Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
179,459 | 13,881,846,541 | IssuesEvent | 2020-10-18 03:03:27 | IzzelAliz/Arclight | https://api.github.com/repos/IzzelAliz/Arclight | closed | 死亡掉落问题 | 1.15 mod need testing | <!-- 在这个尖括号中的内容为注释,无需删除 -->
<!-- 提交的信息请不要放在尖括号内,否则是看不到的 -->
### 我正在运行
* **Arclight** [arclight-1.15.2-1.0.11-SNAPSHOT-ca83918] <!-- 在 Arclight 启动时会打印版本,示例 arclight-1.15.2-1.0.3-SNAPSHOT-9455d03 -->
* **你确认这是最新版吗** [是]
<!-- 最新的构建版本可以在 https://ci.appveyor.com/project/IzzelAliz/arclight/build/artifacts 下载
你所汇报的问题很可能已经修复
如果你确实用不了最新版,请简述为什么 -->
* **你确认所有Mod都安装了依赖** [是]
* **你确认所有插件都已更新至对应版本** [是]
<!-- 市面上大多数整合包,特别是较老版本(1.12.2)的整合包,其自带的插件都无法在高版本环境下运行 -->
* **Java** [jre 261] <!-- 在命令行中键入 java -version 后可以获取版本 -->
* **操作系统** [Debian9]
* **插件列表** <!-- 输入 /plugins 指令 -->
无
* **Mod 列表** <!-- 输入 /forge mods 指令 -->
墓碑GraveStone
### 错误描述
死亡后,不生成墓碑,类似mod均不可以正常工作
<!-- 请尽可能详细。对于描述,请假设开发者不知道 mod 是干什么的。
如果可以的话,在安装尽可能少的 mod 的情况下复现它 -->
叙述这个为什么是一个错误,是哪一方面的,以及其他可能需要的信息
### 重现步骤
1. 安装 xxx
2. 进入服务器后 xxxx
3. ....
<!-- 如果这是 Mod 相关的问题,可以帮助我们在仅安装了 Forge 的环境下测试 -->
**可在 Forge 复现** [否]
<!-- 如果这是插件相关的问题,可以帮助我们在纯净的 Spigot 环境下测试 -->
**可在 Spigot 复现** [否]
### 报错信息
[错误日志]
<!-- 日志位于服务器文件夹的 /logs 目录下,名称为 latest.log -->
<!-- 服务器关闭后,将该文件中内容全部复制,上传至 https://paste.ubuntu.com/ 网站,提交后将链接附在下方即可 -->
<!-- 如果上面的网站打不开,可以将以下几行代码粘贴至 [错误日志],并将日志文本复制进去
<details><pre>
[日志请粘贴于此处]
</pre></details>
-->
| 1.0 | 死亡掉落问题 - <!-- 在这个尖括号中的内容为注释,无需删除 -->
<!-- 提交的信息请不要放在尖括号内,否则是看不到的 -->
### 我正在运行
* **Arclight** [arclight-1.15.2-1.0.11-SNAPSHOT-ca83918] <!-- 在 Arclight 启动时会打印版本,示例 arclight-1.15.2-1.0.3-SNAPSHOT-9455d03 -->
* **你确认这是最新版吗** [是]
<!-- 最新的构建版本可以在 https://ci.appveyor.com/project/IzzelAliz/arclight/build/artifacts 下载
你所汇报的问题很可能已经修复
如果你确实用不了最新版,请简述为什么 -->
* **你确认所有Mod都安装了依赖** [是]
* **你确认所有插件都已更新至对应版本** [是]
<!-- 市面上大多数整合包,特别是较老版本(1.12.2)的整合包,其自带的插件都无法在高版本环境下运行 -->
* **Java** [jre 261] <!-- 在命令行中键入 java -version 后可以获取版本 -->
* **操作系统** [Debian9]
* **插件列表** <!-- 输入 /plugins 指令 -->
无
* **Mod 列表** <!-- 输入 /forge mods 指令 -->
墓碑GraveStone
### 错误描述
死亡后,不生成墓碑,类似mod均不可以正常工作
<!-- 请尽可能详细。对于描述,请假设开发者不知道 mod 是干什么的。
如果可以的话,在安装尽可能少的 mod 的情况下复现它 -->
叙述这个为什么是一个错误,是哪一方面的,以及其他可能需要的信息
### 重现步骤
1. 安装 xxx
2. 进入服务器后 xxxx
3. ....
<!-- 如果这是 Mod 相关的问题,可以帮助我们在仅安装了 Forge 的环境下测试 -->
**可在 Forge 复现** [否]
<!-- 如果这是插件相关的问题,可以帮助我们在纯净的 Spigot 环境下测试 -->
**可在 Spigot 复现** [否]
### 报错信息
[错误日志]
<!-- 日志位于服务器文件夹的 /logs 目录下,名称为 latest.log -->
<!-- 服务器关闭后,将该文件中内容全部复制,上传至 https://paste.ubuntu.com/ 网站,提交后将链接附在下方即可 -->
<!-- 如果上面的网站打不开,可以将以下几行代码粘贴至 [错误日志],并将日志文本复制进去
<details><pre>
[日志请粘贴于此处]
</pre></details>
-->
| non_priority | 死亡掉落问题 我正在运行 arclight 你确认这是最新版吗 最新的构建版本可以在 下载 你所汇报的问题很可能已经修复 如果你确实用不了最新版,请简述为什么 你确认所有mod都安装了依赖 你确认所有插件都已更新至对应版本 java 操作系统 插件列表 无 mod 列表 墓碑gravestone 错误描述 死亡后,不生成墓碑,类似mod均不可以正常工作 请尽可能详细。对于描述,请假设开发者不知道 mod 是干什么的。 如果可以的话,在安装尽可能少的 mod 的情况下复现它 叙述这个为什么是一个错误,是哪一方面的,以及其他可能需要的信息 重现步骤 安装 xxx 进入服务器后 xxxx 可在 forge 复现 可在 spigot 复现 报错信息 如果上面的网站打不开,可以将以下几行代码粘贴至 ,并将日志文本复制进去 | 0 |
144,623 | 19,292,300,370 | IssuesEvent | 2021-12-12 01:29:35 | MidnightBSD/midnightbsd-app-store | https://api.github.com/repos/MidnightBSD/midnightbsd-app-store | opened | CVE-2021-43797 (Medium) detected in netty-codec-http-4.1.69.Final.jar | security vulnerability | ## CVE-2021-43797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.69.Final.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://netty.io/">https://netty.io/</a></p>
<p>Path to dependency file: midnightbsd-app-store/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty-codec-http/4.1.69.Final/netty-codec-http-4.1.69.Final.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-data-elasticsearch-2.4.12.jar (Root Library)
- spring-data-elasticsearch-4.1.14.jar
- transport-netty4-client-7.9.3.jar
- :x: **netty-codec-http-4.1.69.Final.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. Netty prior to version 4.1.7.1.Final skips control chars when they are present at the beginning / end of the header name. It should instead fail fast as these are not allowed by the spec and could lead to HTTP request smuggling. Failing to do the validation might cause netty to "sanitize" header names before it forward these to another remote system when used as proxy. This remote system can't see the invalid usage anymore, and therefore does not do the validation itself. Users should upgrade to version 4.1.7.1.Final to receive a patch.
<p>Publish Date: 2021-12-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43797>CVE-2021-43797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wx5j-54mm-rqqq">https://github.com/advisories/GHSA-wx5j-54mm-rqqq</a></p>
<p>Release Date: 2021-12-09</p>
<p>Fix Resolution: io.netty:netty-codec-http:4.1.71.Final</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-43797 (Medium) detected in netty-codec-http-4.1.69.Final.jar - ## CVE-2021-43797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.69.Final.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://netty.io/">https://netty.io/</a></p>
<p>Path to dependency file: midnightbsd-app-store/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty-codec-http/4.1.69.Final/netty-codec-http-4.1.69.Final.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-data-elasticsearch-2.4.12.jar (Root Library)
- spring-data-elasticsearch-4.1.14.jar
- transport-netty4-client-7.9.3.jar
- :x: **netty-codec-http-4.1.69.Final.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. Netty prior to version 4.1.7.1.Final skips control chars when they are present at the beginning / end of the header name. It should instead fail fast as these are not allowed by the spec and could lead to HTTP request smuggling. Failing to do the validation might cause netty to "sanitize" header names before it forward these to another remote system when used as proxy. This remote system can't see the invalid usage anymore, and therefore does not do the validation itself. Users should upgrade to version 4.1.7.1.Final to receive a patch.
<p>Publish Date: 2021-12-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43797>CVE-2021-43797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wx5j-54mm-rqqq">https://github.com/advisories/GHSA-wx5j-54mm-rqqq</a></p>
<p>Release Date: 2021-12-09</p>
<p>Fix Resolution: io.netty:netty-codec-http:4.1.71.Final</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in netty codec http final jar cve medium severity vulnerability vulnerable library netty codec http final jar library home page a href path to dependency file midnightbsd app store pom xml path to vulnerable library home wss scanner repository io netty netty codec http final netty codec http final jar dependency hierarchy spring boot starter data elasticsearch jar root library spring data elasticsearch jar transport client jar x netty codec http final jar vulnerable library found in base branch master vulnerability details netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers clients netty prior to version final skips control chars when they are present at the beginning end of the header name it should instead fail fast as these are not allowed by the spec and could lead to http request smuggling failing to do the validation might cause netty to sanitize header names before it forward these to another remote system when used as proxy this remote system can t see the invalid usage anymore and therefore does not do the validation itself users should upgrade to version final to receive a patch publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io netty netty codec http final step up your open source security game with whitesource | 0 |
44,259 | 23,532,550,161 | IssuesEvent | 2022-08-19 16:48:09 | PrestaShop/PrestaShop | https://api.github.com/repos/PrestaShop/PrestaShop | closed | Updated links on PS_Linklist not visible if cache is enabled | Bug Waiting for author FO NMI Performance Linklist Module 1.7.8.5 | ### Prerequisites
- [X] I understand and accept the project's [code of conduct](https://github.com/PrestaShop/PrestaShop/blob/develop/CODE_OF_CONDUCT.md)
- [X] I have already [searched in existing issues](https://github.com/PrestaShop/PrestaShop/issues?q=is%3Aissue+label%3ABug) and found no previous report of this bug.
### Describe the bug and add screenshots
If the cache is enabled (Memcache/APC) any update of links is not visible. When the cache is disabled updated links show immediately.
Prestashop v. 1.7.8.5
### Expected behavior
After edited link value (name for example) changes should be visible.
### Steps to reproduce
Login as the system adminstrator
Go to Improve > Design > Link List
Edit Resources in some widget
Click the Save button at the bottom of the page
Note the Succesful Update message indicates the update is completed
Visit a frontend
### PrestaShop version(s) where the bug happened
1.7.8.5
### PHP version(s) where the bug happened
1.7.8.5
### If your bug is related to a module, specify its name and its version
ps_linklist v5.0.4 | True | Updated links on PS_Linklist not visible if cache is enabled - ### Prerequisites
- [X] I understand and accept the project's [code of conduct](https://github.com/PrestaShop/PrestaShop/blob/develop/CODE_OF_CONDUCT.md)
- [X] I have already [searched in existing issues](https://github.com/PrestaShop/PrestaShop/issues?q=is%3Aissue+label%3ABug) and found no previous report of this bug.
### Describe the bug and add screenshots
If the cache is enabled (Memcache/APC) any update of links is not visible. When the cache is disabled updated links show immediately.
Prestashop v. 1.7.8.5
### Expected behavior
After edited link value (name for example) changes should be visible.
### Steps to reproduce
Login as the system adminstrator
Go to Improve > Design > Link List
Edit Resources in some widget
Click the Save button at the bottom of the page
Note the Succesful Update message indicates the update is completed
Visit a frontend
### PrestaShop version(s) where the bug happened
1.7.8.5
### PHP version(s) where the bug happened
1.7.8.5
### If your bug is related to a module, specify its name and its version
ps_linklist v5.0.4 | non_priority | updated links on ps linklist not visible if cache is enabled prerequisites i understand and accept the project s i have already and found no previous report of this bug describe the bug and add screenshots if the cache is enabled memcache apc any update of links is not visible when the cache is disabled updated links show immediately prestashop v expected behavior after edited link value name for example changes should be visible steps to reproduce login as the system adminstrator go to improve design link list edit resources in some widget click the save button at the bottom of the page note the succesful update message indicates the update is completed visit a frontend prestashop version s where the bug happened php version s where the bug happened if your bug is related to a module specify its name and its version ps linklist | 0 |
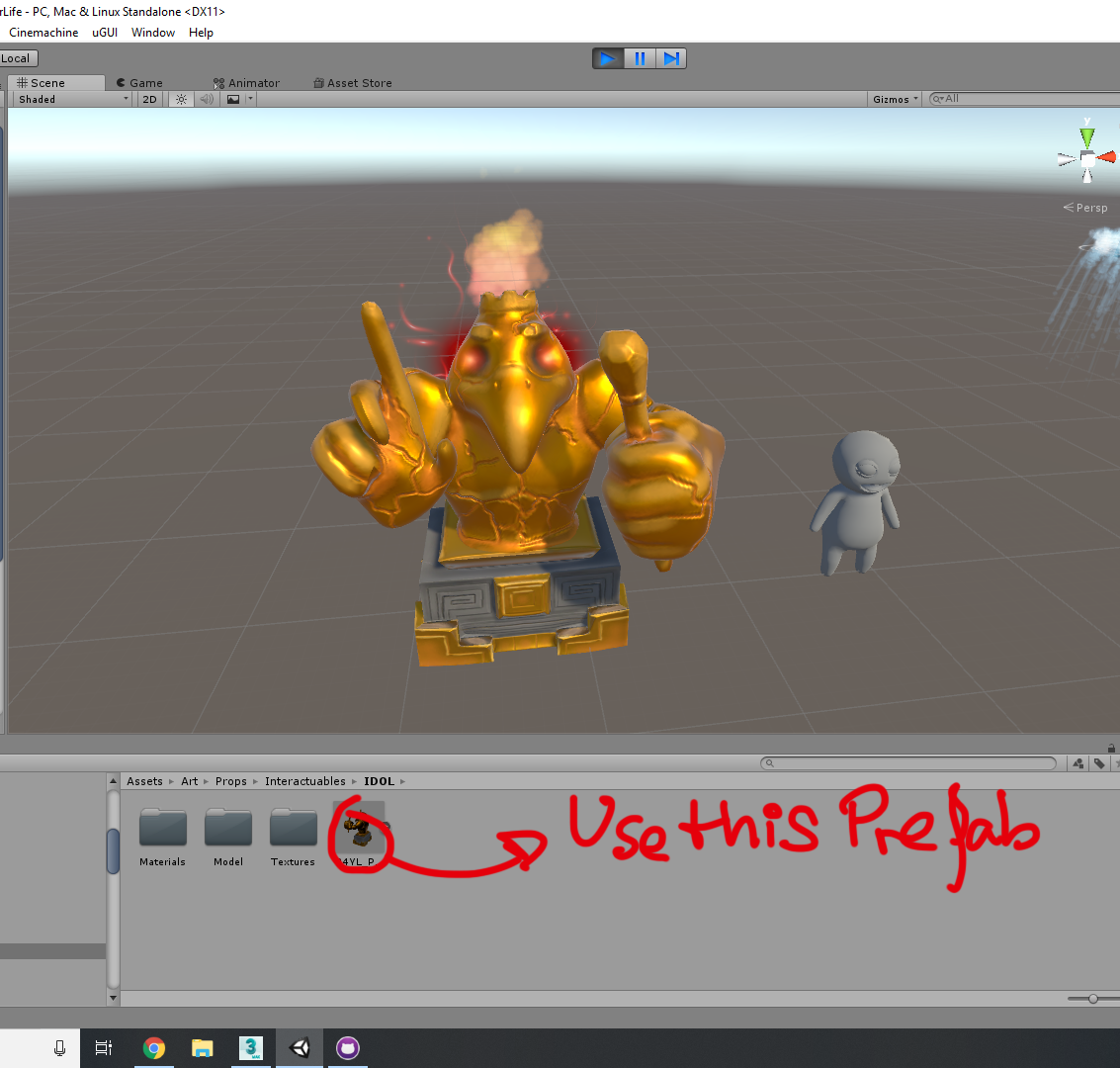
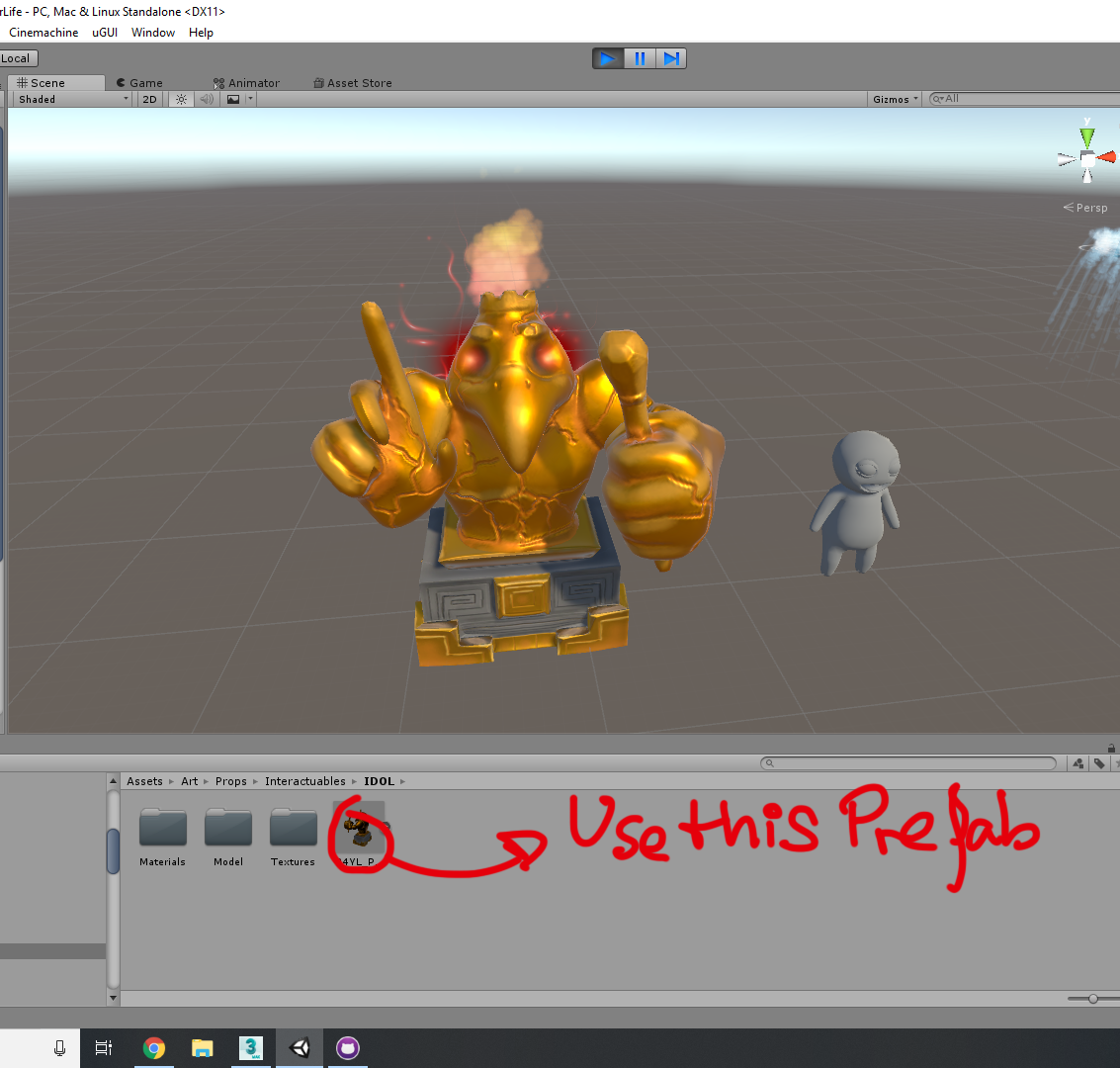
67,599 | 8,149,464,137 | IssuesEvent | 2018-08-22 09:42:06 | HiddenLair/Run4YourLife | https://api.github.com/repos/HiddenLair/Run4YourLife | opened | Implement boss interactuable final killer | design | Hi everyone,
This asset is ready, please find it in the route you can se on the image, note that you should implement the prefab marked and not the model inside models folder because the prefab contains the p.systems of the eyes and fire.
| 1.0 | Implement boss interactuable final killer - Hi everyone,
This asset is ready, please find it in the route you can se on the image, note that you should implement the prefab marked and not the model inside models folder because the prefab contains the p.systems of the eyes and fire.
| non_priority | implement boss interactuable final killer hi everyone this asset is ready please find it in the route you can se on the image note that you should implement the prefab marked and not the model inside models folder because the prefab contains the p systems of the eyes and fire | 0 |
152,427 | 12,104,520,711 | IssuesEvent | 2020-04-20 20:22:10 | clearlinux/swupd-client | https://api.github.com/repos/clearlinux/swupd-client | opened | Testlib: move non public functions to a different file, same for test fixtures | enhancement testing | Testlib at the moment is divided in 2 main groups:
1) it provides test fixtures, stuff like assertions, functions to format tests, etc. All this functionality in general is independent of swupd.
2) It also provides functions to create test resources related to swupd. These can be split in two categories: external functions (these are functions that are intended to be called directly from tests or from the terminal), and internal functions (functions that are only supposed to be used by external functions and not directly from a test or terminal).
The testlib file is getting too big now, I think it may be time to reorganize it in a way that makes more sense. Maybe into 3 different files: one for fixtures, one for internal functions and one for public functions.
| 1.0 | Testlib: move non public functions to a different file, same for test fixtures - Testlib at the moment is divided in 2 main groups:
1) it provides test fixtures, stuff like assertions, functions to format tests, etc. All this functionality in general is independent of swupd.
2) It also provides functions to create test resources related to swupd. These can be split in two categories: external functions (these are functions that are intended to be called directly from tests or from the terminal), and internal functions (functions that are only supposed to be used by external functions and not directly from a test or terminal).
The testlib file is getting too big now, I think it may be time to reorganize it in a way that makes more sense. Maybe into 3 different files: one for fixtures, one for internal functions and one for public functions.
| non_priority | testlib move non public functions to a different file same for test fixtures testlib at the moment is divided in main groups it provides test fixtures stuff like assertions functions to format tests etc all this functionality in general is independent of swupd it also provides functions to create test resources related to swupd these can be split in two categories external functions these are functions that are intended to be called directly from tests or from the terminal and internal functions functions that are only supposed to be used by external functions and not directly from a test or terminal the testlib file is getting too big now i think it may be time to reorganize it in a way that makes more sense maybe into different files one for fixtures one for internal functions and one for public functions | 0 |
24,173 | 12,037,258,293 | IssuesEvent | 2020-04-13 21:26:43 | emergenzeHack/covid19gr_issues | https://api.github.com/repos/emergenzeHack/covid19gr_issues | opened | goods donation and services offering | Missing position form goods donation and services offering | <pre><yamldata>
Beneficiaries: Παιδιά και γονείς
Description: 'Ενθαρρύνετε τα παιδιά να μάθουν ένα διαχρονικό παιχνίδι με αυτή την
onine εφαρμογή! Αυτός ο διασκεδαστικός τρόπος μάθησης θα δώσει κίνητρο στα παιδιά
να μάθουν και να βελτιώσουν τις ικανότητές τους στο σκάκι. Το πιο σημαντικό είναι
ότι η εκμάθηση του σκακιού θα εξασκήσει δεξιότητες που μπορούν να εκμεταλλευτούν
καθ ''όλη τη διάρκεια της ζωής τους: στρατηγική, τακτική, δημιουργικότητα, επιμονή
και υπολογισμό κινδύνων.
Μια ποικιλία εργαλείων μάθησης, γρίφων και σκακιού σε πραγματικό χρόνο εναντίον
ρομπότ ή άλλων ανθρώπων, παρέχει προκλήσεις για τον εγκέφαλο και ώρες ψυχαγωγίας
στα παιδιά!
ΣΗΜΕΙΩΣΗ: Η σελίδα είναι διαθέσιμη μόνο στην αγγλική γλώσσα.'
Institution: Chesskid
Legal: OK
Link: https://www.chesskid.com/
Title: Μάθε σκάκι online!
</yamldata></pre> | 1.0 | goods donation and services offering - <pre><yamldata>
Beneficiaries: Παιδιά και γονείς
Description: 'Ενθαρρύνετε τα παιδιά να μάθουν ένα διαχρονικό παιχνίδι με αυτή την
onine εφαρμογή! Αυτός ο διασκεδαστικός τρόπος μάθησης θα δώσει κίνητρο στα παιδιά
να μάθουν και να βελτιώσουν τις ικανότητές τους στο σκάκι. Το πιο σημαντικό είναι
ότι η εκμάθηση του σκακιού θα εξασκήσει δεξιότητες που μπορούν να εκμεταλλευτούν
καθ ''όλη τη διάρκεια της ζωής τους: στρατηγική, τακτική, δημιουργικότητα, επιμονή
και υπολογισμό κινδύνων.
Μια ποικιλία εργαλείων μάθησης, γρίφων και σκακιού σε πραγματικό χρόνο εναντίον
ρομπότ ή άλλων ανθρώπων, παρέχει προκλήσεις για τον εγκέφαλο και ώρες ψυχαγωγίας
στα παιδιά!
ΣΗΜΕΙΩΣΗ: Η σελίδα είναι διαθέσιμη μόνο στην αγγλική γλώσσα.'
Institution: Chesskid
Legal: OK
Link: https://www.chesskid.com/
Title: Μάθε σκάκι online!
</yamldata></pre> | non_priority | goods donation and services offering beneficiaries παιδιά και γονείς description ενθαρρύνετε τα παιδιά να μάθουν ένα διαχρονικό παιχνίδι με αυτή την onine εφαρμογή αυτός ο διασκεδαστικός τρόπος μάθησης θα δώσει κίνητρο στα παιδιά να μάθουν και να βελτιώσουν τις ικανότητές τους στο σκάκι το πιο σημαντικό είναι ότι η εκμάθηση του σκακιού θα εξασκήσει δεξιότητες που μπορούν να εκμεταλλευτούν καθ όλη τη διάρκεια της ζωής τους στρατηγική τακτική δημιουργικότητα επιμονή και υπολογισμό κινδύνων μια ποικιλία εργαλείων μάθησης γρίφων και σκακιού σε πραγματικό χρόνο εναντίον ρομπότ ή άλλων ανθρώπων παρέχει προκλήσεις για τον εγκέφαλο και ώρες ψυχαγωγίας στα παιδιά σημειωση η σελίδα είναι διαθέσιμη μόνο στην αγγλική γλώσσα institution chesskid legal ok link title μάθε σκάκι online | 0 |
95,598 | 12,016,954,873 | IssuesEvent | 2020-04-10 17:16:12 | cloudfour/cloudfour.com-patterns | https://api.github.com/repos/cloudfour/cloudfour.com-patterns | closed | Odd double quotes and apostrophes with new variable font | size:1 🎨 design 🐛 bug | Tyler recently added some dummy data to the site to prototype the blog listings.
While playing with it I noticed that the double quotes and apostrophes look oddly angular and intense. I tried going in and replacing these with HTML entities for the relevant glyphs but it didn't appear to fix the double quotes.
<img width="1224" alt="Screen Shot 2020-04-09 at 1 18 25 PM" src="https://user-images.githubusercontent.com/5798536/78947960-bdacb580-7a7b-11ea-925e-02ff3d4d528f.png">
<img width="85" alt="Screen Shot 2020-04-09 at 3 48 07 PM" src="https://user-images.githubusercontent.com/5798536/78947968-c1403c80-7a7b-11ea-8ef1-69a6dbd35255.png">
<img width="37" alt="Screen Shot 2020-04-09 at 3 48 14 PM" src="https://user-images.githubusercontent.com/5798536/78947969-c1d8d300-7a7b-11ea-83fb-447d1a7ee1fd.png">
I saw this issue in Firefox on my macbook. | 1.0 | Odd double quotes and apostrophes with new variable font - Tyler recently added some dummy data to the site to prototype the blog listings.
While playing with it I noticed that the double quotes and apostrophes look oddly angular and intense. I tried going in and replacing these with HTML entities for the relevant glyphs but it didn't appear to fix the double quotes.
<img width="1224" alt="Screen Shot 2020-04-09 at 1 18 25 PM" src="https://user-images.githubusercontent.com/5798536/78947960-bdacb580-7a7b-11ea-925e-02ff3d4d528f.png">
<img width="85" alt="Screen Shot 2020-04-09 at 3 48 07 PM" src="https://user-images.githubusercontent.com/5798536/78947968-c1403c80-7a7b-11ea-8ef1-69a6dbd35255.png">
<img width="37" alt="Screen Shot 2020-04-09 at 3 48 14 PM" src="https://user-images.githubusercontent.com/5798536/78947969-c1d8d300-7a7b-11ea-83fb-447d1a7ee1fd.png">
I saw this issue in Firefox on my macbook. | non_priority | odd double quotes and apostrophes with new variable font tyler recently added some dummy data to the site to prototype the blog listings while playing with it i noticed that the double quotes and apostrophes look oddly angular and intense i tried going in and replacing these with html entities for the relevant glyphs but it didn t appear to fix the double quotes img width alt screen shot at pm src img width alt screen shot at pm src img width alt screen shot at pm src i saw this issue in firefox on my macbook | 0 |
18,626 | 4,288,916,124 | IssuesEvent | 2016-07-17 19:34:21 | mwcraig/reducer | https://api.github.com/repos/mwcraig/reducer | closed | Redo image browser screen cap for quickstart | Documentation enhancement | The current one uses the old image renderer, which looked like crap. | 1.0 | Redo image browser screen cap for quickstart - The current one uses the old image renderer, which looked like crap. | non_priority | redo image browser screen cap for quickstart the current one uses the old image renderer which looked like crap | 0 |
451,870 | 32,044,123,320 | IssuesEvent | 2023-09-22 22:33:24 | medplum/medplum | https://api.github.com/repos/medplum/medplum | closed | Document how to enable enterprise observability lambdas | documentation audit-logging | Enterprise observability (e.g. Splunk, Datadog, Sumo-Logic) are enabled via cloudwatch integration. Need to document how to set up the [connector from logs](https://github.com/medplum/medplum/blob/main/packages/infra/src/backend.ts) to the lambda that connects to Splunk while maintaining the integrity of the environment and passing the compliance checks. | 1.0 | Document how to enable enterprise observability lambdas - Enterprise observability (e.g. Splunk, Datadog, Sumo-Logic) are enabled via cloudwatch integration. Need to document how to set up the [connector from logs](https://github.com/medplum/medplum/blob/main/packages/infra/src/backend.ts) to the lambda that connects to Splunk while maintaining the integrity of the environment and passing the compliance checks. | non_priority | document how to enable enterprise observability lambdas enterprise observability e g splunk datadog sumo logic are enabled via cloudwatch integration need to document how to set up the to the lambda that connects to splunk while maintaining the integrity of the environment and passing the compliance checks | 0 |
179,081 | 21,511,908,407 | IssuesEvent | 2022-04-28 05:59:14 | samq-ghdemo/Java-Demo | https://api.github.com/repos/samq-ghdemo/Java-Demo | opened | mysql-connector-java-5.1.25.jar: 7 vulnerabilities (highest severity is: 8.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-3523](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3523) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | mysql-connector-java-5.1.25.jar | Direct | 5.1.41 | ✅ |
| [CVE-2017-3586](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3586) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.4 | mysql-connector-java-5.1.25.jar | Direct | 5.1.42 | ✅ |
| [CVE-2019-2692](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:8.0.16 | ✅ |
| [CVE-2020-2934](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2934) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:5.1.49,8.0.20 | ✅ |
| [CVE-2020-2875](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2875) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.7 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:5.1.49,8.0.15 | ✅ |
| [CVE-2017-3589](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3589) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | mysql-connector-java-5.1.25.jar | Direct | 5.1.42 | ✅ |
| [CVE-2020-2933](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2933) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.2 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:5.1.49 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-3523</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.40 and earlier. Difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 8.5 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3523>CVE-2017-3523</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.oracle.com/technetwork/security-advisory/cpuapr2017-3236618.html">https://www.oracle.com/technetwork/security-advisory/cpuapr2017-3236618.html</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.41</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-3586</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 6.4 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3586>CVE-2017-3586</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1444406">https://bugzilla.redhat.com/show_bug.cgi?id=1444406</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.42</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-2692</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692>CVE-2019-2692</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jcq3-cprp-m333">https://github.com/advisories/GHSA-jcq3-cprp-m333</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: mysql:mysql-connector-java:8.0.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2934</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.19 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data and unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 5.0 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:L/I:L/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2934>CVE-2020-2934</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.oracle.com/security-alerts/cpuapr2020.html">https://www.oracle.com/security-alerts/cpuapr2020.html</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: mysql:mysql-connector-java:5.1.49,8.0.20</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2875</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.14 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker and while the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 4.7 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:N).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2875>CVE-2020-2875</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mysql/mysql-connector-j/commit/79a4336f140499bd22dd07f02b708e163844e3d5">https://github.com/mysql/mysql-connector-j/commit/79a4336f140499bd22dd07f02b708e163844e3d5</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: mysql:mysql-connector-java:5.1.49,8.0.15</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2017-3589</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3589>CVE-2017-3589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.42</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-2933</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 5.1.48 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 2.2 (Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:N/I:N/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2933>CVE-2020-2933</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>2.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING">https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: mysql:mysql-connector-java:5.1.49</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.1.41","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-3523","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.40 and earlier. Difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 8.5 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3523","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.1.42","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-3586","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily \"exploitable\" vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 6.4 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3586","cvss3Severity":"medium","cvss3Score":"6.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:8.0.16","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-2692","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692","cvss3Severity":"medium","cvss3Score":"6.3","cvss3Metrics":{"A":"High","AC":"High","PR":"High","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:5.1.49,8.0.20","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-2934","vulnerabilityDetails":"Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.19 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data and unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 5.0 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:L/I:L/A:L).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2934","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:5.1.49,8.0.15","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-2875","vulnerabilityDetails":"Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.14 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker and while the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 4.7 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:N).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2875","cvss3Severity":"medium","cvss3Score":"4.7","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.1.42","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-3589","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily \"exploitable\" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3589","cvss3Severity":"low","cvss3Score":"3.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:5.1.49","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-2933","vulnerabilityDetails":"Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 5.1.48 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 2.2 (Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:N/I:N/A:L).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2933","cvss3Severity":"low","cvss3Score":"2.2","cvss3Metrics":{"A":"Low","AC":"High","PR":"High","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | mysql-connector-java-5.1.25.jar: 7 vulnerabilities (highest severity is: 8.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2017-3523](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3523) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.5 | mysql-connector-java-5.1.25.jar | Direct | 5.1.41 | ✅ |
| [CVE-2017-3586](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3586) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.4 | mysql-connector-java-5.1.25.jar | Direct | 5.1.42 | ✅ |
| [CVE-2019-2692](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.3 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:8.0.16 | ✅ |
| [CVE-2020-2934](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2934) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:5.1.49,8.0.20 | ✅ |
| [CVE-2020-2875](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2875) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.7 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:5.1.49,8.0.15 | ✅ |
| [CVE-2017-3589](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3589) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | mysql-connector-java-5.1.25.jar | Direct | 5.1.42 | ✅ |
| [CVE-2020-2933](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2933) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.2 | mysql-connector-java-5.1.25.jar | Direct | mysql:mysql-connector-java:5.1.49 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-3523</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.40 and earlier. Difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 8.5 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3523>CVE-2017-3523</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.oracle.com/technetwork/security-advisory/cpuapr2017-3236618.html">https://www.oracle.com/technetwork/security-advisory/cpuapr2017-3236618.html</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.41</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-3586</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 6.4 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3586>CVE-2017-3586</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1444406">https://bugzilla.redhat.com/show_bug.cgi?id=1444406</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.42</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-2692</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692>CVE-2019-2692</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jcq3-cprp-m333">https://github.com/advisories/GHSA-jcq3-cprp-m333</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: mysql:mysql-connector-java:8.0.16</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2934</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.19 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data and unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 5.0 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:L/I:L/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2934>CVE-2020-2934</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.oracle.com/security-alerts/cpuapr2020.html">https://www.oracle.com/security-alerts/cpuapr2020.html</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: mysql:mysql-connector-java:5.1.49,8.0.20</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-2875</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.14 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker and while the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 4.7 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:N).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2875>CVE-2020-2875</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mysql/mysql-connector-j/commit/79a4336f140499bd22dd07f02b708e163844e3d5">https://github.com/mysql/mysql-connector-j/commit/79a4336f140499bd22dd07f02b708e163844e3d5</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: mysql:mysql-connector-java:5.1.49,8.0.15</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2017-3589</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily "exploitable" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).
<p>Publish Date: 2017-04-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3589>CVE-2017-3589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-3589</a></p>
<p>Release Date: 2017-04-24</p>
<p>Fix Resolution: 5.1.42</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-2933</summary>
### Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /repository/mysql/mysql-connector-java/5.1.25/mysql-connector-java-5.1.25.jar</p>
<p>
Dependency Hierarchy:
- :x: **mysql-connector-java-5.1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/7a57885245a9ed9010aa350c184246310435362e">7a57885245a9ed9010aa350c184246310435362e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 5.1.48 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 2.2 (Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:N/I:N/A:L).
<p>Publish Date: 2020-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2933>CVE-2020-2933</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>2.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING">https://docs.oracle.com/javase/7/docs/api/javax/xml/XMLConstants.html#FEATURE_SECURE_PROCESSING</a></p>
<p>Release Date: 2020-04-15</p>
<p>Fix Resolution: mysql:mysql-connector-java:5.1.49</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.1.41","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-3523","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.40 and earlier. Difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 8.5 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3523","cvss3Severity":"high","cvss3Score":"8.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.1.42","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-3586","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily \"exploitable\" vulnerability allows low privileged attacker with network access via multiple protocols to compromise MySQL Connectors. While the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 6.4 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:C/C:L/I:L/A:N).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3586","cvss3Severity":"medium","cvss3Score":"6.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:8.0.16","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-2692","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692","cvss3Severity":"medium","cvss3Score":"6.3","cvss3Metrics":{"A":"High","AC":"High","PR":"High","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:5.1.49,8.0.20","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-2934","vulnerabilityDetails":"Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.19 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data and unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 5.0 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:U/C:L/I:L/A:L).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2934","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:5.1.49,8.0.15","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-2875","vulnerabilityDetails":"Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 8.0.14 and prior and 5.1.48 and prior. Difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker and while the vulnerability is in MySQL Connectors, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data as well as unauthorized read access to a subset of MySQL Connectors accessible data. CVSS 3.0 Base Score 4.7 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:N).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2875","cvss3Severity":"medium","cvss3Score":"4.7","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"5.1.42","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-3589","vulnerabilityDetails":"Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 5.1.41 and earlier. Easily \"exploitable\" vulnerability allows low privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of MySQL Connectors accessible data. CVSS 3.0 Base Score 3.3 (Integrity impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-3589","cvss3Severity":"low","cvss3Score":"3.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"mysql","packageName":"mysql-connector-java","packageVersion":"5.1.25","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"mysql:mysql-connector-java:5.1.25","isMinimumFixVersionAvailable":true,"minimumFixVersion":"mysql:mysql-connector-java:5.1.49","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-2933","vulnerabilityDetails":"Vulnerability in the MySQL Connectors product of Oracle MySQL (component: Connector/J). Supported versions that are affected are 5.1.48 and prior. Difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise MySQL Connectors. Successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service (partial DOS) of MySQL Connectors. CVSS 3.0 Base Score 2.2 (Availability impacts). CVSS Vector: (CVSS:3.0/AV:N/AC:H/PR:H/UI:N/S:U/C:N/I:N/A:L).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-2933","cvss3Severity":"low","cvss3Score":"2.2","cvss3Metrics":{"A":"Low","AC":"High","PR":"High","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_priority | mysql connector java jar vulnerabilities highest severity is vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high mysql connector java jar direct medium mysql connector java jar direct medium mysql connector java jar direct mysql mysql connector java medium mysql connector java jar direct mysql mysql connector java medium mysql connector java jar direct mysql mysql connector java low mysql connector java jar direct low mysql connector java jar direct mysql mysql connector java details cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise mysql connectors while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr l ui n s c c h i h a h publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with network access via multiple protocols to compromise mysql connectors while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data cvss base score confidentiality and integrity impacts cvss vector cvss av n ac l pr l ui n s c c l i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av l ac h pr h ui r s u c h i h a h publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mysql mysql connector java rescue worker helmet automatic remediation is available for this issue cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior and and prior difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data and unauthorized ability to cause a partial denial of service partial dos of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr n ui r s u c l i l a l publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mysql mysql connector java rescue worker helmet automatic remediation is available for this issue cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior and and prior difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise mysql connectors successful attacks require human interaction from a person other than the attacker and while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data cvss base score confidentiality and integrity impacts cvss vector cvss av n ac h pr n ui r s c c l i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mysql mysql connector java rescue worker helmet automatic remediation is available for this issue cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data cvss base score integrity impacts cvss vector cvss av l ac l pr l ui n s u c n i l a n publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql mysql connector java mysql connector java jar dependency hierarchy x mysql connector java jar vulnerable library found in head commit a href found in base branch main vulnerability details vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service partial dos of mysql connectors cvss base score availability impacts cvss vector cvss av n ac h pr h ui n s u c n i n a l publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mysql mysql connector java rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier difficult to exploit vulnerability allows low privileged attacker with network access via multiple protocols to compromise mysql connectors while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr l ui n s c c h i h a h vulnerabilityurl istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with network access via multiple protocols to compromise mysql connectors while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data cvss base score confidentiality and integrity impacts cvss vector cvss av n ac l pr l ui n s c c l i l a n vulnerabilityurl istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion mysql mysql connector java isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av l ac h pr h ui r s u c h i h a h vulnerabilityurl istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion mysql mysql connector java isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior and and prior difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data and unauthorized ability to cause a partial denial of service partial dos of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av n ac h pr n ui r s u c l i l a l vulnerabilityurl istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion mysql mysql connector java isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior and and prior difficult to exploit vulnerability allows unauthenticated attacker with network access via multiple protocols to compromise mysql connectors successful attacks require human interaction from a person other than the attacker and while the vulnerability is in mysql connectors attacks may significantly impact additional products successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data as well as unauthorized read access to a subset of mysql connectors accessible data cvss base score confidentiality and integrity impacts cvss vector cvss av n ac h pr n ui r s c c l i l a n vulnerabilityurl istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and earlier easily exploitable vulnerability allows low privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized update insert or delete access to some of mysql connectors accessible data cvss base score integrity impacts cvss vector cvss av l ac l pr l ui n s u c n i l a n vulnerabilityurl istransitivedependency false dependencytree mysql mysql connector java isminimumfixversionavailable true minimumfixversion mysql mysql connector java isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in the mysql connectors product of oracle mysql component connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with network access via multiple protocols to compromise mysql connectors successful attacks of this vulnerability can result in unauthorized ability to cause a partial denial of service partial dos of mysql connectors cvss base score availability impacts cvss vector cvss av n ac h pr h ui n s u c n i n a l vulnerabilityurl | 0 |
72,940 | 9,632,957,864 | IssuesEvent | 2019-05-15 17:27:04 | FRRouting/frr | https://api.github.com/repos/FRRouting/frr | closed | BGP VPN Label Assignment | documentation | This is just a suggestion to change the wording in the documentation to be a bit more clear:
http://docs.frrouting.org/en/latest/bgp.html#vrf-route-leaking
in the section:
http://docs.frrouting.org/en/latest/bgp.html#clicmd-labelvpnexport(0..1048575)|auto
The current wording is:
Specifies an optional MPLS label to be attached to a route exported from the current unicast VRF to VPN. If label is specified as auto, the label value is automatically assigned from a pool maintained by the zebra daemon. If zebra is not running, automatic label assignment will not complete, which will block corresponding route export.
This can sometimes be misinterpreted that this command is optional, but for an MPLS-VPN to function a VPN label MUST be assigned to routes exported from the VPN.
I think this should be changed to:
Enables an MPLS label to be attached to a route exported from the current unicast VRF to VPN. If label is specified as auto, the label value is automatically assigned from a pool maintained by the zebra daemon. If zebra is not running, or if this command is not configured, automatic label assignment will not complete, which will block corresponding route export.
| 1.0 | BGP VPN Label Assignment - This is just a suggestion to change the wording in the documentation to be a bit more clear:
http://docs.frrouting.org/en/latest/bgp.html#vrf-route-leaking
in the section:
http://docs.frrouting.org/en/latest/bgp.html#clicmd-labelvpnexport(0..1048575)|auto
The current wording is:
Specifies an optional MPLS label to be attached to a route exported from the current unicast VRF to VPN. If label is specified as auto, the label value is automatically assigned from a pool maintained by the zebra daemon. If zebra is not running, automatic label assignment will not complete, which will block corresponding route export.
This can sometimes be misinterpreted that this command is optional, but for an MPLS-VPN to function a VPN label MUST be assigned to routes exported from the VPN.
I think this should be changed to:
Enables an MPLS label to be attached to a route exported from the current unicast VRF to VPN. If label is specified as auto, the label value is automatically assigned from a pool maintained by the zebra daemon. If zebra is not running, or if this command is not configured, automatic label assignment will not complete, which will block corresponding route export.
| non_priority | bgp vpn label assignment this is just a suggestion to change the wording in the documentation to be a bit more clear in the section the current wording is specifies an optional mpls label to be attached to a route exported from the current unicast vrf to vpn if label is specified as auto the label value is automatically assigned from a pool maintained by the zebra daemon if zebra is not running automatic label assignment will not complete which will block corresponding route export this can sometimes be misinterpreted that this command is optional but for an mpls vpn to function a vpn label must be assigned to routes exported from the vpn i think this should be changed to enables an mpls label to be attached to a route exported from the current unicast vrf to vpn if label is specified as auto the label value is automatically assigned from a pool maintained by the zebra daemon if zebra is not running or if this command is not configured automatic label assignment will not complete which will block corresponding route export | 0 |
326,777 | 24,101,007,130 | IssuesEvent | 2022-09-20 00:38:49 | CSClubOfStanState/csclub-website | https://api.github.com/repos/CSClubOfStanState/csclub-website | opened | Fix Author Links | documentation good first issue | - [ ] Fix Hyperlinks in [Archive](https://hopper.csustan.edu/~csclub/archives/archive.html#)
- [ ] Change the name of authors to their Full Name -> Giancarlo Garcia Deleon and Brendan Hutchinson Contreras
- [ ] Add Brendan's [LinkedIn ](https://www.linkedin.com/in/brendan-contreras-4b02181b5/)for his hyperlink | 1.0 | Fix Author Links - - [ ] Fix Hyperlinks in [Archive](https://hopper.csustan.edu/~csclub/archives/archive.html#)
- [ ] Change the name of authors to their Full Name -> Giancarlo Garcia Deleon and Brendan Hutchinson Contreras
- [ ] Add Brendan's [LinkedIn ](https://www.linkedin.com/in/brendan-contreras-4b02181b5/)for his hyperlink | non_priority | fix author links fix hyperlinks in change the name of authors to their full name giancarlo garcia deleon and brendan hutchinson contreras add brendan s his hyperlink | 0 |
186,840 | 15,085,586,682 | IssuesEvent | 2021-02-05 18:54:55 | spsanderson/healthyR.ts | https://api.github.com/repos/spsanderson/healthyR.ts | closed | Resubmit to CRAN with fixed description | documentation | Resubmit to CRAN with fixes,
Description
README
parameter checks | 1.0 | Resubmit to CRAN with fixed description - Resubmit to CRAN with fixes,
Description
README
parameter checks | non_priority | resubmit to cran with fixed description resubmit to cran with fixes description readme parameter checks | 0 |
122,951 | 12,179,205,612 | IssuesEvent | 2020-04-28 10:16:20 | jcs-elpa/flycheck-grammarly | https://api.github.com/repos/jcs-elpa/flycheck-grammarly | reopened | Proper documentation | documentation good first issue | As of now the package's dependencies are completely unknown. Although it can be installed, I don't know how to start it. The official readme should include installation instructions. | 1.0 | Proper documentation - As of now the package's dependencies are completely unknown. Although it can be installed, I don't know how to start it. The official readme should include installation instructions. | non_priority | proper documentation as of now the package s dependencies are completely unknown although it can be installed i don t know how to start it the official readme should include installation instructions | 0 |
136,139 | 18,722,346,461 | IssuesEvent | 2021-11-03 13:11:55 | KDWSS/dd-trace-java | https://api.github.com/repos/KDWSS/dd-trace-java | opened | CVE-2015-1832 (High) detected in derby-10.6.1.0.jar | security vulnerability | ## CVE-2015-1832 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>derby-10.6.1.0.jar</b></p></summary>
<p>Contains the core Apache Derby database engine, which also includes the embedded JDBC driver.</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/jdbc/jdbc.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.apache.derby/derby/10.6.1.0/1137cd636b0e3c22f0d273478adb58aa30e984a/derby-10.6.1.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **derby-10.6.1.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XML external entity (XXE) vulnerability in the SqlXmlUtil code in Apache Derby before 10.12.1.1, when a Java Security Manager is not in place, allows context-dependent attackers to read arbitrary files or cause a denial of service (resource consumption) via vectors involving XmlVTI and the XML datatype.
<p>Publish Date: 2016-10-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-1832>CVE-2015-1832</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-1832">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-1832</a></p>
<p>Release Date: 2016-10-03</p>
<p>Fix Resolution: 10.12.1.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.derby","packageName":"derby","packageVersion":"10.6.1.0","packageFilePaths":["/dd-java-agent/instrumentation/jdbc/jdbc.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.derby:derby:10.6.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.12.1.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-1832","vulnerabilityDetails":"XML external entity (XXE) vulnerability in the SqlXmlUtil code in Apache Derby before 10.12.1.1, when a Java Security Manager is not in place, allows context-dependent attackers to read arbitrary files or cause a denial of service (resource consumption) via vectors involving XmlVTI and the XML datatype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-1832","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2015-1832 (High) detected in derby-10.6.1.0.jar - ## CVE-2015-1832 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>derby-10.6.1.0.jar</b></p></summary>
<p>Contains the core Apache Derby database engine, which also includes the embedded JDBC driver.</p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/jdbc/jdbc.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.apache.derby/derby/10.6.1.0/1137cd636b0e3c22f0d273478adb58aa30e984a/derby-10.6.1.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **derby-10.6.1.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XML external entity (XXE) vulnerability in the SqlXmlUtil code in Apache Derby before 10.12.1.1, when a Java Security Manager is not in place, allows context-dependent attackers to read arbitrary files or cause a denial of service (resource consumption) via vectors involving XmlVTI and the XML datatype.
<p>Publish Date: 2016-10-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-1832>CVE-2015-1832</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-1832">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-1832</a></p>
<p>Release Date: 2016-10-03</p>
<p>Fix Resolution: 10.12.1.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.derby","packageName":"derby","packageVersion":"10.6.1.0","packageFilePaths":["/dd-java-agent/instrumentation/jdbc/jdbc.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.derby:derby:10.6.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"10.12.1.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-1832","vulnerabilityDetails":"XML external entity (XXE) vulnerability in the SqlXmlUtil code in Apache Derby before 10.12.1.1, when a Java Security Manager is not in place, allows context-dependent attackers to read arbitrary files or cause a denial of service (resource consumption) via vectors involving XmlVTI and the XML datatype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-1832","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in derby jar cve high severity vulnerability vulnerable library derby jar contains the core apache derby database engine which also includes the embedded jdbc driver path to dependency file dd trace java dd java agent instrumentation jdbc jdbc gradle path to vulnerable library caches modules files org apache derby derby derby jar dependency hierarchy x derby jar vulnerable library found in head commit a href found in base branch master vulnerability details xml external entity xxe vulnerability in the sqlxmlutil code in apache derby before when a java security manager is not in place allows context dependent attackers to read arbitrary files or cause a denial of service resource consumption via vectors involving xmlvti and the xml datatype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org apache derby derby isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails xml external entity xxe vulnerability in the sqlxmlutil code in apache derby before when a java security manager is not in place allows context dependent attackers to read arbitrary files or cause a denial of service resource consumption via vectors involving xmlvti and the xml datatype vulnerabilityurl | 0 |
12,445 | 7,881,096,589 | IssuesEvent | 2018-06-26 17:55:22 | chapel-lang/chapel | https://api.github.com/repos/chapel-lang/chapel | closed | Enable LayoutCS to have optional sparse sorting | Epic area: Modules type: Performance type: Refactor | As a Chapel user I would expect sparse arrays in Chapel to perform competitively with typical CSR/CSC codes where a major difference today is that LayoutCS sorts the sparse dimension, unlike typical CSR/CSC codes. I would like the ability to specify if sorting should happen in my arrays domain mapped using LayoutCS.
Acceptance Criterion:
+ LayoutCS will support a `param boolean` indicating whether or not sorting should occur on the sparse dimension.
+ No worse than current performance (and potentially better for sparse matrix-matrix multiplication).
| True | Enable LayoutCS to have optional sparse sorting - As a Chapel user I would expect sparse arrays in Chapel to perform competitively with typical CSR/CSC codes where a major difference today is that LayoutCS sorts the sparse dimension, unlike typical CSR/CSC codes. I would like the ability to specify if sorting should happen in my arrays domain mapped using LayoutCS.
Acceptance Criterion:
+ LayoutCS will support a `param boolean` indicating whether or not sorting should occur on the sparse dimension.
+ No worse than current performance (and potentially better for sparse matrix-matrix multiplication).
| non_priority | enable layoutcs to have optional sparse sorting as a chapel user i would expect sparse arrays in chapel to perform competitively with typical csr csc codes where a major difference today is that layoutcs sorts the sparse dimension unlike typical csr csc codes i would like the ability to specify if sorting should happen in my arrays domain mapped using layoutcs acceptance criterion layoutcs will support a param boolean indicating whether or not sorting should occur on the sparse dimension no worse than current performance and potentially better for sparse matrix matrix multiplication | 0 |
4,861 | 25,013,010,321 | IssuesEvent | 2022-11-03 16:33:35 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | opened | Keep records in store while fetching | type: enhancement work: frontend status: ready restricted: maintainers | ## Current behavior
- Before fetching records, we clear all the existing records replacing them with dummy records just so that each cell displays a loading skeleton.
- In the Record Selector, we're auto-sizing the column widths based on the content of the cells.
- The combination of the above two strategies produces some funky loading behavior in the Record Selector. While searching, the table gets too narrow because the cells no longer have content. Then when the search is complete, the table gets wide again. This causes the UI to jump around which can be disorienting to users.
## Desired behavior
- Don't wipe the records out until we have already fetched them. Maintain a separation of concerns between the records _data_ and the records _fetch status_.
- We can still display loading skeletons on the cells by reacting to the fetch status.
| True | Keep records in store while fetching - ## Current behavior
- Before fetching records, we clear all the existing records replacing them with dummy records just so that each cell displays a loading skeleton.
- In the Record Selector, we're auto-sizing the column widths based on the content of the cells.
- The combination of the above two strategies produces some funky loading behavior in the Record Selector. While searching, the table gets too narrow because the cells no longer have content. Then when the search is complete, the table gets wide again. This causes the UI to jump around which can be disorienting to users.
## Desired behavior
- Don't wipe the records out until we have already fetched them. Maintain a separation of concerns between the records _data_ and the records _fetch status_.
- We can still display loading skeletons on the cells by reacting to the fetch status.
| non_priority | keep records in store while fetching current behavior before fetching records we clear all the existing records replacing them with dummy records just so that each cell displays a loading skeleton in the record selector we re auto sizing the column widths based on the content of the cells the combination of the above two strategies produces some funky loading behavior in the record selector while searching the table gets too narrow because the cells no longer have content then when the search is complete the table gets wide again this causes the ui to jump around which can be disorienting to users desired behavior don t wipe the records out until we have already fetched them maintain a separation of concerns between the records data and the records fetch status we can still display loading skeletons on the cells by reacting to the fetch status | 0 |
80,968 | 30,636,065,842 | IssuesEvent | 2023-07-24 17:51:53 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | "Your server isn't responding to some requests" can't be dismissed | T-Defect S-Major A-Config O-Uncommon | Noticed this when working on the Dendrite push notifs stuff — once this appears, it's impossible to dismiss it short of reloading the page. If you click "requests" and try to resend and they don't succeed, you're stuck with it on-screen.
Element version: 1.10.6
Olm version: 3.2.8 | 1.0 | "Your server isn't responding to some requests" can't be dismissed - Noticed this when working on the Dendrite push notifs stuff — once this appears, it's impossible to dismiss it short of reloading the page. If you click "requests" and try to resend and they don't succeed, you're stuck with it on-screen.
Element version: 1.10.6
Olm version: 3.2.8 | non_priority | your server isn t responding to some requests can t be dismissed noticed this when working on the dendrite push notifs stuff — once this appears it s impossible to dismiss it short of reloading the page if you click requests and try to resend and they don t succeed you re stuck with it on screen element version olm version | 0 |
67,163 | 12,885,300,433 | IssuesEvent | 2020-07-13 06:12:08 | Azure/k8s-infra | https://api.github.com/repos/Azure/k8s-infra | closed | Deal with plurality in resource names | CodeGenerator | For example, in `batch_accounts_types_gen.go` the type currently generated is
```
// +kubebuilder:object:root=true
type BatchAccounts struct {
....
}
```
It has a `BatchAccountsSpec`, etc -- these should not be plural.
You can see a similar problem on the VMSS resources as well, for example: `virtual_machine_scale_sets_types_gen.go` has `VirtualMachineScaleSetsSpec` which should probably be `VirtualMachineScaleSetSpec` like it is in the handcrafted code
| 1.0 | Deal with plurality in resource names - For example, in `batch_accounts_types_gen.go` the type currently generated is
```
// +kubebuilder:object:root=true
type BatchAccounts struct {
....
}
```
It has a `BatchAccountsSpec`, etc -- these should not be plural.
You can see a similar problem on the VMSS resources as well, for example: `virtual_machine_scale_sets_types_gen.go` has `VirtualMachineScaleSetsSpec` which should probably be `VirtualMachineScaleSetSpec` like it is in the handcrafted code
| non_priority | deal with plurality in resource names for example in batch accounts types gen go the type currently generated is kubebuilder object root true type batchaccounts struct it has a batchaccountsspec etc these should not be plural you can see a similar problem on the vmss resources as well for example virtual machine scale sets types gen go has virtualmachinescalesetsspec which should probably be virtualmachinescalesetspec like it is in the handcrafted code | 0 |
163,921 | 13,929,958,410 | IssuesEvent | 2020-10-22 01:05:53 | blinklet/usermapper | https://api.github.com/repos/blinklet/usermapper | opened | Add docstrings to modules and functions | documentation enhancement | Add docstrings to the program to document functions and modules | 1.0 | Add docstrings to modules and functions - Add docstrings to the program to document functions and modules | non_priority | add docstrings to modules and functions add docstrings to the program to document functions and modules | 0 |
344,820 | 30,763,266,515 | IssuesEvent | 2023-07-30 01:00:51 | backend-br/vagas | https://api.github.com/repos/backend-br/vagas | closed | [REMOTO - PJ] Tech Lead FullStack - Jusfy | PJ Sênior Node.js Remoto Especialista Testes automatizados TypeScript Git Docker Stale | ## Nossa empresa
A [[Jusfy](https://www.linkedin.com/company/jusfy/)](https://www.linkedin.com/company/jusfy/) está em busca de um **Tech Lead FullStack** para compor o time! Somos uma startup jurídica que busca constantemente soluções para facilitar a vida dos advogados e advogadas brasileiros. Atuamos na área de tecnologia, desenvolvendo produtos e ferramentas que auxiliam na produtividade diária dos nossos clientes.
Somos uma empresa jovem, mas muito promissora. Alcançamos resultados expressivos de crescimento nos últimos anos e sabemos que temos ainda muito mais para conquistar. Buscamos profissionais que queiram fazer parte dessa trajetória junto conosco!
## Descrição da vaga
Responsabilidades:
- Desenvolver novas funcionalidades utilizando ReactJS e APIs RESTful (utilizando Node.js e Express);
- Escrever códigos limpos, de alta qualidade e fácil manutenção seguindo as boas práticas de desenvolvimento;
- Liderar e colaborar com a equipe de desenvolvimento e testes para o sucesso dos projetos;
- Participar ativamente em discussões de arquitetura e tecnologias;
- Realizar code reviews, ajudando outros desenvolvedores a melhorar a qualidade do código;
- Compreender as necessidades de negócio e propor soluções;
- Garantir que a documentação do código e arquitetura esteja sempre atualizada;
- Contribuir em discussões de Design e Produto para garantir a melhor experiência do usuário e resultados de negócio;
- Corrigir bugs.
## Local
100% Remoto!
## Requisitos
Requisitos técnicos:
- Experiência com desenvolvimento de Backend e Frontend;
- Experiência em Typescript e API REST;
- Conhecimento em bancos de dados relacionais e não-relacionais;
- Orquestração de containers (Docker e docker-compose);
- Conhecimento em Styled Components e Context API;
- Experiência com controle de versão utilizando Git.
Desejável
- Experiência com metodologias ágeis;
- Conhecimento de Design Patterns;
- Vivência em Liderança Técnica;
- Experiência em times de desenvolvimento de software ou empresas de tecnologia;
- Conhecimento em testes automatizados e ferramentas de integração contínua;
- Capacidade de contribuir com especificações técnicas para propostas de solução;
- Boa comunicação e capacidade de se adaptar a mudanças;
- Forte habilidade de resolução de problemas e pensamento crítico.
## Benefícios
Oferecemos:
- 100% Remoto;
- Flexibilidade de horário;
- Ambiente de trabalho descontraído e inovador;
- Oportunidade de trabalhar em projetos desafiadores e com grande impacto.
## Contratação
Modelo de Contratação: PJ
## Como se candidatar
Se você é um Desenvolvedor FullStack com boa experiência em desenvolvimento de software e liderança e está buscando uma oportunidade desafiadora em uma empresa inovadora, envie seu currículo para guilherme@jusfy.com.br com o nome da vaga no título do email :)
## Labels
### Nível
- Sênior
- Especialista
### Regime
- PJ
### Alocação
- Remoto | 1.0 | [REMOTO - PJ] Tech Lead FullStack - Jusfy - ## Nossa empresa
A [[Jusfy](https://www.linkedin.com/company/jusfy/)](https://www.linkedin.com/company/jusfy/) está em busca de um **Tech Lead FullStack** para compor o time! Somos uma startup jurídica que busca constantemente soluções para facilitar a vida dos advogados e advogadas brasileiros. Atuamos na área de tecnologia, desenvolvendo produtos e ferramentas que auxiliam na produtividade diária dos nossos clientes.
Somos uma empresa jovem, mas muito promissora. Alcançamos resultados expressivos de crescimento nos últimos anos e sabemos que temos ainda muito mais para conquistar. Buscamos profissionais que queiram fazer parte dessa trajetória junto conosco!
## Descrição da vaga
Responsabilidades:
- Desenvolver novas funcionalidades utilizando ReactJS e APIs RESTful (utilizando Node.js e Express);
- Escrever códigos limpos, de alta qualidade e fácil manutenção seguindo as boas práticas de desenvolvimento;
- Liderar e colaborar com a equipe de desenvolvimento e testes para o sucesso dos projetos;
- Participar ativamente em discussões de arquitetura e tecnologias;
- Realizar code reviews, ajudando outros desenvolvedores a melhorar a qualidade do código;
- Compreender as necessidades de negócio e propor soluções;
- Garantir que a documentação do código e arquitetura esteja sempre atualizada;
- Contribuir em discussões de Design e Produto para garantir a melhor experiência do usuário e resultados de negócio;
- Corrigir bugs.
## Local
100% Remoto!
## Requisitos
Requisitos técnicos:
- Experiência com desenvolvimento de Backend e Frontend;
- Experiência em Typescript e API REST;
- Conhecimento em bancos de dados relacionais e não-relacionais;
- Orquestração de containers (Docker e docker-compose);
- Conhecimento em Styled Components e Context API;
- Experiência com controle de versão utilizando Git.
Desejável
- Experiência com metodologias ágeis;
- Conhecimento de Design Patterns;
- Vivência em Liderança Técnica;
- Experiência em times de desenvolvimento de software ou empresas de tecnologia;
- Conhecimento em testes automatizados e ferramentas de integração contínua;
- Capacidade de contribuir com especificações técnicas para propostas de solução;
- Boa comunicação e capacidade de se adaptar a mudanças;
- Forte habilidade de resolução de problemas e pensamento crítico.
## Benefícios
Oferecemos:
- 100% Remoto;
- Flexibilidade de horário;
- Ambiente de trabalho descontraído e inovador;
- Oportunidade de trabalhar em projetos desafiadores e com grande impacto.
## Contratação
Modelo de Contratação: PJ
## Como se candidatar
Se você é um Desenvolvedor FullStack com boa experiência em desenvolvimento de software e liderança e está buscando uma oportunidade desafiadora em uma empresa inovadora, envie seu currículo para guilherme@jusfy.com.br com o nome da vaga no título do email :)
## Labels
### Nível
- Sênior
- Especialista
### Regime
- PJ
### Alocação
- Remoto | non_priority | tech lead fullstack jusfy nossa empresa a está em busca de um tech lead fullstack para compor o time somos uma startup jurídica que busca constantemente soluções para facilitar a vida dos advogados e advogadas brasileiros atuamos na área de tecnologia desenvolvendo produtos e ferramentas que auxiliam na produtividade diária dos nossos clientes somos uma empresa jovem mas muito promissora alcançamos resultados expressivos de crescimento nos últimos anos e sabemos que temos ainda muito mais para conquistar buscamos profissionais que queiram fazer parte dessa trajetória junto conosco descrição da vaga responsabilidades desenvolver novas funcionalidades utilizando reactjs e apis restful utilizando node js e express escrever códigos limpos de alta qualidade e fácil manutenção seguindo as boas práticas de desenvolvimento liderar e colaborar com a equipe de desenvolvimento e testes para o sucesso dos projetos participar ativamente em discussões de arquitetura e tecnologias realizar code reviews ajudando outros desenvolvedores a melhorar a qualidade do código compreender as necessidades de negócio e propor soluções garantir que a documentação do código e arquitetura esteja sempre atualizada contribuir em discussões de design e produto para garantir a melhor experiência do usuário e resultados de negócio corrigir bugs local remoto requisitos requisitos técnicos experiência com desenvolvimento de backend e frontend experiência em typescript e api rest conhecimento em bancos de dados relacionais e não relacionais orquestração de containers docker e docker compose conhecimento em styled components e context api experiência com controle de versão utilizando git desejável experiência com metodologias ágeis conhecimento de design patterns vivência em liderança técnica experiência em times de desenvolvimento de software ou empresas de tecnologia conhecimento em testes automatizados e ferramentas de integração contínua capacidade de contribuir com especificações técnicas para propostas de solução boa comunicação e capacidade de se adaptar a mudanças forte habilidade de resolução de problemas e pensamento crítico benefícios oferecemos remoto flexibilidade de horário ambiente de trabalho descontraído e inovador oportunidade de trabalhar em projetos desafiadores e com grande impacto contratação modelo de contratação pj como se candidatar se você é um desenvolvedor fullstack com boa experiência em desenvolvimento de software e liderança e está buscando uma oportunidade desafiadora em uma empresa inovadora envie seu currículo para guilherme jusfy com br com o nome da vaga no título do email labels nível sênior especialista regime pj alocação remoto | 0 |
138,436 | 11,201,313,369 | IssuesEvent | 2020-01-04 02:13:44 | ShaneBeee/GriefPreventionFlags | https://api.github.com/repos/ShaneBeee/GriefPreventionFlags | closed | If a player tps away in a claim with fly flag they still have fly | bug need to test | ### Description
If a player has a fly flag enabled in their region and they are flying and then tps to /Spawn they still have fly.
### Steps to Reproduce
Create a claim, add fly flag to it, teleport away from claim while flying in the claim
### Expected Behavior
To disable the fly when the player teleports out of the region
### Server Information
* **Server version/platform:** Paper 1.15.1
* **GriefPrevention Version:** 16.12.0-d4d7ac4
* **GriefPreventionFlags Version:** 5.7.0
### Additional Info
| 1.0 | If a player tps away in a claim with fly flag they still have fly - ### Description
If a player has a fly flag enabled in their region and they are flying and then tps to /Spawn they still have fly.
### Steps to Reproduce
Create a claim, add fly flag to it, teleport away from claim while flying in the claim
### Expected Behavior
To disable the fly when the player teleports out of the region
### Server Information
* **Server version/platform:** Paper 1.15.1
* **GriefPrevention Version:** 16.12.0-d4d7ac4
* **GriefPreventionFlags Version:** 5.7.0
### Additional Info
| non_priority | if a player tps away in a claim with fly flag they still have fly description if a player has a fly flag enabled in their region and they are flying and then tps to spawn they still have fly steps to reproduce create a claim add fly flag to it teleport away from claim while flying in the claim expected behavior to disable the fly when the player teleports out of the region server information server version platform paper griefprevention version griefpreventionflags version additional info | 0 |
87,064 | 8,057,984,936 | IssuesEvent | 2018-08-02 17:00:00 | blockstack/blockstack-core | https://api.github.com/repos/blockstack/blockstack-core | closed | Automate testing of Core on different supported OS | area/testing | We can use VMware Fusion or Virtualbox to test on macOS.
We should be testing on the latest masOS along with earlier versions like Mac OS X 10.10 (Yosemite), Mac OS X 10.9 (Mavericks), Mac OS X 10.8 (Mountain Lion), Mac OS X 10.7 (Lion).
| 1.0 | Automate testing of Core on different supported OS - We can use VMware Fusion or Virtualbox to test on macOS.
We should be testing on the latest masOS along with earlier versions like Mac OS X 10.10 (Yosemite), Mac OS X 10.9 (Mavericks), Mac OS X 10.8 (Mountain Lion), Mac OS X 10.7 (Lion).
| non_priority | automate testing of core on different supported os we can use vmware fusion or virtualbox to test on macos we should be testing on the latest masos along with earlier versions like mac os x yosemite mac os x mavericks mac os x mountain lion mac os x lion | 0 |
184,580 | 21,784,914,003 | IssuesEvent | 2022-05-14 01:47:13 | n-devs/freebitco.in-mobile | https://api.github.com/repos/n-devs/freebitco.in-mobile | closed | WS-2019-0331 (Medium) detected in handlebars-4.1.2.tgz - autoclosed | security vulnerability | ## WS-2019-0331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /freebitco.in-mobile/package.json</p>
<p>Path to vulnerable library: freebitco.in-mobile/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- jest-24.7.1.tgz
- jest-cli-24.8.0.tgz
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.6.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.2. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0331 (Medium) detected in handlebars-4.1.2.tgz - autoclosed - ## WS-2019-0331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /freebitco.in-mobile/package.json</p>
<p>Path to vulnerable library: freebitco.in-mobile/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- jest-24.7.1.tgz
- jest-cli-24.8.0.tgz
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.6.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.2. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in handlebars tgz autoclosed ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file freebitco in mobile package json path to vulnerable library freebitco in mobile node modules handlebars package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz core tgz reporters tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details arbitrary code execution vulnerability found in handlebars before lookup helper fails to validate templates attack may submit templates that execute arbitrary javascript in the system publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
279,468 | 21,161,673,435 | IssuesEvent | 2022-04-07 09:54:44 | karatelabs/karate | https://api.github.com/repos/karatelabs/karate | closed | Cluecumber report integration | documentation | Hello all,
would it be ok if I added instructions on how to add the Cluecumber reporting library for karate in this repository's readme? Or is there another dedicated documentation somewhere that I could contribute to?
Cluecumber is located here and is fully compatible with Karate's JSON format: https://github.com/trivago/cluecumber-report-plugin
* Here is a sample Karate test page: http://cluecumber.softwaretester.blog/pages/scenario-detail/scenario_5.html
* Here is one with docstrings: http://cluecumber.softwaretester.blog/pages/scenario-detail/scenario_13.html | 1.0 | Cluecumber report integration - Hello all,
would it be ok if I added instructions on how to add the Cluecumber reporting library for karate in this repository's readme? Or is there another dedicated documentation somewhere that I could contribute to?
Cluecumber is located here and is fully compatible with Karate's JSON format: https://github.com/trivago/cluecumber-report-plugin
* Here is a sample Karate test page: http://cluecumber.softwaretester.blog/pages/scenario-detail/scenario_5.html
* Here is one with docstrings: http://cluecumber.softwaretester.blog/pages/scenario-detail/scenario_13.html | non_priority | cluecumber report integration hello all would it be ok if i added instructions on how to add the cluecumber reporting library for karate in this repository s readme or is there another dedicated documentation somewhere that i could contribute to cluecumber is located here and is fully compatible with karate s json format here is a sample karate test page here is one with docstrings | 0 |
15,069 | 18,765,576,505 | IssuesEvent | 2021-11-05 23:15:01 | esmero/strawberryfield | https://api.github.com/repos/esmero/strawberryfield | closed | Add SOLR SBF Flavor Document removal when File gets removed | JSON Preprocessors Events and Subscriber Typed Data and Search | # What?
When we remove a file, old SBR documents could end being left in Solr. We may want to remove them automatically (using the Solr tracker) when a node and/or file gets removed.
- Different ways of removing depending if the Node is removed v/s a File from a Node
Important: Revision deletion triggers the same event as a full Node removal. Check that we do not remove everything if a revision is deleted. | 1.0 | Add SOLR SBF Flavor Document removal when File gets removed - # What?
When we remove a file, old SBR documents could end being left in Solr. We may want to remove them automatically (using the Solr tracker) when a node and/or file gets removed.
- Different ways of removing depending if the Node is removed v/s a File from a Node
Important: Revision deletion triggers the same event as a full Node removal. Check that we do not remove everything if a revision is deleted. | non_priority | add solr sbf flavor document removal when file gets removed what when we remove a file old sbr documents could end being left in solr we may want to remove them automatically using the solr tracker when a node and or file gets removed different ways of removing depending if the node is removed v s a file from a node important revision deletion triggers the same event as a full node removal check that we do not remove everything if a revision is deleted | 0 |
12,506 | 9,668,662,458 | IssuesEvent | 2019-05-21 15:34:36 | odoo/odoo | https://api.github.com/repos/odoo/odoo | closed | [12.0] hr_expense: Bad payment generation | 12.0 OE Services | Impacted versions:
12.0
Steps to reproduce:
1. Create a new expense with any values but paid by the company (in the same company currency)
2. Generate the sheet, and process it to generate the entries.
3. Search the payment for the expense
Current behavior:
The payment is generated by $0.00
Expected behavior:
The payment is by the expense total
Video/Screenshot link (optional):
https://www.youtube.com/watch?v=meeXd8f2w6s
| 1.0 | [12.0] hr_expense: Bad payment generation - Impacted versions:
12.0
Steps to reproduce:
1. Create a new expense with any values but paid by the company (in the same company currency)
2. Generate the sheet, and process it to generate the entries.
3. Search the payment for the expense
Current behavior:
The payment is generated by $0.00
Expected behavior:
The payment is by the expense total
Video/Screenshot link (optional):
https://www.youtube.com/watch?v=meeXd8f2w6s
| non_priority | hr expense bad payment generation impacted versions steps to reproduce create a new expense with any values but paid by the company in the same company currency generate the sheet and process it to generate the entries search the payment for the expense current behavior the payment is generated by expected behavior the payment is by the expense total video screenshot link optional | 0 |
370,444 | 25,907,471,559 | IssuesEvent | 2022-12-15 11:22:09 | fga-eps-mds/2022-2-Certifik8 | https://api.github.com/repos/fga-eps-mds/2022-2-Certifik8 | closed | Criar a Release 1 | documentation release_1 | # Descrição
Fazer o lançamento da 1° Release
# Tarefas
Aba responsável por inserir as demandas desta issue.
- [x] Lançar a Release 1.
- [x] Criar documento da Release 1.
# Critérios de Aceitação
- [x] Ambas tarefas concluídas.
| 1.0 | Criar a Release 1 - # Descrição
Fazer o lançamento da 1° Release
# Tarefas
Aba responsável por inserir as demandas desta issue.
- [x] Lançar a Release 1.
- [x] Criar documento da Release 1.
# Critérios de Aceitação
- [x] Ambas tarefas concluídas.
| non_priority | criar a release descrição fazer o lançamento da ° release tarefas aba responsável por inserir as demandas desta issue lançar a release criar documento da release critérios de aceitação ambas tarefas concluídas | 0 |
48,756 | 25,797,695,406 | IssuesEvent | 2022-12-10 18:26:24 | LiUSemWeb/HeFQUIN | https://api.github.com/repos/LiUSemWeb/HeFQUIN | closed | Add logical rewriting to merge identical subplans | good first issue performance improvement | Consider a query with a union over two joins where one the arguments of one of the joins is identical to an argument of the other join. These identical arguments may be represented using different Java objects. The purpose of this issue is to identify such cases and replace one of the Java objects by the other Java object (i.e., use only one of the Java objects for both arguments). That way, in our push-based execution we would have only one executable subplan for the arguments and the output of that subplan is fed as input to both joins. This avoids doing the same thing twice, which will be useful in particular if the subplan consists of more than just a request operator. | True | Add logical rewriting to merge identical subplans - Consider a query with a union over two joins where one the arguments of one of the joins is identical to an argument of the other join. These identical arguments may be represented using different Java objects. The purpose of this issue is to identify such cases and replace one of the Java objects by the other Java object (i.e., use only one of the Java objects for both arguments). That way, in our push-based execution we would have only one executable subplan for the arguments and the output of that subplan is fed as input to both joins. This avoids doing the same thing twice, which will be useful in particular if the subplan consists of more than just a request operator. | non_priority | add logical rewriting to merge identical subplans consider a query with a union over two joins where one the arguments of one of the joins is identical to an argument of the other join these identical arguments may be represented using different java objects the purpose of this issue is to identify such cases and replace one of the java objects by the other java object i e use only one of the java objects for both arguments that way in our push based execution we would have only one executable subplan for the arguments and the output of that subplan is fed as input to both joins this avoids doing the same thing twice which will be useful in particular if the subplan consists of more than just a request operator | 0 |
22,535 | 3,788,904,170 | IssuesEvent | 2016-03-21 16:09:11 | sperez8/Phet-log-analyzer | https://api.github.com/repos/sperez8/Phet-log-analyzer | closed | Propose a design for heatmaps | design sotl | Including:
- a design that matches the sankey
- a color scheme that maintains comparability of values across hues
- better labels
-a higlight effect
| 1.0 | Propose a design for heatmaps - Including:
- a design that matches the sankey
- a color scheme that maintains comparability of values across hues
- better labels
-a higlight effect
| non_priority | propose a design for heatmaps including a design that matches the sankey a color scheme that maintains comparability of values across hues better labels a higlight effect | 0 |
45,300 | 5,921,165,376 | IssuesEvent | 2017-05-22 22:12:16 | azavea/pfb-network-connectivity | https://api.github.com/repos/azavea/pfb-network-connectivity | closed | Add images to "How BNA score is calculated" section on homepage | Design in progress | Or not, depending on how difficult it is to find appropriate images. If we don't do images, remove the HTML placeholders. | 1.0 | Add images to "How BNA score is calculated" section on homepage - Or not, depending on how difficult it is to find appropriate images. If we don't do images, remove the HTML placeholders. | non_priority | add images to how bna score is calculated section on homepage or not depending on how difficult it is to find appropriate images if we don t do images remove the html placeholders | 0 |
71,885 | 18,910,599,858 | IssuesEvent | 2021-11-16 13:46:08 | JuliaGPU/AMDGPU.jl | https://api.github.com/repos/JuliaGPU/AMDGPU.jl | closed | No warning when we fail to find ld.lld, and general build observability | bug build | We don't have any idea that it was `ld.lld` that we failed to find. Also, generally, it would be nice if we could expose more information about *why* the various build steps failed. | 1.0 | No warning when we fail to find ld.lld, and general build observability - We don't have any idea that it was `ld.lld` that we failed to find. Also, generally, it would be nice if we could expose more information about *why* the various build steps failed. | non_priority | no warning when we fail to find ld lld and general build observability we don t have any idea that it was ld lld that we failed to find also generally it would be nice if we could expose more information about why the various build steps failed | 0 |
57,354 | 15,731,358,336 | IssuesEvent | 2021-03-29 16:58:41 | danmar/testissues | https://api.github.com/repos/danmar/testissues | opened | Assign auto variable to parameter false positive (Trac #370) | False positive Incomplete Migration Migrated from Trac defect hyd_danmar | Migrated from https://trac.cppcheck.net/ticket/370
```json
{
"status": "closed",
"changetime": "2009-06-06T19:27:00",
"description": "[c0der@rock ~/samba]$ ~/cppcheck/cppcheck rpc.c -q\n[rpc.c:20]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n[rpc.c:21]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n[rpc.c:23]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n[rpc.c:24]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n\nBut I not see something wrong in this code.\nrpc.c will be attached.\n\nFound during scan Samba sources.",
"reporter": "php-coderrr",
"cc": "",
"resolution": "fixed",
"_ts": "1244316420000000",
"component": "False positive",
"summary": "Assign auto variable to parameter false positive",
"priority": "",
"keywords": "",
"time": "2009-06-06T17:21:11",
"milestone": "1.33",
"owner": "hyd_danmar",
"type": "defect"
}
```
| 1.0 | Assign auto variable to parameter false positive (Trac #370) - Migrated from https://trac.cppcheck.net/ticket/370
```json
{
"status": "closed",
"changetime": "2009-06-06T19:27:00",
"description": "[c0der@rock ~/samba]$ ~/cppcheck/cppcheck rpc.c -q\n[rpc.c:20]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n[rpc.c:21]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n[rpc.c:23]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n[rpc.c:24]: (error) Wrong assignement of an auto-variable to an effective parameter of a function\n\nBut I not see something wrong in this code.\nrpc.c will be attached.\n\nFound during scan Samba sources.",
"reporter": "php-coderrr",
"cc": "",
"resolution": "fixed",
"_ts": "1244316420000000",
"component": "False positive",
"summary": "Assign auto variable to parameter false positive",
"priority": "",
"keywords": "",
"time": "2009-06-06T17:21:11",
"milestone": "1.33",
"owner": "hyd_danmar",
"type": "defect"
}
```
| non_priority | assign auto variable to parameter false positive trac migrated from json status closed changetime description cppcheck cppcheck rpc c q n error wrong assignement of an auto variable to an effective parameter of a function n error wrong assignement of an auto variable to an effective parameter of a function n error wrong assignement of an auto variable to an effective parameter of a function n error wrong assignement of an auto variable to an effective parameter of a function n nbut i not see something wrong in this code nrpc c will be attached n nfound during scan samba sources reporter php coderrr cc resolution fixed ts component false positive summary assign auto variable to parameter false positive priority keywords time milestone owner hyd danmar type defect | 0 |
225,676 | 17,873,790,498 | IssuesEvent | 2021-09-06 21:24:08 | sqlalchemy/sqlalchemy | https://api.github.com/repos/sqlalchemy/sqlalchemy | closed | Tests seem not to catch failures in `test/ext/asincio` | bug tests asyncio | ### Describe the bug
The current master https://github.com/sqlalchemy/sqlalchemy/commit/184e2da5992c55266b37bab5ce3a07e9dfb8caa1
fails a test in `test/ext/asyncio/test_session_py3k.py`:
`FAILED test/ext/asyncio/test_session_py3k.py::OverrideSyncSession::test_init_class - AttributeError: 'AsyncSession' object attribute 'sync_session_class' is read-only`
Looking at the error the current implementation is incompatible with `__slots__` in the `AsyncSession` class.
>
### To Reproduce
```python
pytest --db aiosqlite .\test\ext\asyncio\
```
### Error
FAILED test/ext/asyncio/test_session_py3k.py::OverrideSyncSession::test_init_class - AttributeError: 'AsyncSession' object attribute 'sync_session_class' is read-only
### Versions
- SQLAlchemy: 184e2da5992c55266b37bab5ce3a07e9dfb8caa1
### Additional context
_No response_ | 1.0 | Tests seem not to catch failures in `test/ext/asincio` - ### Describe the bug
The current master https://github.com/sqlalchemy/sqlalchemy/commit/184e2da5992c55266b37bab5ce3a07e9dfb8caa1
fails a test in `test/ext/asyncio/test_session_py3k.py`:
`FAILED test/ext/asyncio/test_session_py3k.py::OverrideSyncSession::test_init_class - AttributeError: 'AsyncSession' object attribute 'sync_session_class' is read-only`
Looking at the error the current implementation is incompatible with `__slots__` in the `AsyncSession` class.
>
### To Reproduce
```python
pytest --db aiosqlite .\test\ext\asyncio\
```
### Error
FAILED test/ext/asyncio/test_session_py3k.py::OverrideSyncSession::test_init_class - AttributeError: 'AsyncSession' object attribute 'sync_session_class' is read-only
### Versions
- SQLAlchemy: 184e2da5992c55266b37bab5ce3a07e9dfb8caa1
### Additional context
_No response_ | non_priority | tests seem not to catch failures in test ext asincio describe the bug the current master fails a test in test ext asyncio test session py failed test ext asyncio test session py overridesyncsession test init class attributeerror asyncsession object attribute sync session class is read only looking at the error the current implementation is incompatible with slots in the asyncsession class to reproduce python pytest db aiosqlite test ext asyncio error failed test ext asyncio test session py overridesyncsession test init class attributeerror asyncsession object attribute sync session class is read only versions sqlalchemy additional context no response | 0 |
81,812 | 23,580,949,454 | IssuesEvent | 2022-08-23 07:37:20 | spatial-model-editor/spatial-model-editor | https://api.github.com/repos/spatial-model-editor/spatial-model-editor | closed | win32 tests segfault | bug build system python | As part of #736 it turns out the win32 tests fail (we don't have a win32 build other than for python wheels, so never actually ran these tests on this platform before, only the python ones)
Seems to occur when symengine tries to call a llvm-compiled expression involving functions (i.e. cos, sin in the failing test case)
See [win32](https://github.com/spatial-model-editor/spatial-model-editor/tree/win32debug) branch to reproduce issue:
```
D:/a/spatial-model-editor/spatial-model-editor/src/core/common/src/symbolic_t.cpp:190: PASSED:
REQUIRE( sym.isCompiled() == true )
with expansion:
true == true
with message:
expr := { "3*x + 4/y - 1.0*x + 0.2*x*y - 0.1", "z - cos(x)*sin(y) - x*y" }
Error: Process completed with exit code 1.
```
Best solution for now might be to simply stop building 32-bit windows wheels, as windows users are mostly using anaconda i.e. 64-bit python anyway, and re-visit this if there is a user who really needs 32-bit wheels. | 1.0 | win32 tests segfault - As part of #736 it turns out the win32 tests fail (we don't have a win32 build other than for python wheels, so never actually ran these tests on this platform before, only the python ones)
Seems to occur when symengine tries to call a llvm-compiled expression involving functions (i.e. cos, sin in the failing test case)
See [win32](https://github.com/spatial-model-editor/spatial-model-editor/tree/win32debug) branch to reproduce issue:
```
D:/a/spatial-model-editor/spatial-model-editor/src/core/common/src/symbolic_t.cpp:190: PASSED:
REQUIRE( sym.isCompiled() == true )
with expansion:
true == true
with message:
expr := { "3*x + 4/y - 1.0*x + 0.2*x*y - 0.1", "z - cos(x)*sin(y) - x*y" }
Error: Process completed with exit code 1.
```
Best solution for now might be to simply stop building 32-bit windows wheels, as windows users are mostly using anaconda i.e. 64-bit python anyway, and re-visit this if there is a user who really needs 32-bit wheels. | non_priority | tests segfault as part of it turns out the tests fail we don t have a build other than for python wheels so never actually ran these tests on this platform before only the python ones seems to occur when symengine tries to call a llvm compiled expression involving functions i e cos sin in the failing test case see branch to reproduce issue d a spatial model editor spatial model editor src core common src symbolic t cpp passed require sym iscompiled true with expansion true true with message expr x y x x y z cos x sin y x y error process completed with exit code best solution for now might be to simply stop building bit windows wheels as windows users are mostly using anaconda i e bit python anyway and re visit this if there is a user who really needs bit wheels | 0 |
69,271 | 9,285,325,153 | IssuesEvent | 2019-03-21 06:35:22 | sylabs/singularity | https://api.github.com/repos/sylabs/singularity | opened | refactor singularity help cache clean text | Documentation | ## Version of Singularity:
3.0.1
* `Clean your local Singularity cache`
changed to: `Remove items from the Singularity cache`
* Description
change to:
<pre>
Remove blob, library, and oci items from the cache. By default only the blob items will be removed from the cache unless the --all option is used.
</pre>
* `clean all cache (will overide all other options)`
change to: `Remove all items from the cache (overrides all other options)`
* `specify a container cache to clean (will clear all
cache with the same name)`
change to: `Remove all items from the cache associated with a named image`
Does that cover it all plus the warning?
* `clean cache type, choose between: library, oci, and
blob (default [blob])`
change to: `Remove specific items from the cache (Default: 'blob')` | 1.0 | refactor singularity help cache clean text - ## Version of Singularity:
3.0.1
* `Clean your local Singularity cache`
changed to: `Remove items from the Singularity cache`
* Description
change to:
<pre>
Remove blob, library, and oci items from the cache. By default only the blob items will be removed from the cache unless the --all option is used.
</pre>
* `clean all cache (will overide all other options)`
change to: `Remove all items from the cache (overrides all other options)`
* `specify a container cache to clean (will clear all
cache with the same name)`
change to: `Remove all items from the cache associated with a named image`
Does that cover it all plus the warning?
* `clean cache type, choose between: library, oci, and
blob (default [blob])`
change to: `Remove specific items from the cache (Default: 'blob')` | non_priority | refactor singularity help cache clean text version of singularity clean your local singularity cache changed to remove items from the singularity cache description change to remove blob library and oci items from the cache by default only the blob items will be removed from the cache unless the all option is used clean all cache will overide all other options change to remove all items from the cache overrides all other options specify a container cache to clean will clear all cache with the same name change to remove all items from the cache associated with a named image does that cover it all plus the warning clean cache type choose between library oci and blob default change to remove specific items from the cache default blob | 0 |
229,880 | 25,387,204,947 | IssuesEvent | 2022-11-21 23:08:01 | UpendoVentures/generator-upendodnn | https://api.github.com/repos/UpendoVentures/generator-upendodnn | closed | CVE-2022-21681 (High) detected in marked-0.8.2.tgz - autoclosed | security vulnerability | ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.8.2.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.8.2.tgz">https://registry.npmjs.org/marked/-/marked-0.8.2.tgz</a></p>
<p>Path to dependency file: /generators/mvc-spa/templates/package.json</p>
<p>Path to vulnerable library: /generators/mvc-spa/templates/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.8.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/UpendoVentures/generator-upendodnn/commit/1c68c9a9ea9734a0a208d80999c86ff1564255dc">1c68c9a9ea9734a0a208d80999c86ff1564255dc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Marked is a markdown parser and compiler. Prior to version 4.0.10, the regular expression `inline.reflinkSearch` may cause catastrophic backtracking against some strings and lead to a denial of service (DoS). Anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected. This issue is patched in version 4.0.10. As a workaround, avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-21681>CVE-2022-21681</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5v2h-r2cx-5xgj">https://github.com/advisories/GHSA-5v2h-r2cx-5xgj</a></p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution: 4.0.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-21681 (High) detected in marked-0.8.2.tgz - autoclosed - ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.8.2.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.8.2.tgz">https://registry.npmjs.org/marked/-/marked-0.8.2.tgz</a></p>
<p>Path to dependency file: /generators/mvc-spa/templates/package.json</p>
<p>Path to vulnerable library: /generators/mvc-spa/templates/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.8.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/UpendoVentures/generator-upendodnn/commit/1c68c9a9ea9734a0a208d80999c86ff1564255dc">1c68c9a9ea9734a0a208d80999c86ff1564255dc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Marked is a markdown parser and compiler. Prior to version 4.0.10, the regular expression `inline.reflinkSearch` may cause catastrophic backtracking against some strings and lead to a denial of service (DoS). Anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected. This issue is patched in version 4.0.10. As a workaround, avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-21681>CVE-2022-21681</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5v2h-r2cx-5xgj">https://github.com/advisories/GHSA-5v2h-r2cx-5xgj</a></p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution: 4.0.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in marked tgz autoclosed cve high severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file generators mvc spa templates package json path to vulnerable library generators mvc spa templates node modules marked package json dependency hierarchy x marked tgz vulnerable library found in head commit a href found in base branch master vulnerability details marked is a markdown parser and compiler prior to version the regular expression inline reflinksearch may cause catastrophic backtracking against some strings and lead to a denial of service dos anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected this issue is patched in version as a workaround avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
261,002 | 19,694,030,335 | IssuesEvent | 2022-01-12 10:13:42 | vaadin/web-components | https://api.github.com/repos/vaadin/web-components | closed | [lumo] Shadows aren't visible in dark mode | bug documentation theme | ### Description
Shadows (e.g. utility classes or direct usage --lumo-box-shadow-m) aren't visible in dark mode.
### Expected outcome
Shadows are visible even in dark mode
### Actual outcome
Shadows aren't visible
### Live demo (optional)
https://vaadin.com/docs/latest/ds/foundation/utility-classes/#box-shadow
Light:
Dark:
### Environment
v23.0-alpha1
### Browsers affected
- Only tested with Firefox | 1.0 | [lumo] Shadows aren't visible in dark mode - ### Description
Shadows (e.g. utility classes or direct usage --lumo-box-shadow-m) aren't visible in dark mode.
### Expected outcome
Shadows are visible even in dark mode
### Actual outcome
Shadows aren't visible
### Live demo (optional)
https://vaadin.com/docs/latest/ds/foundation/utility-classes/#box-shadow
Light:
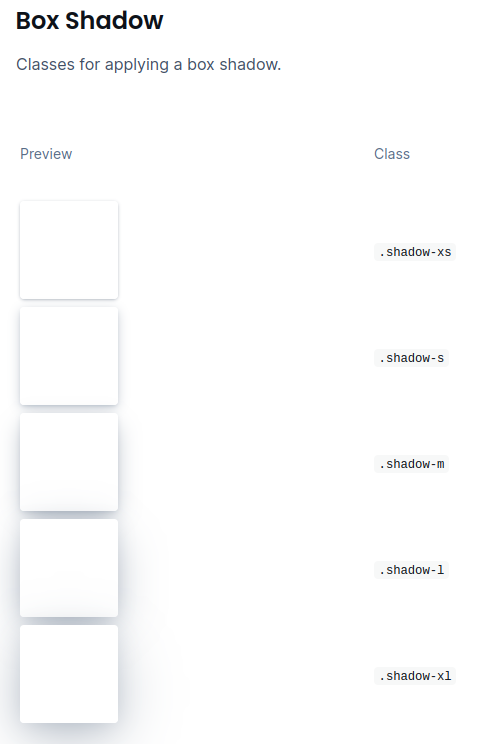
Dark:
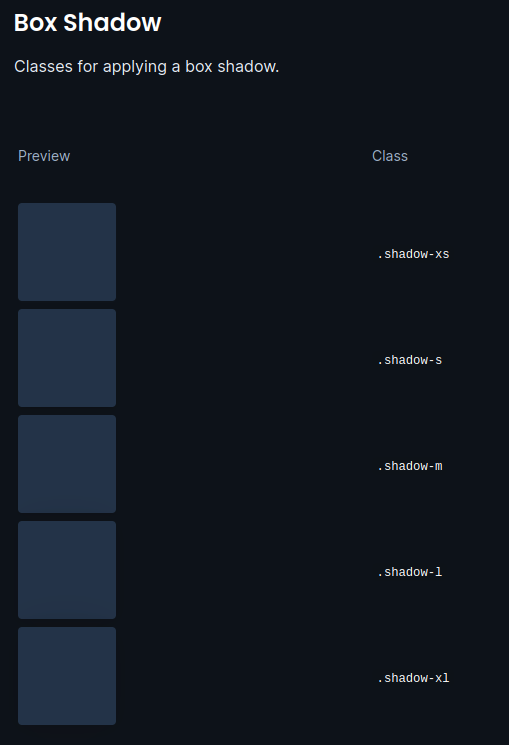
### Environment
v23.0-alpha1
### Browsers affected
- Only tested with Firefox | non_priority | shadows aren t visible in dark mode description shadows e g utility classes or direct usage lumo box shadow m aren t visible in dark mode expected outcome shadows are visible even in dark mode actual outcome shadows aren t visible live demo optional light dark environment browsers affected only tested with firefox | 0 |
118,251 | 11,964,969,155 | IssuesEvent | 2020-04-05 21:32:49 | tot-developers/tot-tse-api | https://api.github.com/repos/tot-developers/tot-tse-api | opened | Atualizar README para próxima entrega | documentation good first issue | Sincronizar o conteúdo do README.md para bater com as features implementadas pra a próxima entrega. | 1.0 | Atualizar README para próxima entrega - Sincronizar o conteúdo do README.md para bater com as features implementadas pra a próxima entrega. | non_priority | atualizar readme para próxima entrega sincronizar o conteúdo do readme md para bater com as features implementadas pra a próxima entrega | 0 |
435,162 | 30,488,897,635 | IssuesEvent | 2023-07-18 06:02:47 | ElektraInitiative/PermaplanT | https://api.github.com/repos/ElektraInitiative/PermaplanT | closed | doc/backend/01setup.md doesn't work | bug documentation urgent | <!--
Please remove this template if you have
a question and do not want
to report a bug.
-->
## Steps to Reproduce the Problem
- checkout master
- run migrations
- build backend
<!--
Please provide a step by step guide on how to reproduce the problem here.
-->
## Expected Result
backend starts
<!--
Please describe what should happen if you follow the steps described above.
-->
## Actual Result
latest migration can't be executed
<!--
Please describe what actually happened.
-->
## System Information
- PermaplanT: master
- Operating System: Linux
<!--
- Versions of other relevant software?
-->
## Further Log Files and Output
<!--
Please add further information here.
-->
To fix this I installed the postgis package
and executed the content of the latest migration manually with the postgres user:
CREATE EXTENSION IF NOT EXISTS postgis;
The problem seems to be that the permaplant user doesn't have the correct privileges to install the extension.
Please change the documentation to match the new installation process and fix the issue with the missing privileges. | 1.0 | doc/backend/01setup.md doesn't work - <!--
Please remove this template if you have
a question and do not want
to report a bug.
-->
## Steps to Reproduce the Problem
- checkout master
- run migrations
- build backend
<!--
Please provide a step by step guide on how to reproduce the problem here.
-->
## Expected Result
backend starts
<!--
Please describe what should happen if you follow the steps described above.
-->
## Actual Result
latest migration can't be executed
<!--
Please describe what actually happened.
-->
## System Information
- PermaplanT: master
- Operating System: Linux
<!--
- Versions of other relevant software?
-->
## Further Log Files and Output
<!--
Please add further information here.
-->
To fix this I installed the postgis package
and executed the content of the latest migration manually with the postgres user:
CREATE EXTENSION IF NOT EXISTS postgis;
The problem seems to be that the permaplant user doesn't have the correct privileges to install the extension.
Please change the documentation to match the new installation process and fix the issue with the missing privileges. | non_priority | doc backend md doesn t work please remove this template if you have a question and do not want to report a bug steps to reproduce the problem checkout master run migrations build backend please provide a step by step guide on how to reproduce the problem here expected result backend starts please describe what should happen if you follow the steps described above actual result latest migration can t be executed please describe what actually happened system information permaplant master operating system linux versions of other relevant software further log files and output please add further information here to fix this i installed the postgis package and executed the content of the latest migration manually with the postgres user create extension if not exists postgis the problem seems to be that the permaplant user doesn t have the correct privileges to install the extension please change the documentation to match the new installation process and fix the issue with the missing privileges | 0 |
58,198 | 14,342,037,192 | IssuesEvent | 2020-11-28 00:47:44 | mtgred/netrunner | https://api.github.com/repos/mtgred/netrunner | closed | Core Experience deck checker does not check for card counts. | bug deckbuilder | For example, I've been able to put 3 Hostile Takeovers into a deck, even though core experience should allow for only 2 | 1.0 | Core Experience deck checker does not check for card counts. - For example, I've been able to put 3 Hostile Takeovers into a deck, even though core experience should allow for only 2 | non_priority | core experience deck checker does not check for card counts for example i ve been able to put hostile takeovers into a deck even though core experience should allow for only | 0 |
58,288 | 16,472,802,523 | IssuesEvent | 2021-05-23 18:58:03 | secureCodeBox/secureCodeBox | https://api.github.com/repos/secureCodeBox/secureCodeBox | closed | 🕸 Extend the Cascading-Scans Hook to generate custom labels or annotations for subsequent scans | defectdojo enhancement hook | ## ➹ New Feature request
<!--
Thank you for reporting an issue in our documentation 🙌
Before opening a new issue, please make sure that we do not have any duplicates already open. You can ensure this by searching the issue list for this repository. If there is a duplicate, please close your issue and add a comment to the existing issue instead.
-->
### Is your feature request related to a problem?
<!-- Please describe a clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
As a secureCodeBox user i would like to use the [cascading rules](https://docs.securecodebox.io/docs/hooks/cascading-scans) in combination with the [**DefectDojo-Persistence Hook**](https://docs.securecodebox.io/docs/hooks/defectdojo) to examine all results efficiently in [OWASP DefectDojo](https://github.com/DefectDojo/django-DefectDojo) (DD).
Imagine a SCB NMAP `scheduledScan` setup for a company with a large network in combination with cascading rules. This results in hundreds or even thousands of subsequent scans started by the [cascading scans hook](https://docs.securecodebox.io/docs/hooks/cascading-scans).
```yaml
apiVersion: execution.securecodebox.io/v1
kind: ScheduledScan
metadata:
name: nmap-large-network-scan
namespace: demo-scans
labels:
organization: "OWASP"
location: barcelona
vlan: lan
spec:
interval: 24h
successfulJobsHistoryLimit: 1
failedJobsHistoryLimit: 1
scanSpec:
scanType: "nmap"
parameters:
- "-T4"
- "-sV"
- "--version-intensity"
- "4"
- "192.168.0.1/24"
cascades:
matchLabels:
# Uses all CascadingRules in the namespace which are labelled as "non-invasive" and a intensiveness level of "light"
securecodebox.io/invasive: non-invasive
securecodebox.io/intensive: light
```
This works really nicely in combination with an [elasticsearch backend](https://docs.securecodebox.io/docs/hooks/elasticsearch).
But trying to do something similar in OWASP DefectDojo would result in hundreds or even thousands DefectDojo products for _each successful subsequent scan_. The name of each imported DefectDojo `Product` would be the generated `scan` name like `ssh-scan-demo-lan-1616202292-ssh-scan-tc754`. To prevent this it is necessary to add some [DefectDojo-Hook specific annotation](https://docs.securecodebox.io/docs/hooks/defectdojo#complete-example-scan) to each _subsequent scan_ to relate them to the correct DefectDojo `Product` or `Engagement` name.
Problem is 🧐: currently this is not possible to configure within the `cascading rules` or a `scan`. But it would be very helpful 😆
There is already a function implemented in the *cascading hook* which ensures that all `parent scan` labels are copied to all subsequent scans:
https://github.com/secureCodeBox/secureCodeBox/blob/0257ddaa07540381d3a056a7cc7b7fc740926f43/hooks/declarative-subsequent-scans/scan-helpers.ts#L79-L90
### Describe the solution you'd like
<!-- A clear and concise description of what you want to happen. -->
It should be possible to define and copy custom labels and annotations for each subsequent scan. There are different scenarios to take into account:
1) Copy all `labels` and `annotations` from the `parent scan` to every `subsequent scan`
2) Generate new labels and annotations based on a lightweight template syntax and the given `parent scan` or `findings` data.
#### Examples
`ScheduledScan` NMAP Definition Example:
```yaml
apiVersion: execution.securecodebox.io/v1
kind: ScheduledScan
metadata:
name: nmap-large-network-scan
namespace: demo-scans
annotations:
defectdojo.securecodebox.io/product-name: "barcelona-network-scan"
defectdojo.securecodebox.io/product-type-name: "OWASP"
defectdojo.securecodebox.io/product-tags: vulnerable,appsec,network
defectdojo.securecodebox.io/engagement-name: "scb-automated-scan"
defectdojo.securecodebox.io/engagement-tags: "automated,daily"
labels:
organization: "OWASP"
location: barcelona
vlan: lan
spec:
interval: 24h
successfulJobsHistoryLimit: 1
failedJobsHistoryLimit: 1
scanSpec:
scanType: "nmap"
parameters:
- "-T4"
- "-sV"
- "192.168.0.1/24"
cascades:
# True if all scan (parent) labels are copied to each subsequent scan (child), otherwise false. Default: true
inheritLabels: true
# True if all scan (parent) annotations are copied to each subsequent scan (child), otherwise false. Default: true
inheritAnnotations: true
# Uses all CascadingRules in the namespace which are labelled as "non-invasive" and a intensiveness level of "light"
matchLabels:
securecodebox.io/invasive: non-invasive
securecodebox.io/intensive: light
```
OWASP ZAP Cascading Rule Example
```yaml
apiVersion: "cascading.securecodebox.io/v1"
kind: CascadingRule
metadata:
name: "zap-http"
labels:
securecodebox.io/invasive: non-invasive
securecodebox.io/intensive: medium
spec:
matches:
anyOf:
- category: "Open Port"
attributes:
service: http
state: open
- category: "Open Port"
attributes:
service: https
state: open
# Configures additional label added to each subsequent scan (child)
scanLabels:
mynewlabel: {{$.metadata.name}}
# Configures additional annotation added to each subsequent scan (child)
scanAnnotations:
defectdojo.securecodebox.io/product-name: "{{$.hostOrIP}}"
defectdojo.securecodebox.io/product-type-name: "{{$.metadata.labels.organization}}"
defectdojo.securecodebox.io/product-tags: vulnerable,appsec,owasp-top-ten,vulnapp
defectdojo.securecodebox.io/engagement-name: "{{$.hostOrIP}}"
scanSpec:
scanType: "zap-baseline"
parameters: ["-t", "{{attributes.service}}://{{$.hostOrIP}}"]
```
### Describe alternatives you've considered
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
### Additional context
<!-- Add any other context or screenshots about the feature request here. -->
| 1.0 | 🕸 Extend the Cascading-Scans Hook to generate custom labels or annotations for subsequent scans - ## ➹ New Feature request
<!--
Thank you for reporting an issue in our documentation 🙌
Before opening a new issue, please make sure that we do not have any duplicates already open. You can ensure this by searching the issue list for this repository. If there is a duplicate, please close your issue and add a comment to the existing issue instead.
-->
### Is your feature request related to a problem?
<!-- Please describe a clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
As a secureCodeBox user i would like to use the [cascading rules](https://docs.securecodebox.io/docs/hooks/cascading-scans) in combination with the [**DefectDojo-Persistence Hook**](https://docs.securecodebox.io/docs/hooks/defectdojo) to examine all results efficiently in [OWASP DefectDojo](https://github.com/DefectDojo/django-DefectDojo) (DD).
Imagine a SCB NMAP `scheduledScan` setup for a company with a large network in combination with cascading rules. This results in hundreds or even thousands of subsequent scans started by the [cascading scans hook](https://docs.securecodebox.io/docs/hooks/cascading-scans).
```yaml
apiVersion: execution.securecodebox.io/v1
kind: ScheduledScan
metadata:
name: nmap-large-network-scan
namespace: demo-scans
labels:
organization: "OWASP"
location: barcelona
vlan: lan
spec:
interval: 24h
successfulJobsHistoryLimit: 1
failedJobsHistoryLimit: 1
scanSpec:
scanType: "nmap"
parameters:
- "-T4"
- "-sV"
- "--version-intensity"
- "4"
- "192.168.0.1/24"
cascades:
matchLabels:
# Uses all CascadingRules in the namespace which are labelled as "non-invasive" and a intensiveness level of "light"
securecodebox.io/invasive: non-invasive
securecodebox.io/intensive: light
```
This works really nicely in combination with an [elasticsearch backend](https://docs.securecodebox.io/docs/hooks/elasticsearch).
But trying to do something similar in OWASP DefectDojo would result in hundreds or even thousands DefectDojo products for _each successful subsequent scan_. The name of each imported DefectDojo `Product` would be the generated `scan` name like `ssh-scan-demo-lan-1616202292-ssh-scan-tc754`. To prevent this it is necessary to add some [DefectDojo-Hook specific annotation](https://docs.securecodebox.io/docs/hooks/defectdojo#complete-example-scan) to each _subsequent scan_ to relate them to the correct DefectDojo `Product` or `Engagement` name.
Problem is 🧐: currently this is not possible to configure within the `cascading rules` or a `scan`. But it would be very helpful 😆
There is already a function implemented in the *cascading hook* which ensures that all `parent scan` labels are copied to all subsequent scans:
https://github.com/secureCodeBox/secureCodeBox/blob/0257ddaa07540381d3a056a7cc7b7fc740926f43/hooks/declarative-subsequent-scans/scan-helpers.ts#L79-L90
### Describe the solution you'd like
<!-- A clear and concise description of what you want to happen. -->
It should be possible to define and copy custom labels and annotations for each subsequent scan. There are different scenarios to take into account:
1) Copy all `labels` and `annotations` from the `parent scan` to every `subsequent scan`
2) Generate new labels and annotations based on a lightweight template syntax and the given `parent scan` or `findings` data.
#### Examples
`ScheduledScan` NMAP Definition Example:
```yaml
apiVersion: execution.securecodebox.io/v1
kind: ScheduledScan
metadata:
name: nmap-large-network-scan
namespace: demo-scans
annotations:
defectdojo.securecodebox.io/product-name: "barcelona-network-scan"
defectdojo.securecodebox.io/product-type-name: "OWASP"
defectdojo.securecodebox.io/product-tags: vulnerable,appsec,network
defectdojo.securecodebox.io/engagement-name: "scb-automated-scan"
defectdojo.securecodebox.io/engagement-tags: "automated,daily"
labels:
organization: "OWASP"
location: barcelona
vlan: lan
spec:
interval: 24h
successfulJobsHistoryLimit: 1
failedJobsHistoryLimit: 1
scanSpec:
scanType: "nmap"
parameters:
- "-T4"
- "-sV"
- "192.168.0.1/24"
cascades:
# True if all scan (parent) labels are copied to each subsequent scan (child), otherwise false. Default: true
inheritLabels: true
# True if all scan (parent) annotations are copied to each subsequent scan (child), otherwise false. Default: true
inheritAnnotations: true
# Uses all CascadingRules in the namespace which are labelled as "non-invasive" and a intensiveness level of "light"
matchLabels:
securecodebox.io/invasive: non-invasive
securecodebox.io/intensive: light
```
OWASP ZAP Cascading Rule Example
```yaml
apiVersion: "cascading.securecodebox.io/v1"
kind: CascadingRule
metadata:
name: "zap-http"
labels:
securecodebox.io/invasive: non-invasive
securecodebox.io/intensive: medium
spec:
matches:
anyOf:
- category: "Open Port"
attributes:
service: http
state: open
- category: "Open Port"
attributes:
service: https
state: open
# Configures additional label added to each subsequent scan (child)
scanLabels:
mynewlabel: {{$.metadata.name}}
# Configures additional annotation added to each subsequent scan (child)
scanAnnotations:
defectdojo.securecodebox.io/product-name: "{{$.hostOrIP}}"
defectdojo.securecodebox.io/product-type-name: "{{$.metadata.labels.organization}}"
defectdojo.securecodebox.io/product-tags: vulnerable,appsec,owasp-top-ten,vulnapp
defectdojo.securecodebox.io/engagement-name: "{{$.hostOrIP}}"
scanSpec:
scanType: "zap-baseline"
parameters: ["-t", "{{attributes.service}}://{{$.hostOrIP}}"]
```
### Describe alternatives you've considered
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
### Additional context
<!-- Add any other context or screenshots about the feature request here. -->
| non_priority | 🕸 extend the cascading scans hook to generate custom labels or annotations for subsequent scans ➹ new feature request thank you for reporting an issue in our documentation 🙌 before opening a new issue please make sure that we do not have any duplicates already open you can ensure this by searching the issue list for this repository if there is a duplicate please close your issue and add a comment to the existing issue instead is your feature request related to a problem as a securecodebox user i would like to use the in combination with the to examine all results efficiently in dd imagine a scb nmap scheduledscan setup for a company with a large network in combination with cascading rules this results in hundreds or even thousands of subsequent scans started by the yaml apiversion execution securecodebox io kind scheduledscan metadata name nmap large network scan namespace demo scans labels organization owasp location barcelona vlan lan spec interval successfuljobshistorylimit failedjobshistorylimit scanspec scantype nmap parameters sv version intensity cascades matchlabels uses all cascadingrules in the namespace which are labelled as non invasive and a intensiveness level of light securecodebox io invasive non invasive securecodebox io intensive light this works really nicely in combination with an but trying to do something similar in owasp defectdojo would result in hundreds or even thousands defectdojo products for each successful subsequent scan the name of each imported defectdojo product would be the generated scan name like ssh scan demo lan ssh scan to prevent this it is necessary to add some to each subsequent scan to relate them to the correct defectdojo product or engagement name problem is 🧐 currently this is not possible to configure within the cascading rules or a scan but it would be very helpful 😆 there is already a function implemented in the cascading hook which ensures that all parent scan labels are copied to all subsequent scans describe the solution you d like it should be possible to define and copy custom labels and annotations for each subsequent scan there are different scenarios to take into account copy all labels and annotations from the parent scan to every subsequent scan generate new labels and annotations based on a lightweight template syntax and the given parent scan or findings data examples scheduledscan nmap definition example yaml apiversion execution securecodebox io kind scheduledscan metadata name nmap large network scan namespace demo scans annotations defectdojo securecodebox io product name barcelona network scan defectdojo securecodebox io product type name owasp defectdojo securecodebox io product tags vulnerable appsec network defectdojo securecodebox io engagement name scb automated scan defectdojo securecodebox io engagement tags automated daily labels organization owasp location barcelona vlan lan spec interval successfuljobshistorylimit failedjobshistorylimit scanspec scantype nmap parameters sv cascades true if all scan parent labels are copied to each subsequent scan child otherwise false default true inheritlabels true true if all scan parent annotations are copied to each subsequent scan child otherwise false default true inheritannotations true uses all cascadingrules in the namespace which are labelled as non invasive and a intensiveness level of light matchlabels securecodebox io invasive non invasive securecodebox io intensive light owasp zap cascading rule example yaml apiversion cascading securecodebox io kind cascadingrule metadata name zap http labels securecodebox io invasive non invasive securecodebox io intensive medium spec matches anyof category open port attributes service http state open category open port attributes service https state open configures additional label added to each subsequent scan child scanlabels mynewlabel metadata name configures additional annotation added to each subsequent scan child scanannotations defectdojo securecodebox io product name hostorip defectdojo securecodebox io product type name metadata labels organization defectdojo securecodebox io product tags vulnerable appsec owasp top ten vulnapp defectdojo securecodebox io engagement name hostorip scanspec scantype zap baseline parameters describe alternatives you ve considered additional context | 0 |
177,949 | 13,754,661,656 | IssuesEvent | 2020-10-06 17:16:13 | dapr/dapr | https://api.github.com/repos/dapr/dapr | opened | [E2E Scenario tests] for Service Invocation across namespaces | P1 area/test/e2e | <!-- If you need to report a security issue with Dapr, send an email to daprct@microsoft.com. -->
## In what area(s)?
<!-- Remove the '> ' to select -->
> /area test-and-release
## Describe the feature
Add e2e tests to cover service invocation across namespaces.
| 1.0 | [E2E Scenario tests] for Service Invocation across namespaces - <!-- If you need to report a security issue with Dapr, send an email to daprct@microsoft.com. -->
## In what area(s)?
<!-- Remove the '> ' to select -->
> /area test-and-release
## Describe the feature
Add e2e tests to cover service invocation across namespaces.
| non_priority | for service invocation across namespaces in what area s to select area test and release describe the feature add tests to cover service invocation across namespaces | 0 |
53,331 | 7,834,936,415 | IssuesEvent | 2018-06-16 20:36:12 | pmd/pmd | https://api.github.com/repos/pmd/pmd | closed | [doc] Make the landing page of the documentation website more useful | has:pr in:documentation | The [current landing page](https://pmd.github.io/pmd-6.3.0/) of the doc website basically repeats the info given in [this paragraph](https://pmd.github.io/#about) of the main landing page, with more `<li>`s and more links -> not that useful for a landing page.
Our Jekyl theme does give us much better alternatives to build a sleek and useful interface using special page layouts, eg a [shuffled layout](https://idratherbewriting.com/documentation-theme-jekyll//mydoc_shuffle.html) or a [knowledge-base layout](https://idratherbewriting.com/documentation-theme-jekyll//mydoc_kb_layout.html).
My personal favourite is the latter, which would allow us to put forward some particular page sets depending on the visitor's goal, eg
* Getting started
* Writing rules
* Rule reference
* Contributing
on a clutter-free and easily navigable page. I personnally think the sidebar could be more useful as a navigation tool *if it didn't fold*, because when you have no idea what you're looking for you have to open all the menus one by one. Even when you do know where to go, having to click 5 times to get to your page is awkward. So having this kind of easily accessible shortcuts is IMO necessary for a more navigable site.
| 1.0 | [doc] Make the landing page of the documentation website more useful - The [current landing page](https://pmd.github.io/pmd-6.3.0/) of the doc website basically repeats the info given in [this paragraph](https://pmd.github.io/#about) of the main landing page, with more `<li>`s and more links -> not that useful for a landing page.
Our Jekyl theme does give us much better alternatives to build a sleek and useful interface using special page layouts, eg a [shuffled layout](https://idratherbewriting.com/documentation-theme-jekyll//mydoc_shuffle.html) or a [knowledge-base layout](https://idratherbewriting.com/documentation-theme-jekyll//mydoc_kb_layout.html).
My personal favourite is the latter, which would allow us to put forward some particular page sets depending on the visitor's goal, eg
* Getting started
* Writing rules
* Rule reference
* Contributing
on a clutter-free and easily navigable page. I personnally think the sidebar could be more useful as a navigation tool *if it didn't fold*, because when you have no idea what you're looking for you have to open all the menus one by one. Even when you do know where to go, having to click 5 times to get to your page is awkward. So having this kind of easily accessible shortcuts is IMO necessary for a more navigable site.
| non_priority | make the landing page of the documentation website more useful the of the doc website basically repeats the info given in of the main landing page with more s and more links not that useful for a landing page our jekyl theme does give us much better alternatives to build a sleek and useful interface using special page layouts eg a or a my personal favourite is the latter which would allow us to put forward some particular page sets depending on the visitor s goal eg getting started writing rules rule reference contributing on a clutter free and easily navigable page i personnally think the sidebar could be more useful as a navigation tool if it didn t fold because when you have no idea what you re looking for you have to open all the menus one by one even when you do know where to go having to click times to get to your page is awkward so having this kind of easily accessible shortcuts is imo necessary for a more navigable site | 0 |
834 | 10,789,155,223 | IssuesEvent | 2019-11-05 11:15:55 | sohaibaslam/learning_site | https://api.github.com/repos/sohaibaslam/learning_site | closed | Broken Crawler: adidasatjd (CN) | crawler broken/unreliable | name: adidasatjd-cn
name: filajd-cn
name: liningatjd-cn
name: nikeatjd-cn
mixin_count: 4 | True | Broken Crawler: adidasatjd (CN) - name: adidasatjd-cn
name: filajd-cn
name: liningatjd-cn
name: nikeatjd-cn
mixin_count: 4 | non_priority | broken crawler adidasatjd cn name adidasatjd cn name filajd cn name liningatjd cn name nikeatjd cn mixin count | 0 |
335,646 | 30,078,876,484 | IssuesEvent | 2023-06-29 00:10:12 | Becksteinlab/MDPOW | https://api.github.com/repos/Becksteinlab/MDPOW | opened | [CI] update micromamba set up | testing | Run mamba-org/provision-with-micromamba@main
Warning: This action is deprecated and no longer maintained. Please use mamba-org/setup-micromamba instead. See https://github.com/mamba-org/provision-with-micromamba#migration-to-setup-micromamba for a migration guide. | 1.0 | [CI] update micromamba set up - Run mamba-org/provision-with-micromamba@main
Warning: This action is deprecated and no longer maintained. Please use mamba-org/setup-micromamba instead. See https://github.com/mamba-org/provision-with-micromamba#migration-to-setup-micromamba for a migration guide. | non_priority | update micromamba set up run mamba org provision with micromamba main warning this action is deprecated and no longer maintained please use mamba org setup micromamba instead see for a migration guide | 0 |
201,310 | 15,802,192,064 | IssuesEvent | 2021-04-03 08:31:16 | fupernova/ped | https://api.github.com/repos/fupernova/ped | opened | Headings in UG are not formatted properly | severity.Medium type.DocumentationBug | From section 4.1.2, List Reviews onwards, the markdown for heading does not render properly. Instead, hashes are seen, which suggests either some other markdown element failed to render properly before it or there is spacing error. Do check on this issue as it reduces the readability of the UG quite substantially.
<!--session: 1617437408259-b9528de8-d92d-455b-8bf5-39703a5bc74c--> | 1.0 | Headings in UG are not formatted properly - From section 4.1.2, List Reviews onwards, the markdown for heading does not render properly. Instead, hashes are seen, which suggests either some other markdown element failed to render properly before it or there is spacing error. Do check on this issue as it reduces the readability of the UG quite substantially.
<!--session: 1617437408259-b9528de8-d92d-455b-8bf5-39703a5bc74c--> | non_priority | headings in ug are not formatted properly from section list reviews onwards the markdown for heading does not render properly instead hashes are seen which suggests either some other markdown element failed to render properly before it or there is spacing error do check on this issue as it reduces the readability of the ug quite substantially | 0 |
280,907 | 24,344,077,793 | IssuesEvent | 2022-10-02 04:04:45 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest/costfuzz: join reordering issue | C-test-failure O-robot O-roachtest branch-master T-sql-queries | roachtest.costfuzz [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6601244?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6601244?buildTab=artifacts#/costfuzz) on master @ [89f4ad907a1756551bd6864c3e8516eeff6b0e0a](https://github.com/cockroachdb/cockroach/commits/89f4ad907a1756551bd6864c3e8516eeff6b0e0a):
```
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runOneRoundQueryComparison
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/query_comparison_util.go:233
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runQueryComparison
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/query_comparison_util.go:66
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runCostFuzz
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/costfuzz.go:41
| main.(*testRunner).runTest.func2
| main/pkg/cmd/roachtest/test_runner.go:928
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1594
Wraps: (4) expected unperturbed and perturbed results to be equal
| []string{
| ... // 3 identical elements
| "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345"...,
| "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345"...,
| + "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345678901234563e-07,1.2345678901234566e-20,1.2345678901234566e-20,1.7976931348623157e+308,1.2345678901234566e-20,6.596932228060170625E+37",
| "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345"...,
| }
| sql: SELECT
| tab_27925.tableoid AS col_61799,
| 1.2345678901234568e-31:::FLOAT8 AS col_61800,
| tab_27923.crdb_internal_mvcc_timestamp AS col_61801,
| 1.2345678901234563e-07:::FLOAT8 AS col_61802,
| tab_27926.col1_1 AS col_61803,
| tab_27924.col1_1 AS col_61804,
| tab_27922.col1_0 AS col_61805,
| tab_27924.col1_1 AS col_61806,
| 6.596932228060170625E+37:::DECIMAL AS col_61807
| FROM
| defaultdb.public.table1@[0] AS tab_27922
| RIGHT JOIN defaultdb.public.table1@[0] AS tab_27923 ON
| (tab_27922.col1_1) = (tab_27923.col1_1)
| AND (tab_27922.crdb_internal_mvcc_timestamp) >= (tab_27923.crdb_internal_mvcc_timestamp)
| AND (tab_27922.col1_1) = (tab_27923.col1_0)
| JOIN defaultdb.public.table1@[0] AS tab_27924 ON
| (tab_27923.col1_0) = (tab_27924.col1_0) AND (tab_27923.col1_1) = (tab_27924.col1_0)
| JOIN defaultdb.public.table1@[0] AS tab_27925 ON
| (tab_27923.col1_0) = (tab_27925.col1_0)
| AND (tab_27924.crdb_internal_mvcc_timestamp) = (tab_27925.crdb_internal_mvcc_timestamp)
| AND (tab_27922.col1_1) = (tab_27925.col1_0)
| AND (tab_27922.crdb_internal_mvcc_timestamp) = (tab_27925.crdb_internal_mvcc_timestamp)
| AND (tab_27924.col1_0) = (tab_27925.col1_0)
| AND (tab_27924.col1_1) = (tab_27925.col1_1)
| JOIN defaultdb.public.table1@[0] AS tab_27926 ON
| (tab_27925.col1_0) = (tab_27926.col1_1)
| AND (tab_27924.col1_1) = (tab_27926.col1_0)
| AND (tab_27924.col1_0) = (tab_27926.col1_0)
| ORDER BY
| tab_27924.crdb_internal_mvcc_timestamp
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.leafError
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #88547 roachtest: costfuzz failed [C-test-failure O-roachtest O-robot T-sql-queries branch-release-22.2]
- #86796 roachtest.costfuzz failed due to scientific notation v. decimal notation [C-test-failure T-sql-queries]
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*costfuzz.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-19846 | 2.0 | roachtest/costfuzz: join reordering issue - roachtest.costfuzz [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6601244?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6601244?buildTab=artifacts#/costfuzz) on master @ [89f4ad907a1756551bd6864c3e8516eeff6b0e0a](https://github.com/cockroachdb/cockroach/commits/89f4ad907a1756551bd6864c3e8516eeff6b0e0a):
```
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runOneRoundQueryComparison
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/query_comparison_util.go:233
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runQueryComparison
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/query_comparison_util.go:66
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runCostFuzz
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/costfuzz.go:41
| main.(*testRunner).runTest.func2
| main/pkg/cmd/roachtest/test_runner.go:928
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1594
Wraps: (4) expected unperturbed and perturbed results to be equal
| []string{
| ... // 3 identical elements
| "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345"...,
| "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345"...,
| + "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345678901234563e-07,1.2345678901234566e-20,1.2345678901234566e-20,1.7976931348623157e+308,1.2345678901234566e-20,6.596932228060170625E+37",
| "104,1.2345678901234568e-31,1664008168391878756.0000000000,1.2345"...,
| }
| sql: SELECT
| tab_27925.tableoid AS col_61799,
| 1.2345678901234568e-31:::FLOAT8 AS col_61800,
| tab_27923.crdb_internal_mvcc_timestamp AS col_61801,
| 1.2345678901234563e-07:::FLOAT8 AS col_61802,
| tab_27926.col1_1 AS col_61803,
| tab_27924.col1_1 AS col_61804,
| tab_27922.col1_0 AS col_61805,
| tab_27924.col1_1 AS col_61806,
| 6.596932228060170625E+37:::DECIMAL AS col_61807
| FROM
| defaultdb.public.table1@[0] AS tab_27922
| RIGHT JOIN defaultdb.public.table1@[0] AS tab_27923 ON
| (tab_27922.col1_1) = (tab_27923.col1_1)
| AND (tab_27922.crdb_internal_mvcc_timestamp) >= (tab_27923.crdb_internal_mvcc_timestamp)
| AND (tab_27922.col1_1) = (tab_27923.col1_0)
| JOIN defaultdb.public.table1@[0] AS tab_27924 ON
| (tab_27923.col1_0) = (tab_27924.col1_0) AND (tab_27923.col1_1) = (tab_27924.col1_0)
| JOIN defaultdb.public.table1@[0] AS tab_27925 ON
| (tab_27923.col1_0) = (tab_27925.col1_0)
| AND (tab_27924.crdb_internal_mvcc_timestamp) = (tab_27925.crdb_internal_mvcc_timestamp)
| AND (tab_27922.col1_1) = (tab_27925.col1_0)
| AND (tab_27922.crdb_internal_mvcc_timestamp) = (tab_27925.crdb_internal_mvcc_timestamp)
| AND (tab_27924.col1_0) = (tab_27925.col1_0)
| AND (tab_27924.col1_1) = (tab_27925.col1_1)
| JOIN defaultdb.public.table1@[0] AS tab_27926 ON
| (tab_27925.col1_0) = (tab_27926.col1_1)
| AND (tab_27924.col1_1) = (tab_27926.col1_0)
| AND (tab_27924.col1_0) = (tab_27926.col1_0)
| ORDER BY
| tab_27924.crdb_internal_mvcc_timestamp
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.leafError
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #88547 roachtest: costfuzz failed [C-test-failure O-roachtest O-robot T-sql-queries branch-release-22.2]
- #86796 roachtest.costfuzz failed due to scientific notation v. decimal notation [C-test-failure T-sql-queries]
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*costfuzz.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-19846 | non_priority | roachtest costfuzz join reordering issue roachtest costfuzz with on master github com cockroachdb cockroach pkg cmd roachtest tests runoneroundquerycomparison github com cockroachdb cockroach pkg cmd roachtest tests query comparison util go github com cockroachdb cockroach pkg cmd roachtest tests runquerycomparison github com cockroachdb cockroach pkg cmd roachtest tests query comparison util go github com cockroachdb cockroach pkg cmd roachtest tests runcostfuzz github com cockroachdb cockroach pkg cmd roachtest tests costfuzz go main testrunner runtest main pkg cmd roachtest test runner go runtime goexit goroot src runtime asm s wraps expected unperturbed and perturbed results to be equal string identical elements sql select tab tableoid as col as col tab crdb internal mvcc timestamp as col as col tab as col tab as col tab as col tab as col decimal as col from defaultdb public as tab right join defaultdb public as tab on tab tab and tab crdb internal mvcc timestamp tab crdb internal mvcc timestamp and tab tab join defaultdb public as tab on tab tab and tab tab join defaultdb public as tab on tab tab and tab crdb internal mvcc timestamp tab crdb internal mvcc timestamp and tab tab and tab crdb internal mvcc timestamp tab crdb internal mvcc timestamp and tab tab and tab tab join defaultdb public as tab on tab tab and tab tab and tab tab order by tab crdb internal mvcc timestamp error types withstack withstack errutil withprefix withstack withstack errutil leaferror parameters roachtest cloud gce roachtest cpu roachtest encrypted false roachtest ssd help see see same failure on other branches roachtest costfuzz failed roachtest costfuzz failed due to scientific notation v decimal notation cc cockroachdb sql queries jira issue crdb | 0 |
54,504 | 13,752,232,197 | IssuesEvent | 2020-10-06 14:17:00 | tensfeldt/openNCA | https://api.github.com/repos/tensfeldt/openNCA | closed | 2020-09-01 tc1580 M3SS inconsistent output for SDEID profiles that contain negative times | 3.0 defect | This issue is in regards to scope item 3.16
### Issue
tc1580 contains a single negative time in each profile, with desired behaviour being NA output for all profiles. This behaviour is inconsistent, with some profiles having non-NA values provided in the output for an unknown reason. One profile shows up with this behaviour when running this locally. The automated report .htmls shows up with 4 SDEID profiles being affected.
These SDEID profiles are not mentioned in the warnings like other profiles with this warning: `No parameters generated due to negative TIME values for SDEID: '3970555705'`
```r
# Check number of negative values per profile (and then see how many unique quantities there are)
d$tmpNEGFLAG <- ifelse(d[mct$ACTTIME] < 0, 1, 0)
d %>%
dplyr::mutate(tmpNEGFLAG = ifelse(d[mct$ACTTIME] < 0, 1, 0)) %>%
dplyr::group_by(SDEID) %>%
dplyr::count(tmpNEGFLAG) %>%
dplyr::filter(tmpNEGFLAG == 1) %>%
dplyr::pull(n) %>% unique()
#> [1] 1
# every profile has 1 negative value
# What is the negative value?
d[d[mct$ACTTIME] < 0, c("PKATPDnew")]
#> [1] -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3
#> [40] -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3
# What profiles are generating output despite having a negative time? (table below)
knitr::kable(r[!is.na(r$CMAX), c(grep("SDEID", names(r)), grep("MAX", names(r)), grep("^CON.+\\d+$", names(r)))])
# Was this ID mentioned in warnings?
capture.output(warnings()) %>% stringr::str_detect("2848066001") %>% any()
#> [1] FALSE
```
| | SDEID|UDSDEID | CMAX| CMAX1| CMAX2| CMAXDN| CMAXDN1| CMAXDN2| TMAX| TMAX1| TMAX2| FLGACCEPTTMAX| CONC1| CONC2| CONC3| CONC4| CONC5| CONC6| CONC7| CONC8| CONC9| CONC10| CONC11| CONC12| CONC13| CONC14| CONC15| CONC16| CONC17| CONCTIME1| CONCTIME2| CONCTIME3| CONCTIME4| CONCTIME5| CONCTIME6| CONCTIME7| CONCTIME8| CONCTIME9| CONCTIME10| CONCTIME11| CONCTIME12| CONCTIME13| CONCTIME14| CONCTIME15| CONCTIME16| CONCTIME17|
|:--|----------:|:-------|-----:|-----:|-----:|------:|-------:|-------:|----:|-----:|-----:|-------------:|-----:|-----:|-----:|-----:|-----:|-----:|-----:|-----:|-----:|------:|------:|------:|------:|------:|------:|------:|------:|---------:|---------:|---------:|---------:|---------:|---------:|---------:|---------:|---------:|----------:|----------:|----------:|----------:|----------:|----------:|----------:|----------:|
|32 | 2848066001|NA | 31000| 31000| 6980| 310| 310| 69.8| 1.5| 1.5| 13| 1| 0| 10600| 25500| 31000| 20200| 12600| 13100| 6980| 1560| 133| 14.5| 0| 0| 0| 0| 0| NA| 0| 0.5| 1.016667| 1.5| 2.5| 6| 9| 13| 24.91667| 48.91667| 72.91667| 96.91667| 120.9167| 168.9167| 337| 505| NA|
| 1.0 | 2020-09-01 tc1580 M3SS inconsistent output for SDEID profiles that contain negative times - This issue is in regards to scope item 3.16
### Issue
tc1580 contains a single negative time in each profile, with desired behaviour being NA output for all profiles. This behaviour is inconsistent, with some profiles having non-NA values provided in the output for an unknown reason. One profile shows up with this behaviour when running this locally. The automated report .htmls shows up with 4 SDEID profiles being affected.
These SDEID profiles are not mentioned in the warnings like other profiles with this warning: `No parameters generated due to negative TIME values for SDEID: '3970555705'`
```r
# Check number of negative values per profile (and then see how many unique quantities there are)
d$tmpNEGFLAG <- ifelse(d[mct$ACTTIME] < 0, 1, 0)
d %>%
dplyr::mutate(tmpNEGFLAG = ifelse(d[mct$ACTTIME] < 0, 1, 0)) %>%
dplyr::group_by(SDEID) %>%
dplyr::count(tmpNEGFLAG) %>%
dplyr::filter(tmpNEGFLAG == 1) %>%
dplyr::pull(n) %>% unique()
#> [1] 1
# every profile has 1 negative value
# What is the negative value?
d[d[mct$ACTTIME] < 0, c("PKATPDnew")]
#> [1] -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3
#> [40] -3 -3 -3 -3 -3 -3 -3 -3 -3 -3 -3
# What profiles are generating output despite having a negative time? (table below)
knitr::kable(r[!is.na(r$CMAX), c(grep("SDEID", names(r)), grep("MAX", names(r)), grep("^CON.+\\d+$", names(r)))])
# Was this ID mentioned in warnings?
capture.output(warnings()) %>% stringr::str_detect("2848066001") %>% any()
#> [1] FALSE
```
| | SDEID|UDSDEID | CMAX| CMAX1| CMAX2| CMAXDN| CMAXDN1| CMAXDN2| TMAX| TMAX1| TMAX2| FLGACCEPTTMAX| CONC1| CONC2| CONC3| CONC4| CONC5| CONC6| CONC7| CONC8| CONC9| CONC10| CONC11| CONC12| CONC13| CONC14| CONC15| CONC16| CONC17| CONCTIME1| CONCTIME2| CONCTIME3| CONCTIME4| CONCTIME5| CONCTIME6| CONCTIME7| CONCTIME8| CONCTIME9| CONCTIME10| CONCTIME11| CONCTIME12| CONCTIME13| CONCTIME14| CONCTIME15| CONCTIME16| CONCTIME17|
|:--|----------:|:-------|-----:|-----:|-----:|------:|-------:|-------:|----:|-----:|-----:|-------------:|-----:|-----:|-----:|-----:|-----:|-----:|-----:|-----:|-----:|------:|------:|------:|------:|------:|------:|------:|------:|---------:|---------:|---------:|---------:|---------:|---------:|---------:|---------:|---------:|----------:|----------:|----------:|----------:|----------:|----------:|----------:|----------:|
|32 | 2848066001|NA | 31000| 31000| 6980| 310| 310| 69.8| 1.5| 1.5| 13| 1| 0| 10600| 25500| 31000| 20200| 12600| 13100| 6980| 1560| 133| 14.5| 0| 0| 0| 0| 0| NA| 0| 0.5| 1.016667| 1.5| 2.5| 6| 9| 13| 24.91667| 48.91667| 72.91667| 96.91667| 120.9167| 168.9167| 337| 505| NA|
| non_priority | inconsistent output for sdeid profiles that contain negative times this issue is in regards to scope item issue contains a single negative time in each profile with desired behaviour being na output for all profiles this behaviour is inconsistent with some profiles having non na values provided in the output for an unknown reason one profile shows up with this behaviour when running this locally the automated report htmls shows up with sdeid profiles being affected these sdeid profiles are not mentioned in the warnings like other profiles with this warning no parameters generated due to negative time values for sdeid r check number of negative values per profile and then see how many unique quantities there are d tmpnegflag ifelse d d dplyr mutate tmpnegflag ifelse d dplyr group by sdeid dplyr count tmpnegflag dplyr filter tmpnegflag dplyr pull n unique every profile has negative value what is the negative value d c pkatpdnew what profiles are generating output despite having a negative time table below knitr kable r was this id mentioned in warnings capture output warnings stringr str detect any false sdeid udsdeid cmax cmaxdn tmax flgaccepttmax na na na | 0 |
269,129 | 20,373,517,850 | IssuesEvent | 2022-02-21 13:33:28 | NetAppDocs/ontap | https://api.github.com/repos/NetAppDocs/ontap | closed | Facts not in evidence: creating audit directories in ONTAP | documentation good first issue | Page: [How the ONTAP auditing process works](https://docs.netapp.com/us-en/ontap/nas-audit/auditing-process-concept.html)
This page refers casually to an audit directory needing to exist before auditing can be created but doesn't discuss how to create one, let alone if there are issues about choosing where to create one. That seems worth a hyperlink to an article on those nuances. | 1.0 | Facts not in evidence: creating audit directories in ONTAP - Page: [How the ONTAP auditing process works](https://docs.netapp.com/us-en/ontap/nas-audit/auditing-process-concept.html)
This page refers casually to an audit directory needing to exist before auditing can be created but doesn't discuss how to create one, let alone if there are issues about choosing where to create one. That seems worth a hyperlink to an article on those nuances. | non_priority | facts not in evidence creating audit directories in ontap page this page refers casually to an audit directory needing to exist before auditing can be created but doesn t discuss how to create one let alone if there are issues about choosing where to create one that seems worth a hyperlink to an article on those nuances | 0 |
1,120 | 2,694,817,829 | IssuesEvent | 2015-04-01 22:37:21 | facebook/react | https://api.github.com/repos/facebook/react | closed | Discussion: Prebuilt binaries and distribution | Component: Build & Tooling | It's nice to have prebuilt binaries available through the current package managers. Right now there's a prebuilt package for [Bower](https://github.com/reactjs/react-bower), but it'd be nice to also have them on npm / component / nlz.io.
What do you think is the best way to create and maintain these packages?
cc/ @zpao | 1.0 | Discussion: Prebuilt binaries and distribution - It's nice to have prebuilt binaries available through the current package managers. Right now there's a prebuilt package for [Bower](https://github.com/reactjs/react-bower), but it'd be nice to also have them on npm / component / nlz.io.
What do you think is the best way to create and maintain these packages?
cc/ @zpao | non_priority | discussion prebuilt binaries and distribution it s nice to have prebuilt binaries available through the current package managers right now there s a prebuilt package for but it d be nice to also have them on npm component nlz io what do you think is the best way to create and maintain these packages cc zpao | 0 |
158,105 | 20,007,587,518 | IssuesEvent | 2022-02-01 00:02:58 | timf-app-sandbox/t1 | https://api.github.com/repos/timf-app-sandbox/t1 | opened | WS-2019-0027 (Medium) detected in marked-0.3.9.tgz | security vulnerability | ## WS-2019-0027 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.9.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.3.9.tgz">https://registry.npmjs.org/marked/-/marked-0.3.9.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.9.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/timf-app-sandbox/t1/commit/ade63e4d4d7f78775fe064056f81c5da1b53aecf">ade63e4d4d7f78775fe064056f81c5da1b53aecf</a></p>
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions 0.3.17 and earlier of marked has Four regexes were vulnerable to catastrophic backtracking. This leaves markdown servers open to a potential REDOS attack.
<p>Publish Date: 2018-02-26
<p>URL: <a href=https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d>WS-2019-0027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d">https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d</a></p>
<p>Release Date: 2018-02-26</p>
<p>Fix Resolution: 0.3.18</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"marked","packageVersion":"0.3.9","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"marked:0.3.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.3.18","isBinary":false}],"baseBranches":["dev"],"vulnerabilityIdentifier":"WS-2019-0027","vulnerabilityDetails":"Versions 0.3.17 and earlier of marked has Four regexes were vulnerable to catastrophic backtracking. This leaves markdown servers open to a potential REDOS attack.","vulnerabilityUrl":"https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0027 (Medium) detected in marked-0.3.9.tgz - ## WS-2019-0027 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.9.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.3.9.tgz">https://registry.npmjs.org/marked/-/marked-0.3.9.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.9.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/timf-app-sandbox/t1/commit/ade63e4d4d7f78775fe064056f81c5da1b53aecf">ade63e4d4d7f78775fe064056f81c5da1b53aecf</a></p>
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions 0.3.17 and earlier of marked has Four regexes were vulnerable to catastrophic backtracking. This leaves markdown servers open to a potential REDOS attack.
<p>Publish Date: 2018-02-26
<p>URL: <a href=https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d>WS-2019-0027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d">https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d</a></p>
<p>Release Date: 2018-02-26</p>
<p>Fix Resolution: 0.3.18</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"marked","packageVersion":"0.3.9","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"marked:0.3.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.3.18","isBinary":false}],"baseBranches":["dev"],"vulnerabilityIdentifier":"WS-2019-0027","vulnerabilityDetails":"Versions 0.3.17 and earlier of marked has Four regexes were vulnerable to catastrophic backtracking. This leaves markdown servers open to a potential REDOS attack.","vulnerabilityUrl":"https://github.com/markedjs/marked/commit/b15e42b67cec9ded8505e9d68bb8741ad7a9590d","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in marked tgz ws medium severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file package json path to vulnerable library node modules marked package json dependency hierarchy x marked tgz vulnerable library found in head commit a href found in base branch dev vulnerability details versions and earlier of marked has four regexes were vulnerable to catastrophic backtracking this leaves markdown servers open to a potential redos attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree marked isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails versions and earlier of marked has four regexes were vulnerable to catastrophic backtracking this leaves markdown servers open to a potential redos attack vulnerabilityurl | 0 |
172,334 | 13,301,907,977 | IssuesEvent | 2020-08-25 13:35:58 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Init:CrashLoopBackOff | kind/failing-test needs-sig triage/support | Hello, im having issues with pode going immediately in crashloopBackoff state.
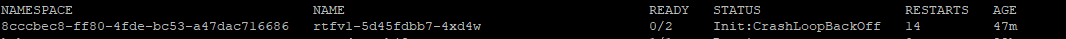
Kubectl describe po -n <namespace>
Init Containers:
init:
Container ID: docker://f2fd33030980aaed48a66b10ff828dfaa835acf64d73c1a01dd89c29136c508b
Image: 494141260463.dkr.ecr.us-east-1.amazonaws.com/mulesoft/rtf-app-init:v1.0.22
Image ID: docker-pullable://494141260463.dkr.ecr.us-east-1.amazonaws.com/mulesoft/rtf-app-init@sha256:fe0be8aaa567db809a7a48f564f5b5c724645862e293fd33fbe316b6e319
Port: <none>
Host Port: <none>
State: Waiting
Reason: CrashLoopBackOff
Last State: Terminated
Reason: Error
Message: Failed to fetch /opt/mule/conf/rtfv1.yml. statusCode=403
Exit Code: 1
Started: Tue, 25 Aug 2020 08:20:35 +0000
Finished: Tue, 25 Aug 2020 08:20:35 +0000
Ready: False
Restart Count: 16
Environment: <none>
Mounts:
/etc/podinfo from podinfo (ro)
/mnt/overlay from overlay (rw)
I can see that it's failing on fetching but why and how to fix this? Where to find detailed logs or something??
Thank you.
| 1.0 | Init:CrashLoopBackOff - Hello, im having issues with pode going immediately in crashloopBackoff state.
Kubectl describe po -n <namespace>
Init Containers:
init:
Container ID: docker://f2fd33030980aaed48a66b10ff828dfaa835acf64d73c1a01dd89c29136c508b
Image: 494141260463.dkr.ecr.us-east-1.amazonaws.com/mulesoft/rtf-app-init:v1.0.22
Image ID: docker-pullable://494141260463.dkr.ecr.us-east-1.amazonaws.com/mulesoft/rtf-app-init@sha256:fe0be8aaa567db809a7a48f564f5b5c724645862e293fd33fbe316b6e319
Port: <none>
Host Port: <none>
State: Waiting
Reason: CrashLoopBackOff
Last State: Terminated
Reason: Error
Message: Failed to fetch /opt/mule/conf/rtfv1.yml. statusCode=403
Exit Code: 1
Started: Tue, 25 Aug 2020 08:20:35 +0000
Finished: Tue, 25 Aug 2020 08:20:35 +0000
Ready: False
Restart Count: 16
Environment: <none>
Mounts:
/etc/podinfo from podinfo (ro)
/mnt/overlay from overlay (rw)
I can see that it's failing on fetching but why and how to fix this? Where to find detailed logs or something??
Thank you.
| non_priority | init crashloopbackoff hello im having issues with pode going immediately in crashloopbackoff state kubectl describe po n init containers init container id docker image dkr ecr us east amazonaws com mulesoft rtf app init image id docker pullable dkr ecr us east amazonaws com mulesoft rtf app init port host port state waiting reason crashloopbackoff last state terminated reason error message failed to fetch opt mule conf yml statuscode exit code started tue aug finished tue aug ready false restart count environment mounts etc podinfo from podinfo ro mnt overlay from overlay rw i can see that it s failing on fetching but why and how to fix this where to find detailed logs or something thank you | 0 |
34,854 | 16,726,116,513 | IssuesEvent | 2021-06-10 13:11:58 | alarm-redist/redist | https://api.github.com/repos/alarm-redist/redist | closed | Draw only needed spanning trees in SMC and M-S | feature request performance | When using counties/multigraph in SMC and M-S, many spanning trees within individual counties don't need to be drawn. Could save a lot of computation by only drawing 2nd-level trees in counties which span a population target | True | Draw only needed spanning trees in SMC and M-S - When using counties/multigraph in SMC and M-S, many spanning trees within individual counties don't need to be drawn. Could save a lot of computation by only drawing 2nd-level trees in counties which span a population target | non_priority | draw only needed spanning trees in smc and m s when using counties multigraph in smc and m s many spanning trees within individual counties don t need to be drawn could save a lot of computation by only drawing level trees in counties which span a population target | 0 |
125,648 | 16,823,175,508 | IssuesEvent | 2021-06-17 15:14:26 | carbon-design-system/carbon-for-ibm-dotcom-website | https://api.github.com/repos/carbon-design-system/carbon-for-ibm-dotcom-website | closed | Project Pupa: Adopter Interview Beta test | design project pupa website: Carbon for ibm.com | ### Objectives:
To evaluate the the latest [interview script ](https://ibm.ent.box.com/notes/820273246361)that Project Pupa developed for the adopter stakeholder interviews by conducting a beta test with [Daniel Ratzenboeck ](https://w3.ibm.com/bluepages/profile.html?uid=059105618)
### Tasks:
- [x] Conduct a mock interview
- [x] Evaluate the flow and timing of our script
- [x] See whether the questions developed reflect our research questions and evoke the intended response from adopters
- [x] Add any follow up questions if necessary
- [x] Clarify any questions that may be ambiguous
Interview is scheduled for Thursday, June 17th @10am EST | 1.0 | Project Pupa: Adopter Interview Beta test - ### Objectives:
To evaluate the the latest [interview script ](https://ibm.ent.box.com/notes/820273246361)that Project Pupa developed for the adopter stakeholder interviews by conducting a beta test with [Daniel Ratzenboeck ](https://w3.ibm.com/bluepages/profile.html?uid=059105618)
### Tasks:
- [x] Conduct a mock interview
- [x] Evaluate the flow and timing of our script
- [x] See whether the questions developed reflect our research questions and evoke the intended response from adopters
- [x] Add any follow up questions if necessary
- [x] Clarify any questions that may be ambiguous
Interview is scheduled for Thursday, June 17th @10am EST | non_priority | project pupa adopter interview beta test objectives to evaluate the the latest project pupa developed for the adopter stakeholder interviews by conducting a beta test with tasks conduct a mock interview evaluate the flow and timing of our script see whether the questions developed reflect our research questions and evoke the intended response from adopters add any follow up questions if necessary clarify any questions that may be ambiguous interview is scheduled for thursday june est | 0 |
244,420 | 20,670,222,766 | IssuesEvent | 2022-03-10 00:47:30 | lawliet7/goddo-editor | https://api.github.com/repos/lawliet7/goddo-editor | closed | test automation without qtbot | test cases | qtbot seems to be more for unit testing, a lot of functionality is mocked or we create a fake event/signal and call appropriate functions for it.
Like for dropping we create a fake drop event and call our callback, for double click on list widget we create fake signal, etc.
The good thing about it though is that it creates the app in background for us to interact but if we have multiple test files it gives a weird access violation error.
Like if i have 2 test modules that both starts the app, if I run them individually they both work fine but if i run everything in the package, the 2nd one would fail. All test cases are green but the overall test suite failed and we see some remanants of the windows so maybe some clean up is not done properly.
However instead of fixing and trying to get it to work, I have decided to just do away with it and see if I can do these tests with simple threading, pyautogui for simulating user interactions and opencv/pil for checking/comparing screens. | 1.0 | test automation without qtbot - qtbot seems to be more for unit testing, a lot of functionality is mocked or we create a fake event/signal and call appropriate functions for it.
Like for dropping we create a fake drop event and call our callback, for double click on list widget we create fake signal, etc.
The good thing about it though is that it creates the app in background for us to interact but if we have multiple test files it gives a weird access violation error.
Like if i have 2 test modules that both starts the app, if I run them individually they both work fine but if i run everything in the package, the 2nd one would fail. All test cases are green but the overall test suite failed and we see some remanants of the windows so maybe some clean up is not done properly.
However instead of fixing and trying to get it to work, I have decided to just do away with it and see if I can do these tests with simple threading, pyautogui for simulating user interactions and opencv/pil for checking/comparing screens. | non_priority | test automation without qtbot qtbot seems to be more for unit testing a lot of functionality is mocked or we create a fake event signal and call appropriate functions for it like for dropping we create a fake drop event and call our callback for double click on list widget we create fake signal etc the good thing about it though is that it creates the app in background for us to interact but if we have multiple test files it gives a weird access violation error like if i have test modules that both starts the app if i run them individually they both work fine but if i run everything in the package the one would fail all test cases are green but the overall test suite failed and we see some remanants of the windows so maybe some clean up is not done properly however instead of fixing and trying to get it to work i have decided to just do away with it and see if i can do these tests with simple threading pyautogui for simulating user interactions and opencv pil for checking comparing screens | 0 |
178,770 | 13,795,269,001 | IssuesEvent | 2020-10-09 17:43:05 | LD4P/sinopia_editor | https://api.github.com/repos/LD4P/sinopia_editor | closed | Write tests for actionCreators/resourceHelpers | tests | Need unit tests for:
- `addEmptyResource`
- `addResourceFromDataset`
- `chooseURI`
- `newSubject`
- `newPropertiesFromTemplates` | 1.0 | Write tests for actionCreators/resourceHelpers - Need unit tests for:
- `addEmptyResource`
- `addResourceFromDataset`
- `chooseURI`
- `newSubject`
- `newPropertiesFromTemplates` | non_priority | write tests for actioncreators resourcehelpers need unit tests for addemptyresource addresourcefromdataset chooseuri newsubject newpropertiesfromtemplates | 0 |
15,081 | 5,050,628,931 | IssuesEvent | 2016-12-20 19:20:33 | apereo/cas | https://api.github.com/repos/apereo/cas | closed | NullPointerException in Resource CRL check | Bug Source Code Trivial X.509 | CAS 5.0.1, Tomcat Spring Boot, X509
ResourceCRLRevocationChecker - Line 204 can return a singleton collection with single null value (haven't tracked down why, but probably b/c i am testing with dummy cert, or bad config)
```
@Override
protected Collection<X509CRL> getCRLs(final X509Certificate cert) {
return Collections.singleton(this.crlIssuerMap.get(cert.getIssuerX500Principal()));
}
```
AbstractCRLRevocationChecker - Line 65 - crls list is not null or empty so it makes it through this block:
```
final Collection<X509CRL> crls = getCRLs(cert);
if (crls == null || crls.isEmpty()) {
logger.warn("CRL data is not available for {}", CertUtils.toString(cert));
this.unavailableCRLPolicy.apply(null);
return;
}
```
The crls collection contains a single null value so there is NPE in CertUtils.isExpired() when the following block executes:
```
crls.stream().filter(CertUtils::isExpired).forEach(crl -> {
logger.warn("CRL data expired on {}", crl.getNextUpdate());
expiredCrls.add(crl);
});
```
ResourceCRLRevocationChecker.getCRLs() should probably return null if this.crlIssuerMap.get(cert.getIssuerX500Principal()) returns null. | 1.0 | NullPointerException in Resource CRL check - CAS 5.0.1, Tomcat Spring Boot, X509
ResourceCRLRevocationChecker - Line 204 can return a singleton collection with single null value (haven't tracked down why, but probably b/c i am testing with dummy cert, or bad config)
```
@Override
protected Collection<X509CRL> getCRLs(final X509Certificate cert) {
return Collections.singleton(this.crlIssuerMap.get(cert.getIssuerX500Principal()));
}
```
AbstractCRLRevocationChecker - Line 65 - crls list is not null or empty so it makes it through this block:
```
final Collection<X509CRL> crls = getCRLs(cert);
if (crls == null || crls.isEmpty()) {
logger.warn("CRL data is not available for {}", CertUtils.toString(cert));
this.unavailableCRLPolicy.apply(null);
return;
}
```
The crls collection contains a single null value so there is NPE in CertUtils.isExpired() when the following block executes:
```
crls.stream().filter(CertUtils::isExpired).forEach(crl -> {
logger.warn("CRL data expired on {}", crl.getNextUpdate());
expiredCrls.add(crl);
});
```
ResourceCRLRevocationChecker.getCRLs() should probably return null if this.crlIssuerMap.get(cert.getIssuerX500Principal()) returns null. | non_priority | nullpointerexception in resource crl check cas tomcat spring boot resourcecrlrevocationchecker line can return a singleton collection with single null value haven t tracked down why but probably b c i am testing with dummy cert or bad config override protected collection getcrls final cert return collections singleton this crlissuermap get cert abstractcrlrevocationchecker line crls list is not null or empty so it makes it through this block final collection crls getcrls cert if crls null crls isempty logger warn crl data is not available for certutils tostring cert this unavailablecrlpolicy apply null return the crls collection contains a single null value so there is npe in certutils isexpired when the following block executes crls stream filter certutils isexpired foreach crl logger warn crl data expired on crl getnextupdate expiredcrls add crl resourcecrlrevocationchecker getcrls should probably return null if this crlissuermap get cert returns null | 0 |
11,334 | 9,311,261,747 | IssuesEvent | 2019-03-25 20:54:47 | ga4gh/dockstore | https://api.github.com/repos/ga4gh/dockstore | closed | Organization and collection names should be case insensitive | enhancement gui web-service | Need to add case constraints to the DB.
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-241)
┆Issue Type: Story
┆Fix Versions: Dockstore 1.6
┆Sprint: Seabright Sprint 6 Ferry
┆Issue Number: DOCK-241
| 1.0 | Organization and collection names should be case insensitive - Need to add case constraints to the DB.
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-241)
┆Issue Type: Story
┆Fix Versions: Dockstore 1.6
┆Sprint: Seabright Sprint 6 Ferry
┆Issue Number: DOCK-241
| non_priority | organization and collection names should be case insensitive need to add case constraints to the db ┆issue is synchronized with this ┆issue type story ┆fix versions dockstore ┆sprint seabright sprint ferry ┆issue number dock | 0 |
45,302 | 7,177,163,964 | IssuesEvent | 2018-01-31 12:41:28 | flyve-mdm/glpi-plugin | https://api.github.com/repos/flyve-mdm/glpi-plugin | closed | Update folder name to install the plugin | documentation | ### Expected behaviour
Update to flyvemdm the setup information to install older versions of Flyve MDM plugin
### Actual behaviour
The version 1.1.0 requires that the uncompressed folder to be named storkmdm in order to be installed
### Environment Details
- HTTP server version:
- GLPi version: 9.1.6
- Flyve MDM version: 1.1.0
- FusionInventory version: 9.1 + 1.0
- Mosquitto version:
- Mosquitto's auth plugin version:
### Steps to reproduce the behaviour
1. Uncompress the Flyve MDM version 1.1.0 in the GLPI plugins directory
2. Rename it to flyvemdm
3. Go to Setup > Plugins on GLPI (Only appears fusioninventory plugin)
4. Rename flyvemdm to storkmdm
5. Go to Setup > Plugins on GLPI (Now both plugins appear)
| 1.0 | Update folder name to install the plugin - ### Expected behaviour
Update to flyvemdm the setup information to install older versions of Flyve MDM plugin
### Actual behaviour
The version 1.1.0 requires that the uncompressed folder to be named storkmdm in order to be installed
### Environment Details
- HTTP server version:
- GLPi version: 9.1.6
- Flyve MDM version: 1.1.0
- FusionInventory version: 9.1 + 1.0
- Mosquitto version:
- Mosquitto's auth plugin version:
### Steps to reproduce the behaviour
1. Uncompress the Flyve MDM version 1.1.0 in the GLPI plugins directory
2. Rename it to flyvemdm
3. Go to Setup > Plugins on GLPI (Only appears fusioninventory plugin)
4. Rename flyvemdm to storkmdm
5. Go to Setup > Plugins on GLPI (Now both plugins appear)
| non_priority | update folder name to install the plugin expected behaviour update to flyvemdm the setup information to install older versions of flyve mdm plugin actual behaviour the version requires that the uncompressed folder to be named storkmdm in order to be installed environment details http server version glpi version flyve mdm version fusioninventory version mosquitto version mosquitto s auth plugin version steps to reproduce the behaviour uncompress the flyve mdm version in the glpi plugins directory rename it to flyvemdm go to setup plugins on glpi only appears fusioninventory plugin rename flyvemdm to storkmdm go to setup plugins on glpi now both plugins appear | 0 |
160,080 | 13,780,795,179 | IssuesEvent | 2020-10-08 15:21:16 | rx-angular/rx-angular | https://api.github.com/repos/rx-angular/rx-angular | opened | Immutability in push and rxLet is not documented | documentation template | Document clearly that `push` and `rxLet` recognize only immutable changes. (same as `onPush`) | 1.0 | Immutability in push and rxLet is not documented - Document clearly that `push` and `rxLet` recognize only immutable changes. (same as `onPush`) | non_priority | immutability in push and rxlet is not documented document clearly that push and rxlet recognize only immutable changes same as onpush | 0 |
181,811 | 21,664,449,476 | IssuesEvent | 2022-05-07 01:23:17 | n-devs/edit-map | https://api.github.com/repos/n-devs/edit-map | closed | WS-2018-0084 (High) detected in sshpk-1.13.0.tgz - autoclosed | security vulnerability | ## WS-2018-0084 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sshpk-1.13.0.tgz</b></p></summary>
<p>A library for finding and using SSH public keys</p>
<p>Library home page: <a href="https://registry.npmjs.org/sshpk/-/sshpk-1.13.0.tgz">https://registry.npmjs.org/sshpk/-/sshpk-1.13.0.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-1.0.13.tgz (Root Library)
- fsevents-1.1.2.tgz
- node-pre-gyp-0.6.36.tgz
- request-2.81.0.tgz
- http-signature-1.1.1.tgz
- :x: **sshpk-1.13.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/n-psk/edit-map/commits/1dc8fdb4f8c25647b64d8935674bd1baedd1438e">1dc8fdb4f8c25647b64d8935674bd1baedd1438e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of sshpk before 1.14.1 are vulnerable to regular expression denial of service when parsing crafted invalid public keys.
<p>Publish Date: 2018-04-25
<p>URL: <a href=https://github.com/joyent/node-sshpk/blob/v1.13.1/lib/formats/ssh.js#L17>WS-2018-0084</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/606">https://nodesecurity.io/advisories/606</a></p>
<p>Release Date: 2018-01-27</p>
<p>Fix Resolution: 1.14.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2018-0084 (High) detected in sshpk-1.13.0.tgz - autoclosed - ## WS-2018-0084 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sshpk-1.13.0.tgz</b></p></summary>
<p>A library for finding and using SSH public keys</p>
<p>Library home page: <a href="https://registry.npmjs.org/sshpk/-/sshpk-1.13.0.tgz">https://registry.npmjs.org/sshpk/-/sshpk-1.13.0.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-1.0.13.tgz (Root Library)
- fsevents-1.1.2.tgz
- node-pre-gyp-0.6.36.tgz
- request-2.81.0.tgz
- http-signature-1.1.1.tgz
- :x: **sshpk-1.13.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/n-psk/edit-map/commits/1dc8fdb4f8c25647b64d8935674bd1baedd1438e">1dc8fdb4f8c25647b64d8935674bd1baedd1438e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of sshpk before 1.14.1 are vulnerable to regular expression denial of service when parsing crafted invalid public keys.
<p>Publish Date: 2018-04-25
<p>URL: <a href=https://github.com/joyent/node-sshpk/blob/v1.13.1/lib/formats/ssh.js#L17>WS-2018-0084</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/606">https://nodesecurity.io/advisories/606</a></p>
<p>Release Date: 2018-01-27</p>
<p>Fix Resolution: 1.14.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in sshpk tgz autoclosed ws high severity vulnerability vulnerable library sshpk tgz a library for finding and using ssh public keys library home page a href dependency hierarchy react scripts tgz root library fsevents tgz node pre gyp tgz request tgz http signature tgz x sshpk tgz vulnerable library found in head commit a href vulnerability details versions of sshpk before are vulnerable to regular expression denial of service when parsing crafted invalid public keys publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
229,948 | 18,460,366,955 | IssuesEvent | 2021-10-15 23:51:39 | eclipse-openj9/openj9 | https://api.github.com/repos/eclipse-openj9/openj9 | closed | NPE running DefaultStaticInvokeTest | comp:jit test failure blocker segfault project:MH | Latest occurrence at https://openj9-jenkins.osuosl.org/job/Test_openjdk17_j9_sanity.openjdk_x86-64_windows_Nightly/8/consoleFull
```
21:27:44 openjdk version "17-internal" 2021-09-14
21:27:44 OpenJDK Runtime Environment (build 17-internal+0-adhoc.****.buildjdk17x86-64windowsnightly)
21:27:44 Eclipse OpenJ9 VM (build v0.28.0-release-18bebe9f4e3, JRE 17 Windows Server 2012 R2 amd64-64-Bit Compressed References 20210829_8 (JIT enabled, AOT enabled)
21:27:44 OpenJ9 - 18bebe9f4e3
21:27:44 OMR - 1d0a329
21:27:44 JCL - 712145ee3f5 based on jdk-17+35)
21:51:08 test DefaultStaticInvokeTest.testMethodHandleInvoke("TestClass7", "TestIF7.TestClass7"): failure
21:51:08 java.lang.NullPointerException: Cannot invoke "java.lang.invoke.MethodHandle.linkToVirtual(java.lang.Object, java.lang.Object, java.lang.invoke.MemberName)" because "<parameter1>" is null
21:51:08 at java.base/java.lang.invoke.LambdaForm$DMH/0x0000000000000000.invokeVirtual(LambdaForm$DMH)
21:51:08 at java.lang.invoke.LambdaForm$MH/0x0000000095dfc060.invoke(LambdaForm$MH)
21:51:08 at java.lang.invoke.LambdaForm$MH/0x0000000095ddf6f0.invoke_MT(LambdaForm$MH)
21:51:08 at DefaultStaticInvokeTest.testMethodHandleInvoke(DefaultStaticInvokeTest.java:169)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
21:51:08 at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
21:51:08 at java.base/java.lang.reflect.Method.invoke(Method.java:568)
21:51:08 at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
21:51:08 at org.testng.internal.TestInvoker.invokeMethod(TestInvoker.java:599)
21:51:08 at org.testng.internal.TestInvoker.invokeTestMethod(TestInvoker.java:174)
21:51:08 at org.testng.internal.MethodRunner.runInSequence(MethodRunner.java:46)
21:51:08 at org.testng.internal.TestInvoker$MethodInvocationAgent.invoke(TestInvoker.java:822)
21:51:08 at org.testng.internal.TestInvoker.invokeTestMethods(TestInvoker.java:147)
21:51:08 at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:146)
21:51:08 at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:128)
21:51:08 at org.testng.TestRunner$$Lambda$129/0x0000000096210428.accept(Unknown Source)
21:51:08 at java.base/java.util.ArrayList.forEach(ArrayList.java:1511)
21:51:08 at org.testng.TestRunner.privateRun(TestRunner.java:764)
21:51:08 at org.testng.TestRunner.run(TestRunner.java:585)
21:51:08 at org.testng.SuiteRunner.runTest(SuiteRunner.java:384)
21:51:08 at org.testng.SuiteRunner.runSequentially(SuiteRunner.java:378)
21:51:08 at org.testng.SuiteRunner.privateRun(SuiteRunner.java:337)
21:51:08 at org.testng.SuiteRunner.run(SuiteRunner.java:286)
21:51:08 at org.testng.SuiteRunnerWorker.runSuite(SuiteRunnerWorker.java:53)
21:51:08 at org.testng.SuiteRunnerWorker.run(SuiteRunnerWorker.java:96)
21:51:08 at org.testng.TestNG.runSuitesSequentially(TestNG.java:1218)
21:51:08 at org.testng.TestNG.runSuitesLocally(TestNG.java:1140)
21:51:08 at org.testng.TestNG.runSuites(TestNG.java:1069)
21:51:08 at org.testng.TestNG.run(TestNG.java:1037)
21:51:08 at com.sun.javatest.regtest.agent.TestNGRunner.main(TestNGRunner.java:94)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
21:51:08 at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
21:51:08 at java.base/java.lang.reflect.Method.invoke(Method.java:568)
21:51:08 at com.sun.javatest.regtest.agent.MainActionHelper$AgentVMRunnable.run(MainActionHelper.java:312)
21:51:08 at java.base/java.lang.Thread.run(Thread.java:884)
21:51:08 ===============================================
21:51:08 java/lang/reflect/DefaultStaticTest/DefaultStaticInvokeTest.java
21:51:08 Total tests run: 276, Passes: 274, Failures: 2, Skips: 0
21:51:08 ===============================================
21:51:08
21:51:08 STDERR:
21:51:08 java.lang.Exception: failures: 2
21:51:08 at com.sun.javatest.regtest.agent.TestNGRunner.main(TestNGRunner.java:96)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
21:51:08 at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
21:51:08 at java.base/java.lang.reflect.Method.invoke(Method.java:568)
21:51:08 at com.sun.javatest.regtest.agent.MainActionHelper$AgentVMRunnable.run(MainActionHelper.java:312)
21:51:08 at java.base/java.lang.Thread.run(Thread.java:884)
21:51:08
21:51:08 JavaTest Message: Test threw exception: java.lang.Exception
21:51:08 JavaTest Message: shutting down test
21:51:08
21:51:08
21:51:08 TEST RESULT: Failed. Execution failed: `main' threw exception: java.lang.Exception: failures: 2
21:51:08 --------------------------------------------------
21:54:09 Test results: passed: 766; failed: 1
21:54:10 Report written to F:\Users\jenkins\workspace\Test_openjdk17_j9_sanity.openjdk_x86-64_windows_Nightly\jvmtest\openjdk\report\html\report.html
21:54:10 Results written to F:\Users\jenkins\workspace\Test_openjdk17_j9_sanity.openjdk_x86-64_windows_Nightly\aqa-tests\TKG\output_16302870106882\jdk_lang_1\work
21:54:10 Error: Some tests failed or other problems occurred.
21:54:10
21:54:10 jdk_lang_1_FAILED
``` | 1.0 | NPE running DefaultStaticInvokeTest - Latest occurrence at https://openj9-jenkins.osuosl.org/job/Test_openjdk17_j9_sanity.openjdk_x86-64_windows_Nightly/8/consoleFull
```
21:27:44 openjdk version "17-internal" 2021-09-14
21:27:44 OpenJDK Runtime Environment (build 17-internal+0-adhoc.****.buildjdk17x86-64windowsnightly)
21:27:44 Eclipse OpenJ9 VM (build v0.28.0-release-18bebe9f4e3, JRE 17 Windows Server 2012 R2 amd64-64-Bit Compressed References 20210829_8 (JIT enabled, AOT enabled)
21:27:44 OpenJ9 - 18bebe9f4e3
21:27:44 OMR - 1d0a329
21:27:44 JCL - 712145ee3f5 based on jdk-17+35)
21:51:08 test DefaultStaticInvokeTest.testMethodHandleInvoke("TestClass7", "TestIF7.TestClass7"): failure
21:51:08 java.lang.NullPointerException: Cannot invoke "java.lang.invoke.MethodHandle.linkToVirtual(java.lang.Object, java.lang.Object, java.lang.invoke.MemberName)" because "<parameter1>" is null
21:51:08 at java.base/java.lang.invoke.LambdaForm$DMH/0x0000000000000000.invokeVirtual(LambdaForm$DMH)
21:51:08 at java.lang.invoke.LambdaForm$MH/0x0000000095dfc060.invoke(LambdaForm$MH)
21:51:08 at java.lang.invoke.LambdaForm$MH/0x0000000095ddf6f0.invoke_MT(LambdaForm$MH)
21:51:08 at DefaultStaticInvokeTest.testMethodHandleInvoke(DefaultStaticInvokeTest.java:169)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
21:51:08 at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
21:51:08 at java.base/java.lang.reflect.Method.invoke(Method.java:568)
21:51:08 at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
21:51:08 at org.testng.internal.TestInvoker.invokeMethod(TestInvoker.java:599)
21:51:08 at org.testng.internal.TestInvoker.invokeTestMethod(TestInvoker.java:174)
21:51:08 at org.testng.internal.MethodRunner.runInSequence(MethodRunner.java:46)
21:51:08 at org.testng.internal.TestInvoker$MethodInvocationAgent.invoke(TestInvoker.java:822)
21:51:08 at org.testng.internal.TestInvoker.invokeTestMethods(TestInvoker.java:147)
21:51:08 at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:146)
21:51:08 at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:128)
21:51:08 at org.testng.TestRunner$$Lambda$129/0x0000000096210428.accept(Unknown Source)
21:51:08 at java.base/java.util.ArrayList.forEach(ArrayList.java:1511)
21:51:08 at org.testng.TestRunner.privateRun(TestRunner.java:764)
21:51:08 at org.testng.TestRunner.run(TestRunner.java:585)
21:51:08 at org.testng.SuiteRunner.runTest(SuiteRunner.java:384)
21:51:08 at org.testng.SuiteRunner.runSequentially(SuiteRunner.java:378)
21:51:08 at org.testng.SuiteRunner.privateRun(SuiteRunner.java:337)
21:51:08 at org.testng.SuiteRunner.run(SuiteRunner.java:286)
21:51:08 at org.testng.SuiteRunnerWorker.runSuite(SuiteRunnerWorker.java:53)
21:51:08 at org.testng.SuiteRunnerWorker.run(SuiteRunnerWorker.java:96)
21:51:08 at org.testng.TestNG.runSuitesSequentially(TestNG.java:1218)
21:51:08 at org.testng.TestNG.runSuitesLocally(TestNG.java:1140)
21:51:08 at org.testng.TestNG.runSuites(TestNG.java:1069)
21:51:08 at org.testng.TestNG.run(TestNG.java:1037)
21:51:08 at com.sun.javatest.regtest.agent.TestNGRunner.main(TestNGRunner.java:94)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
21:51:08 at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
21:51:08 at java.base/java.lang.reflect.Method.invoke(Method.java:568)
21:51:08 at com.sun.javatest.regtest.agent.MainActionHelper$AgentVMRunnable.run(MainActionHelper.java:312)
21:51:08 at java.base/java.lang.Thread.run(Thread.java:884)
21:51:08 ===============================================
21:51:08 java/lang/reflect/DefaultStaticTest/DefaultStaticInvokeTest.java
21:51:08 Total tests run: 276, Passes: 274, Failures: 2, Skips: 0
21:51:08 ===============================================
21:51:08
21:51:08 STDERR:
21:51:08 java.lang.Exception: failures: 2
21:51:08 at com.sun.javatest.regtest.agent.TestNGRunner.main(TestNGRunner.java:96)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
21:51:08 at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:77)
21:51:08 at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
21:51:08 at java.base/java.lang.reflect.Method.invoke(Method.java:568)
21:51:08 at com.sun.javatest.regtest.agent.MainActionHelper$AgentVMRunnable.run(MainActionHelper.java:312)
21:51:08 at java.base/java.lang.Thread.run(Thread.java:884)
21:51:08
21:51:08 JavaTest Message: Test threw exception: java.lang.Exception
21:51:08 JavaTest Message: shutting down test
21:51:08
21:51:08
21:51:08 TEST RESULT: Failed. Execution failed: `main' threw exception: java.lang.Exception: failures: 2
21:51:08 --------------------------------------------------
21:54:09 Test results: passed: 766; failed: 1
21:54:10 Report written to F:\Users\jenkins\workspace\Test_openjdk17_j9_sanity.openjdk_x86-64_windows_Nightly\jvmtest\openjdk\report\html\report.html
21:54:10 Results written to F:\Users\jenkins\workspace\Test_openjdk17_j9_sanity.openjdk_x86-64_windows_Nightly\aqa-tests\TKG\output_16302870106882\jdk_lang_1\work
21:54:10 Error: Some tests failed or other problems occurred.
21:54:10
21:54:10 jdk_lang_1_FAILED
``` | non_priority | npe running defaultstaticinvoketest latest occurrence at openjdk version internal openjdk runtime environment build internal adhoc eclipse vm build release jre windows server bit compressed references jit enabled aot enabled omr jcl based on jdk test defaultstaticinvoketest testmethodhandleinvoke failure java lang nullpointerexception cannot invoke java lang invoke methodhandle linktovirtual java lang object java lang object java lang invoke membername because is null at java base java lang invoke lambdaform dmh invokevirtual lambdaform dmh at java lang invoke lambdaform mh invoke lambdaform mh at java lang invoke lambdaform mh invoke mt lambdaform mh at defaultstaticinvoketest testmethodhandleinvoke defaultstaticinvoketest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal testinvoker invokemethod testinvoker java at org testng internal testinvoker invoketestmethod testinvoker java at org testng internal methodrunner runinsequence methodrunner java at org testng internal testinvoker methodinvocationagent invoke testinvoker java at org testng internal testinvoker invoketestmethods testinvoker java at org testng internal testmethodworker invoketestmethods testmethodworker java at org testng internal testmethodworker run testmethodworker java at org testng testrunner lambda accept unknown source at java base java util arraylist foreach arraylist java at org testng testrunner privaterun testrunner java at org testng testrunner run testrunner java at org testng suiterunner runtest suiterunner java at org testng suiterunner runsequentially suiterunner java at org testng suiterunner privaterun suiterunner java at org testng suiterunner run suiterunner java at org testng suiterunnerworker runsuite suiterunnerworker java at org testng suiterunnerworker run suiterunnerworker java at org testng testng runsuitessequentially testng java at org testng testng runsuiteslocally testng java at org testng testng runsuites testng java at org testng testng run testng java at com sun javatest regtest agent testngrunner main testngrunner java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at com sun javatest regtest agent mainactionhelper agentvmrunnable run mainactionhelper java at java base java lang thread run thread java java lang reflect defaultstatictest defaultstaticinvoketest java total tests run passes failures skips stderr java lang exception failures at com sun javatest regtest agent testngrunner main testngrunner java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at com sun javatest regtest agent mainactionhelper agentvmrunnable run mainactionhelper java at java base java lang thread run thread java javatest message test threw exception java lang exception javatest message shutting down test test result failed execution failed main threw exception java lang exception failures test results passed failed report written to f users jenkins workspace test sanity openjdk windows nightly jvmtest openjdk report html report html results written to f users jenkins workspace test sanity openjdk windows nightly aqa tests tkg output jdk lang work error some tests failed or other problems occurred jdk lang failed | 0 |
261,390 | 27,809,753,908 | IssuesEvent | 2023-03-18 01:38:16 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | closed | CVE-2022-3524 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed | Mend: dependency security vulnerability | ## CVE-2022-3524 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in Linux Kernel. It has been declared as problematic. Affected by this vulnerability is the function ipv6_renew_options of the component IPv6 Handler. The manipulation leads to memory leak. The attack can be launched remotely. It is recommended to apply a patch to fix this issue. The identifier VDB-211021 was assigned to this vulnerability.
<p>Publish Date: 2022-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3524>CVE-2022-3524</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-3524">https://www.linuxkernelcves.com/cves/CVE-2022-3524</a></p>
<p>Release Date: 2022-10-16</p>
<p>Fix Resolution: v4.9.335,v4.14.301,v4.19.268,v5.4.224,v5.10.154,v5.15.77,v6.0.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-3524 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2022-3524 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in Linux Kernel. It has been declared as problematic. Affected by this vulnerability is the function ipv6_renew_options of the component IPv6 Handler. The manipulation leads to memory leak. The attack can be launched remotely. It is recommended to apply a patch to fix this issue. The identifier VDB-211021 was assigned to this vulnerability.
<p>Publish Date: 2022-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3524>CVE-2022-3524</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-3524">https://www.linuxkernelcves.com/cves/CVE-2022-3524</a></p>
<p>Release Date: 2022-10-16</p>
<p>Fix Resolution: v4.9.335,v4.14.301,v4.19.268,v5.4.224,v5.10.154,v5.15.77,v6.0.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files net sockglue c net sockglue c vulnerability details a vulnerability was found in linux kernel it has been declared as problematic affected by this vulnerability is the function renew options of the component handler the manipulation leads to memory leak the attack can be launched remotely it is recommended to apply a patch to fix this issue the identifier vdb was assigned to this vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
225,042 | 24,807,279,124 | IssuesEvent | 2022-10-25 06:22:49 | sast-automation-dev/WebGoat-Legacy-45 | https://api.github.com/repos/sast-automation-dev/WebGoat-Legacy-45 | opened | jquery-1.10.2.min.js: 4 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.10.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-11023](https://www.mend.io/vulnerability-database/CVE-2020-11023) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jquery - 3.5.0 | ❌ |
| [CVE-2020-11022](https://www.mend.io/vulnerability-database/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://www.mend.io/vulnerability-database/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - v3.0.0 | ❌ |
| [CVE-2019-11358](https://www.mend.io/vulnerability-database/CVE-2019-11358) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11023</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-11358</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | True | jquery-1.10.2.min.js: 4 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.10.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-11023](https://www.mend.io/vulnerability-database/CVE-2020-11023) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jquery - 3.5.0 | ❌ |
| [CVE-2020-11022](https://www.mend.io/vulnerability-database/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://www.mend.io/vulnerability-database/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | jQuery - v3.0.0 | ❌ |
| [CVE-2019-11358](https://www.mend.io/vulnerability-database/CVE-2019-11358) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jquery-1.10.2.min.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11023</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-11358</summary>
### Vulnerable Library - <b>jquery-1.10.2.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to dependency file: /newDesign/index.html</p>
<p>Path to vulnerable library: /src/main/webapp/js/jquery/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js,/newDesign/assets/js/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/WebGoat-Legacy-45/commit/43d50a625701e158279691502ea272f61e7eb5a9">43d50a625701e158279691502ea272f61e7eb5a9</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | non_priority | jquery min js vulnerabilities highest severity is vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library src main webapp js jquery jquery min js newdesign assets js jquery min js newdesign assets js jquery min js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in jquery version remediation available medium jquery min js direct jquery medium jquery min js direct jquery medium jquery min js direct jquery medium jquery min js direct details cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library src main webapp js jquery jquery min js newdesign assets js jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library src main webapp js jquery jquery min js newdesign assets js jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library src main webapp js jquery jquery min js newdesign assets js jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery cve vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file newdesign index html path to vulnerable library src main webapp js jquery jquery min js newdesign assets js jquery min js newdesign assets js jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
44,293 | 7,103,525,192 | IssuesEvent | 2018-01-16 05:41:33 | nwjs/nw.js | https://api.github.com/repos/nwjs/nw.js | closed | Allow more communication with embedded devtools | P2 documentation feature-request test-todo | Currently when for the webview embedded devtools, you have only a simple webview.showDevTools(show, [container]) API call.
Please add more extended API for controlling and communicating to the devtools.
@rogerwang We need at least methods to inspectElement(x,y), inspectElement(domNode) and/or inspectElementByQuerySelector(selector) but access to the blackboxed: chrome.devtools api as well settings of the devtools will be really nice.
Electron have already much more extensive about about this: https://github.com/electron/electron/blob/master/docs/api/web-contents.md#webcontentsinspectelementx-y
Thank you!
| 1.0 | Allow more communication with embedded devtools - Currently when for the webview embedded devtools, you have only a simple webview.showDevTools(show, [container]) API call.
Please add more extended API for controlling and communicating to the devtools.
@rogerwang We need at least methods to inspectElement(x,y), inspectElement(domNode) and/or inspectElementByQuerySelector(selector) but access to the blackboxed: chrome.devtools api as well settings of the devtools will be really nice.
Electron have already much more extensive about about this: https://github.com/electron/electron/blob/master/docs/api/web-contents.md#webcontentsinspectelementx-y
Thank you!
| non_priority | allow more communication with embedded devtools currently when for the webview embedded devtools you have only a simple webview showdevtools show api call please add more extended api for controlling and communicating to the devtools rogerwang we need at least methods to inspectelement x y inspectelement domnode and or inspectelementbyqueryselector selector but access to the blackboxed chrome devtools api as well settings of the devtools will be really nice electron have already much more extensive about about this thank you | 0 |
444,901 | 31,155,072,408 | IssuesEvent | 2023-08-16 12:39:04 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | reopened | Document recommendations for shared Kyma cluster usage | area/documentation Epic | **Description**
Document guidance on how to share a Kyma cluster between different teams.
**Reasons**
Our users have expressed interest in sharing a single cluster between different teams.
While Kubernetes does not provide the necessary isolation to provide effective separation within the cluster, we should provide guidance on best practices and potential pitfalls when attempting to share a cluster.
**Acceptance Criteria**
- [ ] Document recommended configuration for sharing a cluster.
- [ ] Document limitations to how much isolation between teams is possible.
- [ ] Document example scenarios where sharing a cluster is acceptable.
**Links**
[Initial issue](https://jira.tools.sap/browse/BITFRTECHNOLOGY-1225)
[Additional findings](https://github.com/kyma-project/busola/issues/1832)
[Additional findings](https://github.com/SAP-docs/btp-cloud-platform/issues/103)
---
<details>
<summary>:warning: Funnel process - do not remove!</summary>
</br>
Name|Value
:--- | :---
theme | Enterprise-grade
business value | 5
technical value | 0
user value | 5
open-source value | 5
effort |
requested by |
</details>
| 1.0 | Document recommendations for shared Kyma cluster usage - **Description**
Document guidance on how to share a Kyma cluster between different teams.
**Reasons**
Our users have expressed interest in sharing a single cluster between different teams.
While Kubernetes does not provide the necessary isolation to provide effective separation within the cluster, we should provide guidance on best practices and potential pitfalls when attempting to share a cluster.
**Acceptance Criteria**
- [ ] Document recommended configuration for sharing a cluster.
- [ ] Document limitations to how much isolation between teams is possible.
- [ ] Document example scenarios where sharing a cluster is acceptable.
**Links**
[Initial issue](https://jira.tools.sap/browse/BITFRTECHNOLOGY-1225)
[Additional findings](https://github.com/kyma-project/busola/issues/1832)
[Additional findings](https://github.com/SAP-docs/btp-cloud-platform/issues/103)
---
<details>
<summary>:warning: Funnel process - do not remove!</summary>
</br>
Name|Value
:--- | :---
theme | Enterprise-grade
business value | 5
technical value | 0
user value | 5
open-source value | 5
effort |
requested by |
</details>
| non_priority | document recommendations for shared kyma cluster usage description document guidance on how to share a kyma cluster between different teams reasons our users have expressed interest in sharing a single cluster between different teams while kubernetes does not provide the necessary isolation to provide effective separation within the cluster we should provide guidance on best practices and potential pitfalls when attempting to share a cluster acceptance criteria document recommended configuration for sharing a cluster document limitations to how much isolation between teams is possible document example scenarios where sharing a cluster is acceptable links warning funnel process do not remove name value theme enterprise grade business value technical value user value open source value effort requested by | 0 |
122,765 | 10,235,849,279 | IssuesEvent | 2019-08-19 10:06:15 | mozilla/iris_firefox | https://api.github.com/repos/mozilla/iris_firefox | reopened | Fix drag_and_drop_bookmark_from_toolbar | test case |
drag_and_drop_bookmark_from_toolbar - Drag and drop a bookmark from 'Bookmark Toolbar' By: Ionut Budeanu
--
1 | 3:28:47 AM | None - [Actual]: None [Expected]: None
| 1.0 | Fix drag_and_drop_bookmark_from_toolbar -
drag_and_drop_bookmark_from_toolbar - Drag and drop a bookmark from 'Bookmark Toolbar' By: Ionut Budeanu
--
1 | 3:28:47 AM | None - [Actual]: None [Expected]: None
| non_priority | fix drag and drop bookmark from toolbar drag and drop bookmark from toolbar drag and drop a bookmark from bookmark toolbar by ionut budeanu am none none none | 0 |
53,093 | 10,988,316,761 | IssuesEvent | 2019-12-02 10:58:24 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | Upgrade to H2 1.4.201 | C: Code Generation C: DB: H2 E: All Editions P: Medium T: Enhancement | H2 version 1.4.201 has not been released yet, but some significant changes to the `INFORMATION_SCHEMA` layout have already been committed, which will mostly affect the `H2Database` in `jOOQ-meta` and thus the code generator. Summary of changes: https://github.com/h2database/h2database/issues/2286#issuecomment-560286207
It would make sense for the `H2Database` to still support older (pre 1.4.201) versions H2 for some time. | 1.0 | Upgrade to H2 1.4.201 - H2 version 1.4.201 has not been released yet, but some significant changes to the `INFORMATION_SCHEMA` layout have already been committed, which will mostly affect the `H2Database` in `jOOQ-meta` and thus the code generator. Summary of changes: https://github.com/h2database/h2database/issues/2286#issuecomment-560286207
It would make sense for the `H2Database` to still support older (pre 1.4.201) versions H2 for some time. | non_priority | upgrade to version has not been released yet but some significant changes to the information schema layout have already been committed which will mostly affect the in jooq meta and thus the code generator summary of changes it would make sense for the to still support older pre versions for some time | 0 |
172,234 | 21,043,281,560 | IssuesEvent | 2022-03-31 14:03:38 | jgeraigery/dynatrace-service-broker | https://api.github.com/repos/jgeraigery/dynatrace-service-broker | opened | CVE-2017-5664 (High) detected in tomcat-embed-core-8.0.15.jar | security vulnerability | ## CVE-2017-5664 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.0.15.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.0.15/tomcat-embed-core-8.0.15.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.1.9.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.1.9.RELEASE.jar
- :x: **tomcat-embed-core-8.0.15.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/dynatrace-service-broker/commit/075c652078643180fb05751cdbc793df371d6844">075c652078643180fb05751cdbc793df371d6844</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.
<p>Publish Date: 2017-06-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664>CVE-2017-5664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664</a></p>
<p>Release Date: 2017-06-06</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.0.15","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.1.9.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.1.9.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.0.15","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-5664","vulnerabilityDetails":"The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-5664 (High) detected in tomcat-embed-core-8.0.15.jar - ## CVE-2017-5664 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.0.15.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.0.15/tomcat-embed-core-8.0.15.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.1.9.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.1.9.RELEASE.jar
- :x: **tomcat-embed-core-8.0.15.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/dynatrace-service-broker/commit/075c652078643180fb05751cdbc793df371d6844">075c652078643180fb05751cdbc793df371d6844</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.
<p>Publish Date: 2017-06-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664>CVE-2017-5664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664</a></p>
<p>Release Date: 2017-06-06</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.0.15","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.1.9.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.1.9.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.0.15","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-5664","vulnerabilityDetails":"The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details the error page mechanism of the java servlet specification requires that when an error occurs and an error page is configured for the error that occurred the original request and response are forwarded to the error page this means that the request is presented to the error page with the original http method if the error page is a static file expected behaviour is to serve content of the file as if processing a get request regardless of the actual http method the default servlet in apache tomcat to to to and to did not do this depending on the original request this could lead to unexpected and undesirable results for static error pages including if the defaultservlet is configured to permit writes the replacement or removal of the custom error page notes for other user provided error pages unless explicitly coded otherwise jsps ignore the http method jsps used as error pages must must ensure that they handle any error dispatch as a get request regardless of the actual method by default the response generated by a servlet does depend on the http method custom servlets used as error pages must ensure that they handle any error dispatch as a get request regardless of the actual method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the error page mechanism of the java servlet specification requires that when an error occurs and an error page is configured for the error that occurred the original request and response are forwarded to the error page this means that the request is presented to the error page with the original http method if the error page is a static file expected behaviour is to serve content of the file as if processing a get request regardless of the actual http method the default servlet in apache tomcat to to to and to did not do this depending on the original request this could lead to unexpected and undesirable results for static error pages including if the defaultservlet is configured to permit writes the replacement or removal of the custom error page notes for other user provided error pages unless explicitly coded otherwise jsps ignore the http method jsps used as error pages must must ensure that they handle any error dispatch as a get request regardless of the actual method by default the response generated by a servlet does depend on the http method custom servlets used as error pages must ensure that they handle any error dispatch as a get request regardless of the actual method vulnerabilityurl | 0 |
58,415 | 7,137,480,454 | IssuesEvent | 2018-01-23 11:09:03 | nextcloud/spreed | https://api.github.com/repos/nextcloud/spreed | closed | Thoughts about the chat UI | design enhancement feature: chat | I just tried the latest version of the chat and it works really good! 😃
During test I found some visual stuff which I think could be improved.
This is how the chat window looks for a guest:

I think the icon of the current user should be next to the input field, not above. I saw that for a logged in user we show the user name next to the icon but for the guest user the name is on the top, quite confusing. Also on top the "copy icon", the user name and the "join call" button looks a bit randomly listed and squeezed together.
A general note about the chat window: I would put the input field on the bottom and scroll the messages from the bottom to the top, like most messengers does.
This is the chat window for a logged in user:

I was a bit confused that at the top I read "You". It looks like it is related to me as a user. Maybe my current display name for the chat? Only after changing it I realized that it is the room name.
Further I don't think we need to have the user name next to the avatar, instead I would just put the avatar left to the input field. We could show the user name on hover if we want to.
Same as on the public page also here the text/input fields at the top looks like randomly put next to each other. I think we should add some structure there.
cc @nextcloud/designers | 1.0 | Thoughts about the chat UI - I just tried the latest version of the chat and it works really good! 😃
During test I found some visual stuff which I think could be improved.
This is how the chat window looks for a guest:

I think the icon of the current user should be next to the input field, not above. I saw that for a logged in user we show the user name next to the icon but for the guest user the name is on the top, quite confusing. Also on top the "copy icon", the user name and the "join call" button looks a bit randomly listed and squeezed together.
A general note about the chat window: I would put the input field on the bottom and scroll the messages from the bottom to the top, like most messengers does.
This is the chat window for a logged in user:

I was a bit confused that at the top I read "You". It looks like it is related to me as a user. Maybe my current display name for the chat? Only after changing it I realized that it is the room name.
Further I don't think we need to have the user name next to the avatar, instead I would just put the avatar left to the input field. We could show the user name on hover if we want to.
Same as on the public page also here the text/input fields at the top looks like randomly put next to each other. I think we should add some structure there.
cc @nextcloud/designers | non_priority | thoughts about the chat ui i just tried the latest version of the chat and it works really good 😃 during test i found some visual stuff which i think could be improved this is how the chat window looks for a guest i think the icon of the current user should be next to the input field not above i saw that for a logged in user we show the user name next to the icon but for the guest user the name is on the top quite confusing also on top the copy icon the user name and the join call button looks a bit randomly listed and squeezed together a general note about the chat window i would put the input field on the bottom and scroll the messages from the bottom to the top like most messengers does this is the chat window for a logged in user i was a bit confused that at the top i read you it looks like it is related to me as a user maybe my current display name for the chat only after changing it i realized that it is the room name further i don t think we need to have the user name next to the avatar instead i would just put the avatar left to the input field we could show the user name on hover if we want to same as on the public page also here the text input fields at the top looks like randomly put next to each other i think we should add some structure there cc nextcloud designers | 0 |
410,089 | 27,766,899,615 | IssuesEvent | 2023-03-16 12:05:02 | ethereum/solidity | https://api.github.com/repos/ethereum/solidity | closed | More detailed libevmasm and libyul optimiser step descriptions in Standard JSON docs | documentation :book: low effort medium impact should have closed-due-inactivity stale | As [discussed on twitter](
https://twitter.com/alexberegszaszi/status/1306681715767865344) auditors are still afraid of the optimiser and currently we only have a [verify brief description hidden within standard json](https://solidity.readthedocs.io/en/v0.7.1/using-the-compiler.html#input-description):
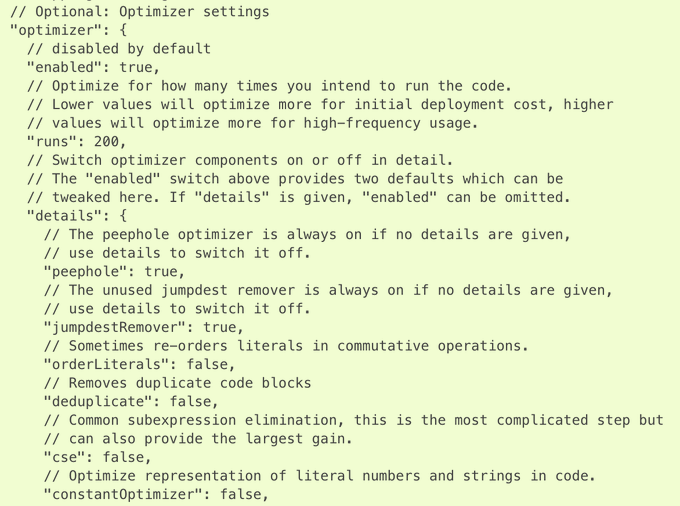
We should create a section under internals explaining all the libevmasm optimiser steps. Later we should extend it with the libyul steps too.
| 1.0 | More detailed libevmasm and libyul optimiser step descriptions in Standard JSON docs - As [discussed on twitter](
https://twitter.com/alexberegszaszi/status/1306681715767865344) auditors are still afraid of the optimiser and currently we only have a [verify brief description hidden within standard json](https://solidity.readthedocs.io/en/v0.7.1/using-the-compiler.html#input-description):
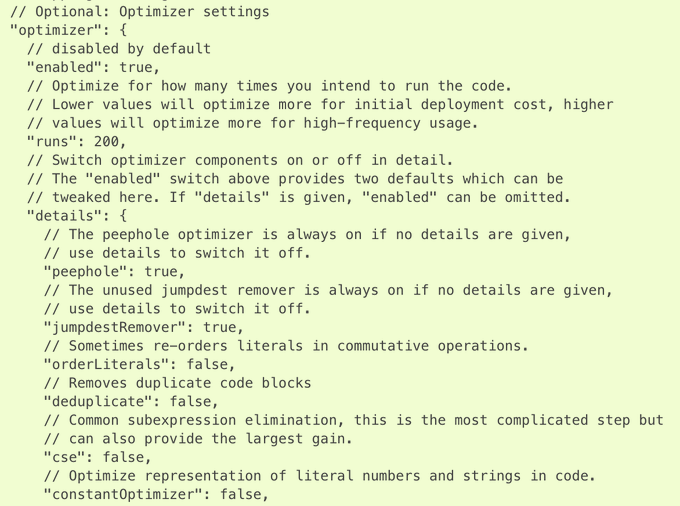
We should create a section under internals explaining all the libevmasm optimiser steps. Later we should extend it with the libyul steps too.
| non_priority | more detailed libevmasm and libyul optimiser step descriptions in standard json docs as auditors are still afraid of the optimiser and currently we only have a we should create a section under internals explaining all the libevmasm optimiser steps later we should extend it with the libyul steps too | 0 |
97,109 | 10,981,352,357 | IssuesEvent | 2019-11-30 21:07:49 | engnogueira/libpythonpro | https://api.github.com/repos/engnogueira/libpythonpro | closed | 3.3 - Flake8 | documentation | Nesse capítulo você vai aprender o que são Dependências. Confira como instalar bibliotecas de terceiros para reutilizar código, como instalar e gerir dependências para outros projetos e como publicar se código no PyPi | 1.0 | 3.3 - Flake8 - Nesse capítulo você vai aprender o que são Dependências. Confira como instalar bibliotecas de terceiros para reutilizar código, como instalar e gerir dependências para outros projetos e como publicar se código no PyPi | non_priority | nesse capítulo você vai aprender o que são dependências confira como instalar bibliotecas de terceiros para reutilizar código como instalar e gerir dependências para outros projetos e como publicar se código no pypi | 0 |
184,937 | 32,074,447,943 | IssuesEvent | 2023-09-25 10:04:13 | ks-fe/smart-factoria | https://api.github.com/repos/ks-fe/smart-factoria | closed | 로그인 페이지 UI 및 기능 구현 | 🎨 Design ✨ Feature | # Progress
- [x] 로그인 페이지 UI 구현
- [x] MUI TextInput 컴포넌트 커스텀하여 시안대로 구현
- [x] 로그인 페이지 기능 구현
- [x] 아이디(4자 이상 20자 이하), 비밀번호(8자 이상 20자 이하) 길이가 맞을 시 로그인 버튼 활성화
- [x] 로그인 성공 시 직전 페이지 이동 - 우선 메인 페이지로 이동하도록 구현
- [x] 실패 시 적절한 UI로 알려주기
- [x] 로그인 버튼 클릭 시 로그인 POST 요청
- [x] 유저 정보 (이름, 아이디, 토큰, 프로필 이미지 URL) 임시로 LocalStorage에 저장
- [x] PrivateAxiosInstance 생성
- [x] 로그인 후
- [x] GNB 프로필 사진 변경, 드롭다운 메뉴 변경
| 1.0 | 로그인 페이지 UI 및 기능 구현 - # Progress
- [x] 로그인 페이지 UI 구현
- [x] MUI TextInput 컴포넌트 커스텀하여 시안대로 구현
- [x] 로그인 페이지 기능 구현
- [x] 아이디(4자 이상 20자 이하), 비밀번호(8자 이상 20자 이하) 길이가 맞을 시 로그인 버튼 활성화
- [x] 로그인 성공 시 직전 페이지 이동 - 우선 메인 페이지로 이동하도록 구현
- [x] 실패 시 적절한 UI로 알려주기
- [x] 로그인 버튼 클릭 시 로그인 POST 요청
- [x] 유저 정보 (이름, 아이디, 토큰, 프로필 이미지 URL) 임시로 LocalStorage에 저장
- [x] PrivateAxiosInstance 생성
- [x] 로그인 후
- [x] GNB 프로필 사진 변경, 드롭다운 메뉴 변경
| non_priority | 로그인 페이지 ui 및 기능 구현 progress 로그인 페이지 ui 구현 mui textinput 컴포넌트 커스텀하여 시안대로 구현 로그인 페이지 기능 구현 아이디 이상 이하 비밀번호 이상 이하 길이가 맞을 시 로그인 버튼 활성화 로그인 성공 시 직전 페이지 이동 우선 메인 페이지로 이동하도록 구현 실패 시 적절한 ui로 알려주기 로그인 버튼 클릭 시 로그인 post 요청 유저 정보 이름 아이디 토큰 프로필 이미지 url 임시로 localstorage에 저장 privateaxiosinstance 생성 로그인 후 gnb 프로필 사진 변경 드롭다운 메뉴 변경 | 0 |
121,773 | 12,133,853,191 | IssuesEvent | 2020-04-23 09:43:37 | libuweber/microgateway | https://api.github.com/repos/libuweber/microgateway | closed | README.md | documentation | Documentation of the DSL Configuration.
- Configure Default DSL
- Configure app
- Configure Custom DSL | 1.0 | README.md - Documentation of the DSL Configuration.
- Configure Default DSL
- Configure app
- Configure Custom DSL | non_priority | readme md documentation of the dsl configuration configure default dsl configure app configure custom dsl | 0 |
161,611 | 20,154,164,175 | IssuesEvent | 2022-02-09 15:04:04 | kapseliboi/OSMBuildings | https://api.github.com/repos/kapseliboi/OSMBuildings | opened | CVE-2021-23337 (High) detected in lodash-4.17.15.tgz, lodash-2.4.2.tgz | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.15.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- documentation-5.5.0.tgz (Root Library)
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/zip-stream/node_modules/lodash/package.json,/node_modules/archiver/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- zip-folder-1.0.0.tgz (Root Library)
- archiver-0.11.0.tgz
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/OSMBuildings/commit/dfd1435f55d83fa05bb3c8833d662571b61c72e8">dfd1435f55d83fa05bb3c8833d662571b61c72e8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (documentation): 6.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23337 (High) detected in lodash-4.17.15.tgz, lodash-2.4.2.tgz - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.15.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.15.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- documentation-5.5.0.tgz (Root Library)
- :x: **lodash-4.17.15.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/zip-stream/node_modules/lodash/package.json,/node_modules/archiver/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- zip-folder-1.0.0.tgz (Root Library)
- archiver-0.11.0.tgz
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/OSMBuildings/commit/dfd1435f55d83fa05bb3c8833d662571b61c72e8">dfd1435f55d83fa05bb3c8833d662571b61c72e8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution (lodash): 4.17.21</p>
<p>Direct dependency fix Resolution (documentation): 6.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in lodash tgz lodash tgz cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file package json path to vulnerable library node modules lodash package json dependency hierarchy documentation tgz root library x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file package json path to vulnerable library node modules zip stream node modules lodash package json node modules archiver node modules lodash package json dependency hierarchy zip folder tgz root library archiver tgz x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash direct dependency fix resolution documentation step up your open source security game with whitesource | 0 |
147,267 | 13,204,760,279 | IssuesEvent | 2020-08-14 16:31:41 | kiudee/chess-tuning-tools | https://api.github.com/repos/kiudee/chess-tuning-tools | opened | Recommendations regarding tuning/calibration conditions | documentation | - How to calibrate the engines for tuning?
- What is a recommended balance to aim for?
| 1.0 | Recommendations regarding tuning/calibration conditions - - How to calibrate the engines for tuning?
- What is a recommended balance to aim for?
| non_priority | recommendations regarding tuning calibration conditions how to calibrate the engines for tuning what is a recommended balance to aim for | 0 |
55,348 | 30,709,209,797 | IssuesEvent | 2023-07-27 08:36:49 | gear-tech/gear | https://api.github.com/repos/gear-tech/gear | opened | Do research on `tail-call` and mb enable it in `wasm-builder` | D7-performance | spec: https://github.com/WebAssembly/tail-call
both `wasmer` and `wasmi` have supported `tail-call`, we can enable the tail-call optimization in wasm-opt with flag `--enable-tail-call`, this could be an optimization for the program size as well | True | Do research on `tail-call` and mb enable it in `wasm-builder` - spec: https://github.com/WebAssembly/tail-call
both `wasmer` and `wasmi` have supported `tail-call`, we can enable the tail-call optimization in wasm-opt with flag `--enable-tail-call`, this could be an optimization for the program size as well | non_priority | do research on tail call and mb enable it in wasm builder spec both wasmer and wasmi have supported tail call we can enable the tail call optimization in wasm opt with flag enable tail call this could be an optimization for the program size as well | 0 |
431,241 | 30,224,252,310 | IssuesEvent | 2023-07-05 22:15:24 | louiiuol/lmc-ui | https://api.github.com/repos/louiiuol/lmc-ui | opened | Sitemap | documentation | ## Contexte 📝
> Définition du `sitemap` sommaire de l'application web (pour les sections public et customer)
## A faire 💪
- Intégrer le diagramme Figma
## Informations complémentaires 🔎 | 1.0 | Sitemap - ## Contexte 📝
> Définition du `sitemap` sommaire de l'application web (pour les sections public et customer)
## A faire 💪
- Intégrer le diagramme Figma
## Informations complémentaires 🔎 | non_priority | sitemap contexte 📝 définition du sitemap sommaire de l application web pour les sections public et customer a faire 💪 intégrer le diagramme figma informations complémentaires 🔎 | 0 |
80,687 | 30,485,212,546 | IssuesEvent | 2023-07-18 01:11:19 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Sessions manager's inline action buttons are not aligned | T-Defect S-Minor Help Wanted O-Frequent | ### Steps to reproduce
1. Open `Sessions` user settings tab
2. Check `Sessions` on the filtered device list header
### Outcome
#### What did you expect?
The inline buttons should be aligned to the center

#### What happened instead?
They are aligned to the top

### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
develop.element.io
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | Sessions manager's inline action buttons are not aligned - ### Steps to reproduce
1. Open `Sessions` user settings tab
2. Check `Sessions` on the filtered device list header
### Outcome
#### What did you expect?
The inline buttons should be aligned to the center

#### What happened instead?
They are aligned to the top

### Operating system
_No response_
### Browser information
_No response_
### URL for webapp
develop.element.io
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
No | non_priority | sessions manager s inline action buttons are not aligned steps to reproduce open sessions user settings tab check sessions on the filtered device list header outcome what did you expect the inline buttons should be aligned to the center what happened instead they are aligned to the top operating system no response browser information no response url for webapp develop element io application version no response homeserver no response will you send logs no | 0 |
329,447 | 28,243,664,382 | IssuesEvent | 2023-04-06 09:07:17 | memorysafety/rav1d | https://api.github.com/repos/memorysafety/rav1d | opened | Test builds with assembly disabled | testing | We generally need to test more combinations of features such as assembly on/off to catch more problems. | 1.0 | Test builds with assembly disabled - We generally need to test more combinations of features such as assembly on/off to catch more problems. | non_priority | test builds with assembly disabled we generally need to test more combinations of features such as assembly on off to catch more problems | 0 |
246,672 | 26,612,017,435 | IssuesEvent | 2023-01-24 01:27:44 | artsking/linux-4.1.15 | https://api.github.com/repos/artsking/linux-4.1.15 | reopened | CVE-2019-19043 (Medium) detected in fedorav4.6 | security vulnerability | ## CVE-2019-19043 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fedorav4.6</b></p></summary>
<p>
<p>Fedora kernel git tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/jwboyer/fedora.git>https://git.kernel.org/pub/scm/linux/kernel/git/jwboyer/fedora.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.1.15/commit/b1c15f7dc4cfe553aeed8332e46f285ee92b5756">b1c15f7dc4cfe553aeed8332e46f285ee92b5756</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/intel/i40e/i40e_main.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/intel/i40e/i40e_main.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the i40e_setup_macvlans() function in drivers/net/ethernet/intel/i40e/i40e_main.c in the Linux kernel through 5.3.11 allows attackers to cause a denial of service (memory consumption) by triggering i40e_setup_channel() failures, aka CID-27d461333459.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19043>CVE-2019-19043</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19043">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19043</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.5-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19043 (Medium) detected in fedorav4.6 - ## CVE-2019-19043 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fedorav4.6</b></p></summary>
<p>
<p>Fedora kernel git tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/jwboyer/fedora.git>https://git.kernel.org/pub/scm/linux/kernel/git/jwboyer/fedora.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.1.15/commit/b1c15f7dc4cfe553aeed8332e46f285ee92b5756">b1c15f7dc4cfe553aeed8332e46f285ee92b5756</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/intel/i40e/i40e_main.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ethernet/intel/i40e/i40e_main.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the i40e_setup_macvlans() function in drivers/net/ethernet/intel/i40e/i40e_main.c in the Linux kernel through 5.3.11 allows attackers to cause a denial of service (memory consumption) by triggering i40e_setup_channel() failures, aka CID-27d461333459.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19043>CVE-2019-19043</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19043">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-19043</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.5-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library fedora kernel git tree library home page a href found in head commit a href found in base branch master vulnerable source files drivers net ethernet intel main c drivers net ethernet intel main c vulnerability details a memory leak in the setup macvlans function in drivers net ethernet intel main c in the linux kernel through allows attackers to cause a denial of service memory consumption by triggering setup channel failures aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
70,037 | 22,796,062,094 | IssuesEvent | 2022-07-10 18:35:37 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | transactionProducer does not commit transaction | T: Defect | ### Expected behavior
After a transactionProducer has been executed (e.g. blocked on) and completes normally, the updates should be committed and visible to later queries.
### Actual behavior
transactionProducer does not seem to commit, meaning updates are lost.
It also logs all sorts of `io.r2dbc.spi.R2dbcNonTransientResourceException: Connection is broken: "session closed"` errors but these don't seem to bubble up as exceptions in the test.
### Steps to reproduce the problem
MVCE incoming
### Versions
- jOOQ: 3.17.2
- Java: openjdk17
- Database (include vendor): have tested against h2 and postgres 12
- OS: ubuntu 20.04
- JDBC Driver (include name if unofficial driver): r2dbc-h2 0.9.1.RELEASE, r2dbc-postgres 0.9.1.RELEASE
| 1.0 | transactionProducer does not commit transaction - ### Expected behavior
After a transactionProducer has been executed (e.g. blocked on) and completes normally, the updates should be committed and visible to later queries.
### Actual behavior
transactionProducer does not seem to commit, meaning updates are lost.
It also logs all sorts of `io.r2dbc.spi.R2dbcNonTransientResourceException: Connection is broken: "session closed"` errors but these don't seem to bubble up as exceptions in the test.
### Steps to reproduce the problem
MVCE incoming
### Versions
- jOOQ: 3.17.2
- Java: openjdk17
- Database (include vendor): have tested against h2 and postgres 12
- OS: ubuntu 20.04
- JDBC Driver (include name if unofficial driver): r2dbc-h2 0.9.1.RELEASE, r2dbc-postgres 0.9.1.RELEASE
| non_priority | transactionproducer does not commit transaction expected behavior after a transactionproducer has been executed e g blocked on and completes normally the updates should be committed and visible to later queries actual behavior transactionproducer does not seem to commit meaning updates are lost it also logs all sorts of io spi connection is broken session closed errors but these don t seem to bubble up as exceptions in the test steps to reproduce the problem mvce incoming versions jooq java database include vendor have tested against and postgres os ubuntu jdbc driver include name if unofficial driver release postgres release | 0 |
165,434 | 12,842,555,647 | IssuesEvent | 2020-07-08 02:20:29 | VOLTTRON/volttron | https://api.github.com/repos/VOLTTRON/volttron | closed | New plotting switches to dark theme automatically | test needed | Selecting a point to Chart switches the user interface to a dark theme in VC, there's no option to disable this that I'm aware of? Was it meant to just switch the container for the plot? It's currently turning the whole screen dark.
Weirdly screen shots are showing correctly? Must be a Chrome/Windows issue?


| 1.0 | New plotting switches to dark theme automatically - Selecting a point to Chart switches the user interface to a dark theme in VC, there's no option to disable this that I'm aware of? Was it meant to just switch the container for the plot? It's currently turning the whole screen dark.
Weirdly screen shots are showing correctly? Must be a Chrome/Windows issue?


| non_priority | new plotting switches to dark theme automatically selecting a point to chart switches the user interface to a dark theme in vc there s no option to disable this that i m aware of was it meant to just switch the container for the plot it s currently turning the whole screen dark weirdly screen shots are showing correctly must be a chrome windows issue | 0 |
211,736 | 23,837,832,794 | IssuesEvent | 2022-09-06 07:46:50 | RG4421/jobcoin-boilerplate | https://api.github.com/repos/RG4421/jobcoin-boilerplate | opened | WS-2021-0638 (Medium) detected in mocha-5.0.5.tgz | security vulnerability | ## WS-2021-0638 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-5.0.5.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-5.0.5.tgz">https://registry.npmjs.org/mocha/-/mocha-5.0.5.tgz</a></p>
<p>Path to dependency file: /node/package.json</p>
<p>Path to vulnerable library: /node/node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-5.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/jobcoin-boilerplate/commit/18b55726c485ed21ac52765d485039bed16c1846">18b55726c485ed21ac52765d485039bed16c1846</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is regular Expression Denial of Service (ReDoS) vulnerability in mocha.
It allows cause a denial of service when stripping crafted invalid function definition from strs.
<p>Publish Date: 2021-09-18
<p>URL: <a href=https://github.com/mochajs/mocha/commit/61b4b9209c2c64b32c8d48b1761c3b9384d411ea>WS-2021-0638</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/1d8a3d95-d199-4129-a6ad-8eafe5e77b9e/">https://huntr.dev/bounties/1d8a3d95-d199-4129-a6ad-8eafe5e77b9e/</a></p>
<p>Release Date: 2021-09-18</p>
<p>Fix Resolution: 6.0.0-0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | WS-2021-0638 (Medium) detected in mocha-5.0.5.tgz - ## WS-2021-0638 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-5.0.5.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-5.0.5.tgz">https://registry.npmjs.org/mocha/-/mocha-5.0.5.tgz</a></p>
<p>Path to dependency file: /node/package.json</p>
<p>Path to vulnerable library: /node/node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-5.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/RG4421/jobcoin-boilerplate/commit/18b55726c485ed21ac52765d485039bed16c1846">18b55726c485ed21ac52765d485039bed16c1846</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is regular Expression Denial of Service (ReDoS) vulnerability in mocha.
It allows cause a denial of service when stripping crafted invalid function definition from strs.
<p>Publish Date: 2021-09-18
<p>URL: <a href=https://github.com/mochajs/mocha/commit/61b4b9209c2c64b32c8d48b1761c3b9384d411ea>WS-2021-0638</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/1d8a3d95-d199-4129-a6ad-8eafe5e77b9e/">https://huntr.dev/bounties/1d8a3d95-d199-4129-a6ad-8eafe5e77b9e/</a></p>
<p>Release Date: 2021-09-18</p>
<p>Fix Resolution: 6.0.0-0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | ws medium detected in mocha tgz ws medium severity vulnerability vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file node package json path to vulnerable library node node modules mocha package json dependency hierarchy x mocha tgz vulnerable library found in head commit a href found in base branch master vulnerability details there is regular expression denial of service redos vulnerability in mocha it allows cause a denial of service when stripping crafted invalid function definition from strs publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
12,449 | 3,274,086,388 | IssuesEvent | 2015-10-26 08:55:00 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | [Windows] in Option Settings, the URL does not look good | bug Platform Specific ReadyToTest | ### Steps to reproduce
1. Install the version 2.0.2
2. Create two accounts (e.g: user1@docker.oc......, user2@docker.oc.....)
3. Right click to icon oC
4. Click on Settings...
### Expected behaviour
You should see the entire URL address
### Actual behaviour
It does not look good at URL

### Server configuration
Desktop v ownCloud-2.0.2.5463-nightly20150915-setup.exe
Server v {"installed":true,"maintenance":false,"version":"8.1.1.3","versionstring":"8.1.1","edition":"Enterprise"} | 1.0 | [Windows] in Option Settings, the URL does not look good - ### Steps to reproduce
1. Install the version 2.0.2
2. Create two accounts (e.g: user1@docker.oc......, user2@docker.oc.....)
3. Right click to icon oC
4. Click on Settings...
### Expected behaviour
You should see the entire URL address
### Actual behaviour
It does not look good at URL

### Server configuration
Desktop v ownCloud-2.0.2.5463-nightly20150915-setup.exe
Server v {"installed":true,"maintenance":false,"version":"8.1.1.3","versionstring":"8.1.1","edition":"Enterprise"} | non_priority | in option settings the url does not look good steps to reproduce install the version create two accounts e g docker oc docker oc right click to icon oc click on settings expected behaviour you should see the entire url address actual behaviour it does not look good at url server configuration desktop v owncloud setup exe server v installed true maintenance false version versionstring edition enterprise | 0 |
9,967 | 2,616,015,624 | IssuesEvent | 2015-03-02 00:58:07 | jasonhall/bwapi | https://api.github.com/repos/jasonhall/bwapi | closed | drawText() can't handle some illegal characters, causes access violation | auto-migrated Security Type-Defect Usability | ```
What steps will reproduce the problem?
I'm not sure exactly how to reproduce it, but I know what the bug is and how to
fix it. I don't mind fixing it myself but I figured someone else is more
qualified.
The bug occurs inside dialog.cpp::GetTextWidth(), when it receives illegal
characters in a certain range.
See this code:
if ( (BYTE)pszString[i] > font->high || (BYTE)pszString[i] < font->low)
continue;
// localize character pointer
fntChr *chr = font->chrs[pszString[i] - font->low];
--------------
pszString[i] is compared after being converted to BYTE (an unsigned char), but
is declared as "const char", which is signed. So, a negative value will pass
the "filtering" (being considered as a value of 128 to 255, and font->high is
255). However, when used to index memory, it will be used as a negative value
and address incorrect memory.
So the solution is one of the two following, each with slightly different
results:
1) declare pszString as "const BYTE" in the function declaration
2) set font->high to 127 or less
What is the expected output? What do you see instead?
What version of the product are you using? On what operating system?
Beta 3.4
Please provide any additional information below.
```
Original issue reported on code.google.com by `erez27` on 23 Dec 2010 at 3:56 | 1.0 | drawText() can't handle some illegal characters, causes access violation - ```
What steps will reproduce the problem?
I'm not sure exactly how to reproduce it, but I know what the bug is and how to
fix it. I don't mind fixing it myself but I figured someone else is more
qualified.
The bug occurs inside dialog.cpp::GetTextWidth(), when it receives illegal
characters in a certain range.
See this code:
if ( (BYTE)pszString[i] > font->high || (BYTE)pszString[i] < font->low)
continue;
// localize character pointer
fntChr *chr = font->chrs[pszString[i] - font->low];
--------------
pszString[i] is compared after being converted to BYTE (an unsigned char), but
is declared as "const char", which is signed. So, a negative value will pass
the "filtering" (being considered as a value of 128 to 255, and font->high is
255). However, when used to index memory, it will be used as a negative value
and address incorrect memory.
So the solution is one of the two following, each with slightly different
results:
1) declare pszString as "const BYTE" in the function declaration
2) set font->high to 127 or less
What is the expected output? What do you see instead?
What version of the product are you using? On what operating system?
Beta 3.4
Please provide any additional information below.
```
Original issue reported on code.google.com by `erez27` on 23 Dec 2010 at 3:56 | non_priority | drawtext can t handle some illegal characters causes access violation what steps will reproduce the problem i m not sure exactly how to reproduce it but i know what the bug is and how to fix it i don t mind fixing it myself but i figured someone else is more qualified the bug occurs inside dialog cpp gettextwidth when it receives illegal characters in a certain range see this code if byte pszstring font high byte pszstring low continue localize character pointer fntchr chr font chrs font low pszstring is compared after being converted to byte an unsigned char but is declared as const char which is signed so a negative value will pass the filtering being considered as a value of to and font high is however when used to index memory it will be used as a negative value and address incorrect memory so the solution is one of the two following each with slightly different results declare pszstring as const byte in the function declaration set font high to or less what is the expected output what do you see instead what version of the product are you using on what operating system beta please provide any additional information below original issue reported on code google com by on dec at | 0 |
31,992 | 7,472,287,806 | IssuesEvent | 2018-04-03 12:11:36 | openshiftio/openshift.io | https://api.github.com/repos/openshiftio/openshift.io | closed | Extend API for interaction with Che workspaces | area/che area/codebases area/workspaces team/che/osio team/che/plugins type/feature | There is need to expose Che workspace API (https://github.com/fabric8-services/fabric8-wit/blob/master/codebase/che/client.go) with the following items:
- [ ] ability to stop workspace
- [ ] ability to create workspace pointing the repository branch ? (maybe here changes for codebases are needed as well to be identified by source location + branch)
- [ ] ability to delete workspace
- [ ] ability to handle workspace statuses
- [ ] add project info (branch / repo) while getting the list of workspaces | 1.0 | Extend API for interaction with Che workspaces - There is need to expose Che workspace API (https://github.com/fabric8-services/fabric8-wit/blob/master/codebase/che/client.go) with the following items:
- [ ] ability to stop workspace
- [ ] ability to create workspace pointing the repository branch ? (maybe here changes for codebases are needed as well to be identified by source location + branch)
- [ ] ability to delete workspace
- [ ] ability to handle workspace statuses
- [ ] add project info (branch / repo) while getting the list of workspaces | non_priority | extend api for interaction with che workspaces there is need to expose che workspace api with the following items ability to stop workspace ability to create workspace pointing the repository branch maybe here changes for codebases are needed as well to be identified by source location branch ability to delete workspace ability to handle workspace statuses add project info branch repo while getting the list of workspaces | 0 |
85,511 | 16,672,534,349 | IssuesEvent | 2021-06-07 12:44:49 | wso2/ballerina-plugin-vscode | https://api.github.com/repos/wso2/ballerina-plugin-vscode | closed | Diagram doesn't work with expression-bodied functions | Area/Diagram Area/LowCode MissingLCSupport Type/Bug | **Description:**
$title.
Works for
```ballerina
import ballerina/http;
service /ser on new http:Listener(8080) {
resource function get res() returns map<json> {
return {greeting: "hello world!"};
}
}
```
"Diagram Not Loaded...!" for
```ballerina
import ballerina/http;
service /ser on new http:Listener(8080) {
resource function get res() returns map<json> => {greeting: "hello world!"};
}
```
**Affected Product Version:**
slbeta1-rc1 | 1.0 | Diagram doesn't work with expression-bodied functions - **Description:**
$title.
Works for
```ballerina
import ballerina/http;
service /ser on new http:Listener(8080) {
resource function get res() returns map<json> {
return {greeting: "hello world!"};
}
}
```
"Diagram Not Loaded...!" for
```ballerina
import ballerina/http;
service /ser on new http:Listener(8080) {
resource function get res() returns map<json> => {greeting: "hello world!"};
}
```
**Affected Product Version:**
slbeta1-rc1 | non_priority | diagram doesn t work with expression bodied functions description title works for ballerina import ballerina http service ser on new http listener resource function get res returns map return greeting hello world diagram not loaded for ballerina import ballerina http service ser on new http listener resource function get res returns map greeting hello world affected product version | 0 |
241,218 | 18,435,050,773 | IssuesEvent | 2021-10-14 12:09:00 | zeikar/issueage | https://api.github.com/repos/zeikar/issueage | closed | test | documentation good first issue | Marked - Markdown Parser
========================
[Marked] lets you convert [Markdown] into HTML. Markdown is a simple text format whose goal is to be very easy to read and write, even when not converted to HTML. This demo page will let you type anything you like and see how it gets converted. Live. No more waiting around.
How To Use The Demo
-------------------
1. Type in stuff on the left.
2. See the live updates on the right.
That's it. Pretty simple. There's also a drop-down option in the upper right to switch between various views:
- **Preview:** A live display of the generated HTML as it would render in a browser.
- **HTML Source:** The generated HTML before your browser makes it pretty.
- **Lexer Data:** What [marked] uses internally, in case you like gory stuff like this.
- **Quick Reference:** A brief run-down of how to format things using markdown.
Why Markdown?
-------------
It's easy. It's not overly bloated, unlike HTML. Also, as the creator of [markdown] says,
> The overriding design goal for Markdown's
> formatting syntax is to make it as readable
> as possible. The idea is that a
> Markdown-formatted document should be
> publishable as-is, as plain text, without
> looking like it's been marked up with tags
> or formatting instructions.
Ready to start writing? Either start changing stuff on the left or
[clear everything](/demo/?text=) with a simple click.
[Marked]: https://github.com/markedjs/marked/
[Markdown]: http://daringfireball.net/projects/markdown/
 | 1.0 | test - Marked - Markdown Parser
========================
[Marked] lets you convert [Markdown] into HTML. Markdown is a simple text format whose goal is to be very easy to read and write, even when not converted to HTML. This demo page will let you type anything you like and see how it gets converted. Live. No more waiting around.
How To Use The Demo
-------------------
1. Type in stuff on the left.
2. See the live updates on the right.
That's it. Pretty simple. There's also a drop-down option in the upper right to switch between various views:
- **Preview:** A live display of the generated HTML as it would render in a browser.
- **HTML Source:** The generated HTML before your browser makes it pretty.
- **Lexer Data:** What [marked] uses internally, in case you like gory stuff like this.
- **Quick Reference:** A brief run-down of how to format things using markdown.
Why Markdown?
-------------
It's easy. It's not overly bloated, unlike HTML. Also, as the creator of [markdown] says,
> The overriding design goal for Markdown's
> formatting syntax is to make it as readable
> as possible. The idea is that a
> Markdown-formatted document should be
> publishable as-is, as plain text, without
> looking like it's been marked up with tags
> or formatting instructions.
Ready to start writing? Either start changing stuff on the left or
[clear everything](/demo/?text=) with a simple click.
[Marked]: https://github.com/markedjs/marked/
[Markdown]: http://daringfireball.net/projects/markdown/
 | non_priority | test marked markdown parser lets you convert into html markdown is a simple text format whose goal is to be very easy to read and write even when not converted to html this demo page will let you type anything you like and see how it gets converted live no more waiting around how to use the demo type in stuff on the left see the live updates on the right that s it pretty simple there s also a drop down option in the upper right to switch between various views preview a live display of the generated html as it would render in a browser html source the generated html before your browser makes it pretty lexer data what uses internally in case you like gory stuff like this quick reference a brief run down of how to format things using markdown why markdown it s easy it s not overly bloated unlike html also as the creator of says the overriding design goal for markdown s formatting syntax is to make it as readable as possible the idea is that a markdown formatted document should be publishable as is as plain text without looking like it s been marked up with tags or formatting instructions ready to start writing either start changing stuff on the left or demo text with a simple click asdf | 0 |
165,508 | 14,004,210,720 | IssuesEvent | 2020-10-28 16:49:02 | microsoft/qsharp-language | https://api.github.com/repos/microsoft/qsharp-language | closed | BigInt literals now accept binary and octal formats | Documentation | microsoft/qsharp-compiler#673 added support for binary and octal BigInt literals to the compiler. The documentation on [BigInt Literals](https://github.com/microsoft/qsharp-language/blob/main/Specifications/Language/3_Expressions/ValueLiterals.md#bigint-literals) in the Q# specification should be updated. | 1.0 | BigInt literals now accept binary and octal formats - microsoft/qsharp-compiler#673 added support for binary and octal BigInt literals to the compiler. The documentation on [BigInt Literals](https://github.com/microsoft/qsharp-language/blob/main/Specifications/Language/3_Expressions/ValueLiterals.md#bigint-literals) in the Q# specification should be updated. | non_priority | bigint literals now accept binary and octal formats microsoft qsharp compiler added support for binary and octal bigint literals to the compiler the documentation on in the q specification should be updated | 0 |
59,145 | 14,367,875,555 | IssuesEvent | 2020-12-01 07:28:40 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 94: firefox-78.3.0esr: 1 advisory [8.8] | 1.severity: security | [search](https://search.nix.gsc.io/?q=firefox&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=firefox+in%3Apath&type=Code)
* [ ] [CVE-2020-15667](https://nvd.nist.gov/vuln/detail/CVE-2020-15667) CVSSv3=8.8 (nixos-20.03, nixos-20.09, nixos-unstable)
Scanned versions: nixos-20.03: eba1d0126b4; nixos-20.09: 0b8799ecaaf; nixos-unstable: 420f89ceb26.
Cc @andir
Cc @edolstra
| True | Vulnerability roundup 94: firefox-78.3.0esr: 1 advisory [8.8] - [search](https://search.nix.gsc.io/?q=firefox&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=firefox+in%3Apath&type=Code)
* [ ] [CVE-2020-15667](https://nvd.nist.gov/vuln/detail/CVE-2020-15667) CVSSv3=8.8 (nixos-20.03, nixos-20.09, nixos-unstable)
Scanned versions: nixos-20.03: eba1d0126b4; nixos-20.09: 0b8799ecaaf; nixos-unstable: 420f89ceb26.
Cc @andir
Cc @edolstra
| non_priority | vulnerability roundup firefox advisory nixos nixos nixos unstable scanned versions nixos nixos nixos unstable cc andir cc edolstra | 0 |
261,435 | 19,712,251,905 | IssuesEvent | 2022-01-13 07:15:36 | wonderflow-bv/design | https://api.github.com/repos/wonderflow-bv/design | closed | Card design spec | documentation feature | ### Feature description
Write design spec for the Card component
### Describe the solution you'd like
_No response_
### Describe alternatives you've considered
_No response_
### Additional context and information
_No response_
### Code of Conduct
- [X] I've searched across open and closed issues for similiar requests | 1.0 | Card design spec - ### Feature description
Write design spec for the Card component
### Describe the solution you'd like
_No response_
### Describe alternatives you've considered
_No response_
### Additional context and information
_No response_
### Code of Conduct
- [X] I've searched across open and closed issues for similiar requests | non_priority | card design spec feature description write design spec for the card component describe the solution you d like no response describe alternatives you ve considered no response additional context and information no response code of conduct i ve searched across open and closed issues for similiar requests | 0 |
271,518 | 23,611,393,482 | IssuesEvent | 2022-08-24 12:43:07 | JonasMuehlmann/bntp.go | https://api.github.com/repos/JonasMuehlmann/bntp.go | closed | Add test to validate if all used validator tags are handled here | tests todo | Add test to validate if all used validator tags are handled here
https://github.com/JonasMuehlmann/bntp.go/blob/b6d1a1411860742bdb11e784c96fc19dc32333eb/internal/config/configuration.go#L73
```golang
// Copyright © 2021-2022 Jonas Muehlmann
//
// Permission is hereby granted, free of charge, to any person obtaining
// a copy of this software and associated documentation files (the "Software"),
// to deal in the Software without restriction, including without limitation
// the rights to use, copy, modify, merge, publish, distribute, sublicense,
// and/or sell copies of the Software, and to permit persons to whom the
// Software is furnished to do so, subject to the following conditions:
//
// The above copyright notice and this permission notice shall be included
// in all copies or substantial portions of the Software.
//
// THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND,
// EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES
// OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT.
// IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM,
// DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT,
// TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE
// OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
package config
import (
"fmt"
"os"
"path"
"github.com/JonasMuehlmann/bntp.go/internal/helper"
"github.com/JonasMuehlmann/goaoi"
"github.com/go-playground/validator/v10"
"github.com/spf13/viper"
"github.com/stoewer/go-strcase"
log "github.com/sirupsen/logrus"
)
var (
PassedConfigPath string
ConfigDir string
ConfigFileBaseName = "bntp"
ConfigSearchPaths []string
)
type message struct {
Level log.Level
Msg string
}
func newMessage(level log.Level, msg string) message {
message := message{}
message.Level = level
message.Msg = msg
return message
}
var DefaultSettings = map[string]any{
LOG_FILE: path.Join(ConfigDir, "bntp.log"),
CONSOLE_LOG_LEVEL: log.ErrorLevel,
FILE_LOG_LEVEL: log.InfoLevel,
}
var pendingLogMessage []message
func addPendingLogMessage(level log.Level, format string, values ...any) {
pendingLogMessage = append(pendingLogMessage, newMessage(level, fmt.Sprintf(format, values...)))
}
func formatValidationError(e validator.FieldError) string {
var message string
// TODO: Add test to validate if all used validator tags are handled here
switch e.Tag() {
case VALIDATOR_LOGRUS_LOG_LEVEL:
message = fmt.Sprintf("value %q is invalid, allowed values are %v", e.Value(), log.AllLevels)
case "required":
message = "setting is required"
case "file":
message = fmt.Sprintf("value %q is not a path", e.Value())
default:
message = e.Error()
}
return message
}
func InitConfig() {
pendingLogMessage = make([]message, 0, 5)
if PassedConfigPath != "" {
viper.SetConfigFile(PassedConfigPath)
}
goaoi.ForeachSliceUnsafe(ConfigSearchPaths, viper.AddConfigPath)
for k, v := range DefaultSettings {
viper.SetDefault(k, v)
}
viper.SetEnvPrefix("BNTP")
viper.SetConfigName(ConfigFileBaseName)
viper.AutomaticEnv() // read in environment variables that match
err := viper.ReadInConfig()
if err != nil {
addPendingLogMessage(log.FatalLevel, "Error reading config: %v", err)
}
//********************* Validate settings ********************//
var config Config
err = viper.Unmarshal(&config)
if err != nil {
panic(err)
}
var consoleLogLevel log.Level
var fileLogLevel log.Level
err = ConfigValidator.Struct(config)
if err != nil {
consoleLogLevel = log.ErrorLevel
fileLogLevel = log.InfoLevel
errs := err.(validator.ValidationErrors)
for _, e := range errs {
addPendingLogMessage(log.FatalLevel, "Error processing setting %v: %v", strcase.SnakeCase(e.Field()), formatValidationError(e))
}
} else {
consoleLogLevel, _ = log.ParseLevel(viper.GetString(CONSOLE_LOG_LEVEL))
fileLogLevel, _ = log.ParseLevel(viper.GetString(FILE_LOG_LEVEL))
}
// ******************** Log pending messages ********************* //
helper.Logger = *helper.NewDefaultLogger(viper.GetString(LOG_FILE), consoleLogLevel, fileLogLevel)
for _, message := range pendingLogMessage {
helper.Logger.Log(message.Level, message.Msg)
if message.Level == log.FatalLevel {
helper.Logger.Exit(1)
}
}
if PassedConfigPath != "" {
helper.Logger.Infof("Using config file %v", viper.ConfigFileUsed())
} else {
helper.Logger.Info("Using internal configuration")
}
}
func init() {
userConfigDir, err := os.UserConfigDir()
if err != nil {
panic(err)
}
cwd, err := os.Getwd()
if err != nil {
panic(err)
}
ConfigDir = path.Join(userConfigDir, "bntp")
ConfigSearchPaths = append(ConfigSearchPaths, ConfigDir)
ConfigSearchPaths = append(ConfigSearchPaths, cwd)
}
```
936e4cbd094660121c55523de83f74ac316d3234 | 1.0 | Add test to validate if all used validator tags are handled here - Add test to validate if all used validator tags are handled here
https://github.com/JonasMuehlmann/bntp.go/blob/b6d1a1411860742bdb11e784c96fc19dc32333eb/internal/config/configuration.go#L73
```golang
// Copyright © 2021-2022 Jonas Muehlmann
//
// Permission is hereby granted, free of charge, to any person obtaining
// a copy of this software and associated documentation files (the "Software"),
// to deal in the Software without restriction, including without limitation
// the rights to use, copy, modify, merge, publish, distribute, sublicense,
// and/or sell copies of the Software, and to permit persons to whom the
// Software is furnished to do so, subject to the following conditions:
//
// The above copyright notice and this permission notice shall be included
// in all copies or substantial portions of the Software.
//
// THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND,
// EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES
// OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT.
// IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM,
// DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT,
// TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE
// OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
package config
import (
"fmt"
"os"
"path"
"github.com/JonasMuehlmann/bntp.go/internal/helper"
"github.com/JonasMuehlmann/goaoi"
"github.com/go-playground/validator/v10"
"github.com/spf13/viper"
"github.com/stoewer/go-strcase"
log "github.com/sirupsen/logrus"
)
var (
PassedConfigPath string
ConfigDir string
ConfigFileBaseName = "bntp"
ConfigSearchPaths []string
)
type message struct {
Level log.Level
Msg string
}
func newMessage(level log.Level, msg string) message {
message := message{}
message.Level = level
message.Msg = msg
return message
}
var DefaultSettings = map[string]any{
LOG_FILE: path.Join(ConfigDir, "bntp.log"),
CONSOLE_LOG_LEVEL: log.ErrorLevel,
FILE_LOG_LEVEL: log.InfoLevel,
}
var pendingLogMessage []message
func addPendingLogMessage(level log.Level, format string, values ...any) {
pendingLogMessage = append(pendingLogMessage, newMessage(level, fmt.Sprintf(format, values...)))
}
func formatValidationError(e validator.FieldError) string {
var message string
// TODO: Add test to validate if all used validator tags are handled here
switch e.Tag() {
case VALIDATOR_LOGRUS_LOG_LEVEL:
message = fmt.Sprintf("value %q is invalid, allowed values are %v", e.Value(), log.AllLevels)
case "required":
message = "setting is required"
case "file":
message = fmt.Sprintf("value %q is not a path", e.Value())
default:
message = e.Error()
}
return message
}
func InitConfig() {
pendingLogMessage = make([]message, 0, 5)
if PassedConfigPath != "" {
viper.SetConfigFile(PassedConfigPath)
}
goaoi.ForeachSliceUnsafe(ConfigSearchPaths, viper.AddConfigPath)
for k, v := range DefaultSettings {
viper.SetDefault(k, v)
}
viper.SetEnvPrefix("BNTP")
viper.SetConfigName(ConfigFileBaseName)
viper.AutomaticEnv() // read in environment variables that match
err := viper.ReadInConfig()
if err != nil {
addPendingLogMessage(log.FatalLevel, "Error reading config: %v", err)
}
//********************* Validate settings ********************//
var config Config
err = viper.Unmarshal(&config)
if err != nil {
panic(err)
}
var consoleLogLevel log.Level
var fileLogLevel log.Level
err = ConfigValidator.Struct(config)
if err != nil {
consoleLogLevel = log.ErrorLevel
fileLogLevel = log.InfoLevel
errs := err.(validator.ValidationErrors)
for _, e := range errs {
addPendingLogMessage(log.FatalLevel, "Error processing setting %v: %v", strcase.SnakeCase(e.Field()), formatValidationError(e))
}
} else {
consoleLogLevel, _ = log.ParseLevel(viper.GetString(CONSOLE_LOG_LEVEL))
fileLogLevel, _ = log.ParseLevel(viper.GetString(FILE_LOG_LEVEL))
}
// ******************** Log pending messages ********************* //
helper.Logger = *helper.NewDefaultLogger(viper.GetString(LOG_FILE), consoleLogLevel, fileLogLevel)
for _, message := range pendingLogMessage {
helper.Logger.Log(message.Level, message.Msg)
if message.Level == log.FatalLevel {
helper.Logger.Exit(1)
}
}
if PassedConfigPath != "" {
helper.Logger.Infof("Using config file %v", viper.ConfigFileUsed())
} else {
helper.Logger.Info("Using internal configuration")
}
}
func init() {
userConfigDir, err := os.UserConfigDir()
if err != nil {
panic(err)
}
cwd, err := os.Getwd()
if err != nil {
panic(err)
}
ConfigDir = path.Join(userConfigDir, "bntp")
ConfigSearchPaths = append(ConfigSearchPaths, ConfigDir)
ConfigSearchPaths = append(ConfigSearchPaths, cwd)
}
```
936e4cbd094660121c55523de83f74ac316d3234 | non_priority | add test to validate if all used validator tags are handled here add test to validate if all used validator tags are handled here golang copyright © jonas muehlmann permission is hereby granted free of charge to any person obtaining a copy of this software and associated documentation files the software to deal in the software without restriction including without limitation the rights to use copy modify merge publish distribute sublicense and or sell copies of the software and to permit persons to whom the software is furnished to do so subject to the following conditions the above copyright notice and this permission notice shall be included in all copies or substantial portions of the software the software is provided as is without warranty of any kind express or implied including but not limited to the warranties of merchantability fitness for a particular purpose and noninfringement in no event shall the authors or copyright holders be liable for any claim damages or other liability whether in an action of contract tort or otherwise arising from out of or in connection with the software or the use or other dealings in the software package config import fmt os path github com jonasmuehlmann bntp go internal helper github com jonasmuehlmann goaoi github com go playground validator github com viper github com stoewer go strcase log github com sirupsen logrus var passedconfigpath string configdir string configfilebasename bntp configsearchpaths string type message struct level log level msg string func newmessage level log level msg string message message message message level level message msg msg return message var defaultsettings map any log file path join configdir bntp log console log level log errorlevel file log level log infolevel var pendinglogmessage message func addpendinglogmessage level log level format string values any pendinglogmessage append pendinglogmessage newmessage level fmt sprintf format values func formatvalidationerror e validator fielderror string var message string todo add test to validate if all used validator tags are handled here switch e tag case validator logrus log level message fmt sprintf value q is invalid allowed values are v e value log alllevels case required message setting is required case file message fmt sprintf value q is not a path e value default message e error return message func initconfig pendinglogmessage make message if passedconfigpath viper setconfigfile passedconfigpath goaoi foreachsliceunsafe configsearchpaths viper addconfigpath for k v range defaultsettings viper setdefault k v viper setenvprefix bntp viper setconfigname configfilebasename viper automaticenv read in environment variables that match err viper readinconfig if err nil addpendinglogmessage log fatallevel error reading config v err validate settings var config config err viper unmarshal config if err nil panic err var consoleloglevel log level var fileloglevel log level err configvalidator struct config if err nil consoleloglevel log errorlevel fileloglevel log infolevel errs err validator validationerrors for e range errs addpendinglogmessage log fatallevel error processing setting v v strcase snakecase e field formatvalidationerror e else consoleloglevel log parselevel viper getstring console log level fileloglevel log parselevel viper getstring file log level log pending messages helper logger helper newdefaultlogger viper getstring log file consoleloglevel fileloglevel for message range pendinglogmessage helper logger log message level message msg if message level log fatallevel helper logger exit if passedconfigpath helper logger infof using config file v viper configfileused else helper logger info using internal configuration func init userconfigdir err os userconfigdir if err nil panic err cwd err os getwd if err nil panic err configdir path join userconfigdir bntp configsearchpaths append configsearchpaths configdir configsearchpaths append configsearchpaths cwd | 0 |
31,755 | 7,445,468,367 | IssuesEvent | 2018-03-28 04:47:38 | krlxfm/amethyst | https://api.github.com/repos/krlxfm/amethyst | opened | Resolve code duplication in resources/assets/js/pages/tracks/edit.js | Code Climate | Code duplication needs to be resolved. Duplicated incidents are found in:
- resources/assets/js/pages/tracks/edit (line 63)
- resources/assets/js/pages/tracks/edit (line 146) | 1.0 | Resolve code duplication in resources/assets/js/pages/tracks/edit.js - Code duplication needs to be resolved. Duplicated incidents are found in:
- resources/assets/js/pages/tracks/edit (line 63)
- resources/assets/js/pages/tracks/edit (line 146) | non_priority | resolve code duplication in resources assets js pages tracks edit js code duplication needs to be resolved duplicated incidents are found in resources assets js pages tracks edit line resources assets js pages tracks edit line | 0 |
26,456 | 6,767,322,023 | IssuesEvent | 2017-10-26 02:34:32 | ahmedahamid/temp-third | https://api.github.com/repos/ahmedahamid/temp-third | closed | display winform in max mode | bug CodePlexMigrationInitiated Impact: Low | http://social.msdn.microsoft.com/Forums/en-US/windowsgeneraldevelopmentissues/thread/d0bc49a1-189a-4ee6-83b7-73a053ba972a
#### This work item was migrated from CodePlex
CodePlex work item ID: '7010'
Vote count: '1'
| 1.0 | display winform in max mode - http://social.msdn.microsoft.com/Forums/en-US/windowsgeneraldevelopmentissues/thread/d0bc49a1-189a-4ee6-83b7-73a053ba972a
#### This work item was migrated from CodePlex
CodePlex work item ID: '7010'
Vote count: '1'
| non_priority | display winform in max mode this work item was migrated from codeplex codeplex work item id vote count | 0 |
73,093 | 19,573,074,225 | IssuesEvent | 2022-01-04 12:23:53 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug] Property pane scrolls when we enable scroll on widgets | Bug Property Pane High UI Building Pod Needs Triaging UI Builders Pod | ## Description
Property pane scrolls when we enable scroll on certain widgets. Loom recording attached:
[](https://www.loom.com/share/c9baa7d93fc64f54bb28c7d1865edd54)
### Steps to reproduce the behaviour:
1. Drag and drop a container widget and enable scroll from property pane
2. Add any widget inside the container and open its property pane
3. Scroll the container. In this case, the property pane moves up while scrolling.
| 2.0 | [Bug] Property pane scrolls when we enable scroll on widgets - ## Description
Property pane scrolls when we enable scroll on certain widgets. Loom recording attached:
[](https://www.loom.com/share/c9baa7d93fc64f54bb28c7d1865edd54)
### Steps to reproduce the behaviour:
1. Drag and drop a container widget and enable scroll from property pane
2. Add any widget inside the container and open its property pane
3. Scroll the container. In this case, the property pane moves up while scrolling.
| non_priority | property pane scrolls when we enable scroll on widgets description property pane scrolls when we enable scroll on certain widgets loom recording attached steps to reproduce the behaviour drag and drop a container widget and enable scroll from property pane add any widget inside the container and open its property pane scroll the container in this case the property pane moves up while scrolling | 0 |
218,945 | 17,031,554,482 | IssuesEvent | 2021-07-04 17:13:23 | CSOIreland/PxStat | https://api.github.com/repos/CSOIreland/PxStat | closed | [BUG] Extend size of GMP_DESCRIPTION column in TD_GEOMAP table. | bug fixed released tested | Extend size of GMP_DESCRIPTION column in TD_GEOMAP table to maximum. Remove validation in C# code that limits this. | 1.0 | [BUG] Extend size of GMP_DESCRIPTION column in TD_GEOMAP table. - Extend size of GMP_DESCRIPTION column in TD_GEOMAP table to maximum. Remove validation in C# code that limits this. | non_priority | extend size of gmp description column in td geomap table extend size of gmp description column in td geomap table to maximum remove validation in c code that limits this | 0 |
206,907 | 23,409,179,354 | IssuesEvent | 2022-08-12 15:38:10 | GNS3/gns3-web-ui | https://api.github.com/repos/GNS3/gns3-web-ui | closed | CVE-2022-33987 (Medium) detected in got-9.6.0.tgz | security vulnerability | ## CVE-2022-33987 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>got-9.6.0.tgz</b></p></summary>
<p>Simplified HTTP requests</p>
<p>Library home page: <a href="https://registry.npmjs.org/got/-/got-9.6.0.tgz">https://registry.npmjs.org/got/-/got-9.6.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/got/package.json</p>
<p>
Dependency Hierarchy:
- ngx-childprocess-0.0.6.tgz (Root Library)
- electron-1.6.10.tgz
- electron-13.6.6.tgz
- get-1.13.1.tgz
- :x: **got-9.6.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The got package before 12.1.0 (also fixed in 11.8.5) for Node.js allows a redirect to a UNIX socket.
<p>Publish Date: 2022-06-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33987>CVE-2022-33987</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987</a></p>
<p>Release Date: 2022-06-18</p>
<p>Fix Resolution: got - 11.8.5,12.1.0</p>
</p>
</details>
<p></p>
| True | CVE-2022-33987 (Medium) detected in got-9.6.0.tgz - ## CVE-2022-33987 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>got-9.6.0.tgz</b></p></summary>
<p>Simplified HTTP requests</p>
<p>Library home page: <a href="https://registry.npmjs.org/got/-/got-9.6.0.tgz">https://registry.npmjs.org/got/-/got-9.6.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/got/package.json</p>
<p>
Dependency Hierarchy:
- ngx-childprocess-0.0.6.tgz (Root Library)
- electron-1.6.10.tgz
- electron-13.6.6.tgz
- get-1.13.1.tgz
- :x: **got-9.6.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The got package before 12.1.0 (also fixed in 11.8.5) for Node.js allows a redirect to a UNIX socket.
<p>Publish Date: 2022-06-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33987>CVE-2022-33987</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-33987</a></p>
<p>Release Date: 2022-06-18</p>
<p>Fix Resolution: got - 11.8.5,12.1.0</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in got tgz cve medium severity vulnerability vulnerable library got tgz simplified http requests library home page a href path to dependency file package json path to vulnerable library node modules got package json dependency hierarchy ngx childprocess tgz root library electron tgz electron tgz get tgz x got tgz vulnerable library found in base branch master vulnerability details the got package before also fixed in for node js allows a redirect to a unix socket publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution got | 0 |
131,531 | 10,698,060,796 | IssuesEvent | 2019-10-23 17:52:15 | phetsims/QA | https://api.github.com/repos/phetsims/QA | opened | RC test: Vector Addition: Equations 1.0.0-rc.1 | QA:rc-test | @KatieWoe, @arouinfar, vector-addition-equations/1.0.0-rc.1 is ready for RC testing.
This release does not include PhET-iO or a11y.
This sim is consists of the _Equations_ screen from Vector Addition. So please document issues in https://github.com/phetsims/vector-addition/issues (not vector-addition-equations) and link to this issue.
Assigning to @ariel-phet for prioritization.
<!---
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
////////// Section 1: General RC Testing [CAN BE OMITTED, SHOULD BE EDITED IF NOT OMITTED]
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
-->
<details>
<summary><b>General RC Test</b></summary>
<!--- [DO NOT OMIT, CAN BE EDITED] -->
<h3>What to Test</h3>
- Click every single button.
- Test all possible forms of input.
- Test all mouse/trackpad inputs.
- Test all touchscreen inputs.
- If there is sound, make sure it works.
- Make sure you can't lose anything.
- Play with the sim normally.
- Try to break the sim.
- Test all query parameters on all platforms. (See [QA Book](https://github.com/phetsims/QA/blob/master/doc/qa-book.md) for a list of query parameters.)
- Download HTML on Chrome and iOS.
- Make sure the iFrame version of the simulation is working as intended on all platforms.
- Make sure the XHTML version of the simulation is working as intended on all platforms.
- Complete the test matrix.
- Don't forget to make sure the sim works with Legends of Learning.
- Check [this](https://docs.google.com/spreadsheets/d/1umIAmhn89WN1nzcHKhYJcv-n3Oj6ps1wITc-CjWYytE/edit#gid=0) LoL spreadsheet and notify AR or AM if it not there.
- If this is rc.1 please do a memory test.
- When making an issue, check to see if it was in a previously published version
- If there is a console available, check for errors and include them in the Problem Description.
<h3>Focus and Special Instructions</h3>
_Vector Addition: Equations_ consists the _Equations_ screen from the _Vector Addition_ sim, with no changes. So this sim does not require a full test matrix. Thorough testing of _Equations_ screen can be done in https://github.com/phetsims/QA/issues/#445, and this sim can be spot tested on a few platforms.
<!--- [CAN BE OMITTED, SHOULD BE EDITED IF NOT OMITTED] -->
<h3>Issues to Verify</h3>
There are no specific issues to verify; all known issues have been addressed.
<!--- [DO NOT OMIT, CAN BE EDITED] -->
<h3>Link(s)</h3>
- **[Simulation](https://phet-dev.colorado.edu/html/vector-addition-equations/1.0.0-rc.1/phet/vector-addition-equations_all_phet.html)**
- **[iFrame](https://phet-dev.colorado.edu/html/vector-addition-equations/1.0.0-rc.1/phet/vector-addition-equations_en_iframe_phet.html)**
- **[XHTML](https://phet-dev.colorado.edu/html/vector-addition-equations/1.0.0-rc.1/phet/xhtml/vector-addition-equations_all.xhtml)**
- **[Test Matrix](link)**
- **[Legends of Learning Harness](https://developers.legendsoflearning.com/public-harness/index.html?startPayload=%7B%22languageCode%22%3A%22en%22%7D)**
<hr>
</details>
<!---
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
////////// Section 0: FAQs for QA Members [DO NOT OMIT, DO NOT EDIT]
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
-->
<details>
<summary><b>FAQs for QA Members</b></summary>
<br>
<!--- Subsection 0.1: There are multiple tests in this issue... What should I test first? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>There are multiple tests in this issue... Which test should I do first?</i></summary>
Test in order! Test the first thing first, the second thing second, and so on.
</details>
<br>
<!--- Subsection 0.2: How should I format my issue? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>How should I format my issue?</i></summary>
Here's a template for making issues:
<b>Test Device</b>
blah
<b>Operating System</b>
blah
<b>Browser</b>
blah
<b>Problem Description</b>
blah
<b>Steps to Reproduce</b>
blah
<b>Visuals</b>
blah
<details>
<summary><b>Troubleshooting Information</b></summary>
blah
</details>
</details>
<br>
<!--- Subsection 0.3: Who should I assign? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>Who should I assign?</i></summary>
We typically assign the developer who opened the issue in the QA repository.
</details>
<br>
<!--- Subsection 0.4: My question isn't in here... What should I do? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>My question isn't in here... What should I do?</i></summary>
You should:
1. Consult the [QA Book](https://github.com/phetsims/QA/blob/master/doc/qa-book.md).
2. Google it.
3. Ask Katie.
4. Ask a developer.
5. Google it again.
6. Cry.
</details>
<br>
<hr>
</details>
| 1.0 | RC test: Vector Addition: Equations 1.0.0-rc.1 - @KatieWoe, @arouinfar, vector-addition-equations/1.0.0-rc.1 is ready for RC testing.
This release does not include PhET-iO or a11y.
This sim is consists of the _Equations_ screen from Vector Addition. So please document issues in https://github.com/phetsims/vector-addition/issues (not vector-addition-equations) and link to this issue.
Assigning to @ariel-phet for prioritization.
<!---
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
////////// Section 1: General RC Testing [CAN BE OMITTED, SHOULD BE EDITED IF NOT OMITTED]
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
-->
<details>
<summary><b>General RC Test</b></summary>
<!--- [DO NOT OMIT, CAN BE EDITED] -->
<h3>What to Test</h3>
- Click every single button.
- Test all possible forms of input.
- Test all mouse/trackpad inputs.
- Test all touchscreen inputs.
- If there is sound, make sure it works.
- Make sure you can't lose anything.
- Play with the sim normally.
- Try to break the sim.
- Test all query parameters on all platforms. (See [QA Book](https://github.com/phetsims/QA/blob/master/doc/qa-book.md) for a list of query parameters.)
- Download HTML on Chrome and iOS.
- Make sure the iFrame version of the simulation is working as intended on all platforms.
- Make sure the XHTML version of the simulation is working as intended on all platforms.
- Complete the test matrix.
- Don't forget to make sure the sim works with Legends of Learning.
- Check [this](https://docs.google.com/spreadsheets/d/1umIAmhn89WN1nzcHKhYJcv-n3Oj6ps1wITc-CjWYytE/edit#gid=0) LoL spreadsheet and notify AR or AM if it not there.
- If this is rc.1 please do a memory test.
- When making an issue, check to see if it was in a previously published version
- If there is a console available, check for errors and include them in the Problem Description.
<h3>Focus and Special Instructions</h3>
_Vector Addition: Equations_ consists the _Equations_ screen from the _Vector Addition_ sim, with no changes. So this sim does not require a full test matrix. Thorough testing of _Equations_ screen can be done in https://github.com/phetsims/QA/issues/#445, and this sim can be spot tested on a few platforms.
<!--- [CAN BE OMITTED, SHOULD BE EDITED IF NOT OMITTED] -->
<h3>Issues to Verify</h3>
There are no specific issues to verify; all known issues have been addressed.
<!--- [DO NOT OMIT, CAN BE EDITED] -->
<h3>Link(s)</h3>
- **[Simulation](https://phet-dev.colorado.edu/html/vector-addition-equations/1.0.0-rc.1/phet/vector-addition-equations_all_phet.html)**
- **[iFrame](https://phet-dev.colorado.edu/html/vector-addition-equations/1.0.0-rc.1/phet/vector-addition-equations_en_iframe_phet.html)**
- **[XHTML](https://phet-dev.colorado.edu/html/vector-addition-equations/1.0.0-rc.1/phet/xhtml/vector-addition-equations_all.xhtml)**
- **[Test Matrix](link)**
- **[Legends of Learning Harness](https://developers.legendsoflearning.com/public-harness/index.html?startPayload=%7B%22languageCode%22%3A%22en%22%7D)**
<hr>
</details>
<!---
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
////////// Section 0: FAQs for QA Members [DO NOT OMIT, DO NOT EDIT]
////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////
-->
<details>
<summary><b>FAQs for QA Members</b></summary>
<br>
<!--- Subsection 0.1: There are multiple tests in this issue... What should I test first? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>There are multiple tests in this issue... Which test should I do first?</i></summary>
Test in order! Test the first thing first, the second thing second, and so on.
</details>
<br>
<!--- Subsection 0.2: How should I format my issue? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>How should I format my issue?</i></summary>
Here's a template for making issues:
<b>Test Device</b>
blah
<b>Operating System</b>
blah
<b>Browser</b>
blah
<b>Problem Description</b>
blah
<b>Steps to Reproduce</b>
blah
<b>Visuals</b>
blah
<details>
<summary><b>Troubleshooting Information</b></summary>
blah
</details>
</details>
<br>
<!--- Subsection 0.3: Who should I assign? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>Who should I assign?</i></summary>
We typically assign the developer who opened the issue in the QA repository.
</details>
<br>
<!--- Subsection 0.4: My question isn't in here... What should I do? [DO NOT OMIT, DO NOT EDIT] -->
<details>
<summary><i>My question isn't in here... What should I do?</i></summary>
You should:
1. Consult the [QA Book](https://github.com/phetsims/QA/blob/master/doc/qa-book.md).
2. Google it.
3. Ask Katie.
4. Ask a developer.
5. Google it again.
6. Cry.
</details>
<br>
<hr>
</details>
| non_priority | rc test vector addition equations rc katiewoe arouinfar vector addition equations rc is ready for rc testing this release does not include phet io or this sim is consists of the equations screen from vector addition so please document issues in not vector addition equations and link to this issue assigning to ariel phet for prioritization section general rc testing general rc test what to test click every single button test all possible forms of input test all mouse trackpad inputs test all touchscreen inputs if there is sound make sure it works make sure you can t lose anything play with the sim normally try to break the sim test all query parameters on all platforms see for a list of query parameters download html on chrome and ios make sure the iframe version of the simulation is working as intended on all platforms make sure the xhtml version of the simulation is working as intended on all platforms complete the test matrix don t forget to make sure the sim works with legends of learning check lol spreadsheet and notify ar or am if it not there if this is rc please do a memory test when making an issue check to see if it was in a previously published version if there is a console available check for errors and include them in the problem description focus and special instructions vector addition equations consists the equations screen from the vector addition sim with no changes so this sim does not require a full test matrix thorough testing of equations screen can be done in and this sim can be spot tested on a few platforms issues to verify there are no specific issues to verify all known issues have been addressed link s link section faqs for qa members faqs for qa members there are multiple tests in this issue which test should i do first test in order test the first thing first the second thing second and so on how should i format my issue here s a template for making issues test device blah operating system blah browser blah problem description blah steps to reproduce blah visuals blah troubleshooting information blah who should i assign we typically assign the developer who opened the issue in the qa repository my question isn t in here what should i do you should consult the google it ask katie ask a developer google it again cry | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.