Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
177,480 | 13,725,923,201 | IssuesEvent | 2020-10-03 20:47:05 | yashvardhan-kukreja/nail-hacktoberfest | https://api.github.com/repos/yashvardhan-kukreja/nail-hacktoberfest | closed | add support for CI testing on every push to the codebase | feature hacktoberfest testing | **Is your feature request related to a problem? Please describe.**
Currently, the project does not have support to test whether the code it contains will successfully run or not. That might lead to exposure to potential human-prone issues.
**Describe the solution you'd like**
Add TravisCI/CircleCI or in general, any CI's testinig support so that, every push will only succeed when the code corresponding to the push passes a certain of tests successfully.
**Describe alternatives you've considered**
NA
**Additional context**
NA. | 1.0 | add support for CI testing on every push to the codebase - **Is your feature request related to a problem? Please describe.**
Currently, the project does not have support to test whether the code it contains will successfully run or not. That might lead to exposure to potential human-prone issues.
**Describe the solution you'd like**
Add TravisCI/CircleCI or in general, any CI's testinig support so that, every push will only succeed when the code corresponding to the push passes a certain of tests successfully.
**Describe alternatives you've considered**
NA
**Additional context**
NA. | non_priority | add support for ci testing on every push to the codebase is your feature request related to a problem please describe currently the project does not have support to test whether the code it contains will successfully run or not that might lead to exposure to potential human prone issues describe the solution you d like add travisci circleci or in general any ci s testinig support so that every push will only succeed when the code corresponding to the push passes a certain of tests successfully describe alternatives you ve considered na additional context na | 0 |
415,039 | 28,014,827,072 | IssuesEvent | 2023-03-27 21:37:21 | pydata/xarray | https://api.github.com/repos/pydata/xarray | closed | The documentation contains some non-descriptive link texts. | topic-documentation contrib-good-first-issue | ### What is your issue?
I've been going through the docs and noticed some links could be more descriptive.
Here are a few examples with options on how we could rewrite them:
- See the [user guide](https://docs.xarray.dev/en/stable/indexing.html) for more. -> Check out the [indexing section in the user guide](https://docs.xarray.dev/en/stable/indexing.html) for a detailed explanation.
- For more, see [the Xarray documentation](https://docs.xarray.dev/en/stable/user-guide/computation.html#automatic-alignment). -> See the [documentation on automatic alignment](https://docs.xarray.dev/en/stable/user-guide/computation.html#automatic-alignment) to learn more.
- [This tutorial notebook](https://tutorial.xarray.dev/fundamentals/02.3_aligning_data_objects.html) also covers alignment and broadcasting (highly recommended)-> You can also check out this [tutorial notebook on alignment and broadcasting](https://tutorial.xarray.dev/fundamentals/02.3_aligning_data_objects.html) (highly recommended).
- For more see the [user guide](https://docs.xarray.dev/en/stable/plotting.html), the [gallery](https://docs.xarray.dev/en/stable/examples/visualization_gallery.html), and [the tutorial material](https://tutorial.xarray.dev/fundamentals/04.0_plotting.html). -> For more information, check out the following resources:
* The [plotting documentation](https://docs.xarray.dev/en/stable/user-guide/plotting.html) in the user guide.
* The [visualization gallery](https://docs.xarray.dev/en/stable/examples/visualization_gallery.html).
* The [plotting and visualization tutorial materials](https://tutorial.xarray.dev/fundamentals/04.0_plotting.html).
With more specific link texts, you get a clearer idea of what to expect when you click on the link which improves the reading experience. It also makes the links more accessible. | 1.0 | The documentation contains some non-descriptive link texts. - ### What is your issue?
I've been going through the docs and noticed some links could be more descriptive.
Here are a few examples with options on how we could rewrite them:
- See the [user guide](https://docs.xarray.dev/en/stable/indexing.html) for more. -> Check out the [indexing section in the user guide](https://docs.xarray.dev/en/stable/indexing.html) for a detailed explanation.
- For more, see [the Xarray documentation](https://docs.xarray.dev/en/stable/user-guide/computation.html#automatic-alignment). -> See the [documentation on automatic alignment](https://docs.xarray.dev/en/stable/user-guide/computation.html#automatic-alignment) to learn more.
- [This tutorial notebook](https://tutorial.xarray.dev/fundamentals/02.3_aligning_data_objects.html) also covers alignment and broadcasting (highly recommended)-> You can also check out this [tutorial notebook on alignment and broadcasting](https://tutorial.xarray.dev/fundamentals/02.3_aligning_data_objects.html) (highly recommended).
- For more see the [user guide](https://docs.xarray.dev/en/stable/plotting.html), the [gallery](https://docs.xarray.dev/en/stable/examples/visualization_gallery.html), and [the tutorial material](https://tutorial.xarray.dev/fundamentals/04.0_plotting.html). -> For more information, check out the following resources:
* The [plotting documentation](https://docs.xarray.dev/en/stable/user-guide/plotting.html) in the user guide.
* The [visualization gallery](https://docs.xarray.dev/en/stable/examples/visualization_gallery.html).
* The [plotting and visualization tutorial materials](https://tutorial.xarray.dev/fundamentals/04.0_plotting.html).
With more specific link texts, you get a clearer idea of what to expect when you click on the link which improves the reading experience. It also makes the links more accessible. | non_priority | the documentation contains some non descriptive link texts what is your issue i ve been going through the docs and noticed some links could be more descriptive here are a few examples with options on how we could rewrite them see the for more check out the for a detailed explanation for more see see the to learn more also covers alignment and broadcasting highly recommended you can also check out this highly recommended for more see the the and for more information check out the following resources the in the user guide the the with more specific link texts you get a clearer idea of what to expect when you click on the link which improves the reading experience it also makes the links more accessible | 0 |
64,420 | 6,902,343,240 | IssuesEvent | 2017-11-25 19:25:06 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | external_auth tokens are not being cleaned up | Bug High Severity Needs Testcase P1 stale | Doesn't look like /var/cache/salt/master/tokens is being properly cleaned:
```
# pwd
/var/cache/salt/master/tokens
# find . -atime +1 | wc -l
301691
```
Running:
```
# salt --versions
Salt: 0.17.5
Python: 2.6.6 (r266:84292, Dec 7 2011, 20:48:22)
Jinja2: 2.2.1
M2Crypto: 0.20.2
msgpack-python: 0.1.13
msgpack-pure: Not Installed
pycrypto: 2.0.1
PyYAML: 3.10
PyZMQ: 2.2.0.1
ZMQ: 3.2.2
```
There was a report in #salt that 2014.1.13 also had a similar issue.
| 1.0 | external_auth tokens are not being cleaned up - Doesn't look like /var/cache/salt/master/tokens is being properly cleaned:
```
# pwd
/var/cache/salt/master/tokens
# find . -atime +1 | wc -l
301691
```
Running:
```
# salt --versions
Salt: 0.17.5
Python: 2.6.6 (r266:84292, Dec 7 2011, 20:48:22)
Jinja2: 2.2.1
M2Crypto: 0.20.2
msgpack-python: 0.1.13
msgpack-pure: Not Installed
pycrypto: 2.0.1
PyYAML: 3.10
PyZMQ: 2.2.0.1
ZMQ: 3.2.2
```
There was a report in #salt that 2014.1.13 also had a similar issue.
| non_priority | external auth tokens are not being cleaned up doesn t look like var cache salt master tokens is being properly cleaned pwd var cache salt master tokens find atime wc l running salt versions salt python dec msgpack python msgpack pure not installed pycrypto pyyaml pyzmq zmq there was a report in salt that also had a similar issue | 0 |
96,866 | 8,635,029,298 | IssuesEvent | 2018-11-22 19:51:54 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Manual test run on OS X for 0.56.x - Release Hotfix 2 | OS/macOS release-notes/exclude tests | ## Per release specialty tests
- [x] Upgrade to Chromium 70.0.3538.110.([#2200](https://github.com/brave/brave-browser/issues/2200))
### Installer
- [x] Check that installer is close to the size of last release
- [x] Check signature: If OS Run `spctl --assess --verbose /Applications/Brave-Browser-Beta.app/` and make sure it returns `accepted`. If Windows right click on the `brave_installer-x64.exe` and go to Properties, go to the Digital Signatures tab and double click on the signature. Make sure it says "The digital signature is OK" in the popup window
### Data(Upgrade from previous release)
- [x] Make sure that data from the last version appears in the new version OK
- [x] With data from the last version, verify that
- [x] bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] cookies are preserved
- [x] installed extensions are retained and work correctly
- [x] opened tabs can be reloaded
- [x] stored passwords are preserved
- [x] unpinned tabs can be pinned
### Widevine
- [x] Verify `Widevine Notification` is shown when you visit Netflix for the first time
- [x] Test that you can stream on Netflix on a fresh profile after installing Widevine
### Geolocation
- [ ] Check that https://developer.mozilla.org/en-US/docs/Web/API/Geolocation/Using_geolocation shows correct location
- [x] Check that https://browserleaks.com/geo works and shows correct location
- [x] Check that https://html5demos.com/geo/ works but doesn't require an accurate location
### Crash Reporting
- [x] Check that loading `brave://crash` causes the new tab to crash
- [x] Check that `brave://crashes` lists all the crashes and includes both Crash Report ID & Local Crash ID
- [x] Verify the crash ID matches the report on brave stats
### Bravery settings
- [x] Verify that HTTPS Everywhere works by loading http://https-everywhere.badssl.com/
- [x] Turning HTTPS Everywhere off and shields off both disable the redirect to https://https-everywhere.badssl.com/
- [x] Verify that toggling `Ads and trackers blocked` works as expected
- [x] Visit https://testsafebrowsing.appspot.com/s/phishing.html, verify that Safe Browsing (via our Proxy) works for all the listed items
- [x] Visit https://brianbondy.com/ and then turn on script blocking, page should not load. Allow it from the script blocking UI in the URL bar and it should load the page correctly
- [x] Test that 3rd party storage results are blank at https://jsfiddle.net/7ke9r14a/9/ when 3rd party cookies are blocked and not blank when 3rd party cookies are unblocked
### Fingerprint Tests
- [ ] Visit https://jsfiddle.net/bkf50r8v/13/, ensure 3 blocked items are listed in shields. Result window should show `got canvas fingerprint 0` and `got webgl fingerprint 00`
- [x] Test that audio fingerprint is blocked at https://audiofingerprint.openwpm.com/ only when `Block all fingerprinting protection` is on
- [x] Test that Brave browser isn't detected on https://extensions.inrialpes.fr/brave/
- [x] Test that https://diafygi.github.io/webrtc-ips/ doesn't leak IP address when `Block all fingerprinting protection` is on
### Content tests
- [x] Open a page with an input control and type some misspellings on a textbox, make sure they are underlined
- [x] Make sure that right clicking on a word with suggestions gives a suggestion and that clicking on the suggestion replaces the text
- [x] Test that https://mixed-script.badssl.com/ shows up as grey not red (no mixed content scripts are run)
### Session storage
- [x] Temporarily move away your browser profile and test that a new profile is created when browser is launched
- macOS - `~/Library/Application\ Support/BraveSoftware/`
- Windows - `%userprofile%\appdata\Local\BraveSoftware\`
- Linux(Ubuntu) - `~/.config/BraveSoftware/`
- [x] Test that windows and tabs restore when closed, including active tab
- [x] Ensure that the tabs in the above session are being lazy loaded when the session is restored
## Chromium upgrade tests
#### Adblock
- [x] Verify referrer blocking works properly for TLD+1. Visit `https://technology.slashdot.org/` and verify adblock works properly similar to `https://slashdot.org/`
#### Components
- [x] Delete Adblock folder from browser profile and restart browser. Visit `brave://components` and verify `Brave Ad Block Updater` downloads and update the component. Repeat for all Brave components
| 1.0 | Manual test run on OS X for 0.56.x - Release Hotfix 2 - ## Per release specialty tests
- [x] Upgrade to Chromium 70.0.3538.110.([#2200](https://github.com/brave/brave-browser/issues/2200))
### Installer
- [x] Check that installer is close to the size of last release
- [x] Check signature: If OS Run `spctl --assess --verbose /Applications/Brave-Browser-Beta.app/` and make sure it returns `accepted`. If Windows right click on the `brave_installer-x64.exe` and go to Properties, go to the Digital Signatures tab and double click on the signature. Make sure it says "The digital signature is OK" in the popup window
### Data(Upgrade from previous release)
- [x] Make sure that data from the last version appears in the new version OK
- [x] With data from the last version, verify that
- [x] bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] cookies are preserved
- [x] installed extensions are retained and work correctly
- [x] opened tabs can be reloaded
- [x] stored passwords are preserved
- [x] unpinned tabs can be pinned
### Widevine
- [x] Verify `Widevine Notification` is shown when you visit Netflix for the first time
- [x] Test that you can stream on Netflix on a fresh profile after installing Widevine
### Geolocation
- [ ] Check that https://developer.mozilla.org/en-US/docs/Web/API/Geolocation/Using_geolocation shows correct location
- [x] Check that https://browserleaks.com/geo works and shows correct location
- [x] Check that https://html5demos.com/geo/ works but doesn't require an accurate location
### Crash Reporting
- [x] Check that loading `brave://crash` causes the new tab to crash
- [x] Check that `brave://crashes` lists all the crashes and includes both Crash Report ID & Local Crash ID
- [x] Verify the crash ID matches the report on brave stats
### Bravery settings
- [x] Verify that HTTPS Everywhere works by loading http://https-everywhere.badssl.com/
- [x] Turning HTTPS Everywhere off and shields off both disable the redirect to https://https-everywhere.badssl.com/
- [x] Verify that toggling `Ads and trackers blocked` works as expected
- [x] Visit https://testsafebrowsing.appspot.com/s/phishing.html, verify that Safe Browsing (via our Proxy) works for all the listed items
- [x] Visit https://brianbondy.com/ and then turn on script blocking, page should not load. Allow it from the script blocking UI in the URL bar and it should load the page correctly
- [x] Test that 3rd party storage results are blank at https://jsfiddle.net/7ke9r14a/9/ when 3rd party cookies are blocked and not blank when 3rd party cookies are unblocked
### Fingerprint Tests
- [ ] Visit https://jsfiddle.net/bkf50r8v/13/, ensure 3 blocked items are listed in shields. Result window should show `got canvas fingerprint 0` and `got webgl fingerprint 00`
- [x] Test that audio fingerprint is blocked at https://audiofingerprint.openwpm.com/ only when `Block all fingerprinting protection` is on
- [x] Test that Brave browser isn't detected on https://extensions.inrialpes.fr/brave/
- [x] Test that https://diafygi.github.io/webrtc-ips/ doesn't leak IP address when `Block all fingerprinting protection` is on
### Content tests
- [x] Open a page with an input control and type some misspellings on a textbox, make sure they are underlined
- [x] Make sure that right clicking on a word with suggestions gives a suggestion and that clicking on the suggestion replaces the text
- [x] Test that https://mixed-script.badssl.com/ shows up as grey not red (no mixed content scripts are run)
### Session storage
- [x] Temporarily move away your browser profile and test that a new profile is created when browser is launched
- macOS - `~/Library/Application\ Support/BraveSoftware/`
- Windows - `%userprofile%\appdata\Local\BraveSoftware\`
- Linux(Ubuntu) - `~/.config/BraveSoftware/`
- [x] Test that windows and tabs restore when closed, including active tab
- [x] Ensure that the tabs in the above session are being lazy loaded when the session is restored
## Chromium upgrade tests
#### Adblock
- [x] Verify referrer blocking works properly for TLD+1. Visit `https://technology.slashdot.org/` and verify adblock works properly similar to `https://slashdot.org/`
#### Components
- [x] Delete Adblock folder from browser profile and restart browser. Visit `brave://components` and verify `Brave Ad Block Updater` downloads and update the component. Repeat for all Brave components
| non_priority | manual test run on os x for x release hotfix per release specialty tests upgrade to chromium installer check that installer is close to the size of last release check signature if os run spctl assess verbose applications brave browser beta app and make sure it returns accepted if windows right click on the brave installer exe and go to properties go to the digital signatures tab and double click on the signature make sure it says the digital signature is ok in the popup window data upgrade from previous release make sure that data from the last version appears in the new version ok with data from the last version verify that bookmarks on the bookmark toolbar and bookmark folders can be opened cookies are preserved installed extensions are retained and work correctly opened tabs can be reloaded stored passwords are preserved unpinned tabs can be pinned widevine verify widevine notification is shown when you visit netflix for the first time test that you can stream on netflix on a fresh profile after installing widevine geolocation check that shows correct location check that works and shows correct location check that works but doesn t require an accurate location crash reporting check that loading brave crash causes the new tab to crash check that brave crashes lists all the crashes and includes both crash report id local crash id verify the crash id matches the report on brave stats bravery settings verify that https everywhere works by loading turning https everywhere off and shields off both disable the redirect to verify that toggling ads and trackers blocked works as expected visit verify that safe browsing via our proxy works for all the listed items visit and then turn on script blocking page should not load allow it from the script blocking ui in the url bar and it should load the page correctly test that party storage results are blank at when party cookies are blocked and not blank when party cookies are unblocked fingerprint tests visit ensure blocked items are listed in shields result window should show got canvas fingerprint and got webgl fingerprint test that audio fingerprint is blocked at only when block all fingerprinting protection is on test that brave browser isn t detected on test that doesn t leak ip address when block all fingerprinting protection is on content tests open a page with an input control and type some misspellings on a textbox make sure they are underlined make sure that right clicking on a word with suggestions gives a suggestion and that clicking on the suggestion replaces the text test that shows up as grey not red no mixed content scripts are run session storage temporarily move away your browser profile and test that a new profile is created when browser is launched macos library application support bravesoftware windows userprofile appdata local bravesoftware linux ubuntu config bravesoftware test that windows and tabs restore when closed including active tab ensure that the tabs in the above session are being lazy loaded when the session is restored chromium upgrade tests adblock verify referrer blocking works properly for tld visit and verify adblock works properly similar to components delete adblock folder from browser profile and restart browser visit brave components and verify brave ad block updater downloads and update the component repeat for all brave components | 0 |
320,098 | 23,801,586,975 | IssuesEvent | 2022-09-03 11:32:48 | Super-Bug-Tracker-Team/super-bug-tracker | https://api.github.com/repos/Super-Bug-Tracker-Team/super-bug-tracker | closed | Design logo | documentation good first issue Frontend | This can be used as the organization's avatar image, in the app itself, and in the README documentation for consistent branding. | 1.0 | Design logo - This can be used as the organization's avatar image, in the app itself, and in the README documentation for consistent branding. | non_priority | design logo this can be used as the organization s avatar image in the app itself and in the readme documentation for consistent branding | 0 |
73,550 | 8,886,713,665 | IssuesEvent | 2019-01-15 01:53:33 | DataBiosphere/job-manager | https://api.github.com/repos/DataBiosphere/job-manager | closed | Move the inputs and outputs tabs int the tab group that contains the list of tasks | Better Error Feedback UI UX/Design | Inputs and outputs are currently too prominent in the job details page. Adding them to the last list tab set will keep them accessible but free up some vertical space. | 1.0 | Move the inputs and outputs tabs int the tab group that contains the list of tasks - Inputs and outputs are currently too prominent in the job details page. Adding them to the last list tab set will keep them accessible but free up some vertical space. | non_priority | move the inputs and outputs tabs int the tab group that contains the list of tasks inputs and outputs are currently too prominent in the job details page adding them to the last list tab set will keep them accessible but free up some vertical space | 0 |
41,496 | 8,996,325,836 | IssuesEvent | 2019-02-02 00:43:52 | rubberduck-vba/Rubberduck | https://api.github.com/repos/rubberduck-vba/Rubberduck | closed | Code Explorer Rename doesn't invoke reparse | bug feature-code-explorer stale | Currently not getting a reparse when naming a TestModule. | 1.0 | Code Explorer Rename doesn't invoke reparse - Currently not getting a reparse when naming a TestModule. | non_priority | code explorer rename doesn t invoke reparse currently not getting a reparse when naming a testmodule | 0 |
269,837 | 23,470,752,033 | IssuesEvent | 2022-08-16 21:32:49 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | [Mac] Add unit tests for AXPlatformNodeMac and AXPlatformNodeCoacoa | a: tests a: accessibility platform-mac a: desktop | We currently run hundreds of tests on the platform-agnostic components of the macOS accessibility implementation, but we don't yet test that we can get the C++ node wrapper class (`AXPlatformNodeMac`) that corresponds to a given `AXNode` or that we can get the native Objective-C macOS accessibility object (`AXPlatformNodeCocoa`) from an `AXPlatformNode`.
Add an initial test that supports adding further platform-specific tests of these wrappers. | 1.0 | [Mac] Add unit tests for AXPlatformNodeMac and AXPlatformNodeCoacoa - We currently run hundreds of tests on the platform-agnostic components of the macOS accessibility implementation, but we don't yet test that we can get the C++ node wrapper class (`AXPlatformNodeMac`) that corresponds to a given `AXNode` or that we can get the native Objective-C macOS accessibility object (`AXPlatformNodeCocoa`) from an `AXPlatformNode`.
Add an initial test that supports adding further platform-specific tests of these wrappers. | non_priority | add unit tests for axplatformnodemac and axplatformnodecoacoa we currently run hundreds of tests on the platform agnostic components of the macos accessibility implementation but we don t yet test that we can get the c node wrapper class axplatformnodemac that corresponds to a given axnode or that we can get the native objective c macos accessibility object axplatformnodecocoa from an axplatformnode add an initial test that supports adding further platform specific tests of these wrappers | 0 |
71,997 | 15,210,130,888 | IssuesEvent | 2021-02-17 06:52:21 | andythinkpower/Proj_02 | https://api.github.com/repos/andythinkpower/Proj_02 | closed | CVE-2020-36186 (High) detected in jackson-databind-2.9.3.jar - autoclosed | security vulnerability | ## CVE-2020-36186 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Proj_02/Proj_02/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.3/jackson-databind-2.9.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/andythinkpower/Proj_02/commit/b7c34d42bb108094d60cbbc332155dca1a1f54ad">b7c34d42bb108094d60cbbc332155dca1a1f54ad</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186>CVE-2020-36186</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2997">https://github.com/FasterXML/jackson-databind/issues/2997</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-36186 (High) detected in jackson-databind-2.9.3.jar - autoclosed - ## CVE-2020-36186 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Proj_02/Proj_02/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.3/jackson-databind-2.9.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/andythinkpower/Proj_02/commit/b7c34d42bb108094d60cbbc332155dca1a1f54ad">b7c34d42bb108094d60cbbc332155dca1a1f54ad</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186>CVE-2020-36186</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2997">https://github.com/FasterXML/jackson-databind/issues/2997</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file proj proj pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp dbcp datasources peruserpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
41,344 | 5,330,700,664 | IssuesEvent | 2017-02-15 17:39:36 | Automattic/jetpack | https://api.github.com/repos/Automattic/jetpack | closed | Admin Page: add link to Settings in page header | Admin Page [Pri] High [Status] Needs Design Review [Type] Enhancement | > It would be useful to have a link to the settings from the main React dashboard like there used to be in the previous version

| 1.0 | Admin Page: add link to Settings in page header - > It would be useful to have a link to the settings from the main React dashboard like there used to be in the previous version

| non_priority | admin page add link to settings in page header it would be useful to have a link to the settings from the main react dashboard like there used to be in the previous version | 0 |
31,394 | 11,924,408,277 | IssuesEvent | 2020-04-01 09:28:46 | mathiasconradt/js-jose | https://api.github.com/repos/mathiasconradt/js-jose | opened | CVE-2012-6708 (Medium) detected in jquery-1.7.1.min.js | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/mathiasconradt/js-jose/commits/34aa30f5623b8738b25b2ea42e1b00fa9f55a8ae">34aa30f5623b8738b25b2ea42e1b00fa9f55a8ae</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.7.1","isTransitiveDependency":false,"dependencyTree":"jquery:1.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v1.9.0"}],"vulnerabilityIdentifier":"CVE-2012-6708","vulnerabilityDetails":"jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the \u0027\u003c\u0027 character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the \u0027\u003c\u0027 character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2012-6708 (Medium) detected in jquery-1.7.1.min.js - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/mathiasconradt/js-jose/commits/34aa30f5623b8738b25b2ea42e1b00fa9f55a8ae">34aa30f5623b8738b25b2ea42e1b00fa9f55a8ae</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.7.1","isTransitiveDependency":false,"dependencyTree":"jquery:1.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v1.9.0"}],"vulnerabilityIdentifier":"CVE-2012-6708","vulnerabilityDetails":"jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the \u0027\u003c\u0027 character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the \u0027\u003c\u0027 character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before is vulnerable to cross site scripting xss attacks the jquery strinput function does not differentiate selectors from html in a reliable fashion in vulnerable versions jquery determined whether the input was html by looking for the character anywhere in the string giving attackers more flexibility when attempting to construct a malicious payload in fixed versions jquery only deems the input to be html if it explicitly starts with the character limiting exploitability only to attackers who can control the beginning of a string which is far less common publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails jquery before is vulnerable to cross site scripting xss attacks the jquery strinput function does not differentiate selectors from html in a reliable fashion in vulnerable versions jquery determined whether the input was html by looking for the character anywhere in the string giving attackers more flexibility when attempting to construct a malicious payload in fixed versions jquery only deems the input to be html if it explicitly starts with the character limiting exploitability only to attackers who can control the beginning of a string which is far less common vulnerabilityurl | 0 |
150,464 | 11,962,009,790 | IssuesEvent | 2020-04-05 10:43:26 | gavv/httpexpect | https://api.github.com/repos/gavv/httpexpect | opened | Add more unit tests for WebSockets | help wanted tests | WebSocket support is covered with a set of [integration tests](https://github.com/gavv/httpexpect/blob/master/e2e_websocket_test.go), but only a few unit tests: [1](https://github.com/gavv/httpexpect/blob/master/websocket_test.go), [2](https://github.com/gavv/httpexpect/blob/master/websocket_message_test.go).
The test coverage is incomplete, see `websocket*` files here: https://coveralls.io/github/gavv/httpexpect?branch=master
It would be nice to add more unit tests and increase test coverage. In particular, most assertion *failures* and some message types are not covered currently. | 1.0 | Add more unit tests for WebSockets - WebSocket support is covered with a set of [integration tests](https://github.com/gavv/httpexpect/blob/master/e2e_websocket_test.go), but only a few unit tests: [1](https://github.com/gavv/httpexpect/blob/master/websocket_test.go), [2](https://github.com/gavv/httpexpect/blob/master/websocket_message_test.go).
The test coverage is incomplete, see `websocket*` files here: https://coveralls.io/github/gavv/httpexpect?branch=master
It would be nice to add more unit tests and increase test coverage. In particular, most assertion *failures* and some message types are not covered currently. | non_priority | add more unit tests for websockets websocket support is covered with a set of but only a few unit tests the test coverage is incomplete see websocket files here it would be nice to add more unit tests and increase test coverage in particular most assertion failures and some message types are not covered currently | 0 |
110,129 | 9,436,218,108 | IssuesEvent | 2019-04-13 04:15:07 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | Test failure: System.Net.WebSockets.Client.Tests.AbortTest/Abort_CloseAndAbort_Success(server: ws://corefx-net-http11.azurewebsites.net/WebSocket/EchoWebSocket.ashx) | area-System.Net os-windows-uwp test-run-uwp-coreclr | Opened on behalf of @AriNuer
The test `System.Net.WebSockets.Client.Tests.AbortTest/Abort_CloseAndAbort_Success(server: ws://corefx-net-http11.azurewebsites.net/WebSocket/EchoWebSocket.ashx)` has failed.
Failure Message:
```
State immediately after ConnectAsync incorrect: Closed\r
Expected: True\r
Actual: False
```
Stack Trace:
```
at System.Net.WebSockets.Client.Tests.WebSocketHelper.<>c__DisplayClass4_0.<<GetConnectedWebSocket>b__0>d.MoveNext() in F:\workspace\_work\1\s\src\System.Net.WebSockets.Client\tests\WebSocketHelper.cs:line 86
--- End of stack trace from previous location where exception was thrown ---
at System.Net.WebSockets.Client.Tests.WebSocketHelper.Retry[T](ITestOutputHelper output, Func`1 func)
at System.Net.WebSockets.Client.Tests.ClientWebSocketTestBase.TestCancellation(Func`2 action, Uri server) in F:\workspace\_work\1\s\src\System.Net.WebSockets.Client\tests\ClientWebSocketTestBase.cs:line 66
at System.Net.WebSockets.Client.Tests.AbortTest.Abort_CloseAndAbort_Success(Uri server) in F:\workspace\_work\1\s\src\System.Net.WebSockets.Client\tests\AbortTest.cs:line 92
--- End of stack trace from previous location where exception was thrown ---
```
Build : 3.0 - 20190407.7 (UWP F5 Tests)
Failing configurations:
- Windows.10.Amd64.ClientRS5-x86
- Release
Details:
https://mc.dot.net/#/product/netcore/30/source/official~2Fdotnet~2Fcorefx~2Frefs~2Fheads~2Fmaster/type/test~2Ffunctional~2Fuwp~2F/build/20190407.7/workItem/System.Net.WebSockets.Client.Tests/analysis/xunit/System.Net.WebSockets.Client.Tests.AbortTest~2FAbort_CloseAndAbort_Success(server:%20ws:~2F~2Fcorefx-net-http11.azurewebsites.net~2FWebSocket~2FEchoWebSocket.ashx) | 1.0 | Test failure: System.Net.WebSockets.Client.Tests.AbortTest/Abort_CloseAndAbort_Success(server: ws://corefx-net-http11.azurewebsites.net/WebSocket/EchoWebSocket.ashx) - Opened on behalf of @AriNuer
The test `System.Net.WebSockets.Client.Tests.AbortTest/Abort_CloseAndAbort_Success(server: ws://corefx-net-http11.azurewebsites.net/WebSocket/EchoWebSocket.ashx)` has failed.
Failure Message:
```
State immediately after ConnectAsync incorrect: Closed\r
Expected: True\r
Actual: False
```
Stack Trace:
```
at System.Net.WebSockets.Client.Tests.WebSocketHelper.<>c__DisplayClass4_0.<<GetConnectedWebSocket>b__0>d.MoveNext() in F:\workspace\_work\1\s\src\System.Net.WebSockets.Client\tests\WebSocketHelper.cs:line 86
--- End of stack trace from previous location where exception was thrown ---
at System.Net.WebSockets.Client.Tests.WebSocketHelper.Retry[T](ITestOutputHelper output, Func`1 func)
at System.Net.WebSockets.Client.Tests.ClientWebSocketTestBase.TestCancellation(Func`2 action, Uri server) in F:\workspace\_work\1\s\src\System.Net.WebSockets.Client\tests\ClientWebSocketTestBase.cs:line 66
at System.Net.WebSockets.Client.Tests.AbortTest.Abort_CloseAndAbort_Success(Uri server) in F:\workspace\_work\1\s\src\System.Net.WebSockets.Client\tests\AbortTest.cs:line 92
--- End of stack trace from previous location where exception was thrown ---
```
Build : 3.0 - 20190407.7 (UWP F5 Tests)
Failing configurations:
- Windows.10.Amd64.ClientRS5-x86
- Release
Details:
https://mc.dot.net/#/product/netcore/30/source/official~2Fdotnet~2Fcorefx~2Frefs~2Fheads~2Fmaster/type/test~2Ffunctional~2Fuwp~2F/build/20190407.7/workItem/System.Net.WebSockets.Client.Tests/analysis/xunit/System.Net.WebSockets.Client.Tests.AbortTest~2FAbort_CloseAndAbort_Success(server:%20ws:~2F~2Fcorefx-net-http11.azurewebsites.net~2FWebSocket~2FEchoWebSocket.ashx) | non_priority | test failure system net websockets client tests aborttest abort closeandabort success server ws corefx net azurewebsites net websocket echowebsocket ashx opened on behalf of arinuer the test system net websockets client tests aborttest abort closeandabort success server ws corefx net azurewebsites net websocket echowebsocket ashx has failed failure message state immediately after connectasync incorrect closed r expected true r actual false stack trace at system net websockets client tests websockethelper c b d movenext in f workspace work s src system net websockets client tests websockethelper cs line end of stack trace from previous location where exception was thrown at system net websockets client tests websockethelper retry itestoutputhelper output func func at system net websockets client tests clientwebsockettestbase testcancellation func action uri server in f workspace work s src system net websockets client tests clientwebsockettestbase cs line at system net websockets client tests aborttest abort closeandabort success uri server in f workspace work s src system net websockets client tests aborttest cs line end of stack trace from previous location where exception was thrown build uwp tests failing configurations windows release details | 0 |
408,543 | 27,695,219,218 | IssuesEvent | 2023-03-14 01:16:36 | nathandh/mywebclass-simulation | https://api.github.com/repos/nathandh/mywebclass-simulation | closed | Research all areas of Legal Compliance | Documentation Sprint 1 (03-11-2023 to 03-24-2023) | Spike research task to understand what is needed for all areas of Legal Compliance for MyWebClass site. | 1.0 | Research all areas of Legal Compliance - Spike research task to understand what is needed for all areas of Legal Compliance for MyWebClass site. | non_priority | research all areas of legal compliance spike research task to understand what is needed for all areas of legal compliance for mywebclass site | 0 |
108,797 | 16,822,683,772 | IssuesEvent | 2021-06-17 14:46:20 | idonthaveafifaaddiction/flink | https://api.github.com/repos/idonthaveafifaaddiction/flink | opened | CVE-2020-11979 (High) detected in ant-1.9.1.jar | security vulnerability | ## CVE-2020-11979 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ant-1.9.1.jar</b></p></summary>
<p>master POM</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/ant/ant/1.9.1/ant-1.9.1.jar</p>
<p>
Dependency Hierarchy:
- hive-exec-2.2.0.jar (Root Library)
- :x: **ant-1.9.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/flink/commit/d77b18bba5da590fb2e8e8aa13f2dcb0674d52be">d77b18bba5da590fb2e8e8aa13f2dcb0674d52be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
As mitigation for CVE-2020-1945 Apache Ant 1.10.8 changed the permissions of temporary files it created so that only the current user was allowed to access them. Unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection, effectively nullifying the effort. This would still allow an attacker to inject modified source files into the build process.
<p>Publish Date: 2020-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11979>CVE-2020-11979</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://ant.apache.org/security.html">https://ant.apache.org/security.html</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: org.apache.ant:ant:1.10.9 </p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.ant","packageName":"ant","packageVersion":"1.9.1","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-exec:2.2.0;org.apache.ant:ant:1.9.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.ant:ant:1.10.9 "}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11979","vulnerabilityDetails":"As mitigation for CVE-2020-1945 Apache Ant 1.10.8 changed the permissions of temporary files it created so that only the current user was allowed to access them. Unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection, effectively nullifying the effort. This would still allow an attacker to inject modified source files into the build process.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11979","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11979 (High) detected in ant-1.9.1.jar - ## CVE-2020-11979 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ant-1.9.1.jar</b></p></summary>
<p>master POM</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/ant/ant/1.9.1/ant-1.9.1.jar</p>
<p>
Dependency Hierarchy:
- hive-exec-2.2.0.jar (Root Library)
- :x: **ant-1.9.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/flink/commit/d77b18bba5da590fb2e8e8aa13f2dcb0674d52be">d77b18bba5da590fb2e8e8aa13f2dcb0674d52be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
As mitigation for CVE-2020-1945 Apache Ant 1.10.8 changed the permissions of temporary files it created so that only the current user was allowed to access them. Unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection, effectively nullifying the effort. This would still allow an attacker to inject modified source files into the build process.
<p>Publish Date: 2020-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11979>CVE-2020-11979</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://ant.apache.org/security.html">https://ant.apache.org/security.html</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: org.apache.ant:ant:1.10.9 </p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.ant","packageName":"ant","packageVersion":"1.9.1","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-exec:2.2.0;org.apache.ant:ant:1.9.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.ant:ant:1.10.9 "}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11979","vulnerabilityDetails":"As mitigation for CVE-2020-1945 Apache Ant 1.10.8 changed the permissions of temporary files it created so that only the current user was allowed to access them. Unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection, effectively nullifying the effort. This would still allow an attacker to inject modified source files into the build process.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11979","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in ant jar cve high severity vulnerability vulnerable library ant jar master pom path to vulnerable library home wss scanner repository org apache ant ant ant jar dependency hierarchy hive exec jar root library x ant jar vulnerable library found in head commit a href found in base branch master vulnerability details as mitigation for cve apache ant changed the permissions of temporary files it created so that only the current user was allowed to access them unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection effectively nullifying the effort this would still allow an attacker to inject modified source files into the build process publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache ant ant isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache hive hive exec org apache ant ant isminimumfixversionavailable true minimumfixversion org apache ant ant basebranches vulnerabilityidentifier cve vulnerabilitydetails as mitigation for cve apache ant changed the permissions of temporary files it created so that only the current user was allowed to access them unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection effectively nullifying the effort this would still allow an attacker to inject modified source files into the build process vulnerabilityurl | 0 |
16,520 | 10,523,579,632 | IssuesEvent | 2019-09-30 11:21:53 | kyma-project/helm-broker | https://api.github.com/repos/kyma-project/helm-broker | closed | Improve controller readiness probe | area/service-catalog enhancement | <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
The `helm-controller` readiness probe is implemented in the dummy way to just return 200OK on every call.
We should return 200OK only when the controller is able to work.
We need to find the best way to implement the checking of the controller status.
**Ideas:**
- In SBU controller we do the test reconcile with the empty object and we expect it to process in order to indicate the readiness of the controller.
- We can wait until the `controller-runtime` probes implementation is ready and use it. https://github.com/kubernetes-sigs/controller-runtime/pull/419
| 1.0 | Improve controller readiness probe - <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
The `helm-controller` readiness probe is implemented in the dummy way to just return 200OK on every call.
We should return 200OK only when the controller is able to work.
We need to find the best way to implement the checking of the controller status.
**Ideas:**
- In SBU controller we do the test reconcile with the empty object and we expect it to process in order to indicate the readiness of the controller.
- We can wait until the `controller-runtime` probes implementation is ready and use it. https://github.com/kubernetes-sigs/controller-runtime/pull/419
| non_priority | improve controller readiness probe thank you for your contribution before you submit the issue search open and closed issues for duplicates read the contributing guidelines description the helm controller readiness probe is implemented in the dummy way to just return on every call we should return only when the controller is able to work we need to find the best way to implement the checking of the controller status ideas in sbu controller we do the test reconcile with the empty object and we expect it to process in order to indicate the readiness of the controller we can wait until the controller runtime probes implementation is ready and use it | 0 |
53,127 | 13,124,621,457 | IssuesEvent | 2020-08-06 04:21:54 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Exception generating tar file in the build process | :Core/Infra/Build >test-failure Team:Core/Infra | https://gradle-enterprise.elastic.co/s/3iszhqpj5hl2e/console-log?anchor=1230
```
[...]
[7.5.2] > Task :distribution:archives:oss-linux-tar:assemble
[7.5.2] build complete, generating: /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/bugfix/build/bwc/checkout-7.5/build/2470.tar.bz2
[7.5.2]
[7.5.2] Deprecated Gradle features were used in this build, making it incompatible with Gradle 6.0.
[7.5.2] Use '--warning-mode all' to show the individual deprecation warnings.
[7.5.2] See https://docs.gradle.org/5.6.2/userguide/command_line_interface.html#sec:command_line_warnings
[7.5.2]
[7.5.2] BUILD SUCCESSFUL in 2m 19s
[7.5.2] 129 actionable tasks: 128 executed, 1 up-to-date
[7.5.2]
[7.5.2] Publishing build scan...
[7.5.2] https://gradle-enterprise.elastic.co/s/ocf4i2mvfdndm
[7.5.2]
Picked up JAVA_TOOL_OPTIONS: -Dfile.encoding=UTF8
Picked up JAVA_TOOL_OPTIONS: -Dfile.encoding=UTF8
build complete, generating: /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/build/2470.tar.bz2
Failed to archive additional logs
org.apache.tools.ant.BuildException: Problem creating TAR: request to write '4367' bytes exceeds size in header of '298999' bytes for entry 'x-pack/qa/rolling-upgrade/build/testclusters/v6.8.7-2/logs/v6.8.7_access.log'
at org.apache.tools.ant.taskdefs.Tar.execute(Tar.java:348)
at org.apache.tools.ant.UnknownElement.execute(UnknownElement.java:292)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.apache.tools.ant.dispatch.DispatchUtils.execute(DispatchUtils.java:99)
at groovy.util.AntBuilder.performTask(AntBuilder.java:333)
at groovy.util.AntBuilder.nodeCompleted(AntBuilder.java:278)
at org.gradle.api.internal.project.ant.BasicAntBuilder.nodeCompleted(BasicAntBuilder.java:80)
at groovy.util.BuilderSupport.doInvokeMethod(BuilderSupport.java:151)
at groovy.util.AntBuilder.doInvokeMethod(AntBuilder.java:213)
at org.gradle.api.internal.project.ant.BasicAntBuilder.doInvokeMethod(BasicAntBuilder.java:107)
at groovy.util.BuilderSupport.invokeMethod(BuilderSupport.java:64)
at org.codehaus.groovy.runtime.callsite.PogoMetaClassSite.call(PogoMetaClassSite.java:43)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCall(CallSiteArray.java:47)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:115)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:135)
at build_complete$_run_closure1.doCall(Unknown Source)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:101)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at org.codehaus.groovy.runtime.metaclass.ClosureMetaClass.invokeMethod(ClosureMetaClass.java:263)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1041)
at groovy.lang.Closure.call(Closure.java:405)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:41)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:25)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:42)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:231)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:150)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:58)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:325)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:235)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:141)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:37)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy16.buildFinished(Unknown Source)
at org.gradle.initialization.DefaultGradleLauncher.finishBuild(DefaultGradleLauncher.java:171)
at org.gradle.initialization.DefaultGradleLauncher.doBuildStages(DefaultGradleLauncher.java:133)
at org.gradle.initialization.DefaultGradleLauncher.executeTasks(DefaultGradleLauncher.java:110)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:60)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:57)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:85)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:78)
at org.gradle.internal.work.DefaultWorkerLeaseService.withLocks(DefaultWorkerLeaseService.java:189)
at org.gradle.internal.work.StopShieldingWorkerLeaseService.withLocks(StopShieldingWorkerLeaseService.java:40)
at org.gradle.internal.invocation.GradleBuildController.doBuild(GradleBuildController.java:78)
at org.gradle.internal.invocation.GradleBuildController.run(GradleBuildController.java:57)
at org.gradle.tooling.internal.provider.ExecuteBuildActionRunner.run(ExecuteBuildActionRunner.java:31)
at org.gradle.launcher.exec.ChainingBuildActionRunner.run(ChainingBuildActionRunner.java:35)
at org.gradle.launcher.exec.BuildOutcomeReportingBuildActionRunner.run(BuildOutcomeReportingBuildActionRunner.java:63)
at org.gradle.tooling.internal.provider.ValidatingBuildActionRunner.run(ValidatingBuildActionRunner.java:32)
at org.gradle.launcher.exec.BuildCompletionNotifyingBuildActionRunner.run(BuildCompletionNotifyingBuildActionRunner.java:39)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:51)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:416)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:406)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:102)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.call(DelegatingBuildOperationExecutor.java:36)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner.run(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:50)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:47)
at org.gradle.composite.internal.DefaultRootBuildState.run(DefaultRootBuildState.java:78)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:47)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:31)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:42)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:28)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:78)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:52)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:59)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:36)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:68)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:38)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:37)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:26)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:43)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:29)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:60)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:32)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:55)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:41)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:48)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:32)
at org.gradle.launcher.daemon.server.exec.ExecuteBuild.doBuild(ExecuteBuild.java:68)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.WatchForDisconnection.execute(WatchForDisconnection.java:39)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ResetDeprecationLogger.execute(ResetDeprecationLogger.java:27)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.RequestStopIfSingleUsedDaemon.execute(RequestStopIfSingleUsedDaemon.java:35)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:78)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:75)
at org.gradle.util.Swapper.swap(Swapper.java:38)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput.execute(ForwardClientInput.java:75)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogAndCheckHealth.execute(LogAndCheckHealth.java:55)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogToClient.doBuild(LogToClient.java:63)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.EstablishBuildEnvironment.doBuild(EstablishBuildEnvironment.java:82)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.StartBuildOrRespondWithBusy$1.run(StartBuildOrRespondWithBusy.java:52)
at org.gradle.launcher.daemon.server.DaemonStateCoordinator$1.run(DaemonStateCoordinator.java:297)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.lang.Thread.run(Thread.java:830)
Caused by: java.io.IOException: request to write '4367' bytes exceeds size in header of '298999' bytes for entry 'x-pack/qa/rolling-upgrade/build/testclusters/v6.8.7-2/logs/v6.8.7_access.log'
at org.apache.tools.tar.TarOutputStream.write(TarOutputStream.java:414)
at org.apache.tools.ant.taskdefs.Tar.tarResource(Tar.java:512)
at org.apache.tools.ant.taskdefs.Tar.tarFile(Tar.java:378)
at org.apache.tools.ant.taskdefs.Tar.tar(Tar.java:695)
at org.apache.tools.ant.taskdefs.Tar.execute(Tar.java:344)
at org.apache.tools.ant.UnknownElement.execute(UnknownElement.java:292)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.apache.tools.ant.dispatch.DispatchUtils.execute(DispatchUtils.java:99)
at groovy.util.AntBuilder.performTask(AntBuilder.java:333)
at groovy.util.AntBuilder.nodeCompleted(AntBuilder.java:278)
at org.gradle.api.internal.project.ant.BasicAntBuilder.nodeCompleted(BasicAntBuilder.java:80)
at groovy.util.BuilderSupport.doInvokeMethod(BuilderSupport.java:151)
at groovy.util.AntBuilder.doInvokeMethod(AntBuilder.java:213)
at org.gradle.api.internal.project.ant.BasicAntBuilder.doInvokeMethod(BasicAntBuilder.java:107)
at groovy.util.BuilderSupport.invokeMethod(BuilderSupport.java:64)
at org.codehaus.groovy.runtime.callsite.PogoMetaClassSite.call(PogoMetaClassSite.java:43)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCall(CallSiteArray.java:47)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:115)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:135)
at build_complete$_run_closure1.doCall(Unknown Source)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:101)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at org.codehaus.groovy.runtime.metaclass.ClosureMetaClass.invokeMethod(ClosureMetaClass.java:263)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1041)
at groovy.lang.Closure.call(Closure.java:405)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:41)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:25)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:42)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:231)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:150)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:58)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:325)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:235)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:141)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:37)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy16.buildFinished(Unknown Source)
at org.gradle.initialization.DefaultGradleLauncher.finishBuild(DefaultGradleLauncher.java:171)
at org.gradle.initialization.DefaultGradleLauncher.doBuildStages(DefaultGradleLauncher.java:133)
at org.gradle.initialization.DefaultGradleLauncher.executeTasks(DefaultGradleLauncher.java:110)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:60)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:57)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:85)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:78)
at org.gradle.internal.work.DefaultWorkerLeaseService.withLocks(DefaultWorkerLeaseService.java:189)
at org.gradle.internal.work.StopShieldingWorkerLeaseService.withLocks(StopShieldingWorkerLeaseService.java:40)
at org.gradle.internal.invocation.GradleBuildController.doBuild(GradleBuildController.java:78)
at org.gradle.internal.invocation.GradleBuildController.run(GradleBuildController.java:57)
at org.gradle.tooling.internal.provider.ExecuteBuildActionRunner.run(ExecuteBuildActionRunner.java:31)
at org.gradle.launcher.exec.ChainingBuildActionRunner.run(ChainingBuildActionRunner.java:35)
at org.gradle.launcher.exec.BuildOutcomeReportingBuildActionRunner.run(BuildOutcomeReportingBuildActionRunner.java:63)
at org.gradle.tooling.internal.provider.ValidatingBuildActionRunner.run(ValidatingBuildActionRunner.java:32)
at org.gradle.launcher.exec.BuildCompletionNotifyingBuildActionRunner.run(BuildCompletionNotifyingBuildActionRunner.java:39)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:51)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:416)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:406)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:102)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.call(DelegatingBuildOperationExecutor.java:36)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner.run(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:50)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:47)
at org.gradle.composite.internal.DefaultRootBuildState.run(DefaultRootBuildState.java:78)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:47)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:31)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:42)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:28)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:78)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:52)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:59)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:36)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:68)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:38)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:37)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:26)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:43)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:29)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:60)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:32)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:55)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:41)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:48)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:32)
at org.gradle.launcher.daemon.server.exec.ExecuteBuild.doBuild(ExecuteBuild.java:68)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.WatchForDisconnection.execute(WatchForDisconnection.java:39)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ResetDeprecationLogger.execute(ResetDeprecationLogger.java:27)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.RequestStopIfSingleUsedDaemon.execute(RequestStopIfSingleUsedDaemon.java:35)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:78)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:75)
at org.gradle.util.Swapper.swap(Swapper.java:38)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput.execute(ForwardClientInput.java:75)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogAndCheckHealth.execute(LogAndCheckHealth.java:55)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogToClient.doBuild(LogToClient.java:63)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.EstablishBuildEnvironment.doBuild(EstablishBuildEnvironment.java:82)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.StartBuildOrRespondWithBusy$1.run(StartBuildOrRespondWithBusy.java:52)
at org.gradle.launcher.daemon.server.DaemonStateCoordinator$1.run(DaemonStateCoordinator.java:297)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.lang.Thread.run(Thread.java:830)
FAILURE: Build failed with an exception.
* Where:
Build file '/dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/build.gradle' line: 245
* What went wrong:
Execution failed for task ':distribution:bwc:bugfix:buildBwcOssLinuxTar'.
> Building 7.5.2 didn't generate expected file /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/bugfix/build/bwc/checkout-7.5/distribution/archives/oss-linux-tar/build/distributions/elasticsearch-oss-7.5.2-SNAPSHOT-linux-x86_64.tar.gz
* Try:
Run with --info or --debug option to get more log output. Run with --scan to get full insights.
* Exception is:
org.gradle.api.tasks.TaskExecutionException: Execution failed for task ':distribution:bwc:bugfix:buildBwcOssLinuxTar'.
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.lambda$executeIfValid$1(ExecuteActionsTaskExecuter.java:187)
at org.gradle.internal.Try$Failure.ifSuccessfulOrElse(Try.java:263)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeIfValid(ExecuteActionsTaskExecuter.java:185)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.execute(ExecuteActionsTaskExecuter.java:166)
at org.gradle.api.internal.tasks.execution.CleanupStaleOutputsExecuter.execute(CleanupStaleOutputsExecuter.java:109)
at org.gradle.api.internal.tasks.execution.FinalizePropertiesTaskExecuter.execute(FinalizePropertiesTaskExecuter.java:46)
at org.gradle.api.internal.tasks.execution.ResolveTaskExecutionModeExecuter.execute(ResolveTaskExecutionModeExecuter.java:62)
at org.gradle.api.internal.tasks.execution.SkipTaskWithNoActionsExecuter.execute(SkipTaskWithNoActionsExecuter.java:57)
at org.gradle.api.internal.tasks.execution.SkipOnlyIfTaskExecuter.execute(SkipOnlyIfTaskExecuter.java:56)
at org.gradle.api.internal.tasks.execution.CatchExceptionTaskExecuter.execute(CatchExceptionTaskExecuter.java:36)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter$1.executeTask(EventFiringTaskExecuter.java:77)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter$1.call(EventFiringTaskExecuter.java:55)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter$1.call(EventFiringTaskExecuter.java:52)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:416)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:406)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:102)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.call(DelegatingBuildOperationExecutor.java:36)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter.execute(EventFiringTaskExecuter.java:52)
at org.gradle.execution.plan.LocalTaskNodeExecutor.execute(LocalTaskNodeExecutor.java:41)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$InvokeNodeExecutorsAction.execute(DefaultTaskExecutionGraph.java:374)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$InvokeNodeExecutorsAction.execute(DefaultTaskExecutionGraph.java:361)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$BuildOperationAwareExecutionAction.execute(DefaultTaskExecutionGraph.java:354)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$BuildOperationAwareExecutionAction.execute(DefaultTaskExecutionGraph.java:340)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.lambda$run$0(DefaultPlanExecutor.java:127)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.execute(DefaultPlanExecutor.java:191)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.executeNextNode(DefaultPlanExecutor.java:182)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.run(DefaultPlanExecutor.java:124)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base/java.lang.Thread.run(Thread.java:830)
Caused by: org.gradle.api.InvalidUserDataException: Building 7.5.2 didn't generate expected file /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/bugfix/build/bwc/checkout-7.5/distribution/archives/oss-linux-tar/build/distributions/elasticsearch-oss-7.5.2-SNAPSHOT-linux-x86_64.tar.gz
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance0(Native Method)
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance(NativeConstructorAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingConstructorAccessorImpl.newInstance(DelegatingConstructorAccessorImpl.java:45)
at java.base/java.lang.reflect.Constructor.newInstanceWithCaller(Constructor.java:500)
at java.base/java.lang.reflect.Constructor.newInstance(Constructor.java:481)
at org.codehaus.groovy.reflection.CachedConstructor.invoke(CachedConstructor.java:80)
at org.codehaus.groovy.reflection.CachedConstructor.doConstructorInvoke(CachedConstructor.java:74)
at org.codehaus.groovy.runtime.callsite.ConstructorSite$ConstructorSiteNoUnwrap.callConstructor(ConstructorSite.java:84)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCallConstructor(CallSiteArray.java:59)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:237)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:249)
at build_cqkew81bvy168mqxti3rluq15$_run_closure1$_closure2$_closure12$_closure36$_closure38.doCall(/dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/build.gradle:245)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:567)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:101)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at org.codehaus.groovy.runtime.metaclass.ClosureMetaClass.invokeMethod(ClosureMetaClass.java:263)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1041)
at groovy.lang.Closure.call(Closure.java:405)
at groovy.lang.Closure.call(Closure.java:421)
at org.gradle.api.internal.AbstractTask$ClosureTaskAction.execute(AbstractTask.java:664)
at org.gradle.api.internal.AbstractTask$ClosureTaskAction.execute(AbstractTask.java:637)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$3.run(ExecuteActionsTaskExecuter.java:539)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:402)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:394)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.run(DefaultBuildOperationExecutor.java:92)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.run(DelegatingBuildOperationExecutor.java:31)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeAction(ExecuteActionsTaskExecuter.java:524)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeActions(ExecuteActionsTaskExecuter.java:507)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.access$300(ExecuteActionsTaskExecuter.java:109)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$TaskExecution.executeWithPreviousOutputFiles(ExecuteActionsTaskExecuter.java:258)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$TaskExecution.execute(ExecuteActionsTaskExecuter.java:247)
at org.gradle.internal.execution.steps.ExecuteStep.lambda$execute$1(ExecuteStep.java:33)
at java.base/java.util.Optional.orElseGet(Optional.java:362)
at org.gradle.internal.execution.steps.ExecuteStep.execute(ExecuteStep.java:33)
at org.gradle.internal.execution.steps.ExecuteStep.execute(ExecuteStep.java:26)
at org.gradle.internal.execution.steps.CleanupOutputsStep.execute(CleanupOutputsStep.java:63)
at org.gradle.internal.execution.steps.CleanupOutputsStep.execute(CleanupOutputsStep.java:35)
at org.gradle.internal.execution.steps.ResolveInputChangesStep.execute(ResolveInputChangesStep.java:49)
at org.gradle.internal.execution.steps.ResolveInputChangesStep.execute(ResolveInputChangesStep.java:34)
at org.gradle.internal.execution.steps.CancelExecutionStep.execute(CancelExecutionStep.java:43)
at org.gradle.internal.execution.steps.TimeoutStep.executeWithoutTimeout(TimeoutStep.java:73)
at org.gradle.internal.execution.steps.TimeoutStep.execute(TimeoutStep.java:54)
at org.gradle.internal.execution.steps.CatchExceptionStep.execute(CatchExceptionStep.java:34)
at org.gradle.internal.execution.steps.CreateOutputsStep.execute(CreateOutputsStep.java:44)
at org.gradle.internal.execution.steps.SnapshotOutputsStep.execute(SnapshotOutputsStep.java:54)
at org.gradle.internal.execution.steps.SnapshotOutputsStep.execute(SnapshotOutputsStep.java:38)
at org.gradle.internal.execution.steps.CacheStep.executeWithoutCache(CacheStep.java:153)
at org.gradle.internal.execution.steps.CacheStep.executeAndStoreInCache(CacheStep.java:129)
at org.gradle.internal.execution.steps.CacheStep.lambda$executeWithCache$2(CacheStep.java:107)
at java.base/java.util.Optional.orElseGet(Optional.java:362)
at org.gradle.internal.execution.steps.CacheStep.lambda$executeWithCache$3(CacheStep.java:107)
at org.gradle.internal.Try$Success.map(Try.java:162)
at org.gradle.internal.execution.steps.CacheStep.executeWithCache(CacheStep.java:76)
at org.gradle.internal.execution.steps.CacheStep.execute(CacheStep.java:66)
at org.gradle.internal.execution.steps.CacheStep.execute(CacheStep.java:41)
at org.gradle.internal.execution.steps.BroadcastChangingOutputsStep.execute(BroadcastChangingOutputsStep.java:49)
at org.gradle.internal.execution.steps.StoreExecutionStateStep.execute(StoreExecutionStateStep.java:44)
at org.gradle.internal.execution.steps.StoreExecutionStateStep.execute(StoreExecutionStateStep.java:33)
at org.gradle.internal.execution.steps.RecordOutputsStep.execute(RecordOutputsStep.java:38)
at org.gradle.internal.execution.steps.RecordOutputsStep.execute(RecordOutputsStep.java:24)
at org.gradle.internal.execution.steps.SkipUpToDateStep.executeBecause(SkipUpToDateStep.java:92)
at org.gradle.internal.execution.steps.SkipUpToDateStep.lambda$execute$0(SkipUpToDateStep.java:85)
at java.base/java.util.Optional.map(Optional.java:258)
at org.gradle.internal.execution.steps.SkipUpToDateStep.execute(SkipUpToDateStep.java:55)
at org.gradle.internal.execution.steps.SkipUpToDateStep.execute(SkipUpToDateStep.java:39)
at org.gradle.internal.execution.steps.ResolveChangesStep.execute(ResolveChangesStep.java:76)
at org.gradle.internal.execution.steps.ResolveChangesStep.execute(ResolveChangesStep.java:37)
at org.gradle.internal.execution.steps.legacy.MarkSnapshottingInputsFinishedStep.execute(MarkSnapshottingInputsFinishedStep.java:36)
at org.gradle.internal.execution.steps.legacy.MarkSnapshottingInputsFinishedStep.execute(MarkSnapshottingInputsFinishedStep.java:26)
at org.gradle.internal.execution.steps.ResolveCachingStateStep.execute(ResolveCachingStateStep.java:94)
at org.gradle.internal.execution.steps.ResolveCachingStateStep.execute(ResolveCachingStateStep.java:49)
at org.gradle.internal.execution.steps.CaptureStateBeforeExecutionStep.execute(CaptureStateBeforeExecutionStep.java:79)
at org.gradle.internal.execution.steps.CaptureStateBeforeExecutionStep.execute(CaptureStateBeforeExecutionStep.java:53)
at org.gradle.internal.execution.steps.ValidateStep.execute(ValidateStep.java:74)
at org.gradle.internal.execution.steps.SkipEmptyWorkStep.lambda$execute$2(SkipEmptyWorkStep.java:78)
at java.base/java.util.Optional.orElseGet(Optional.java:362)
at org.gradle.internal.execution.steps.SkipEmptyWorkStep.execute(SkipEmptyWorkStep.java:78)
at org.gradle.internal.execution.steps.SkipEmptyWorkStep.execute(SkipEmptyWorkStep.java:34)
at org.gradle.internal.execution.steps.legacy.MarkSnapshottingInputsStartedStep.execute(MarkSnapshottingInputsStartedStep.java:39)
at org.gradle.internal.execution.steps.LoadExecutionStateStep.execute(LoadExecutionStateStep.java:40)
at org.gradle.internal.execution.steps.LoadExecutionStateStep.execute(LoadExecutionStateStep.java:28)
at org.gradle.internal.execution.impl.DefaultWorkExecutor.execute(DefaultWorkExecutor.java:33)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeIfValid(ExecuteActionsTaskExecuter.java:174)
... 33 more
* Get more help at https://help.gradle.org
Deprecated Gradle features were used in this build, making it incompatible with Gradle 7.0.
Use '--warning-mode all' to show the individual deprecation warnings.
See https://docs.gradle.org/6.0.1/userguide/command_line_interface.html#sec:command_line_warnings
BUILD FAILED in 12m 1s
345 actionable tasks: 267 executed, 77 from cache, 1 up-to-date
```
I cannot reproduce this but wonder that this might be a bug in one or our dependencies, or maybe due to the fact that the log file was still being appended to? | 1.0 | Exception generating tar file in the build process - https://gradle-enterprise.elastic.co/s/3iszhqpj5hl2e/console-log?anchor=1230
```
[...]
[7.5.2] > Task :distribution:archives:oss-linux-tar:assemble
[7.5.2] build complete, generating: /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/bugfix/build/bwc/checkout-7.5/build/2470.tar.bz2
[7.5.2]
[7.5.2] Deprecated Gradle features were used in this build, making it incompatible with Gradle 6.0.
[7.5.2] Use '--warning-mode all' to show the individual deprecation warnings.
[7.5.2] See https://docs.gradle.org/5.6.2/userguide/command_line_interface.html#sec:command_line_warnings
[7.5.2]
[7.5.2] BUILD SUCCESSFUL in 2m 19s
[7.5.2] 129 actionable tasks: 128 executed, 1 up-to-date
[7.5.2]
[7.5.2] Publishing build scan...
[7.5.2] https://gradle-enterprise.elastic.co/s/ocf4i2mvfdndm
[7.5.2]
Picked up JAVA_TOOL_OPTIONS: -Dfile.encoding=UTF8
Picked up JAVA_TOOL_OPTIONS: -Dfile.encoding=UTF8
build complete, generating: /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/build/2470.tar.bz2
Failed to archive additional logs
org.apache.tools.ant.BuildException: Problem creating TAR: request to write '4367' bytes exceeds size in header of '298999' bytes for entry 'x-pack/qa/rolling-upgrade/build/testclusters/v6.8.7-2/logs/v6.8.7_access.log'
at org.apache.tools.ant.taskdefs.Tar.execute(Tar.java:348)
at org.apache.tools.ant.UnknownElement.execute(UnknownElement.java:292)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.apache.tools.ant.dispatch.DispatchUtils.execute(DispatchUtils.java:99)
at groovy.util.AntBuilder.performTask(AntBuilder.java:333)
at groovy.util.AntBuilder.nodeCompleted(AntBuilder.java:278)
at org.gradle.api.internal.project.ant.BasicAntBuilder.nodeCompleted(BasicAntBuilder.java:80)
at groovy.util.BuilderSupport.doInvokeMethod(BuilderSupport.java:151)
at groovy.util.AntBuilder.doInvokeMethod(AntBuilder.java:213)
at org.gradle.api.internal.project.ant.BasicAntBuilder.doInvokeMethod(BasicAntBuilder.java:107)
at groovy.util.BuilderSupport.invokeMethod(BuilderSupport.java:64)
at org.codehaus.groovy.runtime.callsite.PogoMetaClassSite.call(PogoMetaClassSite.java:43)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCall(CallSiteArray.java:47)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:115)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:135)
at build_complete$_run_closure1.doCall(Unknown Source)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:101)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at org.codehaus.groovy.runtime.metaclass.ClosureMetaClass.invokeMethod(ClosureMetaClass.java:263)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1041)
at groovy.lang.Closure.call(Closure.java:405)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:41)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:25)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:42)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:231)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:150)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:58)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:325)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:235)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:141)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:37)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy16.buildFinished(Unknown Source)
at org.gradle.initialization.DefaultGradleLauncher.finishBuild(DefaultGradleLauncher.java:171)
at org.gradle.initialization.DefaultGradleLauncher.doBuildStages(DefaultGradleLauncher.java:133)
at org.gradle.initialization.DefaultGradleLauncher.executeTasks(DefaultGradleLauncher.java:110)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:60)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:57)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:85)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:78)
at org.gradle.internal.work.DefaultWorkerLeaseService.withLocks(DefaultWorkerLeaseService.java:189)
at org.gradle.internal.work.StopShieldingWorkerLeaseService.withLocks(StopShieldingWorkerLeaseService.java:40)
at org.gradle.internal.invocation.GradleBuildController.doBuild(GradleBuildController.java:78)
at org.gradle.internal.invocation.GradleBuildController.run(GradleBuildController.java:57)
at org.gradle.tooling.internal.provider.ExecuteBuildActionRunner.run(ExecuteBuildActionRunner.java:31)
at org.gradle.launcher.exec.ChainingBuildActionRunner.run(ChainingBuildActionRunner.java:35)
at org.gradle.launcher.exec.BuildOutcomeReportingBuildActionRunner.run(BuildOutcomeReportingBuildActionRunner.java:63)
at org.gradle.tooling.internal.provider.ValidatingBuildActionRunner.run(ValidatingBuildActionRunner.java:32)
at org.gradle.launcher.exec.BuildCompletionNotifyingBuildActionRunner.run(BuildCompletionNotifyingBuildActionRunner.java:39)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:51)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:416)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:406)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:102)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.call(DelegatingBuildOperationExecutor.java:36)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner.run(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:50)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:47)
at org.gradle.composite.internal.DefaultRootBuildState.run(DefaultRootBuildState.java:78)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:47)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:31)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:42)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:28)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:78)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:52)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:59)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:36)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:68)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:38)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:37)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:26)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:43)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:29)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:60)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:32)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:55)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:41)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:48)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:32)
at org.gradle.launcher.daemon.server.exec.ExecuteBuild.doBuild(ExecuteBuild.java:68)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.WatchForDisconnection.execute(WatchForDisconnection.java:39)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ResetDeprecationLogger.execute(ResetDeprecationLogger.java:27)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.RequestStopIfSingleUsedDaemon.execute(RequestStopIfSingleUsedDaemon.java:35)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:78)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:75)
at org.gradle.util.Swapper.swap(Swapper.java:38)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput.execute(ForwardClientInput.java:75)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogAndCheckHealth.execute(LogAndCheckHealth.java:55)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogToClient.doBuild(LogToClient.java:63)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.EstablishBuildEnvironment.doBuild(EstablishBuildEnvironment.java:82)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.StartBuildOrRespondWithBusy$1.run(StartBuildOrRespondWithBusy.java:52)
at org.gradle.launcher.daemon.server.DaemonStateCoordinator$1.run(DaemonStateCoordinator.java:297)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.lang.Thread.run(Thread.java:830)
Caused by: java.io.IOException: request to write '4367' bytes exceeds size in header of '298999' bytes for entry 'x-pack/qa/rolling-upgrade/build/testclusters/v6.8.7-2/logs/v6.8.7_access.log'
at org.apache.tools.tar.TarOutputStream.write(TarOutputStream.java:414)
at org.apache.tools.ant.taskdefs.Tar.tarResource(Tar.java:512)
at org.apache.tools.ant.taskdefs.Tar.tarFile(Tar.java:378)
at org.apache.tools.ant.taskdefs.Tar.tar(Tar.java:695)
at org.apache.tools.ant.taskdefs.Tar.execute(Tar.java:344)
at org.apache.tools.ant.UnknownElement.execute(UnknownElement.java:292)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.apache.tools.ant.dispatch.DispatchUtils.execute(DispatchUtils.java:99)
at groovy.util.AntBuilder.performTask(AntBuilder.java:333)
at groovy.util.AntBuilder.nodeCompleted(AntBuilder.java:278)
at org.gradle.api.internal.project.ant.BasicAntBuilder.nodeCompleted(BasicAntBuilder.java:80)
at groovy.util.BuilderSupport.doInvokeMethod(BuilderSupport.java:151)
at groovy.util.AntBuilder.doInvokeMethod(AntBuilder.java:213)
at org.gradle.api.internal.project.ant.BasicAntBuilder.doInvokeMethod(BasicAntBuilder.java:107)
at groovy.util.BuilderSupport.invokeMethod(BuilderSupport.java:64)
at org.codehaus.groovy.runtime.callsite.PogoMetaClassSite.call(PogoMetaClassSite.java:43)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCall(CallSiteArray.java:47)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:115)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.call(AbstractCallSite.java:135)
at build_complete$_run_closure1.doCall(Unknown Source)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:567)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:101)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at org.codehaus.groovy.runtime.metaclass.ClosureMetaClass.invokeMethod(ClosureMetaClass.java:263)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1041)
at groovy.lang.Closure.call(Closure.java:405)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:41)
at org.gradle.listener.ClosureBackedMethodInvocationDispatch.dispatch(ClosureBackedMethodInvocationDispatch.java:25)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:42)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:231)
at org.gradle.internal.event.BroadcastDispatch$SingletonDispatch.dispatch(BroadcastDispatch.java:150)
at org.gradle.internal.event.AbstractBroadcastDispatch.dispatch(AbstractBroadcastDispatch.java:58)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:325)
at org.gradle.internal.event.BroadcastDispatch$CompositeDispatch.dispatch(BroadcastDispatch.java:235)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:141)
at org.gradle.internal.event.ListenerBroadcast.dispatch(ListenerBroadcast.java:37)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy16.buildFinished(Unknown Source)
at org.gradle.initialization.DefaultGradleLauncher.finishBuild(DefaultGradleLauncher.java:171)
at org.gradle.initialization.DefaultGradleLauncher.doBuildStages(DefaultGradleLauncher.java:133)
at org.gradle.initialization.DefaultGradleLauncher.executeTasks(DefaultGradleLauncher.java:110)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:60)
at org.gradle.internal.invocation.GradleBuildController$1.execute(GradleBuildController.java:57)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:85)
at org.gradle.internal.invocation.GradleBuildController$3.create(GradleBuildController.java:78)
at org.gradle.internal.work.DefaultWorkerLeaseService.withLocks(DefaultWorkerLeaseService.java:189)
at org.gradle.internal.work.StopShieldingWorkerLeaseService.withLocks(StopShieldingWorkerLeaseService.java:40)
at org.gradle.internal.invocation.GradleBuildController.doBuild(GradleBuildController.java:78)
at org.gradle.internal.invocation.GradleBuildController.run(GradleBuildController.java:57)
at org.gradle.tooling.internal.provider.ExecuteBuildActionRunner.run(ExecuteBuildActionRunner.java:31)
at org.gradle.launcher.exec.ChainingBuildActionRunner.run(ChainingBuildActionRunner.java:35)
at org.gradle.launcher.exec.BuildOutcomeReportingBuildActionRunner.run(BuildOutcomeReportingBuildActionRunner.java:63)
at org.gradle.tooling.internal.provider.ValidatingBuildActionRunner.run(ValidatingBuildActionRunner.java:32)
at org.gradle.launcher.exec.BuildCompletionNotifyingBuildActionRunner.run(BuildCompletionNotifyingBuildActionRunner.java:39)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:51)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner$3.call(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:416)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:406)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:102)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.call(DelegatingBuildOperationExecutor.java:36)
at org.gradle.launcher.exec.RunAsBuildOperationBuildActionRunner.run(RunAsBuildOperationBuildActionRunner.java:45)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:50)
at org.gradle.launcher.exec.InProcessBuildActionExecuter$1.transform(InProcessBuildActionExecuter.java:47)
at org.gradle.composite.internal.DefaultRootBuildState.run(DefaultRootBuildState.java:78)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:47)
at org.gradle.launcher.exec.InProcessBuildActionExecuter.execute(InProcessBuildActionExecuter.java:31)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:42)
at org.gradle.launcher.exec.BuildTreeScopeBuildActionExecuter.execute(BuildTreeScopeBuildActionExecuter.java:28)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:78)
at org.gradle.tooling.internal.provider.ContinuousBuildActionExecuter.execute(ContinuousBuildActionExecuter.java:52)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:59)
at org.gradle.tooling.internal.provider.SubscribableBuildActionExecuter.execute(SubscribableBuildActionExecuter.java:36)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:68)
at org.gradle.tooling.internal.provider.SessionScopeBuildActionExecuter.execute(SessionScopeBuildActionExecuter.java:38)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:37)
at org.gradle.tooling.internal.provider.GradleThreadBuildActionExecuter.execute(GradleThreadBuildActionExecuter.java:26)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:43)
at org.gradle.tooling.internal.provider.ParallelismConfigurationBuildActionExecuter.execute(ParallelismConfigurationBuildActionExecuter.java:29)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:60)
at org.gradle.tooling.internal.provider.StartParamsValidatingActionExecuter.execute(StartParamsValidatingActionExecuter.java:32)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:55)
at org.gradle.tooling.internal.provider.SessionFailureReportingActionExecuter.execute(SessionFailureReportingActionExecuter.java:41)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:48)
at org.gradle.tooling.internal.provider.SetupLoggingActionExecuter.execute(SetupLoggingActionExecuter.java:32)
at org.gradle.launcher.daemon.server.exec.ExecuteBuild.doBuild(ExecuteBuild.java:68)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.WatchForDisconnection.execute(WatchForDisconnection.java:39)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ResetDeprecationLogger.execute(ResetDeprecationLogger.java:27)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.RequestStopIfSingleUsedDaemon.execute(RequestStopIfSingleUsedDaemon.java:35)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:78)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput$2.create(ForwardClientInput.java:75)
at org.gradle.util.Swapper.swap(Swapper.java:38)
at org.gradle.launcher.daemon.server.exec.ForwardClientInput.execute(ForwardClientInput.java:75)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogAndCheckHealth.execute(LogAndCheckHealth.java:55)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.LogToClient.doBuild(LogToClient.java:63)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.EstablishBuildEnvironment.doBuild(EstablishBuildEnvironment.java:82)
at org.gradle.launcher.daemon.server.exec.BuildCommandOnly.execute(BuildCommandOnly.java:37)
at org.gradle.launcher.daemon.server.api.DaemonCommandExecution.proceed(DaemonCommandExecution.java:104)
at org.gradle.launcher.daemon.server.exec.StartBuildOrRespondWithBusy$1.run(StartBuildOrRespondWithBusy.java:52)
at org.gradle.launcher.daemon.server.DaemonStateCoordinator$1.run(DaemonStateCoordinator.java:297)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.lang.Thread.run(Thread.java:830)
FAILURE: Build failed with an exception.
* Where:
Build file '/dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/build.gradle' line: 245
* What went wrong:
Execution failed for task ':distribution:bwc:bugfix:buildBwcOssLinuxTar'.
> Building 7.5.2 didn't generate expected file /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/bugfix/build/bwc/checkout-7.5/distribution/archives/oss-linux-tar/build/distributions/elasticsearch-oss-7.5.2-SNAPSHOT-linux-x86_64.tar.gz
* Try:
Run with --info or --debug option to get more log output. Run with --scan to get full insights.
* Exception is:
org.gradle.api.tasks.TaskExecutionException: Execution failed for task ':distribution:bwc:bugfix:buildBwcOssLinuxTar'.
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.lambda$executeIfValid$1(ExecuteActionsTaskExecuter.java:187)
at org.gradle.internal.Try$Failure.ifSuccessfulOrElse(Try.java:263)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeIfValid(ExecuteActionsTaskExecuter.java:185)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.execute(ExecuteActionsTaskExecuter.java:166)
at org.gradle.api.internal.tasks.execution.CleanupStaleOutputsExecuter.execute(CleanupStaleOutputsExecuter.java:109)
at org.gradle.api.internal.tasks.execution.FinalizePropertiesTaskExecuter.execute(FinalizePropertiesTaskExecuter.java:46)
at org.gradle.api.internal.tasks.execution.ResolveTaskExecutionModeExecuter.execute(ResolveTaskExecutionModeExecuter.java:62)
at org.gradle.api.internal.tasks.execution.SkipTaskWithNoActionsExecuter.execute(SkipTaskWithNoActionsExecuter.java:57)
at org.gradle.api.internal.tasks.execution.SkipOnlyIfTaskExecuter.execute(SkipOnlyIfTaskExecuter.java:56)
at org.gradle.api.internal.tasks.execution.CatchExceptionTaskExecuter.execute(CatchExceptionTaskExecuter.java:36)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter$1.executeTask(EventFiringTaskExecuter.java:77)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter$1.call(EventFiringTaskExecuter.java:55)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter$1.call(EventFiringTaskExecuter.java:52)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:416)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$CallableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:406)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.call(DefaultBuildOperationExecutor.java:102)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.call(DelegatingBuildOperationExecutor.java:36)
at org.gradle.api.internal.tasks.execution.EventFiringTaskExecuter.execute(EventFiringTaskExecuter.java:52)
at org.gradle.execution.plan.LocalTaskNodeExecutor.execute(LocalTaskNodeExecutor.java:41)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$InvokeNodeExecutorsAction.execute(DefaultTaskExecutionGraph.java:374)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$InvokeNodeExecutorsAction.execute(DefaultTaskExecutionGraph.java:361)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$BuildOperationAwareExecutionAction.execute(DefaultTaskExecutionGraph.java:354)
at org.gradle.execution.taskgraph.DefaultTaskExecutionGraph$BuildOperationAwareExecutionAction.execute(DefaultTaskExecutionGraph.java:340)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.lambda$run$0(DefaultPlanExecutor.java:127)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.execute(DefaultPlanExecutor.java:191)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.executeNextNode(DefaultPlanExecutor.java:182)
at org.gradle.execution.plan.DefaultPlanExecutor$ExecutorWorker.run(DefaultPlanExecutor.java:124)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base/java.lang.Thread.run(Thread.java:830)
Caused by: org.gradle.api.InvalidUserDataException: Building 7.5.2 didn't generate expected file /dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/bugfix/build/bwc/checkout-7.5/distribution/archives/oss-linux-tar/build/distributions/elasticsearch-oss-7.5.2-SNAPSHOT-linux-x86_64.tar.gz
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance0(Native Method)
at java.base/jdk.internal.reflect.NativeConstructorAccessorImpl.newInstance(NativeConstructorAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingConstructorAccessorImpl.newInstance(DelegatingConstructorAccessorImpl.java:45)
at java.base/java.lang.reflect.Constructor.newInstanceWithCaller(Constructor.java:500)
at java.base/java.lang.reflect.Constructor.newInstance(Constructor.java:481)
at org.codehaus.groovy.reflection.CachedConstructor.invoke(CachedConstructor.java:80)
at org.codehaus.groovy.reflection.CachedConstructor.doConstructorInvoke(CachedConstructor.java:74)
at org.codehaus.groovy.runtime.callsite.ConstructorSite$ConstructorSiteNoUnwrap.callConstructor(ConstructorSite.java:84)
at org.codehaus.groovy.runtime.callsite.CallSiteArray.defaultCallConstructor(CallSiteArray.java:59)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:237)
at org.codehaus.groovy.runtime.callsite.AbstractCallSite.callConstructor(AbstractCallSite.java:249)
at build_cqkew81bvy168mqxti3rluq15$_run_closure1$_closure2$_closure12$_closure36$_closure38.doCall(/dev/shm/elastic+elasticsearch+7.x+multijob+fast+bwc/distribution/bwc/build.gradle:245)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:567)
at org.codehaus.groovy.reflection.CachedMethod.invoke(CachedMethod.java:101)
at groovy.lang.MetaMethod.doMethodInvoke(MetaMethod.java:323)
at org.codehaus.groovy.runtime.metaclass.ClosureMetaClass.invokeMethod(ClosureMetaClass.java:263)
at groovy.lang.MetaClassImpl.invokeMethod(MetaClassImpl.java:1041)
at groovy.lang.Closure.call(Closure.java:405)
at groovy.lang.Closure.call(Closure.java:421)
at org.gradle.api.internal.AbstractTask$ClosureTaskAction.execute(AbstractTask.java:664)
at org.gradle.api.internal.AbstractTask$ClosureTaskAction.execute(AbstractTask.java:637)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$3.run(ExecuteActionsTaskExecuter.java:539)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:402)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:394)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:165)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:250)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:158)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.run(DefaultBuildOperationExecutor.java:92)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.run(DelegatingBuildOperationExecutor.java:31)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeAction(ExecuteActionsTaskExecuter.java:524)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeActions(ExecuteActionsTaskExecuter.java:507)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.access$300(ExecuteActionsTaskExecuter.java:109)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$TaskExecution.executeWithPreviousOutputFiles(ExecuteActionsTaskExecuter.java:258)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$TaskExecution.execute(ExecuteActionsTaskExecuter.java:247)
at org.gradle.internal.execution.steps.ExecuteStep.lambda$execute$1(ExecuteStep.java:33)
at java.base/java.util.Optional.orElseGet(Optional.java:362)
at org.gradle.internal.execution.steps.ExecuteStep.execute(ExecuteStep.java:33)
at org.gradle.internal.execution.steps.ExecuteStep.execute(ExecuteStep.java:26)
at org.gradle.internal.execution.steps.CleanupOutputsStep.execute(CleanupOutputsStep.java:63)
at org.gradle.internal.execution.steps.CleanupOutputsStep.execute(CleanupOutputsStep.java:35)
at org.gradle.internal.execution.steps.ResolveInputChangesStep.execute(ResolveInputChangesStep.java:49)
at org.gradle.internal.execution.steps.ResolveInputChangesStep.execute(ResolveInputChangesStep.java:34)
at org.gradle.internal.execution.steps.CancelExecutionStep.execute(CancelExecutionStep.java:43)
at org.gradle.internal.execution.steps.TimeoutStep.executeWithoutTimeout(TimeoutStep.java:73)
at org.gradle.internal.execution.steps.TimeoutStep.execute(TimeoutStep.java:54)
at org.gradle.internal.execution.steps.CatchExceptionStep.execute(CatchExceptionStep.java:34)
at org.gradle.internal.execution.steps.CreateOutputsStep.execute(CreateOutputsStep.java:44)
at org.gradle.internal.execution.steps.SnapshotOutputsStep.execute(SnapshotOutputsStep.java:54)
at org.gradle.internal.execution.steps.SnapshotOutputsStep.execute(SnapshotOutputsStep.java:38)
at org.gradle.internal.execution.steps.CacheStep.executeWithoutCache(CacheStep.java:153)
at org.gradle.internal.execution.steps.CacheStep.executeAndStoreInCache(CacheStep.java:129)
at org.gradle.internal.execution.steps.CacheStep.lambda$executeWithCache$2(CacheStep.java:107)
at java.base/java.util.Optional.orElseGet(Optional.java:362)
at org.gradle.internal.execution.steps.CacheStep.lambda$executeWithCache$3(CacheStep.java:107)
at org.gradle.internal.Try$Success.map(Try.java:162)
at org.gradle.internal.execution.steps.CacheStep.executeWithCache(CacheStep.java:76)
at org.gradle.internal.execution.steps.CacheStep.execute(CacheStep.java:66)
at org.gradle.internal.execution.steps.CacheStep.execute(CacheStep.java:41)
at org.gradle.internal.execution.steps.BroadcastChangingOutputsStep.execute(BroadcastChangingOutputsStep.java:49)
at org.gradle.internal.execution.steps.StoreExecutionStateStep.execute(StoreExecutionStateStep.java:44)
at org.gradle.internal.execution.steps.StoreExecutionStateStep.execute(StoreExecutionStateStep.java:33)
at org.gradle.internal.execution.steps.RecordOutputsStep.execute(RecordOutputsStep.java:38)
at org.gradle.internal.execution.steps.RecordOutputsStep.execute(RecordOutputsStep.java:24)
at org.gradle.internal.execution.steps.SkipUpToDateStep.executeBecause(SkipUpToDateStep.java:92)
at org.gradle.internal.execution.steps.SkipUpToDateStep.lambda$execute$0(SkipUpToDateStep.java:85)
at java.base/java.util.Optional.map(Optional.java:258)
at org.gradle.internal.execution.steps.SkipUpToDateStep.execute(SkipUpToDateStep.java:55)
at org.gradle.internal.execution.steps.SkipUpToDateStep.execute(SkipUpToDateStep.java:39)
at org.gradle.internal.execution.steps.ResolveChangesStep.execute(ResolveChangesStep.java:76)
at org.gradle.internal.execution.steps.ResolveChangesStep.execute(ResolveChangesStep.java:37)
at org.gradle.internal.execution.steps.legacy.MarkSnapshottingInputsFinishedStep.execute(MarkSnapshottingInputsFinishedStep.java:36)
at org.gradle.internal.execution.steps.legacy.MarkSnapshottingInputsFinishedStep.execute(MarkSnapshottingInputsFinishedStep.java:26)
at org.gradle.internal.execution.steps.ResolveCachingStateStep.execute(ResolveCachingStateStep.java:94)
at org.gradle.internal.execution.steps.ResolveCachingStateStep.execute(ResolveCachingStateStep.java:49)
at org.gradle.internal.execution.steps.CaptureStateBeforeExecutionStep.execute(CaptureStateBeforeExecutionStep.java:79)
at org.gradle.internal.execution.steps.CaptureStateBeforeExecutionStep.execute(CaptureStateBeforeExecutionStep.java:53)
at org.gradle.internal.execution.steps.ValidateStep.execute(ValidateStep.java:74)
at org.gradle.internal.execution.steps.SkipEmptyWorkStep.lambda$execute$2(SkipEmptyWorkStep.java:78)
at java.base/java.util.Optional.orElseGet(Optional.java:362)
at org.gradle.internal.execution.steps.SkipEmptyWorkStep.execute(SkipEmptyWorkStep.java:78)
at org.gradle.internal.execution.steps.SkipEmptyWorkStep.execute(SkipEmptyWorkStep.java:34)
at org.gradle.internal.execution.steps.legacy.MarkSnapshottingInputsStartedStep.execute(MarkSnapshottingInputsStartedStep.java:39)
at org.gradle.internal.execution.steps.LoadExecutionStateStep.execute(LoadExecutionStateStep.java:40)
at org.gradle.internal.execution.steps.LoadExecutionStateStep.execute(LoadExecutionStateStep.java:28)
at org.gradle.internal.execution.impl.DefaultWorkExecutor.execute(DefaultWorkExecutor.java:33)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter.executeIfValid(ExecuteActionsTaskExecuter.java:174)
... 33 more
* Get more help at https://help.gradle.org
Deprecated Gradle features were used in this build, making it incompatible with Gradle 7.0.
Use '--warning-mode all' to show the individual deprecation warnings.
See https://docs.gradle.org/6.0.1/userguide/command_line_interface.html#sec:command_line_warnings
BUILD FAILED in 12m 1s
345 actionable tasks: 267 executed, 77 from cache, 1 up-to-date
```
I cannot reproduce this but wonder that this might be a bug in one or our dependencies, or maybe due to the fact that the log file was still being appended to? | non_priority | exception generating tar file in the build process task distribution archives oss linux tar assemble build complete generating dev shm elastic elasticsearch x multijob fast bwc distribution bwc bugfix build bwc checkout build tar deprecated gradle features were used in this build making it incompatible with gradle use warning mode all to show the individual deprecation warnings see build successful in actionable tasks executed up to date publishing build scan picked up java tool options dfile encoding picked up java tool options dfile encoding build complete generating dev shm elastic elasticsearch x multijob fast bwc build tar failed to archive additional logs org apache tools ant buildexception problem creating tar request to write bytes exceeds size in header of bytes for entry x pack qa rolling upgrade build testclusters logs access log at org apache tools ant taskdefs tar execute tar java at org apache tools ant unknownelement execute unknownelement java at jdk internal reflect nativemethodaccessorimpl native method at jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache tools ant dispatch dispatchutils execute dispatchutils java at groovy util antbuilder performtask antbuilder java at groovy util antbuilder nodecompleted antbuilder java at org gradle api internal project ant basicantbuilder nodecompleted basicantbuilder java at groovy util buildersupport doinvokemethod buildersupport java at groovy util antbuilder doinvokemethod antbuilder java at org gradle api internal project ant basicantbuilder doinvokemethod basicantbuilder java at groovy util buildersupport invokemethod buildersupport java at org codehaus groovy runtime callsite pogometaclasssite call pogometaclasssite java at org codehaus groovy runtime callsite callsitearray defaultcall callsitearray java at org codehaus groovy runtime callsite abstractcallsite call abstractcallsite java at org codehaus groovy runtime callsite abstractcallsite call abstractcallsite java at build complete run docall unknown source at jdk internal reflect nativemethodaccessorimpl native method at jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org codehaus groovy reflection cachedmethod invoke cachedmethod java at groovy lang metamethod domethodinvoke metamethod java at org codehaus groovy runtime metaclass closuremetaclass invokemethod closuremetaclass java at groovy lang metaclassimpl invokemethod metaclassimpl java at groovy lang closure call closure java at org gradle listener closurebackedmethodinvocationdispatch dispatch closurebackedmethodinvocationdispatch java at org gradle listener closurebackedmethodinvocationdispatch dispatch closurebackedmethodinvocationdispatch java at org gradle internal event abstractbroadcastdispatch dispatch abstractbroadcastdispatch java at org gradle internal event broadcastdispatch singletondispatch dispatch broadcastdispatch java at org gradle internal event broadcastdispatch singletondispatch dispatch broadcastdispatch java at org gradle internal event abstractbroadcastdispatch dispatch abstractbroadcastdispatch java at org gradle internal event broadcastdispatch compositedispatch dispatch broadcastdispatch java at org gradle internal event broadcastdispatch compositedispatch dispatch broadcastdispatch java at org gradle internal event listenerbroadcast dispatch listenerbroadcast java at org gradle internal event listenerbroadcast dispatch listenerbroadcast java at org gradle internal dispatch proxydispatchadapter dispatchinginvocationhandler invoke proxydispatchadapter java at com sun proxy buildfinished unknown source at org gradle initialization defaultgradlelauncher finishbuild defaultgradlelauncher java at org gradle initialization defaultgradlelauncher dobuildstages defaultgradlelauncher java at org gradle initialization defaultgradlelauncher executetasks defaultgradlelauncher java at org gradle internal invocation gradlebuildcontroller execute gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller execute gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller create gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller create gradlebuildcontroller java at org gradle internal work defaultworkerleaseservice withlocks defaultworkerleaseservice java at org gradle internal work stopshieldingworkerleaseservice withlocks stopshieldingworkerleaseservice java at org gradle internal invocation gradlebuildcontroller dobuild gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller run gradlebuildcontroller java at org gradle tooling internal provider executebuildactionrunner run executebuildactionrunner java at org gradle launcher exec chainingbuildactionrunner run chainingbuildactionrunner java at org gradle launcher exec buildoutcomereportingbuildactionrunner run buildoutcomereportingbuildactionrunner java at org gradle tooling internal provider validatingbuildactionrunner run validatingbuildactionrunner java at org gradle launcher exec buildcompletionnotifyingbuildactionrunner run buildcompletionnotifyingbuildactionrunner java at org gradle launcher exec runasbuildoperationbuildactionrunner call runasbuildoperationbuildactionrunner java at org gradle launcher exec runasbuildoperationbuildactionrunner call runasbuildoperationbuildactionrunner java at org gradle internal operations defaultbuildoperationexecutor callablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor callablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor call defaultbuildoperationexecutor java at org gradle internal operations delegatingbuildoperationexecutor call delegatingbuildoperationexecutor java at org gradle launcher exec runasbuildoperationbuildactionrunner run runasbuildoperationbuildactionrunner java at org gradle launcher exec inprocessbuildactionexecuter transform inprocessbuildactionexecuter java at org gradle launcher exec inprocessbuildactionexecuter transform inprocessbuildactionexecuter java at org gradle composite internal defaultrootbuildstate run defaultrootbuildstate java at org gradle launcher exec inprocessbuildactionexecuter execute inprocessbuildactionexecuter java at org gradle launcher exec inprocessbuildactionexecuter execute inprocessbuildactionexecuter java at org gradle launcher exec buildtreescopebuildactionexecuter execute buildtreescopebuildactionexecuter java at org gradle launcher exec buildtreescopebuildactionexecuter execute buildtreescopebuildactionexecuter java at org gradle tooling internal provider continuousbuildactionexecuter execute continuousbuildactionexecuter java at org gradle tooling internal provider continuousbuildactionexecuter execute continuousbuildactionexecuter java at org gradle tooling internal provider subscribablebuildactionexecuter execute subscribablebuildactionexecuter java at org gradle tooling internal provider subscribablebuildactionexecuter execute subscribablebuildactionexecuter java at org gradle tooling internal provider sessionscopebuildactionexecuter execute sessionscopebuildactionexecuter java at org gradle tooling internal provider sessionscopebuildactionexecuter execute sessionscopebuildactionexecuter java at org gradle tooling internal provider gradlethreadbuildactionexecuter execute gradlethreadbuildactionexecuter java at org gradle tooling internal provider gradlethreadbuildactionexecuter execute gradlethreadbuildactionexecuter java at org gradle tooling internal provider parallelismconfigurationbuildactionexecuter execute parallelismconfigurationbuildactionexecuter java at org gradle tooling internal provider parallelismconfigurationbuildactionexecuter execute parallelismconfigurationbuildactionexecuter java at org gradle tooling internal provider startparamsvalidatingactionexecuter execute startparamsvalidatingactionexecuter java at org gradle tooling internal provider startparamsvalidatingactionexecuter execute startparamsvalidatingactionexecuter java at org gradle tooling internal provider sessionfailurereportingactionexecuter execute sessionfailurereportingactionexecuter java at org gradle tooling internal provider sessionfailurereportingactionexecuter execute sessionfailurereportingactionexecuter java at org gradle tooling internal provider setuploggingactionexecuter execute setuploggingactionexecuter java at org gradle tooling internal provider setuploggingactionexecuter execute setuploggingactionexecuter java at org gradle launcher daemon server exec executebuild dobuild executebuild java at org gradle launcher daemon server exec buildcommandonly execute buildcommandonly java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec watchfordisconnection execute watchfordisconnection java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec resetdeprecationlogger execute resetdeprecationlogger java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec requeststopifsingleuseddaemon execute requeststopifsingleuseddaemon java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec forwardclientinput create forwardclientinput java at org gradle launcher daemon server exec forwardclientinput create forwardclientinput java at org gradle util swapper swap swapper java at org gradle launcher daemon server exec forwardclientinput execute forwardclientinput java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec logandcheckhealth execute logandcheckhealth java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec logtoclient dobuild logtoclient java at org gradle launcher daemon server exec buildcommandonly execute buildcommandonly java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec establishbuildenvironment dobuild establishbuildenvironment java at org gradle launcher daemon server exec buildcommandonly execute buildcommandonly java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec startbuildorrespondwithbusy run startbuildorrespondwithbusy java at org gradle launcher daemon server daemonstatecoordinator run daemonstatecoordinator java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java lang thread run thread java caused by java io ioexception request to write bytes exceeds size in header of bytes for entry x pack qa rolling upgrade build testclusters logs access log at org apache tools tar taroutputstream write taroutputstream java at org apache tools ant taskdefs tar tarresource tar java at org apache tools ant taskdefs tar tarfile tar java at org apache tools ant taskdefs tar tar tar java at org apache tools ant taskdefs tar execute tar java at org apache tools ant unknownelement execute unknownelement java at jdk internal reflect nativemethodaccessorimpl native method at jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache tools ant dispatch dispatchutils execute dispatchutils java at groovy util antbuilder performtask antbuilder java at groovy util antbuilder nodecompleted antbuilder java at org gradle api internal project ant basicantbuilder nodecompleted basicantbuilder java at groovy util buildersupport doinvokemethod buildersupport java at groovy util antbuilder doinvokemethod antbuilder java at org gradle api internal project ant basicantbuilder doinvokemethod basicantbuilder java at groovy util buildersupport invokemethod buildersupport java at org codehaus groovy runtime callsite pogometaclasssite call pogometaclasssite java at org codehaus groovy runtime callsite callsitearray defaultcall callsitearray java at org codehaus groovy runtime callsite abstractcallsite call abstractcallsite java at org codehaus groovy runtime callsite abstractcallsite call abstractcallsite java at build complete run docall unknown source at jdk internal reflect nativemethodaccessorimpl native method at jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org codehaus groovy reflection cachedmethod invoke cachedmethod java at groovy lang metamethod domethodinvoke metamethod java at org codehaus groovy runtime metaclass closuremetaclass invokemethod closuremetaclass java at groovy lang metaclassimpl invokemethod metaclassimpl java at groovy lang closure call closure java at org gradle listener closurebackedmethodinvocationdispatch dispatch closurebackedmethodinvocationdispatch java at org gradle listener closurebackedmethodinvocationdispatch dispatch closurebackedmethodinvocationdispatch java at org gradle internal event abstractbroadcastdispatch dispatch abstractbroadcastdispatch java at org gradle internal event broadcastdispatch singletondispatch dispatch broadcastdispatch java at org gradle internal event broadcastdispatch singletondispatch dispatch broadcastdispatch java at org gradle internal event abstractbroadcastdispatch dispatch abstractbroadcastdispatch java at org gradle internal event broadcastdispatch compositedispatch dispatch broadcastdispatch java at org gradle internal event broadcastdispatch compositedispatch dispatch broadcastdispatch java at org gradle internal event listenerbroadcast dispatch listenerbroadcast java at org gradle internal event listenerbroadcast dispatch listenerbroadcast java at org gradle internal dispatch proxydispatchadapter dispatchinginvocationhandler invoke proxydispatchadapter java at com sun proxy buildfinished unknown source at org gradle initialization defaultgradlelauncher finishbuild defaultgradlelauncher java at org gradle initialization defaultgradlelauncher dobuildstages defaultgradlelauncher java at org gradle initialization defaultgradlelauncher executetasks defaultgradlelauncher java at org gradle internal invocation gradlebuildcontroller execute gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller execute gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller create gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller create gradlebuildcontroller java at org gradle internal work defaultworkerleaseservice withlocks defaultworkerleaseservice java at org gradle internal work stopshieldingworkerleaseservice withlocks stopshieldingworkerleaseservice java at org gradle internal invocation gradlebuildcontroller dobuild gradlebuildcontroller java at org gradle internal invocation gradlebuildcontroller run gradlebuildcontroller java at org gradle tooling internal provider executebuildactionrunner run executebuildactionrunner java at org gradle launcher exec chainingbuildactionrunner run chainingbuildactionrunner java at org gradle launcher exec buildoutcomereportingbuildactionrunner run buildoutcomereportingbuildactionrunner java at org gradle tooling internal provider validatingbuildactionrunner run validatingbuildactionrunner java at org gradle launcher exec buildcompletionnotifyingbuildactionrunner run buildcompletionnotifyingbuildactionrunner java at org gradle launcher exec runasbuildoperationbuildactionrunner call runasbuildoperationbuildactionrunner java at org gradle launcher exec runasbuildoperationbuildactionrunner call runasbuildoperationbuildactionrunner java at org gradle internal operations defaultbuildoperationexecutor callablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor callablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor call defaultbuildoperationexecutor java at org gradle internal operations delegatingbuildoperationexecutor call delegatingbuildoperationexecutor java at org gradle launcher exec runasbuildoperationbuildactionrunner run runasbuildoperationbuildactionrunner java at org gradle launcher exec inprocessbuildactionexecuter transform inprocessbuildactionexecuter java at org gradle launcher exec inprocessbuildactionexecuter transform inprocessbuildactionexecuter java at org gradle composite internal defaultrootbuildstate run defaultrootbuildstate java at org gradle launcher exec inprocessbuildactionexecuter execute inprocessbuildactionexecuter java at org gradle launcher exec inprocessbuildactionexecuter execute inprocessbuildactionexecuter java at org gradle launcher exec buildtreescopebuildactionexecuter execute buildtreescopebuildactionexecuter java at org gradle launcher exec buildtreescopebuildactionexecuter execute buildtreescopebuildactionexecuter java at org gradle tooling internal provider continuousbuildactionexecuter execute continuousbuildactionexecuter java at org gradle tooling internal provider continuousbuildactionexecuter execute continuousbuildactionexecuter java at org gradle tooling internal provider subscribablebuildactionexecuter execute subscribablebuildactionexecuter java at org gradle tooling internal provider subscribablebuildactionexecuter execute subscribablebuildactionexecuter java at org gradle tooling internal provider sessionscopebuildactionexecuter execute sessionscopebuildactionexecuter java at org gradle tooling internal provider sessionscopebuildactionexecuter execute sessionscopebuildactionexecuter java at org gradle tooling internal provider gradlethreadbuildactionexecuter execute gradlethreadbuildactionexecuter java at org gradle tooling internal provider gradlethreadbuildactionexecuter execute gradlethreadbuildactionexecuter java at org gradle tooling internal provider parallelismconfigurationbuildactionexecuter execute parallelismconfigurationbuildactionexecuter java at org gradle tooling internal provider parallelismconfigurationbuildactionexecuter execute parallelismconfigurationbuildactionexecuter java at org gradle tooling internal provider startparamsvalidatingactionexecuter execute startparamsvalidatingactionexecuter java at org gradle tooling internal provider startparamsvalidatingactionexecuter execute startparamsvalidatingactionexecuter java at org gradle tooling internal provider sessionfailurereportingactionexecuter execute sessionfailurereportingactionexecuter java at org gradle tooling internal provider sessionfailurereportingactionexecuter execute sessionfailurereportingactionexecuter java at org gradle tooling internal provider setuploggingactionexecuter execute setuploggingactionexecuter java at org gradle tooling internal provider setuploggingactionexecuter execute setuploggingactionexecuter java at org gradle launcher daemon server exec executebuild dobuild executebuild java at org gradle launcher daemon server exec buildcommandonly execute buildcommandonly java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec watchfordisconnection execute watchfordisconnection java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec resetdeprecationlogger execute resetdeprecationlogger java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec requeststopifsingleuseddaemon execute requeststopifsingleuseddaemon java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec forwardclientinput create forwardclientinput java at org gradle launcher daemon server exec forwardclientinput create forwardclientinput java at org gradle util swapper swap swapper java at org gradle launcher daemon server exec forwardclientinput execute forwardclientinput java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec logandcheckhealth execute logandcheckhealth java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec logtoclient dobuild logtoclient java at org gradle launcher daemon server exec buildcommandonly execute buildcommandonly java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec establishbuildenvironment dobuild establishbuildenvironment java at org gradle launcher daemon server exec buildcommandonly execute buildcommandonly java at org gradle launcher daemon server api daemoncommandexecution proceed daemoncommandexecution java at org gradle launcher daemon server exec startbuildorrespondwithbusy run startbuildorrespondwithbusy java at org gradle launcher daemon server daemonstatecoordinator run daemonstatecoordinator java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java lang thread run thread java failure build failed with an exception where build file dev shm elastic elasticsearch x multijob fast bwc distribution bwc build gradle line what went wrong execution failed for task distribution bwc bugfix buildbwcosslinuxtar building didn t generate expected file dev shm elastic elasticsearch x multijob fast bwc distribution bwc bugfix build bwc checkout distribution archives oss linux tar build distributions elasticsearch oss snapshot linux tar gz try run with info or debug option to get more log output run with scan to get full insights exception is org gradle api tasks taskexecutionexception execution failed for task distribution bwc bugfix buildbwcosslinuxtar at org gradle api internal tasks execution executeactionstaskexecuter lambda executeifvalid executeactionstaskexecuter java at org gradle internal try failure ifsuccessfulorelse try java at org gradle api internal tasks execution executeactionstaskexecuter executeifvalid executeactionstaskexecuter java at org gradle api internal tasks execution executeactionstaskexecuter execute executeactionstaskexecuter java at org gradle api internal tasks execution cleanupstaleoutputsexecuter execute cleanupstaleoutputsexecuter java at org gradle api internal tasks execution finalizepropertiestaskexecuter execute finalizepropertiestaskexecuter java at org gradle api internal tasks execution resolvetaskexecutionmodeexecuter execute resolvetaskexecutionmodeexecuter java at org gradle api internal tasks execution skiptaskwithnoactionsexecuter execute skiptaskwithnoactionsexecuter java at org gradle api internal tasks execution skiponlyiftaskexecuter execute skiponlyiftaskexecuter java at org gradle api internal tasks execution catchexceptiontaskexecuter execute catchexceptiontaskexecuter java at org gradle api internal tasks execution eventfiringtaskexecuter executetask eventfiringtaskexecuter java at org gradle api internal tasks execution eventfiringtaskexecuter call eventfiringtaskexecuter java at org gradle api internal tasks execution eventfiringtaskexecuter call eventfiringtaskexecuter java at org gradle internal operations defaultbuildoperationexecutor callablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor callablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor call defaultbuildoperationexecutor java at org gradle internal operations delegatingbuildoperationexecutor call delegatingbuildoperationexecutor java at org gradle api internal tasks execution eventfiringtaskexecuter execute eventfiringtaskexecuter java at org gradle execution plan localtasknodeexecutor execute localtasknodeexecutor java at org gradle execution taskgraph defaulttaskexecutiongraph invokenodeexecutorsaction execute defaulttaskexecutiongraph java at org gradle execution taskgraph defaulttaskexecutiongraph invokenodeexecutorsaction execute defaulttaskexecutiongraph java at org gradle execution taskgraph defaulttaskexecutiongraph buildoperationawareexecutionaction execute defaulttaskexecutiongraph java at org gradle execution taskgraph defaulttaskexecutiongraph buildoperationawareexecutionaction execute defaulttaskexecutiongraph java at org gradle execution plan defaultplanexecutor executorworker lambda run defaultplanexecutor java at org gradle execution plan defaultplanexecutor executorworker execute defaultplanexecutor java at org gradle execution plan defaultplanexecutor executorworker executenextnode defaultplanexecutor java at org gradle execution plan defaultplanexecutor executorworker run defaultplanexecutor java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java base java lang thread run thread java caused by org gradle api invaliduserdataexception building didn t generate expected file dev shm elastic elasticsearch x multijob fast bwc distribution bwc bugfix build bwc checkout distribution archives oss linux tar build distributions elasticsearch oss snapshot linux tar gz at java base jdk internal reflect nativeconstructoraccessorimpl native method at java base jdk internal reflect nativeconstructoraccessorimpl newinstance nativeconstructoraccessorimpl java at java base jdk internal reflect delegatingconstructoraccessorimpl newinstance delegatingconstructoraccessorimpl java at java base java lang reflect constructor newinstancewithcaller constructor java at java base java lang reflect constructor newinstance constructor java at org codehaus groovy reflection cachedconstructor invoke cachedconstructor java at org codehaus groovy reflection cachedconstructor doconstructorinvoke cachedconstructor java at org codehaus groovy runtime callsite constructorsite constructorsitenounwrap callconstructor constructorsite java at org codehaus groovy runtime callsite callsitearray defaultcallconstructor callsitearray java at org codehaus groovy runtime callsite abstractcallsite callconstructor abstractcallsite java at org codehaus groovy runtime callsite abstractcallsite callconstructor abstractcallsite java at build run docall dev shm elastic elasticsearch x multijob fast bwc distribution bwc build gradle at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org codehaus groovy reflection cachedmethod invoke cachedmethod java at groovy lang metamethod domethodinvoke metamethod java at org codehaus groovy runtime metaclass closuremetaclass invokemethod closuremetaclass java at groovy lang metaclassimpl invokemethod metaclassimpl java at groovy lang closure call closure java at groovy lang closure call closure java at org gradle api internal abstracttask closuretaskaction execute abstracttask java at org gradle api internal abstracttask closuretaskaction execute abstracttask java at org gradle api internal tasks execution executeactionstaskexecuter run executeactionstaskexecuter java at org gradle internal operations defaultbuildoperationexecutor runnablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor runnablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor run defaultbuildoperationexecutor java at org gradle internal operations delegatingbuildoperationexecutor run delegatingbuildoperationexecutor java at org gradle api internal tasks execution executeactionstaskexecuter executeaction executeactionstaskexecuter java at org gradle api internal tasks execution executeactionstaskexecuter executeactions executeactionstaskexecuter java at org gradle api internal tasks execution executeactionstaskexecuter access executeactionstaskexecuter java at org gradle api internal tasks execution executeactionstaskexecuter taskexecution executewithpreviousoutputfiles executeactionstaskexecuter java at org gradle api internal tasks execution executeactionstaskexecuter taskexecution execute executeactionstaskexecuter java at org gradle internal execution steps executestep lambda execute executestep java at java base java util optional orelseget optional java at org gradle internal execution steps executestep execute executestep java at org gradle internal execution steps executestep execute executestep java at org gradle internal execution steps cleanupoutputsstep execute cleanupoutputsstep java at org gradle internal execution steps cleanupoutputsstep execute cleanupoutputsstep java at org gradle internal execution steps resolveinputchangesstep execute resolveinputchangesstep java at org gradle internal execution steps resolveinputchangesstep execute resolveinputchangesstep java at org gradle internal execution steps cancelexecutionstep execute cancelexecutionstep java at org gradle internal execution steps timeoutstep executewithouttimeout timeoutstep java at org gradle internal execution steps timeoutstep execute timeoutstep java at org gradle internal execution steps catchexceptionstep execute catchexceptionstep java at org gradle internal execution steps createoutputsstep execute createoutputsstep java at org gradle internal execution steps snapshotoutputsstep execute snapshotoutputsstep java at org gradle internal execution steps snapshotoutputsstep execute snapshotoutputsstep java at org gradle internal execution steps cachestep executewithoutcache cachestep java at org gradle internal execution steps cachestep executeandstoreincache cachestep java at org gradle internal execution steps cachestep lambda executewithcache cachestep java at java base java util optional orelseget optional java at org gradle internal execution steps cachestep lambda executewithcache cachestep java at org gradle internal try success map try java at org gradle internal execution steps cachestep executewithcache cachestep java at org gradle internal execution steps cachestep execute cachestep java at org gradle internal execution steps cachestep execute cachestep java at org gradle internal execution steps broadcastchangingoutputsstep execute broadcastchangingoutputsstep java at org gradle internal execution steps storeexecutionstatestep execute storeexecutionstatestep java at org gradle internal execution steps storeexecutionstatestep execute storeexecutionstatestep java at org gradle internal execution steps recordoutputsstep execute recordoutputsstep java at org gradle internal execution steps recordoutputsstep execute recordoutputsstep java at org gradle internal execution steps skipuptodatestep executebecause skipuptodatestep java at org gradle internal execution steps skipuptodatestep lambda execute skipuptodatestep java at java base java util optional map optional java at org gradle internal execution steps skipuptodatestep execute skipuptodatestep java at org gradle internal execution steps skipuptodatestep execute skipuptodatestep java at org gradle internal execution steps resolvechangesstep execute resolvechangesstep java at org gradle internal execution steps resolvechangesstep execute resolvechangesstep java at org gradle internal execution steps legacy marksnapshottinginputsfinishedstep execute marksnapshottinginputsfinishedstep java at org gradle internal execution steps legacy marksnapshottinginputsfinishedstep execute marksnapshottinginputsfinishedstep java at org gradle internal execution steps resolvecachingstatestep execute resolvecachingstatestep java at org gradle internal execution steps resolvecachingstatestep execute resolvecachingstatestep java at org gradle internal execution steps capturestatebeforeexecutionstep execute capturestatebeforeexecutionstep java at org gradle internal execution steps capturestatebeforeexecutionstep execute capturestatebeforeexecutionstep java at org gradle internal execution steps validatestep execute validatestep java at org gradle internal execution steps skipemptyworkstep lambda execute skipemptyworkstep java at java base java util optional orelseget optional java at org gradle internal execution steps skipemptyworkstep execute skipemptyworkstep java at org gradle internal execution steps skipemptyworkstep execute skipemptyworkstep java at org gradle internal execution steps legacy marksnapshottinginputsstartedstep execute marksnapshottinginputsstartedstep java at org gradle internal execution steps loadexecutionstatestep execute loadexecutionstatestep java at org gradle internal execution steps loadexecutionstatestep execute loadexecutionstatestep java at org gradle internal execution impl defaultworkexecutor execute defaultworkexecutor java at org gradle api internal tasks execution executeactionstaskexecuter executeifvalid executeactionstaskexecuter java more get more help at deprecated gradle features were used in this build making it incompatible with gradle use warning mode all to show the individual deprecation warnings see build failed in actionable tasks executed from cache up to date i cannot reproduce this but wonder that this might be a bug in one or our dependencies or maybe due to the fact that the log file was still being appended to | 0 |
20,436 | 11,448,415,571 | IssuesEvent | 2020-02-06 03:19:08 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | VS Code Intellisense: cannot find boost header files (lambda.hpp) | Feature: Configuration Language Service question | Hi all,
Dealing with a frustrating issue here. Running MacOS Catalina 10.15.3, compiler set as /usr/bin/clang.
The title explains my issue quite concisely.
From Boost's "Getting Started" section on their official website [here](https://www.boost.org/doc/libs/1_72_0/more/getting_started/unix-variants.html), I have made sure of the following:
1. To compile anything in Boost, you need a directory containing the boost/ subdirectory in your #include path.
I have done this by properly setting the environment var BOOST_ROOT and adding ${BOOST_ROOT} to 'Browse: path'.
here is my c_cpp_properties.json:
```
{
"configurations": [
{
"name": "Mac",
"includePath": ["${workspaceFolder}/**"],
"defines": [],
"macFrameworkPath": ["/System/Library/Frameworks", "/Library/Frameworks"],
"compilerPath": "/usr/bin/clang",
"cStandard": "c11",
"cppStandard": "c++17",
"intelliSenseMode": "${default}",
"browse": {
"path": ["${BOOST_ROOT}"]
}
}
],
"version": 4
}
```
I set my Intellisense output level to 'Debug' for the sake of investigation and determined that it indeed was able to **locate boost/lambda/lambda.hpp**, but I am not sure as to why it is unable to open it. I have checked the file permissions of the files in boost/lambda, and they consistently readable by all users.
See here for the Intellisense Debug output:
```
tag parsing file: /Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
terminating child process: 1443
tag parsing file: /Users/ajm/Projects/restaurant/cpp/sim/src/Guest.h
tag parsing file: /Users/ajm/Projects/restaurant/cpp/sim/src/Person.h
sending compilation args for /Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
include: /usr/local/include
include: /Library/Developer/CommandLineTools/usr/include/c++/v1
include: /Library/Developer/CommandLineTools/usr/lib/clang/11.0.0/include
include: /Library/Developer/CommandLineTools/usr/include
include: /Library/Developer/CommandLineTools/SDKs/MacOSX10.15.sdk/usr/include
include: /Users/ajm/Projects/restaurant/cpp/sim/src
framework: /System/Library/Frameworks
framework: /Library/Frameworks
framework: /Library/Developer/CommandLineTools/SDKs/MacOSX10.15.sdk/System/Library/Frameworks
define: __llvm__=1
define: __clang__=1
define: __clang_major__=11
define: __clang_minor__=0
define: __clang_patchlevel__=0
define: __clang_version__="11.0.0 (clang-1100.0.33.17)"
define: __GNUC_MINOR__=2
define: __GNUC_PATCHLEVEL__=1
define: __GNUC__=4
define: __GXX_ABI_VERSION=1002
define: __ATOMIC_RELAXED=0
define: __ATOMIC_CONSUME=1
define: __ATOMIC_ACQUIRE=2
define: __ATOMIC_RELEASE=3
define: __ATOMIC_ACQ_REL=4
define: __ATOMIC_SEQ_CST=5
define: __OPENCL_MEMORY_SCOPE_WORK_ITEM=0
define: __OPENCL_MEMORY_SCOPE_WORK_GROUP=1
define: __OPENCL_MEMORY_SCOPE_DEVICE=2
define: __OPENCL_MEMORY_SCOPE_ALL_SVM_DEVICES=3
define: __OPENCL_MEMORY_SCOPE_SUB_GROUP=4
define: __PRAGMA_REDEFINE_EXTNAME=1
define: __VERSION__="4.2.1 Compatible Apple LLVM 11.0.0 (clang-1100.0.33.17)"
define: __STRICT_ANSI__=1
define: __GXX_EXPERIMENTAL_CXX0X__=1
define: __OBJC_BOOL_IS_BOOL=0
define: __CONSTANT_CFSTRINGS__=1
define: __block=__attribute__((__blocks__(byref)))
define: __BLOCKS__=1
define: __EXCEPTIONS=1
define: __GXX_RTTI=1
define: __DEPRECATED=1
define: __GNUG__=4
define: __GXX_WEAK__=1
define: __private_extern__=extern
define: __ORDER_LITTLE_ENDIAN__=1234
define: __ORDER_BIG_ENDIAN__=4321
define: __ORDER_PDP_ENDIAN__=3412
define: __BYTE_ORDER__=__ORDER_LITTLE_ENDIAN__
define: __LITTLE_ENDIAN__=1
define: _LP64=1
define: __LP64__=1
define: __CHAR_BIT__=8
define: __SCHAR_MAX__=127
define: __SHRT_MAX__=32767
define: __INT_MAX__=2147483647
define: __LONG_MAX__=9223372036854775807L
define: __LONG_LONG_MAX__=9223372036854775807LL
define: __WCHAR_MAX__=2147483647
define: __WINT_MAX__=2147483647
define: __INTMAX_MAX__=9223372036854775807L
define: __SIZE_MAX__=18446744073709551615UL
define: __UINTMAX_MAX__=18446744073709551615UL
define: __PTRDIFF_MAX__=9223372036854775807L
define: __INTPTR_MAX__=9223372036854775807L
define: __UINTPTR_MAX__=18446744073709551615UL
define: __SIZEOF_DOUBLE__=8
define: __SIZEOF_FLOAT__=4
define: __SIZEOF_INT__=4
define: __SIZEOF_LONG__=8
define: __SIZEOF_LONG_DOUBLE__=16
define: __SIZEOF_LONG_LONG__=8
define: __SIZEOF_POINTER__=8
define: __SIZEOF_SHORT__=2
define: __SIZEOF_PTRDIFF_T__=8
define: __SIZEOF_SIZE_T__=8
define: __SIZEOF_WCHAR_T__=4
define: __SIZEOF_WINT_T__=4
define: __SIZEOF_INT128__=16
define: __INTMAX_TYPE__=long int
define: __INTMAX_FMTd__="ld"
define: __INTMAX_FMTi__="li"
define: __INTMAX_C_SUFFIX__=L
define: __UINTMAX_TYPE__=long unsigned int
define: __UINTMAX_FMTo__="lo"
define: __UINTMAX_FMTu__="lu"
define: __UINTMAX_FMTx__="lx"
define: __UINTMAX_FMTX__="lX"
define: __UINTMAX_C_SUFFIX__=UL
define: __INTMAX_WIDTH__=64
define: __PTRDIFF_TYPE__=long int
define: __PTRDIFF_FMTd__="ld"
define: __PTRDIFF_FMTi__="li"
define: __PTRDIFF_WIDTH__=64
define: __INTPTR_TYPE__=long int
define: __INTPTR_FMTd__="ld"
define: __INTPTR_FMTi__="li"
define: __INTPTR_WIDTH__=64
define: __SIZE_TYPE__=long unsigned int
define: __SIZE_FMTo__="lo"
define: __SIZE_FMTu__="lu"
define: __SIZE_FMTx__="lx"
define: __SIZE_FMTX__="lX"
define: __SIZE_WIDTH__=64
define: __WCHAR_TYPE__=int
define: __WCHAR_WIDTH__=32
define: __WINT_TYPE__=int
define: __WINT_WIDTH__=32
define: __SIG_ATOMIC_WIDTH__=32
define: __SIG_ATOMIC_MAX__=2147483647
define: __CHAR16_TYPE__=unsigned short
define: __CHAR32_TYPE__=unsigned int
define: __UINTMAX_WIDTH__=64
define: __UINTPTR_TYPE__=long unsigned int
define: __UINTPTR_FMTo__="lo"
define: __UINTPTR_FMTu__="lu"
define: __UINTPTR_FMTx__="lx"
define: __UINTPTR_FMTX__="lX"
define: __UINTPTR_WIDTH__=64
define: __FLT16_DENORM_MIN__=5.9604644775390625e-8F16
define: __FLT16_HAS_DENORM__=1
define: __FLT16_DIG__=3
define: __FLT16_DECIMAL_DIG__=5
define: __FLT16_EPSILON__=9.765625e-4F16
define: __FLT16_HAS_INFINITY__=1
define: __FLT16_HAS_QUIET_NAN__=1
define: __FLT16_MANT_DIG__=11
define: __FLT16_MAX_10_EXP__=4
define: __FLT16_MAX_EXP__=15
define: __FLT16_MAX__=6.5504e+4F16
define: __FLT16_MIN_10_EXP__=(-13)
define: __FLT16_MIN_EXP__=(-14)
define: __FLT16_MIN__=6.103515625e-5F16
define: __FLT_DENORM_MIN__=1.40129846e-45F
define: __FLT_HAS_DENORM__=1
define: __FLT_DIG__=6
define: __FLT_DECIMAL_DIG__=9
define: __FLT_EPSILON__=1.19209290e-7F
define: __FLT_HAS_INFINITY__=1
define: __FLT_HAS_QUIET_NAN__=1
define: __FLT_MANT_DIG__=24
define: __FLT_MAX_10_EXP__=38
define: __FLT_MAX_EXP__=128
define: __FLT_MAX__=3.40282347e+38F
define: __FLT_MIN_10_EXP__=(-37)
define: __FLT_MIN_EXP__=(-125)
define: __FLT_MIN__=1.17549435e-38F
define: __DBL_DENORM_MIN__=4.9406564584124654e-324
define: __DBL_HAS_DENORM__=1
define: __DBL_DIG__=15
define: __DBL_DECIMAL_DIG__=17
define: __DBL_EPSILON__=2.2204460492503131e-16
define: __DBL_HAS_INFINITY__=1
define: __DBL_HAS_QUIET_NAN__=1
define: __DBL_MANT_DIG__=53
define: __DBL_MAX_10_EXP__=308
define: __DBL_MAX_EXP__=1024
define: __DBL_MAX__=1.7976931348623157e+308
define: __DBL_MIN_10_EXP__=(-307)
define: __DBL_MIN_EXP__=(-1021)
define: __DBL_MIN__=2.2250738585072014e-308
define: __LDBL_DENORM_MIN__=3.64519953188247460253e-4951L
define: __LDBL_HAS_DENORM__=1
define: __LDBL_DIG__=18
define: __LDBL_DECIMAL_DIG__=21
define: __LDBL_EPSILON__=1.08420217248550443401e-19L
define: __LDBL_HAS_INFINITY__=1
define: __LDBL_HAS_QUIET_NAN__=1
define: __LDBL_MANT_DIG__=64
define: __LDBL_MAX_10_EXP__=4932
define: __LDBL_MAX_EXP__=16384
define: __LDBL_MAX__=1.18973149535723176502e+4932L
define: __LDBL_MIN_10_EXP__=(-4931)
define: __LDBL_MIN_EXP__=(-16381)
define: __LDBL_MIN__=3.36210314311209350626e-4932L
define: __POINTER_WIDTH__=64
define: __BIGGEST_ALIGNMENT__=16
define: __INT8_TYPE__=signed char
define: __INT8_FMTd__="hhd"
define: __INT8_FMTi__="hhi"
define: __INT8_C_SUFFIX__=
define: __INT16_TYPE__=short
define: __INT16_FMTd__="hd"
define: __INT16_FMTi__="hi"
define: __INT16_C_SUFFIX__=
define: __INT32_TYPE__=int
define: __INT32_FMTd__="d"
define: __INT32_FMTi__="i"
define: __INT32_C_SUFFIX__=
define: __INT64_TYPE__=long long int
define: __INT64_FMTd__="lld"
define: __INT64_FMTi__="lli"
define: __INT64_C_SUFFIX__=LL
define: __UINT8_TYPE__=unsigned char
define: __UINT8_FMTo__="hho"
define: __UINT8_FMTu__="hhu"
define: __UINT8_FMTx__="hhx"
define: __UINT8_FMTX__="hhX"
define: __UINT8_C_SUFFIX__=
define: __UINT8_MAX__=255
define: __INT8_MAX__=127
define: __UINT16_TYPE__=unsigned short
define: __UINT16_FMTo__="ho"
define: __UINT16_FMTu__="hu"
define: __UINT16_FMTx__="hx"
define: __UINT16_FMTX__="hX"
define: __UINT16_C_SUFFIX__=
define: __UINT16_MAX__=65535
define: __INT16_MAX__=32767
define: __UINT32_TYPE__=unsigned int
define: __UINT32_FMTo__="o"
define: __UINT32_FMTu__="u"
define: __UINT32_FMTx__="x"
define: __UINT32_FMTX__="X"
define: __UINT32_C_SUFFIX__=U
define: __UINT32_MAX__=4294967295U
define: __INT32_MAX__=2147483647
define: __UINT64_TYPE__=long long unsigned int
define: __UINT64_FMTo__="llo"
define: __UINT64_FMTu__="llu"
define: __UINT64_FMTx__="llx"
define: __UINT64_FMTX__="llX"
define: __UINT64_C_SUFFIX__=ULL
define: __UINT64_MAX__=18446744073709551615ULL
define: __INT64_MAX__=9223372036854775807LL
define: __INT_LEAST8_TYPE__=signed char
define: __INT_LEAST8_MAX__=127
define: __INT_LEAST8_FMTd__="hhd"
define: __INT_LEAST8_FMTi__="hhi"
define: __UINT_LEAST8_TYPE__=unsigned char
define: __UINT_LEAST8_MAX__=255
define: __UINT_LEAST8_FMTo__="hho"
define: __UINT_LEAST8_FMTu__="hhu"
define: __UINT_LEAST8_FMTx__="hhx"
define: __UINT_LEAST8_FMTX__="hhX"
define: __INT_LEAST16_TYPE__=short
define: __INT_LEAST16_MAX__=32767
define: __INT_LEAST16_FMTd__="hd"
define: __INT_LEAST16_FMTi__="hi"
define: __UINT_LEAST16_TYPE__=unsigned short
define: __UINT_LEAST16_MAX__=65535
define: __UINT_LEAST16_FMTo__="ho"
define: __UINT_LEAST16_FMTu__="hu"
define: __UINT_LEAST16_FMTx__="hx"
define: __UINT_LEAST16_FMTX__="hX"
define: __INT_LEAST32_TYPE__=int
define: __INT_LEAST32_MAX__=2147483647
define: __INT_LEAST32_FMTd__="d"
define: __INT_LEAST32_FMTi__="i"
define: __UINT_LEAST32_TYPE__=unsigned int
define: __UINT_LEAST32_MAX__=4294967295U
define: __UINT_LEAST32_FMTo__="o"
define: __UINT_LEAST32_FMTu__="u"
define: __UINT_LEAST32_FMTx__="x"
define: __UINT_LEAST32_FMTX__="X"
define: __INT_LEAST64_TYPE__=long long int
define: __INT_LEAST64_MAX__=9223372036854775807LL
define: __INT_LEAST64_FMTd__="lld"
define: __INT_LEAST64_FMTi__="lli"
define: __UINT_LEAST64_TYPE__=long long unsigned int
define: __UINT_LEAST64_MAX__=18446744073709551615ULL
define: __UINT_LEAST64_FMTo__="llo"
define: __UINT_LEAST64_FMTu__="llu"
define: __UINT_LEAST64_FMTx__="llx"
define: __UINT_LEAST64_FMTX__="llX"
define: __INT_FAST8_TYPE__=signed char
define: __INT_FAST8_MAX__=127
define: __INT_FAST8_FMTd__="hhd"
define: __INT_FAST8_FMTi__="hhi"
define: __UINT_FAST8_TYPE__=unsigned char
define: __UINT_FAST8_MAX__=255
define: __UINT_FAST8_FMTo__="hho"
define: __UINT_FAST8_FMTu__="hhu"
define: __UINT_FAST8_FMTx__="hhx"
define: __UINT_FAST8_FMTX__="hhX"
define: __INT_FAST16_TYPE__=short
define: __INT_FAST16_MAX__=32767
define: __INT_FAST16_FMTd__="hd"
define: __INT_FAST16_FMTi__="hi"
define: __UINT_FAST16_TYPE__=unsigned short
define: __UINT_FAST16_MAX__=65535
define: __UINT_FAST16_FMTo__="ho"
define: __UINT_FAST16_FMTu__="hu"
define: __UINT_FAST16_FMTx__="hx"
define: __UINT_FAST16_FMTX__="hX"
define: __INT_FAST32_TYPE__=int
define: __INT_FAST32_MAX__=2147483647
define: __INT_FAST32_FMTd__="d"
define: __INT_FAST32_FMTi__="i"
define: __UINT_FAST32_TYPE__=unsigned int
define: __UINT_FAST32_MAX__=4294967295U
define: __UINT_FAST32_FMTo__="o"
define: __UINT_FAST32_FMTu__="u"
define: __UINT_FAST32_FMTx__="x"
define: __UINT_FAST32_FMTX__="X"
define: __INT_FAST64_TYPE__=long long int
define: __INT_FAST64_MAX__=9223372036854775807LL
define: __INT_FAST64_FMTd__="lld"
define: __INT_FAST64_FMTi__="lli"
define: __UINT_FAST64_TYPE__=long long unsigned int
define: __UINT_FAST64_MAX__=18446744073709551615ULL
define: __UINT_FAST64_FMTo__="llo"
define: __UINT_FAST64_FMTu__="llu"
define: __UINT_FAST64_FMTx__="llx"
define: __UINT_FAST64_FMTX__="llX"
define: __USER_LABEL_PREFIX__=_
define: __FINITE_MATH_ONLY__=0
define: __GNUC_GNU_INLINE__=1
define: __GCC_ATOMIC_TEST_AND_SET_TRUEVAL=1
define: __CLANG_ATOMIC_BOOL_LOCK_FREE=2
define: __CLANG_ATOMIC_CHAR_LOCK_FREE=2
define: __CLANG_ATOMIC_CHAR16_T_LOCK_FREE=2
define: __CLANG_ATOMIC_CHAR32_T_LOCK_FREE=2
define: __CLANG_ATOMIC_WCHAR_T_LOCK_FREE=2
define: __CLANG_ATOMIC_SHORT_LOCK_FREE=2
define: __CLANG_ATOMIC_INT_LOCK_FREE=2
define: __CLANG_ATOMIC_LONG_LOCK_FREE=2
define: __CLANG_ATOMIC_LLONG_LOCK_FREE=2
define: __CLANG_ATOMIC_POINTER_LOCK_FREE=2
define: __GCC_ATOMIC_BOOL_LOCK_FREE=2
define: __GCC_ATOMIC_CHAR_LOCK_FREE=2
define: __GCC_ATOMIC_CHAR16_T_LOCK_FREE=2
define: __GCC_ATOMIC_CHAR32_T_LOCK_FREE=2
define: __GCC_ATOMIC_WCHAR_T_LOCK_FREE=2
define: __GCC_ATOMIC_SHORT_LOCK_FREE=2
define: __GCC_ATOMIC_INT_LOCK_FREE=2
define: __GCC_ATOMIC_LONG_LOCK_FREE=2
define: __GCC_ATOMIC_LLONG_LOCK_FREE=2
define: __GCC_ATOMIC_POINTER_LOCK_FREE=2
define: __NO_INLINE__=1
define: __PIC__=2
define: __pic__=2
define: __FLT_EVAL_METHOD__=0
define: __FLT_RADIX__=2
define: __DECIMAL_DIG__=__LDBL_DECIMAL_DIG__
define: __SSP__=1
define: __nonnull=_Nonnull
define: __null_unspecified=_Null_unspecified
define: __nullable=_Nullable
define: __code_model_small_=1
define: __amd64__=1
define: __amd64=1
define: __x86_64=1
define: __x86_64__=1
define: __core2=1
define: __core2__=1
define: __tune_core2__=1
define: __REGISTER_PREFIX__=
define: __NO_MATH_INLINES=1
define: __FXSR__=1
define: __SSE4_1__=1
define: __SSSE3__=1
define: __SSE3__=1
define: __SSE2__=1
define: __SSE2_MATH__=1
define: __SSE__=1
define: __SSE_MATH__=1
define: __MMX__=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_1=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_2=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_4=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_8=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_16=1
define: __APPLE_CC__=6000
define: __APPLE__=1
define: __STDC_NO_THREADS__=1
define: OBJC_NEW_PROPERTIES=1
define: __apple_build_version__=11000033
define: __weak=__attribute__((objc_gc(weak)))
define: __strong=
define: __unsafe_unretained=
define: __DYNAMIC__=1
define: __ENVIRONMENT_MAC_OS_X_VERSION_MIN_REQUIRED__=101500
define: __MACH__=1
define: __STDC__=1
define: __STDC_HOSTED__=1
define: __cplusplus=201703L
define: __STDCPP_DEFAULT_NEW_ALIGNMENT__=16UL
define: __STDC_UTF_16__=1
define: __STDC_UTF_32__=1
other: --clang
other: --clang_version=110000
stdver: c++17
intelliSenseMode: clang-x64
cpptools/getCodeActions: 33
textDocument/hover: 34
IntelliSense client not available, using Tag Parser for go to definition.
IntelliSense client not available, using Tag Parser for quick info.
using Tag Parser for quick info
cpptools/getCodeActions: 35
0 include path suggestion(s) discovered.
idle loop: reparsing the active document
Checking for syntax errors: file:///Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
Queueing IntelliSense update for files in translation unit of: /Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
Database safe to open
cpptools/cpptools_finishUpdateSquiggles
Error squiggle count: 6
terminating child process: 1458
Update IntelliSense time (sec): 5.811
```
This really only started happening recently following the update of my CommandLinesTools and Operating System. It is frustrating the heck out of me and has screwed my flow of development.
Please help. I do not want to waste more time learning a new IDE because this one won't work for me.
Let me know if you need additional information.
Thanks | 1.0 | VS Code Intellisense: cannot find boost header files (lambda.hpp) - Hi all,
Dealing with a frustrating issue here. Running MacOS Catalina 10.15.3, compiler set as /usr/bin/clang.
The title explains my issue quite concisely.
From Boost's "Getting Started" section on their official website [here](https://www.boost.org/doc/libs/1_72_0/more/getting_started/unix-variants.html), I have made sure of the following:
1. To compile anything in Boost, you need a directory containing the boost/ subdirectory in your #include path.
I have done this by properly setting the environment var BOOST_ROOT and adding ${BOOST_ROOT} to 'Browse: path'.
here is my c_cpp_properties.json:
```
{
"configurations": [
{
"name": "Mac",
"includePath": ["${workspaceFolder}/**"],
"defines": [],
"macFrameworkPath": ["/System/Library/Frameworks", "/Library/Frameworks"],
"compilerPath": "/usr/bin/clang",
"cStandard": "c11",
"cppStandard": "c++17",
"intelliSenseMode": "${default}",
"browse": {
"path": ["${BOOST_ROOT}"]
}
}
],
"version": 4
}
```
I set my Intellisense output level to 'Debug' for the sake of investigation and determined that it indeed was able to **locate boost/lambda/lambda.hpp**, but I am not sure as to why it is unable to open it. I have checked the file permissions of the files in boost/lambda, and they consistently readable by all users.
See here for the Intellisense Debug output:
```
tag parsing file: /Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
terminating child process: 1443
tag parsing file: /Users/ajm/Projects/restaurant/cpp/sim/src/Guest.h
tag parsing file: /Users/ajm/Projects/restaurant/cpp/sim/src/Person.h
sending compilation args for /Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
include: /usr/local/include
include: /Library/Developer/CommandLineTools/usr/include/c++/v1
include: /Library/Developer/CommandLineTools/usr/lib/clang/11.0.0/include
include: /Library/Developer/CommandLineTools/usr/include
include: /Library/Developer/CommandLineTools/SDKs/MacOSX10.15.sdk/usr/include
include: /Users/ajm/Projects/restaurant/cpp/sim/src
framework: /System/Library/Frameworks
framework: /Library/Frameworks
framework: /Library/Developer/CommandLineTools/SDKs/MacOSX10.15.sdk/System/Library/Frameworks
define: __llvm__=1
define: __clang__=1
define: __clang_major__=11
define: __clang_minor__=0
define: __clang_patchlevel__=0
define: __clang_version__="11.0.0 (clang-1100.0.33.17)"
define: __GNUC_MINOR__=2
define: __GNUC_PATCHLEVEL__=1
define: __GNUC__=4
define: __GXX_ABI_VERSION=1002
define: __ATOMIC_RELAXED=0
define: __ATOMIC_CONSUME=1
define: __ATOMIC_ACQUIRE=2
define: __ATOMIC_RELEASE=3
define: __ATOMIC_ACQ_REL=4
define: __ATOMIC_SEQ_CST=5
define: __OPENCL_MEMORY_SCOPE_WORK_ITEM=0
define: __OPENCL_MEMORY_SCOPE_WORK_GROUP=1
define: __OPENCL_MEMORY_SCOPE_DEVICE=2
define: __OPENCL_MEMORY_SCOPE_ALL_SVM_DEVICES=3
define: __OPENCL_MEMORY_SCOPE_SUB_GROUP=4
define: __PRAGMA_REDEFINE_EXTNAME=1
define: __VERSION__="4.2.1 Compatible Apple LLVM 11.0.0 (clang-1100.0.33.17)"
define: __STRICT_ANSI__=1
define: __GXX_EXPERIMENTAL_CXX0X__=1
define: __OBJC_BOOL_IS_BOOL=0
define: __CONSTANT_CFSTRINGS__=1
define: __block=__attribute__((__blocks__(byref)))
define: __BLOCKS__=1
define: __EXCEPTIONS=1
define: __GXX_RTTI=1
define: __DEPRECATED=1
define: __GNUG__=4
define: __GXX_WEAK__=1
define: __private_extern__=extern
define: __ORDER_LITTLE_ENDIAN__=1234
define: __ORDER_BIG_ENDIAN__=4321
define: __ORDER_PDP_ENDIAN__=3412
define: __BYTE_ORDER__=__ORDER_LITTLE_ENDIAN__
define: __LITTLE_ENDIAN__=1
define: _LP64=1
define: __LP64__=1
define: __CHAR_BIT__=8
define: __SCHAR_MAX__=127
define: __SHRT_MAX__=32767
define: __INT_MAX__=2147483647
define: __LONG_MAX__=9223372036854775807L
define: __LONG_LONG_MAX__=9223372036854775807LL
define: __WCHAR_MAX__=2147483647
define: __WINT_MAX__=2147483647
define: __INTMAX_MAX__=9223372036854775807L
define: __SIZE_MAX__=18446744073709551615UL
define: __UINTMAX_MAX__=18446744073709551615UL
define: __PTRDIFF_MAX__=9223372036854775807L
define: __INTPTR_MAX__=9223372036854775807L
define: __UINTPTR_MAX__=18446744073709551615UL
define: __SIZEOF_DOUBLE__=8
define: __SIZEOF_FLOAT__=4
define: __SIZEOF_INT__=4
define: __SIZEOF_LONG__=8
define: __SIZEOF_LONG_DOUBLE__=16
define: __SIZEOF_LONG_LONG__=8
define: __SIZEOF_POINTER__=8
define: __SIZEOF_SHORT__=2
define: __SIZEOF_PTRDIFF_T__=8
define: __SIZEOF_SIZE_T__=8
define: __SIZEOF_WCHAR_T__=4
define: __SIZEOF_WINT_T__=4
define: __SIZEOF_INT128__=16
define: __INTMAX_TYPE__=long int
define: __INTMAX_FMTd__="ld"
define: __INTMAX_FMTi__="li"
define: __INTMAX_C_SUFFIX__=L
define: __UINTMAX_TYPE__=long unsigned int
define: __UINTMAX_FMTo__="lo"
define: __UINTMAX_FMTu__="lu"
define: __UINTMAX_FMTx__="lx"
define: __UINTMAX_FMTX__="lX"
define: __UINTMAX_C_SUFFIX__=UL
define: __INTMAX_WIDTH__=64
define: __PTRDIFF_TYPE__=long int
define: __PTRDIFF_FMTd__="ld"
define: __PTRDIFF_FMTi__="li"
define: __PTRDIFF_WIDTH__=64
define: __INTPTR_TYPE__=long int
define: __INTPTR_FMTd__="ld"
define: __INTPTR_FMTi__="li"
define: __INTPTR_WIDTH__=64
define: __SIZE_TYPE__=long unsigned int
define: __SIZE_FMTo__="lo"
define: __SIZE_FMTu__="lu"
define: __SIZE_FMTx__="lx"
define: __SIZE_FMTX__="lX"
define: __SIZE_WIDTH__=64
define: __WCHAR_TYPE__=int
define: __WCHAR_WIDTH__=32
define: __WINT_TYPE__=int
define: __WINT_WIDTH__=32
define: __SIG_ATOMIC_WIDTH__=32
define: __SIG_ATOMIC_MAX__=2147483647
define: __CHAR16_TYPE__=unsigned short
define: __CHAR32_TYPE__=unsigned int
define: __UINTMAX_WIDTH__=64
define: __UINTPTR_TYPE__=long unsigned int
define: __UINTPTR_FMTo__="lo"
define: __UINTPTR_FMTu__="lu"
define: __UINTPTR_FMTx__="lx"
define: __UINTPTR_FMTX__="lX"
define: __UINTPTR_WIDTH__=64
define: __FLT16_DENORM_MIN__=5.9604644775390625e-8F16
define: __FLT16_HAS_DENORM__=1
define: __FLT16_DIG__=3
define: __FLT16_DECIMAL_DIG__=5
define: __FLT16_EPSILON__=9.765625e-4F16
define: __FLT16_HAS_INFINITY__=1
define: __FLT16_HAS_QUIET_NAN__=1
define: __FLT16_MANT_DIG__=11
define: __FLT16_MAX_10_EXP__=4
define: __FLT16_MAX_EXP__=15
define: __FLT16_MAX__=6.5504e+4F16
define: __FLT16_MIN_10_EXP__=(-13)
define: __FLT16_MIN_EXP__=(-14)
define: __FLT16_MIN__=6.103515625e-5F16
define: __FLT_DENORM_MIN__=1.40129846e-45F
define: __FLT_HAS_DENORM__=1
define: __FLT_DIG__=6
define: __FLT_DECIMAL_DIG__=9
define: __FLT_EPSILON__=1.19209290e-7F
define: __FLT_HAS_INFINITY__=1
define: __FLT_HAS_QUIET_NAN__=1
define: __FLT_MANT_DIG__=24
define: __FLT_MAX_10_EXP__=38
define: __FLT_MAX_EXP__=128
define: __FLT_MAX__=3.40282347e+38F
define: __FLT_MIN_10_EXP__=(-37)
define: __FLT_MIN_EXP__=(-125)
define: __FLT_MIN__=1.17549435e-38F
define: __DBL_DENORM_MIN__=4.9406564584124654e-324
define: __DBL_HAS_DENORM__=1
define: __DBL_DIG__=15
define: __DBL_DECIMAL_DIG__=17
define: __DBL_EPSILON__=2.2204460492503131e-16
define: __DBL_HAS_INFINITY__=1
define: __DBL_HAS_QUIET_NAN__=1
define: __DBL_MANT_DIG__=53
define: __DBL_MAX_10_EXP__=308
define: __DBL_MAX_EXP__=1024
define: __DBL_MAX__=1.7976931348623157e+308
define: __DBL_MIN_10_EXP__=(-307)
define: __DBL_MIN_EXP__=(-1021)
define: __DBL_MIN__=2.2250738585072014e-308
define: __LDBL_DENORM_MIN__=3.64519953188247460253e-4951L
define: __LDBL_HAS_DENORM__=1
define: __LDBL_DIG__=18
define: __LDBL_DECIMAL_DIG__=21
define: __LDBL_EPSILON__=1.08420217248550443401e-19L
define: __LDBL_HAS_INFINITY__=1
define: __LDBL_HAS_QUIET_NAN__=1
define: __LDBL_MANT_DIG__=64
define: __LDBL_MAX_10_EXP__=4932
define: __LDBL_MAX_EXP__=16384
define: __LDBL_MAX__=1.18973149535723176502e+4932L
define: __LDBL_MIN_10_EXP__=(-4931)
define: __LDBL_MIN_EXP__=(-16381)
define: __LDBL_MIN__=3.36210314311209350626e-4932L
define: __POINTER_WIDTH__=64
define: __BIGGEST_ALIGNMENT__=16
define: __INT8_TYPE__=signed char
define: __INT8_FMTd__="hhd"
define: __INT8_FMTi__="hhi"
define: __INT8_C_SUFFIX__=
define: __INT16_TYPE__=short
define: __INT16_FMTd__="hd"
define: __INT16_FMTi__="hi"
define: __INT16_C_SUFFIX__=
define: __INT32_TYPE__=int
define: __INT32_FMTd__="d"
define: __INT32_FMTi__="i"
define: __INT32_C_SUFFIX__=
define: __INT64_TYPE__=long long int
define: __INT64_FMTd__="lld"
define: __INT64_FMTi__="lli"
define: __INT64_C_SUFFIX__=LL
define: __UINT8_TYPE__=unsigned char
define: __UINT8_FMTo__="hho"
define: __UINT8_FMTu__="hhu"
define: __UINT8_FMTx__="hhx"
define: __UINT8_FMTX__="hhX"
define: __UINT8_C_SUFFIX__=
define: __UINT8_MAX__=255
define: __INT8_MAX__=127
define: __UINT16_TYPE__=unsigned short
define: __UINT16_FMTo__="ho"
define: __UINT16_FMTu__="hu"
define: __UINT16_FMTx__="hx"
define: __UINT16_FMTX__="hX"
define: __UINT16_C_SUFFIX__=
define: __UINT16_MAX__=65535
define: __INT16_MAX__=32767
define: __UINT32_TYPE__=unsigned int
define: __UINT32_FMTo__="o"
define: __UINT32_FMTu__="u"
define: __UINT32_FMTx__="x"
define: __UINT32_FMTX__="X"
define: __UINT32_C_SUFFIX__=U
define: __UINT32_MAX__=4294967295U
define: __INT32_MAX__=2147483647
define: __UINT64_TYPE__=long long unsigned int
define: __UINT64_FMTo__="llo"
define: __UINT64_FMTu__="llu"
define: __UINT64_FMTx__="llx"
define: __UINT64_FMTX__="llX"
define: __UINT64_C_SUFFIX__=ULL
define: __UINT64_MAX__=18446744073709551615ULL
define: __INT64_MAX__=9223372036854775807LL
define: __INT_LEAST8_TYPE__=signed char
define: __INT_LEAST8_MAX__=127
define: __INT_LEAST8_FMTd__="hhd"
define: __INT_LEAST8_FMTi__="hhi"
define: __UINT_LEAST8_TYPE__=unsigned char
define: __UINT_LEAST8_MAX__=255
define: __UINT_LEAST8_FMTo__="hho"
define: __UINT_LEAST8_FMTu__="hhu"
define: __UINT_LEAST8_FMTx__="hhx"
define: __UINT_LEAST8_FMTX__="hhX"
define: __INT_LEAST16_TYPE__=short
define: __INT_LEAST16_MAX__=32767
define: __INT_LEAST16_FMTd__="hd"
define: __INT_LEAST16_FMTi__="hi"
define: __UINT_LEAST16_TYPE__=unsigned short
define: __UINT_LEAST16_MAX__=65535
define: __UINT_LEAST16_FMTo__="ho"
define: __UINT_LEAST16_FMTu__="hu"
define: __UINT_LEAST16_FMTx__="hx"
define: __UINT_LEAST16_FMTX__="hX"
define: __INT_LEAST32_TYPE__=int
define: __INT_LEAST32_MAX__=2147483647
define: __INT_LEAST32_FMTd__="d"
define: __INT_LEAST32_FMTi__="i"
define: __UINT_LEAST32_TYPE__=unsigned int
define: __UINT_LEAST32_MAX__=4294967295U
define: __UINT_LEAST32_FMTo__="o"
define: __UINT_LEAST32_FMTu__="u"
define: __UINT_LEAST32_FMTx__="x"
define: __UINT_LEAST32_FMTX__="X"
define: __INT_LEAST64_TYPE__=long long int
define: __INT_LEAST64_MAX__=9223372036854775807LL
define: __INT_LEAST64_FMTd__="lld"
define: __INT_LEAST64_FMTi__="lli"
define: __UINT_LEAST64_TYPE__=long long unsigned int
define: __UINT_LEAST64_MAX__=18446744073709551615ULL
define: __UINT_LEAST64_FMTo__="llo"
define: __UINT_LEAST64_FMTu__="llu"
define: __UINT_LEAST64_FMTx__="llx"
define: __UINT_LEAST64_FMTX__="llX"
define: __INT_FAST8_TYPE__=signed char
define: __INT_FAST8_MAX__=127
define: __INT_FAST8_FMTd__="hhd"
define: __INT_FAST8_FMTi__="hhi"
define: __UINT_FAST8_TYPE__=unsigned char
define: __UINT_FAST8_MAX__=255
define: __UINT_FAST8_FMTo__="hho"
define: __UINT_FAST8_FMTu__="hhu"
define: __UINT_FAST8_FMTx__="hhx"
define: __UINT_FAST8_FMTX__="hhX"
define: __INT_FAST16_TYPE__=short
define: __INT_FAST16_MAX__=32767
define: __INT_FAST16_FMTd__="hd"
define: __INT_FAST16_FMTi__="hi"
define: __UINT_FAST16_TYPE__=unsigned short
define: __UINT_FAST16_MAX__=65535
define: __UINT_FAST16_FMTo__="ho"
define: __UINT_FAST16_FMTu__="hu"
define: __UINT_FAST16_FMTx__="hx"
define: __UINT_FAST16_FMTX__="hX"
define: __INT_FAST32_TYPE__=int
define: __INT_FAST32_MAX__=2147483647
define: __INT_FAST32_FMTd__="d"
define: __INT_FAST32_FMTi__="i"
define: __UINT_FAST32_TYPE__=unsigned int
define: __UINT_FAST32_MAX__=4294967295U
define: __UINT_FAST32_FMTo__="o"
define: __UINT_FAST32_FMTu__="u"
define: __UINT_FAST32_FMTx__="x"
define: __UINT_FAST32_FMTX__="X"
define: __INT_FAST64_TYPE__=long long int
define: __INT_FAST64_MAX__=9223372036854775807LL
define: __INT_FAST64_FMTd__="lld"
define: __INT_FAST64_FMTi__="lli"
define: __UINT_FAST64_TYPE__=long long unsigned int
define: __UINT_FAST64_MAX__=18446744073709551615ULL
define: __UINT_FAST64_FMTo__="llo"
define: __UINT_FAST64_FMTu__="llu"
define: __UINT_FAST64_FMTx__="llx"
define: __UINT_FAST64_FMTX__="llX"
define: __USER_LABEL_PREFIX__=_
define: __FINITE_MATH_ONLY__=0
define: __GNUC_GNU_INLINE__=1
define: __GCC_ATOMIC_TEST_AND_SET_TRUEVAL=1
define: __CLANG_ATOMIC_BOOL_LOCK_FREE=2
define: __CLANG_ATOMIC_CHAR_LOCK_FREE=2
define: __CLANG_ATOMIC_CHAR16_T_LOCK_FREE=2
define: __CLANG_ATOMIC_CHAR32_T_LOCK_FREE=2
define: __CLANG_ATOMIC_WCHAR_T_LOCK_FREE=2
define: __CLANG_ATOMIC_SHORT_LOCK_FREE=2
define: __CLANG_ATOMIC_INT_LOCK_FREE=2
define: __CLANG_ATOMIC_LONG_LOCK_FREE=2
define: __CLANG_ATOMIC_LLONG_LOCK_FREE=2
define: __CLANG_ATOMIC_POINTER_LOCK_FREE=2
define: __GCC_ATOMIC_BOOL_LOCK_FREE=2
define: __GCC_ATOMIC_CHAR_LOCK_FREE=2
define: __GCC_ATOMIC_CHAR16_T_LOCK_FREE=2
define: __GCC_ATOMIC_CHAR32_T_LOCK_FREE=2
define: __GCC_ATOMIC_WCHAR_T_LOCK_FREE=2
define: __GCC_ATOMIC_SHORT_LOCK_FREE=2
define: __GCC_ATOMIC_INT_LOCK_FREE=2
define: __GCC_ATOMIC_LONG_LOCK_FREE=2
define: __GCC_ATOMIC_LLONG_LOCK_FREE=2
define: __GCC_ATOMIC_POINTER_LOCK_FREE=2
define: __NO_INLINE__=1
define: __PIC__=2
define: __pic__=2
define: __FLT_EVAL_METHOD__=0
define: __FLT_RADIX__=2
define: __DECIMAL_DIG__=__LDBL_DECIMAL_DIG__
define: __SSP__=1
define: __nonnull=_Nonnull
define: __null_unspecified=_Null_unspecified
define: __nullable=_Nullable
define: __code_model_small_=1
define: __amd64__=1
define: __amd64=1
define: __x86_64=1
define: __x86_64__=1
define: __core2=1
define: __core2__=1
define: __tune_core2__=1
define: __REGISTER_PREFIX__=
define: __NO_MATH_INLINES=1
define: __FXSR__=1
define: __SSE4_1__=1
define: __SSSE3__=1
define: __SSE3__=1
define: __SSE2__=1
define: __SSE2_MATH__=1
define: __SSE__=1
define: __SSE_MATH__=1
define: __MMX__=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_1=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_2=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_4=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_8=1
define: __GCC_HAVE_SYNC_COMPARE_AND_SWAP_16=1
define: __APPLE_CC__=6000
define: __APPLE__=1
define: __STDC_NO_THREADS__=1
define: OBJC_NEW_PROPERTIES=1
define: __apple_build_version__=11000033
define: __weak=__attribute__((objc_gc(weak)))
define: __strong=
define: __unsafe_unretained=
define: __DYNAMIC__=1
define: __ENVIRONMENT_MAC_OS_X_VERSION_MIN_REQUIRED__=101500
define: __MACH__=1
define: __STDC__=1
define: __STDC_HOSTED__=1
define: __cplusplus=201703L
define: __STDCPP_DEFAULT_NEW_ALIGNMENT__=16UL
define: __STDC_UTF_16__=1
define: __STDC_UTF_32__=1
other: --clang
other: --clang_version=110000
stdver: c++17
intelliSenseMode: clang-x64
cpptools/getCodeActions: 33
textDocument/hover: 34
IntelliSense client not available, using Tag Parser for go to definition.
IntelliSense client not available, using Tag Parser for quick info.
using Tag Parser for quick info
cpptools/getCodeActions: 35
0 include path suggestion(s) discovered.
idle loop: reparsing the active document
Checking for syntax errors: file:///Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
Queueing IntelliSense update for files in translation unit of: /Users/ajm/Projects/restaurant/cpp/tests/src/Guest_T.cpp
Database safe to open
cpptools/cpptools_finishUpdateSquiggles
Error squiggle count: 6
terminating child process: 1458
Update IntelliSense time (sec): 5.811
```
This really only started happening recently following the update of my CommandLinesTools and Operating System. It is frustrating the heck out of me and has screwed my flow of development.
Please help. I do not want to waste more time learning a new IDE because this one won't work for me.
Let me know if you need additional information.
Thanks | non_priority | vs code intellisense cannot find boost header files lambda hpp hi all dealing with a frustrating issue here running macos catalina compiler set as usr bin clang the title explains my issue quite concisely from boost s getting started section on their official website i have made sure of the following to compile anything in boost you need a directory containing the boost subdirectory in your include path i have done this by properly setting the environment var boost root and adding boost root to browse path here is my c cpp properties json configurations name mac includepath defines macframeworkpath compilerpath usr bin clang cstandard cppstandard c intellisensemode default browse path version i set my intellisense output level to debug for the sake of investigation and determined that it indeed was able to locate boost lambda lambda hpp but i am not sure as to why it is unable to open it i have checked the file permissions of the files in boost lambda and they consistently readable by all users see here for the intellisense debug output tag parsing file users ajm projects restaurant cpp tests src guest t cpp terminating child process tag parsing file users ajm projects restaurant cpp sim src guest h tag parsing file users ajm projects restaurant cpp sim src person h sending compilation args for users ajm projects restaurant cpp tests src guest t cpp include usr local include include library developer commandlinetools usr include c include library developer commandlinetools usr lib clang include include library developer commandlinetools usr include include library developer commandlinetools sdks sdk usr include include users ajm projects restaurant cpp sim src framework system library frameworks framework library frameworks framework library developer commandlinetools sdks sdk system library frameworks define llvm define clang define clang major define clang minor define clang patchlevel define clang version clang define gnuc minor define gnuc patchlevel define gnuc define gxx abi version define atomic relaxed define atomic consume define atomic acquire define atomic release define atomic acq rel define atomic seq cst define opencl memory scope work item define opencl memory scope work group define opencl memory scope device define opencl memory scope all svm devices define opencl memory scope sub group define pragma redefine extname define version compatible apple llvm clang define strict ansi define gxx experimental define objc bool is bool define constant cfstrings define block attribute blocks byref define blocks define exceptions define gxx rtti define deprecated define gnug define gxx weak define private extern extern define order little endian define order big endian define order pdp endian define byte order order little endian define little endian define define define char bit define schar max define shrt max define int max define long max define long long max define wchar max define wint max define intmax max define size max define uintmax max define ptrdiff max define intptr max define uintptr max define sizeof double define sizeof float define sizeof int define sizeof long define sizeof long double define sizeof long long define sizeof pointer define sizeof short define sizeof ptrdiff t define sizeof size t define sizeof wchar t define sizeof wint t define sizeof define intmax type long int define intmax fmtd ld define intmax fmti li define intmax c suffix l define uintmax type long unsigned int define uintmax fmto lo define uintmax fmtu lu define uintmax fmtx lx define uintmax fmtx lx define uintmax c suffix ul define intmax width define ptrdiff type long int define ptrdiff fmtd ld define ptrdiff fmti li define ptrdiff width define intptr type long int define intptr fmtd ld define intptr fmti li define intptr width define size type long unsigned int define size fmto lo define size fmtu lu define size fmtx lx define size fmtx lx define size width define wchar type int define wchar width define wint type int define wint width define sig atomic width define sig atomic max define type unsigned short define type unsigned int define uintmax width define uintptr type long unsigned int define uintptr fmto lo define uintptr fmtu lu define uintptr fmtx lx define uintptr fmtx lx define uintptr width define denorm min define has denorm define dig define decimal dig define epsilon define has infinity define has quiet nan define mant dig define max exp define max exp define max define min exp define min exp define min define flt denorm min define flt has denorm define flt dig define flt decimal dig define flt epsilon define flt has infinity define flt has quiet nan define flt mant dig define flt max exp define flt max exp define flt max define flt min exp define flt min exp define flt min define dbl denorm min define dbl has denorm define dbl dig define dbl decimal dig define dbl epsilon define dbl has infinity define dbl has quiet nan define dbl mant dig define dbl max exp define dbl max exp define dbl max define dbl min exp define dbl min exp define dbl min define ldbl denorm min define ldbl has denorm define ldbl dig define ldbl decimal dig define ldbl epsilon define ldbl has infinity define ldbl has quiet nan define ldbl mant dig define ldbl max exp define ldbl max exp define ldbl max define ldbl min exp define ldbl min exp define ldbl min define pointer width define biggest alignment define type signed char define fmtd hhd define fmti hhi define c suffix define type short define fmtd hd define fmti hi define c suffix define type int define fmtd d define fmti i define c suffix define type long long int define fmtd lld define fmti lli define c suffix ll define type unsigned char define fmto hho define fmtu hhu define fmtx hhx define fmtx hhx define c suffix define max define max define type unsigned short define fmto ho define fmtu hu define fmtx hx define fmtx hx define c suffix define max define max define type unsigned int define fmto o define fmtu u define fmtx x define fmtx x define c suffix u define max define max define type long long unsigned int define fmto llo define fmtu llu define fmtx llx define fmtx llx define c suffix ull define max define max define int type signed char define int max define int fmtd hhd define int fmti hhi define uint type unsigned char define uint max define uint fmto hho define uint fmtu hhu define uint fmtx hhx define uint fmtx hhx define int type short define int max define int fmtd hd define int fmti hi define uint type unsigned short define uint max define uint fmto ho define uint fmtu hu define uint fmtx hx define uint fmtx hx define int type int define int max define int fmtd d define int fmti i define uint type unsigned int define uint max define uint fmto o define uint fmtu u define uint fmtx x define uint fmtx x define int type long long int define int max define int fmtd lld define int fmti lli define uint type long long unsigned int define uint max define uint fmto llo define uint fmtu llu define uint fmtx llx define uint fmtx llx define int type signed char define int max define int fmtd hhd define int fmti hhi define uint type unsigned char define uint max define uint fmto hho define uint fmtu hhu define uint fmtx hhx define uint fmtx hhx define int type short define int max define int fmtd hd define int fmti hi define uint type unsigned short define uint max define uint fmto ho define uint fmtu hu define uint fmtx hx define uint fmtx hx define int type int define int max define int fmtd d define int fmti i define uint type unsigned int define uint max define uint fmto o define uint fmtu u define uint fmtx x define uint fmtx x define int type long long int define int max define int fmtd lld define int fmti lli define uint type long long unsigned int define uint max define uint fmto llo define uint fmtu llu define uint fmtx llx define uint fmtx llx define user label prefix define finite math only define gnuc gnu inline define gcc atomic test and set trueval define clang atomic bool lock free define clang atomic char lock free define clang atomic t lock free define clang atomic t lock free define clang atomic wchar t lock free define clang atomic short lock free define clang atomic int lock free define clang atomic long lock free define clang atomic llong lock free define clang atomic pointer lock free define gcc atomic bool lock free define gcc atomic char lock free define gcc atomic t lock free define gcc atomic t lock free define gcc atomic wchar t lock free define gcc atomic short lock free define gcc atomic int lock free define gcc atomic long lock free define gcc atomic llong lock free define gcc atomic pointer lock free define no inline define pic define pic define flt eval method define flt radix define decimal dig ldbl decimal dig define ssp define nonnull nonnull define null unspecified null unspecified define nullable nullable define code model small define define define define define define define tune define register prefix define no math inlines define fxsr define define define define define math define sse define sse math define mmx define gcc have sync compare and swap define gcc have sync compare and swap define gcc have sync compare and swap define gcc have sync compare and swap define gcc have sync compare and swap define apple cc define apple define stdc no threads define objc new properties define apple build version define weak attribute objc gc weak define strong define unsafe unretained define dynamic define environment mac os x version min required define mach define stdc define stdc hosted define cplusplus define stdcpp default new alignment define stdc utf define stdc utf other clang other clang version stdver c intellisensemode clang cpptools getcodeactions textdocument hover intellisense client not available using tag parser for go to definition intellisense client not available using tag parser for quick info using tag parser for quick info cpptools getcodeactions include path suggestion s discovered idle loop reparsing the active document checking for syntax errors file users ajm projects restaurant cpp tests src guest t cpp queueing intellisense update for files in translation unit of users ajm projects restaurant cpp tests src guest t cpp database safe to open cpptools cpptools finishupdatesquiggles error squiggle count terminating child process update intellisense time sec this really only started happening recently following the update of my commandlinestools and operating system it is frustrating the heck out of me and has screwed my flow of development please help i do not want to waste more time learning a new ide because this one won t work for me let me know if you need additional information thanks | 0 |
17,334 | 12,302,821,320 | IssuesEvent | 2020-05-11 17:37:27 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | reopened | TestWrappers get built to wrong location | area-Infrastructure-coreclr untriaged | After a coreclr test build, the following directories exist (Windows, x64, Checked):
```
f:\gh\runtime2\artifacts\tests>dir /b f:\gh\runtime2\artifacts\tests\coreclr\Windows_NT.x64.Checked\TestWrappers\JIT.SIMD
JIT.SIMD.XUnitWrapper.cs
JIT.SIMD.XUnitWrapper.csproj
f:\gh\runtime2\artifacts\tests>dir /b f:\gh\runtime2\artifacts\tests\artifacts\tests\coreclr\Windows_NT.x64.Checked\TestWrappers\JIT.SIMD\JIT.SIMD.XUnitWrapper
JIT.SIMD.XUnitWrapper.AssemblyInfo.cs
JIT.SIMD.XUnitWrapper.AssemblyInfoInputs.cache
JIT.SIMD.XUnitWrapper.assets.cache
JIT.SIMD.XUnitWrapper.csproj.CopyComplete
JIT.SIMD.XUnitWrapper.csproj.FileListAbsolute.txt
JIT.SIMD.XUnitWrapper.csproj.nuget.cache
JIT.SIMD.XUnitWrapper.csproj.nuget.dgspec.json
JIT.SIMD.XUnitWrapper.csproj.nuget.g.props
JIT.SIMD.XUnitWrapper.csproj.nuget.g.targets
JIT.SIMD.XUnitWrapper.dll
project.assets.json
```
The built version of the wrappers are getting the wrong directory.
@dotnet/runtime-infrastructure | 1.0 | TestWrappers get built to wrong location - After a coreclr test build, the following directories exist (Windows, x64, Checked):
```
f:\gh\runtime2\artifacts\tests>dir /b f:\gh\runtime2\artifacts\tests\coreclr\Windows_NT.x64.Checked\TestWrappers\JIT.SIMD
JIT.SIMD.XUnitWrapper.cs
JIT.SIMD.XUnitWrapper.csproj
f:\gh\runtime2\artifacts\tests>dir /b f:\gh\runtime2\artifacts\tests\artifacts\tests\coreclr\Windows_NT.x64.Checked\TestWrappers\JIT.SIMD\JIT.SIMD.XUnitWrapper
JIT.SIMD.XUnitWrapper.AssemblyInfo.cs
JIT.SIMD.XUnitWrapper.AssemblyInfoInputs.cache
JIT.SIMD.XUnitWrapper.assets.cache
JIT.SIMD.XUnitWrapper.csproj.CopyComplete
JIT.SIMD.XUnitWrapper.csproj.FileListAbsolute.txt
JIT.SIMD.XUnitWrapper.csproj.nuget.cache
JIT.SIMD.XUnitWrapper.csproj.nuget.dgspec.json
JIT.SIMD.XUnitWrapper.csproj.nuget.g.props
JIT.SIMD.XUnitWrapper.csproj.nuget.g.targets
JIT.SIMD.XUnitWrapper.dll
project.assets.json
```
The built version of the wrappers are getting the wrong directory.
@dotnet/runtime-infrastructure | non_priority | testwrappers get built to wrong location after a coreclr test build the following directories exist windows checked f gh artifacts tests dir b f gh artifacts tests coreclr windows nt checked testwrappers jit simd jit simd xunitwrapper cs jit simd xunitwrapper csproj f gh artifacts tests dir b f gh artifacts tests artifacts tests coreclr windows nt checked testwrappers jit simd jit simd xunitwrapper jit simd xunitwrapper assemblyinfo cs jit simd xunitwrapper assemblyinfoinputs cache jit simd xunitwrapper assets cache jit simd xunitwrapper csproj copycomplete jit simd xunitwrapper csproj filelistabsolute txt jit simd xunitwrapper csproj nuget cache jit simd xunitwrapper csproj nuget dgspec json jit simd xunitwrapper csproj nuget g props jit simd xunitwrapper csproj nuget g targets jit simd xunitwrapper dll project assets json the built version of the wrappers are getting the wrong directory dotnet runtime infrastructure | 0 |
169 | 2,641,537,038 | IssuesEvent | 2015-03-11 18:17:31 | facebook/hhvm | https://api.github.com/repos/facebook/hhvm | opened | HHVM 3.6 binary packages have incorrect mysql socket path | hi-pri php5 incompatibility | - Need rebuilding with mysql-server installed
- Given we're now building a mysqlclient, we should probably error if cmake can't figure out where the socket is | True | HHVM 3.6 binary packages have incorrect mysql socket path - - Need rebuilding with mysql-server installed
- Given we're now building a mysqlclient, we should probably error if cmake can't figure out where the socket is | non_priority | hhvm binary packages have incorrect mysql socket path need rebuilding with mysql server installed given we re now building a mysqlclient we should probably error if cmake can t figure out where the socket is | 0 |
2,839 | 2,650,520,486 | IssuesEvent | 2015-03-16 00:12:19 | openaustralia/righttoknow | https://api.github.com/repos/openaustralia/righttoknow | opened | [responsive styles] remove space between columns on front page | design | There is too much space between the columns on the front page on wide screens:
Responsive styles:

Right To Know:
 | 1.0 | [responsive styles] remove space between columns on front page - There is too much space between the columns on the front page on wide screens:
Responsive styles:

Right To Know:
 | non_priority | remove space between columns on front page there is too much space between the columns on the front page on wide screens responsive styles right to know | 0 |
103,536 | 16,602,912,242 | IssuesEvent | 2021-06-01 22:15:21 | gms-ws-sandbox/nibrs | https://api.github.com/repos/gms-ws-sandbox/nibrs | opened | CVE-2016-1000027 (High) detected in multiple libraries | security vulnerability | ## CVE-2016-1000027 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-5.0.9.RELEASE.jar</b>, <b>spring-web-4.3.11.RELEASE.jar</b>, <b>spring-web-5.1.7.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-web-5.0.9.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/spring-web-5.0.9.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-5.0.9.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-4.3.11.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.11.RELEASE/spring-web-4.3.11.RELEASE.jar,nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/spring-web-4.3.11.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.3.11.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.1.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.1.7.RELEASE/spring-web-5.1.7.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- :x: **spring-web-5.1.7.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Spring Framework 4.1.4 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000027>CVE-2016-1000027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-framework/issues/25379">https://github.com/spring-projects/spring-framework/issues/25379</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: org.springframework:spring-web:5.3.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.0.9.RELEASE","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:5.0.9.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.3.0"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.3.11.RELEASE","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:4.3.11.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.3.0"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.1.7.RELEASE","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework:spring-web:5.1.7.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.3.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2016-1000027","vulnerabilityDetails":"Pivotal Spring Framework 4.1.4 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000027","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-1000027 (High) detected in multiple libraries - ## CVE-2016-1000027 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-5.0.9.RELEASE.jar</b>, <b>spring-web-4.3.11.RELEASE.jar</b>, <b>spring-web-5.1.7.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-web-5.0.9.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-staging-data/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/5.0.9.RELEASE/spring-web-5.0.9.RELEASE.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/spring-web-5.0.9.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-5.0.9.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-4.3.11.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.11.RELEASE/spring-web-4.3.11.RELEASE.jar,nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/spring-web-4.3.11.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.3.11.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.1.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/5.1.7.RELEASE/spring-web-5.1.7.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- :x: **spring-web-5.1.7.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-sandbox/nibrs/commit/9fb1c19bd26c2113d1961640de126a33eacdc946">9fb1c19bd26c2113d1961640de126a33eacdc946</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Spring Framework 4.1.4 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000027>CVE-2016-1000027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-framework/issues/25379">https://github.com/spring-projects/spring-framework/issues/25379</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: org.springframework:spring-web:5.3.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.0.9.RELEASE","packageFilePaths":["/tools/nibrs-staging-data/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:5.0.9.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.3.0"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.3.11.RELEASE","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:4.3.11.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.3.0"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.1.7.RELEASE","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework:spring-web:5.1.7.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.3.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2016-1000027","vulnerabilityDetails":"Pivotal Spring Framework 4.1.4 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000027","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries spring web release jar spring web release jar spring web release jar spring web release jar spring web library home page a href path to dependency file nibrs tools nibrs staging data pom xml path to vulnerable library home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar nibrs web nibrs web target nibrs web web inf lib spring web release jar dependency hierarchy x spring web release jar vulnerable library spring web release jar spring web library home page a href path to dependency file nibrs tools nibrs fbi service pom xml path to vulnerable library home wss scanner repository org springframework spring web release spring web release jar nibrs tools nibrs fbi service target nibrs fbi service web inf lib spring web release jar dependency hierarchy x spring web release jar vulnerable library spring web release jar spring web library home page a href path to dependency file nibrs tools nibrs summary report common pom xml path to vulnerable library home wss scanner repository org springframework spring web release spring web release jar dependency hierarchy spring boot starter web release jar root library x spring web release jar vulnerable library found in head commit a href found in base branch master vulnerability details pivotal spring framework suffers from a potential remote code execution rce issue if used for java deserialization of untrusted data depending on how the library is implemented within a product this issue may or not occur and authentication may be required publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency false dependencytree org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web basebranches vulnerabilityidentifier cve vulnerabilitydetails pivotal spring framework suffers from a potential remote code execution rce issue if used for java deserialization of untrusted data depending on how the library is implemented within a product this issue may or not occur and authentication may be required vulnerabilityurl | 0 |
152,534 | 19,687,579,061 | IssuesEvent | 2022-01-12 00:46:40 | UpendoVentures/Dnn.FipsAesCryptoProvider | https://api.github.com/repos/UpendoVentures/Dnn.FipsAesCryptoProvider | closed | CVE-2018-18325 (High) detected in dotnetnuke.core.9.2.1.533.nupkg | security vulnerability | ## CVE-2018-18325 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dotnetnuke.core.9.2.1.533.nupkg</b></p></summary>
<p>DNN Platform is an open source web application framework.
This package contains only the core ...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/dotnetnuke.core.9.2.1.533.nupkg">https://api.nuget.org/packages/dotnetnuke.core.9.2.1.533.nupkg</a></p>
<p>Path to dependency file: /Libraries/UpendoProvidersFipsAesCryptoProvider/Upendo.Libraries.UpendoProvidersFipsAesCryptoProvider.csproj</p>
<p>Path to vulnerable library: /netnuke.core/9.2.1.533/dotnetnuke.core.9.2.1.533.nupkg</p>
<p>
Dependency Hierarchy:
- :x: **dotnetnuke.core.9.2.1.533.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/UpendoVentures/Dnn.FipsAesCryptoProvider/commit/d6abd56cf0fd6b2d3d2037d2844bf7d7d130c52c">d6abd56cf0fd6b2d3d2037d2844bf7d7d130c52c</a></p>
<p>Found in base branch: <b>development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
DNN (aka DotNetNuke) 9.2 through 9.2.2 uses a weak encryption algorithm to protect input parameters. NOTE: this issue exists because of an incomplete fix for CVE-2018-15811.
<p>Publish Date: 2019-07-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-18325>CVE-2018-18325</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pentest-tools.com/blog/exploit-dotnetnuke-cookie-deserialization/">https://pentest-tools.com/blog/exploit-dotnetnuke-cookie-deserialization/</a></p>
<p>Release Date: 2019-07-03</p>
<p>Fix Resolution: 9.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-18325 (High) detected in dotnetnuke.core.9.2.1.533.nupkg - ## CVE-2018-18325 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dotnetnuke.core.9.2.1.533.nupkg</b></p></summary>
<p>DNN Platform is an open source web application framework.
This package contains only the core ...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/dotnetnuke.core.9.2.1.533.nupkg">https://api.nuget.org/packages/dotnetnuke.core.9.2.1.533.nupkg</a></p>
<p>Path to dependency file: /Libraries/UpendoProvidersFipsAesCryptoProvider/Upendo.Libraries.UpendoProvidersFipsAesCryptoProvider.csproj</p>
<p>Path to vulnerable library: /netnuke.core/9.2.1.533/dotnetnuke.core.9.2.1.533.nupkg</p>
<p>
Dependency Hierarchy:
- :x: **dotnetnuke.core.9.2.1.533.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/UpendoVentures/Dnn.FipsAesCryptoProvider/commit/d6abd56cf0fd6b2d3d2037d2844bf7d7d130c52c">d6abd56cf0fd6b2d3d2037d2844bf7d7d130c52c</a></p>
<p>Found in base branch: <b>development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
DNN (aka DotNetNuke) 9.2 through 9.2.2 uses a weak encryption algorithm to protect input parameters. NOTE: this issue exists because of an incomplete fix for CVE-2018-15811.
<p>Publish Date: 2019-07-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-18325>CVE-2018-18325</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pentest-tools.com/blog/exploit-dotnetnuke-cookie-deserialization/">https://pentest-tools.com/blog/exploit-dotnetnuke-cookie-deserialization/</a></p>
<p>Release Date: 2019-07-03</p>
<p>Fix Resolution: 9.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in dotnetnuke core nupkg cve high severity vulnerability vulnerable library dotnetnuke core nupkg dnn platform is an open source web application framework this package contains only the core library home page a href path to dependency file libraries upendoprovidersfipsaescryptoprovider upendo libraries upendoprovidersfipsaescryptoprovider csproj path to vulnerable library netnuke core dotnetnuke core nupkg dependency hierarchy x dotnetnuke core nupkg vulnerable library found in head commit a href found in base branch development vulnerability details dnn aka dotnetnuke through uses a weak encryption algorithm to protect input parameters note this issue exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
3,900 | 17,359,056,291 | IssuesEvent | 2021-07-29 17:53:15 | carbon-design-system/carbon | https://api.github.com/repos/carbon-design-system/carbon | closed | InlineLoading inactive state animation is broken | status: waiting for maintainer response 💬 type: bug 🐛 | ## Brief description
`InlineLoading` component inactive state animation is broken:

## What package(s) are you using?
<!--
Add an x in one of the options below, for example:
- [] package name
-->
- [x] `carbon-components`
- [x] `carbon-components-react`
## Detailed description
Looks like inactive state in `InlineLoading` component has some weird animation of circle spinning backwards (?).
Versions used:
carbon-components@10.29.0
carbon-components-react@7.29.0
Tested both in Firefox (89.0.2 (64-bit)) and Chrome (Version 91.0.4472.124 (Official Build) (64-bit))
## Steps to reproduce the issue
Have `InlineComponent` with `status='inactive'`.
You could reproduce it in react-components storybook e.g [InlineComponent](https://react.carbondesignsystem.com/?path=/story/components-inlineloading--inline-loading&knob-Description%20(description)=Active%20loading%20indicator)
## Notes:
Looks like it was introduced with` carbon-components-react 7.6.0` | True | InlineLoading inactive state animation is broken - ## Brief description
`InlineLoading` component inactive state animation is broken:

## What package(s) are you using?
<!--
Add an x in one of the options below, for example:
- [] package name
-->
- [x] `carbon-components`
- [x] `carbon-components-react`
## Detailed description
Looks like inactive state in `InlineLoading` component has some weird animation of circle spinning backwards (?).
Versions used:
carbon-components@10.29.0
carbon-components-react@7.29.0
Tested both in Firefox (89.0.2 (64-bit)) and Chrome (Version 91.0.4472.124 (Official Build) (64-bit))
## Steps to reproduce the issue
Have `InlineComponent` with `status='inactive'`.
You could reproduce it in react-components storybook e.g [InlineComponent](https://react.carbondesignsystem.com/?path=/story/components-inlineloading--inline-loading&knob-Description%20(description)=Active%20loading%20indicator)
## Notes:
Looks like it was introduced with` carbon-components-react 7.6.0` | non_priority | inlineloading inactive state animation is broken brief description inlineloading component inactive state animation is broken what package s are you using add an x in one of the options below for example package name carbon components carbon components react detailed description looks like inactive state in inlineloading component has some weird animation of circle spinning backwards versions used carbon components carbon components react tested both in firefox bit and chrome version official build bit steps to reproduce the issue have inlinecomponent with status inactive you could reproduce it in react components storybook e g notes looks like it was introduced with carbon components react | 0 |
24,836 | 12,158,354,615 | IssuesEvent | 2020-04-26 03:23:23 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Make shared_key optional when type is IPSec | enhancement service/virtual-network-gateway | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
Terraform v0.12.19
+ provider.azurerm v1.40.0
### Affected Resource(s)
azurerm_virtual_network_gateway_connection
### Terraform Configuration Files
```hcl
resource azurerm_virtual_network_gateway_connection connection {
name = "any_name"
location = "eastus"
resource_group_name = "demo_group"
type = "IPsec"
virtual_network_gateway_id = var.virtual_network_gateway_id
local_network_gateway_id = azurerm_local_network_gateway.local_gateway.id
}
```
### Debug Output
### Expected Behavior
Connection is created successfully
### Actual Behavior
Error: `local_network_gateway_id` and `shared_key` must be specified when `type` is set to `IPsec
on ..\..\modules\vpn-connection\main.tf line 22, in resource "azurerm_virtual_network_gateway_connection" "connection":
22: resource azurerm_virtual_network_gateway_connection connection {
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform apply`
### Important Factoids
Azure does not require SharedKey to be specified when setting up Site to Site connections (type = IPSec).
We are able to use arm template like below to create the connection and Azure will automatically generate one.
After tracing the code, it appears to be a restriction placed by terraform instead of Azure
```json
{
"apiVersion": "2019-09-01",
"name": "[variables('connectionName')]",
"type": "Microsoft.Network/connections",
"location": "[parameters('location')]",
"dependsOn": [
"[resourceId('Microsoft.Network/localNetworkGateways', variables('localGatewayName'))]"
],
"properties": {
"virtualNetworkGateway1": {
"id": "[resourceId('Microsoft.Network/virtualNetworkGateways', parameters('gatewayName'))]"
},
"localNetworkGateway2": {
"id": "[resourceId('Microsoft.Network/localNetworkGateways', variables('localGatewayName'))]"
},
"connectionType": "IPsec"
}
}
```
### References
https://github.com/terraform-providers/terraform-provider-azurerm/blob/3059f231d3d88b2501a19ebcf7c12692cd5e0e8c/azurerm/internal/services/network/resource_arm_virtual_network_gateway_connection.go
line 523
* #0000
| 1.0 | Make shared_key optional when type is IPSec - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
Terraform v0.12.19
+ provider.azurerm v1.40.0
### Affected Resource(s)
azurerm_virtual_network_gateway_connection
### Terraform Configuration Files
```hcl
resource azurerm_virtual_network_gateway_connection connection {
name = "any_name"
location = "eastus"
resource_group_name = "demo_group"
type = "IPsec"
virtual_network_gateway_id = var.virtual_network_gateway_id
local_network_gateway_id = azurerm_local_network_gateway.local_gateway.id
}
```
### Debug Output
### Expected Behavior
Connection is created successfully
### Actual Behavior
Error: `local_network_gateway_id` and `shared_key` must be specified when `type` is set to `IPsec
on ..\..\modules\vpn-connection\main.tf line 22, in resource "azurerm_virtual_network_gateway_connection" "connection":
22: resource azurerm_virtual_network_gateway_connection connection {
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform apply`
### Important Factoids
Azure does not require SharedKey to be specified when setting up Site to Site connections (type = IPSec).
We are able to use arm template like below to create the connection and Azure will automatically generate one.
After tracing the code, it appears to be a restriction placed by terraform instead of Azure
```json
{
"apiVersion": "2019-09-01",
"name": "[variables('connectionName')]",
"type": "Microsoft.Network/connections",
"location": "[parameters('location')]",
"dependsOn": [
"[resourceId('Microsoft.Network/localNetworkGateways', variables('localGatewayName'))]"
],
"properties": {
"virtualNetworkGateway1": {
"id": "[resourceId('Microsoft.Network/virtualNetworkGateways', parameters('gatewayName'))]"
},
"localNetworkGateway2": {
"id": "[resourceId('Microsoft.Network/localNetworkGateways', variables('localGatewayName'))]"
},
"connectionType": "IPsec"
}
}
```
### References
https://github.com/terraform-providers/terraform-provider-azurerm/blob/3059f231d3d88b2501a19ebcf7c12692cd5e0e8c/azurerm/internal/services/network/resource_arm_virtual_network_gateway_connection.go
line 523
* #0000
| non_priority | make shared key optional when type is ipsec community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform and azurerm provider version terraform provider azurerm affected resource s azurerm virtual network gateway connection terraform configuration files hcl resource azurerm virtual network gateway connection connection name any name location eastus resource group name demo group type ipsec virtual network gateway id var virtual network gateway id local network gateway id azurerm local network gateway local gateway id debug output expected behavior connection is created successfully actual behavior error local network gateway id and shared key must be specified when type is set to ipsec on modules vpn connection main tf line in resource azurerm virtual network gateway connection connection resource azurerm virtual network gateway connection connection steps to reproduce terraform apply important factoids azure does not require sharedkey to be specified when setting up site to site connections type ipsec we are able to use arm template like below to create the connection and azure will automatically generate one after tracing the code it appears to be a restriction placed by terraform instead of azure json apiversion name type microsoft network connections location dependson properties id id connectiontype ipsec references line | 0 |
102,204 | 16,548,287,473 | IssuesEvent | 2021-05-28 04:36:17 | samq-ghdemo/Java-Demo | https://api.github.com/repos/samq-ghdemo/Java-Demo | opened | CVE-2018-14042 (Medium) detected in bootstrap-3.3.7.min.js | security vulnerability | ## CVE-2018-14042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js</a></p>
<p>Path to dependency file: Java-Demo/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: Java-Demo/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html,Java-Demo/.extract/webapps/ROOT/dfi/style_bootstrap.html,Java-Demo/src/main/webapp/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/ebe5ad9510b919e1dd226c70afc5e1115136f8cf">ebe5ad9510b919e1dd226c70afc5e1115136f8cf</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.7","packageFilePaths":["/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html","/.extract/webapps/ROOT/dfi/style_bootstrap.html","/src/main/webapp/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-14042 (Medium) detected in bootstrap-3.3.7.min.js - ## CVE-2018-14042 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.7/js/bootstrap.min.js</a></p>
<p>Path to dependency file: Java-Demo/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: Java-Demo/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html,Java-Demo/.extract/webapps/ROOT/dfi/style_bootstrap.html,Java-Demo/src/main/webapp/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/Java-Demo/commit/ebe5ad9510b919e1dd226c70afc5e1115136f8cf">ebe5ad9510b919e1dd226c70afc5e1115136f8cf</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.3.7","packageFilePaths":["/target/easybuggy-1-SNAPSHOT/dfi/style_bootstrap.html","/.extract/webapps/ROOT/dfi/style_bootstrap.html","/src/main/webapp/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.3.7","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file java demo target easybuggy snapshot dfi style bootstrap html path to vulnerable library java demo target easybuggy snapshot dfi style bootstrap html java demo extract webapps root dfi style bootstrap html java demo src main webapp dfi style bootstrap html dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion org webjars npm bootstrap org webjars bootstrap basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the data container property of tooltip vulnerabilityurl | 0 |
445,043 | 31,162,295,334 | IssuesEvent | 2023-08-16 16:53:44 | microsoft/dynamics365patternspractices | https://api.github.com/repos/microsoft/dynamics365patternspractices | opened | [AREA]: Retire and dispose of assets | documentation business-process acquire to dispose | ### Contact details
sdaggubati@microsoft.com
### Organization type
Microsoft employee
### End-to-end business process
Acquire to dispose
### Specify the business process area name for the article.
Retire and dispose of assets
### Enter any additional comments or information you want us to know about this business process area.
_No response_
### Specify the date you expect the article to be completed and ready for review.
8/31/2023
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | [AREA]: Retire and dispose of assets - ### Contact details
sdaggubati@microsoft.com
### Organization type
Microsoft employee
### End-to-end business process
Acquire to dispose
### Specify the business process area name for the article.
Retire and dispose of assets
### Enter any additional comments or information you want us to know about this business process area.
_No response_
### Specify the date you expect the article to be completed and ready for review.
8/31/2023
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | non_priority | retire and dispose of assets contact details sdaggubati microsoft com organization type microsoft employee end to end business process acquire to dispose specify the business process area name for the article retire and dispose of assets enter any additional comments or information you want us to know about this business process area no response specify the date you expect the article to be completed and ready for review code of conduct i agree to follow this project s code of conduct | 0 |
38,755 | 5,198,150,115 | IssuesEvent | 2017-01-23 17:20:21 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | github.com/cockroachdb/cockroach/pkg/kv: TestMultiRangeBoundedBatchDelRange failed under stress | Robot test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/2b8caa91ab98e65cd587d0c97a4246459a9865a9
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=false
TAGS=deadlock
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=125307&tab=buildLog
```
W170123 10:42:37.898649 2997286 server/status/runtime.go:116 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I170123 10:42:37.900035 2997286 server/config.go:456 1 storage engine initialized
I170123 10:42:37.901870 2997286 server/node.go:426 [n?] store [n0,s0] not bootstrapped
I170123 10:42:37.912170 2997286 server/node.go:355 [n?] **** cluster d263a5ee-e95f-4b9e-80e4-ff89fab495e6 has been created
I170123 10:42:37.912229 2997286 server/node.go:356 [n?] **** add additional nodes by specifying --join=127.0.0.1:52655
I170123 10:42:37.918378 2997286 storage/store.go:1250 [n1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170123 10:42:37.918585 2997286 server/node.go:439 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:0}
I170123 10:42:37.918709 2997286 server/node.go:324 [n1] node ID 1 initialized
I170123 10:42:37.918810 2997286 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:52655" > attrs:<> locality:<>
I170123 10:42:37.925394 2997286 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170123 10:42:37.926053 2997286 server/node.go:571 [n1] connecting to gossip network to verify cluster ID...
I170123 10:42:37.926171 2997286 server/node.go:595 [n1] node connected via gossip and verified as part of cluster "d263a5ee-e95f-4b9e-80e4-ff89fab495e6"
I170123 10:42:37.926470 2997286 server/node.go:374 [n1] node=1: started with [[]=] engine(s) and attributes []
I170123 10:42:37.926579 2997286 sql/executor.go:322 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:52655}
I170123 10:42:37.928953 2997286 server/server.go:629 [n1] starting https server at 127.0.0.1:37472
I170123 10:42:37.929150 2997286 server/server.go:630 [n1] starting grpc/postgres server at 127.0.0.1:52655
I170123 10:42:37.929212 2997286 server/server.go:631 [n1] advertising CockroachDB node at 127.0.0.1:52655
I170123 10:42:37.939553 2998660 sql/event_log.go:95 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:52655} Attrs: Locality:} ClusterID:d263a5ee-e95f-4b9e-80e4-ff89fab495e6 StartedAt:1485168157926437597}
I170123 10:42:37.953162 2997286 sql/event_log.go:95 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueID SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170123 10:42:38.000194 2997286 server/server.go:686 [n1] done ensuring all necessary migrations have run
I170123 10:42:38.000257 2997286 server/server.go:688 [n1] serving sql connections
I170123 10:42:48.111730 2999766 vendor/google.golang.org/grpc/transport/http2_client.go:1123 transport: http2Client.notifyError got notified that the client transport was broken EOF.
I170123 10:42:48.111918 2998903 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:52655->127.0.0.1:45923: use of closed network connection
test_server_shim.go:133: had 1 ranges at startup, expected 5
``` | 1.0 | github.com/cockroachdb/cockroach/pkg/kv: TestMultiRangeBoundedBatchDelRange failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/2b8caa91ab98e65cd587d0c97a4246459a9865a9
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=false
TAGS=deadlock
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=125307&tab=buildLog
```
W170123 10:42:37.898649 2997286 server/status/runtime.go:116 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I170123 10:42:37.900035 2997286 server/config.go:456 1 storage engine initialized
I170123 10:42:37.901870 2997286 server/node.go:426 [n?] store [n0,s0] not bootstrapped
I170123 10:42:37.912170 2997286 server/node.go:355 [n?] **** cluster d263a5ee-e95f-4b9e-80e4-ff89fab495e6 has been created
I170123 10:42:37.912229 2997286 server/node.go:356 [n?] **** add additional nodes by specifying --join=127.0.0.1:52655
I170123 10:42:37.918378 2997286 storage/store.go:1250 [n1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170123 10:42:37.918585 2997286 server/node.go:439 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:0}
I170123 10:42:37.918709 2997286 server/node.go:324 [n1] node ID 1 initialized
I170123 10:42:37.918810 2997286 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:52655" > attrs:<> locality:<>
I170123 10:42:37.925394 2997286 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170123 10:42:37.926053 2997286 server/node.go:571 [n1] connecting to gossip network to verify cluster ID...
I170123 10:42:37.926171 2997286 server/node.go:595 [n1] node connected via gossip and verified as part of cluster "d263a5ee-e95f-4b9e-80e4-ff89fab495e6"
I170123 10:42:37.926470 2997286 server/node.go:374 [n1] node=1: started with [[]=] engine(s) and attributes []
I170123 10:42:37.926579 2997286 sql/executor.go:322 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:52655}
I170123 10:42:37.928953 2997286 server/server.go:629 [n1] starting https server at 127.0.0.1:37472
I170123 10:42:37.929150 2997286 server/server.go:630 [n1] starting grpc/postgres server at 127.0.0.1:52655
I170123 10:42:37.929212 2997286 server/server.go:631 [n1] advertising CockroachDB node at 127.0.0.1:52655
I170123 10:42:37.939553 2998660 sql/event_log.go:95 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:52655} Attrs: Locality:} ClusterID:d263a5ee-e95f-4b9e-80e4-ff89fab495e6 StartedAt:1485168157926437597}
I170123 10:42:37.953162 2997286 sql/event_log.go:95 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueID SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170123 10:42:38.000194 2997286 server/server.go:686 [n1] done ensuring all necessary migrations have run
I170123 10:42:38.000257 2997286 server/server.go:688 [n1] serving sql connections
I170123 10:42:48.111730 2999766 vendor/google.golang.org/grpc/transport/http2_client.go:1123 transport: http2Client.notifyError got notified that the client transport was broken EOF.
I170123 10:42:48.111918 2998903 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:52655->127.0.0.1:45923: use of closed network connection
test_server_shim.go:133: had 1 ranges at startup, expected 5
``` | non_priority | github com cockroachdb cockroach pkg kv testmultirangeboundedbatchdelrange failed under stress sha parameters cockroach proposer evaluated kv false tags deadlock goflags stress build found a failed test server status runtime go could not parse build timestamp parsing time as cannot parse as server config go storage engine initialized server node go store not bootstrapped server node go cluster has been created server node go add additional nodes by specifying join storage store go failed initial metrics computation system config not yet available server node go initialized store capacity available rangecount leasecount server node go node id initialized gossip gossip go nodedescriptor set to node id address attrs locality storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go node started with engine s and attributes sql executor go creating distsqlplanner with address tcp server server go starting https server at server server go starting grpc postgres server at server server go advertising cockroachdb node at sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality clusterid startedat sql event log go event alter table target info tablename eventlog statement alter table system eventlog alter column uniqueid set default uuid user node mutationid cascadedroppedviews server server go done ensuring all necessary migrations have run server server go serving sql connections vendor google golang org grpc transport client go transport notifyerror got notified that the client transport was broken eof vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection test server shim go had ranges at startup expected | 0 |
137,269 | 18,752,672,645 | IssuesEvent | 2021-11-05 05:47:35 | madhans23/linux-4.15 | https://api.github.com/repos/madhans23/linux-4.15 | opened | CVE-2018-5344 (High) detected in linux-stablev4.17.12 | security vulnerability | ## CVE-2018-5344 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stablev4.17.12</b></p></summary>
<p>
<p>Linux kernel stable tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git>https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.15/commit/d96ee498864d1a0b6222cfb17d64ca8196014940">d96ee498864d1a0b6222cfb17d64ca8196014940</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel through 4.14.13, drivers/block/loop.c mishandles lo_release serialization, which allows attackers to cause a denial of service (__lock_acquire use-after-free) or possibly have unspecified other impact.
<p>Publish Date: 2018-01-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-5344>CVE-2018-5344</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-5344">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-5344</a></p>
<p>Release Date: 2018-01-12</p>
<p>Fix Resolution: v4.15-rc8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-5344 (High) detected in linux-stablev4.17.12 - ## CVE-2018-5344 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stablev4.17.12</b></p></summary>
<p>
<p>Linux kernel stable tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git>https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.15/commit/d96ee498864d1a0b6222cfb17d64ca8196014940">d96ee498864d1a0b6222cfb17d64ca8196014940</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel through 4.14.13, drivers/block/loop.c mishandles lo_release serialization, which allows attackers to cause a denial of service (__lock_acquire use-after-free) or possibly have unspecified other impact.
<p>Publish Date: 2018-01-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-5344>CVE-2018-5344</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-5344">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-5344</a></p>
<p>Release Date: 2018-01-12</p>
<p>Fix Resolution: v4.15-rc8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux cve high severity vulnerability vulnerable library linux linux kernel stable tree library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details in the linux kernel through drivers block loop c mishandles lo release serialization which allows attackers to cause a denial of service lock acquire use after free or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
62,725 | 15,351,293,665 | IssuesEvent | 2021-03-01 04:45:11 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | opened | [Feature] Add sticky columns to the table widget | Enhancement Table Widget UI Building Widgets | ## Summary
Add the capability to make columns sticky in the table widget.
## Motivation
When the table renders data with a lot of columns, sticky columns makes it easier for users to be able to scroll through the table horizontally.
## Additional Context
There is an extension available for react-table for this feature.
[https://github.com/GuillaumeJasmin/react-table-sticky](https://github.com/GuillaumeJasmin/react-table-sticky) | 1.0 | [Feature] Add sticky columns to the table widget - ## Summary
Add the capability to make columns sticky in the table widget.
## Motivation
When the table renders data with a lot of columns, sticky columns makes it easier for users to be able to scroll through the table horizontally.
## Additional Context
There is an extension available for react-table for this feature.
[https://github.com/GuillaumeJasmin/react-table-sticky](https://github.com/GuillaumeJasmin/react-table-sticky) | non_priority | add sticky columns to the table widget summary add the capability to make columns sticky in the table widget motivation when the table renders data with a lot of columns sticky columns makes it easier for users to be able to scroll through the table horizontally additional context there is an extension available for react table for this feature | 0 |
151,397 | 23,811,501,799 | IssuesEvent | 2022-09-04 20:38:15 | swarm-game/swarm | https://api.github.com/repos/swarm-game/swarm | closed | Device to give exceptions capability | Z-Feature C-Moderate Effort S-Moderate G-Entities G-Design | Right now the `try` and `raise` commands are available to all robots, but the intention is that there should be a device to give this capability. I don't think it should be available too early in the game. Suggestions welcome!
| 1.0 | Device to give exceptions capability - Right now the `try` and `raise` commands are available to all robots, but the intention is that there should be a device to give this capability. I don't think it should be available too early in the game. Suggestions welcome!
| non_priority | device to give exceptions capability right now the try and raise commands are available to all robots but the intention is that there should be a device to give this capability i don t think it should be available too early in the game suggestions welcome | 0 |
155,504 | 24,472,526,055 | IssuesEvent | 2022-10-07 21:50:38 | CDCgov/prime-simplereport | https://api.github.com/repos/CDCgov/prime-simplereport | closed | Making Spanish test result info more visible | Design Growth & Engagement P2 | During a recent VOC research convo, Spanish content about patient test results was not obvious to the testing facility. They weren't sure how to view or access this info to provide to patients.
This ticket is meant to track what effort(s) are needed to surface this Spanish content for patients (and facilities) in a more obvious way.
- Engineering is working on making preferred patient language in intake forms makes default Spanish for test result info.
**Design needs**
- Facilities need to be aware that they can send patient-facing results in Spanish. They weren't sure how to do it.
- How might facilities find/view or be made aware of these options in a more proactive way?
- Do we need a way for facilities to send Spanish results manually? | 1.0 | Making Spanish test result info more visible - During a recent VOC research convo, Spanish content about patient test results was not obvious to the testing facility. They weren't sure how to view or access this info to provide to patients.
This ticket is meant to track what effort(s) are needed to surface this Spanish content for patients (and facilities) in a more obvious way.
- Engineering is working on making preferred patient language in intake forms makes default Spanish for test result info.
**Design needs**
- Facilities need to be aware that they can send patient-facing results in Spanish. They weren't sure how to do it.
- How might facilities find/view or be made aware of these options in a more proactive way?
- Do we need a way for facilities to send Spanish results manually? | non_priority | making spanish test result info more visible during a recent voc research convo spanish content about patient test results was not obvious to the testing facility they weren t sure how to view or access this info to provide to patients this ticket is meant to track what effort s are needed to surface this spanish content for patients and facilities in a more obvious way engineering is working on making preferred patient language in intake forms makes default spanish for test result info design needs facilities need to be aware that they can send patient facing results in spanish they weren t sure how to do it how might facilities find view or be made aware of these options in a more proactive way do we need a way for facilities to send spanish results manually | 0 |
126,486 | 12,292,602,424 | IssuesEvent | 2020-05-10 15:21:10 | feenkcom/gtoolkit | https://api.github.com/repos/feenkcom/gtoolkit | closed | Image drag leave rest of image while moving | bug documentation | While draging the arrow in the one rendering tree excercise, the arrow does not paint properly on windows 10. See gif:
| 1.0 | Image drag leave rest of image while moving - While draging the arrow in the one rendering tree excercise, the arrow does not paint properly on windows 10. See gif:
| non_priority | image drag leave rest of image while moving while draging the arrow in the one rendering tree excercise the arrow does not paint properly on windows see gif | 0 |
247,575 | 26,718,535,024 | IssuesEvent | 2023-01-28 21:04:40 | samq-ghdemo/webgoat8.1 | https://api.github.com/repos/samq-ghdemo/webgoat8.1 | opened | jsoup-1.11.3.jar: 2 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsoup-1.11.3.jar</b></p></summary>
<p>jsoup is a Java library for working with real-world HTML. It provides a very convenient API for extracting and manipulating data, using the best of DOM, CSS, and jquery-like methods. jsoup implements the WHATWG HTML5 specification, and parses HTML to the same DOM as modern browsers do.</p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/webgoat8.1/commit/60c081f3022a72fded7021d121b82532f51772cf">60c081f3022a72fded7021d121b82532f51772cf</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jsoup version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-37714](https://www.mend.io/vulnerability-database/CVE-2021-37714) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jsoup-1.11.3.jar | Direct | 1.14.2 | ✅ |
| [CVE-2022-36033](https://www.mend.io/vulnerability-database/CVE-2022-36033) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jsoup-1.11.3.jar | Direct | 1.15.3 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37714</summary>
### Vulnerable Library - <b>jsoup-1.11.3.jar</b></p>
<p>jsoup is a Java library for working with real-world HTML. It provides a very convenient API for extracting and manipulating data, using the best of DOM, CSS, and jquery-like methods. jsoup implements the WHATWG HTML5 specification, and parses HTML to the same DOM as modern browsers do.</p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jsoup-1.11.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/webgoat8.1/commit/60c081f3022a72fded7021d121b82532f51772cf">60c081f3022a72fded7021d121b82532f51772cf</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jsoup is a Java library for working with HTML. Those using jsoup versions prior to 1.14.2 to parse untrusted HTML or XML may be vulnerable to DOS attacks. If the parser is run on user supplied input, an attacker may supply content that causes the parser to get stuck (loop indefinitely until cancelled), to complete more slowly than usual, or to throw an unexpected exception. This effect may support a denial of service attack. The issue is patched in version 1.14.2. There are a few available workarounds. Users may rate limit input parsing, limit the size of inputs based on system resources, and/or implement thread watchdogs to cap and timeout parse runtimes.
<p>Publish Date: 2021-08-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37714>CVE-2021-37714</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://jsoup.org/news/release-1.14.2">https://jsoup.org/news/release-1.14.2</a></p>
<p>Release Date: 2021-08-18</p>
<p>Fix Resolution: 1.14.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-36033</summary>
### Vulnerable Library - <b>jsoup-1.11.3.jar</b></p>
<p>jsoup is a Java library for working with real-world HTML. It provides a very convenient API for extracting and manipulating data, using the best of DOM, CSS, and jquery-like methods. jsoup implements the WHATWG HTML5 specification, and parses HTML to the same DOM as modern browsers do.</p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jsoup-1.11.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/webgoat8.1/commit/60c081f3022a72fded7021d121b82532f51772cf">60c081f3022a72fded7021d121b82532f51772cf</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jsoup is a Java HTML parser, built for HTML editing, cleaning, scraping, and cross-site scripting (XSS) safety. jsoup may incorrectly sanitize HTML including `javascript:` URL expressions, which could allow XSS attacks when a reader subsequently clicks that link. If the non-default `SafeList.preserveRelativeLinks` option is enabled, HTML including `javascript:` URLs that have been crafted with control characters will not be sanitized. If the site that this HTML is published on does not set a Content Security Policy, an XSS attack is then possible. This issue is patched in jsoup 1.15.3. Users should upgrade to this version. Additionally, as the unsanitized input may have been persisted, old content should be cleaned again using the updated version. To remediate this issue without immediately upgrading: - disable `SafeList.preserveRelativeLinks`, which will rewrite input URLs as absolute URLs - ensure an appropriate [Content Security Policy](https://developer.mozilla.org/en-US/docs/Web/HTTP/CSP) is defined. (This should be used regardless of upgrading, as a defence-in-depth best practice.)
<p>Publish Date: 2022-08-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-36033>CVE-2022-36033</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jhy/jsoup/security/advisories/GHSA-gp7f-rwcx-9369">https://github.com/jhy/jsoup/security/advisories/GHSA-gp7f-rwcx-9369</a></p>
<p>Release Date: 2022-08-29</p>
<p>Fix Resolution: 1.15.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | jsoup-1.11.3.jar: 2 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsoup-1.11.3.jar</b></p></summary>
<p>jsoup is a Java library for working with real-world HTML. It provides a very convenient API for extracting and manipulating data, using the best of DOM, CSS, and jquery-like methods. jsoup implements the WHATWG HTML5 specification, and parses HTML to the same DOM as modern browsers do.</p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/webgoat8.1/commit/60c081f3022a72fded7021d121b82532f51772cf">60c081f3022a72fded7021d121b82532f51772cf</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jsoup version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-37714](https://www.mend.io/vulnerability-database/CVE-2021-37714) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jsoup-1.11.3.jar | Direct | 1.14.2 | ✅ |
| [CVE-2022-36033](https://www.mend.io/vulnerability-database/CVE-2022-36033) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jsoup-1.11.3.jar | Direct | 1.15.3 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37714</summary>
### Vulnerable Library - <b>jsoup-1.11.3.jar</b></p>
<p>jsoup is a Java library for working with real-world HTML. It provides a very convenient API for extracting and manipulating data, using the best of DOM, CSS, and jquery-like methods. jsoup implements the WHATWG HTML5 specification, and parses HTML to the same DOM as modern browsers do.</p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jsoup-1.11.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/webgoat8.1/commit/60c081f3022a72fded7021d121b82532f51772cf">60c081f3022a72fded7021d121b82532f51772cf</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jsoup is a Java library for working with HTML. Those using jsoup versions prior to 1.14.2 to parse untrusted HTML or XML may be vulnerable to DOS attacks. If the parser is run on user supplied input, an attacker may supply content that causes the parser to get stuck (loop indefinitely until cancelled), to complete more slowly than usual, or to throw an unexpected exception. This effect may support a denial of service attack. The issue is patched in version 1.14.2. There are a few available workarounds. Users may rate limit input parsing, limit the size of inputs based on system resources, and/or implement thread watchdogs to cap and timeout parse runtimes.
<p>Publish Date: 2021-08-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37714>CVE-2021-37714</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://jsoup.org/news/release-1.14.2">https://jsoup.org/news/release-1.14.2</a></p>
<p>Release Date: 2021-08-18</p>
<p>Fix Resolution: 1.14.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-36033</summary>
### Vulnerable Library - <b>jsoup-1.11.3.jar</b></p>
<p>jsoup is a Java library for working with real-world HTML. It provides a very convenient API for extracting and manipulating data, using the best of DOM, CSS, and jquery-like methods. jsoup implements the WHATWG HTML5 specification, and parses HTML to the same DOM as modern browsers do.</p>
<p>Path to dependency file: /webgoat-server/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar,/home/wss-scanner/.m2/repository/org/jsoup/jsoup/1.11.3/jsoup-1.11.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jsoup-1.11.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/webgoat8.1/commit/60c081f3022a72fded7021d121b82532f51772cf">60c081f3022a72fded7021d121b82532f51772cf</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jsoup is a Java HTML parser, built for HTML editing, cleaning, scraping, and cross-site scripting (XSS) safety. jsoup may incorrectly sanitize HTML including `javascript:` URL expressions, which could allow XSS attacks when a reader subsequently clicks that link. If the non-default `SafeList.preserveRelativeLinks` option is enabled, HTML including `javascript:` URLs that have been crafted with control characters will not be sanitized. If the site that this HTML is published on does not set a Content Security Policy, an XSS attack is then possible. This issue is patched in jsoup 1.15.3. Users should upgrade to this version. Additionally, as the unsanitized input may have been persisted, old content should be cleaned again using the updated version. To remediate this issue without immediately upgrading: - disable `SafeList.preserveRelativeLinks`, which will rewrite input URLs as absolute URLs - ensure an appropriate [Content Security Policy](https://developer.mozilla.org/en-US/docs/Web/HTTP/CSP) is defined. (This should be used regardless of upgrading, as a defence-in-depth best practice.)
<p>Publish Date: 2022-08-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-36033>CVE-2022-36033</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jhy/jsoup/security/advisories/GHSA-gp7f-rwcx-9369">https://github.com/jhy/jsoup/security/advisories/GHSA-gp7f-rwcx-9369</a></p>
<p>Release Date: 2022-08-29</p>
<p>Fix Resolution: 1.15.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | jsoup jar vulnerabilities highest severity is vulnerable library jsoup jar jsoup is a java library for working with real world html it provides a very convenient api for extracting and manipulating data using the best of dom css and jquery like methods jsoup implements the whatwg specification and parses html to the same dom as modern browsers do path to dependency file webgoat server pom xml path to vulnerable library home wss scanner repository org jsoup jsoup jsoup jar home wss scanner repository org jsoup jsoup jsoup jar home wss scanner repository org jsoup jsoup jsoup jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in jsoup version remediation available high jsoup jar direct medium jsoup jar direct details cve vulnerable library jsoup jar jsoup is a java library for working with real world html it provides a very convenient api for extracting and manipulating data using the best of dom css and jquery like methods jsoup implements the whatwg specification and parses html to the same dom as modern browsers do path to dependency file webgoat server pom xml path to vulnerable library home wss scanner repository org jsoup jsoup jsoup jar home wss scanner repository org jsoup jsoup jsoup jar home wss scanner repository org jsoup jsoup jsoup jar dependency hierarchy x jsoup jar vulnerable library found in head commit a href found in base branch main vulnerability details jsoup is a java library for working with html those using jsoup versions prior to to parse untrusted html or xml may be vulnerable to dos attacks if the parser is run on user supplied input an attacker may supply content that causes the parser to get stuck loop indefinitely until cancelled to complete more slowly than usual or to throw an unexpected exception this effect may support a denial of service attack the issue is patched in version there are a few available workarounds users may rate limit input parsing limit the size of inputs based on system resources and or implement thread watchdogs to cap and timeout parse runtimes publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jsoup jar jsoup is a java library for working with real world html it provides a very convenient api for extracting and manipulating data using the best of dom css and jquery like methods jsoup implements the whatwg specification and parses html to the same dom as modern browsers do path to dependency file webgoat server pom xml path to vulnerable library home wss scanner repository org jsoup jsoup jsoup jar home wss scanner repository org jsoup jsoup jsoup jar home wss scanner repository org jsoup jsoup jsoup jar dependency hierarchy x jsoup jar vulnerable library found in head commit a href found in base branch main vulnerability details jsoup is a java html parser built for html editing cleaning scraping and cross site scripting xss safety jsoup may incorrectly sanitize html including javascript url expressions which could allow xss attacks when a reader subsequently clicks that link if the non default safelist preserverelativelinks option is enabled html including javascript urls that have been crafted with control characters will not be sanitized if the site that this html is published on does not set a content security policy an xss attack is then possible this issue is patched in jsoup users should upgrade to this version additionally as the unsanitized input may have been persisted old content should be cleaned again using the updated version to remediate this issue without immediately upgrading disable safelist preserverelativelinks which will rewrite input urls as absolute urls ensure an appropriate is defined this should be used regardless of upgrading as a defence in depth best practice publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
107,595 | 9,218,602,159 | IssuesEvent | 2019-03-11 13:46:23 | kcigeospatial/Fred_Co_Land-Management | https://api.github.com/repos/kcigeospatial/Fred_Co_Land-Management | closed | Building - RESUSES - Cannot create a new application | Ready For Retest | A new Building - RESUSES application cannot be created. All required fields are filled out, with the exception of the last Section Complete on the Details tab. The system will not allow typing ('Y') in the box, nor does the dropdown allow any selections, nor is there a search/selection icon to click. The field is required however, so the application cannot be saved/created and cannot move forward.
AP: any new
Logged By: Tara F
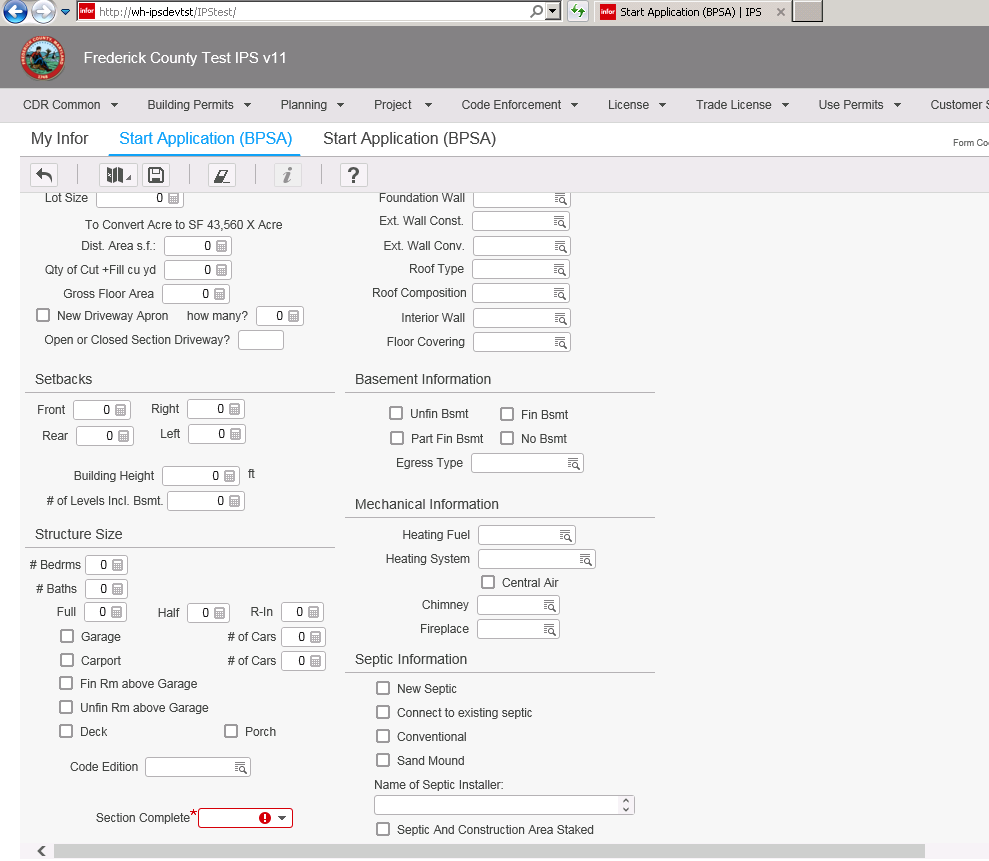
| 1.0 | Building - RESUSES - Cannot create a new application - A new Building - RESUSES application cannot be created. All required fields are filled out, with the exception of the last Section Complete on the Details tab. The system will not allow typing ('Y') in the box, nor does the dropdown allow any selections, nor is there a search/selection icon to click. The field is required however, so the application cannot be saved/created and cannot move forward.
AP: any new
Logged By: Tara F
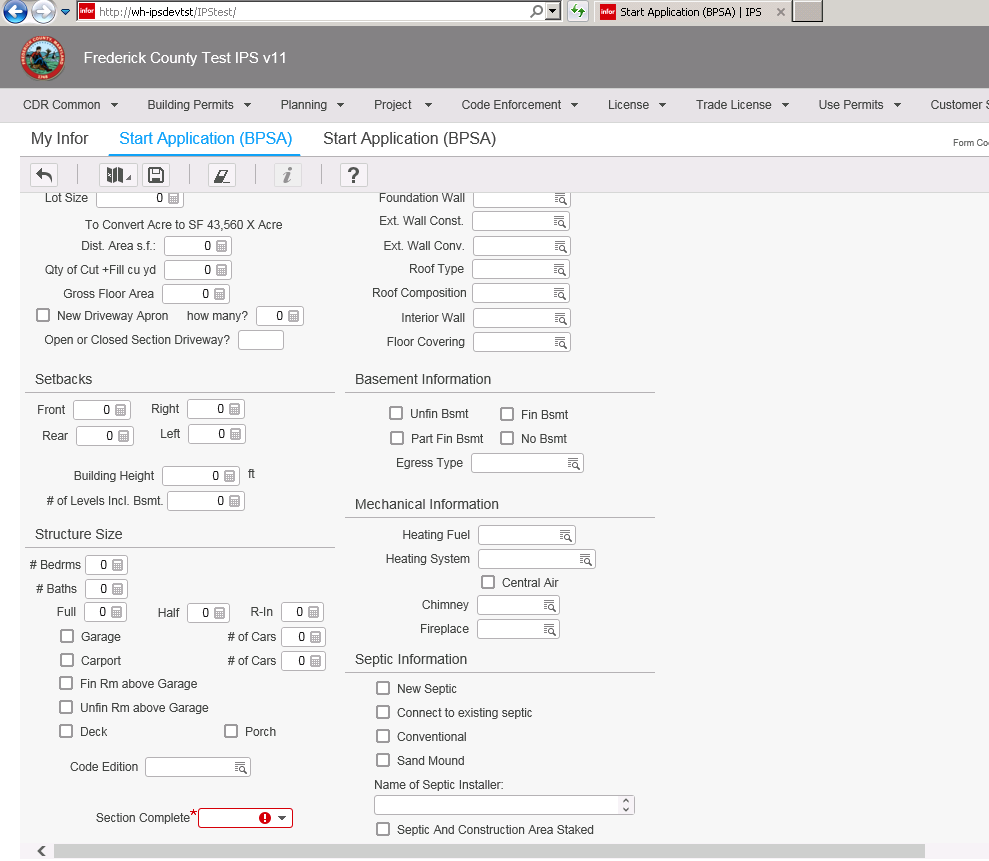
| non_priority | building resuses cannot create a new application a new building resuses application cannot be created all required fields are filled out with the exception of the last section complete on the details tab the system will not allow typing y in the box nor does the dropdown allow any selections nor is there a search selection icon to click the field is required however so the application cannot be saved created and cannot move forward ap any new logged by tara f | 0 |
3,139 | 2,666,617,889 | IssuesEvent | 2015-03-21 19:07:16 | GijsTimmers/kotnetcli | https://api.github.com/repos/GijsTimmers/kotnetcli | opened | Move fabriek.py's contents to __init__.py | @low enhancement software-design | Before going any further, please read [this article](http://mikegrouchy.com/blog/2012/05/be-pythonic-__init__py.html) first (~450 words).
As said in #77 , I'd like to move to a project in which `__init__.py` contains all stuff that's expected to be imported from that directory (or _package_).
Currently, `fabriek.py` makes sure that the right communicator is built and passed to `kotnetcli.py`.
I propose to move everything in `fabriek.py` to `__init__.py`:
Current situation:
from communicator.fabriek import LoginCommunicatorFabriek, LogoutCommunicatorFabriek
Proposed situation:
from communicator import LoginCommunicatorFabriek, LogoutCommunicatorFabriek
This should also resolve strange bugs that we're getting when trying to distribute with `setup.py`, as mentioned in #77 .
@jovanbulck : Please let me know your thoughts about this. | 1.0 | Move fabriek.py's contents to __init__.py - Before going any further, please read [this article](http://mikegrouchy.com/blog/2012/05/be-pythonic-__init__py.html) first (~450 words).
As said in #77 , I'd like to move to a project in which `__init__.py` contains all stuff that's expected to be imported from that directory (or _package_).
Currently, `fabriek.py` makes sure that the right communicator is built and passed to `kotnetcli.py`.
I propose to move everything in `fabriek.py` to `__init__.py`:
Current situation:
from communicator.fabriek import LoginCommunicatorFabriek, LogoutCommunicatorFabriek
Proposed situation:
from communicator import LoginCommunicatorFabriek, LogoutCommunicatorFabriek
This should also resolve strange bugs that we're getting when trying to distribute with `setup.py`, as mentioned in #77 .
@jovanbulck : Please let me know your thoughts about this. | non_priority | move fabriek py s contents to init py before going any further please read first words as said in i d like to move to a project in which init py contains all stuff that s expected to be imported from that directory or package currently fabriek py makes sure that the right communicator is built and passed to kotnetcli py i propose to move everything in fabriek py to init py current situation from communicator fabriek import logincommunicatorfabriek logoutcommunicatorfabriek proposed situation from communicator import logincommunicatorfabriek logoutcommunicatorfabriek this should also resolve strange bugs that we re getting when trying to distribute with setup py as mentioned in jovanbulck please let me know your thoughts about this | 0 |
174,946 | 21,300,587,794 | IssuesEvent | 2022-04-15 02:12:14 | kmorris896/rapture-toy-manager | https://api.github.com/repos/kmorris896/rapture-toy-manager | opened | CVE-2021-43138 (High) detected in async-3.2.1.tgz | security vulnerability | ## CVE-2021-43138 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>async-3.2.1.tgz</b></p></summary>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-3.2.1.tgz">https://registry.npmjs.org/async/-/async-3.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/async/package.json</p>
<p>
Dependency Hierarchy:
- winston-3.3.3.tgz (Root Library)
- :x: **async-3.2.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability exists in Async through 3.2.1 (fixed in 3.2.2) , which could let a malicious user obtain privileges via the mapValues() method.
<p>Publish Date: 2022-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138>CVE-2021-43138</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43138">https://nvd.nist.gov/vuln/detail/CVE-2021-43138</a></p>
<p>Release Date: 2022-04-06</p>
<p>Fix Resolution (async): 3.2.2</p>
<p>Direct dependency fix Resolution (winston): 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-43138 (High) detected in async-3.2.1.tgz - ## CVE-2021-43138 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>async-3.2.1.tgz</b></p></summary>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library home page: <a href="https://registry.npmjs.org/async/-/async-3.2.1.tgz">https://registry.npmjs.org/async/-/async-3.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/async/package.json</p>
<p>
Dependency Hierarchy:
- winston-3.3.3.tgz (Root Library)
- :x: **async-3.2.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability exists in Async through 3.2.1 (fixed in 3.2.2) , which could let a malicious user obtain privileges via the mapValues() method.
<p>Publish Date: 2022-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43138>CVE-2021-43138</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-43138">https://nvd.nist.gov/vuln/detail/CVE-2021-43138</a></p>
<p>Release Date: 2022-04-06</p>
<p>Fix Resolution (async): 3.2.2</p>
<p>Direct dependency fix Resolution (winston): 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in async tgz cve high severity vulnerability vulnerable library async tgz higher order functions and common patterns for asynchronous code library home page a href path to dependency file package json path to vulnerable library node modules async package json dependency hierarchy winston tgz root library x async tgz vulnerable library found in base branch main vulnerability details a vulnerability exists in async through fixed in which could let a malicious user obtain privileges via the mapvalues method publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution async direct dependency fix resolution winston step up your open source security game with whitesource | 0 |
154,322 | 12,200,635,481 | IssuesEvent | 2020-04-30 05:18:48 | dotnet/source-build | https://api.github.com/repos/dotnet/source-build | closed | The source-build infra binlog is overwritten by package-source-build/pack.sh | area-ci-testing triaged | Example:
https://dev.azure.com/dnceng/internal/_build/results?buildId=491337&view=results
https://dev.azure.com/dnceng/public/_build/results?buildId=495856&view=results
Artifact `Logs centos71 Production` => `source-build` => `logs` => `artifacts` => `log` => `Release` => `Build.binlog` seems to be from:
https://github.com/dotnet/source-build/blob/3085962b9d1c17a6c0b746837b94238257966d0a/src/package-source-build/pack.sh#L19
I would expect to see the main binlog here, showing details about project orchestration etc.
Simple solution: have `pack.sh` specify a project-specific binlog location.
However, treating package-source-build as a repository and actually calling a build command seems pretty strange, vs. handing it in process through MSBuild. From the code, I don't see a reason it helps for it to call the build script again. | 1.0 | The source-build infra binlog is overwritten by package-source-build/pack.sh - Example:
https://dev.azure.com/dnceng/internal/_build/results?buildId=491337&view=results
https://dev.azure.com/dnceng/public/_build/results?buildId=495856&view=results
Artifact `Logs centos71 Production` => `source-build` => `logs` => `artifacts` => `log` => `Release` => `Build.binlog` seems to be from:
https://github.com/dotnet/source-build/blob/3085962b9d1c17a6c0b746837b94238257966d0a/src/package-source-build/pack.sh#L19
I would expect to see the main binlog here, showing details about project orchestration etc.
Simple solution: have `pack.sh` specify a project-specific binlog location.
However, treating package-source-build as a repository and actually calling a build command seems pretty strange, vs. handing it in process through MSBuild. From the code, I don't see a reason it helps for it to call the build script again. | non_priority | the source build infra binlog is overwritten by package source build pack sh example artifact logs production source build logs artifacts log release build binlog seems to be from i would expect to see the main binlog here showing details about project orchestration etc simple solution have pack sh specify a project specific binlog location however treating package source build as a repository and actually calling a build command seems pretty strange vs handing it in process through msbuild from the code i don t see a reason it helps for it to call the build script again | 0 |
318,218 | 27,295,748,445 | IssuesEvent | 2023-02-23 20:10:45 | py-mine/mcproto | https://api.github.com/repos/py-mine/mcproto | closed | Increase coverage to at least 75% | t: enhancement z: help wanted p: 1 - high a: tests s: WIP z: large | There was a lot of new code written which doesn't yet have any unit-tests covering it.
Increasing this coverage is absolutely necessary before making the next major release (which will be the first full release), as without it the automated test workflows aren't running all of the code, and there might be some things which were missed and are potentially version incompatible, or just plain broken.
Alongside, it could be a good idea to also add some integration tests, running the examples in readme or similar things, ensuring that everything works properly when put together.
Note that the 75% in the title is just a suggestion, ideally, this should be 100%, but that's probably unrealistic, however generally, we should try to make the coverage as high as possible. | 1.0 | Increase coverage to at least 75% - There was a lot of new code written which doesn't yet have any unit-tests covering it.
Increasing this coverage is absolutely necessary before making the next major release (which will be the first full release), as without it the automated test workflows aren't running all of the code, and there might be some things which were missed and are potentially version incompatible, or just plain broken.
Alongside, it could be a good idea to also add some integration tests, running the examples in readme or similar things, ensuring that everything works properly when put together.
Note that the 75% in the title is just a suggestion, ideally, this should be 100%, but that's probably unrealistic, however generally, we should try to make the coverage as high as possible. | non_priority | increase coverage to at least there was a lot of new code written which doesn t yet have any unit tests covering it increasing this coverage is absolutely necessary before making the next major release which will be the first full release as without it the automated test workflows aren t running all of the code and there might be some things which were missed and are potentially version incompatible or just plain broken alongside it could be a good idea to also add some integration tests running the examples in readme or similar things ensuring that everything works properly when put together note that the in the title is just a suggestion ideally this should be but that s probably unrealistic however generally we should try to make the coverage as high as possible | 0 |
176,993 | 13,673,137,099 | IssuesEvent | 2020-09-29 09:26:04 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/discover/async_scripted_fields·js - discover async search with scripted fields query should show failed shards pop up | failed-test | A test failed on a tracked branch
```
Error: retry.tryForTime timeout: TimeoutError: Waiting for element to be located By(css selector, [data-test-subj="euiToastHeader"])
Wait timed out after 10049ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:842:17
at process._tickCallback (internal/process/next_tick.js:68:7)
at onFailure (/dev/shm/workspace/parallel/2/kibana/test/common/services/retry/retry_for_success.ts:28:9)
at retryForSuccess (/dev/shm/workspace/parallel/2/kibana/test/common/services/retry/retry_for_success.ts:68:13)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/8433/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/discover/async_scripted_fields·js","test.name":"discover async search with scripted fields query should show failed shards pop up","test.failCount":1}} --> | 1.0 | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/discover/async_scripted_fields·js - discover async search with scripted fields query should show failed shards pop up - A test failed on a tracked branch
```
Error: retry.tryForTime timeout: TimeoutError: Waiting for element to be located By(css selector, [data-test-subj="euiToastHeader"])
Wait timed out after 10049ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:842:17
at process._tickCallback (internal/process/next_tick.js:68:7)
at onFailure (/dev/shm/workspace/parallel/2/kibana/test/common/services/retry/retry_for_success.ts:28:9)
at retryForSuccess (/dev/shm/workspace/parallel/2/kibana/test/common/services/retry/retry_for_success.ts:68:13)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/8433/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/discover/async_scripted_fields·js","test.name":"discover async search with scripted fields query should show failed shards pop up","test.failCount":1}} --> | non_priority | failing test chrome x pack ui functional tests x pack test functional apps discover async scripted fields·js discover async search with scripted fields query should show failed shards pop up a test failed on a tracked branch error retry tryfortime timeout timeouterror waiting for element to be located by css selector wait timed out after at dev shm workspace kibana node modules selenium webdriver lib webdriver js at process tickcallback internal process next tick js at onfailure dev shm workspace parallel kibana test common services retry retry for success ts at retryforsuccess dev shm workspace parallel kibana test common services retry retry for success ts first failure | 0 |
304,528 | 23,070,189,501 | IssuesEvent | 2022-07-25 17:16:43 | hms-networks/IgnitionEwonConnector | https://api.github.com/repos/hms-networks/IgnitionEwonConnector | opened | Ignition 8.1 - Add tag cleanup description | Documentation | Add a description to the documentation about how to cleanup tags on Ignition which may have been renamed, deleted, or otherwise modified on the Ewon device. | 1.0 | Ignition 8.1 - Add tag cleanup description - Add a description to the documentation about how to cleanup tags on Ignition which may have been renamed, deleted, or otherwise modified on the Ewon device. | non_priority | ignition add tag cleanup description add a description to the documentation about how to cleanup tags on ignition which may have been renamed deleted or otherwise modified on the ewon device | 0 |
381,297 | 26,445,626,310 | IssuesEvent | 2023-01-16 06:58:22 | GameCache/CodeTemplate | https://api.github.com/repos/GameCache/CodeTemplate | opened | Add Initial Structure | documentation enhancement | <!--- Please search issues before creating a new one. --->
<!--- This is just a template, feel free to customize if prudent. --->
## Wanted Behavior
<!--- Describe the wanted feature. --->
Ability to use this repository as a seed for others.
## Possible Solution
<!--- Optional implementation suggestion. --->
Add a default implementation with the common structure to use for other projects.
## Additional Information
<!--- For example, why do you want the feature. --->
Also provides a way to test new language enhancements for already created projects. | 1.0 | Add Initial Structure - <!--- Please search issues before creating a new one. --->
<!--- This is just a template, feel free to customize if prudent. --->
## Wanted Behavior
<!--- Describe the wanted feature. --->
Ability to use this repository as a seed for others.
## Possible Solution
<!--- Optional implementation suggestion. --->
Add a default implementation with the common structure to use for other projects.
## Additional Information
<!--- For example, why do you want the feature. --->
Also provides a way to test new language enhancements for already created projects. | non_priority | add initial structure wanted behavior ability to use this repository as a seed for others possible solution add a default implementation with the common structure to use for other projects additional information also provides a way to test new language enhancements for already created projects | 0 |
56,498 | 14,078,440,996 | IssuesEvent | 2020-11-04 13:34:40 | themagicalmammal/android_kernel_samsung_j7elte | https://api.github.com/repos/themagicalmammal/android_kernel_samsung_j7elte | opened | CVE-2018-3620 (Medium) detected in linuxv3.10 | security vulnerability | ## CVE-2018-3620 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.10</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/themagicalmammal/android_kernel_samsung_j7elte/commit/adc86a86e0ac98007fd3af905bc71e9f29c1502c">adc86a86e0ac98007fd3af905bc71e9f29c1502c</a></p>
<p>Found in base branch: <b>xsentinel-1.7-experimental</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (5)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable-3level.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable-3level.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable_64.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable_64.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable-3level.h</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Systems with microprocessors utilizing speculative execution and address translations may allow unauthorized disclosure of information residing in the L1 data cache to an attacker with local user access via a terminal page fault and a side-channel analysis.
<p>Publish Date: 2018-08-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3620>CVE-2018-3620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3620">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3620</a></p>
<p>Release Date: 2018-08-14</p>
<p>Fix Resolution: v4.19-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-3620 (Medium) detected in linuxv3.10 - ## CVE-2018-3620 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.10</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/themagicalmammal/android_kernel_samsung_j7elte/commit/adc86a86e0ac98007fd3af905bc71e9f29c1502c">adc86a86e0ac98007fd3af905bc71e9f29c1502c</a></p>
<p>Found in base branch: <b>xsentinel-1.7-experimental</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (5)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable-3level.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable-3level.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable_64.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable_64.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_j7elte/arch/x86/include/asm/pgtable-3level.h</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Systems with microprocessors utilizing speculative execution and address translations may allow unauthorized disclosure of information residing in the L1 data cache to an attacker with local user access via a terminal page fault and a side-channel analysis.
<p>Publish Date: 2018-08-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3620>CVE-2018-3620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3620">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3620</a></p>
<p>Release Date: 2018-08-14</p>
<p>Fix Resolution: v4.19-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch xsentinel experimental vulnerable source files android kernel samsung arch include asm pgtable h android kernel samsung arch include asm pgtable h android kernel samsung arch include asm pgtable h android kernel samsung arch include asm pgtable h android kernel samsung arch include asm pgtable h vulnerability details systems with microprocessors utilizing speculative execution and address translations may allow unauthorized disclosure of information residing in the data cache to an attacker with local user access via a terminal page fault and a side channel analysis publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
202,926 | 15,307,791,644 | IssuesEvent | 2021-02-24 21:26:01 | facebook/TestSlide | https://api.github.com/repos/facebook/TestSlide | closed | Create pytest-testslide | Hacktoberfest enhancement help wanted pytest | Add TestSlide support for pytest:
- Create the PyPI package.
- Add integration tests to `Makefile` for building, installing and using it.
- Add documentation at `doc/` regarding pytest integration.
StrictMock can be used simply by importing it, just document it.
[Patching tools](https://testslide.readthedocs.io/en/2.2.1/patching/index.html) require special pytest integration, which can be done with [@pytest.fixture](https://docs.pytest.org/en/latest/reference.html#pytest-fixture). Naming the fixture `testslide` makes sense:
```python
def test_something(testslide):
testslide.mock_callable(...)
```
but this contrasts with its usage at TestSlide's DSL and Python's Unittest, which access them via `self.mock_callable(...)`, so this is TBD.
The fixture implementation can be copy / pasta from [testslide.TestCase](https://github.com/facebookincubator/TestSlide/blob/master/testslide/__init__.py#L816-L844). | 1.0 | Create pytest-testslide - Add TestSlide support for pytest:
- Create the PyPI package.
- Add integration tests to `Makefile` for building, installing and using it.
- Add documentation at `doc/` regarding pytest integration.
StrictMock can be used simply by importing it, just document it.
[Patching tools](https://testslide.readthedocs.io/en/2.2.1/patching/index.html) require special pytest integration, which can be done with [@pytest.fixture](https://docs.pytest.org/en/latest/reference.html#pytest-fixture). Naming the fixture `testslide` makes sense:
```python
def test_something(testslide):
testslide.mock_callable(...)
```
but this contrasts with its usage at TestSlide's DSL and Python's Unittest, which access them via `self.mock_callable(...)`, so this is TBD.
The fixture implementation can be copy / pasta from [testslide.TestCase](https://github.com/facebookincubator/TestSlide/blob/master/testslide/__init__.py#L816-L844). | non_priority | create pytest testslide add testslide support for pytest create the pypi package add integration tests to makefile for building installing and using it add documentation at doc regarding pytest integration strictmock can be used simply by importing it just document it require special pytest integration which can be done with naming the fixture testslide makes sense python def test something testslide testslide mock callable but this contrasts with its usage at testslide s dsl and python s unittest which access them via self mock callable so this is tbd the fixture implementation can be copy pasta from | 0 |
80,700 | 30,495,787,653 | IssuesEvent | 2023-07-18 10:42:47 | vector-im/element-x-ios | https://api.github.com/repos/vector-im/element-x-ios | closed | Blocks of history are going entirely missing | A-Timeline T-Defect S-Critical O-Uncommon Z-Schedule | ### Steps to reproduce
1. Decide you want to read a room you haven't read before on EIX
2. Filter on roomlist to find it
3. Enter it
4. See the correct most recent message in the room - and then 15 messages are missing from the timeline before older history is visible.
5. Wait a while to see if the older history turns up; it doesn't.
6. Go to room list
7. Go back into the room
8. History is now visible.
This is the second time i've seen this today.
### Outcome
#### What did you expect?
Reliable room history
#### What happened instead?
Big missing block of history. Presumably /messages backwards paginating from the wrong token, or trickle /sync isn't working, or something.
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
257
### Homeserver
_No response_
### Will you send logs?
Yes | 1.0 | Blocks of history are going entirely missing - ### Steps to reproduce
1. Decide you want to read a room you haven't read before on EIX
2. Filter on roomlist to find it
3. Enter it
4. See the correct most recent message in the room - and then 15 messages are missing from the timeline before older history is visible.
5. Wait a while to see if the older history turns up; it doesn't.
6. Go to room list
7. Go back into the room
8. History is now visible.
This is the second time i've seen this today.
### Outcome
#### What did you expect?
Reliable room history
#### What happened instead?
Big missing block of history. Presumably /messages backwards paginating from the wrong token, or trickle /sync isn't working, or something.
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
257
### Homeserver
_No response_
### Will you send logs?
Yes | non_priority | blocks of history are going entirely missing steps to reproduce decide you want to read a room you haven t read before on eix filter on roomlist to find it enter it see the correct most recent message in the room and then messages are missing from the timeline before older history is visible wait a while to see if the older history turns up it doesn t go to room list go back into the room history is now visible this is the second time i ve seen this today outcome what did you expect reliable room history what happened instead big missing block of history presumably messages backwards paginating from the wrong token or trickle sync isn t working or something your phone model no response operating system version no response application version homeserver no response will you send logs yes | 0 |
34,453 | 4,541,876,190 | IssuesEvent | 2016-09-09 19:15:48 | appirio-tech/connect-app | https://api.github.com/repos/appirio-tech/connect-app | opened | Messaging: Style fixes | design | Messaging relies heavily on the Dashboard design, as it is a continuation of the user experience.

The messaging is delivered as part of the Dashboard styling. Speck is here: https://drive.google.com/drive/folders/0B1LbmKnex41fU18zSE9WMEVJNFU?usp=sharing | 1.0 | Messaging: Style fixes - Messaging relies heavily on the Dashboard design, as it is a continuation of the user experience.

The messaging is delivered as part of the Dashboard styling. Speck is here: https://drive.google.com/drive/folders/0B1LbmKnex41fU18zSE9WMEVJNFU?usp=sharing | non_priority | messaging style fixes messaging relies heavily on the dashboard design as it is a continuation of the user experience the messaging is delivered as part of the dashboard styling speck is here | 0 |
2,108 | 3,663,135,387 | IssuesEvent | 2016-02-19 03:24:21 | OS0/culturalyst-yeoman | https://api.github.com/repos/OS0/culturalyst-yeoman | opened | Make culturalyst a Private repo before Public Beta | Security | Work with Victor to make Culturlyst a private repo before public beta. | True | Make culturalyst a Private repo before Public Beta - Work with Victor to make Culturlyst a private repo before public beta. | non_priority | make culturalyst a private repo before public beta work with victor to make culturlyst a private repo before public beta | 0 |
168,748 | 20,811,983,411 | IssuesEvent | 2022-03-18 04:34:37 | UpendoVentures/Upendo-DNN-Auth-Provider | https://api.github.com/repos/UpendoVentures/Upendo-DNN-Auth-Provider | closed | WS-2019-0169 (Medium) detected in marked-0.5.2.tgz - autoclosed | security vulnerability | ## WS-2019-0169 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.5.2.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.5.2.tgz">https://registry.npmjs.org/marked/-/marked-0.5.2.tgz</a></p>
<p>Path to dependency file: /Modules/UpendoDnnAuthProvider/package.json</p>
<p>Path to vulnerable library: /Modules/UpendoDnnAuthProvider/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.5.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/UpendoVentures/Upendo-DNN-Auth-Provider/commit/d61d61f3d02bf47a1e7bcbbfa9e50dcdd3a3ab43">d61d61f3d02bf47a1e7bcbbfa9e50dcdd3a3ab43</a></p>
<p>Found in base branch: <b>development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
marked versions >0.3.14 and < 0.6.2 has Regular Expression Denial of Service vulnerability Email addresses may be evaluated in quadratic time, allowing attackers to potentially crash the node process due to resource exhaustion.
<p>Publish Date: 2019-04-03
<p>URL: <a href=https://github.com/markedjs/marked/pull/1460>WS-2019-0169</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/812">https://www.npmjs.com/advisories/812</a></p>
<p>Release Date: 2019-04-03</p>
<p>Fix Resolution: 0.6.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0169 (Medium) detected in marked-0.5.2.tgz - autoclosed - ## WS-2019-0169 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.5.2.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.5.2.tgz">https://registry.npmjs.org/marked/-/marked-0.5.2.tgz</a></p>
<p>Path to dependency file: /Modules/UpendoDnnAuthProvider/package.json</p>
<p>Path to vulnerable library: /Modules/UpendoDnnAuthProvider/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.5.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/UpendoVentures/Upendo-DNN-Auth-Provider/commit/d61d61f3d02bf47a1e7bcbbfa9e50dcdd3a3ab43">d61d61f3d02bf47a1e7bcbbfa9e50dcdd3a3ab43</a></p>
<p>Found in base branch: <b>development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
marked versions >0.3.14 and < 0.6.2 has Regular Expression Denial of Service vulnerability Email addresses may be evaluated in quadratic time, allowing attackers to potentially crash the node process due to resource exhaustion.
<p>Publish Date: 2019-04-03
<p>URL: <a href=https://github.com/markedjs/marked/pull/1460>WS-2019-0169</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/812">https://www.npmjs.com/advisories/812</a></p>
<p>Release Date: 2019-04-03</p>
<p>Fix Resolution: 0.6.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in marked tgz autoclosed ws medium severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file modules upendodnnauthprovider package json path to vulnerable library modules upendodnnauthprovider node modules marked package json dependency hierarchy x marked tgz vulnerable library found in head commit a href found in base branch development vulnerability details marked versions and has regular expression denial of service vulnerability email addresses may be evaluated in quadratic time allowing attackers to potentially crash the node process due to resource exhaustion publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
15,867 | 9,122,213,794 | IssuesEvent | 2019-02-23 05:31:17 | Electron-Cash/Electron-Cash | https://api.github.com/repos/Electron-Cash/Electron-Cash | opened | LabelSync: Needs some performance tuning | Plugins performance / optimization | In particular when using LabelSync with a high frequency of tx's (as happens in CashShuffle) -- it tends to do a lot of redundant network calls for each tx being sent out.
This normally wouldn't be a problem but when using an automated scheme to send tx's (such as CashShuffle) -- the speed at which tx's get generated overwhelms LabelSync.
LabelSync needs to be refactored to batch updates so as to avoid the overhead of a round-trip http-post per TX sent.
Also, I believe when loading/importing wallet labels from disk, LabelSync ends up doing a round-trip HTTP post *per label* updated.
So, in short: **LabelSync needs refactoring to be faster**.
| True | LabelSync: Needs some performance tuning - In particular when using LabelSync with a high frequency of tx's (as happens in CashShuffle) -- it tends to do a lot of redundant network calls for each tx being sent out.
This normally wouldn't be a problem but when using an automated scheme to send tx's (such as CashShuffle) -- the speed at which tx's get generated overwhelms LabelSync.
LabelSync needs to be refactored to batch updates so as to avoid the overhead of a round-trip http-post per TX sent.
Also, I believe when loading/importing wallet labels from disk, LabelSync ends up doing a round-trip HTTP post *per label* updated.
So, in short: **LabelSync needs refactoring to be faster**.
| non_priority | labelsync needs some performance tuning in particular when using labelsync with a high frequency of tx s as happens in cashshuffle it tends to do a lot of redundant network calls for each tx being sent out this normally wouldn t be a problem but when using an automated scheme to send tx s such as cashshuffle the speed at which tx s get generated overwhelms labelsync labelsync needs to be refactored to batch updates so as to avoid the overhead of a round trip http post per tx sent also i believe when loading importing wallet labels from disk labelsync ends up doing a round trip http post per label updated so in short labelsync needs refactoring to be faster | 0 |
118,702 | 15,358,419,145 | IssuesEvent | 2021-03-01 14:47:28 | anrExperts/xpr | https://api.github.com/repos/anrExperts/xpr | closed | Vue synoptique | design enhancement question | @sardinecan Faire mail à l'équipe pour connaitre les informations qu'ils veulent voir s'afficher au fur et à mesure du remplissage du formulaire. | 1.0 | Vue synoptique - @sardinecan Faire mail à l'équipe pour connaitre les informations qu'ils veulent voir s'afficher au fur et à mesure du remplissage du formulaire. | non_priority | vue synoptique sardinecan faire mail à l équipe pour connaitre les informations qu ils veulent voir s afficher au fur et à mesure du remplissage du formulaire | 0 |
80,321 | 10,169,002,586 | IssuesEvent | 2019-08-07 22:34:50 | universelabs/universe-design | https://api.github.com/repos/universelabs/universe-design | closed | Update README.md | documentation | **Description**
Update README.md.
**Tasks**
- [x] Header
- [x] Header image
- [x] Introduction
- [x] Table of contents
- [x] Quick start
- [x] Status
- [x] Getting started
- [x] Meta & Meta UI
- [x] UX Flow
- [x] Contributing
- [x] Roadmap
- [x] Community
- [x] Maintainers
- [x] License
| 1.0 | Update README.md - **Description**
Update README.md.
**Tasks**
- [x] Header
- [x] Header image
- [x] Introduction
- [x] Table of contents
- [x] Quick start
- [x] Status
- [x] Getting started
- [x] Meta & Meta UI
- [x] UX Flow
- [x] Contributing
- [x] Roadmap
- [x] Community
- [x] Maintainers
- [x] License
| non_priority | update readme md description update readme md tasks header header image introduction table of contents quick start status getting started meta meta ui ux flow contributing roadmap community maintainers license | 0 |
117,594 | 17,512,650,211 | IssuesEvent | 2021-08-11 01:01:55 | harrinry/pulsar | https://api.github.com/repos/harrinry/pulsar | opened | CVE-2018-12022 (High) detected in jackson-databind-2.6.5.jar | security vulnerability | ## CVE-2018-12022 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: pulsar/examples/spark/pom.xml</p>
<p>Path to vulnerable library: 0150316_LVRAMP/downloadResource_AEDNMT/20210810150943/jackson-databind-2.6.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.5.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022>CVE-2018-12022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022</a></p>
<p>Release Date: 2019-03-21</p>
<p>Fix Resolution: 2.7.9.4, 2.8.11.2, 2.9.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.5","packageFilePaths":["/examples/spark/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.7.9.4, 2.8.11.2, 2.9.6"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-12022","vulnerabilityDetails":"An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-12022 (High) detected in jackson-databind-2.6.5.jar - ## CVE-2018-12022 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: pulsar/examples/spark/pom.xml</p>
<p>Path to vulnerable library: 0150316_LVRAMP/downloadResource_AEDNMT/20210810150943/jackson-databind-2.6.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.5.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022>CVE-2018-12022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022</a></p>
<p>Release Date: 2019-03-21</p>
<p>Fix Resolution: 2.7.9.4, 2.8.11.2, 2.9.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.5","packageFilePaths":["/examples/spark/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.7.9.4, 2.8.11.2, 2.9.6"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-12022","vulnerabilityDetails":"An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pulsar examples spark pom xml path to vulnerable library lvramp downloadresource aednmt jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in base branch master vulnerability details an issue was discovered in fasterxml jackson databind prior to and when default typing is enabled either globally or for a specific property the service has the jodd db jar for database access for the jodd framework in the classpath and an attacker can provide an ldap service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails an issue was discovered in fasterxml jackson databind prior to and when default typing is enabled either globally or for a specific property the service has the jodd db jar for database access for the jodd framework in the classpath and an attacker can provide an ldap service to access it is possible to make the service execute a malicious payload vulnerabilityurl | 0 |
14,075 | 8,468,469,874 | IssuesEvent | 2018-10-23 19:50:32 | BCcampus/eypd | https://api.github.com/repos/BCcampus/eypd | closed | Critical Path CSS | MEDIUM - 3 PWA Continuing Performance | is the minimum CSS required to render above the fold content.
ref:
-
https://developers.google.com/speed/docs/insights/PrioritizeVisibleContent?hl=
- https://github.com/addyosmani/critical-path-css-tools
- https://addyosmani.com/blog/detecting-critical-above-the-fold-css-with-paul-kinlan-video/?utm_source=wordpress&utm_medium=plugin&utm_term=optimization&utm_campaign=Above%20The%20Fold%20Optimization
| True | Critical Path CSS - is the minimum CSS required to render above the fold content.
ref:
-
https://developers.google.com/speed/docs/insights/PrioritizeVisibleContent?hl=
- https://github.com/addyosmani/critical-path-css-tools
- https://addyosmani.com/blog/detecting-critical-above-the-fold-css-with-paul-kinlan-video/?utm_source=wordpress&utm_medium=plugin&utm_term=optimization&utm_campaign=Above%20The%20Fold%20Optimization
| non_priority | critical path css is the minimum css required to render above the fold content ref | 0 |
32,824 | 12,151,657,742 | IssuesEvent | 2020-04-24 20:25:24 | LevyForchh/cruise-control | https://api.github.com/repos/LevyForchh/cruise-control | opened | CVE-2019-16335 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-16335 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/cruise-control/buildSrc/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- build-info-extractor-gradle-4.9.5.jar (Root Library)
- build-info-extractor-2.13.5.jar
- build-info-client-2.13.5.jar
- build-info-api-2.13.5.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/LevyForchh/cruise-control/commits/130269f9bed666f5f4862855f315e3bba96ac225">130269f9bed666f5f4862855f315e3bba96ac225</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","isTransitiveDependency":true,"dependencyTree":"org.jfrog.buildinfo:build-info-extractor-gradle:4.9.5;org.jfrog.buildinfo:build-info-extractor:2.13.5;org.jfrog.buildinfo:build-info-client:2.13.5;org.jfrog.buildinfo:build-info-api:2.13.5;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.9.10"}],"vulnerabilityIdentifier":"CVE-2019-16335","vulnerabilityDetails":"A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-16335 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-16335 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/cruise-control/buildSrc/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- build-info-extractor-gradle-4.9.5.jar (Root Library)
- build-info-extractor-2.13.5.jar
- build-info-client-2.13.5.jar
- build-info-api-2.13.5.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/LevyForchh/cruise-control/commits/130269f9bed666f5f4862855f315e3bba96ac225">130269f9bed666f5f4862855f315e3bba96ac225</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","isTransitiveDependency":true,"dependencyTree":"org.jfrog.buildinfo:build-info-extractor-gradle:4.9.5;org.jfrog.buildinfo:build-info-extractor:2.13.5;org.jfrog.buildinfo:build-info-client:2.13.5;org.jfrog.buildinfo:build-info-api:2.13.5;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.9.10"}],"vulnerabilityIdentifier":"CVE-2019-16335","vulnerabilityDetails":"A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm cruise control buildsrc build gradle path to vulnerable library root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy build info extractor gradle jar root library build info extractor jar build info client jar build info api jar x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve vulnerabilityurl | 0 |
67,048 | 20,823,512,830 | IssuesEvent | 2022-03-18 17:51:40 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | opened | Tree: Submitting two selection tree´s inside a form leads to losing selection on the second tree and wrong selection on the first tree | defect | **Describe the defect**
I have two selection tree´s inside a ui:repeat in a form. When i submit the form and the tree´s get processed, the selection of the second tree moves to the selection of the first tree and the selection of the second tree is set to null. The id-attribute of the tree is the same as it is inside a ui:repeat, but the client-id´s are different.
**Environment:**
PF Version: any
PF Theme: any
JSF + version: any
Affected browsers: any
**To Reproduce**
Steps to reproduce the behavior:
1. Just create multiple selection tree´s inside an ui:repeat and give an id to the tree inside the ui:repeat. The ui:repeat in turn should be inside a form, as I want to submit the form and process the form with the selection of the tree´s
2. Select an item for the first tree
3. Select an item for the second tree
4. See error
**Expected behavior**
The expected behaviour should be, that every tree has set the right selected node. But as mentioned, the first tree get´s the selection of the second tree und the selected node of the second tree gets null.
**Example XHTML**
```html
<h:form id="testform">
<ui:repeat id="trees" value="#{treeSelectionView.trees}" var="tree">
<p:tree id="MY_TREE" value="#{tree.root}" var="doc"
selectionMode="single"
selection="#{tree.selectedNode}">
<p:treeNode expandedIcon="pi pi-folder-open" collapsedIcon="pi pi-folder">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="app" icon="pi pi-save">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="document" icon="pi pi-file">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="excel" icon="pi pi-file-excel">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="travel" icon="pi pi-file-pdf">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="picture" icon="pi pi-image">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="video" icon="pi pi-video">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
</p:tree>
</ui:repeat>
</h:form>
<p:commandButton id="submitTreesButton" widgetVar="submitTreesButtonVar"
value="Submit"
process="testform"
actionListener="#{treeSelectionView.saveTrees()}"
partialSubmit="true"
/>
```
**Example Bean**
```java
@Named
@ViewScoped
public class TreeSelectionView implements Serializable {
@Inject
private TreeSelectionService treeSelectionService;
private List<DocumentTreeSelectionModel> trees = new ArrayList<>();
@PostConstruct
public void init() {
DocumentTreeSelectionModel tree1 = new DocumentTreeSelectionModel(treeSelectionService.createDocuments());
DocumentTreeSelectionModel tree2 = new DocumentTreeSelectionModel(treeSelectionService.createCheckboxDocuments());
trees.add(tree1);
trees.add(tree2);
}
public List<DocumentTreeSelectionModel> getTrees() {
return trees;
}
public void saveTrees() {
TreeNode selectedTreeNode1 = trees.get(0).getSelectedNode();
TreeNode selectedTreeNode2 = trees.get(1).getSelectedNode();
// NOW HERE IS WRONG DATA INSIDE THE SELECTED TREE NODES FOR EACH TREE
}
}
```
**DocumentTreeSelectionModel which is used in my example bean**
```java
public class DocumentTreeSelectionModel {
private TreeNode selectedNode;
private TreeNode root;
public DocumentTreeSelectionModel(TreeNode root) {
this.root = root;
}
public TreeNode getSelectedNode() {
return selectedNode;
}
public void setSelectedNode(TreeNode selectedNode) {
this.selectedNode = selectedNode;
}
public TreeNode getRoot() {
return root;
}
}
```
Document.java and DocumentService.java are used from https://www.primefaces.org/showcase/ui/data/tree/selection.xhtml?jfwid=c7d3f
| 1.0 | Tree: Submitting two selection tree´s inside a form leads to losing selection on the second tree and wrong selection on the first tree - **Describe the defect**
I have two selection tree´s inside a ui:repeat in a form. When i submit the form and the tree´s get processed, the selection of the second tree moves to the selection of the first tree and the selection of the second tree is set to null. The id-attribute of the tree is the same as it is inside a ui:repeat, but the client-id´s are different.
**Environment:**
PF Version: any
PF Theme: any
JSF + version: any
Affected browsers: any
**To Reproduce**
Steps to reproduce the behavior:
1. Just create multiple selection tree´s inside an ui:repeat and give an id to the tree inside the ui:repeat. The ui:repeat in turn should be inside a form, as I want to submit the form and process the form with the selection of the tree´s
2. Select an item for the first tree
3. Select an item for the second tree
4. See error
**Expected behavior**
The expected behaviour should be, that every tree has set the right selected node. But as mentioned, the first tree get´s the selection of the second tree und the selected node of the second tree gets null.
**Example XHTML**
```html
<h:form id="testform">
<ui:repeat id="trees" value="#{treeSelectionView.trees}" var="tree">
<p:tree id="MY_TREE" value="#{tree.root}" var="doc"
selectionMode="single"
selection="#{tree.selectedNode}">
<p:treeNode expandedIcon="pi pi-folder-open" collapsedIcon="pi pi-folder">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="app" icon="pi pi-save">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="document" icon="pi pi-file">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="excel" icon="pi pi-file-excel">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="travel" icon="pi pi-file-pdf">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="picture" icon="pi pi-image">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
<p:treeNode type="video" icon="pi pi-video">
<h:outputText value="#{doc.name}"/>
</p:treeNode>
</p:tree>
</ui:repeat>
</h:form>
<p:commandButton id="submitTreesButton" widgetVar="submitTreesButtonVar"
value="Submit"
process="testform"
actionListener="#{treeSelectionView.saveTrees()}"
partialSubmit="true"
/>
```
**Example Bean**
```java
@Named
@ViewScoped
public class TreeSelectionView implements Serializable {
@Inject
private TreeSelectionService treeSelectionService;
private List<DocumentTreeSelectionModel> trees = new ArrayList<>();
@PostConstruct
public void init() {
DocumentTreeSelectionModel tree1 = new DocumentTreeSelectionModel(treeSelectionService.createDocuments());
DocumentTreeSelectionModel tree2 = new DocumentTreeSelectionModel(treeSelectionService.createCheckboxDocuments());
trees.add(tree1);
trees.add(tree2);
}
public List<DocumentTreeSelectionModel> getTrees() {
return trees;
}
public void saveTrees() {
TreeNode selectedTreeNode1 = trees.get(0).getSelectedNode();
TreeNode selectedTreeNode2 = trees.get(1).getSelectedNode();
// NOW HERE IS WRONG DATA INSIDE THE SELECTED TREE NODES FOR EACH TREE
}
}
```
**DocumentTreeSelectionModel which is used in my example bean**
```java
public class DocumentTreeSelectionModel {
private TreeNode selectedNode;
private TreeNode root;
public DocumentTreeSelectionModel(TreeNode root) {
this.root = root;
}
public TreeNode getSelectedNode() {
return selectedNode;
}
public void setSelectedNode(TreeNode selectedNode) {
this.selectedNode = selectedNode;
}
public TreeNode getRoot() {
return root;
}
}
```
Document.java and DocumentService.java are used from https://www.primefaces.org/showcase/ui/data/tree/selection.xhtml?jfwid=c7d3f
| non_priority | tree submitting two selection tree´s inside a form leads to losing selection on the second tree and wrong selection on the first tree describe the defect i have two selection tree´s inside a ui repeat in a form when i submit the form and the tree´s get processed the selection of the second tree moves to the selection of the first tree and the selection of the second tree is set to null the id attribute of the tree is the same as it is inside a ui repeat but the client id´s are different environment pf version any pf theme any jsf version any affected browsers any to reproduce steps to reproduce the behavior just create multiple selection tree´s inside an ui repeat and give an id to the tree inside the ui repeat the ui repeat in turn should be inside a form as i want to submit the form and process the form with the selection of the tree´s select an item for the first tree select an item for the second tree see error expected behavior the expected behaviour should be that every tree has set the right selected node but as mentioned the first tree get´s the selection of the second tree und the selected node of the second tree gets null example xhtml html p tree id my tree value tree root var doc selectionmode single selection tree selectednode p commandbutton id submittreesbutton widgetvar submittreesbuttonvar value submit process testform actionlistener treeselectionview savetrees partialsubmit true example bean java named viewscoped public class treeselectionview implements serializable inject private treeselectionservice treeselectionservice private list trees new arraylist postconstruct public void init documenttreeselectionmodel new documenttreeselectionmodel treeselectionservice createdocuments documenttreeselectionmodel new documenttreeselectionmodel treeselectionservice createcheckboxdocuments trees add trees add public list gettrees return trees public void savetrees treenode trees get getselectednode treenode trees get getselectednode now here is wrong data inside the selected tree nodes for each tree documenttreeselectionmodel which is used in my example bean java public class documenttreeselectionmodel private treenode selectednode private treenode root public documenttreeselectionmodel treenode root this root root public treenode getselectednode return selectednode public void setselectednode treenode selectednode this selectednode selectednode public treenode getroot return root document java and documentservice java are used from | 0 |
258,732 | 27,579,399,500 | IssuesEvent | 2023-03-08 15:13:54 | Dima2021/railsgoat | https://api.github.com/repos/Dima2021/railsgoat | opened | moment-1.7.2.min.js: 5 vulnerabilities (highest severity is: 7.5) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-1.7.2.min.js</b></p></summary>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (moment version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-31129](https://www.mend.io/vulnerability-database/CVE-2022-31129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-1.7.2.min.js | Direct | moment - 2.29.4 | ❌ |
| [CVE-2017-18214](https://www.mend.io/vulnerability-database/CVE-2017-18214) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-1.7.2.min.js | Direct | moment - 2.19.3 | ❌ |
| [CVE-2022-24785](https://www.mend.io/vulnerability-database/CVE-2022-24785) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-1.7.2.min.js | Direct | moment - 2.29.2 | ❌ |
| [CVE-2016-4055](https://www.mend.io/vulnerability-database/CVE-2016-4055) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | moment-1.7.2.min.js | Direct | moment - 2.11.2 | ❌ |
| [WS-2016-0075](https://github.com/moment/moment/commit/663f33e333212b3800b63592cd8e237ac8fabdb9) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | moment-1.7.2.min.js | Direct | moment - 2.15.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-31129</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
moment is a JavaScript date library for parsing, validating, manipulating, and formatting dates. Affected versions of moment were found to use an inefficient parsing algorithm. Specifically using string-to-date parsing in moment (more specifically rfc2822 parsing, which is tried by default) has quadratic (N^2) complexity on specific inputs. Users may notice a noticeable slowdown is observed with inputs above 10k characters. Users who pass user-provided strings without sanity length checks to moment constructor are vulnerable to (Re)DoS attacks. The problem is patched in 2.29.4, the patch can be applied to all affected versions with minimal tweaking. Users are advised to upgrade. Users unable to upgrade should consider limiting date lengths accepted from user input.
<p>Publish Date: 2022-07-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31129>CVE-2022-31129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g">https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g</a></p>
<p>Release Date: 2022-07-06</p>
<p>Fix Resolution: moment - 2.29.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18214</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The moment module before 2.19.3 for Node.js is prone to a regular expression denial of service via a crafted date string, a different vulnerability than CVE-2016-4055.
<p>Publish Date: 2018-03-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-18214>CVE-2017-18214</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-446m-mv8f-q348">https://github.com/advisories/GHSA-446m-mv8f-q348</a></p>
<p>Release Date: 2018-03-04</p>
<p>Fix Resolution: moment - 2.19.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24785</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Moment.js is a JavaScript date library for parsing, validating, manipulating, and formatting dates. A path traversal vulnerability impacts npm (server) users of Moment.js between versions 1.0.1 and 2.29.1, especially if a user-provided locale string is directly used to switch moment locale. This problem is patched in 2.29.2, and the patch can be applied to all affected versions. As a workaround, sanitize the user-provided locale name before passing it to Moment.js.
<p>Publish Date: 2022-04-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24785>CVE-2022-24785</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4">https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4</a></p>
<p>Release Date: 2022-04-04</p>
<p>Fix Resolution: moment - 2.29.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-4055</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The duration function in the moment package before 2.11.2 for Node.js allows remote attackers to cause a denial of service (CPU consumption) via a long string, aka a "regular expression Denial of Service (ReDoS)."
<p>Publish Date: 2017-01-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4055>CVE-2016-4055</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-87vv-r9j6-g5qv">https://github.com/advisories/GHSA-87vv-r9j6-g5qv</a></p>
<p>Release Date: 2017-01-23</p>
<p>Fix Resolution: moment - 2.11.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2016-0075</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular expression denial of service vulnerability in the moment package, by using a specific 40 characters long string in the "format" method.
<p>Publish Date: 2016-10-24
<p>URL: <a href=https://github.com/moment/moment/commit/663f33e333212b3800b63592cd8e237ac8fabdb9>WS-2016-0075</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-10-24</p>
<p>Fix Resolution: moment - 2.15.2</p>
</p>
<p></p>
</details> | True | moment-1.7.2.min.js: 5 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-1.7.2.min.js</b></p></summary>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (moment version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-31129](https://www.mend.io/vulnerability-database/CVE-2022-31129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-1.7.2.min.js | Direct | moment - 2.29.4 | ❌ |
| [CVE-2017-18214](https://www.mend.io/vulnerability-database/CVE-2017-18214) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-1.7.2.min.js | Direct | moment - 2.19.3 | ❌ |
| [CVE-2022-24785](https://www.mend.io/vulnerability-database/CVE-2022-24785) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | moment-1.7.2.min.js | Direct | moment - 2.29.2 | ❌ |
| [CVE-2016-4055](https://www.mend.io/vulnerability-database/CVE-2016-4055) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | moment-1.7.2.min.js | Direct | moment - 2.11.2 | ❌ |
| [WS-2016-0075](https://github.com/moment/moment/commit/663f33e333212b3800b63592cd8e237ac8fabdb9) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | moment-1.7.2.min.js | Direct | moment - 2.15.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-31129</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
moment is a JavaScript date library for parsing, validating, manipulating, and formatting dates. Affected versions of moment were found to use an inefficient parsing algorithm. Specifically using string-to-date parsing in moment (more specifically rfc2822 parsing, which is tried by default) has quadratic (N^2) complexity on specific inputs. Users may notice a noticeable slowdown is observed with inputs above 10k characters. Users who pass user-provided strings without sanity length checks to moment constructor are vulnerable to (Re)DoS attacks. The problem is patched in 2.29.4, the patch can be applied to all affected versions with minimal tweaking. Users are advised to upgrade. Users unable to upgrade should consider limiting date lengths accepted from user input.
<p>Publish Date: 2022-07-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31129>CVE-2022-31129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g">https://github.com/moment/moment/security/advisories/GHSA-wc69-rhjr-hc9g</a></p>
<p>Release Date: 2022-07-06</p>
<p>Fix Resolution: moment - 2.29.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-18214</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The moment module before 2.19.3 for Node.js is prone to a regular expression denial of service via a crafted date string, a different vulnerability than CVE-2016-4055.
<p>Publish Date: 2018-03-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-18214>CVE-2017-18214</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-446m-mv8f-q348">https://github.com/advisories/GHSA-446m-mv8f-q348</a></p>
<p>Release Date: 2018-03-04</p>
<p>Fix Resolution: moment - 2.19.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24785</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Moment.js is a JavaScript date library for parsing, validating, manipulating, and formatting dates. A path traversal vulnerability impacts npm (server) users of Moment.js between versions 1.0.1 and 2.29.1, especially if a user-provided locale string is directly used to switch moment locale. This problem is patched in 2.29.2, and the patch can be applied to all affected versions. As a workaround, sanitize the user-provided locale name before passing it to Moment.js.
<p>Publish Date: 2022-04-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24785>CVE-2022-24785</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4">https://github.com/moment/moment/security/advisories/GHSA-8hfj-j24r-96c4</a></p>
<p>Release Date: 2022-04-04</p>
<p>Fix Resolution: moment - 2.29.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-4055</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The duration function in the moment package before 2.11.2 for Node.js allows remote attackers to cause a denial of service (CPU consumption) via a long string, aka a "regular expression Denial of Service (ReDoS)."
<p>Publish Date: 2017-01-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4055>CVE-2016-4055</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-87vv-r9j6-g5qv">https://github.com/advisories/GHSA-87vv-r9j6-g5qv</a></p>
<p>Release Date: 2017-01-23</p>
<p>Fix Resolution: moment - 2.11.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2016-0075</summary>
### Vulnerable Library - <b>moment-1.7.2.min.js</b></p>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js">https://cdnjs.cloudflare.com/ajax/libs/moment.js/1.7.2/moment.min.js</a></p>
<p>Path to vulnerable library: /app/assets/javascripts/moment.js</p>
<p>
Dependency Hierarchy:
- :x: **moment-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular expression denial of service vulnerability in the moment package, by using a specific 40 characters long string in the "format" method.
<p>Publish Date: 2016-10-24
<p>URL: <a href=https://github.com/moment/moment/commit/663f33e333212b3800b63592cd8e237ac8fabdb9>WS-2016-0075</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-10-24</p>
<p>Fix Resolution: moment - 2.15.2</p>
</p>
<p></p>
</details> | non_priority | moment min js vulnerabilities highest severity is vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library app assets javascripts moment js vulnerabilities cve severity cvss dependency type fixed in moment version remediation available high moment min js direct moment high moment min js direct moment high moment min js direct moment medium moment min js direct moment medium moment min js direct moment details cve vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library app assets javascripts moment js dependency hierarchy x moment min js vulnerable library found in base branch master vulnerability details moment is a javascript date library for parsing validating manipulating and formatting dates affected versions of moment were found to use an inefficient parsing algorithm specifically using string to date parsing in moment more specifically parsing which is tried by default has quadratic n complexity on specific inputs users may notice a noticeable slowdown is observed with inputs above characters users who pass user provided strings without sanity length checks to moment constructor are vulnerable to re dos attacks the problem is patched in the patch can be applied to all affected versions with minimal tweaking users are advised to upgrade users unable to upgrade should consider limiting date lengths accepted from user input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution moment cve vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library app assets javascripts moment js dependency hierarchy x moment min js vulnerable library found in base branch master vulnerability details the moment module before for node js is prone to a regular expression denial of service via a crafted date string a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution moment cve vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library app assets javascripts moment js dependency hierarchy x moment min js vulnerable library found in base branch master vulnerability details moment js is a javascript date library for parsing validating manipulating and formatting dates a path traversal vulnerability impacts npm server users of moment js between versions and especially if a user provided locale string is directly used to switch moment locale this problem is patched in and the patch can be applied to all affected versions as a workaround sanitize the user provided locale name before passing it to moment js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution moment cve vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library app assets javascripts moment js dependency hierarchy x moment min js vulnerable library found in base branch master vulnerability details the duration function in the moment package before for node js allows remote attackers to cause a denial of service cpu consumption via a long string aka a regular expression denial of service redos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution moment ws vulnerable library moment min js parse validate manipulate and display dates library home page a href path to vulnerable library app assets javascripts moment js dependency hierarchy x moment min js vulnerable library found in base branch master vulnerability details regular expression denial of service vulnerability in the moment package by using a specific characters long string in the format method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution moment | 0 |
215,970 | 16,622,558,333 | IssuesEvent | 2021-06-03 04:44:19 | GSA/fedramp-automation | https://api.github.com/repos/GSA/fedramp-automation | opened | Initiate Architectural Decision Records | documentation | # Action Item
Establish the use of [Architectural Decision Records](https://adr.github.io/).
**This is a ...**
- **fix** - Something needs to be different.
- ✔️ **enhancement** - Something could be better.
- **investigation** - Something needs to be investigated further.
**This relates to ...**
- ✔️ **Other**
NOTE: For issues related to the OSCAL syntax itself, please create or add to an [issue in the NIST OSCAL Repository](https://github.com/usnistgov/OSCAL/issues).
## Describe the problem or enhancement
Lack of clarity around key around technical design decisions and how they impact how others will use this work.
## Goals:
Document important decisions around projects in this repository, especially to communicate technical design assumptions to downstream customers of code and artifacts here.
## Dependencies
## Acceptance Criteria
- [ ] All [FedRAMP Documents Related to OSCAL Adoption](https://github.com/GSA/fedramp-automation) affected by the changes in this issue have been updated.
- [ ] A Pull Request (PR) is submitted that fully addresses the goals of this User Story. This issue is referenced in the PR.
## Other Comments
| 1.0 | Initiate Architectural Decision Records - # Action Item
Establish the use of [Architectural Decision Records](https://adr.github.io/).
**This is a ...**
- **fix** - Something needs to be different.
- ✔️ **enhancement** - Something could be better.
- **investigation** - Something needs to be investigated further.
**This relates to ...**
- ✔️ **Other**
NOTE: For issues related to the OSCAL syntax itself, please create or add to an [issue in the NIST OSCAL Repository](https://github.com/usnistgov/OSCAL/issues).
## Describe the problem or enhancement
Lack of clarity around key around technical design decisions and how they impact how others will use this work.
## Goals:
Document important decisions around projects in this repository, especially to communicate technical design assumptions to downstream customers of code and artifacts here.
## Dependencies
## Acceptance Criteria
- [ ] All [FedRAMP Documents Related to OSCAL Adoption](https://github.com/GSA/fedramp-automation) affected by the changes in this issue have been updated.
- [ ] A Pull Request (PR) is submitted that fully addresses the goals of this User Story. This issue is referenced in the PR.
## Other Comments
| non_priority | initiate architectural decision records action item establish the use of this is a fix something needs to be different ✔️ enhancement something could be better investigation something needs to be investigated further this relates to ✔️ other note for issues related to the oscal syntax itself please create or add to an describe the problem or enhancement lack of clarity around key around technical design decisions and how they impact how others will use this work goals document important decisions around projects in this repository especially to communicate technical design assumptions to downstream customers of code and artifacts here dependencies acceptance criteria all affected by the changes in this issue have been updated a pull request pr is submitted that fully addresses the goals of this user story this issue is referenced in the pr other comments | 0 |
31,984 | 4,310,082,174 | IssuesEvent | 2016-07-21 18:03:13 | department-of-veterans-affairs/vets-website | https://api.github.com/repos/department-of-veterans-affairs/vets-website | closed | Footer on VEC page not displaying VCL correctly | bug design | @gnakm
I think you are already aware of different footers on products; pls. review the VEC footer https://www.vets.gov/employment/veterans/235834 as the VCL updates we just made have not been updated here (veterans can't call, text, or chat from homepage). Footer is different--with feedback on the right side, not left.
 | 1.0 | Footer on VEC page not displaying VCL correctly - @gnakm
I think you are already aware of different footers on products; pls. review the VEC footer https://www.vets.gov/employment/veterans/235834 as the VCL updates we just made have not been updated here (veterans can't call, text, or chat from homepage). Footer is different--with feedback on the right side, not left.
 | non_priority | footer on vec page not displaying vcl correctly gnakm i think you are already aware of different footers on products pls review the vec footer as the vcl updates we just made have not been updated here veterans can t call text or chat from homepage footer is different with feedback on the right side not left | 0 |
359,275 | 25,229,631,368 | IssuesEvent | 2022-11-14 18:40:16 | learnwithalfred/recipe-app | https://api.github.com/repos/learnwithalfred/recipe-app | closed | [4pt] Project setup | documentation | Create a new Ruby on Rails Application, setup database, CSS styles and home page
| 1.0 | [4pt] Project setup - Create a new Ruby on Rails Application, setup database, CSS styles and home page
| non_priority | project setup create a new ruby on rails application setup database css styles and home page | 0 |
64,872 | 12,501,112,100 | IssuesEvent | 2020-06-02 00:15:15 | unoplatform/uno | https://api.github.com/repos/unoplatform/uno | closed | Uno.UWPSyncGenerator does not work without Visual Studio 2017 | area/code-generation area/vswin kind/bug kind/contributor-experience | ## Current behavior
`Uno.UWPSyncGenerator` crashes if Visual Studio 2017 is not installed on the developer PC.
## Expected behavior
`Uno.UWPSyncGenerator` should run successfully.
## How to reproduce it (as minimally and precisely as possible)
0. Clean Windows 10, install Visual Studio 2019 with all required workloads 😊
1. Clone `Uno.UI`
2. Open `Uno.UI.sln`
3. Run `Uno.UWPSyncGenerator` for debugging
4. Observe the application crashes in `Generator.cs` on line 1415:
Exception detail:
> System.Reflection.ReflectionTypeLoadException: 'Unable to load one or more of the requested types. Retrieve the LoaderExceptions property for more information.'
Stack trace:
> at System.Reflection.RuntimeModule.GetTypes(RuntimeModule module)
at System.Reflection.RuntimeAssembly.get_DefinedTypes()
at System.Composition.Hosting.ContainerConfiguration.<>c.<WithAssemblies>b__16_0(Assembly a)
at System.Linq.Enumerable.<SelectManyIterator>d__17`2.MoveNext()
at System.Composition.TypedParts.TypedPartExportDescriptorProvider..ctor(IEnumerable`1 types, AttributedModelProvider attributeContext)
at System.Composition.Hosting.ContainerConfiguration.CreateContainer()
at Microsoft.CodeAnalysis.Host.Mef.MefHostServices.Create(IEnumerable`1 assemblies)
at Microsoft.CodeAnalysis.Host.Mef.MSBuildMefHostServices.get_DefaultServices()
at Microsoft.CodeAnalysis.MSBuild.MSBuildWorkspace.Create(IDictionary`2 properties)
at Uno.UWPSyncGenerator.Generator.LoadProject(String projectFile, String targetFramework)
at Uno.UWPSyncGenerator.Generator.Build(String basePath, String baseName, String sourceAssembly)
at Uno.UWPSyncGenerator.Program.Main(String[] args)
App output:
```
*** WARNING: Close all editor files in visual studio, otherwise VS will freeze for a few minutes ****
Press enter to continue...
Generating for Uno.Foundation Windows.Foundation.FoundationContract
Loading for : Uno.UWPSyncGenerator.Reference.csproj
Searching for [Microsoft.CodeAnalysis.Features, Version=2.9.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.CodeAnalysis.CSharp.Features, Version=2.9.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.CodeAnalysis.VisualBasic.Features, Version=2.9.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build.Framework, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
```
## Environment
<!-- For bug reports Check one or more of the following options with "x" -->
Nuget Package:
Package Version(s):
Affected platform(s):
- [ ] iOS
- [ ] Android
- [ ] WebAssembly
- [ ] Windows
- [ ] Build tasks
Visual Studio
- [ ] 2017 (version: )
- [x] 2019 (version: any, tested on 16.1.6)
- [ ] for Mac (version: )
Relevant plugins
- [ ] Resharper (version: )
## Anything else we need to know?
<!-- We would love to know of any friction, apart from knowledge, that prevented you from sending in a pull-request -->
| 1.0 | Uno.UWPSyncGenerator does not work without Visual Studio 2017 - ## Current behavior
`Uno.UWPSyncGenerator` crashes if Visual Studio 2017 is not installed on the developer PC.
## Expected behavior
`Uno.UWPSyncGenerator` should run successfully.
## How to reproduce it (as minimally and precisely as possible)
0. Clean Windows 10, install Visual Studio 2019 with all required workloads 😊
1. Clone `Uno.UI`
2. Open `Uno.UI.sln`
3. Run `Uno.UWPSyncGenerator` for debugging
4. Observe the application crashes in `Generator.cs` on line 1415:
Exception detail:
> System.Reflection.ReflectionTypeLoadException: 'Unable to load one or more of the requested types. Retrieve the LoaderExceptions property for more information.'
Stack trace:
> at System.Reflection.RuntimeModule.GetTypes(RuntimeModule module)
at System.Reflection.RuntimeAssembly.get_DefinedTypes()
at System.Composition.Hosting.ContainerConfiguration.<>c.<WithAssemblies>b__16_0(Assembly a)
at System.Linq.Enumerable.<SelectManyIterator>d__17`2.MoveNext()
at System.Composition.TypedParts.TypedPartExportDescriptorProvider..ctor(IEnumerable`1 types, AttributedModelProvider attributeContext)
at System.Composition.Hosting.ContainerConfiguration.CreateContainer()
at Microsoft.CodeAnalysis.Host.Mef.MefHostServices.Create(IEnumerable`1 assemblies)
at Microsoft.CodeAnalysis.Host.Mef.MSBuildMefHostServices.get_DefaultServices()
at Microsoft.CodeAnalysis.MSBuild.MSBuildWorkspace.Create(IDictionary`2 properties)
at Uno.UWPSyncGenerator.Generator.LoadProject(String projectFile, String targetFramework)
at Uno.UWPSyncGenerator.Generator.Build(String basePath, String baseName, String sourceAssembly)
at Uno.UWPSyncGenerator.Program.Main(String[] args)
App output:
```
*** WARNING: Close all editor files in visual studio, otherwise VS will freeze for a few minutes ****
Press enter to continue...
Generating for Uno.Foundation Windows.Foundation.FoundationContract
Loading for : Uno.UWPSyncGenerator.Reference.csproj
Searching for [Microsoft.CodeAnalysis.Features, Version=2.9.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.CodeAnalysis.CSharp.Features, Version=2.9.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.CodeAnalysis.VisualBasic.Features, Version=2.9.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build.Framework, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
Searching for [Microsoft.Build, Version=15.1.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a] from [C:\Dev\Uno\src\Uno.UWPSyncGenerator\bin\Debug\net461]
```
## Environment
<!-- For bug reports Check one or more of the following options with "x" -->
Nuget Package:
Package Version(s):
Affected platform(s):
- [ ] iOS
- [ ] Android
- [ ] WebAssembly
- [ ] Windows
- [ ] Build tasks
Visual Studio
- [ ] 2017 (version: )
- [x] 2019 (version: any, tested on 16.1.6)
- [ ] for Mac (version: )
Relevant plugins
- [ ] Resharper (version: )
## Anything else we need to know?
<!-- We would love to know of any friction, apart from knowledge, that prevented you from sending in a pull-request -->
| non_priority | uno uwpsyncgenerator does not work without visual studio current behavior uno uwpsyncgenerator crashes if visual studio is not installed on the developer pc expected behavior uno uwpsyncgenerator should run successfully how to reproduce it as minimally and precisely as possible clean windows install visual studio with all required workloads 😊 clone uno ui open uno ui sln run uno uwpsyncgenerator for debugging observe the application crashes in generator cs on line exception detail system reflection reflectiontypeloadexception unable to load one or more of the requested types retrieve the loaderexceptions property for more information stack trace at system reflection runtimemodule gettypes runtimemodule module at system reflection runtimeassembly get definedtypes at system composition hosting containerconfiguration c b assembly a at system linq enumerable d movenext at system composition typedparts typedpartexportdescriptorprovider ctor ienumerable types attributedmodelprovider attributecontext at system composition hosting containerconfiguration createcontainer at microsoft codeanalysis host mef mefhostservices create ienumerable assemblies at microsoft codeanalysis host mef msbuildmefhostservices get defaultservices at microsoft codeanalysis msbuild msbuildworkspace create idictionary properties at uno uwpsyncgenerator generator loadproject string projectfile string targetframework at uno uwpsyncgenerator generator build string basepath string basename string sourceassembly at uno uwpsyncgenerator program main string args app output warning close all editor files in visual studio otherwise vs will freeze for a few minutes press enter to continue generating for uno foundation windows foundation foundationcontract loading for uno uwpsyncgenerator reference csproj searching for from searching for from searching for from searching for from searching for from searching for from searching for from searching for from searching for from searching for from environment nuget package package version s affected platform s ios android webassembly windows build tasks visual studio version version any tested on for mac version relevant plugins resharper version anything else we need to know | 0 |
302,518 | 26,149,341,590 | IssuesEvent | 2022-12-30 11:02:14 | status-im/status-mobile | https://api.github.com/repos/status-im/status-mobile | opened | Bottom sheet is not closed on tapping "Back" | bug e2e test blocker | # Bug Report
## Problem
Currently opened bottom sheet cannot be closed by tapping on "Back" button, it keeps floating in the foreground.
It may lead to issues and stops e2e from navigation.
https://user-images.githubusercontent.com/4557972/210063289-47d16aed-2d30-45ad-a645-8de488348d43.mp4
#### Expected behavior
The bottom sheet is closed
#### Actual behavior
Chat view was navigated to another screen behind the bottom sheet
### Reproduction
1) Start 1-1 chat
2) Send any message
3) Pin the message and tap on the pinned messages
4) Click the system back button
### Additional Information
- Status version: nightly 30/12/22
- Operating System: Android
[comment]: # (Please, add logs/notes if necessary)
| 1.0 | Bottom sheet is not closed on tapping "Back" - # Bug Report
## Problem
Currently opened bottom sheet cannot be closed by tapping on "Back" button, it keeps floating in the foreground.
It may lead to issues and stops e2e from navigation.
https://user-images.githubusercontent.com/4557972/210063289-47d16aed-2d30-45ad-a645-8de488348d43.mp4
#### Expected behavior
The bottom sheet is closed
#### Actual behavior
Chat view was navigated to another screen behind the bottom sheet
### Reproduction
1) Start 1-1 chat
2) Send any message
3) Pin the message and tap on the pinned messages
4) Click the system back button
### Additional Information
- Status version: nightly 30/12/22
- Operating System: Android
[comment]: # (Please, add logs/notes if necessary)
| non_priority | bottom sheet is not closed on tapping back bug report problem currently opened bottom sheet cannot be closed by tapping on back button it keeps floating in the foreground it may lead to issues and stops from navigation expected behavior the bottom sheet is closed actual behavior chat view was navigated to another screen behind the bottom sheet reproduction start chat send any message pin the message and tap on the pinned messages click the system back button additional information status version nightly operating system android please add logs notes if necessary | 0 |
122,401 | 16,110,877,238 | IssuesEvent | 2021-04-27 21:00:42 | PREreview/prereview | https://api.github.com/repos/PREreview/prereview | closed | Design: Wireframe of a new page that would allow users to explore people, communities and events | UX & Design | We want to introduce ways for users to find other people, events and communities on the platform.
**Potential approaches:**
- Individual directory pages for people, communities, and events.
- A directory/search page for information other than preprints, e.g. people, communities, and events).
**Use cases:**
- An editor is looking for reviewers for certain topics or certain types of knowledge. They should be able to search by people who are open to being contacted to do reviews and have offered their expertise in certain areas.
- A user wants to find out about upcoming opportunities and events (e.g. a sprint or a journal club). They should be able to see what is upcoming and find out about how to get involved.
- A user is exploring what communities exist and would like to join them.
- A user is looking for other users who are offering to be mentors. | 1.0 | Design: Wireframe of a new page that would allow users to explore people, communities and events - We want to introduce ways for users to find other people, events and communities on the platform.
**Potential approaches:**
- Individual directory pages for people, communities, and events.
- A directory/search page for information other than preprints, e.g. people, communities, and events).
**Use cases:**
- An editor is looking for reviewers for certain topics or certain types of knowledge. They should be able to search by people who are open to being contacted to do reviews and have offered their expertise in certain areas.
- A user wants to find out about upcoming opportunities and events (e.g. a sprint or a journal club). They should be able to see what is upcoming and find out about how to get involved.
- A user is exploring what communities exist and would like to join them.
- A user is looking for other users who are offering to be mentors. | non_priority | design wireframe of a new page that would allow users to explore people communities and events we want to introduce ways for users to find other people events and communities on the platform potential approaches individual directory pages for people communities and events a directory search page for information other than preprints e g people communities and events use cases an editor is looking for reviewers for certain topics or certain types of knowledge they should be able to search by people who are open to being contacted to do reviews and have offered their expertise in certain areas a user wants to find out about upcoming opportunities and events e g a sprint or a journal club they should be able to see what is upcoming and find out about how to get involved a user is exploring what communities exist and would like to join them a user is looking for other users who are offering to be mentors | 0 |
112,778 | 14,288,295,985 | IssuesEvent | 2020-11-23 17:29:28 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [Ingest] Agent configuration - YAML view, toggle disabled fields | Team:Ingest Management design | Following the decision made in https://github.com/elastic/observability-dev/issues/717, we will now exclude disabled datasources, inputs, and streams from being sent to agent. Disabled meaning that those blocks have the property `enabled: false`. This means that these blocks will not show up in the agent config UI YAML view.
An use case was surfaced where it may be useful to the user to _include_ the disabled blocks in their YAML:
> However from a UX perspective, I can think of one compelling reason to send disabled blocks: user can quickly toggle disabled/enabled when editing the YAML config on agent directly. I think this could happen in agent standalone mode where they use the UI to generate an initial config. Then it could be nice to disable/enable blocks on the fly instead of having to use the UI again just to do that. Maybe this could be solved by having a "Include disabled fields" toggle on the UI YAML views?
Let's use this issue to explore the need for a design around this use case. | 1.0 | [Ingest] Agent configuration - YAML view, toggle disabled fields - Following the decision made in https://github.com/elastic/observability-dev/issues/717, we will now exclude disabled datasources, inputs, and streams from being sent to agent. Disabled meaning that those blocks have the property `enabled: false`. This means that these blocks will not show up in the agent config UI YAML view.
An use case was surfaced where it may be useful to the user to _include_ the disabled blocks in their YAML:
> However from a UX perspective, I can think of one compelling reason to send disabled blocks: user can quickly toggle disabled/enabled when editing the YAML config on agent directly. I think this could happen in agent standalone mode where they use the UI to generate an initial config. Then it could be nice to disable/enable blocks on the fly instead of having to use the UI again just to do that. Maybe this could be solved by having a "Include disabled fields" toggle on the UI YAML views?
Let's use this issue to explore the need for a design around this use case. | non_priority | agent configuration yaml view toggle disabled fields following the decision made in we will now exclude disabled datasources inputs and streams from being sent to agent disabled meaning that those blocks have the property enabled false this means that these blocks will not show up in the agent config ui yaml view an use case was surfaced where it may be useful to the user to include the disabled blocks in their yaml however from a ux perspective i can think of one compelling reason to send disabled blocks user can quickly toggle disabled enabled when editing the yaml config on agent directly i think this could happen in agent standalone mode where they use the ui to generate an initial config then it could be nice to disable enable blocks on the fly instead of having to use the ui again just to do that maybe this could be solved by having a include disabled fields toggle on the ui yaml views let s use this issue to explore the need for a design around this use case | 0 |
8,831 | 11,941,095,537 | IssuesEvent | 2020-04-02 17:50:08 | MicrosoftDocs/vsts-docs | https://api.github.com/repos/MicrosoftDocs/vsts-docs | closed | What about custom groups? | Pri1 devops-cicd-process/tech devops/prod | "If you create an environment within a YAML, contributors and project administrators will be granted Administrator role. This is typically used in provisioning Dev/Test environments."
=> We have custom groups in our projects - When env is created automatically, these groups are added as readers. It would be nice if we have a possibility to change the standard behaviour of the automatic creation - so that it is possible to set own standard permissions (like template or sth.)
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 77d95db6-9983-7346-d0eb-4b7443e4e252
* Version Independent ID: 0a22cccc-318d-592f-d1ab-09ec01d88087
* Content: [Environment - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/environments?view=azure-devops#feedback)
* Content Source: [docs/pipelines/process/environments.md](https://github.com/MicrosoftDocs/vsts-docs/blob/master/docs/pipelines/process/environments.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam** | 1.0 | What about custom groups? - "If you create an environment within a YAML, contributors and project administrators will be granted Administrator role. This is typically used in provisioning Dev/Test environments."
=> We have custom groups in our projects - When env is created automatically, these groups are added as readers. It would be nice if we have a possibility to change the standard behaviour of the automatic creation - so that it is possible to set own standard permissions (like template or sth.)
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 77d95db6-9983-7346-d0eb-4b7443e4e252
* Version Independent ID: 0a22cccc-318d-592f-d1ab-09ec01d88087
* Content: [Environment - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/environments?view=azure-devops#feedback)
* Content Source: [docs/pipelines/process/environments.md](https://github.com/MicrosoftDocs/vsts-docs/blob/master/docs/pipelines/process/environments.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam** | non_priority | what about custom groups if you create an environment within a yaml contributors and project administrators will be granted administrator role this is typically used in provisioning dev test environments gt we have custom groups in our projects when env is created automatically these groups are added as readers it would be nice if we have a possibility to change the standard behaviour of the automatic creation so that it is possible to set own standard permissions like template or sth document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops cicd process github login juliakm microsoft alias jukullam | 0 |
27,201 | 21,417,128,699 | IssuesEvent | 2022-04-22 12:04:24 | XmacsLabs/mogan | https://api.github.com/repos/XmacsLabs/mogan | closed | CMake: the os should be macOS on macOS | Infrastructure | See #153
And here is part of the error messages:
```
System information:
TeXmacs version : 2.1.1
Built by : xmacs
Building date : 2022-04-10T03:46:45
Operating system : linux-gnu
Vendor : pc
Processor : x86_64
Crash date : 2022年 4月10日 星期日 20时45分35秒 CST
``` | 1.0 | CMake: the os should be macOS on macOS - See #153
And here is part of the error messages:
```
System information:
TeXmacs version : 2.1.1
Built by : xmacs
Building date : 2022-04-10T03:46:45
Operating system : linux-gnu
Vendor : pc
Processor : x86_64
Crash date : 2022年 4月10日 星期日 20时45分35秒 CST
``` | non_priority | cmake the os should be macos on macos see and here is part of the error messages system information texmacs version built by xmacs building date operating system linux gnu vendor pc processor crash date 星期日 cst | 0 |
51,224 | 12,691,373,217 | IssuesEvent | 2020-06-21 16:41:44 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | BT_DEBUG is not defined in debug builds | enhancement topic:buildsystem topic:thirdparty | Godot 3.1 ab843b16984d8b62a1100d9b77d8b0dcdc4252bb
I found out that in debug builds of Godot, Bullet may be asserting with `btAssert`, except it expands to no-op, because `BT_DEBUG` is not defined.
It seems only iOS builds (so far) keep the asserts defined regardless (due to how Bullet was written rather than the SCons script).
The result is, for example, someone testing on iOS found crashes that may be happening silently in general with heightmap terrains, where parameters are sent as garbage because `set_shape_data` was not called yet. There was garbage because *like every other shape*, the heightmap one doesn't initialize any of its members in its constructor... (see https://github.com/godotengine/godot/issues/25304)
Is there a reason why BT_DEBUG was not defined? | 1.0 | BT_DEBUG is not defined in debug builds - Godot 3.1 ab843b16984d8b62a1100d9b77d8b0dcdc4252bb
I found out that in debug builds of Godot, Bullet may be asserting with `btAssert`, except it expands to no-op, because `BT_DEBUG` is not defined.
It seems only iOS builds (so far) keep the asserts defined regardless (due to how Bullet was written rather than the SCons script).
The result is, for example, someone testing on iOS found crashes that may be happening silently in general with heightmap terrains, where parameters are sent as garbage because `set_shape_data` was not called yet. There was garbage because *like every other shape*, the heightmap one doesn't initialize any of its members in its constructor... (see https://github.com/godotengine/godot/issues/25304)
Is there a reason why BT_DEBUG was not defined? | non_priority | bt debug is not defined in debug builds godot i found out that in debug builds of godot bullet may be asserting with btassert except it expands to no op because bt debug is not defined it seems only ios builds so far keep the asserts defined regardless due to how bullet was written rather than the scons script the result is for example someone testing on ios found crashes that may be happening silently in general with heightmap terrains where parameters are sent as garbage because set shape data was not called yet there was garbage because like every other shape the heightmap one doesn t initialize any of its members in its constructor see is there a reason why bt debug was not defined | 0 |
72,100 | 19,009,628,427 | IssuesEvent | 2021-11-23 07:37:23 | MovingBlocks/Terasology | https://api.github.com/repos/MovingBlocks/Terasology | opened | Build: Pipeline don't run `test` task of Subsystems | Type: Bug Category: Build/CI Status: Needs Discussion | ### What you were trying to do
I am try to extract subsystems.
I created PR #4930 for this.
### What actually happened
I receive `Requested Changes` because our CI don't runs `test` task for subsystem
Our CI don't run Subsystems's test task.
### How to reproduce
1. Run CI build(PR)
2. Try to find tests which placed in subsystems.
### Additional Infos / Context
Our pipeline ignores test task.
test-related tasks(in run order):
gradle unitTest
gradle check -x test (-x test - excludes test task)
gradle integrationTest
| 1.0 | Build: Pipeline don't run `test` task of Subsystems - ### What you were trying to do
I am try to extract subsystems.
I created PR #4930 for this.
### What actually happened
I receive `Requested Changes` because our CI don't runs `test` task for subsystem
Our CI don't run Subsystems's test task.
### How to reproduce
1. Run CI build(PR)
2. Try to find tests which placed in subsystems.
### Additional Infos / Context
Our pipeline ignores test task.
test-related tasks(in run order):
gradle unitTest
gradle check -x test (-x test - excludes test task)
gradle integrationTest
| non_priority | build pipeline don t run test task of subsystems what you were trying to do i am try to extract subsystems i created pr for this what actually happened i receive requested changes because our ci don t runs test task for subsystem our ci don t run subsystems s test task how to reproduce run ci build pr try to find tests which placed in subsystems additional infos context our pipeline ignores test task test related tasks in run order gradle unittest gradle check x test x test excludes test task gradle integrationtest | 0 |
86,745 | 24,940,936,352 | IssuesEvent | 2022-10-31 18:53:00 | dotnet/arcade | https://api.github.com/repos/dotnet/arcade | closed | Build failed: arcade-services-internal-ci/main #20221031.1 | Build Failed | Build [#20221031.1](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=2033188) partiallySucceeded
## :warning: : internal / arcade-services-internal-ci partiallySucceeded
### Summary
**Finished** - Mon, 31 Oct 2022 18:52:03 GMT
**Duration** - 238 minutes
**Requested for** - DotNet Bot
**Reason** - batchedCI
### Details
#### Deploy
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/193) - Error: Failed to update deployment history. Error: Conflict (CODE: 409)
#### Build
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/29) - Component Governance detected 2 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/29) - Component Governance detected 2 security alert(s) at or above 'High' severity that need to be resolved. On their Due date these alerts will break the build.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/29) - The Component Detection tool partially succeeded. See the logs for more information.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/52) - Could not parse Jtokens from file D:\a\_work\1\s\src\Maestro\maestro-angular\node_modules\resolve\test\resolver\malformed_package_json\package.json.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/61) - Component Governance detected 2 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/61) - Component Governance detected 2 security alert(s) at or above 'High' severity that need to be resolved. On their Due date these alerts will break the build.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/61) - The Component Detection tool partially succeeded. See the logs for more information.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/64) - Could not parse Jtokens from file D:\a\_work\1\s\src\Maestro\maestro-angular\node_modules\resolve\test\resolver\malformed_package_json\package.json.
### Changes
- [ee570d51](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/ee570d5139c7183ec0d9859154ba7b9dbe4de477) - Přemek Vysoký - Generate `THIRD-PARTY-NOTICES.txt` for the VMR (#2076)
- [033f9bb8](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/033f9bb8f88735752210346f409a539747e27c38) - Ricardo Arenas - [automated] Merge branch 'production' => 'main'
- [96b70240](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/96b70240e35894921b5bf33acb16590f0067fb52) - Přemek Vysoký - Handle VMR patches been modified by incoming changes (#2073)
- [97a9158c](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/97a9158c4318c80dd8cea9cea8d7a9a615aab735) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221025.5 (#2075)
- [2e3e2bfa](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/2e3e2bfaa8147ceb2056cb6a11674ecb3ea609e1) - Alitzel Mendez - [Rollout] Production rollout, 2022-10-26
- [f25ed8c1](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/f25ed8c12cf28cdef9d7479703e283eea96f5bf6) - Přemek Vysoký - Add a manager for temporary clones while synchronizing the VMR (#2070)
- [8c66f81e](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/8c66f81ec0a3803dab06db817a83b2e52c3fc94a) - Přemek Vysoký - Fix logging in recursive VMR update (#2068)
- [f456c7f3](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/f456c7f3ee8e0cb7ac3d92c29db2c470932aa25c) - Milena Hristova - Add submodules in source manifest (#2061)
| 1.0 | Build failed: arcade-services-internal-ci/main #20221031.1 - Build [#20221031.1](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=2033188) partiallySucceeded
## :warning: : internal / arcade-services-internal-ci partiallySucceeded
### Summary
**Finished** - Mon, 31 Oct 2022 18:52:03 GMT
**Duration** - 238 minutes
**Requested for** - DotNet Bot
**Reason** - batchedCI
### Details
#### Deploy
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/193) - Error: Failed to update deployment history. Error: Conflict (CODE: 409)
#### Build
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/29) - Component Governance detected 2 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/29) - Component Governance detected 2 security alert(s) at or above 'High' severity that need to be resolved. On their Due date these alerts will break the build.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/29) - The Component Detection tool partially succeeded. See the logs for more information.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/52) - Could not parse Jtokens from file D:\a\_work\1\s\src\Maestro\maestro-angular\node_modules\resolve\test\resolver\malformed_package_json\package.json.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/61) - Component Governance detected 2 security related alerts at or above 'High' severity. Microsoft’s Open Source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components. Vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/61) - Component Governance detected 2 security alert(s) at or above 'High' severity that need to be resolved. On their Due date these alerts will break the build.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/61) - The Component Detection tool partially succeeded. See the logs for more information.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/2033188/logs/64) - Could not parse Jtokens from file D:\a\_work\1\s\src\Maestro\maestro-angular\node_modules\resolve\test\resolver\malformed_package_json\package.json.
### Changes
- [ee570d51](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/ee570d5139c7183ec0d9859154ba7b9dbe4de477) - Přemek Vysoký - Generate `THIRD-PARTY-NOTICES.txt` for the VMR (#2076)
- [033f9bb8](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/033f9bb8f88735752210346f409a539747e27c38) - Ricardo Arenas - [automated] Merge branch 'production' => 'main'
- [96b70240](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/96b70240e35894921b5bf33acb16590f0067fb52) - Přemek Vysoký - Handle VMR patches been modified by incoming changes (#2073)
- [97a9158c](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/97a9158c4318c80dd8cea9cea8d7a9a615aab735) - dotnet-maestro[bot] - Update dependencies from https://github.com/dotnet/arcade build 20221025.5 (#2075)
- [2e3e2bfa](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/2e3e2bfaa8147ceb2056cb6a11674ecb3ea609e1) - Alitzel Mendez - [Rollout] Production rollout, 2022-10-26
- [f25ed8c1](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/f25ed8c12cf28cdef9d7479703e283eea96f5bf6) - Přemek Vysoký - Add a manager for temporary clones while synchronizing the VMR (#2070)
- [8c66f81e](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/8c66f81ec0a3803dab06db817a83b2e52c3fc94a) - Přemek Vysoký - Fix logging in recursive VMR update (#2068)
- [f456c7f3](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/f456c7f3ee8e0cb7ac3d92c29db2c470932aa25c) - Milena Hristova - Add submodules in source manifest (#2061)
| non_priority | build failed arcade services internal ci main build partiallysucceeded warning internal arcade services internal ci partiallysucceeded summary finished mon oct gmt duration minutes requested for dotnet bot reason batchedci details deploy warning error failed to update deployment history error conflict code build warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security alert s at or above high severity that need to be resolved on their due date these alerts will break the build warning the component detection tool partially succeeded see the logs for more information warning could not parse jtokens from file d a work s src maestro maestro angular node modules resolve test resolver malformed package json package json warning component governance detected security related alerts at or above high severity microsoft’s open source policy requires that all high and critical security vulnerabilities found by this task be addressed by upgrading vulnerable components vulnerabilities in indirect dependencies should be addressed by upgrading the root dependency warning component governance detected security alert s at or above high severity that need to be resolved on their due date these alerts will break the build warning the component detection tool partially succeeded see the logs for more information warning could not parse jtokens from file d a work s src maestro maestro angular node modules resolve test resolver malformed package json package json changes přemek vysoký generate third party notices txt for the vmr ricardo arenas merge branch production main přemek vysoký handle vmr patches been modified by incoming changes dotnet maestro update dependencies from build alitzel mendez production rollout přemek vysoký add a manager for temporary clones while synchronizing the vmr přemek vysoký fix logging in recursive vmr update milena hristova add submodules in source manifest | 0 |
231,428 | 17,688,323,845 | IssuesEvent | 2021-08-24 06:38:54 | m3db/m3 | https://api.github.com/repos/m3db/m3 | closed | M3msg usage doc wanted | area:documentation | # Filing M3 Issues
## General Issues
Hi, it's there any doc about how to use m3msg? I find it on the doc that talk about aggregator and coordinator data communicate, but there is nothing more to talk about it in the whole doc, at least I cant find any. So can you guys offer some doc about it?
| 1.0 | M3msg usage doc wanted - # Filing M3 Issues
## General Issues
Hi, it's there any doc about how to use m3msg? I find it on the doc that talk about aggregator and coordinator data communicate, but there is nothing more to talk about it in the whole doc, at least I cant find any. So can you guys offer some doc about it?
| non_priority | usage doc wanted filing issues general issues hi it s there any doc about how to use i find it on the doc that talk about aggregator and coordinator data communicate but there is nothing more to talk about it in the whole doc at least i cant find any so can you guys offer some doc about it | 0 |
149,899 | 23,546,584,508 | IssuesEvent | 2022-08-21 07:46:13 | SubhadeepJasu/Ensembles | https://api.github.com/repos/SubhadeepJasu/Ensembles | closed | Feature Request: Ability to use multiple midi keyboards for specific purposes | Needs Design Status: Wishlist | It would be great if I could set 1 midi keyboard specifically for changing chords, and another one for right hand playing. | 1.0 | Feature Request: Ability to use multiple midi keyboards for specific purposes - It would be great if I could set 1 midi keyboard specifically for changing chords, and another one for right hand playing. | non_priority | feature request ability to use multiple midi keyboards for specific purposes it would be great if i could set midi keyboard specifically for changing chords and another one for right hand playing | 0 |
126,948 | 10,441,209,232 | IssuesEvent | 2019-09-18 10:18:27 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed test: TestDockerCLI | C-test-failure O-robot | The following tests appear to have failed on master (acceptance): TestDockerCLI/test_multiple_nodes.tcl, TestDockerCLI
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+TestDockerCLI).
[#1495152](https://teamcity.cockroachdb.com/viewLog.html?buildId=1495152):
```
TestDockerCLI/test_multiple_nodes.tcl
--- FAIL: acceptance/TestDockerCLI: TestDockerCLI/test_multiple_nodes.tcl (38.020s)
TestDockerCLI
--- FAIL: acceptance/TestDockerCLI (354.660s)
------- Stdout: -------
test_log_scope.go:77: test logs captured to: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/acceptance/logTestDockerCLI925366613
test_log_scope.go:58: use -show-logs to present logs inline
```
Please assign, take a look and update the issue accordingly.
| 1.0 | teamcity: failed test: TestDockerCLI - The following tests appear to have failed on master (acceptance): TestDockerCLI/test_multiple_nodes.tcl, TestDockerCLI
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+TestDockerCLI).
[#1495152](https://teamcity.cockroachdb.com/viewLog.html?buildId=1495152):
```
TestDockerCLI/test_multiple_nodes.tcl
--- FAIL: acceptance/TestDockerCLI: TestDockerCLI/test_multiple_nodes.tcl (38.020s)
TestDockerCLI
--- FAIL: acceptance/TestDockerCLI (354.660s)
------- Stdout: -------
test_log_scope.go:77: test logs captured to: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/acceptance/logTestDockerCLI925366613
test_log_scope.go:58: use -show-logs to present logs inline
```
Please assign, take a look and update the issue accordingly.
| non_priority | teamcity failed test testdockercli the following tests appear to have failed on master acceptance testdockercli test multiple nodes tcl testdockercli you may want to check testdockercli test multiple nodes tcl fail acceptance testdockercli testdockercli test multiple nodes tcl testdockercli fail acceptance testdockercli stdout test log scope go test logs captured to home agent work go src github com cockroachdb cockroach artifacts acceptance test log scope go use show logs to present logs inline please assign take a look and update the issue accordingly | 0 |
137,940 | 30,778,994,881 | IssuesEvent | 2023-07-31 08:42:54 | Makkuusen/TimingSystem | https://api.github.com/repos/Makkuusen/TimingSystem | closed | Sorting by position in trackpage gui's is really slow. | code smell user experience | Add some sort of caching for player positions to make sure the sort goes faster. | 1.0 | Sorting by position in trackpage gui's is really slow. - Add some sort of caching for player positions to make sure the sort goes faster. | non_priority | sorting by position in trackpage gui s is really slow add some sort of caching for player positions to make sure the sort goes faster | 0 |
72,676 | 13,905,575,976 | IssuesEvent | 2020-10-20 10:03:41 | devitocodes/devitoboundary | https://api.github.com/repos/devitocodes/devitoboundary | opened | Add a test to check for correct wavefield behaviour inside a sphere. | better code | Add tests to check for leakage of information outside a spherical boundary, and to check that all energy is reflected back to the center with a reasonable coherency. | 1.0 | Add a test to check for correct wavefield behaviour inside a sphere. - Add tests to check for leakage of information outside a spherical boundary, and to check that all energy is reflected back to the center with a reasonable coherency. | non_priority | add a test to check for correct wavefield behaviour inside a sphere add tests to check for leakage of information outside a spherical boundary and to check that all energy is reflected back to the center with a reasonable coherency | 0 |
189,893 | 14,527,139,438 | IssuesEvent | 2020-12-14 15:01:14 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | SynthAI/SynthAI: kubernetes/pkg/controller/node/nodecontroller_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [SynthAI/SynthAI](https://www.github.com/SynthAI/SynthAI) at [kubernetes/pkg/controller/node/nodecontroller_test.go](https://github.com/SynthAI/SynthAI/blob/4e28fdf2ffd0eaefc0d23049106609421c9290b0/kubernetes/pkg/controller/node/nodecontroller_test.go#L613-L615)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to ds at line 614 may start a goroutine
[Click here to see the code in its original context.](https://github.com/SynthAI/SynthAI/blob/4e28fdf2ffd0eaefc0d23049106609421c9290b0/kubernetes/pkg/controller/node/nodecontroller_test.go#L613-L615)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, ds := range item.daemonSets {
nodeController.daemonSetInformer.Informer().GetStore().Add(&ds)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 4e28fdf2ffd0eaefc0d23049106609421c9290b0
| 1.0 | SynthAI/SynthAI: kubernetes/pkg/controller/node/nodecontroller_test.go; 3 LoC -
Found a possible issue in [SynthAI/SynthAI](https://www.github.com/SynthAI/SynthAI) at [kubernetes/pkg/controller/node/nodecontroller_test.go](https://github.com/SynthAI/SynthAI/blob/4e28fdf2ffd0eaefc0d23049106609421c9290b0/kubernetes/pkg/controller/node/nodecontroller_test.go#L613-L615)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to ds at line 614 may start a goroutine
[Click here to see the code in its original context.](https://github.com/SynthAI/SynthAI/blob/4e28fdf2ffd0eaefc0d23049106609421c9290b0/kubernetes/pkg/controller/node/nodecontroller_test.go#L613-L615)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, ds := range item.daemonSets {
nodeController.daemonSetInformer.Informer().GetStore().Add(&ds)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 4e28fdf2ffd0eaefc0d23049106609421c9290b0
| non_priority | synthai synthai kubernetes pkg controller node nodecontroller test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to ds at line may start a goroutine click here to show the line s of go which triggered the analyzer go for ds range item daemonsets nodecontroller daemonsetinformer informer getstore add ds leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
290,166 | 25,041,021,884 | IssuesEvent | 2022-11-04 20:47:01 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/error_codes·ts - Reporting APIs Reporting error codes places error_code in report output | Feature:Reporting failed-test Team:Global Experience | A test failed on a tracked branch
```
Error: expected undefined to equal 'unknown_error'
at Assertion.assert (node_modules/@kbn/expect/expect.js:100:11)
at Assertion.be.Assertion.equal (node_modules/@kbn/expect/expect.js:227:8)
at Assertion.be (node_modules/@kbn/expect/expect.js:69:22)
at Context.<anonymous> (x-pack/test/reporting_api_integration/reporting_and_security/error_codes.ts:39:64)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Object.apply (node_modules/@kbn/test/target_node/src/functional_test_runner/lib/mocha/wrap_function.js:87:16)
```
First failure: [CI Build - 8.5](https://buildkite.com/elastic/kibana-on-merge/builds/22738#01840b72-1615-4a55-978e-ba0e31c07c48)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/error_codes·ts","test.name":"Reporting APIs Reporting error codes places error_code in report output","test.failCount":2}} --> | 1.0 | Failing test: X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/error_codes·ts - Reporting APIs Reporting error codes places error_code in report output - A test failed on a tracked branch
```
Error: expected undefined to equal 'unknown_error'
at Assertion.assert (node_modules/@kbn/expect/expect.js:100:11)
at Assertion.be.Assertion.equal (node_modules/@kbn/expect/expect.js:227:8)
at Assertion.be (node_modules/@kbn/expect/expect.js:69:22)
at Context.<anonymous> (x-pack/test/reporting_api_integration/reporting_and_security/error_codes.ts:39:64)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Object.apply (node_modules/@kbn/test/target_node/src/functional_test_runner/lib/mocha/wrap_function.js:87:16)
```
First failure: [CI Build - 8.5](https://buildkite.com/elastic/kibana-on-merge/builds/22738#01840b72-1615-4a55-978e-ba0e31c07c48)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/error_codes·ts","test.name":"Reporting APIs Reporting error codes places error_code in report output","test.failCount":2}} --> | non_priority | failing test x pack reporting api integration tests x pack test reporting api integration reporting and security error codes·ts reporting apis reporting error codes places error code in report output a test failed on a tracked branch error expected undefined to equal unknown error at assertion assert node modules kbn expect expect js at assertion be assertion equal node modules kbn expect expect js at assertion be node modules kbn expect expect js at context x pack test reporting api integration reporting and security error codes ts at runmicrotasks at processticksandrejections node internal process task queues at object apply node modules kbn test target node src functional test runner lib mocha wrap function js first failure | 0 |
4,262 | 2,722,755,824 | IssuesEvent | 2015-04-14 07:37:32 | romait2014/57KYXHZ5S3DYAOHNPXRMLQTB | https://api.github.com/repos/romait2014/57KYXHZ5S3DYAOHNPXRMLQTB | closed | kp+HrvlwT/OeS7O5vIKo4tTco4YbXV+lqtyHEONJ89d3fRd8jvot8TyPgmnyoBtSklPrhC1kG2/iAx4qbokjCeQvdWgGzZPlXEVlD5kt7jA7GIStVpBFfnj1eJ0tSQXPIMXpn6pkC24iDMizcDekjehcNBKMHr0ZU7NwWt/k1IM= | design | v5B3LJZs5IWcxxUQWtt/4oamk7yL6Wua4uhkYxuy1518ruXJgdktk0mfg//HNG5Ayum9mbjCP5mBndrgIGDV6BBCB8PLcsac4i6K0EsXowSd5IjXkflbBvS3jcU4nX6n7IUlOZuI+VcwD4E8dFKYAQBMZg6JGdmLDJ4pmxBrhYswSg47GMoJHwnMMjsvfPiVdiyZEA5fDIESOZDAbPRXWcF0HOZrYCEwsBJWD4qgojxfrAaseAjmhz/6VT0SMlVqNxBrknlnUSmlTkbvqtEPpPqf0tfGyGjL3hQeWTjCg26rN8GKq1JMk9SCNOPpWeLh1KhIMLwtQc4y/6AB9YBH+dwDZVG5Lsk70eU7GPuE8P1B06jPdOFzgfDUK8kkLpPk2tOzf2qljWVIFGQp3IwxF1GI8iQJ3lh8J+4G+QWjx5/OyQ27yHt/bsfvM6Lkyams6WZYZ27TUozuphKlj+QyJckiWdUlzxyTH6NIeW5yZlyq/DGzazNHCnSI1LEQBbFZbAr84K3ouPbc+r5Z31hn7xSqdEvBUzauwjFXPtA4ey79p+Na6pdciRHA9CQnne8783cW7blMgH3R55eeaW3GemA7yrPnW/H52L13hmPO5GOc1dlJfmARzANk2nP8eaREbBvKtaowYfjTceiqGvaJq68mTpySqq77U5Y8YsKsIXE2C8KUswc7qiJhxUz+CL9F6utHUGywBi+84B/3c10ywbujL66C9NFoPCrxSI3sc1FFMmdBtjx84AZ4M5eYIhFehU1h5RgCPQ2SpTfYbBEjeCvcISlhPvq2Kwt9+LcPtiZ6kiGIdaB6ECNetS1JWHE4OapU/u8FSaOleWl6HI6uX9wDZVG5Lsk70eU7GPuE8P1GghBvWWtjNFo2XHN+zLQ/Pb+77FJ5Dj7L30gshBXQ/W2hj2AZAZ+WZnqMu6bdJeL3230Y+sJg+QB+HObePyLElO48WEamrk91OZg9tLUMHtwDZVG5Lsk70eU7GPuE8P2Yh6QcxUlv0wQCjxeUr2klDW+UE/rwBmb6XpWehX3Nh8o392J3px00QF9SdCcTCDwgZE7c1N0aTkqJpEaWj20gLhnV8YdNiubh3aHbRvTN0Rnk6B86rwSZ6mefO6jgfyEV0shFUA/PfJEsQVhRnUfcQAlEHJN1MKEDgR5Bf175ySwGZ42NzE+E3vuN+gUPd4dNpsGiATHn9UpiQfRrCvxCEUes0OoM9pfJUDsCtbO/1jKs/Av14j656yq0SuvlIpgH3EzbuNdVJK3JBA8TNiKbt864G7XkJ4kj0RcqcOn1tfnfuaIsp35y8GqM0USHFV6YBubYYDtHo/oZAyDGzyNOOR1g/LDY1cxFzE3TBFCmgKBOoUxvI4cM31XQEtEQAlCYlBBh+sex7y1ljuK3k4MsvC6YMDiQrTjSw59/+MP3olLmUmxsynSZASEPZKemeR/cA2VRuS7JO9HlOxj7hPD9Ux0RC0NxNgNqTEukjgfousCKh98SRRsnpoG3UG3MJW6fUQ8jK+gAYkdngWi3ojTJfdPxVjKg/W8rNguWiBM5B4ufcVcAj4BdtapNOHbG4XcCwZuQA6cC8xud/LYfUUj/LLrCGzwBlFIV5pWCZbF5TyipHacKTj2ELHzFClJ5h5z4fdWLh/FFfHddDwZU8/jB7UmrKEUSr98Qu7gwZmBzgGdUY5wy5KqaObl+YMrrj0GICNMwfrIWV282JCf9MLJrK9whKWE++rYrC334tw+2JtJ9FUtWy1onRbRjEXRl+wE/5kBJ0Y84SRjNziwSVV9MYDvKs+db8fnYvXeGY87kY1+Dln9rlDl7wcHztFwHektasW7ZLHDFV6ouONza6VAspwH/goj4ivYgIg04ktd6Ft90esQf445buIvNFZFw91vv6+FH8qlyzt+t+rtxWv6nrXqde1QRuV5AyxQ/M+LuN3YSbZQv/V1yG7Q5CN5QuCjNIcuFf906zrrWU1aX+d6C0MSS6d45r4zb+nw3mFfSO9dj1DJVMMNUoxaAdfHYy+Ueq8hyq0WgvcwsCZnvWBEcScpNi+dsmSeh7pAvhfQnRMedr6SdcEOj2DqIcbURFU8p/86mVOKttFO7SNHZHkfG9Blxdc3gy/k3Zss+x3iLCDIO3fSg4av/Dzhzysx3CHU7xVciTjVIYuW2/4XIL5WslsPHZgR5Lf2ICdmdRLKSbtuqm4jTiAmPrcQKiivqgGJJyk2L52yZJ6HukC+F9CdEp7cOARsGsnd1ki70Wko4dAk1EzlsNRuEzquSowg4pkzcA2VRuS7JO9HlOxj7hPD9Fb2TilWeUUgFJ4OGiT1+Xbk/gA+6L5AabIcqBIsRwD9lOafTvVOdeuG6vGC+wXgfdsNc2+RJCCL/hUUppM7n/5fQIC2ZhvyKsPhtcwFhn7LOJTUGERPZqcOC8ufJMTW0VY6ZDKvhnaXd6G7KKWpNDVyTPluv597YzBdgDRdd9rNtoY9gGQGflmZ6jLum3SXin4MbG8+pEoLPU05PDN3CjKFwkiO6mes76/OFBl4W7Ctdz2DVxMtis4cQ7nPnL5xxoByKI/5WNKjNhRaNKhqL4+TGTi9KVvSBpmhHILeJfZFfN+wwy+j92Y4w4zXoMGamAEG3ZxinbcECMwKvkYefuZZzU2Kw10yfssJOQh/pC74PHXRR2m0hNTPQ6ihnm5bYkolXVM15WvTOwIMEUnplO5QWOl1OoogTrCB49L8w9p1cEu7BwzDmy0kg/VxEbWByUjasYxZPyxDHAIqiC4LWx0Z6ece1Q1YKaC66vRURSPLMOjqki/o/4n5sfZB/ho+f/ynHrJjBqzJ6HF/pEzk8ZfHL0NeP477m2IZT6OAaP91Z4m2F4Z4V6PJmEa5jf0kiGCWGv33gVF/cUXVuQoOnvhK/J8mYIVeWX1ISgA8K58sroh5+501MIW62+CG/xT/8QT59VdNhqKVpMCVjvex7Y7L2oJAFpIQKSrHdCFfLwp0U8KWhmTjeBZ0EpNHyC/1SjviQcT1kiLNYNX2YOWdh/pxqF4Wa+0g2paY8egVgCUaTD/wegtptgkU5QnRnhb2ifkUSyMZkUN9hM2VMXOoXwKm34a2Inf1NBWLgEuEBBbbDjY8VHMI/vefEAvVvL/+ers7g0QdtEF/8RDrnWdZ+2M74XcZhlhGVInfreILcfeO9rXQWUOsk72GnZvvw+DHhq2yXy4EvKGb9JUzQM18LcFxOZgQHO/+jq3zIYi8PzYx2GkMENRIxGlJ+xJar7Hvt/ux08nNzrL8iwbNYz5Vud8o392J3px00QF9SdCcTCDwoSg9AZwgH7KfJZt6Qqgdcs1F3xt2YygJM+QFG34DrYSyNfA/Gpx8yoyoKRcZ5AplAKJoywf9cJ682I9ufkuqeZKz/jqf2YzWbSaec3HzQZ5TuPFhGpq5PdTmYPbS1DB7cA2VRuS7JO9HlOxj7hPD9vwN4119qOFXdrZKcGSe2Li1AWuJFHzuXjFIgcS50uUWY2q13vBXgKp+DGWN/UZr/dU4KOdKy02nlTu6o20Rm6Xs15pSCTbVOEH0AZdmxA/Im2euEg2GZi3SwtpsbvWRx3ANlUbkuyTvR5TsY+4Tw/fKA/iuBWrTY8sVU+lFdWIJQrwQ/P8EJSPexagbWK5xnK9whKWE++rYrC334tw+2JtiZkSBTYPCxBP4DiIApPiJVGwKmKRUKT21tuR4tAS6L3/3LcMSpIXu8NB9i0nnTKow+/Iyaj+XkUtVSv0ZVF7huScVPeKc37yq50RXCrwg8CN+Nt9H4VbmUSTEYGgluzdCON4xNaTw7RDML+YSYVbKMPvyMmo/l5FLVUr9GVRe47aF8xcqga5/4Fp7iNA2YyJaYWhXUdoqoE4p3Ie+SIvyWYE6HeFxpKhGH0lG945PAfUlkv2UOFLPdiqqPB/IQ2mtm5QbGECHvvC3KEBnwKMj4SKOgZmhmlLcYP5AvpUSQ8cvQ14/jvubYhlPo4Bo/3VYLrvy98C6l6zmS8lYg/93PIdLrNymzwV1pqV7Mjd0Lz5YUTy89znEoRQhtNMX5XZhDeTCaozx+W29hBVb7vMiCg2wZOdRpfaGymmBKOrrO/500CTab4+algVfTjjO2MYU0kcVhZ9KkEXNaXuQS+1Pw8Abg8GumI6GOGdt+TGRxr87fysh9Ul60xMiyLYWq92wczfB0Q7Sp2pWDw+gTno0aQcL5WyurK5GL+71B+qfU | 1.0 | kp+HrvlwT/OeS7O5vIKo4tTco4YbXV+lqtyHEONJ89d3fRd8jvot8TyPgmnyoBtSklPrhC1kG2/iAx4qbokjCeQvdWgGzZPlXEVlD5kt7jA7GIStVpBFfnj1eJ0tSQXPIMXpn6pkC24iDMizcDekjehcNBKMHr0ZU7NwWt/k1IM= - v5B3LJZs5IWcxxUQWtt/4oamk7yL6Wua4uhkYxuy1518ruXJgdktk0mfg//HNG5Ayum9mbjCP5mBndrgIGDV6BBCB8PLcsac4i6K0EsXowSd5IjXkflbBvS3jcU4nX6n7IUlOZuI+VcwD4E8dFKYAQBMZg6JGdmLDJ4pmxBrhYswSg47GMoJHwnMMjsvfPiVdiyZEA5fDIESOZDAbPRXWcF0HOZrYCEwsBJWD4qgojxfrAaseAjmhz/6VT0SMlVqNxBrknlnUSmlTkbvqtEPpPqf0tfGyGjL3hQeWTjCg26rN8GKq1JMk9SCNOPpWeLh1KhIMLwtQc4y/6AB9YBH+dwDZVG5Lsk70eU7GPuE8P1B06jPdOFzgfDUK8kkLpPk2tOzf2qljWVIFGQp3IwxF1GI8iQJ3lh8J+4G+QWjx5/OyQ27yHt/bsfvM6Lkyams6WZYZ27TUozuphKlj+QyJckiWdUlzxyTH6NIeW5yZlyq/DGzazNHCnSI1LEQBbFZbAr84K3ouPbc+r5Z31hn7xSqdEvBUzauwjFXPtA4ey79p+Na6pdciRHA9CQnne8783cW7blMgH3R55eeaW3GemA7yrPnW/H52L13hmPO5GOc1dlJfmARzANk2nP8eaREbBvKtaowYfjTceiqGvaJq68mTpySqq77U5Y8YsKsIXE2C8KUswc7qiJhxUz+CL9F6utHUGywBi+84B/3c10ywbujL66C9NFoPCrxSI3sc1FFMmdBtjx84AZ4M5eYIhFehU1h5RgCPQ2SpTfYbBEjeCvcISlhPvq2Kwt9+LcPtiZ6kiGIdaB6ECNetS1JWHE4OapU/u8FSaOleWl6HI6uX9wDZVG5Lsk70eU7GPuE8P1GghBvWWtjNFo2XHN+zLQ/Pb+77FJ5Dj7L30gshBXQ/W2hj2AZAZ+WZnqMu6bdJeL3230Y+sJg+QB+HObePyLElO48WEamrk91OZg9tLUMHtwDZVG5Lsk70eU7GPuE8P2Yh6QcxUlv0wQCjxeUr2klDW+UE/rwBmb6XpWehX3Nh8o392J3px00QF9SdCcTCDwgZE7c1N0aTkqJpEaWj20gLhnV8YdNiubh3aHbRvTN0Rnk6B86rwSZ6mefO6jgfyEV0shFUA/PfJEsQVhRnUfcQAlEHJN1MKEDgR5Bf175ySwGZ42NzE+E3vuN+gUPd4dNpsGiATHn9UpiQfRrCvxCEUes0OoM9pfJUDsCtbO/1jKs/Av14j656yq0SuvlIpgH3EzbuNdVJK3JBA8TNiKbt864G7XkJ4kj0RcqcOn1tfnfuaIsp35y8GqM0USHFV6YBubYYDtHo/oZAyDGzyNOOR1g/LDY1cxFzE3TBFCmgKBOoUxvI4cM31XQEtEQAlCYlBBh+sex7y1ljuK3k4MsvC6YMDiQrTjSw59/+MP3olLmUmxsynSZASEPZKemeR/cA2VRuS7JO9HlOxj7hPD9Ux0RC0NxNgNqTEukjgfousCKh98SRRsnpoG3UG3MJW6fUQ8jK+gAYkdngWi3ojTJfdPxVjKg/W8rNguWiBM5B4ufcVcAj4BdtapNOHbG4XcCwZuQA6cC8xud/LYfUUj/LLrCGzwBlFIV5pWCZbF5TyipHacKTj2ELHzFClJ5h5z4fdWLh/FFfHddDwZU8/jB7UmrKEUSr98Qu7gwZmBzgGdUY5wy5KqaObl+YMrrj0GICNMwfrIWV282JCf9MLJrK9whKWE++rYrC334tw+2JtJ9FUtWy1onRbRjEXRl+wE/5kBJ0Y84SRjNziwSVV9MYDvKs+db8fnYvXeGY87kY1+Dln9rlDl7wcHztFwHektasW7ZLHDFV6ouONza6VAspwH/goj4ivYgIg04ktd6Ft90esQf445buIvNFZFw91vv6+FH8qlyzt+t+rtxWv6nrXqde1QRuV5AyxQ/M+LuN3YSbZQv/V1yG7Q5CN5QuCjNIcuFf906zrrWU1aX+d6C0MSS6d45r4zb+nw3mFfSO9dj1DJVMMNUoxaAdfHYy+Ueq8hyq0WgvcwsCZnvWBEcScpNi+dsmSeh7pAvhfQnRMedr6SdcEOj2DqIcbURFU8p/86mVOKttFO7SNHZHkfG9Blxdc3gy/k3Zss+x3iLCDIO3fSg4av/Dzhzysx3CHU7xVciTjVIYuW2/4XIL5WslsPHZgR5Lf2ICdmdRLKSbtuqm4jTiAmPrcQKiivqgGJJyk2L52yZJ6HukC+F9CdEp7cOARsGsnd1ki70Wko4dAk1EzlsNRuEzquSowg4pkzcA2VRuS7JO9HlOxj7hPD9Fb2TilWeUUgFJ4OGiT1+Xbk/gA+6L5AabIcqBIsRwD9lOafTvVOdeuG6vGC+wXgfdsNc2+RJCCL/hUUppM7n/5fQIC2ZhvyKsPhtcwFhn7LOJTUGERPZqcOC8ufJMTW0VY6ZDKvhnaXd6G7KKWpNDVyTPluv597YzBdgDRdd9rNtoY9gGQGflmZ6jLum3SXin4MbG8+pEoLPU05PDN3CjKFwkiO6mes76/OFBl4W7Ctdz2DVxMtis4cQ7nPnL5xxoByKI/5WNKjNhRaNKhqL4+TGTi9KVvSBpmhHILeJfZFfN+wwy+j92Y4w4zXoMGamAEG3ZxinbcECMwKvkYefuZZzU2Kw10yfssJOQh/pC74PHXRR2m0hNTPQ6ihnm5bYkolXVM15WvTOwIMEUnplO5QWOl1OoogTrCB49L8w9p1cEu7BwzDmy0kg/VxEbWByUjasYxZPyxDHAIqiC4LWx0Z6ece1Q1YKaC66vRURSPLMOjqki/o/4n5sfZB/ho+f/ynHrJjBqzJ6HF/pEzk8ZfHL0NeP477m2IZT6OAaP91Z4m2F4Z4V6PJmEa5jf0kiGCWGv33gVF/cUXVuQoOnvhK/J8mYIVeWX1ISgA8K58sroh5+501MIW62+CG/xT/8QT59VdNhqKVpMCVjvex7Y7L2oJAFpIQKSrHdCFfLwp0U8KWhmTjeBZ0EpNHyC/1SjviQcT1kiLNYNX2YOWdh/pxqF4Wa+0g2paY8egVgCUaTD/wegtptgkU5QnRnhb2ifkUSyMZkUN9hM2VMXOoXwKm34a2Inf1NBWLgEuEBBbbDjY8VHMI/vefEAvVvL/+ers7g0QdtEF/8RDrnWdZ+2M74XcZhlhGVInfreILcfeO9rXQWUOsk72GnZvvw+DHhq2yXy4EvKGb9JUzQM18LcFxOZgQHO/+jq3zIYi8PzYx2GkMENRIxGlJ+xJar7Hvt/ux08nNzrL8iwbNYz5Vud8o392J3px00QF9SdCcTCDwoSg9AZwgH7KfJZt6Qqgdcs1F3xt2YygJM+QFG34DrYSyNfA/Gpx8yoyoKRcZ5AplAKJoywf9cJ682I9ufkuqeZKz/jqf2YzWbSaec3HzQZ5TuPFhGpq5PdTmYPbS1DB7cA2VRuS7JO9HlOxj7hPD9vwN4119qOFXdrZKcGSe2Li1AWuJFHzuXjFIgcS50uUWY2q13vBXgKp+DGWN/UZr/dU4KOdKy02nlTu6o20Rm6Xs15pSCTbVOEH0AZdmxA/Im2euEg2GZi3SwtpsbvWRx3ANlUbkuyTvR5TsY+4Tw/fKA/iuBWrTY8sVU+lFdWIJQrwQ/P8EJSPexagbWK5xnK9whKWE++rYrC334tw+2JtiZkSBTYPCxBP4DiIApPiJVGwKmKRUKT21tuR4tAS6L3/3LcMSpIXu8NB9i0nnTKow+/Iyaj+XkUtVSv0ZVF7huScVPeKc37yq50RXCrwg8CN+Nt9H4VbmUSTEYGgluzdCON4xNaTw7RDML+YSYVbKMPvyMmo/l5FLVUr9GVRe47aF8xcqga5/4Fp7iNA2YyJaYWhXUdoqoE4p3Ie+SIvyWYE6HeFxpKhGH0lG945PAfUlkv2UOFLPdiqqPB/IQ2mtm5QbGECHvvC3KEBnwKMj4SKOgZmhmlLcYP5AvpUSQ8cvQ14/jvubYhlPo4Bo/3VYLrvy98C6l6zmS8lYg/93PIdLrNymzwV1pqV7Mjd0Lz5YUTy89znEoRQhtNMX5XZhDeTCaozx+W29hBVb7vMiCg2wZOdRpfaGymmBKOrrO/500CTab4+algVfTjjO2MYU0kcVhZ9KkEXNaXuQS+1Pw8Abg8GumI6GOGdt+TGRxr87fysh9Ul60xMiyLYWq92wczfB0Q7Sp2pWDw+gTno0aQcL5WyurK5GL+71B+qfU | non_priority | kp hrvlwt zlq pb sjg qb ue lyfuuj we t m xbk ga rjccl wwy o ho f cuxvuqoonvhk cg xt vefeavvvl dgwn uzr fka lfdwijqrwq iyaj ysyvbkmpvymmo qfu | 0 |
131,002 | 12,467,569,088 | IssuesEvent | 2020-05-28 17:17:34 | henryprescott/raid-helper-sheets | https://api.github.com/repos/henryprescott/raid-helper-sheets | closed | Update read me with project info and discription | documentation | brief discription of how bot and spreadsheet works | 1.0 | Update read me with project info and discription - brief discription of how bot and spreadsheet works | non_priority | update read me with project info and discription brief discription of how bot and spreadsheet works | 0 |
2,839 | 5,007,734,519 | IssuesEvent | 2016-12-12 17:30:37 | IBM-Bluemix/logistics-wizard | https://api.github.com/repos/IBM-Bluemix/logistics-wizard | closed | Initial Data Set Creation | back end erp-service task | Create the data set that will be used as the initial distribution centers, retailers, and shipments when users create a new account or revert their data to a fresh state.
| 1.0 | Initial Data Set Creation - Create the data set that will be used as the initial distribution centers, retailers, and shipments when users create a new account or revert their data to a fresh state.
| non_priority | initial data set creation create the data set that will be used as the initial distribution centers retailers and shipments when users create a new account or revert their data to a fresh state | 0 |
432,286 | 30,276,482,425 | IssuesEvent | 2023-07-07 20:12:04 | SSH-key-rotation-AWS/team-henrique | https://api.github.com/repos/SSH-key-rotation-AWS/team-henrique | closed | Write documentation for python program | documentation | Update README file with detailed documentation on how the program works and how to use it | 1.0 | Write documentation for python program - Update README file with detailed documentation on how the program works and how to use it | non_priority | write documentation for python program update readme file with detailed documentation on how the program works and how to use it | 0 |
59,327 | 14,564,807,406 | IssuesEvent | 2020-12-17 06:00:31 | JuliaLang/julia | https://api.github.com/repos/JuliaLang/julia | closed | Building libssh2 in a clean environment errors | build external dependencies | Looks like it's failing to find libssh2's dependent libraries while building the tests. We could probably either allow the linker to have undefined symbols or have it temporarily set an rpath that includes the mbedtls dependency.
```
make[1]: Entering directory '/workspace/deps'
rm -rf /workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2
mkdir -p /workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/workspace/usr
make -C scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 install DESTDIR="" prefix=/workspace/usr bindir=/workspace/usr/tools libdir=/workspace/usr/lib shlibdir=/workspace/usr/lib libexecdir=/workspace/usr/libexec datarootdir=/workspace/usr/share includedir=/workspace/usr/include sysconfdir=/workspace/usr/etc O= DESTDIR="/workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2"
make[2]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
/usr/local/bin/cmake -H/workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 -B/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 --check-build-system CMakeFiles/Makefile.cmake 0
/usr/local/bin/cmake -E cmake_progress_start /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/CMakeFiles /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/CMakeFiles/progress.marks
make -f CMakeFiles/Makefile2 all
make[3]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f src/CMakeFiles/libssh2.dir/build.make src/CMakeFiles/libssh2.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src/CMakeFiles/libssh2.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f src/CMakeFiles/libssh2.dir/build.make src/CMakeFiles/libssh2.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'src/CMakeFiles/libssh2.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 45%] Built target libssh2
make -f tests/CMakeFiles/copy_test_dependencies.dir/build.make tests/CMakeFiles/copy_test_dependencies.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/copy_test_dependencies.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/copy_test_dependencies.dir/build.make tests/CMakeFiles/copy_test_dependencies.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests && /usr/local/bin/cmake -E make_directory /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/.
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests && /usr/local/bin/cmake -E copy /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src/libssh2.so.1.0.1 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 45%] Built target copy_test_dependencies
make -f tests/CMakeFiles/openssh_fixture.dir/build.make tests/CMakeFiles/openssh_fixture.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/openssh_fixture.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/openssh_fixture.dir/build.make tests/CMakeFiles/openssh_fixture.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'tests/CMakeFiles/openssh_fixture.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 50%] Built target openssh_fixture
make -f tests/CMakeFiles/session_fixture.dir/build.make tests/CMakeFiles/session_fixture.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/session_fixture.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/session_fixture.dir/build.make tests/CMakeFiles/session_fixture.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'tests/CMakeFiles/session_fixture.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 54%] Built target session_fixture
make -f tests/CMakeFiles/runner.dir/build.make tests/CMakeFiles/runner.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/runner.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/runner.dir/build.make tests/CMakeFiles/runner.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'tests/CMakeFiles/runner.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 58%] Built target runner
make -f tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build.make tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build.make tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 60%] Linking C executable test_public_key_auth_succeeds_with_correct_rsa_key
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests && /usr/local/bin/cmake -E cmake_link_script CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/link.txt --verbose=1
/opt/x86_64-linux-gnu/bin/gcc -m64 -Wall -O3 -DNDEBUG -rdynamic CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/test_public_key_auth_succeeds_with_correct_rsa_key.c.o -o test_public_key_auth_succeeds_with_correct_rsa_key -Wl,-rpath,/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src librunner.a libsession_fixture.a ../src/libssh2.so.1.0.1 libopenssh_fixture.a
/opt/x86_64-linux-gnu/lib/gcc/x86_64-linux-gnu/7.3.0/../../../../x86_64-linux-gnu/bin/ld: warning: libmbedtls.so.10, needed by ../src/libssh2.so.1.0.1, not found (try using -rpath or -rpath-link)
/opt/x86_64-linux-gnu/lib/gcc/x86_64-linux-gnu/7.3.0/../../../../x86_64-linux-gnu/bin/ld: warning: libmbedx509.so.0, needed by ../src/libssh2.so.1.0.1, not found (try using -rpath or -rpath-link)
/opt/x86_64-linux-gnu/lib/gcc/x86_64-linux-gnu/7.3.0/../../../../x86_64-linux-gnu/bin/ld: warning: libmbedcrypto.so.0, needed by ../src/libssh2.so.1.0.1, not found (try using -rpath or -rpath-link)
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_update'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_hmac_starts'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_pkcs1_verify'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_entropy_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_entropy_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_fill_random'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_size'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_write_binary'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_hmac_update'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_random'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_finish'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_setkey'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_update'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_entropy_func'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_set_bit'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_setup'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_parse_keyfile'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_finish'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_strerror'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_seed'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_lset'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_set_iv'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_copy'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_exp_mod'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_info_from_type'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_setup'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_info_from_type'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_reset'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_get_type'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_check_privkey'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_starts'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_hmac_finish'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_read_binary'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_parse_key'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_check_pubkey'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_bitlen'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_pkcs1_sign'
collect2: error: ld returned 1 exit status
make[4]: *** [tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build.make:88: tests/test_public_key_auth_succeeds_with_correct_rsa_key] Error 1
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[3]: *** [CMakeFiles/Makefile2:170: tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/all] Error 2
make[3]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[2]: *** [Makefile:163: all] Error 2
make[2]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[1]: *** [/workspace/deps/libssh2.mk:55: /workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2.tgz] Error 2
make[1]: Leaving directory '/workspace/deps'
make: *** [Makefile:60: julia-deps] Error 2
``` | 1.0 | Building libssh2 in a clean environment errors - Looks like it's failing to find libssh2's dependent libraries while building the tests. We could probably either allow the linker to have undefined symbols or have it temporarily set an rpath that includes the mbedtls dependency.
```
make[1]: Entering directory '/workspace/deps'
rm -rf /workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2
mkdir -p /workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/workspace/usr
make -C scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 install DESTDIR="" prefix=/workspace/usr bindir=/workspace/usr/tools libdir=/workspace/usr/lib shlibdir=/workspace/usr/lib libexecdir=/workspace/usr/libexec datarootdir=/workspace/usr/share includedir=/workspace/usr/include sysconfdir=/workspace/usr/etc O= DESTDIR="/workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2"
make[2]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
/usr/local/bin/cmake -H/workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 -B/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 --check-build-system CMakeFiles/Makefile.cmake 0
/usr/local/bin/cmake -E cmake_progress_start /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/CMakeFiles /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/CMakeFiles/progress.marks
make -f CMakeFiles/Makefile2 all
make[3]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f src/CMakeFiles/libssh2.dir/build.make src/CMakeFiles/libssh2.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src/CMakeFiles/libssh2.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f src/CMakeFiles/libssh2.dir/build.make src/CMakeFiles/libssh2.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'src/CMakeFiles/libssh2.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 45%] Built target libssh2
make -f tests/CMakeFiles/copy_test_dependencies.dir/build.make tests/CMakeFiles/copy_test_dependencies.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/copy_test_dependencies.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/copy_test_dependencies.dir/build.make tests/CMakeFiles/copy_test_dependencies.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests && /usr/local/bin/cmake -E make_directory /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/.
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests && /usr/local/bin/cmake -E copy /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src/libssh2.so.1.0.1 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 45%] Built target copy_test_dependencies
make -f tests/CMakeFiles/openssh_fixture.dir/build.make tests/CMakeFiles/openssh_fixture.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/openssh_fixture.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/openssh_fixture.dir/build.make tests/CMakeFiles/openssh_fixture.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'tests/CMakeFiles/openssh_fixture.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 50%] Built target openssh_fixture
make -f tests/CMakeFiles/session_fixture.dir/build.make tests/CMakeFiles/session_fixture.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/session_fixture.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/session_fixture.dir/build.make tests/CMakeFiles/session_fixture.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'tests/CMakeFiles/session_fixture.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 54%] Built target session_fixture
make -f tests/CMakeFiles/runner.dir/build.make tests/CMakeFiles/runner.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/runner.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/runner.dir/build.make tests/CMakeFiles/runner.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[4]: Nothing to be done for 'tests/CMakeFiles/runner.dir/build'.
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 58%] Built target runner
make -f tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build.make tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/depend
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 && /usr/local/bin/cmake -E cmake_depends "Unix Makefiles" /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/srccache/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2 /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/DependInfo.cmake --color=
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make -f tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build.make tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build
make[4]: Entering directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
[ 60%] Linking C executable test_public_key_auth_succeeds_with_correct_rsa_key
cd /workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/tests && /usr/local/bin/cmake -E cmake_link_script CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/link.txt --verbose=1
/opt/x86_64-linux-gnu/bin/gcc -m64 -Wall -O3 -DNDEBUG -rdynamic CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/test_public_key_auth_succeeds_with_correct_rsa_key.c.o -o test_public_key_auth_succeeds_with_correct_rsa_key -Wl,-rpath,/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2/src librunner.a libsession_fixture.a ../src/libssh2.so.1.0.1 libopenssh_fixture.a
/opt/x86_64-linux-gnu/lib/gcc/x86_64-linux-gnu/7.3.0/../../../../x86_64-linux-gnu/bin/ld: warning: libmbedtls.so.10, needed by ../src/libssh2.so.1.0.1, not found (try using -rpath or -rpath-link)
/opt/x86_64-linux-gnu/lib/gcc/x86_64-linux-gnu/7.3.0/../../../../x86_64-linux-gnu/bin/ld: warning: libmbedx509.so.0, needed by ../src/libssh2.so.1.0.1, not found (try using -rpath or -rpath-link)
/opt/x86_64-linux-gnu/lib/gcc/x86_64-linux-gnu/7.3.0/../../../../x86_64-linux-gnu/bin/ld: warning: libmbedcrypto.so.0, needed by ../src/libssh2.so.1.0.1, not found (try using -rpath or -rpath-link)
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_update'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_hmac_starts'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_pkcs1_verify'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_entropy_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_entropy_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_fill_random'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_size'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_write_binary'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_hmac_update'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_random'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_finish'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_setkey'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_update'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_entropy_func'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_set_bit'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_setup'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_parse_keyfile'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_finish'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_strerror'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_ctr_drbg_seed'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_lset'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_set_iv'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_copy'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_exp_mod'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_info_from_type'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_setup'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_info_from_type'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_cipher_reset'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_get_type'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_check_privkey'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_starts'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_hmac_finish'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_read_binary'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_pk_parse_key'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_check_pubkey'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_free'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_mpi_bitlen'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_md_init'
../src/libssh2.so.1.0.1: undefined reference to `mbedtls_rsa_pkcs1_sign'
collect2: error: ld returned 1 exit status
make[4]: *** [tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/build.make:88: tests/test_public_key_auth_succeeds_with_correct_rsa_key] Error 1
make[4]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[3]: *** [CMakeFiles/Makefile2:170: tests/CMakeFiles/test_public_key_auth_succeeds_with_correct_rsa_key.dir/all] Error 2
make[3]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[2]: *** [Makefile:163: all] Error 2
make[2]: Leaving directory '/workspace/deps/scratch/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2'
make[1]: *** [/workspace/deps/libssh2.mk:55: /workspace/usr-staging/libssh2-30e9c1347e3b8baa2951db612f05e6d87fc8e2f2.tgz] Error 2
make[1]: Leaving directory '/workspace/deps'
make: *** [Makefile:60: julia-deps] Error 2
``` | non_priority | building in a clean environment errors looks like it s failing to find s dependent libraries while building the tests we could probably either allow the linker to have undefined symbols or have it temporarily set an rpath that includes the mbedtls dependency make entering directory workspace deps rm rf workspace usr staging mkdir p workspace usr staging workspace usr make c scratch install destdir prefix workspace usr bindir workspace usr tools libdir workspace usr lib shlibdir workspace usr lib libexecdir workspace usr libexec datarootdir workspace usr share includedir workspace usr include sysconfdir workspace usr etc o destdir workspace usr staging make entering directory workspace deps scratch usr local bin cmake h workspace deps srccache b workspace deps scratch check build system cmakefiles makefile cmake usr local bin cmake e cmake progress start workspace deps scratch cmakefiles workspace deps scratch cmakefiles progress marks make f cmakefiles all make entering directory workspace deps scratch make f src cmakefiles dir build make src cmakefiles dir depend make entering directory workspace deps scratch cd workspace deps scratch usr local bin cmake e cmake depends unix makefiles workspace deps srccache workspace deps srccache src workspace deps scratch workspace deps scratch src workspace deps scratch src cmakefiles dir dependinfo cmake color make leaving directory workspace deps scratch make f src cmakefiles dir build make src cmakefiles dir build make entering directory workspace deps scratch make nothing to be done for src cmakefiles dir build make leaving directory workspace deps scratch built target make f tests cmakefiles copy test dependencies dir build make tests cmakefiles copy test dependencies dir depend make entering directory workspace deps scratch cd workspace deps scratch usr local bin cmake e cmake depends unix makefiles workspace deps srccache workspace deps srccache tests workspace deps scratch workspace deps scratch tests workspace deps scratch tests cmakefiles copy test dependencies dir dependinfo cmake color make leaving directory workspace deps scratch make f tests cmakefiles copy test dependencies dir build make tests cmakefiles copy test dependencies dir build make entering directory workspace deps scratch cd workspace deps scratch tests usr local bin cmake e make directory workspace deps scratch tests cd workspace deps scratch tests usr local bin cmake e copy workspace deps scratch src so workspace deps scratch tests make leaving directory workspace deps scratch built target copy test dependencies make f tests cmakefiles openssh fixture dir build make tests cmakefiles openssh fixture dir depend make entering directory workspace deps scratch cd workspace deps scratch usr local bin cmake e cmake depends unix makefiles workspace deps srccache workspace deps srccache tests workspace deps scratch workspace deps scratch tests workspace deps scratch tests cmakefiles openssh fixture dir dependinfo cmake color make leaving directory workspace deps scratch make f tests cmakefiles openssh fixture dir build make tests cmakefiles openssh fixture dir build make entering directory workspace deps scratch make nothing to be done for tests cmakefiles openssh fixture dir build make leaving directory workspace deps scratch built target openssh fixture make f tests cmakefiles session fixture dir build make tests cmakefiles session fixture dir depend make entering directory workspace deps scratch cd workspace deps scratch usr local bin cmake e cmake depends unix makefiles workspace deps srccache workspace deps srccache tests workspace deps scratch workspace deps scratch tests workspace deps scratch tests cmakefiles session fixture dir dependinfo cmake color make leaving directory workspace deps scratch make f tests cmakefiles session fixture dir build make tests cmakefiles session fixture dir build make entering directory workspace deps scratch make nothing to be done for tests cmakefiles session fixture dir build make leaving directory workspace deps scratch built target session fixture make f tests cmakefiles runner dir build make tests cmakefiles runner dir depend make entering directory workspace deps scratch cd workspace deps scratch usr local bin cmake e cmake depends unix makefiles workspace deps srccache workspace deps srccache tests workspace deps scratch workspace deps scratch tests workspace deps scratch tests cmakefiles runner dir dependinfo cmake color make leaving directory workspace deps scratch make f tests cmakefiles runner dir build make tests cmakefiles runner dir build make entering directory workspace deps scratch make nothing to be done for tests cmakefiles runner dir build make leaving directory workspace deps scratch built target runner make f tests cmakefiles test public key auth succeeds with correct rsa key dir build make tests cmakefiles test public key auth succeeds with correct rsa key dir depend make entering directory workspace deps scratch cd workspace deps scratch usr local bin cmake e cmake depends unix makefiles workspace deps srccache workspace deps srccache tests workspace deps scratch workspace deps scratch tests workspace deps scratch tests cmakefiles test public key auth succeeds with correct rsa key dir dependinfo cmake color make leaving directory workspace deps scratch make f tests cmakefiles test public key auth succeeds with correct rsa key dir build make tests cmakefiles test public key auth succeeds with correct rsa key dir build make entering directory workspace deps scratch linking c executable test public key auth succeeds with correct rsa key cd workspace deps scratch tests usr local bin cmake e cmake link script cmakefiles test public key auth succeeds with correct rsa key dir link txt verbose opt linux gnu bin gcc wall dndebug rdynamic cmakefiles test public key auth succeeds with correct rsa key dir test public key auth succeeds with correct rsa key c o o test public key auth succeeds with correct rsa key wl rpath workspace deps scratch src librunner a libsession fixture a src so libopenssh fixture a opt linux gnu lib gcc linux gnu linux gnu bin ld warning libmbedtls so needed by src so not found try using rpath or rpath link opt linux gnu lib gcc linux gnu linux gnu bin ld warning so needed by src so not found try using rpath or rpath link opt linux gnu lib gcc linux gnu linux gnu bin ld warning libmbedcrypto so needed by src so not found try using rpath or rpath link src so undefined reference to mbedtls cipher update src so undefined reference to mbedtls md hmac starts src so undefined reference to mbedtls rsa verify src so undefined reference to mbedtls entropy init src so undefined reference to mbedtls entropy free src so undefined reference to mbedtls mpi fill random src so undefined reference to mbedtls md src so undefined reference to mbedtls cipher init src so undefined reference to mbedtls ctr drbg free src so undefined reference to mbedtls mpi size src so undefined reference to mbedtls mpi write binary src so undefined reference to mbedtls md hmac update src so undefined reference to mbedtls mpi init src so undefined reference to mbedtls ctr drbg random src so undefined reference to mbedtls cipher free src so undefined reference to mbedtls md finish src so undefined reference to mbedtls cipher setkey src so undefined reference to mbedtls md update src so undefined reference to mbedtls md free src so undefined reference to mbedtls entropy func src so undefined reference to mbedtls mpi set bit src so undefined reference to mbedtls cipher setup src so undefined reference to mbedtls pk parse keyfile src so undefined reference to mbedtls cipher finish src so undefined reference to mbedtls strerror src so undefined reference to mbedtls ctr drbg init src so undefined reference to mbedtls rsa free src so undefined reference to mbedtls ctr drbg seed src so undefined reference to mbedtls mpi lset src so undefined reference to mbedtls cipher set iv src so undefined reference to mbedtls rsa copy src so undefined reference to mbedtls mpi exp mod src so undefined reference to mbedtls cipher info from type src so undefined reference to mbedtls pk init src so undefined reference to mbedtls md setup src so undefined reference to mbedtls rsa init src so undefined reference to mbedtls md info from type src so undefined reference to mbedtls cipher reset src so undefined reference to mbedtls pk free src so undefined reference to mbedtls pk get type src so undefined reference to mbedtls rsa check privkey src so undefined reference to mbedtls md starts src so undefined reference to mbedtls md hmac finish src so undefined reference to mbedtls mpi read binary src so undefined reference to mbedtls pk parse key src so undefined reference to mbedtls rsa check pubkey src so undefined reference to mbedtls mpi free src so undefined reference to mbedtls mpi bitlen src so undefined reference to mbedtls md init src so undefined reference to mbedtls rsa sign error ld returned exit status make error make leaving directory workspace deps scratch make error make leaving directory workspace deps scratch make error make leaving directory workspace deps scratch make error make leaving directory workspace deps make error | 0 |
134,195 | 29,924,019,678 | IssuesEvent | 2023-06-22 02:42:22 | vasl-developers/vasl | https://api.github.com/repos/vasl-developers/vasl | closed | LOS engine: hindrance cancelled by trench, foxhole but not by PFZ:Open Grnd | bug 2 - Code | LOS between 12F3 & 12H2 passes through 12G3, a grain hex. With no fortification counters hindrance is reported as one. With foxhole or trench in 12G3 no hindrance is reported. With a pillbox in 12G3 a hindrance of one is reported. With a PFZ:Open Grnd counter in the hex a hindrance of one is reported.
This also affects brush and orchard terrains. And A-T Ditches.
Expected: the presence of a foxhole or trench counter should not affect hindrances.
Desired: a PFZ:Open Grnd counter should affect hindrance
VASSAL version 3.6.11, vasl version 6.6.5 | 1.0 | LOS engine: hindrance cancelled by trench, foxhole but not by PFZ:Open Grnd - LOS between 12F3 & 12H2 passes through 12G3, a grain hex. With no fortification counters hindrance is reported as one. With foxhole or trench in 12G3 no hindrance is reported. With a pillbox in 12G3 a hindrance of one is reported. With a PFZ:Open Grnd counter in the hex a hindrance of one is reported.
This also affects brush and orchard terrains. And A-T Ditches.
Expected: the presence of a foxhole or trench counter should not affect hindrances.
Desired: a PFZ:Open Grnd counter should affect hindrance
VASSAL version 3.6.11, vasl version 6.6.5 | non_priority | los engine hindrance cancelled by trench foxhole but not by pfz open grnd los between passes through a grain hex with no fortification counters hindrance is reported as one with foxhole or trench in no hindrance is reported with a pillbox in a hindrance of one is reported with a pfz open grnd counter in the hex a hindrance of one is reported this also affects brush and orchard terrains and a t ditches expected the presence of a foxhole or trench counter should not affect hindrances desired a pfz open grnd counter should affect hindrance vassal version vasl version | 0 |
216,327 | 24,271,570,833 | IssuesEvent | 2022-09-28 10:42:10 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | opened | [SecurityWeek] Chrome 106 Patches High-Severity Vulnerabilities | SecurityWeek |
**Google this week announced the release of Chrome 106 to the stable channel with patches for 20 vulnerabilities, including 16 reported by external researchers.**
Of the externally reported security bugs, five are rated ‘high’ severity, eight are ‘medium’ severity, and three are ‘low’ severity.
[read more](https://www.securityweek.com/chrome-106-patches-high-severity-vulnerabilities)
<https://www.securityweek.com/chrome-106-patches-high-severity-vulnerabilities>
| True | [SecurityWeek] Chrome 106 Patches High-Severity Vulnerabilities -
**Google this week announced the release of Chrome 106 to the stable channel with patches for 20 vulnerabilities, including 16 reported by external researchers.**
Of the externally reported security bugs, five are rated ‘high’ severity, eight are ‘medium’ severity, and three are ‘low’ severity.
[read more](https://www.securityweek.com/chrome-106-patches-high-severity-vulnerabilities)
<https://www.securityweek.com/chrome-106-patches-high-severity-vulnerabilities>
| non_priority | chrome patches high severity vulnerabilities google this week announced the release of chrome to the stable channel with patches for vulnerabilities including reported by external researchers of the externally reported security bugs five are rated ‘high’ severity eight are ‘medium’ severity and three are ‘low’ severity | 0 |
56,045 | 23,684,758,857 | IssuesEvent | 2022-08-29 04:34:59 | microsoft/BotBuilder-Samples | https://api.github.com/repos/microsoft/BotBuilder-Samples | closed | [sso-with-skills] Authorizartion issues | customer-reported Bot Services customer-replied-to | ### Github issues for [C#](https://github.com/Microsoft/botbuilder-dotnet/issues) /[JS](https://github.com/Microsoft/botbuilder-js/issues) / [Java](https://github.com/Microsoft/botbuilder-java/issues)/ [Python](https://github.com/Microsoft/botbuilder-python/issues) should be used for bugs and feature requests. Use [Stack Overflow](https://stackoverflow.com/questions/tagged/botframework) for general "how-to" questions.
## Sample information
1. Sample type: [\samples\experimental\sso-with-skills]
2. Sample language: [dotnetcore]
3. Sample name: SSO with Simple Skill Consumer and Skill
## Describe the bug
Have a customer who is receiving `"StatusCode": 401,
"RawResponseBody": "{\"error\":{\"code\":\"InvalidAuthenticationToken\",\"message\":\"Access token validation failure. Invalid audience`
I am walking through the repo and getting `"Microsoft.Bot.Schema.ErrorResponseException: Operation returned an invalid status code Unauthorized at Microsoft.Bot.Connector.UserToken.GetTokenWithHttpMessagesAsync(String userId, String connectionName, String channelId, String code, Dictionary 2 customHeaders, CancellationToken cancellationToken) at Microsoft.Bot.Connector.UserTokenExtensions.GetTokenAsync(IUserToken operations, String userId, String connectionName, String channelId, String code, CancellationToken cancellationToken) at Microsoft.Bot.Builder.BotFrameworkAdapter.GetUserTokenAsync(ITurnContext turnContext, AppCredentials oAuthAppCredentials, String connectionName, String magicCode, CancellationToken cancellationToken) at Microsoft.Bot.Builder.Dialogs.UserTokenAccess.GetUserTokenAsync(ITurnContext turnContext, OAuthPromptSettings settings, String magicCode, CancellationToken cancellationToken) at Microsoft.Bot.Builder.Dialogs.OAuthPrompt.BeginDialogAsync(DialogContext dc, Object options, CancellationToken cancellationToken) at Microsoft.Bot.Builder.Dialogs.DialogContext.BeginDialogAsync(String dialogId, Object options, CancellationToken cancellationToken) `
I have confirmed via curl locally that am able to retrieve the correct and valid token.
## To Reproduce
Steps to reproduce the behavior:
1. Launch the code in the emulator after configuring the root and skill bot (Confirmed both are able to get an OAuth Connection)
2. Locally emulator connected to running instance of `RootBot`
3. Welcome message appears
5. Type 'login'
## Expected behavior
Expected to prompted with AAD login screen
## Additional context
Add any other context about the problem here.
| 1.0 | [sso-with-skills] Authorizartion issues - ### Github issues for [C#](https://github.com/Microsoft/botbuilder-dotnet/issues) /[JS](https://github.com/Microsoft/botbuilder-js/issues) / [Java](https://github.com/Microsoft/botbuilder-java/issues)/ [Python](https://github.com/Microsoft/botbuilder-python/issues) should be used for bugs and feature requests. Use [Stack Overflow](https://stackoverflow.com/questions/tagged/botframework) for general "how-to" questions.
## Sample information
1. Sample type: [\samples\experimental\sso-with-skills]
2. Sample language: [dotnetcore]
3. Sample name: SSO with Simple Skill Consumer and Skill
## Describe the bug
Have a customer who is receiving `"StatusCode": 401,
"RawResponseBody": "{\"error\":{\"code\":\"InvalidAuthenticationToken\",\"message\":\"Access token validation failure. Invalid audience`
I am walking through the repo and getting `"Microsoft.Bot.Schema.ErrorResponseException: Operation returned an invalid status code Unauthorized at Microsoft.Bot.Connector.UserToken.GetTokenWithHttpMessagesAsync(String userId, String connectionName, String channelId, String code, Dictionary 2 customHeaders, CancellationToken cancellationToken) at Microsoft.Bot.Connector.UserTokenExtensions.GetTokenAsync(IUserToken operations, String userId, String connectionName, String channelId, String code, CancellationToken cancellationToken) at Microsoft.Bot.Builder.BotFrameworkAdapter.GetUserTokenAsync(ITurnContext turnContext, AppCredentials oAuthAppCredentials, String connectionName, String magicCode, CancellationToken cancellationToken) at Microsoft.Bot.Builder.Dialogs.UserTokenAccess.GetUserTokenAsync(ITurnContext turnContext, OAuthPromptSettings settings, String magicCode, CancellationToken cancellationToken) at Microsoft.Bot.Builder.Dialogs.OAuthPrompt.BeginDialogAsync(DialogContext dc, Object options, CancellationToken cancellationToken) at Microsoft.Bot.Builder.Dialogs.DialogContext.BeginDialogAsync(String dialogId, Object options, CancellationToken cancellationToken) `
I have confirmed via curl locally that am able to retrieve the correct and valid token.
## To Reproduce
Steps to reproduce the behavior:
1. Launch the code in the emulator after configuring the root and skill bot (Confirmed both are able to get an OAuth Connection)
2. Locally emulator connected to running instance of `RootBot`
3. Welcome message appears
5. Type 'login'
## Expected behavior
Expected to prompted with AAD login screen
## Additional context
Add any other context about the problem here.
| non_priority | authorizartion issues github issues for should be used for bugs and feature requests use for general how to questions sample information sample type sample language sample name sso with simple skill consumer and skill describe the bug have a customer who is receiving statuscode rawresponsebody error code invalidauthenticationtoken message access token validation failure invalid audience i am walking through the repo and getting microsoft bot schema errorresponseexception operation returned an invalid status code unauthorized at microsoft bot connector usertoken gettokenwithhttpmessagesasync string userid string connectionname string channelid string code dictionary customheaders cancellationtoken cancellationtoken at microsoft bot connector usertokenextensions gettokenasync iusertoken operations string userid string connectionname string channelid string code cancellationtoken cancellationtoken at microsoft bot builder botframeworkadapter getusertokenasync iturncontext turncontext appcredentials oauthappcredentials string connectionname string magiccode cancellationtoken cancellationtoken at microsoft bot builder dialogs usertokenaccess getusertokenasync iturncontext turncontext oauthpromptsettings settings string magiccode cancellationtoken cancellationtoken at microsoft bot builder dialogs oauthprompt begindialogasync dialogcontext dc object options cancellationtoken cancellationtoken at microsoft bot builder dialogs dialogcontext begindialogasync string dialogid object options cancellationtoken cancellationtoken i have confirmed via curl locally that am able to retrieve the correct and valid token to reproduce steps to reproduce the behavior launch the code in the emulator after configuring the root and skill bot confirmed both are able to get an oauth connection locally emulator connected to running instance of rootbot welcome message appears type login expected behavior expected to prompted with aad login screen additional context add any other context about the problem here | 0 |
6,261 | 3,779,769,365 | IssuesEvent | 2016-03-18 09:59:37 | mapbox/mapbox-gl-native | https://api.github.com/repos/mapbox/mapbox-gl-native | opened | Avoid stripping debug symbols from -symbols builds | build iOS | All iOS SDK make targets currently [invoke `strip -Sx`](https://github.com/mapbox/mapbox-gl-native/blob/0e201eb23d6ae174599c0df5c41eb06fbdd586e0/platform/ios/scripts/package.sh#L176-L184) on the static and dynamic libraries. This step should be limited to `make ipackage-strip` and possibly `make iframework SYMBOLS=NO`. It doesn’t make sense for the `-symbols` builds, which exist for the purpose of debugging crashes, to lack debug symbols.
Per https://github.com/mapbox/mapbox-gl-native/issues/3280#issuecomment-175158420, this stripping step is mostly redundant anyways. It yields only a modest size decrease with respect to the dynamic framework.
/cc @boundsj @friedbunny | 1.0 | Avoid stripping debug symbols from -symbols builds - All iOS SDK make targets currently [invoke `strip -Sx`](https://github.com/mapbox/mapbox-gl-native/blob/0e201eb23d6ae174599c0df5c41eb06fbdd586e0/platform/ios/scripts/package.sh#L176-L184) on the static and dynamic libraries. This step should be limited to `make ipackage-strip` and possibly `make iframework SYMBOLS=NO`. It doesn’t make sense for the `-symbols` builds, which exist for the purpose of debugging crashes, to lack debug symbols.
Per https://github.com/mapbox/mapbox-gl-native/issues/3280#issuecomment-175158420, this stripping step is mostly redundant anyways. It yields only a modest size decrease with respect to the dynamic framework.
/cc @boundsj @friedbunny | non_priority | avoid stripping debug symbols from symbols builds all ios sdk make targets currently on the static and dynamic libraries this step should be limited to make ipackage strip and possibly make iframework symbols no it doesn’t make sense for the symbols builds which exist for the purpose of debugging crashes to lack debug symbols per this stripping step is mostly redundant anyways it yields only a modest size decrease with respect to the dynamic framework cc boundsj friedbunny | 0 |
15,327 | 3,455,928,353 | IssuesEvent | 2015-12-17 22:21:36 | dzitkowskik/mini-dos | https://api.github.com/repos/dzitkowskik/mini-dos | opened | Master failure (TESTS) | test | After implementing #70 and #71 implement master failure test case, when we somehow kill master and want to recreate consistent state from backup. Nodes, should be able to work with a new instance of master. | 1.0 | Master failure (TESTS) - After implementing #70 and #71 implement master failure test case, when we somehow kill master and want to recreate consistent state from backup. Nodes, should be able to work with a new instance of master. | non_priority | master failure tests after implementing and implement master failure test case when we somehow kill master and want to recreate consistent state from backup nodes should be able to work with a new instance of master | 0 |
393,837 | 27,012,034,759 | IssuesEvent | 2023-02-10 16:07:34 | Telefonica/mistica-design | https://api.github.com/repos/Telefonica/mistica-design | closed | Fix inverse state in tags | component: tag library: mobile library: desktop category: documentation platform: ios platform: android platform: web mode: dark brand: all | - [x] Update Tags Specs
- [ ] #920
- [x] [Android ticket](https://jira.tid.es/browse/ANDROID-11348)
- [x] [ iOS ticket](https://jira.tid.es/browse/IOS-7888)
- [x] [Web ticket](https://jira.tid.es/browse/WEB-705)
Las tags sobre imágenes en dark mode se rompen.
Aprovecharía para cambiar quizás la definición actual de los estados inverse en light. @AnaMontes11 comentó en algún momento que aplicaría el mismo estado que el _no-inverse_ en el inverse y no cambiar a blanco puro en estado inverse. | 1.0 | Fix inverse state in tags - - [x] Update Tags Specs
- [ ] #920
- [x] [Android ticket](https://jira.tid.es/browse/ANDROID-11348)
- [x] [ iOS ticket](https://jira.tid.es/browse/IOS-7888)
- [x] [Web ticket](https://jira.tid.es/browse/WEB-705)
Las tags sobre imágenes en dark mode se rompen.
Aprovecharía para cambiar quizás la definición actual de los estados inverse en light. @AnaMontes11 comentó en algún momento que aplicaría el mismo estado que el _no-inverse_ en el inverse y no cambiar a blanco puro en estado inverse. | non_priority | fix inverse state in tags update tags specs las tags sobre imágenes en dark mode se rompen aprovecharía para cambiar quizás la definición actual de los estados inverse en light comentó en algún momento que aplicaría el mismo estado que el no inverse en el inverse y no cambiar a blanco puro en estado inverse | 0 |
121,733 | 17,662,302,078 | IssuesEvent | 2021-08-21 19:12:51 | ghc-dev/Gregory-Pena | https://api.github.com/repos/ghc-dev/Gregory-Pena | opened | CVE-2020-14365 (High) detected in ansible-2.9.9.tar.gz | security vulnerability | ## CVE-2020-14365 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: Gregory-Pena/requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Gregory-Pena/commit/5fbcaef596a4ed03ab44787e2f08df6f043a7b15">5fbcaef596a4ed03ab44787e2f08df6f043a7b15</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Ansible Engine, in ansible-engine 2.8.x before 2.8.15 and ansible-engine 2.9.x before 2.9.13, when installing packages using the dnf module. GPG signatures are ignored during installation even when disable_gpg_check is set to False, which is the default behavior. This flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts. The highest threat from this vulnerability is to integrity and system availability.
<p>Publish Date: 2020-09-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14365>CVE-2020-14365</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1869154">https://bugzilla.redhat.com/show_bug.cgi?id=1869154</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.8.15,2.9.13</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ansible","packageVersion":"2.9.9","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"ansible:2.9.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.8.15,2.9.13"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-14365","vulnerabilityDetails":"A flaw was found in the Ansible Engine, in ansible-engine 2.8.x before 2.8.15 and ansible-engine 2.9.x before 2.9.13, when installing packages using the dnf module. GPG signatures are ignored during installation even when disable_gpg_check is set to False, which is the default behavior. This flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts. The highest threat from this vulnerability is to integrity and system availability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14365","cvss3Severity":"high","cvss3Score":"7.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-14365 (High) detected in ansible-2.9.9.tar.gz - ## CVE-2020-14365 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: Gregory-Pena/requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Gregory-Pena/commit/5fbcaef596a4ed03ab44787e2f08df6f043a7b15">5fbcaef596a4ed03ab44787e2f08df6f043a7b15</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Ansible Engine, in ansible-engine 2.8.x before 2.8.15 and ansible-engine 2.9.x before 2.9.13, when installing packages using the dnf module. GPG signatures are ignored during installation even when disable_gpg_check is set to False, which is the default behavior. This flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts. The highest threat from this vulnerability is to integrity and system availability.
<p>Publish Date: 2020-09-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14365>CVE-2020-14365</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1869154">https://bugzilla.redhat.com/show_bug.cgi?id=1869154</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.8.15,2.9.13</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ansible","packageVersion":"2.9.9","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"ansible:2.9.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.8.15,2.9.13"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-14365","vulnerabilityDetails":"A flaw was found in the Ansible Engine, in ansible-engine 2.8.x before 2.8.15 and ansible-engine 2.9.x before 2.9.13, when installing packages using the dnf module. GPG signatures are ignored during installation even when disable_gpg_check is set to False, which is the default behavior. This flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts. The highest threat from this vulnerability is to integrity and system availability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14365","cvss3Severity":"high","cvss3Score":"7.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in ansible tar gz cve high severity vulnerability vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file gregory pena requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was found in the ansible engine in ansible engine x before and ansible engine x before when installing packages using the dnf module gpg signatures are ignored during installation even when disable gpg check is set to false which is the default behavior this flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts the highest threat from this vulnerability is to integrity and system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree ansible isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails a flaw was found in the ansible engine in ansible engine x before and ansible engine x before when installing packages using the dnf module gpg signatures are ignored during installation even when disable gpg check is set to false which is the default behavior this flaw leads to malicious packages being installed on the system and arbitrary code executed via package installation scripts the highest threat from this vulnerability is to integrity and system availability vulnerabilityurl | 0 |
428,668 | 30,005,470,385 | IssuesEvent | 2023-06-26 12:10:30 | netwerk-digitaal-erfgoed/network-of-terms | https://api.github.com/repos/netwerk-digitaal-erfgoed/network-of-terms | closed | Add licence section to NDE terminology requirements/ datasets? | documentation discuss | Currently the [requirements terminologiebronnen](https://netwerk-digitaal-erfgoed.github.io/requirements-terminologiebronnen/) has no section/ recommendation on licenses (which are mentioned in [NDE dataset requirements](https://netwerk-digitaal-erfgoed.github.io/requirements-datasets/#dataset-license)).
Would be good to discuss license requirements, and add licenses to the [dataset descriptions](https://github.com/netwerk-digitaal-erfgoed/network-of-terms/tree/master/packages/network-of-terms-catalog/catalog/datasets).
| 1.0 | Add licence section to NDE terminology requirements/ datasets? - Currently the [requirements terminologiebronnen](https://netwerk-digitaal-erfgoed.github.io/requirements-terminologiebronnen/) has no section/ recommendation on licenses (which are mentioned in [NDE dataset requirements](https://netwerk-digitaal-erfgoed.github.io/requirements-datasets/#dataset-license)).
Would be good to discuss license requirements, and add licenses to the [dataset descriptions](https://github.com/netwerk-digitaal-erfgoed/network-of-terms/tree/master/packages/network-of-terms-catalog/catalog/datasets).
| non_priority | add licence section to nde terminology requirements datasets currently the has no section recommendation on licenses which are mentioned in would be good to discuss license requirements and add licenses to the | 0 |
209,264 | 16,188,989,249 | IssuesEvent | 2021-05-04 04:40:39 | osmosis-labs/osmosis | https://api.github.com/repos/osmosis-labs/osmosis | opened | Make a spec for x/gamm | documentation x/gamm | We need to clearly explain what x/gamm implements. and then how to navigate all the various code objects in x/gamm.
We should also explain all message types, serialization oddities, and link to CLI parameters | 1.0 | Make a spec for x/gamm - We need to clearly explain what x/gamm implements. and then how to navigate all the various code objects in x/gamm.
We should also explain all message types, serialization oddities, and link to CLI parameters | non_priority | make a spec for x gamm we need to clearly explain what x gamm implements and then how to navigate all the various code objects in x gamm we should also explain all message types serialization oddities and link to cli parameters | 0 |
155,417 | 24,463,255,342 | IssuesEvent | 2022-10-07 13:03:06 | phetsims/quadrilateral | https://api.github.com/repos/phetsims/quadrilateral | opened | Easter egg response questioning number of sides | design:description design:voicing | Related to Shape Maintenance Responses in issue #198 there is a special case when the Quad can look like a triangle. This state is possible for both Convex Quads and Kites and it might only be possible in certain envrironnments - like when using the virtual sim. It might be possible with the virtual the new TMQs or actuated TMQs or other forms of input. It is indeed possible with the virtual environment.
My math understanding is that the following shapes are not mathematically triangles because the shapes still have 4 vertices and 4 sides. That said, they appear like and feel like triangles, so I am wondering if a fun question would be appropriate for a context response.
<img width="613" alt="image" src="https://user-images.githubusercontent.com/1902116/194557914-143837d0-c25a-49a3-9e02-0d7b10e8bbb2.png">
<img width="572" alt="image" src="https://user-images.githubusercontent.com/1902116/194557974-cc5c458b-fe14-492b-ace7-7e499f874894.png">
<img width="491" alt="image" src="https://user-images.githubusercontent.com/1902116/194558100-e4f5ba87-eed9-403d-9535-6b20fcaea73d.png">
Not done with this issue yet.
| 2.0 | Easter egg response questioning number of sides - Related to Shape Maintenance Responses in issue #198 there is a special case when the Quad can look like a triangle. This state is possible for both Convex Quads and Kites and it might only be possible in certain envrironnments - like when using the virtual sim. It might be possible with the virtual the new TMQs or actuated TMQs or other forms of input. It is indeed possible with the virtual environment.
My math understanding is that the following shapes are not mathematically triangles because the shapes still have 4 vertices and 4 sides. That said, they appear like and feel like triangles, so I am wondering if a fun question would be appropriate for a context response.
<img width="613" alt="image" src="https://user-images.githubusercontent.com/1902116/194557914-143837d0-c25a-49a3-9e02-0d7b10e8bbb2.png">
<img width="572" alt="image" src="https://user-images.githubusercontent.com/1902116/194557974-cc5c458b-fe14-492b-ace7-7e499f874894.png">
<img width="491" alt="image" src="https://user-images.githubusercontent.com/1902116/194558100-e4f5ba87-eed9-403d-9535-6b20fcaea73d.png">
Not done with this issue yet.
| non_priority | easter egg response questioning number of sides related to shape maintenance responses in issue there is a special case when the quad can look like a triangle this state is possible for both convex quads and kites and it might only be possible in certain envrironnments like when using the virtual sim it might be possible with the virtual the new tmqs or actuated tmqs or other forms of input it is indeed possible with the virtual environment my math understanding is that the following shapes are not mathematically triangles because the shapes still have vertices and sides that said they appear like and feel like triangles so i am wondering if a fun question would be appropriate for a context response img width alt image src img width alt image src img width alt image src not done with this issue yet | 0 |
140,084 | 18,893,691,232 | IssuesEvent | 2021-11-15 15:41:40 | Zolyn/vuepress-plugin-waline | https://api.github.com/repos/Zolyn/vuepress-plugin-waline | closed | CVE-2021-3749 (Medium) detected in axios-0.21.1.tgz | security vulnerability | ## CVE-2021-3749 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>axios-0.21.1.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.1.tgz">https://registry.npmjs.org/axios/-/axios-0.21.1.tgz</a></p>
<p>Path to dependency file: vuepress-plugin-waline/package.json</p>
<p>Path to vulnerable library: vuepress-plugin-waline/node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- minivaline-5.1.7.tgz (Root Library)
- snyk-1.618.0.tgz
- code-client-3.7.0.tgz
- :x: **axios-0.21.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
axios is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749>CVE-2021-3749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3749 (Medium) detected in axios-0.21.1.tgz - ## CVE-2021-3749 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>axios-0.21.1.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.1.tgz">https://registry.npmjs.org/axios/-/axios-0.21.1.tgz</a></p>
<p>Path to dependency file: vuepress-plugin-waline/package.json</p>
<p>Path to vulnerable library: vuepress-plugin-waline/node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- minivaline-5.1.7.tgz (Root Library)
- snyk-1.618.0.tgz
- code-client-3.7.0.tgz
- :x: **axios-0.21.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
axios is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3749>CVE-2021-3749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in axios tgz cve medium severity vulnerability vulnerable library axios tgz promise based http client for the browser and node js library home page a href path to dependency file vuepress plugin waline package json path to vulnerable library vuepress plugin waline node modules axios package json dependency hierarchy minivaline tgz root library snyk tgz code client tgz x axios tgz vulnerable library found in base branch main vulnerability details axios is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href step up your open source security game with whitesource | 0 |
28,927 | 7,045,310,756 | IssuesEvent | 2018-01-01 17:51:28 | exercism/java | https://api.github.com/repos/exercism/java | opened | word-count: update tests and add version file | code | The word-count tests should be updated to exactly match the canonical data. Also a version file should be added to match the canonical data version. | 1.0 | word-count: update tests and add version file - The word-count tests should be updated to exactly match the canonical data. Also a version file should be added to match the canonical data version. | non_priority | word count update tests and add version file the word count tests should be updated to exactly match the canonical data also a version file should be added to match the canonical data version | 0 |
30,881 | 7,267,710,347 | IssuesEvent | 2018-02-20 06:53:38 | PowerPointLabs/PowerPointLabs | https://api.github.com/repos/PowerPointLabs/PowerPointLabs | closed | Refactor "global" variables in RibbonUI | a-CodeQuality d.Moderate | Some variables are put in Ribbon1.cs for legacy reasons and accessed using this.GetRibbonUI().HighlightBulletsEnabled, but this should be changed into their own labs.
Refer to https://github.com/PowerPointLabs/PowerPointLabs/blob/master/PowerPointLabs/PowerPointLabs/Ribbon1.cs#L122 | 1.0 | Refactor "global" variables in RibbonUI - Some variables are put in Ribbon1.cs for legacy reasons and accessed using this.GetRibbonUI().HighlightBulletsEnabled, but this should be changed into their own labs.
Refer to https://github.com/PowerPointLabs/PowerPointLabs/blob/master/PowerPointLabs/PowerPointLabs/Ribbon1.cs#L122 | non_priority | refactor global variables in ribbonui some variables are put in cs for legacy reasons and accessed using this getribbonui highlightbulletsenabled but this should be changed into their own labs refer to | 0 |
350,719 | 31,931,975,383 | IssuesEvent | 2023-09-19 08:03:38 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix raw_ops.test_tensorflow_Div | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix raw_ops.test_tensorflow_Div - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6111783952/job/16587790899"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix raw ops test tensorflow div numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
114,824 | 9,761,747,234 | IssuesEvent | 2019-06-05 09:31:21 | FluentLenium/FluentLenium | https://api.github.com/repos/FluentLenium/FluentLenium | closed | Add various lifecycle integration tests for JUnit 5 | tests | We have driver lifecycle tests for junit 4 and testng. Junit5 finally supports test suites so we can add SharedWebDriver test suite for this framework as well.
TestNG (fluentlenium-testng) `org.fluentlenium.adapter.testng.integration.shareddriver`
Junit4 (fluentlenium-core) `org.fluentlenium.adapter.sharedwebdriver`
https://junit.org/junit5/docs/current/user-guide/#running-tests-junit-platform-runner-test-suite | 1.0 | Add various lifecycle integration tests for JUnit 5 - We have driver lifecycle tests for junit 4 and testng. Junit5 finally supports test suites so we can add SharedWebDriver test suite for this framework as well.
TestNG (fluentlenium-testng) `org.fluentlenium.adapter.testng.integration.shareddriver`
Junit4 (fluentlenium-core) `org.fluentlenium.adapter.sharedwebdriver`
https://junit.org/junit5/docs/current/user-guide/#running-tests-junit-platform-runner-test-suite | non_priority | add various lifecycle integration tests for junit we have driver lifecycle tests for junit and testng finally supports test suites so we can add sharedwebdriver test suite for this framework as well testng fluentlenium testng org fluentlenium adapter testng integration shareddriver fluentlenium core org fluentlenium adapter sharedwebdriver | 0 |
172,679 | 13,326,654,393 | IssuesEvent | 2020-08-27 12:00:20 | hazelcast/hazelcast-jet | https://api.github.com/repos/hazelcast/hazelcast-jet | opened | com.hazelcast.jet.server.JetCommandLineTest.test_cancelJob_byJobId | test-failure | _master_ (commit f8276874c6b6fa7433e41a51f4ab885c9a40188c)
Failed on Oracle JDK 8: http://jenkins.hazelcast.com/view/Jet%20-%20Compatibility/job/jet-oss-master-oracle-jdk8/266/testReport/com.hazelcast.jet.server/JetCommandLineTest/test_cancelJob_byJobId/
Stacktrace:
```
picocli.CommandLine$ExecutionException: Error while calling command (public void com.hazelcast.jet.server.JetCommandLine.cancel(com.hazelcast.jet.server.JetCommandLine$Verbosity,com.hazelcast.jet.server.JetCommandLine$TargetsMixin,java.lang.String) throws java.io.IOException): com.hazelcast.core.HazelcastException: com.hazelcast.core.HazelcastException: Could not load 'hazelcast-client.yaml' from the classpath
at picocli.CommandLine.execute(CommandLine.java:1207)
at picocli.CommandLine.access$800(CommandLine.java:141)
at picocli.CommandLine$RunAll.handle(CommandLine.java:1416)
at picocli.CommandLine$RunAll.handle(CommandLine.java:1376)
at picocli.CommandLine$AbstractParseResultHandler.handleParseResult(CommandLine.java:1243)
at picocli.CommandLine.parseWithHandlers(CommandLine.java:1526)
at com.hazelcast.jet.server.JetCommandLine.runCommandLine(JetCommandLine.java:162)
at com.hazelcast.jet.server.JetCommandLineTest.run(JetCommandLineTest.java:666)
at com.hazelcast.jet.server.JetCommandLineTest.test_cancelJob_byJobId(JetCommandLineTest.java:200)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:114)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:106)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.lang.Thread.run(Thread.java:748)
Caused by: com.hazelcast.core.HazelcastException: com.hazelcast.core.HazelcastException: Could not load 'hazelcast-client.yaml' from the classpath
at com.hazelcast.internal.config.AbstractConfigLocator.loadConfigurationFromClasspath(AbstractConfigLocator.java:164)
at com.hazelcast.internal.config.AbstractConfigLocator.loadConfigurationFromClasspath(AbstractConfigLocator.java:176)
at com.hazelcast.jet.impl.config.YamlJetClientConfigLocator.locateOnClasspath(YamlJetClientConfigLocator.java:52)
at com.hazelcast.internal.config.AbstractConfigLocator.locateInWorkDirOrOnClasspath(AbstractConfigLocator.java:124)
at com.hazelcast.jet.impl.config.ConfigProvider.locateAndGetClientConfig(ConfigProvider.java:101)
at com.hazelcast.jet.server.JetCommandLine.getClientConfig(JetCommandLine.java:481)
at com.hazelcast.jet.server.JetCommandLine.lambda$getJetClient$13(JetCommandLine.java:463)
at com.hazelcast.jet.impl.util.Util.uncheckCall(Util.java:92)
at com.hazelcast.jet.server.JetCommandLine.getJetClient(JetCommandLine.java:463)
at com.hazelcast.jet.server.JetCommandLine.runWithJet(JetCommandLine.java:454)
at com.hazelcast.jet.server.JetCommandLine.cancel(JetCommandLine.java:253)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at picocli.CommandLine.execute(CommandLine.java:1189)
... 20 more
Caused by: com.hazelcast.core.HazelcastException: Could not load 'hazelcast-client.yaml' from the classpath
at com.hazelcast.internal.config.AbstractConfigLocator.loadConfigurationFromClasspath(AbstractConfigLocator.java:160)
... 35 more
```
Standard output:
```
Hiccups measured while running test 'test_cancelJob_byJobId(com.hazelcast.jet.server.JetCommandLineTest):'
11:51:05, accumulated pauses: 1221 ms, max pause: 340 ms, pauses over 1000 ms: 0
11:51:10, accumulated pauses: 3348 ms, max pause: 253 ms, pauses over 1000 ms: 0
11:51:15, accumulated pauses: 3275 ms, max pause: 423 ms, pauses over 1000 ms: 0
11:51:20, accumulated pauses: 4523 ms, max pause: 890 ms, pauses over 1000 ms: 0
11:51:25, accumulated pauses: 2662 ms, max pause: 264 ms, pauses over 1000 ms: 0
11:51:30, accumulated pauses: 143 ms, max pause: 40 ms, pauses over 1000 ms: 0
```
| 1.0 | com.hazelcast.jet.server.JetCommandLineTest.test_cancelJob_byJobId - _master_ (commit f8276874c6b6fa7433e41a51f4ab885c9a40188c)
Failed on Oracle JDK 8: http://jenkins.hazelcast.com/view/Jet%20-%20Compatibility/job/jet-oss-master-oracle-jdk8/266/testReport/com.hazelcast.jet.server/JetCommandLineTest/test_cancelJob_byJobId/
Stacktrace:
```
picocli.CommandLine$ExecutionException: Error while calling command (public void com.hazelcast.jet.server.JetCommandLine.cancel(com.hazelcast.jet.server.JetCommandLine$Verbosity,com.hazelcast.jet.server.JetCommandLine$TargetsMixin,java.lang.String) throws java.io.IOException): com.hazelcast.core.HazelcastException: com.hazelcast.core.HazelcastException: Could not load 'hazelcast-client.yaml' from the classpath
at picocli.CommandLine.execute(CommandLine.java:1207)
at picocli.CommandLine.access$800(CommandLine.java:141)
at picocli.CommandLine$RunAll.handle(CommandLine.java:1416)
at picocli.CommandLine$RunAll.handle(CommandLine.java:1376)
at picocli.CommandLine$AbstractParseResultHandler.handleParseResult(CommandLine.java:1243)
at picocli.CommandLine.parseWithHandlers(CommandLine.java:1526)
at com.hazelcast.jet.server.JetCommandLine.runCommandLine(JetCommandLine.java:162)
at com.hazelcast.jet.server.JetCommandLineTest.run(JetCommandLineTest.java:666)
at com.hazelcast.jet.server.JetCommandLineTest.test_cancelJob_byJobId(JetCommandLineTest.java:200)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:114)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:106)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.lang.Thread.run(Thread.java:748)
Caused by: com.hazelcast.core.HazelcastException: com.hazelcast.core.HazelcastException: Could not load 'hazelcast-client.yaml' from the classpath
at com.hazelcast.internal.config.AbstractConfigLocator.loadConfigurationFromClasspath(AbstractConfigLocator.java:164)
at com.hazelcast.internal.config.AbstractConfigLocator.loadConfigurationFromClasspath(AbstractConfigLocator.java:176)
at com.hazelcast.jet.impl.config.YamlJetClientConfigLocator.locateOnClasspath(YamlJetClientConfigLocator.java:52)
at com.hazelcast.internal.config.AbstractConfigLocator.locateInWorkDirOrOnClasspath(AbstractConfigLocator.java:124)
at com.hazelcast.jet.impl.config.ConfigProvider.locateAndGetClientConfig(ConfigProvider.java:101)
at com.hazelcast.jet.server.JetCommandLine.getClientConfig(JetCommandLine.java:481)
at com.hazelcast.jet.server.JetCommandLine.lambda$getJetClient$13(JetCommandLine.java:463)
at com.hazelcast.jet.impl.util.Util.uncheckCall(Util.java:92)
at com.hazelcast.jet.server.JetCommandLine.getJetClient(JetCommandLine.java:463)
at com.hazelcast.jet.server.JetCommandLine.runWithJet(JetCommandLine.java:454)
at com.hazelcast.jet.server.JetCommandLine.cancel(JetCommandLine.java:253)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at picocli.CommandLine.execute(CommandLine.java:1189)
... 20 more
Caused by: com.hazelcast.core.HazelcastException: Could not load 'hazelcast-client.yaml' from the classpath
at com.hazelcast.internal.config.AbstractConfigLocator.loadConfigurationFromClasspath(AbstractConfigLocator.java:160)
... 35 more
```
Standard output:
```
Hiccups measured while running test 'test_cancelJob_byJobId(com.hazelcast.jet.server.JetCommandLineTest):'
11:51:05, accumulated pauses: 1221 ms, max pause: 340 ms, pauses over 1000 ms: 0
11:51:10, accumulated pauses: 3348 ms, max pause: 253 ms, pauses over 1000 ms: 0
11:51:15, accumulated pauses: 3275 ms, max pause: 423 ms, pauses over 1000 ms: 0
11:51:20, accumulated pauses: 4523 ms, max pause: 890 ms, pauses over 1000 ms: 0
11:51:25, accumulated pauses: 2662 ms, max pause: 264 ms, pauses over 1000 ms: 0
11:51:30, accumulated pauses: 143 ms, max pause: 40 ms, pauses over 1000 ms: 0
```
| non_priority | com hazelcast jet server jetcommandlinetest test canceljob byjobid master commit failed on oracle jdk stacktrace picocli commandline executionexception error while calling command public void com hazelcast jet server jetcommandline cancel com hazelcast jet server jetcommandline verbosity com hazelcast jet server jetcommandline targetsmixin java lang string throws java io ioexception com hazelcast core hazelcastexception com hazelcast core hazelcastexception could not load hazelcast client yaml from the classpath at picocli commandline execute commandline java at picocli commandline access commandline java at picocli commandline runall handle commandline java at picocli commandline runall handle commandline java at picocli commandline abstractparseresulthandler handleparseresult commandline java at picocli commandline parsewithhandlers commandline java at com hazelcast jet server jetcommandline runcommandline jetcommandline java at com hazelcast jet server jetcommandlinetest run jetcommandlinetest java at com hazelcast jet server jetcommandlinetest test canceljob byjobid jetcommandlinetest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at com hazelcast test failontimeoutstatement callablestatement call failontimeoutstatement java at com hazelcast test failontimeoutstatement callablestatement call failontimeoutstatement java at java util concurrent futuretask run futuretask java at java lang thread run thread java caused by com hazelcast core hazelcastexception com hazelcast core hazelcastexception could not load hazelcast client yaml from the classpath at com hazelcast internal config abstractconfiglocator loadconfigurationfromclasspath abstractconfiglocator java at com hazelcast internal config abstractconfiglocator loadconfigurationfromclasspath abstractconfiglocator java at com hazelcast jet impl config yamljetclientconfiglocator locateonclasspath yamljetclientconfiglocator java at com hazelcast internal config abstractconfiglocator locateinworkdiroronclasspath abstractconfiglocator java at com hazelcast jet impl config configprovider locateandgetclientconfig configprovider java at com hazelcast jet server jetcommandline getclientconfig jetcommandline java at com hazelcast jet server jetcommandline lambda getjetclient jetcommandline java at com hazelcast jet impl util util uncheckcall util java at com hazelcast jet server jetcommandline getjetclient jetcommandline java at com hazelcast jet server jetcommandline runwithjet jetcommandline java at com hazelcast jet server jetcommandline cancel jetcommandline java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at picocli commandline execute commandline java more caused by com hazelcast core hazelcastexception could not load hazelcast client yaml from the classpath at com hazelcast internal config abstractconfiglocator loadconfigurationfromclasspath abstractconfiglocator java more standard output hiccups measured while running test test canceljob byjobid com hazelcast jet server jetcommandlinetest accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms | 0 |
270,161 | 28,960,431,030 | IssuesEvent | 2023-05-10 01:41:24 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | reopened | CVE-2019-19081 (Medium) detected in linuxlinux-4.19.6 | Mend: dependency security vulnerability | ## CVE-2019-19081 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the nfp_flower_spawn_vnic_reprs() function in drivers/net/ethernet/netronome/nfp/flower/main.c in the Linux kernel before 5.3.4 allows attackers to cause a denial of service (memory consumption), aka CID-8ce39eb5a67a.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19081>CVE-2019-19081</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19081 (Medium) detected in linuxlinux-4.19.6 - ## CVE-2019-19081 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the nfp_flower_spawn_vnic_reprs() function in drivers/net/ethernet/netronome/nfp/flower/main.c in the Linux kernel before 5.3.4 allows attackers to cause a denial of service (memory consumption), aka CID-8ce39eb5a67a.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19081>CVE-2019-19081</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details a memory leak in the nfp flower spawn vnic reprs function in drivers net ethernet netronome nfp flower main c in the linux kernel before allows attackers to cause a denial of service memory consumption aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
143,489 | 22,056,693,694 | IssuesEvent | 2022-05-30 13:29:58 | pulumi/pulumi-aws | https://api.github.com/repos/pulumi/pulumi-aws | closed | prompt user for `aws login` | kind/enhancement impact/usability resolution/by-design | ## Hello!
<!-- Please leave this section as-is, it's designed to help others in the community know how to interact with our GitHub issues. -->
- Vote on this issue by adding a 👍 reaction
- If you want to implement this feature, comment to let us know (we'll work with you on design, scheduling, etc.)
## Issue details
Idk if this is reasonable to implement, but it would be nice to improve this flow
```
kdixler@kdixler-20xw004aus ~/Documents/aws-python % pulumi up
Previewing update (dev)
View Live: https://app.pulumi.com/dixler/aws-python/dev/previews/a96bbfbb-02d0-4d09-bf91-9c83d8ed1c48
Type Name Plan Info
+ pulumi:pulumi:Stack aws-python-dev create
└─ aws:s3:Bucket my-bucket 1 error
Diagnostics:
aws:s3:Bucket (my-bucket):
error: unable to discover AWS AccessKeyID and/or SecretAccessKey - see https://pulumi.io/install/aws.html for details on configuration
255 kdixler@kdixler-20xw004aus ~/Documents/aws-python % aws sso login
Attempting to automatically open the SSO authorization page in your default browser.
If the browser does not open or you wish to use a different device to authorize this request, open the following URL:
https://device.sso.us-west-2.amazonaws.com/
Then enter the code:
<redacted>
Successully logged into Start URL: <redacted>
kdixler@kdixler-20xw004aus ~/Documents/aws-python % pulumi up
Previewing update (dev)
View Live: <redacted>
Type Name Plan
+ pulumi:pulumi:Stack aws-python-dev create
+ └─ aws:s3:Bucket my-bucket create
Resources:
+ 2 to create
Do you want to perform this update? [Use arrows to move, enter to select, type to filter]
yes
> no
details
...
```
<!-- Enhancement requests are most helpful when they describe the problem you're having as well as articulating the potential solution you'd like to see built. -->
### Affected area/feature
<!-- If you know the specific area where this feature request would go (e.g. Automation API, the Pulumi Service, the Terraform bridge, etc.), feel free to put that area here. -->
| 1.0 | prompt user for `aws login` - ## Hello!
<!-- Please leave this section as-is, it's designed to help others in the community know how to interact with our GitHub issues. -->
- Vote on this issue by adding a 👍 reaction
- If you want to implement this feature, comment to let us know (we'll work with you on design, scheduling, etc.)
## Issue details
Idk if this is reasonable to implement, but it would be nice to improve this flow
```
kdixler@kdixler-20xw004aus ~/Documents/aws-python % pulumi up
Previewing update (dev)
View Live: https://app.pulumi.com/dixler/aws-python/dev/previews/a96bbfbb-02d0-4d09-bf91-9c83d8ed1c48
Type Name Plan Info
+ pulumi:pulumi:Stack aws-python-dev create
└─ aws:s3:Bucket my-bucket 1 error
Diagnostics:
aws:s3:Bucket (my-bucket):
error: unable to discover AWS AccessKeyID and/or SecretAccessKey - see https://pulumi.io/install/aws.html for details on configuration
255 kdixler@kdixler-20xw004aus ~/Documents/aws-python % aws sso login
Attempting to automatically open the SSO authorization page in your default browser.
If the browser does not open or you wish to use a different device to authorize this request, open the following URL:
https://device.sso.us-west-2.amazonaws.com/
Then enter the code:
<redacted>
Successully logged into Start URL: <redacted>
kdixler@kdixler-20xw004aus ~/Documents/aws-python % pulumi up
Previewing update (dev)
View Live: <redacted>
Type Name Plan
+ pulumi:pulumi:Stack aws-python-dev create
+ └─ aws:s3:Bucket my-bucket create
Resources:
+ 2 to create
Do you want to perform this update? [Use arrows to move, enter to select, type to filter]
yes
> no
details
...
```
<!-- Enhancement requests are most helpful when they describe the problem you're having as well as articulating the potential solution you'd like to see built. -->
### Affected area/feature
<!-- If you know the specific area where this feature request would go (e.g. Automation API, the Pulumi Service, the Terraform bridge, etc.), feel free to put that area here. -->
| non_priority | prompt user for aws login hello vote on this issue by adding a 👍 reaction if you want to implement this feature comment to let us know we ll work with you on design scheduling etc issue details idk if this is reasonable to implement but it would be nice to improve this flow kdixler kdixler documents aws python pulumi up previewing update dev view live type name plan info pulumi pulumi stack aws python dev create └─ aws bucket my bucket error diagnostics aws bucket my bucket error unable to discover aws accesskeyid and or secretaccesskey see for details on configuration kdixler kdixler documents aws python aws sso login attempting to automatically open the sso authorization page in your default browser if the browser does not open or you wish to use a different device to authorize this request open the following url then enter the code successully logged into start url kdixler kdixler documents aws python pulumi up previewing update dev view live type name plan pulumi pulumi stack aws python dev create └─ aws bucket my bucket create resources to create do you want to perform this update yes no details affected area feature | 0 |
219,918 | 16,855,768,384 | IssuesEvent | 2021-06-21 06:24:13 | baloise/design-system | https://api.github.com/repos/baloise/design-system | closed | Error when using with vite | documentation | I tried to import the the baloise DS using vue3 and vite without typescript following https://baloise-ui-library.vercel.app/components/essentials/vue.html#install
I did use the `Vue.use(BaloiseDesignSystem, { useVite: false })` to load the plugin as indicated in the doc.
```
me@computer ~/project/ (git:main) $ npm run dev
> dev
> vite
Pre-bundling dependencies:
vue
@baloise/design-system-components-vue
(this will be run only when your dependencies or config have changed)
vite v2.3.8 dev server running at:
> Local: http://localhost:3000/
> Network: use `--host` to expose
ready in 277ms.
[@vue/compiler-sfc] <script setup> is still an experimental proposal.
Follow its status at https://github.com/vuejs/rfcs/pull/227.
[@vue/compiler-sfc] When using experimental features,
it is recommended to pin your vue dependencies to exact versions to avoid breakage.
12:32:50 AM [vite] warning:
/Users/me/project/node_modules/.vite/@baloise_design-system-components-vue.js
7221| return module[exportName];
7222| }
7223| return import(
| ^
7224| /* webpackInclude: /\.entry\.js$/ */
7225| /* webpackExclude: /\.system\.entry\.js$/ */
The above dynamic import cannot be analyzed by vite.
See https://github.com/rollup/plugins/tree/master/packages/dynamic-import-vars#limitations for supported dynamic import formats. If this is intended to be left as-is, you can use the /* @vite-ignore */ comment inside the import() call to suppress this warning.
Plugin: vite:import-analysis
File: Users/me/project/node_modules/.vite/@baloise_design-system-components-vue.js?v=8639cb5e
``` | 1.0 | Error when using with vite - I tried to import the the baloise DS using vue3 and vite without typescript following https://baloise-ui-library.vercel.app/components/essentials/vue.html#install
I did use the `Vue.use(BaloiseDesignSystem, { useVite: false })` to load the plugin as indicated in the doc.
```
me@computer ~/project/ (git:main) $ npm run dev
> dev
> vite
Pre-bundling dependencies:
vue
@baloise/design-system-components-vue
(this will be run only when your dependencies or config have changed)
vite v2.3.8 dev server running at:
> Local: http://localhost:3000/
> Network: use `--host` to expose
ready in 277ms.
[@vue/compiler-sfc] <script setup> is still an experimental proposal.
Follow its status at https://github.com/vuejs/rfcs/pull/227.
[@vue/compiler-sfc] When using experimental features,
it is recommended to pin your vue dependencies to exact versions to avoid breakage.
12:32:50 AM [vite] warning:
/Users/me/project/node_modules/.vite/@baloise_design-system-components-vue.js
7221| return module[exportName];
7222| }
7223| return import(
| ^
7224| /* webpackInclude: /\.entry\.js$/ */
7225| /* webpackExclude: /\.system\.entry\.js$/ */
The above dynamic import cannot be analyzed by vite.
See https://github.com/rollup/plugins/tree/master/packages/dynamic-import-vars#limitations for supported dynamic import formats. If this is intended to be left as-is, you can use the /* @vite-ignore */ comment inside the import() call to suppress this warning.
Plugin: vite:import-analysis
File: Users/me/project/node_modules/.vite/@baloise_design-system-components-vue.js?v=8639cb5e
``` | non_priority | error when using with vite i tried to import the the baloise ds using and vite without typescript following i did use the vue use baloisedesignsystem usevite false to load the plugin as indicated in the doc me computer project git main npm run dev dev vite pre bundling dependencies vue baloise design system components vue this will be run only when your dependencies or config have changed vite dev server running at local network use host to expose ready in is still an experimental proposal follow its status at when using experimental features it is recommended to pin your vue dependencies to exact versions to avoid breakage am warning users me project node modules vite baloise design system components vue js return module return import webpackinclude entry js webpackexclude system entry js the above dynamic import cannot be analyzed by vite see for supported dynamic import formats if this is intended to be left as is you can use the vite ignore comment inside the import call to suppress this warning plugin vite import analysis file users me project node modules vite baloise design system components vue js v | 0 |
395,564 | 27,075,361,404 | IssuesEvent | 2023-02-14 10:11:45 | ZanattaMichael/SelMVP | https://api.github.com/repos/ZanattaMichael/SelMVP | closed | Update Documentation to include explicit instructions about 64 bit drivers | documentation | An issue was raised in #61 where a recent build of the Firefox gecko driver was 32 bit. If using 64-bit Firefox, will cause PSSelenium (the dependency) to fail. | 1.0 | Update Documentation to include explicit instructions about 64 bit drivers - An issue was raised in #61 where a recent build of the Firefox gecko driver was 32 bit. If using 64-bit Firefox, will cause PSSelenium (the dependency) to fail. | non_priority | update documentation to include explicit instructions about bit drivers an issue was raised in where a recent build of the firefox gecko driver was bit if using bit firefox will cause psselenium the dependency to fail | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.