable version and we are in dev it should probably also run in x child extract text webpack plugin hidden modules error in missing binding ui components node modules node sass vendor darwin binding node node sass could not find a binding for your current environment os x bit with node js x found bindings for the following environments os x bit with node js x this usually happens because your environment has changed since running npm install run npm rebuild node sass to build the binding for your current environment | 0 |
321,781 | 27,554,137,257 | IssuesEvent | 2023-03-07 16:43:55 | Realm667/WolfenDoom | https://api.github.com/repos/Realm667/WolfenDoom | closed | [C3M5_A] Leftover debris | playtesting actor zscript | With the latest git, in c3m5_a, you will find some leftover debris floating. It was cleared from other areas, but not from here.


| 1.0 | [C3M5_A] Leftover debris - With the latest git, in c3m5_a, you will find some leftover debris floating. It was cleared from other areas, but not from here.


| non_priority | leftover debris with the latest git in a you will find some leftover debris floating it was cleared from other areas but not from here | 0 |
80,367 | 15,395,091,756 | IssuesEvent | 2021-03-03 18:45:38 | google/oboe | https://api.github.com/repos/google/oboe | opened | [RhythmGame] Error Invalid packageName when running | bug codelab | Getting the following error when attempting to run the RhythmGame sample:
```
W/ActivityManager: Invalid packageName: com.google.oboe.samples.rhythmgame
``` | 1.0 | [RhythmGame] Error Invalid packageName when running - Getting the following error when attempting to run the RhythmGame sample:
```
W/ActivityManager: Invalid packageName: com.google.oboe.samples.rhythmgame
``` | non_priority | error invalid packagename when running getting the following error when attempting to run the rhythmgame sample w activitymanager invalid packagename com google oboe samples rhythmgame | 0 |
230,310 | 18,536,430,379 | IssuesEvent | 2021-10-21 12:03:04 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | opened | Intermittent UI test failure - < StrictEnhancedTrackingProtectionTest. testStrictVisitDisableExceptionToggle > | eng:intermittent-test eng:ui-test | ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/5933185971491636521/executions/bs.4d160f079e6343be/testcases/1/test-cases)
### Stacktrace:
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:87)
at org.junit.Assert.assertTrue(Assert.java:42)
at org.junit.Assert.assertNotNull(Assert.java:713)
at org.junit.Assert.assertNotNull(Assert.java:723)
at org.mozilla.fenix.helpers.ext.WaitNotNullKt.waitNotNull(WaitNotNull.kt:20)
at org.mozilla.fenix.helpers.ext.WaitNotNullKt.waitNotNull$default(WaitNotNull.kt:17)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobotKt.assertEnhancedTrackingProtectionSheetStatus(EnhancedTrackingProtectionRobot.kt:120)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobotKt.access$assertEnhancedTrackingProtectionSheetStatus(EnhancedTrackingProtectionRobot.kt:1)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobot.verifyEnhancedTrackingProtectionSheetStatus(EnhancedTrackingProtectionRobot.kt:39)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest$testStrictVisitDisableExceptionToggle$8.invoke(StrictEnhancedTrackingProtectionTest.kt:113)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest$testStrictVisitDisableExceptionToggle$8.invoke(StrictEnhancedTrackingProtectionTest.kt:112)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobot$Transition.disableEnhancedTrackingProtectionFromSheet(EnhancedTrackingProtectionRobot.kt:91)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest.testStrictVisitDisableExceptionToggle(StrictEnhancedTrackingProtectionTest.kt:112)
at java.lang.reflect.Method.invoke(Native Method)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at androidx.test.internal.runner.junit4.statement.RunBefores.evaluate(RunBefores.java:80)
at androidx.test.internal.runner.junit4.statement.RunAfters.evaluate(RunAfters.java:61)
at androidx.test.rule.ActivityTestRule$ActivityStatement.evaluate(ActivityTestRule.java:531)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at androidx.test.internal.runner.TestExecutor.execute(TestExecutor.java:56)
at androidx.test.runner.AndroidJUnitRunner.onStart(AndroidJUnitRunner.java:395)
at android.app.Instrumentation$InstrumentationThread.run(Instrumentation.java:2145)
### Build: 10/23 Main
| 2.0 | Intermittent UI test failure - < StrictEnhancedTrackingProtectionTest. testStrictVisitDisableExceptionToggle > - ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/5933185971491636521/executions/bs.4d160f079e6343be/testcases/1/test-cases)
### Stacktrace:
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:87)
at org.junit.Assert.assertTrue(Assert.java:42)
at org.junit.Assert.assertNotNull(Assert.java:713)
at org.junit.Assert.assertNotNull(Assert.java:723)
at org.mozilla.fenix.helpers.ext.WaitNotNullKt.waitNotNull(WaitNotNull.kt:20)
at org.mozilla.fenix.helpers.ext.WaitNotNullKt.waitNotNull$default(WaitNotNull.kt:17)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobotKt.assertEnhancedTrackingProtectionSheetStatus(EnhancedTrackingProtectionRobot.kt:120)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobotKt.access$assertEnhancedTrackingProtectionSheetStatus(EnhancedTrackingProtectionRobot.kt:1)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobot.verifyEnhancedTrackingProtectionSheetStatus(EnhancedTrackingProtectionRobot.kt:39)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest$testStrictVisitDisableExceptionToggle$8.invoke(StrictEnhancedTrackingProtectionTest.kt:113)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest$testStrictVisitDisableExceptionToggle$8.invoke(StrictEnhancedTrackingProtectionTest.kt:112)
at org.mozilla.fenix.ui.robots.EnhancedTrackingProtectionRobot$Transition.disableEnhancedTrackingProtectionFromSheet(EnhancedTrackingProtectionRobot.kt:91)
at org.mozilla.fenix.ui.StrictEnhancedTrackingProtectionTest.testStrictVisitDisableExceptionToggle(StrictEnhancedTrackingProtectionTest.kt:112)
at java.lang.reflect.Method.invoke(Native Method)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at androidx.test.internal.runner.junit4.statement.RunBefores.evaluate(RunBefores.java:80)
at androidx.test.internal.runner.junit4.statement.RunAfters.evaluate(RunAfters.java:61)
at androidx.test.rule.ActivityTestRule$ActivityStatement.evaluate(ActivityTestRule.java:531)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.BlockJUnit4ClassRunner$1.evaluate(BlockJUnit4ClassRunner.java:100)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:366)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:103)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:63)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$4.run(ParentRunner.java:331)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:79)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:329)
at org.junit.runners.ParentRunner.access$100(ParentRunner.java:66)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:293)
at org.junit.runners.ParentRunner$3.evaluate(ParentRunner.java:306)
at org.junit.runners.ParentRunner.run(ParentRunner.java:413)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at androidx.test.internal.runner.TestExecutor.execute(TestExecutor.java:56)
at androidx.test.runner.AndroidJUnitRunner.onStart(AndroidJUnitRunner.java:395)
at android.app.Instrumentation$InstrumentationThread.run(Instrumentation.java:2145)
### Build: 10/23 Main
| non_priority | intermittent ui test failure firebase test run stacktrace java lang assertionerror at org junit assert fail assert java at org junit assert asserttrue assert java at org junit assert assertnotnull assert java at org junit assert assertnotnull assert java at org mozilla fenix helpers ext waitnotnullkt waitnotnull waitnotnull kt at org mozilla fenix helpers ext waitnotnullkt waitnotnull default waitnotnull kt at org mozilla fenix ui robots enhancedtrackingprotectionrobotkt assertenhancedtrackingprotectionsheetstatus enhancedtrackingprotectionrobot kt at org mozilla fenix ui robots enhancedtrackingprotectionrobotkt access assertenhancedtrackingprotectionsheetstatus enhancedtrackingprotectionrobot kt at org mozilla fenix ui robots enhancedtrackingprotectionrobot verifyenhancedtrackingprotectionsheetstatus enhancedtrackingprotectionrobot kt at org mozilla fenix ui strictenhancedtrackingprotectiontest teststrictvisitdisableexceptiontoggle invoke strictenhancedtrackingprotectiontest kt at org mozilla fenix ui strictenhancedtrackingprotectiontest teststrictvisitdisableexceptiontoggle invoke strictenhancedtrackingprotectiontest kt at org mozilla fenix ui robots enhancedtrackingprotectionrobot transition disableenhancedtrackingprotectionfromsheet enhancedtrackingprotectionrobot kt at org mozilla fenix ui strictenhancedtrackingprotectiontest teststrictvisitdisableexceptiontoggle strictenhancedtrackingprotectiontest kt at java lang reflect method invoke native method at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at androidx test internal runner statement runbefores evaluate runbefores java at androidx test internal runner statement runafters evaluate runafters java at androidx test rule activitytestrule activitystatement evaluate activitytestrule java at org junit runners parentrunner evaluate parentrunner java at org junit runners evaluate java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org junit runners suite runchild suite java at org junit runners suite runchild suite java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org junit runner junitcore run junitcore java at org junit runner junitcore run junitcore java at androidx test internal runner testexecutor execute testexecutor java at androidx test runner androidjunitrunner onstart androidjunitrunner java at android app instrumentation instrumentationthread run instrumentation java build main | 0 |
50,968 | 26,861,378,921 | IssuesEvent | 2023-02-03 18:43:38 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | kv: make disk I/O asynchronous with respect to Raft state machine | C-performance A-kv-replication T-kv | ⚠️ **EDIT: The original optimization proposed here was implemented in https://github.com/cockroachdb/cockroach/pull/38954. See https://github.com/cockroachdb/cockroach/issues/17500#issuecomment-425689048 for the remainder of this issue.**
Raft, along with most consensus protocols in the Paxos family, distinguishes committed entries from executed entries. An entry is committed when the Raft protocol has completed and the entry has been sufficiently replicated and persisted in the Raft log. The entry is then executed when it is applied to a given replica's state machine. This distinction is important because in cases where the execution of an entry onto the state machine does not produce a result, it is not necessary to wait for execution before sending a commit notification to clients.
Currently in Cockroach, the proposing replica [waits until command execution](https://github.com/cockroachdb/cockroach/blob/2e76b6e567311330041c97e2f564ece8485feefd/pkg/storage/replica.go#L4220) before responding to clients. However, changes made for PropEval KV assured that all MVCC related logic is made upstream of Raft and that by the time we reach entry execution, we're simply applying a `WriteBatch` to RockDB. While some of these execution steps can create `ReplicaCorruptionError`s, I don't think it's necessary or possibly even correct that we attach these errors to the proposal response itself. This is because the entry has already been replicated through Raft, so a local `ReplicaCorruptionError` doesn't mean that all replicas are corrupted or that the command failed. In fact, after looking at the code I don't think that `proposalResult` needs anything populated at execution time for correctness. Because of this, I have a suspicion that all of the time spent in `applyRaftCommand`, including writing to RocksDB and performing stats computations, is unnecessary latency.
Preliminary results from a (very) [rough draft of the change](https://github.com/nvanbenschoten/cockroach/commit/06b4cba909e5a79900833f5443580b1b85e47694) show a **2-3%** improvement on average latency for the [KV](https://github.com/cockroachdb/loadgen/tree/master/kv) benchmark with a `--batch` size of 4:
_Without change (batch=4):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
600.0s 0 597164 995.3 32.2 32.5 41.9 65.0 939.5
BenchmarkBlocks 597164 1004753.2 ns/op
```
_With change (batch=4):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
600.0s 0 612652 1021.1 31.4 30.4 41.9 58.7 604.0
BenchmarkBlocks 612652 979351.4 ns/op
```
With a `--batch` size of 40, the results were even more pronounced:
_Without change (batch=40):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
300.0s 0 616040 2053.4 134.0 54.5 151.0 2415.9 10200.5
BenchmarkBlocks 616040 486990.5 ns/op
```
_With change (batch=40):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
300.0s 0 708040 2360.1 114.7 54.5 130.0 1140.9 10200.5
BenchmarkBlocks 708040 423713.8 ns/op
```
Note that while I think we can respond to clients sooner, I don't think we can pop the command out of the `CommandQueue` until after it has actually been executed because of how proposer evaluated kv works upstream of Raft.
@tschottdorf @bdarnell
Jira issue: CRDB-6037
Epic CRDB-22644 | True | kv: make disk I/O asynchronous with respect to Raft state machine - ⚠️ **EDIT: The original optimization proposed here was implemented in https://github.com/cockroachdb/cockroach/pull/38954. See https://github.com/cockroachdb/cockroach/issues/17500#issuecomment-425689048 for the remainder of this issue.**
Raft, along with most consensus protocols in the Paxos family, distinguishes committed entries from executed entries. An entry is committed when the Raft protocol has completed and the entry has been sufficiently replicated and persisted in the Raft log. The entry is then executed when it is applied to a given replica's state machine. This distinction is important because in cases where the execution of an entry onto the state machine does not produce a result, it is not necessary to wait for execution before sending a commit notification to clients.
Currently in Cockroach, the proposing replica [waits until command execution](https://github.com/cockroachdb/cockroach/blob/2e76b6e567311330041c97e2f564ece8485feefd/pkg/storage/replica.go#L4220) before responding to clients. However, changes made for PropEval KV assured that all MVCC related logic is made upstream of Raft and that by the time we reach entry execution, we're simply applying a `WriteBatch` to RockDB. While some of these execution steps can create `ReplicaCorruptionError`s, I don't think it's necessary or possibly even correct that we attach these errors to the proposal response itself. This is because the entry has already been replicated through Raft, so a local `ReplicaCorruptionError` doesn't mean that all replicas are corrupted or that the command failed. In fact, after looking at the code I don't think that `proposalResult` needs anything populated at execution time for correctness. Because of this, I have a suspicion that all of the time spent in `applyRaftCommand`, including writing to RocksDB and performing stats computations, is unnecessary latency.
Preliminary results from a (very) [rough draft of the change](https://github.com/nvanbenschoten/cockroach/commit/06b4cba909e5a79900833f5443580b1b85e47694) show a **2-3%** improvement on average latency for the [KV](https://github.com/cockroachdb/loadgen/tree/master/kv) benchmark with a `--batch` size of 4:
_Without change (batch=4):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
600.0s 0 597164 995.3 32.2 32.5 41.9 65.0 939.5
BenchmarkBlocks 597164 1004753.2 ns/op
```
_With change (batch=4):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
600.0s 0 612652 1021.1 31.4 30.4 41.9 58.7 604.0
BenchmarkBlocks 612652 979351.4 ns/op
```
With a `--batch` size of 40, the results were even more pronounced:
_Without change (batch=40):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
300.0s 0 616040 2053.4 134.0 54.5 151.0 2415.9 10200.5
BenchmarkBlocks 616040 486990.5 ns/op
```
_With change (batch=40):_
```
_elapsed___errors_____ops(total)___ops/sec(cum)__avg(ms)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
300.0s 0 708040 2360.1 114.7 54.5 130.0 1140.9 10200.5
BenchmarkBlocks 708040 423713.8 ns/op
```
Note that while I think we can respond to clients sooner, I don't think we can pop the command out of the `CommandQueue` until after it has actually been executed because of how proposer evaluated kv works upstream of Raft.
@tschottdorf @bdarnell
Jira issue: CRDB-6037
Epic CRDB-22644 | non_priority | kv make disk i o asynchronous with respect to raft state machine ⚠️ edit the original optimization proposed here was implemented in see for the remainder of this issue raft along with most consensus protocols in the paxos family distinguishes committed entries from executed entries an entry is committed when the raft protocol has completed and the entry has been sufficiently replicated and persisted in the raft log the entry is then executed when it is applied to a given replica s state machine this distinction is important because in cases where the execution of an entry onto the state machine does not produce a result it is not necessary to wait for execution before sending a commit notification to clients currently in cockroach the proposing replica before responding to clients however changes made for propeval kv assured that all mvcc related logic is made upstream of raft and that by the time we reach entry execution we re simply applying a writebatch to rockdb while some of these execution steps can create replicacorruptionerror s i don t think it s necessary or possibly even correct that we attach these errors to the proposal response itself this is because the entry has already been replicated through raft so a local replicacorruptionerror doesn t mean that all replicas are corrupted or that the command failed in fact after looking at the code i don t think that proposalresult needs anything populated at execution time for correctness because of this i have a suspicion that all of the time spent in applyraftcommand including writing to rocksdb and performing stats computations is unnecessary latency preliminary results from a very show a improvement on average latency for the benchmark with a batch size of without change batch elapsed errors ops total ops sec cum avg ms ms ms ms pmax ms benchmarkblocks ns op with change batch elapsed errors ops total ops sec cum avg ms ms ms ms pmax ms benchmarkblocks ns op with a batch size of the results were even more pronounced without change batch elapsed errors ops total ops sec cum avg ms ms ms ms pmax ms benchmarkblocks ns op with change batch elapsed errors ops total ops sec cum avg ms ms ms ms pmax ms benchmarkblocks ns op note that while i think we can respond to clients sooner i don t think we can pop the command out of the commandqueue until after it has actually been executed because of how proposer evaluated kv works upstream of raft tschottdorf bdarnell jira issue crdb epic crdb | 0 |
99,049 | 12,395,348,419 | IssuesEvent | 2020-05-20 18:30:06 | pnp/sp-dev-list-formatting | https://api.github.com/repos/pnp/sp-dev-list-formatting | closed | Using () in JSON STYLE attribute causes column formatter to fail | ✔ By Design 🌭 List Formatting General | #### Category
- [ ] Question
- [X ] Bug
- [ ] Enhancement
#### Expected or Desired Behavior
Using a CSS style attribute in a column formatter containing brackets "()" it should render the condition / attribute.
#### Observed Behavior
As soon as I start using brackets "()" within CSS style attributes the whole column formatter stops working and no output is displayed.
#### Steps to Reproduce
"style": {
"background-color": {
"rgba(0,0,0,0)"
}
}
"style": {
"background-image": {
"url(/path/to/my/image.png)"
}
}
"style": {
"color": {
"rgb(0,0,0)"
}
}
"style": {
"color": {
"rgba(0,0,0,0)"
}
}
"style": {
"width": {
"calc(100px - 1px)"
}
}
"style": {
"height": {
"calc(100px - 1px)"
}
}
"style": {
"max-width": {
"calc(100px - 1px)"
}
}
"style": {
"max-height": {
"calc(100px - 1px)"
}
}
| 1.0 | Using () in JSON STYLE attribute causes column formatter to fail - #### Category
- [ ] Question
- [X ] Bug
- [ ] Enhancement
#### Expected or Desired Behavior
Using a CSS style attribute in a column formatter containing brackets "()" it should render the condition / attribute.
#### Observed Behavior
As soon as I start using brackets "()" within CSS style attributes the whole column formatter stops working and no output is displayed.
#### Steps to Reproduce
"style": {
"background-color": {
"rgba(0,0,0,0)"
}
}
"style": {
"background-image": {
"url(/path/to/my/image.png)"
}
}
"style": {
"color": {
"rgb(0,0,0)"
}
}
"style": {
"color": {
"rgba(0,0,0,0)"
}
}
"style": {
"width": {
"calc(100px - 1px)"
}
}
"style": {
"height": {
"calc(100px - 1px)"
}
}
"style": {
"max-width": {
"calc(100px - 1px)"
}
}
"style": {
"max-height": {
"calc(100px - 1px)"
}
}
| non_priority | using in json style attribute causes column formatter to fail category question bug enhancement expected or desired behavior using a css style attribute in a column formatter containing brackets it should render the condition attribute observed behavior as soon as i start using brackets within css style attributes the whole column formatter stops working and no output is displayed steps to reproduce style background color rgba style background image url path to my image png style color rgb style color rgba style width calc style height calc style max width calc style max height calc | 0 |
192,972 | 15,363,976,568 | IssuesEvent | 2021-03-01 21:23:01 | ProfKleberSouza/projeto-pratico-grupo-5 | https://api.github.com/repos/ProfKleberSouza/projeto-pratico-grupo-5 | closed | Especificações do Projeto - Persona | documentation | > **Links Úteis**:
> - [Rock Content](https://rockcontent.com/blog/personas/)
> - [Hotmart](https://blog.hotmart.com/pt-br/como-criar-persona-negocio/)
> - [O que é persona?](https://resultadosdigitais.com.br/blog/persona-o-que-e/)
> - [Persona x Público-alvo](https://flammo.com.br/blog/persona-e-publico-alvo-qual-a-diferenca/)
> - [Mapa de Empatia](https://resultadosdigitais.com.br/blog/mapa-da-empatia/)
> - [Mapa de Stalkeholders](https://www.racecomunicacao.com.br/blog/como-fazer-o-mapeamento-de-stakeholders/) | 1.0 | Especificações do Projeto - Persona - > **Links Úteis**:
> - [Rock Content](https://rockcontent.com/blog/personas/)
> - [Hotmart](https://blog.hotmart.com/pt-br/como-criar-persona-negocio/)
> - [O que é persona?](https://resultadosdigitais.com.br/blog/persona-o-que-e/)
> - [Persona x Público-alvo](https://flammo.com.br/blog/persona-e-publico-alvo-qual-a-diferenca/)
> - [Mapa de Empatia](https://resultadosdigitais.com.br/blog/mapa-da-empatia/)
> - [Mapa de Stalkeholders](https://www.racecomunicacao.com.br/blog/como-fazer-o-mapeamento-de-stakeholders/) | non_priority | especificações do projeto persona links úteis | 0 |
7,473 | 10,679,024,157 | IssuesEvent | 2019-10-21 18:26:44 | openopps/openopps-platform | https://api.github.com/repos/openopps/openopps-platform | closed | Tracking Data: Who edited internship | Admin Data Requirements Ready |
Who: System Admin
What: Ability to track who edited an internship
Why: in order to provide data to state if necessary
Acceptance Criteria:
Also track who edited an internship, when it was edited, and if possible what fields were edited. | 1.0 | Tracking Data: Who edited internship -
Who: System Admin
What: Ability to track who edited an internship
Why: in order to provide data to state if necessary
Acceptance Criteria:
Also track who edited an internship, when it was edited, and if possible what fields were edited. | non_priority | tracking data who edited internship who system admin what ability to track who edited an internship why in order to provide data to state if necessary acceptance criteria also track who edited an internship when it was edited and if possible what fields were edited | 0 |
13,864 | 10,058,287,603 | IssuesEvent | 2019-07-22 13:37:47 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | Upgrade istio to 1.2.x | area/service-mesh enhancement | <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
We need to upgrade istio to 1.2.X (1.2.2 at least) in order to have https://github.com/istio/istio/commit/5c1f917439a49f53bba8c6104fd2ec00a7866c4a
As agreed with @hisarbalik we will not touch `kiali` directory - it is excluded from the upgrade. Hisar will upgrade kiali manually.
Support for HTTP 1.0 in ingress available in the kyma. Once this will be done, the application connector can fully migrate to istio and get rid of nginx.
<!-- Provide a clear and concise description of the feature. -->
**Reasons**
Allow application connector to fully switch to istio asap.
<!-- Explain why we should add this feature. Provide use cases to illustrate its benefits. -->
**Attachments**
<!-- Attach any files, links, code samples, or screenshots that will convince us to your idea. -->
| 1.0 | Upgrade istio to 1.2.x - <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
We need to upgrade istio to 1.2.X (1.2.2 at least) in order to have https://github.com/istio/istio/commit/5c1f917439a49f53bba8c6104fd2ec00a7866c4a
As agreed with @hisarbalik we will not touch `kiali` directory - it is excluded from the upgrade. Hisar will upgrade kiali manually.
Support for HTTP 1.0 in ingress available in the kyma. Once this will be done, the application connector can fully migrate to istio and get rid of nginx.
<!-- Provide a clear and concise description of the feature. -->
**Reasons**
Allow application connector to fully switch to istio asap.
<!-- Explain why we should add this feature. Provide use cases to illustrate its benefits. -->
**Attachments**
<!-- Attach any files, links, code samples, or screenshots that will convince us to your idea. -->
| non_priority | upgrade istio to x thank you for your contribution before you submit the issue search open and closed issues for duplicates read the contributing guidelines description we need to upgrade istio to x at least in order to have as agreed with hisarbalik we will not touch kiali directory it is excluded from the upgrade hisar will upgrade kiali manually support for http in ingress available in the kyma once this will be done the application connector can fully migrate to istio and get rid of nginx reasons allow application connector to fully switch to istio asap attachments | 0 |
68,042 | 13,064,416,365 | IssuesEvent | 2020-07-30 18:03:22 | drag-time/drag-time-fe | https://api.github.com/repos/drag-time/drag-time-fe | closed | Create Eval Presentation (FE & BE) | CODEFREEZE documentation | Create a google slides presentation for our evaluation on Thursday, 7/30/20.
Group has 20 minutes total - 10 minutes for the back-end, and 10 minutes for the front-end. The presentation should use the rubric as a guideline for what needs to be covered.
- [x] Project board
- [x] Demo of application
- [x] Technologies used
- [x] Tasks completed
- [x] Testing
- [x] Challenges | 1.0 | Create Eval Presentation (FE & BE) - Create a google slides presentation for our evaluation on Thursday, 7/30/20.
Group has 20 minutes total - 10 minutes for the back-end, and 10 minutes for the front-end. The presentation should use the rubric as a guideline for what needs to be covered.
- [x] Project board
- [x] Demo of application
- [x] Technologies used
- [x] Tasks completed
- [x] Testing
- [x] Challenges | non_priority | create eval presentation fe be create a google slides presentation for our evaluation on thursday group has minutes total minutes for the back end and minutes for the front end the presentation should use the rubric as a guideline for what needs to be covered project board demo of application technologies used tasks completed testing challenges | 0 |
5 | 2,490,614,733 | IssuesEvent | 2015-01-02 17:33:13 | CrazyPants/EnderZoo | https://api.github.com/repos/CrazyPants/EnderZoo | closed | Config needs configurable enchantment ID | bug Code Complete | ID:8 is already taken on my server, there doesn't appear to be a way to alter this via the config.
I am using the latest version of EnderZoo available. | 1.0 | Config needs configurable enchantment ID - ID:8 is already taken on my server, there doesn't appear to be a way to alter this via the config.
I am using the latest version of EnderZoo available. | non_priority | config needs configurable enchantment id id is already taken on my server there doesn t appear to be a way to alter this via the config i am using the latest version of enderzoo available | 0 |
54,949 | 7,933,433,688 | IssuesEvent | 2018-07-08 06:05:33 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | default values should be returned rather than None or [] or {} or '' | Core Documentation Feature Pillar stale | ## The Problem
Consider some simple pillar/grain data:
```
somekey:
```
If I call `pillar.get` with a `default` value of an empty array (`[]`):
```
salt-call pillar.get somekey []
```
It will return `None` rather than the default (`[]`). This is because the value is present in the file (although entirely undefined).
If I delete the pillar/grain value entirely and call the same `pillar.get` it returns an empty string (`''`).
If I change the pillar to:`somekey: []` it will return an empty array, if I change the pillar to `somekey: {}` it will return an empty dictionary.
So there are 4 different possible values for something that doesn't really exist (or its existence implies nothing) and only one of these variations will actually trigger/use the `default` argument: deleting the entry entirely.
This leads to very verbose code endlessly checking for the various different versions of **doesn't-really-exist** to avoid template compilation errors and runtime `state.apply` issues. This is particularly frustrating when iterating over values where you hope to do a simple `for x in salt['pillar.get']('y')`. This can be dealt with by being really pedantic with your YAML but for solid code you need to cater for all options as you can't guarantee that people will populate the data in a consistent fashion, and why should you care.
I'm not sure what the fix should be but improving this area could make salt programming a lot more efficient.
## Background
There are two types of YAML notation to express lists/dictionaries:
- Multi-line - [block notation](http://www.yaml.org/spec/1.2/spec.html#id2798057)
- Single-line - [flow notation](http://www.yaml.org/spec/1.2/spec.html#id2790832)
A dictionary item with no child elements/items can be expressed in many different ways (along with removing the key entirely):
```
somekey:
somekey: ''
somekey: {}
somekey: []
somekey:
{}
somekey:
[]
somekey: |
etc.etc.etc
```
.... but they are all essentially nothing.
| 1.0 | default values should be returned rather than None or [] or {} or '' - ## The Problem
Consider some simple pillar/grain data:
```
somekey:
```
If I call `pillar.get` with a `default` value of an empty array (`[]`):
```
salt-call pillar.get somekey []
```
It will return `None` rather than the default (`[]`). This is because the value is present in the file (although entirely undefined).
If I delete the pillar/grain value entirely and call the same `pillar.get` it returns an empty string (`''`).
If I change the pillar to:`somekey: []` it will return an empty array, if I change the pillar to `somekey: {}` it will return an empty dictionary.
So there are 4 different possible values for something that doesn't really exist (or its existence implies nothing) and only one of these variations will actually trigger/use the `default` argument: deleting the entry entirely.
This leads to very verbose code endlessly checking for the various different versions of **doesn't-really-exist** to avoid template compilation errors and runtime `state.apply` issues. This is particularly frustrating when iterating over values where you hope to do a simple `for x in salt['pillar.get']('y')`. This can be dealt with by being really pedantic with your YAML but for solid code you need to cater for all options as you can't guarantee that people will populate the data in a consistent fashion, and why should you care.
I'm not sure what the fix should be but improving this area could make salt programming a lot more efficient.
## Background
There are two types of YAML notation to express lists/dictionaries:
- Multi-line - [block notation](http://www.yaml.org/spec/1.2/spec.html#id2798057)
- Single-line - [flow notation](http://www.yaml.org/spec/1.2/spec.html#id2790832)
A dictionary item with no child elements/items can be expressed in many different ways (along with removing the key entirely):
```
somekey:
somekey: ''
somekey: {}
somekey: []
somekey:
{}
somekey:
[]
somekey: |
etc.etc.etc
```
.... but they are all essentially nothing.
| non_priority | default values should be returned rather than none or or or the problem consider some simple pillar grain data somekey if i call pillar get with a default value of an empty array salt call pillar get somekey it will return none rather than the default this is because the value is present in the file although entirely undefined if i delete the pillar grain value entirely and call the same pillar get it returns an empty string if i change the pillar to somekey it will return an empty array if i change the pillar to somekey it will return an empty dictionary so there are different possible values for something that doesn t really exist or its existence implies nothing and only one of these variations will actually trigger use the default argument deleting the entry entirely this leads to very verbose code endlessly checking for the various different versions of doesn t really exist to avoid template compilation errors and runtime state apply issues this is particularly frustrating when iterating over values where you hope to do a simple for x in salt y this can be dealt with by being really pedantic with your yaml but for solid code you need to cater for all options as you can t guarantee that people will populate the data in a consistent fashion and why should you care i m not sure what the fix should be but improving this area could make salt programming a lot more efficient background there are two types of yaml notation to express lists dictionaries multi line single line a dictionary item with no child elements items can be expressed in many different ways along with removing the key entirely somekey somekey somekey somekey somekey somekey somekey etc etc etc but they are all essentially nothing | 0 |
238,295 | 26,095,266,050 | IssuesEvent | 2022-12-26 18:20:23 | uriel-naor/BigProduct | https://api.github.com/repos/uriel-naor/BigProduct | opened | spring-security-data-4.2.3.RELEASE.jar: 6 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-data-4.2.3.RELEASE.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (spring-security-data version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2018-1273](https://www.mend.io/vulnerability-database/CVE-2018-1273) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | spring-data-commons-1.13.4.RELEASE.jar | Transitive | 4.2.6.RELEASE | ✅ |
| [CVE-2018-1274](https://www.mend.io/vulnerability-database/CVE-2018-1274) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | spring-data-commons-1.13.4.RELEASE.jar | Transitive | 4.2.6.RELEASE | ✅ |
| [CVE-2018-1259](https://www.mend.io/vulnerability-database/CVE-2018-1259) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | spring-data-commons-1.13.4.RELEASE.jar | Transitive | 4.2.6.RELEASE | ✅ |
| [CVE-2019-11272](https://www.mend.io/vulnerability-database/CVE-2019-11272) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | spring-security-core-4.2.3.RELEASE.jar | Transitive | 4.2.13.RELEASE | ✅ |
| [CVE-2020-5408](https://www.mend.io/vulnerability-database/CVE-2020-5408) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | spring-security-core-4.2.3.RELEASE.jar | Transitive | 4.2.16.RELEASE | ✅ |
| [CVE-2019-3795](https://www.mend.io/vulnerability-database/CVE-2019-3795) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-security-core-4.2.3.RELEASE.jar | Transitive | 4.2.12.RELEASE | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1273</summary>
### Vulnerable Library - <b>spring-data-commons-1.13.4.RELEASE.jar</b></p>
<p>Global parent pom.xml to be used by Spring Data modules</p>
<p>Library home page: <a href="http://www.spring.io/spring-data">http://www.spring.io/spring-data</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/data/spring-data-commons/1.13.4.RELEASE/spring-data-commons-1.13.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-data-commons-1.13.4.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Data Commons, versions prior to 1.13 to 1.13.10, 2.0 to 2.0.5, and older unsupported versions, contain a property binder vulnerability caused by improper neutralization of special elements. An unauthenticated remote malicious user (or attacker) can supply specially crafted request parameters against Spring Data REST backed HTTP resources or using Spring Data's projection-based request payload binding hat can lead to a remote code execution attack.
<p>Publish Date: 2018-04-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1273>CVE-2018-1273</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1273">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1273</a></p>
<p>Release Date: 2018-04-11</p>
<p>Fix Resolution (org.springframework.data:spring-data-commons): 1.13.11.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.6.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1274</summary>
### Vulnerable Library - <b>spring-data-commons-1.13.4.RELEASE.jar</b></p>
<p>Global parent pom.xml to be used by Spring Data modules</p>
<p>Library home page: <a href="http://www.spring.io/spring-data">http://www.spring.io/spring-data</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/data/spring-data-commons/1.13.4.RELEASE/spring-data-commons-1.13.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-data-commons-1.13.4.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Data Commons, versions 1.13 to 1.13.10, 2.0 to 2.0.5, and older unsupported versions, contain a property path parser vulnerability caused by unlimited resource allocation. An unauthenticated remote malicious user (or attacker) can issue requests against Spring Data REST endpoints or endpoints using property path parsing which can cause a denial of service (CPU and memory consumption).
<p>Publish Date: 2018-04-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1274>CVE-2018-1274</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1274">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1274</a></p>
<p>Release Date: 2018-04-18</p>
<p>Fix Resolution (org.springframework.data:spring-data-commons): 1.13.11.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.6.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1259</summary>
### Vulnerable Library - <b>spring-data-commons-1.13.4.RELEASE.jar</b></p>
<p>Global parent pom.xml to be used by Spring Data modules</p>
<p>Library home page: <a href="http://www.spring.io/spring-data">http://www.spring.io/spring-data</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/data/spring-data-commons/1.13.4.RELEASE/spring-data-commons-1.13.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-data-commons-1.13.4.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Data Commons, versions 1.13 prior to 1.13.12 and 2.0 prior to 2.0.7, used in combination with XMLBeam 1.4.14 or earlier versions, contains a property binder vulnerability caused by improper restriction of XML external entity references as underlying library XMLBeam does not restrict external reference expansion. An unauthenticated remote malicious user can supply specially crafted request parameters against Spring Data's projection-based request payload binding to access arbitrary files on the system.
<p>Publish Date: 2018-05-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1259>CVE-2018-1259</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1259">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1259</a></p>
<p>Release Date: 2018-05-11</p>
<p>Fix Resolution (org.springframework.data:spring-data-commons): 1.13.12.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.6.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-11272</summary>
### Vulnerable Library - <b>spring-security-core-4.2.3.RELEASE.jar</b></p>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-security-core-4.2.3.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security, versions 4.2.x up to 4.2.12, and older unsupported versions support plain text passwords using PlaintextPasswordEncoder. If an application using an affected version of Spring Security is leveraging PlaintextPasswordEncoder and a user has a null encoded password, a malicious user (or attacker) can authenticate using a password of "null".
<p>Publish Date: 2019-06-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11272>CVE-2019-11272</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272</a></p>
<p>Release Date: 2019-06-26</p>
<p>Fix Resolution (org.springframework.security:spring-security-core): 4.2.13.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.13.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-5408</summary>
### Vulnerable Library - <b>spring-security-core-4.2.3.RELEASE.jar</b></p>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-security-core-4.2.3.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security versions 5.3.x prior to 5.3.2, 5.2.x prior to 5.2.4, 5.1.x prior to 5.1.10, 5.0.x prior to 5.0.16 and 4.2.x prior to 4.2.16 use a fixed null initialization vector with CBC Mode in the implementation of the queryable text encryptor. A malicious user with access to the data that has been encrypted using such an encryptor may be able to derive the unencrypted values using a dictionary attack.
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5408>CVE-2020-5408</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5408">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5408</a></p>
<p>Release Date: 2020-05-14</p>
<p>Fix Resolution (org.springframework.security:spring-security-core): 4.2.16.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.16.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-3795</summary>
### Vulnerable Library - <b>spring-security-core-4.2.3.RELEASE.jar</b></p>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-security-core-4.2.3.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security versions 4.2.x prior to 4.2.12, 5.0.x prior to 5.0.12, and 5.1.x prior to 5.1.5 contain an insecure randomness vulnerability when using SecureRandomFactoryBean#setSeed to configure a SecureRandom instance. In order to be impacted, an honest application must provide a seed and make the resulting random material available to an attacker for inspection.
<p>Publish Date: 2019-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-3795>CVE-2019-3795</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pivotal.io/security/cve-2019-3795">https://pivotal.io/security/cve-2019-3795</a></p>
<p>Release Date: 2019-04-09</p>
<p>Fix Resolution (org.springframework.security:spring-security-core): 4.2.12.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.12.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | spring-security-data-4.2.3.RELEASE.jar: 6 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-data-4.2.3.RELEASE.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (spring-security-data version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2018-1273](https://www.mend.io/vulnerability-database/CVE-2018-1273) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | spring-data-commons-1.13.4.RELEASE.jar | Transitive | 4.2.6.RELEASE | ✅ |
| [CVE-2018-1274](https://www.mend.io/vulnerability-database/CVE-2018-1274) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | spring-data-commons-1.13.4.RELEASE.jar | Transitive | 4.2.6.RELEASE | ✅ |
| [CVE-2018-1259](https://www.mend.io/vulnerability-database/CVE-2018-1259) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | spring-data-commons-1.13.4.RELEASE.jar | Transitive | 4.2.6.RELEASE | ✅ |
| [CVE-2019-11272](https://www.mend.io/vulnerability-database/CVE-2019-11272) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | spring-security-core-4.2.3.RELEASE.jar | Transitive | 4.2.13.RELEASE | ✅ |
| [CVE-2020-5408](https://www.mend.io/vulnerability-database/CVE-2020-5408) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | spring-security-core-4.2.3.RELEASE.jar | Transitive | 4.2.16.RELEASE | ✅ |
| [CVE-2019-3795](https://www.mend.io/vulnerability-database/CVE-2019-3795) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-security-core-4.2.3.RELEASE.jar | Transitive | 4.2.12.RELEASE | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1273</summary>
### Vulnerable Library - <b>spring-data-commons-1.13.4.RELEASE.jar</b></p>
<p>Global parent pom.xml to be used by Spring Data modules</p>
<p>Library home page: <a href="http://www.spring.io/spring-data">http://www.spring.io/spring-data</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/data/spring-data-commons/1.13.4.RELEASE/spring-data-commons-1.13.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-data-commons-1.13.4.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Data Commons, versions prior to 1.13 to 1.13.10, 2.0 to 2.0.5, and older unsupported versions, contain a property binder vulnerability caused by improper neutralization of special elements. An unauthenticated remote malicious user (or attacker) can supply specially crafted request parameters against Spring Data REST backed HTTP resources or using Spring Data's projection-based request payload binding hat can lead to a remote code execution attack.
<p>Publish Date: 2018-04-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1273>CVE-2018-1273</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1273">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1273</a></p>
<p>Release Date: 2018-04-11</p>
<p>Fix Resolution (org.springframework.data:spring-data-commons): 1.13.11.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.6.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1274</summary>
### Vulnerable Library - <b>spring-data-commons-1.13.4.RELEASE.jar</b></p>
<p>Global parent pom.xml to be used by Spring Data modules</p>
<p>Library home page: <a href="http://www.spring.io/spring-data">http://www.spring.io/spring-data</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/data/spring-data-commons/1.13.4.RELEASE/spring-data-commons-1.13.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-data-commons-1.13.4.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Data Commons, versions 1.13 to 1.13.10, 2.0 to 2.0.5, and older unsupported versions, contain a property path parser vulnerability caused by unlimited resource allocation. An unauthenticated remote malicious user (or attacker) can issue requests against Spring Data REST endpoints or endpoints using property path parsing which can cause a denial of service (CPU and memory consumption).
<p>Publish Date: 2018-04-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1274>CVE-2018-1274</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1274">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1274</a></p>
<p>Release Date: 2018-04-18</p>
<p>Fix Resolution (org.springframework.data:spring-data-commons): 1.13.11.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.6.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1259</summary>
### Vulnerable Library - <b>spring-data-commons-1.13.4.RELEASE.jar</b></p>
<p>Global parent pom.xml to be used by Spring Data modules</p>
<p>Library home page: <a href="http://www.spring.io/spring-data">http://www.spring.io/spring-data</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/data/spring-data-commons/1.13.4.RELEASE/spring-data-commons-1.13.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-data-commons-1.13.4.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Data Commons, versions 1.13 prior to 1.13.12 and 2.0 prior to 2.0.7, used in combination with XMLBeam 1.4.14 or earlier versions, contains a property binder vulnerability caused by improper restriction of XML external entity references as underlying library XMLBeam does not restrict external reference expansion. An unauthenticated remote malicious user can supply specially crafted request parameters against Spring Data's projection-based request payload binding to access arbitrary files on the system.
<p>Publish Date: 2018-05-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1259>CVE-2018-1259</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1259">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1259</a></p>
<p>Release Date: 2018-05-11</p>
<p>Fix Resolution (org.springframework.data:spring-data-commons): 1.13.12.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.6.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-11272</summary>
### Vulnerable Library - <b>spring-security-core-4.2.3.RELEASE.jar</b></p>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-security-core-4.2.3.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security, versions 4.2.x up to 4.2.12, and older unsupported versions support plain text passwords using PlaintextPasswordEncoder. If an application using an affected version of Spring Security is leveraging PlaintextPasswordEncoder and a user has a null encoded password, a malicious user (or attacker) can authenticate using a password of "null".
<p>Publish Date: 2019-06-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11272>CVE-2019-11272</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11272</a></p>
<p>Release Date: 2019-06-26</p>
<p>Fix Resolution (org.springframework.security:spring-security-core): 4.2.13.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.13.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-5408</summary>
### Vulnerable Library - <b>spring-security-core-4.2.3.RELEASE.jar</b></p>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-security-core-4.2.3.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security versions 5.3.x prior to 5.3.2, 5.2.x prior to 5.2.4, 5.1.x prior to 5.1.10, 5.0.x prior to 5.0.16 and 4.2.x prior to 4.2.16 use a fixed null initialization vector with CBC Mode in the implementation of the queryable text encryptor. A malicious user with access to the data that has been encrypted using such an encryptor may be able to derive the unencrypted values using a dictionary attack.
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-5408>CVE-2020-5408</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5408">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5408</a></p>
<p>Release Date: 2020-05-14</p>
<p>Fix Resolution (org.springframework.security:spring-security-core): 4.2.16.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.16.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-3795</summary>
### Vulnerable Library - <b>spring-security-core-4.2.3.RELEASE.jar</b></p>
<p>spring-security-core</p>
<p>Library home page: <a href="http://spring.io/spring-security">http://spring.io/spring-security</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/security/spring-security-core/4.2.3.RELEASE/spring-security-core-4.2.3.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-security-data-4.2.3.RELEASE.jar (Root Library)
- :x: **spring-security-core-4.2.3.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/BigProduct/commit/ec45057b29d0802809578770364c129481ad39d1">ec45057b29d0802809578770364c129481ad39d1</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security versions 4.2.x prior to 4.2.12, 5.0.x prior to 5.0.12, and 5.1.x prior to 5.1.5 contain an insecure randomness vulnerability when using SecureRandomFactoryBean#setSeed to configure a SecureRandom instance. In order to be impacted, an honest application must provide a seed and make the resulting random material available to an attacker for inspection.
<p>Publish Date: 2019-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-3795>CVE-2019-3795</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pivotal.io/security/cve-2019-3795">https://pivotal.io/security/cve-2019-3795</a></p>
<p>Release Date: 2019-04-09</p>
<p>Fix Resolution (org.springframework.security:spring-security-core): 4.2.12.RELEASE</p>
<p>Direct dependency fix Resolution (org.springframework.security:spring-security-data): 4.2.12.RELEASE</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | spring security data release jar vulnerabilities highest severity is vulnerable library spring security data release jar path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework security spring security core release spring security core release jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in spring security data version remediation available high spring data commons release jar transitive release high spring data commons release jar transitive release high spring data commons release jar transitive release high spring security core release jar transitive release medium spring security core release jar transitive release medium spring security core release jar transitive release details cve vulnerable library spring data commons release jar global parent pom xml to be used by spring data modules library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework data spring data commons release spring data commons release jar dependency hierarchy spring security data release jar root library x spring data commons release jar vulnerable library found in head commit a href found in base branch main vulnerability details spring data commons versions prior to to to and older unsupported versions contain a property binder vulnerability caused by improper neutralization of special elements an unauthenticated remote malicious user or attacker can supply specially crafted request parameters against spring data rest backed http resources or using spring data s projection based request payload binding hat can lead to a remote code execution attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework data spring data commons release direct dependency fix resolution org springframework security spring security data release rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring data commons release jar global parent pom xml to be used by spring data modules library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework data spring data commons release spring data commons release jar dependency hierarchy spring security data release jar root library x spring data commons release jar vulnerable library found in head commit a href found in base branch main vulnerability details spring data commons versions to to and older unsupported versions contain a property path parser vulnerability caused by unlimited resource allocation an unauthenticated remote malicious user or attacker can issue requests against spring data rest endpoints or endpoints using property path parsing which can cause a denial of service cpu and memory consumption publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework data spring data commons release direct dependency fix resolution org springframework security spring security data release rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring data commons release jar global parent pom xml to be used by spring data modules library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework data spring data commons release spring data commons release jar dependency hierarchy spring security data release jar root library x spring data commons release jar vulnerable library found in head commit a href found in base branch main vulnerability details spring data commons versions prior to and prior to used in combination with xmlbeam or earlier versions contains a property binder vulnerability caused by improper restriction of xml external entity references as underlying library xmlbeam does not restrict external reference expansion an unauthenticated remote malicious user can supply specially crafted request parameters against spring data s projection based request payload binding to access arbitrary files on the system publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework data spring data commons release direct dependency fix resolution org springframework security spring security data release rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring security core release jar spring security core library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework security spring security core release spring security core release jar dependency hierarchy spring security data release jar root library x spring security core release jar vulnerable library found in head commit a href found in base branch main vulnerability details spring security versions x up to and older unsupported versions support plain text passwords using plaintextpasswordencoder if an application using an affected version of spring security is leveraging plaintextpasswordencoder and a user has a null encoded password a malicious user or attacker can authenticate using a password of null publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security core release direct dependency fix resolution org springframework security spring security data release rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring security core release jar spring security core library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework security spring security core release spring security core release jar dependency hierarchy spring security data release jar root library x spring security core release jar vulnerable library found in head commit a href found in base branch main vulnerability details spring security versions x prior to x prior to x prior to x prior to and x prior to use a fixed null initialization vector with cbc mode in the implementation of the queryable text encryptor a malicious user with access to the data that has been encrypted using such an encryptor may be able to derive the unencrypted values using a dictionary attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security core release direct dependency fix resolution org springframework security spring security data release rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring security core release jar spring security core library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework security spring security core release spring security core release jar dependency hierarchy spring security data release jar root library x spring security core release jar vulnerable library found in head commit a href found in base branch main vulnerability details spring security versions x prior to x prior to and x prior to contain an insecure randomness vulnerability when using securerandomfactorybean setseed to configure a securerandom instance in order to be impacted an honest application must provide a seed and make the resulting random material available to an attacker for inspection publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security core release direct dependency fix resolution org springframework security spring security data release rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
3,857 | 6,049,597,530 | IssuesEvent | 2017-06-12 19:06:52 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Environment Variables and Secrets missing from container/SG details page | area/container area/service area/ui kind/bug status/resolved status/to-test | **Rancher versions:** 5/24
**Steps to Reproduce:**
1. Create a container or scaling group that has environment variables and stuff in the secrets section
2. Go to their details pages
**Results:** Environment variables and the Secrets you added are not showing anywhere
| 1.0 | Environment Variables and Secrets missing from container/SG details page - **Rancher versions:** 5/24
**Steps to Reproduce:**
1. Create a container or scaling group that has environment variables and stuff in the secrets section
2. Go to their details pages
**Results:** Environment variables and the Secrets you added are not showing anywhere
| non_priority | environment variables and secrets missing from container sg details page rancher versions steps to reproduce create a container or scaling group that has environment variables and stuff in the secrets section go to their details pages results environment variables and the secrets you added are not showing anywhere | 0 |
315,663 | 23,590,886,821 | IssuesEvent | 2022-08-23 15:05:59 | arturo-lang/arturo | https://api.github.com/repos/arturo-lang/arturo | closed | [Reflection\complex?] add documentation example | documentation library todo easy | [Reflection\complex?] add documentation example
https://github.com/arturo-lang/arturo/blob/3a89302d1b1f33da097ed6e7bd6dfb05fc338482/src/library/Reflection.nim#L292
```text
builtin "color?",
alias = unaliased,
rule = PrefixPrecedence,
description = "checks if given value is of type :color",
args = {
"value" : {Any}
},
attrs = NoAttrs,
returns = {Logical},
# TODO(Reflection\color?) add documentation example
# labels: library, documentation, easy
example = """
""":
##########################################################
push(newLogical(x.kind==Color))
builtin "complex?",
alias = unaliased,
rule = PrefixPrecedence,
description = "checks if given value is of type :complex",
args = {
"value" : {Any}
},
attrs = NoAttrs,
returns = {Logical},
# TODO(Reflection\complex?) add documentation example
# labels: library, documentation, easy
example = """
""":
##########################################################
push(newLogical(x.kind==Complex))
builtin "database?",
alias = unaliased,
rule = PrefixPrecedence,
```
618f5b7315934d100b1650e62313cf8d69700ce6 | 1.0 | [Reflection\complex?] add documentation example - [Reflection\complex?] add documentation example
https://github.com/arturo-lang/arturo/blob/3a89302d1b1f33da097ed6e7bd6dfb05fc338482/src/library/Reflection.nim#L292
```text
builtin "color?",
alias = unaliased,
rule = PrefixPrecedence,
description = "checks if given value is of type :color",
args = {
"value" : {Any}
},
attrs = NoAttrs,
returns = {Logical},
# TODO(Reflection\color?) add documentation example
# labels: library, documentation, easy
example = """
""":
##########################################################
push(newLogical(x.kind==Color))
builtin "complex?",
alias = unaliased,
rule = PrefixPrecedence,
description = "checks if given value is of type :complex",
args = {
"value" : {Any}
},
attrs = NoAttrs,
returns = {Logical},
# TODO(Reflection\complex?) add documentation example
# labels: library, documentation, easy
example = """
""":
##########################################################
push(newLogical(x.kind==Complex))
builtin "database?",
alias = unaliased,
rule = PrefixPrecedence,
```
618f5b7315934d100b1650e62313cf8d69700ce6 | non_priority | add documentation example add documentation example text builtin color alias unaliased rule prefixprecedence description checks if given value is of type color args value any attrs noattrs returns logical todo reflection color add documentation example labels library documentation easy example push newlogical x kind color builtin complex alias unaliased rule prefixprecedence description checks if given value is of type complex args value any attrs noattrs returns logical todo reflection complex add documentation example labels library documentation easy example push newlogical x kind complex builtin database alias unaliased rule prefixprecedence | 0 |
74,421 | 14,248,119,928 | IssuesEvent | 2020-11-19 12:28:50 | feelpp/feelpp | https://api.github.com/repos/feelpp/feelpp | closed | GLPK interface of what() returns address to temporary | type:bug type:clean-code | we have this message:
```
home/prudhomm/Devel/feelpp.quick/feelpp/feel/feelopt/glpk.cpp:140:12: warning: returning address of local temporary object [-Wreturn-stack-address]
[build] return OptimizationLinearProgramming::check(M_e).c_str();
[build] ^~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
```
indeed check() returns a temporary and what() return the adress of the this temporary
/cc @romainhild | 1.0 | GLPK interface of what() returns address to temporary - we have this message:
```
home/prudhomm/Devel/feelpp.quick/feelpp/feel/feelopt/glpk.cpp:140:12: warning: returning address of local temporary object [-Wreturn-stack-address]
[build] return OptimizationLinearProgramming::check(M_e).c_str();
[build] ^~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
```
indeed check() returns a temporary and what() return the adress of the this temporary
/cc @romainhild | non_priority | glpk interface of what returns address to temporary we have this message home prudhomm devel feelpp quick feelpp feel feelopt glpk cpp warning returning address of local temporary object return optimizationlinearprogramming check m e c str indeed check returns a temporary and what return the adress of the this temporary cc romainhild | 0 |
306,786 | 26,495,433,285 | IssuesEvent | 2023-01-18 04:58:55 | ConaireD/TolimanWIP | https://api.github.com/repos/ConaireD/TolimanWIP | closed | The Three A's of Unit Testing. | tests | Hi all,
The three A's of unit testing are Arrange, Act and Assert. This is a pretty self explanatory structure, but one feature is that every test does exactly one thing. Therefore, instead of testing `test___init__` we would have `test___init__with_scenario` and `test___init__with_other_scenario`.
Regards
Jordan. | 1.0 | The Three A's of Unit Testing. - Hi all,
The three A's of unit testing are Arrange, Act and Assert. This is a pretty self explanatory structure, but one feature is that every test does exactly one thing. Therefore, instead of testing `test___init__` we would have `test___init__with_scenario` and `test___init__with_other_scenario`.
Regards
Jordan. | non_priority | the three a s of unit testing hi all the three a s of unit testing are arrange act and assert this is a pretty self explanatory structure but one feature is that every test does exactly one thing therefore instead of testing test init we would have test init with scenario and test init with other scenario regards jordan | 0 |
194,682 | 22,262,073,235 | IssuesEvent | 2022-06-10 02:04:36 | Trinadh465/device_renesas_kernel_AOSP10_r33_CVE-2021-33034 | https://api.github.com/repos/Trinadh465/device_renesas_kernel_AOSP10_r33_CVE-2021-33034 | reopened | CVE-2019-15505 (High) detected in linuxlinux-4.19.239 | security vulnerability | ## CVE-2019-15505 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.239</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/device_renesas_kernel_AOSP10_r33_CVE-2021-33034/commit/19525e8c58fe9ba0d7cb0f7a1a87d31d30380de6">19525e8c58fe9ba0d7cb0f7a1a87d31d30380de6</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/media/usb/dvb-usb/technisat-usb2.c in the Linux kernel through 5.2.9 has an out-of-bounds read via crafted USB device traffic (which may be remote via usbip or usbredir).
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-15505>CVE-2019-15505</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505</a></p>
<p>Release Date: 2019-09-04</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-15505 (High) detected in linuxlinux-4.19.239 - ## CVE-2019-15505 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.239</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/device_renesas_kernel_AOSP10_r33_CVE-2021-33034/commit/19525e8c58fe9ba0d7cb0f7a1a87d31d30380de6">19525e8c58fe9ba0d7cb0f7a1a87d31d30380de6</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/media/usb/dvb-usb/technisat-usb2.c in the Linux kernel through 5.2.9 has an out-of-bounds read via crafted USB device traffic (which may be remote via usbip or usbredir).
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-15505>CVE-2019-15505</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505</a></p>
<p>Release Date: 2019-09-04</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers media usb dvb usb technisat c drivers media usb dvb usb technisat c vulnerability details drivers media usb dvb usb technisat c in the linux kernel through has an out of bounds read via crafted usb device traffic which may be remote via usbip or usbredir publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
112,236 | 17,080,656,310 | IssuesEvent | 2021-07-08 04:21:25 | MohamedElashri/Zotero-Docker | https://api.github.com/repos/MohamedElashri/Zotero-Docker | closed | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz, glob-parent-5.1.1.tgz | security vulnerability | ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: Zotero-Docker/client/zotero-client/package.json</p>
<p>Path to vulnerable library: Zotero-Docker/client/zotero-client/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- chokidar-2.1.8.tgz (Root Library)
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: Zotero-Docker/client/zotero-client/package.json</p>
<p>Path to vulnerable library: Zotero-Docker/client/zotero-client/node_modules/@babel/cli/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.12.1.tgz (Root Library)
- chokidar-3.4.3.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/MohamedElashri/Zotero-Docker/commit/6f83bd2bfd0767b41690936c81cfaee93c63820e">6f83bd2bfd0767b41690936c81cfaee93c63820e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz, glob-parent-5.1.1.tgz - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: Zotero-Docker/client/zotero-client/package.json</p>
<p>Path to vulnerable library: Zotero-Docker/client/zotero-client/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- chokidar-2.1.8.tgz (Root Library)
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: Zotero-Docker/client/zotero-client/package.json</p>
<p>Path to vulnerable library: Zotero-Docker/client/zotero-client/node_modules/@babel/cli/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.12.1.tgz (Root Library)
- chokidar-3.4.3.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/MohamedElashri/Zotero-Docker/commit/6f83bd2bfd0767b41690936c81cfaee93c63820e">6f83bd2bfd0767b41690936c81cfaee93c63820e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz glob parent tgz cve high severity vulnerability vulnerable libraries glob parent tgz glob parent tgz glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file zotero docker client zotero client package json path to vulnerable library zotero docker client zotero client node modules glob parent package json dependency hierarchy chokidar tgz root library x glob parent tgz vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file zotero docker client zotero client package json path to vulnerable library zotero docker client zotero client node modules babel cli node modules glob parent package json dependency hierarchy cli tgz root library chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch main vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent step up your open source security game with whitesource | 0 |
244,320 | 26,375,270,064 | IssuesEvent | 2023-01-12 01:32:37 | guardicore/monkey | https://api.github.com/repos/guardicore/monkey | opened | Use common function for generating random strings. | Impact: Low Complexity: Low Security Refactor | # Refactor
## Component(s) to be refactored
- A bunch of stuff that generates random strings
## Explanation
There are a number of different places where `random.choices()` is used to generate random strings. We need to reduce code duplication by using a common function.
A new function has been added at `common.utils.code_utils.insecure_generate_random_string()` to generate random strings. It allows the user to pass a string length and an allowed character set. Use this (or a secure version of it) everywhere we're generating random strings.
## Tasks
- [ ] Create `secure_generate_random_string()` that uses a cryptographically secure source of randomness.
- [ ] Replace all other random string generation code with calls to either of the new functions. | True | Use common function for generating random strings. - # Refactor
## Component(s) to be refactored
- A bunch of stuff that generates random strings
## Explanation
There are a number of different places where `random.choices()` is used to generate random strings. We need to reduce code duplication by using a common function.
A new function has been added at `common.utils.code_utils.insecure_generate_random_string()` to generate random strings. It allows the user to pass a string length and an allowed character set. Use this (or a secure version of it) everywhere we're generating random strings.
## Tasks
- [ ] Create `secure_generate_random_string()` that uses a cryptographically secure source of randomness.
- [ ] Replace all other random string generation code with calls to either of the new functions. | non_priority | use common function for generating random strings refactor component s to be refactored a bunch of stuff that generates random strings explanation there are a number of different places where random choices is used to generate random strings we need to reduce code duplication by using a common function a new function has been added at common utils code utils insecure generate random string to generate random strings it allows the user to pass a string length and an allowed character set use this or a secure version of it everywhere we re generating random strings tasks create secure generate random string that uses a cryptographically secure source of randomness replace all other random string generation code with calls to either of the new functions | 0 |
315,595 | 27,088,690,375 | IssuesEvent | 2023-02-14 19:04:20 | rancher/rancher | https://api.github.com/repos/rancher/rancher | opened | [BUG] System Default Private Registry not being used to pull images | kind/bug [zube]: To Test | **Rancher Server Setup**
- Rancher version: v2.6.10
**Information about the Cluster**
- Kubernetes version:
- Cluster Type (Local/Downstream):
- If downstream, what type of cluster? (Custom/Imported or specify provider for Hosted/Infrastructure Provider): Custom
**Describe the bug**
<!--A clear and concise description of what the bug is.-->
The rancher/shell image for helm-operation Pods is pulled from Docker Hub not the system-default-registry (i.e. where the user has a registry without authentication, per https://ranchermanager.docs.rancher.com/v2.6/how-to-guides/new-user-guides/authentication-permissions-and-global-configuration/global-default-private-registry#setting-a-private-registry-with-no-credentials-as-the-default-registry) nor the cluster private registry (i.e. when a user has a registry with authentication, per https://ranchermanager.docs.rancher.com/v2.6/how-to-guides/new-user-guides/authentication-permissions-and-global-configuration/global-default-private-registry#setting-a-private-registry-with-no-credentials-as-the-default-registry). As a result users in an air-gapped environment are unable to perform chart installations/upgrades/deletions via Apps & Marketplace in Rancher v2.6.10.
**To Reproduce**
<!--Steps to reproduce the behavior-->
- Provision a Rancher v2.6.10 instance and a single all-role node custom RKE cluster
- Populate a Docker registry with the images for Rancher v2.6.10 (and v2.6.9 for regression testing)
- Set system-default-registry to the registry.
- Navigate to Apps & Marketplace and install the rancher-logging chart
- Observe the helm-operation Pod within the cattle-system Namespace created to run the helm install uses the rancher/shell image without a registry prefix, i.e. pulls from Docker Hub by default
- Set registry to private versus public access and repeat the test for downstream cluster with cluster private registry configured and observe same result.
- Repeat tests in Rancher v2.6.9 and observe rancher/shell image is pulled from custom registry as expected.
**Result**
Images are pulled from Docker Hub
**Expected Result**
<!--A clear and concise description of what you expected to happen.-->
Images should be pulled from registries
**Additional context**
<!--Add any other context about the problem here.-->
This issue is believed to be solved based on validation during https://github.com/rancher/rancher/issues/40457
SURE-5881 | 1.0 | [BUG] System Default Private Registry not being used to pull images - **Rancher Server Setup**
- Rancher version: v2.6.10
**Information about the Cluster**
- Kubernetes version:
- Cluster Type (Local/Downstream):
- If downstream, what type of cluster? (Custom/Imported or specify provider for Hosted/Infrastructure Provider): Custom
**Describe the bug**
<!--A clear and concise description of what the bug is.-->
The rancher/shell image for helm-operation Pods is pulled from Docker Hub not the system-default-registry (i.e. where the user has a registry without authentication, per https://ranchermanager.docs.rancher.com/v2.6/how-to-guides/new-user-guides/authentication-permissions-and-global-configuration/global-default-private-registry#setting-a-private-registry-with-no-credentials-as-the-default-registry) nor the cluster private registry (i.e. when a user has a registry with authentication, per https://ranchermanager.docs.rancher.com/v2.6/how-to-guides/new-user-guides/authentication-permissions-and-global-configuration/global-default-private-registry#setting-a-private-registry-with-no-credentials-as-the-default-registry). As a result users in an air-gapped environment are unable to perform chart installations/upgrades/deletions via Apps & Marketplace in Rancher v2.6.10.
**To Reproduce**
<!--Steps to reproduce the behavior-->
- Provision a Rancher v2.6.10 instance and a single all-role node custom RKE cluster
- Populate a Docker registry with the images for Rancher v2.6.10 (and v2.6.9 for regression testing)
- Set system-default-registry to the registry.
- Navigate to Apps & Marketplace and install the rancher-logging chart
- Observe the helm-operation Pod within the cattle-system Namespace created to run the helm install uses the rancher/shell image without a registry prefix, i.e. pulls from Docker Hub by default
- Set registry to private versus public access and repeat the test for downstream cluster with cluster private registry configured and observe same result.
- Repeat tests in Rancher v2.6.9 and observe rancher/shell image is pulled from custom registry as expected.
**Result**
Images are pulled from Docker Hub
**Expected Result**
<!--A clear and concise description of what you expected to happen.-->
Images should be pulled from registries
**Additional context**
<!--Add any other context about the problem here.-->
This issue is believed to be solved based on validation during https://github.com/rancher/rancher/issues/40457
SURE-5881 | non_priority | system default private registry not being used to pull images rancher server setup rancher version information about the cluster kubernetes version cluster type local downstream if downstream what type of cluster custom imported or specify provider for hosted infrastructure provider custom describe the bug the rancher shell image for helm operation pods is pulled from docker hub not the system default registry i e where the user has a registry without authentication per nor the cluster private registry i e when a user has a registry with authentication per as a result users in an air gapped environment are unable to perform chart installations upgrades deletions via apps marketplace in rancher to reproduce provision a rancher instance and a single all role node custom rke cluster populate a docker registry with the images for rancher and for regression testing set system default registry to the registry navigate to apps marketplace and install the rancher logging chart observe the helm operation pod within the cattle system namespace created to run the helm install uses the rancher shell image without a registry prefix i e pulls from docker hub by default set registry to private versus public access and repeat the test for downstream cluster with cluster private registry configured and observe same result repeat tests in rancher and observe rancher shell image is pulled from custom registry as expected result images are pulled from docker hub expected result images should be pulled from registries additional context this issue is believed to be solved based on validation during sure | 0 |
42,290 | 22,441,784,370 | IssuesEvent | 2022-06-21 02:10:44 | sympy/sympy | https://api.github.com/repos/sympy/sympy | closed | Hangs: integrate((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1)) | integrals Performance integrals.manualintegrate | The `Integral(...).n()` works, but the same `integrate(...)` hangs:
```
In [1]: Integral((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1))
Out[1]:
1
⌠
⎮ 3 2
⎮ 3⋅x - x + 2⋅x - 4
⎮ ─────────────────── dx
⎮ ______________
⎮ ╱ 2
⎮ ╲╱ x - 3⋅x + 2
⌡
0
In [2]: i = Integral((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1))
In [3]: i.n()
Out[3]: -2.98126694400554
In [4]: integrate((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1))
[HANGS]
``` | True | Hangs: integrate((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1)) - The `Integral(...).n()` works, but the same `integrate(...)` hangs:
```
In [1]: Integral((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1))
Out[1]:
1
⌠
⎮ 3 2
⎮ 3⋅x - x + 2⋅x - 4
⎮ ─────────────────── dx
⎮ ______________
⎮ ╱ 2
⎮ ╲╱ x - 3⋅x + 2
⌡
0
In [2]: i = Integral((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1))
In [3]: i.n()
Out[3]: -2.98126694400554
In [4]: integrate((3*x**3-x**2+2*x-4)/sqrt(x**2-3*x+2), (x, 0, 1))
[HANGS]
``` | non_priority | hangs integrate x x x sqrt x x x the integral n works but the same integrate hangs in integral x x x sqrt x x x out ⌠ ⎮ ⎮ ⋅x x ⋅x ⎮ ─────────────────── dx ⎮ ⎮ ╱ ⎮ ╲╱ x ⋅x ⌡ in i integral x x x sqrt x x x in i n out in integrate x x x sqrt x x x | 0 |
408,679 | 27,702,640,349 | IssuesEvent | 2023-03-14 09:08:50 | BetterThanTomorrow/calva | https://api.github.com/repos/BetterThanTomorrow/calva | closed | Improve deps.edn and Leiningen `+ shadow-cljs` project support | documentation jack-in connect ux | The connect sequences involving deps.edn or Leiningen + shadow-cljs often cause troubles for people. I think it is due to that shadow-cljs dependencies are assumed to be present.
Many of these projects are configured so that shadow-cljs uses deps.edn or Leiningen for dependencies and then it is a better Calva workflow to start them that way. I think we can improve the documentation to help with this a bit. But we should also look at how the Jack-in process can guide better. And when the dependencies are not met, we need better error messaging (or inject the dependency, which I am a bit hesitant to do, because we used to inject Figwheel dependencies and that caused troubles in other ways).
Two related issues:
* #1285
* #1307
Here's a thread illustrating where the current state of affairs cause confusion: https://clojureverse.org/t/understanding-jack-in-in-calva/ | 1.0 | Improve deps.edn and Leiningen `+ shadow-cljs` project support - The connect sequences involving deps.edn or Leiningen + shadow-cljs often cause troubles for people. I think it is due to that shadow-cljs dependencies are assumed to be present.
Many of these projects are configured so that shadow-cljs uses deps.edn or Leiningen for dependencies and then it is a better Calva workflow to start them that way. I think we can improve the documentation to help with this a bit. But we should also look at how the Jack-in process can guide better. And when the dependencies are not met, we need better error messaging (or inject the dependency, which I am a bit hesitant to do, because we used to inject Figwheel dependencies and that caused troubles in other ways).
Two related issues:
* #1285
* #1307
Here's a thread illustrating where the current state of affairs cause confusion: https://clojureverse.org/t/understanding-jack-in-in-calva/ | non_priority | improve deps edn and leiningen shadow cljs project support the connect sequences involving deps edn or leiningen shadow cljs often cause troubles for people i think it is due to that shadow cljs dependencies are assumed to be present many of these projects are configured so that shadow cljs uses deps edn or leiningen for dependencies and then it is a better calva workflow to start them that way i think we can improve the documentation to help with this a bit but we should also look at how the jack in process can guide better and when the dependencies are not met we need better error messaging or inject the dependency which i am a bit hesitant to do because we used to inject figwheel dependencies and that caused troubles in other ways two related issues here s a thread illustrating where the current state of affairs cause confusion | 0 |
33,036 | 27,157,089,170 | IssuesEvent | 2023-02-17 08:50:22 | SonarSource/sonarlint-visualstudio | https://api.github.com/repos/SonarSource/sonarlint-visualstudio | closed | Fix namespaces in TestInfrastructure Assembly | Infrastructure | Currently, the namespace of the files in TestInfrastructure is "**SonarLint.VisualStudio.Integration.UnitTests**" this leads to confusion when referencing projects. Should change it to a new namespace. | 1.0 | Fix namespaces in TestInfrastructure Assembly - Currently, the namespace of the files in TestInfrastructure is "**SonarLint.VisualStudio.Integration.UnitTests**" this leads to confusion when referencing projects. Should change it to a new namespace. | non_priority | fix namespaces in testinfrastructure assembly currently the namespace of the files in testinfrastructure is sonarlint visualstudio integration unittests this leads to confusion when referencing projects should change it to a new namespace | 0 |
53,284 | 13,150,557,450 | IssuesEvent | 2020-08-09 12:14:44 | mrfdev/1MB | https://api.github.com/repos/mrfdev/1MB | closed | Handling old, current, new, pause and check for latest | 1MB-BuildTools.sh enhancement todo | Currently it checks only for the version json of the _minecraftVersion we set manually in the buildtools script, if it can't find it - it stops the script. If it can find it, it will compare it against our cache, and if mismatches.. it asks if we are certain we wish to continue. And otherwise it just continues comparing versions (and perhaps it figures out if there's a new jar to make)
What it doesn't do is check against latest, it just says `(Script Halted!) Failed to get version from https://hub.spigotmc.org/stash/projects/SPIGOT/repos/builddata/raw/info.json, quitting script!` It could say: build a jar using --1.16.1 instead? (and read user input for y/n key)
`java -jar BuildTools.jar --rev latest` | 1.0 | Handling old, current, new, pause and check for latest - Currently it checks only for the version json of the _minecraftVersion we set manually in the buildtools script, if it can't find it - it stops the script. If it can find it, it will compare it against our cache, and if mismatches.. it asks if we are certain we wish to continue. And otherwise it just continues comparing versions (and perhaps it figures out if there's a new jar to make)
What it doesn't do is check against latest, it just says `(Script Halted!) Failed to get version from https://hub.spigotmc.org/stash/projects/SPIGOT/repos/builddata/raw/info.json, quitting script!` It could say: build a jar using --1.16.1 instead? (and read user input for y/n key)
`java -jar BuildTools.jar --rev latest` | non_priority | handling old current new pause and check for latest currently it checks only for the version json of the minecraftversion we set manually in the buildtools script if it can t find it it stops the script if it can find it it will compare it against our cache and if mismatches it asks if we are certain we wish to continue and otherwise it just continues comparing versions and perhaps it figures out if there s a new jar to make what it doesn t do is check against latest it just says script halted failed to get version from quitting script it could say build a jar using instead and read user input for y n key java jar buildtools jar rev latest | 0 |
63,869 | 15,727,171,374 | IssuesEvent | 2021-03-29 12:20:19 | hashicorp/packer | https://api.github.com/repos/hashicorp/packer | closed | AMI tag not persisting after build | builder/amazon remote-plugin/amazon upstream-bug |
#### Overview of the Issue
When I set `tags` on `amazon-ebs` builder I see the tags being applied in packer log output during the running of packer. However I do not see the final tag in AWS console when I go and check on my AMI's.
#### Reproduction Steps
- Use this amazon-ebs builder defintion:
```
{
"name": "t3a.micro",
"profile": "{{user `profile`}}",
"region": "{{user `aws_region`}}",
"type": "amazon-ebs",
"source_ami_filter": {
"filters": {
"virtualization-type": "hvm",
"name": "ubuntu/images/hvm-ssd/ubuntu-focal-20.04-amd64-server-20200609",
"root-device-type": "ebs"
},
"owners": ["099720109477"],
"most_recent": false
},
"ami_users": ["320176959135", "351145466100", "485438916218"],
"instance_type": "t3a.micro",
"ssh_username": "ubuntu",
"ami_name": "foooo-{{timestamp}}",
"subnet_filter": {
"filters": {
"tag:Group": "meta-new",
"tag:Name": "meta-new-private-*"
},
"most_free": true,
"random": false
},
"ssh_interface": "private_ip",
"ami_regions": ["us-east-2", "ap-southeast-2"],
"tags": {
"Release": "{{user `release_tag`}}"
},
"run_tags":{
"Release": "{{user `release_tag`}}"
}
}
```
- Run packer
- Go to AWS CLI and see that the AMI that was generated and subsequently copied to the other regions doesn't have the tag defined:
<img width="1515" alt="Screen Shot 2020-10-20 at 1 09 24 PM" src="https://user-images.githubusercontent.com/5511749/96620557-9873ec00-12d5-11eb-8f82-379b502d8cc4.png">
### Packer version
```
rixhersajazi@hostyhost packer-dev (ticketT-7772)*$ packer --version
1.6.0
```
### Packer build output
```
==> t3a.micro: Waiting for the instance to stop...
==> t3a.micro: Creating AMI fooooo-1603212597 from instance i-06aa58418cfc94449
t3a.micro: AMI: ami-00275c4502a4e0dba
==> t3a.micro: Waiting for AMI to become ready...
==> t3a.micro: Copying/Encrypting AMI (ami-00275c4502a4e0dba) to other regions...
t3a.micro: Copying to: us-east-2
t3a.micro: Copying to: ap-southeast-2
t3a.micro: Waiting for all copies to complete...
==> t3a.micro: Modifying attributes on AMI (ami-0b2881c5cba17e5b0)...
t3a.micro: Modifying: users
==> t3a.micro: Modifying attributes on AMI (ami-00275c4502a4e0dba)...
t3a.micro: Modifying: users
==> t3a.micro: Modifying attributes on AMI (ami-0752628f480d59636)...
t3a.micro: Modifying: users
==> t3a.micro: Modifying attributes on snapshot (snap-04a99f316e19fced0)...
==> t3a.micro: Modifying attributes on snapshot (snap-032d3d88e4844f1dd)...
==> t3a.micro: Modifying attributes on snapshot (snap-0bd7cae46477fc6ca)...
==> t3a.micro: Adding tags to AMI (ami-00275c4502a4e0dba)...
==> t3a.micro: Tagging snapshot: snap-04a99f316e19fced0
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
==> t3a.micro: Creating snapshot tags
==> t3a.micro: Adding tags to AMI (ami-0752628f480d59636)...
==> t3a.micro: Tagging snapshot: snap-032d3d88e4844f1dd
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
==> t3a.micro: Creating snapshot tags
==> t3a.micro: Adding tags to AMI (ami-0b2881c5cba17e5b0)...
==> t3a.micro: Tagging snapshot: snap-0bd7cae46477fc6ca
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
==> t3a.micro: Creating snapshot tags
==> t3a.micro: Terminating the source AWS instance...
==> t3a.micro: Cleaning up any extra volumes...
==> t3a.micro: No volumes to clean up, skipping
==> t3a.micro: Deleting temporary security group...
==> t3a.micro: Deleting temporary keypair...
Build 't3a.micro' finished.
==> Builds finished. The artifacts of successful builds are:
--> t3a.micro: AMIs were created:
ap-southeast-2: ami-0752628f480d59636
us-east-2: ami-0b2881c5cba17e5b0
us-west-2: ami-00275c4502a4e0dba
```
Notice there are lines saying:
```
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
```
### Operating system and Environment details
MacOS Catalina - 10.15.7
### Log Fragments and crash.log files
| 1.0 | AMI tag not persisting after build -
#### Overview of the Issue
When I set `tags` on `amazon-ebs` builder I see the tags being applied in packer log output during the running of packer. However I do not see the final tag in AWS console when I go and check on my AMI's.
#### Reproduction Steps
- Use this amazon-ebs builder defintion:
```
{
"name": "t3a.micro",
"profile": "{{user `profile`}}",
"region": "{{user `aws_region`}}",
"type": "amazon-ebs",
"source_ami_filter": {
"filters": {
"virtualization-type": "hvm",
"name": "ubuntu/images/hvm-ssd/ubuntu-focal-20.04-amd64-server-20200609",
"root-device-type": "ebs"
},
"owners": ["099720109477"],
"most_recent": false
},
"ami_users": ["320176959135", "351145466100", "485438916218"],
"instance_type": "t3a.micro",
"ssh_username": "ubuntu",
"ami_name": "foooo-{{timestamp}}",
"subnet_filter": {
"filters": {
"tag:Group": "meta-new",
"tag:Name": "meta-new-private-*"
},
"most_free": true,
"random": false
},
"ssh_interface": "private_ip",
"ami_regions": ["us-east-2", "ap-southeast-2"],
"tags": {
"Release": "{{user `release_tag`}}"
},
"run_tags":{
"Release": "{{user `release_tag`}}"
}
}
```
- Run packer
- Go to AWS CLI and see that the AMI that was generated and subsequently copied to the other regions doesn't have the tag defined:
<img width="1515" alt="Screen Shot 2020-10-20 at 1 09 24 PM" src="https://user-images.githubusercontent.com/5511749/96620557-9873ec00-12d5-11eb-8f82-379b502d8cc4.png">
### Packer version
```
rixhersajazi@hostyhost packer-dev (ticketT-7772)*$ packer --version
1.6.0
```
### Packer build output
```
==> t3a.micro: Waiting for the instance to stop...
==> t3a.micro: Creating AMI fooooo-1603212597 from instance i-06aa58418cfc94449
t3a.micro: AMI: ami-00275c4502a4e0dba
==> t3a.micro: Waiting for AMI to become ready...
==> t3a.micro: Copying/Encrypting AMI (ami-00275c4502a4e0dba) to other regions...
t3a.micro: Copying to: us-east-2
t3a.micro: Copying to: ap-southeast-2
t3a.micro: Waiting for all copies to complete...
==> t3a.micro: Modifying attributes on AMI (ami-0b2881c5cba17e5b0)...
t3a.micro: Modifying: users
==> t3a.micro: Modifying attributes on AMI (ami-00275c4502a4e0dba)...
t3a.micro: Modifying: users
==> t3a.micro: Modifying attributes on AMI (ami-0752628f480d59636)...
t3a.micro: Modifying: users
==> t3a.micro: Modifying attributes on snapshot (snap-04a99f316e19fced0)...
==> t3a.micro: Modifying attributes on snapshot (snap-032d3d88e4844f1dd)...
==> t3a.micro: Modifying attributes on snapshot (snap-0bd7cae46477fc6ca)...
==> t3a.micro: Adding tags to AMI (ami-00275c4502a4e0dba)...
==> t3a.micro: Tagging snapshot: snap-04a99f316e19fced0
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
==> t3a.micro: Creating snapshot tags
==> t3a.micro: Adding tags to AMI (ami-0752628f480d59636)...
==> t3a.micro: Tagging snapshot: snap-032d3d88e4844f1dd
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
==> t3a.micro: Creating snapshot tags
==> t3a.micro: Adding tags to AMI (ami-0b2881c5cba17e5b0)...
==> t3a.micro: Tagging snapshot: snap-0bd7cae46477fc6ca
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
==> t3a.micro: Creating snapshot tags
==> t3a.micro: Terminating the source AWS instance...
==> t3a.micro: Cleaning up any extra volumes...
==> t3a.micro: No volumes to clean up, skipping
==> t3a.micro: Deleting temporary security group...
==> t3a.micro: Deleting temporary keypair...
Build 't3a.micro' finished.
==> Builds finished. The artifacts of successful builds are:
--> t3a.micro: AMIs were created:
ap-southeast-2: ami-0752628f480d59636
us-east-2: ami-0b2881c5cba17e5b0
us-west-2: ami-00275c4502a4e0dba
```
Notice there are lines saying:
```
==> t3a.micro: Creating AMI tags
t3a.micro: Adding tag: "Release": "FEATURE_BRANCH_QA_ONLY"
```
### Operating system and Environment details
MacOS Catalina - 10.15.7
### Log Fragments and crash.log files
| non_priority | ami tag not persisting after build overview of the issue when i set tags on amazon ebs builder i see the tags being applied in packer log output during the running of packer however i do not see the final tag in aws console when i go and check on my ami s reproduction steps use this amazon ebs builder defintion name micro profile user profile region user aws region type amazon ebs source ami filter filters virtualization type hvm name ubuntu images hvm ssd ubuntu focal server root device type ebs owners most recent false ami users instance type micro ssh username ubuntu ami name foooo timestamp subnet filter filters tag group meta new tag name meta new private most free true random false ssh interface private ip ami regions tags release user release tag run tags release user release tag run packer go to aws cli and see that the ami that was generated and subsequently copied to the other regions doesn t have the tag defined img width alt screen shot at pm src packer version rixhersajazi hostyhost packer dev tickett packer version packer build output micro waiting for the instance to stop micro creating ami fooooo from instance i micro ami ami micro waiting for ami to become ready micro copying encrypting ami ami to other regions micro copying to us east micro copying to ap southeast micro waiting for all copies to complete micro modifying attributes on ami ami micro modifying users micro modifying attributes on ami ami micro modifying users micro modifying attributes on ami ami micro modifying users micro modifying attributes on snapshot snap micro modifying attributes on snapshot snap micro modifying attributes on snapshot snap micro adding tags to ami ami micro tagging snapshot snap micro creating ami tags micro adding tag release feature branch qa only micro creating snapshot tags micro adding tags to ami ami micro tagging snapshot snap micro creating ami tags micro adding tag release feature branch qa only micro creating snapshot tags micro adding tags to ami ami micro tagging snapshot snap micro creating ami tags micro adding tag release feature branch qa only micro creating snapshot tags micro terminating the source aws instance micro cleaning up any extra volumes micro no volumes to clean up skipping micro deleting temporary security group micro deleting temporary keypair build micro finished builds finished the artifacts of successful builds are micro amis were created ap southeast ami us east ami us west ami notice there are lines saying micro creating ami tags micro adding tag release feature branch qa only operating system and environment details macos catalina log fragments and crash log files | 0 |
169,566 | 26,824,484,803 | IssuesEvent | 2023-02-02 11:53:17 | swarm-game/swarm | https://api.github.com/repos/swarm-game/swarm | closed | Sand should not be so easy to get | Z-Feature C-Low Hanging Fruit S-Nice to have G-Entities G-Design G-Recipes | Right now, `sand` respawns immediately and infinitely. This is not very realistic and it also makes it far too easy to get sand.
Perhaps we should make sand more like `rock` and `copper ore`: it does not regrow, but there is a way to produce more of it. For example, perhaps drilling a `rock` produces some number of `sand`. | 1.0 | Sand should not be so easy to get - Right now, `sand` respawns immediately and infinitely. This is not very realistic and it also makes it far too easy to get sand.
Perhaps we should make sand more like `rock` and `copper ore`: it does not regrow, but there is a way to produce more of it. For example, perhaps drilling a `rock` produces some number of `sand`. | non_priority | sand should not be so easy to get right now sand respawns immediately and infinitely this is not very realistic and it also makes it far too easy to get sand perhaps we should make sand more like rock and copper ore it does not regrow but there is a way to produce more of it for example perhaps drilling a rock produces some number of sand | 0 |
50,595 | 10,532,541,569 | IssuesEvent | 2019-10-01 11:00:04 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Japanese text does not render in a uniform size with the large font | Bug Code |  (Loading screen)
 (Server browser)
Japanese override font for GUI.LargeFont (NotoSansCJKsc-Bold.otf) does not render all text with the same size | 1.0 | Japanese text does not render in a uniform size with the large font -  (Loading screen)
 (Server browser)
Japanese override font for GUI.LargeFont (NotoSansCJKsc-Bold.otf) does not render all text with the same size | non_priority | japanese text does not render in a uniform size with the large font loading screen server browser japanese override font for gui largefont notosanscjksc bold otf does not render all text with the same size | 0 |
412,855 | 27,877,127,810 | IssuesEvent | 2023-03-21 16:42:49 | bigbluebutton/bigbluebutton | https://api.github.com/repos/bigbluebutton/bigbluebutton | opened | docs: split pages into smaller chunks | target: documentation | The current docs md-files have become veeery long in some cases. We should start splitting them into smaller chunks. | 1.0 | docs: split pages into smaller chunks - The current docs md-files have become veeery long in some cases. We should start splitting them into smaller chunks. | non_priority | docs split pages into smaller chunks the current docs md files have become veeery long in some cases we should start splitting them into smaller chunks | 0 |
117,945 | 17,570,033,961 | IssuesEvent | 2021-08-14 13:47:05 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 105: asterisk-16.17.0: 2 advisories [7.5] | 1.severity: security | [search](https://search.nix.gsc.io/?q=asterisk&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=asterisk+in%3Apath&type=Code)
* [ ] [CVE-2021-32558](https://nvd.nist.gov/vuln/detail/CVE-2021-32558) CVSSv3=7.5 (nixos-21.05, nixos-unstable)
* [ ] [CVE-2021-31878](https://nvd.nist.gov/vuln/detail/CVE-2021-31878) CVSSv3=6.5 (nixos-21.05, nixos-unstable)
## CVE details
### CVE-2021-32558
An issue was discovered in Sangoma Asterisk 13.x before 13.38.3, 16.x before 16.19.1, 17.x before 17.9.4, and 18.x before 18.5.1, and Certified Asterisk before 16.8-cert10. If the IAX2 channel driver receives a packet that contains an unsupported media format, a crash can occur.
### CVE-2021-31878
An issue was discovered in PJSIP in Asterisk before 16.19.1 and before 18.5.1. To exploit, a re-INVITE without SDP must be received after Asterisk has sent a BYE request.
-----
Scanned versions: nixos-21.05: ad6e733d633; nixos-unstable: 4138cbd913f.
Cc @DerTim1
Cc @auntieNeo
Cc @yorickvp
| True | Vulnerability roundup 105: asterisk-16.17.0: 2 advisories [7.5] - [search](https://search.nix.gsc.io/?q=asterisk&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=asterisk+in%3Apath&type=Code)
* [ ] [CVE-2021-32558](https://nvd.nist.gov/vuln/detail/CVE-2021-32558) CVSSv3=7.5 (nixos-21.05, nixos-unstable)
* [ ] [CVE-2021-31878](https://nvd.nist.gov/vuln/detail/CVE-2021-31878) CVSSv3=6.5 (nixos-21.05, nixos-unstable)
## CVE details
### CVE-2021-32558
An issue was discovered in Sangoma Asterisk 13.x before 13.38.3, 16.x before 16.19.1, 17.x before 17.9.4, and 18.x before 18.5.1, and Certified Asterisk before 16.8-cert10. If the IAX2 channel driver receives a packet that contains an unsupported media format, a crash can occur.
### CVE-2021-31878
An issue was discovered in PJSIP in Asterisk before 16.19.1 and before 18.5.1. To exploit, a re-INVITE without SDP must be received after Asterisk has sent a BYE request.
-----
Scanned versions: nixos-21.05: ad6e733d633; nixos-unstable: 4138cbd913f.
Cc @DerTim1
Cc @auntieNeo
Cc @yorickvp
| non_priority | vulnerability roundup asterisk advisories nixos nixos unstable nixos nixos unstable cve details cve an issue was discovered in sangoma asterisk x before x before x before and x before and certified asterisk before if the channel driver receives a packet that contains an unsupported media format a crash can occur cve an issue was discovered in pjsip in asterisk before and before to exploit a re invite without sdp must be received after asterisk has sent a bye request scanned versions nixos nixos unstable cc cc auntieneo cc yorickvp | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.